Page 1

Configuration Guide
T1500-28TC (TL-SL2428)/T1500-28PCT(TL-SL2428P)
1910012115 REV2.0.0
March 2017
Page 2
FCC STATEMENT
This equipment has been tested and found to comply with the limits for a Class A digital
device, pursuant to part 15 of the FCC Rules. These limits are designed to provide
reasonable protection against harmful interference when the equipment is operated in a
commercial environment. This equipment generates, uses, and can radiate radio frequency
energy and, if not installed and used in accordance with the instruction manual, may cause
harmful interference to radio communications. Operation of this equipment in a residential
area is likely to cause harmful interference in which case the user will be required to correct
the interference at his own expense.
This device complies with part 15 of the FCC Rules. Operation is subject to the following
two conditions:
1) This device may not cause harmful interference.
2) This device must accept any interference received, including interference that may
cause undesired operation.
Any changes or modifications not expressly approved by the party responsible for
compliance could void the user’s authority to operate the equipment.
CE Mark Warning
This is a class A product. In a domestic environment, this product may cause radio
interference, in which case the user may be required to take adequate measures.
Canadian Compliance Statement
This device complies with Industry Canada license-exempt RSSs. Operation is subject to
the following two conditions:
1) This device may not cause interference, and
2) This device must accept any interference, including interference that may cause
undesired operation of the device.
Le présent appareil est conforme aux CNR d’Industrie Canada applicables aux appareils
radio exempts de licence. L’exploitation est autorisée aux deux conditions suivantes :
1) l’appareil ne doit pas produire de brouillage;
2) l’utilisateur de l’appareil doit accepter tout brouillage radioélectrique subi, meme si le
brouillage est susceptible d’en compromettre le fonctionnement.
Page 3

Industry Canada Statement
CAN ICES-3 (A)/NMB-3(A)
NCC Notice
注意!
依據 低功率電波輻射性電機管理辦法
第十二條 經型式認證合格之低功率射頻電機,非經許可,公司、商號或使用者均不得擅自變
更頻率、加大功率或變更原設計之特性或功能。
第十四條 低功率射頻電機之使用不得影響飛航安全及干擾合法通行;經發現有干擾現象時,
應立即停用,並改善至無干擾時方得繼續使用。前項合法通信,指依電信規定作業之無線電信。
低功率射頻電機需忍受合法通信或工業、科學以及醫療用電波輻射性電機設備之干擾。
BSMI Notice
安全諮詢及注意事項
•請使用原裝電源供應器或只能按照本產品注明的電源類型使用本產品。
•清潔本產品之前請先拔掉電源線。請勿使用液體、噴霧清潔劑或濕布進行清潔。
•注意防潮,請勿將水或其他液體潑灑到本產品上。
•插槽與開口供通風使用,以確保本產品的操作可靠並防止過熱,請勿堵塞或覆蓋開口。
•請勿將本產品置放於靠近熱源的地方。除非有正常的通風,否則不可放在密閉位置中。
•請不要私自打開機殼,不要嘗試自行維修本產品,請由授權的專業人士進行此項工作。
此為甲類資訊技術設備,于居住環境中使用時,可能會造成射頻擾動,在此種情況下,使用者
會被要求採取某些適當的對策。
Продукт сертифіковано згідно с правилами системи УкрСЕПРО на відповідність
вимогам нормативних документів та вимогам, що передбачені чинними законодавчими
актами України.
Page 4
この装置は、クラス A 情報技術装置です。この装置を家庭環境で使用すると電波妨害を引き
起こすことがあります。この場合には使用者が適切な対策を講ずるよう要求されることがあ
ります。 VCCI-A
Safety Information
When product has power button, the power button is one of the way to shut off the
product; When there is no power button, the only way to completely shut off power is to
disconnect the product or the power adapter from the power source.
Don’t disassemble the product, or make repairs yourself. You run the risk of electric
shock and voiding the limited warranty. If you ne ed service, please contact us.
Avoid water and wet locations.
Explanation of the symbols on the product label
Symbol Explanation
AC voltage.
Indoor use only
RECYCLING
This product bears the selective sorting symbol for Waste electrical and
electronic equipment (WEEE). This means that this product must be handled
pursuant to European directive 2012/19/EU in order to be recycled or
dismantled to minimize its impact on the environment.
User has the choice to give his product to a competent recycling
organization or to the retailer when he buys a new electrical or electronic
equipment.
Page 5

CONTENTS
About This Guide
Intended Readers ................................................................................................................................................................1
Conventions ...........................................................................................................................................................................1
More Information .................................................................................................................................................................2
Accessing the Switch
Overview ................................................................................................................................................................................4
Web Interface Access ........................................................................................................................................................5
Login 5
Save Config Function ..............................................................................................................................................................................6
Disable the Web Server .........................................................................................................................................................................7
Configure the Switch's IP Address and Default Gateway ...................................................................................................7
Command Line Interface Access .................................................................................................................................. 9
Console Login (only for switch with console port) ..................................................................................................................9
Telnet Login ...............................................................................................................................................................................................11
SSH Login ...................................................................................................................................................................................................12
Disable Telnet login ...............................................................................................................................................................................16
Disable SSH login ...................................................................................................................................................................................17
Copy running-config startup-config ............................................................................................................................................17
Change the Switch's IP Address and Default Gateway .....................................................................................................18
Managing System
System .................................................................................................................................................................................. 20
Overview ......................................................................................................................................................................................................20
Supported Features ..............................................................................................................................................................................20
System Info Configurations .......................................................................................................................................... 22
Using the GUI ............................................................................................................................................................................................22
Viewing the System Summary ...........................................................................................................................................22
Specifying the Device Description ..................................................................................................................................24
Setting the System Time ......................................................................................................................................................25
Setting the Daylight Saving Time .....................................................................................................................................26
Specifying the System IP ......................................................................................................................................................27
Using the CLI .............................................................................................................................................................................................28
Viewing the System Summary ...........................................................................................................................................28
Page 6

Specifying the Device Description ..................................................................................................................................29
Setting the System Time ......................................................................................................................................................30
Setting the Daylight Saving Time .....................................................................................................................................33
Specifying the System IP......................................................................................................................35
User Management Configurations ............................................................................................................................. 38
Using the GUI ............................................................................................................................................................................................38
Creating Admin Accounts ....................................................................................................................................................38
Creating Accounts of Other Types .................................................................................................................................39
Using the CLI .............................................................................................................................................................................................41
Creating Admin Accounts ....................................................................................................................................................41
Creating Accounts of Other Types .................................................................................................................................42
System Tools Configurations ...................................................................................................................................... 46
Using the GUI ............................................................................................................................................................................................46
Configuring the Boot File ......................................................................................................................................................46
Restoring the Configuration of the Switch .................................................................................................................47
Backing up the Configuration File ....................................................................................................................................48
Upgrading the Firmware ........................................................................................................................................................48
Rebooting the switch ..............................................................................................................................................................49
Reseting the Switch .................................................................................................................................................................49
Using the CLI .............................................................................................................................................................................................50
Configuring the Boot File ......................................................................................................................................................50
Restoring the Configuration of the Switch .................................................................................................................50
Backing up the Configuration File ....................................................................................................................................51
Upgrading the firmware .........................................................................................................................................................52
Rebooting the switch ..............................................................................................................................................................52
Reseting the Switch .................................................................................................................................................................52
Access Security Configurations ................................................................................................................................. 54
Using the GUI ............................................................................................................................................................................................54
Configuring the Access Control Feature .....................................................................................................................54
Configuring the HTTP Function ........................................................................................................................................56
Configuring the HTTPS Function .....................................................................................................................................57
Configuring the SSH Feature .............................................................................................................................................59
Enabling the Telnet Function ..............................................................................................................................................60
Using the CLI .............................................................................................................................................................................................60
Configuring the Access Control .......................................................................................................................................60
Configuring the HTTP Function ........................................................................................................................................62
Configuring the HTTPS Function .....................................................................................................................................63
Configuring the SSH Feature .............................................................................................................................................66
Page 7

Enabling the Telnet Function ..............................................................................................................................................68
Appendix: Default Parameters ..................................................................................................................................... 69
Managing Physical Interfaces
Physical Interface ............................................................................................................................................................. 73
Overview ......................................................................................................................................................................................................73
Supported Features ..............................................................................................................................................................................73
Basic Parameters Configurations ............................................................................................................................... 74
Using the GUI ............................................................................................................................................................................................74
Using the CLI .............................................................................................................................................................................................75
Port Mirror Configuration ............................................................................................................................................... 78
Using the GUI ............................................................................................................................................................................................78
Using the CLI .............................................................................................................................................................................................80
Port Security Configuration .......................................................................................................................................... 82
Using the GUI ............................................................................................................................................................................................82
Using the CLI .............................................................................................................................................................................................83
Port Isolation Configurations ....................................................................................................................................... 85
Using the GUI ............................................................................................................................................................................................85
Using the CLI .............................................................................................................................................................................................86
Loopback Detection Configuration ........................................................................................................................... 88
Using the GUI ............................................................................................................................................................................................88
Using the CLI .............................................................................................................................................................................................89
Configuration Examples ................................................................................................................................................. 92
Example for Port Mirror .......................................................................................................................................................................92
Network Requirements ..........................................................................................................................................................92
Configuration Scheme ...........................................................................................................................................................92
Using the GUI ...............................................................................................................................................................................92
Using the CLI ...............................................................................................................................................................................94
Example for Port Isolation ..................................................................................................................................................................94
Network Requirements ..........................................................................................................................................................94
Configuration Scheme ...........................................................................................................................................................95
Using the GUI ...............................................................................................................................................................................95
Using the CLI ...............................................................................................................................................................................96
Example for Loopback Detection..................................................................................................................................................97
Network Requirements ..........................................................................................................................................................97
Configuration Scheme ...........................................................................................................................................................97
Using the GUI ...............................................................................................................................................................................97
Page 8

Using the CLI ...............................................................................................................................................................................98
Appendix: Default Parameters ...................................................................................................................................100
Configuring LAG
LAG ......................................................................................................................................................................................103
Overview ...................................................................................................................................................................................................103
Supported Features ...........................................................................................................................................................................103
LAG Configuration ..........................................................................................................................................................104
Using the GUI .........................................................................................................................................................................................105
Configuring Load-balancing Algorithm .....................................................................................................................105
Configuring Static LAG or LACP....................................................................................................................................106
Using the CLI ..........................................................................................................................................................................................108
Configuring Load-balancing Algorithm .....................................................................................................................108
Configuring Static LAG or LACP....................................................................................................................................109
Configuration Example .................................................................................................................................................113
Network Requirements .....................................................................................................................................................................113
Configuration Scheme .....................................................................................................................................................................113
Using the GUI .........................................................................................................................................................................................114
Using the CLI ..........................................................................................................................................................................................115
Appendix: Default Parameters ...................................................................................................................................117
Monitoring Traffic
Traffic Monitor .................................................................................................................................................................119
Using the GUI .........................................................................................................................................................................................119
Viewing the Traffic Summary ..........................................................................................................................................119
Viewing the Traffic Statistics in Detail ........................................................................................................................120
Using the CLI ..........................................................................................................................................................................................122
Appendix: Default Parameters ...................................................................................................................................123
Managing MAC Address Table
MAC Address Table .......................................................................................................................................................125
Overview ...................................................................................................................................................................................................125
Supported Features ...........................................................................................................................................................................125
Address Configurations ...............................................................................................................................................126
Using the GUI .........................................................................................................................................................................................126
Adding Static MAC Address Entries ..........................................................................................................................126
Modifying the Aging Time of Dynamic Address Entries...................................................................................128
Page 9

Adding MAC Filtering Address Entries.......................................................................................................................129
Viewing Address Table Entries .......................................................................................................................................129
Using the CLI ..........................................................................................................................................................................................130
Adding Static MAC Address Entries ..........................................................................................................................130
Modifying the Aging Time of Dynamic Address Entries...................................................................................131
Adding MAC Filtering Address Entries.......................................................................................................................132
Appendix: Default Parameters ...................................................................................................................................134
Configuring 802.1Q VLAN
Overview ...........................................................................................................................................................................136
802.1Q VLAN Configuration .......................................................................................................................................137
Using the GUI .........................................................................................................................................................................................137
Configuring the PVID of the Port ...................................................................................................................................137
Configuring the VLAN ..........................................................................................................................................................138
Using the CLI ..........................................................................................................................................................................................139
Creating a VLAN .....................................................................................................................................................................139
Configuring the PVID of the Port ...................................................................................................................................140
Adding the Port to the Specified VLAN .....................................................................................................................141
Configuration Example .................................................................................................................................................143
Network Requirements .....................................................................................................................................................................143
Configuration Scheme .....................................................................................................................................................................143
Network Topology ...............................................................................................................................................................................144
Using the GUI .........................................................................................................................................................................................144
Using the CLI ..........................................................................................................................................................................................146
Appendix: Default Parameters ..................................................................................................................................148
Configuring Spanning Tree
Spanning Tree ..................................................................................................................................................................150
Overview ...................................................................................................................................................................................................150
Basic Concepts ....................................................................................................................................................................................150
STP/RSTP Concepts ............................................................................................................................................................150
MSTP Concepts .....................................................................................................................................................................154
STP Security ...........................................................................................................................................................................................155
STP/RSTP Configurations ...........................................................................................................................................158
Using the GUI .........................................................................................................................................................................................158
Configuring STP/RSTP Parameters on Ports .........................................................................................................158
Configuring STP/RSTP Globally .....................................................................................................................................160
Page 10

Verifying the STP/RSTP Configurations ....................................................................................................................162
Using the CLI ..........................................................................................................................................................................................163
Configuring STP/RSTP Parameters on Ports .........................................................................................................163
Configuring Global STP/RSTP Parameters .............................................................................................................165
Enabling STP/RSTP Globally ............................................................................................................................................166
MSTP Configurations ....................................................................................................................................................168
Using the GUI .........................................................................................................................................................................................168
Configuring Parameters on Ports in CIST ................................................................................................................168
Configuring the MSTP Region ........................................................................................................................................170
Configuring MSTP Globally ...............................................................................................................................................175
Verifying the MSTP Configurations .............................................................................................................................177
Using the CLI ..........................................................................................................................................................................................178
Configuring Parameters on Ports in CIST ................................................................................................................178
Configuring the MSTP Region .......................................................................................................................................180
Configuring Global MSTP Parameters .......................................................................................................................183
Enabling Spanning Tree Globally...................................................................................................................................185
STP Security Configurations ......................................................................................................................................188
Using the GUI .........................................................................................................................................................................................188
Configuring the STP Security ..........................................................................................................................................188
Using the CLI ..........................................................................................................................................................................................189
Configuring the STP Security ..........................................................................................................................................189
Configuration Example for MSTP .............................................................................................................................192
Network Requirements .....................................................................................................................................................................192
Configuration Scheme .....................................................................................................................................................................192
Using the GUI .........................................................................................................................................................................................193
Using the CLI ..........................................................................................................................................................................................204
Appendix: Default Parameters ...................................................................................................................................211
Configuring Layer 2 Multicast
Layer 2 Multicast .............................................................................................................................................................216
Overview ...................................................................................................................................................................................................216
Supported Layer 2 Multicast Protocols ..................................................................................................................................217
IGMP Snooping Configurations .................................................................................................................................218
Using the GUI .........................................................................................................................................................................................218
Configuring IGMP Snooping Globally .........................................................................................................................218
Enabling IGMP Snooping Globally ................................................................................................................218
(Optional) Configuring Unknown Multicast ..............................................................................................218
Page 11

