zyxel Ethernet Switch cli reference guide
CLI Reference Guide
Ethernet Switch Series
Managed Ethernet Switches
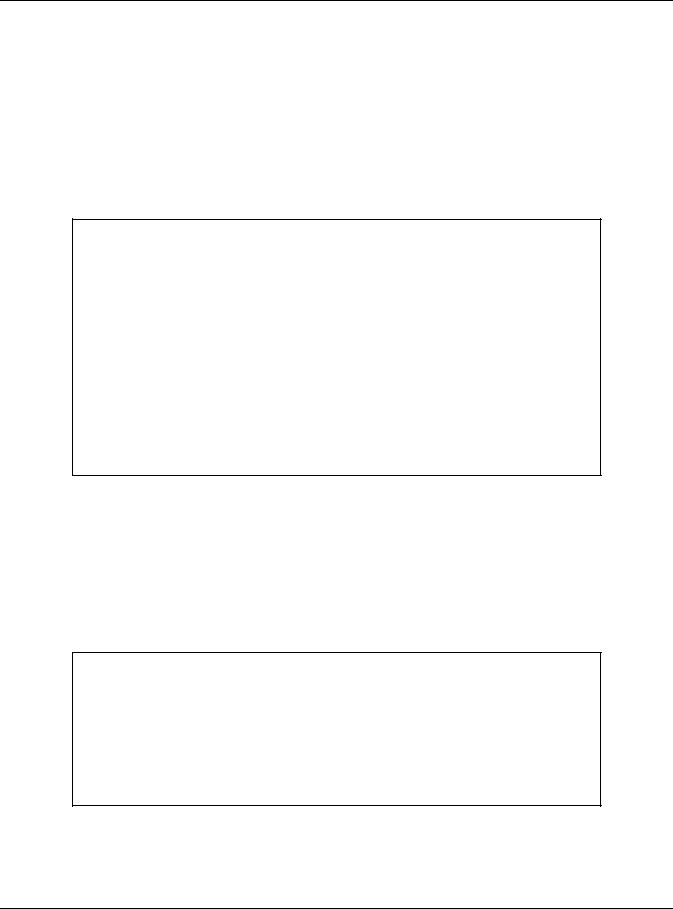
Default Login Details
Version 3.79~4.60 Edition 3, 12/2019
Out-of-Band |
|
|
|
|
|
|
|
|
http://192.168.0.1 |
|
|
|
|
|
|
|
||||||
MGMT Port |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|||||||||
In-Band Ports |
|
|
|
|
|
http://DHCP-assigned IP |
|
|
|
|
|
|
||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
or |
|
|
|
|
|
|
|||
|
|
|
|
|
|
|
|
|
|
|
http://192.168.1.1 |
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
||||
User Name |
|
|
|
|
|
|
|
|
|
|
admin |
|
|
|
|
|
|
|||||
|
|
|
|
|
|
|
|
|
|
|||||||||||||
Password |
|
1234 |
|
|
|
|
|
|
|
|||||||||||||
|
|
|
|
|
|
|||||||||||||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Copyright © 2019 Zyxel Communications Corporation
IMPORTANT!
READ CAREFULLY BEFORE USE.
KEEP THIS GUIDE FOR FUTURE REFERENCE.
This is a Reference Guide for a series of products intended for people who want to configure the Switch via Command Line Interface (CLI).
Note: Some commands or command options in this guide may not be available in your product. See your product's User’s Guide for a list of supported features. Every effort has been made to ensure that the information in this guide is accurate.
How To Use This Guide
1Read Chapter 1 on page 10 for how to access and use the CLI (Command Line Interface).
2Read Chapter 2 on page 13 to learn about the CLI user and privilege modes.
Do not use commands not documented in this guide.
Related Documentation
•Quick Start Guide
The Quick Start Guide shows how to connect the Switch and access the Web Configurator.
•User’s Guide
The User’s Guide explains how to use the Web Configurator to configure the Switch.
Note: It is recommended you use the Web Configurator to configure the Switch.

About This CLI Reference Guide
About This CLI Reference Guide
Intended Audience
This manual is intended for people who want to configure Zyxel Switches via Command Line Interface (CLI).
The version number on the cover page refers to the latest firmware version supported by the Zyxel Switches. This guide applies to versions 3.79, 3.80, 3.90, 4.00, 4.10, 4.20, 4.30, 4.40, 4.50 and 4.60 at the time of writing.
Note: This guide is intended as a command reference for a series of products. Therefore many commands in this guide may not be available in your product. See your User’s Guide for a list of supported features and details about feature implementation.
Please refer to www.zyxel.com for product specific User Guides and product certifications.
How To Use This Guide
•Read the How to Access the CLI chapter for an overview of various ways you can get to the command interface on your Switch.
•Use the Reference section in this guide for command syntax, description and examples. Each chapter describes commands related to a feature.
•To find specific information in this guide, use the Contents Overview, the Index of Commands, or search the PDF file.
Ethernet Switch CLI Reference Guide
3

Document Conventions
Document Conventions
Warnings and Notes
These are how warnings and notes are shown in this CLI Reference Guide.
Warnings tell you about things that could harm you or your device. See your User’s Guide for product specific warnings.
Note: Notes tell you other important information (for example, other things you may need to configure or helpful tips) or recommendations.
Syntax Conventions
This manual follows these general conventions:
•Zyxel’s switches may be referred to as the “Switch”, the “device”, the “system” or the “product” in this Reference Guide.
•Units of measurement may denote the “metric” value or the “scientific” value. For example, “k” for kilo may denote “1000” or “1024”, “M” for mega may denote “1000000” or “1048576” and so on.
Command descriptions follow these conventions:
•Commands are in courier new font.
•Required input values are in angle brackets <>; for example, ping <ip> means that you must specify an IP address for this command.
•Optional fields are in square brackets []; for instance show logins [name], the name field is optional.
The following is an example of a required field within an optional field: snmp-server [contact <system contact>], the contact field is optional. However, if you use contact, then you must provide the system contact information.
•In some commands you specify slots or interfaces by the Access ID <aid>, use “?” to show which types of interfaces you can specify. For example, you might be able to use: slot-<slot> | <ge|msc>-<slot>-<port> | <ge|msc>-<slot>-<port>&&-<port>.
•Use “msc-<slot>-<port>” for an uplink slot on the management switch card.
•Use “ge-<slot>-<port>” for a Gigabit Ethernet port or switch settings on a PON interface.
•Use “pon-<slot>-<port>” to configure PON interface settings.
•A “slot” is a chassis slot.
•The “port” is 1-N where N is the number of ports on the card.
•Use && to specify a range of ports.
•Lists (such as <port-list>) consist of one or more elements separated by commas. Each element might be a single value (1, 2, 3, ...) or a range of values (1-2, 3-5, ...) separated by a dash.
•The | (bar) symbol means “or”.
•italic terms represent user-defined input values; for example, in snmp-server [contact <system contact>], system contact can be replaced by the administrator’s name.
•A key stroke is denoted by square brackets and uppercase text, for example, [ENTER] means the “Enter” or “Return” key on your keyboard.
Ethernet Switch CLI Reference Guide
4

