TP-Link TL-SG2008 User Manual
TL-SG2008
8-Port Gigabit Smart Switch
REV1.0.0
1910010984

COPYRIGHT & TRADEMARKS
Specifications are subject to change without notice.  is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make any derivative such as translation, transformation, or adaptation without permission from TP-LINK TECHNOLOGIES CO., LTD. Copyright © 2014 TP-LINK TECHNOLOGIES CO., LTD. All rights reserved.
http://www.tp-link.com
FCC STATEMENT
This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is operated in a commercial environment. This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the instruction manual, may cause harmful interference to radio communications. Operation of this equipment in a residential area is likely to cause harmful interference in which case the user will be required to correct the interference at his own expense.
This device complies with part 15 of the FCC Rules. Operation is subject to the following two conditions:
1)This device may not cause harmful interference.
2)This device must accept any interference received, including interference that may cause undesired operation.
Any changes or modifications not expressly approved by the party responsible for compliance could void the user’s authority to operate the equipment.
CE Mark Warning
This is a class A product. In a domestic environment, this product may cause radio interference, in which case the user may be required to take adequate measures.
Продукт сертифіковано згідно с правилами системи УкрСЕПРО на відповідність вимогам нормативних документів та вимогам, що передбачені чинними законодавчими актами України.
I

Safety Information
zWhen product has power button, the power button is one of the way to shut off the product; When there is no power button, the only way to completely shut off power is to disconnect the product or the power adapter from the power source.
zDon’t disassemble the product, or make repairs yourself. You run the risk of electric shock and voiding the limited warranty. If you need service, please contact us.
zAvoid water and wet locations.
This product can be used in the following countries:
AT |
BG |
BY |
CA |
CZ |
DE |
DK |
EE |
|
|
|
|
|
|
|
|
ES |
FI |
FR |
GB |
GR |
HU |
IE |
IT |
|
|
|
|
|
|
|
|
LT |
LV |
MT |
NL |
NO |
PL |
PT |
RO |
|
|
|
|
|
|
|
|
RU |
SE |
SK |
TR |
UA |
|
|
|
|
|
|
|
|
|
|
|
II
|
|
|
CONTENTS |
Package Contents .......................................................................................................................... |
1 |
||
Chapter 1 About this Guide........................................................................................................... |
2 |
||
1.1 |
Intended Readers ......................................................................................................... |
2 |
|
1.2 |
Conventions.................................................................................................................. |
2 |
|
1.3 |
Overview of This Guide ................................................................................................ |
2 |
|
Chapter 2 |
Introduction .................................................................................................................. |
5 |
|
2.1 |
Overview of the Switch ................................................................................................. |
5 |
|
2.2 |
Main Features............................................................................................................... |
5 |
|
2.3 |
Appearance Description ............................................................................................... |
5 |
|
2.3.1 |
Front Panel ........................................................................................................ |
5 |
|
2.3.2 |
Rear Panel ......................................................................................................... |
6 |
|
Chapter 3 Login to the Switch....................................................................................................... |
7 |
||
3.1 |
Login |
............................................................................................................................. |
7 |
3.2 |
Configuration ................................................................................................................ |
7 |
|
Chapter 4 |
System ......................................................................................................................... |
9 |
|
4.1 |
System ...................................................................................................................Info |
9 |
|
4.1.1 ............................................................................................... |
System Summary |
9 |
|
4.1.2 ........................................................................................... |
Device Description |
10 |
|
4.1.3 .................................................................................................... |
System Time |
11 |
|
4.1.4 ....................................................................................... |
Daylight Saving Time |
12 |
|
4.1.5 ......................................................................................................... |
System IP |
13 |
|
4.2 |
User Management ...................................................................................................... |
14 |
|
4.2.1 ........................................................................................................ |
User Table |
14 |
|
4.2.2 ...................................................................................................... |
User Config |
15 |
|
4.3 |
System ..............................................................................................................Tools |
16 |
|
4.3.1 ................................................................................................. |
Config Restore |
16 |
|
4.3.2 .................................................................................................. |
Config Backup |
17 |
|
4.3.3 ........................................................................................... |
Firmware Upgrade |
17 |
|
4.3.4 ................................................................................................ |
System Reboot |
18 |
|
4.3.5 ................................................................................................... |
System Reset |
18 |
|
4.4 |
Access ..........................................................................................................Security |
19 |
|
4.4.1 ................................................................................................. |
Access Control |
19 |
|
4.4.2 ....................................................................................................... |
SSL Config |
20 |
|
4.4.3 ...................................................................................................... |
SSH Config |
22 |
|
Chapter 5 |
Switching.................................................................................................................... |
28 |
|
5.1 |
Port ............................................................................................................................. |
|
28 |
|
|
|
III |
5.1.1 |
Port Config ....................................................................................................... |
28 |
|
5.1.2 |
Port Mirror ........................................................................................................ |
29 |
|
5.1.3 |
Port Security .................................................................................................... |
31 |
|
5.1.4 |
Port Isolation .................................................................................................... |
32 |
|
5.1.5 |
Loopback Detection ......................................................................................... |
33 |
|
5.2 |
LAG ............................................................................................................................ |
|
34 |
5.2.1 |
LAG Table ........................................................................................................ |
35 |
|
5.2.2 |
Static LAG ........................................................................................................ |
36 |
|
5.2.3 |
LACP Config .................................................................................................... |
37 |
|
5.3 |
Traffic Monitor............................................................................................................. |
39 |
|
5.3.1 |
Traffic Summary............................................................................................... |
39 |
|
5.3.2 |
Traffic Statistics ................................................................................................ |
40 |
|
5.4 |
MAC Address.............................................................................................................. |
41 |
|
5.4.1 |
Address Table .................................................................................................. |
42 |
|
5.4.2 |
Static Address .................................................................................................. |
43 |
|
5.4.3 |
Dynamic Address ............................................................................................. |
44 |
|
5.4.4 |
Filtering Address .............................................................................................. |
46 |
|
5.5 |
DHCP Filtering............................................................................................................ |
47 |
|
Chapter 6 |
VLAN.......................................................................................................................... |
|
51 |
6.1 |
802.1Q VLAN.............................................................................................................. |
52 |
|
6.1.1 |
VLAN Config .................................................................................................... |
53 |
|
6.2 |
Application Example for 802.1Q VLAN ....................................................................... |
55 |
|
Chapter 7 |
Spanning Tree............................................................................................................ |
57 |
|
7.1 |
STP Config ................................................................................................................. |
62 |
|
7.1.1 |
STP Config....................................................................................................... |
62 |
|
7.1.2 |
STP Summary.................................................................................................. |
64 |
|
7.2 |
Port Config.................................................................................................................. |
64 |
|
7.3 |
MSTP Instance ........................................................................................................... |
66 |
|
7.3.1 |
Region Config .................................................................................................. |
66 |
|
7.3.2 |
Instance Config ................................................................................................ |
66 |
|
7.3.3 |
Instance Port Config......................................................................................... |
68 |
|
7.4 |
STP Security............................................................................................................... |
