TP-Link TL-SL3428 CLI Reference Guide
TL-SL3428
JetStream L2 Managed Switch
Rev: 1.1.0
1910010622

TL-SL3428 JetStream L2 Managed Switch CLI Guide
COPYRIGHT & TRADEMARKS
Specifications are subject to change without notice.  is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
is a registered trademark of TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or registered trademarks of their respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make any derivative such as translation, transformation, or adaptation without permission from TP-LINK TECHNOLOGIES CO., LTD. Copyright © 2012 TP-LINK TECHNOLOGIES CO., LTD. All rights reserved.
http://www.tp-link.com
i

TL-SL3428 JetStream L2 Managed Switch CLI Guide
CONTENTS
Preface |
.............................................................................................................. |
1 |
|
Chapter 1 Using the CLI ....................................................................................... |
4 |
||
1.1 |
Accessing the CLI ........................................................................................................... |
4 |
|
|
1.1.1 Logon by a console port ....................................................................................... |
4 |
|
|
1.1.2 |
Logon by Telnet .................................................................................................... |
6 |
1.2 |
CLI Command Modes ..................................................................................................... |
8 |
|
1.3 |
Security Levels ............................................................................................................. |
11 |
|
1.4 |
Conventions.................................................................................................................. |
11 |
|
|
1.4.1 |
Format Conventions ........................................................................................... |
11 |
|
1.4.2 |
Special Characters.............................................................................................. |
11 |
|
1.4.3 |
Parameter Format............................................................................................... |
12 |
Chapter 2 |
User Interface .................................................................................... |
13 |
|
enable.................................................................................................................................... |
|
13 |
|
enable password ................................................................................................................... |
13 |
||
disable ................................................................................................................................... |
|
14 |
|
configure................................................................................................................................ |
|
14 |
|
exit......................................................................................................................................... |
|
|
14 |
end ........................................................................................................................................ |
|
|
15 |
Chapter 3 IEEE 802.1Q VLAN Commands ........................................................ |
16 |
||
vlan database ........................................................................................................................ |
16 |
||
vlan........................................................................................................................................ |
|
|
16 |
interface vlan ......................................................................................................................... |
17 |
||
description ............................................................................................................................. |
17 |
||
switchport type ...................................................................................................................... |
18 |
||
switchport allowed vlan.......................................................................................................... |
18 |
||
switchport pvid....................................................................................................................... |
19 |
||
switchport general egress-rule .............................................................................................. |
19 |
||
show vlan .............................................................................................................................. |
|
20 |
|
show interface switchport ...................................................................................................... |
20 |
||
Chapter 4 Protocol VLAN Commands............................................................... |
21 |
||
protocol-vlan template ........................................................................................................... |
21 |
||
protocol-vlan vlan .................................................................................................................. |
21 |
||
protocol-vlan interface ........................................................................................................... |
22 |
||
ii

|
TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
show protocol-vlan template.................................................................................................. |
23 |
|
show protocol-vlan vlan ......................................................................................................... |
23 |
|
show protocol-vlan interface.................................................................................................. |
23 |
|
Chapter 5 Voice VLAN Commands.................................................................... |
25 |
|
voice-vlan enable .................................................................................................................. |
25 |
|
voice-vlan aging-time ............................................................................................................ |
25 |
|
voice-vlan oui ........................................................................................................................ |
26 |
|
switchport voice-vlan mode ................................................................................................... |
27 |
|
show voice-vlan global .......................................................................................................... |
27 |
|
show voice-vlan oui ............................................................................................................... |
28 |
|
show voice-vlan switchport.................................................................................................... |
28 |
|
Chapter 6 |
GVRP Commands.............................................................................. |
29 |
gvrp ....................................................................................................................................... |
|
29 |
gvrp (interface) ...................................................................................................................... |
29 |
|
gvrp registration..................................................................................................................... |
30 |
|
gvrp timer .............................................................................................................................. |
|
30 |
show gvrp global ................................................................................................................... |
31 |
|
show gvrp interface ............................................................................................................... |
32 |
|
Chapter 7 |
LAG Commands ................................................................................ |
33 |
interface link-aggregation ...................................................................................................... |
33 |
|
interface range link-aggregation ............................................................................................ |
33 |
|
link-aggregation..................................................................................................................... |
34 |
|
link-aggregation hash-algorithm ............................................................................................ |
35 |
|
description ............................................................................................................................. |
35 |
|
show interface link-aggregation............................................................................................. |
36 |
|
Chapter 8 |
LACP Commands .............................................................................. |
37 |
lacp system-priority ............................................................................................................... |
37 |
|
lacp (interface)....................................................................................................................... |
37 |
|
lacp admin-key ...................................................................................................................... |
38 |
|
lacp port-priority..................................................................................................................... |
38 |
|
show lacp interface................................................................................................................ |
39 |
|
show lacp system-priority ...................................................................................................... |
39 |
|
Chapter 9 User Manage Commands.................................................................. |
41 |
|
user add ................................................................................................................................ |
|
41 |
user remove .......................................................................................................................... |
42 |
|
|
iii |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
user modify status ................................................................................................................. |
42 |
user modify type .................................................................................................................... |
43 |
user modify password............................................................................................................ |
43 |
user access-control disable ................................................................................................... |
44 |
user access-control ip-based................................................................................................. |
44 |
user access-control mac-based............................................................................................. |
45 |
user access-control port-based ............................................................................................. |
45 |
user max-number .................................................................................................................. |
46 |
user idle-timeout.................................................................................................................... |
46 |
show user account-list........................................................................................................... |
47 |
show user configuration......................................................................................................... |
47 |
Chapter 10 Binding Table Commands................................................................. |
49 |
binding-table user-bind .......................................................................................................... |
49 |
binding-table remove ............................................................................................................. |
50 |