Document Conventions
•<cr> means press the [ENTER] key.
•An arrow (-->) indicates that this line is a continuation of the previous line.
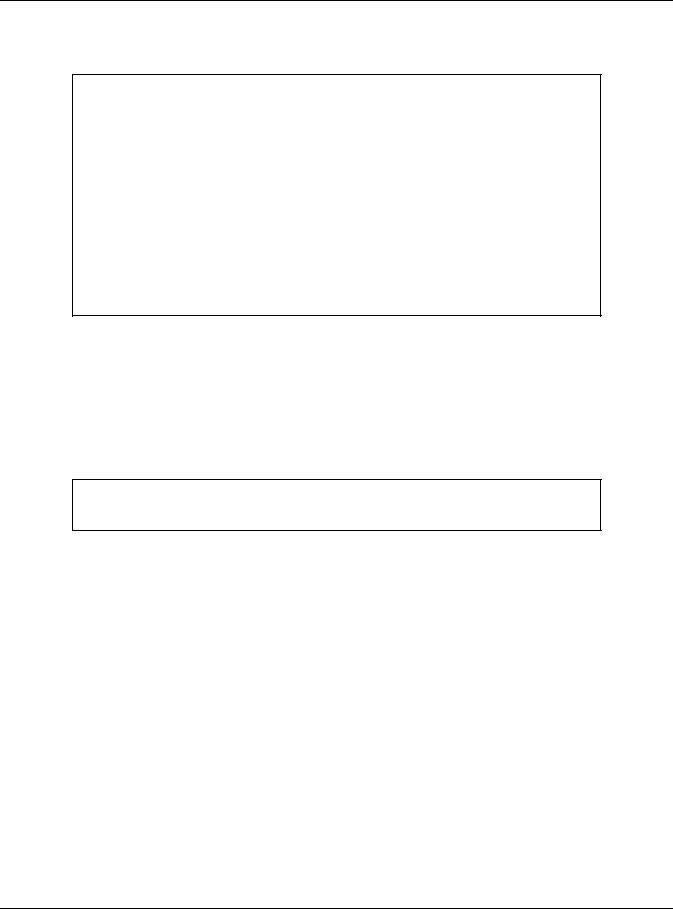
Command summary tables are organized as follows:
Table 1 Example: Command Summary Table
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
show vlan |
Displays the status of all VLANs. |
E |
3 |
vlan <1-4094> |
Enters config-vlan mode for the specified VLAN. Creates |
C |
13 |
|
the VLAN, if necessary. |
|
|
inactive |
Disables the specified VLAN. |
C |
13 |
no inactive |
Enables the specified VLAN. |
C |
13 |
no vlan <1-4094> |
Deletes a VLAN. |
C |
13 |
The Table title identifies commands or the specific feature that the commands configure.
The COMMAND column shows the syntax of the command.
•If a command is not indented, you run it in the enable or config mode. See Chapter 2 on page 13 for more information on command modes.
•If a command is indented, you run it in a sub-command mode.
The DESCRIPTION column explains what the command does. It also identifies legal input values, if necessary.
The M column identifies the mode in which you run the command.
•E: The command is available in enable mode. It is also available in user mode if the privilege level (P) is less than 13.
•C: The command is available in config (not indented) or one of the sub-command modes (indented).
The P column identifies the privilege level of the command. If you don’t have a high enough privilege level you may not be able to view or execute some of the commands. See Chapter 2 on page 13 for more information on privilege levels.
Ethernet Switch CLI Reference Guide
5