(Optional) Configuring Report Message Suppression ......................................................................219
Configuring Router Port Time and Member Port Time .....................................................................219
Configuring IGMP Snooping Last Listener Query ...............................................................................219
Verifying IGMP Snooping Status ...................................................................................................................220
Configuring the Port’s Basic IGMP Snooping Features....................................................................................221
Enabling IGMP Snooping on the Port .........................................................................................................221
(Optional) Configuring Fast Leave ................................................................................................................221
Configuring IGMP Snooping in the VLAN .................................................................................................................222
Configuring IGMP Snooping Globally in the VLAN ..............................................................................222
(Optional) Configuring the Static Router Ports in the VLAN ..........................................................223
(Optional) Configuring the Forbidden Router Ports in the VLAN ................................................223
Configuring the Multicast VLAN ....................................................................................................................................223
Creating Multicast VLAN and Configuring Basic Settings ..............................................................224
(Optional) Creating Replace Source IP ......................................................................................................225
Viewing Dynamic Router Ports in the Multicast VLAN ......................................................................225
(Optional) Configuring the Static Router Ports ......................................................................................225
(Optional) Configuring the Forbidden Router Ports ............................................................................225
(Optional) Configuring the Querier ................................................................................................................................226
Configuring the Querier ......................................................................................................................................226
Viewing Settings of IGMP Querier ................................................................................................................227
Configuring IGMP Profile ....................................................................................................................................................227
Creating Profile .......................................................................................................................................................227
Searching Profile ....................................................................................................................................................227
Editing IP Range of the Profile ........................................................................................................................228
Binding Profile and Member Ports ................................................................................................................................228
Binding Profile and Member Ports ...............................................................................................................229
Configuring Max Groups a Port Can Join.................................................................................................229
Viewing IGMP Statistics on Each Port ........................................................................................................................230
Configuring Auto Refresh .................................................................................................................................230
Viewing IGMP Statistics .....................................................................................................................................231
Configuring Static Member Port ....................................................................................................................................231
Configuring Static Member Port ...................................................................................................................231
Viewing IGMP Static Multicast Groups ......................................................................................................232
Using the CLI ..........................................................................................................................................................................................232
Enabling IGMP Snooping Globally ................................................................................................................................232
Enabling IGMP Snooping on the Port .........................................................................................................................232
Configuring IGMP Snooping Parameters Globally ..............................................................................................234
Configuring Report Message Suppression ............................................................................................234
Page 12

Configuring Unknown Multicast ....................................................................................................................235
Configuring IGMP Snooping Parameters on the Port .......................................................................................236
Configuring Router Port Time and Member Port Time .....................................................................236
Configuring Fast Leave ......................................................................................................................................237
Configuring Max Group and Overflow Action on the Port ..............................................................238
Configuring IGMP Snooping Last Listener Query ...............................................................................................239
Configuring IGMP Snooping Parameters in the VLAN ......................................................................................240
Configuring Router Port Time and Member Port Time .....................................................................240
Configuring Static Router Port .......................................................................................................................241
Configuring Forbidden Router Port .............................................................................................................242
Configuring Static Multicast (Multicast IP and Forward Port)........................................................243
Configuring IGMP Snooping Parameters in the Multicast VLAN ................................................................244
Configuring Router Port Time and Member Port Time .....................................................................244
Configuring Static Router Port .......................................................................................................................245
Configuring Forbidden Router Port .............................................................................................................246
Configuring Replace Source IP ......................................................................................................................247
Configuring the Querier ......................................................................................................................................................248
Enabling IGMP Querier ........................................................................................................................................248
Configuring Query Interval, Max Response Time and General Query Source IP ...............248
Configuring Multicast Filtering ........................................................................................................................................250
Creating Profile .......................................................................................................................................................250
Binding Profile to the Port .................................................................................................................................251
Viewing Multicast Snooping Configurations ........................................................................................................253
Using the GUI .........................................................................................................................................................................................253
Viewing IPv4 Multicast Snooping Configurations ................................................................................................253
Using the CLI ..........................................................................................................................................................................................253
Viewing IPv4 Multicast Snooping Configurations ................................................................................................253
Configuration Examples ...............................................................................................................................................255
Example for Configuring Basic IGMP Snooping .................................................................................................................255
Network Requirements .......................................................................................................................................................255
Configuration Scheme ........................................................................................................................................................255
Using the GUI ............................................................................................................................................................................256
Using the CLI ............................................................................................................................................................................259
Example for Configuring Multicast VLAN ...............................................................................................................................261
Network Requirements .......................................................................................................................................................261
Configuration Scheme ........................................................................................................................................................261
Network Topology .................................................................................................................................................................261
Using the GUI ............................................................................................................................................................................262
Page 13

Using the CLI ............................................................................................................................................................................265
Example for Configuring Unknown Multicast and Fast Leave ....................................................................................267
Network Requirement ..........................................................................................................................................................267
Configuration Scheme ........................................................................................................................................................268
Using the GUI ............................................................................................................................................................................268
Using the CLI ............................................................................................................................................................................271
Example for Configuring Multicast Filtering ..........................................................................................................................272
Network Requirements .......................................................................................................................................................272
Configuration Scheme ........................................................................................................................................................272
Network Topology .................................................................................................................................................................272
Using the GUI ............................................................................................................................................................................273
Using the CLI ............................................................................................................................................................................280
Appendix: Default Parameters ..................................................................................................................................283
Default Parameters for IGMP Snooping .................................................................................................................................283
Configuring QoS
QoS ......................................................................................................................................................................................285
Overview ...................................................................................................................................................................................................285
Supported Features ...........................................................................................................................................................................285
DiffServ Configuration ..................................................................................................................................................286
Using the GUI .........................................................................................................................................................................................287
Configuring Priority Mode .................................................................................................................................................287
Configuring Schedule Mode ............................................................................................................................................289
Using CLI ..................................................................................................................................................................................................290
Configuring Priority Mode .................................................................................................................................................290
Configuring Schedule Mode ............................................................................................................................................294
Bandwidth Control Configuration .............................................................................................................................296
Using the GUI .........................................................................................................................................................................................296
Configuring Rate Limit .........................................................................................................................................................296
Configuring Storm Control ...............................................................................................................................................297
Using the CLI ..........................................................................................................................................................................................298
Configuring Rate Limit on Port .......................................................................................................................................298
Configuring Storm Control ...............................................................................................................................................299
Configuration Examples ...............................................................................................................................................301
Example for Configuring SP Mode .............................................................................................................................................301
Network Requirements .......................................................................................................................................................301
Configuration Scheme ........................................................................................................................................................301
Page 14

Using the GUI ............................................................................................................................................................................302
Using the CLI ............................................................................................................................................................................302
Example for Configuring WRR Mode ........................................................................................................................................303
Network Requirements .......................................................................................................................................................303
Configuration Scheme ........................................................................................................................................................304
Using the GUI ............................................................................................................................................................................304
Using the CLI ............................................................................................................................................................................313
Appendix: Default Parameters ...................................................................................................................................317
Configuring Voice VLAN
Overview ...........................................................................................................................................................................319
Voice VLAN Configuration ..........................................................................................................................................321
Using the GUI .........................................................................................................................................................................................322
(Optional) Configuring OUI Addresses .......................................................................................................................322
Configuring Voice VLAN Globally .................................................................................................................................323
Configuring Voice VLAN Mode on Ports ..................................................................................................................324
Using the CLI .........................................................................................................................................................................................325
Configuration Example .................................................................................................................................................328
Network Requirements .....................................................................................................................................................................328
Configuration Scheme .....................................................................................................................................................................328
Network Topology..............................................................................................................................................................................328
Using the GUI .........................................................................................................................................................................................329
Using the CLI ..........................................................................................................................................................................................337
Appendix: Default Parameters ...................................................................................................................................341
Configuring PoE
PoE ......................................................................................................................................................................................343
Overview ...................................................................................................................................................................................................343
Supported Features ...........................................................................................................................................................................343
PoE Power Management Configurations ..............................................................................................................344
Using the GUI .........................................................................................................................................................................................344
Configuring the PoE Parameters Manually ..............................................................................................................344
Configuring the PoE Parameters Using the Profile .............................................................................................346
Using the CLI ..........................................................................................................................................................................................348
Configuring the PoE Parameters Manually ..............................................................................................................348
Configuring the PoE Parameters Using the Profile .............................................................................................350
Time-Range Function Configurations .....................................................................................................................352
Page 15

Using the GUI .........................................................................................................................................................................................352
Creating a Time-Range .......................................................................................................................................................352
Configuring the Holiday Parameters ...........................................................................................................................354
Viewing the Time-Range Table ......................................................................................................................................354
Using the CLI ..........................................................................................................................................................................................355
Configuring a Time-Range ................................................................................................................................................355
Configuring the Holiday Parameters ...........................................................................................................................357
Viewing the Time-Range Table ......................................................................................................................................358
Example for PoE Configurations ...............................................................................................................................359
Network Requirements .....................................................................................................................................................................359
Configuring Scheme ..........................................................................................................................................................................359
Using the GUI .........................................................................................................................................................................................359
Using the CLI ..........................................................................................................................................................................................361
Appendix: Default Parameters ...................................................................................................................................363
Configuring ACL
ACL ......................................................................................................................................................................................365
Overview ...................................................................................................................................................................................................365
Supported Features ...........................................................................................................................................................................365
ACL Configurations ........................................................................................................................................................366
Using the GUI .........................................................................................................................................................................................366
Creating an ACL ......................................................................................................................................................................366
Configuring ACL Rules ........................................................................................................................................................367
Configuring Policy ..................................................................................................................................................................370
Configuring the ACL Binding and Policy Binding .................................................................................................371
Using the CLI ..........................................................................................................................................................................................376
Configuring ACL .....................................................................................................................................................................376
Configuring Policy ..................................................................................................................................................................380
ACL Binding and Policy Binding .....................................................................................................................................381
Configuration Example for ACL .................................................................................................................................384
Network Requirements .....................................................................................................................................................................384
Network Topology ...............................................................................................................................................................................384
Configuration Scheme .....................................................................................................................................................................384
Using the GUI .........................................................................................................................................................................................385
Using the CLI ..........................................................................................................................................................................................389
Appendix: Default Parameters ...................................................................................................................................391
Page 16

Configuring Network Security
Network Security ............................................................................................................................................................393
Overview ...................................................................................................................................................................................................393
Supported Features ...........................................................................................................................................................................393
IP-MAC Binding Configurations.................................................................................................................................397
Using the GUI .........................................................................................................................................................................................397
Binding Entries Manually ....................................................................................................................................................397
Binding Entries Dynamically .............................................................................................................................................398
Viewing the Binding Entries ..............................................................................................................................................400
Using the CLI ..........................................................................................................................................................................................401
Binding Entries Manually ....................................................................................................................................................401
Viewing Binding Entries ......................................................................................................................................................403
DHCP Snooping Configuration ..................................................................................................................................404
Using the GUI .........................................................................................................................................................................................404
Enabling DHCP Snooping on VLAN .............................................................................................................................404
Configuring DHCP Snooping on Ports ......................................................................................................................405
(Optional) Configuring Option 82 ..................................................................................................................................406
Using the CLI ..........................................................................................................................................................................................407
Enabling DHCP Snooping on VLAN .............................................................................................................................407
Configuring DHCP Snooping on Ports ......................................................................................................................408
(Optional) Configuring Option 82 ..................................................................................................................................410
ARP Inspection Configurations .................................................................................................................................412
Using the GUI .........................................................................................................................................................................................412
Configuring ARP Detection ..............................................................................................................................................412
Configuring ARP Defend ....................................................................................................................................................413
Viewing ARP Statistics ........................................................................................................................................................414
Using the CLI ..........................................................................................................................................................................................416
Configuring ARP Detection ..............................................................................................................................................416
Configuring ARP Defend ....................................................................................................................................................417
Viewing ARP Statistics ........................................................................................................................................................418
DoS Defend Configuration ..........................................................................................................................................419
Using the GUI .........................................................................................................................................................................................419
Using the CLI ..........................................................................................................................................................................................420
802.1X Configuration ....................................................................................................................................................423
Using the GUI .........................................................................................................................................................................................423
Configuring the RADIUS Server .....................................................................................................................................423
Configuring 802.1X Globally ............................................................................................................................................427
Page 17

Configuring 802.1X on Ports ...........................................................................................................................................429
Using the CLI ..........................................................................................................................................................................................430
Configuring the RADIUS Server .....................................................................................................................................430
Configuring 802.1X Globally ............................................................................................................................................432
Configuring 802.1X on Ports ...........................................................................................................................................434
AAA Configuration ..........................................................................................................................................................437
Using the GUI .........................................................................................................................................................................................438
Globally Enabling AAA .........................................................................................................................................................438
Adding Servers ........................................................................................................................................................................438
Configuring Server Groups ...............................................................................................................................................440
Configuring the Method List ............................................................................................................................................441
Configuring the AAA Application List .........................................................................................................................442
Configuring Login Account and Enable Password .............................................................................................443
Using the CLI ..........................................................................................................................................................................................444
Globally Enabling AAA .........................................................................................................................................................444
Adding Servers ........................................................................................................................................................................444
Configuring Server Groups ...............................................................................................................................................447
Configuring the Method List ............................................................................................................................................448
Configuring the AAA Application List .........................................................................................................................449
Configuring Login Account and Enable Password .............................................................................................454
Configuration Examples ...............................................................................................................................................456
Example for DHCP Snooping and ARP Detection ............................................................................................................456
Network Requirements .......................................................................................................................................................456
Configuration Scheme ........................................................................................................................................................456
Using the GUI ............................................................................................................................................................................457
Using the CLI ............................................................................................................................................................................460
Example for 802.1X ............................................................................................................................................................................462
Network Requirements .......................................................................................................................................................462
Configuration Scheme ........................................................................................................................................................462
Network Topology .................................................................................................................................................................463
Using the GUI ............................................................................................................................................................................463
Using the CLI ............................................................................................................................................................................466
Example for AAA ..................................................................................................................................................................................468
Network Requirements .......................................................................................................................................................468
Configuration Scheme ........................................................................................................................................................469
Using the GUI ............................................................................................................................................................................469
Using the CLI ............................................................................................................................................................................472
Appendix: Default Parameters ...................................................................................................................................475
Page 18

Configuring SNMP & RMON
SNMP Overview ...............................................................................................................................................................483
SNMP Configurations ....................................................................................................................................................484
Using the GUI .........................................................................................................................................................................................485
Enabling SNMP ........................................................................................................................................................................485
Creating an SNMP View......................................................................................................................................................485
Creating an SNMP Group ..................................................................................................................................................486
Creating SNMP Users .........................................................................................................................................................488
Creating SNMP Communities .........................................................................................................................................489
Using the CLI ..........................................................................................................................................................................................490
Enabling SNMP ........................................................................................................................................................................490
Creating an SNMP View......................................................................................................................................................492
Creating an SNMP Group ..................................................................................................................................................493
Creating SNMP Users ..........................................................................................................................................................495
Creating SNMP Communities .........................................................................................................................................496
Notification Configurations .........................................................................................................................................498
Using the GUI .........................................................................................................................................................................................498
Using the CLI ..........................................................................................................................................................................................500
Configuring the Host ............................................................................................................................................................500
Enabling SNMP Notification .............................................................................................................................................501
RMON Overview ..............................................................................................................................................................505
RMON Configurations ...................................................................................................................................................506
Using the GUI .........................................................................................................................................................................................506
Configuring Statistics ..........................................................................................................................................................506
Configuring History ...............................................................................................................................................................507
Configuring Event ..................................................................................................................................................................508
Configuring Alarm ..................................................................................................................................................................509
Using the CLI ..........................................................................................................................................................................................511
Configuring Statistics ..........................................................................................................................................................511
Configuring History ...............................................................................................................................................................512
Configuring Event ..................................................................................................................................................................513
Configuring Alarm ..................................................................................................................................................................515
Configuration Example ................................................................................................................................................517
Network Requirements .....................................................................................................................................................................517
Configuration Scheme .....................................................................................................................................................................517
Network Topology ...............................................................................................................................................................................518
Using the GUI .........................................................................................................................................................................................518
Page 19

Using the CLI ..........................................................................................................................................................................................523
Appendix: Default Parameters ...................................................................................................................................529
Configuring LLDP
LLDP .....................................................................................................................................................................................534
Overview ...................................................................................................................................................................................................534
Supported Features ...........................................................................................................................................................................534
LLDP Configurations .....................................................................................................................................................535
Using the GUI .........................................................................................................................................................................................535
Global Config ............................................................................................................................................................................535
Port Config .................................................................................................................................................................................537
Using the CLI ..........................................................................................................................................................................................538
Global Config ............................................................................................................................................................................538
Port Config .................................................................................................................................................................................540
LLDP-MED Configurations ..........................................................................................................................................542
Using the GUI .........................................................................................................................................................................................542
Global Config ............................................................................................................................................................................542
Port Config .................................................................................................................................................................................543
Using the CLI ..........................................................................................................................................................................................545
Global Config ............................................................................................................................................................................545
Port Config .................................................................................................................................................................................546
Viewing LLDP Settings..................................................................................................................................................549
Using GUI ..................................................................................................................................................................................................549
Viewing LLDP Device Info .................................................................................................................................................549
Viewing LLDP Statistics .....................................................................................................................................................552
Using CLI ..................................................................................................................................................................................................553
Viewing LLDP-MED Settings ......................................................................................................................................554
Using GUI ..................................................................................................................................................................................................554
Using CLI ..................................................................................................................................................................................................556
Configuration Example .................................................................................................................................................558
Example for Configuring LLDP ....................................................................................................................................................558
Network Requirements .......................................................................................................................................................558
Network Topology .................................................................................................................................................................558
Configuration Scheme ........................................................................................................................................................558
Using the GUI ............................................................................................................................................................................558
Using CLI .....................................................................................................................................................................................559
Example for Configuring LLDP-MED ........................................................................................................................................565
Page 20

