Page 1
D-Link ™ DES-3550
Managed 48-port 10/100Mbps and 2GE ports Layer 2
Ethernet Switch
Release II
Manual
Second Edition (June 2004)
Printed In Taiwan
RECYCLABLE
Page 2

__________________________________________________________________________________
Information in this document is subject to change without notice.
© 2004 D-Link Computer Corporation. All rights reserved.
Reproduction in any manner whatsoever without the written permission of D-Link Computer Corporation is strictly forbidden.
Trademarks used in this text: D-Link and the D-LINK logo are trademarks of D-Link Computer Corporation; Microsoft and Windows are registered
trademarks of Microsoft Corporation.
Other trademarks and trade names may be used in this document to refer to either the entities claiming the marks and names or their products. D-Link
Computer Corporation disclaims any proprietary interest in trademarks and trade names other than its own.
June 2004 P/N 651ES3550025
Page 3

DES-3550 Fast Ethernet Layer 2 Switch
Table of Contents
Preface............................................................................................................................................................................. viii
Intended Readers................................................................................................................................................................ix
Typographical Conventions.............................................................................................................................................................. ix
Notes, Notices, and Cautions..............................................................................................................................................ix
Safety Instructions...............................................................................................................................................................x
Safety Cautions.................................................................................................................................................................................. x
General Precautions for Rack-Mountable Products.......................................................................................................................... xi
Protecting Against Electrostatic Discharge...................................................................................................................................... xii
Introduction..............................................................................................................................................................................1
Fast Ethernet...................................................................................................................................................................................... 1
Gigabit Ethernet Technology............................................................................................................................................................. 1
Switching Technology....................................................................................................................................................................... 2
Switch Description............................................................................................................................................................................. 2
Features.............................................................................................................................................................................................. 2
Ports................................................................................................................................................................................................... 3
Front-Panel Components ................................................................................................................................................................... 4
LED Indicators .................................................................................................................................................................................. 4
Rear Panel Description ...................................................................................................................................................................... 5
Side Panel Description....................................................................................................................................................................... 5
Gigabit Combo Ports ......................................................................................................................................................................... 6
Installation................................................................................................................................................................................7
Package Contents............................................................................................................................................................................... 7
Before You Connect to the Network.................................................................................................................................................. 8
Installing the Switch Without the Rack ............................................................................................................................................. 8
Installing the Switch in a Rack .......................................................................................................................................................... 9
Mounting the Switch in a Standard 19" Rack.................................................................................................................................... 9
Power On .................................................................................................................................................................10
Power Failure...........................................................................................................................................................10
Connecting The Switch ..........................................................................................................................................................10
Switch To End Node........................................................................................................................................................................ 10
Switch to Hub or Switch.................................................................................................................................................................. 11
Connecting To Network Backbone or Server.................................................................................................................................. 11
Introduction To Switch Management.....................................................................................................................................12
Management Options ........................................................................................................................................................13
Web-based Management Interface................................................................................................................................................... 13
SNMP-Based Management.............................................................................................................................................................. 13
Command Line Console Interface Through The Serial Port............................................................................................................ 13
Connecting the Console Port (RS-232 DCE)...........................................................................................................13
First Time Connecting to The Switch.............................................................................................................................................. 14
i
Page 4

DES-3550 Fast Ethernet Layer 2 Switch
Password Protection......................................................................................................................................................................... 16
SNMP Settings ................................................................................................................................................................................ 16
Traps ........................................................................................................................................................................17
MIBs ........................................................................................................................................................................17
IP Address Assignment.................................................................................................................................................................... 17
Connecting Devices to the Switch................................................................................................................................................... 19
Introduction to Web-based Switch Configuration..................................................................................................................20
Introduction .......................................................................................................................................................................20
Login to Web Manager.................................................................................................................................................................... 20
Web-based User Interface................................................................................................................................................................ 21
Areas of the User Interface ......................................................................................................................................21
Web Pages ....................................................................................................................................................................................... 22
Configuring The Switch.........................................................................................................................................................23
Switch Information............................................................................................................................................................23
IP Address .........................................................................................................................................................................24
Setting the Switch's IP Address using the Console Interface...................................................................................26
Advanced Settings.............................................................................................................................................................26
Port Configurations ...........................................................................................................................................................28
Port Description.................................................................................................................................................................30
Port Mirroring ...................................................................................................................................................................32
Link Aggregation ..............................................................................................................................................................33
Understanding Port Trunk Groups...........................................................................................................................33
LACP Port Setting.............................................................................................................................................................35
MAC Notification..............................................................................................................................................................37
MAC Notification Global Settings ..........................................................................................................................37
MAC Notification Port Settings...............................................................................................................................37
IGMP.................................................................................................................................................................................39
IGMP Snooping .......................................................................................................................................................39
Static Router Ports ...................................................................................................................................................41
Spanning Tree ...................................................................................................................................................................42
802.1s MSTP ...........................................................................................................................................................42
802.1w Rapid Spanning Tree...................................................................................................................................43
Port Transition States...............................................................................................................................................43
Edge Port .................................................................................................................................................................44
P2P Port ...................................................................................................................................................................44
802.1d / 802.1w / 802.1s Compatibility...................................................................................................................44
STP Bridge Global Settings............................................................................................................................................................. 44
MST Configuration Table................................................................................................................................................................ 47
MSTI Settings.................................................................................................................................................................................. 50
STP Instance Settings ...................................................................................................................................................................... 51
MSTP Port Information ................................................................................................................................................................... 51
ii
Page 5

DES-3550 Fast Ethernet Layer 2 Switch
Forwarding Filtering..........................................................................................................................................................54
Unicast Forwarding ......................................................................................................................................................................... 54
Static Multicast Forwarding............................................................................................................................................................. 54
Multicast Port Filtering.................................................................................................................................................................... 56
VLANs ..............................................................................................................................................................................57
Understanding IEEE 802.1p Priority ............................................................................................................................................... 57
VLAN Description........................................................................................................................................................................... 57
Notes About VLANs on the DES-3550...................................................................................................................58
IEEE 802.1Q VLANs ...................................................................................................................................................................... 58
802.1Q VLAN Tags.................................................................................................................................................59
Port VLAN ID .........................................................................................................................................................60
Tagging and Untagging............................................................................................................................................60
Ingress Filtering .......................................................................................................................................................61
Default VLANs........................................................................................................................................................61
Port-based VLANs...................................................................................................................................................61
VLAN Segmentation ...............................................................................................................................................62
VLAN and Trunk Groups........................................................................................................................................62
Static VLAN Entry .......................................................................................................................................................................... 62
GVRP Setting .................................................................................................................................................................................. 64
Traffic Control................................................................................................................................................................................. 66
Port Security......................................................................................................................................................................67
QoS....................................................................................................................................................................................69
The Advantages of QoS................................................................................................................................................................... 69
Understanding QoS.......................................................................................................................................................................... 70
Port Bandwidth................................................................................................................................................................................ 71
Scheduling ....................................................................................................................................................................................... 73
802.1p Default Priority .................................................................................................................................................................... 74
802.1p User Priority......................................................................................................................................................................... 76
Traffic Segmentation ....................................................................................................................................................................... 76
System Log Server........................................................................................................................................................................... 78
SNTP Settings.................................................................................................................................................................................. 80
Current Time Settings..............................................................................................................................................80
Time Zone and DST ................................................................................................................................................81
Access Profile Table..........................................................................................................................................................83
Configuring the Access Profile Table.............................................................................................................................................. 83
PAE Access Entity (802.1X).............................................................................................................................................96
802.1x Port-Based and MAC-Based Access Control....................................................................................................................... 96
Authentication Server ..............................................................................................................................................97
Authenticator ...........................................................................................................................................................98
Client........................................................................................................................................................................99
Authentication Process .................................................................................................................................................................... 99
iii
Page 6

DES-3550 Fast Ethernet Layer 2 Switch
Port-Based Network Access Control ............................................................................................................................................... 99
MAC-Based Network Access Control........................................................................................................................................... 101
Configure Authenticator ................................................................................................................................................................ 101
PAE System Control...................................................................................................................................................................... 104
Port Capability .......................................................................................................................................................104
Initializing Ports for Port Based 802.1x.................................................................................................................106
Initializing Ports for MAC Based 802.1x ..............................................................................................................108
Reauthenticate Port(s) for Port Based 802.1x........................................................................................................108
RADIUS Server............................................................................................................................................................................. 109
Layer 3 IP Networking ....................................................................................................................................................111
Static ARP Table ........................................................................................................................................................................... 111
Management.........................................................................................................................................................................113
Security IP .......................................................................................................................................................................113
User Accounts .................................................................................................................................................................113
Admin and User Privileges....................................................................................................................................114
Access Authentication Control........................................................................................................................................115
Policy & Parameters ...................................................................................................................................................................... 116
Application's Authentication Settings............................................................................................................................................ 116
Authentication Server Group Settings ........................................................................................................................................... 117
Authentication Server Hosts.......................................................................................................................................................... 118
Login Method Lists........................................................................................................................................................................ 120
Enable Method Lists...................................................................................................................................................................... 122
Local Enable Password.................................................................................................................................................................. 123
Enable Admin................................................................................................................................................................................ 124
Secure Socket Layer (SSL) .............................................................................................................................................125
Download Certificate..................................................................................................................................................................... 125
Ciphersuite..................................................................................................................................................................................... 126
Secure Shell (SSH)..........................................................................................................................................................127
SSH Configuration......................................................................................................................................................................... 128
SSH Algorithm .............................................................................................................................................................................. 129
SSH User Authentication............................................................................................................................................................... 131
SNMP Manager...............................................................................................................................................................133
SNMP Settings .............................................................................................................................................................................. 133
Traps ......................................................................................................................................................................133
MIBs ......................................................................................................................................................................133
SNMP User Table.......................................................................................................................................................................... 134
SNMP View Table......................................................................................................................................................................... 136
SNMP Group Table ....................................................................................................................................................................... 137
SNMP Community Table Configuration....................................................................................................................................... 139
SNMP Host Table.......................................................................................................................................................................... 140
SNMP Engine ID........................................................................................................................................................................... 141
iv
Page 7

DES-3550 Fast Ethernet Layer 2 Switch
Monitoring ...........................................................................................................................................................................142
Port Utilization ................................................................................................................................................................142
CPU Utilization ...............................................................................................................................................................143
Packets.............................................................................................................................................................................144
Received(RX) ................................................................................................................................................................................ 144
UMB Cast(RX).............................................................................................................................................................................. 146
Transmitted (TX)........................................................................................................................................................................... 148
Errors...............................................................................................................................................................................150
Received (RX) ............................................................................................................................................................................... 151
Transmitted (TX)........................................................................................................................................................................... 153
Size..................................................................................................................................................................................155
MAC Address..................................................................................................................................................................157
Switch History.................................................................................................................................................................159
IGMP Snooping Group ...................................................................................................................................................160
IGMP Snooping Forwarding...........................................................................................................................................161
VLAN Status ...................................................................................................................................................................161
Router Port ......................................................................................................................................................................162
Port Access Control.........................................................................................................................................................163
Authenticator State ................................................................................................................................................163
Layer 3 Feature................................................................................................................................................................165
Browse ARP Table ........................................................................................................................................................................ 165
Maintenance .........................................................................................................................................................................166
TFTP Services .................................................................................................................................................................166
Download Firmware From TFTP Server....................................................................................................................................... 166
Download Configuration File ........................................................................................................................................................ 168
Upload Configuration .................................................................................................................................................................... 168
Upload Log.................................................................................................................................................................................... 168
Ping Test..........................................................................................................................................................................169
Save Changes ..................................................................................................................................................................169
Reset................................................................................................................................................................................170
Reset System ...................................................................................................................................................................170
Reset Config....................................................................................................................................................................171
Reboot Device .................................................................................................................................................................171
Logout .............................................................................................................................................................................171
D-Link Single IP Management ............................................................................................................................................173
Single IP Management (SIM) Overview.........................................................................................................................173
SIM Using The Web Interface ........................................................................................................................................174
Topology .........................................................................................................................................................................175
Tool Tips .........................................................................................................................................................................178
Right Click..................................................................................................................................................................................... 180
v
Page 8

DES-3550 Fast Ethernet Layer 2 Switch
Group Icon.............................................................................................................................................................180
Commander Switch Icon........................................................................................................................................181
Member Switch Icon..............................................................................................................................................182
Candidate Switch Icon ...........................................................................................................................................183
Menu Bar....................................................................................................................................................................................... 184
Group .....................................................................................................................................................................185
Device....................................................................................................................................................................185
View.......................................................................................................................................................................185
Firmware Upgrade...........................................................................................................................................................185
Configuration File Backup/Restore.................................................................................................................................186
Appendix A..........................................................................................................................................................................187
Appendix B ..........................................................................................................................................................................189
Cables and Connectors...........................................................................................................................................189
Appendix C ..........................................................................................................................................................................190
Cable Lengths ........................................................................................................................................................190
Glossary ...............................................................................................................................................................................191
Warranty and Registration Information ...............................................................................................................................198
vi
Page 9

DES-3550 Fast Ethernet Layer 2 Switch
vii
Page 10
DES-3550 Fast Ethernet Layer 2 Switch
Preface
The DES-3550 Manual is divided into sections that describe the system installation and operating instructions with
examples.
Section 1, “Introduction”– Describes the Switch and its features.
Section 2, “Installation” – Helps you get started with the basic installation of the Switch and also describes the front panel,
rear panel, side panels, and LED indicators of the Switch.
Section 3, “Connecting the Switch” – Tells how you can connect the Switch to your Ethernet/Fast Ethernet network.
Section 4, “Introduction to Switch Management” – Introduces basic Switch management features, including password
protection, SNMP settings, IP address assignment and connecting devices to the Switch.
Section 5, “Introduction to Web-based Switch Management” – Talks about connecting to and using the Web-based switch
management feature on the Switch.
Section 6, “Configuring the Switch” – A detailed discussion about configuring some of the basic functions of the Switch,
including accessing the Switch information, using the Switch's utilities and setting up network configurations, such as
Quality of Service, The Access Profile Table, port mirroring and configuring the Spanning Tree.
Section 7, “Management” – A discussion of the security features of the Switch, including Security IP, User Accounts,
Access Authentication Control, and SNMP.
Section 8, “Monitoring” – Features graphs and screens used in monitoring features and packets on the Switch.
Section 9, “Maintenance” – Features information on Switch utility functions, including TFTP Services, Switch History,
Ping Test Save Changes and Rebooting Services.
Section 10, “Single IP Management” – Discussion on the Single IP Management function of the Switch, including
functions and features of the Java based user interface and the utilities of the SIM function.
Appendix A, “Technical Specifications” – The technical specifications of the DES-3550
Appendix B, “Cables and Connectors” – Describes the RJ-45 receptacle/connector, straight-through and crossover cables
and standard pin assignments.
Appendix C, “Cable Lengths” – Information on cable types and maximum distances.
Glossary - Lists definitions for terms and acronyms used in this document.
viii
Page 11
DES-3550 Fast Ethernet Layer 2 Switch
Intended Readers
The DES-3550 Manual contains information for setup and management of the Switch. This manual is intended for
network managers familiar with network management concepts and terminology.
Typographical Conventions
Convention Description
[ ]
Bold font
Boldface
Typewriter Font
Initial capital letter
Italics
Menu Name > Menu
Option
In a command line, square brackets indicate an optional entry. For example: [copy
filename] means that optionally you can type copy followed by the name of the file.
Do not type the brackets.
Indicates a button, a toolbar icon, menu, or menu item. For example: Open the File
menu and choose Cancel. Used for emphasis. May also indicate system messages
or prompts appearing on your screen. For example: You have mail. Bold font is also
used to represent filenames, program names and commands. For example: use the
copy command.
Indicates commands and responses to prompts that must be typed exactly as printed
in the manual.
Indicates a window name. Names of keys on the keyboard have initial capitals. For
example: Click Enter.
Indicates a window name or a field. Also can indicate a variables or parameter that is
replaced with an appropriate word or string. For example: type filename means that
you should type the actual filename instead of the word shown in italic.
Menu Name > Menu Option Indicates the menu structure. Device > Port > Port
Properties means the Port Properties menu option under the Port menu option that
is located under the Device menu.
Notes, Notices, and Cautions
A NOTE indicates important information that helps you make better use of
your device.
A NOTICE indicates either potential damage to hardware or loss of data
and tells you how to avoid the problem.
A CAUTION indicates a potential for property damage, personal injury, or
death.
ix
Page 12
DES-3550 Fast Ethernet Layer 2 Switch
Safety Instructions
Use the following safety guidelines to ensure your own personal safety and to help protect your system from potential
damage. Throughout this safety section, the caution icon (
) is used to indicate cautions and precautions that you
need to review and follow.
Safety Cautions
To reduce the risk of bodily injury, electrical shock, fire, and damage to the equipment, observe the following precautions.
•
Observe and follow service markings.
•
Do not service any product except as explained in your system documentation.
•
Opening or removing covers that are marked with the triangular symbol with a lightning bolt may expose you to
electrical shock.
•
Only a trained service technician should service components inside these compartments.
•
If any of the following conditions occur, unplug the product from the electrical outlet and replace the part or contact
your trained service provider:
•
The power cable, extension cable, or plug is damaged.
•
An object has fallen into the product.
•
The product has been exposed to water.
•
The product has been dropped or damaged.
•
The product does not operate correctly when you follow the operating instructions.
•
Keep your system away from radiators and heat sources. Also, do not block cooling vents.
•
Do not spill food or liquids on your system components, and never operate the product in a wet environment. If the
system gets wet, see the appropriate section in your troubleshooting guide or contact your trained service provider.
•
Do not push any objects into the openings of your system. Doing so can cause fire or electric shock by shorting out
interior components.
•
Use the product only with approved equipment.
•
Allow the product to cool before removing covers or touching internal components.
•
Operate the product only from the type of external power source indicated on the electrical ratings label. If you are
not sure of the type of power source required, consult your service provider or local power company.
•
To help avoid damaging your system, be sure the voltage selection switch (if provided) on the power supply is set to
match the power available at your location:
•
115 volts (V)/60 hertz (Hz) in most of North and South America and some Far Eastern countries such as South
Korea and Taiwan
•
100 V/50 Hz in eastern Japan and 100 V/60 Hz in western Japan
•
230 V/50 Hz in most of Europe, the Middle East, and the Far East
•
Also be sure that attached devices are electrically rated to operate with the power available in your location.
•
Use only approved power cable(s). If you have not been provided with a power cable for your system or for any ACpowered option intended for your system, purchase a power cable that is approved for use in your country. The power
cable must be rated for the product and for the voltage and current marked on the product's electrical ratings label.
The voltage and current rating of the cable should be greater than the ratings marked on the product.
•
To help prevent electric shock, plug the system and peripheral power cables into properly grounded electrical outlets.
These cables are equipped with three-prong plugs to help ensure proper grounding. Do not use adapter plugs or
x
Page 13
DES-3550 Fast Ethernet Layer 2 Switch
remove the grounding prong from a cable. If you must use an extension cable, use a 3-wire cable with properly
grounded plugs.
•
Observe extension cable and power strip ratings. Make sure that the total ampere rating of all products plugged into
the extension cable or power strip does not exceed 80 percent of the ampere ratings limit for the extension cable or
power strip.
•
To help protect your system from sudden, transient increases and decreases in electrical power, use a surge
suppressor, line conditioner, or uninterruptible power supply (UPS).
•
Position system cables and power cables carefully; route cables so that they cannot be stepped on or tripped over. Be
sure that nothing rests on any cables.
•
Do not modify power cables or plugs. Consult a licensed electrician or your power company for site modifications.
Always follow your local/national wiring rules.
•
When connecting or disconnecting power to hot-pluggable power supplies, if offered with your system, observe the
following guidelines:
•
Install the power supply before connecting the power cable to the power supply.
•
Unplug the power cable before removing the power supply.
•
If the system has multiple sources of power, disconnect power from the system by unplugging all power cables
from the power supplies.
•
Move products with care; ensure that all casters and/or stabilizers are firmly connected to the system. Avoid sudden
stops and uneven surfaces.
General Precautions for Rack-Mountable Products
Observe the following precautions for rack stability and safety. Also refer to the rack installation documentation
accompanying the system and the rack for specific caution statements and procedures.
Systems are considered to be components in a rack. Thus, "component" refers to any system as well as to various
•
peripherals or supporting hardware.
Before working on the rack, make sure that the stabilizers are secured to the rack, extended to the floor, and that the
•
full weight of the rack rests on the floor. Install front and side stabilizers on a single rack or front stabilizers for joined
multiple racks before working on the rack.
•
Always load the rack from the bottom up, and load the heaviest item in the rack first.
•
Make sure that the rack is level and stable before extending a component from the rack.
CAUTION: Installing systems in a rack without the front and side
stabilizers installed could cause the rack to tip over, potentially resulting in
bodily injury under certain circumstances. Therefore, always install the
stabilizers before installing components in the rack. After installing
system/components in a rack, never pull more than one component out of
the rack on its slide assemblies at one time. The weight of more than one
extended component could cause the rack to tip over and may result in
serious injury.
•
Use caution when pressing the component rail release latches and sliding a component into or out of a rack; the slide
rails can pinch your fingers.
•
After a component is inserted into the rack, carefully extend the rail into a locking position, and then slide the
component into the rack.
•
Do not overload the AC supply branch circuit that provides power to the rack. The total rack load should not exceed
80 percent of the branch circuit rating.
•
Ensure that proper airflow is provided to components in the rack.
xi
Page 14
DES-3550 Fast Ethernet Layer 2 Switch
Do not step on or stand on any component when servicing other components in a rack. •
NOTE: A qualified electrician must perform all connections to DC power
and to safety grounds. All electrical wiring must comply with applicable
local or national codes and practices.
CAUTION: Never defeat the ground conductor or operate the equipment
in the absence of a suitably installed ground conductor. Contact the
appropriate electrical inspection authority or an electrician if you are
uncertain that suitable grounding is available.
CAUTION: The system chassis must be positively grounded to the rack
cabinet frame. Do not attempt to connect power to the system until
grounding cables are connected. Completed power and safety ground
wiring must be inspected by a qualified electrical inspector. An energy
hazard will exist if the safety ground cable is omitted or disconnected.
Protecting Against Electrostatic Discharge
Static electricity can harm delicate components inside your system. To prevent static damage, discharge static electricity
from your body before you touch any of the electronic components, such as the microprocessor. You can do so by
periodically touching an unpainted metal surface on the chassis.
You can also take the following steps to prevent damage from electrostatic discharge (ESD):
1. When unpacking a static-sensitive component from its shipping carton, do not remove the component from the
antistatic packing material until you are ready to install the component in your system. Just before unwrapping the
antistatic packaging, be sure to discharge static electricity from your body.
2. When transporting a sensitive component, first place it in an antistatic container or packaging.
3. Handle all sensitive components in a static-safe area. If possible, use antistatic floor pads, workbench pads and an
antistatic grounding strap.
xii
Page 15

