Zyxel MES-3528 user manual
MES-3528
Layer 2+ Metro Ethernet Switch
Default Login Details
IP Address |
http://192.168.1.1 |
User Name |
admin |
Password |
1234 |
|
|
Firmware Version 3.90
Edition 1, 3/2009
www.zyxel.com
Copyright © 2009
ZyXEL Communications Corporation
About This User's Guide
About This User's Guide
Intended Audience
This manual is intended for people who want to configure the Switch using the web configurator.
Related Documentation
•Command Line Interface (CLI) Reference Guide
The Command Reference Guide explains how to use the Command-Line Interface (CLI) and CLI commands to configure the Switch.
•Web Configurator Online Help
The embedded Web Help contains descriptions of individual screens and supplementary information.
Note: It is recommended you use the web configurator to configure the Switch.
•Support Disc
Refer to the included CD for support documents.
Documentation Feedback
Send your comments, questions or suggestions to: techwriters@zyxel.com.tw
Thank you!
The Technical Writing Team, ZyXEL Communications Corp.,
6 Innovation Road II, Science-Based Industrial Park, Hsinchu, 30099, Taiwan.
Need More Help?
More help is available at www.zyxel.com.
|
3 |
MES-3528 User’s Guide |
|
|
|

About This User's Guide
•Download Library
Search for the latest product updates and documentation from this link. Read the Tech Doc Overview to find out how to efficiently use the User Guide, Quick Start Guide and Command Line Interface Reference Guide in order to better understand how to use your product.
•Knowledge Base
If you have a specific question about your product, the answer may be here. This is a collection of answers to previously asked questions about ZyXEL products.
•Forum
This contains discussions on ZyXEL products. Learn from others who use ZyXEL products and share your experiences as well.
Customer Support
Should problems arise that cannot be solved by the methods listed above, you should contact your vendor. If you cannot contact your vendor, then contact a ZyXEL office for the region in which you bought the device.
See http://www.zyxel.com/web/contact_us.php for contact information. Please have the following information ready when you contact an office.
•Product model and serial number.
•Warranty Information.
•Date that you received your device.
•Brief description of the problem and the steps you took to solve it.
4 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

Document Conventions
Document Conventions
Warnings and Notes
These are how warnings and notes are shown in this User’s Guide.
Warnings tell you about things that could harm you or your device.
Note: Notes tell you other important information (for example, other things you may need to configure or helpful tips) or recommendations.
Syntax Conventions
•The MES-3528 may be referred to as the “Switch”, the “device”, the “system” or the “product” in this User’s Guide.
•Product labels, screen names, field labels and field choices are all in bold font.
•A key stroke is denoted by square brackets and uppercase text, for example, [ENTER] means the “enter” or “return” key on your keyboard.
•“Enter” means for you to type one or more characters and then press the [ENTER] key. “Select” or “choose” means for you to use one of the predefined choices.
•A right angle bracket ( > ) within a screen name denotes a mouse click. For example, Maintenance > Log > Log Setting means you first click Maintenance in the navigation panel, then the Log sub menu and finally the Log Setting tab to get to that screen.
•Units of measurement may denote the “metric” value or the “scientific” value. For example, “k” for kilo may denote “1000” or “1024”, “M” for mega may denote “1000000” or “1048576” and so on.
•“e.g.,” is a shorthand for “for instance”, and “i.e.,” means “that is” or “in other words”.
|
5 |
MES-3528 User’s Guide |
|
|
|
Document Conventions
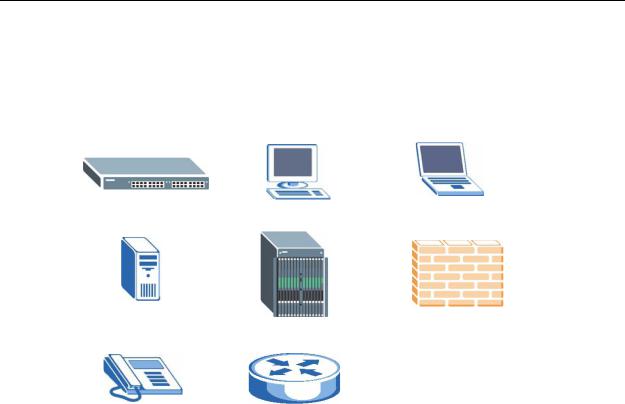
Icons Used in Figures
Figures in this User’s Guide may use the following generic icons. The Switch icon is not an exact representation of your device.
The Switch |
Computer |
Notebook computer |
|
|
|
Server |
DSLAM |
Firewall |
|
|
|
Telephone |
Router |
|
|
|
|
6 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|
Safety Warnings
Safety Warnings
•Do NOT use this product near water, for example, in a wet basement or near a swimming pool.
•Do NOT expose your device to dampness, dust or corrosive liquids.
•Do NOT store things on the device.
•Do NOT install, use, or service this device during a thunderstorm. There is a remote risk of electric shock from lightning.
•Do not obstruct the device ventillation slots as insufficient airflow may harm your device.
•Connect ONLY suitable accessories to the device.
•Do NOT open the device or unit. Opening or removing covers can expose you to dangerous high voltage points or other risks. ONLY qualified service personnel should service or disassemble this device. Please contact your vendor for further information.
•Make sure to connect the cables to the correct ports.
•Place connecting cables carefully so that no one will step on them or stumble over them.
•Always disconnect all cables from this device before servicing or disassembling.
•Use ONLY an appropriate power adaptor or cord for your device. Connect it to the right supply voltage (for example, 110V AC in North America or 230V AC in Europe).
•Use ONLY power wires of the appropriate wire gauge (see Chapter 41 on page 335 for details) for your device. Connect it to a power supply of the correct voltage (see Chapter 41 on page 335 for details).
•Do NOT allow anything to rest on the power adaptor or cord and do NOT place the product where anyone can walk on the power adaptor or cord.
•Do NOT use the device if the power adaptor or cord is damaged as it might cause electrocution.
•If the power adaptor or cord is damaged, remove it from the device and the power source.
•Do NOT attempt to repair the power adaptor or cord. Contact your local vendor to order a new one.
•Fuse Warning! Replace a fuse only with a fuse of the same type and rating.
•The length of exposed (bare) power wire should not exceed 7 mm.
Your product is marked with this symbol, which is known as the WEEE mark. WEEE stands for Waste Electronics and Electrical Equipment. It means that used electrical and electronic products should not be mixed with general waste. Used electrical and electronic equipment should be treated separately.
|
7 |
MES-3528 User’s Guide |
|
|
|

