Page 1

ZyAIR G-2000
802.11g Wireless 4-port Router
User's Guide
Version 3.60
February 2004
Page 2

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Copyright
Copyright © 2003 by ZyXEL Communications Corporation.
The contents of this publication may not be reproduced in any part or as a whole, transcribed, stored in a
retrieval system, translated into any language, or transmitted in any form or by any means, electronic,
mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise, without the prior written
permission of ZyXEL Communications Corporation.
Published by ZyXEL Communications Corporation. All rights reserved.
Disclaimer
ZyXEL does not assume any liability arising out of the application or use of any products, or software
described herein. Neither does it convey any license under its patent rights nor the patent rights of others.
ZyXEL further reserves the right to make changes in any products described herein without notice. This
publication is subject to change without notice.
Trademarks
ZyNOS (ZyXEL Network Operating System) is a registered trademark of ZyXEL Communications, Inc.
Other trademarks mentioned in this publication are used for identification purposes only and may be
properties of their respective owners.
ii Copyright
Page 3

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Federal Communications Commission
(FCC) Interference Statement
This device complies with Part 15 of FCC rules. Operation is subject to the following two conditions:
• This device may not cause harmful interference.
• This device must accept any interference received, including interference that may cause undesired
operations.
This equipment has been tested and found to comply with the limits for a Class B digital device pursuant to
Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful
interference in a commercial environment. This equipment generates, uses, and can radiate radio frequency
energy, and if not installed and used in accordance with the instructions, may cause harmful interference to
radio communications.
If this equipment does cause harmful interference to radio/television reception, which can be determined by
turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of
the following measures:
1. Reorient or relocate the receiving antenna.
2. Increase the separation between the equipment and the receiver.
3. Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
4. Consult the dealer or an experienced radio/TV technician for help.
Notice 1
Changes or modifications not expressly approved by the party responsible for compliance could void the
user's authority to operate the equipment.
Certifications
1. Go to www.zyxel.com
2. Select your product from the drop-down list box on the ZyXEL home page to go to that product's page.
3. Select the certification you wish to view from this page
FCC Statement iii
Page 4

ZyAIR G-2000 Wireless 4-port Router User’s Guide
ZyXEL Limited Warranty
ZyXEL warrants to the original end user (purchaser) that this product is free from any defects in materials
or workmanship for a period of up to two years from the date of purchase. During the warranty period, and
upon proof of purchase, should the product have indications of failure due to faulty workmanship and/or
materials, ZyXEL will, at its discretion, repair or replace the defective products or components without
charge for either parts or labor, and to whatever extent it shall deem necessary to restore the product or
components to proper operating condition. Any replacement will consist of a new or re-manufactured
functionally equivalent product of equal value, and will be solely at the discretion of ZyXEL. This warranty
shall not apply if the product is modified, misused, tampered with, damaged by an act of God, or subjected
to abnormal working conditions.
Note
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This
warranty is in lieu of all other warranties, express or implied, including any implied warranty of
merchantability or fitness for a particular use or purpose. ZyXEL shall in no event be held liable for
indirect or consequential damages of any kind of character to the purchaser.
To obtain the services of this warranty, contact ZyXEL's Service Center for your Return Material
Authorization number (RMA). Products must be returned Postage Prepaid. It is recommended that the unit
be insured when shipped. Any returned products without proof of purchase or those with an out-dated
warranty will be repaired or replaced (at the discretion of ZyXEL) and the customer will be billed for parts
and labor. All repaired or replaced products will be shipped by ZyXEL to the corresponding return address,
Postage Paid. This warranty gives you specific legal rights, and you may also have other rights that vary
from country to country.
Safety Warnings
1. To reduce the risk of fire, use only No. 26 AWG or larger telephone wire.
2. Do not use this product near water, for example, in a wet basement or near a swimming pool.
3. Avoid using this product during an electrical storm. There may be a remote risk of electric shock from
lightening.
iv ZyXEL Warranty
Page 5
ZyAIR G-2000 Wireless 4-port Router User’s Guide
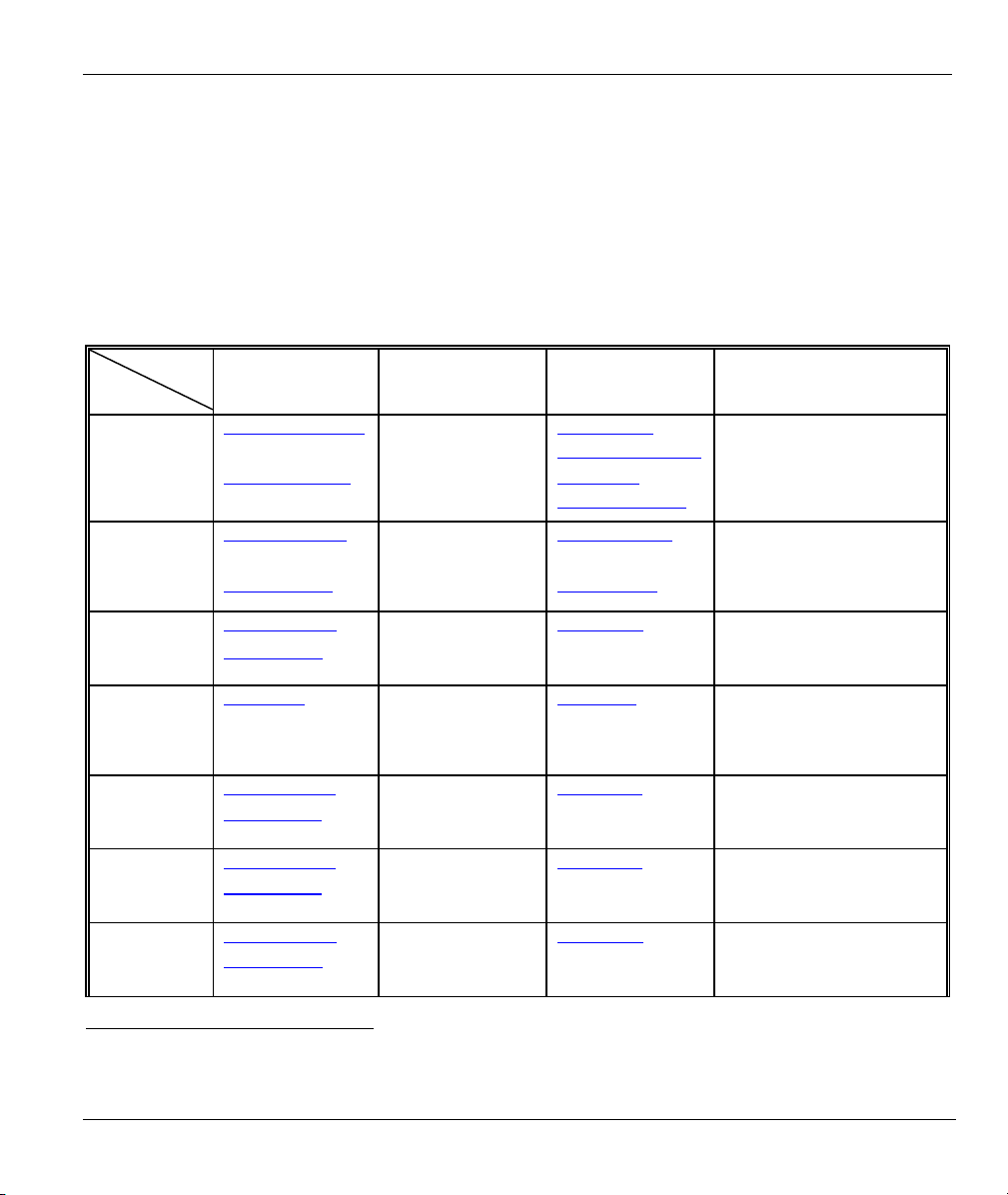
/
Customer Support
Please have the following information ready when you contact customer support.
• Product model and serial number.
• Warranty Information.
• Date that you received your device.
• Brief description of the problem and the steps you took to solve it.
REGULAR MAIL
ZyXEL Communications Corp.
6 Innovation Road II
Science Park
Hsinchu 300
Taiwan
ZyXEL Communications Inc.
1130 N. Miller St.
Anaheim
CA 92806-2001
U.S.A.
ZyXEL Deutschland GmbH.
Adenauerstr. 20/A2 D-52146
Wuerselen
Germany
1 rue des Vergers
Bat. 1 / C
69760 Limonest
France
Alejandro Villegas 33
1º, 28043 Madrid
Spain
ZyXEL Communications A/S
Columbusvej 5
2860 Soeborg
Denmark
ZyXEL Communications A
Nils Hansens vei 13
0667 Oslo
Norway
S
LOCATION
WORLDWIDE
AMERICA
SUPPORT E-MAIL TELEPHONE1 WEB SITE METHOD
SALES E-MAIL FAX1 FTP SITE
support@zyxel.com.tw +886-3-578-3942 www.zyxel.com
sales@zyxel.com.tw
support@zyxel.com +1-800-255-4101
sales@zyxel.com
support@zyxel.de +49-2405-6909-0 www.zyxel.de GERMANY
sales@zyxel.de
support@zyxel.es +34 902 195 420 SPAIN
sales@zyxel.es
support@zyxel.dk +45 39 55 07 00 www.zyxel.dk DENMARK
sales@zyxel.dk
support@zyxel.no +47 22 80 61 80 www.zyxel.no NORWAY
sales@zyxel.no
+886-3-578-2439 ftp.zyxel.com
+1-714-632-0882
+1-714-632-0858 ftp.us.zyxel.com
+49-2405-6909-99
+33 (0)4 72 52 97 97 FRANCE info@zyxel.fr
+33 (0)4 72 52 19 20
+34 913 005 345
+45 39 55 07 07
+47 22 80 61 81
www.europe.zyxel.com
ftp.europe.zyxel.com
www.us.zyxel.com NORTH
www.zyxel.fr ZyXEL France
www.zyxel.es
ZyXEL Communications
1
“+” is the (prefix) number you enter to make an international telephone call.
Customer Support v
Page 6
ZyAIR G-2000 Wireless 4-port Router User’s Guide
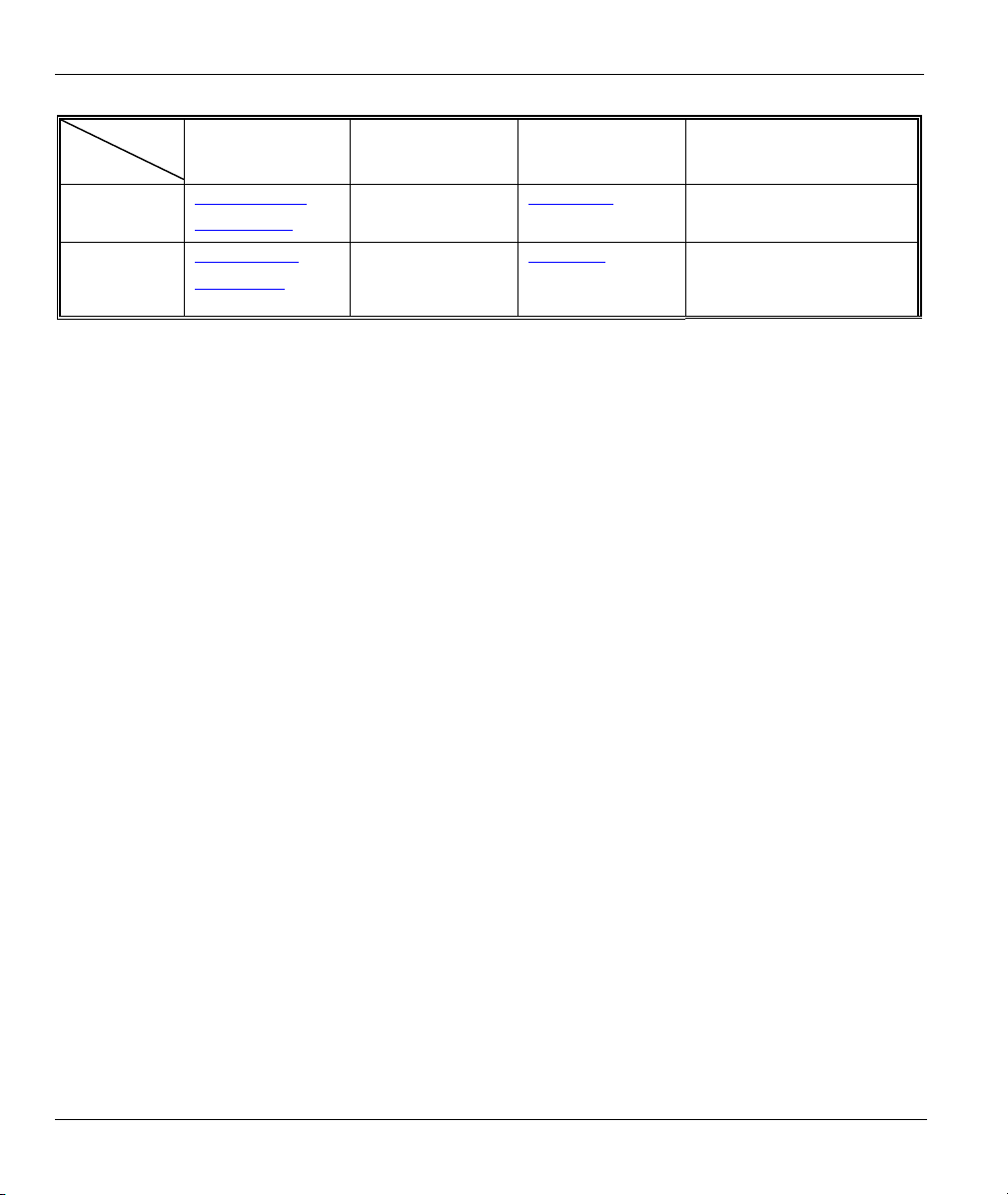
LOCATION
SUPPORT E-MAIL TELEPHONE1 WEB SITE METHOD
SALES E-MAIL FAX1 FTP SITE
support@zyxel.se +46 31 744 7700 www.zyxel.se SWEDEN
sales@zyxel.se
support@zyxel.fi +358-9-4780-8411 www.zyxel.fi FINLAND
sales@zyxel.fi
+46 31 744 7701
+358-9-4780 8448
REGULAR MAIL
ZyXEL Communications A/S
Sjöporten 4, 41764 Göteborg
Sweden
ZyXEL Communications Oy
Malminkaari 10
00700 Helsinki
Finland
vi Customer Support
Page 7

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table of Contents
Copyright.........................................................................................................................................................ii
Federal Communications Commission (FCC) Interference Statement.....................................................iii
ZyXEL Limited Warranty.............................................................................................................................iv
Customer Support........................................................................................................................................... v
List of Figures...............................................................................................................................................xvi
List of Tables.................................................................................................................................................xxi
Preface.........................................................................................................................................................xxiv
OVERVIEW.................................................................................................................................................... I
Chapter 1 Getting to Know Your ZyAIR...................................................................................................1-1
1.1 Introducing the ZyAIR...............................................................................................................1-1
1.2 ZyAIR Features..........................................................................................................................1-1
1.3 Application for the ZyAIR .........................................................................................................1-6
1.3.1 Internet Access Application ...............................................................................................1-6
Chapter 2 Introducing the Web Configurator...........................................................................................2-1
2.1 Web Configurator Overview......................................................................................................2-1
2.2 Accessing the ZyAIR Web Configurator ...................................................................................2-1
2.3 Resetting the ZyAIR ..................................................................................................................2-2
2.3.1 Procedure to Use the Reset Button.....................................................................................2-2
2.4 Navigating the ZyAIR Web Configurator..................................................................................2-3
Chapter 3 Wizard Setup ..............................................................................................................................3-1
3.1 Wizard Setup Overview .............................................................................................................3-1
3.1.1 Channel ..............................................................................................................................3-1
3.1.2 ESS ID................................................................................................................................3-1
3.1.3 WEP Encryption.................................................................................................................3-1
3.2 Wizard Setup: General Setup.....................................................................................................3-1
3.3 Wizard Setup: Wireless LAN Setup...........................................................................................3-3
3.4 Wizard Setup: ISP Parameters ...................................................................................................3-5
3.4.1 Ethernet ..............................................................................................................................3-5
3.4.2 PPPoE Encapsulation.........................................................................................................3-7
3.4.3 PPTP Encapsulation ...........................................................................................................3-9
3.5 Wizard Setup: WAN and DNS.................................................................................................3-11
3.5.1 WAN IP Address Assignment..........................................................................................3-11
3.5.2 IP Address and Subnet Mask............................................................................................3-12
3.5.3 DNS Server Address Assignment ....................................................................................3-12
3.5.4 WAN MAC Address........................................................................................................3-13
3.6 Basic Setup Complete ..............................................................................................................3-15
SYSTEM, LAN AND WIRELESS................................................................................................................II
Chapter 4 System Screens ...........................................................................................................................4-1
4.1 System Overview .......................................................................................................................4-1
Table of Contents vii
Page 8

ZyAIR G-2000 Wireless 4-port Router User’s Guide
4.2 Configuring General Setup ........................................................................................................4-1
4.3 Dynamic DNS............................................................................................................................ 4-2
4.3.1 DYNDNS Wildcard...........................................................................................................4-3
4.4 Configuring Dynamic DNS .......................................................................................................4-3
4.5 Configuring Password................................................................................................................4-4
4.6 Configuring Time Setting ..........................................................................................................4-5
Chapter 5 LAN Screens............................................................................................................................... 5-1
5.1 LAN Overview ..........................................................................................................................5-1
5.2 LANs and WANs....................................................................................................................... 5-1
5.2.1 LANs, WANs and the ZyAIR............................................................................................ 5-1
5.3 DHCP Setup...............................................................................................................................5-2
5.3.1 DNS Servers ......................................................................................................................5-2
5.4 Factory LAN Defaults................................................................................................................5-2
5.5 RIP Setup ................................................................................................................................... 5-2
5.6 Multicast ....................................................................................................................................5-3
5.7 Configuring the LAN IP Screens............................................................................................... 5-3
Chapter 6 Wireless Configuration and Roaming...................................................................................... 6-1
6.1 Wireless LAN Overview............................................................................................................6-1
6.1.1 IBSS...................................................................................................................................6-1
6.1.2 BSS ....................................................................................................................................6-1
6.1.3 ESS ....................................................................................................................................6-2
6.2 Wireless LAN Basics.................................................................................................................6-3
6.2.1 RTS/CTS............................................................................................................................6-3
6.2.2 Fragmentation Threshold................................................................................................... 6-4
6.3 Configuring Wireless................................................................................................................. 6-5
6.4 Configuring Roaming ................................................................................................................6-7
6.4.1 Requirements for Roaming................................................................................................ 6-9
Chapter 7 Wireless Security........................................................................................................................7-1
7.1 Wireless Security Overview.......................................................................................................7-1
7.2 WEP Overview ..........................................................................................................................7-1
7.2.1 Data Encryption .................................................................................................................7-2
7.2.2 Authentication.................................................................................................................... 7-2
7.2.3 Preamble Type ...................................................................................................................7-3
7.3 Configuring WEP Encryption....................................................................................................7-3
7.4 MAC Filter.................................................................................................................................7-6
7.5 802.1x Overview........................................................................................................................7-8
7.6 Dynamic WEP Key Exchange................................................................................................... 7-8
7.7 Introduction to WPA.................................................................................................................. 7-9
7.7.1 User Authentication ...........................................................................................................7-9
7.7.2 Encryption..........................................................................................................................7-9
7.8 WPA-PSK Application Example............................................................................................. 7-10
viii Table of Contents
Page 9