Network Requirements .......................................................................................................................................................565
Configuration Scheme ........................................................................................................................................................565
Network Topology .................................................................................................................................................................565
Using the GUI ............................................................................................................................................................................566
Using the CLI ............................................................................................................................................................................570
Appendix: Default Parameters ...................................................................................................................................577
Configuring Maintenance
Maintenance ....................................................................................................................................................................579
Overview ...................................................................................................................................................................................................579
Supported Features ...........................................................................................................................................................................579
Monitoring the System .................................................................................................................................................580
Using the GUI .........................................................................................................................................................................................580
Monitoring the CPU ..............................................................................................................................................................580
Monitoring the Memory ......................................................................................................................................................581
Using the CLI ..........................................................................................................................................................................................582
Monitoring the CPU ..............................................................................................................................................................582
Monitoring the Memory ......................................................................................................................................................582
System Log Configurations .......................................................................................................................................583
Using the GUI .........................................................................................................................................................................................584
Configuring the Local Log .................................................................................................................................................584
Configuring the Remote Log ...........................................................................................................................................584
Backing up the Log File .....................................................................................................................................................585
Viewing the Log Table .........................................................................................................................................................586
Using the CLI ..........................................................................................................................................................................................586
Configuring the Local Log .................................................................................................................................................586
Configuring the Remote Log ...........................................................................................................................................588
Diagnosing the Device ..................................................................................................................................................590
Using the GUI .........................................................................................................................................................................................590
Using the CLI ..........................................................................................................................................................................................591
Diagnosing the Network ...............................................................................................................................................592
Using the GUI .........................................................................................................................................................................................592
Configuring the Ping Test ..................................................................................................................................................592
Configuring the Tracert Test ...........................................................................................................................................593
Using the CLI ..........................................................................................................................................................................................593
Configuring the Ping Test ..................................................................................................................................................593
Configuring the Tracert Test ...........................................................................................................................................594
Page 21

Configuration Example for Remote Log .................................................................................................................596
Network Requirements .....................................................................................................................................................................596
Configuration Scheme .....................................................................................................................................................................596
Using the GUI ........................................................................................................................................................................................596
Using the CLI .........................................................................................................................................................................................597
Appendix: Default Parameters ...................................................................................................................................598
Page 22
About This Guide Intended Readers
About This Guide
This Configuration Guide provides information for managing T1600G Series Switches.
Please read this guide carefully before operation.
Intended Readers
This Guide is intended for network managers familiar with IT concepts and network
terminologies.
Conventions
Some models featured in this guide may be unavailable in your country or region. For local
sales information, visit http://www.tp-link.com.
When using this guide, please notice that features of the switch may vary slightly
depending on the model and software version you have. All screenshots, images,
parameters and descriptions documented in this guide are used for demonstration only.
The information in this document is subject to change without notice. Every effort has
been made in the preparation of this document to ensure accuracy of the contents, but
all statements, information, and recommendations in this document do not constitute
the warranty of any kind, express or implied. Users must take full responsibility for their
application of any products.
In this Guide, the following conventions are used:
The symbol
make better use of your device.
For GUI:
Menu Name > Submenu Name > Tab page indicates the menu structure. System >
System Info > System Summary means the System Summary page under the System Info
menu option that is located under the System menu.
stands for
. Notes contains suggestions or references that helps you
Note
Bold font indicates a button, a toolbar icon, menu or menu item.
For CLI:
Bold Font An unalterable keyword.
For example: show logging
Configuration Guide 1
Page 23
About This Guide More Information
Normal Font A constant (several options are enumerated and only one can be
selected).
For example: no bandwidth {all | ingress | egress}
{} Items in braces { } are required.
[] Items in square brackets [ ] are optional.
| Alternative items are grouped in braces and separated by vertical bars |.
For example: speed {10 | 100 | 1000}
Italic Font
Common combination:
{[ ][ ][ ]} A least one item in the square brackets must be selected.
A variable (an actual value must be assigned).
For example: bridge aging-time
For example: bandwidth {[ingress
This command can be used on three occasions:
bandwidth ingress
bandwidth egress
bandwidth ingress
ingress and egress bandwidth.
i
ngress-rate
egress-rate
ingress-rate
aging-time
ingress-rate
is used to restrict ingress bandwidth.
is used to restrict egress bandwidth.
egress
egress-rate
] [egress
egress-rate
is used to restrict
More Information
The latest software and documentations can be found at Download Center at http://
www.tp-link.com/support.
The Installation Guide (IG) can be found where you find this guide or inside the package
of the switch.
]}
Specifications can be found on the product page at http://www.tp-link.com.
A Technical Support Forum is provided for you to discuss our products at http://forum.
tp-link.com.
Our Technical Support contact information can be found at the Contact Technical
Support page at http://www.tp-link.com/support.
Configuration Guide 2
Page 24
Part 1
Accessing the Switch
CHAPTERS
1. Overview
2. Web Interface Access
3. Command Line Interface Access
Page 25

Accessing the Switch Overview
1
Overview
You can access and manage the switch using the GUI (Graphical User Interface, also called
web interface in this text) or using the CLI (Command Line Interface). There are equivalent
functions in the web interface and the command line interface, while web configuration is
easier and more visual than the CLI configuration. You can choose the method according
to their available applications and preference.
Configuration Guide 4
Page 26
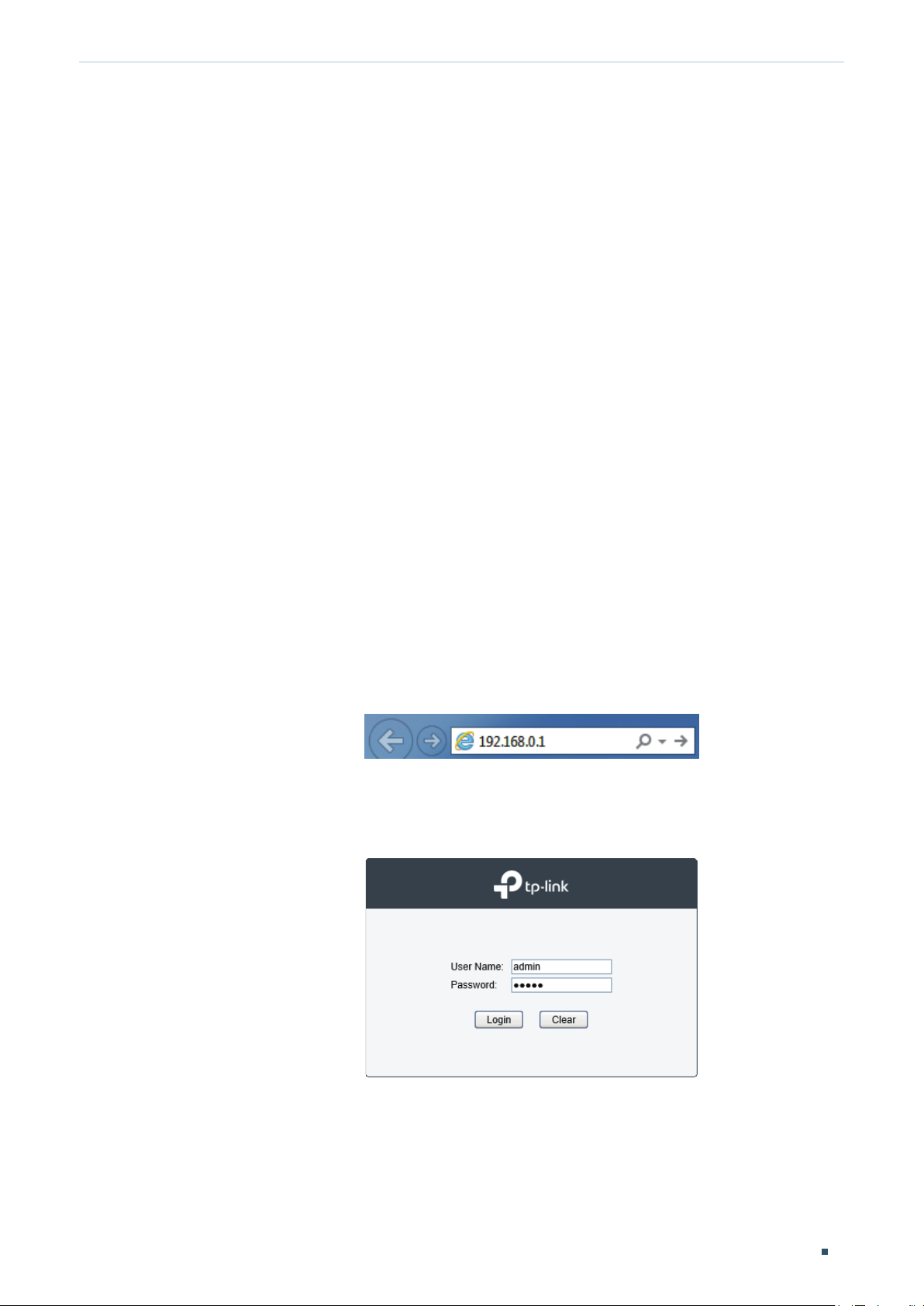
Accessing the Switch Web Interface Access
2
Web Interface Access
You can access the switch’s web interface through the web-based authentication.
The switch uses two built-in web servers, HTTP server and HTTPS server, for user
authentication.
The following example shows how to login via the HTTP server.
2.1 Login
To manage your switch through a web browser in the host PC:
1) Make sure that the route between the host PC and the switch is available.
2) Launch a web browser. The supported web browsers include, but are not limited to, the
following types:
IE 8.0, 9.0, 10.0, 11.0
Firefox 26.0, 27.0
Chrome 32.0, 33.0
3) Enter the switch’s IP address in the web browser’s address bar. The switch’s default IP
address is 192.168.0.1.
Figure 2-1 Enter the switch's IP addresss in the browser
4) Enter the username and password in the pop-up login window. Use admin for both
username and password in lower case letters.
Figure 2-2 Login authentication
5) The typical web interface displays below. You can view the switch’s running status and
configure the switch on this interface.
Configuration Guide
5
Page 27
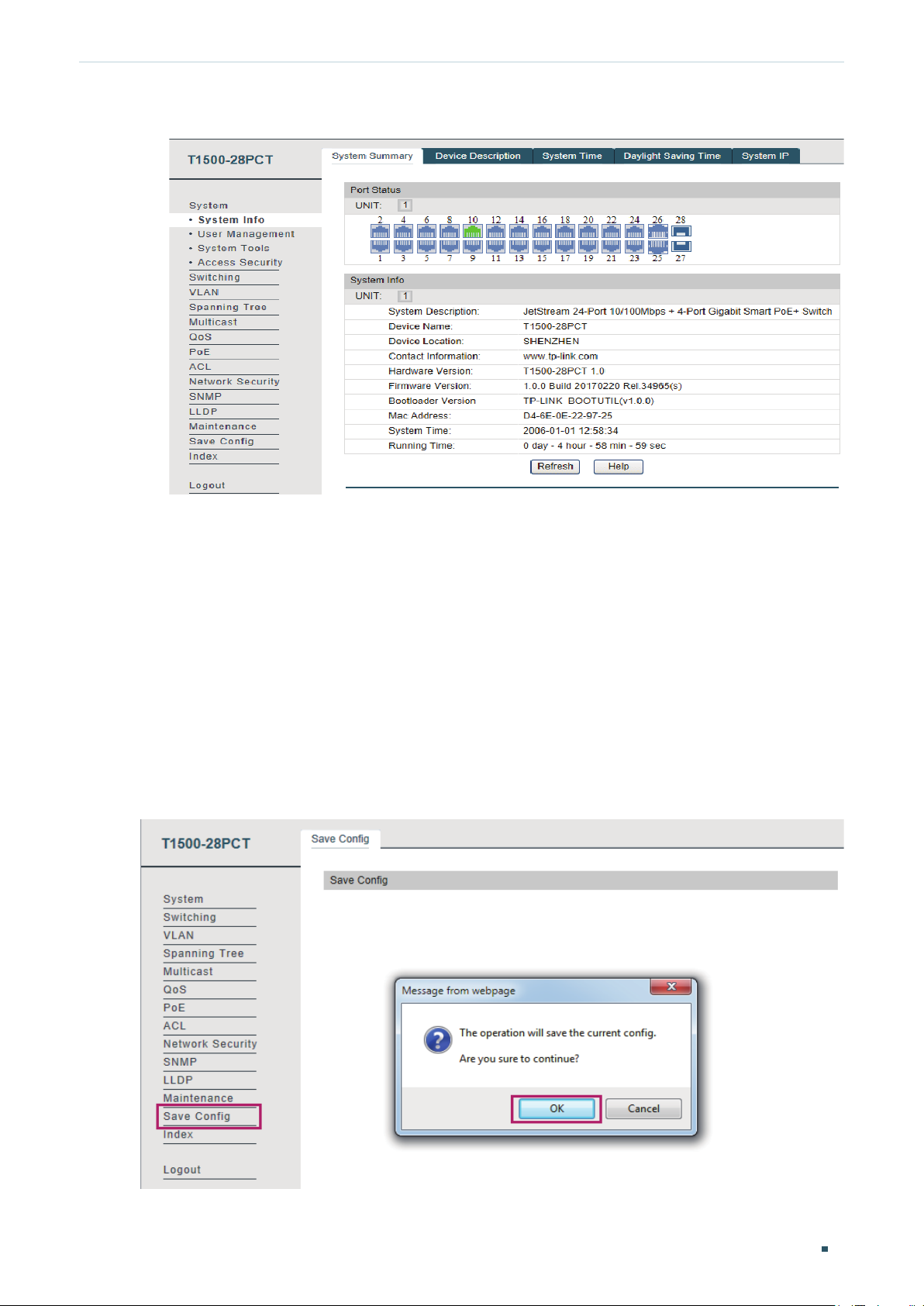
Accessing the Switch Web Interface Access
Figure 2-3 Web interface
2.2 Save Config Function
The switch’s configuration files fall into two types: the running configuration file and the
start-up configuration file.
After you perform configurations on the sub-interfaces and click Apply, the modifications
will be saved in the running configuration file. The configurations will be lost when the
switch reboots.
If you need to keep the configurations after the switch reboots, please user the Save Config
function on the main interface to save the configurations in the start-up configuration file.
Figure 2-4 Save Config
Configuration Guide 6
Page 28