Introduction
Ethernet Technology
Switch Description
Features
Ports
Front-Panel Components
Side Panel Description
Rear Panel Description
Gigabit Combo Ports
Ethernet Technology
Fast Ethernet Technology
DES-3550 Fast Ethernet Layer 2 Switch
Section 1
Fast Ethernet
The growing importance of LANs and the increasing complexity of desktop computing applications are fueling the need
for high performance networks. A number of high-speed LAN technologies are proposed to provide greater bandwidth and
improve client/server response times. Among them, Fast Ethernet, or 100BASE-T, provides a non-disruptive, smooth
evolution from 10BASE-T technology.
100Mbps Fast Ethernet is a standard specified by the IEEE 802.3 LAN committee. It is an extension of the 10Mbps
Ethernet standard with the ability to transmit and receive data at 100Mbps, while maintaining the Carrier Sense Multiple
Access with Collision Detection (CSMA/CD) Ethernet protocol.
Gigabit Ethernet Technology
Gigabit Ethernet is an extension of IEEE 802.3 Ethernet utilizing the same packet structure, format, and support for
CSMA/CD protocol, full duplex, flow control, and management objects, but with a tenfold increase in theoretical
throughput over 100Mbps Fast Ethernet and a one hundred-fold increase over 10Mbps Ethernet. Since it is compatible with
all 10Mbps and 100Mbps Ethernet environments, Gigabit Ethernet provides a straightforward upgrade without wasting a
company's existing investment in hardware, software, and trained personnel.
The increased speed and extra bandwidth offered by Gigabit Ethernet are essential to coping with the network bottlenecks
that frequently develop as computers and their busses get faster and more users use applications that generate more traffic.
Upgrading key components, such as your backbone and servers to Gigabit Ethernet can greatly improve network response
times as well as significantly speed up the traffic between your subnetworks.
Gigabit Ethernet enables fast optical fiber connections to support video conferencing, complex imaging, and similar dataintensive applications. Likewise, since data transfers occur 10 times faster than Fast Ethernet, servers outfitted with Gigabit
Ethernet NIC's are able to perform 10 times the number of operations in the same amount of time.
In addition, the phenomenal bandwidth delivered by Gigabit Ethernet is the most cost-effective method to take advantage
of today and tomorrow's rapidly improving switching and routing internetworking technologies.
1
Page 16

DES-3550 Fast Ethernet Layer 2 Switch
Switching Technology
Another key development pushing the limits of Ethernet technology is in the field of switching technology. A switch
bridges Ethernet packets at the MAC address level of the Ethernet protocol transmitting among connected Ethernet or Fast
Ethernet LAN segments.
Switching is a cost-effective way of increasing the total network capacity available to users on a local area network. A
switch increases capacity and decreases network loading by making it possible for a local area network to be divided into
different segments, which are not competing with each other for network transmission capacity, and therefore decreasing
the load on each segment.
The Switch acts as a high-speed selective bridge between the individual segments. Traffic that needs to go from one
segment to another (from one port to another) is automatically forwarded by the Switch, without interfering with any other
segments (ports). This allows the total network capacity to be multiplied, while still maintaining the same network cabling
and adapter cards.
For Fast Ethernet or Gigabit Ethernet networks, a switch is an effective way of eliminating problems of chaining hubs
beyond the "two-repeater limit." A switch can be used to split parts of the network into different collision domains, for
example, making it possible to expand your Fast Ethernet network beyond the 205-meter network diameter limit for
100BASE-TX networks. Switches supporting both traditional 10Mbps Ethernet and 100Mbps Fast Ethernet are also ideal
for bridging between existing 10Mbps networks and new 100Mbps networks.
Switching LAN technology is a marked improvement over the previous generation of network bridges, which were
characterized by higher latencies. Routers have also been used to segment local area networks, but the cost of a router and
the setup and maintenance required make routers relatively impractical. Today's switches are an ideal solution to most
kinds of local area network congestion problems.
Switch Description
The DES-3550 is equipped with unshielded twisted-pair (UTP) cable ports providing dedicated 10 or 100 Mbps bandwidth.
The Switch has 48 UTP ports and Auto MDI-X/MDI-II convertible ports that can be used for uplinking to another switch.
These ports can be used for connecting PCs, printers, servers, hubs, routers, switches and other networking devices. The
dual speed ports use standard twisted-pair cabling and are ideal for segmenting networks into small, connected
subnetworks for superior performance. Each 10/100 port can support up to 200 Mbps of throughput in full-duplex mode.
In addition, the Switch has 2 Mini-GBIC combo ports. These two gigabit combo ports are ideal for connecting to a server
or network backbone.
This stand-alone Switch enables the network to use some of the most demanding multimedia and imaging applications
concurrently with other user applications without creating bottlenecks. The built-in console interface can be used to
configure the Switch's settings for priority queuing, VLANs, and port trunk groups, port monitoring, and port speed.
Features
IEEE 802.3 10BASE-T compliant •
•
IEEE 802.3u 100BASE-TX compliant
•
IEEE 802.1p Priority Queues
•
IEEE 802.3x flow control in full duplex mode
•
IEEE 802.3ad Link Aggregation Control Protocol support.
•
IEEE 802.1x Port-based and MAC-based Access Control
•
IEEE 802.1Q VLAN
•
IEEE 802.1D Spanning Tree, IEEE 802.1W Rapid Spanning Tree and IEEE 802.1s Multiple Spanning Tree
support
•
Access Control List (ACL) support
•
Single IP Management support
•
Access Authentication Control utilizing TACACS, XTACACS and TACACS+
2
Page 17