dhcp-snooping....................................................................................................................... |
50 |
dhcp-snooping global ............................................................................................................ |
51 |
dhcp-snooping information enable ........................................................................................ |
52 |
dhcp-snooping information strategy ...................................................................................... |
52 |
dhcp-snooping information user-defined ............................................................................... |
53 |
dhcp-snooping information remote-id .................................................................................... |
53 |
dhcp-snooping information circuit-id...................................................................................... |
54 |
dhcp-snooping trusted........................................................................................................... |
54 |
dhcp-snooping mac-verify ..................................................................................................... |
55 |
dhcp-snooping rate-limit ........................................................................................................ |
55 |
dhcp-snooping decline........................................................................................................... |
56 |
show binding-table................................................................................................................. |
56 |
show dhcp-snooping global ................................................................................................... |
57 |
show dhcp-snooping information........................................................................................... |
57 |
show dhcp-snooping interface............................................................................................... |
58 |
Chapter 11 ARP Inspection Commands.............................................................. |
59 |
arp detection (global)............................................................................................................. |
59 |
arp detection trust-port .......................................................................................................... |
59 |
arp detection (interface)......................................................................................................... |
60 |
arp detection limit-rate........................................................................................................... |
60 |
arp detection recover............................................................................................................. |
61 |
show arp detection global...................................................................................................... |
62 |
show arp detection interface.................................................................................................. |
62 |
iv |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
show arp detection statistic ................................................................................................... |
63 |
show arp detection statistic reset .......................................................................................... |
63 |
Chapter 12 DoS Defend Command...................................................................... |
64 |
dos-prevent ........................................................................................................................... |
64 |
dos-prevent type.................................................................................................................... |
64 |
show dos-prevent .................................................................................................................. |
65 |
Chapter 13 IEEE 802.1X Commands ................................................................... |
66 |
dot1x...................................................................................................................................... |
66 |
dot1x auth-method ................................................................................................................ |
66 |
dot1x guest-vlan .................................................................................................................... |
67 |
dot1x quiet-period.................................................................................................................. |
68 |
dot1x timer............................................................................................................................. |
68 |
dot1x retry ............................................................................................................................. |
69 |
dot1x...................................................................................................................................... |
69 |
dot1x guest-vlan .................................................................................................................... |
70 |
dot1x port-control .................................................................................................................. |
70 |
dot1x port-method ................................................................................................................. |
71 |
radius authentication primary-ip ............................................................................................ |
72 |
radius authentication secondary-ip........................................................................................ |
73 |
radius authentication port ...................................................................................................... |
73 |
radius authentication key....................................................................................................... |
74 |
radius accounting enable....................................................................................................... |
74 |
radius accounting primary-ip ................................................................................................. |
75 |
radius accounting secondary-ip............................................................................................. |
75 |
radius accounting port ........................................................................................................... |
76 |
radius accounting key............................................................................................................ |
76 |
radius response-timeout ........................................................................................................ |
77 |
show dot1x global.................................................................................................................. |
78 |
show dot1x interface ............................................................................................................. |
78 |
show radius authentication .................................................................................................... |
79 |
show radius accounting......................................................................................................... |
79 |
Chapter 14 Log Commands ................................................................................. |
80 |
logging local buffer ................................................................................................................ |
80 |
logging local flash.................................................................................................................. |
81 |
logging clear .......................................................................................................................... |
81 |
logging loghost ...................................................................................................................... |
82 |
v |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
show logging local-config ...................................................................................................... |
83 |
show logging loghost............................................................................................................. |
83 |
show logging buffer ............................................................................................................... |
84 |
show logging flash................................................................................................................. |
84 |
Chapter 15 SSH Commands................................................................................. |
86 |
ssh server enable .................................................................................................................. |
86 |
ssh version ............................................................................................................................ |
86 |
ssh idle-timeout ..................................................................................................................... |
87 |
ssh max-client ....................................................................................................................... |
87 |
ssh download ........................................................................................................................ |
88 |
show ssh ............................................................................................................................... |
88 |
Chapter 16 SSL Commands ................................................................................. |
90 |
ssl enable .............................................................................................................................. |
90 |
ssl download certificate ......................................................................................................... |
90 |
ssl download key ................................................................................................................... |
91 |
show ssl................................................................................................................................. |
91 |
Chapter 17 Address Commands.......................................................................... |
93 |
bridge address port-security .................................................................................................. |
93 |
bridge address static ............................................................................................................. |
94 |
bridge aging-time................................................................................................................... |
95 |
bridge address filtering .......................................................................................................... |
95 |
show bridge port-security ...................................................................................................... |
96 |
show bridge address ............................................................................................................. |
96 |
show bridge aging-time ......................................................................................................... |
97 |
Chapter 18 System Commands ........................................................................... |
98 |
system-descript ..................................................................................................................... |
98 |
system-time gmt .................................................................................................................... |
98 |
system-time manual .............................................................................................................. |
99 |
system-time dst ..................................................................................................................... |
99 |
ip address............................................................................................................................ |
