Page 1

User’s Guide
Default Login Details
EMG3415-B10A
Dual-Band Wireless AC/N Gigabit Ethernet Gateway
LAN IP Address http://192.168.200.1
Login Login account and
Password
password are not needed.
Simply click I Agree to go
to the Web Configurator.
Version 5.12 Edition 1, 02/2017
Copyright © 2017 Zyxel Communications Corporation
Page 2
IMPORTANT!
READ CAREFULLY BEFORE USE.
KEEP THIS GUIDE FOR FUTURE REFERENCE.
This is a User’s Guide for a system managing a series of products. Not all products support all features.
Menushots and graphics in this book may differ slightly from what you see due to differences in release
versions or your computer operating system. Every effort has been made to ensure that the information
in this manual is accurate.
Related Documentation
•Quick Start Guide
The Quick Start Guide shows how to connect the managed device, such as the Nebula AP, gateway
or security gateway.
EMG3415-B10A User’s Guide
2
Page 3

Contents Overview
Contents Overview
User’s Guide ......................................................................................................................................12
Introducing the EMG ............................................................................................................................ 13
The Web Configurator ......................................................................................................................... 20
Tutorials .................................................................................................................................................. 27
Technical Reference ........................................................................................................................44
Network Map and Status Screens ...................................................................................................... 45
Broadband ............................................................................................................................................ 50
Wireless ................................................................................................................................................... 64
Home Networking ................................................................................................................................. 88
Routing ................................................................................................................................................. 102
Quality of Service (QoS) .................................................................................................................... 109
Network Address Translation (NAT) ................................................................................................... 127
DNS ....................................................................................................................................................... 143
VLAN Group ........................................................................................................................................ 147
Interface Grouping ............................................................................................................................ 149
Firewall ................................................................................................................................................. 153
MAC Filter ............................................................................................................................................ 160
Parental Control ................................................................................................................................. 162
Scheduler Rule .................................................................................................................................... 167
Certificates .......................................................................................................................................... 169
Log ....................................................................................................................................................... 175
Traffic Status ....................................................................................................................................... 178
ARP Table ............................................................................................................................................ 181
Routing Table ...................................................................................................................................... 183
Multicast Status .................................................................................................................................. 185
System .................................................................................................................................................. 187
User Account ...................................................................................................................................... 188
Remote Management ....................................................................................................................... 191
SNMP .................................................................................................................................................... 194
Time Settings ........................................................................................................................................ 196
E-mail Notification .............................................................................................................................. 198
Log Setting .......................................................................................................................................... 200
Firmware Upgrade .............................................................................................................................. 203
Backup/Restore .................................................................................................................................. 205
Diagnostic ........................................................................................................................................... 208
Troubleshooting .................................................................................................................................. 210
Appendices ............................................ ........................................................... ..............................215
EMG3415-B10A User’s Guide
3
Page 4

Table of Contents
Table of Contents
Contents Overview .............................................................................................................................3
Table of Contents.................................................................................................................................4
Part I: User’s Guide.......................................................................................... 12
Chapter 1
Introducing the EMG.................................................................................................. ........................13
1.1 Overview ......................................................................................................................................... 13
1.2 Ways to Manage the EMG ............................................................................................................ 13
1.3 Good Habits for Managing the EMG ...........................................................................................13
1.4 Applications for the EMG ............................................................................................................. 13
1.4.1 Internet Access ...................................................................................................................... 13
1.4.2 Dual-Band .............................................................................................................................. 14
1.4.3 Triple Play ............................................................................................................................... 15
1.5 LEDs (Lights) ..................................................................................................................................... 15
1.6 The RESET Button ............................................................................................................................. 17
1.7 Wireless Access ............................................................................................................................... 17
1.7.1 Using the WPS Button ............................................................................................................ 18
1.8 Wall Mounting ................................................................................................................................. 18
Chapter 2
The Web Configurator........................................................................................................................20
2.1 Overview ......................................................................................................................................... 20
2.1.1 Accessing the Web Configurator ....................................................................................... 20
2.2 Web Configurator Layout .............................................................................................................. 22
2.2.1 Title Bar ................................................................................................................................... 22
2.2.2 Navigation Panel .................................................................................................................. 23
Chapter 3
Tutorials...............................................................................................................................................27
3.1 Overview ......................................................................................................................................... 27
3.2 Setting Up a New WAN Connection ............................................................................................27
3.3 Setting Up a Secure Wireless Network ......................................................................................... 30
3.3.1 Configuring the Wireless Network Settings ......................................................................... 30
3.3.2 Using WPS ............................................................................................................................... 32
3.3.3 Without WPS ........................................................................................................................... 35
3.4 Configuring Static Route for Routing to Another Network ........................................................ 36
EMG3415-B10A User’s Guide
4
Page 5

Table of Contents
3.5 Configuring QoS Queue and Class Setup ................................................................................... 38
3.6 Access the EMG Using DDNS ........................................................................................................ 41
3.6.1 Registering a DDNS Account on www.dyndns.org ........................................................... 41
3.6.2 Configuring DDNS on Your EMG ......................................................................................... 41
3.6.3 Testing the DDNS Setting ...................................................................................................... 42
3.7 Configuring the MAC Address Filter ............................................................................................. 42
Part II: Technical Reference........................................................................... 44
Chapter 4
Network Map and Status Screens....................................................................................................45
4.1 Overview ......................................................................................................................................... 45
4.2 The Network Map Screen .............................................................................................................. 45
4.3 The Status Screen ........................................................................................................................... 46
Chapter 5
Broadband..........................................................................................................................................50
5.1 Overview ......................................................................................................................................... 50
5.1.1 What You Can Do in this Chapter ....................................................................................... 50
5.1.2 What You Need to Know ..................................................................................................... 50
5.1.3 Before You Begin ................................................................................................................... 53
5.2 The Broadband Screen .................................................................................................................. 53
5.2.1 Add/Edit Internet Connection .............................................................................................54
5.3 Technical Reference ...................................................................................................................... 59
Chapter 6
Wireless...............................................................................................................................................64
6.1 Overview ......................................................................................................................................... 64
6.1.1 What You Can Do in this Chapter ....................................................................................... 64
6.1.2 What You Need to Know ..................................................................................................... 64
6.2 The General Screen ...................................................................................................................... 65
6.2.1 No Security ............................................................................................................................. 67
6.2.2 Basic (WEP Encryption) ......................................................................................................... 67
6.2.3 More Secure (WPA(2)-PSK) .................................................................................................. 68
6.3 MAC Authentication ...................................................................................................................... 69
6.4 The WPS Screen .............................................................................................................................. 70
6.5 The WMM Screen ............................................................................................................................ 72
6.6 The Others Screen .......................................................................................................................... 73
6.7 The Channel Status Screen ........................................................................................................... 74
6.8 Technical Reference ...................................................................................................................... 75
6.8.1 Wireless Network Overview .................................................................................................. 75
EMG3415-B10A User’s Guide
5
Page 6

Table of Contents
6.8.2 Additional Wireless Terms ..................................................................................................... 77
6.8.3 Wireless Security Overview ................................................................................................... 77
6.8.4 Signal Problems ..................................................................................................................... 79
6.8.5 BSS ........................................................................................................................................... 80
6.8.6 Preamble Type ...................................................................................................................... 80
6.8.7 WiFi Protected Setup (WPS) ................................................................................................. 81
Chapter 7
Home Networking..............................................................................................................................88
7.1 Overview ......................................................................................................................................... 88
7.1.1 What You Can Do in this Chapter ....................................................................................... 88
7.1.2 What You Need To Know ..................................................................................................... 89
7.1.3 Before You Begin ................................................................................................................... 90
7.2 The LAN Setup Screen .................................................................................................................... 90
7.3 The Static DHCP Screen ................................................................................................................. 94
7.4 The UPnP Screen ............................................................................................................................. 95
7.4.1 Turning On UPnP in Windows 7 Example ............................................................................ 96
7.5 The Additional Subnet Screen ....................................................................................................... 98
7.6 The STB Vendor ID Screen .............................................................................................................. 99
7.7 The Wake on LAN Screen .............................................................................................................. 99
7.8 The TFTP Server Name Screen ..................................................................................................... 100
7.9 Technical Reference .................................................................................................................... 100
7.9.1 LANs, WANs and the EMG .................................................................................................. 100
7.9.2 DHCP Setup ......................................................................................................................... 101
7.9.3 DNS Server Addresses ......................................................................................................... 101
Chapter 8
Routing..............................................................................................................................................102
8.1 Overview ...................................................................................................................................... 102
8.2 The Routing Screen ...................................................................................................................... 102
8.2.1 Add/Edit Static Route ......................................................................................................... 103
8.3 The DNS Route Screen ................................................................................................................. 104
8.3.1 The DNS Route Add Screen ............................................................................................... 105
8.4 The Policy Route Screen .............................................................................................................. 105
8.4.1 Add/Edit Policy Route ........................................................................................................ 107
8.5 RIP ............................................................................................................................................... 107
8.5.1 The RIP Screen ..................................................................................................................... 108
Chapter 9
Quality of Service (QoS) ........................................ ..........................................................................109
9.1 Overview ...................................................................................................................................... 109
9.1.1 What You Can Do in this Chapter ..................................................................................... 109
9.2 What You Need to Know ............................................................................................................. 110
EMG3415-B10A User’s Guide
6
Page 7

Table of Contents
9.3 The Quality of Service General Screen .....................................................................................111
9.4 The Queue Setup Screen ............................................................................................................. 112
9.4.1 Adding a QoS Queue ........................................................................................................ 114
9.5 The Classification Setup Screen .................................................................................................. 115
9.5.1 Add/Edit QoS Class ............................................................................................................ 115
9.6 The QoS Shaper Setup Screen .................................................................................................... 119
9.6.1 Add/Edit a QoS Shaper ..................................................................................................... 120
9.7 The QoS Policer Setup Screen ..................................................................................................... 120
9.7.1 Add/Edit a QoS Policer ..................................................................................................... 121
9.8 Technical Reference .................................................................................................................... 122
Chapter 10
Network Address Translation (NAT)................................................................................................127
10.1 Overview ..................................................................................................................................... 127
10.1.1 What You Can Do in this Chapter ................................................................................... 127
10.1.2 What You Need To Know ................................................................................................. 127
10.2 The Port Forwarding Screen ..................................................................................................... 128
10.2.1 Add/Edit Port Forwarding ................................................................................................ 130
10.3 The Applications Screen ............................................................................................................ 131
10.3.1 Add New Application ....................................................................................................... 132
10.4 The Port Triggering Screen ......................................................................................................... 133
10.4.1 Add/Edit Port Triggering Rule ..........................................................................................134
10.5 The DMZ Screen .......................................................................................................................... 135
10.6 The ALG Screen .......................................................................................................................... 136
10.7 The Address Mapping Screen ................................................................................................... 137
10.7.1 Add/Edit Address Mapping Rule ..................................................................................... 138
10.8 The Sessions Screen .................................................................................................................... 139
10.9 Technical Reference .................................................................................................................. 139
10.9.1 NAT Definitions ................................................................................................................... 139
10.9.2 What NAT Does ................................................................................................................. 140
10.9.3 How NAT Works .................................................................................................................. 140
10.9.4 NAT Application ................................................................................................................ 141
Chapter 11
DNS....................................................................................................................................................143
11.1 Overview ..................................................................................................................................... 143
11.1.1 What You Can Do in this Chapter ................................................................................... 143
11.1.2 What You Need To Know ................................................................................................. 143
11.2 The DNS Entry Screen ................................................................................................................. 144
11.2.1 Add/Edit DNS Entry ........................................................................................................... 144
11.3 The Dynamic DNS Screen .......................................................................................................... 145
Chapter 12
VLAN Group......................................................................................................................................147
EMG3415-B10A User’s Guide
7
Page 8

Table of Contents
12.1 Overview ..................................................................................................................................... 147
12.1.1 What You Can Do in this Chapter ................................................................................... 147
12.2 The VLAN Group Screen ............................................................................................................ 147
12.2.1 Add/Edit a VLAN Group ...................................................................................................148
Chapter 13
Interface Grouping..........................................................................................................................149
13.1 Overview ..................................................................................................................................... 149
13.1.1 What You Can Do in this Chapter ................................................................................... 149
13.2 The Interface Grouping Screen ................................................................................................ 149
13.2.1 Interface Group Configuration ....................................................................................... 150
13.2.2 Interface Grouping Criteria ............................................................................................151
Chapter 14
Firewall..............................................................................................................................................153
14.1 Overview ..................................................................................................................................... 153
14.1.1 What You Can Do in this Chapter ................................................................................... 153
14.1.2 What You Need to Know ................................................................................................. 154
14.2 The Firewall Screen ..................................................................................................................... 154
14.3 The Protocol Screen .................................................................................................................. 155
14.3.1 Add/Edit a Service ........................................................................................................... 156
14.4 The Access Control Screen ....................................................................................................... 157
14.4.1 Add/Edit an ACL Rule ..................................................................................................... 157
14.5 The DoS Screen ........................................................................................................................... 159
Chapter 15
MAC Filter .........................................................................................................................................160
15.1 Overview .................................................................................................................................... 160
15.2 The MAC Filter Screen ................................................................................................................ 160
Chapter 16
Parental Control...............................................................................................................................162
16.1 Overview ..................................................................................................................................... 162
16.2 The Parental Control Screen ..................................................................................................... 162
16.2.1 Add/Edit a Parental Control Profile ................................................................................ 163
Chapter 17
Scheduler Rule .................................................................................................................................167
17.1 Overview ..................................................................................................................................... 167
17.2 The Scheduler Rule Screen ........................................................................................................ 167
17.2.1 Add/Edit a Schedule ........................................................................................................ 167
Chapter 18
Certificates .......................................................................................................................................169
EMG3415-B10A User’s Guide
8
Page 9

Table of Contents
18.1 Overview ..................................................................................................................................... 169
18.1.1 What You Can Do in this Chapter ................................................................................... 169
18.2 What You Need to Know ........................................................................................................... 169
18.3 The Local Certificates Screen ................................................................................................... 169
18.3.1 Create Certificate Request ............................................................................................ 170
18.3.2 Load Signed Certificate .................................................................................................. 171
18.4 The Trusted CA Screen ............................................................................................................... 172
18.4.1 View Trusted CA Certificate ............................................................................................ 173
18.4.2 Import Trusted CA Certificate .......................................................................................... 174
Chapter 19
Log ..................................... ................................................ ...............................................................175
19.1 Overview ..................................................................................................................................... 175
19.1.1 What You Can Do in this Chapter ................................................................................... 175
19.1.2 What You Need To Know ................................................................................................. 175
19.2 The System Log Screen .............................................................................................................. 176
19.3 The Security Log Screen ............................................................................................................. 176
Chapter 20
Traffic Status .....................................................................................................................................178
20.1 Overview ..................................................................................................................................... 178
20.1.1 What You Can Do in this Chapter ................................................................................... 178
20.2 The WAN Status Screen .............................................................................................................. 178
20.3 The LAN Status Screen ............................................................................................................... 179
20.4 The NAT Status Screen ................................................................................................................ 180
Chapter 21
ARP Table..........................................................................................................................................181
21.1 Overview ..................................................................................................................................... 181
21.1.1 How ARP Works .................................................................................................................. 181
21.2 ARP Table Screen ....................................................................................................................... 181
Chapter 22
Routing Table....................................................................................................................................183
22.1 Overview ..................................................................................................................................... 183
22.2 The Routing Table Screen .......................................................................................................... 183
Chapter 23
Multicast Status ...............................................................................................................................185
23.1 Overview ..................................................................................................................................... 185
23.2 The IGMP Status Screen ............................................................................................................. 185
23.3 The MLD Status Screen ............................................................................................................... 185
EMG3415-B10A User’s Guide
9
Page 10

Table of Contents
Chapter 24
System...............................................................................................................................................187
24.1 Overview ..................................................................................................................................... 187
24.2 The System Screen ...................................................................................................................... 187
Chapter 25
User Account................. .... .... .... .......................................................................................................188
25.1 Overview .................................................................................................................................... 188
25.2 The User Account Screen .......................................................................................................... 188
25.2.1 The User Account Add/Edit Screen ................................................................................ 189
Chapter 26
Remote Management.....................................................................................................................191
26.1 Overview ..................................................................................................................................... 191
26.2 The MGMT Services Screen ....................................................................................................... 191
26.3 The Trust Domain Screen ............................................................................................................ 192
26.3.1 The Add Trust Domain Screen ......................................................................................... 193
Chapter 27
SNMP .................................................................................................................................................194
27.1 Overview ..................................................................................................................................... 194
27.2 The SNMP Screen ........................................................................................................................ 194
Chapter 28
Time Settings.....................................................................................................................................196
28.1 Overview ..................................................................................................................................... 196
28.2 The Time Screen ......................................................................................................................... 196
Chapter 29
E-mail Notification ...........................................................................................................................198
29.1 Overview .................................................................................................................................. 198
29.2 The E-mail Notification Screen .................................................................................................. 198
29.2.1 E-mail Notification Edit .................................................................................................... 198
Chapter 30
Log Setting .......................................................................................................................................200
30.1 Overview .................................................................................................................................... 200
30.2 The Log Settings Screen ............................................................................................................. 200
30.2.1 Example E-mail Log ........................................................................................................... 201
Chapter 31
Firmware Upgrade..................................................... ... ............................................. ......................203
31.1 Overview ..................................................................................................................................... 203
EMG3415-B10A User’s Guide
10
Page 11

Table of Contents
31.2 The Firmware Screen .................................................................................................................. 203
Chapter 32
Backup/Restore ...............................................................................................................................205
32.1 Overview ..................................................................................................................................... 205
32.2 The Backup/Restore Screen ...................................................................................................... 205
32.3 The ROM-D Screen ..................................................................................................................... 207
32.4 The Reboot Screen ..................................................................................................................... 207
Chapter 33
Diagnostic.........................................................................................................................................208
33.1 Overview ..................................................................................................................................... 208
33.1.1 What You Can Do in this Chapter ................................................................................... 208
33.2 What You Need to Know ........................................................................................................... 208
33.3 Ping & TraceRoute & NsLookup ................................................................................................ 209
Chapter 34
Troubleshooting................................................................................................................................210
34.1 Power, Hardware Connections, and LEDs ............................................................................... 210
34.2 EMG Access and Login .............................................................................................................. 211
34.3 Internet Access ........................................................................................................................... 212
34.4 Wireless Internet Access ............................................................................................................. 213
34.5 UPnP ............................................................................................................................................. 214
Part III: Appendices......................................................................................215
Appendix A Customer Support ..................................................................................................... 216
Appendix B Wireless LANs............................................................................................................... 222
Appendix C IPv6.............................................................................................................................. 234
Appendix D Services....................................................................................................................... 242
Appendix E Legal Information ....................................................................................................... 246
Index.................................................................................................................................................254
EMG3415-B10A User’s Guide
11
Page 12
PART I
User’s Guide
12
Page 13