69 |
|
7.4.1 |
Port Protect ...................................................................................................... |
69 |
|
7.4.2 |
TC Protect........................................................................................................ |
71 |
|
7.5 |
Application Example for STP Function ....................................................................... |
72 |
|
Chapter 8 |
Multicast..................................................................................................................... |
76 |
|
8.1 |
IGMP Snooping .......................................................................................................... |
78 |
|
|
|
IV |
|
8.1.1 |
Snooping Config .............................................................................................. |
79 |
|
8.1.2 |
Port Config ....................................................................................................... |
80 |
|
8.1.3 |
VLAN Config .................................................................................................... |
81 |
|
8.1.4 |
Multicast VLAN ................................................................................................ |
82 |
|
8.2 |
Multicast IP ................................................................................................................. |
85 |
|
8.2.1 |
Multicast IP Table ............................................................................................. |
85 |
|
8.2.2 |
Static Multicast IP ............................................................................................. |
86 |
|
8.3 |
Multicast Filter............................................................................................................. |
87 |
|
8.3.1 |
IP - Range .......................................................................................................... |
88 |
|
8.3.2 |
Port Filter ......................................................................................................... |
88 |
|
8.4 |
Packet Statistics.......................................................................................................... |
90 |
|
Chapter 9 |
QoS |
............................................................................................................................ |
92 |
9.1 |
DiffServ....................................................................................................................... |
95 |
|
9.1.1 ...................................................................................................... |
Port Priority |
95 |
|
9.1.2 ....................................................................................... |
802.1P/CoS Mapping |
96 |
|
9.1.3 ................................................................................................... |
DSCP Priority |
97 |
|
9.1.4 ................................................................................................ |
Schedule Mode |
98 |
|
9.2 |
Bandwidth ......................................................................................................Control |
99 |
|
9.2.1 ......................................................................................................... |
Rate Limit |
99 |
|
9.2.2 ................................................................................................. |
Storm Control |
100 |
|
9.3 |
Voice ..............................................................................................................VLAN |
101 |
|
9.3.1 ................................................................................................. |
Global Config |
103 |
|
9.3.2 ..................................................................................................... |
Port Config |
104 |
|
9.3.3 ..................................................................................................... |
OUI Config |
105 |
|
Chapter 10 ACL .......................................................................................................................... |
|
107 |
|
10.1 |
ACL ...............................................................................................................Config |
107 |
|
10.1.1 ................................................................................................ |
ACL Summary |
107 |
|
10.1.2 .................................................................................................... |
ACL Create |
107 |
|
10.1.3 ....................................................................................................... |
MAC ACL |
108 |
|
10.1.4 ............................................................................................ |
Standard - IP ACL |
109 |
|
10.1.5 ............................................................................................... |
Extend - IP ACL |
109 |
|
10.2 |
Policy .............................................................................................................Config |
110 |
|
10.2.1 ............................................................................................. |
Policy Summary |
110 |
|
10.2.2 .................................................................................................. |
Policy Create |
111 |
|
10.2.3 ................................................................................................. |
Action Create |
111 |
|
10.3 |
Policy ...........................................................................................................Binding |
112 |
|
10.3.1 ................................................................................................. |
Binding Table |
112 |
|
|
|
|
V |
|
10.3.2 |
Port Binding ................................................................................................... |
113 |
|
10.3.3 |
VLAN Binding................................................................................................. |
113 |
10.4 |
Application Example for ACL .................................................................................... |
114 |
|
Chapter 11 SNMP....................................................................................................................... |
117 |
||
11.1 |
SNMP Config ............................................................................................................ |
119 |
|
|
11.1.1 |
Global Config ................................................................................................. |
119 |
|
11.1.2 |
SNMP View.................................................................................................... |
120 |
|
11.1.3 |
SNMP Group.................................................................................................. |
120 |
|
11.1.4 |
SNMP User .................................................................................................... |
122 |
|
11.1.5 |
SNMP Community.......................................................................................... |
124 |
11.2 |
Notification................................................................................................................ |
126 |
|
11.3 |
RMON....................................................................................................................... |
127 |
|
|
11.3.1 |
History Control ............................................................................................... |
128 |
|
11.3.2 |
Event Config .................................................................................................. |
129 |
|
11.3.3 |
Alarm Config .................................................................................................. |
129 |
Chapter 12 Maintenance ............................................................................................................ |
132 |
||
12.1 |
System Monitor......................................................................................................... |
132 |
|
|
12.1.1 |
CPU Monitor .................................................................................................. |
132 |
|
12.1.2 |
Memory Monitor ............................................................................................. |
133 |
12.2 |
Log............................................................................................................................ |
|
133 |
|
12.2.1 |
Log Table ....................................................................................................... |
134 |
|
12.2.2 |
Local Log ....................................................................................................... |
135 |
|
12.2.3 |
Remote Log ................................................................................................... |
136 |
|
12.2.4 |
Backup Log .................................................................................................... |
136 |
12.3 |
Device Diagnostics ................................................................................................... |
137 |
|
|
12.3.1 |
Cable Test ...................................................................................................... |
137 |
|
12.3.2 |
Loopback ....................................................................................................... |
138 |
12.4 |
Network Diagnostics ................................................................................................. |
138 |
|
|
12.4.1 |
Ping................................................................................................................ |
139 |
|
12.4.2 |
Tracert............................................................................................................ |
139 |
Appendix A: Specifications ......................................................................................................... |
141 |
||
Appendix B: Configuring the PCs ............................................................................................... |
142 |
||
Appendix C: Glossary................................................................................................................. |
144 |
||
VI

Package Contents
The following items should be found in your box:
¾One TL-SG2008 8-Port Gigabit Smart Switch
¾One power adapter
¾Four rubber cushions
¾Quick Installation Guide
¾Resource CD for TL-SG2008 switch, including:
•This User Guide
•Other Helpful Information
 Note:
Note:
Make sure that the package contains the above items. If any of the listed items are damaged or missing, please contact your distributor.
1
Chapter 1 About this Guide
This User Guide contains information for setup and management of TL-SG2008 8-Port Gigabit Smart Switch. Please read this guide carefully before operation.
1.1 Intended Readers
This Guide is intended for network managers familiar with IT concepts and network terminologies.
1.2 Conventions
In this Guide the following conventions are used:
¾The switch or TL-SG2008 mentioned in this Guide stands for TL-SG2008 8-Port Gigabit Smart Switch without any explanation.
¾Menu Name→Submenu Name→Tab page indicates the menu structure. System→System Info→System Summary means the System Summary page under the System Info menu option that is located under the System menu.
¾Bold font indicates a button, a toolbar icon, menu or menu item.
Symbols in this Guide
|
Symbol |
Description |
|
|
|
|
Note: |
Ignoring this type of note might result in a malfunction or damage to the device. |
|
|
This format indicates important information that helps you make better use of Tips: your device.
