Page 1
53-1001944-01
September 2010
Brocade Mobility
RFS7000-GR Controller
®
System Reference Guide
Supporting software release 4.1.0.0-040GR and later
Page 2
Copyright © 2010 Brocade Communications Systems, Inc. All Rights Reserved.
Brocade, the B-wing symbol, BigIron, DCX, Fabric OS, FastIron, IronPoint, IronShield, IronView, IronWare, JetCore, NetIron,
SecureIron, ServerIron, StorageX, and TurboIron are registered trademarks, and DCFM, Extraordinary Networks, and SAN Health
are trademarks of Brocade Communications Systems, Inc., in the United States and/or in other countries. All other brands,
products, or service names are or may be trademarks or service marks of, and are used to identify, products or services of their
respective owners.
Notice: This document is for informational purposes only and does not set forth any warranty, expressed or implied, concerning
any equipment, equipment feature, or service offered or to be offered by Brocade. Brocade reserves the right to make changes to
this document at any time, without notice, and assumes no responsibility for its use. This informational document describes
features that may not be currently available. Contact a Brocade sales office for information on feature and product availability.
Export of technical data contained in this document may require an export license from the United States government.
The authors and Brocade Communications Systems, Inc. shall have no liability or responsibility to any person or entity with
respect to any loss, cost, liability, or damages arising from the information contained in this book or the computer programs that
accompany it.
The product described by this document may contain “open source” software covered by the GNU General Public License or other
open source license agreements. To find out which open source software is included in Brocade products, view the licensing
terms applicable to the open source software, and obtain a copy of the programming source code, please visit
http://www.brocade.com/support/oscd.
Brocade Communications Systems, Incorporated
Corporate and Latin American Headquarters
Brocade Communications Systems, Inc.
130 Holger Way
San Jose, CA 95134
Tel: 1-408-333-8000
Fax: 1-408-333-8101
E-mail: info@brocade.com
European Headquarters
Brocade Communications Switzerland Sàrl
Centre Swissair
Tour B - 4èm e étag e
29, Route de l'Aéroport
Case Postale 105
CH-1215 Genève 15
Switzerland
Tel: +41 22 799 5640
Fax: +41 22 799 5641
E-mail: emea-info@brocade.com
Asia-Pacific Headquarters
Brocade Communications Systems China HK, Ltd.
No. 1 Guanghua Road
Chao Yang District
Units 2718 and 2818
Beijing 100020, China
Tel: +8610 6588 8888
Fax: +8610 6588 9999
E-mail: china-info@brocade.com
Asia-Pacific Headquarters
Brocade Communications Systems Co., Ltd. (Shenzhen WFOE)
Citic Plaza
No. 233 Tian He Road North
Unit 1308 – 13th Floor
Guangzhou, China
Tel: +8620 3891 2000
Fax: +8620 3891 2111
E-mail: china-info@brocade.com
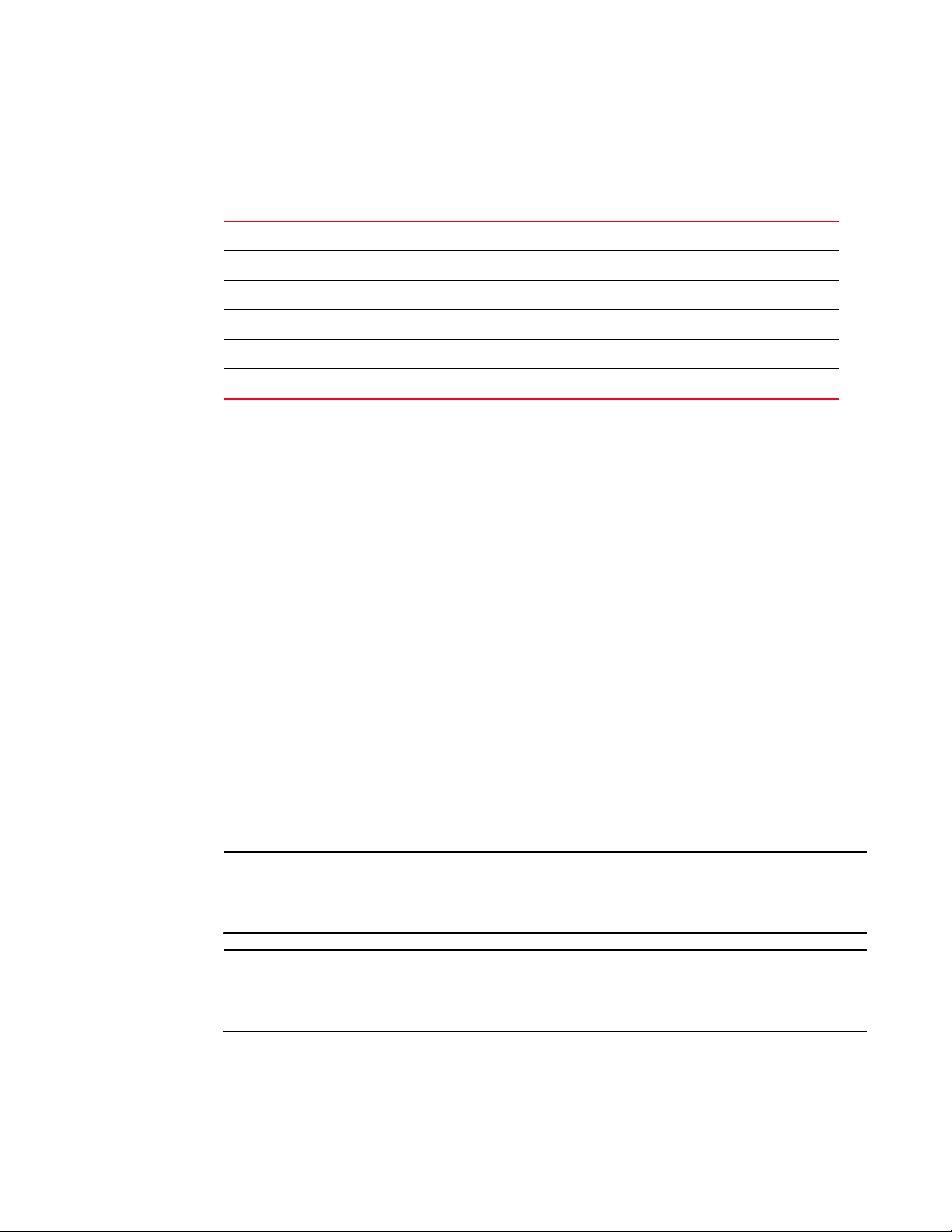
Document History
Title Publication number Summary of changes Date
Brocade Mobility RFS7000-GR Controller
System Reference Guide
53-1001944-01 New document September 2010
Page 3

Table of Contents
1 Overview 1
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1
Hardware overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1
Physical specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2
Software overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3
Infrastructure features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Wireless switching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Wired switching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Management features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Security features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
Supported Access Ports/Points . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Standards support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
2 Controller Web UI Access and Image Upgrades 33
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Accessing the switch Web UI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .33
Web UI requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Connecting to the switch Web UI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
Switch password recovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .35
Upgrading the switch image . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .35
Auto installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
3 Controller Information 39
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Viewing the switch interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Setting the switch country code . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Viewing the switch configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Switch dashboard details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Viewing switch statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Viewing switch port information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Viewing the port configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Viewing the ports runtime status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 49
Reviewing port statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
Viewing switch configurations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .55
Viewing the detailed contents of a config file . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 56
Transferring a config file . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
Viewing switch firmware information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 59
Editing the switch firmware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 60
Updating the switch firmware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Switch file management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
Transferring files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
Viewing files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Configuring automatic updates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .68
Viewing the switch alarm log . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Viewing alarm log details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
Brocade Mobility RFS7000-GR Controller System Reference Guide iii
53-1001944-01
Page 4

Viewing switch licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
How to use the filter option . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 74
4 Network Setup 75
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
Displaying the network interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
Viewing network IP information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77
Configuring DNS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77
Configuring IP forwarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 79
Viewing address resolution . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82
Viewing and configuring Layer 2 virtual LANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82
Viewing and configuring VLANs by port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
Editing the details of an existing VLAN by port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
Viewing and configuring ports by VLAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
Configuring switch virtual interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87
Configuring the virtual interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87
Viewing virtual interface statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 91
Viewing and configuring switch WLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 96
Configuring WLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 96
Viewing WLAN statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130
Configuring WMM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 137
Configuring the NAC inclusion list . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
Configuring the NAC exclusion list . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
NAC configuration examples using the switch CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
Viewing associated MU details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150
Viewing MU status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150
Configuring Mobile Units . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 155
Viewing MU statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 156
Viewing voice statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 161
Viewing Access Port Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 162
Configuring access port radios . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 162
Viewing AP statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 175
Configuring WLAN assignment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 179
Configuring WMM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 181
Configuring access point radio bandwidth . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 184
Configuring radio groups for MU load balancing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 185
Viewing Active Calls (AC) statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 186
Viewing mesh statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 187
Smart RF . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 189
Voice statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 198
Viewing access port adoption defaults . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
Configuring AP adoption defaults . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
Configuring Layer 3 access port adoption . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 206
Configuring WLAN assignment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 207
Configuring WMM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 209
Configuring access ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
iv Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 5

Viewing adopted access ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
Viewing unadopted access ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
Access port configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Configuring Adaptive AP firmware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 217
Multiple spanning tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .219
Configuring a bridge . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 220
Viewing and configuring bridge instance details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 222
Configuring a port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 224
Viewing and configuring port instance details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 228
IGMP Snooping . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .230
IGMP Snoop configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
IGMP Snoop Querier configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 231
5 Controller Services 235
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
Displaying the services interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
DHCP server settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .237
Configuring the switch DHCP server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
Viewing the attributes of existing host pools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
Configuring excluded IP address information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 246
Configuring the DHCP server relay . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 247
Viewing DDNS bindings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 249
Viewing DHCP bindings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
Reviewing DHCP dynamic bindings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Configuring the DHCP user class . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
Configuring DHCP pool class . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 255
Configuring secure NTP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 258
Defining the SNTP configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 258
Configuring symmetric key . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 260
Defining a NTP neighbor configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 262
Adding an NTP neighbor . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 264
Viewing NTP associations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 265
Viewing NTP status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 267
Configuring switch redundancy & clustering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 269
Configuring redundancy settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 271
Reviewing redundancy status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 273
Configuring redundancy group membership . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 275
Redundancy group license aggregation rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 279
Managing clustering using the Web UI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 280
Layer 3 Mobility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 281
Configuring Layer 3 Mobility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 282
Defining the Layer 3 peer list . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 284
Reviewing Layer 3 peer list statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 285
Reviewing Layer 3 MU status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 287
Configuring self healing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .288
Configuring self healing neighbor details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 289
Configuring switch discovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .292
Brocade Mobility RFS7000-GR Controller System Reference Guide v
53-1001944-01
Page 6

Configuring Discovery Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 292
Viewing discovered switches . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 295
Locationing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 297
RTLS overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
SOLE - Smart Opportunistic Location Engine . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
Defining site parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
Configuring SOLE parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 301
Configuring Aeroscout parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 303
Configuring Ekahau parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 304
6 Controller Security 307
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 307
Displaying the main security interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 307
AP intrusion detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Enabling and configuring AP detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Authorized APs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 312
Unauthorized APs (AP reported) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 314
Unauthorized APs (MU reported) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
AP containment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
MU intrusion detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 318
Configuring wireless intrusion detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 318
Viewing filtered MUs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 320
Configuring firewalls and access control lists . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 321
ACL overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 322
Attaching an ACL on a WLAN interface/port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 326
Attaching an ACL Layer 2/Layer 3 configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Configuring the role based firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
Attaching adaptive AP WLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 331
Attaching adaptive AP LANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 334
Configuring wireless filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 335
Editing an existing wireless filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 337
Adding a new wireless filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 338
Associating an ACL with WLAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 340
Configuring the firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 341
Configuring Layer 2 firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 345
Configuring WLAN firewall rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 348
Configuring Denial of Service (DoS) Attack firewall rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 351
Configuring the role . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 353
Configuring firewall logging options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 356
Reviewing firewall and ACL statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 358
Configuring NAT information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 364
Defining Dynamic NAT translations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 365
Defining static NAT translations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 368
Configuring NAT interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 371
Viewing NAT status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 373
Configuring IKE settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 374
Defining the IKE configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 374
vi Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 7

Setting IKE policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 376
Viewing SA statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 380
Configuring IPSec VPN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 382
Defining the IPSec configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 384
Defining the IPSec VPN remote configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 388
Configuring IPSEC VPN authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 389
Configuring Crypto Maps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 392
Viewing IPSec security associations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 401
Configuring the RADIUS Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 403
RADIUS overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 403
Using the switch’s RADIUS Server versus an External RADIUS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 406
Defining the RADIUS configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 406
RADIUS client configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 408
Configuring RADIUS authentication and accounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 408
Configuring RADIUS users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 411
Configuring RADIUS user groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 413
Viewing RADIUS accounting logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 417
Creating server certificates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 418
Using trustpoints to configure certificates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 418
Configuring trustpoint associated keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 429
Configuring enhanced beacons and probes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .432
Configuring the beacon table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 433
Configuring the probe table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 435
Reviewing found beacons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 436
Reviewing found probes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 437
7 Controller Management 439
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 439
Displaying the Management Access Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .439
Configuring Access Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 440
Configuring SNMP Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .442
Configuring SNMP v3 Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 442
Accessing Message Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 445
Accessing SNMP v3 Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 445
Configuring SNMP Traps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .447
Enabling trap configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 447
Configuring Trap Thresholds . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 450
Configuring SNMP trap receivers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 453
Editing SNMP trap receivers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 455
Adding SNMP trap receivers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 455
Configuring management users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .456
Configuring local users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 456
Configuring switch authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 462
8 Diagnostics 467
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 467
Brocade Mobility RFS7000-GR Controller System Reference Guide vii
53-1001944-01
Page 8

Displaying the main diagnostic interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 467
Switch environment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 467
CPU performance . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 469
Switch memory allocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 470
Switch disk allocation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 471
Switch memory processes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 471
Other switch resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 472
Configuring system logging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 473
Log options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 473
File management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 475
Debugging the applet . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479
Configuring a ping . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 481
Modifying the configuration of an existing ping test . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 482
Adding a new ping test . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 483
Viewing ping statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 485
A Adaptive AP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 487
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 487
Where to go from here . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 487
Adaptive AP management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 488
Licensing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 488
Switch discovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 488
Securing a configuration channel between switch and AP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 489
Adaptive AP WLAN topology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 489
Configuration updates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 490
Securing data tunnels between the switch and AAP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 490
Adaptive AP switch failure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 490
Remote Site Survivability (RSS) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 491
Adaptive mesh support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 491
Supported Adaptive AP topologies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 494
Topology deployment considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 494
Extended WLANs only . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 495
Independent WLANs only . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 495
Extended WLANs with independent WLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 495
Extended VLAN with mesh networking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 495
How the AP receives its adaptive configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 495
Adaptive AP pre-requisites . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 496
Configuring the Adaptive AP for adoption by the switch . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 496
Configuring the switch for Adaptive AP adoption . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 496
Establishing basic Adaptive AP connectivity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 497
Adaptive AP configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 497
Switch configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 499
Adaptive AP deployment considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 502
Sample switch configuration file for IPSec and independent WLAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 503
B Troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 507
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 507
viii Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 9

General troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .507
Wireless switch issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 507
Access Port Issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 510
Mobile unit issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 511
Miscellaneous issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 512
System logging mechanism . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 513
Troubleshooting SNMP issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .513
MIB browser not able to contact the agent . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 513
Not able to SNMP WALK for a GET . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
MIB not visible in the MIB browser . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
SNMP SETs not working . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
Not receiving SNMP traps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
Additional Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
Security issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
Switch password recovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 514
RADIUS troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 515
Troubleshooting RADIUS Accounting issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 517
Rogue AP detection troubleshooting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .517
Troubleshooting Firewall configuration issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 518
C How To Tutorials . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 521
In this chapter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 521
Wireless IDS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 521
Unauthorized Access Point Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 522
Unauthorized Access Point Containment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 522
Wireless Intrusion Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 523
Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 524
Restrictions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 524
Configuring a Wireless IDS Deployment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .525
Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 525
Components . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 526
Unauthorized AP Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 526
Unauthorized AP Containment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 529
Mobile Unit Intrusion Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 531
SNMP Traps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 534
RF Switch Running Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 537
Brocade Mobility RFS7000-GR Controller System Reference Guide ix
53-1001944-01
Page 10

x Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 11
About This Document
In this chapter
•Audience. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
•Supported hardware and software. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
•Document conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
•Web support sites . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xiii
Audience
This document is designed for system administrators with a working knowledge of Layer 2 and
Layer 3 switching and routing.
If you are using a Brocade Layer 3 router, you should be familiar with the following protocols if
applicable to your network – IP, RIP, OSPF, BGP, ISIS, IGMP, PIM, and VRRP.
Supported hardware and software
The following hardware platforms are supported by this release of this guide:
• Brocade Brocade Mobility RFS7000-GR Controller
The following software version is supported by this release of this guide:
• Software version 4.1.0.0-040GR and later
Document conventions
This section describes text formatting conventions and important notice formats used in this
document.
Text formatting
The narrative-text formatting conventions that are used are as follows:
Brocade Mobility RFS7000-GR Controller System Reference Guide xi
53-1001944-01
Page 12
bold text Identifies command names
Identifies the names of user-manipulated GUI elements
Identifies keywords
Identifies text to enter at the GUI or CLI
italic text Provides emphasis
Identifies variables
Identifies document titles
code text Identifies CLI output
For readability, command names in the narrative portions of this guide are presented in mixed
lettercase: for example, controllerShow. In actual examples, command lettercase is often all
lowercase. Otherwise, this manual specifically notes those cases in which a command is case
sensitive.
.
Command syntax conventions
Command syntax in this manual follows these conventions:
command and
parameters
[ ] Optional parameter.
variable Variables are printed in italics enclosed in angled brackets < >.
... Repeat the previous element, for example “member[;member...]”
| Choose from one of the parameters.
Commands and parameters are printed in bold.
Notes, cautions, and warnings
The following notices and statements are used in this manual. They are listed below in order of
increasing severity of potential hazards.
NOTE
A note provides a tip, guidance or advice, emphasizes important information, or provides a
reference to related information.
CAUTION
A Caution statement alerts you to situations that can be potentially hazardous to you or cause
damage to hardware, firmware, software, or data.
xii Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 13
DANGER
A Danger statement indicates conditions or situations that can be potentially lethal or extremely
hazardous to you. Safety labels are also attached directly to products to warn of these conditions
or situations.
Web support sites
Customer Support Web Site
Brocade Support Central Web site, located at www.brocade.com/support provides information and
online assistance including developer tools, software downloads, product manuals and online
repair requests.
Downloads
http://www.brocade.com/support/
Manuals
http://www.brocade.com/support/
Because quality is our first concern at Brocade, we have made every effort to ensure the accuracy
and completeness of this document. However, if you find an error or an omission, or you think that
a topic needs further development, we want to hear from you. Forward your feedback to:
documentation@brocade.com
Provide the title and version number and as much detail as possible about your comment,
including the topic heading and page number and your suggestions for improvement.
.
E-mail and telephone access
Go to http://www.brocade.com/services-support/index.page for email and telephone contact
information.
Brocade Mobility RFS7000-GR Controller System Reference Guide xiii
53-1001944-01
Page 14

xiv Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 15

In this chapter
A Brocade wireless controller is a centralized management solution for wireless networking. It
connects to non-legacy Access Ports through Layer 2 or Layer 3 (Layer 2 is preferable, if the
situation allows it).
Access ports function as radio antennas for data traffic management and routing. System
configuration and intelligence for the wireless network resides with the switch. The switch uses
Access Ports to bridge data to and from wireless devices. The wireless switch applies appropriate
policies to data packets before forwarding them to their destination.
Chapter
1Overview
•Hardware overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1
•Software overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
•Standards support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
All data packets to and from wireless devices are processed by the switch, where appropriate
policies are applied before they are decapsulated and sent to their destination.
NOTE
Access port configuration is managed by the switch through a Web UI Graphical User Interface (GUI),
SNMP or the switch Command Line Interface (CLI). The discussion of the switch GUI within t his guide
is presented generically, making it equally relevant to the Brocade Mobility RFS7000-GR Controller.
However, some subtle differences do exist amongst these baselines. These differences are noted
within the specific GUI elements impacted. When these differences are noted, the options available
to each switch baseline are described in detail.
Hardware overview
The Brocade Mobility RFS7000-GR Controller is a rack-mountable device that manage all inbound
and outbound traffic on the wireless network. They provide security, network service and system
management applications.
Unlike traditional wireless infrastructure devices that reside at the edge of a network, the switch
uses centralized, policy-based management to apply sets of rules or actions to all devices on the
wireless network. The switch collects management “intelligence” from individual Access
Ports/Points and moves the collected information to the centralized switch.
Access ports (APs) are 48V Power-over-Ethernet devices connected to the switch by an Ethernet
cable. An Access Port receives 802.11x data from MUs and forwards the data to the switch which
applies the appropriate policies and routes the packets to their destinations.
Access ports do not have software or firmware upon initial receipt from the factory. When the
Access Port is first powered on and cleared for the network, the switch initializes the Access Port
and installs a small firmware file automatically. Therefore, installation and firmware upgrades are
automatic and transparent.
Brocade Mobility RFS7000-GR Controller System Reference Guide 1
53-1001944-01
Page 16
Hardware overview
1
Physical specifications
The physical dimensions and operating parameters of the Brocade Mobility RFS7000-GR Controller
include:
Width
Height
Depth
Weight
Operating Temperature
Operating Humidity
A power cord is not supplied with a Brocade Mobility RFS7000-GR Controller. Use only a correctly
rated power cord certified for the country of operation
440mm (17.32 in)
44.45mm (1.75 in)
390.8mm (15.38 in)
6.12 Kg (13.5 lbs)
0°C - 40°C (32°F - 104°F)
5% - 85% RH, non-condensing
.
Power protection
To best protect the switch from unexpected power surges or other power-related problems, ensure
the switch installation meets the following guidelines:
• If possible, use a dedicated circuit to protect data processing equipment. Commercial
electrical contractors are familiar with wiring for data processing equipment and can help with
the load balancing of dedicated circuits.
• Install surge protection. Use a surge protection device between the electricity source and the
switch.
• Install an Uninterruptible Power Supply (UPS). A UPS provides continuous power during a
power outage. Some UPS devices have integral surge protection. UPS equipment requires
periodic maintenance to ensure reliability.
Cabling requirements
• A minimum of one category 6 Ethernet cables (not supplied) are required to connect the switch
to the LAN and WLAN. The cable(s) are used with the Ethernet ports on the front panel of the
switch.
NOTE
On a Brocade Mobility RFS7000-GR Controller, Brocade recommends connecting via the
Management Ethernet (ME) interface to better ensure secure and easier management. The ME
interface is connected to the management VLAN, and is therefore separate from production VLANs.
NOTE
On the Brocade Mobility RFS7000-GR Controller, the Uplink (UP) port is the preferred method of
connecting the switch to the network. The Uplink port has its own dedicated 1Gbps connection
which is unaffected by internal traffic across the GE ports.
The console cable included with the switch connects the switch to a computer running a serial
terminal emulator program to access the switch’s Command Line Interface (CLI) for initial
configuration. An initial configuration is described within the Installation Guide shipped with each
switch.
2 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 17
Software overview
The switch includes a robust set of features. The features are listed and described in the following
sections:
• Infrastructure features
• Wireless switching
• Wired switching
• Management features
• Security features
• Supported Access Ports/Points
Infrastructure features
The switch includes the following Infrastructure features:
• Installation feature
• Configuration management
• Diagnostics
• Serviceability
• Tracing / logging
• Process monitor
• Hardware abstraction layer and drivers
• Redundancy
• Secure Network Time Protocol (SNTP)
• Password recovery
Software overview
1
Installation feature
The upgrade/downgrade of the switch can be performed at boot time using one of the following
methods:
• Web UI
• DHCP
• CLI
• SNMP
• Patches
The switch has sufficient non-volatile memory to store two firmware images. Having a second
firmware image provides a backup in case of failure of the primary image. It also allows for testing
of new firmware on a switch with the ability to easily revert to a previous image.
Configuration management
The switch supports the redundant storage of configuration files to protect against corruption
during a write operation and ensure (at any given time) a valid configuration file exists. If writing the
configuration file fails, it is rolled back and a pre-write file is used.
Brocade Mobility RFS7000-GR Controller System Reference Guide 3
53-1001944-01
Page 18

Software overview
1
Text based configuration
The configuration is stored in a human readable format (as a set of CLI commands).
Diagnostics
The following diagnostics are available:
1. In-service Diagnostics – In-service diagnostics provide a range of automatic health monitoring
features ensuring both the system hardware and software are in working order.
In-service-diagnostics continuously monitor available physical characteristics (as detailed
below) and issue log messages when warning or error thresholds are reached. There are three
types of in-service diagnostics:
• Hardware – Ethernet ports, chip failures, system temperature via the temperature sensors
provided by the hardware, etc.
• Software – CPU load, memory usage, etc.
• Environmental – CPU and air temperature, fans speed, etc.
2. Out-of-service Diagnostics – Out-of-service diagnostics are a set of intrusive tests run from the
user interface. Out-of-service diagnostics cannot be run while the switch is in operation.
Intrusive tests include:
Ethernet loopback tests
RAM tests, Real Time Clock tests, etc.
3. Manufacturing Diagnostics – Manufacturing diagnostics are a set of diagnostics used by
manufacturing to inspect quality of hardware.
Serviceability
A special set of Service CLI commands are available to provide additional troubleshooting
capabilities for service personnel (access to Linux services, panic logs, etc.). Only authorized users
or service personnel are provided access to the Service CLI.
A built-in Packet Sniffer enables service personnel and users to capture incoming and outgoing
packets in a buffer.
The switch also collects statistics for RF activity, Ethernet port activity etc. RF statistics include
roaming stats, packet counters, octets tx/rx, signal, noise SNR, retry, and information for each MU.
Tracing / logging
Log messages are well-defined and documented system messages with various destinations. They
are numbered and referenced by ID. Each severity level group, can be configured separately to go
to either the serial console, telnet interface, log file or remote syslog server.
Trace messages are more free-form and are used mainly by support personnel for tracking
problems. They are enabled or disabled via CLI commands. Trace messages can go to a log file, the
serial console, or the current tty.
Log and trace messages are interleaved in the same log file, so chronological order is preserved.
Log and trace messages from different processes are similarly interleaved in the same file for the
same reason.
4 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 19

Software overview
Log message format is similar to the format used by syslog messages (RFC 3164). Log messages
include message severity, source (facility), the time the message was generated and a textual
message describing the situation triggering the event. For more information on using the switch
logging functionality, see “Configuring system logging” on page 473.
1
Process monitor
The switch Process Monitor checks to ensure processes under its control are up and running. Each
monitored process sends periodic heartbeat messages. A process that is down (due to a software
crash or stuck in an endless loop) is detected when its heartbeat is not received. Such a process is
terminated (if still running) and restarted (if configured) by the Process Monitor.
Hardware abstraction layer and drivers
The Hardware Abstraction Layer (HAL) provides an abstraction library with an interface hiding
hardware/platform specific data. Drivers include platform specific components such as Ethernet,
Flash Memory storage and thermal sensors.
Redundancy
Using the switch redundancy, up to 12 switches can be configured in a redundancy group (and
provide group monitoring). In the event of a switch failure, an existing cluster member assumes
control. Therefore, the switch supported network is always up and running even if a switch fails or is
removed for maintenance or a software upgrade.
The following redundancy features are supported:
• Up to 12 switch redundancy members are supported in a single group. Each member is
capable of tracking statistics for the entire group in addition to their own.
• Each redundancy group is capable of supporting an Active/Active configuration responsible for
group load sharing.
• Members within the same redundancy group can be deployed across different subnets.
• APs are load balanced across members of the group.
• Licenses are aggregated across the group. When a new member joins the group, the new
member can leverage the Access Port adoption license(s) of existing members.
• Each member of the redundancy group (including the reporting switch) is capable of displaying
cluster performance statistics for all members in addition to their own.
• Centralized redundancy group management using the switch CLI.
For more information on configuring the switch for redundancy support, see
“Configuring switch redundancy & clustering” on page 269.
Secure Network Time Protocol (SNTP)
Secure Network Time Protocol (SNTP) manages time and/or network clock synchronization within
the switch managed network. SNTP is a client/server implementation. The switch (a SNTP client)
periodically synchronizes its clock with a master clock (an NTP server). For example, the switch
resets its clock to 07:04:59 upon reading a time of 07:04:59 from its designated NTP server. Time
synchronization is recommended for the switch’s network operations. The following holds true:
• The switch can be configured to provide NTP services to NTP clients.
Brocade Mobility RFS7000-GR Controller System Reference Guide 5
53-1001944-01
Page 20
Software overview
1
• The switch can provide NTP support for user authentication.
• Secure Network Time Protocol (SNTP) clients can be configured to synchronize switch time with
an external NTP server.
For information on configuring the switch to support SNTP, see “Configuring secure NTP” on
page 258.
Password recovery
The access point has a means of restoring its password to its default value. Doing so also reverts
the access point’s security, radio and power management configuration to their default settings.
Only an installation professional should reset the access point’s password and promptly define a
new restrictive password.
To contact Brocade Support in the event of a password reset requirement, go to
http://www.brocade.com/support/
CAUTION
Only a qualified installation professional should set or restore the access point’s radio and power
management configuration in the event of a password reset.
Wireless switching
The switch includes the following wireless switching features:
• Adaptive AP
• Physical layer features
• Rate limiting
• Proxy-ARP
• HotSpot / IP Redirect
• IDM (identity driven management)
• Voice prioritization
• Self healing
• Wireless capacity
• AP and MU load balancing
• Wireless roaming
• Power save polling
• QoS
• Wireless Layer 2 switching
• Automatic channel selection
• WMM-unscheduled APSD
• Multiple VLANs per WLAN
6 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 21

Software overview
1
Adaptive AP
An adaptive AP (AAP) is a Brocade Mobility 7131N-FGR Access Point adopted by a wireless switch.
The management of an AAP is conducted by the switch, once the Access Point connects to the
switch and receives its AAP configuration.
An AAP provides:
• local 802.11 traffic termination
• local encryption/decryption
• local traffic bridging
• tunneling of centralized traffic to the wireless switch
The connection between the AAP and the switch can be secured using IPSec depending on
whether a secure WAN link from a remote site to the central site already exists.
The switch can be discovered using one of the following mechanisms:
• DHCP
• Switch fully qualified domain name (FQDN)
• Static IP addresses
The benefits of an AAP deployment include:
• Centralized Configuration Management & Compliance - Wireless configurations across
distributed sites can be centrally managed by the wireless switch or cluster.
• WAN Survivability - Local WLAN services at a remote sites are unaffected in the case of a WAN
outage.
• Securely extend corporate WLAN's to stores for corporate visitors - Small home or office
deployments can utilize the feature set of a corporate WLAN from their remote location.
• Maintain local WLAN's for specific applications - WLANs created and supported locally can be
concurrently supported with your existing infrastructure.
For an overview of AAP and how it is configured and deployed using the switch and Access Point,
see “Ad aptive AP ” on page 487.
Physical layer features
802.11a
• DFS Radar Avoidance – Dynamic Frequency Selection (DFS) is mandatory for WLAN equipment
intended to operate in the frequency bands 5150 MHz to 5350 MHz and 5470 MHz to 5725
MHz when in countries of the EU.
The purpose of DFS is:
• Detect interference from other systems and avoid co-channeling with those systems (most
notably radar systems).
• Provide uniform spectrum loading across all devices.
This feature is enabled automatically when the country code indicates that DFS is required
for at least one of the frequency bands that are allowed in the country.
• TPC – Tr an s m i t P ower Control (TPC) meets the regulatory requirement for maximum power and
mitigation for each channel. TPC functionality is enabled automatically for every AP that
operates on the channel.
Brocade Mobility RFS7000-GR Controller System Reference Guide 7
53-1001944-01
Page 22

Software overview
1
802.11bg
• Dual mode b/g protection – ERP builds on the payload data rates of 1 and 2 Mbit/s that use
DSSS modulation and builds on the payload data rates of 1, 2, 5.5, and 11 Mbit/s, that use
DSSS, CCK, and optional PBCC modulations. ERP provides additional payload data rates of 6,
9, 12, 18, 24, 36, 48, and 54 Mbit/s. The transmission and reception capability for 1, 2, 5.5,
11, 6, 12, and 24 Mbit/s data rates is mandatory.
Two additional optional ERP-PBCC modulation modes with payload data rates of 22 and 33
Mbit/s are defined. An ERP-PBCC station may implement 22 Mbit/s alone or 22 and 33
Mbit/s. An optional modulation mode (known as DSSS-OFDM) is also incorporated with
payload data rates of 6, 9, 12, 18, 24, 36, 48, and 54 Mbit/s.
• Short slot protection – The slot time is 20 µs, except an optional 9 µs slot time may be used
when the BSS consists of only ERP STAs capable of supporting this option. The optional 9 µs
slot time should not be used if the network has one or more non-ERP STAs associated. For
IBSS, the Short Slot Time field is set to 0, corresponding to a 20 µs slot time.
Rate limiting
Rate Limiting limits the maximum rate sent to or received from the wireless network per mobile
unit. It prevents any single user from overwhelming the wireless network. It can also provide
differential service for service providers. The uplink and downlink rate limits are usually configured
on the RADIUS server using Brocade vendor specific attributes. The switch extracts the rate limits
from RADIUS server response. When such attributes are not present, the global settings on the
switch are then applied.
Proxy-ARP
Proxy ARP is provided for MU's whose IP address is known. The WLAN generates an ARP reply on
behalf of a MU (if the MU's IP address is known). The ARP reply contains the MAC address of the
MU (not the MAC address of switch). Thus, the MU does not awaken to send ARP replies (increasing
MU battery life and conserving wireless bandwidth).
If an MU goes into PSP without transmitting at least one packet, its Proxy ARP will not work.
HotSpot / IP Redirect
A hotspot is a Web page users are forced to visit before they are granted access to the Internet.
With the advent of Wi-Fi enabled client devices (such as laptops and PDAs) commercial hotspots
are common and can be found at many airports, hotels and coffee shops. The hotspot re-directs
the user’s traffic on hotspot enabled WLANs to a web page that requires them to authenticate
before granting access to the WLAN. The following is a typical sequence for hotspot access:
1. A visitor with a laptop requires hotspot access at a site.
2. A user ID/ Password and hotspot ESSID is issued by the site receptionist or IT staff.
3. The user connects their laptop to this ESSID.
4. The laptop receives its IP configuration via DHCP.
5. The user opens a Web browser and connects to their home page.
6. The switch re-directs them to the hotspot Web page for authentication.
7. The user enters their User ID/ Password.
8 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 23

