Page 1

CLI Reference Guide
T2500G-10TS (TL-SG3210)
1910012494 REV2.0.0
November 2018
Page 2
COPYRIGHT & TRADEMARKS
Specifications are subject to change without notice. is a registered trademark of
TP-Link Technologies Co., Ltd. Other brands and product names are trademarks or registered
trademarks of their respective holders.
No part of the specifications may be reproduced in any form or by any means or used to make
any derivative such as translation, transformation, or adaptation without permission from
TP-Link Technologies Co., Ltd. Copyright © 2018 TP-Link Technologies Co., Ltd. All rights
reserved.
https://www.tp-link.com
I
Page 3

............................................................................................................................ 1
................................................................................................... 5
............................................................................................... 17
................................................................. 24
.......................................................... 28
CONTENTS
Preface
Chapter 1 Using the CLI
Chapter 2 User Interface
1.1 Accessing the CLI ......................................................................................................................... 5
1.1.1 Logon by Telnet ........................................................................................................... 5
1.1.2 Logon by SSH ............................................................................................................... 6
1.2 CLI Command Modes ................................................................................................................. 12
1.3 Privilege Restrictions .................................................................................................................. 15
1.4 Conventions ................................................................................................................................. 15
1.4.1 Format Conventions .................................................................................................. 15
1.4.2 Special Characters .................................................................................................... 16
1.4.3 Parameter Format ...................................................................................................... 16
2.1 enable ................................................................................................................................... 17
2.2 service password-encryption .......................................................................................... 17
2.3 enable password ................................................................................................................ 18
2.4 enable secret ...................................................................................................................... 19
2.5 configure ............................................................................................................................. 20
2.6 exit ........................................................................................................................................ 21
2.7 end ........................................................................................................................................ 21
2.8 clipaging .............................................................................................................................. 22
2.9 history .................................................................................................................................. 22
2.10 history clear ........................................................................................................................ 23
Chapter 3 User Management Commands
3.1 user name (password) ....................................................................................................... 24
3.2 user name (secret) ............................................................................................................. 25
3.3 show user account-list ...................................................................................................... 26
3.4 show user configuration ................................................................................................... 27
Chapter 4 System Configuration Commands
4.1 system-time manual .......................................................................................................... 28
4.2 system-time ntp ................................................................................................................. 28
4.3 system-time dst predefined............................................................................................. 30
4.4 system-time dst date ........................................................................................................ 31
4.5 system-time dst recurring ................................................................................................ 32
II
Page 4

................................................................. 55
4.6 hostname ............................................................................................................................. 33
4.7 location ................................................................................................................................ 34
4.8 contact-info ........................................................................................................................ 34
4.9 ip address ............................................................................................................................ 35
4.10 ip management-vlan .......................................................................................................... 36
4.11 ip address-alloc .................................................................................................................. 36
4.12 reset ..................................................................................................................................... 37
4.13 reboot................................................................................................................................... 38
4.14 reboot-schedule ................................................................................................................ 38
4.15 copy running-config startup-config ............................................................................... 39
4.16 copy startup-config tftp ................................................................................................... 40
4.17 copy tftp startup-config ................................................................................................... 40
4.18 copy backup-config tftp ................................................................................................... 41
4.19 copy backup-config startup-config ............................................................................... 42
4.20 copy running-config backup-config ............................................................................... 42
4.21 copy tftp backup-config ................................................................................................... 43
4.22 boot application ................................................................................................................. 44
4.23 boot config .......................................................................................................................... 44
4.24 remove backup-image ...................................................................................................... 45
4.25 firmware upgrade ............................................................................................................... 46
4.26 ping ....................................................................................................................................... 47
4.27 tracert .................................................................................................................................. 48
4.28 show system-info............................................................................................................... 49
4.29 show image-info ................................................................................................................. 49
4.30 show boot ............................................................................................................................ 50
4.31 show running-config ......................................................................................................... 50
4.32 show startup-config .......................................................................................................... 51
4.33 show system-time ............................................................................................................. 51
4.34 show system-time dst ....................................................................................................... 52
4.35 show system-time ntp....................................................................................................... 52
4.36 show cable-diagnostics interface ................................................................................... 53
4.37 show cpu-utilization ...........................................................................................................
4.38 show memory-utilization .................................................................................................. 54
Chapter 5 EEE Configuration Commands
5.1 eee ........................................................................................................................................ 55
5.2 show interface eee ............................................................................................................ 55
III
53
Page 5

........................................................................ 57
............................................................................. 59
................................................................ 64
.......................................................................... 73
............................................................. 75
Chapter 6 SDM Template Commands
6.1 sdm prefer ........................................................................................................................... 57
6.2 show sdm prefer ................................................................................................................ 58
Chapter 7 Time Range Commands
7.1 time-range ........................................................................................................................... 59
7.2 absolute ............................................................................................................................... 59
7.3 periodic ................................................................................................................................ 60
7.4 holiday (time-range mode) ............................................................................................... 61
7.5 holiday .................................................................................................................................. 62
7.6 show holiday ....................................................................................................................... 62
7.7 show time-range ................................................................................................................ 63
Chapter 8 Port Configuration Commands
8.1 interface gigabitEthernet .................................................................................................. 64
8.2 interface range gigabitEthernet ...................................................................................... 64
8.3 description .......................................................................................................................... 65
8.4 shutdown ............................................................................................................................. 66
8.5 flow-control ......................................................................................................................... 67
8.6 duplex ................................................................................................................................... 67
8.7 jumbo-size ........................................................................................................................... 68
8.8 speed ................................................................................................................................... 69
8.9 clear counters ..................................................................................................................... 69
8.10 show interface status ........................................................................................................ 70
8.11 show interface counters ................................................................................................... 71
8.12 show interface configuration ........................................................................................... 71
Chapter 9 Port Isolation Commands
9.1 port isolation ....................................................................................................................... 73
9.2 show port isolation interface ........................................................................................... 74
Chapter 10 Loopback Detection Commands
10.1 loopback-detection (global) ............................................................................................. 75
10.2 loopback-detection interval ............................................................................................. 75
10.3 loopback-detection recovery-time ................................................................................ 76
10.4 loopback-detection (interface) ........................................................................................ 77
10.5 loopback-detection config process-mode ................................................................... 77
10.6 loopback-detection recover ............................................................................................ 78
10.7 show loopback-detection global .................................................................................... 79
IV
Page 6
.......................................................................................... 81
.......................................................................... 89
.......................................................................... 96
10.8 show loopback-detection interface ............................................................................... 79
Chapter 11 DDM Commands
11.1 ddm state enable ............................................................................................................... 81
11.2 ddm shutdown .................................................................................................................... 81
11.3 ddm temperature_threshold ............................................................................................ 82
11.4 ddm voltage_threshold ..................................................................................................... 83
11.5 ddm bias_current_threshold ............................................................................................ 84
11.6 ddm tx_power_threshold .................................................................................................. 85
11.7 ddm rx_power_threshold.................................................................................................. 86
11.8 show ddm configuration ................................................................................................... 87
11.9 show ddm status ................................................................................................................ 88
Chapter 12 Etherchannel Commands
12.1 channel-group .................................................................................................................... 89
12.2 port-channel load-balance ............................................................................................... 90
12.3 lacp system-priority .......................................................................................................... 91
12.4 lacp port-priority ................................................................................................................ 92
12.5 show etherchannel ............................................................................................................ 92
12.6 show etherchannel load-balance .................................................................................... 93
12.7 show lacp ............................................................................................................................. 94
12.8 show lacp sys-id ................................................................................................................. 94
Chapter 13 MAC Address Commands
13.1 mac address-table static .................................................................................................. 96
13.2 mac address-table aging-time ........................................................................................ 97
13.3 mac address-table filtering .............................................................................................. 97
13.4 mac address-table notification ....................................................................................... 98
13.5 mac address-table max-mac-count ............................................................................... 99
13.6 mac address-table notification (interface) .................................................................. 100
13.7 mac address-table security ........................................................................................... 101
13.8 mac address-table vlan-security .................................................................................. 102
13.9 show mac address-table ................................................................................................ 103
13.10 clear mac address-table ................................................................................................. 103
13.11 show mac address-table aging-time ............................................................................ 104
13.12 show mac address-table max-mac-count .................................................................. 104
13.13 show mac address-table interface ............................................................................... 105
13.14 show mac address-table count ..................................................................................... 106
13.15 show mac address-table address ................................................................................. 106
V
Page 7

............................................................... 109
................................................................ 116
........................................................ 119
............................................................................. 123
13.16 show mac address-table vlan ........................................................................................ 107
13.17 show mac address-table notification ........................................................................... 107
13.18 show mac address-table vlan-security ........................................................................ 108
Chapter 14 IEEE 802.1Q VLAN Commands
14.1 vlan ..................................................................................................................................... 109
14.2 name ................................................................................................................................... 110
14.3 switchport general allowed vlan .................................................................................... 110
14.4 switchport pvid ................................................................................................................. 111
14.5 switchport check ingress ............................................................................................... 112
14.6 switchport acceptable frame ......................................................................................... 113
14.7 show vlan summary ......................................................................................................... 113
14.8 show vlan brief .................................................................................................................. 114
14.9 show vlan ........................................................................................................................... 114
14.10 show interface switchport .............................................................................................. 115
Chapter 15 MAC-based VLAN Commands
15.1 mac-vlan mac-address ................................................................................................... 116
15.2 mac-vlan ............................................................................................................................ 117
15.3 show mac-vlan .................................................................................................................. 117
15.4 show mac-vlan interface ................................................................................................ 118
Chapter 16 Protocol-based VLAN Commands
16.1 protocol-vlan template ................................................................................................... 119
16.2 protocol-vlan vlan ............................................................................................................ 120
16.3 protocol-vlan group ......................................................................................................... 121
16.4 show protocol-vlan template ......................................................................................... 122
16.5 show protocol-vlan vlan .................................................................................................. 122
Chapter 17 VLAN-VPN Commands
17.1 dot1q-tunnel ..................................................................................................................... 123
17.2 switchport dot1q-tunnel tpid ......................................................................................... 123
17.3 dot1q-tunnel mapping .................................................................................................... 124
17.4 switchport dot1q-tunnel mode ..................................................................................... 125
17.5 switchport dot1q-tunnel missdrop ............................................................................... 126
17.6 switchport dot1q-tunnel mapping ................................................................................ 126
17.7 show dot1q-tunnel........................................................................................................... 127
17.8 show dot1q-tunnel mapping .......................................................................................... 128
17.9 show dot1q-tunnel interface ......................................................................................... 128
VI
Page 8

