TP-Link TL-SG3216, TL-SG3424 CLI Reference Guide
TL-SG3210/TL-SG3216/TL-SG3424/TL-SG3424P
JetStream L2 Managed Switch
REV2.1.0
1910011082
COPYRIGHT & TRADEMARKS
Specifications are subject to change without notice.  is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make any derivative such as translation, transformation, or adaptation without permission from TP-LINK TECHNOLOGIES CO., LTD. Copyright © 2014 TP-LINK TECHNOLOGIES CO., LTD. All rights reserved.
http://www.tp-link.com
I
CONTENTS
Preface |
|
............................................................................................................................ |
1 |
Chapter 1 |
Using the CLI.................................................................................................... |
4 |
|
1.1 |
Accessing the CLI ........................................................................................................ |
4 |
|
|
1.1.1 |
Logon by a console port..................................................................................... |
4 |
|
1.1.2 |
Configuring the Privileged EXEC Mode Password.............................................. |
6 |
|
1.1.3 |
Logon by Telnet.................................................................................................. |
7 |
|
1.1.4 |
Logon by SSH................................................................................................... |
11 |
1.2 |
CLI Command Modes ................................................................................................ |
16 |
|
1.3 |
Security Levels........................................................................................................... |
18 |
|
1.4 |
Conventions............................................................................................................... |
18 |
|
|
1.4.1 |
Format Conventions......................................................................................... |
18 |
|
1.4.2 |
Special Characters........................................................................................... |
19 |
|
1.4.3 |
Parameter Format............................................................................................ |
19 |
Chapter 2 |
User Interface ................................................................................................. |
20 |
|
enable ................................................................................................................................ |
|
20 |
|
service password-encryption............................................................................................... |
20 |
||
enable password ................................................................................................................ |
21 |
||
enable secret...................................................................................................................... |
22 |
||
disable................................................................................................................................ |
|
23 |
|
configure ............................................................................................................................ |
|
23 |
|
exit ..................................................................................................................................... |
|
|
24 |
end..................................................................................................................................... |
|
|
24 |
history................................................................................................................................. |
|
24 |
|
history clear........................................................................................................................ |
25 |
||
Chapter 3 |
IEEE 802.1Q VLAN Commands.................................................................. |
26 |
|
vlan |
.................................................................................................................................... |
|
26 |
interface vlan...................................................................................................................... |
26 |
||
name .................................................................................................................................. |
|
27 |
|
switchport mode ................................................................................................................. |
27 |
||
switchport access vlan........................................................................................................ |
28 |
||
switchport trunk allowed vlan.............................................................................................. |
28 |
||
switchport general allowed vlan .......................................................................................... |
29 |
||
switchport pvid.................................................................................................................... |
30 |
||
II
show vlan summary ............................................................................................................ |
30 |
|
show vlan brief.................................................................................................................... |
31 |
|
show vlan |
........................................................................................................................... |
31 |
Chapter 4 |
MAC - based VLAN Commands .................................................................... |
32 |
mac-vlan mac .......................................................................................................-address |
32 |
|
show mac- ....................................................................................................................vlan |
32 |
|
Chapter 5 .............................................................. |
Protocol - based VLAN Commands |
34 |
protocol-vlan ........................................................................................................template |
34 |
|
protocol-vlan ...............................................................................................................vlan |
35 |
|
protocol-vlan .............................................................................................................group |
35 |
|
show protocol ...............................................................................................-vlan template |
36 |
|
show protocol ......................................................................................................-vlan vlan |
36 |
|
Chapter 6 ............................................................................... |
Voice VLAN Commands |
37 |
voice vlan ........................................................................................................................... |
|
37 |
voice vlan ..........................................................................................................aging time |
37 |
|
voice vlan ................................................................................................................priority |
38 |
|
voice vlan ......................................................................................................mac-address |
38 |
|
switchport .................................................................................................voice vlan mode |
39 |
|
switchport ..............................................................................................voice vlan security |
40 |
|
show voice ..................................................................................................................vlan |
40 |
|
show voice .............................................................................................................vlan oui |
41 |
|
show voice .................................................................................................vlan switchport |
41 |
|
Chapter 7 ......................................................................................... |
GVRP Commands |
42 |
gvrp(global) ........................................................................................................................ |
42 |
|
gvrp(interface) .................................................................................................................... |
42 |
|
gvrp registration.................................................................................................................. |
43 |
|
gvrp timer ........................................................................................................................... |
|
43 |
show gvrp .................................................................................................................global |
44 |
|
show gvrp .............................................................................................................interface |
45 |
|
Chapter 8 ............................................................................. |
Etherchannel Commands |
46 |
channel-group .................................................................................................................... |
46 |
|
port-channel ..................................................................................................load-balance |
47 |
|
lacp system .............................................................................................................-priority |
47 |
|
lacp port-priority.................................................................................................................. |
48 |
|
|
III |
|
show etherchannel ............................................................................................................. |
49 |
|
show etherchannel load-balance ........................................................................................ |
49 |
|
show lacp |
........................................................................................................................... |
50 |
show lacp .................................................................................................................sys-id |
50 |
|
Chapter 9 ............................................................................. |
User Manage Commands |
51 |
user name ........................................................................................................(password) |
51 |
|
user name .............................................................................................................(secret) |
52 |
|
user access ..............................................................................................-control ip-based |
53 |
|
user access ..........................................................................................-control mac-based |
54 |
|
user access ...........................................................................................-control port-based |
54 |
|
user max-number ............................................................................................................... |
55 |
|
user idle-timeout................................................................................................................. |
56 |
|
line ..................................................................................................................................... |
|
56 |
password............................................................................................................................ |
|
57 |
login ................................................................................................................................... |
|
58 |
login local ........................................................................................................................... |
|
59 |
show user ........................................................................................................account-list |
59 |
|
show user ......................................................................................................configuration |
60 |
|