100 |
ip management-vlan............................................................................................................ |
101 |
ip dhcp-alloc ........................................................................................................................ |
101 |
ip bootp-alloc ....................................................................................................................... |
101 |
reset .................................................................................................................................... |
102 |
reboot .................................................................................................................................. |
102 |
user-config backup .............................................................................................................. |
103 |
vi |
|

TL-SL3428 JetStream L2 Managed Switch CLI Guide |
|
user-config load................................................................................................................... |
103 |
user-config save .................................................................................................................. |
104 |
firmware upgrade ................................................................................................................ |
104 |
ping ..................................................................................................................................... |
105 |
tracert .................................................................................................................................. |
105 |
loopback .............................................................................................................................. |
106 |
show system-info................................................................................................................. |
106 |
show ip address .................................................................................................................. |
107 |
show system-time................................................................................................................ |
107 |
show system-time dst.......................................................................................................... |
108 |
show system-time source .................................................................................................... |
108 |
show system-time mode...................................................................................................... |
108 |
Chapter 19 Ethernet Configuration Commands ................................................ |
110 |
interface ethernet ................................................................................................................ |
110 |
interface range ethernet ...................................................................................................... |
110 |
description ........................................................................................................................... |
111 |
shutdown ............................................................................................................................. |
111 |
flow-control .......................................................................................................................... |
112 |
negotiation........................................................................................................................... |
112 |
storm-control ....................................................................................................................... |
113 |
port rate-limit ....................................................................................................................... |
114 |
port rate-limit disable ingress............................................................................................... |
114 |
port rate-limit disable egress ............................................................................................... |
115 |
show interface configuration................................................................................................ |
115 |
show interface status........................................................................................................... |
116 |
show interface counters....................................................................................................... |
116 |
show storm-control ethernet ................................................................................................ |
117 |
show port rate-limit .............................................................................................................. |
117 |
Chapter 20 QoS Commands................................................................................ |
119 |
qos ...................................................................................................................................... |
119 |
qos dot1p enable................................................................................................................. |
119 |
qos dot1p config .................................................................................................................. |
120 |
qos dscp enable .................................................................................................................. |
121 |
qos dscp config ................................................................................................................... |
121 |
qos scheduler ...................................................................................................................... |
122 |
show qos port-based ........................................................................................................... |
123 |
show qos dot1p ................................................................................................................... |
124 |
vii |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
show qos dscp..................................................................................................................... |
124 |
show qos scheduler............................................................................................................. |
124 |
Chapter 21 Port Mirror Commands .................................................................... |
126 |
mirror add ............................................................................................................................ |
126 |
mirror remove group............................................................................................................ |
127 |
mirror remove mirrored........................................................................................................ |
127 |
show mirror.......................................................................................................................... |
128 |
Chapter 22 Port isolation Commands ................................................................ |
129 |
port isolation ........................................................................................................................ |
129 |
show port isolation............................................................................................................... |
129 |
Chapter 23 ACL Commands................................................................................ |
131 |
acl time-segment ................................................................................................................. |
131 |
acl edit time-segment .......................................................................................................... |
132 |
acl holiday ........................................................................................................................... |
133 |
acl create............................................................................................................................. |
133 |
acl rule mac-acl ................................................................................................................... |
134 |
acl edit rule mac-acl ............................................................................................................ |
135 |
acl rule std-acl ..................................................................................................................... |
136 |
acl edit rule std-acl............................................................................................................... |
137 |
acl policy policy-add ............................................................................................................ |
138 |
acl policy action-add............................................................................................................ |
139 |
acl edit action ...................................................................................................................... |
140 |
acl bind to-port..................................................................................................................... |
141 |
acl bind to-vlan .................................................................................................................... |
141 |
show acl time-segment........................................................................................................ |
142 |
show acl holiday .................................................................................................................. |
142 |
show acl config.................................................................................................................... |
142 |
show acl bind....................................................................................................................... |
143 |
Chapter 24 MSTP Commands ............................................................................. |
144 |
spanning-tree global ............................................................................................................ |
144 |
spanning-tree common-config ............................................................................................. |
145 |
spanning-tree region............................................................................................................ |
146 |
spanning-tree msti............................................................................................................... |
147 |
spanning-tree msti............................................................................................................... |
148 |
spanning-tree tc-defend....................................................................................................... |
149 |
spanning-tree security ......................................................................................................... |
149 |
viii |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
spanning-tree mcheck ......................................................................................................... |
150 |
show spanning-tree global-info............................................................................................ |
151 |
show spanning-tree global-config........................................................................................ |
151 |
show spanning-tree port-config ........................................................................................... |
151 |
show spanning-tree region .................................................................................................. |
152 |
show spanning-tree msti config ........................................................................................... |
152 |
show spanning-tree msti port .............................................................................................. |
153 |
show spanning-tree security tc-defend ................................................................................ |
