Konica Minolta bizhub C650 User Manual

User’s Guide [Network Scanner Operations]

Introduction
Introduction
Thank you for choosing this machine.
This User’s Guide contains details on making network connections and on the operations required to use the
scanning functions of the bizhub C650, precautions on its use, and basic troubleshooting procedures. In
order to ensure that this machine is used correctly and efficiently, carefully read this User’s Guide before
using the machine.
In addition, for details on the operation of PageScope Web Connection, which can be used to operate this
machine over a network, refer to the User’s Guide [PageScope Web Connection Operations].
Views of the actual equipment may be slightly different from the illustrations used in this manual.
C650 x-1
Introduction
Trademarks and registered trademarks
KONICA MINOLTA, KONICA MINOLTA Logo, and The essentials of imaging are registered trademarks or
trademarks of KONICA MINOLTA HOLDINGS, INC.
PageScope and bizhub are registered trademarks or trademarks of KONICA MINOLTA BUSINESS
TECHNOLOGIES, INC.
Netscape is a registered trademark of Netscape Communications Corporation in the United States and other
countries.
This machine and PageScope Box Operator are based in part on the work of the Independent JPEG Group.
Compact-VJE
Copyright 1986-2003 VACS Corp.
RC4® is a registered trademark or trademark of RSA Security Inc. in the United States and/or other countries.
RSA® is a registered trademark or trademark of RSA Security Inc. RSA BSAFE® is a registered trademark or
trademark of RSA Security Inc. in the United States and/or other countries.
License information
This product includes RSA BSAFE Cryptographic software from RSA Security Inc.
®
This product contains Adobe
Copyright © 1995-2007 Adobe Macromedia Software LLC. All rights reserved.
Adobe and Flash are either registered trademarks or trademarks of Adobe Systems Incorporated in the
United States and/or other countries.
All other product and brand names are trademarks or registered trademarks of their respective companies or
organizations.
NetFront statement
This product contains ACCESS Co., Ltd.’s NetFront Internet browser software.
NetFront is a trademark or registered trademark of ACCESS Co., Ltd. in Japan and in other countries.
Copyright © 2004 Adobe Systems Incorporated. All rights reserved. Patents Pending.
OpenSSL statement
Flash® Player under license from Adobe Systems Incorporated.
OpenSSL license
Copyright © 1998-2005 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following
acknowledgment:
"This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit.
(http://www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to endorse or promote
products derived from this software without prior written permission. For written permission, please
contact openssl-core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their
names without prior written permission of the OpenSSL Project.
C650 x-2

Introduction
6. Redistributions of any form whatsoever must retain the following acknowledgment:
"This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit
(http://www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT "AS IS" AND ANY EXPRESSED OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL
PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
EXEMPLARY, OR CONSEQENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product
includes software written by Tim Hudson (tjh@cryptsoft.com).
Original SSLeay license
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are aheared
to. The following conditions apply to all code found in this distribution, be it the RC4, RSA, Ihash, DES, etc.,
code; not just the SSL code.
The SSL documentation included with this distribution is covered by the same copyright terms except that
the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young’s, and as such any Copyright notices in the code are not to be removed. If this
package is used in a product, Eric Young should be given attribution as the author of the parts of the library
used. This can be in the form of a textual message at program startup or in documentation (online or textual)
provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
1. Redistributions of source code must retain the copyright notice, this list of conditions and the following
disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following
acknowledgement:
"This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)"
The word ‘cryptographic’ can be left out if the rouines from the library being used are not cryptographic
related.
4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application
code) you must include an acknowledgement:
"This product includes software written by Tin Hudson (tjh@cryptsoft.com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS
FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be
changed. i.e. this code cannot simply be copied and put under another distribution licence [including the
GNU Public Licence.]
NetSNMP Licenses
Part 1: CMU/UCD copyright notice: (BSD like)
Copyright 1989, 1991, 1992 by Carnegie Mellon University Derivative Work - 1996, 1998-2000
Copyright 1996, 1998-2000 The Regents of the University of California All Rights Reserved
Permission to use, copy, modify and distribute this software and its documentation for any purpose and
without fee is hereby granted, provided that the above copyright notice appears in all copies and that both
C650 x-3

Introduction
that copyright notice and this permission notice appear in supporting documentation, and that the name of
CMU and The Regents of the University of California not be used in advertising or publicity pertaining to
distribution of the software without specific written permission.
CMU AND THE REGENTS OF THE UNIVERSITY OF CALIFORNIA DISCLAIM ALLWARRANTIES WITH
REGARD TO THIS SOFTWARE, INCLUDING ALL IMPLIEDWARRANTIES OF MERCHANTABILITY AND
FITNESS. IN NO EVENT SHALL CMU OR THE REGENTS OF THE UNIVERSITY OF CALIFORNIA BE LIABLE
FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER
RESULTING FROM THE LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF CONTRACT,
NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE USE OR
PERFORMANCE OF THIS SOFTWARE.
Part 2: Networks Associates Technology, Inc copyright notice (BSD)
Copyright © 2001-2003, Networks Associates Technology, Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of the Networks Associates Technology, Inc nor the names of its contributors may be
used to endorse or promote products derived from this software without specific prior written
permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT,
INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED
TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 3: Cambridge Broadband Ltd. copyright notice (BSD)
Portions of this code are copyright © 2001-2003, Cambridge Broadband Ltd.
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
- The name of Cambridge Broadband Ltd. may not be used to endorse or promote products derived from
this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDER "AS IS" AND ANY EXPRESS OR IMPLIED
WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY
AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT
HOLDER BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER
CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT
(INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 4: Sun Microsystems, Inc. copyright notice (BSD)
Copyright © 2003 Sun Microsystems, Inc., 4150 Network Circle, Santa Clara, California 95054, U.S.A. All
rights reserved.
Use is subject to license terms below.
This distribution may include materials developed by third parties.
C650 x-4

Introduction
Sun, Sun Microsystems, the Sun logo and Solaris are trademarks or registered trademarks of Sun
Microsystems, Inc. in the U.S. and other countries.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of the Sun Microsystems, Inc. nor the names of its contributors may be used to
endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT,
INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED
TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 5: Sparta, Inc copyright notice (BSD)
Copyright © 2003-2004, Sparta, Inc All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of Sparta, Inc nor the names of its contributors may be used to endorse or promote
products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT,
INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED
TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Part 6: Cisco/BUPTNIC copyright notice (BSD)
Copyright © 2004, Cisco, Inc and Information Network Center of Beijing University of Posts and
Telecommunications. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of Cisco, Inc, Beijing University of Posts and Telecommunications, nor the names of
their contributors may be used to endorse or promote products derived from this software without
specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE COPYRIGHT HOLDERS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT,
INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED
TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
C650 x-5

Introduction
All other product names mentioned are trademarks or registered trademarks of their respective companies
Kerberos
Copyright © 1985-2005 by the Massachusetts Institute of Technology. All rights reserved.
permission notice
WITHIN THAT CONSTRAINT, permission to use, copy, modify, and distribute this software and its
documentation for any purpose and without fee is hereby granted, provided that the above copyright notice
appear in all copies and that both that copyright notice and this permission notice appear in supporting
documentation, and that the name of M.I.T. not be used in advertising or publicity pertaining to distribution
of the software without specific, written prior permission. Furthermore if you modify this software you must
label your software as modified software and not distribute it in such a fashion that it might be confused with
the original MIT software.
M.I.T. makes no representations about the suitability of this software for any purpose. It is provided "as is"
without express or implied warranty.
THIS SOFTWARE IS PROVIDED "AS IS" AND WITHOUT ANY EXPRESS OR IMPLIED WARRANTIES,
INCLUDING, WITHOUT LIMITATION, THE IMPLIED WARRANTIES OF MERCHANTIBILITY AND FITNESS
FOR A PARTICULAR PURPOSE.
THIS SOFTWARE IS NOT ORIGINAL MIT SOFTWARE, MODIFIED BY KONICA MINOLTA BUSINESS
TECHNOLOGIES, INC.
Mersenne Twister
A C-program for MT19937, with initialization improved 2002/1/26.
Coded by Takuji Nishimura and Makoto Matsumoto.
Before using, initialize the state by using init_genrand(seed) or init_by_array(init_key, key_length).
Copyright © 1997-2002, Makoto Matsumoto and Takuji Nishimura, All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that
the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the
following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the
following disclaimer in the documentation and/or other materials provided with the distribution.
3. The names of its contributors may not be used to endorse or promote products derived from this
software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY
EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT,
INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED
TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR
BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Any feedback is very welcome.
http://www.math.sci.hiroshima-u.ac.jp/~m-mat/MT/emt.html
email: m-mat @ math.sci.hiroshima-u.ac.jp (remove space)
C650 x-6