1.3 Overview of This Guide
Chapter |
|
Introduction |
|
|
|
Chapter 1 About This Guide |
Introduces the guide structure and conventions. |
|
|
|
|
Chapter 2 |
Introduction |
Introduces the features, application and appearance of |
|
|
TL-SG2008 switch. |
|
|
|
Chapter 3 |
Login to the Switch |
Introduces how to log on to the Web management page. |
|
|
|
2
Chapter |
Introduction |
|
|
|
|
|
|
Chapter 4 System |
This module is used to configure system properties of the |
||
|
switch. Here mainly introduces: |
|
|
|
z System Info: Configure the description, system time and |
||
|
|
network parameters of the switch. |
|
|
z |
User Management: Configure the user name and password |
|
|
|
for users to log on to the Web management page with a |
|
|
|
certain access level. |
|
|
z System Tools: Manage the configuration file of the switch. |
||
|
z |
Access Security: Provide different security measures for the |
|
|
|
login to enhance the configuration management security. |
|
|
|
||
Chapter 5 Switching |
This module is used to configure basic functions of the switch. |
||
|
Here mainly introduces: |
|
|
|
z Port: Configure the basic features for the port. |
|
|
|
z LAG: Configure Link Aggregation Group. LAG is to combine a |
||
|
|
number of ports together to make a single high-bandwidth |
|
|
|
data path. |
|
|
z Traffic Monitor: Monitor the traffic of each port. |
|
|
|
z MAC Address: Configure the address table of the switch. |
||
|
z DHCP Filtering: Monitor the process of the host obtaining the |
||
|
|
IP address from DHCP server. |
|
|
|
||
Chapter 6 VLAN |
This module is used to configure VLANs to control broadcast in |
||
|
LANs. Here mainly introduces: |
|
|
|
z 802.1Q VLAN: Configure port-based VLAN. |
|
|
|
|
||
Chapter 7 Spanning Tree |
This module is used to configure spanning tree function of the |
||
|
switch. Here mainly introduces: |
|
|
|
z STP Config: Configure and view the global |
settings of |
|
|
|
spanning tree function. |
|
|
z Port Config: Configure CIST parameters of ports. |
|
|
|
z MSTP Instance: Configure MSTP instances. |
|
|
|
z STP Security: Configure protection function |
to prevent |
|
|
|
devices from any malicious attack against STP features. |
|
|
|
||
Chapter 8 Multicast |
This module is used to configure multicast function of the switch. |
||
|
Here mainly introduces: |
|
|
|
z IGMP Snooping: Configure global parameters of IGMP |
||
|
|
Snooping function, port properties, VLAN and multicast |
|
|
|
VLAN. |
|
|
z Multicast IP: Configure multicast IP table. |
|
|
|
z |
Multicast Filter: Configure multicast filter feature to restrict |
|
|
|
users ordering multicast programs. |
|
|
z |
Packet Statistics: View the multicast data traffic on each port |
|
|
|
of the switch, which facilitates you to monitor the IGMP |
|
|
|
messages in the network. |
|
|
|
|
|
3
Chapter |
Introduction |
|
|
|
|
Chapter 9 QoS |
This module is used to configure QoS function to provide |
|
|
different quality of service for various network applications and |
|
|
requirements. Here mainly introduces: |
|
|
z |
DiffServ: Configure priorities, port priority, 802.1P priority and |
|
|
DSCP priority. |
|
z |
Bandwidth Control: Configure rate limit feature to control the |
|
|
traffic rate on each port; configure storm control feature to |
|
|
filter broadcast, multicast and UL frame in the network. |
|
z |
Voice VLAN: Configure voice VLAN to transmit voice data |
|
|
stream within the specified VLAN so as to ensure the |
|
|
transmission priority of voice data stream and voice quality. |
|
|
|
Chapter 10 ACL |
This module is used to configure match rules and process |
|
|
policies of packets to filter packets in order to control the access |
|
|
of the illegal users to the network. Here mainly introduces: |
|
|
z ACL Config: ACL rules. |
|
|
z Policy Config: Configure operation policies. |
|
|
z |
Policy Binding: Bind the policy to a port/VLAN to take its |
|
|
effect on a specific port/VLAN. |
|
|
|
Chapter 11 SNMP |
This module is used to configure SNMP function to provide a |
|
|
management frame to monitor and maintain the network |
|
|
devices. Here mainly introduces: |
|
|
z SNMP Config: Configure global settings of SNMP function. |
|
|
z |
Notification: Configure notification function for the |
|
|
management station to monitor and process the events. |
|
z |
RMON: Configure RMON function to monitor network more |
|
|
efficiently. |
|
|
|
Chapter 12 Maintenance |
This module is used to assemble the commonly used system |
|
|
tools to manage the switch. Here mainly introduces: |
|
|
z System Monitor: Monitor the memory and CPU of the switch. |
|
|
z Log: View configuration parameters on the switch. |
|
|
z |
Device Diagnostics: Test the connection status of the cable |
|
|
connected to the switch, test if the port of the switch and the |
|
|
connected device are available. |
|
z |
Network Diagnostics: Test if the destination is reachable and |
|
|
the account of router hops from the switch to the destination. |
|
|
|
Appendix A Specifications |
Lists the hardware specifications of the switch. |
|
|
|
|
Appendix B Configure the PCs |
Introduces how to configure the PCs. |
|
|
|
|
Appendix C Glossary |
Lists the glossary used in this manual. |
|
|
|
|
Return to CONTENTS
4

Chapter 2 Introduction
Thanks for choosing the TL-SG2008 8-Port Gigabit Smart Switch!
2.1 Overview of the Switch
Designed for workgroups and departments, TL-SG2008 from TP-LINK provides wire-speed performance and full set of layer 2 management features. It provides a variety of service features and multiple powerful functions with high security.
The EIA-standardized framework and smart configuration capacity can provide flexible solutions for a variable scale of networks. QoS and IGMP snooping/filtering optimize voice and video application. Link aggregation (LACP) increase aggregated bandwidth, optimizing the transport of business critical data. SNMP, RMON, WEB/Telnet Log-in bring abundant management policies. TL-SG2008 switch integrates multiple functions with excellent performance, and is friendly to manage, which can fully meet the need of the users demanding higher networking performance.
2.2 Main Features
•Resiliency and Availability
+IEEE 802.1s Multiple Spanning Tree provides high link availability in multiple VLAN environments.
+Multicast snooping automatically prevents flooding of IP multicast traffic.
+Root Guard protects root bridge from malicious attack or configuration mistakes
•Layer 2 Switching
+Supports up to 512 VLANs simultaneously (out of 4K VLAN IDs).
•Quality of Service
+Supports L2/L3 granular CoS with 4 priority queues per port.
+Rate limiting confines the traffic flow accurately according to the preset value.