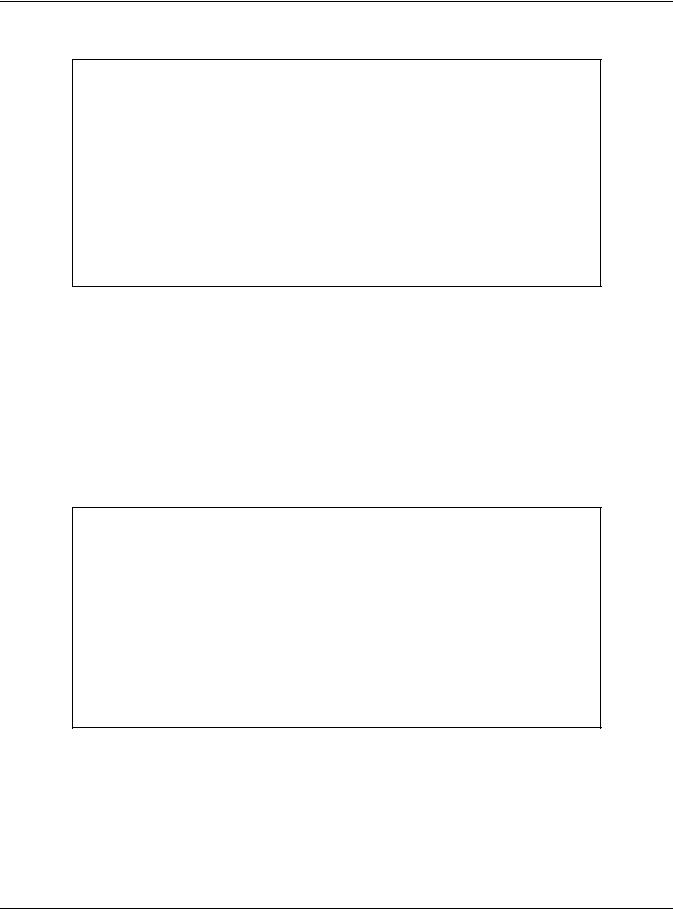
Contents Overview |
|
Contents Overview |
|
Introduction ......................................................................................................................................... |
9 |
How to Access and Use the CLI .......................................................................................................... |
10 |
Privilege Level and Command Mode ................................................................................................ |
13 |
Initial Setup ............................................................................................................................................ |
18 |
Reference A-G .................................................................................................................................. |
25 |
AAA Commands .................................................................................................................................. |
27 |
Anti-Arpscan ......................................................................................................................................... |
30 |
ARP Commands ................................................................................................................................... |
32 |
ARP Inspection Commands ................................................................................................................ |
34 |
ARP Learning Commands ................................................................................................................... |
39 |
Auto Configuration Commands ......................................................................................................... |
40 |
Bandwidth Commands ........................................................................................................................ |
42 |
BPDU Guard .......................................................................................................................................... |
45 |
Broadcast Storm Commands .............................................................................................................. |
46 |
CFM Commands .................................................................................................................................. |
49 |
Certificates Commands ...................................................................................................................... |
58 |
Classifier Commands ........................................................................................................................... |
60 |
Cluster Commands .............................................................................................................................. |
64 |
CLV Commands ................................................................................................................................... |
67 |
Custom Default Commands ............................................................................................................... |
73 |
Date and Time Commands ................................................................................................................. |
74 |
Data Center Bridging Commands ..................................................................................................... |
77 |
DHCP Commands ................................................................................................................................ |
85 |
DHCP Snooping & DHCP VLAN Commands ..................................................................................... |
90 |
DiffServ Commands ............................................................................................................................. |
94 |
Display Commands .............................................................................................................................. |
95 |
DVMRP Commands .............................................................................................................................. |
96 |
Error Disable and Recovery Commands ........................................................................................... |
98 |
Ethernet OAM Commands ................................................................................................................ |
102 |
External Alarm Commands ............................................................................................................... |
107 |
GARP Commands .............................................................................................................................. |
109 |
Green Ethernet Commands .............................................................................................................. |
111 |
GVRP Commands .............................................................................................................................. |
115 |
Reference H-M ................................................................................................................................ |
116 |
HTTPS Server Commands ................................................................................................................... |
118 |
IEEE 802.1x Authentication Commands ........................................................................................... |
121 |
Ethernet Switch CLI Reference Guide |
|
6

Contents Overview |
|
IGMP and Multicasting Commands ................................................................................................. |
124 |
IGMP Snooping Commands ............................................................................................................. |
126 |
IGMP Filtering Commands ................................................................................................................. |
134 |
Interface Commands ........................................................................................................................ |
136 |
Interface Loopback Mode ................................................................................................................ |
141 |
Interface Route-domain Mode ........................................................................................................ |
143 |
IP Commands ..................................................................................................................................... |
144 |
IP Source Binding Commands .......................................................................................................... |
149 |
IPv6 Commands ................................................................................................................................. |
151 |
Layer 2 Protocol Tunnel (L2PT) Commands ..................................................................................... |
176 |
Link Layer Discovery Protocol (LLDP) Commands .......................................................................... |
179 |
Load Sharing Commands .................................................................................................................. |
191 |
Logging Commands .......................................................................................................................... |
193 |
Login Account Commands ............................................................................................................... |
194 |
Loopguard Commands ..................................................................................................................... |
195 |
MAC Address Commands ................................................................................................................. |
197 |
MAC Authentication Commands .................................................................................................... |
199 |
MAC-based VLAN .............................................................................................................................. |
202 |
MAC Filter Commands ....................................................................................................................... |
204 |
MAC Forward Commands ................................................................................................................ |
206 |
MAC Pinning Commands .................................................................................................................. |
207 |
Mirror Commands ............................................................................................................................... |
209 |
MRSTP Commands ............................................................................................................................. |
213 |
MSTP Commands ................................................................................................................................ |
216 |
Multiple Login Commands ................................................................................................................ |
221 |
MVR Commands ................................................................................................................................ |
222 |
Reference N-S ................................................................................................................................. |
224 |
NLB Commands .................................................................................................................................. |
226 |
OSPF Commands ................................................................................................................................ |
230 |
Password Commands ........................................................................................................................ |
239 |
PoE Commands .................................................................................................................................. |
241 |
Policy Commands .............................................................................................................................. |
248 |
Policy Route Commands ................................................................................................................... |
252 |
Port Security Commands ................................................................................................................... |
254 |
Port-based VLAN Commands ........................................................................................................... |
256 |
PPPoE IA Commands ......................................................................................................................... |
257 |
Private VLAN Commands .................................................................................................................. |
263 |
Protocol-based VLAN Commands ................................................................................................... |
268 |
Queuing Commands ......................................................................................................................... |
270 |
RADIUS Commands ............................................................................................................................ |
274 |
Remote Management Commands ................................................................................................. |
276 |
RIP Commands ................................................................................................................................... |
279 |
Ethernet Switch CLI Reference Guide |
|
7

|
Contents Overview |
RMON ................................................................................................................................................... |
282 |
Running Configuration Commands ................................................................................................. |
289 |
Service Register ................................................................................................................................... |
292 |
sFlow ..................................................................................................................................................... |
293 |
Smart Isolation Commands ............................................................................................................... |
295 |
SNMP Server Commands ................................................................................................................... |
298 |
Stacking Commands ......................................................................................................................... |
303 |
STP and RSTP Commands .................................................................................................................. |
309 |
SSH Commands .................................................................................................................................. |
313 |
Static Multicast Commands .............................................................................................................. |
315 |
Static Route Commands ................................................................................................................... |
317 |
Subnet-based VLAN Commands ..................................................................................................... |
320 |
Syslog Commands .............................................................................................................................. |
322 |
Reference T-Z .................................................................................................................................. |
323 |
TACACS+ Commands ........................................................................................................................ |
324 |
Tech Support Commands ................................................................................................................. |
325 |
TFTP Commands ................................................................................................................................. |
328 |
Time Range Commands .................................................................................................................... |
329 |
Traceroute Commands ..................................................................................................................... |
331 |
Trunk Commands ................................................................................................................................ |
332 |
trTCM Commands .............................................................................................................................. |
335 |
Vendor ID-based VLAN ...................................................................................................................... |
338 |
VLAN Commands ............................................................................................................................... |
341 |
VLAN IP Commands ........................................................................................................................... |
347 |
VLAN Mapping Commands .............................................................................................................. |
349 |
VLAN Port Isolation Commands ........................................................................................................ |
351 |
VLAN Stacking Commands ............................................................................................................... |
352 |
VLAN Trunking Commands ................................................................................................................ |
355 |
Voice VLAN Commands .................................................................................................................... |
356 |
VRRP Commands ............................................................................................................................... |
359 |
ZULD Commands ................................................................................................................................ |
362 |
Wol Relay Commands ....................................................................................................................... |
364 |
Additional Commands ...................................................................................................................... |
365 |
Appendices and Index of Commands ......................................................................................... |
378 |
Ethernet Switch CLI Reference Guide
8
PART I
Introduction
How to Access and Use the CLI (10)
Privilege Level and Command Mode (13)
Initial Setup (18)
9