153 |
show spanning-tree security port-defend............................................................................. |
154 |
Chapter 25 IGMP Commands.............................................................................. |
155 |
igmp-snooping global .......................................................................................................... |
155 |
igmp-snooping config .......................................................................................................... |
155 |
igmp-snooping vlan-config-add ........................................................................................... |
156 |
igmp-snooping vlan-config................................................................................................... |
157 |
igmp-snooping multi-vlan-config.......................................................................................... |
158 |
igmp-snooping static-entry-add ........................................................................................... |
159 |
igmp-snooping filter-add ...................................................................................................... |
160 |
igmp-snooping filter-config .................................................................................................. |
160 |
igmp-snooping filter ............................................................................................................. |
161 |
show igmp-snooping global-config ...................................................................................... |
162 |
show igmp-snooping port-config.......................................................................................... |
162 |
show igmp-snooping vlan-config ......................................................................................... |
163 |
show igmp-snooping multi-vlan ........................................................................................... |
163 |
show igmp-snooping multi-ip-list ......................................................................................... |
164 |
show igmp-snooping filter-ip-addr ....................................................................................... |
164 |
show igmp-snooping port-filter ............................................................................................ |
164 |
show igmp-snooping packet-stat ......................................................................................... |
165 |
show igmp-snooping packet-stat-clear ................................................................................ |
165 |
Chapter 26 SNMP Commands............................................................................. |
167 |
snmp global ......................................................................................................................... |
167 |
snmp view-add .................................................................................................................... |
168 |
snmp group-add .................................................................................................................. |
168 |
snmp user-add .................................................................................................................... |
170 |
snmp community-add .......................................................................................................... |
171 |
snmp notify-add................................................................................................................... |
172 |
snmp-rmon history sample-cfg ............................................................................................ |
173 |
snmp-rmon history owner .................................................................................................... |
174 |
ix |
|

TL-SL3428 |
JetStream L2 Managed Switch CLI Guide |
snmp-rmon history enable ................................................................................................... |
174 |
snmp-rmon event user......................................................................................................... |
175 |
snmp-rmon event description .............................................................................................. |
176 |
snmp-rmon event type......................................................................................................... |
176 |
snmp-rmon event owner...................................................................................................... |
177 |
snmp-rmon event enable..................................................................................................... |
177 |
snmp-rmon alarm config...................................................................................................... |
178 |
snmp-rmon alarm owner...................................................................................................... |
179 |
snmp-rmon alarm enable..................................................................................................... |
180 |
show snmp global-config ..................................................................................................... |
180 |
show snmp view .................................................................................................................. |
181 |
show snmp group ................................................................................................................ |
181 |
show snmp user .................................................................................................................. |
182 |
show snmp community........................................................................................................ |
182 |
show snmp destination-host ................................................................................................ |
182 |
show snmp-rmon history ..................................................................................................... |
183 |
show snmp-rmon event ....................................................................................................... |
183 |
show snmp-rmon alarm ....................................................................................................... |
184 |
Chapter 27 Cluster Commands........................................................................... |
185 |
cluster ndp........................................................................................................................... |
185 |
cluster ntdp.......................................................................................................................... |
186 |
cluster explore ..................................................................................................................... |
187 |
cluster.................................................................................................................................. |
187 |
cluster manage role-change ................................................................................................ |
188 |
show cluster ndp global ....................................................................................................... |
188 |
show cluster ndp port-status................................................................................................ |
189 |
show cluster neighbour........................................................................................................ |
189 |
show cluster ntdp global ...................................................................................................... |
189 |
show cluster ntdp port-status............................................................................................... |
190 |
show cluster ntdp device ..................................................................................................... |
190 |
show cluster manage role.................................................................................................... |
191 |
x

TL-SL3428 JetStream L2 Managed Switch CLI Guide
Preface
This Guide is intended for network administrator to provide referenced information about CLI (Command Line Interface). The device mentioned in this Guide stands for TL-SL3428 JetStream L2 Managed Switch.
Overview of this Guide
Chapter 1: Using the CLI
Provide information about how to use the CLI, CLI Command Modes, Security Levels and some Conventions.
Chapter 2: User Interface
Provide information about the commands used to switch between five CLI Command Modes.
Chapter 3: IEEE 802.1Q VLAN Commands
Provide information about the commands used for configuring IEEE 802.1Q VLAN.
Chapter 4: Protocol VLAN Commands
Provide information about the commands used for configuring Protocol VLAN.
Chapter 5: Voice VLAN Commands
Provide information about the commands used for configuring Voice VLAN.
Chapter 6: GVRP Commands
Provide information about the commands used for configuring GVRP (GARP VLAN registration protocol).
Chapter 7: LAG Commands
Provide information about the commands used for configuring LAG (Link Aggregation Group).
Chapter 8: LACP Commands
Provide information about the commands used for configuring LACP (Link Aggregation Control Protocol).
Chapter 9: User Manage Commands
Provide information about the commands used for user management.
Chapter 10: Binding Table Commands
Provide information about the commands used for binding the IP address, MAC address, VLAN and the connected Port number of the Host together.
Chapter 11: ARP Inspection Commands
Provide information about the commands used for protecting the switch from the ARP cheating or ARP Attack.
1

TL-SL3428 JetStream L2 Managed Switch CLI Guide
Chapter 12: DoS Defend Command
Provide information about the commands used for DoS defend and detecting the DoS attack.
Chapter 13: IEEE 802.1X Commands
Provide information about the commands used for configuring IEEE 802.1X function.
Chapter 14: Log Commands
Provide information about the commands used for configuring system log.
Chapter 15: SSH Commands
Provide information about the commands used for configuring and managing SSH (Security Shell).
Chapter 16: SSL Commands
Provide information about the commands used for configuring and managing SSL (Secure Sockets Layer).
Chapter 17: Address Commands
Provide information about the commands used for Address configuration.
Chapter 18: System Commands
Provide information about the commands used for configuring the System information and System IP, reboot and reset the switch, upgrade the switch system and other operations.
Chapter 19: Ethernet Configuration Commands
Provide information about the commands used for configuring the Bandwidth Control, Negotiation Mode, and Storm Control for Ethernet ports.
Chapter 20: QoS Commands
Provide information about the commands used for configuring the QoS function.
Chapter 21: Port Mirror Commands
Provide information about the commands used for configuring the Port Mirror function.
Chapter 22: Port isolation Commands
Provide information about the commands used for configuring the Port isolation function.
Chapter 23: ACL Commands
Provide information about the commands used for configuring the ACL (Access Control List).
Chapter 24: MSTP Commands
Provide information about the commands used for configuring the MSTP (Multiple Spanning Tree Protocol).
Chapter 25: IGMP Commands
Provide information about the commands used for configuring the IGMP Snooping (Internet Group Management Protocol Snooping).
2

TL-SL3428 JetStream L2 Managed Switch CLI Guide
Chapter 26: SNMP Commands
Provide information about the commands used for configuring the SNMP (Simple Network Management Protocol) functions.
Chapter 27: Cluster Commands
Provide information about the commands used for configuring the Cluster Management function.
3
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Chapter 1 Using the CLI
1.1Accessing the CLI
You can log on to the switch and access the CLI by the following two methods:
1.Log on to the switch by the console port on the switch.