Introduction
Contents
Introduction
Trademarks and registered trademarks ..............................................................................................................x-2
NetFront statement ..................................................................................................................................x-2
OpenSSL statement ................................................................................................................................x-2
NetSNMP Licenses ..................................................................................................................................x-3
Kerberos ..................................................................................................................................................x-6
Mersenne Twister ....................................................................................................................................x-6
Contents ..................................................................................................................................................................x-7
About this manual.................................................................................................................................................x-12
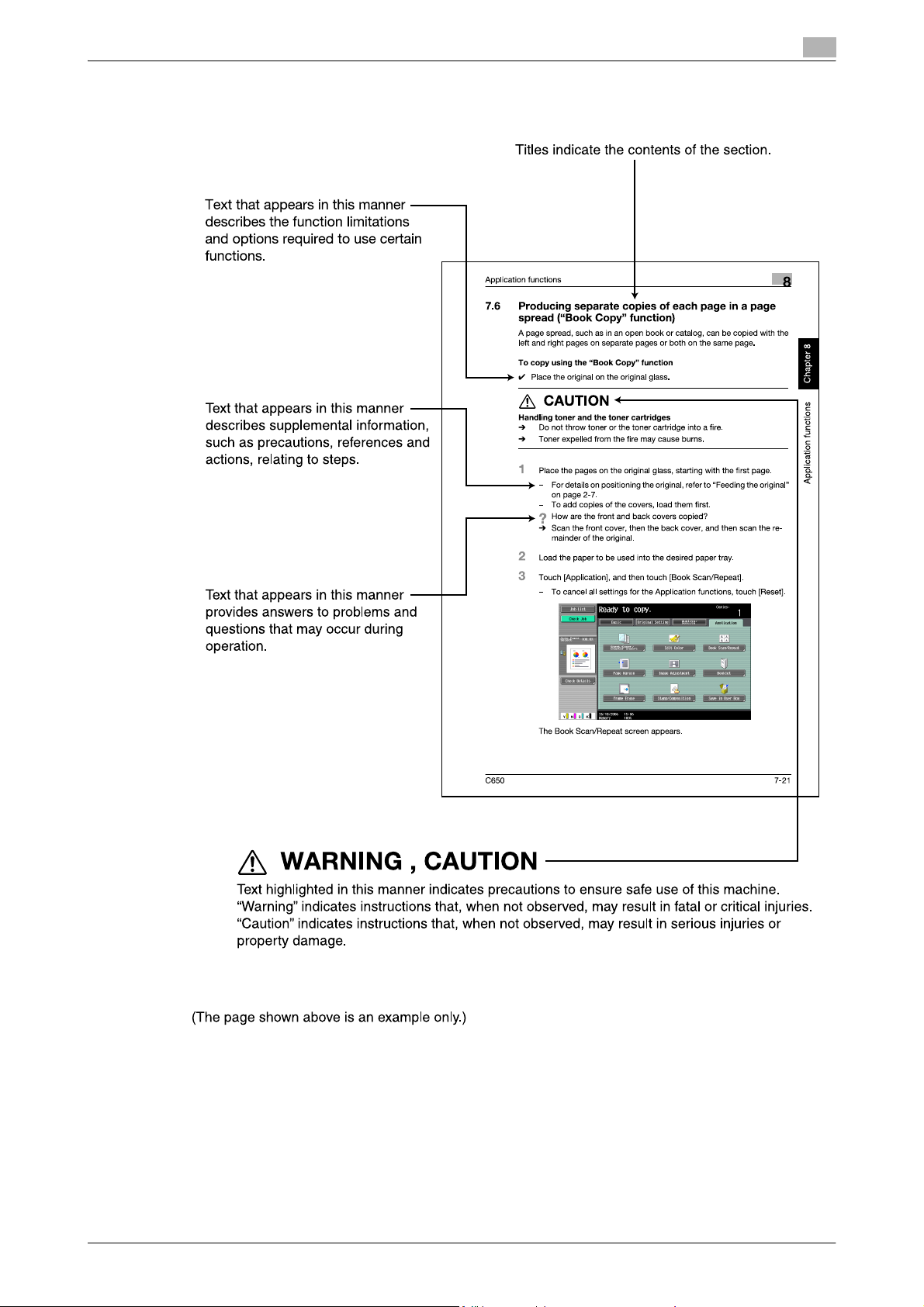
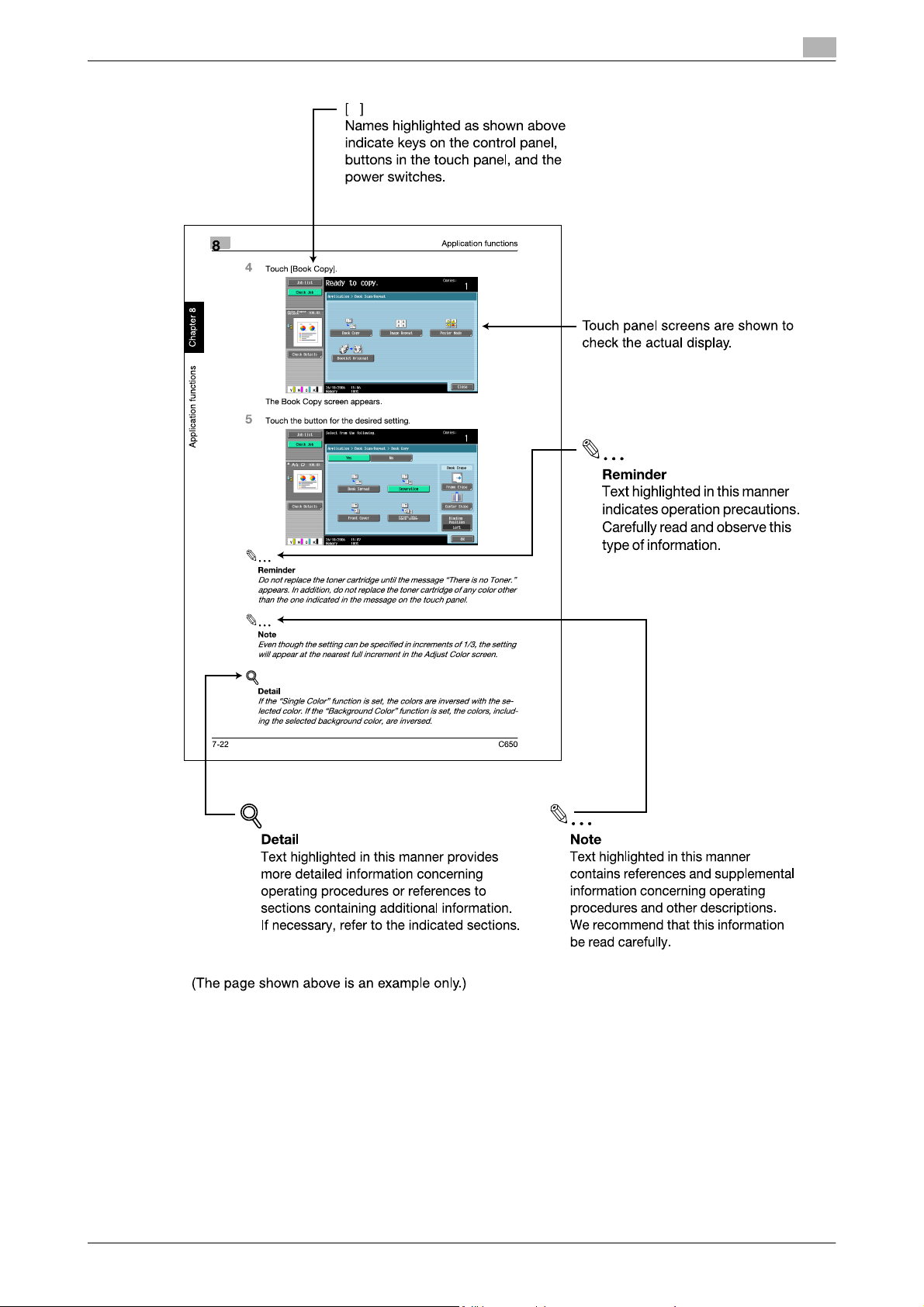
Explanation of manual conventions....................................................................................................................x-13
User’s guides ........................................................................................................................................................x-15
Structure of the manual .........................................................................................................................x-12
Notation .................................................................................................................................................x-12
Printed manuals .....................................................................................................................................x-15
User’s Guide CD manuals .....................................................................................................................x-15
1 Before using scanning functions
1.1 Environment required for using scanning functions .......................................................................... 1-2
1.2 Available scanning functions................................................................................................................ 1-3
1.3 When first used ...................................................................................................................................... 1-7
1.4 Using Web services ............................................................................................................................... 1-9
Scan to E-Mail ..........................................................................................................................................1-3
Scan to FTP ..............................................................................................................................................1-3
Scan to SMB.............................................................................................................................................1-4
Saving in user boxes ................................................................................................................................1-4
Scan to WebDAV ......................................................................................................................................1-5
Web Service..............................................................................................................................................1-5
Using the machine as a scanner ..............................................................................................................1-6
Network connection .................................................................................................................................1-7
Network settings.......................................................................................................................................1-7
Specifying the E-Mail address of the machine.........................................................................................1-7
Address Registration ................................................................................................................................1-7
Registration of address book destination.................................................................................................1-7
Registration of group destination .............................................................................................................1-8
Fax/Scan programs ..................................................................................................................................1-8
Setting display contents...........................................................................................................................1-8
Settings required for using Web services.................................................................................................1-9
Installing the driver of this machine on the computer ..............................................................................1-9
Installation procedure.............................................................................................................................1-10
When using SSL to communicate from Windows Vista to this machine ...............................................1-11
When using SSL to communicate from this machine to Windows Vista ...............................................1-11
2 Scanning
2.1 Control panel.......................................................................................................................................... 2-2
2.2 Fax/Scan mode screen ......................................................................................................................... 2-4
Screen layout............................................................................................................................................2-4
Icons on the touch panel ..........................................................................................................................2-4
Display with/without optional settings......................................................................................................2-5
2.3 Display and operation of the left panel................................................................................................ 2-7
C650 x-7
Job List .....................................................................................................................................................2-7
Job List - Delete .......................................................................................................................................2-8
Job List - Job Details................................................................................................................................2-8
Check Job - Check Job Settings ...........................................................................................................2-11
Check Job - Check Job Settings - Destination Settings........................................................................2-12
Check Job - Check Job Settings - Scan Settings..................................................................................2-12
Check Job - Check Job Settings - Original Settings..............................................................................2-12
Check Job - Check Job Settings - Check E-Mail Settings ....................................................................2-13

