Page 1

D-Link ™ DGS-3224TGR
Managed 24-Port Gigabit Ethernet Switch
User’s Guide
Page 2
Information in this document is subject to change without notice.
© 2004 D-Link Computer Corporation. All rights reserved.
Reproduction in any manner whatsoever without the written permission of D-Link Computer Corporation is strictly
forbidden.
Trademarks used in this text: D-Link and the D-Link logo are trademarks of D-Link Computer Corporation; Microsoft and
Windows are registered trademarks of Microsoft Corporation.
Other trademarks and trade names may be used in this document to refer to either the entities claiming the marks and names
or their products. D-Link Computer Corporation disclaims any proprietary interest in trademarks and trade names other than
its own.
FCC Warning
This equipment has been tested and found to comply with the limits for a Class A digital device, pursuant to Part 15 of the
FCC Rules. These limits are designed to provide reasonable protection against harmful interference when the equipment is
operated in a commercial environment. This equipment generates, uses, and can radiate radio frequency energy and, if not
installed and used in accordance with this user’s guide, may cause harmful interference to radio communications. Operation
of this equipment in a residential area is likely to cause harmful interference in which case the user will be required to
correct the interference at his own expense.
CE Mark Warning
This is a Class A product. In a domestic environment, this product may cause radio interference in which case the user may
be required to take adequate measures.
Warnung!
Dies ist ein Produkt der Klasse A. Im Wohnbereich kann dieses Produkt Funkstoerungen verursachen. In diesem Fall kann
vom Benutzer verlangt werden, angemessene Massnahmen zu ergreifen.
Precaución!
Este es un producto de Clase A. En un entorno doméstico, puede causar interferencias de radio, en cuyo case, puede
requerirse al usuario para que adopte las medidas adecuadas.
Attention!
Ceci est un produit de classe A. Dans un environnement domestique, ce produit pourrait causer des interférences radio,
auquel cas l`utilisateur devrait prendre les mesures adéquates.
Attenzione!
Il presente prodotto appartiene alla classe A. Se utilizzato in ambiente domestico il prodotto può
causare interferenze radio, nel cui caso è possibile che l`utente debba assumere provvedimenti
adeguati.
VCCI Warning
September 2004 P/N 6GS3224TGR03
Page 3

Table of Contents
Preface ................................................................................................................................................................................ vii
Intended Readers............................................................................................................................................................. vii
Notes, Notices, and Cautions .......................................................................................................................................... vii
Safety Instructions.................................................................................................................................................................ix
Introduction............................................................................................................................................................................. 1
Features ................................................................................................................................................................................ 1
Ports .................................................................................................................................................................................. 1
Performance Features........................................................................................................................................................ 1
Management...................................................................................................................................................................... 2
Unpacking and Setup.............................................................................................................................................................. 3
Unpacking............................................................................................................................................................................. 3
Installation ............................................................................................................................................................................ 3
Desktop or Shelf Installation............................................................................................................................................. 4
Rack Installation ............................................................................................................................................................... 4
Power on ............................................................................................................................................................................... 5
Power Failure .................................................................................................................................................................... 6
External Redundant Power System ....................................................................................................................................... 6
Identifying External Components ......................................................................................................................................... 7
Front Panel ........................................................................................................................................................................... 7
Rear Panel ............................................................................................................................................................................ 7
Side Panels............................................................................................................................................................................ 8
LED Indicators...................................................................................................................................................................... 8
Connecting The Switch........................................................................................................................................................... 9
Switch to End Node............................................................................................................................................................... 9
Switch to Hub or Switch...................................................................................................................................................... 10
Switch Management and Operating Concepts................................................................................................................... 11
Local Console Management ............................................................................................................................................... 11
Diagnostic (console) port (RS-232 DCE) ....................................................................................................................... 11
IP Addresses and SNMP Community Names...................................................................................................................... 12
Setting an IP Address.......................................................................................................................................................... 12
Traps ................................................................................................................................................................................... 12
MIBs.................................................................................................................................................................................... 13
SNMP .................................................................................................................................................................................. 13
Authentication................................................................................................................................................................. 14
Packet Forwarding .......................................................................................................................................................... 14
MAC Address Aging Time ............................................................................................................................................. 14
Filtering .............................................................................................................................................................................. 14
Page 4

Spanning Tree ..................................................................................................................................................................... 15
802.1w Rapid Spanning Tree.......................................................................................................................................... 15
VLANs ................................................................................................................................................................................. 16
IEEE 802.1Q VLANs ..................................................................................................................................................... 16
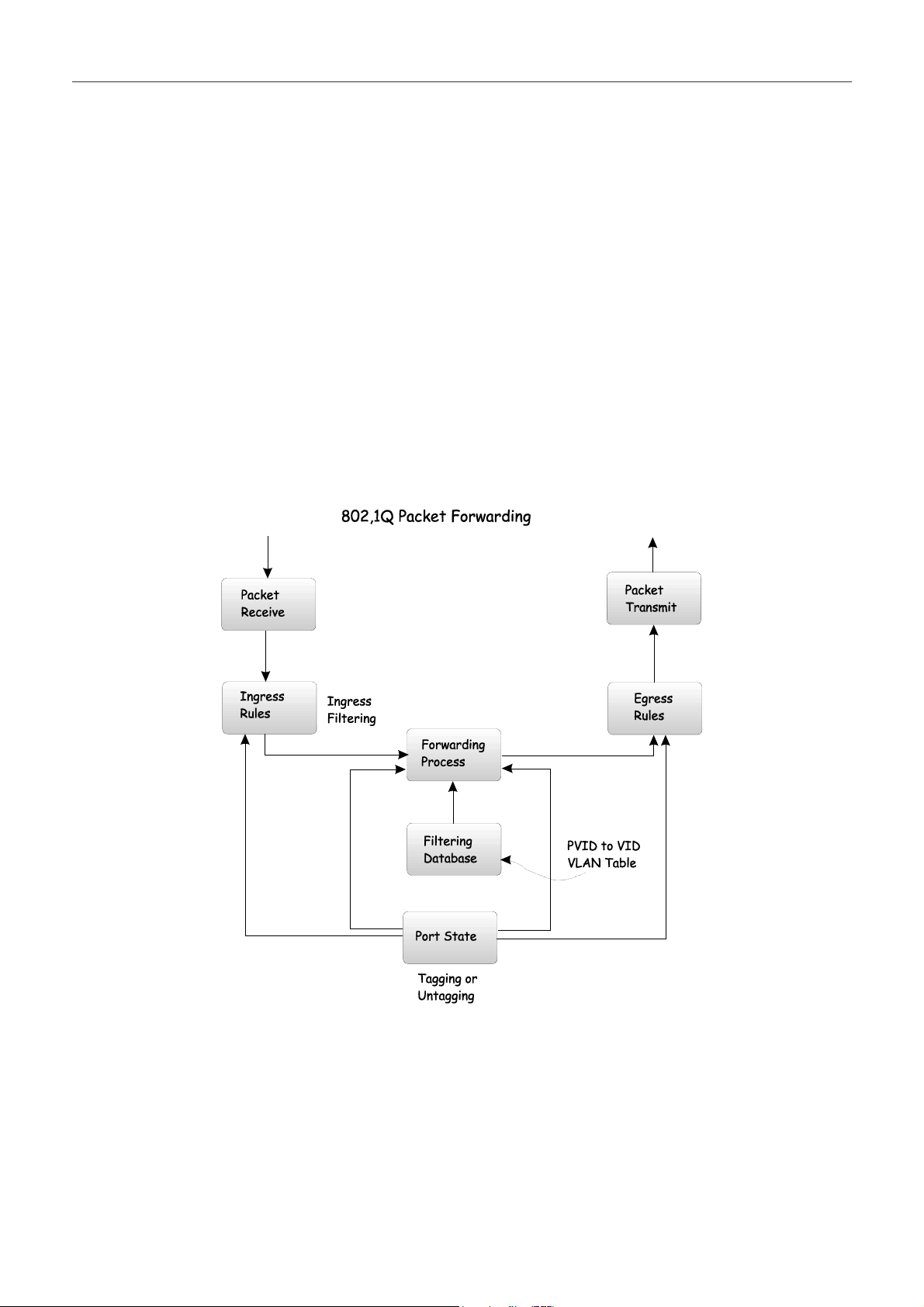
802.1Q VLAN Packet Forwarding ................................................................................................................................. 17
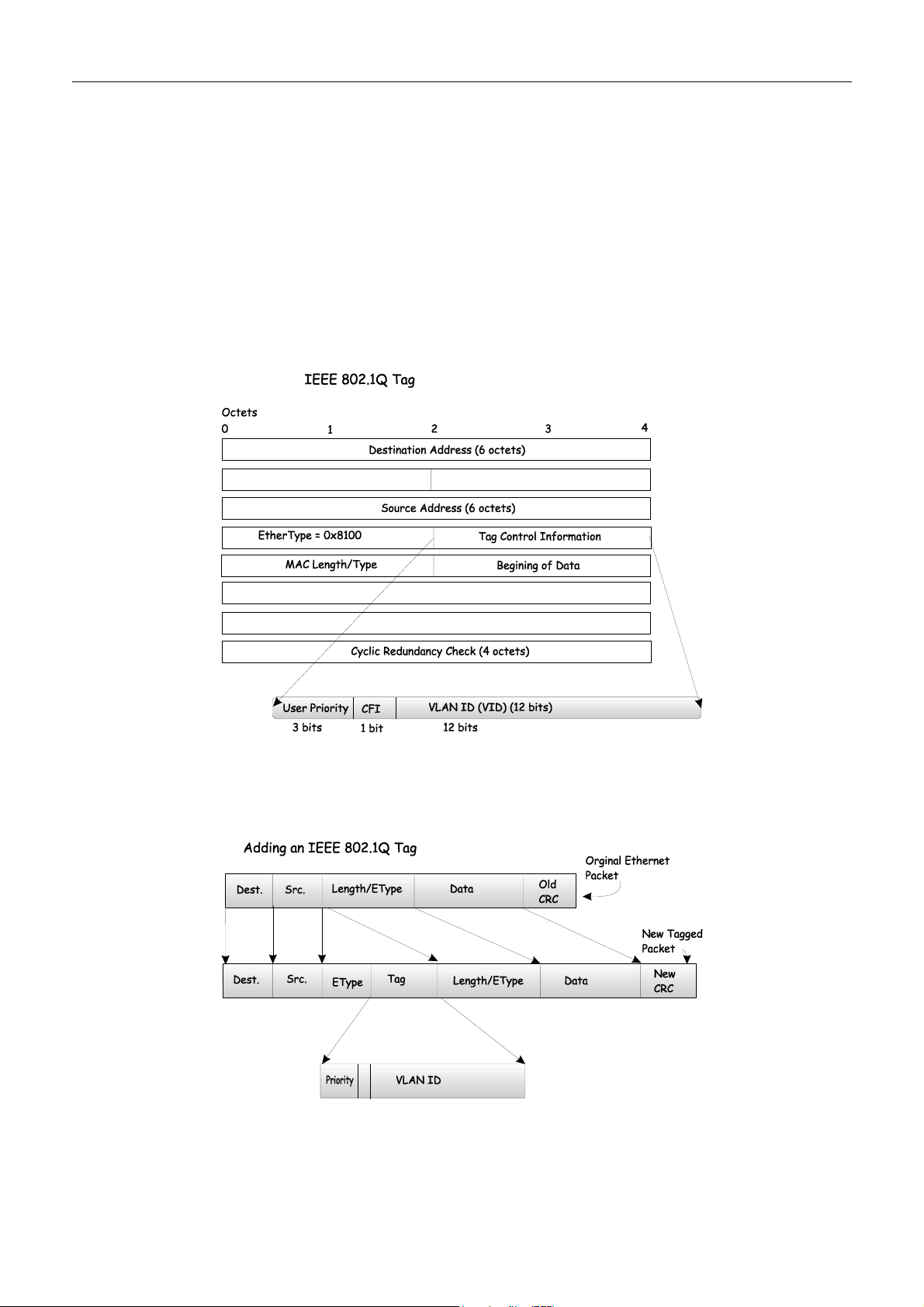
802.1Q VLAN Tags........................................................................................................................................................ 18
Port VLAN ID................................................................................................................................................................. 19
Tagging and Untagging................................................................................................................................................... 19
Ingress Filtering .............................................................................................................................................................. 19
802.1x Port-Based and MAC-Based Access Control.......................................................................................................... 20
Authentication Server ..................................................................................................................................................... 21
Authenticator................................................................................................................................................................... 21
Client............................................................................................................................................................................... 22
Authentication Process.................................................................................................................................................... 23
Port-Based Network Access Control .............................................................................................................................. 23
MAC-Based Network Access Control ............................................................................................................................ 25
DHCP.................................................................................................................................................................................. 25
Web-Based Network Management...................................................................................................................................... 27
Introduction ........................................................................................................................................................................ 27
Getting Started .................................................................................................................................................................... 27
Basic Setup.......................................................................................................................................................................... 31
Switch Information ......................................................................................................................................................... 31
Basic Switch Setup.......................................................................................................................................................... 33
Serial Port Settings.......................................................................................................................................................... 34
Port Configurations ............................................................................................................................................................ 35
Port Description Settings ................................................................................................................................................ 37
Traffic Segmentation Table............................................................................................................................................. 38
User Accounts ..................................................................................................................................................................... 39
SNMP Network Management.............................................................................................................................................. 41
SNMP V3........................................................................................................................................................................ 41
SNMP View Table.......................................................................................................................................................... 41
SNMP Community Table................................................................................................................................................ 42
SNMP Host Table ........................................................................................................................................................... 43
SNMP Group Table ........................................................................................................................................................ 44
Engine ID ........................................................................................................................................................................ 46
SNMP User Table ........................................................................................................................................................... 46
Management Station IP Addresses ..................................................................................................................................... 48
Switch Utilities .................................................................................................................................................................... 48
TFTP Services................................................................................................................................................................. 48
Network Monitoring............................................................................................................................................................ 52
Statistics .......................................................................................................................................................................... 52
Address Tables................................................................................................................................................................ 55
Status............................................................................................................................................................................... 57
Factory Reset ...................................................................................................................................................................... 60
Save Changes...................................................................................................................................................................... 60
Restart System................................................................................................................................................................. 61
Logout............................................................................................................................................................................. 61
Advanced Setup..................................................................................................................................................................... 61
Switch Advanced Settings.................................................................................................................................................... 62
Page 5

