Page 1

Default Login Details
CLI Reference Guide
Ethernet Switch Series
Managed Ethernet Switches
Out-of-Band
MGMT Port
In-Band Ports http://DHCP-assigned IP
User Name admin
Password 1234
http://192.168.0.1
or
http://192.168.1.1
Version 3.79~4.60 Edition 3, 12/2019
Copyright © 2019 Zyxel Communications Corporation
Page 2

IMPORTANT!
READ CAREFULLY BEFORE USE.
KEEP THIS GUIDE FOR FUTURE REFERENCE.
This is a Reference Guide for a series of products intended for people who want to configure the Switch
via Command Line Interface (CLI).
Note: Some commands or command options in this guide may not be available in your
product. See your product's User’s Guide for a list of supported features. Every effort has
been made to ensure that the information in this guide is accurate.
How To Use This Guide
1 Read Chapter 1 on page 10 for how to access and use the CLI (Command Line Interface).
2 Read Chapter 2 on page 13 to learn about the CLI user and privilege modes.
Do not use commands not documented in this guide.
Related Documentation
•Quick Start Guide
The Quick Start Guide shows how to connect the Switch and access the Web Configurator.
• User’s Guide
The User’s Guide explains how to use the Web Configurator to configure the Switch.
Note: It is recommended you use the Web Configurator to configure the Switch.
Page 3
About This CLI Reference Guide
About This CLI Reference Guide
Intended Audience
This manual is intended for people who want to configure Zyxel Switches via Command Line Interface
(CLI).
The version number on the cover page refers to the latest firmware version supported by the Zyxel
Switches. This guide applies to versions 3.79, 3.80, 3.90, 4.00, 4.10, 4.20, 4.30, 4.40, 4.50 and 4.60 at the
time of writing.
Note: This guide is intended as a command reference for a series of products. Therefore many
commands in this guide may not be available in your product. See your User’s Guide
for a list of supported features and details about feature implementation.
Please refer to www.zyxel.com for product specific User Guides and product certifications.
How To Use This Guide
• Read the How to Access the CLI chapter for an overview of various ways you can get to the
command interface on your Switch.
• Use the Reference section in this guide for command syntax, description and examples. Each chapter
describes commands related to a feature.
• To find specific information in this guide, use the Contents Overview, the Index of Commands, or
search the PDF file.
Ethernet Switch CLI Reference Guide
3
Page 4

Document Conventions
Document Conventions
Warnings and Notes
These are how warnings and notes are shown in this CLI Reference Guide.
Warnings tell you about things that could harm you or your device. See
your User’s Guide for product specific warnings.
Note: Notes tell you other important information (for example, other things you may need to
configure or helpful tips) or recommendations.
Syntax Conventions
This manual follows these general conventions:
• Zyxel’s switches may be referred to as the “Switch”, the “device”, the “system” or the “product” in this
Reference Guide.
• Units of measurement may denote the “metric” value or the “scientific” value. For example, “k” for
kilo may denote “1000” or “1024”, “M” for mega may denote “1000000” or “1048576” and so on.
Command descriptions follow these conventions:
• Commands are in courier new font.
• Required input values are in angle brackets <>; for example,
specify an IP address for this command.
• Optional fields are in square brackets []; for instance show logins [name], the name field is optional.
The following is an example of a required field within an optional field: snmp-server [contact
<system contact>], the contact field is optiona l. However, if you use contact, then you must
provide the system contact information.
• In some commands you specify slots or interfaces by the Access ID <aid>, use “?” to show which
types of interfaces you can specify. For example, you might be able to use: slot-<slot> |
<ge|msc>-<slot>-<port> | <ge|msc>-<slot>-<port>&&-<port>.
• Use “msc-<slot>-<port>” for an uplink slot on the management switch card.
• Use “ge-<slot>-<port>” for a Gigabit Ethernet port or switch settings on a PON interface.
• Use “pon-<slot>-<port>” to configure PON interface settings.
• A “slot” is a chassis slot.
• The “port” is 1-N where N is the number of ports on the card.
• Use && to specify a range of ports.
•Lists (such as <port-list>) consist of one or more elements separated by commas. Each element
might be a single value (1, 2, 3, ...) or a range of values (1-2, 3-5, ...) separated by a dash.
• The | (bar) symbol means “or”.
• italic terms represent user-defined input values; for example, in snmp-server [contact <system
contact>], system contact can be replaced by the administrator’s name.
• A key stroke is denoted by square brackets and uppercase text, for example, [ENTER] means the
“Enter” or “Return” key on your keyboard.
ping <ip> means that you must
Ethernet Switch CLI Reference Guide
4
Page 5
Document Conventions
• <cr> means press the [ENTER] key.
• An arrow (-->) indicates that this line is a continuation of the previous line.
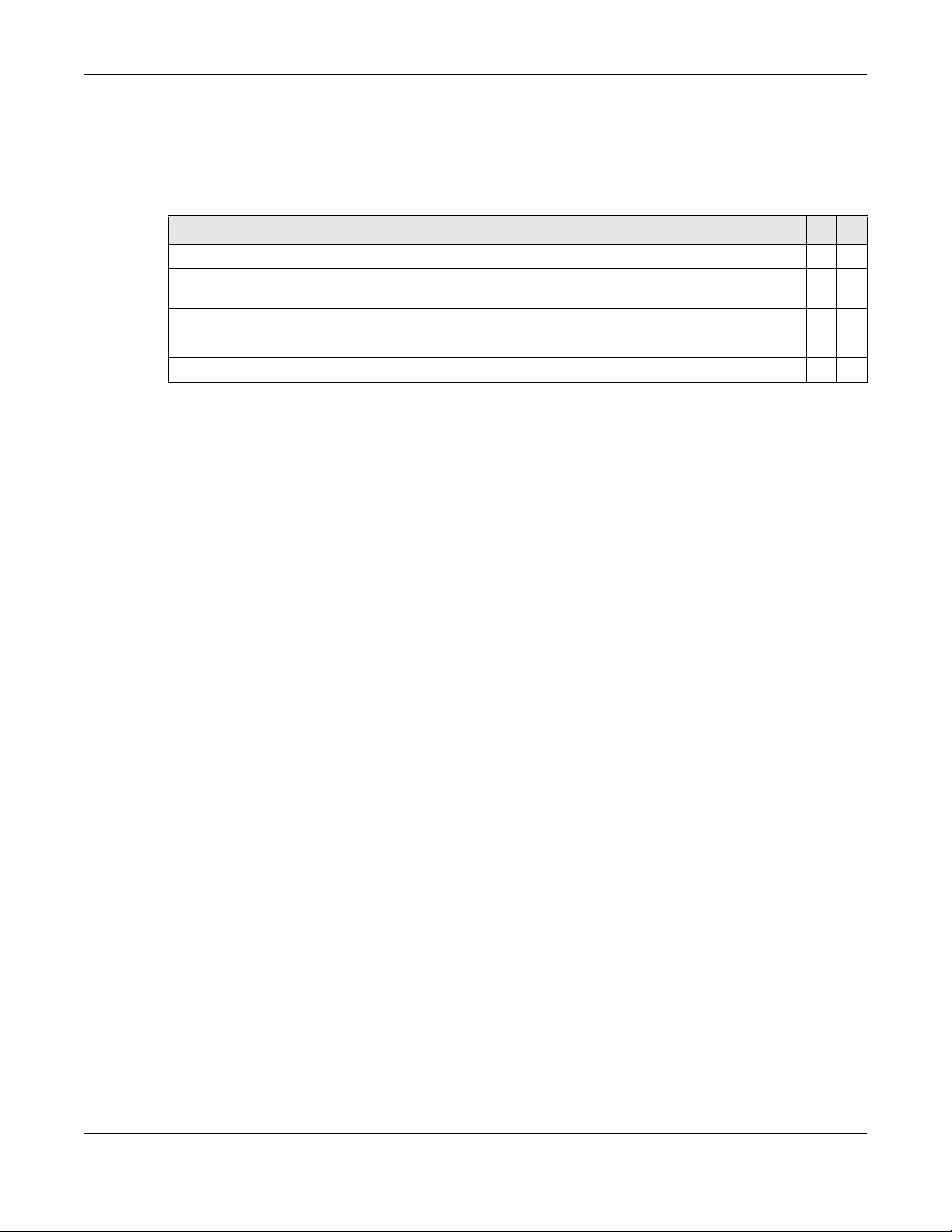
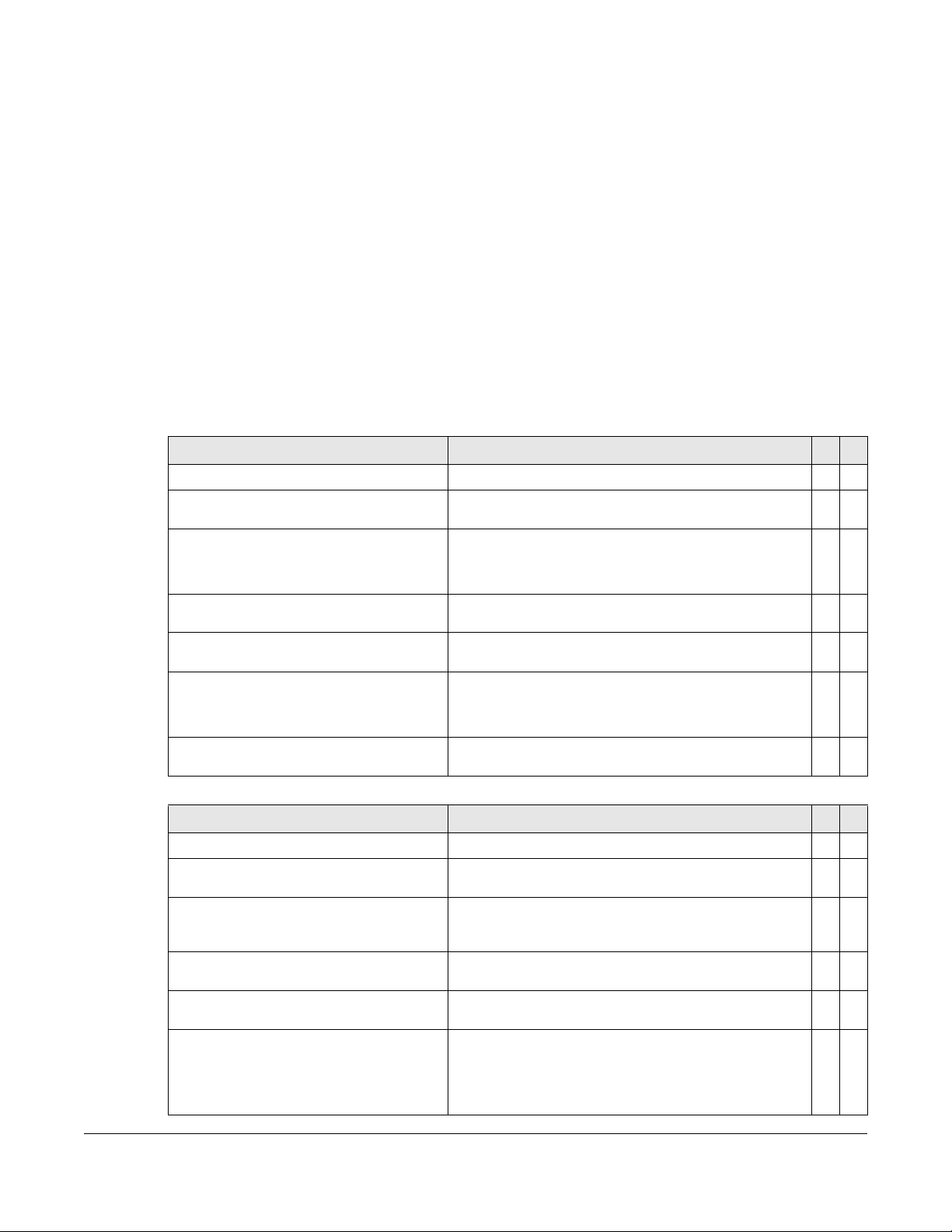
Command summary tables are organized as follows:
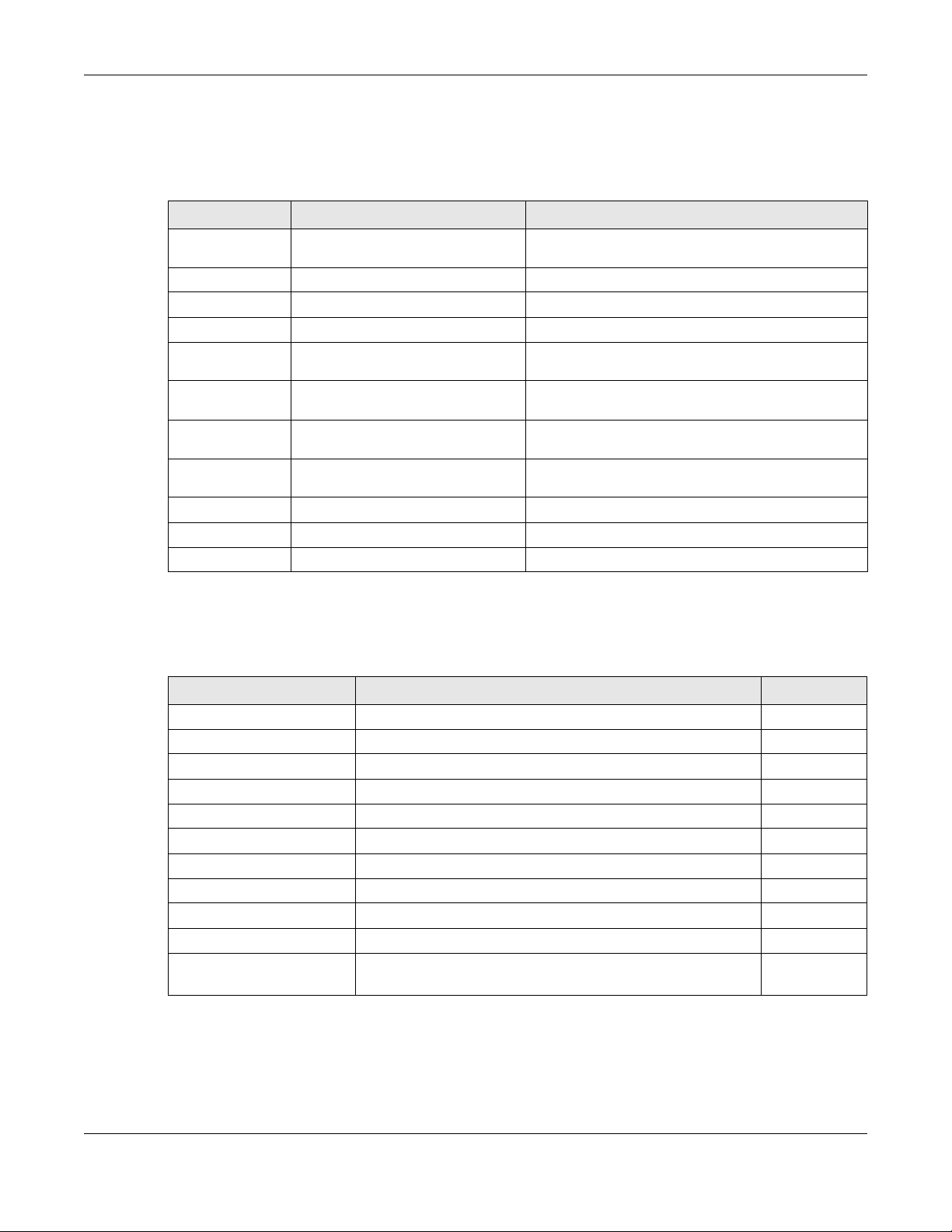
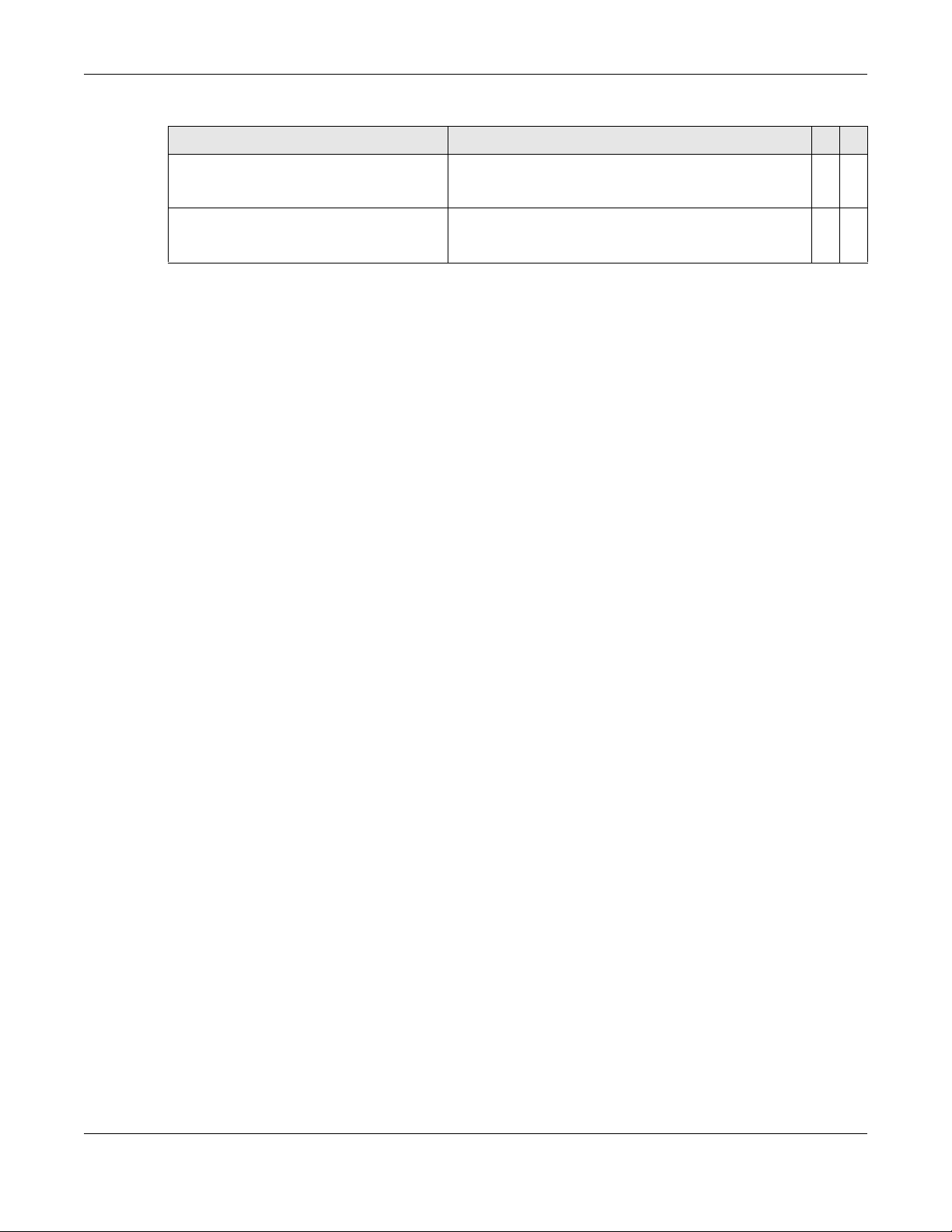
Table 1 Example: Command Summary Table
COMMAND DESCRIPTION M P
show vlan
vlan <1-4094>
inactive
no inactive
no vlan <1-4094>
Displays the status of all VLANs. E 3
Enters config-vlan mode for the specified VLAN. Creates
the VLAN, if necessary.
Disables the specified VLAN. C 13
Enables the specified VLAN. C 13
Deletes a VLAN. C 13
C13
The Table title identifies commands or the specific feature that the commands configure.
The COMMAND column shows the syntax of the command.
• If a command is not indented, you run it in the enable or config mode. See Chapter 2 on page 13 for
more information on command modes.
• If a command is indented, you run it in a sub-command mode.
The DESCRIPTION column explains what the command does. It also identifies legal input values, if
necessary.
The M column identifies the mode in which you run the command.
• E: The command is available in enable mode. It is also available in user mode if the privilege level (P)
is less than 13.
• C: The command is available in config (not indented) or one of the sub-command modes (indented).
The P column identifies the privilege level of the command. If you don’t have a high enough privilege
level you may not be able to view or execute some of the commands. See Chapter 2 on page 13 for
more information on privilege levels.
Ethernet Switch CLI Reference Guide
5
Page 6

Contents Overview
Contents Overview
Introduction .........................................................................................................................................9
How to Access and Use the CLI .......................................................................................................... 10
Privilege Level and Command Mode .................................................................... ....... ....... ....... ....... 13
Initial Setup ............................................................................................................................................ 18
Reference A-G ..................................................................................................................................25
AAA Commands .................................................................................................................................. 27
Anti-Arpscan ......................................................................................................................................... 30
ARP Commands ................................................................................................................................... 32
ARP Inspection Commands ................................................................................................................ 34
ARP Learning Commands ......................... .......................................................................................... 39
Auto Configuration Commands ......................................................................................................... 40
Bandwidth Commands ........................................................................................................................ 42
BPDU Guard .......................................................................................................................................... 45
Broadcast Storm Commands .............................................................................................................. 46
CFM Commands .................................................................................................................................. 49
Certificates Commands ...................................................................................................................... 58
Classifier Commands ........................................................................................................................... 60
Cluster Commands ........................................................ ....... ....... ....... ....... ....... ....... ....... ..................... 64
CLV Commands ................................................................................................................................... 67
Custom Default Commands ............................................................................................................... 73
Date and Time Commands ................................................................................................................. 74
Data Center Bridging Commands ..................................................................................................... 77
DHCP Commands ................................................................................................................................ 85
DHCP Snooping & DHCP VLAN Commands ..................................................................................... 90
DiffServ Commands ............................................................................................................................. 94
Display Commands .............................................................................................................................. 95
DVMRP Commands .............................................................................................................................. 96
Error Disable and Recovery Commands ........................................................................................... 98
Ethernet OAM Commands ................................................................................................................ 102
External Alarm Commands ............................................................................................................... 107
GARP Commands .............................................................................................................................. 109
Green Ethernet Commands ........ ....... ....... ...... ....... ....... ....... ....... .............. ....... ....... ....... ....... ............ 111
GVRP Commands .............................................................................................................................. 115
Reference H-M ................................................................................................................................116
HTTPS Server Commands ................................................................................................................... 118
IEEE 802.1x Authentication Commands ......... .................................................................................. 121
Ethernet Switch CLI Reference Guide
6
Page 7

Contents Overview
IGMP and Multicasting Commands .................................... ....... ....... ....... ....... ....... ....... ....... ............124
IGMP Snooping Commands ............................................................................ ....... ....... ....... ............ 126
IGMP Filtering Commands ........................................................... ....... .............. ....... ....... ....... ............ 134
Interface Commands ........................................................................................................................ 136
Interface Loopback Mode ................................................................................................................ 141
Interface Route-domain Mode ........................................................................................................ 143
IP Commands ..................................................................................................................................... 144
IP Source Binding Commands .......................................................................................................... 149
IPv6 Commands ................................................................................................................................. 151
Layer 2 Protocol Tunnel (L2PT) Commands ..................................................................................... 176
Link Layer Discovery Protocol (LLDP) Commands .......................................................................... 179
Load Sharing Commands .................................................................................................................. 191
Logging Commands .......................................................................................................................... 193
Login Account Commands ............................................................................................ ................... 194
Loopguard Commands ..................................................................................................................... 195
MAC Address Commands ................................................................................................................. 197
MAC Authentication Commands ....................................................................................................199
MAC-based VLAN .............................................................................................................................. 202
MAC Filter Commands ....................................................................................................................... 204
MAC Forward Commands ................................................................................................................ 206
MAC Pinning Commands .................................................................................................................. 207
Mirror Commands ............................................................................................................................... 209
MRSTP Commands ............................................................................................................................. 213
MSTP Commands ..................................................... ....... ....... ....... ....... ....... ....... ....... ....... ................... 216
Multiple Login Commands .............................. ....... .............. ....... ....... ....... ....... ....... ....... ....... ............ 221
MVR Commands ................................................................................................................................ 222
Reference N-S .................................................................................................................................224
NLB Commands .................................................................................................................................. 226
OSPF Commands ................................................................................................................................ 230
Password Commands ........................................................................................................................ 239
PoE Commands .................................................................................................................................. 241
Policy Commands .............................................................................................................................. 248
Policy Route Commands ................................................................................................................... 252
Port Security Commands ................................................................................................................... 254
Port-based VLAN Commands ........................................................................................................... 256
PPPoE IA Commands ......................................................................................................................... 257
Private VLAN Commands .................................................................................................................. 263
Protocol-based VLAN Commands ...................................................................................................268
Queuing Commands ......................................................................................................................... 270
RADIUS Commands ............... ............................................................................................................. 274
Remote Management Commands ................................................................................................. 276
RIP Commands ................................................................................................................................... 279
Ethernet Switch CLI Reference Guide
7
Page 8

