HP 1920-48G, 1920-24G, 1920-16G, 1920-8G, 1920-24G-PoE+ User Manual
...
HP 1920 Gigabit Ethernet Switch Series
User Guide
Part number: 5998-5627
Software version: Release 1102
Document version: 5W100-20140620
Legal and notice information
© Copyright 2014 Hewlett-Packard Development Company, L.P.
No part of this documentation may be reproduced or transmitted in any form or by any means without prior written consent of Hewlett-Packard Development Company, L.P.
The information contained herein is subject to change without notice.
HEWLETT-PACKARD COMPANY MAKES NO WARRANTY OF ANY KIND WITH REGARD TO THIS MATERIAL, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. Hewlett-Packard shall not be liable for errors contained herein or for incidental or consequential damages in connection with the furnishing, performance, or use of this material.
The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. HP shall not be liable for technical or editorial errors or omissions contained herein.

Contents
Overview ······································································································································································ 1
Configuring the switch in the Web interface ············································································································· 2
Restrictions and guidelines···············································································································································2 Operating system requirements ······························································································································2 Web browser requirements·····································································································································2 Others ········································································································································································5 Overview············································································································································································6 Logging in to the Web interface······································································································································6 Logging out of the Web interface ···································································································································7 Web interface ···································································································································································7 Web user level ··································································································································································8 Web-based NM functions················································································································································8 Common items on the Web pages ······························································································································ 16
Configuring the switch at the CLI ······························································································································20
Getting started with the CLI··········································································································································· 20 Setting up the configuration environment ··········································································································· 20 Setting terminal parameters·································································································································· 21 Logging in to the CLI ············································································································································· 24 CLI commands ································································································································································ 24 initialize·································································································································································· 25 ipsetup ···································································································································································· 25 ipsetup ipv6 ··························································································································································· 26 password································································································································································ 26 ping········································································································································································· 27 ping ipv6································································································································································ 27 quit ·········································································································································································· 28 reboot ····································································································································································· 29 summary ································································································································································· 29 upgrade·································································································································································· 30 upgrade ipv6 ························································································································································· 31
Configuration example for upgrading the system software image at the CLI ························································· 32
Configuration wizard·················································································································································34
Basic service setup ················································································································································ 34 Entering the configuration wizard homepage···································································································· 34 Configuring system parameters ··························································································································· 34 Configuring management IP address·················································································································· 36 Finishing configuration wizard ···························································································································· 37
Configuring stack ·······················································································································································39
Overview········································································································································································· 39 Configuration task list ···················································································································································· 39 Configuring global parameters of a stack ·················································································································· 40 Configuring stack ports ················································································································································· 41 Displaying topology summary of a stack ···················································································································· 42 Displaying device summary of a stack ························································································································ 42 Logging in to a member device from the master ········································································································ 42 Stack configuration example ········································································································································ 43 Configuration guidelines ··············································································································································· 46
i
Displaying system and device information···············································································································47
Displaying system information······································································································································ 47 Displaying basic system information··················································································································· 47 Displaying the system resource state··················································································································· 48 Displaying recent system logs ······························································································································ 48 Setting the refresh period ····································································································································· 48
Displaying device information ······································································································································ 48
Configuring basic device settings·····························································································································50
Configuring system name·············································································································································· 50 Configuring idle timeout period ··································································································································· 50
Maintaining devices···················································································································································52
Software upgrade ·························································································································································· 52 Device reboot ································································································································································· 53 Electronic label ······························································································································································· 54 Diagnostic information ·················································································································································· 54
Configuring system time ············································································································································56
Overview········································································································································································· 56 Displaying the current system time ······························································································································· 56 Manually configuring the system time·························································································································· 56 Configuring system time by using NTP ························································································································ 57 System time configuration example ····························································································································· 58
Network requirements··········································································································································· 58 Configuring the system time ································································································································· 59 Verifying the configuration··································································································································· 59 Configuration guidelines ··············································································································································· 59
Configuring syslog ·····················································································································································61
Displaying syslogs·························································································································································· 61 Setting the log host························································································································································· 62 Setting buffer capacity and refresh interval ················································································································ 63
Managing the configuration······································································································································64
Backing up the configuration········································································································································ 64 Restoring the configuration ··········································································································································· 64 Saving the configuration ··············································································································································· 65 Resetting the configuration············································································································································ 66
Managing files ···························································································································································67
Displaying files ······························································································································································· 67 Downloading a file ························································································································································ 67 Uploading a file ····························································································································································· 68 Removing a file······························································································································································· 68 Specifying the main boot file ········································································································································ 68
Managing ports··························································································································································69
Setting operation parameters for a port ······················································································································ 69 Displaying port operation parameters························································································································· 73 Displaying a specified operation parameter for all ports················································································· 73 Displaying all the operation parameters for a port ··························································································· 74 Port management configuration example···················································································································· 75 Network requirements··········································································································································· 75 Configuring the switch ·········································································································································· 75
Configuring port mirroring ········································································································································79
Terminology ···································································································································································· 79
ii
Mirroring source···················································································································································· 79 Mirroring destination ············································································································································ 79 Mirroring direction ················································································································································ 79 Mirroring group····················································································································································· 79 Local port mirroring ······················································································································································· 79 Configuration restrictions and guidelines···················································································································· 80 Recommended configuration procedures···················································································································· 80 Configuring a mirroring group····································································································································· 80 Configuring ports for the mirroring group··················································································································· 81 Local port mirroring configuration example················································································································ 83 Network requirements··········································································································································· 83 Configuration procedure ······································································································································ 83
Managing users ·························································································································································86
Adding a local user ······················································································································································· 86 Setting the super password··········································································································································· 87 Switching to the management level ····························································································································· 88
Configuring a loopback test······································································································································89
Configuration guidelines ··············································································································································· 89 Configuration procedure··············································································································································· 89
Configuring VCT ························································································································································91
Overview········································································································································································· 91 Testing cable status ························································································································································ 91
Configuring the flow interval·····································································································································92
Viewing port traffic statistics ········································································································································· 92
Configuring RMON ···················································································································································93
Overview········································································································································································· 93 Working mechanism············································································································································· 93 RMON groups ······················································································································································· 93 RMON configuration task list ······································································································································· 95 Configuring a statistics entry································································································································ 97 Configuring a history entry··································································································································· 98 Configuring an event entry··································································································································· 99 Configuring an alarm entry································································································································100 Displaying RMON statistics································································································································101 Displaying RMON history sampling information·····························································································103 Displaying RMON event logs ····························································································································104 RMON configuration example ···································································································································105
Configuring energy saving····································································································································· 109
Configuring energy saving on a port ························································································································109
Configuring SNMP·················································································································································· 111
Overview·······································································································································································111 SNMP mechanism ···············································································································································111 SNMP protocol versions ·····································································································································112 Recommended configuration procedure····················································································································112 Enabling SNMP agent ········································································································································113 Configuring an SNMP view········································································································································115 Creating an SNMP view·····································································································································115 Adding rules to an SNMP view ·························································································································116 Configuring an SNMP community ·····························································································································117 Configuring an SNMP group······································································································································118
iii
Configuring an SNMP user·········································································································································120 Configuring SNMP trap function································································································································121 Displaying SNMP packet statistics ·····························································································································123 SNMPv1/v2c configuration example························································································································124 SNMPv3 configuration example ································································································································127
Displaying interface statistics ································································································································· 132
Configuring VLANs ················································································································································· 133
Overview·······································································································································································133 VLAN fundamentals·············································································································································133 VLAN types ··························································································································································134 Port-based VLAN ·················································································································································135 Recommended VLAN configuration procedures·······································································································137 Recommended configuration procedure for assigning an access port to a VLAN ······································137 Recommended configuration procedure for assigning a trunk port to a VLAN ···········································137 Recommended configuration procedure for assigning a hybrid port to a VLAN·········································138 Creating VLANs ···························································································································································139 Configuring the link type of a port·····························································································································140 Setting the PVID for a port···········································································································································141 Selecting VLANs···························································································································································142 Modifying a VLAN·······················································································································································143 Modifying ports ····························································································································································144 VLAN configuration example······································································································································145 Network requirements·········································································································································145 Configuring Switch A··········································································································································145 Configuring Switch B ··········································································································································149 Configuration guidelines ·············································································································································149