DES-3550 Fast Ethernet Layer 2 Switch
Dual Image Firmware •
•
Simple Network Time Protocol support
•
MAC Notification support
•
Asymmetric VLAN support
•
System and Port Utilization support
•
System Log Support
•
High performance switching engine performs forwarding and filtering at full wire speed, maximum 14, 881
packets/sec on each 10Mbps Ethernet port, and maximum 148,810 packet/sec on 100Mbps Fast Ethernet port.
•
Full- and half-duplex for both 10Mbps and 100Mbps connections. Full duplex allows the switch port to
simultaneously transmit and receive data. It only works with connections to full-duplex-capable end stations and
switches. Connections to a hub must take place at half-duplex
•
Support broadcast storm filtering
•
Non-blocking store and forward switching scheme capability to support rate adaptation and protocol conversion
•
Supports by-port Egress/Ingress rate control.
•
Efficient self-learning and address recognition mechanism enables forwarding rate at wire speed
•
Support port-based enable and disable
•
Address table: Supports up to 8K MAC addresses per device
•
Supports a packet buffer of up to 3 Mbits
•
Supports Port-based VLAN Groups
•
Port Trunking with flexible load distribution and fail-over function
•
IGMP Snooping support
•
SNMP support
•
Secure Sockets Layer (SSL) and Secure Shell (SSH) support
•
Port Mirroring support
•
MIB support for:
•
RFC1213 MIB II
•
RFC1493 Bridge
•
RFC1757 RMON
•
RFC1643 Ether-like MIB
•
RFC2233 Interface MIB
•
Private MIB
•
RFC2674 for 802.1p
•
IEEE 802.1x MIB
•
•
Ports
•
•
RS-232 DCE console port for Switch management
Provides parallel LED display for port status such as link/act, speed, etc.
Forty-eight (48) high-performance (MDI-X/MDI-II) ports for connecting to end stations, servers, hubs and other
networking devices.
All UTP ports can auto-negotiate between 10Mbps and 100Mbps, half-duplex and full duplex, and feature flow
control.
3
Page 18
DES-3550 Fast Ethernet Layer 2 Switch
Two 1000BASE-T Mini-GBIC combo ports for connecting to another switch, server, or network backbone. •
• RS-232 DCE Diagnostic port (console port) for setting up and managing the Switch via a connection to a
console terminal or PC using a terminal emulation program.
NOTE: For customers interested in D-View, D-Link Corporation's
proprietary SNMP management software, go to the D-Link Website
(www.dlink.com.cn) and download the software and manual.
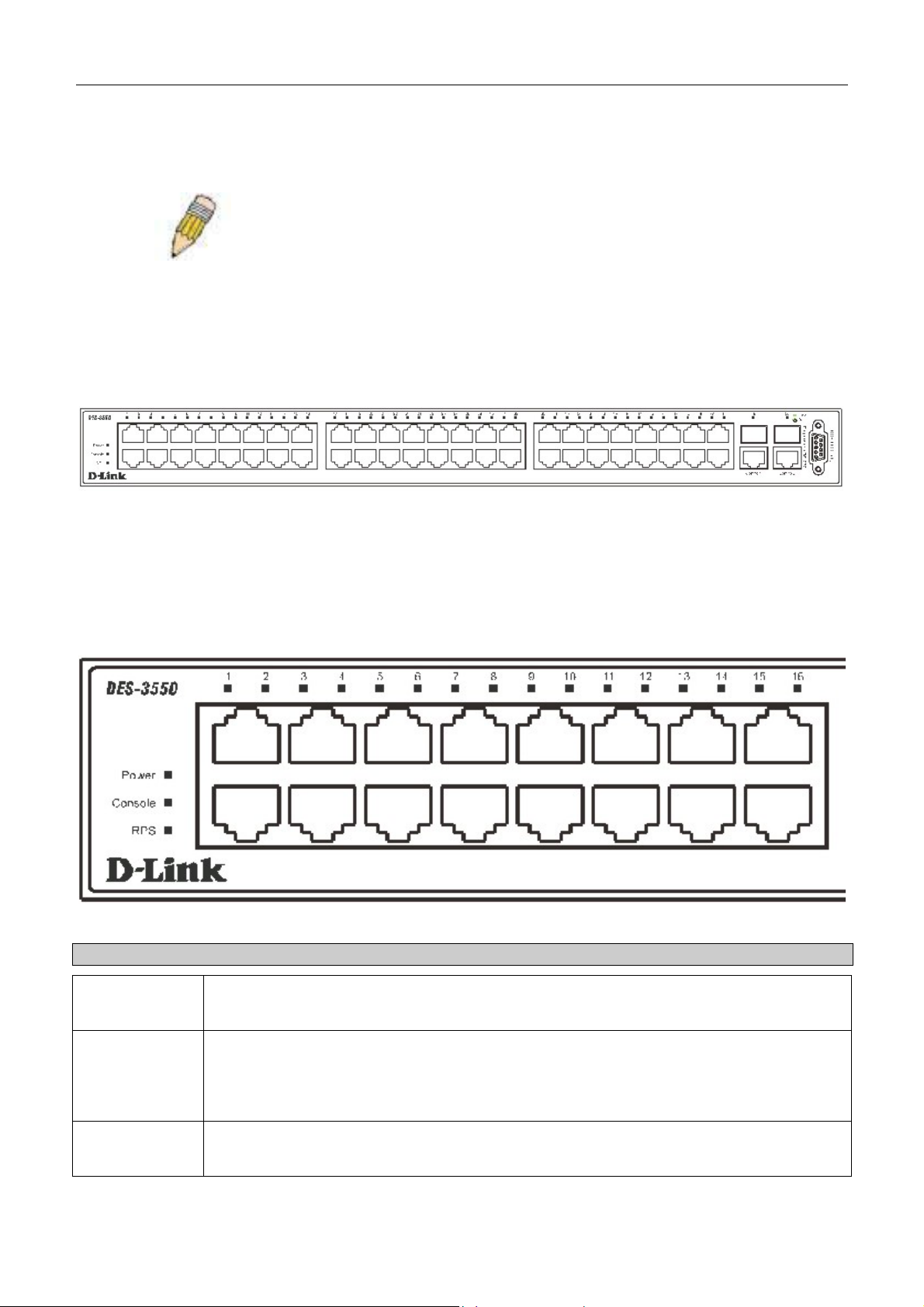
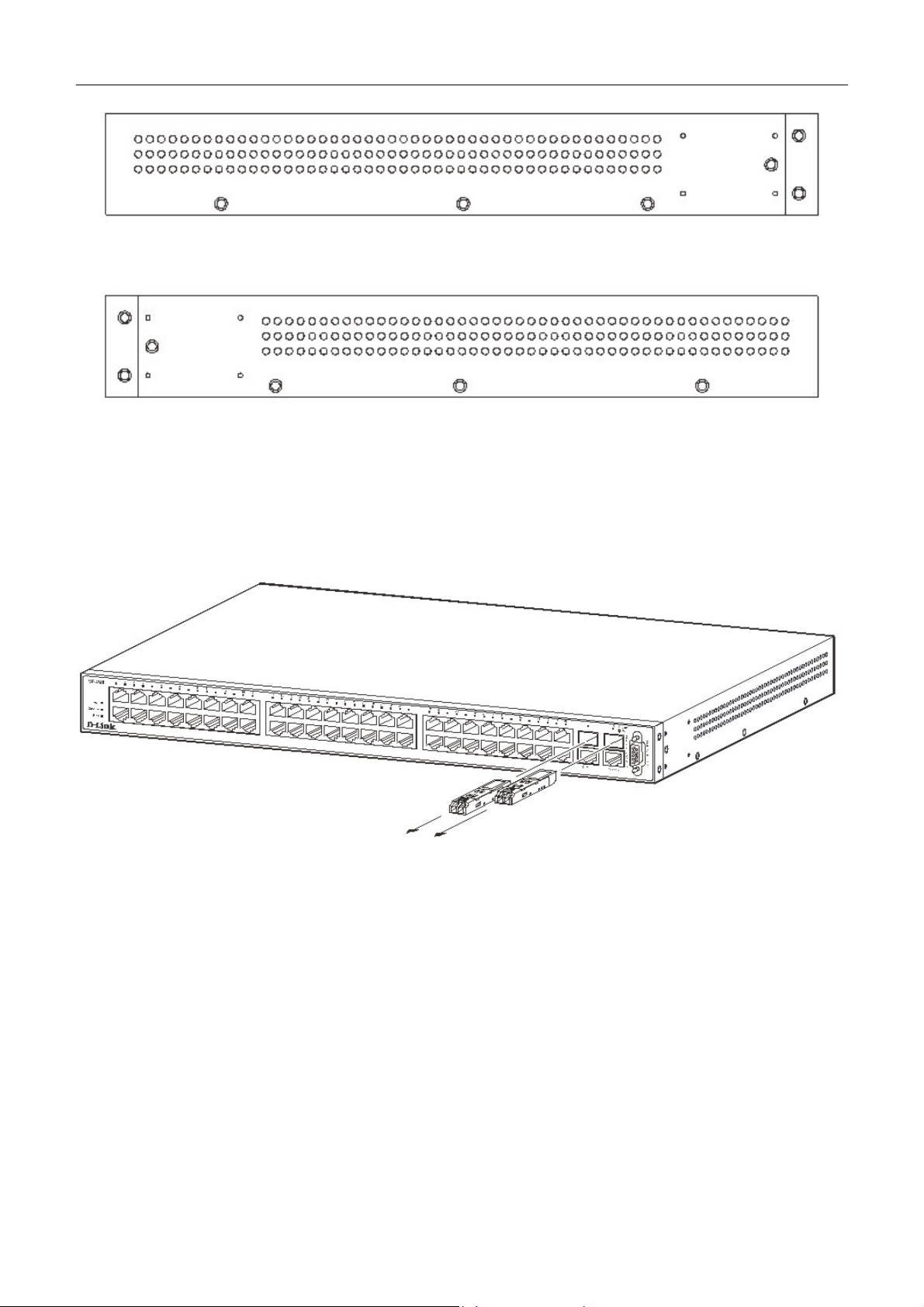
Front-Panel Components
The front panel of the Switch consists of LED indicators for power and for each 10/100 Mbps twisted-pair ports, and two
1000BASE-T Mini-GBIC ports.
DES-3550
Figure 1- 1. Front Panel View of the DES-3550 as shipped
Comprehensive LED indicators display the status of the Switch and the network.
LED Indicators
The Switch supports LED indicators for Power, Console, RPS and Port LEDs. The following shows the LED indicators for
the Switch along with an explanation of each indicator.
Figure 1- 2. LED Indicators
LED Description
Power
Console
RPS
This LED will light green after the Switch is powered on to indicate the ready state of the
device. The indicator is dark when the Switch is powered off.
This LED should blink during the Power-On Self Test (POST). When the POST is finished,
the LED goes dark. This indicator is lit sold green when the Switch is being logged into via
out-of-band/local console management through the RS-232 console port in the back of the
Switch using a straight-through serial cable.
This LED will be lit when the redundant power supply is present and in use. Otherwise it will
remain dark.
4
Page 19
DES-3550 Fast Ethernet Layer 2 Switch
Port LEDs
100M/10M
Gigabit Ports
One row of LEDs for each port is located above the ports on the front panel. The first LED is
for the top port and the second one is for the bottom ports. These port LEDs will light two
different colors for 10M and 100M.
•
Amber - For speeds of 10 Mbps. A solid light denotes activity on the port while a
blinking light indicates a valid link.
•
Green - For speeds of 100 Mbps. A solid light denotes activity on the port while a
blinking light indicates a valid link.
These LEDs will light steady green to indicate that the port is transferring data at 100Mbps.
The Switch's two Mini GBIC ports have their own corresponding LEDs:
Speed - This LED will light solid green when the port is transferring at a rate of 1000Mbps.
When dark, the port is transferring at 10/100Mbps.·
Link/Act - This LED will light solid green when there is a valid link. A blinking LED indicates
current activity on the port. A dark LED indicates no activity on the port.
Rear Panel Description
The rear panel of the Switch contains an AC power connector.
Figure 1- 3. Rear panel view of the Switch
The AC power connector is a standard three-pronged connector that supports the power cord. Plug-in the female connector
of the provided power cord into this socket, and the male side of the cord into a power outlet. The Switch automatically
adjusts its power setting to any supply voltage in the range from 100 ~ 240 VAC at 50 ~ 60 Hz.
The rear panel also includes an outlet for an optional external power supply. When power fails, the optional external RPS
will take over all the power immediately and automatically.
Side Panel Description
The right-hand side panel of the Switch contains a system fan, while the left hand panel includes a system fan and a heat
vent.
The system fans are used to dissipate heat. The sides of the system also provide heat vents to serve the same purpose. Do
not block these openings, and leave at least 6 inches of space at the rear and sides of the Switch for proper ventilation. Be
reminded that without proper heat dissipation and air circulation, system components might overheat, which could lead to
system failure.
5
Page 20
DES-3550 Fast Ethernet Layer 2 Switch
Figure 1- 4. Side Panels
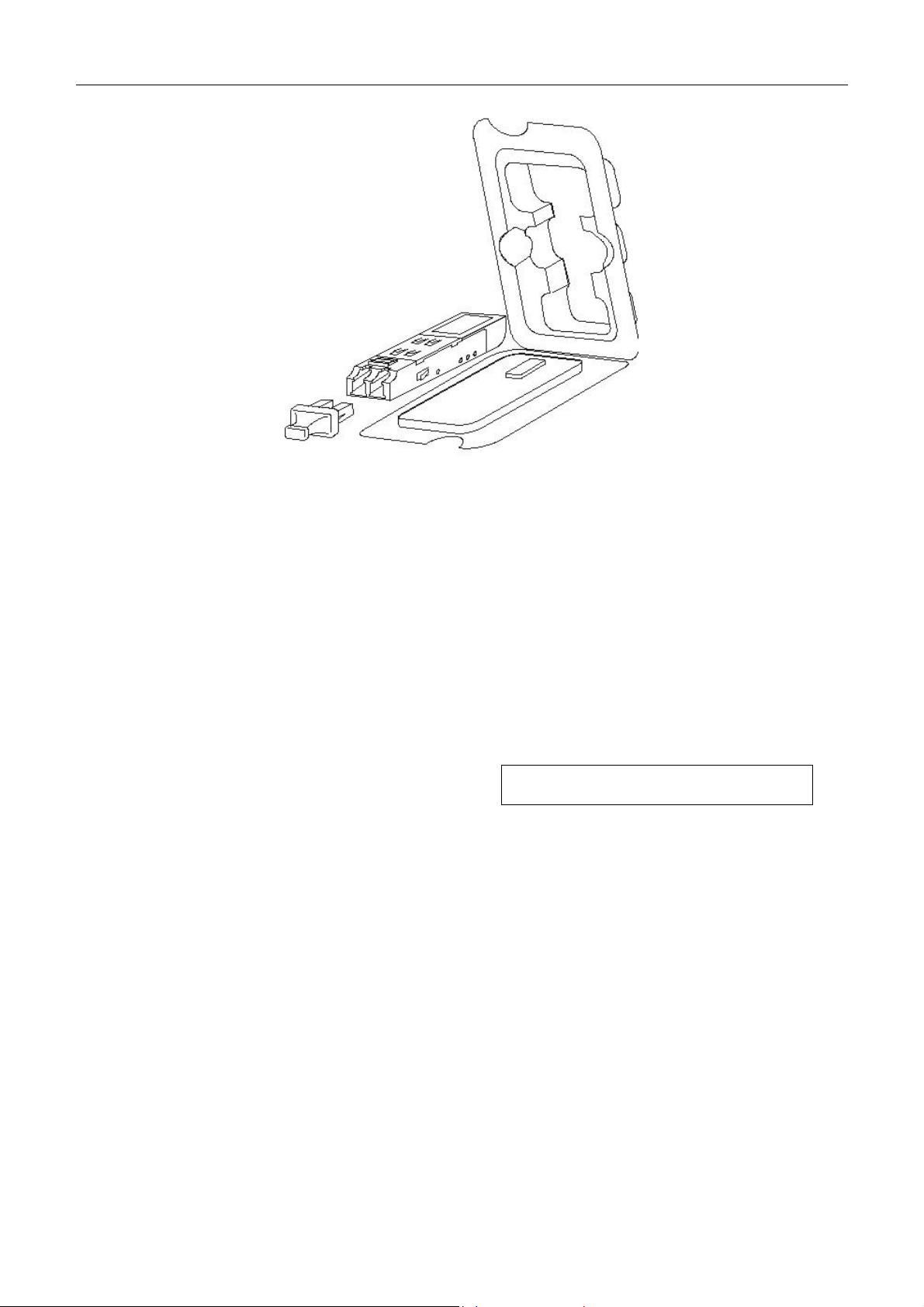
Gigabit Combo Ports
In addition to the 48 10/100 Mbps ports, the Switch features two Gigabit Ethernet Combo ports. These two ports are
1000BASE-T copper ports (provided) and Mini-GBIC ports (optional). See the diagram below to view the two Mini-GBIC
port modules being plugged into the Switch. Please note that although these two front panel modules can be used
simultaneously, the ports must be different. The GBIC port will always have the highest priority.
Figure 1- 5. Mini-GBIC modules plug-in to the Switch
6
Page 21
DES-3550 Fast Ethernet Layer 2 Switch
Figure 1- 6. Installing the Mini-GBIC Module
Installation
Package Contents
Before You Connect to the Network
SECTION 2
Installing the Switch Without the Rack
Rack Installation
Power On
Package Contents
Open the shipping carton of the Switch and carefully unpack its contents. The carton should contain the following items:
7
Page 22
DES-3550 Fast Ethernet Layer 2 Switch
One DES-3550 Stand-alone Switch •
•
One AC power cord
•
This Manual
•
Registration card
•
Mounting kit (two brackets and screws)
•
Four rubber feet with adhesive backing
•
RS-232 console cable
If any item is found missing or damaged, please contact your local D-Link Reseller for replacement.
Before You Connect to the Network
The site where you install the Switch may greatly affect its performance. Please follow these guidelines for setting up the
Switch.
•
Install the Switch on a sturdy, level surface that can support at least 6.6 lb. (3 kg) of weight. Do not place heavy
objects on the Switch.
•
The power outlet should be within 1.82 meters (6 feet) of the Switch.
•
Visually inspect the power cord and see that it is fully secured to the AC power port.
•
Make sure that there is proper heat dissipation from and adequate ventilation around the Switch. Leave at least
10 cm (4 inches) of space at the front and rear of the Switch for ventilation.
•
Install the Switch in a fairly cool and dry place for the acceptable temperature and humidity operating ranges.
•
Install the Switch in a site free from strong electromagnetic field generators (such as motors), vibration, dust,
and direct exposure to sunlight.
•
When installing the Switch on a level surface, attach the rubber feet to the bottom of the device. The rubber feet
cushion the Switch, protect the casing from scratches and prevent it from scratching other surfaces.
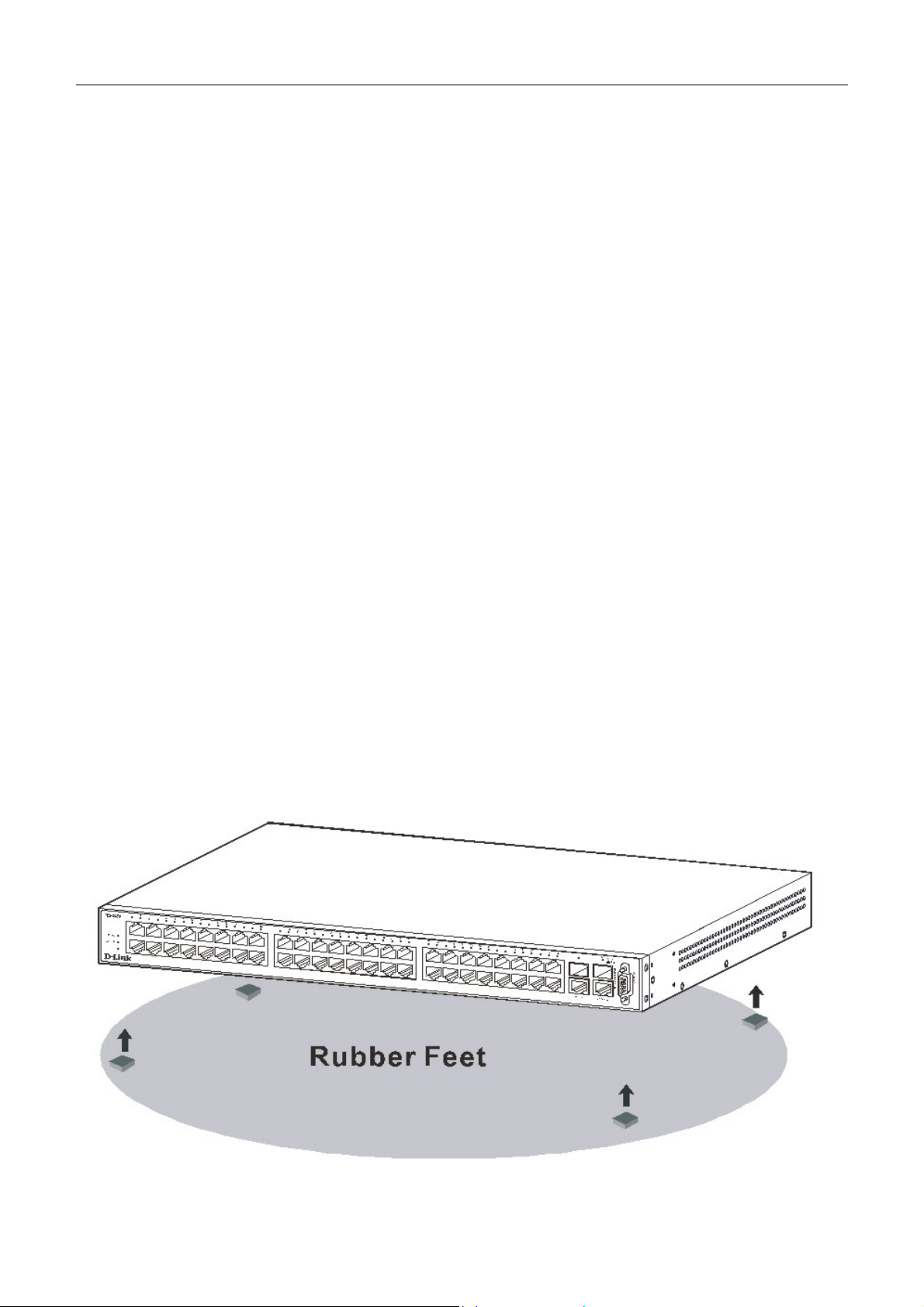
Installing the Switch Without the Rack
When installing the Switch on a desktop or shelf, the rubber feet included with the Switch should first be attached. Attach
these cushioning feet on the bottom at each corner of the device. Allow enough ventilation space between the Switch and
any other objects in the vicinity.
Figure 2- 1. Prepare Switch for installation on a desktop or shelf
8
Page 23
DES-3550 Fast Ethernet Layer 2 Switch
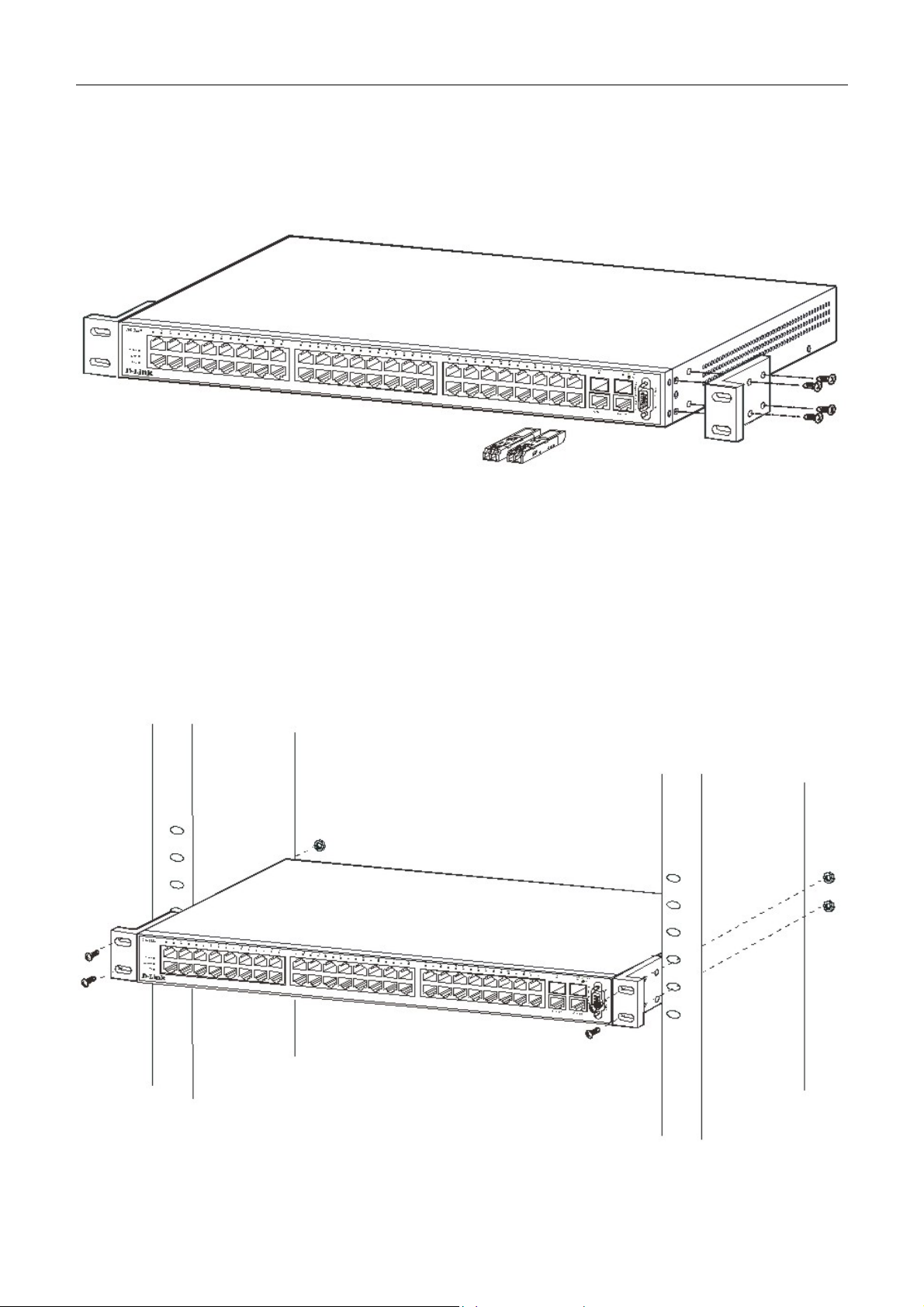
Installing the Switch in a Rack
The Switch can be mounted in a standard 19" rack. Use the following diagrams to guide you.
Figure 2- 2. Fasten mounting brackets to Switch
Fasten the mounting brackets to the Switch using the screws provided. With the brackets attached securely, you can mount
the Switch in a standard rack as shown in Figure 2-3 on the following page.
Mounting the Switch in a Standard 19" Rack
Figure 2- 3. Installing Switch in a rack
9
Page 24
DES-3550 Fast Ethernet Layer 2 Switch
Power On
Plug one end of the AC power cord into the power connector of the Switch and the other end into the local power source
outlet.
After the Switch is powered on, the LED indicators will momentarily blink. This blinking of the LED indicators represents
a reset of the system.
Power Failure
As a precaution, in the event of a power failure, unplug the Switch. When power is resumed, plug the Switch back in.
Connecting The Switch
Switch To End Node
Switch To Hub or Switch
Connecting To Network Backbone or Server
NOTE: All 48 high-performance NWay Ethernet ports can support both
MDI-II and MDI-X connections.
Section 3
Switch To End Node
End nodes include PCs outfitted with a 10, 100 or 1000 Mbps RJ?45 Ethernet/Fast Ethernet Network Interface Card (NIC)
and most routers.
An end node can be connected to the Switch via a twisted-pair Category 3, 4, or 5 UTP/STP cable. The end node should be
connected to any of the ports of the Switch.
10
Page 25

DES-3550 Fast Ethernet Layer 2 Switch
Figure 3- 1. Switch connected to an end node
The Link/Act LEDs for each UTP port will light green or amber when the link is valid. A blinking LED indicates packet
activity on that port.
Switch to Hub or Switch
These connections can be accomplished in a number of ways using a normal cable.
A 10BASE-T hub or switch can be connected to the Switch via a twisted-pair Category 3, 4 or 5 UTP/STP
•
cable.
• A 100BASE-TX hub or switch can be connected to the Switch via a twisted -pair Category 5 UTP/STP cable.
Figure 3- 2. Switch connected to a port on a hub or switch using either a straight or crossover cable-
any normal cable is fine
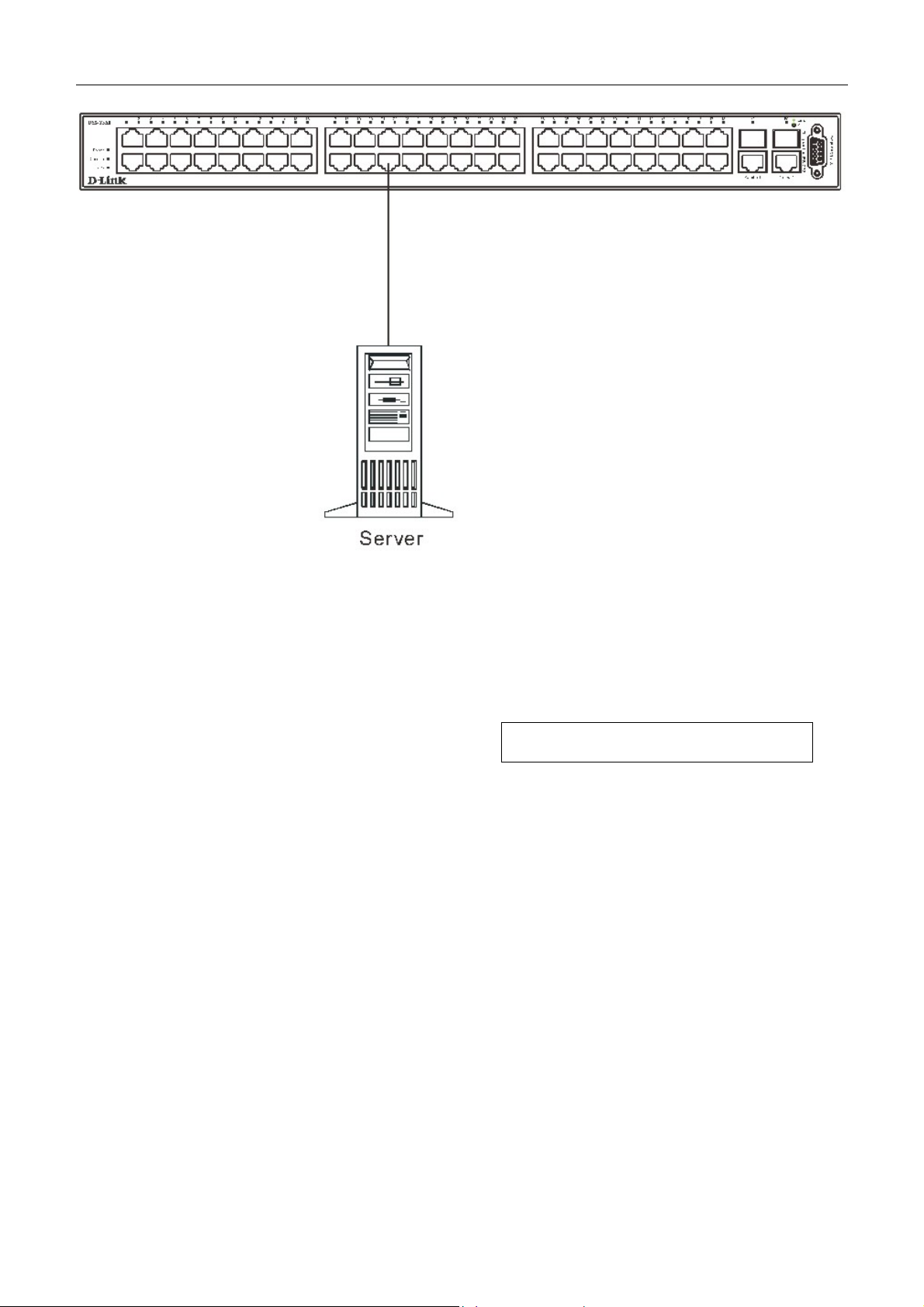
Connecting To Network Backbone or Server
The two Mini-GBIC combo ports are ideal for uplinking to a network backbone or server. The copper ports operate at a
speed of 1000, 100 or 10Mbps in full or half duplex mode. The fiber optic ports can operate at 1000Mbps in full duplex
mode.
Connections to the Gigabit Ethernet ports are made using fiber optic cable or Category 5 copper cable, depending on the
type of port. A valid connection is indicated when the Link LED is lit.
11
Page 26
DES-3550 Fast Ethernet Layer 2 Switch
Figure 3- 3. Uplink Connection to a server.
Section 4
Introduction To Switch Management
Management Options
Web-based Management Interface
SNMP-Based Management
Managing User Accounts
Command Line Console Interface Through The Serial Port
Connecting the Console Port (RS-232 DCE)
First Time Connecting to The Switch
Password Protection
SNMP Settings
IP Address Assignment
Connecting Devices to the Switch
12
Page 27

