Page 1

Quick Start Guide
NWA5301-NJ
802.11 b/g/n In-wall Managed Access Point
Version 4.10
Edition 2, 05/2014
User’s Guide
Default Login Details
(Standalone AP Mode)
LAN IP Address http://192.168.1.2
User Name admin
Password 1234
www.zyxel.com
Copyright © 2014 ZyXEL Communications Corporation
Page 2

IMPORTANT!
READ CAREFULLY BEFORE USE.
KEEP THIS GUIDE FOR FUTURE REFERENCE.
Screenshots and graphics in this book may differ slightly from your product due to differences in
your product firmware or your computer operating system. Every effort has been made to ensure
that the information in this manual is accurate.
Related Documentation
•Quick Start Guide
The Quick Start Guide shows how to connect the NWA and access the Web Configurator.
• CLI Reference Guide
The CLI Reference Guide explains how to use the Command-Line Interface (CLI) and CLI
commands to configure the NWA.
Note: It is recommended you use the Web Configurator to configure the NWA.
• Web Configurator Online Help
Click the help icon in any screen for help in configuring that screen and supplementary
information.
NWA5301-NJ User’s Guide
2
Page 3
Contents Overview
Contents Overview
User’s Guide .......................................................................................................................................10
Introduction ............................................................................................................................................. 11
The Web Configurator .............................................................................................................................21
Technical Reference ..........................................................................................................................32
Dashboard ...............................................................................................................................................33
Monitor ....................................................................................................................................................38
Management Mode .................................................................................................................................48
Network ...................................................................................................................................................52
Wireless ..................................................................................................................................................59
User .........................................................................................................................................................67
AP Profile ................................................................................................................................................74
WDS Profile .............................................................................................................................................92
Certificates ..............................................................................................................................................94
System .................................................................................................................................................. 111
Log and Report .....................................................................................................................................136
File Manager .........................................................................................................................................148
Diagnostics ............................................................................................................................................159
Reboot ...................................................................................................................................................161
Shutdown ..............................................................................................................................................162
Troubleshooting ....................................................................................................................................163
NWA5301-NJ User’s Guide
3
Page 4

Table of Contents
Table of Contents
Contents Overview ..............................................................................................................................3
Table of Contents .................................................................................................................................4
Part I: User’s Guide .........................................................................................10
Chapter 1
Introduction.........................................................................................................................................11
1.1 Overview .......................................................................................................................................... 11
1.1.1 Management Mode ..................................................................................................................12
1.1.2 MBSSID ...................................................................................................................................12
1.1.3 Root AP ...................................................................................................................................13
1.1.4 Repeater ..................................................................................................................................14
1.2 Ways to Manage the NWA ................................................................................................................15
1.3 Good Habits for Managing the NWA .................................................................................................16
1.4 Hardware Connections ......................................................................................................................16
1.4.1 110 Punch-Down Block ............................................................................................................16
1.4.2 Phone Port ...............................................................................................................................18
1.4.3 Console Port ............................................................................................................................18
1.5 LEDs .................................................................................................................................................19
1.6 Starting and Stopping the NWA .........................................................................................................20
Chapter 2
The Web Configurator........................................................................................................................21
2.1 Overview ...........................................................................................................................................21
2.2 Access ...............................................................................................................................................21
2.3 Navigating the Web Configurator ......................................................................................................22
2.3.1 Title Bar ...................................................................................................................................23
2.3.2 Navigation Panel .....................................................................................................................26
2.3.3 Warning Messages ..................................................................................................................29
2.3.4 Tables and Lists .......................................................................................................................29
Part II: Technical Reference............................................................................32
Chapter 3
Dashboard...........................................................................................................................................33
NWA5301-NJ User’s Guide
4
Page 5

Table of Contents
3.1 Overview ...........................................................................................................................................33
3.1.1 What You Can Do in this Chapter ............................................................................................33
3.2 Dashboard .......................................................................................................................................33
3.2.1 CPU Usage ..............................................................................................................................36
3.2.2 Memory Usage ........................................................................................................................37
Chapter 4
Monitor.................................................................................................................................................38
4.1 Overview ...........................................................................................................................................38
4.1.1 What You Can Do in this Chapter ............................................................................................38
4.2 Network Status ..................................................................................................................................38
4.3 Radio List .........................................................................................................................................40
4.3.1 AP Mode Radio Information ....................................................................................................41
4.4 Station List ........................................................................................................................................43
4.5 WDS Link Info ...................................................................................................................................44
4.6 View Log ...........................................................................................................................................45
Chapter 5
Management Mode .............................................................................................................................48
5.1 Overview ...........................................................................................................................................48
5.2 About CAPWAP ................................................................................................................................48
5.2.1 CAPWAP Discovery and Management ...................................................................................48
5.2.2 Managed AP Finds the Controller ...........................................................................................49
5.2.3 CAPWAP and IP Subnets ........................................................................................................49
5.2.4 Notes on CAPWAP ..................................................................................................................50
5.3 Management Mode Screen ...............................................................................................................50
Chapter 6
Network................................................................................................................................................52
6.1 Overview ...........................................................................................................................................52
6.1.1 What You Can Do in this Chapter ............................................................................................52
6.2 IP Setting ..........................................................................................................................................52
6.3 VLAN .................................................................................................................................................54
6.3.1 Port Setting Edit .......................................................................................................................56
6.3.2 VLAN Add/Edit .........................................................................................................................57
Chapter 7
Wireless...............................................................................................................................................59
7.1 Overview ...........................................................................................................................................59
7.1.1 What You Can Do in this Chapter ............................................................................................59
7.1.2 What You Need to Know ..........................................................................................................60
7.2 AP Management ...............................................................................................................................60
7.3 Load Balancing .................................................................................................................................61
NWA5301-NJ User’s Guide
5
Page 6

Table of Contents
7.3.1 Disassociating and Delaying Connections ..............................................................................62
7.4 DCS ..................................................................................................................................................63
7.5 Technical Reference ..........................................................................................................................65
Chapter 8
User......................................................................................................................................................67
8.1 Overview ...........................................................................................................................................67
8.1.1 What You Can Do in this Chapter ............................................................................................67
8.1.2 What You Need To Know .........................................................................................................67
8.2 User Summary ..................................................................................................................................68
8.2.1 Add/Edit User ..........................................................................................................................68
8.3 Setting ..............................................................................................................................................70
8.3.1 Edit User Authentication Timeout Settings ..............................................................................72
Chapter 9
AP Profile.............................................................................................................................................74
9.1 Overview ...........................................................................................................................................74
9.1.1 What You Can Do in this Chapter ............................................................................................74
9.1.2 What You Need To Know .........................................................................................................74
9.2 Radio .................................................................................................................................................75
9.2.1 Add/Edit Radio Profile .............................................................................................................76
9.3 SSID .................................................................................................................................................80
9.3.1 SSID List ..................................................................................................................................80
9.3.2 Add/Edit SSID Profile ..............................................................................................................81
9.4 Security List .......................................................................................................................................83
9.4.1 Add/Edit Security Profile ..........................................................................................................84
9.5 MAC Filter List ...................................................................................................................................87
9.5.1 Add/Edit MAC Filter Profile ......................................................................................................88
9.6 Layer-2 Isolation List .........................................................................................................................89
9.6.1 Add/Edit Layer-2 Isolation Profile ............................................................................................90
Chapter 10
WDS Profile .........................................................................................................................................92
10.1 Overview .........................................................................................................................................92
10.1.1 What You Can Do in this Chapter ..........................................................................................92
10.2 WDS Profile ....................................................................................................................................92
10.2.1 Add/Edit WDS Profile ............................................................................................................93
Chapter 11
Certificates..........................................................................................................................................94
11.1 Overview .........................................................................................................................................94
11.1.1 What You Can Do in this Chapter ..........................................................................................94
11.1.2 What You Need to Know ........................................................................................................94
NWA5301-NJ User’s Guide
6
Page 7

Table of Contents
11.1.3 Verifying a Certificate .............................................................................................................96
11.2 My Certificates ................................................................................................................................97
11.2.1 Add My Certificates ................................................................................................................98
11.2.2 Edit My Certificates ..............................................................................................................102
11.2.3 Import Certificates ...............................................................................................................104
11.3 Trusted Certificates .......................................................................................................................105
11.3.1 Edit Trusted Certificates .......................................................................................................107
11.3.2 Import Trusted Certificates ...................................................................................................109
11.4 Technical Reference ...................................................................................................................... 110
Chapter 12
System...............................................................................................................................................111
12.1 Overview ....................................................................................................................................... 111
12.1.1 What You Can Do in this Chapter ........................................................................................ 111
12.2 Host Name .................................................................................................................................... 111
12.3 Date and Time .............................................................................................................................. 112
12.3.1 Pre-defined NTP Time Servers List ..................................................................................... 114
12.3.2 Time Server Synchronization ...............................................................................................114
12.4 WWW Overview ............................................................................................................................ 115
12.4.1 Service Access Limitations .................................................................................................. 116
12.4.2 System Timeout ................................................................................................................... 116
12.4.3 HTTPS ................................................................................................................................. 116
12.4.4 Configuring WWW Service Control ..................................................................................... 117
12.4.5 HTTPS Example .................................................................................................................. 118
12.5 SSH ............................................................................................................................................126
12.5.1 How SSH Works ..................................................................................................................126
12.5.2 SSH Implementation on the NWA .......................................................................................127
12.5.3 Requirements for Using SSH ...............................................................................................128
12.5.4 Configuring SSH ..................................................................................................................128
12.5.5 Examples of Secure Telnet Using SSH ...............................................................................128
12.6 Telnet ............................................................................................................................................130
12.7 FTP ..............................................................................................................................................130
12.8 SNMP ...........................................................................................................................................131
12.8.1 Supported MIBs ...................................................................................................................132
12.8.2 SNMP Traps ........................................................................................................................133
12.8.3 Configuring SNMP ...............................................................................................................133
12.8.4 Adding or Editing an SNMPv3 User Profile .........................................................................134
Chapter 13
Log and Report .................................................................................................................................136
13.1 Overview .......................................................................................................................................136
13.1.1 What You Can Do In this Chapter ........................................................................................136
13.2 Email Daily Report ........................................................................................................................136
NWA5301-NJ User’s Guide
7
Page 8

Table of Contents
13.3 Log Setting ...................................................................................................................................138
13.3.1 Log Setting Screen ..............................................................................................................138
13.3.2 Edit System Log Settings ...................................................................................................140
13.3.3 Edit Remote Server ............................................................................................................142
13.3.4 Active Log Summary ..........................................................................................................144
Chapter 14
File Manager......................................................................................................................................148
14.1 Overview .......................................................................................................................................148
14.1.1 What You Can Do in this Chapter ........................................................................................148
14.1.2 What you Need to Know ......................................................................................................148
14.2 Configuration File ..........................................................................................................................149
14.2.1 Example of Configuration File Download Using FTP ..........................................................153
14.3 Firmware Package .......................................................................................................................154
14.3.1 Example of Firmware Upload Using FTP ............................................................................156
14.4 Shell Script ...................................................................................................................................156
Chapter 15
Diagnostics .......................................................................................................................................159
15.1 Overview .......................................................................................................................................159
15.1.1 What You Can Do in this Chapter ........................................................................................159
15.2 Diagnostics ..................................................................................................................................159
Chapter 16
Reboot ...............................................................................................................................................161
16.1 Overview .......................................................................................................................................161
16.1.1 What You Need To Know .....................................................................................................161
16.2 Reboot ...........................................................................................................................................161
Chapter 17
Shutdown...........................................................................................................................................162
17.1 Overview .......................................................................................................................................162
17.1.1 What You Need To Know .....................................................................................................162
17.2 Shutdown ......................................................................................................................................162
Chapter 18
Troubleshooting................................................................................................................................163
18.1 Overview .......................................................................................................................................163
18.2 Power, Hardware Connections, and LED ......................................................................................163
18.3 NWA Access and Login ................................................................................................................164
18.4 Internet Access .............................................................................................................................165
18.5 Wireless Connections ...................................................................................................................166
18.6 Resetting the NWA ........................................................................................................................169
NWA5301-NJ User’s Guide
8
Page 9

Table of Contents
18.7 Getting More Troubleshooting Help ..............................................................................................169
Appendix A Importing Certificates ...................................................................................................170
Appendix B IPv6 ..............................................................................................................................183
Appendix C Customer Support........................................................................................................192
Appendix D Legal Information .........................................................................................................198
Index ..................................................................................................................................................203
NWA5301-NJ User’s Guide
9
Page 10
PART I
User’s Guide
10
Page 11

1.1 Overview
The NWA is an in-the-wall IEEE 802.11b/g/n wireless access point that supports Power over
Ethernet (PoE) to eliminate the need for power sockets.
The NWA extends the range of your existing wired network without additional wiring, providing
easy network access to mobile users. You can set up a wireless network with other IEEE 802.11b/g/
n compatible devices.
In the following example, you connect a PoE switch to a broadband router/modem that has Internet
access. You then use the swicth to provide power and Internet access to three NWAs in different
rooms via Ethernet cables.
CHAPTER 1
Introduction
You can set the NWA to operate in either standalone AP or managed AP mode. When the NWA is in
standalone AP mode, it can serve as a normal AP, or even as a root AP or a wireless repeater to
establish wireless links with other APs in a WDS (Wireless Distribution System). A WDS is a wireless
connection between two or more APs.
Your NWA’s business-class reliability, SMB features, and centralized wireless management make it
ideally suited for advanced service delivery in mission-critical networks. It uses Multiple BSSID and
VLAN to provide simultaneous independent virtual APs. Additionally, innovations in roaming
technology and QoS features eliminate voice call disruptions.
NWA5301-NJ User’s Guide
11
Page 12
The NWA controls network access with Media Access Control (MAC) address filtering. It also
provides a high level of network traffic security, supporting IEEE 802.1x, Wi-Fi Protected Access
(WPA), WPA2 and Wired Equivalent Privacy (WEP) data encryption.
Your NWA is easy to install, configure and use. The embedded Web-based configurator enables
simple, straightforward management and maintenance. See the Quick Start Guide for how to make
hardware connections.
1.1.1 Management Mode
An AP controller can use Control And Provisioning of Wireless Access Points (CAPWAP, see RFC
5415) to discover and configure multiple managed APs.
The NWA is a managed AP by default and needs to be managed by an AP controller, such as the
NXC2500. When the NWA is in managed AP mode, it acts as a DHCP client and obtains an IP
address from the AP controller. It can be configured ONLY by the AP controller. To change the NWA
back to standalone AP mode, you need to check the AP controller for the NWA’s IP address and use
FTP to upload NWA’s firmware for standalone AP mode.
When the NWA is in standalone AP mode, the NWA is set to have a static management IP address
(192.168.1.2) by default. You can use either the web configurator or FTP to upload firmware. See
Section 14.3 on page 154 for more information about firmware uploading. To switch the NWA from
being a standalone AP to acting as a managed AP, see Chapter 5 on page 48.
Chapter 1 Introduction
Table 1 NWA Management Mode Comparison
MANAGEMENT MODE DEFAULT IP ADDRESS UPLOAD FIRMWARE VIA
Standalone AP
Managed AP Dynamic FTP
1.1.2 MBSSID
A Basic Service Set (BSS) is the set of devices forming a single wireless network (usually an access
point and one or more wireless clients). The Service Set IDentifier (SSID) is the name of a BSS. In
Multiple BSS (MBSSID) mode, the NWA provides multiple virtual APs, each forming its own BSS and
using its own individual SSID profile.
You can configure multiple SSID profiles, and have all of them active at any one time.
You can assign different wireless and security settings to each SSID profile. This allows you to
compartmentalize groups of users, set varying access privileges, and prioritize network traffic to
and from certain BSSs.
To the wireless clients in the network, each SSID appears to be a different access point. As in any
wireless network, clients can associate only with the SSIDs for which they have the correct security
settings.
For example, you might want to set up a wireless network in your office where Internet telephony
(VoIP) users have priority. You also want a regular wireless network for standard users, as well as a
‘guest’ wireless network for visitors. In the following figure, VoIP_SSID users have QoS priority,
SSID01 is the wireless network for standard users, and Guest_SSID is the wireless network for
guest users. In this example, the guest user is forbidden access to the wired Land Area Network
(LAN) behind the AP and can access only the Internet.
Static (192.168.1.2) Web Configurator or FTP
NWA5301-NJ User’s Guide
12
Page 13
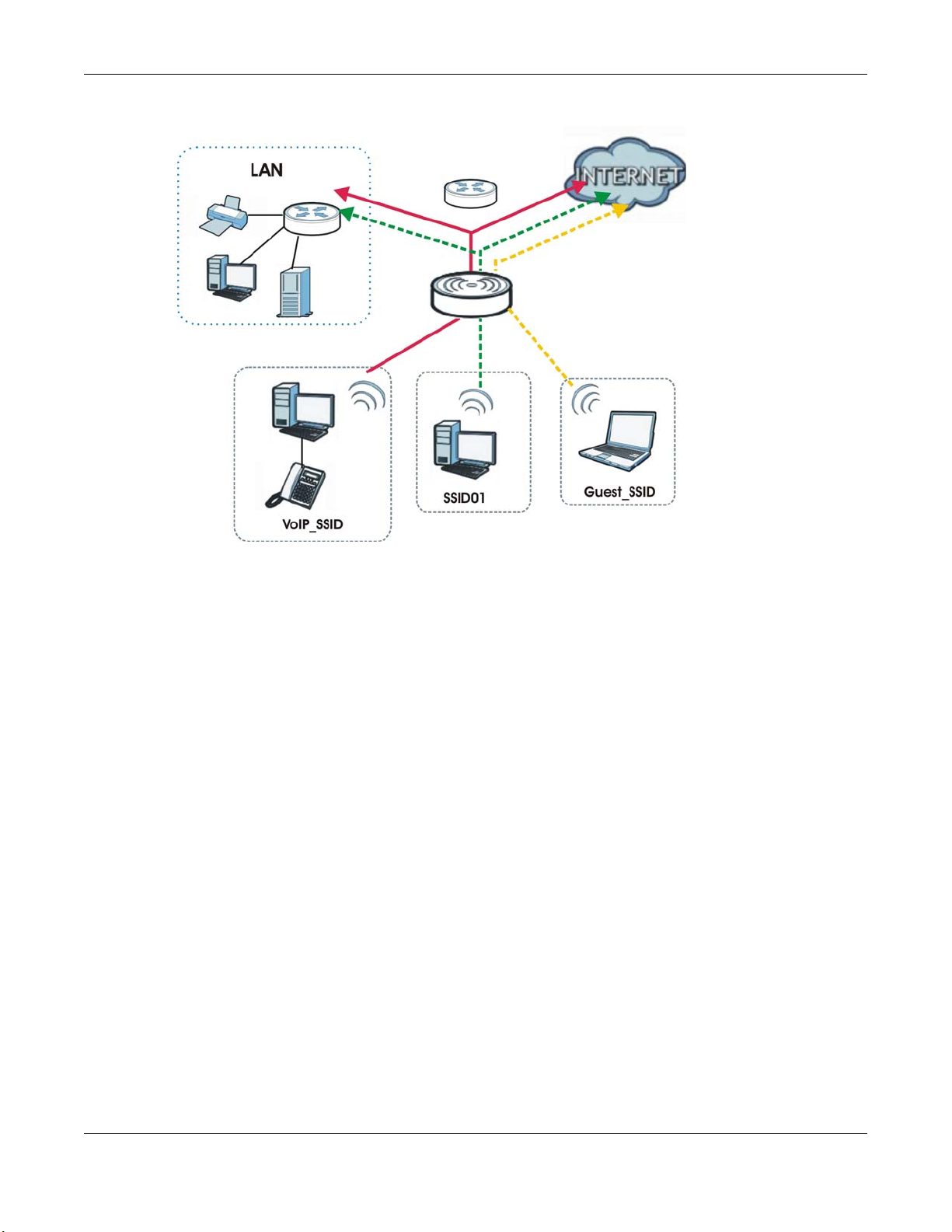
Figure 1 Multiple BSSs
Chapter 1 Introduction
1.1.3 Root AP
In Root AP mode, the NWA (Z) can act as the root AP in a wireless network and also allow repeaters
(X and Y) to extend the range of its wireless network at the same time. In the figure below, both
clients A, B and C can access the wired network through the root AP.
NWA5301-NJ User’s Guide
13
Page 14

