Chapter 8 AP Profile
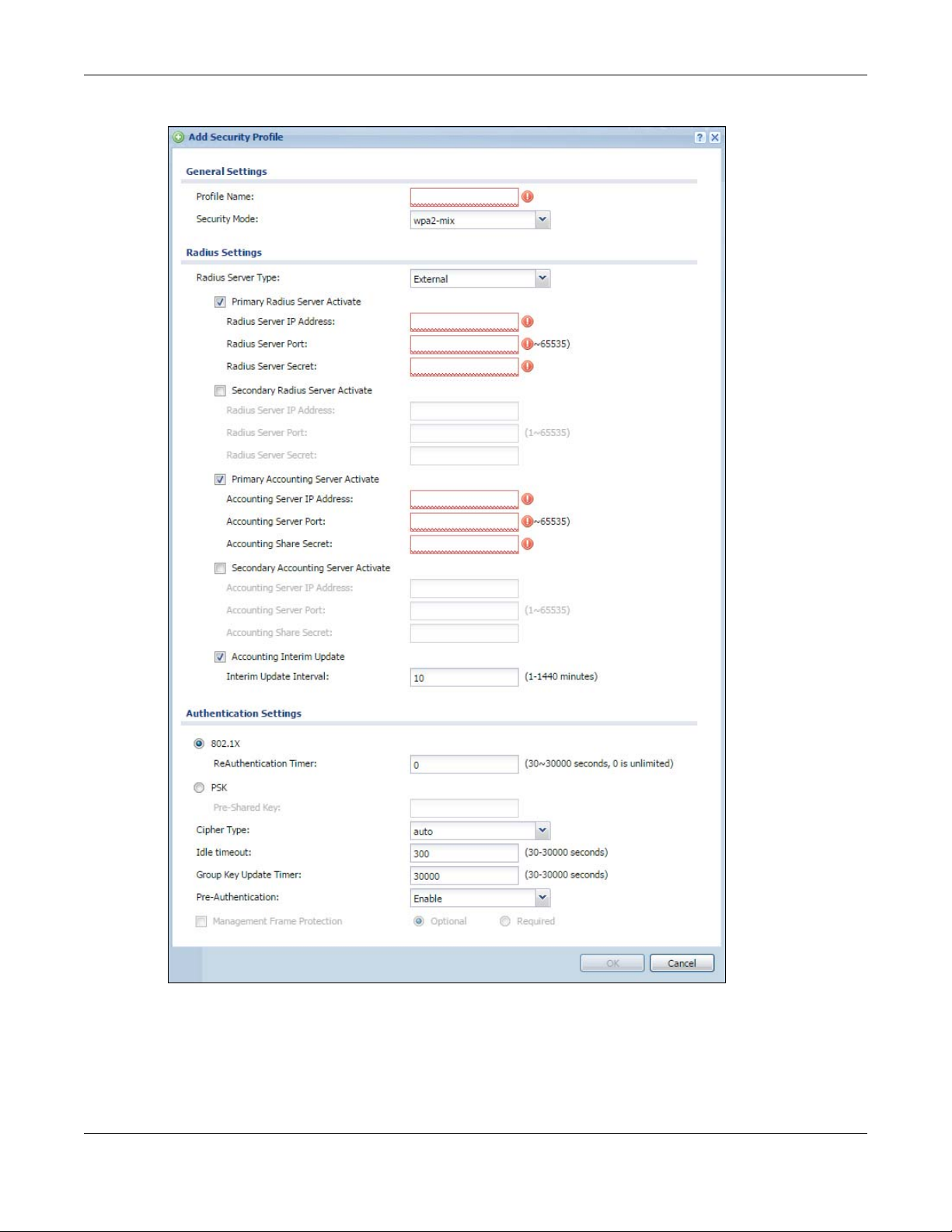
Figure 56 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile
NWA / WAC Series User’s Guide
101
Chapter 8 AP Profile
The following table describes the labels in this screen.
Table 48 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the
Security Mode Select a security mode from the list: none, wep, wpa2, or wpa2-mix.
Radius Server Type This shows External and the NWA/WAC uses an external RADIUS server for authentication.
Primary / Secondary
Radius Server
Activate
Radius Server IP
Address
Radius Server
Port
Radius Server
Secret
Primary / Secondary
Accounting Server
Activate
Accounting
Server IP Address
Accounting
Server Port
Accounting
Share Secret
Accounting Interim
Update
Interim Update
Interval
802.1X Select this to enable 802.1x secure authentication.
ReAuthenticatio
n Timer
WEP Authentication Settings
Idle Timeout Enter the idle interval (in seconds) that a client can be idle before authentication is
Authentication Type Select a WEP authentication method. Choices are Open or Share key. Share key is only
Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
Select this to have the NWA/WAC use the specified RADIUS server.
Enter the IP address of the RADIUS server to be used for authentication.
Enter the port number of the RADIUS server to be used for authentication.
Enter the shared secret password of the RADIUS server to be used for authentication.
Select the check box to enable user accounting through an external authentication server.
Enter the IP address of the external accounting server in dotted decimal notation.
Enter the port number of the external accounting server. The default port number is 1813.
You need not change this value unless your network administrator instructs you to do so with
additional information.
Enter a password (up to 128 alphanumeric characters) as the key to be shared between the
external accounting server and the NWA/WAC. The key must be the same on the external
accounting server and your NWA/WAC. The key is not sent over the network.
This field is available only when you enable user accounting through an external
authentication server.
Select this to have the NWA/WAC send subscriber status updates to the accounting server
at the interval you specify.
Specify the time interval for how often the NWA/WAC is to send a subscriber status update
to the accounting server.
Enter the interval (in seconds) between authentication requests. Enter a 0 for unlimited
requests.
discontinued.
available if you are not using 802.1x.
NWA / WAC Series User’s Guide
102
Chapter 8 AP Profile
Table 48 Configuration > Object > AP Profile > SSID > Security List > Add/Edit Security Profile (continued)
LABEL DESCRIPTION
Key Length Select the bit-length of the encryption key to be used in WEP connections.
If you select WEP-64:
• Enter 10 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x11AA22BB33) for each Key used.
or
• Enter 5 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey) for each Key used.
If you select WEP-128:
• Enter 26 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x00112233445566778899AABBCC) for each Key used.
or
• Enter 13 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey12345678) for each Key used.
Key 1~4 Based on your Key Length selection, enter the appropriate length hexadecimal or ASCII key.
WPA2/WPA2-Mix Authentication Settings
PSK This field is available when you select the wpa2, or wpa2-mix security mode.
Select this option to use a Pre-Shared Key with WPA2 encryption.
Pre-Shared Key Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including
spaces and symbols) or 64 hexadecimal characters.
Cipher Type Select an encryption cipher type from the list.
• auto - This automatically chooses the best available cipher based on the cipher in use
by the wireless client that is attempting to make a connection.
• aes - This is the Advanced Encryption Standard encryption method. It is a more recent
development over TKIP and considerably more robust. Not all wireless clients may
support this.
Idle Timeout Enter the interval (in seconds) that a client can be idle before authentication is
discontinued.
Group Key Update
Timer
Management
Frame Protection
OK Click OK to save your changes back to the NWA/WAC.
Cancel Click Cancel to exit this screen without saving your changes.
Enter the interval (in seconds) at which the AP updates the group WPA2 encryption key.
This field is available only when you select wpa2 in the Security Mode field and set Cipher
Type to aes.
Data frames in 802.11 WLANs can be encrypted and authenticated with WEP, WPA or
WPA2. But 802.11 management frames, such as beacon/probe response, association
request, association response, de-authentication and disassociation are always
unauthenticated and unencrypted. IEEE 802.11w Protected Management Frames allows
APs to use the existing security mechanisms (encryption and authentication methods
defined in IEEE 802.11i WPA/WPA2) to protect management frames. This helps prevent
wireless DoS attacks.
Select the check box to enable management frame protection (MFP) to add security to
802.11 management frames.
Select Optional if you do not require the wireless clients to support MFP. Management
frames will be encrypted if the clients support MFP.
Select Required and wireless clients must support MFP in order to join the NWA/WAC’s
wireless network.
NWA / WAC Series User’s Guide
103
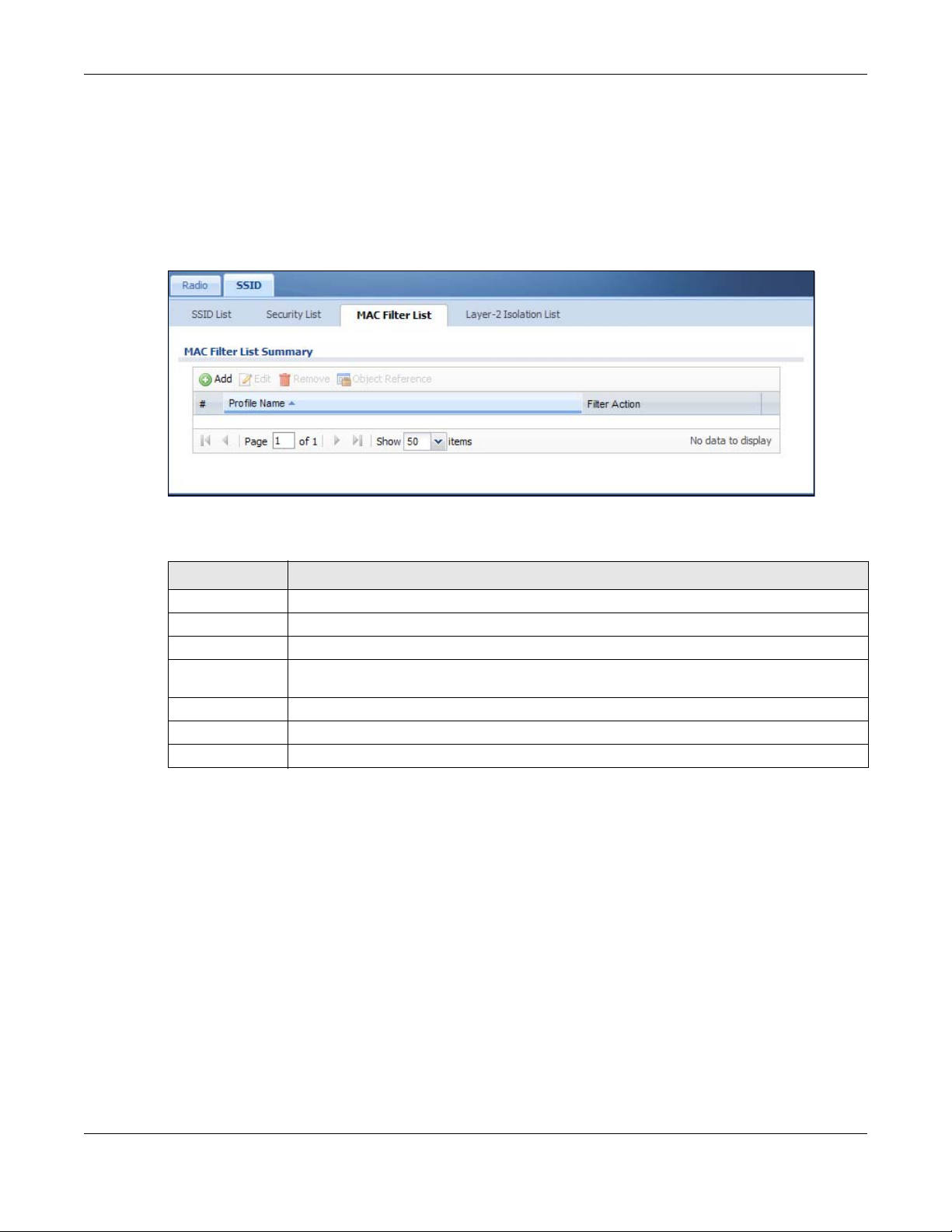
8.5 MAC Filter List
This screen allows you to create and manage security configurations that can be used by your SSIDs. To
access this screen click Configuration > Object > AP Profile > SSID > MAC Filter List.
Note: You can have a maximum of 32 MAC filtering profiles on the NWA/WAC.
Figure 57 Configuration > Object > AP Profile > SSID > MAC Filter List
Chapter 8 AP Profile
The following table describes the labels in this screen.
Table 49 Configuration > Object > AP Profile > SSID > MAC Filter List
LABEL DESCRIPTION
Add Click this to add a new MAC filtering profile.
Edit Click this to edit the selected MAC filtering profile.
Remove Click this to remove the selected MAC filtering profile.
Object
Reference
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the MAC filtering profile.
Filter Action This field indicates this profile’s filter action (if any).
Click this to view which other objects are linked to the selected MAC filtering profile (for
example, SSID profile).
8.5.1 Add/Edit MAC Filter Profile
This screen allows you to create a new MAC filtering profile or edit an existing one. To access this screen,
click the Add button or select a MAC filter profile from the list and click the Edit button.