Safety Warnings
8 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

Contents Overview
Contents Overview
Introduction and Hardware ................................................................................................... |
21 |
Getting to Know Your Switch ..................................................................................................... |
23 |
Hardware Installation and Connection ....................................................................................... |
29 |
Hardware Overview ................................................................................................................... |
33 |
Basic Configuration ............................................................................................................... |
43 |
The Web Configurator ............................................................................................................... |
45 |
Initial Setup Example ................................................................................................................. |
55 |
Tutorials ..................................................................................................................................... |
61 |
System Status and Port Statistics .............................................................................................. |
71 |
Basic Setting ............................................................................................................................. |
77 |
Advanced ................................................................................................................................ |
89 |
VLAN ......................................................................................................................................... |
91 |
Static MAC Forward Setup ....................................................................................................... |
111 |
Static Multicast Forward Setup ................................................................................................. |
115 |
Filtering ..................................................................................................................................... |
119 |
Spanning Tree Protocol ........................................................................................................... |
121 |
Bandwidth Control ................................................................................................................... |
143 |
Broadcast Storm Control ......................................................................................................... |
147 |
Mirroring .................................................................................................................................. |
149 |
Link Aggregation ...................................................................................................................... |
151 |
Port Authentication .................................................................................................................. |
161 |
Port Security ............................................................................................................................ |
165 |
Classifier .................................................................................................................................. |
169 |
Policy Rule .............................................................................................................................. |
175 |
Queuing Method ...................................................................................................................... |
181 |
VLAN Stacking ......................................................................................................................... |
185 |
Multicast .................................................................................................................................. |
193 |
AAA ......................................................................................................................................... |
209 |
IP Source Guard ...................................................................................................................... |
223 |
Loop Guard .............................................................................................................................. |
249 |
Layer 2 Protocol Tunneling ...................................................................................................... |
253 |
IP Application ....................................................................................................................... |
257 |
Static Route ............................................................................................................................. |
259 |
Differentiated Services ............................................................................................................. |
263 |
MES-3528 User’s Guide |
9 |

Contents Overview
DHCP ...................................................................................................................................... |
267 |
Management ......................................................................................................................... |
275 |
Maintenance ............................................................................................................................ |
277 |
Access Control ........................................................................................................................ |
285 |
Diagnostic ................................................................................................................................ |
307 |
Syslog ...................................................................................................................................... |
309 |
Cluster Management ............................................................................................................... |
313 |
MAC Table ............................................................................................................................... |
321 |
ARP Table ................................................................................................................................ |
325 |
Configure Clone ....................................................................................................................... |
327 |
Troubleshooting & Product Specifications ....................................................................... |
329 |
Troubleshooting ....................................................................................................................... |
331 |
Product Specifications ............................................................................................................. |
335 |
Appendices and Index ......................................................................................................... |
343 |
10 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

Table of Contents
Table of Contents
About This User's Guide .......................................................................................................... |
3 |
|
Document Conventions............................................................................................................ |
5 |
|
Safety Warnings........................................................................................................................ |
7 |
|
Contents Overview ................................................................................................................... |
9 |
|
Table of Contents.................................................................................................................... |
11 |
|
Part I: Introduction and Hardware ........................................................ |
21 |
|
Chapter 1 |
|
|
Getting to Know Your Switch................................................................................................. |
23 |
|
1.1 |
Introduction .......................................................................................................................... |
23 |
|
1.1.1 Backbone Application ................................................................................................. |
23 |
|
1.1.2 Bridging Example ....................................................................................................... |
24 |
|
1.1.3 High Performance Switching Example ....................................................................... |
25 |
|
1.1.4 IEEE 802.1Q VLAN Application Examples ................................................................ |
25 |
|
1.1.5 Metro Ethernet ........................................................................................................... |
26 |
1.2 |
Ways to Manage the Switch ................................................................................................ |
27 |
1.3 |
Good Habits for Managing the Switch ................................................................................. |
28 |
Chapter 2 |
|
|
Hardware Installation and Connection ................................................................................. |
29 |
|
2.1 |
Installation Scenarios .......................................................................................................... |
29 |
2.2 |
Desktop Installation Procedure ........................................................................................... |
29 |
2.3 |
Mounting the Switch on a Rack .......................................................................................... |
29 |
|
2.3.1 Rack-mounted Installation Requirements .................................................................. |
30 |
|
2.3.2 Attaching the Mounting Brackets to the Switch .......................................................... |
30 |
|
2.3.3 Mounting the Switch on a Rack .................................................................................. |
31 |
Chapter 3 |
|
|
Hardware Overview................................................................................................................. |
33 |
|
3.1 |
Front Panel ......................................................................................................................... |
33 |
|
3.1.1 Console Port .............................................................................................................. |
34 |
|
3.1.2 Gigabit Ethernet Ports ............................................................................................... |
34 |
|
3.1.3 Mini-GBIC Slots .......................................................................................................... |
35 |
MES-3528 User’s Guide |
11 |
|