Figure 2 Root AP Application
Chapter 1 Introduction
On the NWA in Root AP mode, you can have multiple SSIDs active for reqular wireless connections
and one SSID for the connection with a repeater (repeater SSID). Wireless clients can use either
SSID to associate with the NWA in Root AP mode. A repeater must use the repeater SSID to
connect to the NWA in Root AP mode.
When the NWA is in Root AP mode, repeater security between the NWA and other repeater is
independent of the security between the wireless clients and the AP or repeater. When repeater
security is enabled, both APs and repeaters must use the same pre-shared key. See Section 7.2 on
page 60 and Section 10.2 on page 92 for more details.
Unless specified, the term “security settings” refers to the traffic between the wireless clients and
the AP. At the time of writing, repeater security is compatible with the NWA only.
1.1.4 Repeater
The NWA can act as a wireless network repeater to extend a root AP’s wireless network range, and
also establish wireless connections with wireless clients.
Using Repeater mode, your NWA can extend the range of the WLAN. In the figure below, the NWA
in Repeater mode (Z) has a wireless connection to the NWA in Root AP mode (X) which is
connected to a wired network and also has a wireless connection to another NWA in Repeater mode
(Y) at the same time. Z and Y act as repeaters that forward traffic between associated wireless
clients and the wired LAN. Clients A and B access the AP and the wired network behind the AP
throught repeaters Z and Y.
NWA5301-NJ User’s Guide
14
Page 15
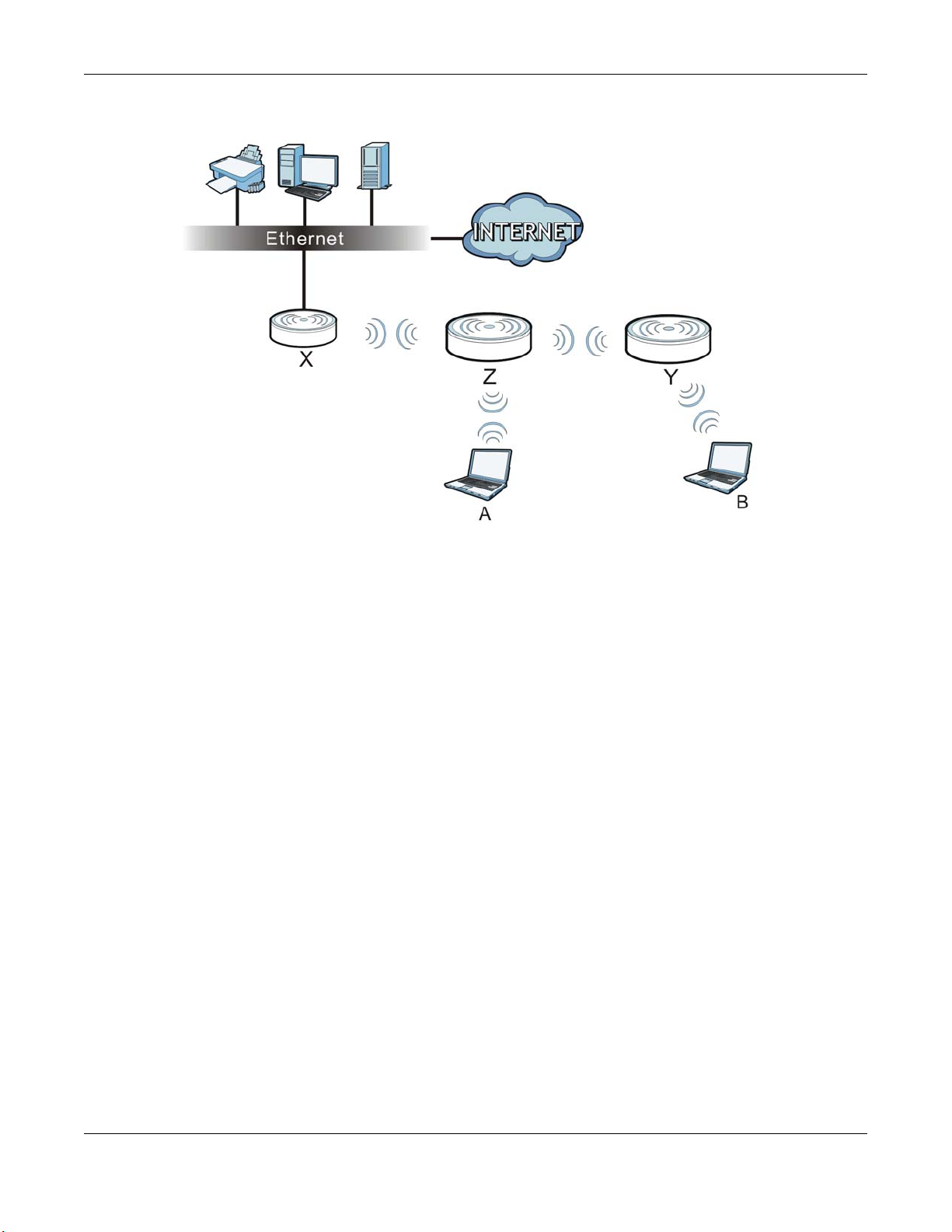
Figure 3 Repeater Application
Chapter 1 Introduction
When the NWA is in Repeater mode, repeater security between the NWA and other repeater is
independent of the security between the wireless clients and the AP or repeater. When repeater
security is enabled, both APs and repeaters must use the same pre-shared key. See Section 7.2 on
page 60 and Section 10.2 on page 92 for more details.
Once the security settings of peer sides match one another, the connection between devices is
made.
At the time of writing, repeater security is compatible with the NWA only.
1.2 Ways to Manage the NWA
You can use the following ways to manage the NWA.
Web Configurator
The Web Configurator allows easy NWA setup and management using an Internet browser. This
User’s Guide provides information about the Web Configurator.
Command-Line Interface (CLI)
The CLI allows you to use text-based commands to configure the NWA. You can access it using
remote management (for example, SSH or Telnet). See the Command Reference Guide for more
information.
NWA5301-NJ User’s Guide
15
Page 16
Chapter 1 Introduction
File Transfer Protocol (FTP)
This protocol can be used for firmware upgrades and configuration backup and restore.
Simple Network Management Protocol (SNMP)
The NWA can be monitored by an SNMP manager. See the SNMP chapter in this User’s Guide.
1.3 Good Habits for Managing the NWA
Do the following things regularly to make the NWA more secure and to manage it more effectively.
• Change the password often. Use a password that’s not easy to guess and that consists of
different types of characters, such as numbers and letters.
• Write down the password and put it in a safe place.
• Back up the configuration (and make sure you know how to restore it). Restoring an earlier
working configuration may be useful if the device becomes unstable or even crashes. If you
forget your password, you will have to reset the NWA to its factory default settings. If you backed
up an earlier configuration file, you won’t have to totally re-configure the NWA; you can simply
restore your last configuration.
1.4 Hardware Connections
See your Quick Start Guide for more information on making hardware connections.
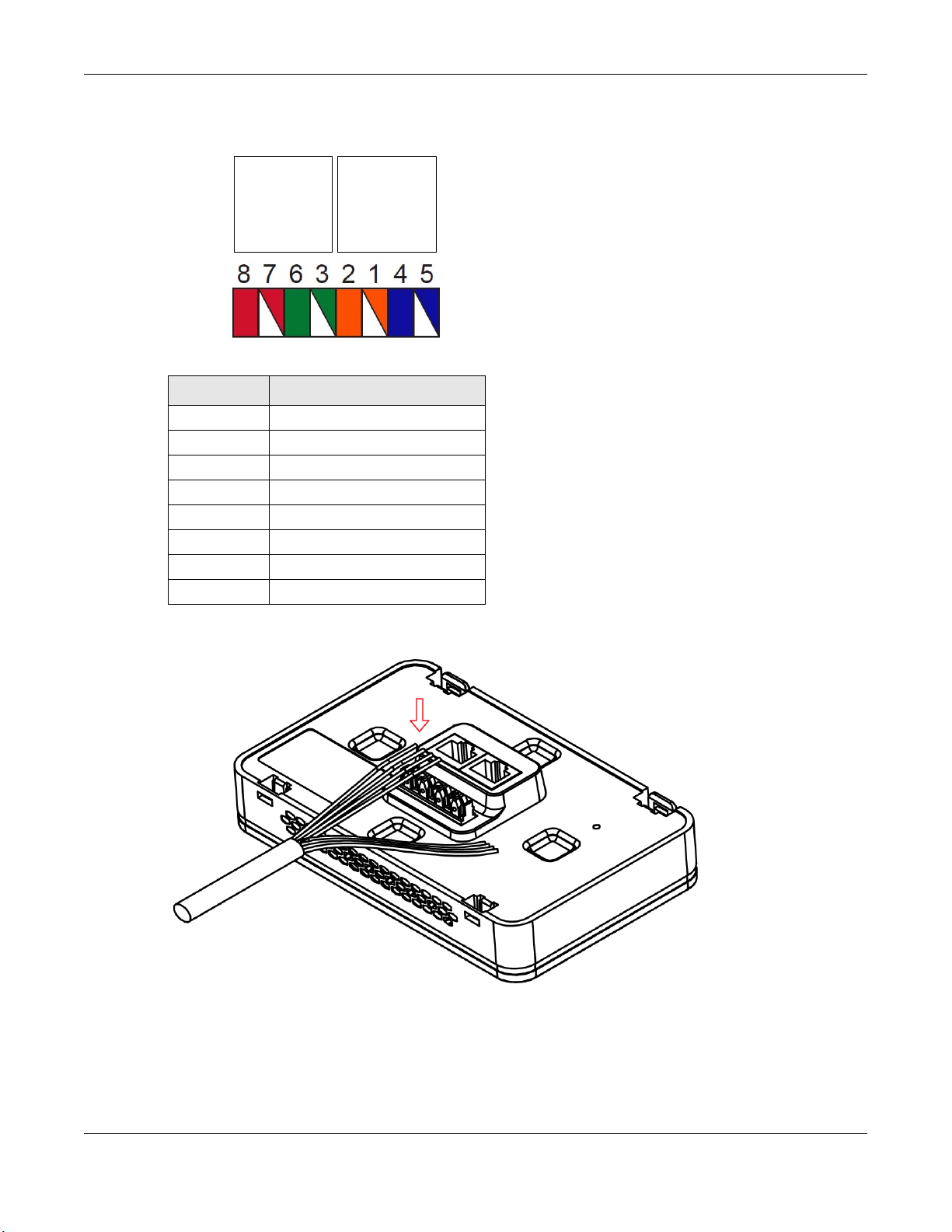
1.4.1 110 Punch-Down Block
This section shows you how to use a punch-down tool to seat an 8-wire Ethernet cable to the 110
punch-down block. You can connect a PoE switch to the 110 punch-down block to provide power
and Internet access to the NWA through this connection. An 8-pin Ethernet cable has four pairs of
color coded wires.
1 Cut out one and a half inches of the jacket from the Ethenet cable to expose the wires.
2 Untwist the wire pairs no more than one inch.
3 Match each wire to the correct slot according to the color codes for wiring shown below.
NWA5301-NJ User’s Guide
16
Page 17
Chapter 1 Introduction
PIN#
PHONE
PORT
UPLINK
PORT
NWA Rear Panel
Table 2 Color Codes for 110 Punch Down Block Wiring
PIN# WIRE COLOR
1White/Orange
2Orange
3White/Green
4Blue
5White/Blue
6Green
7White/Brown
8Brown
4 Use a punch-down tool to seat the wires down properly into the slot.
5 Trim any excess wires. Place the dust caps over the terminated wires.
NWA5301-NJ User’s Guide
17
Page 18
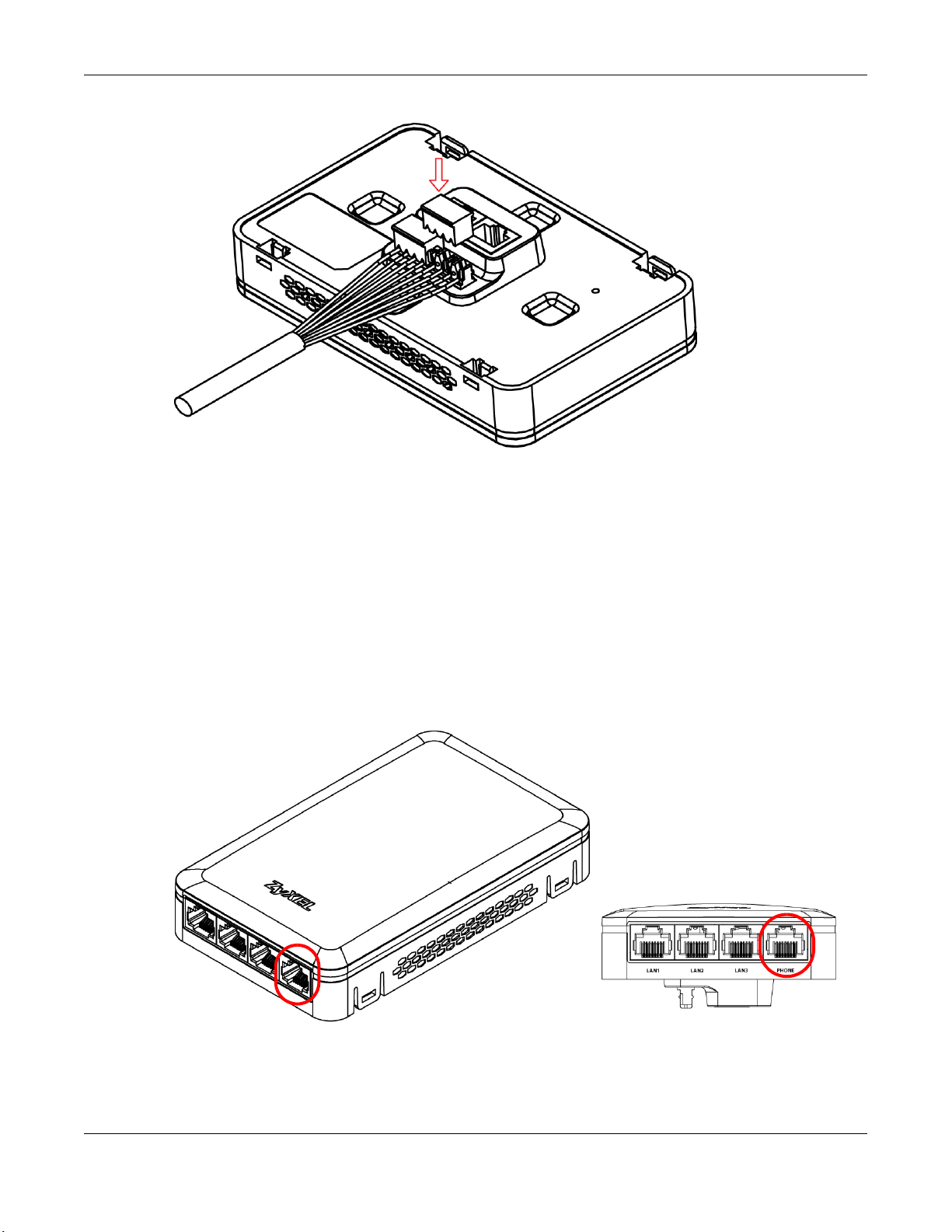
1.4.2 Phone Port
Chapter 1 Introduction
Connect a digital telephone to the RJ-45 PHONE port at the bottom of the NWA to forward voice
traffic to/from the telephone switchboard that is connected to the RJ-45 PHONE port on the back of
the NWA. The NWA does not support VoIP (Voice over Internet Protocol) and the PHONE port is
NOT for making calls over the regular networking network (PSTN), either.
1.4.3 Console Port
To use the CLI commands to configure the NWA, connect an RJ-45-to-DB-9 cable to the PHONE
port at the bottom of the NWA.
For local management, you can use a computer with terminal emulation software configured to the
following parameters:
• VT100 terminal emulation
NWA5301-NJ User’s Guide
18
Page 19
Chapter 1 Introduction
• 115200 bps
• No parity, 8 data bits, 1 stop bit
• No flow control
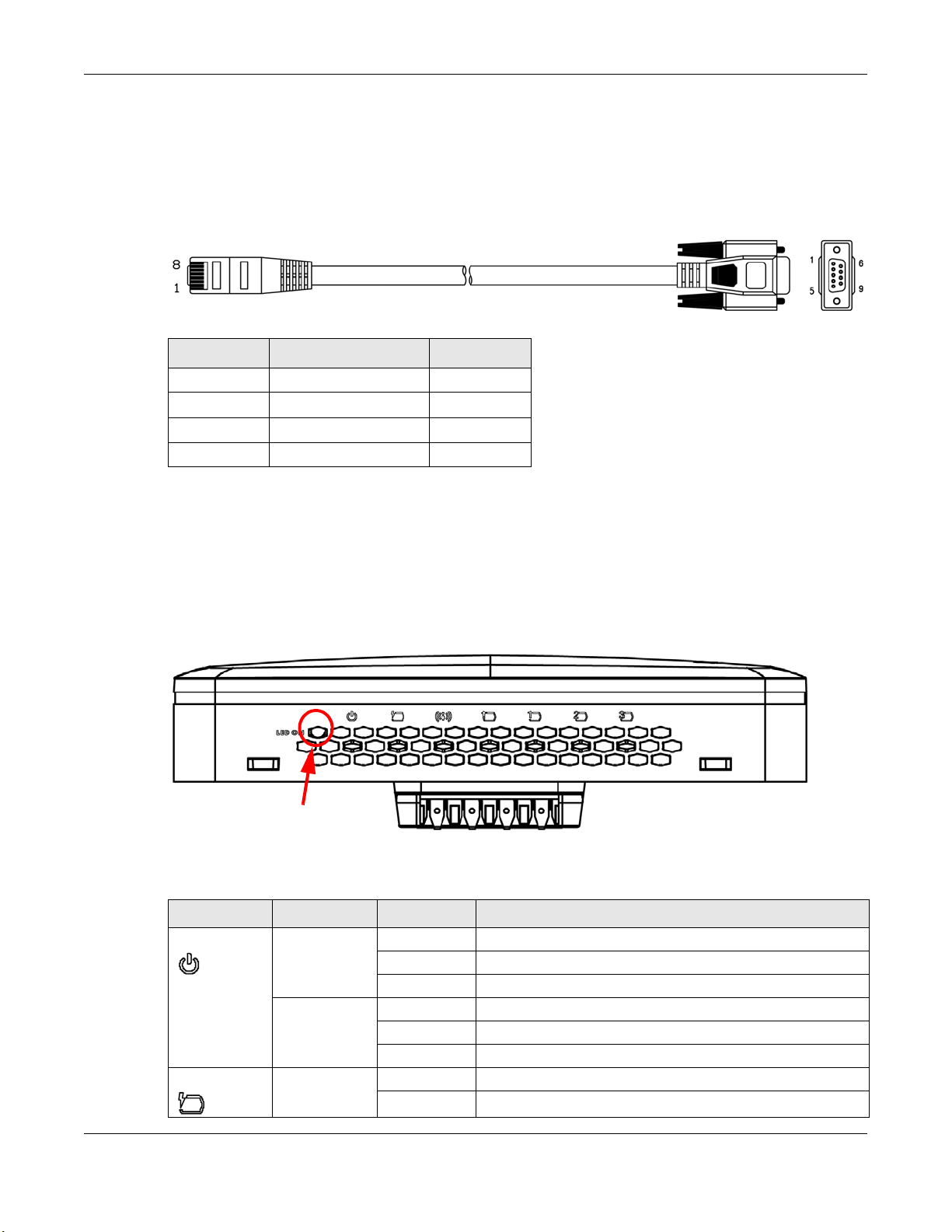
The following table shows you the wire color codes and pin assignment for the console cable.
Table 3 RJ45-to-DB-9 Console Cable Color Codes
RJ45 PIN# WIRE COLOR DB-9 PIN#
1Black 1
7Brown 2
2Blue 3
8Purple 5
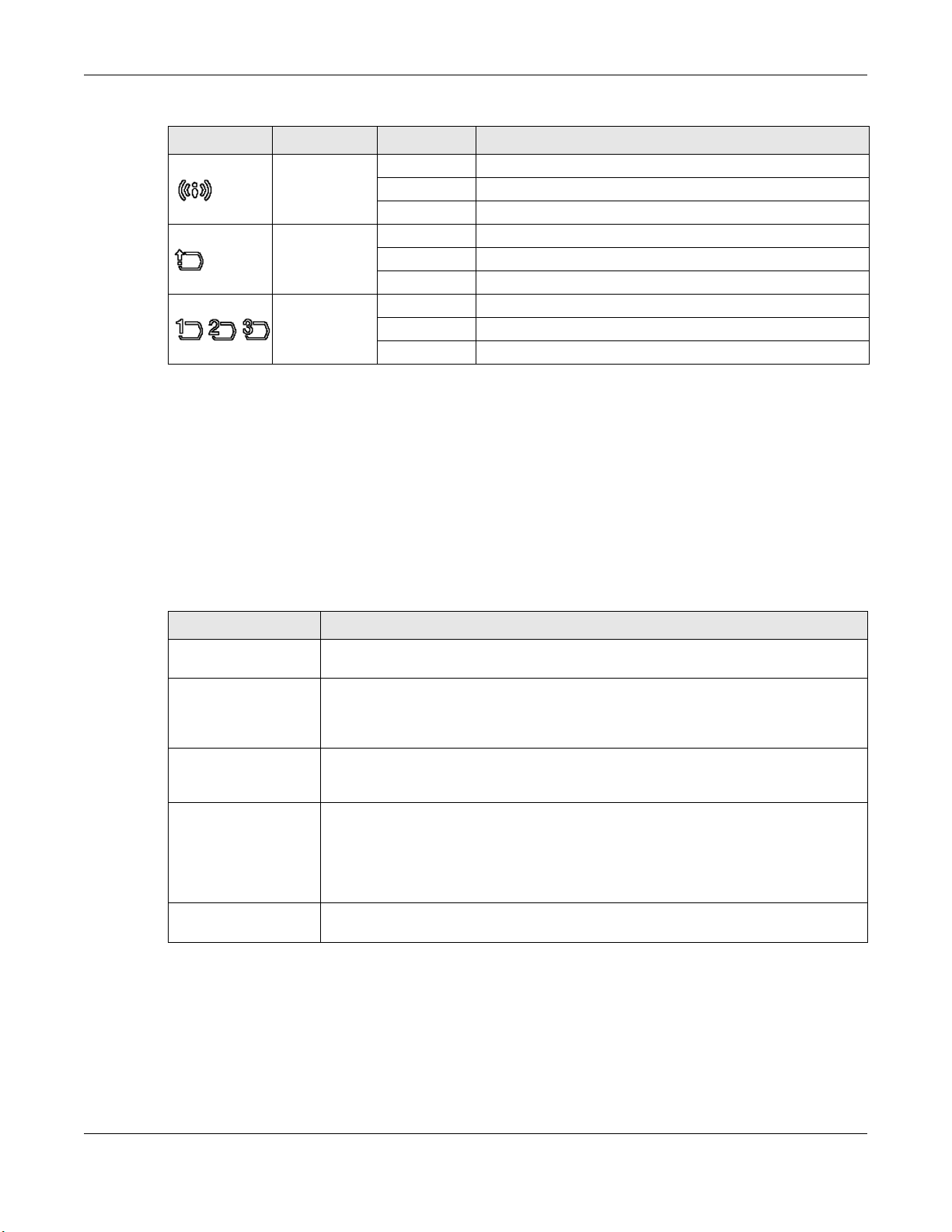
1.5 LEDs
The LEDs automatically turn off when the NWA is ready. You can press the LED ON button for one
second to turn on the LEDs again. The LEDs will blink and turn off after two minuters.
Figure 4 NWA Side Panel
The following are the LED descriptions for your NWA.
Table 4 NWA LEDs
LABEL COLOR STATUS DESCRIPTION
PWR/SYS Green On The NWA is receiving power.
PoE Green On Power is supplied to the yellow PoE Ethernet port (LAN1).
Blinking The NWA is starting up.
Off The NWA is not receiving power.
Amber On There is system error and the NWA cannot boot up.
Blinking Firmware upgrade is in progress.
Off The NWA is ready for use.
Off There is no power supply.
NWA5301-NJ User’s Guide
19
Page 20
Chapter 1 Introduction
Table 4 NWA LEDs (continued)
LABEL COLOR STATUS DESCRIPTION
WLAN Green On The WLAN is active.
Blinking The WLAN is transmitting or receiving data.
Off The WLAN is not active.
UPLINK Green On The port is connected.
Blinking The NWA is sending/receiving data through the port.
Off The port is not connected.
LAN1-3 Green On The port is connected.
Blinking The NWA is sending/receiving data through the port.
Off The port is not connected.
1.6 Starting and Stopping the NWA
Here are some of the ways to start and stop the NWA.
Always use Maintenance > Shutdown or the shutdown command before
you turn off the NWA or remove the power. Not doing so can cause the
firmware to become corrupt.
Table 5 Starting and Stopping the NWA
METHOD DESCRIPTION
Turning on the power A cold start occurs when you turn on the power to the NWA. The NWA powers up,
Rebooting the NWA A warm start (without powering down and powering up again) occurs when you use
Using the RESET
button
Clicking
Maintenance >
Shutdown >
Shutdown or using
the shutdown
command
Disconnecting the
power
checks the hardware, and starts the system processes.
the Reboot button in the Reboot screen or when you use the reboot command. The
NWA writes all cached data to the local storage, stops the system processes, and then
does a warm start.
If you press the RESET button on the back of the NWA, the NWA sets the
configuration to its default values and then reboots. See Section 18.6 on page 169 for
more information.
Clicking Maintenance > Shutdown > Shutdown or using the shutdown command
writes all cached data to the local storage and stops the system processes. Wait for
the device to shut down and then manually turn off or remove the power. It does not
turn off the power.
Power off occurs when you turn off the power to the NWA. The NWA simply turns off.
It does not stop the system processes or write cached data to local storage.
The NWA does not stop or start the system processes when you apply configuration files or run
shell scripts although you may temporarily lose access to network resources.
NWA5301-NJ User’s Guide
20
Page 21
2.1 Overview
The NWA Web Configurator allows easy management using an Internet browser.
In order to use the Web Configurator, you must:
• Use Internet Explorer 7.0 and later versions, Mozilla Firefox 9.0 and later versions, Safari 4.0 and
later versions, or Google Chrome 10.0 and later versions.
• Allow pop-up windows.
• Enable JavaScript (enabled by default).
• Enable Java permissions (enabled by default).
• Enable cookies.
CHAPTER 2
The Web Configurator
The recommended screen resolution is 1024 x 768 pixels and higher.
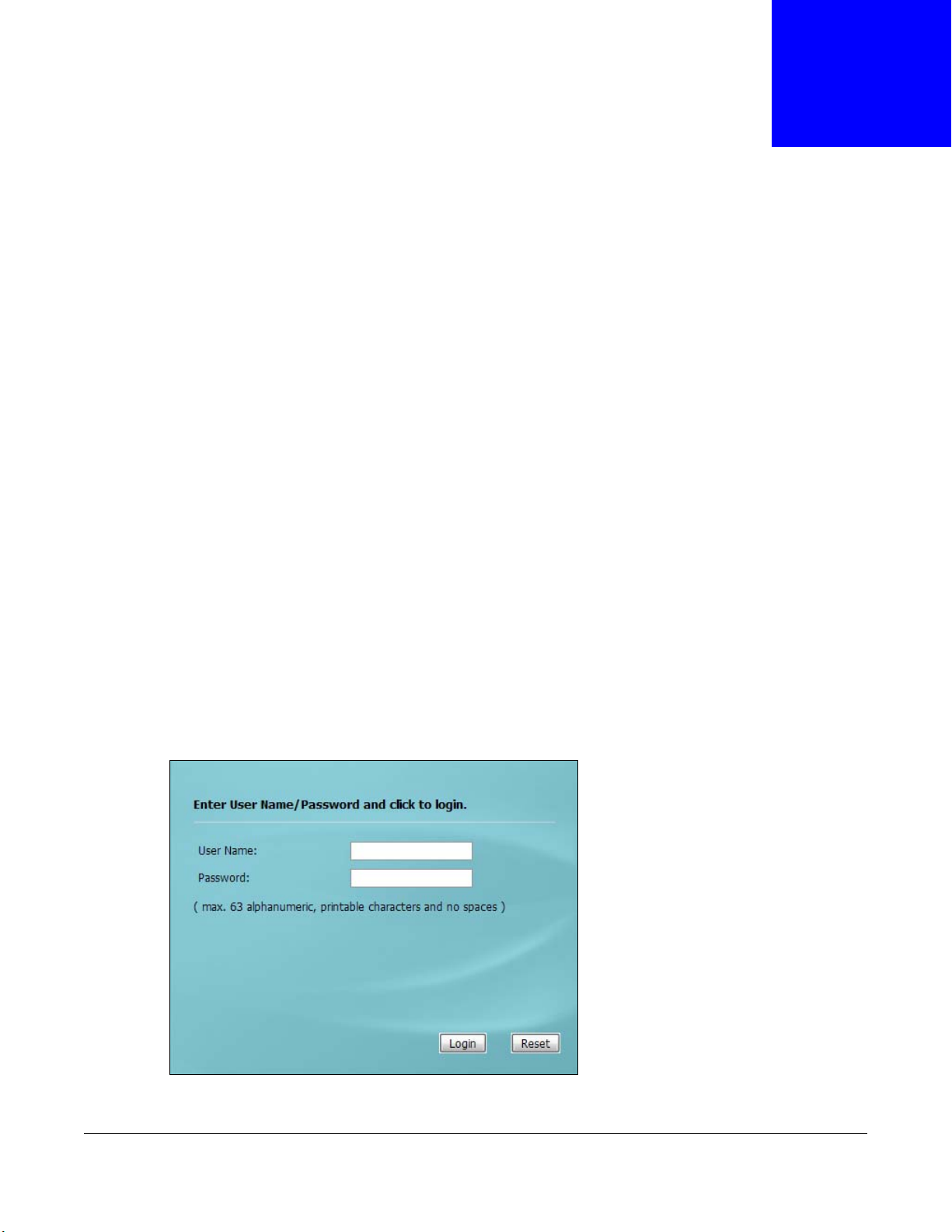
2.2 Access
1 Make sure your NWA is working in standalone AP mode (see Section 1.1.1 on page 12) and
hardware is properly connected. See the Quick Start Guide.
2 Browse to https://192.168.1.2. The Login screen appears.
3 Enter the user name (default: “admin”) and password (default: “1234”).
NWA5301-NJ User’s Guide
21
Page 22
Chapter 2 The Web Configurator
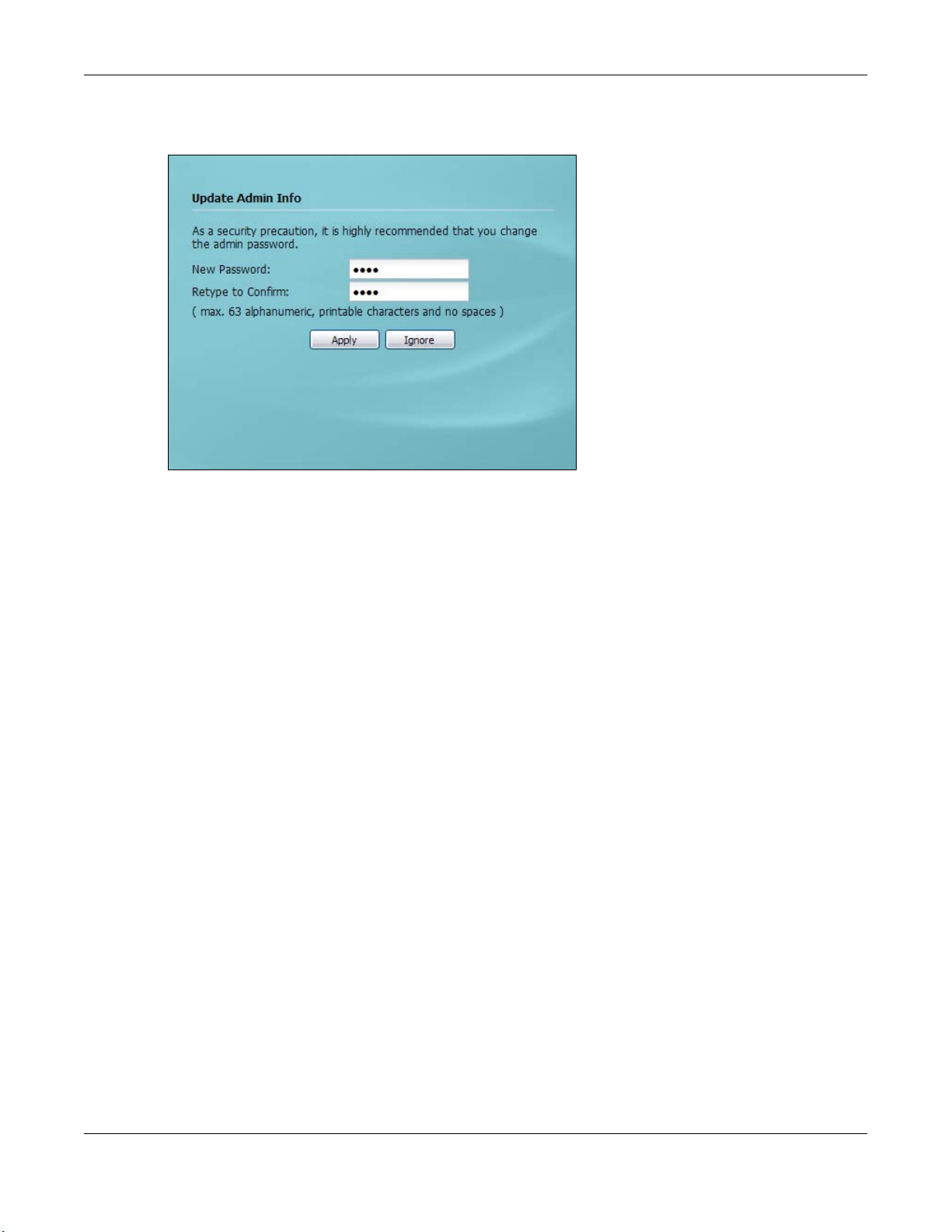
4 Click Login. If you logged in using the default user name and password, the Update Admin Info
screen appears. Otherwise, the dashboard appears.
The Update Admin Info screen appears every time you log in using the default user name and
default password. If you change the password for the default user account, this screen does not
appear anymore.
2.3 Navigating the Web Configurator
The following summarizes how to navigate the web configurator from the Dashboard screen.
NWA5301-NJ User’s Guide
22
Page 23
Chapter 2 The Web Configurator
A
C
B
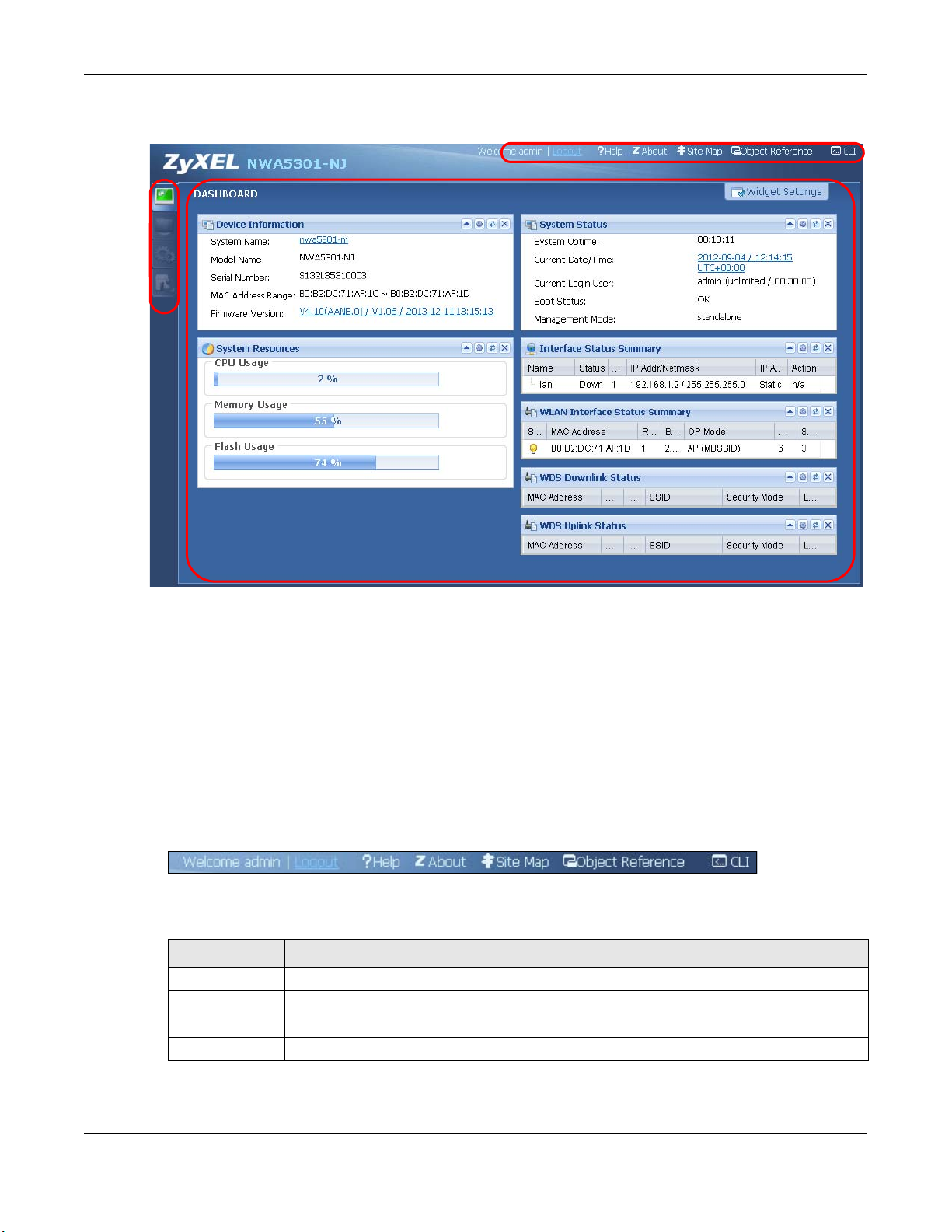
Figure 5 The Web Configurator’s Main Screen
The Web Configurator’s main screen is divided into these parts:
• A - Title Bar
• B - Navigation Panel
• C - Main Window
2.3.1 Title Bar
The title bar provides some useful links that always appear over the screens below, regardless of
how deep into the Web Configurator you navigate.
Figure 6 Title Bar
The icons provide the following functions.
Table 6 Title Bar: Web Configurator Icons
LABEL DESCRIPTION
Logout Click this to log out of the Web Configurator.
Help Click this to open the help page for the current screen.
About Click this to display basic information about the NWA.
Site Map Click this to see an overview of links to the Web Configurator screens.
NWA5301-NJ User’s Guide
23
Page 24
Chapter 2 The Web Configurator
Table 6 Title Bar: Web Configurator Icons (continued)
LABEL DESCRIPTION
Object
Reference
CLI Click this to open a popup window that displays the CLI commands sent by the Web
Click this to open a screen where you can check which configuration items reference an
object.
Configurator.
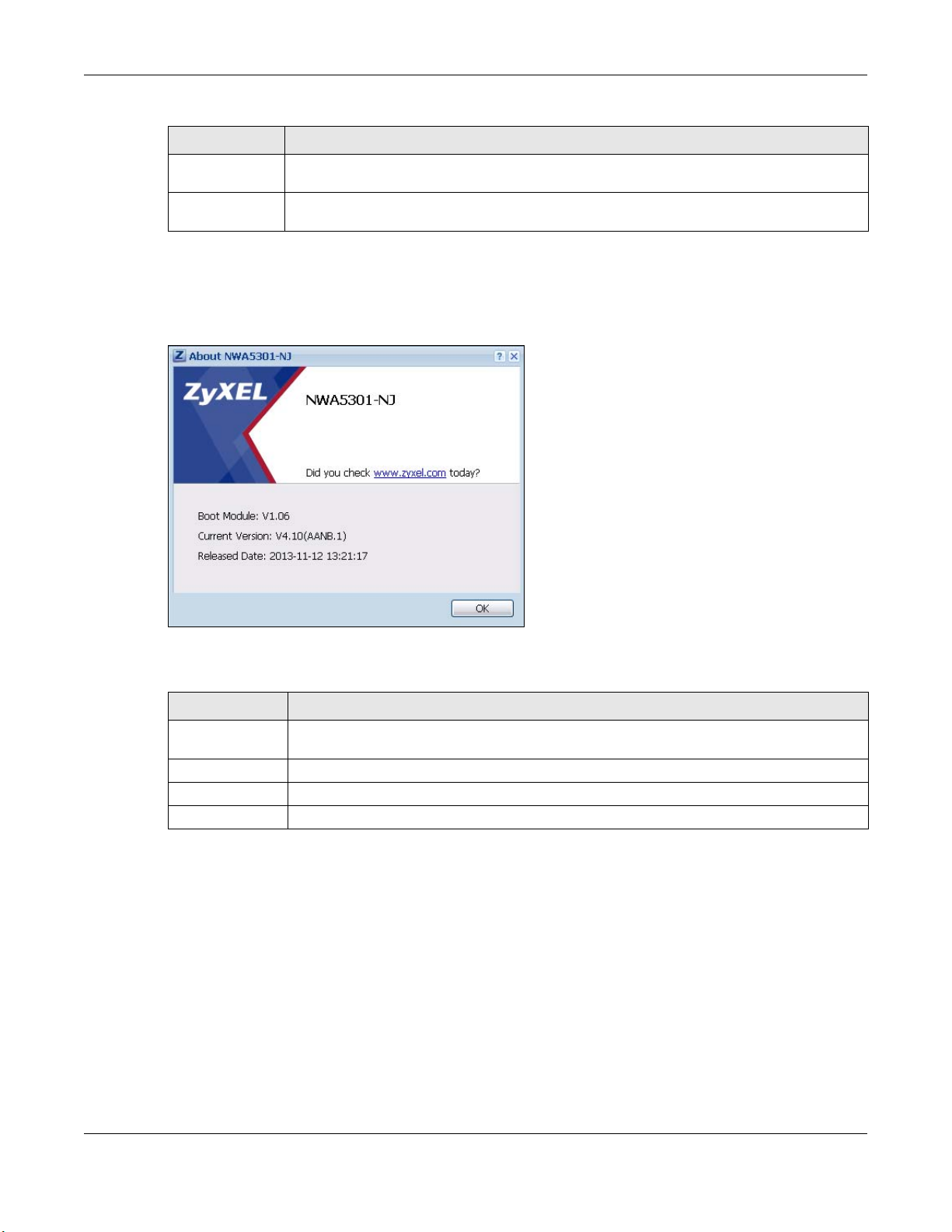
About
Click About to display basic information about the NWA.
Figure 7 About
The following table describes labels that can appear in this screen.
Table 7 About
LABEL DESCRIPTION
Boot Module This shows the version number of the software that handles the booting process of the
Current Version This shows the firmware version of the NWA.
Released Date This shows the date (yyyy-mm-dd) and time (hh:mm:ss) when the firmware is released.
OK Click this to close the screen.
NWA.
Site Map
Click Site MAP to see an overview of links to the Web Configurator screens. Click a screen’s link to
go to that screen.
NWA5301-NJ User’s Guide
24
Page 25
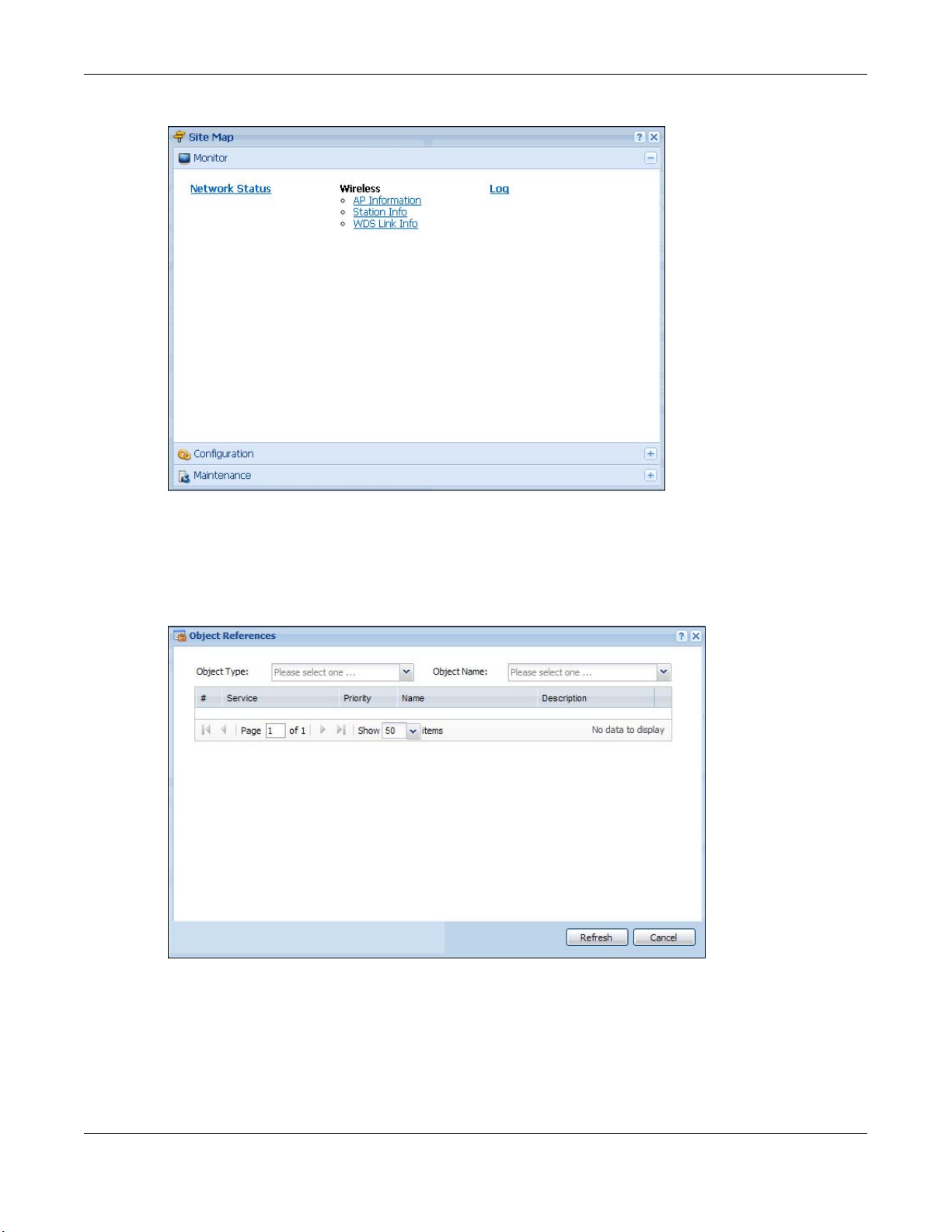
Figure 8 Site Map
Chapter 2 The Web Configurator
Object Reference
Click Object Reference to open the Object Reference screen. Select the type of object and the
individual object and click Refresh to show which configuration settings reference the object.
Figure 9 Object Reference
NWA5301-NJ User’s Guide
25
Page 26