DES-3550 Fast Ethernet Layer 2 Switch
Management Options
This system may be managed out-of-band through the console port on the front panel or in-band using Telnet. The user
may also choose the web-based management, accessible through a web browser.
Web-based Management Interface
After you have successfully installed the Switch, you can configure the Switch, monitor the LED panel, and display
statistics graphically using a web browser, such as Netscape Navigator (version 6.2 and higher) or Microsoft® Internet
Explorer (version 5.0).
SNMP-Based Management
You can manage the Switch with an SNMP-compatible console program. The Switch supports SNMP version 1.0, version
2.0 and version 3.0. The SNMP agent decodes the incoming SNMP messages and responds to requests with MIB objects
stored in the database. The SNMP agent updates the MIB objects to generate statistics and counters.
Command Line Console Interface Through The Serial Port
You can also connect a computer or terminal to the serial console port to access the Switch. The command-line-driven
interface provides complete access to all Switch management features.
Connecting the Console Port (RS-232 DCE)
The Switch provides an RS-232 serial port that enables a connection to a computer or terminal for monitoring and
configuring the Switch. This port is a female DB-9 connector, implemented as a data terminal equipment (DTE)
connection.
To use the console port, you need the following equipment:
A terminal or a computer with both a serial port and the ability to emulate a terminal. •
• A null modem or crossover RS-232 cable with a female DB-9 connector for the console port on the Switch.
To connect a terminal to the console port:
1. Connect the female connector of the RS-232 cable directly to the console port on the Switch, and tighten the
captive retaining screws.
2. Connect the other end of the cable to a terminal or to the serial connector of a computer running terminal
emulation software. Set the terminal emulation software as follows:
3. Select the appropriate serial port (COM port 1 or COM port 2).
4. Set the data rate to 9600 baud.
5. Set the data format to 8 data bits, 1 stop bit, and no parity.
6. Set flow control to none.
7. Under Properties, select VT100 for Emulation mode.
8. Select Terminal keys for Function, Arrow, and Ctrl keys. Ensure that you select Terminal keys (not Windows
keys).
9. After you have correctly set up the terminal, plug the power cable into the power receptacle on the back of the
Switch. The boot sequence appears in the terminal.
NOTE: When you use HyperTerminal with the Microsoft® Windows® 2000
operating system, ensure that you have Windows 2000 Service Pack 2 or
later installed. Windows 2000 Service Pack 2 allows you to use arrow keys
in HyperTerminal's VT100 emulation. See www.microsoft.com for
information on Windows 2000 service packs.
13
Page 28

DES-3550 Fast Ethernet Layer 2 Switch
10. After the boot sequence completes, the console login screen displays.
11. If you have not logged into the command line interface (CLI) program, press the Enter key at the User name and
password prompts. There is no default user name and password for the Switch. User names and passwords must
first be created by the administrator. If you have previously set up user accounts, log in and continue to configure
the Switch.
12. Enter the commands to complete your desired tasks. Many commands require administrator-level access
privileges. Read the next section for more information on setting up user accounts. See the DES-3550 Command
Line Interface Reference Manual on the documentation CD for a list of all commands and additional information
on using the CLI.
13. When you have completed your tasks, exit the session with the logout command or close the emulator program.
Make sure the terminal or PC you are using to make this connection is configured to match these settings.
If you are having problems making this connection on a PC, make sure the emulation is set to VT-100. You will be able to
set the emulation by clicking on the File menu in you HyperTerminal window, clicking on Properties in the drop-down
menu, and then clicking the Settings tab. This is where you will find the Emulation options. If you still do not see
anything, try rebooting the Switch by disconnecting its power supply.
Once connected to the console, the screen below will appear on your console screen. This is where the user will enter
commands to perform all the available management functions. The Switch will prompt the user to enter a user name and a
password. Upon the initial connection, there is no user name or password and therefore just press enter twice to access the
command line interface.
Figure 4- 1. Initial screen after first connection.
First Time Connecting to The Switch
The Switch supports user-based security that can allow you to prevent unauthorized users from accessing the Switch or
changing its settings. This section tells how to log onto the Switch.
NOTE: The passwords used to access the Switch are case-sensitive;
therefore, "S" is not the same as "s."
When you first connect to the Switch, you will be presented with the first login screen (shown below).
14
Page 29
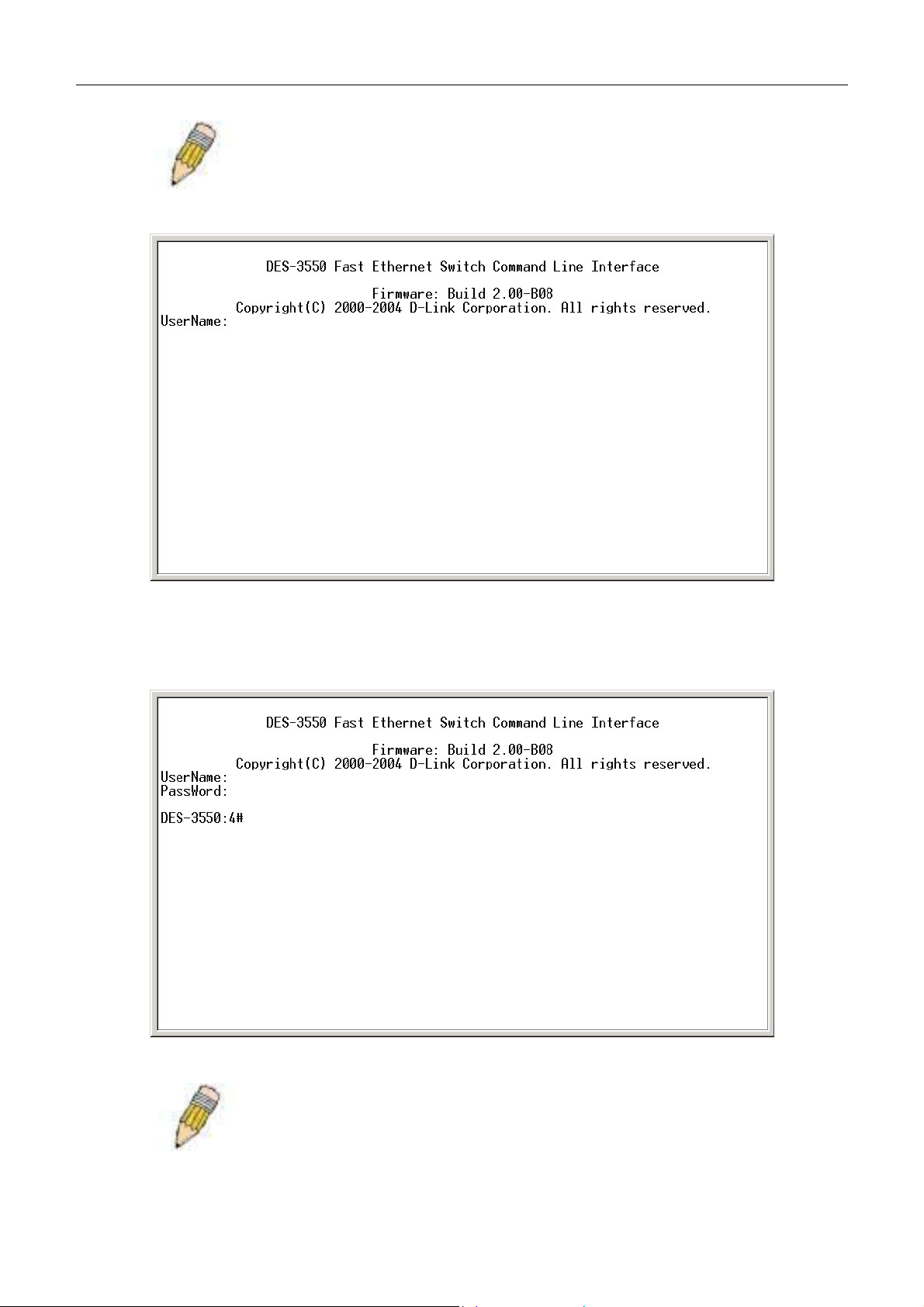
DES-3550 Fast Ethernet Layer 2 Switch
NOTE: Press Ctrl+R to refresh the screen. This command can be used at
any time to force the console program in the Switch to refresh the console
screen.
Figure 4- 2. Initial screen, first time connecting to the Switch
Press Enter in both the Username and Password fields. You will be given access to the command prompt DES-3550:4#
shown below:
There is no initial username or password. Leave the Username and Password fields blank.
Figure 4- 3. Command Prompt
NOTE: The first user automatically gets Administrator level privileges. It is
recommended to create at least one Admin-level user account for the
Switch.
15
Page 30
DES-3550 Fast Ethernet Layer 2 Switch
Password Protection
The DES-3550 does not have a default user name and password. One of the first tasks when settings up the Switch is to
create user accounts. If you log in using a predefined administrator-level user name, you have privileged access to the
Switch's management software.
After your initial login, define new passwords for both default user names to prevent unauthorized access to the Switch,
and record the passwords for future reference.
To create an administrator-level account for the Switch, do the following:
At the CLI login prompt, enter create account admin followed by the <user name> and press the Enter key. •
•
You will be asked to provide a password. Type the <password> used for the administrator account being
created and press the Enter key.
•
You will be prompted to enter the same password again to verify it. Type the same password and press the Enter
key.
•
Successful creation of the new administrator account will be verified by a Success message.
NOTE: Passwords are case sensitive. User names and passwords can be
up to 15 characters in length.
The sample below illustrates a successful creation of a new administrator-level account with the user name "newmanager".
DES-3550:4#create account admin newmanager
Command: create account admin newmanager
Enter a case-sensitive new password:********
Enter the new password again for confirmation:********
Success.
DES-3550:4#
NOTICE: CLI configuration commands only modify the running
configuration file and are not saved when the Switch is rebooted. To save
all your configuration changes in nonvolatile storage, you must use the
save command to copy the running configuration file to the startup
configuration.
SNMP Settings
Simple Network Management Protocol (SNMP) is an OSI Layer 7 (Application Layer) designed specifically for managing
and monitoring network devices. SNMP enables network management stations to read and modify the settings of
gateways, routers, switches, and other network devices. Use SNMP to configure system features for proper operation,
monitor performance and detect potential problems in the Switch, switch group or network.
Managed devices that support SNMP include software (referred to as an agent), which runs locally on the device. A
defined set of variables (managed objects) is maintained by the SNMP agent and used to manage the device. These objects
are defined in a Management Information Base (MIB), which provides a standard presentation of the information
16
Page 31

DES-3550 Fast Ethernet Layer 2 Switch
controlled by the on-board SNMP agent. SNMP defines both the format of the MIB specifications and the protocol used to
access this information over the network.
The DES-3550 supports SNMP versions 1, 2c, and 3. You can specify which version of SNMP you want to use to monitor
and control the Switch. The three versions of SNMP vary in the level of security provided between the management
station and the network device.
In SNMP v.1 and v.2, user authentication is accomplished using 'community strings', which function like passwords. The
remote user SNMP application and the Switch SNMP must use the same community string. SNMP packets from any
station that has not been authenticated are ignored (dropped).
The default community strings for the Switch used for SNMP v.1 and v.2 management access are:
public - Allows authorized management stations to retrieve MIB objects. •
• private - Allows authorized management stations to retrieve and modify MIB objects.
SNMP v.3 uses a more sophisticated authentication process that is separated into two parts. The first part is to maintain a
list of users and their attributes that are allowed to act as SNMP managers. The second part describes what each user on
that list can do as an SNMP manager.
The Switch allows groups of users to be listed and configured with a shared set of privileges. The SNMP version may also
be set for a listed group of SNMP managers. Thus, you may create a group of SNMP managers that are allowed to view
read-only information or receive traps using SNMP v.1 while assigning a higher level of security to another group,
granting read/write privileges using SNMP v.3.
Using SNMP v.3 individual users or groups of SNMP managers can be allowed to perform or be restricted from
performing specific SNMP management functions. The functions allowed or restricted are defined using the Object
Identifier (OID) associated with a specific MIB. An additional layer of security is available for SNMP v.3 in that SNMP
messages may be encrypted. To read more about how to configure SNMP v.3 settings for the Switch read the section
entitled Management.
Traps
Traps are messages that alert network personnel of events that occur on the Switch. The events can be as serious as a
reboot (someone accidentally turned OFF the Switch), or less serious like a port status change. The Switch generates traps
and sends them to the trap recipient (or network manager). Typical traps include trap messages for Authentication Failure,
Topology Change and Broadcast\Multicast Storm.
MIBs
Management and counter information are stored by the Switch in the Management Information Base (MIB). The Switch
uses the standard MIB-II Management Information Base module. Consequently, values for MIB objects can be retrieved
from any SNMP-based network management software. In addition to the standard MIB-II, the Switch also supports its own
proprietary enterprise MIB as an extended Management Information Base. The proprietary MIB may also be retrieved by
specifying the MIB Object Identifier. MIB values can be either read-only or read-write.
IP Address Assignment
Each Switch must be assigned its own IP Address, which is used for communication with an SNMP network manager or
other TCP/IP application (for example BOOTP, TFTP). The Switch's default IP address is 10.90.90.90. You can change
the default Switch IP address to meet the specification of your networking address scheme.
17
Page 32

DES-3550 Fast Ethernet Layer 2 Switch
The Switch is also assigned a unique MAC address by the factory. This MAC address cannot be changed, and can be found
by entering the command "show switch" into the command line interface, as shown below.
Figure 4- 4. Show switch command
The Switch's MAC address can also be found from the Web management program on the Switch Information (Basic
Settings) window on the Configuration menu.
The IP address for the Switch must be set before it can be managed with the Web-based manager. The Switch IP address
can be automatically set using BOOTP or DHCP protocols, in which case the actual address assigned to the Switch must be
known.
The IP address may be set using the Command Line Interface (CLI) over the console serial port as follows:
Starting at the command line prompt, enter the commands config ipif System ipaddress
xxx.xxx.xxx.xxx/yyy.yyy.yyy.yyy, where the x's represent the IP address to be assigned to the IP interface named System
and the y's represent the corresponding subnet mask.
Alternatively, you can enter config ipif System ipaddress xxx.xxx.xxx.xxx/z. Where the x's represent the IP address to be
assigned to the IP interface named System and the z represents the corresponding number of subnets in CIDR notation.
The IP interface named System on the Switch can be assigned an IP address and subnet mask which can then be used to
connect a management station to the Switch's Telnet or Web-based management agent.
18
Page 33

DES-3550 Fast Ethernet Layer 2 Switch
Figure 4- 5. Assigning the Switch an IP Address
In the above example, the Switch was assigned an IP address of 10.53.13.144 with a subnet mask of 255.0.0.0. The system
message Success indicates that the command was executed successfully. The Switch can now be configured and managed
via Telnet and the CLI or via the Web-based management.
Connecting Devices to the Switch
After you assign IP addresses to the Switch, you can connect devices to the Switch.
To connect a device to an SFP transceiver port:
Use your cabling requirements to select an appropriate SFP transceiver type. •
•
Insert the SFP transceiver (sold separately) into the SFP transceiver slot.
•
Use the appropriate network cabling to connect a device to the connectors on the SFP transceiver.
NOTICE: When the SFP transceiver acquires a link, the associated
integrated 10/100/ 1000BASE-T port is disabled.
19
Page 34

DES-3550 Fast Ethernet Layer 2 Switch
Section 5
Introduction to Web-based Switch
Configuration
Introduction
Login To Web manager
Web-Based User Interface
Basic Setup
Reboot
Basic Switch Setup
Network Management
Switch Utilities
Network Monitoring
IGMP Snooping Status
Introduction
All software functions of the DES-3550 can be managed, configured and monitored via the embedded web-based (HTML)
interface. The Switch can be managed from remote stations anywhere on the network through a standard browser such as
Netscape Navigator/Communicator or Microsoft Internet Explorer. The browser acts as a universal access tool and can
communicate directly with the Switch using the HTTP protocol.
The Web-based management module and the Console program (and Telnet) are different ways to access the same internal
switching software and configure it. Thus, all settings encountered in web-based management are the same as those found
in the console program.
Login to Web Manager
To begin managing your Switch, simply run the browser you have installed on your computer and point it to the IP address
you have defined for the device. The URL in the address bar should read something like: http://123.123.123.123, where the
numbers 123 represent the IP address of the Switch.
NOTE: The Factory default IP address for the Switch is 10.90.90.90.
In the page that opens, click on the Login to make a setup button:
Figure 5- 1. Login Button
This opens the management module's user authentication window, as seen below.
20
Page 35

DES-3550 Fast Ethernet Layer 2 Switch
Figure 5- 2. Enter Network Password window
Leave both the User Name field and the Password field blank and click OK. This will open the Web-based user interface.
The Switch management features available in the web-based manager are explained below.
Web-based User Interface
The user interface provides access to various Switch configuration and management screens, allows you to view
performance statistics, and permits you to graphically monitor the system status.
Areas of the User Interface
The figure below shows the user interface. The user interface is divided into 3 distinct areas as described in the table.
Area 2
Area 3
Area 1
Figure 5- 3. Main Web-Manager Screen
Area Function
Area 1
Area 2
Select the menu or window to be displayed. The folder icons can be opened to
display the hyperlinked menu buttons and subfolders contained within them. Click
the D-Link logo to go to the D-Link website.
Presents a graphical near real-time image of the front panel of the Switch. This area
displays the Switch's ports and expansion modules, showing port activity, duplex
mode, or flow control, depending on the specified mode.
Various areas of the graphic can be selected for performing management functions,
including port configuration.
21
Page 36

DES-3550 Fast Ethernet Layer 2 Switch
Area 3
Presents switch information based on your selection and the entry of configuration
data.
NOTICE: Any changes made to the Switch configuration during the
current session must be saved in the Save Changes web menu (explained
below) or use the command line interface (CLI) command save.
Web Pages
When you connect to the management mode of the Switch with a web browser, a login screen is displayed. Enter a user
name and password to access the Switch's management mode.
Below is a list and description of the main folders available in the web interface:
Configurations- Contains screens concerning configurations for IP Address, Switch Information, Advanced Settings, Port
Configuration, IGMP, Spanning Tree, Forwarding Filtering, VLANs, Port Bandwidth, SNTP Settings, Port Security, QoS,
MAC Notification, LACP, Access Profile Table, System Log Servers, PAE Access Entity, and Layer 3 IP Networking.
Security Management - Contains screens concerning configurations for Security IP, User Accounts, Access
Authentication Control (TACACS), Secure Sockets Layer (SSL), Secure Shell (SSH) and SNMP V3.
Monitoring - Contains screens concerning monitoring the Switch, pertaining to Port Utilization, CPU Utilization, Packets,
Errors Size, MAC Address, IGMP Snooping Group, IGMP Snooping Forwarding, VLAN Status, Router Port, Port Access
Control and Layer 3 Feature.
Maintenance - Contains screens concerning configurations and information about Switch maintenance, including TFTP
Services, Switch History, Ping Test, Save Changes, Reboot Services and Logout.
Single IP Management - Contains screens concerning information on Single IP Management, including SIM Settings,
Topology and Firmware/Configuration downloads.
NOTE: Be sure to configure the user name and password in the User
Accounts menu before connecting the Switch to the greater network.
22
Page 37

DES-3550 Fast Ethernet Layer 2 Switch
Configuring The Switch
Switch Information
IP Address
Advanced Settings
Port Configuration
Port Description
Port Mirroring
Link Aggregation
LACP Port Setting
MAC Notification
IGMP
Section 6
Spanning Tree
Forward Filtering
VLANs
Port Security
QoS
System Log Servers
SNTP Settings
Access Profile Table
PAE Access Entity
Layer 3 IP Networking
Switch Information
The subsections below describe how to change some of the basic settings for the Switch such as changing IP settings and
assigning user names and passwords for management access privileges, as well as how to save the changes and restart the
Switch.
Click the Switch Information link in the Configuration menu.
23
Page 38

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 1. Switch Information (Basic Settings) window
The Switch Information window shows the Switch's MAC Address (assigned by the factory and unchangeable), the
Boot PROM, Firmware Version, and Hardware Version. This information is helpful to keep track of PROM and
firmware updates and to obtain the Switch's MAC address for entry into another network device's address table, if
necessary. The user may also enter a System Name, System Location and System Contact to aid in defining the Switch,
to the user's preference.
IP Address
The IP Address may initially be set using the console interface prior to connecting to it through the Ethernet. If the Switch
IP address has not yet been changed, read the introduction of the DES-3550 Command Line Interface Manual or return to
Section 4 of this manual for more information.
To change IP settings using the web manager you must access the IP Address menu located in the Configuration folder.
To configure the Switch's IP address:
Open the Configuration folder and click the IP Address menu link. The web manager will display the Switch's current IP
settings in the IP configuration menu, as seen below.
Figure 6- 2. IP Address Settings window
To manually assign the Switch's IP address, subnet mask, and default gateway address:
1. Select Manual from the Get IP From drop-down menu.
2. Enter the appropriate IP Address and Subnet Mask.
24
Page 39

