Page 1

WA6102X-2
2.4 GHz / 5 GHz
Wireless Access Point
User Guide
www.edge-core.com
Page 2

Page 3

User Guide
2.4 GHz / 5 GHz Wireless Access Point
IEEE 802.11g and 802.11a Dual-band Access Point
with 1 10/100BASE-TX (RJ-45) Port
Page 4

WA6102X-2AG-17
F4.3.2.0 E012006-R01
149100033300E
Page 5

COMPLIANCES
Federal Communication Commission Interference
Statement
This equipment has been tested and found to comply with the limits for a Class B
digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to
provide reasonable protection against harmful interference in a residential
installation. This equipment generates, uses and can radiate radio frequency
energy and, if not installed and used in accordance with the instructions, may
cause harmful interference to radio communications. However, there is no
guarantee that interference will not occur in a particular installation. If this
equipment does cause harmful interference to radio or television reception, which
can be determined by turning the equipment off and on, the user is encouraged to
try to correct the interference by one of the following measures:
• Reorient or relocate the receiving antenna
• Increase the separation between the equipment and receiver
• Connect the equipment into an outlet on a circuit different from that to which the
receiver is connected
• Consult the dealer or an experienced radio/TV technician for help
FCC Caution: Any changes or modifications not expressly approved by the party
responsible for compliance could void the user's authority to operate this
equipment. This device complies with Part 15 of the FCC Rules. Operation is
subject to the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received, including
interference that may cause undesired operation.
IMPORTANT NOTE:
FCC Radiation Exposure Statement
This equipment complies with FCC radiation exposure limits set forth for an
uncontrolled environment. This equipment should be installed and operated with a
minimum distance of 20 centimeters (8 inches) between the radiator and your
body. This transmitter must not be co-located or operating in conjunction with any
other antenna or transmitter.
Wireless 5 GHz Band Statements:
As the Access Point can operate in the 5150-5250 MHz frequency band it is
limited by the FCC, Industry Canada and some other countries to indoor use only
so as to reduce the potential for harmful interference to co-channel Mobile
Satellite systems.
i
Page 6
COMPLIANCES
High power radars are allocated as primary users (meaning they have priority) of
the 5250-5350 MHz and 5650-5850 MHz bands. These radars could cause
interference and /or damage to the access point when used in Canada.
The term “IC” before the radio certification number only signifies that Industry
Canada technical specifications were met.
Industry Canada - Class B
This digital apparatus does not exceed the Class B limits for radio noise emissions
from digital apparatus as set out in the interference-causing equipment standard
entitled “Digital Apparatus,” ICES-003 of Industry Canada.
Cet appareil numérique respecte les limites de bruits radioélectriques applicables
aux appareils numériques de Classe B prescrites dans la norme sur le matérial
brouilleur: “Appareils Numériques,” NMB-003 édictée par l’Industrie.
Japan VCCI Class B
Australia/New Zealand AS/NZS 4771
ACN 066 352010
ii
Page 7

C
OMPLIANCES
EC Conformance Declaration
Marking by the above symbol indicates compliance with the Essential
Requirements of the R&TTE Directive of the European Union (1999/5/
EC). This equipment meets the following conformance standards:
• EN 60950-1 (IEC 60950-1) - Product Safety
• EN 301 893 - Technical requirements for 5 GHz radio equipment
• EN 300 328 - Technical requirements for 2.4 GHz radio equipment
• EN 301 489-1 / EN 301 489-17 - EMC requirements for radio equipment
Countries of Operation & Conditions of Use in the European
Community
This device is intended to be operated in all countries of the European
Community. Requirements for indoor vs. outdoor operation, license
requirements and allowed channels of operation apply in some countries
as described below:
Note: The user must use the configuration utility provided with this
product to ensure the channels of operation are in conformance
with the spectrum usage rules for European Community countries
as described below.
• This device requires that the user or installer properly enter the current
country of operation in the command line interface as described in the
user guide, before operating this device.
• This device will automatically limit the allowable channels determined
by the current country of operation. Incorrectly entering the country of
operation may result in illegal operation and may cause harmful
interference to other systems. The user is obligated to ensure the
device is operating according to the channel limitations, indoor/outdoor
restrictions and license requirements for each European Community
country as described in this document.
• This device employs a radar detection feature required for European
Community operation in the 5 GHz band. This feature is automatically
enabled when the country of operation is correctly configured for any
European Community country. The presence of nearby radar operation
may result in temporary interruption of operation of this device. The
radar detection feature will automatically restart operation on a channel
free of radar.
iii
Page 8

COMPLIANCES
• The 5 GHz Turbo Mode feature is not allowed for operation in any
European Community country. The current setting for this feature is
found in the 5 GHz 802.11a Radio Settings Window as described in the
user guide.
• The 5 GHz radio's Auto Channel Select setting described in the user
guide must always remain enabled to ensure that automatic 5 GHz
channel selection complies with European requirements. The current
setting for this feature is found in the 5 GHz 802.11a Radio Settings
Window as described in the user guide.
• This device is restricted to indoor use when operated in the European
Community using the 5.15 - 5.35 GHz band: Channels 36, 40, 44, 48,
52, 56, 60, 64. See table below for allowed 5 GHz channels by country.
• This device may be operated indoors or outdoors in all countries of the
European Community using the 2.4 GHz band: Channels 1 - 13, except
where noted below.
- In Italy the end-user must apply for a license from the national
spectrum authority to operate this device outdoors.
- In Belgium outdoor operation is only permitted using the 2.46 -
2.4835 GHz band: Channel 13.
- In France outdoor operation is only permitted using the 2.4 - 2.454
GHz band: Channels 1 - 7.
iv
Page 9
C
OMPLIANCES
Operation Using 5 GHz Channels in the European
Community
The user/installer must use the provided configuration utility to check the
current channel of operation and make necessary configuration changes
to ensure operation occurs in conformance with European National
spectrum usage laws as described below and elsewhere in this
document.
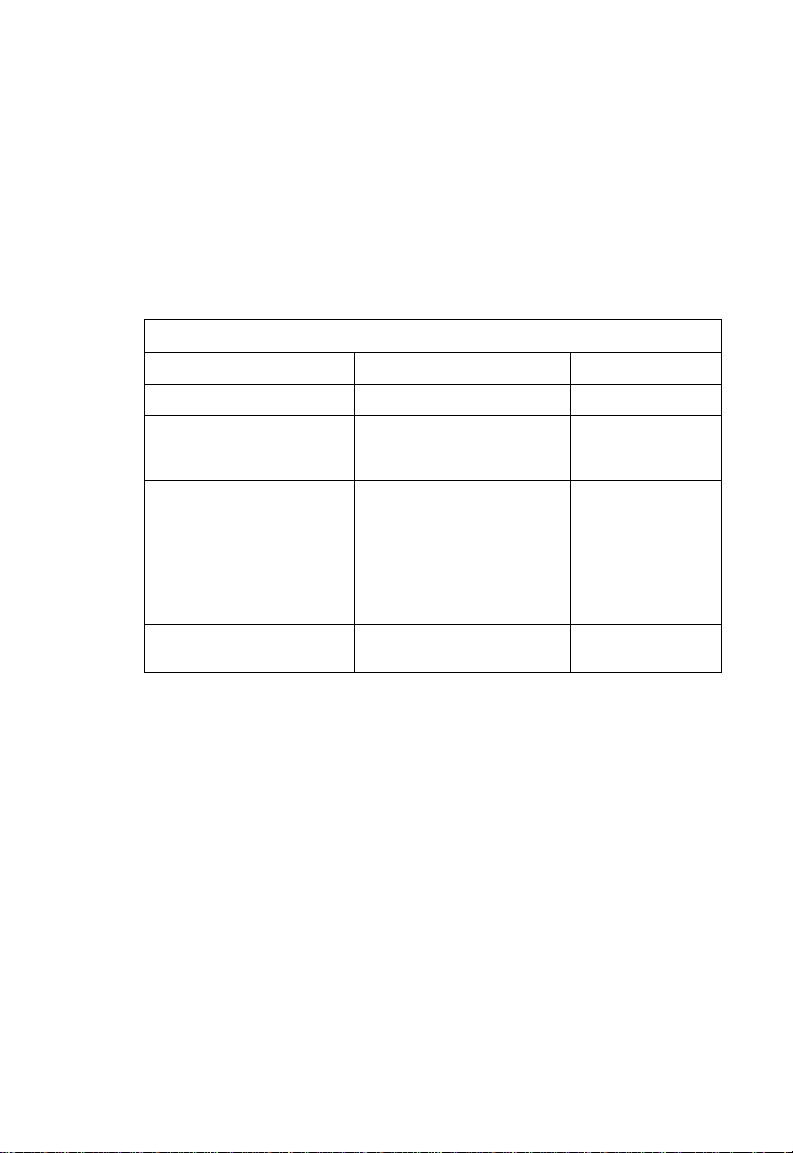
Allowed 5GHz Channels in Each European Community Country
Allowed Frequency Bands Allowed Channel Numbers Countries
5.15 - 5.25 GHz* 36, 40, 44, 48 Austria, Belgium
5.15 - 5.35 GHz* 36, 40, 44, 48, 52, 56, 60, 64 France,
5.15 - 5.35* & 5.470 - 5.725
GHz
5 GHz Operation Not
Allowed
* Outdoor operation is not allowed using 5.15-5.35 GHz bands (Channels 36 -
64).
36, 40, 44, 48, 52, 56, 60, 64,
100, 104, 108, 112, 116, 120,
124, 128, 132, 136, 140
None Greece
Switzerland,
Liechtenstein
Denmark, Finland,
Germany, Iceland,
Ireland, Italy,
Luxembourg,
Netherlands,
Norway, Portugal,
Spain, Sweden,
U.K.
v
Page 10
COMPLIANCES
Declaration of Conformity in Languages of the European
Community
English Hereby, SMC, declares that this Radio LAN device is in
Finnish Valmistaja SMC vakuuttaa täten että Radio LAN device tyyppinen
Dutch Hierbij verklaart SMC dat het toestel Radio LAN device in
French Par la présente SMC déclare que l'appareil Radio LAN device est
Swedish Härmed intygar SMC att denna Radio LAN device står I
Danish Undertegnede SMC erklærer herved, at følgende udstyr Radio
German Hiermit erklärt SMC, dass sich dieser/diese/dieses Radio LAN
Greek με την παρουσα SMC δηλωνει οτι radio LAN device
Italian Con la presente SMC dichiara che questo Radio LAN device è
compliance with the essential requirements and other relevant
provisions of Directive 1999/5/EC.
laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä
koskevien direktiivin muiden ehtojen mukainen.
overeenstemming is met de essentiële eisen en de andere
relevante bepalingen van richtlijn 1999/5/EG
Bij deze SMC dat deze Radio LAN device voldoet aan de
essentiële eisen en aan de overige relevante bepalingen van
Richtlijn 1999/5/EC.
conforme aux exigences essentielles et aux autres dispositions
pertinentes de la directive 1999/5/CE
överensstämmelse med de väsentliga egenskapskrav och övriga
relevanta bestämmelser som framgår av direktiv 1999/5/EG.
LAN device overholder de væsentlige krav og øvrige relevante
krav i direktiv 1999/5/EF
device in Übereinstimmung mit den grundlegenden
Anforderungen und den anderen relevanten Vorschriften der
Richtlinie 1999/5/EG befindet". (BMWi)
Hiermit erklärt SMC die Übereinstimmung des Gerätes Radio
LAN device mit den grundlegenden Anforderungen und den
anderen relevanten Festlegungen der Richtlinie 1999/5/EG.
(Wien)
συμμορφωνεται προσ τισ ουσιωδεισ απαιτησεισ και τισ λοιπεσ
σΧετικεσ διαταξεισ τησ οδηγιασ 1999/5/εκ
conforme ai requisiti essenziali ed alle altre disposizioni pertinenti
stabilite dalla direttiva 1999/5/CE.
vi
Page 11
C
OMPLIANCES
Spanish Por medio de la presente Manufacturer declara que el Radio LAN
Portuguese Manufacturer declara que este Radio LAN device está conforme
device cumple con los requisitos esenciales y cualesquiera otras
disposiciones aplicables o exigibles de la Directiva 1999/5/CE
com os requisitos essenciais e outras disposições da Directiva
1999/5/CE.
Safety Compliance
Power Cord Safety
Please read the following safety information carefully before installing the access
point:
WARNING: Installation and removal of the unit must be carried out by qualified
personnel only.
• The unit must be connected to an earthed (grounded) outlet to comply with
international safety standards.
• Do not connect the unit to an A.C. outlet (power supply) without an earth
(ground) connection.
• The appliance coupler (the connector to the unit and not the wall plug) must have
a configuration for mating with an EN 60320/IEC 320 appliance inlet.
• The socket outlet must be near to the unit and easily accessible. You can only
remove power from the unit by disconnecting the power cord from the outlet.
• This unit operates under SELV (Safety Extra Low Voltage) conditions according
to IEC 60950. The conditions are only maintained if the equipment to which it is
connected also operates under SELV conditions.
France and Peru only
This unit cannot be powered from IT
unit must be powered by 230 V (2P+T) via an isolation transformer ratio 1:1, with
the secondary connection point labelled Neutral, connected directly to earth
(ground).
†
Impédance à la terre
†
supplies. If your supplies are of IT type, this
vii
Page 12
COMPLIANCES
Important! Before making connections, make sure you have the correct cord set.
Check it (read the label on the cable) against the following:
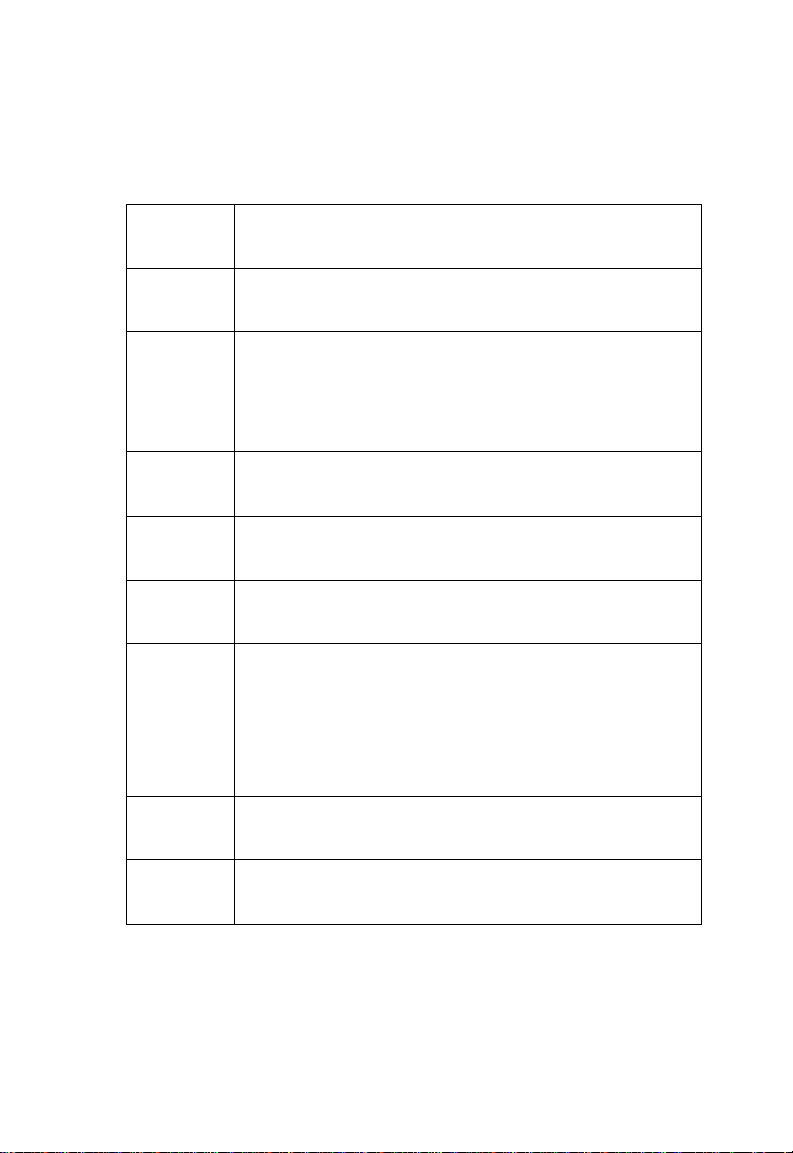
Power Cord Set
U.S.A. and
Canada
Denmark The supply plug must comply with Section 107-2-D1,
Switzerland The supply plug must comply with SEV/ASE 1011.
U.K. The supply plug must comply with BS1363 (3-pin 13 A) and
Europe The supply plug must comply with CEE7/7 (“SCHUKO”).
The cord set must be UL-approved and CSA certified.
The minimum specifications for the flexible cord are:
- No. 18 AWG - not longer than 2 meters, or 16 AWG.
- Type SV or SJ
- 3-conductor
The cord set must have a rated current capacity of at least
10 A
The attachment plug must be an earth-grounding type with
NEMA 5-15P (15 A, 125 V) or NEMA 6-15P (15 A, 250 V)
configuration.
Standard DK2-1a or DK2-5a.
be fitted with a 5 A fuse which complies with BS1362.
The mains cord must be <HAR> or <BASEC> marked and
be of type HO3VVF3GO.75 (minimum).
The mains cord must be <HAR> or <BASEC> marked and
be of type HO3VVF3GO.75 (minimum).
IEC-320 receptacle.
viii
Page 13
C
OMPLIANCES
Veuillez lire à fond l'information de la sécurité suivante avant
d'installer le access point:
AVERTISSEMENT: L’installation et la dépose de ce groupe doivent être confiés à un
personnel qualifié.
• Ne branchez pas votre appareil sur une prise secteur (alimentation électrique)
lorsqu'il n'y a pas de connexion de mise à la terre (mise à la masse).
• Vous devez raccorder ce groupe à une sortie mise à la terre (mise à la masse) afin
de respecter les normes internationales de sécurité.
• Le coupleur d’appareil (le connecteur du groupe et non pas la prise murale) doit
respecter une configuration qui permet un branchement sur une entrée d’appareil
EN 60320/IEC 320.
• La prise secteur doit se trouver à proximité de l’appareil et son accès doit être
facile. Vous ne pouvez mettre l’appareil hors circuit qu’en débranchant son cordon
électrique au niveau de cette prise.
• L’appareil fonctionne à une tension extrêmement basse de sécurité qui est
conforme à la norme IEC 60950. Ces conditions ne sont maintenues que si
l’équipement auquel il est raccordé fonctionne dans les mêmes conditions.
France et Pérou uniquement:
Ce groupe ne peut pas être alimenté par un dispositif à impédance à la terre. Si vos
alimentations sont du type impédance à la terre, ce groupe doit être alimenté par
une tension de 230 V (2 P+T) par le biais d’un transformateur d’isolement à rapport
1:1, avec un point secondaire de connexion portant l’appellation Neutre et avec
raccordement direct à la terre (masse).
Cordon électrique - Il doit être agréé dans le pays d’utilisation
Etats-Unis et
Canada:
Danemark: La prise mâle d’alimentation doit respecter la section 107-2
Le cordon doit avoir reçu l’homologation des UL et un
certificat de la CSA.
Les spécifications minimales pour un cable flexible sont
AWG No. 18, ou AWG No. 16 pour un cable de longueur
inférieure à 2 mètres.
- type SV ou SJ
- 3 conducteurs
Le cordon doit être en mesure d’acheminer un courant
nominal d’au moins 10 A.
La prise femelle de branchement doit être du type à mise à
la terre (mise à la masse) et respecter la configuration NEMA
5-15P (15 A, 125 V) ou NEMA 6-15P (15 A, 250 V).
D1 de la norme DK2 1a ou DK2 5a.
ix
Page 14
COMPLIANCES
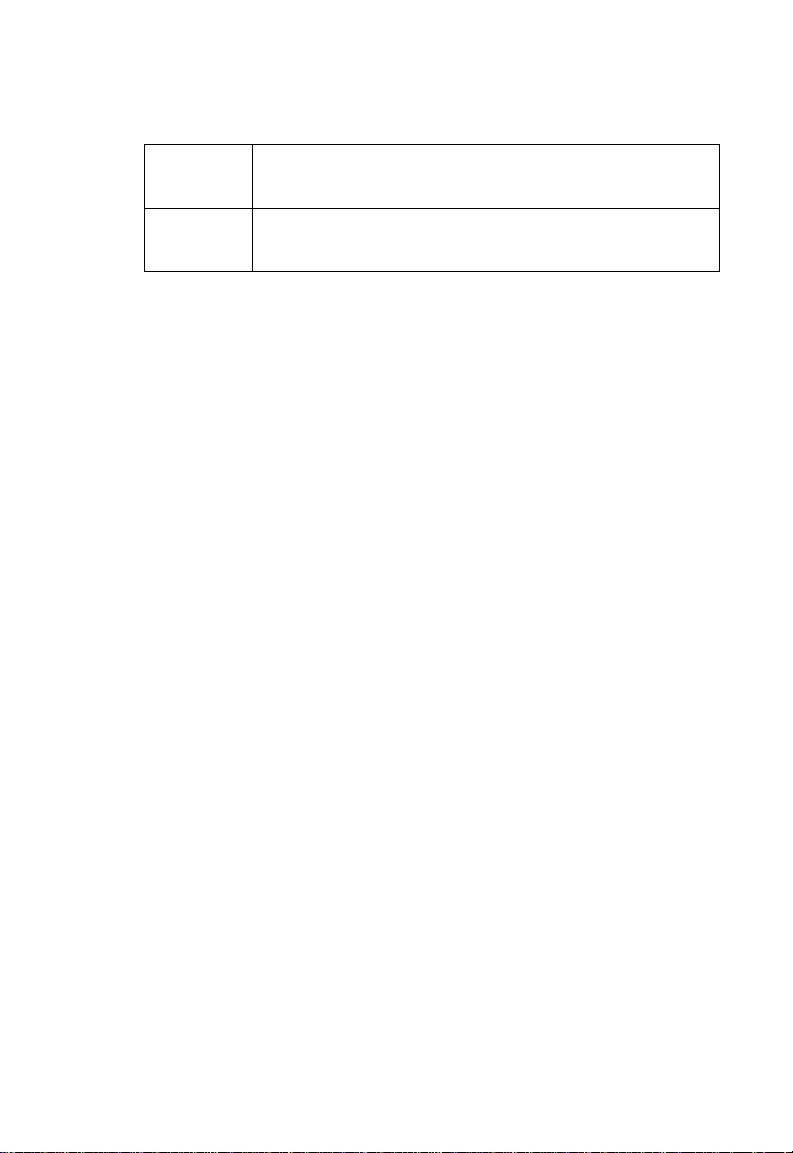
Cordon électrique - Il doit être agréé dans le pays d’utilisation
Suisse: La prise mâle d’alimentation doit respecter la norme SEV/
Europe La prise secteur doit être conforme aux normes CEE 7/7
Bitte unbedingt vor dem Einbauen des Access Point die folgenden
Sicherheitsanweisungen durchlesen
WARNUNG: Die Installation und der Ausbau des Geräts darf nur durch
Fachpersonal erfolgen.
• Das Gerät sollte nicht an eine ungeerdete Wechselstromsteckdose
angeschlossen werden.
• Das Gerät muß an eine geerdete Steckdose angeschlossen werden, welche die
internationalen Sicherheitsnormen erfüllt.
• Der Gerätestecker (der Anschluß an das Gerät, nicht der
Wandsteckdosenstecker) muß einen gemäß EN 60320/IEC 320 konfigurierten
Geräteeingang haben.
• Die Netzsteckdose muß in der Nähe des Geräts und leicht zugänglich sein. Die
Stromversorgung des Geräts kann nur durch Herausziehen des
Gerätenetzkabels aus der Netzsteckdose unterbrochen werden.
• Der Betrieb dieses Geräts erfolgt unter den SELV-Bedingungen
(Sicherheitskleinstspannung) gemäß IEC 60950. Diese Bedingungen sind nur
gegeben, wenn auch die an das Gerät angeschlossenen Geräte unter
•
SELV-Bedingungen betrieben werden.
ASE 1011.
(“SCHUKO”)
LE cordon secteur doit porter la mention <HAR> ou
<BASEC> et doit être de type HO3VVF3GO.75 (minimum).
(Germany):
x
Page 15
C
OMPLIANCES
Stromkabel. Dies muss von dem Land, in dem es benutzt wird geprüft werden:
U.S.A und
Kanada
Danemark Dieser Stromstecker muß die ebene 107-2-D1, der
Schweiz Dieser Stromstecker muß die SEV/ASE
Europe Das Netzkabel muß vom Typ HO3VVF3GO.75
Der Cord muß das UL gepruft und war das CSA
beglaubigt.
Das Minimum spezifikation fur der Cord sind:
- Nu. 18 AWG - nicht mehr als 2 meter, oder 16 AWG.
- Der typ SV oder SJ
- 3-Leiter
Der Cord muß haben eine strombelastbarkeit aus
wenigstens 10 A
Dieser Stromstecker muß hat einer erdschluss mit der typ
NEMA 5-15P (15A, 125V) oder NEMA 6-15P (15A, 250V)
konfiguration.
standard DK2-1a oder DK2-5a Bestimmungen einhalten.
1011Bestimmungen einhalten.
(Mindestanforderung) sein und die Aufschrift <HAR> oder
<BASEC> tragen.
Der Netzstecker muß die Norm CEE 7/7 erfüllen
(”SCHUKO”).
xi
Page 16