•Manageability
+Supports Telnet, SNMP v1/v2c/v3, RMON and web access.
+Port Mirroring enables monitoring selected ingress/egress traffic.
2.3 Appearance Description
2.3.1 Front Panel
The front panel of TL-SG2008 is shown as Figure 2-1.
Figure 2-1 Front Panel of TL-SG2008
5
The following parts are located on the front panel of the switch:
¾Reset: Press this button for five seconds or above to reset the software setting back to factory default setting.
¾LEDs
|
Name |
|
Status |
|
Indication |
|
|
Power |
|
On(Green) |
|
The switch is powered on. |
|
|
|
|
|
|
|
|
|
|
Flashing/Off |
The switch is powered off or power supply is abnormal. |
|||
|
|
|
||||
|
|
|
|
|
|
|
|
|
|
Flashing |
The switch is working normally. |
||
|
System |
|
|
|
|
|
|
|
On/Off |
|
The switch is working abnormally. |
||
|
|
|
|
|||
|
|
|
|
|
|
|
|
|
|
|
On |
|
A 1000Mbps device is connected to the corresponding port, but |
|
|
|
Green |
|
no activity. |
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
Link/Act |
|
|
Flashing |
|
Data is being transmitted or received. |
|
|
|
|
|
|
|
|
|
|
On |
|
A 10/100Mbps device is connected to the corresponding port, but |
|
|
|
|
|
|
||
|
|
|
Yellow |
|
no activity. |
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
Flashing |
|
Data is being transmitted or received. |
|
|
|
|
|
|
|
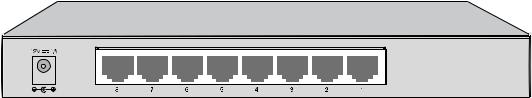
2.3.2 Rear Panel
The rear panel of TL-SG2008 features a power socket and eight ports. Its rear panel is shown as the following figure.
Figure 2-2 Rear Panel of TL-SG2008
¾1000Mbps Ports: Designed to connect to the device with a bandwidth of 10Mbps, 100Mbps or 1000Mbps. Each has a corresponding LED on the front panel.
¾Power Socket: Connect the female connector of the power cord here, and the male connector to the DC power outlet. Please make sure the voltage of the power supply meets the requirement of the input voltage (12V/1A for TL-SG2008).
Return to CONTENTS
6
Chapter 3 Login to the Switch
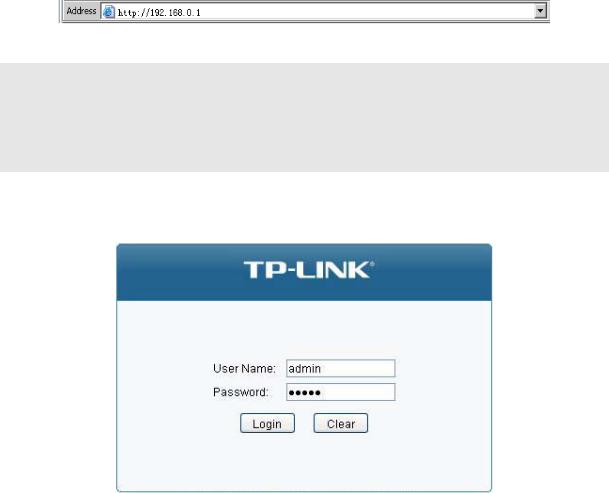
3.1Login
1)To access the configuration utility, open a web-browser and type in the default address http://192.168.0.1 in the address field of the browser, then press the Enter key.
Figure 3-1 Web-browser
 Tips:
Tips:
To log in to the switch, the IP address of your PC should be set in the same subnet addresses of the switch. The IP address is 192.168.0.x ("x" is any number from 2 to 254), Subnet Mask is 255.255.255.0. For the detailed instructions as to how to do this, please refer to Appendix B.
2)After a moment, a login window will appear, as shown in Figure 3-2. Enter admin for the User Name and Password, both in lower case letters. Then click the Login button or press the Enter key.
Figure 3-2 Login
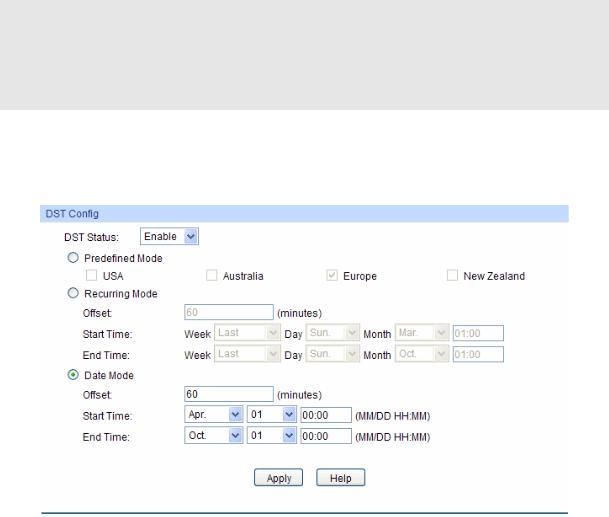
3.2 Configuration
After a successful login, the main page will appear as Figure 3-3, and you can configure the function by clicking the setup menu on the left side of the screen.
7
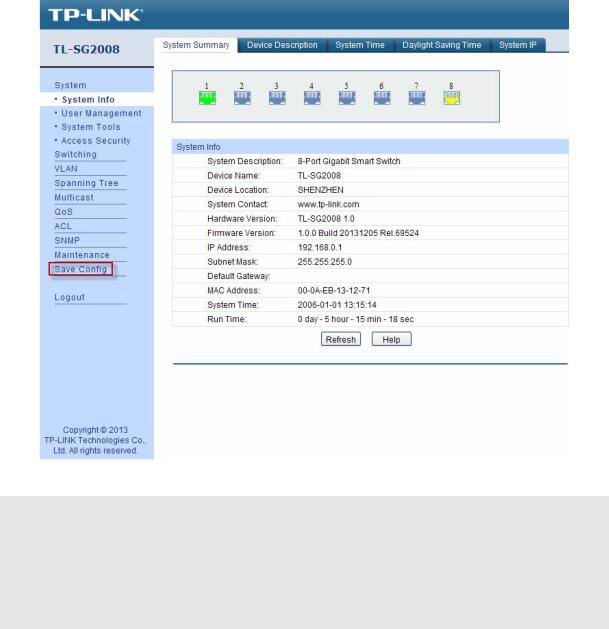
Figure 3-3 Main Setup-Menu
 Note:
Note:
Clicking Apply can only make the new configurations effective before the switch is rebooted. If you want to keep the configurations effective even the switch is rebooted, please click Save Config. You are suggested to click Save Config before cutting off the power or rebooting the switch to avoid losing the new configurations.
Return to CONTENTS
8
Chapter 4 System
The System module is mainly for system configuration of the switch, including four submenus:
System Info, User Management, System Tools and Access Security.
