Page 1
TL-ER6020
SafeStream
TM
Gigabit Dual-WAN VPN Router
Rev: 1.0.0
1910010695
Page 2
COPYRIGHT & TRADEMARKS
Specifications are subject to change without notice. is a registered trademark of
TP-LINK TECHNOLOGIES CO., LTD. Other brands and product names are trademarks of their
respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make any
derivative such as translation, transformation, or adaptation without permission from TP-LINK
TECHNOLOGIES CO., LTD. Copyright © 2012 TP-LINK TECHNOLOGIES CO., LTD. All rights
reserved.
http://www.tp-link.com
FCC STATEMENT
This equipment has been tested and found to comply with the limits for a Class A digital device,
pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable protection
against harmful interference when the equipment is operated in a commercial environment. This
equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in
accordance with the instruction manual, may cause harmful interference to radio communications.
Operation of this equipment in a residential area is likely to cause harmful interference in which case
the user will be required to correct the interference at his own expense.
This device complies with part 15 of the FCC Rules. Operation is subject to the following two
conditions:
1) This device may not cause harmful interference.
2) This device must accept any interference received, including interference that may cause
undesired operation.
Any changes or modifications not expressly approved by the party responsible for compliance could
void the user’s authority to operate the equipment.
CE Mark Warning
This is a class A product. In a domestic environment, this product may cause radio interference, in
which case the user may be required to take adequate measures.
-I-
Page 3

CONTENTS
Package Contents..................................................................................................................1
Chapter 1 About this Guide
1.1 Intended Readers ..................................................................................................................2
1.2 Conventions ...........................................................................................................................2
1.3 Overview of this Guide...........................................................................................................2
Chapter 2 Introduction
2.1 Overview of the Router ..........................................................................................................4
2.2 Features.................................................................................................................................5
2.3 Appearance............................................................................................................................6
2.3.1 Front Panel ................................................................................................................6
2.3.2 Rear Panel.................................................................................................................8
Chapter 3 Configuration
3.1 Network..................................................................................................................................9
...................................................................................................2
..........................................................................................................4
........................................................................................................9
3.1.1 Status.........................................................................................................................9
3.1.2 System Mode.............................................................................................................9
3.1.3 WAN ........................................................................................................................12
3.1.4 LAN..........................................................................................................................29
3.1.5 DMZ.........................................................................................................................32
3.1.6 MAC Address...........................................................................................................34
3.1.7 Switch ......................................................................................................................36
3.2 User Group ..........................................................................................................................42
3.2.1 Group.......................................................................................................................43
3.2.2 User .........................................................................................................................43
3.2.3 View.........................................................................................................................44
3.3 Advanced .............................................................................................................................45
3.3.1 NAT..........................................................................................................................45
3.3.2 Traffic Control ..........................................................................................................54
-II-
Page 4

3.3.3 Session Limit ...........................................................................................................58
3.3.4 Load Balance...........................................................................................................59
3.3.5 Routing ....................................................................................................................64
3.4 Firewall.................................................................................................................................69
3.4.1 Anti ARP Spoofing ...................................................................................................69
3.4.2 Attack Defense ........................................................................................................72
3.4.3 MAC Filtering ...........................................................................................................74
3.4.4 Access Control.........................................................................................................75
3.4.5 App Control..............................................................................................................81
3.5 VPN......................................................................................................................................83
3.5.1 IKE...........................................................................................................................83
3.5.2 IPsec........................................................................................................................87
3.5.3 L2TP/PPTP..............................................................................................................94
3.6 Services ...............................................................................................................................98
3.6.1 PPPoE Server..........................................................................................................98
3.6.2 E-Bulletin ...............................................................................................................104
3.6.3 Dynamic DNS ........................................................................................................106
3.6.4 UPnP .....................................................................................................................112
3.7 Maintenance ......................................................................................................................113
3.7.1 Admin Setup .......................................................................................................... 113
3.7.2 Management..........................................................................................................
3.7.3 License ..................................................................................................................118
3.7.4 Statistics.................................................................................................................119
116
3.7.5 Diagnostics ............................................................................................................121
3.7.6 Time.......................................................................................................................124
3.7.7 Logs.......................................................................................................................125
Chapter 4 Application
4.1 Network Requirements.......................................................................................................127
........................................................................................................127
-III-
Page 5

4.2 Network Topology...............................................................................................................128
4.3 Configurations....................................................................................................................128
4.3.1 Internet Setting ......................................................................................................128
4.3.2 VPN Setting ...........................................................................................................130
4.3.3 Network Management............................................................................................136
4.3.4 Network Security....................................................................................................140
Chapter 5 CLI
5.1 Configuration......................................................................................................................146
5.2 Interface Mode ...................................................................................................................149
5.3 Online Help ........................................................................................................................150
5.4 Command Introduction.......................................................................................................152
Appendix A Hardware Specifications
....................................................................................................................146
5.4.1 ip............................................................................................................................152
5.4.2 ip-mac....................................................................................................................152
5.4.3 sys .........................................................................................................................153
5.4.4 user........................................................................................................................154
5.4.5 history ....................................................................................................................155
5.4.6 exit .........................................................................................................................156
..................................................................................157
Appendix B FAQ
Appendix C Glossary
................................................................................................................158
.........................................................................................................160
-IV-
Page 6
Package Contents
The following items should be found in your package:
One TL-ER6020 Router
One Power Cord
One Console Cable
Two mounting brackets and other fittings
Installation Guide
Resource CD
Note:
Make sure that the package contains the above items. If any of the listed items is damaged or missing,
please contact with your distributor.
-1-
Page 7
Chapter 1 About this Guide
This User Guide contains information for setup and management of TL-ER6020 Router. Please read
this guide carefully before operation.
1.1 Intended Readers
This Guide is intended for Network Engineer and Network Administrator.
1.2 Conventions
In this Guide the following conventions are used:
The Router or TL-ER6020 mentioned in this Guide stands for TL-ER6020 SafeStream
Dual-WAN VPN Router without any explanation.
Menu Name→Submenu Name→Tab page indicates the menu structure. Advanced→NAT
→Basic NAT means the Basic NAT page under the NAT menu option that is located under the
Advanced menu.
Bold font indicates a toolbar icon, menu or menu item.
<Font> indicate a button.
Symbols in this Guide:
Symbol Description
Ignoring this type of note might result in a malfunction or damage to the
Note:
Tips:
device.
This format indicates important information that helps you make better use of
your device.
TM
Gigabit
1.3 Overview of this Guide
Chapter 1 About This Guide Introduces the guide structure and conventions.
Chapter 2 Introduction Introduces the features an
Chapter 3 Configurations Introduces how to configure the Router via Web management page.
Chapter 4 Application Introduces the practical application of the Router on the enterprise
network.
Chapter5 CLI Introduces how to log in and set up the Router using CLI commands by
console port.
-2-
d appearance of TL-ER6020 router.
Page 8

Appendix A Hardware
Lists the hardware specifications of this Router.
Specifications
Appendix B FAQ Provides the possible solutions to the problems that may occur during
the installation and operation of the router.
Appendix C Glossary Lists the glossary used in this guide.
-3-
Page 9

Chapter 2 Introduction
Thanks for choosing the SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020.
2.1 Overview of the Router
The SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020 from TP-LINK possesses excellent
data processing capability and multiple powerful functions including IPsec/PPTP/L2TP VPN, Load
Balance, Access Control, Bandwidth Control, Session Limit, IM/P2P Blocking, PPPoE Server and so
on, which consumedly meet the needs of small and medium enterprise, hotels and communities with
volumes of users demanding a efficient and easy-to-manage network with high security.
Powerful Data Processing Capability
+ Built-in ARM 32 network processor and 128MB DDRII high-speed RAM allows the stability and
reliability for operation.
Virtual Private Network (VPN)
+ Providing comprehensive IPsec VPN with DES/3DES/AES encryptions, MD5/SHA1
identifications and automatically/manually IKE Pre-Share Key exchanges.
+ Supporting PPTP/L2TP VPN Server mode to allow the staff on business or remote branch office
to access the headquarter network.
Online Behavior Management
+ Complete Functions of Access Rules can allow managers to select the network service levels to
block or allow applications of FTP downloading, Email, Web browsing and so on.
+ Deploying One-Click restricting of IM/P2P applications to save time & energy while reserving
exceptional groups for certain users.
+ Supporting URL Filtering to prevent potential hazards from visiting the malicious Web sites.
Powerful Firewall
+ Supporting One-Click IP-MAC Binding to avoid ARP spoofing and guarantee a network without
stagnation.
+ Featured Attack Defense to protect the network from a variety of flood attack and packet
anomaly attack.
+ Possessing MAC Filtering function to block the access of illegal hosts.
Flexible Traffic Control
+ Featured Bandwidth Control with flexible bandwidth management to automatically control the
bandwidth of the host in bi-direction to avoid bandwidth over occupation, as well as optimize
bandwidth usage.
+ Supporting Session Limit to avoid the complaint of a few people to force whole sessions.
-4-
Page 10