Note: Each MAC filtering profile can include a maximum of 512 MAC addresses.
NWA / WAC Series User’s Guide
104
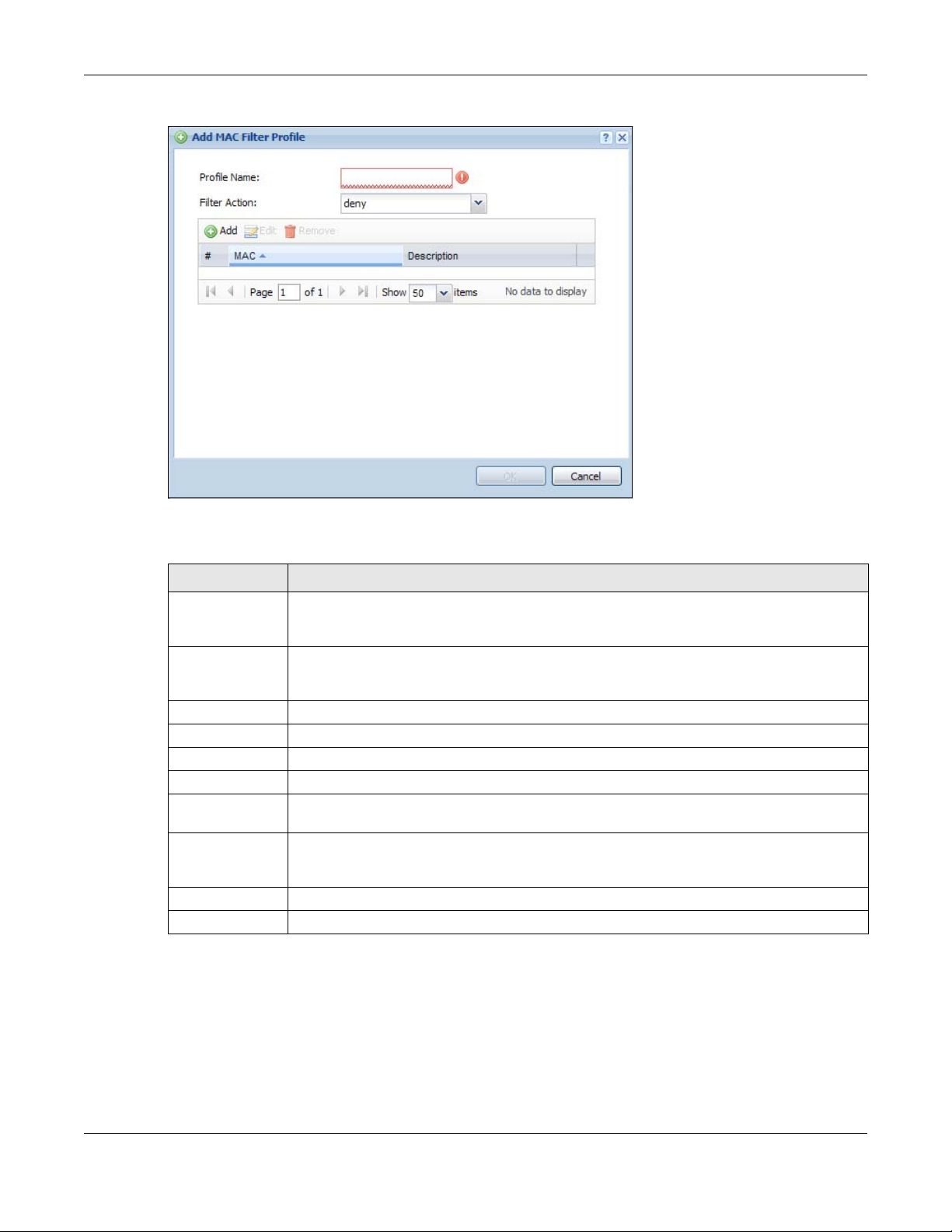
Chapter 8 AP Profile
Figure 58 Configuration > Object > AP Profile > SSID > MAC Filter List > Add/Edit MAC Filter Profile
The following table describes the labels in this screen.
Table 50 Configuration > Object > AP Profile > SSID > MAC Filter List > Add/Edit MAC Filter Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the
Filter Action Select allow to permit the wireless client with the MAC addresses in this profile to connect to the
Add Click this to add a MAC address to the profile’s list.
Edit Click this to edit the selected MAC address in the profile’s list.
Remove Click this to remove the selected MAC address from the profile’s list.
# This field is a sequential value, and it is not associated with a specific user.
MAC This field specifies a MAC address associated with this profile. You can click the MAC address to
Description This field displays a description for the MAC address associated with this profile. You can click
OK Click OK to save your changes back to the NWA/WAC.
Cancel Click Cancel to exit this screen without saving your changes.
Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
network through the associated SSID; select deny to block the wireless clients with the specified
MAC addresses.
make it editable.
the description to make it editable. Enter up to 60 characters, spaces and underscores
allowed.
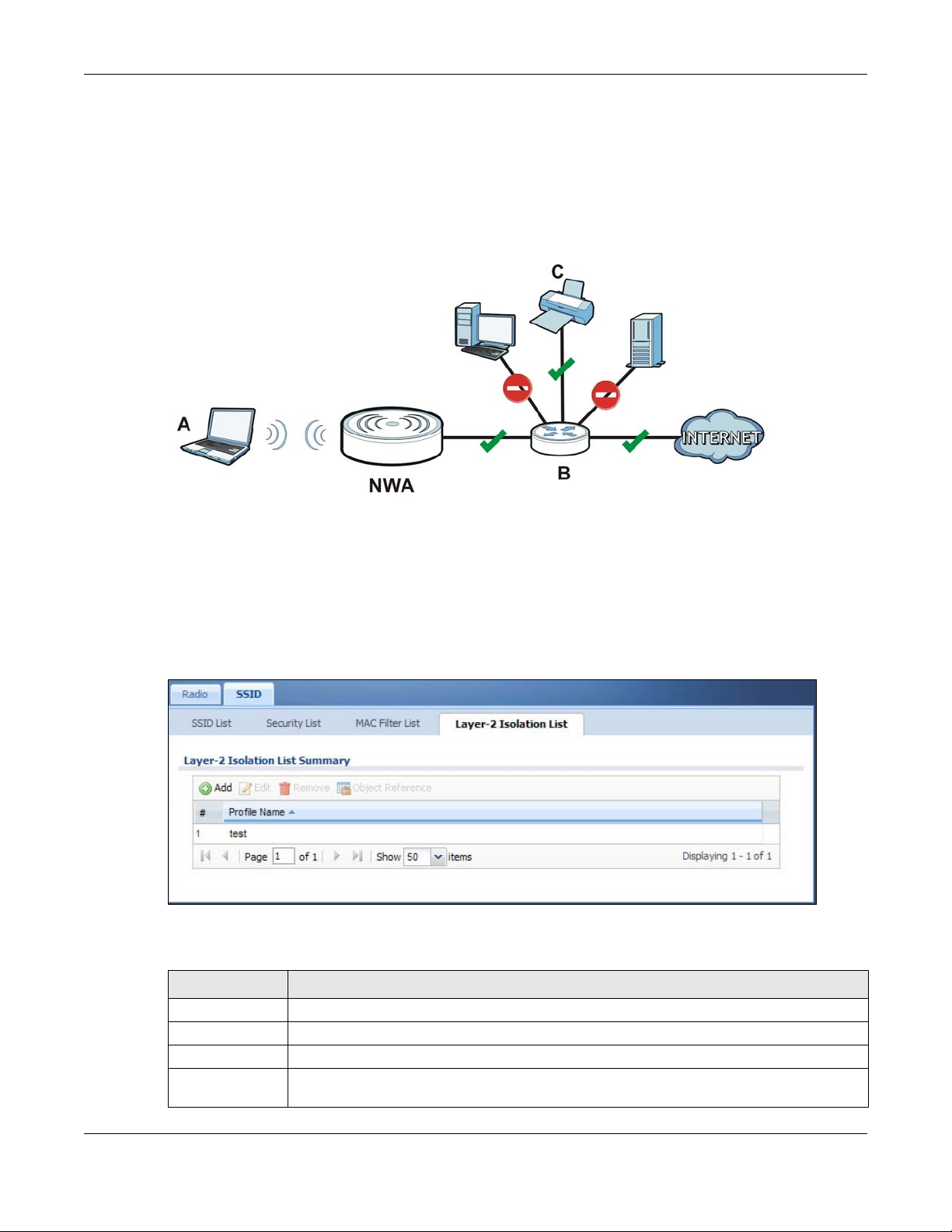
8.6 Layer-2 Isolation List
Layer-2 isolation is used to prevent wireless clients associated with your NWA/WAC from communicating
with other wireless clients, APs, computers or routers in a network.
NWA / WAC Series User’s Guide
105
Chapter 8 AP Profile
In the following example, layer-2 isolation is enabled on the NWA/WAC to allow a guest wireless client
(A) to access the main network router (B). The router provides access to the Internet and the network
printer (C) while preventing the client from accessing other computers and servers on the network. The
client can communicate with other wireless clients only if Intra-BSS Traffic blocking is disabled.
Note: Intra-BSS Traffic Blocking is activated when you enable layer-2 isolation.
Figure 59 Layer-2 Isolation Application
MAC addresses that are not listed in the layer-2 isolation table are blocked from communicating with
the NWA/WAC’s wireless clients except for broadcast packets. Layer-2 isolation does not check the
traffic between wireless clients that are associated with the same AP. Intra-BSS traffic allows wireless
clients associated with the same AP to communicate with each other.
This screen allows you to specify devices you want the users on your wireless networks to access. To
access this screen click Configuration > Object > AP Profile > SSID > Layer-2 Isolation List.
Figure 60 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
The following table describes the labels in this screen.
Table 51 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List
LABEL DESCRIPTION
Add Click this to add a new MAC filtering profile.
Edit Click this to edit the selected MAC filtering profile.
Remove Click this to remove the selected MAC filtering profile.
Object
Reference
Click this to view which other objects are linked to the selected MAC filtering profile (for
example, SSID profile).
NWA / WAC Series User’s Guide
106
Chapter 8 AP Profile
Table 51 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List (continued)
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific user.
Profile Name This field indicates the name assigned to the layer-2 isolation profile.
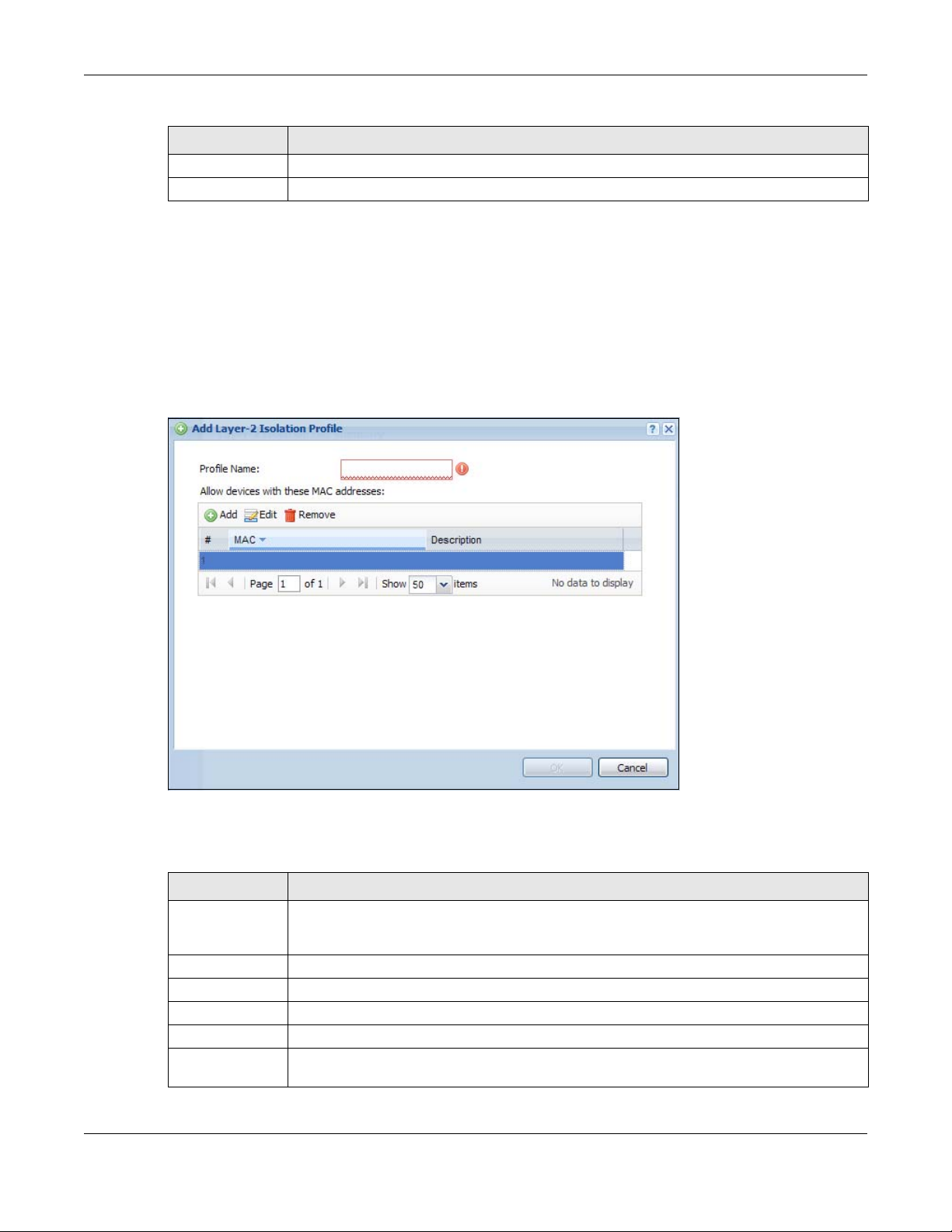
8.6.1 Add/Edit Layer-2 Isolation Profile
This screen allows you to create a new layer-2 isolation profile or edit an existing one. To access this
screen, click the Add button or select a layer-2 isolation profile from the list and click the Edit button.
