Page 1
VN/UN764:G"
46/Rqtv"321322Odru"-"6/Rqtv"Ikicdkv"
LgvUvtgco"N4"Ocpcigf"Uykvej"
"
"
TGX40302"
3;32233636"
Page 2
EQR[TKIJV"("VTCFGOCTMU"
Specifications are subject to change without notice. is a registered trademark of
TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks or
registered trademarks of their respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make any
derivative such as translation, transformation, or adaptation without permission from TP-LINK
TECHNOLOGIES CO., LTD. Copyright © 2015 TP-LINK TECHNOLOGIES CO., LTD. All rights
reserved.
http://www.tp-link.com
"
HEE"UVCVGOGPV"
This equipment has been tested and found to comply with the limits for a Class A digital device,
pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection
against harmful interference when the equipment is operated in a commercial environment. This
equipment generates, uses, and can radiate radio frequency energy and, if not installed and used
in accordance with the instruction manual, may cause harmful interference to radio
communications. Operation of this equipment in a residential area is likely to cause harmful
interference in which case the user will be required to correct the interference at his own expense.
This device complies with part 15 of the FCC Rules. Operation is subject to the following two
conditions:
1) This device may not cause harmful interference.
2) This device must accept any interference received, including interference that may cause
undesired operation.
Any changes or modifications not expressly approved by the party responsible for compliance
could void the user’s authority to operate the equipment.
EG"Octm"Yctpkpi"
"
This is a class A product. In a domestic environment, this product may cause radio interference, in
which case the user may be required to take adequate measures.
Продукт сертифіковано згідно с правилами системи УкрСЕПРО на відповідність вимогам
нормативних документів та вимогам, що передбачені чинними законодавчими актами
України.
I
Page 3
"
Kpfwuvt{"Ecpcfc"Uvcvgogpv"
CAN ICES-3 (A)/NMB-3(A)
Uchgv{"Kphqtocvkqp"
When product has power button, the power button is one of the way to shut off the product;
When there is no power button, the only way to completely shut off power is to disconnect the
product or the power adapter from the power source.
Don’t disassemble the product, or make repairs yourself. You run the risk of electric shock and
voiding the limited warranty. If you need service, please contact us.
Avoid water and wet locations.
安全諮詢及注意事項
請使用原裝電源供應器或只能按照本產品注明的電源類型使用本產品。
清潔本產品之前請先拔掉電源線。請勿使用液體、噴霧清潔劑或濕布進行清潔。
注意防潮,請勿將水或其他液體潑灑到本產品上。
插槽與開口供通風使用,以確保本產品的操作可靠並防止過熱,請勿堵塞或覆蓋開口。
請勿將本產品置放於靠近熱源的地方。除非有正常的通風,否則不可放在密閉位置中。
請不要私自打開機殼,不要嘗試自行維修本產品,請由授權的專業人士進行此項工作。
This product can be used in the following countries:
AT BG BY CA CZ DE DK EE
ES FI FR GB GR HU IE IT
LT LV MT NL NO PL PT RO
RU SE SG SK TR UA US
II III
Page 4
FGENCTCVKQP"QH"EQPHQTOKV["
Eqorcp{<"VR/NKPM"VGEJPQNQIKGU"EQ0."NVF0"
We declare under our own responsibility for the following equipment:
Product Description:"46/Rqtv"321322Odru"-"6/Rqtv"Ikicdkv"LgvUvtgco"N4"Ocpcigf"
Uykvej"
Model No.: VN/UN764:G
Trademark: VR/NKPM"
The above products satisfy all the technical regulations applicable to the product
within the scope of Council Directives:
Fktgevkxgu"4226132:1GE."42281;71GE."42331871GW"
The above product is in conformity with the following standards or other normative
documents:
GP"77244<"4232"-"CE<"4233" " ""
GP"83222/5/4<"4228"-"C3<"422;"-"C4<"422;" " "
GP"83222/5/5<"4235" "
GP"77246<"4232" " """"
GP"82;72/3<"4228"-"C33<"422;"-"C3<"4232"-"C34<"4233-C4<"4235"
Person is responsible for marking this declaration:
"
"
"
Date of Issue: 2015-11-04
"
"
CFF<"Dwknfkpi"46*hnqqtu"3.5.6.7+"cpf"4:*hnqqtu3/6+"Egpvtcn"Uekgpeg"cpf" "
Vgejpqnqi{"Rctm."Ujgppcp"Tf."Pcpujcp."Ujgp|jgp.Ejkpc"
Ygdukvg<"yyy0vr/nkpm0eqo"
Page 5
VGPVU"
EQP
Package Contents ..........................................................................................................................1
Chapter 1 About This Guide .........................................................................................................2
1.1 Intended Readers .........................................................................................................2
1.2 Conventions..................................................................................................................2
1.3 Overview of This Guide ................................................................................................2
Chapter 2 Introduction ..................................................................................................................7
2.1 Overview of the Switch .................................................................................................7
2.2 Appearance Description ...............................................................................................7
2.2.1 Front Panel ........................................................................................................7
2.2.2 Rear Panel.........................................................................................................8
Chapter 3 Login to the Switch....................................................................................................... 9
3.1 Login.............................................................................................................................9
3.2 Configuration ................................................................................................................9
Chapter 4 System ....................................................................................................................... 11
4.1 System Info................................................................................................................. 11
4.1.1 System Summary............................................................................................. 11
4.1.2 Device Description ...........................................................................................13
4.1.3 System Time ....................................................................................................13
4.1.4 Daylight Saving Time .......................................................................................14
4.1.5 System IP.........................................................................................................15
4.1.6 System IPv6.....................................................................................................17
4.2 User Management ......................................................................................................
25
4.2.1 User Table ........................................................................................................25
4.2.2 User Config ...................................................................................................... 25
4.3 System Tools ..............................................................................................................26
4.3.1 Config Restore ................................................................................................. 27
4.3.2 Config Backup..................................................................................................27
4.3.3 Firmware Upgrade ...........................................................................................28
4.3.4 System Reboot ................................................................................................28
4.3.5 System Reset...................................................................................................29
4.4 Access Security ..........................................................................................................29
4.4.1 Access Control.................................................................................................29
4.4.2 SSL Config....................................................................................................... 31
4.4.3 SSH Config ......................................................................................................32
Chapter 5 Switching....................................................................................................................39
5.1 Port .............................................................................................................................39
I
Page 6
5.1.1 Port Config.......................................................................................................39
5.1.2 Port Mirror........................................................................................................40
5.1.3 Port Security ....................................................................................................41
5.1.4 Port Isolation....................................................................................................43
5.1.5 Loopback Detection .........................................................................................44
5.2 LAG ............................................................................................................................45
5.2.1 LAG Table ........................................................................................................46
5.2.2 Static LAG ........................................................................................................ 47
5.2.3 LACP Config ....................................................................................................48
5.3 Traffic Monitor.............................................................................................................50
5.3.1 Traffic Summary...............................................................................................50
5.3.2 Traffic Statistics ................................................................................................51
5.4 MAC Address..............................................................................................................52
5.4.1 Address Table ..................................................................................................53
5.4.2 Static Address ..................................................................................................54
5.4.3 Dynamic Address .............................................................................................55
5.4.4 Filtering Address ..............................................................................................57
Chapter 6 VLAN..........................................................................................................................59
6.1 802.1Q VLAN..............................................................................................................60
6.1.1 VLAN Config ....................................................................................................61
6.1.2 Port Config.......................................................................................................
63
6.2 MAC VLAN .................................................................................................................65
6.2.1 MAC VLAN.......................................................................................................66
6.2.2 Port Enable ......................................................................................................67
6.3 Protocol VLAN ............................................................................................................67
6.3.1 Protocol VLAN .................................................................................................68
6.3.2 Protocol Template ............................................................................................69
6.3.3 Port Enable ......................................................................................................70
6.4 Application Example for 802.1Q VLAN .......................................................................70
6.5 Application Example for MAC VLAN...........................................................................72
6.6 Application Example for Protocol VLAN......................................................................73
6.7 VLAN VPN..................................................................................................................75
6.7.1 VPN Config ......................................................................................................76
6.7.2 VLAN Mapping.................................................................................................76
6.7.3 Port Enable ......................................................................................................77
6.8 Private VLAN ..............................................................................................................79
6.8.1 PVLAN Config..................................................................................................82
II
Page 7

6.8.2 Port Config.......................................................................................................83
6.9 GVRP .........................................................................................................................85
6.10 Application Example for Private VLAN........................................................................88
Chapter 7 Spanning Tree............................................................................................................91
7.1 STP Config .................................................................................................................95
7.1.1 STP Config.......................................................................................................95
7.1.2 STP Summary..................................................................................................97
7.2 Port Config..................................................................................................................98
7.3 MSTP Instance ...........................................................................................................99
7.3.1 Region Config ..................................................................................................99
7.3.2 Instance Config ..............................................................................................100
7.3.3 Instance Port Config.......................................................................................101
7.4 STP Security.............................................................................................................103
7.4.1 Port Protect.................................................................................................... 103
7.4.2 TC Protect......................................................................................................105
7.5 Application Example for STP Function .....................................................................106
Chapter 8 Ethernet OAM .......................................................................................................... 110
8.1 Basic Config ............................................................................................................. 113
8.1.1 Basic Config................................................................................................... 113
8.1.2 Discov
ery Info ................................................................................................ 115
8.2 Link Monitoring .........................................................................................................117
8.3 RFI............................................................................................................................11 8
8.4 Remote Loopback..................................................................................................... 119
8.5 Statistics ...................................................................................................................120
8.5.1 Statistics......................................................................................................... 120
8.5.2 Event Log.......................................................................................................121
8.6 DLDP ........................................................................................................................122
8.7 Application Example for DLDP..................................................................................125
Chapter 9 DHCP .......................................................................................................................128
9.1 DHCP Relay .............................................................................................................132
Chapter 10 Multicast................................................................................................................... 136
10.1 IGMP Snooping ........................................................................................................ 140
10.1.1 Snooping Config ............................................................................................141
10.1.2 VLAN Config ..................................................................................................142
10.1.3 Port Config .....................................................................................................143
10.1.4 IP-Range ........................................................................................................ 145
10.1.5 Multicast VLAN ..............................................................................................146
III
Page 8

10.1.6 Static Multicast IP...........................................................................................149
10.1.7 Packet Statistics.............................................................................................150
10.1.8 Querier Config................................................................................................151
10.1.9 IGMP Authentication ......................................................................................152
10.2 MLD Snooping..........................................................................................................153
10.2.1 Global Config .................................................................................................155
10.2.2 VLAN Config ..................................................................................................156
10.2.3 Filter Config....................................................................................................158
10.2.4 Port Config .....................................................................................................158
10.2.5 Static Multicast............................................................................................... 159
10.2.6 Querier Config................................................................................................160
10.2.7 Packet Statistics.............................................................................................161
10.3 Multicast Table ..........................................................................................................162
10.3.1 IPv4 Multicast Table .......................................................................................163
10.3.2 IPv6 Multicast Table .......................................................................................163
Chapter 11 QoS.......................................................................................................................... 165
11.1 DiffServ.....................................................................................................................168
11.1.1 Port Priority ....................................................................................................168
11.1.2 DSCP Priority.................................................................................................169
11.1.3 802.1P/CoS Mapping .....................................................................................
170
11.1.4 Schedule Mode ..............................................................................................171
11.2 Bandwidth Control ....................................................................................................172
11.2.1 Rate Limit.......................................................................................................172
11.2.2 Storm Control.................................................................................................173
11.3 Voice VLAN ..............................................................................................................175
11.3.1 Global Config .................................................................................................177
11.3.2 Port Config .....................................................................................................177
11.3.3 OUI Config ..................................................................................................... 179
Chapter 12 ACL..........................................................................................................................181
12.1 Time-Range..............................................................................................................181
12.1.1 Time-Range Summary ...................................................................................181
12.1.2 Time-Range Create........................................................................................ 182
12.1.3 Holiday Config................................................................................................183
12.2 ACL Config ...............................................................................................................183
12.2.1 ACL Summary................................................................................................183
12.2.2 ACL Create ....................................................................................................184
12.2.3 MAC ACL .......................................................................................................185
IV
Page 9

12.2.4 Standard-IP ACL ............................................................................................ 185
12.2.5 Extend-IP ACL ...............................................................................................186
12.2.6 Combined ACL...............................................................................................188
12.3 Policy Config.............................................................................................................189
12.3.1 Policy Summary .............................................................................................189
12.3.2 Policy Create..................................................................................................190
12.3.3 Action Create .................................................................................................190
12.4 Policy Binding ...........................................................................................................192
12.4.1 Binding Table .................................................................................................192
12.4.2 Port Binding ...................................................................................................192
12.4.3 VLAN Binding.................................................................................................193
12.5 Application Example for ACL ....................................................................................194
Chapter 13 Network Security......................................................................................................196
13.1 IP-MAC Binding ........................................................................................................196
13.1.1 Binding Table .................................................................................................196
13.1.2 Manual Binding ..............................................................................................197
13.1.3 ARP Scanning................................................................................................199
13.2 DHCP Snooping .......................................................................................................200
13.2.1
DHCP
Snooping............................................................................................. 204
13.2.2 Option 82 .......................................................................................................205
13.3 ARP Inspection.........................................................................................................206
13.3.1 ARP Detect ....................................................................................................209
13.3.2 ARP Defend ................................................................................................... 211
13.3.3 ARP Statistics ................................................................................................212
13.4 IP Source Guard.......................................................................................................212
13.5 DoS Defend ..............................................................................................................213
13.5.1 DoS Defend ...................................................................................................215
13.5.2 DoS Detect..................................................................................................... 216
13.6 802.1X ......................................................................................................................216
13.6.1 Global Config .................................................................................................220
13.6.2 Port Config .....................................................................................................222
13.7 AAA .......................................................................................................................... 223
13.7.1 Global Config .................................................................................................224
13.7.2 Privilege Elevation .........................................................................................225
13.7.3 RADIUS Server Config ..................................................................................225
13.7.4 TACACS+ Server Config................................................................................226
13.7.5 Authentication Server Group Config ..............................................................227
V
Page 10

13.7.6 Authentication Method List Config .................................................................228
13.7.7 Application Authentication List Config ............................................................ 229
13.7.8 802.1X Authentication Server Config .............................................................230
13.7.9 Default Settings..............................................................................................230
13.8 PPPoE Config...........................................................................................................231
Chapter 14 SNMP.......................................................................................................................234
14.1 SNMP Config............................................................................................................236
14.1.1 Global Config .................................................................................................236
14.1.2 SNMP View....................................................................................................237
14.1.3 SNMP Group..................................................................................................237
14.1.4 SNMP User ....................................................................................................239
14.1.5 SNMP Community..........................................................................................241
14.2 Notification................................................................................................................243
14.2.1 Notification Config ..........................................................................................243
14.2.2 Traps Config...................................................................................................244
14.3 RMON.......................................................................................................................247
14.3.1 History Control ...............................................................................................248
14.3.2 Event Config ..................................................................................................249
14.3.3 Alarm Config ..................................................................................................250
Chapte
r 15 LLDP........................................................................................................................252
15.1 Basic Config .............................................................................................................255
15.1.1 Global Config .................................................................................................256
15.1.2 Port Config .....................................................................................................257
15.2 Device Info................................................................................................................257
15.2.1 Local Info .......................................................................................................257
15.2.2 Neighbor Info .................................................................................................258
15.3 Device Statistics........................................................................................................260
Chapter 16 Cluster......................................................................................................................262
16.1 NDP..........................................................................................................................263
16.1.1 Neighbor Info .................................................................................................263
16.1.2 NDP Summary ...............................................................................................264
16.1.3 NDP Config ....................................................................................................266
16.2 NTDP........................................................................................................................ 267
16.2.1 Device Table ..................................................................................................267
16.2.2 NTDP Summary .............................................................................................269
16.2.3 NTDP Config .................................................................................................. 270
16.3 Cluster ......................................................................................................................271
VI VII
Page 11

16.3.1 Cluster Summary ...........................................................................................271
16.3.2 Cluster Config ................................................................................................274
16.3.3 Member Config ..............................................................................................276
16.3.4 Cluster Topology ............................................................................................277
Chapter 17 Maintenance ............................................................................................................280
17.1 System Monitor.........................................................................................................280
17.1.1 CPU Monitor ..................................................................................................280
17.1.2 Memory Monitor .............................................................................................281
17.2 Log............................................................................................................................281
17.2.1 Log Table .......................................................................................................282
17.2.2 Local Log .......................................................................................................283
17.2.3 Remote Log ...................................................................................................283
17.2.4 Backup Log ....................................................................................................284
17.3 Device Diagnostics ...................................................................................................285
17.4 Network Diagnostics.................................................................................................286
17.4.1 Ping................................................................................................................286
17.4.2 Tracert............................................................................................................ 287
Chapter 18 System Maintenance via FTP ..................................................................................288
Appendix A: Specifications .........................................................................................................291
Appendix B: Glossary
.................................................................................................................292
Page 12