....................................................................................... 130
..................................................................... 135
Chapter 18 GVRP Commands
18.1 gvrp..................................................................................................................................... 130
18.2 gvrp (interface) ................................................................................................................. 130
18.3 gvrp registration ............................................................................................................... 131
18.4 gvrp timer .......................................................................................................................... 132
18.5 show gvrp interface ......................................................................................................... 133
18.6 show gvrp global .............................................................................................................. 134
Chapter 19 IGMP Snooping Commands
19.1 ip igmp snooping (global) ................................................................................................ 135
19.2 ip igmp snooping version ............................................................................................... 135
19.3 ip igmp snooping drop-unknown .................................................................................. 136
19.4 ip igmp snooping header-validation ............................................................................. 137
19.5 ip igmp snooping vlan-config ........................................................................................ 137
19.6 ip igmp snooping vlan-config (immediate-leave) ....................................................... 139
19.7 ip igmp snooping vlan-config (report-suppression) .................................................. 139
19.8 ip igmp snooping vlan-config (router-ports-forbidden) ............................................ 140
19.9 ip igmp snooping vlan-config (rport interface) ........................................................... 141
19.10 ip igmp snooping vlan-config (static) ........................................................................... 142
19.11 ip igmp snooping vlan-config (querier) ........................................................................ 143
19.12 ip igmp snooping (interface) .......................................................................................... 144
19.13 ip igmp snooping max-groups ....................................................................................... 145
19.14 ip igmp snooping immediate-leave............................................................................... 146
19.15 ip igmp snooping authentication ................................................................................... 147
19.16 ip igmp snooping accounting ........................................................................................ 147
19.17 ip igmp profile ................................................................................................................... 148
19.18 deny .................................................................................................................................... 149
19.19 permit ................................................................................................................................. 149
19.20 range .................................................................................................................................. 150
19.21 ip igmp filter ...................................................................................................................... 150
19.22 clear ip igmp snooping statistics .................................................................................. 151
19.23 show ip igmp snooping ................................................................................................... 151
19.24 show ip igmp snooping interface .................................................................................. 152
19.25 show ip igmp snooping vlan ........................................................................................... 153
19.26 show ip igmp snooping groups ..................................................................................... 153
19.27 show ip igmp profile ......................................................................................................... 154
VII
Page 9

...................................................................... 156
......................................................................................... 174
Chapter 20 MLD Snooping Commands
20.1 ipv6 mld snooping (global) .............................................................................................. 156
20.2 ipv6 mld snooping drop-unknown ................................................................................ 156
20.3 ipv6 mld snooping vlan-config ...................................................................................... 157
20.4 ipv6 mld snooping vlan-config (immediate-leave) ..................................................... 158
20.5 ipv6 mld snooping vlan-config (report-suppression) ................................................ 159
20.6 ipv6 mld snooping vlan-config (router-ports-forbidden) .......................................... 160
20.7 ipv6 mld snooping vlan-config (rport interface) ......................................................... 161
20.8 ipv6 mld snooping vlan-config (static) ......................................................................... 161
20.9 ipv6 mld snooping vlan-config (querier) ...................................................................... 162
20.10 ipv6 mld snooping (interface) ........................................................................................ 164
20.11 ipv6 mld snooping max-groups ..................................................................................... 164
20.12 ipv6 mld snooping immediate-leave ............................................................................ 166
20.13 ipv6 mld profile ................................................................................................................. 166
20.14 deny .................................................................................................................................... 167
20.15 permit ................................................................................................................................. 167
20.16 range .................................................................................................................................. 168
20.17 ipv6 mld filter .................................................................................................................... 169
20.18 clear ipv6 mld snooping statistics ................................................................................ 169
20.19 show ipv6 mld snooping ................................................................................................. 170
20.20 show ipv6 mld snooping interface ................................................................................ 170
20.21 show ipv6 mld snooping vlan ......................................................................................... 171
20.22 show ipv6 mld snooping groups ................................................................................... 172
20.23 show ipv6 mld profile ...................................................................................................... 172
Chapter 21 MVR Commands
21.1 mvr (global) ........................................................................................................................ 174
21.2 mvr group .......................................................................................................................... 174
21.3 mvr mode........................................................................................................................... 175
21.4 mvr querytime ................................................................................................................... 176
21.5 mvr vlan .............................................................................................................................. 177
21.6 mvr (interface) ................................................................................................................... 177
21.7 mvr type ............................................................................................................................. 178
21.8 mvr immediate .................................................................................................................. 179
21.9 mvr vlan (group) ................................................................................................................ 179
21.10 show mvr ........................................................................................................................... 180
21.11 show mvr interface .......................................................................................................... 181
21.12 show mvr members ......................................................................................................... 181
VIII
Page 10

....................................................................................... 183
........................................................................................ 203
21.13 show mvr traffic ................................................................................................................ 182
Chapter 22 MSTP Commands
22.1 debug spanning-tree ....................................................................................................... 183
22.2 spanning-tree (global) ..................................................................................................... 184
22.3 spanning-tree (interface) ................................................................................................ 184
22.4 spanning-tree common-config ..................................................................................... 185
22.5 spanning-tree mode ........................................................................................................ 186
22.6 spanning-tree mst configuration .................................................................................. 187
22.7 instance ............................................................................................................................. 188
22.8 name ................................................................................................................................... 188
22.9 revision .............................................................................................................................. 189
22.10 spanning-tree mst instance ........................................................................................... 190
22.11 spanning-tree mst ........................................................................................................... 190
22.12 spanning-tree priority ..................................................................................................... 191
22.13 spanning-tree timer ......................................................................................................... 192
22.14 spanning-tree hold-count .............................................................................................. 193
22.15 spanning-tree max-hops ................................................................................................ 193
22.16 spanning-tree bpdufilter ................................................................................................. 194
22.17 spanning-tree bpduflood ................................................................................................ 195
22.18 spanning-tree bpduguard .............................................................................................. 195
22.19 spanning-tree guard loop ............................................................................................... 196
22.20 spanning-tree guard root ............................................................................................... 197
22.21 spanning-tree guard tc ................................................................................................... 197
22.22 spanning-tree mcheck .................................................................................................... 198
22.23 show spanning-tree active ............................................................................................. 199
22.24 show spanning-tree bridge ............................................................................................ 199
22.25 show spanning-tree interface ........................................................................................ 200
22.26 show spanning-tree interface-security ....................................................................... 201
22.27 show spanning-tree mst ................................................................................................. 201
Chapter 23 LLDP Commands
23.1 lldp ...................................................................................................................................... 203
23.2 lldp forward_message ..................................................................................................... 203
23.3 lldp hold-multiplier ........................................................................................................... 204
23.4 lldp timer ............................................................................................................................ 205
23.5 lldp receive ........................................................................................................................ 206
23.6 lldp transmit ...................................................................................................................... 206
IX
Page 11

........................................................................................ 216
............................................................. 220
........................................................................... 225
23.7 lldp snmp-trap .................................................................................................................. 207
23.8 lldp tlv-select .................................................................................................................... 208
23.9 lldp management-address ............................................................................................. 208
23.10 lldp med-fast-count ......................................................................................................... 209
23.11 lldp med-status ................................................................................................................ 210
23.12 lldp med-tlv-select ........................................................................................................... 210
23.13 lldp med-location ............................................................................................................. 211
23.14 show lldp ............................................................................................................................ 212
23.15 show lldp interface ........................................................................................................... 213
23.16 show lldp local-information interface ........................................................................... 213
23.17 show lldp neighbor-information interface ................................................................... 214
23.18 show lldp traffic interface ............................................................................................... 214
Chapter 24 L2PT Commands
24.1 l2protocol-tunnel ............................................................................................................. 216
24.2 l2protocol-tunnel type .................................................................................................... 216
24.3 show l2protocol-tunnel global ....................................................................................... 218
24.4 show l2protocol-tunnel interface .................................................................................. 218
Chapter 25 PPPoE ID-Insertion Commands
25.1 pppoe id-insertion (global) ............................................................................................. 220
25.2 pppoe circuit-id (interface) ............................................................................................. 221
25.3 pppoe circuit-id type ....................................................................................................... 221
25.4 pppoe remote-id .............................................................................................................. 222
25.5 show pppoe id-insertion global ..................................................................................... 223
25.6 show pppoe id-insertion interface ................................................................................ 223
Chapter 26 DHCP Relay Commands
26.1 service dhcp relay ............................................................................................................ 225
26.2 ip dhcp relay hops ............................................................................................................ 225
26.3 ip dhcp relay time ............................................................................................................. 226
26.4 ip dhcp relay vlan ............................................................................................................. 227
26.5 ip dhcp relay information ................................................................................................ 227
26.6 ip dhcp relay information strategy ................................................................................ 228
26.7 ip dhcp relay information format ................................................................................... 229
26.8 ip dhcp relay information circuit-id ............................................................................... 230
26.9 ip dhcp relay information remote-id ............................................................................. 230
26.10 ip dhcp relay default-interface ...................................................................................... 231
26.11 show ip dhcp relay ........................................................................................................... 232
X
Page 12

..................................................................... 233
.......................................................................................... 239
.............................................................. 249
........................................................................... 255
Chapter 27 DHCP L2 Relay Commands
27.1 ip dhcp l2relay .................................................................................................................. 233
27.2 ip dhcp l2relay vlan .......................................................................................................... 233
27.3 ip dhcp l2relay information ............................................................................................. 234
27.4 ip dhcp l2relay information strategy ............................................................................. 234
27.5 ip dhcp l2relay information format ................................................................................ 235
27.6 ip dhcp l2relay information circuit-id ............................................................................ 236
27.7 ip dhcp l2relay information remote-id .......................................................................... 237
27.8 show ip dhcp l2relay ........................................................................................................ 237
27.9 show ip dhcp l2relay interface ....................................................................................... 238
Chapter 28 QoS Commands
28.1 qos trust mode ................................................................................................................. 239
28.2 qos port-priority ............................................................................................................... 240
28.3 qos cos-map ..................................................................................................................... 240
28.4 qos dot1p-remap ............................................................................................................. 241
28.5 qos dscp-map................................................................................................................... 242
28.6 qos dscp-remap ............................................................................................................... 243
28.7 qos queue mode .............................................................................................................. 243
28.8 show qos cos-map .......................................................................................................... 244
28.9 show qos dot1p-remap .................................................................................................. 245
28.10 show qos dscp-map ........................................................................................................ 245
28.11 show qos dscp-remap .................................................................................................... 246
28.12 show qos port-priority interface ................................................................................... 246
28.13 show qos trust interface ................................................................................................. 247
28.14 show qos queue interface .............................................................................................. 247
Chapter 29 Bandwidth Control Commands
29.1 storm-control rate-mode ............................................................................................... 249
29.2 storm-control.................................................................................................................... 250
29.3 storm-control exceed ..................................................................................................... 251
29.4 storm-control recover .................................................................................................... 251
29.5 bandwidth .......................................................................................................................... 252
29.6 show storm-control ......................................................................................................... 253
29.7 show bandwidth ............................................................................................................... 253
Chapter 30 Voice VLAN Commands
30.1 voice vlan ........................................................................................................................... 255
XI
Page 13

