Acronis Backup for Linux Server 11.7 User Manual

Acronis Backup
Version 11.7
APPLIES TO THE FOLLOWING PRODUCTS
For Linux Server
USER GUIDE
Copyright Statement
Copyright © Acronis International GmbH, 2002-2016. All rights reserved.
“Acronis” and “Acronis Secure Zone” are registered trademarks of Acronis International GmbH.
"Acronis Compute with Confidence", “Acronis Startup Recovery Manager”, “Acronis Active Restore”, “Acronis Instant Restore” and the Acronis logo are trademarks of Acronis International GmbH.
Linux is a registered trademark of Linus Torvalds.
VMware and VMware Ready are trademarks and/or registered trademarks of VMware, Inc. in the United States and/or other jurisdictions.
Windows and MS-DOS are registered trademarks of Microsoft Corporation.
All other trademarks and copyrights referred to are the property of their respective owners.
Distribution of substantively modified versions of this document is prohibited without the explicit permission of the copyright holder.
Distribution of this work or derivative work in any standard (paper) book form for commercial purposes is prohibited unless prior permission is obtained from the copyright holder.
DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID.
Third party code may be provided with the Software and/or Service. The license terms for such third-parties are detailed in the license.txt file located in the root installation directory. You can always find the latest up-to-date list of the third party code and the associated license terms used with the Software and/or Service at http://kb.acronis.com/content/7696
Acronis patented technologies
Technologies, used in this product, are covered and protected by one or more U.S. Patent Numbers: 7,047,380; 7,275,139; 7,281,104; 7,318,135; 7,353,355; 7,366,859; 7,475,282; 7,603,533; 7,636,824; 7,650,473; 7,721,138; 7,779,221; 7,831,789; 7,886,120; 7,895,403; 7,934,064; 7,937,612; 7,949,635; 7,953,948; 7,979,690; 8,005,797; 8,051,044; 8,069,320; 8,073,815; 8,074,035; 8,145,607; 8,180,984; 8,225,133; 8,261,035; 8,296,264; 8,312,259; 8,347,137; 8,484,427; 8,645,748; 8,732,121 and patent pending applications.
2 |
Copyright © Acronis International GmbH, 2002-2016 |
Table of contents
1 |
Introducing Acronis Backup.............................................................................................. |
8 |
|
1.1 |
What's new in Acronis Backup 11.7........................................................................................... |
8 |
|
1.2 |
Acronis Backup components ..................................................................................................... |
8 |
|
1.2.1 |
Agent for Linux ................................................................................................................................................ |
8 |
|
1.2.2 |
Management Console..................................................................................................................................... |
9 |
|
1.2.3 |
Bootable Media Builder.................................................................................................................................. |
9 |
|
1.3 |
About using the product in the trial mode ................................................................................ |
9 |
|
1.4 |
Supported file systems ............................................................................................................ |
10 |
|
1.5 |
Technical Support .................................................................................................................... |
10 |
|
2 |
Getting started .............................................................................................................. |
11 |
|
2.1 |
Using the management console .............................................................................................. |
12 |
|
2.1.1 |
"Navigation" pane......................................................................................................................................... |
13 |
|
2.1.2 Main area, views and action pages.............................................................................................................. |
14 |
||
2.1.3 |
Console options............................................................................................................................................. |
17 |
|
3 |
Understanding Acronis Backup....................................................................................... |
20 |
3.1 |
Owners..................................................................................................................................... |
20 |
3.2 |
Credentials used in backup plans and tasks ............................................................................ |
20 |
3.3 |
User privileges on a managed machine................................................................................... |
22 |
3.4 |
Full, incremental and differential backups .............................................................................. |
22 |
3.5 |
What does a disk or volume backup store?............................................................................. |
23 |
3.6 |
Backup and recovery of logical volumes and MD devices (Linux) ........................................... |
24 |
3.6.1 Backing up logical volumes........................................................................................................................... |
24 |
|
3.6.2 Backing up MD devices................................................................................................................................. |
25 |
|
3.6.3 Backing up hardware RAID arrays (Linux) ................................................................................................... |
25 |
|
3.6.4 Assembling MD devices for recovery (Linux) .............................................................................................. |
26 |
|
3.6.5 Recovering MD devices and logical volumes .............................................................................................. |
26 |
|
3.7 |
Support for Advanced Format (4K-sector) hard disks ............................................................. |
30 |
3.8 |
Support for UEFI-based machines ........................................................................................... |
31 |
3.9 |
Support for SNMP.................................................................................................................... |
31 |
4 |
Backup .......................................................................................................................... |
|
33 |
|
4.1 |
Back up now............................................................................................................................. |
|
33 |
|
4.2 |
Creating a backup plan ............................................................................................................ |
|
33 |
|
4.2.1 |
Selecting data to back up.............................................................................................................................. |
|
35 |
|
4.2.2 |
Access credentials for source ....................................................................................................................... |
|
36 |
|
4.2.3 |
Source files exclusion.................................................................................................................................... |
|
36 |
|
4.2.4 |
Backup location selection............................................................................................................................. |
|
38 |
|
4.2.5 |
Access credentials for archive location........................................................................................................ |
|
40 |
|
4.2.6 |
Backup schemes............................................................................................................................................ |
|
41 |
|
4.2.7 |
Archive validation.......................................................................................................................................... |
|
50 |
|
4.2.8 |
Backup plan's credentials ............................................................................................................................. |
|
51 |
|
4.2.9 |
Label (Preserving machine properties in a backup).................................................................................... |
51 |
||
4.2.10 |
Sequence of operations in a backup plan ................................................................................................... |
|
53 |
|
4.2.11 |
Why is the program asking for the password? ........................................................................................... |
|
53 |
|
3 |
|
|
Copyright © Acronis International GmbH, 2002-2016 |
|
4.3 |
Simplified naming of backup files............................................................................................ |
|
53 |
|
4.3.1 |
The [DATE] variable....................................................................................................................................... |
|
54 |
|
4.3.2 |
Backup splitting and simplified file naming................................................................................................. |
|
55 |
|
4.3.3 |
Usage examples............................................................................................................................................. |
|
55 |
|
4.4 |
Scheduling................................................................................................................................ |
|
58 |
|
4.4.1 |
Daily schedule................................................................................................................................................ |
|
59 |
|
4.4.2 |
Weekly schedule ........................................................................................................................................... |
|
61 |
|
4.4.3 |
Monthly schedule.......................................................................................................................................... |
|
63 |
|
4.4.4 |
Conditions...................................................................................................................................................... |
|
65 |
|
4.5 |
Replication and retention of backups...................................................................................... |
|
67 |
|
4.5.1 |
Supported locations...................................................................................................................................... |
|
69 |
|
4.5.2 |
Setting up replication of backups................................................................................................................. |
|
69 |
|
4.5.3 |
Setting up retention of backups................................................................................................................... |
|
70 |
|
4.5.4 |
Retention rules for the Custom scheme...................................................................................................... |
|
71 |
|
4.5.5 |
Usage examples............................................................................................................................................. |
|
72 |
|
4.6 |
How to disable backup cataloging ........................................................................................... |
|
74 |
|
4.7 |
Default backup options............................................................................................................ |
|
74 |
|
4.7.1 |
Additional settings......................................................................................................................................... |
|
76 |
|
4.7.2 |
Archive protection......................................................................................................................................... |
|
77 |
|
4.7.3 |
Backup cataloging ......................................................................................................................................... |
|
78 |
|
4.7.4 |
Backup performance..................................................................................................................................... |
|
78 |
|
4.7.5 |
Backup splitting ............................................................................................................................................. |
|
79 |
|
4.7.6 |
Compression level......................................................................................................................................... |
|
80 |
|
4.7.7 |
Disaster recovery plan (DRP)........................................................................................................................ |
|
81 |
|
4.7.8 |
E-mail notifications........................................................................................................................................ |
|
82 |
|
4.7.9 |
Error handling................................................................................................................................................ |
|
83 |
|
4.7.10 |
Event tracing.................................................................................................................................................. |
|
84 |
|
4.7.11 |
Fast incremental/differential backup .......................................................................................................... |
|
84 |
|
4.7.12 |
File-level backup snapshot ........................................................................................................................... |
|
85 |
|
4.7.13 |
LVM snapshotting ......................................................................................................................................... |
|
85 |
|
4.7.14 |
Media components....................................................................................................................................... |
|
87 |
|
4.7.15 |
Pre/Post commands...................................................................................................................................... |
|
87 |
|
4.7.16 |
Pre/Post data capture commands............................................................................................................... |
|
89 |
|
4.7.17 |
Replication/cleanup inactivity time ............................................................................................................. |
|
91 |
|
4.7.18 |
Sector-by-sector backup............................................................................................................................... |
|
91 |
|
4.7.19 |
Task failure handling ..................................................................................................................................... |
|
91 |
|
4.7.20 |
Task start conditions ..................................................................................................................................... |
|
92 |
|
5 |
Recovery ....................................................................................................................... |
|
94 |
|
5.1 |
Creating a recovery task .......................................................................................................... |
|
94 |
|
5.1.1 |
What to recover ............................................................................................................................................ |
|
95 |
|
5.1.2 |
Access credentials for location..................................................................................................................... |
|
98 |
|
5.1.3 |
Access credentials for destination ............................................................................................................... |
|
99 |
|
5.1.4 |
Where to recover .......................................................................................................................................... |
|
99 |
|
5.1.5 |
When to recover ......................................................................................................................................... |
|
105 |
|
5.1.6 |
Task credentials........................................................................................................................................... |
|
105 |
|
5.2 |
Bootability troubleshooting................................................................................................... |
|
106 |
|
5.2.1 |
How to reactivate GRUB and change its configuration |
............................................................................ 107 |