COMPLIANCES
xii
Page 17
Table of Contents
Chapter 1: Introduction 1-1
Package Checklist 1-2
Hardware Description 1-2
Component Description 1-3
Features and Benefits 1-5
Applications 1-6
System Defaults 1-6
Chapter 2: Hardware Installation 2-1
Chapter 3: External Antennas 3-1
Instalati on Procedures 3-1
Chapter 4: Network Configuration 4-1
Network Topologies 4-2
Ad Hoc Wireless LAN (no Access Point) 4-2
Infrastructure Wireless LAN 4-3
Infrastructure Wireless LAN for Roaming Wireless PCs 4-4
Infrastructure Wireless Bridge 4-5
Infrastructure Wireless Repeate r 4-6
Chapter 5: Initial Configuration 5-1
Initial Setup through the CLI 5-1
Required Connections 5-1
Initial Configuration Steps 5-2
Logging In 5-3
Chapter 6: System Configuration 6-1
Advanced Configuratio n 6-2
System Identification 6-3
TCP / IP Settings 6-5
RADIUS 6-7
SSH Settings 6-11
Authentication 6-12
xiii
Page 18
Contents
Filter Control 6-17
VLAN 6-19
WDS Settings 6-21
AP Management 6-27
Administration 6-28
System Log 6-33
RSSI 6-37
SNMP 6-37
Configuring SNMP and Trap Message Parameters 6-38
Configuring SNMPv3 Users 6-42
Configuring SNMPv3 Trap Filters 6-44
Configuring SNMPv3 Targets 6-46
Radio Interface 6-48
Radio Settings A (802.11a) 6-49
Radio Settings G (802.11g) 6-63
Security 6-66
Status Information 6-84
Access Point Status 6-84
Station Status 6-87
Event Logs 6-90
Chapter 7: Command Line Interfa ce 7-1
Using the Command Line Interface 7-1
Accessing the CLI 7-1
Console Connection 7-1
Telnet Connection 7-1
Entering Commands 7-2
Keywords and Arguments 7-2
Minimum Abbreviation 7-2
Command Completion 7-3
Getting Help on Commands 7-3
Partial Keyword Lookup 7-4
Negating the Effect of Commands 7-4
Using Command History 7-4
Understanding Command Modes 7-4
Exec Commands 7-5
Configuration Commands 7-5
Command Line Processing 7-6
Command Groups 7-6
General Commands 7-7
configure 7-8
end 7-8
exit 7-8
ping 7-9
xiv
Page 19

Contents
reset 7-10
show history 7-10
show line 7-11
System Management Commands 7-11
country 7-12
prompt 7-14
system name 7-14
username 7-15
password 7-15
ip ssh-server enable 7-16
ip ssh-server port 7-16
ip telnet-server enable 7-17
ip http port 7-17
ip http server 7-18
ip https port 7-18
ip https server 7-19
web-redirect 7-20
APmgmtIP 7-21
APmgmtUI 7-22
show apmanagement 7-22
show system 7-23
show version 7-24
show config 7-24
show hardware 7-28
System Logging Commands 7-28
logging on 7-29
logging host 7-29
logging console 7-30
logging level 7-30
logging facility-type 7-31
logging clear 7-32
show logging 7-32
show event-log 7-33
System Clock Commands 7-33
sntp-server ip 7-34
sntp-server enable 7-34
sntp-server date-time 7-35
sntp-server daylight-saving 7-36
sntp-server timezone 7-36
show sntp 7-37
DHCP Relay Commands 7-38
dhcp-relay enable 7-38
dhcp-relay 7-39
show dhcp-relay 7-39
SNMP Commands 7-40
xv
Page 20

Contents
snmp-server community 7-41
snmp-server contact 7-41
snmp-server location 7-42
snmp-server enable server 7-42
snmp-server host 7-43
snmp-server trap 7-44
snmp-server engine-id 7-45
snmp-server user 7-46
snmp-server targets 7-48
snmp-server filter 7-49
snmp-server filter-assignments 7-50
show snmp groups 7-50
show snmp users 7-51
show snmp group-assignments 7-51
show snmp target 7-52
show snmp filter 7-52
show snmp filter-assignments 7-53
show snmp 7-54
Flash/File Commands 7-55
bootfile 7-55
copy 7-56
delete 7-57
dir 7-58
show bootfile 7-58
RADIUS Client 7-59
radius-server address 7-59
radius-server port 7-60
radius-server key 7-60
radius-server retransmit 7-61
radius-server timeout 7-61
radius-server port-accounting 7-62
radius-server timeout-interim 7-62
radius-server radius-mac-format 7-63
radius-server vlan-format 7-63
show radius 7-64
802.1X Authentication 7-65
802.1x 7-65
802.1x broadcast-key-refresh-rate 7-66
802.1x session-key-refresh-rate 7-67
802.1x session-timeout 7-67
802.1x-supplicant enable 7-68
802.1x-supplicant user 7-68
show authentication 7-69
MAC Address Authentication 7-70
address filter default 7-70
xvi
Page 21

Contents
address filter entry 7-71
address filter delete 7-71
mac-authentication server 7-72
mac-authentication session-timeout 7-72
Filtering Commands 7-73
filter local-bridge 7-73
filter ap-manage 7-74
filter ethernet-type enable 7-74
filter ethernet-type protocol 7-75
show filters 7-76
WDS Bridge Commands 7-76
bridge role (WDS) 7-77
bridge-link parent 7-77
bridge-link child 7-78
bridge dynamic-entry age-time 7-78
show bridge aging-time 7-79
show bridge filter-entry 7-80
show bridge link 7-80
Spanning Tree Commands 7-82
bridge stp enable 7-82
bridge stp forwarding-delay 7-83
bridge stp hello-time 7-83
bridge stp max-age 7-84
bridge stp priority 7-84
bridge-link path-cost 7-85
bridge-link port-priority 7-85
show bridge stp 7-86
Ethernet Interface Commands 7-87
interface ethernet 7-87
dns server 7-88
ip address 7-88
ip dhcp 7-89
speed-duplex 7-90
shutdown 7-91
show interface ethernet 7-91
Wireless Interface Command s 7-92
interface wireless 7-94
vap 7-94
speed 7-95
turbo 7-95
multicast-data-rate 7-96
channel 7-96
transmit-power 7-97
radio-mode 7-98
preamble 7-98
xvii
Page 22

Contents
antenna control 7-99
antenna id 7-100
antenna location 7-100
beacon-interval 7-101
dtim-period 7-101
fragmentation-length 7-102
rts-threshold 7-103
super-a 7-104
super-g 7-104
description 7-105
ssid 7-105
closed-system 7-106
max-association 7-106
assoc-timeout-interval 7-107
auth-timeout-value 7-107
shutdown 7-107
show interface wireless 7-109
show station 7-110
Rogue AP Detection Commands 7-111
rogue-ap enable 7-111
rogue-ap authenticate 7-112
rogue-ap duration 7-113
rogue-ap interval 7-113
rogue-ap scan 7-114
show rogue-ap 7-115
Wireless Security Command s 7-115
auth 7-116
encryption 7-118
key 7-119
transmit-key 7-120
cipher-suite 7-121
mic_mode 7-122
wpa-pre-shared-key 7-123
pmksa-lifetime 7-123
pre-authentication 7-124
Link Integrity Commands 7-125
link-integrity ping-detect 7-126
link-integrity pin g-host 7-126
link-integrity ping-interval 7-127
link-integrity ping-fail-retry 7-127
link-integrity ethernet-detect 7-127
show link-integrity 7-128
IAPP Commands 7-129
iapp 7-129
VLAN Commands 7-130
xviii
Page 23
Contents
vlan 7-130
management-vlanid 7-131
vlan-id 7-131
WMM Commands 7-132
wmm 7-133
wmm-acknowledge-policy 7-133
wmmparam 7-134
Appendix A: Troubleshooting A-1
Appendix B: Cables and Pinouts B-1
Twisted-Pair Cable Assignments B-1
10/100BASE-TX Pin Assignments B-1
Straight-Through Wiring B-2
Crossover Wiring B-3
Console Port Pin Assignments B-3
Wiring Map for Serial Cable B-4
Appendix C: Specifications C-1
General Specifications C-1
Sensitivity C-4
Transmit Power C-5
Operating Range C-6
Glossary
Index
xix
Page 24