2.Log on to the switch remotely by a Telnet or SSH connection through an Ethernet port.
1.1.1Logon by a console port
To log on to the switch by the console port on the switch, please take the following steps:
1.Connect the PCs or Terminals to the console port on the switch by a provided cable.
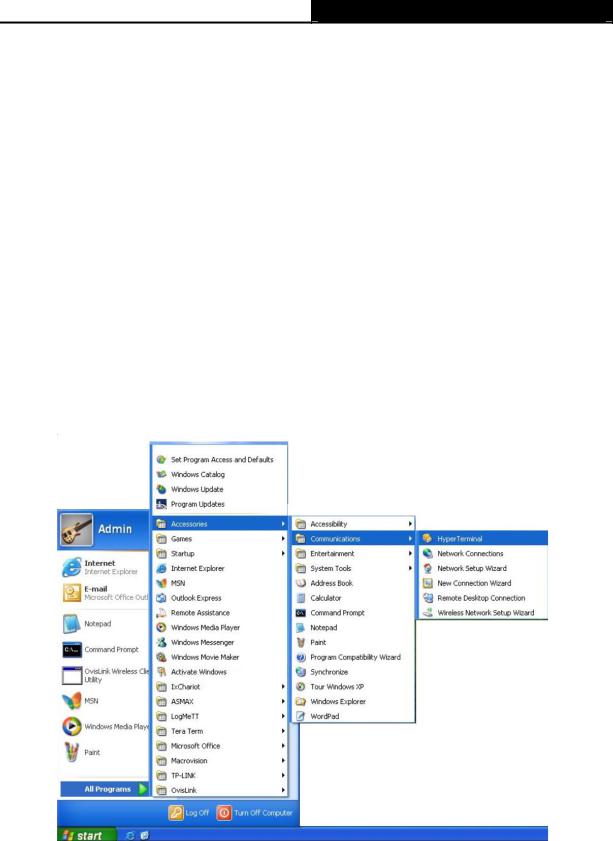
2.Click Start →All Programs →Accessories→Communications →Hyper Terminal to open the Hyper Terminal as the figure 1-1 shown.
Figure 1-1 Open Hyper Terminal
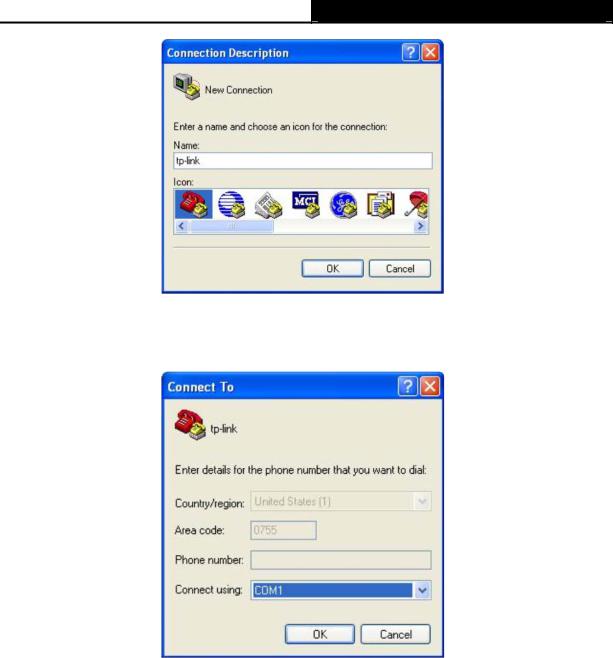
3.The Connection Description Window will prompt as figure1-2. Enter a name into the Name field and click OK.
4
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Figure 1-2 Connection Description
4.Select the port to connect in figure 1-3, and click OK.
Figure 1-3 Select the port to connect
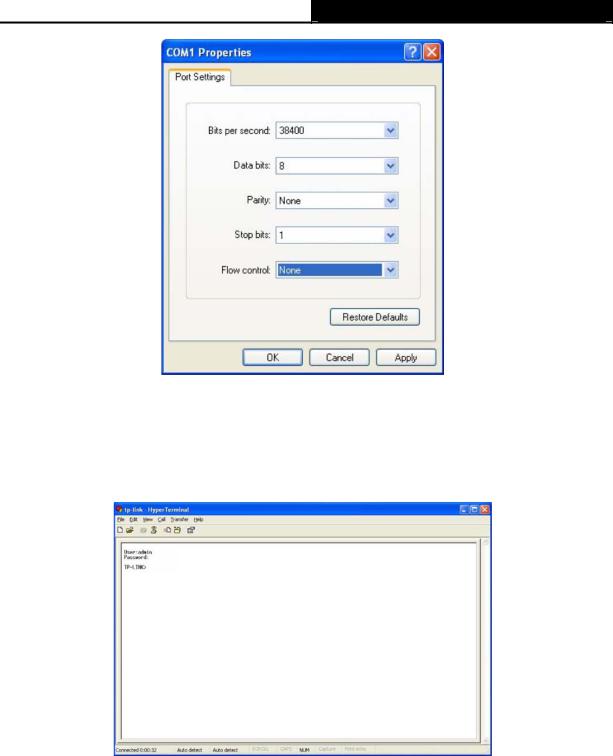
5.Configure the port selected in the step above as the following figure1-4 shown. Configure Bits per second as 38400, Data bits as 8, Parity as None, Stop bits as 1, Flow control as None, and then click OK.
5
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Figure 1-4 Port Settings
6.Type the User name and Password in the Hyper Terminal window, the factory default value for both of them is admin. The DOS prompt” TP-LINK>” will appear after pressing the Enter button as figure1-5 shown. It indicates that you can use the CLI now.
Figure 1-5 Log in the Switch
1.1.2Logon by Telnet
To log on to the switch by a Telnet connection, please take the following steps:
1.Make sure the switch and the PC are in the same LAN.