Software overview
8. A RADIUS server authenticates the user.
9. Upon successful authentication, the user is directed to a Welcome Page that lists (among other
things) an Acceptable Use Policy.
10. The user agrees to the usage terms and is granted access to the Internet. (or other network
services).
To setup a hotspot, create a WLAN ESSID and select Hotspot authentication from the
Authentication menu. This is simply another way to authenticate a WLAN user, as it would be
impractical to authenticate visitors using 802.1x. For information on configuring a hotspot, see
“Configuring hotspots” on page 107.
1
IDM (identity driven management)
RADIUS authentication is performed for all protocols using a RADIUS-based authentication scheme
(such as EAP). Identity driven management is provided using a RADIUS client. The following IDMs
are supported:
• User based SSID authentication — Denies authentication to MUs if associated to a ESSID
configured differently by their RADIUS server.
• User based VLAN assignment — Allows the switch to extract VLAN information from the RADIUS
server.
• User based QoS — Enables QoS for the MU based on settings within the RADIUS Server.
Voice prioritization
The switch has the capability of having its QoS policy configured to prioritize network traffic
requirements for associated MUs. Use QoS to enable voice prioritization for devices using voice as
its transmission priority.
Voice prioritization allows you to assign priority to voice traffic over data traffic, and (if necessary)
assign legacy voice supported devices (non WMM supported voice devices) additional priority.
Currently voice support implies the following:
• Spectralink voice prioritization - Spectralink sends packets that allow the switch to identify
these MU's as voice MU's. Thereafter, any UDP packet sent by these MU's is prioritized ahead
of data.
• Strict priority - The prioritization is strict.
• Multicast prioritization - Multicast frames that match a configured multicast mask bypass the
PSP queue. This features permits intercom mode operation without delay (even in the
presence of PSP MU's).
For more information on configuring voice prioritization for a target WLAN, see “Configuring WMM”
on page 137.
Self healing
Self healing is the ability to dynamically adjust the RF network by modifying transmit power and/or
supported rates upon an AP failure.
In a typical RF network deployment, APs are configured for Transmit Power below their maximum
level. This allows the Tx Power to be increased when there is a need to increase coverage when an
AP fails.
Brocade Mobility RFS7000-GR Controller System Reference Guide 9
53-1001944-01
Page 24

Software overview
1
When an AP fails, the Tx Power/Supported rates of APs neighboring the failed AP are adjusted. The
Tx power is increased and/or Supported rates are decreased. When the failed AP becomes
operational again, Neighbor AP’s Tx Power/Supported rates are brought back to the levels before
the self healing operation changed them.
The switch detects an AP failure when:
• AP stops sending heartbeats.
• AP beacons are no longer being sent. This is determined when other detector APs are no longer
hearing beacons from a particular AP.
Configure 0 (Zero) or more APs to act as either:
• Detector APs — Detector APs scan all channels and send beacons to the switch which uses the
information for self-healing.
• Neighbor APs — When an AP fails, neighbor APs assist in self healing.
• Self Healing Actions — When an AP fails, actions are taken on the neighbor APs to do
self-healing.
Detector APs
Configure an AP in either – Data mode (the regular mode) or Detector mode.
In Detector mode, an AP scans all channels at a configurable rate and forwards received beacons
the switch. The switch uses the information to establish a receive signal strength baseline over a
period of time and initiates self-healing procedures (if necessary).
Neighbor configuration
Neighbor detect is a mechanism allowing an AP to detect its neighbors as well as their signal
strength. This enables you to verify your installation and configure it for self-healing when an AP
fails.
Self healing actions
If AP1 detects AP2 and AP3 as its neighbors, you can assign failure actions to AP2 and AP3
whenever AP1 fails.
Assign up to four self healing actions:
1. No action
2. Decrease supported rates
3. Increase Tx power
4. Both 2 and 3.
You can specify the Detector AP (AP2 or AP3) to stop detecting and adopt the RF settings of the
failed AP. For more information on configuring self healing, see “Configuring self healing” on
page 288.
Wireless capacity
Wireless capacity specifies the maximum numbers of MUs, Access Ports and wireless networks
usable by a switch. Wireless capacity is largely independent of performance. Aggregate switch
performance is divided among the switch clients (MUs and Access Ports) to find the performance
experienced by a given user. Each switch platform is targeted at specific market segments, so the
capacity of each platform is chosen appropriately. Wireless switch capacity is measured by:
10 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 25

Software overview
1
• The maximum number of WLANs per switch
• The maximum number of Access Ports adopted per switch
• The maximum number of MUs per switch
• The maximum number of MUs per Access Port.
The actual number of Access Ports adoptable by a switch is defined by the switch licenses or the
total licenses in the cluster in which this switch is a member.
AP and MU load balancing
Fine tune a network to evenly distribute data and/or processing across available resources. Refer
to the following:
• MU balancing across multiple APs
• AP balancing across multiple switches
MU balancing across multiple APs
Per the 802.11 standard, AP and MU association is a process conducted independently of the
switch. 802.11 provides message elements used by the MU firmware to influence roaming
decisions. The switch implements the following MU load balancing techniques:
• 802.11e admission control — 1 byte: channel utilization % and 1 byte: MU count is sent in
QBSS Load Element in beacons to MU.
• Load balancing element — 2 byte: MU Count are sent in beacon to MU.
AP balancing across multiple switches
At adoption, the AP solicits and receives multiple adoption responses from the switches on the
network. These adoption responses contain preference and loading information the AP uses to
select the optimum switch to be adopted by. Use this mechanism to define which APs are adopted
by which switches. By default, the adoption algorithm generally distributes AP adoption evenly
among the switches available.
NOTE
Port adoption per switch is determined by the number of licenses acquired.
For more information on Access Port adoption in a layer 3 environment, see “Configuring Layer 3
access port adoption” on page 206.
Wireless roaming
The following types of wireless roaming are supported by the switch:
• Interswitch Layer 2 roaming
• Interswitch Layer 3 roaming
• Fast roaming
• International roaming
• MU move command
• Power save polling
Brocade Mobility RFS7000-GR Controller System Reference Guide 11
53-1001944-01
Page 26

Software overview
1
Interswitch Layer 2 roaming
An associated MU (connected to a switch) can roam to another Access Port connected to a
different switch. Both switches must be on the same Layer 2 domain. Authentication information is
not shared between the switches, nor are buffered packets on one switch transferred to the other.
Pre-authentication between the switch and MU allows faster roaming.
Interswitch Layer 3 roaming
Interswitch Layer 3 roaming allows MUs to roam between switches which are not on the same LAN
or IP subnet without the MUs or the rest of the network noticing. This allows switches to be placed
in different locations on the network without having to extend the MU VLANs to every switch.
Fast roaming
Using 802.11i can speed up the roaming process from one AP to another. Instead of doing a
complete 802.1x authentication each time a MU roams between APs, 802.11i allows a MU to
re-use previous PMK authentication credentials and perform a four-way handshake. This speeds
up the roaming process. In addition to reusing PMKs on previously visited APs, Opportunistic Key
Caching allows multiple APs to share PMKs amongst themselves. This allows an MU to roam to an
AP it has not previously visited and reuse a PMK from another AP to skip the 802.1x authentication.
International roaming
The wireless switch supports international roaming per the 802.11d specification.
MU move command
As a value added proprietary feature between Brocade infrastructure products and Brocade MUs, a
move command has been introduced. The move command permits an MU to roam between ports
connected to the same switch without the need to perform the full association and authentication
defined by the 802.11 standard. The move command is a simple packet up/packet back exchange
with the Access Port. Verification of this feature is dependent on its implementation in one or more
mobile units.
Power save polling
An MU uses Power Save Polling (PSP) to reduce power consumption. When an MU is in PSP mode,
the switch buffers its packets and delivers them using the DTIM interval. The PSP-Poll packet polls
the AP for buffered packets. The PSP null data frame is used by the MU to signal the current PSP
state to the AP.
QoS
QoS provides a data traffic prioritization scheme. QoS reduces congestion from excessive traffic.
If there is enough bandwidth for all users and applications (unlikely because excessive bandwidth
comes at a ver y high cost), then applying QoS has very little value. QoS provides policy enforcement
for mission-critical applications and/or users that have critical bandwidth requirements when the
switch’s bandwidth is shared by different users and applications.
QoS helps ensure each WLAN on the switch receives a fair share of the overall bandwidth, either
equally or as per the proportion configured. Packets directed towards MUs are classified into
categories such as Management, Voice and Data. Packets within each category are processed
based on the weights defined for each WLAN.
The switch supports the following QoS mechanisms:
12 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 27

Software overview
802.11e QoS
802.11e enables real-time audio and video streams to be assigned a higher priority over data
traffic. The switch supports the following 802.11e features:
1
• Basic WMM
• WMM Linked to 802.1p Priorities
• WMM Linked to DSCP Priorities
• Fully Configurable WMM
• Admission Control
• Unscheduled-APSD
• TSPEC Negotiation
• Block ACKQBSS Beacon Element
802.1p support
802.1p is a standard for providing QoS in 802-based networks. 802.1p uses three bits to allow
switches to re-order packets based on priority level.
Voice QoS
When switch resources are shared between a Voice over IP (VoIP) conversation and a file transfer,
bandwidth is normally exploited by the file transfer, thus reducing the quality of the conversation or
even causing it to disconnect. With QoS, a VoIP conversation (a real-time session), receives priority,
maintaining a high level of voice quality. Voice QoS ensures:
• Strict Priority
• Spectralink Prioritization
• VOIP Prioritization (IP ToS Field)
• Multicast Prioritization
Data QoS
The switch supports the following data QoS techniques:
• Egress Prioritization by WLAN
• Egress Prioritization by ACL
DCSCP to AC mapping
The switch provides arbitrary mapping between Differentiated Services Code Point (DCSCP) values
and WMM Access Categories. This mapping can be set manually.
Wireless Layer 2 switching
The switch supports the following layer 2 wireless switching techniques:
• WLAN to VLAN
• MU User to VLAN
• WLAN to GRE
Automatic channel selection
Automatic channel selection works sequentially as follows:
Brocade Mobility RFS7000-GR Controller System Reference Guide 13
53-1001944-01
Page 28

Software overview
1
1. When a new AP is adopted, it scans each channel. However, the switch does not forward traffic
at this time.
2. The switch then selects the least crowded channel based on the noise and traffic detected on
each channel.
3. The algorithm used is a simplified maximum entropy algorithm for each radio, where the signal
strength from adjoining AP's/MU's associated to adjoining AP's is minimized.
4. The algorithm ensures adjoining AP's are as far away from each other as possible (in terms of
channel assignment).
NOTE
Individual radios can be configured to perform automatic channel selection.
WMM-unscheduled APSD
This feature is also known as WMM Power Save or WMM-UPSD (Unscheduled Power Save Delivery).
WMM-UPSD defines an unscheduled service period, which are contiguous periods of time during
which the switch is expected to be awake. If the switch establishes a downlink flow and specifies
UPSD power management, it requests (and the AP delivers) buffered frames associated with that
flow during an unscheduled service period. The switch initiates an unscheduled service period by
transmitting a trigger frame. A trigger frame is defined as a data frame (e.g. an uplink voice frame)
associated with an uplink flow with UPSD enabled. After the AP acknowledges the trigger frame, it
transmits the frames in its UPSD power save buffer addressed to the triggering switch.
UPSD is well suited to support bi-directional frame exchanges between a voice STA and its AP.
Multiple VLANs per WLAN
The switch permits the mapping of a WLAN to more than one VLAN. When a MU associates with a
WLAN, the MU is assigned a VLAN by means of load balance distribution. The VLAN is picked from a
pool assigned to the WLAN. The switch tracks the number of MUs per VLAN, and assigns the least
used/loaded VLAN to the MU. This number is tracked on a per-WLAN basis.
A broadcast key, unique to the VLAN, encrypts packets coming from the VLAN. If two or more MUs
are on two different VLANs, they both hear the broadcast packet, but only one can decrypt it. The
switch provides each MU a unique VLAN broadcast key as part of the WPA2 handshake or group
key update message of a WPA handshake.
Limiting users per VLAN
Not all VLANs within a single WLAN must have the same DHCP pool size. Assign a user limit to each
VLAN to allow the mapping of different pool sizes.
Specify the VLAN user limit. This specifies the maximum number of MUs associated with a VLAN
(for a particular WLAN). When the maximum MU limit is reached, no more MUs can be assigned to
that VLAN.
Packet flows
There are four packet flows supported when the switch is configured to operate with multiple VLAN
per WLAN:
14 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 29

Software overview
1
• Unicast From Mobile Unit – Frames are decrypted, converted from 802.11 to 802.3 and
switched to the wired side of the VLAN dynamically assigned to the mobile device. If the
destination is another mobile device on the wireless side, the frame is encrypted and switched
over the air.
• Unicast To Mobile Unit – The frame is checked to ensure the VLAN is same as that assigned to
the mobile device. It is then converted to an 802.11 frame, encrypted, and sent over the air.
• Multicast/Broadcast From Mobile Unit – The frame is treated as a unicast frame from the MU,
with the exception that it is encrypted with the per-VLAN broadcast key and then transmitted
over the air.
• Multicast/Broadcast from Wired Side – If the frame comes from a VLAN mapped to the WLAN,
it’s encrypted using a per-VLAN broadcast key and transmitted over the air. Only MUs on that
VLAN have a broadcast key that can decrypt this frame. Other MUs receive it, but discard it.
In general, when there are multiple VLANs mapped to the same WLAN, the broadcast buffer
queue size scales linearly to accommodate a potential increase in the broadcast packet
stream.
Roaming within the switch
When a MU is assigned to a VLAN, the switch registers the VLAN assignment in its credential cache.
If the MU roams, it is assigned back to its earlier assigned VLAN. The cache is flushed upon
detected MU inactivity or if the MU associates over a different WLAN (on the same switch).
Roaming across a cluster
MUs roam amongst switch cluster members. The switch must ensure a VLAN remains unchanged
as an MU roams. This is accomplished by passing MU VLAN information across the cluster using
the interface used by a hotspot. It automatically passes the username/password across the
credential caches of the member switches. This ensures a VLAN MU association is maintained
even while the MU roams amongst cluster members.
Roaming across a Layer 3 mobility domain
When an MU roams amongst switches in different Layer 3 mobility domains, Layer 3 ensures traffic
is tunneled back to the correct VLAN (on the home switch).
Interaction with RADIUS assigned VLANs
Multiple VLANs per WLAN can co-exist with VLANs assigned by a RADIUS server. Upon association,
an MU is assigned to a VLAN from a pool of available VLANs. When the RADIUS server assigns the
user another VLAN, MU traffic is forwarded to that VLAN.
When 802.1x is used, traffic from the MU is dropped until authentication is completed. None of the
MU data is switched onto the temporarily VLAN. A RADIUS assigned VLAN overrides the statically
assigned VLAN.
If the RADIUS assigned VLAN is among the VLANs assigned to a WLAN, it is available for VLAN
assignment in the future. If the RADIUS assigned VLAN is not one of the VLANs assigned to a
WLAN, it is not available for future VLAN assignment. To configure Multiple VLANs for a single
WLAN, see “Assigning multiple VLANs per WLAN” on page 104.
Wired switching
The switch includes the following wired switching features:
• DHCP servers
Brocade Mobility RFS7000-GR Controller System Reference Guide 15
53-1001944-01
Page 30
Software overview
1
• DHCP user class options
• DDNS
• VLAN enhancements
• Interface management
DHCP servers
Dynamic Host Configuration Protocol (DHCP) allows hosts on an IP network to request and be
assigned IP addresses as well as discover information about the network to which they are
attached. Each subnet may be configured with its own address pool. Whenever a DHCP client
requests an IP address, the DHCP server assigns an IP address from that subnet’s address pool.
When a DHCP server allocates an address for a DHCP client, the client is assigned a lease, which
expires after an pre-determined interval. Before a lease expires, clients (to which leases are
assigned) are expected to renew them to continue to use the addresses. Once the lease expires,
the client is no longer permitted to use the leased IP address. For information on defining the
switch DHCP configuration, see “DHCP server settings” on page 237.
DHCP user class options
A DHCP Server groups clients based on defined user-class option values. Clients with a defined set
of user-class values are segregated by class. The DHCP Server can associate multiple classes to
each pool. Each class in a pool is assigned an exclusive range of IP addresses.
DHCP clients are compared against classes. If the client matches one of the classes assigned to
the pool, it receives an IP address from the range assigned to the class. If the client doesn't match
any of the classes in the pool, it receives an IP address from a default pool range (if defined).
Multiple IP addresses for a single VLAN allow the configuration of multiple IP addresses, each
belonging to different subnet. Class configuration allows a DHCP client to obtain an address from
the first pool to which the class is assigned. For more information, see “Configuring the DHCP user
class” on page 252.
DDNS
Dynamic DNS (DDNS) keeps a domain name linked to a changing IP address. Typically, when a user
connects to a network, the user’s ISP assigns it an unused IP address from a pool of IP addresses.
This address is only valid for a short period. Dynamically assigning IP addresses increases the pool
of assignable IP addresses. DNS maintains a database to map a given name to an IP address used
for communication on the Internet. The dynamic assignment of IP addresses makes it necessary to
update the DNS database to reflect the current IP address for a given name. Dynamic DNS updates
the DNS database to reflect the correct mapping of a given name to an IP address.
VLAN enhancements
The switch has incorporated the following VLAN enhancements:
• Network interfaces operate in either trunk or access modes.
• A network interface in access mode can only send and receive untagged packets.
• A trunk port can now receive both tagged and untagged packets. Each ethernet port is
assigned a native VLAN.
16 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 31