||
5.3 |
Default recovery options ....................................................................................................... |
|
108 |
|
5.3.1 |
Additional settings....................................................................................................................................... |
|
110 |
|
5.3.2 |
E-mail notifications...................................................................................................................................... |
|
111 |
|
5.3.3 |
Error handling.............................................................................................................................................. |
|
112 |
|
5.3.4 |
Event tracing................................................................................................................................................ |
|
112 |
|
5.3.5 |
File-level security......................................................................................................................................... |
|
113 |
|
4 |
|
|
Copyright © Acronis International GmbH, 2002-2016 |
|
5.3.6 |
Pre/Post commands.................................................................................................................................... |
113 |
5.3.7 |
Recovery priority ......................................................................................................................................... |
115 |
6 |
Conversion to a virtual machine ................................................................................... |
116 |
|
6.1 |
Conversion methods.............................................................................................................. |
116 |
|
6.2 |
Conversion to an automatically created virtual machine...................................................... |
116 |
|
6.2.1 |
Considerations before conversion............................................................................................................. |
117 |
|
6.2.2 Setting up regular conversion to a virtual machine.................................................................................. |
118 |
||
6.2.3 Recovery to the ''New virtual machine'' destination................................................................................ |
121 |
||
6.3 |
Recovery to a manually created virtual machine .................................................................. |
124 |
|
6.3.1 |
Considerations before conversion............................................................................................................. |
124 |
|
6.3.2 |
Steps to perform ......................................................................................................................................... |
125 |
|
7 |
Storing the backed up data........................................................................................... |
126 |
|
7.1 |
Vaults ..................................................................................................................................... |
126 |
|
7.1.1 |
Working with vaults .................................................................................................................................... |
127 |
|
7.1.2 |
Personal vaults ............................................................................................................................................ |
127 |
|
7.2 |
Acronis Secure Zone .............................................................................................................. |
130 |
|
7.2.1 Creating Acronis Secure Zone .................................................................................................................... |
130 |
||
7.2.2 Managing Acronis Secure Zone.................................................................................................................. |
132 |
||
7.3 |
Removable devices ................................................................................................................ |
133 |
|
8 Operations with archives and backups.......................................................................... |
135 |
|
8.1 Validating archives and backups............................................................................................ |
135 |
|
8.1.1 |
Archive selection ......................................................................................................................................... |
136 |
8.1.2 |
Backup selection.......................................................................................................................................... |
136 |
8.1.3 |
Vault selection ............................................................................................................................................. |
136 |
8.1.4 |
Access credentials for source ..................................................................................................................... |
137 |
8.1.5 |
When to validate......................................................................................................................................... |
137 |
8.1.6 |
Task credentials........................................................................................................................................... |
138 |
8.2 Exporting archives and backups ............................................................................................ |
138 |
|
8.2.1 |
Archive selection ......................................................................................................................................... |
140 |
8.2.2 |
Backup selection.......................................................................................................................................... |
141 |
8.2.3 |
Access credentials for source ..................................................................................................................... |
141 |
8.2.4 |
Destination selection .................................................................................................................................. |
141 |
8.2.5 |
Access credentials for destination ............................................................................................................. |
142 |
8.3 Mounting an image................................................................................................................ |
143 |
|
8.3.1 |
Archive selection ......................................................................................................................................... |
144 |
8.3.2 |
Backup selection.......................................................................................................................................... |
144 |
8.3.3 |
Access credentials ....................................................................................................................................... |
144 |
8.3.4 |
Volume selection......................................................................................................................................... |
145 |
8.3.5 |
Managing mounted images........................................................................................................................ |
145 |
8.4 Operations available in vaults................................................................................................ |
146 |
|
8.4.1 |
Operations with archives............................................................................................................................ |
146 |
8.4.2 |
Operations with backups............................................................................................................................ |
147 |
8.4.3 |
Converting a backup to full......................................................................................................................... |
147 |
8.4.4 |
Deleting archives and backups................................................................................................................... |
148 |
9 |
Bootable media ........................................................................................................... |
149 |
|
9.1 |
Linux-based bootable media ................................................................................................. |
149 |
|
9.1.1 |
Kernel parameters....................................................................................................................................... |
150 |
|
9.1.2 |
Network settings ......................................................................................................................................... |
152 |
|
9.1.3 |
Network port ............................................................................................................................................... |
153 |
|
5 |
|
|
Copyright © Acronis International GmbH, 2002-2016 |
9.2 |
Preparing to work under bootable media ............................................................................. |
153 |
|
9.3 |
Working under bootable media............................................................................................. |
154 |
|
9.3.1 |
Setting up a display mode .......................................................................................................................... |
154 |
|
9.3.2 |
Configuring iSCSI and NDAS devices .......................................................................................................... |
154 |
|
9.4 |
List of commands and utilities available in Linux-based bootable media ............................. |
155 |
|
9.5 |
Acronis Startup Recovery Manager ....................................................................................... |
156 |
|
10 |
|
Administering a managed machine ......................................................................... |
158 |
10.1 |
Backup plans and tasks.......................................................................................................... |
158 |
|
10.1.1 |
Actions on backup plans and tasks ............................................................................................................ |
158 |
|
10.1.2 |
States and statuses of backup plans and tasks ......................................................................................... |
160 |
|
10.1.3 |
Export and import of backup plans ............................................................................................................ |
162 |
|
10.1.4 |
Deploying backup plans as files .................................................................................................................. |
165 |
|
10.1.5 |
Backup plan details ..................................................................................................................................... |
167 |
|
10.1.6 |
Task/activity details ..................................................................................................................................... |
168 |
|
10.2 |
Log |
.......................................................................................................................................... |
168 |
10.2.1 |
Actions on log entries .................................................................................................................................. |
168 |
|
10.2.2 .......................................................................................................................................... |
Log entry details |
169 |
|
10.3 |
Alerts...................................................................................................................................... |
170 |
|
10.4 |
Changing .................................................................................................................a license |
171 |
|
10.5 |
Collecting ...............................................................................................system information |
171 |
|
10.6 |
Adjusting ....................................................................................................machine options |
172 |
|
10.6.1 ............................................................................................................................................................ |
Alerts |
172 |
|
10.6.2 ............................................................................................................................................. |
E - mail settings |
172 |
|
10.6.3 ................................................................................................................................................ |
Event tracing |
174 |
|
10.6.4 ......................................................................................................................................... |
Log cleanup rules |
175 |
|
10.6.5 ..................................................................................................................................... |
Cloud backup proxy |
175 |
|
11 |
......................................................................................................... |
Cloud backup |
177 |
11.1 |
Introduction ...................................................................................to Acronis Cloud Backup |
177 |
|
11.1.1 .................................................................................................................. |
What is Acronis Cloud Backup? |
177 |
|
11.1.2 ...................................................................................................... |
What data can I back up and recover? |
177 |
|
11.1.3 ........................................................................ |
How long will my backups be kept in the cloud storage? |
177 |
|
11.1.4 .......................................................................................................................... |
How do I secure my data? |
178 |
|
11.1.5 ...................................................................... |
Supported operating systems and virtualization products |
178 |
|
11.1.6 .......................................................................................................................... |
Backup and recovery FAQ |
179 |
|
11.1.7 ...................................................................................................................................... |
Initial Seeding FAQ |
181 |
|
11.1.8 .......................................................................................................................... |
Large Scale Recovery FAQ |
186 |
|
11.1.9 .......................................................................................................................... |
Subscription lifecycle FAQ |
187 |
|
11.2 |
Where ...................................................................................................................do I start? |
190 |
|
11.3 |
Choosing .........................................................................................................a subscription |
190 |
|
11.4 |
Configuring .....................................................................................................proxy settings |
191 |
|
11.5 |
Checking ................................................................................................the firewall settings |
191 |
|
11.6 |
Activating ..................................................................................cloud backup subscriptions |
191 |
|
11.6.1 ............................................................................................... |
Activating subscriptions in Acronis Backup |
192 |
|
11.6.2 ....................................................................................................... |
Reassigning an activated subscription |
192 |
|
11.7 |
Retrieving ..........................................files from the cloud storage by using a web browser |
193 |
|
11.8 |
Limitations ............................................................................................of the cloud storage |
194 |
|
11.9 |
Terminology ..........................................................................................................reference |
195 |
|
6 |
|
Copyright © Acronis International GmbH, 2002 - 2016 |
|
12 |
Glossary................................................................................................................. |
198 |
7 |
Copyright © Acronis International GmbH, 2002-2016 |
1 Introducing Acronis Backup
1.1What's new in Acronis Backup 11.7
Licensing
Support for the subscription licensing model. For more information, please refer to the Acronis Backup Licensing FAQ.