............................................................................... 260
.................................................................... 266
................................................................. 271
30.2 voice vlan (interface) ....................................................................................................... 255
30.3 voice vlan priority ............................................................................................................. 256
30.4 voice vlan oui .................................................................................................................... 257
30.5 show voice vlan ................................................................................................................ 257
30.6 show voice vlan oui-table ............................................................................................... 258
30.7 show voice vlan interface ............................................................................................... 258
Chapter 31 Auto VoIP Commands
31.1 auto-voip ........................................................................................................................... 260
31.2 auto-voip (interface) ........................................................................................................ 260
31.3 auto-voip dot1p ................................................................................................................ 261
31.4 auto-voip untagged ......................................................................................................... 262
31.5 auto-voip none ................................................................................................................. 262
31.6 no auto-voip (interface) ................................................................................................... 263
31.7 auto-voip dscp ................................................................................................................. 263
31.8 auto-voip data priority ..................................................................................................... 264
31.9 show auto-voip ................................................................................................................. 265
Chapter 32 Access Control Commands
32.1 user access-control ip-based enable .......................................................................... 266
32.2 user access-control ip-based ....................................................................................... 266
32.3 user access-control mac-based enable ...................................................................... 267
32.4 user access-control mac-based ................................................................................... 268
32.5 user access-control port-based enable ...................................................................... 269
32.6 user access-control port-based ................................................................................... 269
Chapter 33 HTTP and HTTPS Commands
33.1 ip http server ..................................................................................................................... 271
33.2 ip http port ......................................................................................................................... 272
33.3 ip http max-users ............................................................................................................. 272
33.4 ip http session timeout ................................................................................................... 273
33.5 ip http secure-server ....................................................................................................... 274
33.6 ip http secure-port ........................................................................................................... 274
33.7 ip http secure-protocol ................................................................................................... 275
33.8 ip http secure-ciphersuite .............................................................................................. 276
33.9 ip http secure-max-users ............................................................................................... 277
33.10 ip http secure-session timeout ..................................................................................... 278
33.11 ip http secure-server download certificate ................................................................. 278
33.12 ip http secure-server download key ............................................................................. 279
XII
Page 14

.......................................................................................... 282
...................................................................................... 288
.............................................................................. 290
......................................................................................... 291
33.13 show ip http configuration .............................................................................................. 280
33.14 show ip http secure-server ............................................................................................ 281
Chapter 34 SSH Commands
34.1 ip ssh server ...................................................................................................................... 282
34.2 ip ssh port .......................................................................................................................... 282
34.3 ip ssh version .................................................................................................................... 283
34.4 ip ssh algorithm ................................................................................................................ 284
34.5 ip ssh timeout ................................................................................................................... 284
34.6 ip ssh max-client .............................................................................................................. 285
34.7 ip ssh download ................................................................................................................ 286
34.8 remove public-key ........................................................................................................... 286
34.9 show ip ssh ........................................................................................................................ 287
Chapter 35 Telnet Commands
35.1 telnet enable ..................................................................................................................... 288
35.2 telnet port .......................................................................................................................... 288
35.3 show telnet-status ........................................................................................................... 289
Chapter 36 Serial Port Commands
36.1 serial_port baud-rate ....................................................................................................... 290
Chapter 37 AAA Commands
37.1 tacacas-server host ........................................................................................................ 291
37.2 show tacacs-server ......................................................................................................... 292
37.3 radius-server host ........................................................................................................... 293
37.4 show radius-server .......................................................................................................... 294
37.5 aaa group ........................................................................................................................... 295
37.6 server ................................................................................................................................. 296
37.7 show aaa group ................................................................................................................ 296
37.8 aaa authentication login .................................................................................................. 297
37.9 aaa authentication enable .............................................................................................. 298
37.10 aaa authentication dot1x default................................................................................... 299
37.11 aaa accounting dot1x default ........................................................................................ 300
37.12 show aaa authentication ................................................................................................. 300
37.13 show aaa accounting ....................................................................................................... 301
37.14 line telnet ........................................................................................................................... 301
37.15 login authentication (telnet) ............................................................................................ 302
37.16 line ssh ............................................................................................................................... 303
XIII
Page 15

............................................................................ 309
......................................................................... 323
....................................................................... 325
.......................................................................................... 329
37.17 login authentication (ssh) ................................................................................................ 303
37.18 enable authentication (telnet) ........................................................................................ 304
37.19 enable authentication (ssh) ............................................................................................ 305
37.20 ip http login authentication............................................................................................. 305
37.21 ip http enable authentication ......................................................................................... 306
37.22 show aaa global ................................................................................................................ 307
37.23 enable-admin .................................................................................................................... 307
Chapter 38 IEEE 802.1x Commands
38.1 dot1x system-auth-control ............................................................................................ 309
38.2 dot1x handshake.............................................................................................................. 310
38.3 dot1x auth-protocol ........................................................................................................ 310
38.4 dot1x vlan-assignment ................................................................................................... 311
38.5 dot1x accounting ............................................................................................................. 312
38.6 dot1x mab ......................................................................................................................... 313
38.7 dot1x guest-vlan .............................................................................................................. 313
38.8 dot1x timeout quiet-period ............................................................................................ 314
38.9 dot1x timeout supp-timeout .......................................................................................... 315
38.10 dot1x max- req ................................................................................................................. 316
38.11 dot1x .................................................................................................................................. 317
38.12 dot1x port-control ........................................................................................................... 317
38.13 dot1x port-method .......................................................................................................... 318
38.14 dot1x auth-init .................................................................................................................. 319
38.15 dot1x auth-reauth ............................................................................................................ 320
38.16 show dot1x global ............................................................................................................ 320
38.17 show dot1x interface ....................................................................................................... 321
38.18 show dot1x auth-state .................................................................................................... 322
Chapter 39 Port Security Commands
39.1 mac address-table max-mac count .............................................................................. 323
39.2 show mac address-table max-mac-count .................................................................. 323
Chapter 40 Port Mirroring Commands
40.1 monitor session destination interface ......................................................................... 325
40.2 monitor session source .................................................................................................. 326
40.3 show monitor session ..................................................................................................... 327
Chapter 41 ACL Commands
41.1 access-list create ............................................................................................................ 329
XIV
Page 16

............................................................................... 345
............................................................................... 351
41.2 access-list resequence .................................................................................................. 329
41.3 access-list mac ................................................................................................................ 330
41.4 access-list ip ..................................................................................................................... 332
41.5 access-list combined ...................................................................................................... 333
41.6 access-list ipv6 ................................................................................................................ 335
41.7 access-list action ............................................................................................................. 337
41.8 redirect interface ............................................................................................................. 338
41.9 s-condition ........................................................................................................................ 339
41.10 s-mirror .............................................................................................................................. 339
41.11 qos-remark ........................................................................................................................ 340
41.12 access bind ....................................................................................................................... 341
41.13 show access-list .............................................................................................................. 342
41.14 show access-list bind ...................................................................................................... 342
41.15 show access-list status .................................................................................................. 343
41.16 show access-list counter ............................................................................................... 343
41.17 clear access-list ............................................................................................................... 344
Chapter 42 IPv4 IMPB Commands
42.1 ip source binding .............................................................................................................. 345
42.2 ip dhcp snooping ............................................................................................................. 346
42.3 ip dhcp snooping vlan ..................................................................................................... 347
42.4 ip dhcp snooping max-entries ....................................................................................... 347
42.5 show ip source binding ................................................................................................... 348
42.6 show ip dhcp snooping ................................................................................................... 349
42.7 show ip dhcp snooping interface .................................................................................. 349
Chapter 43 IPv6 IMPB Commands
43.1 Ipv6 source binding ......................................................................................................... 351
43.2 ipv6 dhcp snooping ......................................................................................................... 352
43.3 ipv6 dhcp snooping vlan ................................................................................................. 353
43.4 ipv6 dhcp snooping max-entries .................................................................................. 353
43.5 ipv6 nd snooping .............................................................................................................. 354
43.6 ipv6 nd snooping vlan ..................................................................................................... 355
43.7 ipv6 nd snooping max-entries ....................................................................................... 355
43.8 show ipv6 source binding ............................................................................................... 356
43.9 show ipv6 dhcp snooping............................................................................................... 357
43.10 show ipv6 dhcp snooping interface ............................................................................. 357
43.11 show ipv6 nd snooping ................................................................................................... 358
XV
Page 17
................................................................... 359
.............................................................. 362
....................................................................... 365
....................................................................... 372
........................................................................... 378
....................................................................................... 382
Chapter 44 IP Verify Source Commands
44.1 ip verify source ................................................................................................................. 359
44.2 ip verify source logging ................................................................................................... 360
44.3 show ip verify source ...................................................................................................... 360
44.4 show ip verify source interface ..................................................................................... 361
Chapter 45 IPv6 Verify Source Commands
45.1 ipv6 verify source ............................................................................................................. 362
45.2 show ipv6 verify source .................................................................................................. 363
45.3 show ipv6 verify source interface ................................................................................. 363
Chapter 46 DHCPv4 Filter Commands
46.1 ip dhcp filter ...................................................................................................................... 365
46.2 ip dhcp filter (interface) ................................................................................................... 365
46.3 ip dhcp filter mac-verify .................................................................................................. 366
46.4 ip dhcp filter limit rate ...................................................................................................... 367
46.5 ip dhcp filter decline rate ................................................................................................ 368
46.6 ip dhcp filter server permit-entry .................................................................................. 368
46.7 show ip dhcp filter ............................................................................................................ 369
46.8 show ip dhcp filter interface ........................................................................................... 370
46.9 show ip dhcp filter server permit-entry ........................................................................ 370
Chapter 47 DHCPv6 Filter Commands
47.1 ipv6 dhcp filter .................................................................................................................. 372
47.2 ipv6 dhcp filter (interface) ............................................................................................... 372
47.3 ipv6 dhcp filter limit rate ................................................................................................. 373
47.4 ipv6 dhcp filter decline rate ............................................................................................ 374
47.5 ipv6 dhcp filter server permit-entry .............................................................................. 375
47.6 show ipv6 dhcp filter ....................................................................................................... 376
47.7 show ipv6 dhcp filter interface ...................................................................................... 376
47.8 show ip dhcp filter server permit-entry ........................................................................ 377
Chapter 48 DoS Defend Commands
48.1 ip dos-prevent .................................................................................................................. 378
48.2 ip dos-prevent type ......................................................................................................... 378
48.3 show ip dos-prevent ........................................................................................................ 380
Chapter 49 DLDP Commands
49.1 dldp (global) ....................................................................................................................... 382
XVI
Page 18