Introducing the EMG
1.1 Overview
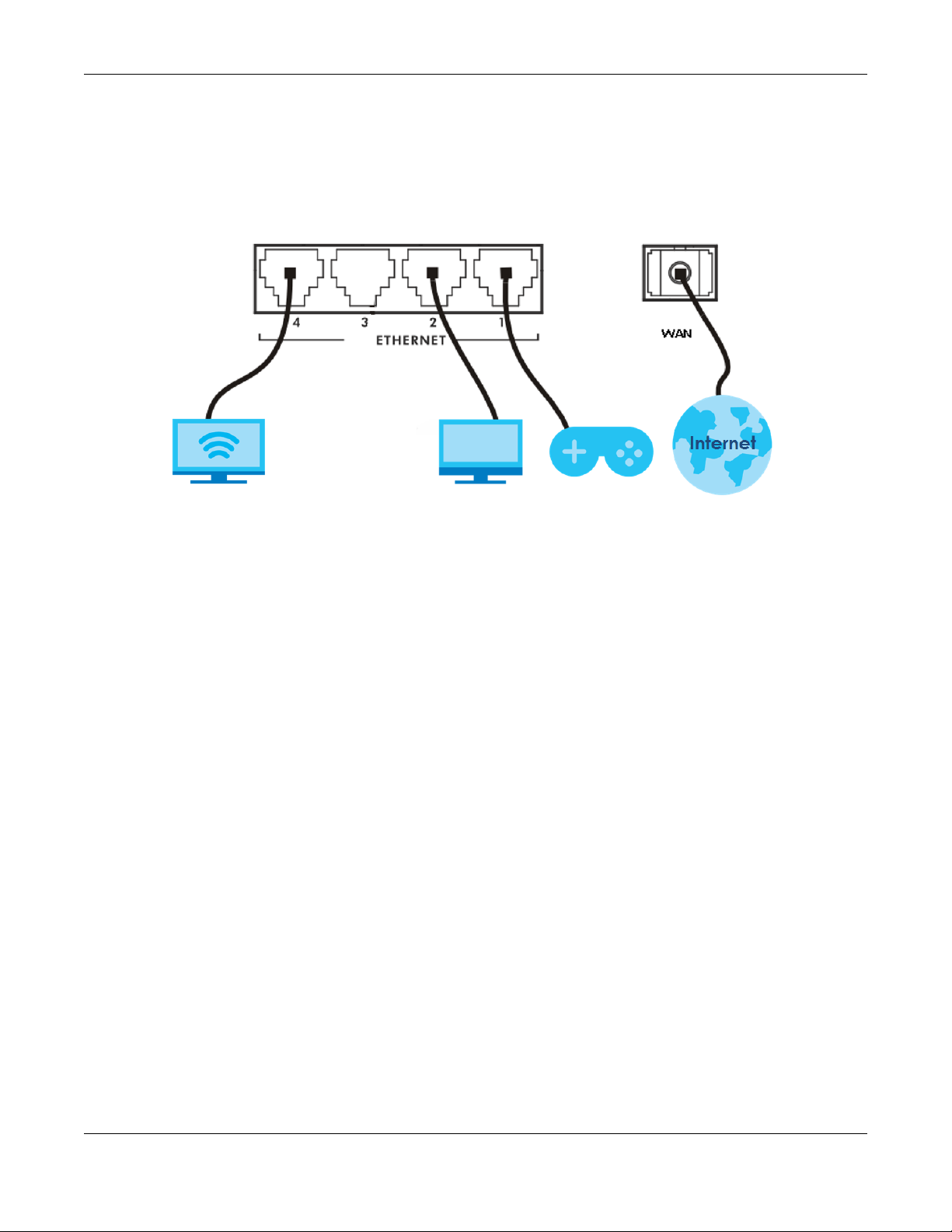
The EMG is an Ethernet gateway providing triple-play services and optimized HD IPTV services at home
or office. This model offers a Gigabit Ethernet (GbE) WAN with interfaces of Ethernet and WAN ports. The
EMG offers 2.4G and 5G Wi-Fi networks that operate simultaneously, providing a simple and unified
network management.
Only use firmware for your EMG’s specific model.
1.2 Ways to Manage the EMG
Use any of the following methods to manage the EMG.
CHAPTER 1
• Web Configurator. This is recommended for everyday management of the EMG using a (supported)
web browser.
1.3 Good Habits for Managing the EMG
Do the following regularly to make the EMG more secure and to manage the EMG more effectively.
• Back up the configuration (and make sure you know how to restore it). Restoring an earlier working
configuration may be useful if the device becomes unstable or even crashes. If you backed up an
earlier configuration file, you would not have to totally re-configure the EMG. You could simply restore
your last configuration.
1.4 Applications for the EMG
Here are some example uses for which the EMG is well suited.
1.4.1 Internet Access
Computers can connect to the EMG’s LAN ports (or wirelessly).
You can also configure IP filtering on the EMG for secure Internet access. When the IP filter is on, all
incoming traffic from the Internet to your network is blocked by default unless it is initiated from your
network. This means that probes from the outside to your network are not allowed, but you can safely
browse the Internet and download files.
EMG3415-B10A User’s Guide
13
Page 14
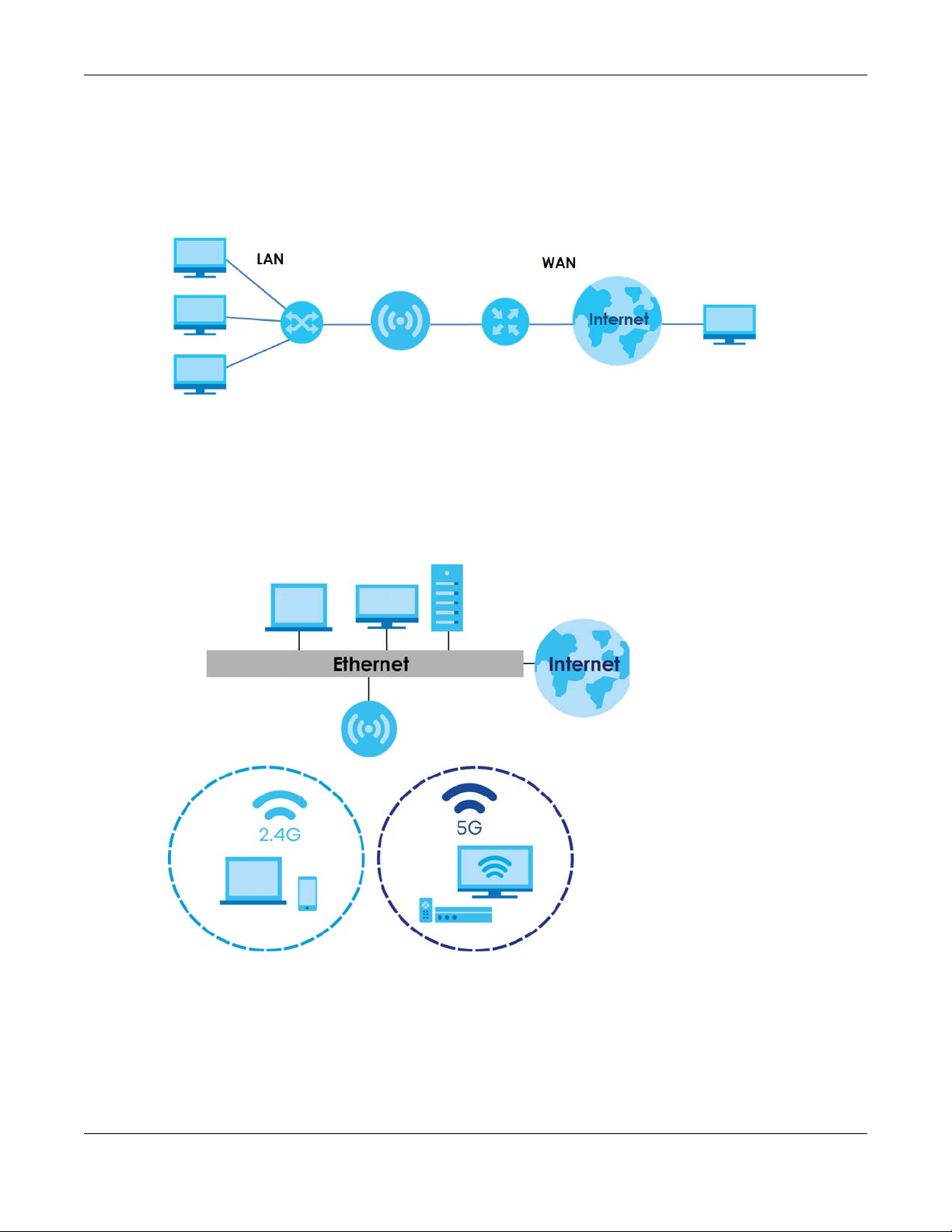
1.4.1.1 Ethernet WAN
If you have another broadband modem or router available, you can connect the WAN port to the
broadband modem or router. This way, you can access the Internet via an Ethernet connection and still
use the QoS, Firewall and parental control functions on the EMG.
Figure 1 EMG’s Internet Access Application: Ethernet WAN
1.4.2 Dual-Band
The EMG is a dual-band gateway and able to function both 2.4G and 5G networks at the same time.
You could use the 2.4 GHz band for regular Intern et surfing and downloading while using the 5 GHz
band for time sensitive traffic like high-definition video, music, and gaming.
Chapter 1 Introducing the EMG
Figure 2 Dual-Band Application
EMG3415-B10A User’s Guide
14
Page 15
1.4.3 Triple Play
The ISP may provide “triple play” service to the EMG. This allows you to take advantage of such
features as broadband Internet access, and streaming video/audio media, all at the same time with
no noticeable loss in bandwidth.
Figure 3 Triple Play Example
Chapter 1 Introducing the EMG
1.5 LEDs (Lights)
The following graphic displays the labels of the LEDs.
EMG3415-B10A User’s Guide
15
Page 16
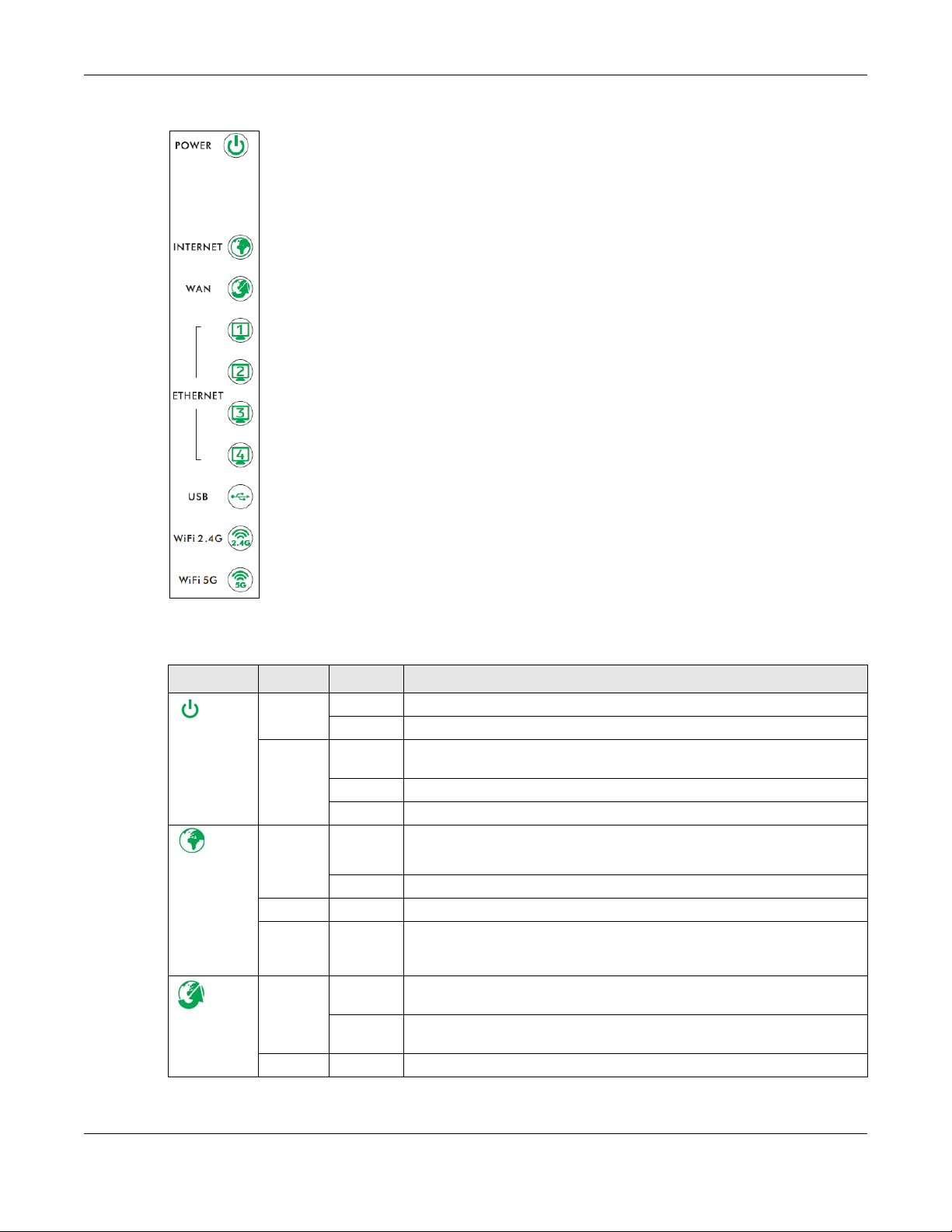
Figure 4 LEDs on the EMG
Chapter 1 Introducing the EMG
None of the LEDs are on if the EMG is not receiving power.
Table 1 LED Descriptions
LED COLOR STATUS DESCRIPTION
Green On The EMG is receiving power and ready for use.
Power
Red On The EMG detected an error while self-testing, or there is a device
Green On The EMG has an IP connection but no traffic.
Internet
Red On The EMG attempted to make an IP connection but failed. Possible causes
Green On The EMG has a successful 10/100/1000 Mbps Ethernet connection on the
WAN
Blinking The EMG is self-testing.
malfunction.
Blinking The EMG is upgrading its firmware.
Off The EMG is not receiving power.
Blinking The EMG is sending or receiving IP traffic.
Off There is no Internet connection or the gateway is in bridged mode.
are no response from a DHCP server, no PPPoE response, PPPoE
authentication failed.
WAN.
Blinking The EMG is sending or receiving data to/from the WAN at 10/100/1000
Mbps.
Off There is no Ethernet connection on the WAN.
EMG3415-B10A User’s Guide
16
Page 17
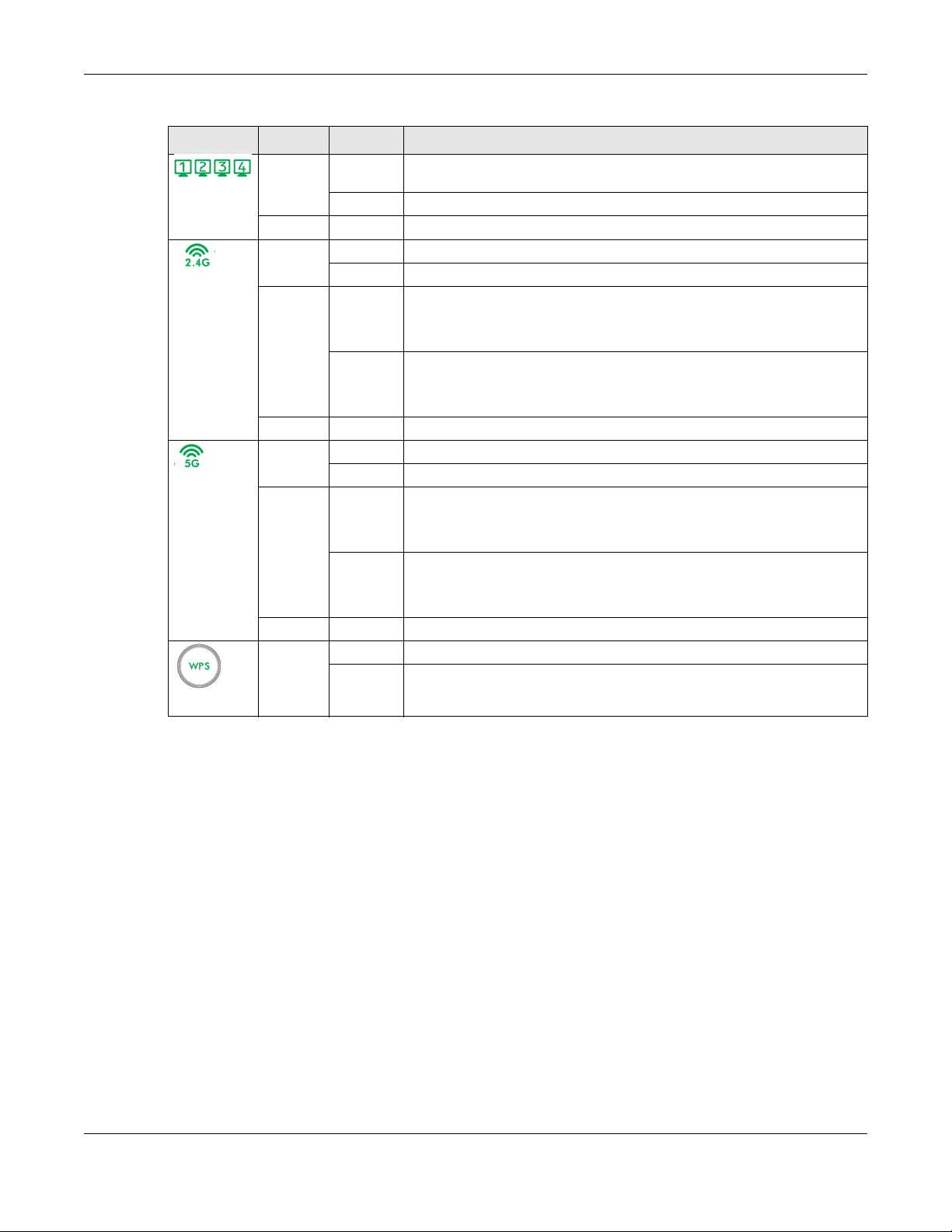
Chapter 1 Introducing the EMG
Table 1 LED Descriptions (continued)
LED COLOR STATUS DESCRIPTION
Green On The EMG has a successful 1000 Mbps Ethernet connection with a device on
Ethernet 1~4
WiFi 2.4G
WiFi 5G
Blinking The EMG is sending or receiving data to/from the LAN at 1000 Mbps.
Off The EMG does not have an Ethernet connection with the LAN.
Green On The 2.4 GHz wireless network is activated.
Blinking The EMG is communicating with 2.4 GHz wireless clients.
Amber On The EMG is setting up a WPS connection with a 2.4 GHz wireless client via
Blinking The EMG is setting up a WPS connection with a 2.4 GHz wireless client via
Off The 2.4 GHz wireless network is not activated.
Green On The 5 GHz wireless network is activated.
Blinking The EMG is communicating with 5 GHz wireless clients.
Amber On The EMG is setting up a WPS connection with a 5 GHz wireless client via WPS
Blinking The EMG is setting up a WPS connection with a 5 GHz wireless client via WPS
Off The 5 GHz wireless network is not activated.
Amber On The 2.4 Ghz or 5 GHz wireless network and WPS are enabled.
Off Both 2.4 Ghz or 5 GHz wireless network and WPS are disabled.
the Local Area Network (LAN).
WPS method 3.
See Section 6.4 on page 70 to learn each method.
WPS method 1 or 2.
See Section 6.4 on page 70 to learn each method.
method 3.
See Section 6.4 on page 70 to learn each method.
method 1 or 2.
See Section 6.4 on page 70 to learn each method.
WPS
1.6 The RESET Button
You will need to use the RESET button at the back of the device to reload the factory-default
configuration file. This means that you will lose all configurations that you had previously.
1 Make sure the POWER LED is on (not blinking).
2 To set the device back to the factory default settings, press the RESET button for five seconds or until the
POWER LED begins to blink and then release it. When the POWER LED begins to blink, the defaults have
been restored and the device restarts.
1.7 Wireless Access
You can configure your wireless network in either the built-in Web Configurator, or using the WPS button.
EMG3415-B10A User’s Guide
17
Page 18

Figure 5 Wireless Access Example
1.7.1 Using the WPS Button
Once the WiFi LED turns green, the wireless network is active. If the wireless network is turned off, see
Section 6.2 on page 65 for how to enable the wireless network on the EMG.
You can also use the WPS button to quickly set up a secure wireless connection between the EMG and
a WPS-compatible client by adding one device at a time.
Chapter 1 Introducing the EMG
To activate WPS:
1 Make sure the POWER LED is on and not blinking.
2 Press the WPS button for five seconds and release it.
3 Press the WPS button on another WPS-enabled device within range of the EMG. The WiFi LED flashes
amber while the EMG sets up a WPS connection with the other wireless device.
4 Once the connection is successfully made, the WPS LED shines amber.
The WPS LED turns off when the wireless network is off.
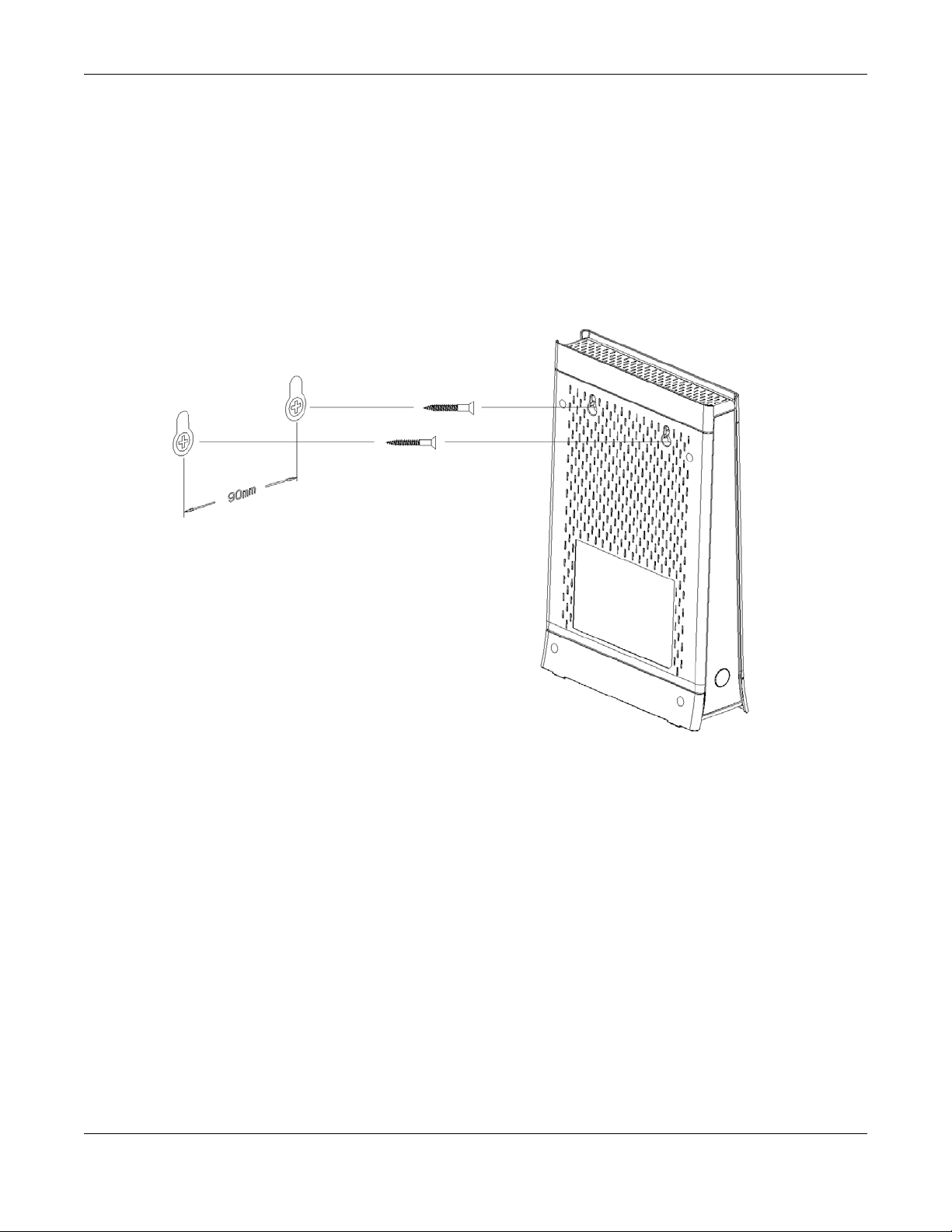
1.8 Wall Mounting
You may need screw anchors if mounting on a concrete or brick wall.
Table 2 Wall Mounting Information
Distance between holes 90 mm
M4 Screws Two
Screw anchors (optional) Two
5 Select a position free of obstructions on a wall strong enough to hold the weight of the device.
6 Mark two holes on the wall at the appropriate distance apart for the screws.
Be careful to avoid damaging pipes or cables located inside the wall
when drilling holes for the screws.
EMG3415-B10A User’s Guide
18
Page 19
Chapter 1 Introducing the EMG
7 If using screw anchors, drill two holes for the screw anchors into the wall. Push the anchors into the full
depth of the holes, then insert the screws into the anchors. Do not insert the screws all the way in - leave
a small gap of about 0.5 cm.
If not using screw anchors, use a screwdriver to insert the screws into the wall. Do not insert the screws all
the way in - leave a gap of about 0.5 cm.
8 Make sure the screws are fastened well enough to hold the weight of the EMG with the connection
cables.
9 Align the holes on the back of the EMG with the screws on the wall. Hang the EMG on the screws.
Figure 6 Wall Mounting Example
EMG3415-B10A User’s Guide
19
Page 20
2.1 Overview
The web configurator is an HTML-based management interface that allows easy EMG setup and
management via Internet browser. Use Internet Explorer 8.0 and later versions or Mozilla Firefox 3 and
later versions or Safari 2.0 and later versions.* The recommended screen resolution is 1024 by 768 pixels.
In order to use the web configurator you need to allow:
CHAPTER 2
The Web Configurator
• Web browser pop-up windows from your
Windows XP SP (Service Pack) 2.
• JavaScript (enabled by default).
• Java permissions (enabled by default).
EMG. Web pop-up blocking is enabled by default in
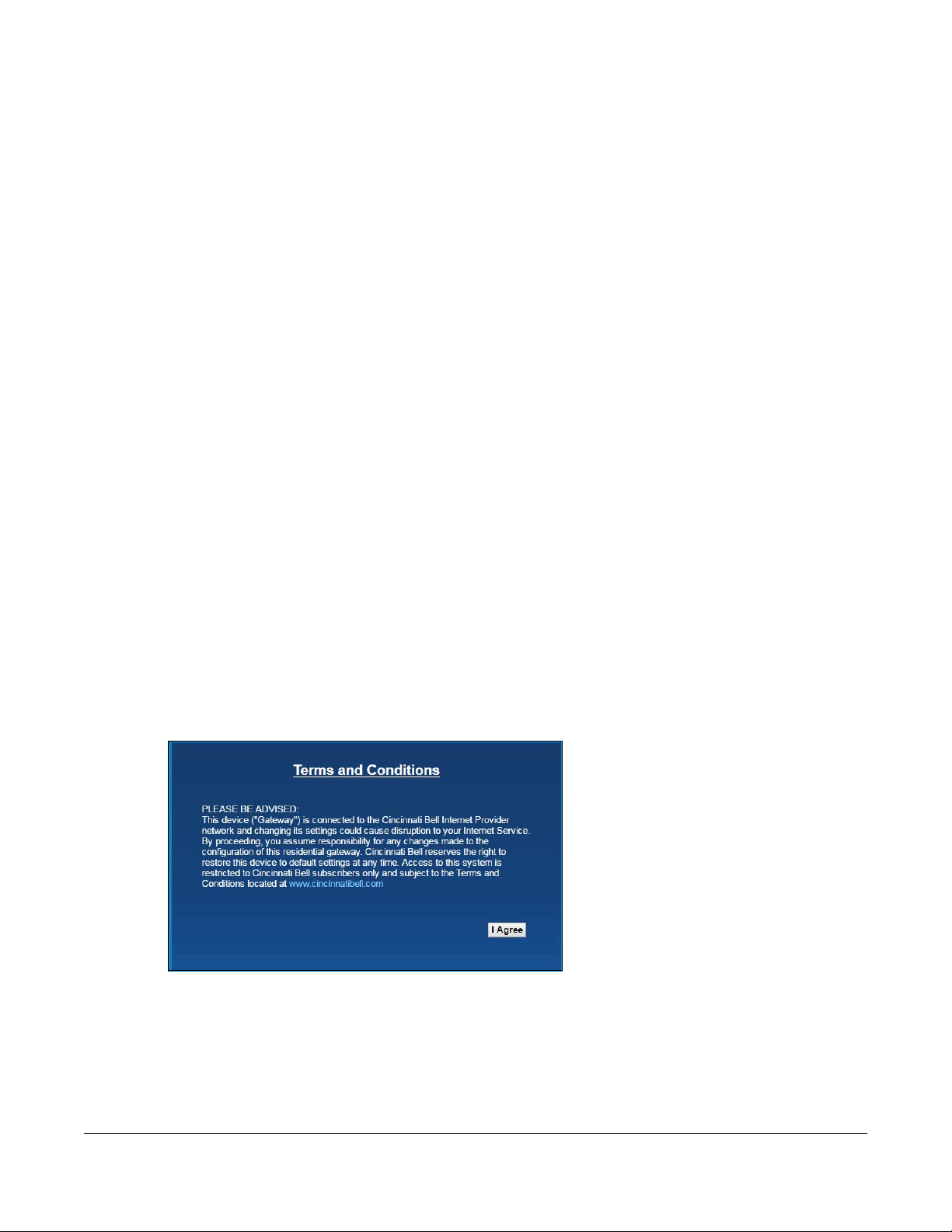
2.1.1 Accessing the Web Configurator
1 Make sure your EMG hardware is properly connected (refer to the Quick Start Guide).
2 Launch your web browser. If the EMG does not automatically re-direct you to the login screen, go to
http://192.168.200.1.
3 The Terms and Conditions screen displays. To access the administrative Web Configurator and manage
the EMG, click on the I Agree button as shown below.
Figure 7 The Terms and Conditions Screen
4 The Network Map page appears.
EMG3415-B10A User’s Guide
20
Page 21