Dual-WAN Ports
+ Providing two 10/100/1000M WAN ports for users to connect two Internet lines for bandwidth
expansion.
+ Supporting multiple Load Balance modes, including Bandwidth Based Balance Routing,
Application Optimized Routing, and Policy Routing to optimize bandwidth usage.
+ Featured Link Backup to switch all the new sessions from dropped line automatically to another
for keeping an always on-line network.
Easy-to-use
+ Providing easy-to-use GUI with clear configuration steps and detailed help information for the
users to configure the Router simply.
+ Helping administrators to monitor the whole network status and take actions to malfunctions
according to the recorded log information.
+ Supporting remote management to manage the Router from remote places.
2.2 Features
Hardware
2 gigabit WAN ports, 2 gigabit LAN ports, 1 gigabit LAN/DMZ port and 1 Console port
Built-in high-quality power supply with non-fan system design for quietness
Possesses standard-sized, 19-inch outfit for standard rack
Supports Professional 4kV common mode
Complies with IEEE 802.3, IEEE 802.3u, IEEE 802.3ab standards
Supports AH, ESP, IKE, PPP protocols
Supports TCP/IP, DHCP, ICMP, NAT, NAPT protocols
Supports PPPoE, SNTP, HTTP, DDNS, UPnP, NTP protocols
Basic Functions
Supports Static IP, Dynamic IP, PPPoE/Russian PPPoE, L2TP/Russian L2TP, PPTP/Russian
lightning protection
PPTP, Dual Access, BigPond Internet connections
Supports Virtual Server, Port Triggering, ALG, Static Route and RIP v1/v2
Built-in Switch supporting Port Mirror, Port VLAN, Rate Control and so on
Supports to change the MAC address of LAN, WAN, DMZ port
Supports Logs, Statistics, Time setting
Supports Remote and Web management
-5-
Page 11
Supports Diagnostic (Ping/Tracert) and Online Detection
VPN
Supports IPsec VPN and provides up to 50 IPsec VPN tunnels
Supports IPSec VPN in LAN-to-LAN or Client-to-LAN
Provides DES, 3DES, AES128, AES152, AES256 encryption, MD5, SHA1 authentication
Supports IKE Pre-Share Key and DH1/DH2/DH5 Key Exchanges
Supports PPTP/L2TP Server/Client
Traffic Control
Supports Bandwidth Control
Supports Session Limit
Security
Built-in firewall supporting URL/MAC Filtering
Supports Access Control
Supports Attack Defense
Supports IP-MAC Binding
Supports GARP (Gratuitous ARP)
Deploys One-Click restricting of IM/P2P applications
2.3 Appearance
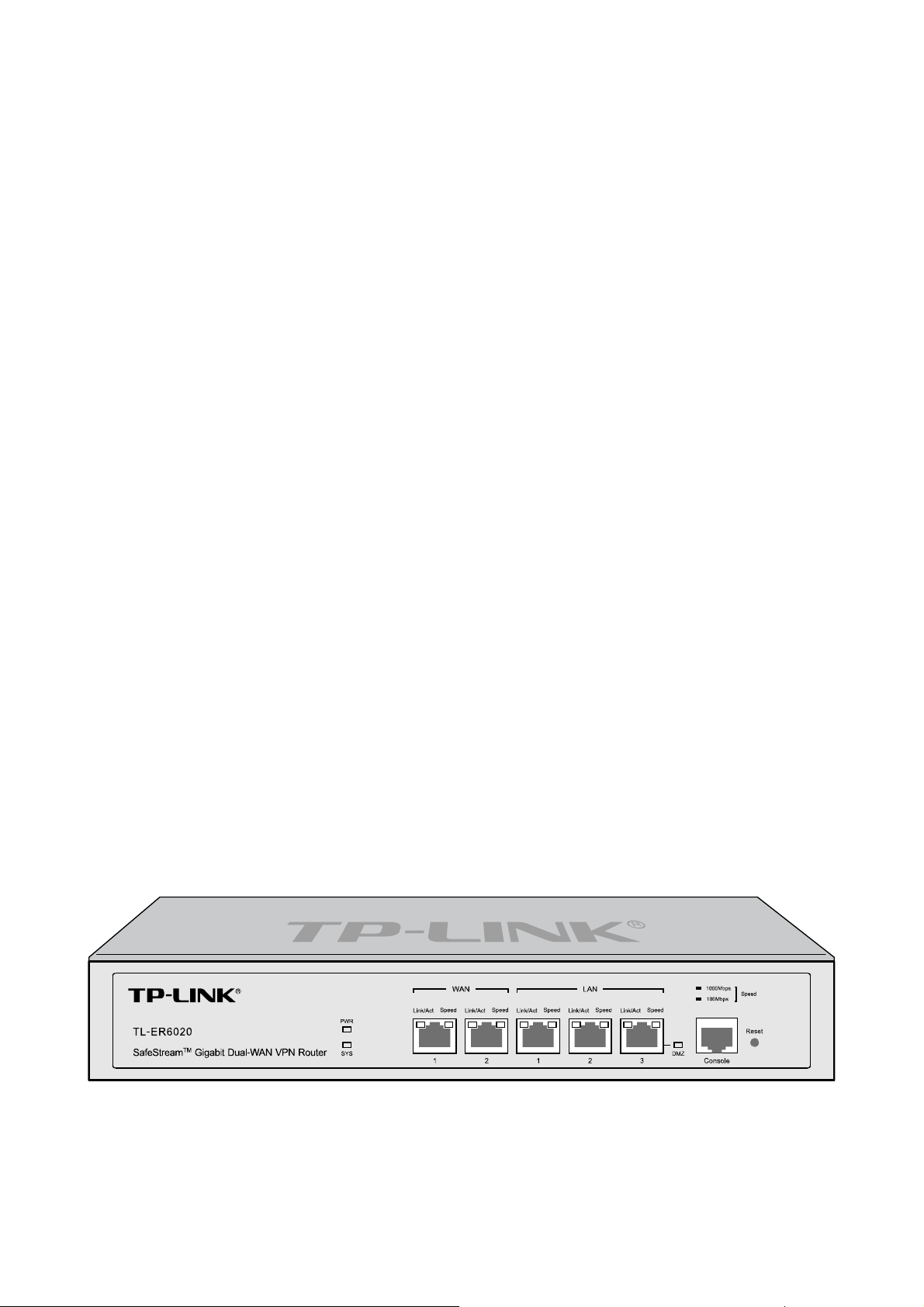
2.3.1 Front Panel
The front panel of TL-ER6020 is shown as the following figure.
-6-
Page 12
LEDs
LED Status Indication
On The Router is powered on
PWR
Off The Router is powered off or power supply is abnormal
Flashing The Router works properly
SYS
On/Off The Router works improperly
On There is a device linked to the corresponding port
Link/Act
Off There is no device linked to the corresponding port
Flashing The corresponding port is transmitting or receiving data
On (Green) The linked device is running at 1000Mbps
Speed
On (Yellow) The linked device is running at 100Mbps
Off
There is no device linked to the corresponding port or the
linked device is running at 10Mbps
On The port is working in DMZ mode
DMZ
Off The port is working in LAN mode
Interface Description
Interface Port Description
WAN 1~2
The WAN port is for connecting the Router to a DSL/Cable
modem or Ethernet by the RJ45 cable
LAN 1~3
The LAN port is for connecting the Router to the local PCs or
switches by the RJ45 cable
DMZ 3 The DMZ port is for connecting the Router to the servers
Console N/A
Reset button
The Console port is for connecting with the serial port of a
computer or terminal to monitor and configure the Router
Use the button to restore the Router to the factory defaults. With the Router powered on, use a pin to
press and hold the Reset button (about 4~5 seconds). After the SYS LED goes out, release the Reset
button. If the SYS LED is flashing with a high frequency about two or three seconds, it means the Router
is restored successfully.
-7-
Page 13
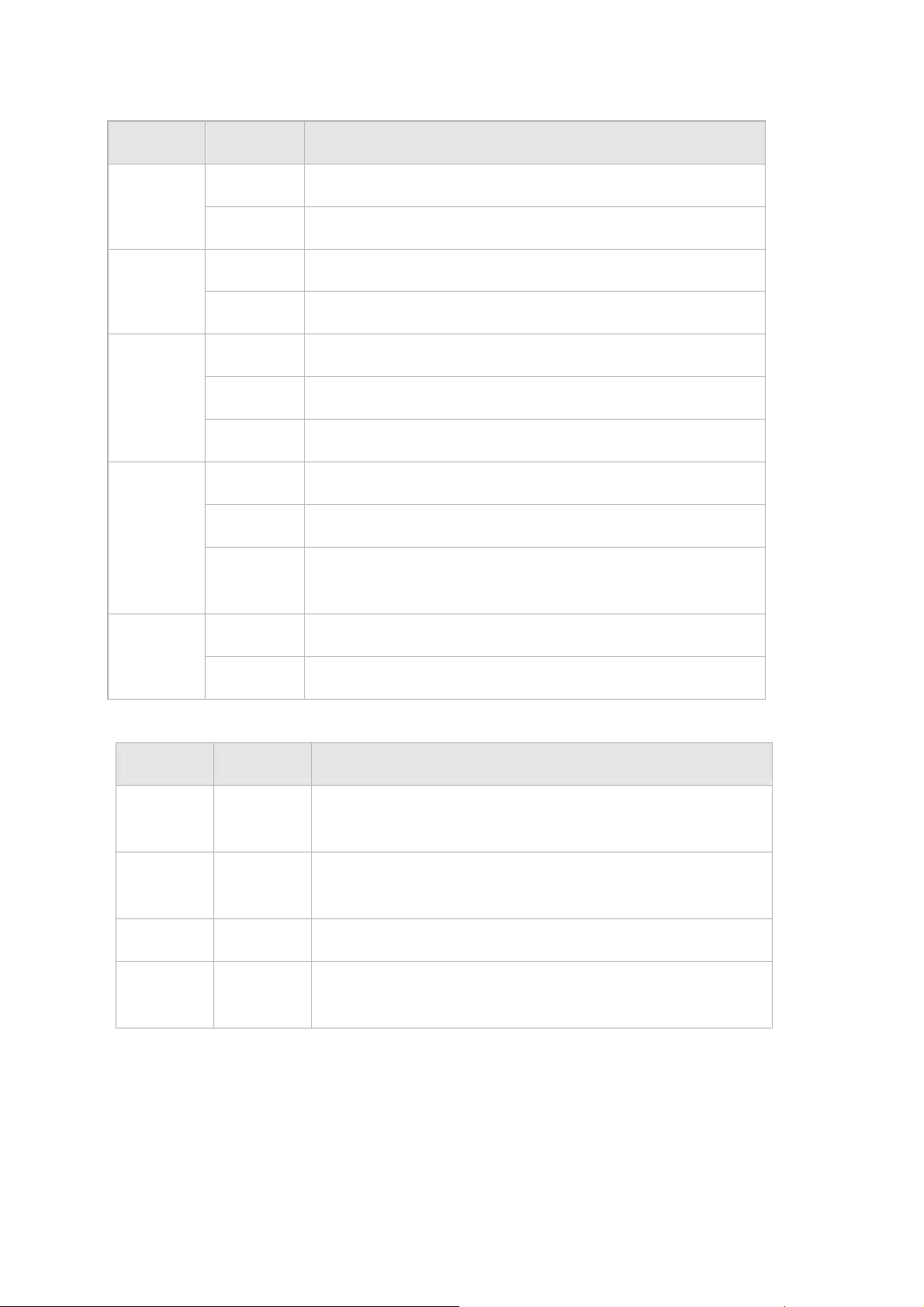
2.3.2 Rear Panel
The rear panel of TL-ER6020 is shown as the following figure.
Power Socket
Connect the female connector of the power cord to this power socket, and the male connector to the AC
power outlet. Please make sure the voltage of the power supply meets the requirement of the input
voltage (100-240V~ 50/60Hz).
Grounding Terminal
The Router already comes with lightning protection mechanism. You can also ground the Router through
the PE (Protecting Earth) cable of AC cord or with Ground Cable.
Kensington Security Slot
The Router provides one security slot.
Note:
Please use only the power cord provided with this Router.
-8-
Page 14
Chapter 3 Configuration
3.1 Network
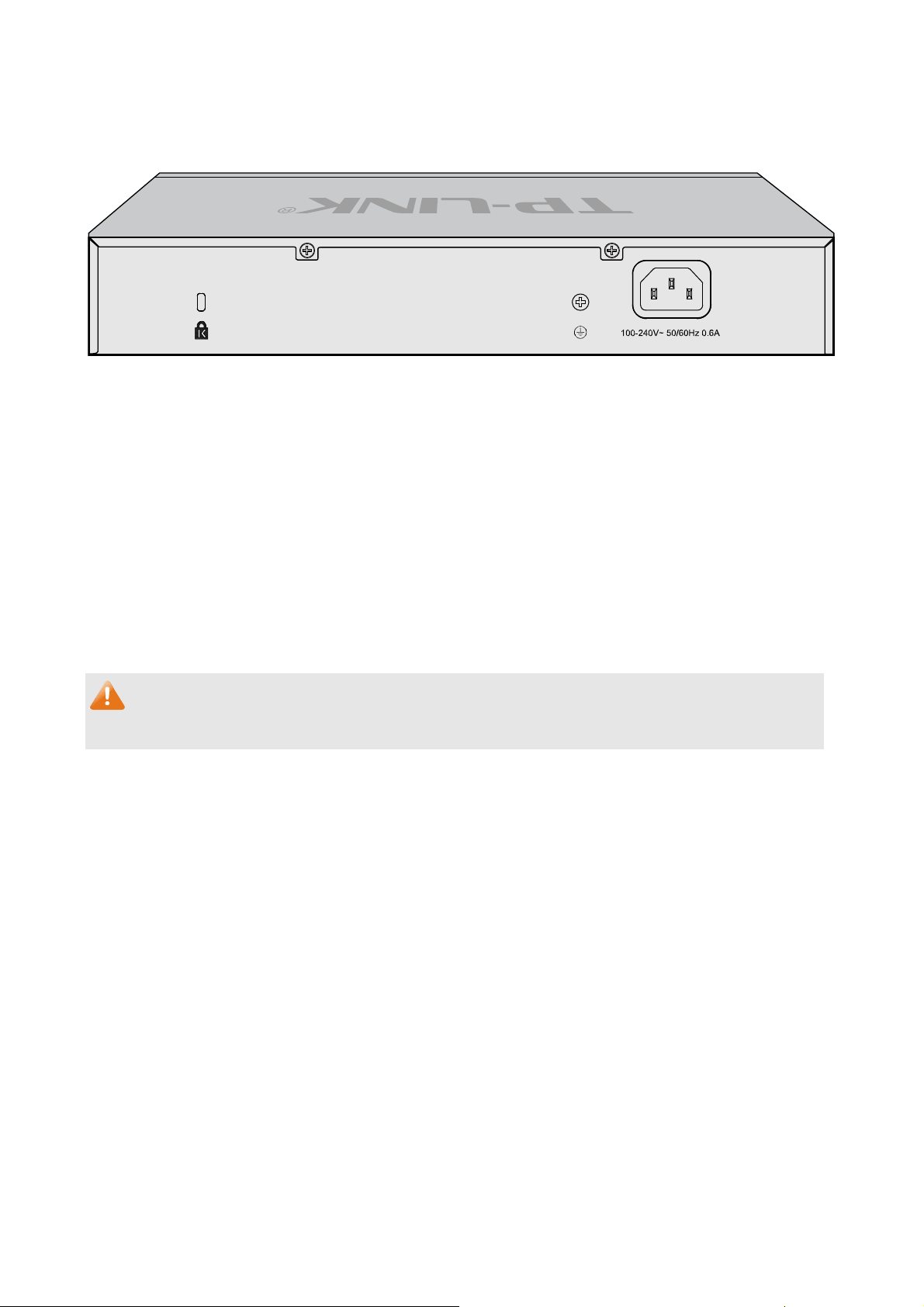
3.1.1 Status
The Status page shows the system information, the port connection status and other information
related to this Router.
Choose the menu Network→Status to load the following page.
Figure 3-1 Status
3.1.2 System Mode
The TL-ER6020 Router can work in three modes: NAT, Non-NAT and Classic.
If your Router is hosting your local network’s connection to the Internet with a network topology as the
Figure 3-2 shown, you can set it to NAT mode.
-9-
Page 15
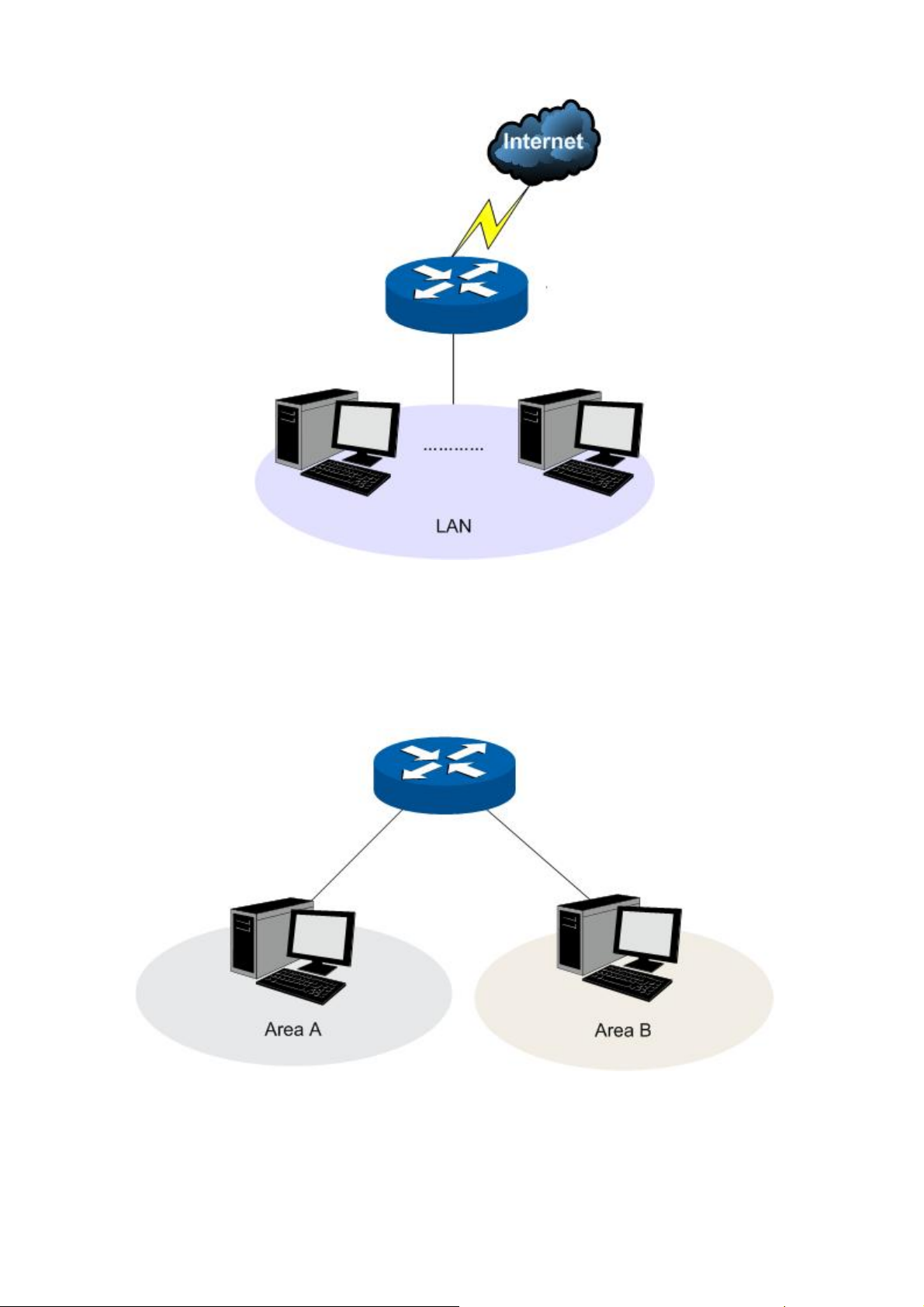
Figure 3-2 Network Topology - NAT Mode
If your Router is connecting the two networks of different areas in a large network environment with a
network topology as the Figure 3-3 shown, and forwards the packets betwe
en these two networks by
the Routing rules, you can set it to Non-NAT mode.
Figure 3-3 Network Topology – Non-NAT Mode
If your Router is connected in a combined network topology as the Figure 3-4 shown, you can set it to
Classic Mode.
-10-
Page 16