Chapter 10 ............................................................................. |
Binding Table Commands |
61 |
ip source binding ................................................................................................................ |
61 |
|
ip source binding .......................................................................................................index |
62 |
|
ip dhcp snooping ................................................................................................................ |
63 |
|
ip dhcp snooping ......................................................................................................global |
63 |
|
ip dhcp snooping ....................................................................................information option |
64 |
|
ip dhcp snooping .................................................................................information strategy |
65 |
|
ip dhcp snooping ..............................................................................information remote-id |
65 |
|
ip dhcp snooping ................................................................................information circuit-id |
66 |
|
ip dhcp snooping .........................................................................................................trust |
67 |
|
ip dhcp snooping ...............................................................................................mac-verify |
67 |
|
ip dhcp snooping ..................................................................................................limit rate |
68 |
|
ip dhcp snooping ....................................................................................................decline |
68 |
|
show ip source .......................................................................................................binding |
69 |
|
show ip dhcp .......................................................................................................snooping |
69 |
|
show ip dhcp .....................................................................................snooping information |
70 |
|
show ip dhcp ................................................................snooping interface gigabitEthernet |
70 |
|
Chapter 11 ......................................................................... |
ARP Inspection Commands |
72 |
|
IV |
|
ip arp inspection(global)...................................................................................................... |
72 |
ip arp inspection trust.......................................................................................................... |
72 |
ip arp inspection(interface).................................................................................................. |
73 |
ip arp inspection limit-rate................................................................................................... |
74 |
ip arp inspection recover..................................................................................................... |
74 |
show ip arp inspection........................................................................................................ |
75 |
show ip arp inspection interface.......................................................................................... |
75 |
show ip arp inspection statistics.......................................................................................... |
76 |
clear ip arp inspection statistics .......................................................................................... |
76 |
Chapter 12 DoS Defend Command................................................................................. |
77 |
ip dos-prevent..................................................................................................................... |
77 |
ip dos-prevent type............................................................................................................. |
77 |
show ip dos-prevent............................................................................................................ |
78 |
Chapter 13 IEEE 802.1X Commands.............................................................................. |
79 |
dot1x system-auth-control................................................................................................... |
79 |
dot1x auth-method.............................................................................................................. |
79 |
dot1x guest-vlan(global)...................................................................................................... |
80 |
dot1x quiet-period............................................................................................................... |
81 |
dot1x timeout...................................................................................................................... |
81 |
dot1x max-reauth-req ......................................................................................................... |
82 |
dot1x .................................................................................................................................. |
82 |
dot1x guest-vlan(interface) ................................................................................................. |
83 |
dot1x port-control................................................................................................................ |
83 |
dot1x port-method .............................................................................................................. |
84 |
radius ................................................................................................................................. |
85 |
radius server-account......................................................................................................... |
86 |
show dot1x global............................................................................................................... |
87 |
show dot1x interface........................................................................................................... |
87 |
show radius accounting ...................................................................................................... |
88 |
show radius authentication ................................................................................................. |
88 |
Chapter 14 System Log Commands ............................................................................... |
89 |
logging buffer...................................................................................................................... |
89 |
logging file flash.................................................................................................................. |
90 |
logging file flash frequency ................................................................................................. |
90 |
logging file flash level.......................................................................................................... |
91 |
clear logging....................................................................................................................... |
91 |
|
V |
logging host index............................................................................................................... |
92 |
|
show logging local-config.................................................................................................... |
93 |
|
show logging loghost.......................................................................................................... |
93 |
|
show logging buffer............................................................................................................. |
94 |
|
show logging flash.............................................................................................................. |
94 |
|
Chapter 15 |
SSH Commands ............................................................................................ |
96 |
ip ssh server....................................................................................................................... |
96 |
|
ip ssh version ..................................................................................................................... |
96 |
|
ip ssh timeout ..................................................................................................................... |
97 |
|
ip ssh max-client................................................................................................................. |
97 |
|
ip ssh download.................................................................................................................. |
98 |
|
show ip ssh......................................................................................................................... |
99 |
|
Chapter 16 |
SSL Commands ........................................................................................... |
100 |
ip http secure-server......................................................................................................... |
100 |
|
ip http secure-server download certificate......................................................................... |
100 |
|
ip http secure-server download key................................................................................... |
101 |
|
show ip http secure-server................................................................................................ |
102 |
|
Chapter 17 |
MAC Address Commands .......................................................................... |
103 |
mac address-table static................................................................................................... |
103 |
|
mac address-table aging-time........................................................................................... |
104 |
|
mac address-table filtering................................................................................................ |
104 |
|
mac address-table max-mac-count................................................................................... |
105 |
|
show mac address-table................................................................................................... |
106 |
|
show mac address-table aging-time.................................................................................. |
107 |
|
show mac address-table max-mac-count interface gigabitEthernet................................... |
107 |
|
show mac address-table interface gigabitEthernet............................................................ |
108 |
|
show mac address-table count ......................................................................................... |
108 |
|
show mac address-table address...................................................................................... |
109 |
|
show mac address-table vlan............................................................................................ |
109 |
|
Chapter 18 |
System Configuration Commands ............................................................ |
110 |
system-time manual........................................................................................................... |
110 |
|
system-time ntp ................................................................................................................. |
110 |
|
system-time dst predefined................................................................................................ |
112 |
|
system-time dst date.......................................................................................................... |
113 |
|
system-time dst recurring................................................................................................... |
114 |
|
|
VI |
|
hostname .......................................................................................................................... |
|
115 |
location.............................................................................................................................. |