Linux
Support for Linux kernel version 4.2, 4.3, and 4.4
Support for Red Hat Enterprise Linux 7.2, Oracle Linux 7.2, ClearOS, Debian 8.2, Ubuntu 15.10, and Fedora 23.
Other
It is possible to use compression in combination with third-party hardware or software deduplication (for disk-level backups only). This effectively reduces the storage space occupied by the backups.
32-bit Linux-based bootable media was optimized in size by removing the rarely used acrocmd utility.
1.2Acronis Backup components
This section contains a list of Acronis Backup components with a brief description of their functionality.
Components for a managed machine (agents)
These are applications that perform data backup, recovery and other operations on the machines managed with Acronis Backup. Agents require a license to perform operations on each managed machine.
Console
The console provides Graphical User Interface to the agents. Usage of the console is not licensed. The console is installed together with the agent and cannot be disconnected from it.
Bootable Media Builder
With Bootable Media Builder, you can create bootable media in order to use the agents and other rescue utilities in a rescue environment. Bootable Media Builder is installed together with the agent.
1.2.1Agent for Linux
This agent enables disk-level and file-level data protection under Linux.
Disk backup
Disk-level data protection is based on backing up either a disk or a volume file system as a whole, along with all information necessary for the operating system to boot; or all the disk sectors using the sector-by-sector approach (raw mode.) A backup that contains a copy of a disk or a volume in a
8 |
Copyright © Acronis International GmbH, 2002-2016 |
packaged form is called a disk (volume) backup or a disk (volume) image. It is possible to recover disks or volumes as a whole from such backup, as well as individual folders or files.
File backup
File-level data protection is based on backing up files and directories residing on the machine where the agent is installed or on a network share accessed using the smb or nfs protocol. Files can be recovered to their original location or to another place. It is possible to recover all files and directories that were backed up or select which of them to recover.
Conversion to a virtual machine
Agent for Linux performs the conversion by recovering a disk backup to a new virtual machine of any of the following types: VMware Workstation, Microsoft Virtual PC, Citrix XenServer Open Virtual Appliance (OVA) or Red Hat Kernel-based Virtual Machine (KVM). Files of the fully configured and operational machine will be placed in the directory you select. You can start the machine using the respective virtualization software or prepare the machine files for further usage.
1.2.2Management Console
Acronis Backup Management Console is an administrative tool for local access to Acronis Backup agent. Remote connection to the agent is not possible.
1.2.3Bootable Media Builder
Acronis Bootable Media Builder is a dedicated tool for creating bootable media (p. 200). The media builder that installs on Linux creates bootable media based on Linux kernel.
1.3About using the product in the trial mode
Before buying an Acronis Backup license, you may want to try the software. This can be done without a license key.
To install the product in the trial mode, run the setup program locally or use the remote installation functionality. Unattended installation and other ways of installation are not supported.
Limitations of the trial mode
When working under bootable media:
The disk management functionality is not available. You can try the user interface, but there is no option to commit the changes.
The recovery functionality is available, but the backup functionality is not. To try the backup functionality, install the software in the operating system.
Upgrading to the full mode
After the trial period expires, the product GUI displays a notification requesting you to specify or obtain a license key.
To specify a license key, click Help > Change License (p. 171). Specifying the key by running the setup program is not possible.
9 |
Copyright © Acronis International GmbH, 2002-2016 |
If you have activated a trial or purchased a subscription for the cloud backup service (p. 177), cloud backup will be available until the subscription period expires, regardless of whether you specify a license key.
1.4Supported file systems
Acronis Backup can back up and recover the following file systems with the following limitations:
FAT16/32
NTFS
ReFS - volume recovery without the volume resize capability. Supported in Windows Server 2012/2012 R2 and Windows Server 2016 only.
Ext2/Ext3/Ext4
ReiserFS3 - particular files cannot be recovered from disk backups located on Acronis Backup Storage Node
ReiserFS4 - volume recovery without the volume resize capability; particular files cannot be recovered from disk backups located on Acronis Backup Storage Node
XFS - volume recovery without the volume resize capability; particular files cannot be recovered from disk backups located on Acronis Backup Storage Node
JFS - particular files cannot be recovered from disk backups located on Acronis Backup Storage Node
Linux SWAP
Acronis Backup can back up and recover corrupted or non-supported file systems using the sector-by-sector approach.
1.5Technical Support
Maintenance and Support Program
If you need assistance with your Acronis product, please go to
http://www.acronis.com/en-us/support/
Product Updates
You can download the latest updates for all your registered Acronis software products from our website at any time after logging into your Account (http://www.acronis.com/en-us/my) and registering the product. See Registering Acronis Products at the Website
(http://kb.acronis.com/content/4834) and Acronis Website User Guide (http://kb.acronis.com/content/8128).
10 |
Copyright © Acronis International GmbH, 2002-2016 |

2 Getting started
 Step 1. Installation
Step 1. Installation
 These brief installation instructions enable you to start using the product quickly. For the complete description of installation methods and procedures, please refer to the Installation documentation.
These brief installation instructions enable you to start using the product quickly. For the complete description of installation methods and procedures, please refer to the Installation documentation.
Before installation, make sure that:
Your hardware meets the system requirements.
You have a license key for Acronis Backup for Linux Server.
You have the setup program. You can download it from the Acronis website.
Make sure that the RPM Package Manager (RPM) and the following Linux packages are installed: gcc, make, and kernel-devel. The names of these packages may vary depending on the Linux distribution.
To install Acronis Backup
Run the AcronisBackupL.i686 or the AcronisBackupL.x86_64 installation file and follow the on-screen instructions.
 Step 2. Running
Step 2. Running
Log in as root or log in as an ordinary user and then switch user as required. Start the console with the command
/usr/sbin/acronis_console
 For understanding of the GUI elements see "Using the management console" (p. 12).