Chapter 2 The Web Configurator
The fields vary with the type of object. The following table describes labels that can appear in this
screen.
Table 8 Object References
LABEL DESCRIPTION
Object Name This identifies the object for which the configuration settings that use it are displayed. Click
# This field is a sequential value, and it is not associated with any entry.
Service This is the type of setting that references the selected object. Click a service’s name to
Priority If it is applicable, this field lists the referencing configuration item’s position in its list,
Name This field identifies the configuration item that references the object.
Description If the referencing configuration item has a description configured, it displays here.
Refresh Click this to update the information in this screen.
Cancel Click Cancel to close the screen.
the object’s name to display the object’s configuration screen in the main window.
display the service’s configuration screen in the main window.
otherwise N/A displays.
CLI Messages
Click CLI to look at the CLI commands sent by the Web Configurator. These commands appear in a
popup window, such as the following.
Figure 10 CLI Messages
Click Clear to remove the currently displayed information.
Note: See the Command Reference Guide for information about the commands.
2.3.2 Navigation Panel
Use the menu items on the navigation panel to open screens to configure NWA features. Click the
arrow in the middle of the right edge of the navigation panel to hide the navigation panel menus or
drag it to resize them. The following sections introduce the NWA’s navigation panel menus and their
screens.
NWA5301-NJ User’s Guide
26
Page 27
Chapter 2 The Web Configurator
Figure 11 Navigation Panel
Dashboard
The dashboard displays general device information, system status, system resource usage, and
interface status in widgets that you can re-arrange to suit your needs.
For details on the Dashboard’s features, see Chapter 3 on page 33.
Monitor Menu
The monitor menu screens display status and statistics information.
Table 9 Monitor Menu Screens Summary
FOLDER OR LINK TAB FUNCTION
Network Status Display general LAN interface information and packet statistics.
Wireless
AP Information Radio List Display information about the radio of the NWA.
Station Info Station List Display information about the connected stations.
WDS Link Info Display statistics about the NWA’s WDS connections.
Log View Log Display log entries for the NWA.
Configuration Menu
Use the configuration menu screens to configure the NWA’s features.
Table 10 Configuration Menu Screens Summary
FOLDER OR LINK TAB FUNCTION
MGNT Mode Configure the NWA as a standalone AP, or a managed AP
Network IP Setting Configuer the IP address for the NWA Ethernet interface.
VLAN Manage the Ethernet interface VLAN settings.
Wireless
AP Management WLAN Setting Edit wireless AP information, remove APs, and reboot them.
NWA5301-NJ User’s Guide
27
Page 28
Chapter 2 The Web Configurator
Table 10 Configuration Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
Load Balancing Configure load balancing for traffic moving to and from wireless
clients.
DCS Configure dynamic wireless channel selection.
Object
Users User Create and manage users.
Setting Manage default settings for all users, general settings for user
sessions, and rules to force user authentication.
AP Profile Radio Create and manage wireless radio settings files that can be
SSID Create and manage wireless SSID, security, MAC filtering, and
WDS Profile Create and manage WDS profiles that can be used to connect to
Certificate My Certificates Create and manage the NWA’s certificates.
Trusted Certificates Import and manage certificates from trusted sources.
System
Host Name Configure the system and domain name for the NWA.
Date/Time Configure the current date, time, and time zone in the NWA.
WWW Configure HTTP, HTTPS, and general authentication.
SSH Configure SSH server and SSH service settings.
TELNET Configure telnet server settings for the NWA.
FTP Configure FTP server settings.
SNMP Configure SNMP communities and services.
Log & Report
Email Daily
Report
Log Setting Configure the system log, e-mail logs, and remote syslog servers.
associated with different APs.
layer-2 isolation files that can be associated with different APs.
different APs in WDS.
Configure where and how to send daily reports and what reports
to send.
Maintenance Menu
Use the maintenance menu screens to manage configuration and firmware files, run diagnostics,
and reboot or shut down the NWA.
Tab le 11 Maintenance Menu Screens Summary
FOLDER OR LINK TAB FUNCTION
File Manager Configuration File Manage and upload configuration files for the NWA.
Firmware Package View the current firmware version and to upload firmware.
Shell Script Manage and run shell script files for the NWA.
Diagnostics Diagnostics Collect diagnostic information.
Reboot Restart the NWA.
Shutdown Turn off the NWA.
NWA5301-NJ User’s Guide
28
Page 29
Chapter 2 The Web Configurator
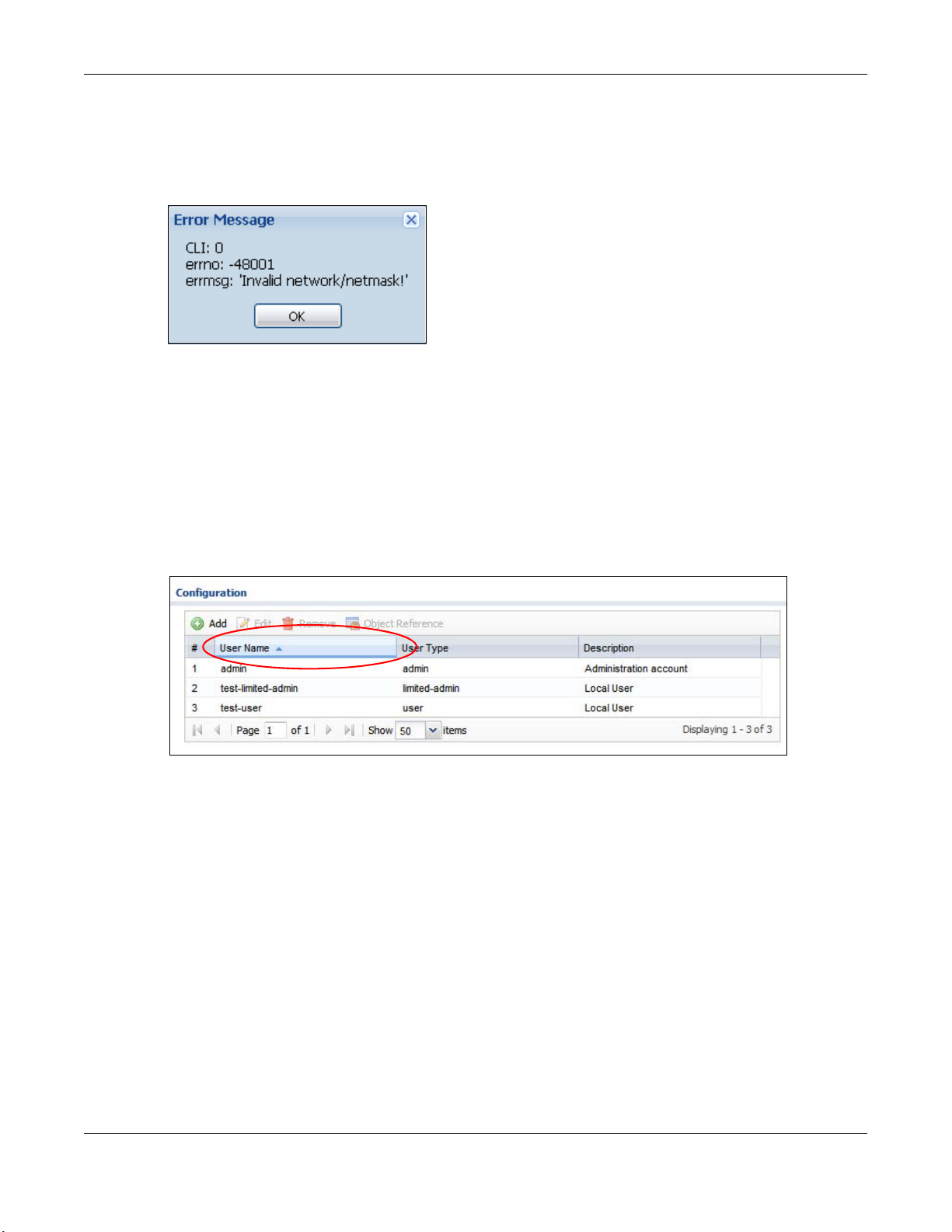
2.3.3 Warning Messages
Warning messages, such as those resulting from misconfiguration, display in a popup window.
Figure 12 Warning Message
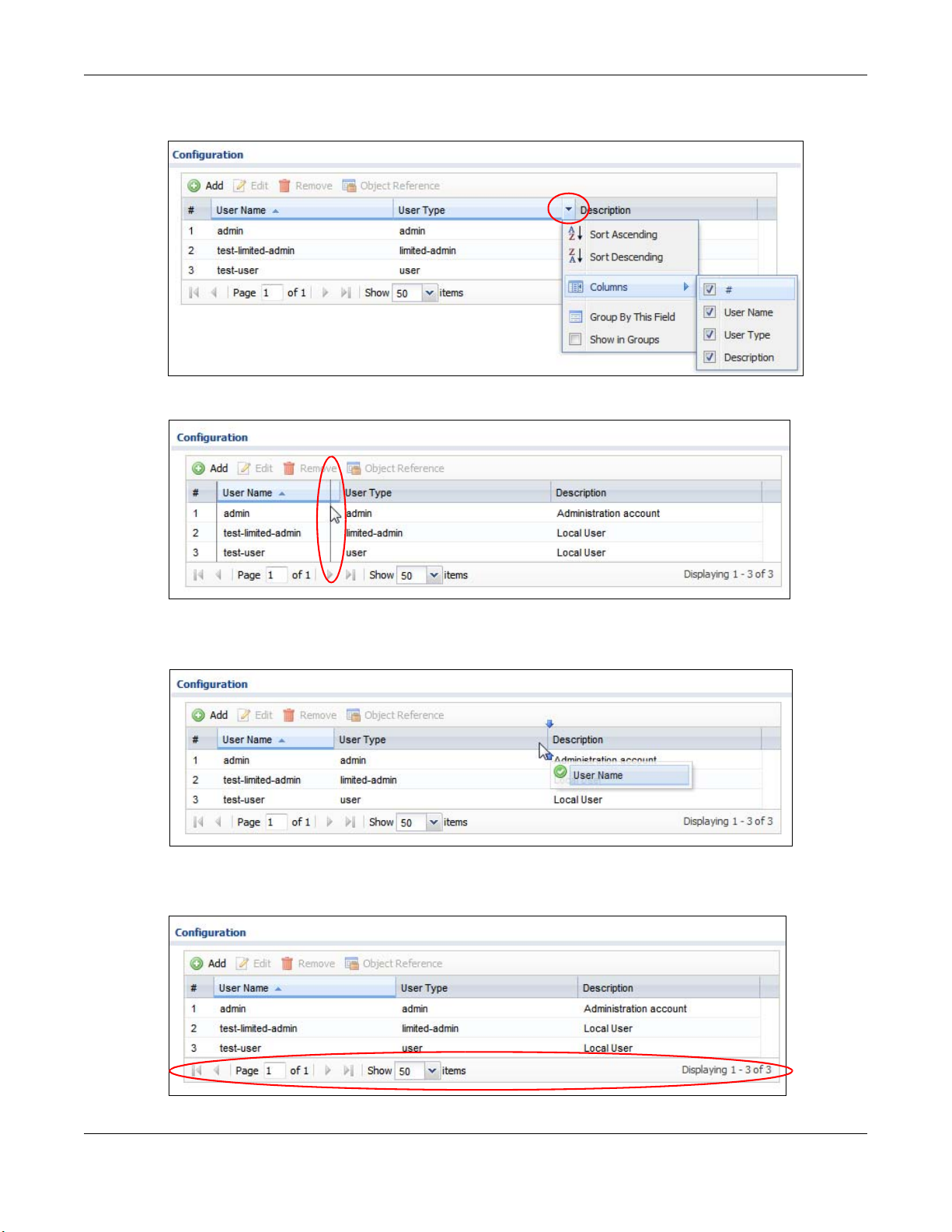
2.3.4 Tables and Lists
The Web Configurator tables and lists are quite flexible and provide several options for how to
display their entries.
2.3.4.1 Manipulating Table Display
Here are some of the ways you can manipulate the Web Configurator tables.
1 Click a column heading to sort the table’s entries according to that column’s criteria.
2 Click the down arrow next to a column heading for more options about how to display the entries.
The options available vary depending on the type of fields in the column. Here are some examples
of what you can do:
• Sort in ascending alphabetical order
• Sort in descending (reverse) alphabetical order
• Select which columns to display
• Group entries by field
• Show entries in groups
NWA5301-NJ User’s Guide
29
Page 30
Chapter 2 The Web Configurator
• Filter by mathematical operators (<, >, or =) or searching for text.
3 Select a column heading cell’s right border and drag to re-size the column.
4 Select a column heading and drag and drop it to change the column order. A green check mark
displays next to the column’s title when you drag the column to a valid new location.
5 Use the icons and fields at the bottom of the table to navigate to different pages of entries and
control how many entries display at a time.
NWA5301-NJ User’s Guide
30
Page 31