Chapter 2 The Web Configurator
Figure 8 The Network Map Screen
5 Click Status to display the Status screen, where you can view the EMG’s interface and system
information.
EMG3415-B10A User’s Guide
21
Page 22
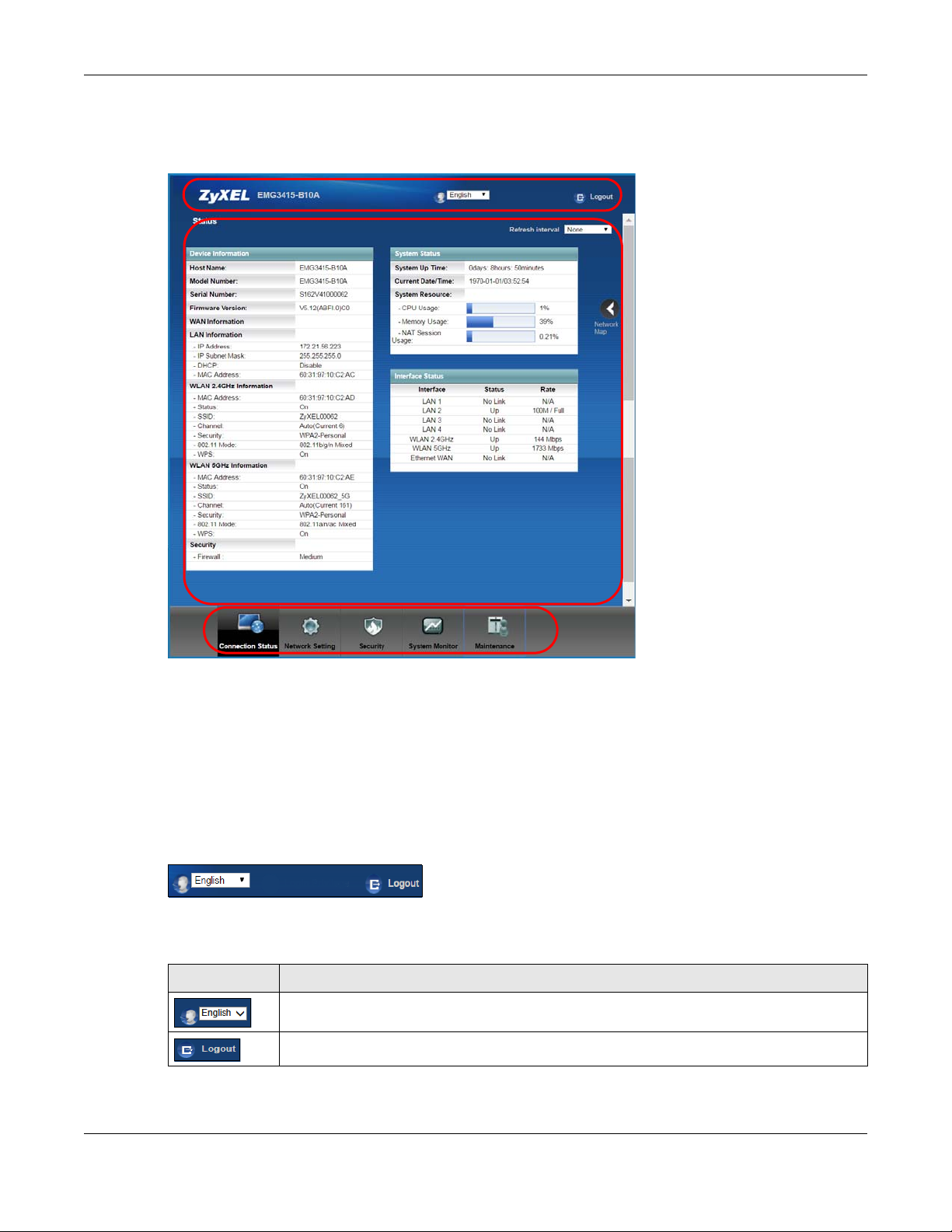
Chapter 2 The Web Configurator
A
B
C
2.2 Web Configurator Layout
Figure 9
As illustrated above, the main screen is divided into these parts:
• A - title bar
• B - main window
• C - navigation panel
2.2.1 Title Bar
The title bar provides some icons in the upper right corner.
The icons provide the following functions.
Table 3 Web Configurator Icons in the Title Bar
ICON DESCRIPTION
Language: Select the language you prefer.
Logout: Click this icon to log out of the web configurator.
EMG3415-B10A User’s Guide
22
Page 23
2.2.2 Navigation Panel
Use the menu items on the navigation panel to open screens to configure EMG features. The following
tables describe each menu item.
Table 4 Navigation Panel Summary
LINK TAB FUNCTION
Connection Status This screen shows the network status of the EMG and computers/devices
Network Setting
Broadband Broadband Use this screen to view and configure ISP parameters, WAN IP address
Wireless General Use this screen to configure the wireless LAN settings and WLAN
MAC
Authentication
WPS Use this screen to configure and view your WPS (Wi-Fi Protected Setup)
WMM Use this screen to enable or disable Wi-Fi MultiMedia (WMM).
Others Use this screen to configure advanced wireless settings.
Channel Status Use this screen to scan wireless LAN channel noises and view the results.
Home
Networking
Routing Static Route Use this screen to view and set up static routes on the EMG.
QoS General Use this screen to enable QoS and traffic prioritizing. You can also
LAN Setup Use this screen to configure LAN TCP/IP settings, and other advanced
Static DHCP Use this screen to assign specific IP addresses to individual MAC
UPnP Use this screen to turn UPnP and UPnP NAT-T on or off.
Additional
Subnet
STB Vendor ID Use this screen to configure the Vendor IDs of the connected Set Top Box
Wake on LAN Use this screen to remotely turn on a device on the local network.
TFTP Server Name Configure a TFTP server name which is sent to clients using DHCP option
DNS Route
Policy Route
RIP Use this screen to configure Routing Information Protocol to exchange
Queue Setup Use this screen to configure QoS queues.
Classification
Setup
Shaper Setup Use this screen to limit outgoing traffic rate on the selected interface.
Policer Setup Use this screen to configure QoS policers.
Chapter 2 The Web Configurator
connected to it.
assignment, and other advanced properties. You can also add new
WAN connections.
authentication/security settings.
Use this screen to block or allow wireless traffic from wireless devices of
certain SSIDs and MAC addresses to the EMG.
settings.
properties.
addresses.
Use this screen to configure IP alias and public static IP.
(STB) devices, which have the EMG automatically create static DHCP
entries for the STB devices when they request IP addresses.
66.
Use this screen to forward DNS queries for certain domain names through
a specific WAN interface to its DNS server(s).
Use this screen to configure policy routing on the EMG.
routing information with other routers.
configure the QoS rules and actions.
Use this screen to define a classifier.
EMG3415-B10A User’s Guide
23
Page 24
Chapter 2 The Web Configurator
Table 4 Navigation Panel Summary (continued)
LINK TAB FUNCTION
NAT Port Forwarding Use this screen to make your local servers visible to the outside world.
Applications
Port Triggering Use this screen to change your EMG’s port triggering settings.
DMZ Use this screen to configure a default server which receives packets from
ALG Use this screen to enable or disable SIP ALG.
Address Mapping Use this screen to change your EMG’s address mapping settings.
Sessions Use this screen to configure the maximum number of NAT sessions each
DNS DNS Entry Use this screen to view and configure DNS routes.
Dynamic DNS Use this screen to allow a static hostname alias for a dynamic IP address.
Vlan Group Vlan Group Use this screen to group and tag VLAN IDs to outgoing traffic from the
Interface
Grouping
Security
Firewall General Use this screen to configure the security level of your firewall.
MAC Filter MAC Filter Use this screen to block or allow traffic from devices of certain MAC
Parental
Control
Scheduler Rules Scheduler Rules Use this screen to configure the days and times when a configured
Certificates Local Certificates Use this screen to view a summary list of certificates and manage
System Monitor
Interface
Grouping
Protocol Use this screen to add Internet services and configure firewall rules.
Access Control Use this screen to enable specific traffic directions for network services.
DoS Use this screen to activate protection against Denial of Service (DoS)
Parental Control Use this screen to block web sites with the specific URL.
Trusted CA
Use this screen to configure servers behind the EMG.
ports that are not specified in the Port Forwarding screen.
client host is allowed to have through the EMG.
specified interface.
Use this screen to map a port to a PVC or bridge group.
attacks.
addresses to the EMG.
restriction (such as parental control) is enforced.
certificates and certification requests.
Use this screen to view and manage the list of the trusted CAs.
EMG3415-B10A User’s Guide
24
Page 25
Chapter 2 The Web Configurator
Table 4 Navigation Panel Summary (continued)
LINK TAB FUNCTION
Log System Log Use this screen to view the status of events that occurred to the EMG.
You can export or e-mail the logs.
Security Log Use this screen to view all security related events. You can select level
and category of the security events in their proper drop-down list
window.
Levels include:
•Emergency
•Alert
• Critical
• Error
• Warning
•Notice
• Informational
•Debugging
Categories include:
• Account
• Attack
•Firewall
• MAC Filter
Traffic Status WAN Use this screen to view the status of all network traffic going through the
WAN port of the EMG.
LAN Use this screen to view the status of all network traffic going through the
NAT Use this screen to view NAT statistics for connected hosts.
ARP table ARP table Use this screen to view the ARP table. It displays the IP and MAC address
Routing Table Routing Table Use this screen to view the routing table on the EMG.
Multicast Status IGMP Status Use this screen to view the status of all IGMP settings on the EMG.
MLD Status Use this screen to view the status of all MLD settings on the EMG.
Maintenance
System System
User Account User Account Use this screen to change user password on the EMG.
Remote
Management
SNMP SNMP Use this screen to configure SNMP (Simple Network Management
Time Time Use this screen to change your EMG’s time and date.
E-mail
Notification
Log Setting Log Setting Use this screen to change your EMG’s log settings.
Firmware
Upgrade
MGMT Services Use this screen to enable specific traffic directions for network services.
Trust Domain Use this screen to view a list of public IP addresses which are allowed to
E-mail
Notification
Firmware
Upgrade
LAN ports of the EMG.
of each DHCP connection.
Use this screen to set Device name and Domain name.
access the EMG through the services configured in the Maintenance >
Remote Management screen.
Protocol) settings.
Use this screen to configure up to two mail servers and sender addresses
on the EMG.
Use this screen to upload firmware to your EMG.
EMG3415-B10A User’s Guide
25
Page 26
Chapter 2 The Web Configurator
Table 4 Navigation Panel Summary (continued)
LINK TAB FUNCTION
Backup/Restore Backup/Restore Use this screen to backup and restore your EMG’s configuration (settings)
or reset the factory default settings.
ROM-D Use this screen to save and/or clean the configuration to/from the ROM-
D file which can store customized default settings.
Reboot Reboot Use this screen to reboot the EMG without turning the power off.
Diagnostic Ping&Traceroute
&Nslookup
Use this screen to identify problems with the Ethernet WAN connection.
You can use Ping, TraceRoute, or Nslookup to help you identify problems.
EMG3415-B10A User’s Guide
26
Page 27
3.1 Overview
This chapter shows you how to use the EMG’s various features.
• Setting Up a New WAN Connection, see page 27
• Setting Up a Secure Wireless Network, see page 30
• Configuring Static Route for Routing to Another Network, see page 36
• Configuring QoS Queue and Class Setup, see page 38
• Access the EMG Using DDNS, see page 41
• Configuring the MAC Address Filter, see page 42
CHAPTER 3
Tutorials
3.2 Setting Up a New WAN Connection
This tutorial shows you how to set up a new WAN Internet connection using the Web Configurator.
If you have another broadband modem or router available, you can connect the WAN port to the
router and access the Internet via an Ethernet connection.
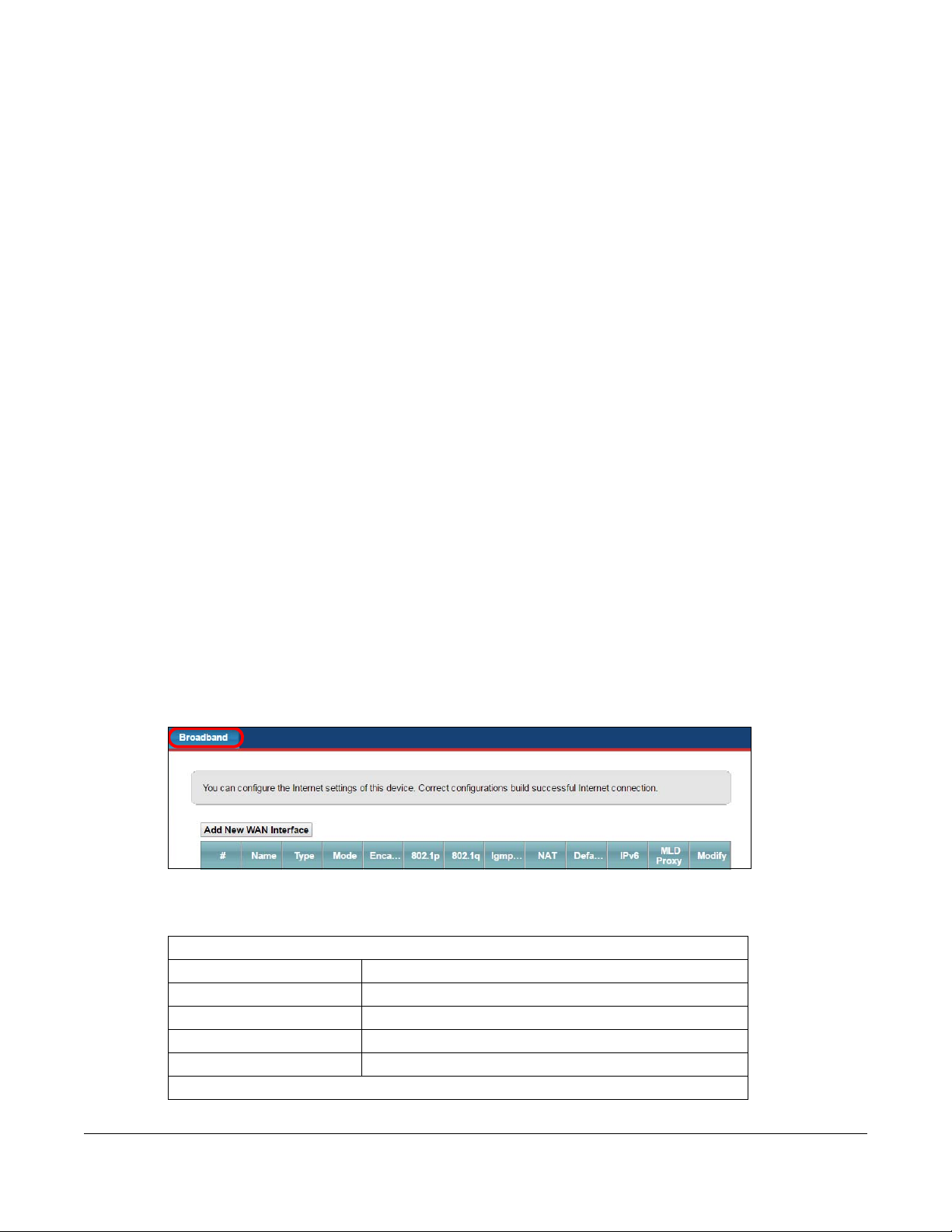
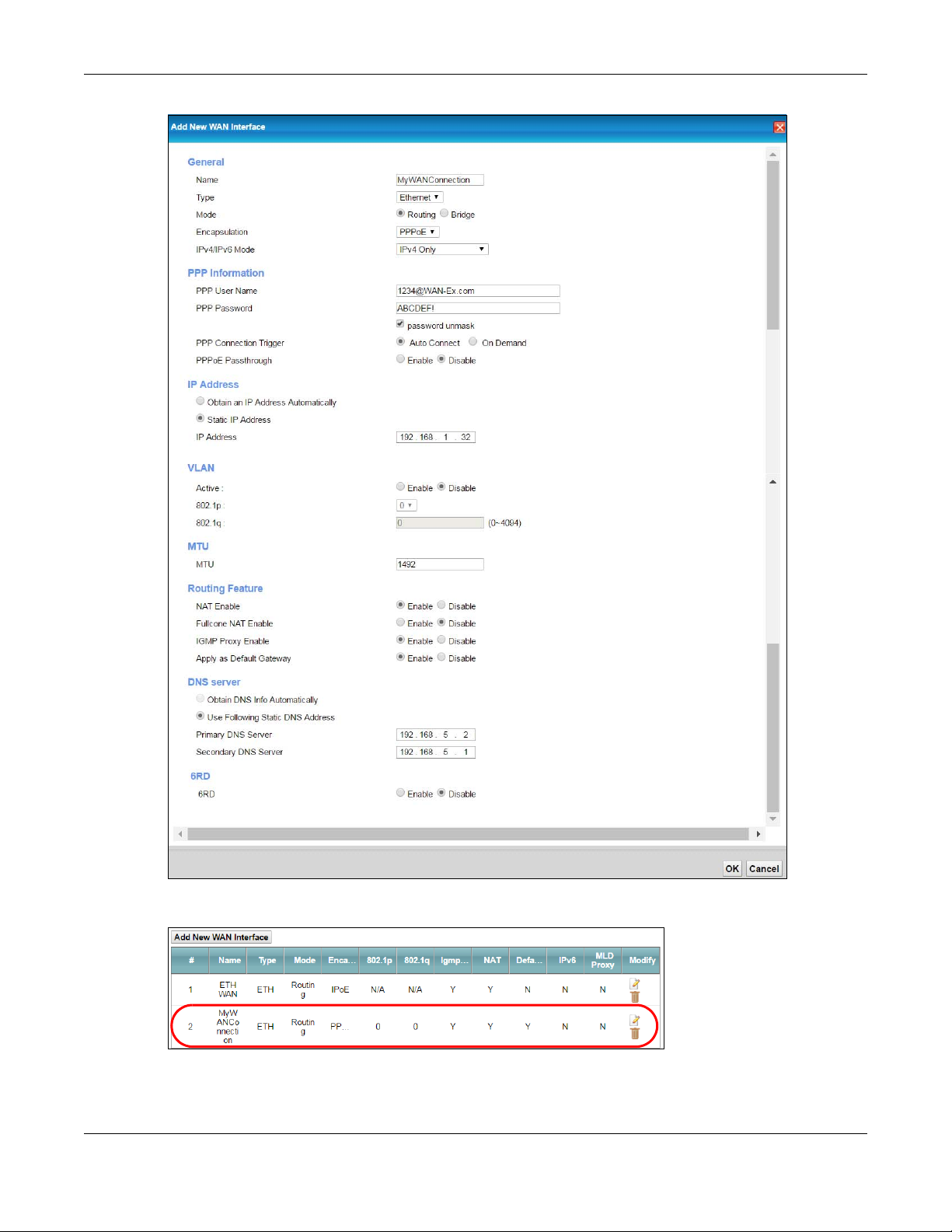
1 Click Network Setting > Broadband to open the following screen. Click Add New WAN Interface.
2 In this example, the Ethernet WAN connection has the following information.
General
Name MyWANConnection
Type Ethernet
Connection Mode Routing
Encapsulation PPPoE
IPv6/IPv4 Mode IPv4
Account Information
EMG3415-B10A User’s Guide
27
Page 28
Chapter 3 Tutorials
PPP User Name 1234@WAN-Ex.com
PPP Password ABCDEF!
PPPoE Service Name MyWAN
Static IP Address 192.168.1.32
Others Authentication Method: AUTO
PPPoE Passthrough: Disabled
NAT: Enabled
IGMP Multicast Proxy: Enabled
Apply as Default Gateway: Enabled
VLAN: Enabled
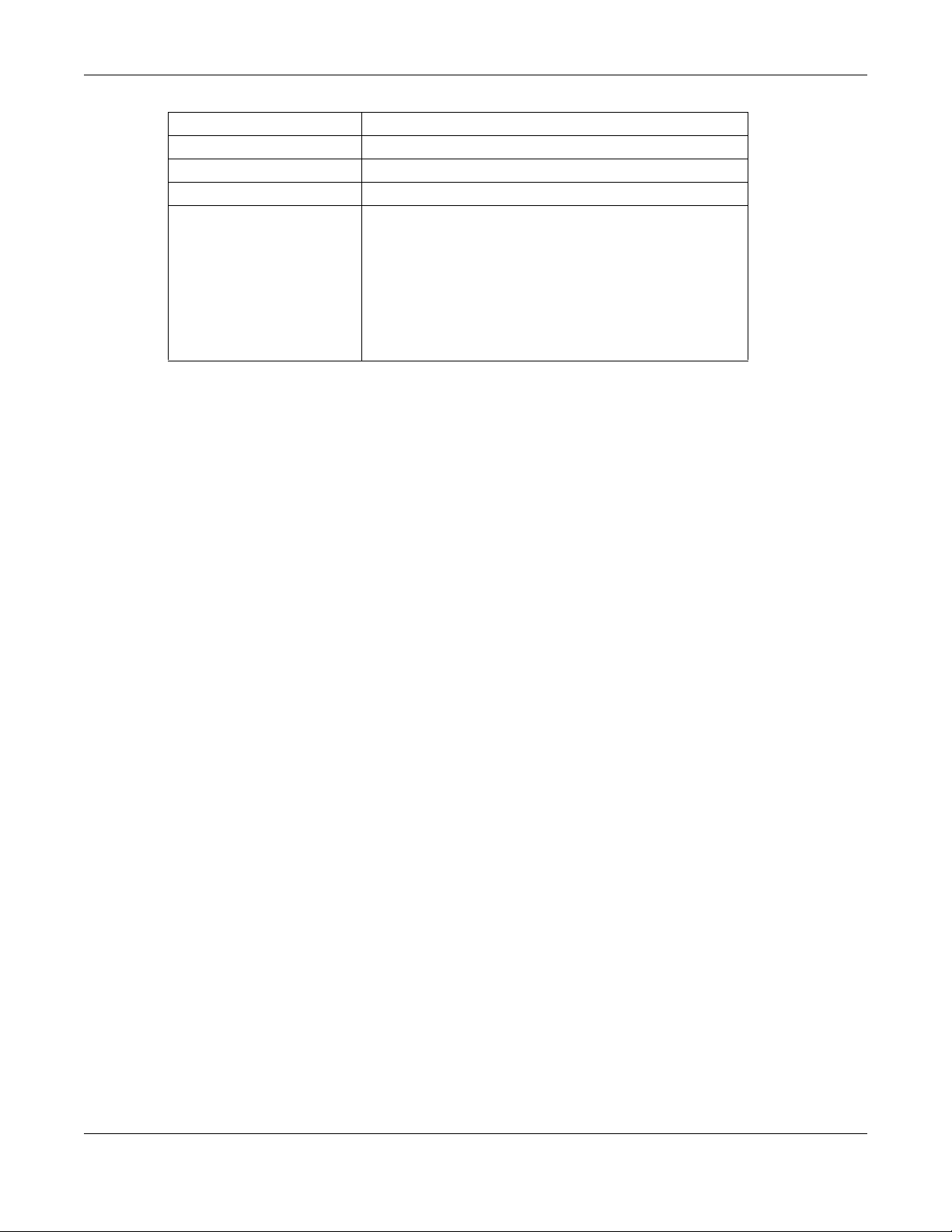
3 Select the Active check box. Enter the General and Account Information settings as provided above.
Set the Type to Ethernet.
Choose the Encapsulation specified by your service provider. For this example, the service provider
requires a username and password to establish Internet connection. Therefore, select PPPoE as the WAN
encapsulation type.
Set the IPv6/IPv4 Mode to IPv4 Only.
4 Enter the account information provided to you by your service provider.
5 Configure this rule as your default Internet connection by selecting the Apply as Default Gateway check
box. Then select DNS as Static and enter the DNS server addresses provided to you, such as 192.168.5.2
(DNS server1)/192.168.5.1 (DNS server2).
6 Leave the rest of the fields to the default settings.
7 Click Apply to save your settings.
EMG3415-B10A User’s Guide
28
Page 29
Chapter 3 Tutorials
8 You should see a summary of your new WAN connection setup in the Broadband screen as follows.
Try to connect to a website to see if you have correctly set up your Internet connection.
EMG3415-B10A User’s Guide
29
Page 30