For understanding of the GUI elements see "Using the management console" (p. 12).
 Step 3. Bootable media
Step 3. Bootable media
To be able to recover an operating system that fails to start, or deploy it on bare metal, create bootable media.
1.Select  Tools >
Tools >  Create bootable media in the menu.
Create bootable media in the menu.
2.Click Next in the welcome screen. Keep clicking Next until the list of components appears.
3.Proceed as described in "Linux-based bootable media" (p. 149).
 Step 4. Backup
Step 4. Backup
 Back up now (p. 33)
Back up now (p. 33)
Click Back up now to do a one-time backup in a few simple steps. The backup process will start immediately after you perform the required steps.
To save your machine to a file:
Under Where to back up, click Location, and select the location where the backup will be saved. Click OK to confirm your selection. Click OK at the bottom of the window to start the backup.
11 |
Copyright © Acronis International GmbH, 2002-2016 |
Tip. Using the bootable media, you can do off-line ("cold") backups in the same way as in the operating system.
 Create backup plan (p. 33)
Create backup plan (p. 33)
Create a backup plan if you need a long-term backup strategy including backup schemes, schedules and conditions, timely deleting of backups, or moving them to different locations.
 Step 5. Recovery
Step 5. Recovery
 Recover (p. 94)
Recover (p. 94)
To recover data, you need to select the backed-up data and the destination the data will be recovered to. As a result, a recovery task will be created.
Recovery of a disk or volume over a volume locked by the operating system requires a reboot. After the recovery is completed, the recovered operating system goes online automatically.
If the machine fails to boot or if you need to recover a system to bare metal, boot the machine using the bootable media and configure the recovery operation in the same way as the recovery task.
 Step 6. Management
Step 6. Management
The Navigation pane (at the left part of the console) enables you to navigate across the product views that are used for different administering purposes.
Use the  Backup plans and tasks view to manage backup plans and tasks: run, edit, stop and delete plans and tasks, view their states and progress.
Backup plans and tasks view to manage backup plans and tasks: run, edit, stop and delete plans and tasks, view their states and progress.
Use the  Alerts view to rapidly identify and solve the problems.
Alerts view to rapidly identify and solve the problems.
Use the  Log view to browse the operations log.
Log view to browse the operations log.
The location where you store backup archives is called a vault (p. 210). Navigate to the  Vaults (p. 126) view to obtain information about your vaults. Navigate further to the specific vault to view backups and their contents. You can also select the data to recover and perform manual operations with backups (mounting, validating, deleting).
Vaults (p. 126) view to obtain information about your vaults. Navigate further to the specific vault to view backups and their contents. You can also select the data to recover and perform manual operations with backups (mounting, validating, deleting).
2.1Using the management console
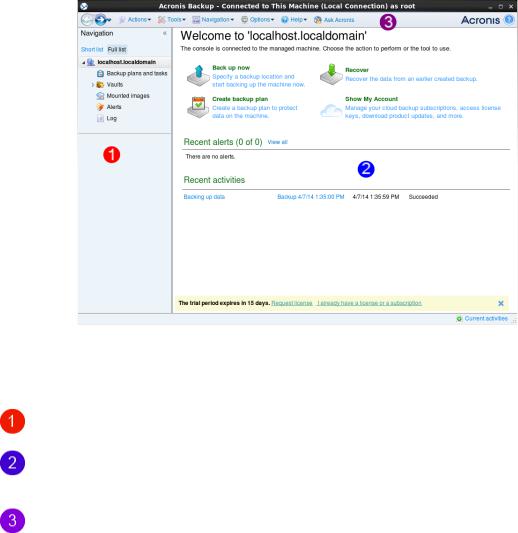
As soon as the console starts, the respective items appear across the console's workspace (in the menu, in the main area with the Welcome screen, or in the Navigation pane) enabling you to perform machine-specific operations.
12 |
Copyright © Acronis International GmbH, 2002-2016 |
|
|
Acronis Backup Management Console - Welcome screen |
|
Key elements of the console workspace |
|||
|
Name |
|
Description |
|
|
|
|
|
Navigation pane |
|
Contains the Navigation tree. Lets you navigate to the different views. For |
|
|
|
details, see Navigation pane (p. 13). |
|
|
|
|
|
Main area |
|
Here you configure and monitor backup, recovery and other operations. The |
|
|
|
main area displays views and action pages (p. 14) depending on the items |
|
|
|
selected in the menu or Navigation tree. |
|
|
|
|
|
Menu bar |
|
Appears across the top of the program window. Lets you perform most of |
|
|
|
operations available in Acronis Backup. The menu items change dynamically |
|
|
|
depending on the item selected in the Navigation tree and the main area. |
|
|
|
|
2.1.1"Navigation" pane
The navigation pane includes the Navigation tree.
Navigation tree
The Navigation tree enables you to navigate across the program views. You can choose between the Full list or the Short list of views. The Short list contains the most frequently used views from the
Full list.
The Short list displays
 [Machine name]. This is the root of the tree also called a Welcome screen. It displays the name of the machine the console is currently connected to. Use this view for quick access to the main operations, available on the managed machine.
[Machine name]. This is the root of the tree also called a Welcome screen. It displays the name of the machine the console is currently connected to. Use this view for quick access to the main operations, available on the managed machine.
 Backup plans and tasks. Use this view to manage backup plans and tasks on the managed machine: run, edit, stop and delete plans and tasks, view their progress.
Backup plans and tasks. Use this view to manage backup plans and tasks on the managed machine: run, edit, stop and delete plans and tasks, view their progress.
 Vaults. Use this view to manage personal vaults and archives stored in there, add new vaults, rename and delete the existing ones, validate vaults, explore backup content, perform operations on archives and backups, etc.
Vaults. Use this view to manage personal vaults and archives stored in there, add new vaults, rename and delete the existing ones, validate vaults, explore backup content, perform operations on archives and backups, etc.
13 |
Copyright © Acronis International GmbH, 2002-2016 |
 Alerts. Use this view to examine warning messages for the managed machine. The Full list additionally displays
Alerts. Use this view to examine warning messages for the managed machine. The Full list additionally displays
 Disk management. Use this view to perform operations on the machine's hard disk drives.
Disk management. Use this view to perform operations on the machine's hard disk drives.
 Log. Use this view to examine information on operations performed by the program on the managed machine.
Log. Use this view to examine information on operations performed by the program on the managed machine.
 Mounted images. This node is displayed if at least one volume is mounted. Use this view to manage mounted images.
Mounted images. This node is displayed if at least one volume is mounted. Use this view to manage mounted images.
Operations with pane
How to expand/minimize panes
By default, the Navigation pane appears expanded. You might need to minimize the pane in order to free some additional workspace. To do this, click the chevron ( ). The pane will be minimized and the chevron changes its direction (
). The pane will be minimized and the chevron changes its direction ( ). Click the chevron once again to expand the pane.
). Click the chevron once again to expand the pane.
How to change the panes' borders
1.Point to the pane's border.
2.When the pointer becomes a double-headed arrow, drag the pointer to move the border.
2.1.2Main area, views and action pages
The main area is a basic place where you work with the console. Here you create, edit and manage backup plans, recovery tasks and perform other operations. The main area displays different views and action pages according the items you select in the menu, or Navigation tree.
2.1.2.1Views
A view appears on the main area when clicking any item in the Navigation tree in the Navigation pane (p. 13).
14 |
Copyright © Acronis International GmbH, 2002-2016 |
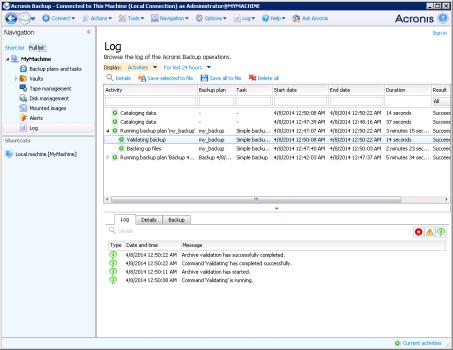
"Log" view
Common way of working with views
Generally, every view contains a table of items, a table toolbar with buttons, and the Information panel.