ZyAIR G-2000 Wireless 4-port Router User’s Guide
7.9 WPA with RADIUS Application Example ..............................................................................7-10
7.10 Security Parameters Summary .................................................................................................7-11
7.11 Wireless Client WPA Supplicants............................................................................................7-12
7.12 Configuring 802.1x and WPA..................................................................................................7-12
7.12.1 Authentication Required: 802.1x .....................................................................................7-13
7.12.2 Authentication Required: WPA........................................................................................7-16
7.12.3 Authentication Required: WPA-PSK...............................................................................7-18
7.13 Introduction to Local User Database........................................................................................7-20
7.14 Configuring Local User Database ............................................................................................7-20
7.15 Introduction to RADIUS..........................................................................................................7-22
7.15.1 EAP Authentication Overview.........................................................................................7-23
7.16 Configuring RADIUS ..............................................................................................................7-24
WAN .............................................................................................................................................................. III
Chapter 8 WAN Screens ..............................................................................................................................8-1
8.1 WAN Overview .........................................................................................................................8-1
8.2 Configuring WAN ISP...............................................................................................................8-1
8.2.1 Ethernet Encapsulation.......................................................................................................8-1
8.2.2 PPPoE Encapsulation.........................................................................................................8-3
8.2.3 PPTP Encapsulation ...........................................................................................................8-5
8.3 TCP/IP Priority (Metric) ............................................................................................................8-6
8.4 Configuring WAN IP .................................................................................................................8-7
8.5 Configuring WAN MAC..........................................................................................................8-10
SUA/NAT AND STATIC ROUTE............................................................................................................... IV
Chapter 9 Single User Account (SUA) / Network Address Translation (NAT).......................................9-1
9.1 NAT Overview...........................................................................................................................9-1
9.1.1 NAT Definitions.................................................................................................................9-1
9.1.2 What NAT Does.................................................................................................................9-2
9.1.3 How NAT Works ...............................................................................................................9-2
9.1.4 NAT Application................................................................................................................9-3
9.1.5 NAT Mapping Types .........................................................................................................9-4
9.1.6 SUA (Single User Account) Versus NAT..........................................................................9-5
9.2 SUA Server ................................................................................................................................9-6
9.2.1 Port Forwarding: Services and Port Numbers....................................................................9-6
9.2.2 Configuring Servers Behind SUA (Example)....................................................................9-7
9.3 Configuring SUA Server............................................................................................................9-7
9.4 Configuring Address Mapping...................................................................................................9-9
9.4.1 Configuring Address Mapping Rule ................................................................................9-11
Chapter 10 Static Route.............................................................................................................................10-1
10.1 Static Route Overview .............................................................................................................10-1
10.2 Configuring IP Static Route .....................................................................................................10-1
10.2.1 Configuring Route Entry..................................................................................................10-3
Table of Contents ix
Page 10

ZyAIR G-2000 Wireless 4-port Router User’s Guide
FIREWALL AND REMOTE MANAGEMENT ......................................................................................... V
Chapter 11 Introduction to Firewalls....................................................................................................... 11-1
11.1 Firewall Overview ...................................................................................................................11-1
11.2 Types of Firewalls....................................................................................................................11-1
11.2.1 Packet Filtering Firewalls ................................................................................................11-1
11.2.2 Application-level Firewalls..............................................................................................11-1
11.2.3 Stateful Inspection Firewalls............................................................................................11-2
11.3 Introduction to ZyXEL’s Firewall ...........................................................................................11-2
11.4 Denial of Service .....................................................................................................................11-2
11.4.1 Basics...............................................................................................................................11-3
11.4.2 Types of DoS Attacks...................................................................................................... 11-4
11.5 Stateful Inspection ...................................................................................................................11-7
Chapter 12 Firewall Screens .....................................................................................................................12-1
12.1 Access Methods .......................................................................................................................12-1
12.2 Firewall Policies Overview......................................................................................................12-1
12.3 Rule Logic Overview...............................................................................................................12-2
12.3.1 Rule Checklist..................................................................................................................12-2
12.3.2 Security Ramifications.....................................................................................................12-2
12.3.3 Key Fields For Configuring Rules...................................................................................12-3
12.4 Guidelines For Enhancing Security With Your Firewall......................................................... 12-3
12.5 Connection Direction Examples ..............................................................................................12-4
12.5.1 LAN to WAN Rules.........................................................................................................12-4
12.5.2 WAN to LAN Rules.........................................................................................................12-5
12.6 Enabling Firewall..................................................................................................................... 12-6
12.6.1 Configuring Content Filtering..........................................................................................12-8
12.6.2 Configuring Firewall Services ....................................................................................... 12-11
12.6.3 Predefined Services........................................................................................................12-13
Chapter 13 Remote Management.............................................................................................................13-1
13.1 Remote Management Overview...............................................................................................13-1
13.1.1 Remote Management Limitations.................................................................................... 13-1
13.1.2 Remote Management and NAT .......................................................................................13-2
13.1.3 System Timeout ...............................................................................................................13-2
13.2 Telnet .......................................................................................................................................13-2
13.3 Configuring TELNET..............................................................................................................13-3
13.4 Configuring FTP ...................................................................................................................... 13-4
13.5 Configuring WWW..................................................................................................................13-5
13.6 Configuring SNMP ..................................................................................................................13-6
13.6.1 Supported MIBs............................................................................................................... 13-8
13.6.2 SNMP Traps ....................................................................................................................13-8
13.6.3 REMOTE MANAGEMENT: SNMP ..............................................................................13-9
13.7 Configuring DNS................................................................................................................... 13-10
x Table of Contents
Page 11

ZyAIR G-2000 Wireless 4-port Router User’s Guide
13.8 Configuring Security..............................................................................................................13-11
UPNP AND LOGS........................................................................................................................................ VI
Chapter 14 UPnP Screen ...........................................................................................................................14-1
14.1 Universal Plug and Play Overview ..........................................................................................14-1
14.1.1 How Do I Know If I'm Using UPnP?...............................................................................14-1
14.1.2 NAT Traversal .................................................................................................................14-1
14.1.3 Cautions with UPnP.........................................................................................................14-2
14.2 UPnP and ZyXEL ....................................................................................................................14-2
14.3 Configuring UPnP....................................................................................................................14-2
14.4 Installing UPnP in Windows Example.....................................................................................14-4
14.4.1 Installing UPnP in Windows Me......................................................................................14-4
14.4.2 Installing UPnP in Windows XP......................................................................................14-5
14.5 Using UPnP in Windows XP Example ....................................................................................14-6
14.5.1 Auto-discover Your UPnP-enabled Network Device.......................................................14-6
14.5.2 Web Configurator Easy Access........................................................................................14-8
Chapter 15 Logs Screens ...........................................................................................................................15-1
15.1 Using the View Log Screen .....................................................................................................15-1
15.2 Configuring Log Settings .........................................................................................................15-3
15.3 Configuring Reports.................................................................................................................15-6
15.3.1 Viewing Protocol/Port......................................................................................................15-8
15.3.2 Viewing LAN IP Address ..............................................................................................15-10
15.3.3 Reports Specifications....................................................................................................15-11
MAINTENANCE........................................................................................................................................VII
Chapter 16 Maintenance ...........................................................................................................................16-1
16.1 Maintenance Overview ............................................................................................................16-1
16.2 System Status Screen ...............................................................................................................16-1
16.2.1 System Statistics...............................................................................................................16-2
16.3 DHCP Table Screen .................................................................................................................16-3
16.4 Wireless Screen........................................................................................................................16-4
16.5 F/W Upload Screen..................................................................................................................16-5
16.6 Configuration Screen ...............................................................................................................16-8
16.6.1 Backup Configuration ......................................................................................................16-8
16.6.2 Restore Configuration ......................................................................................................16-9
16.6.3 Back to Factory Defaults................................................................................................16-11
SMT GETTING STARTED MENUS...................................................................................................... VIII
Chapter 17 Introducing the SMT .............................................................................................................17-1
17.1 Connect to your ZyAIR Using Telnet ......................................................................................17-1
17.1.1 Entering Password............................................................................................................17-1
17.2 Changing the System Password ...............................................................................................17-1
17.3 ZyAIR SMT Menu Overview Example ...................................................................................17-2
17.4 Navigating the SMT Interface..................................................................................................17-4
Table of Contents xi
Page 12

ZyAIR G-2000 Wireless 4-port Router User’s Guide
17.4.1 System Management Terminal Interface Summary......................................................... 17-5
Chapter 18 General and WAN Setup ....................................................................................................... 18-1
18.1 General Setup...........................................................................................................................18-1
18.1.1 Dynamic DNS..................................................................................................................18-1
18.1.2 Procedure To Configure Menu 1......................................................................................18-1
18.1.3 Procedure to Configure Dynamic DNS............................................................................18-3
18.2 WAN Setup.............................................................................................................................. 18-5
Chapter 19 LAN Setup.............................................................................................................................. 19-1
19.1 LAN Setup ............................................................................................................................... 19-1
19.1.1 General Ethernet Port Filter Setup...................................................................................19-1
19.2 TCP/IP Ethernet and DHCP Setup...........................................................................................19-2
19.3 IP Alias ....................................................................................................................................19-4
19.3.1 IP Alias Setup ..................................................................................................................19-5
19.4 Wireless LAN Setup ................................................................................................................19-6
19.4.1 Configuring MAC Address Filter .................................................................................... 19-9
19.4.2 Configuring Roaming on the ZyAIR .............................................................................19-11
Chapter 20 Internet Access ....................................................................................................................... 20-1
20.1 Internet Access Configuration .................................................................................................20-1
20.2 Internet Access Setup............................................................................................................... 20-2
SMT ADVANCED APPLICATION MENUS .............................................................................................IX
Chapter 21 Remote Node Configuration .................................................................................................21-1
21.1 Remote Node Profile................................................................................................................21-1
21.1.1 Encapsulation Scenarios ..................................................................................................21-1
21.1.2 Outgoing Authentication Protocol ...................................................................................21-4
21.1.3 Remote Node Setup .........................................................................................................21-5
21.2 Remote Node Filter.................................................................................................................. 21-6
21.2.1 IP Static Route Setup ....................................................................................................... 21-7
Chapter 22 Dial-in User Setup..................................................................................................................22-1
22.1 Dial-in User Setup ...................................................................................................................22-1
Chapter 23 Network Address Translation (NAT)....................................................................................23-1
23.1 Introduction..............................................................................................................................23-1
23.1.1 Applying NAT................................................................................................................. 23-1
23.2 NAT Setup ............................................................................................................................... 23-2
23.2.1 Address Mapping Sets .....................................................................................................23-3
23.2.2 Configuring Individual Rule............................................................................................23-6
23.3 Port Forwarding Setup - NAT Server Sets...............................................................................23-7
23.3.1 Configuring a Server behind NAT................................................................................... 23-8
23.4 General NAT Examples...........................................................................................................23-9
23.4.1 Example 1: Internet Access Only..................................................................................... 23-9
23.4.2 Example 2: Internet Access with an Inside Server......................................................... 23-11
23.4.3 Example 3: Multiple Public IP Addresses With Inside Servers ..................................... 23-11
xii Table of Contents
Page 13

ZyAIR G-2000 Wireless 4-port Router User’s Guide
23.4.4 Example 4: NAT Unfriendly Application Programs......................................................23-15
23.5 Trigger Port Setup..................................................................................................................23-16
SMT ADVANCED MANAGEMENT MENUS............................................................................................X
Chapter 24 Filter and Firewall Configuration.........................................................................................24-1
24.1 About Filtering.........................................................................................................................24-1
24.2 Configuring a Filter Set............................................................................................................24-3
24.2.1 Filter Rules Summary Menus...........................................................................................24-5
24.3 Configuring a Filter Rule .........................................................................................................24-6
24.3.1 TCP/IP Filter Rule............................................................................................................24-6
24.3.2 Generic Filter Rule.........................................................................................................24-11
24.4 Filter Types and NAT ............................................................................................................24-12
24.5 Example Filter........................................................................................................................24-13
24.6 Applying Filters and Factory Defaults ...................................................................................24-15
24.6.1 Ethernet Traffic..............................................................................................................24-16
24.6.2 Remote Node Filters.......................................................................................................24-16
24.7 Firewall Setup ........................................................................................................................24-17
Chapter 25 SNMP Configuration .............................................................................................................25-1
25.1 SNMP Configuration ...............................................................................................................25-1
Chapter 26 System Security ......................................................................................................................26-1
26.1 System Security........................................................................................................................26-1
26.1.1 System Password..............................................................................................................26-1
26.1.2 Configuring External RADIUS Server.............................................................................26-1
26.1.3 802.1x...............................................................................................................................26-3
Chapter 27 System Information and Diagnosis.......................................................................................27-1
27.1 Overview..................................................................................................................................27-1
27.2 System Status ...........................................................................................................................27-1
27.3 System Information..................................................................................................................27-3
27.3.1 System Information ..........................................................................................................27-3
27.3.2 Console Port Speed ..........................................................................................................27-4
27.4 Log and Trace ..........................................................................................................................27-5
27.4.1 Viewing Error Log...........................................................................................................27-5
27.4.2 UNIX Syslog....................................................................................................................27-6
27.4.3 Call-Triggering Packet.....................................................................................................27-7
27.5 Diagnostic ................................................................................................................................27-7
Chapter 28 Firmware and Configuration File Maintenance..................................................................28-1
28.1 Filename Conventions..............................................................................................................28-1
28.2 Backup Configuration ..............................................................................................................28-2
28.2.1 Backup Configuration ......................................................................................................28-3
28.2.2 Using the FTP Command from the Command Line.........................................................28-3
28.2.3 Example of FTP Commands from the Command Line....................................................28-4
28.2.4 GUI-based FTP Clients ....................................................................................................28-4
Table of Contents xiii
Page 14

ZyAIR G-2000 Wireless 4-port Router User’s Guide
28.2.5 TFTP and FTP over WAN Management Limitations......................................................28-4
28.2.6 Backup Configuration Using TFTP ................................................................................. 28-5
28.2.7 TFTP Command Example ...............................................................................................28-5
28.2.8 GUI-based TFTP Clients .................................................................................................28-5
28.3 Restore Configuration..............................................................................................................28-6
28.3.1 Restore Using FTP........................................................................................................... 28-6
28.3.2 Restore Using FTP Session Example...............................................................................28-7
28.4 Uploading Firmware and Configuration Files .........................................................................28-8
28.4.1 Firmware File Upload...................................................................................................... 28-8
28.4.2 Configuration File Upload............................................................................................... 28-9
28.4.3 FTP File Upload Command from the DOS Prompt Example........................................ 28-10
28.4.4 FTP Session Example of Firmware File Upload............................................................ 28-10
28.4.5 TFTP File Upload .......................................................................................................... 28-10
28.4.6 TFTP Upload Command Example................................................................................. 28-11
Chapter 29 System Maintenance and SMT Menu 24.8 to 24.10........................................................... 29-1
29.1 Command Interpreter Mode.....................................................................................................29-1
29.2 Call Control Support................................................................................................................ 29-2
29.2.1 Call Control Parameters................................................................................................... 29-2
29.2.2 Blacklist ........................................................................................................................... 29-3
29.2.3 Budget Management........................................................................................................29-4
29.2.4 Call History......................................................................................................................29-5
29.3 Time and Date Setting .............................................................................................................29-5
29.3.1 Resetting the Time...........................................................................................................29-7
Chapter 30 Remote Management.............................................................................................................30-1
30.1 Telnet .......................................................................................................................................30-1
30.2 FTP ..........................................................................................................................................30-1
30.3 Web.......................................................................................................................................... 30-1
30.4 Remote Management ...............................................................................................................30-1
30.4.1 Remote Management Setup............................................................................................. 30-2
30.4.2 Remote Management Limitations.................................................................................... 30-3
30.5 Remote Management and NAT ...............................................................................................30-4
30.6 System Timeout ....................................................................................................................... 30-4
Chapter 31 Call Scheduling ......................................................................................................................31-1
31.1 Introduction..............................................................................................................................31-1
APPENDICES...............................................................................................................................................XI
Appendix A Troubleshooting...................................................................................................................... A-1
Problems Starting Up the ZyAIR......................................................................................................... A-1
Problems with the Password ................................................................................................................A-1
Problems with the Ethernet Interface................................................................................................... A-2
Problems with the WAN Interface....................................................................................................... A-2
Problems with Internet Access............................................................................................................. A-3
xiv Table of Contents
Page 15

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Problems with Telnet ...........................................................................................................................A-3
Problems with the WLAN Interface.....................................................................................................A-4
Appendix B Brute-Force Password Guessing Protection ........................................................................B-1
Appendix C Setting up Your Computer’s IP Address..............................................................................C-1
Appendix D Wireless LAN and IEEE 802.11............................................................................................D-1
Appendix E Wireless LAN With IEEE 802.1x.......................................................................................... E-1
Appendix F Types of EAP Authentication................................................................................................. F-1
Appendix G Antenna Selection and Positioning Recommendation ....................................................... G-1
Appendix H PPPoE.................................................................................................................................... H-1
Appendix I PPTP .........................................................................................................................................I-1
Appendix J IP Subnetting............................................................................................................................J-1
Appendix K Triangle Route ...................................................................................................................... K-1
Appendix L Command Interpreter ...........................................................................................................L-1
Appendix M NetBIOS Filter Commands.................................................................................................M-1
Appendix N Log Descriptions ....................................................................................................................N-1
Appendix O Power Adaptor Specifications.............................................................................................. O-1
Appendix P Index........................................................................................................................................ P-1
Table of Contents xv
Page 16

ZyAIR G-2000 Wireless 4-port Router User’s Guide
List of Figures
Figure 1-1 Internet Access Application Example ........................................................................................1-6
Figure 2-1 Web Browser Address Field .......................................................................................................2-1
Figure 2-2 Change Password Screen ...........................................................................................................2-2
Figure 2-3 Navigating the ZyAIR Web Configurator ..................................................................................2-3
Figure 3-1 Wizard 1: General Setup ............................................................................................................3-2
Figure 3-2 Wizard 2: Wireless LAN Setup ..................................................................................................3-4
Figure 3-3 Wizard 3: Ethernet Encapsulation..............................................................................................3-6
Figure 3-4 Wizard 3: PPPoE Encapsulation ................................................................................................3-8
Figure 3-5 Wizard 3: PPTP Encapsulation.................................................................................................3-10
Figure 3-6 Wizard 4: WAN and DNS ........................................................................................................3-14
Figure 3-7 Setup Complete........................................................................................................................ 3-16
Figure 4-1 System General Setup ................................................................................................................ 4-1
Figure 4-2 DDNS.........................................................................................................................................4-3
Figure 4-3 Password ....................................................................................................................................4-5
Figure 4-4 Time Setting...............................................................................................................................4-6
Figure 5-1 LAN & WAN IPs .......................................................................................................................5-1
Figure 5-2 IP................................................................................................................................................5-4
Figure 6-1 IBSS (Ad-hoc) Wireless LAN.................................................................................................... 6-1
Figure 6-2 Basic Service set ........................................................................................................................6-2
Figure 6-3 Extended Service Set..................................................................................................................6-3
Figure 6-4 RTS/CTS .................................................................................................................................... 6-4
Figure 6-5 Wireless......................................................................................................................................6-6
Figure 6-6 Roaming Example......................................................................................................................6-8
Figure 6-7 Roaming.....................................................................................................................................6-9
Figure 7-1 ZyAIR Wireless Security Levels................................................................................................ 7-1
Figure 7-2 WEP Authentication Steps .........................................................................................................7-2
Figure 7-3 Wireless......................................................................................................................................7-4
Figure 7-4 MAC Address Filter...................................................................................................................7-7
Figure 7-5 WPA - PSK Authentication ......................................................................................................7-10
Figure 7-6 WPA with RADIUS Application Example............................................................................... 7-11
Figure 7-7 Wireless LAN: 802.1x/WPA ....................................................................................................7-13
Figure 7-8 Wireless LAN: 802.1x/WPA for 802.1x Protocol ....................................................................7-14
Figure 7-9 Wireless LAN: 802.1x/WPA for WPA Protocol.......................................................................7-17
Figure 7-10 Wireless LAN: 802.1x/WPA for WPA-PSK Protocol ............................................................7-19
Figure 7-11 Local User Database...............................................................................................................7-21
Figure 7-12 EAP Authentication................................................................................................................ 7-23
Figure 7-13 RADIUS................................................................................................................................. 7-24
Figure 8-1 Ethernet Encapsulation .................................................................................................................8-1
Figure 8-2 Service Type................................................................................................................................8-2
xvi List of Figures
Page 17