Chapter 3 Tutorials
3.3 Setting Up a Secure Wireless Network
Thomas wants to set up a wireless network so that he can use his notebook to access the Internet. In this
wireless network, the EMG serves as an access point (AP), and the notebook is the wireless client. The
wireless client can access the Internet through the AP.
Thomas has to configure the wireless network settings on the EMG. Then he can set up a wireless network
using WPS (Section 3.3.2 on page 32) or manual configuration (Section 3.3.3 on page 35).
3.3.1 Configuring the Wireless Network Settings
This example uses the following parameters to set up a wireless network.
SSID Example
Security Mode WPA2-PSK
Pre-Shared Key DoNotStealMyWirelessNetwork
802.11 Mode 802.11b/g/n Mixed
1 Click Network Setting > Wireless to open the General screen. Select More Secure as the security level
and WPA2-PSK as the security mode. Configure the screen using the provided parameters (see
page 30). Click Apply.
EMG3415-B10A User’s Guide
30
Page 31

Chapter 3 Tutorials
2 Go to the Wireless > Others screen and select 802.11b/g/n Mixed in the 802.11 Mode field. Click Apply.
Thomas can now use the WPS feature to establish a wireless connection between his notebook and the
EMG (see Section 3.3.2 on page 32). He can also use the notebook’s wireless client to search for the
EMG (see Section 3.3.3 on page 35).
EMG3415-B10A User’s Guide
31
Page 32

3.3.2 Using WPS
1
2
3
This section shows you how to set up a wireless network using WPS. It uses the EMG as the AP and Zyxel
NWD210N as the wireless client which connects to the notebook.
Note: The wireless client must be a WPS-aware device (for example, a WPS USB adapter or
PCMCIA card).
There are two WPS methods to set up the wireless client settings:
• Push Button Configuration (PBC) - simply press a button. This is the easier of the two methods.
• PIN Configuration - configure a Personal Identification Number (PIN) on the EMG. A wireless client
must also use the same PIN in order to download the wireless network settings from the EMG.
Push Button Configuration (PBC)
1 Make sure that your EMG is turned on and your notebook is within the cover range of the wireless signal.
2 Make sure that you have installed the wireless client driver and utility in your notebook.
Chapter 3 Tutorials
3 In the wireless client utility, go to the WPS setting page. Enable WPS and press the WPS button for more
than five seconds (Start or WPS button).
4 Push and hold the WPS button located on the EMG’s front panel for more than 5 seconds. Alternatively,
you may log into EMG’s web configurator and go to the Network Setting > Wireless > WPS screen.
Enable the WPS function for method 1 and click Apply. Then click the WPS button.
Note: Your EMG has a WPS button located on its front panel as well as a WPS button in its
configuration utility. Both buttons have exactly the same function: you can use one or
the other.
Note: It doesn’t matter which button is pressed first. You must press the second button within
two minutes of pressing the first one.
EMG3415-B10A User’s Guide
32
Page 33

Chapter 3 Tutorials
The EMG sends the proper configuration settings to the wireless client. This may take up to two minutes.
The wireless client is then able to communicate with the EMG securely.
The following figure shows you an example of how to set up a wireless network and its security by
pressing a button on both EMG and wireless client.
Example WPS Process: PBC MethodZyxel
PIN Configuration
When you use the PIN configuration method, you need to use both the EMG’s web configurator and the
wireless client’s utility.
1 Launch your wireless client’s configuration utility. Go to the WPS settings and select the PIN method to
get a PIN number.
2 Log into EMG’s web configurator and go to the Network Setting > Wireless > WPS screen. Enable the WPS
function and click Apply.
EMG3415-B10A User’s Guide
33
Page 34

Chapter 3 Tutorials
1
2
3
3 Enter the PIN number of the wireless client and click the Register button. Activate WPS function on the
wireless client utility screen within two minutes.
The EMG authenticates the wireless client and sends the proper configuration settings to the wireless
client. This may take up to two minutes. The wireless client is then able to communicate with the EMG
securely.
The following figure shows you how to set up a wireless network and its security on a EMG and a wireless
client by using PIN method.
EMG3415-B10A User’s Guide
34
Page 35

Example WPS Process: PIN Method
Chapter 3 Tutorials
3.3.3 Without WPS
Use the wireless adapter’s utility installed on the notebook to search for the “Example” SSID. Then enter
the “DoNotStealMyWirelessNetwork” pre-shared key to establish an wireless Internet connection.
Note: The EMG supports IEEE 802.11b and IEEE 802.11g wireless clients. Make sure that your
notebook or computer’s wireless adapter supports one of these standards.
EMG3415-B10A User’s Guide
35
Page 36

Chapter 3 Tutorials
3.4 Configuring Static Route for Routing to Another
Network
In order to extend your Intranet and control traffic flowing directions, you may connect a router to the
EMG’s LAN. The router may be used to separate two department networks. This tutorial shows how to
configure a static routing rule for two network routings.
In the following figure, router R is connected to the EMG’s LAN. R connects to two networks, N1
(192.168.1.x/24) and N2 (192.168.10.x/24). If you want to send traffic from computer A (in N1 network) to
computer B (in N2 network), the traffic is sent to the EMG’s WAN default gateway by default. In this
case, B will never receive the traffic.
You need to specify a static routing rule on the EMG to specify R as the router in charge of forwarding
traffic to N2. In this case, the EMG routes traffic from A to R and then R routes the traffic to B.
EMG3415-B10A User’s Guide
36
Page 37

Chapter 3 Tutorials
This tutorial uses the following example IP settings:
Table 5 IP Settings in this Tutorial
DEVICE / COMPUTER IP ADDRESS
The EMG’s WAN 172.16.1.1
The EMG’s LAN 192.168.200.1
IP Type IPv4
Use Interface ETHWAN
A 192.168.1.34
R’s N1 192.168.1.253
R’s N2 192.168.10.2
B 192.168.10.33
To configure a static route to route traffic from N1 to N2:
1 Log into the EMG’s Web Configurator.
2 Click Network Setting > Routing.
3 Click Add new Static Route in the Static Route screen.
4 Configure the Static Route Setup screen using the following settings:
4a Select the Enable in the Active field. Enter the Route Name as R.
4b Set IP Type to IPv4.
4c Type 192.168.10.0 and subnet mask 255.255.255.0 for the destination, N2.
4d Select Enable in the Use Gateway IP Address field. Type 192.168.1.253 (R’s N1 address) in the
Gateway IP Address field.
4e Select ETHWAN as the Use Interface.
EMG3415-B10A User’s Guide
37
Page 38

Chapter 3 Tutorials
4a Click OK.
Now B should be able to receive traffic from A. You may need to additionally configure B’s firewall
settings to allow specific traffic to pass through.
3.5 Configuring QoS Queue and Class Setup
This section contains tutorials on how you can configure the QoS screen.
Let’s say you are a team leader of a small sales branch office. You want to prioritize e-mail traffic
because your task includes sending urgent updates to clients at least twice every hour. You also upload
data files (such as logs and e-mail archives) to the FTP server throughout the day. Your colleagues use
the Internet for research, as well as chat applications for communicating with other branch offices.
In the following figure, your Internet connection has an upstream transmission bandwidth of 10,000 kbps.
For this example, you want to configure QoS so that e-mail traffic gets the highest priority with at least
5,000 kbps. You can do the following:
• Configure a queue to assign the highest priority queue (1) to e-mail traffic going to the WAN
interface, so that e-mail traffic would not get delayed when there is network congestion.
• Note the IP address (192.168.1.23 for example) and/or MAC address (AA:FF:AA:FF:AA:FF for example)
of your computer and map it to queue 7.
Note: QoS is applied to traffic flowing out of the EMG.
Traffic that does not match this class is assigned a priority queue based on the internal QoS mapping
table on the EMG.
QoS Example
1 Click Network Setting > QoS > General and select Enable. Set your WAN Managed Upstream Bandwidth
to 10,000 kbps (or leave this blank to have the EMG automatically determine this figure). Click Apply.
EMG3415-B10A User’s Guide
38
Page 39

Chapter 3 Tutorials
Tutorial: Advanced > QoS
2 Click Queue Setup > Add new Queue to create a new queue. In the screen that opens, select Enable in
the Active field and enter or select the following values:
• Name: E-mail
• Interface: WAN
• Priority: 1 (High)
• Weight: 8
• Rate Limit: 5,000 (kbps)
Tutorial: Advanced > QoS > Queue Setup
3 Click Classification Setup > Add new Classification to create a new class. Select Enable in the Active
field and follow the settings as shown in the screen below.
EMG3415-B10A User’s Guide
39
Page 40

Tutorial: Advanced > QoS > Class Setup
Chapter 3 Tutorials
Class Name Give a class name to this traffic, such as E-mail in this example.
From Interface This is the interface from which the traffic will be coming from. Select LAN1 for this example.
Ether Type Select IP to identify the traffic source by its IP address or MAC address.
IP Address Type the IP address of your computer - 192.168.1.23. Type the IP Subnet Mask if you know it.
MAC Address Type the MAC address of your computer - AA:FF:AA:FF:AA:FF. Type the MAC Mask if you know it.
To Queue Index Link this to an item in the Network Setting > QoS > Queue Setup screen, which is the E-mail queue
created in this example.
This maps e-mail traffic coming from port 25 to the highest priority, which you have created in the
previous screen (see the IP Protocol field). This also maps your computer’s IP address and MAC address
to the E-mail queue (see the Source fields).
EMG3415-B10A User’s Guide
40
Page 41

Chapter 3 Tutorials
3.6 Access the EMG Using DDNS
If you connect your EMG to the Internet and it uses a dynamic WAN IP address, it is inconvenient for you
to manage the device from the Internet. The EMG’s WAN IP address changes dynamically. Dynamic
DNS (DDNS) allows you to access the EMG using a domain name.
To use this feature, you have to apply for DDNS service at www.dyndns.org.
This tutorial covers:
• Registering a DDNS Account on www.dyndns.org
• Configuring DDNS on Your EMG
• Testing the DDNS Setting
Note: If you have a private WAN IP address, then you cannot use DDNS.
3.6.1 Registering a DDNS Account on www.dyndns.org
1 Open a browser and type http://www.dyndns.org.
2 Apply for a user account. This tutorial uses UserName1 and 12345 as the username and password.
3 Log into www.dyndns.org using your account.
4 Add a new DDNS host name. This tutorial uses the following settings as an example.
• Hostname: zyxelrouter.dyndns.org
• Service Type: Host with IP address
• IP Address: Enter the WAN IP address that your EMG is currently using. You can find the IP address on
the EMG’s Web Configurator Status page.
Then you will need to configure the same account and host name on the EMG later.
3.6.2 Configuring DDNS on Your EMG
Configure the following settings in the Network Setting > DNS > Dynamic DNS screen.
•Select Enable Dynamic DNS.
•Select www.DynDNS.com as the service provider.
•Type zyxelrouter.dyndns.org in the Host Name field.
EMG3415-B10A User’s Guide
41
Page 42

• Enter the user name (UserName1) and password (12345).
Click Apply.
3.6.3 Testing the DDNS Setting
Chapter 3 Tutorials
Now you should be able to access the EMG from the Internet. To test this:
1 Open a web browser on the computer (using the IP address a.b.c.d) that is connected to the Internet.
2 Type http://zyxelrouter.dyndns.org and press [Enter].
3 The EMG’s login page should appear. You can then log into the EMG and manage it.
3.7 Configuring the MAC Address Filter
Thomas noticed that his daughter Josephine spends too much time surfing the web and downloading
media files. He decided to prevent Josephine from accessing the Internet so that she can concentrate
on preparing for her final exams.
Josephine’s computer connects wirelessly to the Internet through the EMG. Thomas decides to use the
Security > MAC Filter screen to grant wireless network access to his computer but not to Josephine’s
computer.
EMG3415-B10A User’s Guide
42
Page 43

Chapter 3 Tutorials
1 Click Security > MAC Filter to open the MAC Filter screen. Select the Enable check box to activate MAC
filter function.
2 Select Allow. Then enter the host name and MAC address of Thomas’ computer in this screen. Click
Apply.
Thomas can also grant access to the computers of other members of his family and friends. However,
Josephine and others not listed in this screen will no longer be able to access the Internet through the
EMG.
EMG3415-B10A User’s Guide
43
Page 44

PART II
Technical Reference
44
Page 45

Network Map and Status
4.1 Overview
After you log into the Web Configurator, the Network Map screen appears. This shows the network
connection status of the EMG and clients connected to it.
You can use the Status screen to look at the current status of the EMG, system resources, and interfaces
(LAN, WAN, and WLAN).
4.2 The Network Map Screen
CHAPTER 4
Screens
Use this screen to view the network connection status of the device and its clients. A warning message
appears if there is a connection problem.
Figure 10 Connection Status: Icon View
EMG3415-B10A User’s Guide
45
Page 46

Chapter 4 Network Map and Status Screens
If you want to view information about a client, click the client’s name and Info. Click the IP address if
you want to change it. If you want to change the name or icon of the client, click Change name/icon.
If you prefer to view the status in a list, click List View in the Viewing mode selection box. You can
configure how often you want the EMG to update this screen in Refresh interval.
Figure 11 Connection Status: List View
4.3 The Status Screen
Use this screen to view the status of the EMG. Click Status to open this screen.
EMG3415-B10A User’s Guide
46
Page 47

Chapter 4 Network Map and Status Screens
Figure 12 System Info Screen
Each field is described in the following table.
Table 6 Status Screen
LABEL DESCRIPTION
Refresh Interval Select how often you want the EMG to update this screen.
Device Information
Host Name This field displays the EMG system name. It is used for identification.
Model Number This shows the model number of your EMG.
Serial Number This field displays the serial number of the EMG.
Firmware
Version
WAN Information (These fields display when you have a WAN connection.)
Encapsulation This field displays the current encapsulation method.
IP Address This field displays the current IP address of the EMG in the WAN.
IP Subnet Mask This field displays the current subnet mask in the WAN.
MAC Address This shows the WAN Ethernet adapter MAC (Media Access Control) Address of your EMG.
Primary DNS
server
Secondary DNS
server
This is the current version of the firmware inside the EMG.
This field displays the first DNS server address assigned by the ISP.
This field displays the second DNS server address assigned by the ISP.
EMG3415-B10A User’s Guide
47
Page 48

Chapter 4 Network Map and Status Screens
Table 6 Status Screen (continued)
LABEL DESCRIPTION
DHCP This field displays whether the WAN interface is using a DHCP IP address or a static IP address.
Choices are:
Client - The WAN interface can obtain an IP address from a DHCP server.
None - The WAN interface is using a static IP address.
LAN Information
IP Address This is the current IP address of the EMG in the LAN.
IP Subnet Mask This is the current subnet mask in the LAN.
IPv6 Link Local
Address
DHCP This field displays what DHCP services the EMG is providing to the LAN. The possible values
MAC Address This shows the LAN Ethernet adapter MAC (Media Access Control) Address of your EMG.
WLAN 2.4GHz/5GHz Information
MAC Address This shows the wireless adapter MAC (Media Access Control) Address of the wireless
Status This displays whether the WLAN is activated.
SSID This is the descriptive name used to identify the EMG in a wireless LAN.
Channel This is the channel number used by the wireless interface now.
Security This displays the type of security mode the wireless interface is using in the wireless LAN.
802.11 Mode This displays the type of 802.11 mode the wireless interface is using in the wireless LAN.
WPS This displays whether WPS is activated on the wireless interface.
Security
Firewall This displays the firewall’s current security level.
System Status
System Up Time This field displays how long the EMG has been running since it last started up. The EMG starts
Current Date/
Time
System Resource
CPU Usage This field displays what percentage of the EMG’s processing ability is currently used. When
Memory Usage This field displays what percentage of the EMG’s memory is currently used. Usually, this
NAT Session
Usage
Interface Status
This field displays the current link-local address of the EMG for the LAN interface.
are:
Server - The EMG is a DHCP server in the LAN. It assigns IP addresses to other computers in the
LAN.
Relay - The EMG acts as a surrogate DHCP server and relays DHCP requests and responses
between the remote server and the clients.
Disable - The EMG is not providing any DHCP services to the LAN.
interface.
up when you plug it in, when you restart it (Maintenance > Reboot), or when you reset it.
This field displays the current date and time in the EMG. You can change this in
Maintenance> Time Setting.
this percentage is close to 100%, the EMG is running at full load, and the throughput is not
going to improve anymore. If you want some applications to have more throughput, you
should turn off other applications (for example, using QoS; see Chapter 9 on page 109).
percentage should not increase much. If memory usage does get close to 100%, the EMG is
probably becoming unstable, and you should restart the device. See Section 32.2 on page
205, or turn off the device (unplug the power) for a few seconds.
This field displays what percentage of the EMG supported NAT sessions are currently being
used. This field also displays the number of active NAT sessions and the maximum number of
NAT sessions the EMG can support.
EMG3415-B10A User’s Guide
48
Page 49