Accessing the Switch Web Interface Access
2.3 Disable the Web Server
You can shut down the HTTP server or HTTPS server to block any access to the web
interface.
System > Access Security > HTTP Config, disable the HTTP server and click Apply.
Go to
Figure 2-5 Shut down HTTP server
System > Access Security > HTTPS Config, disable the HTTPS server and click Apply.
Go to
Figure 2-6 Disbale the HTTPS Server
2.4 Configure the Switch's IP Address and Default Gateway
The default IP address of the switch is 192.168.0.1, and the default gateway is 0.0.0.0. You
can change the IP address and default gateway of the switch according to your needs.
System > System Info > System IP
Go to
to load the following page.
Configuration Guide
7
Page 29
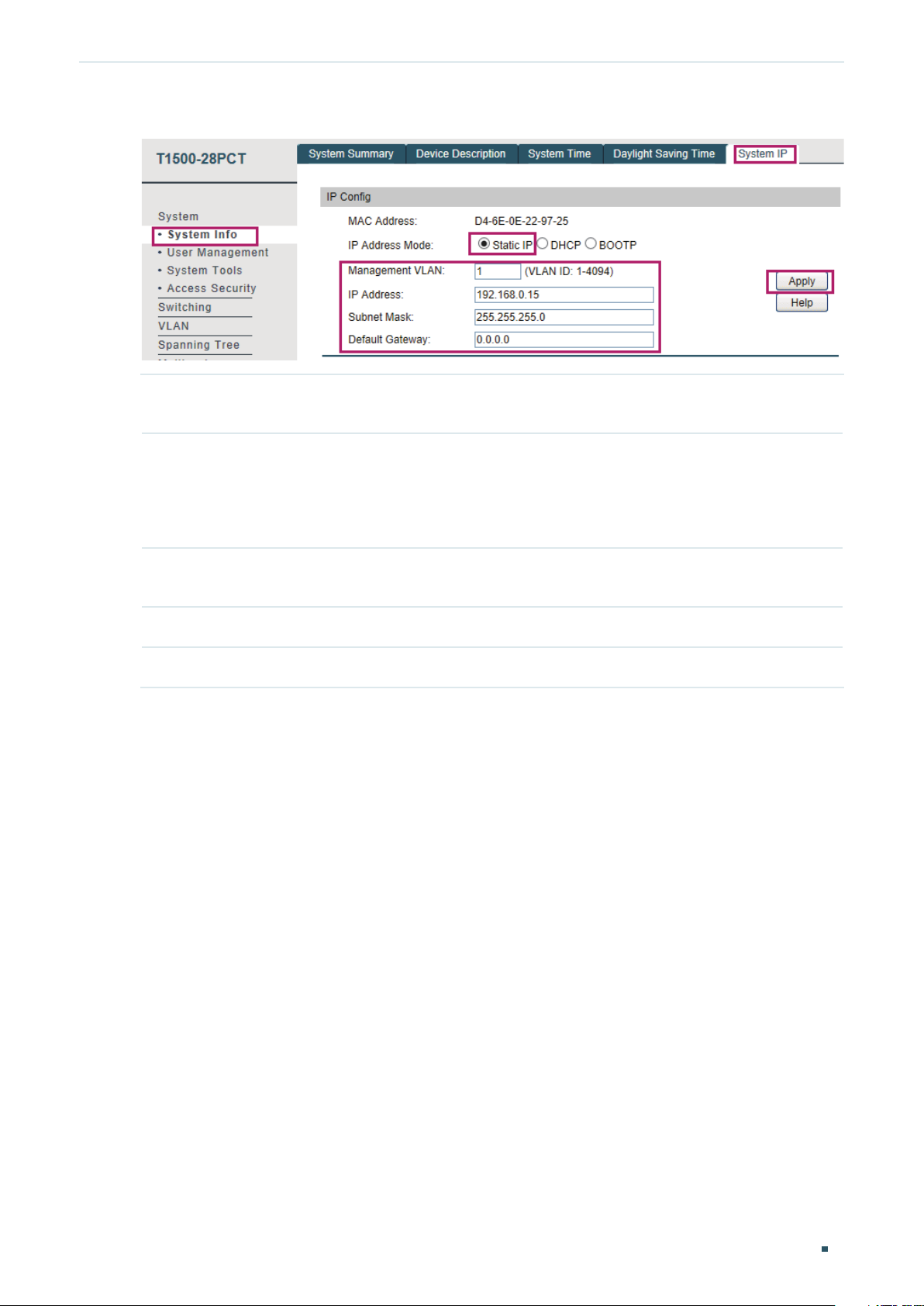
Accessing the Switch Web Interface Access
Figure 2-7 Change the default IP address
IP Address
Mode
Management
VLAN
IP Address Enter a new IP address. Make sure the route between the management host and the
Subnet Mask Enter a new subnet mask.
Default Gateway Enter your desired default gateway.
Choose the IP address mode as Static IP.
This is the only VLAN through which you can get access to the switch. By default, all
the ports are belonged to VLAN 1, and VLAN 1 is the Management VLAN, you can
connect to the switch through VLAN 1. However, if another VLAN is created and set to
be the Management VLAN, you may have to reconnect the management station to a
port that is a member of the Management VLAN.
switch’s new IP address id available.
Configuration Guide 8
Page 30
Accessing the Switch Command Line Interface Access
3
Command Line Interface Access
Users can access the switch's command line interface through the console (only for switch
with console port), Telnet or SSH connection, and manage the switch with the command
lines.
Console connection requires the host PC connecting to the switch’s console port directly,
while Telnet and SSH connection support both local and remote access.
The following table shows the typical applications used in the CLI access.
Table 3-1 Method list
Method Using Port Typical Applications
Console Console port (connected
directly)
Telnet RJ-45 port CMD
SSH RJ-45 port Putty
Hyper Terminal
3.1 Console Login (only for switch with console port)
Follow these steps to log in to the switch via the Console port:
1) Connect the PC or terminal to the Console port on the switch with the serial cable.
2) Start the terminal emulation program (such as the Hyper Terminal) on the PC and
configure the terminal emulation program as follows:
·Baud Rate: 38400bps
·Data Bits: 8
·Parity: None
·Stop Bits: 1
·Flow Control: None
3) Press Enter in the main window and Switch> will appear, indicating that you have
successfully logged in to the switch and you can use the CLI now.
Configuration Guide
9
Page 31

Accessing the Switch Command Line Interface Access
Figure 3-1 CLI Main Window
4) Enter enable to enter the User EXEC Mode to further configure the switch.
Figure 3-2 User EXEC Mode
Note:
In Windows XP, go to Start > All Programs > Accessories > Communications > Hyper Terminal to
open the Hyper Terminal and configure the above settings to log in to the switch.
Configuration Guide 10
Page 32

Accessing the Switch Command Line Interface Access
3.2 Telnet Login
The switch supports Login Local Mode for authentication by default.
Login Local Mode: Username and password are required, which are both admin by default.
The following steps show how to manage the switch via the Login Local Mode:
1) Make sure the switch and the PC are in the same LAN (Local Area Network). Click Start
and type in cmd in the Search bar and press Enter.
Figure 3-3 Open the cmd Window
2) Type in telnet 192.168.0.1 in the cmd window and press Enter.
Figure 3-4 Log In to the Switch
3) Type in the login username and password (both admin by default). Press Enter and you
will enter User EXEC Mode.
Figure 3-5 Enter User EXEC Mode
4) Type in enable command and you will enter Privileged EXEC Mode. By default no
password is needed. Later you can set a password for users who want to access the
Privileged EXEC Mode.
Configuration Guide
11
Page 33

Accessing the Switch Command Line Interface Access
Figure 3-6 Enter Privileged EXEC Mode
Now you can manage your switch with CLI commands through Telnet connection.
3.3 SSH Login
SSH login supports the following two modes: Password Authentication Mode and Key
Authentication Mode. You can choose one according to your needs:
Password Authentication Mode: Username and password are required, which are both
admin by default.
Key Authentication Mode (Recommended): A public key for the switch and a private key
for the client software (PuTTY) are required. You can generate the public key and the
private key through the PuTTY Key Generator.
Before logging in via SSH, follow the steps below to enable SSH on the terminal emulation
program:
Figure 3-7 Enable SSH
Password Authentication Mode
1) Open PuTTY and go to the Session page. Enter the IP address of the switch in the Host
Name field and keep the default value 22 in the Port field; select SSH as the Connection
type. Click Open.
Configuration Guide 12
Page 34

Accessing the Switch Command Line Interface Access
Figure 3-8 Configurations in PuTTY
2) Enter the login username and password to log in to the switch, and you can continue to
configure the switch.
Figure 3-9 Log In to the Switch
Key Authentication Mode
1) Open the PuTTY Key Generator. In the Parameters section, select the key type and
enter the key length. In the Actions section, click Generate to generate a public/private
key pair. In the following figure, an SSH-2 RSA key pair is generated, and the length of
each key is 1024 bits.
Configuration Guide
13
Page 35

Accessing the Switch Command Line Interface Access
Figure 3-10 Generate a Public/Private Key Pair
Note:
The key length should be between 512 and 3072 bits.
•
You can accelerate the key generation process by moving the mouse quickly and randomly in
•
the Key section.
2) After the keys are successfully generated, click Save public key to save the public key
to a TFTP server; click Save private key to save the private key to the host PC.
Figure 3-11 Save the Generated Keys
Configuration Guide 14
Page 36

Accessing the Switch Command Line Interface Access
3) On Hyper Terminal, download the public key file from the TFTP server to the switch as
shown in the following figure:
Figure 3-12 Download the Public Key to the Switch
Note:
The key type should accord with the type of the key file. In the above CLI, v1 corresponds to
•
SSH-1 (RSA), and v2 corresponds to SSH-2 RSA and SSH-2 DSA.
The key downloading process cannot be interrupted.
•
4) After the public key is downloaded, open PuTTY and go to the Session page. Enter the
IP address of the switch and select SSH as the Connection type (keep the default value
in the Port field).
Figure 3-13 Configure the Host Name and Connection Type
5) Go to Connection > SSH > Auth. Click Browse to download the private key file to
PuTTY. Click Open to start the connection and negotiation.
Configuration Guide
15
Page 37

Accessing the Switch Command Line Interface Access
Figure 3-14 Download the Private Key to PuTTY
6) After negotiation is completed, enter the username to log in. If you can log in without
entering the password, the key authentication completed successfully.
Figure 3-15 Log In to the Switch
3.4 Disable Telnet login
You can shut down the Telnet function to block any Telnet access to the CLI interface.
Using the GUI:
System > Access Security > Telnet Config, disable the Telnet function and click Apply.
Go to
Figure 3-16 Disable Telnet login
Configuration Guide 16
Page 38

Accessing the Switch Command Line Interface Access
Using the CLI:
Switch#configure
Switch(config)#telnet disable
3.5 Disable SSH login
You can shut down the SSH server to block any SSH access to the CLI interface.
Using the GUI:
System > Access Security > SSH Config, disable the SSH server and click Apply.
Go to
Figure 3-17 Shut down SSH server
Using the CLI:
Switch#configure
Switch(config)#no ip ssh server
3.6 Copy running-config startup-config
The switch’s configuration files fall into two types: the running configuration file and the
start-up configuration file.
After you enter each command line, the modifications will be saved in the running
configuration file. The configurations will be lost when the switch reboots.
If you need to keep he configurations after the switch reboots, please use the command
copy running-config startup-config to save the configurations in the start-up
configuration file.
Switch(config)#end
Switch#copy running-config startup-config
Configuration Guide
17
Page 39

Accessing the Switch Command Line Interface Access
3.7 Change the Switch's IP Address and Default Gateway
If you want to access the switch via a specified port (hereafter referred to as the access
port), you can configure the port as a routed port and specify its IP address, or configure
the IP address of the VLAN which the access port belongs to.
Change the IP Address
By default, all the ports belong to VLAN 1 with the VLAN interface IP 192.168.0.1/24. In
the following example, we will show how to replace the switch’s default access IP address
192.168.0.1/24 with 192.168.0.10/24.
Switch#configure
Switch(config)#interface vlan 1
Switch(config-if)#ip address 192.168.0.10 255.255.255.0
The connection will be interrupted and you should telnet to the switch's new IP address
192.168.0.10.
C:\Users\Administrator>telnet 192.168.0.10
User:admin
Password:admin
Switch>enable
Switch#copy running-config startup-config
Configure the Default Gateway
In the following example, we will show how to configure the switch’s gateway as
192.168.0.100. By default, the switch has no default gateway.
Switch#configure
Switch(config)#ip route 0.0.0.0 255.255.255.0 192.168.0.100 1
Switch(config)#end
Switch#copy running-config startup-config
Configuration Guide 18
Page 40

Part 2
Managing System
CHAPTERS
1. System
2. System Info Configurations
3. User Management Configurations
4. System Tools Configurations
5. Access Security Configurations
6. Appendix: Default Parameters
Page 41

Managing System System
1
System
1.1 Overview
The System module is mainly used to configure and view the system information of the
switch. It provides controls over the type of the access users and the access security.
1.2 Supported Features
System Info
The System Info is mainly used for the basic properties configuration. You can view the
switch’s port status and system information, and configure the device description, system
time, and daylight saving time.
User management
User Management function is used to configure the user name and password for users to
log into the switch with a certain access level so as to protect the settings of the switch
from being randomly changed.
System Tools
The System Tools are used to manage the configuration file of the switch. With these tools,
you can configure the boot file of the switch, backup and restore the configurations of the
switch, update the firmware, reset the switch, and reboot the switch.
Boot Config function is used to configure the boot file of the switch uploaded before, and
the switch will boot up according to your configuration file.
Access Security
Access Security provides different security measures for accessing the switch remotely
so as to enhance the configuration management security.
Access Control function is used to control the users’ access to the switch by filtering IP
address, MAC address or port.
HTTP Config function is based on the HTTP protocol. It can allow or deny users to access
the switch via a web browser.
HTTPS Config function is based on the SSL or TLS protocol working in transport layer. It
supports a security access via a web browser.
Configuration Guide 20
Page 42

Managing System System
SSH Config function is based on the SSH protocol, a security protocol established on
application and transport layers. The function with SSH is similar to a telnet connection, but
SSH can provide information security and powerful authentication.
Configuration Guide
21
Page 43

Managing System System Info Configurations
2
System Info Configurations
With system information configurations, you can:
View the system summary
Specify the device description
Set the system time
Set the daylight saving time
Specify the system IP
2.1 Using the GUI
2.1.1 Viewing the System Summary
Choose the menu System > System Info > System Summary to load the following page.
Figure 2-1 Viewing the System Summary
Port Status Indication
Configuration Guide 22
Page 44

Managing System System Info Configurations
Indicates that the corresponding 100Mbps port is not connected to a device.
Indicates that the corresponding 1000Mbps port is at the speed of 100Mbps.
Indicates that the corresponding 1000Mbps port is not connected to a device.
Indicates that the corresponding 1000Mbps port is at the speed of 1000Mbps.
Indicates that the corresponding 1000Mbps port is at the speed of 10Mbps or
100Mbps.
Indicates that the corresponding SFP port is not connected to a device.
Indicates the SFP port is at the speed of 1000Mbps.
Move the cursor to the port to view the detailed information of the port.
Figure 2-2 Port Information
Port Information Indication
Port Displays the port number of the switch.
Type Displays the type of the port.
Speed Displays the maximum transmission rate of the port.
Status Displays the connection status of the port.
Click a port to view the bandwidth utilization on this port.
Configuration Guide
23
Page 45

Managing System System Info Configurations
Figure 2-3 Bnadwidth Utilization
Rx Select Rx to view the bandwidth utilization of receiving packets on this port.
Tx Select Tx to view the bandwidth utilization of sending packets on this port.
2.1.2 Specifying the Device Description
Choose the menu System > System Info > Device Description to load the following page.
Figure 2-4 Specifying the Device Description
1) In the Device Description section, specify the following information.
Device Name Enter the name of the switch.
Device Location Enter the location of the switch.
System Contact Enter the contact information.
2) Click Apply.
Configuration Guide 24
Page 46