Use filtering and sorting (p. 15) capabilities to search the table for the item in question.
In the table, select the desired item.
In the information panel (collapsed by default), view the item's details. To expand the panel, click the arrow mark ( ).
).
Perform actions on the selected item. There are several ways of performing the same action on selected items:
By clicking the buttons on the table toolbar.
By selecting the items in the Actions menu.
By right-clicking the item and selecting the operation in the context menu.
Sorting, filtering and configuring table items
The following is a guideline to sort, filter and configure table items in any view.
To |
|
Do the following |
|
|
|
|
|
|
Sort items by any column |
|
Click a column's header to sort items in ascending order. |
|
|
Click it once again to sort items in descending order. |
|
|
|
Filter items by predefined |
|
In a field below the corresponding column's header, select the required value |
column value |
|
from the drop-down list. |
|
|
|
Filter items by entered value |
|
In a field below the corresponding column's header, type a value. |
|
|
As a result you will see the list of values, fully or just partly coincide with the |
|
|
entered value. |
|
|
|
Filter items by predefined |
|
Click the appropriate buttons above the table. |
parameters |
|
For example, in the Log view, you can filter the log entries by event type |
|
|
|
|
|
(Error, Warning, Information) or by the period when the event occurred (For |
|
|
last 24 hours, For last week, For last three months, or For custom period). |
|
|
|
Show or hide table columns |
|
By default, any table has a fixed number of columns that are shown, others |
|
|
are hidden. If required, you can hide the shown columns and show the hidden |
|
|
ones. |
|
|
To show or hide columns |
|
|
1. Right-click any column header to open the context menu. |
|
|
2. Click the items you want to be displayed/hidden. |
|
|
|
2.1.2.2Action pages
An action page appears in the main area when clicking any action item in the Actions menu. It contains steps you need to perform in order to create and launch any task or a backup plan.
15 |
Copyright © Acronis International GmbH, 2002-2016 |
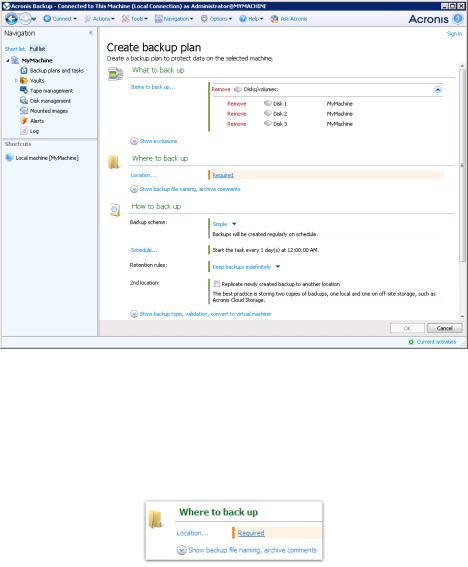
Action page - Create backup plan
Using controls and specifying settings
Use active controls to specify a backup plan or recovery task settings and parameters. By default, such fields as credentials, options, comments, and some others are hidden. Most settings are configured by clicking the respective Show… links. Others are selected from the drop-down list, or typed manually in the page's fields.
Action page - Controls
Acronis Backup remembers the changes you made on the action pages. For example, if you started to create a backup plan, and then for any reason switched to another view without accomplishing the plan creation, you can click the Back navigation button on the menu. Or, if you have passed several steps forward, click the Down arrow and select the page where you started the plan creation from the list. Thus, you can perform the remaining steps and accomplish the backup plan creation.
16 |
Copyright © Acronis International GmbH, 2002-2016 |

Navigation buttons
2.1.3Console options
The console options define the way information is represented in the Graphical User Interface of Acronis Backup.
To access the console options, select Options > Console options from the top menu.
2.1.3.1Alert display options
The option specifies which alerts to show and which to hide in the Alerts view.
The preset is: All alerts.
To show (hide) alerts, select (clear) the check boxes next to the respective alert types.
2.1.3.2Credentials cache
The option specifies whether to store the credentials entered while using the management console.
The preset is: Enabled.
If the option is enabled, the credentials for various locations that you enter during a console session are saved for use during later sessions. In Windows, the credentials are stored in the Windows Credential Manager. In Linux, the credentials are stored in a special encrypted file.
If the option is disabled, the credentials are stored only until the console is closed.
To clear the credentials cache for the current user account, click the Clear credentials cache button.
2.1.3.3Fonts
The option defines the fonts to be used in the Graphical User Interface of Acronis Backup. The Menu font setting affects the drop-down and context menus. The Application font setting affects all other GUI elements.
The preset is: System Default font for both the menus and the application interface items.
To make a selection, choose the font from the respective combo-box and set the font's properties. You can preview the font's appearance by clicking Browse to the right.
17 |
Copyright © Acronis International GmbH, 2002-2016 |

2.1.3.4Pop-up messages
The “Interaction Required” dialog
This option defines whether to display a pop-up window when one or more activities require user interaction. This window enables you to specify your decision, such as to confirm reboot or to retry after freeing-up the disk space, on all the activities in the same place. Until at least one activity requires interaction, you can open this window at any time from the managed machine's welcome screen. Alternatively, you can review the task execution states in the Backup plans and tasks view and specify your decision on each task in the information panel.
The preset is: Enabled.
To make a selection, select or clear the The “Interaction Required” dialog check box.
The “Feedback Confirmation” dialog
This option defines whether to display a pop-up window with the information about your system after an error occurs. You can send this information to Acronis technical support.
The preset is: Enabled.
To make a selection, select or clear the The “Feedback Confirmation” dialog check box.
Notify if bootable media is not created
This option defines whether to display a pop-up window when the management console is launched on a machine and no bootable media has been created on that machine.
The preset is: Enabled.
To make a selection, select or clear the Notify if bootable media is not created check box.
Notify when the management console is connected to a component of a different version
This option defines whether to display a pop-up window when a console is connected to an agent and their versions differ.
The preset is: Enabled.
To make a selection, select or clear the Notify when the management console is connected to a component of a different version check box.
Request description when ejecting a tape
This option defines whether to display a prompt for you to describe a tape when you eject it from a tape device by using Acronis Backup. For example, you may describe the physical location where the tape will be kept (recommended). If a tape is ejected automatically according to the Eject tapes after successful backups option, no such prompt is displayed.
The preset is: Enabled.
To make a selection, select or clear the Request description when ejecting a tape check box.
Note Tape devices are available only if you have upgraded from Acronis Backup & Recovery 10.
18 |
Copyright © Acronis International GmbH, 2002-2016 |
About the task execution results
The option defines whether to display the pop-up messages about task run results: successful completion, failure or success with warnings. When the displaying of pop-up messages is disabled, you can review the task execution states and results in the Backup plans and tasks view.
The preset is: Enabled for all results.
To make a setting for each result (successful completion, failure or success with warnings) individually, select or clear the respective check box.
19 |
Copyright © Acronis International GmbH, 2002-2016 |
3 Understanding Acronis Backup
This section attempts to give its readers a clear understanding of the product so that they can use the product in various circumstances without step-by-step instructions.
3.1Owners
This section explains the concept of a backup plan (task) owner and an archive owner.
Plan (task) owner
A local backup plan owner is the user who created or last modified the plan.
Tasks, belonging to a backup plan, are owned by the backup plan owner.
Tasks that do not belong to a backup plan, such as the recovery task, are owned by the user who has created or last modified the task.
Managing a plan (task) owned by another user
Having Administrator privileges on the machine, a user can modify tasks and local backup plans owned by any user registered in the operating system.
When a user opens a plan or task for editing, which is owned by another user, all passwords set in the task are cleared. This prevents the "modify settings, leave passwords" trick. The program displays a warning each time you are trying to edit a plan (task) last modified by another user. On seeing the warning, you have two options:
Click Cancel and create your own plan or task. The original task will remain intact.
Continue editing. You will have to enter all credentials required for the plan or task execution.
Archive owner
An archive owner is the user who saved the archive to the destination. To be more precise, this is the user whose account was specified when creating the backup plan in the Where to back up step. By default, the plan's credentials are used.