Note: You need to know the MAC address of each wireless client, AP, computer or router that
you want to allow to communicate with the NWA/WAC's wireless clients.
Figure 61 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List > Add/Edit Layer-2 Isolation
Profile
The following table describes the labels in this screen.
Table 52 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List > Add/Edit Layer-2 Isolation
Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the
Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
Add Click this to add a MAC address to the profile’s list.
Edit Click this to edit the selected MAC address in the profile’s list.
Remove Click this to remove the selected MAC address from the profile’s list.
# This field is a sequential value, and it is not associated with a specific user.
MAC This field specifies a MAC address associated with this profile. You can click the MAC address to
make it editable.
NWA / WAC Series User’s Guide
107
Chapter 8 AP Profile
Table 52 Configuration > Object > AP Profile > SSID > Layer-2 Isolation List > Add/Edit Layer-2 Isolation
Profile (continued)
LABEL DESCRIPTION
Description This field displays a description for the MAC address associated with this profile. You can click
OK Click OK to save your changes back to the NWA/WAC.
Cancel Click Cancel to exit this screen without saving your changes.
the description to make it editable. Enter up to 60 characters, spaces and underscores
allowed.
NWA / WAC Series User’s Guide
108
9.1 Overview
This screen allows you to set up monitor mode configurations that allow your NWA/WAC to scan for
other wireless devices in the vicinity. Once detected, you can use the Wireless > MON Mode screen
(Section 6.3 on page 74) to classify them as either rogue or friendly.
Not all NWA/WACs support monitor mode and rogue APs detection.
9.1.1 What You Can Do in this Chapter
The MON Profile screen (Section 9.2 on page 109) creates preset monitor mode configurations that can
be used by the NWA/WAC.
CHAPTER 9
MON Profile
9.2 MON Profile
This screen allows you to create monitor mode configurations that can be used by the APs. To access
this screen, login to the Web Configurator, and click Configuration > Object > MON Profile.
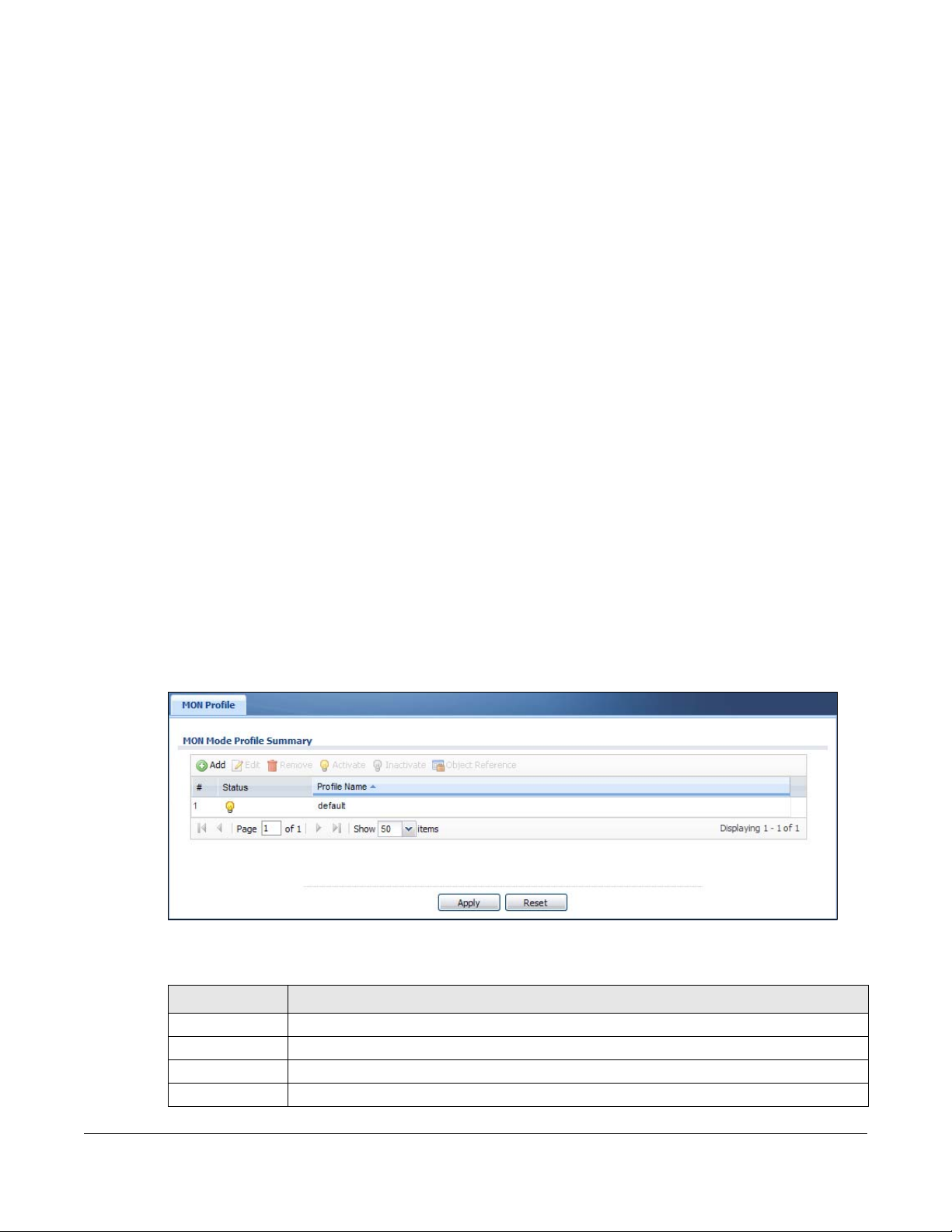
Figure 62 Configuration > Object > MON Profile
The following table describes the labels in this screen.
Table 53 Configuration > Object > MON Profile
LABEL DESCRIPTION
Add Click this to add a new monitor mode profile.
Edit Click this to edit the selected monitor mode profile.
Remove Click this to remove the selected monitor mode profile.
Activate To turn on an entry, select it and click Activate.
NWA / WAC Series User’s Guide
109
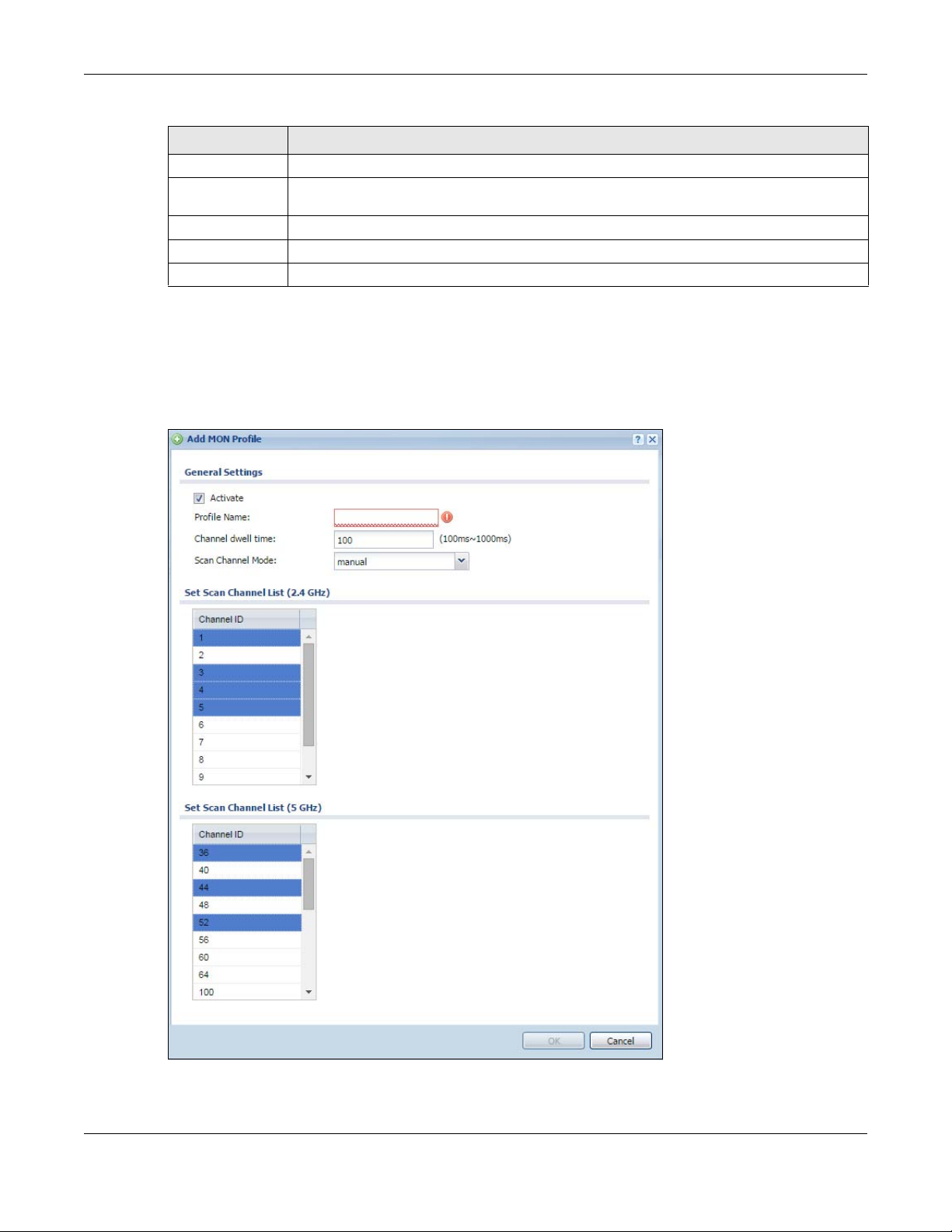
Table 53 Configuration > Object > MON Profile (continued)
LABEL DESCRIPTION
Inactivate To turn off an entry, select it and click Inactivate.
Object
Reference
# This field is a sequential value, and it is not associated with a specific profile.
Status This field shows whether or not the entry is activated.
Profile Name This field indicates the name assigned to the monitor profile.
Click this to view which other objects are linked to the selected monitor mode profile (for
example, an AP management profile).
9.2.1 Add/Edit MON Profile
This screen allows you to create a new monitor mode profile or edit an existing one. To access this
screen, click the Add button or select and existing monitor mode profile and click the Edit button.
Figure 63 Configuration > Object > MON Profile > Add/Edit MON Profile
Chapter 9 MON Profile
NWA / WAC Series User’s Guide
110
Chapter 9 MON Profile
The following table describes the labels in this screen.
Table 54 Configuration > Object > MON Profile > Add/Edit MON Profile
LABEL DESCRIPTION
Activate Select this to activate this monitor mode profile.
Profile Name This field indicates the name assigned to the monitor mode profile.
Channel dwell time Enter the interval (in milliseconds) before the NWA/WAC switches to another channel for
Scan Channel Mode Select auto to have the NWA/WAC switch to the next sequential channel once the
Set Scan Channel List
(2.4 GHz)
Set Scan Channel List
(5 GHz)
OK Click OK to save your changes back to the NWA/WAC.
Cancel Click Cancel to exit this screen without saving your changes.
monitoring.
Channel dwell time expires.
Select manual to set specific channels through which to cycle sequentially when the
Channel dwell time expires. Selecting this options makes the Scan Channel List options
available.
Select one or more than one channel to have the NWA/WAC using this profile scan the
channel(s) when Scan Channel Mode is set to manual.
These channels are limited to the 2.4 GHz range (802.11 b/g/n).
Select one or more than one channel to have the NWA/WAC using this profile scan the
channel(s) when Scan Channel Mode is set to manual.
These channels are limited to the 5 GHz range (802.11 a/n). Not all NWA/WACs support
both 2.4 GHz and 5 GHz frequency bands.