Configuring VLAN interfaces ································································································································· 150
Overview·······································································································································································150 Creating a VLAN interface··········································································································································150 Modifying a VLAN interface·······································································································································152 Configuration guidelines ·············································································································································155
Configuring a voice VLAN ····································································································································· 156
Overview·······································································································································································156 OUI addresses ·····················································································································································156 Voice VLAN assignment modes·························································································································156 Security mode and normal mode of voice VLANs···························································································158 Recommended voice VLAN configuration procedure ······························································································159 Configuring voice VLAN globally ······························································································································160 Configuring voice VLAN on ports ······························································································································161 Adding OUI addresses to the OUI list ·······················································································································162 Voice VLAN configuration examples ·························································································································163 Configuring voice VLAN on a port in automatic voice VLAN assignment mode·········································163 Configuring a voice VLAN on a port in manual voice VLAN assignment mode ·········································167 Configuration guidelines ·············································································································································172
Configuring the MAC address table ····················································································································· 173
Overview·······································································································································································173 How a MAC address entry is created ··············································································································173 Types of MAC address entries···························································································································174 Displaying and configuring MAC address entries ···································································································174 Setting the aging time of MAC address entries········································································································175 MAC address table configuration example ··············································································································175 Network requirements·········································································································································175
iv
Creating a static MAC address entry················································································································176
Configuring MSTP ··················································································································································· 177
Overview·······································································································································································177 Introduction to STP ·······················································································································································177 STP protocol packets ···········································································································································177 Basic concepts in STP··········································································································································178 Calculation process of the STP algorithm ·········································································································179 Introduction to RSTP ·····················································································································································184 Introduction to MSTP····················································································································································185 MSTP features ······················································································································································185 MSTP basic concepts ··········································································································································185 How MSTP works ················································································································································189 MSTP implementation on devices ······················································································································189 Protocols and standards ·····································································································································190 Configuration guidelines ·············································································································································190 Recommended MSTP configuration procedure·········································································································190 Configuring an MST region ········································································································································191 Configuring MSTP globally ·········································································································································192 Configuring MSTP on a port·······································································································································195 Displaying MSTP information of a port ·····················································································································197 MSTP configuration example······································································································································199 Network requirements·········································································································································199 Configuration procedure ····································································································································200
Configuring link aggregation and LACP··············································································································· 205
Overview·······································································································································································205 Basic concepts ·····················································································································································205 Link aggregation modes ·····································································································································206
Configuration procedures ···········································································································································208 Configuring a static aggregation group···········································································································208 Configuring a dynamic aggregation group ·····································································································208 Creating a link aggregation group ···················································································································208 Displaying aggregate interface information·····································································································209 Setting LACP priority ···········································································································································211 Displaying LACP-enabled port information·······································································································211
Link aggregation and LACP configuration example·································································································213 Configuration guidelines ····································································································································215
Configuring LLDP····················································································································································· 217
Overview·······································································································································································217 Basic concepts ·····················································································································································217 LLDP operating modes·········································································································································221 Working mechanism···········································································································································221 Protocols and standards ··············································································································································222 Recommended LLDP configuration procedure···········································································································222 Enabling LLDP on ports ················································································································································223 Setting LLDP parameters on ports ·······························································································································224 Setting LLDP parameters for a single port ·········································································································224 Setting LLDP parameters for ports in batch ·······································································································227 Configuring LLDP globally ···········································································································································227 Displaying LLDP information for a port ······················································································································229 Displaying global LLDP information ···························································································································234 Displaying LLDP information received from LLDP neighbors····················································································236 LLDP configuration example········································································································································236 Network requirements·········································································································································236
v
Configuring Switch A··········································································································································236 Configuring Switch B ··········································································································································239 Verifying the configuration·································································································································239 LLDP configuration guidelines ·····································································································································241
Configuring ARP······················································································································································ 242
Overview·······································································································································································242 ARP message format ···········································································································································242 ARP operating mechanism ·································································································································242 ARP table······························································································································································243 Gratuitous ARP·····················································································································································244
Configuring ARP entries ··············································································································································244 Displaying ARP entries········································································································································244 Creating a static ARP entry ································································································································245 Removing ARP entries ··················································································································································245 Configuring gratuitous ARP·········································································································································246 Static ARP configuration example ·····················································································································246
Configuring ARP attack protection························································································································· 250
Overview·······································································································································································250 User validity check ··············································································································································250 ARP packet validity check ··································································································································250 Configuring ARP detection··········································································································································250
Configuring IGMP snooping ·································································································································· 252
Overview·······································································································································································252 Basic IGMP snooping concepts ·························································································································252 How IGMP snooping works ·······························································································································254 Protocols and standards ·····································································································································255 Recommended configuration procedure····················································································································255 Enabling IGMP snooping globally ·····························································································································256 Configuring IGMP snooping in a VLAN····················································································································257 Configuring IGMP snooping port functions···············································································································258 Displaying IGMP snooping multicast forwarding entries·························································································259 IGMP snooping configuration example·····················································································································260 Network requirements·········································································································································260 Configuration procedure ····································································································································261 Verifying the configuration·································································································································264
Configuring MLD snooping ···································································································································· 266
Overview·······································································································································································266 Basic MLD snooping concepts ···························································································································266 How MLD snooping works ·································································································································268 Protocols and standards ·····································································································································269 Recommended configuration procedure····················································································································269 Enabling MLD snooping globally ······················································································································270 Configuring MLD snooping in a VLAN ·············································································································270 Configuring MLD snooping port functions········································································································272 Displaying MLD snooping multicast forwarding entries··················································································273 MLD snooping configuration example·······················································································································274 Network requirements·········································································································································274 Configuration procedure ····································································································································274 Verifying the configuration·································································································································277
Configuring IPv4 and IPv6 routing ························································································································ 278
Overview·······································································································································································278 Routing table························································································································································278
vi
Static route ···························································································································································278 Default route·························································································································································279 Displaying the IPv4 active route table ·······················································································································279 Creating an IPv4 static route·······································································································································280 Displaying the IPv6 active route table ·······················································································································281 Creating an IPv6 static route·······································································································································281 IPv4 static route configuration example·····················································································································283 Network requirements·········································································································································283 Configuration considerations ·····························································································································283 Configuration procedure ····································································································································283 Verifying the configuration·································································································································286 IPv6 static route configuration example·····················································································································287 Network requirements·········································································································································287 Configuration considerations ·····························································································································287 Configuration procedure ····································································································································287 Verifying the configuration·································································································································290 Configuration guidelines ·············································································································································291
DHCP overview ······················································································································································· 292
DHCP address allocation ············································································································································292 Allocation mechanisms ·······································································································································292 IP address allocation process·····························································································································293 IP address lease extension··································································································································293
DHCP message format·················································································································································294 DHCP options ·······························································································································································295 Common DHCP options······································································································································295 Option 82 ····························································································································································295 Protocols and standards ··············································································································································296
Configuring DHCP relay agent ······························································································································ 297
Overview·······································································································································································297 Recommended configuration procedure····················································································································298 Enabling DHCP and configuring advanced parameters for the DHCP relay agent ·············································299 Creating a DHCP server group ··································································································································300 Enabling the DHCP relay agent on an interface ······································································································301 Configuring and displaying clients' IP-to-MAC bindings ·························································································302 DHCP relay agent configuration example·················································································································303
Configuring DHCP snooping·································································································································· 306
Overview·······································································································································································306 Application of trusted ports ································································································································306 DHCP snooping support for Option 82············································································································308 Recommended configuration procedure····················································································································308 Enabling DHCP snooping ···········································································································································309 Configuring DHCP snooping functions on an interface···························································································309 Displaying clients' IP-to-MAC bindings ······················································································································310 DHCP snooping configuration example ····················································································································311