Contents
xx
Page 25

Chapter 1: Introduction
The 2.4 GHz/5 GHz Wireless Access Point is an IEEE 802.11a/g access point that
provides transparent, wire le ss hig h- speed data communications between the wired
LAN and fixed or mobile devices equipped with an 802.11a, 802.11b, or 802.11g
wireless adapter.
This solution offers fast, re liable wireless c onnectivity with co nsiderable cost savings
over wired LANs (which include long-term maintenance overhead for cabling). Using
802.11a and 802.11g technology, this access point can easily repl ace a 10 Mbps
Ethernet connection or se am lessly integrate into a 10/100 M bps Eth er net LAN.
The access point supports up to ei ght Virtual Acc ess Points per physical radio
interface, that is eight on the 802. 11a radio and eight on the 802.11g radio. This
allows traffic to be separated for different user groups using an access point t hat
services one area. For each VAP, different security settings, VLAN assignments, and
other parameters can be appl ied.
Each radio interface on the access point can operate in one of four modes:
• Access Point – Providing conectivity to wireless clie nt s in th e service area.
• Repeater – Providing an extended link to a remote access point from the wired
LAN. In this mode, the access point does not have a cable connection to the wired
Ethernet LAN.
• Bridge – Providing links to access points operating in “Bridge” or “Roo t Bri dge ”
mode and thereby connecting other wired LAN segments.
• Root Bridge – Providing links to other access points operating in “Bridge” mode
and thereb y connecting other wir ed LAN segments. Only one un it in the wireless
bridge network can be set to “Root Bridge” mode.
In addition, the access point offers full network management capabilities through an
easy to configure web in te rface, a command line interfa ce for ini tial co nf ig ur at io n
and troubleshooting, and su pport for Simple Network M anagement Protocol tool s.
Radio Characteristics – The IEEE 802.11a/g standard uses a radio mod ul at i on
technique known as Orthogonal Frequency Division Multiplexing (OFDM) , and a
shared collision domain (CSM A/CA). It operates at the 5 GH z U nl icensed National
Information Infrastru ct ur e (UNII) band for connections to 802.11a clients, and at 2.4
GHz for connections to 802.11g clients.
IEEE 802.11g includes backward compatibility with the IE EE 802.11b standard.
IEEE 802.11b also operates at 2.4 GHz, but uses Direct Se qu ence Spread
Spectrum (DSSS) and Complementary Code Keying (CCK) modulation t echnology
to achieve a communication rate of up to 11 Mbps.
The access point supports a 54 M bps half -d upl ex connection to Ethernet ne t w or ks
for each active channel (o r up to 108 M bps w hen using turbo mode on the 802.11a
interface).
1-1
Page 26
Introduction
1
Package Checklist
The 2.4 GHz/5 GHz Wirel ess Access Point package includes :
• One 2.4 GHz/5 GHz Wireless Access Point
• One Category 5 network cable
• One RS-232 console cable
• One AC power adapter and pow er cord
• Four rubber feet
• User Guide CD
Inform your dealer if there are any incorrect, missing or damaged parts. If possible,
retain the carton, including the original packing materials. Use them again to repack
the product in case there is a need to return it.
Hardware Description
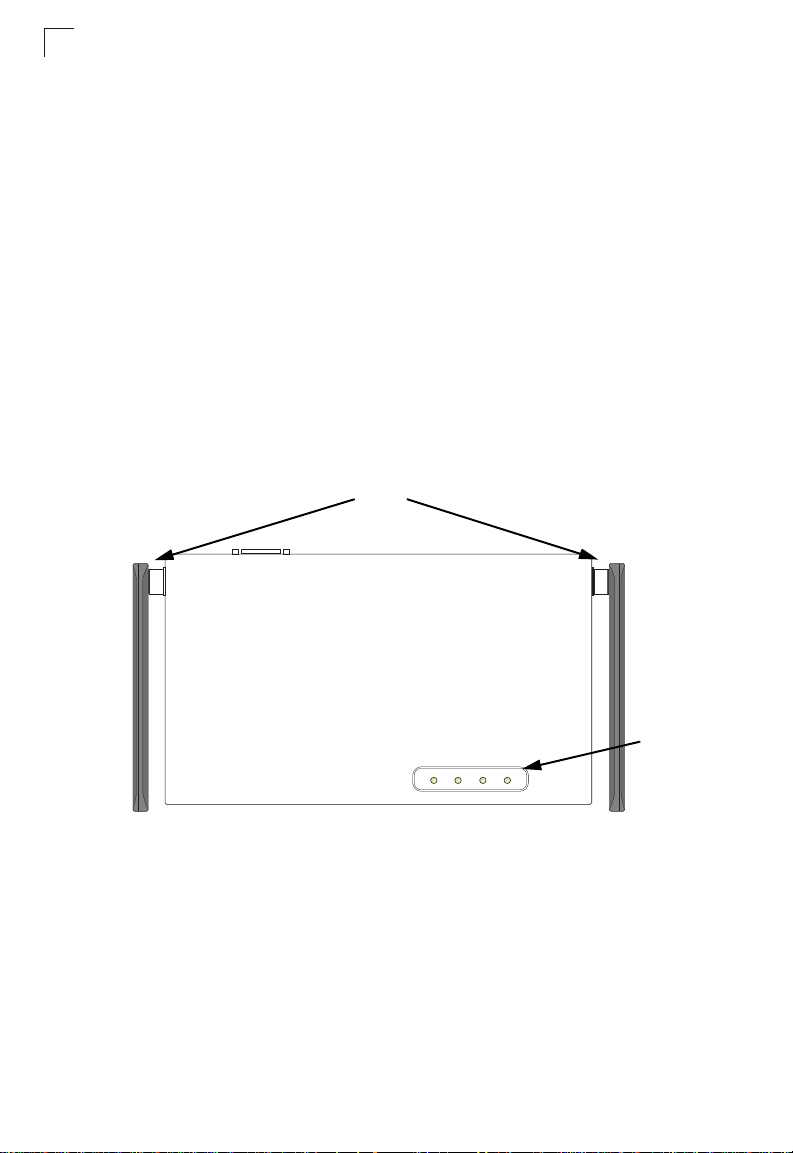
Top Panel
Antennas
PWR Link 11a 11g
LED
Indicators
1-2
Page 27
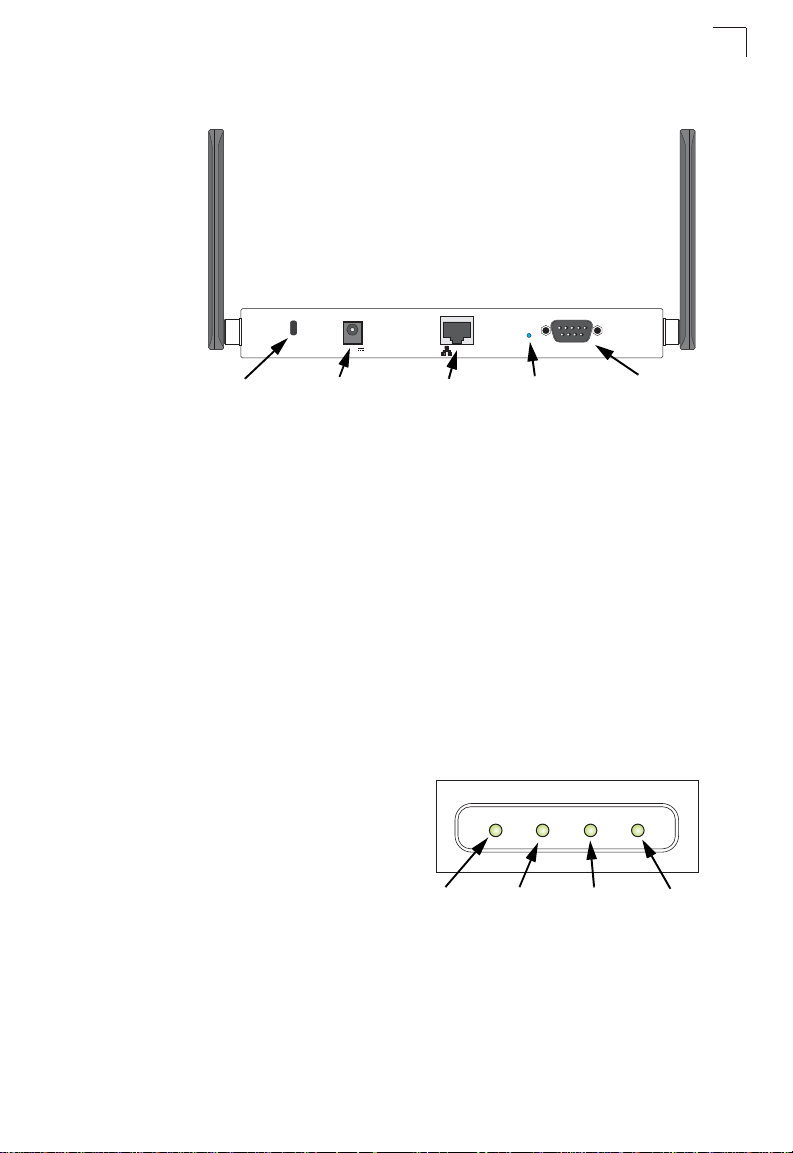
Rear Panel
Lock ConsolePOE In ResetDC 5V
Hardware Description
1
Security Slot
5 VDC
Power Socket
RJ-45 Port,
PoE Connector
Reset
Button
Console
Port
Component Description
Antennas
The access point includes integrated diversity antennas for wireless
communications. A diversity antenna system uses two identical antennas to receive
and transmit signals, he lpi ng t o av oi d m ul t ipath fadi ng effects. When receiving, the
access point checks bot h antennas and selects the on e wi th the st ro ngest signal.
When transmitting, it will continue to use the antenna previously selected for
receiving. The access point never transmits from both antennas at the same time.
The antennas transmit the outgoing signal as a toroidal sphere (doughnut shape d) ,
with the coverage extend ing most in a direction perp endicular to t he antenna. Th e
antenna should be adjus te d to an angle that provides the appr op riat e coverage for
the service area. For further information, see “Positionin g th e Ant ennas” on 2-2.
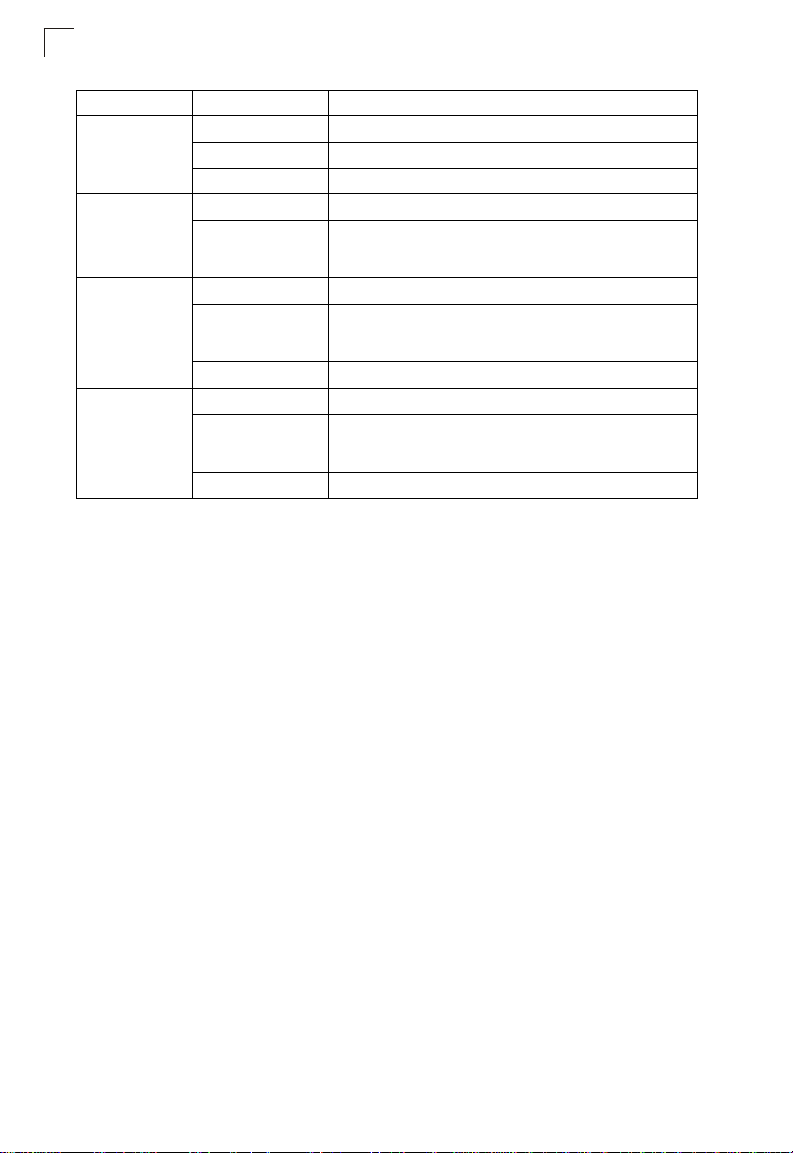
LED Indicators
The access point includes four status LED
indicators, as described in the following
figure and table.
PWR Link 11a 11g
Power
Ethernet
Link/Activity
802.11a
Wireless
Link/Activity
802.11b/g
Wireless
Link/Activity
1-3
Page 28
Introduction
1
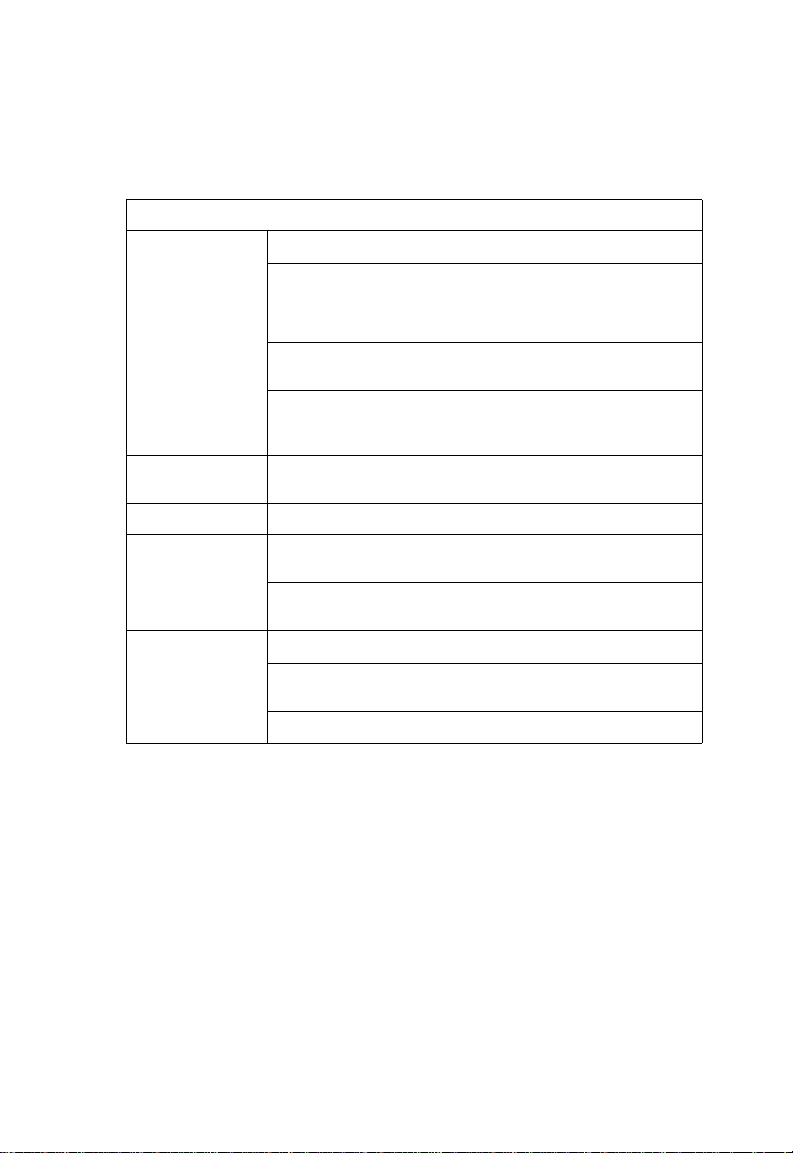
LED Status Description
PWR On Indicates that the system is working normally.
Flashing Indicates running a self-test or loading the software program.
Flashing (Prolonged) Indicates system errors.
Link On Indicates a valid 10/100 Mbps Ethernet cable link.
Flashing Indicates that the access point is transmitting or receiving data
11a On Indicates that the 802.11a radio is enabled.
Flashing Indicates that the access point is transmitting or receiving data
Off Indicates that the 802.11a radio is disabled.
11g On Indicates that the 802.11b/g radio is enabled.
Flashing Indicates that the access point is transmitting or receiving data
Off Indicates that the 802.11b/g radio is disabled.
on a 10/100 Mbps Ethernet LAN. Flashing rate is proportional
to network activity.
through wireless links. Flashing rate is proportional to network
activity.
through wireless links. Flashing rate is proportional to network
activity.
Security Slot
The access point includes a Kensington security slo t on th e re ar panel. You can
prevent unauthorized removal of the access point by w r apping the Kensington
securit y cab le (n ot pr ov id ed ) ar oun d an un mo va bl e object, inserting th e lo ck in to th e
slot, and turning the key.
Console Port
This port is used to connect a con sole device to the access po int through a serial
cable. This connection is described under “Co nsole Port Pin Assignments” on page
B-3. The console device can be a PC or wo rk station running a VT-100 terminal
emulator, or a VT-100 terminal.
Ethernet Port
The access point has one 10BASE-T/100BASE-TX RJ-45 port that can be attached
directly to 10BASE-T/100BASE-TX LAN segments. These segments must conform
to the IEEE 802.3 or 802.3u spe cif ic ati ons.
This port uses an MDI (i.e., inte rn al st ra ig ht -through) pin configuration . You can
therefore use straight-through twisted-pair cable to connect this port to most network
interconnection devices such as a switch or router tha t provide MDI-X ports.
However, when connecting the acce ss point to a workstation or othe r de vi ce that
does not have MDI-X po rts, you mu st use crossover twisted-pair ca ble.
The access point appears as an Ethernet node and perfor ms a bridging function by
moving packets from the wired LAN to remote workstations on t he w ir el ess
infrastructure.
1-4
Page 29

Features and Benefits
Note: The RJ-45 port also supports Power over Ethernet (PoE) based on the IEEE
802.3af standard. Refer to the description for the “Power Connector” for
information on supplying power to the access point’s network port from a network
device, such as a switch, that prov ides Power over Et hernet (PoE).
Reset Button
This button is used to reset the access point or restore the factory default
configuration. If you hold down the button for less than 5 seconds, the access point
will perform a hardware res et . If you hold down the button for 5 seconds or more,
any configuration changes you may have made are removed, and the factory default
configuration is restor ed to the access point.
Power Connector
The access point does not have a power switch. It is powered on when connected to
the AC power adapter, and the power adapter is connected to a power sourc e. The
power adapter automat i cally adjusts to any voltage betw een 100-240 volts at 50 or
60 Hz. No voltage range settings are required.
The access point may also r eceive Power over Ethernet (PoE) from a switch or
other network device that supplies power over the network cable based on the IEEE
802.3af standard.
Note that if the access poi nt is connected to a PoE source dev ic e an d al so
connected to a local power source through the AC power adapter, PoE will be
disabled.
1
Features and Benefits
• Local network connection via 10/100 Mbps Ethernet po rt s or 54 Mbps wireless
interface (supporting up to 128 m obile users)
• IEEE 802.11a, 802.11b, and 802.11g compliant
• Interoperable with multipl e ve ndors based on the IEEE 802.11f protocol
• Advanced security throug h 64/ 128/152-bit Wired Equival ent Protection (WEP)
encryption, IEEE 802.1X authentication via a RADIUS server, Wi-Fi Protected
Access (WPA), and MAC address filtering features to protect your sensitive data
and authenticate only au th or iz ed users to your network
• Provides seamless roaming within the IEEE 802.11a, 802.11b and 802.11g WLAN
environment
• Scans all available channels and selects the best channel for each client based on
the signal-to-noise rati o
1-5
Page 30
Introduction
1
Applications
Wireless network products offer a high speed, reliable, cos t -e ffective solution for
wireless Ethernet client access to the network in applications such as:
• Remote access to corporate network information –
E-mail, file transfer, and terminal emulation.
• Difficult-to-wire environments –
Historical or old buildings, asbestos installations, and open areas where wiring is
difficult to employ.
• Frequently changing en vi ro nm ents –
Retailers, manufactur ers, and banks that freque nt l y re ar ra nge the workplace or
change location.
• Temporary LANs for speci al pr oj ects or peak times –
Trade shows, exhibitions and construction sites th at need temporary setup for a
short time period. Retailers, airline and shipping companies that need additional
workstations for a peak per iod. Auditors who require wo rk gr oups at customer
sites.
• Access to databases for mobile work ers –
Doctors, nurses, retailers, or white-colla r workers who ne ed access to databases
while being mobile in a hospi t al , retai l st or e, or an of fice campus.
• SOHO users –
SOHO (Small Office and Home Office) users who need easy and quick installation
of a small computer netw or k.
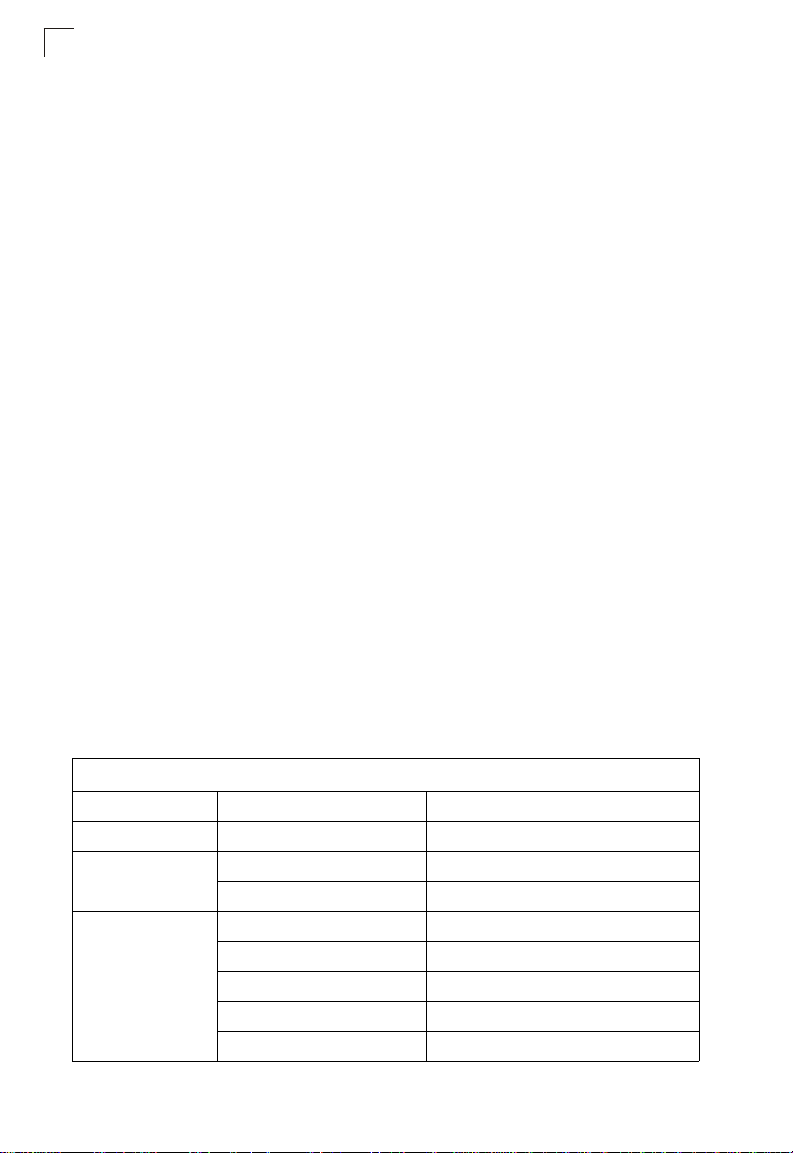
System Defaults
The following table lists some of the acc ess point’s basic system defaul ts. To reset
the access point defaults, use the CLI command “reset configuration” from the Exec
level pr o mpt.
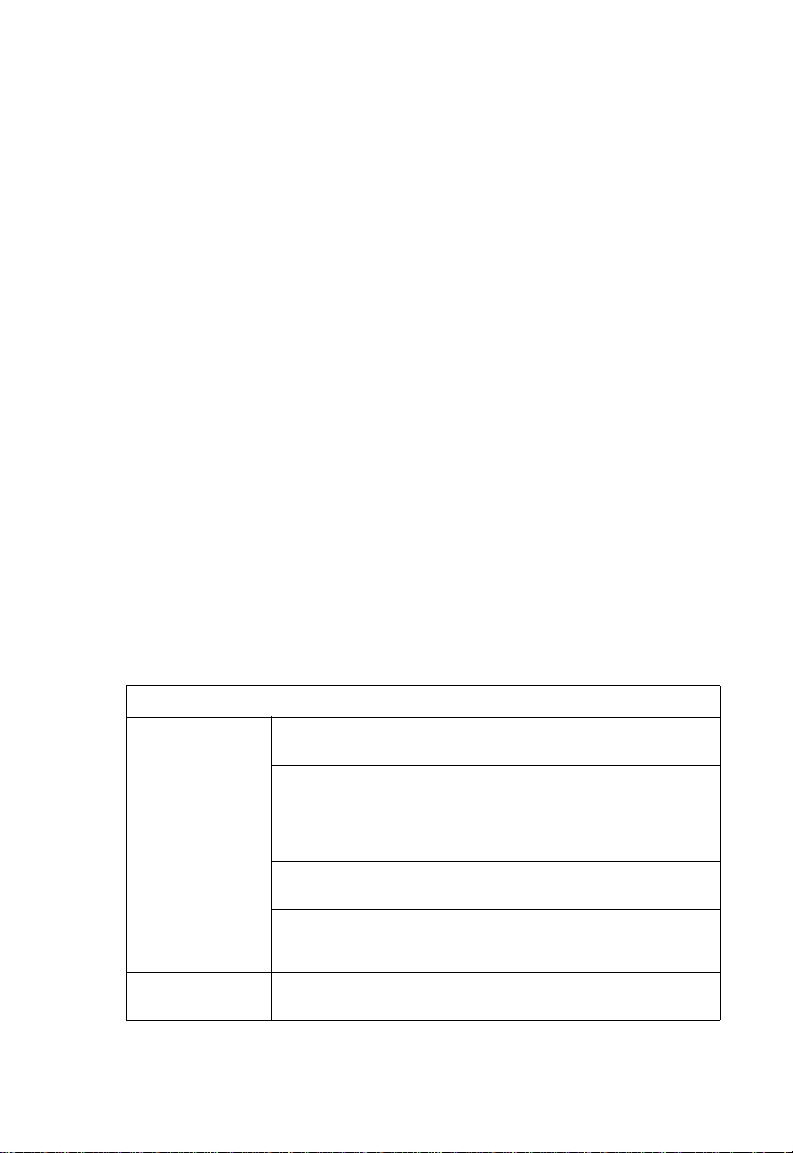
Table1-1. System Defaults
Feature Parameter Default
Identification System Name SMC
Administration User Name admin
Password null
General HTTP Server Enabled
HTTP Server Port 80
HTTPS Server Enabled
HTTPS Server Port 443
Web Redirect Disabled
1-6
Page 31