Chapter 2 The Web Configurator
2.3.4.2 Working with Table Entries
The tables have icons for working with table entries. A sample is shown next. You can often use the
[Shift] or [Ctrl] key to select multiple entries to remove, activate, or deactivate.
Table 12 Common Table Icons
Here are descriptions for the most common table icons.
Table 13 Common Table Icons
LABEL DESCRIPTION
Add Click this to create a new entry. For features where the entry’s position in the numbered
list is important (features where the NWA applies the table’s entries in order like the
firewall for example), you can select an entry and click Add to create a new entry after
the selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings. In some tables you can just click a table entry and edit it directly in
the table. For those types of tables small red triangles display for table entries with
changes that you have not yet applied.
Remove To remove an entry, select it and click Remove. The NWA confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object Reference Select an entry and click Object Reference to open a screen that shows which settings
use the entry.
2.3.4.3 Working with Lists
When a list of available entries displays next to a list of selected entries, you can often just doubleclick an entry to move it from one list to the other. In some lists you can also use the [Shift] or
[Ctrl] key to select multiple entries, and then use the arrow button to move them to the other list.
Figure 13 Working with Lists
NWA5301-NJ User’s Guide
31
Page 32

PART II
Technical Reference
32
Page 33

3.1 Overview
B
C
D
E
A
Use the Dashboard screens to check status information about the NWA.
3.1.1 What You Can Do in this Chapter
•The main Dashboard screen (Section 3.2 on page 33) displays the NWA’s general device
information, system status, system resource usage, and interface status. You can also display
other status screens for more information.
3.2 Dashboard
CHAPTER 3
Dashboard
This screen is the first thing you see when you log into the NWA. It also appears every time you
click the Dashboard icon in the navigation panel. The Dashboard displays general device
information, system status, system resource usage, and interface status in widgets that you can rearrange to suit your needs. You can also collapse, refresh, and close individual widgets.
Figure 14 Dashboard
NWA5301-NJ User’s Guide
33
Page 34

Chapter 3 Dashboard
The following table describes the labels in this screen.
Table 14 Dashboard
LABEL DESCRIPTION
Widget Settings (A) Use this link to re-open closed widgets. Widgets that are already open appear grayed
Up Arrow (B) Click this to collapse a widget.
Refresh Time
Setting (C)
Refresh Now (D) Click this to update the widget’s information immediately.
Close Widget (E) Click this to close the widget. Use Widget Setting to re-open it.
Device Information
System Name This field displays the name used to identify the NWA on any network. Click the icon to
Model Name This field displays the model name of this NWA.
Serial Number This field displays the serial number of this NWA.
MAC Address
Range
Firmware
Version
System Resources
CPU Usage This field displays what percentage of the NWA’s processing capability is currently being
Memory Usage This field displays what percentage of the NWA’s RAM is currently being used. Hover
Flash Usage This field displays what percentage of the NWA’s onboard flash memory is currently
System Status
System Uptime This field displays how long the NWA has been running since it last restarted or was
Current Date/
Time
Current Login
User
out.
Set the interval for refreshing the information displayed in the widget.
open the screen where you can change it.
This field displays the MAC addresses used by the NWA. Each physical port or wireless
radio has one MAC address. The first MAC address is assigned to the Ethernet LAN port,
the second MAC address is assigned to the first radio, and so on.
This field displays the version number and date of the firmware the NWA is currently
running. Click the icon to open the screen where you can upload firmware.
used. Hover your cursor over this field to display the Show CPU Usage icon that takes
you to a chart of the NWA’s recent CPU usage.
your cursor over this field to display the Show Memory Usage icon that takes you to a
chart of the NWA’s recent memory usage.
being used.
turned on.
This field displays the current date and time in the NWA. The format is yyyy-mm-dd
hh:mm:ss.
This field displays the user name used to log in to the current session, the amount of
reauthentication time remaining, and the amount of lease time remaining.
NWA5301-NJ User’s Guide
34
Page 35

Chapter 3 Dashboard
Table 14 Dashboard (continued)
LABEL DESCRIPTION
Boot Status This field displays details about the NWA’s startup state.
OK - The NWA started up successfully.
Firmware update OK - A firmware update was successful.
Problematic configuration after firmware update - The application of the
configuration failed after a firmware upgrade.
System default configuration - The NWA successfully applied the system default
configuration. This occurs when the NWA starts for the first time or you intentionally
reset the NWA to the system default settings.
Fallback to lastgood configuration - The NWA was unable to apply the startupconfig.conf configuration file and fell back to the lastgood.conf configuration file.
Fallback to system default configuration - The NWA was unable to apply the
lastgood.conf configuration file and fell back to the system default configuration file
(system-default.conf).
Booting in progress - The NWA is still applying the system configuration.
Management
Mode
Interface Status
Summary
Name This field displays the name of each interface.
Status This field displays the current status of each interface. The possible values depend on
This shows whether the NWA is set to work as a stand alone AP.
If an Ethernet interface does not have any physical ports associated with it, its entry is
displayed in light gray text. Click the Detail icon to go to a (more detailed) summary
screen of interface statistics.
what type of interface it is.
Inactive - The Ethernet interface is disabled.
Down - The Ethernet interface is enabled but not connected.
Speed / Duplex - The Ethernet interface is enabled and connected. This field displays
the port speed and duplex setting (Full or Half).
VID This field displays the VLAN ID to which the interface belongs.
IP Addr/
Netmask
IP Assignment This field displays how the interface gets its IP address.
Action If the interface has a static IP address, this shows n/a.
WLAN Interface
Status Summary
Status This displays whether or not the WLAN interface is activated.
MAC Address This displays the MAC address of the radio.
Radio This indicates the radio number on the NWA.
Band This indicates the wireless frequency band currently being used by the radio.
OP Mode This indicates the radio’s operating mode. Operating modes are AP (MBSSID), Root
Channel This indicates the channel number the radio is using.
This field displays the current IP address and subnet mask assigned to the interface. If
the IP address is 0.0.0.0, the interface is disabled or did not receive an IP address and
subnet mask via DHCP.
Static - This interface has a static IP address.
DHCP Client - This interface gets its IP address from a DHCP server.
If the interface has a dynamic IP address, use this field to get or to update the IP
address for the interface. Click Renew to send a new DHCP request to a DHCP server.
This displays status information for the WLAN interface.
AP or Repeater.
NWA5301-NJ User’s Guide
35
Page 36

Chapter 3 Dashboard
Table 14 Dashboard (continued)
LABEL DESCRIPTION
Station This displays the number of wireless clients connected to the NWA.
WDS Downlink
Status
WDS Uplink Status
MAC Address This is the MAC address of the root AP or repeater to which the NWA is connected using
Radio This is the radio number on the root AP or repeater to which the NWA is connected
Channel This is the channel number(s) used by the root AP or repeater to which the NWA is
SSID This indicates the name of the wireless network to which the NWA is connected using
Security Mode This indicates which secure encryption methods is being used by the NWA to connect to
Link Status This indicates whether the WDS link is up. A yellow bulb signifies that this link is up. A
This displays status information for the WDS links.
Uplink refers to the WDS link from the repeaters to the root AP.
Downlink refers to the WDS link from the root AP to the repeaters.
When the NWA is in root AP mode and connected to a repeater, only the downlink
information is displayed.
When the NWA is in repeater mode and connected to a root AP directly or via another
repeater, the uplink information is displayed.
When the NWA is in repeater mode and connected to a root AP and other repeater(s),
both the uplink and downlink information would be displayed.
WDS.
using WDS.
connected using WDS.
WDS.
the root AP or repeater using WDS.
gray bulb signifies that this link is down.
3.2.1 CPU Usage
Use this screen to look at a chart of the NWA’s recent CPU usage. To access this screen, click CPU
Usage in the dashboard.
Figure 15 Dashboard > CPU Usage
NWA5301-NJ User’s Guide
36
Page 37