9.3 Technical Reference
The following section contains additional technical information about the features described in this
chapter.
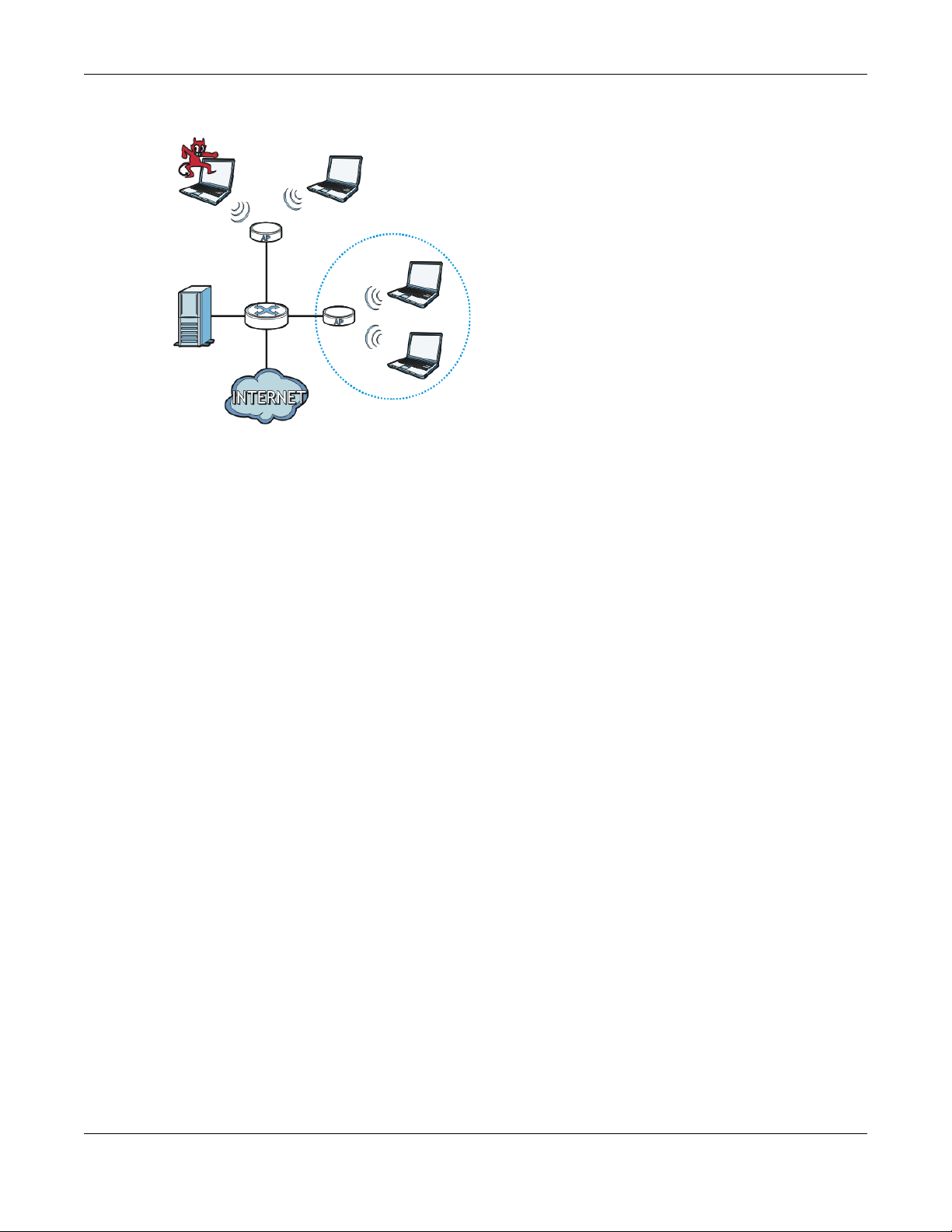
Rogue APs
Rogue APs are wireless access points operating in a network’s coverage area that are not under the
control of the network’s administrators, and can open up holes in a network’s security. Attackers can
take advantage of a rogue AP’s weaker (or non-existent) security to gain access to the network, or set
up their own rogue APs in order to capture information from wireless clients. If a scan reveals a rogue AP,
you can use commercially-available software to physically locate it.
NWA / WAC Series User’s Guide
111
Chapter 9 MON Profile
RG
AX
B
C
Figure 64 Rogue AP Example
In the example above, a corporate network’s security is compromised by a rogue AP (RG) set up by an
employee at his workstation in order to allow him to connect his notebook computer wirelessly (A). The
company’s legitimate wireless network (the dashed ellipse B) is well-secured, but the rogue AP uses
inferior security that is easily broken by an attacker (X) running readily available encryption-cracking
software. In this example, the attacker now has access to the company network, including sensitive
data stored on the file server (C).
Friendly APs
If you have more than one AP in your wireless network, you should also configure a list of “friendly” APs.
Friendly APs are other wireless access points that are detected in your network, as well as any others that
you know are not a threat (those from recognized networks, for example). It is recommended that you
export (save) your list of friendly APs often, especially if you have a network with a large number of
access points.
NWA / WAC Series User’s Guide
112
10.1 Overview
This chapter shows you how to configure WDS (Wireless Disbribution System) profiles for the NWA/WAC to
form a WDS with other APs.
10.1.1 What You Can Do in this Chapter
The WDS Profile screen (Section 10.2 on page 113) creates preset WDS configurations that can be used
by the NWA/WAC.
10.2 WDS Profile
CHAPTER 10
WDS Profile
This screen allows you to manage and create WDS profiles that can be used by the APs. To access this
screen, click Configuration > Object > WDS Profile.
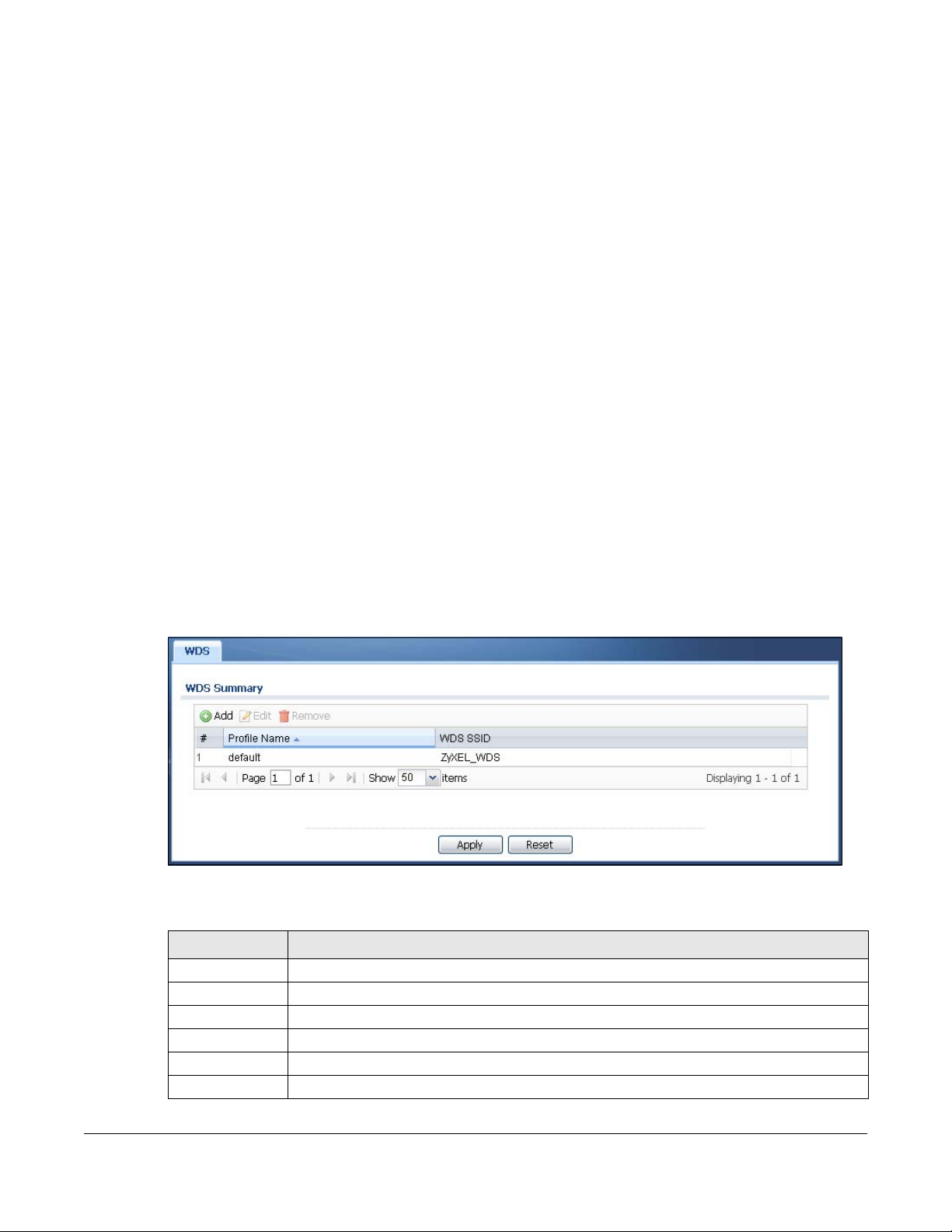
Figure 65 Configuration > Object > WDS Profile
The following table describes the labels in this screen.
Table 55 Configuration > Object > WDS Profile
LABEL DESCRIPTION
Add Click this to add a new profile.
Edit Click this to edit the selected profile.
Remove Click this to remove the selected profile.
# This field is a sequential value, and it is not associated with a specific profile.
Profile Name This field indicates the name assigned to the profile.
WDS SSID This field shows the SSID specified in this WDS profile.
NWA / WAC Series User’s Guide
113
10.2.1 Add/Edit WDS Profile
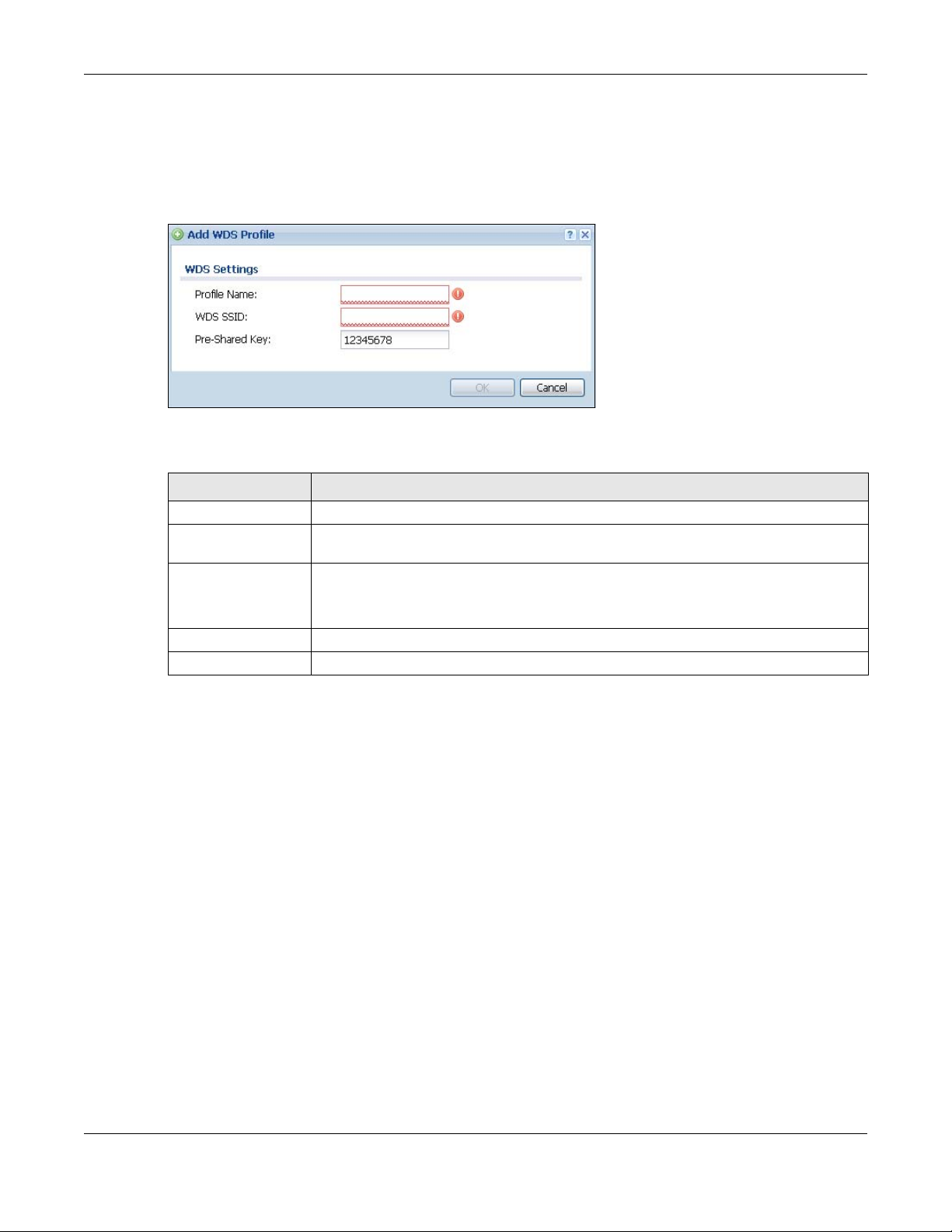
This screen allows you to create a new WDS profile or edit an existing one. To access this screen, click the
Add button or select and existing profile and click the Edit button.