Table1-1. System Defaults
Feature Parameter Default
TCP/IP DHCP Enabled
IP Address 192.168.1.1
Subnet Mask 255.255.255.0
Default Gateway 0.0.0.0
Primary DNS IP 0.0.0.0
Secondary DNS IP 0.0.0.0
RADIUS (Primary and
Secondary)
SSH Server Status Enabled
PPPoE PPPoE Status Disabled
MAC Authentication MAC Disabled
802.1X Authentication Status Disabled
VLAN Man age me nt VLAN ID 1
QoS QoS Mode Off
IP Address 0.0.0.0
Port 1812
Key DEFAULT
Timeout 5 seconds
Retransmit attempts 3
Accounting Port 0 (Disabled)
Interim Update Timeout 3600 seconds
Server Port 22
Authentication Session Timeout 0 minutes (disabled)
Local MAC System Default Allowed
Local MAC Permission Allowed
Broadcast Key Refresh 0 minutes (disabled)
Session Key Refresh 0 minutes (disabled)
Reauthentication Refresh Rate 0 seconds (disabled)
Supplicant Disabled
VLAN ID (VAP Interface) 1
VLAN Tag Support Disabled
SVP (SpectraLink Voice Priority) Disabled
System Defaults
1
1-7
Page 32

Introduction
1
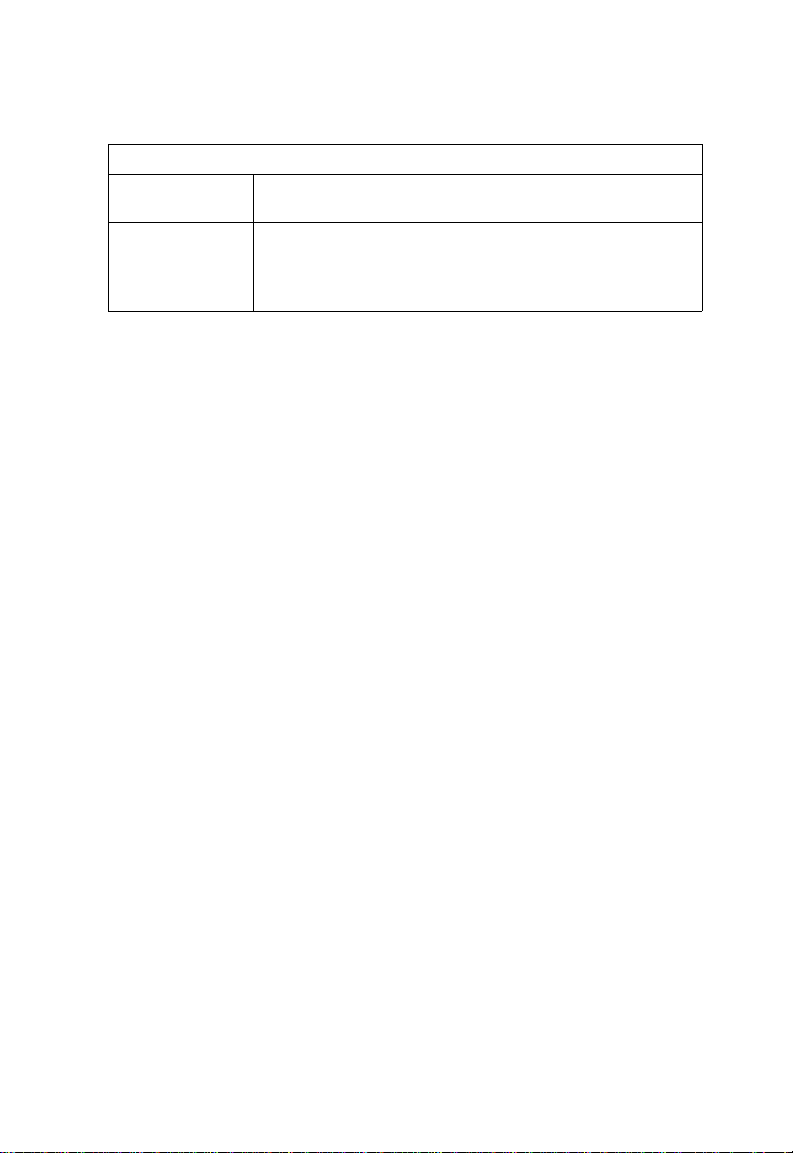
Table1-1. System Defaults
Feature Parameter Default
Filter Control Local Bridge Disabled
AP Management Enabled
Ethernet Type Disabled
SNMP Status Enabled
Location null
Contact null
Community (Read Only) Public
Community
(Read/Write)
Traps Enabled
Trap Destination (1-4) Disabled
Trap Destination IP Address null
Trap Destination Community
Name
SNMP v3 Groups RO
SNMP v3 Users none
System Logging Syslog Disabled
Logging Host Disabled
Logging Console Disabled
IP Address / Host Name 0.0.0.0
Logging Level Informational
Logging Facility Type 16
System Clock SNTP Server Status Enabled
SNTP Server 1 IP 137.92.140.80
SNTP Server 2 IP 192.43.244.18
Date and Time 00:00, Jan 1, 1970 (when there is no time
Daylight Saving Time Disabled
Time Zone GMT-5 (Eastern Time, US and Canada)
Ethernet Interface Speed and Duplex Auto
Private
Public
RWAuth
RWPriv
server)
1-8
Page 33

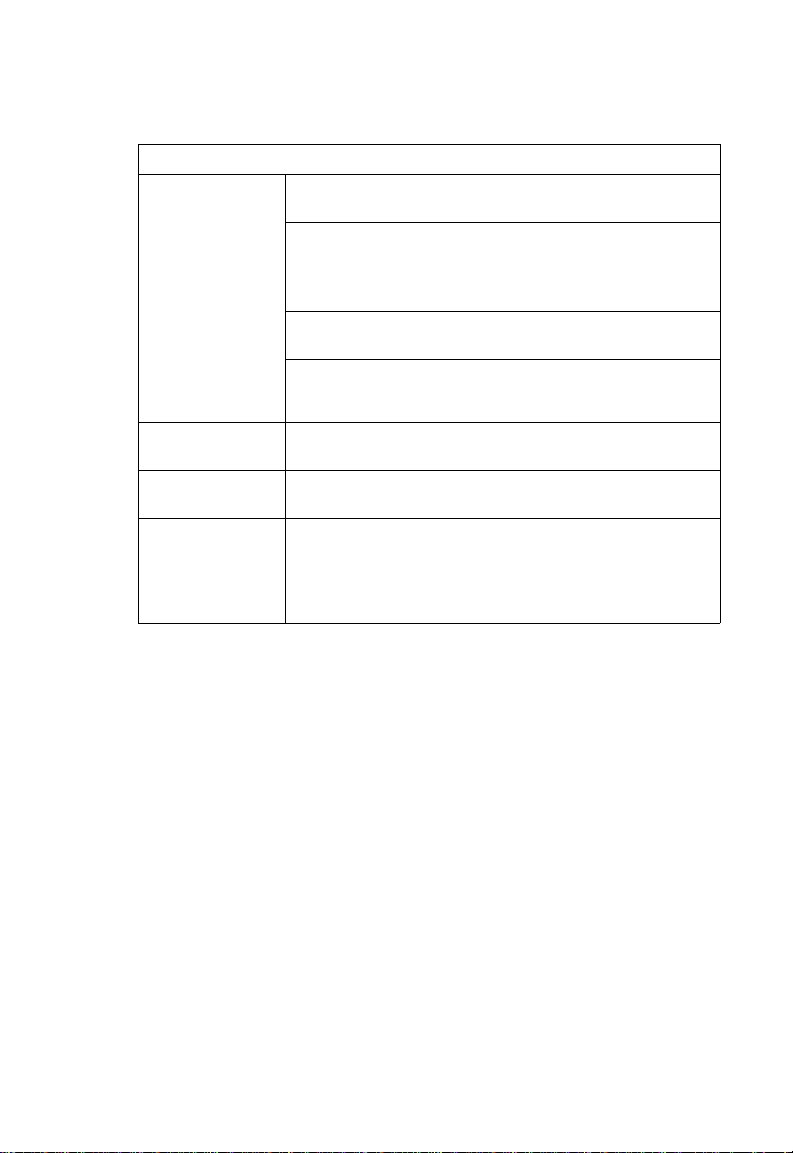
Table1-1. System Defaults
Feature Parameter Default
Wireless Interface
802.11a
Wireless Security
802.11a
IAPP Enabled
SSID VAP_TEST_11A (0 to 7)
Turbo Mode Disabled
Status Disabled
Auto Channel Select Enabled
Closed System Disabled
Transmit Power Full
Max Station Data Rate 54 Mbps
Multicast Data Rate 6 Mbps
Beacon Interval 100 TUs
Data Beacon Rate (DTIM Interval) 1 beacon
RTS Threshold 2347 bytes
Association Timeou t Interval 30 minutes
Authentication Timeout Interval 60 minutes
Rogue AP Detection Disabled
Antenna Control Method Diversity
Antenna ID 0x0000
Antenna Location Indoor
Authentication Type Open System
Data Encryption Disabled
WEP Key Length 128 bits
WEP Key Type Hexadecimal
WEP Transmit Key Number 1
WEP Keys null
WPA Configuration Mode WEP Only (Disabled)
WPA Key Management WPA Pre-shared Key
WPA PSK Type Alphanumeric
Multicast Cipher WEP
System Defaults
1
1-9
Page 34

Introduction
1
Table1-1. System Defaults
Feature Parameter Default
Wireless Interface
802.11b/g
Wireless Security
802.11b/g
IAPP Enabled
SSID VAP_TEST_11G (0 to 7)
Radio Mode b+g
Status Disabled
Auto Channel Select Enabled
Closed System Disabled
Transmit Power Full
Max Station Data Rate 54 Mbps
Multicast Data Rate 5.5 Mbps
Preamble Length Long
Beacon Interval 100 TUs
Data Beacon Rate (DTIM Interval) 1 beacon
RTS Threshold 2347 bytes
Association Timeou t Interval 30 minutes
Authentication Timeout Interval 60 minutes
Rogue AP Detection Disabled
Antenna Control Method Diversity
Antenna ID 0x0000
Antenna Location Indoor
Authentication Type Open System
Data Encryption Disabled
WEP Key Length 128 bits
WEP Key Type Hexadecimal
WEP Transmit Key Number 1
WEP Keys null
WPA Configuration Mode WEP Only (Disabled)
WPA Key Management WPA Pre-shared Key
WPA PSK Type Alphanumeric
Multicast Cipher WEP
1-10
Page 35

Table1-1. System Defaults
Feature Parameter Default
Link Integrity Status Disabled
Ping Interval 30 seconds
Fail Retry Count 6
System Defaults
1
1-11
Page 36

1
Introduction
1-12
Page 37

Chapter 2: Hardware Installation
1. Select a Site – Choose a proper place for the access point. In general, the best
location is at the center of your wireless coverage area, within line of sight of all
wireless devices. Try to place the access poi nt in a posi tion that can best c over
its Basic Service Set (refer to “Infrastructure Wireless LAN” on page 4-3). For
optimum performance, consider these points:
• Mount the access point as high as possible above any obstructions in the
coverage area.
• Avoid mounting next to or near building support columns or other obstructions
that may cause reduced signal or null zones in parts of the coverage area.
• Mount away from any signal absorbing or reflecting structures (such as those
containing metal).
2. Mount the Acc ess Point – The access point can be mounted on any
horizontal surface.
Mounting on a horizontal surface – T o keep the access point from sliding on the
surface, attach the four rubber feet provided in the accessory kit to the marked
circles on the bottom of th e ac cess point.
Lock the Access Point in Plac e – To prevent unauthorized removal of t he
access point, you can use a Kensington Slim MicroSaver security cable (not
included) to attach the acc e ss po int to a fixed object.
3. Connect the Pow er Cord – Conne ct the power adapter to the access po in t ,
and the power cord to an AC pow er out let .
Otherwis e, the access poi nt can derive its operat ing power dire ctly from the
RJ-45 port when connected to a device that provide s IEEE 802.3af compliant
Power over Ethernet (PoE).
Note: If the access point is connected to both a PoE source device and an AC power
source, PoE will be disabled.
Caution: Use ONLY the power adapter supplied with this access point. Otherwise, the
product may be damaged.
2-1
Page 38

Hardware Installation
2
4. Observ e t he Sel f Test – When you power on the access point, verify that the
PWR indica tor st op s fl ashi ng an d rema ins o n, and that the othe r indi cat ors sta rt
functioning as described under “LED Indicators” on page 1-3. If the PW R LED
does not stop flashing, the self test has not completed correctly. Refer to
“Troubleshooting” on page A-1.
5. Connect the Et her net C able – The access point can be wired to a 10/100
Mbps Ethernet through a network device such as a hub or a swi tc h. C onnect
your network to the RJ-45 por t on th e back panel with category 3, 4, or 5 UT P
Ethernet cable. When th e acc ess point and the connected device are powered
on, the Ethernet Link LED should light indicating a valid net work connection. If
this LED fails to turn on refer to “Troubleshooti ng ” on page A-1 .
Note: The RJ-45 port on the access point uses an MDI pin configuration, so you must
use straight-through cable for network connections to switches that only have
MDI-X ports, and crossover cable for network connections to PCs, servers or
other devices that only have MDI ports. However, if the connected device
supports auto-MDI/MDI-X operation, you can use either straight-through or
crossover cable.
6. Position the Antenn as – Each antenna emits a radiation pattern that is
toroidal (doughnut shaped), with the coverage extending most in the direction
perpendi cular to the antenna. Ther efore, the antennas should be oriented so
that the radio coverage patter n f ills t he intended horizontal space. Also, the
diversity antennas should both be positioned alo ng t he same axes, providing
the same coverage area. For example, if the access point is mounted on a
horizontal surface, both ant en nas should be positioned pointing vertically up to
provide optimum coverage.
7. Connect the Cons ole Por t – Co nnect the console cable (included) to the
RS-232 console port for accessing the command- line interface. You can
manage the ac cess point using the conso le port (Chapter 6), the web interface
(Chapter 5), or SNMP management software such as HP’s OpenView.
2-2
Page 39

Chapter 3: External Antennas
The SMC WA6102X-2AG provides a variety of external antenna options for
extending the radio range and shaping the cover ge area. These an tennas of fer a
number of different mounting locations, including indoor or outdoor, wall,
ceiling, or radio mast.
This chapter shows you how to install an external antenna for your
WA6102X-2AG.
Only the SMC antennas listed in this guide are permitted to be connected to the
WA6102X-2AG. You must use the appropriate antennas, cables, and where
applicable, surge arrestors, for your given region. You are responsible for
verifying local regulations or legi slation that may impose restri ctions on the use
of specific antenna and cable combinations. For this reason, SMC recommends
that you consult with a professional installer who is trained in RF installation
and knowledgeable in the local regulations prior to connecting an external
antenna to your wireless radio product. It is the responsibility of the end user to
ensure that the antenna installation complies with the local radio regulations.
Instalation Procedures
Follow these steps to install an exte rn al ant enna and connect it to the
WA6102X-2AG.
Caution: Never mount the access point outdoors to be near an external antenna.
1. Plan the Installation
The access point must always be installed indoors.
• Pigtail Cables - Use the coax pigtail cable attached to the antenna to connect
to the access point. Because most pigtail cables are a relatively short length
(83 cm or 33 inches), be sur e to find a suitable mounting posit io n for the
antenna that is not too far from the access point. If an extension cable is
required, please cont act a professional installer who is trained in RF
installation and knowledgeable in the local regul at ions.
• Installation Location - Plan t he an te nna’s position and orient at ion.
Warning: The radiated output power of this device is below the FCC radio
exposure limits. Nevertheless, the device should be used in such a
manner that the potential for human contact during normal operation
is minimized. To avoid the possibility of exceeding the FCC radio
frequency exposure limits, human proximity to the antennas should
not be less than 20 cm (8 inches) during normal operation.
3-1
Page 40

External Antennas
3
Consider these points:
• Use the antenna’s mounti ng bracket or other hardwar e, if in cluded.
• For optimum performance, mount antennas as high as possible above any
obstructions, and awa y f rom any signal absorbing or ref le ct ing structures
(such as those containing metal)
• Be sure there are no other radio ant enn as mounted within 2 m (6 ft).
• Consider the antenna’s radio coverage pattern so that it can properly cover
the intended service area.
• Omnidirectional Antennas - Consider these factors when selecting a
location for these antennas:
• Always mount the antenna in a vertical orientation so that th e ra di o
coverage pattern fills the i nt ended horizontal space.
• For optimum coverage, mount the antenna at the center of the area with a
line-of-sight path to all point s w it hi n th e ar ea.
• Avoid mounting next to or nea r bu ildi n g support columns or other
obstructions that ma y cause reduced signal or null z ones in parts of the
coverage area.
• When mounting outdoors using a mast, make sure that the antenna extends
beyond the top of the mas t.
• Directional Antennas - Consider t hes e fa ct or s whe n se le ct in g a lo ca ti on for
these antennas:
• For optimum coverage, m ount the antenna above any obstructions,
directed at the center of th e coverage area sector.
• High-gain directional ante nnas provide a flattened rad io cov erage pattern
in the horizontal plane. Us e th e t iltin g or arti culated mounts to point the
antennas towards th e cov er age area.
• Outdoor Installation - When installing an antenn a out doors, be sure to
consider these addit ional f act or s:
• Always place the antenna aw ay from power and telephone lines
• Make sure that the antenn a, any supporting structure, and cables are all
properly grounded.
• For lightning protection, con si der us in g a l ight ni ng arrestor immediately
before the cable enters th e building.
Warning: Never install an antenna or construct a radio mast near overhead
power lines.
2. Mount the Antenn a
Install the antenna in its planned location using the brackets, clips, or other hardware
included in the antenna package.
Refer to documentation incl uded with the antenna for sp eci f ic in f ormation and
installation instructions.
3-2
Page 41

Instalation Procedures
3. Connect Pigtail Cables to the Access Point
Use the pigtail cables that are at tache d t o th e antenna, or are included in the
antenna package. If an extension cable is required, plea se contact a professional
installer who is trained in RF installation and knowledgeable in the local regulations.
Note that diversity antennas have two pigtail cables. A diversity antenna includes
two internal antenna elements that are identical. Both antenna pigtail cables must be
connected to the acce ss point for correct operati on.
Other non-diversity an te nnas, which have only one pi gtail cable, attach to the
access point’s right antenna c onnector. The access point’s right antenna is the one
on the side closest to the LE D in dicat or s. When using a non-diversi t y antenna, a
50-ohm terminator (in cl uded with the antenna) mu st be connected to the access
point’s left antenna connector.
To connect pigtail cables to the acce ss point, follow these steps:
1. Disable the access point radio using the w eb br ow s er interface, CLI, or SNMP.
2. Remove p ow er to th e access point.
3. Remove b ot h of th e access point’s antennas by uns cr ewi ng them at their base.
Right antenna
3
Unscrew antenna
to remove
4. For diversity antennas, connect the antenna pigtail cables to the exp osed
Reverse SMA connectors on both sides of the access point.
For non-diversity antennas, be sure to connect the s in gl e pigtail cable to the
Reverse SMA connec tor on the access point’s right side. Wh en using a
non-diversity antenna, you must also connect th e 50-ohm terminator
(5092-0933), included with the antenna, to the access point’s left-side Reverse
SMA connector.
3-3
Page 42

3
External Antennas
Screw onto access point’s
5. Reconnect power to the access point.
Note: Before enabling the radio with an external antenna attached, be sure to first
configure the access point’s antenna mode and transmit power settings.
Antenna pigtail cable
3-4
Page 43