The following table describes the labels in this screen.
Table 15 Dashboard > CPU Usage
LABEL DESCRIPTION
% The y-axis represents the percentage of CPU usage.
time The x-axis shows the time period over which the CPU usage occurred
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
3.2.2 Memory Usage
Use this screen to look at a chart of the NWA’s recent memory (RAM) usage. To access this screen,
click Memory Usage in the dashboard.
Figure 16 Dashboard > Memory Usage
Chapter 3 Dashboard
The following table describes the labels in this screen.
Table 16 Dashboard > Memory Usage
LABEL DESCRIPTION
The y-axis represents the percentage of RAM usage.
The x-axis shows the time period over which the RAM usage occurred
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
NWA5301-NJ User’s Guide
37
Page 38

4.1 Overview
Use the Monitor screens to check status and statistics information.
4.1.1 What You Can Do in this Chapter
•The Network Status screen (Section 4.2 on page 38) displays general Ethernet interface
information and packet statistics.
•The Radio List screen (Section 4.3 on page 40) displays statistics about the wireless radio
transmitter in the NWA.
•The Station Info screen (Section 4.4 on page 43) displays statistics pertaining to the associated
stations.
•The WDS Link Info screen (Section 4.5 on page 44) displays statistics about the NWA’s WDS
connections.
•The View Log screen (Section 4.6 on page 45) displays the NWA’s current log messages. You
can change the way the log is displayed, you can e-mail the log, and you can also clear the log in
this screen.
CHAPTER 4
Monitor
4.2 Network Status
Use this screen to look at general Ethernet interface information and packet statistics. To access
this screen, click Monitor > Network Status.
NWA5301-NJ User’s Guide
38
Page 39

Chapter 4 Monitor
Figure 17 Monitor > Network Status
The following table describes the labels in this screen.
Table 17 Monitor > Network Status
LABEL DESCRIPTION
Interface
Summary
IPv6 Interface
Summary
IP Addr/Netmask
IP Address
IP Assignment This field displays how the interface gets its IPv4 address.
Action Use this field to get or to update the IP address for the interface. Click Renew to send a
Port Statistics
Tabl e
Poll Interval Enter how often you want this window to be updated automatically, and click Set Interval.
Set Interval Click this to set the Poll Interval the screen uses.
Stop Click this to stop the window from updating automatically. You can start it again by setting
Name This field displays the name of the Ethernet port on the NWA.
Use the Interface Summary section for IPv4 network settings. Use the IPv6 Interface
Summary section for IPv6 network settings if you connect your NWA to an IPv6 network.
Both sections have similar fields as described below.
This field displays the current IP address (and subnet mask) of the interface. If the IP
address is 0.0.0.0 (in the IPv4 network) or :: (in the IPv6 network), the interface does not
have an IP address yet.
Static - This interface has a static IPv4 address.
DHCP Client - This interface gets its IPv4 address from a DHCP server.
new DHCP request to a DHCP server. If the interface cannot use one of these ways to get
or to update its IP address, this field displays n/a.
the Poll Interval and clicking Set Interval.
NWA5301-NJ User’s Guide
39
Page 40

Chapter 4 Monitor
Table 17 Monitor > Network Status (continued)
LABEL DESCRIPTION
Status This field displays the current status of the physical port.
Down - The physical port is not connected.
Speed / Duplex - The physical port is connected. This field displays the port speed and
duplex setting (Full or Half).
TxPkts This field displays the number of packets transmitted from the NWA on the physical port
RxPkts This field displays the number of packets received by the NWA on the physical port since it
Collisions This field displays the number of collisions on the physical port since it was last connected.
Tx This field displays the transmission speed, in bytes per second, on the physical port in the
Rx This field displays the reception speed, in bytes per second, on the physical port in the
Up Time This field displays how long the physical port has been connected.
System Up Time This field displays how long the NWA has been running since it last restarted or was turned
since it was last connected.
was last connected.
one-second interval before the screen updated.
one-second interval before the screen updated.
on.
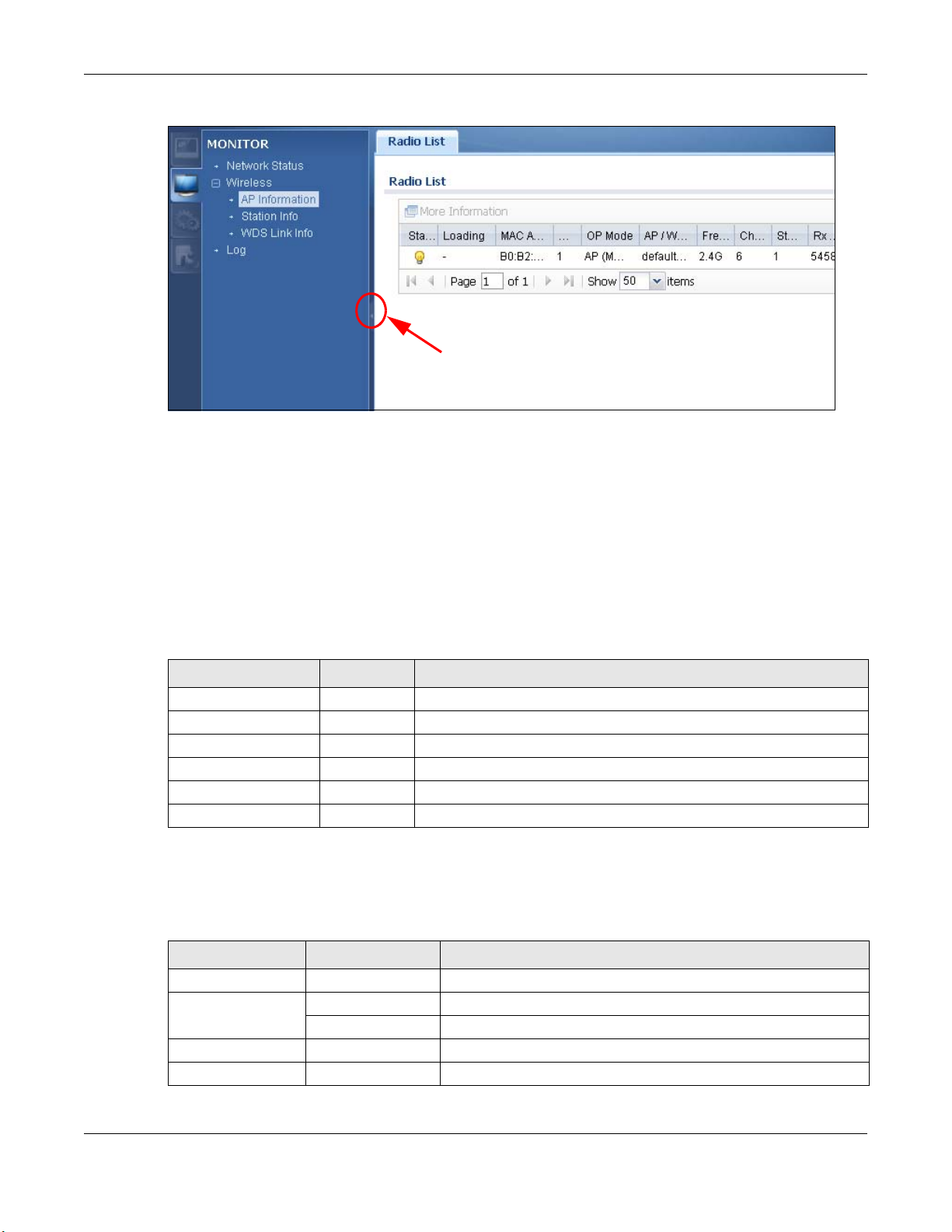
4.3 Radio List
Use this screen to view statistics for the NWA’s wireless radio transmitter. To access this screen,
click Monitor > Wireless > AP Information > Radio List.
Figure 18 Monitor > Wireless > AP Information > Radio List
The following table describes the labels in this screen.
Table 18 Monitor > Wireless > AP Information > Radio List
LABEL DESCRIPTION
More
Information
Status This displays whether or not the radio is enabled.
Loading This indicates the AP’s load balance status (UnderLoad or OverLoad) when load
MAC Address This displays the MAC address of the radio.
Click this to view additional information about the selected radio’s wireless traffic and
station count. Information spans a 24 hour period.
balancing is enabled on the NWA. Otherwise, it shows - when load balancing is disabled.
NWA5301-NJ User’s Guide
40
Page 41

Table 18 Monitor > Wireless > AP Information > Radio List (continued)
LABEL DESCRIPTION
Radio This indicates the radio number on the NWA to which it belongs.
OP Mode This indicates the radio’s operating mode. Operating modes are A P (MB SSID), Root AP
or Repeater.
AP/WDS Profile This indicates the AP profile name and WDS profile name to which the radio belongs.
Frequency Band This indicates the wireless frequency band currently being used by the radio.
Channel ID This indicates the radio’s channel ID.
Station This displays the number of wireless clients connected to this radio on the NWA.
Rx PKT This displays the total number of packets received by the radio.
Tx PKT This displays the total number of packets transmitted by the radio.
Rx FCS Error
Count
Tx Retry Count This indicates the number of times the radio has attempted to re-transmit packets.
This indicates the number of received packet errors accrued by the radio.
4.3.1 AP Mode Radio Information
This screen allows you to view a selected radio’s SSID details, wireless traffic statistics and station
count for the preceding 24 hours. To access this window, select a radio and click the More
Information button in the Radio List screen.
Chapter 4 Monitor
NWA5301-NJ User’s Guide
41
Page 42

Chapter 4 Monitor
Figure 19 Monitor > Wireless > AP Information > Radio List > More Information
NWA5301-NJ User’s Guide
42
Page 43

Chapter 4 Monitor
The following table describes the labels in this screen.
Table 19 Monitor > Wireless > AP Information > Radio List > More Information
LABEL DESCRIPTION
SSID Detail This list shows information about all the wireless clients that have connected to the
# This is the items sequential number in the list. It has no bearing on the actual data in this
SSID Name This displays an SSID associated with this radio. There can be up to eight maximum.
BSSID This displays a BSSID associated with this radio. The BSSID is tied to the SSID.
Security
Mode
VLAN This displays the VLAN ID associated with the SSID.
Traffic Statistics This graph displays the overall traffic information of the radio over the preceding 24 hours.
Station Count This graph displays the connected station information of the radio over the preceding 24
Last Update This field displays the date and time the information in the window was last updated.
OK Click this to close this window.
Cancel Click this to close this window.
specified radio over the preceding 24 hours.
list.
This displays the security mode in which the SSID is operating.
This y-axis represents the amount of data moved across this radio in megabytes per
second.
This x-axis represents the amount of time over which the data moved across this radio.
hours
The y-axis represents the number of connected stations.
The x-axis shows the time period over which a station was connected.
4.4 Station List
Use this screen to view statistics pertaining to the associated stations (or “wireless clients”). Click
Monitor > Wireless > Station Info to access this screen.
Figure 20 Monitor > Wireless > Station Info
NWA5301-NJ User’s Guide
43
Page 44

Chapter 4 Monitor
The following table describes the labels in this screen.
Table 20 Monitor > Wireless > Station Info
LABEL DESCRIPTION
# This is the station’s index number in this list.
MAC Address This is the station’s MAC address.
Radio This is the radio number on the NWA to which the station is connected.
SSID Name This indicates the name of the wireless network to which the station is connected. A single
Security Mode This indicates which secure encryption methods is being used by the station to connect to
Signal Strength This is the RSSI (Received Signal Strength Indicator) of the station’s wireless connection.
Tx Rate This is the maximum transmission rate of the station.
Rx Rate This is the maximum reception rate of the station.
Association Time This displays the time the station first associated with the NWA’s wireless network.
Refresh Click this to refresh the items displayed on this page.
AP can have multiple SSIDs or networks.
the network.
4.5 WDS Link Info
Use this screen to view the WDS traffic statistics between the NWA and a root AP or repeaters. Click
Monitor > Wireless > WDS Link Info to access this screen.
Figure 21 Monitor > Wireless > WDS Link Info
NWA5301-NJ User’s Guide
44
Page 45

Chapter 4 Monitor
The following table describes the labels in this screen.
Table 21 Monitor > Wireless > WDS Link Info
LABEL DESCRIPTION
WDS Uplink Info
WDS Downlink
Info
# This is the index number of the root AP or repeater in this list.
MAC Address This is the MAC address of the root AP or repeater to which the NWA is connected using
Radio This is the radio number on the root AP or repeater to which the NWA is connected using
SSID Name This indicates the name of the wireless network to which the NWA is connected using WDS.
Security Mode This indicates which secure encryption methods is being used by the NWA to connect to the
Signal Strength This is the RSSI (Received Signal Strength Indicator) of the wireless connection in WDS.
Tx Rate This is the maximum transmission rate of the root AP or repeater to which the NWA is
Rx Rate This is the maximum reception rate of the root AP or repeater to which the NWA is
Association Time This displays the time the NWA first associated with the wireless network using WDS.
Refresh Click this to refresh the items displayed on this page.
Uplink refers to the WDS link from the repeaters to the root AP.
Downlink refers to the WDS link from the root AP to the repeaters.
When the NWA is in root AP mode and connected to a repeater, only the downlink
information is displayed.
When the NWA is in repeater mode and connected to a root AP directly or via another
repeater, the uplink information is displayed.
When the NWA is in repeater mode and connected to a root AP and other repeater(s), both
the uplink and downlink information would be displayed.
WDS.
WDS.
root AP or repeater using WDS.
connected using WDS.
connected using WDS.
4.6 View Log
Log messages are stored in two separate logs, one for regular log messages and one for debugging
messages. In the regular log, you can look at all the log messages by selecting All Logs, or you can
select a specific category of log messages (for example, user). You can also look at the debugging
log by selecting Debug Log. All debugging messages have the same priority.
To access this screen, click Monitor > Log. The log is displayed in the following screen.
Note: When a log reaches the maximum number of log messages, new log messages
automatically overwrite existing log messages, starting with the oldest existing log
message first.
Events that generate an alert (as well as a log message) display in red. Regular logs display in
black. Click a column’s heading cell to sort the table entries by that column’s criteria. Click the
heading cell again to reverse the sort order.
NWA5301-NJ User’s Guide
45
Page 46

Figure 22 Monitor > Log > View Log
Chapter 4 Monitor
The following table describes the labels in this screen.
Table 22 Monitor > Log > View Log
LABEL DESCRIPTION
Show Filter /
Hide Filter
Display Select the category of log message(s) you want to view. You can also view All Logs at one
Priority This displays when you show the filter. Select the priority of log messages to display. The
Source Address This displays when you show the filter. Type the source IP address of the incoming packet
Destination
Address
Click this button to show or hide the filter settings.
If the filter settings are hidden, the Display, Email Log Now, Refresh, and Clear Log
fields are available.
If the filter settings are shown, the Display, Priority, Source Address, Destination
Address, Service, Keyword, and Search fields are available.
time, or you can view the Debug Log.
log displays the log messages with this priority or higher. Choices are: any, emerg, alert,
crit, error, warn, notice, and info, from highest priority to lowest priority. This field is
read-only if the Category is Debug Log.
that generated the log message. Do not include the port in this filter.
This displays when you show the filter. Type the IP address of the destination of the
incoming packet when the log message was generated. Do not include the port in this filter.
NWA5301-NJ User’s Guide
46
Page 47

Chapter 4 Monitor
Table 22 Monitor > Log > View Log (continued)
LABEL DESCRIPTION
Source Interface This displays when you show the filter. Select the source interface of the packet that
generated the log message.
Destination
Interface
Protocol This displays when you show the filter. Select a service protocol whose log messages you
Keyword This displays when you show the filter. Type a keyword to look for in the Message,
Search This displays when you show the filter. Click this button to update the log using the current
Email Log Now Click this button to send log messages to the Active e-mail addresses specified in the
Refresh Click this to update the list of logs.
Clear Log Click this button to clear the whole log, regardless of what is currently displayed on the
# This field is a sequential value, and it is not associated with a specific log message.
Time This field displays the time the log message was recorded.
Priority This field displays the priority of the log message. It has the same range of values as the
Category This field displays the log that generated the log message. It is the same value used in the
Message This field displays the reason the log message was generated. The text “[count=x]”, where
Source This field displays the source IP address and the port number in the event that generated
Destination This field displays the destination IP address and the port number of the event that
Note This field displays any additional information about the log message.
This displays when you show the filter. Select the destination interface of the packet that
generated the log message.
would like to see.
Source, Destination and Note fields. If a match is found in any field, the log message is
displayed. You can use up to 63 alphanumeric characters and the underscore, as well as
punctuation marks ()’ ,:;?! +-*/= #$% @ ; the period, double quotes, and brackets are
not allowed.
filter settings.
Send Log To field on the Configuration > Log & Report > Log Settings screen.
screen.
Priority field above.
Display and (other) Category fields.
x is a number, appears at the end of the Message field if log consolidation is turned on and
multiple entries were aggregated to generate into this one.
the log message.
generated the log message.
The Web Configurator saves the filter settings if you leave the View Log screen and return to it
later.
NWA5301-NJ User’s Guide
47
Page 48

5.1 Overview
This chapter discusses using the NWA in management mode, which determines whether the NWA is
used in its default standalone mode, or as part of a Control And Provisioning of Wireless Access
Points (CAPWAP) network.
5.2 About CAPWAP
The NWA supports CAPWAP. This is ZyXEL’s implementation of the CAPWAP protocol (RFC 5415).
The CAPWAP dataflow is protected by Datagram Transport Layer Security (DTLS).
CHAPTER 5
Management Mode
The following figure illustrates a CAPWAP wireless network. You (U) configure the AP controller (C),
which then automatically updates the configurations of the managed APs (M1 ~ M4).
Figure 23 CAPWAP Network Example
Note: The NWA can be a standalone AP (default), or a CAPWAP managed AP.
5.2.1 CAPWAP Discovery and Management
The link between CAPWAP-enabled access points proceeds as follows:
NWA5301-NJ User’s Guide
48
Page 49

Chapter 5 Management Mode
1 An AP in managed AP mode joins a wired network (receives a dynamic IP address).
2 The AP sends out a discovery request, looking for a CAPWAP AP controller.
3 If there is an AP controller on the network, it receives the discovery request. If the AP controller is
in Manual mode it adds the details of the AP to its Unmanaged Access Points list, and you
decide which available APs to manage. If the AP is in Always Accept mode, it automatically adds
the AP to its Managed Access Points list and provides the managed AP with default configuration
information, as well as securely transmitting the DTLS pre-shared key. The managed AP is ready for
association with wireless clients.
5.2.2 Managed AP Finds the Controller
A managed NWA can find the controller in one of the following ways:
• Manually specify the controller’s IP address in the Web Configurator’s MGNT Mode screen.
• Get the controller’s IP address from a DHCP server with the controller’s IP address configured as
option 138.
• Broadcasting to discover the controller within the broadcast domain.
Note: The AP controller needs to have a static IP address. If it is a DHCP client, set the
DHCP server to reserve an IP address for the AP controller.
5.2.3 CAPWAP and IP Subnets
By default, CAPWAP works only between devices with IP addresses in the same subnet.
However, you can configure CAPWAP to operate between devices with IP addresses in different
subnets by doing the following.
• Activate DHCP. Your network’s DHCP server must support option 138 defined in RFC 5415.
• Configure DHCP option 138 with the IP address of the CAPWAP AP controller on your network.
DHCP Option 138 allows the CAPWAP management request (from the AP in managed AP mode) to
reach the AP controller in a different subnet, as shown in the following figure.
NWA5301-NJ User’s Guide
49
Page 50

Figure 24 CAPWAP and DHCP Option 138
5.2.4 Notes on CAPWAP
Chapter 5 Management Mode
This section lists some additional features of ZyXEL’s implementation of the CAPWAP protocol.
• When the AP controller uses its internal Remote Authentication Dial In User Service (RADIUS)
server, managed APs also use the AP controller’s authentication server to authenticate wireless
clients.
• If a managed AP’s link to the AP controller is broken, the managed AP continues to use the
wireless settings with which it was last provided.
5.3 Management Mode Screen
Use this screen to configure the NWA as a CAPWAP managed AP, or to use it in standalone AP
mode. To access this screen, click Configuration > MGNT Mode.
Note: After you change the operation mode, the NWA resets to its default settings for the
mode you set it to, including the IP address of 192.168.1.2 (in standalone AP
mode).
NWA5301-NJ User’s Guide
50
Page 51

Chapter 5 Management Mode
Figure 25 Configuration > MGNT Mode
Each field is described in the following table.
Table 23 Configuration > MGNT Mode
LABEL DESCRIPTION
Standalone AP Select this to manage the NWA using its own web configurator, neither managing nor
Managed AP Select this to have the NWA managed by an AP controller on your network. When you
managed by other devices.
do this, the NWA can be configured ONLY by the AP controller.
Note: If you want to return the NWA to standalone AP mode, you must check the AP
controller for the NWA’s IP address and use FTP to upload firmware for standalone
AP mode.
Auto Select this option to use DHCP option 138 (CAPWAP Access Controller addresses) to get
the AP controller’s IP address.
Manual Select this option and enter the IP address of the AP controller manually.
Primary/
Secondary static
AC IP
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
Specify the primary and secondary IP address of the AP controller to which the NWA
connects.
If you change the mode in this screen, the NWA restarts. Wait a short while before you
attempt to log in again. If you changed the mode to Managed AP, the AP controller
uploads the firmware package for managed AP mode to the NWA and you cannot log in
as the web configurator is disabled; you must manage the NWA through the AP
controller on your network.
NWA5301-NJ User’s Guide
51
Page 52