Software overview
1
• You can now configure a set of allowed VLANs on a trunk port. Packets received on this port
that belong to other VLANs are discarded.
Interface management
The switch’s physical interfaces auto-negotiate speed and duplex. The switch also allows:
• Manual bandwidth configuration of a physical interface speed to 10/100/1000Mbps.
• Manual duplex configuration of a physical interface to Full Duplex or Half Duplex.
• Manual configuration of administrative shutdown of a physical interface.
Management features
The switch supports the following management features:
• A secure, browser-based management console
• A Command Line Interface (CLI) accessible via the serial port or through Telnet or a Secure
Shell (SSH) application
• A CLI Service mode enabling the capture of system status information that can be sent to
Brocade personnel for use in problem resolution
• The support for Simple Network Management Protocol (SNMP) version 3 as well as SNMP
version 2
• Upload and download of Access Port firmware and configuration files using TFTP and FTP
• Transfer of firmware and configuration files using Compact Flash or USB
• The graphing of wireless statistics
• A GUI dashboard summary of system status
• Multi switch management via MSP application
• Heat map support for RF deployment
• Secure guest access with specific permission intervals
• Switch discovery enabling users to discover each Brocade switch on the specified network.
Security features
Switch security can be classified into wireless security and wired security.
The switch includes the following wireless security features:
• Encryption and authentication
• MU authentication
• Secure beacon
• MU to MU disallow
• 802.1x authentication
• WIPS
• Rogue AP detection
The switch includes the following wired security features:
• ACLs
Brocade Mobility RFS7000-GR Controller System Reference Guide 17
53-1001944-01
Page 32

Software overview
1
• Local RADIUS server
• IPSec VPN
• NAT
• Certificate management
Encryption and authentication
The switch can implement the following encryption and authentication types:
• WEP
• WPA
• WPA2
• Keyguard-WEP
WEP
Wired Equivalent Privacy (WEP) is an encryption scheme used to secure wireless networks. WEP
was intended to provide comparable confidentiality to a traditional wired network, hence the name.
WEP had many serious weaknesses and hence was superseded by Wi-Fi Protected Access (WPA).
Regardless, WEP still provides a level of security that can deter casual snooping. For more
information on configuring WEP for a target WLAN, see “Configuring WEP 64” on page 125 or
“Configuring WEP 128 / KeyGuard” on page 126.
WEP uses passwords entered manually at both ends (Pre Shared Keys). Using the RC4 encryption
algorithm, WEP originally specified a 40-bit key, but was later boosted to 104 bits. Combined with a
24-bit initialization vector, WEP is often touted as having a 128-bit key.
WPA
WPA is designed for use with an 802.1X authentication server, which distributes different keys to
each user. However, it can also be used in a less secure pre-shared key (PSK) mode, where every
user is given the same passphrase.
WPA uses Temporal Key Integrity Protocol (TKIP), which dynamically changes keys as the system is
used. When combined with the much larger Initialization Vector, it defeats well-known key recovery
attacks on WEP. For information on configuring WPA for a WLAN, see “Configuring WPA/WPA2 using
TKIP and CCMP” on page 128.
WPA2
WPA2 uses a sophisticated key hierarchy that generates new encryption keys each time a MU
associates with an Access Point. Protocols including 802.1X, EAP and RADIUS are used for strong
authentication. WPA2 also supports the TKIP and AES-CCMP encryption protocols. For information
on configuring WPA for a WLAN, see “Configuring WPA/WPA2 using TKIP and CCMP” on page 128.
Keyguard-WEP
KeyGuard is Brocade’s proprietary dynamic WEP solution. Brocade (upon hearing of the
vulnerabilities of WEP) developed a non standard method of rotating keys to prevent compromises.
Basically, KeyGuard is TKIP without the message integrity check. KeyGuard is proprietary to
Brocade MUs only. For information on configuring KeyGuard for a WLAN, see “Configuring WEP 128
/ KeyGuard” on page 126.
18 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 33

Software overview
1
MU authentication
The switch uses the following authentication schemes for MU association:
• Kerberos
• 802.1x EAP
• MAC ACL
Refer to “Editing the WLAN configuration” on page 100 for additional information.
Kerberos
Kerberos allows for mutual authentication and end-to-end encryption. All traffic is encrypted and
security keys are generated on a per-client basis. Keys are never shared or reused, and are
automatically distributed in a secure manner. For information on configuring Kerberos for a WLAN,
see “Configuring Kerberos” on page 106.
802.1x EAP
802.1x EAP is the most secure authentication mechanism for wireless networks and includes
EAP-TLS, EAP-TTLS and PEAP. The switch is a proxy for RADIUS packets. An MU does a full 802.11
authentication and association and begins transferring data frames. The switch realizes the MU
needs to authenticate with a RADIUS server and denies any traffic not RADIUS related. Once
RADIUS completes its authentication process, the MU is allowed to send other data traffic. You can
use either an onboard RADIUS server or internal RADIUS Server for authentication. For information
on configuring 802.1x EAP for a WLAN, see “Configuring 802.1x EAP” on page 105.
MAC ACL
The MAC ACL feature is basically a dynamic MAC ACL where MUs are allowed/denied access to the
network based on their configuration on the RADIUS server. The switch allows 802.11
authentication and association, then checks with the RADIUS server to see if the MAC address is
allowed on the network. The RADIUS packet uses the MAC address of the MU as both the
username and password (this configuration is also expected on the RADIUS server). MAC-Auth
supports all encryption types, and (in case of 802.11i) the handshake is completed before the
RADIUS lookup begins. For information on configuring 802.1x EAP for a WLAN, see “Configuring
MAC authentication” on page 116.
Secure beacon
Devices in a wireless network use Service Set Identifiers (SSIDs) to communicate. An SSID is a text
string up to 32 bytes long. An AP in the network announces its status by using beacons. To avoid
others from accessing the network, the most basic security measure adopted is to change the
default SSID to one not easily recognizable, and disable the broadcast of the SSID.
The SSID is a code attached to all packets on a wireless network to identify each packet as part of
that network. All wireless devices attempting to communicate with each other must share the same
SSID. Apart from identifying each packet, the SSID also serves to uniquely identify a group of
wireless network devices used in a given service set.
Brocade Mobility RFS7000-GR Controller System Reference Guide 19
53-1001944-01
Page 34

Software overview
1
MU to MU disallow
Use MU to MU Disalllow to restrict MU to MU communication within a WLAN. The default is ‘no’,
which allows MUs to exchange packets with other MUs. It does not prevent MUs on other WLANs
from sending packets to this WLAN. You would have to enable MU to MU Disallow on the other
WLAN. To define how MU to MU traffic is permitted for a WLAN, see “Editing the WLAN
configuration” on page 100.
802.1x authentication
802.1x Authentication cannot be disabled (it is always enabled). A factory delivered out-of-the-box
Brocade Mobility 7131N-FGR Access Point supports 802.1x authentication using a default
username and password. EAP-MD5 is used for 802.1x.
When you initially switch packets on an out-of-the-box Brocade Mobility 7131N-FGR Access Point
port, it immediately attempts to authenticate using 802.1x. Since 802.1x supports supplicant
initiated authentication, the Brocade Mobility 7131N-FGR Access Point attempts to initiate the
authentication process.
On reset (all resets including power-up), the Brocade Mobility 7131N-FGR Access Point sends an
EAPOL start message every time it sends a Hello message (periodically every 1 second). The EAPOL
start is the supplicant initiated attempt to become authenticated.
If an appropriate response is received in response to the EAPOL start message, the Brocade
Mobility 7131N-FGR Access Point attempts to proceed with the authentication process to
completion. Upon successful authentication, the Brocade Mobility 7131N-FGR Access Point
transmits the Hello message and the download proceeds the way as it does today.
If no response is received from the EAPOL start message, or if the authentication attempt is not
successful, the Brocade Mobility 7131N-FGR Access Point continues to transmit Hello messages
followed by LoadMe messages. If a parent reply is received in response to the Hello message, then
downloading continue normally - without authentication. In this case, you need not enable or
disable the port authentication.
802.1x authentication is conducted:
• At power up
• On an Brocade Mobility 7131N-FGR Access Point operator initiated reset (such as pulling
Ethernet cable)
• When the switch administrator initiates a reset of the Brocade Mobility 7131N-FGR Access
Point.
• When re-authentication is initiated by the Authenticator (say the switch in between)
Change username/password after AP adoption
Once the Brocade Mobility 7131N-FGR Access Point is adopted using 802.1x authentication (say
default username/password) OR using a non-secure access method (hub or switch without 802.1x
enabled), use the CLI/SNMP/UI to reconfigure the username/password combination.
Reset username/password to factory defaults
To restore the BrocadeMobility 7131N-FGR Access Point username/password to factory defaults,
adopt the Brocade Mobility 7131N-FGR Access Point using a non-secure access method (a hub or
switch without 802.1x enabled), then reconfigure the username/password combination.
20 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 35

Software overview
The Access Port does not make use of any parameters (such as MAC based authentication, VLAN
based etc.) configured on RADIUS Server.
1
WIPS
The Brocade Wireless Intrusion Protection Software (WIPS) monitors for any presence of
unauthorized rogue Access Points. Unauthorized attempts to access the WLAN is generally
accompanied by anomalous behavior as intruding MUs try to find network vulnerabilities. Basic
forms of this behavior can be monitored and reported without needing a dedicated WIPS. When the
parameters exceed a configurable threshold, the switch generates an SNMP trap and reports the
result via the management interfaces. Basic WIPS functionality does not require monitoring APs
and does not perform off-channel scanning.
NOTE
When converting a Brocade Mobility 7131N-FGR Access Point to an Intrusion Detection Sensor, the
conversion requires approximately 60 seconds.
Rogue AP detection
The switch supports the following techniques for rogue AP detection:
• RF scan by Access Port on one channel
• RF scan by Access Port on all channels
• SNMP Trap on discovery
• Authorized AP lists
• Rogue AP report
RF scan by Access Port on one channel
This process requires an Access Port to assist in Rogue AP detection. It functions as follows:
• The switch sends a new configuration message to the adopted AP informing it to detect Rogue
APs.
• The Access Port listens for beacons on its present channel.
• It passes the beacons to the switch as it receives them without any modification.
• The switch processes these beacon messages to generate the list of APs
By choosing this option for detection, all capable Access Ports will be polled.
RF scan by Access Port on all channels
The process used to scan for Rogue APs on all available channels functions as follows:
• The switch sends a configuration message (with the ACS bit set and channel dwell time) to the
Access Port.
• An Access Port starts scanning each channel and passes the beacons it hears on each
channel to the switch.
• An Access Port resets itself after scanning all channels.
• An switch then processes this information
Brocade Mobility RFS7000-GR Controller System Reference Guide 21
53-1001944-01
Page 36

Software overview
1
SNMP Trap on discovery
An SNMP trap is sent for each detected and Rogue AP. Rogue APs are only detected, and
notification is provided via a SNMP trap.
NOTE
Wired side scanning for Rogue APs using WNMP is not supported. Similarly, RADIUS lookup for
approved AP is not provided.
Authorized AP lists
Configure a list of authorized Access Ports based on their MAC addresses. The switch evaluates the
APs against the configured authorized list after obtaining Rogue AP information from one of the 2
mechanisms as mentioned in “Rogue AP detection” on page 21.
Rogue AP report
After determining which are authorized APs and which are Rogue, the switch prepares a report.
ACLs
ACLs control access to the network through a set of rules. Each rule specifies an action taken when
a packet matches a set of rules. If the action is deny, the packet is dropped. If the action is permit,
the packet is allowed. If the action is to mark, the packet is tagged for priority. The switch supports
the following types of ACLs:
• IP Standard ACLs
• IP Extended ACLs
• MAC Extended ACLs
• Wireless LAN ACLs
For information on creating an ACL, see “Configuring firewalls and access control lists” on
page 321.
Local RADIUS server
RADIUS is a common authentication protocol utilized by the 802.1x wireless security standard.
RADIUS improves the WEP encryption key standard, in conjunction with other security methods
such as EAP-PEAP. The switch has one onboard RADIUS server. For information on configuring the
switch’s resident RADIUS Server, see “Configuring the RADIUS Server” on page 403.
IPSec VPN
IP Sec is a security protocol providing authentication and encryption over the Internet. Unlike SSL
(which provides services at layer 4 and secures two applications), IPsec works at Layer 3 and
secures the network. Also unlike SSL (which is typically built into the Web browser), IPsec requires a
client installation. IPsec can access both Web and non-Web applications, whereas SSL requires
workarounds for non-Web access such as file sharing and backup.
A VPN is used to provide secure access between two subnets separated by an unsecured network.
There are two types of VPNs:
• Site-Site VPN — For example, a company branching office traffic to another branch office
traffic with an unsecured link between the two locations.
22 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 37

Software overview
• Remote VPN — Provides remote user ability to access company resources from outside the
company premises.
The switch supports:
• IPSec termination for site to site
• IPSec termination for remote access
• IPSec traversal of firewall filtering
• IPSec traversal of NAT
• IPSec/L2TP (client to switch)
NAT
Network Address Translation (NAT) is supported for packets routed by the switch. The following
types of NAT are supported:
• Port NAT– Port NAT (also known as NAPT) entails multiple local addresses are mapped to
single global address and a dynamic port number. The user is not required to configure any
NAT IP address. Instead IP address of the public interface of the switch is used to NAT packets
going out from private network and vice versa for packets entering private network.
• Static NAT– Static NAT is similar to Port NAT with the only difference being that it allows the
user to configure a source NAT IP address and/or destination NAT IP address to which all the
packets will be NATted to. The source NAT IP address is used when hosts on a private network
are trying to access a host on a public network. A destination NAT IP address can be used for
public hosts to talk to a host on a private network.
1
Certificate management
Certificate Management is used to provide a standardized procedure to:
• Generate a Server certificate request and upload the server certificate signed by certificate
authority (CA).
• Uploading of CA's root certificate
• Creating a self-signed certificate
Certificate management will be used by the applications HTTPS, VPN, HOTSPOT and RADIUS. For
information on configuring switch certificate management, see “Creating server certificates” on
page 418.
NAC
Using Network Access Control (NAC), the switch hardware and software grants access to specific
network resources. NAC performs a user and MU authorization check for resources that do not
have a NAC agent. NAC verifies a MU’s compliance with the switch’s security policy. The switch
supports only the EAP/802.1x type of NAC. However, the switch also provides a mean to bypass
NAC authentication for MU’s that do not have NAC 802.1x support (printers, phones, PDAs etc.). For
information on configuring NAC support, see “Configuring NAC server support” on page 122.
Supported Access Ports/Points
A Brocade Mobility RFS7000-GR Controller supports the adoption of the following Brocade
Enterprise Access Ports and Access Points:
Brocade Mobility RFS7000-GR Controller System Reference Guide 23
53-1001944-01
Page 38

Software overview
1
• Brocade Mobility 7131N-FGR Access Point
24 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 39

Software overview
1.1 IEEE standards support
IEEE Standard Supported Notes
IEEE 802.11a Yes The IEEE 802.11a standard is
fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11a standard is
fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.11b Yes The IEEE 802.11b standard is
fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11b standard is
fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.11g Yes The IEEE 802.11g standard is
fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11g standard is
fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.11d Yes The IEEE 802.1d standard is
implemented as part of the IEEE
802.1s standard on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11d standard is
implemented for Mesh
networking on the following AP
Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
1
Brocade Mobility RFS7000-GR Controller System Reference Guide 25
53-1001944-01
Page 40

Software overview
1
IEEE Standard Supported Notes
IEEE 802.11i Yes We fully support the 802.11i
standard for encryption and
authentication. Additionally we
also implement 802.11i PMK
Caching, Opportunistic PMK
Caching and Pre-Authentication.
The IEEE 802.11i standard is
fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11i standard is
fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.11n Yes The IEEE 802.11n standard is
fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.11n standard is
fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point (Standalone
and Adaptive)
26 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 41

Software overview
IEEE Standard Supported Notes
IEEE 802.1x Yes Full support IEEE 802.1x
authentication ether with a fully
functional integrated RADIUS
server built into our RF Switches
and Access Points or an external
RADIUS server such as Microsoft
IAS, Microsoft NPS, Cisco Secure
ACS, Free RADIUS and Juniper
Steel Belted RADIUS (to name a
few).
When using the integrated
RADIUS server we support the
following EAP methods:
• EAP-TLS
• EAP-GTC (PEAPv1)
• EAP-MSCHAPv2 (PEAPv0)
• EAP-TTLS (MD5, PAP,
MSCHAPv2)
When using an external RADIUS
server the EAP type is
transparent to the WLAN
infrastructure allowing any
standard EAP method to be
supported.
The IEEE 802.1x standard is fully
supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.1x standard is fully
supported on the following AP
Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.3u Yes The IEEE 802.3u (100BASE-T)
standard is fully supported on
the following Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.3u (100BASE-T)
standard is fully supported on
the following AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
1
Brocade Mobility RFS7000-GR Controller System Reference Guide 27
53-1001944-01
Page 42

Software overview
1
IEEE Standard Supported Notes
IEEE 802.3ab Yes The IEEE 802.3ab (1000BASE-T)
standard is fully supported on
the following Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.3ab (1000BASE-T)
standard is fully supported on
the following AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.3z Yes The IEEE 802.3z (1000BASE-X)
standard is fully supported on
the following Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
(SFP Pluggable Optics)
IEEE 802.1P Yes The IEEE 802.1P (QoS) standard
is fully supported on the following
Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.1P (QoS) standard
is fully supported on the following
AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
IEEE 802.1Q Yes The IEEE 802.1Q (VLAN Tagging)
standard is fully supported on
the following Switch Platforms:
• Brocade Mobility
RFS7000-GR Controller
The IEEE 802.1Q (VLAN Tagging)
standard is fully supported on
the following AP Platforms:
• Brocade Mobility
7131N-FGR Access Point
Access Point
28 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 43