I
Page 13
Rcemcig"Eqpvgpvu"
The following items should be found in your box:
One TL-SL5428E switch
One power cord
One console cable
Two mounting brackets and other fittings
Installation Guide
Resource CD for TL-SL5428E switch, including:
This User Guide
The CLI Reference Guide
SNMP Mibs
802.1X Client Software
Other Helpful Information
Pqvg<"
Make sure that the package contains the above items. If any of the listed items are damaged or
missing, please contact your distributor.
1
Page 14
Ejcrvgt"3" Cdqwv"Vjku"Iwkfg"
This User Guide contains information for setup and management of TL-SL5428E switch. Please
read this guide carefully before operation.
303" Kpvgpfgf"Tgcfgtu"
This Guide is intended for network managers familiar with IT concepts and network terminologies.
304" Eqpxgpvkqpu"
In this Guide the following conventions are used:
The switch or TL-SL5428E mentioned in this Guide stands for TL-SL5428E 24-Port
10/100Mbps + 4-Port Gigabit JetStream L2 Managed Switch without any explanation.
Ogpw"Pcog→Uwdogpw"Pcog→Vcd"rcig"indicates"the menu structure. U{uvgo→U{uvgo"
Kphq→U{uvgo"Uwooct{" means the System Summary page under the System Info menu
option that is located under the System menu."
Dqnf"hqpv indicates a button, a toolbar icon, menu or menu item.
Symbols in this Guide:
U{odqn" Fguetkrvkqp"
Ignoring this type of note might result in a malfunction or damage to the
Pqvg<
Vkru<
device.
This format indicates important information that helps you make better use of
your device.
305" Qxgtxkgy"qh"Vjku"Iwkfg"
Ejcrvgt" Kpvtqfwevkqp"
Chapter 1 About This Guide Introduces the guide structure and conventions.
Chapter 2 Introduction Introduces the features, application and appearance of
TL-SL5428E switch.
Chapter 3 Login to the switch Introduces how to log on to TL-SL5428E Web management page.
2
Page 15
Ejcrvgt" Kpvtqfwevkqp"
Chapter 4 System This module is used to configure system properties of the switch.
Here mainly introduces:
System Info: Configure the description, system time and
network parameters of the switch.
User Management: Configure the user name and password for
users to log on to the Web management page with a certain
access level.
System Tools: Manage the configuration file of the switch.
Access Security: Provide different security measures for the
login to enhance the configuration management security.
Chapter 5 Switching This module is used to configure basic functions of the switch.
Here mainly introduces:
Port: Configure the basic features for the port.
LAG: Configure Link Aggregation Group. LAG is to combine a
number of ports together to make a single high-bandwidth data
path.
Traffic Monitor: Monitor the traffic of each port
MAC Address: Configure the address table of the switch.
Chapter 6 VLAN This module is used to configure VLANs to control broadcast in
LANs. Here mainly introduces:
802.1Q VLAN: Configure port-based VLAN.
MAC VLAN: Configure MAC-based VLAN without changing
the 802.1Q VLAN configuration.
Protocol VLAN: Create VLANs in application layer to make
some special data transmitted in the specified VLAN.
VLAN VPN: VLAN VPN allows the packets with VLAN tags of
private networks to be encapsulated with VLAN tags of public
networks at the network access terminal of the Internet Service
Provider.
GVRP: GVRP allows the switch to automatically add or remove
the VLANs via the dynamic VLAN registration information and
propagate the local VLAN registration information to other
switches, without having to individually configure each VLAN.
Private VLAN: Designed to save VLAN resources of uplink
devices and decrease broadcast. Private VLAN mainly used in
campus or enterprise networks to achieve user layer-2separation and to save VLAN resources of uplink devices.
Chapter 7 Spanning Tree This module is used to configure spanning tree function of the
switch. Here mainly introduces:
STP Config: Configure and view the global settings of
spanning tree function.
Port Config: Configure CIST parameters of ports.
MSTP Instance: Configure MSTP instances.
STP Security: Configure protection function to prevent devices
from any malicious attack against STP features.
3
Page 16
Ejcrvgt" Kpvtqfwevkqp"
Chapter 8 Ethernet OAM This module is used to configure Ethernet OAM function of the
switch. Here mainly introduces:
Basic Config: Enable the Ethernet OAM function, configure its
OAM mode, and check out the connection status.
Link Monitoring: Configure the parameters about OAM link
events and choose whether to notify the link event.
RFI: Choose whether to notify the link faults like dying gasp
and critical event.
Remote Loopback: Start or stop the remote loopback; choose
to ignore or to process the received remote loopback request.
Statistics: View the statistics about the detailed Ethernet OAM
traffic information and event log information
DLDP: Configure the DLDP function to allow the switch to
monitor the physical configuration of the cables and detect
whether a unidirectional link exists.
Chapter 9 DHCP This module is used to configure DHCP function of the switch.
The switch can work as DHCP relay, and here mainly introduces
DHCP relay function.
DHCP Relay: Configure the DHCP relay feature.
Chapter 10 Multicast This module is used to configure multicast function of the switch.
Here mainly introduces:
IGMP Snooping: Configure global parameters of IGMP
Snooping function, port properties, VLAN and multicast VLAN.
MLD Snooping: Configure global parameters of MLD Snooping
function, port properties, VLAN and multicast VLAN.
Multicast Table: View the information of IPv4 and IPv6
multicast groups already on the switch.
Chapter 11 QoS This module is used to configure QoS function to provide different
quality of service for various network applications and
requirements. Here mainly introduces:
DiffServ: Configure priorities, port priority, 802.1P priority and
DSCP priority.
Bandwidth Control: Configure rate limit feature to control the
traffic rate on each port; configure storm control feature to filter
broadcast, multicast and UL frame in the network.
Voice VLAN: Configure voice VLAN to transmit voice data
stream within the specified VLAN so as to ensure the
transmission priority of voice data stream and voice quality.
Chapter 12 ACL This module is used to configure match rules and process policies
of packets to filter packets in order to control the access of the
illegal users to the network. Here mainly introduces:
Time-Range: Configure the effective time for ACL rules.
ACL Config: ACL rules.
Policy Config: Configure operation policies.
Policy Binding: Bind the policy to a port/VLAN to take its effect
on a specific port/VLAN.
4
Page 17
Ejcrvgt" Kpvtqfwevkqp"
Chapter 13 Network Security This module is used to configure the multiple protection measures
for the network security. Here mainly introduces:
IP-MAC Binding: Bind the IP address, MAC address, VLAN ID
and the connected Port number of the Host together.
DHCP Snooping: DHCP Snooping functions to monitor the
process of the Host obtaining the IP address from DHCP
server, and record the IP address, MAC address, VLAN and
the connected Port number of the Host for automatic binding.
ARP Inspection: Configure ARP inspection feature to prevent
the network from ARP attacks.
IP Source Guard: Configure IP source guard feature to filter IP
packets in the LAN.
DoS Defend: Configure DoS defend feature to prevent DoS
attack.
802.1X: Configure common access control mechanism for
LAN ports to solve mainly authentication and security
problems.
AAA: Configure the AAA function protect the device from
unauthorized operations.
PPPoE Config: Configure the PPPoE Circuit-ID Insertion
function to support the authentication, authorization, and
accounting (AAA) access requests on an Ethernet interface.
Chapter 14 SNMP This module is used to configure SNMP function to provide a
management frame to monitor and maintain the network devices.
Here mainly introduces:
SNMP Config: Configure global settings of SNMP function.
Notification: Configure notification function for the
management station to monitor and process the events.
RMON: Configure RMON function to monitor network more
efficiently.
Chapter 15 LLDP This module is used to configure LLDP function to provide
information for SNMP applications to simplify troubleshooting.
Here mainly introduces:
Basic Config: Configure the LLDP parameters of the device.
Device Info: View the LLDP information of the local device and
its neighbors
Device Statistics: View the LLDP statistics of the local device
Chapter 16 Cluster This module is used to configure cluster function to central
manage the scattered devices in the network. Here mainly
introduces:
NDP: Configure NDP function to get the information of the
directly connected neighbor devices.
NTDP: Configure NTDP function for the commander switch to
collect NDP information.
Cluster: Configure cluster function to establish and maintain cluster.
5
Page 18
Ejcrvgt" Kpvtqfwevkqp"
Chapter 17 Maintenance This module is used to assemble the commonly used system
tools to manage the switch. Here mainly introduces:
System Monitor: Monitor the memory and CPU of the switch.
Log: View configuration parameters on the switch.
Network Diagnostics: Including Cable Test and Loopback.
Cable Test tests the connection status of the cable connected
to the switch; and Loopback tests if the port of the switch and
the connected device are available.
Network Diagnostics: Test if the destination is reachable and
the account of router hops from the switch to the destination.
Chapter 18 System
Maintenance via FTP
Introduces how to download firmware of the switch via FTP
function.
Appendix A Specifications Lists the glossary used in this manual.
Appendix B Glossary Lists the glossary used in this manual.
Return to CONTENTS
6
Page 19
Ejcrvgt"4" Kpvtqfwevkqp"
Thanks for choosing the TL-SL5428E 24-Port 10/100Mbps + 4-Port Gigabit JetStream L2
Managed Switch!
403" Qxgtxkgy"qh"vjg"Uykvej"
Designed for workgroups and departments, TL-SL5428E from TP-LINK provides wire-speed
performance and full set of layer 2 management features. It provides a variety of service features
and multiple powerful functions with high security.
The EIA-standardized framework and smart configuration capacity can provide flexible solutions for
a variable scale of networks. ACL, 802.1x, IP Source Guard and Dynamic ARP Inspection provide
robust security strategy. QoS and IGMP snooping/filtering optimize voice and video application.
Link aggregation (LACP) increases aggregated bandwidth, optimizing the transport of business
critical data. SNMP, RMON, WEB/CLI/Telnet Log-in bring abundant management policies.
TL-SL5428E switch integrates multiple functions with excellent performance, and is friendly to
manage, which can fully meet the need of the users demanding higher networking performance.
404" Crrgctcpeg"Fguetkrvkqp"
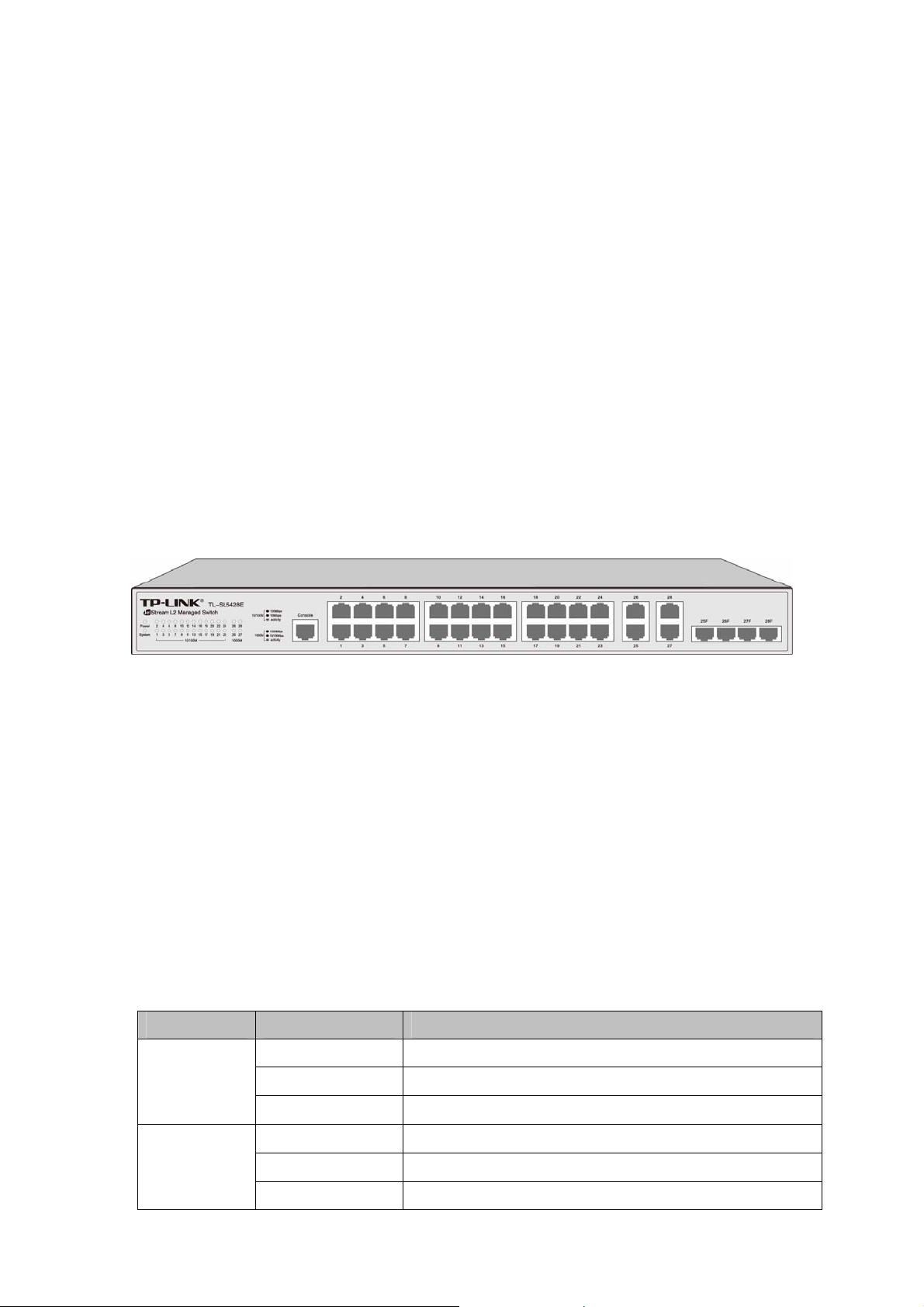
40403"Htqpv"Rcpgn"
Figure 2-1 Front Panel
The following parts are located on the front panel of the switch:
321322Odru"TL67" Rqtvu< Designed to connect to a device with the bandwidth of 10Mbps or
100Mbps. Each has a corresponding 10/100M LED."
32132213222Odru"TL67"Rqtvu< Designed to connect to a device with the bandwidth of 10Mbps,
100Mbps or 1000Mbps. Each has a corresponding 1000M LED.
UHR"Rqtvu< Designed to install the SFP module. Port 25F–28F share the same LED with Port
25–28 respectively.
Eqpuqng"Rqtv<"Designed to connect with the serial port of a computer or terminal for monitoring
and configuring the switch.
NGFu"
Pcog" Uvcvwu" Kpfkecvkqp"
On Power is on.
Power
System
Flashing Power supply is abnormal.
Off Power is off or power supply is abnormal.
On The switch is working abnormally.
Flashing The switch is working normally.
Off The switch is working abnormally.
7
Page 20
Pcog" Uvcvwu" Kpfkecvkqp"
A 100Mbps device is connected to the corresponding
port, but no activity.
A 10Mbps device is connected to the corresponding
port, but no activity.
A 1000Mbps device is connected to the corresponding
port, but no activity.
A 10/100Mbps device is connected to the corresponding
port, but no activity.
10/100M
1000M
Green
On
Yellow
Flashing Data is being transmitted or received.
Off No device is connected to the corresponding port.
Green
On
Yellow
Flashing Data is being transmitted or received.
Off No device is connected to the corresponding port.
40404"Tgct"Rcpgn"
The rear panel of TL-SL5428E features a power socket and a Grounding Terminal (marked
).
with
Figure 2-2 Rear Panel
Itqwpfkpi"Vgtokpcn< TL-SL5428E already comes with Lightning Protection Mechanism. You
can also ground the switch through the PE (Protecting Earth) cable of AC cord or with Ground
Cable. For detail information, please refer to Installation Guide.
CE" Rqygt" Uqemgv< Connect the female connector of the power cord here, and the male
connector to the AC power outlet. Please make sure the voltage of the power supply meets the
requirement of the input voltage (100-240V~ 50/60Hz 0.6A).
Return to CONTENTS
8
Page 21
Ejcrvgt"5" Nqikp"vq"vjg"Uykvej"
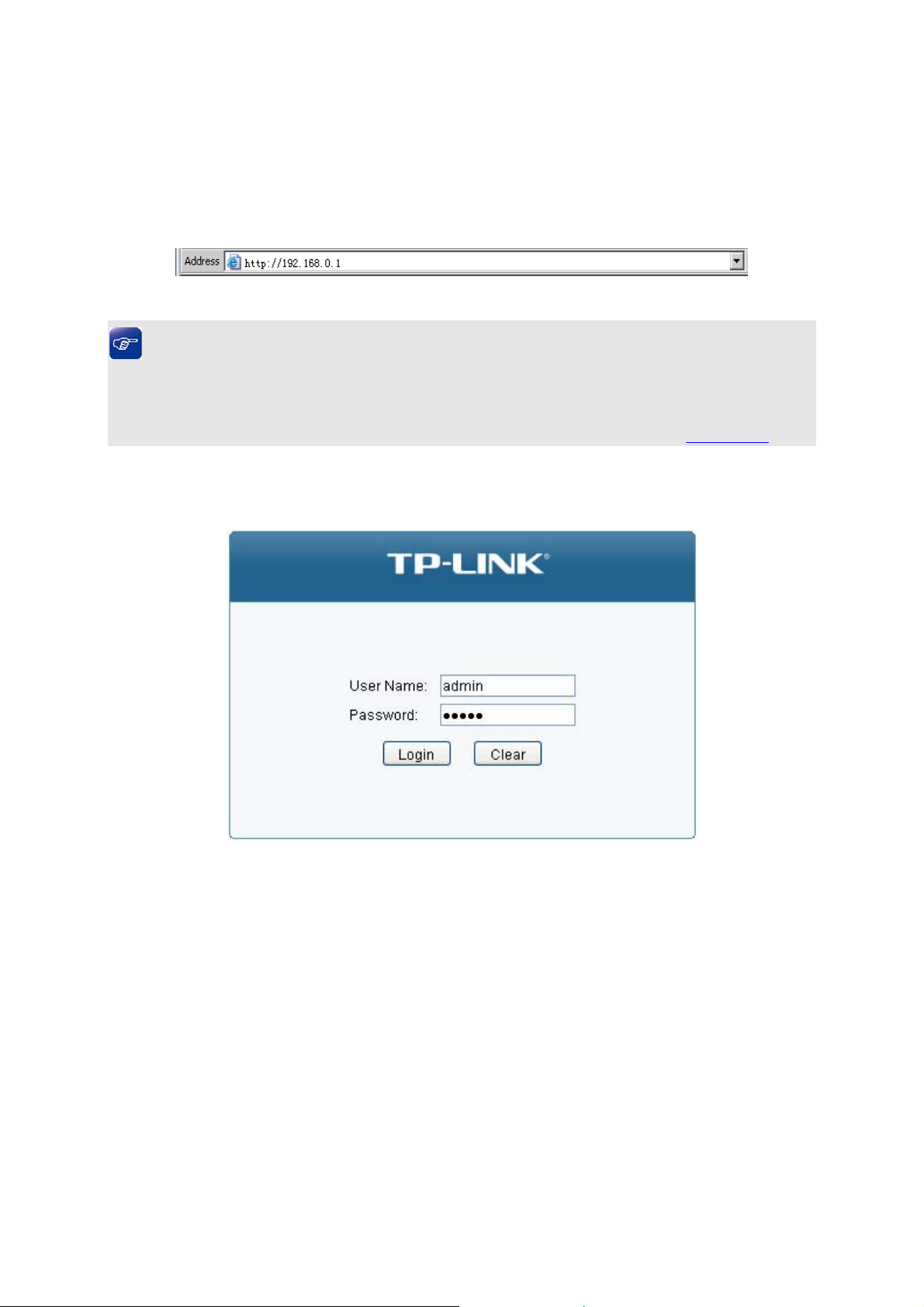
503" Nqikp"
1. To access the configuration utility, open a web-browser and type in the default address
http://192.168.0.1 in the address field of the browser, then press the Gpvgt"key.
Figure 3-1 Web-browser
"Vkru<"
To log in to the switch, the IP address of your PC should be set in the same subnet addresses of
the switch. The IP address is 192.168.0.x ("x" is any number from 2 to 254), Subnet Mask is
255.255.255.0. For the detailed instructions as to how to do this, please refer to Appendix B.
2. After a moment, a login window will appear, as shown in Figure 3-2. Enter cfokp for
Name and Password, both in lower case letters. Then click the Nqikp button or press the Gpvgt
key.
Figure 3-2 Login
the User
504" Eqphkiwtcvkqp"
After a successful login, the main page will appear as Figure 3-3, and you can configure the
function by clicking the setup menu on the left side of the screen.
9
Page 22
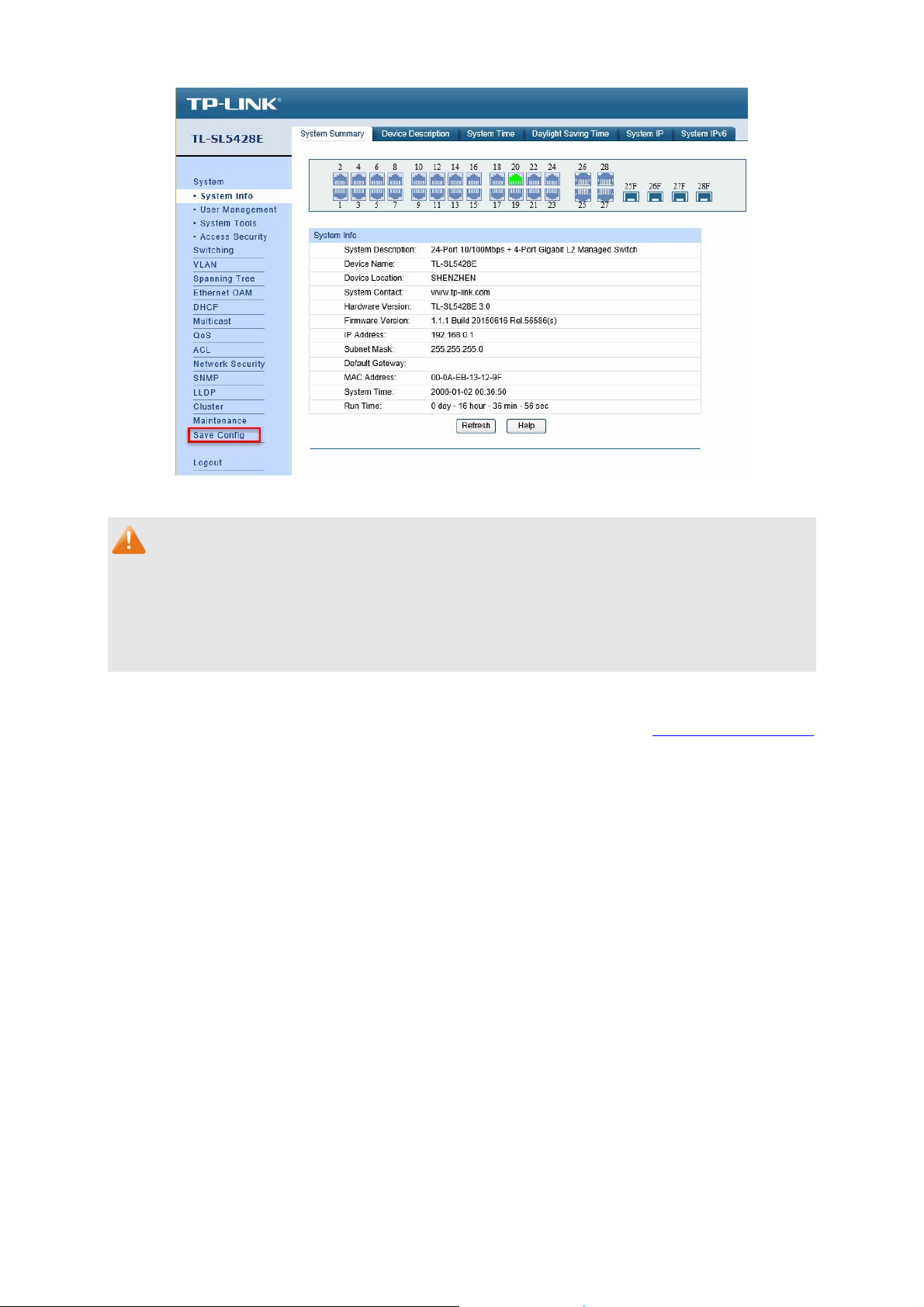
Figure 3-3 Main Setup-Menu
Pqvg<"
Clicking Crrn{ can only make the new configurations effective before the switch is rebooted. If
you want to keep the configurations effective even the switch is rebooted, please click Ucxg"
Eqphki. You are suggested to click Ucxg"Eqphki" before cutting off the power or rebooting the
switch to avoid losing the new configurations.
Return to CONTENTS
10
Page 23
Ejcrvgt"6" U{uvgo"
The System module is mainly for system configuration of the switch, including four submenus:"
U{uvgo"Kphq, Wugt"Ocpcigogpv."U{uvgo"Vqqnu and Ceeguu"Ugewtkv{.
603" U{uvgo"Kphq"
The System Info, mainly for basic properties configuration, can be implemented on U{uvgo"
Uwooct{, Fgxkeg"Fguetkrvkqp, U{uvgo"Vkog, Fc{nkijv"Ucxkpi"Vkog, U{uvgo"KR and"U{uvgo"
KRx8 pages.
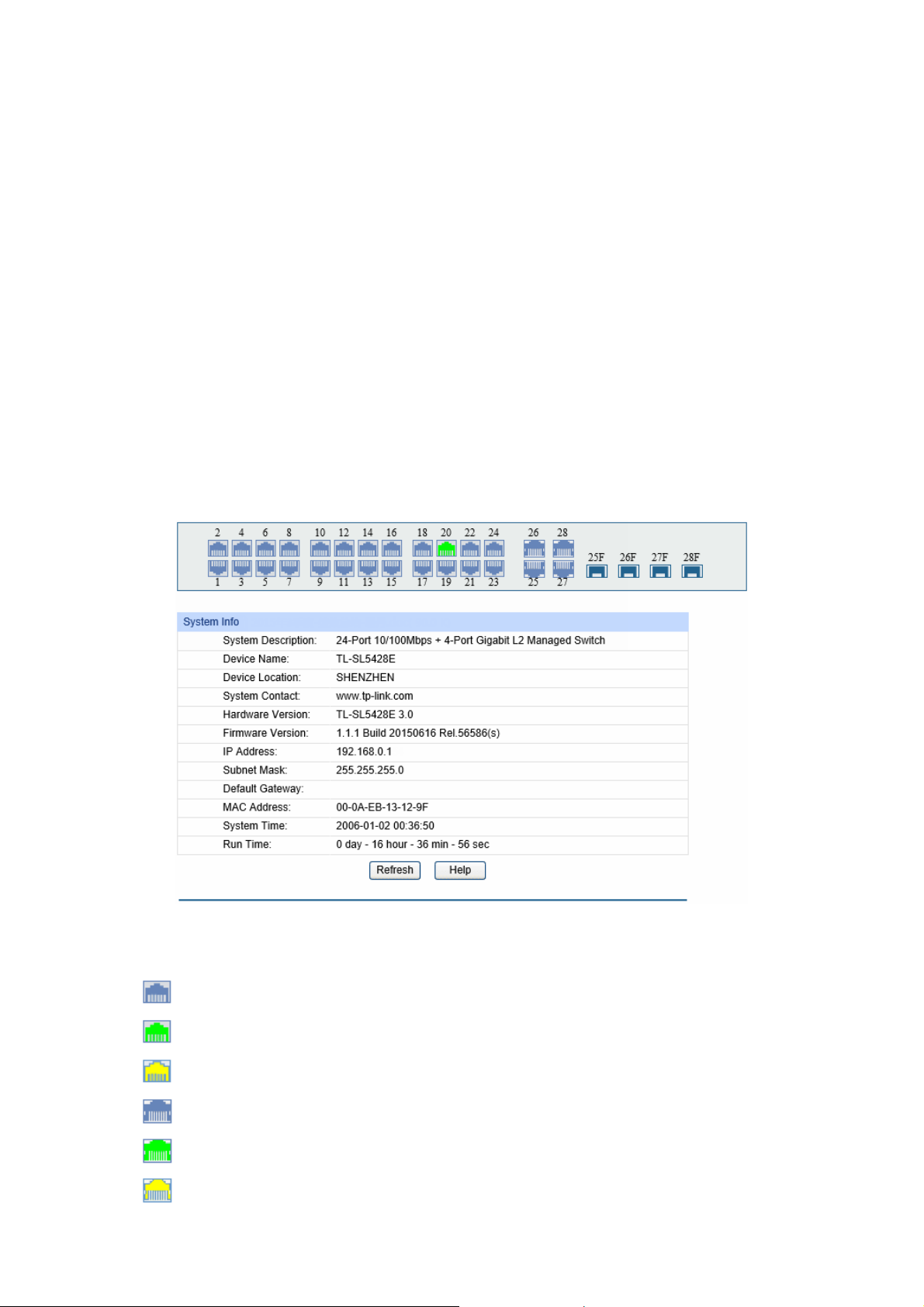
60303"U{uvgo"Uwooct{"
On this page you can view the port connection status and the system information.
The port status diagram shows the working status of 24 10/100Mbps RJ45 ports, 4
10/100/1000Mbps RJ45 ports and 2 SFP ports of the switch. Ports 1 to 24 are 10/100Mbps ports.
Ports 25-26 and 27T-28T are 10/100/1000Mbps ports, among which ports 27T and 28T are
Combo ports with SFP ports labeled 27F and 28F.
Choose the menu"U{uvgo→U{uvgo"Kphq→U{uvgo"Uwooct{"to load the following page.
" Rqtv"Uvcvwu"
"
"
"
"
"
"
"
Figure 4-1 System Summary
Indicates the 100Mbps port is not connected to a device.
Indicates the 100Mbps port is at the speed of 100Mbps.
Indicates the 100Mbps port is at the speed of 10Mbps.
Indicates the 1000Mbps port is not connected to a device.
Indicates the 1000Mbps port is at the speed of 1000Mbps.
Indicates the 1000Mbps port is at the speed of 10Mbps or 100Mbps.
11
Page 24
"
"
"
Indicates the SFP port is not connected to a device.
Indicates the SFP port is at the speed of 1000Mbps.
Indicates the SFP port is at the speed of 100Mbps.
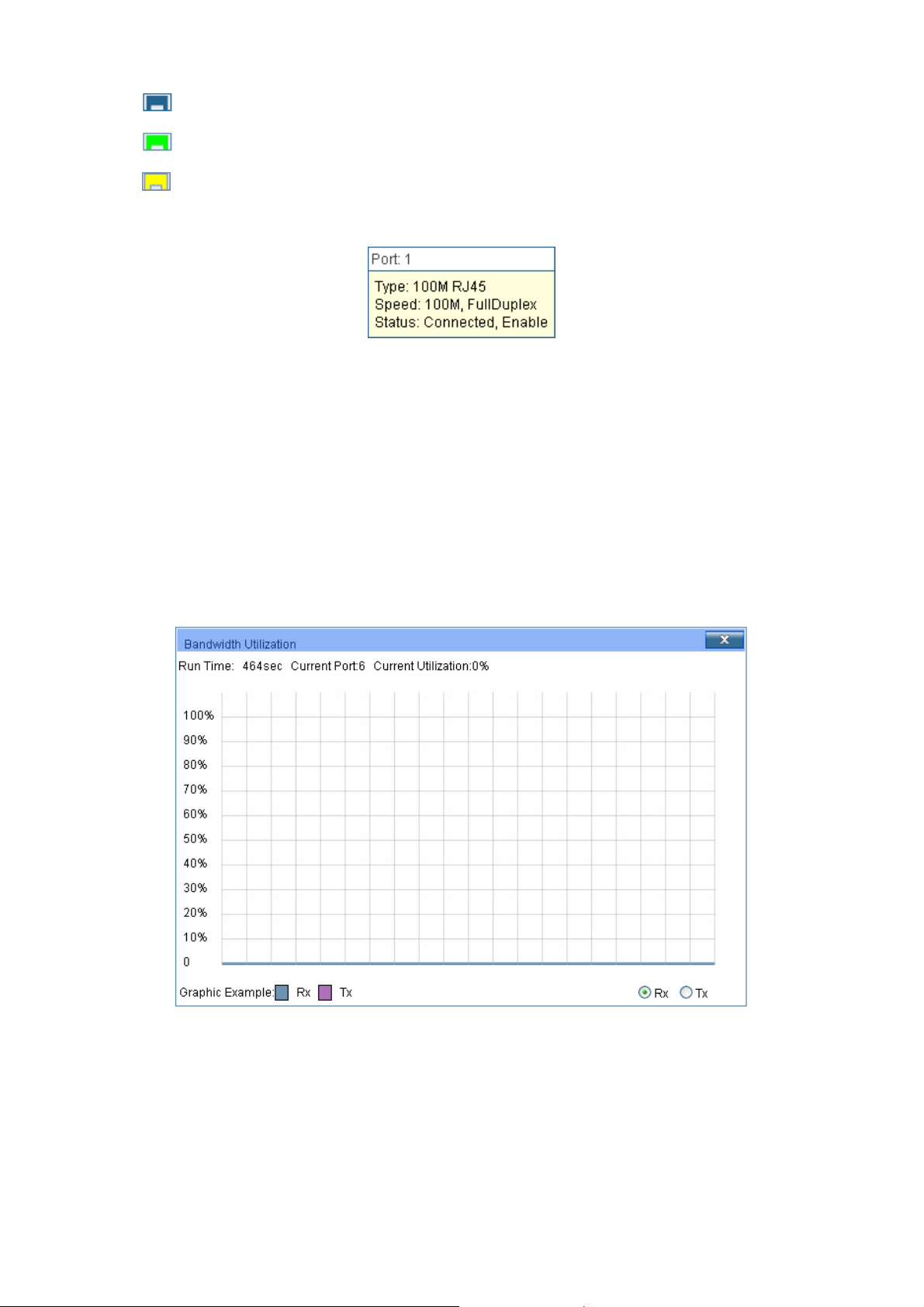
When the cursor moves on the port, the detailed information of the port will be displayed.
Figure 4-2 Port Information
" Rqtv"Kphq"
Rqtv<"
V{rg<"
Tcvg<"
Uvcvwu<"
Displays the port number of the switch.
Displays the type of the port.
Displays the maximum transmission rate of the port.
Displays the connection status of the port.
Click a port to display the bandwidth utilization on this port. The actual rate divided by theoretical
maximum rate is the bandwidth utilization.
Figure 4-3 displays the bandwidth utilization monitored
every four seconds. Monitoring the bandwidth utilization on each port facilitates you to monitor the
network traffic and analyze the network abnormities.
" Dcpfykfvj"Wvknk|cvkqp"
Tz<"
Vz<"
Figure 4-3 Bandwidth Utilization
Select Rx to display the bandwidth utilization of receiving packets
on this port.
Select Tx to display the bandwidth utilization of sending packets
on this port.
12
Page 25
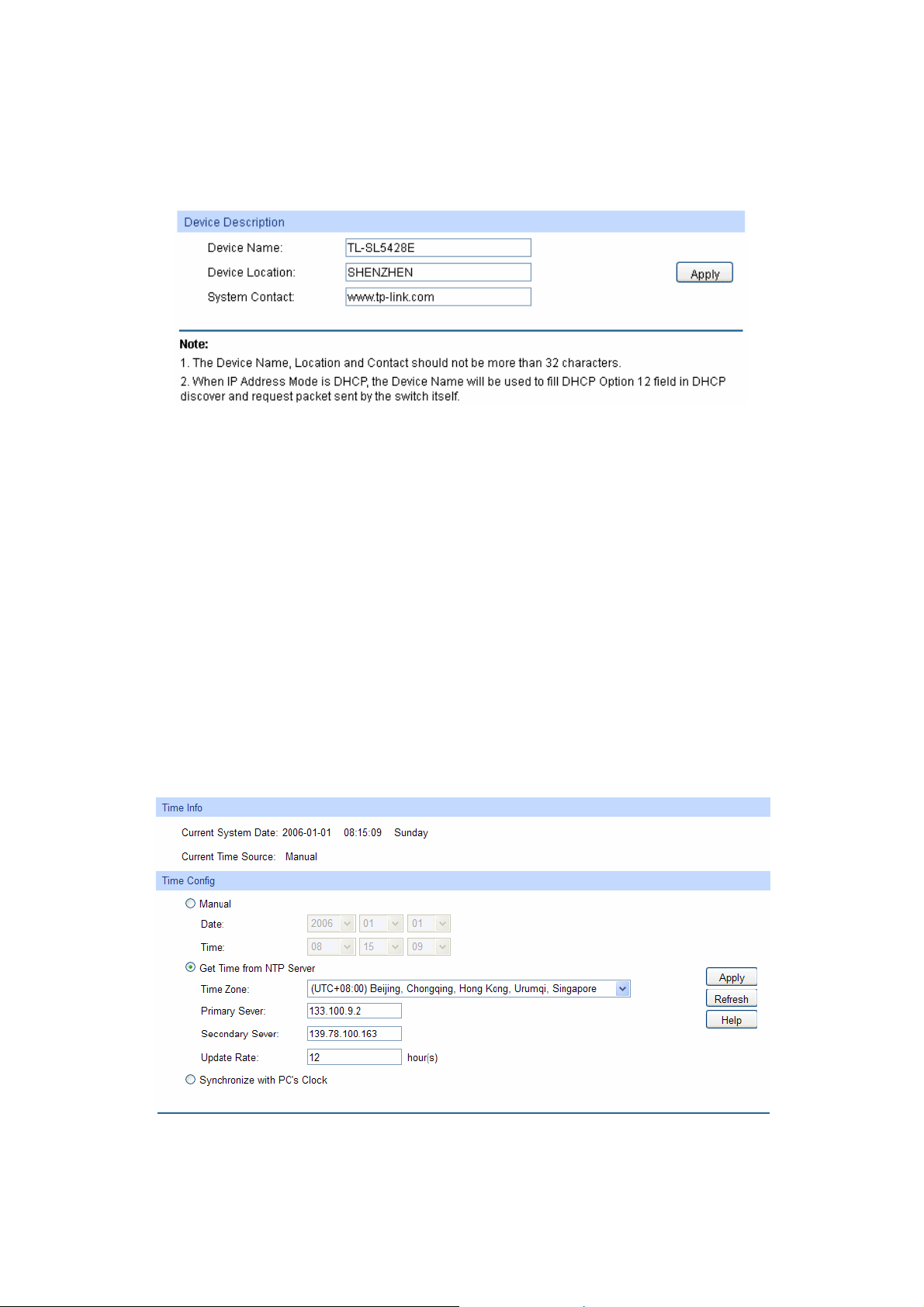
60304"Fgxkeg"Fguetkrvkqp"
On this page you can configure the description of the switch, including device name, device location
and system contact.
Choose the menu"U{uvgo→U{uvgo"Kphq→Fgxkeg"Fguetkrvkqp"to load the following page."
Figure 4-4 Device Description
The following entries are displayed on this screen:
" Fgxkeg"Fguetkrvkqp"
Fgxkeg"Pcog<"
Fgxkeg"Nqecvkqp<"
U{uvgo"Eqpvcev<"
Enter the name of the switch.
Enter the location of the switch.
Enter your contact information.
60305"U{uvgo"Vkog"
System Time is the time displayed while the switch is running. On this page you can configure the
system time and the settings here will be used for other time-based functions like"ACL.
You can manually set the system time, get UTC automatically if it has connected to an NTP server
or synchronize with PC’s clock as the system time.
Choose the menu U{uvgo→U{uvgo"Kphq→U{uvgo"Vkog to load the following page.
Figure 4-5 System Time
13
Page 26
The followin
" Vkog"Kphq"
g entries are displayed on this screen:
Ewttgpv"U{uvgo"Fcvg<"
Ewttgpv"Vkog"Uqwteg<"
" Vkog"Eqphki"
Ocpwcn<"
Igv" Vkog" htqo" PVR"
Ugtxgt<"
U{pejtqpk|g"ykvj"
RE‚U"Enqem<"
Displays the current date and time of the switch.
Displays the current time source of the switch.
When this option is selected, you can set the date and time
manually.
When this option is selected, you can configure the time zone
and the IP Address for the NTP Server. The switch will get UTC
automatically if it has connected to an NTP Server.
Vkog"\qpg< Select your local time.
Rtkoct{1Ugeqpfct{"PVR"Ugtxgt< Enter the IP Address for
the NTP Server.
Wrfcvg" Tcvg<" Specify the rate fetching time from NTP
server.
When this option is selected, the administrator PC’s clock is
utilized.
Pqvg<"
1. The system time will be restored to the default when the switch is restarted and you need to
reconfigure the system time of the switch.
2. When Get Time from NTP Server is selected and no time server is configured, the switch will
get time from the time server of the Internet if it has connected to the Internet.
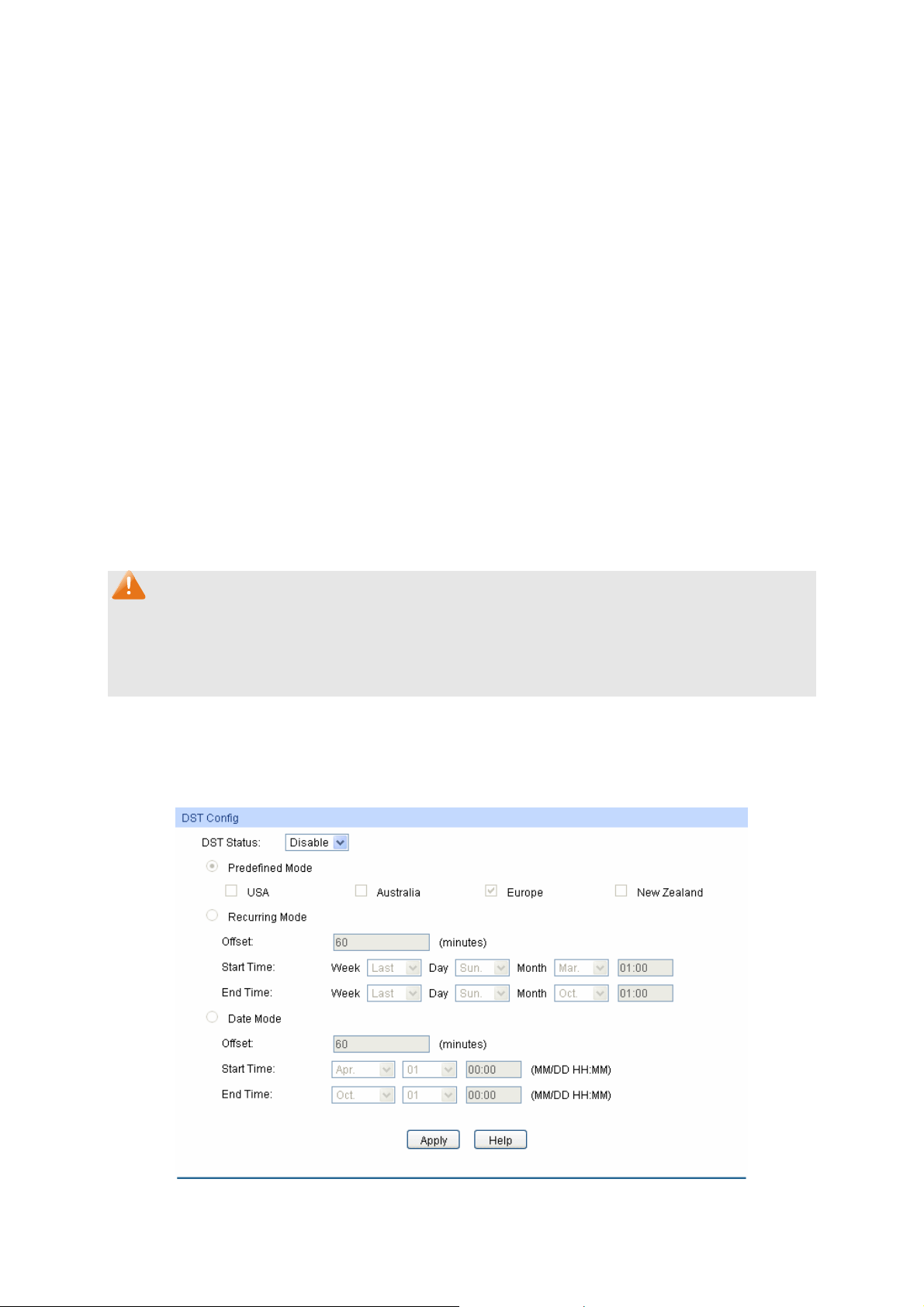
60306"Fc{nkijv"Ucxkpi"Vkog"
Here you can configure the Daylight Saving Time of the switch.
Choose the menu U{uvgo→U{uvgo"Kphq→Fc{nkijv"Ucxkpi"Vkog to load the following page.
Figure 4-6 Daylight Saving Time
14
Page 27
The followin
" FUV"Eqphki"
g entries are displayed on this screen:
FUV"Uvcvwu<"
Rtgfghkpgf"Oqfg<"
Tgewttkpi"Oqfg<"
Enable or Disable DST.
Select a predefined DST configuration:
USA: Second Sunday in March, 02:00 – First Sunday in
November, 02:00.
Australia: First Sunday in October, 02:00 – First Sunday in
April, 03:00.
Europe: Last Sunday in March, 01:00 – Last Sunday in
October, 01:00.
New Zealand: Last Sunday in September, 02:00 – First
Sunday in April, 03:00.
Specify the DST configuration in recurring mode. This
configuration is recurring in use:
Offset: Specify the time adding in minutes when Daylight
Saving Time comes.
Start/End Time: Select starting time and ending time of
Daylight Saving Time.
Fcvg"Oqfg<"
Specify the DST configuration in Date mode. This configuration
is one-off in use:
Offset: Specify the time adding in minutes when Daylight
Saving Time comes.
Start/End Time: Select starting time and ending time of
Daylight Saving Time.
Pqvg<"
1. When the DST is disabled, the predefined mode, recurring mode and date mode cannot be
configured.
2. When the DST is enabled, the default daylight saving time is of Europe in predefined mode.
60307"U{uvgo"KR"
Each device in the network possesses a unique IP Address. You can log on to the Web
management page to operate the switch using this IP Address. The switch supports three modes
to obtain an IP address: Static IP, DHCP and BOOTP. The IP address obtained using a new mode
will replace the original IP address. On this page you can configure the system IP of the switch.
15
Page 28
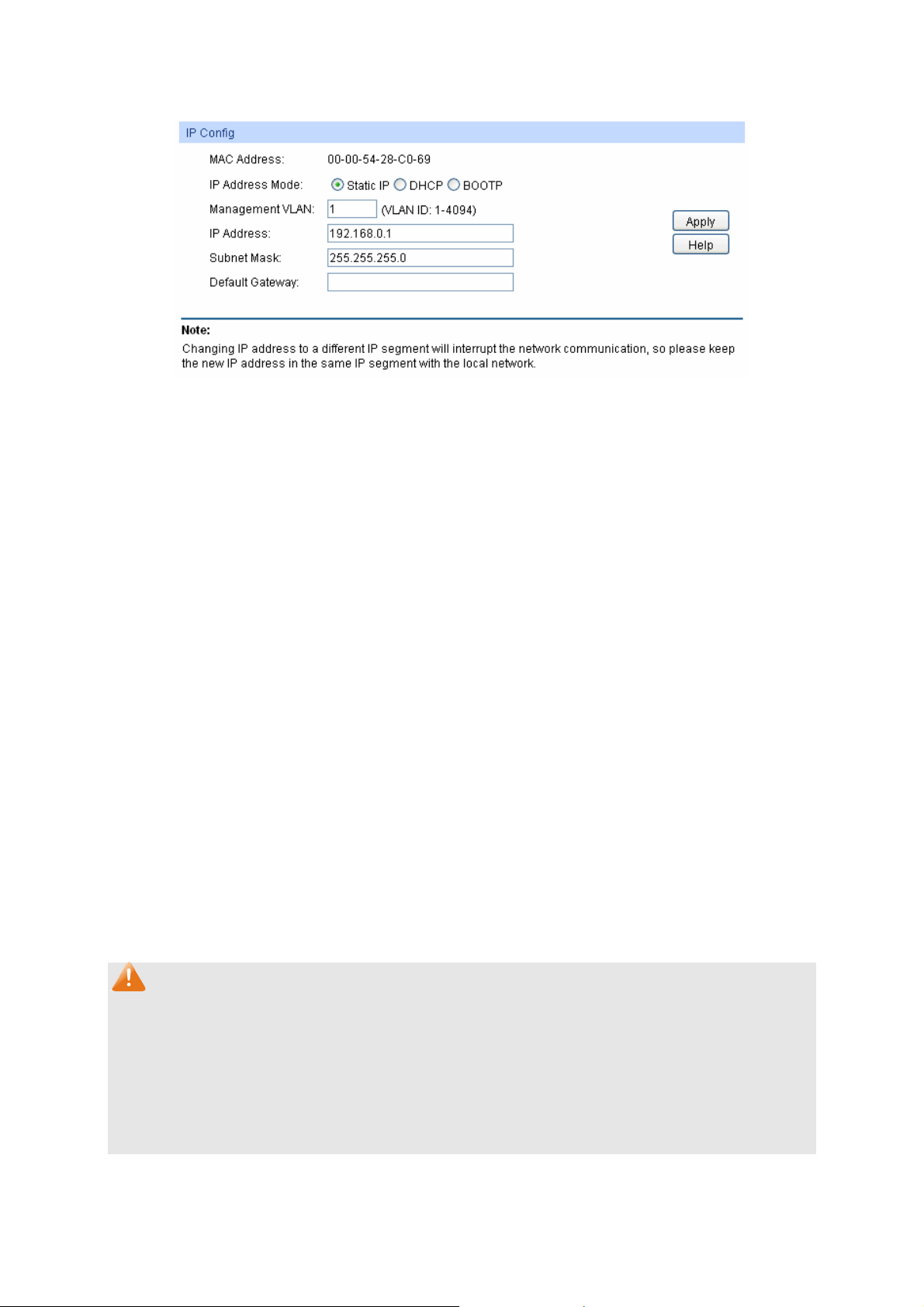
Choose the
menu U{uvgo→U{uvgo"Kphq→U{uvgo"KR"to load the following page."
Figure 4-7 System IP
The following entries are displayed on this screen:
" KR"Eqphki"
OCE"Cfftguu<"
KR"Cfftguu"Oqfg<"
Displays MAC Address of the switch.
Select the mode to obtain IP Address for the switch.
Uvcvke" KR< When this option is selected, you should enter IP
Address, Subnet Mask and Default Gateway manually.
FJER<" When this option is selected, the switch will obtain
network parameters from the DHCP Server.
DQQVR<" When this option is selected, the switch will obtain
network parameters from the BOOTP Server.
Ocpcigogpv"XNCP<"
Enter the ID of management VLAN, the only VLAN through which
you can get access to the switch. By default VLAN1 owning all the
ports is the Management VLAN and you can access the switch via
any port on the switch. However, if another VLAN is created and set
to be the Management VLAN, you may have to reconnect the
management station to a port that is a member of the Management
VLAN.
KR"Cfftguu<"
Enter the system IP of the switch. The default system IP is
192.168.0.1 and you can change it appropriate to your needs.
Uwdpgv"Ocum<"
Fghcwnv"Icvgyc{<"
Enter the subnet mask of the switch.
Enter the default gateway of the switch.
Pqvg<"
1. Changing the IP address to a different IP segment will interrupt the network communication,
so please keep the new IP address in the same IP segment with the local network.
2. The switch only possesses an IP address. The IP address configured will replace the original
IP address.
3. If the switch gets the IP address from DHCP server, you can see the configuration of the
switch in the DHCP server; if DHCP option is selected but no DHCP server exists in the
network, the switch will keep obtaining IP address from DHCP server until success.
16
Page 29