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 8-3 PPPoE Encapsulation....................................................................................................................8-4
Figure 8-4 PPTP Encapsulation......................................................................................................................8-5
Figure 8-5 IP Setup........................................................................................................................................8-7
Figure 8-6 MAC Setup ................................................................................................................................8-10
Figure 9-1 How NAT Works ........................................................................................................................9-3
Figure 9-2 NAT Application with IP Alias ...................................................................................................9-4
Figure 9-3 Multiple Servers Behind NAT Example.....................................................................................9-7
Figure 9-4 SUA/NAT Setup .........................................................................................................................9-8
Figure 9-5 Address Mapping......................................................................................................................9-10
Figure 9-6 Address Mapping Rule .............................................................................................................9-11
Figure 10-1 Example of Static Routing Topology......................................................................................10-1
Figure 10-2 IP Static Route Summary........................................................................................................10-2
Figure 10-3 Edit IP Static Route ................................................................................................................10-3
Figure 11-1 Firewall Application...............................................................................................................11-3
Figure 11-2 Three-Way Handshake............................................................................................................11-4
Figure 11-3 SYN Flood..............................................................................................................................11-5
Figure 11-4 Smurf Attack...........................................................................................................................11-6
Figure 11-5 Stateful Inspection ..................................................................................................................11-8
Figure 12-1 LAN to WAN Traffic..............................................................................................................12-5
Figure 12-2 WAN to LAN Traffic..............................................................................................................12-6
Figure 12-3 Firewall Settings.....................................................................................................................12-7
Figure 12-4 Firewall Filter.........................................................................................................................12-9
Figure 12-5 Firewall Services .................................................................................................................. 12-11
Figure 13-1 Telnet Configuration on a TCP/IP Network ...........................................................................13-2
Figure 13-2 Telnet......................................................................................................................................13-3
Figure 13-3 FTP.........................................................................................................................................13-4
Figure 13-4 WWW.....................................................................................................................................13-5
Figure 13-5 SNMP Management Model....................................................................................................13-7
Figure 13-6 SNMP.....................................................................................................................................13-9
Figure 13-7 DNS...................................................................................................................................... 13-11
Figure 13-8 Security.................................................................................................................................13-12
Figure 14-1 Configuring UPnP ..................................................................................................................14-3
Figure 15-1 View Log ................................................................................................................................15-2
Figure 15-2 Log Settings............................................................................................................................15-4
Figure 15-3 Reports ...................................................................................................................................15-7
Figure 15-4 Protocol/Port Report...............................................................................................................15-9
Figure 15-5 LAN IP Address Report........................................................................................................15-10
Figure 16-1 System Status .........................................................................................................................16-1
Figure 16-2 System Status: Show Statistics ...............................................................................................16-2
Figure 16-3 DHCP Table............................................................................................................................16-4
Figure 16-4 Association List......................................................................................................................16-5
List of Figures xvii
Page 18

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 16-5 Firmware Upgrade .................................................................................................................16-6
Figure 16-6 Firmware Upload In Process.................................................................................................. 16-7
Figure 16-7 Network Temporarily Disconnected....................................................................................... 16-7
Figure 16-8 Firmware Upload Error..........................................................................................................16-8
Figure 16-9 Backup Configuration ............................................................................................................ 16-9
Figure 16-10 Restore Configuration .......................................................................................................... 16-9
Figure 16-11 Configuration Upload Successful.......................................................................................16-10
Figure 16-12 Network Temporarily Disconnected...................................................................................16-10
Figure 16-13 Configuration Upload Error ...............................................................................................16-11
Figure 16-14 Back to Factory Default .....................................................................................................16-11
Figure 16-15 Reset Warning Message .....................................................................................................16-12
Figure 17-1 Login Screen ..........................................................................................................................17-1
Figure 17-2 Menu 23.1 System Security : Change Password.................................................................... 17-2
Figure 17-3 ZyAIR SMT Menu Overview Example ................................................................................. 17-3
Figure 17-4 ZyAIR SMT Main Menu........................................................................................................17-5
Figure 18-1 Menu 1 General Setup............................................................................................................18-2
Figure 18-2 Menu 1.1 Configure Dynamic DNS.......................................................................................18-3
Figure 18-3 Menu 2 WAN Setup ...............................................................................................................18-5
Figure 19-1 Menu 3 LAN Setup................................................................................................................ 19-1
Figure 19-2 Menu 3.1 LAN Port Filter Setup............................................................................................19-1
Figure 19-3 Menu 3.2 TCP/IP and DHCP Ethernet Setup......................................................................... 19-2
Figure 19-4 Physical Network ...................................................................................................................19-4
Figure 19-5 Partitioned Logical Networks.................................................................................................19-4
Figure 19-6 Menu 3.2 TCP/IP and DHCP Ethernet Setup......................................................................... 19-5
Figure 19-7 Menu 3.2.1 IP Alias Setup......................................................................................................19-5
Figure 19-8 Menu 3.5 Wireless LAN Setup ..............................................................................................19-7
Figure 19-9 Menu 3.5 Wireless LAN Setup ..............................................................................................19-9
Figure 19-10 Menu 3.5.1 WLAN MAC Address Filter ...........................................................................19-10
Figure 19-11 Menu 3.5 Wireless LAN Setup........................................................................................... 19-11
Figure 19-12 Menu 3.5.2 Roaming Configuration ..................................................................................19-11
Figure 20-1 Menu 4 Internet Access Setup................................................................................................20-2
Figure 21-1 Menu 11.1 Remote Node Profile............................................................................................21-2
Figure 21-2 Menu 11.3 Remote Node Network Layer Options................................................................. 21-5
Figure 21-3 Menu 11.5 Remote Node Filter (Ethernet Encapsulation ) ....................................................21-7
Figure 21-4 Menu 11.5 Remote Node Filter (PPTP or PPPoE Encapsulation).......................................... 21-7
Figure 21-5 Menu 12.1 IP Static Route Setup ...........................................................................................21-8
Figure 21-6 Menu 12.1 Edit IP Static Route..............................................................................................21-8
Figure 22-1 Menu 14 Dial-in User Setup...................................................................................................22-1
Figure 22-2 Menu 14.1 Edit Dial-in User..................................................................................................22-1
Figure 23-1 Menu 4 Internet Access Setup................................................................................................23-1
Figure 23-2 Menu 11.3 Remote Node Network Layer Options................................................................. 23-2
xviii List of Figures
Page 19

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 23-3 Menu 15 NAT Setup...............................................................................................................23-3
Figure 23-4 Menu 15.1 Address Mapping Sets..........................................................................................23-3
Figure 23-5 Menu 15.1.255 SUA Address Mapping Rules........................................................................23-4
Figure 23-6 Menu 15.1.1 Address Mapping Rules ....................................................................................23-5
Figure 23-7 Menu 15.1.1.1 Address Mapping Rule ...................................................................................23-6
Figure 23-8 Menu 15.2 Port Forwarding Setup .........................................................................................23-9
Figure 23-9 NAT Example 1 ....................................................................................................................23-10
Figure 23-10 Menu 4 Internet Access Setup ............................................................................................23-10
Figure 23-11 NAT Example 2 .................................................................................................................. 23-11
Figure 23-12 Menu 15.2.1 NAT Server Setup..........................................................................................23-11
Figure 23-13 NAT Example 3 ..................................................................................................................23-12
Figure 23-14 Menu 11.3 Remote Node Network Layer Options.............................................................23-13
Figure 23-15 Menu 15.1.1.1 Address Mapping Rule ...............................................................................23-13
Figure 23-16 Menu 15.1.1 Address Mapping Rules ................................................................................23-14
Figure 23-17 NAT Example 4 ..................................................................................................................23-15
Figure 23-18 Menu 15.1.1.1 Address Mapping Rule ...............................................................................23-15
Figure 23-19 Menu 15.1.1 Address Mapping Rules ................................................................................23-16
Figure 23-20 Trigger Port Forwarding Process: Example........................................................................23-16
Figure 23-21 Menu 15.3 Trigger Port Setup ............................................................................................23-17
Figure 24-1 Outgoing Packet Filtering Process .........................................................................................24-1
Figure 24-2 Filter Rule Process..................................................................................................................24-2
Figure 24-3 Menu 21.1 Filter Set Configuration........................................................................................24-3
Figure 24-4 NetBIOS_WAN Filter Rules Summary ..................................................................................24-4
Figure 24-5 NetBIOS_LAN Filter Rules Summary...................................................................................24-4
Figure 24-6 TEL_FTP_WEB_WAN Filter Rules Summary ......................................................................24-4
Figure 24-7 Menu 21.1.1 TCP/IP Filter Rule.............................................................................................24-7
Figure 24-8 Executing an IP Filter...........................................................................................................24-10
Figure 24-9 Menu 21.1.4.1 Generic Filter Rule.......................................................................................24-11
Figure 24-10 Protocol and Device Filter Sets ..........................................................................................24-13
Figure 24-11 Sample Telnet Filter............................................................................................................24-13
Figure 24-12 Sample Filter - Menu 21.1.3.1............................................................................................24-14
Figure 24-13 Sample Filter Rules Summary - Menu 21.1.3 ....................................................................24-15
Figure 24-14 Filtering Ethernet Traffic....................................................................................................24-16
Figure 24-15 Filtering Remote Node Traffic ...........................................................................................24-16
Figure 25-1 Menu 22 SNMP Configuration...............................................................................................25-1
Figure 26-1 Menu 23 System Security.......................................................................................................26-1
Figure 26-2 Menu 23 System Security.......................................................................................................26-1
Figure 26-3 Menu 23.2 System Security : RADIUS Server ......................................................................26-2
Figure 26-4 Menu 23 System Security.......................................................................................................26-3
Figure 26-5 Menu 23.4 System Security : IEEE802.1x.............................................................................26-4
Figure 27-1 Menu 24 System Maintenance ...............................................................................................27-1
List of Figures xix
Page 20

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 27-2 Menu 24.1 System Maintenance : Status ...............................................................................27-2
Figure 27-3 Menu 24.2 System Information and Console Port Speed....................................................... 27-3
Figure 27-4 Menu 24.2.1 System Maintenance : Information ...................................................................27-4
Figure 27-5 Menu 24.2.2 System Maintenance : Change Console Port Speed..........................................27-5
Figure 27-6 Menu 24.3 System Maintenance : Log and Trace.................................................................. 27-5
Figure 27-7 Sample Error and Information Messages...............................................................................27-6
Figure 27-8 Menu 24.3.2 System Maintenance : UNIX Syslog ................................................................27-6
Figure 27-9 Menu 24.4 System Maintenance : Diagnostic........................................................................ 27-7
Figure 28-1 Telnet in Menu 24.5 ...............................................................................................................28-3
Figure 28-2 FTP Session Example.............................................................................................................28-4
Figure 28-3 Telnet into Menu 24.6 ............................................................................................................28-7
Figure 28-4 Restore Using FTP Session Example ..................................................................................... 28-8
Figure 28-5 Telnet Into Menu 24.7.1 Upload System Firmware ...............................................................28-9
Figure 28-6 Telnet Into Menu 24.7.2 System Maintenance ....................................................................... 28-9
Figure 28-7 FTP Session Example of Firmware File Upload..................................................................28-10
Figure 29-1 Menu 24 System Maintenance............................................................................................... 29-1
Figure 29-2 Valid CI Commands ...............................................................................................................29-1
Figure 29-3 Menu24.9 System Maintenance : Call Control ......................................................................29-2
Figure 29-4 Menu 24.9.1 Call Control Parameters.................................................................................... 29-2
Figure 29-5 Menu 24.9.2 Blacklist ............................................................................................................29-3
Figure 29-6 Menu 24.9.3 Budget Management......................................................................................... 29-4
Figure 29-7 Menu 24.9.2 Call History....................................................................................................... 29-5
Figure 29-8 Menu 24.10 System Maintenance : Time and Date Setting ...................................................29-6
Figure 30-1 Telnet Configuration on a TCP/IP Network ...........................................................................30-1
Figure 30-2 Menu 24.11 Remote Management Control ............................................................................30-2
Figure 31-1 Menu 26 Schedule Setup........................................................................................................ 31-1
Figure 31-2 Menu 26.1 Schedule Set Setup...............................................................................................31-2
Figure 31-3 Applying Schedule Set(s) to a Remote Node (PPTP) ............................................................31-4
xx List of Figures
Page 21

ZyAIR G-2000 Wireless 4-port Router User’s Guide
List of Tables
Table 3-1 Wizard 1: General Setup ..............................................................................................................3-3
Table 3-2 Wizard 2: Wireless LAN Setup....................................................................................................3-4
Table 3-3 Wizard 3: Ethernet Encapsulation................................................................................................3-6
Table 3-4 Wizard 3: PPPoE Encapsulation ..................................................................................................3-8
Table 3-5 Wizard 3: PPTP Encapsulation ..................................................................................................3-10
Table 3-6 Private IP Address Ranges .........................................................................................................3-11
Table 3-7 Example of Network Properties for LAN Servers with Fixed IP Addresses..............................3-13
Table 3-8 Wizard 4: WAN and DNS ..........................................................................................................3-14
Table 4-1 System General Setup..................................................................................................................4-2
Table 4-2 DDNS...........................................................................................................................................4-4
Table 4-3 Password ......................................................................................................................................4-5
Table 4-4 Time Setting.................................................................................................................................4-6
Table 5-1 IP..................................................................................................................................................5-4
Table 6-1 Wireless........................................................................................................................................6-7
Table 6-2 Roaming.....................................................................................................................................6-10
Table 7-1 Wireless : WEP Fields..................................................................................................................7-5
Table 7-2 MAC Address Filter.....................................................................................................................7-8
Table 7-3 Wireless Security Relational Matrix ..........................................................................................7-12
Table 7-4 Wireless LAN: 802.1x/WPA ......................................................................................................7-13
Table 7-5 Wireless LAN: 802.1x/WPA for 802.1x Protocol ......................................................................7-14
Table 7-6 Wireless LAN: 802.1x/WPA for WPA Protocol.........................................................................7-17
Table 7-7 Wireless LAN: 802.1x/WPA for WPA-PSK Protocol ................................................................7-19
Table 7-8 Local User Database ..................................................................................................................7-22
Table 7-9 RADIUS.....................................................................................................................................7-25
Table 8-1 Ethernet Encapsulation...................................................................................................................8-2
Table 8-2 Service Type..................................................................................................................................8-3
Table 8-3 PPPoE Encapsulation .....................................................................................................................8-4
Table 8-4 PPTP Encapsulation .......................................................................................................................8-6
Table 8-5 IP Setup .........................................................................................................................................8-7
Table 9-1 NAT Definitions...........................................................................................................................9-1
Table 9-2 NAT Mapping Types....................................................................................................................9-5
Table 9-3 Services and Port Numbers..........................................................................................................9-6
Table 9-4 SUA/NAT Setup...........................................................................................................................9-8
Table 9-5 Address Mapping .......................................................................................................................9-10
Table 9-6 Address Mapping Rule............................................................................................................... 9-11
Table 10-1 IP Static Route Summary .........................................................................................................10-2
Table 10-2 Edit IP Static Route..................................................................................................................10-3
Table 11-1 Common IP Ports .....................................................................................................................11-3
Table 11-2 ICMP Commands That Trigger Alerts......................................................................................11-6
Lists of Tables xxi
Page 22

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 11-3 Legal NetBIOS Commands .....................................................................................................11-6
Table 11-4 Legal SMTP Commands.......................................................................................................... 11-7
Table 12-1 Firewall Settings ...................................................................................................................... 12-7
Table 12-2 Firewall Filter ........................................................................................................................12-10
Table 12-3 Creating/Editing A Firewall Rule ..........................................................................................12-12
Table 12-4 Predefined Services ...............................................................................................................12-13
Table 13-1 Telnet .......................................................................................................................................13-3
Table 13-2 FTP ..........................................................................................................................................13-4
Table 13-3 WWW...................................................................................................................................... 13-5
Table 13-4 SNMP Traps.............................................................................................................................13-8
Table 13-5 Ports and Interface Types......................................................................................................... 13-8
Table 13-6 SNMP ......................................................................................................................................13-9
Table 13-7 DNS .......................................................................................................................................13-11
Table 13-8 Security..................................................................................................................................13-12
Table 14-1 Configuring UPnP ...................................................................................................................14-3
Table 15-1 View Log .................................................................................................................................15-2
Table 15-2 Log Settings.............................................................................................................................15-5
Table 15-3 Reports..................................................................................................................................... 15-8
Table 15-4 Protocol/Port Report ................................................................................................................ 15-9
Table 15-5 LAN IP Address Report ......................................................................................................... 15-11
Table 15-6 Report Specifications............................................................................................................. 15-11
Table 16-1 System Status...........................................................................................................................16-2
Table 16-2 System Status: Show Statistics ................................................................................................16-3
Table 16-3 DHCP Table............................................................................................................................. 16-4
Table 16-4 Association List .......................................................................................................................16-5
Table 16-5 Firmware Upgrade...................................................................................................................16-6
Table 16-6 Restore Configuration............................................................................................................16-10
Table 17-1 Main Menu Commands ...........................................................................................................17-4
Table 17-2 Main Menu Summary.............................................................................................................. 17-5
Table 18-1 Menu 1 General Setup .............................................................................................................18-2
Table 18-2 Menu 1.1 Configure Dynamic DNS ........................................................................................18-3
Table 18-3 Menu 2 WAN Setup.................................................................................................................18-5
Table 19-1 Menu 3.2 DHCP Ethernet Setup..............................................................................................19-3
Table 19-2 Menu3.2 TCP/IP Ethernet Setup.............................................................................................. 19-3
Table 19-3 Menu 3.2.1 IP Alias Setup .......................................................................................................19-6
Table 19-4 Menu 3.5 Wireless LAN Setup ................................................................................................ 19-7
Table 19-5 Menu 3.5.1 WLAN MAC Address Filter...............................................................................19-10
Table 19-6 Menu 3.5.2 Roaming Configuration...................................................................................... 19-11
Table 20-1 Internet Account Information...................................................................................................20-1
Table 20-2 Menu 4 Internet Access Setup .................................................................................................20-2
Table 21-1 Menu 11.1 Remote Node Profile .............................................................................................21-2
xxii Lists of Tables
Page 23