Managing services·················································································································································· 314
Overview·······································································································································································314 Managing services·······················································································································································315
Using diagnostic tools············································································································································· 317
Ping················································································································································································317 Traceroute ·····································································································································································317 Ping operation ······························································································································································318 Traceroute operation···········································································································································319
vii
Configuring 802.1X ··············································································································································· 321
802.1X overview ·························································································································································321
802.1X architecture ············································································································································321 Access control methods ······································································································································321 Controlled/uncontrolled port and port authorization status ···········································································322 Packet formats······················································································································································322 EAP over RADIUS ················································································································································323 Initiating 802.1X authentication ························································································································324 802.1X authentication procedures····················································································································325 802.1X timers ······················································································································································328 Using 802.1X authentication with other features ····························································································329
Configuration prerequisites·········································································································································331 Recommended configuration procedure····················································································································332 Configuring 802.1X globally ·····································································································································332 Configuring 802.1X on a port ···································································································································333 Configuring an 802.1X guest VLAN·················································································································335 Configuring an Auth-Fail VLAN ·························································································································336 802.1X configuration examples·································································································································336 MAC-based 802.1X configuration example····································································································336 802.X with ACL assignment configuration example ·······················································································343
Configuring AAA ···················································································································································· 352
Overview·······································································································································································352 AAA application··················································································································································352 Domain-based user management ······················································································································353 Configuration prerequisites·········································································································································353 Recommended configuration procedure···········································································································353 Configuring an ISP domain································································································································354 Configuring authentication methods for the ISP domain·················································································355 Configuring authorization methods for the ISP domain ··················································································356 Configuring accounting methods for the ISP domain······················································································357 AAA configuration example ·······································································································································359
Configuring RADIUS ··············································································································································· 363
Overview·······································································································································································363 Client/server model ············································································································································363 Security and authentication mechanisms ··········································································································364 Basic RADIUS message exchange process ······································································································364 RADIUS packet format ········································································································································365 Extended RADIUS attributes ·······························································································································367 Protocols and standards ·····································································································································368
Configuring a RADIUS scheme···································································································································368 Configuring common parameters······················································································································369 Adding RADIUS servers ······································································································································373 RADIUS configuration example ··································································································································374 Configuration guidelines ·············································································································································378
Configuring users ···················································································································································· 380
Configuring a local user··············································································································································380 Configuring a user group············································································································································382
Managing certificates ············································································································································· 384
Overview·······································································································································································384 PKI terms·······························································································································································384 PKI architecture····················································································································································384 How PKI works·····················································································································································385
viii
PKI applications ···················································································································································386 Recommended configuration procedures··················································································································386 Recommended configuration procedure for manual request··········································································386 Recommended configuration procedure for automatic request······································································388 Creating a PKI entity····················································································································································388 Creating a PKI domain ················································································································································390 Generating an RSA key pair·······································································································································393 Destroying the RSA key pair ·······································································································································394 Retrieving and displaying a certificate ······················································································································394 Requesting a local certificate······································································································································396 Retrieving and displaying a CRL ································································································································398 PKI configuration example ··········································································································································399 Configuration guidelines ·············································································································································403
Configuring MAC authentication··························································································································· 404
Overview·······································································································································································404 User account policies ··········································································································································404 Authentication methods·······································································································································404 MAC authentication timers·································································································································405 Using MAC authentication with other features ·········································································································405 VLAN assignment ················································································································································405 ACL assignment ···················································································································································405 Auth-Fail VLAN ····················································································································································405 Configuration prerequisites·········································································································································406 Recommended configuration procedure····················································································································406 Configuring MAC authentication globally ················································································································406 Configuring MAC authentication on a port ·····································································································408 MAC authentication configuration examples············································································································408 Local MAC authentication configuration example···························································································408 ACL assignment configuration example············································································································411
Configuring port security ········································································································································ 421
Overview·······································································································································································421 Port security features ···········································································································································421 Port security modes ·············································································································································421
Configuration guidelines ·············································································································································423 Recommended configuration procedure····················································································································423 Configuring global settings for port security ·············································································································424 Configuring basic port security control······················································································································425 Configuring secure MAC addresses ··························································································································427 Configuring advanced port security control··············································································································428 Configuring permitted OUIs········································································································································429 Port security configuration examples ·························································································································430
Basic port security mode configuration example·····························································································430 Advanced port security mode configuration example ····················································································433
Configuring port isolation······································································································································· 440
Configuring the isolation group··································································································································440 Port isolation configuration example··························································································································441
Configuring authorized IP ······································································································································ 443
Configuration procedure·············································································································································443 Authorized IP configuration example·························································································································444 Network requirements·········································································································································444 Configuration procedure ····································································································································444
ix
Configuring loopback detection ···························································································································· 447
Recommended configuration procedure····················································································································447 Configuring loopback detection globally··················································································································447 Configuring loopback detection on a port················································································································448
Configuring ACLs···················································································································································· 450
Overview·······································································································································································450 ACL categories ····················································································································································450 Match order ·························································································································································450 Implementing time-based ACL rules···················································································································452 IPv4 fragments filtering with ACLs ·····················································································································452
Configuration guidelines ·············································································································································452 Recommend ACL configuration procedures ··············································································································452 Recommended IPv4 ACL configuration procedure ··························································································452 Recommended IPv6 ACL configuration procedure ··························································································453 Configuring a time range ···································································································································453 Adding an IPv4 ACL ···········································································································································454 Configuring a rule for a basic IPv4 ACL···········································································································455 Configuring a rule for an advanced IPv4 ACL·································································································456 Configuring a rule for an Ethernet frame header ACL ····················································································459 Adding an IPv6 ACL ···········································································································································461 Configuring a rule for a basic IPv6 ACL···········································································································462 Configuring a rule for an advanced IPv6 ACL·································································································463
Configuring QoS····················································································································································· 466
Overview·······································································································································································466 Networks without QoS guarantee ·····················································································································466 QoS requirements of new applications·············································································································466 Congestion: causes, impacts, and countermeasures·······················································································467 End-to-end QoS····················································································································································468 Traffic classification·············································································································································468 Packet precedences·············································································································································469 Queue scheduling ···············································································································································471 Rate limit·······························································································································································473 Priority mapping ··················································································································································474 Introduction to priority mapping tables·············································································································475
Configuration guidelines ·············································································································································476 Recommended QoS configuration procedures·········································································································476 Adding a class ·····························································································································································478 Configuring classification rules···································································································································479 Adding a traffic behavior············································································································································480 Configuring traffic mirroring and traffic redirecting for a traffic behavior ····························································481 Configuring other actions for a traffic behavior ·······································································································481 Adding a policy ···························································································································································483 Configuring classifier-behavior associations for the policy ·····················································································484 Applying a policy to a port·········································································································································484 Configuring queue scheduling on a port···················································································································485 Configuring rate limit on a port··································································································································486 Configuring priority mapping tables··························································································································487 Configuring priority trust mode on a port ·················································································································488
ACL and QoS configuration example ··················································································································· 489
Network requirements ·················································································································································489 Configuring Switch ······················································································································································489
x
Configuring PoE ······················································································································································ 497
Overview·······································································································································································497 Configuring PoE ···························································································································································498 Configuring PoE ports·········································································································································498 Configuring non-standard PD detection············································································································499 Displaying information about PSE and PoE ports ····························································································500 PoE configuration example ·········································································································································501
Support and other resources ·································································································································· 503
Contacting HP ······························································································································································503 Subscription service ············································································································································503 Related information······················································································································································503 Documents····························································································································································503 Websites·······························································································································································503 Conventions ··································································································································································504
Index ········································································································································································ 506
xi