Chapter 4: Network Configuration
Wireless networks su pport a stand-alone configurat i on as well as an integrated
configuration with 10/10 0 Mbps Ethernet LANs. The 2. 4 G Hz/ 5 G H z Wi r eless
Access Point also provide s re peater and bridging servic es t hat can be configured
independently on either th e 5 GH z or 2.4 GHz radio interfaces .
Access points can be deployed to support wireless clients and connect wired LANs
in the following configurat i ons:
• Ad hoc for departmental, SOHO or enterpris e LAN s
• Infrastructure for wireless LAN s
• Infrastructure wireless LAN for roaming wireless PCs
• Infrastructure wireless b ridge to connect wired LANs
• Infrastructure wireless repeater for extended range
The 802.11b and 802.11g frequency band which operates at 2.4 GHz can easily
encounter interferen ce f ro m other 2.4 GHz devices, suc h as other 802.11b or g
wireless devices, cordless phones and microwave ovens. If you experience poor
wireless LAN perform ance, try the following meas ur es:
• Limit any possible sources of radio interference within the service area
• Increase the distance between n ei ghb or in g access points
• Decrease the signal strength of nei ghboring access points
• Increase the channel separation of neighboring access po in ts (e.g . up to 5
channels of separation for 802 .11b and 802.11g)
4-1
Page 44

Network Configuration
p
4
Network Topologies
Ad Hoc Wireless LAN (no Access Point)
An ad hoc wireless LAN cons ists of a gr oup of computers, each equip ped with a
wireless adapter, connected via radio signals as an independent wir eless LAN.
Computers in a specific ad hoc wireless LAN must ther ef or e be configured to the
same radio channel. An ad hoc wireless LAN can be us ed for a br anc h offic e or
SOHO operation.
Ad HocWireless LAN
Notebook with
Wireless USB Adapter
Notebook with
Wireless PC Card
PC with Wireless
PCI Ada
ter
4-2
Page 45

Network Topologies
Infrastructure Wireless LAN
The access point also provides access to a wir ed LAN for wireless work stations. An
integrated wired/wireless LAN is called an Infrastruct u re c onf i guration. A Basic
Service Set (BSS) consists of a gr oup of wi r eless PC users, and an access poi nt
that is directly connected to the wired LAN. Each wireless PC in this BSS can talk to
any computer in its wireless group via a radio link, or access other computers or
network resources in t he wi re d LAN infrastructure via th e acc ess point.
The infrastructure configuration not only extends the accessibility of wireless PCs to
the wired LAN, but also increases the effective wireless transmission range for
wireless PCs by passing their signal through one or more access points.
A wireless infrastructur e c an be used for access to a cent ra l databa se , or fo r
connection between mo bi l e workers, as shown in the follo wi ng f ig ur e.
Wired LAN Extension
to Wireless Clients
Server
4
Desktop PC
Switch
Access Point
Notebook PC
Desktop PC
4-3
Page 46

Network Configuration
4
Infrastructure Wireless LAN for Roaming Wireless PCs
The Basic Service Set (BSS) defines the communications domain for each access
point and its associated wirele ss cl ients. The BSS ID is a 48-bit binary number
based on the access po int ’s wirel es s M A C add ress, and is set automati call y and
transparently as clients associa te w i th the access point. The BSS ID is used in
frames sent between t he access point and its clients to iden tify t ra ffic in the ser vi ce
area.
The BSS ID is only set by the access point, never by its clients. The clients on ly
need to set the Service Set Iden tifi er (SSID ) that ide nti fies the ser vice set provided
by one or more access points. The SSID can be m anually configured by the clien ts,
can be detected in an access point’s beacon, or can be obtained by querying for the
identity of the nearest access point. For clients that do not need to roam, set the
SSID for the wireless card to that used by the access point to which you want to
connect.
A wireless infrastructure can also support roaming for mobile workers. More than
one access point can be conf igured to create an Extended S er vice Set (ESS). By
placing the access poi nts so tha t a c ont i nuous coverage area is creat ed, wireless
users within this ESS can roam freely. All wireless network cards and adapters and
wireless access points within a specific ESS must be configured with the same
SSID.
Seamless Roaming
Between Access Points
4-4
Desktop PC
Switch
Access Point
Desktop PC
Server
Notebook PC
<BSS 1>
Switch
Access Point
Notebook PC
<BSS 2>
<ESS>
Page 47

Network Topologies
Infrastructure Wireless Bridge
The IEEE 802.11 standard defines a WIreless Distribution System (WDS) for bridge
connections between BSS areas (access points). The access point uses WDS to
forward traffic on links between units.
The access point suppo rts WDS br i dge links on either the 5 GHz (802.11a) or
2.4 GHz (802.11b/g) bands and can be used with various external antennas to offer
flexible deployment opti ons.
Up to six WDS bridge links can be specified for each unit in th e wi re le ss bridge
network. One unit only must be configured as the “root bridge” in the wireless
network. The root bridge sh oul d be the unit connected to the mai n core of the wired
LAN. Other bridges must configure one “parent” link to the root bridge or to a bridge
connected to the root bridge. The other five available WDS links can be specified as
“child” links to other bridges. This forms a tiered-star topology for the wireless bridge
network.
When using WDS on a radi o band, only wireless bridge uni ts ca n ass ociate to each
other. Wireless clients can only associate with the access point using a radi o band
set to access point or repea t er m ode.
4
802.11g Radio
AP Link
802.11g Radio
AP Link
Network
Core
802.11a Radio
Bridge Link
Bridge
Root Bridge
Wireless Bridge Links
Between Access Points
802.11a Radio
Bridge Link
802.11g Radio
802.11g Radio
AP Link
802.11a Radio
Bridge Link
AP Link
Bridge
Bridge
4-5
Page 48

Network Configuration
4
Infrastructure Wireless Repeater
The access point can also operate in a bridge “repeater ” mode to extend the range
of links to wireless clients. The ac cess point uses WDS to forw ar d t ra ffic between
the repeater bridge and th e ro ot br idge. The access point supports up to si x W D S
repeater links.
In repeater mode, the access point does not support an Ethernet link to a wired LAN.
Note that when the acce ss point operates in this mode only half the normal
throughput is possible . Th is is bec ause the access point has to receive and then
re-transmit all data on the same channel.
Network
Core
Wireless Repeater Links
Between Access Points
Root Bridge
802.11gRadio
802.11gRadio
Repeater Link
Repeater Link
4-6
802.11gRadio
AP Link
Repeater
802.11gRadio
AP Link
Repeater
Page 49

Chapter 5: Initial Configuration
The 2.4 GHz/5 GHz Wireless Access Point offers a variety of management options,
including a web-based i nte r f ace , a direct connection to the cons ol e po rt , Telnet,
Secure Shell (SSH), or using SNMP software.
The initial configuration steps can be made through the web browser interface or
CLI. The access point requests an IP address via DHCP by default. If no response is
received from the DHCP server, then the access point uses the default address
192.168.1.1. If this address is not compatible with your network, you can first use the
command line interfac e (C L I) as d escribed below to configu re a val id address.
Note: Units sold in countries outside the United States are not configured with a specific
country code. You must use the CLI to set the country code and enable wireless
operation (page 5-3).
Initial Setup through the CLI
Required Connections
The access point provides an RS-232 serial port that en abl es a connection to a PC
or terminal for monitoring and configuration. Attach a VT100-compatible terminal, or
a PC running a terminal emul at ion program to the access point . You can use the
console cable provide d w i th th is package, or use a cable that com pli es w i t h the
wiring assignments shown on page B-3.
To connect to the console port, co m pl et e the following steps:
1. Connect the con sol e c abl e t o t he serial port on a terminal, or a PC run ni ng
terminal emulation software, and tighten the captive retaining screws on the
DB-9 connector.
2. Connect the oth er end of the cable to the RS-232 se rial port on the access
point.
3. Make sure the terminal emulation software is set as follows:
• Select the appropri ate serial port (COM port 1 or 2) .
• Set the data rate to 9600 baud.
• Set the data format to 8 data bits, 1 stop bit, and no parity.
• Set flow control to none.
• Set the emulation mode to VT10 0.
• When using HyperTermin al , s elect Terminal keys, not Wind ow s k eys.
5-1
Page 50

Initial Configura tion
5
Note: When using HyperTerminal with Microsoft® Windows® 2000, make sure that you
have Windows 2000 Service Pack 2 or later installed. Windows 2000 Service
Pack 2 fixes the problem of arrow keys not functioning in HyperTerminal’s VT100
emulation. See www.microsoft.com for information on Windows 2000 service
packs.
4. Once you have set up the terminal correctly, press the [Enter] key to initiate the
console connection. The console login screen will be displayed.
For a description of how to use the CLI, see “Using the Command Line Interface” on
page 7-1. For a list of all the CLI commands and detailed information on using the
CLI, refer to “Command Groups” on page 7-6.
Initial Configuration Ste p s
Logging In – Enter “admin” for the user name. The default password is null, so just
press [Enter] at the passwor d pr ompt. The CLI prompt appe ars displaying the
access point’s name.
Username: admin
Password:
Enterprise AP#
Setting the IP Address – By default, the access point is configured to obtain IP
address settings from a DHCP server. If a DHCP server is not available, the IP
address defaults to 192.168 . 1. 1, w hich m ay not be compatible with your net w or k.
You will therefore have to use the command line interface (CLI) to assign an IP
address that is compatible with your network.
Type “configure” to enter configuration mo de, th en type “interface ethernet ” to
access the Ethernet interf ac e- configuration mode.
Enterprise AP#configure
Enterprise AP(config)#interface ethernet
Enterprise AP(config-if)#
First type “no ip dhcp” to disable DHCP client mode. Then type “ip a ddr ess
ip-address netmask gat ew ay,” where “ip-address” is the access point’s IP addr ess,
“netmask” is the network mask for the network, and “gateway” is the default gateway
router. Check with your system admin istrat or to obtain an IP address that is
compatible with your network.
Enterprise AP(if-ethernet)#no ip dhcp
Enterprise AP(if-ethernet)#ip address 192.168.2.2
255.255.255.0 192.168.2.254
Enterprise AP(if-ethernet)#
5-2
Page 51

Logging In
After configuring the access point’s IP parameters, you can access the management
interface from anywhe re wi t hin t he at tac hed network. The command l i ne int er f ace
can also be accessed usi ng Telne t fro m any computer attached to the net work.
Setting the Country Code – U ni ts sold in t he U nited States are configured by
default to use only radio cha nnels 1-11 in 802.11b or 802.11g mode as defined by
FCC regulations. Units sold in other countrie s are configured by default without a
country code (i.e., 99). You must use the CLI to set the country code. Setting the
country code restricts ope ra tion of the access point to the ra di o channels and
transmit power levels permitted for wireless networks in the specified country .
Type “exit” to leave configuration mode. Then type “country ?” to display the list of
countries. Select the code for your country, and enter the country comma nd again,
following by your countr y code (e.g., tw for Taiwan).
Enterprise AP#country tw
Enterprise AP#
Note: Command examples shown later in this manual abbreviate the console prompt to
“AP” for simplicity.
Logging In
There are only a few basic st e ps yo u ne ed t o complete to connect th e acc ess point
to your corporate netwo rk , and pr ovide network access to wirel ess clients.
5
The access point can be managed by any computer usi ng a web browser (Internet
Explorer 5.0 or above, or Netscape Navigator 6.2 or above). Enter the default IP
address: http://192.1 68. 1. 1
Logging In – Enter the username “admin,” the password is null, so just press just
leave it blank and click LO G IN. For inf or mation on configuring a use r na m e and
password, see page 6-28.
5-3
Page 52

Initial Configura tion
5
The home page displays the Main Menu.
5-4
Page 53

Chapter 6: System Configuration
Before continuing with advanced configuration, first complete the initial configuration
steps described in Chapte r 4 t o set up an IP address for the acc ess point.
The access point can be managed by any computer usi ng a web browser (Internet
Explorer 5.0 or above, or Netscape Navigator 6.2 or above). Enter the configured IP
address of the access point, or use the default address: http://192.168.1.1
To log into the access point, enter the defa ult us er nam e “admin”, leave the
password blank, and press “LOGIN”. When the home page displays, click on
Advanced Setup. The following page will display.
The information in this chap te r is or ganized to reflect the struc tu re of the we b
screens for easy refer enc e. H ow e ver, it is recomme nded that you configure a use r
name and password as the f irst st ep u nde r advanced configurati on t o control
management acces s to th is dev ic e ( page 6- 28).
6-1
Page 54

System Configuration
6
Advanced Configuration
The Advanced Configur at i on pages include the following o pt ions.
Table 6-2. Menu
Menu Description Page
System Configures basic administrative and client access 6-3
Identification Specifies the host name 6-3
TCP / IP Settings Configures the IP address, subnet mask, gateway, and domain
RADIUS Configures the RADIUS server for wireless client authentication
SSH Settings Configures Secure Shell management access 6-11
Authentication Configures 802.1X client authentication, with an option for MAC
Filter Control Filters communications between wireless clients, access to the
VLAN Enables VLAN support and sets the management VLAN ID 6-19
WDS Settings Configures bridge or repeater modes for each radio interface and
AP Management Configures access to management interfaces 6-27
Administration Configures user name and password for management
System Log Controls logging of error messages; sets the system clock via
Mesh Settings Configures meshing functions. 6-37
SNMP Configures SNMP settings 6-37
SNMP Controls access to this access point from management stations
SNMP Trap Filters Defines trap filters for SNMPv3 users 6-44
SNMP Targets Specifies SNMPv3 users that will receive trap messages 6-46
Radio Interface A Configures the IEEE 802.11a interface 6-48
Radio Settings Configures common radio signal parameters and other settings for
Security Enables each virtual access point (VAP) interface, sets the Service
Radio Interface G Configures the IEEE 802.11g interface 6-48
Radio Settings Configures common radio signal parameters and other settings for
name servers
and accounting
address authentication
management interface from wireless clients, and traffic matching
specific Ethernet protocol types
sets spanning tree parameters
upgrades software from local file, FTP or TFTP server;
configuration settings to facto ry def ault s; and res ets the acces s
point
SNTP server or manual configuration
using SNMP, as well as the hosts that will receive trap messages
each VAP interface
Set Identifier (SSID), and configures wireless security
each VAP interface
access;
resets
6-5
6-7
6-12
6-17
6-21
6-28
6-33
6-37
6-49
6-66
6-63
6-2
Page 55

Advanced Configuration
Table 6-2. Menu
Menu Description Page
Security Enables each VAP interface, sets the SSID, and configures
Status Displays information about the access point and wireless clients 6-84
AP Status Displays configuration settings for the basic system and the
Station Station Shows the wireless clients currently associated with the access
Event Logs Shows log messages stored in memory 6-90
Mesh Status Displays information on the mesh configuration settings and
wireless security
wireless interface
point
current network topology
6-66
6-84
6-87
6-91
System Identification
The system name for the ac cess point can be left at its default setting. Ho w ev er,
modifyin g thi s p a ra met er can he lp you to mor e ea si ly di st in gui s h di f f er ent devi ce s in
your network.
6
System Name – An alias for the access point, enabling the device to be uniquely
identified on the network. (D ef aul t: SMC; Range: 1-32 characters)
6-3
Page 56

System Configuration
6
CLI Commands for Sy st em I den ti f ic at io n – Ent er th e gl oba l co nf i gur at i on m ode , an d
use the system name command to specify a new system name. Then return to the
Exec mode, an d use the show system command to display the changes to the
system identification settings.
Enterprise AP#config
Enterprise AP(config)#system name R&D
Enterprise AP(config)#end 7-87
Enterprise AP#show system 7-23
Enterprise AP#config 7-8
Enter configuration commands, one per line.
Enterprise AP(config)#system name R&D
Enterprise AP(config)#end 7-87
Enterprise AP#show system 7-23
System Information
==============================================================
Serial Number :
System Up time : 0 days, 0 hours, 32 minutes, 22 seconds
System Name : R&D
System Location :
System Contact : Contact
System Country Code : US - UNITED STATES
MAC Address : 00-12-CF-12-34-60
Radio A MAC Address : 00-12-CF-12-34-61
Radio G MAC Address : 00-12-CF-12-34-65
IP Address : 192.168.1.1
Subnet Mask : 255.255.255.0
Default Gateway : 0.0.0.0
VLAN State : DISABLED
Management VLAN ID(AP): 1
IAPP State : ENABLED
DHCP Client : ENABLED
HTTP Server : ENABLED
HTTP Server Port : 80
HTTPS Server : ENABLED
HTTPS Server Port : 443
Slot Status : Dual band(a/g)
Boot Rom Version : v1.1.5
Software Version : v4.3.2.0b01
SSH Server : ENABLED
SSH Server Port : 22
Telnet Server : ENABLED
WEB Redirect : DISABLED
DHCP Relay : DISABLED
==============================================================
Enterprise AP#
7-14
7-14
6-4
Page 57

Advanced Configuration
TCP / IP Settings
Configuring the access point with an IP address expands your ability to manage the
access point. A number of access point features depend on IP addressing to
operate.
Note: You can use the web browser interface to access IP addressing only if the access
point already has an IP address that is reachable through your network.
By default, the access point will be automatically configured with IP settings from a
Dynamic Host Configuration Protocol (DHCP) server. However, if you are not using
a DHCP server to configure IP addressing, use the CLI to manually configure the
initial IP values (see page 5-2). After y ou have network access to th e access point,
you can use the web brow ser in te rface to modify the initial IP co nf iguration, if
needed.
Note: If there is no DHCP server on your network, or DHCP fails, the access point will
automatically start up with a default IP address of 192.168.1.1.
6
DHCP Client (Enable) – Select this option to obtain the IP settings for th e access
point from a DHCP (Dynamic Host Configuration Protocol) server. The IP address,
subnet mask, default ga te way, and Domain Name Se rv er (DNS) address are
dynamically assigned to the access point by the network DHCP server.
(Default: Enabled)
DHCP Client (Disable) – Select this option to manually configure a static address for
the access point.
• IP Address: The IP address of the access point. Valid IP addresses consist of four
decimal numbers, 0 to 255, separated by periods.
6-5
Page 58

System Configuration
6
• Subnet Mask: The mask that identifies the host address b its us ed for routing to
specific subnets.
• Default Gateway: The defaul t gat ew ay is the IP address of the rout er fo r the
access point, which is used if the requested destination address is not on the local
subnet.
If you have management st at ions, DNS, RADIUS, or othe r network servers
located on another subnet, type the IP address of the default gateway router in the
text field provided. Otherwise, leave the address as all zeros (0.0.0.0).
• Primary and Secondary DNS Address: The IP address of Domain Name Servers
on the network. A DNS maps numerical IP addresses to domain names and can
be used to identify network hosts by familiar names instead of the IP addresses.
If you have one or more DNS servers located on the local network, type the IP
addresses in the text fields provided. Otherwise, leave the addresses as all zeros
(0.0.0.0).
CLI Commands for TCP/IP Settings – From the global configuration mode, enter the
interface configuration mode with the interfac e et hernet command. Use t he ip
dhcp command to enable the DHCP client, or no ip dhcp to disable it. To manually
configure an address, specify the new IP address, subnet mask, and default
gateway using the ip address command. To specify DNS server addresses use the
dns server command. Then use the show interface ethernet command from t he
Exec mode to display the current IP settings.
Enterprise AP(config)#interface ethernet 7-87
Enter Ethernet configuration commands, one per line.
Enterprise AP(if-ethernet)#no ip dhcp
Enterprise AP(if-ethernet)#ip address 192.168.1.2
255.255.255.0 192.168.1.253
Enterprise AP(if-ethernet)#dns primary-server 192.168.1.55 7-88
Enterprise AP(if-ethernet)#dns secondary-server 10.1.0.55 7-88
Enterprise AP(config)#end 7-8
Enterprise AP#show interface ethernet 7-91
Ethernet Interface Information
========================================
IP Address : 192.168.1.2
Subnet Mask : 255.255.255.0
Default Gateway : 192.168.1.253
Primary DNS : 192.168.1.55
Secondary DNS : 10.1.0.55
Speed-duplex : 100Base-TX Full Duplex
Admin status : Up
Operational status : Up
========================================
Enterprise AP#
7-89
7-88
6-6
Page 59

Advanced Configuration
RADIUS
Remote Authentication D ial - in User Ser vi ce (RAD I US) is an authentication protocol
that uses software running on a central server to contr ol access to RADIUS-awar e
devices on the network. An authentication server co ntains a datab ase of user
credentials for each user that requires access to the network.
A primary RADIUS server must be specified for the access point to implement IEEE
802.1X network access control and Wi-Fi Protected Access (WPA) wireless security.
A secondary RADIUS ser ve r m ay als o be specified as a backup should the primary
server fail or become inaccessible.
In addition, the configured R A DI U S server can also act as a RADI US Accounting
server and receive user -s ession accounting info rmation from the access poin t .
RADIUS Accounting c an be used to provide valuable inf or m at io n on user activity in
the network.
Note: This guide assumes that you have already configured RADIUS server(s) to
support the access point. Configuration of RADIUS server software is beyond the
scope of this guide, refer to the document ation provided with the RADIUS server
software.
6
6-7
Page 60