4. If DHCP or BOOTP option is selected, the switch will get network parameters dynamically
from the Internet, which means that its IP address, subnet mask and default gateway cannot
be configured.
5. By default, the IP address is 192.168.0.1.
60308"U{uvgo"KRx8"
IPv6 (Internet Protocol version 6), also called IPng (IP next generation), was developed by the
IETF (Internet Engineering Task Force) as the successor to IPv4 (Internet Protocol version 4).
Compared with IPv4, IPv6 increases the IP address size from 32 bits to 128 bits; this solves the
IPv4 address exhaustion problem.
KRx8"hgcvwtgu"
IPv6 has the following features:
1. Cfgswcvg"cfftguu"urceg<"The source and destination IPv6 addresses are both 128 bits (16
38
bytes) long. IPv6 can provide 3.4 x 10
addresses to completely meet the requirements of
hierarchical address division as well as allocation of public and private addresses.
2. Jgcfgt"hqtocv"ukornkhkecvkqp<"IPv6 cuts down some IPv4 header fields or move them to IPv6
extension headers to reduce the load of basic IPv6 headers, thus making IPv6 packet handling
simple and improving the forwarding efficiency. Although the IPv6 address size is four times
that of IPv4 addresses, the size of basic IPv6 headers is 40 bytes and is only twice that of IPv4
headers (excluding the Options field).
3. Hngzkdng" gzvgpukqp" jgcfgtu< IPv6 cancels the Options field in IPv4 packets but introduces
multiple extension headers. In this way, IPv6 enhances the flexibility greatly to provide
scalability for IP while improving the handling efficiency. The Options field in IPv4 packets
contains 40 bytes at most, while the size of IPv6 extension headers is restricted by that of IPv6
packets.
4. Dwknv/kp" ugewtkv{< IPv6 uses IPSec as its standard extension header to provide end-to-end
security. This feature provides a standard for network security solutions and improves the
interoperability between different IPv6 applications.
5. Cwvqocvke" cfftguu"eqphkiwtcvkqp<"To simplify the host configuration, IPv6 supports stateful
and stateless address configuration.
Stateful address configuration means that a host acquires an IPv6 address and related
information from a server (for example, DHCP server).
Stateless address configuration means that a host automatically configures an IPv6
address and related information on basis of its own link-layer address and the prefix
information advertised by a router.
In addition, a host can generate a link-local address on basis of its own link-layer address and
the default prefix (FE80::/64) to communicate with other hosts on the link.
6. Gpjcpegf" pgkijdqt" fkueqxgt{" ogejcpkuo<" The IPv6 neighbor discovery protocol is a
group of Internet control message protocol version 6 (ICMPv6) messages that manages the
information exchange between neighbor nodes on the same link. The group of ICMPv6
17
Page 30
messages
takes the place of Address Resolution Protocol (ARP) message, Internet Control
Message Protocol version 4 (ICMPv4) router discovery message, and ICMPv4 redirection
message to provide a series of other functions.
Kpvtqfwevkqp"vq"KRx8"cfftguu"
1. IPv6 address format
An IPv6 address is represented as a series of 16-bit hexadecimals, separated by colons (:).
An IPv6 address is divided into eight groups, and the 16 bits of each group are represented by
four hexadecimal numbers which are separated by colons, for example,
2001:0d02:0000:0000:0014: 0000:0000:0095. The hexadecimal letters in IPv6 addresses are
not case-sensitive.
To simplify the representation of IPv6 addresses, zeros in IPv6 addresses can be handled as
follows:
Leading zeros in each group can be removed. For example, the above-mentioned address
can be represented in shorter format as 2001:d02:0:0:14:0:0:95.
Two colons (::) may be used to compress successive hexadecimal fields of zeros at the
beginning, middle, or end of an IPv6 address. For example, the above-mentioned address
can be represented in the shortest format as 2001:d02::14:0:0:95.
Pqvg<
Two colons (::) can be used only once in an IPv6 address to represent the longest successive
hexadecimal fields of zeros. Otherwise, the device is unable to determine how many zeros
double-colons represent when converting them to zeros to restore a 128-bit IPv6 address.
An IPv6 address consists of two parts: address prefix and interface ID. The address prefix and
the interface ID are respectively equivalent to the network ID and the host ID in an IPv4
address.
An IPv6 address prefix is represented in "IPv6 address/prefix length" format, where "IPv6
address" is an IPv6 address in any of the above-mentioned formats and "prefix length" is a
decimal number indicating how many leftmost bits from the preceding IPv6 address are used
as the address prefix.
2. IPv6 address classification
IPv6 addresses fall into three types: unicast address, multicast address, and anycast address.
Unicast address: An identifier for a single interface, on a single node. A packet that is sent to
a unicast address is delivered to the interface identified by that address.
Multicast address: An identifier for a set of interfaces (typically belonging to different nodes),
similar to an IPv4 multicast address. A packet sent to a multicast address is delivered to all
interfaces identified by that address. There are no broadcast addresses in IPv6. Their
function is superseded by multicast addresses.
18
Page 31