Introduction
Check Job - Delete.................................................................................................................................2-13
2.4 Previewing............................................................................................................................................ 2-14
Preview screen .......................................................................................................................................2-14
Preview - View Pages - Change Setting.................................................................................................2-15
Preview - View Status.............................................................................................................................2-15
Sending after previewing........................................................................................................................2-15
2.5 Using Scan/Fax programs .................................................................................................................. 2-18
Recalling a Scan/Fax program ...............................................................................................................2-18
Registering Scan/Fax programs.............................................................................................................2-21
Editing and deleting Scan/Fax programs ...............................................................................................2-25
2.6 Sending data in an e-mail message (Scan to E-Mail)....................................................................... 2-27
Scan to E-Mail ........................................................................................................................................2-27
Selecting a destination from the address book......................................................................................2-27
Selecting a group destination.................................................................................................................2-28
Entering addresses directly ....................................................................................................................2-30
Selecting a destination that was searched for .......................................................................................2-31
Selecting a destination with an Address Search ....................................................................................2-33
2.7 Sending data to a computer on the network (Scan to SMB)........................................................... 2-36
Scan to SMB...........................................................................................................................................2-36
Scan to SMB operations with Windows File Sharing (Mac OS X)/Samba (Linux/Unix) .........................2-36
Scan to SMB operations with Windows 98 SE and Windows Me .........................................................2-36
Selecting a destination from the address book......................................................................................2-37
Entering addresses directly ....................................................................................................................2-38
2.8 Sending data to a server (Scan to FTP)............................................................................................. 2-41
Scan to FTP ............................................................................................................................................2-41
Selecting a destination from the address book......................................................................................2-41
Entering addresses directly ....................................................................................................................2-43
2.9 Sending data to a server (WebDAV)................................................................................................... 2-45
WebDAV .................................................................................................................................................2-45
Selecting a destination from the address book......................................................................................2-45
Entering addresses directly ....................................................................................................................2-47
2.10 Using Web Service............................................................................................................................... 2-49
2.11 Specifying scan and transmission settings
Specifying the scan command from the control panel of the machine..................................................2-49
Checking the Web Service destinations.................................................................................................2-50
Searching for a Web Service destination ...............................................................................................2-50
Giving a scan command from a computer.............................................................................................2-51
(Scan Settings/Original Settings/Communication Settings) ........................................................... 2-53
Settings that can be specified................................................................................................................2-53
Original Type...........................................................................................................................................2-54
Simplex/Duplex ......................................................................................................................................2-56
Resolution...............................................................................................................................................2-57
File Type .................................................................................................................................................2-58
Density....................................................................................................................................................2-61
Separate Scan ........................................................................................................................................2-62
Color (Quality Adjustment)......................................................................................................................2-62
Background Removal (Quality Adjustment)............................................................................................2-64
Sharpness (Quality Adjustment) .............................................................................................................2-65
Frame Erase (Erase)................................................................................................................................2-66
Book Copy (Book Scan) .........................................................................................................................2-67
Scan Size (Application)...........................................................................................................................2-69
Annotation (Application) .........................................................................................................................2-72
Date/Time (Application) ..........................................................................................................................2-72
Page Number (Application).....................................................................................................................2-75
Stamp (Application) ................................................................................................................................2-79
Header/Footer (Application)....................................................................................................................2-82
Send & Print (Application).......................................................................................................................2-86
Document Name.....................................................................................................................................2-88
Original Settings .....................................................................................................................................2-89
E-Mail Setting .........................................................................................................................................2-91
URL Notification Setting .........................................................................................................................2-92
E-Mail Encryption ...................................................................................................................................2-93
Digital Signature .....................................................................................................................................2-94
C650 x-8
Introduction
3 Specifying Utility mode parameters
3.1 Settings that can be specified from Utility mode ............................................................................... 3-2
Utility mode parameters ...........................................................................................................................3-2
Other related parameters..........................................................................................................................3-2
PageScope Web Connection ...................................................................................................................3-2
3.2 Displaying settings screens.................................................................................................................. 3-3
Displaying the Create One-Touch Destination screen .............................................................................3-3
Displaying the User Settings screen.........................................................................................................3-4
Displaying the Administrator Settings screen...........................................................................................3-5
3.3 Registering an address book destination ........................................................................................... 3-7
3.4 Registering a group destination......................................................................................................... 3-23
3.5 Specifying e-mail settings .................................................................................................................. 3-25
3.6 Limiting Access to Destinations......................................................................................................... 3-28
3.7 Custom Display Settings..................................................................................................................... 3-31
3.8 Scan/Fax Settings................................................................................................................................ 3-36
3.9 Reset Data After Job ........................................................................................................................... 3-42
3.10 Header/Footer Settings....................................................................................................................... 3-43
3.11 Printing registered destination lists................................................................................................... 3-49
3.12 Open API Settings................................................................................................................................ 3-55
E-Mail destination.....................................................................................................................................3-7
User Box...................................................................................................................................................3-9
PC (SMB) ................................................................................................................................................3-12
FTP .........................................................................................................................................................3-15
WebDAV .................................................................................................................................................3-19
Subject....................................................................................................................................................3-25
E-Mail Text..............................................................................................................................................3-26
Limiting Access to Destinations .............................................................................................................3-28
Specifying limited access settings .........................................................................................................3-28
Default Tab .............................................................................................................................................3-31
Program Default......................................................................................................................................3-31
Address Book Index Default...................................................................................................................3-32
Shortcut Key...........................................................................................................................................3-33
Default Address Book.............................................................................................................................3-34
Search Option Settings ..........................................................................................................................3-35
JPEG Compression Level.......................................................................................................................3-36
Black Compression Level.......................................................................................................................3-37
TWAIN Lock Time...................................................................................................................................3-38
Default Scan/Fax Settings......................................................................................................................3-39
Compact PDF/XPS Compression Level .................................................................................................3-39
Color TIFF Type ......................................................................................................................................3-40
Registering headers/footers ...................................................................................................................3-43
Deleting headers/footers ........................................................................................................................3-47
Address Book List ..................................................................................................................................3-49
Group List ...............................................................................................................................................3-50
Program List ...........................................................................................................................................3-51
E-Mail Subject/Text List .........................................................................................................................3-53
Access Setting........................................................................................................................................3-55
Port Number ...........................................................................................................................................3-56
SSL .........................................................................................................................................................3-57
Authentication.........................................................................................................................................3-58
4 Network Settings
4.1 Available Network Settings parameters.............................................................................................. 4-2
4.2 Network settings with external server authentication ....................................................................... 4-3
When SSL is installed ...............................................................................................................................4-3
Using Active Directory ..............................................................................................................................4-3
Using NTLM v1 and NTLM v2 ..................................................................................................................4-6
Using Novell NDS .....................................................................................................................................4-8
Using LDAP ..............................................................................................................................................4-9
C650 x-9

Introduction
4.3 TCP/IP Settings.................................................................................................................................... 4-12
Displaying the TCP/IP Settings screen...................................................................................................4-12
IP Settings ..............................................................................................................................................4-13
DNS Host................................................................................................................................................4-14
DNS Domain...........................................................................................................................................4-15
DNS Server Settings...............................................................................................................................4-16
RAW Port Number ..................................................................................................................................4-17
IP Filtering (Permit Access).....................................................................................................................4-18
IP Filtering (Deny Access).......................................................................................................................4-19
IPv6 Settings...........................................................................................................................................4-20
IKE Settings (IPsec Settings) ..................................................................................................................4-22
IPsec SA Settings (IPsec Settings) .........................................................................................................4-23
Peer (IPsec Settings) ..............................................................................................................................4-26
4.4 NetWare Settings................................................................................................................................. 4-28
4.5 http Server Settings............................................................................................................................. 4-33
4.6 FTP Settings......................................................................................................................................... 4-39
4.7 SMB Settings........................................................................................................................................ 4-42
4.8 LDAP Settings ...................................................................................................................................... 4-47
4.9 E-Mail TX (SMTP)................................................................................................................................. 4-54
4.10 E-Mail RX (POP) ................................................................................................................................... 4-61
4.11 S/MIME Communication Settings...................................................................................................... 4-65
4.12 SNMP Settings ..................................................................................................................................... 4-69
4.13 AppleTalk Settings............................................................................................................................... 4-76
4.14 Bonjour Settings .................................................................................................................................. 4-77
4.15 TCP Socket Settings ........................................................................................................................... 4-78
4.16 WebDAV Client Settings...................................................................................................................... 4-81
4.17 WebDAV Server Settings..................................................................................................................... 4-83
4.18 Web Service Settings .......................................................................................................................... 4-84
4.19 Device Setting ...................................................................................................................................... 4-86
4.20 Time Adjustment Setting .................................................................................................................... 4-87
4.21 Status Notification Setting.................................................................................................................. 4-89
IPX Settings ............................................................................................................................................4-28
NetWare Print Settings ...........................................................................................................................4-29
User Authentication Setting (NDS) .........................................................................................................4-31
Support Information................................................................................................................................4-35
Printer Information ..................................................................................................................................4-36
FTP TX Settings ......................................................................................................................................4-39
FTP Server Settings................................................................................................................................4-40
Client Settings ........................................................................................................................................4-42
Print Setting ............................................................................................................................................4-43
WINS Settings ........................................................................................................................................4-44
Direct Hosting Setting ............................................................................................................................4-45
Enabling LDAP........................................................................................................................................4-47
Setting Up LDAP.....................................................................................................................................4-48
Default Search Settings..........................................................................................................................4-53
SMTP Server Address ............................................................................................................................4-58
SMTP Authentication..............................................................................................................................4-59
POP Server Address...............................................................................................................................4-64
Before specifying settings to use S/MIME .............................................................................................4-65
Specifying S/MIME communication settings..........................................................................................4-66
SNMP v1/v2c Settings............................................................................................................................4-70
SNMP v3 Settings ..................................................................................................................................4-72
TCP Socket.............................................................................................................................................4-78
TCP Socket (ASCII Mode) ......................................................................................................................4-79
Web Service Common Settings .............................................................................................................4-84
Scanner Settings ....................................................................................................................................4-85
NTP server address ................................................................................................................................4-87
Specifying an IP address........................................................................................................................4-89
Specifying an IPX address......................................................................................................................4-91
Specifying an e-mail address .................................................................................................................4-92
Notification Item .....................................................................................................................................4-94
C650 x-10