CHAPTER 1
How to Access and Use the CLI
This chapter introduces the command line interface (CLI).
1.1 Accessing the CLI
Use any of the following methods to access the CLI.
1.1.1 Console Port
1Connect your computer to the console port on the Switch using the appropriate cable.
2Use terminal emulation software with the following settings: Table 2 Default Settings for the Console Port
SETTING |
DEFAULT VALUE |
|
|
Terminal Emulation |
VT100 |
|
|
Baud Rate |
9600 or 115200 bps |
|
|
Parity |
None |
|
|
Number of Data Bits |
8 |
|
|
Number of Stop Bits |
1 |
|
|
Flow Control |
None |
|
|
3Press [ENTER] to open the login screen.
1.1.2Telnet
1Connect your computer to one of the Ethernet ports.
2Open a Telnet session to the Switch’s IP address. If this is your first login, use the default values.
Ethernet Switch CLI Reference Guide
10

Chapter 1 How to Access and Use the CLI
Table 3 Default Management IP Address
SETTING |
DEFAULT VALUE |
|
|
IP Address |
192.168.1.1 |
|
|
Subnet Mask |
255.255.255.0 |
|
|
Make sure your computer IP address is in the same subnet, unless you are accessing the Switch through one or more routers.
1.1.3 SSH
1Connect your computer to one of the Ethernet ports.
2Use a SSH client program to access the Switch. If this is your first login, use the default values in Table 3 on page 11 and Table 4 on page 11. Make sure your computer IP address is in the same subnet, unless you are accessing the Switch through one or more routers.
1.2Logging in
Use the administrator username and password. If this is your first login, use the default values.
Table 4 Default User Name and Password
SETTING |
DEFAULT VALUE |
|
|
User Name |
admin |
|
|
Password |
1234 |
|
|
Note: The Switch automatically logs you out of the management interface after five minutes of inactivity. If this happens to you, simply log back in again.
1.3 Using Shortcuts and Getting Help
This table identifies some shortcuts in the CLI, as well as how to get help.
Table 5 CLI Shortcuts and Help
COMMAND / KEY(S) |
DESCRIPTION |
|
|
history |
Displays a list of recently-used commands. |
(up/down arrow keys) |
Scrolls through the list of recently-used commands. You can edit any |
|
command or press [ENTER] to run it again. |
[CTRL]+U |
Clears the current command. |
[TAB] |
Auto-completes the keyword you are typing if possible. For example, type |
|
config, and press [TAB]. The Switch finishes the word configure. |
? |
Displays the keywords and/or input values that are allowed in place of the ?. |
help |
Displays the (full) commands that are allowed in place of help. |
Ethernet Switch CLI Reference Guide
11
Chapter 1 How to Access and Use the CLI
1.4 Saving Your Configuration
When you run a command, the Switch saves any changes to its run-time memory. The Switch loses these changes if it is turned off or loses power. Use the write memory command in enable mode to save the current configuration permanently to non-volatile memory.
sysname# write memory
Note: You should save your changes after each CLI session. All unsaved configuration changes are lost once you restart the Switch.
1.5 Logging Out
Enter logout to log out of the CLI. You have to be in user, enable, or config mode. See Chapter 2 on page 13 for more information about modes.
Ethernet Switch CLI Reference Guide
12

CHAPTER 2
Privilege Level and
Command Mode
This chapter introduces the CLI privilege levels and command modes.
•The privilege level determines whether or not a user can run a particular command.
•If a user can run a particular command, the user has to run it in the correct mode.
2.1Privilege Levels
Every command has a privilege level (0-14). Users can run a command if the session’s privilege level is greater than or equal to the command’s privilege level. The session’s privilege level initially comes from the login account’s privilege level, though it is possible to change the session’s privilege level after logging in.
2.1.1 Privilege Levels for Commands
The privilege level of each command is listed in the Reference A-G chapters on page 25.
At the time of writing, commands have a privilege level of 0, 3, 13, or 14. The following table summarizes the types of commands at each of these privilege levels.
Table 6 Types of Commands at Different Privilege Levels
PRIVILEGE LEVEL |
TYPES OF COMMANDS AT THIS PRIVILEGE LEVEL |
|
|
0 |
Display basic system information. |
|
|
3 |
Display configuration or status. |
13Configure features except for login accounts, SNMP user accounts, the authentication method sequence and authorization settings, multiple logins, administrator and enable passwords, and configuration information display.
14Configure login accounts, SNMP user accounts, the authentication method sequence and authorization settings, multiple logins, and administrator and enable passwords, and display configuration information.
2.1.2Privilege Levels for Login Accounts
You can manage the privilege levels for login accounts in the following ways:
•Using commands. Login accounts can be configured by the admin account or any login account with a privilege level of 14. See Chapter 47 on page 194.
Ethernet Switch CLI Reference Guide
13