Standards support
Standard Supported Notes
RFC 768 UDP Yes The Brocade Mobility
RFC 791 IP Yes In addition we provide full IP4
RFC 792 ICMP Yes
RFC 793 TCP Yes
RFC 826 ARP Yes
RFC 1122 Requirements for
Internet Hosts
RFC 1519 CIDR Yes
RFC 1542 BOOTP Yes BOOTP is implemented as part of
RFC 2131 DHCP Yes DHCP client and server.
RFC 1321 MD5 Message-Digest
Algorithm
RFC 1851 The ESP Triple DES
Tra nsfor m
RFC 2104 HMAC: Keyed Hashing
for Message Authentication
RFC 2246 TLS Protocol Version
1.0
RFC 2401 Security Architecture
for the Internet Protocol
RFC 2403 HMAC-MD5-96 within
ESP and AH
RFC 2404 HMAC-SHA-1-96 within
ESP and AH
RFC 2405 ESP DES-CBC Cipher
Algorithm with Explicit IV
RFC 2406 IPsec Yes
RFC 2407 Interpretation for
ISAKMP
Standards support
RFS7000-GR Controller supports
IP, UDP, TCP for various
management and control
functions and Switch -> AP
communications.
routing support on the RF Switch
as well as support IPv4 on our
wired / wireless stateful
inspection firewall.
Yes
the Integrated DHCP server.
BOOTP clients are implemented
on the Brocade Mobility
7131N-FGR Access Point Access
Point.
Yes Imple mented for IPS ec VP N,
SNMPv3 and EAP-TTLS.
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
1
Brocade Mobility RFS7000-GR Controller System Reference Guide 29
53-1001944-01
Page 44

Standards support
1
Standard Supported Notes
RFC 2408 ISAKMP Yes
RFC 2409 IKE Yes
RFC 2451 ESP CBC-Mode Cipher
Algorithms
RFC 2459 Internet X.509 PKI
Certificate and CRL Profile
RFC 3602 The AES-CBC Cipher
Algorithm and Its Use with IPsec
SSL and TLS: RC4 128-bit and
RSA 1024- and 2048-bit
IPSec: DES-CBC, 3DES, AES-CBC Yes
RFC 2548 Microsoft
Vendor-Specific RADIUS Attributes
RFC 2716 PPP EAP-TLS Yes
RFC 2865 RADIUS Authentication Yes Integrated and Pass-through
RFC 2866 RADIUS Accounting Yes Integrated and Pass-through
RFC 2867 RADIUS Tunnel
Accounting
RFC 2869 RADIUS Extensions Yes
RFC 3576 Dynamic Authorization
Extensions to RADIUS
RFC 3579 RADIUS Support for
EAP
RFC 3580 IEEE 802.1X RADIUS
Guidelines
RFC 3748 Extensible
Authentication Protocol
Web-based authentication Yes Using internal and external
SNMP v1, v2c, v3 Yes
RFC 854 Telnet Yes Client and Server.
RFC 1155 Management
Information for TCP/IP-Based
Internets
RFC 1156 MIB Yes
RFC 1157 SNMP Yes
RFC 1213 SNMP MIB II Yes
RFC 1350 TFTP Yes Client only.
RFC 1643 Ethernet MIB Yes This RFC is obsolete
RFC 2030 SNTP Yes Client and Server.
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
hosting.
Yes
http://tools.ietf.org/html/rfc363
8.
30 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 45

Standards support
Standard Supported Notes
RFC 2616 HTTP Yes
RFC 2674 Definitions of Managed
Objects for Bridges with Traffic
Classes, Multicast Filtering, and
Virtual LAN Extensions
RFC 2819 RMON MIB Yes
RFC 2863 Interfaces Group MIB Yes We support ifTable but do not
RFC 3164 Syslog Yes
RFC 3414 User-Based Security
Model (USM) for SNMPv3
RFC 3418 MIB for SNMP Yes
Web-based: HTTP/HTTPS Yes
Command-line interface: Telnet,
SSH, serial port
Yes We support everything except the
pBridge MIB.
support ifMIB (mib-2 dot 31)
which are later extensions of
ifTable (mib-2 dot 2 dot 2).
Yes
Yes
1
Brocade Mobility RFS7000-GR Controller System Reference Guide 31
53-1001944-01
Page 46

Standards support
1
32 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 47

In this chapter
• Accessing the switch Web UI
• Switch password recovery
• Upgrading the switch image
• Auto installation
Accessing the switch Web UI
Web UI requirements
Chapter
2Controller Web UI Access and Image Upgrades
The switch Web UI is accessed using Internet Explorer version 5.5 (or later) and SUN JRE (Java
Runtime Environment) 1.5 (or later). Refer to the Sun Microsystems Web site for information on
downloading JRE.
NOTE
To successfully access the switch Web UI through a firewall, UDP por t 161 must be open in order for
the switch’s SNMP backend to function.
To prepare Internet Explorer to run the Web UI:
1. Open IE’s Tools > Inte r n e t Op tio ns panel and select the Advanced tab.
2. Uncheck the following checkboxes:
• Use HTTP 1.1
• Java console enabled (requires restart)
• Java logging enabled
• JIT compiler for virtual enabled (requires restart).
Connecting to the switch Web UI
To display the Web UI, launch a Web browser on a computer with the capability of accessing the
switch.
NOTE
Ensure you have HTTP connectivity to the switch, as HTTP is a required to launch the switch Web UI
from a browser.
To d i s play the sw it c h Web UI:
Brocade Mobility RFS7000-GR Controller System Reference Guide 33
53-1001944-01
Page 48

Accessing the switch Web UI
2
1. Point the browser to the IP address assigned to the wired Ethernet port (port 2). Specify a
secure connection using the https:// protocol.
The switch login screen displays:
2. Enter the Username admin, and Password admin123. Both are case-sensitive. Click the Login
button.
NOTE
If using HTTP to login into the switch, you may encounter a Warning screen if a self-signed certificate
has not been created and implemented for the switch. This warning screen will continue to display
on future login attempts until a self-signed certificate is implemented. Brocade recommends only
using the default certificate for the first few login attempts until a self-signed certificate can be
generated.
NOTE
If your p assword is lost, t here is a means to a ccess th e switch , but you are fo rced to rever t th e switch
back to its factory default settings and lose your existing configuration (unless saved to a secure
location). Consequently, Brocade recommends keeping the password in a secure location so it can
be retrieved. For information on password recovery, see “The chapters within this System Reference
Guide are arranged to be complimentary with the main menu items in the menu tree of the switch
Web UI. Refer to this content to configure switch network addressing, security and diagnostics as
required.” on page 35.
34 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 49

Once the Web UI is accessed, the Switch main menu item displays a configuration tab with
high-level switch information. Click the Show Dashboard button to display an overall indicator of
switch health. Once the switch is fully configured, the dashboard is the central display for the user
to view the version of firmware running on the switch, quickly assess the last 5 alarms generated
by the switch, view the status of the switch’s Ethernet connections and view switch CPU and
memory utilization statistics.
NOTE
The chapters within this System Reference Guide are arranged to be complimentary with the main
menu items in the menu tree of the switch Web UI. Refer to this content to configure switch network
addressing, security and diagnostics as required.
Switch password recovery
The access point has a means of restoring its password to its default value. Doing so also reverts
the access point’s security, radio and power management configuration to their default settings.
Only an installation professional should reset the access point’s password and promptly define a
new restrictive password.
To contact Brocade Support in the event of a password reset requirement, go to
Switch password recovery
2
http://www.brocade.com/support/
CAUTION
Only a qualified installation professional should set or restore the access point’s radio and power
management configuration in the event of a password reset.
Upgrading the switch image
The switch ships with a factory installed firmware image with the full feature functionality described
in this System Reference Guide. However, Brocade periodically releases switch firmware that
includes enhancements or resolutions to known issues. Verify your current switch firmware version
with the latest version available from the Brocade Web site before determining if your system
requires an upgrade.
Auto installation
The switch auto install function can be configured manually or using a DHCP server. When
configuring auto installation using DHCP, the server requires the definition of a vendor class and
four sub-options under option 43 namely:
• Option 186 - defines the tftp/ftp server and ftp username, password information
• Option 187 - defines the firmware path and file name
• Option 188 - defines the config path and file name
• Option 190 - defines the cluster config path and file name.
Brocade Mobility RFS7000-GR Controller System Reference Guide 35
53-1001944-01
Page 50

Auto installation
2
The individual features (config, cluster-config and image) can be enabled separately using the CLI,
SNMP or Web UI. If a feature is disabled, it is skipped when auto install is triggered.
For manual configuration (where the URLs for the configuration and image files are not supplied by
DHCP), the URLs can be specified using the CLI, SNMP or Applet. Use the CLI to define the
expected firmware image version. If the image version is not specified, the switch will derive it from
the header of the firmware image file.
Configuration files are tracked by their MD5 checksum. Configuration files are tracked by their
contents. If a file is renamed its contents remain the same and the file will not be reloaded.
The requested image file version (if any) is checked against the current version before any attempt
is made to load it. If the requested version is the same as the running version, no action is taken. If
the image file version (embedded in the file header) does not match the expected version, no
further action is taken. If the version has not been specified, the image file header is compared to
the local version. If they are the same, no action is taken.
NOTE
Once the system has been operating for ten minutes, Auto Install is disabled, though it may still be
reconfigured. This is to prevent the system from attempting to re-install each time a DHCP lease is
renewed.
Configuring auto install using the CLI
There are three compulsory and four optional configuration parameters.
The compulsory parameters are:
• configuration upgrade enable
• cluster configuration upgrade enable
• image upgrade enable
Optional (only for the static case):
• configuration file URL
• cluster configuration file URL
• image file URL
• expected image version
To set default to no, and the URLs and the version default to "" (blank):
RF Switch(config)#show autoinstall
feature enabled URL
config no --not-set-cluster cfg no --not-set-image no --not-set-expected image version --not-set--
Enables are set using the autoinstall <feature> command:
RF Switch>en
RF Switch#conf t
RF Switch(config)#autoinstall image
RF Switch(config)#autoinstall config
RF Switch(config)#autoinstall cluster-config
After this configuration update, any switch reboot with DHCP enabled on the RON port will trigger
an auto install, provided the DHCP Server is configured with appropriate options.
36 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 51

Auto installation
2
The "enables" are cleared using the no autoinstall <feature>
URLs and the version string are stored in the configuration file as text and can be cleared using an
empty pair of double quotes to denote the blank string. In the following example, define the three
URLs and the expected version of the image file, then enable all three features for the auto install.
RF Switch(config)#autoinstall config url
ftp://ftp:ftp@192.9.200.1/RFSwitch/config
RF Switch(config)#autoinstall cluster-config url
ftp://ftp:ftp@192.9.200.1/RFSwitch/cluster-config
RF Switch(config)#autoinstall image url
ftp://ftp:ftp@147.11.1.11/RFSwitch/images/RFS7000-GR.img
RF Switch(config)#autoinstall image version 4.1.0.0-040GR
RF Switch(config)#autoinstall config
RF Switch(config)#autoinstall cluster-config
RF Switch(config)#autoinstall image
RF Switch(config)#show autoinstall
feature enabled URL
config yes ftp://ftp:ftp@192.9.200.1/RFSwitch/config
cluster cfg yes ftp://ftp:ftp@192.9.200.1/RFSwitch/cluster-config
image yes ftp://ftp:ftp@147.11.1.11/RFSwitch/images/RFS7000-GR.img
expected image version 4.1.0.0-040GR
Once again, for DHCP option based auto install the URLs is ignored and those passed by DHCP are
not stored.
Whenever a string is blank it is shown as --not-set--.
Brocade Mobility RFS7000-GR Controller System Reference Guide 37
53-1001944-01
Page 52

Auto installation
2
38 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 53

In this chapter
This chapter describes the Switch main menu information used to configure the switch. This
chapter consists of the following sections:
• Viewing the switch interface
• Viewing switch port information
• Viewing switch configurations
• Viewing switch firmware information
• Switch file management
• Configuring automatic updates
• Viewing the switch alarm log
• Viewing switch licenses
• How to use the filter option
Chapter
3Controller Information
Viewing the switch interface
The Switch Configuration tab provides high-level system, switch name and address information
accessible from one location. Use this information to assess whether the current firmware version
is the most recent and if the number of licenses available is correct to support the number of radio
devices deployed. The values displayed within the screen can be defined in numerous additional
locations throughout the switch applet.
The switch screen displays two tabs supporting the following configuration activities:
• “Setting the switch country code” on page 40
• Viewing switch statistics
NOTE
When the switch’s configuration is successfully updated (using the Web UI), the effected screen is
closed without informing the user their change was successful. However, if an error were to occur,
the error displays within the effected screen’s Status field and the screen remains displayed. With
file transfer operations, the transfer screen remains open during the transfer and remains open
upon completion (with status displayed within the Status field).
Brocade Mobility RFS7000-GR Controller System Reference Guide 39
53-1001944-01
Page 54

Viewing the switch interface
3
Setting the switch country code
When initially logging into the system, the switch requests that you enter the correct country code
for your region. If a country code is not configured, a warning message will display stating that an
incorrect country setting will lead to the illegal use of the switch. Consequently, selecting the
correct country is extremely important. Each country has its own regulatory restrictions concerning
electromagnetic emissions (channel range) and the maximum RF signal strength transmitted. To
ensure compliance with national and local laws, be sure to set the Country value correctly.
Viewing the switch configuration
To view a high-level display of the switch configuration:
1. Select Switch from the main menu tree.
2. Click the Configuration tab.
3. Refer the System field to view or define the following information:
System Name
Location
Contact
40 Brocade Mobility RFS7000-GR Controller System Reference Guide
Displays the designated system name. Provide a system name serving as a
reminder of the user base the switch supports (engineering, retail, etc.).
The Location parameter serves as a reminder of where the switch can be found.
Define the System Name as a specific identifier of the switch’s location. Use the
System Name and Location parameters together to optionally define the switch
name by the radio coverage type it supports and physical location. For example,
“second floor engineering.”
Displays a Contact value for system administration and troubleshooting. This name
should be the network administrator responsible for switch operations.
53-1001944-01
Page 55

Viewing the switch interface
3
Uptime
Firmware
AP License Count
AAP License Count
Date (MM/DD/YYYY)
Time
Time Zone
Country
Displays the current operational time for the device name defined within the
System Name field. Uptime is the cumulative time since the switch was last
rebooted or lost power.
Displays the current firmware version running on the switch. This version should be
periodically compared to the most recent version available on the Brocade Web
site, as versions with increased functionality are periodically released.
Displays the number of Access Port licenses currently available for the switch. This
value represents the maximum number of Access Ports the switch is licensed to
adopt.
The AAP License Count value displays the number of Adaptive AP licenses installed
on this member.
Displays the day, month and year currently used with the switch.
Displays the time of day used by the switch.
Use the drop-down menu to specify the time zone used with the switch. Adjusting
the time zone will in turn, cause an adjustment to the time displayed.
Use the drop-down menu to specify the correct country of operation. Selecting the
country incorrectly could render your switch as operating illegally.
4. Click the Restart button to reboot the switch. The switch itself does not include a hardware
reset feature:
CAUTION
When rebooting the switch, the RADIUS Server will also be restarted regardless of its state before
the reboot.
5. Click the Shutdown button to shutdown and power off the switch.
NOTE
On the Brocade Mobility RFS7000-GR Controller, the shutdown command will shutdown the switch
but the fans on the switch will remain on.
6. Click the Show Dashboard button to display a screen with important indicators of switch health
and status. For more information, see “Switch dashboard details” on page 41. Referencing the
Details screen is recommended before new configurations are employed that utilize increased
switch bandwidth.
7. Cl ic k t h e Revert button to undo any changes. Click the Revert button before selecting the Apply
button for any changes.
8. Click the Apply button to save the updates (to the Time Zone or Country parameters
specifically).
Switch dashboard details
The Brocade Mobility RFS7000-GR Controller contains a dashboard which represents a high-level
graphical overview of central switch processes and hardware. When logging into the switch, the
dashboard should be the first place you go to assess overall switch performance and any potential
performance issues.
Brocade Mobility RFS7000-GR Controller System Reference Guide 41
53-1001944-01
Page 56

Viewing the switch interface
3
Click the Show Dashboard button (within the Switch screen’s Configuration tab) to display the
current health of the switch.
Brocade Mobility RFS7000-GR Controller dashboard
The Dashboard screen displays the current health of the switch and is divided into fields
representing the following important diagnostics:
• Alarms
• Ports
• Environment
• CPU/Memory
• File Systems
Apart from the sections mentioned above, it also displays the following status:
Redundancy State
Displays the Redundancy State of the switch. The status can be either Enabled or
Disabled.
• Enabled - Defined a green state.
• Disabled - Defined by a yellow state.
Firmware
42 Brocade Mobility RFS7000-GR Controller System Reference Guide
Displays the firmware version of the current software running on the wireless
switch.
53-1001944-01
Page 57

Viewing the switch interface
3
Management IP
Access Ports
Mobile Units
Up Time
Displays the management IP address of the switch.
Displays the total number of Access Ports adopted by the switch.
Displays the total number of MUs associated with the switch.
Displays the actual switch uptime. The Up Time is the current operational time of
the device defined within the System Name field. Uptime is the cumulative time
since the switch was last rebooted or lost power.
1. Refer to the Alarms field for details of all the unacknowledged alarms generated during the
past 48 hours. The alarms are classified as:
• Critical — Denoted by a red indicator. These alarms warrant immediate attention.
• Major — Denoted by a yellow indicator. These alarms warrant attention.
• Others — Denoted by a blue indicator.
The alarms field also displays details (in a tabular format) of the 5 most recent
unacknowledged critical/major alarms raised during the past 48 hours. The table displays the
following details:
Severity
Last Occurrence
Message
# Occurrences
Displays the severity of the alarm. It can be either Critical or Major.
Displays the time when the alarm was reported.
Displays the message associated with the alarm.
Displays the number of times during the past 48 hours such an alarm was
generated.
2. Refer to the Ports field for link, speed and duplex status of each physical port on the switch’s
front panel. It displays the following details in a tabular format:
Name
Status
Speed
Duplex
Displays the name of the port (ge1, ge2, ge3, ge4 and me1).
Displays the status of the port, either— Up or Down
Displays the speed at which the port transmits or receives data.
Displays the status of the port, either— Full Duplex or Unknown.
3. The Environment section displays the CPU temperature . It displays the valid threshold range
set by the user.
4. The CPU/Memory section displays the free memory available with the RAM.
5. The File Systems section displays the free file system available for:
• flash
• nvram
Brocade Mobility RFS7000-GR Controller System Reference Guide 43
53-1001944-01
Page 58