Introduction
4.22 Total Counter Notification Settings ................................................................................................... 4-95
Notification Schedule Setting .................................................................................................................4-95
Address Setting ......................................................................................................................................4-98
4.23 PING Confirmation............................................................................................................................. 4-100
4.24 SLP Setting......................................................................................................................................... 4-102
4.25 LPD Setting ........................................................................................................................................ 4-103
4.26 Prefix/Suffix Setting........................................................................................................................... 4-104
ON/OFF Setting ....................................................................................................................................4-104
Prefix/Suffix Setting..............................................................................................................................4-105
4.27 Action for Invalid Certificate............................................................................................................. 4-107
5 Scan function troubleshooting
5.1 Troubleshooting..................................................................................................................................... 5-2
If an error message appears when connecting to the machine from a computer....................................5-2
If "SMTP cannot be used." or "FTP cannot be used." appears...............................................................5-2
If the HDD Ready indicator indicates an HDD malfunction......................................................................5-2
5.2 Network error message list .................................................................................................................. 5-3
6 Appendix
6.1 Product specifications .......................................................................................................................... 6-2
Scanning functions ...................................................................................................................................6-2
Network Functions....................................................................................................................................6-2
6.2 Entering text........................................................................................................................................... 6-3
Enlarging the keyboard.............................................................................................................................6-4
To type text...............................................................................................................................................6-5
List of Available Characters......................................................................................................................6-5
6.3 Glossary.................................................................................................................................................. 6-6
7Index
C650 x-11

Introduction
About this manual
This User’s Guide covers the bizhub C650 network and scanning functions.
This section introduces the structure of the manual and notations used for product names, etc.
This manual is intended for users who understand the basic operations of computers and the machine. For
operating procedures of the Windows or Macintosh operating system and application programs, refer to the
respective manuals.
Structure of the manual
This manual consists of the following chapters.
Chapter 1 Before using scanning functions
Chapter 2 Scanning
Chapter 3 Specifying Utility mode parameters
Chapter 4 Network Settings
Chapter 5 Scan function troubleshooting
Chapter 6 Appendix
Chapter 7 Index
Lists the product specifications and the characters that can be entered from the control panel.
Notation
Product name Notation in the manual
bizhub C650 This machine, C650
Microsoft Windows NT 4.0 Windows NT 4.0
Microsoft Windows 2000 Windows 2000
Microsoft Windows XP Windows XP
Microsoft Windows Vista Windows Vista
When the operating systems above are written together Windows NT 4.0/2000/XP/Vista
C650 x-12
Introduction
Explanation of manual conventions
C650 x-13
Introduction
C650 x-14

Introduction
User’s guides
This machine is provided with printed manuals and PDF manuals on the User’s Guide CD.
Printed manuals
Quick Guide [Copy/Print/Fax/Scan/Box Operations]
This manual contains operating procedures and descriptions of the most frequently used functions, allowing
the machine to immediately be used.
In addition, this manual contains notes and precautions that should be followed for safe use of the machine.
Be sure to read this manual before using the machine.
User’s Guide [Enlarge Display Operations]
This manual contains details on operating procedures in Enlarge Display mode.
Refer to this manual for details on using copy, network scanner and fax functions in Enlarge Display mode.
User’s Guide CD manuals
User’s Guide [Copy Operations]
This manual contains descriptions of the Copy mode operations and machine maintenance. Refer to this
manual for details on the paper and documents, copy procedures using convenient Application functions,
replacing consumables, and troubleshooting operations such as clearing paper misfeeds.
User’s Guide [Print Operations]
This manual contains details of the printing functions that can be specified with the standard built-in printer
controller. Refer to this manual for operating procedures on using the printing functions.
User’s Guide [Box Operations]
This manual contains operating procedures for using the user boxes on the hard disk. Refer to this manual
for details on saving data in user boxes, retrieving data from user boxes and transferring data.
User’s Guide [Network Scanner Operations] (this manual)
This manual contains descriptions on specifying network settings for standard equipment and operating
procedures for scanning functions. Refer to this User’s Guide for details on using network functions and the
Scan to E-Mail, Scan to FTP and Scan to SMB operations.
User’s Guide [PageScope Web Connection Operations]
This manual contains descriptions on the machine settings that can be specified remotely with PageScope
Web Connection from a Web browser on a computer. Refer to this manual for details on operating
procedures for using PageScope Web Connection.
User’s Guide [Fax Operations]
This manual contains descriptions of the G3 fax operations. Refer to this manual for details on using the G3
fax operations when the optional fax kit is installed.
In order to use the fax functions, the optional fax kit must be purchased separately.
User’s Guide [Network Fax Operations]
This manual contains details on the network fax functions. Refer to this manual for operating procedures on
Internet faxing and IP address faxing.
User’s Guide [FAX Driver Operations]
This manual contains details of the fax driver functions that can be used to send a fax directly from a
computer. Refer to this manual for operating procedures on using the PC-FAX functions.
In order to use the fax functions, the optional fax kit must be purchased separately.
User’s Guide [Advanced Function Operations]
This User’s Guide describes overview and usage of functions that become available by registering the
optional license kit and enabling its function, and functions that become available by connecting the MFP
with applications.
In order to use the functions effectively, please read this User’s Guide.
The following models support the advanced function.
bizhub C650/C550/C451/C353/C253/C203
C650 x-15