6.1 Overview
This chapter describes how you can configure the management IP address and VLAN settings of
your NWA.
The Internet Protocol (IP) address identifies a device on a network. Every networking device
(including computers, servers, routers, printers, etc.) needs an IP address to communicate across
the network. These networking devices are also known as hosts.
Figure 26 IP Setup
CHAPTER 6
Network
The figure above illustrates one possible setup of your NWA. The gateway IP address is 192.168.1.1
and the IP address of the NWA is 192.168.1.2 (default). The gateway and the NWA must belong in
the same subnet mask to be able to communicate with each other.
6.1.1 What You Can Do in this Chapter
•The IP Setting screen (Section 6.2 on page 52) configures the NWA’s LAN IP address.
•The VLAN screen (Section 6.3 on page 54) configures the NWA’s VLAN settings.
6.2 IP Setting
Use this screen to configure the IP address for your NWA. To access this screen, click
Configuration > Network > IP Setting.
NWA5301-NJ User’s Guide
52
Page 53

Chapter 6 Network
Figure 27 Configuration > Network > IP Setting
Each field is described in the following table.
Table 24 Configuration > Network > IP Setting
LABEL DESCRIPTION
IP Address
Assignment
Get
Automatically
Use Fixed IP
Address
IP Address Enter the IP address for this interface.
Subnet Mask Enter the subnet mask of this interface in dot decimal notation. The subnet mask
Gateway Enter the IP address of the gateway. The NWA sends packets to the gateway when it
DNS Server IP
Address
IPv6 Address
Assignment
Enable Stateless
Address Autoconfiguration
(SLAAC)
Select this to make the interface a DHCP client and automatically get the IP address,
subnet mask, and gateway address from a DHCP server.
Select this if you want to specify the IP address, subnet mask, and gateway manually.
indicates what part of the IP address is the same for all computers in the network.
does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Enter the IP address of the DNS server.
Select this to enable IPv6 stateless auto-configuration on the NWA. The NWA will
generate an IPv6 address itself from a prefix obtained from an IPv6 router in the
network.
NWA5301-NJ User’s Guide
53
Page 54

Chapter 6 Network
A
B
Table 24 Configuration > Network > IP Setting (continued)
LABEL DESCRIPTION
Link-Local
Address
IPv6 Address/
Prefix Length
Gateway Enter the IPv6 address of the default outgoing gateway using colon (:) hexadecimal
Metric Enter the priority of the gateway (if any) on the LAN interface. The NWA decides which
DHCPv6 Select this option to set the NWA to act as a DHCPv6 client.
DUID This field displays the DHCP Unique IDentifier (DUID) of the NWA, which is unique and
Request Address
DHCPv6 Request
Options
DNS Server Select this option to obtain the IP address of the DNS server.
NTP Server Select this option to obtain the IP address of the NTP server.
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
This displays the IPv6 link-local address and the network prefix that the NWA generates
itself for the LAN interface.
Enter the IPv6 address and the prefix length for the LAN interface if you want to use a
static IP address. This field is optional.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
notation.
gateway to use based on this priority. The lower the number, the higher the priority. If
two or more gateways have the same priority, the NWA uses the one that was
configured first.
used for identification purposes when the NWA is exchanging DHCPv6 messages with
others. See Appendix B on page 183 for more information.
Select this option to determine what additional information to get from the DHCPv6
server.
6.3 VLAN
This section discusses how to configure the NWA’s VLAN settings.
Figure 28 Management VLAN Setup
In the figure above, to access and manage the NWA from computer A, the NWA and switch B’s
ports to which computer A and the NWA are connected should be in the same VLAN.
NWA5301-NJ User’s Guide
54
Page 55

Chapter 6 Network
A Virtual Local Area Network (VLAN) allows a physical network to be partitioned into multiple logical
networks. Devices on a logical network belong to one group. A device can belong to more than one
group. With VLAN, a device cannot directly talk to or hear from devices that are not in the same
group(s); the traffic must first go through a router.
In Multi-Tenant Unit (MTU) applications, VLAN is vital in providing isolation and security among the
subscribers. When properly configured, VLAN prevents one subscriber from accessing the network
resources of another on the same LAN, thus a user will not see the printers and hard disks of
another user in the same building.
VLAN also increases network performance by limiting broadcasts to a smaller and more
manageable logical broadcast domain. In traditional switched environments, all broadcast packets
go to each and every individual port. With VLAN, all broadcasts are confined to a specific broadcast
domain.
IEEE 802.1Q Tag
The IEEE 802.1Q standard defines an explicit VLAN tag in the MAC header to identify the VLAN
membership of a frame across bridges. A VLAN tag includes the 12-bit VLAN ID and 3-bit user
priority. The VLAN ID associates a frame with a specific VLAN and provides the information that
devices need to process the frame across the network.
Use this screen to configure the VLAN settings for your NWA and enable or disable a port. To access
this screen, click Configuration > Network > VLAN.
Figure 29 Configuration > Network > VLAN
NWA5301-NJ User’s Guide
55
Page 56

Chapter 6 Network
Each field is described in the following table.
Table 25 Configuration > Network > VLAN
LABEL DESCRIPTION
VLAN Settings
Management
VLAN ID
As Native VLAN Select this option to treat this VLAN ID as a VLAN created on the NWA and not one
Port Setting
# This is the port’s index number in this list.
Status This displays whether or not the port is activated.
Port This shows the name of the physical Ethernet port on the NWA.
PVID This shows the port’s PVID.
VLAN Member
Configuration
# This is the VLAN’s index number in this list.
Status This displays whether or not the VLAN is activated.
Name This shows the name of the VLAN.
VID This shows the VLAN ID number.
Member This field displays the Ethernet port(s) that is a member of this VLAN.
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
Enter a VLAN ID for the NWA.
assigned to it from outside the network.
A PVID (Port VLAN ID) is a tag that adds to incoming untagged frames received on a
port so that the frames are forwarded to the VLAN group that the tag defines.
U indicates that the port does not tag outbound traffic with this VLAN’s ID
T indicates that the port tags outbound traffic with this VLAN’s ID.
6.3.1 Port Setting Edit
Use this screen to enable or disable a port and configure the port’s PVID.
To access this screen, select a port and click the Edit button in the Configuration > Network >
VLAN screen.
Figure 30 Configuration > Network > VLAN > Edit Port
NWA5301-NJ User’s Guide
56
Page 57

Each field is described in the following table.
Table 26 Configuration > Network > VLAN > Edit Port
LABEL DESCRIPTION
Enable Select this option to activate the port. Otherwise, deselect it.
Name This shows the name of the port.
Native VID (PVID) A PVID (Port VLAN ID) is a tag that adds to incoming untagged frames received on a
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to close the window with changes unsaved.
6.3.2 VLAN Add/Edit
Use this screen to create a new VLAN or configure an existing VLAN on the NWA.
To access this screen, click Add or select a VLAN and click the Edit button in the Configuration >
Network > VLAN screen.
Chapter 6 Network
port so that the frames are forwarded to the VLAN group that the tag defines.
Enter the PVID from 1 to 4094 for this port.
Figure 31 Configuration > Network > VLAN > Edit VLAN
Each field is described in the following table.
Table 27 Configuration > Network > VLAN > Edit VLAN
LABEL DESCRIPTION
Enable Select this option to activate the VLAN. Otherwise, deselect it.
Name This field is read-only if you are editing an existing VLAN.
Enter the number of the VLAN. You can use a number from 0~4095. For example,
vlan0, vlan8, and so on.
VID Enter the VLAN ID. This 12-bit number uniquely identifies each VLAN. Allowed values
are 1 - 4094. (0 and 4095 are reserved.)
NWA5301-NJ User’s Guide
57
Page 58

Chapter 6 Network
Table 27 Configuration > Network > VLAN > Edit VLAN (continued)
LABEL DESCRIPTION
Member
Configuration
Edit Click this to edit the selected port’s membership values.
# This is sequential indicator of the port number.
Port Name This indicates the port name.
Member This indicates whether the selected port is a member or not of the VLAN which is
Tx Tagging This indicates whether the selected port tags outbound traffic with this VLAN’s ID .
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to close the window with changes unsaved.
Use these settings to assign ports to this VLAN as members.
currently being edited.
Click this field to edit the value.
Click this field to edit the value.
NWA5301-NJ User’s Guide
58
Page 59

7.1 Overview
This chapter discusses how to configure the wireless network settings in your NWA.
The following figure provides an example of a wireless network.
Figure 32 Example of a Wireless Network
CHAPTER 7
Wireless
The wireless network is the part in the blue circle. In this wireless network, devices A and B are
called wireless clients. The wireless clients use the access point (AP) to interact with other devices
(such as the printer) or with the Internet. Your NWA is the AP.
7.1.1 What You Can Do in this Chapter
•The AP Management screen (Section 7.2 on page 60) manages the NWA’s general wireless
settings.
•The Load Balancing screen (Section 7.3 on page 61) configures network traffic load balancing
between the APs and the NWA.
•The DCS screen (Section 7.4 on page 63) configures dynamic radio channel selection.
NWA5301-NJ User’s Guide
59
Page 60

7.1.2 What You Need to Know
The following terms and concepts may help as you read this chapter.
Station / Wireless Client
A station or wireless client is any wireless-capable device that can connect to an AP using a wireless
signal.
Dynamic Channel Selection (DCS)
Dynamic Channel Selection (DCS) is a feature that allows an AP to automatically select the radio
channel upon which it broadcasts by scanning the area around it and determining what channels
are currently being used by other devices.
Load Balancing (Wireless)
Wireless load balancing is the process where you limit the number of connections allowed on an
wireless access point (AP) or you limit the amount of wireless traffic transmitted and received on it
so the AP does not become overloaded.
Chapter 7 Wireless
7.2 AP Management
Use this screen to manage the NWA’s general wireless settings. Click Configuration > Wireless >
AP Management to access this screen.
Figure 33 Configuration > Wireless > AP Management
NWA5301-NJ User’s Guide
60
Page 61

Chapter 7 Wireless
Each field is described in the following table.
Table 28 Configuration > Wireless > AP Management
LABEL DESCRIPTION
Model This field displays the NWA’s model name.
Radio 1 Activate Select the check box to enable the NWA’s first (default) radio.
Radio 1 OP Mode Select the operating mode for the radio.
AP Mode means the radio can receive connections from wireless clients and pass their
data traffic through to the NWA to be managed (or subsequently passed on to an
upstream gateway for managing).
Root AP means the radio acts as an AP and also supports the wireless connections with
other APs (in repeater mode) to form a WDS to extend its wireless network.
Repeater means the radio can establish a wireless connection with other APs (in either
root AP or repeater mode) to form a WDS.
Radio 1 Profile Select the radio profile the radio uses.
Radio 1 WDS Profile This field is available only when the radio is in Root AP or Repeater mode.
Select the WDS profile the radio uses to connect to a root AP or repeater.
Uplink Selection
Mode
Radio 1 Uplink MAC
Address
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
This field is available only when the radio is in Repeater mode.
Select AUTO to have the NWA automatically use the settings in the applied WDS profile
to connect to a root AP or repeater.
Select Manual to have the NWA connect to the root AP or repeater with tbe MAC
address specified in the Radio 1 Uplink MAC Address field.
Enter the MAC address of the root AP or repeater with which you want the NWA to
associate.
7.3 Load Balancing
Use this screen to configure wireless network traffic load balancing between the APs on your
network. Click Configuration > Wireless > Load Balancing to access this screen.
Figure 34 Configuration > Wireless > Load Balancing
NWA5301-NJ User’s Guide
61
Page 62

Chapter 7 Wireless
Each field is described in the following table.
Table 29 Configuration > Wireless > Load Balancing
LABEL DESCRIPTION
Enable Load
Balancing
Mode Select a mode by which load balancing is carried out.
Max Station
Number
Traffic Level Select the threshold traffic level at which the AP begins load balancing its connections
Disassociate
station when
overloaded
Select this to enable load balancing on the NWA.
Select By Station Number to balance network traffic based on the number of specified
stations connect to an AP.
Select By Traffic Level to balance network traffic based on the volume generated by
the stations connected to an AP.
Once the threshold is crossed (either the maximum station numbers or with network
traffic), then the AP delays association request and authentication request packets from
any new station that attempts to make a connection. This allows the station to
automatically attempt to connect to another, less burdened AP if one is available.
Enter the threshold number of stations at which an AP begins load balancing its
connections.
(Low, Medium, High).
Select this option to disassociate wireless clients connected to the AP when it becomes
overloaded. If you do not enable this option, then the AP simply delays the connection
until it can afford the bandwidth it requires, or it transfers the connection to another AP
within its broadcast radius.
The disassociation priority is determined automatically by the NWA and is as follows:
• Idle Timeout - Devices that have been idle the longest will be kicked first. If none
of the connected devices are idle, then the priority shifts to Signal Strength.
• Signal Strength - Devices with the weakest signal strength will be kicked first.
Note: If you enable this function, you should ensure that there are multiple APs within the
broadcast radius that can accept any rejected or kicked wireless clients; otherwise,
a wireless client attempting to connect to an overloaded AP will be disassociated
permanently and never be allowed to connect.
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
7.3.1 Disassociating and Delaying Connections
When your AP becomes overloaded, there are two basic responses it can take. The first one is to
“delay” a client connection. This means that the AP withholds the connection until the data transfer
throughput is lowered or the client connection is picked up by another AP. If the client is picked up
by another AP then the original AP cannot resume the connection.
For example, here the AP has a balanced bandwidth allotment of 6 Mbps. If laptop R connects and
it pushes the AP over its allotment, say to 7 Mbps, then the AP delays the red laptop’s connection
until it can afford the bandwidth or the laptop is picked up by a different AP with bandwidth to
spare.
NWA5301-NJ User’s Guide
62
Page 63

Chapter 7 Wireless
Figure 35 Delaying a Connection
The second response your AP can take is to kick the connections that are pushing it over its
balanced bandwidth allotment.
Figure 36 Kicking a Connection
Connections are kicked based on either idle timeout or signal strength. The NWA first looks to
see which devices have been idle the longest, then starts kicking them in order of highest idle time.
If no connections are idle, the next criteria the NWA analyzes is signal strength. Devices with the
weakest signal strength are kicked first.
7.4 DCS
Use this screen to configure dynamic radio channel selection. Click Configuration > Wireless >
DCS to access this screen.
NWA5301-NJ User’s Guide
63
Page 64

Chapter 7 Wireless
Figure 37 Configuration > Wireless > DCS
Each field is described in the following table.
Table 30 Configuration > Wireless > DCS
LABEL DESCRIPTION
Select Now Click this to have the NWA scan for and select an available channel immediately.
Enable Dynamic
Channel Selection
DCS Time Interval Enter a number of minutes. This regulates how often the NWA surveys the other APs
Enable DCS Client
Aware
2.4 GHz Channel
Selection Method
Select this to have the NWA automatically select the radio channel upon which it
broadcasts by scanning the area around it and determining what channels are currently
being used by other devices.
within its broadcast radius. If the channel on which it is currently broadcasting suddenly
comes into use by another AP, the NWA will then dynamically select the next available
clean channel or a channel with lower interference.
Select this to have the AP wait until all connected clients have disconnected before
switching channels.
If you disable this then the AP switches channels immediately regardless of any client
connections. In this instance, clients that are connected to the AP when it switches
channels are dropped.
Select how you want to specify the channels the NWA switches between for 2.4 GHz
operation.
Select auto to have the NWA display a 2.4 GHz Channel Deployment field you can
use to limit channel switching to 3 or 4 channels.
Select manual to select the individual channels the NWA switches between. Select
channels from the Available channels list and use the right arrow button to move
them to the Channels selected list.
NWA5301-NJ User’s Guide
64
Page 65

Table 30 Configuration > Wireless > DCS (continued)
LABEL DESCRIPTION
2.4 GHz Channel
Deployment
Apply Click Apply to save your changes back to the NWA.
Reset Click Reset to return the screen to its last-saved settings.
This is available when the 2.4 GHz Channel Selection Method is set to auto.
Select Three-Channel Deployment to limit channel switching to channels 1,6, and
11, the three channels that are sufficiently attenuated to have almost no impact on one
another. In other words, this allows you to minimize channel interference by limiting
channel-hopping to these three “safe” channels.
Select Four-Channel Deployment to limit channel switching to four channels.
Depending on the country domain, if the only allowable channels are 1-11 then the
NWA uses channels 1, 4, 7, 11 in this configuration; otherwise, the NWA uses channels
1, 5, 9, 13 in this configuration. Four channel deployment expands your pool of possible
channels while keeping the channel interference to a minimum.
7.5 Technical Reference
The following section contains additional technical information about the features described in this
chapter.
Chapter 7 Wireless
Dynamic Channel Selection
When numerous APs broadcast within a given area, they introduce the possibility of heightened
radio interference, especially if some or all of them are broadcasting on the same radio channel. If
the interference becomes too great, then the network administrator must open his AP configuration
options and manually change the channel to one that no other AP is using (or at least a channel
that has a lower level of interference) in order to give the connected stations a minimum degree of
interference. Dynamic channel selection frees the network administrator from this task by letting
the AP do it automatically. The AP can scan the area around it looking for the channel with the least
amount of interference.
Load Balancing
Because there is a hard upper limit on an AP’s wireless bandwidth, load balancing can be crucial in
areas crowded with wireless users. Rather than let every user connect and subsequently dilute the
available bandwidth to the point where each connecting device receives a meager trickle, the load
balanced AP instead limits the incoming connections as a means to maintain bandwidth integrity.
There are two kinds of wireless load balancing available on the NWA:
Load balancing by station number limits the number of devices allowed to connect to your AP. If
you know exactly how many stations you want to let connect, choose this option.
For example, if your company’s graphic design team has their own AP and they have 10 computers,
you can load balance for 10. Later, if someone from the sales department visits the graphic design
team’s offices for a meeting and he tries to access the network, his computer’s connection is
delayed, giving it the opportunity to connect to a different, neighboring AP. If he still connects to
the AP regardless of the delay, then the AP may boot other people who are already connected in
order to associate with the new connection.
NWA5301-NJ User’s Guide
65
Page 66

Chapter 7 Wireless
Load balancing by traffic level limits the number of connections to the AP based on maximum
bandwidth available. If you are uncertain as to the exact number of wireless connections you will
have then choose this option. By setting a maximum bandwidth cap, you allow any number of
devices to connect as long as their total bandwidth usage does not exceed the configured
bandwidth cap associated with this setting. Once the cap is hit, any new connections are rejected or
delayed provided that there are other APs in range.
Imagine a coffee shop in a crowded business district that offers free wireless connectivity to its
customers. The coffee shop owner can’t possibly know how many connections his AP will have at
any given moment. As such, he decides to put a limit on the bandwidth that is available to his
customers but not on the actual number of connections he allows. This means anyone can connect
to his wireless network as long as the AP has the bandwidth to spare. If too many people connect
and the AP hits its bandwidth cap then all new connections must basically wait for their turn or get
shunted to the nearest identical AP.
NWA5301-NJ User’s Guide
66
Page 67

8.1 Overview
This chapter describes how to set up user accounts and user settings for the NWA.
8.1.1 What You Can Do in this Chapter
•The User screen (see Section 8.2 on page 68) provides a summary of all user accounts.
•The Setting screen (see Section 8.3 on page 70) controls default settings, login settings, lockout
settings, and other user settings for the NWA.
8.1.2 What You Need To Know
The following terms and concepts may help as you read this chapter.
CHAPTER 8
User
User Account
A user account defines the privileges of a user logged into the NWA. User accounts are used in
controlling access to configuration and services in the NWA.
User Types
These are the types of user accounts the NWA uses.
Table 31 Types of User Accounts
TYPE ABILITIES LOGIN METHOD(S)
Admin Users
admin Change NWA configuration (web, CLI) WWW, TELNET, SSH, FTP
limited-admin Look at NWA configuration (web, CLI)
Perform basic diagnostics (CLI)
Access Users
user Used for the embedded RADIUS server and
SNMPv3 user access
Browse user-mode commands (CLI)
Note: The default admin account is always authenticated locally, regardless of the
authentication method setting.
WWW, TELNET, SSH
NWA5301-NJ User’s Guide
67
Page 68

8.2 User Summary
The User screen provides a summary of all user accounts. To access this screen click
Configuration > Object > User.
Figure 38 Configuration > Object > User
Chapter 8 User
The following table describes the labels in this screen.
Table 32 Configuration > Object > User
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
Remove To remove an entry, select it and click Remove. The NWA confirms you want to remove it
Object Reference Select an entry and click Object Reference to open a screen that shows which settings
# This field is a sequential value, and it is not associated with a specific user.
User Name This field displays the user name of each user.
User Type This field displays type of user this account was configured as.
Description This field displays the description for each user.
8.2.1 Add/Edit User
the entry’s settings.
before doing so.
use the entry.
• admin - this user can look at and change the configuration of the NWA
• limited-admin - this user can look at the configuration of the NWA but not to change
it
• user - this user has access to the NWA’s services but cannot look at the configuration
The User Add/Edit screen allows you to create a new user account or edit an existing one.
8.2.1.1 Rules for User Names
Enter a user name from 1 to 31 characters.
The user name can only contain the following characters:
NWA5301-NJ User’s Guide
68
Page 69

Chapter 8 User
• Alphanumeric A-z 0-9 (there is no unicode support)
• _ [underscores]
•- [dashes]
The first character must be alphabetical (A-Z a-z), an underscore (_), or a dash (-). Other
limitations on user names are:
• User names are case-sensitive. If you enter a user 'bob' but use 'BOB' when connecting via CIFS
or FTP, it will use the account settings used for 'BOB' not ‘bob’.
• User names have to be different than user group names.
• Here are the reserved user names:
•adm •admin •any •bin •daemon
•debug •devicehaecived•ftp •games •halt
•ldap-users •lp •mail •news •nobody
•operator •radius-users •root •shutdown •sshd
•sync •uucp •zyxel
To access this screen, go to the User screen, and click Add or Edit.
Figure 39 Configuration > Object > User > Add/Edit A User
NWA5301-NJ User’s Guide
69
Page 70