Viewing the switch interface
3
Viewing switch statistics
The Switch Statistics tab displays an overview of the recent network traffic and RF status for the
switch.
To display the Switch Statistics tab:
1. Select Switch from the main menu tree.
2. Click the Switch Statistics tab at the top of the Switch screen.
• system
3. Refer to the Switch Statistics field for the following read-only information about associated
MUs:
Number of MUs
Associated
Number of APs Adopted
Number of Radios
Adopted
Displays the total number of MUs currently associated to the switch.
Displays the total number of Access Ports currently adopted by the switch.
Displays the total number of radios currently adopted by the switch.
4. Refer to the Traf fic field to assess network traffic for associated APs and radios:
Pkts per second
Throughput
44 Brocade Mobility RFS7000-GR Controller System Reference Guide
Displays the packet transmission rate for received and transmitted packets over
last 30 seconds and 1 hour.
Displays the traffic throughput for packets received, packets transmitted and total
packets over last 30 seconds and 1 hour.
53-1001944-01
Page 59

Viewing switch port information
3
Avg. Bit Speed
% Non-unicast pkts
Displays the average bit speed for the switch over last 30 seconds and 1 hour. Use
the average bit speed value to help determine overall network speeds and
troubleshoot network congestion.
Displays the percentage of non-unicast packets seen (received & transmitted) by
the switch over last 30 seconds and 1 hour. Non-unicast traffic includes both
multicast and broadcast traffic.
Broadcasted, multicasted, and flooded packets are sent over the air at the slowest
rate on every radio in the WLAN and therefore have a much larger airtime
utilization than unicast packets a greater chance of causing collisions.
5. The RF Status section displays the following read-only RF radio signal information for
associated APs and radios:
Avg Signal
Avg Noise
Avg SNR (dB)
Displays the average signal strength for MUs associated with the switch over the
last 30 seconds and 1 hour. Typically, the higher the signal, the closer the MU.
Displays the average RF noise for all MUs associated with the selected WLAN. MU
noise for the last 30 seconds is displayed in black and the number in blue
represents MU noise for the last hour. If MU noise is excessive, consider moving
the MU closer to the Access Port, or in area with less conflicting network traffic.
Excessive noise may also be an indication of network interference.
Displays the average Signal to Noise Ratio (SNR) in decibels for all MUs associated
with the switch. The Signal to Noise Ratio is an indication of overall RF
performance on the wireless network.
6. Refer to the Errors field for read-only packet error and loss information for associated Access
Ports and radios:
Average Number of
Retries
% Gave Up Pkts
% Non-decryptable Pkts
Displays the average number of retries for all MUs associated with the switch. The
number in black represents average retries for the last 30 seconds and the
number in blue represents average retries for the last hour.
If the Average Number of Retries starts increasing, this indicates that MUs are not
linked back to the AP.
Displays the percentage of packets which the switch gave up on for all MUs
associated with the switch. The number in black represents this statistic for the
last 30 seconds and the number in blue represents this statistic for the last hour.
If this field displays a non-zero number, it indicates bad links causing packets to
the MUs
Displays the percentage of undecryptable packets for all MUs associated with the
switch. The number in black represents undecryptable pkts for the last 30 seconds
and the number in blue represents undecryptable pkts for the last hour.
If this field displays a non-zero number, it can indicate outside intrusion into the
network or an MU using incorrect cryptography such as a a misconfigured static
key.
Viewing switch port information
The Port screen displays configuration, runtime status, and statistics of the ports on the switch.
NOTE
The ports available on the Brocade Mobility RFS7000-GR Controller are: ge1, ge2, ge3, ge4 and
me1
Brocade Mobility RFS7000-GR Controller System Reference Guide 45
53-1001944-01
Page 60

Viewing switch port information
3
The port types are defined as follows:
GE#
ME#
The Port screen contains three tabs supporting the following port assessment activities:
GE ports are available on the Brocade Mobility RFS7000-GR Controller. GE ports
on the Brocade Mobility RFS7000-GR Controller can be RJ-45 or fiber ports which
support 10/100/1000Mbps.
ME ports are available on the Brocade Mobility RFS7000-GR Controller platforms.
ME ports are out-of-band management ports which can be used to manage the
switch via CLI or Web UI even when the other ports on the switch are unreachable.
• Viewing the port configuration
• Viewing the ports runtime status
• Reviewing port statistics
Viewing the port configuration
The Configuration tab displays the current configuration for the switch ports. Use the port
configuration information to determine whether an existing port configuration can be used as is or
requires modification for use within the switch managed network.
To view configuration details for the uplink and downlink ports:
1. Select Switch > Ports from the main menu tree.
2. Select the Configuration tab to display the following read-only information:
46 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 61

Viewing switch port information
3
Name
Aggregation
Membership
MAC Address
Admin Status
Speed
Duplex
Medium Type
Displays the current port name. On the Brocade Mobility RFS7000-GR Controller,
the available ports are named as follows:
Brocade Mobility RFS7000-GR Controller: ge1, ge2, ge3, ge4, me1
The Aggregation Membership value displays the channel group the port is a
member of.
Displays the port’s MAC Address. This value is read-only, set at the factory and
cannot be modified.
Displays whether the port is currently Up or Down.
Displays the current speed of the data transmitted and received over the port.
Displays the port as either half or full duplex.
The Medium Type value displays the physical connection type of the port. Medium
types are:
• Copper: Used on RJ-45 Ethernet Ports
• Optical: Used on Fiber Optic Gigabit Ethernet Ports
NOTE
On a Brocade Mobility RFS7000-GR Controller, the MAC address for the me1 port changes when the
switch firmware is updated to the 1.3 version. This addresses an issue where the switch MAC
address and ge1 interface shared the same MAC address in previous versions.
3. Select a port and click the Edit button to modify the port configuration. For additional
information, see “Editing the port configuration” on page 47.
Editing the port configuration
To modify the port configuration:
1. Select a port from the table displayed within the Configuration screen.
2. Click the Edit button.
Brocade Mobility RFS7000-GR Controller System Reference Guide 47
53-1001944-01
Page 62

Viewing switch port information
3
A Port Change Warning screen displays, stating any change to the port setting could disrupt
access to the switch. Communication errors may occur even if modifications made are
successful.
3. Click the OK button to continue.
Optionally, select the Don’t show this message again for the rest of the session , checkbox to
prevent the pop-up from being displayed for the rest of the session..
4. Use the Edit screen to modify the following port configurations for the selected port.
Name
Displays the read-only name assigned to the port.
Speed
Select the speed at which the port can receive and transmit the data. Select from
the following range:
• 10 Mbps
• 100 Mbps
• 1000 Mbps
• Auto
48 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 63

Viewing switch port information
3
Duplex
Modify the duplex status by selecting one of the following options:
• Half
• Full
• Auto
Channel Group
Description
Admin Status
Medium
Read-only details about the port’s cabling connection also display within the Edit screen. This
information should be used to determine the configuration defined for this port.
5. Click the OK button to commit the changes made to the port configurations.
6. Click Cancel to disregard any changes and revert back to the last saved configuration.
Optionally, set the Channel Group defined for the port. The switch bundles
individual Ethernet links (over the selected channel) into a single logical link that
provides bandwidth between the switch and another switch or host. The port
speed used is dependant on the Duplex value selected (full, half or auto). If a
segment within a channel fails, traffic previously carried over the failed link is
routed to the remaining segments within the channel. A trap is sent upon a failure
identifying the switch, channel and failed link.
Enter a brief description for the port. The description should reflect the port’s
intended function to differentiate it from others with similar configurations.
Either Enable (activate) or Disable (shutdown) the admin status of the port.
Displays the current (read-only) connection medium used by this port.
Viewing the ports runtime status
The Runtime tab displays read-only runtime configuration for uplink and downlink ports.
To view the runtime configuration details of the uplink and downlink ports:
Brocade Mobility RFS7000-GR Controller System Reference Guide 49
53-1001944-01
Page 64

Viewing switch port information
3
1. Select Switch > Ports from the main menu tree.
2. Select the Runtime tab to display the following read-only information:
Name
MAC Address
Oper Status
Speed
Duplex
MTU
Displays the port’s current name.
Displays the port’s MAC Address. This value is read-only, set at the factory and
cannot be modified.
Displays the link status of the port. The port status can be either Up or Down.
Displays the current speed of the data transmitted and received over the port.
Displays the port as either half duplex, full duplex or Unknown.
Displays the Maximum Transmission Unit (MTU) setting configured on the port. The
MTU value represents the largest packet size that can be sent over a link.
10/100 Ethernet ports have a maximum MTU setting of 1500.
Reviewing port statistics
The Statistics tab displays read-only statistics for ethernet ports. Use this information to assess if
configuration changes are required to improve network performance.
To view the runtime configuration details of the switch ports:
50 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 65

1. Select Switch > Ports from the main menu tree.
2. Select the Statistics tab.
Viewing switch port information
3
3. Refer to the Statistics tab to display the following read-only information:
Name
Bytes In
Packets In
Packets In Dropped
Packets In Error
Bytes Out
Packets Out
Packets Out Dropped
Packets Out Error
Defines the port name. On the Brocade Mobility RFS7000-GR Controller the
available ports are named as follows:
Brocade Mobility RFS7000-GR Controller: ge1, ge2, ge3, ge4, me1
Displays the total number of bytes received by the port.
Displays the total number of packets received by the port.
Displays the number of packets dropped by the port. If the number appears
excessive, a different port could be required.
Displays the number of erroneous packets received by the port. If the number
appears excessive, try using a different port and see if the problem persists.
Displays the total number of bytes transmitted by the port.
Displays the total number of packets transmitted by the port. A low value could be
an indication of a network problem.
Displays the total number of packets dropped during transmission. A high value
may be an indication of network throughput issue.
Displays the total number of erroneous transmitted packets.
4. Select a port and click on Details button to see the detailed port statistics. For more
information, refer to “Detailed port statistics” on page 52.
5. Select a port and click on Graph button to view the port statistics in a graphical format. For
more information, refer to “Viewing the port statistics graph” on page 53.
Brocade Mobility RFS7000-GR Controller System Reference Guide 51
53-1001944-01
Page 66

Viewing switch port information
3
Detailed port statistics
To view detailed statistics for a port:
1. Select a port from the table displayed within the Statistics screen.
2. Click the Details button.
3. The Interface Statistics screen displays. This screen displays the following statistics for the
selected port:
Name
MAC Address
Input Bytes
Input Unicast Packets
Input NonUnicast
Packets
Input Total Packets
Input Packets Dropped
Input Packets Error
Output Bytes
Displays the port name.
Displays physical address information associated with the interface. This address
is read-only (hard-coded at the factory) and cannot be modified.
Displays the number of bytes received on the interface.
Displays the number of unicast packets (packets directed towards the interface)
received on the interface.
Displays the number of Non-Unicast Packets (Multicast and Broadcast Packets)
received on the interface.
Displays the total number of packets received on the interface.
Displays the number of received packets dropped by the interface by the input
queue of the hardware unit /software module associated with the VLAN. Packets
are dropped when the input Queue is full or unable to processing incoming traffic.
Displays the number of packets with errors received on the interface. Input Packet
Errors are input errors due to: no buffer space/ignored packets due to broadcast
storms, packets larger than maximum packet size, framing errors, input rate
exceeding the receiver's date handling rate or cyclic redundancy check errors. In all
of these cases, an error is reported and logged.
Displays the number of bytes transmitted from the interface.
52 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 67

Viewing switch port information
3
Output Unicast Packets
Output NonUnicast
Packets
Output Total Packets
Output Packets
Dropped
Output Packets Error
Displays the number of unicast packets (packets directed towards a single
destination address) transmitted from the interface.
Displays the number of unicast packets transmitted from the interface.
Displays the total number of packets transmitted from the interface.
Displays the number of transmitted packets dropped from the interface. Output
Packets Dropped are packets dropped when the output queue of the device
associated with the interface is saturated.
Displays the number of transmitted packets with errors. Output Packet Errors are
the sum of all the output packet errors, malformed packets and misaligned
packets received.
4. The Status is the current state of the requests made from the applet. Requests are any
“SET/GET” operation from the applet. The Status field displays error messages if something
goes wrong in the transaction between the applet and the switch.
5. Click on the Refresh button to refresh the port statistics.
6. Click on the Close button to exit out of the screen.
Viewing the port statistics graph
The switch continuously collects data for port statistics. Even when the port statistics graph is
closed, data is still tallied. Periodically display the port statistics graph for assessing the latest
information.
To view a detailed graph for a port:
1. Select a port from the table displayed in the Statistics screen.
2. Click the Graph button.
Brocade Mobility RFS7000-GR Controller System Reference Guide 53
53-1001944-01
Page 68

Viewing switch port information
3
The Interface Statistics screen displays for the selected port. The screen provides the option to
view the following:
• Input Bytes
• Input Pkts Dropped
• Output Pkts Total
• Output Pkts Error
• Input Pkts Total
• Input Pkts Error
• Output Pkts NUCast
• Input Pkts NUCast
• Output Bytes
• Output Pkts Dropped
3. Display any of the above by selecting the checkbox associated with it.
NOTE
You are not allowed to select (display) more than four parameters at any given time.
4. Click on the Close button to exit out of the screen.
54 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 69

Viewing switch configurations
Use the Configurations screen to review the configuration files available to the switch. The details
of each configuration can be viewed individually. Optionally, edit the file to modify its name or use
the file as the switch startup configuration. A file can be deleted from the list of available
configurations or transferred to a user specified location.
NOTE
To view the entire switch configuration using SNMP, the switch CLI provides a better medium to
review the entire switch configuration.
To view the Configuration files available to the switch:
1. Select Switch > Configurations from the main menu tree.
Viewing switch configurations
3
The following information is displayed in tabular format. Configuration files (with the exception of
startup-config and running-config) can be edited, viewed in detail, or deleted.
Name
Size (Bytes)
Created
Modified
Path
Brocade Mobility RFS7000-GR Controller System Reference Guide 55
53-1001944-01
Displays the name of each existing configuration file.
Displays the size (in bytes) of each available configuration file.
Displays the date and time each configuration file was created. Use this
information as a baseline for troubleshooting problems by comparing event log
data with configuration file creation data.
Displays the date and time each configuration file was last modified. Compare this
column against the Created column to discern which files were modified and make
informed decisions whether existing files should be further modified or deleted.
Displays the path (location) to the configuration file.
Page 70

Viewing switch configurations
3
2. To view the contents of a config file in detail, select a config file by selecting a row from the
3. Select a configuration (other than the start-up-config or running config) and click the Install
NOTE
Selecting either the startup-config or running-config does not enable the Edit button. A different
configuration must be available to enable the Edit function for the purposes of replacing the existing
startup-config.
4. To permanently remove a file from the list of configurations available to the switch, select a
5. To restore the system’s default configuration and revert back to factory default, click the
table and click the View button. For more information, see “Viewing the detailed contents of a
config file” on page 56.
button to install the file on the switch and replace the existing startup-config file.
If a file (for example, sample-config) is selected, a message displays stating, “When
sample-config is installed, it will replace start-up config. Are you sure you want to install
sample-config.” Click Yes to continue.
configuration file from the table and click the Delete button.
If startup-config is deleted, a prompt displays stating the default switch startup-config will
automatically take its place. The switch running-config cannot be deleted.
Restore Defaults button.
NOTE
After setting the switch to revert to factory default settings, the system must be rebooted before the
default settings take effect. When this occurs, the switch IP address may change.
6. Click the Transfer Files button to move a target configuration file to a secure location for later
use. For more information, see “Transferring a config file” on page 57.
Viewing the detailed contents of a config file
The View screen displays the entire contents of a configuration file. Brocade recommends a file be
reviewed carefully before it is selected from the Config Files screen for edit or designation as the
switch startup configuration.
1. Select a configuration file from the Configuration screen by highlighting the file.
2. Click the View button to see the contents of the selected configuration file.
56 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 71

Viewing switch configurations
3
Use the up and down navigation facilities on the right-hand side of the screen to view the
entire page.
3. The Page parameter displays the portion of the configuration file in the main viewing area.
The total number of pages in the file are displayed to the right of the current page. The total
number of lines in the file display in the Status field at the bottom of the screen.
Scroll to corresponding pages as required to view the entire contents of the file. To navigate to
a specific page, enter the page number in the text area (next to Page item) and click on the Go
button. The source parameter differs depending on the source selected.
4. Refer to the Status field for the current state of the requests made from the applet. Requests
are any “SET/GET” operation from the applet. The Status field displays error messages if
something goes wrong in the transaction between the applet and the switch.
5. Click the Refresh button to get the most recent updated version of the configuration file.
6. Click Close to close the dialog without committing updates to the running configuration.
Transferring a config file
Transfer a configuration file to and from the switch using the Transfer screen. Transferring the
switch configuration is recommended to keep viable configurations available in a secure location.
The following file transfer configurations are possible:
• switch to switch, server, or local disk
Brocade Mobility RFS7000-GR Controller System Reference Guide 57
53-1001944-01
Page 72