Spanning Tree ..................................................................................................................................................................... 62
STP Switch Settings........................................................................................................................................................ 63
STP Port Settings ............................................................................................................................................................ 64
Forwarding ......................................................................................................................................................................... 65
MAC Address Aging Time ............................................................................................................................................. 65
Unicast MAC Address Settings ...................................................................................................................................... 66
Multicast MAC Address Settings.................................................................................................................................... 67
Broadcast/Multicast Storm Control................................................................................................................................. 68
Configure QOS.................................................................................................................................................................... 69
QOS Output Scheduling ................................................................................................................................................. 70
802.1p Default Priority ................................................................................................................................................... 71
802.1p User Priority........................................................................................................................................................ 72
Bandwidth Control Table................................................................................................................................................ 72
Access Profile Mask Setting................................................................................................................................................ 73
Port Security ....................................................................................................................................................................... 83
Port Mirroring Configurations ........................................................................................................................................... 86
VLAN Configurations.......................................................................................................................................................... 87
Asymmetric VLAN State................................................................................................................................................ 87
Switch GVRP.................................................................................................................................................................. 87
802.1Q VLANs............................................................................................................................................................... 88
802.1Q Port Settings ....................................................................................................................................................... 90
Link Aggregation ................................................................................................................................................................ 91
Link Aggregation Algorithm .......................................................................................................................................... 91
Link Aggregation Group................................................................................................................................................. 91
LACP Port Settings......................................................................................................................................................... 93
802.1X ................................................................................................................................................................................. 95
802.1X State.................................................................................................................................................................... 95
802.1X Auth Mode Settings............................................................................................................................................ 96
802.1X Port Settings ....................................................................................................................................................... 96
802.1X Port Auth State ................................................................................................................................................. 100
802.1X Initialize / Reauthenticate Ports........................................................................................................................ 101
RADIUS Server Settings ................................................................................................................................................... 102
802.1X Local User Settings............................................................................................................................................... 103
802.1X Auth Diagnostics .................................................................................................................................................. 104
802.1X Auth Statistics ....................................................................................................................................................... 105
802.1X Auth Session Statistics .......................................................................................................................................... 106
802.1X Auth Client............................................................................................................................................................ 107
802.1X Accounting Client ............................................................................................................................................ 107
TACACS ............................................................................................................................................................................ 107
TACACS State Configuration ...................................................................................................................................... 107
TACACS Server Settings.............................................................................................................................................. 108
TACACS Group............................................................................................................................................................ 109
TACACS Group Settings.............................................................................................................................................. 109
TACACS Method List .................................................................................................................................................. 110
Authentication............................................................................................................................................................... 111
Enable Admin ............................................................................................................................................................... 111
System Log ........................................................................................................................................................................ 112
System Log State .......................................................................................................................................................... 112
System Log Host........................................................................................................................................................... 112
Multicast Configuration.................................................................................................................................................... 114
IGMP Snooping Global ................................................................................................................................................ 114
Page 6
IGMP Snooping Configurations ................................................................................................................................... 115
Static Router Port Settings ............................................................................................................................................ 116
SSH Management.............................................................................................................................................................. 116
SSH Configurations ...................................................................................................................................................... 117
SSH Account Configuration ......................................................................................................................................... 118
SSL Management .............................................................................................................................................................. 119
Download Certificate .................................................................................................................................................... 119
Cipher Suite Configuration ........................................................................................................................................... 120
SSL V3 Configuration .................................................................................................................................................. 121
TLS V1 Configuration .................................................................................................................................................. 122
Single IP Management........................................................................................................................................................ 123
SIM Settings ...................................................................................................................................................................... 123
SIM Using the Web Interface............................................................................................................................................ 124
Topology ........................................................................................................................................................................... 126
Tool Tips....................................................................................................................................................................... 128
Right-Click.................................................................................................................................................................... 129
Commander Switch Icon............................................................................................................................................... 130
Menu Bar ...................................................................................................................................................................... 133
Device ........................................................................................................................................................................... 134
View.............................................................................................................................................................................. 134
Firmware Upgrade ........................................................................................................................................................... 135
Configuration Backup/Restore.......................................................................................................................................... 135
Technical Specifications ..................................................................................................................................................... 136
Cable Lengths...................................................................................................................................................................... 138
Glossary ............................................................................................................................................................................... 139
Warranty and Registration Information .......................................................................................................................... 142
Page 7
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Preface
The DGS-3224TGR User’s Guide is divided into chapters that describe the system installation and operating instructions
with examples.
Chapter 1, “Introduction” – Describes the Switch and its features.
Chapter 2, “Unpacking and Setup” – Helps you get started with the basic installation of the Switch.
Chapter 3, “Identifying External Components” – Describes the front panel, rear panel, and LED indicators of the
Switch.
Chapter 4, “Connecting the Switch” – Tells how you can connect the DGS-3224TGR to your Gigabit Ethernet
network.
Chapter 5, “Switch Management and Operating Concepts” – Talks about management via the RS-232 DCE console
port and other aspects about how to manage the Switch.
Chapter 6, “Web-Based Network Management” – Tells how to manage the Switch through an Internet browser.
Chapter 7, “D-Link’s Single IP Management” – An introduction to the new D-Link switch management feature used
to manage multiple switches through a single Switch.
Appendix A, “Technical Specifications” – Lists the technical specifications of the DGS-3224TGR.
Appendix B, “Cable Lengths” – Contains chart for fiber-optic and copper cable maximum distances.
Glossary – Lists definitions for terms and acronyms used in this document.
Intended Readers
The DGS-3224TGR User’s Guide contains information for setup and management and of the DGS-3224TGR switch. This
guide is intended for network managers familiar with network management concepts and terminology.
Notes, Notices, and Cautions
NOTE: A NOTE indicates important information that helps you make
better use of your device.
NOTICE: A NOTICE indicates either potential damage to hardware or loss
of data and tells you how to avoid the problem.
vii
Page 8
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
CAUTION: A CAUTION indicates a potential for property damage,
personal injury, or death.
viii
Page 9
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Safety Instructions
Use the following safety guidelines to ensure your own personal safety and to help protect your system from potential
damage. Throughout this safety section, the caution icon ( ) is used to indicate cautions and precautions that you need to
review and follow.
Safety Cautions
To reduce the risk of bodily injury, electrical shock, fire, and damage to the equipment, observe the following precautions.
Observe and follow service markings. Do not service any product except as explained in your system documentation.
Opening or removing covers that are marked with the triangular symbol with a lightning bolt
may expose you to electrical shock. Only a trained service technician should service components inside these
compartments.
If any of the following conditions occur, unplug the product from the electrical outlet and replace the part or contact your
trained service provider:
– The power cable, extension cable, or plug is damaged.
– An object has fallen into the product.
– The product has been exposed to water.
– The product has been dropped or damaged.
– The product does not operate correctly when you follow the operating instructions.
• Keep your system away from radiators and heat sources. Also, do not block cooling vents.
• Do not spill food or liquids on your system components, and never operate the product in a wet environment. If the
system gets wet, see the appropriate section in your troubleshooting guide or contact your trained service provider.
• Do not push any objects into the openings of your system. Doing so can cause fire or electric shock by shorting out
interior components.
• Use the product only with approved equipment.
• Allow the product to cool before removing covers or touching internal components.
• Operate the product only from the type of external power source indicated on the electrical ratings label. If you are
not sure of the type of power source required, consult your service provider or local power company.
• To help avoid damaging your system, be sure the voltage selection switch (if provided) on the power supply is set
to match the power available at your location:
– 115 volts (V)/60 hertz (Hz) in most of North and South America and some Far Eastern countries such as South
Korea and Taiwan
– 100 V/50 Hz in eastern Japan and 100 V/60 Hz in western Japan
– 230 V/50 Hz in most of Europe, the Middle East, and the Far East
• Also be sure that attached devices are electrically rated to operate with the power available in your location.
• Use only approved power cable(s). If you have not been provided with a power cable for your system or for any
AC-powered option intended for your system, purchase a power cable that is approved for use in your country.
The power cable must be rated for the product and for the voltage and current marked on the product's electrical
ratings label. The voltage and current rating of the cable should be greater than the ratings marked on the product.
ix
Page 10
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Safety Instructions (continued)
• To help prevent electric shock, plug the system and peripheral power cables into properly grounded electrical
outlets. These cables are equipped with three-prong plugs to help ensure proper grounding. Do not use adapter
plugs or remove the grounding prong from a cable. If you must use an extension cable, use a 3-wire cable with
properly grounded plugs.
• Observe extension cable and power strip ratings. Make sure that the total ampere rating of all products plugged
into the extension cable or power strip does not exceed 80 percent of the ampere ratings limit for the extension
cable or power strip.
• To help protect your system from sudden, transient increases and decreases in electrical power, use a surge
suppressor, line conditioner, or uninterruptible power supply (UPS).
• Position system cables and power cables carefully; route cables so that they cannot be stepped on or tripped over.
Be sure that nothing rests on any cables.
• Do not modify power cables or plugs. Consult a licensed electrician or your power company for site modifications.
Always follow your local/national wiring rules.
• When connecting or disconnecting power to hot-pluggable power supplies, if offered with your system, observe
the following guidelines:
– Install the power supply before connecting the power cable to the power supply.
– Unplug the power cable before removing the power supply.
– If the system has multiple sources of power, disconnect power from the system by
unplugging all power cables from the power supplies.
• Move products with care; ensure that all casters and/or stabilizers are firmly connected to the system. Avoid
sudden stops and uneven surfaces.
General Precautions for Rack-Mountable Products
Observe the following precautions for rack stability and safety. Also refer to the rack installation documentation
accompanying the system and the rack for specific caution statements and procedures.
Systems are considered to be components in a rack. Thus, "component" refers to any system as well as to various
peripherals or supporting hardware.
CAUTION: Installing systems in a rack without the front and side stabilizers
installed could cause the rack to tip over, potentially resulting in bodily injury under
certain circumstances. Therefore, always install the stabilizers before installing
components in the rack.
After installing system/components in a rack, never pull more than one component
out of the rack on its slide assemblies at one time. The weight of more than one
extended component could cause the rack to tip over and may result in serious
injury.
• Before working on the rack, make sure that the stabilizers are secured to the rack, extended to the floor, and that
the full weight of the rack rests on the floor. Install front and side stabilizers on a single rack or front stabilizers for
joined multiple racks before working on the rack.
x
Page 11
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Safety Instructions (continued)
Always load the rack from the bottom up, and load the heaviest item in the rack first.
Make sure that the rack is level and stable before extending a component from the rack.
Use caution when pressing the component rail release latches and sliding a component into or out of a rack; the slide rails
can pinch your fingers.
After a component is inserted into the rack, carefully extend the rail into a locking position, and then slide the component
into the rack.
Do not overload the AC supply branch circuit that provides power to the rack. The total rack load should not exceed 80
percent of the branch circuit rating.
Ensure that proper airflow is provided to components in the rack.
Do not step on or stand on any component when servicing other components in a rack.
NOTE: A qualified electrician must perform all connections to DC power
and to safety grounds. All electrical wiring must comply with applicable
local or national codes and practices.
CAUTION: Never defeat the ground conductor or operate the equipment in the
absence of a suitably installed ground conductor. Contact the appropriate electrical
inspection authority or an electrician if you are uncertain that suitable grounding is
available.
CAUTION: The system chassis must be positively grounded to the rack cabinet
frame. Do not attempt to connect power to the system until grounding cables are
connected. Completed power and safety ground wiring must be inspected by a
qualified electrical inspector. An energy hazard will exist if the safety ground cable
is omitted or disconnected.
xi
Page 12
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Protecting Against Electrostatic Discharge
Static electricity can harm delicate components inside your system. To prevent static damage, discharge static electricity
from your body before you touch any of the electronic components, such as the microprocessor. You can do so by
periodically touching an unpainted metal surface on the chassis.
You can also take the following steps to prevent damage from electrostatic discharge (ESD):
1. When unpacking a static-sensitive component from its shipping carton, do not remove the component
from the antistatic packing material until you are ready to install the component in your system. Just
before unwrapping the antistatic packaging, be sure to discharge static electricity from your body.
2. When transporting a sensitive component, first place it in an antistatic container or packaging.
3. Handle all sensitive components in a static-safe area. If possible, use antistatic floor pads and workbench
pads and an antistatic grounding strap.
Battery Handling Reminder
CAUTION: Danger of explosion if battery is incorrectly replaced. Replace only with
the same or equivalent type recommended by the manufacturer. Discard used
batteries according to the manufacturer's instructions.
xii
Page 13

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
1
Introduction
This section describes the features of the DGS-3224TGR.
Features
The DGS-3224TGR was designed for departmental and enterprise connections. As an all-gigabit-port switch, it is ideal for
backbone and server connection. Powerful and versatile, the switch eliminates network bottlenecks while giving users the
capability to fine-tune performance
Switch features include:
Ports
• Twenty-four high performance 1000BASE-T ports for making 10/100/1000 connections to a backbone, end stations,
and servers.
• Four mini-GBIC (SFP) combo ports to connect fiber optic media to another switch, server or network backbone.
• RS-232 DCE Diagnostic port (console port) for setting up and managing the Switch via a connection to a console
terminal or PC using a terminal emulation program.
Performance Features
• Store-and-forward switching scheme.
• Switching fabric: 48Gbps
• Max. Forwarding Rate: 35.7 million packets per second
• High-speed data forwarding rate of 1,488,095 pps per port at 100% of wire-speed for 1000 Mbps speed.
• Supports 16K MAC address.
• Supports eight priority queues per port.
• Supports 2Mbytes buffer memory per switch.
• Jumbo Frame support (up to 9216 bytes).
• Multi-layer (Layer 2 to Layer 4) ACL and CoS support.
• Administrator-definable port security.
• 802.1D Spanning Tree support. Can be disabled on the entire switch or on a per-port basis.
• 802.1w Rapid Reconfiguration of Spanning Tree.
• 802.1Q Tagged VLAN support, including GVRP (GARP VLAN Registration Protocol).
• Support for up to 255 VLANs.
• IGMP snooping support per switch and fast-leave.
• Link aggregation support for up to 32 trunk groups and 8 trunk members per group. Support LACP and Static mode.
• Both port-based and MAC-based 802.1x port access control.
• Per-port bandwidth control.
1
Page 14

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Management
• RS-232 console port for out-of-band network management via a console terminal.
• Spanning Tree Algorithm Protocol for creation of alternative backup paths and prevention of network loops.
• SNMP V.1, V2c1, and V3 network management, 4 groups of RMON.
• Flash memory for software upgrades. This can be done in-band via TFTP or out-of-band via the console.
• Built-in SNMP management:
Bridge MIB (RFC 1493)
MIB-II (RFC 1213)
802.1P/Q MIB (RFC 2674)
Interface MIB (RFC 2233)
Ethernet-like MIB (RFC 1643)
Mini-RMON MIB (RFC 1757) – 4 groups. The RMON specification defines the counters for the receive
functions only. However, the DGS-3224TGR provides counters for both receive and transmit functions.
• Supports Web-based management.
• TFTP support.
• BOOTP support.
• DHCP Client support.
• Password enabled.
• Telnet remote control console.
• Broadcast storm control.
• Multicast storm control.
• Command Line Interface support.
• Port security support.
• TACACS and TACACS+ protocol support.
• SYSLOG support.
• Destination Lookup Fail control.
• SSL support.
• Single IP Management v1.0 support.
2
Page 15