Figure 66 Configuration > Object > WDS Profile > Add/Edit WDS Profile
The following table describes the labels in this screen.
Table 56 Configuration > Object > WDS Profile > Add/Edit WDS Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name.
WDS SSID Enter the SSID with which you want the NWA/WAC to connect to a root AP or repeater to
form a WDS.
Pre-Shared Key Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including
spaces and symbols) or 64 hexadecimal characters.
The key is used to encrypt the traffic between the APs.
OK Click OK to save your changes back to the NWA/WAC.
Cancel Click Cancel to exit this screen without saving your changes.
Chapter 10 WDS Profile
NWA / WAC Series User’s Guide
114

11.1 Overview
The NWA/WAC can use certificates (also called digital IDs) to authenticate users. Certificates are based
on public-private key pairs. A certificate contains the certificate owner’s identity and public key.
Certificates provide a way to exchange public keys for use in authentication.
11.1.1 What You Can Do in this Chapter
• The My Certificate screens (Section 11.2 on page 118) generate and export self-signed certificates or
certification requests and import the NWA/WAC’s CA-signed certificates.
• The Trusted Certificates screens (Section 11.3 on page 126) save CA certificates and trusted remote
host certificates to the NWA/WAC. The NWA/WAC trusts any valid certificate that you have imported
as a trusted certificate. It also trusts any valid certificate signed by any of the certificates that you
have imported as a trusted certificate.
CHAPTER 11
Certificates
11.1.2 What You Need to Know
The following terms and concepts may help as you read this chapter.
When using public-key cryptology for authentication, each host has two keys. One key is public and can
be made openly available. The other key is private and must be kept secure.
These keys work like a handwritten signature (in fact, certificates are often referred to as “digital
signatures”). Only you can write your signature exactly as it should look. When people know what your
signature looks like, they can verify whether something was signed by you, or by someone else. In the
same way, your private key “writes” your digital signature and your public key allows people to verify
whether data was signed by you, or by someone else.
This process works as follows:
1 Tim wants to send a message to Jenny. He needs her to be sure that it comes from him, and that the
message content has not been altered by anyone else along the way. Tim generates a public key pair
(one public key and one private key).
2 Tim keeps the private key and makes the public key openly available. This means that anyone who
receives a message seeming to come from Tim can read it and verify whether it is really from him or not.
3 Tim uses his private key to sign the message and sends it to Jenny.
4 Jenny receives the message and uses Tim’s public key to verify it. Jenny knows that the message is from
Tim, and that although other people may have been able to read the message, no-one can have
altered it (because they cannot re-sign the message with Tim’s private key).
NWA / WAC Series User’s Guide
115

Chapter 11 Certificates
5 Additionally, Jenny uses her own private key to sign a message and Tim uses Jenny’s public key to verify
the message.
The NWA/WAC uses certificates based on public-key cryptology to authenticate users attempting to
establish a connection, not to encrypt the data that you send after establishing a connection. The
method used to secure the data that you send through an established connection depends on the
type of connection.
The certification authority uses its private key to sign certificates. Anyone can then use the certification
authority’s public key to verify the certificates.
A certification path is the hierarchy of certification authority certificates that validate a certificate. The
NWA/WAC does not trust a certificate if any certificate on its path has expired or been revoked.
Certification authorities maintain directory servers with databases of valid and revoked certificates. A
directory of certificates that have been revoked before the scheduled expiration is called a CRL
(Certificate Revocation List). The NWA/WAC can check a peer’s certificate against a directory server’s
list of revoked certificates. The framework of servers, software, procedures and policies that handles keys
is called PKI (public-key infrastructure).
Advantages of Certificates
Certificates offer the following benefits.
• The NWA/WAC only has to store the certificates of the certification authorities that you decide to
trust, no matter how many devices you need to authenticate.
• Key distribution is simple and very secure since you can freely distribute public keys and you never
need to transmit private keys.
Self-signed Certificates
You can have the NWA/WAC act as a certification authority and sign its own certificates.
Factory Default Certificate
The NWA/WAC generates its own unique self-signed certificate when you first turn it on. This certificate is
referred to in the GUI as the factory default certificate.
Certificate File Formats
Any certificate that you want to import has to be in one of these file formats:
• Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates.
• PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters, uppercase
letters and numerals to convert a binary X.509 certificate into a printable form.
• Binary PKCS#7: This is a standard that defines the general syntax for data (including digital signatures)
that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The private key is not
included. The NWA/WAC currently allows the importation of a PKS#7 file that contains a single
certificate.
• PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase letters,
uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable form.
NWA / WAC Series User’s Guide
116
• Binary PKCS#12: This is a format for transferring public key and private key certificates.The private key
in a PKCS #12 file is within a password-encrypted envelope. The file’s password is not connected to
your certificate’s public or private passwords. Exporting a PKCS #12 file creates this and you must
provide it to decrypt the contents when you import the file into the NWA/WAC.
Note: Be careful not to convert a binary file to text during the transfer process. It is easy for this
to occur since many programs use text files by default.
11.1.3 Verifying a Certificate
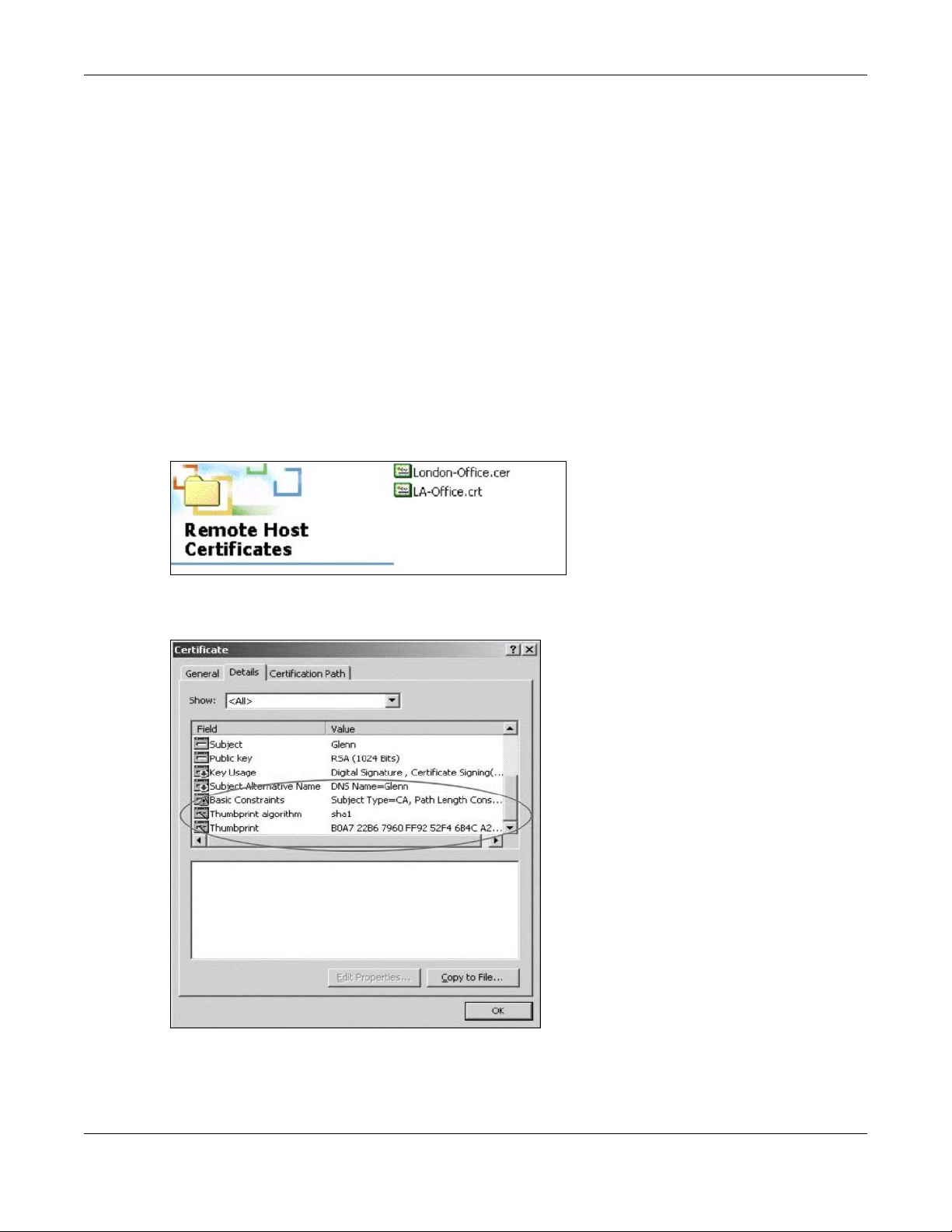
Before you import a trusted certificate into the NWA/WAC, you should verify that you have the correct
certificate. You can do this using the certificate’s fingerprint. A certificate’s fingerprint is a message
digest calculated using the MD5 or SHA1 algorithm. The following procedure describes how to check a
certificate’s fingerprint to verify that you have the actual certificate.
1 Browse to where you have the certificate saved on your computer.
2 Make sure that the certificate has a “.cer” or “.crt” file name extension.
Chapter 11 Certificates
3 Double-click the certificate’s icon to open the Certificate window. Click the Details tab and scroll down
to the Thumbprint Algorithm and Thumbprint fields.
4 Use a secure method to verify that the certificate owner has the same information in the Thumbprint
Algorithm and Thumbprint fields. The secure method may very based on your situation. Possible
examples would be over the telephone or through an HTTPS connection.
NWA / WAC Series User’s Guide
117
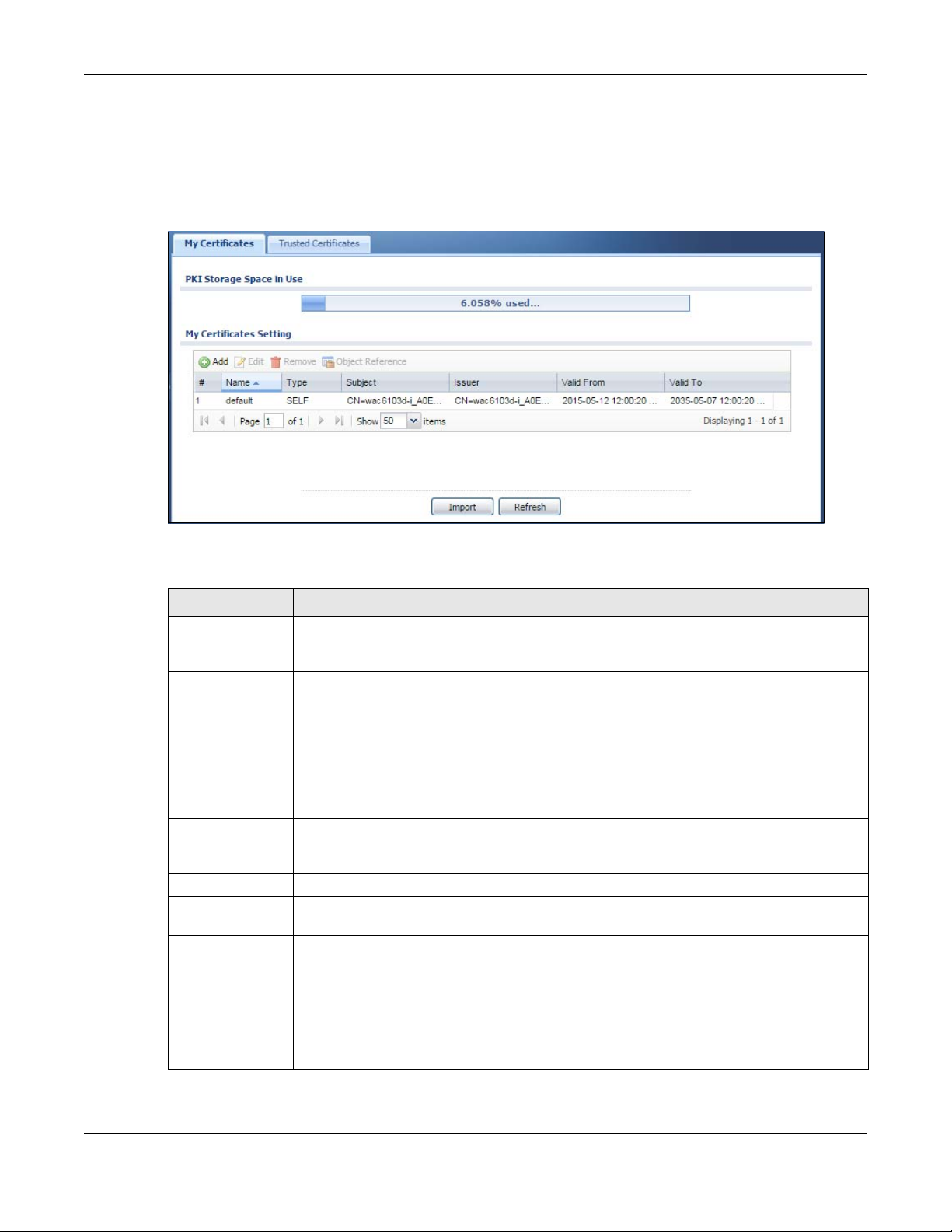
11.2 My Certificates
Click Configuration > Object > Certificate > My Certificates to open this screen. This is the NWA/WAC’s
summary list of certificates and certification requests.