Chapter 4 Network Map and Status Screens
Table 6 Status Screen (continued)
LABEL DESCRIPTION
Interface This column displays each interface the EMG has.
Status This field indicates the interface’s use status.
For the LAN and Ethernet WAN interfaces, this field displays Up when using the interface and
NoLink when not using the interface.
For a WLAN interface, this field displays the enabled (Up) or disabled (Disable) state of the
interface.
Rate For the Ethernet WAN and LAN interfaces, this displays the port speed and duplex setting.
For the WLAN interface, it displays the maximum transmission rate or N/A with WLAN
disabled.
EMG3415-B10A User’s Guide
49
Page 50

5.1 Overview
This chapter discusses the EMG’s Broadband screens. Use these screens to configure your EMG for
Internet access.
A WAN (Wide Area Network) connection is an outside connection to another network or the Internet. It
connects your private networks, such as a LAN (Local Area Network) and other networks, so that a
computer in one location can communicate with computers in other locations.
Figure 13 LAN and WAN
CHAPTER 5
Broadband
5.1.1 What You Can Do in this Chapter
• Use the Broadband screen to view, remove or add a WAN interface. You can also configure the WAN
settings on the EMG for Internet access (Section 5.2 on page 53).
Table 7 WAN Setup Overview
LAYER-2
INTERFACE
CONNECTION MODE ENCAPSULATION CONNECTION SETTINGS
Ethernet Routing PPPoE PPP user name and password, WAN
INTERNET CONNECTION
IPoE WAN IPv4/IPv6 IP address, NAT, DNS
Bridge N/A VLAN
5.1.2 What You Need to Know
The following terms and concepts may help as you read this chapter.
IPv4/IPv6 IP address, routing feature,
DNS server, VLAN, and MTU
server and routing feature
EMG3415-B10A User’s Guide
50
Page 51

Chapter 5 Broadband
WAN IP Address
The WAN IP address is an IP address for the EMG, which makes it accessible from an outside network. It is
used by the EMG to communicate with other devices in other networks. It can be static (fixed) or
dynamically assigned by the ISP each time the EMG tries to access the Internet.
If your ISP assigns you a static WAN IP address, they should also assign you the subnet mask and DNS
server IP address(es).
IPv6 Introduction
IPv6 (Internet Protocol version 6), is designed to enhance IP address size and features. The increase in
IPv6 address size to 128 bits (from the 32-bit IPv4 address) allows up to 3.4 x 10
can use IPv4/IPv6 dual stack to connect to IPv4 and IPv6 networks, and supports IPv6 rapid deployment
(6RD).
38
IP addresses. The EMG
IPv6 Addressing
The 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons (:). This is an
example IPv6 address 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
IPv6 addresses can be abbreviated in two ways:
• Leading zeros in a block can be omitted. So
2001:0db8:1a2b:0015:0000:0000:1a2f:0000 can be written as
2001:db8:1a2b:15:0:0:1a2f:0.
• Any number of consecutive blocks of zeros can be replaced by a double colon. A double
colon can only appear once in an IPv6 address. So
2001:0db8:0000:0000:1a2f:0000:0000:0015 can be written as
2001:0db8::1a2f:0000:0000:0015, 2001:0db8:0000:0000:1a2f::0015,
2001:db8::1a2f:0:0:15 or 2001:db8:0:0:1a2f::15.
IPv6 Prefix and Prefix Length
Similar to an IPv4 subnet mask, IPv6 uses an address prefix to represent the network address. An IPv6
prefix length specifies how many most significant bits (start from the left) in the address compose the
network address. The prefix length is written as “/x” where x is a number. For example,
2001:db8:1a2b:15::1a2f:0/32
means that the first 32 bits (2001:db8) is the subnet prefix.
IPv6 Subnet Masking
Both an IPv6 address and IPv6 subnet mask compose of 128-bit binary digits, which are divided into
eight 16-bit blocks and written in hexadecimal notation. Hexadecimal uses four bits for each character
(1 ~ 10, A ~ F). Each block’s 16 bits are then represented by four hexadecimal characters. For example,
FFFF:FFFF:FFFF:FFFF:FC00:0000:0000:0000.
EMG3415-B10A User’s Guide
51
Page 52

Chapter 5 Broadband
IPv6 Rapid Deployment
Use IPv6 Rapid Deployment (6rd) when the local network uses IPv6 and the ISP has an IPv4 network.
When the EMG has an IPv4 WAN address and you set IPv4/IPv6 Mode to IPv4 Only, you can enable 6rd
to encapsulate IPv6 packets in IPv4 packets to cross the ISP’s IPv4 network.
The EMG generates a global IPv6 prefix from its IPv4 WAN address and tunnels IPv6 traffic to the ISP’s
Border Relay router (BR in the figure) to connect to the native IPv6 Internet. The local network can also
use IPv4 services. The EMG uses it’s configured IPv4 WAN IP to route IPv4 traffic to the IPv4 Internet.
Figure 14 IPv6 Rapid Deployment
Dual Stack Lite
Use Dual Stack Lite when local network computers use IPv4 and the ISP has an IPv6 network. When the
EMG has an IPv6 WAN address and you set IPv4/IPv6 Mode to IPv6 Only, you can enable Dual Stack Lite
to use IPv4 computers and services.
The EMG tunnels IPv4 packets inside IPv6 encapsulation packets to the ISP’s Address Family Transition
Router (AFTR in the graphic) to connect to the IPv4 Internet. The local network can also use IPv6 services.
The EMG uses it’s configured IPv6 WAN IP to route IPv6 traffic to the IPv6 Internet.
EMG3415-B10A User’s Guide
52
Page 53

Figure 15 Dual Stack Lite
Chapter 5 Broadband
5.1.3 Before You Begin
You need to know your Internet access settings such as encapsulation and WAN IP address. Get this
information from your ISP.
5.2 The Broadband Screen
Use this screen to change your EMG’s Internet access settings. Click Network Setting > Broadband from
the menu. The summary table shows you the configured WAN services (connections) on the EMG.
Figure 16 Network Setting > Broadband
The following table describes the labels in this screen.
Table 8 Network Setting > Broadband
LABEL DESCRIPTION
Add New WAN
Interface
# This is the index number of the entry.
Name This is the service name of the connection.
Type This shows whether it is an ATM, Ethernet or a PTM connection.
Mode This shows whether the connection is in routing or bridge mode.
Encapsulation This is the method of encapsulation used by this connection.
Click this button to create a new connection.
EMG3415-B10A User’s Guide
53
Page 54

Chapter 5 Broadband
Table 8 Network Setting > Broadband (continued)
LABEL DESCRIPTION
802.1p This indicates the 802.1p priority level assigned to traffic sent through this connection. This
displays N/A when there is no priority level assigned.
802.1q This indicates the VLAN ID number assigned to traffic sent through this connection. This displays
N/A when there is no VLAN ID number assigned.
IGMP Proxy This shows whether the EMG act as an IGMP proxy on this connection.
NAT This shows whether NAT is activated or not for this connection.
Default
Gateway
IPv6 This shows whether IPv6 is activated or not for this connection. IPv6 is not available when the
MLD Proxy This shows whether Multicast Listener Discovery (MLD) is activated or not for this connection. MLD
Modify Click the Edit icon to configure the WAN connection.
This shows whether the EMG use the WAN interface of this connection as the system default
gateway.
connection uses the bridging service.
is not available when the connection uses the bridging service.
Click the Delete icon to remove the WAN connection.
5.2.1 Add/Edit Internet Connection
Click Add New WAN Interfac e in the Broadband screen or the Edit icon next to an existing WAN interface
to configure a WAN connection. The screen varies depending on the interface type, mode,
encapsulation, and IPv6/IPv4 mode you select.
5.2.1.1 Routing Mode
Use Routing mode if your ISP give you one IP address only and you want multiple computers to share an
Internet account.
The following example screen displays when you select the Ethernet connection type, Routing mode,
and PPPoE encapsulation. The screen varies when you select other encapsulation and IPv4/IPv6 mode.
EMG3415-B10A User’s Guide
54
Page 55

Chapter 5 Broadband
Figure 17 Network Setting > Broadband > Add New WAN Interface/Edit (Routing Mode)
The following table describes the labels in this screen.
Table 9 Network Setting > Broadband > Add New WAN Interface/Edit (Routing Mode)
LABEL DESCRIPTION
General
Name Specify a descriptive name for this connection.
Type Select an Ethernet connection.
Mode Select Routing if your ISP give you one IP address only and you want multiple computers to share
Encapsulation Select the method of encapsulation used by your ISP from the drop-down list box. This option is
IPv4/IPv6 Mode Select IPv4 Only if you want the EMG to run IPv4 only.
an Internet account.
available only when you select Routing in the Mode field.
The choices are PPPoE and IPoE.
Select IPv4 IPv6 DualStack to allow the EMG to run IPv4 and IPv6 at the same time.
Select IPv6 Only if you want the EMG to run IPv6 only.
EMG3415-B10A User’s Guide
55
Page 56

Chapter 5 Broadband
Table 9 Network Setting > Broadband > Add New WAN Interface/Edit (Routing Mode) (continued)
LABEL DESCRIPTION
PPP Information (This is available only when you select PPPoE in the Mode field.)
PPP User Name Enter the user name exactly as your ISP assigned. If assigned a name in the form user@domain
where domain identifies a service name, then enter both components exactly as given.
PPP Password Enter the password associated with the user name above. Select password unmask to show your
entered password in plain text.
PPP Connection
Trigger
Idle Timeout This value specifies the time in minutes that elapses before the router automatically disconnects
PPPoE
Passthrough
Select when to have the EMG establish the PPP connection.
Auto Connect - select this to not let the connection time out.
On Demand - select this to automatically bring up the connection when the EMG receives
packets destined for the Internet.
from the PPPoE server.
This field is not available if you select On Demand in the PPP Connection Trigger field.
This field is available when you select PPPoE encapsulation.
In addition to the EMG’s built-in PPPoE client, you can enable PPPoE pass through to allow up to
ten hosts on the LAN to use PPPoE client software on their computers to connect to the ISP via
the EMG. Each host can have a separate account and a public WAN IP address.
PPPoE pass through is an alternative to NAT for application where NAT is not appropriate.
Disable PPPoE pass through if you do not need to allow hosts on the LAN to use PPPoE client
software on their computers to connect to the ISP.
IP Address (This is available only when you select IPv4 Only or IPv4 IPv6 DualStack in the IPv4/IPv6 Mode field.)
Obtain an IP
Address
Automatically
Static IP Address Select this option If the ISP assigned a fixed IP address
IP Address Enter the static IP address provided by your ISP.
Subnet Mask Enter the subnet mask provided by your ISP.
Gateway IP
Address
VLAN
Active Select this to enable VLAN on this WAN interface.
802.1p IEEE 802.1p defines up to 8 separate traffic types by inserting a tag into a MAC-layer frame that
802.1q Type the VLAN ID number (from 1 to 4094) for traffic through this connection.
MTU
MTU Enter the MTU (Maximum Transfer Unit) size for this traffic.
Routing Feature (This is available only when you select IPv4 Only or IPv4 IPv6 DualStack in the IPv4/IPv6 Mode field.)
NAT Enable Select this option to activate NAT on this connection.
Fullcone NAT
Enable
A static IP address is a fixed IP that your ISP gives you. A dynamic IP address is not fixed; the ISP
assigns you a different one each time you connect to the Internet. Select this if you have a
dynamic IP address.
Enter the gateway IP address provided by your ISP.
contains bits to define class of service.
Select the IEEE 802.1p priority level (from 0 to 7) to add to traffic through this connection. The
greater the number, the higher the priority level.
Select this option to enable full cone NAT on this connection. This field is available only when you
activate NAT. In full cone NAT, the EMG maps all outgoing packets from an internal IP address
and port to a single IP address and port on the external network. The EMG also maps packets
coming to that external IP address and port to the internal IP address and port.
EMG3415-B10A User’s Guide
56
Page 57

Chapter 5 Broadband
Table 9 Network Setting > Broadband > Add New WAN Interface/Edit (Routing Mode) (continued)
LABEL DESCRIPTION
IGMP Proxy
Enable
Apply as Default
Gateway
DNS Server (This is available only when you select IPv4 Only or IPv4 IPv6 DualStack in the IPv4/IPv6 Mode field.)
Primary DNS
Server
Secondary DNS
Server
Tunnel
The DS-Lite (Dual Stack Lite) fields display when you set the IPv4/IPv6 Mode field to IPv6 Only.
Enable Dual Stack Lite to let local computers use IPv4 through an ISP’s IPv6 network. See Dual Stack Lite on page 52
for more information.
Enable DS-Lite This is available only when you select IPv6 Only in the IPv4/IPv6 Mode field. Select Enable to let
DS-Lite Relay
Server IP
6RD
Internet Group Multicast Protocol (IGMP) is a network-layer protocol used to establish
membership in a Multicast group - it is not used to carry user data.
Select this option to have the EMG act as an IGMP proxy on this connection. This allows the EMG
to get subscribing information and maintain a joined member list for each multicast group. It can
reduce multicast traffic significantly.
Select this option to have the EMG use the WAN interface of this connection as the system
default gateway.
Select Obtain DNS Info Automically if you want the EMG to use the DNS server addresses
assigned by your ISP.
Select Use Following Static DNS Address if you want the EMG to use the DNS server addresses you
configure manually.
Enter the first DNS server address assigned by the ISP.
Enter the second DNS server address assigned by the ISP.
local computers use IPv4 through an ISP’s IPv6 network.
Specify the transition router’s IPv6 address.
The 6RD (IPv6 rapid deployment) fields display when you set the IPv6/IPv4 Mode field to IPv4 Only. See IPv6 Rapid
Deployment on page 52 for more information.
6RD Select Enable to tunnel IPv6 traffic from the local network through the ISP’s IPv4 network.
Select Manually Configured if you have the IPv4 address of the relay server. Otherwise, select
Automatically configured by DHCPC to have the EMG detect it automatically through DHCP.
The Automatically configured by DHCPC option is configurable only when you set the method of
encapsulation to IPoE.
Service Provider
IPv6 Prefix
IPv4 Mask
Length
Border Relay
IPv4 Address
DHCPC Options (This is available only when you select IPv4 Only or IPv4 IPv6 DualStack in the IPv4/IPv6 Mode field.)
Request Options Select Option 43 to have the EMG automatically add vendor specific information in the DHCP
Sent Options
option 60 Select this and enter the device identity you want the EMG to add in the DHCP discovery
Vendor ID Enter the Vendor Class Identifier, such as the type of the hardware or firmware.
Enter an IPv6 prefix for tunneling IPv6 traffic to the ISP’s border relay router and connecting to the
native IPv6 Internet.
Enter the subnet mask number (1~32) for the IPv4 network.
When you select Manually Configured, specify the relay server’s IPv4 address in this field.
packets to request the vendor specific options from the DHCP server.
Select Option 121 to have the EMG push static routes to clients.
packets that go to the DHCP server.
EMG3415-B10A User’s Guide
57
Page 58

Chapter 5 Broadband
Table 9 Network Setting > Broadband > Add New WAN Interface/Edit (Routing Mode) (continued)
LABEL DESCRIPTION
option 61 Select this and enter any string that identifies the device.
IAID Enter the Identity Association Identifier (IAID) of the device, for example, the WAN connection
index number.
DUID Enter the hardware type, a time value and the MAC address of the device.
option 125 Select this to have the EMG automatically generate and add vendor specific parameters in the
DHCP discovery packets that go to the DHCP server.
IPv6 Address (This is available only when you select IPv4 IPv6 DualStack or IPv6 Only in the IPv4/IPv6 Mode field.)
Obtain an IPv6
Address
Automatically
Static IPv6
Address
IPv6 Address Enter an IPv6 IP address that your ISP gave to you for this WAN interface.
Prefix Length Enter the address prefix length to specify how many most significant bits in an IPv6 address
IPv6 Default
Gateway
IPv6 Routing Feature (This is available only when you select IPv4 IPv6 DualStack or IPv6 Only in the IPv4/IPv6 Mode
field. You can enable IPv6 routing features in the following section.)
MLD Proxy
Enable
Apply as Default
Gateway
IPv6 DNS Server
This is available only when you select IPv4 IPv6 DualStack or IPv6 Only in the IPv4/IPv6 Mode field. Configure the
IPv6 DNS server in the following section.
Obtain IPv6 DNS
Info
Automatically
Use Following
Static IPv6 DNS
Address
Primary DNS
Server
Secondary DNS
Server
Apply Click Apply to save your changes back to the EMG.
Cancel Click Cancel to exit this screen without saving.
Select Obtain an IPv6 Address Automatically if you want to have the EMG use the IPv6 prefix
from the connected router’s Router Advertisement (RA) to generate an IPv6 address.
Select Static IPv6 Address if you have a fixed IPv6 address assigned by your ISP. When you select
this, the following fields appear.
compose the network address.
Enter the IP address of the next-hop gateway. The gateway is a router or switch on the same
segment as your EMG's interface(s). The gateway helps forward packets to their destinations.
Select this checkbox to have the EMG act as an MLD proxy on this connection. This allows the
EMG to get subscription information and maintain a joined member list for each multicast group.
It can reduce multicast traffic significantly.
Select this option to have the EMG use the WAN interface of this connection as the system
default gateway.
Select Obtain IPv6 DNS Info Automatically to have the EMG get the IPv6 DNS server addresses
from the ISP automatically.
Select Use Following Static IPv6 DNS Address to have the EMG use the IPv6 DNS server addresses
you configure manually.
Enter the first IPv6 DNS server address assigned by the ISP.
Enter the second IPv6 DNS server address assigned by the ISP.
5.2.1.2 Bridge Mode
Click the Add new WAN Interface in the Network Setting > Broadband screen or the Edit icon next to the
connection you want to configure. Select Bridge as the encapsulation mode. The screen varies
depending on the interface type you select.
If you select Ethernet as the interface type, the following screen appears.
EMG3415-B10A User’s Guide
58
Page 59

Chapter 5 Broadband
Figure 18 Network Setting > Broadband > Add New WAN Interface/Edit (Ethernet-Bridge Mode)
The following table describes the fields in this screen.
Table 10 Network Setting > Broadband > Add New WAN Interface/Edit (Ethernet-Bridge)
LABEL DESCRIPTION
General
Name Enter a service name of the connection.
Type Select Ethernet as the interface that you want to configure.
Mode Select Bridge when your ISP provides you more than one IP address and you want the connected
computers to get individual IP address from ISP’s DHCP server directly. If you select Bridge, you
cannot use routing functions, such as QoS, Firewall, DHCP server and NAT on traffic from the
selected LAN port(s).
VLAN This section is available only when you select ADSL/VDSL over PTM in the Type field.
Active Select Enable to enable VLAN on this WAN interface.
802.1p IEEE 802.1p defines up to 8 separate traffic types by inserting a tag into a MAC-layer frame that
contains bits to define class of service.
Select the IEEE 802.1p priority level (from 0 to 7) to add to traffic through this connection. The greater
the number, the higher the priority level.
802.1q Type the VLAN ID number (from 0 to 4094) for traffic through this connection.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving.
5.3 Technical Reference
The following section contains additional technical information about the EMG features described in this
chapter.
EMG3415-B10A User’s Guide
59
Page 60

Chapter 5 Broadband
Encapsulation
Be sure to use the encapsulation method required by your ISP. The EMG can work in bridge mode or
routing mode. When the EMG is in routing mode, it supports the following methods.
IP over Ethernet
IP over Ethernet (IPoE) is an alternative to PPPoE. IP packets are being delivered across an Ethernet
network, without using PPP encapsulation. They are routed between the Ethernet interface and the
WAN interface and then formatted so that they can be understood in a bridged environment. For
instance, it encapsulates routed Ethernet frames into bridged Ethernet cells.
PPP over Ethernet (PPPoE)
Point-to-Point Protocol over Ethernet (PPPoE) provides access control and billing functionality in a
manner similar to dial-up services using PPP. PPPoE is an IETF standard (RFC 2516) specifying how a
personal computer (PC) interacts with a broadband modem (DSL, cable, wireless, etc.) connection.
For the service provider, PPPoE offers an access and authentication method that works with existing
access control systems (for example RADIUS).
One of the benefits of PPPoE is the ability to let you access one of multiple network services, a function
known as dynamic service selection. This enables the service provider to easily create and offer new IP
services for individuals.
Operationally, PPPoE saves significant effort for both you and the ISP or carrier, as it requires no specific
configuration of the broadband modem at the customer site.
By implementing PPPoE directly on the EMG (rather than individual computers), the computers on the
LAN do not need PPPoE software installed, since the EMG does that part of the task. Furthermore, with
NAT, all of the LANs’ computers will have access.
Multiplexing
There are two conventions to identify what protocols the virtual circuit (VC) is carrying. Be sure to use the
multiplexing method required by your ISP.
VC-based Multiplexing
In this case, by prior mutual agreement, each protocol is assigned to a specific virtual circuit; for
example, VC1 carries IP, etc. VC-based multiplexing may be dominant in environments where dynamic
creation of large numbers of ATM VCs is fast and economical.
LLC-based Multiplexing
In this case one VC carries multiple protocols with protocol identifying information being contained in
each packet header. Despite the extra bandwidth and processing overhead, this method may be
advantageous if it is not practical to have a separate VC for each carried protocol, for example, if
charging heavily depends on the number of simultaneous VCs.
EMG3415-B10A User’s Guide
60
Page 61