1
Before using scanning
functions

Before using scanning functions
1 Before using scanning functions
1.1 Environment required for using scanning functions
The following conditions are required in order to use the network scanning features.
- The machine is connected to the network. (required)
The machine can be used over a TCP/IP network. First, connect the cable for connecting to the
network. For details, refer to "Network connection" on page 1-7. In order to use this machine on a
network, settings such as the IP address of the machine must be specified. For details, refer to chapter
4, "Network Settings" on page 4-2.
- The driver software is installed on the computer.
In order to use this machine as a scanner, the dedicated software KONICA MINOLTA TWAIN must be
installed. For details, refer to the TWAIN driver manual on the User Software CD-ROM.
1
C650 1-2
Before using scanning functions
1.2 Available scanning functions
"Scanning" refers to the operation of reading the image of a document fed through the ADF or placed on the
original glass. The Scan functions can be used to temporarily store the scan data on the internal memory of
the machine and transmit the data over the network.
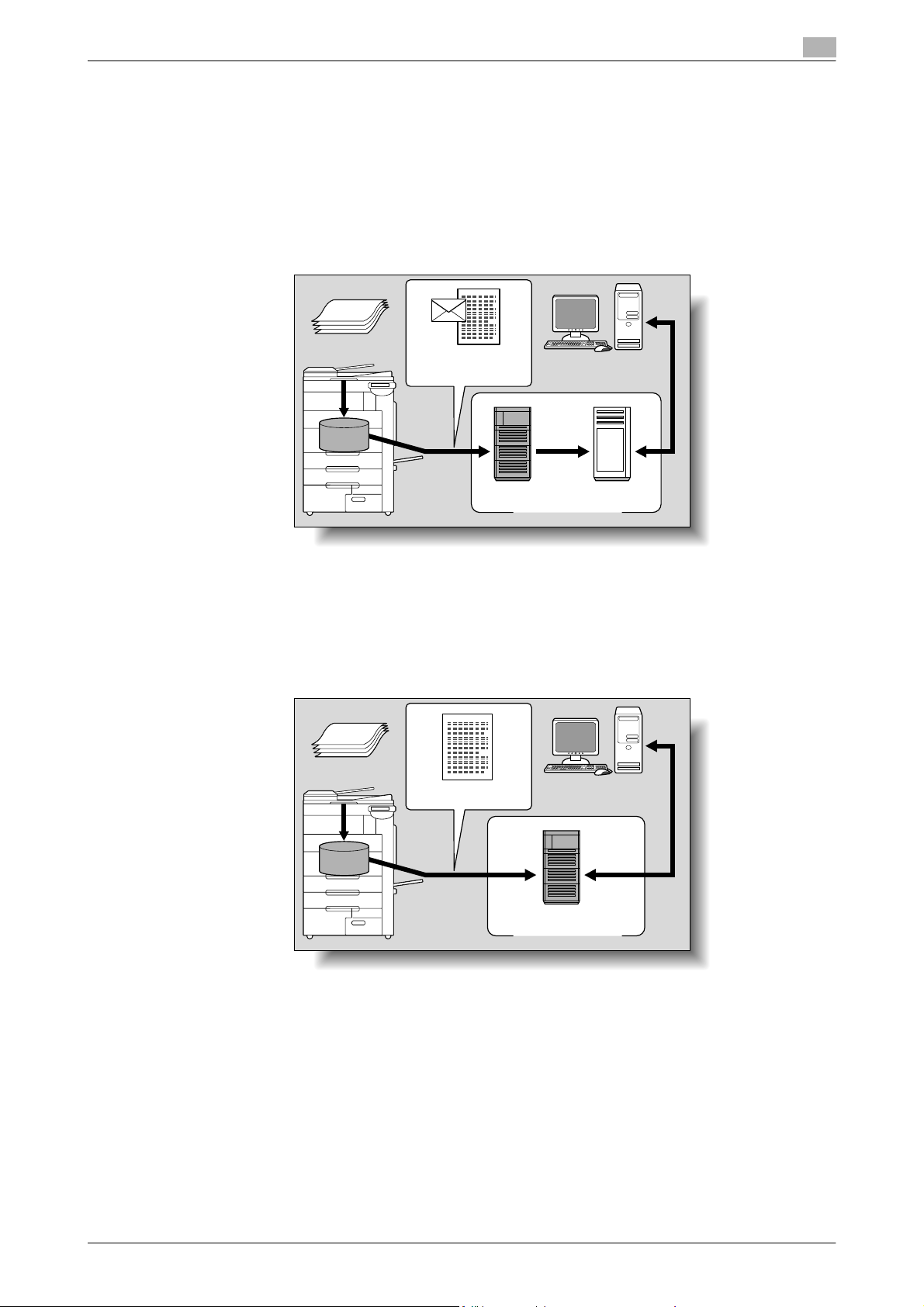
Scan to E-Mail
The scan data can be sent to the specified e-mail address. Destinations can be selected from the touch panel
of this machine, and the scan data is sent as an e-mail attachment.
Original
1
Machine
E-mail and scan data
Memory
SMTP server POP server
E-mail reception
Internet
Scan to FTP
The scan data can be uploaded to the specified FTP server. The FTP server address, logon password and
other information are entered from the touch panel of this machine.
The data uploaded to the FTP server can be downloaded from a computer on the network.
Original
Machine
Scan data
Download
Memory
FTP server
Internet
C650 1-3
Before using scanning functions
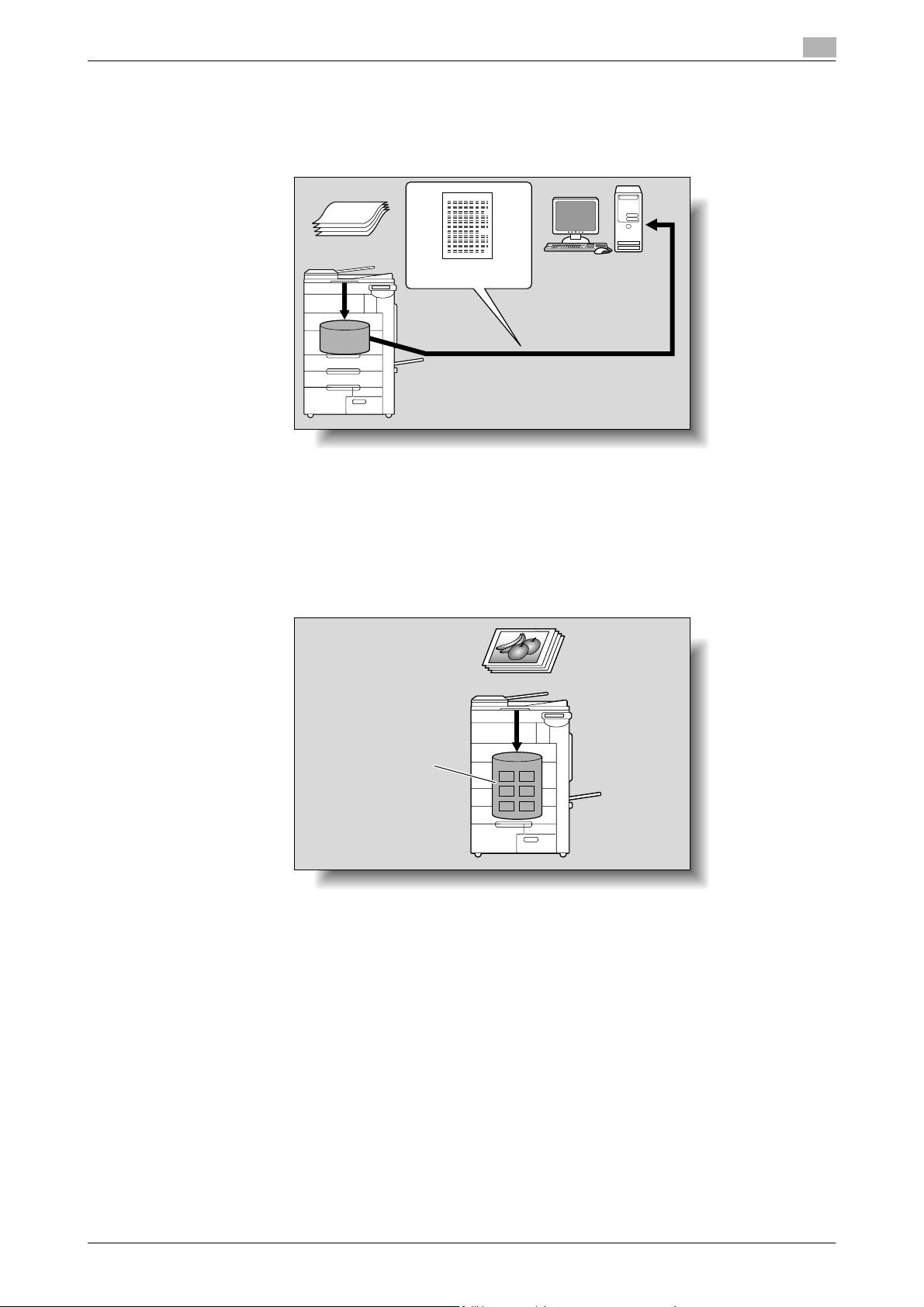
Scan to SMB
The scan data can be sent to a shared folder on a specified computer. The host name, file path and other
information are entered from the touch panel of this machine.
1
Original
Machine
Scan data
Memory
Save to a shared folder
Saving in user boxes
The scan data can be saved in a user box created on the hard disk of this machine, allowing the data to be
reused. The file name can be entered from the touch panel of this machine when the data is saved.
Other data such as received fax data can also be stored in user boxes. For details, refer to the User’s Guide
[Box Operations].
Machine
Hard disk
C650 1-4
Before using scanning functions
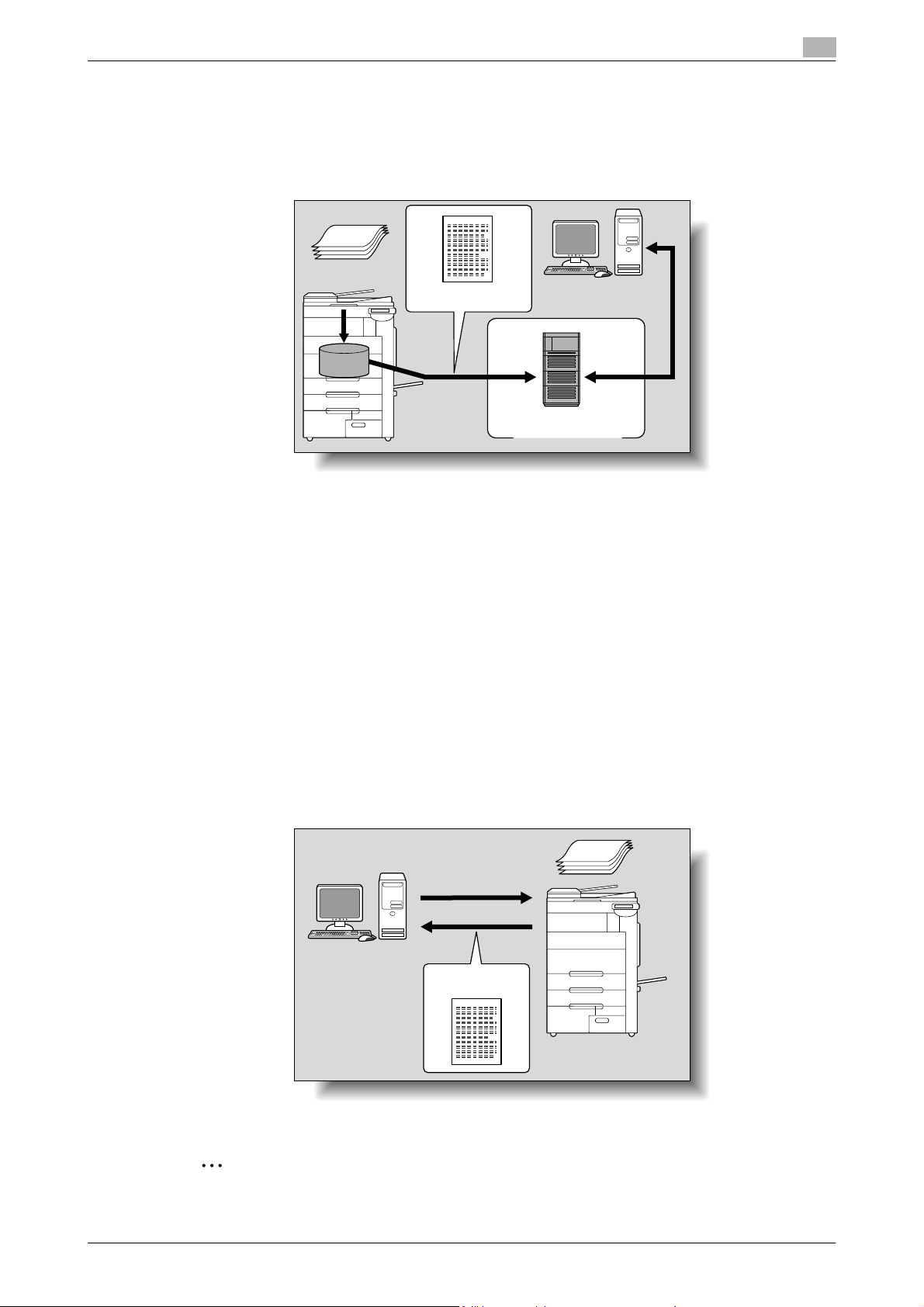
Scan to WebDAV
Scanned data can be uploaded to a specified server. Enter the server address, login password and other
information from the touch panel of the machine.
The data uploaded to the server can be downloaded from a computer on the network.
1
Original
Machine
Scan data
Memory
Download
Server
Internet
!
Detail
Since HTTP extensions are used, WebDAV allows HTTP security technology to be used as it is. Files
can be transmitted more safely when communications with the WebDAV server are encrypted with SSL.
If a proxy server is available in the network environment, a WebDAV server on the Internet can be
accessed through the proxy server.
Web Service
Scanning can be performed using the Web Service Function provided with Windows Vista.
If this machine is recognized by a computer (Windows Vista) on the network and installed, a scan command
can be sent from the computer, or this machine can scan using the specified operation and send the scan
data to the computer.
By specifying this machine (installed as a scanner) when scanning from Windows Vista, scanning is possible
using Web Service for communication.
Original
Scanning instruction
Windows Vista
Scan data
2
Note
If optional image controller IC-409 has been installed this function is not available.
C650 1-5
Before using scanning functions
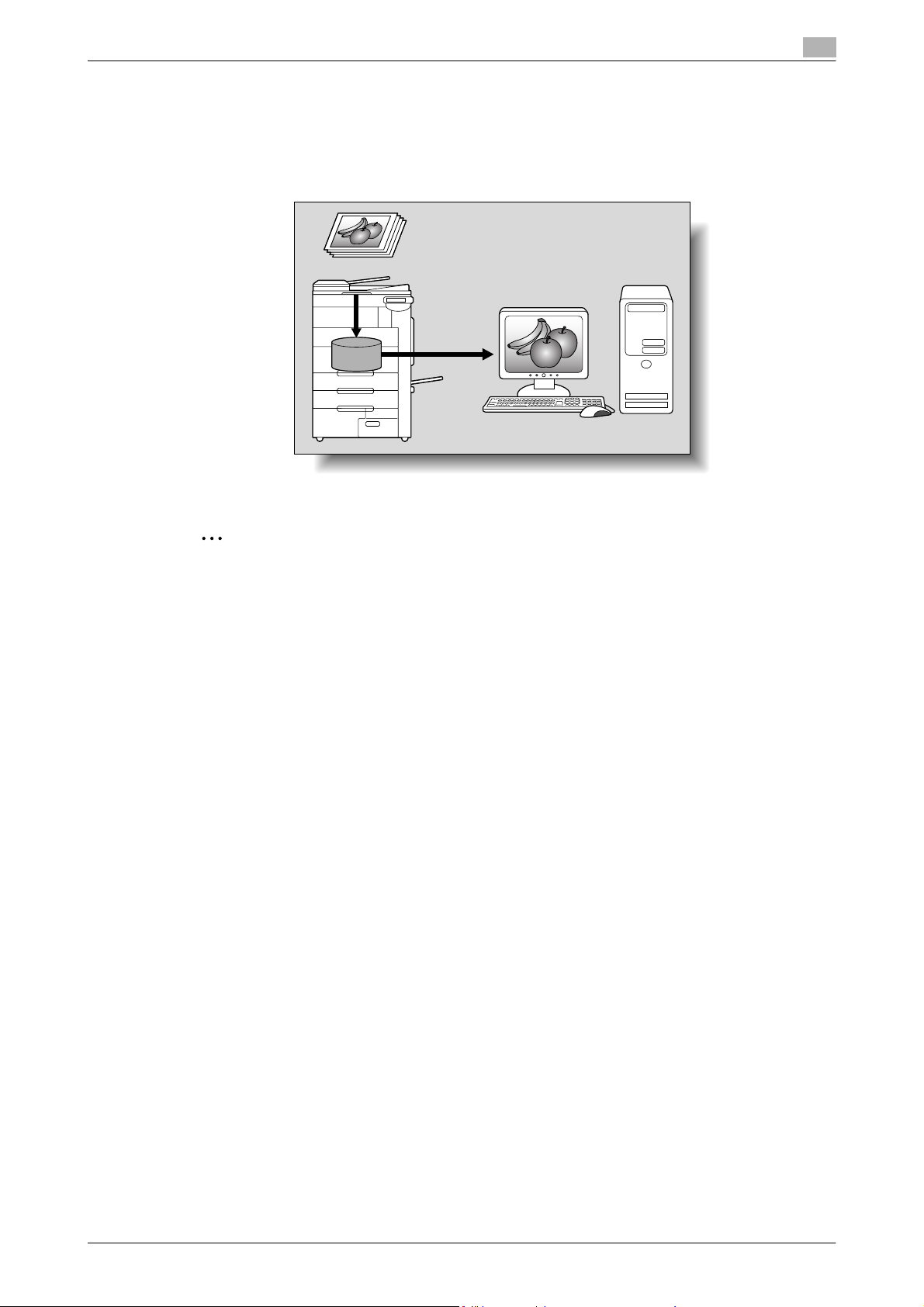
Using the machine as a scanner
This machine can be used as a scanner. The scanner can be controlled from a computer connected to the
network, and the scanned image can be imported into an application on the computer to be processed.
For more details, refer to the TWAIN driver manual on the User Software CD-ROM.
1
Original
Machine
Memory
2
Note
If optional image controller IC-409 has been installed this function is not available.
C650 1-6
Before using scanning functions
1.3 When first used
The network connections and settings must be specified before the network scanning functions can be used.
Any other settings should be specified as necessary.
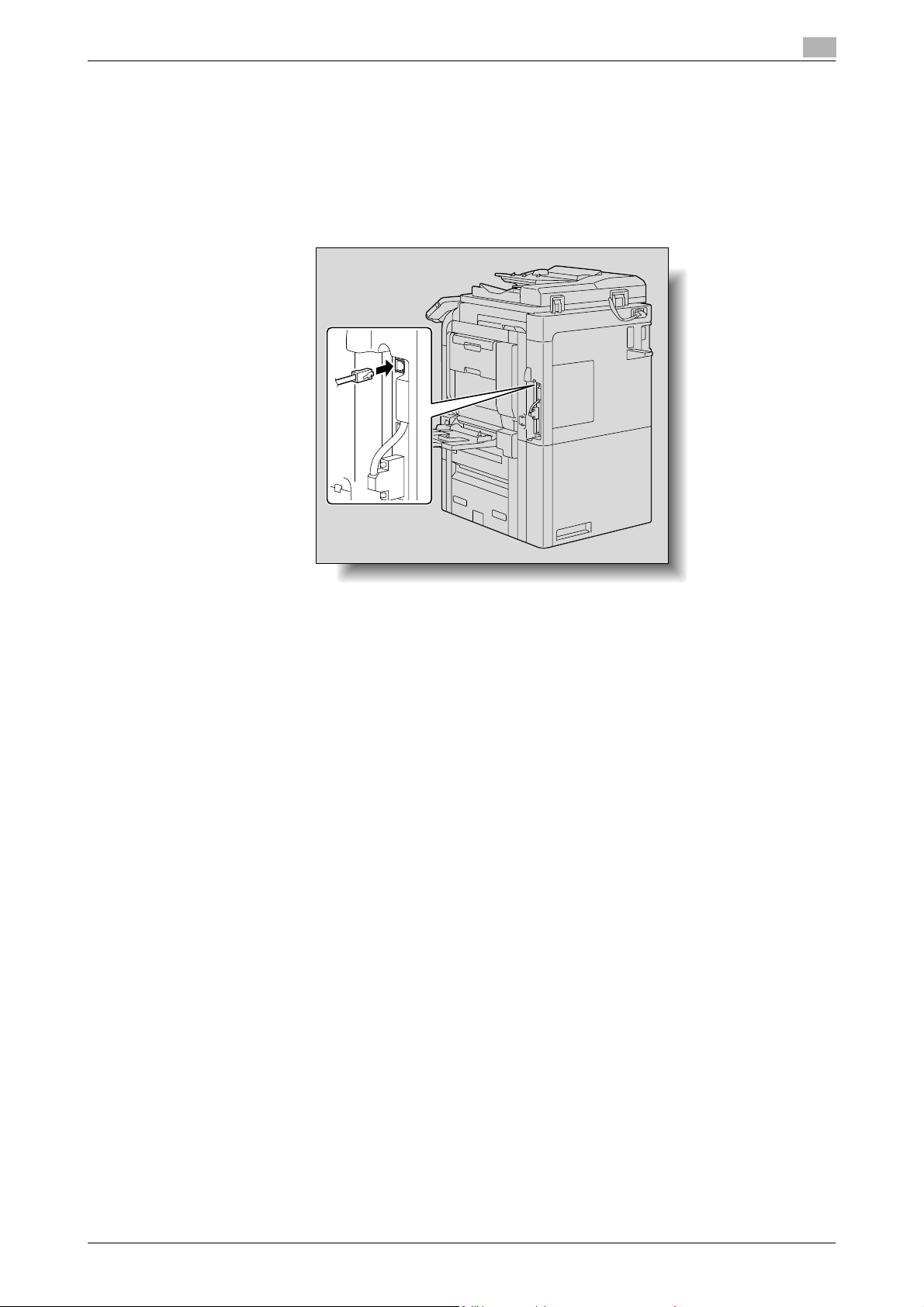
Network connection
Connect a UTP cable (category 5 or later recommended) from the network to the Ethernet connector on the
machine.
1
Network settings