3.2Credentials used in backup plans and tasks
This section explains the concept of access credentials, backup plan's credentials and task credentials.
Access credentials
When browsing backup locations, setting up backups, or creating recovery tasks, you may need to provide credentials for accessing various resources, such as the data you are going to back up or the location where the backups are (or will be) stored.
If the Credentials cache (p. 17) option is enabled (it is enabled by default), the credentials which you provide during a console session are saved for use during the later sessions. Thus, there is no need to enter the credentials next time. The credentials are cached independently for each user who uses the console on the machine.
20 |
Copyright © Acronis International GmbH, 2002-2016 |
Backup plan's credentials
Any backup plan running on a machine runs on behalf of a user.
In Windows
By default, the plan runs under the agent service account, if created by a user having administrative privileges on the machine. If created by a regular user, such as a member of the Users group, the plan runs under this user's account.
When creating a backup plan, you are only asked for credentials in specific cases. For example:
You are scheduling backups as a regular user and did not enter credentials when connecting the console to the machine. This may be the case when the console is installed on the same machine that you are backing up.
You are backing up a Microsoft Exchange cluster to a storage node.
Specifying the credentials explicitly
You have the option to explicitly specify a user account under which the backup plan will run. To do this, on the backup plan creation page:
1.In the Plan parameters section, click Show plan's credentials, comments, label.
2.Click Plan's credentials.
3.Enter the credentials under which the plan will run. When entering the name of an Active Directory user account, be sure to also specify the domain name (DOMAIN\Username or Username@domain).
In Linux
You do not need to specify backup plan's credentials. In Linux, backup plans always run under the root user account.
Task credentials
Like a backup plan, any task runs on behalf of a user.
In Windows
When creating a task, you have the option to explicitly specify an account under which the task will run. Your choice depends on whether the task is intended for manual start or for executing on schedule.
Manual start
Every time you manually start the task, the task will run under the credentials with which you are currently logged on. Any person that has administrative privileges on the machine can also start the task. The task will run under this person's credentials.
The task will always run under the same credentials, regardless of the user who actually starts the task, if you specify the task credentials explicitly.
Scheduled or postponed start
The task credentials are mandatory. You cannot complete the task creation until you specify the task credentials. Task credentials are specified on the task creation page in a similar manner as the plan’s credentials are specified.
In Linux
You do not need to specify task credentials. In Linux, tasks always run under the root user account.
21 |
Copyright © Acronis International GmbH, 2002-2016 |
3.3User privileges on a managed machine
When managing a machine running Linux, the user has or obtains the root privileges, and so can:
Back up and recover any data or the entire machine, having full control over all Acronis Backup agent operations and log files on the machine.
Manage local backup plans and tasks owned by any user registered in the operating system.
To avoid routine logging on to the system as root, the root user can log on with the ordinary user credentials and then switch user as required.
3.4Full, incremental and differential backups
Acronis Backup provides the capability to use popular backup schemes, such as Grandfather-Father-Son and Tower of Hanoi, as well as to create custom backup schemes. All backup schemes are based on full, incremental and differential backup methods. The term "scheme" in fact denotes the algorithm of applying these methods plus the algorithm of the archive cleanup.
Comparing backup methods with each other does not make much sense because the methods work as a team in a backup scheme. Each method should play its specific role according to its advantages. A competent backup scheme will benefit from the advantages of all backup methods and lessen the influence of all the methods’ shortcomings. For example, weekly differential backup facilitates archive cleanup because it can be easily deleted along with the weekly set of daily incremental backups depending on it.
Backing up with the full, incremental or differential backup method results in a backup (p. 199) of the corresponding type.
Full backup
A full backup stores all data selected for backup. A full backup underlies any archive and forms the base for incremental and differential backups. An archive can contain multiple full backups or consist of only full backups. A full backup is self-sufficient - you do not need access to any other backup to recover data from a full backup.
It is widely accepted that a full backup is the slowest to do but the fastest to restore. With Acronis technologies, recovery from an incremental backup may be not slower than recovery from a full one.
A full backup is most useful when:
you need to roll back the system to its initial state
this initial state does not change often, so there is no need for regular backup.
Example: An Internet cafe, school or university lab where the administrator often undoes changes made by the students or guests but rarely updates the reference backup (in fact, after installing software updates only). The backup time is not crucial in this case and the recovery time will be minimal when recovering the systems from the full backup. The administrator can have several copies of the full backup for additional reliability.
Incremental backup
An incremental backup stores changes to the data against the latest backup. You need access to other backups from the same archive to recover data from an incremental backup.
An incremental backup is most useful when:
22 |
Copyright © Acronis International GmbH, 2002-2016 |

you need the possibility to roll back to any one of multiple saved states
the data changes tend to be small as compared to the total data size.
It is widely accepted that incremental backups are less reliable than full ones because if one backup in the "chain" is corrupted, the next ones can no longer be used. However, storing multiple full backups is not an option when you need multiple prior versions of your data, because reliability of an oversized archive is even more questionable.
Example: Backing up a database transaction log.
Differential backup
A differential backup stores changes to the data against the latest full backup. You need access to the corresponding full backup to recover the data from a differential backup. A differential backup is most useful when:
you are interested in saving only the most recent data state
the data changes tend to be small as compared to the total data size.
The typical conclusion is: "differential backups take longer to do and are faster to restore, while incremental ones are quicker to do and take longer to restore." In fact, there is no physical difference between an incremental backup appended to a full backup and a differential backup appended to the same full backup at the same point of time. The above mentioned difference implies creating a differential backup after (or instead of) creating multiple incremental backups.
An incremental or differential backup created after disk defragmentation might be considerably larger than usual because defragmentation changes file locations on the disk and the backup reflects these changes. It is recommended that you re-create a full backup after disk defragmentation.
The following table summarizes the advantages and shortcomings of each backup type as they appear based on common knowledge. In real life, these parameters depend on numerous factors such as the amount, speed and pattern of data changes; the nature of the data, the physical specifications of the devices, the backup/recovery options you set, to name a few. Practice is the best guide to selecting the optimal backup scheme.
Parameter |
Full backup |
Differential backup |
Incremental backup |
|
|
|
|
Storage space |
Maximal |
Medium |
Minimal |
|
|
|
|
|
|
|
|
Creation time |
Maximal |
Medium |
Minimal |
|
|
|
|
|
|
|
|
Recovery time |
Minimal |
Medium |
Maximal |
|
|
|
|
|
|
|
|
3.5What does a disk or volume backup store?
A disk or volume backup stores a disk or a volume file system as a whole and includes all of the information necessary for the operating system to boot. It is possible to recover disks or volumes as a whole from such backups as well as individual folders or files.
Windows
A volume backup stores all files and folders of the selected volume independent of their attributes (including hidden and system files), the boot record, the file allocation table (FAT) if it exists, the root and the zero track of the hard disk with the master boot record (MBR).
A disk backup stores all volumes of the selected disk (including hidden volumes such as the vendor's maintenance partitions) and the zero track with the master boot record.
The following items are not included in a disk or volume backup (as well as in a file-level backup):
23 |
Copyright © Acronis International GmbH, 2002-2016 |
The swap file (pagefile.sys) and the file that keeps the RAM content when the machine goes into hibernation (hiberfil.sys). After recovery, the files will be re-created in the appropriate place with the zero size.
Windows shadow storage. The path to it is determined in the registry value VSS Default Provider which can be found in the registry key
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\BackupRestore\FilesNotToBa ckup. This means that in operating systems starting with Windows Vista, Windows Restore Points are not backed up.
Linux
A volume backup stores all files and directories of the selected volume independent of their attributes, a boot record, and the file system super block.
A disk backup stores all disk volumes as well as the zero track with the master boot record.
With the sector-by-sector (raw mode) option enabled, a disk backup stores all the disk sectors. The sector-by-sector backup can be used for backing up disks with unrecognized or unsupported file systems and other proprietary data formats.
3.6Backup and recovery of logical volumes and MD
devices (Linux)
This section explains how you would back up and recover volumes managed by Linux Logical Volume Manager (LVM), called logical volumes; and multiple-disk (MD) devices, called Linux Software RAID.