System Configuration
6
6-8
Page 61

Advanced Configuration
Primary Radius Server Setup – Configure the following settings to use RADIUS
authentication on the ac cess point.
• IP Address: Specifies the IP address or host name of the RADIU S server.
• Port: The UDP port number used by the RADIU S server for authentication
messages. (Range: 1024-65535; Default: 1812)
• Key: A shared text string used to encrypt messages between the access point and
the RADIUS server. Be sure that the same text string is specified on the RADIUS
server. Do not use blank s paces in the string. (Maximum length: 255 characte rs )
• Timeout: Number of seconds the access point waits for a reply from the RADIUS
server before resending a request. (Range: 1-60 seconds; Default: 5)
• Retransmit attempts: The number of times the access point tries to resend a
request to the RADIUS server before authentication fails. (Range: 1-30; Default: 3)
• Interim Update Timeout: The interval between transmitting accounting updates to
the RADIUS server. (Range: 60-86400; Defau lt: 3600 seconds)
Note: For the Timeout and Retransmit attempts fields, accept the default values unless
you experience problems connecting to the RADIUS server over the network.
Secondary Radius Server Setup – Configure a secondary RADIUS server to provide
a backup in case the prim ar y server fails. The access poin t uses the secondary
server if the primary server fails or becomes inaccessible. Once the access point
switches over to the sec ondary server, it periodically attempts to establish
communication aga in w i th prim ar y server. If communication with the primar y server
is re-established, the secondary server reverts to a backup role.
6
6-9
Page 62

System Configuration
6
CLI Commands for RADIUS – From the global configuration m ode, use the
radius-server address com m and to specify the addres s of th e pr imary or
secondary RADIUS servers. (The following example configures the settings for the
primary RADIUS server.) Configure the other parameters for the RADIUS server.
Then use the show show radius command from the Exec mode to display the
current settings for the p rimary and secondary RADIUS servers.
Enterprise AP(config)#radius-server address 192.168.1.25 7-59
Enterprise AP(config)#radius-server port 181 7-60
Enterprise AP(config)#radius-server key green 7-60
Enterprise AP(config)#radius-server timeout 10 7-61
Enterprise AP(config)#radius-server retransmit 5 7-61
Enterprise AP(config)#radius-server port-accounting 1813 7-62
Enterprise AP(config)#radius-server timeout-interim 500 7-62
Enterprise AP(config)#exit
Enterprise AP#show radius
Radius Server Information
========================================
IP : 192.168.1.25
Port : 181
Key : *****
Retransmit : 5
Timeout : 10
Radius MAC format : no-delimiter
Radius VLAN format : HEX
========================================
Radius Secondary Server Information
========================================
IP : 0.0.0.0
Port : 1812
Key : *****
Retransmit : 3
Timeout : 5
Radius MAC format : no-delimiter
Radius VLAN format : HEX
========================================
Enterprise AP#
7-64
6-10
Page 63

Advanced Configuration
SSH Settings
Teln et is a remote management tool tha t can be used to configure the acc ess point
from anywhere in the ne twork. However, Telnet is not secure from hostile attacks.
The Secure Shell (SSH) can act as a se cur e r epl acement for Telnet. The SSH
protocol uses generated public keys to encrypt all data tra nsfers passing between
the access point and SSH -e nabled management station cl ie nts and ensures that
data traveling over the netw or k ar rives unaltered. Clients can th en securely use the
local user name and password for access authentication.
Note that SSH client software nee ds to be installed on the manageme nt statio n to
access the access poi nt for m anagement via the SSH proto col.
Notes: 1. The access point supports only SSH version 2.0.
2. After boot up, the SSH server needs about two minutes to generate host
encryption keys. The SSH server is disabled while the keys are being
generated.
6
SSH Settings
• SSH Server Status: Enables or disables t he SSH server. (Default: Enabled)
• SSH Server Port: Sets the UDP port for the SSH server. (Range: 1-65535;
Default: 22)
CLI Commands for SSH – To enable the SSH server, use the ip ssh-server enable
command from the CLI Et her ne t inter f ace configuration mode. To set the SSH
server UDP port, use the ip ssh-server port command. To view the current settings,
use the show system command from the CLI Exec mode (not shown i n the
following example).
Enterprise AP(if-ethernet)#ip ssh-server enable 7-16
Enterprise AP(if-ethernet)#ip ssh-server port 1124 7-16
Enterprise AP(if-ethernet)#exit
Enterprise AP(if-ethernet)#configure
6-11
Page 64

System Configuration
6
Authentication
Wireless clients can be auth ent i cat e d for network access by checki ng their MAC
address against the local database configured on the ac cess point, or by using a
database configured on a ce nt ra l RADIUS server. Alternatively, authentication can
be implemented using the IEEE 802.1X network access control protocol.
A client’s MAC address provides relatively weak user aut hen tication, since MAC
addresses can be easily captured and used by anot her station to break into the
network. Using 802.1X pr ov id es more robust user authe ntic at i on us i ng user names
and passwords or digital certificates. You can configure the access point to use both
MAC address and 802.1X authentication, with client station MAC authentication
occurring prior to IEEE 802.1X authentication. However, it is better to choose one or
the other, as appropriate.
Take note of the following points befor e configuring MAC addres s or 802. 1X
authentication:
• Use MAC address authentication for a small network w ith a li m ited number of
users. MAC addresses can be manually confi gured on the access point itse lf
without the need to set up a RADIUS server, but managing a large number of MAC
addresses across many access points is very cumbersome. A RADIUS server can
be used to centrally manage a larger database of user MAC addresses.
• Use IEEE 802.1X authentication for networks with a larger number of users and
where secu r ity is the mo st importan t i ssue. When using 802.1X authentica t i on, a
RADIUS server is required in the wired network to centrally manage the
credentials of the wireless clients. It also provides a mechanism for enhanced
network security using dynamic encryption key rotation or W-Fi Protected Access
(WPA).
Note: If you configure RADIUS MAC authentication together with 802.1X, RADIUS MAC
address authentication is performed prior to 802.1X authentication. If RADIUS
MAC authentication succeeds, then 802.1X authentication is performed. If
RADIUS MAC authentication fails, 802.1X authentication is not performed.
• The access point can als o ope rate in a 802. 1X s uppl ican t mo de. T his enabl es the
access point itself to be authenticated with a RADI US ser ve r using a configured
MD5 user name and password. This prevents rog ue access points from gaini ng
access to the network.
Note: The 802.1X supplicant mode is only configurable using the CLI.
6-12
Page 65

Advanced Configuration
6
MAC Authentication – You can configure a list of the MAC addresses for wireless
clients that are authorized to access the network. This provides a basic level of
authentication for wireless cli ents attempting to gain access to the network. A
database of authorized MAC addresses can be stored locally on the access point or
remotely on a central RADIUS server.
(Default: Disabled)
• Disabled: No checks are perfor med on an associating sta tion’s MAC address.
• Local MAC: The MAC address of the associating station is compared against the
local database stored on t he access point. Use the Lo cal MAC Authentication
section of this web page to se t up th e l oca l d at abase, and configure all access
points in the wireless network service area with the same MAC address database.
• Radius MAC: The MAC address of the associating station is sent to a configured
RADIUS server for au thent i cation. When using a RADIU S authentication server
for MAC ad dre ss a ut hen ti cat i o n, th e se rv er mu st fi r st be co nf ig ur ed i n t he R adius
window (see “RADIUS” on page 6-7). The database of MA C addresses and
filtering policy must be de f ined i n t he R ADIUS server.
Note: MAC addresses on the RADIUS server can be entered in four different formats
(see “radius-server radius-mac-format” on page 7-63).
6-13
Page 66

System Configuration
6
MAC Authentication Session Timeout – Sets the interval at which associated clients
will be re-authenticate d wi th the R AD I US server. (Range: 0-1440 minutes; Default :
0, that is, disabled)
WEB Redirect – Enables web-based authentication of wireless clients. This feature
supports billing for a public access wireless network without requiring 802.1X or
MAC authentication. After suc ces sf ul association to an access po i nt, a c lient is
“redirected” to an acces s point login web page as soon as Internet access is
attempted. The client is then authenticated by entering a user name and password
on the web page. Authentication is determined by checking these credentials
against a database of user names and passwords stored n a RADIUS server that is
attached to the wired networ k. Fo r infor m at ion on configuring the RADIU S server’s
details on the access point, se e “RADIUS Client” on page 6-54. (De fa ul t: Di sa bl ed)
Note: Enabling Web Redirect will cause the system to reboot after 5 seconds.
Local MAC Authentication – Configures the local MAC authentication database. The
MAC database provides a me chanism to take certain actions ba sed on a wireless
client’s MAC address. The MA C lis t ca n be configured to allow or deny net w or k
access to specific clients.
• System Default: Specifies a def aul t act ion f or al l un known MAC addresses (that
is, those not listed in the local MAC database).
• D en y: Bl ocks access for all MAC addr ess es except those listed in the lo cal
database as “Allow.”
• Al l ow : Per mits access for all MAC addr esses except those list ed i n th e local
database as “Deny.”
• MAC Authentication Settings: E nter s specified MAC addresses and permissions
into the local MAC database.
• MAC Address: Physical address of a client. Enter six pairs of hexadecimal digits
separated by hyphens; for example, 00-90-D1-12-AB-89.
• Permission: Select Allow to permit access or Deny to block access. If Delete is
selected, the specified MAC address entry is rem oved from the database.
• Update: Enters the specified MAC address and permission setting into the local
database.
• MAC Authentication Table: Displ ay s current entries in the local MA C dat abase.
6-14
Page 67

Advanced Configuration
CLI Commands for Local MAC Authentication – Use th e mac-authentication
server command from the global configur at i on m ode to enable local MAC
authentication. Use the m ac-authentication session -ti m eout command to set the
authentication interval , an d w eb-redirect command to enable web-based
authentication for service billing. Set the default action for MAC addresses not in the
local table using the address filter default command, then enter MAC addresses in
the local table using the address filter entry command. To remove an entry from
the table, use the address filt er del et e command. To display the current settings,
use the show authentica tion command from the Exec mode.
Enterprise AP(config)#mac-authentication server local 7-72
Enterprise AP(config)#mac-authentication session-timeout 5 7-72
Enterprise AP(config)#web-redirect 7-20
Enterprise AP(config)#address filter default denied 7-70
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1a denied
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1b allowed
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1c allowed
Enterprise AP(config)#address filter delete
00-70-50-cc-99-1c
Enterprise AP(config)#exit
Enterprise AP#show authentication
Authentication Information
===========================================================
MAC Authentication Server : LOCAL
MAC Auth Session Timeout Value : 0 min
802.1x supplicant : DISABLED
802.1x supplicant user : EMPTY
802.1x supplicant password : EMPTY
Address Filtering : DENIED
System Default : ALLOW addresses not found in filter table.
Filter Table
MAC Address Status
----------------- ---------00-70-50-cc-99-1a DENIED
00-70-50-cc-99-1b ALLOWED
=========================================================
Enterprise AP#
7-71
7-71
7-68
6
6-15
Page 68

System Configuration
6
CLI Commands for RADIUS MAC Authentication – Use the mac-authentication
server command from the global configur at i on m ode to enable remote MAC
authentication. Set the tim eou t val ue f or re-authentication using the macauthenti cation session-timeout command. Be sure to als o configure connection
settings for the RADIUS server (not shown in the following example). To display the
current settings, use the show authentication comm and from the Exec mode.
Enterprise AP(config)#mac-authentication server remote 7-72
Enterprise AP(config)#mac-authentication
session-timeout 300
Enterprise AP(config)#exit
Enterprise AP#show authentication
Authentication Information
===========================================================
MAC Authentication Server : REMOTE
MAC Auth Session Timeout Value : 300 min
802.1x supplicant : DISABLED
802.1x supplicant user : EMPTY
802.1x supplicant password : EMPTY
Address Filtering : DENIED
System Default : DENY addresses not found in filter table.
Filter Table
MAC Address Status
----------------- ---------00-70-50-cc-99-1a DENIED
00-70-50-cc-99-1b ALLOWED
=========================================================
Enterprise AP#
7-72
7-68
CLI Command for Web Redirect – To configure the access point to use web redirect,
first use the web-redirect command under global configuration mode. To display the
current settings, use the show system command from the Exec mode (not shown in
the following example).
Enterprise AP(config)#web-redirect
Enterprise AP(config)#
7-68
CLI Command for 802.1x Sup pl ic an t – To configure the access point to operate as a
802.1X supplicant, first us e t he 802.1X supplicant user command to set a user
name and password for the access point, then use the 802.1X supplicant command
to enable the feature. To display the current settings, use the show authentication
command from the Exec m ode (not shown in the followi ng e xam ple)
Enterprise AP(config)#802.1X supplicant user WA6102 dot1xpass
Enterprise AP(config)#802.1X supplicant 7-68
Enterprise AP(config)#
7-68
6-16
Page 69

Advanced Configuration
Filter Control
The access point can empl oy network traffic frame filterin g to control access to
network resources and increase security. You can prevent communications between
wireless clients and prevent access point management from wireless clie nt s. Also,
you can block specific Eth er net tr af f ic fr om being forwarded by the access point.
6
IAPP – Enables roaming between multi-vendor access points.
Local Bridge Filter – Controls wireless-to-wireless communications between clients
through the access poin t. H ow e ver, it does not affect communications betwee n
wireless clients and the wired net w or k. (Default: Enabled)
• Disabled: Allows wireless-to-wireless communications between clients through
the access point.
• Enabled: Blocks wireless-to-wireless communications between clients through the
access point.
AP Management Filter – Controls managem e n t access to the access point from
wireless clients. Management interfaces include the web, Telnet, or SNMP.
(Default: Disabled)
• Disabled: Allows managem ent access from wireless cli ents.
• Enabled: Blocks management access from wireless cli ents.
6-17
Page 70

System Configuration
6
Ethernet Type Filter – Controls checks on the Eth er net ty pe of all incoming and
outgoing Ethernet packets again st the protocol filtering table. (Default: Disabled)
• Disabled: Access point doe s no t filt er Eth ernet protocol types.
• Enabled: Access point filters Ethernet protocol types based on t he configuration
of protocol types in the filter ta bl e. If the st at us of a protocol is set to “ON,” the
protocol is filtered from the access point.
Note: Ethernet protocol types not listed in the filtering table are always forwarded by the
access point.
CLI Commands for Bridge Filtering – Use the filter local-bridge command from the
global configuration m ode to prevent wireless-to -wi r el ess communications through
the access point. Use the fil te r ap-manage command to restrict management
access from wireless cl i ents. To configure Ethernet protocol filte ring, use the filter
ethernet-type enable command to enable filter ing and the filter ethernet-type
protocol command to define the protocols that you want to filter. T o remove an entry
from the table, use the address filter delete command. To display the current
settings, use the show filters command from the Exec mode.
Enterprise AP(config)#filter local-bridge 7-73
Enterprise AP(config)#filter ap-manage 7-74
Enterprise AP(config)#filter ethernet-type enable 7-74
Enterprise AP(config)#filter ethernet-type protocol ARP 7-75
Enterprise AP(config)#exit
Enterprise AP#show filters
Protocol Filter Information
=========================================================
Local Bridge :ENABLED
AP Management :ENABLED
Ethernet Type Filter :ENABLED
Enabled Protocol Filters
--------------------------------------------------------Protocol: ARP ISO: 0x0806
=========================================================
Enterprise AP#
7-76
6-18
Page 71

Advanced Configuration
VLAN
The access point can employ VLAN tagging support to control access to network
resources and increase security. VLANs separate traffic passing between the
access point, associat ed cl ients, and the wired network. Ther e can be a VLAN
assigned to each associ at ed client, a default VLAN for each VAP (Virtual Access
Point) interface, and a management VLAN for the access point.
Note the following points about the access point’s VLAN supp or t:
• The management VLAN is for man ag in g t he ac cess point through remote
management tools, such as the web interface, SSH, SNMP, or Telnet. The access
point only accepts management traffic that is tagg ed wit h t he specified
management VLAN ID.
• All wireless clients associated to the access point are assigned to a VLAN. If IEEE
802.1X is being used to authenticate wireless clients, specific VLAN IDs can be
configured on the RADI US server to be assigned to eac h cl ient . If a cl i ent is not
assigned to a specific VLAN or if 802.1X is not used, the client is assigned to the
default VLAN for the VAP interfa ce wi t h whi ch it is associated. The access po i nt
only allows traffic tagged with assigned VLAN IDs or default VLAN IDs to access
clients associated on ea ch VAP interface.
• When VLAN support is enabled on th e ac cess point, traffic passed to th e w ired
network is tagged with the appropriate VLAN ID, either an assigned client VLAN
ID, default VLAN ID, or the management VLAN ID. Traffic receiv ed from the wired
network must also be tagged with one of these known VLAN IDs. Received traffic
that has an unknown VLAN ID or no VLAN t ag is dropped.
• When VLAN support is disabled, th e access point does not tag traff i c passed to
the wired network and ignores the VLAN tags on any rece iv ed frames.
Note: Before enabling VLAN tagging on the access point, be sure to configure the
attached network switch port to support tagged VLAN frames from the access
point’s management VLAN ID, default VLAN IDs, and other client VLAN IDs.
Otherwise, connectivity to the access point will be lost when you enable the VLAN
feature.
6
Using IEEE 802.1X and a cen t ral RA DI U S server, up to 64 VLAN IDs can be
mapped to specific wirel ess clients, allowing users to remai n w ith in th e sam e VLAN
as they move around a campus site. This feature can also be used to control access
to network resources f rom clients, thereby improving security.
A VLAN ID (1-4094) can be ass i gned to a client after successful IEEE 802.1X
authentication. The client VLAN IDs must be configured on t he RA DIUS server for
each user authorized to access the network. If a client does not have a configured
VLAN ID on the RADIUS server, the access point assigns the client to the
configured default VLAN I D fo r the VAP interface.
Note: When using IEEE 802.1X to dynamically assign VLAN IDs, the access point must
have 802.1X authentication enabled and a RADIUS server configured. Wireless
clients must also support 802.1X client software.
6-19
Page 72

System Configuration
6
When setting up VLAN IDs for each user on the RADIUS server, be sure to use the
RADIUS attributes an d values as indicated in the fol low i ng tab le .
Number RADIUS Attribute Value
64 Tunnel-Type VLAN (13)
65 Tunnel-Medium-Type 802
81 Tunnel-Private-Group-ID VLANID
VLAN IDs on the RADIUS ser ver can be entered as hexadeci m al digi t s or a stri ng
(see “radius-server vlan-format” on page 7-63).
Note: The specific configuration of RADIUS server software is beyond the scope of this
guide. Refer to the documentation provided with the RADIUS server software.
(1 to 4094 as hexadecimal or string)
Management Native VLAN I D – The VLAN ID that traffic must have to be able to
manage the access point . (Range 1-4094; Default: 1 )
System VLAN status (forces AP reboot) – Enab l es or disables VLAN tagging
support on the access poi nt . Ch anging this parameter automatically reboots the
access point. (Default : Disable)
6-20
Page 73

Advanced Configuration
WDS Settings
Each access point radio inte rface can be configured to oper at e i n a br i dge or
repeater mode, which al low s i t to fo rward traffic directly to other acce ss point units.
To set up br i dge links between access poi nt units, you must configure the W Irel es s
Distribution System (WDS) forwarding table by specifying the wireless MAC address
of all units to which you want to forw ar d tr affic. Up t o si x W D S br i dge or r epeater
links can be specified fo r ea ch unit in the wireless bridge ne twork.
The Spanning Tree Protocol (STP) can be used to detect and disable network loops,
and to provide backup links between bridges. This allows a wireless bridge to
interact with other bridgi ng devices (that is, an STP-com pliant switch, bridge or
router) in your network to ensure that only one route exists between any two stations
on the network, and provi de b ac kup links which automatic al ly take o ver w hen a
primary link goes down.
6
WDS Bridge – Up to six WDS bridg e or rep eater links (MAC addresses ) pe r r adio
interface can be specified for each unit in the wireless bridge network. One unit only
must be configured as the “root br id ge” in the wireless network. The root bridge is
the unit connected to the main core of the wired LAN. Other bridges need to specify
one “Parent” link to the root br id ge or to a bridge connected to th e ro ot bridge. The
other five WDS links are avai labl e as “Child” links to other bridg es.
• Bridge Role – Each radio interface can be s et to op er at e in one of the following
four modes: (Default: AP)
• AP (Access Point): Operates as an access point for wireless clients, providing
connectivity to a wired LAN.
6-21
Page 74