Managing System System Info Configurations
2.1.3 Setting the System Time
Choose the menu System > System Info > System Time to load the following page.
Figure 2-5 Setting the System Time
In the Time Info section, view the current time information of the switch.
Current System
Time
Current Time
Source
Displays the current date and time of the switch.
Displays the current time source of the switch.
In the Time Config section, follow these steps to configure the system time:
1) Choose one method to set the system time and specify the information.
Manual Set the system time manually.
Date: Specify the date of the system.
Time: Specify the time of the system.
Configuration Guide
25
Page 47
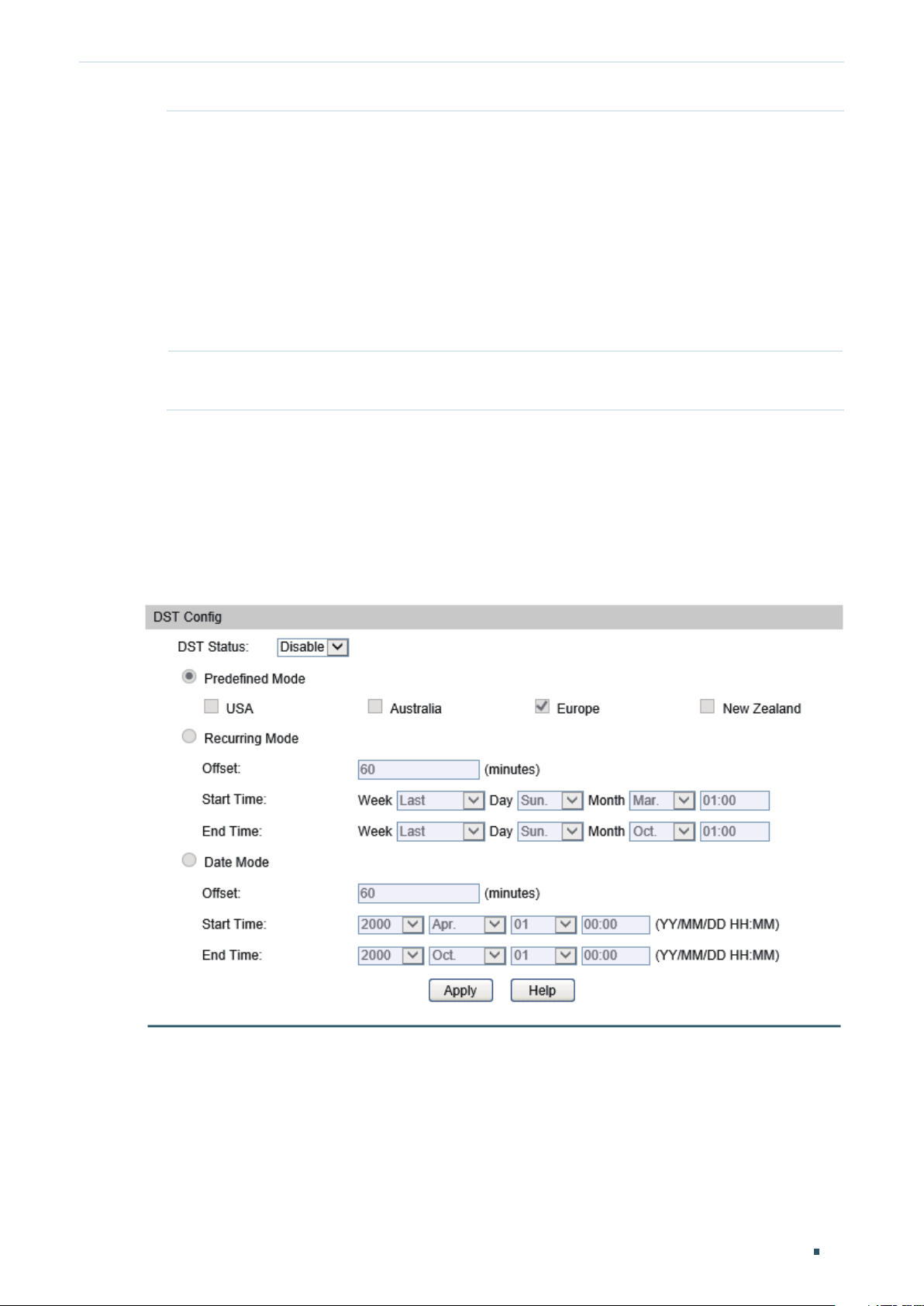
Managing System System Info Configurations
Get Time from
NTP Server
Synchronize
with PC’s Clock
Set the system time by getting time from NTP server. Make sure the NTP server
is accessible on your network. If the NTP server is on the Internet, connect the
switch to the Internet first.
Time Zone: Select your local time zone.
Primary Server: Enter the IP Address of the primary NTP server.
Secondary Server: Enter the IP Address of the secondary NTP server.
Update Rate: Specify the interval the switch fetching time from NTP server, which
ranges from 1 to 24 hours. The default value is 12 hours.
Synchronize the system time of the switch with PC’s clock.
2) Click Apply.
2.1.4 Setting the Daylight Saving Time
Choose the menu System > System Info > Daylight Saving Time to load the following
page.
Figure 2-6 Setting the Daylight Saving Time
Follow these steps to configure Daylight Saving Time:
1) In the DST Config section, select Enable to enable the Daylight Saving Time function.
2) Choose one method to set the Daylight Saving Time of the switch and specify the
information.
Configuration Guide 26
Page 48

Managing System System Info Configurations
Predefined
Mode
Recurring Mode If you select Recurring Mode, specify a cycle time range for the Daylight Saving
If you select Predefined Mode, choose a predefined DST schedule for the switch.
USA: Select the Daylight Saving Time of the USA. It is from 2: 00 a.m. on the
Second Sunday in March to 2:00 a.m. on the First Sunday in November.
Australia: Select the Daylight Saving Time of Australia. It is from 2:00 a.m. on the
First Sunday in October to 3:00 a.m. on the First Sunday in April.
Europe: Select the Daylight Saving Time of Europe. It is from 1: 00 a.m. on the Last
Sunday in March to 1:00 a.m. on the Last Sunday in October.
New Zealand: Select the Daylight Saving Time of New Zealand. It is from 2: 00 a.m.
on the Last Sunday in September to 3:00 a.m. on the First Sunday in April.
Time of the switch. This configuration will be used every year.
Offset: Specify the time to set the clock forward by.
Start Time: Specify the start time of Daylight Saving Time. The interval between
start time and end time should be more than 1 day and less than 1 year(365 days).
End Time: Specify the end time of Daylight Saving Time. The interval between
start time and end time should be more than 1 day and less than 1 year (365 days).
Date Mode If you select Date Mode, specify an absolute time range for the Daylight Saving
Time of the switch. This configuration will be used only one time.
Offset: Specify the time to set the clock forward by.
Start Time: Specify the start time of Daylight Saving Time. The interval between
start time and end time should be more than 1 day and less than 1 year(365 days).
End Time: Specify the end time of Daylight Saving Time. The interval between
start time and end time should be more than 1 day and less than 1 year (365 days).
3) Click Apply.
2.1.5 Specifying the System IP
Note:
Before configuring Management VLAN, make sure the VLAN will be set as the management VLAN is
configured correctly and at least one port’s PVID is set as the management VLAN ID.
Choose the menu System > System Info > System IP to load the following page.
Configuration Guide
27
Page 49

Managing System System Info Configurations
Figure 2-7 Configuring the system IP
1) In the IP Config section, specify the following information.
IP Address
Mode
Management
VLAN
IP address Enter the IP address for the switch.
Subnet Mask Enter the subnet mask for the switch.
Default Gateway Enter the default gateway for the switch.
2) Click Apply.
2.2 Using the CLI
Select the mode to obtain IP address for the switch.
Static IP: Select to specify the IP address, subnet mask and default gateway
manually.
DHCP: Select to let the switch obtain network parameters from the DHCP server.
BOOTP: Select to let the switch obtain network parameters from the BOOTP
server.
Enter the ID for management VLAN. Only the members belong to the management
VLAN can access to the switch.
2.2.1 Viewing the System Summary
On privileged EXEC mode or any other configuration mode, you can use the following
command to view the system information of the switch:
show interface status [ fastEthernet
View status of the interface.
: Enter the number of the Ethernet port.
port
show system-info
View the system information including system Description, Device Name, Device Location, System
Contact, Hardware Version, Firmware Version, System Time, Run Time and so on.
| gigabitEthernet
port
| ten-gigabitEthernet
port
]
port
Configuration Guide 28
Page 50

Managing System System Info Configurations
The following example shows how to view the interface status and the system information
of the switch.
Switch#show interface status
Port Status Speed Duplex FlowCtrl Jumbo Active-Medium
------- ----------- ----- ------ -------- --------- -------------
Fa1/0/1 LinkDown N/A N/A N/A Disable Copper
Fa1/0/2 LinkDown N/A N/A N/A Disable Copper
Fa1/0/3 LinkUp 100M Full Disable Disable Copper
...
Gi1/0/26 LinkDown N/A N/A N/A Disable Copper
Gi1/0/27 LinkDown N/A N/A N/A Disable Fiber
Gi1/0/28 LinkDown N/A N/A N/A Disable Fiber
Switch#show system-info
System Description - JetStream 24-Port 10/100Mbps + 4-port Gigabit Smart PoE+ Switch
System Name - T1500-28PTC
System Location - SHENZHEN
Contact Information - www.tp-link.com
Hardware Version - T1500-28PTC 1.0
Software Version - 1.0.3 Build 20170220 Rel.34965(s)
System Time - 2016-01-04 10:07:38
Running Time - 3 day - 2 hour - 8 min - 26 sec
2.2.2 Specifying the Device Description
Follow these steps to specify the device description:
Step 1 configure
Enter global configuration mode.
Step 2 hostname [
Specify the system name of the switch.
hostname
default, it is the model name of the switch.
: Enter the system name. The length of the name ranges from 1 to 32 characters. By
hostname
]
Configuration Guide
29
Page 51

Managing System System Info Configurations
Step 3 location [
Specify the system location of the switch.
location
it is “SHENZHEN”.
Step 4 contact-info [
Specify the system contact Information.
contact-info
default, it is “www.tp-link.com”.
Step 5 show system-info
Verify the system information including system Description, Device Name, Device Location,
System Contact, Hardware Version, Firmware Version, System Time, Run Time and so on.
Step 6 end
Return to privileged EXEC mode.
Step 7 copy running-config startup-config
Save the settings in the configuration file.
location
: Enter the device location. It should consist of no more than 32 characters. By default,
]
contact-info
: Enter the contact information. It should consist of no more than 32 characters. By
]
The following example shows how to set the device name as Switch_A, set the location as
BEIJING and set the contact information as http://www.tp-link.com.
Switch#configure
Switch(config)#hostname Switch_A
Switch(config)#location BEIJING
Switch(config)#contact-info http://www.tp-link.com
Switch(config)#show system-info
System Description - JetStream 48-Port Gigabit Smart Switch with 4 SFP Slots
System Name - Switch_A
System Location - BEIJING
Contact Information - http://www.tp-link.com
...
Switch(config)#end
Switch#copy running-config startup-config
2.2.3 Setting the System Time
Follow these steps and choose one method to set the system time:
Configuration Guide 30
Page 52

Managing System System Info Configurations
Step 1 configure
Enter global configuration mode.
Step 2 Use the following command to set the system time manually:
system-time manual
Configure the system time manually.
: Specify the date and time manually in the format of MM/DD/YYYY-HH:MM:SS. The valid
time
value of the year ranges from 2000 to 2037.
Use the following command to set the system time by getting time from the NTP server:
system-time ntp {
Configure the time zone and the NTP server to get time from the NTP server. Ensure the NTP
server is accessible. If the NTP server is on the Internet, connect the switch to the Internet first.
timezone
: Enter your local time-zone, which ranges from UTC-12:00 to UTC+13:00.
time
timezone
} {
ntp-server
} {
backup-ntp-server
} {
fetching-rate
}
Configuration Guide
31
Page 53

Managing System System Info Configurations
The detailed information of each time-zone are displayed as follows:
UTC-12:00 —— TimeZone for International Date Line West.
UTC-11:00 —— TimeZone for Coordinated Universal Time-11.
UTC-10:00 —— TimeZone for Hawaii.
UTC-09:00 —— TimeZone for Alaska.
UTC-08:00 —— TimeZone for Pacific Time (US Canada).
UTC-07:00 —— TimeZone for Mountain Time (US Canada).
UTC-06:00 —— TimeZone for Central Time (US Canada).
UTC-05:00 —— TimeZone for Eastern Time (US Canada).
UTC-04:30 —— TimeZone for Caracas.
UTC-04:00 —— TimeZone for Atlantic Time (Canada).
UTC-03:30 —— TimeZone for Newfoundland.
UTC-03:00 —— TimeZone for Buenos Aires, Salvador, Brasilia.
UTC-02:00 —— TimeZone for Mid-Atlantic.
UTC-01:00 —— TimeZone for Azores, Cape Verde Is.
UTC —— TimeZone for Dublin, Edinburgh, Lisbon, London.
UTC+01:00 —— TimeZone for Amsterdam, Berlin, Bern, Rome, Stockholm, Vienna.
UTC+02:00 —— TimeZone for Cairo, Athens, Bucharest, Amman, Beirut, Jerusalem.
UTC+03:00 —— TimeZone for Kuwait, Riyadh, Baghdad.
UTC+03:30 —— TimeZone for Tehran.
UTC+04:00 —— TimeZone for Moscow, St.Petersburg, Volgograd, Tbilisi, Port Louis.
UTC+04:30 —— TimeZone for Kabul.
UTC+05:00 —— TimeZone for Islamabad, Karachi, Tashkent.
UTC+05:30 —— TimeZone for Chennai, Kolkata, Mumbai, New Delhi.
UTC+05:45 —— TimeZone for Kathmandu.
UTC+06:00 —— TimeZone for Dhaka,Astana, Ekaterinburg.
UTC+06:30 —— TimeZone for Yangon (Rangoon).
UTC+07:00 —— TimeZone for Novosibrisk, Bangkok, Hanoi, Jakarta.
UTC+08:00 —— TimeZone for Beijing, Chongqing, Hong Kong, Urumqi, Singapore.
UTC+09:00 —— TimeZone for Seoul, Irkutsk, Osaka, Sapporo, Tokyo.
UTC+09:30 —— TimeZone for Darwin, Adelaide.
UTC+10:00 —— TimeZone for Canberra, Melbourne, Sydney, Brisbane.
UTC+11:00 —— TimeZone for Solomon Is., New Caledonia, Vladivostok.
UTC+12:00 —— TimeZone for Fiji, Magadan, Auckland, Welington.
UTC+13:00 —— TimeZone for Nuku’alofa, Samoa.
ntp-server
backup-ntp-server
fetching-rate
: Specify the IP address of the primary NTP server.
: Specify the IP address of the backup NTP server.
: Specify the interval fetching time from the NTP server.
Configuration Guide 32
Page 54

Managing System System Info Configurations
Step 3 Use the following command to verify the system time information.
show system-time
Verify the system time information.
Use the following command to verify the NTP mode configuration information.
show system-time ntp
Verify the system time information of NTP mode.
Step 4 end
Return to privileged EXEC mode.
Step 5 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to set the system time by Get Time from NTP Server and
set the time zone as UTC+08:00, set the NTP server as 133.100.9.2, set the backup NTP
server as 139.78.100.163 and set the update rate as 11.
Switch#configure
Switch(config)#system-time ntp UTC+08:00 133.100.9.2 139.78.100.163 11
Switch(config)#show system-time ntp
Time zone : UTC+08:00
Prefered NTP server: 133.100.9.2
Backup NTP server: 139.78.100.163
Last successful NTP server: 133.100.9.2
Update Rate: 11 hour(s)
Switch(config)#end
Switch#copy running-config startup-config
2.2.4 Setting the Daylight Saving Time
Follow these steps and choose one method to set the Daylight Saving Time:
Step 1 configure
Enter global configuration mode.
Configuration Guide
33
Page 55

Managing System System Info Configurations
Step 2 Use the following command to select a predefined Daylight Saving Time configuration:
system-time dst predefined [ USA | Australia | Europe | New-Zealand ]
Specify the Daylight Saving Time using a predefined schedule.
USA | Australia | Europe | New-Zealand: Select one mode of Daylight Saving Time.
USA: 02:00 a.m. on the Second Sunday in March ~ 02:00 a.m. on the First Sunday in November.
Australia: 02:00 a.m. on the First Sunday in October ~ 03:00 a.m. on the First Sunday in April.
Europe: 01:00 a.m. on the Last Sunday in March ~ 01:00 a.m. on the Last Sunday in October.
New Zealand: 02:00 a.m. on the Last Sunday in September ~ 03:00 a.m. on the First Sunday in
April.
Use the following command to set the Daylight Saving Time in recurring mode:
system-time dst recurring {
} [
etime
Specify the Daylight Saving Time in Recuring mode.
: Enter the start week of Daylight Saving Time. There are 5 values showing as follows:
sweek
first, second, third, fourth, last.
: Enter the start day of Daylight Saving Time. There are 7 values showing as follows: Sun,
sday
Mon, Tue, Wed, Thu, Fri, Sat.
smonth
Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
: Enter the start time of Daylight Saving Time,in the format of HH:MM.
stime
: Enter the end week of Daylight Saving Time. There are 5 values showing as follows:
eweek
first, second, third, fourth, last.
: Enter the end day of Daylight Saving Time. There are 7 values showing as follows: Sun,
eday
Mon, Tue, Wed, Thu, Fri, Sat.
emonth
Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
: Enter the end time of Daylight Saving Time,in the format of HH:MM.
etime
: Enter the offset of Daylight Saving Time. The default value is 60.
offset
]
offset
: Enter the start month of Daylight Saving Time. There are 12 values showing as follows:
: Enter the end month of Daylight Saving Time. There are 12 values showing as follows:
sweek
} {
sday
} {
smonth
} {
stime
} {
eweek
} {
eday
} {
emonth
} {
Use the following command to set the Daylight Saving Time in date mode:
system-time dst date {
]
offset
Specify the Daylight Saving Time in Date mode.
smonth
} {
sday
} {
stime
} {
syear
} {
emonth
} {
eday
Configuration Guide 34
} {
etime
} {
eyear
} [
Page 56