Figure 3-4 Network Topology – Classic Mode
Choose the menu Network→System Mode to load the following page.
Figure 3-5 System Mode
You can select a System Mode for your Router according to your network need.
NAT Mode
NAT (Network Address Translation) mode allows the Router to translate private IP addresses within
internal networks to public IP addresses for traffic transport over external networks, such as the
Internet. Incoming traffic is translated back for delivery within the internal network. However, the
Router will drop all the packets whose source IP addresses are in different subnet of LAN port. For
example: If the LAN port of the Router is set to 192.168.0.1 for IP address and 255.255.255.0 for the
Subnet Mask, then the subnet of LAN port is 192.168.0.0/24. The packet with 192.168.0.123 as its
source IP address can be transported by NAT, whereas the packet with 20.31.76.80 as its source IP
address will be dropped.
-11-
Page 17
Non-NAT Mode
In this mode, the Router functions as the traditional Gateway and forwards the packets via routing
protocol. The Hosts in different subnets can communicate with one another via the routing rules
whereas no NAT is employed. For example: If the DMZ port of the Router is in WAN mode, the Hosts
in the subnet of DMZ port can access the servers in Internet only when the Static Router rules permit.
Note:
In Non-NAT mode, all the NAT forwarding rules will be disabled.
Classic Mode
It's the combined mode of NAT mode and Non-NAT mode. In Classic mode, the Router will first
transport the packets which are compliant with NAT forwarding rules and then match the other packets
to the static routing rules. The matched packets will be transmitted based on the static routing rules
and the unmatched ones will be dropped. In this way, the Router can implement NAT for the packets
without blocking the packets in the different subnet of the ports.
3.1.3 WAN
TL-ER6020 provides the following six Internet connection types: Static IP, Dynamic IP, PPPoE/Russian
PPPoE, L2TP/Russian L2TP, PPTP/Russian PPTP and BigPond. To configure the WAN, please first
select the type of Internet connection provided by your ISP (Internet Service Provider).
Tips:
It’s allowed to set the IP addresses of both the WAN ports within the same subnet. However, to
guarantee a normal communication, make sure that the WAN ports can access the same network,
such as Internet or a local area network.
Choose the menu Network→WAN to load the configuration page.
1) Static IP
If a static IP address has been provided by your ISP, please choose the Static IP connection type to
configure the parameters for WAN port manually.
-12-
Page 18
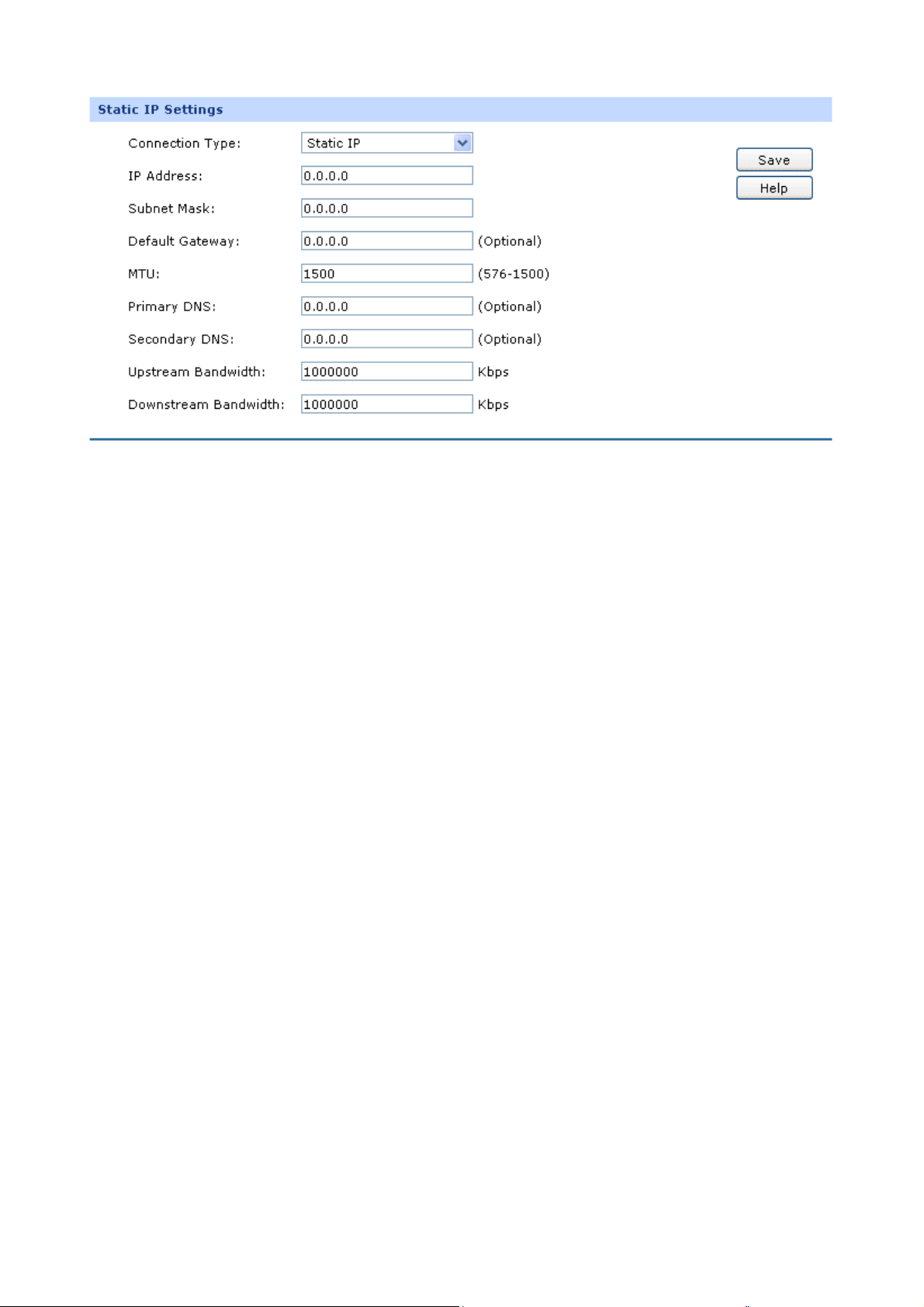
Figure 3-6 WAN – Static IP
The following items are displayed on this screen:
Static IP
Connection Type:
IP Address:
Subnet Mask:
Default Gateway:
MTU:
Select Static IP if your ISP has assigned a static IP address for your
computer.
Enter the IP address assigned by your ISP. If you are not clear,
please consult your ISP.
Enter the Subnet Mask assigned by your ISP.
Optional. Enter the Gateway assigned by your ISP.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1500. The default MTU is 1500. It is recommended to keep the
default value if no other MTU value is provided by your ISP.
Primary DNS:
Secondary DNS:
Enter the IP address of your ISP’s Primary DNS (Domain Name
Server). If you are not clear, please consult your ISP. It’s not allowed
to access the Internet via domain name if the Primary DNS field is
blank.
Optional. If a Secondary DNS Server address is available, enter it.
-13-
Page 19
Upstream Bandwidth:
Downstream
Specify the bandwidth for transmitting packets on the port.
Specify the bandwidth for receiving packets on the port.
Bandwidth:
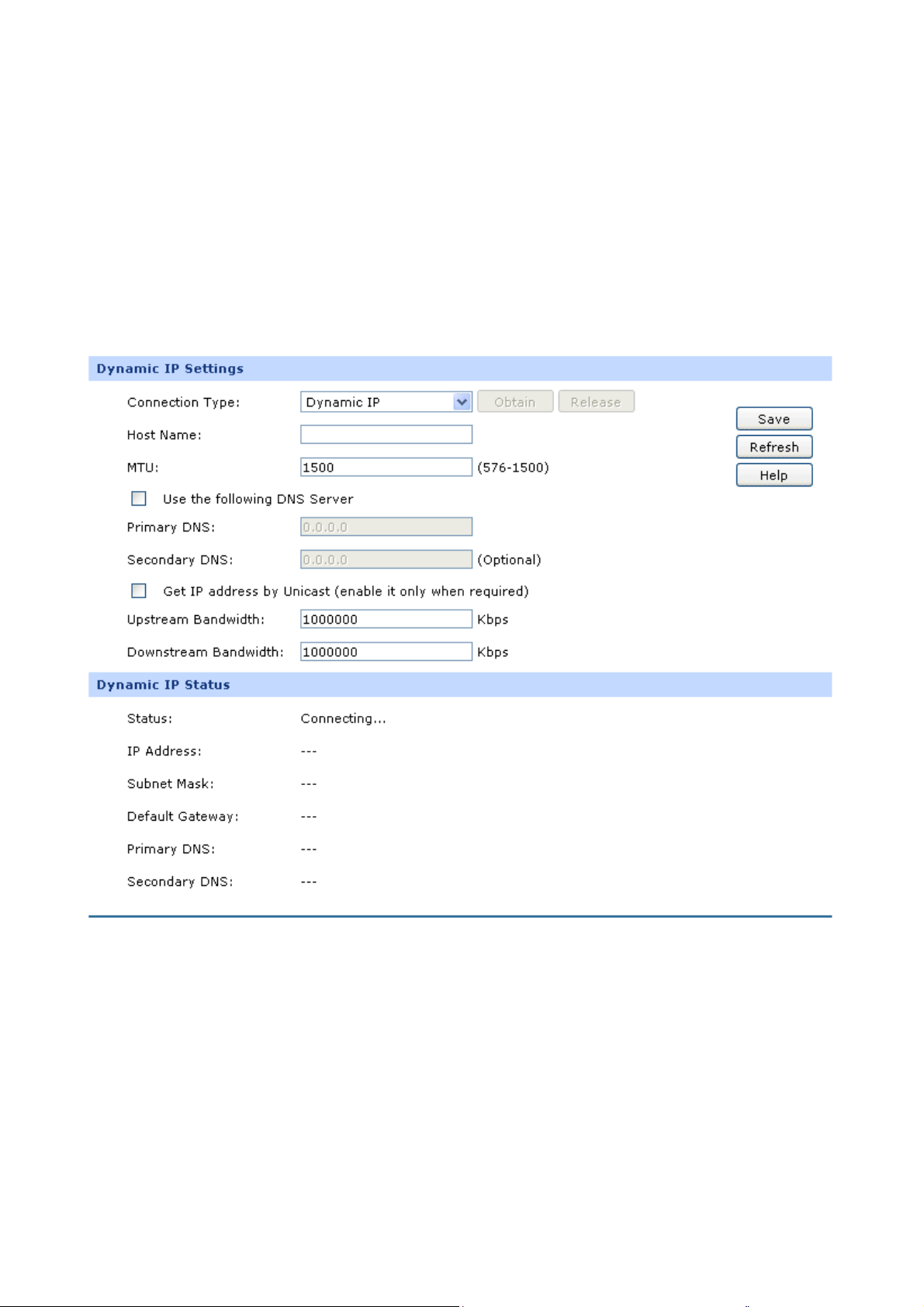
2) Dynamic IP
If your ISP (Internet Service Provider) assigns the IP address automatically, please choose the
Dynamic IP connection type to obtain the parameters for WAN port automatically.
Figure 3-7 WAN – Dynamic IP
The following items are displayed on this screen:
-14-
Page 20

Dynamic IP
Connection Type:
Host Name:
MTU:
Get IP Address by
Unicast:
Select Dynamic IP if your ISP assigns the IP address
automatically. Click <Obtain> to get the IP address from your
ISP’s server. Click <Release> to release the current IP address of
WAN port.
Optional. This field allows you to give a name for the Router. It's
blank by default.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1500. The default MTU is 1500. It is recommended to keep
the default value if no other MTU value is provided by your ISP.
The broadcast requirement may not be supported by a few ISPs.
Select this option if you can not get the IP address from your ISP
even if with a normal network connection. This option is not
required generally.
Use the following DNS
Server:
Primary DNS:
Select this option to enter the DNS (Domain Name Server)
address manually.
Enter the IP address of your ISP’s Primary DNS (Domain Name
Server). If you are not clear, please consult your ISP.
Secondary DNS:
Optional. If a Secondary DNS Server address is available, enter
it.
Upstream Bandwidth:
Downstream
Specify the bandwidth for transmitting packets on the port.
Specify the bandwidth for receiving packets on the port.
Bandwidth:
-15-
Page 21

Dynamic IP Status
Status:
IP Address:
Subnet Mask:
Displays the status of obtaining an IP address from your ISP.
“Disabled” indicates that the Dynamic IP connection type is not
applied.
“Connecting” indicates that the Router is obtaining the IP
parameters from your ISP.
“Connected” indicates that the Router has successfully
obtained the IP parameters from your ISP.
“Disconnected” indicates that the IP address has been
manually released or the request of the Router gets no
response from your ISP. Please check your network
connection and consult your ISP if this problem remains.
Displays the IP address assigned by your ISP.
Displays the Subnet Mask assigned by your ISP.
Gateway Address:
Primary DNS:
Secondary DNS:
Displays the Gateway Address assigned by your ISP.
Displays the IP address of your ISP’s Primary DNS.
Displays the IP address of your ISP’s Secondary DNS.
3) PPPoE
If your ISP (Internet Service Provider) has provided the account information for the PPPoE connection,
please choose the PPPoE connection type (Used mainly for DSL Internet service).
-16-
Page 22
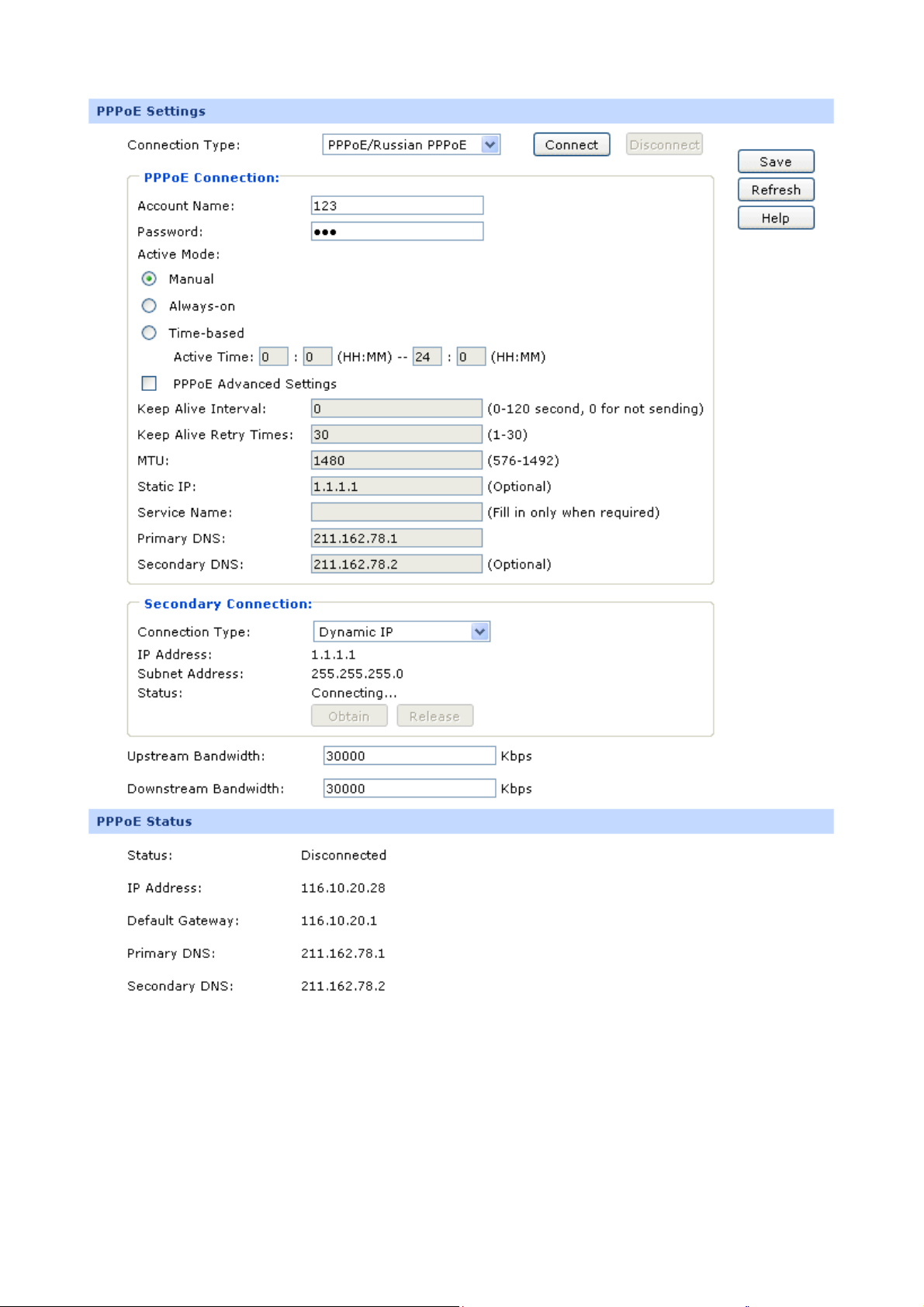
Figure 3-8 WAN - PPPoE
-17-
Page 23

The following items are displayed on this screen:
PPPoE Settings
Connection Type:
Account Name:
Password:
Active Mode:
Select PPPoE if your ISP provides xDSL Virtual Dial-up connection.
Click <Connect> to dial-up to the Internet and obtain the IP address.
Click <Disconnect> to disconnect the Internet connection and
release the current IP address.
Enter the Account Name provided by your ISP. If you are not clear,
please consult your ISP.
Enter the Password provided by your ISP.
You can select the proper Active mode according to your need.
Manual: Select this option to manually activate or terminate the
Internet connection by the <Connect> or <Disconnect> button.
It is optimum for the dial-up connection charged on time.
Always-on: Select this option to keep the connection always
on. The connection can be re-established automatically when it
PPPoE Advanced
Settings:
Keep Alive:
MTU:
is down.
Time-based: Select this option to keep the connection on
during the Active time you set.
Check here to enable PPPoE advanced settings.
Once PPPoE is connected, the Router will send keep-alive packets
every "Keep Alive Interval" sec and "Keep Alive Retry Times" to
make sure the connection is still alive. If the Router does not get the
response from ISP after sending keep-alive packets, then the
Router will terminate the connection.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1492. The default MTU is 1480. It is recommended to keep the
default value if no other MTU value is provided by your ISP.
-18-
Page 24

ISP Address:
Service Name:
Primary DNS:
Secondary DNS:
Secondary Connection:
Connection Type:
IP Address:
Optional. Enter the ISP address provided by your ISP. It's null by
default.
Optional. Enter the Service Name provided by your ISP. It's null by
default.
Enter the IP address of your ISP’s Primary DNS.
Optional. Enter the IP address of your ISP’s Secondary DNS.
Here allows you to configure the secondary connection. Dynamic IP
and Static IP connection types are provided.
Select the secondary connection type. Options include Disable,
Dynamic IP and Static IP.
If Static IP is selected, configure the IP address of WAN port. If
Subnet Address:
Status:
Upstream Bandwidth:
Downstream Bandwidth:
Dynamic IP is selected, the obtained IP address of WAN port is
displayed.
If Static IP is selected, configure the subnet address of WAN port. If
Dynamic IP is selected, the obtained subnet address of WAN port is
displayed.
Displays the status of secondary connection.
Specify the bandwidth for transmitting packets on the port.
Specify the bandwidth for receiving packets on the port.
-19-
Page 25