|
115 |
contact-info........................................................................................................................ |
116 |
|
ip management-vlan.......................................................................................................... |
116 |
|
ip address.......................................................................................................................... |
|
117 |
ip address-alloc dhcp......................................................................................................... |
118 |
|
ip address-alloc bootp........................................................................................................ |
118 |
|
reset.................................................................................................................................. |
|
119 |
reboot................................................................................................................................ |
|
119 |
copy running-config startup-config..................................................................................... |
119 |
|
copy startup-config tftp...................................................................................................... |
120 |
|
copy tftp startup-config...................................................................................................... |
121 |
|
firmware upgrade.............................................................................................................. |
121 |
|
ping .................................................................................................................................. |
|
122 |
tracert............................................................................................................................... |
|
123 |
show system-time ............................................................................................................. |
124 |
|
show system-time dst ....................................................................................................... |
124 |
|
show system-time ntp ....................................................................................................... |
125 |
|
show system-info.............................................................................................................. |
125 |
|
show running-config.......................................................................................................... |
125 |
|
show cable-diagnostics interface ...................................................................................... |
126 |
|
Chapter 19 |
IPv6 Address Configuration Commands .................................................. |
127 |
ipv6 enable....................................................................................................................... |
127 |
|
ipv6 address autoconfig.................................................................................................... |
127 |
|
ipv6 address link-local ...................................................................................................... |
128 |
|
ipv6 address dhcp ............................................................................................................ |
128 |
|
ipv6 address ra................................................................................................................. |
129 |
|
ipv6 address eui-64 .......................................................................................................... |
130 |
|
ipv6 address..................................................................................................................... |
130 |
|
show ipv6 interface vlan.................................................................................................... |
131 |
|
Chapter 20 |
Ethernet Configuration Commands........................................................... |
132 |
interface gigabitEthernet................................................................................................... |
132 |
|
interface range gigabitEthernet......................................................................................... |
132 |
|
description........................................................................................................................ |
133 |
|
shutdown.......................................................................................................................... |
|
134 |
flow-control....................................................................................................................... |
134 |
|
|
VII |
|
media-type........................................................................................................................ |
135 |
|
duplex............................................................................................................................... |
|
135 |
speed ............................................................................................................................... |
|
136 |
storm-control broadcast.................................................................................................... |
136 |
|
storm-control multicast...................................................................................................... |
137 |
|
storm-control unicast ........................................................................................................ |
138 |
|
bandwidth......................................................................................................................... |
|
139 |
clear counters................................................................................................................... |
140 |
|
show interface status........................................................................................................ |
140 |
|
show interface counters.................................................................................................... |
141 |
|
show interface description ................................................................................................ |
141 |
|
show interface flowcontrol................................................................................................. |
142 |
|
show interface configuration ............................................................................................. |
142 |
|
show storm-control ........................................................................................................... |
143 |
|
show bandwidth................................................................................................................ |
143 |
|
Chapter 21 |
QoS Commands........................................................................................... |
145 |
qos ................................................................................................................................... |
|
145 |
qos dscp........................................................................................................................... |
|
146 |
qos queue cos-map.......................................................................................................... |
146 |
|
qos queue dscp-map........................................................................................................ |
147 |
|
qos queue mode............................................................................................................... |
148 |
|
show qos interface............................................................................................................ |
149 |
|
show qos cos-map............................................................................................................ |
150 |
|
show qos dscp-map.......................................................................................................... |
150 |
|
show qos queue mode...................................................................................................... |
151 |
|
show qos status................................................................................................................ |
151 |
|
Chapter 22 |
Port Mirror Commands................................................................................ |
152 |
monitor session destination interface................................................................................ |
152 |
|
monitor session source interface ...................................................................................... |
153 |
|
show monitor session ....................................................................................................... |
154 |
|
Chapter 23 |
Port Isolation Commands ........................................................................... |
155 |
port isolation..................................................................................................................... |
155 |
|
show port isolation interface ............................................................................................. |
156 |
|
Chapter 24 |
Loopback Detection Commands ............................................................... |
157 |
loopback-detection(global)................................................................................................ |
157 |
|
|
VIII |
|
loopback-detection interval............................................................................................... |
157 |
|
loopback-detection recovery-time ..................................................................................... |
158 |
|
loopback-detection(interface)............................................................................................ |
158 |
|
loopback-detection config................................................................................................. |
159 |
|
loopback-detection recover............................................................................................... |
160 |
|
show loopback-detection global........................................................................................ |
160 |
|
show loopback-detection interface.................................................................................... |
161 |
|
Chapter 25 |
PoE Commands ........................................................................................... |
162 |
power inline consumption (global)..................................................................................... |
162 |
|
power inline disconnect-method........................................................................................ |
162 |
|
power profile..................................................................................................................... |
163 |
|
power time-range.............................................................................................................. |
164 |
|
power holiday ................................................................................................................... |
165 |
|
absolute............................................................................................................................ |
|
165 |
periodic............................................................................................................................. |
|
166 |
holiday.............................................................................................................................. |
|
167 |
power inline consumption(interface).................................................................................. |
168 |
|
power inline priority........................................................................................................... |
168 |
|
power inline supply........................................................................................................... |
169 |
|
power inline profile............................................................................................................ |
170 |
|