4.1 System Info
The System Info, mainly for basic properties configuration, can be implemented on System Summary, Device Description, System Time, Daylight Saving Time and System IP pages.
4.1.1 System Summary
On this page you can view the port connection status and the system information.
The port status diagram shows the working status of 8 1000Mbps RJ45 ports of the switch. Choose the menu System→System Info→System Summary to load the following page.
Figure 4-1 System Summary
¾Port Status
Indicates the corresponding port is not connected to a device.
Indicates the corresponding port is at the speed of 1000Mbps.
Indicates the corresponding port is at the speed of 10/100Mbps.
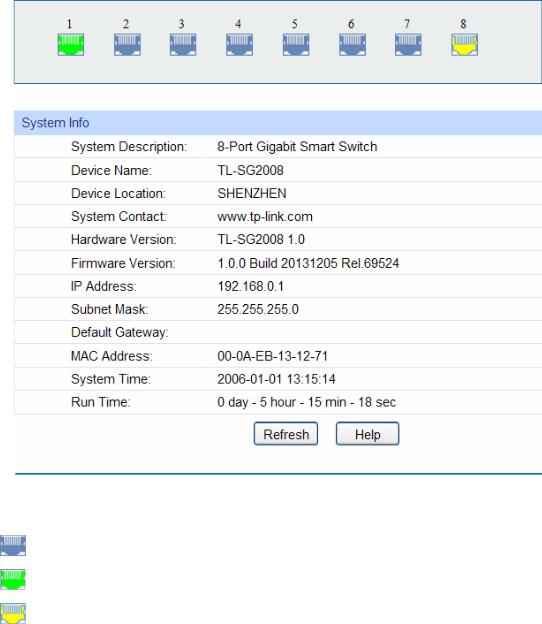
When the cursor moves on the port, the detailed information of the port will be displayed.
9
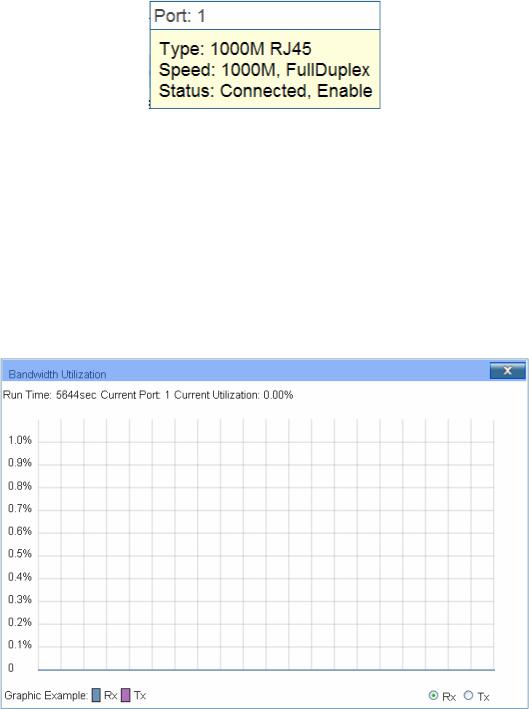
Figure 4-2 Port Information
¾Port Info
Port: |
Displays the port number of the switch. |
Type: |
Displays the type of the port. |
Rate: |
Displays the maximum transmission rate of the port. |
Status: |
Displays the connection status of the port. |
Click a port to display the bandwidth utilization on this port. The actual rate divided by theoretical maximum rate is the bandwidth utilization. The following figure displays the bandwidth utilization monitored every four seconds. Monitoring the bandwidth utilization on each port facilitates you to monitor the network traffic and analyze the network abnormities.
|
Figure 4-3 Bandwidth Utilization |
¾ Bandwidth Utilization |
|
Rx: |
Select Rx to display the bandwidth utilization of receiving packets |
|
on this port. |
Tx: |
Select Tx to display the bandwidth utilization of sending packets |
|
on this port. |
4.1.2 Device Description
On this page you can configure the description of the switch, including device name, device location and system contact.
Choose the menu System→System Info→Device Description to load the following page.
10

Figure 4-4 Device Description
The following entries are displayed on this screen:
¾Device Description
Device Name: Enter the name of the switch.
Device Location: Enter the location of the switch.
System Contact: Enter your contact information.
4.1.3 System Time
System Time is the time displayed while the switch is running. On this page you can configure the system time and the settings here will be used for other time-based functions.
You can manually set the system time or synchronize with PC’s clock as the system time.
Choose the menu System→System Info→System Time to load the following page.
Figure 4-5 System Time
The following entries are displayed on this screen:
¾Time Info
Current System Date: Displays the current date and time of the switch.
Current Time Source: Displays the current time source of the switch.
11
¾Time Config
Manual: When this option is selected, you can set the date and time
Get Time from NTP Server:
manually.
When this option is selected, you can configure the time zone and the IP Address for the NTP Server. The switch will get UTC automatically if it has connected to an NTP Server.
|
|
z Time Zone: Select your local time. |
|
|
z Primary/Secondary NTP Server: Enter the IP Address for |
|
|
the NTP Server. |
|
|
z Update Rate: Specify the rate fetching time from NTP server. |
Synchronize |
with |
When this option is selected, the administrator PC’s clock is |
PC’S Clock: |
|
utilized. |

 Note:
Note:
1.The system time will be restored to the default when the switch is restarted and you need to reconfigure the system time of the switch.
2.When Get Time from NTP Server is selected and no time server is configured, the switch will get time from the time server of the Internet if it has connected to the Internet.
4.1.4 Daylight Saving Time
Here you can configure the Daylight Saving Time of the switch.
Choose the menu System→System Info→Daylight Saving Time to load the following page.
Figure 4-6 Daylight Saving Time
The following entries are displayed on this screen:
¾DST Config
DST Status: |
Enable or disable the DST. |
12
Predefined Mode: Select a predefined DST configuration.
zUSA: Second Sunday in March, 02:00 ~ First Sunday in November, 02:00.
zAustralia: First Sunday in October, 02:00 ~ First Sunday in April, 03:00.
zEurope: Last Sunday in March, 01:00 ~ Last Sunday in October, 01:00.
zNew Zealand: Last Sunday in September, 02:00 ~ First Sunday in April, 03:00.
Recurring Mode: Specify the DST configuration in recurring mode. This configuration is recurring in use.
zOffset: Specify the time adding in minutes when Daylight Saving Time comes.
zStart/End Time: Select starting time and ending time of Daylight Saving Time.
Date Mode: Specify the DST configuration in Date mode. This configuration is recurring in use.
zOffset: Specify the time adding in minutes when Daylight Saving Time comes.
zStart/End Time: Select starting time and ending time of Daylight Saving Time.
 Note:
Note:
1.When the DST is disabled, the predefined mode, recurring mode and date mode cannot be configured.
2.When the DST is enabled, the default daylight saving time is of Europe in predefined mode.