DES-3550 Fast Ethernet Layer 2 Switch
3. If you want to access the Switch from a different subnet from the one it is installed on, enter the IP address of the
Default Gateway. If you will manage the Switch from the subnet on which it is installed, you can leave the
default address (0.0.0.0) in this field.
4. If no VLANs have been previously configured on the Switch, you can use the default VLAN Name. The default
VLAN contains all of the Switch ports as members. If VLANs have been previously configured on the Switch,
you will need to enter the VLAN ID of the VLAN that contains the port connected to the management station that
will access the Switch. The Switch will allow management access from stations with the same VID listed here.
NOTE: The Switch's factory default IP address is 10.90.90.90 with a
subnet mask of 255.0.0.0 and a default gateway of 0.0.0.0.
To use the BOOTP or DHCP protocols to assign the Switch an IP address, subnet mask, and default gateway address:
Use the Get IP From pull-down menu to choose from BOOTP or DHCP. This selects how the Switch will be assigned an
IP address on the next reboot.
The IP Address Settings options are:
Parameter Description
BOOTP
DHCP
Manual
Subnet Mask
Default
Gateway
The Switch will send out a BOOTP broadcast request when it is powered up. The BOOTP
protocol allows IP addresses, network masks, and default gateways to be assigned by a
central BOOTP server. If this option is set, the Switch will first look for a BOOTP server to
provide it with this information before using the default or previously entered settings.
The Switch will send out a DHCP broadcast request when it is powered up. The DHCP protocol allows IP addresses, network masks, and default gateways to be assigned by a DHCP
server. If this option is set, the Switch will first look for a DHCP server to provide it with this
information before using the default or previously entered settings.
Allows the entry of an IP address, Subnet Mask, and a Default Gateway for the Switch.
These fields should be of the form xxx.xxx.xxx.xxx, where each xxx is a number
(represented in decimal form) between 0 and 255. This address should be a unique address
on the network assigned for use by the network administrator.
A Bitmask that determines the extent of the subnet that the Switch is on. Should be of the
form xxx.xxx.xxx.xxx, where each xxx is a number (represented in decimal) between 0 and
255. The value should be 255.0.0.0 for a Class A network, 255.255.0.0 for a Class B
network, and 255.255.255.0 for a Class C network, but custom subnet masks are allowed.
IP address that determines where packets with a destination address outside the current
subnet should be sent. This is usually the address of a router or a host acting as an IP gateway. If your network is not part of an intranet, or you do not want the Switch to be accessible
outside your local network, you can leave this field unchanged.
VLAN Name
Admin State
This allows the entry of a VLAN Name from which a management station will be allowed to
manage the Switch using TCP/IP (in-band via web manager or Telnet). Management
stations that are on VLANs other than the one entered here will not be able to manage the
Switch in-band unless their IP addresses are entered in the Security IP Management menu.
If VLANs have not yet been configured for the Switch, the default VLAN contains all of the
Switch's ports. There are no entries in the Security IP Management table, by default, so
any management station that can connect to the Switch can access the Switch until a
management VLAN is specified or Management Station IP Addresses are assigned.
This field will allow the user the enable or disable the Admin State for the IP interface, by
the using the pull-down menu. Disabling this feature will render all remote management
inoperable, and thus the only way to configure the Switch will be to use the Console port for
the Command Line Interface.
25
Page 40

DES-3550 Fast Ethernet Layer 2 Switch
Click Apply to let your changes take effect.
Setting the Switch's IP Address using the Console Interface
Each Switch must be assigned its own IP Address, which is used for communication with an SNMP network manager or
other TCP/IP application (for example BOOTP, TFTP). The Switch's default IP address is 10.90.90.90. You can change
the default Switch IP address to meet the specification of your networking address scheme.
The IP address for the Switch must be set before it can be managed with the Web-based manager. The Switch IP address
can be automatically set using BOOTP or DHCP protocols, in which case the actual address assigned to the Switch must be
known. The IP address may be set using the Command Line Interface (CLI) over the console serial port as follows:
•
Starting at the command line prompt, enter the commands config ipif System ipaddress xxx.xxx.xxx.xxx/
yyy.yyy.yyy.yyy. Where the x's represent the IP address to be assigned to the IP interface named System and the
y's represent the corresponding subnet mask.
•
Alternatively, you can enter config ipif System ipaddress xxx.xxx.xxx.xxx/z. Where the x's represent the IP
address to be assigned to the IP interface named System and the z represents the corresponding number of
subnets in CIDR notation.
The IP interface named System on the Switch can be assigned an IP address and subnet mask which can then be used to
connect a management station to the Switch's Telnet or Web-based management agent.
The system message Success indicates that the command was executed successfully. The Switch can now be configured
and managed via Telnet and the CLI or via the Web-based management agent using the above IP address to connect to the
Switch.
Advanced Settings
The Switch Information (Advanced Settings) window contains the main settings for all major functions for the Switch.
To view this window, click its link in the Configuration folder. This will enable the following window to be viewed and
configured.
Figure 6- 3. Switch Information (Advanced Settings)
26
Page 41

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
Serial Port Auto
Logout Time
MAC Address
Aging Time
IGMP Snooping
GVRP Status
Telnet Status
TCP Port Number
(1-65535)
Web Status
Select the logout time used for the console interface. This automatically logs the user
out after an idle period of time, as defined. Choose from the following options: 2
Minutes, 5 Minutes, 10 Minutes, 15 Minutes or Never. The default setting is 10 minutes.
This field specifies the length of time a learned MAC Address will remain in the
forwarding table without being accessed (that is, how long a learned MAC Address is
allowed to remain idle). The default age-out time for the Switch is 300 seconds. To
change this, type in a different value representing the MAC address age-out time in
seconds. The MAC Address Aging Time can be set to any value between 10 and
1,000,000 seconds. The default setting is 300 seconds.
To enable system-wide IGMP Snooping capability select Enabled. IGMP snooping is
Disabled by default. Enabling IGMP snooping allows you to specify use of a multicast
router only (see below). To configure IGMP Snooping for individual VLANs, use the
IGMP Snooping page under the IGMP folder.
Use this pull-down menu to enable or disable GVRP on the Switch.
Telnet configuration is Enabled by default. If you do not want to allow configuration of
the system through Telnet choose Disabled.
The TCP port number. TCP ports are numbered between 1 and 65535. The "wellknown" TCP port for the Telnet protocol is 23.
Web-based management is Enabled by default. If you choose to disable this by selecting Disabled, you will lose the ability to configure the system through the web interface
as soon as these settings are applied.
Web TCP Port
Number
Link Aggregation
Algorithm
RMON Status
802.1x Status
802.1x
Authentication
Protocol
The TCP port number currently being utilized by the Switch to connect to the web
interface. The "well-known" TCP port for the Web interface is 80.
The algorithm that the Switch uses to balance the load across the ports that make up
the port trunk group is defined by this definition. Choose MAC Source, MAC Destination,
MAC Src & Dest, IP Source, IP Destination or IP Src & Dest (See the Link Aggregation
section of this manual).
Remote monitoring (RMON) of the Switch is Enabled or Disabled here.
The Switch’s 802.1x function may be enabled by port or by MAC Address; the default is
Disabled. This field must be enabled to view and configure certain windows for 802.1x.
More information regarding 802.1x, its functions and implementation can be found later
in this section, under the Port Access Entity folder.
Port-Based 802.1x specifies that ports configured for 802.1x are initialized based on the
port number only and are subject to any authorization parameters configured.
MAC-based Authorization specifies that ports configured for 802.1x are initialized based
on the port number and the MAC address of the computer being authorized and are
then subject to any authorization parameters configured.
The user may use the pull down menu to choose between radius eap and radius pap for
the 802.1x authentication protocol on the Switch. The default setting is radius eap.
Asymmetric VLAN
This field will enable or disable Asymmetric VLANs on the Switch. The default is
Disabled.
27
Page 42

DES-3550 Fast Ethernet Layer 2 Switch
Syslog Global
State
Click Apply to implement changes made.
Enables or disables Syslog State; default is Disabled.
NOTE: When the Asymmetric VLAN function is Disabled, the user must
change the VLAN setting on the Switch to its default configurations.
Port Configurations
This section contains information for configuring various attributes and properties for individual physical ports, including
port speed and flow control. Clicking on Port Configurations in the Configuration menu will display the following
window for the user:
28
Page 43

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 4. Port Configuration and The Port Information Table window
To configure switch ports:
1. Choose the port or sequential range of ports using the From…To… port pull-down menus.
2. Use the remaining pull-down menus to configure the parameters described below:
29
Page 44

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
State <Enabled>
Speed/Duplex <Auto>
Flow Control
Learn
Click Apply to implement the new settings on the Switch.
Toggle the State field to either enable or disable a given port or group of ports.
Toggle the Speed/Duplex field to either select the speed and duplex/half-duplex
state of the port. Auto denotes auto-negotiation between 10 and 100 Mbps
devices, in full- or half-duplex. The Auto setting allows the port to automatically
determine the fastest settings the device the port is connected to can handle, and
then to use those settings. The other options are Auto, 10M/Half, 10M/Full,
100M/Half and 100M/Full. There is no automatic adjustment of port settings with
any option other than Auto.
Displays the flow control scheme used for the various port configurations. Ports
configured for full-duplex use 802.3x flow control, half-duplex ports use
backpressure flow control, and Auto ports use an automatic selection of the two.
The default is Disabled.
Enable or disable MAC address learning for the selected ports. When Enabled,
destination and source MAC addresses are automatically listed in the forwarding
table. When learning is Disabled, MAC addresses must be manually entered into
the forwarding table. This is sometimes done for reasons of security or efficiency.
See the section on Forwarding/Filtering for information on entering MAC
addresses into the forwarding table. The default setting is Disabled.
Port Description
The DES-3550 supports a port description feature where the user may name various ports on the Switch. To assign names
to various ports, click the Port Description on the Configuration menu:
30
Page 45

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 5. Port Description Setting and Port Description Table
31
Page 46

DES-3550 Fast Ethernet Layer 2 Switch
Use the From and To pull down menu to choose a port or range of ports to describe, and then enter a description of the
port(s). Click Apply to set the descriptions in the Port Description Table.
Port Mirroring
The Switch allows you to copy frames transmitted and received on a port and redirect the copies to another port. You can
attach a monitoring device to the mirrored port, such as a sniffer or an RMON probe, to view details about the packets
passing through the first port. This is useful for network monitoring and troubleshooting purposes. To view the Port
Mirroring window, click Port Mirroring in the Configuration folder.
To configure a mirror port:
Select the Source Port from where you want to copy frames and the Target Port, which receives the copies
•
from the source port.
•
Select the Source Direction, Ingress, Egress, or Both and change the Status drop-down menu to Enabled.
•
Click Apply to let the changes take effect.
Figure 6- 6. Setup Port Mirroring window
NOTE: You cannot mirror a fast port onto a slower port. For example, if
you try to mirror the traffic from a 100 Mbps port onto a 10 Mbps port, this
can cause throughput problems. The port you are copying frames from
should always support an equal or lower speed than the port to which you
are sending the copies. Also, the target port for the mirroring cannot be a
member of a trunk group. Please note a target port and a source port
cannot be the same port.
32
Page 47

DES-3550 Fast Ethernet Layer 2 Switch
Link Aggregation
Understanding Port Trunk Groups
Port trunk groups are used to combine a number of ports together to make a single high-bandwidth data pipeline.
The DES-3550 supports up to 6 port trunk groups with 2 to 8 ports in each group. A potential bit rate of 8000 Mbps can be
achieved.
Figure 6- 7. Example of Port Trunk Group
The Switch treats all ports in a trunk group as a single port. Data transmitted to a specific host (destination address) will
always be transmitted over the same port in a trunk group. This allows packets in a data stream to arrive in the same order
they were sent.
NOTE: If any ports within the trunk group become disconnected, packets
intended for the disconnected port will be load shared among the other
uplinked ports of the link aggregation group.
Link aggregation allows several ports to be grouped together and to act as a single link. This gives a bandwidth that is a
multiple of a single link's bandwidth.
Link aggregation is most commonly used to link a bandwidth intensive network device or devices, such as a server, to the
backbone of a network.
The Switch allows the creation of up to 6 link aggregation groups, each group consisting of 2 to 8 links (ports). The
aggregated links must be contiguous (they must have sequential port numbers) except the two (optional) Gigabit ports,
which can only belong to a single link aggregation group. All of the ports in the group must be members of the same
VLAN, and their STP status, static multicast, traffic control, traffic segmentation and 802.1p default priority configurations
must be identical. Port locking, port mirroring and 802.1X must not be enabled on the trunk group. Further, the aggregated
links must all be of the same speed and should be configured as full-duplex.
The Master Port of the group is to be configured by the user, and all configuration options, including the VLAN
configuration that can be applied to the Master Port, are applied to the entire link aggregation group.
Load balancing is automatically applied to the ports in the aggregated group, and a link failure within the group causes the
network traffic to be directed to the remaining links in the group.
33
Page 48

DES-3550 Fast Ethernet Layer 2 Switch
The Spanning Tree Protocol will treat a link aggregation group as a single link, on the switch level. On the port level, the
STP will use the port parameters of the Master Port in the calculation of port cost and in determining the state of the link
aggregation group. If two redundant link aggregation groups are configured on the Switch, STP will block one entire
group, in the same way STP will block a single port that has a redundant link.
To configure port trunking, click on the Link Aggregation hyperlink in the Configuration folder to bring up the Port
Link Aggregation Group table:
Figure 6- 8. Port Link Aggregation Group Entries window
To configure port trunk groups, click the Add button to add a new trunk group and use the Link Aggregation Settings
menu (see example below) to set up trunk groups. To modify a port trunk group, click the Modify button corresponding to
the entry you wish to alter. To delete a port trunk group, click the corresponding
Current Link Aggregation Group Entries table.
Figure 6- 9. Link Aggregation Settings window – Add
under the Delete heading in the
34
Page 49

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 10. Link Aggregation Group Configuration window - Modify
The user-changeable parameters are as follows:
Parameter Description
Group ID
State
Master Port
Member Ports
Flooding Port
Active Port
Type
Select an ID number for the group, between 1 and 6.
Trunk groups can be toggled between Enabled and Disabled. This is used to turn a
port trunking group on or off. This is useful for diagnostics, to quickly isolate a
bandwidth intensive network device or to have an absolute backup aggregation
group that is not under automatic control.
Choose the Master Port for the trunk group using the pull down menu.
Choose the members of a trunked group. Up to 8 ports per group can be assigned
to a group.
A trunking group must designate one port to allow transmission of broadcasts and
unknown unicasts.
Shows the port that is currently forwarding packets.
This pull-down menu allows you to select between Static and LACP (Link
Aggregation Control Protocol). LACP allows for the automatic detection of links in a
Port Trunking Group.
After setting the previous parameters, click Apply to allow your changes to be implemented. Successfully created trunk
groups will be show in the Current Link Aggregation Group Entries as seen in Figure 6-8.
LACP Port Setting
The LACP Port Setting window is used in conjunction with the Link Aggregation window to create port trunking groups
on the Switch. Using the following window, the user may set which ports will be active and passive in processing and
sending LACP control frames.
35
Page 50

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 11. LACP Port Settings and LACP Port Table
The user may set the following parameters:
36
Page 51

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
From/To
Mode
After setting the previous parameters, click Apply to allow your changes to be implemented. The LACP Port Table
shows which ports are active and/or passive.
A consecutive group of ports may be configured starting with the selected port.
Active - Active LACP ports are capable of processing and sending LACP control
frames. This allows LACP compliant devices to negotiate the aggregated link so the
group may be changed dynamically as needs require. In order to utilize the ability to
change an aggregated port group, that is, to add or subtract ports from the group, at
least one of the participating devices must designate LACP ports as active. Both
devices must support LACP.
Passive - LACP ports that are designated as passive cannot initially send LACP
control frames. In order to allow the linked port group to negotiate adjustments and
make changes dynamically, one end of the connection must have "active" LACP
ports (see above).
MAC Notification
MAC Notification is used to monitor MAC addresses learned and entered into the forwarding database.
MAC Notification Global Settings
To globally set MAC notification on the Switch, open the following screen by opening the MAC Notification folder and
clicking the MAC Notification Global Settings link:
Figure 6- 12. MAC Notification Global Setting window.
The following parameters may be modified:
Parameter Description
State
Interval (sec)
History size
Enable or disable MAC notification globally on the Switch
The time in seconds between notifications.
The maximum number of entries listed in the history log used for notification. Up to
500 entries can be specified.
MAC Notification Port Settings
To change MAC notification settings for a port or group of ports on the Switch, click Port Settings in the MAC
Notification folder, which will display the following screen:
37
Page 52

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 13. MAC Notification Port Settings and Port State Table
38
Page 53

DES-3550 Fast Ethernet Layer 2 Switch
The following parameters may be set:
Parameter Description
From…To
State
Click Apply to implement changes made.
Select a port or group of ports to enable for MAC notification using the pull
down menus.
Enable MAC Notification for the ports selected using the pull down menu.
IGMP
Internet Group Management Protocol (IGMP) snooping allows the Switch to recognize IGMP queries and reports sent
between network stations or devices and an IGMP host. When enabled for IGMP snooping, the Switch can open or close a
port to a specific device based on IGMP messages passing through the Switch.
In order to use IGMP Snooping it must first be enabled for the entire Switch (see Advanced Settings). You may then
fine-tune the settings for each VLAN using the IGMP Snooping link in the Configuration folder. When enabled for
IGMP snooping, the Switch can open or close a port to a specific multicast group member based on IGMP messages sent
from the device to the IGMP host or vice versa. The Switch monitors IGMP messages and discontinues forwarding
multicast packets when there are no longer hosts requesting that they continue.
IGMP Snooping
Use the Current IGMP Snooping Group Entries window to view IGMP Snooping settings. To modify the settings,
click the Modify button of the VLAN ID you want to change.
Figure 6- 14. Current IGMP Snooping Group Entries
Clicking the Modify button will open the IGMP Snooping Settings menu, shown below:
39
Page 54

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 15. IGMP Snooping Settings window
The following parameters may be viewed or modified:
Parameter Description
VLAN ID
This is the VLAN ID that, along with the VLAN Name, identifies the VLAN the user
wishes to modify the IGMP Snooping Settings for.
VLAN Name
This is the VLAN Name that, along with the VLAN ID, identifies the VLAN the user
wishes to modify the IGMP Snooping Settings for.
Query Interval
The Query Interval field is used to set the time (in seconds) between transmitting
IGMP queries. Entries between 1 and 65535 seconds are allowed. Default = 125.
Max Response Time
This determines the maximum amount of time in seconds allowed before sending an
IGMP response report. The Max Response Time field allows an entry between 1 and
25 (seconds). Default = 10.
Robustness Variable
Adjust this variable according to expected packet loss. If packet loss on the VLAN is
expected to be high, the Robustness Variable should be increased to accommodate
increased packet loss. This entry field allows an entry of 1 to 255. Default = 2.
Last Member Query
Interval
This field specifies the maximum amount of time between group-specific query
messages, including those sent in response to leave group messages. Default = 1.
Host Timeout
Route Timeout
This is the maximum amount of time in seconds allowed for a host to continue
membership in a multicast group without the Switch receiving a host membership
report. Default = 260.
This is the maximum amount of time in seconds a route is kept in the forwarding table
without receiving a membership report. Default = 260.
40
Page 55

DES-3550 Fast Ethernet Layer 2 Switch
Leave Timer
This specifies the maximum amount of time in seconds between the Switch receiving
a leave group message from a host, and the Switch issuing a group membership
query. If no response to the membership query is received before the Leave Timer
expires, the (multicast) forwarding entry for that host is deleted.
Querier State
Choose Enabled to enable transmitting IGMP Query packets or Disabled to disable.
The default is Disabled.
State
Select Enabled to implement IGMP Snooping. This field is Disabled by default.
Click Apply to implement the new settings. Click the Show All IGMP Group Entries link to return to the Current IGMP
Snooping Group Entries window.
Static Router Ports
A static router port is a port that has a multicast router attached to it. Generally, this router would have a connection to a
WAN or to the Internet. Establishing a router port will allow multicast packets coming from the router to be propagated
through the network, as well as allowing multicast messages (IGMP) coming from the network to be propagated to the
router.
A router port has the following behavior:
All IGMP Report packets will be forwarded to the router port. •
•
IGMP queries (from the router port) will be flooded to all ports.
•
All UDP multicast packets will be forwarded to the router port. Because routers do not send IGMP reports or
implement IGMP snooping, a multicast router connected to the router port of a Layer 3 switch would not be able
to receive UDP data streams unless the UDP multicast packets were all forwarded to the router port.
A router port will be dynamically configured when IGMP query packets, RIPv2 multicast, DVMRP multicast or PIM-DM
multicast packets are detected flowing into a port.
Open the IGMP folder and the click on the Static Router Ports Entry link to open the Current Static Router Ports
Entries page, as shown below.
Figure 6- 16. Current Static Router Ports Entries window
The Current Static Router Ports Entries page (shown above) displays all of the current entries to the Switch's static
router port table. To modify an entry, click the Modify button. This will open the Static Router Ports Settings page, as
shown below.
41
Page 56