power inline time-range .................................................................................................... |
170 |
|
show power inline ............................................................................................................. |
171 |
|
show power inline configuration interface.......................................................................... |
171 |
|
show power inline information interface ............................................................................ |
172 |
|
show power profile............................................................................................................ |
172 |
|
show power holiday .......................................................................................................... |
173 |
|
show power time-range .................................................................................................... |
173 |
|
Chapter 26 |
ACL Commands ........................................................................................... |
174 |
time-range........................................................................................................................ |
174 |
|
absolute............................................................................................................................ |
|
174 |
periodic............................................................................................................................. |
|
175 |
holiday.............................................................................................................................. |
|
176 |
holiday(global).................................................................................................................. |
176 |
|
access-list create.............................................................................................................. |
177 |
|
mac access-list................................................................................................................. |
178 |
|
access-list standard.......................................................................................................... |
178 |
|
|
|
IX |
access-list extended......................................................................................................... |
179 |
rule................................................................................................................................... |
181 |
access-list policy name..................................................................................................... |
182 |
access-list policy action .................................................................................................... |
182 |
redirect interface............................................................................................................... |
183 |
redirect vlan...................................................................................................................... |
184 |
s-condition........................................................................................................................ |
184 |
s-mirror............................................................................................................................. |
185 |
qos-remark....................................................................................................................... |
185 |
access-list bind(interface)................................................................................................. |
186 |
access-list bind(vlan)........................................................................................................ |
187 |
show time-range............................................................................................................... |
187 |
show holiday..................................................................................................................... |
188 |
show access-list ............................................................................................................... |
188 |
show access-list policy ..................................................................................................... |
188 |
show access-list bind........................................................................................................ |
189 |
Chapter 27 MSTP Commands........................................................................................ |
190 |
spanning-tree(global)........................................................................................................ |
190 |
spanning-tree(interface).................................................................................................... |
190 |
spanning-tree common-config........................................................................................... |
191 |
spanning-tree mode.......................................................................................................... |
192 |
spanning-tree mst configuration........................................................................................ |
193 |
instance............................................................................................................................ |
193 |
name ................................................................................................................................ |
194 |
revision............................................................................................................................. |
194 |
spanning-tree mst instance............................................................................................... |
195 |
spanning-tree mst............................................................................................................. |
196 |
spanning-tree priority........................................................................................................ |
196 |
spanning-tree tc-defend.................................................................................................... |
197 |
spanning-tree timer........................................................................................................... |
198 |
spanning-tree hold-count.................................................................................................. |
199 |
spanning-tree max-hops ................................................................................................... |
199 |
spanning-tree bpdufilter.................................................................................................... |
200 |
spanning-tree bpduguard.................................................................................................. |
200 |
spanning-tree guard loop.................................................................................................. |
201 |
spanning-tree guard root................................................................................................... |
202 |
spanning-tree guard tc...................................................................................................... |
202 |
|
X |
spanning-tree mcheck ...................................................................................................... |
203 |
|
show spanning-tree active................................................................................................ |
203 |
|
show spanning-tree bridge................................................................................................ |
204 |
|
show spanning-tree interface............................................................................................ |
204 |
|
show spanning-tree interface-security............................................................................... |
205 |
|
show spanning-tree mst.................................................................................................... |
206 |
|
Chapter 28 |
IGMP Snooping Commands ...................................................................... |
207 |
ip igmp snooping(global)................................................................................................... |
207 |
|
ip igmp snooping(interface)............................................................................................... |
207 |
|
ip igmp snooping immediate-leave.................................................................................... |
208 |
|
ip igmp snooping drop-unknown ....................................................................................... |
208 |
|
ip igmp snooping vlan-config ............................................................................................ |
209 |
|
ip igmp snooping multi-vlan-config.................................................................................... |
210 |
|
ip igmp snooping filter add-id............................................................................................. |
211 |
|
ip igmp snooping filter(global)........................................................................................... |
212 |
|
ip igmp snooping filter(interface)....................................................................................... |
213 |
|
ip igmp snooping filter maxgroup ...................................................................................... |
213 |
|
ip igmp snooping filter mode............................................................................................. |
214 |
|
show ip igmp snooping ..................................................................................................... |
214 |
|
show ip igmp snooping interface....................................................................................... |
215 |
|
show ip igmp snooping vlan.............................................................................................. |
216 |
|
show ip igmp snooping multi-vlan ..................................................................................... |
216 |
|
show ip igmp snooping groups.......................................................................................... |
217 |
|
show ip igmp snooping filter.............................................................................................. |
218 |
|
Chapter 29 |
MLD Snooping Commands ........................................................................ |
219 |
ipv6 mld snooping............................................................................................................. |
219 |
|
ipv6 mld snooping router-aging-time................................................................................. |
219 |
|
ipv6 mld snooping member-aging-time ............................................................................. |
220 |
|
ipv6 mld snooping report-suppression .............................................................................. |
220 |
|
ipv6 mld snooping unknown-filter...................................................................................... |
221 |
|
ipv6 mld snooping last-listener query-inteval..................................................................... |
221 |
|
ipv6 mld snooping last-listener query-count ...................................................................... |
222 |
|
ipv6 mld snooping multicast-vlan ...................................................................................... |
222 |
|
ipv6 mld snooping multicast-vlan vlan-id........................................................................... |
223 |
|
ipv6 mld snooping vlan ..................................................................................................... |
223 |
|
ipv6 mld snooping vlan router-aging-time.......................................................................... |
224 |
|
|
|
XI |
ipv6 mld snooping vlan member-aging-time...................................................................... |
224 |
ipv6 mld snooping vlan immediate-leave........................................................................... |
225 |