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
2
Unpacking and Setup
This chapter provides unpacking and setup information for the switch.
Unpacking
Open the shipping carton of the switch and carefully unpack its contents. The carton should contain the following items:
• A DGS-3224TGR 24-Port Gigabit Layer 2 Ethernet switch
• A mounting kit: 2 mounting brackets and screws
• Four rubber feet with adhesive backing
• One or two AC power cords
• A printed QIG
• A printed User’s Guide
• D-View 5.1 demo CD-ROM
• This User’s Guide with Registration Card on CD-ROM
If any item is found missing or damaged, please contact your local D-Link reseller for replacement.
Installation
Use the following guidelines when choosing a place to install the switch:
• The surface must support at least 4 kg.
• The power outlet should be within 1.82 meters (6 feet) of the device.
• Visually inspect the power cord and see that it is secured to the AC power connector.
• Make sure that there is proper heat dissipation from and adequate ventilation around the switch. Do not place heavy
objects on the switch.
3
Page 16
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
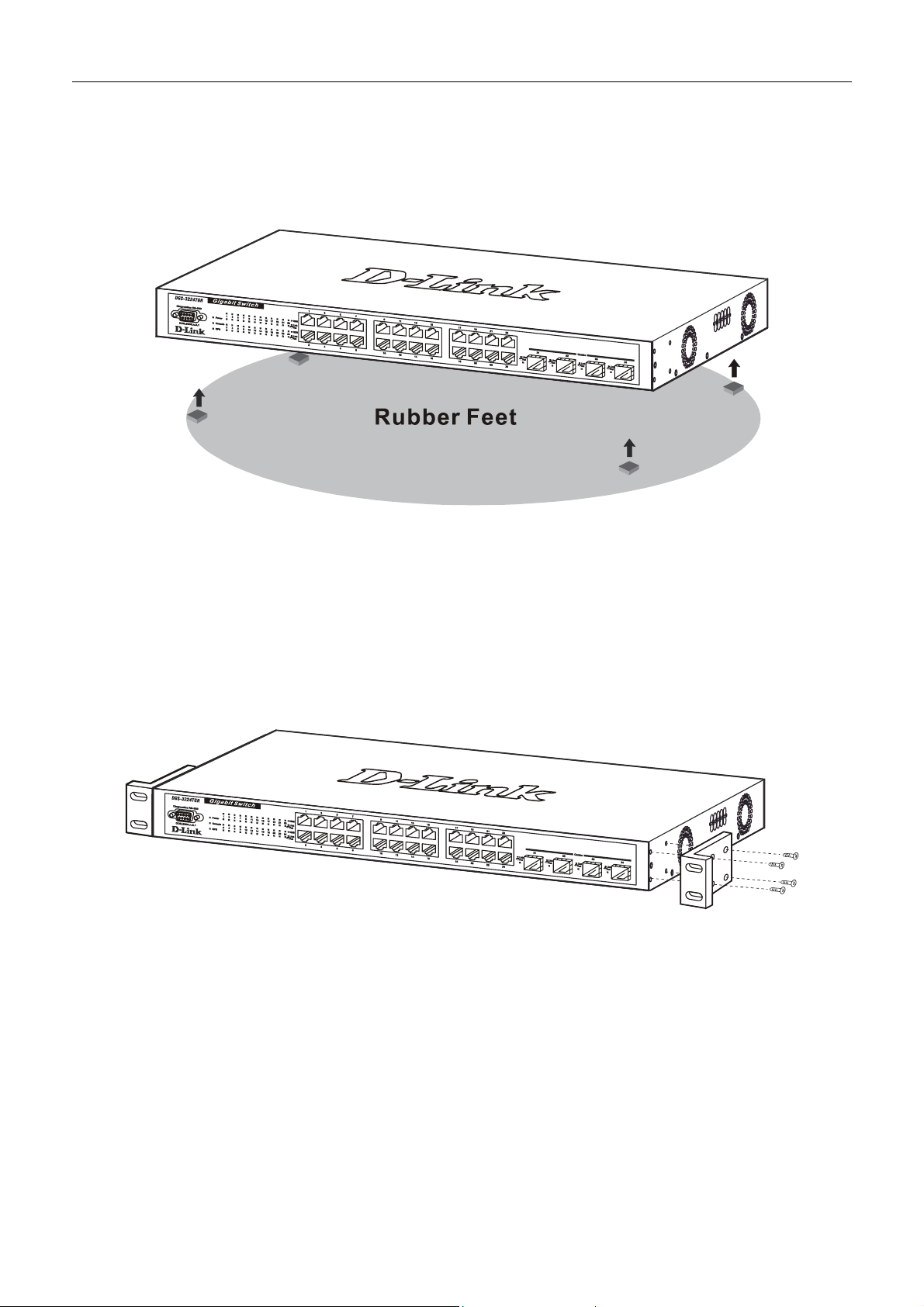
Desktop or Shelf Installation
When installing the switch on a desktop or shelf, the rubber feet included with the device should first be attached. Attach
these cushioning feet on the bottom at each corner of the device. Allow adequate space for ventilation between the device
and the objects around it.
Figure 2-1. Installing rubber feet for desktop installation
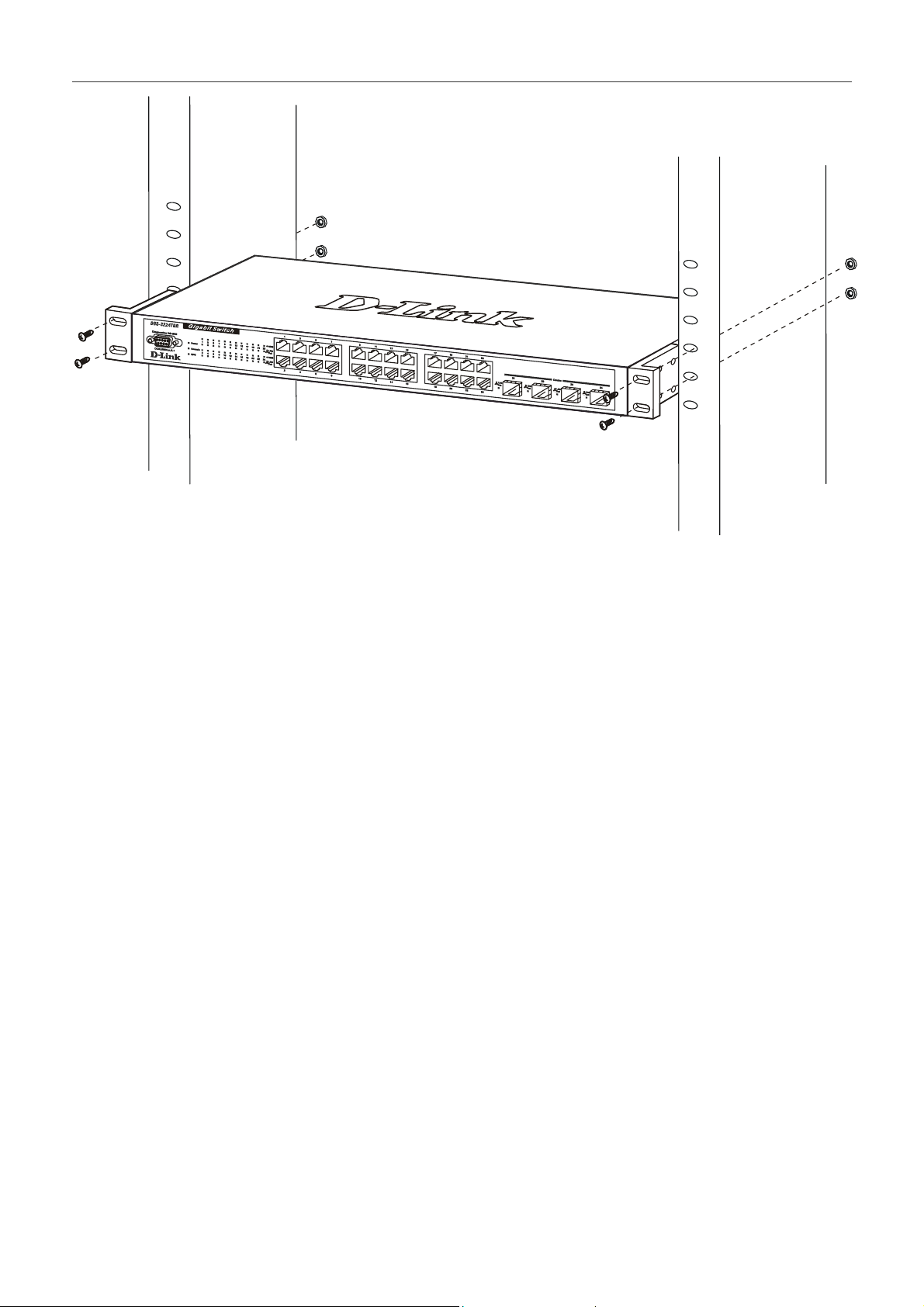
Rack Installation
The DGS-3224TGR can be mounted in an EIA standard-sized, 19-inch rack, which can be placed in a wiring closet with
other equipment. To install, attach the mounting brackets on the switch’s side panels (one on each side) and secure them
with the screws provided.
Figure 2- 2A. Attaching the mounting brackets
Then, use the screws provided with the equipment rack to mount the witch on the rack.
4
Page 17
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 2- 2B. Installing in an equipment rack
Power on
The switch can be used with AC power supply 100-240 VAC, 50 - 60 Hz. The switch’s power supply will adjust to the
local power source automatically and may be powered on without having any or all LAN segment cables connected.
After the switch is plugged in, the LED indicators should respond as follows:
• All LED indicators except console will momentarily blink. This blinking of the LEDs indicates a reset of the system.
• The console LED indicator will blink while the switch loads onboard software and performs a self-test. When the
POST is passed, the LED will become dark. If the POST fails, the indicator will light solid amber. This indicator lights
solid green when the switch is being logged-in via out-of-band/local console management through the RS-232 console
port using a straight-through serial cable.
5
Page 18
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Power Failure
As a precaution in the event of a power failure, unplug the switch. When power is resumed, plug the switch back in.
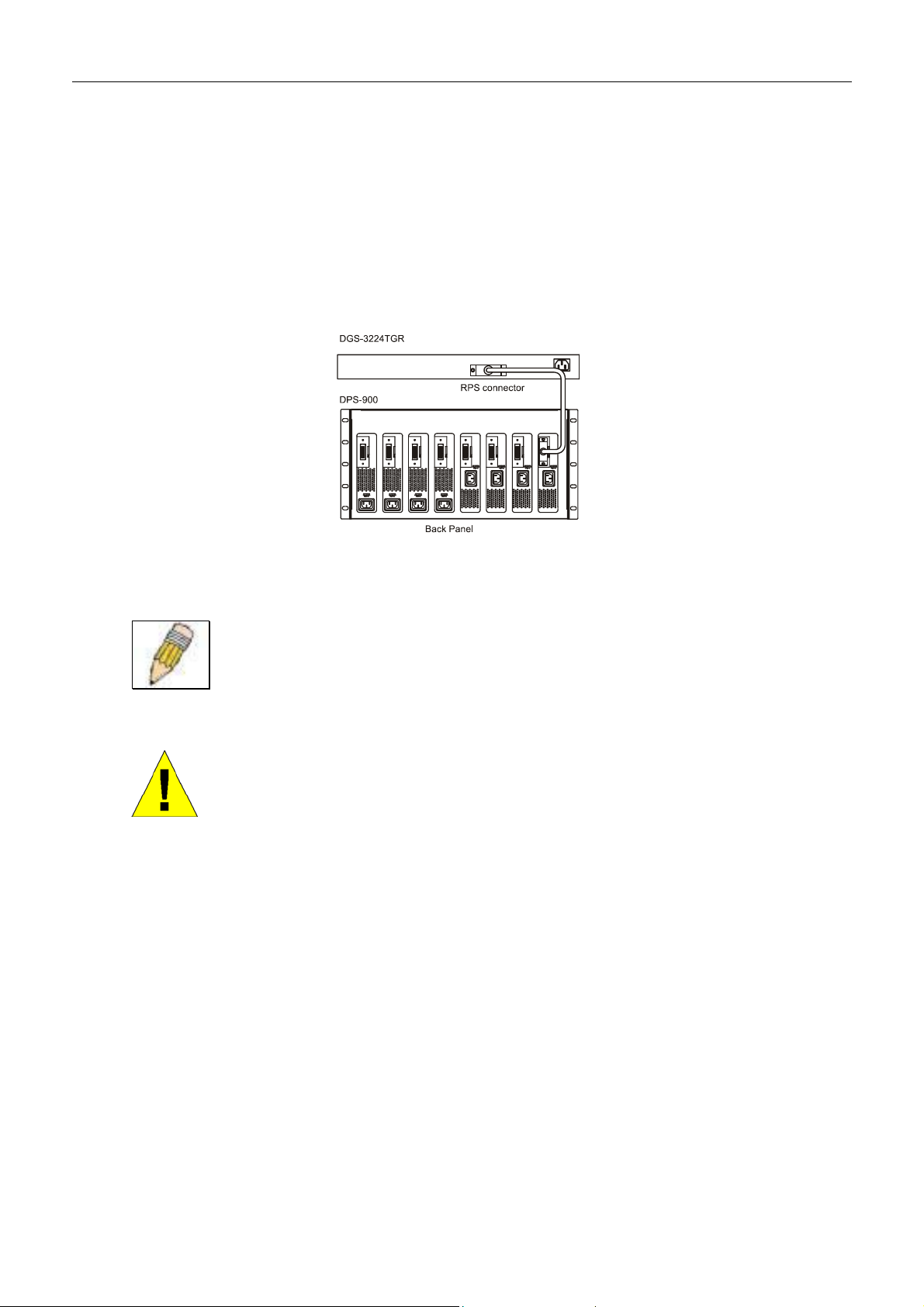
External Redundant Power System
The switch supports an external redundant power system.
Figure 2-3. DPS-300 in DPS-900 with DGS-3224TGR
NOTE: See the DPS-300 documentation for more information.
CAUTION: Do not use the switch with any redundant power system other than
the DPS-300.
6
Page 19
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
3
Identifying External Components
This chapter describes the front panel, rear panel, side panels, and LED indicators of the DGS-3224TGR.
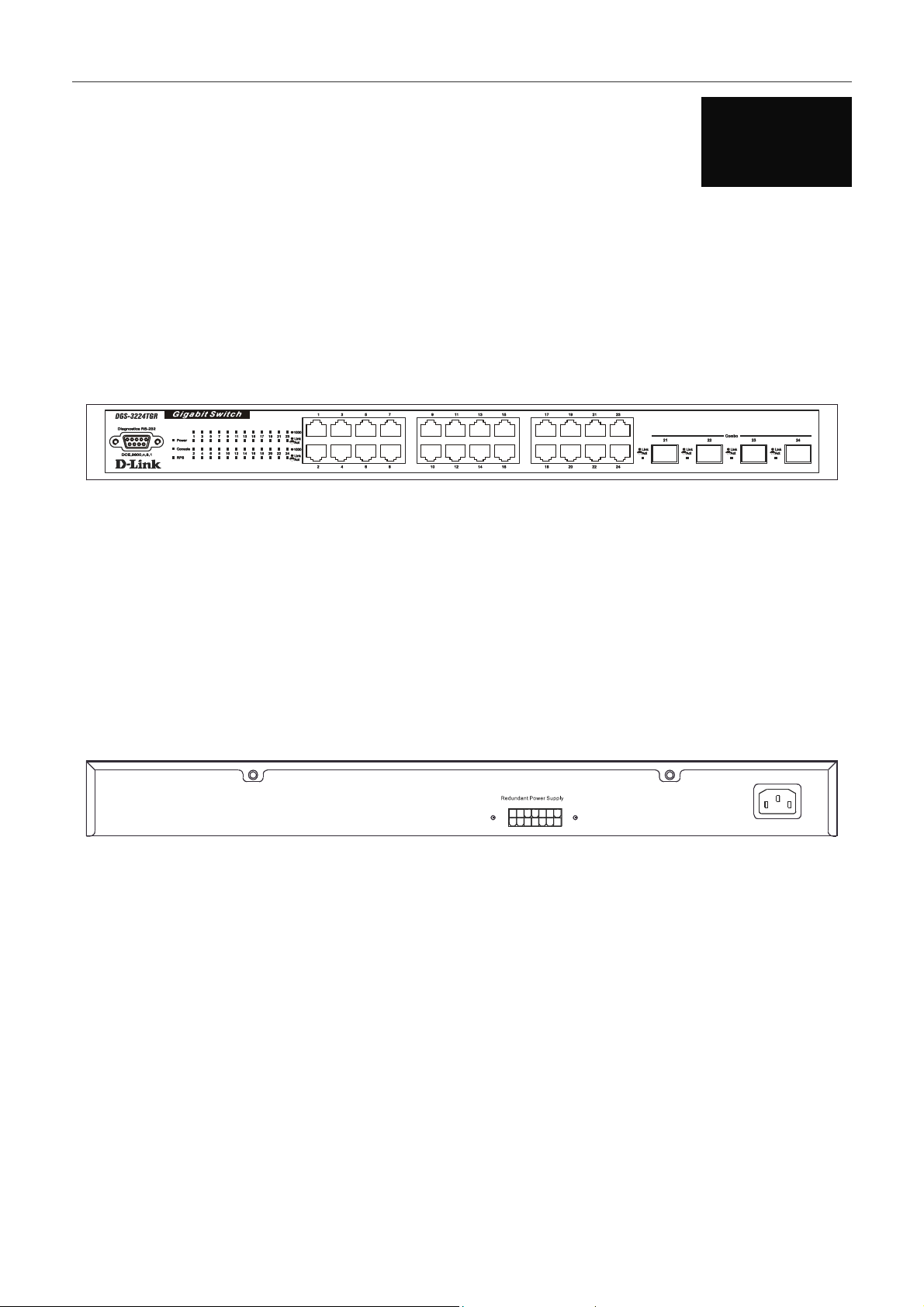
Front Panel
The front panel of the switch consists of LED indicators, an RS-232 communication port, 24 1000BASE-T ports, and 4
mini-GBIC combo ports.
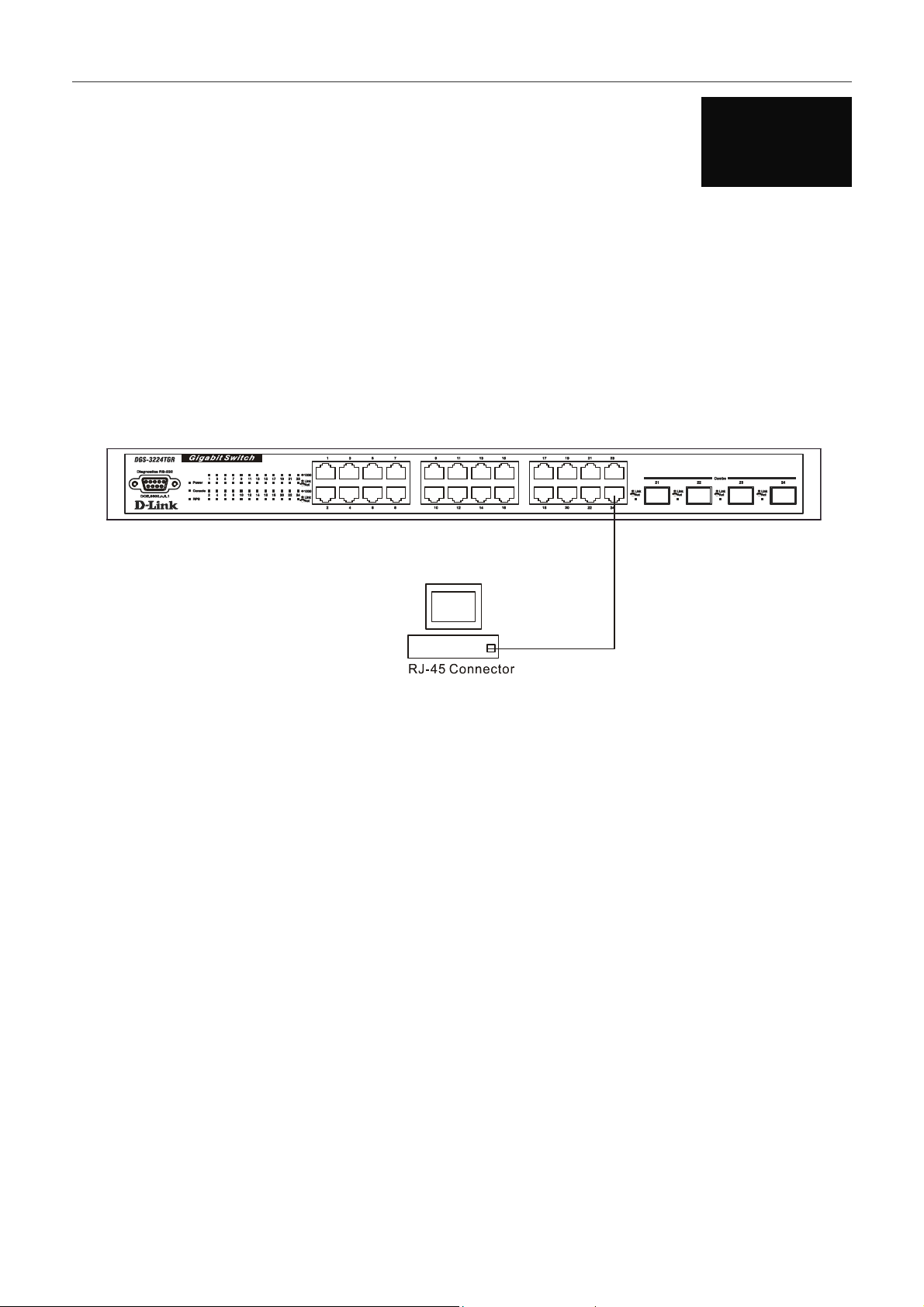
Figure 3-1. Front panel view
• An RS-232 DCE console port for setting up and managing the switch via a connection to a console terminal or PC
using a terminal emulation program.
• Comprehensive LED indicators display the status of the switch and the network (see the LED Indicators section
below).
• Twenty-four 1000BASE-T Ethernet ports for 10/100/1000 connections to a backbone, end stations, and servers.
• Four mini-GBIC combo ports to connect fiber optic media to another switch, server, or network backbone.
Rear Panel
The rear panel of the switch contains an external Redundant Power Supply connector and an AC power connector.
Figure 3-2. Rear panel view
• The external Redundant Power Supply connector is used to connect the DGS-3224TGR to a DPS-300. An auto-switch
circuit automatically switches to an external RPS once the internal power supply fails. Transition from internal to
external supply shall not disturb normal operation.
• The AC power connector is a standard three-pronged connector that supports the power cord. Plug-in the female
connector of the provided power cord into this socket, and the male side of the cord into a power outlet. Supported
input voltages range from 100 ~ 240 VAC at 50 ~ 60 Hz.
7
Page 20
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Side Panels
The right side panel of the switch contains two system fans (see the top part of the diagram below). The left side panel
contains heat vents.
Figure 3-3. Side panel views of the Switch
• The system fans are used to dissipate heat. The sides of the system also provide heat vents to serve the same purpose.
Do not block these openings, and leave at least 6 inches of space at the rear and sides of the switch for proper
ventilation. Be reminded that without proper heat dissipation and air circulation, system components might overheat,
which could lead to system failure.
LED Indicators
The LED indicators of the switch include Power, Console, RPS, Speed, and Link/Activity. The following shows the LED
indicators for the switch along with an explanation of each indicator.
Figure 3-4. LED indicators
• Power – This indicator on the front panel lights solid green when the system is powered up and remains dark when the
system is not powered on.
• Console – This indicator blinks green when the system is booting up. It remains solid green when the system is
operating properly. The LED is solid amber when the POST fails.
• RPS – This indicator is lit solid amber when the external Redundant Power Supply is in operation and remains dark
when it is not in use or the main power is working normally.
• Speed – This row of indicators will light solid green when the connection speed is operating at 1000 Mbps. An unlit
LED indicates a connection speed of either 10 or 100 Mbps.
• Link/Act – This row of indicators for the 24 copper ports light solid green when there is a secure connection (or link)
to a device on any of the ports. The LEDs blink green whenever there is reception or transmission (i.e. Activity--Act)
of data occurring on a port.
8
Page 21
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
4
Connecting The Switch
This chapter describes how to connect the DGS-3224TGR to your Gigabit Ethernet network.
Switch to End Node
End nodes include PCs outfitted with a 10, 100, or 1000 Mbps RJ-45 Ethernet/Fast Ethernet/Gigabit Ethernet Network
Interface Card (NIC) and most routers.
An end node can be connected to the switch via a Category 3, 4, 5, or 5e UTP/STP cable—for optimal performance,
Category 5e is recommended. The end node should be connected to any of the ports of the switch.
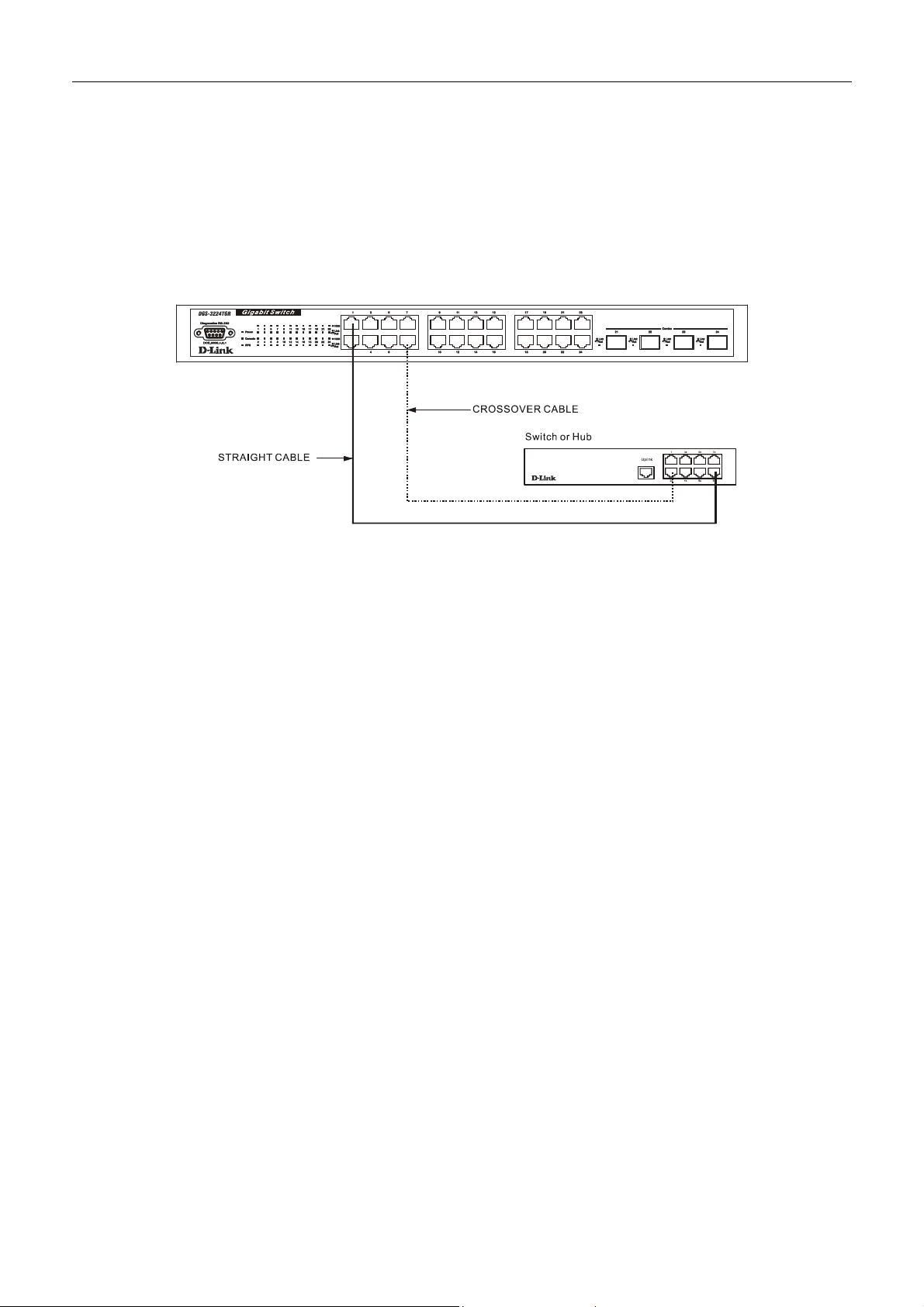
Figure 4-1. Switch connected to an End Node
The Link/Act LEDs light green when the link is valid. A blinking green LED indicates packet activity on that port. The
Speed LEDs indicate port speed and will light solid green for 1000 Mbps connections. They will remain off for 10 or 100
Mbps connections.
9
Page 22
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Switch to Hub or Switch
These connections can be accomplished in a number of ways using a normal cable.
• A 10BASE-T hub or switch can be connected to the switch via a two-pair Category 3, 4, 5, or 5e UTP/STP cable.
• A 100BASE-TX hub or switch can be connected to the switch via a two-pair Category 5 or 5e UTP/STP cable.
• A 1000BASE-T switch can be connected to the switch via four-pair straight Category 5 or 5e UTP/STP cable.
Figure 4-2. Switch connected to a normal (non-Uplink) port on a hub or switch using a straight or
crossover cable
10
Page 23