...................................................................................... 386
49.2 dldp interval....................................................................................................................... 382
49.3 dldp shut-mode ................................................................................................................ 383
49.4 dldp(interface) .................................................................................................................. 384
49.5 show dldp .......................................................................................................................... 384
49.6 show dldp interface ......................................................................................................... 385
Chapter 50 SNMP Commands
50.1 snmp-server...................................................................................................................... 386
50.2 snmp-server view ............................................................................................................ 386
50.3 snmp-server group .......................................................................................................... 387
50.4 snmp-server user ............................................................................................................. 389
50.5 snmp-server community ................................................................................................ 390
50.6 snmp-server host............................................................................................................. 391
50.7 snmp-server engineID .................................................................................................... 393
50.8 snmp-server traps snmp ................................................................................................ 393
50.9 snmp-server traps ........................................................................................................... 394
50.10 snmp-server traps ddm .................................................................................................. 396
50.11 snmp-server traps vlan ................................................................................................... 397
50.12 snmp-server traps security ............................................................................................ 398
50.13 snmp-server traps acl ..................................................................................................... 399
50.14 snmp-server traps ip ....................................................................................................... 399
50.15 snmp-server traps link-status ....................................................................................... 400
50.16 rmon history ...................................................................................................................... 400
50.17 rmon event ........................................................................................................................ 401
50.18 rmon alarm ........................................................................................................................ 402
50.19 rmon statistics .................................................................................................................. 404
50.20 show snmp-server ........................................................................................................... 405
50.21 show snmp-server view .................................................................................................. 405
50.22 show snmp-server group ............................................................................................... 406
50.23 show snmp-server user .................................................................................................. 406
50.24 show snmp-server community ...................................................................................... 407
50.25 show snmp-server host .................................................................................................. 407
50.26 show snmp-server engineID .......................................................................................... 407
50.27 show rmon history ........................................................................................................... 408
50.28 show rmon event .............................................................................................................. 408
50.29 show rmon alarm .............................................................................................................. 409
50.30 show rmon statistics ....................................................................................................... 410
XVII
Page 19
..................................................................... 411
........................................................................ 420
........................................................................... 424
Chapter 51 ARP Inspection Commands
51.1 ip arp inspection ............................................................................................................... 411
51.2 ip arp inspection validate ................................................................................................ 411
51.3 ip arp inspection vlan ...................................................................................................... 412
51.4 ip arp inspection vlan logging ........................................................................................ 413
51.5 ip arp inspection trust ..................................................................................................... 414
51.6 ip arp inspection limit-rate .............................................................................................. 414
51.7 ip arp inspection burst-interval ..................................................................................... 415
51.8 ip arp inspection recover ................................................................................................ 416
51.9 show ip arp inspection .................................................................................................... 416
51.10 show ip arp inspection interface ................................................................................... 417
51.11 show ip arp inspection vlan ............................................................................................ 418
51.12 show ip arp inspection statistics ................................................................................... 418
51.13 clear ip arp inspection statistics ................................................................................... 419
Chapter 52 ND Detection Commands
52.1 ipv6 nd detection ............................................................................................................. 420
52.2 ipv6 nd detection vlan ..................................................................................................... 420
52.3 ipv6 nd detection vlan logging....................................................................................... 421
52.4 ipv6 nd detection trust .................................................................................................... 421
52.5 show ipv6 nd detection ................................................................................................... 422
52.6 show ipv6 nd detection interface .................................................................................. 422
52.7 show ipv6 nd detection vlan .......................................................................................... 423
Chapter 53 System Log Commands
53.1 logging buffer ................................................................................................................... 424
53.2 logging buffer level .......................................................................................................... 424
53.3 logging file flash ............................................................................................................... 425
53.4 logging file flash frequency ............................................................................................ 426
53.5 logging file flash level ...................................................................................................... 427
53.6 logging host index ............................................................................................................ 427
53.7 logging console ................................................................................................................ 428
53.8 logging console level ....................................................................................................... 429
53.9 logging monitor ................................................................................................................ 430
53.10 logging monitor level ....................................................................................................... 430
53.11 clear logging ..................................................................................................................... 431
53.12 show logging local-config .............................................................................................. 432
53.13 show logging loghost ...................................................................................................... 432
XVIII
Page 20

53.14 show logging buffer ......................................................................................................... 433
53.15 show logging flash ........................................................................................................... 433
XIX
Page 21

Preface
This Guide is intended for network administrator to provide referenced information about CLI
(Command Line Interface). The device mentioned in this Guide stands for T2500G-10TS
JetStream 8-Port Gigabit L2 Managed Switch with 2 SFP Slots without any explanation.
Overview of this Guide
Chapter 1: Using the CLI
Provide information about how to use the CLI, CLI Command Modes, Security Levels and some
Conventions.
Chapter 2: User Interface
Provide information about the commands used to switch between five CLI Command Modes.
Chapter 3: User Management Commands
Provide information about the commands used for user management.
Chapter 4: System Configuration Commands
Provide information about the commands used for configuring the System information and
System IP, reboot and reset the switch, upgrade the switch system and commands used for
cable test.
Chapter 5: EEE Configuration Commands
Provide information about the commands used for configuring EEE.
Chapter 6: SDM Template Commands
Provide information about the commands used for configuring the SDM templates.
Chapter 7: Time Range Commands
Provide information about the commands used for configuring the time range.
Chapter 8: Port Configuration Commands
Provide information about the commands used for configuring the Speed, Negotiation Mode,
and Flow Control for Ethernet ports.
Chapter 9: Port Isolation Commands
Provide information about the commands used for configuring Port Isolation function.
Chapter 10: Loopback Detection Commands
Provide information about the commands used for configuring the Loopback Detection
function.
Chapter 11: DDM Commands
Provide information about the commands used for DDM (Digital Diagnostic Monitoring)
function.
1
Page 22

Chapter 12: Etherchannel Commands
Provide information about the commands used for configuring LAG (Link Aggregation Group)
and LACP (Link Aggregation Control Protocol).
Chapter 13: MAC Address Commands
Provide information about the commands used for Address configuration.
Chapter 14 IEEE 802.1Q VLAN Commands
Provide information about the commands used for configuring IEEE 802.1Q VLAN.
Chapter 15: MAC-based VLAN Commands
Provide information about the commands used for configuring MAC-based VLAN.
Chapter 16: Protocol-based VLAN Commands
Provide information about the commands used for configuring Protocol VLAN.
Chapter 17: VLAN-VPN Commands
Provide information about the commands used for configuring VLAN-VPN (Virtual Private
Network) function.
Chapter 18: GVRP Commands
Provide information about the commands used for configuring GVRP (GARP VLAN registration
protocol).
Chapter 19: IGMP Snooping Commands
Provide information about the commands used for configuring the IGMP Snooping (Internet
Group Management Protocol Snooping).
Chapter 20: MLD Snooping Commands
Provide information about the commands used for configuring the MLD Snooping (Multicast
Listener Discovery Snooping).
Chapter 21: MVR Commands
Provide information about the commands used for configuring the MVR.
Chapter 22: MSTP Commands
Provide information about the commands used for configuring the MSTP (Multiple Spanning
Tree Protocol).
Chapter 23: LLDP Commands
Provide information about the commands used for configuring LLDP function.
Chapter 24: L2PT Commands
Provide information about the commands used for configuring L2PT (Layer 2 Protocol
Tunneling).
Chapter 25: PPPoE ID-Insertion Commands
Provide information about the commands used for configuring PPPoE ID-Insertion.
2
Page 23

Chapter 26: DHCP Relay Commands
Provide information about the commands used for configuring the DHCP Relay function.
Chapter 27: DHCP L2 Relay Commands
Provide information about the commands used for configuring the DHCP L2 Relay function.
Chapter 28: QoS Commands
Provide information about the commands used for configuring the QoS function.
Chapter 29: Bandwidth Commands
Provide information about the commands used for configuring the Bandwidth Control.
Chapter 30: Voice VLAN Commands
Provide information about the commands used for configuring Voice VLAN.
Chapter 31: Auto VoIP Commands
Provide information about the commands used for configuring Auto VoIP.
Chapter 32: Access Control Commands
Provide information about the commands used for configuring Access Control.
Chapter 33: HTTP and HTTPS Commands
Provide information about the commands used for configuring the HTTP and HTTPS logon.
Chapter 34: SSH Commands
Provide information about the commands used for configuring and managing SSH (Security
Shell).
Chapter 35: Telnet Commands
Provide information about the commands used for configuring and managing SSH (Security
Shell).
Chapter 36: Serial Port Commands
Provide information about the commands used for configuring and managing SSH (Security
Shell).
Chapter 37: AAA Commands
Provide information about the commands used for configuring AAA (authentication,
authorization and accounting).
Chapter 38: IEEE 802.1X Commands
Provide information about the commands used for configuring IEEE 802.1X function.
Chapter 39: Port Security Commands
Provide information about the commands used for configuring Port Security.
3
Page 24