Chapter 2 Privilege Level and Command Mode
•Using vendor-specific attributes in an external authentication server. See the User’s Guide for more information.
The admin account has a privilege level of 14, so the administrator can run every command. You cannot change the privilege level of the admin account.
2.1.3 Privilege Levels for Sessions
The session’s privilege level initially comes from the privilege level of the login account the user used to log in to the Switch. After logging in, the user can use the following commands to change the session’s privilege level.
2.1.3.1 enable Command
This command raises the session’s privilege level to 14. It also changes the session to enable mode (if not already in enable mode). This command is available in user mode or enable mode, and users have to know the enable password.
In the following example, the login account user0 has a privilege level of 0 but knows that the enable password is 123456. Afterwards, the session’s privilege level is 14, instead of 0, and the session changes to enable mode.
sysname> enable Password: 123456 sysname#
The default enable password is 1234. Use this command to set the enable password.
password <password>
<password> consists of 1-32 alphanumeric characters. For example, the following command sets the enable password to 123456. See Chapter 106 on page 365 for more information about this command.
sysname(config)# password 123456
The password is sent in plain text and stored in the Switch’s buffers. Use this command to set the cipher password for password encryption.
password cipher <password>
<password> consists of 32 alphanumeric characters. For example, the following command encrypts the enable password with a 32-character cipher password. See Chapter 62 on page 239 for more information about this command.
sysname(config)# password cipher qwertyuiopasdfghjklzxcvbnm123456
2.1.3.2 enable <0-14> Command
This command raises the session’s privilege level to the specified level. It also changes the session to enable mode, if the specified level is 13 or 14. This command is available in user mode or enable mode, and users have to know the password for the specified privilege level.
Ethernet Switch CLI Reference Guide
14
Chapter 2 Privilege Level and Command Mode
In the following example, the login account user0 has a privilege level of 0 but knows that the password for privilege level 13 is pswd13. Afterwards, the session’s privilege level is 13, instead of 0, and the session changes to enable mode.
sysname> enable 13 Password: pswd13 sysname#
Users cannot use this command until you create passwords for specific privilege levels. Use the following command to create passwords for specific privilege levels.
password <password> privilege <0-14>
<password> consists of 1-32 alphanumeric characters. For example, the following command sets the password for privilege level 13 to pswd13. See Chapter 106 on page 365 for more information about this command.
sysname(config)# password pswd13 privilege 13
2.1.3.3 disable Command
This command reduces the session’s privilege level to 0. It also changes the session to user mode. This command is available in enable mode.
2.1.3.4 show privilege command
This command displays the session’s current privilege level. This command is available in user mode or enable mode.
sysname# show privilege Current privilege level : 14
2.2 Command Modes
The CLI is divided into several modes. If a user has enough privilege to run a particular command, the user has to run the command in the correct mode. The modes that are available depend on the session’s privilege level.
2.2.1 Command Modes for Privilege Levels 0-12
If the session’s privilege level is 0-12, the user and all of the allowed commands are in user mode. Users do not have to change modes to run any allowed commands.
Ethernet Switch CLI Reference Guide
15

Chapter 2 Privilege Level and Command Mode
2.2.2 Command Modes for Privilege Levels 13-14
If the session’s privilege level is 13-14, the allowed commands are in one of several modes. Table 7 Command Modes for Privilege Levels 13-14 and the Types of Commands in Each One
MODE |
PROMPT |
COMMAND FUNCTIONS IN THIS MODE |
|
|
|
enable |
sysname# |
Display current configuration, diagnostics, |
|
|
maintenance. |
config |
sysname(config)# |
Configure features other than those below. |
config-interface |
sysname(config-interface)# |
Configure ports. |
config-mvr |
sysname(config-mvr)# |
Configure multicast VLAN. |
config-route- |
sysname(config-if)# |
Enable and enter configuration mode for an IPv4 or |
domain |
|
IPv6 routing domain. |
config-dvmrp |
sysname(config-dvmrp)# |
Configure Distance Vector Multicast Routing Protocol |
|
|
(DVRMP). |
config-igmp |
sysname(config-igmp)# |
Configure Internet Group Management Protocol |
|
|
(IGMP). |
config-ma |
sysname(config-ma)# |
Configure an Maintenance Association (MA) in |
|
|
Connectivity Fault Management (CFM). |
config-ospf |
sysname(config-ospf)# |
Configure Open Shortest Path First (OSPF) protocol. |
config-rip |
sysname(config-rip)# |
Configure Routing Information Protocol (RIP). |
config-vrrp |
sysname(config-vrrp)# |
Configure Virtual Router Redundancy Protocol (VRRP). |
Each command is usually in one and only one mode. If a user wants to run a particular command, the user has to change to the appropriate mode. The command modes are organized like a tree, and users start in enable mode. The following table explains how to change from one mode to another.
Table 8 Changing Between Command Modes for Privilege Levels 13-14
MODE |
ENTER MODE |
LEAVE MODE |
|
|
|
enable |
-- |
-- |
config |
configure |
exit |
config-interface |
interface port-channel <port-list> |
exit |
config-mvr |
mvr <1-4094> |
exit |
config-vlan |
vlan <1-4094> |
exit |
config-route-domain |
interface route domain <ip-address>/<mask-bits> |
exit |
config-dvmrp |
router dvmrp |
exit |
config-igmp |
router igmp |
exit |
config-ospf |
router ospf <router-id> |
exit |
config-rip |
router rip |
exit |
config-vrrp |
router vrrp network <ip-address>/<mask-bits> |
exit |
|
vr-id <1~7> uplink-gateway <ip-address> |
|
Ethernet Switch CLI Reference Guide
16
Chapter 2 Privilege Level and Command Mode
2.3 Listing Available Commands
Use the help command to view the executable commands on the Switch. You must have the highest privilege level in order to view all the commands. Follow these steps to create a list of supported commands:
1Log into the CLI. This takes you to the enable mode.
2Type help and press [ENTER]. A list comes up which shows all the commands available in enable mode. The example shown next has been edited for brevity’s sake.
sysname# help Commands available:
help logout exit history
enable <0-14> enable <cr>
.
.
traceroute <ip|host-name> [vlan <vlan-id>][..] traceroute help
ssh <1|2> <[user@]dest-ip> <cr>
ssh <1|2> <[user@]dest-ip> [command </>] sysname#
3Copy and paste the results into a text editor of your choice. This creates a list of all the executable commands in the user and enable modes.
4Type configure and press [ENTER]. This takes you to the config mode.
5Type help and press [ENTER]. A list is displayed which shows all the commands available in config mode and all the sub-commands. The sub-commands are preceded by the command necessary to enter that sub-command mode. For example, the command name <name-str> as shown next, is preceded by the command used to enter the config-vlan sub-mode: vlan <1-4094>.
sysname# help
.
.
no arp inspection log-buffer logs no arp inspection filter-aging-time no arp inspection <cr>
vlan <1-4094>
vlan <1-4094> name <name-str> vlan <1-4094> normal <port-list> vlan <1-4094> fixed <port-list>
6Copy and paste the results into a text editor of your choice. This creates a list of all the executable commands in config and the other submodes, for example, the config-vlan mode.
Ethernet Switch CLI Reference Guide
17