Figure 6- 17. Static Router Ports Settings window
The following parameters can be set:
Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
VID (VLAN ID)
VLAN Name
Member Ports
Click Apply to implement the new settings, Click the Show All Static Router Port Entries link to return to the Current
Static Router Port Entries window.
This is the VLAN ID that, along with the VLAN Name, identifies the VLAN where the
multicast router is attached.
This is the name of the VLAN where the multicast router is attached.
There are the ports on the Switch that will have a multicast router attached to them.
Spanning Tree
This Switch supports three versions of the Spanning Tree Protocol; 802.1d STP, 802.1w Rapid STP and 802.1s MSTP.
802.1d STP will be familiar to most networking professionals. However, since 802.1w RSTP and 802.1s MSTP has been
recently introduced to D-Link managed Ethernet switches, a brief introduction to the technology is provided below
followed by a description of how to set up 802.1d STP, 802.1w RSTP and 802.1s MSTP.
802.1s MSTP
Multiple Spanning Tree Protocol, or MSTP, is a standard defined by the IEEE community that allows multiple VLANs to
be mapped to a single spanning tree instance, which will provide multiple pathways across the network. Therefore, these
MSTP configurations will balance the traffic load, preventing wide scale disruptions when a single spanning tree instance
fails. This will allow for faster convergences of new topologies for the failed instance. Frames designated for these VLANs
will be processed quickly and completely throughout interconnected bridges utilizing either of the three spanning tree
protocols (STP, RSTP or MSTP).
This protocol will also tag BDPU packets so receiving devices can distinguish spanning tree instances, spanning tree
regions and the VLANs asscociated with them. These instances will be classified by an MSTI ID. MSTP will connect
multiple spanning trees with a Common and Internal Spanning Tree (CIST). The CIST will automatically determine each
MSTP region, its maximum possible extent and will appear as one virtual bridge that runs a single spanning tree.
Consequentially, frames assigned to different VLANs will follow different data routes within administratively established
regions on the network, continuing to allow simple and full processing of frames, regardless of administrative errors in
defining VLANs and their respective spanning trees.
Each switch utilizing the MSTP on a network will have a single MSTP configuration that will have the following three
attributes:
42
Page 57

DES-3550 Fast Ethernet Layer 2 Switch
1. A configuration name defined by an alphanumeric string of up to 32 characters (defined in the STP Bridge
Global Settings window in the Configuration Name field).
2. A configuration revision number (named here as a Revision Level and found in the STP Bridge Global Settings
window) and;
3. A 4096 element table (defined here as a VID List in the MST Configuration Table window) which will
associate each of the possible 4096 VLANs supported by the Switch for a given instance.
To utilize the MSTP function on the Switch, three steps need to be taken:
1. The Switch must be set to the MSTP setting (found in the STP Bridge Global Settings window in the STP
Version field)
2. The correct spanning tree priority for the MSTP instance must be entered (defined here as a Priority in the MST
Configuration Table window when configuring an MSTI ID settings).
3. VLANs that will be shared must be added to the MSTP Instance ID (defined here as a VID List in the MST
Configuration Table window when configuring an MSTI ID settings).
802.1w Rapid Spanning Tree
The Switch implements three versions of the Spanning Tree Protocol, the Multiple Spanning Tree Protocol (MSTP) as
defined by the IEEE 802.1s, the Rapid Spanning Tree Protocol (RSTP) as defined by the IEEE 802.1w specification and a
version compatible with the IEEE 802.1d STP. RSTP can operate with legacy equipment implementing IEEE 802.1d,
however the advantages of using RSTP will be lost.
The IEEE 802.1w Rapid Spanning Tree Protocol (RSTP) evolved from the 802.1d STP standard. RSTP was developed in
order to overcome some limitations of STP that impede the function of some recent switching innovations, in particular,
certain Layer 3 functions that are increasingly handled by Ethernet switches. The basic function and much of the
terminology is the same as STP. Most of the settings configured for STP are also used for RSTP. This section introduces
some new Spanning Tree concepts and illustrates the main differences between the two protocols.
Port Transition States
An essential difference between the three protocols is in the way ports transition to a forwarding state and in the way this
transition relates to the role of the port (forwarding or not forwarding) in the topology. MSTP and RSTP combine the
transition states disabled, blocking and listening used in 802.1d and creates a single state Discarding. In either case, ports
do not forward packets. In the STP port transition states disabled, blocking or listening or in the RSTP/MSTP port state
discarding, there is no functional difference, the port is not active in the network topology. Table 6-1 below compares how
the three protocols differ regarding the port state transition.
All three protocols calculate a stable topology in the same way. Every segment will have a single path to the root bridge.
All bridges listen for BPDU packets. However, BPDU packets are sent more frequently - with every Hello packet. BPDU
packets are sent even if a BPDU packet was not received. Therefore, each link between bridges is sensitive to the status of
the link. Ultimately this difference results in faster detection of failed links, and thus faster topology adjustment. A drawback of 802.1d is this absence of immediate feedback from adjacent bridges.
802.1d MSTP 802.1w RSTP 802.1d STP Forwarding Learning
Discarding Discarding Disabled No No
Discarding Discarding Blocking No No
Discarding Discarding Listening No No
Learning Learning Learning No Yes
Forwarding Forwarding Forwarding Yes Yes
Table 6- 1. Comparing Port States
RSTP is capable of a more rapid transition to a forwarding state - it no longer relies on timer configurations - RSTP
compliant bridges are sensitive to feedback from other RSTP compliant bridge links. Ports do not need to wait for the
43
Page 58

DES-3550 Fast Ethernet Layer 2 Switch
topology to stabilize before transitioning to a forwarding state. In order to allow this rapid transition, the protocol
introduces two new variables: the edge port and the point-to-point (P2P) port.
Edge Port
The edge port is a configurable designation used for a port that is directly connected to a segment where a loop cannot be
created. An example would be a port connected directly to a single workstation. Ports that are designated as edge ports
transition to a forwarding state immediately without going through the listening and learning states. An edge port loses its
status if it receives a BPDU packet, immediately becoming a normal spanning tree port.
P2P Port
A P2P port is also capable of rapid transition. P2P ports may be used to connect to other bridges. Under RSTP/MSTP, all
ports operating in full-duplex mode are considered to be P2P ports, unless manually overridden through configuration.
802.1d / 802.1w / 802.1s Compatibility
MSTP or RSTP can interoperate with legacy equipment and is capable of automatically adjusting BPDU packets to 802.1d
format when necessary. However, any segment using 802.1d STP will not benefit from the rapid transition and rapid
topology change detection of MSTP or RSTP. The protocol also provides for a variable used for migration in the event that
legacy equipment on a segment is updated to use RSTP or MSTP.
The Spanning Tree Protocol (STP) operates on two levels:
1. On the switch level, the settings are globally implemented.
2. On the port level, the settings are implemented on a per user-defined group of ports basis.
STP Bridge Global Settings
To open the following window, open the Spanning Tree folder in the Configuration menu and click the STP Bridge
Global Settings link.
Figure 6- 18. STP Bridge Global Settings - STP
44
Page 59

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 19. STP Bridge Global Settings - RSTP (default)
Figure 6- 20. STP Bridge Global Settings
The following parameters can be set:
Parameter Description
STP Status
STP Version
Use the pull-down menu to enable or disable STP globally on the Switch. The
default is Disabled.
Use the pull-down menu to choose the desired version of STP to be implemented
on the Switch. There are three choices:
MST Configuration Identification
45
Page 60

DES-3550 Fast Ethernet Layer 2 Switch
STP - Select this parameter to set the Spanning Tree Protocol(STP) globally on
the switch.
RSTP - Select this parameter to set the Rapid Spanning Tree Protocol (RSTP)
globally on the Switch.
MSTP - Select this parameter to set the Multiple Spanning Tree Protocol (MSTP)
globally on the Switch.
Hello Time: (1 - 10 sec)
<2>
Max Age: (6 - 40 sec)
<20>
Forward Delay: (4 - 30
sec) <15 >
Max Hops (1-20) <20>
The Hello Time can be set from 1 to 10 seconds. This is the interval between two
transmissions of BPDU packets sent by the Root Bridge to tell all other switches
that it is indeed the Root Bridge. This field will only appear here when STP or
RSTP is selected for the STP Version. For MSTP, the Hello Time must be set on
a port per port basis. See the MST Port Settings section for further details.
The Max Age may be set to ensure that old information does not endlessly
circulate through redundant paths in the network, preventing the effective
propagation of the new information. Set by the Root Bridge, this value will aid in
determining that the Switch has spanning tree configuration values consistent with
other devices on the bridged LAN. If the value ages out and a BPDU has still not
been received from the Root Bridge, the Switch will start sending its own BPDU to
all other switches for permission to become the Root Bridge. If it turns out that
your switch has the lowest Bridge Identifier, it will become the Root Bridge. The
user may choose a time between 6 and 40 seconds. The default value is 20.
The Forward Delay can be from 4 to 30 seconds. Any port on the Switch spends
this time in the listening state while moving from the blocking state to the forwarding state.
Used to set the number of hops between devices in a spanning tree region before
the BPDU (bridge protocol data unit) packet sent by the Switch will be discarded.
Each switch on the hop count will reduce the hop count by one until the value
reaches zero. The Switch will then discard the BDPU packet and the information
held for the port will age out. The user may set a hop count from 1 to 20. The
default is 20.
TX Hold Count (1-10) <3>
Used to set the maximum number of Hello packets transmitted per interval. The
count can be specified from 1 to 10. The default is 3.
Forwarding BPDU
<Enabled >
Configuration Name
This field can be Enabled or Disabled. When Enabled, it allows the forwarding of
STP BPDU packets from other network devices. The default is Enabled.
Enter an alphanumeric string of up to 32 characters to uniquely identify the MSTP
region on the Switch. This Configuration Name, along with the Revision Level
value will identify the MSTP region configured on the Switch. If no name is
entered, the default name will be the MAC address of the device. This field is only
valid when MSTP is the version of STP globally set on the Switch.
Revision Level (0-65535)
Enter a number between 0 and 65535 to identify the MSTP region. This value,
along with the name will identify the MSTP region configured on the Switch. The
default setting is 0. This field is only valid when MSTP is the version of STP
globally set on the Switch.
Click Apply to implement changes made.
MST Configuration Identification
46
Page 61

DES-3550 Fast Ethernet Layer 2 Switch
NOTE: The Hello Time cannot be longer than the Max. Age. Otherwise, a
configuration error will occur. Observe the following formulas when setting
the above parameters:
Max. Age = 2 x (Forward Delay - 1 second)
Max. Age = 2 x (Hello Time + 1 second)
MST Configuration Table
The following screens in the MST Configuration Table window allow the user to configure a MSTI instance on the
Switch. These settings will uniquely identify a multiple spanning tree instance set on the Switch. The Switch initially
possesses one CIST or Common Internal Spanning Tree of which the user may modify the parameters for but cannot
change the MSTI ID for, and cannot be deleted. To view the Current MST Configuration Identification window, click
Configuration > Spanning Tree > MST Configuration Table:
Figure 6- 21. Current MST Configuration Identification window
The window above contains the following information:
Parameter Description
Configuration Name
Revision Level
MSTI ID
VID List
Clicking the Add button will reveal the following window to configure:
A previously configured name set on the Switch to uniquely identify the MSTI (Multiple
Spanning Tree Instance). If a configuration name is not set, this field will show the
MAC address to the device running MSTP. This field can be set in the STP Bridge
Global Settings window.
This value, along with the Configuration Name will identify the MSTP region configured on the Switch. This field can also be set in the STP Bridge Global Settings
window.
This field shows the MSTI IDs currently set on the Switch. This field will always have
the CIST MSTI, which may be configured but not deleted. Clicking the hyperlinked
name will open a new window for configuring parameters associated with that
particular MSTI.
This field displays the VLAN IDs associated with the specific MSTI.
47
Page 62

DES-3550 Fast Ethernet Layer 2 Switch
p
Figure 6- 22. Instance ID Settings window- Add
The user may configure the following parameters to create a MSTI in the Switch.
Parameter Description
MSTI ID
Type
Enter a number between 1 and 15 to set a new MSTI on the Switch.
Create is selected to create a new MSTI. No other choices are available for this field
when creating a new MSTI.
VID List (1-4094)
This field is used to specify the VID range from configured VLANs set on the Switch.
Supported VIDs on the Switch range from ID number 1 to 4094.
Priority (0-61440)
Select a value between 0 and 61440 to specify the priority for a specified MSTI for
forwarding packets. The lower the value, the higher the priority. This entry must be
divisible by 4094.
Click Apply to implement changes made.
To configure the settings for the CIST, click on its hyperlinked name in the Current MST Configuration Identification
window, which will reveal the following window to configure:
Figure 6- 23. Instance ID Settings window - CIST modify
The user may configure the following parameters to configure the CIST on the Switch.
Parameter Description
MSTI ID
Type
The MSTI ID of the CIST is 0 and cannot be altered.
The type of configuration about to be processed. This window is used to set the
riority for the CIST only. All other parameters are permanently set and therefore
48
Page 63

DES-3550 Fast Ethernet Layer 2 Switch
unchangeable.
VID List (1-4094)
This field is used to specify the VID range from configured VLANs set on the Switch.
Supported VIDs on the Switch range from ID number 1 to 4094. This field is
inoperable when configuring the CIST.
Priority (0-61440)
Select a value between 0 and 61440 to specify the priority for a specified MSTI for
forwarding packets. The lower the value, the higher the priority. This entry must be
divisible by 4094.
Click Apply to implement changes made.
To configure the parameters for a previously set MSTI, click on its hyperlinked MSTI ID number, which will reveal the
following screen for configuration.
Figure 6- 24. Instance ID Settings window - modify
The user may configure the following parameters for a MSTI on the Switch.
Parameter Description
MSTI ID
Type
Displays the MSTI ID previously set by the user.
This field allows the user to choose a desired method for altering the MSTI settings.
The user has 4 choices.
•
Add - Select this parameter to add VIDs to the MSTI ID, in conjunction with
the VID List parameter.
•
Remove - Select this parameter to remove VIDs from the MSTI ID, in conjunction with the VID List parameter.
•
Delete - Select this parameter to delete this MSTI ID.
•
Set Priority Only - Select this parameter to set the priority for the MSTI ID.
This field is used in conjunction with the Priority field.
VID List (1-4094)
This field is used to specify the VID range from configured VLANs set on the Switch
that the user wishes to add to this MSTI ID. Supported VIDs on the Switch range from
ID number 1 to 4094. This parameter can only be utilized if the Type chosen is Add or
Remove.
Priority (0-61440)
Select a value between 0 and 61440 to specify the priority for a specified MSTI for
forwarding packets. The lower the value, the higher the priority. This entry must be
divisible by 4094 and can only be utilized if the Type chosen is Set Priority Only.
Click Apply to implement changes made.
49
Page 64

DES-3550 Fast Ethernet Layer 2 Switch
MSTI Settings
This window displays the current MSTI configuration settings and can be used to update the port configuration for an
MSTI ID. If a loop occurs, the MSTP function will use the port priority to select an interface to put into the forwarding
state. Set a higher priority value for interfaces to be selected for forwarding first. In instances where the priority value is
identical, the MSTP function will implement the lowest MAC address into the forwarding state and other interfaces will be
blocked. Remember that lower priority values mean higher priorities for forwarding packets.
To view the following window, click Configuration > Spanning Tree > MSTP Settings:
Figure 6- 25. MSTP Port Information window
To view the MSTI settings for a particular port, select the Port number, located in the top left hand corner of the screen
and click Apply. To modify the settings for a particular MSTI Instance, click on its hyperlinked MSTI ID, which will
reveal the following window.
Figure 6- 26. MSTI Settings window
Parameter Description
Instance ID <0>
Displays the MSTI ID of the instance being configured. An entry of 0 in this field denotes
the CIST (default MSTI).
Internal cost
(0=Auto) <200000>
This parameter is set to represent the relative cost of forwarding packets to specified
ports when an interface is selected within a STP instance. The default setting is 0
(auto). There are two options:
•
0 (auto) - Selecting this parameter for the internalCost will set quickest route
automatically and optimally for an interface. The default value is derived from
the media speed of the interface.
•
value 1-2000000 - Selecting this parameter with a value in the range of 12000000 will set the quickest route when a loop occurs. A lower Internal cost
represents a quicker transmission.
50
Page 65

DES-3550 Fast Ethernet Layer 2 Switch
Priority <128>
Click Apply to implement changes made.
Enter a value between 0 and 240 to set the priority for the port interface. A higher
priority will designate the interface to forward packets first. A lower number denotes a
higher priority.
STP Instance Settings
The following window displays MSTIs currently set on the Switch. To view the following table, click Configuration >
Spanning Tree > STP Instance Settings:
Figure 6- 27. STP Instance Settings
The following information is displayed:
Parameter Description
Instance Type
Displays the instance type(s) currently configured on the Switch. Each instance type
is classified by a MSTI ID. CIST refers to the default MSTI configuration set on the
Switch.
Instance Status
Instance Priority
Click Apply to implement changes made.
Displays the current status of the corresponding MSTI ID
Displays the priority of the corresponding MSTI ID. The lowest priority will be the root
bridge.
MSTP Port Information
STP can be set up on a port per port basis. To view the following window click Configuration > Spanning Tree > MST
Port Information:
51
Page 66

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 28. STP Port Settings and MSTP Port Information Table
52
Page 67

DES-3550 Fast Ethernet Layer 2 Switch
(
In addition to setting Spanning Tree parameters for use on the switch level, the Switch allows for the configuration of
groups of ports, each port-group of which will have its own spanning tree, and will require some of its own configuration
settings. An STP Group will use the switch-level parameters entered above, with the addition of Port Priority and Port
Cost.
An STP Group spanning tree works in the same way as the switch-level spanning tree, but the root bridge concept is
replaced with a root port concept. A root port is a port of the group that is elected based on port priority and port cost, to be
the connection to the network for the group. Redundant links will be blocked, just as redundant links are blocked on the
switch level.
The STP on the switch level blocks redundant links between switches (and similar network devices). The port level STP
will block redundant links within an STP Group.
It is advisable to define an STP Group to correspond to a VLAN group of ports.
The following fields can be set:
Parameter Description
From/To <Port 1>
External Cost < 0 =
Auto>
Hello Time <1>
Migration <Yes>
A consecutive group of ports may be configured starting with the selected port.
External Cost - This defines a metric that indicates the relative cost of forwarding
packets to the specified port list. Port cost can be set automatically or as a metric
value. The default value is 0(auto).
•
0 (auto) - Setting 0 for the external cost will automatically set the speed for
forwarding packets to the specified port(s) in the list for optimal efficiency.
Default port cost: 100Mbps port = 200000. Gigabit port = 20000.
•
value 1-200000000 - Define a value between 1 and 200000000 to
determine the external cost. The lower the number, the greater the
probability the port will be chosen to forward packets.
The time interval between the transmission of configuration messages by the designated port, to other devices on the bridged LAN, thus stating that the Switch is still
functioning. The user may choose a time between 1 and 10 seconds. The default is
2 seconds. This field is only operable when the Switch is enabled for MSTP.
Setting this parameter as "yes" will set the ports to send out BDPU packets to other
bridges, requesting information on their STP setting If the Switch is configured for
RSTP, the port will be capable to migrate from 802.1d STP to 802.1w RSTP. If the
Switch is configured for MSTP, the port is capable of migrating from 802.1d STP to
802.1s MSTP. RSTP and MSTP can coexist with standard STP, however the
benefits of RSTP and MSTP are not realized on a port where an 802.1d network
connects to an 802.1w or 802.1s enabled network. Migration should be set as yes
on ports connected to network stations or segments that are capable of being
upgraded to 802.1w RSTP or 802.1s MSTP on all or some portion of the segment.
Edge <False>
Choosing the true parameter designates the port as an edge port. Edge ports
cannot create loops, however an edge port can lose edge port status if a topology
change creates a potential for a loop. An edge port normally should not receive
BPDU packets. If a BPDU packet is received, it automatically loses edge port
status. Choosing the false parameter indicates that the port does not have edge
port status.
P2P <True>
Choosing the true parameter indicates a point-to-point (P2P) shared link. P2P ports
are similar to edge ports, however they are restricted in that a P2P port must
operate in full-duplex. Like edge ports, P2P ports transition to a forwarding state
rapidly thus benefiting from RSTP. A p2p value of false indicates that the port
cannot have p2p status. Auto allows the port to have p2p status whenever possible
and operate as if the p2p status were true. If the port cannot maintain this status,
for example if the port is forced to half-duplex operation) the p2p status changes to
53
Page 68

DES-3550 Fast Ethernet Layer 2 Switch
operate as if the p2p value were false. The default setting for this parameter is true.
State <Disabled>
Click Apply to implement changes made.
This drop-down menu allows you to enable or disable STP for the selected group of
ports. The default is Enabled.
Forwarding Filtering
Unicast Forwarding
Open the Forwarding Filtering folder in the Configuration menu and click on the Unicast Forwarding link. This will
open the Setup Static Unicast Forwarding Table, as shown below:
Figure 6- 29. Setup Static Unicast Forwarding Table and Static Unicast Forwarding Table
To add or edit an entry, define the following parameters and then click Add/Modify:
Parameter Description
VLAN ID (VID)
MAC Address
Allowed to Go Port
Click Apply to implement the changes made. To delete an entry in the Static Unicast Forwarding Table, click the
corresponding
under the Delete heading.
The VLAN ID number of the VLAN on which the above Unicast MAC address
resides.
The MAC address to which packets will be statically forwarded. This must be a
unicast MAC address.
Allows the selection of the port number on which the MAC address entered above
resides.
Static Multicast Forwarding
The following figure and table describe how to set up Multicast Forwarding on the Switch. Open the Forwarding
Filtering folder and click on the Multicast Forwarding link to see the entry screen below:
54
Page 69