To learn more about LVM please visit http://tldp.org/HOWTO/LVM-HOWTO/ or http://www.centos.org/docs/5/html/5.1/Deployment_Guide/ch-lvm.html.
3.6.1Backing up logical volumes
Acronis Backup Agent for Linux can access, back up, and recover logical volumes when running in Linux starting with 2.6.x kernel or under Linux-based bootable media.
Backup
In Acronis Backup GUI, logical volumes appear under Dynamic volumes at the end of the list of volumes available for backup. If you select logical volumes for backup, the logical volume structure will be saved to the backup along with the volume contents. This structure can be automatically recreated when you recover these volumes under a Linux-based bootable media.
To back up all available disks, specify all logical volumes plus basic volumes not belonging to them. This is the default choice when you open the Create backup plan page.
Basic volumes included in logical volumes are shown in the list with None in the File system column. If you select such volumes, the program will back them up sector-by-sector. Normally this is not required.
Recovery
When recovering logical volumes, you have two options:
Recovering volume contents only. The type or other properties of the target volume will not change.
This option is available both in the operating system and under bootable media.
24 |
Copyright © Acronis International GmbH, 2002-2016 |
This option is useful in the following cases:
When some data on the volume was lost, but no hard disks were replaced.
When recovering a logical volume over a basic disk or volume. You can resize the resulting volume in this case.
A system, recovered from a logical volume backup to a basic disk, cannot boot because its kernel tries to mount the root file system at the logical volume. To boot the system, change the loader configuration and /etc/fstab so that LVM is not used and reactivate your boot loader (p. 107).
When recovering a basic or logical volume to an existing logical volume.
If the boot partition (/boot) was located on a basic volume, we recommend recovering it to a basic volume, even if your boot loader supports booting from logical volumes.
Recovering both the structure of logical volumes and their contents.
Such is the case when recovering on bare metal or on a machine with different volume structure. The structure of logical volumes can be automatically created at the time of recovery (p. 27).
This option is available only under bootable media.
For detailed instructions on how to recover logical volumes, see Recovering MD devices and logical volumes (p. 26).
3.6.2Backing up MD devices
MD devices, known as Linux Software RAID, combine several volumes and make solid block devices (/dev/md0, /dev/md1, ..., /dev/md31). The information about MD devices is stored in /etc/raidtab or in dedicated areas of those volumes.
You can back up active (mounted) MD devices in the same way as logical volumes. The MD devices appear at the end of the list of volumes available for backup. If you select MD devices for backup, the structure of the MD devices will be backed up along with their contents.
Backing up volumes included in MD devices does not make sense when an MD device is mounted, as it won’t be possible to recover them.
When recovering MD devices under bootable media, the structure of MD devices can be recreated automatically. For detailed information about recovering MD devices under bootable media, see Recovering MD devices and logical volumes (p. 26).
For information about assembling MD devices when performing recovery in Linux, see Assembling MD devices for recovery (Linux) (p. 26).
3.6.3Backing up hardware RAID arrays (Linux)
Hardware RAID arrays under Linux combine several physical drives to create a single partitionable disk. The special file related to a hardware RAID array is usually located in /dev/ataraid. You can back up hardware RAID arrays in the same way as ordinary hard disks.
Physical drives that are part of hardware RAID arrays may be listed alongside other disks as if they had a bad partition table or no partition table at all. Backing up such disks does not make sense as it won’t be possible to recover them.
25 |
Copyright © Acronis International GmbH, 2002-2016 |
3.6.4Assembling MD devices for recovery (Linux)
In Linux, when performing recovery from a disk backup to an existing MD device (also called Linux Software RAID), make sure that this device is assembled at the time of recovery.
If the device is not assembled, assemble it by using the mdadm utility. Here are two examples:
Example 1. The following command assembles the device /dev/md0 combined from the volumes /dev/sdb1 and /dev/sdc1:
mdadm --assemble /dev/md0 -ayes /dev/sdb1 /sdc1
Example 2. The following command assembles the device /dev/md0 combined from the disks /dev/sdb and /dev/sdc:
mdadm --assemble /dev/md0 -ayes /dev/sdb /dev/sdc
If the recovery requires the machine to be rebooted (usually, when the volumes to recover include the boot partition), follow these guidelines:
If all parts of the MD device are volumes (a typical case, such as in the first example), make sure that each volume type—called partition type or system ID—is Linux raid automount; the hexadecimal code of this partition type is 0xFD. This will guarantee that the device will be automatically assembled following the reboot. To view or change the partition type, use a disk partitioning utility such as fdisk.
Otherwise (such as in the second example), perform the recovery from bootable media. No reboot will be required in that case. In bootable media, you may need to create the MD device manually or automatically, as described in Recovering MD devices and logical volumes (p. 26).
3.6.5Recovering MD devices and logical volumes
Recovering MD devices and/or volumes created by Logical Volume Manager (logical volumes) assumes that the corresponding volume structure will be recreated.
In Linux-based bootable media, you can choose to recreate the volume structure automatically (p. 27).
This functionality is intended primarily for bare-metal recovery of an entire machine. The software backs up and recreates the entire logical volume structure, even if not all MD devices or logical volumes are being backed up or recovered. Therefore, you need at least as many disks as the original volume structure used.
Do not try to recreate the volume structure automatically in any of the following cases:
The machine has data that must be preserved. The software will destroy all data on the disks that it chooses to recreate the volume structure on.
The machine has fewer physical disks than the original volume structure used. The software will fail to recreate the volume structure even if the capacity of the physical disks is enough to fit all the data being recovered.
The backup does not contain the volume structure information. This information might be absent in backups created by Acronis Backup & Recovery 10, because saving it was optional.
In these cases, create the volume structure manually (p. 27) prior to recovery. You can do this by using the mdadm and lvm utilities, either in Linux-based bootable media or in Linux.
26 |
Copyright © Acronis International GmbH, 2002-2016 |
3.6.5.1Creating the volume structure automatically
Use the following procedure to automatically recreate the logical volume structure on a machine.
Caution As a result of the following procedure, the current volume structure on the machine will be replaced with the one stored in the backup. This will destroy the data that is currently stored on some or all of the machine's hard disks.
If disk configuration has changed. An MD device or a logical volume resides on one or more disks. If you replaced any of these disks between backup and recovery (or if you are recovering the volumes to a different machine), ensure that the new disk configuration includes at least the same number of disks as the original volume structure did. The capacity of the disks must be enough to fit all the data being recovered.
To create the volume structure automatically
1.Boot the machine from a Linux-based bootable media.
2.Click Acronis Bootable Agent. Then, click Run management console.
3.In the management console, click Recover.
Under the archive contents, Acronis Backup will display a message saying that it detected information about the volume structure.
4.Click Details in the area with that message.
5.Review the volume structure, and then click Apply RAID/LVM to create it.
3.6.5.2Creating the volume structure manually
The following is a general procedure for recovering MD devices and logical volumes by using a Linux-based bootable media, and an example of such recovery. You can use a similar procedure in Linux.
To create the volume structure manually
1.Boot the machine from a Linux-based bootable media.
2.Click Acronis Backup. Then, click Run management console.
3.On the toolbar, click Actions, and then click Start shell. Alternatively, you can press CTRL+ALT+F2.
4.If necessary, examine the structure of volumes which are stored in the archive, by using the acrocmd utility. Also, you can use this utility to mount one or more of these volumes as if they were regular volumes (see "Mounting backup volumes" later in this topic).
5.Create the volume structure according to that in the archive, by using the mdadm utility (for MD devices), the lvm utility (for logical volumes), or both.
Note: Logical Volume Manager utilities such as pvcreate and vgcreate, which are normally available in Linux, are not included in the bootable media environment, so you need to use the lvm utility with a corresponding command. For example: lvm pvcreate, lvm vgcreate, and lvm lvcreate.
6.If you previously mounted the backup by using the acrocmd utility, use this utility again to unmount the backup (see "Mounting backup volumes" later in this topic).
7.Return to the management console by pressing ALT+F1.