CHAPTER 3
Initial Setup
This chapter identifies tasks you might want to do when you first configure the Switch.
3.1 Changing the Administrator Password
Note: It is recommended you change the default administrator password. You can encrypt the password using the password encryption command. See Chapter 62 on page 239 for more information.
Use this command to change the administrator password.
admin-password <pw-string> <Confirm-string>
where <pw-string> may be 1-32 alphanumeric characters long.
sysname# configure
sysname(config)# admin-password t1g2y7i9 t1g2y7i9
3.2 Changing the Enable Password
Note: It is recommended you change the default enable password. You can encrypt the password using the password encryption command. See Chapter 62 on page 239 for more information.
Use this command to change the enable password.
password <password>
where <password> may be 1-32 alphanumeric characters long.
sysname# configure
sysname(config)# password k8s8s3dl0
Ethernet Switch CLI Reference Guide
18

Chapter 3 Initial Setup
3.3 Prohibiting Concurrent Logins
By default, multiple CLI sessions are allowed via the console port or Telnet. See the User’s Guide for the maximum number of concurrent sessions for your Switch. Use this command to prohibit concurrent logins.
no multi-login
Console port has higher priority than Telnet. See Chapter 58 on page 221 for more multi-login commands.
sysname# configure sysname(config)# no multi-login
3.4 Changing the Management IP Address
The Switch has a different IP address in each VLAN. By default, the Switch has VLAN 1 with IP address 192.168.1.1 and subnet mask 255.255.255.0. Use this command in config-vlan mode to change the management IP address in a specific VLAN.
ip address <ip> <mask>
This example shows you how to change the management IP address in VLAN 1 to 172.16.0.1 with subnet mask 255.255.255.0.
sysname# configure sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management 172.16.0.1 255.255.255.0
Note: Afterwards, you have to use the new IP address to access the Switch.
3.5 Changing the Out-of-band Management IP Address
If your Switch has a MGMT port (also referred to as the out-of-band management port), then the Switch can also be managed via this interface. By default, the MGMT port IP address is 192.168.0.1 and the subnet mask is 255.255.255.0. Use this command in config mode to change the out-of-band management IP address.
ip address <ip> <mask>
This example shows you how to change the out-of-band management IP address to 10.10.10.1 with subnet mask 255.255.255.0 and the default gateway 10.10.10.254.
sysname# configure
sysname(config)# ip address 10.10.10.1 255.255.255.0 sysname(config)# ip address default-gateway 10.10.10.254
Ethernet Switch CLI Reference Guide
19

Chapter 3 Initial Setup
3.6 Using Auto Configuration
Follow the steps below to set up configurations on the Switch, so you can load an auto configuration file automatically from a TFTP server when you reboot the Switch.
Note: You need to set up configurations on a DHCP server and TFTP server first to use auto configuration.
1Use this command to enable auto configuration on the Switch. auto-config
sysname# config sysname(config)# auto-config
2Use this command to enable the DHCP mode for auto configuration. auto-config dhcp
sysname# config
sysname(config)# auto-config dhcp
3Use this command to configure the Switch as a DHCP client. ip address default-management dhcp-bootp
sysname# config sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp
4Use this command to enable DHCP option 60.
ip address default-management dhcp-bootp option-60
When you enable DHCP option 60, make sure you set up a Vendor Class Identifier. The Vendor Class Identifier specifies the Zyxel switch that should receive the auto configuration file.
Skip this step if you are not enabling DHCP option 60.
sysname# config sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp option-60
5Use this command to define a Vendor Class Identifier for DHCP option 60.
ip address default-management dhcp-bootp option-60 class-id <class-id>
In this example, we use “ZyxelCorp”.
Skip this step if you don’t need to define a Vendor Class Identifier.
sysname# config sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp option-60 class-id ZyxelCorp
Ethernet Switch CLI Reference Guide
20
Chapter 3 Initial Setup
6Use this command to check the settings for auto configuration. show running-config
GS2210# show running-config
Building configuration...
Current configuration:
vlan 1 name 1
normal "" fixed 1-50 forbidden "" untagged 1-50
ip address default-management dhcp-bootp
ip address default-management dhcp-bootp option-60 class-id ZyxelCorp exit
pwr mode consumption auto-config
7You need to save the current configuration in a configuration file, so the Switch will load the auto configuration files from the TFTP server automatically when rebooting
Use this command to save the current configuration in a configuration file. write memory [<index>]
For [<index>], you can enter a value to save the current configuration to a specified configuration file. 1 is for Config 1, and 2 is for Config 2.
In this example, we save the current configuration to Config 1.
sysname# write memory 1
........................................................................
............................
8Use this command to reboot the Switch. reload config [1|2]
For [1|2], 1 is for Config 1, and 2 is for Config 2.
In this example, we load Config 1 to reboot the Switch.
Ethernet Switch CLI Reference Guide
21

Chapter 3 Initial Setup
sysname# reload config 1
Do you really want to reboot system with configuration file 1? [y/N]y Bootbase Version: V1.05 | 12/19/2013 16:57:54
DRAM calibration...PASSED RAM: Size = 131072 Kbytes
ZyNOS Version: V4.50(AAHW.0)b3_20171020_1 | 10/20/2017 16:9:36
Press any key to enter debug mode within 1 second.
....................
(Compressed)
Version: GS2210, start: b4962430
Length: 16F0668, Checksum: 03AA
Compressed Length: 2EE424, Checksum: 87A5
Copyright (c) 1994 - 2017 Zyxel Communications Corp.
initialize mgmt, initialize switch, ethernet address: 00:19:cb:00:00:01
Initializing MSTP.............
Initializing VLAN Database...
Initializing IP Interface...
Initializing Advanced Applications...
Initializing Command Line Interface...
Initializing Web Interface...
Restore System Configuration...
Start Auto Configuration...
..............
Try to download and restore configuration file from TFTP://10.90.90.11/
TestConf2
Downloading....
Get the file TestConf2, length 289 bytes.
Restoring......
Auto-config processes successfully.
Press ENTER to continue...
9Use this command to check whether the auto configuration file was loaded successfully.
Show auto-config
Mode: DHCP
State: Success
Filename: TFTP://10.90.90.11/TestConf2
3.7 Using Custom Default
Follow the steps below to set up configurations on the Switch, so you can load a customized default file when you reboot the Switch.
1Use this command to enable custom default on the Switch. custom-default
sysname# config sysname(config)# custom-default
Ethernet Switch CLI Reference Guide
22