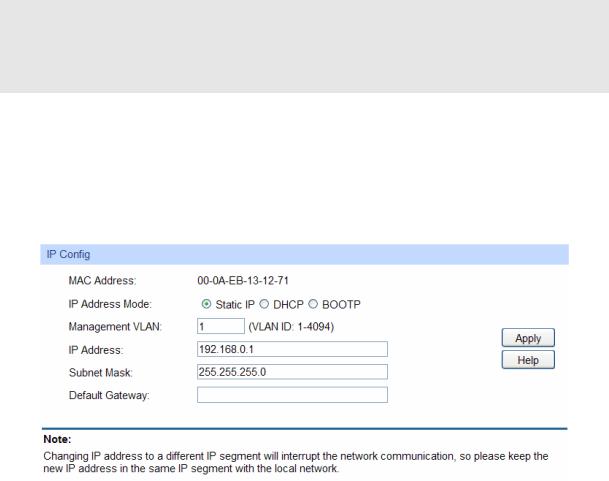
4.1.5 System IP
Each device in the network possesses a unique IP Address. You can log on to the Web management page to operate the switch using this IP Address. The switch supports three modes to obtain an IP address: Static IP, DHCP and BOOTP. The IP address obtained using a new mode will replace the original IP address. On this page you can configure the system IP of the switch.
Choose the menu System→System Info→System IP to load the following page.
Figure 4-7 System IP
The following entries are displayed on this screen:
13
¾IP Config
MAC Address: Displays MAC Address of the switch.
IP Address Mode: Select the mode to obtain IP Address for the switch.
zStatic IP: When this option is selected, you should enter IP Address, Subnet Mask and Default Gateway manually.
zDHCP: When this option is selected, the switch will obtain network parameters from the DHCP Server.
zBOOTP: When this option is selected, the switch will obtain network parameters from the BOOTP Server.
Management VLAN: Enter the ID of management VLAN, the only VLAN through which you can get access to the switch. By default VLAN1 owning all the ports is the Management VLAN and you can access the switch via any port on the switch. However, if another VLAN is created and set to be the Management VLAN, you may have to reconnect the management station to a port that is a member of the Management VLAN.
IP Address: Enter the system IP of the switch. The default system IP is 192.168.0.1 and you can change it appropriate to your needs.
Subnet Mask: Enter the subnet mask of the switch.
Default Gateway: Enter the default gateway of the switch.

 Note:
Note:
1.Changing the IP address to a different IP segment will interrupt the network communication, so please keep the new IP address in the same IP segment with the local network.
2.The switch only possesses an IP address. The IP address configured will replace the original IP address.
3.If the switch gets the IP address from DHCP server, you can see the configuration of the switch in the DHCP server; if DHCP option is selected but no DHCP server exists in the network, the switch will keep obtaining IP address from DHCP server until success.
4.If DHCP or BOOTP option is selected, the switch will get network parameters dynamically from the Internet, which means that IP address, subnet mask and default gateway can not be configured.
5.By default, the IP address is 192.168.0.1.
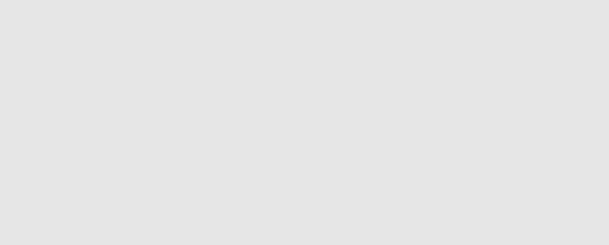
4.2 User Management
User Management functions to configure the user name and password for users to log on to the Web management page with a certain access level so as to protect the settings of the switch from being randomly changed.
The User Management function can be implemented on User Table and User Config pages.
4.2.1 User Table
On this page you can view the information about the current users of the switch.
Choose the menu System→User Management→User Table to load the following page.
14
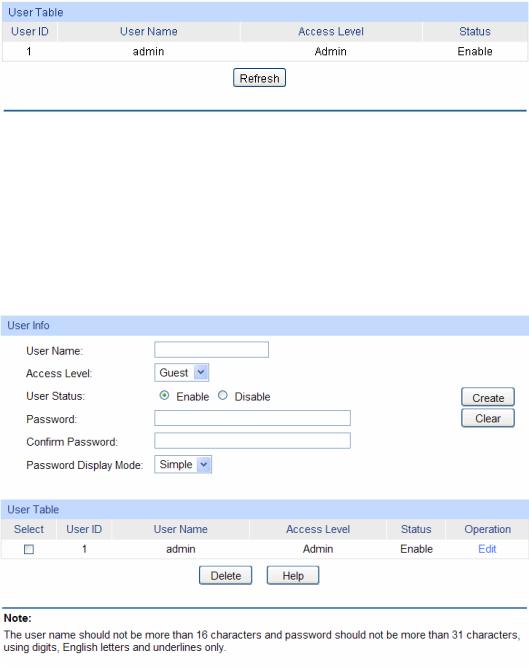
Figure 4-8 User Table
4.2.2 User Config
On this page you can configure the access level of the user to log on to the Web management page. The switch provides two access levels: Guest and Admin. The guest only can view the settings without the right to configure the switch; the admin can configure all the functions of the switch. The Web management pages contained in this guide are subject to the admin’s login without any explanation.
Choose the menu System→User Management→User Config to load the following page.
Figure 4-9 User Config
The following entries are displayed on this screen:
¾User Info
User Name: Create a name for users’ login.
Access Level: Select the access level to login.
zAdmin: Admin can edit, modify and view all the settings of different functions.
zGuest: Guest only can view the settings without the right to edit or modify.
User Status: |
Select Enable/Disable the user configuration. |
Password: |
Type in a password for users’ login. |
|
15 |
Confirm Password:
Password Display
Mode:
Retype the password.
zSimple: Select a simple password display mode.
zCipher: Select a cipher password display mode.
¾User Table
Select: Select the desired entry to delete the corresponding user
User ID, Name, Access Level and status:
Operation:
information. It is multi-optional. The current user information can’t be deleted.
Displays the current user ID, user name, access level and user status.
Click the Edit button of the desired entry, and you can edit the corresponding user information. After modifying the settings, please click the Modify button to make the modification effective. Access level and user status of the current user information can’t be modified.
4.3 System Tools
The System Tools function, allowing you to manage the configuration file of the switch, can be implemented on Config Restore, Config Backup, Firmware Upgrade, System Reboot and System Reset pages.
4.3.1 Config Restore
On this page you can upload a backup configuration file to restore your switch to this previous configuration.
Choose the menu System→System Tools→Config Restore to load the following page.
Figure 4-10 Config Restore
The following entries are displayed on this screen:
¾Config Restore
Restore Config: Click the Restore Config button to restore the backup
configuration file. It will take effect after the switch automatically reboots.
16
 Note:
Note:
1.It will take a few minutes to restore the configuration. Please wait without any operation.
2.To avoid any damage, please don’t power down the switch while being restored.