Table of Contents
|
3.1.4 Power Connector ....................................................................................................... |
37 |
|
3.1.5 ALARM Slot ................................................................................................................ |
37 |
3.2 |
LEDs ................................................................................................................................... |
40 |
Part II: Basic Configuration................................................................... |
43 |
|
Chapter 4 |
|
|
The Web Configurator ............................................................................................................ |
45 |
|
4.1 |
Introduction .......................................................................................................................... |
45 |
4.2 |
System Login .................................................................................................................... |
45 |
4.3 |
The Status Screen .......................................................................................................... |
46 |
|
4.3.1 Change Your Password .......................................................................................... |
51 |
4.4 |
Saving Your Configuration ................................................................................................... |
51 |
4.5 |
Switch Lockout .................................................................................................................. |
52 |
4.6 |
Resetting the Switch ......................................................................................................... |
52 |
|
4.6.1 Reload the Configuration File .................................................................................... |
52 |
4.7 |
Logging Out of the Web Configurator ................................................................................. |
53 |
4.8 |
Help .................................................................................................................................... |
54 |
Chapter 5 |
|
|
Initial Setup Example.............................................................................................................. |
55 |
|
5.1 |
Overview .............................................................................................................................. |
55 |
|
5.1.1 Creating a VLAN ........................................................................................................ |
55 |
|
5.1.2 Setting Port VID ......................................................................................................... |
57 |
5.2 |
Configuring Switch Management IP Address ...................................................................... |
58 |
Chapter 6 |
|
|
Tutorials ................................................................................................................................... |
|
61 |
6.1 |
How to Use DHCP Snooping on the Switch ........................................................................ |
61 |
6.2 |
How to Use DHCP Relay on the Switch .............................................................................. |
65 |
|
6.2.1 DHCP Relay Tutorial Introduction .............................................................................. |
65 |
|
6.2.2 Creating a VLAN ........................................................................................................ |
66 |
|
6.2.3 Configuring DHCP Relay ........................................................................................... |
69 |
|
6.2.4 Troubleshooting ......................................................................................................... |
69 |
Chapter 7 |
|
|
System Status and Port Statistics......................................................................................... |
71 |
|
7.1 |
Overview .............................................................................................................................. |
71 |
7.2 |
Port Status Summary ...................................................................................................... |
72 |
|
7.2.1 Status: Port Details ................................................................................................ |
73 |
12 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

|
|
Table of Contents |
Chapter 8 |
|
|
Basic Setting .......................................................................................................................... |
77 |
|
8.1 |
Overview .............................................................................................................................. |
77 |
8.2 |
System Information ........................................................................................................... |
77 |
8.3 |
General Setup ................................................................................................................. |
78 |
8.4 |
Introduction to VLANs ......................................................................................................... |
80 |
8.5 |
Switch Setup Screen ........................................................................................................ |
81 |
8.6 |
IP Setup .............................................................................................................................. |
82 |
|
8.6.1 Management IP Addresses ........................................................................................ |
83 |
8.7 |
Port Setup ........................................................................................................................... |
85 |
Part III: Advanced................................................................................... |
89 |
|
Chapter 9 |
|
|
VLAN ........................................................................................................................................ |
|
91 |
9.1 |
Introduction to IEEE 802.1Q Tagged VLANs .................................................................. |
91 |
|
9.1.1 Forwarding Tagged and Untagged Frames ................................................................ |
91 |
9.2 |
Automatic VLAN Registration ............................................................................................. |
92 |
|
9.2.1 GARP ......................................................................................................................... |
92 |
|
9.2.2 GVRP ......................................................................................................................... |
92 |
9.3 |
Port VLAN Trunking ............................................................................................................ |
93 |
9.4 |
Select the VLAN Type ........................................................................................................ |
94 |
9.5 |
Static VLAN ......................................................................................................................... |
94 |
|
9.5.1 VLAN Status .............................................................................................................. |
95 |
|
9.5.2 VLAN Details ............................................................................................................. |
96 |
|
9.5.3 Configure a Static VLAN ........................................................................................ |
97 |
|
9.5.4 Configure VLAN Port Settings ................................................................................ |
99 |
9.6 |
Subnet Based VLANs ....................................................................................................... |
100 |
9.7 |
Configuring Subnet Based VLAN .................................................................................... |
101 |
9.8 |
Protocol Based VLANs ..................................................................................................... |
103 |
9.9 |
Configuring Protocol Based VLAN .................................................................................. |
104 |
9.10 Create an IP-based VLAN Example ................................................................................ |
106 |
|
9.11 Port-based VLAN Setup .............................................................................................. |
107 |
|
|
9.11.1 Configure a Port-based VLAN ............................................................................... |
108 |
Chapter 10 |
|
|
Static MAC Forward Setup................................................................................................... |
111 |
|
10.1 Overview ........................................................................................................................... |
111 |
|
10.2 Configuring Static MAC Forwarding ............................................................................ |
111 |
|
Chapter 11 |
|
|
Static Multicast Forward Setup............................................................................................ |
115 |
|
|
13 |
MES-3528 User’s Guide |
|
|
|