ipv6 mld snooping vlan mrouter........................................................................................ |
225 |
ipv6 mld snooping vlan static............................................................................................ |
226 |
ipv6 mld snooping querier vlan ......................................................................................... |
226 |
ipv6 mld snooping querier vlan max-response-time .......................................................... |
227 |
ipv6 mld snooping querier vlan query-interval................................................................... |
228 |
ipv6 mld snooping querier vlan query-source.................................................................... |
228 |
ipv6 mld snooping filter(global) ......................................................................................... |
229 |
ipv6 mld snooping filter(interface) ..................................................................................... |
229 |
ipv6 mld snooping filter-mode........................................................................................... |
230 |
ipv6 mld snooping filter-id................................................................................................. |
230 |
ipv6 mld snooping max-group........................................................................................... |
231 |
clear ipv6 mld snooping statistics...................................................................................... |
231 |
show ipv6 mld snooping.................................................................................................... |
232 |
show ipv6 mld snooping vlan............................................................................................ |
232 |
show ipv6 mld snooping static-mcast................................................................................ |
233 |
show ipv6 mld snooping group.......................................................................................... |
233 |
show ipv6 mld snooping filter............................................................................................ |
233 |
show ipv6 mld snooping interface..................................................................................... |
234 |
show ipv6 mld snooping interface filter.............................................................................. |
234 |
show ipv6 mld snooping querier........................................................................................ |
235 |
show ipv6 mld snooping statistics..................................................................................... |
235 |
Chapter 30 SNMP Commands ....................................................................................... |
236 |
snmp-server ..................................................................................................................... |
236 |
snmp-server view ............................................................................................................. |
236 |
snmp-server group ........................................................................................................... |
237 |
snmp-server user.............................................................................................................. |
238 |
snmp-server community.................................................................................................... |
240 |
snmp-server host.............................................................................................................. |
241 |
snmp-server engineID ...................................................................................................... |
242 |
snmp-server traps snmp ................................................................................................... |
243 |
snmp-server traps link-status............................................................................................ |
244 |
snmp-server traps............................................................................................................. |
244 |
snmp-server traps mac..................................................................................................... |
245 |
snmp-server traps vlan ..................................................................................................... |
246 |
rmon history...................................................................................................................... |
247 |
XII |
|
rmon event ....................................................................................................................... |
248 |
|
rmon alarm....................................................................................................................... |
249 |
|
show snmp-server ............................................................................................................ |
250 |
|
show snmp-server view .................................................................................................... |
251 |
|
show snmp-server group .................................................................................................. |
251 |
|
show snmp-server user .................................................................................................... |
252 |
|
show snmp-server community .......................................................................................... |
252 |
|
show snmp-server host..................................................................................................... |
252 |
|
show snmp-server engineID ............................................................................................. |
253 |
|
show rmon history ............................................................................................................ |
253 |
|
show rmon event .............................................................................................................. |
254 |
|
show rmon alarm.............................................................................................................. |
254 |
|
Chapter 31 |
LLDP Commands......................................................................................... |
256 |
lldp ................................................................................................................................... |
|
256 |
lldp hold-multiplier............................................................................................................. |
256 |
|
lldp timer........................................................................................................................... |
|
257 |
lldp med-fast-count........................................................................................................... |
258 |
|
lldp receive....................................................................................................................... |
259 |
|
lldp transmit...................................................................................................................... |
259 |
|
lldp snmp-trap................................................................................................................... |
260 |
|
lldp tlv-select..................................................................................................................... |
260 |
|
lldp med-location .............................................................................................................. |
261 |
|
lldp med-status................................................................................................................. |
262 |
|
lldp med-tlv-select............................................................................................................. |
262 |
|
show lldp .......................................................................................................................... |
|
263 |
show lldp interface............................................................................................................ |
263 |
|
show lldp local-information interface ................................................................................. |
264 |
|
show lldp neighbor-information interface........................................................................... |
264 |
|
show lldp traffic interface .................................................................................................. |
265 |
|
Chapter 32 |
Cluster Commands ...................................................................................... |
266 |
cluster ndp........................................................................................................................ |
266 |
|
cluster ntdp....................................................................................................................... |
267 |
|
cluster explore.................................................................................................................. |
268 |
|
cluster............................................................................................................................... |
|
269 |
cluster candidate .............................................................................................................. |
269 |
|
cluster individual............................................................................................................... |
270 |
|
|
|
XIII |
show cluster ndp............................................................................................................... |
270 |
show cluster ntdp.............................................................................................................. |
271 |
show cluster neighbour..................................................................................................... |
271 |
show cluster manage role................................................................................................. |
272 |
XIV
Preface
This Guide is intended for network administrator to provide referenced information about CLI (Command Line Interface). The switch mentioned in this Guide stands for TL-SG3210/TL-SG3216/TL-SG3424/TL-SG3424P without any explanation. The commands in this guilde apply to these four models if not specially noted, and TL-SG3424 is taken as an example model in the example commands.
Overviewof this Guide
Chapter 1: Using the CLI
Provide information about how to use the CLI, CLI Command Modes, Security Levels and some Conventions.
Chapter 2: User Interface
Provide information about the commands used to switch between five CLI Command Modes.
Chapter 3: IEEE 802.1Q VLAN Commands
Provide information about the commands used for configuring IEEE 802.1Q VLAN.
Chapter 4: MAC-Based VLAN Commands
Provide information about the commands used for configuring MAC-Based VLAN.
Chapter 5: Protocol-Based VLAN Commands
Provide information about the commands used for configuring Protocol-Based VLAN.
Chapter 6: Voice VLAN Commands
Provide information about the commands used for configuring Voice VLAN.
Chapter 7: GVRP Commands
Provide information about the commands used for configuring GVRP (GARP VLAN registration protocol).
Chapter 8: Etherchannel Commands
Provide information about the commands used for configuring LAG (Link Aggregation Group) and LACP (Link Aggregation Control Protocol).
Chapter 9: User Manage Commands
Provide information about the commands used for user management.
Chapter 10: Binding Table Commands
Provide information about the commands used for binding the IP address, MAC address, VLAN and the connected Port number of the Host together. Besides it also provide information about the commands used for monitoring the process of the Host obtaining the IP address from DHCP server,
1
and record the IP address, MAC address, VLAN and the connected Port number of the Host for automatic binding.
Chapter 11:ARP Inspection Commands
Provide information about the commands used for protecting the switch from the ARP cheating or ARP Attack.