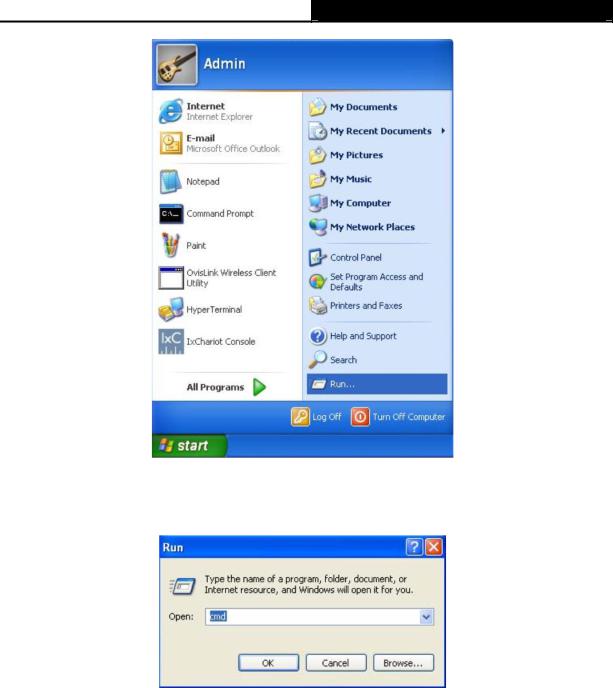
2.Click Start → Run to open the Run window.
6
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Figure 1-6 Open the Run window
3.Type cmd in the prompt Run window as figure 1-7 and click OK.
Figure 1-7 Run Window
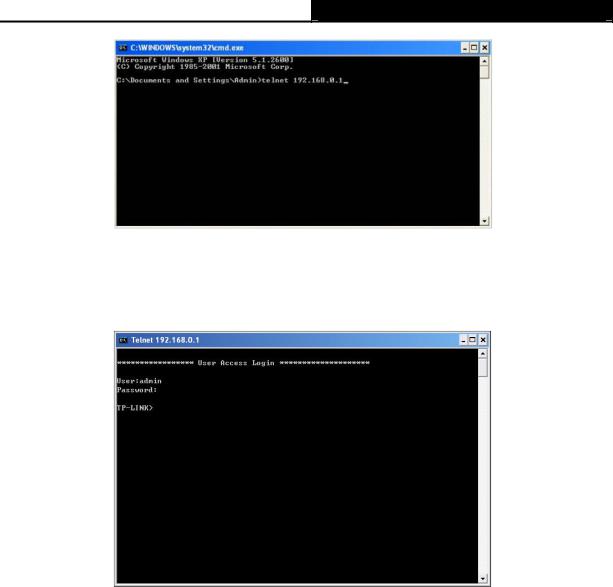
4.Type telnet 192.168.0.1 in the command prompt shown as figure1-8, and press the Enter button.
7
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Figure 1-8 Connecting to the Switch
5.Type the User name and Password (the factory default value for both of them is admin) and press the Enter button, then you can use the CLI now, which is shown as figure1-9.
Figure 1-9 Log in the Switch
1.2CLI Command Modes
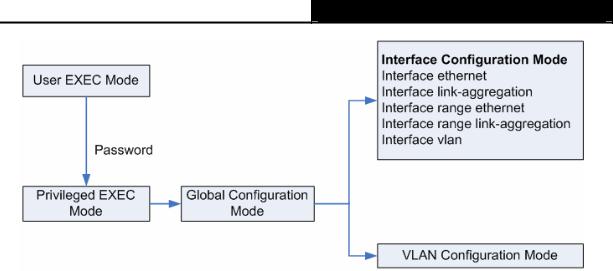
The CLI is divided into different command modes: User EXEC Mode, Privileged EXEC Mode, Global Configuration Mode, Interface Configuration Mode and VLAN Database (VLAN Configuration Mode). Interface Configuration Mode can also be divided into Interface Ethernet, Interface link-aggregation and some other modes, which is shown as the following diagram.
8
TL-SL3428 JetStream L2 Managed Switch CLI Guide
The following table gives detailed information about the Accessing path, Prompt of each mode and how to exit the current mode and access the next mode.