System Configuration
6
• Bridge: Operates as a bridge to other access points. The “Parent” link to the root
bridge must be configur ed. Up to five other ”Child” links ar e available to other
bridges.
• R ep eater: Operates as a wireless repeater, extending th e range for remote
wireless clients and connecting them to the root bridge. The “Parent” link to the
root bridge must be conf ig ur ed. In th is mo de, traffic is not forwarded to the
Ethernet port from the radio interf ace.
• Root Bridge: Operates as the root bridge in the wireless bridge network. Up to
six ”Child” links are avai labl e to ot her br id ges in the network.
• Bridge Parent – The physical layer address of the root bridge unit or the bridge unit
connected to the root bridge. (12 hexadecimal digits in the form
“xx-xx-xx-xx-xx-xx”)
• Bridge Child – The physical layer address of other bridge units for which this unit
serves as the bridge par ent or the roo t bridge. Note that the first entry under the
list of child nodes is reserved for the root bridge, and can only be configured if the
role is set to “Root Bridge.” (12 hexadecimal digits in the form “xx-xx-xx-xx-xx-xx”)
• Bridge Link Timer – Sets th e m ax imum time the bridge waits to recei ve a link
message from the parent br id ge. (Range: 0 -100; Default: 0, tha t is disabled)
Child bridges periodically send requests for link information from the parent bridge.
The Parent bridge responds with the information and checks that it was received
by the child bridge. The message includes link information on the connection path
to the root bridge and conf irm s t hat the l in k is valid. If a link is detected as down ,
the bridge restarts the association process to try and recover the link.
6-22
Page 75

Advanced Configuration
6
Spanning Tree Protocol – STP uses a distributed algorithm to select a bridging
device (STP-compliant sw i t ch , br idge or router) that serves as the root of the
spanning tree network. It se l ects a roo t po rt on each bridging device (except for the
root device) which incurs the lowest path cost when forwarding a packet from that
device to the root device. Then it selects a designated bridging device from each
LAN which incurs the lowest path cost when forwarding a packet from that LAN to
the root device. All ports connec te d to designated bridging devic es are assigned as
6-23
Page 76

System Configuration
6
designated ports. After determining the lowest cost spanning tree, it enables all root
ports and designated ports, an d di sables all other ports. Network pack ets ar e
therefor e only forwarded between root ports and designated ports, eli m i nating any
possible network loops.
Once a stable network topol ogy has been established, all brid ges listen for Hello
BPDUs (Bridge Protocol Data Units) transmitted from the root bridge. If a bridge
does not get a Hello BPDU after a pre def i ne d in t erv al (M aximum Age), the bridge
assumes that the link to th e ro ot bridge is down. This bridge will the n i ni tia te
negotiations with othe r bri dges to reconfigure the network to reestablish a valid
network to pology.
• Bridge – Enables/disables STP on the wireless bridge or repeater.
(Default: Disabled)
• Bridge Priority – Used in selecting the root device, root port, and designated port.
The device with the highest priority becomes the STP root device. However, if all
devices have the same priority, the device with the lowest MAC address will then
become the root devic e. (Not e tha t low er numeric values indic at e higher priority.)
• R an ge: 0-65535
• D ef au l t: 32768
• Bridge Max Age – The maximum time (in seconds) a device can wait without
receiving a configurati on m essage before attempt ing t o re configure. All device
ports (except for design at ed ports) should receive configuration messag es at
regular intervals. Any port tha t ages out STP i nf or m ati on ( pr ovi d ed i n th e last
configuration message) becomes the designated port for the attached LAN. If it is
a root port, a new root port is se le ct ed from among the device por t s at ta ch ed t o
the network. (Range: 6-40 seconds)
• D ef au l t: 20
• M i nim um: The higher of 6 or [2 x (Hello Tim e + 1) ] .
• M aximum: The lower of 40 or [2 x (Fo rw ard D el ay - 1)]
• Bridge Hello Time – Interval (in seconds) at which the r oot device transmits a
configuration message. (Range: 1-10 seconds)
• D ef au l t: 2
• Minimum: 1
• M aximum: The lower of 10 or [(Max . Message Age / 2) -1]
• Bridge Forwarding Delay – The maximum time (in seconds) this device waits
before changing states ( i.e. , di sca rding to learning to forwarding). This delay is
required because every device must receive information about topology changes
before it starts to forward frames. In addition, each port needs time to listen for
conflicting informa tion tha t wo ul d m ake it return to a discarding st at e; ot herwise,
temporary data loops might result. (Range: 4-30 seconds)
• D ef au l t: 15
• M i nimum: The higher of 4 or [(Max. M essage Age / 2) + 1]
• Maximum: 30
• Link Pa th Cost – This parameter is used by the STP to determine the best path
6-24
Page 77

Advanced Configuration
between devices. Therefore, lower values should be assigned to ports attached to
faster media, and higher values assigned to ports w ith slo w er m edi a. (Path cost
takes precedence over port priority.)
• R an ge: 1-65535
• D efault: Ethernet interface: 19 ; Wire l ess in te rface: 40
• Link Port Priority – Defines the priority used for this port in the Spanning Tree
Protocol. If the path cost for all ports on a switch are the same, the port with the
highest priority (i.e., low est value) will be configured as an act iv e l ink i n th e
spanning tree. This makes a port with higher priority less likely to be blocked if the
Spanning Tree Protocol is detecting network loops. Where more than one port is
assigned the highest pri or ity , the port with lowest numeric ident i fie r w ill be
enabled.
• D ef au l t: 128
• Range: 0-240, in steps of 16
CLI Commands for WDS Settings – To set the role of th e ac cess point radio
interface, use the bridge role command from the CLI wireless interface
configuration mode. If th e ro le of the rad io in terf ac e i s set t o “Br idge” or “Repeater,”
the MAC address of the paren t no de must also be configure d us in g t he bridge-link
parent command. If the role is set to anything other than “Access Point,” then you
should also configure th e M A C addresses of the child nod es using the bridge-link
child command. You can also use the bridge-link link-timer command to adjust the
interval at which a node will wait f or a spa nning-tre e message from i t’ s p are nt before
trying to recover. To view t he current bridge link settings, use the show bridge link
command.
6
Enterprise AP(if-wireless a)#bridge role bridge 6-96
Enterprise AP(if-wireless a)#bridge-link child 2
00-08-3e-84-bc-6d 6-98
Enterprise AP(if-wireless a)#bridge-link child 3
00-08-3e-85-13-f2
Enterprise AP(if-wireless a)#bridge-link child 4
00-08-3e-84-79-31
Enterprise AP(if-wireless a)#bridge-link parent
00-08-2d-69-3a-51 6-97
Enterprise AP(if-wireless a)#exit
Enterprise AP#show bridge link wireless a 6-101
Interface Wireless A WDS Information
====================================
AP Role: Bridge
Parent: 00-08-2d-69-3a-51
Child:
Child 2: 00-08-3e-84-bc-6d
Child 3: 00-08-3e-85-13-f2
Child 4: 00-08-3e-84-79-31
Child 5: 00-00-00-00-00-00
Child 6: 00-00-00-00-00-00
STAs:
No WDS Stations.
Enterprise AP#
6-25
Page 78

System Configuration
6
CLI Commands for STP Settings – If the role of a radio interface is set to Repeater,
Bridge or Root Bridge, STP can be en abl ed on the access point to maintain a va lid
network topology. To globally enable STP, use th e br id ge st p enable command
from the CLI configuration mo de. Then configure the other glo bal STP parameters
for the bridge. The path cost and priority for each bridge link can be set using the
bridge-link path-cost and bridge-link port-priority comma nd from the Wireless
Interface configuration mode. The path cost and prio rit y can also be set for the
Ethernet port from the Ether net I nt er fa ce c onf i gur at ion mode. To view the current
STP settings, use the show bridge stp command.
Enterprise AP(config)#bridge stp enable 6-104
Enterprise AP(config)#bridge stp forwarding-delay 2500 6-105
Enterprise AP(config)#bridge stp hello-time 500 6-106
Enterprise AP(config)#bridge stp max-age 4000 6-107
Enterprise AP(config)#bridge stp priority 40000 6-108
Enterprise AP(config)#interface wireless a
Enterprise AP(if-wireless a)#bridge-link path-cost 2 40 6-109
Enterprise AP(if-wireless a)#bridge-link port-priority 2 64 6-110
Enterprise AP(if-wireless a)#exit
Enterprise AP#show bridge stp 6-111
Bridge MAC : 00:30:F1:F0:9A:9C
Status : Disabled
priority : 32768
desiginated-root : priority = 0, MAC = 00:00:00:00:00:00
root-path-cost : 0
root-Port-no : 0
Hold Time : 0 Seconds
Hello Time : 0 Seconds
Maximum Age : 0 Seconds
Forward Delay : 0 Seconds
bridge Hello Time : 2 Seconds
bridge Maximum Age : 20 Seconds
bridge Forward Delay : 5 Seconds
time-since-top-change: 3168 Seconds
topology-change-count: 0
Enterprise AP#
6-26
Page 79

Advanced Configuration
AP Management
The Web, Telnet, and SNMP management interfaces are enabled and open to all IP
addresses by default. To provide more security for management access to the
access point, specific in te rfaces can be disabled and m anagement restricted to a
single IP address or a limi ted ra nge of IP addresses.
Once you specify an IP ad dress or range of addresses, access to management
interfaces is restricted to the specified addresses. If anyone tries to access a
management interface from an unauthorized address, the access point will reject the
connection.
6
UI Manageme nt – Enables or disables management access through Telnet, the Web
(HTTP), or SNMP interfaces. (Default: Enabled)
Note: Secure Web (HTTPS) connections are not affected by the UI Management or IP
Management settings.
IP Management – R est r ic ts management access to Telnet, Web, and SNMP
interfaces to specified IP addresses. (Default: Any IP)
• Any IP: Indicates that any IP address is allowed management access.
• Single IP: Specifies a single IP address that is allowed management access.
• Multiple IP: Specifies an address range as defined by the entered IP address and
subnet mask. For exam pl e, IP address 192.168.1.6 and subnet mask
255.255.255.0, defin es al l IP addr esses from 192.168.1.1 to 192.168.1.254.
6-27
Page 80

System Configuration
6
CLI Commands for AP Management features.
Enterprise AP(config)#apmgmtip multiple 192.168.1.50 255.255.255.0 7-21
Enterprise AP(config)#apmgmtui SNMP enable 7-22
Enterprise AP(config)#ip http server
Enterprise AP(config)#ip http port 769 7-17
Enterprise AP(config)#ip https server 7-18
Enterprise AP(config)#ip https port 1234 7-18
Administration
Changing the Password
Management acces s t o th e web and CLI interface on the ac cess point is controlled
through a single user na m e and password. You can also gain additional access
security by using contro l fi lter s ( see “Filter Control” on page 6-17) .
To protect access to the management interface , you need to confi gure an
Administ r ator’s user name and password as soon as possible. If the user name and
password are not configur ed, th en anyone having access to th e access point may
be able to compromise access point and network security. Once a new Administrator
has been configured, you can delete the default “admin” user name from the system.
Note: Pressing the Reset button on the back of the access point for more than five
seconds resets the user name and password to the factory defaults. For this
reason, we recommend that you protect the access point from physical access by
unauthorized persons.
7-18
Username – The name of the user. The default name is “admin.” (Length: 3-16
characters, case sensitive)
New Password – The password for managem ent access. (Length: 3-16 cha ra ct er s,
case sensitive)
Confirm New Password – Enter the password again for verification.
6-28
Page 81

Advanced Configuration
CLI Commands for the Ad m in istrat or’s User Name and Pa ssword – Use the
username and password com m ands from the CLI configur at io n m ode.
Enterprise AP(config)#username bob 7-15
Enterprise AP(config)#password admin 7-15
Enterprise AP#
Upgrading Firmware
You can upgrade new access point software from a local file on t he management
workstation, or from an FTP or TFTP server. New software may be provided
periodically from your dist ributor.
After upgrading new software, you must reboot the access point to implement the
new code. Until a reboot occu rs , the ac cess point will continue to run the software it
was using before the upgrade started. Also note that new software that is
incompatible with the current configuration automatically restores the access point to
the factory default settin gs when first activated after a reboot.
6
6-29
Page 82

System Configuration
6
Before upgrading new software, verify that the access point is connected to the
network and has been configured with a com patible IP ad dress and subnet mask.
If you need to download from an F TP or TFTP server, take the following additional
steps:
• Obtain the IP address of the FTP or TFTP server where the access point software
is stored.
• If upgrading from an FTP server, be sure that you have an account configured on
the server with a user name and password.
6-30
Page 83

Advanced Configuration
• If VLANs are configured on the acces s point, determine the VLAN ID w ith wh ich
the FTP or TFTP server is asso ciat ed, and then configure the management
station, or the network port to which it is attached, with the same VLAN ID. If you
are managing the access point from a wireless client, the VLAN ID for the wireless
client must be configured on a RADIUS server.
Current version – Ver si on number of runtime code .
Firmware Upgrade Local – D ownloads an operation code image file from the web
managemen t station to the access point using HTTP. Use the Browse button to
locate the image file locall y on the management station an d cl ic k Start Upgrade to
proceed.
• New firmware file: Specifies the na m e of th e code file on the server. The new
firmware file name should no t co nt ai n sl as hes (\ or /), the leading letter of the file
name should not be a peri od ( .), and the maximum length for file names is 32
characters for files on the access point. (Valid characters: A-Z, a-z, 0-9, “.”, “-”, “_”)
Firmware Upgrade Remote – Downloads an operat i on code image file from a
specified remote FTP or TFTP server. After filling in the following fields, click Start
Upgrade to proceed.
• New firmware file: Specifies the na m e of th e code file on the server.
firmware file name should not contain slashes (\ or /),
name should not be a peri od ( .), and the maximum length for file names on the
FTP/TFTP server is 255 characters or 32 characters for files on the access point.
(Valid characters: A -Z, a-z, 0-9, “. ”, “-”, “_”)
• IP Address: IP address or host name of FTP or TFTP server.
• Username: The user ID used for login on an FTP server.
• Password: The password used fo r login on an FTP server.
Restore Fa ctory Settings – Click the Restore button to reset the configuration
settings for the access point to the factory defaults and reboot the system. Note that
all user configured information will be lost. You will have to re-enter the default user
name (admin) to re-gain management access to this device.
Reboot Access Point – Click the Reset button to reboot the system.
Note: If you have upgraded system software, then you must reboot the access point to
implement the new operation code. New software that is incompatible with the
current configuration automatically restores the access point to default values
when first activated after a reboot.
the leading letter of the file
The new
6
6-31
Page 84

System Configuration
6
CLI Commands for Downloading Software from a TFTP Server – Use the copy tftp
file command from the Exec mode and then specify the file type , na m e, and IP
address of the TFTP server. When the download is complete, the dir command can
be used to check that the ne w fil e is pre sent in the access point file system. To run
the new software, use the reset boar d command to reboot the ac cess point.
Enterprise AP#copy tftp file 7-56
1. Application image
2. Config file
3. Boot block image
Select the type of download<1,2,3>: [1]:1
TFTP Source file name:img.bin
TFTP Server IP:192.168.1.19
Enterprise AP#dir
File Name Type File Size
-------------------------- ---- ----------dflt-img.bin 2 1319939
img.bin 2 1629577
syscfg 5 17776
syscfg_bak 5 17776
262144 byte(s) available
Enterprise AP#reset board
Reboot system now? <y/n>: y
7-58
7-10
6-32
Page 85

Advanced Configuration
System Log
The access point can be co nf igur ed to send event and error mes sages to a System
Log Server. The system clock can also be synchronized with a time server, so that
all the messages sent to the Syslog server are stamped with the correct time and
date.
6
Enabling System Logging
The access point supports a logging process that can control error messages saved
to memory or sent to a Syslog server. The logged messages serve as a valuable tool
for isolating access poin t an d network problems.
System Log Setup – Enab le s t he logging of error messages . (D ef au lt: D isable)
Server (1-4) – Enables the sending of log messages to a Sy sl og ser ver host. Up to
four Syslog servers ar e supported on the access po i nt . (D ef ault: Disable)
Server Name/IP – The IP address or name of a Syslog serv er. (Default: 0.0.0. 0)
UDP Port – The UDP port used by a Syslog ser ver. (Range: 514 or 11024-65535;
Default: 514)
Logging Console – Enables the logging of error messages to the console.
(Default: Disable)
6-33
Page 86

System Configuration
6
Logging Level – Sets the minimum severity level for event logging.
(Default: Informational)
The system allows you to lim i t the messages that are logge d by specifying a
minimum severity level . The following table li sts the erro r me ssage levels from the
most severe (Emergency) to least severe (Debug). The message levels that are
logged include the speci fied minimum level up to the Emerg ency level.
Error Level Description
Emergency System unusable
Alerts Immediate action needed
Critical Critical conditions (e.g., memory allocation, or free memory error - resource
Error Error conditions (e.g., invalid input, default used)
Warning Warning conditions (e.g., return false, unexpected return)
Notice Normal but significant condition, such as cold start
Informational Informational messages only
Debug Debugging messages
Note: The access point error log can be viewed using the Event Logs window in the
Status section (page 6-90). The Event Logs window displays the last 128
messages logged in chronological order, from the newest to the oldest. Log
messages saved in the access point’s memory are erased when the device is
rebooted.
exhausted)
Logging Facility Type – Sets the facility type for remote logging of syslog messages.
The command specifies the facility type tag sent in syslog messages. (See RFC
3164.) This type has no effect on th e ki nd o f messages reported by the sw i t ch.
However, it may be used by the syslog serv er to sor t m es sages or to store
messages in the corresponding database. (Range : 16 -2 3; Def aul t : 16)
6-34
Page 87

Advanced Configuration
CLI Commands for System Logging – To enable logging on the access point, use
the logging on comm and from the global configu ra tion mode. The logging level
command sets the minimum l ev el of message to log. Use the logging co nsole
command to enable logging to the console. Use the logging host command to
specify up to four Syslog servers. The CLI also allows the logging facility-type
command to set the facility-type number to use on the Syslog server. To view the
current logging settings, use the show logging command.
Enterprise AP(config)#logging on 7-29
Enterprise AP(config)#logging level alert 7-30
Enterprise AP(config)#logging console 7-30
Enterprise AP(config)#logging host 1 IP 10.1.0.3 514 7-29
Enterprise AP(config)#logging host 1 Port 514 7-29
Enterprise AP(config)#logging facility-type 19 7-31
Enterprise AP(config)#exit
Enterprise AP#show logging
Logging Information
============================================
Syslog State : Enabled
Logging Console State : Enabled
Logging Level : Alert
Logging Facility Type : 19
Servers
1: 10.1.0.3, UDP Port: 514, State: Enabled
2: 0.0.0.0, UDP Port: 514, State: Disabled
3: 0.0.0.0, UDP Port: 514, State: Disabled
4: 0.0.0.0, UDP Port: 514, State: Disabled
=============================================
Enterprise AP#
7-32
6
Configuring SNTP
Simple Network Time Protocol (SNTP) allows the access point to set its internal
clock based on periodic updates from a time server (SNTP or NTP). Maintaining an
accurate time on the access point enables the sys te m lo g to rec or d m eaningful
dates and times for event entries. If the clock is not set, the access point will only
record the time from the fac tory default set at the last bootup.
The access point acts as an SNTP client, periodically sending time synchronization
requests to specific time s er ver s. You can configure up to two time server IP
addresses. The access point will attempt to poll each server in the configured
sequence.
SNTP Server – Configure s t he ac cess point to operate as an SNTP client. When
enabled, at least one time ser ver IP address must be sp ecif i ed.
• Primary Server: The IP address of an SNTP or N TP t ime ser ver that the access
point attempts to poll for a time update.
• Secondary Server: The IP address of a secondary SNTP or NTP time server. The
access point first attempts to update the time from the primary server; if this fails
it attempts an update fro m the sec ondary server.
6-35
Page 88