Contents Overview
RMON ............................................................................... .................................................................... 282
Running Configuration Commands ......................................................... ....... ....... ....... ....... ....... .....289
Service Register ................................................................................................................................... 292
sFlow ................................................................................. .................................................................... 293
Smart Isolation Commands ..................................................................................... ....... ....... ............ 295
SNMP Server Commands ................................................................................................................... 298
Stacking Commands ........................................................................................ ....... ....... ................... 303
STP and RSTP Commands .................................................................................................................. 309
SSH Commands .................................................................................................................................. 313
Static Multicast Commands .............................................................................................................. 315
Static Route Commands ................................................................................................................... 317
Subnet-based VLAN Commands .....................................................................................................320
Syslog Commands .............................................................................................................................. 322
Reference T-Z ..................................................................................................................................323
TACACS+ Commands ........................................................................................................................ 324
Tech Support Commands .... ....... ....... ............. ....... ....... ....... ....... ....... ....... ....... ....... ....... ....... ............ 325
TFTP Commands ................................................................................................................................. 328
Time Range Commands ................................................ .................................................................... 329
Traceroute Commands ..................................................................................................................... 331
Trunk Commands ................................................................... ....... ....... ....... ....... ....... ....... ................... 332
trTCM Commands ............................................................................... ............................................... 335
Vendor ID-based VLAN ...................................................................................................................... 338
VLAN Commands ............................................................................................................................... 341
VLAN IP Commands ........................................................................................................................... 347
VLAN Mapping Commands .............................................................................................................. 349
VLAN Port Isolation Commands ........................................................................................................ 351
VLAN Stacking Commands ............................................................................................................... 352
VLAN Trunking Commands ............................................................................................. ................... 355
Voice VLAN Commands .................................................................................................................... 356
VRRP Commands ............................................................................................................................... 359
ZULD Commands ................................................................................................................................ 362
Wol Relay Commands ....................................................................................................................... 364
Additional Commands ...................................................................................................................... 365
Appendices and Index of Commands .........................................................................................378
Ethernet Switch CLI Reference Guide
8
Page 9
PART I
Introduction
How to Access and Use the CLI (10)
Privilege Level and Command Mode (13)
Initial Setup (18)
9
Page 10
CHAPTER 1
How to Access and Use the
This chapter introduces the command line interface (CLI).
1.1 Accessing the CLI
Use any of the following methods to access the CLI.
1.1.1 Console Port
CLI
1 Connect your computer to the console port on the Switch using the appropriate cable.
2 Use terminal emulation software with the following settings:
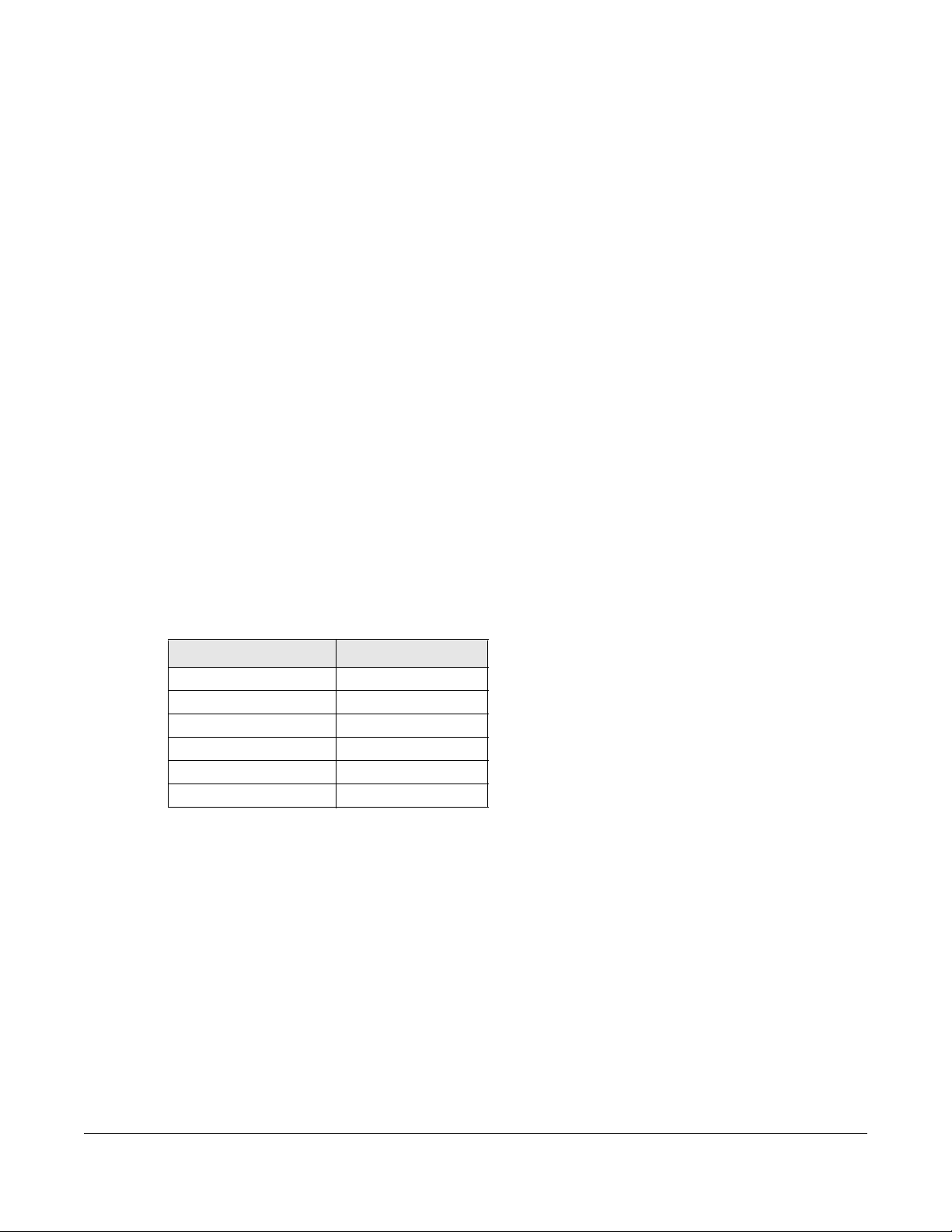
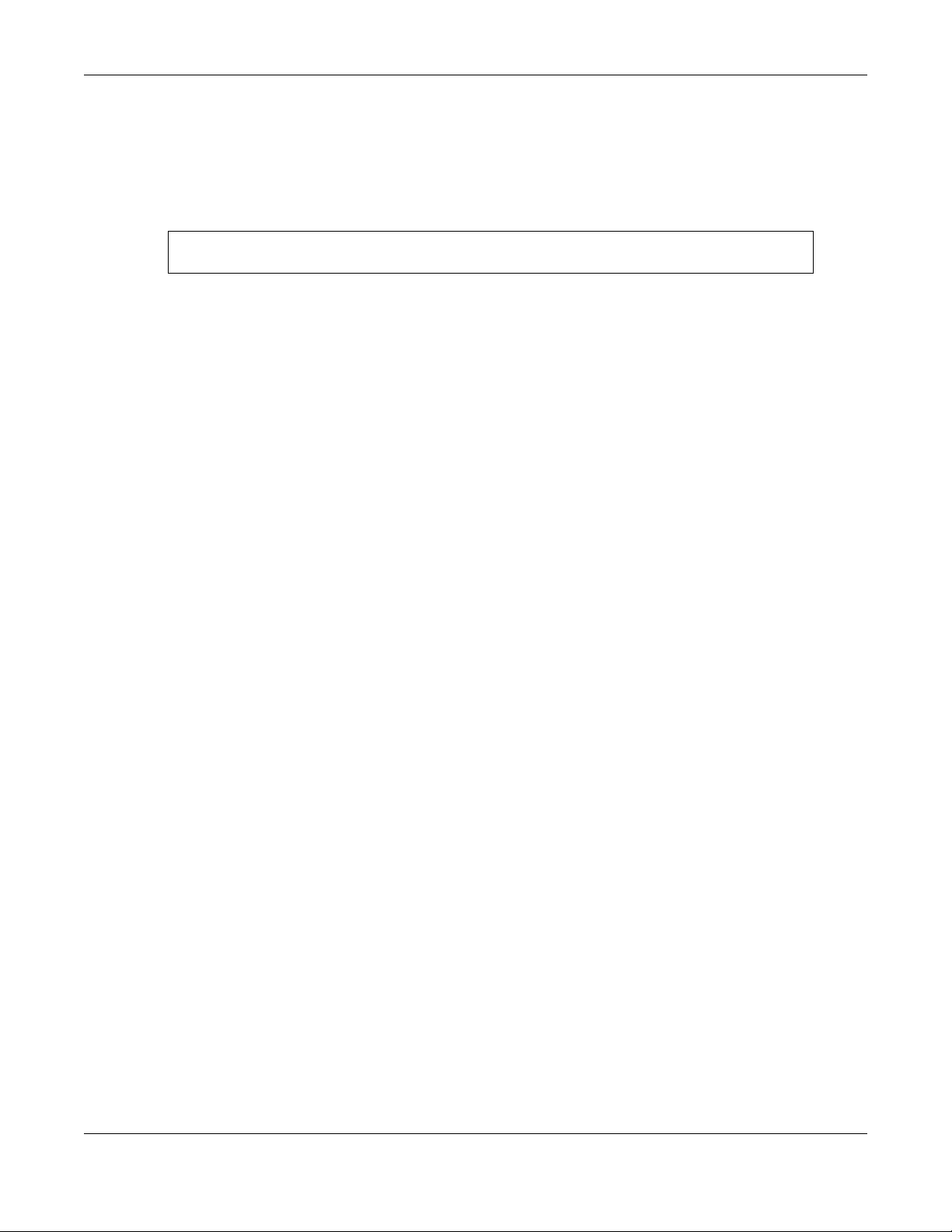
Table 2 Default Settings for the Console Port
SETTING DEFAULT VALUE
Terminal Emulation VT100
Baud Rate 9600 or 115200 bps
Parity None
Number of Data Bits 8
Number of Stop Bits 1
Flow Control None
3 Press [ENTER] to open the login screen.
1.1.2 Telnet
1 Connect your computer to one of the Ethernet ports.
2 Open a Telnet session to the Switch’s IP address. If this is your first login, use the default values.
Ethernet Switch CLI Reference Guide
10
Page 11
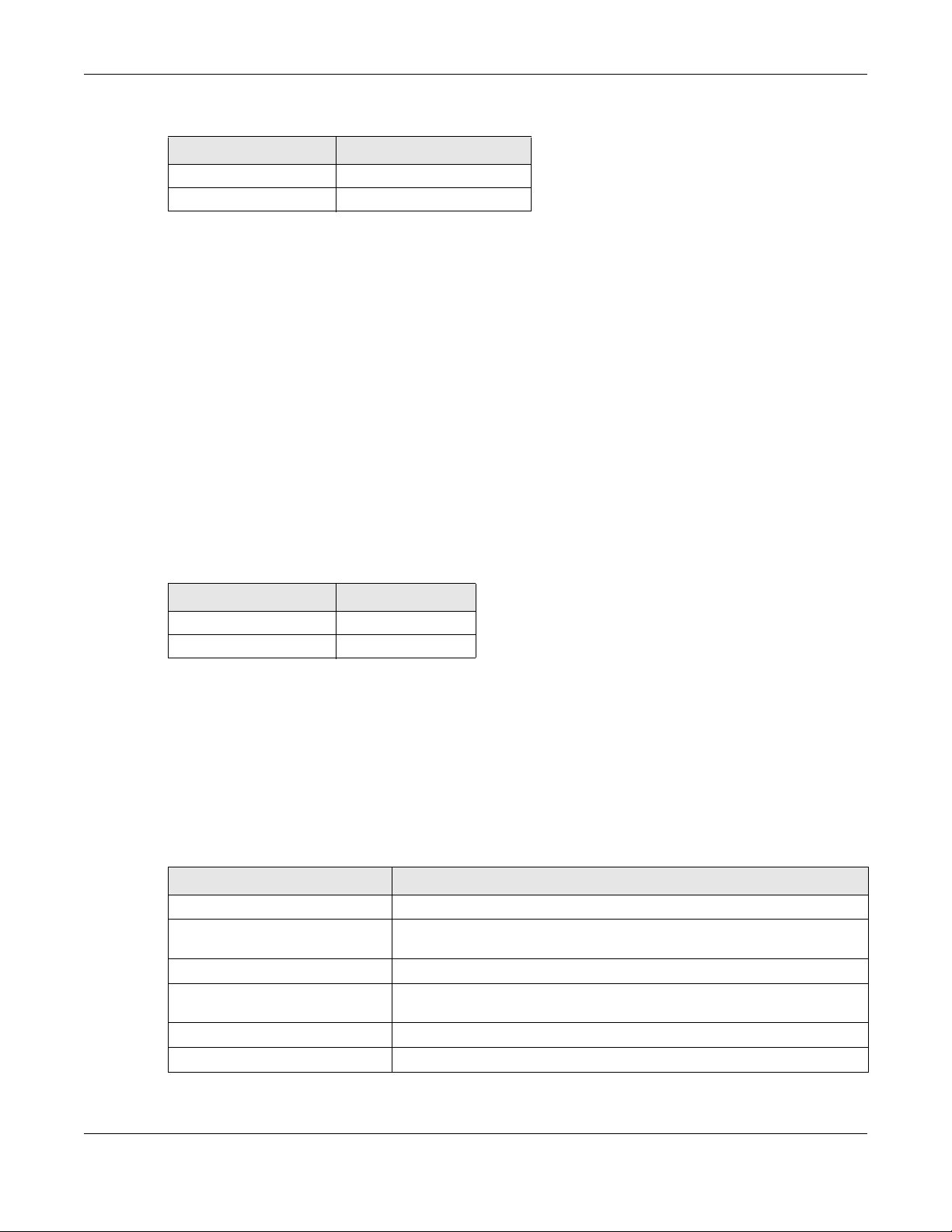
Table 3 Default Management IP Address
SETTING DEFAULT VALUE
IP Address 192.168.1.1
Subnet Mask 255.255.255.0
Make sure your computer IP address is in the same subnet, unless you are accessing the Switch through
one or more routers.
1.1.3 SSH
1 Connect your computer to one of the Ethernet ports.
2 Use a SSH client program to access the Switch. If this is your first login, use the default values in Table 3 on
page 11 and Table 4 on page 11. Make sure your computer IP address is in the same subnet, unless you
are accessing the Switch through one or more routers.
1.2 Logging in
Chapter 1 How to Access and Use the CLI
Use the administrator username and password. If this is your first login, use the default values.
Table 4 Default User Name and Password
SETTING DEFAULT VALUE
User Name admin
Password 1234
Note: The Switch automatically logs you out of the management interface after five minutes
of inactivity. If this happens to you, simply log back in again.
1.3 Using Shortcuts and Getting Help
This table identifies some shortcuts in the CLI, as well as how to get help.
Table 5 CLI Shortcuts and Help
COMMAND / KEY(S) DESCRIPTION
history
(up/down arrow keys)
[CTRL]+U
[TAB]
?
help
Displays a list of recently-used commands.
Scrolls through the list of recently-used commands. You can edit any
command or press [ENTER] to run it again.
Clears the current command.
Auto-completes the keyword you are typing if possible. For example, type
config, and press [TAB]. The Switch finishes the word configure.
Displays the keywords and/or input values that are allowed in place of the ?.
Displays the (full) commands that are allowed in place of help.
Ethernet Switch CLI Reference Guide
11
Page 12
Chapter 1 How to Access and Use the CLI
1.4 Saving Your Configuration
When you run a command, the Switch saves any changes to its run-time memory. The Switch loses these
changes if it is turned off or loses power. Use the
current configuration permanently to non-volatile memory.
sysname# write memory
Note: You should save your changes after each CLI session. All unsaved configuration
changes are lost once you restart the Switch.
1.5 Logging Out
Enter logout to log out of the CLI. You have to be in user, enable, or config mode. See Chapter 2 on
page 13 for more information about modes.
write memory command in enable mode to save the
Ethernet Switch CLI Reference Guide
12
Page 13
This chapter introduces the CLI privilege levels and command modes.
• The privilege level determines whether or not a user can run a particular command.
• If a user can run a particular command, the user has to run it in the correct mode.
2.1 Privilege Levels
Every command has a privilege level (0-14). Users can run a command if the session’s privilege level is
greater than or equal to the command’s privilege level. The session’s privilege level initially comes from
the login account’s privilege level, though it is possible to change the session’s privilege level after
logging in.
CHAPTER 2
Privilege Level and
Command Mode
2.1.1 Privilege Levels for Commands
The privilege level of each command is listed in the Reference A-G chapters on page 25.
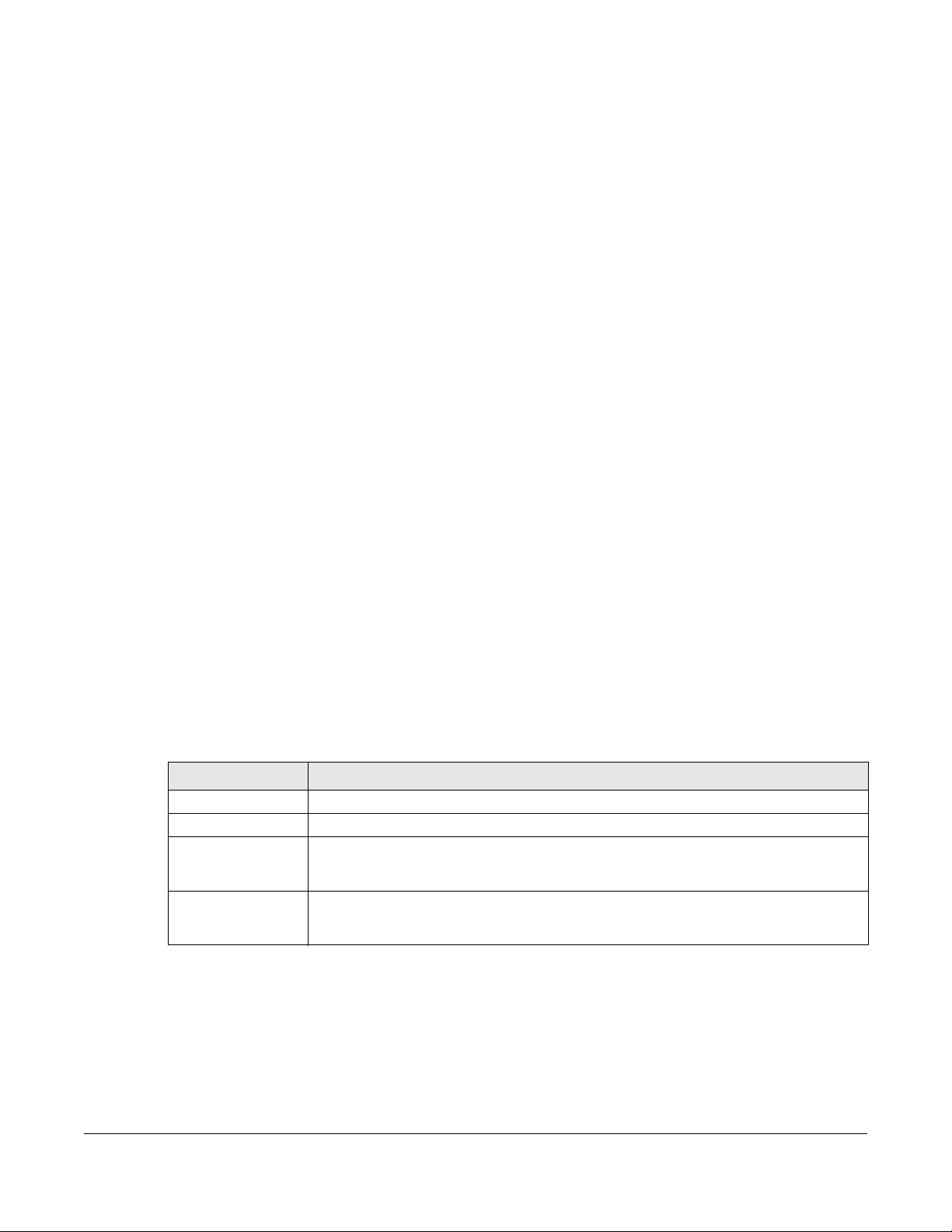
At the time of writing, commands have a privilege level of 0, 3, 13, or 14. The following table summarizes
the types of commands at each of these privilege levels.
Table 6 Types of Commands at Different Privilege Levels
PRIVILEGE LEVEL TYPES OF COMMANDS AT THIS PRIVILEGE LEVEL
0 Display basic system information.
3 Display configuration or status.
13 Configure features except for login accounts, SNMP user accounts, the authentication
method sequence and authorization settings, multiple logins, admi nistrator and enable
passwords, and configuration information display.
14 Configure login accounts, SNMP user accounts, the authentication method sequence and
authorization settings, multiple logins, and administrator and enable passwords, and display
configuration information.
2.1.2 Privilege Levels for Login Accounts
You can manage the privilege levels for login accounts in the following ways:
• Using commands. Login accounts can be configured by the admin account or any login account
with a privilege level of 14. See Chapter 47 on page 194.
Ethernet Switch CLI Reference Guide
13
Page 14
Chapter 2 Privilege Level and Command Mode
• Using vendor-specific attributes in an external authentication server. See the User’s Guide for more
information.
The admin account has a privilege level of 14, so the administrator can run every command. You
cannot change the privilege level of the admin account.
2.1.3 Privilege Levels for Sessions
The session’s privilege level initially comes from the privilege level of the login account the user used to
log in to the Switch. After logging in, the user can use the following commands to change the session’s
privilege level.
2.1.3.1 enable Command
This command raises the session’s privilege level to 14. It also changes the session to enable mode (if not
already in enable mode). This command is available in user mode or enable mode, and users have to
know the enable password.
In the following example, the login account user0 has a privilege level of 0 but knows that the enable
password is 123456. Afterwards, the session’s privilege level is 14, instead of 0, and the session changes to
enable mode.
sysname> enable
Password: 123456
sysname#
The default enable password is 1234. Use this command to set the enable password.
password <password>
<password> consists of 1-32 alphanumeric characters. For example, the following command sets the
enable password to 123456. See Chapter 106 on page 365 for more information about this command.
sysname(config)# password 123456
The password is sent in plain text and stored in the Switch’s buffers. Use this command to set the cipher
password for password encryption.
password cipher <password>
<password> consists of 32 alphanumeric characters. For example, the following command encrypts the
enable password with a 32-character cipher password. See Chapter 62 on page 239 for more
information about this command.
sysname(config)# password cipher qwertyuiopasdfghjklzxcvbnm123456
2.1.3.2 enable <0-14> Command
This command raises the session’s privilege level to the specified level. It also changes the session to
enable mode, if the specified level is 13 or 14. This command is available in user mode or enable mode,
and users have to know the password for the specified privilege level.
Ethernet Switch CLI Reference Guide
14
Page 15
In the following example, the login account user0 has a privilege level of 0 but knows that the password
for privilege level 13 is pswd13. Afterwards, the session’s privilege level is 13, instead of 0, and the session
changes to enable mode.
sysname> enable 13
Password: pswd13
sysname#
Users cannot use this command until you create passwords for specific privilege levels. Use the following
command to create passwords for specific privilege levels.
password <password> privilege <0-14>
<password> consists of 1-32 alphanumeric characters. For example, the following command sets the
password for privilege level 13 to pswd13. See Chapter 106 on page 365 for more information about this
command.
sysname(config)# password pswd13 privilege 13
2.1.3.3 disable Command
Chapter 2 Privilege Level and Command Mode
This command reduces the session’s privilege level to 0. It also changes the session to user mode. This
command is available in enable mode.
2.1.3.4 show privilege command
This command displays the session’s current privilege level. This command is available in user mode or
enable mode.
sysname# show privilege
Current privilege level : 14
2.2 Command Modes
The CLI is divided into several modes. If a user has enough privilege to run a particular command, the
user has to run the command in the correct mode. The modes that are available depend on the
session’s privilege level.
2.2.1 Command Modes for Privilege Levels 0-12
If the session’s privilege level is 0-12, the user and all of the allowed commands are in user mode. Users
do not have to change modes to run any allowed commands.
Ethernet Switch CLI Reference Guide
15
Page 16
Chapter 2 Privilege Level and Command Mode
2.2.2 Command Modes for Privilege Levels 13-14
If the session’s privilege level is 13-14, the allowed commands are in one of several modes.
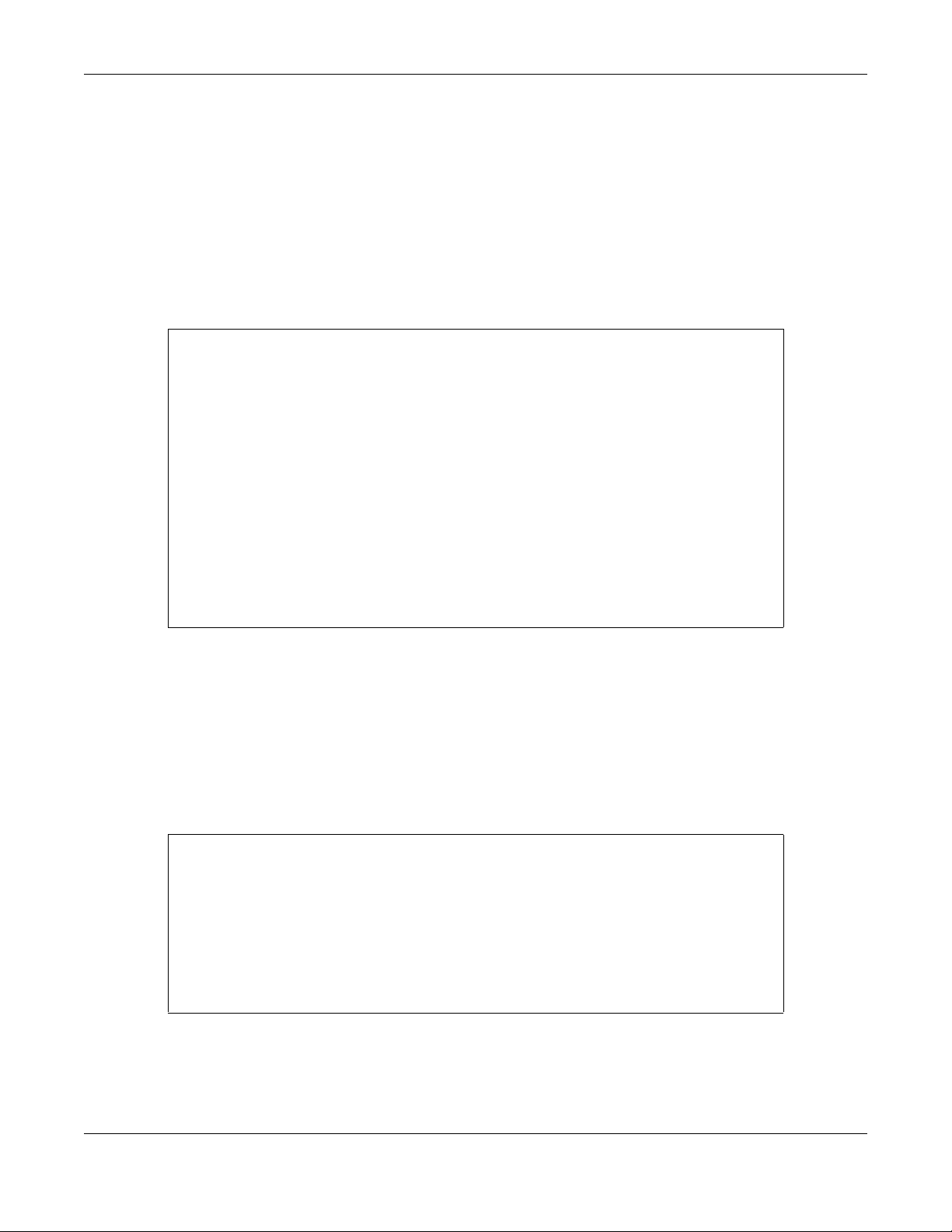
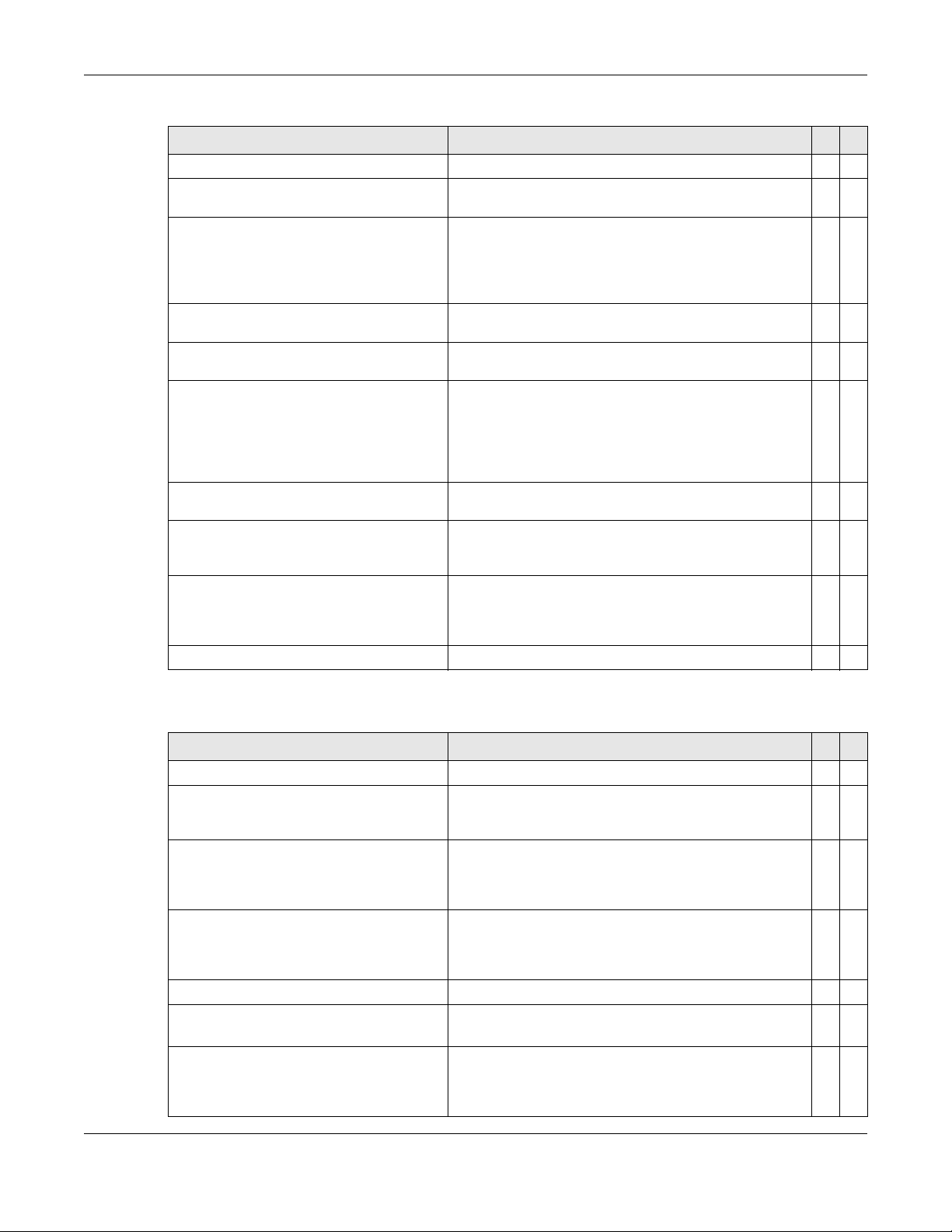
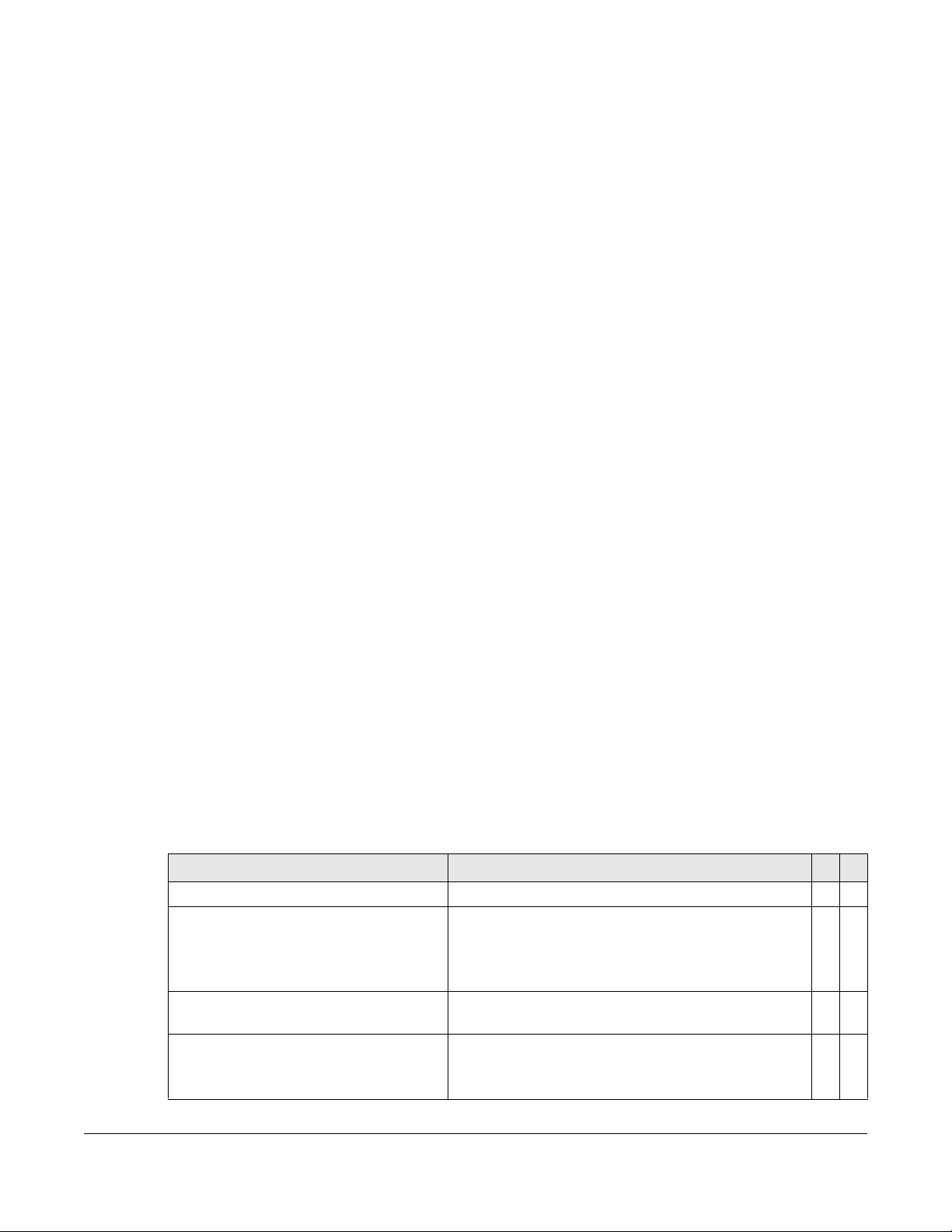
Table 7 Command Modes for Privilege Levels 13-14 and the Types of Commands in Each One
MODE PROMPT COMMAND FUNCTIONS IN THIS MODE
enable
config
config-interface
config-mvr
config-route-
domain
config-dvmrp
config-igmp
config-ma
config-ospf
config-rip
config-vrrp
sysname#
sysname(config)#
sysname(config-interface)#
sysname(config-mvr)#
sysname(config-if)#
sysname(config-dvmrp)#
sysname(config-igmp)#
sysname(config-ma)#
sysname(config-ospf)#
sysname(config-rip)#
sysname(config-vrrp)#
Display current configuration, diagnostics,
maintenance.
Configure features other than those below.
Configure ports.
Configure multicast VLAN.
Enable and enter configuration mode for an IPv4 or
IPv6 routing domain.
Configure Distance Vector Multicast Routing Protocol
(DVRMP).
Configure Internet Group Management Protocol
(IGMP).
Configure an Maintenance Association (MA) in
Connectivity Fault Management (CFM).
Configure Open Shortest Path First (OSPF) protocol.
Configure Routing Information Protocol (RIP).
Configure Virtual Router Redundancy Protocol (VRRP).
Each command is usually in one and only one mode. If a user wants to run a particular comm an d, the
user has to change to the appropriate mode. The command modes are organized like a tree, and users
start in enable mode. The following table explains how to change from one mode to another.
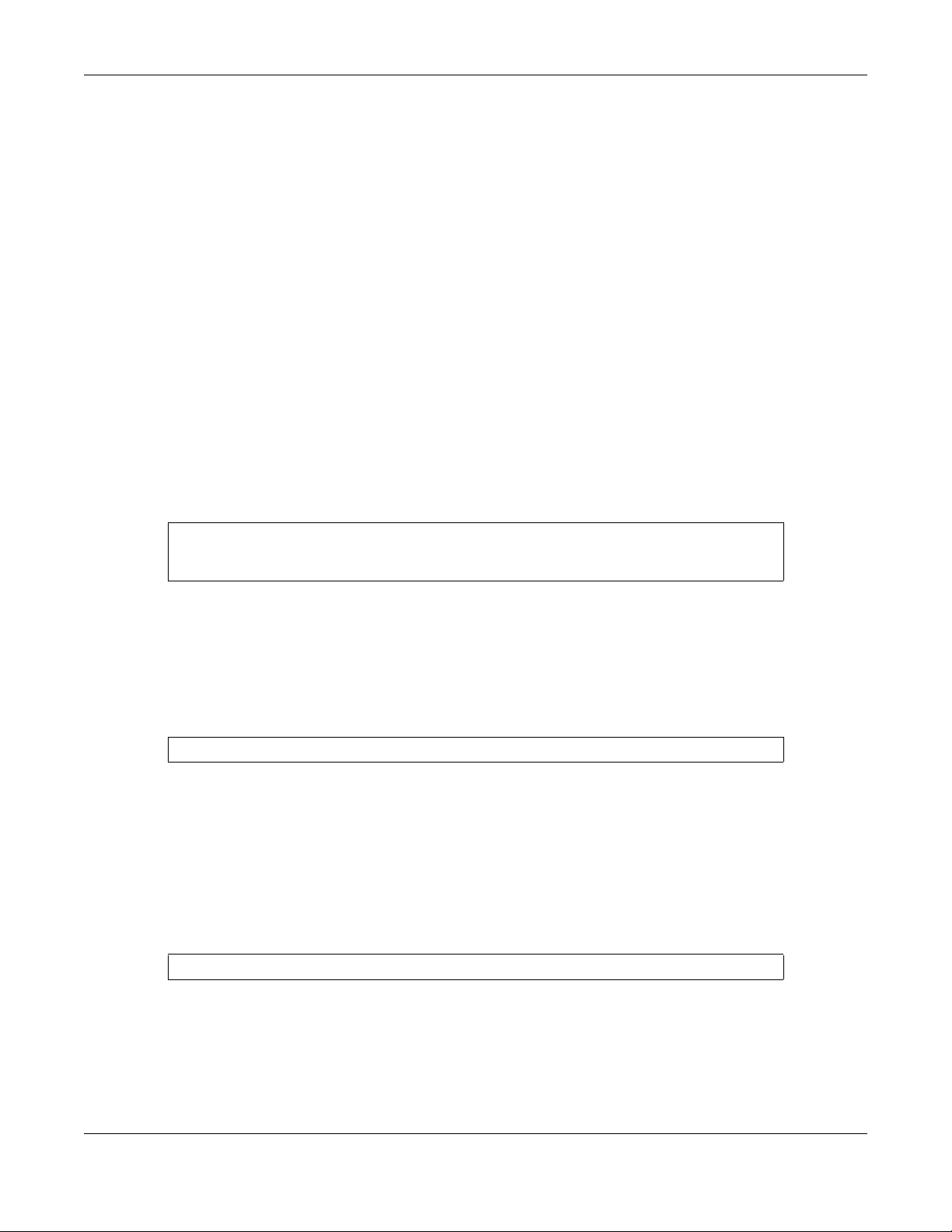
Table 8 Changing Between Command Modes for Privilege Levels 13-14
MODE ENTER MODE LEAVE MODE
enable
config
-configure
config-interface interface port-channel <port-list>
config-mvr mvr <1-4094>
config-vlan vlan <1-4094>
config-route-domain interface route domain <ip-address>/<mask-bits>
config-dvmrp router dvmrp
config-igmp router igmp
config-ospf router ospf <router-id>
config-rip router rip
config-vrrp router vrrp network <ip-address>/<mask-bits>
-exit
exit
exit
exit
exit
exit
exit
exit
exit
exit
vr-id <1~7> uplink-gateway <ip-address>
Ethernet Switch CLI Reference Guide
16
Page 17
Chapter 2 Privilege Level and Command Mode
2.3 Listing Available Commands
Use the help command to view the executable commands on the Switch. You must have the highest
privilege level in order to view all the commands. Follow these steps to create a list of supported
commands:
1 Log into the CLI. This takes you to the enable mode.
2 Type help and press [ENTER]. A list comes up which shows all the commands available in enable mode.
The example shown next has been edited for brevity’s sake.
sysname# help
Commands available:
help
logout
exit
history
enable <0-14>
enable <cr>
.
.
traceroute <ip|host-name> [vlan <vlan-id>][..]
traceroute help
ssh <1|2> <[user@]dest-ip> <cr>
ssh <1|2> <[user@]dest-ip> [command </>]
sysname#
3 Copy and paste the results into a text editor of your choice. This creates a list of all the executable
commands in the user and enable modes.
4 Type configure and press [ENTER]. This takes you to the config mode.
5 Type help and press [ENTER]. A list is displayed which shows all the commands available in config mode
and all the sub-commands. The sub-commands are preceded by the command necessary to enter
that sub-command mode. For example, the command name <name-str> as shown next, is preceded
by the command used to enter the config-vlan sub-mode: vlan <1-4094>.
sysname# help
.
.
no arp inspection log-buffer logs
no arp inspection filter-aging-time
no arp inspection <cr>
vlan <1-4094>
vlan <1-4094> name <name-str>
vlan <1-4094> normal <port-list>
vlan <1-4094> fixed <port-list>
6 Copy and paste the results into a text editor of your choice. This creates a list of all the executable
commands in config and the other submodes, for example, the config-vlan mode.
Ethernet Switch CLI Reference Guide
17
Page 18
CHAPTER 3
Initial Setup
This chapter identifies tasks you might want to do when you first configure the Switch.
3.1 Changing the Administrator Password
Note: It is recommended you change the default administrator password. You can encrypt
the password using the password encryption command. See Chapter 62 on page
239 for more information.
Use this command to change the administrator password.
admin-password <pw-string> <Confirm-string>
where <pw-string> may be 1-32 alphanumeric characters long.
sysname# configure
sysname(config)# admin-password t1g2y7i9 t1g2y7i9
3.2 Changing the Enable Password
Note: It is recommended you change the default enable password. You can encrypt the
password using the password encryption command. See Chapter 62 on page 239 for
more information.
Use this command to change the enable password.
password <password>
where <password> may be 1-32 alphanumeric characters long.
sysname# configure
sysname(config)# password k8s8s3dl0
Ethernet Switch CLI Reference Guide
18
Page 19
Chapter 3 Initial Setup
3.3 Prohibiting Concurrent Logins
By default, multiple CLI sessions are allowed via the console port or Telnet. See the User’s Guide for the
maximum number of concurrent sessions for your Switch. Use this command to prohibit concurrent
logins.
no multi-login
Console port has higher priority than Telnet. See Chapter 58 on page 221 for more
commands.
sysname# configure
sysname(config)# no multi-login
3.4 Changing the Management IP Address
The Switch has a different IP address in each VLAN. By default, the Switch has VLAN 1 with IP address
192.168.1.1 and subnet mask 255.255.255.0. Use this command in config-vlan mode to change the
management IP address in a specific VLAN.
ip address <ip> <mask>
This example shows you how to change the management IP address in VLAN 1 to 172.16.0.1 with subnet
mask 255.255.255.0.
sysname# configure
sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management 172.16.0.1 255.255.255.0
multi-login
Note: Afterwards, you have to use the new IP address to access the Switch.
3.5 Changing the Out-of-band Management IP Address
If your Switch has a MGMT port (also referred to as the out-of-band management port), then the Switch
can also be managed via this interface. By default, the MGMT port IP address is 192.168.0.1 and the
subnet mask is 255.255.255.0. Use this command in config mode to change the out-of-band
management IP address.
ip address <ip> <mask>
This example shows you how to change the out-of-band management IP address to 10.10.10.1 with
subnet mask 255.255.255.0 and the default gateway 10.10.10.254.
sysname# configure
sysname(config)# ip address 10.10.10.1 255.255.255.0
sysname(config)# ip address default-gateway 10.10.10.254
Ethernet Switch CLI Reference Guide
19
Page 20