Overview
The HP 1920 Switch Series can be configured through the command line interface (CLI), Web interface, and SNMP/MIB. These configuration methods are suitable for different application scenarios.
•The Web interface supports all 1920 Switch Series configurations.
•The CLI provides configuration commands to facilitate your operation. To perform other configurations not supported by the CLI, use the Web interface.
1

Configuring the switch in the Web interface
Restrictions and guidelines
To ensure a successful login, verify that your operating system and Web browser meet the requirements, and follow the guidelines in this section.
Operating system requirements
•The device supports the following operating systems:
{Windows XP
{Windows 2000
{Windows Server 2003 Enterprise Edition
{Windows Server 2003 Standard Edition
{Windows Vista
{Windows 7
{Linux
{MAC OS
•If you are using a Windows operating system, turn off the Windows firewall. The Windows firewall limits the number of TCP connections. When the limit is reached, you cannot log in to the Web interface.
Web browser requirements
•HP recommends that you use the following Web browsers:
{Internet Explorer 6 SP2 or higher
{Mozilla Firefox 3 or higher
{Google Chrome 2.0.174.0 or higher
•If you are using a Microsoft Internet Explorer browser, you must enable the security settings (see "Enabling securing settings in a Microsoft Internet Explorer browser"), including Run ActiveX controls and plug-ins, Script ActiveX controls marked safe for scripting, and Active scripting.
•If you are using a Mozilla Firefox browser, you must enable JavaScript (see "Enabling JavaScript in a Firefox browserEnabling JavaScript in a Firefox browser").
Enabling securing settings in a Microsoft Internet Explorer browser
1.Launch the Internet Explorer, and select Tools > Internet Options from the main menu.
2.Select the Security tab, and select the content zone where the target Website resides, as shown in Figure 1.
2
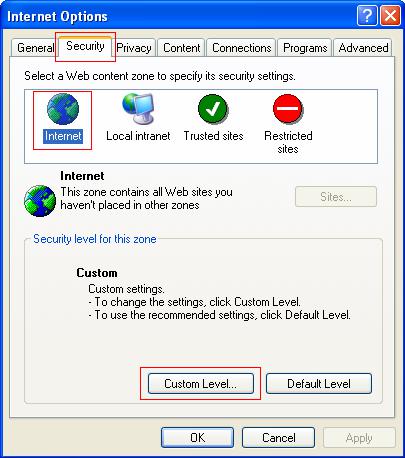
Figure 1 Internet Explorer settings (1)
3.Click Custom Level.
4.In the Security Settings dialog box, enable Run ActiveX controls and plug-ins, Script ActiveX controls marked safe for scripting, and Active scripting.
3
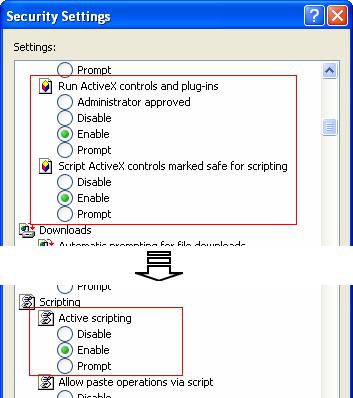
Figure 2 Internet Explorer settings (2)
5. Click OK to save your settings.
Enabling JavaScript in a Firefox browser
1.Launch the Firefox browser, and select Tools > Options.
2.In the Options dialog box, click the Content icon, and select Enable JavaScript.
4

Figure 3 Firefox browser settings
3.Click OK to save your settings.
Others
•The Web interface does not support the Back, Next, and Refresh buttons provided by the browser. Using these buttons might result in abnormal display of Web pages.
•To ensure correct display of Web page contents after software upgrade or downgrade, clear data cached by the browser before you log in.
•If you click the verification code displayed on the Web login page, you can get a new verification code.
•Up to five users can concurrently log in to the device through the Web interface.
•A list can contain a maximum of 20000 entries if displayed in pages.
•The PC where you configure the device is not necessarily a Web-based network management terminal. A Web-based network management terminal is a PC used to log in to the Web interface and is required to be reachable to the device.
•After logging in to the Web interface, you can select Device > Users from the navigation tree, create a new user, and select Wizard or Network > VLAN interface to configure the IP address of the VLAN interface acting as the management interface. For more information, see the corresponding configuration guides of these modules.
5

Overview
The device provides web-based configuration interfaces for visual device management and maintenance.
Figure 4 Web-based network management operating environment
Logging in to the Web interface
You can use the following default settings to log in to the web interface through HTTP:
•Username—admin
•Password—None
•IP address of VLAN-interface 1 on the device—IP address of the device, depending on the status of the network where the device resides.
{If the device is not connected to the network, or no DHCP server exists in the subnet where the device resides, you can get the IP address of the device on the label on the device. IP address is 169.254.xxx.xxx. If the MAC address is 08004E000102, the IP address would be 169.254.1.2.
{If a DHCP server exists in the subnet where the device resides, the device will dynamically obtain its IP address through the DHCP server.
You can log in to the device through the console port, and execute the summary command to view the information about its IP address.
<Sysname> summary |
|
Select menu option: |
Summary |
IP Method: |
DHCP |
IP address: |
169.254.1.2 |
Subnet mask: |
255.255.0.0 |
Default gateway: |
0.0.0.0 |
<Omitted> |
|
Assuming that the IP address of the device is 169.254.1.2, to log in to the Web interface of the device from a PC:
1.Connect the Ethernet interface of the device to a PC by using a crossover Ethernet cable. By default, all interfaces belong to VLAN 1.
2.Configure an IP address for the PC and make sure that the PC and device can reach each other.
For example, assign the PC an IP address (for example, 169.254.1.27) within 169.254.0.0/16 (except for the IP address of the device).
3.Open the browser, and input the login information.
a.Type the IP address http:// 169.254.1.2 in the address bar and press Enter. The login page of the web interface (see Figure 5) appears.
6
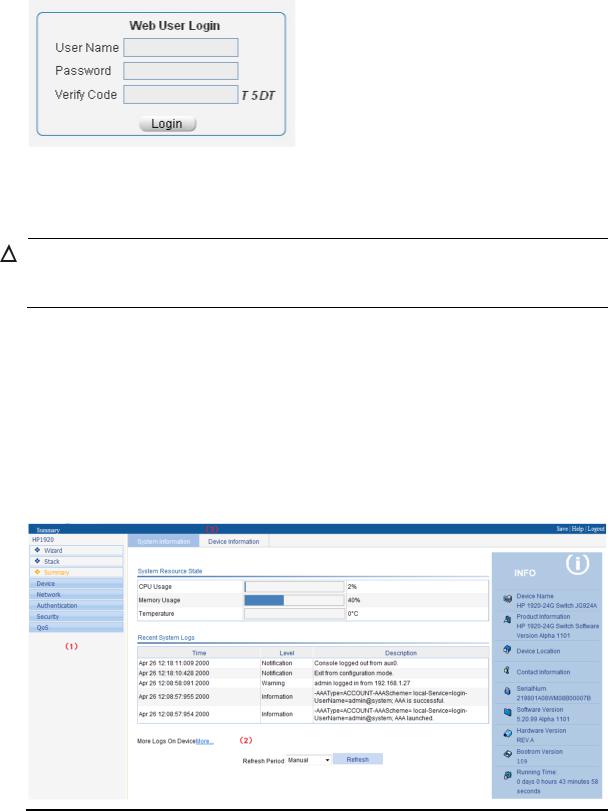
b.Enter the username admin and the verification code, leave the password blank, and click
Login.
Figure 5 Login page of the Web interface
Logging out of the Web interface
CAUTION:
•You cannot log out by directly closing the browser.
•For security purposes, log out of the Web interface after you finish your operations.
1.Save the current configuration.
Because the system does not save the current configuration automatically, HP recommends that you perform this step to avoid loss of configuration.
2.Click Logout in the upper-right corner of the Web interface.
Web interface
The Web interface includes three parts: navigation tree, title area, and body area, as shown in Figure 6.
Figure 6 Web-based configuration interface
(1) Navigation tree |
(2) Body area |
(3) Title area |
7