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
5
Switch Management and Operating Concepts
This chapter discusses many of the concepts and features used to manage the switch, as well as the concepts necessary for
the user to understand the functioning of the switch. Further, this chapter explains many important points regarding these
features.
Configuring the switch to implement these concepts and make use of its many features is discussed in detail in the next
chapters.
Local Console Management
A local console is a terminal or a workstation running a terminal emulation program that is connected directly to the switch
via the RS-232 console port on the front of the switch. A console connection is referred to as an ‘Out-of-Band’ connection,
meaning that console is connected to the switch using a different circuit than that used for normal network communications.
So, the console can be used to set up and manage the switch even if the network is down.
Local console management uses the terminal connection to operate the console program built-in to the switch (see the DGS-
3224TGR Command Line Interface Reference manual). A network administrator can manage, control and monitor the
switch from the console program.
The DGS-3224TGR contains a CPU, memory for data storage, flash memory for configuration data, operational programs,
and SNMP agent firmware.
Diagnostic (console) port (RS-232 DCE)
Out-of-band management requires connecting a terminal, such as a VT-100 or a PC running a terminal emulation program
(such as HyperTerminal, which is automatically installed with Microsoft Windows) a to the RS-232 DCE console port of
the switch. Switch management using the RS-232 DCE console port is called Local Console Management to differentiate it
from management performed via management platforms, such as D-View, HP OpenView, etc.
The console port is set at the factory for the following configuration:
• Baud rate: 9,600
• Data width: 8 bits
• Parity: none
• Stop bits: 1
• Flow Control None
Make sure the terminal or PC you are using to make this connection is configured to match these settings.
If you are having problems making this connection on a PC, make sure the emulation is set to VT-100. If you still don’t see
anything, try hitting <Ctrl> + r to refresh the screen.
11
Page 24

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
IP Addresses and SNMP Community Names
Each switch must be assigned its own IP Address, which is used for communication with an SNMP network manager or
other TCP/IP application (for example BOOTP, TFTP). The switch’s default IP address is 10.90.90.90. You can change the
default switch IP Address to meet the specification of your networking address scheme.
The switch is also assigned a unique MAC address by the factory. This MAC address cannot be changed, and can be found
when using the command “show switch.”
In addition, you can also set an IP address for a gateway router. This becomes necessary when the network management
station is located on a different IP network from the switch, making it necessary for management packets to go through a
router to reach the network manager, and vice-versa.
For security, you can set in the switch a list of IP Addresses of the network managers that allow you to manage the switch.
You can also change the default SNMP Community Strings in the switch and set the access rights of these Community
Strings. In addition, a VLAN may be designated as a Management VLAN.
Setting an IP Address
The IP address for the switch must be set before it can be managed with the Web-based manager. The switch IP address
may be automatically set using BOOTP or DHCP protocols, in which case the actual address assigned to the switch must be
known.
The IP address may alternatively be set using the Command Line Interface (CLI) over the console serial port as follows:
1. Starting at the command line prompt local>, enter the commands config ipif System ipaddress
xxx.xxx.xxx.xxx/yyy.yyy.yyy.yyy. Where the x’s represent the IP address to be assigned to the IP interface
named System and the y’s represent the corresponding subnet mask.
2. Alternatively, you can enter the commands config ipif System ipaddress xxx.xxx.xxx.xxx/z. Where the x’s
represent the IP address to be assigned to the IP interface named System and the z represents the
corresponding number of subnets in CIDR notation.
Using this method, the switch can be assigned an IP address and subnet mask that can then be used to connect a
management station to the switch’s Web-based management agent.
Traps
Traps are messages that alert you of events that occur on the switch. The events can be as serious as a reboot (someone
accidentally turned OFF the switch), or less serious like a port status change. The switch generates traps and sends them to
the network manager (trap recipient).
Trap recipients are special users of the network who are given certain rights and access in overseeing the maintenance of
the network. Trap recipients will receive traps sent from the switch; they must immediately take certain actions to avoid
future failure or breakdown of the network.
You can also specify which network managers may receive traps from the switch by entering a list of the IP addresses of
authorized network managers. Up to four trap recipient IP addresses, and four corresponding SNMP community strings can
be entered.
SNMP community strings function like passwords in that the community string entered for a given IP address must be used
in the management station software, or a trap will be sent.
The following are trap types the switch can send to a trap recipient:
• Cold Start –This trap signifies that the switch has been powered up and initialized such that software settings are
reconfigured and hardware systems are rebooted. A cold start is different from a factory reset in that configuration
settings saved to non-volatile RAM used to reconfigure the switch.
• Authentication Failure – This trap signifies that someone has tried to logon to the switch using an invalid SNMP
community string. The switch automatically stores the source IP address of the unauthorized user.
12
Page 25

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
• New Root – This trap indicates that the switch has become the new root of the Spanning Tree, the trap is sent by
the switch soon after its election as the new root. This implies that upon expiration of the Topology Change Timer
the new root trap is sent out immediately after the switch’s election as the new root.
• Topology Change (STP) – A Topology Change trap is sent by the switch when any of its configured ports
transitions from the Learning state to the Forwarding state, or from the Forwarding state to the Blocking state. The
trap is not sent if a new root trap is sent for the same transition.
• Connected and Working – This trap is sent when the Redundant Power Supply is connected and working.
• Disconnect or Malfunction – This trap is sent whenever the Redundant Power Supply malfunctions.
• MAC Notification – This trap indicates that the switch had learned a new MAC address.
MIBs
Management and counter information are stored in the switch in the Management Information Base (MIB. The switch uses
the standard MIB-II Management Information Base module. Consequently, values for MIB objects can be retrieved from
any SNMP-based network management software. In addition to the standard MIB-II, the switch also supports its own
proprietary enterprise MIB as an extended Management Information Base. These MIBs may also be retrieved by specifying
the MIB’s Object-Identity (OID) at the network manager. MIB values can be either read-only or read-write.
Read-only MIBs variables can be either constants that are programmed into the switch, or variables that change while the
switch is in operation. Examples of read-only constants are the number of port and type of ports. Examples of read-only
variables are the statistics counters such as the number of errors that have occurred, or how many kilobytes of data have
been received and forwarded through a port.
Read-write MIBs are variables usually related to user-customized configurations. Examples of these are the switch’s IP
Address, Spanning Tree Algorithm parameters, and port status.
If you use a third-party vendors’ SNMP software to manage the switch, a diskette listing the switch’s propriety enterprise
MIBs can be obtained by request. If your software provides functions to browse or modify MIBs, you can also get the MIB
values and change them (if the MIBs’ attributes permit the write operation). This process however can be quite involved,
since you must know the MIB OIDs and retrieve them one by one.
SNMP
The Simple Network Management Protocol (SNMP) is an OSI layer 7 (the application layer) protocol for remotely
monitoring and configuring network devices. SNMP enables network management stations to read and modify the settings
of gateways, routers, switches, and other network devices. SNMP can be used to perform many of the same functions as a
directly connected console, or can be used within an integrated network management software package such as HP
OpenView or DView.
SNMP performs the following functions:
• Sending and receiving SNMP packets through the IP protocol.
• Collecting information about the status and current configuration of network devices.
• Modifying the configuration of network devices.
The DGS-3224TGR has a software program called an ‘agent’ that processes SNMP requests, but the user program that
makes the requests and collects the responses runs on a management station (a designated computer on the network). The
SNMP agent and the user program both use the UDP/IP protocol to exchange packets.
13
Page 26

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Authentication
The authentication protocol ensures that both the router SNMP agent and the remote user SNMP application program
discard packets from unauthorized users. Authentication is accomplished using ‘community strings’, which function like
passwords. The remote user SNMP application and the router SNMP must use the same community string.
Packet Forwarding
The switch enters the relationship between destination MAC or IP addresses and the Ethernet port or gateway router the
destination resides on into its forwarding table. This information is then used to forward packets. This reduces the traffic
congestion on the network, because packets, instead of being transmitted to all ports, are transmitted to the destination port
only. Example: if Port 1 receives a packet destined for a station on Port 2, the switch transmits that packet through Port 2
only, and transmits nothing through the other ports. This process is referred to as ‘learning’ the network topology.
MAC Address Aging Time
The Aging Time affects the learning process of the Switch. Dynamic forwarding table entries, which are made up of the
source and destination MAC addresses and their associated port numbers, are deleted from the table if they are not accessed
within the aging time.
The aging time can be from 10 to 1,000,000 seconds with a default value of 300 seconds. A very long aging time can result
in dynamic forwarding table entries that are out-of-date or no longer exist. This may cause incorrect packet forwarding
decisions by the Switch.
If the Aging Time is too short however, many entries may be aged out too soon. This will result in a high percentage of
received packets whose source addresses cannot be found in the forwarding table, in which case the switch will broadcast
the packet to all ports, negating many of the benefits of having a switch.
Static forwarding entries are not affected by the aging time.
Filtering
The switch uses a filtering database to segment the network and control communication between segments. It can also filter
packets off the network for intrusion control. Static filtering entries can be made by MAC Address filtering.
Each port on the switch is a unique collision domain and the switch filters (discards) packets whose destination lies on the
same port as where it originated. This keeps local packets from disrupting communications on other parts of the network.
For intrusion control, whenever a switch encounters a packet originating from or destined to a MAC address entered into
the filter table, the switch will discard the packet.
Some filtering is done automatically by the switch:
• Dynamic filtering – automatic learning and aging of MAC addresses and their location on the network. Filtering
occurs to keep local traffic confined to its segment.
• Filtering done by the Spanning Tree Protocol that can filter packets based on topology, making sure that signal
loops don’t occur.
• Filtering done for VLAN integrity. Packets from a member of a VLAN (VLAN 2, for example) destined for a
device on another VLAN (VLAN 3) will be filtered.
14
Page 27
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Spanning Tree
802.1w Rapid Spanning Tree
The DGS-3224TGR implements two versions of the Spanning Tree Protocol, the Rapid Spanning Tree Protocol (RSTP) as
defined by the IEE 802.1w specification and a version compatible with the IEEE 802.1d STP. RSTP can operate with
legacy equipment implementing IEEE 802.1d, however the advantages of using RSTP will be lost.
The IEEE 802.1w Rapid Spanning Tree Protocol (RSTP) evolved from the 802.1d STP standard. RSTP was developed in
order to overcome some limitations of STP that impede the function of some recent switching innovations, in particular,
certain Layer 3 function that are increasingly handled by Ethernet switches. The basic function and much of the
terminology is the same as STP. Most of the settings configured for STP are also used for RSTP. This section introduces
some new Spanning Tree concepts and illustrates the main differences between the two protocols.
Port Transition States
An essential difference between the two protocols is in the way ports transition to a forwarding state and the in the way this
transition relates to the role of the port (forwarding or not forwarding) in the topology. RSTP combines the transition states
disabled, blocking and listening used in 802.1d and creates a single state Discarding. In either case, ports do not forward
packets; in the STP port transition states disabled, blocking or listening or in the RSTP port state discarding there is no
functional difference, the port is not active in the network topology. The table below compares how the two protocols differ
regarding the port state transition.
Both protocols calculate a stable topology in the same way. Every segment will have a single path to the root bridge. All
bridges listen for BPDU packets. However, BPDU packets are sent more frequently – with every Hello packet. BPDU
packets are sent even if a BPDU packet was not received. Therefore, each link between bridges is sensitive to the status of
the link. Ultimately this difference results faster detection of failed links, and thus faster topology adjustment. A drawback
of 802.1d is this absence of immediate feedback from adjacent bridges.
STP/RSTP Comparison
802.1d STP 802.1w RSTP Forwarding? Learning?
Disabled Discarding No No
Blocking Discarding No No
Listening Discarding No No
Learning Learning No Yes
Forwarding Forwarding Yes Yes
Comparing Port States
RSTP is capable of more rapid transition to a forwarding state – it no longer relies on timer configurations – RSTP
compliant bridges are sensitive to feedback from other RSTP compliant bridge links. Ports do not need to wait for the
topology to stabilize before transitioning to a forwarding state. In order to allow this rapid transition, the protocol
introduces two new variables: the edge port and the point-to-point (P2P) port.
Edge Port
The edge port is a configurable designation used for a port that is directly connected to a segment where a loop cannot be
created. An example would be a port connected directly to a single workstation. Ports that are designated as edge ports
transition to a forwarding state immediately without going through the listening and learning states. An edge port loses its
status if it receives a BPDU packet, immediately becoming a normal spanning tree port.
P2P Port
A P2P port is also capable of rapid transition. P2P ports may be used to connect to other bridges. Under RSTP, all ports
operating in full-duplex mode are considered to be P2P ports, unless manually overridden through configuration.
15
Page 28