Chapter 3 Initial Setup
3.6 Using Auto Configuration
Follow the steps below to set up configurations on the Switch, so you can load an auto configuration file
automatically from a TFTP server when you reboot the Switch.
Note: You need to set up configurations on a DHCP server and TFTP server first to use auto
configuration.
1 Use this command to enable auto configuration on the Switch.
auto-config
sysname# config
sysname(config)# auto-config
2 Use this command to enable the DHCP mode for auto configuration.
auto-config dhcp
sysname# config
sysname(config)# auto-config dhcp
3 Use this command to configure the Switch as a DHCP client.
ip address default-management dhcp-bootp
sysname# config
sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp
4 Use this command to enable DHCP option 60.
ip address default-management dhcp-bootp option-60
When you enable DHCP option 60, make sure you set up a Vendor Class Identifier. The Vendor Class
Identifier specifies the Zyxel switch that should receive the auto configuration file.
Skip this step if you are not enabling DHCP option 60.
sysname# config
sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp option-60
5 Use this command to define a Vendor Class Identifier for DHCP option 60.
ip address default-management dhcp-bootp option-60 class-id <class-id>
In this example, we use “ZyxelCorp”.
Skip this step if you don’t need to define a Vendor Class Identifier.
sysname# config
sysname(config)# vlan 1
sysname(config-vlan)# ip address default-management dhcp-bootp option-60
class-id ZyxelCorp
Ethernet Switch CLI Reference Guide
20
Page 21
Chapter 3 Initial Setup
6 Use this command to check the settings for auto configuration.
show running-config
GS2210# show running-config
Building configuration...
Current configuration:
vlan 1
name 1
normal ""
fixed 1-50
forbidden ""
untagged 1-50
ip address default-management dhcp-bootp
ip address default-management dhcp-bootp option-60 class-id ZyxelCorp
exit
pwr mode consumption
auto-config
7 You need to save the current configuration in a configuration file, so the Switch will load the auto
configuration files from the TFTP server automatically when rebooting
Use this command to save the current configuration in a configuration file.
write memory [<index>]
For [<index>], you can enter a value to save the current configuration to a specified configuration file.
1 is for Config 1, and 2 is for Config 2.
In this example, we save the current configuration to Config 1.
sysname# write memory 1
........................................................................
............................
8 Use this command to reboot the Switch.
reload config [1|2]
For [1|2], 1 is for Config 1, and 2 is for Config 2.
In this example, we load Config 1 to reboot the Switch.
Ethernet Switch CLI Reference Guide
21
Page 22
Chapter 3 Initial Setup
sysname# reload config 1
Do you really want to reboot system with configuration file 1? [y/N]y
Bootbase Version: V1.05 | 12/19/2013 16:57:54
DRAM calibration...PASSED
RAM: Size = 131072 Kbytes
ZyNOS Version: V4.50(AAHW.0)b3_20171020_1 | 10/20/2017 16:9:36
Press any key to enter debug mode within 1 second.
....................
(Compressed)
Version: GS2210, start: b4962430
Length: 16F0668, Checksum: 03AA
Compressed Length: 2EE424, Checksum: 87A5
Copyright (c) 1994 - 2017 Zyxel Communications Corp.
initialize mgmt, initialize switch, ethernet address: 00:19:cb:00:00:01
Initializing MSTP.............
Initializing VLAN Database...
Initializing IP Interface...
Initializing Advanced Applications...
Initializing Command Line Interface...
Initializing Web Interface...
Restore System Configuration...
Start Auto Configuration...
..............
Try to download and restore configuration file from TFTP://10.90.90.11/
TestConf2
Downloading....
Get the file TestConf2, length 289 bytes.
Restoring......
Auto-config processes successfully.
Press ENTER to continue...
9 Use this command to check whether the auto configuration file was loaded successfully.
Show auto-config
Mode: DHCP
State: Success
Filename: TFTP://10.90.90.11/TestConf2
3.7 Using Custom Default
Follow the steps below to set up configurations on the Switch, so you can load a customized default file
when you reboot the Switch.
1 Use this command to enable custom default on the Switch.
custom-default
sysname# config
sysname(config)# custom-default
Ethernet Switch CLI Reference Guide
22
Page 23
Chapter 3 Initial Setup
2 Use this command to save the current configuration settings permanently to a customized default file on
the Switch.
copy running-config custom-default
sysname# copy running-config custom-default
........................................................................
............................
3 Use this command to reboot the system and load a saved customized default file on the Switch.
reload custom-default
sysname# reload custom-default
Do you really want to restore system to custom default settings and
reboot?[y/N]y
.......
Bootbase Version: V1.05 | 12/19/2013 16:57:54
DRAM calibration...PASSED
RAM: Size = 131072 Kbytes
ZyNOS Version: V4.50(AAHW.0)b3_20171020_1 | 10/20/2017 16:9:36
Press any key to enter debug mode within 1 second.
....................
(Compressed)
Version: GS2210, start: b4962430
Length: 16F0668, Checksum: 03AA
Compressed Length: 2EE424, Checksum: 87A5
Copyright (c) 1994 - 2017 Zyxel Communications Corp.
initialize mgmt, initialize switch, ethernet address: 00:19:cb:00:00:01
Initializing MSTP.............
Initializing VLAN Database...
Initializing IP Interface...
Initializing Advanced Applications...
Initializing Command Line Interface...
Initializing Web Interface...
Restore System Configuration...
Press ENTER to continue...
3.8 Looking at Basic System Information
Use this command to look at general system information about the Switch.
show system-information
Ethernet Switch CLI Reference Guide
23
Page 24
Chapter 3 Initial Setup
This is illustrated in the following example.
sysname# show system-information
Product Model : sysname
System Name : sysname
System Mode : Standalone
System Contact :
System Location :
System up Time : 98:26:28 (151f8939 ticks)
Ethernet Address : 00:19:cb:00:00:02
Bootbase Version : V1.02 | 08/27/2014
ZyNOS F/W Version : V4.20(AASS.0)b3 | 09/24/2014
Config Boot Image : 1
Current Boot Image : 1
RomRasSize : 8336318
sysname#
See Chapter 106 on page 365 for more information about these attributes.
3.9 Looking at the Operating Configuration
Use this command to look at the current operating configuration.
show running-config
This is illustrated in the following example.
sysname# show running-config
Building configuration...
Current configuration:
vlan 1
name 1
normal ""
fixed 1-52
forbidden ""
untagged 1-52
ip address 192.168.1.1 255.255.255.0
exit
interface route-domain 192.168.1.1/24
exit
pwr mode consumption
Ethernet Switch CLI Reference Guide
24
Page 25
PART II
Reference A-G
AAA Commands (27)
ARP Commands (32)
ARP Inspection Commands (34)
ARP Learning Commands (39)
Auto Configuration Commands (40)
Bandwidth Commands (42)
Broadcast Storm Commands (46)
CFM Commands (49)
Certificates Commands (58)
Classifier Commands (60)
Cluster Commands (64)
CLV Commands (67)
Custom Default Commands (73)
Date and Time Commands (74)
Data Center Bridging Commands (77)
DHCP Commands (85)
DHCP Snooping & DHCP VLAN Commands (90)
25
Page 26