PPPoE Status
Status:
IP Address:
Displays the status of PPPoE connection.
“Disabled” indicates that the PPPoE connection type is not
applied.
“Connecting” indicates that the Router is obtaining the IP
parameters from your ISP.
“Connected” indicates that the Router has successfully
obtained the IP parameters from your ISP.
“Disconnected” indicates that the connection has been
manually terminated or the request of the Router has no
response from your ISP. Please ensure that your settings are
correct and your network is connected well. Consult your ISP if
this problem remains.
Displays the IP address assigned by your ISP.
Gateway Address:
Primary DNS:
Secondary DNS:
Displays the Gateway Address assigned by your ISP.
Displays the IP address of your ISP’s Primary DNS.
Displays the IP address of your ISP’s Secondary DNS.
4) L2TP
If your ISP (Internet Service Provider) has provided the account information for the L2TP connection,
please choose the L2TP connection type.
-20-
Page 26
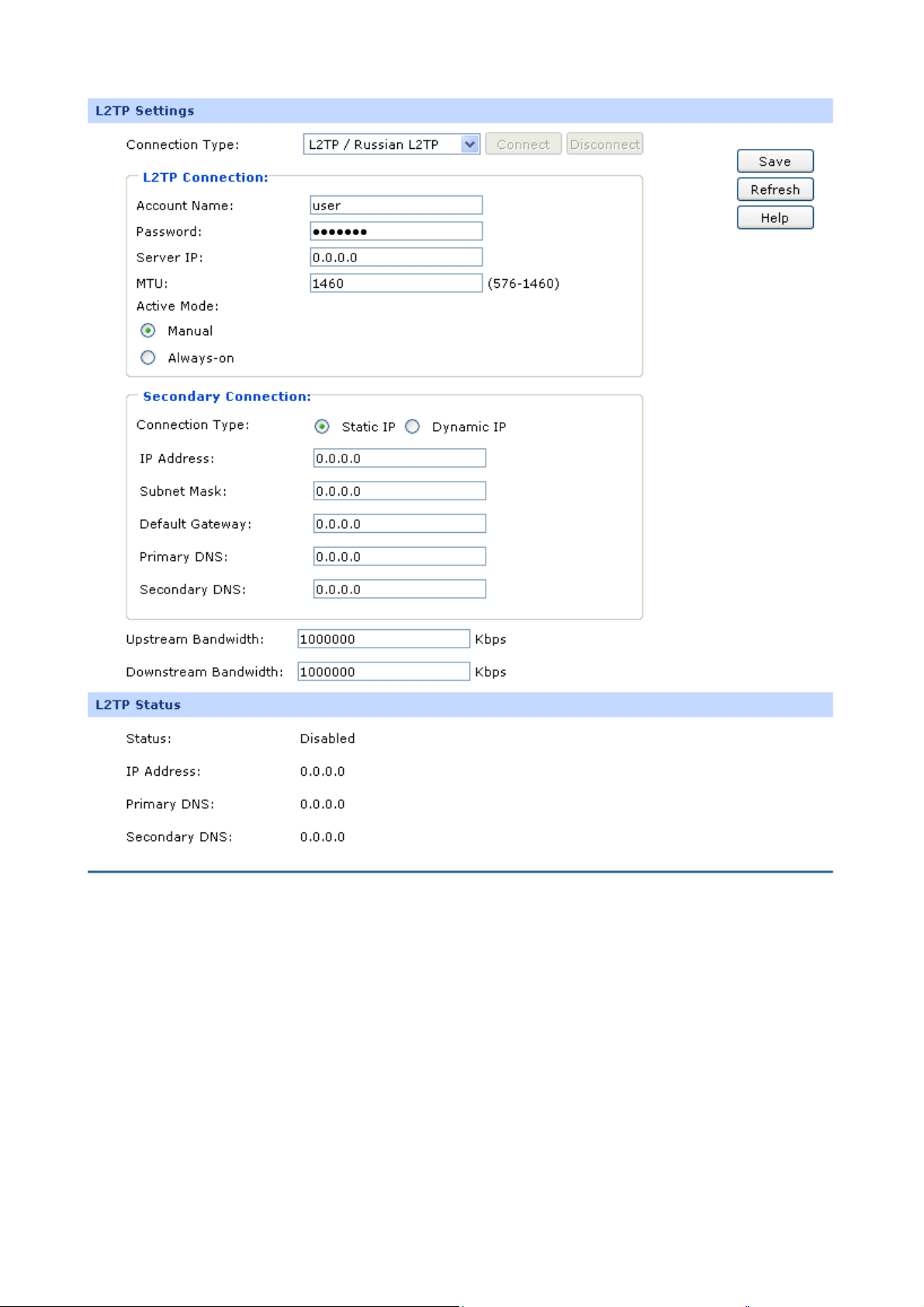
Figure 3-9 WAN - L2TP
The following items are displayed on this screen:
L2TP Settings
Connection Type:
Select L2TP if your ISP provides a L2TP connection. Click <Connect>
to dial-up to the Internet and obtain the IP address. Click
<Disconnect> to disconnect the Internet connection and release the
current IP address.
-21-
Page 27

Account Name:
Password:
Server IP:
MTU:
Active Mode:
Enter the Account Name provided by your ISP. If you are not clear,
please consult your ISP.
Enter the Password provided by your ISP.
Enter the Server IP provided by your ISP.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1460. The default MTU is 1460. It is recommended to keep the
default value if no other MTU value is provided by your ISP.
You can select the proper Active Mode according to your need.
Manual: Select this option to manually activate or terminate the
Internet connection by the <Connect> or <Disconnect> button. It
is optimum for the dial-up connection charged on time.
Secondary
Connection:
Connection Type:
IP Address:
Subnet Mask:
Always-on: Select this option to keep the connection always on.
The connection can be re-established automatically when it is
down.
Here allows you to configure the secondary connection. Dynamic IP
and Static IP connection types are provided.
Select the secondary connection type. Options include Disable,
Dynamic IP and Static IP.
If Static IP is selected, configure the IP address of WAN port. If
Dynamic IP is selected, the IP address of WAN port obtained is
displayed.
If Static IP is selected, configure the subnet mask of WAN port. If
Dynamic IP is select, the subnet mask of WAN port obtained is
displayed.
Default Gateway:
If Static IP is selected, configure the default gateway. If Dynamic IP is
selected, the obtained default gateway is displayed.
-22-
Page 28

Primary DNS/
Secondary DNS:
Upstream Bandwidth:
Downstream
Bandwidth:
L2TP Status
Status:
If Static IP is selected, configure the DNS. If Dynamic IP is selected,
the obtained DNS is displayed.
Specify the bandwidth for transmitting packets on the port.
Specify the bandwidth for receiving packets on the port.
Displays the status of PPPoE connection.
“Disabled” indicates that the L2TP connection type is not applied.
“Connecting” indicates that the Router is obtaining the IP
parameters from your ISP.
“Connected” indicates that the Router has successfully obtained
IP Address:
Primary DNS:
Secondary DNS:
the IP parameters from your ISP.
“Disconnected” indicates that the connection has been manually
terminated or the request of the Router has no response from
your ISP. Please ensure that your settings are correct and your
network is connected well. Consult your ISP if this problem
remains.
Displays the IP address assigned by your ISP.
Displays the IP address of your ISP’s Primary DNS.
Displays the IP address of your ISP’s Secondary DNS.
-23-
Page 29
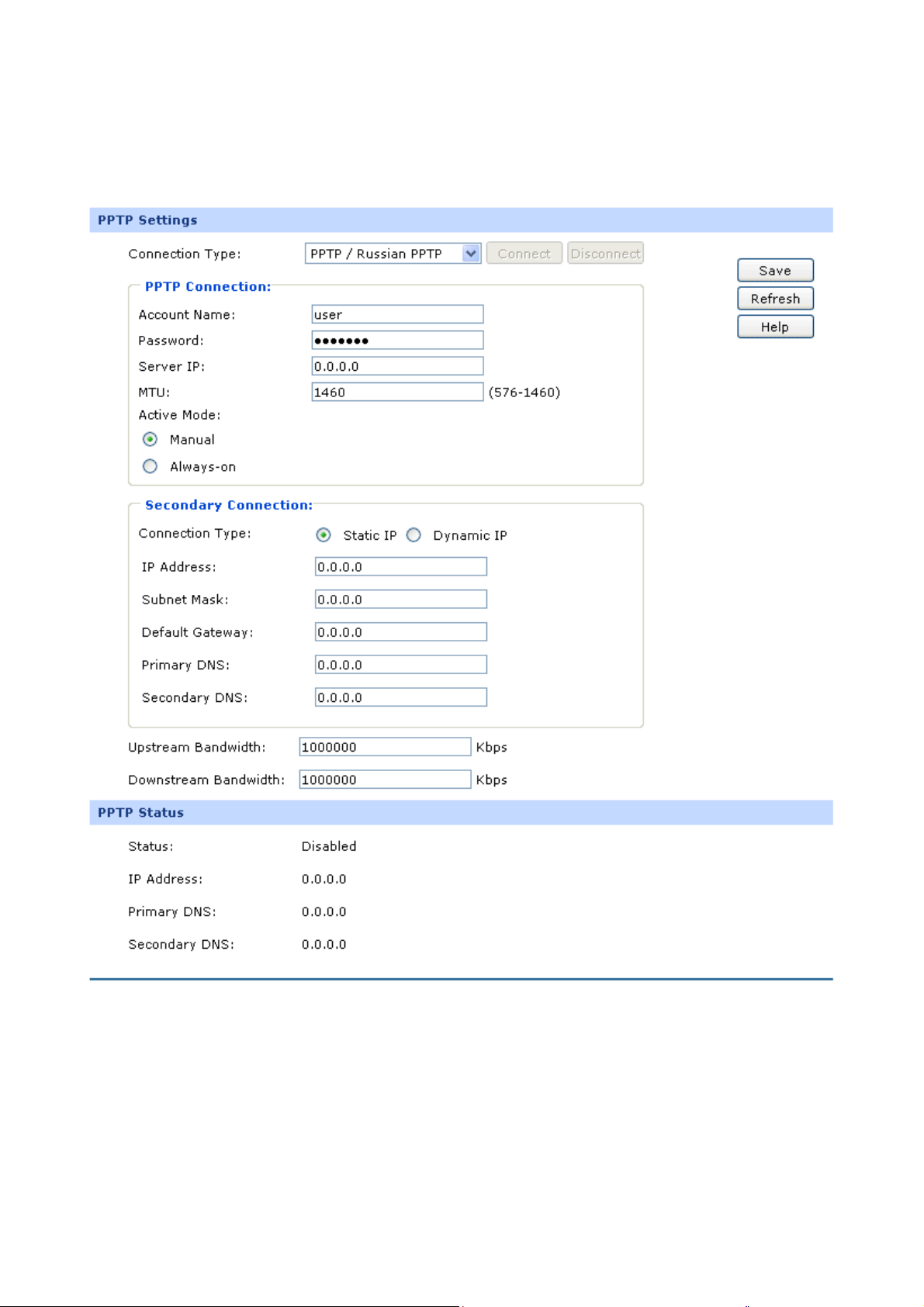
5) PPTP
If your ISP (Internet Service Provider) has provided the account information for the PPTP connection,
please choose the PPTP connection type.
Figure 3-10 WAN - PPTP
The following items are displayed on this screen:
PPTP Settings
Connection Type:
Select PPTP if your ISP provides a PPTP connection. Click
<Connect> to dial-up to the Internet and obtain the IP address. Click
-24-
Page 30

<Disconnect> to disconnect the Internet connection and release the
current IP address.
Account Name:
Password:
Server IP:
MTU:
Active Mode:
Enter the Account Name provided by your ISP. If you are not clear,
please consult your ISP.
Enter the Password provided by your ISP.
Enter the Server IP provided by your ISP.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1460. The default MTU is 1460. It is recommended to keep the
default value if no other MTU value is provided by your ISP.
You can select the proper Active mode according to your need.
Manual: Select this option to manually activate or terminate the
Internet connection by the <Connect> or <Disconnect> button.
It’s optimum for the dial-up connection charged on time.
Secondary
Connection:
Connection Type:
IP Address:
Subnet Mask:
Always-on: Select this option to keep the connection always on.
The connection can be re-established automatically when it is
down.
Here allows you to configure the secondary connection. Dynamic IP
and Static IP connection types are provided.
Select the secondary connection type. Options include Disable,
Dynamic IP and Static IP.
If Static IP is selected, configure the IP address of WAN port. If
Dynamic IP is selected, the IP address of WAN port obtained is
displayed.
If Static IP is selected, configure the subnet mask of WAN port. If
Dynamic IP is select, the subnet mask of WAN port obtained is
displayed.
Default Gateway:
If Static IP is selected, configure the default gateway. If Dynamic IP is
selected, the obtained default gateway is displayed.
-25-
Page 31

Primary DNS/
Secondary DNS:
Upstream Bandwidth:
Downstream
Bandwidth:
PPTP Status
Status:
If Static IP is selected, configure the DNS. If Dynamic IP is selected,
the obtained DNS is displayed.
Specify the bandwidth for transmitting packets on the port.
Specify the bandwidth for receiving packets on the port.
Displays the status of PPTP connection.
“Disabled” indicates that the PPTP connection type is not
applied.
“Connecting” indicates that the Router is obtaining the IP
parameters from your ISP.
“Connected” indicates that the Router has successfully obtained
the IP parameters from your ISP.
“Disconnected” indicates that the connection has been manually
terminated or the request of the Router has no response from
your ISP. Please ensure that your settings are correct and your
network is connected well. Consult your ISP if this problem
remains.
IP Address:
Primary DNS:
Secondary DNS:
Displays the IP address assigned by your ISP.
Displays the IP address of your ISP’s Primary DNS.
Displays the IP address of your ISP’s Secondary DNS.
6) BigPond
If your ISP (Internet Service Provider) has provided the account information for the BigPond
connection, please choose the BigPond connection type.
-26-
Page 32

Figure 3-11 WAN – Bigpond
The following items are displayed on this screen:
BigPond Settings
Connection Type:
Select BigPond if your ISP provides a BigPond connection. Click
<Connect> to dial-up to the Internet and obtain the IP address. Click
<Disconnect> to disconnect the Internet connection and release the
current IP address.
Account Name:
Enter the Account Name provided by your ISP. If you are not clear,
please consult your ISP.
Password:
Enter the Password provided by your ISP. If you are not clear, please
consult your ISP.
Auth Server:
Enter the address of authentication server. It can be IP address or
server name.
-27-
Page 33

Auth Domain:
Auth Mode:
MTU:
Upstream/Downstream
Enter the domain name of authentication server. It's only required
when the address of Auth Server is a server name.
You can select the proper Active mode according to your need.
Manual: Select this option to manually activate or terminate the
Internet connection by the <Connect> or <Disconnect> button.
It’s optimum for the dial-up connection charged on time.
Always-on: Select this option to keep the connection always on.
The connection can be re-established automatically when it is
down.
MTU (Maximum Transmission Unit) is the maximum data unit
transmitted by the physical network. It can be set in the range of
576-1500. The default MTU is 1500.
Specify the Upstream/Downstream Bandwidth for the port. To make
Bandwidth:
BigPond Status
Status:
"Load Balance" and "Bandwidth Control" take effect, please set
these parameters correctly.
Displays the status of BigPond connection.
“Disabled” indicates that the BigPond connection type is not
applied.
“Connecting” indicates that the Router is obtaining the IP
parameters from your ISP.
“Connected” indicates that the Router has successfully
obtained the IP parameters from your ISP.
“Disconnected” indicates that the connection has been
manually terminated or the request of the Router has no
response from your ISP. Please ensure that your settings are
IP Address:
Subnet Mask:
correct and your network is connected well. Consult your ISP if
this problem remains.
Displays the IP address assigned by your ISP.
Displays the Subnet Mask assigned by your ISP.
-28-
Page 34
Default Gateway:
Note:
To ensure the BigPond connection re-established normally, please restart the connection at least 5
seconds after the connection is off.
Displays the IP address of the default gateway assigned by your
ISP.
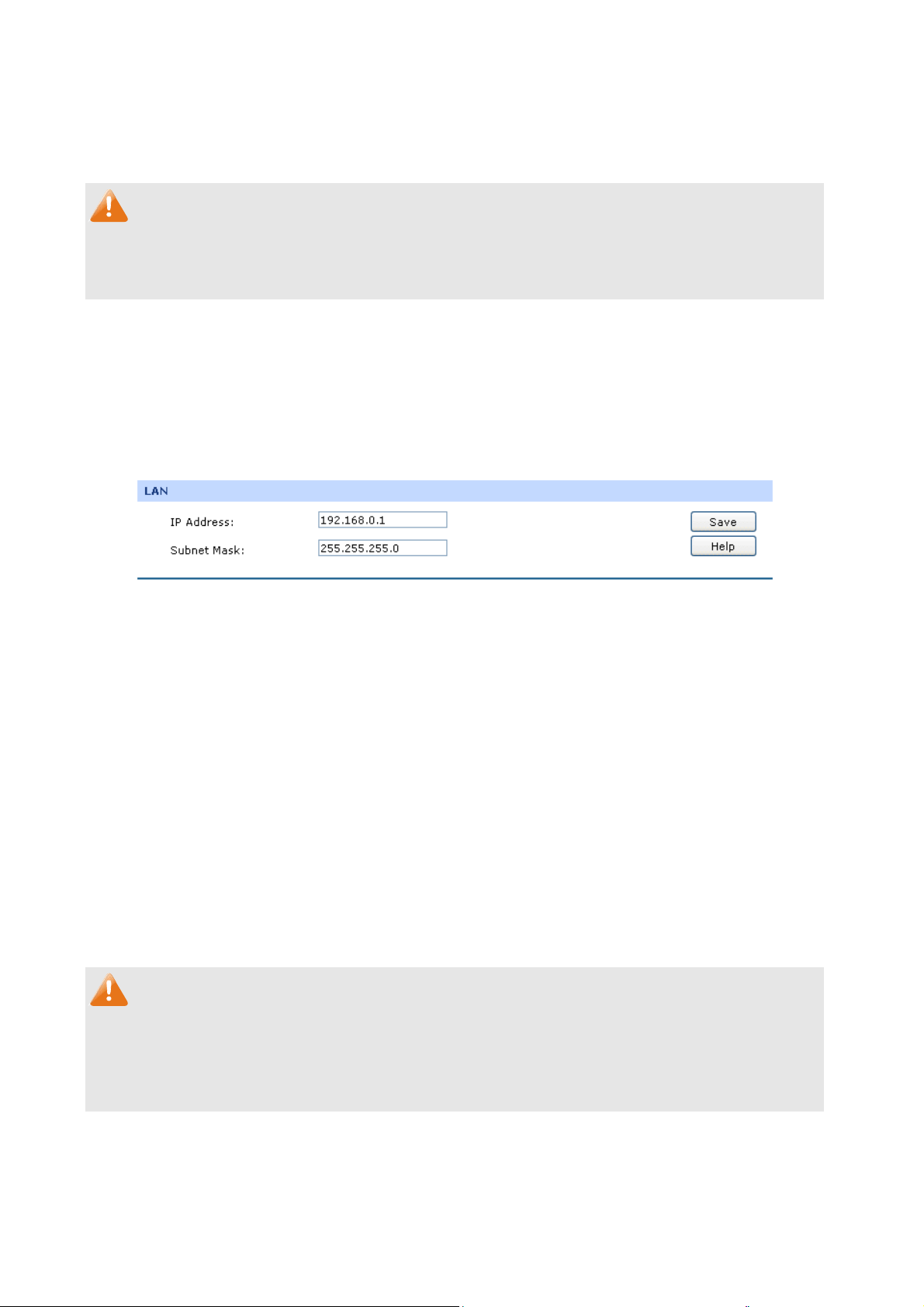
3.1.4 LAN
3.1.4.1 LAN
On this page, you can configure the parameters for LAN port of this router.
Choose the menu Network→LAN→LAN to load the following page.
Figure 3-12 LAN
The following items are displayed on this screen:
LAN
IP Address:
Subnet Mask:
Note:
Enter the LAN IP address of the Router. 192.168.0.1 is the
default IP address. The Hosts in LAN can access the Router
via this IP address. It can be changed according to your
network.
Enter the Subnet Mask. The default subnet mask is
255.255.255.0.
If the LAN IP address is changed, you must use the new IP address to log into the Router. To
guarantee a normal communication, be sure to set the Gateway address and the Subnet Mask of the
Hosts on the LAN to the new LAN IP address and the Subnet Mask of the Router.
3.1.4.2 DHCP
The Router with its DHCP (Dynamic Host Configuration Protocol) server enabled can automatically
assign an IP address to the computers in the local area network.
-29-
Page 35