Table of Contents
11.1 |
Static Multicast Forwarding Overview ............................................................................... |
115 |
11.2 |
Configuring Static Multicast Forwarding ............................................................................ |
116 |
Chapter 12 |
|
|
||
Filtering.................................................................................................................................. |
|
119 |
|
|
12.1 |
Configure a Filtering Rule .............................................................................................. |
119 |
|
|
Chapter 13 |
|
|
||
Spanning Tree Protocol........................................................................................................ |
121 |
|
||
13.1 |
STP/RSTP Overview ...................................................................................................... |
121 |
|
|
|
13.1.1 STP Terminology ................................................................................................... |
121 |
|
|
|
13.1.2 How STP Works .................................................................................................... |
122 |
|
|
|
13.1.3 STP Port States ..................................................................................................... |
123 |
|
|
|
13.1.4 Multiple RSTP ....................................................................................................... |
123 |
|
|
|
13.1.5 Multiple STP ........................................................................................................... |
124 |
|
|
13.2 |
Spanning Tree Protocol Status Screen ............................................................................ |
127 |
|
|
13.3 |
Spanning Tree Configuration .......................................................................................... |
128 |
|
|
13.4 |
Configure Rapid Spanning Tree Protocol ..................................................................... |
129 |
|
|
13.5 |
Rapid Spanning Tree Protocol Status ........................................................................ |
131 |
|
|
13.6 |
Configure Multiple Rapid Spanning Tree Protocol ........................................................ |
133 |
|
|
13.7 |
Multiple Rapid Spanning Tree Protocol Status .......................................................... |
135 |
|
|
13.8 |
Configure Multiple Spanning Tree Protocol .................................................................. |
137 |
|
|
13.9 |
Multiple Spanning Tree Protocol Status ..................................................................... |
140 |
|
|
Chapter 14 |
|
|
||
Bandwidth Control................................................................................................................ |
143 |
|
||
14.1 |
Bandwidth Control Overview .......................................................................................... |
143 |
|
|
14.2 |
Bandwidth Control Setup ................................................................................................. |
144 |
|
|
Chapter 15 |
|
|
||
Broadcast Storm Control ..................................................................................................... |
147 |
|
||
15.1 |
Broadcast Storm Control Setup ...................................................................................... |
147 |
|
|
Chapter 16 |
|
|
||
Mirroring ................................................................................................................................ |
|
149 |
|
|
16.1 |
Port Mirroring Setup ....................................................................................................... |
149 |
|
|
Chapter 17 |
|
|
||
Link Aggregation .................................................................................................................. |
151 |
|
||
17.1 |
Link Aggregation Overview ............................................................................................. |
151 |
|
|
17.2 |
Dynamic Link Aggregation .............................................................................................. |
151 |
|
|
|
17.2.1 Link Aggregation ID ............................................................................................... |
152 |
|
|
17.3 |
Link Aggregation Status .................................................................................................. |
153 |
|
|
|
|
|
|
|
14 |
|
|
|
|
|
|
MES-3528 User’s Guide |
|
|
|
|
|
|
|

|
|
Table of Contents |
17.4 |
Link Aggregation Setting ................................................................................................ |
155 |
17.5 |
Link Aggregation Control Protocol ................................................................................ |
157 |
17.6 |
Static Trunking Example .................................................................................................. |
158 |
Chapter 18 |
|
|
Port Authentication............................................................................................................... |
161 |
|
18.1 |
Port Authentication Overview ......................................................................................... |
161 |
18.1.1 IEEE 802.1x Authentication ................................................................................... |
161 |
|
18.2 |
Port Authentication Configuration .................................................................................... |
162 |
18.2.1 Activate IEEE 802.1x Security ........................................................................... |
163 |
|
Chapter 19 |
|
|
Port Security.......................................................................................................................... |
165 |
|
19.1 |
About Port Security ......................................................................................................... |
165 |
19.2 |
Port Security Setup .......................................................................................................... |
166 |
Chapter 20 |
|
|
Classifier................................................................................................................................ |
|
169 |
20.1 |
About the Classifier and QoS .......................................................................................... |
169 |
20.2 |
Configuring the Classifier ............................................................................................... |
169 |
20.3 |
Viewing and Editing Classifier Configuration ................................................................... |
172 |
20.4 |
Classifier Example ........................................................................................................... |
173 |
Chapter 21 |
|
|
Policy Rule............................................................................................................................ |
175 |
|
21.1 |
Policy Rules Overview .................................................................................................... |
175 |
21.2 |
Configuring Policy Rules ................................................................................................. |
175 |
21.3 |
Viewing and Editing Policy Configuration ........................................................................ |
178 |
21.4 |
Policy Example ................................................................................................................ |
179 |
Chapter 22 |
|
|
Queuing Method.................................................................................................................... |
181 |
|
22.1 |
Queuing Method Overview ............................................................................................. |
181 |
22.1.1 Strictly Priority Queuing .......................................................................................... |
181 |
|
22.1.2 Weighted Fair Queuing .......................................................................................... |
181 |
|
22.1.3 Weighted Round Robin Scheduling (WRR) ........................................................... |
182 |
|
22.2 |
Configuring Queuing ........................................................................................................ |
183 |
Chapter 23 |
|
|
VLAN Stacking ...................................................................................................................... |
185 |
|
23.1 |
VLAN Stacking Overview ................................................................................................ |
185 |
23.1.1 VLAN Stacking Example ........................................................................................ |
185 |
|
23.2 |
VLAN Stacking Port Roles ............................................................................................... |
186 |
MES-3528 User’s Guide |
15 |
|