Figure 67 Configuration > Object > Certificate > My Certificates
Chapter 11 Certificates
The following table describes the labels in this screen.
Table 57 Configuration > Object > Certificate > My Certificates
LABEL DESCRIPTION
PKI Storage Space
in Use
Add Click this to go to the screen where you can have the NWA/WAC generate a certificate or a
Edit Double-click an entry or select it and click Edit to open a screen with an in-depth list of
Remove The NWA/WAC keeps all of your certificates unless you specifically delete them. Uploading a
Object Reference You cannot delete certificates that any of the NWA/WAC’s features are configured to use.
# This field displays the certificate index number. The certificates are listed in alphabetical order.
Name This field displays the name used to identify this certificate. It is recommended that you give
Type This field displays what kind of certificate this is.
This bar displays the percentage of the NWA/WAC’s PKI storage space that is currently in use.
When the storage space is almost full, you should consider deleting expired or unnecessary
certificates before adding more certificates.
certification request.
information about the certificate.
new firmware or default configuration file does not delete your certificates. To remove an
entry, select it and click Remove. The NWA/WAC confirms you want to remove it before doing
so. Subsequent certificates move up by one when you take this action.
Select an entry and click Object Reference to open a screen that shows which settings use
the entry.
each certificate a unique name.
REQ represents a certification request and is not yet a valid certificate. Send a certification
request to a certification authority, which then issues a certificate. Use the My Certificate
Import screen to import the certificate and replace the request.
SELF represents a self-signed certificate.
CERT represents a certificate issued by a certification authority.
NWA / WAC Series User’s Guide
118
Table 57 Configuration > Object > Certificate > My Certificates (continued)
LABEL DESCRIPTION
Subject This field displays identifying information about the certificate’s owner, such as CN (Common
Name), OU (Organizational Unit or department), O (Organization or company) and C
(Country). It is recommended that each certificate have unique subject information.
Issuer This field displays identifying information about the certificate’s issuing certification authority,
such as a common name, organizational unit or department, organization or company and
country. With self-signed certificates, this is the same information as in the Subject field.
Valid From This field displays the date that the certificate becomes applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes an
Expired! message if the certificate has expired.
Import Click Import to open a screen where you can save a certificate to the NWA/WAC.
Refresh Click Refresh to display the current validity status of the certificates.
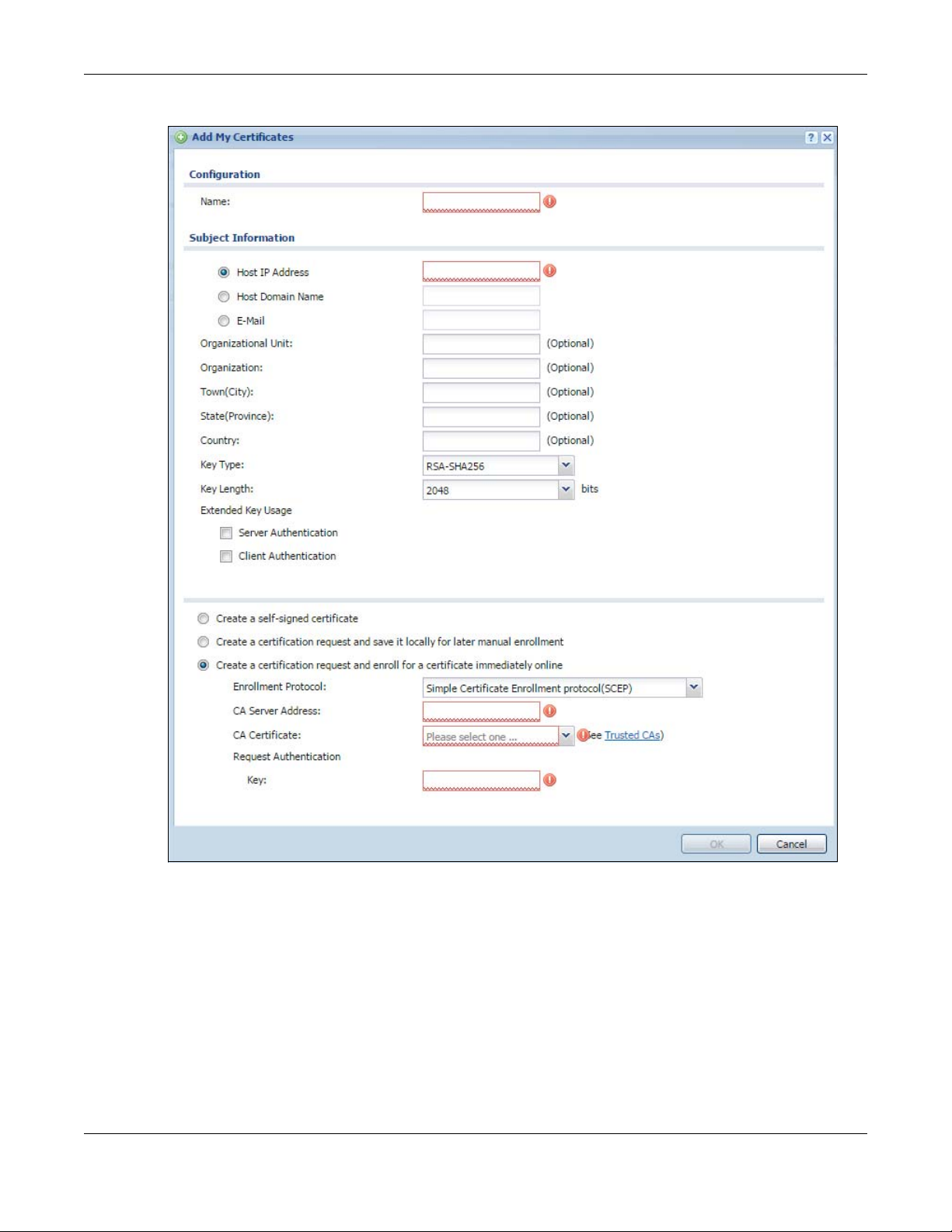
11.2.1 Add My Certificates
Click Configuration > Object > Certificate > My Certificates and then the Add icon to open the Add My
Certificates screen. Use this screen to have the NWA/WAC create a self-signed certificate, enroll a
certificate with a certification authority or generate a certification request.
Chapter 11 Certificates
NWA / WAC Series User’s Guide
119
Chapter 11 Certificates
Figure 68 Configuration > Object > Certificate > My Certificates > Add
NWA / WAC Series User’s Guide
120
Chapter 11 Certificates
The following table describes the labels in this screen.
Table 58 Configuration > Object > Certificate > My Certificates > Add
LABEL DESCRIPTION
Name Type a name to identify this certificate. You can use up to 31 alphanumeric and
Subject Information Use these fields to record information that identifies the owner of the certificate. You do
Organizational Unit Identify the organizational unit or department to which the certificate owner belongs. You
Organization Identify the company or group to which the certificate owner belongs. You can use up to
Town (City) Identify the town or city where the certificate owner is located. You can use up to 31
State (Province) Identify the state or province where the certificate owner is located. You can use up to 31
Country Identify the nation where the certificate owner is located. You can use up to 31
Key Type The NWA/WAC uses the RSA (Rivest, Shamir and Adleman) public-key encryption
Key Length Select a number from the drop-down list box to determine how many bits the key should
Extended Key Usage Select Server Authentication to allow a web server to send clients the certificate to
Create a self-signed
certificate
Create a certification
request and save it
locally for later
manual enrollment
;‘~!@#$%^&()_+[]{}’,.=-
not have to fill in every field, although you must specify a Host IP Address, Host Domain
Name, or E-Mail. The certification authority may add fields (such as a serial number) to the
subject information when it issues a certificate. It is recommended that each certificate
have unique subject information.
Select a radio button to identify the certificate’s owner by IP address, domain name or email address. Type the IP address (in dotted decimal notation), domain name or e-mail
address in the field provided. The domain name or e-mail address is for identification
purposes only and can be any string.
A domain name can be up to 255 characters. You can use alphanumeric characters, the
hyphen and periods.
An e-mail address can be up to 63 characters. You can use alphanumeric characters, the
hyphen, the @ symbol, periods and the underscore.
can use up to 31 characters. You can use alphanumeric characters, the hyphen and the
underscore.
31 characters. You can use alphanumeric characters, the hyphen and the underscore.
characters. You can use alphanumeric characters, the hyphen and the underscore.
characters. You can use alphanumeric characters, the hyphen and the underscore.
characters. You can use alphanumeric characters, the hyphen and the underscore.
algorithm. SHA1 (Secure Hash Algorithm) and SHA2 are hash algorithms used to
authenticate packet data. SHA2-256 or SHA2-512 are part of the SHA2 set of
cryptographic functions and they are considered even more secure than SHA1.
Select a key type from RSA-SHA256 and RSA-SHA512.
use (1024 to 2048). The longer the key, the more secure it is. A longer key also uses more PKI
storage space.
authenticate itself.
Select Client Authentication to use the certificate’s key to authenticate clients to the
secure gateway.
These radio buttons deal with how and when the certificate is to be generated.
Select this to have the NWA/WAC generate the certificate and act as the Certification
Authority (CA) itself. This way you do not need to apply to a certification authority for
certificates.
Select this to have the NWA/WAC generate and store a request for a certificate. Use the
My Certificate Edit screen to view the certification request and copy it to send to the
certification authority.
Copy the certification request from the My Certificate Edit screen and then send it to the
certification authority.
characters.
NWA / WAC Series User’s Guide
121
Chapter 11 Certificates
Table 58 Configuration > Object > Certificate > My Certificates > Add (continued)
LABEL DESCRIPTION
Create a certification
request and enroll for
a certificate
immediately online
Enrollment Protocol This field applies when you select Create a certification request and enroll for a certificate
CA Server Address This field applies when you select Create a certification request and enroll for a certificate
Select this to have the NWA/WAC generate a request for a certificate and apply to a
certification authority for a certificate.
You must have the certification authority’s certificate already imported in the Trusted
Certificates screen.
When you select this option, you must select the certification authority’s enrollment
protocol and the certification authority’s certificate from the drop-down list boxes and
enter the certification authority’s server address. You also need to fill in the Reference
Number and Key if the certification authority requires them.
immediately online. Select the certification authority’s enrollment protocol from the drop-
down list box.
Simple Certificate Enrollment Protocol (SCEP) is a TCP-based enrollment protocol that was
developed by VeriSign and Cisco.
Certificate Management Protocol (CMP) is a TCP-based enrollment protocol that was
developed by the Public Key Infrastructure X.509 working group of the Internet
Engineering Task Force (IETF) and is specified in RFC 2510.
immediately online. Enter the IP address (or URL) of the certification authority server.
For a URL, you can use up to 511 of the following characters. a-zA-Z0-9'()+,/:.=?;!*#@$_%-
CA Certificate This field applies when you select Create a certification request and enroll for a certificate
Request
Authentication
OK Click OK to begin certificate or certification request generation.
Cancel Click Cancel to quit and return to the My Certificates screen.
immediately online. Select the certification authority’s certificate from the CA Certificate
drop-down list box.
You must have the certification authority’s certificate already imported in the Trusted
Certificates screen. Click Trusted CAs to go to the Trusted Certificates screen where you
can view (and manage) the NWA/WAC's list of certificates of trusted certification
authorities.
When you select Create a certification request and enroll for a certificate immediately
online, the certification authority may want you to include a reference number and key to
identify you when you send a certification request.
Fill in both the Reference Number and the Key fields if your certification authority uses the
CMP enrollment protocol. Just the Key field displays if your certification authority uses the
SCEP enrollment protocol.
For the reference number, use 0 to 99999999.