Assign an IP address to the machine and complete settings for the SMTP server, etc. For details, refer to the
"Network Settings" on page 4-2.
Specifying the E-Mail address of the machine
To send scanned data as an E-Mail message or to use the Internet fax function, register the E-Mail address
on the machine beforehand. This E-Mail address is used when sending and receiving data. Generally, it is
recommended that the E-Mail address registered for the administrator be used.
If the E-Mail address registered for the administrator is not specified, the E-Mail address of the sender must
be entered for each Scan to E-Mail operation. Scan to E-Mail operations are not possible without address
entry.
!
Detail
When user authentication is enabled, the E-Mail address specified for each user is used as the sender’s
address.
Address Registration
Register the destination (address) of scanned/faxed data. Use one of the following registration methods.
- Using the touch panel of the machine
- Using PageScope Web Connection from a computer on the network
Registration of address book destination
The following types of destination information can be registered in the Address Book. For details on
registering destinations in Address Book, refer to "Registering an address book destination" on page 3-7.
- E-Mail
- User Box
- PC (SMB)
- FTP
- WebDAV
C650 1-7
Before using scanning functions
!
Detail
Destinations in Address Book cannot be registered by Web service. Specify the destination by directly
entering the address.
Registration of group destination
A set of addresses registered in the Address Book can be registered as a group. Group registration is useful
for sending a message to more than one address at the same time.
Fax/Scan programs
The destination and scan settings can be registered together as a single program. This is convenient for
frequently scanning documents and sending data under the same conditions. Use the touch panel of the
machine to specify the settings.
2
Note
For details, refer to "Using Scan/Fax programs" on page 2-18.
Setting display contents
Set the contents to be displayed when the [Fax/Scan] key is touched on the control panel.
1
2
Note
For details, refer to "Custom Display Settings" on page 3-31.
C650 1-8
Before using scanning functions
1.4 Using Web services
It is possible to give a scan command from a computer (Windows Vista) on the network or to perform
scanning according to the purpose from the machine and to send the scanned data to the computer. This
section describes settings that should be specified on the computer in advance.
Settings required for using Web services
The following settings are required for using Web services:
- Install the driver of the machine on the computer.
- Specify settings for Web services on the machine.
!
Detail
Settings for Web services on this machine can be specified in the Administrator Settings screen. For
details, refer to "Web Service Settings" on page 4-84.
Installing the driver of this machine on the computer
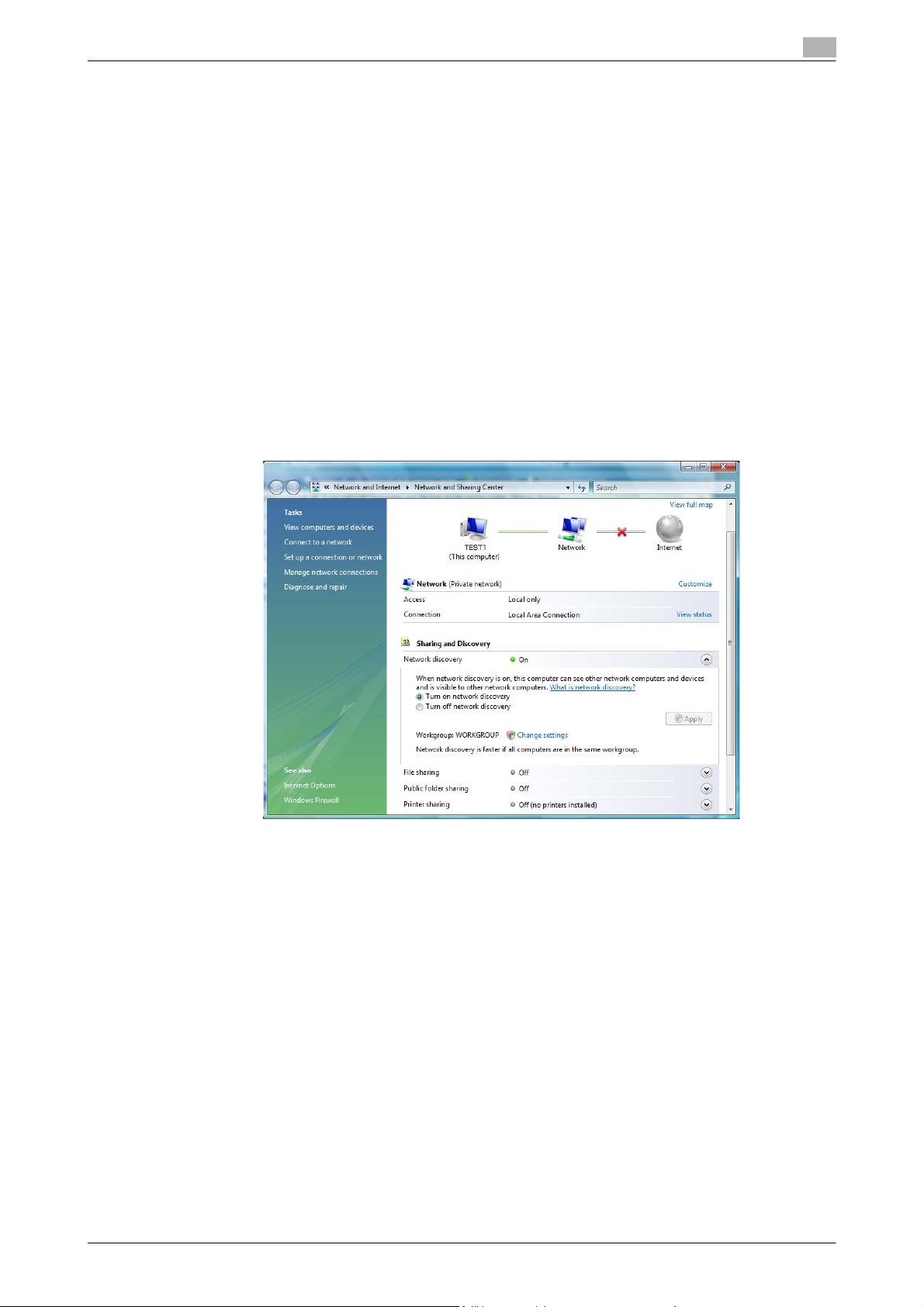
Before installation, check that "Network discovery" is enabled in [Network and Sharing Center] accessed
from [Control Panel].
1
C650 1-9
Before using scanning functions
Installation procedure
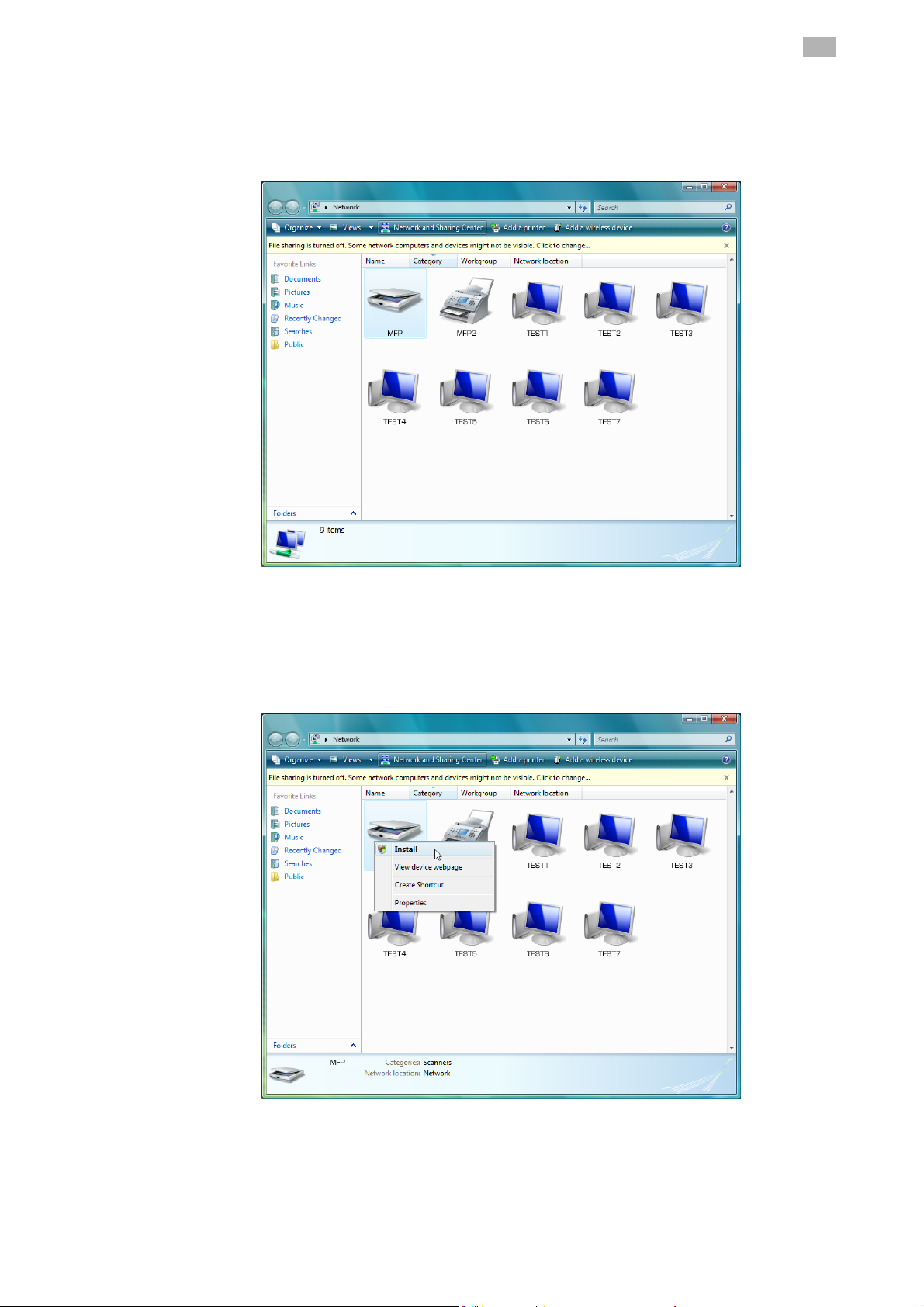
1 Click the [Start] button, and then select [Network].
Devices connected to the network are listed.
1
2 Right-click the scanner icon on the machine, and then select [Install].
– Depending on the settings on the computer, the UAC (User Account Control) dialog box may
appear. Check the contents, and then continue.
– If both scanning and printing using Web Service have been enabled on this machine, this machine
appears as a printer icon.
C650 1-10
Before using scanning functions
– The driver software is installed automatically. When the confirmation dialog box appears, click the
[Close] button.
3 On the control panel of the machine, select [Web Service] and check that the connection destination is
displayed.
When using SSL to communicate from Windows Vista to this machine
In order to apply SSL encryption to communications from a computer running Windows Vista to this machine,
the computer must be able to use DNS to resolve the name of this machine. First, register this machine with
the DNS server and specify the DNS settings from the computer. If the certificate for this machine was not
issued by the certification authority, be sure to register the certificate for this machine as a certificate from a
publisher trusted for computer accounts by Windows Vista.
1
When using SSL to communicate from this machine to Windows Vista
In order to apply SSL encryption to communications from this machine to a computer running Windows Vista,
create a certificate from the computer, and then link it to the communications port.
C650 1-11