Table of Contents
23.3 |
VLAN Tag Format ............................................................................................................ |
187 |
23.3.1 Frame Format ........................................................................................................ |
187 |
|
23.4 |
Configuring VLAN Stacking ............................................................................................. |
189 |
23.4.1 Configuring SVLAN ................................................................................................ |
190 |
|
Chapter 24 |
|
|
Multicast ................................................................................................................................ |
|
193 |
24.1 |
Multicast Overview ......................................................................................................... |
193 |
24.1.1 IP Multicast Addresses ........................................................................................... |
193 |
|
24.1.2 IGMP Filtering ........................................................................................................ |
193 |
|
24.1.3 IGMP Snooping ..................................................................................................... |
194 |
|
24.1.4 IGMP Snooping and VLANs ................................................................................... |
194 |
|
24.2 |
Multicast Status .............................................................................................................. |
194 |
24.3 |
Multicast Setting ............................................................................................................. |
195 |
24.4 IGMP Snooping VLAN .................................................................................................... |
198 |
|
24.5 |
IGMP Filtering Profile ..................................................................................................... |
199 |
24.6 MVR Overview ................................................................................................................ |
201 |
|
24.6.1 Types of MVR Ports ............................................................................................... |
201 |
|
24.6.2 MVR Modes ........................................................................................................... |
202 |
|
24.6.3 How MVR Works .................................................................................................... |
202 |
|
24.7 |
General MVR Configuration ............................................................................................ |
203 |
24.8 |
MVR Group Configuration .............................................................................................. |
205 |
24.8.1 MVR Configuration Example .................................................................................. |
206 |
|
Chapter 25 |
|
|
AAA ........................................................................................................................................ |
|
209 |
25.1 |
Authentication, Authorization and Accounting (AAA) ..................................................... |
209 |
25.1.1 Local User Accounts .............................................................................................. |
210 |
|
25.1.2 RADIUS and TACACS+ ........................................................................................ |
210 |
|
25.2 |
AAA Screens ................................................................................................................... |
210 |
25.2.1 RADIUS Server Setup ......................................................................................... |
211 |
|
25.2.2 TACACS+ Server Setup ..................................................................................... |
213 |
|
25.2.3 AAA Setup ............................................................................................................. |
215 |
|
25.2.4 Vendor Specific Attribute ........................................................................................ |
218 |
|
25.3 |
Supported RADIUS Attributes ......................................................................................... |
219 |
25.3.1 Attributes Used for Authentication .......................................................................... |
220 |
|
25.3.2 Attributes Used for Accounting ............................................................................... |
221 |
|
Chapter 26 |
|
|
IP Source Guard.................................................................................................................... |
223 |
|
26.1 |
IP Source Guard Overview .............................................................................................. |
223 |
|
26.1.1 DHCP Snooping Overview |
..................................................................................... 224 |
|
|
26.1.2 ARP Inspection Overview ...................................................................................... |
226 |
|
|
|
|
|
16 |
|
|
|
|
MES - 3528 User’s Guide |
|
|
|
|
|
|

|
|
Table of Contents |
26.2 |
IP Source Guard .............................................................................................................. |
227 |
26.3 |
IP Source Guard Static Binding ....................................................................................... |
228 |
26.4 DHCP Snooping .............................................................................................................. |
230 |
|
26.5 |
DHCP Snooping Configure .............................................................................................. |
234 |
26.5.1 DHCP Snooping Port Configure ............................................................................. |
236 |
|
26.5.2 DHCP Snooping VLAN Configure .......................................................................... |
237 |
|
26.6 |
ARP Inspection Status ..................................................................................................... |
239 |
26.6.1 ARP Inspection VLAN Status ................................................................................. |
240 |
|
26.6.2 ARP Inspection Log Status .................................................................................... |
241 |
|
26.7 |
ARP Inspection Configure ............................................................................................... |
242 |
26.7.1 ARP Inspection Port Configure .............................................................................. |
244 |
|
26.7.2 ARP Inspection VLAN Configure ........................................................................... |
246 |
|
Chapter 27 |
|
|
Loop Guard............................................................................................................................ |
249 |
|
27.1 |
Loop Guard Overview ..................................................................................................... |
249 |
27.2 |
Loop Guard Setup ........................................................................................................... |
251 |
Chapter 28 |
|
|
Layer 2 Protocol Tunneling.................................................................................................. |
253 |
|
28.1 |
Layer 2 Protocol Tunneling Overview ............................................................................. |
253 |
28.1.1 Layer 2 Protocol Tunneling Mode .......................................................................... |
254 |
|
28.2 |
Configuring Layer 2 Protocol Tunneling .......................................................................... |
255 |
Part IV: IP Application.......................................................................... |
257 |
|
Chapter 29 |
|
|
Static Route ........................................................................................................................... |
259 |
|
29.1 |
Static Routing Overview .................................................................................................. |
259 |
29.2 |
Configuring Static Routing ............................................................................................... |
260 |
Chapter 30 |
|
|
Differentiated Services ......................................................................................................... |
263 |
|
30.1 |
DiffServ Overview ........................................................................................................... |
263 |
30.1.1 DSCP and Per-Hop Behavior ................................................................................ |
263 |
|
30.1.2 DiffServ Network Example .................................................................................... |
264 |
|
30.2 |
Activating DiffServ .......................................................................................................... |
264 |
30.3 |
DSCP-to-IEEE 802.1p Priority Settings ......................................................................... |
265 |
30.3.1 Configuring DSCP Settings .................................................................................... |
266 |
|
Chapter 31 |
|
|
DHCP...................................................................................................................................... |
|
267 |
|
17 |
MES-3528 User’s Guide |
|
|
|

Table of Contents
31.1 DHCP Overview ............................................................................................................. |
267 |
|
31.1.1 DHCP Modes ........................................................................................................ |
267 |
|
31.1.2 DHCP Configuration Options ................................................................................. |
267 |
|
31.2 |
DHCP Status ................................................................................................................... |
268 |
31.3 DHCP Relay ................................................................................................................... |
268 |
|
31.3.1 DHCP Relay Agent Information ............................................................................. |
268 |
|
31.3.2 Configuring DHCP Global Relay ............................................................................ |
269 |
|
31.3.3 Global DHCP Relay Configuration Example .......................................................... |
270 |
|
31.4 |
Configuring DHCP VLAN Settings ................................................................................ |
271 |
31.4.1 Example: DHCP Relay for Two VLANs .................................................................. |
273 |
|
Part V: Management............................................................................. |
275 |
|
Chapter 32 |
|
|
Maintenance .......................................................................................................................... |
277 |
|
32.1 |
The Maintenance Screen .............................................................................................. |
277 |
32.2 |
Load Factory Default ...................................................................................................... |
278 |
32.3 |
Save Configuration .......................................................................................................... |
279 |
32.4 |
Reboot System ................................................................................................................ |
279 |
32.5 |
Firmware Upgrade ........................................................................................................ |
279 |
32.6 |
Restore a Configuration File ......................................................................................... |
280 |
32.7 |
Backup a Configuration File ......................................................................................... |
281 |
32.8 FTP Command Line ........................................................................................................ |
281 |
|
32.8.1 Filename Conventions .......................................................................................... |
281 |
|
32.8.2 FTP Command Line Procedure ............................................................................ |
282 |
|
32.8.3 GUI-based FTP Clients .......................................................................................... |
283 |
|
32.8.4 FTP Restrictions .................................................................................................... |
283 |
|
Chapter 33 |
|
|
Access Control...................................................................................................................... |
285 |
|
33.1 |
Access Control Overview ............................................................................................ |
285 |
33.2 |
The Access Control Main Screen .................................................................................... |
285 |
33.3 About SNMP .................................................................................................................. |
286 |
|
33.3.1 SNMP v3 and Security ........................................................................................... |
287 |
|
33.3.2 Supported MIBs .................................................................................................... |
287 |
|
33.3.3 SNMP Traps .......................................................................................................... |
288 |
|
33.3.4 Configuring SNMP ................................................................................................ |
292 |
|
33.3.5 Configuring SNMP Trap Group ........................................................................... |
294 |
|
33.3.6 Setting Up Login Accounts ................................................................................. |
295 |
|
33.4 |
SSH Overview ................................................................................................................. |
297 |
33.5 How SSH works ............................................................................................................... |
298 |
|
18 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