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
802.1d/802.1w Compatibility
RSTP can interoperate with legacy equipment and is capable of automatically adjusting BPDU packets to 802.1d format
when necessary. However, any segment using 802.1 STP will not benefit from the rapid transition and rapid topology
change detection of RSTP. The protocol also provides for a variable used for migration in the event that legacy equipment
on a segment is updated to use RSTP.
The Spanning Tree Protocol (STP) operates on two levels: on the switch level, the settings are globally implemented. On
the port level, the settings are implemented on a user-defined Group of ports basis.
VLANs
A Virtual Local Area Network (VLAN) is a network topology configured according to a logical scheme rather than the
physical layout. VLANs can be used to combine any collection of LAN segments into an autonomous user group that
appears as a single LAN. VLANs also logically segment the network into different broadcast domains so that packets are
forwarded only between ports within the VLAN. Typically, a VLAN corresponds to a particular subnet, although not
necessarily.
VLANs can enhance performance by conserving bandwidth, and improve security by limiting traffic to specific domains.
A VLAN is a collection of end nodes grouped by logic instead of physical location. End nodes that frequently communicate
with each other are assigned to the same VLAN, regardless of where they are physically on the network. Logically, a
VLAN can be equated to a broadcast domain, because broadcast packets are forwarded to only members of the VLAN on
which the broadcast was initiated.
Note: VLANs on the DGS-3224TGR
No matter what basis is used to uniquely identify end nodes and assign
these nodes VLAN membership, packets cannot cross VLANs without a
network device performing a routing function between the VLANs.
The DGS-3224TGR supports only IEEE 802.1Q VLANs. The port
untagging function can be used to remove the 802.1Q tag from packet
headers to maintain compatibility with devices that are tag-unaware.
The switch’s default is to assign all ports to a single 802.1Q VLAN named
“default.”
The default VLAN has a VID = 1
IEEE 802.1Q VLANs
Some relevant terms:
• Tagging – The act of putting 802.1Q VLAN information into the header of a packet.
• Untagging – The act of stripping 802.1Q VLAN information out of the packet header.
• Ingress port – A port on a switch where packets are flowing into the switch and VLAN decisions must be
made.
• Egress port – A port on a switch where packets are flowing out of the switch, either to another switch or to an
end station, and tagging decisions must be made.
IEEE 802.1Q (tagged) VLANs are implemented on the DGS-3224TGR 802.1Q VLANs require tagging, which enables
them to span the entire network (assuming all switches on the network are IEEE 802.1Q-compliant).
VLANs allow a network to be segmented in order to reduce the size of broadcast domains. All packets entering a VLAN
will only be forwarded to the stations (over IEEE 802.1Q enabled switches) that are members of that VLAN, and this
includes broadcast, multicast and unicast packets from unknown sources.
VLANs can also provide a level of security to your network. IEEE 802.1Q VLANs will only deliver packets between
stations that are members of the VLAN.
16
Page 29
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Any port can be configured as either tagging or untagging. The untagging feature of IEEE 802.1Q VLANs allows VLANs
to work with legacy switches that don’t recognize VLAN tags in packet headers. The tagging feature allows VLANs to
span multiple 802.1Q-compliant switches through a single physical connection and allows Spanning Tree to be enabled on
all ports and work normally.
The IEEE 802.1Q standard restricts the forwarding of untagged packets to the VLAN the receiving port is a member of.
The main characteristics of IEEE 802.1Q are as follows:
• Assigns packets to VLANs by filtering.
• Assumes the presence of a single global spanning tree.
• Uses an explicit tagging scheme with one-level tagging
802.1Q VLAN Packet Forwarding
Packet forwarding decisions are made based upon the following three types of rules:
• Ingress rules – rules relevant to the classification of received frames belonging to a VLAN.
• Forwarding rules between ports – decides filter or forward the packet
• Egress rules – determines if the packet must be sent tagged or untagged.
Figure 5- 1. IEEE 802.1Q Packet Forwarding
17
Page 30
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
802.1Q VLAN Tags
The figure below shows the 802.1Q VLAN tag. There are four additional octets inserted after the source MAC address.
Their presence is indicated by a value of 0x8100 in the EtherType field. When a packet’s EtherType field is equal to
0x8100, the packet carries the IEEE 802.1Q/802.1p tag. The tag is contained in the following two octets and consists of
three bits of user priority, one bit of Canonical Format Identifier (CFI – used for encapsulating Token Ring packets so they
can be carried across Ethernet backbones) and twelve bits of VLAN ID (VID). The three bits of user priority are used by
802.1p. The VID is the VLAN identifier and is used by the 802.1Q standard. Because the VID is twelve bits long, 4094
unique VLANs can be identified.
The tag is inserted into the packet header making the entire packet longer by four octets. All of the information contained in
the packet originally is retained.
Figure 5- 2. IEEE 802.1Q Tag
The EtherType and VLAN ID are inserted after the MAC source address, but before the original EtherType/Length or
Logical Link Control. Because the packet is now a bit longer than it was originally, the Cyclic Redundancy Check (CRC)
must be recalculated.
Figure 5- 3. Adding an IEEE 802.1Q Tag
18
Page 31

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Port VLAN ID
Packets that are tagged (are carrying the 802.1Q VID information) can be transmitted from one 802.1Q compliant network
device to another with the VLAN information intact. This allows 802.1Q VLANs to span network devices (and indeed, the
entire network – if all network devices are 802.1Q compliant).
Unfortunately, not all network devices are 802.1Q compliant. These devices are referred to as tag-unaware. 802.1Q
devices are referred to as tag-aware.
Prior to the adoption 802.1Q VLANs, port-based and MAC-based VLANs were in common use. These VLANs relied upon
a Port VLAN ID (PVID) to forward packets. A packet received on a given port would be assigned that port’s PVID and
then be forwarded to the port that corresponded to the packet’s destination address (found in the switch’s forwarding table).
If the PVID of the port that received the packet is different from the PVID of the port that is to transmit the packet, the
switch will drop the packet.
Within the switch, different PVIDs mean different VLANs (remember that two VLANs cannot communicate without an
external router). So, VLAN identification based upon the PVIDs cannot create VLANs that extend outside a given switch.
Every physical port on a switch has a PVID. 802.1Q ports are also assigned a PVID, for use within the switch. If no
VLANs are defined on the switch, all ports are then assigned to a default VLAN with a PVID equal to 1. Untagged packets
are assigned the PVID of the port on which they were received. Forwarding decisions are based upon this PVID, in so far as
VLANs are concerned. Tagged packets are forwarded according to the VID contained within the tag. Tagged packets are
also assigned a PVID, but the PVID is not used to make packet forwarding decisions, the VID is.
Tag-aware switches must keep a table to relate PVIDs within the switch to VIDs on the network. The switch will compare
the VID of a packet to be transmitted to the VID of the port that is to transmit the packet. If the two VIDs are different, the
switch will drop the packet. Because of the existence of the PVID for untagged packets and the VID for tagged packets,
tag-aware and tag-unaware network devices can coexist on the same network.
A switch port can have only one PVID, but can have as many VIDs as the switch has memory in its VLAN table to store
them.
Because some devices on a network may be tag-unaware, a decision must be made at each port on a tag-aware device
before packets are transmitted – should the packet to be transmitted have a tag or not? If the transmitting port is connected
to a tag-unaware device, the packet should be untagged. If the transmitting port is connected to a tag-aware device, the
packet should be tagged.
Tagging and Untagging
Every port on an 802.1Q compliant switch can be configured as tagging or untagging.
Ports with tagging enabled will put the VID number, priority and other VLAN information into the header of all packets
that flow into and out of it. If a packet has previously been tagged, the port will not alter the packet, thus keeping the VLAN
information intact. The VLAN information in the tag can then be used by other 802.1Q-compliant devices on the network to
make packet forwarding decisions.
Ports with untagging enabled will strip the 802.1Q tag from all packets that flow into and out of those ports. If the packet
doesn’t have an 802.1Q VLAN tag, the port will not alter the packet. Thus, all packets received by and forwarded by an
untagging port will have no 802.1Q VLAN information (Remember that the PVID is only used internally within the
switch). Untagging is used to send packets from an 802.1Q-compliant network device to a non-compliant network device.
Ingress Filtering
A port on a switch where packets are flowing into the switch and VLAN decisions must be made is referred to as an ingress
port. If ingress filtering is enabled for a port, the switch will examine the VLAN information in the packet header (if
present) and decide whether or not to forward the packet.
If the packet is tagged with VLAN information, the ingress port will first determine if the ingress port itself is a member of
the tagged VLAN. If it is not, the packet will be dropped. If the ingress port is a member of the 802.1Q VLAN, the switch
then determines if the destination port is a member of the 802.1Q VLAN. If it is not, the packet is dropped. If the
destination port is a member of the 802.1Q VLAN, the packet is forwarded and the destination port transmits it to its
attached network segment.
19
Page 32

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
If the packet is not tagged with VLAN information, the ingress port will tag the packet with its own PVID as a VID. The
switch then determines if the destination port is a member of the same VLAN (has the same VID) as the ingress port. If it
does not, the packet is dropped. If it has the same VID, the packet is forwarded and the destination port transmits it on its
attached network segment.
This process is referred to as ingress filtering and is used to conserve bandwidth within the switch by dropping packets that
are not on the same VLAN as the ingress port at the point of reception. This eliminates the subsequent processing of
packets that will just be dropped by the destination port.
802.1x Port-Based and MAC-Based Access Control
The IEEE 802.1x standard is a security measure for authorizing and authenticating users to gain access to various wired or
wireless devices on a specified Local Area Network by using a Client and Server based access control model. This is
accomplished by using a RADIUS server to authenticate users trying to access a network by relaying Extensible
Authentication Protocol over LAN (EAPOL) packets between the Client and the Server. The following figure represents a
basic EAPOL packet:
Figure 5- 4. The EAPOL Packet
Utilizing this method, unauthorized devices are restricted from connecting to a LAN through a port to which the user is
connected. EAPOL packets are the only traffic that can be transmitted through the specific port until authorization is
granted. The 802.1x Access Control method holds three roles, each of which are vital to creating and upkeeping a stable
and working Access Control security method.
Figure 5- 5. The three roles of 802.1x
The following section will explain the three roles of Client, Authenticator and Authentication Server in greater detail.
20
Page 33

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Authentication Server
The Authentication Server is a remote device that is connected to the same network as the Client and Authenticator, must be
running a RADIUS Server program and must be configured properly on the Authenticator (Switch). Clients connected to a
port on the Switch must be authenticated by the Authentication Server (RADIUS) before attaining any services offered by
the Switch on the LAN. The role of the Authentication Server is to certify the identity of the Client attempting to access the
network by exchanging secure information between the RADIUS server and the Client through EAPOL packets and, in
turn, informs the Switch whether or not the Client is granted access to the LAN and/or switches services.
Figure 5- 6. The Authentication Server
Authenticator
The Authenticator (the Switch) is an intermediary between the Authentication Server and the Client. The Authenticator
servers two purposes when utilizing 802.1x. The first purpose is to request certification information from the Client through
EAPOL packets, which is the only information allowed to pass through the Authenticator before access is granted to the
Client. The second purpose of the Authenticator is to verify the information gathered from the Client with the
Authentication Server, and to then relay that information back to the Client.
Three steps must be implemented on the Switch to properly configure the Authenticator.
1. The 802.1x State must be Enabled. (Configuration / Switch Information / Advanced Settings / 802.1x Status)
2. The 802.1x settings must be implemented by port (Port Access Entity / PAE System Control / Port Capability /
Capability)
3. A RADIUS server must be configured on the Switch. (Port Access Entity / RADIUS Server / Authentic
RADIUS Server)
21
Page 34

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 5- 7. The Authenticator
Client
The Client is simply the endstation that wishes to gain access to the LAN or switch services. All endstations must be
running software that is compliant with the 802.1x protocol. For users running Windows XP, that software is included
within the operating system. All other users are required to attain 802.1x client software from an outside source. The Client
will request access to the LAN and or Switch through EAPOL packets and, in turn will respond to requests from the
Switch.
Figure 5- 8. The Client
22
Page 35

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Authentication Process
Utilizing the three roles stated above, the 802.1x protocol provides a stable and secure way of authorizing and
authenticating users attempting to access the network. Only EAPOL traffic is allowed to pass through the specified port
before a successful authentication is made. This port is “locked” until the point when a Client with the correct username and
password (and MAC address if 802.1x is enabled by MAC address) is granted access and therefore successfully “unlocks”
the port. Once unlocked, normal traffic is allowed to pass through the port. The following figure displays a more detailed
explanation of how the authentication process is completed between the three roles stated above.
Figure 5- 9. The 802.1x Authentication Process
The D-Link implementation of 802.1x allows network administrators to choose between two types of Access Control used
on the Switch, which are:
1. Port-Based Access Control – This method requires only one user to be authenticated per port by a remote RADIUS
server to allow the remaining users on the same port access to the network.
2. MAC-Based Access Control – Using this method, the Switch will automatically learn up to three MAC addresses
by port and set them in a list. Each MAC address must be authenticated by the Switch using a remote RADIUS
server before being allowed access to the Network.
Port-Based Network Access Control
The original intent behind the development of 802.1x was to leverage the characteristics of point-to-point in LANs. Any
single LAN segment in such an infrastructures has no more than two devices attached to it, one of which is a Bridge Port.
The Bridge Port detects events that indicate the attachment of an active device at the remote end of the link, or an active
device becoming inactive. These events can be used to control the authorization state of the Port and initiate the process of
authenticating the attached device if the Port is unauthorized. This is the Port-Based Network Access Control.
23
Page 36

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
RADIUS
Server
Ethernet Switch
…
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
Network access controlled port
Network access uncontrolled port
Figure 5- 10. Example of Typical Port-Based Configuration
Once the connected Client has successfully been authenticated, the Port then becomes Authorized, and all subsequent traffic
on the Port is not subject to access control restriction until an event occurs that causes the Port to become Unauthorized.
Hence, if the Port is actually connected to a shared media LAN segment with more than one attached device, successfully
authenticating one of the attached devices effectively provides access to the LAN for all devices on the shared segment.
Clearly, the security offered in this situation is open to attack.
24
Page 37

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
MAC-Based Network Access Control
Ethernet Switch
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
802.1X
Client
…
802.1X
Client
RADIUS
Server
802.1X
Client
802.1X
Client
Network access controlled port
Network access uncontrolled port
Figure 5- 11. Example of Typical MAC-Based Configuration
In order to successfully make use of 802.1x in a shared media LAN segment, it would be necessary to create “virtual” Ports,
one for each attached device that required access to the LAN. The Switch would regard the single physical Port connecting
it to the shared media segment as consisting of a number of distinct virtual Ports, each virtual Port being independently
controlled from the point of view of EAPOL exchanges and authorization state. The Switch learns each attached device’s
individual MAC address, and effectively creates a virtual Port that the attached device can then use to communicate with
the LAN via the Switch.
DHCP
The Dynamic Host Configuration Protocol (DHCP) can reduce the administrative burden of assigning and maintaining IP
address information. DHCP provides reliable and simple TCP/IP network configuration, ensures that address conflicts do
not occur, and helps to conserve the use of IP addresses through the centralized management of address allocation.
Dynamic address allocation enables a client to be assigned an IP address from a pool of free addresses. Each address is
assigned with a lease and a lease expiration period. The client must renew the lease to continue using the assigned address.
Dynamically assigned addresses can be returned to the free address pool if the computer is not being used, if it is moved to
another subnet, of if its lease expires. Usually, network policy ensures that the same IP address is assigned to a client each
time and that addresses returned to the free address pool are reassigned.
When the address lease expires, the DHCP client enters the renewing state. The client sends a request message to the DHCP
server that provided the address. The DHCP server sends an acknowledgement that contains the new lease and
configuration parameters. The client then updates its configuration values and returns to the bound state.
25
Page 38

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
When the DHCP client is in the renewing state, it must release its address immediately in the rare event that the DHCP
server sends a negative acknowledgment. The DHCP server sends this message to inform a client that it has incorrect
configuration information, forcing it to release its current address and acquire new information.
If the DHCP client cannot successfully renew its lease, the client enters a rebinding state. The client then sends a request
message to all DHCP servers in its range, attempting to renew its lease. Any DHCP server that can extend the lease sends
an acknowledgement containing the extended lease and updated configuration information. If the lease expires or if a
DHCP server responds with a negative acknowledgement, the client must release its current configuration, and then return
to the initializing state.
If the DHCP client uses more than one network adapter to connect to multiple networks, this protocol is followed for each
adapter that the user wants to configure for TCP/IP. Multi-homed systems are selectively configured for any combination of
the system’s interfaces.
When a DHCP-enabled computer is restarted, it sends a message to the DHCP server with its current configuration
information. The DHCP server either confirms this configuration or sends a negative reply so that the client must begin the
initializing state again. System startup might, therefore, result in a new IP address for a client computer, but neither the user
nor the network administrator has to take any action in the configuration process.
Before loading TCP/IP with an address acquired from the DHCP server, DHCP clients check for an IP address conflict by
sending an Address Resolution Protocol (ARP) request containing the address. If a conflict is found, TCP/IP does not start,
and the user receives an error message. The conflicting address should be removed for the list of active leases or it should
be excluded until the conflict is identified and resolved.
26
Page 39

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
6
Web-Based Network Management
Introduction
The DGS-3224TGR offers an embedded Web-based (HTML) interface allowing users to manage the switch from anywhere
on the network through a standard browser, such as Opera, Netscape Navigator/Communicator, or Microsoft Internet
Explorer. The Web browser acts as a universal access tool and can communicate directly with the switch using the HTTP
protocol. Your browser window may vary with the screen shots (pictures) in this guide.
The Web-based management module and the Console program (and Telnet) are different ways to access the same internal
switching software and configure it. Thus, all settings encountered in Web-based management are the same as those found
in the console program.
NOTE: This Web-based Management Module does not accept Chinese
language input (or other languages requiring 2 bytes per character).
NOTE: It is necessary to download Java Runtime Environment 1.4.2 to
display the Topology windows located in the Single IP Management folder.
Getting Started
The first step in getting started in using Web-based management for your switch is to secure a browser. A Web browser is a
program that allows a person to read hypertext, for example, Opera, Netscape Navigator, or Microsoft Internet Explorer.
Follow the installation instructions for the browser.
The second and last step is to configure the IP interface of the switch. This should be done manually through a console (see
the Configure IP Address section in the “Using The Console Interface” chapter).
You are now ready to begin managing your switch by simply running the browser installed on your computer and pointing
it to the IP address you have defined for the device. The URL in the address bar should read something like:
http://123.123.123.123, where the numbers 123 represent the IP address of the switch. Please note that the proxy for session
connection should be turned off.
Depending on which browser you are using, a dialog box similar to the following will open:
27
Page 40