Choose the menu Network→LAN→DHCP to load the following page.
Figure 3-13 DHCP Settings
The following items are displayed on this screen:
DHCP Settings
DHCP Server:
Start IP Address:
End IP Address:
Lease Time:
Enable or disable the DHCP server on your Router. To enable the
Router to assign the TCP/IP parameters to the computers in the LAN
automatically, please select Enable.
Enter the Start IP address to define a range for the DHCP server to
assign dynamic IP addresses. This address should be in the same IP
address subnet with the Router’s LAN IP address. The default
address is 192.168.0.2.
Enter the End IP address to define a range for the DHCP server to
assign dynamic IP addresses. This address should be in the same IP
address subnet with the Router’s LAN IP address. The default
address is 192.168.0.254.
Specify the length of time the DHCP server will reserve the IP address
Default Gateway:
Default Domain:
for each computer. After the IP address expired, the client will be
automatically assigned a new one.
Optional. Enter the Gateway address to be assigned. It is
recommended to enter the IP address of the LAN port of the Router.
Optional. Enter the domain name of your network.
-30-
Page 36

Primary DNS:
Secondary DNS:
Optional. Enter the Primary DNS server address provided by your
ISP. It is recommended to enter the IP address of the LAN port of the
Router.
Optional. If a Secondary DNS Server address is available, enter it.
3.1.4.3 DHCP Client
On this page, you can view the information about all the DHCP clients connected to the Router.
Choose the menu Network→LAN→DHCP Client to load the following page.
Figure 3-14 DHCP Client
You can view the information of the DHCP clients in this table. Click the Refresh button for the updated
information.
3.1.4.4 DHCP Reservation
DHCP Reservation feature allows you to reserve an IP address for the specified MAC address. The
client with this MAC address will always get the same IP address every time when it accesses the
DHCP server.
Choose the menu Network→LAN→DHCP Reservation to load the following page.
Figure 3-15 DHCP Reservation
The following items are displayed on this screen:
-31-
Page 37

DHCP Reservation
MAC Address:
IP Address:
Description:
Status:
List of Reserved Address
In this table, you can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-15 indicates: The IP address 192.168.0.101 is reserved for the
computer with the MAC address 00-19
Enter the MAC address of the computer for which you want to reserve
the IP address.
Enter the reserved IP address.
Optional. Enter a description for the entry. Up to 28 characters can be
entered.
Activate or Inactivate the corresponding entry.
-66-83-53-CF, and this entry is activated.
Note:
It's recommended that users bind the IP address and the MAC address in 3.4.1.1 IP-MAC Binding ,
then import the entries from the IP-MAC binding table to the List of Reserved Address in buck by
clicking <Import> button in Figure 3-15 DHCP Reservation.
3.1.5 DMZ
DMZ (Demilitarized Zone) is a network which has fewer default firewall restrictions than the LAN does.
TL-ER6020 provides a DMZ port to allow all the local hosts connected to this port to be exposed to the
Internet for some special-purpose services, such as such as Internet gaming and video-conferencing.
The DMZ physical port can work in Public mode and Private mode.
In Public mode, the DMZ port allows the Hosts in DMZ to directly communicate with Internet via routing
mode using public IP address. However, the Hosts in DMZ cannot access LAN.
-32-
Page 38

Figure 3-
In Private mode, the DMZ port allows the Hosts in DMZ to access Internet via NAT mode which
translates private IP addresses within DMZ to public IP addresses for transport over Internet. The
Hosts in DMZ can directly communicate with LAN using the private IP addresses within the different
subnet of LAN.
16 DMZ – Public Mode
Figure 3-
17 DMZ – Private Mode
3.1.5.1 DMZ
This page allows you to configure the DMZ port of TL-ER6020.
Choose the menu Network→DMZ→DMZ to load the following page.
-33-
Page 39

Figure 3-18 DMZ
The following items are displayed on this screen:
DMZ
Status:
Mode:
IP Address:
Subnet Mask:
Tips:
The DHCP service, DHCP Client and DHCP Reservation functions are available when the DMZ port is
enabled. For the configuration instructions, please refer to section 3.1.4.1 to 3.1.4.4.
Note:
Activate or inactivate this entry. The DMZ port functions as a normal
LAN port when it’s disabled.
Select the mode for DMZ port to control the connection way among
DMZ, LAN and Internet. Options include: Public and Private.
Enter the IP address of DMZ port.
Enter the Subnet Mask of DMZ port.
When the DMZ port is enabled in Public Mode, please do not enable the DHCP service of DMZ port if
your ISP provides a single public IP address. Otherwise, the Hosts in DMZ will be unable to access
Internet normally. If an IP address range is provided by your ISP, please configure the DHCP pool
based on the IP address range.
3.1.6 MAC Address
The MAC (Media Access Control) address, as the unique identifier of the router in network, does not
need to be changed commonly.
-34-
Page 40

Set the MAC Address for LAN port:
In a complex network topology with all the ARP bound devices, if you want to use TL-ER6020 instead
of the current router in a network node, you can just set the MAC address of TL-ER6020‘s LAN port
the same to the MAC address of the previous router, which can avoid all the devices under this
network node to update their ARP binding tables.
Set the MAC Address for WAN port:
In the condition that your ISP has bound the account and the MAC address of the dial-up device, if you
want to change the dial-up device to be TL-ER6020, you can just set the MAC address of
TL-ER6020’s WAN port the same to the MAC address of the previous dial-up device for a normal
Internet connection.
Set the MAC Address for DMZ port:
The application of MAC address for DMZ port is similar to that for LAN port.
Choose the menu Network→MAC Address→MAC Address to load the following page.
Figure 3-19 MAC Address
The following items are displayed on this screen:
MAC Address
Port:
Current MAC Address:
Displays the port type of the Router.
Displays the current MAC address of the port.
-35-
Page 41

MAC Clone:
Note:
To avoid a conflict of MAC address on the local area network, it’s not allowed to set the MAC address
of the Router’s LAN port to the MAC address of the current management PC.
It’s only available for WAN port. Click the <Restore Factory MAC>
button to restore the MAC address to the factory default value or
click the <Clone Current PC’s MAC> button to clone the MAC
address of the PC you are currently using to configure the Router.
Then click <Save> to apply.
3.1.7 Switch
Some basic switch port management functions are provided by TL-ER6020, which facilitates you to
monitor the traffic and manage the network effectively.
3.1.7.1 Statistics
Statistics screen displays the detailed traffic information of each port, which allows you to monitor the
traffic and locate faults promptly.
Choose the menu Network→Switch→Statistics to load the following page.
Figure 3-20 Statistics
-36-
Page 42

The following items are displayed on this screen:
Statistics
Unicast:
Broadcast:
Pause:
Multicast:
Undersize:
Normal:
Displays the number of normal unicast packets received or transmitted
on the port.
Displays the number of normal broadcast packets received or
transmitted on the port.
Displays the number of flow control frames received or transmitted on
the port.
Displays the number of normal multicast packets received or transmitted
on the port.
Displays the number of the received frames (including error frames) that
are less than 64 bytes long.
Displays the number of the received packets (including error frames) that
are between 64 bytes and the maximum frame length. The maximum
untagged frame this Router can support is 1518 bytes long and the
maximum tagged frame is 1522 bytes long.
Oversize:
Total (Bytes):
Click the <Clear All> button to clear all the traffic statistics.
Tips:
The Port 1/2/3/4/5 mentioned in this User Guide refers to the WAN1/2 port and LAN1/2/3 port on the
Router.
Displays the number of the received packets (including error frames) that
are longer than the maximum frame.
Displays the total number of the received or transmitted packets
(including error frames).
3.1.7.2 Port Mirror
Port Mirror, the packets obtaining technology, functions to forward copies of packets from one/multiple
ports (mirrored port) to a specific port (mirroring port). Usually, the mirroring port is connected to a data
diagnose device, which is used to analyze the mirrored packets for monitoring and troubleshooting the
network.
-37-
Page 43

Choose the menu Network→Switch→Port Mirror to load the following page.
Figure 3-21 Port Mirror
The following items are displayed on this screen:
General
Enable Port Mirror:
Mode:
Port Mirror
Check the box to enable the Port Mirror function. If unchecked, it will
be disabled.
Select the mode for the port mirror function. Options include:
Ingress: When this mode is selected, only the incoming packets
received by the mirrored port will be copied to the mirroring port.
Egress: When this mode is selected, only the outgoing packets
sent by the mirrored port will be copied to the mirroring port.
Ingress&Egress: When this mode is selected, both the incoming
and outgoing packets through the mirrored port will be copied to
the mirroring port.
Mirroring Port:
Mirrored Port:
Select the Mirroring Port to which the traffic is copied. Only one port
can be selected as the mirroring port.
Select the Mirrored Port from which the traffic is mirrored. One or
multiple ports can be selected as the mirrored ports.
-38-
Page 44

The entry in Figure 3-21 indicates: The outgoing packets sent by port 1, port 2, port 3 and port 5
(mirrored ports) will be copied to port 4 (mirroring port).
Application Example:
To monitor all the traffic and analyze the network abnormity for an enterprise’s network, please set the
Port Mirror function as below:
1) Check the box before Enable Port Mirror to enable the Port Mirror function and select the
Ingress & Egress mode.
2) Select Port 3 to be the Mirroring Port to monitor all the packets of the other ports.
3) Select all the other ports to be the Mirrored Ports.
4) Click the <Save> button to apply.
3.1.7.3 Rate Control
On this page, you can control the traffic rate for the specific packets on each port so as to manage your
network flow.
Choose the menu Network→Switch→Rate Control to load the following page.
-39-
Page 45

Figure 3-22 Rate Control
The following items are displayed on this screen:
Rate Control
Port:
Ingress Limit:
Ingress Rate:
Egress Limit:
Egress Rate:
The first entry in Figure 3-22 indicates: The Ingress and Egress Limits are enabled for port 1. The
Ingress and
1Mbps, and the transmitting rate for all the egress packets will not exceed 1Mbps.
Egress Rates are 1Mbps. That is, the receiving rate for the ingress packets will not exceed
Displays the port number.
Specify whether to enable the Ingress Limit feature.
Specify the limit rate for the ingress packets.
Specify whether to enable Egress Limit feature.
Specify the limit rate for the egress packets.
3.1.7.4 Port Config
On this page, you can configure the basic parameters for the ports.
Choose the menu Network→Switch→Port Config to load the following page.
-40-
Page 46

Figure 3-23 Port Config
The following items are displayed on this screen:
Port Config
Status:
Flow Control:
Negotiation Mode:
All Ports:
Specify whether to enable the port. The packets can be
transported via this port after being enabled.
Allows you to enable/disable the Flow Control function.
Select the Negotiation Mode for the port.
Allows you to configure the parameters for all the ports at
one time.
3.1.7.5 Port Status
On this page, you can view the current status of each port.
Choose the menu Network→Switch→Port Status to load the following page.
Figure 3-24 Port Status
-41-
Page 47

3.1.7.6 Port VLAN
A VLAN (Virtual Local Area Network) is a network topology configured according to a logical scheme
rather than the physical layout, which allows you to divide the physical LAN into multiple logical LANs
so as to control the communication among the ports
The VLAN function can prevent the broadcast storm in LANs and enhance the network security. By
creating VLANs in a physical LAN, you can divide the LAN into multiple logical LANs, each of which
has a broadcast domain of its own. Hosts in the same VLAN communicate with one another as if they
are in a LAN. However, hosts in different VLANs cannot communicate with one another directly.
Therefore, broadcast packets are limited in a VLAN.
TL-ER6020 provides the Port VLAN function, which allows you to create multiple logical VLANs for the
LAN ports based on their port numbers.
Choose the menu Network→Switch→Port VLAN to load the following page.
.
Figure 3-25 Port VLAN
The following items are displayed on this screen:
Port VLAN
Network:
VLAN:
Tips:
● The Port VLAN can only be created among the LAN ports.
● The change of DMZ status will affect the configurations of Port VLAN. You're recommended to
check or reconfigure the Port VLAN if the status of DMZ is changed.
Displays the current logical network of the physical port.
Select the desired VLAN for the port.
3.2 User Group
The User Group function is used to group different users for unified management, so that you can
perform other applications such as Bandwidth Control, Session Limit, and Access Control etc. on per
group.
-42-
Page 48

3.2.1 Group
On this page you can define the group for management.
Choose the menu User Group→Group to load the following page.
3-26 Group Configuration
Figure
The following items are displayed on this screen:
Group Config
Group Name: Specify a unique name for the group.
Description: Give a description for the group. It's optional.
List of Group
In this table, you can view the information of the Groups and edit them by the Action buttons.
3.2.2 User
On this page, you can configure the User for the group.
Choose the menu User Group→User to load the following page.
Figure 3-27 User Configuration
The following items are displayed on this screen:
-43-
Page 49

User Config
User Name:
IP Address:
Specify a unique name for the user.
Enter the IP Address of the user. It cannot be the network address or
broadcast address of the port.
Description:
List of User
Give a description to the user for identification. It's optional.
In this table, you can view the information of the Users and edit them by the Action buttons.
3.2.3 View
On this page, you can configure the User View or Group View.
Choose the menu User Group→View to load the following page.
Figure 3-28 View Configuration
The following items are displayed on this screen:
View Config
View:
Select the desired view for configuration.
-44-
Page 50

User Name:
Available Group:
Selected Group:
Group Name:
Group Structure:
Available Member:
Selected Member:
Select the name of the desired User.
Displays the Groups that the User can join.
Displays the Groups to which this User belongs.
Select the name of the desired Group.
Click this button to view the tree structure of this group. All the members of
this group will be displayed, including Users and sub-Groups. The Group
Names are displayed in bold.
Displays the Users and the Groups which can be added into this group.
Displays the members of this group, including Users and Groups.
3.3 Advanced
3.3.1 NAT
NAT (Network Address Translation) is the translation between private IP and public IP, which allows
private network users to visit the public network using private IP addresses.
With the explosion of the Internet, the number of available IP addresses is not enough. NAT provides a
way to allow multiple private hosts to access the public network with one public IP at the same time,
which alleviates the shortage of IP addresses. Furthermore, NAT strengthens the LAN (Local Area
Network) security of the network since the address of LAN host never appears on the Internet.
3.3.1.1 NAT Setup
On this page, you can set up the NAT function.
Choose the menu Advanced→NAT→NAT Setup to load the following page.
Figure 3-29 NAT Setup
-45-
Page 51