Chapter 3 Initial Setup
2Use this command to save the current configuration settings permanently to a customized default file on the Switch.
copy running-config custom-default
sysname# copy running-config custom-default
........................................................................
............................
3Use this command to reboot the system and load a saved customized default file on the Switch. reload custom-default
sysname# reload custom-default
Do you really want to restore system to custom default settings and reboot?[y/N]y
.......
Bootbase Version: V1.05 | 12/19/2013 16:57:54
DRAM calibration...PASSED
RAM: Size = 131072 Kbytes
ZyNOS Version: V4.50(AAHW.0)b3_20171020_1 | 10/20/2017 16:9:36
Press any key to enter debug mode within 1 second.
....................
(Compressed)
Version: GS2210, start: b4962430
Length: 16F0668, Checksum: 03AA
Compressed Length: 2EE424, Checksum: 87A5
Copyright (c) 1994 - 2017 Zyxel Communications Corp.
initialize mgmt, initialize switch, ethernet address: 00:19:cb:00:00:01
Initializing MSTP.............
Initializing VLAN Database...
Initializing IP Interface...
Initializing Advanced Applications...
Initializing Command Line Interface...
Initializing Web Interface...
Restore System Configuration...
Press ENTER to continue...
3.8 Looking at Basic System Information
Use this command to look at general system information about the Switch.
show system-information
Ethernet Switch CLI Reference Guide
23
Chapter 3 Initial Setup
This is illustrated in the following example.
sysname# show system-information
Product Model |
: sysname |
|
System Name |
: sysname |
|
System Mode |
: Standalone |
|
System Contact |
: |
|
System Location |
: |
98:26:28 (151f8939 ticks) |
System up Time |
: |
|
Ethernet Address |
: 00:19:cb:00:00:02 |
|
Bootbase Version |
: V1.02 | 08/27/2014 |
|
ZyNOS F/W Version |
: V4.20(AASS.0)b3 | 09/24/2014 |
|
Config Boot Image |
: 1 |
|
Current Boot Image |
: 1 |
|
RomRasSize |
: 8336318 |
|
sysname# |
|
|
See Chapter 106 on page 365 for more information about these attributes.
3.9 Looking at the Operating Configuration
Use this command to look at the current operating configuration.
show running-config
This is illustrated in the following example.
sysname# show running-config
Building configuration...
Current configuration:
vlan 1 name 1 normal ""
fixed 1-52 forbidden "" untagged 1-52
ip address 192.168.1.1 255.255.255.0 exit
interface route-domain 192.168.1.1/24 exit
pwr mode consumption
Ethernet Switch CLI Reference Guide
24

PART II
Reference A-G
AAA Commands (27)
ARP Commands (32)
ARP Inspection Commands (34)
ARP Learning Commands (39)
Auto Configuration Commands (40)
Bandwidth Commands (42)
Broadcast Storm Commands (46)
CFM Commands (49)
Certificates Commands (58)
Classifier Commands (60)
Cluster Commands (64)
CLV Commands (67)
Custom Default Commands (73)
Date and Time Commands (74)
Data Center Bridging Commands (77)
DHCP Commands (85)
DHCP Snooping & DHCP VLAN Commands (90)
25

DiffServ Commands (94)
Display Commands (95)
DVMRP Commands (96)
Error Disable and Recovery Commands (98)
Ethernet OAM Commands (102)
External Alarm Commands (107)
GARP Commands (109)
Green Ethernet Commands (111)
GVRP Commands (115)
26

CHAPTER 4
AAA Commands
Use these commands to configure authentication, authorization and accounting on the Switch.
4.1 Command Summary
The following section lists the commands for this feature.
Table 9 aaa authentication Command Summary
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
show aaa authentication |
Displays what methods are used for authentication. |
E |
3 |
show aaa authentication enable |
Displays the authentication method(s) for checking |
E |
3 |
|
privilege level of administrators. |
|
|
aaa authentication enable |
Specifies which method should be used first, second, and |
C |
14 |
<method1> [<method2> ...] |
third for checking privileges. |
|
|
|
method: enable, radius, or tacacs+. |
|
|
no aaa authentication enable |
Resets the method list for checking privileges to its default |
C |
14 |
|
value. |
|
|
show aaa authentication login |
Displays the authentication methods for administrator login |
E |
3 |
|
accounts. |
|
|
aaa authentication login |
Specifies which method should be used first, second, and |
C |
14 |
<method1> [<method2> ...] |
third for the authentication of login accounts. |
|
|
|
method: local, radius, or tacacs+. |
|
|
no aaa authentication login |
Resets the method list for the authentication of login |
C |
14 |
|
accounts to its default value. |
|
|
Table 10 Command Summary: aaa accounting |
|
|
|
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
show aaa accounting |
Displays accounting settings configured on the Switch. |
E |
3 |
show aaa accounting update |
Display the update period setting on the Switch for |
E |
3 |
|
accounting sessions. |
|
|
aaa accounting update periodic |
Sets the update period (in minutes) for accounting |
C |
13 |
<1-2147483647> |
sessions. This is the time the Switch waits to send an update |
|
|
|
to an accounting server after a session starts. |
|
|
no aaa accounting update |
Resets the accounting update interval to the default |
C |
13 |
|
value. |
|
|
show aaa accounting commands |
Displays accounting settings for recording command |
E |
3 |
|
events. |
|
|
aaa accounting commands |
Enables accounting of command sessions and specifies |
C |
13 |
<privilege> stop-only tacacs+ |
the minimum privilege level (0-14) for the command |
|
|
[broadcast] |
sessions that should be recorded. Optionally, sends |
|
|
accounting information for command sessions to all |
|
|
|
|
|
|
|
|
configured accounting servers at the same time. |
|
|
|
|
|
|
Ethernet Switch CLI Reference Guide
27