Anycast address: An identifier for a set of interfaces (typically belonging to different
nodes). A packet sent to an anycast address is delivered to one of the interfaces identified
by that address (the nearest one, according to the routing protocols’ measure of distance).
The type of an IPv6 address is designated by the first several bits called format prefix. The
following table lists the mappings between address types and format prefixes.
Type Format Prefix (binary) IPv6 Prefix ID
Unassigned address 00…0 (128 bits) ::/128
Loopback address 00…1 (128 bits) ::1/128
Unicast
Link-local address 11111110 1 0 FE 80 ::/10
address
Site-local address 1111111011 FEC0 ::/10
Global unicast address
(currently assigned)
Reserved type
(to be assigned in future)
001 2xxx::/4 or 3xxx::/4
Other formats
Multicast address 11111111 FF00::/8
Anycast addresses are taken from unicast
Anycast address
address space and are not syntactically
distinguishable from unicast addresses.
Table 4-1 Mappings between address types and format prefixes
IPv6 unicast address can be classified into several types, including global unicast address,
link-local address, and site-local address. The two most common types are introduced below:
Global unicast address
A Global unicast address is an IPv6 unicast address that is globally unique and is routable
on the global Internet.
Global unicast addresses are defined by a global routing prefix, a subnet ID, and an
interface ID. Except for addresses that start with binary 000, all global unicast addresses
have a 64-bit interface ID. The IPv6 global unicast address allocation uses the range of
addresses that start with binary value 001 (2000::/3). The figure below shows the structure
of a global unicast address.
19
Page 32

Figure 4-8 Global Unicast Address Format
An interface ID is used to identify interfaces on a link. The interface ID must be unique to
the link. It may also be unique over a broader scope. In many cases, an interface ID will be
the same as or based on the link-layer address of an interface. Interface IDs used in global
unicast and other IPv6 address types must be 64 bits long and constructed in the modified
extended universal identifier (EUI)-64 format.
For all IEEE 802 interface types (for example, Ethernet and FDDI interfaces), Interface IDs
in the modified EUI-64 format are constructed in the following way:
the first three octets (24 bits) are taken from the Organizationally Unique Identifier (OUI) of
the 48-bit link-layer address (the media access control, or MAC, address) of the interface,
the fourth and fifth octets (16 bits) are a fixed hexadecimal value of FFFE, and the last
three octets (24 bits) are taken from the last three octets of the MAC address. The
construction of the interface ID is completed by setting the universal/local (U/L) bit--the
seventh bit of the first octet--to a value of 0 or 1. A value of 0 indicates a locally
administered identifier; a value of 1 indicates a globally unique IPv6 interface identifier.
Take MAC address 0012:0B0A:2D51 as an example. Insert HHHG to the middle of the
address to get 0012:0BHH<HG0A:2D51. Then set the U/L bit to 1 to obtain an interface ID in
EUI-64 format as 0412:0BFF:FE0A:2D51.
Link-local address
A link-local address is an IPv6 unicast address that can be automatically configured on any
interface using the link-local prefix FE80::/10 (1111 1110 10) and the interface identifier in
the modified EUI-64 format. Link-local addresses are used in the neighbor discovery
protocol and the stateless autoconfiguration process. Nodes on a local link can use
link-local addresses to communicate; the nodes do not need globally unique addresses to
communicate. The figure below shows the structure of a link-local address.
Figure 4-9 Link-local Address Format
IPv6 devices must not forward packets that have link-local source or destination addresses
to other links.
20
Page 33

Pqvg<
You can configure multiple IPv6 addresses per interface, but only one link-local address.
KRx8"Pgkijdqt"Fkueqxgt{"
The IPv6 neighbor discovery process uses ICMP messages and solicited-node multicast
addresses to determine the link-layer address of a neighbor on the same network (local link),
verify the reachability of a neighbor, and track neighboring devices.
1. IPv6 Neighbor Solicitation Message
A value of 135 in the Type field of the ICMP packet header identifies a neighbor solicitation
(NS) message. Neighbor solicitation messages are sent on the local link when a node wants
to determine the link-layer address of another node on the same local link. After receiving the
neighbor solicitation message, the destination node replies by sending a neighbor
advertisement (NA) message, which has a value of 136 in the Type field of the ICMP packet
header, on the local link. After the source node receives the neighbor advertisement, the
source node and destination node can communicate.
Neighbor advertisement messages are also sent when there is a change in the link-layer
address of a node on a local link.
Neighbor solicitation messages are also used to verify the reachability of a neighbor after the
link-layer address of a neighbor is identified.
Neighbor solicitation messages are also used in the stateless autoconfiguration process to
verify the uniqueness of unicast IPv6 addresses before the addresses are assigned to an
interface. Duplicate address detection is performed first on a new, link-local IPv6 address
before the address is assigned to an interface (the new address remains in a tentative state
while duplicate address detection is performed). Specifically, a node sends a neighbor
solicitation message with an unspecified source address and a tentative link-local address in
the body of the message. If another node is already using that address, the node returns a
neighbor advertisement message that contains the tentative link-local address. If another
node is simultaneously verifying the uniqueness of the same address, that node also returns a
neighbor solicitation message. If no neighbor advertisement messages are received in
response to the neighbor solicitation message and no neighbor solicitation messages are
received from other nodes that are attempting to verify the same tentative address, the node
that sent the original neighbor solicitation message considers the tentative link-local address
to be unique and assigns the address to the interface.
Every IPv6 unicast address (global or link-local) must be verified for uniqueness on the link;
however, until the uniqueness of the link-local address is verified, duplicate address detection
is not performed on any other IPv6 addresses associated with the link-local address.
2. IPv6 Router Advertisement Message
Router advertisement (RA) messages, which have a value of 134 in the Type field of the ICMP
packet header, are periodically sent out each configured interface of an IPv6 router.
21
Page 34

messages typically include the following information:
RA
One or more onlink IPv6 prefixes that nodes on the local link can use to automatically
configure their IPv6 addresses
Lifetime information for each prefix included in the advertisement
Sets of flags that indicate the type of autoconfiguration (stateless or stateful) that can be
completed
Default router information (whether the device sending the advertisement should be used
as a default router and, if so, the amount of time, in seconds, the device should be used as
a default router)
Additional information for hosts, such as the hop limit and maximum transmission unit (MTU)
a host should use in packets that it originates
RAs are also sent in response to device solicitation messages. Device solicitation messages,
which have a value of 133 in the Type field of the ICMP packet header, are sent by hosts at
system startup or anytime needed so that the host can immediately autoconfigure without
needing to wait for the next scheduled RA message.
Hosts discover and select default devices by listening to Router Advertisements (RAs).
Stateless address autoconfiguration means that the node automatically configures an IPv6
address and other information for its interface according to the address prefix and other
configuration parameters in the received RA messages.
3. IPv6 Neighbor Redirect Message
A value of 137 in the type field of the ICMP packet header identifies an IPv6 neighbor redirect
message. Devices send neighbor redirect messages to inform hosts of better first-hop nodes
on the path to a destination.
A device will send an IPv6 ICMP redirect message when the following conditions are satisfied:
The receiving interface is the forwarding interface.
The selected route itself is not created or modified by an IPv6 ICMP redirect message.
The selected route is not the default route.
The forwarded IPv6 packet does not contain any routing header.
22
Page 35

Choose the
menu U{uvgo"→U{uvgo"Kphq"→U{uvgo"KRx8"to load the following page."
Figure 4-10 System IPv6
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
KRx8<"
" Nkpm/nqecn"Cfftguu"Eqphki"
Eqphki"Oqfg<"
Nkpm/nqecn"Cfftguu<"
Enable/Disable IPv6 function globally on the Switch.
Select the link-local address configuration mode.
Ocpwcn< When this option is selected, you should assign a
link-local address manually.
Cwvq<"When this option is selected, the switch will generate a
link-local address automatically.
Enter a link-local address.
23
Page 36

Uvcvwu<"
Displays the st
Pqtocn< Indicates that the link-local address is normal.
Vt{< Indicates that the link-local address may be newly
atus of the link-local address.
configured
Tgrgcv< Indicates that the link-local address is duplicate. It is
illegal to access the switch using the IPv6 address (including
link-local and global address).
" Inqdcn"Cfftguu"Cwvqeqphki"xkc"TC"Oguucig"
Gpcdng"inqdcn"cfftguu"
cwvq" eqphkiwtcvkqp" xkc"
TC"oguucig<"
When this option is enabled, the switch automatically configures a
global address and other information according to the address
prefix and other configuration parameters from the received RA
(Router Advertisement) message.
" Inqdcn"Cfftguu"Cwvqeqphki"xkc"FJERx8"Ugtxgt"
Gpcdng" Inqdcn"
Cfftguu" Cwvqeqphki"
When this option is enabled, the system will try to obtain the global
address from the DHCPv6 Server.
xkc"FJERx8"Ugtxgt<"
" Cff"c"inqdcn"cfftguu"ocpwcnn{"
Cfftguu"Hqtocv<"
Inqdcn"Cfftguu<"
" Inqdcn"cfftguu"Vcdng"
Ugngev<"
Inqdcn"Cfftguu<"
Rtghkz"Ngpivj<"
V{rg<"
You can select the global address format according to your
requirements.
GWK/86< Indicates that you only need to specify an address
prefix, and then the system will create a global address
automatically.
Pqv"GWK/86<"Indicates that you have to specify an intact global
address.
When selecting the mode of EUI-64, please input the address
prefix here, otherwise, please input an intact IPv6 address here.
Select the desired entry to delete or modify the corresponding
global address.
Modify the global address.
Modify the prefix length of the global address.
Displays the configuration mode of the global address.
Ocpwcn< Indicates that the corresponding address is
configured manually
Cwvq< Indicates that the corresponding address is created
automatically using the RA message or obtained from the
DHCPv6 Server.
Rtghgttgf" Nkhgvkog"
1Xcnkf"Nkhgvkog<"
Displays the preferred time and valid time of the global address.
24
Page 37

Uvcvwu<"
"Vkru<"
After adding a global IPv6 address to your switch manually here, you can configure your PC’s
global IPv6 address in the same subnet with the switch and login to the switch via its global IPv6
address.
Displays the st
Pqtocn< Indicates that the global address is normal.
Vt{< Indicates that the global address may be newly
configured.
Tgrgcv< Indicates that the corresponding address is duplicate.
It is illegal to access the switch using this address.
atus of the global address.
604" Wugt"Ocpcigogpv"
User Management functions to configure the user name and password for users to log on to the
Web management page with a certain access level so as to protect the settings of the switch from
being randomly changed.
The User Management function can be implemented on Wugt"Vcdng and Wugt"Eqphki pages.
60403"Wugt"Vcdng"
On this page you can view the information about the current users of the switch.
Choose the menu"U{uvgo→Wugt"Ocpcigogpv→Wugt"Vcdng to load the following page.
Figure 4-11 User Table
60404"Wugt"Eqphki"
On this page you can configure the access level of the user to log on to the Web management
page. The switch provides two access levels: Guest and Admin. The guest only can view the
settings without the right to configure the switch; the admin can configure all the functions of the
switch. The Web management pages contained in this guide are subject to the admin’s login without any
explanation.
25
Page 38

Choose the
menu U{uvgo→Wugt"Ocpcigogpv→Wugt"Eqphki"to load the following page.
Figure 4-12 User Config
The following entries are displayed on this screen:
" Wugt"Kphq"
Wugt"Pcog<"
Ceeguu"Ngxgn<"
Rcuuyqtf<"
Eqphkto"Rcuuyqtf<"
" Wugt"Vcdng"
Ugngev<"
Wugt" KF." Pcog" cpf"
Ceeguu"Ngxgn<"
Qrgtcvkqp<"
Create a name for users’ login.
Select the access level to login.
Cfokp<" Admin can edit, modify and view all the settings of
different functions.
Iwguv<" Guest only can view the settings without the right to
edit and modify.
Type a password for users’ login.
Retype the password.
Select the desired entry to delete the corresponding user
information. It is multi-optional The current user information can’t
be deleted.
Displays the current user ID, user name and access level.
Click the Gfkv button of the desired entry, and you can edit the
corresponding user information. After modifying the settings,
please click the Oqfkh{ button to make the modification effective.
Access level and user status of the current user information can’t
be modified.
605" U{uvgo"Vqqnu"
The System Tools function, allowing you to manage the configuration file of the switch, can be
implemented on Eqphki" Tguvqtg," Eqphki" Dcemwr," Hktoyctg" Writcfg," U{uvgo" Tgdqqv and
U{uvgo"Tgugv pages.
26
Page 39

60503"Eqphki"Tguvqtg"
On this page you can upload a backup configuration file to restore your switch to this previous
configuration.
Choose the menu U{uvgo→U{uvgo"Vqqnu→Eqphki"Tguvqtg"to load the following page.
Figure 4-13 Config Restore
The following entries are displayed on this screen:
" Eqphki"Tguvqtg"
Tguvqtg"Eqphki<"
Pqvg<"
1. It will take a few minutes to restore the configuration. Please wait without any operation.
2. To avoid any damage, please don’t power down the switch while being restored.
3. After being restored, the current settings of the switch will be lost. Wrong uploaded
configuration file may cause the switch unmanaged.
Click the Tguvqtg" Eqphki button to restore the backup
configuration file. It will take effect after the switch automatically
reboots.
60504"Eqphki"Dcemwr"
On this page you can download the current configuration and save it as a file to your computer for
your future configuration restore.
Choose the menu"U{uvgo→U{uvgo"Vqqnu→Eqphki"Dcemwr"to load the following page."
Figure 4-14 Config Backup
27
Page 40

The followin
" Eqphki"Dcemwr"
Dcemwr"Eqphki<"
Pqvg<"
It will take a few minutes to back up the configuration. Please wait without any operation.
g entries are displayed on this screen:
Click the Backup Config button to save the current configuration
as a file to your computer. You are suggested to take this
measure before upgrading.
60505"Hktoyctg"Writcfg"
The switch system can be upgraded via the Web management page. To upgrade the system is to
get more functions and better performance. Go to http://www.tp-link.com
firmware.
Choose the menu U{uvgo→U{uvgo"Vqqnu→Hktoyctg"Writcfg"to load the following page.
to download the updated
Figure 4-15 Firmware Upgrade
Pqvg<"
1. Don’t interrupt the upgrade.
2. Please select the proper software version matching with your hardware to upgrade.
3. To avoid damage, please don't turn off the device while upgrading.
4. After upgrading, the device will reboot automatically.
5. You are suggested to back up the configuration before upgrading.
60506"U{uvgo"Tgdqqv"
On this page you can reboot the switch and return to the login page. Please save the current
configuration before rebooting to avoid losing the configuration unsaved
Choose the menu U{uvgo→U{uvgo"Vqqnu→U{uvgo"Tgdqqv"to load the following page.
Figure 4-16 System Reboot
28
Page 41

Pqvg<"
To avoid damage, please don't turn off the device while rebooting.
60507"U{uvgo"Tgugv"
On this page you can reset the switch to the default. All the settings will be cleared after the switch
is reset.
Choose the menu U{uvgo→U{uvgo"Vqqnu→U{uvgo"Tgugv"to load the following page.
Figure 4-17 System Reset
Pqvg<"
After the system is reset, the switch will be reset to the default and all the settings will be cleared.
606" Ceeguu"Ugewtkv{"
Access Security provides different security measures for the remote login so as to enhance the
configuration management security. It can be implemented on Ceeguu"Eqpvtqn,"UUN"Eqphki and
UUJ"Eqphki pages.
60603"Ceeguu"Eqpvtqn"
On this page you can control the users logging on to the Web management page to enhance the
configuration management security. The definitions of Admin and Guest refer to 4.2 User
Management.
29
Page 42