|
Mode |
|
|
|
Accessing |
|
|
Prompt |
|
|
Logout or Access the next |
||||
|
|
|
|
Path |
|
|
|
|
|
mode |
|
||||
|
|
|
|
|
|
|
|
|
|
|
|
||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Primary mode once it is |
|
|
|
|
Use the exit command to disconnect the |
||||||
|
User EXEC |
connected with the |
|
TP-LINK> |
|
switch (except that the switch is |
|||||||||
|
Mode |
|
switch. |
|
|
|
|
|
connected through the Console port). |
||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
Use the enable command to access |
|||
|
|
|
|
|
|
|
|
|
|
|
|
Privileged EXEC mode. |
|
||
|
|
|
|
|
|
|
|
|
|
|
|
||||
|
|
|
|
Use |
the |
enable |
|
|
|
|
Use the exit command to disconnect the |
||||
|
|
|
|
command to enter this |
|
|
|
|
switch (except that the switch is |
||||||
|
Privileged |
|
mode from User EXEC |
|
|
|
|
connected through the Console port). |
|||||||
|
|
mode. |
|
|
|
|
TP-LINK# |
|
Enter the disable command to return to |
||||||
|
EXEC Mode |
|
|
|
|
|
|
||||||||
|
|
|
|
|
|
|
|
|
|
User EXEC mode. |
|
|
|||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
Enter configure command to access |
|||
|
|
|
|
|
|
|
|
|
|
|
|
Global Configuration mode. |
|
||
|
|
|
|
|
|
|
|
|
|
|
|
||||
|
|
|
|
Use |
the |
configure |
|
|
|
|
Use the exit or the end command or |
||||
|
|
|
|
command to enter this |
|
|
|
|
press Ctrl+Z to return to Privileged |
||||||
|
Global |
|
mode |
from |
Privileged |
|
|
|
|
EXEC mode. |
|
|
|
||
|
|
EXEC mode. |
|
|
|
|
|
|
Use the interface type number |
||||||
|
Configuration |
|
|
|
|
TP-LINK(config)# |
|
||||||||
|
|
|
|
|
|
|
|
||||||||
|
Mode |
|
|
|
|
|
|
|
|
|
command |
to |
access |
interface |
|
|
|
|
|
|
|
|
|
|
|
Configuration mode. |
|
|
|||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
Use the vlan database to access VLAN |
|||
|
|
|
|
|
|
|
|
|
|
|
|
Configuration mode. |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
9 |
|
|
|
|
|
|
|

TL-SL3428 JetStream L2 Managed Switch CLI Guide
|
|
Use the interface type |
|
Use the end command or press Ctrl+Z |
|
|
Interface |
number |
command to |
|
to return to Privileged EXEC mode. |
|
enter this mode from |
TP-LINK(config-if |
Enter exit command to return to Global |
||
|
Configuration |
||||
|
Global |
Configuration |
)# |
Configuration mode. |
|
|
Mode |
||||
|
mode. |
|
|
|
|
|
|
|
|
A port number must be specified in the |
|
|
|
|
|
|
|
|
|
|
|
|
interface command. |
|
|
|
|
|
|
|
VLAN |
Use the vlan database |
|
Use the end command or press Ctrl+Z |
|
|
command to enter this |
TP-LINK(config- |
to return to Privileged EXEC mode. |
||
|
Configuration |
||||
|
mode |
from Global |
vlan)# |
|
|
|
Mode |
Enter the exit command to return to |
|||
|
Configuration mode. |
|
|
||
|
|
|
Global configuration mode. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Note: |
|
|
|
|
|
1.The user is automatically in User EXEC Mode after the connection between the PC and the switch is established by a console port or by a telnet connection.
2.Each command mode has its own set of specific commands. To configure some commands, you should access the corresponding command mode firstly.
Global Configuration Mode: In this mode, global commands are provided, such as the Spanning Tree, Schedule Mode and so on.
Interface Configuration Mode: In this mode, users can configure one or several ports, different ports corresponds to different commands
a). Interface Ethernet: Configure parameters for an Ethernet port, such as Duplex-mode, flow control status.
b). Interface range Ethernet: The commands contained are the same as that of the Interface Ethernet. Configure parameters for several Ethernet ports.
c). Interface link-aggregation: Configure parameters for a link-aggregation, such as broadcast storm.
d). Interface range link-aggregation: Configure parameters for multi-trunks. e). Interface vlan: Configure parameters for the vlan-port.
Vlan Configuration Mode: In this mode, users can create a VLAN and add a specified port to the VLAN.
3.Some commands are global, that means they can be performed in all modes:
show: display all information of switch, for example: statistic information, port information, VLAN information.
10

TL-SL3428 JetStream L2 Managed Switch CLI Guide
history: Display the commands history.
1.3Security Levels
This switch’s security is divided into two levels: User level and Admin level.
User level only allows users to do some simple operations in User EXEC Mode; Admin level allows you to monitor, configure and manage the switch in Privileged EXEC Mode, Global Configuration Mode, Interface Configuration Mode and VLAN Configuration Mode.
Users get the privilege to the User level once connecting console port with the switch or logging in by Telnet. However, Guest users are restricted to access the CLI..
Users can enter Privileged EXEC mode from User EXEC mode by using the enable command. In default case, no password is needed. In Global Configuration Mode, you can configure password for Admin level by enable password command. Once password is configured, you are required to enter it to access Privileged EXEC mode.
1.4Conventions
1.4.1Format Conventions
The following conventions are used in this Guide:
Items in square brackets [ ] are optional
Items in braces { } are required
Alternative items are grouped in braces and separated by vertical bars. For example: speed {10 | 100 | 1000 }
Bold indicates an unalterable keyword. For example: show logging
Normal Font indicates a constant (several options are enumerated and only one can be selected). For example: switchport type { access | trunk | general }
Italic Font indicates a variable (an actual value must be assigned). For example: bridge aging-time aging-time
1.4.2Special Characters
You should pay attentions to the description below if the variable is a character string:
These six characters ” < > , \ & can not be input.
11

TL-SL3428 JetStream L2 Managed Switch CLI Guide
If a blank is contained in a character string, single or double quotation marks should be used, for example ’hello world’, ”hello world”, and the words in the quotation marks will be identified as a string. Otherwise, the words will be identified as several strings.
1.4.3Parameter Format
Some parameters must be entered in special formats which are shown as follows:
MAC Address must be enter in the format of xx:xx:xx:xx:xx:xx
One or several values can be typed for a port-list or a vlan-list using comma to separate. Use a hyphen to designate a range of values, for instance, 1,3-5,7 indicates choosing 1,3,4,5,and 7.
12

TL-SL3428 JetStream L2 Managed Switch CLI Guide
Chapter 2 User Interface
enable
Description
The enable command is used to access Privileged EXEC Mode from User EXEC Mode.
Syntax
enable
Command Mode
User EXEC Mode
Example
If you have set the password to access Privileged EXEC Mode from User EXEC Mode:
TP-LINK>enable
Enter password
TP-LINK#
enable password
Description
The enable password command is used to set the password for users to access Privileged EXEC Mode from User EXEC Mode. To return to the default configuration, please use no enable password command.