|
|
Table of Contents |
33.6 |
SSH Implementation on the Switch ................................................................................. |
299 |
33.6.1 Requirements for Using SSH ................................................................................. |
299 |
|
33.7 |
Introduction to HTTPS ..................................................................................................... |
299 |
33.8 HTTPS Example .............................................................................................................. |
300 |
|
33.8.1 Internet Explorer Warning Messages ..................................................................... |
300 |
|
33.8.2 Netscape Navigator Warning Messages ................................................................ |
301 |
|
33.8.3 The Main Screen .................................................................................................... |
303 |
|
33.9 |
Service Port Access Control ......................................................................................... |
303 |
33.10 Remote Management ............................................................................................... |
304 |
|
Chapter 34 |
|
|
Diagnostic |
.............................................................................................................................. |
307 |
34.1 |
Diagnostic ....................................................................................................................... |
307 |
Chapter 35 |
|
|
Syslog .................................................................................................................................... |
|
309 |
35.1 .............................................................................................................. |
Syslog Overview |
309 |
35.2 .................................................................................................................. |
Syslog Setup |
310 |
35.3 ........................................................................................................ |
Syslog Server Setup |
311 |
Chapter 36 |
|
|
Cluster Management............................................................................................................. |
313 |
|
36.1 ........................................................................... |
Cluster Management Status Overview |
313 |
36.2 ........................................................................................... |
Cluster Management Status |
314 |
36.2.1 ...................................................................Cluster Member Switch Management |
315 |
|
36.3 .......................................................................... |
Clustering Management Configuration |
318 |
Chapter 37 |
|
|
MAC Table.............................................................................................................................. |
|
321 |
37.1 ...................................................................................................... |
MAC Table Overview |
321 |
37.2 ................................................................................................... |
Viewing the MAC Table |
322 |
Chapter 38 |
|
|
ARP Table .............................................................................................................................. |
|
325 |
38.1 ....................................................................................................... |
ARP Table Overview |
325 |
38.1.1 ....................................................................................................How ARP Works |
325 |
|
38.2 ................................................................................................... |
Viewing the ARP Table |
326 |
Chapter 39 |
|
|
Configure Clone .................................................................................................................... |
327 |
|
39.1 .............................................................................................................. |
Configure Clone |
327 |
|
19 |
MES-3528 User’s Guide |
|
|
|

Table of Contents
Part VI: Troubleshooting & Product Specifications.......................... |
329 |
|
Chapter 40 |
|
|
Troubleshooting.................................................................................................................... |
331 |
|
40.1 |
Power, Hardware Connections, and LEDs ...................................................................... |
331 |
40.2 |
Switch Access and Login ................................................................................................. |
332 |
40.3 |
Switch Configuration ........................................................................................................ |
334 |
Chapter 41 |
|
|
Product Specifications ......................................................................................................... |
335 |
|
Part VII: Appendices and Index .......................................................... |
343 |
||
Appendix |
A |
Changing a Fuse .............................................................................................. |
345 |
Appendix |
B |
Common Services............................................................................................. |
347 |
Appendix |
C Legal Information .............................................................................................. |
351 |
|
Index....................................................................................................................................... |
|
|
355 |
20 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|
PART I
Introduction and
Hardware
Getting to Know Your Switch (23)
Hardware Installation and Connection (29)
Hardware Overview (33)
21