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 21-2 Menu 11.3 Remote Node Network Layer Options...................................................................21-5
Table 21-3 Menu 12.1 Edit IP Static Route................................................................................................21-8
Table 22-1 Menu 14.1- Edit Dial-in User...................................................................................................22-2
Table 23-1 Applying NAT in Menus 4 & 11.3 ...........................................................................................23-2
Table 23-2 Menu 15.1.255 SUA Address Mapping Rules .........................................................................23-4
Table 23-3 Menu 15.1.1 Address Mapping Rules ......................................................................................23-5
Table 23-4 Menu 15.1.1.1 Address Mapping Rule.....................................................................................23-6
Table 23-5 Services & Port Numbers.........................................................................................................23-8
Table 23-6 Menu 15.3 Trigger Port Setup................................................................................................23-17
Table 24-1 Abbreviations Used in the Filter Rules Summary Menu..........................................................24-5
Table 24-2 Rule Abbreviations Used .........................................................................................................24-5
Table 24-3 Menu 21.1.1 TCP/IP Filter Rule ..............................................................................................24-7
Table 24-4 Menu 21.1.4.1 Generic Filter Rule.........................................................................................24-11
Table 24-5 Filter Sets Table .....................................................................................................................24-15
Table 25-1 Menu 22 SNMP Configuration................................................................................................25-1
Table 26-1 Menu 23.2 System Security : RADIUS Server........................................................................26-2
Table 26-2 Menu 23.4 System Security : IEEE802.1x...............................................................................26-4
Table 27-1 Menu 24.1 System Maintenance : Status .................................................................................27-2
Table 27-2 Menu 24.2.1 System Maintenance – Information....................................................................27-4
Table 27-3 Menu 24.3.2 System Maintenance : UNIX Syslog ..................................................................27-6
Table 27-4 Menu 24.4 System Maintenance : Diagnostic..........................................................................27-8
Table 28-1 Filename Conventions..............................................................................................................28-2
Table 28-2 General Commands for GUI-based FTP Clients......................................................................28-4
Table 28-3 General Commands for GUI-based TFTP Clients ...................................................................28-6
Table 29-1 Menu 24.9.1 Call Control Parameters......................................................................................29-3
Table 29-2 Menu 24.9.1 Budget Management...........................................................................................29-4
Table 29-3 Menu 24.9.2 Call History.........................................................................................................29-5
Table 29-4 Menu 24.10 System Maintenance : Time and Date Setting .....................................................29-6
Table 30-1 Menu 24.11 Remote Management Control ..............................................................................30-3
Table 31-1 Menu 26.1 Schedule Set Setup.................................................................................................31-2
Lists of Tables xxiii
Page 24
ZyAIR G-2000 Wireless 4-port Router User’s Guide
Preface
Congratulations on your purchase from the ZyAIR G-2000 802.11g Wireless 4-port Router.
A wireless router is an access point and router rolled into one. It is a cost-effect solution to share Internet
access with multiple computers and expand your wired network.
This User’s Guide is designed to guide you through the configuration of your ZyAIR using the web
configurator or the SMT.
Use the web configurator, System Management Terminal (SMT) or command
interpreter interface to configure your ZyAIR. Not all features can be configured
through all interfaces.
The web configurator parts of this guide contain background information on features configurable by the
web configurator and the SMT. The SMT parts of this guide contain background information solely on
features not configurable by the web configurator.
Register your product online to receive e-mail notices of firmware upgrades and
information at www.zyxel.com for global products, or at www.us.zyxel.com for
North American products.
Related Documentation
Supporting Disk
Refer to the included CD for support documents.
Quick Installation Guide
Our Quick Installation Guide is designed to help you get up and running right away. It contains
information on the configuration of key features and hardware connections and installation.
ZyXEL Web Site
The ZyXEL download library at www.zyxel.com
Please also refer to www.zyxel.com for an online glossary of networking terms.
contains additional support documentation.
Syntax Conventions
• “Enter” means for you to type one or more characters (and press the carriage return). “Select” or
“Choose” means for you to use one predefined choices.
• Enter, or carriage return, key; [ESC] means the escape key and [SPACE BAR] means the space bar.
[UP] and [DOWN] are the up and down arrow keys.
xxiv Preface
Page 25
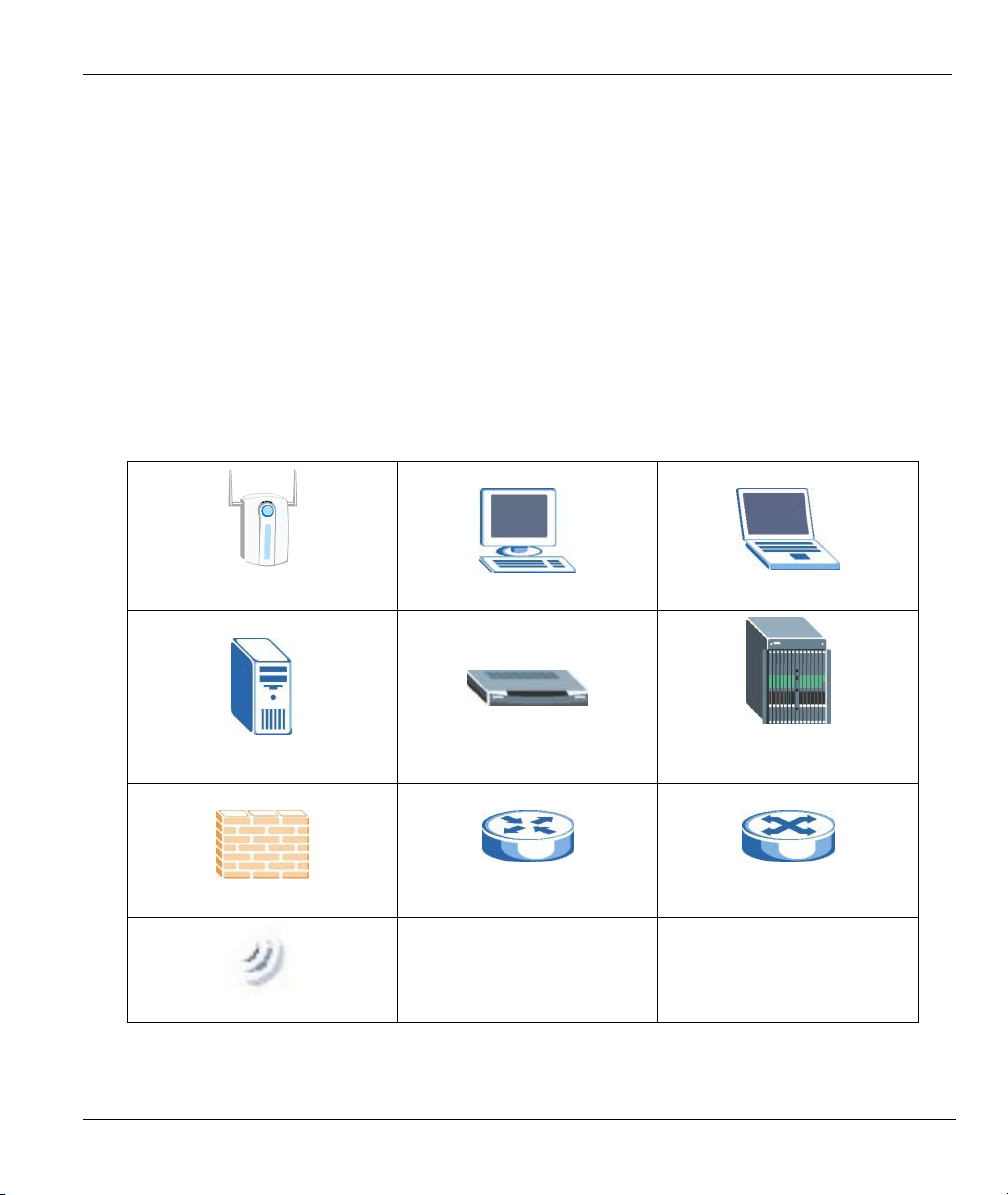
ZyAIR G-2000 Wireless 4-port Router User’s Guide
• Mouse action sequences are denoted using a comma. For example, “click the Apple icon, Control
Panels and then Modem” means first click the Apple icon, then point your mouse pointer to Control
Panels and then click Modem.
• For brevity’s sake, we will use “e.g.,” as a shorthand for “for instance”, and “i.e.,” for “that is” or “in
other words” throughout this manual.
• The ZyAIR G-2000 802.11g Wireless 4-port Router may be referred to simply as the ZyAIR in the
user’s guide.
User Guide Feedback
Help us help you. E-mail all User Guide-related comments, questions or suggestions for improvement to
techwriters@zyxel.com.tw or send regular mail to The Technical Writing Team, ZyXEL Communications
Corp., 6 Innovation Road II, Science-Based Industrial Park, Hsinchu, 300, Taiwan. Thank you.
Graphics Icons Key
ZyAIR
Server
Firewall
Wireless Signal
Computer
Modem
Router
Notebook Computer
DSLAM (Digital Subscriber
Line Access Multiplexer)
Switch
Preface xxv
Page 26

Page 27
Overview
Part I:
OVERVIEW
This part introduces the main features and applications of the ZyAIR and shows how to access
the web configurator and use the Wizard to configure for Internet Access.
I
Page 28

Page 29

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Chapter 1
Getting to Know Your ZyAIR
This chapter introduces the main features and applications of the ZyAIR.
1.1 Introducing the ZyAIR
The ZyAIR G-2000, an IEEE802.11b/g compliant broadband wireless sharing gateway, provides wireless
connectivity. As an Internet gateway, your ZyAIR can share an Internet connection (through a cable or
xDSL modem) with multiple computers using SUA/NAT and DHCP. The ZyAIR offers highly secured
wireless connectivity to your wired network with IEEE 802.1x, WEP data encryption, WPA (Wi-Fi
Protected Access) and MAC address filtering.
The ZyAIR is easy to install and configure. The embedded web-based configurator and SNMP network
management enables remote configuration and management of your ZyAIR.
1.2 ZyAIR Features
The following sections describe the features of the ZyAIR.
4-Port Switch
A combination of switch and router makes your ZyAIR a cost-effective and viable network solution. You
can connect up to four computers to the LAN ports on you ZyAIR without the cost of a hub.
10/100M Auto-negotiating Ethernet/Fast Ethernet Interface
This auto-negotiating feature allows the ZyAIR to detect the speed of incoming transmissions and adjust
appropriately without manual intervention. It allows data transfer of either 10 Mbps or 100 Mbps in either
half-duplex or full-duplex mode depending on your Ethernet network.
10/100M Auto-crossover Ethernet/Fast Ethernet Interface
The LAN interface automatically adjusts to either a crossover or straight-through Ethernet cable.
10/100 Mbps Ethernet WAN
The 10/100 Mbps Ethernet WAN port attaches to the Internet via broadband modem or router.
Getting to Know Your ZyAIR 1-1
Page 30
ZyAIR G-2000 Wireless 4-port Router User’s Guide
Reset Button
The ZyAIR reset button is built into the side panel. Use this button to restore the factory default password
to 1234; IP address to 192.168.1.1, subnet mask to 255.255.255.0 and DHCP sever enabled with a pool of
32 IP addresses starting at 192.168.1.33.
Brute-Force Password Guessing Protection
The ZyAIR has a special protection mechanism to discourage brute-force password guessing attacks on the
ZyAIR's management interfaces. You can specify a wait-time that must expire before entering a fourth
password after three incorrect passwords have been entered. Please see the appendix for details about this
feature.
ZyAIR LED
The blue ZyAIR LED (also known as the Breathing LED) is on when the ZyAIR is on and blinks (or
breaths) when data is being transmitted to/from its wireless stations. You may use the web configurator to
turn this LED off even when the ZyAIR is on and data is being transmitted/received.
802.11b Wireless LAN Standard
ZyAIR products containing the letter “B” in the model name, such as ZyAIR B-2000, ZyAIR B-2000 v.2,
comply with the 802.11b wireless standard.
The 802.11b data rate and corresponding modulation techniques are as follows. The modulation technique
defines how bits are encoded onto radio waves.
802.11b
Data Rate (Mbps) Modulation
1 DBPSK (Differential Binary Phase Shift Keyed)
2
5.5 / 11 CCK (Complementary Code Keying)
DQPSK (Differential Quadrature Phase Shift Keying
)
The ZyAIR may be prone to RF (Radio Frequency) interference from other 2.4 GHz
devices such as microwave ovens, wireless phones, Bluetooth enabled devices,
and other wireless LANs.
802.11g Wireless LAN Standard
ZyAIR products containing the letter “G” in the model name, such as ZyAIR G-1000 and ZyAIR G-2000,
comply with the 802.11g wireless standard.
802.11g will be fully compatible with the 802.11b standard. This means an 802.11b radio card can interface
directly with an 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. 802.11g
1-2 Getting to Know Your ZyAIR
Page 31

ZyAIR G-2000 Wireless 4-port Router User’s Guide
has several intermediate rate steps between the maximum and minimum data rates. The 802.11g data rate
and modulation are as follows:
802.11g
Data Rate (Mbps) Modulation
1 ~ 54 OFDM (Orthogonal Frequency Division Multiplexing)
Wi-Fi Protected Access
Wi-Fi Protected Access (WPA) is a subset of the IEEE 802.11i security specification draft. Key differences
between WPA and WEP are user authentication and improved data encryption.
SSL Passthrough
SSL (Secure Sockets Layer) uses a public key to encrypt data that's transmitted over an SSL connection.
Both Netscape Navigator and Internet Explorer support SSL, and many web sites use the protocol to obtain
confidential user information, such as credit card numbers. By convention, URLs that require an SSL
connection start with “https” instead of “http”. The ZyAIR allows SSL connections to take place through
the ZyAIR.
Firewall
The ZyAIR employs a stateful inspection firewall with DoS (Denial of Service) protection. By default,
when the firewall is activated, all incoming traffic from the WAN to the LAN is blocked unless it is
initiated from the LAN. The ZyAIR firewall supports TCP/UDP inspection, DoS detection and prevention,
real time alerts, reports and logs.
IEEE 802.1x Network Security
The ZyAIR supports the IEEE 802.1x standard to enhance user authentication. Use the built-in user profile
database to authenticate up to 32 users using MD5 encryption. Use an EAP-compatible RADIUS
(RFC2138, 2139 - Remote Authentication Dial In User Service) server to authenticate a limitless number of
users using EAP (Extensible Authentication Protocol). EAP is an authentication protocol that supports
multiple types of authentication.
Wireless LAN MAC Address Filtering
Your ZyAIR checks the MAC address of the wireless station against a list of allowed or denied MAC
addresses.
WEP Encryption
WEP (Wired Equivalent Privacy) encrypts data frames before transmitting over the wireless network to
help keep network communications private.
Getting to Know Your ZyAIR 1-3
Page 32

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Universal Plug and Play (UPnP)
Using the standard TCP/IP protocol, the ZyAIR and other UPnP-enabled devices can dynamically join a
network, obtain an IP address and convey its capabilities to other devices on the network.
Dynamic DNS Support
With Dynamic DNS support, you can have a static hostname alias for a dynamic IP address, allowing the
host to be more easily accessible from various locations on the Internet. You must register for this service.
PPPoE Support (RFC2516)
PPPoE (Point-to-Point Protocol over Ethernet) emulates a dial-up connection. It allows your ISP to use
their existing network configuration with newer broadband technologies such as ADSL. The PPPoE driver
on the ZyAIR is transparent to the computers on the LAN, which see only Ethernet and are not aware of
PPPoE thus saving you from having to manage PPPoE clients on individual computers.
PPTP Encapsulation
Point-to-Point Tunneling Protocol (PPTP) is a network protocol that enables secure transfer of data from a
remote client to a private server, creating a Virtual Private Network (VPN) using a TCP/IP-based network.
PPTP supports on-demand, multi-protocol and virtual private networking over public networks, such as the
Internet. Use PPTP to connect to a broadband modem to achieve access to high-speed data networks via a
familiar "dial-up networking" user interface.
Network Address Translation (NAT)
NAT (Network Address Translation - NAT, RFC 1631) allows the translations of multiple IP addresses
used within one network to different IP addresses known within another network.
NAT for Single-IP-address Internet Access
The ZyAIR's SUA (Single User Account) feature allows multiple-user Internet access for the cost of a
single IP account. NAT supports popular Internet applications such as MS traceroute, CuSeeMe, IRC,
RealPlayer, VDOLive, Quake, and PPTP. No configuration is needed to support these applications.
DHCP (Dynamic Host Configuration Protocol)
DHCP (Dynamic Host Configuration Protocol) allows the individual clients (computers) to obtain the
TCP/IP configuration at start-up from a centralized DHCP server. The ZyAIR has built-in DHCP server
capability enabled by default. It can assign IP addresses, an IP default gateway and DNS servers to DHCP
clients. The ZyAIR also acts as a surrogate DHCP server (DHCP Relay) where it relays IP address
assignment from the actual real DHCP server to the clients.
Multicast
Traditionally, IP packets are transmitted in two ways - unicast or broadcast. Multicast is a third way to
deliver IP packets to a group of hosts. IGMP (Internet Group Management Protocol) is the protocol used to
1-4 Getting to Know Your ZyAIR
Page 33

ZyAIR G-2000 Wireless 4-port Router User’s Guide
support multicast groups. The latest version is version 2 (see RFC 2236). The ZyAIR supports versions 1
and 2.
IP Alias
IP Alias allows you to partition a physical network into logical networks over the same Ethernet interface.
The ZyAIR supports three logical LAN interfaces via its single physical Ethernet LAN interface with the
ZyAIR itself as the gateway for each LAN network.
IP Policy Routing
IP Policy Routing provides a mechanism to override the default routing behavior and alter packet
forwarding based on the policies defined by the network administrator.
SNMP
SNMP (Simple Network Management Protocol) is a protocol used for exchanging management
information between network devices. SNMP is a member of the TCP/IP protocol suite. Your ZyAIR
supports SNMP agent functionality, which allows a manger station to manage and monitor the ZyAIR
through the network. The ZyAIR supports SNMP version one (SNMPv1) and version two c (SNMPv2c).
Full Network Management
The embedded web configurator is an all-platform web-based utility that allows you to easily access the
ZyAIR’s management settings. Most functions of the ZyAIR are also software configurable via the SMT
(System Management Terminal) interface. The SMT is a menu-driven interface that you can access from a
terminal emulator over a telnet connection.
Logging and Tracing
♦ Built-in message logging and packet tracing.
♦ Unix syslog facility support.
Diagnostics Capabilities
The ZyAIR can perform self-diagnostic tests. These tests check the integrity of the following circuitry:
♦ FLASH memory
♦ DRAM
♦ LAN port
♦ Wireless port
Embedded FTP and TFTP Servers
The ZyAIR’s embedded FTP and TFTP servers enable fast firmware upgrades as well as configuration file
backups and restoration.
Getting to Know Your ZyAIR 1-5
Page 34