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Click OK as there is no preset user name or password on the switch. This opens the main page in the management module.
The top panel shows a real-time front panel display of the DGS-3224TGR. Clicking on an individual port on this display
will connect you to the Port Configurations window (see Basic Setup → Port Configurations for a detailed description).
The panel on the left-hand side contains the main menu. The folders in the main menu are directories for Basic Setup,
Advanced Setup, and Single IP Management. In these folders or directories are links to configuration windows and
subdirectories containing more windows used to setup, manage and monitor the Switch.
28
Page 41

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
29
Page 42

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
These are the major categories for switch management. If the sub-menus for each main category do not appear, click on the
small square hyperlink to the left of the folder icon.
The switch management features available in the Web-based are explained below.
30
Page 43

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Basic Setup
The first category includes: Switch Information, Basic Switch Setup, Serial Port Settings, Port Configurations, Port
Description Settings, Traffic Segmentation Table, User Accounts, Network Management, Switch Utilities, Network
Monitoring, Factory Reset, Save Changes, Restart System, and Logout, as well as secondary windows.
Switch Information
Figure 6- 1. Switch Information window
31
Page 44

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
The information is described as follows:
Parameter Description
Device Type
MAC Address
Get IP From
IP Address
VLAN Name
Subnet Mask
Default Gateway
Boot PROM Version
Firmware Version
Hardware Version
Name
A description of the switch type.
The Ethernet address for the device. Also known as the physical address.
There are three choices for how the switch receives its IP Address settings: Manual,
BOOTP, and DHCP.
The host address for the device on the TCP/IP network.
The VLAN name. The switch includes a pre-configured VLAN named “default.”
The address mask that controls subnetting on your TCP/IP network.
The IP address of the device—usually a router—that handles connections to other
subnets and/or other TCP/IP networks.
Version number for the firmware chip. This information is needed for new runtime
software downloads.
Version number of the firmware installed on the switch. This can be updated by using
the Download Firmware from TFTP Server window in the TFTP Services folder (Basic
Setup → Switch Utilities).
Version of the switch hardware.
A user-assigned name for the switch.
Location
Contact
Spanning Tree
GVRP
IGMP Snooping
SSH
TELNET
WEB
A user-assigned description for the physical location of the switch.
Name of the person to contact should there be any problems or questions with the
system. You may also want to include a phone number or extension.
This indicates if Spanning Tree is enabled on the switch. The switch’s global STP
settings can be changed on the STP Switch Settings window (Advanced Setup →
Spanning Tree).
This indicates if Group VLAN Registration Protocol (GVRP) is enabled on the switch.
GVRP is a protocol that allows members to dynamically join VLANs. The switch’s
GVRP settings can be changed on the Switch GVRP window (Advanced Setup →
VLAN Configurations → Switch GVRP).
This indicates if Internet Group Management Protocol (IGMP) Snooping is enabled on
the switch. When enabled, this feature instructs the switch to read IGMP packets being
forwarded through the switch in order to obtain forwarding information from them (learn
which ports contain Multicast members). The switch’s IGMP snooping state can be
changed on the IGMP Snooping State window (Advanced Setup → Multicast
Configuration → IGMP Snooping Global).
This indicates if the Secure Shell protocol is currently enabled on the switch.
This indicates if a Telnet connection is currently enabled on the switch.
This indicates if the Web manager is currently enabled on the switch.
RMON
This indicates if RMON is enabled on the switch.
32
Page 45

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Basic Switch Setup
Figure 6- 2. Basic Switch Setup window
This window is used to enter name, location, and contact information, as well as to determine whether the switch should get
its IP Address settings from the user (Manual), a BOOTP server, or a DHCP server. If you are not using either BOOTP or
DHCP, enter the IP Address, Subnet Mask, and Default Gateway of the switch. If you enable BOOTP, you do not need to
configure any IP parameters because a BOOTP server automatically assigns IP configuration parameters to the switch. If
you enable DHCP, a Dynamic Host Configuration Protocol request will be sent when the switch is powered up. Once you
have selected a setting under Get IP From, click Apply to activate the new settings.
The information is described as follows:
Parameter Description
Get IP From
IP Address
There are three choices for how the switch receives its IP Address settings: Manual,
BOOTP, and DHCP.
The host address for the device on the TCP/IP network.
33
Page 46

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Subnet Mask
Default Gateway
VLAN Name
Name
Location
Contact
State
The address mask that controls subnetting on your TCP/IP network.
The IP address of the device—usually a router—that handles connections to other
subnets and/or other TCP/IP networks.
The VLAN name. The switch includes a pre-configured VLAN named “default.”
A user-assigned name for the switch.
A user-assigned description for the physical location of the switch.
Name of the person to contact should there be any problems or questions with the
system. You may also want to include a phone number or extension.
This allows you to enable or disable the IP interface.
Serial Port Settings
Figure 6- 3. Serial Port Settings window
The following fields can be set:
Parameter Description
Baud Rate
Auto Logout
Determines the serial port bit rate that will be used the next time the switch is restarted.
Available speeds are 9600, 19,200, 38,400, and 115,200 bits per second. The default
setting is 9600.
This setting for the restart of the console is 2 mins, 5 mins, 10 mins, 15 mins, or Never.
34
Page 47

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Port Configurations
Figure 6- 4. first Port Configurations window
To make changes to port configurations, select a port and click Edit. The following Port Configurations window will
open:
35
Page 48

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 5. second Port Configurations window
Select the port(s) you want to configure by using the drop-down menus in the Port and Configure Ports from __ to fields.
Follow these steps:
1. Enable or disable the port. If you choose Disabled in the State field, devices connected to that port cannot use the
switch, and the switch purges their addresses from its address table after the MAC address aging time elapses.
2. Configure the Speed/Duplex setting for the twenty 10/100/1000 ports. Select Auto to allow the port to select the best
transmission speed, duplex mode, and flow control settings based on the capabilities of the device at the other end.
The other selections allow you to force the port to operate in the specified manner. Select 1000M/Full for port
operation at 1000 Mbps and full duplex. Select 100M/Half for port operation at 100 Mbps and half duplex Select
100M/Full for port operation at 100 Mbps and full duplex. Select 100M/Half for port operation at 100 Mbps and half
duplex. Select 10M/Full for port operation at 10 Mbps and full duplex. Select 10M/Half for port operation at 10 Mbps
and half duplex. For 1000BASE-T ports, if 1000M/Full_M is selected on one end of the link pair, then 1000M/Full_S
must be selected on the other end of your D-Link switch, and vice versa. For 1000M connections to switches that do
not possess master/slave capability, the port speed must be set to 1000/Full. Any other configuration will result in a
link down status for both ports. The four mini-GBIC ports are 1000M/Full only.
3. Configure the Flow Control setting for the port. Selecting Enabled in full-duplex mode will implement IEEE 802.3x
flow control. Select Disabled for no flow control. Also, if the port is set for Auto (NWay) in the speed/duplex field
above and flow control is enabled, flow control (whether full- or half-duplex) will only be implemented if the other
device can auto-negotiate flow control.
4. Enable or disable Address Learning.
5. Click Apply to let your changes take effect.
CAUTION: For 1000BASE-T ports, the master and slave parameters refer to connections
running a 1000BASE-T cable for connection between the switch port and another device
capable of a gigabit connection. If one connection is set for 1000 master, the other side of the
connection must be set for 1000 slave, for devices with master/slave capability. For connection
to a device without this capability, the port speed must be set to 1000/full on the switch
connected to the DGS-3224TGR. Any other configuration will result in a link down status for both
ports.
36
Page 49

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Port Description Settings
The DGS-3224TGR supports a port description feature where the user may name various ports on the Switch. To assign
names to various ports:
1. Click Port Description Settings on the Basic Setup menu.
2. Use the From and To pull-down menu to choose a port or range of ports to describe, and then enter a description
of the port(s).
3. Click Apply to set the descriptions in the Port Description Table.
Figure 6- 6. Port Description Settings window
37
Page 50

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Traffic Segmentation Table
The Traffic Segmentation feature prevents the traffic of a specific port on the switch from being transferred to other ports
on the switch. When an incoming packet from a specific port is received, it is only forwarded to the ports that have been
user-defined, even if it is a unicast packet.
Figure 6- 7. Traffic Segmentation Table window
38
Page 51

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Select a Traffic Segmentation Table entry and click Edit to modify an entry.
Figure 6- 8. Traffic Segmentation Table – Edit window
User Accounts
The switch allows you to set up and manage user accounts in the following windows.
Figure 6- 9. User Accounts window
The information on the window is described as follows:
The following fields can be set:
Parameter Description
User Name
Access Level
New
Displays all current users for the switch.
Displays the current access level assigned to each corresponding user. There are two
access levels: User and Admin. Admin has full read/write access, while a User has
read-only access.
Click this button to add a new user to the table.
39
Page 52

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
User Accounts – Add
Figure 6- 10. User Accounts – Add window
To add a User Account, fill in the appropriate information in the Username, New Password, and Confirm New
Password fields. Then select the desired access, Admin or User, in the Access Level drop-down menu and click
Apply.
The information on the window is described as follows:
Parameter Description
User Name
New Password
Confirm New
Password
Access Level
Enter a user name in this field.
Enter the desired new password in this field.
Enter the new password a second time.
Displays the current access level assigned to each corresponding user. There are two
access levels: Admin and User. An Admin user has full read/write access, while a User
has read-only access.
User Accounts – Edit
Figure 6- 11. User Accounts – Edit window
To edit a User Account, fill in the appropriate information in the Old Password, New Password, and Confirm New
Password fields. Click Apply to let your change take effect.
40
Page 53

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
The information on the window is described as follows:
Parameter Description
User Name
Old Password
New Password
Confirm New
Password
The user name being edited.
Enter the last password used in this field.
Enter the desired new password in this field.
Enter the new password a second time.
SNMP Network Management
SNMP V3
The DGS-3224TGR supports the Simple Network Management Protocol (SNMP) versions 1, 2c1, and 3. The SNMP
version used to monitor and control the switch can be specified by the administrator. The three versions of SNMP vary in
the level of security provided between the management station and the network device.
SNMP settings are configured using the menus located on the SNMP V3 folder of the Web manager. Workstations on the
network that are allowed SNMP privileged access to the switch can be restricted with the Management Station IP
Addresses window.
SNMP View Table
The SNMP View Table is used to assign views to community strings that define which MIB objects can be accessed by an
SNMP manager.
Figure 6- 12. SNMP View Table window
To delete an existing SNMP View Table entry, click Delete in the right-hand column that corresponds to the view name
you wish to remove. To create a new entry, click the New button, a separate window will appear.
41
Page 54

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 13. SNMP View Table – Add window
The information on the SNMP View Table windows is described as follows:
Parameter Description
View Name
Subtree
View Type
Type an alphanumeric string of up to 32 characters. This is used to identify the new
SNMP view being created.
Type the Object Identifier (OID) Subtree for the view. The OID identifies an object tree
(MIB tree) that will be included or excluded from access by an SNMP manager.
Select Included to include this object in the list of objects that an SNMP manager can
access. Select Excluded to exclude this object from the list of objects that an SNMP
manager can access.
SNMP Community Table
Figure 6- 14. SNMP Community Table window
To delete an entry, select it on the SNMP Community Table and then click Delete. To create a new entry, click the New
button, a separate window will appear.
42
Page 55

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 15. SNMP Community Table – Add window
SNMP Host Table
Use the SNMP Host Table to set up trap recipients.
Figure 6- 16. SNMP Host Table window
To delete an existing entry, click the selection button in the right-hand column that corresponds to the port you want to
remove and then click Delete. To create a new entry, click the New button, a separate window will appear.
Figure 6- 17. SNMP Host Table – Add window
The following parameters are used in the SNMP Host Table windows:
Parameter Description
43
Page 56

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Host IP
SNMP Version
Community String
/SNMPv3 User Name
Type the IP address of the remote management station that will serve as the SNMP
host for the switch.
From the pull-down menu select:
V1 – To specifies that SNMP version 1 will be used.
V2c – To specify that SNMP version 2 will be used.
V3-NoAuth-NoPriv – To specify that the SNMP version 3 will be used, with a NoAuth-
NoPriv security level.
V3-Auth-NoPriv – To specify that the SNMP version 3 will be used, with an Auth-NoPriv
security level.
V3-Auth-Priv – To specify that the SNMP version 3 will be used, with an Auth-Priv
security level.
Type in the community string or SNMP V3 user name as appropriate.
SNMP Group Table
The SNMP Group created with this table maps SNMP users (identified in the SNMP User Table) to the views created in the
previous window.
Figure 6- 18. SNMP Group Table window
To delete an existing entry, click the selection button in the right-hand column that corresponds to the port you want to
remove. To create a new entry, click the New button, a separate window will appear.
44
Page 57

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 19. SNMP Group Table – Add window
The following parameters are used in the SNMP Group Table windows:
Parameter Description
Group Name
Read View Name
Write View Name
Notify View Name
Security Model
Security Level
Type an alphanumeric string of up to 32 characters. This is used to identify the new
SNMP group of SNMP users.
This name is used to specify the SNMP group created can request SNMP messages.
Specify a SNMP group name for users that are allowed SNMP write privileges to the
switch’s SNMP agent.
Specify a SNMP group name for users that can receive SNMP trap messages
generated by the switch’s SNMP agent.
Use the pull-down menu to select the SNMP version. Select one of the following:
SNMPv1 – Specifies that SNMP version 1 will be used.
SNMPv2 – Specifies that SNMP version 2c will be used. The SNMP v2c supports both
centralized and distributed network management strategies. It includes improvements
in the Structure of Management Information (SMI) and adds some security features.
SNMPv3 – Specifies that the SNMP version 3 will be used. SNMP v3 provides secure
access to devices through a combination of authentication and encrypting packets over
the network.
Use the pull-down menu to select the SNMP version:
NoAuthNoPriv − Specifies that there will be no authorization and no encryption of
packets sent between the switch and a remote SNMP manager.
AuthNoPriv − Specifies that authorization will be required, but there will be no
encryption of packets sent between the switch and a remote SNMP manager.
AuthPriv − Specifies that authorization will be required, and that packets sent between
the switch and a remote SNMP manger will be encrypted.
45
Page 58

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Engine ID
The Engine ID is a unique identifier used for SNMP V3 implementations. This is an alphanumeric string used to identify
the SNMP engine on the switch.
Figure 6- 20. Engine ID window
To change the Engine ID, type the new Engine ID in the space provided and click the Apply button.
SNMP User Table
Use the SNMP User Table to create a new SNMP user and add the user to an existing SNMP group or to a newly created
group.
Figure 6- 21. SNMP User Table window
To delete an existing entry, click the selection button in the right-hand column that corresponds to the port you want to
configure and then click Delete. To create a new entry, click the New button, a separate window will appear.
46
Page 59

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 22. SNMP User Table – Add window
The following parameters are used in the SNMP User Table windows:
Parameter Description
User Name
Type in the new SNMP V3 user name or community string for V1 or V2. This can be
any alphanumeric name of up to 32 characters that will identify the new SNMP user.
Group Name
Type in the new SNMP V3 group name. Again, this can be any alphanumeric name of
up to 32 characters that will identify the SNMP group the new SNMP user will be
associated with.
SNMP Version
From the pull-down menu select:
V1 – To specifies that SNMP version 1 will be used.
V2c– To specify that SNMP version 2 will be used.
V3 – To specify that the SNMP version 3 will be used.
If Encryption (V3 only) is
checked configure also:
Auth-Protocol
In the space provided, type an alphanumeric sting of between 8 and 20 characters that
will be used to authorize the agent to receive packets for the host.
From the pull-down menu select:
MD5 − To specify that the HMAC-MD5-96 authentication level will be used.
SHA − To specify that the HMAC-SHA-96 authentication level will be used.
If Encryption (V3 only) is
checked configure also:
PrivProtocol
In the space provided, type an alphanumeric string of between 8 and 16 characters that
will be used to encrypt the contents of messages the host sends to the agent.
Method
From the pull-down menu select:
by_password– The auth_password string length ranges from 4 to 8.
by_key– The auth_key string length is 16 and must be hexadecimal.
47
Page 60

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Management Station IP Addresses
Management stations are computers on the network that will be used to manage the switch. You can limit the number of
possible management stations by entering up to three IP addresses. If the three IP Address fields contain all zeros (“0”),
then any station with any IP address can access the switch to manage and configure it. If there is one or more IP addresses
entered in the IP Address fields, then only stations with the IP addresses entered will be allowed to access the switch to
manage or configure it.
Figure 6- 23. Management Station IP Addresses window
Switch Utilities
TFTP Services
Trivial File Transfer Protocol (TFTP) services allow the switch firmware to be upgraded by downloading a new firmware
file from a TFTP server to the switch. A configuration file can also be loaded into the switch, and switch settings can be
saved to a TFTP server. In addition, the switch’s history log can be uploaded to a TFTP server.
Please note that TFTP server software must be running on the management station for the TFTP services listed here to
work.
Download Firmware from TFTP Server
Figure 6- 24. Download Firmware from TFTP Server window
Enter the IP address of the TFTP server in the Server IP Address field and the complete path and file name of the firmware
file for the switch in the Path/Filename field. Click Download to initiate the file transfer.
48
Page 61