DiffServ Commands (94)
Display Commands (95)
DVMRP Commands (96)
Error Disable and Recovery Commands (98)
Ethernet OAM Commands (102)
External Alarm Commands (107)
GARP Commands (109)
Green Ethernet Commands (111)
GVRP Commands (115)
26
Page 27
Use these commands to configure authentication, authorization and accounting on the Switch.
4.1 Command Summary
The following section lists the commands for this feature.
Table 9 aaa authentication Command Summary
COMMAND DESCRIPTION M P
show aaa authentication
show aaa authentication enable
aaa authentication enable
<method1> [<method2> ...]
no aaa authentication enable
show aaa authentication login
aaa authentication login
<method1> [<method2> ...]
no aaa authentication login
CHAPTER 4
AAA Commands
Displays what methods are used for authentication. E 3
Displays the authentication method(s) for checking
privilege level of administrators.
Specifies which method should be used first, second, and
third for checking privileges.
method: enable, radius, or tacacs+.
Resets the method list for checking privileges to its default
value.
Displays the authentication methods for administrator login
accounts.
Specifies which method should be used first, second, and
third for the authentication of login accounts.
method: local, radius, or tacacs+.
Resets the method list for the authentication of login
accounts to its default value.
E3
C14
C14
E3
C14
C14
Table 10 Command Summary: aaa accounting
COMMAND DESCRIPTION M P
show aaa accounting
show aaa accounting update
aaa accounting update periodic
<1-2147483647>
no aaa accounting update
show aaa accounting commands
aaa accounting commands
<privilege> stop-only tacacs+
[broadcast]
Ethernet Switch CLI Reference Guide
Displays accounting settings configured on the Switch. E 3
Display the update period setting on the Switch for
accounting sessions.
Sets the update period (in minutes) for accounting
sessions. This is the time the Switch waits to send an update
to an accounting server after a session starts.
Resets the accounting update interval to the default
value.
Displays accounting settings for recording command
events.
Enables accounting of command sessions and specifies
the minimum privilege level (0-14) for the command
sessions that should be recorded. Optionally, sends
accounting information for command sessions to all
configured accounting servers at the same time.
E3
C13
C13
E3
C13
27
Page 28
Chapter 4 AAA Commands
Table 10 Command Summary: aaa accounting (continued)
COMMAND DESCRIPTION M P
no aaa accounting commands
show aaa accounting dot1x
aaa accounting dot1x <startstop|stop-only>
<radius|tacacs+> [broadcast]
no aaa accounting dot1x
show aaa accounting exec
aaa accounting exec <startstop|stop-only>
<radius|tacacs+> [broadcast]
no aaa accounting exec
show aaa accounting system
aaa accounting system
<radius|tacacs+> [broadcast]
no aaa accounting system
Disables accounting of command sessions on the Switch. C 13
Displays accounting settings for recording IEEE 802.1x
session events.
Enables accounting of IEEE 802.1x authentication sessions
and specifies the mode and protocol method. Optionally,
sends accounting information for IEEE 802.1x
authentication sessions to all configured accounting
servers at the same time.
Disables accounting of IEEE 802.1x authentication sessions
on the Switch.
Displays accounting settings for recording administrative
sessions via SSH, Telnet or the console port.
Enables accounting of administrative sessions via SSH,
Telnet and console port and specifies the mode and
protocol method. Optionally, sends accou nting
information for administrative sessions via SSH, Telnet and
console port to all configured accounting servers at the
same time.
Disables accounting of administrative sessions via SSH,
Telnet or console on the Switch.
Displays accounting settings for recording system events,
for example system shut down, start up, accounting
enabled or accounting disabled.
Enables accounting of system events and specifies the
protocol method. Optionally, sends accou nting
information for system events to all configured accounting
servers at the same time.
Disables accounting of system events on the Switch. C 13
E3
C13
C13
E3
C13
C13
E3
C13
Table 11 aaa authorization Command Summary
COMMAND DESCRIPTION M P
show aaa authorization
show aaa authorization dot1x
show aaa authorization exec
aaa authorization console
aaa authorization dot1x radius
aaa authorization exec
<radius|tacacs+>
no aaa authorization console
Displays authorization settings configured on the Switch. E 3
Displays the authorization method used to allow an IEEE
802.1x client to have different bandwidth limit or VLAN ID
assigned via the external server.
Displays the authorization method used to allow an
administrator which logs in the Switch through Telnet or SSH
to have different access privilege level assigned via the
external server.
Enables authorization of allowing an administrator which
logs in the Switch through the console port to have
different access privilege level assigned via the external
server.
Enables authorization for IEEE 802.1x clients using RADIUS. C 14
Specifies which method (radius or tacacs+) should be
used for administrator authorization.
Disables authorization of allowing an administrator which
logs in the Switch through the console port to have
different access privilege level assigned via the external
server.
E3
E3
C14
C14
C14
Ethernet Switch CLI Reference Guide
28
Page 29
Chapter 4 AAA Commands
Table 11 aaa authorization Command Summary (continued)
COMMAND DESCRIPTION M P
no aaa authorization dot1x
no aaa authorization exec
Disables authorization of allowing an IEEE 802.1x client to
have different bandwidth limit or VLAN ID assigned via the
external server.
Disables authorization of allowing an administrator which
logs in the Switch through Telnet or SSH to have different
access privilege level assigned via the external server.
C14
C14
Ethernet Switch CLI Reference Guide
29
Page 30
Use these commands to configure anti-Arpscan on the Switch.
5.1 Anti-Arpscan Overview
Address Resolution Protocol (ARP), RFC 826, is a protocol used to convert a network-layer IP address to a
link-layer MAC address. ARP scan is used to scan the network of a certain interface for alive hosts. It
shows the IP address and MAC addresses of all hosts found. Hackers could use ARP scan to find targets
in your network. Anti-arpscan is used to detect unusual ARP scan activity and block suspicious hosts or
ports.
Unusual ARP scan activity is determined by port and host thresholds that you set. A port threshold is
determined by the number of packets received per second on the port. If the received packet rate is
over the threshold, then the port is put into an Err-Disable state. You can recover the normal state of the
port manually if this happens and after you identify the cause of the problem.
CHAPTER 5
Anti-Arpscan
A host threshold is determined by the number of ARP-request packets received per second. There is a
global threshold rate for all hosts. If the rate of a host is over the threshold, then that host is blocked by
using a MAC address filter. A blocked host is released automatically after the MAC aging time expires.
Note: A port-based threshold must be larger than the host-based threshold or the host-based
threshold will not work.
5.2 Command Summary
The following section lists the commands for this feature.
Table 12 anti arpscan Command Summary
COMMAND DESCRIPTION M P
anti arpscan
anti arpscan host threshold <2-
100>
anti arpscan port threshold <2255>
anti arpscan trust host <ip-
address> <mask> [ name <name> ]
Enables Anti-arpscan on the Switch. C 13
Sets the maximum number of ARP-request packets
allowed by a host before it is blocked. If the rate of a host is
over the threshold, then that host is blocked by using a
MAC address filter. A blocked host is released
automatically after the MAC aging time expires.
Sets the maximum number of packets per second allowed
on the port before it is blocked.
Creates a trusted host identified by IP address and subnet
mask.
Anti-arpscan is not performed on trusted hosts.
C13
C13
C13
Ethernet Switch CLI Reference Guide
30
Page 31

Chapter 5 Anti-Arpscan
Table 12 anti arpscan Command Summary (continued)
COMMAND DESCRIPTION M P
clear anti arpscan host
clear anti arpscan host
Unblocks all hosts. E 13
Unblocks all hosts connected to the specified port(s). E 13
interface port-channel <portlist>
interface port-channel <port-
Enters config-interface mode for the specified port(s). C 13
list>
anti arpscan trust
no anti arpscan
no anti arpscan host threshold
no anti arpscan port threshold
no anti arpscan trust host <ip-
Sets the port as a trusted port. This prevents the port from
being shutdown due to receiving too many ARP
messages.
Disables Anti-arpscan on the Switch. C 13
Resets the host threshold to its default value. C 13
Resets the port threshold to its default value. C 13
Removes a trusted host. C 13
C13
address> <mask>
show anti arpscan
show anti arpscan host
Displays what ports are trusted and are forwarding traffic
or are disabled.
Displays the host that has been blocked. E 3
E3
Ethernet Switch CLI Reference Guide
31
Page 32

Use these commands to look at IP-to-MAC address mapping(s).
6.1 Command Summary
The following section lists the commands for this feature.
Table 13 arp Command Summary
COMMAND DESCRIPTION M P
arp aging-time <60-1000000>
arp name <name> ip <ip-address>
mac <mac-addr> vlan <vlan-id>
interface port-channel <port-
list>
arp name <name> ip <ip-address>
mac <mac-addr> vlan <vlan-id>
interface port-channel <port-
list> inactive
no arp ip <ip-address> mac <mac-
addr> vlan <vlan-id>
no arp ip <ip-address> mac <mac-
addr> vlan <vlan-id> inactive
show ip arp
show ip arp count
clear ip arp
clear ip arp interface port-
channel <port-list>
clear ip arp ip <ip-address>
CHAPTER 6
ARP Commands
Sets how long dynamically learned ARP entries remain in
the ARP table before they age out (and must be
relearned).
Creates a static ARP entry which will not age out. C 13
Creates a static ARP entry but disables it. C 13
Deletes a static ARP entry from the ARP table. C 13
Enables the specified static ARP entry. C 13
Displays the ARP table. E 3
Displays the number of ARP entries in the ARP table. E 3
Removes all of the dynamic entries from the ARP table. E 13
Removes the dynamic entries learned on the specified
port.
Removes the dynamic entries learned with the specified IP
address.
C13
E13
E13
Ethernet Switch CLI Reference Guide
32
Page 33

Chapter 6 ARP Commands
6.2 Command Examples
This example creates a static ARP entry and shows the ARP table on the Switch.
sysname# config
sysname(config)# arp name test ip 192.168.1.99 mac 00:c5:d8:01:23:45 vlan
1 interface port-channel 3
sysname(config)# exit
sysname# show ip arp
Index IP MAC VLAN Port Age(s) Type
1 192.168.1.1 00:19:cb:37:00:49 1 CPU 0 static
2 192.168.1.99 00:c5:d8:01:23:45 1 3 0 sta tic
3 192.168.2.1 00:19:cb:37:00:49 465 CPU 0 static
sysname#
The following table describes the labels in this screen.
Table 14 show ip arp
LABEL DESCRIPTION
Index This field displays the index number.
IP This field displays the learned IP address of the device.
MAC This field displays the MAC address of the device.
VLAN This field displays the VLAN to which the device belongs.
Port This field displays the number of the port from which the IP address was learned.
CPU indicates this IP address is the Switch’s management IP address.
Age(s) This field displays how long the entry remains valid.
Type This field displays how the entry was learned.
dynamic: The Switch learned this entry from ARP packets.
Ethernet Switch CLI Reference Guide
33
Page 34

ARP Inspection Commands
Use these commands to filter unauthorized ARP packets in your network.
7.1 Command Summary
The following section lists the commands for this feature.
Table 15 arp inspection Command Summary
COMMAND DESCRIPTION M P
arp inspection
no arp inspection
show arp inspection
clear arp inspection statistics
clear arp inspection statistics
vlan <vlan-list>
show arp inspection statistics
show arp inspection statistics
vlan <vlan-list>
CHAPTER 7
Enables ARP inspection on the Switch. You still have to
enable ARP inspection on specific VLAN and specify
trusted ports.
Disables ARP inspection on the Switch. C 13
Displays ARP inspection configuration details. E 3
Removes all ARP inspection statistics on the Switch. E 3
Removes ARP inspection stat istics for the specified
VLAN(s).
Displays all ARP inspection statistics on the Switch. E 3
Displays ARP inspection statistics for the specified VLAN(s). E 3
C13
E3
Table 16 Command Summary: arp inspection filter
COMMAND DESCRIPTION M P
show arp inspection filter
[<mac-addr>] [vlan <vlan-id>]
clear arp inspection filter
arp inspection filter-aging-time
<1-2147483647>
arp inspection filter-aging-time
none
no arp inspection filter-agingtime
Ethernet Switch CLI Reference Guide
Displays the current list of MAC address filters that were
created because the Switch identified an unauthorized
ARP packet. Optionally, lists MAC address filters based on
the MAC address or VLAN ID in the filter.
Deletes all ARP inspection filters from the Switch. E 13
Specifies how long (1-2147483647 seconds) MAC address
filters remain in the Switch after the Switch identifies an
unauthorized ARP packet. The Switch automatically
deletes the MAC address filter af terwards.
Specifies the MAC address filter to be permanent. C 13
Resets how long (1-2147483647 seconds) the MAC address
filter remains in the Switch after the Switch identifies an
unauthorized ARP packet to the default value.
E3
C13
C13
34
Page 35

Chapter 7 ARP Inspection Commands
Table 17 Command Summary: arp inspection log
COMMAND DESCRIPTION M P
show arp inspection log
clear arp inspection log
arp inspection log-buffer
entries <0-1024>
arp inspection log-buffer logs
<0-1024> interval <0-86400>
no arp inspection log-buffer
entries
no arp inspection log-buffer
logs
Displays the log settings configured on the Switch. It also
displays the log entries recorded on the Switch.
Delete all ARP inspection log entries from the Switch. E 13
Specifies the maximum number (1-1024) of log messages
that can be generated by ARP packets and not sent to
the syslog server.
If the number of log messages in the Switch exceeds this
number, the Switch stops recording log messages and
simply starts counting the number of entries that were
dropped due to unavailable buffer.
Specifies the number of syslog messages that can be sent
to the syslog server in one batch and how often (1-86400
seconds) the Switch sends a batch of syslog messages to
the syslog server.
Resets the maximum number (1-1024) of log messages that
can be generated by ARP packets and not sent to the
syslog server to the default value.
Resets the maximum number of syslog messages the
Switch can send to the syslog server in one batch to the
default value.
E3
C13
C13
C13
C13
Table 18 Command Summary: interface arp inspection
COMMAND DESCRIPTION M P
show arp inspection interface
port-channel <port-list>
interface port-channel <port-
Displays the ARP inspection settings for the specified
port(s).
Enters config-interface mode for the specified port(s). C 13
E3
list>
arp inspection trust
no arp inspection trust
Sets the port to be a trusted port for arp inspection. The
Switch does not discard ARP packets on trusted ports for
any reason.
Disables this port from being a trusted port for ARP
inspection.
C13
C13
Table 19 Command Summary: arp inspection vlan
COMMAND DESCRIPTION M P
show arp inspection vlan <vlan-
Displays ARP inspection settings for the specified VLAN(s). E 3
list>
arp inspection vlan <vlan-list>
no arp inspection vlan <vlan-
Enables ARP inspection on the specified VLAN(s). C 13
Disables ARP inspection on the specified VLAN(s). C 13
list>
arp inspection vlan <vlan-list>
logging [all|none|permit|deny]
no arp inspection vlan <vlan-
list> logging
Enables logging of ARP inspection events on the specified
VLAN(s). Optionally specifies which types of events to log.
Disables logging of messages generated by ARP
inspection for the specified VLAN(s).
C13
C13
Ethernet Switch CLI Reference Guide
35
Page 36

Chapter 7 ARP Inspection Commands
7.2 Command Examples
This example looks at the current list of MAC address filters that were created because the Switch
identified an unauthorized ARP packet. When the Switch identifies an unauthorized ARP packet, it
automatically creates a MAC address filter to block traffic from the source MAC address and source
VLAN ID of the unauthorized ARP packet.
sysname# show arp inspection filter
Filtering aging timeout : 300
MacAddress VLAN Port Expiry (sec) Reason
----------------- ---- ----- ------------ ------------- Total number of bindings: 0
The following table describes the labels in this screen.
Table 20 show arp inspection filter
LABEL DESCRIPTION
Filtering aging timeout This field displays how long the MAC address filters remain in the Switch after the Switch
identifies an unauthorized ARP packet. The Switch automatically deletes the MAC
address filter afterwards.
MacAddress This field displays the source MAC address in the MAC address filter.
VLAN This field displays the source VLAN ID in the MAC address filter.
Port This field displays the source port of the discarded AR P packet .
Expiry (sec) This field displays how long (in seconds) the MAC address filter remains in the Switch.
You can also delete the record manually (Delete).
Reason This field displays the reason the ARP packet was discarded.
MAC+VLAN: The MAC address and VLAN ID were not in the binding table.
IP: The MAC address and VLAN ID were in the binding table, but the IP address was not
valid.
Port: The MAC address, VLAN ID, and IP address were in the binding table, but the port
number was not valid.
This example looks at log messages that were generated by ARP packets and that have not been sent
to the syslog server yet.
sysname# show arp inspection log
Total Log Buffer Size : 32
Syslog rate : 5 entries per 1 seconds
Port Vlan Sender MAC Sender IP Pkts Reason
Time
---- ---- ----------------- --------------- ---- ---------- ----
-------------------- Total number of logs: 0
Ethernet Switch CLI Reference Guide
36
Page 37

Chapter 7 ARP Inspection Commands
The following table describes the labels in this screen.
Table 21 show arp inspection log
LABEL DESCRIPTION
Total Log Buffer Size This field displays the maximum number (1-1024) of log messages that were
Syslog rate This field displays the maximum number of syslog messages the Switch can send to
Port This field displays the source port of the ARP packet.
Vlan This field displays the source VLAN ID of the ARP packet.
Sender MAC This field displays the source MAC address of the ARP packet.
Sender IP This field displays the source IP address of the ARP packet.
Pkts This field displays the number of ARP packets that were consolidated into this log
Reason This field displays the reason the log message was generated.
generated by ARP packets and have not been sent to the syslog server yet.
If the number of log messages in the Switch exceeds this number, the Switch stops
recording log messages and simply starts counting the number of entries that were
dropped due to unavailable buffer.
the syslog server in one batch. This number is ex pressed as a rate because the batch
frequency is determined by the Log Interval.
message. The Switch consolidates identical log messages generated by ARP
packets in the log consolidation interval into one log message.
dhcp deny: An ARP packet was discarded because it violated a dynamic binding
with the same MAC address and VLAN ID.
static deny: An ARP packet was discarded because it violated a static binding with
the same MAC address and VLAN ID.
deny: An ARP packet was discarded because there were no bindings with the same
MAC address and VLAN ID.
static permit: An ARP packet was forwarded because it matched a static binding.
dhcp permit: An ARP packet was forwarded because it matched a dynamic
binding.
Time This field displays when the log message was generated.
Total number of logs This field displays the number of log messages that were generated by ARP packets
and that have not been sent to the syslog server yet. If one or more log messages
are dropped due to unavailable buffer, there is an entry called overflow with the
current number of dropped log messages.
This example displays whether ports are trusted or untrusted ports for ARP inspection.
sysname# show arp inspection interface port-channel 1
Interface Trusted State Rate (pps) Burst Interval
--------- ------------- ---------- ------------- 1 Untrusted 15 1
Ethernet Switch CLI Reference Guide
37
Page 38

Chapter 7 ARP Inspection Commands
The following table describes the labels in this screen.
Table 22 show arp inspection interface port-channel
LABEL DESCRIPTION
Interface This field displays the port number. If you configure the * port, the settings are applied
Trusted State This field displays whether this port is a trusted port (Trusted) or an untrusted port
Rate (pps) Thi s field displays the maximum number for DHCP packets that the Switch receives from
Burst Interval This field displays the length of time over which the rate of ARP packets is monitored for
to all of the ports.
(Untrusted).
Trusted ports are connected to DHCP servers or other switches, and the Switch discards
DHCP packets from trusted ports only if the rate at which DHCP packets arrive is too
high.
each port each second. The Switch discards any additional DHCP packets.
each port. For example, if the Rate is 15 pps and the burst interval is 1 second, then the
Switch accepts a maximum of 15 ARP packets in every one-second interval. If the burst
interval is 5 seconds, then the Switch accepts a maximum of 75 ARP packets in every
five-second interval.
Ethernet Switch CLI Reference Guide
38
Page 39

ARP Learning Commands
Use these commands to configure how the Switch updates the ARP table.
8.1 Command Summary
The following section lists the commands for this feature.
Table 23 arp-learning Command Summary
COMMAND DESCRIPTION M P
interface port-channel <portlist>
arp-learning <arpreply|gratuitous-arp|arprequest>
no arp-learning
CHAPTER 8
Enters config-interface mode for the specified port(s). C 13
Sets the ARP learning mode the Switch uses on the port.
arp-reply: the Switch updates the ARP table only with
the ARP replies to the ARP requests sent by the Switch.
gratuitous-arp: the Switch updates its ARP table with
either an ARP reply or a gratuitous ARP request. A
gratuitous ARP is an ARP request in which both the source
and destination IP address fields are set to the IP address of
the device that sends this request and the destination
MAC address field is set to the broadcast address.
arp-request: the Switch updates the ARP table with both
ARP replies, gratuitous ARP requests and ARP requests.
Resets the ARP learning mode to its default setting (arp-
reply).
C13
C13
8.2 Command Examples
This example changes the ARP learning mode on port 8 from arp-reply to arp-request.
sysname# configure
sysname(config)# interface port-channel 8
sysname(config-interface)# arp-learning arp-request
Ethernet Switch CLI Reference Guide
39
Page 40

Auto Configuration
Use these commands to configure auto configuration on the Switch.
9.1 Auto Configuration Overview
The Switch can download a pre-saved auto configuration file automatically when you reboot the
Switch using the DHCP or HTTPS mode. This will overwrite the running configuration stored in the Switch’s
RAM instead of the startup configuration stored in the Switch’s flash memory.
You can use the DHCP mode to load an auto configuration file from a TFTP server automatically when
you reboot the Switch. The Switch must have a dynamic IP address assigned by a DHCP server. Also,
make sure the Switch can communicate with the TFTP server.
CHAPTER 9
Commands
Note: You need to set up configurations on a DHCP server and TFTP server first to use auto
configuration.
9.2 Command Summary
The following section lists the commands for this feature.
Table 24 auto-config Command Summary
COMMAND DESCRIPTION M P
auto-config
no auto-config
auto-config <dhcp | https>
Enables auto configuration. When auto configuration is
enabled, the Switch can receive an auto configuration
file.
Disables auto configuration. C 14
Selects the DHCP or HTTPS mode for auto configuration.
dhcp: Enables the DHCP mode for auto configuration.
When auto configuration DHCP is enabled, the Switch can
receive an auto configuration file from a TFTP server. The
location of the TFTP server is provided by a DHCP server.
https: Enables the HTTPS mode for auto configuration.
When auto configuration HTTPS is enabled, the Switch will
use the URL you specified using the auto-config url
command to access a web server and download the
auto configuration file using HTTPS.
C14
C14
Ethernet Switch CLI Reference Guide
40
Page 41

Chapter 9 Auto Configuration Commands
Table 24 auto-config Command Summary (continued)
COMMAND DESCRIPTION M P
auto-config url <https://host/
filename>
auto-config vlan <vlan-id>
show auto-config
See Chapter 97 on page 347 for the commands to enable and disable DHCP option 60.
9.3 Command Examples
Types the URL that can be used to access and download
the auto configuration file from a web server using HTTPS.
For example, https://
webserverIPaddressconfigfilename.cfg.
Enters the VLAN ID of the DHCP server that assigns the TF TP
server IP address and auto configuration file name to the
Switch.
The following information is displayed:
• The mode that is used for auto configuration.
• The status to see whether an auto configuration file is
successfully loaded to the Switch after you reboot the
Switch.
• The name of the auto configuration file that is loaded
after you reboot the Switch.
C14
C14
E3
See Section 3.6 on page 20 for an example of how to configure auto configuration using the DHCP
mode on the Switch.
Ethernet Switch CLI Reference Guide
41
Page 42