The following items are displayed on this screen:
NAPT
Source Port Range:
Enter the source port range between 2049 and 65000, the span of which
must be not less than 100.
NAT-DMZ
NAT-DMZ:
Enable or disable NAT-DMZ. NAT DMZ is a special service of NAT
application, which can be considered as a default forwarding rule. When
NAT DMZ (Pseudo DMZ) is enabled, all the data initiated by external
network falling short of the current connections or forwarding rules will be
forwarded to the preset NAT DMZ host.
Host IP Address:
Enter the IP address of the host specified as NAT DMZ server.
3.3.1.2 One-to-One NAT
On this page, you can configure the One-to-One NAT.
Choose the menu Advanced→NAT→One-to-One NAT to load the following page.
Figure 3-30 One to One NAT
The following items are displayed on this screen:
One-to-One NAT
Mapping IP Address:
Enter the Original IP Address in the first checkbox and Translated
IP Address in the second checkbox. TL-ER6020 allows mapping from LAN
port to WAN port and DMZ in LAN Mode.
-46-
Page 52

Interface:
DMZ Forwarding:
Select an interface for forwarding data packets.
Enable or disable DMZ Forwarding. The packets transmitted to the
Translated IP Address will be forwarded to the host of Original IP if DMZ
Forwarding is enabled.
Description:
Status:
List of Rules
Give a description for the entry.
Activate or inactivate the entry.
In this table, you can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-30 indicates: The IP address of host1 in local network is 192.16
8.0.128 and
the WAN IP address after NAT mapping is specified to be 222.135.48.128. The data packets are
transmitted from WAN1 port. DMZ Forwarding and this entry are both activated.
Note:
One-to-One NAT entries take effect only when the Connection Type of WAN is Static IP. Changing the
Connection type from Static IP to other ones will make the entries attached to the interface disabled.
3.3.1.3 Multi-Nets NAT
Multi-Nets NAT function allows the IP under LAN or DMZ port within multiple subnets to access the
Internet via NAT.
Choose the menu Advanced→NAT→Multi-Nets NAT to load the following page.
Figure 3-31 Multi-Nets NAT
The following items are displayed on this screen:
Multi-Nets NAT
-47-
Page 53

Subnet/Mask:
Interface:
Description:
Status:
Enter the subnet/mask to make the address range for the entry.
Select the interface for the entry. You can select LAN or DMZ port.
Give a description for the entry.
Activate or inactivate the entry.
list of Rules
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-31 indicates that: This is a Multi-Net
s NAT entry named tplink1. The subnet
under the LAN port of the Router is 192.168.2.0/24 and this entry is activated. After the corresponding
Static Route entry is set, the hosts within this subnet can access the Internet through the Router via
NAT.
Note:
● Multi-Nets NAT entry takes effect only when cooperating with the corresponding Static Route
entries.
● The DMZ port will display in the drop-down list only when the DMZ port is enabled.
● For detailed setting of subnet mask, please refer to the Appendix B FAQ
Application Example:
Net
work Requirements
The LAN subnet of TL-ER6020 is 192.168.0.0 /24, the subnet of VLAN2 under a three layer switch is
192.168.2.0 /24, while the subnet of VLAN3 is 192.168.3.0 /24. The IP of VLAN for cascading the
switch to the Router is 192.168.0.2. Now the hosts within VLAN2 and VLAN3 desire to access the
Internet.
The network topology is shown as the following:
-48-
Page 54

Configuration procedure
1. Establish the Multi-Nets NAT entries with Subnet/Mask of VLAN2 and VLAN3.
The configured entries are as follows:
2. Then set the corresponding Static Route entry, enter the IP address of the interface connecting
the Router and the three layer switch into the Next Hop field.
-49-
Page 55

Choose the menu Advanced→Routing→Static Route to load the following page.
The Static Route entry is as follows:
3.3.1.4 Virtual Server
Virtual server sets up public services in your private network, such as DNS, Email and FTP, and
defines a service port. All the service requests to this port will be transmitted to the LAN server
appointed by the Router via IP address.
Choose the menu Advanced→NAT→Virtual Server to load the following page.
-50-
Page 56

The fo layed
llowing items are disp on this screen:
Virtual Server
Name:
Enter a name for Virtual Server
entered.
Interface:
External Port:
Select an interface for forwarding data packets.
Enter the service port or port range the Router provided for accessing
external network. All the requests from Internet
port range will be redirected to the specified server in local network.
Internal Port:
Protocol:
Specify the service port of the LAN host as virtual server.
Specify the protocol used for the entry.
Figure 3-32 Virtual Server
entries. Up to 28 characters can be
to this service port or
Internal Server IP:
Enter the IP address of the specified internal server for the entry. All
the requests from the Internet to the specified LAN port will be
redirected to this host.
Status:
Activate or inactivate the entry.
-51-
Page 57

Note:
● The External port and Internal Port should be set in the range of 1-65535.
● The external ports of different entries should be different, whereas the internal ports can be the
same.
List of Rules
In this table, you can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-32 indicates: This is a Virtual Server
packets from WAN1 to port 65534-65535 of the Router will be redirected to the port 65534-65535 of
the LAN host with IP address of 192.168.0.103, and this entry is activated.
entry named host, all the TCP data
3.3.1.5 Port Triggering
Some applications require multiple connections, such as Internet games, video conferencing, Internet
calling, P2P download and so on. Port Triggering is used for those applications requiring multiple
connections.
When an application initiates a connection to the trigger port, all the ports corresponding to the
incoming port will open for follow-up c
Choose the menu Advanced→NAT→Port Trigge
onnections.
ring to load the following page.
Port Triggering
Figure 3-33 Port Triggering
d on this screen: The following items are displaye
-52-
Page 58

Name:
Interface:
Trigger Port:
Trigger Protocol:
Incoming Port:
Incoming Protocol:
Enter a name for Port Triggering entries. U
p to 28
characters can be
entered.
Select an interface for forwarding data packets.
Enter the trigger port number or the range of port. Only when the
trigger port initiates connection will all the corresponding incoming
ports open and provide service for the applications, otherwise the
incoming ports will not open.
Select the protocol used for trigger port.
Enter the incoming port number or range of port numbers. The
incoming port
will open for follow-up connection after the trigger port
initiates connection.
Select the protocol used for incoming port.
Status:
Activate or inactivate the entry.
Note:
● The Trigger Port and Incoming Port should be set in the range of 1-65535. The Incoming Port can
be set in a continuous range such as 8690-8696.
● The Router supports up to 16 Port Triggering entries. Each entry supports at most 5 groups of
trigger ports and overlapping between the ports is not allowed.
● Each entry supports at most 5 groups of incoming ports and the sum of incoming ports you set for
each entry should not be more than 100.
List of Rules
In this table, you can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-33 indicates that: This is a Port Triggeri
ng entry named host1, When the LAN
host initiates a TCP request via port of 535 rt 5355 of WAN1 will open for TCP and 4, the incoming po
UDP protocol. This entry is activated.
-53-
Page 59

3.3.1.6
Some special protocols such as
(Application Layer Gateway) service is enabled.
Choose the menu Advanced→NAT→ALG to load the following page.
The following items are displayed on this screen:
ALG
ALG
FTP, H.323, SIP, IPsec and PPTP will work properly only when ALG
Figure 3-34 ALG
ALG:
FTP
H.323 ALG:
SIP ALG:
IPsec ALG:
PPTP ALG:
Enable or disable FTP ALG. The default setting is enabled. It is
recommended to keep the default setting if no special
requirement.
Enable or disable H.323 ALG. The default setting is enabled.
H.323 is used for various applications such as NetMeeting and
VoIP.
Enable or disable SIP ALG. The default setting is enabled. It is
recommended to keep the default setting if no special
requirement.
Enable or disable IPsec ALG. The default setting is enabled. It is
recommended to keep default if no special requirement.
Enable or disable PPTP ALG. The default setting is enabled. It is
recommended to keep default if no special requirement.
3.3.2 Traffic Control
Traffic Control functions to control the bandwidth by configuring rules for limiting various data flows. In
this way, the network bandwidth can be reasonably distributed and utilized.
-54-
Page 60

3.3.2.1 Setup
Choose the menu Advanced→Traffic Control→Setup to load the following page.
Figure 3-35 Configuration
The following items are displayed on this screen:
G
eneral
Disable Bandwidth
Control:
Enable Bandwidth
Control all the t
Enable Bandwidth
Control Whe
D
efault Limit
ime:
n:
Select this option to disable Bandwidth Control.
Select this option to enable Bandwidth Control all the time.
With this option selected, the Bandwidth Control will take effect when the
bandwidth usage reaches the specified value.
Limited
Bandwidth:
lt Limit applies only for users that are not constrained by Bandwidth
Defau
Control Rules. These users share certain bandwidth with upper limit
configured here. Value 0 means all the remained bandwidth is available to
use.
-55-
Page 61

Interface B ndwidth
Interface:
Upstream
Bandwidth:
Downstream
Bandwidth:
Note:
● The Upstream/Downstream Bandwidth of WAN port you set must not be more than the bandwidth
provided by ISP. Otherwise the Traffic Control will be invalid.
● If there are data flowing into the Router from interface A and out from interface B while the
downstream bandwidth of A is different from the upstream bandwidth of B, then the smaller one
a
Displays the current enabled WAN port(s). The To
the sum of bandwidth of the enabled WAN ports.
Displays the bandwidth of each WAN port for transmitting data. The
Upstream Bandwidth of WAN port can be configured on WAN page.
Displays the bandwidth of each WAN port for receiving data. Th
Downstream Bandwidth of WAN port can be configured on WAN page.
tal bandwidth is equal to
e
should be considered as the effective bandwidth, and vice versa.
● Click the <View IP Traffic Statistics> button to jump to IP Traffic Statistics page.
3.3.2.2 Bandwidth Control
On this page, you can configure the Bandwidth Control function.
Choose the
menu Advanced→Traffic Control→Bandwidth Control to load the following page.
Figure 3-36 Bandwidth Control
d on this screen: The following items are displaye
-56-
Page 62

Band Rule
width Control
Direction:
Group:
Mode:
Guarantee
d Bandwidth
Select the data stream direction for the entry. The direction of
arrowhead indicates the data stream direction The DMZ port
displays in the drop-down list only when the DMZ port is
enabled. WAN-ALL means all WAN ports through which the
data flow might pass. Individual
WAN port cannot be selected if
WAN-ALL rules are added.
Select the group to define the controlled users.
Individual: The bandwidth of eac
h user equals to the current
bandwidth of this entry.
Shared: The total bandwidth of all controlled IP
addresses
equals to the current bandwidth of this entry.
Specify the Guaranteed Upstream Bandwidth for this entry.
(Up):
Limited Bandwidth (Up):
Guarantee
d Bandwidth
(Down):
Limited B
andwidth
(Down):
Effective Time
Description:
Status:
List of Rules
Specify the Limited Upstream Bandwidth for this entry.
Specify the Guaranteed Downstream Bandwidth for this entry.
Specify the Limited Downstream Bandwidth for this entry.
:
Specify the time for the entry to t
Give a description for the entry.
ake effect.
Activate or inactivate the entry.
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-36 indicates: The users within group “sales” share the band
width and the
Downstream/Upstream Guaranteed Bandwidth is 5000kbps, while the Downstream/Upstream Limite
bandwidth is 10000kbps. This entry takes effect at 8 a.m. to 10 p.m. from Monday to Friday.
-57-
d
Page 63

Note:
● The premise for single rule taking effect is that the bandwidth of the interface for this rule is
sufficient and not used up.
● It is impossible to satisfy all the guaranteed bandwidth if the total guaranteed bandwidth specified
by all Bandwidth Control rules for certain interface exceeds the physical bandwidth of this
interface.
● When DMZ port is disabled, it is only allowed deleting operation to the related rules.
3.3.3 Session Limit
The amount of TCP and UDP sessions supported by the Router is finite. If som
too many TCP and UDP sess
hosts will be affected, thus it is necessary to limit the sessions of those hosts.
ions to the public network, the communication quality of the other local
3.3.3.1 Session Limit
On this page, you can configure the session limit to specified PCs.
Choose the
menu Advanced→Session Limit→Session Limit to load the following page.
e local hosts transmit
The following items are displayed on t
G
eneral
Enable Session
Limit:
Check here to enable Session Limit, otherwise all the Session Limit
entries will be disabled.
Figure 3-37 Session Limit
his screen:
-58-
Page 64

Session Limit
Group:
Max. Sessions:
Descript
Status:
List of Session Limit
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-37 indicates: The amount of maximum se
is 100 and this entry is en
ion:
Select a group to define the controlled
Enter the max. Sessions for the users.
Give a description for the entry.
Activate or inactivate the entry.
ed.
abl
users.
ssions
for the hosts within group1
3.3.3.2 Session List
On this page, you can view the Session Limit information of hosts configured with Session
Limit.
Choose the menu Advanced→Session Limit→Session List to load the following page.
Figure 3-38 Session List
In this table, you can view the session limit information of users configured with Session Limit. Click
the <Refresh
> button to get the
latest information.
3.3.4 Load Balance
In this part
utilization.
, you can configure the traf
3.3.4.1 Configuration
Choose the menu Advan
ced→Load Balance→Configuration to load the following page.
fic sharing mode of the WAN ports to optimize the resource
-59-
Page 65

Figure 3-39 Configuration
With the box before Enable Application Optimized Routing checked, the Router will consider the
source IP address and destination IP address of the packets as a whole and record the WAN port they
pass t And then the packets with the same source IP address and destination IP address or
hrough.
destination port will be forwarded to the recorded WAN port. This feature is to ensure the
multi-connected applications to work properly.
Check
Load Balance of the specified WAN port will be enabled automatically if no routing rules are set.
Then click the <Save> button to apply
The WAN ports not connecting to the Internet don’t support Intelligent Balance, please do not select
them.
the box before Enable Bandwidth Based Balance Routing and select the WAN port below,
.
Note:
3.3.4.2 Policy Routing
Policy Routing provides an accurate way to control the routing based on the policy defined by the
network administrator.
Choose the menu Advanced→Load Balance→Policy Routing to load the following page.
Figure 3-40 Policy Routing
-60-
Page 66

The following items are displa is screen:
General
Protocol:
Source IP:
Destination IP:
Source Port:
yed on th
Select the protocol for the entry in the drop-down list. If the protocol you
want to set is not in the list, you can add it to the list on 3.3.4.4 Protocol
page.
Enter the source IP range for the entry. 0.0.0.0 - 0.0.0.0 means any IP is
acceptable.
Enter the destination IP range for the entry. 0.0.0.0 - 0.0.0.0 means any
IP is acceptable.
Enter the source Port range for the entry, which is effective only when the
protocol is TCP, UDP or TCP/UDP. The default value is 1 – 65535, which
means any port is acceptable.
Destination Port:
WAN :
Effective Time:
Status:
List of Rules
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-40 indicates: All the packets with Source IP
192.168.0.199 and Destination IP between 116.10.20.28 and 1
WAN1 port, regardless of the port and protocol. This entry is activated d and will take effect at 8 am to
Enter the destination port range for the entry, which is effective only when
the protocol is TCP, UDP or TCP/UDP. The default value is 1 – 65535,
which means any port is acceptable.
Select the WAN port for transmitting packets.
Specify the time for the entry to take effect.
Activate or inactivate the entry.
between 192.168.0.100 and
16.10.20.29 will be forwarded from
10 pm from Monday to Friday.
3.3.4.3 Link Backup
With Link Backup function, the Router will switch all the new sessions from dropped line automatically
to another to keep an always on-line network.
-61-
Page 67

On this page, you can configure the Link Backup function based on actual need to reduce the traffic
burden of WAN port and improve the network efficiency.
Choose the menu Advanced→Load Balance→Link Backup to load the following page.
The fo are displaye
llowing items d on this screen:
General
WAN Ports:
Displays all the WAN ports in use. You can drag the light-blue WAN
button to primary and backup WAN list. The color of WAN button
changing to gray indicates that the WAN port is already in the primary
and backup WAN list.
WAN Config:
The WAN port in the secondary WAN list will share the traffic for the
WAN in the primary WAN list under the specified condition.
Mode:
You can select Timing or Failover Mode.
Figure 3-41 Link Backup
-62-
Page 68