3.After being restored, the current settings of the switch will be lost. Wrong uploaded configuration file may cause the switch unmanaged.
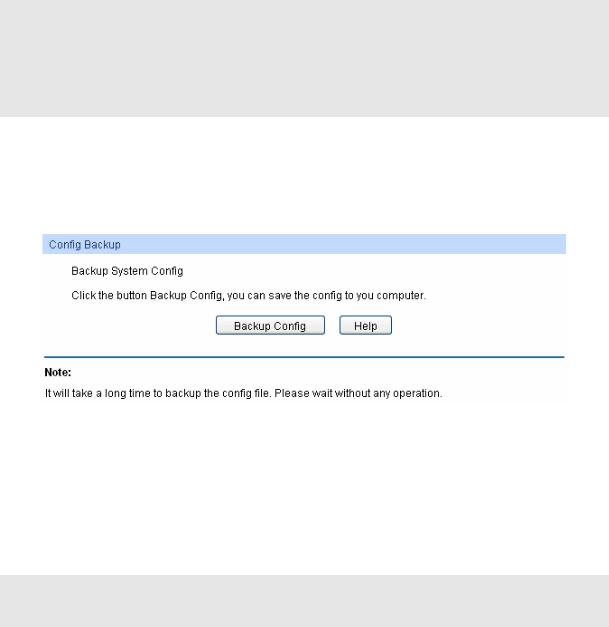
4.3.2 Config Backup
On this page you can download the current configuration and save it as a file to your computer for your future configuration restore.
Choose the menu System→System Tools→Config Backup to load the following page.
Figure 4-11 Config Backup
The following entries are displayed on this screen:
¾Config Backup
Backup Config: Click the Backup Config button to save the current configuration
as a file to your computer. You are suggested to take this measure before upgrading.

 Note:
Note:
It will take a few minutes to backup the configuration. Please wait without any operation.
4.3.3 Firmware Upgrade
The switch system can be upgraded via the Web management page. To upgrade the system is to get more functions and better performance. Go to http://www.tp-link.com to download the updated firmware.
Choose the menu System→System Tools→Firmware Upgrade to load the following page.
17
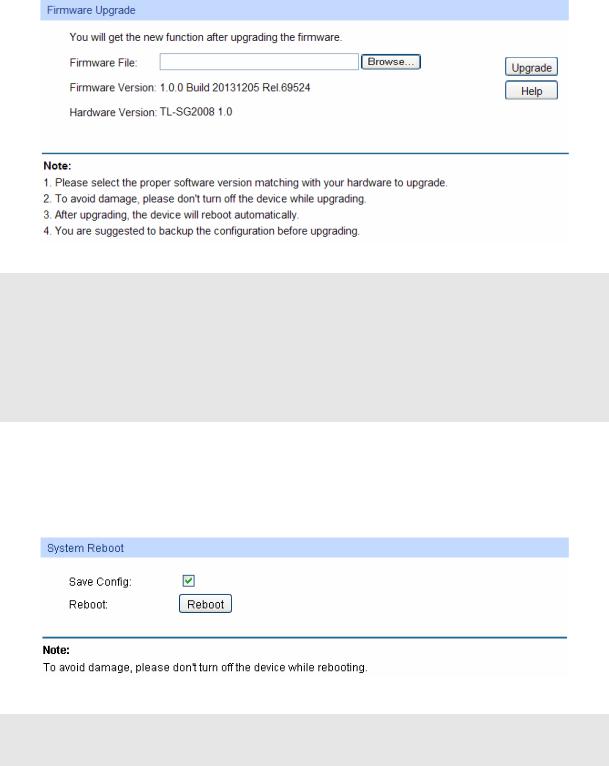
Figure 4-12 Firmware Upgrade
 Note:
Note:
1.Don’t interrupt the upgrade.
2.Please select the proper software version matching with your hardware to upgrade.
3.To avoid damage, please don't turn off the device while upgrading.
4.After upgrading, the device will reboot automatically.
5.You are suggested to backup the configuration before upgrading.
4.3.4 System Reboot
On this page you can reboot the switch and return to the login page. Please save the current configuration before rebooting to avoid losing the configuration unsaved
Choose the menu System→System Tools→System Reboot to load the following page.
Figure 4-13 System Reboot
 Note:
Note:
To avoid damage, please don't turn off the device while rebooting.
4.3.5 System Reset
On this page you can reset the switch to the default. All the settings will be cleared after the switch is reset.
Choose the menu System→System Tools→System Reset to load the following page.
18
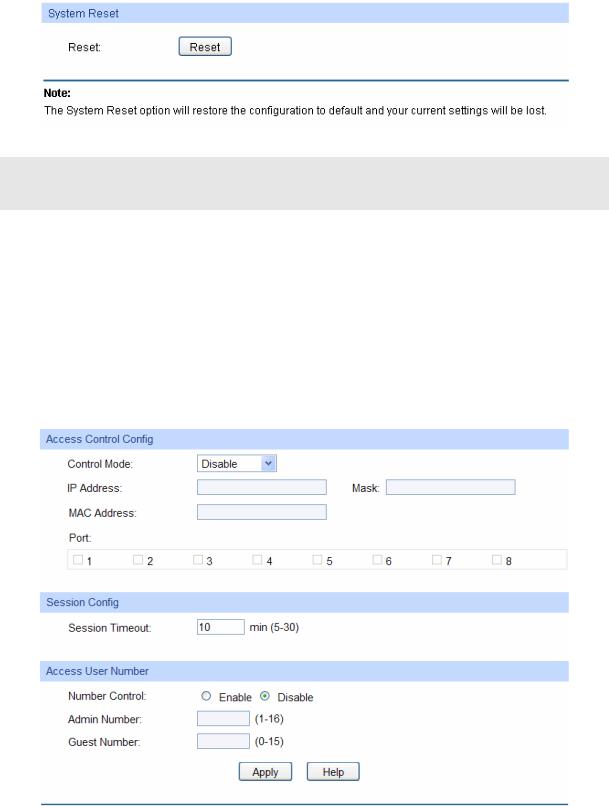
Figure 4-14 System Reset
 Note:
Note:
After the system is reset, the switch will be reset to the default and all the settings will be cleared.
4.4 Access Security
Access Security provides different security measures for the remote login so as to enhance the configuration management security. It can be implemented on Access Control page.
4.4.1 Access Control
On this page you can control the users logging on to the Web management page to enhance the configuration management security. The definitions of Admin and Guest refer to 4.2 User Management.
Choose the menu System→Access Security→Access Control to load the following page.