•Navigation tree—Organizes the Web-based NM functions as a navigation tree, where you can select and configure functions as needed. The result is displayed in the body area.
•Body area—Allows you to configure and display features.
•Title area—On the left, displays the path of the current configuration interface in the navigation area; on the right, provides the Save button to quickly save the current configuration, the Help button to display the Web-related help information, and the Logout button to log out of the Web interface.
Web user level
Web user levels, from low to high, are visitor, monitor, configure, and management. A user with a higher level has all the operating rights of a user with a lower level.
•Visitor—Users of this level can only use the network diagnostic tools ping and Trace Route. They can neither access the device data nor configure the device.
•Monitor—Users of this level can only access the device data but cannot configure the device.
•Configure—Users of this level can access device data and configure the device, but they cannot upgrade the host software, add/delete/modify users, or backup/restore configuration files.
•Management—Users of this level can perform any operations to the device.
Web-based NM functions
User level in Table 1 indicates that users of this level or users of a higher level can perform the corresponding operations.
Table 1 Web-based NM function description
Function menu |
|
Description |
User level |
|||
Wizard |
|
IP Setup |
Perform quick configuration of the device. |
Management |
||
|
|
|
|
|
|
|
|
|
|
Setup |
Display global settings and port settings of a stack. |
Configure |
|
|
|
|
|
|
||
|
|
|
Configure global parameters and stack ports. |
Management |
||
|
|
|
|
|||
|
|
|
|
|
|
|
Stack |
|
Topology |
Display the topology summary of a stack. |
Configure |
||
|
|
|
Summary |
|||
|
|
|
|
|
||
|
|
|
Device |
Display the control panels of stack members. |
Configure |
|
|
|
|
Summary |
|||
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
System |
Display the basic system information, system |
Monitor |
|
|
|
|
Information |
resource state, and recent system operation logs. |
||
Summary |
|
|||||
|
|
|
||||
Device |
Display the port information about the device. |
Monitor |
||||
|
|
|
||||
|
|
|
Information |
|||
|
|
|
|
|
||
|
|
|
|
|
|
|
|
|
|
System Name |
Display and configure the system name. |
Configure |
|
|
|
Basic |
|
|
|
|
|
|
Web Idle |
Display and configure the idle timeout period for |
Configure |
||
|
|
|
||||
Devi |
|
|
Timeout |
logged-in users. |
||
|
|
|||||
|
|
|
|
|||
ce |
Device |
Software |
Upload upgrade file from local host, and upgrade |
Management |
||
|
|
|||||
|
|
Upgrade |
the system software. |
|||
|
|
Maintenanc |
|
|||
|
|
|
|
|
||
|
|
e |
Reboot |
Reboot the device. |
Management |
|
|
|
|
||||
|
|
|
|
|
|
|
8

Function menu |
|
Description |
User level |
|
|
|
Electronic |
Display the electronic label of the device. |
Monitor |
|
|
Label |
||
|
|
|
|
|
|
|
|
|
|
|
|
Diagnostic |
Generate diagnostic information file and view or |
Management |
|
|
Information |
save the file to local host. |
|
|
|
|
||
|
|
|
|
|
|
|
System Time |
Display and configure the system date and time. |
Configure |
|
System Time |
|
|
|
|
Net Time |
Display the synchronization status of the system |
Monitor |
|
|
|
|||
|
|
clock and configure the network time. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Loglist |
Display and refresh system logs. |
Monitor |
|
|
|
|
|
|
|
Clear system logs. |
Configure |
|
|
|
|
||
|
Syslog |
|
|
|
|
Loghost |
Display and configure the loghost. |
Configure |
|
|
|
|||
|
|
|
|
|
|
|
Log Setup |
Display and configure the buffer capacity and |
Configure |
|
|
interval for refreshing system logs. |
||
|
|
|
|
|
|
|
|
|
|
|
|
|
Back up the configuration file to be used at the next |
|
|
|
Backup |
startup from the device to the host of the current |
Management |
|
|
|
user. |
|
|
|
|
|
|
|
Configurati |
|
Upload the configuration file to be used at the next |
|
|
Restore |
startup from the host of the current user to the |
Management |
|
|
on |
|
device. |
|
|
|
|
|
|
|
|
Save |
Save the current configuration to the configuration |
Configure |
|
|
file to be used at the next startup. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Initialize |
Restore the factory default settings. |
Configure |
|
|
|
|
|
|
File |
File |
Manage files on the device, such as displaying the |
|
|
Manageme |
file list, downloading a file, uploading a file, and |
Management |
|
|
Management |
|||
|
nt |
removing a file. |
|
|
|
|
|
||
|
|
|
|
|
|
|
Summary |
Display port information by features. |
Monitor |
|
Port |
|
|
|
|
Detail |
Display feature information by ports. |
Monitor |
|
|
Manageme |
|||
|
|
|
|
|
|
|
|
|
|
|
nt |
Setup |
Create, modify, delete, and enable/disable a port, |
Configure |
|
|
and clear port statistics. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Summary |
Display the configuration information about a port |
Monitor |
|
|
mirroring group. |
||
|
|
|
|
|
|
Port |
|
|
|
|
Add |
Create a port mirroring group. |
Configure |
|
|
Mirroring |
|
|
|
|
Remove |
Remove a port mirroring group. |
Configure |
|
|
|
|||
|
|
|
|
|
|
|
Modify Port |
Configure ports for a mirroring group. |
Configure |
|
|
|
|
|
|
|
Summary |
Display the brief information about FTP and Telnet |
Monitor |
|
|
users. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Super |
Configure a password for a lower-level user to |
|
|
|
switch from the current access level to the |
Management |
|
|
|
Password |
||
|
Users |
management level. |
|
|
|
|
|
||
|
|
|
|
|
|
|
Create |
Create an FTP or Telnet user. |
Management |
|
|
|
|
|
|
|
Modify |
Modify FTP or Telnet user information. |
Management |
|
|
|
|
|
|
|
Remove |
Remove an FTP or a Telnet user. |
Management |
|
|
|
|
|
9