Timing:
Failover:
Backup Effective Time:
Status: Activate or inactivate the entry.
Link Backup will be enabled if the specified effective time is reached.
All the traffic on the primary WAN will switch to the backup WAN at the
beginning of the effective time; the traffic on the backup WAN will
switch to the primary WAN at the ending of the effective time.
Specify the premise for Failover Mode. The backup WAN port will be
enabled only when the premise is met.
Specify the backup effective time if Timing Mode has been selected.
Then the backup WAN port will be enabled, while the primary WAN
port is disabled in the specified time period. When the start time you
enter is not earlier than the end time, the default effective time is from
the start time of the day to the end time of the next day.
List of Rules
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-41 indicates: WAN1 is the primary port and WAN2 is the backup port. WAN2
will be enabled while WAN1 is failed. This entry i
Note:
The same WAN port cannot be added to the primary and secondary WAN lists at the same time, and
one WAN port should be added to only one list.
s enabled.
3.3.4.4 Protocol
On this page, you can specify the protocol for routing rules conveniently. A protocol constitutes of the
name and number. The Router predefines three commonly used protocols such as TCP, UDP and
TCP/UDP. Moreover, you can also add new protocols as your wish.
Choose the menu Advanced→Load Balance→Protocol to load the following page.
-63-
Page 69

Figure 3-42 Protocol
The following items are displayed on this screen:
Protocol
Name:
Number:
List of Protocol
You can view the information of the entries and edit them by the Action buttons.
Note:
The system predefined protocols cannot be configured.
Enter a name to indicate a protocol. The name will display in the
drop-down list of Protocol on Access Rule page.
Enter the Number of the protocol in the range of 0-255.
3.3.5 Routing
3.3.5.1 Static Route
Routing is the process of selecting optimized paths in a network along which to send network traffic.
Static Route is a kind of special routing configured by the administrator, which is simple, efficient, and
reliable.
Commonly used in small-sized network with fixed topology, Static Route does not change along with
the network topology automatically. The administrator should modify the static route information
manually as long as the network topology or link status is changed.
-64-
Page 70

Choose the menu Advanced→Routing→Static Route to load the following page.
Figure 3-43 Static Route
The following items are displayed on this screen:
Static Route
Destination:
Subnet Mask:
Next Hop:
Interface:
Enter the destination host the route leads to.
Enter the Subnet Mask of the destination network.
Enter the gateway IP address to which the packet should be sent next.
Select the physical network interface, through which this route is
accessible.
Metric:
Defines the priority of the route. The smaller the value is, the higher the
priority is. The default value is 0. It is recommended to keep the default
value.
Description:
Status:
Give a description for the entry.
Activate or inactivate the entry.
List of Rules
You can view the information of the entries and edit them by the Action buttons.
-65-
Page 71

The first entry in Figure 3-43 indicates: If there are packets being sent to a device with IP address of
211.162.1.0 and subnet mask of 255.255.255.0, the Router will forward the packets from WAN1 port to
the next hop of 211.200.1.1.
Application Example
There is a network topology as the following figure shown:
If the LAN port of TL-ER6020(with Non-NAT or Classic system mode)is connected to LAN1 with
subnet of 192.168.0.0/24, while the LAN port of another Router R1 is connected to LAN2 with network
of 192.168.2.0/24. Meanwhile, the WAN ports of the two routers are interconnected and within the
same network. Now a host under TL-ER6020 and within network of LAN1 desires to communicate with
the host within network of LAN2.
You can set a Static Route entry: Enter the WAN IP address of R1 (116.31.88.16) in the Next Hop field
on the Static Route page of TL-ER6020 as the following figure shown, then click the <Add> button to
save the entry.
3.3.5.2 RIP
RIP (Routing Information Protocol) is a dynamic route protocol using distance vector algorithm to select
the optimal path. With features of easy configuration, management and implementation, it is widely used
in small and medium-sized networks such as the campus network.
-66-
Page 72

The distance of RIP refers to the hop counts that a data packet passes through before reaching its
destination, the value range of which is 1–15. It means the destination cannot be reached if the value is
more than 15. Optimal path indicates the path with the fewest hop counts. RIP exchanges the route
information every 30 seconds by broadcasting UDP packets. If one Router has not sent route information
in 180 seconds, the RIP of the other routers would set the distance to this Router into infinity and delete
the corresponding information from route table.
RIP develops from initial RIPv1 to RIPv2 gradually. Compared with RIPv1, RIPv2 supports VLSM
(Variable Length Subnet Mask), simple plain text authentication, MD5 cryptograph authentication, CIDR
(Classless Inter-Domain Routing) and multicast.
TL-ER6020 supports both RIPv1 version and RIPv2 version, thus you can configure the RIP version
based on the actual need to improve the network performance.
Choose the menu Advanced→Routing→RIP to load the following page.
Figure 3-44 RIP
The following items are displayed on this screen:
General
Interface:
Displays the interfaces which has been physically connected or assigned
static IP.
Status:
RIP Version:
Password
Enable or disable RIP protocol.
Select RIPv1 or RIPv2. RIPv2 supports multicast and broadcast.
If RIPv2 is enabled, set the Password Authentication according to the actual
-67-
Page 73

Authentication:
All Interfaces:
List of RIP
After RIP is enabled, the information of RIP forwarding the packets received by the Router will be
displayed in the list.
The first entry in Figure 3-44 indicates: when receivi
Router will select WAN1 which is in the same network with the destination IP as next hop and forward
data via this port. The IP address of next hop is 116.10.1.254 and the hop count is 1. The effective
time of this entry is 1 second.
Note:
● RIP function cannot be set if the Router is in NAT Mode. To set RIP function, please change the
System Mode to Routing or Full Mode.
network situation, and the password should not be more than 15 characters.
Here you can operate all the interfaces in bulk. All the interfaces will not apply
RIP if “Enable” option for All Interfaces is selected.
ng packets with destination IP is 116.10.20.28, the
● The RIP function of WAN port takes effects only when the Connection Type of this WAN port is
Static IP.
3.3.5.3 Route Table
This page displays the information of the system route table.
Choose the menu Advanced→Routing→Route Table to load the following page.
Destination:
Gateway:
Figure 3-45 RIP
The Destination of route entry.
The Gateway of route entry.
-68-
Page 74

Flags:
Logical Interface:
Physical
Interface:
Metric
The Flags of route entry. The Flags describe certain characteristics of the
route.
The logical interface of route entry.
The physical interface of route entry.
The Metric of route entry.
3.4 Firewall
3.4.1 Anti ARP Spoofing
ARP (Address Resolution Protocol) is used for analyzing and mapping IP addresses to the
corresponding MAC addresses so that packets can be delivered to their destinations correctly.
ARP functions to translate the IP address into the corresponding MAC address and maintain an ARP
Table in which the latest used IP address-to-MAC address mapping entries are stored. ARP protocol
can facilitate the Hosts in the same network segment to communicate with one another or access to
external network via Gateway. However, since ARP protocol is implemented with the premise that all
the Hosts and Gateways are trusted, there are high security risks during ARP Implementation
Procedure in the actual complex network.
The attacker may send the ARP spoofing packets with false IP address-to-MAC address mapping
entries, and then the device will automatically update the ARP table after receiving wrong ARP
packets, which results in a breakdown of the normal communication. Thus, ARP defense technology is
generated to prevent the network from this kind of attack.
3.4.1.1 IP-MAC Binding
IP-MAC Binding functions to bind the IP address, MAC address of the host together and only allows the
Hosts matching the bound entries to access the network.
Choose the menu Firewall→Anti ARP Spoofing→IP-MAC Binding to load the following page.
-69-
Page 75

Figure 3-46 IP-MAC Binding
The following items are displayed on this screen:
General
It is recommended to check all the options. You should import the IP and MAC address of the host to
IP-MAC Binding List and enable the corresponding entry before enabling “Permit the packets
matching the IP-MAC Binding entries only”.
When suffered ARP attack, the correct ARP information will be sent to the device suffering attack
initiatively by GARP (Gratuitous ARP) packets, thus the error ARP information of the device will be
replaced. You can set the packets sending rate in the Interval field.
With the box before Enable ARP Logs checked, the Router will send ARP logs to the specified
server. The IP address of server is the Server IP set on 3.7.7 Logs.
IP-MAC Binding
IP Address:
Enter the IP Address to be bound.
MAC Address:
Description:
Status:
List of Rules
Enter the MAC Address corresponding to the IP Address.
Give a description for the entry.
Activate or inactivate the entry.
-70-
Page 76

You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-46 indicates: The IP address of 192.168.1.101 and MAC address of
9-66-83-53-CF have been bound and this entry is activated.
00-1
Note:
If all the entries in the binding list are disabled and “Permit the packets of IP-MAC Binding entries only”
option is selected and saved, the WEB management page of the Router cannot be login. At the
moment, you should restore the Router to factory default and login again.
3.4.1.2 ARP Scanning
ARP Scanning feature enables the Router to scan the IP address and corresponding MAC address
and display them on the List of Scanning Result.
Choose the menu Firewall→Anti ARP Spoofing→ARP Scanning to load the following page.
Figure 3-47 ARP Scanning
Enter the start and the end IP addresses into the Scanning IP Range field. Then click the <Scan>
button, the Router will scan all the active hosts within the scanning range and display the result in the
list.
The entries displayed on the List of Scanning Result do not mean the IP and MAC addresses are
already bound. The current status for the entry will display in the “Status” field.
--- Indicates that the IP and MAC address of this entry are not bound and may be
replaced by error ARP information.
Indicates that this entry is imported to the list on IP-MAC Binding page, but not
effective yet.
-71-
Page 77

To bind the entries in the list, check these entries and click the <Import> button, then the settings will
take effect if the entries do not conflict with the existed entries.
Note:
If the local hosts suffered from ARP attack, you cannot add IP-MAC Binding entries on this page.
Please add entries manually on 3.4.1.1 IP-MAC Binding.
Indicates that the IP and MAC address of this entry are already bound.
3.4.1.3 ARP List
On this page, the IP-MAC information of the hosts which communicated with the Router recently will
be saved in the ARP list.
Choose the menu Firewall→Anti ARP Spoofing→ARP List to load the following page.
Figure 3-48 ARP List
The configurations for the entries is the same as the configuration of List of Scanning Result on 3.4.1.2
ARP Scanning p
The unbound IP-MAC information will be replaced by new IP-MAC information or be automatically
removed from the list if it has not been communicated with others for a long time. This period is
regarded as the aging time of the ARP information.
age.
3.4.2 Attack Defense
With Attack Defense function enabled, the Router can distinguish the malicious packets and prevent
the port scanning from external network, so as to guarantee the network security.
Choose the menu Firewall→Attack Defense→Attack Defense to load the following page.
-72-
Page 78

Figure 3-49 Attack Defense
The following items are displayed on this screen:
General
Flood Defense:
Flood attack is a commonly used DoS (Denial of Service) attack,
including TCP SYN, UDP, ICMP and so on. It is recommended to
select all the Flood Defense options and specify the
corresponding thresholds. Keep the default settings if you are not
sure.
-73-
Page 79

Packet Anomaly
Defense:
Enable Attack
Defense Logs:
Packet Anomaly refers to the abnormal packets. It is
recommended to select all the Packet Anomaly Defense options.
With this box checked, the Router will record the defense logs.
3.4.3 MAC Filtering
On this page, you can control the Internet access of local hosts by specifying their MAC addresses.
Choose the menu Firewall→MAC Filtering→MAC Filtering to load the following page.
Figure 3-50 MAC Filtering
The following items are displayed on this screen:
General
To control the access to Internet for hosts in you private network, it is recommended to check the
box before Enable MAC Filtering and select a filtering mode according to actual situation.
MAC Filtering
MAC Address:
Description:
Enter the MAC Address to be filtered.
Give a description for the entry.
-74-
Page 80

List of Rules
You can view the information of the entries and edit them by the Action buttons.
3.4.4 Access Control
3.4.4.1 URL Filtering
URL (Uniform Resource Locator) specifies where an identified resource is available and the
mechanism for retrieving it. URL Filter functions to filter the Internet URL address, so as to provide a
convenient way for controlling the access to Internet from LAN hosts.
Choose the menu Firewall→Access Control→URL Filtering to load the following page.
Figure 3-51 URL Filtering
The following items are displayed on this screen:
General
To control the access to Internet for hosts in your private network, you are recommended to
check the box before Enable URL Filtering and select a filtering rule based on the actual
situation.
URL Filtering Rule
Object:
Select the range in which the URL Filtering takes effect:
ANY: URL Filtering will take effect to all the users.
-75-
Page 81

Group: URL Filtering will take effect to all the users in group.
Mode:
Select the mode for URL Filtering. “Keyword’’ indicates that all the
URL addresses including the specified keywords will be filtered.
“URL Path” indicates that the URL address will be filtered only
when it exactly matches the specified URL.
Description:
Give a description for the entry.
List of Rules
You can view the information of the entries and edit them by the Action buttons.
Application Example:
Network Requirements:
Prevent the local hosts from accessing Internet website www.aabbcc.com and downloading the files
with suffix of “exe”.
Configuration Procedure:
Select Keywords mode and type ”exe“ in the field, select URL mode and type “www.aabbcc.com” as
the following figure shows, and then click the <Add> button to make the setting take effect.
-76-
Page 82

3.4.4.2 Web Filtering
On this page, you can filter the desired web components.
Choose the menu Firewall→Access Control→Web Filtering to load the following page.
Figure 3-52 Web Filtering
Check the box before Enable Web Filtering and select the web components to be filtered.
3.4.4.3 Access Rules
Choose the menu Firewall→Access Control→Access Rules to load the following page.
Figure 3-53 Access Rule
The following items are displayed on this screen:
Access Rules
-77-
Page 83

Policy:
Service:
Interface
Select a policy for the entry:
Block: When this option is selected, the packets obeyed the
rule will not be permitted to pass through the Router.
Allow: When this option is selected, the packets obeyed the
rule will be allowed to pass through the Router.
Select the service for the entry. Only the service belonging to the
specified service type is limited by the entry. For example, if you
select “Block” for Policy and only FTP for Service, the packets of
other service types can still pass through the Router. You can add
new service types on 3.4.4.4 Service.
:
Select interface for the entry. The entry will take effect when the
interface to which the data is flowing is selected. WAN, LAN or
DMZ refers to all the WAN, LAN or DMZ interfaces.
Source:
Destination:
Select the Source IP Range for the entries, including the following
three ways:
IP/MASK: Enter an IP address or subnet mask. ("0.0.0.0/32"
means any IP).
Group: Select a predefined group of users. You can set the
group on3.2.1 Group.
ANY: means for any users.
Select the Destination IP Range for the entries, including the
following two ways:
IP/MASK: Enter an IP address or subnet mask. ("0.0.0.0/32"
means any IP is acceptable).
ANY: means for any users.
Effective Time:
Description:
Specify the time for the entry to take effect.
Give a description for the entry.
-78-
Page 84

Priority:
List of Rules
You can view the information of the entries and edit them by the Action buttons. The smaller the value
is, the higher the priority is.
The first entry in Figure 3-53 indicates: The TELNET packets transmitted from the hosts within the
network of 192.168.0.0/24 will be not
to Saturday.
Note:
● For the users in the private network and not being set access rule, the default Policy is Allow.
Select this option to specify the priority for the added entries. The
latest enabled entry will be displayed at the end of the list by
default.
allowed to pass through the Router at 8:00-20:00 from Tuesday
● To specify all IP addresses, type “0.0.0.0 / 32” in the Policy field.
● For detailed setting of subnet mask, please refer to Appendix B FAQ.
3.4.4.4 Service
The Service function allows you to specify the protocol and port number to be filtered for Firewall
function conveniently. Protocol name and port range constitute a service type. The Router predefines
three commonly used services such as HTTP, FTP and TELNET and you can also add customized
services if needed.
Choose the menu Firewall→Access Control→Service to load the following page.
-79-
Page 85

Figure 3-54 Service
The following items are displayed on this screen:
Service
Name:
Enter a name for the service. The name should not be more than 28
characters. The name will display in the drop-down list of Protocol on
Access Rule page.
Protocol:
Select the protocol for the service. The system predefined protocols
include TCP, UDP and TCP/UDP.
Dest. Port:
Enter the start and end ports to make a destination port range for the
service. The start port number cannot be greater than the end port
number.
List of Service
You can view the information of the entries and edit them by the Action buttons.
Note:
The service types predefined by the system cannot be modified.
-80-
Page 86

3.4.5 App Control
3.4.5.1 Control Rules
On this page, you can enable the Application Rules function.
Choose the menu Firewall→App Control→Control Rules to load the following page.
Figure 3-55 Application Rules
The following items are displayed on this screen:
General
Check the box before Enable Application Control to make the Application Control function
take effect. The specified application used by the specified local users will be not allowed to
access the Internet if the Application Control entry is enabled.
Control Rules
Object:
Group:
Specify the object for the entry. You can select “Group” to limit the
predefined group, or select “ANY” to limit all the users.
If select “Group” as object, you can select the group in the drop-down list.
To establish new group, please refer to 3.2.1 Group.
-81-
Page 87