Figure 4-15 Access Control
The following entries are displayed on this screen:
19
¾Access Control Config
Control Mode: Select the control mode for users to log on to the Web
|
management page. |
|
z Disable Disable the access control function. |
|
z IP-based: Select this option to limit the IP-range of the users |
|
for login. |
|
z MAC-based: Select this option to limit the MAC Address of the |
|
users for login. |
|
z Port-based: Select this option to limit the ports for login. |
IP Address & Mask |
These fields can be available for configuration only when IP-based |
|
mode is selected. Only the users within the IP-range you set here |
|
are allowed for login. |
MAC Address: |
The field can be available for configuration only when MAC-based |
|
mode is selected. Only the user with this MAC Address you set |
|
here is allowed for login. |
Port: |
The field can be available for configuration only when Port-based |
|
mode is selected. Only the users connected to these ports you set |
|
here are allowed for login. |
¾Session Config
Session Timeout: If you do nothing with the Web management page within the
timeout time, the system will log out automatically. If you want to reconfigure, please login again.
¾Access User Number
Number Control: Select Enable/Disable the Number Control function.
Admin Number: Enter the maximum number of the users logging on to the Web management page as Admin.
Guest Number: Enter the maximum number of the users logging on to the Web management page as Guest.
4.4.2 SSL Config
SSL (Secure Sockets Layer), a security protocol, is to provide a secure connection for the application layer protocol (e.g. HTTP) communication based on TCP. SSL is widely used to secure the data transmission between the Web browser and servers. It is mainly applied through ecommerce and online banking.
SSL mainly provides the following services:
1.Authenticate the users and the servers based on the certificates to ensure the data are transmitted to the correct users and servers;
2.Encrypt the data transmission to prevent the data being intercepted;
3.Maintain the integrality of the data to prevent the data being altered in the transmission.
Adopting asymmetrical encryption technology, SSL uses key pair to encrypt/decrypt information. A key pair refers to a public key (contained in the certificate) and its corresponding private key. By
20

default the switch has a certificate (self-signed certificate) and a corresponding private key. The Certificate/Key Download function enables the user to replace the default key pair.
After SSL is effective, you can log on to the Web management page via https://192.168.0.1. For the first time you use HTTPS connection to log into the switch with the default certificate, you will be prompted that “The security certificate presented by this website was not issued by a trusted certificate authority” or “Certificate Errors”. Please add this certificate to trusted certificates or continue to this website.
On this page you can configure the SSL function.
Choose the menu System→Access Security→SSL Config to load the following page.
Figure 4-16 SSL Config
The following entries are displayed on this screen:
¾Global Config
SSL: |
Select Enable/Disable the SSL function on the switch. |
¾Certificate Download
Certificate File: Select the desired certificate to download to the switch. The
certificate must be BASE64 encoded.
¾Key Download
Key File: |
Select the desired SSL key to download to the switch. The key |
|
must be BASE64 encoded. |

 Note:
Note:
1.The SSL certificate and key downloaded must match each other; otherwise the HTTPS connection will not work.
2.The SSL certificate and key downloaded will not take effect until the switch is rebooted.
3.To establish a secured connection using https, please enter https:// into the URL field of the browser.
21
4.It may take more time for https connection than that for http connection, because https connection involves authentication, encryption and decryption etc.
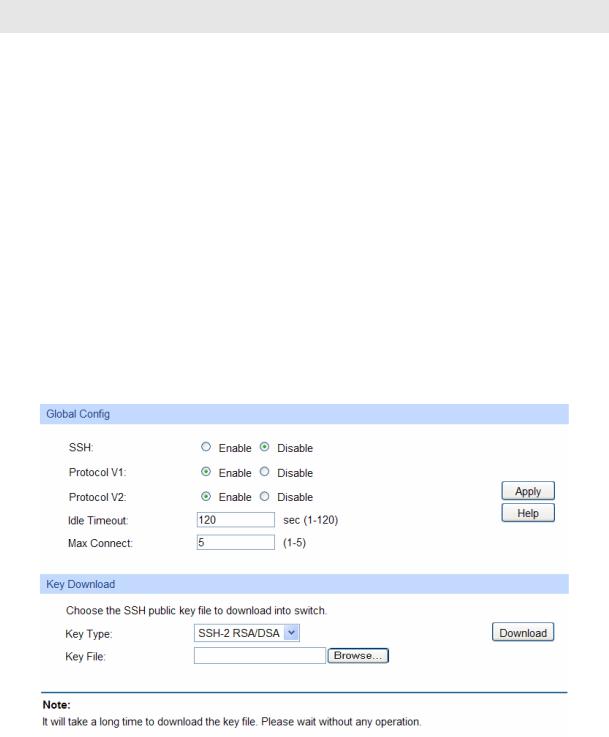
4.4.3 SSH Config
As stipulated by IFTF (Internet Engineering Task Force), SSH (Secure Shell) is a security protocol established on application and transport layers. SSH-encrypted-connection is similar to a telnet connection, but essentially the old telnet remote management method is not safe, because the password and data transmitted with plain-text can be easily intercepted. SSH can provide information security and powerful authentication when you log on to the switch remotely through an insecure network environment. It can encrypt all the transmission data and prevent the information in a remote management being leaked.
Comprising server and client, SSH has two versions, V1 and V2 which are not compatible with each other. In the communication, SSH server and client can auto-negotiate the SSH version and the encryption algorithm. After getting a successful negotiation, the client sends authentication request to the server for login, and then the two can communicate with each other after successful authentication. This switch supports SSH server and you can log on to the switch via SSH connection using SSH client software.
SSH key can be downloaded into the switch. If the key is successfully downloaded, the certificate authentication will be preferred for SSH access to the switch.
Choose the menu System→Access Security→SSH Config to load the following page.
Figure 4-17 SSH Config
The following entries are displayed on this screen:
¾Global Config
SSH: |
Select Enable/Disable SSH function. |
Protocol V1: Select Enable/Disable SSH V1 to be the supported protocol.
Protocol V2: Select Enable/Disable SSH V2 to be the supported protocol.
22
Idle Timeout: Specify the idle timeout time. The system will automatically release the connection when the time is up. The default time is 120 seconds.
Max Connect: Specify the maximum number of the connections to the SSH server. No new connection will be established when the number of the connections reaches the maximum number you set. The default value is 5.
¾Key Download
Key Type: Select the type of SSH key to download. The switch supports
three types: SSH-1 RSA, SSH-2 RSA and SSH-2 DSA.
Key File: Select the desired key file to download.
Download: Click the Download button to down the desired key file to the switch.

 Note:
Note:
1.Please ensure the key length of the downloaded file is in the range of 256 to 3072 bits.
2.After the key file is downloaded, the user’s original key of the same type will be replaced. The wrong uploaded file will result in the SSH access to the switch via Password authentication.
Application Example 1 for SSH:
¾ |
Network Requirements |
1. |
Log on to the switch via password authentication using SSH and the SSH function is enabled |
|
on the switch. |
2. |
PuTTY client software is recommended. |
¾ |
Configuration Procedure |
1.Open the software to log on to the interface of PuTTY. Enter the IP address of the switch into Host Name field; keep the default value 22 in the Port field; select SSH as the Connection type.
23
 Loading...
Loading...