Managing System System Info Configurations
: Enter the start month of Daylight Saving Time. There are 12 values showing as follows:
smonth
Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
: Enter the start day of Daylight Saving Time, which ranges from 1 to 31.
sday
: Enter the start time of Daylight Saving Time,in the format of HH:MM.
stime
: Enter the start year of Daylight Saving Time.
syear
: Enter the end month of Daylight Saving Time. There are 12 values showing as follows:
emonth
Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
: Enter the end day of Daylight Saving Time, which ranges from 1 to 31.
eday
: Enter the end time of Daylight Saving Time,in the format of HH:MM.
etime
: Enter the end year of Daylight Saving Time.
eyear
: Enter the offset of Daylight Saving Time. The default value is 60.
offset
Step 3 show system-time dst
Verify the DST information of the switch.
Step 4 end
Return to privileged EXEC mode.
Step 5 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to set the Daylight Saving Time by Date Mode. Set the
start time as 01:00 August 1st, 2016, set the end time as 01:00 September 1st, 2016 and
set the offset as 50.
Switch#configure
Switch(config)#system-time dst date Aug 1 01:00 2016 Sep 1 01:00 2016 50
Switch(config)#show system-time dst
DST starts at 01:00:00 on Aug 1 2016
DST ends at 01:00:00 on Sep 1 2016
DST offset is 50 minutes
DST configuration is one-off
Switch(config)#end
Switch#copy running-config startup-config
2.2.5 Specifying the System IP
Note:
Before configuring Management VLAN, make sure the VLAN will be set as the management VLAN is
configured correctly and at least one port’s PVID is set as the management VLAN ID.
Configuration Guide
35
Page 57

Managing System System Info Configurations
Follow these steps and choose one method to specify the system IP:
Step 1 configure
Enter global configuration mode.
Step 2 ip management-vlan
Specify the ID for management VLAN. Only the members belong to the management VLAN
can access to the switch.
: Enter the ID for management VLAN.
vlan-id
Step 3 interface vlan
Enter the Interface Configuration Mode of the management VLAN.
: Enter the IEEE 802.1Q VLAN ID of the management VLAN, ranging from 1 to 4094.
vlan-id
Step 4 Use the following command to specify the network parameters manually.
ip address {
Specify the system lP of the switch manually.
ip-addr
ip-mask
gateway
Use the following command to let the switch obtain network parameters from DHCP server or
BOOTP server.
ip-addr
: Enter the system IP for the switch. By default, it is 192.168.0.1.
: Enter the subnet mask for the switch. By default, it is 255.255.255.0.
: Enter the gateway for the switch.
vlan-id
vlan-id
} {
ip-mask
} [
gateway
]
ip address-alloc { dhcp | bootp }
Specify the method how the switch obtains network parameters.
dhcp: Select to let the switch obtain network parameters from DHCP server.
bootp: Select to let the switch obtain network parameters from BOOTP server.
Step 5 end
Return to privileged EXEC mode.
Step 6 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to set the management VLAN as VLAN 2. Set the IP
address as 192.168.0.12 and set the subnet mask as 255.255.255.0.
Switch#configure
Switch(config)#ip management-vlan 2
#2006-01-01 08:08:44,[NETIF]/5/Line protocol on Interface Vlan1, changed state to down
by admin on vty0 (192.168.0.100).
#2006-01-01 08:09:19,[NETIF]/5/Line protocol on Interface Vlan2, changed state to up.
Configuration Guide 36
Page 58

Managing System System Info Configurations
Switch(config)#interface vlan 2
Switch(config-if)#ip address 192.168.0.12 255.255.255.0
Configuration Guide
37
Page 59

Managing System User Management Configurations
3
User Management Configurations
With user management configurations, you can:
Create Admin accounts
Create accounts of other types
3.1 Using the GUI
3.1.1 Creating Admin Accounts
Choose the menu System > User Management > User Config to load the following page.
Figure 3-1 Create Admin Accounts
Follow these steps to create an Admin account:
1) In the User Info section, select Admin from the drop-down list and specify the user
name and password.
User Name Create a user name for users' login. It contains 16 characters at most,
composed of digits, English letters and underscore only.
Configuration Guide 38
Page 60

Managing System User Management Configurations
Access Level Select the access level as Admin.
Admin: Admin can edit, modify and view all the settings of different
functions.
Operator: Operator can edit, modify and view most of the settings of
different functions.
Power User: Power User can edit, modify and view some of the settings of
different functions.
User: User can only view the settings without the right to edit or modify.
Password Type a password for users' login. It is a string from 1 to 31 alphanumeric
characters or symbols. You can use digits, English letters (case sensitive),
underscore and sixteen special characters.
Confirm
Password
Retype the password.
2) Click Create.
3.1.2 Creating Accounts of Other Types
You can create accounts with the access level of Operator,Power User and User here. You
also need to go to the AAA section to create an Enable Password for these accounts. The
Enable Password is used to change the users’ access level to Admin.
Creating an Account
Choose the menu System > User Management > User Config to load the following page.
Figure 3-2 Create Accounts of Other Types
Follow these steps to create an account of other types:
1) In the User Info section, select the access level from the drop-down list and specify the
user name and password.
Configuration Guide
39
Page 61

Managing System User Management Configurations
User Name Create a user name for users' login. It contains 16 characters at most,
composed of digits, English letters and under dashes only.
Access Level Select the access level as Operator, Power User or User.
Admin: Admin can edit, modify and view all the settings of different
functions.
Operater: Operator can edit, modify and view most of the settings of
different functions.
Power User: Power User can edit, modify and view some of the settings of
different functions.
User: User can only view the settings without the right to edit or modify.
Password Type a password for users' login. It is a string from 1 to 31 alphanumeric
characters or symbols. You can use digits, English letters (case sensitive),
underscore and sixteen special characters.
Confirm
Password
Retype the password.
2) Click Create.
Configuring Enable Password
Choose the menu Network Security > AAA > Global Config to load the following page.
Figure 3-3 Configure the AAA Function
1) Select Enable and Click Apply to enable the AAA function.
2) Specify the Enable Password and Click Apply.
Tips:
The AAA function applies another method to manage the access users' name and
password. For details, refer to
The logged-in users can enter the Enable Password on this page to get the
AAA Configuration
in
Configuring Network Security.
administrative privileges.
Configuration Guide 40
Page 62

Managing System User Management Configurations
3.2 Using the CLI
3.2.1 Creating Admin Accounts
Follow these steps to create an Admin account:
Step 1 configure
Enter global configuration mode.
Step 2 Use the following command to create an account unencrypted or symmetric encrypted.
user name
Create an account whose access level is Admin.
: Enter a user name for users’ login. It contains 16 characters at most, composed of
name
digits, English letters and underscore only.
admin: Select the access level for the user. Admin can edit, modify and view all the settings of
different functions.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, and
the password is saved to the configuration file unencrypted. By default, the encryption type is 0.
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
7: Specify the encryption type. 7 indicates that the password you entered is symmetric
encrypted, and the password is saved to the configuration file symmetric encrypted.
encrypted-password
copy from another switch’s configuration file. After the encrypted password is configured, you
should use the corresponding unencrypted password to reenter this mode.
Use the following command to create an account MD5 encrypted.
user name
: Enter a password for users’ login. It is a string from 1 to 31 alphanumeric characters
{ privilege admin } password { [ 0 ]
name
: Enter a symmetric encrypted password with fixed length, which you can
{ privilege admin } secret { [ 0 ]
name
password
password
| 7
encrypted-password
| 5
encrypted-password
}
}
Create an account whose access level is Admin.
: Enter a user name for users’ login. It contains 16 characters at most, composed of
name
digits, English letters and underscore only.
admin: Select the access level for the user. Admin can edit, modify and view all the settings of
different functions.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, but
the password is saved to the configuration file MD5 encrypted. By default, the encryption type
is 0.
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
5: Specify the encryption type. 5 indicates that the password you entered is MD5 encrypted,
and the password is saved to the configuration file MD5 encrypted.
encrypted-password
from another switch’s configuration file.
: Enter a password for users’ login. It is a string from 1 to 31 alphanumeric characters
: Enter a MD5 encrypted password with fixed length, which you can copy
Configuration Guide
41
Page 63

Managing System User Management Configurations
Step 3 show user account-list
Verify the information of the current users.
Step 4 end
Return to privileged EXEC mode.
Step 5 copy running-config startup-config
Save the settings in the configuration file.
3.2.2 Creating Accounts of Other Types
You can create accounts with the access level of Operator, Power user and User here. You
also need to go to the AAA section to create an Enable Password for these accounts. The
Enable Password is used to change the users’ access level to Admin.
Follow these steps to create an account of other type:
Step 1 configure
Enter global configuration mode.
Configuration Guide 42
Page 64

Managing System User Management Configurations
Step 2 Use the following command to create an account unencrypted or symmetric encrypted.
user name
encrypted-password
Create an account whose access level is Operator, Power User or User.
: Enter a user name for users’ login. It contains 16 characters at most, composed of
name
digits, English letters and underscore only.
operator | power_user | user: Select the access level for the user. Operator can edit, modify
and view mostly the settings of different functions. Power User can edit, modify and view some
the settings of different functions. User only can view the settings without the right to edit and
modify.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, and
the password is saved to the configuration file unencrypted. By default, the encryption type is 0.
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
7: Specify the encryption type. 7 indicates that the password you entered is symmetric
encrypted, and the password is saved to the configuration file symmetric encrypted.
: Enter a password for users’ login. It is a string from 1 to 31 alphanumeric characters
encrypted-password
copy from another switch’s configuration file. After the encrypted password is configured, you
should use the corresponding unencrypted password to reenter this mode.
{ privilege operator | power_user | user } password { [ 0 ]
name
}
: Enter a symmetric encrypted password with fixed length, which you can
password
| 7
Use the following command to create an account MD5 encrypted.
user name
password
Create an account whose access level is Operator, Power User or User.
name
digits, English letters and underscore only.
operator | power_user | user: Select the access level for the user. Operator can edit, modify
and view mostly the settings of different functions. Power User can edit, modify and view some
the settings of different functions. User only can view the settings without the right to edit and
modify.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, but
the password is saved to the configuration file MD5 encrypted. By default, the encryption type
is 0.
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
5: Specify the encryption type. 5 indicates that the password you entered is MD5 encrypted,
and the password is saved to the configuration file MD5 encrypted.
}
: Enter a user name for users’ login. It contains 16 characters at most, composed of
: Enter a password for users’ login. It is a string from 1 to 31 alphanumeric characters
encrypted-password
from another switch’s configuration file. After the encrypted password is configured, you
should use the corresponding unencrypted password to reenter this mode.
{ privilege operator | power_user | user } secret { [ 0 ]
name
: Enter a MD5 encrypted password with fixed length, which you can copy
password
| 5
encrypted-
Step 3 aaa enable
Globally enable the AAA function.
Configuration Guide
43
Page 65

Managing System User Management Configurations
Step 4 Use the following command to create an enable password unencrypted or symmetric
encrypted.
enable admin password { [ 0 ]
Create an Enable Password. It can change the users’ access level to Admin. By default, it is
empty.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, and
the password is saved to the configuration file unencrypted. By default, the encryption type is 0.
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
7: Specify the encryption type. 7 indicates that the password you entered is symmetric
encrypted, and the password is saved to the configuration file symmetric encrypted.
encrypted-password
copy from another switch’s configuration file. After the encrypted password is configured, you
should use the corresponding unencrypted password to reenter this mode.
Use the following command to create an enable password unencrypted or MD5 encrypted.
enable admin secret { [ 0 ]
Create an Enable Password. It can change the users’ access level to Admin. By default, it is
empty.
0: Specify the encryption type. 0 indicates that the password you entered is unencrypted, but
the password is saved to the configuration file MD5 encrypted. By default, the encryption type
is 0.
: Enter an enable password. It is a string from 1 to 31 alphanumeric characters
: Enter a symmetric encrypted password with fixed length, which you can
password
password
| 7
encrypted-password
| 5
encrypted-password
}
}
password
or symbols. The password is case sensitive, allows digits, English letters (case sensitive),
underlines and sixteen special characters.
5: Specify the encryption type. 5 indicates that the password you entered is MD5 encrypted,
and the password is saved to the configuration file MD5 encrypted.
encrypted-password
from another switch’s configuration file. After the encrypted password is configured, you
should use the corresponding unencrypted password to reenter this mode.
Step 5 show user account-list
Verify the information of the current users.
Step 6 end
Return to privileged EXEC mode.
Step 7 copy running-config startup-config
Save the settings in the configuration file.
: Enter an enable password. It is a string from 1 to 31 alphanumeric characters
: Enter a MD5 encrypted password with fixed length, which you can copy
Tips:
The AAA function applies another method to manage the access users’ name and
password. For details, refer to
AAA Configuration
in
Configuring Network Security
.
The logged-in users can enter the Enable Password on this page to get the
administrative privileges.
Configuration Guide 44
Page 66

Managing System User Management Configurations
The following example shows how to create a uesr with the access level of Operator, set
the user name as user1 and set the password as 123. Enable AAA function and set the
enable password as abc123.
Switch#configure
Switch(config)#user name user1 privilege operator password 123
Switch(config)#aaa enable
Switch(config)#enable admin password abc123
Switch(config)#show user account-list
Index User-Name User-Type
----- --------- ---------
1 user1 Operator
2 admin Admin
Switch(config)#end
Switch#copy running-config startup-config
Configuration Guide
45
Page 67

Managing System System Tools Configurations
4
System Tools Configurations
With system tools configurations, you can:
Configure the boot file
Restore the configuration of the switch
Back up the configuration file
Upgrade the firmware
Reboot the switch
Reset the switch
4.1 Using the GUI
4.1.1 Configuring the Boot File
Choose the menu System > System Tools > Boot Config to load the following page.
Figure 4-1 Configuring the Boot File
Follow these steps to configure the boot file:
1) In the Boot Table section, select one or more units and configure the relevant
parameters.
Select Select one or more units to be configured.
Configuration Guide 46
Page 68

Managing System System Tools Configurations
Unit Displays the number of the unit.
Current Startup
Image
Next Startup
Image
Backup Image Select the backup image. When the switch fails to start up with the next startup
Displays the current startup image.
Select the next startup image. When the switch is powered on, it will try to start up
with the next startup image. The next startup and backup image should not be the
same.
image, it will try to start up with the backup image. The next startup and backup
image should not be the same.
2) Click Apply.
4.1.2 Restoring the Configuration of the Switch
Choose the menu System > System Tools > Config Restore to load the following page.
Figure 4-2 Restoring the Configuration of the Switch
Follow these steps to restore the configuration of the switch:
1) In the Config Restore section, select one unit and one configuration file.
Target Unit Select a member switch to import configuration file. .
Config file Select the desired configuration file to import.
2) Click Import to import the configuration file.
Note:
It will take a long time to restore the configuration. Please wait without any operation.
•
After the configuration is restored successfully, the device will reboot to make the configura-
•
tion change effective.
Configuration Guide
47
Page 69

Managing System System Tools Configurations
4.1.3 Backing up the Configuration File
Choose the menu System > System Tools > Config Backup to load the following page.
Figure 4-3 Backing up the Configuration File
In the Config Backup section, select one unit and click Export to export the configuration
file.
4.1.4 Upgrading the Firmware
Choose the menu System > System Tools > Firmware Upgrade to load the following
page.
Figure 4-4 Upgrading the Firmware
In the Firmware Upgrade section, select one file and click Upgrade to upgrade the system.
Firmware File Select the desired firmware file to upgrade the system.
Image Name Displays the image to upgrade. It means that the operation will only effect the
backup image.
Firmware Version Displays the current firmware version of the system.
Hardware Version
Displays the current hardware version of the system.
Configuration Guide 48
Page 70

Managing System System Tools Configurations
After upgrading, the
device will reboot
automatically with
the backup image
Select this option to reboot automatically with the backup image after upgrading.
4.1.5 Rebooting the switch
Choose the menu System > System Tools > System Reboot to load the following page.
Figure 4-5 Rebooting the switch
In the System Reboot section, select the desired unit and click Reboot.
Target Unit Select the desired unit to reboot. By default, it is ALL Unit.
Save Config Select this option to save the configuration before the reboot.
4.1.6 Reseting the Switch
Choose the menu System > System Tools > System Reset to load the following page.
Figure 4-6 Reseting the Switch
In the System Reset section, select the desired unit and click Reset.
Target Unit Select the desired unit to reset. By default, it is ALL Unit.
Note:
After the system is reset, configurations of the switch will be reset to the default.
Configuration Guide
49
Page 71