For the key, use up to 31 of the following characters. a-zA-Z0-9;|`~!@#$%^&*()_+\{}':,./
<>=-
If you configured the Add My Certificates screen to have the NWA/WAC enroll a certificate and the
certificate enrollment is not successful, you see a screen with a Return button that takes you back to the
Add My Certificates screen. Click Return and check your information in the Add My Certificates screen.
Make sure that the certification authority information is correct and that your Internet connection is
working properly if you want the NWA/WAC to enroll a certificate online.
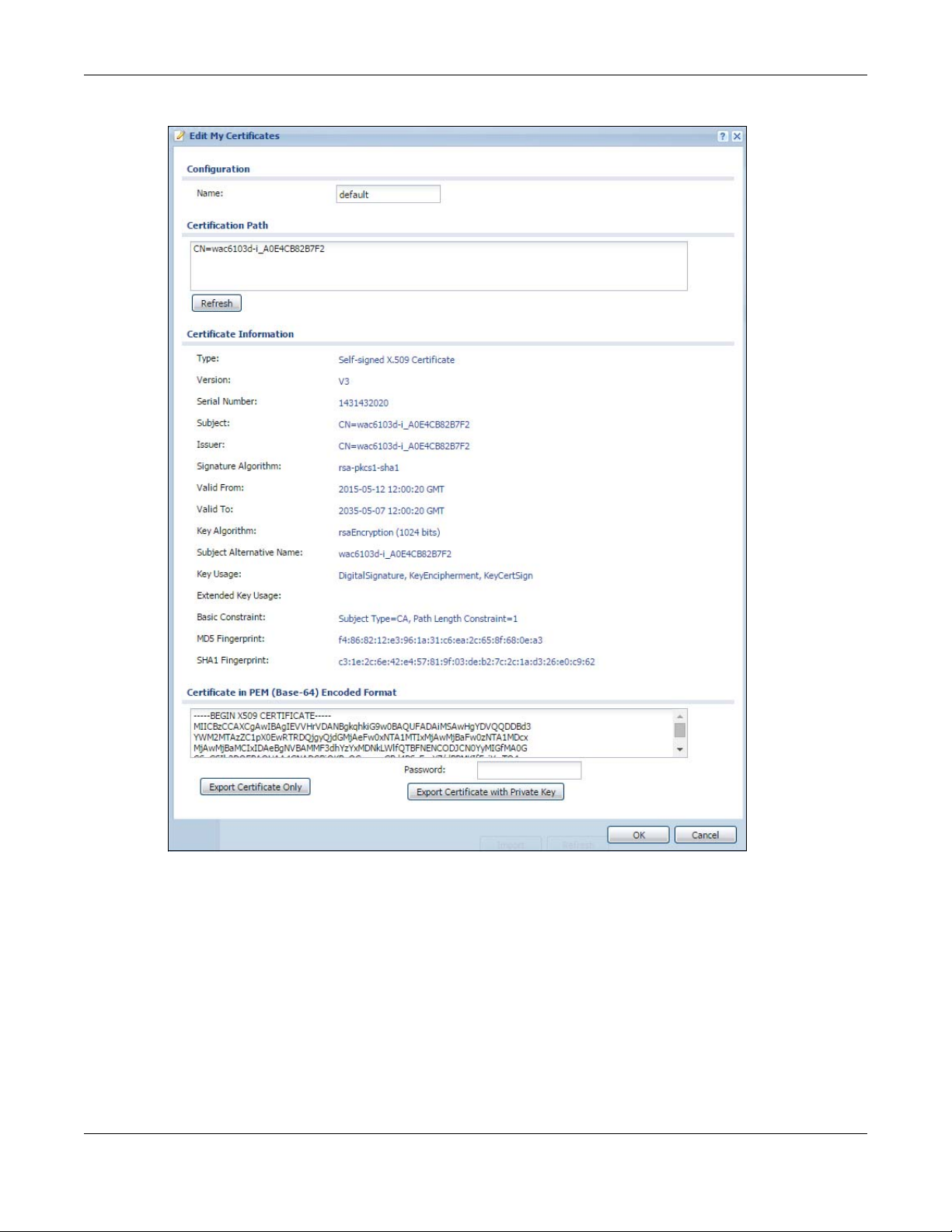
11.2.2 Edit My Certificates
Click Configuration > Object > Certificate > My Certificates and then the Edit icon to open the My
Certificate Edit screen. You can use this screen to view in-depth certificate information and change the
certificate’s name.
NWA / WAC Series User’s Guide
122
Chapter 11 Certificates
Figure 69 Configuration > Object > Certificate > My Certificates > Edit
NWA / WAC Series User’s Guide
123
Chapter 11 Certificates
The following table describes the labels in this screen.
Table 59 Configuration > Object > Certificate > My Certificates > Edit
LABEL DESCRIPTION
Name This field displays the identifying name of this certificate. You can use up to 31 alphanumeric
Certification Path This field displays for a certificate, not a certification request.
Refresh Click Refresh to display the certification path.
Certificate
Information
Type This field displays general information about the certificate. CA-signed means that a
Version This field displays the X.509 version number. “
Serial Number This field displays the certificate’s identification number given by the certification authority
Subject This field displays information that identifies the owner of the certificate, such as Common
Issuer This field displays identifying information about the certificate’s issuing certification authority,
and ;‘~!@#$%^&()_+[]{}’,.=-
Click the Refresh button to have this read-only text box display the hierarchy of certification
authorities that validate the certificate (and the certificate itself).
If the issuing certification authority is one that you have imported as a trusted certification
authority, it may be the only certification authority in the list (along with the certificate itself).
If the certificate is a self-signed certificate, the certificate itself is the only one in the list. The
NWA/WAC does not trust the certificate and displays “Not trusted” in this field if any
certificate on the path has expired or been revoked.
These read-only fields display detailed information about the certificate.
Certification Authority signed the certificate. Self-signed means that the certificate’s owner
signed the certificate (not a certification authority). “X.509” means that this certificate was
created and signed according to the ITU-T X.509 recommendation that defines the formats
for public-key certificates.
or generated by the NWA/WAC.
Name (CN), Organizational Unit (OU), Organization (O), State (ST), and Country (C).
such as Common Name, Organizational Unit, Organization and Country.
With self-signed certificates, this is the same as the Subject Name field.
characters.
“none” displays for a certification request.
Signature Algorithm This field displays the type of algorithm that was used to sign the certificate.
Valid From This field displays the date that the certificate becomes applicable. “none” displays for a
Valid To This field displays the date that the certificate expires. The text displays in red and includes
Key Algorithm This field displays the type of algorithm that was used to generate the certificate’s key pair
Subject Alternative
Name
Key Usage This field displays for what functions the certificate’s key can be used. For example,
Extended Key Usage This field displays for what EKU (Extended Key Usage) functions the certificate’s key can be
Basic Constraint This field displays general information about the certificate. For example, Subject Type=CA
certification request.
an Expired! message if the certificate has expired. “none” displays for a certification
request.
(the NWA/WAC uses RSA encryption) and the length of the key set in bits (1024 bits for
example).
This field displays the certificate owner‘s IP address (IP), domain name (DNS) or e-mail
address (EMAIL).
“DigitalSignature” means that the key can be used to sign certificates and
“KeyEncipherment” means that the key can be used to encrypt text.
used.
means that this is a certification authority’s certificate and “Path Length Constraint=1”
means that there can only be one certification authority in the certificate’s path. This field
does not display for a certification request.
NWA / WAC Series User’s Guide
124
Chapter 11 Certificates
Table 59 Configuration > Object > Certificate > My Certificates > Edit
LABEL DESCRIPTION
MD5 Fingerprint This is the certificate’s message digest that the NWA/WAC calculated using the MD5
algorithm.
SHA1 Fingerprint This is the certificate’s message digest that the NWA/WAC calculated using the SHA1
algorithm.
Certificate in PEM
(Base-64) Encoded
Format
Export Certificate
Only
Password If you want to export the certificate with its private key, create a password and type it here.
Export Certificate
with Private Key
OK Click OK to save your changes back to the NWA/WAC. You can only change the name.
Cancel Click Cancel to quit and return to the My Certificates screen.
This read-only text box displays the certificate or certification request in Privacy Enhanced
Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a
binary certificate into a printable form.
You can copy and paste a certification request into a certification authority’s web page,
an e-mail that you send to the certification authority or a text editor and save the file on a
management computer for later manual enrollment.
You can copy and paste a certificate into an e-mail to send to friends or colleagues or you
can copy and paste a certificate into a text editor and save the file on a management
computer for later distribution (via floppy disk for example).
Use this button to save a copy of the certificate without its private key. Click this button and
then Save in the File Download screen. The Save As screen opens, browse to the location
that you want to use and click Save.
Make sure you keep this password in a safe place. You will need to use it if you import the
certificate to another device.
Use this button to save a copy of the certificate with its private key. Type the certificate’s
password and click this button. Click Save in the File Download screen. The Save As screen
opens, browse to the location that you want to use and click Save.
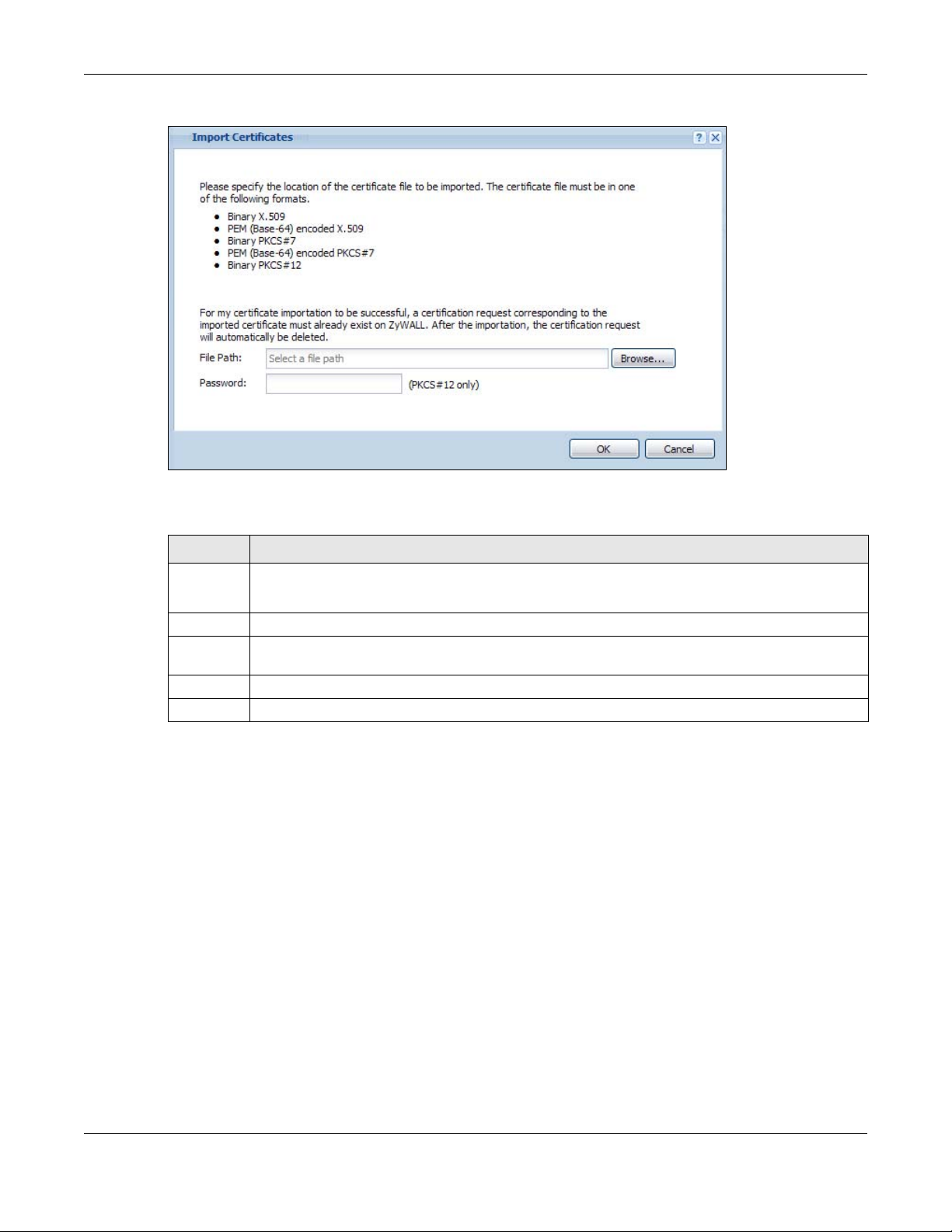
11.2.3 Import Certificates
Click Configuration > Object > Certificate > My Certificates > Import to open the My Certificate Import
screen. Follow the instructions in this screen to save an existing certificate to the NWA/WAC.
Note: You can import a certificate that matches a corresponding certification request that
was generated by the NWA/WAC. You can also import a certificate in PKCS#12 format,
including the certificate’s public and private keys.