Chapter 40: Port Mirroring Commands
Provide information about the commands used for configuring the Port Mirror function.
Chapter 41: ACL Commands
Provide information about the commands used for configuring the ACL (Access Control List).
Chapter 42: IPv4 IMPB Commands
Provide information about the commands used for binding the IP address, MAC address, VLAN
and the connected Port number of the Host together.
Chapter 43: IPv6 IMPB Commands
Provide information about the commands used for binding the IPv6 address, MAC address,
VLAN and the connected Port number of the Host together.
Chapter 44: IP Verify Source Commands
Provide information about the commands used for guarding the IP Source by filtering the IP
packets based on the IP-MAC Binding entries.
Chapter 45: IPv6 Verify Source Commands
Provide information about the commands used for guarding the IPv6 Source by filtering the IP
packets based on the IP-MAC Binding entries.
Chapter 46: DHCPv4 Filter Commands
Provide information about the commands used for configuring the DHCPv4 Filter.
Chapter 47: DHCPv6 Filter Commands
Provide information about the commands used for configuring the DHCPv6 Filter.
Chapter 48: DoS Defend Command
Provide information about the commands used for DoS defend and detecting the DoS attack.
Chapter 49: DLDP Commands
Provide information about the commands used for configuring the DLDP (Device Link
Detection Protocol).
Chapter 50: SNMP Commands
Provide information about the commands used for configuring the SNMP (Simple Network
Management Protocol) functions.
Chapter 51: ARP Inspection Commands
Provide information about the commands used for protecting the switch from the ARP
cheating or ARP Attack.
Chapter 52: ND Detection Commands
Provide information about the commands used for configuring ND detection.
Chapter 53: System Log Commands
Provide information about the commands used for configuring system log.
4
Page 25
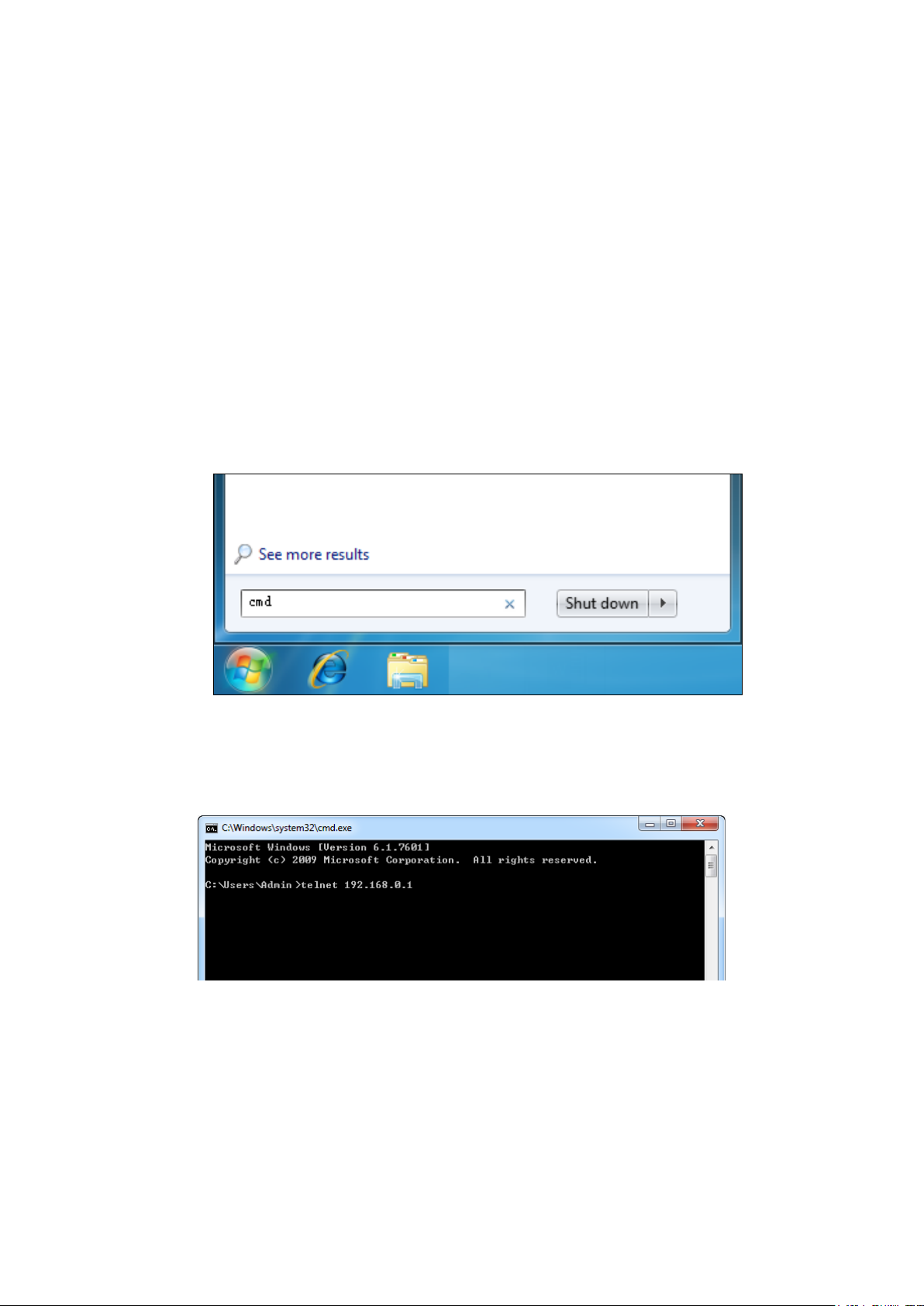
Logon by Telnet
Chapter 1 Using the CLI
1.1 Accessing the CLI
You can log on to the switch and access the CLI by logging on to the switch remotely by a
Telnet or SSH connection through an Ethernet port.
1.1.1
To log on to the switch by a Telnet connection, please take the following steps:
1. Click Start and type in cmd in the Search programs and files window and press the Enter
2. Telnet the switch’s IP address (factory setting is 192.168.0.1) in the prompt cmd window
button.
Figure 1-1 Run Window
and press Enter.
Figure 1-2 Type in the telnet command
5
Page 26
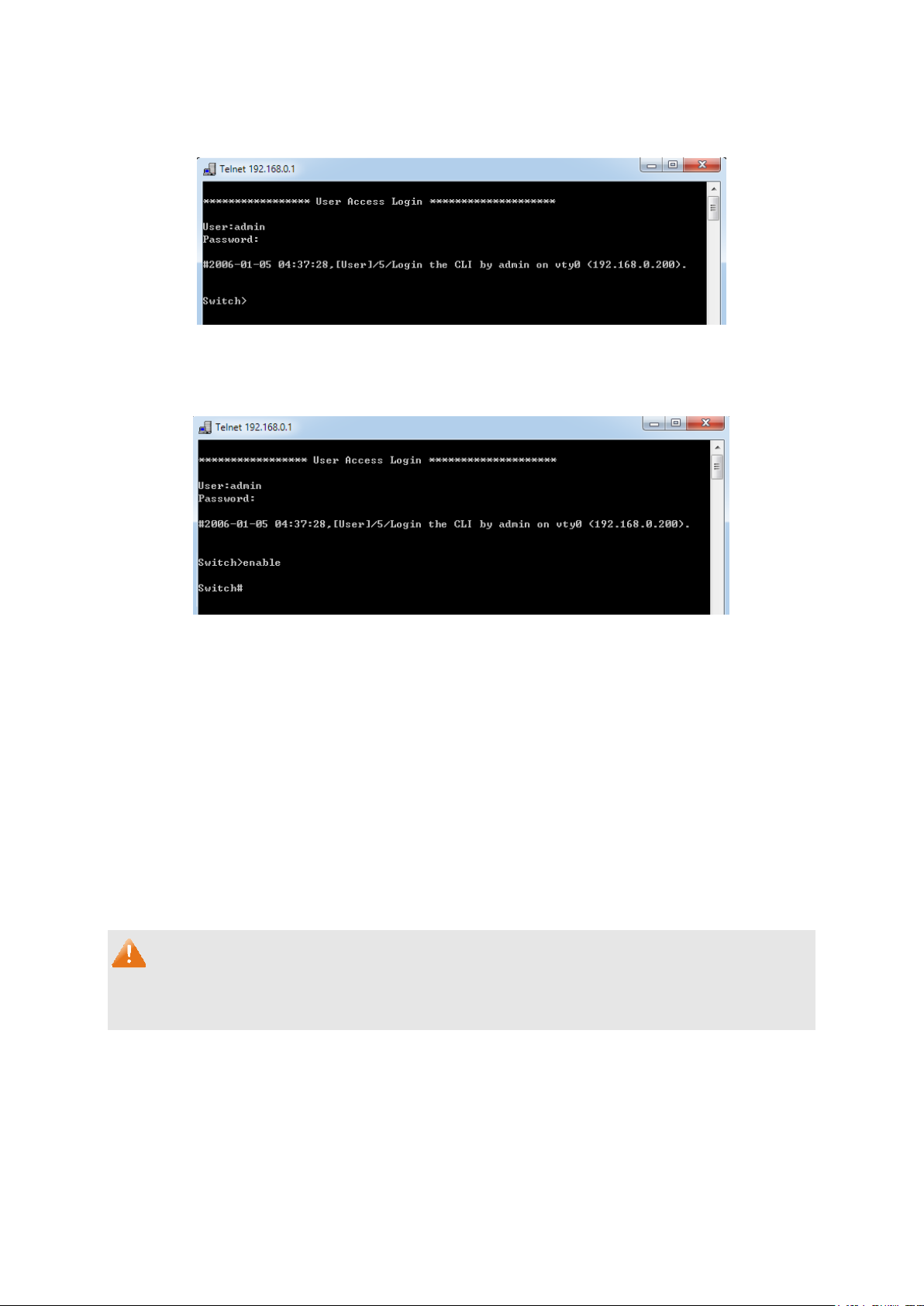
Logon by SSH
3. Type in the User name and Password (the factory default value for both of them are admin)
and press the Enter button to enter User EXEC Mode , which is shown as Figure 1-3.
Figure 1-3 Log in the Switch
4. Type in enable command to enter Privileged EXEC Mode.
Figure 1-4 Enter into Priviledged EXEC Mode
1.1.2
To log on by SSH, a Putty client software is recommended. There are two authentication modes
to set up an SSH connection:
Password Authentication Mode: It requires username and password, which are both admin by
default.
Key Authentication Mode: It requires a public key for the switch and a private key for the SSH
client software. You can generate the public key and the private key through Putty Key
Generator.
Before SSH login, please follow the steps shown in Figure 1-5 to enable the SSH function
through Telnet connection.
Note:
6
Page 27
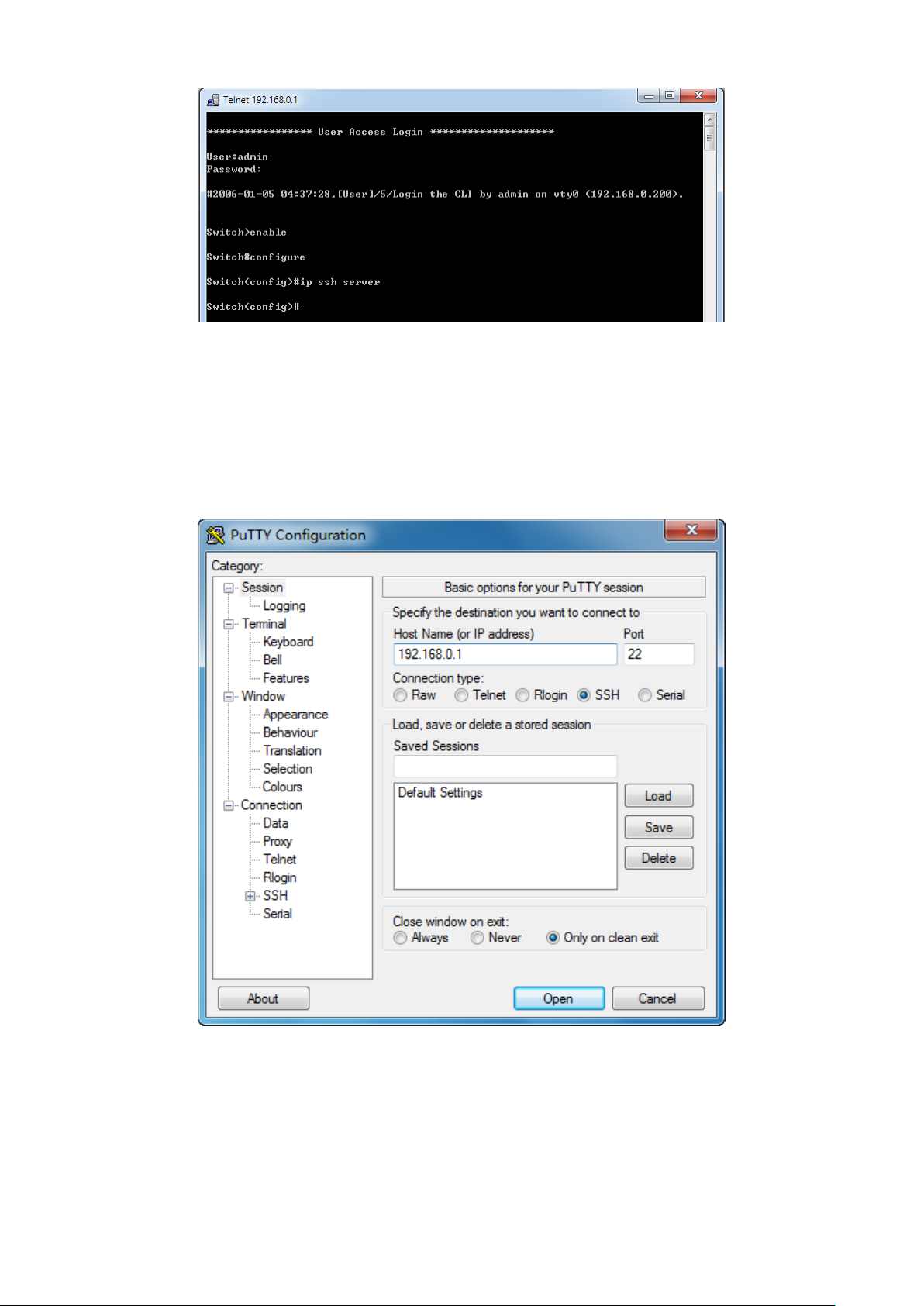
Figure 1-5 Enable SSH function
Password Authentication Mode
1. Open the software to log on to the interface of PuTTY. Enter the IP address of the switch
into Host Name field; keep the default value 22 in the Port field; select SSH as the
Connection type.
Figure 1-6 SSH Connection Config
7
Page 28
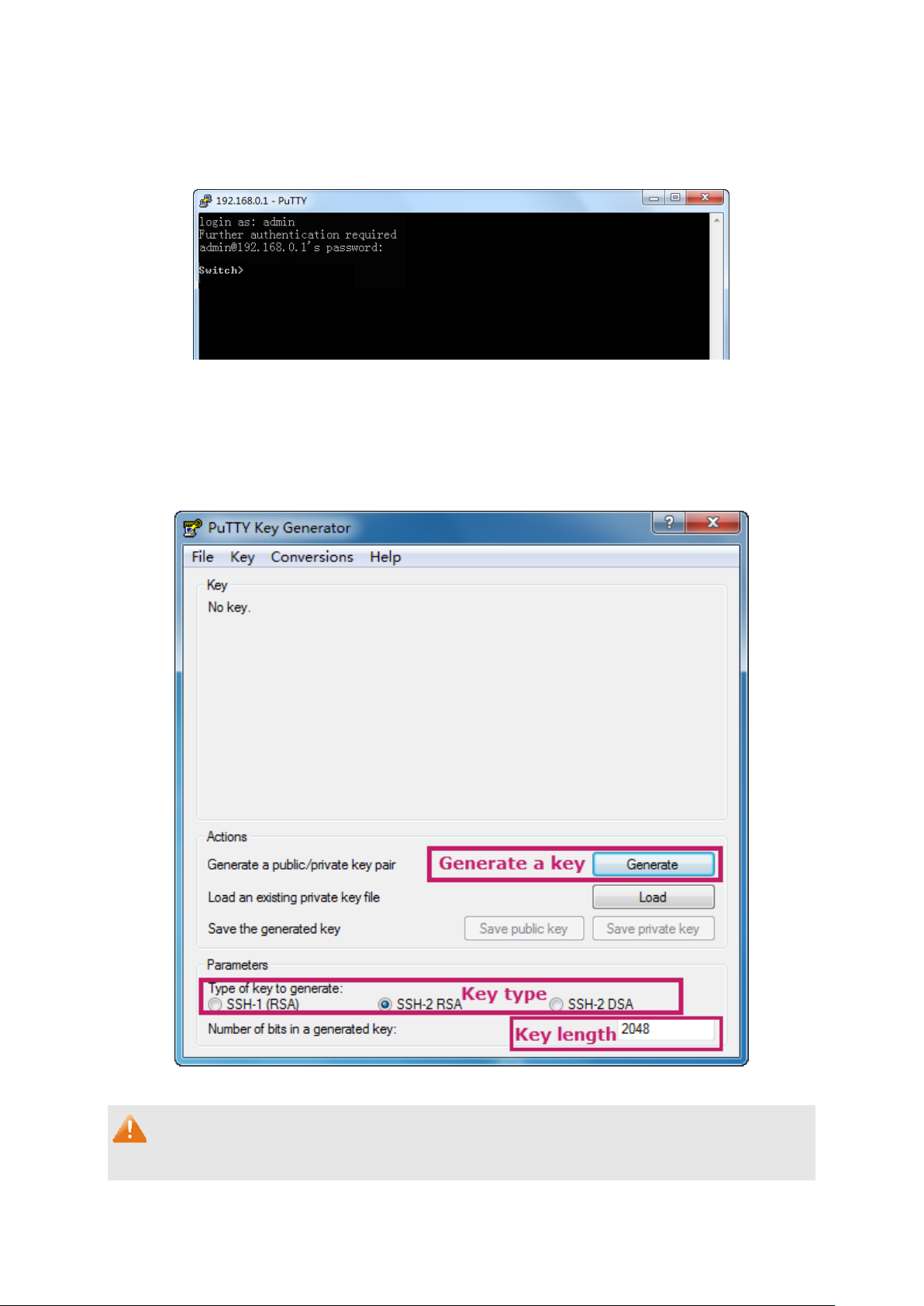
2. Click the Open button in the above figure to log on to the switch. Enter the login user name
and password to log on the switch, and then enter enable to enter Privileged EXEC Mode,
so you can continue to configure the switch.
Figure 1-7 Log on the Switch
Key Authentication Mode
1. Select the key type and key length, and generate SSH key.
Figure 1-8 Generate SSH Key
Note:
1. The key length is in the range of 512 to 3072 bits.
8
Page 29
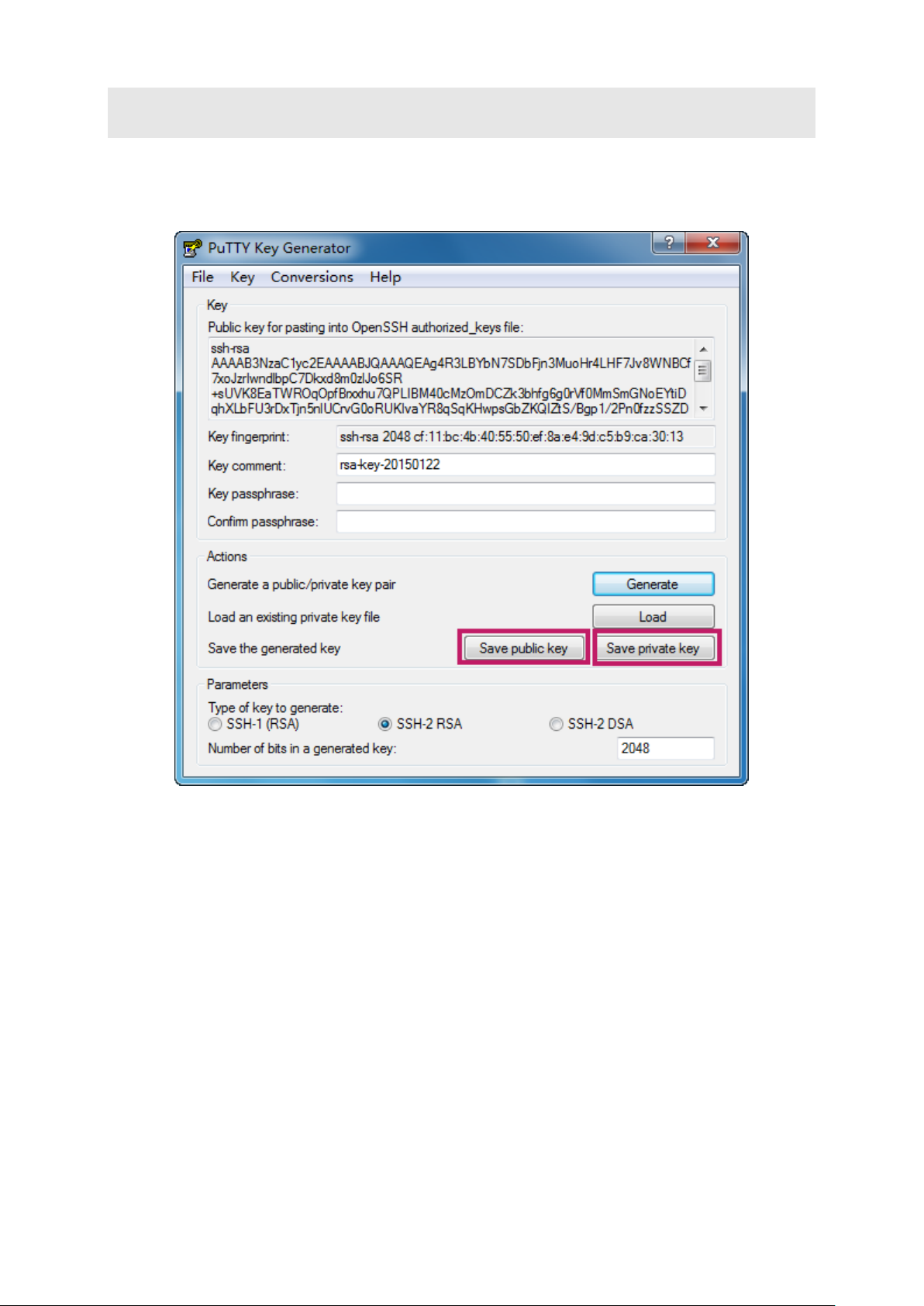
2. During the key generation, randomly moving the mouse quickly can accelerate the key
generation.
2. After the key is successfully generated, please save the public key and private key to a
TFTP server.
Figure 1-9 Save the Generated Key
9
Page 30
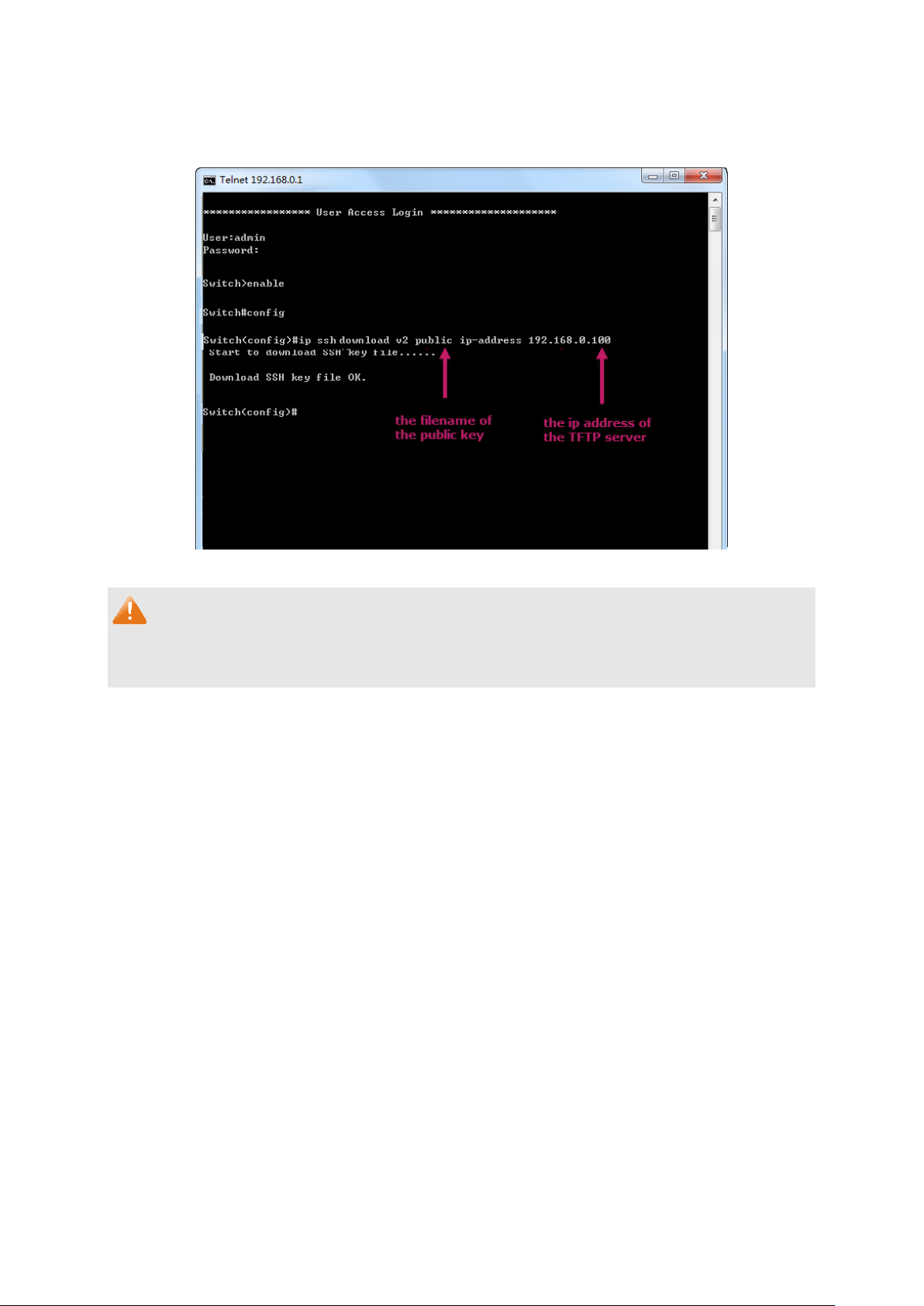
3. Log on to the switch by Telnet and download the public key file from the TFTP server to the
switch, as the following figure shows:
Figure 1-10 Download the Public Key
Note:
1. The key type should accord with the type of the key file.
2. The SSH key downloading can not be interrupted.
10
Page 31