Function menu |
|
Description |
User level |
|
|
|
Switch To |
Switch the current user level to the management |
Visitor |
|
|
Management |
level. |
|
|
|
|
||
|
|
|
|
|
|
Loopback |
Loopback |
Perform loopback tests on Ethernet interfaces. |
Configure |
|
|
|
|
|
|
VCT |
VCT |
Check the status of the cables connected to Ethernet |
Configure |
|
ports. |
|||
|
|
|
|
|
|
|
|
|
|
|
Flow |
Port Traffic |
Display the average rate at which the interface |
|
|
receives and sends packets within a specified time |
Monitor |
||
|
Interval |
Statistics |
||
|
interval. |
|
||
|
|
|
|
|
|
|
|
|
|
|
|
Statistics |
Display, create, modify, and clear RMON |
Configure |
|
|
statistics. |
||
|
|
|
|
|
|
|
|
|
|
|
|
History |
Display, create, modify, and clear RMON history |
Configure |
|
|
sampling information. |
||
|
RMON |
|
|
|
|
|
|
|
|
|
Alarm |
Display, create, modify, and clear alarm entries. |
Configure |
|
|
|
|||
|
|
|
|
|
|
|
Event |
Display, create, modify, and clear event entries. |
Configure |
|
|
|
|
|
|
|
Log |
Display log information about RMON events. |
Configure |
|
|
|
|
|
|
Energy |
Energy Saving |
Display and configure the energy saving settings of |
Configure |
|
Saving |
an interface. |
||
|
|
|
||
|
|
|
|
|
|
|
|
Display and refresh SNMP configuration and |
Monitor |
|
|
Setup |
statistics information. |
|
|
|
|
||
|
|
|
|
|
|
|
|
Configure SNMP. |
Configure |
|
|
|
|
|
|
|
Community |
Display SNMP community information. |
Monitor |
|
|
|
|
|
|
|
Create, modify, and delete an SNMP community. |
Configure |
|
|
|
|
||
|
|
|
|
|
|
|
Group |
Display SNMP group information. |
Monitor |
|
|
|
|
|
|
|
Create, modify, and delete an SNMP group. |
Configure |
|
|
|
|
||
|
SNMP |
|
|
|
|
|
Display SNMP user information. |
Monitor |
|
|
|
User |
||
|
|
|
|
|
|
|
Create, modify, and delete an SNMP user. |
Configure |
|
|
|
|
||
|
|
|
|
|
|
|
|
Display the status of the SNMP trap function and |
Monitor |
|
|
|
information about target hosts. |
|
|
|
Trap |
|
|
|
|
|
|
|
|
|
Enable or disable the SNMP trap function; create, |
Configure |
|
|
|
|
||
|
|
|
modify, and delete a target host. |
|
|
|
|
|
|
|
|
|
|
|
|
|
View |
Display SNMP view information. |
Monitor |
|
|
|
|
|
|
|
Create, modify, and delete an SNMP view. |
Configure |
|
|
|
|
||
|
|
|
|
|
|
Interface |
Interface |
Display and clear the statistics information about |
Configure |
|
Statistics |
Statistics |
an interface. |
|
|
|
|||
|
|
|
|
|
10

Function menu |
Description |
User level |
Net work
|
Select VLAN |
Select a VLAN range. |
Monitor |
|
|
|
|
|
|
|
Create |
Create VLANs. |
Configure |
|
|
|
|
|
|
|
Port Detail |
Display the VLAN-related details of a port. |
Monitor |
|
|
|
|
|
|
|
Detail |
Display the member port information about a |
Monitor |
|
VLAN |
VLAN. |
|||
|
|
|||
|
|
|
|
|
|
Modify VLAN |
Modify the description and member ports of a |
Configure |
|
|
VLAN. |
|||
|
|
|
||
|
|
|
|
|
|
Modify Port |
Change the VLAN to which a port belongs. |
Configure |
|
|
|
|
|
|
|
Remove |
Remove VLANs. |
Configure |
|
|
|
|
|
|
|
Summary |
Display information about VLAN interfaces by |
Monitor |
|
|
address type. |
|||
|
|
|
||
|
|
|
|
|
VLAN |
Create |
Create VLAN interfaces and configure IP addresses |
Configure |
|
for them. |
||||
|
|
|||
Interface |
|
|
|
|
Modify |
Modify the IP addresses and status of VLAN |
Configure |
||
|
||||
|
interfaces. |
|||
|
|
|
||
|
|
|
|
|
|
Remove |
Remove VLAN interfaces. |
Configure |
|
|
|
|
|
|
|
Summary |
Display voice VLAN information globally or on a |
Monitor |
|
|
port. |
|||
|
|
|
||
|
|
|
|
|
|
Setup |
Configure the global voice VLAN. |
Configure |
|
|
|
|
|
|
|
Port Setup |
Configure a voice VLAN on a port. |
Configure |
|
|
|
|
|
|
Voice VLAN |
OUI Summary |
Display the addresses of the OUIs that can be |
Monitor |
|
|
identified by voice VLAN. |
|||
|
|
|
||
|
OUI Add |
Add the address of an OUI that can be identified |
Configure |
|
|
by voice VLAN. |
|||
|
|
|
||
|
|
|
|
|
|
OUI Remove |
Remove the address of an OUI that can be |
Configure |
|
|
identified by voice VLAN. |
|||
|
|
|
||
|
|
|
|
|
|
MAC |
Display MAC address information. |
Monitor |
|
|
|
|
||
MAC |
Create and remove MAC addresses. |
Configure |
||
|
||||
|
|
|
|
|
|
Setup |
Display and configure MAC address aging time. |
Configure |
|
|
|
|
|
|
|
Region |
Display information about MST regions. |
Monitor |
|
|
|
|
||
|
Modify MST regions. |
Configure |
||
|
|
|||
|
|
|
|
|
MSTP |
Global |
Set global MSTP parameters. |
Configure |
|
|
|
|
|
|
|
Port Summary |
Display the MSTP information about ports. |
Monitor |
|
|
|
|
|
|
|
Port Setup |
Set MSTP parameters on ports. |
Configure |
|
|
|
|
|
|
|
Summary |
Display information about link aggregation |
Monitor |
|
|
groups. |
|||
Link |
|
|
||
|
|
|
||
Create |
Create link aggregation groups. |
Configure |
||
Aggregatio |
||||
|
|
|
||
n |
Modify |
Modify link aggregation groups. |
Configure |
|
|
||||
|
|
|
|
|
|
Remove |
Remove link aggregation groups. |
Configure |
11