Choose the
menu U{uvgo→Ceeguu"Ugewtkv{→Ceeguu"Eqpvtqn"to load the following page."
Figure 4-18 Access Control
The following entries are displayed on this screen:
" Ceeguu"Eqpvtqn"Eqphki"
Eqpvtqn"Oqfg<"
Select the control mode for users to log on to the Web
management page.
KR/dcugf<"Select this option to limit the IP-range of the users
for login.
OCE/dcugf< Select this option to limit the MAC Address of
the users for login.
Rqtv/dcugf< Select this option to limit the ports for login.
KR"Cfftguu(Ocum:"
These fields can be available for configuration only when
IP-based mode is selected. Only the users within the IP-range
you set here are allowed for login.
OCE"Cfftguu<" "
The field can be available for configuration only when MAC-based
mode is selected. Only the user with this MAC Address you set
here is allowed for login.
30
Page 43

Rqtv<"
The field can be availa
ble for configuration only when Port-based
mode is selected. Only the users connected to these ports you
set here are allowed for login.
" Uguukqp"Eqphki"
Uguukqp"Vkogqwv<"
If you do nothing with the Web management page within the
timeout time, the system will log out automatically. If you want to
reconfigure, please login again.
" Ceeguu"Wugt"Pwodgt"
Pwodgt"Eqpvtqn;"
Cfokp"Pwodgt<"
Enable/Disable the Number Control function.
Enter the maximum number of the users logging on to the Web
management page as Admin.
Iwguv"Pwodgt<"
Enter the maximum number of the users logging on to the Web
management page as Guest.
60604"UUN"Eqphki"
SSL (Secure Sockets Layer), a security protocol, is to provide a secure connection for the
application layer protocol (e.g. HTTP) communication based on TCP. SSL is widely used to secure
the data transmission between the Web browser and servers. It is mainly applied through
ecommerce and online banking.
SSL mainly provides the following services:
1. Authenticate the users and the servers based on the certificates to ensure the data are
transmitted to the correct users and servers;
2. Encrypt the data transmission to prevent the data being intercepted;
3. Maintain the integrality of the data to prevent the data being altered in the transmission.
Adopting asymmetrical encryption technology, SSL uses key pair to encrypt/decrypt information. A
key pair refers to a public key (contained in the certificate) and its corresponding private key. By
default the switch has a certificate (self-signed certificate) and a corresponding private key. The
Certificate/Key Download function enables the user to replace the default key pair.
After SSL is effective, you can log on to the Web management page via https://192.168.0.1
. For
the first time you use HTTPS connection to log into the switch with the default certificate, you will
be prompted that “The security certificate presented by this website was not issued by a trusted
certificate authority” or “Certificate Errors”. Please add this certificate to trusted certificates or
continue to this website.
The switch also supports HTTPS connection for IPv6. After configuring an IPv6 address (for
example, 3001::1) for the switch, you can log on to the switch’s Web management page via
https://[3001::1].
31
Page 44

On this p
age you can configure the SSL function.
Choose the menu"U{uvgo→Ceeguu"Ugewtkv{→UUN"Eqphki to load the following page."
Figure 4-19 SSL Config
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
UUN<" "
" Egtvkhkecvg"Fqypnqcf"
Egtvkhkecvg"Hkng<" "
Enable/Disable the SSL function on the switch.
Select the desired certificate to download to the switch. The
certificate must be BASE64 encoded.
" Mg{"Fqypnqcf"
Mg{"Hkng<"
Select the desired SSL Key to download to the switch. The key
must be BASE64 encoded.
Pqvg<"
1. The SSL certificate and key downloaded must match each other; otherwise the HTTPS
connection will not work.
2. The SSL certificate and key downloaded will not take effect until the switch is rebooted.
3. To establish a secured connection using https, please enter https:// into the URL field of the
browser.
4. It may take more time for https connection than that for http connection, because https
connection involves authentication, encryption and decryption etc.
60605"UUJ"Eqphki" "
As stipulated by IFTF (Internet Engineering Task Force), SSH (Secure Shell) is a security protocol
established on application and transport layers. SSH-encrypted-connection is similar to a telnet
connection, but essentially the old telnet remote management method is not safe, because the
password and data transmitted with plain-text can be easily intercepted. SSH can provide
information security and powerful authentication when you log on to the switch remotely through
32
Page 45

an insecure
network environment. It can encrypt all the transmission data and prevent the
information in a remote management being leaked.
Comprising server and client, SSH has two versions, V1 and V2 which are not compatible with
each other. In the communication, SSH server and client can auto-negotiate the SSH version and
the encryption algorithm. After getting a successful negotiation, the client sends authentication
request to the server for login, and then the two can communicate with each other after successful
authentication. This switch supports SSH server and you can log on to the switch via SSH
connection using SSH client software.
SSH key can be downloaded into the switch. If the key is successfully downloaded, the certificate
authentication will be preferred for SSH access to the switch.
Choose the menu U{uvgo→Ceeguu"Ugewtkv{→UUJ"Eqphki to load the following page.
Figure 4-20 SSH Config
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
UUJ<"
Rtqvqeqn"X3<"
Rtqvqeqn"X4<"
Kfng"Vkogqwv<"
Enable/Disable SSH function.
Enable/Disable SSH V1 to be the supported protocol.
Enable/Disable SSH V2 to be the supported protocol.
Specify the idle timeout time. The system will automatically
release the connection when the time is up. The default time is
120 seconds.
Ocz"Eqppgev<"
Specify the maximum number of the connections to the SSH
server. No new connection will be established when the number
of the connections reaches the maximum number you set. The
default value is 5.
" Mg{"Fqypnqcf"
Mg{"V{rg<"
Select the type of SSH Key to download. The switch supports
three types: SSH-1 RSA, SSH-2 RSA and SSH-2 DSA.
33
Page 46

Mg{
"Hkng<"
Select the desired key file to download.
Fqypnqcf<"
Click the" Fqypnqcf button to down the desired key file to the
switch.
Pqvg<"
1. Please ensure the key length of the downloaded file is in the range of 256 to 3072 bits.
2. After the Key File is downloaded, the user’s original key of the same type will be replaced.
The wrong uploaded file will result in the SSH access to the switch via Password
authentication.
Crrnkecvkqp"Gzcorng"3"hqt"UUJ<"
" Pgvyqtm"Tgswktgogpvu"
1. Log on to the switch via password authentication using SSH and the SSH function is enabled
on the switch.
2. PuTTY client software is recommended.
" Eqphkiwtcvkqp"Rtqegfwtg"
1. Open the software to log on to the interface of PuTTY. Enter the IP address of the switch into
Jquv"Pcog field; keep the default value 22 in the Rqtv field; select UUJ as the Connection
type.
2. Click the Qrgp button in the above figure to log on to the switch. Enter the login user name and
password, and then you can continue to configure the switch.
34
Page 47

Crrnkecvkqp"Gzcorng"4"hqt"UUJ<"
" Pgvyqtm"Tgswktgogpvu"
1. Log on to the switch via key authentication using SSH and the SSH function is enabled on the
switch.
2. PuTTY client software is recommended.
" Eqphkiwtcvkqp"Rtqegfwtg"
1. Select the key type and key length, and generate SSH key.
Pqvg<"
1. The key length is in the range of 512 to 3072 bits.
2. During the key generation, randomly moving the mouse quickly can accelerate the key
generation.
35
Page 48

After the key is successfully generated, please save the public key and private key to the
2.
computer.
3. On the Web management page of the switch, download the public key file saved in the
computer to the switch.
Pqvg<"
1. The key type should accord with the type of the key file.
2. The SSH key downloading cannot be interrupted.
4. After the public key is downloaded, please log on to the interface of PuTTY and enter the IP
address for login.
36
Page 49

5. Click Dtqyug to download the private key file to SSH client software and click Qrgp.
After successful authentication, please enter the login user name. If you log on to the switch
without entering password, it indicates that the key has been successfully loaded.
37
Page 50

Pqvg<"
Following the steps above, you have already entered the User EXEC Mode of the switch. However,
to configure the switch, you need a password to enter the Privileged EXEC Mode first. For a switch
with factory settings, the Privileged EXEC Mode password can only be configured through the
console connection. For complete information about how to configure the Privileged EXEC Mode
password, please refer to the CLI Reference Guide in the provided Resource CD.
Return to CONTENTS
38
Page 51

Ejcrvgt"7" Uykvejkpi"
Switching module is used to configure the basic functions of the switch, including four submenus:
Rqtv,"NCI,"Vtchhke"Oqpkvqt and"OCE"Cfftguu.
703" Rqtv"
The Port function, allowing you to configure the basic features for the port, is implemented on the
Rqtv"Eqphki, Rqtv"Okttqt, Rqtv"Ugewtkv{, Rqtv"Kuqncvkqp"and"Nqqrdcem"Fgvgevkqp pages.
70303"Rqtv"Eqphki"
On this page, you can configure the basic parameters for the ports. When the port is disabled, the
packets on the port will be discarded. Disabling the port which is vacant for a long time can reduce
the power consumption effectively. And you can enable the port when it is in need.
The parameters will affect the working mode of the port, please set the parameters appropriate to
your needs.
Choose the menu Uykvejkpi→Rqtv→Rqtv"Eqphki to load the following page.
Figure 5-1 Port Config
The following entries are displayed on this screen.
Rqtv"Eqphki
Rqtv"Ugngev<"
Ugngev<"
Rqtv<"
Fguetkrvkqp<"
Click the Ugngev"button to quick-select the corresponding port
based on the port number you entered.
Select the desired port for configuration. It is multi-optional.
Displays the port number.
Give a description to the port for identification.
39
Page 52

Uvcvwu<"
Urggf"cpf"Fwrngz<"
Hnqy"Eqpvtqn<"
NCI<"
Pqvg<"
1. The switch cannot be managed through the disabled port. Please enable the port which is
used to manage the switch.
2. The parameters of the port members in a LAG should be set as the same.
Allows you to Enable/Disable the port. When Enable is
selected, the port can forward the packets normally.
Select the Speed and Duplex mode for the port. The device
connected to the switch should be in the same Speed and
Duplex mode with the switch. When “Auto” is selected, the
Speed and Duplex mode will be determined by
auto-negotiation.
Allows you to Enable/Disable the Flow Control feature. When
Flow Control is enabled, the switch can synchronize the speed
with its peer to avoid the packet loss caused by congestion.
Displays the LAG number which the port belongs to.
70304"Rqtv"Okttqt"
Port Mirror, the packets obtaining technology, functions to forward copies of packets from
one/multiple ports (mirrored port) to a specific port (mirroring port). Usually, the mirroring port is
connected to a data diagnose device, which is used to analyze the mirrored packets for monitoring
and troubleshooting the network.
Choose the menu Uykvejkpi→Rqtv→Rqtv"Okttqt to load the following page."
Figure 5-2 Port Mirror Config
40
Page 53

e following entries are displayed on this screen.
Th
" Okttqtkpi"Rqtv"
Okttqtkpi"Rqtv<"
" Okttqtgf"Rqtv"
Rqtv"Ugngev<"
Ugngev<"
Rqtv<"
Kpitguu<"
Gitguu<"
NCI<"
Pqvg<"
Select a port from the pull-down list as the mirroring port. When
disable is selected, the Port Mirror feature will be disabled.
Click the Ugngev" button to quick-select the corresponding port
based on the port number you entered.
Select the desired port as a mirrored port. It is multi-optional.
Displays the port number.
Enable/Disable the Ingress feature. When the Ingress is enabled,
the incoming packets received by the mirrored port will be copied
to the mirroring port.
Enable/Disable the Egress feature. When the Egress is enabled,
the outgoing packets sent by the mirrored port will be copied to the
mirroring port.
Displays the LAG number which the port belongs to. The LAG
member cannot be selected as the mirrored port or mirroring port.
1. The LAG member cannot be selected as the mirrored port or mirroring port.
2. A port cannot be set as the mirrored port and the mirroring port simultaneously.
3. The Port Mirror function can take effect span the multiple VLANs.
70305"Rqtv"Ugewtkv{"
MAC Address Table maintains the mapping relationship between the port and the MAC address of
the connected device, which is the base of the packet forwarding. The capacity of MAC Address
Table is fixed. MAC Address Attack is the attack method that the attacker takes to obtain the
network information illegally. The attacker uses tools to generate the cheating MAC address and
quickly occupy the MAC Address Table. When the MAC Address Table is full, the switch will
broadcast the packets to all the ports. At this moment, the attacker can obtain the network
information via various sniffers and attacks. When the MAC Address Table is full, the packets
traffic will flood to all the ports, which results in overload, lower speed, packets drop and even
breakdown of the system.
Port Security is to protect the switch from the malicious MAC Address Attack by limiting the
maximum number of MAC addresses that can be learned on the port. The port with Port Security
feature enabled will learn the MAC address dynamically. When the learned MAC address number
reaches the maximum, the port will stop learning. Thereafter, the other devices with the MAC
address unlearned cannot access to the network via this port.
41
Page 54

Choose the
menu Uykvejkpi→Rqtv→Rqtv"Ugewtkv{ to load the following page.
Figure 5-3 Port Security
The following entries are displayed on this screen:
" Rqtv"Ugewtkv{"
Ugngev<"
Select the desired port for Port Security configuration. It is
multi-optional.
Rqtv<"
Ocz"Ngctpgf"OCE<"
Displays the port number.
Specify the maximum number of MAC addresses that can be
learned on the port.
Ngctpgf"Pwo<"
Displays the number of MAC addresses that have been learned
on the port.
Ngctp"Oqfg<"
Select the Learn Mode for the port.
F{pcoke< When Dynamic mode is selected, the learned
MAC address will be deleted automatically after the aging
time.
Uvcvke< When Static mode is selected, the learned MAC
address will be out of the influence of the aging time and can
only be deleted manually. The learned entries will be cleared
after the switch is rebooted.
Rgtocpgpv< When Permanent mode is selected, the
learned MAC address will be out of the influence of the
aging time and can only be deleted manually. The learned
entries will be saved even the switch is rebooted.
Uvcvwu<"
Enable/Disable the Port Security feature for the port.
42
Page 55

Pqvg<"
1. The Port Security function is disabled for the LAG port member. Only the port is removed from
the LAG, will the Port Security function be available for the port.
2. The Port Security function is disabled when the 802.1X function is enabled.
70306"Rqtv"Kuqncvkqp"
Port Isolation provides a method of restricting traffic flow to improve the network security by
forbidding the port to forward packets to the ports that are not on its forward portlist.
Choose the menu Uykvejkpi→Rqtv→Rqtv"Kuqncvkqp to load the following page.
Figure 5-4 Port Isolation Config
The following entries are displayed on this screen:
" Rqtv"Kuqncvkqp"Eqphki"
Htqo1Vq"Rqtv<"
Hqtyctf"Rqtvnkuv<"
" Rqtv"Kuqncvkqp"Nkuv"
Rqtv<"
Hqtyctf"Rqtvnkuv<"
Select the port number to set its forwardlist.
Select the port(s) to be forwarded to.
Display the port number.
Display the forwardlist.
43
Page 56

70307"Nqqrdcem"Fgvgevkqp"
With loopback detection feature enabled, the switch can detect loops using loopback detection
packets. When a loop is detected, the switch will display an alert or further block the corresponding
port according to the port configuration.
Choose the menu Uykvejkpi→Rqtv→NqqrdcemFgvgevkqp to load the following page.
Figure 5-5 Loopback Detection Config
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
NqqrdcemFgvgevkqp"
Uvcvwu<"
Fgvgevkqp"Kpvgtxcn<"
Here you can enable or disable Loopback Detection function
globally.
Set a Loopback Detection interval between 1 and 1000 seconds.
By default, it’s 30 seconds.
Cwvqocvke"
Tgeqxgt{"Vkog<"
Ygd"Tghtguj"Uvcvwu<"
Ygd"Tghtguj"Kpvgtxcn<"
Time after which the blocked port would automatically recover to
normal status. It can be set as integral times of detection interval.
Here you can enable or disable web automatic refresh.
Set a web refresh interval between 3 and 100 seconds. By
default, it’s 6 seconds.
" Rqtv"Eqphki"
Rqtv"Ugngev<"
Click the Ugngev" button to quick-select the corresponding port
based on the port number you entered.
44
Page 57

Ugngev<"
Rqtv<"
Uvcvwu<"
Qrgtcvkqp"Oqfg<""
Tgeqxgt{"Oqfg<"
Nqqr"Uvcvwu<"
Dnqem"Uvcvwu<"
NCI<"
Ocpwcn"Tgeqxgt<"
Select the desired po
rt for Loopback Detection configuration. It is
multi-optional.
Displays the port number.
Enable or disable Loopback Detection function for the port.
Select the mode how the switch processes the detected loops.
Cngtv<"When a loop is detected, display an alert.
Rqtv" dcugf< When a loop is detected, display an alert and
block the port.
Select the mode how the blocked port recovers to normal status.
Cwvq< Block status can be automatically removed after
recovery time.
Ocpwcn<"Block status only can be removed manually.
Displays the port status whether a loopback is detected.
Displays the port status about block or unblock.
Displays the LAG number the port belongs to.
Manually remove the block status of selected ports.
Pqvg<"
1. Recovery Mode is not selectable when Alert is chosen in Operation Mode.
2. Loopback Detection must coordinate with storm control.
704" NCI"
LAG (Link Aggregation Group) is to combine a number of ports together to make a single
high-bandwidth data path, so as to implement the traffic load sharing among the member ports in
the group and to enhance the connection reliability.
For the member ports in an aggregation group, their basic configuration must be the same. The
basic configuration includes UVR,"SqU, IXTR, XNCP, rqtv"cvvtkdwvgu, OCE"Cfftguu"Ngctpkpi"
oqfg and other associated settings. The further explains are as following:
If the ports, which are enabled for the IXTR, :2403S"XNCP, Xqkeg"XNCP, UVR, SqU,"Rqtv"
Kuqncvkqp," FJER"Upqqrkpi and Rqtv"Eqphkiwtcvkqp (Urggf,"Hnqy"Eqpvtqn), are in a LAG,
their configurations should be the same.
The ports, which are enabled for the Rqtv" Ugewtkv{, Rqtv" Okttqt, OCE"Cfftguu" Hknvgtkpi,
Uvcvke"OCE"Cfftguu"Dkpfkpi,":2403Z"Cwvjgpvkecvkqp,"KR"Uqwteg"Iwctf, and jcnh/fwrngz"
cannot be added to the LAG.
It’s not suggested to add the ports with CTR"Kpurgevkqp and FqU" Fghgpf enabled to the
LAG.
If the LAG is needed, you are suggested to configure the LAG function here before configuring the
other functions for the member ports.
45
Page 58

"Vkru<"
1. Calculate the bandwidth for a LAG: If a LAG consists of the four ports in the speed of
1000Mbps Full Duplex, the whole bandwidth of the LAG is up to 8000Mbps (2000Mbps * 4)
because the bandwidth of each member port is 2000Mbps counting the up-linked speed of
1000Mbps and the down-linked speed of 1000Mbps.
2. The traffic load of the LAG will be balanced among the ports according to the Aggregate
Arithmetic. If the connections of one or several ports are broken, the traffic of these ports will
be transmitted on the normal ports, so as to guarantee the connection reliability.
Depending on different aggregation modes, aggregation groups fall into two types: Uvcvke" NCI
and NCER"Eqphki. The LAG function is implemented on the"NCI"Vcdng, Uvcvke"NCI and NCER"
Eqphki"configuration"pages.
70403"NCI"Vcdng"
On this page, you can view the information of the current LAG of the switch.
Choose the menu Uykvejkpi→NCI→NCI"Vcdng to load the following page.
Figure 5-6 LAG Table
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
Jcuj"Cniqtkvjo<"
Select the applied scope of aggregate hash arithmetic,
which results in choosing a port to transfer the packets.
UTE" OCE" -" FUV"OCE< When this option is selected,
the Aggregate Arithmetic will apply to the source and
destination MAC addresses of the packets. "
UTE"KR"-"FUV"KR<"When this option is selected, the
Aggregate Arithmetic will apply to the source and
destination IP addresses of the packets."
" NCI"Vcdng"
Ugngev<"
Itqwr"Pwodgt<"
Fguetkrvkqp<"
Select the desired LAG. It is multi-optional.
Displays the LAG number here.
Displays the description of LAG.
Ogodgt<"
Displays the LAG member.
46
Page 59

Qrgtcvkqp<
"
Allows you to view or modify the information for each LAG.
Gfkv< Click to modify the settings of the LAG.
Fgvckn< Click to get the information of the LAG.
Click the Fgvckn button for the detailed information of your selected LAG.
Figure 5-7 Detail Information
70404"Uvcvke"NCI"
On this page, you can manually configure the LAG. The LACP feature is disabled for the member
ports of the manually added Static LAG.
Choose the menu Uykvejkpi→NCI→Uvcvke"NCI to load the following page.
Figure 5-8 Static LAG Config
The following entries are displayed on this screen:
" NCI"Eqphki"
Itqwr"Pwodgt<"
Select a Group Number for the LAG.
47
Page 60

f
Fguetkrvkqp<
" NCI"Vcdng"
Ogodgt"Rqtv<"
"
Give a description to the LAG for identification.
Select the port as the LAG member. Clearing all the ports o
the LAG will delete this LAG.
"Vkru<"
1. The LAG can be deleted by clearing its all member ports.
2. A port can only be added to a LAG. If a port is the member of a LAG or is dynamically
aggregated as the LACP member, the port number will be displayed in gray and cannot be
selected.
70405"NCER"Eqphki"
LACP (Link Aggregation Control Protocol) is defined in IEEE802.3ad/802.1ax and enables the
dynamic link aggregation and disaggregation by exchanging LACP packets with its partner. The
switch can dynamically group similarly configured ports into a single logical link, which will highly
extend the bandwidth and flexibly balance the load.
With the LACP feature enabled, the port will notify its partner of the system priority, system MAC,
port priority, port number and operation key (operation key is determined by the physical
properties of the port, upper layer protocol and admin key). The device with higher priority will lead
the aggregation and disaggregation. System priority and system MAC decide the priority of the
device. The smaller the system priority, the higher the priority of the device is. With the same
system priority, the device owning the smaller system MAC has the higher priority. The device with
the higher priority will choose the ports to be aggregated based on the port priority, port number
and operation key. Only the ports with the same operation key can be selected into the same
aggregation group. In an aggregation group, the port with smaller port priority will be considered
as the preferred one. If the two port priorities are equal, the port with smaller port number is
preferred. After an aggregation group is established, the selected ports can be aggregated
together as one port to transmit packets.
On this page, you can configure the LACP feature of the switch.
48
Page 61