22

1
Getting to Know Your Switch
This chapter introduces the main features and applications of the Switch.
1.1 Introduction
The Switch is a layer-2 standalone Ethernet switch with additional layer-2, layer-3, and layer-4 features suitable for metro ethernets. The Switch has twenty-four 10/ 100 Mbps Ethernet ports. It also has four GbE dual personality interfaces with each interface comprising one mini-GBIC slot and one 100/1000 Mbps RJ-45 port, with either port or slot active at a time.
With its built-in web configurator, managing and configuring the Switch is easy. In addition, the Switch can also be managed via Telnet, any terminal emulator program on the console port, or third-party SNMP management.
See Chapter 41 on page 335 for a full list of software features available on the Switch.
This section shows a few examples of using the Switch in various network environments.
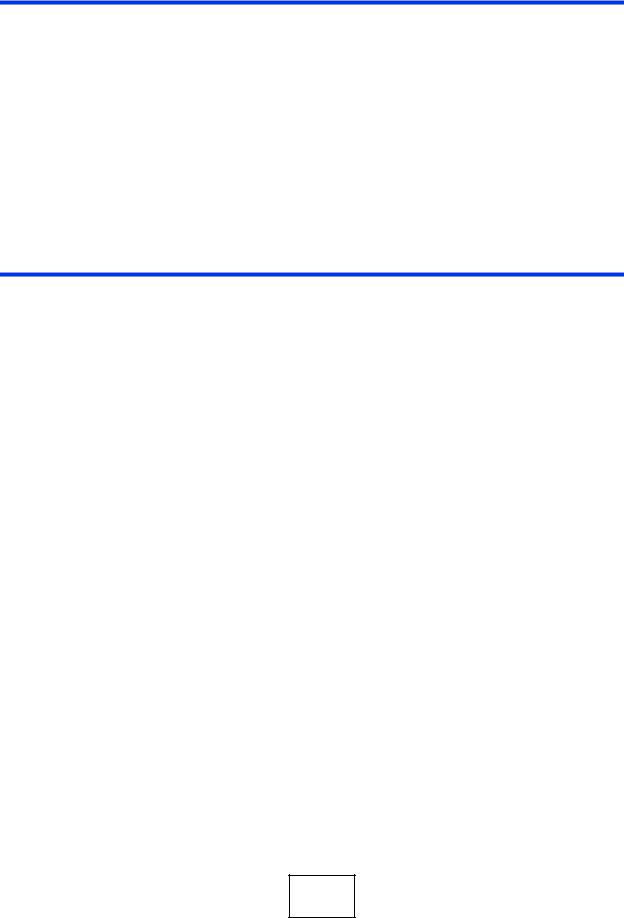
1.1.1 Backbone Application
The Switch is an ideal solution for small networks where rapid growth can be expected in the near future. The Switch can be used standalone for a group of heavy traffic users. You can connect computers and servers directly to the Switch’s port or connect other switches to the Switch.
|
23 |
MES-3528 User’s Guide |
|
|
|
Chapter 1 Getting to Know Your Switch
In this example, all computers can share high-speed applications on the server. To expand the network, simply add more networking devices such as switches, routers, computers, print servers etc.
Figure 1 Backbone Application
1.1.2 Bridging Example
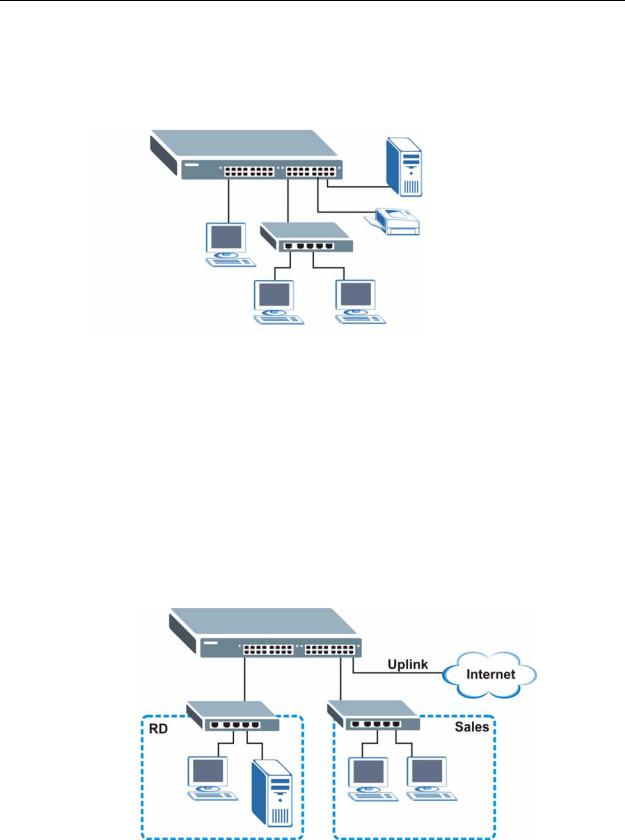
In this example, the Switch connects different company departments (RD and Sales) to the corporate backbone. It can alleviate bandwidth contention and eliminate server and network bottlenecks. All users that need high bandwidth can connect to high-speed department servers via the Switch. You can provide a super-fast uplink connection by using a Gigabit Ethernet/mini-GBIC port on the Switch.
Moreover, the Switch eases supervision and maintenance by allowing network managers to centralize multiple servers at a single location.
Figure 2 Bridging Application
24 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|
Chapter 1 Getting to Know Your Switch
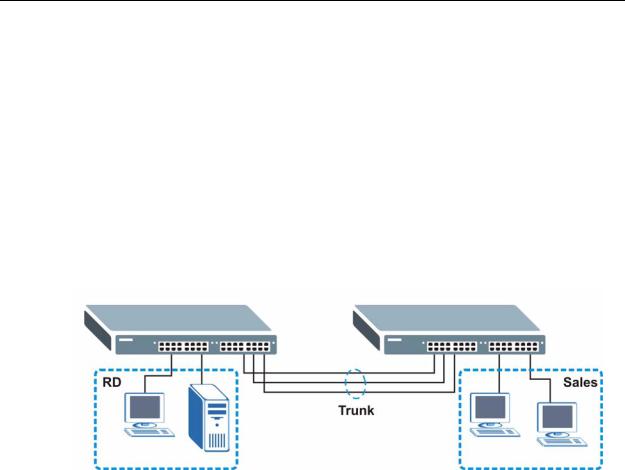
1.1.3 High Performance Switching Example
The Switch is ideal for connecting two networks that need high bandwidth. In the following example, use trunking to connect these two networks.
Switching to higher-speed LANs such as ATM (Asynchronous Transmission Mode) is not feasible for most people due to the expense of replacing all existing Ethernet cables and adapter cards, restructuring your network and complex maintenance. The Switch can provide the same bandwidth as ATM at much lower cost while still being able to use existing adapters and switches. Moreover, the current LAN structure can be retained as all ports can freely communicate with each other.
Figure 3 High Performance Switched Workgroup Application
1.1.4 IEEE 802.1Q VLAN Application Examples
A VLAN (Virtual Local Area Network) allows a physical network to be partitioned into multiple logical networks. Stations on a logical network belong to one group. A station can belong to more than one group. With VLAN, a station cannot directly talk to or hear from stations that are not in the same group(s) unless such traffic first goes through a router.
For more information on VLANs, refer to Chapter 9 on page 91.
1.1.4.1 Tag-based VLAN Example
Ports in the same VLAN group share the same frame broadcast domain thus increase network performance through reduced broadcast traffic. VLAN groups can be modified at any time by adding, moving or changing ports without any recabling.
|
25 |
MES-3528 User’s Guide |
|
|
|