Chapter 5 Broadband
Traffic Shaping
Traffic Shaping is an agreement between the carrier and the subscriber to regulate the average rate
and fluctuations of data transmission over an ATM network. This agreement helps eliminate congestion,
which is important for transmission of real time data such as audio and video connections.
Peak Cell Rate (PCR) is the maximum rate at which the sender can send cells. This parameter may be
lower (but not higher) than the maximum line speed. 1 ATM cell is 53 bytes (424 bits), so a maximum
speed of 832Kbps gives a maximum PCR of 1962 cells/sec. This rate is not guaranteed because it is
dependent on the line speed.
Sustained Cell Rate (SCR) is the mean cell rate of each bursty traffic source. It specifies the maximum
average rate at which cells can be sent over the virtual connection. SCR may not be greater than the
PCR.
Maximum Burst Size (MBS) is the maximum number of cells that can be sent at the PCR. After MBS is
reached, cell rates fall below SCR until cell rate averages to the SCR again. At this time, more cells (up to
the MBS) can be sent at the PCR again.
If the PCR, SCR or MBS is set to the default of "0", the system will assign a maximum value that correlates
to your upstream line rate.
The following figure illustrates the relationship between PCR, SCR and MBS.
Figure 19 Example of Traffic Shaping
IP Address Assignment
A static IP is a fixed IP that your ISP gives you. A dynamic IP is not fixed; the ISP assigns you a different one
each time. The Single User Account feature can be enabled or disabled if you have either a dynamic or
static IP. However the encapsulation method assigned influences your choices for IP address and
default gateway.
Introduction to VLANs
A Virtual Local Area Network (VLAN) allows a physical network to be partitioned into multiple logical
networks. Devices on a logical network belong to one group. A device can belong to more than one
group. With VLAN, a device cannot directly talk to or hear from devices that are not in the same
group(s); the traffic must first go through a router.
EMG3415-B10A User’s Guide
61
Page 62

Chapter 5 Broadband
In Multi-Tenant Unit (MTU) applications, VLAN is vital in providing isolation and security among the
subscribers. When properly configured, VLAN prevents one subscriber from accessing the network
resources of another on the same LAN, thus a user will not see the printers and hard disks of another user
in the same building.
VLAN also increases network performance by limiting broadcasts to a smaller and more manageable
logical broadcast domain. In traditional switched environments, all broadcast packets go to each and
every individual port. With VLAN, all broadcasts are confined to a specific broadcast domain.
Introduction to IEEE 802.1Q Tagged VLAN
A tagged VLAN uses an explicit tag (VLAN ID) in the MAC header to identify the VLAN membership of a
frame across bridges - they are not confined to the switch on which they were created. The VLANs can
be created statically by hand or dynamically through GVRP. The VLAN ID associates a frame with a
specific VLAN and provides the information that switches need to process the frame across the network.
A tagged frame is four bytes longer than an untagged frame and contains two bytes of TPID (Tag
Protocol Identifier), residing within the type/length field of the Ethernet frame) and two bytes of TCI (Tag
Control Information), starts after the source address field of the Ethernet frame).
The CFI (Canonical Format Indicator) is a single-bit flag, always set to zero for Ethernet switches. If a
frame received at an Ethernet port has a CFI set to 1, then that frame should not be forwarded as it is to
an untagged port. The remaining twelve bits define the VLAN ID, giving a possible maximum number of
4,096 VLANs. Note that user priority and VLAN ID are independent of each other. A frame with VID
(VLAN Identifier) of null (0) is called a priority frame, meaning that only the priority level is significant and
the default VID of the ingress port is given as the VID of the frame. Of the 4096 possible VIDs, a VID of 0 is
used to identify priority frames and value 4095 (FFF) is reserved, so the maximum possible VLAN
configurations are 4,094.
TPID
2 Bytes
User Priority
3 Bits
CFI
1 Bit
VLAN ID
12 Bits
Multicast
IP packets are transmitted in either one of two ways - Unicast (1 sender - 1 recipient) or Broadcast (1
sender - everybody on the network). Multicast delivers IP packets to a group of hosts on the network not everybody and not just 1.
Internet Group Multicast Protocol (IGMP) is a network-layer protocol used to establish membership in a
Multicast group - it is not used to carry user data. IGMP version 2 (RFC 2236) is an improvement over
version 1 (RFC 1112) but IGMP version 1 is still in wide use. If you would like to read more detailed
information about interoperability between IGMP version 2 and version 1, please see sections 4 and 5 of
RFC 2236. The class D IP address is used to identify host groups and can be in the range 224.0.0.0 to
239.255.255.255. The address 224.0.0.0 is not assigned to any group and is used by IP multicast
computers. The address 224.0.0.1 is used for query messages and is assigned to the permanent group of
all IP hosts (including gateways). All hosts must join the 224.0.0.1 group in order to participate in IGMP.
The address 224.0.0.2 is assigned to the multicast routers group.
At start up, the EMG queries all directly connected networks to gather group membership. After that,
the EMG periodically updates this information.
EMG3415-B10A User’s Guide
62
Page 63

Chapter 5 Broadband
DNS Server Address Assignment
Use Domain Name System (DNS) to map a domain name to its corresponding IP address and vice versa,
for instance, the IP address of www.zyxel.com is 204.217.0.2. The DNS server is extremely important
because without it, you must know the IP address of a computer before you can access it.
The EMG can get the DNS server addresses in the following ways.
1 The ISP tells you the DNS server addresses, usually in the form of an information sheet, when you sign up.
If your ISP gives you DNS server addresses, manually enter them in the DNS server fields.
2 If your ISP dynamically assigns the DNS server IP addresses (along with the EMG’s WAN IP address), set
the DNS server fields to get the DNS server address from the ISP.
IPv6 Addressing
The 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons (:). This is an
example IPv6 address 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
IPv6 addresses can be abbreviated in two ways:
• Leading zeros in a block can be omitted. So 2001:0db8:1a2b:0015:0000:0000:1a2f:0000 can be
written as 2001:db8:1a2b:15:0:0:1a2f:0.
• Any number of consecutive blocks of zeros can be replaced by a double colon. A double colon can
only appear once in an IPv6 address. So 2001:0db8:0000:0000:1a2f:0000:0000:0015 can be
written as 2001:0db8::1a2f:0000:0000:0015, 2001:0db8:0000:0000:1a2f::0015,
2001:db8::1a2f:0:0:15 or 2001:db8:0:0:1a2f::15.
IPv6 Prefix and Prefix Length
Similar to an IPv4 subnet mask, IPv6 uses an address prefix to represent the network address. An IPv6
prefix length specifies how many most significant bits (start from the left) in the address compose the
network address. The prefix length is written as “/x” where x is a number. For example,
2001:db8:1a2b:15::1a2f:0/32
means that the first 32 bits (2001:db8) is the subnet prefix.
EMG3415-B10A User’s Guide
63
Page 64

6.1 Overview
This chapter describes the EMG’s Network Setting > Wireless screens. Use these screens to set up your
EMG’s wireless connection.
6.1.1 What You Can Do in this Chapter
This section describes the EMG’s Wireless screens. Use these screens to set up your EMG’s wireless
connection.
• Use the General screen to enable the Wireless LAN, enter the SSID and select the wireless security
mode (Section 6.2 on page 65).
• Use the MAC Authentication screen to allow or deny wireless clients based on their MAC addresses
from connecting to the EMG (Section 6.3 on page 69).
• Use the WPS screen to enable or disable WPS, view or generate a security PIN (Personal Identification
Number) (Section 6.4 on page 70).
• Use the WMM screen to enable Wi-Fi MultiMedia (WMM) to ensure quality of service in wireless
networks for multimedia applications (Section 6.5 on page 72).
• Use the Others screen to configure wireless advanced features, such as the RTS/CTS Threshold
(Section 6.6 on page 73).
• Use the Channel Status screen to scan wireless LAN channel noises and view the results (Section 6.7 on
page 74).
CHAPTER 6
Wireless
6.1.2 What You Need to Know
Wireless Basics
“Wireless” is essentially radio communication. In the same way that walkie-talkie radios send and
receive information over the airwowaves, wireless networking devices exchange information with one
another. A wireless networking device is just like a radio that lets your computer exchange information
with radios attached to other computers. Like walkie-talkies, most wireless networking devices operate
at radio frequency bands that are open to the public and do not require a license to use. However,
wireless networking is different from that of most traditional radio communications in that there a
number of wireless networking standards available with different methods of data encryption.
Finding Out More
See Section 6.8 on page 75 for advanced technical information on wireless networks.
EMG3415-B10A User’s Guide
64
Page 65

6.2 The General Screen
Use this screen to enable the Wireless LAN, enter the SSID and select the wireless security mode.
Note: If you are configuring the EMG from a computer connected to the wireless LAN and
you change the EMG’s SSID, channel or security settings, you will lose your wireless
connection when you press Apply to confirm. You must then change the wireless
settings of your computer to match the EMG’s new settings.
Click Network Setting > Wireless to open the General screen.
Figure 20 Network Setting > Wireless > General
Chapter 6 Wireless
EMG3415-B10A User’s Guide
65
Page 66

Chapter 6 Wireless
The following table describes the general wireless LAN labels in this screen.
Table 11 Network Setting > Wireless > General
LABEL DESCRIPTION
Wireless Network Setup
Band This shows the wireless band which this radio profile is using. 2.4GHz is the frequency used by IEEE
Wireless You can Enable or Disable the wireless LAN in this field.
Channel Use Auto to have the EMG automatically determine a channel to use.
Bandwidth Select whether the EMG uses a wireless channel width of 20MHz, 40MHz or 80MHz.
Control
Sideband
Wireless Network Settings
Wireless
Network Name
(SSID)
Max Clients Specify the maximum number of clients that can connect to this network at the same time.
Hide SSID Select this check box to hide the SSID in the outgoing beacon frame so a station cannot obtain
Multicast
Forwarding
Max. Upstream
Bandwidth
Max.
Downstream
Bandwidth
BSSID This shows the MAC address of the wireless interface on the EMG when wireless LAN is enabled.
Security Level Select Basic (WEP) or More Secure (WPA(2)-PSK) to add security on this wireless network. The
802.11b/g/n wireless clients while 5GHz is used by IEEE 802.11a/ac wireless clients.
A standard 20MHz channel offers transfer speeds of up to 150Mbps whereas a 40MHz channel
uses two standard channels and offers speeds of up to 300 Mbps.
40MHz (channel bonding or dual channel) bonds two adjacent radio channels to increase
throughput. The wireless clients must also support 40 MHz. It is often better to use the 20 MHz
setting in a location where the environment hinders the wireless signal.
An 80MHz channel groups adjacent 40MHz channels into pairs to increase bandwidth even
higher.
Select 20MHz if you want to lessen radio interference with other wireless devices in your
neighborhood or the wireless clients do not support channel bonding.
This is available for some regions when you select a specific channel and set the Bandwidth field
to 40MHz. Set whether the control channel (set in the Channel field) should be in the Lower or
Upper range of channel bands.
The SSID (Service Set IDentity) identifies the service set with which a wireless device is associated.
Wireless devices associating to the access point (AP) must have the same SSID.
Enter a descriptive name (up to 32 English keyboard characters) for the wireless LAN.
the SSID through scanning using a site survey tool.
Select this check box to allow the EMG to convert wireless multicast traffic into wireless unicast
traffic.
Specify the maximum rate for upstream wireless traffic to the WAN from this WLAN in kilobits per
second (Kbps).
Specify the maximum rate for downstream wireless traffic to this WLAN from the WAN in kilobits
per second (Kbps).
wireless clients which want to associate to this network must have same wireless security settings
as the EMG. When you select to use a security, additional options appears in this screen.
Or you can select No Security to allow any client to associate this network without any data
encryption or authentication.
See the following sections for more details about this field.
Apply Click Apply to save your changes.
Cancel Click Cancel to restore your previously saved settings.
EMG3415-B10A User’s Guide
66
Page 67

6.2.1 No Security
Select No Security to allow wireless stations to communicate with the access points without any data
encryption or authentication.
Note: If you do not enable any wireless security on your EMG, your network is accessible to
any wireless networking device that is within range.
Figure 21 Wireless > General: No Security
The following table describes the labels in this screen.
Table 12 Wireless > General: No Security
LABEL DESCRIPTION
Security Level Choose No Security to allow all wireless connections without data encryption or authentication.
Chapter 6 Wireless
6.2.2 Basic (WEP Encryption)
WEP encryption scrambles the data transmitted between the wireless stations and the access points
(AP) to keep network communications private. Both the wireless stations and the access points must use
the same WEP key.
Note: WEP is extremely insecure. Its encryption can be broken by an attacker, using widely-
available software. It is strongly recommended that you use a more effective security
mechanism. Use the strongest security mechanism that all the wireless devices in your
network support. For example, use WPA-PSK or WPA2-PSK if all your wireless devices
support it, or use WPA or WPA2 if your wireless devices support it and you have a RADIUS
server. If your wireless devices support nothing stronger than WEP, use the highest
encryption level available.
Your EMG allows you to configure up to four 64-bit or 128-bit WEP keys but only one key can be enabled
at any one time.
Note: WEP is not available when you set the wireless band to 5GHz.
In order to configure and enable WEP encryption, click Network Setting > Wireless to display the General
screen, then select Basic as the security level.
EMG3415-B10A User’s Guide
67
Page 68

Chapter 6 Wireless
Figure 22 Wireless > General: Basic (WEP)
The following table describes the labels in this screen.
Table 13 Wireless > General: Basic (WEP)
LABEL DESCRIPTION
Security Level Select Basic to enable WEP data encryption.
Security Mode This shows WEP when you set Security Level to Basic.
Generate
password
automatically
Password 1~4 The password (WEP keys) are used to encrypt data. Both the EMG and the wireless stations must
more.../hide Click more... to show more fields in this section. Click hide to hide them.
WEP Encryption Select 64-bit or 128-bit.
Select this option to have the EMG automatically generate a password. The password field will
not be configurable when you select this option.
use the same password (WEP key) for data transmission.
If you chose 64-bit WEP, then enter any 5 ASCII characters or 10 hexadecimal characters ("0-9",
"A-F").
If you chose 128-bit WEP, then enter 13 ASCII characters or 26 hexadecimal characters ("0-9", "A-
F").
You must configure at least one password, only one password can be activated at any one
time.
Select password unmask to display the entered password in plain text. Clear it to hide the
password to avoid shoulder surfing.
This dictates the length of the security key that the network is going to use.
6.2.3 More Secure (WPA(2)-PSK)
The WPA-PSK security mode provides both improved data encryption and user authentication over
WEP. Using a Pre-Shared Key (PSK), both the EMG and the connecting client share a common password
in order to validate the connection. This type of encryption, while robust, is not as strong as WPA, WPA2
or even WPA2-PSK. The WPA2-PSK security mode is a newer, more robust version of the WPA encryption
standard. It offers slightly better security, although the use of PSK makes it less robust than it could be.
Note: WPA-PSK is not available if you enable WPS before you configure them.
EMG3415-B10A User’s Guide
68
Page 69

Chapter 6 Wireless
Click Network Setting > Wireless to display the General screen. Select More Secure as the security level.
Then select WPA-PSK or WPA2-PSK from the Security Mode list.
Figure 23 Wireless > General: More Secure: WPA(2)-PSK
The following table describes the labels in this screen.
Table 14 Wireless > General: More Secure: WPA(2)-PSK
LABEL DESCRIPTION
Security Level Select More Secure to enable WPA(2)-PSK data encryption.
Security Mode Select WPA-PSK or WPA2-PSK from the drop-down list box.
Generate
password
automatically
Password The encryption mechanisms used for WPA(2) and WPA(2)-PSK are the same. The only difference
more.../hide Click more... to show more fields in this section. Click hide to hide them.
Encryption Select the encryption type (TKIP, AES or TKIP+AES) for data encryption.
Group Key
Update Timer
Select this option to have the EMG automatically generate a password. The password field will
not be configurable when you select this option.
between the two is that WPA(2)-PSK uses a simple common password, instead of user-specific
credentials.
If you did not select Generate password automatically, you can manually type a pre-shared key
from 8 to 64 case-sensitive keyboard characters. Select password unmask to display the entered
password in plain text. Clear it to hide the password to avoid shoulder surfing.
Select TKIP if your wireless clients can all use TKIP.
Select AES if your wireless clients can all use AES.
Select TKIP+AES to allow the wireless clients to use either TKIP or AES.
The Group Key Update Timer is the rate at which the RADIUS server sends a new group key out to
all clients.
6.3 MAC Authentication
This screen allows you to configure the Zyxel Device to give exclusive access to specific devices (Allow)
or exclude specific devices from accessing the Zyxel Device (Deny). Every Ethernet device has a unique
MAC (Media Access Control) address. The MAC address is assigned at the factory and consists of six
EMG3415-B10A User’s Guide
69
Page 70

Chapter 6 Wireless
pairs of hexadecimal characters, for example, 00:A0:C5:00:00:02. You need to know the MAC addresses
of the devices to configure this screen.
Use this screen to view your EMG’s MAC filter settings and add new MAC filter rules. Click Network
Setting > Wireless > MAC Authentication. The screen appears as shown.
Figure 24 Wireless > MAC Authentication
The following table describes the labels in this screen.
Table 15 Wireless > MAC Authentication
LABEL DESCRIPTION
SSID Select the SSID for which you want to configure MAC filter settings.
MAC Restrict
Mode
Add new MAC
address
# This is the index number of the entry.
MAC Address This is the MAC addresses of the wireless devices that are allowed or denied access to the EMG.
Modify Click the Edit icon and type the MAC address of the peer device in a valid MAC address format
Apply Click Apply to save your changes.
Cancel Click Cancel to exit this screen without saving.
Define the filter action for the list of MAC addresses in the MAC Address table.
Select Disable to turn off MAC filtering.
Select Deny to block access to the EMG. MAC addresses not listed will be allowed to access the
EMG.
Select Allow to permit access to the EMG. MAC addresses not listed will be denied access to the
EMG.
Click this if you want to add a new MAC address entry to the MAC filter list below.
Enter the MAC addresses of the wireless devices that are allowed or denied access to the EMG
in these address fields. Enter the MAC addresses in a valid MAC address format, that is, six
hexadecimal character pairs, for example, 12:34:56:78:9a:bc.
(six hexadecimal character pairs, for example 12:34:56:78:9a:bc).
Click the Delete icon to delete the entry.
6.4 The WPS Screen
Use this screen to configure WiFi Protected Setup (WPS) on your EMG.
EMG3415-B10A User’s Guide
70
Page 71

Chapter 6 Wireless
WPS allows you to quickly set up a wireless network with strong security, without having to configure
security settings manually. Set up each WPS connection between two devices. Both devices must
support WPS. See Section 6.8.7.3 on page 83 for more information about WPS.
Note: The EMG applies the security settings of the SSID1 profile (see Section 6.2 on page 65). If
you want to use the WPS feature, make sure you have set the security mode of SSID1 to
WPA2-PSK or No Security.
Click Network Setting > Wireless > WPS. The following screen displays. Select Enable and click Apply to
activate the WPS function. Then you can configure the WPS settings in this screen.
Figure 25 Network Setting > Wireless > WPS
The following table describes the labels in this screen.
Table 16 Network Setting > Wireless > WPS
LABEL DESCRIPTION
General
WPS Select Enable to activate WPS on this EMG.
Add a new device with WPS Method
Method 1 Use this section to set up a WPS wireless network using Push Button Configuration (PBC). Select
Enable and click Apply to activate WPS method 1 on the EMG.
WPS Click this button to add another WPS-enabled wireless device (within wireless range of the
EMG) to your wireless network. This button may either be a physical button on the outside of
device, or a menu button similar to the WPS button on this screen.
Note: You must press the other wireless device’s WPS button within two minutes of
pressing this button.
Method 2 Use this section to set up a WPS wireless network by entering the PIN of the client into the EMG.
Select Enable and click Apply to activate WPS method 2 on the EMG.
Register Enter the PIN of the device that you are setting up a WPS connection with and click Register to
authenticate and add the wireless device to your wireless network.
You can find the PIN either on the outside of the device, or by checking the device’s settings.
Note: You must also activate WPS on that device within two minutes to have it
present its PIN to the EMG.
EMG3415-B10A User’s Guide
71
Page 72

Table 16 Network Setting > Wireless > WPS (continued)
LABEL DESCRIPTION
Method 3 Use this section to set up a WPS wireless network by entering the PIN of the EMG into the client.
Select Enable and click Apply to activate WPS method 3 on the EMG.
Release
Configuration
Generate
New PIN
Number
Apply Click Apply to save your changes.
Cancel Click Cancel to restore your previously saved settings.
The default WPS status is configured.
Click this button to remove all configured wireless and wireless security settings for WPS
connections on the EMG.
If this method has been enabled, the PIN (Personal Identification Number) of the EMG is shown
here. Enter this PIN in the configuration utility of the device you want to connect to using WPS.
The PIN is not necessary when you use WPS push-button method.
Click the Generate New PIN button to have the EMG create a new PIN.
6.5 The WMM Screen
Use this screen to enable Wi-Fi MultiMedia (WMM) and WMM Power Save in wireless networks for
multimedia applications.
Chapter 6 Wireless
Click Network Setting > Wireless > WMM. The following screen displays.
Figure 26 Network Setting > Wireless > WMM
The following table describes the labels in this screen.
Table 17 Network Setting > Wireless > WMM
LABEL DESCRIPTION
2.4GHz WMM Setup / 5GHz WMM Setup
WMM of SSID1~4 Select On to have the EMG automatically give the wireless network (SSIDx) a priority level
according to the ToS value in the IP header of packets it sends. WMM QoS (Wifi MultiMedia
Quality of Service) gives high priority to voice and video, which makes them run more smoothly.
WMM
Automatic
Power Save
Delivery(APSD)
Select this option to extend the battery life of your mobile devices (especially useful for small
devices that are running multimedia applications). The EMG goes to sleep mode to save power
when it is not transmitting data. The AP buffers the packets sent to the EMG until the EMG "wakes
up". The EMG wakes up periodically to check for incoming data.
Note: This works only if the wireless device to which the EMG is connected also
supports this feature.
Apply Click Apply to save your changes.
Cancel Click Cancel to restore your previously saved settings.
EMG3415-B10A User’s Guide
72
Page 73