Managing System System Tools Configurations
4.2 Using the CLI
4.2.1 Configuring the Boot File
Follow these steps to configure the boot file:
Step 1 configure
Enter global configuration mode.
Step 2 boot application filename { image1 | image2 } { startup | backup }
Specify the configuration of the boot file. By default, the image1.bin is the startup image and
the image2.bin is the backup image.
image1 | image2: Select the image file to be configured.
startup | backup: Select the property of the image file.
Step 3 show boot
Verify the boot configuration of the system.
Step 4 end
Return to privileged EXEC mode.
Step 5 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to set the next startup image as image 1 and set the
backup image as image 2.
Switch#configure
Switch(config)#boot application filename image1 startup
Switch(config)#boot application filename image2 backup
Switch(config)#show boot
Boot config:
Current Startup Image - image1.bin
Next Startup Image - image1.bin
Backup Image - image2.bin
Switch(config)#end
Switch#copy running-config startup-config
4.2.2 Restoring the Configuration of the Switch
Follow these steps to restore the configuration of the switch:
Configuration Guide 50
Page 72

Managing System System Tools Configurations
Step 1 enable
Enter privileged mode.
Step 2 copy tftp startup-config ip-address
Download the configuration file to the switch from TFTP server.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
: Specify the name of the configuration file to be downloaded.
name
ip-addr
filename
name
Note:
It will take a long time to restore the configuration. Please wait without any operation.
•
After the configuration is restored successfully, the device will reboot to make the configura-
•
tion change effective.
The following example shows how to restore the configuration file named file1 from the
TFTP server with IP address 192.168.0.100.
Switch>enable
Switch#copy tftp startup-config ip-address 192.168.0.100 filename file1
Start to load user config file......
Operation OK! Now rebooting system......
4.2.3 Backing up the Configuration File
Follow these steps to back up the current configuration of the switch in a file:
Step 1 enable
Enter privileged mode.
Step 2 copy startup-config tftp ip-address
Back up the configuration file to TFTP server.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
: Specify the name of the configuration file to be saved.
name
The following example shows how to backup the configuration file named file2 from TFTP
server with IP address 192.168.0.100.
Switch>enable
ip-addr
filename
name
Switch#copy startup-config tftp ip-address 192.168.0.100 filename file2
Start to backup user config file......
Backup user config file OK.
Configuration Guide
51
Page 73

Managing System System Tools Configurations
4.2.4 Upgrading the firmware
Follow these steps to upgrade the firmware:
Step 1 enable
Enter privileged mode.
Step 2 firmware upgrade ip-address
Upgrade the switch’s backup image via TFTP server. To boot up with the new firmware, you
need to choose to reboot the switch with the backup image.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
: Specify the name of the desired firmware file.
name
Step 3 Enter Y to continue then enter Y to reboot.
ip-addr
filename
name
The following example shows how to upgrade the firmware using the configuration file
named file3.bin. The TFTP server is 190.168.0.100.
Switch>enable
Switch#firmware upgrade ip-address 192.168.0.100 filename file3.bin
It will only upgrade the backup image. Continue? (Y/N):Y
Operation OK!
Reboot with the backup image? (Y/N): Y
4.2.5 Rebooting the switch
Follow these steps to reboot the switch:
Step 1 enable
Enter privileged mode.
Step 2 reboot
Reboot the switch.
4.2.6 Reseting the Switch
Follow these steps to reset the switch:
Step 1 enable
Enter privileged mode.
Step 2 reset
Reset the switch.
Configuration Guide 52
Page 74

Managing System System Tools Configurations
Note:
After the system is reset, configurations of the switch will be reset to the default.
Configuration Guide
53
Page 75

Managing System Access Security Configurations
5
Access Security Configurations
With access security configurations, you can:
Configure the Access Control feature
Configure the HTTP feature
Configure the HTTPS feature
Configure the SSH feature
Enable the telnet function
5.1 Using the GUI
5.1.1 Configuring the Access Control Feature
Choose the menu System > Access Security > Access Control to load the following page.
Figure 5-1 Configuring the Access Control
1) In the Access Control section, select one control mode and specify the parameters.
Control Mode Select the control mode for users to log in to the web management page.
Disable: The Access Control function is disabled.
IP-based: Only the users within the IP-range you set here are allowed to access
the switch.
MAC-based: Only the users with the MAC address you set here are allowed to
access the switch.
Port-based: Only the users connecting to the ports you set here are allowed to
access the switch.
Configuration Guide 54
Page 76

Managing System Access Security Configurations
Access
Interface
IP Address/
Mask
MAC Address
Select the interface to control the methods for users’ accessing. The selected
access interfaces will only affect the users you set before.
SNMP: A function to manage the network devices via NMS.
Telnet: A connection type for users to remote login.
SSH: A connection type based on SSH protocol.
HTTP: A connection type based on HTTP protocol.
HTTPS: A connection type based on SSL protocol.
Ping: A communication protocol to test the connection of the network.
If you select IP-based mode, enter the IP address and mask to specify an IP
range. Only the users within this IP range can access the switch.
If you select MAC-based mode, specify the MAC address. Only the users with the
correct MAC address can access the switch.
When the IP-based mode is selected, the following section will display.
IP Address Displays the IP range of the entry.
Access
Interface
Operation
Displays the access interface you set of the entry.
Click Edit to modify the parameters of the desired entry.
When the Port-based mode is selected, the following section will display.
Port Select one or more ports to configure. Only the users connected to these ports are
allowed to access the switch.
2) Click Apply.
Configuration Guide
55
Page 77

Managing System Access Security Configurations
5.1.2 Configuring the HTTP Function
Choose the menu System > Access Security > HTTP Config to load the following page.
Figure 5-2 Configuring the HTTP Function
1) In the Global Control section, Select Enable and click Apply to enable the HTTP
function.
HTTP HTTP function is based on the HTTP protocol. It allows users to manage the
switch through a web browser.
2) In the Session Config section, specify the Session Timeout and click Apply.
Session
Timeout
The system will log out automatically if users do nothing within the Session
Timeout time.
3) In the Access User Number section, select Enable and specify the parameters.
Number Control Select Enable to control the number of the users logging on to the web
management page at the same time. The total number of users should be no more
than 16.
Admin Number Specify the maximum number of users whose access levels are Admin.
Operator
Number
Power User
Number
Specify the maximum number of users whose access levels are Operatorr.
Specify the maximum number of users whose access levels are Power User.
User Number Specify the maximum number of users whose access levels are User.
4) Click Apply.
Configuration Guide 56
Page 78

Managing System Access Security Configurations
5.1.3 Configuring the HTTPS Function
Choose the menu System > Access Security > HTTPS Config to load the following page.
Table 5-1 Configuring the HTTPS Function
1) In the Global Config section, select Enable to enable HTTPS function and select the
protocol the switch supports. Click Apply.
HTTPS Select Enable to enable the HTTPS function.
HTTPS function is based on the SSL or TLS protocol. It provides a secure
connection between the client and the switch.
Configuration Guide
57
Page 79

Managing System Access Security Configurations
SSL Version 3 Select Enable to make the switch support SSL Version 3 protocol.
SSL is a transport protocol. It can provide server authentication, encryption and
message integrity to allow secure HTTP connection.
TLS Version 1 Select Enable to make the switch support TLS Version 1 protocol.
TLS is a transport protocol upgraded from SSL. It supports a different encryption
algorithm from SSL, so TLS and SSL are not compatible. TLS can support a more
secure connection.
2) In the CipherSuite Config section, select the algorithm to be enabled and click Apply.
RSA_WITH_
RC4_128_MD5
RSA_WITH_
RC4_128_SHA
RSA_WITH_
DES_CBC_SHA
RSA_
WITH_3DES_
EDE_CBC_SHA
Key exchange with RC4 128-bit encryption and MD5 for message digest.
Key exchange with RC4 128-bit encryption and SHA for message digest.
Key exchange with DES-CBC for message encryption and SHA for message
digest.
Key exchange with 3DES and DES-EDE3-CBC for message encryption and SHA
for message digest.
3) In the Session Config section, specify the Session Timeout and click Apply.
Session
Timeout
The system will log out automatically if users do nothing within the Session
Timeout time.
4) In the Access User Number section, select Enable and specify the parameters. Click
Apply.
Number Control Select Enable to control the number of the users logging in to the web
management page at the same time.
Admin Number Specify the maximum number of users whose access levels are Admin.
Operator
Number
Power User
Number
User Number Specify the maximum number of users whose access levels are User.
Specify the maximum number of users whose access levels are Operator.
Specify the maximum number of users whose access levels are Power User.
5) In the Certificate Download and Key Download section, download the certificate and
key.
Certificate File Select the desired certificate to download to the switch. The certificate must be
BASE64 encoded. The SSL certificate and key downloaded must match each
other, otherwise the HTTPS connection will not work.
Configuration Guide 58
Page 80

Managing System Access Security Configurations
Key File Select the desired Key to download to the switch. The key must be BASE64
encoded. The SSL certificate and key downloaded must match each other,
otherwise the HTTPS connection will not work.
5.1.4 Configuring the SSH Feature
Choose the menu System > Access Security > SSH Config to load the following page.
Figure 5-3 Configuring the SSH Feature
1) In the Global Config section, select Enable to enable SSH function and specify other
parameters.
SSH Select Enable to enable the SSH function.
SSH is a protocol working in application layer and transport layer. It can provide a
secure, remote connection to a device. It is more secure than Telnet protocol as it
provides strong encryption.
Protocol V1 Select Enable to enable SSH version 1.
Protocol V2 Select Enable to enable SSH version 2.
Idle Timeout Specify the idle timeout time. The system will automatically release the
connection when the time is up.
Configuration Guide
59
Page 81

Managing System Access Security Configurations
Max Connect Specify the maximum number of the connections to the SSH server. New
connection will not be established when the number of the connections reaches
the maximum number you set.
2) In the Encryption Algorithm section, select the encryption algorithm you want the
switch to support and click Apply.
3) In Data Integrity Algorithm section, select the integrity algorithm you want the switch
to support and click Apply.
4) In Key Download section, select key type from the drop-down list and select the
desired key file to down.
Key Type Select the key type. The algorithm of the corresponding type is used for both key
generation and authentication.
Key File Select the desired public key to download to the switch. The key length of the
downloaded file ranges of 512 to 3072 bits.
Note:
It will take a long time to download the key file. Please wait without any operation.
5.1.5 Enabling the Telnet Function
Choose the menu System > Access Security > Telnet Config to load the following page.
Figure 5-4 Configuring the Telnet Function
In Global Config section, select Enable and click Apply.
Telnet Select Enable to make the Telnet function effective. Telnet function is based on the
Telnet protocol subjected to TCP/IP protocol. It allows users to log on to the switch
remotely.
5.2 Using the CLI
5.2.1 Configuring the Access Control
Follow these steps to configure the access control:
Step 1 configure
Enter global configuration mode.
Configuration Guide 60
Page 82

Managing System Access Security Configurations
Step 2 Use the following command to control the users’ access by limiting the IP address:
user access-control ip-based {
] [ all ]
Only the users within the IP-range you set here are allowed to access the switch.
: Specify the IP address of the user.
ip-addr
ip-mask
[ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping ] [ all ]: Select to control the types for users’
accessing. By default, these types are all enabled.
Use the following command to control the users’ access by limiting the MAC address:
user access-control mac-based {
all ]
Only the users with the MAC address you set here are allowed to access the switch.
mac-addr
[ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping ] [ all ]: Select to control the types for users’
accessing. By default, these types are all enabled.
Use the following command to control the users’ access by limiting the ports connected to the
users:
: Specify the subnet mask of the user.
: Specify the MAC address of the user.
ip-addr ip-mask
mac-addr
} [ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping
} [ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping ] [
user access-control port-based interface { fastEthernet
ten-gigabitEthernet
Only the users connecting to the ports you set here are allowed to access the switch.
: Specify the list of Ethernet port, in the format of 1/0/1-4. You can appoint 5 ports at
port-list
most.
[ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping ] [ all ]: Select to control the types for users’
accessing. By default, these types are all enabled.
Step 3 show user configuration
Verify the security configuration information of the user authentication information and the
access interface.
Step 4 end
Return to privileged EXEC mode.
Step 5 copy running-config startup-config
Save the settings in the configuration file.
} [ snmp ] [ telnet ] [ ssh ] [ http ] [ https ] [ ping ] [ all ]
port-list
| gigabitEthernet
port-list
port-list
|
The following example shows how to set the type of access control as IP-based. Set the
IP address as 192.168.0.100,set the subnet mask as 255.255.255.0 and make the switch
support snmp, telnet, http and https.
Switch#configure
Switch(config)#user access-control ip-based 192.168.0.100 255.255.255.0 snmp telnet
http https
Switch(config)#show user configuration
Configuration Guide
61
Page 83

Managing System Access Security Configurations
User authentication mode: IP based
Index IP Address Access Interface
----- ----------------- -------------------------------
1 192.168.0.0/24 SNMP Telnet HTTP HTTPS
Switch(config)#end
Switch#copy running-config startup-config
5.2.2 Configuring the HTTP Function
Follow these steps to configure the HTTP function:
Step 1 configure
Enter global configuration mode.
Step 2 ip http server
Enable the HTTP function. By default, it is enabled.
Step 3 ip http session timeout
Specify the Session Timeout time. The system will log out automatically if users do nothing
within the Session Timeout time.
minutes
Step 4 ip http max-users
Specify the maximum number of users that are allowed to connect to the HTTP server. The
total number of users should be no more than 16.
admin-num
are from 1 to 16.
operator-num
User or User. The valid values are from 0 to 15.
power-user-num
valid values are from 0 to 15.
user-num
are from 0 to 15.
: Specify the timeout time, which ranges from 5 to 30 minutes. The default value is 10.
admin-num operator-num power-user-num user-num
: Enter the maximum number of users whose access level is Admin. The valid values
: Enter the maximum number of users whose access level is Operator, Power
: Enter the maximum number of users whose access level is Power User,. The
: Enter the maximum number of users whose access level is User,. The valid values
minutes
Step 5 show ip http configuration
Verify the configuration information of the HTTP server, including status, session timeout,
access-control, max-user number and the idle-timeout, etc.
Step 6 end
Return to privileged EXEC mode.
Step 7 copy running-config startup-config
Save the settings in the configuration file.
Configuration Guide 62
Page 84

Managing System Access Security Configurations
The following example shows how to set the session timeout as 9, set the maximum admin
number as 6, and set the maximum guest number as 5.
Switch#configure
Switch(config)#ip http server
Switch(config)#ip http session timeout 9
Switch(config)#ip http max-user 6 5
Switch(config)#show ip http configuration
HTTP Status: Enabled
HTTP Session Timeout: 9
HTTP User Limitation: Enabled
HTTP Max Admin Users: 6
HTTP Max Guest Users: 5
Switch(config)#end
Switch#copy running-config startup-config
5.2.3 Configuring the HTTPS Function
Follow these steps to configure the HTTPS function:
Step 1 configure
Enter global configuration mode.
Step 2 ip http secure-server
Enable the HTTPS function. By default, it is enabled.
Step 3 ip http secure-protocol { [ ssl3 ] [ tls1 ] }
Configure to make the switch support the corresponding protocol. By default, the switch
supports SSLv3 and TLSv1.
ssl3: Enable the SSL version 3 protocol. SSL is a transport protocol. It can provide server
authentication, encryption and message integrity to allow secure HTTP connection.
tls1: Enable the TLS version 1 protocol. TLS is s transport protocol upgraded from SSL. It
supports different encryption algorithm from SSL, so TLS and SSL are not compatible. TLS
can support a more secure connection.
Configuration Guide
63
Page 85