System Configuration
6
Note: The access point also allows you to disable SNTP and set the system clock
manually.
Set Time Zone – SNTP uses Coordinated Universal Time (or UTC, formerly
Greenwich Mean Time, or GMT) base d on the time at the Earth’s prime merid ia n,
zero degrees longitude. To display a time corresponding to your local time, you must
indicate the number of hour s your time zone is located b ef or e (e ast ) or after (west)
UTC.
Enable Daylight Saving – The access point provides a wa y t o aut om atically adjust
the system clock for Dayl i ght Savings Time changes. To use this feature you must
define the month and date to b egi n and to end the change from standard time.
During this period the sys t em cl ock is set back by one hour.
CLI Commands for SNTP – To enable SNTP support on the access point, from the
global configuration mode specify SNTP server IP addresses using the sntp-server
ip command, then use the sntp-server enable command to enable the service. Use
the sntp-server timezone command to set the time zone for your location, and th e
sntp-server daylight-saving comma nd t o set daylight savings. To view the current
SNTP settings, use the show snt p co mmand.
Enterprise AP(config)#sntp-server ip 1 10.1.0.19 7-34
Enterprise AP(config)#sntp-server enable 7-34
Enterprise AP(config)#sntp-server timezone +8 7-36
Enterprise AP(config)#sntp-server daylight-saving 7-36
Enter Daylight saving from which month<1-12>: 3
and which day<1-31>: 31
Enter Daylight saving end to which month<1-12>: 10
and which day<1-31>: 31
Enterprise AP(config)#exit
Enterprise AP#show sntp
SNTP Information
=========================================================
Service State : Enabled
SNTP (server 1) IP : 10.1.10.19
SNTP (server 2) IP : 192.43.244.18
Current Time : 19 : 35, Oct 10th, 2003
Time Zone : +8 (TAIPEI, BEIJING)
Daylight Saving : Enabled, from Mar, 31st to Oct, 31st
=========================================================
Enterprise AP#
7-37
6-36
Page 89

SNMP
CLI Commands for the Sy st em C lock – The following example shows how to
manually set the system time when SNTP server support is disabled on the access
point.
Enterprise AP(config)#no sntp-server enable 7-34
Enterprise AP(config)#sntp-server date-time 7-35
Enter Year<1970-2100>: 2003
Enter Month<1-12>: 10
Enter Day<1-31>: 10
Enter Hour<0-23>: 18
Enter Min<0-59>: 35
Enterprise AP(config)#
RSSI
The RSSI page displays the ambi en t no i se flo or fo r bo th rad ios A and G. These
values only apply to exter nal used antennas. The disp la yed values are
non-configurable.
6
dBm – Decibel referenced to milliwatts.
SNMP
Simple Net w ork Management Protocol ( SN MP) is a communic ation protocol
designed specifically f or managing devices on a net work. Equipment commonl y
managed with SNMP in cludes switches, routers and host computers. SNMP is
typically used to configure these devices for proper operation in a network
environment, as well as to monitor them to evaluate performance or detect potential
problems.
Managed devices sup por t in g SNM P contain software, which runs local l y on th e
device and is referred to as an agent. A defined set of variables, known as managed
objects, is maintained by the SNM P agent and used to manage the device. These
objects are defined in a Management Information Base (M I B) th at pr ovi de s a
standard presentation of the information controlled by the agent. SNMP defines both
the format of the MIB specifications and the protocol used to access this information
over the network.
6-37
Page 90

System Configuration
6
The access point includes an onboard agent that supports SNMP versions 1, 2c,
and 3 clients. This agent continuously monitors the status of the acc ess point, as
well as the traffic passing to and from wirel es s cl i ents. A ne twork management
station can access this inform at i on using SNMP manageme nt softw ar e th at is
compliant with MIB II. To implement SNMP management, the access point must first
have an IP address and subnet mask, configured ei t her m anually or dynamically.
Access to the onboard agent using SNMP v1 and v2c is controlled by community
strings. To communicate with the access point, the management station must first
submit a valid communi ty st ring for authentication.
Access to th e acces s poi nt us ing SNMP v3 pr ovid es ad diti ona l sec urit y fea ture s that
cover message integr i ty, authentication, and en cryption; as well as contro lli ng
notifications that are sent to specified user targets.
Configuring SNMP and Trap Message Parameters
The access point SNMP agent must be enabled to funct ion (for versions 1, 2c, and
3 clients). Management acc ess using SNMP v1 and v2c als o re quires community
strings to be configure d fo r au th entication. Trap notifications can be enabled and
sent to up to four management stations.
6-38
Page 91

SNMP
SNMP – Enables or disable s SN M P management access and also enables the
access point to send SNM P traps (n ot ifications). (Default: Disable )
Location – A text strin g t hat describes the system location. (Maximum lengt h: 255
characters)
Contact – A text string that describe s t he system contact. (Maximum l ength: 255
characters)
Community Name (Read Only) – Defines the SNM P community access stri ng t hat
has read-only access. A ut hor i ze d management stations are onl y able to retrieve
MIB objects. (Maximum len gt h: 23 characters, case sensitive; Default: public)
Community Name (Read/Write) – Defines the SNMP community access string that
has read/write access . Au th or iz ed ma nagement stations are able to bot h r et rieve
and modify MIB objects. (Max imum length: 23 characters , case sensitive;
Default: private)
Trap Destination (1 to 4) – Enables recipients (up to four) of SNMP notificat ions.
• Trap Destination IP Address – Specifies the recipient of SNMP notifications. Enter
the IP address or the host name. (Host Name: 1 to 63 characters, case sensitive)
• Trap Destination Community Name – The community string sent with the
notification operation. (Maximum length: 23 chara ct er s, case sensitive;
Default: public)
Engine ID – Sets the engine identifier for the S N M Pv3 agent that resides on the
access point. This engine protects against message replay, delay, and redirection.
The engine ID is also used in combination with user passwords to generate the
security keys for authen tic at ing and encrypting SNMPv3 pack ets. A def au l t en gine
ID is automatically generated that is unique to the acc ess point. (Range: 10 to 64
hexadecimal char acters)
Note: If the local engine ID is deleted or changed, all SNMP users will be cleared. All
existing users will need to be re-configured. If you want to change the default
engine ID, change it first before configuring other SNMP v3 parameters.
6
6-39
Page 92

System Configuration
6
Trap Configuration – Allows selection of specific SNMP notifications to send. The
following items are avail abl e:
• sysSystemUp - The access point is up and running.
• sysSystemDown - The acces s poi nt is about to shutdown and reboot.
• sysRadiusServerChange d - Th e access point has changed fr om th e pr im ary
RADIUS server to the secondary, or from the sec on dary to the primary.
• sysConfigFileVersionChanged - The access point’s confi guration file has been
changed.
• dot11StationAssociation - A client station has successfully associated with the
access point.
• dot11StationReAssociation - A client station has successfully re-associated with
the access point.
• dot11StationAuthentication - A client station has been successfully authenticated.
• dot11StationRequestFa il - A client station has failed asso ciat i on, re -a ssociation,
or authentication.
• dot11InterfaceBFail - The 802.11b interface has failed.
• dot11InterfaceAGFail - The 802 .1 1a or 802.11g interface has failed .
• dot1xMacAddrAuthSucce ss - A clie nt sta t ion has successfully authen ticated its
MAC address with the RA D IU S ser ver.
6-40
Page 93

SNMP
• dot1xMacAddrAuthFail - A client stat i on has failed MAC address authentication
with the RADIUS server.
• dot1xAuthNotInitiated - A client st at ion di d not initiate 802.1X authentication.
• dot1xAuthSuccess - A 802.1X clie nt st at ion has been successfully auth enticated
by the RADIUS server.
• dot1xAuthFail - A 802.1X clie nt st at io n has failed RADIUS authentication.
• localMacAddrAuthSuccess - A client station has successfully authenticated its
MAC address with the loc al dat abase on the access point .
• localMacAddrAuthFail - A client station has failed authentication with the local
MAC address datab ase on t he access point.
• iappStationRoamedFrom - A client station has roamed from another access point
(identified by its IP addres s) .
• iappStationRoamedTo - A client station has roamed to anot her access point
(identified by its IP addres s) .
• iappContextDataSent - A client st at io n’s C ontext Data has been sent to another
access point with which th e st at ion has associated.
• sntpServerFail - The access po int ha s f ai led t o set t he t ime fr om t he co nf i gur ed
SNTP server.
• Enable All Traps - Click the butto n to ena bl e al l the available traps.
• Disable All Traps - Cl ick th e button to disable all the availabl e traps.
CLI Commands for SNMP and Trap Configuration – Use the snmp-server enab l e
server comman d fr om t he glo bal co nf ig ur at i on m ode to enable the SNMP age nt.
Use the snmp-s erver location and snmp-server contact commands to in di cate
the physical location of the access point and define a system contact. To set the
read-only and read/wr ite c om m unity names, use the snm p- ser ver community
command. Use the sn mp-server host command to define a trap receiver host and
the snmp-s er ver tr ap command to enable or disable specific traps.
6
Enterprise AP(config)#snmp-server enable server 7-42
Enterprise AP(config)#snmp-server community alpha rw 7-41
Enterprise AP(config)#snmp-server community beta ro
Enterprise AP(config)#snmp-server location WC-19
Enterprise AP(config)#snmp-server contact Paul 7-41
Enterprise AP(config)#snmp-server host 192.168.1.9 alpha 7-43
Enterprise AP(config)#snmp-server trap dot11StationAssociation 7-44
Enterprise AP(config)#
7-42
6-41
Page 94

System Configuration
6
To view the current SNMP settings, use the show snmp command.
Enterprise AP#show snmp 7-54
SNMP Information
==============================================
Service State : Enable
Community (ro) : *****
Community (rw) : *****
Location : WC-19
Contact : Paul
EngineId :80:00:07:e5:80:00:00:2e:62:00:00:00:18
EngineBoots:1
Trap Destinations:
1: 192.168.1.9, Community: *****, State: Enabled
2: 0.0.0.0, Community: *****, State: Disabled
3: 0.0.0.0, Community: *****, State: Disabled
4: 0.0.0.0, Community: *****, State: Disabled
dot11InterfaceAGFail Enabled dot11InterfaceBFail Enabled
dot11StationAssociation Enabled dot11StationAuthentication Enabled
dot11StationReAssociation Enabled dot11StationRequestFail Enabled
dot1xAuthFail Enabled dot1xAuthNotInitiated Enabled
dot1xAuthSuccess Enabled dot1xMacAddrAuthFail Enabled
dot1xMacAddrAuthSuccess Enabled iappContextDataSent Enabled
iappStationRoamedFrom Enabled iappStationRoamedTo Enabled
localMacAddrAuthFail Enabled localMacAddrAuthSuccess Enabled
pppLogonFail Enabled sntpServerFail Enabled
configFileVersionChanged Enabled radiusServerChanged Enabled
systemDown Enabled systemUp Enabled
=============================================
Enterprise AP#
Configuring SNMPv3 Users
The access point allows up to 10 SN M P v3 users to be configured . Ea ch us er mu st
be defined by a unique name, assi gned to one of three pre-defined security groups,
and configured with spe ci f ic aut hentication and encryp tion settings.
User – The SNMPv3 user name. (3 2 ch ar act ers maximum)
Group – The SNMPv3 group name. (Options: RO, RWAuth, or RWPriv; Default: RO)
• RO – Read-only access.
• RWAuth – Read/write acce ss wit h user authentication.
• RWPriv – Read/write access w ith both user authenticatio n an d dat a encryption.
Auth Type – The authentication type used for the SNMP user; eithe r MD 5 or no ne.
When MD5 is selected, ent er a password in the correspondi ng Passphrase field.
Priv Type – The data encryption type used for the SNMP user; either DES or none.
When DES is selected, en te r a ke y i n the corresponding Passphrase field.
6-42
Page 95

SNMP
Passphrase – The password or key associated with the authentication and privacy
settings. A minimum of eigh t plain text characters is require d.
Action – Click the Add button to add a new user to the list. Click the edit button to
change details of an existing user. Click the Del button to remove a user from the list.
Note: Users must be assigned to groups that have the same security levels. For
example, a user who has “Auth Type” and “Priv Type” configured to MD5 and
DES respectively (that it, uses both authentication and data encryption) must be
assigned to the RWPriv group. If this same user were instead assigned to the
read-only (RO) group, the user would not be able to access the database.
CLI Commands for Configuring SNMPv3 Users – Use the snmp-server engine-id
command to define the SNM P v3 engine before assigni ng users to groups. Use the
snmp-server user command to assign users to one of the three groups and set the
appropriate authenti ca tion and encryption types to be used. To vie w th e current
SNMP v3 engine ID, use the show snmp command. To view SNMP users and
group settings, use the sh ow snm p users or show snmp group-assignments
commands.
Enterprise AP(config)#snmp-server engine-id 1a:2b:3c:4d:00:ff 7-45
Enterprise AP(config)#snmp-server user 7-46
User Name<1-32> :chris
Group Name<1-32> :RWPriv
Authtype(md5,<cr>none):md5
Passphrase<8-32>:a good secret
Privacy(des,<cr>none) :des
Passphrase<8-32>:a very good secret
Enterprise AP(config)#exit
Enterprise AP#show snmp users
=============================================
UserName :chris
GroupName :RWPriv
AuthType :MD5
Passphrase:****************
PrivType :DES
Passphrase:****************
=============================================
Enterprise AP#show snmp group-assignments
7-51
7-51
6
GroupName :RWPriv
UserName :chris
Enterprise AP#
6-43
Page 96

System Configuration
6
Configuring SNMPv3 Trap Filters
SNMP v3 users can be configured to receive notification messages from the access
point. An SNMP Target ID is created that specifies the SNMP v3 us er, IP address,
and UDP port. A user-defi ned not i fic at io n filt er can be created so that specifi c
notifications can be prev ent ed from being sent to particular targets.
The access point allows up to 10 notification filters to be created. Each filter can be
defined by up to 20 MIB subtree ID entries.
To conf igure a new notification filter, click the New button. A new page opens to
configure the filter (see below). To edit an existing filter, select the radio button next
to the entry in the table and then click th e Edit button. To delete a filter, select the
radio button next to the entr y in t he tab le and t hen click the Delete button.
When you click on the New but t on in the SNMP Trap Filters page, a new page
opens where the filter parameters are configured. Define a filter name, subtree ID to
be filtered, and a mask if required. Select the filter type, include or exclude, from the
drop-down list. Click Appl y t o cr eat e the filter.
To add more subtree IDs to the filter, return to th e SNMP Trap Filters page and click
the Edit button. In the Edit page, click the New button to access the Add SNMP
Notification Subtree page and configure a new subtree ID to be f iltered.
6-44
Page 97

SNMP
Note: Only the New Filter page allows the Filter ID to be configured.
Filter ID – A user-defined name th at ident i fies th e fil t er. (Maximum lengt h: 32
characters)
Subtree OI D – Specifies MIB subtree to be filtered. The MIB subtree must be
defined in the form “.1.3.6 . 1” and al ways start with a “.”.
Subtree Mask – A hexadecimal value with each bit masking the corresponding ID in
the MIB subtree. A “1” in the mask indicates an exact match and a “0” indicates a
“wild card.” For example, a mask value of 0xFFBF provides a bit mask “1111 1111
1011 111 1.” If applied to the subtree “1.3.6.1.2.1.2.2.1.1.23,” the zero corresponds to
the 10th subtree ID. When th ere are more subtree IDs than bi ts in the mask, the
mask is padded with ones.
Filter Type – Indicates if the filter is to “include” or “exclude” the MIB subtree objects
from the filter. Note that MIB objects included in the filter are not sent to the receiving
target and objects excluded are sent. By default all traps are sent, so yo u can first
use an “include” filter entry f or all t rap obj ec ts. Then use “exclude” entries fo r t he
required trap objects to send t o t he target . N ot e th at th e fil t er ent ries are applied in
the sequence that they ar e d ef in ed.
6
6-45
Page 98

System Configuration
6
CLI Commands for Configuring SNMPv3 Trap Filters – To create a notification filter,
use the snmp-server fil te r co m m and from the CLI configurat i on m ode. Use the
command more than once with the same filter ID to bui l d a f ilter th at inc ludes or
excludes multiple MIB obj ec ts . To view the current SNMP filters, use the show
snmp filter comma nd f ro m th e CLI Exec mode.
Enterprise AP(config)#snmp-server filter trapfilter
include .1
Enterprise AP(config)#snmp-server filter trapfilter
exclude .1.3.6.1.2.1.2.2.1.1.23
Enterprise AP(config)#exit
Enterprise AP#show snmp filter
Filter: trapfilter
Type: include
Subtree: iso
Type: exclude
Subtree: iso.3.6.1.2.1.2.2.1.1.23
=============================
Enterprise AP#
7-49
7-52
Configuring SNMPv3 Targets
An SNMP v3 notification Target ID is specified by the SNMP v3 user, IP address,
and UDP port. A user-defi ned filter can also be assigned t o specific targets to limit
the notifications receive d t o specific MIB objects. (Note that th e filt er mu st firs t be
configured. see “Confi gur i ng SNMPv3 Trap Filters” on page 6- 44)
To conf igure a new notification rec eiver targ et , clic k th e New button. A new page
opens to configure the set tings (see below). To edit an existing target, select the
radio button next to the entry i n t he tab le and t hen click the Edit button. To delete
targets, select the radio button next to the entry in the table and then click the Delete
button.
When you click on the New or Edit button in the SNMP Targets page, a new page
opens where the target paramet er s ar e configured. Define the parameters and
select a filter, if required. Note that the SNM P v3 u ser name must first be define d
(see “Configuring SNMPv3 Users” on page 6-42). Click Apply.
6-46
Page 99

SNMP
Note: The Target ID cannot be changed in the Edit Target page. Only the New Target
page allows the Target ID to be configured.
Ta rget I D – A user-defined name that identifies a receiver of no tific ati ons. The
access point supports up to 10 target IDs. (Maximum leng th : 32 cha racters)
IP Address – Specifies the IP address of the receiving management station.
UDP Port – The UDP port that is used on the re ceiving management station for
notification messages .
SNMP User – The defined SNMP v3 user that is to receive notificati on m essages.
Assigned Filter – The name of a user - def i ned notification filter that is appli ed t o the
target.
6
CLI Commands for Configuring SNMPv3 Targets – To cr eat e a notification target,
use the snmp-server targets command from the CLI conf igur at ion mod e. To assign
a filter to a target, use the snmp-server filter-assignment command. To view the
current SNMP targets, use the show sn mp target command from t he C LI Exec
mode. To view filter assignment to targets, use th e show snmp filter-assignments
command.
6-47
Page 100

System Configuration
6
Enterprise AP(config)#snmp-server targets mytraps
192.168.1.33 chris
Enterprise AP(config)#snmp-server filter-assignment
mytraps trapfilter
Enterprise AP(config)#exit
Enterprise AP#show snmp target
Host ID : mytraps
User : chris
IP Address : 192.168.1.33
UDP Port : 162
=============================
Enterprise AP#show snmp filter-assignments
HostID FilterID
mytraps trapfilter
Enterprise AP#
7-48
7-50
7-52
7-53
Radio Interface
The IEEE 802.11a and 802.11g interfaces include configuration optio ns for radio
signal characteristic s and wireless security features. The configuration op tions are
nearly id entical, and are therefore both covered in this secti on of the manual.
The access point can operate in three modes, IEEE 802.11a only , 802.11b/g only, or
a mixed 802.11a/b/g mode. Also note that 802.11g is backward compatible w ith
802.11b. These interfaces are configured independently under the followi ng web
pages:
• Radio Interface A: 802.11a
• Radio Interface G: 802.11b/g
Each radio supports up to four virtual access point (VAP) interfaces numbered 0 to
3. Each VAP functions as a separate access point, and can be configured with its
own Service Set Identification (SSID) and security settings. However, most radio
signal parameters apply to all four VAP interfaces.
The VAPs function similar to a VLAN, with each VAP mapped to its own VLAN ID.
Traffic to specific VAPs can segregated based on user groups or applicati on t ra ffic.
Each VAP can have up to 64 wireless clients, whereby the cl ients associate with
these VAPs the same as they would with a physical access point.
Note: The radio channel settings for the access point are limited by local regulations,
which determine the number of channels that are available. Refer to “General
Specifications” on page C-1 for additional information on the maximum number
channels available.
6-48
 Loading...
Loading...