6.6 The Others Screen
Use this screen to configure advanced wireless settings. Click Network Setting > Wireless > Others. The
screen appears as shown.
See Section 6.8.2 on page 77 for detailed definitions of the terms listed in this screen.
Figure 27 Network Setting > Wireless > Others
The following table describes the labels in this screen.
Chapter 6 Wireless
Table 18 Network Setting > Wireless > Others
LABEL DESCRIPTION
RTS/CTS
Threshold
Fragmentation
Threshold
Output Power Set the output power of the EMG. If there is a high density of APs in an area, decrease the
Beacon Interval When a wirelessly networked device sends a beacon, it includes with it a beacon interval. This
DTIM Interval Delivery Traffic Indication Message (DTIM) is the time period after which broadcast and
802.11 Mode Select 802.11b Only to allow only IEEE 802.11b compliant WLAN devices to associate with the
Data with its frame size larger than this value will perform the RTS (Request To Send)/CTS (Clear
To Send) handshake.
Enter a value between 0 and 2347.
This is the maximum data fragment size that can be sent. Enter a value between 256 and 2346.
output power to reduce interference with other APs. Select one of the following: 20%, 40%,
60%, 80% or 100%.
specifies the time period before the device sends the beacon again.
The interval tells receiving devices on the network how long they can wait in low power mode
before waking up to handle the beacon. This value can be set from 50ms to 1000ms. A high
value helps save current consumption of the access point.
multicast packets are transmitted to mobile clients in the Power Saving mode. A high DTIM
value can cause clients to lose connectivity with the network. This value can be set from 1 to
255.
EMG.
Select 802.11g Only to allow only IEEE 802.11g compliant WLAN devices to associate with the
EMG.
Select 802.11n Only to allow only IEEE 802.11n compliant WLAN devices to associate with the
EMG.
Select 802.11b/g Mixed to allow either IEEE 802.11b or IEEE 802.11g compliant WLAN devices to
associate with the EMG. The transmission rate of your EMG might be reduced.
Select 802.11b/g/n Mixed to allow IEEE 802.11b, IEEE 802.11g or IEEE802.11n compliant WLAN
devices to associate with the EMG. The transmission rate of your EMG might be reduced.
EMG3415-B10A User’s Guide
73
Page 74

Chapter 6 Wireless
Table 18 Network Setting > Wireless > Others (continued)
LABEL DESCRIPTION
802.11 Protection Enabling this feature can help prevent collisions in mixed-mode networks (networks with both
IEEE 802.11b and IEEE 802.11g traffic).
Select Auto to have the wireless devices transmit data after a RTS/CTS handshake. This helps
improve IEEE 802.11g performance.
Select Off to disable 802.11 protection. The transmission rate of your EMG might be reduced in a
mixed-mode network.
This field displays Off and is not configurable when you set 802.11 Mode to 802.11b Only.
Preamble Select a preamble type from the drop-down list box. Choices are Long or Short. See Section
6.8.6 on page 80 for more information.
This field is configurable only when you set 802.11 Mode to 802.11b.
OBSS
Coexistence
Apply Click Apply to save your changes.
Cancel Click Cancel to restore your previously saved settings.
Select Enable to allow the coexistence of 20 MHz and 40 MHz Overlapping Basic Service Sets
(OBSS) in wireless local area networks. Select Disabled to disable this feature.
6.7 The Channel Status Screen
Use the Channel Status screen to scan wireless LAN channel noises and view the results. Click Network
Setting > Wireless > Channel Status. The screen appears as shown. Click Scan to scan the wireless LAN
channels. You can view the results in the Channel Scan Result section.
Note: The Scan button only works when the EMG uses 20MHz for the wireless channel width.
You can go to the
then change the channel width setting in the Bandwidth field.
Network Setting > Wireless > General screen, click the more link, and
EMG3415-B10A User’s Guide
74
Page 75

Chapter 6 Wireless
Figure 28 Network Setting > Wireless > Channel Status
6.8 Technical Reference
This section discusses wireless LANs in depth. For more information, see Appendix B on page 222.
6.8.1 Wireless Network Overview
Wireless networks consist of wireless clients, access points and bridges.
• A wireless client is a radio connected to a user’s computer.
• An access point is a radio with a wired connection to a network, which can connect with numerous
wireless clients and let them access the network.
• A bridge is a radio that relays communications between access points and wireless clients, extending
a network’s range.
Traditionally, a wireless network operates in one of two ways.
• An “infrastructure” type of network has one or more access points and one or more wireless clients.
The wireless clients connect to the access points.
• An “ad-hoc” type of network is one in which there is no access point. Wireless clients connect to one
another in order to exchange information.
EMG3415-B10A User’s Guide
75
Page 76

Chapter 6 Wireless
The following figure provides an example of a wireless network.
Figure 29 Example of a Wireless Network
The wireless network is the part in the blue circle. In this wireless network, devices A and B use the access
point (AP) to interact with the other devices (such as the printer) or with the Internet. Your EMG is the AP.
Every wireless network must follow these basic guidelines.
• Every device in the same wireless network must use the same SSID.
The SSID is the name of the wireless network. It stands for Service Set IDentifier.
• If two wireless networks overlap, they should use a different channel.
Like radio stations or television channels, each wireless network uses a specific channel, or frequency,
to send and receive information.
• Every device in the same wireless network must use security compatible with the AP.
Security stops unauthorized devices from using the wireless network. It can also protect the
information that is sent in the wireless network.
Radio Channels
In the radio spectrum, there are certain frequency bands allocated for unlicensed, civilian use. For the
purposes of wireless networking, these bands are divided into numerous channels. This allows a variety of
networks to exist in the same place without interfering with one another. When you create a network,
you must select a channel to use.
Since the available unlicensed spectrum varies from one country to another, the number of available
channels also varies.
EMG3415-B10A User’s Guide
76
Page 77

6.8.2 Additional Wireless Terms
The following table describes some wireless network terms and acronyms used in the EMG’s Web
Configurator.
Table 19 Additional Wireless Terms
TERM DESCRIPTION
RTS/CTS Threshold In a wireless network which covers a large area, wireless devices are sometimes not
aware of each other’s presence. This may cause them to send information to the AP at
the same time and result in information colliding and not getting through.
By setting this value lower than the default value, the wireless devices must sometimes get
permission to send information to the EMG. The lower the value, the more often the
devices must get permission.
If this value is greater than the fragmentation threshold value (see below), then wireless
devices never have to get permission to send information to the EMG.
Preamble A preamble affects the timing in your wireless network. There are two preamble modes:
long and short. If a device uses a different preamble mode than the EMG does, it cannot
communicate with the EMG.
Authentication The process of verifying whether a wireless device is allowed to use the wireless network.
Fragmentation
Threshold
A small fragmentation threshold is recommended for busy networks, while a larger
threshold provides faster performance if the network is not very busy.
Chapter 6 Wireless
6.8.3 Wireless Security Overview
By their nature, radio communications are simple to intercept. For wireless data networks, this means
that anyone within range of a wireless network without security can not only read the data passing over
the airwaves, but also join the network. Once an unauthorized person has access to the network, he or
she can steal information or introduce malware (malicious software) intended to compromise the
network. For these reasons, a variety of security systems have been developed to ensure that only
authorized people can use a wireless data network, or understand the data carried on it.
These security standards do two things. First, they authenticate. This means that only people presenting
the right credentials (often a username and password, or a “key” phrase) can access the network.
Second, they encrypt. This means that the information sent over the air is encoded. Only people with
the code key can understand the information, and only people who have been authenticated are
given the code key.
These security standards vary in effectiveness. Some can be broken, such as the old Wired Equivalent
Protocol (WEP). Using WEP is better than using no security at all, but it will not keep a determined
attacker out. Other security standards are secure in themselves but can be broken if a user does not use
them properly. For example, the WPA-PSK security standard is very secure if you use a long key which is
difficult for an attacker’s software to guess - for example, a twenty-letter long string of apparently
random numbers and letters - but it is not very secure if you use a short key which is very easy to guess for example, a three-letter word from the dictionary.
Because of the damage that can be done by a malicious attacker, it’s not just people who have
sensitive information on their network who should use security. Everybody who uses any wireless network
should ensure that effective security is in place.
A good way to come up with effective security keys, passwords and so on is to use obscure information
that you personally will easily remember, and to enter it in a way that appears random and does not
include real words. For example, if your mother owns a 1970 Dodge Challenger and her favorite movie is
EMG3415-B10A User’s Guide
77
Page 78

Vanishing Point (which you know was made in 1971) you could use “70dodchal71vanpoi” as your
security key.
The following sections introduce different types of wireless security you can set up in the wireless
network.
6.8.3.1 SSID
Normally, the EMG acts like a beacon and regularly broadcasts the SSID in the area. You can hide the
SSID instead, in which case the EMG does not broadcast the SSID. In addition, you should change the
default SSID to something that is difficult to guess.
This type of security is fairly weak, however, because there are ways for unauthorized wireless devices to
get the SSID. In addition, unauthorized wireless devices can still see the information that is sent in the
wireless network.
6.8.3.2 MAC Address Filter
Chapter 6 Wireless
Every device that can use a wireless network has a unique identification number, called a MAC
address.
00A0C5000002 or 00:A0:C5:00:00:02. To get the MAC address for each device in the wireless network,
see the device’s User’s Guide or other documentation.
You can use the MAC address filter to tell the EMG which devices are allowed or not allowed to use the
wireless network. If a device is allowed to use the wireless network, it still has to have the correct
information (SSID, channel, and security). If a device is not allowed to use the wireless network, it does
not matter if it has the correct information.
This type of security does not protect the information that is sent in the wireless network. Furthermore,
there are ways for unauthorized wireless devices to get the MAC address of an authorized device. Then,
they can use that MAC address to use the wireless network.
1
A MAC address is usually written using twelve hexadecimal characters2; for example,
6.8.3.3 User Authentication
Authentication is the process of verifying whether a wireless device is allowed to use the wireless
network. You can make every user log in to the wireless network before using it. However, every device
in the wireless network has to support IEEE 802.1x to do this.
For wireless networks, you can store the user names and passwords for each user in a RADIUS server. This
is a server used in businesses more than in homes. If you do not have a RADIUS server, you cannot set up
user names and passwords for your users.
Unauthorized wireless devices can still see the information that is sent in the wireless network, even if they
cannot use the wireless network. Furthermore, there are ways for unauthorized wireless users to get a
valid user name and password. Then, they can use that user name and password to use the wireless
network.
1. Some wireless devices, such as scanners, can detect wireless networks but cannot use wireless networks. These
kinds of wireless devices might not have MAC addresses.
2. Hexadecimal characters are 0, 1, 2, 3, 4, 5, 6, 7, 8, 9, A, B, C, D, E, and F.
EMG3415-B10A User’s Guide
78
Page 79

6.8.3.4 Encryption
Wireless networks can use encryption to protect the information that is sent in the wireless network.
Encryption is like a secret code. If you do not know the secret code, you cannot understand the
message.
The types of encryption you can choose depend on the type of authentication. (See Section 6.8.3.3 on
page 78 for information about this.)
Table 20 Types of Encryption for Each Type of Authentication
Weakest No Security WPA
Strongest WPA2-PSK WPA2
For example, if the wireless network has a RADIUS server, you can choose WPA or WPA2. If users do not
log in to the wireless network, you can choose no encryption, Static WEP, WPA-PSK, or WPA2-PSK.
Chapter 6 Wireless
NO AUTHENTICATION RADIUS SERVER
Static WEP
WPA-PSK
Usually, you should set up the strongest encryption that every device in the wireless network supports. For
example, suppose you have a wireless network with the EMG and you do not have a RADIUS server.
Therefore, there is no authentication. Suppose the wireless network has two devices. Device A only
supports WEP, and device B supports WEP and WPA. Therefore, you should set up Static WEP in the
wireless network.
Note: It is recommended that wireless networks use WPA-PSK, WPA, or stronger encryption.
The other types of encryption are better than none at all, but it is still possible for
unauthorized wireless devices to figure out the original information pretty quickly.
When you select WPA2 or WPA2-PSK in your EMG, you can also select an option (WPA compatible) to
support WPA as well. In this case, if some of the devices support WPA and some support WPA2, you
should set up WPA2-PSK or WPA2 (depending on the type of wireless network login) and select the WPA
compatible option in the EMG.
Many types of encryption use a key to protect the information in the wireless network. The longer the
key, the stronger the encryption. Every device in the wireless network must have the same key.
6.8.4 Signal Problems
Because wireless networks are radio networks, their signals are subject to limitations of distance,
interference and absorption.
Problems with distance occur when the two radios are too far apart. Problems with interference occur
when other radio waves interrupt the data signal. Interference may come from other radio
transmissions, such as military or air traffic control communications, or from machines that are
coincidental emitters such as electric motors or microwaves. Problems with absorption occur when
physical objects (such as thick walls) are between the two radios, muffling the signal.
EMG3415-B10A User’s Guide
79
Page 80

6.8.5 BSS
Chapter 6 Wireless
A Basic Service Set (BSS) exists when all communications between wireless stations or between a wireless
station and a wired network client go through one access point (AP).
Intra-BSS traffic is traffic between wireless stations in the BSS. When Intra-BSS traffic blocking is disabled,
wireless station A and B can access the wired network and communicate with each other. When IntraBSS traffic blocking is enabled, wireless station A and B can still access the wired network but cannot
communicate with each other.
Figure 30 Basic Service set
6.8.6 Preamble Type
Preamble is used to signal that data is coming to the receiver. Short and long refer to the length of the
synchronization field in a packet.
Short preamble increases performance as less time sending preamble means more time for sending
data. All IEEE 802.11 compliant wireless adapters support long preamble, but not all support short
preamble.
Use long preamble if you are unsure what preamble mode other wireless devices on the network
support, and to provide more reliable communications in busy wireless networks.
Use short preamble if you are sure all wireless devices on the network support it, and to provide more
efficient communications.
Use the dynamic setting to automatically use short preamble when all wireless devices on the network
support it, otherwise the EMG uses long preamble.
EMG3415-B10A User’s Guide
80
Page 81

Chapter 6 Wireless
Note: The wireless devices MUST use the same preamble mode in order to communicate.
6.8.7 WiFi Protected Setup (WPS)
Your EMG supports WiFi Protected Setup (WPS), which is an easy way to set up a secure wireless network.
WPS is an industry standard specification, defined by the WiFi Alliance.
WPS allows you to quickly set up a wireless network with strong security, without having to configure
security settings manually. Each WPS connection works between two devices. Both devices must
support WPS (check each device’s documentation to make sure).
Depending on the devices you have, you can either press a button (on the device itself, or in its
configuration utility) or enter a PIN (a unique Personal Identification Number that allows one device to
authenticate the other) in each of the two devices. When WPS is activated on a device, it has two
minutes to find another device that also has WPS activated. Then, the two devices connect and set up
a secure network by themselves.
6.8.7.1 Push Button Configuration
WPS Push Button Configuration (PBC) is initiated by pressing a button on each WPS-enabled device, and
allowing them to connect automatically. You do not need to enter any information.
Not every WPS-enabled device has a physical WPS button. Some may have a WPS PBC button in their
configuration utilities instead of or in addition to the physical button.
Take the following steps to set up WPS using the button.
1 Ensure that the two devices you want to set up are within wireless range of one another.
2 Look for a WPS button on each device. If the device does not have one, log into its configuration utility
and locate the button (see the device’s User’s Guide for how to do this - for the EMG, see Section 6.5 on
page 72).
3 Press the button on one of the devices (it doesn’t matter which). For the EMG you must press the WPS
button for more than five seconds.
4 Within two minutes, press the button on the other device. The registrar sends the network name (SSID)
and security key through an secure connection to the enrollee.
If you need to make sure that WPS worked, check the list of associated wireless clients in the AP’s
configuration utility. If you see the wireless client in the list, WPS was successful.
6.8.7.2 PIN Configuration
Each WPS-enabled device has its own PIN (Personal Identification Number). This may either be static (it
cannot be changed) or dynamic (in some devices you can generate a new PIN by clicking on a button
in the configuration interface).
Use the PIN method instead of the push-button configuration (PBC) method if you want to ensure that
the connection is established between the devices you specify, not just the first two devices to activate
WPS in range of each other. However, you need to log into the configuration interfaces of both devices
to use the PIN method.
EMG3415-B10A User’s Guide
81
Page 82

Chapter 6 Wireless
When you use the PIN method, you must enter the PIN from one device (usually the wireless client) into
the second device (usually the Access Point or wireless router). Then, when WPS is activated on the first
device, it presents its PIN to the second device. If the PIN matches, one device sends the network and
security information to the other, allowing it to join the network.
Take the following steps to set up a WPS connection between an access point or wireless router
(referred to here as the AP) and a client device using the PIN method.
1 Ensure WPS is enabled on both devices.
2 Access the WPS section of the AP’s configuration interface. See the device’s User’s Guide for how to do
this.
3 Look for the client’s WPS PIN; it will be displayed either on the device, or in the WPS section of the client’s
configuration interface (see the device’s User’s Guide for how to find the WPS PIN - for the EMG, see
Section 6.4 on page 70).
4 Enter the client’s PIN in the AP’s configuration interface.
5 If the client device’s configuration interface has an area for entering another device’s PIN, you can
either enter the client’s PIN in the AP, or enter the AP’s PIN in the client - it does not matter which.
6 Start WPS on both devices within two minutes.
7 Use the configuration utility to activate WPS, not the push-button on the device itself.
8 On a computer connected to the wireless client, try to connect to the Internet. If you can connect, WPS
was successful.
If you cannot connect, check the list of associated wireless clients in the AP’s configuration utility. If you
see the wireless client in the list, WPS was successful.
The following figure shows a WPS-enabled wireless client (installed in a notebook computer) connecting
to the WPS-enabled AP via the PIN method.
EMG3415-B10A User’s Guide
82
Page 83

Chapter 6 Wireless
Figure 31 Example WPS Process: PIN Method
6.8.7.3 How WPS Works
When two WPS-enabled devices connect, each device must assume a specific role. One device acts
as the registrar (the device that supplies network and security settings) and the other device acts as the
enrollee (the device that receives network and security settings. The registrar creates a secure EAP
(Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the WPA-PSK or
WPA2-PSK pre-shared key to the enrollee. Whether WPA-PSK or WPA2-PSK is used depends on the
standards supported by the devices. If the registrar is already part of a network, it sends the existing
information. If not, it generates the SSID and WPA(2)-PSK randomly.
The following figure shows a WPS-enabled client (installed in a notebook computer) connecting to a
WPS-enabled access point.
EMG3415-B10A User’s Guide
83
Page 84

Figure 32 How WPS works
Chapter 6 Wireless
The roles of registrar and enrollee last only as long as the WPS setup process is active (two minutes). The
next time you use WPS, a different device can be the registrar if necessary.
The WPS connection process is like a handshake; only two devices participate in each WPS transaction.
If you want to add more devices you should repeat the process with one of the existing networked
devices and the new device.
Note that the access point (AP) is not always the registrar, and the wireless client is not always the
enrollee. All WPS-certified APs can be a registrar, and so can some WPS-enabled wireless clients.
By default, a WPS devices is “unconfigured”. This means that it is not part of an existing network and can
act as either enrollee or registrar (if it supports both functions). If the registrar is unconfigured, the security
settings it transmits to the enrollee are randomly-generated. Once a WPS-enabled device has
connected to another device using WPS, it becomes “configured”. A configured wireless client can still
act as enrollee or registrar in subsequent WPS connections, but a configured access point can no longer
act as enrollee. It will be the registrar in all subsequent WPS connections in which it is involved. If you
want a configured AP to act as an enrollee, you must reset it to its factory defaults.
6.8.7.4 Example WPS Network Setup
This section shows how security settings are distributed in an example WPS setup.
The following figure shows an example network. In step 1, both AP1 and Client 1 are unconfigured.
When WPS is activated on both, they perform the handshake. In this example, AP1 is the registrar, and
Client 1 is the enrollee. The registrar randomly generates the security information to set up the network,
since it is unconfigured and has no existing information.
EMG3415-B10A User’s Guide
84
Page 85

Chapter 6 Wireless
Figure 33 WPS: Example Network Step 1
In step 2, you add another wireless client to the network. You know that Client 1 supports registrar mode,
but it is better to use AP1 for the WPS handshake with the new client since you must connect to the
access point anyway in order to use the network. In this case, AP1 must be the registrar, since it is
configured (it already has security information for the network). AP1 supplies the existing security
information to Client 2.
Figure 34 WPS: Example Network Step 2
In step 3, you add another access point (AP2) to your network. AP2 is out of range of AP1, so you cannot
use AP1 for the WPS handshake with the new access point. However, you know that Client 2 supports
the registrar function, so you use it to perform the WPS handshake instead.
EMG3415-B10A User’s Guide
85
Page 86

Chapter 6 Wireless
Figure 35 WPS: Example Network Step 3
6.8.7.5 Limitations of WPS
WPS has some limitations of which you should be aware.
• WPS works in Infrastructure networks only (where an AP and a wireless client communicate). It does
not work in Ad-Hoc networks (where there is no AP).
• When you use WPS, it works between two devices only. You cannot enroll multiple devices
simultaneously, you must enroll one after the other.
For instance, if you have two enrollees and one registrar you must set up the first enrollee (by pressing
the WPS button on the registrar and the first enrollee, for example), then check that it successfully
enrolled, then set up the second device in the same way.
• WPS works only with other WPS-enabled devices. However, you can still add non-WPS devices to a
network you already set up using WPS.
WPS works by automatically issuing a randomly-generated WPA-PSK or WPA2-PSK pre-shared key
from the registrar device to the enrollee devices. Whether the network uses WPA-PSK or WPA2-PSK
depends on the device. You can check the configuration interface of the registrar device to discover
the key the network is using (if the device supports this feature). Then, you can enter the key into the
non-WPS device and join the network as normal (the non-WPS device must also support WPA-PSK or
WPA2-PSK).
• When you use the PBC method, there is a short period (from the moment you press the button on one
device to the moment you press the button on the other device) when any WPS-enabled device
could join the network. This is because the registrar has no way of identifying the “correct” enrollee,
and cannot differentiate between your enrollee and a rogue device. This is a possible way for a
hacker to gain access to a network.
You can easily check to see if this has happened. WPS works between only two devices
simultaneously, so if another device has enrolled your device will be unable to enroll, and will not
have access to the network. If this happens, open the access point’s configuration interface and look
at the list of associated clients (usually displayed by MAC address). It does not matter if the access
EMG3415-B10A User’s Guide
86
Page 87