2
Scanning
Scanning
2 Scanning
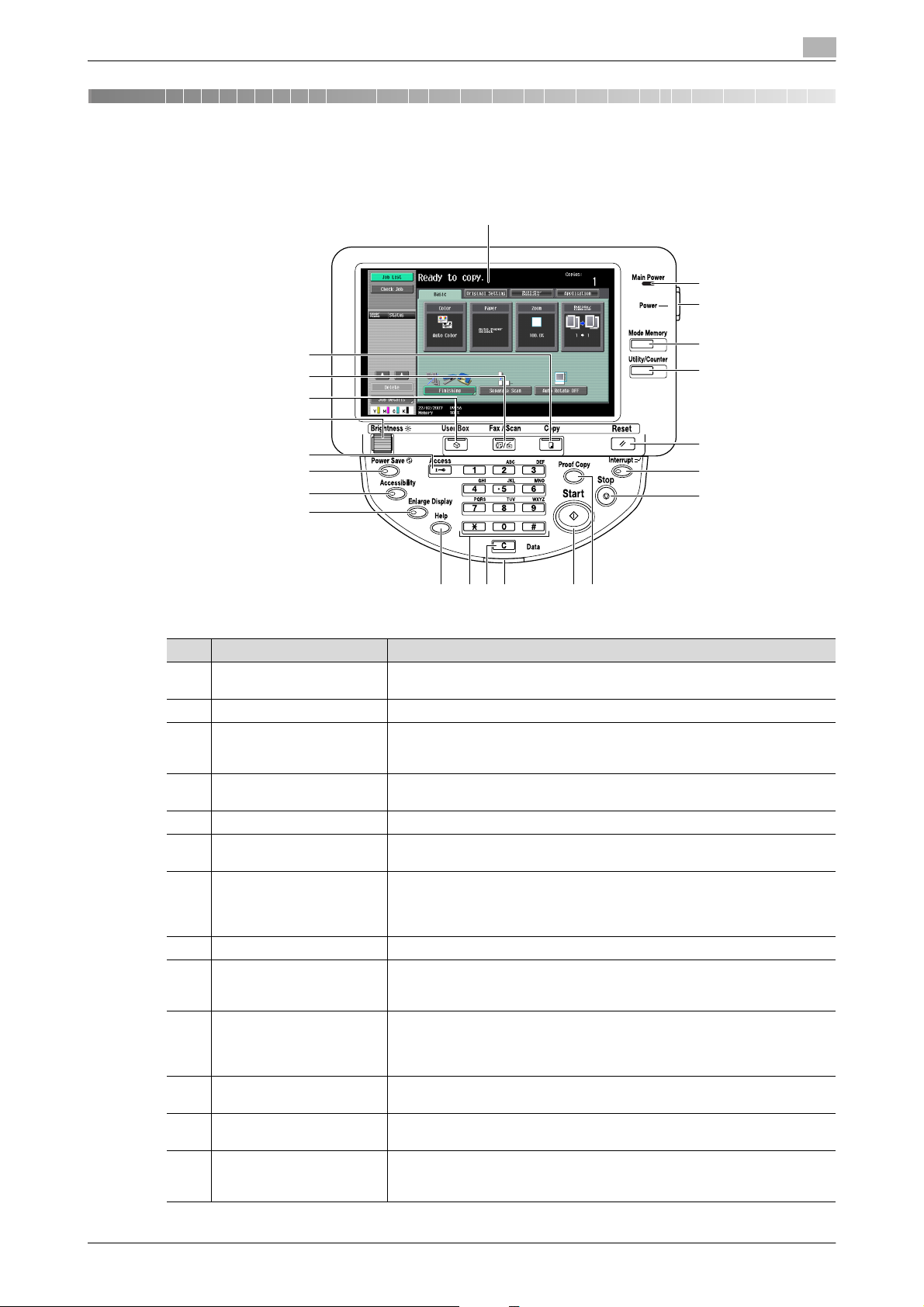
2.1 Control panel
2
1
2
3
22
21
20
19
18
17
16
15
1314
12 9
11 10
No. Part Name Description
1 Touch panel Displays various screens and messages. Specify the various settings by di-
2 Main Power indicator Lights up in blue when the machine is turned on with the main power switch
3 Sub power switch Press to turn on/off machine operations, for example, for copying, printing or
4 [Mode Memory] key Press to register (store) the desired scan settings as a program or to recall a
5 [Utility/Counter] key Press to display the Meter Count screen and the Utility screen.
6 [Reset] key Press to clear all settings (except programmed settings) entered in the control
7 [Interrupt] key Press to enter Interrupt mode. While the machine is in Interrupt mode, the in-
8 [Stop] key Pressing the [Stop] key during scanning temporarily stops the scan operation.
9 [Proof Copy] key Press to print a single proof copy to be checked before printing a large number
10 [Start] key Press to start scanning. When this machine is ready to begin scanning, the in-
11 Data indicator Flashes in blue while a print job is being received.
12 [C] (clear) key Press to erase a value (such as the number of copies, a zoom ratio, or a size)
13 Keypad Use to type in the number of copies to be produced.
rectly touching the panel.
scanning. When turned off, the machine enters a state where it conserves energy.
registered scan program.
panel and touch panel.
dicator on the [Interrupt] key lights up in green and the message "Now in Interrupt mode." appears on the touch panel. To cancel Interrupt mode, press the
[Interrupt] key again.
of copies. By pressing the [Proof Copy] key before scanning or copying, the
result can be viewed on the touch panel.
dicator on the [Start] key lights up in blue. If the indicator on the [Start] key
lights up in orange, scanning cannot begin.
Press to restart a stopped job.
Lights up in blue when data is being printed.
entered using the keypad.
Use to type in the zoom ratio.
Use to type in the various settings.
4
5
6
7
8
C650 2-2