Chapter 8 User
The following table describes the labels in this screen.
Table 33 Configuration > User > User > Add/Edit A User
LABEL DESCRIPTION
User Name Type the user name for this user account. You may use 1-31 alphanumeric characters,
User Type Select what type of user this is. Choices are:
Password Enter the password of this user account. It can consist of 4 - 31 alphanumeric
Retype Re-enter the password to make sure you have entered it correctly.
Description Enter the description of each user, if any. You can use up to 60 printable ASCII
Authentication
Timeout Settings
Lease Time This field is not available if the user type is user.
Reauthentication
Time
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
underscores(
case-sensitive. User names have to be different than user group names, and some
words are reserved.
• admin - this user can look at and change the configuration of the NWA
• limited-admin - this user can look at the configuration of the NWA but not to
change it
• user - this is used for embedded RADIUS server and SNMPv3 user access
characters.
characters. Default descriptions are provided.
This field is not available if the user type is user.
If you want to set authentication timeout to a value other than the default settings,
select Use Manual Settings then fill your preferred values in the fields that follow.
Enter the number of minutes this user has to renew the current session before the user
is logged out. You can specify 1 to 1440 minutes. You can enter 0 to make the number
of minutes unlimited. Admin users renew the session every time the main screen
refreshes in the Web Configurator.
This field is not available if the user type is user.
Type the number of minutes this user can be logged into the NWA in one session before
the user has to log in again. You can specify 1 to 1440 minutes. You can enter 0 to make
the number of minutes unlimited. Unlike Lease Time, the user has no opportunity to
renew the session without logging out.
_), or dashes (-), but the first character cannot be a number. This value is
8.3 Setting
This screen controls default settings, login settings, lockout settings, and other user settings for the
NWA.
To access this screen, login to the Web Configurator, and click Configuration > Object > User >
Setting.
NWA5301-NJ User’s Guide
70
Page 71

Chapter 8 User
Figure 40 Configuration > Object > User > Setting
The following table describes the labels in this screen.
Table 34 Configuration > Object > User > Setting
LABEL DESCRIPTION
User Default Setting
Default Authentication
Timeout Settings
Edit Double-click an entry or select it and click Edit to open a screen where you can
# This field is a sequential value, and it is not associated with a specific entry.
User Type These are the kinds of user account the NWA supports.
Lease Time This is the default lease time in minutes for each type of user account. It
Reauthentication Time This is the default reauthentication time in minutes for each type of user
These authentication timeout settings are used by default when you create a
new user account. They also control the settings for any existing user accounts
that are set to use the default settings. You can still manually configure any
user account’s authentication timeout settings.
modify the entry’s settings.
• admin - this user can look at and change the configuration of the NWA
• limited-admin - this user can look at the configuration of the NWA but not
to change it
• user - this is used for embedded RADIUS server and SNMPv3 user access
defines the number of minutes the user has to renew the current session before
the user is logged out.
Admin users renew the session every time the main screen refreshes in the
Web Configurator.
account. It defines the number of minutes the user can be logged into the NWA
in one session before having to log in again. Unlike Lease Time, the user has
no opportunity to renew the session without logging out.
NWA5301-NJ User’s Guide
71
Page 72

Chapter 8 User
Table 34 Configuration > Object > User > Setting (continued)
LABEL DESCRIPTION
User Logon Settings
Limit the number of
simultaneous logons for
administration account
Maximum number per
administration account
User Lockout Settings
Enable logon retry limit Select this check box to set a limit on the number of times each user can login
Maximum retry count This field is effective when Enable logon retry limit is checked. Type the
Lockout period This field is effective when Enable logon retry limit is checked. Type the
Apply Click Apply to save the changes.
Reset Click Reset to return the screen to its last-saved settings.
Select this check box if you want to set a limit on the number of simultaneous
logins by admin users. If you do not select this, admin users can login as many
times as they want at the same time using the same or different IP addresses.
This field is effective when Limit ... for administration account is checked.
Type the maximum number of simultaneous logins by each admin user.
unsuccessfully (for example, wrong password) before the IP address is locked
out for a specified amount of time.
maximum number of times each user can login unsuccessfully before the IP
address is locked out for the specified lockout period. The number must be
between 1 and 99.
number of minutes the user must wait to try to login again, if logon retry limit
is enabled and the maximum retry count is reached. This number must be
between 1 and 65,535 (about 45.5 days).
8.3.1 Edit User Authentication Timeout Settings
This screen allows you to set the default authentication timeout settings for the selected type of
user account. These default authentication timeout settings also control the settings for any
existing user accounts that are set to use the default settings. You can still manually configure any
user account’s authentication timeout settings.
To access this screen, go to the Configuration > Object > User > Setting screen, select one of
the Default Authentication Timeout Settings entry and click the Edit icon.
Figure 41 User > Setting > Edit User Authentication Timeout Settings
NWA5301-NJ User’s Guide
72
Page 73

Chapter 8 User
The following table describes the labels in this screen.
Table 35 User > Setting > Edit User Authentication Timeout Settings
LABEL DESCRIPTION
User Type This read-only field identifies the type of user account for which you are configuring the
Lease Time Enter the number of minutes this type of user account has to renew the current session
Reauthentication
Time
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
default settings.
• admin - this user can look at and change the configuration of the NWA.
• limited-admin - this user can look at the configuration of the NWA but not to
change it.
before the user is logged out. You can specify 1 to 1440 minutes. You can enter 0 to
make the number of minutes unlimited.
Admin users renew the session every time the main screen refreshes in the Web
Configurator. Access users can renew the session by clicking the Renew button on their
screen. If you allow access users to renew time automatically, the users can select this
check box on their screen as well. In this case, the session is automatically renewed
before the lease time expires.
Type the number of minutes this type of user account can be logged into the NWA in one
session before the user has to log in again. You can specify 1 to 1440 minutes. You can
enter 0 to make the number of minutes unlimited. Unlike Lease Time, the user has no
opportunity to renew the session without logging out.
NWA5301-NJ User’s Guide
73
Page 74

9.1 Overview
This chapter shows you how to configure preset wireless profiles for the NWA.
9.1.1 What You Can Do in this Chapter
•The Radio screen (Section 9.2 on page 75) creates radio configurations that can be used by the
APs.
•The SSID screen (Section 9.3 on page 80) configures three different types of profiles for your
networked APs.
9.1.2 What You Need To Know
CHAPTER 9
AP Profile
The following terms and concepts may help as you read this chapter.
Wireless Profiles
At the heart of all wireless AP configurations on the NWA are profiles. A profile represents a group
of saved settings that you can use across any number of connected APs. You can set up the
following wireless profile types:
• Radio - This profile type defines the properties of an AP’s radio transmitter. You can have a
maximum of 32 radio profiles on the NWA.
• SSID - This profile type defines the properties of a single wireless network signal broadcast by
an AP. Each radio on a single AP can broadcast up to 8 SSIDs. You can have a maximum of 32
SSID profiles on the NWA.
• Security - This profile type defines the security settings used by a single SSID. It controls the
encryption method required for a wireless client to associate itself with the SSID. You can have a
maximum of 32 security profiles on the NWA.
• MAC Filtering - This profile provides an additional layer of security for an SSID, allowing you to
block access or allow access to that SSID based on wireless client MAC addresses. If a client’s
MAC address is on the list, then it is either allowed or denied, depending on how you set up the
MAC Filter profile. You can have a maximum of 32 MAC filtering profiles on the NWA.
• Layer-2 Isolation - This profile defines the MAC addresses of the devices that you want to allow
the associated wireless clients to have access to when layer-2 isolation is enabled.
SSID
The SSID (Service Set IDentifier) is the name that identifies the Service Set with which a wireless
station is associated. Wireless stations associating to the access point (AP) must have the same
SSID. In other words, it is the name of the wireless network that clients use to connect to it.
NWA5301-NJ User’s Guide
74
Page 75

Chapter 9 AP Profile
WEP
WEP (Wired Equivalent Privacy) encryption scrambles all data packets transmitted between the AP
and the wireless stations associated with it in order to keep network communications private. Both
the wireless stations and the access points must use the same WEP key for data encryption and
decryption.
WPA and WPA2
Wi-Fi Protected Access (WPA) is a subset of the IEEE 802.11i standard. WPA2 (IEEE 802.11i) is a
wireless security standard that defines stronger encryption, authentication and key management
than WPA. Key differences between WPA(2) and WEP are improved data encryption and user
authentication.
IEEE 802.1x
The IEEE 802.1x standard outlines enhanced security methods for both the authentication of
wireless stations and encryption key management. Authentication is done using an external
RADIUS server.
9.2 Radio
This screen allows you to create radio profiles for the NWA. A radio profile is a list of settings that an
NWA can use to configure its radio transmitter(s). To access this screen click Configuration >
Object > AP Profile.
Note: You can have a maximum of 32 radio profiles on the NWA.
Figure 42 Configuration > Object > AP Profile > Radio
The following table describes the labels in this screen.
Table 36 Configuration > Object > AP Profile > Radio
LABEL DESCRIPTION
Add Click this to add a new radio profile.
Edit Click this to edit the selected radio profile.
Remove Click this to remove the selected radio profile.
NWA5301-NJ User’s Guide
75
Page 76

Table 36 Configuration > Object > AP Profile > Radio (continued)
LABEL DESCRIPTION
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object Reference Click this to view which other objects are linked to the selected radio profile.
# This field is a sequential value, and it is not associated with a specific user.
Status This field shows whether or not the entry is activated.
Profile Name This field indicates the name assigned to the radio profile.
Frequency Band This field indicates the frequency band which this radio profile is configured to use.
Channel ID This field indicates the broadcast channel which this radio profile is configured to use.
9.2.1 Add/Edit Radio Profile
This screen allows you to create a new radio profile or edit an existing one. To access this screen,
click the Add button or select a radio profile from the list and click the Edit button.
Chapter 9 AP Profile
NWA5301-NJ User’s Guide
76
Page 77

Chapter 9 AP Profile
Figure 43 Configuration > Object > AP Profile > Add/Edit Profile
NWA5301-NJ User’s Guide
77
Page 78

Chapter 9 AP Profile
The following table describes the labels in this screen.
Table 37 Configuration > Object > AP Profile > Add/Edit Profile
LABEL DESCRIPTION
Hide / Show
Advanced Settings
Create New Object Select an item from this menu to create a new object of that type. Any objects created
General Settings
Activate Select this option to make this profile active.
Profile Name Enter up to 31 alphanumeric characters to be used as this profile’s name. Spaces and
802.11 Band Select the wireless band which this radio profile should use.
Mode If you set 802.11 Band to 2.4G, you can select from the following:
Channel Select the wireless channel which this radio profile should use.
Click this to hide or show the Advanced Settings in this window.
in this way are automatically linked to this radio profile.
underscores are allowed.
2.4 GHz is the frequency used by IEEE 802.11b/g/n wireless clients.
• b/g: allows either IEEE 802.11b or IEEE 802.11g compliant WLAN devices to
associate with the NWA. The NWA adjusts the transmission rate automatically
according to the wireless standard supported by the wireless devices.
• b/g/n: allows IEEE802.11b, IEEE802.11g and IEEE802.11n compliant WLAN
devices to associate with the NWA. The transmission rate of your NWA might be
reduced.
It is recommended that you choose the channel least in use by other APs in the region
where this profile will be implemented. This will reduce the amount of interference
between wireless clients and the AP to which this profile is assigned.
Advanced Settings
Channel Width Select the channel bandwidth you want to use for your wireless network.
Select Auto to allow the NWA to adjust the channel bandwidth depending on network
conditions.
Select 20 MHz if you want to lessen radio interference with other wireless devices in
your neighborhood.
Guard Interval Set the guard interval for this radio profile to either short or long.
The guard interval is the gap introduced between data transmission from users in order
to reduce interference. Reducing the interval increases data transfer rates but also
increases interference. Increasing the interval reduces data transfer rates but also
reduces interference.
Enable A-MPDU
Aggregation
Enable A-MSDU
Aggregation
Select this to enable A-MPDU aggregation.
Message Protocol Data Unit (MPDU) aggregation collects Ethernet frames along with
their 802.11n headers and wraps them in a 802.11n MAC header. This method is useful
for increasing bandwidth throughput in environments that are prone to high error
rates.
Select this to enable A-MSDU aggregation.
Mac Service Data Unit (MSDU) aggregation collects Ethernet frames without any of
their 802.11n headers and wraps the header-less payload in a single 802.11n MAC
header. This method is useful for increasing bandwidth throughput. It is also more
efficient than A-MPDU except in environments that are prone to high error rates.
NWA5301-NJ User’s Guide
78
Page 79

Chapter 9 AP Profile
Table 37 Configuration > Object > AP Profile > Add/Edit Profile (continued)
LABEL DESCRIPTION
RTS/CTS
Threshold
Beacon Interval When a wirelessly networked device sends a beacon, it includes with it a beacon
DTIM Delivery Traffic Indication Message (DTIM) is the time period after which broadcast and
Output Power Set the output power of the AP in this field. If there is a high density of APs in an area,
Use RTS/CTS to reduce data collisions on the wireless network if you have wireless
clients that are associated with the same AP but out of range of one another. When
enabled, a wireless client sends an RTS (Request To Send) and then waits for a CTS
(Clear To Send) before it transmits. This stops wireless clients from transmitting
packets at the same time (and causing data collisions).
A wireless client sends an RTS for all packets larger than the number (of bytes) that
you enter here. Set the RTS/CTS equal to or higher than the fragmentation threshold to
turn RTS/CTS off.
interval. This specifies the time period before the device sends the beacon again. The
interval tells receiving devices on the network how long they can wait in low-power
mode before waking up to handle the beacon. A high value helps save current
consumption of the access point.
multicast packets are transmitted to mobile clients in the Active Power Management
mode. A high DTIM value can cause clients to lose connectivity with the network. This
value can be set from 1 to 255.
decrease the output power of the NWA5160N to reduce interference with other APs.
Select one of the following Max, -3db (50%), -6db (25%), -9dB (12.5%) or Min.
See the product specifications for more information on your NWA’s output power.
Note: Reducing the output power also reduces the NWA’s effective broadcast radius.
Enable Signal
Threshold
Station Signal
Threshold
Disassociate
Station
Threshold
Allow Station
Connection after
Multiple Retries
Station Retry
Count
Rate Configuration This section controls the data rates permitted for clients.
Multicast Settings
Select the check box to use the signal threshold to ensure wireless clients receive good
throughput. This allows only wireless clients with a strong signal to connect to the AP.
Clear the check box to not require wireless clients to have a minimum signal strength
to connect to the AP.
Set a minimum client signal strength. A wireless client is allowed to connect to the AP
only when its signal strength is stronger than the specified threshold.
-20 dBm is the strongest signal you can require and -76 is the weakest.
Set a minimum kick-off signal strength. When a wireless client’s signal strength is
lower than the specified threshold, the NWA disconnects the wireless client from the AP.
-20 dBm is the strongest signal you can require and -90 is the weakest.
Select this option to allow a wireless client to try to associate with the AP again after it
is disconnected due to weak signal strength.
Set the maximum number of times a wireless client can attempt to re-connect to the
AP
For each rate, select a rate option from its list. The rates are:
• Basic Rate (Mbps) - Set the basic rate configuration in Mbps. Clients can always
connect to the NWA at this speed.
• Support Rate (Mbps) - Set the support rate configuration in Mbps. Clients can
connect to the NWA at this speed, when permitted to do so by the NWA.
• MCS Rate - Set the MCS rate configuration. EEE 802.11n supports many different
data rates which are called MCS rates. MCS stands for Modulation and Coding
Scheme. This is an 802.11n feature that increases the wireless network
performance in terms of throughput.
NWA5301-NJ User’s Guide
79
Page 80

Chapter 9 AP Profile
Table 37 Configuration > Object > AP Profile > Add/Edit Profile (continued)
LABEL DESCRIPTION
Tra nsmiss i o n
Mode
Multicast
Rate(Mbps)
MBSSID Settings This section displays if you set the Operating Mo de to MBSSID. It allows you to
Edit Select an SSID and click this button to reassign it. The selected SSID becomes editable
SSID Profile Indicates which SSID profile is associated with this radio profile.
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
Specify how the NWA handles wireless multicast traffic.
Select Multicast to Unicast to broadcast wireless multicast traffic to all of the wireless
clients as unicast traffic. Unicast traffic dynamically changes the data rate based on the
application’s bandwidth requirements. The retransmit mechanism of unicast traffic
provides more reliable transmission of the multicast traffic, although it also produces
duplicate packets.
Select Fixed Multicast Rate to send multicast traffic to all wireless clients at a single
data rate. You must know the multicast application’s bandwidth requirements and set it
in the following field.
If you set Transmission Mode to Fixed Multicast Rate, select a data rate at which
the NWA transmits multicast packets to wireless clients. For example, to deploy 4 Mbps
video, select a fixed multicast rate higher than 4 Mbps.
associate an SSID profile with the radio profile.
immediately upon clicking.
9.3 SSID
The SSID screens allow you to configure three different types of profiles for your networked APs: an
SSID list, which can assign specific SSID configurations to your APs; a security list, which can
assign specific encryption methods to the APs when allowing wireless clients to connect to them;
and a MAC filter list, which can limit connections to an AP based on wireless clients MAC addresses.
9.3.1 SSID List
This screen allows you to create and manage SSID configurations that can be used by the APs. An
SSID, or Service Set IDentifier, is basically the name of the wireless network to which a wireless
client can connect. The SSID appears as readable text to any device capable of scanning for
wireless frequencies (such as the WiFi adapter in a laptop), and is displayed as the wireless network
name when a person makes a connection to it.
To access this screen click Configuration > Object > AP Profile > SSID.
Note: You can have a maximum of 32 SSID profiles on the NWA.
NWA5301-NJ User’s Guide
80
Page 81

Chapter 9 AP Profile
Figure 44 Configuration > Object > AP Profile > SSID List
The following table describes the labels in this screen.
Table 38 Configuration > Object > AP Profile > SSID List
LABEL DESCRIPTION
Add Click this to add a new SSID profile.
Edit Click this to edit the selected SSID profile.
Remove Click this to remove the selected SSID profile.
Object Reference Click this to view which other objects are linked to the selected SSID profile (for example,
radio profile).
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the SSID profile.
SSID This field indicates the SSID name as it appears to wireless clients.
Security Profile This field indicates which (if any) security profile is associated with the SSID profile.
QOS This field indicates the QoS type associated with the SSID profile.
MAC Filtering
Profile
Layer-2 Isolation
Profile
VLAN ID This field indicates the VLAN ID associated with the SSID profile.
This field indicates which (if any) MAC filter Profile is associated with the SSID profile.
This field indicates which (if any) layer-2 isolation Profile is associated with the SSID
profile.
9.3.2 Add/Edit SSID Profile
This screen allows you to create a new SSID profile or edit an existing one. To access this screen,
click the Add button or select an SSID profile from the list and click the Edit button.
NWA5301-NJ User’s Guide
81
Page 82

Chapter 9 AP Profile
Figure 45 Configuration > Object > AP Profile > Add/Edit SSID Profile
The following table describes the labels in this screen.
Table 39 Configuration > Object > AP Profile > Add/Edit SSID Profile
LABEL DESCRIPTION
Create new
Object
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in
SSID Enter the SSID name for this profile. This is the name visible on the network to wireless
Security Profile Select a security profile from this list to associate with this SSID. If none exist, you can use
Select an object type from the list to create a new one associated with this SSID profile.
the Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
clients. Enter up to 32 characters, spaces and underscores are allowed.
the Create new Object menu to create one.
Note: It is highly recommended that you create security profiles for all of your SSIDs to
enhance your network security.
MAC Filtering
Profile
Layer-2 Isolation
Profile
Select a MAC filtering profile from the list to associate with this SSID. If none exist, you can
sue the Create new Object menu to create one.
MAC filtering allows you to limit the wireless clients connecting to your network through a
particular SSID by wireless client MAC addresses. Any clients that have MAC addresses not
in the MAC filtering profile of allowed addresses are denied connections.
The disable setting means no MAC filtering is used.
Select a layer-2 isolation profile from the list to associate with this SSID. If none exist, you
can sue the Create new Object menu to create one.
Layer-2 isolation allows you to prevent wireless clients associated with your NWA from
communicating with other wireless clients, APs, computers or routers in a network.
The disable setting means no layer-2 isolation is used.
NWA5301-NJ User’s Guide
82
Page 83

Chapter 9 AP Profile
Table 39 Configuration > Object > AP Profile > Add/Edit SSID Profile (continued)
LABEL DESCRIPTION
QoS Select a Quality of Service (QoS) access category to associate with this SSID. Access
categories minimize the delay of data packets across a wireless network. Certain
categories, such as video or voice, are given a higher priority due to the time sensitive
nature of their data packets.
QoS access categories are as follows:
disable: Turns off QoS for this SSID. All data packets are treated equally and not tagged
with access categories.
WMM: Enables automatic tagging of data packets. The NWA assigns access categories to
the SSID by examining data as it passes through it and making a best guess effort. If
something looks like video traffic, for instance, it is tagged as such.
WMM_VOICE: All wireless traffic to the SSID is tagged as voice data. This is
recommended if an SSID is used for activities like placing and receiving VoIP phone calls.
WMM_VIDEO: All wireless traffic to the SSID is tagged as video data. This is
recommended for activities like video conferencing.
WMM_BEST_EFFORT: All wireless traffic to the SSID is tagged as “best effort,” meaning
the data travels the best route it can without displacing higher priority traffic. This is good
for activities that do not require the best bandwidth throughput, such as surfing the
Internet.
WMM_BACKGROUND: All wireless traffic to the SSID is tagged as low priority or
“background traffic”, meaning all other access categories take precedence over this one. If
traffic from an SSID does not have strict throughput requirements, then this access
category is recommended. For example, an SSID that only has network printers connected
to it.
VLAN ID Enter a VLAN ID for the NWA to use to tag traffic originating from this SSID.
Hidden SSID Select this if you want to “hide” your SSID from wireless clients. This tells any wireless
clients in the vicinity of the AP using this SSID profile not to display its SSID name as a
potential connection. Not all wireless clients respect this flag and display it anyway.
Enable Intra-BSS
Traffic Blocking
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
9.4 Security List
This screen allows you to manage wireless security configurations that can be used by your SSIDs.
Wireless security is implemented strictly between the AP broadcasting the SSID and the stations
that are connected to it.
To access this screen click Configuration > Object > AP Profile > SSID > Security Li st.
Note: You can have a maximum of 32 security profiles on the NWA.
When an SSID is “hidden” and a wireless client cannot see it, the only way you can connect
to the SSID is by manually entering the SSID name in your wireless connection setup
screen(s) (these vary by client, client connectivity software, and operating system).
Select this option to prevent crossover traffic from within the same SSID.
Note: If you associate a layer-2 isolation profile with the SSID, this option will be selected
automatically and cannot be configured.
NWA5301-NJ User’s Guide
83
Page 84