Viewing switch configurations
3
• server to switch
• local disk to switch
To transfer the contents of a configuration file:
1. Click the Transfer Files button on the bottom of the Configuration screen.
2. Refer to the Source field to define the location and address information for the source config
file.
From
File
Using
IP Address
User ID
Password
Path
Select the location representing the source file’s current location using the From
drop-down menu. Options include Server, Local Disk and Switch.
Specify a source file for the file transfer. If the switch is selected, the file used at
startup automatically displays within the File parameter.
Refer to the Using drop down-menu to configure whether the log file transfer is
conducted using SFTP transfers require a valid user ID and password.
Enter the IP Address of the server or system receiving the source configuration.
Ensure the IP address is valid or risk jeopardizing the success of the file transfer.
Enter the User ID credentials required to transfer the configuration file from a SFTP
server.
Enter the Password required to send the configuration file from an SFTP server.
Specify an appropriate Path name to the target directory on the local system disk
or server. The Target options are different depending on the target selected.
3. Refer to the Target field to specify the details of the target file.
To
File
Use the To drop-down menu to define the location of the configuration file. Options
include the switch (default location), external server or local disk.
Use the File field to specify a target file for the file transfer. Use the File Browser
icon to search attached files systems for target file location.
4. Refer to the Status field for the current state of the requests made from the applet. Requests
are any “SET/GET” operation from the applet. The Status field displays error messages if
something goes wrong in the transaction between the applet and the switch.
5. Click the Transfer button when ready to move the target file to the specified location. Repeat
the process as necessary to move each desired configuration file to the specified location.
58 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 73

6. Click the Abort button to cancel the file transfer process before it is complete.
7. Cl i c k t h e Close button to exit the Transfer screen and return to the Config Files screen. Once a
file is transferred, there is nothing else to be saved within the Transfer screen.
Viewing switch firmware information
The switch can store (retain) two software versions (primary and secondary). Information
supporting the two versions displays within the Firmware screen. The Version column displays the
version string. The Build Time is the date and time each version was generated. Install represents
the date and time the upgrade was performed. Next Boot indicates which version should be used
on the next reboot. The Next Boot version should match the Running Version, unless the system
has failed over to another version.
Viewing switch firmware information
3
To view the firmware files available to the switch:
1. Select Switch > Firmware from the main menu tree.
2. Refer to the following information displayed within the Firmware screen:
Image
Version
Current Boot
Next Boot
Brocade Mobility RFS7000-GR Controller System Reference Guide 59
53-1001944-01
Displays whether a firmware image is the primary image or a secondary image. The
primary image is typically the image loaded when the switch boots.
Displays a unique alphanumeric version for each firmware file listed.
A check mark within this column designates this version as the version used by the
switch the last time it was booted. An “X” in this column means this version was
not used the last time the switch was booted.
A check mark within this column designates this version as the version to be used
the next time the switch is booted. An “X” in this column means this version will not
be used the next time the switch is booted. To change the boot designation,
highlight an image and click the Edit button.
Page 74

Viewing switch firmware information
3
Built Time
Install Time
3. Refer to the Patch field for a listing of those Patches available to the switch. The name and
version of each patch file is displayed. Each patch file has an associated .txt file designation.
the text file describes nuances associated with the file that may make it optimal for use with
the switch.
4. Select an existing firmware version and click the Edit button to change the firmware version
used when the switch is booted the next. For more information, see “Editing the switch
firmware” on page 60.
5. Click on the Update Firmware button to update the firmware file loaded onto the switch. For
more information, see “Updating the switch firmware” on page 61.
Displays the time the version was created (built). Do not confuse the Built Time
with the time the firmware was last loaded on the switch.
The Install Time is the time this version was loaded with on the switch. Periodically
review this information to assess the relevance of older files.
NOTE
To apply a patch to the switch follow the same instructions for updating the switch’s firmware.
6. To remove a patch, select it from amongst those displayed within the Patch field and click the
Remove Patch button.
Editing the switch firmware
The Edit screen enables the user to select a firmware file and designate it as the version used the
next time the switch is booted.
1. Select the primary firmware image from the Firmware screen.
2. Click the Edit button.
The Firmware screen displays the current firmware version and whether this version is used
for the next reboot.
3. Select the checkbox to use this version on the next boot of the switch.
4. To edit the secondary image, select the secondary image, click the Edit button and select the
Use this firmware on next reboot checkbox.
This firmware version will now be invoked after the next reboot of the switch.
60 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 75

Viewing switch firmware information
5. Refer to the Status field for the current state of the requests made from the applet. Requests
are any “SET/GET” operation from the applet. The Status field displays error messages if
something goes wrong in the transaction between the applet and the switch.
6. Click the OK button to commit the changes made and exit the screen.
3
Updating the switch firmware
Use the Update screen to update the firmware version currently used by the switch.
NOTE
When performing a firmware update using the switch CLI, use the following syntax (specific to SFTP)
ftp://username:password@ipaddress:port/path/filename. If using TFTP, use
tftp://ipaddress/path/filename.
NOTE
When per for ming a f irmwa re update using SFTP be sure th at TC P por t 21 is open between the switch
and the FTP server where the firmware file is located.
1. Select an image from the table in the Firmware screen.
2. Click the Update Firmware button.
3. Use the From drop-down menu to specify the location from which the file is sent.
4. Enter the name of the file containing the firmware update in the File text field.
This is the file that will append the file currently in use.
5. From the Using drop down menu, select SFTP as a medium to update the firmware.
a. Use SFTP to get the firmware update from a Secure File Transfer Protocol (SFTP) server. A
user account must be established on the SFTP server specified for the firmware update.
NOTE
On the Brocade Mobility RFS7000-GR Controller, users can also transfer firmware files using USB
or Compact Flash.
6. Enter the IP address for the SFTP server in the IP address field.
Brocade Mobility RFS7000-GR Controller System Reference Guide 61
53-1001944-01
Page 76

Switch file management
3
7. Enter the username for SFTP server login in the User ID field.
8. Enter the password for SFTP server login in the Password field.
9. Enter the complete file path for the file that contains the firmware update in the Path field.
10. Click the Do Update button to initiate the update.
A warning prompt displays. Upon confirming the firmware update, the switch reboots and
completes the firmware update.
CAUTION
When restarting or rebooting the switch, the RADIUS server is restarted regardless of its state
before the reboot.
11. Click OK to add the changes to the running configuration and close the dialog.
12. Refer to the Status field for the current state of the requests made from the applet. Requests
are any “SET/GET” operation from the applet. The Status field displays error messages if
something goes wrong in the transaction between the applet and the switch.
13. Click Close to close the dialog without committing updates to the running configuration.
Switch file management
Use the File Management screen to transfer configuration file to and from the switch and review
the files available.
Transferring files
Use the Transfer Files screen to transfer files to and from the switch.Transferring files is
recommended to keep files in a secure location. The following file transfer options are available:
• wireless switch to wireless switch
• wireless switch to server
• server to wireless switch
To define the properties of the file transfer configuration:
62 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 77

Switch file management
1. Select Switch > File Management from the main menu tree.
3
2. Refer to the Source field to specify the details of the source file.
From
Use the From drop-down menu to select the source file’s current location. The
options include Wireless Switch and Server. The following transfer options are
possible:
• wireless switch to wireless switch
• wireless switch to server
• server to wireless switch.
The parameters displayed in the Source and Tar ge t fields differ based on the
above selection. These different kinds of file transfer techniques are described in
the sections that follow.
File
Use the Browse button to navigate to a target file for transfer. If the switch is
selected from the From drop-down menu (within the Source field), the file used at
startup automatically displays.
Transferring a file from wireless switch to wireless switch
To transfer a file from one switch to another:
Brocade Mobility RFS7000-GR Controller System Reference Guide 63
53-1001944-01
Page 78

Switch file management
3
1. Select Wireless Switch from the From drop-down menu
2. Use the Browse button to locate a target file for the file transfer.
3. Use the To drop-down menu (within the Tar g et field) and select Wireless Switch. This defines
the location of the file.
4. Use the Browse button to define a location for the transferred file.
5. Click the Transfer button to complete the file transfer.
6. The Message section in the main menu area displays the file transfer message.
7. C l i c k Abort at any time during the transfer process to abort the file transfer.
Transferring a file from a wireless switch to a server
To transfer a file from the switch to a Server:
64 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 79

Switch file management
1. Refer to the Source field to specify the source file. Use the From drop-down menu and select
Wireless Switch.
3
2. Use the Browse button and select a file for transfer.
3. Use the To drop-down menu (within the Target field) and select Server. This defines the
transfer location of the configuration file. Enter the file location marked to store the transferred
file.
4. Use the Using drop down-menu to configure the log file transfer by using SFTP. This field
display the default port for SFTP. The value in this field can be configured as required. Enter
the IP Address of the server receiving the source configuration. Ensure the IP address is valid
or risk jeopardizing the success of the file transfer. Enter the User ID credentials required to
transfer the configuration file from a FTP server.
NOTE
On the Brocade Mobility RFS7000-GR Controller users can also transfer files using USB or Compact
Flash. On the Brocade Mobility RFS7000-GR Controller users can also transfer files using USB.
5. Enter the Password required to send the configuration file from the SFTP server.
6. Specify the appropriate Path name to the target directory on the server. The target options are
different depending on the target selected.
7. Cl i c k t h e Transfer button to complete the file transfer. The Message section in the main menu
area displays the file transfer message.
8. Click Abort at any time during the transfer process to abort the file transfer.
Transferring a file from a server to a wireless switch
To transfer a file from a Server to the switch:
Brocade Mobility RFS7000-GR Controller System Reference Guide 65
53-1001944-01
Page 80

Switch file management
3
1. Refer to the Source field to specify the details of the source file. Use the From drop-down menu
and select Server.
2. Provide the name of the File.
3. Use the Using drop-down menu to configure whether the file transfer is conducted using SFTP.
SFTP transfers require a valid user ID and password.
4. Enter an IP Address of the server receiving the configuration file. Ensure the IP address is valid
or risk jeopardizing the success of the file transfer.
5. Enter the User ID credentials required to transfer the configuration file from the SFTP server.
6. Enter the Password required to send the configuration file from the SFTP server.
7. Specify the appropriate Path name to the target directory on the server. The Target options are
different depending on the target selected.
8. Use the To drop-down menu (within the Target field) and select Wireless Switch.
9. Use the Browse button to browse and select the location to store the file marked for transfer.
10. Click the Transfer button to complete the file transfer. The Message section displays the status
of the file transfer message.
11. Click Abort button any time during the transfer process to abort the file transfer.
66 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 81

Switch file management
3
Viewing files
Use the File System tab to review the files available to the switch. The switch maintains the
following file types:
• flash
• nvram
• system
NOTE
USB1, USB2 and Compact Flash are available on the Brocade Mobility RFS7000-GR Controller.
Transfer files between the switch and the server from any one of the above mentioned locations.
Since compact flash (CF) and USB are external memory locations, the File System window displays
the status of these devices. Transfer files to compact flash and USB only if they are connected and
available.
To view the file systems currently available to the switch:
1. Select Switch > File Management from the main menu tree.
2. Select the File System tab.
3. Refer to the following File Systems information.
Name
Brocade Mobility RFS7000-GR Controller System Reference Guide 67
53-1001944-01
Displays the memory locations available to the switch.
Page 82

Configuring automatic updates
3
Available
Displays the current status of the memory resource. By default, nvram and system
are always available.
• A green check indicates the device is currently connected to the switch and is
available.
• A red “X” indicates the device is currently not available.
Formatted
This displays the format status of the memory devices. This ensures that the
external and internal memory device store the files securely. A formatted memory
device is less prone to crash and loss of data.
• A green check mark indicates the device is currently connected to the switch
and is available.
• A red “X” indicates the device is currently not available.
Configuring automatic updates
Use the Automatic Updates screen to enable a facility that will poll a server address (you
designate) when the switch is booted. If updates are found since the last time the switch was
booted, the updated version is uploaded to the switch the next time the switch is booted. Enable
this option for either the firmware, configuration file or cluster configuration file. Brocade
recommends leaving this setting disabled if a review of a new file is required before it is
automatically uploaded by the switch.
To enable and configure the automatic update feature for switch firmware, configuration files and
cluster configurations:
1. Select Switch > Automatic Updates from the main menu tree.
68 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 83

Configuring automatic updates
2. Refer to the Switch Configuration field to enable and define the configuration for automatic
configuration file updates. If enabled, the located (updated) configuration file will be used with
the switch the next time the switch boots.
3
Enable
IP Address
User ID
File Name (With Path)
Protocol/Device
Password
Select the Enable checkbox to allow an automatic configuration file update when a
newer (updated) file is detected (upon the boot of the switch) at the specified IP
address.
Define the IP address of the server where the configuration files reside. If a new
version is detected when the switch is booted, it is uploaded to the switch and
used upon the next boot of the switch.
Enter the User ID required to access the FTP or TFTP server.
Provide the complete and accurate path to the location of the configuration files on
the server. This path must be accurate to ensure the most recent file is retrieved.
Use the Protocol drop-down menu to specify the SFTP or resident switch FLASH
medium used for the file update from the server. FLASH is the default setting.
Enter the password required to access the server.
NOTE
In addition to the Protocols listed, on the Brocade Mobility RFS7000-GR Controller, users can also
auto-update using USB or Compact Flash.
3. Refer to the Redundancy Configuration field to enable and define the configuration for
automatic cluster file updates.
Enable
IP Address
User ID
Select the Enable checkbox to allow an automatic cluster file update when a new
(updated) file is detected (upon the boot of the switch) at the specified IP address.
Define the IP address of the server where the cluster files reside. If a new version
is detected when the switch is booted it will be uploaded to the switch and used
upon the next boot of the switch.
Enter the User ID required to access the FTP or TFTP server.
File Name (With Path)
Protocol/Device
Password
Provide the complete and accurate path to the location of the cluster files on the
server. This path must be accurate to ensure the most recent file is retrieved.
Use the Protocol drop-down menu to specify the SFTP or resident switch FLASH
medium used for the file update from the server. FLASH is the default setting.
Enter the password required to access the server.
4. Refer to the Firmware field to enable and define the configuration for automatic firmware
updates. If enabled, the located (updated) switch firmware is used with the switch the next
time the switch boots.
Enable
IP Address
User ID
Brocade Mobility RFS7000-GR Controller System Reference Guide 69
53-1001944-01
Select the Enable checkbox to allow an automatic firmware update when a new
(updated) version is detected (upon the boot of the switch) at the specified IP
address.
Define the IP address of the server where the firmware files reside. If a new version
is detected when the switch is booted it will be uploaded to the switch and used
upon the next boot of the switch.
Enter the User ID required to access the SFTP server.
Page 84

Viewing the switch alarm log
3
File Name (With Path)
Protocol/Device
Password
Version
Provide the complete and accurate path to the location of the firmware files on the
server. This path must be accurate to ensure the file is retrieved.
Use the Protocol drop-down menu to specify the SFTP or resident switch FLASH
medium used for the file update from the server. FLASH is the default setting.
Enter the password required to access the server.
Provide the target firmware version to ensure the switch is upgrading to the
intended baseline.
5. Select the Start Update button to begin the file updates for the enabled switch configuration,
cluster configuration, or firmware facilities.
6. Click the Apply button to save the changes to the configuration.
7. Cl i c k t h e Revert button to revert back to the last saved configuration.
Viewing the switch alarm log
Use the Alarm Log screen as an initial snapshot for alarm log information. Expand alarms (as
needed) for greater detail, delete alarms, acknowledge alarms, or export alarm data to a
user-specified location for archive and network performance analysis.
To view switch alarm log information:
1. Select Switch > Alarm Log from the main menu tree.
2. Use the Alarm Log screen’s filtering options to view alarm log data by page or the by its entire
content.
70 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 85

Viewing the switch alarm log
3. Select either of the two available options to view alarm log information:
3
View By Page
View All
Select the View By Page radio button to view alarm log information on a per page
basis. Use the View By Page option to page through alarm logs. If there are a large
number of alarms, the user can navigate to the page that has been completely
loaded. All operations can be performed on the currently loaded data. Enter a page
number next to “Page” and click the Go button to move to the specific page.
Select the View All radio button to display the complete alarm log with in the table.
If there are a large number of alarms, the View All option will take several minutes
to load.
4. Refer to the table within the Alarm Log screen for the following information:
Index
Status
Time Stamp
Severity
Displays the unique numerical identifier for trap events (alarms) generated in the
system. Use the index to help differentiate an alarm from others with similar
attributes.
Displays the current state of the requests made from the applet. Requests are any
“SET/GET” operation from the applet. The Status area displays error messages if
something goes wrong in the transaction between the applet and the switch.
Displays the date, year and time the alarm was raised (as well as the time zone of
the system). The time stamp only states the time the alarm was generated, not the
time it was acknowledged.
Displays the severity level of the event. Use this (non numerical and verbal)
description to assess the criticality of the alarms. Severity levels include:
• Critical
• Major
• Warning
• Informational
• Normal
Module Name
Type
Displays the module name that triggered this alarm. Use this information to assess
if this alarm is a recurring problem or if it is an isolated incident.
Displays the alarm type.
Message
Displays a detailed event message corresponding to the alarm event. It contains
an event specific message for information about the alarm. Use this value along
with the Details description for optimal problem event identification.
5. Select an alarm and click the Details button to display an alarm description along with a
system proposed solution and possible causes. For more information, see
“Viewing alarm log details” on page 72.
6. Select the alarm(s) from those listed and click the Delete button to remove them from the list
of alarms.
This is not recommended in instances where the problem is unacknowledged and the
criticality has not yet been assessed.
7. Select the unacknowledged alarm(s) from those listed and click the Acknowledge button to
acknowledge them.
8. Click the Export button to export the content of the table to a Comma Separated Values (CSV).
Brocade Mobility RFS7000-GR Controller System Reference Guide 71
53-1001944-01
Page 86