Choose the
menu Uykvejkpi→NCI→NCER"Eqphki to load the following page.
Figure 5-9 LACP Config
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
U{uvgo"Rtkqtkv{<"
Specify the system priority for the switch. The system priority and
MAC address constitute the system identification (ID). A lower system
priority value indicates a higher system priority. When exchanging
information between systems, the system with higher priority
determines which link aggregation a link belongs to, and the system
with lower priority adds the proper links to the link aggregation
according to the selection of its partner.
" NCER"Eqphki"
Rqtv"Ugngev<"
Click the Ugngev"button to quick-select the corresponding port based
on the port number you entered.
Ugngev<"
Rqtv<"
Select the desired port for LACP configuration. It is multi-optional.
Displays the port number.
Cfokp"Mg{<"
Rqtv"Rtkqtkv{<"
Specify an Admin Key for the port. The member ports in a dynamic
aggregation group must have the same Admin Key.
Specify a Port Priority for the port. This value determines the priority
of the port to be selected as the dynamic aggregation group
member. The port with smaller Port Priority will be considered as the
preferred one. If the two port priorities are equal; the port with
smaller port number is preferred.
49
Page 62

r
Uvcvwu<"
NCI<"
Enable/Disa
Displays the LAG number which the port belongs to.
ble the LACP feature for your selected port.
705" Vtchhke"Oqpkvqt"
The Traffic Monitor function, monitoring the traffic of each port, is implemented on the"Vtchhke"
Uwooct{ and Vtchhke"Uvcvkuvkeu"pages.
70503"Vtchhke"Uwooct{"
Traffic Summary screen displays the traffic information of each port, which facilitates you to
monitor the traffic and analyze the network abnormity.
Choose the menu Uykvejkpi→Vtchhke"Oqpkvqt→Vtchhke"Uwooct{ to load the following page.
Figure 5-10 Traffic Summary
The following entries are displayed on this screen:
" Cwvq"Tghtguj"
Cwvq"Tghtguj<"
Tghtguj"Tcvg<"
" Vtchhke"Uwooct{"
Rqtv"Ugngev<"
Rqtv<"
Rcemgvu"Tz<"
Allows you to Enable/Disable refreshing the Traffic Summary
automatically.
Enter a value in seconds to specify the refresh interval.
Click the"Ugngev"button to quick-select the corresponding port based
on the port number you entered.
Displays the port number.
Displays the number of packets received on the port. The erro
packets are not counted in.
50
Page 63

Rcemgv
Qevgvu"Tz<"
u"Vz<"
Displays the number of packets transmitted on the port.
Displays the number of octets received on the port. The error octets
are counted in.
Qevgvu"Vz<"
Uvcvkuvkeu<"
Displays the number of octets transmitted on the port.
Click the Uvcvkuvkeu"button to view the detailed traffic statistics of the
port.
70504"Vtchhke"Uvcvkuvkeu"
Traffic Statistics screen displays the detailed traffic information of each port, which facilitates you to
monitor the traffic and locate faults promptly.
Choose the menu Uykvejkpi→Vtchhke"Oqpkvqt→Vtchhke"Uvcvkuvkeu to load the following page.
Figure 5-11 Traffic Statistics
The following entries are displayed on this screen:
" Cwvq"Tghtguj"
Cwvq"Tghtguj<"
Allows you to Enable/Disable refreshing the Traffic Summary
automatically.
Tghtguj"Tcvg<"
" Uvcvkuvkeu"
Rqtv<"
Enter a value in seconds to specify the refresh interval.
Enter a port number and click the Ugngev"button to view the traffic
statistics of the corresponding port.
Tgegkxgf<"
Displays the details of the packets received on the port.
51
"
Page 64

r
r
r
r
r
r
r
Ugpv<"
Dtqcfecuv<"
Ownvkecuv<"
Wpkecuv<"
Cnkipogpv"Gttqtu<"
Wpfgtuk|gRmvu<"
Rmvu86Qevgvu<"
Rmvu87vq349Qevgvu<"
Displays the det
Displays the number of good broadcast packets received o
transmitted on the port. The error frames are not counted in.
Displays the number of good multicast packets received o
transmitted on the port. The error frames are not counted in.
Displays the number of good unicast packets received or
transmitted on the port. The error frames are not counted in.
Displays the number of the received packets that have a bad
Frame Check Sequence (FCS) with a non-integral octet
(Alignment Error) and have a bad FCS with an integral octet
(CRC Error). The length of the packet is between 64 bytes and
1518 bytes.
Displays the number of the received packets (excluding erro
packets) that are less than 64 bytes long.
Displays the number of the received packets (including erro
packets) that are 64 bytes long.
Displays the number of the received packets (including error
packets) that are between 65 and 127 bytes long.
ails of the packets transmitted on the port.
Rmvu34:vq477Qevgvu<"
Rmvu478vq733Qevgvu<"
Rmvu734vq3245Qevgvu<"
RmvuQxgt3245Qevgvu<"
Eqnnkukqpu<"
Displays the number of the received packets (including erro
packets) that are between 128 and 255 bytes long.
Displays the number of the received packets (including error
packets) that are between 256 and 511 bytes long.
Displays the number of the received packets (including erro
packets) that are between 512 and 1023 bytes long.
Displays the number of the received packets (including erro
packets) that are more than 1023 bytes long.
Displays the number of collisions experienced by a port during
packet transmissions.
706" OCE"Cfftguu"
The main function of the switch is forwarding the packets to the correct ports based on the
destination MAC address of the packets. Address Table contains the port-based MAC address
information, which is the base for the switch to forward packets quickly. The entries in the Address
Table can be updated by auto-learning or configured manually. Most the entries are generated and
updated by auto-learning. In the stable networks, the static MAC address entries can facilitate the
switch to reduce broadcast packets and enhance the efficiency of packets forwarding remarkably.
The address filtering feature allows the switch to filter the undesired packets and forbid its
forwarding so as to improve the network security.
52
Page 65

The types an
V{rg"
Static
Address
Table
Dynamic
Address
Table
Filtering
Address
d the features of the MAC Address Table are listed as the following:
Eqphkiwtcvkqp"
Yc{"
Manually
configuring
Cikpi"
qwv"
Dgkpi"mgrv"chvgt"tgdqqv"
(if the configuration is saved)
No Yes The bound MAC address cannot be
Tgncvkqpujkr"dgvyggp"vjg"dqwpf"
OCE"cfftguu"cpf"vjg"rqtv"
learned by the other ports in the
same VLAN.
Automatically
learning
Yes No The bound MAC address can be
learned by the other ports in the
same VLAN.
Manually
No Yes -
configuring
Table
Table 5-1 Types and features of Address Table
This function includes four submenus: Cfftguu"Vcdng, Uvcvke"Cfftguu, F{pcoke"Cfftguu and
Hknvgtkpi"Cfftguu.
70603"Cfftguu"Vcdng"
On this page, you can view all the information of the Address Table.
Choose the menu Uykvejkpi→OCE"Cfftguu→Cfftguu"Vcdng to load the following page.
Figure 5-12 Address Table
The following entries are displayed on this screen:
" Ugctej"Qrvkqp"
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
Enter the MAC address of your desired entry.
Enter the VLAN ID of your desired entry.
Select the corresponding port number of your desired entry.
53
Page 66

V{
rg<"
" Cfftguu"Vcdng"
Select the type of your desired entry.
Cnn<" This option allows the address table to display all the
address entries.
Uvcvke<"This option allows the address table to display the static
address entries only.""
F{pcoke<" This option allows the address table to display the
dynamic address entries only."
Hknvgtkpi<" This option allows the address table to display the
filtering address entries only."
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
V{rg<"
Cikpi"Uvcvwu<"
Displays the MAC address learned by the switch.
Displays the corresponding VLAN ID of the MAC address.
Displays the corresponding Port number of the MAC address.
Displays the Type of the MAC address.
Displays the Aging status of the MAC address.
70604"Uvcvke"Cfftguu"
The static address table maintains the static address entries which can be added or removed
manually, independent of the aging time. In the stable networks, the static MAC address entries
can facilitate the switch to reduce broadcast packets and remarkably enhance the efficiency of
packets forwarding without learning the address. The static MAC address learned by the port with
Rqtv"Ugewtkv{"enabled in the static learning mode will be displayed in the Static Address Table.
Choose the menu Uykvejkpi→OCE"Cfftguu→Uvcvke"Cfftguu to load the following page.
Figure 5-13 Static Address
54
Page 67

e following entries are displayed on this screen:
Th
" Etgcvg"Uvcvke"Cfftguu"
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
" Ugctej"Qrvkqp"
Ugctej"Qrvkqp<"
" Uvcvke"Cfftguu"Vcdng"
Ugngev<"
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
Enter the static MAC Address to be bound.
Enter the corresponding VLAN ID of the MAC address.
Select a port from the pull-down list to be bound.
Select a Search Option from the pull-down list and click the Ugctej
button to find your desired entry in the Static Address Table.
OCE<"Enter the MAC address of your desired entry.
XNCP"KF<"Enter the VLAN ID number of your desired entry."
Rqtv< Enter the Port number of your desired entry.
Select the entry to delete or modify the corresponding port number. It
is multi-optional.
Displays the static MAC Address.
Displays the corresponding VLAN ID of the MAC address.
Displays the corresponding Port number of the MAC address. Here
you can modify the port number to which the MAC address is bound.
The new port should be in the same VLAN.
V{rg<"
Cikpi"Uvcvwu<"
Displays the Type of the MAC address.
Displays the Aging Status of the MAC address.
Pqvg<" "
1. If the corresponding port number of the MAC address is not correct, or the connected port (or
the device) has been changed, the switch cannot be forward the packets correctly. Please
reset the static address entry appropriately.
2. If the MAC address of a device has been added to the Static Address Table, connecting the
device to another port will cause its address not to be recognized dynamically by the switch.
Therefore, please ensure the entries in the Static Address Table are correct and valid.
3. The MAC address in the Static Address Table cannot be added to the Filtering Address Table
or bound to a port dynamically.
4. This static MAC address bound function is not available if the 802.1X feature is enabled.
70605"F{pcoke"Cfftguu"
The dynamic address can be generated by the auto-learning mechanism of the switch. The
Dynamic Address Table can update automatically by auto-learning or the MAC address aging out
mechanism.
To fully utilize the MAC address table, which has a limited capacity, the switch adopts an aging
mechanism for updating the table. That is, the switch removes the MAC address entries related to
a network device if no packet is received from the device within the aging time.
55
Page 68

On this p
age, you can configure the dynamic MAC address entry.
Choose the menu Uykvejkpi→OCE"Cfftguu→F{pcoke"Cfftguu to load the following page.
Figure 5-14 Dynamic Address
The following entries are displayed on this screen:
" Cikpi"Eqphki"
Cwvq"Cikpi<"
Cikpi"Vkog<"
" Ugctej"Qrvkqp"
Ugctej"Qrvkqp<"
Allows you to Enable/Disable the Auto Aging feature.
Enter the Aging Time for the dynamic address.
Select a Search Option from the pull-down list and click the Ugctej
button to find your desired entry in the Dynamic Address Table.
OCE<"Enter the MAC address of your desired entry.
XNCP"KF<"Enter the VLAN ID number of your desired entry."
Rqtv< Enter the Port number of your desired entry.
NCI"KF<"Enter the LAG ID number of your desired entry.
" F{pcoke"Cfftguu"Vcdng"
Ugngev<"
Select the entry to delete the dynamic address or to bind the MAC
address to the corresponding port statically. It is multi-optional.
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
V{rg<"
Cikpi"Uvcvwu<"
Displays the dynamic MAC Address.
Displays the corresponding VLAN ID of the MAC address.
Displays the corresponding port number of the MAC address.
Displays the Type of the MAC address.
Displays the Aging Status of the MAC address.
56
Page 69

Dkpf<"
lick the"Dkpf"button to bind the MAC address of your selected entry
C
to the corresponding port statically.
"Vkru<"
Setting aging time properly helps implement effective MAC address aging. The aging time that is
too long or too short results decreases the performance of the switch. If the aging time is too long,
excessive invalid MAC address entries maintained by the switch may fill up the MAC address table.
This prevents the MAC address table from updating with network changes in time. If the aging time
is too short, the switch may remove valid MAC address entries. This decreases the forwarding
performance of the switch. It is recommended to keep the default value.
70606"Hknvgtkpi"Cfftguu"
The filtering address is to forbid the undesired packets to be forwarded. The filtering address can
be added or removed manually, independent of the aging time. The filtering MAC address allows
the switch to filter the packets which includes this MAC address as the source address or
destination address, so as to guarantee the network security. The filtering MAC address entries
act on all the ports in the corresponding VLAN.
Choose the menu Uykvejkpi→OCE"Cfftguu→Hknvgtkpi"Cfftguu to load the following page.
Figure 5-15 Filtering Address
The following entries are displayed on this screen:
" Etgcvg"Hknvgtkpi"Cfftguu"
OCE"Cfftguu<"
XNCP"KF<"
" Ugctej"Qrvkqp"
Ugctej"Qrvkqp<"
Enter the MAC Address to be filtered.
Enter the corresponding VLAN ID of the MAC address.
Select a Search Option from the pull-down list and click the Ugctej
button to find your desired entry in the Filtering Address Table.
OCE"Cfftguu<"Enter the MAC address of your desired entry.
XNCP"KF<"Enter the VLAN ID number of your desired entry."
57
Page 70

" Hknvgtkpi"Cfftguu"Vcdng"
Ugngev<"
Select the entry to delete the corresponding filtering address. It is
multi-optional.
OCE"Cfftguu<"
XNCP"KF<"
Rqtv<"
V{rg<"
Cikpi"Uvcvwu<"
Displays the filtering MAC Address.
Displays the corresponding VLAN ID.
Here the symbol “__” indicates no specified port.
Displays the Type of the MAC address.
Displays the Aging Status of the MAC address.
Pqvg<"
1. The MAC address in the Filtering Address Table cannot be added to the Static Address Table
or bound to a port dynamically.
2. This MAC address filtering function is not available if the 802.1X feature is enabled.
Return to CONTENTS
58
Page 71

Ejcrvgt"8" XNCP"
The traditional Ethernet is a data network communication technology basing on CSMA/CD (Carrier
Sense Multiple Access/Collision Detect) via shared communication medium. Through the
traditional Ethernet, the overfull hosts in LAN will result in serious collision, flooding broadcasts,
poor performance or even breakdown of the Internet. Though connecting the LANs through
switches can avoid the serious collision, the flooding broadcasts cannot be prevented, which will
occupy plenty of bandwidth resources, causing potential serious security problems.
A Virtual Local Area Network (VLAN) is a network topology configured according to a logical
scheme rather than the physical layout. The VLAN technology is developed for switches to control
broadcast in LANs. By creating VLANs in a physical LAN, you can divide the LAN into multiple
logical LANs, each of which has a broadcast domain of its own. Hosts in the same VLAN
communicate with one another as if they are in a LAN. However, hosts in different VLANs cannot
communicate with one another directly. Therefore, broadcast packets are limited in a VLAN. Hosts
in the same VLAN communicate with one another via Ethernet whereas hosts in different VLANs
communicate with one another through the Internet devices such as Router, the Layer3 switch, etc.
The following figure illustrates a VLAN implementation.
Figure 6-1 VLAN implementation
Compared with the traditional Ethernet, VLAN enjoys the following advantages.
1. Broadcasts are confined to VLANs. This decreases bandwidth utilization and improves
network performance.
2. Network security is improved. VLANs cannot communicate with one another directly. That is, a
host in a VLAN cannot access resources in another VLAN directly, unless routers or Layer 3
switches are used.
3. Network configuration workload for the host is reduced. VLAN can be used to group specific
hosts. When the physical position of a host changes within the range of the VLAN, you need
not to change its network configuration.
A VLAN can span across multiple switches, or even routers. This enables hosts in a VLAN to be
dispersed in a looser way. That is, hosts in a VLAN can belong to different physical network
segment. This switch supports three ways, namely, 802.1Q VLAN, MAC VLAN and Protocol VLAN,
to classify VLANs. VLAN tags in the packets are necessary for the switch to identify packets of
different VLANs. The switch can analyze the received untagged packets on the port and match the
packets with the MAC VLAN, Protocol VLAN and 802.1Q VLAN in turn. If a packet is matched, the
switch will add a corresponding VLAN tag to it and forward it in the corresponding VLAN.
59
Page 72

803" :2403S"XNCP"
VLAN tags in the packets are necessary for the switch to identify packets of different VLANs. The
switch works at the data link layer in OSI model and it can identify the data link layer encapsulation
of the packet only, so you can add the VLAN tag field into the data link layer encapsulation for
identification.
In 1999, IEEE issues the IEEE 802.1Q protocol to standardize VLAN implementation, defining the
structure of VLAN-tagged packets. IEEE 802.1Q protocol defines that a 4-byte VLAN tag is
encapsulated after the destination MAC address and source MAC address to show the information
about VLAN.
As shown in the following figure, a VLAN tag contains four fields, including TPID (Tag Protocol
Identifier), Priority, CFI (Canonical Format Indicator), and VLAN ID.
Figure 6-2 Format of VLAN Tag
1. TPID: TPID is a 16-bit field, indicating that this data frame is VLAN-tagged. By default, it is
0x8100.
2. Priority: Priority is a 3-bit field, referring to 802.1p priority. Refer to section “QoS & QoS profile”
for details.
3. CFI: CFI is a 1-bit field, indicating whether the MAC address is encapsulated in the standard
format in different transmission media. This field is not described in detail in this chapter.
4. VLAN ID: VLAN ID is a 12-bit field, indicating the ID of the VLAN to which this packet belongs.
It is in the range of 0 to 4,095. Generally, 0 and 4,095 is not used, so the field is in the range of
1 to 4,094.
VLAN ID identifies the VLAN to which a packet belongs. When the switch receives an
un-VLAN-tagged packet, it will encapsulate a VLAN tag with the default VLAN ID of the inbound
port for the packet, and the packet will be assigned to the default VLAN of the inbound port for
transmission.
In this User Guide, the tagged packet refers to the packet with VLAN tag whereas the untagged
packet refers to the packet without VLAN tag, and the priority-tagged packet refers to the packet
with VLAN tag whose VLAN ID is 0.
" Nkpm"V{rgu"qh"rqtvu"
When creating the 802.1Q VLAN, you should set the link type for the port according to its
connected device. The link types of port including the following three types:
1. ACCESS: The ACCESS port can be added in a single VLAN, and the egress rule of the port is
UNTAG. The PVID is same as the current VLAN ID. If the ACCESS port is added to another
VLAN, it will be removed from the current VLAN automatically.
2. TRUNK: The TRUNK port can be added in multiple VLANs, and the egress rule of the port is
TAG. The TRUNK port is generally used to connect the cascaded network devices for it can
receive and forward the packets of multiple VLANs. When the packets are forwarded by the
TRUNK port, its VLAN tag will not be changed.
3. GENERAL: The GENERAL port can be added in multiple VLANs and set various egress rules
according to the different VLANs. The default egress rule is UNTAG. The PVID can be set as
the VID number of any VLAN the port belongs to.
60
Page 73

" RXKF"
PVID (Port VLAN ID) is the default VID of the port. When the switch receives an un-VLAN-tagged
packet, it will add a VLAN tag to the packet according to the PVID of its received port and forward
the packets.
When creating VLANs, the PVID of each port, indicating the default VLAN to which the port
belongs, is an important parameter with the following two purposes:
1. When the switch receives an un-VLAN-tagged packet, it will add a VLAN tag to the packet
according to the PVID of its received port
2. PVID determines the default broadcast domain of the port, i.e. when the port receives UL
packets or broadcast packets, the port will broadcast the packets in its default VLAN.
Different packets, tagged or untagged, will be processed in different ways, after being received by
ports of different link types, which is illustrated in the following table.
Receiving Packets
Port Type
Forwarding Packets
Untagged Packets Tagged Packets
If the VID of packet is the
same as the PVID of the
port, the packet will be
Access
Trunk
General
When untagged
packets are received,
the port will add the
default VLAN tag, i.e.
the PVID of the
ingress port, to the
packets.
received.
If the VID of packet is not
the same as the PVID of
the port, the packet will
be dropped.
If the VID of packet is
allowed by the port, the
packet will be received.
If the VID of packet is
forbidden by the port, the
packet will be dropped.
The packet will be forwarded after
removing its VLAN tag.
The packet will be forwarded with
its current VLAN tag.
If the egress rule of port is TAG,
the packet will be forwarded with
its current VLAN tag.
If the egress rule of port is
UNTAG, the packet will be
forwarded after removing its
VLAN tag.
Table 6-1 Relationship between Port Types and VLAN Packets Processing
IEEE 802.1Q VLAN function is implemented on the XNCP"Eqphki"and Rqtv"Eqphki"pages.
80303"XNCP"Eqphki"
On this page, you can view the current created 802.1Q VLAN.
Choose the menu XNCP→:2403S"XNCP→XNCP"Eqphki to load the following page.
Figure 6-3 VLAN Table
61
Page 74

o ensure the normal communication of the factory switch, the default VLAN of all ports is set to
T
VLAN1.
The following entries are displayed on this screen:
" XNCP"Vcdng"
XNCP"KF"Ugngev:"
Click the Ugngev" button to quick-select the corresponding entry
based on the VLAN ID number you entered.
Ugngev:"
Select the desired entry to delete the corresponding VLAN. It is
multi-optional.
XNCP"KF:"
Pcog:"
Ogodgtu:"
Qrgtcvkqp:"
Displays the ID number of VLAN.
Displays the user-defined name of VLAN.
Displays the port members in the VLAN.
Allows you to view or modify the information for each entry.
Gfkv<"Click to modify the settings of VLAN.
Fgvckn< Click to get the information of VLAN.
Click Gfkv"button to modify the settings of the corresponding VLAN. Click Etgcvg button to create a
new VLAN.
Figure 6-4 Create or Modify 802.1Q VLAN
62
Page 75

e following entries are displayed on this screen:
Th
" XNCP"Eqphki"
XNCP"KF<"
Fguetkrvkqp<"
Ejgem<"
" XNCP"Ogodgtu"
Rqtv"Ugngev<"
Ugngev<"
Rqtv<"
Nkpm"V{rg<"
Gitguu"Twng<"
NCI<"
Enter the ID number of VLAN.
Give a description to the VLAN for identification.
Click the Ejgem"button to check whether the VLAN ID you entered
is valid or not.
Click the Ugngev" button to quick-select the corresponding entry
based on the port number you entered.
Select the desired port to be a member of VLAN or leave it blank.
It's multi-optional.
Displays the port number.
Displays the Link Type of the port. It can be reset on Port Config
screen.
Select the Egress Rule for the VLAN port member. The default
egress rule is UNTAG.
VC I< " All packets forwarded by the port are tagged. The
packets contain VLAN information.
WPVCI< Packets forwarded by the port are untagged.
Displays the LAG to which the port belongs.
80304"Rqtv"Eqphki"
Before creating the 802.1Q VLAN, please acquaint yourself with all the devices connected to the
switch in order to configure the ports properly.
63
Page 76