4. After the public key is downloaded, please log on to the interface of PuTTY and enter the IP
address for login.
Figure 1-11 SSH Connection Config
11
Page 32
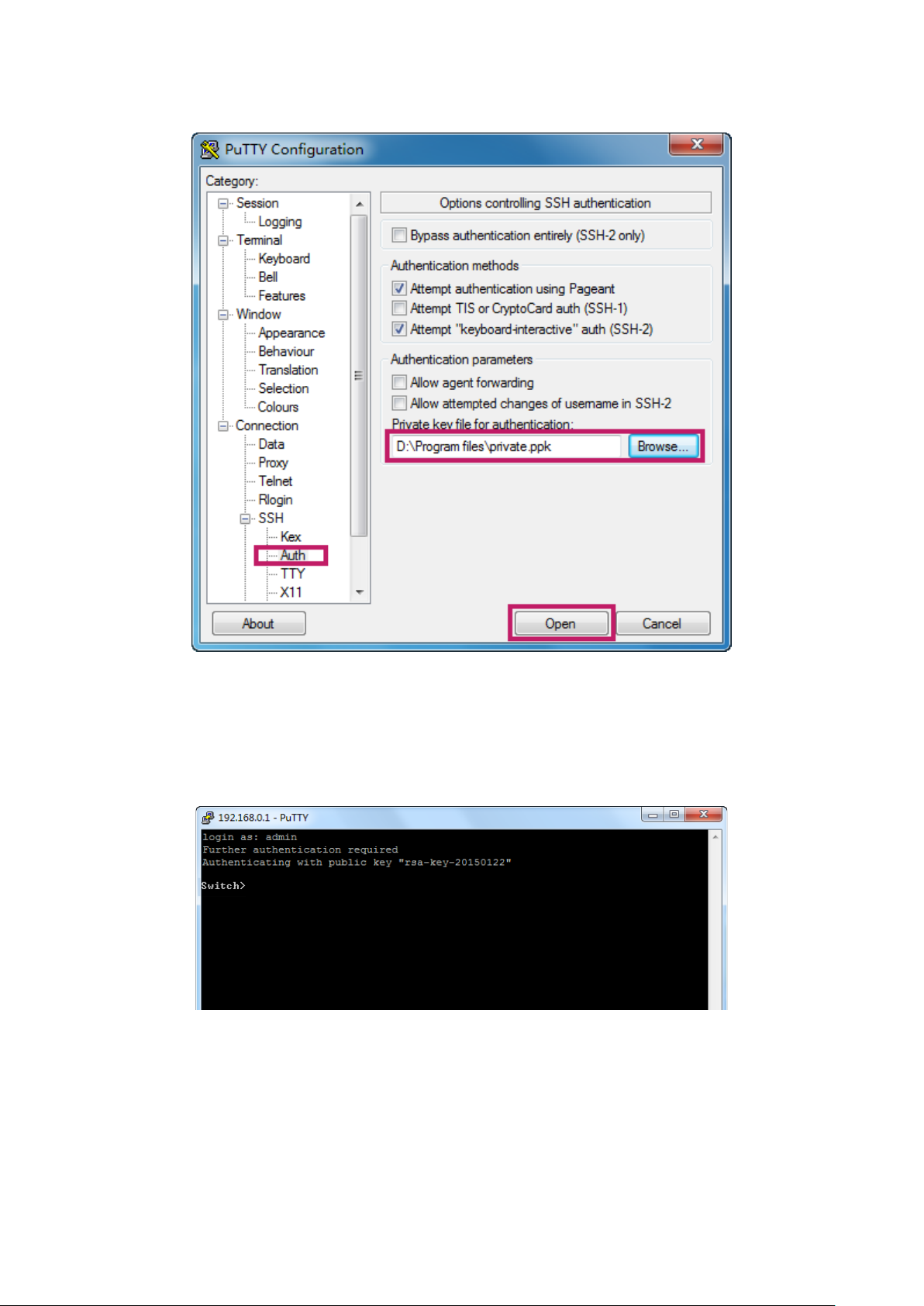
5. Click Browse to download the private key file to SSH client software and click Open.
Figure 1-12 Download the Private Key
6. After successful authentication, please enter the login user name. If you log on to the
switch without entering password, it indicates that the key has been successfully
downloaded.
Figure 1-13 Log on the Switch
1.2 CLI Command Modes
The CLI is divided into different command modes: User EXEC Mode, Privileged EXEC Mode,
Global Configuration Mode, Interface Configuration Mode and VLAN Configuration Mode.
12
Page 33