The certificate you import replaces the corresponding request in the My Certificates screen.
You must remove any spaces in the certificate’s filename before you can import it.
NWA / WAC Series User’s Guide
125
Chapter 11 Certificates
Figure 70 Configuration > Object > Certificate > My Certificates > Import
The following table describes the labels in this screen.
Table 60 Configuration > Object > Certificate > My Certificates > Import
LABEL DESCRIPTION
File Path Type in the location of the file you want to upload in this field or click Browse to find it.
You cannot import a certificate with the same name as a certificate that is already in the NWA/WAC.
Browse Click Browse to find the certificate file you want to upload.
Password This field only applies when you import a binary PKCS#12 format file. Type the file’s password that was
created when the PKCS #12 file was exported.
OK Click OK to save the certificate on the NWA/WAC.
Cancel Click Cancel to quit and return to the My Certificates screen.
11.3 Trusted Certificates
Click Configuration > Object > Certificate > Trusted Certificates to open the Trusted Certificates screen.
This screen displays a summary list of certificates that you have set the NWA/WAC to accept as trusted.
The NWA/WAC also accepts any valid certificate signed by a certificate on this list as being trustworthy;
thus you do not need to import any certificate that is signed by one of these certificates.
NWA / WAC Series User’s Guide
126
Chapter 11 Certificates
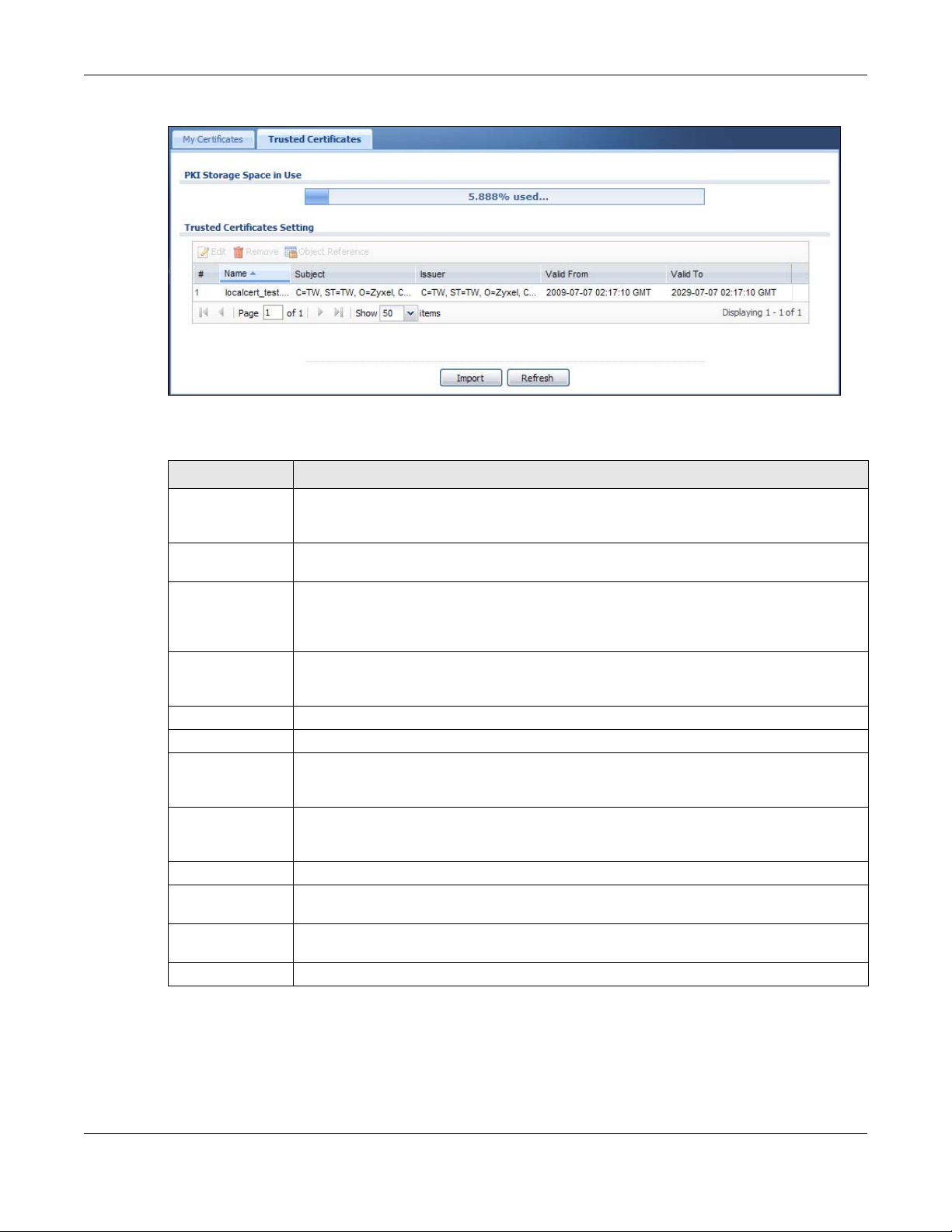
Figure 71 Configuration > Object > Certificate > Trusted Certificates
The following table describes the labels in this screen.
Table 61 Configuration > Object > Certificate > Trusted Certificates
LABEL DESCRIPTION
PKI Storage Space
in Use
Edit Double-click an entry or select it and click Edit to open a screen with an in-depth list of
Remove The NWA/WAC keeps all of your certificates unless you specifically delete them. Uploading a
Object Reference You cannot delete certificates that any of the NWA/WAC’s features are configured to use.
# This field displays the certificate index number. The certificates are listed in alphabetical order.
Name This field displays the name used to identify this certificate.
Subject This field displays identifying information about the certificate’s owner, such as CN (Common
Issuer This field displays identifying information about the certificate’s issuing certification authority,
Valid From This field displays the date that the certificate becomes applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes an
Import Click Import to open a screen where you can save the certificate of a certification authority
Refresh Click this button to display the current validity status of the certificates.
This bar displays the percentage of the NWA/WAC’s PKI storage space that is currently in use.
When the storage space is almost full, you should consider deleting expired or unnecessary
certificates before adding more certificates.
information about the certificate.
new firmware or default configuration file does not delete your certificates. To remove an
entry, select it and click Remove. The NWA/WAC confirms you want to remove it before doing
so. Subsequent certificates move up by one when you take this action.
Select an entry and click Object Reference to open a screen that shows which settings use the
entry.
Name), OU (Organizational Unit or department), O (Organization or company) and C
(Country). It is recommended that each certificate have unique subject information.
such as a common name, organizational unit or department, organization or company and
country. With self-signed certificates, this is the same information as in the Subject field.
Expired! message if the certificate has expired.
that you trust, from your computer to the NWA/WAC.
11.3.1 Edit Trusted Certificates
Click Configuration > Object > Certificate > Trusted Certificates and then a certificate’s Edit icon to open
the Trusted Certificates Edit screen. Use this screen to view in-depth information about the certificate,
NWA / WAC Series User’s Guide
127
Chapter 11 Certificates
change the certificate’s name and set whether or not you want the NWA/WAC to check a certification
authority’s list of revoked certificates before trusting a certificate issued by the certification authority.
Figure 72 Configuration > Object > Certificate > Trusted Certificates > Edit
NWA / WAC Series User’s Guide
128
Chapter 11 Certificates
The following table describes the labels in this screen.
Table 62 Configuration > Object > Certificate > Trusted Certificates > Edit
LABEL DESCRIPTION
Name This field displays the identifying name of this certificate. You can change the name. You
Certification Path Click the Refresh button to have this read-only text box display the end entity’s certificate
Refresh Click Refresh to display the certification path.
Enable X.509v3 CRL
Distribution Points
and OCSP checking
OCSP Server Select this check box if the directory server uses OCSP (Online Certificate Status Protocol).
URL Type the protocol, IP address and pathname of the OCSP server.
ID The NWA/WAC may need to authenticate itself in order to assess the OCSP server. Type the
Password Type the password (up to 31 ASCII characters) from the entity maintaining the OCSP server
LDAP Server Select this check box if the directory server uses LDAP (Lightweight Directory Access
Address Type the IP address (in dotted decimal notation) of the directory server.
Port Use this field to specify the LDAP server port number. You must use the same server port
ID The NWA/WAC may need to authenticate itself in order to assess the CRL directory server.
Password Type the password (up to 31 ASCII characters) from the entity maintaining the CRL directory
Certificate
Information
Type This field displays general information about the certificate. CA-signed means that a
Version This field displays the X.509 version number.
Serial Number This field displays the certificate’s identification number given by the certification authority.
Subject This field displays information that identifies the owner of the certificate, such as Common
Issuer This field displays identifying information about the certificate’s issuing certification authority,
Signature Algorithm This field displays the type of algorithm that was used to sign the certificate. Some
can use up to 31 alphanumeric and ;‘~!@#$%^&()_+[]{}’,.=-
and a list of certification authority certificates that shows the hierarchy of certification
authorities that validate the end entity’s certificate. If the issuing certification authority is one
that you have imported as a trusted certificate, it may be the only certification authority in
the list (along with the end entity’s own certificate). The NWA/WAC does not trust the end
entity’s certificate and displays “Not trusted” in this field if any certificate on the path has
expired or been revoked.
Select this check box to have the NWA/WAC check incoming certificates that are signed
by this certificate against a Certificate Revocation List (CRL) or an OCSP server. You also
need to configure the OSCP or LDAP server details.
login name (up to 31 ASCII characters) from the entity maintaining the server (usually a
certification authority).
(usually a certification authority).
Protocol). LDAP is a protocol over TCP that specifies how clients access directories of
certificates and lists of revoked certificates.
number that the directory server uses. 389 is the default server port number for LDAP.
Type the login name (up to 31 ASCII characters) from the entity maintaining the server
(usually a certification authority).
server (usually a certification authority).
These read-only fields display detailed information about the certificate.
Certification Authority signed the certificate. Self-signed means that the certificate’s owner
signed the certificate (not a certification authority). X.509 means that this certificate was
created and signed according to the ITU-T X.509 recommendation that defines the formats
for public-key certificates.
Name (CN), Organizational Unit (OU), Organization (O) and Country (C).
such as Common Name, Organizational Unit, Organization and Country.
With self-signed certificates, this is the same information as in the Subject Name field.
certification authorities use rsa-pkcs1-sha1 (RSA public-private key encryption algorithm and
the SHA1 hash algorithm). Other certification authorities may use rsa-pkcs1-md5 (RSA
public-private key encryption algorithm and the MD5 hash algorithm).
characters.
NWA / WAC Series User’s Guide
129
Chapter 11 Certificates
Table 62 Configuration > Object > Certificate > Trusted Certificates > Edit (continued)
LABEL DESCRIPTION
Valid From This field displays the date that the certificate becomes applicable. The text displays in red
and includes a Not Yet Valid! message if the certificate has not yet become applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes
an Expiring! or Expired! message if the certificate is about to expire or has already expired.
Key Algorithm This field displays the type of algorithm that was used to generate the certificate’s key pair
Subject Alternative
Name
Key Usage This field displays for what functions the certificate’s key can be used. For example,
Basic Constraint This field displays general information about the certificate. For example, Subject Type=CA
MD5 Fingerprint This is the certificate’s message digest that the NWA/WAC calculated using the MD5
SHA1 Fingerprint This is the certificate’s message digest that the NWA/WAC calculated using the SHA1
Certificate This read-only text box displays the certificate or certification request in Privacy Enhanced
Export Certificate Click this button and then Save in the File Download screen. The Save As screen opens,
OK Click OK to save your changes back to the NWA/WAC. You can only change the name.
Cancel Click Cancel to quit and return to the Trusted Certificates screen.
(the NWA/WAC uses RSA encryption) and the length of the key set in bits (1024 bits for
example).
This field displays the certificate’s owner‘s IP address (IP), domain name (DNS) or e-mail
address (EMAIL).
“DigitalSignature” means that the key can be used to sign certificates and
“KeyEncipherment” means that the key can be used to encrypt text.
means that this is a certification authority’s certificate and “Path Length Constraint=1”
means that there can only be one certification authority in the certificate’s path.
algorithm. You can use this value to verify with the certification authority (over the phone for
example) that this is actually their certificate.
algorithm. You can use this value to verify with the certification authority (over the phone for
example) that this is actually their certificate.
Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a
binary certificate into a printable form.
You can copy and paste the certificate into an e-mail to send to friends or colleagues or
you can copy and paste the certificate into a text editor and save the file on a
management computer for later distribution (via floppy disk for example).
browse to the location that you want to use and click Save.
11.3.2 Import Trusted Certificates
Click Configuration > Object > Certificate > Trusted Certificates > Import to open the Import Trusted
Certificates screen. Follow the instructions in this screen to save a trusted certificate to the NWA/WAC.
Note: You must remove any spaces from the certificate’s filename before you can import the
certificate.
NWA / WAC Series User’s Guide
130
 Loading...
Loading...