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Wireless Association List
With the Wireless Association List, you can see the list of the wireless stations that are currently using the
ZyAIR to access your wired network.
1.3 Application for the ZyAIR
Here is an application example of what you can do with your ZyAIR.
1.3.1 Internet Access Application
Add a wireless LAN to your existing network without expensive network cables. Wireless stations can
move freely anywhere in the coverage area and use resources on the wired network.
Figure 1-1 Internet Access Application Example
1-6 Getting to Know Your ZyAIR
Page 35

ZyAIR G-2000 Wireless 4-port Router User’s Guide
A
Chapter 2
Introducing the Web Configurator
This chapter describes how to access the ZyAIR web configurator and provides an overview of its
screens.
2.1 Web Configurator Overview
The web configurator makes it easy to configure and manage the ZyAIR. The screens you see in the web
configurator may vary somewhat from the ones shown in this document due to differences between
individual ZyAIR models or firmware versions.
2.2 Accessing the ZyAIR Web Configurator
Step 1. Make sure your ZyAIR hardware is properly connected (refer to the Quick Installation Guide).
Step 2. Prepare your computer to connect to the ZyAIR (refer to the Setting Up Your Computer’s IP
Address appendix).
Step 3. Launch your web browser.
Step 4. Type "192.168.1.1" as the URL.
ddress field.
Figure 2-1 Web Browser Address Field
Step 5. Type "1234" (default) as the password and click Login. In some versions, the default password
appears automatically - if this is the case, click Login.
Step 6. You should see a screen asking you to change your password (highly recommended) as shown
next. Type a new password (and retype it to confirm) and click Apply or click Ignore to allow
access without password change.
Introducing the Web Configurator 2-1
Page 36

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 2-2 Change Password Screen
Step 7. You should now see the SYSTEM screen.
The management session automatically times out when the time period set in the
Administrator Inactivity Timer field expires (default five minutes). Simply log back into
the ZyAIR if this happens to you.
2.3 Resetting the ZyAIR
If you forget your password or cannot access the ZyAIR, you will need to reload the factory-default
configuration file or use the RESET button on the side panel of the ZyAIR. Uploading this configuration file
replaces the current configuration file with the factory-default configuration file. This means that you will
lose all configurations that you had previously. The password will be reset to “1234”, also.
2.3.1 Procedure to Use the Reset Button
Make sure the SYS LED is on (not blinking) before you begin this procedure.
Step 1. Press the RESET button for more than five seconds, and then release it. If the SYS LED begins
to blink, the defaults have been restored and the ZyAIR restarts. Otherwise, go to step 2.
Step 2. Turn the ZyAIR off.
Step 3. While pressing the RESET button, turn the ZyAIR on.
Step 4. Continue to hold the RESET button. The SYS LED will begin to blink and flicker very quickly
after about 10 or 15 seconds. This indicates that the defaults have been restored and the ZyAIR is
now restarting.
Step 5. Release the RESET button and wait for the ZyAIR to finish restarting.
2-2 Introducing the Web Configurator
Page 37

ZyAIR G-2000 Wireless 4-port Router User’s Guide
gs(
2.4 Navigating the ZyAIR Web Configurator
The following summarizes how to navigate the web configurator.
Follow the instructions below or click the icon (located in the top right corner
of most screens) to view online help.
The icon does not appear in the main screen.
Click WIZARD SETUP for initial configuration including general
setup, wireless LAN setup, ISP Parameters for Internet Access
and WAN IP/DNS/MAC Address Assignment.
Click the links under MAINTENANCE to view information about your ZyAIR or
Click LOGOUT at
any time to exit the
web configurator.
upgrade configuration/firmware files. Maintenance includes SYSTEM STATUS
(Statistics), DHCP TABLE, F/W (Firmware) UPLOAD, CONFIGURATION
(Backup, Restore Default) and WIRELESS (Association List).
Click the links under ADVANCED to configure advanced features
such as SYSTEM (General Setup, Dynamic DNS, Password and
Time Setting), LAN (DHCP and TCP/IP Setup), WLAN (WLAN
and WLAN Security Setup), WAN, SUA/NAT, STATIC ROUTE
(Route Entry), FIREWALL (Settings, Filter and Services),
REMOTE MGNT (Telnet, FTP, WWW, SNMP, DNS and Security),
UPnP and Lo
View Log, Log Settings and Reports).
Figure 2-3 Navigating the ZyAIR Web Configurator
Introducing the Web Configurator 2-3
Page 38

Page 39

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Chapter 3
Wizard Setup
This chapter provides information on the Wizard Setup screens in the web configurator.
3.1 Wizard Setup Overview
The web configurator’s setup wizard helps you configure your ZyAIR for Internet access and set up wireless
LAN.
3.1.1 Channel
A channel is the radio frequency(ies) used by IEEE 802.11b wireless devices. Channels available depend on
your geographical area. You may have a choice of channels (for your region) so you should use a different
channel than an adjacent AP (access point) to reduce interference. Interference occurs when radio signals
from different access points overlap causing interference and degrading performance.
Adjacent channels partially overlap however. To avoid interference due to overlap, your AP should be on a
channel at least five channels away from a channel that an adjacent AP is using. For example, if your region
has 11 channels and an adjacent AP is using channel 1, then you need to select a channel between 6 or 11.
3.1.2 ESS ID
An Extended Service Set (ESS) is a group of access points or wireless gateways connected to a wired LAN
on the same subnet. An ESS ID uniquely identifies each set. All access points or wireless gateways and their
associated wireless stations in the same set must have the same ESSID.
3.1.3 WEP Encryption
WEP (Wired Equivalent Privacy) encrypts data frames before transmitting over the wireless network. WEP
encryption scrambles the data transmitted between the wireless stations and the access points to keep network
communications private. It encrypts unicast and multicast communications in a network. Both the wireless
stations and the access points must use the same WEP key for data encryption and decryption.
3.2 Wizard Setup: General Setup
General Setup contains administrative and system-related information.
Wizard Setup 3-1
Page 40

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-1 Wizard 1: General Setup
The following table describes the labels in this screen.
3-2 Wizard Setup
Page 41

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-1 Wizard 1: General Setup
LABEL DESCRIPTION
System Name It is recommended you type your computer's "Computer name". some ISPs check this name
you should enter your computer's "Computer Name".
In Windows 95/98 click Start, Settings, Control Panel, Network. Click the Identification
tab, note the entry for the Computer Name field and enter it as the System Name.
In Windows 2000, click Start, Settings, Control Panel and then double-click System.
Click the Network Identification tab and then the Properties button. Note the entry for
the Computer name field and enter it as the System Name.
In Windows XP, click Start, My Computer, View system information and then click the
Computer Name tab. Note the entry in the Full computer name field and enter it as the
ZyAIR System Name.
This name can be up to 30 alphanumeric characters long. Spaces are not allowed, but
dashes "-" and underscores "_" are accepted.
Domain Name
Next
The Domain Name entry is what is propagated to the DHCP clients on the LAN. Type the
domain name (if you know it) here. If you leave this field blank, the ISP may assign a domain
name via DHCP. The domain name entered by you is given priority over the ISP assigned
domain name.
Click Next to proceed to the next screen.
3.3 Wizard Setup: Wireless LAN Setup
Set up your wireless LAN using the second wizard screen.
Wizard Setup 3-3
Page 42

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-2 Wizard 2: Wireless LAN Setup
The following table describes the labels in this screen.
Table 3-2 Wizard 2: Wireless LAN Setup
LABEL DESCRIPTION
ESSID
Choose
Channel ID
Enter a descriptive name (up to 32 printable 7-bit ASCII characters) for the wireless LAN.
If you change this field on the ZyAIR, make sure all wireless stations use the same ESSID in
order to access the network.
Select a channel from the drop-down list box.
3-4 Wizard Setup
Page 43

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-2 Wizard 2: Wireless LAN Setup
LABEL DESCRIPTION
WEP
Encryption
ASCII Select this option in order to enter ASCII characters as the WEP keys.
HEX Select this option to enter hexadecimal characters as the WEP keys.
Key 1 to Key 4
Next
Back
Select Disable allows all wireless computers to communicate with the access points without
any data encryption.
Select 64-bit WEP or 128-bit WEP to allow data encryption.
The preceding “0x” is entered automatically.
The WEP keys are used to encrypt data. Both the ZyAIR and the wireless stations must use
the same WEP key for data transmission.
If you chose 64-bit WEP, then enter any 5 ASCII characters or 10 hexadecimal characters
("0-9", "A-F").
If you chose 128-bit WEP, then enter 13 ASCII characters or 26 hexadecimal characters
("0-9", "A-F").
You must configure all four keys, but only one key can be activated at any one time. The
default key is key 1.
Click Next to continue.
Click Back to return to the previous screen.
Refer to the chapter on wireless LAN for more information.
3.4 Wizard Setup: ISP Parameters
The ZyAIR offers three choices of encapsulation. They are Ethernet, PPTP or PPPoE. The screen varies
depending upon the type chosen.
3.4.1 Ethernet
Choose Ethernet when the WAN port is used as a regular Ethernet.
Wizard Setup 3-5
Page 44

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-3 Wizard 3: Ethernet Encapsulation
The following table describes the labels in this screen.
Table 3-3 Wizard 3: Ethernet Encapsulation
LABEL DESCRIPTION
ISP Parameters for Internet Access
Encapsulation
Service Type
You must choose the Ethernet option when the WAN port is used as a regular
Ethernet. Otherwise, choose PPPoE or PPTP for a dial-up connection.
Select from Standard, RR-Toshiba (RoadRunner Toshiba authentication method),
RR-Manager (Roadrunner Manager authentication method), RR-Telstra or Telia
Login. Choose a Roadrunner service type if your ISP is Time Warner's Roadrunner;
otherwise choose Standard.
The User Name, Password and Login Server IP Address fields are not applicable
(N/A) for the Standard service type.
3-6 Wizard Setup
Page 45

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-3 Wizard 3: Ethernet Encapsulation
LABEL DESCRIPTION
User Name Type the username given to you by your ISP.
Password Type the password associated with the username above.
Login Server IP
Address
Login Server
(Telia Login only)
Relogin
Every(min) (Telia
Login only)
Next
Back
The ZyAIR will find the Roadrunner Server IP if this field is left blank. If it does not,
then you must enter the authentication server IP address.
Type the domain name of the Telia login server, for example "login1.telia.com".
The Telia server logs the ZyAIR out if the ZyAIR does not log in periodically. Type the
number of minutes from 1 to 59 (30 recommended) for the ZyAIR to wait between
logins.
Click Next to proceed to the next page.
Click Back to go back to the previous page.
3.4.2 PPPoE Encapsulation
Point-to-Point Protocol over Ethernet (PPPoE) functions as a dial-up connection. PPPoE is an IETF (Internet
Engineering Task Force) draft standard specifying how a host personal computer interacts with a broadband
modem (for example xDSL, cable, wireless, etc.) to achieve access to high-speed data networks. It preserves
the existing Microsoft Dial-Up Networking experience and requires no new learning or procedures.
For the service provider, PPPoE offers an access and authentication method that works with existing access
control systems (for instance, RADIUS). For the user, PPPoE provides a login and authentication method
that the existing Microsoft Dial-Up Networking software can activate, and therefore requires no new learning
or procedures for Windows users.
One of the benefits of PPPoE is the ability to let end users access one of multiple network services, a function
known as dynamic service selection. This enables the service provider to easily create and offer new IP
services for specific users.
Operationally, PPPoE saves significant effort for both the subscriber and the ISP/carrier, as it requires no
specific configuration of the broadband modem at the subscriber’s site.
By implementing PPPoE directly on the ZyAIR (rather than individual computers), the computers on the
LAN do not need PPPoE software installed, since the ZyAIR does that part of the task. Furthermore, with
NAT, all of the LAN's computers will have Internet access.
Refer to the appendix for more information on PPPoE.
Wizard Setup 3-7
Page 46

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-4 Wizard 3: PPPoE Encapsulation
The following table describes the labels in this screen.
Table 3-4 Wizard 3: PPPoE Encapsulation
LABEL DESCRIPTION
ISP Parameter for Internet Access
Encapsulation Choose an encapsulation method from the pull-down list box. PPPoE forms a dial-up
connection.
Service Name Type the name of your service provider.
User Name Type the user name given to you by your ISP.
Password Type the password associated with the user name above.
3-8 Wizard Setup
Page 47
ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-4 Wizard 3: PPPoE Encapsulation
LABEL DESCRIPTION
Nailed-Up
Connection
Idle Timeout Type the time in seconds that elapses before the ZyAIR automatically disconnects from
Next
Back
Select Nailed-Up Connection if you do not want the connection to time out.
the PPPoE server.
Click Next to continue.
Click Back to return to the previous screen.
3.4.3 PPTP Encapsulation
Point-to-Point Tunneling Protocol (PPTP) is a network protocol that enables transfers of data from a remote
client to a private server, creating a Virtual Private Network (VPN) using TCP/IP-based networks.
PPTP supports on-demand, multi-protocol, and virtual private networking over public networks, such as the
Internet.
Refer to the appendix for more information on PPTP.
The ZyAIR supports one PPTP server connection at any given time.
Wizard Setup 3-9
Page 48

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-5 Wizard 3: PPTP Encapsulation
The following table describes the labels in this screen.
Table 3-5 Wizard 3: PPTP Encapsulation
LABEL DESCRIPTION
ISP Parameters for Internet Access
Encapsulation
User Name Type the user name given to you by your ISP.
Password Type the password associated with the User Name above.
Nailed-Up
Connection
Select PPTP from the drop-down list box.
Select Nailed-Up Connection if you do not want the connection to time out.
3-10 Wizard Setup
Page 49

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-5 Wizard 3: PPTP Encapsulation
LABEL DESCRIPTION
Idle Timeout Type the time in seconds that elapses before the ZyAIR automatically disconnects
from the PPTP server.
PPTP Configuration
My IP Address Type the (static) IP address assigned to you by your ISP.
My IP Subnet
Mask
Server IP Address Type the IP address of the PPTP server.
Connection
ID/Name
Next
Back
Type the subnet mask assigned to you by your ISP (if given).
If your ISP has provided a connection ID name, enter it in this field exactly as
provided.
Click Next to continue.
Click Back to return to the previous screen.
3.5 Wizard Setup: WAN and DNS
The fourth wizard screen allows you to configure WAN IP address assignment, DNS server address
assignment and the WAN MAC address.
3.5.1 WAN IP Address Assignment
Every computer on the Internet must have a unique IP address. If your networks are isolated from the
Internet, for instance, only between your two branch offices, you can assign any IP addresses to the hosts
without problems. However, the Internet Assigned Numbers Authority (IANA) has reserved the following
three blocks of IP addresses specifically for private networks.
Table 3-6 Private IP Address Ranges
10.0.0.0 - 10.255.255.255
172.16.0.0 - 172.31.255.255
192.168.0.0 - 192.168.255.255
You can obtain your IP address from the IANA, from an ISP or have it assigned by a private network. If you
belong to a small organization and your Internet access is through an ISP, the ISP can provide you with the
Internet addresses for your local networks. On the other hand, if you are part of a much larger organization,
you should consult your network administrator for the appropriate IP addresses.
Wizard Setup 3-11
Page 50

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Regardless of your particular situation, do not create an arbitrary IP address;
always follow the guidelines above. For more information on address assignment,
please refer to RFC 1597, Address Allocation for Private Internets and RFC 1466,
Guidelines for Management of IP Address Space.
3.5.2 IP Address and Subnet Mask
Similar to the way houses on a street share a common street name, so too do computers on a LAN share one
common network number.
Where you obtain your network number depends on your particular situation. If the ISP or your network
administrator assigns you a block of registered IP addresses, follow their instructions in selecting the IP
addresses and the subnet mask.
If the ISP did not explicitly give you an IP network number, then most likely you have a single user account
and the ISP will assign you a dynamic IP address when the connection is established. If this is the case, it is
recommended that you select a network number from 192.168.0.0 to 192.168.255.0 and you must enable the
Network Address Translation (NAT) feature of the ZyAIR. The Internet Assigned Number Authority
(IANA) reserved this block of addresses specifically for private use; please do not use any other number
unless you are told otherwise. Let's say you select 192.168.1.0 as the network number; which covers 254
individual addresses, from 192.168.1.1 to 192.168.1.254 (zero and 255 are reserved). In other words, the first
three numbers specify the network number while the last number identifies an individual computer on that
network.
Once you have decided on the network number, pick an IP address that is easy to remember, for instance,
192.168.1.1, for your ZyAIR, but make sure that no other device on your network is using that IP address.
The subnet mask specifies the network number portion of an IP address. Your ZyAIR will compute the
subnet mask automatically based on the IP address that you entered. You don't need to change the subnet
mask computed by the ZyAIR unless you are instructed to do otherwise.
3.5.3 DNS Server Address Assignment
Use DNS (Domain Name System) to map a domain name to its corresponding IP address and vice versa, for
instance, the IP address of www.zyxel.com is 204.217.0.2. The DNS server is extremely important because
without it, you must know the IP address of a computer before you can access it.
There are two ways that an ISP disseminates the DNS server addresses.
1. The ISP tells you the DNS server addresses, usually in the form of an information sheet, when you sign
up. If your ISP gives you DNS server addresses, enter them in the DNS Server fields in DHCP Setup.
2. Leave the DNS Server fields in DHCP Setup blank (for example 0.0.0.0). The ZyAIR acts as a DNS
proxy when this field is blank.
3-12 Wizard Setup
Page 51

ZyAIR G-2000 Wireless 4-port Router User’s Guide
3.5.4 WAN MAC Address
Every Ethernet device has a unique MAC (Media Access Control) address. The MAC address is assigned at
the factory and consists of six pairs of hexadecimal characters, for example, 00:A0:C5:00:00:02.
You can configure the WAN port's MAC address by either using the factory default or cloning the MAC
address from a workstation on your LAN. Once it is successfully configured, the address will be copied to
the "rom" file (ZyNOS configuration file). It will not change unless you change the setting or upload a
different "rom" file.
ZyXEL recommends you clone the MAC address from a workstation on your LAN
even if your ISP does not require MAC address authentication.
Your ZyAIR WAN port is always set at half-duplex mode as most cable/DSL modems only support halfduplex mode. Make sure your modem is in half-duplex mode. Your ZyAIR supports full duplex mode on the
LAN side.
Table 3-7 Example of Network Properties for LAN Servers with Fixed IP Addresses
Choose an IP address 192.168.1.2-192.168.1.32; 192.168.1.65-192.168.1.254.
Subnet mask 255.255.255.0
Gateway (or default route) 192.168.1.1(ZyAIR LAN IP)
Wizard Setup 3-13
Page 52

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 3-6 Wizard 4: WAN and DNS
The following table describes the labels in this screen.
Table 3-8 Wizard 4: WAN and DNS
LABEL DESCRIPTION
WAN IP Address Assignment
Get automatically from
Use fixed IP address Select this option If the ISP assigned a fixed IP address.
My WAN IP Address
Select this option If your ISP did not assign you a fixed IP address. This is the
ISP
default selection.
Enter your WAN IP address in this field if you selected Use fixed IP Address.
3-14 Wizard Setup
Page 53