Chapter 12: DoS Defend Command
Provide information about the commands used for DoS defend and detecting the DoS attack.
Chapter 13: IEEE 802.1X Commands
Provide information about the commands used for configuring IEEE 802.1X function.
Chapter 14: System Log Commands
Provide information about the commands used for configuring system log.
Chapter 15: SSH Commands
Provide information about the commands used for configuring and managing SSH (Security Shell).
Chapter 16: SSL Commands
Provide information about the commands used for configuring and managing SSL (Secure Sockets Layer).
Chapter 17: MAC Address Commands
Provide information about the commands used for Address configuration.
Chapter 18: System Configuration Commands
Provide information about the commands used for configuring the System information and System IP, reboot and reset the switch, upgrade the switch system and commands used for cable test.
Chapter 19: IPv6 Address Configuration Commands
Provide information about the commands used for configuring the System IPv6 addresses.
Chapter 20: Ethernet Configuration Commands
Provide information about the commands used for configuring the Bandwidth Control, Negotiation Mode, and Storm Control for Ethernet ports.
Chapter 21: QoS Commands
Provide information about the commands used for configuring the QoS function.
Chapter 22: Port Mirror Commands
Provide information about the commands used for configuring the Port Mirror function.
Chapter 23: Port Isolation Commands
Provide information about the commands used for configuring the Port Isolation function.
Chapter 24: Loopback Detection Commands
Provide information about the commands used for configuring the Loopback Detection function.
2
Chapter 25: PoE Commands
Provide information about the commands used for configuring PoE function.
Chapter 26:ACL Commands
Provide information about the commands used for configuring the ACL (Access Control List).
Chapter 27: MSTP Commands
Provide information about the commands used for configuring the MSTP (Multiple Spanning Tree Protocol).
Chapter 28: IGMP Snooping Commands
Provide information about the commands used for configuring the IGMP Snooping (Internet Group Management Protocol Snooping).
Chapter 29: MLD Snooping Commands
Provide information about the commands used for configuring the MLD Snooping (Multicast Listener Discovery Snooping).
Chapter 30: SNMP Commands
Provide information about the commands used for configuring the SNMP (Simple Network Management Protocol) functions.
Chapter 31: LLDP Commands
Provide information about the commands used for configuring LLDP function.
Chapter 32: Cluster Commands
Provide information about the commands used for configuring the Cluster Management function.
3

Chapter 1 Using the CLI
1.1 Accessing the CLI
You can log on to the switch and access the CLI by the following two methods:
1.Log on to the switch by the console port on the switch.
2.Log on to the switch remotely by a Telnet or SSH connection through an Ethernet port.
1.1.1Logon by a console port
To log on to the switch by the console port on the switch, please take the following steps:
1.Connect the PCs or Terminals to the console port on the switch by a provided cable.
2.Click Start →All Programs →Accessories→Communications →Hyper Terminal to open the Hyper Terminal as the Figure 1-1 shown.
Figure 1-1 Open Hyper Terminal
4
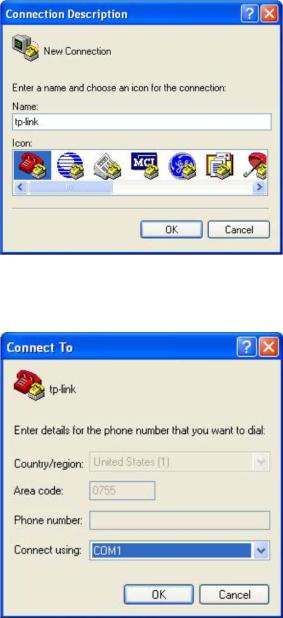
3.The Connection Description Window will prompt as Figure 1-2 shown. Enter a name into the Name field and click OK.
Figure 1-2 Connection Description
4.Select the port to connect in Figure 1-3, and click OK.
Figure 1-3 Select the port to connect
5
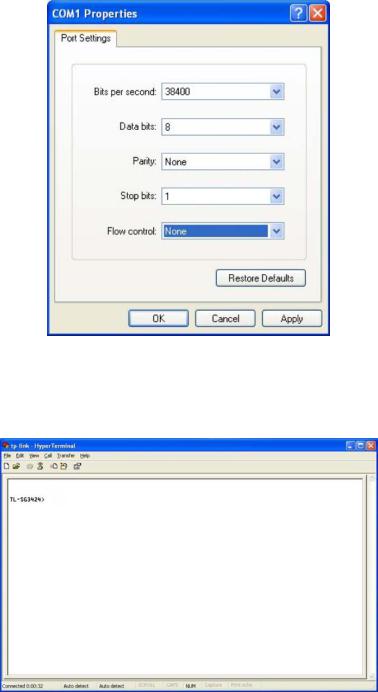
5.Configure the port selected in the step above as the following Figure 1-4 shown. Configure Bits per second as 38400, Data bits as 8, Parity as None, Stop bits as 1,
Flow control as None, and then click OK.
Figure 1-4 Port Settings
6.The DOS prompt” TL-SG3424>” will appear after pressing the Enter button as Figure 1-5 shown. It indicates that you can use the CLI now.