mode.
Configuration mode.
mode.
Interface Configuration Mode can also be divided into Interface Ethernet, Interface
link-aggregation and some other modes, which is shown as the following diagram.
The following table gives detailed information about the Accessing path, Prompt of each mode
and how to exit the current mode and access the next mode.
Mode Accessing Path Prompt
User EXEC
Mode
Privileged
EXEC Mode
Global
Configuration
Primary mode once it
is connected with the
switch.
Use the enable
command to enter this
mode from User EXEC
mode.
Use the configure
command to enter this
mode from Privileged
T2500G-10TS>
T2500G-10TS#
T2500G-10TS(config)#
Mode
EXEC mode.
Logout or Access the
next mode
Use the exit command to
disconnect the switch.
Use the enable command
to access Privileged EXEC
Enter the exit command to
return to User EXEC mode.
Enter configure command
to access Global
Use the exit or the end
command or press Ctrl+Z
to return to Privileged EXEC
mode.
Use the interface
port
gigabitEthernet
interface range
fastEthernet
gigabitEthernet
command to access
interface Configuration
mode.
port-list
or
|
port-list
13
Use the vlan
access VLAN Configuration
vlan-list
to
Page 34
mode.
mode.
Global configuration mode.
Mode Accessing Path Prompt
Layer 2 Interface:
Use the interface
Interface
Configuration
Mode
Interface
Configuration
Mode
fastEthernet
interface
gigabitEthernet
interface
port-channel
interface range
fastEthernet
gigabitEthernet
port-list
enter this mode from
Global Configuration
Use the interface vlan
vlan-id
enter VLAN Interface
mode from Global
Configuration mode.
Use the interface
loopback
to enter Loopback
Interface mode from
Global Configuration
port,
port,
lagid
port-list
command to
command to
id
command
or
T2500G-10TS(config-if)#
T2500G-10TS(config-if-range)#
|
T2500G-10TS(config-if)#
T2500G-10TS(config-if-range)#
or
or
Logout or Access the
next mode
Use the end command or
press Ctrl+Z to return to
Privileged EXEC mode.
Enter the exit or the #
command to return to
Global Configuration mode.
A port number must be
specified in the interface
command.
Use the switchport
command to switch to the
Layer 2 interface mode.
Use the end command or
press Ctrl+Z to return to
Privileged EXEC mode.
Enter the exit or the #
command to return to
Global Configuration mode.
Use the end command or
VLAN
Configuration
Mode
Use the vlan
command to enter this
mode from Global
Configuration mode.
vlan-list
T2500G-10TS(config-vlan)#
press Ctrl+Z to return to
Privileged EXEC mode.
Enter the exit command or
the # command to return to
Note:
1. The user is automatically in User EXEC Mode after the connection between the PC and the
switch is established by a Telnet/SSH connection.
2. Each command mode has its own set of specific commands. To configure some
commands, you should access the corresponding command mode firstly.
Global Configuration Mode: In this mode, global commands are provided, such as the
Spanning Tree, Schedule Mode and so on.
14
Page 35
Interface Configuration Mode: In this mode, users can configure one or several ports,
different ports corresponds to different commands
a). Interface gigabitEthernet: Configure parameters for an Ethernet port, such as
Duplex-mode, flow control status.
b). Interface range gigabitEthernet: Configure parameters for several Ethernet ports.
c). Interface link-aggregation: Configure parameters for a link-aggregation, such as
broadcast storm.
d). Interface range link-aggregation: Configure parameters for multi-trunks.
e). Interface vlan: Configure parameters for the vlan-port.
VLAN Configuration Mode: In this mode, users can create a VLAN and add a specified
port to the VLAN.
3. Some commands are global, that means they can be performed in all modes:
show: Display all information of switch, for example: statistic information, port information,
VLAN information.
history: Display the commands history.
1.3 Privilege Restrictions
This switch’s security is divided into four privilege levels: User level, Power User level, Operator
level and Admin level. You can define username and password pairs, and assign a specific
privilege level to each pair. Different privilege levels have access to specified commands,
which is illustrated in the Privilege Requirement in each command. For details about how to
configure usename and password pairs, please refer to user name (password) and user name
(secret).
Users can enter Privileged EXEC mode from User EXEC mode by using the enable command. In
default case, no password is needed. In Global Configuration Mode, you can configure
password for Admin level by enable password command. Once password is configured, you
are required to enter it to access Privileged EXEC mode.
1.4 Conventions
1.4.1 Format Conventions
The following conventions are used in this Guide:
Items in square brackets [ ] are optional
Items in braces { } are required
15
Page 36