Choose the
menu XNCP→:2403S"XNCP→Rqtv"Eqphki to load the following page.
Figure 6-5 802.1Q VLAN – Port Config
The following entries are displayed on this screen:
" XNCP"Rqtv"Eqphki"
Rqtv"Ugngev<"
Click the Ugngev" button to quick-select the corresponding entry
based on the port number you entered.
Ugngev<"
Rqtv<"
Nkpm"V{rg<"
Select the desired port for configuration. It is multi-optional.
Displays the port number.
Select the Link Type from the pull-down list for the port.
CEEGUU<"The ACCESS port can be added in a single VLAN,
and the egress rule of the port is UNTAG. The PVID is same
as the current VLAN ID. If the current VLAN is deleted, the
PVID will be set to 1 by default.
VTWPM<"The TRUNK port can be added in multiple VLANs,
and the egress rule of the port is TAG. The PVID can be set as
the VID number of any VLAN the port belongs to.
IGPGTCN<" The GENERAL port can be added in multiple
VLANs and set various egress rules according to the different
VLANs. The default egress rule is UNTAG. The PVID can be
set as the VID number of any VLAN the port belongs to.
RXKF<"
NCI<"
XNCP<"
Enter the PVID number of the port.
Displays the LAG to which the port belongs.
Click the Fgvckn" button to view the information of the VLAN to
which the port belongs.
64
Page 77

lick the Fgvckn button to view the information of the corresponding VLAN.
C
Figure 6-6 View the Current VLAN of Port
The following entries are displayed on this screen:
" XNCP"qh"Rqtv"
XNCP"KF"Ugngev<"
XNCP"KF:"
XNCP"Pcog<"
Qrgtcvkqp<"
Click the Ugngev" button to quick-select the corresponding entry
based on the VLAN ID number you entered.
Displays the ID number of VLAN.
Displays the user-defined description of VLAN.
Allows you to remove the port from the current VLAN.
Configuration Procedure:
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Set the link type for
port.
2 Create VLAN. Required. On the XNCP→:2403S" XNCP→XNCP" Eqphki page,
3 Modify/View VLAN. Optional. On the XNCP→:2403S" XNCP→XNCP" Eqphki page,
Required. On the XNCP→:2403S"XNCP→Rqtv"Eqphki page, set
the link type for the port basing on its connected device.
click the Etgcvg"button to create a VLAN. Enter the VLAN ID and
the description for the VLAN. Meanwhile, specify its member
ports.
click the Gfkv1Fgvckn button to modify/view the information of the
corresponding VLAN.
4 Delete VLAN Optional. On the XNCP→:2403S" XNCP→XNCP" Eqphki page,
select the desired entry to delete the corresponding VLAN by
clicking the Fgngvg"button.
804" OCE"XNCP"
MAC VLAN technology is the way to classify VLANs according to the MAC addresses of Hosts. A
MAC address corresponds to a single VLAN ID. For the device in a MAC VLAN, if its MAC address
is bound to VLAN, the device can be connected to another member port in this VLAN and still
takes its member role effect without changing the configuration of VLAN members.
The packet in MAC VLAN is processed in the following way:
1. When receiving an untagged packet, the switch matches the packet with the current MAC
VLAN. If the packet is matched, the switch will add a corresponding MAC VLAN tag to it. If no
MAC VLAN is matched, the switch will add a tag to the packet according to the PVID of the
65
Page 78

received p
ort. Thus, the packet is assigned automatically to the corresponding VLAN for
transmission.
2. When receiving tagged packet, the switch will process it basing on the 802.1Q VLAN. If the
received port is the member of the VLAN to which the tagged packet belongs, the packet will
be forwarded normally. Otherwise, the packet will be discarded.
3. If the MAC address of a Host is classified into 802.1Q VLAN, please set its connected port of
switch to be a member of this 802.1Q VLAN so as to ensure the packets forwarded normally.
80403"OCE"XNCP"
On this page, you can create MAC VLAN and view the current MAC VLANs in the table.
Choose the menu XNCP→OCE"XNCP to load the following page.
Figure 6-7 Create and View MAC VLAN
The following entries are displayed on this screen:
" XNCP"Vcdng"
OCE"Cfftguu<"
Fguetkrvkqp<"
XNCP"KF<"
Enter the MAC address.
Give a description to the MAC address for identification.
Enter the ID number of the MAC VLAN. This VLAN should be one
of the 802.1Q VLANs the ingress port belongs to.
" OCE"XNCP"Vcdng"
OCE"Ugngev<"
Click the Ugngev" button to quick-select the corresponding entry
based on the MAC address you entered.
Ugngev<"
OCE"Cfftguu<"
Fguetkrvkqp<"
Select the desired entry. It is multi-optional.
Displays the MAC address.
Displays the user-defined description of the MAC address.
XNCP"KF<"
Qrgtcvkqp<"
Displays the corresponding VLAN ID of the MAC address.
Click the Gfkv"button to modify the settings of the entry. And click
the Oqfkh{ button to apply your settings.
66
Page 79

80404"Rqtv"Gpcdng"
On this page, you can enable the port for the MAC VLAN feature. Only the port is enabled, can the
configured MAC VLAN take effect.
Choose the menu XNCP→OCE"XNCP→Rqtv"Gpcdng to load the following page.
Figure 6-8 Enable MAC VLAN for Port
Select your desired port for VLAN Mapping function. All the ports are disabled for VLAN Mapping
function by default.
Configuration Procedure:
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Set the link type for
port.
2 Create VLAN. Required. On the XNCP→:2403S" XNCP→XNCP" Eqphki page,
3 Create MAC VLAN. Required. On the XNCP→OCE"XNCP page, create the MAC VLAN.
4 Select your desired
ports for MAC VLAN
feature.
Required. On the XNCP→:2403S" XNCP→Rqtv" Eqphki page, set
the link type for the port basing on its connected device.
click the Etgcvg button to create a VLAN. Enter the VLAN ID and
the description for the VLAN. Meanwhile, specify its member ports.
For the device in a MAC VLAN, it’s required to set its connected
port of switch to be a member of this VLAN so as to ensure the
normal communication.
Required. On the XNCP→OCE"XNCP→Rqtv" Gpcdng page, select
and enable the desired ports for MAC VLAN feature.
805" Rtqvqeqn"XNCP"
Protocol VLAN is another way to classify VLANs basing on network protocol. Protocol VLANs can
be sorted by IP, IPX, DECnet, AppleTalk, Banyan and so on. Through the Protocol VLANs, the
broadcast domain can span over multiple switches and the Host can change its physical position
in the network with its VLAN member role always effective. By creating Protocol VLANs, the
network administrator can manage the network clients basing on their actual applications and
services effectively.
This switch can classify VLANs basing on the common protocol types listed in the following table.
Please create the Protocol VLAN to your actual need.
Protocol Type Type value
ARP 0x0806
IP 0x0800
MPLS 0x8847/0x8848
67
Page 80

Protocol Type Type value
IPX 0x8137
IS-IS 0x8000
LACP 0x8809
802.1X 0x888E
Table 6-2 Protocol types in common use
The packet in Protocol VLAN is processed in the following way:
1. When receiving an untagged packet, the switch matches the packet with the current Protocol
VLAN. If the packet is matched, the switch will add a corresponding Protocol VLAN tag to it. If
no Protocol VLAN is matched, the switch will add a tag to the packet according to the PVID of
the received port. Thus, the packet is assigned automatically to the corresponding VLAN for
transmission.
2. When receiving tagged packet, the switch will process it basing on the 802.1Q VLAN. If the
received port is the member of the VLAN to which the tagged packet belongs, the packet will
be forwarded normally. Otherwise, the packet will be discarded.
3. If the Protocol VLAN is created, please set its enabled port to be the member of
corresponding 802.1Q VLAN so as to ensure the packets forwarded normally.
80503"Rtqvqeqn"XNCP"
On this page, you can create Protocol VLAN and view the information of the current defined
Protocol VLANs.
Choose the menu XNCP→Rtqvqeqn"XNCP→Rtqvqeqn"XNCP to load the following page.
Figure 6-9 Create Protocol VLAN
The following entries are displayed on this screen:
" Etgcvg"Rtqvqeqn"XNCP"
Rtqvqeqn<"
XNCP"KF<"
Select the defined protocol template.
Enter the ID number of the Protocol VLAN. This VLAN should be one
of the 802.1Q VLANs the ingress port belongs to.
68
Page 81

" Rtqvqeqn"XNCP"Vcdng"
Ugngev<"
Rtqvqeqn<"
Gvjgt"V{rg<"
XNCP"KF<"
Qrgtcvkqp<"
Select the desired entry. It is multi-optional.
Displays the protocol template of the VLAN.
Displays the Ethernet protocol type field in the protocol template.
Displays the corresponding VLAN ID of the protocol.
Click the Gfkv"button to modify the settings of the entry. And click the
Oqfkh{"button to apply your settings.
80504"Rtqvqeqn"Vgorncvg"
The Protocol Template should be created before configuring the Protocol VLAN. By default, the
switch has defined the IP Template, ARP Template, RARP Template, etc. You can add more
Protocol Template on this page.
Choose the menu XNCP→Rtqvqeqn"XNCP→Rtqvqeqn"Vgorncvg to load the following page.
Figure 6-10 Create and View Protocol Template
The following entries are displayed on this screen:
" Etgcvg"Rtqvqeqn"Vgorncvg"
Rtqvqeqn"Pcog<"
Gvjgt"V{rg<"
" Rtqvqeqn"Vgorncvg"Vcdng"
Ugngev<"
Rtqvqeqn"Pcog<"
Gvjgt"V{rg<"
Give a name for the Protocol Template.
Enter the Ethernet protocol type field in the protocol template.
Select the desired entry. It is multi-optional.
Displays the name of the protocol template.
Displays the Ethernet protocol type field in the protocol template.
Pqvg<"
The Protocol Template bound to VLAN cannot be deleted.
69
Page 82

80505"Rqtv"Gpcdng"
On this page, you can enable the port for the Protocol VLAN feature. Only the port is enabled, can
the configured Protocol VLAN take effect.
Choose the menu XNCP→Rtqvqeqn"XNCP→Rqtv"Gpcdng to load the following page.
Figure 6-11 Enable Protocol VLAN for Port
Select your desired port for VLAN Mapping function. All the ports are disabled for VLAN Mapping
function by default.
Configuration Procedure:
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Set the link type for port. Required. On the XNCP→:2403S"XNCP→Rqtv"Eqphki page,
set the link type for the port basing on its connected device.
2 Create VLAN. Required. On the XNCP→:2403S" XNCP→XNCP" Eqphki
page, click the Etgcvg button to create a VLAN. Enter the
VLAN ID and the description for the VLAN. Meanwhile,
specify its member ports.
3 Create Protocol Template. Required. On the XNCP→Rtqvqeqn" XNCP→Rtqvqeqn"
Vgornc v g page, create the Protocol Template before
configuring Protocol VLAN.
4 Select your desired ports for
Protocol VLAN feature.
5 Create Protocol VLAN. Required. On the XNCP→Rtqvqeqn" XNCP→Rtqvqeqn"
6 Modify/View VLAN. Optional. On the XNCP→Rtqvqeqn"XNCP→Rtqvqeqn"XNCP"
Required. On the XNCP→Rtqvqeqn" XNCP→Rqtv" Gpcdng
page, select and enable the desired ports for Protocol
VLAN feature.
XNCP"page, select the protocol type and enter the VLAN ID
to create a Protocol VLAN.
page, click the Gfkv button to modify/view the information of
the corresponding VLAN.
7 Delete VLAN. Optional. On the XNCP→Rtqvqeqn"XNCP→Rtqvqeqn"XNCP"
page, select the desired entry to delete the corresponding
VLAN by clicking the Fgngvg button.
806" Crrnkecvkqp"Gzcorng"hqt":2403S"XNCP"
Pgvyqtm"Tgswktgogpvu"
Switch A is connecting to PC A and Server B;
70
Page 83

Switch B is connecting to PC B and Server A;
PC A and Server A is in the same VLAN;
PC B and Server B is in the same VLAN;
PCs in the two VLANs cannot communicate with each other.
Pgvyqtm"Fkcitco"
Eqphkiwtcvkqp"Rtqegfwtg"
Configure switch A
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
ports
Required. On XNCP→:2403S" XNCP→Rqtv" Eqphki"page, configure
the link type of Port 2, Port 3 and Port 4 as ACCESS, TRUNK and
ACCESS respectively
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki"page, create a
VLAN with its VLAN ID as 10, owning Port 2 and Port 3.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki"page, create a
VLAN with its VLAN ID as 20, owning Port 3 and Port 4.
Configure switch B
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
ports
Required. On XNCP→:2403S" XNCP→Rqtv" Eqphki"page, configure
the link type of Port 7, Port 6 and Port 8 as ACCESS, TRUNK and
ACCESS respectively.
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki"page, create a
VLAN with its VLAN ID as 10, owning Port 6 and Port 8.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki"page, create a
VLAN with its VLAN ID as 20, owning Port 6 and Port 7.
71
Page 84

807" Crrnkecvkqp"Gzcorng"hqt"OCE"XNCP"
Pgvyqtm"Tgswktgogpvu"
Switch A and switch B are connected to meeting room A and meeting room B respectively, and
the two rooms are for all departments;
Notebook A and Notebook B, special for meeting room, are of two different departments;
The two departments are in VLAN10 and VLAN20 respectively. The two notebooks can just
access the server of their own departments, that is, Server A and Server B, in the two meeting
rooms;
The MAC address of Notebook A is 00-19-56-8A-4C-71, Notebook B’s MAC address is
00-19-56-82-3B-70.
Pgvyqtm"Fkcitco"
Eqphkiwtcvkqp"Rtqegfwtg"
Configure switch A
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
Required. On XNCP→:2403S"XNCP→Rqtv"Eqphki"page, configure the
link type of Port 11 and Port 12 as GENERAL and TRUNK respectively.
ports
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 10, owning Port 11 and Port 12, and
configure the egress rule of Port 11 as Untag.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 20, owning Port 11 and Port 12, and
configure the egress rule of Port 11 as Untag.
72
Page 85

Uvgr" Qrgtcvkqp" Fguetkrvkqp"
4 Configure MAC
VLAN 10
5 Configure MAC
VLAN 20
On XNCP→OCE"XNCP→OCE"XNCP"page, create MAC VLAN10 with
the MAC address as 00-19-56-8A-4C-71.
On XNCP→OCE"XNCP→OCE"XNCP"page, create MAC VLAN10 with
the MAC address as 00-19-56-82-3B-70.
6 Port Enable Required. On the XNCP→OCE"XNCP→Rqtv"Gpcdng page, select and
enable Port 11 and Port 12 for MAC VLAN feature.
Configure switch B
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
Required. On XNCP→:2403S"XNCP→Rqtv"Eqphki"page, configure the
link type of Port 21 and Port 22 as GENERAL and TRUNK respectively.
ports
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 10, owning Port 21 and Port 22, and
configure the egress rule of Port 21 as Untag.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 20, owning Port 21 and Port 22, and
configure the egress rule of Port 21 as Untag.
4 Configure MAC
VLAN 10
5 Configure MAC
VLAN 20
On XNCP→OCE"XNCP→OCE"XNCP"page, create MAC VLAN10 with
the MAC address as 00-19-56-8A-4C-71.
On XNCP→OCE"XNCP→OCE"XNCP"page, create MAC VLAN10 with
the MAC address as 00-19-56-82-3B-70.
6 Port Enable Required. On the XNCP→OCE"XNCP→Rqtv"Gpcdng page, select and
enable Port 21 and Port 22 for MAC VLAN feature.
Configure switch C
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
ports
Required. On XNCP→:2403S"XNCP→Rqtv"Eqphki"page, configure the
link type of Port 2 and Port 3 as GENERAL, and configure the link type
of Port 4 and Port 5 as ACCESS.
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 10, owning Port 2, Port 3 and Port 5,
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 20, owning Port 2, Port 3 and Port 4,
808" Crrnkecvkqp"Gzcorng"hqt"Rtqvqeqn"XNCP"
Pgvyqtm"Tgswktgogpvu"
Department A is connected to the company LAN via Port12 of switch A;
Department A has IP host and AppleTalk host;
73
Page 86

IP host, in VLAN10, is served by IP server while AppleTalk host is served by AppleTalk server;
Switch B is connected to IP server and AppleTalk server.
Pgvyqtm"Fkcitco"
Eqphkiwtcvkqp"Rtqegfwtg"
Configure switch A
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
ports
Required. On XNCP→:2403S"XNCP→Rqtv"Eqphki"page, configure the
link type of Port 11 and Port 13 as ACCESS, and configure the link type
of Port 12 as GENERAL.
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 10, owning Port 12 and Port 13, and
configure the egress rule of Port 12 as Untag.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 20, owning Port 11 and Port 12, and
configure the egress rule of Port 12 as Untag.
Configure switch B
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Configure the
Link Type of the
ports
Required. On XNCP→:2403S"XNCP→Rqtv"Eqphki"page, configure the
link type of Port 4 and Port 5 as ACCESS, and configure the link type of
Port 3 as GENERAL.
2 Create VLAN10 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 10, owning Port 3 and Port 4, and configure
the egress rule of Port 3 as Untag.
3 Create VLAN20 Required. On XNCP→:2403S" XNCP→XNCP" Eqphki" page, create a
VLAN with its VLAN ID as 20, owning Port 3 and Port 5, and configure
the egress rule of Port 3 as Untag.
74
Page 87

Uvgr" Qrgtcvkqp" Fguetkrvkqp"
4 Create Protocol
Tem pl at e
5 Port Enable Required. On the XNCP→Rtqvqeqn"XNCP→Rqtv"Gpcdng page, select
6 Create Protocol
VLAN 10
7 Create Protocol
VLAN 20
Required. On XNCP→Rtqvqeqn" XNCP→Rtqvqeqn" Vgorncvg" page,
configure the protocol template practically. E.g. the Ether Type of IP
network packets is 0800 and that of AppleTalk network packets is 809B.
and enable Port 3, Port 4 and Port 5 for Protocol VLAN feature.
On XNCP→Rtqvqeqn" XNCP→Rtqvqeqn" XNCP" page, create protocol
VLAN 10 with Protocol as IP.
On XNCP→Rtqvqeqn" XNCP→Rtqvqeqn" XNCP" page, create protocol
VLAN 20 with Protocol as AppleTalk.
809" XNCP"XRP"
With the increasing application of the Internet, the VPN (Virtual Private Network) technology is
developed and used to establish the private network through the operators’ backbone networks.
VLAN-VPN (Virtual Private Network) function, the implement of a simple and flexible Layer 2 VPN
technology, allows the packets with VLAN tags of private networks to be encapsulated with VLAN
tags of public networks at the network access terminal of the Internet Service Provider. And these
packets will be transmitted with double-tag across the public networks.
The VLAN-VPN function provides you with the following benefits:
1. Provides simple Layer 2 VPN solutions for small-sized MANs or intranets.
2. Saves public network VLAN ID resource.
3. You can have VLAN IDs of your own, which is independent of public network VLAN IDs.
4. When the network of the Internet Service Provider is upgraded, the user’s network with a
relative independence can still work normally without changing the current configurations.
In addition, the switch supports the feature to adjust the TPID Values of VLAN VPN Packets. TPID
(Tag Protocol Identifier) is a field of the VLAN tag. IEEE 802.1Q specifies the value of TPID to be
0x8100. This switch adopts the default value of TPID (0x8100) defined by the protocol. Other
manufacturers use other TPID values (such as 0x9100 or 0x9200) in the outer tags of VLAN-VPN
packets. To be compatible with devices coming from other manufacturers, this switch can adjust
the TPID values of VLAN-VPN packets globally. You can configure TPID values by yourself. When
a port receives a packet, this port will replace the TPID value in the outer VLAN tag of this packet
with the user-defined value and then send the packet again. Thus, the VLAN-VPN packets sent to
the public network can be recognized by devices of other manufacturers.
The position of the TPID field in an Ethernet packet is the same as the position of the protocol type
field in the packet without VLAN Tag. Thus, to avoid confusion happening when the switch
forwards or receives a packet, you must not configure the following protocol type values listed in
the following table as the TPID value.
Rtqvqeqn"v{rg" Xcnwg"
ARP 0x0806
IP 0x0800
MPLS 0x8847/0x8848
IPX 0x8137
IS-IS 0x8000
75
Page 88

Rtqvqeqn"v{rg" Xcnwg"
LACP 0x8809
802.1X 0x888E
Table 6-3 Values of Ethernet frame protocol type in common use
This VLAN VPN function is implemented on the XRP"Eqphki, XNCP" Ocrrkpi and Rqtv" Gpcdng
pages.
80903"XRP"Eqphki"
This page allows you to enable the VPN function, adjust the global TPID for VLAN-VPN packets
and enable the VPN up-link port. When VPN mode is enabled, the switch will add a tag to the
received tagged packet basing on the VLAN mapping entries.
Choose the menu XNCP→XNCP"XRP→XRP"Eqphki to load the following page.
Figure 6-12 VPN Global Config
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
XRP"Oqfg<"
Inqdcn"VRKF<"
" XRP"Wr/nkpm"Rqtvu"
Allows you to Enable/Disable the VLAN-VPN function.
Enter the global TPID (Tag protocol identifier).
Select the desired port as the VPN Up-link port. It’s required to set the port connected to the
operators’ backbone networks to be up-link port.
Pqvg<"
If VPN mode is enabled, please create VLAN Mapping entries on the VLAN Mapping function
page.
80904"XNCP"Ocrrkpi"
VLAN Mapping function allows the VLAN TAG of the packets to be replaced with the new VLAN
TAG according to the VLAN Mapping entries. And these packets can be forwarded in the new
VLAN. If VLAN VPN function is enabled, a received packet already carrying a VLAN tag will be
tagged basing on the VLAN Mapping entries and becomes a double-tagged packet to be
forwarded in the new VLAN.
76
Page 89