Function menu |
|
Description |
User level |
|
|
|
Summary |
Display information about LACP-enabled ports and |
Monitor |
|
LACP |
their partner ports. |
||
|
|
|
||
|
|
|
|
|
|
|
Setup |
Set LACP priorities. |
Configure |
|
|
|
|
|
|
|
|
Display the LLDP configuration information, local |
|
|
|
Port Setup |
information, neighbor information, statistics |
Monitor |
|
|
information, and status information about a port. |
|
|
|
|
|
|
|
|
|
|
Modify LLDP configuration on a port. |
Configure |
|
|
|
|
|
|
LLDP |
Global Setup |
Display global LLDP configuration information. |
Monitor |
|
|
|
||
|
Configure global LLDP parameters. |
Configure |
||
|
|
|
||
|
|
|
|
|
|
|
Global |
Display global LLDP local information and statistics. |
Monitor |
|
|
Summary |
||
|
|
|
|
|
|
|
|
|
|
|
|
Neighbor |
Display global LLDP neighbor information. |
Monitor |
|
|
Summary |
||
|
|
|
|
|
|
|
|
|
|
|
|
ARP Table |
Display ARP table information. |
Monitor |
|
|
|
|
|
|
ARP |
Add, modify, and remove ARP entries. |
Configure |
|
|
|
|||
|
|
|
|
|
|
Manageme |
|
Display the configuration information about |
Monitor |
|
nt |
|
||
|
Gratuitous ARP |
gratuitous ARP. |
||
|
|
|
||
|
|
|
|
|
|
|
|
Configure gratuitous ARP. |
Configure |
|
|
|
|
|
|
ARP |
ARP Detection |
Display ARP detection configuration information. |
Monitor |
|
|
|
||
|
Anti-Attack |
Configure ARP detection. |
Configure |
|
|
|
|||
|
|
|
||
|
|
|
|
|
|
|
|
Display global IGMP snooping configuration |
|
|
|
|
information or the IGMP snooping configuration |
Monitor |
|
|
Basic |
information in a VLAN, and the IGMP snooping |
|
|
|
|
||
|
|
multicast entry information. |
|
|
|
IGMP |
|
|
|
|
|
|
|
|
|
|
Configure IGMP snooping globally or in a VLAN. |
Configure |
|
|
Snooping |
|
||
|
|
|
|
|
|
|
|
Display the IGMP snooping configuration |
Monitor |
|
|
Advanced |
information on a port. |
|
|
|
|
||
|
|
|
|
|
|
|
|
Configure IGMP snooping on a port. |
Configure |
|
|
|
|
|
|
|
|
Display global MLD snooping configuration |
|
|
|
|
information or the MLD snooping configuration |
Monitor |
|
|
Basic |
information in a VLAN, and the MLD snooping |
|
|
|
|
||
|
|
multicast entry information. |
|
|
|
MLD |
|
|
|
|
|
|
|
|
|
|
Configure MLD snooping globally or in a VLAN. |
Configure |
|
|
Snooping |
|
||
|
|
|
|
|
|
|
|
Display the MLD snooping configuration |
Monitor |
|
|
Advanced |
information on a port. |
|
|
|
|
||
|
|
|
|
|
|
|
|
Configure MLD snooping on a port. |
Configure |
|
|
|
|
|
|
|
Summary |
Display the IPv4 active route table. |
Monitor |
|
|
|
|
|
|
IPv4 Routing |
Create |
Create an IPv4 static route. |
Configure |
|
|
|
|
|
|
|
Remove |
Delete the selected IPv4 static routes. |
Configure |
|
|
|
|
|
12

Function menu |
|
Description |
User level |
||
|
|
Summary |
Display the IPv6 active route table. |
Monitor |
|
|
|
|
|
|
|
|
IPv6 Routing |
Create |
Create an IPv6 static route. |
Configure |
|
|
|
|
|
|
|
|
|
Remove |
Delete the selected IPv6 static routes. |
Configure |
|
|
|
|
|
|
|
|
|
|
Display information about the DHCP status, |
|
|
|
|
|
advanced configuration information about the |
|
|
|
|
|
DHCP relay agent, DHCP server group |
Monitor |
|
|
|
|
configuration, DHCP relay agent interface |
|
|
|
|
DHCP Relay |
configuration, and the DHCP client information. |
|
|
|
|
|
|
||
|
|
|
Enable/disable DHCP, configure advanced DHCP |
|
|
|
DHCP |
|
relay agent settings, configure a DHCP server |
Configure |
|
|
|
group, and enable/disable the DHCP relay agent |
|||
|
|
|
|
||
|
|
|
on an interface. |
|
|
|
|
|
|
|
|
|
|
|
Display the status, trusted and untrusted ports and |
Monitor |
|
|
|
DHCP |
DHCP client information about DHCP snooping. |
||
|
|
|
|||
|
|
|
|
||
|
|
Snooping |
Enable/disable DHCP snooping, and configure |
Configure |
|
|
|
|
|||
|
|
|
DHCP snooping trusted and untrusted ports. |
||
|
|
|
|
||
|
|
|
|
||
|
|
|
Display the states of services: enabled or disabled. Configure |
||
|
Service |
Service |
|
|
|
|
Enable/disable services, and set related |
Management |
|||
|
|
|
|||
|
|
|
parameters. |
||
|
|
|
|
||
|
|
|
|
|
|
|
|
IPv4 Ping |
Ping an IPv4 address. |
Visitor |
|
|
|
|
|
|
|
|
|
IPv6 Ping |
Ping an IPv6 address. |
Visitor |
|
|
Diagnostic |
|
|
|
|
|
IPv4 |
Perform IPv4 trace route operations. |
Visitor |
||
|
Tools |
||||
|
Traceroute |
||||
|
|
|
|
||
|
|
|
|
|
|
|
|
IPv6 |
Perform IPv6 trace route operations. |
Visitor |
|
|
|
Traceroute |
|||
|
|
|
|
||
|
|
|
|
|
|
|
MAC |
MAC |
Display MAC authentication configuration |
Monitor |
|
|
information. |
||||
|
Authenticati |
|
|||
|
Authentication |
|
|
||
|
on |
Configure MAC authentication. |
Configure |
||
|
|
||||
|
|
|
|||
|
|
|
|
|
|
|
|
|
Display 802.1X configuration information globally |
Monitor |
|
|
802.1X |
802.1X |
or on a port. |
||
|
|
||||
|
|
|
|||
|
|
|
Configure 802.1X globally or on a port. |
Configure |
|
|
|
|
|
|
|
|
Port Security |
Port Security |
Display port security configuration information. |
Monitor |
|
Auth |
|
|
|||
Configure port security. |
Configure |
||||
|
|
||||
entic |
|
|
|
|
|
|
|
Display ISP domain configuration information. |
Monitor |
||
ation |
|
Domain Setup |
|||
|
|
Add and remove ISP domains. |
Management |
||
|
|
|
|||
|
|
|
|
|
|
|
|
|
Display the authentication configuration |
Monitor |
|
|
|
Authentication |
information about an ISP domain. |
||
|
AAA |
|
|||
|
|
|
|||
|
|
Specify authentication methods for an ISP domain. |
Management |
||
|
|
|
|||
|
|
|
|
|
|
|
|
|
Display the authorization method configuration |
Monitor |
|
|
|
Authorization |
information about an ISP domain. |
||
|
|
|
|||
|
|
|
|
||
|
|
|
Specify authorization methods for an ISP domain. |
Management |
|
|
|
|
|
|
|
13