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 3-8 Wizard 4: WAN and DNS
LABEL DESCRIPTION
My WAN IP Subnet
Mask
Gateway/Remote IP
Address
Remote IP Subnet
Mask
DNS Server Address Assignment
Get automatically from
ISP
Use fixed IP address DNS Server IP Address
Primary/Secondary
DNS Server
WAN MAC Address: The MAC address field allows you to configure the WAN port's MAC address by
either using the factory default or cloning the MAC address from a workstation on your LAN.
Factory Default Select this option to use the factory assigned default MAC address.
Spoof this Computer's
MAC address - IP
Address
Back
Next
Enter the IP subnet mask in this field if you selected Use fixed IP Address.
This field is not available when you select PPPoE and PPTP encapsulation in
the previous wizard screen.
Enter the gateway IP address in this field if you selected Use fixed IP Address.
This field is not available when you select PPPoE encapsulation in the previous
wizard screen.
Enter the gateway IP subnet mask (if your ISP gave you one) in this field if you
selected Use fixed IP Address. This field is available only when you select
PPTP encapsulation in the previous wizard screen.
Select this option if your ISP does not give you DNS server addresses. This
option is selected by default.
Select this option If your ISP provides you a DNS server address.
If you selected the Use fixed IP address –DNS Server IP Address option,
enter the provided DNS addresses in these fields.
Select this option and enter the IP address of the computer on the LAN whose
MAC address you are cloning. Once it is successfully configured, the MAC
address will be copied to the rom file (ZyNOS configuration file). It will not
change unless you change the setting or upload a different rom file. It is
advisable to clone the MAC address from a computer on your LAN even if your
ISP does not presently require MAC address authentication.
Click Back to return to the previous screen.
Click Next to continue.
3.6 Basic Setup Complete
Click Finish to complete and save the wizard setup.
Wizard Setup 3-15
Page 54

ZyAIR G-2000 Wireless 4-port Router User’s Guide
If you are currently using a wireless (LAN) adapter to access this ZyAIR and you made changes to the
ESSID, then you will need to make the same changed to your wireless (LAN) adapter after you click the
Finish button.
Figure 3-7 Setup Complete
Well done! You have successfully set up your ZyAIR to operate on your network and access the Internet.
3-16 Wizard Setup
Page 55

System, LAN and Wireless
Part II:
SYSTEM, LAN AND WIRELESS
This part discusses the System, LAN, and Wireless setup screens.
II
Page 56

Page 57

ZyAIR G-2000 Wireless 4-port Router User’s Guide
This chapter provides information on the System screens.
4.1 System Overview
This section provides information on general system setup.
4.2 Configuring General Setup
Click SYSTEM to open the General screen.
Chapter 4
System Screens
Figure 4-1 System General Setup
The following table describes the labels in this screen.
System Screens 4-1
Page 58

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 4-1 System General Setup
LABEL DESCRIPTION
System Name Type a descriptive name for identification purposes. Some ISPs check this name, so it
is recommended you enter your computer's "Computer name"
This name can be up to 30 alphanumeric characters long. Spaces are not allowed, but
dashes "-" and underscores "_" are accepted.
Domain Name Type the domain name (if you know it) here. If you leave this field blank, the ISP may
assign a domain name via DHCP. The domain name entered by you is given priority
over the ISP assigned domain name.
Administrator
Inactivity Timer
System DNS Servers
First DNS Server
Second DNS
Server
Third DNS
Server
Apply
Reset
Type how many minutes a management session (either via the web configurator or
SMT) can be left idle before the session times out.
The default is 5 minutes. After it times out you have to log in with your password again.
Very long idle timeouts may have security risks.
A value of "0" means a management session never times out, no matter how long it
has been left idle (not recommended).
Select From ISP if your ISP dynamically assigns DNS server information (and the
ZyAIR's WAN IP address). The field to the right displays the (read-only) DNS server IP
address that the ISP assigns.
Select User-Defined if you have the IP address of a DNS server. Enter the DNS
server's IP address in the field to the right. If you chose User-Defined, but leave the IP
address set to 0.0.0.0, User-Defined changes to None after you click Apply. If you set
a second choice to User-Defined, and enter the same IP address, the second User-
Defined changes to None after you click Apply.
Select None if you do not want to configure DNS servers. If you do not configure a
DNS server, you must know the IP address of a machine in order to access it.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
4.3 Dynamic DNS
Dynamic DNS allows you to update your current dynamic IP address with one or many dynamic DNS
services so that anyone can contact you (in NetMeeting, CU-SeeMe, etc.). You can also access your FTP
server or web site on your own computer using a domain name (for instance myhost.dhs.org, where myhost
is a name of your choice) that will never change instead of using an IP address that changes each time you
reconnect. Your friends or relatives will always be able to call you even if they don't know your IP address.
4-2 System Screens
Page 59

ZyAIR G-2000 Wireless 4-port Router User’s Guide
First of all, you need to have registered a dynamic DNS account with www.dyndns.org. This is for people
with a dynamic IP from their ISP or DHCP server that would still like to have a domain name. The dynamic
DNS service provider will give you a password or key.
4.3.1 DYNDNS Wildcard
Enabling the wildcard feature for your host causes *.yourhost.dyndns.org to be aliased to the same IP address
as yourhost.dyndns.org. This feature is useful if you want to be able to use, for example,
www.yourhost.dyndns.org and still reach your hostname.
If you have a private WAN IP address, then you cannot use Dynamic DNS.
4.4 Configuring Dynamic DNS
To change your ZyAIR’s DDNS, click SYSTEM and then the DDNS tab. The screen appears as shown.
Figure 4-2 DDNS
System Screens 4-3
Page 60

ZyAIR G-2000 Wireless 4-port Router User’s Guide
The following table describes the labels in this screen.
Table 4-2 DDNS
LABEL DESCRIPTION
Enable DDNS Select this check box to activate DDNS.
Service Provider Select the name of your DDNS service provider.
DDNS Type Select the type of service that you are registered for from your DDNS service
provider. Options are Dynamic DNS, Static DNS or Custom DNS.
Host Names 1~3 Enter your host names in the three fields provided. You can specify up to two
host names in each field separated by a comma (",").
User Name Type your user name.
Password Type the password assigned to you.
Enable Wildcard
Option
Enable off line option
IP Address Update Policy:
Use WAN IP address Select this option to update the IP address of the host name(s) to the WAN IP
DDNS server auto
detect IP Address
Use specified IP
Address
IP Address
Apply
Reset
Your ZyAIR supports DYNDNS wildcard. Select the check box to enable.
This option is available when CustomDNS is selected in the DDNS Type field.
Check with your dynamic DNS service provider to have traffic redirected to a URL
(that you can specify) while you are off line.
address.
Select this option to update the IP address of the host name(s) automatically by
the DDNS server. It is recommended that you select this option.
Select this option to update the IP address of the host name(s) to the IP address
specified below. Use this option if you have a static IP address.
Enter the IP address if you select the Use specified IP Address option.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
4.5 Configuring Password
To change your ZyAIR’s password (recommended), click SYSTEM and then the Password tab. The screen
appears as shown. This screen allows you to change the ZyAIR’s password.
If you forget your password (or the ZyAIR IP address), you will need to reset the ZyAIR. See the Resetting
the ZyAIR section for details.
4-4 System Screens
Page 61

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 4-3 Password
The following table describes the labels in this screen.
Table 4-3 Password
LABEL DESCRIPTION
Old Password Type in your existing system password (1234 is the default password).
New Password Type your new system password (up to 31 characters). Note that as you type a
password, the screen displays an asterisk (*) for each character you type.
Retype to Confirm Retype your new system password for confirmation.
Apply
Reset
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
4.6 Configuring Time Setting
To change your ZyAIR’s time and date, click SYSTEM and then the Time Setting tab. The screen appears
as shown. Use this screen to configure the ZyAIR’s time based on your local time zone.
System Screens 4-5
Page 62

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 4-4 Time Setting
The following table describes the labels in this screen.
Table 4-4 Time Setting
LABEL DESCRIPTION
Time Protocol Select the time service protocol that your time server sends when you turn on the
ZyAIR. Not all time servers support all protocols, so you may have to check with
your ISP/network administrator or use trial and error to find a protocol that works.
The main difference between them is the format.
Daytime (RFC 867) format is day/month/year/time zone of the server.
Time (RFC 868) format displays a 4-byte integer giving the total number of seconds
since 1970/1/1 at 0:0:0.
The default, NTP (RFC 1305), is similar to Time (RFC 868).
Select None to enter the time and date manually.
4-6 System Screens
Page 63

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 4-4 Time Setting
LABEL DESCRIPTION
Time Server
Address
Current Time
(hh:mm:ss)
New Time
(hh:mm:ss)
Current Date
(yyyy/mm/dd)
New Date
(yyyy/mm/dd)
Time Zone Choose the time zone of your location. This will set the time difference between your
Daylight Savings Select this option if you use daylight savings time. Daylight saving is a period from
Start Date (mm-dd) Enter the month and day that your daylight-savings time starts on if you selected
End Date (mm-dd) Enter the month and day that your daylight-savings time ends on if you selected
Apply
Reset
Enter the IP address or the URL of your time server. Check with your ISP/network
administrator if you are unsure of this information (the default is tick.stdtime.gov.tw).
This field displays the time of your ZyAIR.
Each time you reload this page, the ZyAIR synchronizes the time with the time
server.
This field displays the last updated time from the time server.
When you select None in the Time Protocol field, enter the new time in this field
and then click Apply.
This field displays the date of your ZyAIR.
Each time you reload this page, the ZyAIR synchronizes the time with the time
server.
This field displays the last updated date from the time server.
When you select None in the Time Protocol field, enter the new date in this field
and then click Apply.
time zone and Greenwich Mean Time (GMT).
late spring to early fall when many countries set their clocks ahead of normal local
time by one hour to give more daytime light in the evening.
Daylight Savings.
Daylight Savings.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
System Screens 4-7
Page 64

Page 65

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Chapter 5
LAN Screens
This chapter describes how to configure LAN settings.
5.1 LAN Overview
Local Area Network (LAN) is a shared communication system to which many computers are attached. The
LAN screens can help you configure a LAN DHCP server, manage IP addresses, and partition your physical
network into logical networks.
Please see the Wizard Setup chapter for the background information about Primary and Secondary DNS
Server and IP Address and Subnet Mask.
5.2 LANs and WANs
A LAN is a computer network limited to the immediate area, usually the same building or floor of a building.
A WAN (Wide Area Network), on the other hand, is an outside connection to another network or the
Internet.
5.2.1 LANs, WANs and the ZyAIR
The actual physical connection determines whether the ZyAIR ports are LAN or WAN ports. There are two
separate IP networks, one inside, the LAN network; the other outside: the WAN network as shown next:
Figure 5-1 LAN & WAN IPs
LAN Screens 5-1
Page 66

ZyAIR G-2000 Wireless 4-port Router User’s Guide
5.3 DHCP Setup
DHCP (Dynamic Host Configuration Protocol, RFC 2131 and RFC 2132) allows individual clients to obtain
TCP/IP configuration at start-up from a server. You can configure the ZyAIR as a DHCP server or disable it.
When configured as a server, the ZyAIR provides the TCP/IP configuration for the clients. If set to None,
DHCP service will be disabled and you must have another DHCP server on your LAN, or else the computer
must be manually configured.
5.3.1 DNS Servers
Use the LAN screen to configure the DNS server information that the ZyAIR sends to the DHCP client
devices on the LAN.
There are three places where you can configure DNS setup on the ZyAIR.
1. Use the SYSTEM General screen to configure the ZyAIR to use a DNS server to resolve domain
names for ZyAIR system features like DDNS and the time server.
2. Use the LAN screen to configure the DNS server information that the ZyAIR sends to the DHCP
client devices on the LAN.
3. Use the REMOTE MGNT DNS screen to configure the ZyAIR to accept or discard DNS queries.
5.4 Factory LAN Defaults
The LAN parameters of the ZyAIR are preset in the factory with the following values:
• IP address of 192.168.1.1 with subnet mask of 255.255.255.0 (24 bits)
• DHCP server enabled with 32 client IP addresses starting from 192.168.1.33.
IP Pool Setup
The ZyAIR is pre-configured with a pool of 32 IP addresses starting from 192.168.1.33 to 192.168.1.64. This
configuration leaves 31 IP addresses (excluding the ZyAIR itself) in the lower range for other server
computers, for instance, servers for mail, FTP, TFTP, web, etc., that you may have.
These parameters should work for the majority of installations. If your ISP gives you explicit DNS server
address(es), read the embedded web configurator help regarding what fields need to be configured.
5.5 RIP Setup
RIP (Routing Information Protocol, RFC 1058 and RFC 1389) allows a router to exchange routing
information with other routers. RIP Direction controls the sending and receiving of RIP packets. When set
to:
1. Both - the ZyAIR will broadcast its routing table periodically and incorporate the RIP information that
it receives.
2. In Only - the ZyAIR will not send any RIP packets but will accept all RIP packets received.
3. Out Only - the ZyAIR will send out RIP packets but will not accept any RIP packets received.
5-2 LAN Screens
Page 67

ZyAIR G-2000 Wireless 4-port Router User’s Guide
4. None - the ZyAIR will not send any RIP packets and will ignore any RIP packets received.
RIP Version controls the format and the broadcasting method of the RIP packets that the ZyAIR sends (it
recognizes both formats when receiving). RIP-1 is universally supported; but RIP-2 carries more
information. RIP-1 is probably adequate for most networks, unless you have an unusual network topology.
Both RIP-2B and RIP-2M send routing data in RIP-2 format; the difference being that RIP-2B uses subnet
broadcasting while RIP-2M uses multicasting. Multicasting can reduce the load on non-router machines
since they generally do not listen to the RIP multicast address and so will not receive the RIP packets.
However, if one router uses multicasting, then all routers on your network must use multicasting, also.
By default, RIP Direction is set to Both and RIP Version to RIP-1.
5.6 Multicast
Traditionally, IP packets are transmitted in one of either two ways - Unicast (1 sender - 1 recipient) or
Broadcast (1 sender - everybody on the network). Multicast delivers IP packets to a group of hosts on the
network - not everybody and not just 1.
IGMP (Internet Group Multicast Protocol) is a network-layer protocol used to establish membership in a
Multicast group - it is not used to carry user data. IGMP version 2 (RFC 2236) is an improvement over
version 1 (RFC 1112) but IGMP version 1 is still in wide use. If you would like to read more detailed
information about interoperability between IGMP version 2 and version 1, please see sections 4 and 5 of
RFC 2236. The class D IP address is used to identify host groups and can be in the range 224.0.0.0 to
239.255.255.255. The address 224.0.0.0 is not assigned to any group and is used by IP multicast computers.
The address 224.0.0.1 is used for query messages and is assigned to the permanent group of all IP hosts
(including gateways). All hosts must join the 224.0.0.1 group in order to participate in IGMP. The address
224.0.0.2 is assigned to the multicast routers group.
The ZyAIR supports both IGMP version 1 (IGMP-v1) and IGMP version 2 (IGMP-v2). At start up, the
ZyAIR queries all directly connected networks to gather group membership. After that, the ZyAIR
periodically updates this information. IP multicasting can be enabled/disabled on the ZyAIR LAN and/or
WAN interfaces in the web configurator (LAN; WAN). Select None to disable IP multicasting on these
interfaces.
5.7 Configuring the LAN IP Screens
Click LAN to open the IP screen.
LAN Screens 5-3
Page 68

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 5-2 IP
The following table describes the labels in this screen.
Table 5-1 IP
LABEL DESCRIPTION
DHCP Setup (refer to your User's Guide for background information)
DHCP Server Select this option to allow your ZyAIR to assign IP addresses, an IP default gateway
and DNS servers to Windows 95, Windows NT and other systems that support the
DHCP client.
When DHCP is used, the following items need to be set:
IP Pool Starting
Address
This field specifies the first of the contiguous addresses in the IP address pool.
5-4 LAN Screens
Page 69
ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 5-1 IP
LABEL DESCRIPTION
Pool Size This field specifies the size or count of the IP address pool.
DNS Servers Assigned by DHCP Server
First DNS Server
Second DNS
Server
Third DNS Server
LAN TCP/IP
IP Address Type the IP address of your ZyAIR in dotted decimal notation, for example,
IP Subnet Mask Type the subnet mask assigned to you by your ISP (if given).
RIP Direction
RIP Version
Multicast IGMP (Internet Group Multicast Protocol) is a session-layer protocol used to
Windows Networking (NetBIOS over TCP/IP)
NetBIOS (Network Basic Input/Output System) are TCP or UDP broadcast packets that enable a computer
to connect to and communicate with a LAN. For some dial-up services such as PPPoE or PPTP, NetBIOS
packets cause unwanted calls. However it may sometimes be necessary to allow NetBIOS packets to pass
through to the WAN in order to find a computer on the WAN.
Select From ISP if your ISP dynamically assigns DNS server information (and the
ZyAIR's WAN IP address). The field to the right displays the (read-only) DNS server
IP address that the ISP assigns.
Select User-Defined if you have the IP address of a DNS server. Enter the DNS
server's IP address in the field to the right. If you chose User-Defined, but leave the
IP address set to 0.0.0.0, User-Defined changes to None after you click Apply. If
you set a second choice to User-Defined, and enter the same IP address, the
second User-Defined changes to None after you click Apply.
Select DNS Relay to have the ZyAIR act as a DNS proxy. The ZyAIR's LAN IP
address displays in the field to the right (read-only). The ZyAIR tells the DHCP
clients on the LAN that the ZyAIR itself is the DNS server. When a computer on the
LAN sends a DNS query to the ZyAIR, the ZyAIR forwards the query to the ZyAIR's
system DNS server (configured in the SYSTEM General screen) and relays the
response back to the computer. You can only select DNS Relay for one of the three
servers; if you select DNS Relay for a second or third DNS server, that choice
changes to None after you click Apply.
Select None if you do not want to configure DNS servers. If you do not configure a
DNS server, you must know the IP address of a machine in order to access it.
192.168.1.1 (factory default).
Select the RIP direction from None, Both, In Only and Out Only.
Select the RIP version from RIP-1, RIP-2B and RIP-2M.
establish membership in a multicast group. The ZyAIR supports both IGMP version 1
(IGMP-v1) and IGMP-v2. Select None to disable it.
LAN Screens 5-5
Page 70

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 5-1 IP
LABEL DESCRIPTION
Allow between
LAN and WAN
Apply
Reset
Select this check box to forward NetBIOS packets from the LAN to the WAN and
from the WAN to the LAN. If your firewall is enabled with the default policy set to
block WAN to LAN traffic, you also need to enable the default WAN to LAN firewall
rule that forwards NetBIOS traffic.
Clear this check box to block all NetBIOS packets going from the LAN to the WAN
and from the WAN to the LAN.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
5-6 LAN Screens
Page 71

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Chapter 6
Wireless Configuration and Roaming
This chapter discusses how to configure the Wireless and Roaming screens on the ZyAIR.
6.1 Wireless LAN Overview
This section introduces the wireless LAN (WLAN) and some basic scenarios.
6.1.1 IBSS
An Independent Basic Service Set (IBSS), also called an Ad-hoc network, is the simplest WLAN
configuration. An IBSS is defined as two or more computers with wireless adapters within range of each
other that from an independent (wireless) network without the need of an access point (AP).
Figure 6-1 IBSS (Ad-hoc) Wireless LAN
6.1.2 BSS
A Basic Service Set (BSS) exists when all communications between wireless stations or between a wireless
station and a wired network client go through one access point (AP).
Intra-BSS traffic is traffic between wireless stations in the BSS. When Intra-BSS is enabled, wireless station
A and B can access the wired network and communicate with each other. When Intra-BSS is disabled,
wireless station A and B can still access the wired network but cannot communicate with each other.
Wireless Configuration and Roaming 6-1
Page 72