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 30. Static Multicast Forwarding Settings and Current Multicast Forwarding Entries
The Static Multicast Forwarding Settings page displays all of the entries made into the Switch's static multicast
forwarding table. Click the Add button to open the Setup Static Multicast Forwarding Table, as shown below:
Figure 6- 31. Setup Static Multicast Forwarding Table
The following parameters can be set:
Parameter Description
VID
Multicast MAC
Address
Port Settings
The VLAN ID of the VLAN the corresponding MAC address belongs to.
The MAC address of the static source of multicast packets. This must be a multicast
MAC address.
Allows the selection of ports that will be members of the static multicast group and
ports that are either forbidden from joining dynamically, or that can join the multicast
group dynamically, using GMRP. The options are:
None - No restrictions on the port dynamically joining the multicast group. When None
is chosen, the port will not be a member of the Static Multicast Group.
Egress - The port is a static member of the multicast group.
Click Apply to implement the changes made. To delete an entry in the Static Multicast Forwarding Table, click the
corresponding
under the Delete heading. Click the Show All Multicast Forwarding Entries link to return to the
Static Multicast Forwarding Settings window.
55
Page 70

DES-3550 Fast Ethernet Layer 2 Switch
Multicast Port Filtering
The following figure and table describe how to set up multicast forwarding on the Switch. Open the Forwarding Filtering
folder and click on the Multicast Port Filtering Mode Setup link to see the entry screen below:
Figure 6- 32. Multicast Port Filtering Mode Setup and Multicast port Filtering Mode Table
The following parameters can be set:
56
Page 71

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
From/To
Mode
Click Apply to implement changes made.
These two drop-down menus allow you to select a range of ports that the filter
settings will be applied to.
This drop-down menu allows you to select the action the Switch will take when it
receives a multicast packet that is to be forwarded to one of the ports in the range
specified above.
•
Forward All Groups - This will instruct the Switch to forward a multicast
packet to all multicast groups residing within the range of ports specified
above.
•
Forward Unregistered Groups - This will instruct the Switch to forward a
multicast packet whose destination is an unregistered multicast group
residing within the range of ports specified above.
•
Filter Unregistered Groups - This will instruct the Switch to filter any
multicast packets whose destination is an unregistered multicast group
residing within the range of ports specified above.
VLANs
Understanding IEEE 802.1p Priority
Priority tagging is a function defined by the IEEE 802.1p standard designed to provide a means of managing traffic on a
network where many different types of data may be transmitted simultaneously. It is intended to alleviate problems
associated with the delivery of time critical data over congested networks. The quality of applications that are dependent on
such time critical data, such as video conferencing, can be severely and adversely affected by even very small delays in
transmission.
Network devices that are in compliance with the IEEE 802.1p standard have the ability to recognize the priority level of
data packets. These devices can also assign a priority label or tag to packets. Compliant devices can also strip priority tags
from packets. This priority tag determines the packet's degree of expeditiousness and determines the queue to which it will
be assigned.
Priority tags are given values from 0 to 7 with 0 being assigned to the lowest priority data and 7 assigned to the highest.
The highest priority tag 7 is generally only used for data associated with video or audio applications, which are sensitive to
even slight delays, or for data from specified end users whose data transmissions warrant special consideration.
The Switch allows you to further tailor how priority tagged data packets are handled on your network. Using queues to
manage priority tagged data allows you to specify its relative priority to suit the needs of your network. There may be
circumstances where it would be advantageous to group two or more differently tagged packets into the same queue.
Generally, however, it is recommended that the highest priority queue, Queue 1, be reserved for data packets with a
priority value of 7. Packets that have not been given any priority value are placed in Queue 0 and thus given the lowest
priority for delivery.
A weighted round robin system is employed on the Switch to determine the rate at which the queues are emptied of
packets. The ratio used for clearing the queues is 4:1. This means that the highest priority queue, Queue 1, will clear 4
packets for every 1 packet cleared from Queue 0.
Remember, the priority queue settings on the Switch are for all ports, and all devices connected to the Switch will be
affected. This priority queuing system will be especially beneficial if your network employs switches with the capability of
assigning priority tags.
VLAN Description
A Virtual Local Area Network (VLAN) is a network topology configured according to a logical scheme rather than the
physical layout. VLANs can be used to combine any collection of LAN segments into an autonomous user group that
57
Page 72

DES-3550 Fast Ethernet Layer 2 Switch
appears as a single LAN. VLANs also logically segment the network into different broadcast domains so that packets are
forwarded only between ports within the VLAN. Typically, a VLAN corresponds to a particular subnet, although not necessarily.
VLANs can enhance performance by conserving bandwidth, and improve security by limiting traffic to specific domains.
A VLAN is a collection of end nodes grouped by logic instead of physical location. End nodes that frequently
communicate with each other are assigned to the same VLAN, regardless of where they are physically on the network.
Logically, a VLAN can be equated to a broadcast domain, because broadcast packets are forwarded to only members of the
VLAN on which the broadcast was initiated.
Notes About VLANs on the DES-3550
No matter what basis is used to uniquely identify end nodes and assign these nodes VLAN membership, packets cannot
cross VLANs without a network device performing a routing function between the VLANs.
The DES-3550 supports IEEE 802.1Q VLANs and Port-Based VLANs. The port untagging function can be used to remove
the 802.1Q tag from packet headers to maintain compatibility with devices that are tag-unaware.
The Switch's default is to assign all ports to a single 802.1Q VLAN named "default."
The "default" VLAN has a VID = 1.
The member ports of Port-based VLANs may overlap, if desired.
IEEE 802.1Q VLANs
Some relevant terms:
Tagging - The act of putting 802.1Q VLAN information into the header of a packet.
Untagging - The act of stripping 802.1Q VLAN information out of the packet header.
Ingress port - A port on a switch where packets are flowing into the Switch and VLAN decisions must be made.
Egress port - A port on a switch where packets are flowing out of the Switch, either to another switch or to an end station,
and tagging decisions must be made.
IEEE 802.1Q (tagged) VLANs are implemented on the Switch. 802.1Q VLANs require tagging, which enables them to
span the entire network (assuming all switches on the network are IEEE 802.1Q-compliant).
VLANs allow a network to be segmented in order to reduce the size of broadcast domains. All packets entering a VLAN
will only be forwarded to the stations (over IEEE 802.1Q enabled switches) that are members of that VLAN, and this
includes broadcast, multicast and unicast packets from unknown sources.
VLANs can also provide a level of security to your network. IEEE 802.1Q VLANs will only deliver packets between
stations that are members of the VLAN.
Any port can be configured as either tagging or untagging. The untagging feature of IEEE 802.1Q VLANs allows VLANs
to work with legacy switches that don't recognize VLAN tags in packet headers. The tagging feature allows VLANs to
span multiple 802.1Q-compliant switches through a single physical connection and allows Spanning Tree to be enabled on
all ports and work normally.
The IEEE 802.1Q standard restricts the forwarding of untagged packets to the VLAN the receiving port is a member of.
The main characteristics of IEEE 802.1Q are as follows:
Assigns packets to VLANs by filtering. •
•
Assumes the presence of a single global spanning tree.
•
Uses an explicit tagging scheme with one-level tagging.
•
802.1Q VLAN Packet Forwarding
•
Packet forwarding decisions are made based upon the following three types of rules:
•
Ingress rules - rules relevant to the classification of received frames belonging to a VLAN.
•
Forwarding rules between ports - decides whether to filter or forward the packet.
•
Egress rules - determines if the packet must be sent tagged or untagged.
58
Page 73

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 33. IEEE 802.1Q Packet Forwarding
802.1Q VLAN Tags
The figure below shows the 802.1Q VLAN tag. There are four additional octets inserted after the source MAC address.
Their presence is indicated by a value of 0x8100 in the EtherType field. When a packet's EtherType field is equal to
0x8100, the packet carries the IEEE 802.1Q/802.1p tag. The tag is contained in the following two octets and consists of 3
bits of user priority, 1 bit of Canonical Format Identifier (CFI - used for encapsulating Token Ring packets so they can be
carried across Ethernet backbones), and 12 bits of VLAN ID (VID). The 3 bits of user priority are used by 802.1p. The
VID is the VLAN identifier and is used by the 802.1Q standard. Because the VID is 12 bits long, 4094 unique VLANs can
be identified.
The tag is inserted into the packet header making the entire packet longer by 4 octets. All of the information originally
contained in the packet is retained.
Figure 6- 34. IEEE 802.1Q Tag
59
Page 74

DES-3550 Fast Ethernet Layer 2 Switch
The EtherType and VLAN ID are inserted after the MAC source address, but before the original EtherType/Length or
Logical Link Control. Because the packet is now a bit longer than it was originally, the Cyclic Redundancy Check (CRC)
must be recalculated.
Figure 6- 35. Adding an IEEE 802.1Q Tag
Port VLAN ID
Packets that are tagged (are carrying the 802.1Q VID information) can be transmitted from one 802.1Q compliant network
device to another with the VLAN information intact. This allows 802.1Q VLANs to span network devices (and indeed, the
entire network, if all network devices are 802.1Q compliant).
Unfortunately, not all network devices are 802.1Q compliant. These devices are referred to as tag-unaware. 802.1Q devices
are referred to as tag-aware.
Prior to the adoption of 802.1Q VLANs, port-based and MAC-based VLANs were in common use. These VLANs relied
upon a Port VLAN ID (PVID) to forward packets. A packet received on a given port would be assigned that port's PVID
and then be forwarded to the port that corresponded to the packet's destination address (found in the Switch's forwarding
table). If the PVID of the port that received the packet is different from the PVID of the port that is to transmit the packet,
the Switch will drop the packet.
Within the Switch, different PVIDs mean different VLANs (remember that two VLANs cannot communicate without an
external router). So, VLAN identification based upon the PVIDs cannot create VLANs that extend outside a given switch
(or switch stack).
Every physical port on a switch has a PVID. 802.1Q ports are also assigned a PVID, for use within the Switch. If no
VLANs are defined on the Switch, all ports are then assigned to a default VLAN with a PVID equal to 1. Untagged packets
are assigned the PVID of the port on which they were received. Forwarding decisions are based upon this PVID, in so far
as VLANs are concerned. Tagged packets are forwarded according to the VID contained within the tag. Tagged packets
are also assigned a PVID, but the PVID is not used to make packet forwarding decisions, the VID is.
Tag-aware switches must keep a table to relate PVIDs within the Switch to VIDs on the network. The Switch will compare
the VID of a packet to be transmitted to the VID of the port that is to transmit the packet. If the two VIDs are different, the
Switch will drop the packet. Because of the existence of the PVID for untagged packets and the VID for tagged packets,
tag-aware and tag-unaware network devices can coexist on the same network.
A switch port can have only one PVID, but can have as many VIDs as the Switch has memory in its VLAN table to store
them.
Because some devices on a network may be tag-unaware, a decision must be made at each port on a tag-aware device
before packets are transmitted - should the packet to be transmitted have a tag or not? If the transmitting port is connected
to a tag-unaware device, the packet should be untagged. If the transmitting port is connected to a tag-aware device, the
packet should be tagged.
Tagging and Untagging
Every port on an 802.1Q compliant switch can be configured as tagging or untagging.
Ports with tagging enabled will put the VID number, priority and other VLAN information into the header of all packets
that flow into and out of it. If a packet has previously been tagged, the port will not alter the packet, thus keeping the
60
Page 75

DES-3550 Fast Ethernet Layer 2 Switch
VLAN information intact. The VLAN information in the tag can then be used by other 802.1Q compliant devices on the
network to make packet-forwarding decisions.
Ports with untagging enabled will strip the 802.1Q tag from all packets that flow into and out of those ports. If the packet
doesn't have an 802.1Q VLAN tag, the port will not alter the packet. Thus, all packets received by and forwarded by an
untagging port will have no 802.1Q VLAN information. (Remember that the PVID is only used internally within the
Switch). Untagging is used to send packets from an 802.1Q-compliant network device to a non-compliant network device.
Ingress Filtering
A port on a switch where packets are flowing into the Switch and VLAN decisions must be made is referred to as an
ingress port. If ingress filtering is enabled for a port, the Switch will examine the VLAN information in the packet header
(if present) and decide whether or not to forward the packet.
If the packet is tagged with VLAN information, the ingress port will first determine if the ingress port itself is a member of
the tagged VLAN. If it is not, the packet will be dropped. If the ingress port is a member of the 802.1Q VLAN, the Switch
then determines if the destination port is a member of the 802.1Q VLAN. If it is not, the packet is dropped. If the
destination port is a member of the 802.1Q VLAN, the packet is forwarded and the destination port transmits it to its
attached network segment.
If the packet is not tagged with VLAN information, the ingress port will tag the packet with its own PVID as a VID (if the
port is a tagging port). The switch then determines if the destination port is a member of the same VLAN (has the same
VID) as the ingress port. If it does not, the packet is dropped. If it has the same VID, the packet is forwarded and the
destination port transmits it on its attached network segment.
This process is referred to as ingress filtering and is used to conserve bandwidth within the Switch by dropping packets that
are not on the same VLAN as the ingress port at the point of reception. This eliminates the subsequent processing of
packets that will just be dropped by the destination port.
Default VLANs
The Switch initially configures one VLAN, VID = 1, called "default." The factory default setting assigns all ports on the
Switch to the "default." As new VLANs are configured in Port-based mode, their respective member ports are removed
from the "default."
Packets cannot cross VLANs. If a member of one VLAN wants to connect to another VLAN, the link must be through an
external router.
NOTE: If no VLANs are configured on the Switch, then all packets will be
forwarded to any destination port. Packets with unknown source
addresses will be flooded to all ports. Broadcast and multicast packets will
also be flooded to all ports.
An example is presented below:
VLAN Name VID Switch Ports
System (default) 1 5, 6, 7, 8, 21, 22, 23, 24
Engineering 2 9, 10, 11, 12
Marketing 3 13, 14, 15, 16
Finance 4 17, 18, 19, 20
Sales 5 1, 2, 3, 4
Table 6- 2. VLAN Example - Assigned Ports
Port-based VLANs
Port-based VLANs limit traffic that flows into and out of switch ports. Thus, all devices connected to a port are members
of the VLAN(s) the port belongs to, whether there is a single computer directly connected to a switch, or an entire
department.
61
Page 76

DES-3550 Fast Ethernet Layer 2 Switch
On port-based VLANs, NICs do not need to be able to identify 802.1Q tags in packet headers. NICs send and receive
normal Ethernet packets. If the packet's destination lies on the same segment, communications take place using normal
Ethernet protocols. Even though this is always the case, when the destination for a packet lies on another switch port,
VLAN considerations come into play to decide if the packet gets dropped by the Switch or delivered.
VLAN Segmentation
Take for example a packet that is transmitted by a machine on Port 1 that is a member of VLAN 2. If the destination lies on
another port (found through a normal forwarding table lookup), the Switch then looks to see if the other port (Port 10) is a
member of VLAN 2 (and can therefore receive VLAN 2 packets). If Port 10 is not a member of VLAN 2, then the packet
will be dropped by the Switch and will not reach its destination. If Port 10 is a member of VLAN 2, the packet will go
through. This selective forwarding feature based on VLAN criteria is how VLANs segment networks. The key point being
that Port 1 will only transmit on VLAN 2.
Network resources such as printers and servers however, can be shared across VLANs. This is achieved by setting up
overlapping VLANs. That is ports can belong to more than one VLAN group. For example, setting VLAN 1 members to
ports 1, 2, 3, and 4 and VLAN 2 members to ports 1, 5, 6, and 7. Port 1 belongs to two VLAN groups. Ports 8, 9, and 10
are not configured to any VLAN group. This means ports 8, 9, and 10 are in the same VLAN group.
VLAN and Trunk Groups
The members of a trunk group have the same VLAN setting. Any VLAN setting on the members of a trunk group will
apply to the other member ports.
NOTE: In order to use VLAN segmentation in conjunction with port trunk
groups, you can first set the port trunk group(s), and then you may
configure VLAN settings. If you wish to change the port trunk grouping
with VLANs already in place, you will not need to reconfigure the VLAN
settings after changing the port trunk group settings. VLAN settings will
automatically change in conjunction with the change of the port trunk
group settings.
Static VLAN Entry
In the Configuration folder, open the VLAN folder and click the Static VLAN Entry link to open the following window:
Figure 6- 36. Current 802.1Q Static VLANs Entries window
The 802.1Q Static VLANs menu lists all previously configured VLANs by VLAN ID and VLAN Name. To delete an
existing 802.1Q VLAN, click the corresponding
To create a new 802.1Q VLAN, click the Add button in the 802.1Q Static VLANs menu. A new menu will appear, as
shown below, to configure the port settings and to assign a unique name and number to the new VLAN. See the table
below for a description of the parameters in the new menu.
button under the Delete heading.
62
Page 77

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 37. 802.1Q Static VLANs - Add
To return to the Current 802.1Q Static VLANs Entries window, click the Show All Static VLAN Entries
an existing 802.1Q VLAN entry, click the Modify button of the corresponding entry you wish to modify. A new menu will
appear to configure the port settings and to assign a unique name and number to the new VLAN. See the table below for a
description of the parameters in the new menu.
link. To change
Figure 6- 38. 802.1Q Static VLANs Entry Settings - Modify
The following fields can then be set in either the Add or Modify 802.1Q Static VLANs menus:
63
Page 78

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
VID (VLAN ID)
VLAN Name
Advertisement
Port Settings
Tag
None
Egress
Forbidden
Click Apply to implement changes made.
Allows the entry of a VLAN ID in the Add dialog box, or displays the VLAN ID of an
existing VLAN in the Modify dialog box. VLANs can be identified by either the VID or
the VLAN name.
Allows the entry of a name for the new VLAN in the Add dialog box, or for editing the
VLAN name in the Modify dialog box.
Enabling this function will allow the Switch to send out GVRP packets to outside
sources, notifying that they may join the existing VLAN.
Allows an individual port to be specified as member of a VLAN.
Specifies the port as either 802.1Q tagging or 802.1Q untagged. Checking the box will
designate the port as Tagged.
Allows an individual port to be specified as a non-VLAN member.
Select this to specify the port as a static member of the VLAN. Egress member ports are
ports that will be transmitting traffic for the VLAN. These ports can be either tagged or
untagged.
Select this to specify the port as not being a member of the VLAN and that the port is
forbidden from becoming a member of the VLAN dynamically.
GVRP Setting
In the Configuration menu, open the VLANs folder and click GVRP Setting.
The 802.1Q Port Settings dialog box, shown below, allows you to determine whether the Switch will share its VLAN
configuration information with other GARP VLAN Registration Protocol (GVRP) enabled switches. In addition, Ingress
Checking can be used to limit traffic by filtering incoming packets whose PVID does not match the PVID of the port.
Results can be seen in the table under the configuration settings, as seen below.
64
Page 79

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 39. 802.1Q Port Settings and 802.1Q Port Table
The following fields can be set:
Parameter Description
From/To
PVID
These two fields allow you to specify the range of ports that will be included in the
Port-based VLAN that you are creating using the 802.1Q Port Settings page.
The read only field in the 802.1Q Port Table shows the current PVID assignment
for each port, which may be manually assigned to a VLAN when created in the
65
Page 80

DES-3550 Fast Ethernet Layer 2 Switch
802.1Q Port Settings table. The Switch's default is to assign all ports to the default
VLAN with a VID of 1.The PVID is used by the port to tag outgoing, untagged
packets, and to make filtering decisions about incoming packets. If the port is
specified to accept only tagged frames - as tagging, and an untagged packet is
forwarded to the port for transmission, the port will add an 802.1Q tag using the
PVID to write the VID in the tag. When the packet arrives at its destination, the
receiving device will use the PVID to make VLAN forwarding decisions. If a packet
is received by the port, and Ingress filtering is enabled, the port will compare the
VID of the incoming packet to its PVID. If the two are unequal, the port will drop the
packet. If the two are equal, the port will receive the packet.
GVRP
Ingress
Acceptable Frame
Type
Click Apply to implement changes made.
The Group VLAN Registration Protocol (GVRP) enables the port to dynamically
become a member of a VLAN. GVRP is Disabled by default.
This field can be toggled using the space bar between Enabled and Disabled.
Enabled enables the port to compare the VID tag of an incoming packet with the
PVID number assigned to the port. If the two are different, the port filters (drops) the
packet. Disabled disables ingress filtering. Ingress Checking is Disabled by default.
This field denotes the type of frame that will be accepted by the port. The user may
choose between Tagged Only, which means only VLAN tagged frames will be
accepted, and Admit_All, which means both tagged and untagged frames will be
accepted. Admit_All is enabled by default.
Traffic Control
Use the Traffic Control menu to enable or disable storm control and adjust the threshold for multicast and broadcast
storms, as well as DLF (Destination Look Up Failure). Traffic control settings are applied to individual Switch modules.
To view the following window, click Configuration > VLANs > Traffic Control:
Figure 6- 40. Traffic Control Settings and Traffic Control Table window
66
Page 81