Function menu |
|
Description |
User level |
||
|
|
|
Display the accounting method configuration |
Monitor |
|
|
|
Accounting |
information about an ISP domain. |
||
|
|
|
|||
|
|
|
|
||
|
|
|
Specify accounting methods for an ISP domain. |
Management |
|
|
|
|
|
|
|
|
RADIUS |
RADIUS Server |
Display and configure RADIUS server information. |
Management |
|
|
|
|
|
||
|
RADIUS Setup |
Display and configure RADIUS parameters. |
Management |
||
|
|
||||
|
|
|
|
|
|
|
|
|
Display configuration information about local |
Monitor |
|
|
|
Local User |
users. |
||
|
|
|
|||
|
|
|
|
||
|
Users |
|
Create, modify, and remove a local user. |
Management |
|
|
|
|
|
||
|
|
Display configuration information about user |
Monitor |
||
|
|
|
|||
|
|
User Group |
groups. |
||
|
|
|
|||
|
|
|
|
||
|
|
|
Create, modify, and remove a user group. |
Management |
|
|
|
|
|
|
|
|
|
Entity |
Display information about PKI entities. |
Monitor |
|
|
|
|
|
||
|
|
Add, modify, and delete a PKI entity. |
Configure |
||
|
|
|
|||
|
|
|
|
|
|
|
|
Domain |
Display information about PKI domains. |
Monitor |
|
|
|
|
|
||
|
|
Add, modify, and delete a PKI domain. |
Configure |
||
|
|
|
|||
|
Certificate |
|
|
|
|
|
|
Display the certificate information about PKI |
Monitor |
||
|
Manageme |
|
|||
|
|
domains and the contents of a certificate. |
|||
|
nt |
|
|
||
|
Certificate |
|
|
||
|
Generate a key pair, destroy a key pair, retrieve a |
|
|||
|
|
|
|||
|
|
|
|
||
|
|
|
certificate, request a certificate, and delete a |
Configure |
|
|
|
|
certificate. |
|
|
|
|
|
|
|
|
|
|
CRL |
Display the contents of the CRL. |
Monitor |
|
|
|
|
|
||
|
|
Receive the CRL of a domain. |
Configure |
||
|
|
|
|||
|
|
|
|
|
|
|
Port Isolate |
Summary |
Display port isolation group information. |
Monitor |
|
|
|
|
|
||
|
Group |
Port Setup |
Configure the ports in an isolation group. |
Configure |
|
|
|
||||
|
|
|
|
|
|
|
|
|
Display the configurations of authorized IP, the |
|
|
Secu |
Authorized |
Summary |
associated IPv4 ACL list, and the associated IPv6 |
Management |
|
|
ACL list. |
|
|||
rity |
IP |
|
|
||
|
|
|
|||
Setup |
Configure authorized IP. |
Management |
|||
|
|
||||
|
|
|
|
|
|
|
Loopback |
Loopback |
Display and configure system loopback detection |
|
|
|
parameters and port loopback detection |
Configure |
|||
|
Detection |
Detection |
|||
|
parameters. |
|
|||
|
|
|
|
||
|
|
|
|
|
|
|
|
Summary |
Display time range configuration information. |
Monitor |
|
|
|
|
|
|
|
|
Time Range |
Create |
Create a time range. |
Configure |
|
|
|
|
|
|
|
|
|
Remove |
Delete a time range. |
Configure |
|
|
|
|
|
|
|
QoS |
|
Summary |
Display IPv4 ACL configuration information. |
Monitor |
|
|
|
|
|
||
|
Create |
Create an IPv4 ACL. |
Configure |
||
|
|
||||
|
ACL IPv4 |
|
|
|
|
|
Basic Setup |
Configure a rule for a basic IPv4 ACL. |
Configure |
||
|
|
||||
|
|
|
|
|
|
|
|
Advanced |
Configure a rule for an advanced IPv4 ACL. |
Configure |
|
|
|
Setup |
|||
|
|
|
|
||
|
|
|
|
|
|
14

Function menu |
|
Description |
User level |
|
|
|
Link Setup |
Create a rule for a link layer ACL. |
Configure |
|
|
|
|
|
|
|
Remove |
Delete an IPv4 ACL or its rules. |
Configure |
|
|
|
|
|
|
|
Summary |
Display IPv6 ACL configuration information. |
Monitor |
|
|
|
|
|
|
|
Create |
Create an IPv6 ACL. |
Configure |
|
|
|
|
|
|
ACL IPv6 |
Basic Setup |
Configure a rule for a basic IPv6 ACL. |
Configure |
|
|
|
|
|
|
Advanced |
Configure a rule for an advanced IPv6 ACL. |
Configure |
|
|
|
|||
|
|
Setup |
||
|
|
|
|
|
|
|
|
|
|
|
|
Remove |
Delete an IPv6 ACL or its rules. |
Configure |
|
|
|
|
|
|
Queue |
Summary |
Display the queue information about a port. |
Monitor |
|
|
|
|
|
|
Setup |
Configure a queue on a port. |
Configure |
|
|
|
|||
|
|
|
|
|
|
Line Rate |
Summary |
Display line rate configuration information. |
Monitor |
|
|
|
|
|
|
Setup |
Configure the line rate. |
Configure |
|
|
|
|||
|
|
|
|
|
|
|
Summary |
Display classifier configuration information. |
Monitor |
|
|
|
|
|
|
Classifier |
Create |
Create a class. |
Configure |
|
|
|
|
|
|
Setup |
Configure the classification rules for a class. |
Configure |
|
|
|
|||
|
|
|
|
|
|
|
Remove |
Delete a class or its classification rules. |
Configure |
|
|
|
|
|
|
|
Summary |
Display traffic behavior configuration information. |
Monitor |
|
|
|
|
|
|
|
Create |
Create a traffic behavior. |
Configure |
|
|
|
|
|
|
Behavior |
Setup |
Configure actions for a traffic behavior. |
Configure |
|
|
|
|
|
|
Port Setup |
Configure traffic mirroring and traffic redirecting |
Configure |
|
|
|
|||
|
|
for a traffic behavior |
||
|
|
|
|
|
|
|
|
|
|
|
|
Remove |
Delete a traffic behavior. |
Configure |
|
|
|
|
|
|
|
Summary |
Display QoS policy configuration information. |
Monitor |
|
|
|
|
|
|
|
Create |
Create a QoS policy. |
Configure |
|
|
|
|
|
|
QoS Policy |
Setup |
Configure the classifier-behavior associations for a |
Configure |
|
|
QoS policy. |
||
|
|
|
|
|
|
|
Remove |
Delete a QoS policy or its classifier-behavior |
Configure |
|
|
associations. |
||
|
|
|
|
|
|
|
|
|
|
|
|
Summary |
Display the QoS policy applied to a port. |
Monitor |
|
|
|
|
|
|
Port Policy |
Setup |
Apply a QoS policy to a port. |
Configure |
|
|
|
|
|
|
|
Remove |
Remove the QoS policy from the port. |
Configure |
|
|
|
|
|
|
Priority |
Priority |
Display priority mapping table information. |
Monitor |
|
|
|
||
|
Mapping |
Mapping |
Modify the priority mapping entries. |
Configure |
|
|
|
||
|
|
|
|
|
|
Port Priority |
Port Priority |
Display port priority and trust mode information. |
Monitor |
|
|
|
||
|
Modify port priority and trust mode. |
Configure |
||
|
|
|
||
|
|
|
|
|
15

Function menu |
|
Description |
User level |
||
|
|
Summary |
Display PSE information and PoE interface |
Monitor |
|
|
|
information. |
|||
|
|
|
|
||
PoE |
PoE |
|
|
|
|
PSE Setup |
Configure a PoE interface. |
Configure |
|||
|
|
||||
|
|
|
|
|
|
|
|
Port Setup |
Configure a port. |
Configure |
|
|
|
|
|
|
|
Common items on the Web pages
Buttons and icons
Table 2 Commonly used buttons and icons
Button and icon |
Function |
|
Applies the configuration on the current page. |
|
|
|
Cancels the configuration on the current page. |
|
|
|
Refreshes the current page. |
|
|
|
Clears all entries in a list or all statistics. |
|
|
|
Adds an item. |
|
|
, |
Removes the selected items. |
|
|
|
|
|
Selects all the entries in a list. |
|
|
|
Clears selection of all entries in a list. |
|
|
|
Buffers but does not apply the configuration of the current step, and enters |
|
the next configuration step. |
|
|
|
Buffers but does not apply the configuration of the current step, and returns |
|
to the previous configuration step. |
|
|
|
Applies the configurations of all configuration steps. |
|
|
|
Enters the modification page of an item so that you can modify the |
|
configurations of the item. |
|
|
|
Deletes the item corresponding to this icon. |
|
|
Page display function
The Web interface can display contents by pages, as shown in Figure 7. You can set the number of entries displayed per page, and view the contents on the first, previous, next, and last pages, or go to any page that you want to check.
16

Figure 7 Content display by pages
Search function
The Web interface provides you with the basic and advanced searching functions to display only the entries that match specific searching criteria.
•Basic search—As shown in Figure 7, type the keyword in the text box above the list, select a search item from the list and click Search to display the entries that match the criteria. Figure 8 shows an example of searching for entries with LLDP disabled.
Figure 8 Basic search function example
•Advanced search—As shown in Figure 9, you can click the Advanced Search link to open the advanced search area. Specify the search criteria, and click Apply to display the entries that match the criteria.
17
 Loading...
Loading...