Scanning
2
No. Part Name Description
14 [Help] key Press to display the Help Menu screen, which can be used to display descrip-
tions of the various functions and details of operations.
15 [Enlarge Display] key Press to enter Enlarge Display mode. If authentication is performed with Pag-
eScope Authentication Manager, it does not enter Enlarge Display mode.
16 [Accessibility] key Press to display the screen for specifying settings for user accessibility func-
tions.
17 [Power Save] key Press to enter Power Save mode. While the machine is in Power Save mode,
the indicator on the [Power Save] key lights up in green and the touch panel
goes off. To cancel Power Save mode, press the [Power Save] key again.
18 [Access] key If user authentication or account track settings have been applied, press this
key after entering the user name and password (for user authentication) or the
account name and password (for account track) in order to use this machine.
19 [Brightness] dial Use to adjust the contrast of the touch panel.
20 [User Box] key Press to enter User Box mode.
While the machine is in User Box mode, the indicator on the [User Box] key
lights up in green. For details, refer to the User’s Guide [Box Operations].
21 [Fax/Scan] key Press to enter Fax/Scan mode.
While the machine is in Fax/Scan mode, the indicator on the [Fax/Scan] key
lights up in green. For details, refer to the User’s Guide [Fax Operations].
22 [Copy] key Press to enter Copy mode. (As a default, the machine is in Copy mode.) While
the machine is in Copy mode, the indicator on the [Copy] key lights up in green.
For details, refer to the User’s Guide [Copy Operations].
7 CAUTION
Do not apply extreme pressure to the touch panel, otherwise it may be scratched or damaged.
% Never push down on the touch panel with force, and never use a hard or pointed object to make a
selection in the touch panel.
C650 2-3
 Loading...
Loading...