Chapter 6 Wireless
point is the WPS registrar, the enrollee, or was not involved in the WPS handshake; a rogue device
must still associate with the access point to gain access to the network. Check the MAC addresses of
your wireless clients (usually printed on a label on the bottom of the device). If there is an unknown
MAC address you can remove it or reset the AP.
EMG3415-B10A User’s Guide
87
Page 88

7.1 Overview
A Local Area Network (LAN) is a shared communication system to which many networking devices are
connected. It is usually located in one immediate area such as a building or floor of a building.
Use the LAN screens to help you configure a LAN DHCP server and manage IP addresses.
CHAPTER 7
Home Networking
7.1.1 What You Can Do in this Chapter
• Use the LAN Setup screen to set the LAN IP address, subnet mask, and DHCP settings of your EMG
(Section 7.2 on page 90).
• Use the Static DHCP screen to assign IP addresses on the LAN to specific individual computers based
on their MAC Addresses (Section 7.3 on page 94).
• Use the UPnP screen to enable UPnP and UPnP NAT traversal on the EMG (Section 7.4 on page 95).
• Use the Additional Subnet screen to configure IP alias and public static IP (Section 7.5 on page 98).
• Use the STB Vendor ID screen to configure the Vendor IDs of the connected Set Top Box (STB) devices,
which have the EMG automatically create static DHCP entries for the STB devices when they request
IP addresses (Section 7.6 on page 99).
• Use the Wake on LAN screen to remotely turn on a device on the network. (Section 7.7 on page 99).
• Use the TFTP Server Name screen to set a TFTP server address which is passed to the clients using DHCP
option 66. (Section 7.8 on page 100).
EMG3415-B10A User’s Guide
88
Page 89

Chapter 7 Home Networking
7.1.2 What You Need To Know
7.1.2.1 About LAN
IP Address
IP addresses identify individual devices on a network. Every networking device (including computers,
servers, routers, printers, etc.) needs an IP address to communicate across the network. These
networking devices are also known as hosts.
Subnet Mask
Subnet masks determine the maximum number of possible hosts on a network. You can also use subnet
masks to divide one network into multiple sub-networks.
DHCP
A DHCP (Dynamic Host Configuration Protocol) server can assign your EMG an IP address, subnet mask,
DNS and other routing information when it's turned on.
DNS
DNS (Domain Name System) is for mapping a domain name to its corresponding IP address and vice
versa. The DNS server is extremely important because without it, you must know the IP address of a
networking device before you can access it.
RADVD (Router Advertisement Daemon)
When an IPv6 host sends a Router Solicitation (RS) request to discover the available routers, RADVD with
Router Advertisement (RA) messages in response to the request. It specifies the minimum and maximum
intervals of RA broadcasts. RA messages containing the address prefix. IPv6 hosts can be generated
with the IPv6 prefix an IPv6 address.
7.1.2.2 About UPnP
Identifying UPnP Devices
UPnP hardware is identified as an icon in the Network Connections folder (Windows XP). Each UPnP
compatible device installed on your network will appear as a separate icon. Selecting the icon of a
UPnP device will allow you to access the information and properties of that device.
NAT Traversal
UPnP NAT traversal automates the process of allowing an application to operate through NAT. UPnP
network devices can automatically configure network addressing, announce their presence in the
network to other UPnP devices and enable exchange of simple product and service descriptions. NAT
traversal allows the following:
• Dynamic port mapping
• Learning public IP addresses
EMG3415-B10A User’s Guide
89
Page 90

Chapter 7 Home Networking
• Assigning lease times to mappings
Windows Messenger is an example of an application that supports NAT traversal and UPnP.
See the Chapter 10 on page 127 for more information on NAT.
Cautions with UPnP
The automated nature of NAT traversal applications in establishing their own services and opening
firewall ports may present network security issues. Network information and configuration may also be
obtained and modified by users in some network environments.
When a UPnP device joins a network, it announces its presence with a multicast message. For security
reasons, the EMG allows multicast messages on the LAN only.
All UPnP-enabled devices may communicate freely with each other without additional configuration.
Disable UPnP if this is not your intention.
UPnP and Zyxel
Zyxel has achieved UPnP certification from the Universal Plug and Play Forum UPnP™ Implementers
Corp. (UIC). Zyxel's UPnP implementation supports Internet Gateway Device (IGD) 1.0.
See Section 7.4.1 on page 96 for examples of installing and using UPnP.
Finding Out More
See Section 7.9 on page 100 for technical background information on LANs.
7.1.3 Before You Begin
Find out the MAC addresses of your network devices if you intend to add them to the DHCP Client List
screen.
7.2 The LAN Setup Screen
Use this screen to set the Local Area Network IP address and subnet mask of your EMG. Click Network
Setting > Home Networking to open the LAN Setup screen.
Follow these steps to configure your LAN settings.
1 Enter an IP address into the IP Address field. The IP address must be in dotted decimal notation. This will
become the IP address of your EMG.
2 Enter the IP subnet mask into the Subnet Mask field. Unless instructed otherwise it is best to leave this
alone, the configurator will automatically compute a subnet mask based upon the IP address you
entered.
EMG3415-B10A User’s Guide
90
Page 91

Chapter 7 Home Networking
3 Click Apply to save your settings.
Figure 36 Network Setting > Home Networking > LAN Setup
EMG3415-B10A User’s Guide
91
Page 92

Chapter 7 Home Networking
The following table describes the fields in this screen.
Table 21 Network Setting > Home Networking > LAN Setup
LABEL DESCRIPTION
Interface Group
Group Name Select the interface group name for which you want to configure LAN settings. See Chapter 13
LAN IP Setup
IP Address Enter the LAN IPv4 address you want to assign to your EMG in dotted decimal notation, for
Subnet Mask Type the subnet mask of your network in dotted decimal notation, for example 255.255.255.0
IGMP Snooping
Active Select Enable to allows the EMG to passively learn multicast group.
IGMP Mode Select Standard Mode to allow the EMG to forward traffic only to ports that want to receive it.
DHCP Server State
DHCP Select Enable to have the EMG act as a DHCP server or DHCP relay agent.
on page 149 for how to create a new interface group.
example, 192.168.200.1 (factory default).
(factory default). Your EMG automatically computes the subnet mask based on the IP Address
you enter, so do not change this field unless you are instructed to do so.
Select Blocking Mode to allow the EMG to block unknown muticast adresses.
Select Disable to stop the DHCP server on the EMG.
Select DHCP Relay to have the EMG forward DHCP request to the DHCP server.
DHCP Relay
Server Address
IP Address Enter the IPv4 address of the actual remote DHCP server in this field.
IP Addressing
Values
Beginning IP
Address
Ending IP
Address
Auto reserve IP
for the same
host
DHCP Server
Lease Time
Days/Hours/
Minutes
DNS Values This field is only available when you select Enable in the DHCP field.
DNS Select From ISP if your ISP dynamically assigns DNS server information.
This field is only available when you select DHCP Relay in the DHCP field.
This field is only available when you select Enable in the DHCP field.
This field specifies the first of the contiguous addresses in the IP address pool.
This field specifies the last of the contiguous addresses in the IP address pool.
Select Enable to have the EMG record DHCP IP addresses with the MAC addresses the IP
addresses are assigned to. The EMG assigns the same IP address to the same MAC address
when the host requests an IP address again through DHCP.
This is the period of time DHCP-assigned addresses is used. DHCP automatically assigns IP
addresses to clients when they log in. DHCP centralizes IP address management on central
computers that run the DHCP server program. DHCP leases addresses, for a period of time,
which means that past addresses are “recycled” and made available for future reassignment to
other systems.
This field is only available when you select Enable in the DHCP field.
Enter the lease time of the DHCP server.
Select DNS Proxy if you have the DNS proxy service. The EMG redirects clients’ DNS queries to a
DNS server for resolving domain names.
Select Static if you have the IP address of a DNS server.
DNS Server 1/2 This field is only available when you select Static in the DNS field. Enter the first and second DNS
(Domain Name System) server IP addresses the EMG passes to the DHCP clients.
EMG3415-B10A User’s Guide
92
Page 93

Chapter 7 Home Networking
Table 21 Network Setting > Home Networking > LAN Setup (continued)
LABEL DESCRIPTION
LAN IPv6 Mode Setup
IPv6 Active
Link Local Address Type
EUI64
Manual
Lan Global Identifier Type
EUI64
Manual
LAN IPv6 Prefix Setup
Delegate prefix
from WAN
Static
MLD Snooping Multicast Listener Discovery (MLD) allows an IPv6 switch or router to discover the presence of
Active
MLD Mode
LAN IPv6
Address Assign
Setup
LAN IPv6 DNS
Assign Setup
DHCPv6 Configuration
DHCPv6 Active
IPv6 Router Advertisement State
RADVD Active
IPv6 DNS Values
IPv6 DNS Server
1-3
Select Enable to activate the IPv6 mode and configure IPv6 settings on the EMG.
Select this to have the EMG generate an interface ID for the LAN interface’s link-local address
using the EUI-64 format.
Select this to manually enter an interface ID for the LAN interface’s link-local address.
Select this to have the EMG generate an interface ID using the EUI-64 format for its global
address .
Select this to manually enter an interface ID for the LAN interface’s global IPv6 address.
Select this option to automatically obtain an IPv6 network prefix from the service provider or an
uplink router.
Select this option to configure a fixed IPv6 address for the EMG’s LAN IPv6 address.
MLD hosts who wish to receive multicast packets and the IP addresses of multicast groups the
hosts want to join on its network.
Select Enable to activate MLD Snooping on the EMG. This allows the EMG to check MLD packets
passing through it and learn the multicast group membership. It helps reduce multicast traffic.
Select Standard Mode to allow the EMG to forward MLD packets only to ports that want to
receive it.
Select MLD Mode to allow the EMG to block MLD packets for a specific multicast group.
Select how you want to obtain an IPv6 address:
• Stateless: The EMG uses IPv6 stateless autoconfiguration. RADVD (Router Advertisement
Daemon) is enabled to have the EMG send IPv6 prefix information in router advertisements
periodically and in response to router solicitations. DHCPv6 server is disabled.
• Stateful: The EMG uses IPv6 stateful autoconfiguration. The DHCPv6 server is enabled to have
the EMG act as a DHCPv6 server and pass IPv6 addresses to DHCPv6 clients.
Select how the EMG provide DNS server and domain name information to the clients:
• From Router Advertisement: The EMG provides DNS information through router
advertisements.
• From DHCPv6 Server: The EMG provides DNS information through DHCPv6.
• From RA & DHCPv6 Server: The EMG provides DNS information through both router
advertisements and DHCPv6.
This shows the status of the DHCPv6. DHCPv6 Server displays if you configured the EMG to act as
a DHCPv6 server which assigns IPv6 addresses and/or DNS information to clients.
This shows whether RADVD is enabled or not.
Select From ISP if your ISP dynamically assigns IPv6 DNS server information.
Select User-Defined if you have the IPv6 address of a DNS server. Enter the DNS server IPv6
addresses the EMG passes to the DHCP clients.
Select None if you do not want to configure IPv6 DNS servers.
EMG3415-B10A User’s Guide
93
Page 94

Chapter 7 Home Networking
Table 21 Network Setting > Home Networking > LAN Setup (continued)
LABEL DESCRIPTION
DNS Query
Scenario
Apply
Cancel Click Cancel to restore your previously saved settings.
Select how the EMG handles clients’ DNS information requests.
• IPv4/IPv6 DNS Server: The EMG forwards the requests to both the IPv4 and IPv6 DNS servers
and sends clients the first DNS information it receives.
• IPv6 DNS Server Only: The EMG forwards the requests to the IPv6 DNS server and sends clients
the DNS information it receives.
• IPv4 DNS Server Only: The EMG forwards the requests to the IPv4 DNS server and sends clients
the DNS information it receives.
• IPv6 DNS Server First: The EMG forwards the requests to the IPv6 DNS server first and then the
IPv4 DNS server. Then it sends clients the first DNS information it receives.
• IPv4 DNS Server First: The EMG forwards the requests to the IPv4 DNS server first and then the
IPv6 DNS server. Then it sends clients the first DNS information it receives.
Click Apply to save your changes.
7.3 The Static DHCP Screen
This table allows you to assign IP addresses on the LAN to specific individual computers based on their
MAC Addresses.
Every Ethernet device has a unique MAC (Media Access Control) address. The MAC address is assigned
at the factory and consists of six pairs of hexadecimal characters, for example, 00:A0:C5:00:00:02.
Use this screen to change your EMG’s static DHCP settings. Click Network Setting > Home Networking >
Static DHCP to open the following screen.
Figure 37 Network Setting > Home Networking > Static DHCP
The following table describes the labels in this screen.
Table 22 Network Setting > Home Networking > Static DHCP
LABEL DESCRIPTION
Static DHCP
Configuration
# This is the index number of the entry.
Status This field displays whether the client is connected to the EMG.
MAC Address The MAC (Media Access Control) or Ethernet address on a LAN (Local Area Network) is
IP Address This field displays the IP address relative to the # field listed above.
Modify Click the Edit icon to have the IP address field editable and change it.
Click this to add a new static DHCP entry.
unique to your computer (six pairs of hexadecimal notation).
A network interface card such as an Ethernet adapter has a hardwired address that is
assigned at the factory. This address follows an industry standard that ensures no other
adapter has a similar address.
Click the Delete icon to delete a static DHCP entry. A window displays asking you to confirm
that you want to delete the selected entry.
EMG3415-B10A User’s Guide
94
Page 95

Chapter 7 Home Networking
If you click Static DHCP Configuration in the Static DHCP screen or the Edit icon next to a static DHCP
entry, the following screen displays.
Figure 38 Static DHCP: Static DHCP Configuration/Edit
The following table describes the labels in this screen.
Table 23 Static DHCP: Static DHCP Configuration/Edit
LABEL DESCRIPTION
Active Select Enable to activate the connection between the client and the EMG.
Group Name Select the interface group name for which you want to configure static DHCP settings. See
Chapter 13 on page 149 for how to create a new interface group.
IP Type This field displays IPv4 for the type of the DHCP IP address. At the time of writing, it is not
allowed to select other type.
Select Device Info Select a device or computer from the drop-down list or select Manual Input to manually enter
MAC Address If you select Manual Input, enter the MAC address of a computer on your LAN.
IP Address If you select Manual Input, enter the IP address that you want to assign to the computer on
OK
Cancel Click Cancel to exit this screen without saving.
a device’s MAC address and IP address in the following fields.
your LAN with the MAC address that you will also specify.
Click OK to save your changes.
7.4 The UPnP Screen
Universal Plug and Play (UPnP) is a distributed, open networking standard that uses TCP/IP for simple
peer-to-peer network connectivity between devices. A UPnP device can dynamically join a network,
obtain an IP address, convey its capabilities and learn about other devices on the network. In turn, a
device can leave a network smoothly and automatically when it is no longer in use.
See page 89 for more information on UPnP.
EMG3415-B10A User’s Guide
95
Page 96

Chapter 7 Home Networking
Use the following screen to configure the UPnP settings on your EMG. Click Network Setting > Home
Networking > UPnP to display the screen shown next.
Figure 39 Network Setting > Home Networking > UPnP
The following table describes the labels in this screen.
Table 24 Network Setting > Home Networking > UPnP
LABEL DESCRIPTION
UPnP State
UPnP Select Enable to activate UPnP. Be aware that anyone could use a UPnP application to open
UPnP NAT-T State
UPnP NAT-T Select Enable to allow UPnP-enabled applications to automatically configure the EMG so that
# This is the index number of the UPnP NAT-T connection.
Description This is the description of the UPnP NAT-T connection.
Destination IP
Address
External Port This is the external port number that identifies the service.
Internal Port This is the internal port number that identifies the service.
Protocol This is the transport layer protocol used for the service.
Apply Click Apply to save your changes.
Cancel
the web configurator's login screen without entering the EMG's IP address.
they can communicate through the EMG by using NAT traversal. UPnP applications
automatically reserve a NAT forwarding port in order to communicate with another UPnP
enabled device; this eliminates the need to manually configure port forwarding for the UPnP
enabled application.
The table below displays the NAT port forwarding rules added automatically by UPnP NAT-T.
This is the IP address of the other connected UPnP-enabled device.
Click Cancel to exit this screen without saving.
7.4.1 Turning On UPnP in Windows 7 Example
This section shows you how to use the UPnP feature in Windows 7. UPnP server is installed in Windows 7.
Activate UPnP on the EMG.
Make sure the computer is connected to a LAN port of the EMG. Turn on your computer and the EMG.
1 Click the start icon, Control Panel and then the Network and Sharing Center.
EMG3415-B10A User’s Guide
96
Page 97

Chapter 7 Home Networking
2 Click Change Advanced Sharing Settings.
3 Select Turn on network discovery and click Save Changes. Network discovery allows your computer to
find other computers and devices on the network and other computers on the network to find your
computer. This makes it easier to share files and printers.
EMG3415-B10A User’s Guide
97
Page 98

Chapter 7 Home Networking
7.5 The Additional Subnet Screen
Use the Additional Subnet screen to configure IP alias and public static IP.
IP alias allows you to partition a physical network into different logical networks over the same Ethernet
interface. The EMG supports multiple logical LAN interfaces via its physical Ethernet interface with the
EMG itself as the gateway for the LAN network. When you use IP alias, you can also configure firewall
rules to control access to the LAN's logical network (subnet).
If your ISP provides the Public LAN service, the EMG may use an LAN IP address that can be accessed
from the WAN.
Click Network Setting > Home Networking > Additional Subnet to display the screen shown next.
Figure 40 Network Setting > Home Networking > Additional Subnet
The following table describes the labels in this screen.
Table 25 Network Setting > Home Networking > Additional Subnet
LABEL DESCRIPTION
IP Alias Setup
Group Name Select the interface group name for which you want to configure the IP alias settings. See
Chapter 13 on page 149 for how to create a new interface group.
Active Select Enable to configure a LAN network for the EMG.
IPv4 Address Enter the IP address of your EMG in dotted decimal notation.
Subnet Mask Enter the subnet mask of your network in dotted decimal notation, for example 255.255.255.0
(factory default).
Public LAN
Active Select Enable to enable the Public LAN feature. Your ISP must support Public LAN and Static IP.
IPv4 Address Enter the public IP address provided by your ISP.
Subnet Mask Enter the public IPv4 subnet mask provided by your ISP.
Offer Public IP
by DHCP
Enable ARP
Proxy
Select Enable to enable the EMG to provide public IP addresses by DHCP server.
Select Enable to enable the ARP (Address Resolution Protocol) proxy.
EMG3415-B10A User’s Guide
98
Page 99

Chapter 7 Home Networking
Table 25 Network Setting > Home Networking > Additional Subnet (continued)
LABEL DESCRIPTION
Apply Click Apply to save your changes.
Cancel
Click Cancel to exit this screen without saving.
7.6 The STB Vendor ID Screen
Set Top Box (STB) devices with dynamic IP addresses sometimes don’t renew their IP addresses before
the lease time expires. This could lead to IP address conflicts if the STB continues to use an IP address that
gets assigned to another device. Use this screen to configure the Vendor IDs of connected STBs, which
have the EMG automatically created static DHCP entries for them when they request IP addresses.
Click Network Setting > Home Networking > STB Vendor ID to open this screen.
Figure 41 Network Setting > Home Networking > STB Vendor ID
The following table describes the labels in this screen.
Table 26 Network Setting > Home Networking > STB Vendor ID
LABEL DESCRIPTION
Vendor ID 1~5 These are STB’s Vendor Class Identifiers (DHCP option 60). A Vendor Class Identifier is usually
Apply Click Apply to save your changes.
Cancel
used to inform the DHCP server a DHCP client’s vendor and functionality.
Click Cancel to exit this screen without saving.
7.7 The Wake on LAN Screen
Use this screen to turn on a device on the LAN network. To use this feature, the remote device must also
support Wake On LAN.
You need to know the MAC address of the LAN device. It may be on a label on the device or in its
documentation.
Click Network Setting > Home Networking > Wake on LAN to open this screen.
Figure 42 Network Setting > Home Networking > Wake on LAN
EMG3415-B10A User’s Guide
99
Page 100

Chapter 7 Home Networking
The following table describes the labels in this screen.
Table 27 Network Setting > Home Networking > Wake on LAN
LABEL DESCRIPTION
Wake by
Address
IP Address Enter the IPv4 IP address of the device to turn it on.
MAC Address Enter the MAC address of the device to turn it on. A MAC address consists of six hexadecimal
Wake up Click this to send a wake up packet to wake up the specified device.
Select Manual and enter the IP address or MAC address of the device to turn it on remotely. The
drop-down list also lists the IP addresses that can be found in the EMG’s ARP table. Select an IP
address and it will then automatically update the IP address and MAC address in the following
fields.
character pairs.
7.8 The TFTP Server Name Screen
Use the TFTP Server Name screen to set the TFTP server address which is passed to the clients using DHCP
option 66. The DHCP clients in the EMG local network, such as STB devices that support the TFTP booting
mechanism, can then use the TFTP server address or domain name for initial system settings download.
RFC 2132 defines the option 66 open standard. DHCP option 66 carries the IP address or the domain
name of a single TFTP server.
Click Network Setting > Home Networking > TFTP Server Name to open this screen.
Figure 43 Network Setting > Home Networking > TFTP Server Name
The following table describes the labels in this screen.
Table 28 Network Setting > Home Networking > TFTP Server Name
LABEL DESCRIPTION
TFTP Server
Name
Apply Click Apply to save your changes.
Cancel Click Cancel to exit this screen without saving.
Enter the IP address or the domain name of a single TFTP server.
7.9 Technical Reference
This section provides some technical background information about the topics covered in this chapter.
7.9.1 LANs, WANs and the EMG
The actual physical connection determines whether the EMG ports are LAN or WAN ports. There are two
separate IP networks, one inside the LAN network and the other outside the WAN network as shown
next.
EMG3415-B10A User’s Guide
100
 Loading...
Loading...