Choose the
menu XNCP→XNCP"XRP→XNCP"Ocrrkpi to load the following page.
Figure 6-13 Create VLAN Mapping Entry
The following entries are displayed on this screen:
" XNCP"Ocrrkpi"Eqphki"
E"XNCP<"
Enter the ID number of the Customer VLAN. C VLAN refers to the
VLAN to which the packet received by switch belongs.
UR"XNCP<"
Fguetkrvkqp<"
" XNCP"Ocrrkpi"Vcdng"
E"XNCP"Ugngev<"
Enter the ID number of the Service Provider VLAN.
Give a description to the VLAN Mapping entry or leave it blank.
Click the Ugngev button to quick-select the corresponding entry
based on the C VLAN ID you entered.
Ugngev<"
Select the desired entry to delete the corresponding VLAN
Mapping entry. It is multi-optional.
Qrgtcvkqp<"
Click the Gfkv"button to modify the settings of the entry and click
the Oqfkh{"button to apply.
80905"Rqtv"Gpcdng"
On this page, you can enable the port for the VLAN Mapping function. Only the port is enabled,
can the configured VLAN Mapping function take effect.
77
Page 90

Figure 6-14 Enable VLAN Mapping for Port
Select your desired port for VLAN Mapping function. All the ports are disabled for VLAN Mapping
function by default.
Eqphkiwtcvkqp"Rtqegfwtg"qh"XNCP"XRP"Hwpevkqp<"
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Enable VPN mode. Required. On the XNCP→XNCP"XRP→XRP"Eqphki"page,
enable the VPN mode.
2 Configure the global TPID. Optional. On the XNCP→XNCP" XRP→XRP" Eqphki"page,
configure the global TPID basing on the devices connected
to the up-link port.
3 Set the VPN up-link port. Required. On the XNCP→XNCP"XRP→XRP"Eqphki"page,
specify the desired port to be the VPN up-link port. It’s
required to set the port connected to the backbone
networks to be up-link port.
4 Create VLAN Mapping
entries.
Required. On the XNCP→XNCP" XRP→XNCP" Ocrrkpi"
page, configure the VLAN Mapping entries basing on the
actual application.
5 Create SP (Service
Provider) VLAN.
Optional. On the XNCP→:2403S" XNCP" page, create the
SP VLAN. For the steps of creating VLAN, please refer to
802.1Q VLAN
.
Eqphkiwtcvkqp"Rtqegfwtg"qh"XNCP"Ocrrkpi"Hwpevkqp<"
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Create VLAN Mapping
entries.
Required. On the XNCP→XNCP" XRP→XNCP" Ocrrkpi"
page, configure the VLAN Mapping entries basing on the
actual application.
2 Enable VLAN Mapping
function for port.
3 Create SP (Service
Provider) VLAN
Required. On the XNCP→XNCP"XRP→Rqtv"Gpcdng"page,
enable VLAN Mapping function for the ports.
Optional. On the XNCP→:2403S" XNCP" page, create the
SP VLAN. For the steps of creating VLAN, please refer to
802.1Q VLAN
78
.
Page 91

80:" Rtkxcvg"XNCP"
Private VLANs, designed to save VLAN resources of uplink devices and decrease broadcast, are
sets of VLAN pairs that share a common primary identifier. To guarantee user information security,
the ease with which to manage and account traffic for service providers, in campus network,
service providers usually require that each individual user is layer-2 separated. VLAN feature can
solve this problem. However, as stipulated by IEEE 802.1Q protocol, a device can only support up
to 4094 VLANs. If a service provider assigns one VLAN per user, the VLANs will be far from
enough; as a result, the number of users this service provider can support is limited.
Private VLAN adopts Layer 2 VLAN structure. A Private VLAN consists of a Primary VLAN and a
Secondary VLAN, providing a mechanism for achieving layer-2-separation between ports. For
uplink devices, all the packets received from the downstream are without VLAN tags. Uplink
devices need to identify Primary VLANs but not Secondary VLANs. Therefore, they can save
VLAN resources without considering the VLAN configuration in the lower layer. Meanwhile, the
service provider can assign each user an individual Secondary VLAN, so that users are separated
at the Layer 2 level.
Private VLAN technology is mainly used in campus or enterprise networks to achieve user
layer-2-separation and to save VLAN resources of uplink devices.
Vjg"Gngogpvu"qh"c"Rtkxcvg"XNCP
Rtkoct{"XNCP<"A Private VLAN has one Primary VLAN and one Secondary VLAN. Primary VLAN
is the user VLAN uplink device can identify but it is not the actual VLAN the end user is in. Every
port in a private VLAN is a member of the primary VLAN. The primary VLAN carries unidirectional
traffic downstream from the promiscuous ports to the host ports and to other promiscuous ports.
Ugeqpfct{"XNCP< .Secondary VLAN is the actual VLAN the end user is in. Secondary VLANs are
associated with a primary VLAN, and are used to carry traffic from hosts to uplink devices."
Rtqokuewqwu< A promiscuous port connects to and communicates with the uplink device. The
PVID of the promiscuous port is the same with the Primary VLAN ID. One promiscuous port can
only join to one Primary VLAN.
Jquv<"A host port connects to and communicates with terminal device. The PVID of the host port is
the same as the Secondary VLAN ID. One host port can only belong to one Private VLAN.
Hgcvwtgu"qh"Rtkxcvg"XNCP"
1. A Private VLAN contains one Primary VLAN and one Secondary VLAN.
2. A VLAN cannot be set as the Primary VLAN and Secondary VLAN simultaneously.
3. A Secondary VLAN can only join one private VLAN.
4. A Primary VLAN can be associated with multi-Secondary VLANs to create multi-Private
VLANs.
Rtkxcvg"XNCP"Korngogpvcvkqp"
To hide Secondary VLANs from uplink devices and save VLAN resources, Private VLAN
containing one Primary VLAN and one Secondary VLAN requires the following characteristics:
79
Page 92

Packets from different Secondary VLANs can be forwarded to the uplink device via
promiscuous port and carry no corresponding Secondary VLAN information.
Packets from Primary VLANs can be sent to end users via host port and carry no Primary
VLAN information.
Private VLAN is designed to save VLAN resource by means of Port configuration synchronization
among the MAC address tables of VLANs and MAC address duplication. To achieve these
requirements described above, the following two aspects are required:
1) Create Private VLAN: A Private VLAN includes one Primary VLAN and one Secondary VLAN,
the PVID of the promiscuous port is equal to the Primary VLAN ID and the PVID of the host
port is the same as the corresponding Secondary VLAN ID, moreover, the egress rule of all
ports is untag by default, that is, only those untagged packets can be forwarded, but you can
modify the egress rule on XNCP→:2403S"XNCP→XNCP"Eqphki"page.
2) Port configuration and MAC address duplication should be synchronized on the switch. Port
configuration synchronization is completed in the whole configuration progress and MAC
address duplication is implemented while FDB is changing.
Port configuration synchronization: when configuring promiscuous and host ports for a
Private VLAN, the system will automatically add the promiscuous port and the host port
synchronously to the corresponding Primary VLAN and Secondary VLAN. Through port
configuration synchronization, the promiscuous port forwards the packets from the Primary
VLAN as well as from all the Primary VLAN-associated Secondary VLANs; the host port
forwards the packets from the Primary VLAN and the Secondary VLAN owning this host port.
Here we take a Private VLAN to illustrate port configuration synchronization. As shown in
the figure below, Port2, Port3 and Port5 belong to VLAN 2, VLAN 3 and VLAN 5
respectively. Configure VLAN 2 and VLAN 3 as Secondary VLANs, and VLAN5 as Primary
VLAN. After this configuration is completed, the settings of these ports are changed as
shown in Table 6-5.
Figure 6-15
80
Page 93

Port PVID Allowed VLANs
Port5 5 VLAN5
Port2 2 VLAN2
Port3 3 VLAN3
Table 6-4 Port settings before configuration synchronization
Port PVID Allowed VLANs
Port5 5 VLAN2, 3, 5
Port2 2 VLAN2, 5
Port3 3 VLAN2, 5
Table 6-5 Port settings after configuration synchronization
MAC address duplication: After port configuration synchronization, packets from Secondary
VLAN can be forwarded via the promiscuous port untagged, and those from Primary VLAN
can be sent via the host port untagged. In order for these packets can be forwarded in
unicast via the right port, MAC address duplication is used to expand the VLANs the MAC
address is in. Normally, the egress ports for forwarding these packets are identified through
MAC address learning. For example the switch in
table shown in Table 6-6. The MAC address duplication process has
Figure 6-15 maintains a MAC address
two aspects, that is,
duplicating the dynamic MAC addresses learned by the host ports in the secondary VLANs
to the Primary VLAN and copying the dynamic MAC addresses learned by the promiscuous
ports in the Primary VLAN to the secondary VLANs. As shown in
Figure 6-15, supposing the
Router sends a packet with the source MAC as mac_2 and the destination Mac as mac_a.
The MAC address table on the switch is changed to the one shown in Table 6-7.
Destination MAC VLAN Egress Port
mac_a 5 port 5
mac_2 2 port 2
mac_3 3 port 3
Table 6-6 MAC address table before duplication
Destination MAC VLAN Egress Port
mac_a 5 port 5
mac_a 2 port 5
mac_a 3 port 5
mac_2 2 port 2
mac_2 5 port 2
mac_3 3 port 3
mac_3 5 port 3
Table 6-7 MAC address table after duplication
81
Page 94

Rcemgv"hqtyctfkpi"kp"Rtkxcvg"XNCP"
The Private VLAN packet forwarding process (here we take traffic transmission for PC2) based on
the figure above is illustrated as follows:
1) PC2 sends out its first upstream packet with the source MAC as mac_2 and the destination
MAC as mac_a. This packet is untagged.
2) When the host port Port2 on the switch receives this packet, it adds a default VLAN ID 2 to
this packet and learns its source MAC address. The MAC address entry,
mac_2+VLAN2+Port2 is created, indicating that the egress port for the traffic with
destination MAC address mac_2 and VLAN ID 2 is Port2.
3) According to the MAC address duplication, this MAC address entry is copied to VLAN 5, and
the switch adds the MAC address entry mac_2+VLAN5+Port2 to its address table.
4) As mac_a is not in the MAC address table of the switch, the switch will broadcast this packet
in VLAN 2.
5) As the switch has performed the port configuration synchronization, Port5 can receive this
packet from VLAN 2 and forward it to the Router untagged.
6) The Router responds to the switch upon receiving this packet.
7) When the promiscuous port Port5 receives the response packet, it tags this packet a default
VLAN ID 5 and learns the MAC address entry mac_a+VLAN5+Port5.
8) According to the MAC address duplication, this MAC address entry is copied to VLAN 2 and
VLAN 3, and the switch adds two more MAC address entries mac_a+VLAN2+Port5 and
mac_a+VLAN3+Port5 to its address table.
9) The switch looks up the MAC address table based on mac_2+VLAN5. It finds out the egress
port Port2 through which the packet is forwarded to PC2 untagged.
After all the steps above are finished, the bidirectional communication between PC2 and the
Router is achieved.
Private VLAN functions are implemented on the RXNCP"Eqphki"and Rqtv"Eqphki"pages.
80:03"RXNCP"Eqphki"
On this page, you can create Private VLAN and view the information of the current defined Private
VLANs.
82
Page 95

Choose the
menu XNCP→Rtkxcvg"XNCP→RXNCP Eqphki to load the following page.
Figure 6-16 Create Private VLAN
The following entries are displayed on this screen:
" Etgcvg"Rtkxcvg"XNCP"
Rtkoct{"XNCP<"
Ugeqpfct{"XNCP<
" Ugctej"Qrvkqp"
Ugctej"Qrvkqp<"
" Rtkxcvg"XNCP"Vcdng"
Ugngev<"
Rtkoct{"XNCP<"
Ugeqpfct{"XNCP<
Rqtv<"
Enter the ID number of the Primary VLAN.
Enter the ID number of the Secondary VLAN.
Select a Search Option from the pull-down list and click the Ugctej"
button to find your desired entry in Private VLAN.
Rtkoct{" XNCP"KF<" Enter the Primary VLAN ID number of the
desired Private VLAN.
Ugeqpfct{"XNCP"KF<"Enter the Secondary VLAN ID number of
the desired Private VLAN.
Select the entry to delete. It is multi-optional.
Displays the Primary VLAN ID number of the Private VLAN.
Displays the Secondary VLAN ID number of the Private VLAN.
Displays the Port number of the Private VLAN.
80:04"Rqtv"Eqphki"
The Private VLAN provides two Port Types for the ports, Promiscuous and Host. Usually, the
Promiscuous port is used to connect to uplink devices while the Host port is used to connect to the
he terminal hosts, such as PC and Server.
83
Page 96

Choose the
menu XNCP→Rtkxcvg"XNCP→Rqtv"Eqphki to load the following page.
Figure 6-17 Create and View Protocol Template
The following entries are displayed on this screen:
" Rqtv"Eqphki"
Rqtv<"
Rqtv"V{rg<"
Rtkoct{"XNCP<"
Select the desired port for configuration.
Select the Port Type from the pull-down list for the port.
Specify the Primary VLAN the port belongs to.
Ugeqpfct{"XNCP<
" Rtkxcvg"XNCP"Rqtv"Vcdng"
Rqtv"KF<"
Rqtv"V{rg<"
Qrgtcvkqp<"
Specify the Secondary VLAN the port belongs to.
Displays the port number.
Displays the corresponding Port Type.
Click Tgoqxg to delete the port.
Pqvg<"
1. A Host Port can only join to a Private VLAN.
2. A Promiscuous Port can only join to a Primary VLAN.
3. If you want to add a Promiscuous port to different Private VLANs with the same Primary VLAN,
you need to add the Promiscuous port to any one of these Private VLANs.
Eqphkiwtcvkqp"Rtqegfwtg<"
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Create Private VLAN. Required. On the XNCP→Rtkxcvg"XNCP→RXNCP" Eqphki"
page, Enter the Primary VLAN and Secondary VLAN, and
then click the Etgcvg button.
2 Add ports to Private VLAN Required. On the XNCP→Rtkxcvg" XNCP→Rqtv" Eqphki
page, select the desired ports and configure the port types
and click the Cff"button.
3 Modify VLAN. Optional. On the XNCP→Rtkxcvg" XNCP→RXNCP" Eqphki
page, select the desired Private VLAN and do the
modification, then click the Crrn{ button to modify the
information of the corresponding VLAN.
84
Page 97

Uvgr" Qrgtcvkqp" Fguetkrvkqp"
4 Delete VLAN. Optional. On the XNCP→Rtkxcvg" XNCP→RXNCP" Eqphki
page, select the desired entry to delete the corresponding
VLAN by clicking the Fgngvg button.
80;" IXTR"
GVRP (GARP VLAN Registration Protocol) is an implementation of GARP (generic attribute
registration protocol). GVRP allows the switch to automatically add or remove the VLANs via the
dynamic VLAN registration information and propagate the local VLAN registration information to
other switches, without having to individually configure each VLAN.
" ICTR"
GARP provides the mechanism to assist the switch members in LAN to deliver, propagate and
register the information among the members. GARP itself does not work as the entity among the
devices. The application complied with GARP is called GARP implementation, and GVRP is the
implementation of GARP. When GARP is implemented on a port of device, the port is called
GARP entity.
The information exchange between GARP entities is completed by messages. GARP defines the
messages into three types: Join, Leave and LeaveAll.
Lqkp" Oguucig<" When a GARP entity expects other switches to register certain attribute
information of its own, it sends out a Join message. And when receiving the Join message
from the other entity or configuring some attributes statically, the device also sends out a Join
message in order to be registered by the other GARP entities.
Ngcxg"Oguucig< When a GARP entity expects other switches to deregister certain attribute
information of its own, it sends out a Leave message. And when receiving the Leave message
from the other entity or deregistering some attributes statically, the device also sends out a
Leave message.
NgcxgCnn"Oguucig<"Once a GARP entity starts up, it starts the LeaveAll timer. After the timer
times out, the GARP entity sends out a LeaveAll message. LeaveAll message is to deregister
all the attribute information so as to enable the other GARP entities to re-register attribute
information of their own.
Through message exchange, all the attribute information to be registered can be propagated to all
the switches in the same switched network.
The interval of GARP messages is controlled by timers. GARP defines the following timers:
Jqnf" Vkogt<" When a GARP entity receives a piece of registration information, it does not
send out a Join message immediately. Instead, to save the bandwidth resources, it starts the
Hold timer, puts all registration information it receives before the timer times out into one Join
message and sends out the message after the timer times out.
Lqkp" Vkogt<" To transmit the Join messages reliably to other entities, a GARP entity sends
each Join message two times. The Join timer is used to define the interval between the two
sending operations of each Join message.
Ngcxg" Vkogt< When a GARP entity expects to deregister a piece of attribute information, it
sends out a Leave message. Any GARP entity receiving this message starts its Leave timer,
and deregisters the attribute information if it does not receives a Join message again before
the timer times out.
85
Page 98

NgcxgC
nn"Vkogt<"Once a GARP entity starts up, it starts the LeaveAll timer, and sends out a
LeaveAll message after the timer times out, so that other GARP entities can re-register all the
attribute information on this entity. After that, the entity restarts the LeaveAll timer to begin a
new cycle.
" IXTR"
GVRP, as an implementation of GARP, maintains dynamic VLAN registration information and
propagates the information to other switches by adopting the same mechanism of GARP.
After the GVRP feature is enabled on a switch, the switch receives the VLAN registration
information from other switches to dynamically update the local VLAN registration information,
including VLAN members, ports through which the VLAN members can be reached, and so on.
The switch also propagates the local VLAN registration information to other switches so that all the
switching devices in the same switched network can have the same VLAN information. The VLAN
registration information includes not only the static registration information configured locally, but
also the dynamic registration information, which is received from other switches.
In this switch, only the port with TRUNK link type can be set as the GVRP application entity to
maintain the VLAN registration information. GVRP has the following three port registration modes:
Normal, Fixed, and Forbidden.
Pqtocn<" In this mode, a port can dynamically register/deregister a VLAN and propagate the
dynamic/static VLAN information.
Hkzgf<"In this mode, a port cannot register/deregister a VLAN dynamically. It only propagates
static VLAN information. That is, the port in Fixed mode only permits the packets of its static
VLAN to pass.
Hqtdkffgp< In this mode, a port cannot register/deregister VLANs. It only propagates VLAN 1
information. That is, the port in Forbidden mode only permits the packets of the default VLAN
(namely VLAN 1) to pass.
86
Page 99

Choose the
menu XNCP→IXTR→IXTR"Eqphki to load the following page.
Figure 6-18 GVRP Config
Pqvg<"
If the GVRP feature is enabled for a member port of LAG, please ensure all the member ports of
this LAG are set to be in the same status and registration mode.
The following entries are displayed on this screen:
" Inqdcn"Eqphki"
IXTR<"
" Rqtv"Eqphki"
Rqtv"Ugngev<"
Allows you to Enable/Disable the GVRP function.
Click the Ugngev"button to quick-select the corresponding entry based
on the port number you entered.
Ugngev<"
Rqtv<"
Uvcvwu<"
Select the desired port for configuration. It is multi-optional.
Displays the port number.
Enable/Disable the GVRP feature for the port. The port type should
be set to TRUNK before enabling the GVRP feature.
Tgikuvtcvkqp"
Oqfg<"
Select the Registration Mode for the port.
Pqtocn< In this mode, a port can dynamically register/deregister
a VLAN and propagate the dynamic/static VLAN information.
Hkzgf< In this mode, a port cannot register/deregister a VLAN
dynamically. It only propagates static VLAN information.
Hqtdkffgp< In this mode, a port cannot register/deregister
VLANs. It only propagates VLAN 1 information.
87
Page 100

NgcxgCnn"Vkogt<"
Once the LeaveAll Timer is set, the port with GVRP enabled can send
a LeaveAll message after the timer times out, so that other GARP
ports can re-register all the attribute information. After that, the
LeaveAll timer will start to begin a new cycle. The LeaveAll Timer
ranges from 1000 to 30000 centiseconds.
Lqkp"Vkogt<"
To guarantee the transmission of the Join messages, a GARP port
sends each Join message two times. The Join Timer is used to define
the interval between the two sending operations of each Join
message. The Join Timer ranges from 20 to 1000 centiseconds.
Ngcxg"Vkogt<"
Once the Leave Timer is set, the GARP port receiving a Leave
message will start its Leave timer, and deregister the attribute
information if it does not receive a Join message again before the
timer times out. The Leave Timer ranges from 60 to 3000
centiseconds.
NCI<"
Displays the LAG to which the port belongs.
Pqvg<"
LeaveAll Timer >= 10* Leave Timer, Leave Timer >= 2*Join Timer
Eqphkiwtcvkqp"Rtqegfwtg<"
Uvgr" Qrgtcvkqp" Fguetkrvkqp"
1 Set the link type for port. Required. On the XNCP→:2403S" XNCP→Rqtv" Eqphki
page, set the link type of the port to be TRUNK.
2 Enable GVRP function. Required. On the XNCP→IXTR page, enable GVRP
function.
3 Configure the registration
mode and the timers for the
Required. On the XNCP→IXTR page, configure the
parameters of ports basing on actual applications.
port.
8032"Crrnkecvkqp"Gzcorng"hqt"Rtkxcvg"XNCP"
Pgvyqtm"Tgswktgogpvu"
Switch A is connecting to switch B, switch B is connecting to switch C;
Switch B is connecting to PC1, PC2 and PC3;
Switch C is connecting to PC4, PC5 and PC6;
PCs in different VLANs cannot communicate with each other;;
For switch A, packets from switch B and switch C have no VLAN tags. Switch A needs not to
consider the VLANs of switch B and switch C;
88
 Loading...
Loading...