Chapter 9 AP Profile
Figure 46 Configuration > Object > AP Profile > SSID > Security List
The following table describes the labels in this screen.
Table 40 Configuration > Object > AP Profile > SSID > Security List
LABEL DESCRIPTION
Add Click this to add a new security profile.
Edit Click this to edit the selected security profile.
Remove Click this to remove the selected security profile.
Object Reference Click this to view which other objects are linked to the selected security profile (for
example, SSID profile).
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the security profile.
Security Mode This field indicates this profile’s security mode (if any).
9.4.1 Add/Edit Security Profile
This screen allows you to create a new security profile or edit an existing one. To access this screen,
click the Add button or select a security profile from the list and click the Edit button.
Note: This screen’s options change based on the Security Mode selected. Only the default
screen is displayed here.
NWA5301-NJ User’s Guide
84
Page 85

Chapter 9 AP Profile
Figure 47 SSID > Security Profile > Add/Edit Security Profile
The following table describes the labels in this screen.
Table 41 SSID > Security Profile > Add/Edit Security Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in
the Web Configurator and is only for management purposes. Spaces and underscores
are allowed.
Security Mode Select a security mode from the list: none, wep, wpa, wpa2, or wpa2-mix.
NWA5301-NJ User’s Guide
85
Page 86

Chapter 9 AP Profile
Table 41 SSID > Security Profile > Add/Edit Security Profile (continued)
LABEL DESCRIPTION
Radius Server Type This shows External and the NWA uses an external RADIUS server for authentication.
Primary /
Secondary Radius
Server Activate
Radius Server
IP Address
Radius Server
Port
Radius Server
Secret
Primary /
Secondary
Accounting Server
Activate
Accounting
Server IP
Address
Accounting
Server Port
Accounting
Share Secret
802.1X Select this to enable 802.1x secure authentication.
ReAuthenticatio
n Timer
Idle Timeout Enter the idle interval (in seconds) that a client can be idle before authentication is
Authentication Type Select a WEP authentication method. Choices are Open or Share key. Share key is
Key Length Select the bit-length of the encryption key to be used in WEP connections.
Select this to have the NWA use the specified RADIUS server.
Enter the IP address of the RADIUS server to be used for authentication.
Enter the port number of the RADIUS server to be used for authentication.
Enter the shared secret password of the RADIUS server to be used for authentication.
Select the check box to enable user accounting through an external authentication
server.
Enter the IP address of the external accounting server in dotted decimal notation.
Enter the port number of the external accounting server. The default port number is
1813. You need not change this value unless your network administrator instructs you
to do so with additional information.
Enter a password (up to 128 alphanumeric characters) as the key to be shared between
the external accounting server and the NWA. The key must be the same on the external
accounting server and your NWA. The key is not sent over the network.
Enter the interval (in seconds) between authentication requests. Enter a 0 for unlimited
requests.
discontinued.
only available if you are not using 802.1x.
If you select WEP-64:
• Enter 10 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x11AA22BB33) for each Key used.
or
• Enter 5 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey) for each Key used.
If you select WEP-128:
• Enter 26 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x00112233445566778899AABBCC) for each Key used.
or
• Enter 13 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey12345678) for each Key used.
Key 1~4 Based on your Key Length selection, enter the appropriate length hexadecimal or
ASCII key.
PSK This field is available when you select the wpa, wpa2, or wpa2-mix security mode.
Select this option to use a Pre-Shared Key with WPA encryption.
Pre-Shared Key Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including
spaces and symbols) or 64 hexadecimal characters.
NWA5301-NJ User’s Guide
86
Page 87

Chapter 9 AP Profile
Table 41 SSID > Security Profile > Add/Edit Security Profile (continued)
LABEL DESCRIPTION
Cipher Type Select an encryption cipher type from the list.
• auto - This automatically chooses the best available cipher based on the cipher in
use by the wireless client that is attempting to make a connection.
• tkip - This is the Temporal Key Integrity Protocol encryption method added later to
the WEP encryption protocol to further secure. Not all wireless clients may support
this.
• aes - This is the Advanced Encryption Standard encryption method. It is a more
recent development over TKIP and considerably more robust. Not all wireless clients
may support this.
Group Key Update
Timer
Pre-Authentication This is available when the profile is set to use wpa2 or wpa2-mix and 802.1x. Enable
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
Enter the interval (in seconds) at which the AP updates the group WPA encryption key.
or Disable pre-authentication to allow the NWA to send authentication information to
other APs on the network, allowing connected wireless clients to switch APs without
having to re-authenticate their network connection.
9.5 MAC Filter List
This screen allows you to create and manage security configurations that can be used by your
SSIDs. To access this screen click Configuration > Object > AP Profile > SSID > MAC Filter
List.
Note: You can have a maximum of 32 MAC filtering profiles on the NWA.
Figure 48 Configuration > Object > AP Profile > SSID > MAC Filter List
The following table describes the labels in this screen.
Table 42 Configuration > Object > AP Profile > SSID > MAC Filter List
LABEL DESCRIPTION
Add Click this to add a new MAC filtering profile.
Edit Click this to edit the selected MAC filtering profile.
Remove Click this to remove the selected MAC filtering profile.
Object Reference Click this to view which other objects are linked to the selected MAC filtering profile (for
example, SSID profile).
NWA5301-NJ User’s Guide
87
Page 88

Table 42 Configuration > Object > AP Profile > SSID > MAC Filter List (continued)
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the MAC filtering profile.
Filter Action This field indicates this profile’s filter action (if any).
9.5.1 Add/Edit MAC Filter Profile
This screen allows you to create a new MAC filtering profile or edit an existing one. To access this
screen, click the Add button or select a MAC filter profile from the list and click the Edit button.
Note: Each MAC filtering profile can include a maximum of 512 MAC addresses.
Figure 49 SSID > MAC Filter List > Add/Edit MAC Filter Profile
Chapter 9 AP Profile
The following table describes the labels in this screen.
Table 43 SSID > MAC Filter List > Add/Edit MAC Filter Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in
Filter Action Select allow to permit the wireless client with the MAC addresses in this profile to connect
Add Click this to add a MAC address to the profile’s list.
Edit Click this to edit the selected MAC address in the profile’s list.
Remove Click this to remove the selected MAC address from the profile’s list.
# This field is a sequential value, and it is not associated with a specific user.
MAC This field specifies a MAC address associated with this profile.
the Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
to the network through the associated SSID; select deny to block the wireless clients with
the specified MAC addresses.
NWA5301-NJ User’s Guide
88
Page 89

Table 43 SSID > MAC Filter List > Add/Edit MAC Filter Profile (continued)
LABEL DESCRIPTION
Description This field displays a description for the MAC address associated with this profile. You can
click the description to make it editable. Enter up to 60 characters, spaces and underscores
allowed.
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
9.6 Layer-2 Isolation List
Layer-2 isolation is used to prevent wireless clients associated with your NWA from communicating
with other wireless clients, APs, computers or routers in a network.
In the following example, layer-2 isolation is enabled on the NWA to allow a guest wireless client
(A) to access the main network router (B). The router provides access to the Internet and the
network printer (C) while preventing the client from accessing other computers and servers on the
network. The client can communicate with other wireless clients only if Intra-BSS Traffic blocking is
disabled.
Chapter 9 AP Profile
Note: Intra-BSS Traffic Blocking is activated when you enable layer-2 isolation.
Figure 50 Layer-2 Isolation Application
MAC addresses that are not listed in the layer-2 isolation table are blocked from communicating
with the NWA’s wireless clients except for broadcast packets. Layer-2 isolation does not check the
traffic between wireless clients that are associated with the same AP. Intra-BSS traffic allows
wireless clients associated with the same AP to communicate with each other.
This screen allows you to specify devices you want the users on your wireless networks to access.
To access this screen click Configuratio n > Object > AP Prof ile > SSID > Layer-2 Isolation
List.
NWA5301-NJ User’s Guide
89
Page 90

Chapter 9 AP Profile
Figure 51 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
The following table describes the labels in this screen.
Table 44 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
LABEL DESCRIPTION
Add Click this to add a new MAC filtering profile.
Edit Click this to edit the selected MAC filtering profile.
Remove Click this to remove the selected MAC filtering profile.
Object Reference Click this to view which other objects are linked to the selected MAC filtering profile (for
example, SSID profile).
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the layer-2 isolation profile.
9.6.1 Add/Edit Layer-2 Isolation Profile
This screen allows you to create a new layer-2 isolation profile or edit an existing one. To access
this screen, click the Add button or select a layer-2 isolation profile from the list and click the Edit
button.
Note: You need to know the MAC address of each wireless client, AP, computer or router
that you want to allow to communicate with the NWA's wireless clients.
NWA5301-NJ User’s Guide
90
Page 91

Chapter 9 AP Profile
Figure 52 SSID > MAC Filter List > Add/Edit Layer-2 Isolation Profile
The following table describes the labels in this screen.
Table 45 SSID > MAC Filter List > Add/Edit Layer-2 Isolation Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in
the Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
Add Click this to add a MAC address to the profile’s list.
Edit Click this to edit the selected MAC address in the profile’s list.
Remove Click this to remove the selected MAC address from the profile’s list.
# This field is a sequential value, and it is not associated with a specific user.
MAC This field specifies a MAC address associated with this profile.
Description This field displays a description for the MAC address associated with this profile. You can
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
click the description to make it editable. Enter up to 60 characters, spaces and underscores
allowed.
NWA5301-NJ User’s Guide
91
Page 92

CHAPTER 10
10.1 Overview
This chapter shows you how to configure WDS profiles for the NWA to form a WDS with other APs.
10.1.1 What You Can Do in this Chapter
The WDS Profile screen (Section 10.2 on page 92) creates preset WDS configurations that can be
used by the NWA.
10.2 WDS Profile
WDS Profile
This screen allows you to manage and create WDS profiles that can be used by the APs. To access
this screen, click Configuration > Object > WDS Profile.
Figure 53 Configuration > Object > WDS Profile
The following table describes the labels in this screen.
Table 46 Configuration > Object > WDS Profile
LABEL DESCRIPTION
Add Click this to add a new profile.
Edit Click this to edit the selected profile.
Remove Click this to remove the selected profile.
# This field is a sequential value, and it is not associated with a specific profile.
Profile Name This field indicates the name assigned to the profile.
WDS SSID This field shows the SSID specified in this WDS profile.
NWA5301-NJ User’s Guide
92
Page 93

10.2.1 Add/Edit WDS Profile
This screen allows you to create a new WDS profile or edit an existing one. To access this screen,
click the Add button or select and existing profile and click the Edit button.
Figure 54 Configuration > Object > WDS Profile > Add/Edit WDS Profile
The following table describes the labels in this screen.
Table 47 Configuration > Object > WDS Profile > Add/Edit WDS Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name.
WDS SSID Enter the SSID with which you want the NWA to connect to a root AP or repeater to
form a WDS.
Pre-Shared Key Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including
spaces and symbols) or 64 hexadecimal characters.
The key is used to encrypt the traffic between the APs.
OK Click OK to save your changes back to the NWA.
Cancel Click Cancel to exit this screen without saving your changes.
Chapter 10 WDS Profile
NWA5301-NJ User’s Guide
93
Page 94

CHAPTER 11
11.1 Overview
The NWA can use certificates (also called digital IDs) to authenticate users. Certificates are based
on public-private key pairs. A certificate contains the certificate owner’s identity and public key.
Certificates provide a way to exchange public keys for use in authentication.
11.1.1 What You Can Do in this Chapter
•The My Certificate screens (Section 11.2 on page 97) generate and export self-signed
certificates or certification requests and import the NWA’s CA-signed certificates.
•The Trusted Certificates screens (Section 11.3 on page 105) save CA certificates and trusted
remote host certificates to the NWA. The NWA trusts any valid certificate that you have imported
as a trusted certificate. It also trusts any valid certificate signed by any of the certificates that
you have imported as a trusted certificate.
Certificates
11.1.2 What You Need to Know
The following terms and concepts may help as you read this chapter.
When using public-key cryptology for authentication, each host has two keys. One key is public and
can be made openly available. The other key is private and must be kept secure.
These keys work like a handwritten signature (in fact, certificates are often referred to as “digital
signatures”). Only you can write your signature exactly as it should look. When people know what
your signature looks like, they can verify whether something was signed by you, or by someone
else. In the same way, your private key “writes” your digital signature and your public key allows
people to verify whether data was signed by you, or by someone else.
This process works as follows:
1 Tim wants to send a message to Jenny. He needs her to be sure that it comes from him, and that
the message content has not been altered by anyone else along the way. Tim generates a public
key pair (one public key and one private key).
2 Tim keeps the private key and makes the public key openly available. This means that anyone who
receives a message seeming to come from Tim can read it and verify whether it is really from him
or not.
3 Tim uses his private key to sign the message and sends it to Jenny.
4 Jenny receives the message and uses Tim’s public key to verify it. Jenny knows that the message is
from Tim, and that although other people may have been able to read the message, no-one can
have altered it (because they cannot re-sign the message with Tim’s private key).
NWA5301-NJ User’s Guide
94
Page 95

Chapter 11 Certificates
5 Additionally, Jenny uses her own private key to sign a message and Tim uses Jenny’s public key to
verify the message.
The NWA uses certificates based on public-key cryptology to authenticate users attempting to
establish a connection, not to encrypt the data that you send after establishing a connection. The
method used to secure the data that you send through an established connection depends on the
type of connection.
The certification authority uses its private key to sign certificates. Anyone can then use the
certification authority’s public key to verify the certificates.
A certification path is the hierarchy of certification authority certificates that validate a certificate.
The NWA does not trust a certificate if any certificate on its path has expired or been revoked.
Certification authorities maintain directory servers with databases of valid and revoked certificates.
A directory of certificates that have been revoked before the scheduled expiration is called a CRL
(Certificate Revocation List). The NWA can check a peer’s certificate against a directory server’s list
of revoked certificates. The framework of servers, software, procedures and policies that handles
keys is called PKI (public-key infrastructure).
Advantages of Certificates
Certificates offer the following benefits.
• The NWA only has to store the certificates of the certification authorities that you decide to trust,
no matter how many devices you need to authenticate.
• Key distribution is simple and very secure since you can freely distribute public keys and you
never need to transmit private keys.
Self-signed Certificates
You can have the NWA act as a certification authority and sign its own certificates.
Factory Default Certificate
The NWA generates its own unique self-signed certificate when you first turn it on. This certificate is
referred to in the GUI as the factory default certificate.
Certificate File Formats
Any certificate that you want to import has to be in one of these file formats:
• Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates.
• PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters,
uppercase letters and numerals to convert a binary X.509 certificate into a printable form.
• Binary PKCS#7: This is a standard that defines the general syntax for data (including digital
signatures) that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The
private key is not included. The NWA currently allows the importation of a PKS#7 file that
contains a single certificate.
• PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase
letters, uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable
form.
NWA5301-NJ User’s Guide
95
Page 96

• Binary PKCS#12: This is a format for transferring public key and private key certificates.The
private key in a PKCS #12 file is within a password-encrypted envelope. The file’s password is not
connected to your certificate’s public or private passwords. Exporting a PKCS #12 file creates this
and you must provide it to decrypt the contents when you import the file into the NWA.
Note: Be careful not to convert a binary file to text during the transfer process. It is easy
for this to occur since many programs use text files by default.
11.1.3 Verifying a Certificate
Before you import a trusted certificate into the NWA, you should verify that you have the correct
certificate. You can do this using the certificate’s fingerprint. A certificate’s fingerprint is a message
digest calculated using the MD5 or SHA1 algorithm. The following procedure describes how to check
a certificate’s fingerprint to verify that you have the actual certificate.
1 Browse to where you have the certificate saved on your computer.
2 Make sure that the certificate has a “.cer” or “.crt” file name extension.
Chapter 11 Certificates
3 Double-click the certificate’s icon to open the Certificate window. Click the Details tab and scroll
down to the Thumbprint Algorithm and Thumbprint fields.
4 Use a secure method to verify that the certificate owner has the same information in the
Thumbprint Algorithm and Thumbprint fields. The secure method may very based on your
situation. Possible examples would be over the telephone or through an HTTPS connection.
NWA5301-NJ User’s Guide
96
Page 97

11.2 My Certificates
Click Configuration > Object > Certificate > My Certificates to open this screen. This is the
NWA’s summary list of certificates and certification requests.
Figure 55 Configuration > Object > Certificate > My Certificates
Chapter 11 Certificates
The following table describes the labels in this screen.
Table 48 Configuration > Object > Certificate > My Certificates
LABEL DESCRIPTION
PKI Storage
Space in Use
Add Click this to go to the screen where you can have the NWA generate a certificate or a
Edit Double-click an entry or select it and click Edit to open a screen with an in-depth list of
Remove The NWA keeps all of your certificates unless you specifically delete them. Uploading a
Object Reference You cannot delete certificates that any of the NWA’s features are configured to use. Select
# This field displays the certificate index number. The certificates are listed in alphabetical
Name This field displays the name used to identify this certificate. It is recommended that you
Type This field displays what kind of certificate this is.
This bar displays the percentage of the NWA’s PKI storage space that is currently in use.
When the storage space is almost full, you should consider deleting expired or
unnecessary certificates before adding more certificates.
certification request.
information about the certificate.
new firmware or default configuration file does not delete your certificates. To remove an
entry, select it and click Remove. The NWA confirms you want to remove it before doing
so. Subsequent certificates move up by one when you take this action.
an entry and click Object Reference to open a screen that shows which settings use the
entry.
order.
give each certificate a unique name.
REQ represents a certification request and is not yet a valid certificate. Send a
certification request to a certification authority, which then issues a certificate. Use the My
Certificate Import screen to import the certificate and replace the request.
SELF represents a self-signed certificate.
CERT represents a certificate issued by a certification authority.
NWA5301-NJ User’s Guide
97
Page 98

Table 48 Configuration > Object > Certificate > My Certificates (continued)
LABEL DESCRIPTION
Subject This field displays identifying information about the certificate’s owner, such as CN
(Common Name), OU (Organizational Unit or department), O (Organization or company)
and C (Country). It is recommended that each certificate have unique subject
information.
Issuer This field displays identifying information about the certificate’s issuing certification
authority, such as a common name, organizational unit or department, organization or
company and country. With self-signed certificates, this is the same information as in the
Subject field.
Valid From This field displays the date that the certificate becomes applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and
includes an Expired! message if the certificate has expired.
Import Click Import to open a screen where you can save a certificate to the NWA.
Refresh Click Refresh to display the current validity status of the certificates.
11.2.1 Add My Certificates
Click Configuration > Object > Certificate > My Certificates and then the Add icon to open
the Add My Certificates screen. Use this screen to have the NWA create a self-signed certificate,
enroll a certificate with a certification authority or generate a certification request.
Chapter 11 Certificates
NWA5301-NJ User’s Guide
98
Page 99

Chapter 11 Certificates
Figure 56 Configuration > Object > Certificate > My Certificates > Add
NWA5301-NJ User’s Guide
99
Page 100

Chapter 11 Certificates
The following table describes the labels in this screen.
Table 49 Configuration > Object > Certificate > My Certificates > Add
LABEL DESCRIPTION
Name Type a name to identify this certificate. You can use up to 31 alphanumeric and
Subject Information Use these fields to record information that identifies the owner of the certificate. You
Organizational Unit Identify the organizational unit or department to which the certificate owner belongs.
Organization Identify the company or group to which the certificate owner belongs. You can use up
Town (City) Identify the town or city where the certificate owner is located. You can use up to 31
State (Province) Identify the state or province where the certificate owner is located. You can use up to
Country Identify the nation where the certificate owner is located. You can use up to 31
Key Type Select RSA to use the Rivest, Shamir and Adleman public-key algorithm.
;‘~!@#$%^&()_+[]{}’,.=-
do not have to fill in every field, although you must specify a Host IP Address, Host
Domain Name, or E-Mail. The certification authority may add fields (such as a serial
number) to the subject information when it issues a certificate. It is recommended
that each certificate have unique subject information.
Select a radio button to identify the certificate’s owner by IP address, domain name or
e-mail address. Type the IP address (in dotted decimal notation), domain name or email address in the field provided. The domain name or e-mail address is for
identification purposes only and can be any string.
A domain name can be up to 255 characters. You can use alphanumeric characters,
the hyphen and periods.
An e-mail address can be up to 63 characters. You can use alphanumeric characters,
the hyphen, the @ symbol, periods and the underscore.
You can use up to 31 characters. You can use alphanumeric characters, the hyphen
and the underscore.
to 31 characters. You can use alphanumeric characters, the hyphen and the
underscore.
characters. You can use alphanumeric characters, the hyphen and the underscore.
31 characters. You can use alphanumeric characters, the hyphen and the underscore.
characters. You can use alphanumeric characters, the hyphen and the underscore.
characters.
Select DSA to use the Digital Signature Algorithm public-key algorithm.
Key Length Select a number from the drop-down list box to determine how many bits the key
Enrollment Options These radio buttons deal with how and when the certificate is to be generated.
Create a self-signed
certificate
Create a certification
request and save it
locally for later
manual enrollment
should use (512 to 2048). The longer the key, the more secure it is. A longer key also
uses more PKI storage space.
Select this to have the NWA generate the certificate and act as the Certification
Authority (CA) itself. This way you do not need to apply to a certification authority for
certificates.
Select this to have the NWA generate and store a request for a certificate. Use the My
Certificate Edit screen to view the certification request and copy it to send to the
certification authority.
Copy the certification request from the My Certificate Edit screen and then send it to
the certification authority.
NWA5301-NJ User’s Guide
100
 Loading...
Loading...