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Enter the information described below to download firmware from a TFTP server:
Parameter Description
Server IP Address
Path/File Name
The IP address of the TFTP server.
The full file name (including path) of the setting file on the TFTP server.
Download Configuration from TFTP Server
A configuration file can be downloaded from a TFTP server to the switch. This file is then used by the switch to configure
itself.
Figure 6- 25. Download Configuration from TFTP Server window
Enter the IP address of the TFTP Server in the Server IP Address field and the complete path and file name of the firmware
file for the switch in the Path/Filename field. Click Download to initiate the file transfer.
Enter the information described below to download a configuration file from a TFTP server:
Parameter Description
Server IP Address
Path/File Name
Increment
The IP address of the TFTP server.
The full file name (including path) of the setting file on the TFTP server.
Checking this box allows the switch to add the current configuration file to any
previously downloaded partial configuration files. If this box is not checked, the new
configuration file will completely replace the previous configuration file(s).
49
Page 62

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Upload Settings to TFTP Server
The switch’s current settings can be uploaded to a TFTP Server by the switch’s management agent.
Figure 6- 26. Upload Settings to TFTP Server window
Enter the IP address of the TFTP Server in the Server IP Address field and the complete path and file name of the firmware
file for the switch in the Path/Filename field. Click Upload to initiate the file transfer.
Please note that if the user does not save configurations to NV-RAM, the configurations the user is uploading to a TFTP
server will not be saved correctly.
Enter the information described below to upload Switch configuration settings to a TFTP server:
Parameter Description
Server IP Address
Path/File Name
The IP address of the TFTP server.
The full file name (including path) of the setting file on the TFTP server.
Upload History Log to TFTP Server
The switch’s management agent can upload its history log file to a TFTP server.
Please note that an empty history file on the TFTP server must exist on the server before the switch can upload its history
file.
Figure 6- 27. Upload History Log to TFTP Server window
Enter the IP address of the TFTP Server in the Server IP Address field and the complete path and file name of the firmware
file for the switch in the Path/Filename field. Click Upload to initiate the file transfer.
The information is described as follows:
50
Page 63

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Parameter Description
Server IP Address
Path/File Name
The IP address of the TFTP server.
The full file name (including path) of the setting file on the TFTP server.
Ping Test
The switch is able to test the connection with another network device using Ping.
Figure 6- 28. Ping Test window
Enter the IP address of the network device to be Pinged in the first field, select the number of test packets to be sent (three
is usually enough) in the second field, and enter a time-out value in the third field. Click Start to initiate the Ping program.
51
Page 64

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Network Monitoring
The switch’s monitoring features are located in the following three folders: Statistics, Address Tables, and Status.
Statistics
The Statistics windows include CPU Utilization, Port Utilization, Port Error Packets, and Port Packet Analysis.
CPU Utilization
Figure 6- 29. CPU Utilization window
The CPU Utilization window displays the percentage of the CPU being used, expressed as an integer percentage and
calculated as a simple average by time interval.
52
Page 65

Port Utilization
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 30. Port Utilization window
The information is described as follows:
Parameter Description
Refresh Interval
Clear
Select the desired setting between 2 seconds and 60 second, or Suspend.
Clicking this button clears all statistics counters on this window.
Port Error Packets
Figure 6- 31. Port Error Packets window
The information is described as follows:
Parameter Description
53
Page 66

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Port
Interval
Clear
CrcError
Undersize
Oversize
Fragment
Jabber
Drop Packets
Excessive
Deferral
CRC Error
Select the port you want port error packet statistics for from the drop-down menu.
Select the desired setting between 2 seconds and 60 seconds or Suspend.
Clicking this button clears all statistics counters on this window.
Counts otherwise valid frames that did not end on a byte (octet) boundary.
The number of frames detected that are less than the minimum permitted frame size of 64
bytes and have a good CRC. Undersize frames usually indicate collision fragments, a
normal network occurrence.
Counts packets received that were longer than 1518 octets, or if a VLAN frame 1522
octets, and less than the MAX_PKT_LEN. Internally, MAX_PKT_LEN is equal to 1522.
The number of packets less than 64 bytes with either bad framing or an invalid CRC.
These are normally the result of collisions.
The number of frames with lengths more than the MAX_PKT_LEN bytes. Internally,
MAX_PKT_LEN is equal to 1522.
The number of frames that are dropped by this port since the last Switch reboot.
Counts the number of frames for which the first transmission attempt on a particular
interface was delayed because the medium was busy.
For 10 Mbps ports, the counter records CRC errors (FCS or alignment errors). For 100
Mbps ports, the counter records the sum of CRC errors and code errors (frames received
with rxerror signal).
Late Collision
Excessive
Collision
Single Collision
Collision
Counts the number of times that a collision is detected later than 512 bit-times into the
transmission of a packet.
The number of frames for which transmission failed due to excessive collisions.
The number of successfully transmitted frames for which transmission is inhibited by more
than one collision.
An estimate of the total number of collisions on this network segment.
Port Packet Analysis
Figure 6- 32. Port Packet Analysis window
The information is described as follows:
54
Page 67

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Parameter Description
Port
Interval
Clear
64
65-127
128-255
256-511
512-1023
1024-1518
Unicast RX
Multicast RX
Select the port you want port error analysis statistics for from the drop-down menu.
Select the desired setting between 2 seconds and 60 second, or Suspend.
Clicking this button clears all statistics counters on this window.
The total number of packets (including bad packets) received that were 64 octets in length
(excluding framing bits but including FCS octets).
The total number of packets (including bad packets) received that were between 65 and
127 octets in length inclusive (excluding framing bits but including FCS octets).
The total number of packets (including bad packets) received that were between 128 and
255 octets in length inclusive (excluding framing bits but including FCS octets).
The total number of packets (including bad packets) received that were between 256 and
511 octets in length inclusive (excluding framing bits but including FCS octets).
The total number of packets (including bad packets) received that were between 512 and
1023 octets in length inclusive (excluding framing bits but including FCS octets).
The total number of packets (including bad packets) received that were between 1024 and
1518 octets in length inclusive (excluding framing bits but including FCS octets).
Displays the number of unicast packets received by the switch in total number (Frames)
and the rate (Frames/sec).
Displays the number of multicast packets received by the switch in total number (Frames)
and the rate (Frames/sec).
Broadcast RX
RX Bytes
RX Frames
TX Bytes
Displays the number of broadcast packets received by the switch in total number
(Frames) and the rate (Frames/sec).
Displays the number of bytes (octets) received by the switch in total number (Total), and
rate (Total/sec).
Displays the number of packets (frames) received by the switch in total number (Total),
and rate (Total/sec).
Displays the number of bytes (octets) transmitted by the switch in total number (Total),
and rate (Total/sec).
Address Tables
The Address Tables include the MAC Address Table and ARP Table.
55
Page 68

MAC Address Table
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 33. MAC Address Table window
The information is described as follows:
Parameter Description
Browse
Clear
Click this button to initiate the desired method for viewing MAC addresses.
Clicking this button clears all statistics counters on this window.
56
Page 69

ARP Table
DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 34. ARP Table window
Search the ARP entry table by Interface Name or by IP Address. You may also specify Static or Dynamic entries only by
selecting the Type and specifying Static or Dynamic from the pull-down menu. Click the Find button to initiate the search
for the ARP Table. Clicking the Clear Table button to clear all statistics counters on this window.
Status
The Status windows include GVRP Status, Router Ports, IGMP Snooping Group Table, and Switch History.
GVRP Status
This allows the GVRP status for each of the switch’s ports to be viewed by VLAN. This window displays the ports on the
switch that are currently Egress or Untagged ports.
57
Page 70

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 35. GVRP Status window
Router Ports
This displays which of the switch’s ports are currently configured as router ports. A router port configured by a user (using
the console or Web-based management interfaces) is displayed as a static router port, designated by S. A router port that is
dynamically configured by the switch is designated by D.
Figure 6- 36. Router Ports window
IGMP Snooping Group Table
This allows the switch’s IGMP Snooping table to be viewed. IGMP Snooping allows the switch to read the Multicast Group
IP address and the corresponding MAC address from IGMP packets that pass through the switch. The ports where the
IGMP packets were snooped are displayed, signified with an M. The number of IGMP reports that were snooped is also
displayed in the Reports field.
58
Page 71

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 37. IGMP Snooping Group Table window
Switch History
The Web manager allows the switch’s history log, as compiled by the switch’s management agent, to be viewed.
Figure 6- 38. Switch History window
59
Page 72

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
The switch can record event information in its own logs, to designated SNMP trap receiving stations, and to the PC
connected to the console manager. Clicking Next at the bottom of the window will allow you to display all the switch Trap
Logs.
The information in the Switch History log is described as follows:
Parameter Description
Sequence
Time
Log Text
A counter incremented whenever an entry to the switch’s history log is made. The table
displays the last entry (highest sequence number) first.
Displays the time in days, hours, and minutes since the switch was last restarted.
Displays text describing the event that triggered the history log entry.
Factory Reset
The following window allows you to Reset, Reset Config, or Reset System. See the on-screen instructions for the
differences among each option.
Note that all changes are kept in normal memory. If a user does not save the result into NV-RAM with the Save Changes
function, the switch will recover all the settings the last user configured after the switch is rebooted.
Figure 6- 39. Factory Reset window
Save Changes
The DGS-3224TGR has two levels of memory, normal RAM and non-volatile or NV-RAM.
To retain any configuration changes permanently, highlight Save Changes on the Basic Setup window. The following
window will appear to verify that your new settings have been saved to NV-RAM.
Figure 6- 40. Save Changes window
60
Page 73

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Once the switch configuration settings have been saved to NV-RAM, they become the default settings for the switch. These
settings will be used every time the switch is rebooted.
Restart System
Figure 6- 41. Restart System window
Logout
Figure 6- 42. Logout window
Advanced Setup
This category includes: Switch Advanced Settings, Spanning Tree, Forwarding, Configure QOS, Access Profile Mask
Setting, Port Security, Port Mirroring Configurations, VLAN Configurations, Link Aggregation, 802.1X, TACACS,
System Log, Multicast Configuration, SSH Management, and SSL Management, as well as secondary windows.
61
Page 74

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Switch Advanced Settings
Figure 6- 43. Switch Advanced Settings window
The information is described as follows:
Parameter Description
SSH State
HOL Prevention
Jumbo Frame
ARP Aging Time
(minute)
Year/Month/Date
Hour/Minute/Secon
d
This allows you to enable or disable the Secure Shell feature.
This allows you to enable or disable Head of Line prevention.
This allows you to enable or disable Jumbo Frame support.
This allows you to configure the timeout value of an entry maintained in the ARP table.
This allows you to set the year, month, and date.
This allows you to set the hour, minute, and second.
Spanning Tree
The Switch supports 802.1d Spanning Tree Protocol (STP) and 802.1w Rapid Spanning Tree Protocol (RSTP). 802.1d STP
will be familiar to most networking professionals. However since 802.1w RSTP has been recently introduced to D-Link
managed Ethernet switches, a brief introduction to the technology is provided in Chapter Five’s “Spanning Tree” section.
The Spanning Tree section includes two windows, STP Switch Settings and STP Port Settings.
62
Page 75

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
STP Switch Settings
The switch supports 802.1W Rapid Spanning Tree Protocol, which allows you to create alternative paths (with multiple
switches or other types of bridges) in your network. See the Spanning Tree Algorithm section of the “Switch Management
and Operating Concepts” chapter for a detailed explanation.
Figure 6- 44. STP Switch Settings window
Click Apply after making changes to the window above.
The STP Switch parameters that you can change are:
Parameter Description
Status
Max Age (6-40 sec) <20>
Hello Time (1-10 sec) <2>
Forward Delay (4-30 sec)
<15>
This drop-down menu allows you to enable the Spanning Tree Protocol setting.
The Maximum Age can be from 6 to 40 seconds. At the end of the Maximum
Age, if a BPDU has still not been received from the Root Bridge, your switch
will start sending its own BPDU to all other switches for permission to become
the Root Bridge. If it turns out that your switch has the lowest Bridge Identifier,
it will become the Root Bridge.
The Hello Time can be from 1 to 10 seconds. This is the interval between two
transmissions of BPDU packets sent by the Root Bridge to tell all other
switches that it is indeed the Root Bridge. If you set a Hello Time for your
switch, and it is not the Root Bridge, the set Hello Time will be used if and
when your switch becomes the Root Bridge.
The Forward Delay can be from 4 to 30 seconds. This is the time any port on
the switch spends in the listening state while moving from the blocking state to
the forwarding state.
63
Page 76

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Priority (0-61440) <32768>
STP Version
TX Hold Count (1-10) <3>
Forwarding BPDU
STP Port Settings
A Bridge Priority can be from 0 to 61440. Zero is equal to the highest Bridge
Priority.
Choose RSTP (default) or STP compatible. Both versions use STP parameters
in the same way. RSTP is fully compatible with IEEE 802.1d STP and will
function with legacy equipment.
This is the maximum number of Hello packets transmitted per interval. The
count can be specified from 1 to 10. The default value is 3.
This drop-down menu allows you to configure whether to forward BPDU when
the Spanning Tree Protocol is disabled.
Figure 6- 45. STP Port Settings window
To configure Spanning Tree Protocol functions for individual ports, enter the desired information in the fields on this
window and then click Apply.
64
Page 77

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
The STP Port settings are described as follows:
Parameter Description
From __ To __
State
Cost
Priority
Migrate
Edge
P2P
A consecutive group of ports may be configured starting with the selected port.
The Spanning Tree Protocol state for a selected port can either be Enabled or
Disabled.
A Port Cost can be set from 1 to 200000000. The lower the number, the greater
the probability the port will be chosen to forward packets. Default port cost:
100Mbps port = 19, Gigabit ports = 4.
A Port Priority can be from 0 to 240. The lower the number, the greater the
probability the port will be chosen as the Root Port.
Select Yes or No. Choosing Yes will enable the port to migrate from 802.1d STP
status to 802.1w RSTP status. RSTP can coexist with standard STP, however
the benefits of RSTP are not realized on a port where an 802.1d network
connects to an 802.1w enabled network. Migration should be enabled (Yes) on
ports connected to network stations or segments that will be upgraded to 802.1w
RSTP on all or some portion of the segment
Select Yes or No. Choosing Yes designates the port as an edge port. Edge ports
cannot create loops, however an edge port can lose edge port status if a
topology change creates a potential for a loop. An edge port normally should not
receive BPDU packets. If a BPDU packet is received it automatically loses edge
port status. No indicates the port does not have edge port status.
Select Yes, No, or Auto. Choosing Yes indicates a point-to-point (p2p) shared
link. These are similar to edge ports however they are restricted in that a p2p
port must operate in full duplex. Like edge ports, p2p ports transition to a
forwarding state rapidly thus benefiting from RSTP. The Auto setting instructs
the switch to force a connection to a non-P2P port when it detects 1 or more
BPDUs.
Forwarding
Configuration menus for MAC Address Forwarding including Multicast and Unicast forwarding can be found in the
Forwarding folder. The MAC Address Aging Time and Broadcast/Multicast Storm Control menus are located here as well.
MAC Address Aging Time
Figure 6- 46. MAC Address Aging Time window
65
Page 78

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Set the MAC Address Aging Time and click the Apply button. MAC Address Aging Time specifies the length of time a
learned MAC Address will remain in the forwarding table without being accessed (that is, how long a learned MAC
Address is allowed to remain idle). The Aging Time can be set to any value between 10 and 1,000,000 seconds.
NOTE: A very long Aging Time can result with the out-of-date Dynamic Entries
that may cause incorrect packet filtering/forwarding decisions. A very short
aging time may cause entries to be aged out to soon, resulting in a high
percentage of received packets whose source addresses cannot be found in
the address table, in which case the switch will broadcast the packet to all
ports, negating many of the benefits of having a switch.
Unicast MAC Address Settings
Figure 6- 47. Unicast MAC Address Settings window
To modify a unicast MAC address on the table above, select it and then click Edit.
To add a unicast MAC address to the table above, click New.
Figure 6- 48. Unicast MAC Address Settings – Add window
The following fields can be set:
Parameter Description
MAC Address
Allows the entry of the MAC address of an end station that will be entered into the
switch’s static forwarding table when adding a new entry. Displays the currently
selected MAC address when editing.
66
Page 79

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
VLAN Name
Type
Port
Allows the entry of the VLAN Name of the VLAN the MAC address below is a member
of − when editing. Displays the VLAN the currently selected MAC address is a member
of − when editing an existing entry.
This is the type of the Unicast MAC Address entry.
Allows the entry of the port number on which the MAC address entered above resides.
Multicast MAC Address Settings
Multicast MAC addresses can be statically entered into the switch’s MAC Address Forwarding Table. These addresses will
never age out.
Figure 6- 49. Multicast MAC Address Settings window
Click New to add multicast MAC addresses to the table above. To make changes to an existing entry, select the entry on the
table above and click Edit.
Figure 6- 50. Multicast MAC Address Settings – Add window
The following fields can be set:
Parameter Description
MAC Address
VLAN Name
Allows the entry of the MAC address of an end station that will be entered into the
switch’s static forwarding table.
Allows the entry of the VLAN name of the VLAN the MAC address below is a member
of − when adding a new entry to the table. Displays the VLAN name of the VLAN the
MAC address is a member of − when editing an existing entry.
67
Page 80

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Port
None
Egress
Allows the entry of the port number on which the MAC address entered above
resides.
Specifies the port as being none.
Specifies the port as being a source of multicast packets originating from the MAC
address specified above.
Broadcast/Multicast Storm Control
Broadcast and multicast storms consist of broadcast or multicast packets that flood and/or are looped on a network causing
noticeable performance degradation and, in extreme cases, network failure.
The DGS-3224TGR allows some control over broadcast/multicast storms by setting thresholds on the number of
broadcast/multicast packets received (in thousands of packets per second or Kpps), and then following a user-specified
course of action when this threshold is exceeded.
Figure 6- 51. Broadcast/Multicast Storm Control window
68
Page 81