Syntax
enable password password no enable password
Parameter
password —— super password which contains 16 characters at most, composing digits, English letters and underdashes only. By default, it is empty.
Command Mode
Global Configuration Mode
Example
Set the super password as admin to access Privileged EXEC Mode from User EXEC Mode:
TP-LINK(config)# enable password admin
13

TL-SL3428 JetStream L2 Managed Switch CLI Guide
disable
Description
The disable command is used to return to User EXEC Mode from Privileged
EXEC Mode.
Syntax
disable
Command Mode
Privileged EXEC Mode
Example
Return to User EXEC Mode from Privileged EXEC Mode:
TP-LINK# disable
TP-LINK>
configure
Description
The configure command is used to access Global Configuration Mode from Privileged EXEC Mode.
Syntax
configure
Command Mode
Privileged EXEC Mode
Example
Access Global Configuration Mode from Privileged EXEC Mode:
TP-LINK# configure
TP-LINK(config)#
exit
Description
The exit command is used to return to the previous Mode from the current Mode.
Syntax
14

TL-SL3428 JetStream L2 Managed Switch CLI Guide
exit
Command Mode
Any Configuration Mode
Example
Return to Global Configuration Mode from Interface Configuration Mode, and then return to Privileged EXEC Mode:
TP-LINK(config-if)# exit
TP-LINK(config)#exit
TP-LINK#
end
Description
The end command is used to return to Privileged EXEC Mode.
Syntax
end
Command Mode
Any Configuration Mode
Example
Return to Privileged EXEC Mode from Interface Configuration Mode:
TP-LINK(config-if)#end
TP-LINK#
15
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Chapter 3 IEEE 802.1Q VLAN Commands
VLAN (Virtual Local Area Network) technology is developed for the switch to divide the LAN into multiple logical LANs flexibly. Hosts in the same VLAN can communicate with each other, regardless of their physical locations. VLAN can enhance performance by conserving bandwidth, and improve security by limiting traffic to specific domains.
vlan database
Description
The vlan database command is used to access VLAN Configuration Mode for creating, deleting 802.1Q VLAN and other operations.
Syntax
vlan database
Command Mode
Global Configuration Mode
Example
Access VLAN Configuration Mode:
TP-LINK(config)# vlan database
TP-LINK(config-vlan)#
vlan
Description
The vlan command is used to create IEEE 802.1Q VLAN. To delete the IEEE 802.1Q VLAN, please use no vlan command.
Syntax
vlan VLAN_ID_LIST no vlan VLAN_ID_LIST
Parameter
VLAN_ID_LIST ——The list of VLAN ID, in the format of 2-5,7, ranging from 2 to 4094.
Command Mode
VLAN Configuration Mode
16
TL-SL3428 JetStream L2 Managed Switch CLI Guide
Example
Create several VLANs with the vid as 2-5, 7:
TP-LINK(config)# vlan database
TP-LINK(config-vlan)#vlan 2-5,7
interface vlan
Description
The interface vlan command is used to access VLAN Interface Mode to configure the specified VLAN.
Syntax
interface vlan vlan-id
Parameter
vlan-id ——VLAN ID, ranging from 1 to 4094.
Command Mode
Global Configuration Mode
Example
Configure the VLAN2:
TP-LINK(config)# interface vlan 2
description
Description
The description command is used to assign a description string to a VLAN. To clear the description, please use no description command.
Syntax
description descript no description
Parameter
descript ——String to describe the VLAN, which contains 16 characters at most.
Command Mode
Interface Configuration Mode interface vlan
Example
Specify the description string of the VLAN 2 as “vlan 2”:
17
TL-SL3428 JetStream L2 Managed Switch CLI Guide
TP-LINK(config)# interface vlan 2
TP-LINK(config-if)#description vlan2
switchport type
Description
The switchport type command is used to configure the Link Types for the ports.
Syntax
switchport type { access | trunk | general }
Parameter
access | trunk | general —— Link Types. There are three Link Types for the ports.
Command Mode
Interface Configuration Mode ( interface ethernet / interface range ethernet )
Example
Specify the Link Type of port 5 as general:
TP-LINK(config)# interface ethernet 5
TP-LINK(config-if)#switchport type general
switchport allowed vlan
Description
The switchport allowed vlan command is used to add the desired port to IEEE 802.1Q VLAN, or to remove a port from the corresponding VLAN.
Syntax
switchport allowed vlan add vlan-list switchport allowed vlan remove vlan-list
Parameter
vlan-list —— VLAN ID list, it is multi-optional.
Command Mode
Interface Configuration Mode ( interface ethernet / interface range ethernet )
Example
Add port 2 to IEEE 802.1Q VLAN:
18
TL-SL3428 JetStream L2 Managed Switch CLI Guide
TP-LINK(config)# interface ethernet 2
TP-LINK(config-if)# switchport allowed vlan add 2
switchport pvid
Description
The switchport pvid command is used to configure the PVID for the switch ports.
Syntax
switchport pvid vlan-id
Parameter
vlan-id —— VLAN ID, ranging from 1 to 4094.
Command Mode
Interface Configuration Mode (interface ethernet / interface range ethernet )
Example
Specify the PVID of port 2 as 2:
TP-LINK(config)# interface ethernet 2
TP-LINK(config-if)# switchport pvid 2
switchport general egress-rule
Description
The switchport general egress-rule command is used to configure the egress-rule of the general port.
Syntax
switchport general egress-rule vlan-id { untagged | tagged }
Parameter
vlan-id —— VLAN ID, ranging from 1 to 4094. untagged | tagged ——egress-rule untagged or tagged
Command Mode
Interface Configuration Mode ( interface ethernet / interface range ethernet )
Example
Specify the egress-rule of port 2 in vlan 3 as tagged:
19
 Loading...
Loading...