Managing System Access Security Configurations
Step 4 ip http secure-ciphersuite { [ 3des-ede-cbc-sha ] [ rc4-128-md5 ] [ rc4-128-sha ] [ des-cbc-
sha ] }
Enable the corresponding ciphersuite. By default, these types are all enabled.
[ 3des-ede-cbc-sha ]: Key exchange with 3DES and DES-EDE3-CBC for message encryption
and SHA for message digest.
[ rc4-128-md5 ]: Key exchange with RC4 128-bit encryption and MD5 for message digest.
[ rc4-128-sha ]: Key exchange with RC4 128-bit encryption and SHA for message digest.
[ des-cbc-sha ]: Key exchange with DES-CBC for message encryption and SHA for message
digest.
Step 5 ip http secure-session timeout
Specify the Session Timeout time. The system will log out automatically if users do nothing
within the Session Timeout time.
minutes
Step 6 ip http secure-max-users
Specify the maximum number of users that are allowed to connect to the HTTPS server. The
total number of users should be no more than 16.
admin-num
are from 1 to 16.
operator-num
User or User. The valid values are from 0 to 15.
power-user-num
valid values are from 0 to 15.
user-num
are from 0 to 15.
Step 7 ip http secure-server download certificate
Download the desired certificate to the switch from TFTP server.
: Specify the timeout time, which ranges from 5 to 30 minutes. The default value is 10.
: Enter the maximum number of users whose access level is Admin. The valid values
: Enter the maximum number of users whose access level is Operator, Power
: Enter the maximum number of users whose access level is Power User,. The
: Enter the maximum number of users whose access level is User,. The valid values
minutes
admin-num operator-num power-user-num user-num
ssl-cert
ip-address
ip-addr
: Specify the name of the SSL certificate, which ranges from 1 to 25 characters. The
ssl-cert
certificate must be BASE64 encoded. The SSL certificate and key downloaded must match
each other.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
Step 8 ip http secure-server download key
Download the desired key to the switch from TFTP server.
: Specify the name of the key file saved in TFTP server. The key must be BASE64
ssl-key
encoded.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
Step 9 show ip http secure-server
Verify the global configuration of HTTPS.
ssl-key
ip-address
ip-addr
Configuration Guide 64
Page 86

Managing System Access Security Configurations
Step 10 end
Return to privileged EXEC mode.
Step 11 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to configure the HTTPS function. Enable SSL3 and TLS1
protocol. Enable the ciphersuite of 3des-ede-cbc-sha. Set the session timeout time as 15,
the admin number as 1 and the guest number as 2. Download the certificate named ca.crt
and the key named ca.key from the TFTP server with the IP address 192.168.0.100.
Switch#configure
Switch(config)#ip http secure-server
Switch(config)#ip http secure-protocol ssl3 tls1
Switch(config)#ip http secure-ciphersuite 3des-ede-cbc-sha
Switch(config)#ip http secure-session timeout 15
Switch(config)#ip http secure-max-users 1 2
Switch(config)#ip http secure-server download certificate ca.crt ip-address
192.168.0.100
Start to download SSL certificate......
Download SSL certificate OK.
Switch(config)#ip http secure-server download key ca.key ip-address 192.168.0.100
Start to download SSL key......
Download SSL key OK.
Switch(config)#show ip http secure-server
HTTPS Status: Enabled
SSL Protocol Level(s): ssl3 tls1
SSL CipherSuite: 3des-ede-cbc-sha
HTTPS Session Timeout: 15
HTTPS User Limitation: Enabled
HTTPS Max Admin Users: 1
HTTPS Max Guest Users: 2
Switch(config)#end
Switch#copy running-config startup-config
Configuration Guide
65
Page 87

Managing System Access Security Configurations
5.2.4 Configuring the SSH Feature
Follow these steps to configure the SSH function:
Step 1 configure
Enter global configuration mode.
Step 2 ip ssh server
Enable the SSH function. By default, it is disabled.
Step 3 ip ssh version { v1 | v2 }
Configure to make the switch support the corresponding protocol. By default, the switch
supports SSHv1 and SSHv3.
v1 | v2: Select to enable the corresponding protocol.
Step 4 ip ssh timeout
Specify the idle timeout time. The system will automatically release the connection when the
time is up.
: Enter the value of the timeout time, which ranges from 1 to 120 seconds. The default
value
value is 120 seconds.
Step 5 ip ssh max-client
Specify the maximum number of the connections to the SSH server. New connection will not
be established when the number of the connections reaches the maximum number you set.
: Enter the number of the connections, which ranges from 1 to 5. The default value is 5.
num
Step 6 ip ssh algorithm { AES128-CBC | AES192-CBC | AES256-CBC | Blowfish-CBC | Cast128-CBC |
3DES-CBC | HMAC-SHA1 | HMAC-MD5 }
Enable the corresponding algorithm. By default, these types are all enabled.
AES128-CBC | AES192-CBC | AES256-CBC | Blowfish-CBC | Cast128-CBC | 3DES-CBC:
Specify the encryption algorithm you want the switch supports.
HMAC-SHA1 | HMAC-MD5: Specify the data integrity algorithm you want the switch supports.
Step 7 ip ssh download { v1 | v2 }
value
num
key-file
ip-address
ip-addr
Select the type of the key file and download the desired file to the switch from TFTP server.
v1 | v2: Select the key type. The algorithm of the corresponding type is used for both key
generation and authentication.
: Specify the name of the key file saved in TFTP server. Ensure the key length of the
key-file
downloaded file is in the range of 512 to 3072 bits.
: Specify the IP address of the TFTP server. Both IPv4 and IPv6 addresses are
ip-addr
supported.
Step 8 show ip ssh
Verify the global configuration of SSH.
Configuration Guide 66
Page 88

Managing System Access Security Configurations
Step 9 end
Return to privileged EXEC mode.
Step 10 copy running-config startup-config
Save the settings in the configuration file.
Note:
It will take a long time to download the key file. Please wait without any operation.
The following example shows how to configure the SSH function. Set the version as SSH
V1 and SSH V2. Enable the AES128-CBC and Cast128-CBC encryption algorithm. Enable
the HMAC-MD5 data integrity algorithm. Choose the key type as SSH-2 RSA/DSA.
Switch(config)#ip ssh server
Switch(config)#ip ssh version v1
Switch(config)#ip ssh version v2
Switch(config)#ip ssh timeout 100
Switch(config)#ip ssh max-client 4
Switch(config)#ip ssh algorithm AES128-CBC
Switch(config)#ip ssh algorithm Cast128-CBC
Switch(config)#ip ssh algorithm HMAC-MD5
Switch(config)#ip ssh download v2 publickey ip-address 192.168.0.100
Start to download SSH key file......
Download SSH key file OK.
Switch(config)#show ip ssh
Global Config:
SSH Server: Enabled
Protocol V1: Enabled
Protocol V2: Enabled
Idle Timeout: 100
MAX Clients: 4
Encryption Algorithm:
AES128-CBC: Enabled
AES192-CBC: Disabled
AES256-CBC: Disabled
Configuration Guide
67
Page 89

Managing System Access Security Configurations
Blowfish-CBC: Disabled
Cast128-CBC: Enabled
3DES-CBC: Disabled
Data Integrity Algorithm:
HMAC-SHA1: Disabled
HMAC-MD5: Enabled
Key Type: SSH-2 RSA/DSA
Key File:
---- BEGIN SSH2 PUBLIC KEY ----
Comment: “dsa-key-20160711”
Switch(config)#end
Switch#copy running-config startup-config
5.2.5 Enabling the Telnet Function
Follow these steps enable the Telnet function:
Step 1 configure
Enter global configuration mode.
Step 2 telnet enable
Enable the telnet function. By default, it is enabled.
Step 3 end
Return to privileged EXEC mode.
Step 4 copy running-config startup-config
Save the settings in the configuration file.
Configuration Guide 68
Page 90

Managing System Appendix: Default Parameters
6
Appendix: Default Parameters
Default settings of System Info are listed in the following tables.
Table 6-1 Default Settings of Device Description Configuration
Parameter Default Setting
Device Name The model name
of the switch.
Device Location SHENZHEN
System Contact www.tp-link.com
Table 6-2 Default Settings of System Time Configuration
Parameter Default Setting
Time Source Manual
System Time 2006-01-01
08:01:56 Sunday
Table 6-3 Default Settings of Daylight Saving Time Configuration
Parameter Default Setting
DST status Disabled
Default settings of User Management are listed in the following table.
Table 6-4 Default Settings of User Configuration
Parameter Default Setting
User Name admin
Password admin
Access Level Admin
Default settings of System Tools are listed in the following table.
Table 6-5 Default Settings of Boot Configuration
Parameter Default Setting
Current Startup Image image1.bin
Next Startup Image image1.bin
Backup Image image2.bin
Configuration Guide
69
Page 91

Managing System Appendix: Default Parameters
Default settings of Access Security are listed in the following tables.
Table 6-6 Default Settings of Access Control Configuration
Parameter Default Setting
Control Mode Disabled
Table 6-7 Default Settings of HTTP Configuration
Parameter Default Setting
HTTP Enabled
Session Timeout 10 minutes
Number Control Disabled
Table 6-8 Default Settings of HTTPS Configuration
Parameter Default Setting
HTTPS Enabled
SSL Version 3 Enabled
TLS Version 1 Enabled
RSA_WITH_RC4_128_MD5 Enabled
RSA_WITH_RC4_128_SHA Enabled
RSA_WITH_DES_CBC_SHA Enabled
RSA_WITH_3DES_EDE_CBC_
SHA
Session Timeout 10 minutes
Number Control Disabled
Table 6-9 Default Settings of SSH Configuration
Parameter Default Setting
SSH Disabled
Protocol V1 Enabled
Protocol V2 Enabled
Idle Timeout 120 seconds
Enabled
Max Connect 5
AES128-CBC Enabled
AES192-CBC Enabled
AES256-CBC Enabled
Blowfish-CBC Enabled
Cast128-CBC Enabled
3DES-CBC Enabled
Configuration Guide 70
Page 92
Managing System Appendix: Default Parameters
Parameter Default Setting
HMAC-SHA1 Enabled
HMAC-MD5 Enabled
Key Type: SSH-2 RSA/DSA
Table 6-10 Default Settings of Telnet Configuration
Parameter Default Setting
Control Mode Enabled
Configuration Guide
71
Page 93

Part 3
Managing Physical Interfaces
CHAPTERS
1. Physical Interface
2. Basic Parameters Configurations
3. Port Mirror Configuration
4. Port Security Configuration
5. Port Isolation Configurations
6. Loopback Detection Configuration
7. Configuration Examples
Page 94

Managing Physical Interfaces Physical Interface
1
Physical Interface
1.1 Overview
Interfaces of a device are used to exchange data and interact with other network devices.
Interfaces are classified into physical interfaces and logical interfaces.
Physical interfaces are the ports on the front panel or rear panel of the switch.
Logical interfaces are manually configured and do not physically exist, such as
loopback interfaces and routing interfaces.
This chapter introduces the configurations for physical interfaces.
1.2 Supported Features
The switch supports the following features about physical interfaces:
Basic Parameters
You can configure port status, speed mode, duplex mode, flow control and other basic
parameters for ports.
Port Mirror
This function allows the switch to forward packet copies of the monitored ports to a
specific monitoring port. Then you can analyze the copied packets to monitor network
traffic and troubleshoot network problems.
Port Security
You can use this feature to limit the number of MAC addresses that can be learned on each
port, thus preventing the MAC address table from being exhausted by the attack packets.
Port Isolation
You can use this feature to restrict a specific port to send packets to only the ports in the
forward-port list that you configure.
Loopback Detection
This function allows the switch to detect loops in the network. When a loop is detected on a
port, the switch will send a trap message, generate an entry on the log file and further block
the corresponding port according to your configurations.
Configuration Guide
73
Page 95

Managing Physical Interfaces Basic Parameters Configurations
2
Basic Parameters Configurations
2.1 Using the GUI
Choose the menu Switching > Port > Port Config to load the following page.
Figure 2-1 Configuring Basic Parameters
Follow these steps to set basic parameters for ports:
1) Set the jumbo frame value and click Apply. The default MTU (Maximum Transmission
Unit) size for frames received and sent on all ports is 1518 bytes. A higher value means
allowing the port to send jumbo frames. The valid values are from 1518 to 9216 bytes.
2) Select and configure your desired ports or LAGs. Then click Apply.
UNIT:1/LAGS Click 1 to configure physical ports. Click LAGS to configure LAGs.
Type Displays the port type. Copper indicates an Ethernet port, and Sfp indicates a fiber
port.
Description Give a port description for identification.
Status With this option enabled, the port forwards packets normally. Otherwise, the port
discards all the received packets. By default, it is enabled.
Configuration Guide 74
Page 96

Managing Physical Interfaces Basic Parameters Configurations
Speed Select the appropriate speed mode for the port. When Auto is selected, the port
autonegotiates speed mode with the connected device. The default setting is Auto.
This value is recommended if both ends of the line support auto-negotiation.
Duplex Select the appropriate duplex mode for the port. There are three options: Half, Full
and Auto. When Auto is selected, the port autonegotiates duplex mode with the
connected device. The default setting is Auto.
Flow Control With this option enabled, the switch synchronizes the data transmission speed with
the peer device, thus avoiding the packet loss caused by congestion. By default, it is
disabled.
Note:
We recommend that you set the ports on both ends of a link as the same speed and duplex mode.
2.2 Using the CLI
Follow these steps to set basic parameters for the ports.
Step 1 configure
Enter global configuration mode.
Step 2 interface { fastEthernet
gigabitEthernet
}
id-list
Enter interface configuration mode.
port-list |
| range fastEthernet port-list | gigabitEthernet
port
port-channel
port-channel-id |
range port-channel
| range
port
port-channel-
Configuration Guide
75
Page 97

Managing Physical Interfaces Basic Parameters Configurations
Step 3 Configure basic parameters for the port:
description
Give a port description for identification.
string
shutdown
no shutdown
Use shutdown to disable the port, and use no shutdown to enable the port. When the
status is enabled, the port can forward packets normally, otherwise it will discard the
received packets. By default, all ports are enabled.
speed { 10 | 100 | 1000 | auto }
Set the appropriate speed mode for the port.
10 | 100 | 1000 | auto: Speed mode of the port. The options are subject to your actual
product. The device connected to the port should be in the same speed and duplex
mode with the port. When auto is selected, the speed mode will be determined by auto
negotiation.
string
: Content of a port description, ranging from 1 to 16 characters.
duplex { auto | full | half }
Set the appropriate duplex mode for the port.
auto | full | half: Duplex mode of the port. The device connected to the port should be in the
same speed and duplex mode with the port. When auto is selected, the duplex mode will be
determined by auto negotiation.
flow-control
Enable the switch to synchronize the data transmission speed with the peer device,
avoiding the packet loss caused by congestion. By default, this feature is disabled.
jumbo-size
Change the MTU (Maximum Transmission Unit) size on the port to support jumbo frames.
The default MTU size for frames received and sent on all ports is 1518 bytes. For the port
with Jumbo enabled, the MTU size is up to 9216 bytes, thus allowing the port to send jumbo
frames.
Step 4 show interface configuration [ fastEthernet
port-channel-id
Verify the configuration of the port or LAG.
Step 5 end
Return to privileged EXEC mode.
size
]
| gigabitEthernet
port
| port-channel
port
Step 6 copy running-config startup-config
Save the settings in the configuration file.
The following example shows how to implement the basic configurations of port1/0/1,
including setting a description for the port, making the port autonegotiate speed and
duplex with the neighboring port, and enabling the flow-control feature.
Switch#configure
Configuration Guide 76
Page 98

Managing Physical Interfaces Basic Parameters Configurations
Switch(config)#interface fastEthernet 1/0/1
Switch(config-if)#no shutdown
Switch(config-if)#description
router connection
Switch(config-if)#speed auto
Switch(config-if)#duplex auto
Switch(config-if)#flow-control
Switch(config-if)#show interface configuration fastEthernet 1/0/1
Port State Speed Duplex FlowCtrl Description
-------- ----- -------- ------ -------- -----------
Fa1/0/1 Enable Auto Auto Enable router connection
Switch(config-if)#end
Switch#copy running-config startup-config
The following example shows how to globally configure the jumbo size as 9216 bytes:
Switch#configure
Switch(config)#jumbo-size 9216
Switch(config)#show jumbo-size
Global jumbo size : 9216
Switch(config)#end
Switch#copy running-config startup-config
Configuration Guide
77
Page 99

Managing Physical Interfaces Port Mirror Configuration
3
3.1 Using the GUI
Port Mirror Configuration
Choose the menu Switching > Port > Port Mirror to load the following page.
Figure 3-1 Mirror Session List
The above page displays a mirror session, and no more session can be created. Click Edit
to configure this mirror session on the following page.
Configuration Guide 78
Page 100

Managing Physical Interfaces Port Mirror Configuration
Figure 3-2 Configuring Port Mirror
Follow these steps to configure Port Mirror:
1) In the Destination Port section, specify a monitoring port for the mirror session, and
click Apply.
2) In the Source Port section, select one or multiple monitored ports for configuration.
Then set the parameters and click Apply.
UNIT:1/LAGS Click 1 to select physical ports. Click LAGS to select LAGs.
Ingress With this option enabled, the packets received by the monitored port will be
copied to the monitoring port. By default, it is disabled.
Egress With this option enabled, the packets sent by the monitored port will be copied to
the monitoring port. By default, it is disabled.
Configuration Guide
79
 Loading...
Loading...