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 52. Broadcast/Multicast Storm Control – Edit window
The BS/MS/DLF Upper Threshold sets the rate of broadcast/multicast/destination lookup fail packets received on a port or
group of ports that will trigger the action to be taken by the switch, as detailed below. A range of thousands of packets
received per second (Kpps) between 0 and 255 can be specified.
When a port or group of ports receives more broadcast, multicast, or destination lookup fail packets per second than is
specified in the respective Upper Threshold (0-255 Kpps) field, the switch will take the actions specified in the Broadcast
Storm Mode, Multicast Storm Mode, and the Destination Lookup Fail pull-down menus.
The Broadcast Storm Mode is Enabled or Disabled using a pull-down menu. When the Broadcast Storm Mode is Enabled,
and a port contained within the corresponding port group receives more broadcast packets than specified in the Upper
Threshold (0-255 Kpps) field, the switch will drop all broadcast packets received by any port in the port group until the rate
of broadcast packets received by the port group falls.
The Multicast Storm Mode is Enabled or Disabled using a pull-down menu. When the Multicast Storm Mode is Enabled,
and a port contained within the corresponding port group receives more multicast packets than specified in the Upper
Threshold (0-255 Kpps) field, the switch will drop all multicast packets received by any port in the port group until the rate
of multicast packets received by the port group falls.
The Destination Lookup Fail is Enabled or Disabled using a pull-down menu. When the Destination Lookup Fail is
Enabled, and a port contained within the corresponding port group receives more destination lookup failed packets than
specified in the Upper Threshold (0-255 Kpps) field, the switch will drop all destination lookup failed packets received by
any port in the port group until the rate of destination lookup failed packets received by the port group falls.
Configure QOS
The DGS-3224TGR supports 802.1p priority queuing. The switch has eight priority queues. These priority queues are
numbered from 0 — the lowest priority queue — to 7 — the highest priority queue. The eight priority queues specified in
IEEE 802.1p (Q0 to Q7) are mapped to the switch’s priority queues as follows:
Q0 is assigned to the switch’s Q2 queue.
Q1 is assigned to the switch’s Q0 queue.
Q2 is assigned to the switch’s Q1 queue.
Q3 is assigned to the switch’s Q3 queue.
69
Page 82

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Q4 is assigned to the switch’s Q4 queue.
Q5 is assigned to the switch’s Q5 queue.
Q6 is assigned to the switch’s Q6 queue.
Q7 is assigned to the switch’s Q7 queue.
For strict priority-based scheduling, any packets residing in the higher priority queues are transmitted first. Only when these
queues are empty, are packets of lower priority transmitted.
For weighted round-robin queuing, the number of packets sent from each priority queue depends upon the assigned weight.
For a configuration of eight CoS queues, A~H with their respective weight value: 8~1, the packets are sent in the following
sequence: A1, B1, C1, D1, E1, F1, G1, H1, A2, B2, C2, D2, E2, F2, G2, A3, B3, C3, D3, E3, F3, A4, B4, C4, D4, E4, A5,
B5, C5, D5, A6, B6, C6, A7, B7, A8, A1, B1, C1, D1, E1, F1, G1, H1.
For weighted round-robin queuing, if each CoS queue has the same weight value, then each CoS queue has an equal
opportunity to send packets just like round-robin queuing.
For weighted round-robin queuing, if the weight for a CoS is set to 0, then it will continue processing the packets from this
CoS until there are no more packets for this CoS. The other CoS queues that has been given a nonzero value, and depending
upon the weight, they will follow a common weighted round-robin scheme.
Remember that the DGS-3224TGR has eight priority queues (and thus eight Classes of Service) for each port on the switch.
QOS Output Scheduling
Figure 6- 53. QOS Output Scheduling window
70
Page 83

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
802.1p Default Priority
The switch allows the assignment of a default 802.1p priority to each port on the switch.
Figure 6- 54. 802.1p Default Priority window
This window allows you to assign a default 802.1p priority to any given port on the switch. The priority queues are
numbered from 0 − the lowest priority − to 7 − the highest priority.
71
Page 84

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
802.1p User Priority
The DGS-3224TGR allows the assignment of a User Priority to each of the 802.1p priorities.
Figure 6- 55. 802.1p User Priority window
Bandwidth Control Table
The bandwidth control settings are used to place a ceiling on the transmitting and receiving data bit rates for any port.
72
Page 85

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 56. Bandwidth Control Table window
To change the maximum allowed bandwidth for a given port in the Bandwidth Control Table window, click the selection
button in the far left column that corresponds to the port you want to configure and click the Edit button. A new window
opens:
Figure 6- 57. Bandwidth Control Table – Edit window
To limit either the Rx or Tx rates, deselect the No Limit check box and enter the desired rate. Rates can be expressed using
whole numbers up to the maximum available rate for the port.
Access Profile Mask Setting
Access profiles allow you to establish criteria to determine whether or not the switch will forward packets based on the
information contained in each packet’s header. These criteria can be specified on a basis of VLAN, MAC address or IP
address.
73
Page 86

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Creating an access profile is divided into two basic parts. The first is to specify which part or parts of a frame the switch
will examine, such as the MAC source address or the IP destination address. The second part is entering the criteria the
switch will use to determine what to do with the frame. The entire process is described below in two parts.
Figure 6- 58. Access Profile Mask Setting window
To create an Access Profile Mask:
To add an entry to the Access Profile Mask Setting window, click the New button. This will open an Access Profile Mask
Setting – Add window, as shown below. There are three Access Profile Mask Setting – Add windows; one for Ethernet
(or MAC address-based) profile configuration, one for IP address-based profile configuration and one for the Packet
Content Mask. You can switch among the three windows by using the Access Profile drop-down menu.
Use the Access Profile Mask Setting – Add windows to create access profiles and specify what criteria are used to
examine frames. Once a profile has been created, you can set up the rule applied to the profile as described later in this
section.
Figure 6- 59. Access Profile Mask Setting – Add (Ethernet) window
74
Page 87

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
The following parameters can be set, for the Ethernet type:
Parameter Description
Profile ID
Auto Assign
Access Profile
VLAN
Source MAC
Destination MAC
802.1p
Type in a unique identifier number for this profile set. This value can be set from 1 to
8.
Checking this box instructs the Switch to automatically assign a Profile ID.
Select profile based on Ethernet (MAC Address), IP address or packet content mask.
This will change the window according to the requirements for the type of profile.
Ethernet instructs the Switch to examine the layer 2 part of each packet header.
Select IP to instruct the Switch to examine the IP address in each frame's header.
Select Packet Content Mask to specify a mask to hide the content of the packet
header.
Selecting this option instructs the Switch to examine the VLAN identifier of each
packet header and use this as the full or partial criterion for forwarding.
Source MAC Mask - Enter a MAC address mask for the source MAC address.
Destination MAC Mask - Enter a MAC address mask for the destination MAC
address.
Selecting this option instructs the Switch to examine the 802.1p priority value of each
packet header and use this as the, or part of the criterion for forwarding.
Ethernet Type
Selecting this option instructs the Switch to examine the Ethernet type value in each
frame's header.
Port The user may set the Access Profile Mask Setting window on a per-port basis by
entering a port number in this field. The port list is specified by listing the beginning
port number on that switch and the highest port number of the range. The beginning
and end of the port list range are separated by a dash. For example, 3-8 specifies all
of the ports between port 3 and port 8 − in numerical order. Entering all will denote all
ports on the Switch.
75
Page 88

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 60. Access Profile Mask Setting – Add (IP) window
The following parameters can be set, for IP:
Parameter Description
Profile ID
Type in a unique identifier number for this profile set. This value can be set from 1 to
8.
Auto Assign
Type
Checking this box instructs the Switch to automatically assign a Profile ID.
Select profile based on Ethernet (MAC Address), IP address or packet content mask.
This will change the window according to the requirements for the type of profile.
IP instructs the Switch to examine the IP address in each frame's header.
Select Ethernet to instruct the Switch to examine the layer 2 part of each packet
header.
Select Packet Content Mask to specify a mask to hide the content of the packet
header.
VLAN
Selecting this option instructs the Switch to examine the VLAN part of each packet
header and use this as the, or part of the criterion for forwarding.
76
Page 89

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Source IP Mask
Destination IP Mask
DSCP
Protocol
Enter an IP address mask for the source IP address.
Enter an IP address mask for the destination IP address.
Selecting this option instructs the Switch to examine the DiffServ Code part of each
packet header and use this as the, or part of the criterion for forwarding.
Selecting this option instructs the Switch to examine the protocol type value in each
frame's header. You must then specify what protocol(s) to include according to the
following guidelines:
Select ICMP to instruct the Switch to examine the Internet Control Message Protocol
(ICMP) field in each frame's header.
Select Type to further specify that the access profile will apply an ICMP type
value, or specify Code to further specify that the access profile will apply an
ICMP code value.
Select IGMP to instruct the Switch to examine the Internet Group Management
Protocol (IGMP) field in each frame's header.
Select Type to further specify that the access profile will apply an IGMP type
value
Select TCP to use the TCP port number contained in an incoming packet as the
forwarding criterion. Selecting TCP requires that you specify a source port mask
and/or a destination port mask. The user may also identify which flag bits to filter by
checking the flag bit box. Flag bits are parts of a packet that determine what to do
with the packet. The user may filter packets by filtering certain flag bits within the
packets, by checking the boxes corresponding to the flag bits of the TCP field. The
user may choose among urg (urgent), ack (acknowledgement), psh (push), rst (reset),
syn (synchronize), and fin (finish).
Source Port Mask 0x - Specify a TCP port mask for the source port in hex form
(hex 0x0-0xffff), which you wish to filter.
Destination Port Mask 0x - Specify a TCP port mask for the destination port in hex
form (hex 0x0-0xffff) which you wish to filter.
Select UDP to use the UDP port number contained in an incoming packet as the
forwarding criterion. Selecting UDP requires that you specify a source port mask
and/or a destination port mask.
Source Port Mask 0x - Specify a TCP port mask for the source port in hex form
(hex 0x0-0xffff).
Destination Port Mask 0x - Specify a TCP port mask for the destination port in hex
form (hex 0x0-0xffff).
Protocol ID - Enter a value defining the protocol ID in the packet header to mask.
Specify the protocol ID mask in hex form (hex 0x0-0xffffffff).
Port The user may set the Access Profile Mask Setting window on a per-port basis by
entering a port number in this field. The port list is specified by listing the beginning
port number on that switch and the highest port number of the range. The beginning
and end of the port list range are separated by a dash. For example, 3-8 specifies all
of the ports between port 3 and port 8 − in numerical order. Entering all will denote all
ports on the Switch.
77
Page 90

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 61. Access Profile Mask Setting – Add (Package Content Mask) window
This window will aid the user in configuring the Switch to mask packet headers beginning with the offset value specified.
The following fields are used to configure the Packet Content Mask:
Parameter Description
Profile ID (1-8)
Auto Assign
Type
Type in a unique identifier number for this profile set. This value can be set from 1 - 8.
Checking this box instructs the Switch to automatically assign a Profile ID.
Select profile based on Ethernet (MAC Address), IP address or packet content mask.
This will change the menu according to the requirements for the type of profile.
Packet Content Mask specifies a mask to hide the content of the packet header.
78
Page 91

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Select Ethernet to instruct the Switch to examine the layer 2 part of each packet
header.
Select IP to instruct the Switch to examine the IP address in each frame's header.
Offset
This field will instruct the Switch to mask the packet header beginning with the offset
value specified:
value (0-15) - Enter a value in hex form to mask the packet from the beginning of
the packet to the 15th byte.
value (16-31) – Enter a value in hex form to mask the packet from byte 16 to byte
31.
value (32-47) – Enter a value in hex form to mask the packet from byte 32 to byte
47.
value (48-63) – Enter a value in hex form to mask the packet from byte 48 to byte
63.
value (64-79) – Enter a value in hex form to mask the packet from byte 64 to byte
79.
Port The user may set the Access Profile Mask Setting window on a per-port basis by
entering a port number in this field. The port list is specified by listing the beginning
port number on that switch and the highest port number of the range. The beginning
and end of the port list range are separated by a dash. For example, 3-8 specifies all
of the ports between port 3 and port 8 − in numerical order. Entering all will denote all
ports on the Switch.
To establish the rule for a previously created Access Profile Mask:
Select the Access Profile from the Access Profile Mask Setting window and click the Edit Rule button.
Figure 6- 62. Access Profile Rule Setting (Ethernet) window
79
Page 92

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 63. Access Profile Rule Setting (IP) window
Figure 6- 64. Access Profile Rule Setting (Packet Content Mask) window
To create a new rule set for an access profile, click the New button. A new window is displayed. To remove a previously
created rule, select it and click the Delete button.
80
Page 93

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 65. Access Profile Rule Setting – Add (Ethernet) window
Figure 6- 66. Access Profile Rule Setting – Add (IP) window
81
Page 94

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 67. Access Profile Rule Setting – Add (Package Content Mask) window
Configure the following Access Profile Rule Settings:
Parameter Description
Profile ID
Access Rule ID
This is the identifier number for this profile set.
Type in a unique identifier number for this access. This value can be set from 0 to 255.
82
Page 95

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Access Profile
Mode
VLAN
replace priority
(0-7)
replace_dscp (0-
63)
Selected profile based on Ethernet (MAC Address), IP address, or Packet Content Mask.
Ethernet instructs the Switch to examine the layer 2 part of each packet header.
IP instructs the Switch to examine the IP address in each frame's header.
Packet Content Mask instructs the Switch to examine the packet header
Select Permit to specify that the packets that match the access profile are forwarded by
the Switch, according to any additional rule added (see below).
Select Deny to specify that packets that do not match the access profile are not forwarded
by the Switch and will be filtered.
Selecting this option instructs the Switch to examine the VLAN part of each packet header
and use this as the, or part of the criterion for forwarding.
Select this option to instruct the switch to replace the 802.1p value (in a packet that meets
the selected criteria). In this way, packets meeting the criteria can have their priority
handling modified for use within the switch, and then have a different priority value
assigned when they leave the switch.
Select this option to instruct the switch to replace the DSCP value (in a packet that meets
the selected criteria) with the value entered in the adjacent field.
Protocol
Offset Settings:
Selecting this option instructs the Switch to examine the protocol type value in each
frame's header. You must then specify what protocol(s) to include according to the
following guidelines:
Select ICMP to instruct the Switch to examine the Internet Control Message Protocol
(ICMP) field in each frame's header.
This field will instruct the Switch to mask the packet header beginning with the offset value
specified:
value (0-15) - Enter a value in hex form to mask the packet from the beginning of the
packet to the 15th byte.
value (16-31) - Enter a value in hex form to mask the packet from byte 16 to byte 31.
value (32-47) - Enter a value in hex form to mask the packet from byte 32 to byte 47.
value (48-63) - Enter a value in hex form to mask the packet from byte 48 to byte 63.
value (64-79) - Enter a value in hex form to mask the packet from byte 64 to byte 79.
Port Security
A given port’s (or a range of port’s) dynamic MAC address learning can be locked such that the current source MAC
addresses entered into the MAC address forwarding table can not be changed once the port lock is enabled. The port can be
locked by changing the Admin State pull-down menu to Enabled on the Port Security Settings – Edit window, shown
below, and clicking Apply.
This is a security feature that prevents unauthorized computers (with source MAC addresses unknown to the switch prior to
locking the port (or ports) from connecting to the switch’s locked ports and gaining access to the network.
83
Page 96

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 68. Port Security Settings window
Click Edit to open the following window:
84
Page 97

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Figure 6- 69. Port Security Settings – Edit window
The following fields can be set:
Parameter Description
Admin State <Disabled>
Allows the selected port(s) dynamic MAC address learning to be locked such
that new source MAC addresses cannot be entered into the MAC address
table for the locked port or group of ports. It can be changed by toggling
between Disabled and Enabled.
Max. Addr (0 - 10) <1 >
Select the maximum number of addresses that may be learned for the port.
The port can be restricted to 10 or less MAC addresses that are allowed for
dynamically learned MAC addresses in the forwarding table.
Mode<DeleteOnReset>
Select DeleteOnTimeout to clear dynamic entries for the ports on timeout of
the Forwarding Data Base (FDB). When DeleteOnReset is selected, the
locked addresses will not age out until the Switch has been reset. Select
Permanent to automatically save the new learned address and never age out
even if the system rebooting. You can use the Port Security menu to either
clear or delete port security entries.
Configure Ports from __ to
Use this to specify a consecutively numbered group of ports on the switch for
configuration.
Click Clear Port Security Entry in the Port Security folder to access the following window:
Figure 6- 70. Clear Port Security Entry window
Select the range of port security entries and then click Clear.
85
Page 98

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Click Delete Port Security Entry in the Port Security folder to access the following window:
Figure 6- 71. Delete Port Security Entry window
Enter the VLAN Name, MAC Address, and port, and then click Delete to remove a port security entry.
Port Mirroring Configurations
Figure 6- 72. Port Mirroring Configurations window
The target port is the port where information will be duplicated and sent for capture and network analysis. This is the port
where a network analyzer would be attached to capture packets duplicated from the source port.
Up to 25 entries can be made to the port mirroring table, but it should be noted that a faster port (a 1000 Mbps Gigabit
Ethernet port, for example) should not be mirrored to a slower port, because many packets will be dropped.
The following fields can be set:
Parameter Description
Mirror Status
Target Port
This enables or disables mirroring.
This is the port where information will be duplicated and sent for capture and network
analysis.
86
Page 99

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
Mirrored Port
This field can be toggled among None, Both, Rx and Tx. Rx mirrors only received
packets, while Tx mirrors only transmitted packets.
VLAN Configurations
This section includes Asymmetric VLAN State, Switch GVRP, 802.1Q VLANs, and IEEE 802.1Q Settings.
Asymmetric VLAN State
Figure 6- 73. Asymmetric VLAN State window
To set Asymmetric VLANs on the DGS-3224TGR, select Enabled from the drop-down menu and then click Apply.
Switch GVRP
Figure 6- 74. Switch GVRP window
To enable ports from dynamically joining VLANs, select Enabled from the drop-down menu and then click Apply.
87
Page 100

DGS-3224TGR Gigabit Ethernet Switch User’s Guide
802.1Q VLANs
Figure 6- 75. 802.1Q VLANs window
To delete an existing 802.1Q VLAN, click the corresponding click-box to the left of the VLAN you want to delete from the
switch and then click the Delete button.
To create a new 802.1Q VLAN, click the New button:
Figure 6- 76. 802.1Q VLANs – Add window
88
 Loading...
Loading...