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 6-2 Basic Service set
6.1.3 ESS
An Extended Service Set (ESS) consists of a series of overlapping BSSs, each containing an access point,
with each access point connected together by a wired network. This wired connection between APs is called
a Distribution System (DS). An ESSID (ESS IDentification) uniquely identifies each ESS. All access points
and their associated wireless stations within the same ESS must have the same ESSID in order to
communicate.
6-2 Wireless Configuration and Roaming
Page 73

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 6-3 Extended Service Set
6.2 Wireless LAN Basics
Refer also to the Wizard Setup chapter for more background information on Wireless LAN features, such as
channels.
6.2.1 RTS/CTS
A hidden node occurs when two stations are within range of the same access point, but are not within range
of each other. The following figure illustrates a hidden node. Both stations (STA) are within range of the
access point (AP) or wireless gateway, but out-of-range of each other, so they cannot “hear” each other, that
is they do not know if the channel is currently being used. Therefore, they are considered hidden from each
other.
Wireless Configuration and Roaming 6-3
Page 74

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 6-4 RTS/CTS
When station A sends data to the ZyAIR, it might not know that station B is already using the channel. If
these two stations send data at the same time, collisions may occur when both sets of data arrive at the AP at
the same time, resulting in a loss of messages for both stations.
RTS/CTS is designed to prevent collisions due to hidden nodes. An RTS/CTS defines the biggest size data
frame you can send before an RTS (Request To Send)/CTS (Clear to Send) handshake is invoked.
When a data frame exceeds the RTS/CTS value you set (between 0 to 2432 bytes), the station that wants to
transmit this frame must first send an RTS (Request To Send) message to the AP for permission to send it.
The AP then responds with a CTS (Clear to Send) message to all other stations within its range to notify
them to defer their transmission. It also reserves and confirms with the requesting station the time frame for
the requested transmission.
Stations can send frames smaller than the specified RTS/CTS directly to the AP without the RTS (Request
To Send)/CTS (Clear to Send) handshake.
You should only configure RTS/CTS if the possibility of hidden nodes exists on your network and the “cost”
of resending large frames is more than the extra network overhead involved in the RTS (Request To
Send)/CTS (Clear to Send) handshake.
If the RTS/CTS value is greater than the Fragmentation Threshold value (see next), then the RTS (Request
To Send)/CTS (Clear to Send) handshake will never occur as data frames will be fragmented before they
reach RTS/CTS size.
Enabling the RTS Threshold causes redundant network overhead that could
negatively affect the throughput performance instead of providing a remedy.
6.2.2 Fragmentation Threshold
A Fragmentation Threshold is the maximum data fragment size (between 256 and 2432 bytes) that can be
sent in the wireless network before the ZyAIR will fragment the packet into smaller data frames.
6-4 Wireless Configuration and Roaming
Page 75
ZyAIR G-2000 Wireless 4-port Router User’s Guide
A large Fragmentation Threshold is recommended for networks not prone to interference while you should
set a smaller threshold for busy networks or networks that are prone to interference.
If the Fragmentation Threshold value is smaller than the RTS/CTS value (see previously) you set, then the
RTS (Request To Send)/CTS (Clear to Send) handshake will never occur as data frames will be fragmented
before they reach RTS/CTS size.
6.3 Configuring Wireless
If you are configuring the ZyAIR from a computer connected to the wireless LAN
and you change the ZyAIR’s ESSID or WEP settings, you will lose your wireless
connection when you press Apply to confirm. You must then change the wireless
settings of your computer to match the ZyAIR’s new settings.
Click the WIRELESS link under ADVANCED to open the Wireless screen.
Wireless Configuration and Roaming 6-5
Page 76

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 6-5 Wireless
The following table describes the general wireless LAN labels in this screen.
6-6 Wireless Configuration and Roaming
Page 77

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 6-1 Wireless
LABEL DESCRIPTION
Enable
Wireless LAN
ESSID (Extended Service Set IDentity) The ESSID identifies the Service Set with which a
Click the check box to activate wireless LAN.
wireless station is associated. Wireless stations associating to the access point (AP)
must have the same ESSID. Enter a descriptive name (up to 32 printable 7-bit ASCII
characters) for the wireless LAN.
If you are configuring the ZyAIR from a computer connected to
the wireless LAN and you change the ZyAIR’s ESSID or WEP
settings, you will lose your wireless connection when you press
Apply to confirm. You must then change the wireless settings of
your computer to match the ZyAIR’s new settings.
Hide ESSID Select this check box to hide the ESSID in the outgoing beacon frame so a station cannot
obtain the ESSID through passive scanning using a site survey tool.
Choose
Channel ID
RTS/CTS
Threshold
Fragmentation
Threshold
Apply
Reset
Set the operating frequency/channel depending on your particular region.
Select a channel from the drop-down list box.
Refer to the Wizard Setup chapter for more information on channels.
Enter a value between 0 and 2432. The default is 2432.
Enter a value between 256 and 2432. The default is 2432. It is the maximum data
fragment size that can be sent.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
See the Wireless Security chapter for information on the other labels in this screen.
6.4 Configuring Roaming
A wireless station is a device with an IEEE 802.11mode compliant wireless adapter. An access point (AP)
acts as a bridge between the wireless and wired networks. An AP creates its own wireless coverage area. A
wireless station can associate with a particular access point only if it is within the access point’s coverage
area.
In a network environment with multiple access points, wireless stations are able to switch from one access
point to another as they move between the coverage areas. This is roaming. As the wireless station moves
Wireless Configuration and Roaming 6-7
Page 78

ZyAIR G-2000 Wireless 4-port Router User’s Guide
from place to place, it is responsible for choosing the most appropriate access point depending on the signal
strength, network utilization or other factors.
The roaming feature on the access points allows the access points to relay information about the wireless
stations to each other. When a wireless station moves from a coverage area to another, it scans and uses the
channel of a new access point, which then informs the access points on the LAN about the change. The new
information is then propagated to the other access points on the LAN. An example is shown in Figure 6-6.
Enable roaming to exchange the latest bridge information of all wireless stations between APs when a
wireless station moves between coverage areas. Wireless stations can still associate with other APs even if
you disable roaming. Enabling roaming ensures correct traffic forwarding (bridge tables are updated) and
maximum AP efficiency. The AP deletes records of wireless stations that associate with other APs (NonZyXEL APs may not be able to perform this). 802.1x authentication information is not exchanged (at the
time of writing).
Figure 6-6 Roaming Example
The steps below describe the roaming process.
Step 1. As wireless station Y moves from the coverage area of access point AP 1 to that of access point
AP 2, it scans and uses the signal of access point AP 2.
Step 2. Access point AP 2 acknowledges the presence of wireless station Y and relays this information
to access point AP 1 through the wired LAN.
Step 3. Access point AP 1 updates the new position of wireless station.
6-8 Wireless Configuration and Roaming
Page 79

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Step 4. Wireless station Y sends a request to access point AP 2 for re-authentication.
6.4.1 Requirements for Roaming
The following requirements must be met in order for wireless stations to roam between the coverage areas.
1. All the access points must be on the same subnet and configured with the same ESSID.
2. If IEEE 802.1x user authentication is enabled and to be done locally on the access point, the new
access point must have the user profile for the wireless station.
3. The adjacent access points should use different radio channels when their coverage areas overlap.
4. All access points must use the same port number to relay roaming information.
5. The access points must be connected to the Ethernet and be able to get IP addresses from a DHCP
server if using dynamic IP address assignment.
To enable roaming on your ZyAIR, click the WIRELESS link under ADVANCED and then the Roaming
tab. The screen appears as shown.
Figure 6-7 Roaming
The following table describes the labels in this screen.
Wireless Configuration and Roaming 6-9
Page 80

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 6-2 Roaming
LABEL DESCRIPTION
Active
Select Yes from the drop-down list box to enable roaming on the ZyAIR if you have two
or more ZyAIRs on the same subnet.
All APs on the same subnet and the wireless stations must have
the same ESSID to allow roaming.
Port Enter the port number to communicate roaming information between APs. The port
number must be the same on all APs. The default is 16290. Make sure this port is not
used by other services.
Apply
Reset
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
6-10 Wireless Configuration and Roaming
Page 81

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Chapter 7
Wireless Security
This Chapter describes how to use the MAC Filter, 802.1x, Local User Database and RADIUS to
configure wireless security on your ZyAIR.
7.1 Wireless Security Overview
Wireless security is vital to your network to protect wireless communication between wireless stations,
access points and the wired network.
The figure below shows the possible wireless security levels on your ZyAIR. EAP (Extensible
Authentication Protocol) is used for authentication and utilizes dynamic WEP key exchange. It requires
interaction with a RADIUS (Remote Authentication Dial-In User Service) server either on the WAN or your
LAN to provide authentication service for wireless stations.
Figure 7-1 ZyAIR Wireless Security Levels
If you do not enable any wireless security on your ZyAIR, your network is accessible to any wireless
networking device that is within range.
7.2 WEP Overview
WEP (Wired Equivalent Privacy) as specified in the IEEE 802.11 standard provides methods for both data
encryption and wireless station authentication.
Wireless Security 7-1
Page 82

ZyAIR G-2000 Wireless 4-port Router User’s Guide
7.2.1 Data Encryption
WEP provides a mechanism for encrypting data using encryption keys. Both the AP and the wireless stations
must use the same WEP key to encrypt and decrypt data. Your ZyAIR allows you to configure up to four 64bit or 128-bit WEP keys, but only one key can be enabled at any one time.
7.2.2 Authentication
Three different methods can be used to authenticate wireless stations to the network: Open System, Shared
Key, and Auto. The following figure illustrates the steps involved.
Figure 7-2 WEP Authentication Steps
Open system authentication involves an unencrypted two-message procedure. A wireless station sends an
open system authentication request to the AP, which will then automatically accept and connect the wireless
station to the network. In effect, open system is not authentication at all as any station can gain access to the
network.
7-2 Wireless Security
Page 83

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Shared key authentication involves a four-message procedure. A wireless station sends a shared key
authentication request to the AP, which will then reply with a challenge text message. The wireless station
must then use the AP’s default WEP key to encrypt the challenge text and return it to the AP, which attempts
to decrypt the message using the AP’s default WEP key. If the decrypted message matches the challenge text,
the wireless station is authenticated.
When your ZyAIR's authentication method is set to open system, it will only accept open system
authentication requests. The same is true for shared key authentication. However, when it is set to auto
authentication, the ZyAIR will accept either type of authentication request and the ZyAIR will fall back to
use open authentication if the shared key does not match.
7.2.3 Preamble Type
A preamble is used to synchronize the transmission timing in your wireless network. There are two preamble
modes: Long and Short.
Short preamble takes less time to process and minimizes overhead, so it should be used in a good wireless
network environment when all wireless clients support it.
Select Long if you have a ‘noisy’ network or are unsure of what preamble mode your wireless clients support
as all IEEE 802.11b compliant wireless adapters must support long preamble. However, not all wireless
adapters support short preamble. Use long preamble if you are unsure what preamble mode the wireless
adapters support, to ensure interpretability between the ZyAIR and the wireless stations and to provide more
reliable communication in ‘noisy’ networks.
Select Auto to have the ZyAIR automatically use short preamble when all wireless clients support it,
otherwise the ZyAIR uses long preamble.
The ZyAIR and the wireless stations MUST use the same preamble mode in order
to communicate.
7.3 Configuring WEP Encryption
In order to configure and enable WEP encryption; click the WIRELESS link under ADVANCED to display
the Wireless screen.
Wireless Security 7-3
Page 84

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-3 Wireless
The following table describes the wireless LAN security labels in this screen.
7-4 Wireless Security
Page 85

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-1 Wireless : WEP Fields
LABEL DESCRIPTION
WEP
Encryption
Authentication
Method
ASCII Select this option in order to enter ASCII characters as the WEP keys.
Hex Select this option in order to enter hexadecimal characters as the WEP keys.
Key 1 to Key
4
Enable
Breathing
LED
Preamble
802.11 Mode
Apply
Reset
Select Disable to allow wireless stations to communicate with the access points without
any data encryption.
Select 64-bit WEP or 128-bit WEP to enable data encryption.
This field is activated when you select 64-bit WEP or 128-bit WEP in the WEP
Encryption field.
Select Auto, Open System or Shared Key from the drop-down list box.
The preceding "0x", that identifies a hexadecimal key, is entered automatically.
The WEP keys are used to encrypt data. Both the ZyAIR and the wireless stations must
use the same WEP key for data transmission.
If you chose 64-bit WEP, then enter any 5 ASCII characters or 10 hexadecimal
characters ("0-9", "A-F").
If you chose 128-bit WEP, then enter 13 ASCII characters or 26 hexadecimal characters
("0-9", "A-F").
You must configure all four keys, but only one key can be activated at any one time. The
default key is key 1.
Select this check box to enable the Breathing LED, also known as the ZyAIR LED.
The blue ZyAIR LED is on when the ZyAIR is on and blinks (or breaths) when data is
being transmitted to/from its wireless stations. Clear the check box to turn this LED off
even when the ZyAIR is on and data is being transmitted/received.
Select a preamble type from the drop-down list menu. Choices are Long, Short and
Auto. The default setting is Auto.
See the section on preamble for more information.
Select 802.11b Only to allow only IEEE 802.11b compliant WLAN devices to associate
with the ZyAIR.
Select 802.11g Only to allow only IEEE 802.11g compliant WLAN devices to associate
with the ZyAIR.
Select Mixed to allow either IEEE802.11b or IEEE802.11g compliant WLAN devices to
associate with the ZyAIR. The transmission rate of your ZyAIR might be reduced.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
Wireless Security 7-5
Page 86

ZyAIR G-2000 Wireless 4-port Router User’s Guide
7.4 MAC Filter
The MAC filter screen allows you to configure the ZyAIR to give exclusive access to up to 32 devices
(Allow Association) or exclude up to 32 devices from accessing the ZyAIR (Deny Association). Every
Ethernet device has a unique MAC (Media Access Control) address. The MAC address is assigned at the
factory and consists of six pairs of hexadecimal characters, for example, 00:A0:C5:00:00:02. You need to
know the MAC address of the devices to configure this screen.
To change your ZyAIR’s MAC filter settings, click the WIRELESS link under ADVANCED and then the MAC Filter tab. The screen appears as shown.
7-6 Wireless Security
Page 87

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-4 MAC Address Filter
The following table describes the labels in this menu.
Wireless Security 7-7
Page 88

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-2 MAC Address Filter
LABEL DESCRIPTION
Active
Filter Action
Set This is the index number of the MAC address.
MAC
Address
Apply
Reset
Select Yes from the drop down list box to enable MAC address filtering.
Define the filter action for the list of MAC addresses in the MAC Address table.
Select Deny Association to block access to the ZyAIR, MAC addresses not listed will be
allowed to access the ZyAIR
Select Allow Association to permit access to the ZyAIR, MAC addresses not listed will be
denied access to the ZyAIR.
Enter the MAC addresses (in XX:XX:XX:XX:XX:XX format) of the wireless station that are
allowed or denied access to the ZyAIR in these address fields.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
7.5 802.1x Overview
The IEEE 802.1x standard outlines enhanced security methods for both the authentication of wireless stations
and encryption key management. Authentication can be done using the local user database internal to the
ZyAIR (authenticate up to 32 users) or an external RADIUS server for an unlimited number of users.
See also the section on RADIUS in this User’s Guide.
7.6 Dynamic WEP Key Exchange
The AP maps a unique key that is generated with the RADIUS server. This key expires when the wireless
connection times out, disconnects or reauthentication times out. A new WEP key is generated each time
reauthentication is performed.
If this feature is enabled, it is not necessary to configure a default encryption key in the Wireless screen. You
may still configure and store keys here, but they will not be used while Dynamic WEP is enabled.
To use Dynamic WEP, enable and configure the RADIUS server (see section 7.15) and enable Dynamic
WEP Key Exchange in the 802.1x screen. Ensure that the wireless station’s EAP type is configured to one of
the following:
• EAP-TLS
• EAP-TTLS
• PEAP
7-8 Wireless Security
Page 89

ZyAIR G-2000 Wireless 4-port Router User’s Guide
EAP-MD5 cannot be used with Dynamic WEP Key Exchange.
7.7 Introduction to WPA
Wi-Fi Protected Access (WPA) is a subset of the IEEE 802.11i security specification draft. Key differences
between WPA and WEP are user authentication and improved data encryption.
7.7.1 User Authentication
WPA applies IEEE 802.1x and Extensible Authentication Protocol (EAP) to authenticate wireless clients
using an external RADIUS database. You can’t use the ZyAIR’s Local User Database for WPA
authentication purposes since the Local User Database uses EAP-MD5 which cannot be used to generate
keys. See later in this chapter and the appendices for more information on IEEE 802.1x, RADIUS and EAP.
Therefore, if you don’t have an external RADIUS server you should use WPA-PSK (WPA -Pre-Shared Key)
that only requires a single (identical) password entered into each access point, wireless gateway and wireless
client. As long as the passwords match, a client will be granted access to a WLAN.
7.7.2 Encryption
WPA improves data encryption by using Temporal Key Integrity Protocol (TKIP), Message Integrity Check
(MIC) and IEEE 802.1x.
Temporal Key Integrity Protocol (TKIP) uses 128-bit keys that are dynamically generated and distributed by
the authentication server. It includes a per-packet key mixing function, a Message Integrity Check (MIC)
named Michael, an extended initialization vector (IV) with sequencing rules, and a re-keying mechanism.
TKIP regularly changes and rotates the encryption keys so that the same encryption key is never used twice.
The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then sets up a key hierarchy
and management system, using the pair-wise key to dynamically generate unique data encryption keys to
encrypt every data packet that is wirelessly communicated between the AP and the wireless clients. This all
happens in the background automatically.
The Message Integrity Check (MIC) is designed to prevent an attacker from capturing data packets, altering
them and resending them. The MIC provides a strong mathematical function in which the receiver and the
transmitter each compute and then compare the MIC. If they do not match, it is assumed that the data has
been tampered with and the packet is dropped.
By generating unique data encryption keys for every data packet and by creating an integrity checking
mechanism (MIC), TKIP makes it much more difficult to decode data on a Wi-Fi network than WEP, making
it difficult for an intruder to break into the network.
The encryption mechanisms used for WPA and WPA-PSK are the same. The only difference between the
two is that WPA-PSK uses a simple common password, instead of user-specific credentials. The commonpassword approach makes WPA-PSK susceptible to brute-force password-guessing attacks but it’s still an
improvement over WEP as it employs an easier-to-use, consistent, single, alphanumeric password.
Wireless Security 7-9
Page 90