CHAPTER 10
Bandwidth Commands
Use these commands to configure the maximum allowable bandwidth for incoming or outgoing traffic
flows on a port.
Note: Bandwidth management implementation differs across Switch models.
• Some models use a single command (bandwidth-limit ingress) to control the incoming rate of
traffic on a port.
• Other models use two separate commands (bandwidth-limit cir and bandwidth-limit pir) to
control the Committed Information Rate (CIR) and the Peak Information Rate (PIR) allowed on a port.
The CIR and PIR should be set for all ports that use the same uplink bandwidth. If the CIR is reached,
packets are sent at the rate up to the PIR. When network congestion occurs, packets through the
ingress port exceeding the CIR will be marked for drop.
Note: The CIR should be less than the PIR.
See Section 10.2 on page 43 and Section 10.3 on page 44 for examples.
See also Chapter 94 on page 335 for information on how to use trTCM (Two Rate Three Color Marker) to
control traffic flow.
10.1 Command Summary
The following table describes user-input values available in multiple commands for this feature.
Table 25 User-input Values: running-config
COMMAND DESCRIPTION
port-list
rate
The following section lists the commands for this feature.
Table 26 Command Summary: bandwidth-control & bandwidth-limit
COMMAND DESCRIPTION M P
show interfaces config <portlist> bandwidth-control
bandwidth-control
no bandwidth-control
interface port-channel <port-
list>
The port number or a range of port numbers that you want to configure.
The rate represents a bandwidth limit. Different models support different rate limiting
incremental steps. See your User’s Guide for more information.
Displays the current settings for bandwidth control on the
specified ports.
Enables bandwidth control on the Switch. C 13
Disables bandwidth control on the Switch. C 13
Enters subcommand mode for configuring the specified
ports.
E3
C13
Ethernet Switch CLI Reference Guide
42
Page 43

Chapter 10 Bandwidth Commands
Table 26 Command Summary: bandwidth-control & bandwidth-limit (continued)
COMMAND DESCRIPTION M P
bandwidth-limit ingress
bandwidth-limit ingress
<rate>
bandwidth-limit egress
bandwidth-limit egress
<rate>
no bandwidth-limit ingress
no bandwidth-limit egress
bandwidth-limit cir
bandwidth-limit cir <rate>
Enables bandwidth limits for incoming traffic on the port(s). C 13
Sets the maximum bandwidth allowed for incoming traffic
on the port(s).
Enables bandwidth limits for outgoing traffic on the port(s). C 13
Sets the maximum bandwidth allowed for outgoing traffic
on the port(s).
Disables ingress bandwidth limits on the specified port(s). C 13
Disables egress bandwidth limits on the specified port(s). C 13
Enables commit rate limits on the specified port(s). C 13
Sets the guaranteed bandwidth allowed for the incoming
traffic flow on a port. The commit rate should be less than
the peak rate. The sum of commit rates cannot be greater
than or equal to the uplink bandwidth.
C13
C13
C13
Note: The sum of CIRs cannot be greater than or
equal to the uplink bandwidth.
bandwidth-limit pir
bandwidth-limit pir <rate>
no bandwidth-limit cir
no bandwidth-limit pir
Enables peak rate limits on the specified port(s). C 13
Sets the maximum bandwidth allowed for the incoming
traffic flow on the specified port(s).
Disables commit rate limits on the specified port(s). C 13
Disables peak rate limits on the specified port(s). C 13
C13
10.2 Command Examples: ingress
This example sets the outgoing traffic bandwidth limit to 5000 Kbps and the incoming traffic bandwidth
limit to 4000 Kbps for port 1.
sysname# configure
sysname(config)# bandwidth-control
sysname(config)# interface port-channel 1
sysname(config-interface)# bandwidth-limit egress 5000
sysname(config-interface)# bandwidth-limit ingress 4000
sysname(config-interface)# exit
sysname(config)# exit
This example deactivates the outgoing bandwidth limit on port 1.
sysname# configure
sysname(config)# interface port-channel 1
sysname(config-interface)# no bandwidth-limit egress
sysname(config-interface)# exit
sysname(config)# exit
Ethernet Switch CLI Reference Guide
43
Page 44

Chapter 10 Bandwidth Commands
10.3 Command Examples: cir & pir
This example sets the guaranteed traffic bandwidth limit on port 1 to 4000 Kbps and the maximum traffic
bandwidth limit to 5000 Kbps for port 1.
sysname# configure
sysname(config)# bandwidth-control
sysname(config)# interface port-channel 1
sysname(config-interface)# bandwidth-limit cir
sysname(config-interface)# bandwidth-limit cir 4000
sysname(config-interface)# bandwidth-limit pir
sysname(config-interface)# bandwidth-limit pir 5000
sysname(config-interface)# exit
sysname(config)# exit
This example displays the bandwidth limits configured on port 1.
sysname# show running-config interface port-channel 1 bandwidth-limit
Building configuration...
Current configuration:
interface port-channel 1
bandwidth-limit cir 4000
bandwidth-limit cir
bandwidth-limit pir 5000
bandwidth-limit pir
Ethernet Switch CLI Reference Guide
44
Page 45

Use these commands to configure BPDU guard on the Switch.
11.1 BPDU Guard Overview
A BPDU (Bridge Protocol Data Units) is a data frame that contains information about STP. STP-aware
switches exchange BPDUs periodically.
The BPDU guard feature allows you to prevent any new STP-aware switch from connecting to an existing
network and causing STP topology changes in the network. If there is any BPDU detected on the port(s)
on which BPDU guard is enabled, the Switch disables the port(s) automatically. You can then enable the
port(s) manually via the web configurator or the commands. With error-disable recovery, you can also
have the port(s) become active after a certain time interval.
CHAPTER 11
BPDU Guard
11.2 Command Summary
The following section lists the commands for this feature.
Table 27 bpduguard Command Summary
COMMAND DESCRIPTION M P
bpduguard
no bpduguard
interface port-channel <port-
list>
bpduguard
no bpduguard
show bpdupguard
Enabled BPDU guard on the Switch. C 13
Disables BPDU guard on the Switch. C 13
Enters config-interface mode for the specified port(s). C 13
Enabled BPDU guard on the port(s). C 13
Disables BPDU guard on the port(s). C 13
Displays whether BPDU guard is enabled on the Switch and
the port status.
E3
Ethernet Switch CLI Reference Guide
45
Page 46

CHAPTER 12
Broadcast Storm Commands
Use these commands to limit the number of broadcast, multicast and destination lookup failure (DLF)
packets the Switch receives per second on the ports.
Note: Broadcast storm control implementation differs across Switch models.
• Some models use a single command (bmstorm-limit) to control the combined rate of broadcast,
multicast and DLF packets accepted on Switch ports.
• Other models use three separate commands (broadcast-limit, multicast-limit, dlf-limit) to
control the number of individual types of packets accepted on Switch ports.
See Section 12.2 on page 47 and Section 12.3 on page 47 for examples.
12.1 Command Summary
The following table describes user-input values available in multiple commands for this feature.
Table 28 User-input Values: broadcast-limit, multicast-limit & dlf-limit
COMMAND DESCRIPTION
pkt/s
The following section lists the commands for this feature.
Table 29 Command Summary: storm-control, bmstorm-limit, and bstorm-control
COMMAND DESCRIPTION M P
show interfaces config <portlist> bstorm-control
storm-control
no storm-control
interface port-channel <port-
list>
bmstorm-limit
bmstorm-limit <rate>
no bmstorm-limit
broadcast-limit
Specifies the maximum number of packets per second accepted by a Switch port.
Displays the current settings for broadcast storm control on
the specified ports.
Enables broadcast storm control on the Switch. C 13
Disables broadcast storm control on the Switch. C 13
Enters subcommand mode for configuring the specified
ports.
Enables broadcast storm control on the specified port(s). C 13
Specifies the maximum rate at which the Switch receives
broadcast, multicast, and destination lookup failure (DLF)
packets on the specified port(s).
Different models support different rate limiting incremental
steps. See your User’s Guide for more information.
Disables broadcast storm control on the specified port(s). C 13
Enables the broadcast packet limit on the specified
port(s).
E3
C13
C13
C13
Ethernet Switch CLI Reference Guide
46
Page 47

Chapter 12 Broadcast Storm Commands
Table 29 Command Summary: storm-control, bmstorm-limit, and bstorm-control (continued)
COMMAND DESCRIPTION M P
broadcast-limit <pkt/s>
no broadcast-limit
multicast-limit
multicast-limit <pkt/s>
no multicast-limit
dlf-limit
dlf-limit <pkt/s>
no dlf-limit
Specifies the maximum number of broadcast packets the
Switch accepts per second on the specified port(s).
The Switch will generate a trap and/or log when the
actual rate is higher than the specified threshold.
Disables broadcast packet limit no the specified port(s). C 13
Enables the multicast packet limit on the specified port(s). C 13
Specifies the maximum number of multicast packets the
Switch accepts per second on the specified port(s).
The Switch will generate a trap and/or log when the
actual rate is higher than the specified threshold.
Disables multicast packet limit on the specified port(s). C 13
Enables the DLF packet limit on the specified port(s). C 13
Specifies the maximum number of DLF packets the Switch
accepts per second on the specified port (s).
Disables DLF packet limits no the specified port(s). C 13
C13
C13
C13
12.2 Command Example: bmstorm-limit
This example enables broadcast storm control on port 1 and limits the combined maximum rate of
broadcast, multicast and DLF packets to 128 Kbps.
sysname# configure
sysname(config)# storm-control
sysname(config)# interface port-channel 1
sysname(config-interface)# bmstorm-limit
sysname(config-interface)# bmstorm-limit 128
sysname(config-interface)# exit
sysname(config)# exit
12.3 Command Example: broadcast-limit, multicast-limit & dlf-limit
This example enables broadcast storm control on the Switch, and configures port 1 to accept up to:
• 128 broadcast packets per second,
• 256 multicast packets per second,
Ethernet Switch CLI Reference Guide
47
Page 48

Chapter 12 Broadcast Storm Commands
• 64 DLF packets per second.
sysname# configure
sysname(config)# storm-control
sysname(config)# interface port-channel 1
sysname(config-interface)# broadcast-limit
sysname(config-interface)# broadcast-limit 128
sysname(config-interface)# multicast-limit
sysname(config-interface)# multicast-limit 256
sysname(config-interface)# dlf-limit
sysname(config-interface)# dlf-limit 64
sysname(config)# exit
sysname# show interfaces config 1 bstorm-control
Broadcast Storm Control Enabled: Yes
Port Broadcast|Enabled Multicast|Enabled DLF-Limit|Enabled
1 128 pkt/s|Yes 256 pkt/s|Yes 64 pkt/s|Yes
Ethernet Switch CLI Reference Guide
48
Page 49

Use these commands to configure the Connectivity Fault Management (CFM) on the Switch.
CPE
Service Provider Network
CPE
13.1 CFM Overview
The route between two users may go through aggregated switches, routers and/or DSLAMs owned by
independent organizations. A connectivity fault point generally takes time to discover and impacts
subscribers’ network access. IEEE 802.1ag is a Connectivity Fault Management (CFM) specification
which allows network administrators to identify and manage connection faults in order to ease
management and maintenance. Through discovery and verification of the path, CFM can detect and
analyze connectivity faults in bridged LANs.
The figure shown below is an example of a connection fault between switches in the service provider’s
network. CFM can be used to identify and management this kind of connection problem.
CHAPTER 13
CFM Commands
Figure 1 Connectivity Fault Example
13.1.1 How CFM Works
CFM sends pro-active Connectivity Check (CC) packets between two CFM-aware devices in the same
MD (Maintenance Domain) network. An MA (Maintenance Association) defines a VLAN and associated
ports on the device under an MD level. In this MA, a port can be an MEP (Maintenance End Point) port
or an MIP (Maintenance Intermediate Point) port.
•MEP port - has the ability to send pro-active connectivity check (CC) packets and get other MEP
port information from neighbor switches’ CC packets within an MA.
•MIP port - only forwards the CC packets.
Ethernet Switch CLI Reference Guide
49
Page 50

Chapter 13 CFM Commands
C
(port 17, MIP)
(port 2, MEP)
(port 18, MIP)
B
(port 8, MEP)
A
CFM provides two tests to discover connectivity faults.
•Loopback test - similar to using “ping” in Microsoft DOS mode to check connectivity from your
computer to a host. In a loopback test, a MEP port sends a LBM (Loop Back Message) to a MIP port
and checks for an LBR (Loop Back Response). If no response is received, there might be a
connectivity fault between them.
•Link trace test - similar to using “tracert” in the Microsoft DOS mode to check connectivity from your
computer to a host. A link trace test provides additional connectivity fault analysis to get more
information on where the fault is. In a link trace test, a MEP port sends a LTM (Link Trace Message) to
a MIP port and checks for an LTR (Link Trace Response). If an MIP or MEP port does not respond to
the source MEP, this may indicate a fault. Administrators can take further action to check the fault
and resume services according to the line connectivity status report.
An example is shown next. A user cannot access the Internet. To check the problem, the administrator
starts the link trace test from A which is an MEP port to B which is also an MEP port. Each aggregation MIP
port between aggregated devices responds to the LTM packets and also forwards them to the next
port. A fault occurs at port C. A discovers the fault since it only gets the LTR packets from the ports
before port C.
Figure 2 MIP and MEP Example
13.2 CFM Term Definition
This section lists the common term definition which appears in this chapter. Refer to User’s Guide for
more detailed information about CFM.
Table 30 CFM Term Definitions
TERM DESCRIPTION
CFM CFM (Connectivity Fault Management) is used to detect and analyze connectivity faults in
bridged LANs.
MD An MD (Maintenance Domain) is part of a network, where CFM can be done. The MD is
identified by a level number and contains both MEPs and MIPs. The Switch supports up to
eight MD levels (0 ~ 7) in a network. You can create multiple MDs on one MD level and
multiple MA groups in one MD.
MA An MA (Maintenance Association) is a group of MEPs and identified by a VLAN ID. One MA
should belong to one and only one MD group.
MEP An MEP (Maintenance End Point) port has the ab ility to send and reply to the CCMs, LBMs and
MIP An MIP (Maintenance Intermediate Point) port forwards the CCMs, LBMs, and LTMs and replies
Connectivity
Check
LTMs. It also gets other MEP port information from neighbor switches’ CCMs in an MA.
the LBMs and LTMs by sending Loop Back Responses (LBRs) and Link Trace Responses (LTRs).
Connectivity Check (CC) enables an MEP port sending Connectivity Check Messages
(CCMs) periodically to other MEP ports. An MEP port collects CCMs to get other MEP
information within an MA.
Ethernet Switch CLI Reference Guide
50
Page 51

Table 30 CFM Term Definitions
TERM DESCRIPTION
Loop Back Test Loop Back Test (LBT) checks if an MEP port receives its LBR (Loop Back Response) from its
target after it sends the LBM (Loop Back Message). If no response is received, there might be a
connectivity fault between them.
Link Trace Test Link Trace Test (LTT) provides additional connectivity fault analysis to get more information on
where the fault is. In the link trace test, MIP ports also send LTR (Link Trace Response) to
response the source MEP port’s LTM (Link Trace Message). If an MIP or MEP port does not
respond to the source MEP, this may indicate a fault. Administrators can take further action to
check and resume services from the fault according to the line connectivity status report.
13.3 User Input Values
This section lists the common term definition appears in this chapter. Refer to User’s Guide for more
detailed information about CFM.
Table 31 CFM command user input values
USER INPUT DESCRIPTION
mep-id
ma-index
md-index
mac-address
Chapter 13 CFM Commands
This is the maintenance endpoint identifier (1~8191).
This is the maintenance association (MA) index number (1~4294967295).
This is the maintenance domain (MD) index number (1~4294967295).
This is the remote maintenance endpoint’s MAC address or a virtual MAC
address assigned to a port.
A Switch has one or two MAC addresses only. If you do not use virtual MAC
addresses with CFM, all CFM ports will use the Switch’s MAC address and
appear as one port. If you want unique CFM ports, you need to assign virtual
MAC addresses. If you use virtual MAC addresses, make sure that all virtual
MAC addresses are unique in both the Switch and the network to which it
belongs.
13.4 Command Summary
The following section lists the commands for this feature.
Table 32 CFM Command Summary
COMMAND DESCRIPTION M P
clear ethernet cfm linktrace
clear ethernet cfm mep-ccmdb
clear ethernet cfm mip-ccmdb
clear ethernet cfm mep-defects
ethernet cfm
Clears the link trace database. E 13
Clears the MEP CCM database. E 13
Clears the MIP CCM database. E 13
Clears the MEP-defects database. E 13
Enables CFM on the Switch. C 13
Ethernet Switch CLI Reference Guide
51
Page 52

Chapter 13 CFM Commands
Table 32 CFM Command Summary (continued)
COMMAND DESCRIPTION M P
ethernet cfm loopback remote-mep
<mep-id> mep <mep-id> ma <ma-index>
md <md-index> [size <0-1500>][count
<1-1024>]
ethernet cfm loopback mac <mac-
address> mep <mep-id> ma <ma-index>
md <md-index> [size <0-1500>][count
<1-1024>]
ethernet cfm linktrace remote-mep
<mep-id> mep <mep-id> ma <ma-index>
md <md-index> [mip-ccmdb][[ttl
<ttl>]
ethernet cfm linktrace mac <mac-
address> mep <mep-id> ma <ma-index>
md <md-index> [mip-ccmdb][[ttl
<ttl>]
Specifies the remote MEP ID, local MEP ID, MA index
and MD index to perform a loopback test.
This enables the MEP port (with the specified MEP ID)
in a specified CFM domain to send the LBMs (Loop
Back Messages) to a specified remote end point.
You can also define the packet size (from 0 to 1500
bytes) and how many times the Switch sends the
LBMs.
Specifies the destination MAC address, local MEP ID,
MA index and MD index to perform a loopback test.
This enables the MEP port (with the specified MEP ID)
in a specified CFM domain to send the LBMs (Loop
Back Messages) to a specified remote end point.
You can also define the packet size (from 0 to 1500
bytes) and how many times the Switch sends the
LBMs.
Specifies the remote MEP ID, local MEP ID, MA index
and MD index to perform a link trace test.
This enables the MEP port (with the specified MEP ID)
in a specified CFM domain to send the LTMs (Link
Trace Messages) to a specified remote end point.
mip-ccmdb: Specifies the MIP CCM DB, a database
that stores information (tuples of {Port, VID, MAC
address}) about MEPs in the MD when receiving
CCMs. The MIP CCM DB is used for fault isolation, such
as link trace and loop back. An entry can remains in
the MIP CCM DB for at least 24 hours.
ttl: This is the time-to-live value (the number of
transmissions, 64 hops by default). Sets this to stop a
test once it exceeds the time duration without
receiving any response.
Specifies the destination MAC address, local MEP ID,
MA index and MD index to perform a link trace test.
This enables the MEP port (with the specified MEP ID)
in a specified CFM domain to send the LTMs (Link
Trace Messages) to a specified remote end point.
E13
E13
E13
E13
mip-ccmdb: Specifies the MIP CCM DB, a database
that stores information (tuples of {Port, VID, MAC
address}) about MEPs in the MD when receiving
CCMs. The MIP CCM DB is used for fault isolation, such
as link trace and loop back. An entry can remains in
the MIP CCM DB for at least 24 hours.
ttl: This is the time-to-live value (the number of
transmissions, 64 hops by default). Sets this to stop a
test once it exceeds the time duration without
receiving any response.
Ethernet Switch CLI Reference Guide
52
Page 53

Chapter 13 CFM Commands
Table 32 CFM Command Summary (continued)
COMMAND DESCRIPTION M P
ethernet cfm ma <ma-index> format
<vid|string|integer> name <ma-name>
md <md-index> primary-vlan <1-4094>
Creates an MA (Maintenance Association) and
defines its VLAN ID under the MD. You can also define
the format which the Switch uses to send this MA
information in the domain (MD).
ma-name: Enters a VLAN ID, a descriptive name or a 2octet integer for the MA.
C13
Note: If you set the format to vid, the VLAN ID
should be the same as the VLAN ID you
use to identify the MA.
cc-interval
<100ms|1s|10s|1min|10min>
mhf-creation < none | default |
explicit>
id-permission < none | chassis
| management | chassismanagement>
Sets how often an MEP sends a connectivity check
message (CCM).
Sets MHF (MIP Half Function).
Select none and no MIP can be created
automatically for this MA.
Select default to automatically create MIPs for this
MA and on the ports belonging to this MA’s VLAN
when there are no lower configured MD levels or
there is an MEP at the next lower configured MD level
on the port.
Select explicit to automatically create MIPs for this
MA and on the ports belonging to this MA’s VLAN only
when there is an MEP at the next lower configured MD
level on the port.
Sets what’s to be included in the sender ID TLV (TypeLength-Value) transmitted by CFM packets.
Select none to not include the sender ID TLV.
C13
C13
C13
exit
remote-mep <mep-id>
mep <mep-id> interface port-
channel <port> direction
<up|down> priority <0-7>
mep <mep-id> interface portchannel <port> direction
<up|down> priority <0-7>
inactive
mep <mep-id> interface portchannel <port> direction
<up|down> priority <0-7> ccenable
no remote-mep <mep-id>
Select chassis to include the chassis information.
Select management to include the management
information.
Select chassis-management to include both chassis
and management information.
Exits from the config-ma mode. C 13
Sets a remote MEP in an MA. C 13
Sets an MEP in an MA.
up|down: The traffic direction.
0-7: The priority value of the CCMs or LTMs transmitted
by the MEP. 1 is the lowest, then 2, 0 and 3 ~ 7.
Disables a specified MEP. C 13
Enables Connectivity Check (CC) to allow an MEP
sending Connectivity Check Messages (CCMs)
periodically to other MEPs.
Deletes a specified destination MEP. C 13
C13
C13
Ethernet Switch CLI Reference Guide
53
Page 54

Chapter 13 CFM Commands
Table 32 CFM Command Summary (continued)
COMMAND DESCRIPTION M P
no mep <mep-id>
no mep <mep-id> inactive
no mep <mep-id> cc-enable
ethernet cfm md <md-index> format
<dns|mac|string> name <md-name>
level <0-7>
ethernet cfm management-addressdomain ip [<ip-addr>]
interface port-channel <port-list>
ethernet cfm virtual-mac <mac-
addr>
no ethernet cfm virtual-mac
no ethernet cfm
no ethernet cfm md <md-index>
no ethernet cfm ma <ma-index> md
Deletes a specified MEP. C 13
Enables an MEP. C 13
Disallows an MEP sending Connectivity Check
Messages (CCMs) periodically to other MEPs.
Creates an MD (Maintenance Domain) with the
specified name and level number.
md-name: Enters a domain name, MAC address or a
descriptive name for the MD.
Sets the Switch to carry the host name and
management IP address for the VLAN to which an
MEP belongs or the specified IP address in CFM
packets.
This helps you to easily identify a remote MEP by its
host name and management IP address showed in
the link trace database and MEP-CCM database.
Enters config-interface mode for configuring the
specified port(s).
Assigns a virtual MAC address(es) to the specified
port(s) so that each specified port can have its own
MAC address for CFM.
You cannot use the copy running-config
interface port-channel command to copy the
virtual MAC address from the specified port to other
ports.
Removes the virtual MAC address(es) and sets the
port(s) to use the default system MAC address.
Disables CFM on the Switch. C 13
Deletes the specified MD. C 13
Deletes an MA from the specified MD. C 13
C13
C13
C13
C13
C13
C13
<md-index>
no ethernet cfm management-address-
domain
show ethernet cfm linktrace
show ethernet cfm local
show ethernet cfm local stack
show ethernet cfm local stack mep
show ethernet cfm local stack mep
<mep-id> ma <ma-index> md <md-
index>
show ethernet cfm local stack mep
<mep-id> ma <ma-index> md <md-
index> mep-ccmdb [remote-mep <mepid>]
show ethernet cfm local stack mip
show ethernet cfm local stack mip
Sets the Switch to not carry the host name and
management IP address in CFM packets.
Displays the CFM link trace database information. E 13
Displays the detailed settings of the configured MD(s)
and MA(s).
Displays a list of all maintenance points, such as MIP
and MEP.
Displays a list of the MEP(s). E 13
Displays the specified MEP’s general, fault notification
generator, continuity-check, loopback and link trace
information.
Displays the specified MEP’s MEP-CCM database
information. Each MEP maintains an MEP CCM
database which stores information about remote
MEPs in the MA when receiving CCMs.
Displays a list of the MIP(s). E 13
Displays the MIP-CCM database. E 13
C13
E13
E13
E13
E13
mip-ccmdb
Ethernet Switch CLI Reference Guide
54
Page 55