(Do not reboot the machine at this point. Otherwise, you will have to create the volume structure again.)
8.Click Recover, then specify the path to the archive and any other required parameters, and then click OK.
27 |
Copyright © Acronis International GmbH, 2002-2016 |
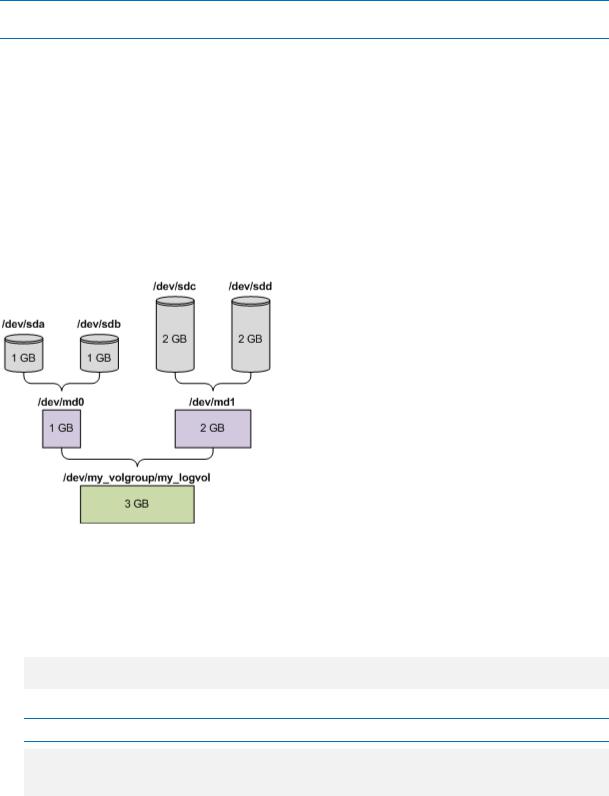
Note: This procedure will not work if you connect to Acronis Backup Bootable Agent remotely, because the command shell is not available in this case.
Example
Suppose that you previously performed a disk-level backup of a machine with the following disk configuration:
The machine has two 1-gigabyte and two 2-gigabyte SCSI hard disks, mounted on /dev/sda,
/dev/sdb, /dev/sdc, and /dev/sdd, respectively.
The first and second pairs of hard disks are configured as two MD devices; both are in the RAID-1 configuration, and are mounted on /dev/md0 and /dev/md1, respectively.
A logical volume is based on the two MD devices and is mounted on
/dev/my_volgroup/my_logvol.
The following picture illustrates this configuration.
Do the following to recover data from this archive.
Step 1: Creating the volume structure
1.Boot the machine from a Linux-based bootable media.
2.In the management console, press CTRL+ALT+F2.
3.Run the following commands to create the MD devices:
mdadm --create /dev/md0 --level=1 --raid-devices=2 /dev/sd[ab] mdadm --create /dev/md1 --level=1 --raid-devices=2 /dev/sd[cd]
4.Run the following commands to create the logical volume group:
Caution: The pvcreate command destroys all data on the /dev/md0 and /dev/md1 devices.
lvm pvcreate /dev/md0 /dev/md1
lvm vgcreate my_volgroup /dev/md0 /dev/md1 lvm vgdisplay
The output of the lvm vgdisplay command will contain lines similar to the following:
28 |
Copyright © Acronis International GmbH, 2002-2016 |
--- Volume group ---
VG Name |
my_volgroup |
... |
|
VG Access |
read/write |
VG Status |
resizable |
... |
|
VG Size |
1.99 GB |
... |
|
VG UUID |
0qoQ4l-Vk7W-yDG3-uF1l-Q2AL-C0z0-vMeACu |
5.Run the following command to create the logical volume; in the -L parameter, specify the size given by VG Size:
lvm lvcreate -L1.99G --name my_logvol my_volgroup
6.Activate the volume group by running the following command: lvm vgchange -a y my_volgroup
7.Press ALT+F1 to return to the management console.
Step 2: Starting the recovery
1.In the management console, click Recover.
2.In Archive, click Change and then specify the name of the archive.
3.In Backup, click Change and then select the backup from which you want to recover data.
4.In Data type, select Volumes.
5.In Items to recover, select the check box next to my_volgroup-my_logvol.
6.Under Where to recover, click Change, and then select the logical volume that you created in Step 1. Click the chevron buttons to expand the list of disks.
7.Click OK to start the recovery.
For a complete list of commands and utilities that you can use in the bootable media environment, see List of commands and utilities available in Linux-based bootable media (p. 155). For detailed descriptions of the acrocmd utility, see the Acronis Backup command-line reference.
Mounting backup volumes
You may want to mount a volume stored in a disk backup, for example, to view some files in it before starting the recovery.
To mount a backup volume
1.Use the acrocmd list content command to list the disks and volumes that are stored in the backup. For example, the following command lists the content of the latest backup of the linux_machine archive:
acrocmd list content --loc=\\server\backups --credentials=user,MyPassWd --arc=linux_machine
The output will contain lines similar to the following:
29 |
Copyright © Acronis International GmbH, 2002-2016 |
type: disk |
|
|
|
|
|
|
|
Num |
Partition |
Flags |
Size |
|
Type |
GUID |
|
---------- |
-------------------- |
---------- |
---------- |
------------- |
------ |
||
-- |
|
|
|
|
|
|
|
Dyn1 |
my_volgroup-my_lo... |
|
4 |
GB |
|
Ext 3 |
|
Dyn2 |
md0 |
|
2.007 |
GB |
Ext 2 |
|
|
Disk 1 |
sda |
|
16 GB |
|
DT_FIXED |
|
|
1-1 |
sda1 |
Act,Pri |
203.9 |
MB |
Ext 2 |
|
|
1-2 |
sda2 |
Pri |
11.72 |
GB |
Reiser |
|
|
1-3 |
sda3 |
Pri |
1.004 |
GB |
Linux swap |
|
|
Disk 2 |
sdb |
|
8 |
GB |
|
DT_FIXED |
|
2-1 |
sdb1 |
Pri |
2.007 |
GB |
Ext 2 |
|
|
2-2 |
sdb2 |
Pri |
2.007 |
GB |
None |
|
|
Disk 3 |
sdc |
|
1 |
GB |
|
DT_FIXED |
|
Disk 4 |
sdd |
|
8 |
GB |
|
DT_FIXED |
|
4-1 |
sdd1 |
Pri |
2.007 |
GB |
Ext 2 |
|
|
4-2 |
sdd2 |
Pri |
2.007 |
GB |
None |
|
|
2.Use the acrocmd mount command, specifying the volume's name in the --volume parameter. For example:
acrocmd mount --loc=\\server\backups --arc=linux_machine --mount_point=/mnt --volume=DYN1
This command mounts the logical volume DYN1 on the mount point /mnt.
To unmount a backup volume
Use the acrocmd umount command, specifying the volume's mount point as a parameter. For example:
acrocmd umount --mount_point=/mnt
3.7Support for Advanced Format (4K-sector) hard disks
Acronis Backup can back up hard disks with a sector size of 4 KB (known as Advanced Format disks), as well as traditional hard disks that have 512-byte sectors.
Acronis Backup can recover data from one disk to another as long as both disks have the same logical sector size. (This is the sector size presented to the operating system.) Acronis Backup automatically aligns the disk’s volumes (p. 103) if necessary. This way, the start of a cluster in the file system always matches the start of a physical sector on the disk.
The disk management functionality of Acronis Backup is not available for disks with a 4-KB logical sector size.
Determining the logical sector size
By disk specification
Development of the Advanced Format technology is coordinated by the International Disk Drive Equipment and Materials Association (IDEMA). For more details, see http://www.idema.org/?page_id=2.
In terms of the logical sector size, IDEMA specifies two types of Advanced Format disks:
512 Byte emulation (512e) disks have 512-byte logical sector size. These disks are supported in Windows starting with Windows Vista, and in modern Linux distributions. Microsoft and Western Digital use the term “Advanced Format” exclusively for this type of disk.
30 |
Copyright © Acronis International GmbH, 2002-2016 |
 Loading...
Loading...