Figure 1-5 Log in the Switch
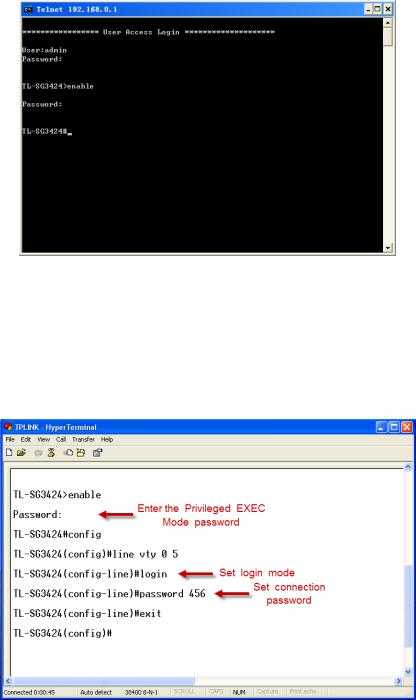
1.1.2Configuring the Privileged EXEC Mode Password
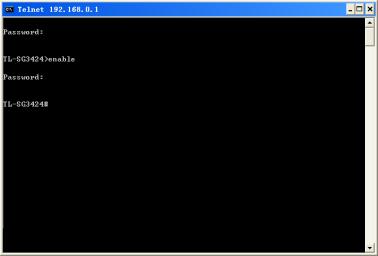
To configure the switch remotely by a Telnet or SSH connection, please set a password for entering the Privileged EXEC Mode through the console connection first. Follow the steps in 1.1.1 Logon by a console port to log on to the switch, and then follow the steps shown in Figure 1-6 to configure the Privileged EXEC Mode password.
6

Figure 1-6 Configure the Privileged EXEC Mode Password
1.1.3Logon by Telnet
To successfully create Telnet connection, firstly CLI commands about configuring Telnet login mode, login authentication information and Privileged EXEC Mode password should be configured through Console connection.
Telnet login has the following two modes, you can choose one according to your needs:
Login local Mode: It requires username and password, which are both admin by default.
Login Mode: It requires no username and password, but a connection password is required.
Note:
Before Telnet login, you are required to configure Telnet login mode and login authentication information through console connection.
Login Local Mode
Firstly, enter the Privileged EXEC Mode password set in 1.1.2 Configuring the Priviledged EXEC Mode Password and configure the Telnet login mode as “login local” in the prompted DOS screen shown in Figure 1-7.
Figure 1-7 Configure login local mode
7

Now, you can logon by Telnet in login local mode.
1.Make sure the switch and the PC are in the same LAN. Click Start → Run to open the Run window, and type cmd in the prompt Run window as Figure 1-8 and click OK.
Figure 1-8 Run Window
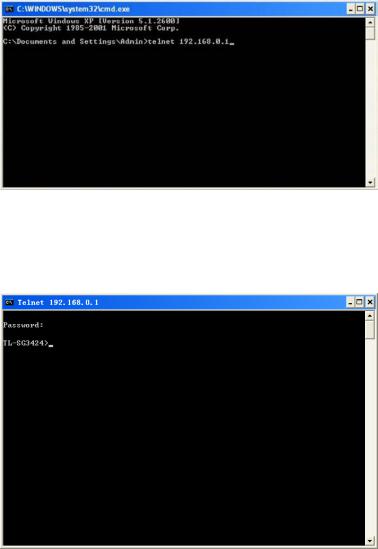
2.Open Telnet and type telnet 192.168.0.1 in the command prompt shown as Figure 1-9, and press the Enter button.
Figure 1-9 Connecting to the Switch
3.Type the default user name and password admin/admin, then press the Enter button so as to enter User EXEC Mode.
Figure 1-10 Enter into the User EXEC Mode
Now you can manage your switch with CLI commands through Telnet connection.
8
4.Type enable command to enter Privileged EXEC Mode. A password that you have set through Console port connection is required. Here the password is set as 123.
Figure 1-11 Enter into the Privileged EXEC Mode
Login Mode
Firstly enter the Privileged EXEC Mode password set in 1.1.2 Configuring the Priviledged EXEC Mode Password and configure the Telnet login mode as “login” and the connection password and 456 in the prompted DOS screen shown in Figure 1-12.
Figure 1-12 Configure login mode
9
Now, you can logon by Telnet in login mode:
1.Open Telnet and type telnet 192.168.0.1 in the command prompt shown as Figure 1-13, and press the Enter button.
Figure 1-13 Connecting to the Switch
2.You are prompted to enter the connection password 456 you have set through Console port connection, and then you are in User EXEC Mode.
Figure 1-14 Enter into the User EXEC Mode
10
3.When entering enable command to access Privileged EXEC Mode, you are required to give the password 123 you have set through Console port connection.
Figure 1-15 Enter into the Privileged EXEC Mode
Now you can manage your switch with CLI commands through Telnet connection.
Note:
You can refer to Chapter 9 User Manage Commands for detailed commands information of the Telnet connection configuration.
1.1.4Logon by SSH
To log on by SSH, a Putty client software is recommended. There are two authentication modes to set up an SSH connection:
Password Authentication Mode: It requires username and password, which are both admin by default.
Key Authentication Mode: It requires a public key for the switch and a private key for the SSH client software. You can generate the public key and the private key through Putty Key Generator.
11
Note:
Before SSH login, please follow the steps shown in Figure 1-16 to enable the SSH function through console connection.
Figure 1-16 Enable SSH function
Password Authentication Mode
1.Open the software to log on to the interface of PuTTY. Enter the IP address of the switch into Host Name field; keep the default value 22 in the Port field; select SSH as the Connection type.
Figure 1-17 SSH Connection Config
12
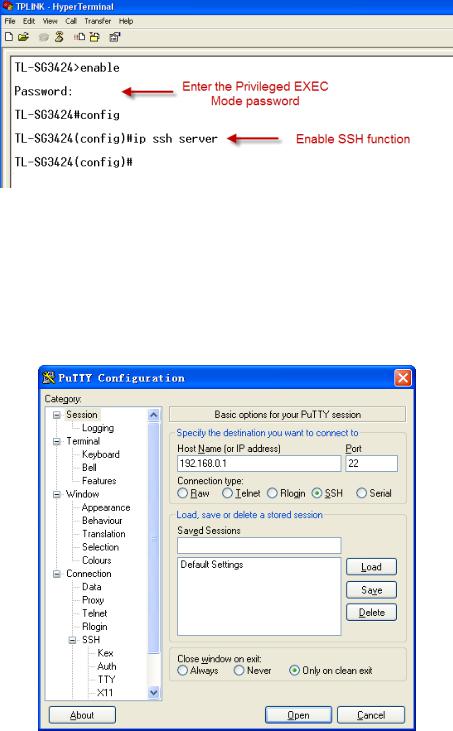
2.Click the Open button in the above figure to log on to the switch. Enter the login user name and password to log on the switch, and then enter the Privileged EXEC Mode password, so you can continue to configure the switch.