Chapter 13 CFM Commands
Table 32 CFM Command Summary (continued)
COMMAND DESCRIPTION M P
show ethernet cfm remote
show ethernet cfm virtual-mac
show ethernet cfm virtual-mac port
<port-list>
13.5 Command Examples
This example creates MD1 (with MD index 1 and level 1) and MA2 (with MA index 2 and VLAN ID 2) under
MD1 that defines a CFM domain.
sysname# config
sysname(config)# ethernet cfm md 1 format string name MD1 level 1
sysname(config)# ethernet cfm ma 2 format string name MA2 md 1 primaryvlan 2
sysname(config-ma)# exit
sysname(config)# exit
sysname# write memory
Displays a list of MA(s), MEP(s) and the remote MEP(s)
under the configured MD(s).
Displays all virtual MAC addresses. E 13
Displays the MAC address(es) of the specified port(s). E 13
E13
Note: Remember to save new settings using the write memory command.
This example deletes MA2 (with MA index 2) from MD1 (with MD index 1).
sysname# config
sysname(config)# no ethernet cfm ma 2 md 1
sysname(config)# exit
sysname# write mem
This example creates MA3 (with MA index 3 and VLAN ID 123) under MD1, and associates port 1 as an
MEP port with MEP ID 301 in the specified CFM domain. This also sets MHF (MIP half function) to default to
have the Switch automatically create MIPs for this MA and on the ports belonging to this MA's VLAN
when there are no lower configured MD levels or there is a MEP at the next lower configured MD level
on the port. This also sets a remote MEP in MA3.
sysname# config
sysname(config)# ethernet cfm ma 3 format string name MA3 md 1 primary-vlan
123
sysname(config-ma)# mep 301 interface port-channel 1 direction up priority 2
sysname(config-ma)# mep 301 interface port-channel 1 direction up priority 2
cc-enable
sysname(config-ma)# mhf-creation default
sysname(config-ma)# remote-mep 117
sysname(config-ma)# exit
sysname(config)# exit
sysname# write mem
Ethernet Switch CLI Reference Guide
55
Page 56

Chapter 13 CFM Commands
This example lists all CFM domains. In this example, only one MD (MD1) is configured. The MA3 with the
associated MEP port 1 is under this MD1.
sysname# show ethernet cfm local
MD Index: 1
MD Name: MD1(string)
MD Level: 1
MA Index: 3
MA Name: MA3(string)
Primary Vlan: 123
CC Interval: 1000 millisecond(s)
MHF Creation: default
ID Permission: none
MEP:301 (ACTIVE ) Port:1 Direction:DOWN Priority:5 CC-Enable:FALSE
sysname#
This example starts a loopback test and displays the test result on the console.
sysname# ethernet cfm loopback remote-mep 2 mep 1 ma 1 md 1
Sending 5 Ethernet CFM Loopback messages to remote-mepid 2, timeout is 5
seconds .....
sysname# Loopback: Successful
Success rate is 100 percent, round-trip min/avg/max = 0/0/0 ms
sysname#
This example displays all neighbors’ MEP port information in the MIP-CCM databases.
sysname# show ethernet cfm local stack mip mip-ccmdb
MIP CCM DB
Port VID Source Address Retained
---- ---- ----------------- -------- 2 1 00:19:cb:00:00:04 0 hr(s)
7 1 00:19:cb:00:00:06 0 hr(s)
sysname#
The following table describes the labels in this screen.
Table 33 show cfm-action mipccmdb
LABEL DESCRIPTION
Port Displays the number of the port on which this CCM was received.
VID Displays the MA VLAN ID of the last received CCM.
Source Address Displays the MAC address of the remote MEP.
Retained Displays how long an entry has been kept in the database.
Ethernet Switch CLI Reference Guide
56
Page 57

Chapter 13 CFM Commands
This example assigns a virtual MAC address to port 3 and displays the MAC addresses of the ports 2 ~ 4.
The assigned virtual MAC address should be unique in both the Switch and the network to which it
belongs.
sysname# config
sysname(config)# interface port-channel 3
sysname(config-interface)# ethernet cfm virtual-mac 00:19:cb:12:34:56
sysname(config-interface)# exit
sysname(config)# exit
sysname# show ethernet cfm virtual-mac port 2-4
Virtual MACPort MAC
---- ----------------2 00:19:cb:00:00:02
3 00:19:cb:12:34:56
4 00:19:cb:00:00:02
sysname#
This example sets the Switch to carry its host name and management IP address 192.168.100.1 in CFM
packets.
sysname# config
sysname(config)# ethernet cfm management-address-domain ip 192.168.100.1
This example shows remote MEP database information. The remote MEP has been configured to carry its
host name and a specified IP address in CFM packets.
sysnam# show ethernet cfm remote
MD Index: 1
MD Name: customer123(string)
MD Level: 2
MA Index: 1
MA Name: 123(vid)
Primary Vlan: 123
MEP: 11
Remote MEP ID: 1
MAC Address: 00:19:cb:6f:91:5a
Chassis Id: MGS-3712F
Management Address: 192.168.100.1:161
sysname#
Ethernet Switch CLI Reference Guide
57
Page 58

Certificates Commands
Use these commands to import an HTTPS certificate to the Switch. You can also clear or show the HTTPS
certificate imported to the Switch.
14.1 Certificates Overview
The Switch can use HTTPS certificates that are verified by a third party to create secure HTTPS
connections between your computer and the Switch. This way, you may securely access the Switch
using the web configurator. See Section 52.8 on page 451 for more information about HTTPS.
Certificates are based on public-private key pairs. A certificate contains the certificate owner’s identity
and public key. Certificates provide a way to exchange public keys for use in authentication.
CHAPTER 14
14.2 Command Summary
The following section lists the commands for this feature.
Table 34 auto-config Command Summary
COMMAND DESCRIPTION M P
import certificate https
clear certificate https
show https certificate
14.3 Command Example
This example shows you how to import the HTTPS certificate to the Switch.
FTP Server
First, we need to upload an HTTPS certificate file to the FTP server. The Switch is the FTP server.
Imports the HTTPS certificate from the FTP server to the
Switch. See Section 14.3 on page 58 for the example.
Note: You need to upload an HTTPS certificate file to
the FTP server first. The Switch is the FTP server.
Removes the HTTPS certificate uploaded to the Switch. E 13
Displays the HTTPS certificates. E 3
E13
1 Select Start > All Programs > Accessories > Command Prompt.
Ethernet Switch CLI Reference Guide
58
Page 59

Chapter 14 Certificates Commands
2 Use the ftp <ip address> command and enter the Switch IP address to have your computer ping the
Switch. In this example, we use the default out-of-band IP address (192.168.0.1) for the Switch IP address.
Use the default in-band management IP address (192.168.1.1), DHCP -assigned IP address, static IP
address, or the default out-of-band IP address (192.168.0.1). It doesn’t matter which IP address you use
as long as your computer can ping the Switch.
3 Enter the login username and password of the Switch. The default username is admin and associated
default password is 1234.
C:\Users>ftp 192.168.0.1
Connected to 192.168.0.1
220 XS3800 FTP version 1.0 ready at Fri Oct 19 05:14:22 2018
User (192.168.0.1:(none)): admin
331 Enter PASS command
Password:
230 Logged in
ftp>
4 Enter the put <file name> https-cert command to upload an HTTPS certificate file to the Switch.
ftp> put CAfile.pfx https-cert
The Switch
Access the CLI. See Chapter 1 on page 10 for more information about how to access the CLI.
1 Enter the import certificate https command to import the HTTPS certificate from the FTP server to
the Switch.
2 Type the certificate file’s password that was created when the PKCS #12 file was exported.
sysname# import certificate https
Password:*****
Import Successfully
Ethernet Switch CLI Reference Guide
59
Page 60

Classifier Commands
Use these commands to classify packets into traffic flows. After classifying traffic, policy commands
(Chapter 64 on page 248) can be used to ensure that a traffic flow gets the requested treatment in the
network.
15.1 Command Summary
The following section lists the commands for this feature.
Table 35 Command Summary: classifier
COMMAND DESCRIPTION M P
show classifier [<name>]
clear classifier match-count
[<name>]
CHAPTER 15
Displays classifier configuration details. E 3
Removes the number of times all or the specified classifier rule is
applied.
E3
Ethernet Switch CLI Reference Guide
60
Page 61

Chapter 15 Classifier Commands
Table 35 Command Summary: classifier (continued)
COMMAND DESCRIPTION M P
classifier <name> < [weight
<0-65535> ][packet- format
<802.3untag|802.3tag|
EtherIIuntag|EtherIItag>]
[priority <0-7>] [ innerpriority <0-7> ] [vlan
<vlan-id>] [ inner-vlan
<vlan-id-list> ][ethernet-
type <ether-
num|ip|ipx|arp|rarp|appletal
k|decnet|IPv6>] [source-mac
<src-mac-addr> [mask
<mask>]] [source-port <port-
list>] [ source-trunk
<trunk-list> ] [
destination-port <port-list>
] [destination-mac <dest-
mac-addr> [mask <mask>]]
[ip-packet-length <0-65535>
to <0-65525>] [dscp <0-63>]
[precedence <0-7>] [tos <0-
255>] [ipv6-dscp <0-63>]
[ip-protocol <protocol-
num|tcp|udp|icmp|egp|
ospf|rsvp|igmp|igp|pim|ipsec
> [establish-only]][ipv6next-header <protocol-
num|tcp|udp|icmpv6>
[establish-only]][source-ip
<src-ip-addr> [mask-bits
<mask-bits>]] [ipv6-source-
ip <src-ipv6-addr> [prefixlength <prefix-length>] ]
[source-socket <socket-num>
[to <socket-num>] ]]
[destination-ip <dest-ip-
addr> [mask-bits <maskbits>]] [ipv6-destination-ip
<dest-ipv6-addr> [prefix-
length <prefix-length>] ]
[destination-socket <socket-
num> [to <socket-num>] ]]
[time-range <name>] [log]
[count] [inactive]>
no classifier <name>
no classifier <name>
Configures a classifier. Specify the parameters to identify the
traffic flow:
• weight: Enter the weight the priority of the Classifier rule
when the match order is in manual mode. A higher weight
means a higher priority.
• priority: Type 0 to classify traffic from any priority level or
type a priority level with 1 being the highest priority.
• inner-priority: Type 0 to classify traffic from any inner priority
level or type a priority level with 1 being the highest priority.
• vlan-id: Type 0 to classify traffic from any VLAN or type a
specific VLAN ID number.
• inner-vlan-id: Type 0 to classify traffic from any inner VLAN or
type a specific inner VLAN ID number.
• ethernet-type: Enter one of the Ethernet types or type the
hexadecimal number that identifies an Ethernet type (see
Table 36 on page 62).
• source-mac: Enter the source MAC address of the packet.
• source-port: Enter any to classify traffic received on any
port or type a specific port number.
• source-trunk: Enter any to classify traffic from any trunk
group or type a specific trunk group ID number.
• destination-port: Enter any to classify traffic to any
destination port or type a specific port number.
• destination-mac: Enter the destination MAC address of
the packet.
• ip-protocol: Enter one of the protocols or type the port
number that identifies the protocol (see Table 37 on page
62).
• mask: type the mask for the specified MAC address to
determine which bits a packet’s MAC address should
match. Enter “f” for each bit of the specified MAC address
that the traffic’s MAC address should match. Enter “0” for
the bit(s) of the matched traffic’s MAC address, which can
be of any hexadecimal character(s). For example, if you set
the MAC address to 00:13:49:00:00:00 and the mask to
ff:ff:ff:00:00:00, a packet with a MAC address of
00:13:49:12:34:56 matches this criteria.
• tos: Enter any to classify traffic from any ToS, or set an IP
Precedence (the first 3 bits of the 8-bit ToS field) value and a
Type of Service (the last 5 bits of the 8-bit ToS field) value.
• establish-only: Enter this to identify only TCP packets
used to establish TCP connections.
• source-ip: Enter the source IPv4 address of the packet.
• ipv6-source-ip: Enter the source IPv6 address of the
packet.
• source-socket: (for UDP or TCP protocols only) Specify the
protocol port number.
• destination-ip: Enter the destination IPv4 address of the
packet.
• ipv6-destination-ip
of the packet.
• destination-socket: (for UDP or TCP protocols only)
specify the protocol port number.
• time-range: Enter the name of a pre-defined time-range
rule.
• inactive: Disables this classifier.
Deletes the classifier.
If you delete a classifier you cannot use policy rule related
information.
Enables a classifier. C 13
: Enter the destination IPv6 address
C13
C13
inactive
Ethernet Switch CLI Reference Guide
61
Page 62

Chapter 15 Classifier Commands
Table 35 Command Summary: classifier (continued)
COMMAND DESCRIPTION M P
classifier match-order
<auto|manual>
classifier logging
classifier logging interval
<0-65535>
no classifier logging
Use manual to have classifier rules applied according to the
weight of each rule you configured. Use auto to have classifier
rules applied according to the layer of the item configured in
the rule.
Creates a log when packets match a classifier rule during a
defined time interval.
Enter the length of the time period (in seconds) to count
matched packets for a classifier rule. Enter an integer from 0-
65535. 0 means that no logging is done.
Disallows the Switch to create a log message when packets
match a classifier rule during a defined time interval.
C13
C13
C13
C13
The following table shows some other common Ethernet types and the corresponding protocol number.
Table 36 Common Ethernet Types and Protocol Number
ETHERNET TYPE PROTOCOL NUMBER
IP ETHII 0800
X.75 Internet 0801
NBS Internet 0802
ECMA Internet 0803
Chaosnet 0804
X.25 Level 3 0805
XNS Compat 0807
Banyan Systems 0BAD
BBN Simnet 5208
IBM SNA 80D5
AppleTalk AARP 80F3
In an IPv4 packet header, the “Protocol” field identifies the next level protocol. The following table
shows some common IPv4 protocol types and the corresponding protocol number. Refer to http://
www.iana.org/assignments/protocol-numbers for a complete list.
Table 37 Common IPv4Protocol Types and Protocol Numbers
PROTOCOL TYPE PROTOCOL NUMBER
ICMP 1
TCP 6
UDP 17
EGP 8
L2TP 115
Ethernet Switch CLI Reference Guide
62
Page 63

Chapter 15 Classifier Commands
15.2 Command Examples
This example creates a classifier for packets with a VLAN ID of 3. The resulting traffic flow is identified by
the name VLAN3. The policy command can use the name VLAN3 to apply policy rules to this traffic
flow. See the policy example in Chapter 64 on page 248.
sysname# config
sysname(config)# classifier VLAN3 vlan 3
sysname(config)# exit
sysname# show classifier
Index Active Name Rule
1 Yes VLAN3 VLAN = 3;
This example creates a classifier (Class1) for packets which have a source MAC address of
11:22:33:45:67:89 and are received on port 1. You can then use the policy command and the name
Class1 to apply policy rules to this traffic flow. See the policy example in Chapter 64 on page 248.
sysname# config
sysname(config)# classifier Class1 source-mac 11:22:33:45:67:89 source-port
1
sysname(config)# exit
sysname# show classifier
Index Active Name Rule
1 Yes Class1 SrcMac = 11:22:33:45:67:89; S...
The default value of match-order is auto. Use the following command to make weight work by
changing the default value of match-order to manual and configuring a classifier weight value where
the higher the weight, the higher the priority.
sysname# config
sysname(config)#classifier match-order manual
sysname(config)#classifier 1 weight 12345 source-port 1/1
Ethernet Switch CLI Reference Guide
63
Page 64

Cluster Commands
Use these commands to configure cluster management.
16.1 Command Summary
The following section lists the commands for this feature.
Table 38 cluster Command Summary
COMMAND DESCRIPTION M P
show cluster
cluster <vlan-id>
no cluster
cluster name <cluster name>
show cluster candidates
cluster member <mac> password
<password>
show cluster member
show cluster member config
show cluster member mac <mac>
cluster rcommand <mac>
no cluster member <mac>
CHAPTER 16
Displays cluster management status. E 3
Enables clustering in the specified VLAN group. C 13
Disables cluster management on the Switch. C 13
Sets a descriptive name for the cluster.
<cluster name>: You may use up to 32 printable
characters (spaces are allowed).
Displays the switches that are potential cluster members.
The switches must be directly connected.
Adds the specified device to the cluster. You have to
specify the password of the device too.
Displays the cluster member(s) and their running status. E 3
Displays the current cluster member(s). E 3
Displays the running status of the cluster member(s). E 3
Logs into the CLI of the specified cluster member. C 13
Removes the cluster member. C 13
C13
E3
C13
Ethernet Switch CLI Reference Guide
64
Page 65

Chapter 16 Cluster Commands
16.2 Command Examples
This example creates the cluster CManage in VLAN 1. Then, it looks at the current list of candidates for
membership in this cluster and adds two switches to cluster.
sysname# configure
sysname(config)# cluster 1
sysname(config)# cluster name CManage
sysname(config)# exit
sysname# show cluster candidates
Clustering Candidates:
Index Candidates(MAC/HostName/Model)
0 00:13:49:00:00:01/ES-2108PWR/ES-2108PWR
1 00:13:49:00:00:02/GS-3012/GS-3012
2 00:19:cb:00:00:02/ES-3124/ES-3124
sysname# configure
sysname(config)# cluster member 00:13:49:00:00:01 password 1234
sysname(config)# cluster member 00:13:49:00:00:02 password 1234
sysname(config)# exit
sysname# show cluster member
Clustering member status:
Index MACAddr Name Status
1 00:13:49:00:00:01 ES-2108PWR Online
2 00:13:49:00:00:02 GS-3012 Online
The following table describes the labels in this screen.
Table 39 show cluster member
LABEL DESCRIPTION
Index This field displays an entry number for each member.
MACAddr This field displays the member’s MAC address.
Name This field displays the member’s system name.
Status This field displays the current status of the member in the cluster.
Online: The member is accessible.
Error: The member is connected but not accessible. For example, the member’s
password has changed, or the member was set as the manager and so left the
member list. This status also appears while the Switch finishes adding a ne w member to
the cluster.
Offline: The member is disconnected. It takes approximately 1.5 minutes after the link
goes down for this status to appear.
Ethernet Switch CLI Reference Guide
65
Page 66

Chapter 16 Cluster Commands
This example logs in to the CLI of member 00:13:49:00:00:01, looks at the current firmware version on the
member Switch, logs out of the member’s CLI, and returns to the CLI of the manager.
sysname# configure
sysname(config)# cluster rcommand 00:13:49:00:00:01
Connected to 127.0.0.2
Escape character is '^]'.
User name: admin
Password: ****
Copyright (c) 1994 - 2007 ZyXEL Communications Corp.
ES-2108PWR# show version
Current ZyNOS version: V3.80(ABS.0)b2 | 05/28/2007
ES-2108PWR# exit
Telnet session with remote host terminated.
Closed
sysname(config)#
This example looks at the current status of the Switch’s cluster.
sysname# show cluster
Cluster Status: Manager
VID: 1
Manager: 00:13:49:ae:fb:7a
The following table describes the labels in this screen.
Table 40 show cluster
LABEL DESCRIPTION
Cluster Status This field displays the role of this Switch within the cluster.
Manager: This Switch is the device through which you manage the cluster member
switches.
Member: This Switch is managed by the specified manager.
None: This Switch is not in a cluster.
VID This field displays the VLAN ID used by the cluster.
Manager This field displays the cluster manager’s MAC address.
Ethernet Switch CLI Reference Guide
66
Page 67

CHAPTER 17
CLV Commands
Use these commands to configure VLAN settings on the Switch in clv mode. In Zyxel configuration mode,
you need to use the VLAN commands to configure a VLAN first, then specify the port(s) which you want
to configure and tag all outgoing frames with the specified VLAN ID. In clv mode, you need to specify
the port(s) first, then configure frames which you want to tag with the specified VLAN ID.
Note: CLV mode is supported only in the Command Line Interface (CLI). If you've enabled
CLV mode to configure the Switch's VLAN settings, further VLAN changes you make via
the web configurator will not be saved and applied completely. You can still use the
web configurator to view the VLAN status.
If you want to configure VLAN settings in both the web configurator and the CLI, just
return to Zyxel configuration mode by turning off CLV mode.
17.1 Command Summary
The following section lists the commands for this feature. There are three different ways that you can
configure ports on the Switch. Use Access mode to untag outgoing frames; usually connect a port in
Access mode to a computer. Use Trunk mode to tag outgoing frames; usually connect a port in Trunk
mode to another Switch. Use Hybrid mode to tag or untag outgoing frames; usually connect a port in
Hybrid mode to another Switch or computer.
Suppose port 1 is configured as a native VLAN with VLAN ID 100. Then all untagged incoming traffic that
goes out from port 1 will be tagged with VLAN ID 100.
Suppose port 2 is configured in Access mode. Then all outgoing traffic from port 2 will be untagged.
Suppose port 3 is configured in Trunk mode. Then all outgoing traffic from port 3 will be tagged with
VLAN ID 100.
Ethernet Switch CLI Reference Guide
67
Page 68

Chapter 17 CLV Commands
Figure 3 Trunk - Access Mode Example
Table 41 vlan Command Summary
COMMAND DESCRIPTION M P
show vlan
show vlan <vlan-id>
Displays the status of all VLANs. E 3
Displays the status of the specified VLAN. E 3
Table 42 clv Command Summary
COMMAND DESCRIPTION M P
clv
no clv
Enables clv mode. C 13
Disables clv mode. C 13
Table 43 switchport mode Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-
Enters config-interface mode for the specified port(s). C 13
list>
switchport mode
<access|trunk|hybrid>
no switchport mode
Specifies VLAN configuration mode on the specified
port(s).
•Use Access to untag outgoing frames with a VLAN ID.
•Use Trunk to tag outgoing frames with a VLAN ID.
•Use Hybrid to tag or untag outgoing frames with a
VLAN ID.
Resets VLAN configuration mode to the default switchport
mode. The default switchport mode is hybrid mode.
C13
C13
Ethernet Switch CLI Reference Guide
68
Page 69

Chapter 17 CLV Commands
Table 44 switchport access Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-
Enters config-interface mode for the specified port(s). C 13
list>
switchport mode access
switchport access <vlan-id>
no switchport access vlan
Sets the specified interface in access mode. C 13
Untags all outgoing frames with the specified VLAN ID. C 13
Resets all outgoing frames to the default VLAN ID. The
default VLAN ID is VLAN 1.
C13
Table 45 switchport trunk Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-
Enters config-interface mode for the specified port(s). C 13
list>
switchport mode trunk
switchport trunk allowed
Sets the specified interface in trunk mode. C 13
Tags all outgoing frames with the specified VLAN ID. C 13
vlan <vlan-list>
no switchport trunk allowed
Disables the specified VLAN trunk on the port(s). C 13
vlan <vlan-list>
switchport trunk allowed
Tags all outgoing frames for all VLANs. C 13
vlan all
no switchport trunk allowed
Disables all VLAN trunks on the port(s). C 13
vlan all
switchport trunk native vlan
<vlan-id>
no switchport trunk native
vlan
Tags all incoming untagged frames with the specified
VLAN ID. The default VLAN ID is VLAN 1 for all ports. Sets a
VLAN ID in the range 1 to 4094.
Resets all incoming untagged frames to the default VLAN
ID. The default VLAN ID is VLAN 1.
C13
C13
Table 46 switchport hybrid Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-
Enters config-interface mode for the specified port(s). C 13
list>
switchport mode hybrid
switchport hybrid allowed
Sets the specified interface in hybrid mode. C 13
Tags all outgoing frames with the specified VLAN ID. C 13
vlan <vlan-list> tagged
switchport hybrid allowed
Untags all outgoing frames with the specified VLAN ID. C 13
vlan <vlan-list> untagged
no switchport hybrid allowed
Disables the specified VLAN ID on the port(s). C 13
vlan <vlan-list>
switchport hybrid pvid
<vlan-id>
no switchport hybrid pvid
<vlan-id>
Tags all incoming untagged frames with the specified
VLAN ID.
Resets all incoming untagged frames to the default VLAN
ID. The default VLAN ID is VLAN 1.
C13
C13
Ethernet Switch CLI Reference Guide
69
Page 70

Chapter 17 CLV Commands
Table 47 switchport forbidden Command Summary
COMMAND DESCRIPTION M P
interface port-channel <portlist>
switchport forbidden vlan
add <vlan-list>
switchport forbidden vlan
add all
switchport forbidden vlan
remove <vlan-list>
switchport forbidden vlan
remove all
17.2 Command Examples
This example configures clv mode.
Enters config-interface mode for the specified port(s). C 13
Prohibits the specified port(s) from joining the specified
VLAN group.
Prohibits the specified port(s) from joining all VLAN groups. C 13
Sets forbidden port(s) in the specified VLAN to normal
port(s).
Sets all forbidden port(s) in the port list to normal port(s). C 13
C13
C13
sysname# config
sysname(config)# clv
Note: The following commands all have clv mode enabled.
This example configures clv for VLAN 20 on port 1.
sysname# config
sysname(config)# interface port-channel 1
sysname(config-interface)# switchport mode access
sysname(config-interface)# switchport access vlan 20
sysname(config-interface)# exit
This example activates clv for VLAN 100 and VLAN 20 on ports 1 to 3. This example prohibits ports 1 to 3
from joining VLAN 200.
sysname# config
sysname(config)# interface port-channel 1-3
sysname(config-interface)# switchport mode trunk
sysname(config-interface)# switchport trunk allowed vlan 100
sysname(config-interface)# switchport trunk native vlan 20
sysname(config-interface)# switchport forbidden vlan add 200
sysname(config-interface)# exit
Ethernet Switch CLI Reference Guide
70
Page 71