Application:
Effective Time:
Description:
Status:
List of Rules
You can view the information of the entries and edit them by the Action buttons.
The first entry in Figure 3-55 indicates: The group1 is applied with
<View> to view the limited applications in the popup checkbox. The effective time of this entry is
Click the <Application List> button to select applications from the popup
checkbox. The applications include IM, Web IM, SNS, P2P, Media, Basic
and Proxy. The default setting is to limit all the applications in the
application list except for Basic and Proxy.
Specify the time for the entry to take effect.
Give a description for the entry.
Activate or inactivate the entry.
Application Rules. You can click
7:00-9:00 on Monday, Tuesday, Friday, Saturday and Sunday. This entry is enabled.
Note:
To set the group and group members, please refer to 3.2.1 Group.
3.4.5.2 Database
On this page, you can upgrade the application database.
Choose the menu Firewall→App Control→Database to load the following page.
Figure 3-56 Database
The database refers to all the applications in the application list on the Application Rules page, you can
download the latest database from http://www.tp-link.com
file, and then click the <Upgrade> button to upgrade the database.
-82-
, Click the <Browse> button and select the
Page 88

3.5 VPN
VPN (Virtual Private Network) is a private network established via the public network, generally via the
Internet. However, the private network is a logical network without any physical network lines, so it is
called Virtual Private Network.
With the wide application of the Internet, more and more data are needed to be shared through the
Internet. Connecting the local network to the Internet directly, though can allow the data exchange, will
cause the private data to be exposed to all the users on the Internet. The VPN (Virtual Private Network)
technology is developed and used to establish the private network through the public network, which
can guarantee a secured data exchange.
VPN adopts the tunneling technology to establish a private connection between two endpoints. It is a
connection secured by encrypting the data and using point-to-point authentication. The following
diagram is a typical VPN topology.
Figure 3-57 VPN – Network Topology
As the packets are encapsulated and de-encapsulated in the Router, the tunneling topology
implemented by encapsulating packets is transparent to users. The tunneling protocols supported by
TL-ER6020 contain Layer 3 IPsec and Layer 2 L2TP/PPTP.
3.5.1 IKE
In the IPsec VPN, to ensure a secure communication, the two peers should encapsulate and
de-encapsulate the packets using the information both known. Therefore the two peers need to
negotiate a security key for communication with IKE (Internet Key Exchange) protocols.
Actually IKE is a hybrid protocol based on three underlying security protocols, ISAKMP (Internet
Security Association and Key Management Protocol), Oakley Key Determination Protocol, and
SKEME Security Key Exchange Protocol. ISAKMP provides a framework for Key Exchange and SA
(Security Association) negotiation. Oakley describes a series of key exchange modes. SKEME
describes another key exchange mode different from those described by Oakley.
IKE consists of two phases. Phase 1 is used to negotiate the parameters, key exchange algorithm and
encryption to establish an ISAKMP SA for securely exchanging more information in Phase 2. During
phase 2, the IKE peers use the ISAKMP SA established in Phase 1 to negotiate the parameters for
security protocols in IPsec and create IPsec SA to secure the transmission data.
-83-
Page 89

3.5.1.1 IKE Policy
On this page you can configure the related parameters for IKE negotiation.
Choose the menu VPN→IKE→IKE Policy to load the following page.
Figure 3-58 IKE Policy
The following items are displayed on this screen:
IKE Policy
Policy Name:
Specify a unique name to the IKE policy for identification and
management purposes. The IKE policy can be applied to IPsec
policy.
-84-
Page 90

Exchange Mode:
Local ID Type:
Local ID:
Select the IKE Exchange Mode in phase 1, and ensure the
remote VPN peer uses the same mode.
Main: Main mode provides identity protection and exchanges
more information, which applies to the scenarios with higher
requirement for identity protection.
Aggressive: Aggressive Mode establishes a faster
connection but with lower security, which applies to scenarios
with lower requirement for identity protection.
Select the local ID type for IKE negotiation. IP Address: uses an
IP address as the ID in IKE negotiation. FQDN: uses a name as
the ID.
The local WAN IP will be inputted automatically if IP Address type
is selected. If Name type is selected, enter a name for the local
device as the ID in IKE negotiation
Remote ID Type:
Remote ID:
IKE Proposal:
Pre-shared Key:
SA Lifetime:
Select the remote ID type for IKE negotiation. IP Address: uses an
IP address as the ID in IKE negotiation. FQDN: uses a name as
the ID.
The remote gateway IP will be inputted automatically if IP Address
type is selected. If Name type is selected, enter the name of the
remote peer as the ID in IKE negotiation.
Select the Proposal for IKE negotiation phase 1. Up to four
proposals can be selected.
Enter the Pre-shared Key for IKE authentication, and ensure both
the two peers use the same key. The key should consist of visible
characters without blank space.
Specify ISAKMP SA Lifetime in IKE negotiation.
DPD:
Enable or disable DPD (Dead Peer Detect) function. If enabled,
the IKE endpoint can send a DPD request to the peer to inspect
whether the IKE peer is alive.
-85-
Page 91

DPD Interval:
Enter the interval after which the DPD is triggered.
List of IKE Policy
In this table, you can view the information of IKE Policies and edit them by the action buttons.
3.5.1.2 IKE Proposal
On this page, you can define and edit the IKE Proposal.
Choose the menu VPN→IKE→IKE Proposal to load the following page.
Figure 3-59 IKE Proposal
The following items are displayed on this screen:
IKE Proposal
Proposal Name:
Specify a unique name to the IKE proposal for identification and
management purposes. The IKE proposal can be applied to IPsec
proposal.
Authentication:
Select the authentication algorithm for IKE negotiation. Options
include:
MD5: MD5 (Message Digest Algorithm) takes a message of
arbitrary length and generates a 128-bit message digest.
SHA1: SHA1 (Secure Hash Algorithm) takes a message less
than 2^64 (the 64th power of 2) in bits and generates a
160-bit message digest.
-86-
Page 92

Encryption:
DH Group:
Specify the encryption algorithm for IKE negotiation. Options
include:
DES: DES (Data Encryption Standard) encrypts a 64-bit
block of plain text with a 56-bit key.
3DES: Triple DES, encrypts a plain text with 168-bit key.
AES128: Uses the AES algorithm and 128-bit key for
encryption.
AES192: Uses the AES algorithm and 192-bit key for
encryption.
AES256: Uses the AES algorithm and 256-bit key for
encryption.
Select the DH (Diffie-Hellman) group to be used in key negotiation
phase 1. The DH Group sets the strength of the algorithm in bits.
Options include DH1, DH2 and DH5.
DH1: 768 bits
DH2: 1024 bits
DH3: 1536 bits
List of IKE Proposal
In this table, you can view the information of IKE Proposals and edit them by the action buttons.
3.5.2 IPsec
IPsec (IP Security) is a set of services and protocols defined by IETF (Internet Engineering Task Force)
to provide high security for IP packets and prevent attacks.
To ensure a secured communication, the two IPsec peers use IPsec protocol to negotiate the data
encryption algorithm and the security protocols for checking the integrity of the transmission data, and
exchange the key to data de-encryption.
IPsec has two important security protocols, AH (Authentication Header) and ESP (Encapsulating
Security Payload). AH is used to guarantee the data integrity. If the packet has been tampered during
transmission, the receiver will drop this packet when validating the data integrity. ESP is used to check
the data integrity and encrypt the packets. Even if the encrypted packet is intercepted, the third party
still cannot get the actual information.
-87-
Page 93

3.5.2.1 IPsec Policy
On this page, you can define and edit the IPsec policy.
Choose the menu VPN→IPsec→IPsec Policy to load the following page.
Figure 3-60 IPsec Policy
The following items are displayed on this screen:
General
You can enable/disable IPsec function for the Router here.
IPsec Policy
Policy Name:
Specify a unique name to the IPsec policy. Up to 28 characters
can be entered.
-88-
Page 94

Mode:
Local Subnet:
Remote Subnet:
WAN :
Select the network mode for IPsec policy. Options include:
LAN-to-LAN: Select this option when the client is a
network.
Client-to-LAN: Select this option when the client is a host.
Specify IP address range on your local LAN to identify which
PCs on your LAN are covered by this policy. It's formed by IP
address and subnet mask.
Specify IP address range on your remote network to identify
which PCs on the remote network are covered by this policy. It's
formed by IP address and subnet mask.
Specify the local WAN port for this Policy. The "Remote
Gateway" of the remote peer should be set to the IP address of
this WAN port.
Remote Gateway:
Policy Mode:
IKE Mode
IKE Policy:
IPsec Proposal:
Enter the Remote Gateway. It can be IP address or Domain
name.
Select the negotiation mode for the policy.
IKE: The parameters for the VPN tunnel are generated
automatically via IKE negotiations.
Manual: All settings (including the keys) for the VPN tunnel
are manually inputted and no key negotiation is needed.
It is available when IKE is selected as the negotiation mode.
Specify the IKE policy. If there is no policy selection, add new
policy on VPN→IKE→IKE Policy page.
Select IPsec Proposal on IKE mode. Up to four IPsec Proposals
PFS:
can be selected on IKE mode.
Select the PFS (Perfect Forward Security) for IKE mode to
enhance security. This setting should match the remote peer.
With PFS feature, IKE negotiates to create a new key in
-89-
Page 95

Phase2. As it is independent of the key created in Phase1, this
key can be secure even when the key in Phase1 is
de-encrypted. Without PFS, the key in Phase2 is created based
on the key in Phase1 and thus once the key in Phase1 is
de-encrypted, the key in Phase2 is easy to be de-encrypted, in
this case, the communication secrecy is threatened.
SA Lifetime:
Status:
Manual Mode
IPsec Proposal:
Incoming SPI:
AH Authentication Key-In:
Specify IPsec SA Lifetime for IKE mode.
Activate or inactivate the entry.
Select the IPsec Proposal. Only one proposal can be selected
on Manual mode. You need to first create the IPsec Proposal.
Specify the Incoming SPI (Security Parameter Index) manually.
The Incoming SPI here must match the Outgoing SPI value at
the other end of the tunnel, and vice versa.
Specify the inbound AH Authentication Key manually if AH
protocol is used in the corresponding IPsec Proposal. The
inbound key here must match the outbound AH authentication
key at the other end of the tunnel, and vice versa.
ESP Authentication Key-In:
ESP Encryption: Key-In:
Outgoing SPI:
Specify the inbound ESP Authentication Key manually if ESP
protocol is used in the corresponding IPsec Proposal. The
inbound key here must match the outbound ESP authentication
key at the other end of the tunnel, and vice versa.
Specify the inbound ESP Encryption Key manually if ESP
protocol is used in the corresponding IPsec Proposal. The
inbound key here must match the outbound ESP encryption key
at the other end of the tunnel, and vice versa.
Specify the Outgoing SPI (Security Parameter Index) manually.
The Outgoing SPI here must match the Incoming SPI value at
the other end of the tunnel, and vice versa.
-90-
Page 96

AH Authentication Key-Out:
ESP Authentication Key-Out:
ESP Encryption Key-Out:
List of IPsec Policy IPsec
Specify the outbound AH Authentication Key manually if AH
protocol is used in the corresponding IPsec Proposal. The
outbound key here must match the inbound AH authentication
key at the other end of the tunnel, and vice versa.
Specify the outbound ESP Authentication Key manually if ESP
protocol is used in the corresponding IPsec Proposal. The
outbound key here must match the inbound ESP authentication
key at the other end of the tunnel, and vice versa.
Specify the outbound ESP Encryption Key manually if ESP
protocol is used in the corresponding IPsec Proposal. The
outbound key here must match the inbound ESP encryption key
at the other end of the tunnel, and vice versa.
In this table, you can view the information of IPsec policies and edit them by the action buttons.
The first entry in Figure 3-60 indicates: this is an IPsec tunnel, the local sub
the remote subnet is 192.168.3.0/24 and this tunnel is using IKE automatic negotiation. It is
enabled.
Tips:
● 0.0.0.0.0/32 indicates all IP addresses.
● Refer to Appendix Troubleshooting 5 for the configuration of subnet.
net is 192.168.0.0/24,
3.5.2.2 IPsec Proposal
On this page, you can define and edit the IPsec proposal.
Choose the menu VPN→IPsec→IPsec Proposal to load the following page.
-91-
Page 97

Figure 3-61 IPsec Proposal
The following items are displayed on this screen:
IPsec Proposal
Proposal Name:
Specify a unique name to the IPsec Proposal for identification and
management purposes. The IPsec proposal can be applied to IPsec
policy.
Security Protocol:
AH Authentication:
Select the security protocol to be used. Options include:
AH: AH (Authentication Header) provides data origin
ESP: ESP (Encapsulating Security Payload) provides data
Select the algorithm used to verify the integrity of the data for AH
authentication. Options include:
authentication, data integrity and anti-replay services.
encryption in addition to origin authentication, data integrity, and
anti-replay services.
MD5: MD5 (Message Digest Algorithm) takes a message of
arbitrary length and generates a 128-bit message digest.
SHA: SHA (Secure Hash Algorithm) takes a message less than the
64th power of 2 in bits and generates a 160-bit message digest.
-92-
Page 98

ESP Authentication:
ESP Encryption:
Select the algorithm used to verify the integrity of the data for ESP
authentication. Options include:
MD5: MD5 (Message Digest Algorithm) takes a message of
arbitrary length and generates a 128-bit message digest.
SHA: SHA (Secure Hash Algorithm) takes a message less than the
64th power of 2 in bits and generates a 160-bit message digest.
Select the algorithm used to encrypt the data for ESP encryption.
Options include:
NONE: Performs no encryption.
DES: DES (Data Encryption Standard) encrypts a 64-bit block of plain
text with a 56-bit key. The key should be 8 characters.
3DES: Triple DES, encrypts a plain text with 168-bit key. The key should
be 24 characters.
AES128: Uses the AES algorithm and 128-bit key for encryption. The
key should be 16 characters.
List of IPsec Proposal
In this table, you can view the information of IPsec Proposals and edit them by the action buttons.
3.5.2.3 IPsec SA
This page displays the information of the IPsec SA (Security Association).
Choose the menu VPN→IPsec→IPsec SA to load the following page.
Figure 3-62 IPsec SA
Figure 3-62 displays the connection status of the NO.1 entry in the List of IPsec policy in Figure 3-60.
As shown in the figure, the Router is using WAN2 for tunnel connection, and the IP address of WAN2
and the default gateway of remote peer are 172.30.70.151 and 172.30.70.161 respectively. Security
protocol and other parameters for IPsec tunnel and the remote router should be configured the same.
As Security Association is unidirectional, an ingoing SA and an outgoing SA are created to protect data
flows for each tunnel after IPsec tunnel is successfully established. The ingoing SPI value and
-93-
Page 99

outgoing SPI value are different. However, the Incoming SPI value must match the Outgoing SPI value
at the other end of the tunnel, and vice versa. The connection status on the remote endpoint of this
tunnel is as the following figure shows. The SPI value is obtained via auto-negotiation.
3.5.3 L2TP/PPTP
Layer 2 VPN tunneling protocol consists of L2TP (Layer 2 Tunneling Protocol) and PPTP (Point to
Point Tunneling Protocol).
Both L2TP and PPTP encapsulate packet and add extra header to the packet by using PPP (Point to
Point Protocol). Table depicts the difference between L2TP and PPTP.
Protocol Media Tunnel Length of Header Authentication
PPTP IP network Single tunnel 6 bytes at least Not supported
IP network of
UDP, frame relay
L2TP
virtual circuit,
X.25 virtual
circuit
Multiple tunnels 4 bytes at least Supported
3.5.3.1 L2TP/PPTP Tunnel
On this page, you can configure the L2TP/PPTP VPN.
Choose the menu VPN→L2TP/PPTP→L2TP/PPTP Tunnel to load the following page.
-94-
Page 100

Figure 3-63 L2TP/PPTP Tunnel
The following items are displayed on this screen:
General
Enable VPN-to-Internet:
Specify whether to enable VPN-to-Internet function. If enabled, the
VPN client is permitted to access the LAN of the server and Internet.
Hello Interval:
Specify the interval to send hello packets.
L2TP/PPTP Tunnel
Protocol:
Mode:
Select the protocol for VPN tunnel. Options include L2TP and PPTP.
Specify the working mode for this Router. Options include:
Client: In this mode, the device sends a request to the remote
L2TP/PPTP server initiatively for establishing a tunnel.
Server: In this mode, the Router responds the request from the
remote client for establishing a tunnel.
-95-
 Loading...
Loading...