Chapter 1 Getting to Know Your Switch
Shared resources such as a server can be used by all ports in the same VLAN as the server. In the following figure only ports that need access to the server need to be part of VLAN 1. Ports can belong to other VLAN groups too.
Figure 4 Shared Server Using VLAN Example
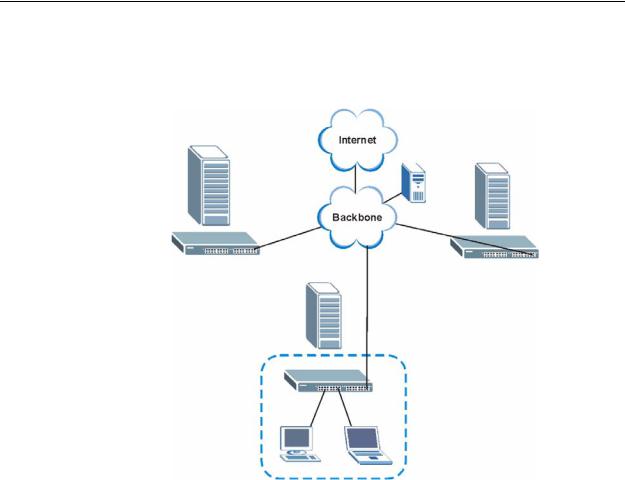
1.1.5 Metro Ethernet
The Switch is ideal for connecting users to an Ethernet network that spans a metropolitan area.
In the following example, the Switch is one of many switches that connect users in the metropolitan area to the Internet. The metro ethernet is based on a star (or hub-and-spoke) topology, though other topologies, such as ring or mesh, are also
26 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|
Chapter 1 Getting to Know Your Switch
possible. The Switch is connected to the backbone and the metropolitan servers over an optical network that provides higher bandwidth than copper.
Figure 5 Metro Ethernet
1.2 Ways to Manage the Switch
Use any of the following methods to manage the Switch.
•Web Configurator. This is recommended for everyday management of the Switch using a (supported) web browser. See Chapter 4 on page 45.
•Command Line Interface. Line commands offer an alternative to the web configurator and in some cases are necessary to configure advanced features. See the CLI Reference Guide.
•FTP. Use FTP for firmware upgrades and configuration backup/restore. See Section 32.8 on page 281.
•SNMP. The Switch can be monitored by an SNMP manager. See Section 33.3 on page 286.
•Cluster Management. Cluster Management allows you to manage multiple switches through one switch, called the cluster manager. See Chapter 36 on page 313.
|
27 |
MES-3528 User’s Guide |
|
|
|

Chapter 1 Getting to Know Your Switch
1.3 Good Habits for Managing the Switch
Do the following things regularly to make the Switch more secure and to manage the Switch more effectively.
•Change the password. Use a password that’s not easy to guess and that consists of different types of characters, such as numbers and letters.
•Write down the password and put it in a safe place.
•Back up the configuration (and make sure you know how to restore it). Restoring an earlier working configuration may be useful if the device becomes unstable or even crashes. If you forget your password, you will have to reset the Switch to its factory default settings. If you backed up an earlier configuration file, you would not have to totally re-configure the Switch. You could simply restore your last configuration.
28 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|

2
Hardware Installation and
Connection
This chapter shows you how to install and connect the Switch.
2.1 Installation Scenarios
The Switch can be placed on a desktop or rack-mounted on a standard EIA rack. Use the rubber feet in a desktop installation and the brackets in a rack-mounted installation.
Note: For proper ventilation, allow at least 4 inches (10 cm) of clearance at the front and 3.4 inches (8 cm) at the back of the Switch. This is especially important for enclosed rack installations.
2.2 Desktop Installation Procedure
1Make sure the Switch is clean and dry.
2Set the Switch on a smooth, level surface strong enough to support the weight of the Switch and the connected cables. Make sure there is a power outlet nearby.
3Make sure there is enough clearance around the Switch to allow air circulation and the attachment of cables and the power cord.
2.3Mounting the Switch on a Rack
The Switch can be mounted on an EIA standard size, 19-inch rack or in a wiring closet with other equipment. Follow the steps below to mount your Switch on a standard EIA rack using a rack-mounting kit.
|
29 |
MES-3528 User’s Guide |
|
|
|

Chapter 2 Hardware Installation and Connection
2.3.1Rack-mounted Installation Requirements
•Two mounting brackets.
•Eight M3 flat head screws and a #2 Philips screwdriver.
•Four M5 flat head screws and a #2 Philips screwdriver.
Failure to use the proper screws may damage the unit.
2.3.1.1Precautions
•Make sure the rack will safely support the combined weight of all the equipment it contains.
•Make sure the position of the Switch does not make the rack unstable or topheavy. Take all necessary precautions to anchor the rack securely before installing the unit.
2.3.2Attaching the Mounting Brackets to the Switch
1Position a mounting bracket on one side of the Switch, lining up the four screw holes on the bracket with the screw holes on the side of the Switch.
Figure 6 Attaching the Mounting Brackets
2Using a #2 Philips screwdriver, install the M3 flat head screws through the mounting bracket holes into the Switch.
3Repeat steps 1 and 2 to install the second mounting bracket on the other side of the Switch.
4You may now mount the Switch on a rack. Proceed to the next section.
30 |
|
|
MES-3528 User’s Guide |
|
|
|
|
|
 Loading...
Loading...