Figure 1-18 Log on the Switch
Key Authentication Mode
1.Select the key type and key length, and generate SSH key.
Figure 1-19 Generate SSH Key
 Note:
Note:
1.The key length is in the range of 256 to 3072 bits.
2.During the key generation, randomly moving the mouse quickly can accelerate the key generation.
13
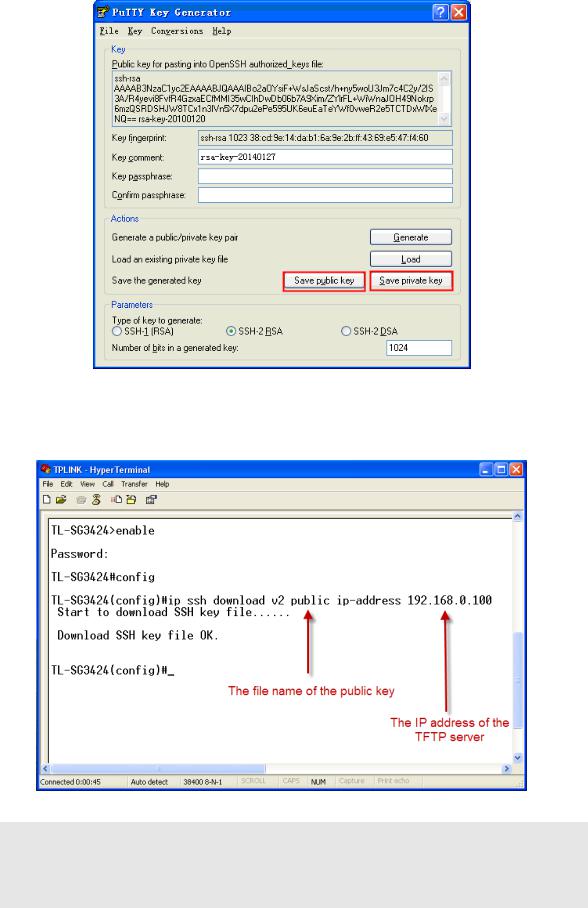
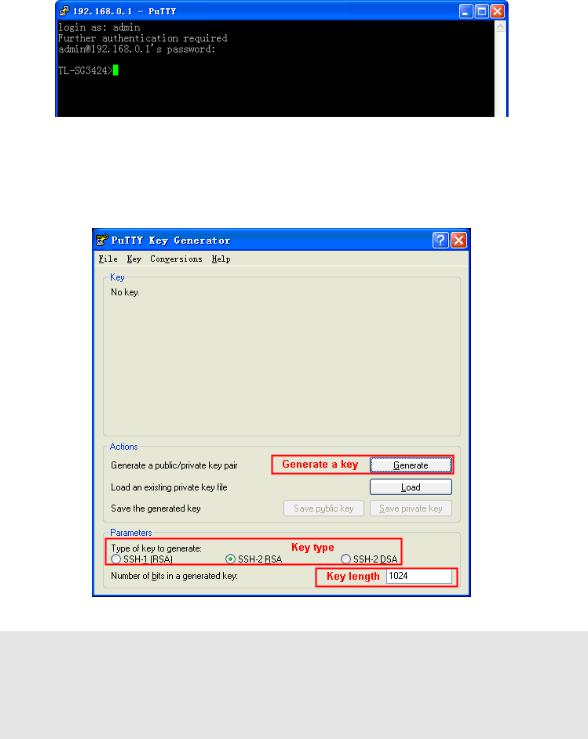
2.After the key is successfully generated, please save the public key and private key to a TFTP server.
Figure 1-20 Save the Generated Key
3.Log on to the switch by the console port, and download the public key file from the TFTP server to the switch, as the following figure shows:
Figure 1-21 Download the Public Key
 Note:
Note:
1.The key type should accord with the type of the key file.
2.The SSH key downloading can not be interrupted.
14
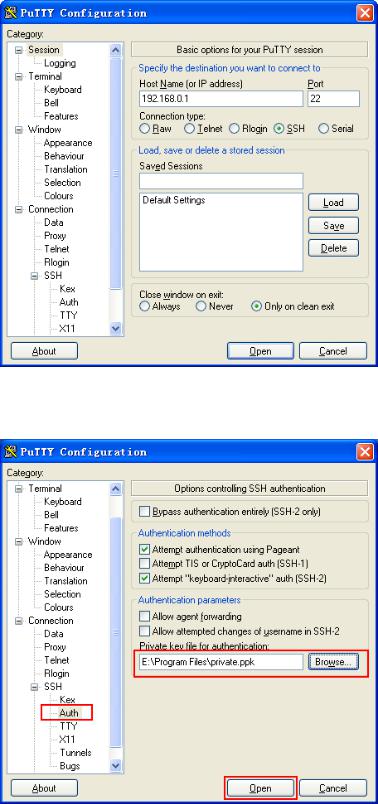
4.After the public key is loaded, please log on to the interface of PuTTY and enter the IP address for login.
Figure 1-22 SSH Connection Config
5.Click Browse to load the private key file to SSH client software and click Open.
Figure 1-23 Load the Private Key
15
 Loading...
Loading...