Chapter 17 CLV Commands
This example configures port 4 as the tagged port in VLAN 20 and the untagged port in VLAN 100. This
example also configures 200 as the PVID on port 4.
sysname# config
sysname(config)# interface port-channel 4
sysname(config-interface)# switchport mode hybrid
sysname(config-interface)# switchport hybrid allowed vlan 20 tagged
sysname(config-interface)# switchport hybrid allowed vlan 100 untagged
sysname(config-interface)# switchport hybrid pvid 200
sysname(config-interface)# exit
This example shows the VLAN table.
sysname# show vlan
The Number of VLAN : 4
Idx. VID Status Elap-Time TagCtl
---- ---- --------- ----------- ----------------------------------
---
1 1 Static 145:03:37 Access :1-3,6-52
Trunk :
2 20 Static 1:47:09 Access :
Trunk :4
3 100 Static 26:04:36 Access :4
Trunk :1-3
4 200 Static 2:01:54 Access :
Trunk :
The following table describes the labels in this screen.
Table 48 show vlan
LABEL DESCRIPTION
The Number of VLAN This field displays the number of VLANs on the Switch.
Idx. This field displays an entry number for each VLAN.
VID This field displays the VLAN identification number.
Status This field displays how this VLAN was added to the Switch.
Dynamic: The VLAN was added via GVRP.
Static: The VLAN was added as a permanent entry
Other: The VLAN was added in another way, such as Multicast VLAN Registration
(MVR).
Elap-Time This field displays how long it has been si nce a dynamic VLAN was registered or a stati c
TagCtl This field displays untagged and tagged ports.
VLAN was set up.
Access: These ports do not tag outgoing frames with the VLAN ID.
Trunk: These ports tag outgoing frames with the VLAN ID.
Ethernet Switch CLI Reference Guide
71
Page 72

Chapter 17 CLV Commands
This example shows the VLAN 100 status.
sysname# show vlan 100
802.1Q VLAN ID : 100
Name :
Status : Static
Elapsed Time : 26:05:15
Port Information Mode
---------------- --- 1 Trunk
2 Trunk
3 Trunk
4 Hybrid
Ethernet Switch CLI Reference Guide
72
Page 73

CHAPTER 18
Custom Default Commands
Use these commands to use custom default on the Switch.
18.1 Custom Default Overview
You can save the current configuration settings to a customized default file, so you can load it when
you reboot the Switch.
Note: For the GS2210 Series, when the custom default feature is enabled, Config 2 can’t be
used.
18.2 Command Summary
The following section lists the commands for this feature.
Table 49 custom-default Command Summary
COMMAND DESCRIPTION M P
custom-default
no custom-default
See Chapter 76 on page 289 for the commands to save the current configuration settings permanently
to a customized default file, and load it when rebooting the Switch.
18.3 Command Examples
See Section 3.7 on page 22 for an example of how to configure custom default on the Switch.
Enables custom default. C 14
Disables custom default. C 14
Ethernet Switch CLI Reference Guide
73
Page 74

Date and Time Commands
Use these commands to configure the date and time on the Switch.
19.1 Command Summary
The following table describes user-input values available in multiple commands for this feature.
Table 50 time User-input Values
COMMAND DESCRIPTION
week
day
month
o’clock
Possible values (daylight-saving-time commands only): first, second, third, fourth,
last.
Possible values ( daylight-saving-time commands only): Sunday, Monday, Tuesday, ....
Possible values ( daylight-saving-time commands only): January, February, March, ....
Possible values ( daylight-saving-time commands only): 0-23
CHAPTER 19
The following section lists the commands for this feature.
Table 51 time Command Summary
COMMAND DESCRIPTION M P
show time
time <hour:min:sec>
time date <month/day/year>
time timezone <-1200|...|1200>
time daylight-saving-time
Displays current system time an d date. E 3
Sets the current time on the Switch.
hour: 0-23
min: 0-59
sec: 0-59
Note: If you configure Daylight Saving Time after
you configure the time, the Switch will apply
Daylight Saving Time.
Sets the current date on the Switch.
month: 1-12
day: 1-31
year: 1970-2037
Selects the time difference between UTC (formerly known
as GMT) and your time zone.
Note: You can configure a time zone with a 30-
minute offset (for example, UTC -630).
Enables daylight saving time. The current time is updated if
daylight saving time has started.
C13
C13
C13
C13
Ethernet Switch CLI Reference Guide
74
Page 75

Chapter 19 Date and Time Commands
Table 51 time Command Summary (continued)
COMMAND DESCRIPTION M P
time daylight-saving-time startdate <week> <day> <month>
<o’clock>
time daylight-saving-time enddate <week> <day> <month>
<o’clock>
no time daylight-saving-time
time daylight-saving-time help
Sets the day and time when Daylight Saving Time starts.
In most parts of the United States, Daylight Saving Time
starts on the second Sunday of March at 2 A.M. local time.
In the European Union, Daylight Saving Time starts on the
last Sunday of March at 1 A.M. GMT or UTC, so the
o’clock field depends on your time zone.
Sets the day and time when Daylight Saving Time ends.
In most parts of the United States, Daylight Saving Time
ends on the first Sunday of November at 2 A.M. local time.
In the European Union, Daylight Saving Time ends on the
last Sunday of October at 1 A.M. GMT or UTC, so the
o’clock field depends on your time zone.
Disables daylight saving on the Swi t ch. C 13
Provides more information about the specified command. C 13
C13
C13
Table 52 timesync Command Summary
COMMAND DESCRIPTION M P
show timesync
timesync server <ip|domain name>
timesync <daytime|time|ntp>
no timesync
Displays time server information. E 3
Sets the IP address or domain name of the timeserver. The
Switch attempts to connect to the timeserver for up to 60
seconds.
The Switch synchronizes with the time server in the
following situations:
• When the Switch starts up.
• Every 24 hours after the Switch starts up.
• When the time server IP address or protocol is
updated.
Sets the time server protocol. You have to configure a time
server before you can specify the protocol.
Disables timeserver settings. C 13
C13
C13
19.2 Command Examples
This example sets the current date, current time, time zone, and daylight savings time.
sysname# configure
sysname(config)# time date 06/04/2007
sysname(config)# time timezone -600
sysname(config)# time daylight-saving-time
sysname(config)# time daylight-saving-time start-date second Sunday
--> March 2
sysname(config)# time daylight-saving-time end-date first Sunday
--> November 2
sysname(config)# time 13:24:00
sysname(config)# exit
sysname# show time
Current Time 13:24:03 (UTC-05:00 DST)
Current Date 2007-06-04
Ethernet Switch CLI Reference Guide
75
Page 76

Chapter 19 Date and Time Commands
This example looks at the current time server settings.
sysname# show timesync
Time Configuration
---------------------------- Time Zone :UTC -600
Time Sync Mode :USE_DAYTIME
Time Server IP Address :172.16.37.10
Time Server Sync Status:CONNECTING
The following table describes the labels in this screen.
Table 53 show timesync
LABEL DESCRIPTION
Time Zone This field displays the time zone.
Time Sync Mode This field displays the time server protocol the Switch uses. It displays NO_TIMESERVICE if
the time server is disabled.
Time Server IP Address This field displays the IP address of the time server.
Time Server Sync Status This field displays the status of the connection with the time server.
NONE: The time server is disabled.
CONNECTING: The Switch is trying to connect with the specified time server.
OK: Synchronize with time server done.
FAIL: Synchronize with time server fail.
Ethernet Switch CLI Reference Guide
76
Page 77

At the time of writing, data center bridging can only be configured using commands on the Switch.
20.1 Overview
A traditional Ethernet network is best-effort, that is, frames may be dropped due to network congestion.
FCoE (Fiber Channel over Ethernet) transparently encapsulates fiber channel traffic into Ethernet, so
that you don’t need separate fiber channel and Ethernet switches.
Data Center Bridging (DCB) enhances Ethernet technology to adapt to the FCoE. It supports lossless
Ethernet traffic (no frames discarded when there is network congestion) and can allocate bandwidth
for different traffic classes, based on IEEE802.1p priority with a guaranteed minimum bandwidth. LAN
traffic (large number of flows and not latency-sensitive), SAN traffic (Storage Area Network, large
packet sizes and requires lossless performance), and IPC traffic (Inter-Process Communication, latencysensitive messages) can share the same physical connection while still having their own priority and
guaranteed minimum bandwidth.
CHAPTER 20
Data Center Bridging
Commands
You should configure DCB on any port that has both Ethernet and fiber channel traffic.
20.1.1 PFC, ETS, and DCBX Standards
DCB may use PFC, ETS, application priority and DCBX to adapt to the FCoE.
• PFC (Priority-based Flow Control, IEEE 802.1Qbb -2011) is a flow control mechanism that uses a PAUSE
frame to suspend traffic of a certain priority rather than drop it when there is network congestion
(lossless). If an outgoing (egress) port buffer is almost full, the Switch transmits a PAUSE frame to the
sender who just transmitted traffic requesting it to stop sending traffic of a certain priority to that port.
For example, say outgoing port 8 is receiving too much traffic of priorities 3-6 from port 1. Then if port 1
is configured with PFC priorities 3-6, port 1 can request the sender to suspend traffic with priorities 3-6.
Similarly, if the outgoing (egress) port 8 receives a PAUSE frame with PFC priorities 0-1, then if port 8 is
configured with PFC, it can suspend sending traffic with PFC priorities 0-1.
• ETS (Enhanced Transmission Selection, IEEE 802.1Qaz -2011) is used to allocate bandwidth for different
traffic classes, based on IEEE802.1p priority (0 to 7, allowing for eight types of traffic) with a
guaranteed minimum bandwidth.
• Application priority is used to globally assign a priority to all FCoE traffic on the Switch.
• DCBX (Data Center Bridging capability eXchange, IEEE 802.1Qaz -2011) uses LLDP (Link Layer
Discovery Protocol) to advertize PFC, ETS and application priority information between switches. PFC
information should be consistent between connected switches, so PFC can be configured
automatically using DCBX.
Ethernet Switch CLI Reference Guide
77
Page 78

Chapter 20 Data Center Bridging Commands
The following table describes user-input values available in multiple commands for this feature.
Table 54 dcb User-input Values
COMMAND DESCRIPTION
<priority-list> Possible values range from 0 to 7.
<port-list> Possible values range from 1 to the number of ports on your Switch.
<id> Possible values for traffic class ID range from 1 to 100. 0 is a default traffic class and
<tc-idN> The traffic class ID for priority N (0 to 7). The traffic class ID range is from 1 to 100.
<name> Up to 32 printable ASCII characters. Names with spaces must be enclosed in quotes. For
<weight> Possible values range from 1 to 127 for unicast or multicast weights.
cannot be modified or deleted.
example, “My Class”.
Possible values range from 1 to 100 for WFQ traffic class weight.
20.2 Command Summary
This section shows the commands and examples for PFC, ETS, Application Priority and DCBX.
20.2.1 PFC
PFC should be configured the same on connected switch ports. If DCBX is used, then one switch port
must be configured to accept network configuration from the peer switch port (auto). If both switch
ports are configured to accept configuration (auto on both switch ports), then the configuration of the
switch port with the lowest MAC address hex value sum is used.
The following table lists the commands for this feature.
Table 55 priority-flow-control Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-list>
show priority-flow-control
show priority-flow-control
statistics interface port-channel
<port-list>
clear priority-flow-control
statistics interface port-channel
<port-list>
priority-flow-control
no priority-flow-control
priority-flow-control auto
priority-flow-control priority
<priority-list>
no priority-flow-control
priority
Enters config-interface mode for the specified port(s). C 13
Enables PFC on the specified port(s). C 13
Disables PFC on the specified port(s). C 13
Sets the port to accept PFC configuration from the
connected Switch port.
Sets the priority value(s) on the specified port(s). C 13
Clears the priority value(s) on the specified port(s). C 13
Displays PFC settings. E 3
Displays PFC statistics on the specified port(s). E 3
Clears PFC statistics on the specified port(s). E 13
C13
Ethernet Switch CLI Reference Guide
78
Page 79

Chapter 20 Data Center Bridging Commands
20.2.2 PFC Command Examples
In the following example, PFC on switch A, port 1, is set to auto, so that it can accept the priority
configuration from the peer switch B. If switch A did not receive PFC PDU from switch B, then priority 2,
will be used by switch A.
switchA# configure
switchA(config)# interface port-channel 1
switchA(config-interface)# priority-flow-control auto
switchA(config-interface)# priority-flow-control priority 2
switchB# configure
switchB(config)# interface port-channel 1
switchB(config-interface)# priority-flow-control
switchB(config-interface)# priority-flow-control priority 3-5
Use the show command to see the PFC configuration. Operation-Priority shows whether switch A is using
switch B’s configured priorities or not.
In the following example, Switch A is using Switch B’s configured priorities.
switchA# show priority-flow-control
Port Admin Operation Admin-Priority Operation-Priority
-------------------------------------------------------------------1 Auto On 2 3-5
In the following example, Switch A is NOT using Switch B’s configured priorities.
switchA# show priority-flow-control
Port Admin Operation Admin-Priority Operation-Priority
------------------------------------------------------------------- 1 Auto On 2 2
Ethernet Switch CLI Reference Guide
79
Page 80

Chapter 20 Data Center Bridging Commands
This is an example showing how many pause frames of certain priorities were temporarily stopped
(transmitted or received) on port 1.
sysname# show priority-flow-control statistics interface port-channel 1
Port Number: 1
PFC Tx
Priority 0: 0
Priority 1: 0
Priority 2: 0
Priority 3: 0
Priority 4: 0
Priority 5: 0
Priority 6: 0
Priority 7: 0
PFC Rx
Priority 0: 0
Priority 1: 0
Priority 2: 0
Priority 3: 0
Priority 4: 0
Priority 5: 0
Priority 6: 0
Priority 7: 0
sysname#
20.2.3 ETS
An IEEE 802.1p priority is assigned to a traffic class with guaranteed minimum bandwidth. A traffic class
can use SP (Strict Priority) or WFQ (Weighted Fair Queue) queuing method. Available link bandwidth is
reserved first for SP traffic. The guaranteed minimum bandwidth for non-SP traffic (WFQ) is its weight
value by remaining available bandwidth. If a non-strict-priority-traffic-class does not consume its
allocated bandwidth, other non-strict-priority- traffic-classes can share the unused b andwidth according
to the weight ratio.
20.2.3.1 Notes on ETS
• Priority 0 does not mean the highest or lowest priority. Priority level of importance is mapped to a
queue level (with queue level 0, the lowest importance).
• You don’t automatically configure ETS using DCBX negotiation. ETS is configured manually on each
Switch.
• All priorities are mapped to traffic class ID 0 by default.
• The default traffic class (named Default) has ID 0, and is an SP traffic-class. It cannot be modified or
deleted.
• You can create up to 100 traffic class profiles, with ID from 1 to 100.
• The weight range of WFQ traffic-class can be from 1 to 100.
• Bandwidth can also be prioritized depending on whether traffic is unicast traffic or non-unicast
(broadcast, multicast, DLF) traffic. For example, 100:50 means twice as much unicast traffic to nonunicast traffic is allowed when there is network congestion. The weight ranges of unicast and nonunicast traffic can be from 1 to 127.
Ethernet Switch CLI Reference Guide
80
Page 81

Chapter 20 Data Center Bridging Commands
The following table lists the commands for this feature.
Table 56 ets Command Summary
COMMAND DESCRIPTION M P
traffic-class <id> scheduler <sp |
ets <weight>> [name <name>]
no traffic-class <id>
show traffic-class
interface port-channel <port-list>
ets
ets traffic-class binding <tcid0> <tc-id1> <tc-id2> <tc-id3>
Creates a WFQ or SP traffic class with ID, weight and
(optional) name.
Deletes the SP/WFQ traffic class with specified ID. C 13
Shows a summary of traffic class(es) created on the
Switch.
Enters config-interface mode for the specified port(s). C 13
Enable Enhanced Transmission Selection (ETS) queuing
method. See Chapter 71 on page 270 for other
queuing methods.
Binds priorities to a traffic class(es) on the specified
port(s).
C13
E3
C13
C13
<tc-id4> <tc-id5> <tc-id6> <tcid7>
no ets traffic-class binding
unicast-nonunicast-weight
<weight> <weight>
Resets traffic class binding priorities to default settings
on the specified port(s).
Sets the unicast to non-unicast traffic weight ratio on
the specified port(s).
C13
C13
20.2.4 ETS Command Example 1
This is an example where the non-editable default traffic class, ID 0, uses SP queuing. LAN and SAN traffic
uses WFQ queuing with equal weighting of 50 each.
Table 57 ETS Example Traffic Classes
TRAFFIC CLASS ID GUARANTEED BANDWIDTH NAME
0 SP Default
150SAN
250LAN
The guaranteed minimum bandwidth for both SAN and LAN traffic is 2.5Gbps with a link bandwidth of
10Gbps.
Table 58 ETS Example Traffic Bandwidths
NAME
Default 5 5 (SP) 5
SAN 3 (10-5) * (50/(50+50)) = 2.5 2.5
LAN 4 (10-5) * (50/(50+50)) = 2.5 2.5
Create and name traffic class IDs, with weights for the non-SP traffic type.
INCOMING TRAFFIC
BANDWIDTH (GBPS)
GUARANTEED
MINIMUM BANDWIDTH
OUTGOING TRAFFIC
BANDWIDTH (GBPS)
sysname# configure
sysname(config)# traffic-class 1 scheduler ets 50 name LAN
sysname(config)# traffic-class 2 scheduler ets 50 name SAN
Ethernet Switch CLI Reference Guide
81
Page 82

Chapter 20 Data Center Bridging Commands
This command shows traffic class.
switch# show traffic-class
Traffic Class Profile Configuration:
Traffic Class ID Scheduler Weight Name
---------------- --------- ------ ------------------------------ 0 sp - Default
1 ets 50 LAN
2 ets 50 SAN
Next, configure a port for traffic class(es) and bind priorities to traffic classes on a port. In the next
example, we configure port 1 and bind priorities 0, 1 and 2 to traffic class 2 (LAN), 3, 4, 5 and 6 to class 1
(SAN) and 7 to class 0, the default traffic class.
Table 59 ETS Example Priority Traffic Class ID Mapping
PRIORITY TRAFFIC CLASS ID NAME
02LAN
12LAN
22LAN
31SAN
41SAN
51SAN
61SAN
7 0 Default
sysname(config)# interface port-channel 1
sysname(config-interface)# ets
sysname(config-interface)# ets traffic-class binding 2 2 2 1 1 1 1 0
sysname(config-interface)# unicast-nonunicast-weight 100 100
sysname(config-interface)# exit
20.2.5 Application Priority
Use the application priority command to assign a priority to all FCoE traffic on a switch.
The following table lists the commands for this feature.
Table 60 application priority Command Summary
COMMAND DESCRIPTION M P
lldp dcbx application <ethertype><fcoe> priority <0-7>
no lldp dcbx application <ethertype > <fcoe>
Assigns the specified priority value to all FCoE traffic
on the Switch.
Clears priority value for all FCoE traffic on the Switch. C 13
C13
Ethernet Switch CLI Reference Guide
82
Page 83

Chapter 20 Data Center Bridging Commands
20.2.6 Application Priority Command Examples
In the following example, all FCoE traffic on the switch is assigned with priority 3.
switchA# configure
switchA(config)# lldp dcbx application ether-type fcoe priority 3
Application priority can then be used in conjunction with ETS and PFC as shown in the following
examples.
This is an application priority command example with PFC.
switchA(config)# interface port-channel 5
switchA(config-interface)# priority-flow-control
switchA(config-interface)# priority-flow-control priority 3
switchB(config)# interface port-channel 6
switchB(config-interface)# priority-flow-control
switchB(config-interface)# priority-flow-control priority 3
This is an application priority command example with ETS.
• Default traffic class 0 with strict priority for priorities 0, 1, 2, 6, 7
• Traffic class 3 (for legacy Ethernet traffic): Guarantee bandwidth 40% for priority 4, 5
• Traffic class 4 (for FCoE traffic): Guarantee bandwidth 60% for priority 3
• Unicast to Non-Unicast weight ratio is 100:100
Table 61 ETS Example 2 Traffic Classes
PRIORITY TRAFFIC CLASS ID NAME
0 0 Default
1 0 Default
2 0 Default
34 FCoE
43Ethernet
53Ethernet
6 0 Default
7 0 Default
sysname# configure
sysname(config)# traffic-class 3 scheduler ets 40 name ethernet
sysname (config)# traffic-class 4 scheduler ets 60 name fcoe
sysname (config)# interface port-channel 6
sysname (config-interface)# ets
sysname (config-interface)# ets traffic-class binding 0 0 0 4 3 3 0 0
sysname (config-interface)# unicast-nonunicast-weight 100 100
Ethernet Switch CLI Reference Guide
83
Page 84

20.2.7 DCBX
DCBX uses LLDP (Link Layer Discovery Protocol) to exchange PFC, ETS and application priority
information between switches. PFC information should be consistent between switches, so this can be
configured automatically using DCBX.
See Chapter 44 on page 179 for more information on LLDP.
In order for switches to exchange information, they must send their type-length values (TLVs) in order to
be able to read each other’s information.
The following table lists the commands for this feature.
Table 62 dcbx Command Summary
COMMAND DESCRIPTION M P
interface port-channel <port-list>
Chapter 20 Data Center Bridging Commands
lldp org-specific-tlv dot1
dcbx-ets-configuration
lldp org-specific-tlv dot1
dcbx-pfc-configuration
lldp org-specific-tlv dot1
dcbx-application-priority
Enters config-interface mode for the specified port(s). C 13
Enables the sending of ETS TLVs on the specified
port(s).
Enables the sending of PFC TLVs on the specified
port(s).
Enables the sending of application priority TLVs on the
specified port(s).
C13
C13
C13
This is a DCBX command example.
sysname# configure
sysname(config)# lldp
interface port-channel 2
sysname(config-interface)# lldp admin-status tx-rx
sysname(config-interface)# lldp org-specific-tlv dot1 dcbx-etsconfiguration
sysname(config-interface)# lldp org-specific-tlv dot1 dcbx-pfcconfiguration
sysname(config-interface)# lldp org-specific-tlv dot1 dcbx-applicationpriority
sysname(config-interface)#exit
sysname(config)# exit
sysname#
See Chapter 44 on page 179 for LLDP command examples.
Ethernet Switch CLI Reference Guide
84
Page 85

DHCP Commands
Use these commands to configure DHCP features on the Switch.
• Use the dhcp option commands to configure DHCP Option 82 profiles.
• Use the dhcp relay commands to configure DHCP relay for specific VLAN.
• Use the dhcp smart-relay commands to configure DHCP relay for all broadcast domains.
• Use the dhcp server commands to configure the Switch as a DHCP server. (This command is
available on a layer 3 Switch only.)
21.1 Command Summary
The following section lists the commands for this feature.
Table 63 dhcp option Command Summary
COMMAND DESCRIPTION M P
dhcp option profile <name>
[ circuit-id [slot-port] [vlan]
[hostname] [string <string>] ] [
remote-id [mac] [string
<string>] ]
no dhcp option profile <name>
show dhcp option profile
CHAPTER 21
Creates a DHCPv4 option 82 profile. C 13
Deletes the specified DHCPv4 option 82 profile. C 13
Displays DHCP option 82 profile settings. E 3
Table 64 dhcp relay Command Summary
COMMAND DESCRIPTION M P
show dhcp relay <vlan-id>
dhcp relay <vlan-id> helper-
address <remote-dhcp-server1>
[<remote-dhcp-server2>]
[<remote-dhcp-server3>]
[option] [information]
dhcp relay <vlan-id> helperaddress <remote-dhcp-server1>
[<remote-dhcp-server2>]
[<remote-dhcp-server3>] [option
profile <name>]
Ethernet Switch CLI Reference Guide
Displays DHCP relay settings for the specified VLAN. E 3
Enables DHCP relay on the specified VLAN and sets the IP
address of up to 3 DHCP servers. Optionally, sets the Switch
to add relay agent information and system name.
Note: You have to configure the VLAN before you
configure a DHCP relay for the VLAN. You
have to disable dhcp smart-relay before
you can enable dhcp relay.
Enables DHCP relay on the specified VLAN and sets the IP
address of up to 3 DHCP servers. Optionally, specify a predefined DHCP option 82 profile that the Switch applies to
all ports in this VLAN.
Note: You have to configure the VLAN before you
configure a DHCP relay for the VLAN. You
have to disable dhcp smart-relay before
you can enable dhcp relay.
C13
C13
85
Page 86