Viewing switch licenses
3
Viewing alarm log details
Use the Details option when additional information is required for a specific alarm to make an
informed decision on whether to delete, acknowledge or export the alarm.
To review switch alarm details:
1. Select Switch > Alarm Log from the main menu tree.
1. Select an alarm and click the Details button.
2. Refer to the Alarm Details and Alarm Message for the following information:
Description
Solution
Possible Causes
Alarm Message
3. Click Close to exit the dialog.
Viewing switch licenses
Use the Licenses screen to install and add a new switch license.
To install a new license:
Displays the details of the alarm log event. This information can be used in
conjunction with the Solution and Possible Causes items to troubleshoot the event
and determine how the event can be avoided in the future.
Displays a possible solution to the alarm event. The solution should be attempted
first to rectify the described problem.
Describes the probable causes that could have raised this specific alarm.
Determine whether the causes listed can be remedied to avoid this alarm from
being raised in the future.
Displays the radio (and MAC address if relevant) reporting the alarm detail
information.
72 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 87

1. Select Switch > Licenses from the main menu tree.
Viewing switch licenses
3
2. Refer to the Install License field for the following information:
License Key
Feature Name
Serial Number
Enter the license key required to install a particular feature. The license key is
returned when you supply the switch serial number to Brocade support.
Enter the name of the feature you wish to install/upgrade using the license.
Displays the serial number of the switch used for generating the license key.
3. Click the Install button to install the selected license.
4. Refer to the Feature Licenses table for the following license specific information:
Feature Name
Displays the name of the feature either installed or upgraded on the switch.
Available feature licenses on the switch are:
• Access Port licenses - AP: This enables you to adopt a specified number of
Access Ports to the switch. The available number of Access Port licences
varies by switch platform.
• Adaptive AP licenses - AAP: This enables you to adopt a specified number of
Adaptive APs to the switch. The available number of Adaptive AP licences
varies by switch platform.
• Advanced Security license - ADSEC: This enables the Role Based Firewall
feature and increases the number of IPSec VPN tunnels. The number of IPSec
tunnels varies by switch platform.
• Location Application License - LOC-APP: This enables the switch's integrated
RTLS engine which allows for locationing of wireless clients and Wi-Fi tags. It
also enables RFID support and reader management and Gen2 tag support. In
addition this license enables Application Level Event support for sending
location updates to 3rd par ty applications.
License Count
Displays the number of licenses applied while entering the license key.
Brocade Mobility RFS7000-GR Controller System Reference Guide 73
53-1001944-01
Page 88

How to use the filter option
3
License Usage
License Key
Lists the number of license in use. Determine whether this number adequately
represents the number of switches needed to deploy.
The license key for the feature installed/upgraded.
How to use the filter option
Use the Filter Option to sort the display details of screen that employ the filtering option as a
means of sorting how data is displayed within the screen.
1. Click the Show Filtering Option to expand the Filter Option zone, whenever it appears in any
screen.
2. Enter the filter criteria as per the options provided in the Filter Option zone.
The parameters in the Filter Option field are populated with the parameters of the screen in
which it appears. Not all switch Web UI’s contain the filtering option.
3. Click the Filter Entire Table button to filter the entire table in which the filter zone appears.
The result of the filtering operation displays at the bottom of the table
4. Click the Turn Off Filtering button to disable the filtering option for the screen where it appears.
Filtering status (when filtering is turned off) displays at the bottom of the table.
5. Click the Hide Filtering Option button to hide the Filter Option zone.
74 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 89

In this chapter
This chapter describes the Network Setup menu information used to configure the switch. This
chapter consists of the following switch Network configuration activities:
Chapter
4Network Setup
•Displaying the network interface
•Viewing network IP information
•Viewing and configuring Layer 2 virtual LANs
•Configuring switch virtual interfaces
•Viewing and configuring switch WLANs
•Viewing associated MU details
•Viewing Access Port Information
•Viewing access port adoption defaults
•Viewing adopted access ports
•IGMP Snooping
NOTE
HTTPS must be enabled to access the switch applet. Ensure HTTPS access has been enabled before
using the login screen to access the switch applet.
Displaying the network interface
The main Network interface displays a high-level overview of the configuration (default or
otherwise) as defined within the Network main menu. Use the information to determine if items
require additional configuration using the sub-menu items under the main Network menu item.
NOTE
When the switch’s configuration is successfully updated (using the Web UI), the effected screen is
closed without informing the user their change was successful. However, if an error were to occur,
the error displays within the effected screen’s Status field and the screen remains displayed. In the
case of file transfer operations, the transfer screen remains open during the transfer operation and
remains open upon completion (with status displayed within the Status field).
To view the switch’s Network configuration:
Brocade Mobility RFS7000-GR Controller System Reference Guide 75
53-1001944-01
Page 90

Displaying the network interface
4
1. Select Network from the main menu tree.
2. Refer to the following information to discern if configuration changes are warranted:
DNS Servers
IP Routes
Address Resolution
Entries
Switch Virtual
Interfaces
Wireless LANs
Mobile Units
Access Ports
Radios
Displays the number of DNS Servers configured thus far for use with the switch. For more
information, see “Viewing network IP information” on page 77.
Displays the number of IP routes for routing packets to a defined destination. For information
on defining IP Routes, see “Configuring IP forwarding” on page 79.
Displays the number of layer three (IP) address to layer two (MAC) address mappings. For
more information, see “Viewing address resolution” on page 82.
Displays the number of virtual interfaces (VLANs) defined thus far for the switch. New VLANs
can be defined or existing VLANs can be modified as needed. For more information, see
“Configuring switch vir tual interfaces” on page 87.
Displays the number of WLANs currently defined on the switch. The switch has 32 default
WLANs. New WLANs can be added as needed, and their descriptions, VLAN assignments and
security schemes modified. For more information, see “Viewing and configuring switch
WLANs” on page 96.
Displays the number of MUs currently associated to (and interacting with) the switch. The
details of individual MUs can be displayed as needed. For more information, see “Viewing
associated MU details” on page 150.
Displays the number of Access Ports (APs) active on the switch. Access ports can be added or
existing APs can have their VLAN assignments changed, their descriptions modified and their
current authentication and encryption schemes modified. For more information, see “Viewing
Access Por t Information” on page 162.
Displays the number of AP radios detected over the switch managed network. Displayed with
this information is the number of radios detected that have been adopted by the switch. For
more information, see “Configuring access port radios” on page 162.
76 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 91

The Apply and Revert buttons are greyed out within this screen, as there is no data to be
configured or saved.
Viewing network IP information
Use the Internet Protocol screen to view and configure network associated IP details. The Internet
Protocol screen contains tabs supporting the following configuration activities:
• Configuring DNS
• Configuring IP forwarding
• Viewing address resolution
Configuring DNS
Use the Domain Name System tab to view Server address information and delete or add severs to
the list of servers available. To configure DNS:
1. Select Network > Internet Protocol from the main tree menu.
2. Select the Domain Network System tab (displayed by default).
Viewing network IP information
4
Use the Show Filtering Options link to view the details displayed in the table.
Brocade Mobility RFS7000-GR Controller System Reference Guide 77
53-1001944-01
Page 92

Viewing network IP information
4
3. The Domain Name System tab displays DNS details in a tabular format.
Server IP Address
Server Type
4. Select an IP Address from the table and click the Delete button to remove the selected entry
from the list.
5. Click the Add button to display a screen used to add another domain name server. For more
information, see “Adding an IP address for a DNS server” on page 78.
6. Click the Global Settings button to open a screen that allows the domain lookup to be
enabled/disabled and the domain name to be specified. For more information, see
“Configuring global settings” on page 78.
Displays the IP address of the domain name server(s) the system can use for
resolving domain names to IP addresses. Domain look up order is determined by
the order of the servers listed. The first server queried is the first server displayed.
Therefore, ensure obsolete addresses are periodically removed.
Displays whether the DNS IP address entry has been created statically (manually)
or dynamically. The DHCP server provides the dynamic DNS IP address entry
displayed. A static DNS IP address can be created by clicking the Add button.
Adding an IP address for a DNS server
Add an IP address for a new domain server using the Add screen.
1. Click the Add button within the Domain Network System screen.
The new Configuration screen displays enabling you to add IP address for the DNS Server.
2. Enter the Server IP Address to define the IP address of the new static domain name server.
3. Refer to the Status field for the current state of the requests made from applet. This field
displays error messages if something goes wrong in the transaction between the applet and
the switch.
4. Click OK to use the changes to the running configuration and close the dialog.
5. Click Cancel to close the dialog without committing updates to the running configuration.
Configuring global settings
Use the Global Settings screen to query domain name servers to resolve domain names to IP
addresses. Use this screen to enable/disable the Domain look up, which allows you to use
commands like ping, traceroute etc. using hostnames rather than IP addresses.
78 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 93

Viewing network IP information
1. Click the Global Settings button in the main Domain Network System screen.
A Configuration screen displays for editing the DNS settings of the server.
2. Select the Domain Look Up checkbox to enable the switch to query domain name servers to
resolve domain names to IP addresses.
4
NOTE
The order of look up is determined by the order of the servers within Domain Name System tab. The
first server queried is the first server displayed.
3. Enter a Domain Name in the text field. This is the switch’s domain.
4. Refer to the Status field for the current state of the requests made from applet. This field
displays error messages if something goes wrong in the transaction between the applet and
the switch.
5. Click OK to use the changes to the running configuration and close the dialog.
6. Click Cancel to close the dialog without committing updates to the running configuration.
Configuring IP forwarding
The IP Forwarding table lists all the routing entries to route the packets to a specific destination. To
view the IP forwarding configuration:
1. Select Network > Internet Protocol from the main tree menu.
2. Select the IP Forwarding tab.
Use the Filtering Option to view the details displayed in the table.
Brocade Mobility RFS7000-GR Controller System Reference Guide 79
53-1001944-01
Page 94

Viewing network IP information
4
3. The read-only IP Forwarding tab displays the current status between VLANs. To toggle the
status of routing between VLANs, use the Enable/Disable options located at the bottom of the
screen.
The following details display in the table:
Destination Subnet
Subnet Mask
Gateway Address
Interface
Protocol
Displays the mask used for destination subnet entries. The Subnet Mask is the IP
mask used to divide internet addresses into blocks (known as subnets). A value of
255.255.255.0 will support 256 IP addresses.
Displays the mask used for destination subnet entries. The Subnet Mask is the IP
mask used to divide internet addresses into blocks (known as subnets). A value of
255.255.255.0 will support 256 IP addresses.
Displays the IP address of the Gateway used to route the packets to the specified
destination subnet. Do not set the gateway address to any VLAN interface used by
the switch.
Displays the interface name with which the destination subnet entries are
attached.
Displays the name of the routing protocol with which this route was obtained.
Possible values are:
• Static — Routes are statically added by the operator.
• DHCP — Routes obtained from the DHCP server.
• Connected — Routes automatically installed by the switch for directly
connected networks based on interface IP addresses.
• Kernel/ ICMP — Routes added as a result of receiving an ICMP redirect from
an intermediate router.
Active
When IP Forwarding is enabled for the selected subnet, a green check displays in
the Active column. A red X defines the subnet as disabled.
80 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 95

Viewing network IP information
4. Select an entry and click the Delete button to remove the selected entry from the IP forwarding
table.
5. Click the Add button to create a new static route. For more information, see “Adding a new
static route” on page 81.
6. Click Enable (to allow) or Disable (to deny) routing between VLANs.
4
Adding a new static route
Use the Add screen to add a new destination subnet, subnet mask and gateway for routing packets
to a defined destination. Use the screen when an existing destination subnet does not meet the
needs of the network.
To add a new static route:
1. Click the Add button.
A new Configuration screen displays enabling you to add a new destination subnet, subnet
mask and gateway for routing packets to a defined destination.
2. In the Destination Subnet field, enter an IP address to route packets to a specific destination
address.
3. Enter a subnet mask for the destination subnet in the Subnet Mask field.
The Subnet Mask is the IP mask used to divide internet addresses into blocks known as
subnets. A value of 255.255.255.0 support 256 IP addresses.
4. In the Gateway Address field, enter the IP address of the gateway used to route the packets to
the specified destination subnet. Do not set the gateway address to any VLAN interface used
by the switch.
5. Refer to the Status field for the current state of the requests made from applet. This field
displays error messages if something goes wrong in the transaction between the applet and
the switch.
6. Click OK to use the changes to the running configuration and close the dialog.
7. C l i c k Cancel to close the dialog without committing updates to the running configuration.
Brocade Mobility RFS7000-GR Controller System Reference Guide 81
53-1001944-01
Page 96

Viewing and configuring Layer 2 virtual LANs
4
Viewing address resolution
The Address Resolution table displays the mapping of layer three (IP) addresses to layer two (MAC)
addresses. To view address resolution details:
1. Select Network > Internet Protocol from the main tree menu.
2. Select the Address Resolution tab.
3. Refer to the Address Resolution table for the following information:
Interface
IP Address
MAC Address
Type
4. Click the Clear button to remove the selected AP entry if no longer usable.
Displays the name of the actual interface where the IP address
was found (typically a VLAN).
Displays the IP address being resolved.
Displays the MAC address corresponding to the IP address being
resolved.
Defines whether the entry was added statically or created
dynamically in respect to network traffic. Entries are typically
static.
Viewing and configuring Layer 2 virtual LANs
A virtual LAN (VLAN) is similar to a Local Area Network (LAN), however devices do not need to be
connected to the same segment physically. Devices operate as if connected to the same LAN, but
could be connected at different physical connections across the LAN segment. The VLAN can be
connected at various physical points but react as if it were connected directly. One of the biggest
82 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 97

Viewing and configuring Layer 2 virtual LANs
4
advantages of a VLAN, is when a computer is physically moved to another location, it can stay on
the same VLAN without reconfiguration. The switch can support multiple VLANs. Use the Layer 2
Virtual LANs screen to view and configure VLANs by Port and Ports by VLAN information. Refer to
the following VLAN configuration activities:
• Viewing and configuring VLANs by port
• Viewing and configuring ports by VLAN
Viewing and configuring VLANs by port
1. Select Network > Layer 2 Virtual LANs from the main menu tree. VLAN by Port details display
within the Virtual LANs screen.
2. Refer to following details within the table:
Name
Mode
Displays the name of the VLAN to which the switch is currently connected.
It can be either Access or Trunk.
• Access– This ethernet interface accepts packets only form the native VLANs.
• Tru nk– The Ethernet interface allows packets from the given list of VLANs you
add to the trunk.
Native VLAN
Allowed VLANs
Tagged Native VLAN
Brocade Mobility RFS7000-GR Controller System Reference Guide 83
53-1001944-01
Displays the tag assigned to the native VLAN.
Displays VLAN tags allowed on this interface
Displays if the Native VLAN for each port is tagged or not. The column displays a
green check mark if the Native VLAN is tagged. If the Native VLAN is not tagged the
column will display a red “x”.
A Native VLAN is the VLAN which untagged traffic will be directed over when using
a port in trunk mode.
Page 98

Viewing and configuring Layer 2 virtual LANs
4
NOTE
For Adaptive AP to work properly with Brocade Mobility RFS7000-GR Controller you need to have
independent and extended WLANs mapped to a different VLAN than the ge port.
3. Select a record from the table and click the Edit button to modify the record. For more
information, see “Editing the details of an existing VLAN by port” on page 84.
Editing the details of an existing VLAN by port
To revise the configuration of an existing VLAN:
1. Select Network > Virtual LANs from the main menu tree.
2. Select an Ethernet for which you want to configure the VLAN and click on the Edit button.
The system prompts you with a Port VLAN Change Warning message stating communication
disruptions could occur with the switch.
3. Click OK to continue.
4. Use the Edit screen to modify the VLAN’s mode, access VLAN and allowed VLAN designation.
84 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
Page 99

Viewing and configuring Layer 2 virtual LANs
5. Use the Edit screen to modify the following:
4
Name
Mode
Displays a read only field and with the name of the Ethernet to which the VLAN is
associated.
Use the drop-down menu to select the mode. It can be either:
• Access – This Ethernet interface accepts packets only form the native VLANs.
If this mode is selected, the Allowed VLANs field is unavailable.
• Tru nk–The Ethernet interface allows packets from the given list of VLANs you
can add to the trunk.
Native VLAN
Allowed VLANs
Use this field to change the tag assigned to the native VLAN.
This section has the following 2 options (and is only available when Trunk is
selected from the Mode drop-down menu):
• No VLANs– Select this option if you do not wish to add any additional VLANs.
• Selected VLANs– Select this option if you wish to add additional VLANs.
6. Refer to the Status field for the current state of the requests made from applet. This field
displays error messages if something goes wrong in the transaction between the applet and
the switch.
7. C l i c k OK to use the changes to the running configuration and close the dialog.
8. Click Cancel to close the dialog without committing updates to the running configuration.
Viewing and configuring ports by VLAN
A Virtual Local Area Network (VLAN) is a switched network segmented by function or application
rather than a traditional LAN segmentation (based on physical location). VLANs allow a greater
level of flexibility and enable changes to the network infrastructure without physically
disconnecting network equipment.
To view VLAN by Port information:
1. Select Network > Layer 2 Virtual LANs from the main menu tree.
2. Select the Ports by VLAN tab.
Brocade Mobility RFS7000-GR Controller System Reference Guide 85
53-1001944-01
Page 100

Viewing and configuring Layer 2 virtual LANs
4
VLAN details display within the VLANs by Port tab.
3. Highlight an existing VLAN and click the Edit button. The system displays a Port VLAN Change
Warning message. Be advised, changing VLAN designations could disrupt access to the switch.
86 Brocade Mobility RFS7000-GR Controller System Reference Guide
53-1001944-01
 Loading...
Loading...