ZyAIR G-2000 Wireless 4-port Router User’s Guide
7.8 WPA-PSK Application Example
A WPA-PSK application looks as follows.
Step 1. First enter identical passwords into the AP and all wireless clients. The Pre-Shared Key (PSK)
must consist of between 8 and 63 ASCII characters (including spaces and symbols).
Step 2. The AP checks each client’s password and (only) allows it to join the network if it matches its
password.
Step 3. The AP derives and distributes keys to the wireless clients.
Step 4. The AP and wireless clients use the TKIP encryption process to encrypt data exchanged between
them.
Figure 7-5
WPA - PSK Authentication
7.9 WPA with RADIUS Application Example
You need the IP address of the RADIUS server, its port number (default is 1812), and the RADIUS shared
secret. A WPA application example with an external RADIUS server looks as follows. “A” is the RADIUS
server. “DS” is the distribution system.
Step 1. The AP passes the wireless client’s authentication request to the RADIUS server.
Step 2. The RADIUS server then checks the user's identification against its database and grants or denies
network access accordingly.
Step 3. The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then sets up a
key hierarchy and management system, using the pair-wise key to dynamically generate unique
7-10 Wireless Security
Page 91
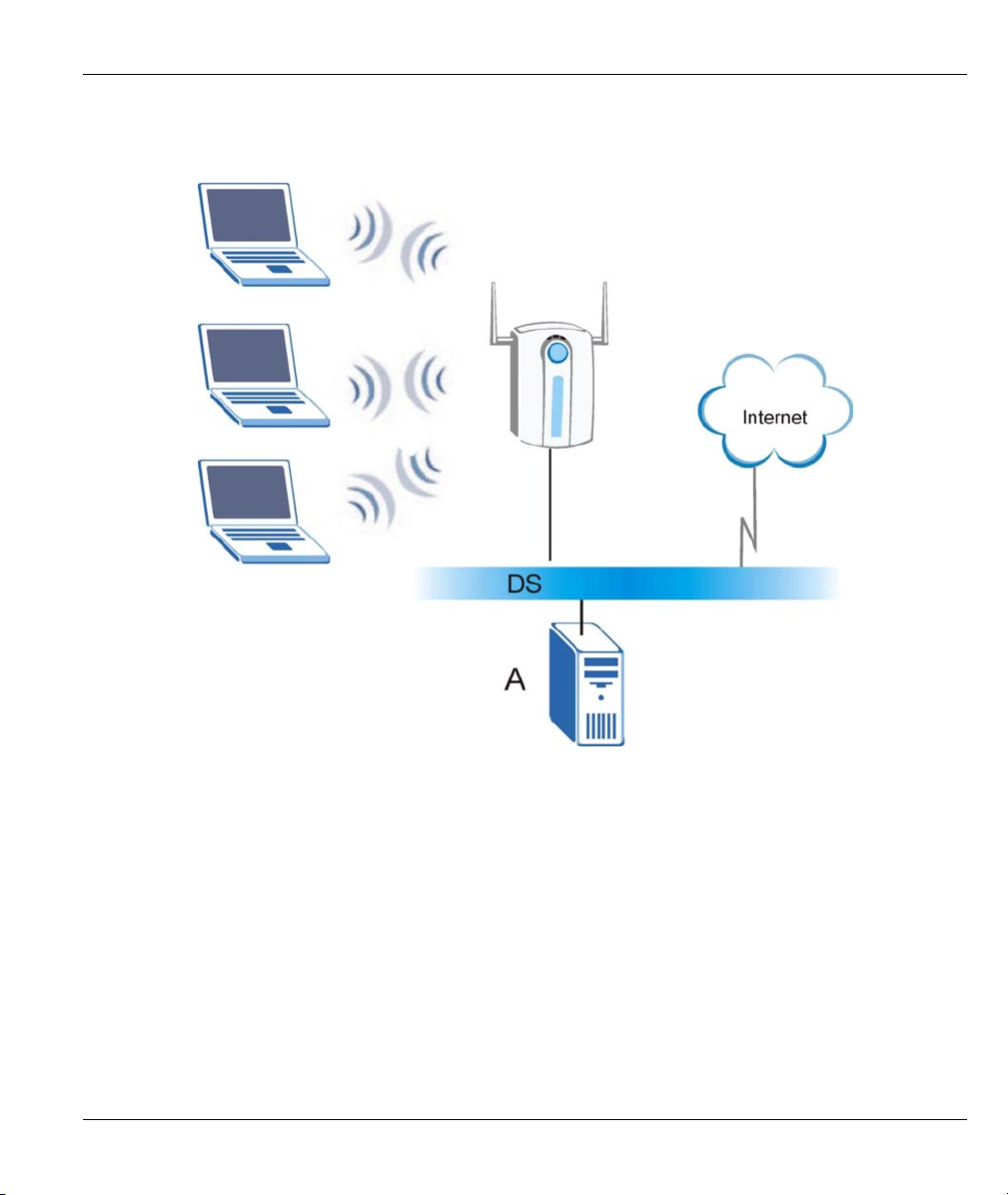
ZyAIR G-2000 Wireless 4-port Router User’s Guide
data encryption keys to encrypt every data packet that is wirelessly communicated between the
AP and the wireless clients.
Figure 7-6 WPA with RADIUS Application Example
7.10 Security Parameters Summary
Refer to this table to see what other security parameters you should configure for each Authentication
Method/ key management protocol type. You enter manual keys by first selecting 64-bit WEP or 128-bit
WEP from the WEP Encryption field and then typing the keys (in ASCII or hexadecimal format) in the key
text boxes. MAC address filters are not dependent on how you configure these security features.
Wireless Security 7-11
Page 92

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-3 Wireless Security Relational Matrix
AUTHENTICATION
METHOD/ KEY
MANAGEMENT PROTOCOL
Open None No Disable
Open WEP
Shared WEP
WPA WEP No Enable
WPA TKIP No Enable
WPA-PSK WEP Yes Enable
WPA-PSK TKIP Yes Enable
ENCRYPTION
METHOD
ENTER
MANUAL KEY
No Enable with Dynamic WEP Key
Yes Enable without Dynamic WEP Key
Yes Disable
No Enable with Dynamic WEP Key
Yes Enable without Dynamic WEP Key
Yes Disable
IEEE 802.1X
7.11 Wireless Client WPA Supplicants
A wireless client supplicant is the software that runs on an operating system instructing the wireless client
how to use WPA. At the time of writing, the most widely available supplicants are the WPA patch for
Windows XP, Funk Software's Odyssey client, and Meetinghouse Data Communications' AEGIS client.
The Windows XP patch is a free download that adds WPA capability to Windows XP's built-in "Zero
Configuration" wireless client. However, you must run Windows XP to use it.
7.12 Configuring 802.1x and WPA
To change your ZyAIR’s authentication settings, click the WIRELESS link under ADVANCED and then
the 802.1x/WPA tab.
You see the next screen when you select No Access Allowed or No Authentication Required in the
Wireless Port Control field.
7-12 Wireless Security
The screen varies by the key management protocol you select.
Page 93

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-7 Wireless LAN: 802.1x/WPA
The following table describes the labels in this screen.
Table 7-4 Wireless LAN: 802.1x/WPA
LABEL DESCRIPTION
Wireless Port
Control
To control wireless stations access to the wired network, select a control method from
the drop-down list box. Choose from No Access Allowed, No Authentication
Required and Authentication Required.
No Access Allowed blocks all wireless stations access to the wired network.
No Authentication Required allows all wireless stations access to the wired network
without entering usernames and passwords. This is the default setting.
Authentication Required means that all wireless stations have to enter usernames
and passwords before access to the wired network is allowed.
Select Authentication Required to configure Key Management Protocol and other
related fields.
7.12.1 Authentication Required: 802.1x
Select Authentication Required in the Wireless Port Control field and 802.1x in the Key Management
Protocol field to display the next screen.
Wireless Security 7-13
Page 94

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-8 Wireless LAN: 802.1x/WPA for 802.1x Protocol
The following table describes the labels in this screen.
Table 7-5 Wireless LAN: 802.1x/WPA for 802.1x Protocol
LABEL DESCRIPTION
Wireless Port
Control
To control wireless stations access to the wired network, select a control method from
the drop-down list box. Choose from No Authentication Required, Authentication
Required and No Access Allowed.
No Authentication Required allows all wireless stations access to the wired network
without entering usernames and passwords. This is the default setting.
Authentication Required means that all wireless stations have to enter usernames
and passwords before access to the wired network is allowed.
No Access Allowed blocks all wireless stations access to the wired network.
The following fields are only available when you select Authentication Required.
7-14 Wireless Security
Page 95

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-5 Wireless LAN: 802.1x/WPA for 802.1x Protocol
LABEL DESCRIPTION
ReAuthentication
Timer
(in seconds)
Specify how often wireless stations have to reenter usernames and passwords in
order to stay connected. This field is activated only when you select Authentication
Required in the Wireless Port Control field.
Enter a time interval between 10 and 9999 seconds. The default time interval is 1800
seconds (30 minutes).
If wireless station authentication is done using a RADIUS
server, the reauthentication timer on the RADIUS server has
priority.
Idle Timeout The ZyAIR automatically disconnects a wireless station from the wired network after
a period of inactivity. The wireless station needs to enter the username and password
again before access to the wired network is allowed.
This field is activated only when you select Authentication Required in the Wireless
Port Control field. The default time interval is 3600 seconds (or 1 hour).
Key Management
Protocol
Dynamic WEP
Key Exchange
Choose 802.1x from the drop-down list.
This field is activated only when you select Authentication Required in the Wireless
Port Control field. Also set the Authentication Databases field to RADIUS Only.
Local user database may not be used.
Select Disable to allow wireless stations to communicate with the access points
without using dynamic WEP key exchange.
Select 64-bit WEP or 128-bit WEP to enable data encryption.
Up to 32 stations can access the ZyAIR when you configure dynamic WEP key
exchange.
This field is not available when you set Key Management Protocol to WPA or WPA-
PSK.
Wireless Security 7-15
Page 96

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-5 Wireless LAN: 802.1x/WPA for 802.1x Protocol
LABEL DESCRIPTION
Authentication
Databases
Apply
Reset
The authentication database contains wireless station login information. The local
user database is the built-in database on the ZyAIR. The RADIUS is an external
server. Use this drop-down list box to select which database the ZyAIR should use
(first) to authenticate a wireless station.
Before you specify the priority, make sure you have set up the corresponding
database correctly first.
Select Local User Database Only to have the ZyAIR just check the built-in user
database on the ZyAIR for a wireless station's username and password.
Select RADIUS Only to have the ZyAIR just check the user database on the
specified RADIUS server for a wireless station's username and password.
Select Local first, then RADIUS to have the ZyAIR first check the user database on
the ZyAIR for a wireless station's username and password. If the user name is not
found, the ZyAIR then checks the user database on the specified RADIUS server.
Select RADIUS first, then Local to have the ZyAIR first check the user database on
the specified RADIUS server for a wireless station's username and password. If the
ZyAIR cannot reach the RADIUS server, the ZyAIR then checks the local user
database on the ZyAIR. When the user name is not found or password does not
match in the RADIUS server, the ZyAIR will not check the local user database and
the authentication fails.
Click Apply to save your changes back to the ZyAIR.
Click Reset to reload the previous configuration for this screen.
Once you enable user authentication, you need to specify an external RADIUS
server or create local user accounts on the ZyAIR for authentication.
7.12.2 Authentication Required: WPA
Select Authentication Required in the Wireless Port Control field and WPA in the Key Management
Protocol field to display the next screen.
7-16 Wireless Security
Page 97

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-9 Wireless LAN: 802.1x/WPA for WPA Protocol
The following table describes the labels not previously discussed
Table 7-6 Wireless LAN: 802.1x/WPA for WPA Protocol
LABEL DESCRIPTION
Key Management
Protocol
WPA Mixed Mode
Choose WPA in this field.
The ZyAIR can operate in WPA Mixed Mode, which supports both clients running
WPA and clients running WEP security in the same Wi-Fi network.
Select Enable to activate WPA mixed mode. Otherwise, select Disable and configure
the Group Data Privacy field.
Wireless Security 7-17
Page 98

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-6 Wireless LAN: 802.1x/WPA for WPA Protocol
LABEL DESCRIPTION
Group Data
Privacy
WPA Group Key
Update Timer
Authentication
Databases
Group Data Privacy allows you to choose TKIP (recommended) or WEP for
broadcast and multicast (“group”) traffic if the Key Management Protocol is WPA
and WPA Mixed Mode is disabled. WEP is used automatically if you have enabled
WPA Mixed Mode.
All unicast traffic is automatically encrypted by TKIP when WPA or WPA-PSK Key
Management Protocol is selected.
The WPA Group Key Update Timer is the rate at which the AP (if using WPA-PSK
key management) or RADIUS server (if using WPA key management) sends a new
group key out to all clients. The re-keying process is the WPA equivalent of
automatically changing the WEP key for an AP and all stations in a WLAN on a
periodic basis. Setting of the WPA Group Key Update Timer is also supported in
WPA-PSK mode. The ZyAIR default is 1800 seconds (30 minutes).
When you configure Key Management Protocol to WPA, the Authentication
Databases must be RADIUS Only. You can only use the Local User Database
Only with 802.1x Key Management Protocol.
7.12.3 Authentication Required: WPA-PSK
Select Authentication Required in the Wireless Port Control field and WPA-PSK in the Key
Management Protocol field to display the next screen.
7-18 Wireless Security
Page 99
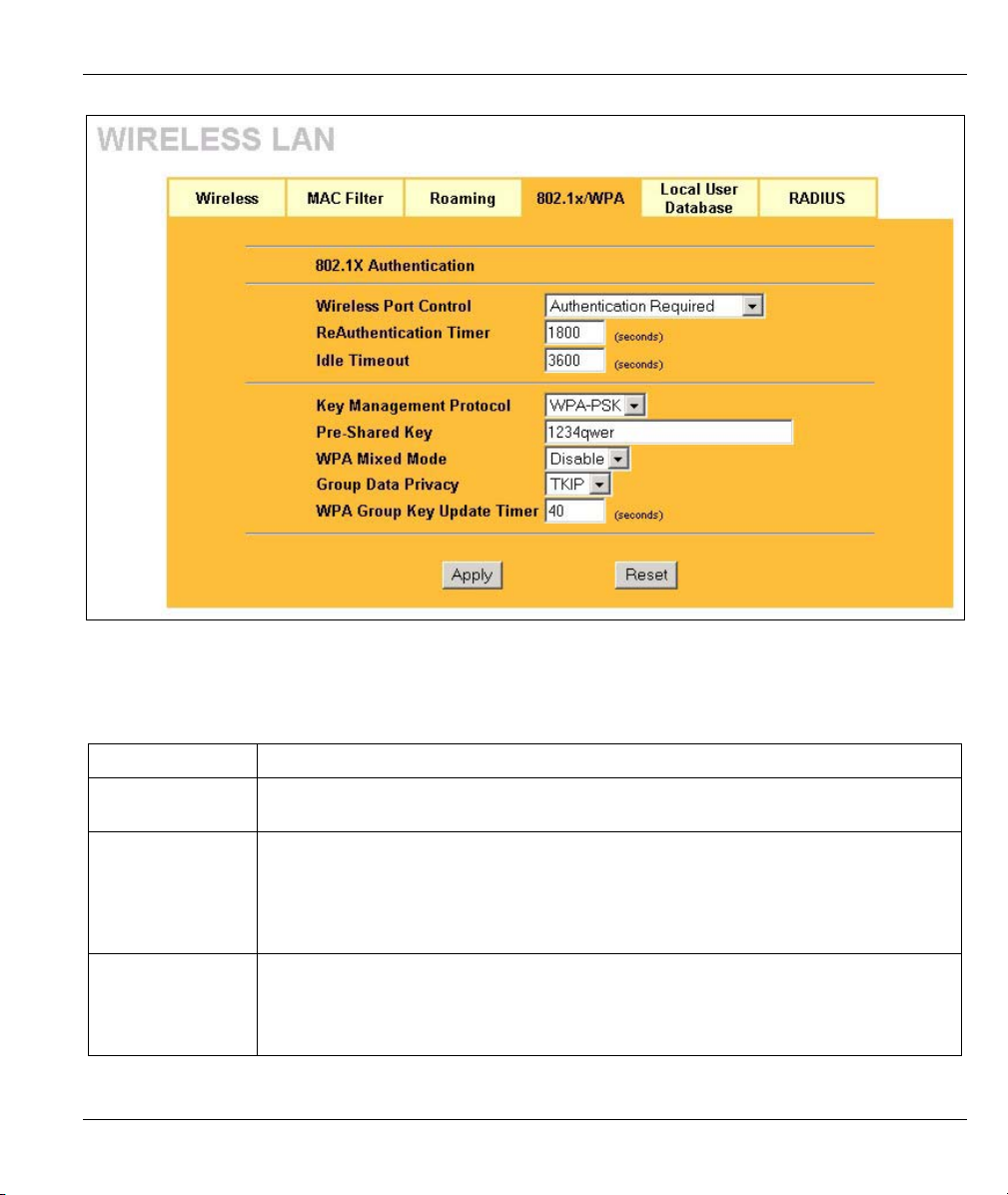
ZyAIR G-2000 Wireless 4-port Router User’s Guide
Figure 7-10 Wireless LAN: 802.1x/WPA for WPA-PSK Protocol
The following table describes the labels not previously discussed
Table 7-7 Wireless LAN: 802.1x/WPA for WPA-PSK Protocol
LABEL DESCRIPTION
Key Management
Protocol
Pre-Shared Key
WPA Mixed Mode
Choose WPA-PSK in this field.
The encryption mechanisms used for WPA and WPA-PSK are the same. The only
difference between the two is that WPA-PSK uses a simple common password,
instead of user-specific credentials.
Type a pre-shared key from 8 to 63 case-sensitive ASCII characters (including
spaces and symbols).
The ZyAIR can operate in WPA Mixed Mode, which supports both clients running
WPA and clients running WEP security in the same Wi-Fi network.
Select Enable to activate WPA mixed mode. Otherwise, select Disable and configure
the Group Data Privacy field.
Wireless Security 7-19
Page 100

ZyAIR G-2000 Wireless 4-port Router User’s Guide
Table 7-7 Wireless LAN: 802.1x/WPA for WPA-PSK Protocol
LABEL DESCRIPTION
Group Data
Privacy
WPA Group Key
Update Timer
Authentication
Databases
Group Data Privacy allows you to choose TKIP (recommended) or WEP for
broadcast and multicast (“group”) traffic if the Key Management Protocol is WPA
and WPA Mixed Mode is disabled. WEP is used automatically if you have enabled
WPA Mixed Mode.
All unicast traffic is automatically encrypted by TKIP when WPA or WPA-PSK Key
Management Protocol is selected.
The WPA Group Key Update Timer is the rate at which the AP (if using WPA-PSK
key management) or RADIUS server (if using WPA key management) sends a new
group key out to all clients. The re-keying process is the WPA equivalent of
automatically changing the WEP key for an AP and all stations in a WLAN on a
periodic basis. Setting of the WPA Group Key Update Timer is also supported in
WPA-PSK mode. The ZyAIR default is 1800 seconds (30 minutes).
This field is only visible when WPA Mixed Mode is enabled.
When you configure Key Management Protocol to WPA, the Authentication
Databases must be RADIUS Only. You can only use the Local User Database
Only with 802.1x Key Management Protocol.
7.13 Introduction to Local User Database
By storing user profiles locally on the ZyAIR, your ZyAIR is able to authenticate wireless users without
interacting with a network RADIUS server. However, there is a limit on the number of users you may
authenticate in this way. You can only use Local User Database with 802.1x key management protocol.
7.14 Configuring Local User Database
To change your ZyAIR’s local user database, click the WIRELESS link under ADVANCED and then the
Local User Database tab. The screen appears as shown.
7-20 Wireless Security
 Loading...
Loading...