Chapter 4 AAA Commands
Table 10 Command Summary: aaa accounting (continued)
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
no aaa accounting commands |
Disables accounting of command sessions on the Switch. |
C |
13 |
show aaa accounting dot1x |
Displays accounting settings for recording IEEE 802.1x |
E |
3 |
|
session events. |
|
|
aaa accounting dot1x <start- |
Enables accounting of IEEE 802.1x authentication sessions |
C |
13 |
stop|stop-only> |
and specifies the mode and protocol method. Optionally, |
|
|
<radius|tacacs+> [broadcast] |
sends accounting information for IEEE 802.1x |
|
|
authentication sessions to all configured accounting |
|
|
|
|
|
|
|
|
servers at the same time. |
|
|
|
|
|
|
no aaa accounting dot1x |
Disables accounting of IEEE 802.1x authentication sessions |
C |
13 |
|
on the Switch. |
|
|
show aaa accounting exec |
Displays accounting settings for recording administrative |
E |
3 |
|
sessions via SSH, Telnet or the console port. |
|
|
aaa accounting exec <start- |
Enables accounting of administrative sessions via SSH, |
C |
13 |
stop|stop-only> |
Telnet and console port and specifies the mode and |
|
|
<radius|tacacs+> [broadcast] |
protocol method. Optionally, sends accounting |
|
|
information for administrative sessions via SSH, Telnet and |
|
|
|
|
|
|
|
|
console port to all configured accounting servers at the |
|
|
|
same time. |
|
|
|
|
|
|
no aaa accounting exec |
Disables accounting of administrative sessions via SSH, |
C |
13 |
|
Telnet or console on the Switch. |
|
|
show aaa accounting system |
Displays accounting settings for recording system events, |
E |
3 |
|
for example system shut down, start up, accounting |
|
|
|
enabled or accounting disabled. |
|
|
|
|
|
|
aaa accounting system |
Enables accounting of system events and specifies the |
C |
13 |
<radius|tacacs+> [broadcast] |
protocol method. Optionally, sends accounting |
|
|
|
information for system events to all configured accounting |
|
|
|
servers at the same time. |
|
|
|
|
|
|
no aaa accounting system |
Disables accounting of system events on the Switch. |
C |
13 |
Table 11 aaa authorization Command Summary |
|
|
|
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
show aaa authorization |
Displays authorization settings configured on the Switch. |
E |
3 |
show aaa authorization dot1x |
Displays the authorization method used to allow an IEEE |
E |
3 |
|
802.1x client to have different bandwidth limit or VLAN ID |
|
|
|
assigned via the external server. |
|
|
|
|
|
|
show aaa authorization exec |
Displays the authorization method used to allow an |
E |
3 |
|
administrator which logs in the Switch through Telnet or SSH |
|
|
|
to have different access privilege level assigned via the |
|
|
|
external server. |
|
|
|
|
|
|
aaa authorization console |
Enables authorization of allowing an administrator which |
C |
14 |
|
logs in the Switch through the console port to have |
|
|
|
different access privilege level assigned via the external |
|
|
|
server. |
|
|
|
|
|
|
aaa authorization dot1x radius |
Enables authorization for IEEE 802.1x clients using RADIUS. |
C |
14 |
aaa authorization exec |
Specifies which method (radius or tacacs+) should be |
C |
14 |
<radius|tacacs+> |
used for administrator authorization. |
|
|
no aaa authorization console |
Disables authorization of allowing an administrator which |
C |
14 |
|
logs in the Switch through the console port to have |
|
|
|
different access privilege level assigned via the external |
|
|
|
server. |
|
|
|
|
|
|
Ethernet Switch CLI Reference Guide
28

Chapter 4 AAA Commands
Table 11 aaa authorization Command Summary (continued)
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
no aaa authorization dot1x |
Disables authorization of allowing an IEEE 802.1x client to |
C |
14 |
|
have different bandwidth limit or VLAN ID assigned via the |
|
|
|
external server. |
|
|
|
|
|
|
no aaa authorization exec |
Disables authorization of allowing an administrator which |
C |
14 |
|
logs in the Switch through Telnet or SSH to have different |
|
|
|
access privilege level assigned via the external server. |
|
|
|
|
|
|
Ethernet Switch CLI Reference Guide
29

CHAPTER 5
Anti-Arpscan
Use these commands to configure anti-Arpscan on the Switch.
5.1 Anti-Arpscan Overview
Address Resolution Protocol (ARP), RFC 826, is a protocol used to convert a network-layer IP address to a link-layer MAC address. ARP scan is used to scan the network of a certain interface for alive hosts. It shows the IP address and MAC addresses of all hosts found. Hackers could use ARP scan to find targets in your network. Anti-arpscan is used to detect unusual ARP scan activity and block suspicious hosts or ports.
Unusual ARP scan activity is determined by port and host thresholds that you set. A port threshold is determined by the number of packets received per second on the port. If the received packet rate is over the threshold, then the port is put into an Err-Disable state. You can recover the normal state of the port manually if this happens and after you identify the cause of the problem.
A host threshold is determined by the number of ARP-request packets received per second. There is a global threshold rate for all hosts. If the rate of a host is over the threshold, then that host is blocked by using a MAC address filter. A blocked host is released automatically after the MAC aging time expires.
Note: A port-based threshold must be larger than the host-based threshold or the host-based threshold will not work.
5.2 Command Summary
The following section lists the commands for this feature.
Table 12 anti arpscan Command Summary
COMMAND |
DESCRIPTION |
M |
P |
|
|
|
|
anti arpscan |
Enables Anti-arpscan on the Switch. |
C |
13 |
anti arpscan host threshold <2- |
Sets the maximum number of ARP-request packets |
C |
13 |
100> |
allowed by a host before it is blocked. If the rate of a host is |
|
|
|
over the threshold, then that host is blocked by using a |
|
|
|
MAC address filter. A blocked host is released |
|
|
|
automatically after the MAC aging time expires. |
|
|
|
|
|
|
anti arpscan port threshold <2- |
Sets the maximum number of packets per second allowed |
C |
13 |
255> |
on the port before it is blocked. |
|
|
anti arpscan trust host <ip- |
Creates a trusted host identified by IP address and subnet |
C |
13 |
address> <mask> [ name <name> ] |
mask. |
|
|
|
Anti-arpscan is not performed on trusted hosts. |
|
|
|
|
|
|
Ethernet Switch CLI Reference Guide
30
 Loading...
Loading...