DES-3550 Fast Ethernet Layer 2 Switch
Traffic or storm control is used to stop broadcast, multicast or ARP request storms that may result when a loop is created.
The Destination Look Up Failure control is a method of shutting down a loop when a storm is formed because a MAC
address cannot be located in the Switch's forwarding database and it must send a packet to all ports or all ports on a VLAN.
To configure Traffic Control, first select a group of ports by using the Group pull down menu. As seen in the figure
above, this section is set by 5 specified groups of ports on the Switch.
Group 1 refers to ports 1 through 8; •
•
Group 2 refers to ports 9 through 16;
•
Group 3 refers to ports 17 through 24;
•
Group 4 refers to ports 25 through 32;
•
Group 5 refers to ports 33 through 40;
•
Group 6 refers to ports 41 through 48;
•
Group 7 refers to mini GBIC port 49;
•
Group 8 refers to mini GBIC port 50.
Broadcast Storm, Multicast Storm and Destination Unknown may be Enabled or Disabled for either group.
The Threshold value is the upper threshold at which the specified traffic control is switched on. This is the number of
Broadcast, Multicast or DLF packets, in Kbps, received by the Switch that will trigger the storm traffic control measures.
The Threshold value can be set from 0 to 255 packets. The default setting is 128. The settings of each port may be viewed
in the Traffic Control Table in the same window. Click Apply to implement changes made.
Port Security
A given port's (or a range of ports') dynamic MAC address learning can be locked such that the current source MAC
addresses entered into the MAC address forwarding table can not be changed once the port lock is enabled. The port can be
locked by using the Admin State pull-down menu to Enabled, and clicking Apply.
Port Security is a security feature that prevents unauthorized computers (with source MAC addresses) unknown to the
Switch prior to locking the port (or ports) from connecting to the Switch's locked ports and gaining access to the network.
67
Page 82

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 41. Port Security Settings window
68
Page 83

The following parameters can be set:
Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
From/To
Admin State
Max. Learning
Addr. (0-10)
Lock Address
Mode
Click Apply to implement changes made.
A consecutive group of ports may be configured starting with the selected port.
This pull-down menu allows you to enable or disable Port Security (locked MAC address
table for the selected ports).
The number of MAC addresses that will be in the MAC address forwarding table for the
selected switch and group of ports.
This pull-down menu allows you to select how the MAC address table locking will be
implemented on the Switch, for the selected group of ports. The options are:
•
Permanent – The locked addresses will not age out after the aging timer
expires.
•
DeleteOnTimeout – The locked addresses will age out after the aging timer
expires.
•
DeleteOnReset – The locked addresses will not age out until the Switch has
been reset.
QoS
The DES-3550 supports 802.1p priority queuing Quality of Service. The following section discusses the implementation of
QoS (Quality of Service) and benefits of using 802.1p priority queuing.
The Advantages of QoS
QoS is an implementation of the IEEE 802.1p standard that allows network administratiors a method of reserving
bandwidth for important functions that require a large bandwidth or have a high priority, such as VoIP (voice-over Internet
Protocol), web browsing applications, file server applications or video conferencing. Not only can a larger bandwidth be
created, but other less critical traffic can be limited, so excessive bandwidth can be saved. The Switch has separate
hardware queues on every physical port to which packets from various applications can be mapped to, and, in turn
prioritized. View the following map to see how the DES-3550 implements 802.1P priority queuing.
69
Page 84

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 42. Mapping QoS on the Switch
The picture above shows the default priority setting for the Switch. Class-3 has the highest priority of the four priority
queues on the Switch. In order to implement QoS, the user is required to instruct the Switch to examine the header of a
packet to see if it has the proper identifying tag tagged. Then the user may forward these tagged packets to designated
queues on the Switch where they will be emptied, based on priority.
For example, lets say a user wishes to have a video conference between two remotely set computers. The administrator can
add priority tags to the video packets being sent out, utilizing the Access Profile commands. Then, on the receiving end,
the administrator instructs the Switch to examine packets for this tag, acquires the tagged packets and maps them to a class
queue on the Switch. Then in turn, the administrator will set a priority for this queue so that will be emptied before any
other packet is forwarded. This results in the end user receiving all packets sent as quickly as possible, thus prioritizing the
queue and allowing for an uninterrupted stream of packets, which optimizes the use of bandwidth available for the video
conference.
Understanding QoS
The Switch has four priority queues. These priority queues are labeled as 3, the high queue to 0, the lowest queue. The
eight priority tags, specified in IEEE 802.1p are mapped to the Switch's priority tags as follows:
Priority 0 is assigned to the Switch's Q1 queue. •
•
Priority 1 is assigned to the Switch's Q0 queue.
•
Priority 2 is assigned to the Switch's Q0 queue.
•
Priority 3 is assigned to the Switch's Q1 queue.
•
Priority 4 is assigned to the Switch's Q2 queue.
•
Priority 5 is assigned to the Switch's Q2 queue.
•
Priority 6 is assigned to the Switch's Q3 queue.
•
Priority 7 is assigned to the Switch's Q3 queue.
For strict priority-based scheduling, any packets residing in the higher priority queues are transmitted first. Multiple strict
priority queues empty based on their priority tags. Only when these queues are empty, are packets of lower priority
transmitted.
70
Page 85

DES-3550 Fast Ethernet Layer 2 Switch
For weighted round-robin queuing, the number of packets sent from each priority queue depends upon the assigned weight.
For a configuration of 8 CoS queues, A~H with their respective weight value: 8~1, the packets are sent in the following
sequence: A1, B1, C1, D1, E1, F1, G1, H1, A2, B2, C2, D2, E2, F2, G2, A3, B3, C3, D3, E3, F3, A4, B4, C4, D4, E4, A5,
B5, C5, D5, A6, B6, C6, A7, B7, A8, A1, B1, C1, D1, E1, F1, G1, H1.
For weighted round-robin queuing, if each CoS queue has the same weight value, then each CoS queue has an equal
opportunity to send packets just like round-robin queuing.
For weighted round-robin queuing, if the weight for a CoS is set to 0, then it will continue processing the packets from this
CoS until there are no more packets for this CoS. The other CoS queues that have been given a nonzero value, and
depending upon the weight, will follow a common weighted round-robin scheme.
Remember that the DES-3550 has 4 priority queues (and four Classes of Service) for each port on the Switch.
Port Bandwidth
The bandwidth control settings are used to place a ceiling on the transmitting and receiving data rates for any selected port.
In the Configuration folder, click Port Bandwidth, to view the screen shown below.
71
Page 86

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 43. Bandwidth Settings and Port Bandwidth Table
72
Page 87

DES-3550 Fast Ethernet Layer 2 Switch
The following parameters can be set or are displayed:
Parameter Description
From/To
Type
no_limit
Rate
Click Apply to set the bandwidth control for the selected ports. Results of configured Bandwidth Settings will be
displayed in the Port Bandwidth Table.
A consecutive group of ports may be configured starting with the selected port.
This drop-down menu allows you to select between RX (receive,) TX (transmit,) and
Both. This setting will determine whether the bandwidth ceiling is applied to receiving,
transmitting, or both receiving and transmitting packets.
This drop-down menu allows you to specify that the selected port will have no
bandwidth limit. Enabled disables the limit.
This field allows you to enter the data rate, in kb/s, that will be the limit for the selected
port.
Scheduling
QoS can be customized by changing the output scheduling used for the hardware queues in the Switch. As with any
changes to QoS implementation, careful consideration should be given to how network traffic in lower priority queues is
affected. Changes in scheduling may result in unacceptable levels of packet loss or significant transmission delay. If you
choose to customize this setting, it is important to monitor network performance, especially during peak demand, as
bottlenecks can quickly develop if the QoS settings are not suitable. In the Configuration folder open the QoS folder and
click QoS Output Scheduling, to view the screen shown below.
Figure 6- 44. QoS Output Scheduling Configuration window
You may assign the following values to the QoS classes to set the scheduling.
Parameter Description
Max. Packets(0-255)
Max. Latency(0-255)
Click Apply to implement changes made.
Specifies the maximum number of packets the above specified hardware priority
queue will be allowed to transmit before allowing the next lowest priority queue to
transmit its packets. A value between 0 and 255 can be specified.
Specifies the maximum amount of time the above specified hardware priority
queue will be allowed to transmit packets before allowing the next lowest
hardware priority queue to begin transmitting its packets. A value between 0 and
255 can be specified - with this value multiplied by 16 ms to arrive at the total
allowed time for the queue to transmit packets. For example, a value of 3
specifies 3 X 16 = 48 ms. The queue will continue transmitting the last packet until
it is finished when the max latency timer expires.
73
Page 88

DES-3550 Fast Ethernet Layer 2 Switch
NOTE: The settings you assign to the queues, numbers 0-7, represent the
IEEE 802.1p priority tag number. Do not confuse these settings with port
numbers.
802.1p Default Priority
The Switch allows the assignment of a default 802.1p priority to each port on the Switch. In the Configuration folder open
the QoS folder and click 802.1p Default Priority, to view the screen shown below.
74
Page 89

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 45. 802.1p Default Priority window
75
Page 90

DES-3550 Fast Ethernet Layer 2 Switch
This page allows you to assign a default 802.1p priority to any given port on the Switch. The priority queues are numbered
from 0, the lowest priority, to 7, the highest priority. Click Apply to implement your settings.
802.1p User Priority
The DES-3550 allows the assignment of a user priority to each of the 802.1p priorities. In the Configuration folder open
the QoS folder and click 802.1p User Priority, to view the screen shown below.
Figure 6- 46. QoS Class of Traffic window
Once you have assigned a priority to the port groups on the Switch, you can then assign this Class to each of the 4 levels of
802.1p priorities. Click Apply to set your changes.
Traffic Segmentation
Traffic segmentation is used to limit traffic flow from a single port to a group of ports on either a single switch (in
standalone mode) or a group of ports on another switch in a switch stack (Single IP). This method of segmenting the flow
of traffic is similar to using VLANs to limit traffic, but is more restrictive. It provides a method of directing traffic that
does not increase the overhead of the Master switch CPU.
In the Configuration folder open the QoS folder and click Traffic Segmentation, to view the screen shown below.
76
Page 91

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 47. Traffic Segmentation Setting and Traffic Segmentation Table window
77
Page 92

DES-3550 Fast Ethernet Layer 2 Switch
This page allows you to determine which port on a given switch will be allowed to forward packets to other ports on that
switch.
The user may set the following parameters:
Parameter Description
Port
Forward Portlist
Clicking the Apply button will enter the combination of transmitting port and allowed receiving ports into the Switch's
Traffic Segmentation Table.
Check the corresponding boxes for the port(s) you wish to transmit packets.
Check the boxes to select which of the ports on the Switch will be able to forward
packets. These ports will be allowed to receive packets from the port specified above.
System Log Server
The Switch can send Syslog messages to up to four designated servers using the System Log Server. In the Configuration
folder, click System Log Server, to view the screen shown below.
Figure 6- 48. System Log Servers window
The parameters configured for adding and editing System Log Server settings are the same. See the table below for a
description.
Figure 6- 49. System Log Servers - Add
The following parameters can be set:
Parameter Description
Index
Syslog server settings index (1-4).
78
Page 93

DES-3550 Fast Ethernet Layer 2 Switch
Server IP
Severity
Facility
The IP address of the Syslog server.
This drop-down menu allows you to select the level of messages that will be sent. The
options are Warning, Informational, and All.
Some of the operating system daemons and processes have been assigned Facility
values. Processes and daemons that have not been explicitly assigned a Facility may
use any of the "local use" facilities or they may use the "user-level" Facility. Those
Facilities that have been designated are shown in the following: Bold font means the
facility values that the Switch currently now.
Numerical Facility
Code
0 kernel messages
1 user-level messages
2 mail system
3 system daemons
4 security/authorization messages
5 messages generated internally by syslog line printer subsystem
7 network news subsystem
8 UUCP subsystem
UDP Port (514 or
6000-65535)
9 clock daemon
10 security/authorization messages
11 FTP daemon
12 NTP subsystem
13 log audit
14 log alert
15 clock daemon
16 local use 0 (local0)
17 local use 1 (local1)
18 local use 2 (local2)
19 local use 3 (local3)
20 local use 4 (local4)
21 local use 5 (local5)
22 local use 6 (local6)
23 local use 7 (local7)
Type the UDP port number used for sending Syslog messages. The default is 0.
Status
Choose Enabled or Disabled to activate or deactivate.
To set the System Log Server configuration, click Apply. To delete an entry from the System Log Server window, click
the corresponding
under the Delete heading of the entry you wish to delete. To return to the Current System Log
Servers window, click the Show All System Log Servers link.
79
Page 94

DES-3550 Fast Ethernet Layer 2 Switch
SNTP Settings
Current Time Settings
To configure the time settings for the Switch, open the Configuration folder, then the SNTP folder and click on the
Current Time Setting link, revealing the following screen for the user to configure.
Figure 6- 50. Time Settings Page
The following parameters can be set or are displayed:
Parameter Description
Current Time: Status
Current Time
Time Source
SNTP State
SNTP Primary Server
SNTP Secondary
Server
SNTP Poll Interval in
Seconds
Displays the time when the Switch was initially started for this session.
Displays the time source for the system.
Current Time: SNTP Settings
Use this pull-down menu to Enable or Disable SNTP.
This is the IP address of the primary server the SNTP information will be taken from.
This is the IP address of the secondary server the SNTP information will be taken
from.
This is the interval, in seconds, between requests for updated SNTP information.
Current Time: Set Current Time
80
Page 95

DES-3550 Fast Ethernet Layer 2 Switch
Year
Month
Day
Time in HH MM
Click Apply to implement your changes.
Enter the current year, if you want to update the system clock.
Enter the current month, if you would like to update the system clock.
Enter the current day, if you would like to update the system clock.
Enter the current time in hours and minutes, if you would like to update the system
clock.
Time Zone and DST
The following are screens used to configure time zones and Daylight Savings time settings for SNTP. Open the
Configuration folder, then the SNTP folder and click on the Time Zone and DST link, revealing the following screen.
Figure 6- 51. Time Zone and DST Settings Page
The following parameters can be set:
Parameter Description
Time Zone and DST Settings
81
Page 96

DES-3550 Fast Ethernet Layer 2 Switch
Daylight Saving
Use this pull-down menu to Enable or Disable the DST Settings.
Time State
Daylight Saving
Time Offset in
Use this pull-down menu to specify the amount of time that will constitute your local DST
offset - 30, 60, 90, or 120 minutes.
Minutes
Time Zone Offset
from GMT in +/-
Use these pull-down menus to specify your local time zone's offset from Greenwich
Mean Time (GMT.)
HH:MM
DST Repeating Settings - Using repeating mode will enable DST seasonal time adjustment. Repeating mode
requires that the DST beginning and ending date be specified using a formula. For example, specify to begin
DST on Saturday during the second week of April and end DST on Sunday during the last week of October.
From: Which Day
From: Day of Week
From: Month
From: time in
Enter the week of the month that DST will start.
Enter the day of the week that DST will start on.
Enter the month DST will start on.
Enter the time of day that DST will start on.
HH:MM
To: Which Day
Enter the week of the month the DST will end.
To: Day of Week
To: Month
To: time in HH:MM
Enter the day of the week that DST will end.
Enter the month that DST will end.
Enter the time DST will end.
DST Annual Settings - Using annual mode will enable DST seasonal time adjustment. Annual mode requires
that the DST beginning and ending date be specified consisely. For example, specify to begin DST on April 3
and end DST on October 14.
From: Month
From: Day
From: Time in
Enter the month DST will start on, each year.
Enter the day of the week DST will start on, each year.
Enter the time of day DST will start on, each year.
HH:MM
To: Month
To: Day
To: Time in HH:MM
Enter the month DST will end on, each year.
Enter the day of the week DST will end on, each year.
Enter the time of day that DST will end on, each year.
Click Apply to implement changes made to the Time Zone and DST window.
82
Page 97

DES-3550 Fast Ethernet Layer 2 Switch
Access Profile Table
Configuring the Access Profile Table
Access profiles allow you to establish criteria to determine whether or not the Switch will forward packets based on the
information contained in each packet's header. These criteria can be specified on a basis of VLAN, MAC address or IP
address.
Creating an access profile is divided into two basic parts. The first is to specify which part or parts of a frame the Switch
will examine, such as the MAC source address or the IP destination address. The second part is entering the criteria the
Switch will use to determine what to do with the frame. The entire process is described below in two parts.
To display the currently configured Access Profiles on the Switch, open the Configuration folder and click on the Access
Profile Table link. This will open the Access Profile Table page, as shown below.
Figure 6- 52. Access Profile Table
To add an entry to the Access Profile Table, click the Add button. This will open the Access Profile Configuration page,
as shown below. There are three Access Profile Configuration pages; one for Ethernet (or MAC address-based) profile
configuration, one for IP address-based profile configuration and one for the Packet Content Mask. You can switch
between the three Access Profile Configuration pages by using the Type drop-down menu. The page shown below is the
Ethernet Access Profile Configuration page.
Figure 6- 53. Access Profile Table (Ethernet)
The following parameters can be set, for the Ethernet type:
83
Page 98

Parameter Description
DES-3550 Fast Ethernet Layer 2 Switch
Profile ID (1-255)
Type
VLAN
Source Mac
Destination Mac
802.1p
Ethernet type
Type in a unique identifier number for this profile set. This value can be set from 1 -
255.
Select profile based on Ethernet (MAC Address), IP address or packet content mask.
This will change the menu according to the requirements for the type of profile.
•
Select Ethernet to instruct the Switch to examine the layer 2 part of each
packet header.
•
Select IP to instruct the Switch to examine the IP address in each frame's
header.
•
Select Packet Content Mask to specify a mask to hide the content of the
packet header.
Selecting this option instructs the Switch to examine the VLAN identifier of each
packet header and use this as the full or partial criterion for forwarding.
Source MAC Mask - Enter a MAC address mask for the source MAC address.
Destination MAC Mask - Enter a MAC address mask for the destination MAC
address.
Selecting this option instructs the Switch to examine the 802.1p priority value of each
packet header and use this as the, or part of the criterion for forwarding.
Selecting this option instructs the Switch to examine the Ethernet type value in each
frame's header.
Port
The user may set the Access Profile Table on a per-port basis by entering a port
number in this field.
The page shown below is the IP Access Profile Configuration page.
84
Page 99

DES-3550 Fast Ethernet Layer 2 Switch
Figure 6- 54. Access Profile Configuration (IP)
The following parameters can be set, for IP:
Parameter Description
Profile ID (1-255)
Type in a unique identifier number for this profile set. This value can be set from 1 -
255.
Type
Select profile based on Ethernet (MAC Address), IP address or packet content mask.
This will change the menu according to the requirements for the type of profile.
•
Select Ethernet to instruct the Switch to examine the layer 2 part of each
packet header.
•
Select IP to instruct the Switch to examine the IP address in each frame's
header.
85
Page 100

DES-3550 Fast Ethernet Layer 2 Switch
• Select Packet Content Mask to specify a mask to hide the content of the
packet header.
VLAN
Source IP Mask
Destination IP Mask
DSCP
Protocol
Selecting this option instructs the Switch to examine the VLAN part of each packet
header and use this as the, or part of the criterion for forwarding.
Enter an IP address mask for the source IP address.
Enter an IP address mask for the destination IP address.
Selecting this option instructs the Switch to examine the DiffServ Code part of each
packet header and use this as the, or part of the criterion for forwarding.
Selecting this option instructs the Switch to examine the protocol type value in each
frame's header. You must then specify what protocol(s) to include according to the
following guidelines:
Select ICMP to instruct the Switch to examine the Internet Control Message Protocol
(ICMP) field in each frame's header.
•
Select Type to further specify that the access profile will apply an ICMP type
value, or specify Code to further specify that the access profile will apply an
ICMP code value.
Select IGMP to instruct the Switch to examine the Internet Group Management
Protocol (IGMP) field in each frame's header.
•
Select Type to further specify that the access profile will apply an IGMP type
value
Select TCP to use the TCP port number contained in an incoming packet as the
forwarding criterion. Selecting TCP requires that you specify a source port mask
and/or a destination port mask. The user may also identify which flag bits to deny.
Flag bits are parts of a packet that determine what to do with the packet. The user
may deny packets by denying certain flag bits within the packets, by checking the
boxes corresponding to the flag bits of the TCP field. The user may choose between
urg (urgent), ack (acknowledgement), psh (push), rst (reset), syn (synchronize), fin
(finish).
•
src port mask - Specify a TCP port mask for the source port in hex form
(hex 0x0-0xffff), which you wish to deny.
•
dest port mask - Specify a TCP port mask for the destination port in hex
form (hex 0x0-0xffff) which you wish to deny.
Select UDP to use the UDP port number contained in an incoming packet as the
forwarding criterion. Selecting UDP requires that you specify a source port mask
and/or a destination port mask.
•
src port mask - Specify a TCP port mask for the source port in hex form
(hex 0x0-0xffff).
•
dest port mask - Specify a TCP port mask for the destination port in hex
form (hex 0x0-0xffff).
protocol id - Enter a value defining the protocol ID in the packet header to mask.
Specify up to 5, Layer 4 port masks for the destination port in hex form (hex 0x00xffffffff).
Port
The user may set the Access Profile Table on a per-port basis by entering an entry
in this field. Entering all will denote all ports on the Switch.
The page shown below is the Packet Content Mask configuration window.
86
 Loading...
Loading...