Chapter 21 DHCP Commands
Table 64 dhcp relay Command Summary (continued)
COMMAND DESCRIPTION M P
dhcp relay <vlan-id> interface
port-channel <port-list> option
profile <name>
dhcp relay <vlan-id> sourceaddress <ip-addr>
no dhcp relay <vlan-id>
no dhcp relay <vlan-id>
information
no dhcp relay <vlan-id>
interface port-channel <port-
Specifies a pre-defined DHCP option 82 profile that the
Switch applies to the specified port(s) in this VLAN. The
Switch adds the Circuit ID sub-option and/or Remote ID
sub-option specified in the profile to DHCP requests that it
relays to a DHCP server.
Specifies the source IP address that the Switch adds to
DHCP requests from clients in this VLAN before forwarding
them.
The source IP address helps DHCP clients obtain an
appropriate IP address when you configure multiple
routing domains on a VLAN.
Disables DHCP relay. C 13
System name is not appended to option 82 information
field.
Sets the Switch to not apply a DHCP option 82 profile to the
specified port(s) in this V LAN.
C13
C13
C13
C13
list> option
no dhcp relay <vlan-id> source-
address
no dhcp relay <vlan-id> option
Removes the source IP address setting and sets this field set
to 0.0.0.0. The Switch automatically sets the source IP
address of the DHCP requests to the IP address of the
interface on which the packet is received.
Disables the relay agent information option 82. C 13
C13
Table 65 dhcp relay-broadcast Command Summary
COMMAND DESCRIPTION M P
dhcp relay-broadcast
no dhcp relay-broadcast
The broadcast behavior of DHCP packets (within the
VLAN(s) on which DHCP relay is enabled) will not be
terminated by the Switch.
The Switch terminates the broadcast behavior of DHCP
packets within the VLAN(s) on which DHCP relay is
enabled.
C13
C13
Table 66 dhcp smart-relay Command Summary
COMMAND DESCRIPTION M P
show dhcp smart-relay
dhcp smart-relay
Displays global DHCP relay settings. E 3
Enables DHCP relay for all broadcast domains on the
Switch.
C13
Note: You have to disable dhcp relay before you
can enable dhcp smart-relay.
no dhcp smart-relay
dhcp smart-relay helper-address
Disables global DHCP relay settings. C 13
Sets the IP addresses of up to 3 DHCP servers. C 13
<remote-dhcp-server1> [<remote-
dhcp-server2>] [<remote-dhcpserver3>]
dhcp smart-relay information
no dhcp smart-relay information
Allows the Switch to add system name to agent
information.
System name is not appended to option 82 information
field for global dhcp set tings.
C13
C13
Ethernet Switch CLI Reference Guide
86
Page 87

Chapter 21 DHCP Commands
Table 66 dhcp smart-relay Command Summary (continued)
COMMAND DESCRIPTION M P
dhcp smart-relay interface portchannel <port-list> option
Specifies a pre-defined DHCP option 82 profile that the
Switch applies to the specified port(s).
C13
profile <name>
Note: The profile you specify here has priority over
the one you set using the dhcp smart-relay
option profile <name> command.
dhcp smart-relay option
dhcp smart-relay option profile
<name>
no dhcp smart-relay interface
port-channel <port-list>
no dhcp smart-relay option
Allows the Switch to add DHCP relay agent information. C 13
Specifies a pre-defined DHCPv4 option 82 profile that the
Switch applies to all ports. The Switch adds the Circuit ID
sub-option and/or Remote ID sub-option specified in the
profile to DHCP requests that it relays to a DHCP server.
Sets the Switch to not apply a DHCP option 82 profile to
the specified port(s).
Disables the relay agent information option 82 for global
dhcp settings.
C13
C13
C13
Table 67 dhcp server Command Summary
COMMAND DESCRIPTION M P
dhcp server <vlan-id> startingaddress <ip-addr> <subnet-mask>
Enables DHCP server for the specified VLAN and specifies
the TCP/IP configuration details to send to DHCP clients.
C13
size-of-client-ip-pool <1-1024>
dhcp server <vlan-id> starting-
address <ip-addr> <subnet-mask>
size-of-client-ip-pool <1-1024>
[default-gateway <ip-addr>]
[primary-dns <ip-addr>]
Enables DHCP server for the specified VLAN and specifies
the TCP/IP configuration details to send to DHCP clients.
Including default gateway IP address and DNS server
information.
C13
[secondary-dns <ip-addr>]
no dhcp server <vlan-id>
no dhcp server <vlan-id>
Disables DHCP server for the specified VLAN. C 13
Disables DHCP server default gateway settings. C 13
default-gateway
no dhcp server <vlan-id>
Disables DHCP primary DNS server settings. C 13
primary-dns
no dhcp server <vlan-id>
Disables DHCP server secondary DNS settings. C 13
secondary-dns
show dhcp server
show dhcp server <vlan-id>
Displays DHCP server settings. E 13
Displays DHCP server settings in a specified VLAN. E 13
21.2 Command Examples
In this example, the Switch relays DHCP requests for the VLAN1 and VLAN2 domains. There is only one
DHCP server for DHCP clients in both domains.
Ethernet Switch CLI Reference Guide
87
Page 88

Chapter 21 DHCP Commands
VLAN1
VLAN2
192.168.1.100
DHCP Server:
VLAN 1
VLAN 2
DHCP:
192.168.1.100
DHCP:
172.16.10.100
Figure 4 Example: Global DHCP Relay
This example shows how to configure the Switch for this configuration. DHCP relay agent information
option 82 is also enabled.
sysname# configure
sysname(config)# dhcp smart-relay
sysname(config)# dhcp smart-relay helper-address 192.168.1.100
sysname(config)# dhcp smart-relay option
sysname(config)# exit
sysname# show dhcp smart-relay
DHCP Relay Agent Configuration
Active: Yes
Remote DHCP Server 1:192.168.1.100
Remote DHCP Server 2: 0.0.0.0
Remote DHCP Server 3: 0.0.0.0
Option82: Enable Option82Inf: Disable
In this example, there are two VLANs (VIDs 1 and 2) in a campus network. Two DHCP servers are installed
to serve each VLAN. The Switch forwards DHCP requests from the dormitory rooms (VLAN 1) to the DHCP
server with IP address 192.168.1.100. DHCP requests from the academic buildings (VLAN 2) are sent to
the other DHCP server with IP address 172.16.10.100.
Figure 5 Example: DHCP Relay for Two VLANs
Ethernet Switch CLI Reference Guide
88
Page 89

Chapter 21 DHCP Commands
VLAN 1
VLAN 2
DHCP Pool:
192.168.1.100-192.168.1.200
DHCP Pool:
172.16.1.30-172.16.1.130
This example shows how to configure these DHCP servers. The VLANs are already configured.
sysname# configure
sysname(config)# dhcp relay 1 helper-address 192.168.1.100
sysname(config)# dhcp relay 2 helper-address 172.16.10.100
sysname(config)# exit
In this example, the Switch is a DHCP server for clients on VLAN 1 and VLAN 2. The DHCP clients in VLAN 1
are assigned IP addresses in the range 192.168.1.100 to 192.168.1.200 and clients on VLAN 2 are assigned
IP addresses in the range 172.16.1.30 to 172.16.1.130.
Figure 6 Example: DHCP Relay for Two VLANs
This example shows how to configure the DHCP server for VLAN 1 with the configuration shown in Figure
6 on page 89. It also provides the DHCP clients with the IP address of the default gateway and the DNS
server.
sysname# configure
sysname(config)# dhcp server 1 starting-address 192.168.1.100
255.255.255.0 size-of-client-ip-pool 100 default-gateway 192.168.1.1
primary-dns 192.168.5.1
Ethernet Switch CLI Reference Guide
89
Page 90

DHCP Snooping & DHCP
VLAN Commands
Use the dhcp snooping commands to configure the DHCP snooping on the Switch and the dhcp vlan
commands to specify a DHCP VLAN on your network. DHCP snooping filters unauthorized DHCP packets
on the network and builds the binding table dynamically.
22.1 Command Summary
The following section lists the commands for this feature.
Table 68 dhcp snooping Command Summary
COMMAND DESCRIPTION M P
show dhcp snooping
show dhcp snooping binding
show dhcp snooping database
show dhcp snooping database
detail
show dhcp snooping option [vlan
<vlan-list>] [interface <port-
list>]
dhcp snooping
no dhcp snooping
dhcp snooping database <tftp://
host/filename>
no dhcp snooping database
dhcp snooping database timeout
<seconds>
no dhcp snooping database
timeout
dhcp snooping database writedelay <seconds>
CHAPTER 22
Displays DHCP snooping configuration on the Switch. E 3
Displays the DHCP binding table. E 3
Displays DHCP snooping database update statistics and
settings.
Displays DHCP snooping database update statistics in full
detail form.
Displays the DHCP option 82 profile that the Switch applies
to ports in the specified VLAN or to the specified port(s).
Enables DHCP Snooping on the Switch. C 13
Disables DHCP Snooping on the Switch. C 13
Specifies the location of the DHCP snooping database.
The location should be expressed like this: tftp://{domain
name or IP address}/directory, if applicable/file name; for
example, tftp://192.168.10.1/database.txt.
Removes the location of the DHCP snooping database. C 13
Specifies how long (10-65535 seconds) the Switch tries to
complete a specific update in the DHCP snooping
database before it gives up.
Resets how long (10-65535 seconds) the Switch tries to
complete a specific update in the DHCP snooping
database before it gives up to the default value (300).
Specifies how long (10-65535 seconds) the Switch waits to
update the DHCP snooping database the first time the
current bindings change after an update.
E3
E3
E3
C13
C13
C13
C13
Ethernet Switch CLI Reference Guide
90
Page 91

Chapter 22 DHCP Snooping & DHCP VLAN Commands
Table 68 dhcp snooping Command Summary (continued)
COMMAND DESCRIPTION M P
no dhcp snooping database writedelay
dhcp snooping vlan <vlan-list>
no dhcp snooping vlan <vlan-
list>
dhcp snooping vlan <vlan-list>
information
no dhcp snooping vlan <vlan-
list> information
dhcp snooping vlan <vlan-list>
interface port-channel <port-
list> option profile <name>
no dhcp snooping vlan <vlan-
list> interface port-channel
Resets how long (10-65535 seconds) the Switch waits to
update the DHCP snooping database the first time the
current bindings change after an update to the default
value (300).
Specifies the VLAN IDs for VLANs you want to enable DHCP
snooping on.
Specifies the VLAN IDs for VLANs you want to disable DHCP
snooping on.
Sets the Switch to add the system name to DHCP requests
that it broadcasts to the DHCP VLAN, if specified, or VLAN.
Sets the Switch to not add the system name to DHCP
requests that it broadcasts to the DHCP VLAN, if specified,
or VLAN.
Specifies a pre-defined DHCP option 82 profile that the
Switch applies to the specified port(s) in the specified
VLAN.
Sets the Switch to not apply a DHCP option 82 profile to the
specified port(s).
C13
C13
C13
C13
C13
C13
C13
<port-list> option
dhcp snooping vlan <vlan-list>
option
no dhcp snooping vlan <vlan-
list> option
dhcp snooping vlan <vlan-list>
option profile <name>
no dhcp snooping vlan <vlan-
list> option
clear dhcp snooping database
statistics
renew dhcp snooping database
renew dhcp snooping database
<tftp://host/filename>
interface port-channel <port-
Sets the Switch to add the slot number, port number and
VLAN ID to DHCP requests that it broadcasts to the DHCP
VLAN, if specified, or VLAN.
Sets the Switch to not add the slot number, port number
and VLAN ID to DHCP requests that it broadcasts to the
DHCP VLAN, if specified, or VLAN.
Specifies a pre-defined DHCP option 82 profile that the
Switch applies to all ports in the specified VLAN.
Sets the Switch to not apply a DHCP option 82 profile to all
ports in the specified VLAN.
Delete all statistics records of DHCP requests going through
the Switch.
Loads dynamic bindings from the default DHCP snooping
database.
Loads dynamic bindings from the sp ecified DHCP
snooping database.
Enables a port or a list of ports for configuration. C 13
C13
C13
C13
C13
E13
E13
E13
list>
dhcp snooping trust
dhcp snooping limit rate
<pps>
no dhcp snooping trust
no dhcp snooping limit rate
Sets this port as a trusted DHCP snooping port. Trusted ports
are connected to DHCP servers or other switches, and the
Switch discards DHCP packets from trusted ports only if the
rate at which DHCP packets arrive is too high.
Sets the maximum rate in packets per second (pps) that
DHCP packets are allowed to arrive at a trusted DHCP
snooping port.
Disables this port from being a trusted port for DHCP
snooping.
Resets the DHCP snooping rate to the default (0). C 13
C13
C13
C13
Ethernet Switch CLI Reference Guide
91
Page 92

Chapter 22 DHCP Snooping & DHCP VLAN Commands
The following table describes the dhcp-vlan commands.
Table 69 dhcp-vlan Command Summary
COMMAND DESCRIPTION M P
dhcp dhcp-vlan <vlan-id>
no dhcp dhcp-vlan
22.2 Command Examples
This example:
• Enables DHCP snooping Switch.
• Sets up an external DHCP snooping database on a network server with IP address 172.16.37.17.
• Enables DHCP snooping on VLANs 1,2,3,200 and 300.
• Sets the Switch to add the slot number, port number and VLAN ID to DHCP requests that it broadcasts
to the DHCP VLAN.
• Sets ports 1 - 5 as DHCP snooping trusted ports.
• Sets the maximum number of DHCP packets that can be received on ports 1 - 5 to 100 packets per
second.
• Configures a DHCP VLAN with a VLAN ID 300.
Specifies the VLAN ID of the DHCP VLAN. C 13
Disables DHCP VLAN on the Switch. C 13
Ethernet Switch CLI Reference Guide
92
Page 93

Chapter 22 DHCP Snooping & DHCP VLAN Commands
•Displays DHCP snooping configuration details.
sysname(config)# dhcp snooping
sysname(config)# dhcp snooping database tftp://172.16.37.17/
snoopdata.txt
sysname(config)# dhcp snooping vlan 1,2,3,200,300
sysname(config)# dhcp snooping vlan 1,2,3,200,300 option
sysname(config)# interface port-channel 1-5
sysname(config-interface)# dhcp snooping trust
sysname(config-interface)# dhcp snooping limit rate 100
sysname(config-interface)# exit
sysname(config)# dhcp dhcp-vlan 300
sysname(config)# exit
sysname# show dhcp snooping
Switch DHCP snooping is enabled
DHCP Snooping is configured on the following VLANs:
1-3,200,300
Option 82 is configured on the following VLANs:
1-3,200,300
Appending system name is configured on the following VLANs:
DHCP VLAN is enabled on VLAN 300
Interface Trusted Rate Limit (pps)
--------- ------- --------------- 1 yes 100
2 yes 100
3 yes 100
4 yes 100
5 yes 100
6 no unlimited
7 no unlimited
8 no unlimited
Ethernet Switch CLI Reference Guide
93
Page 94

DiffServ Commands
Use these commands to configure Differentiated Services (DiffServ) on the Switch.
23.1 Command Summary
The following section lists the commands for this feature.
Table 70 diffserv Command Summary
COMMAND DESCRIPTION M P
show diffserv
diffserv
no diffserv
diffserv dscp <0-63> priority
<0-7>
interface port-channel <port-
list>
diffserv
no diffserv
CHAPTER 23
Displays general DiffServ settings. E 3
Enables DiffServ on the Switch. C 13
Disables DiffServ on the Switch. C 13
Sets the DSCP-to-IEEE 802.1q mappings. C 13
Enters config-interface mode for the specified port(s). C 13
Enables DiffServ on the port(s). C 13
Disables DiffServ on the port(s). C 13
Ethernet Switch CLI Reference Guide
94
Page 95

Display Commands
Use these commands to display configuration information.
24.1 Command Summary
The following section lists the commands for this feature.
Table 71 display Command Summary
COMMAND DESCRIPTION M P
display user <[system][snmp]>
no display user <[system][snmp]>
display aaa
<[authentication][authorization][
server]>
CHAPTER 24
Displays all or specific user account information in the
configuration file.
system: Displays system account information, such as
admin, enable or login username and password.
snmp: Displays SNMP user account information.
Hide all or specific user account information in the
configuration file.
Displays all or specific AAA information in the
configuration file.
authentication: Displays authentication information in
the configuration file.
C14
C14
C14
no display aaa
<[authentication][authorization][
server]>
Ethernet Switch CLI Reference Guide
authorization: Displays authorization information in the
configuration file.
server: Displays authentication server information in the
configuration file.
Hide all or specific AAA information in the configuration
file.
C14
95
Page 96

DVMRP Commands
This chapter explains how to use commands to activate the Distance Vector Multicast Routing Protocol
(DVMRP) on the Switch.
25.1 DVMRP Overview
DVMRP (Distance Vector Multicast Routing Protocol) is a protocol used for routing multicast data.
DVMRP is used when a router receives multicast traffic and it wants to find out if other multicast routers it
is connected to need to receive the data. DVMRP sends the data to all attached routers and waits for a
reply. Routers which do not need to receive the data (do not have multicast group member
connected) return a “prune” message, which stops further multicast traffic for that group from reaching
the router.
CHAPTER 25
25.2 Command Summary
The following section lists the commands for this feature.
Table 72 Command Summary: DVMRP
COMMAND DESCRIPTION M P
show ip dvmrp group
show ip dvmrp interface
show ip dvmrp neighbor
show ip dvmrp prune
show ip dvmrp route
show router dvmrp
router dvmrp
exit
threshold <ttl-value>
no router dvmrp
interface route-domain <ip-address>/
<mask-bits>
ip dvmrp
no ip dvmrp
Displays DVMRP group information. E 3
Displays DVMRP interface information. E 3
Displays DVMRP neighbor information. E 3
Displays the DVMRP prune information. E 3
Displays the DVMRP routes. E 3
Displays DVMRP settings. E 3
Enables and enters the DVMRP configuration
mode.
Leaves the DVMRP configuration mode. C 13
Sets the DVMRP threshold value. Multicast
packets with TTL (Time-To-Live) value lower than
the threshold are not forwarded by the Switch.
Disables DVMRP on the Switch. C 13
Enters the configuration mode for this routing
domain.
Activates this routing domain in participating in
DVMRP.
Disables this routing domain from participating in
DVMRP.
C13
C13
C13
C13
C13
Ethernet Switch CLI Reference Guide
96
Page 97

Chapter 25 DVMRP Commands
A
B
C
D
E
10.10.10.254
172.16.1.254
25.3 Command Examples
In this example, the Switch is configured to exchange DVMRP information with other DVMRP enabled
routers as shown next. The Switch is a DVMRP router (C). DVMRP is activated on IP routing domains
10.10.10.1/24 and 172.16.1.1/24 so that it can exchange DVMRP information with routers A and B.
Figure 7 DVMRP Network Example
• Enables IGMP and DVMRP on the Switch.
• Enables DVMRP on the following routing domains: 10.10.10.1/24, 172.16.1.1/24.
• Displays DVMRP settings configured on the Switch.
sysname(config)# router igmp
sysname(config-igmp)# exit
sysname(config)# router dvmrp
sysname(config-dvmrp)# exit
sysname(config)# interface route-domain 10.10.10.1/24
sysname(config-if)# ip dvmrp
sysname(config-if)# exit
sysname(config)# interface route-domain 172.16.1.1/24
sysname(config-if)# ip dvmrp
sysname(config-if)# exit
sysname(config)# exit
sysname# show router dvmrp
TTL threshold: 50
IP Address Subnet Mask Active
----------------------------------------
10.10.10.1 255.255.255.0 Yes
172.16.1.1 255.255.255.0 Yes
192.168.1.1 255.255.255.0 No
Ethernet Switch CLI Reference Guide
97
Page 98

Error Disable and Recovery
Use these commands to configure the CPU protection and error disable recovery features on the
Switch.
26.1 CPU Protection Overview
Switches exchange protocol control packets in a network to get the latest networking information. If a
Switch receives large numbers of control packets, such as ARP, BPDU or IGMP packets, which are to be
processed by the CPU, the CPU may become overloaded and be unable to handle regular tasks
properly.
CHAPTER 26
Commands
The CPU protection feature allows you to limit the rate of ARP, BPDU and IGMP packets to be delivered
to the CPU on a port. This enhances the CPU efficiency and protects against potential DoS attacks or
errors from other network(s). You then can choose to drop control packets that exceed the specified
rate limit or disable a port on which the packets are received.
26.2 Error-Disable Recovery Overview
Some features, such as loop guard or CPU protection, allow the Switch to shut down a port or discard
specific packets on a port when an error is detected on the port. For example, if the Switch detects that
packets sent out the port(s) loop back to the Switch, the Switch can shut down the port(s)
automatically. After that, you need to enable the port(s) or allow the packets on a port manually via the
web configurator or the commands. With error-disable recovery, you can set the disabled port(s) to
become active or start receiving the packets again after the time interval you specify.
26.3 User Input Values
This section lists the common term definition appears in this chapter.
Table 73 errdisable recovery command user input values
USER INPUT DESCRIPTION
port-list
The port number or a range of port numbers that you want to configure.
Ethernet Switch CLI Reference Guide
98
Page 99

Chapter 26 Error Disable and Recovery Commands
26.4 Command Summary
The following section lists the commands for this feature.
Table 74 cpu-protection Command Summary
COMMAND DESCRIPTION M P
interface port-channel <portlist>
cpu-protection cause
<ARP|BPDU|IGMP> rate-limit
<0-256>
clear cpu-protection interface
port-channel <port-list> cause
<ARP|BPDU|IGMP>
reset cpu-protection interface
port-channel <port-list> cause
<ARP|BPDU|IGMP>
show cpu-protection interface
port-channel <port-list>
Enables a port or a list of ports for configuration. C 13
Sets the maximum number of ARP, BPDU or IGMP packets
that the specified port(s) are allowed to receive or transmit
per second. 0 means no rate limit.
Resets the “Total Drop” counters for the specified port(s) to
zero (0). You can see the counter using the show cpu-
protection command. The “Total Drops” means the
number of ARP, BPDU or IGMP packets that have been
dropped due to the Error Disable feature in rate-
limitation mode.
Sets the specified port(s) to handle all ARP, BPDU or IGMP
packets in stead of ignoring them, if the port(s) are in
inactive-reason mode (set by using the errdisable
detet cause command).
Shows the CPU Protection settings and the number of ARP,
BPDU and/or IGMP packets that has been dropped by the
Error Disable feature for the specified port(s).
C13
E13
E13
E13
Table 75 errdisable recovery Command Summary
COMMAND DESCRIPTION M P
errdisable detect cause
<ARP|BPDU|IGMP>
errdisable detect cause
<ARP|BPDU|IGMP> mode <inactiveport|inactive-reason|ratelimitation>
errdisable recovery
errdisable recovery cause
<loopguard|ARP|BPDU|IGMP>
errdisable recovery cause
<loopguard|ARP|BPDU|IGMP>
Sets the Switch to detect if the number of ARP, BPDU or
IGMP packets exceeds the rate limit on port(s) (set by
using the cpu-protection cause command).
Sets the action that the Switch takes when the number of
ARP, BPDU or IGMP packets exceeds the rate limit on
port(s).
inactive-port: The Switch shuts down the port.
inactive-reason: The Switch bypasses the processing of
the specified control packets (such as ARP or IGMP
packets), or drops all the specified control packets (such
as BPDU) on the port.
rate-limitation: The Switch drops the additional control
packets the port(s) have to handle in every one second.
Turns on the disabled port recovery function on the Switch. C 13
Enables the recovery timer for the specified feature that
causes the Switch to shut down port(s).
Sets how many seconds the Switch waits before enabling
the port(s) which was shut down.
C13
C13
C13
C13
interval <30-2592000>
no errdisable detect cause
<ARP|BPDU|IGMP>
no errdisable recovery
no errdisable recovery cause
<loopguard|ARP|BPDU|IGMP>
Disables the rate limit for ARP, BPDU or IGMP packets on
port(s), set by using the cpu-protection cause
command.
Turns off the disabled port recovery function on the Switch. C 13
Disables the recovery timer for the specified feature that
causes the Switch to shut down a port.
C13
C13
Ethernet Switch CLI Reference Guide
99
Page 100

Chapter 26 Error Disable and Recovery Commands
Table 75 errdisable recovery Command Summary (continued)
COMMAND DESCRIPTION M P
show errdisable
show errdisable detect
show errdisable recovery
26.5 Command Examples
This example shows you how to configure the following:
• limit the number of ARP packets that port 7 can handle to 100 packets per second.
• set to shut down port 7 when the number ARP packets the port should handle exceeds the rate limit.
• display the CPU protection settings that you just set for port 7.
• display the Error Disable status and action mode for ARP packet handling.
systemname# config
systemname(config)# interface port-channel 7
systemname(config-interface)# cpu-protection cause ARP rate-limit 100
systemname(config-interface)# exit
systemname(config)# errdisable detect cause ARP
systemname(config)# errdisable detect cause ARP mode inactive-port
systemname(config)# exit
systemname# show cpu-protection interface port-channel 7
Port : 7
Displays which port(s) are detected (by Error Disable), the
mode of the ports, and which packets (ARP, BPDU or
IGMP) are being detected.
Displays the Error Disable settings including the available
protocol of packets (ARP, BPDU or IGMP), the current
status (enabled or disabled), and the corresponding
action the Switch takes when a detected port is handling
packets over the limit.
Displays the disabled port recovery settings and after how
many seconds which port(s) will be activated.
E13
E13
E13
Reason Rate Mode Total Drops
------ ------- --------------- ---------- ARP 100 inactive-port BPDU 0 inactive-port IGMP 0 inactive-port -
systemname# show errdisable detect
Reason Status Mode
------ ------- -------------- ARP enable inactive-port
BPDU enable rate-limitation
IGMP enable inactive-port
systemname#
This example enables the disabled port recovery function and the recovery timer for the loopguard
feature on the Switch. If a port is shut down due to the specified reason, the Switch activates the port
Ethernet Switch CLI Reference Guide
100
 Loading...
Loading...