Alternative items are grouped in braces and separated by vertical bars. For example:
speed {10 | 100 | 1000 }
Bold indicates an unalterable keyword. For example: show logging
Normal Font indicates a constant (several options are enumerated and only one can be
selected). For example: mode {dynamic | static | permanent}
Italic Font indicates a variable (an actual value must be assigned). For example: bridge
aging-time
aging-time
1.4.2 Special Characters
You should pay attentions to the description below if the variable is a character string:
These six characters ” < > , \ & cannot be input.
If a blank is contained in a character string, single or double quotation marks should be
used, for example ’hello world’, ”hello world”, and the words in the quotation marks will be
identified as a string. Otherwise, the words will be identified as several strings.
1.4.3 Parameter Format
Some parameters must be entered in special formats which are shown as follows:
MAC address must be enter in the format of xx:xx:xx:xx:xx:xx.
One or several values can be typed for a port-list or a vlan-list using comma to separate.
Use a hyphen to designate a range of values, for instance, 1/0/1, 1/0/3-5, 1/0/7 indicates
choosing port 1/0/1, 1/0/3, 1/0/4, 1/0/5, 1/0/7.
16
Page 37

Chapter 2 User Interface
2.1 enable
Description
The enable command is used to access Privileged EXEC Mode from User
EXEC Mode.
Syntax
enable
Command Mode
User EXEC Mode
Privilege Requirement
None.
Example
If you have set the password to access Privileged EXEC Mode from User
EXEC Mode:
T2500G-10TS>enable
Enter password:
T2500G-10TS#
2.2 service password-encryption
Description
The service password-encryption command is used to encrypt the
password when the password is defined or when the configuration is written,
using the symmetric encryption algorithm. Encryption prevents the password
from being readable in the configuration file. To disable the global encryption
Syntax
function, please use no service password-encryption command.
service password-encryption
no service password-encryption
17
Page 38

Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Enable the global encryption function:
T2500G-10TS(config)# service password-encryption
2.3 enable password
Description
The enable password command is used to set or change the password for
users to access Privileged EXEC Mode from User EXEC Mode. To remove the
password, please use no enable password command. This command uses
the symmetric encryption.
Syntax
enable password { [ 0 ]
no enable password
Parameter
0 —— Specify the encryption type. 0 indicates that an unencrypted password
will follow. By default, the encryption type is 0.
password
characters or symbols. The password is case sensitive, allows digits, English
letters (case sensitive), underlines and sixteen special characters
( !$%'()*,-./[]{|} ). By default, it is empty.
7 —— Indicates a symmetric encrypted password with fixed length will follow.
encrypted-password
password
—— Super password, a string from 1 to 31 alphanumeric
—— A symmetric encrypted password with fixed length,
| 7
encrypted-password
}
which you can copy from another switch’s configuration file. After the
encrypted password is configured, you should use the corresponding
unencrypted password if you re-enter this mode.
Command Mode
Global Configuration Mode
18
Page 39
Privilege Requirement
Only Admin level users have access to these commands.
User Guidelines
If the password you configured here is unencrypted and the global
encryption function is enabled in service password-encryption, the
password in the configuration file will be displayed in the symmetric
encrypted form.
Example
Set the super password as “admin” and unencrypted to access Privileged
EXEC Mode from User EXEC Mode:
T2500G-10TS(config)#enable password 0 admin
2.4 enable secret
Description
The enable secret command is used to set a secret password, which is using
an MD5 encryption algorithm, for users to access Privileged EXEC Mode from
User EXEC Mode. To return to the default configuration, please use no enable
secret command. This command uses the MD5 encryption.
Syntax
enable secret { [ 0 ]
no enable secret
Parameter
0 —— Specify the encryption type. 0 indicates that an unencrypted password
will follow. By default, the encryption type is 0.
password
characters or symbols. The password is case sensitive, allows digits, English
letters (case sensitive), underlines and sixteen special characters
password
—— Super password, a string from 1 to 31 alphanumeric
| 5
encrypted-password
}
( !$%'()*,-./[]{|} ). By default, it is empty. The password in the configuration file
will be displayed in the MD5 encrypted form.
5 —— Indicates an MD5 encrypted password with fixed length will follow.
encrypted-password
which you can copy from another switch’s configuration file. After the
—— An MD5 encrypted password with fixed length,
19
Page 40

encrypted password is configured, you should use the corresponding
unencrypted password if you re-enter this mode.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
User Guidelines
If both the enable password and enable secret are defined, you must enter
the password set in enable secret.
Example
Set the secret password as “admin” and unencrypted to access Privileged
EXEC Mode from User EXEC Mode. The password will be displayed in the
encrypted form.
T2500G-10TS(config)#enable secret 0 admin
2.5 configure
Description
The configure command is used to access Global Configuration Mode from
Privileged EXEC Mode.
Syntax
configure
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Access Global Configuration Mode from Privileged EXEC Mode:
T2500G-10TS# configure
T2500G-10TS(config)#
20
Page 41

2.6 exit
Description
The exit command is used to return to the previous Mode from the current
Mode.
Syntax
exit
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Return to Global Configuration Mode from Interface Configuration Mode, and
then return to Privileged EXEC Mode:
T2500G-10TS(config-if)# exit
T2500G-10TS(config)#exit
T2500G-10TS#
2.7 end
Description
The end command is used to return to Privileged EXEC Mode.
Syntax
end
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Return to Privileged EXEC Mode from Interface Configuration Mode:
T2500G-10TS(config-if)#end
T2500G-10TS#
21
Page 42

2.8 clipaging
Description
The clipaging command is used to enable the pause function for the screen
display. If you want to display all the related information of the switch at once
when using the show command, please use no clipaging command.
Syntax
clipaging
no clipaging
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Disable the pause function for the screen display:
T2500G-10TS(config)#no clipaging
2.9 history
Description
The history command is used to show the latest 20 commands you entered
in the current mode since the switch is powered.
Syntax
history
Command Mode
Privileged EXEC Mode and any Configuration Mode
Privilege Requirement
None.
Example
Show the commands you have entered in the current mode:
T2500G-10TS (config)# history
1 history
22
Page 43

2.10 history clear
Description
The history clear command is used to clear the commands you have entered
in the current mode, therefore these commands will not be shown next time
you use the history command.
Syntax
history clear
Command Mode
Privileged EXEC Mode and any Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Clear the commands you have entered in the current mode:
T2500G-10TS(config)#history clear
23
Page 44

Chapter 3 User Management Commands
User Management commands are used to manage the user’s logging information by Web,
Telnet or SSH, so as to protect the settings of the switch from being randomly changed.
3.1 user name (password)
Description
The user name command is used to add a new user or modify the existed
users’ information. To delete the existed users, please use no user name
command. This command uses the symmetric encryption.
Syntax
user name
{ [ 0 ]
no user name
Parameter
name
composed of digits, English letters and under dashes only.
admin | operator | power_user | user —— Access level. “admin” means that
you can edit, modify and view all the settings of different functions. “operator”
means that you can edit, modify and view most of the settings of different
functions. “power-user” means that you can edit, modify and view some of
the settings of different functions. “user” means that you can only view some
of the settings of different functions without the right to edit or modify. It is
“admin” by default. For more details about privilege restrictions, please refer
to the Privilege Requirement part in each command.
0 —— Specify the encryption type. 0 indicates that an unencrypted password
name
[ privilege admin | operator | power_user | user ] password
password
| 7
encrypted-password
}
name
——Type a name for users' login, which contains 16 characters at most,
will follow. By default, the encryption type is 0.
password
characters or symbols. The password is case sensitive, allows digits, English
letters (case sensitive), underlines and sixteen special characters
( !$%'()*,-./[]{|} ).
7 —— Indicates a symmetric encrypted password with fixed length will follow.
encrypted-password
which you can copy from another switch’s configuration file. After the
—— Users’ login password, a string from 1 to 31 alphanumeric
—— A symmetric encrypted password with fixed length,
24
Page 45

encrypted password is configured, you should use the corresponding
unencrypted password if you re-enter this mode.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
User Guidelines
If the password you configured here is unencrypted and the global
encryption function is enabled in service password-encryption, the
password in the configuration file will be displayed in the symmetric
encrypted form.
Example
Add and enable a new admin user named “tplink”, of which the password is
“admin” and unencrypted:
T2500G-10TS(config)#user name tplink privilege admin password 0 admin
3.2 user name (secret)
Description
The user name command is used to add a new user or modify the existed
users’ information. To delete the existed users, please use no user name
command. This command uses the MD5 encryption.
Syntax
user name
password
no user name
Parameter
name
name
[ privilege admin | operator | power_user | user ] secret { [ 0 ]
| 5
encrypted-password
name
——Type a name for users' login, which contains 16 characters at most,
}
composed of digits, English letters and under dashes only.
admin | operator | power_user | user —— Access level. “admin” means that
you can edit, modify and view all the settings of different functions. “operator”
means that you can edit, modify and view most of the the settings of different
functions. “power-user” means that you can edit, modify and view some of
25
Page 46

the the settings of different functions. “user” means that you can only view
some of the the settings of different functions without the right to edit or
modify. It is “admin” by default.
0 —— Specify the encryption type. 0 indicates that an unencrypted password
will follow. By default, the encryption type is 0.
password
characters or symbols. The password is case sensitive, allows digits, English
letters (case sensitive), underlines and sixteen special characters
( !$%'()*,-./[]{|} ). The password will be saved to the configuration file using the
MD5 encrypted algorithm.
5 —— Indicates an MD5 encrypted password with fixed length will follow.
——Users’ login password, a string from 1 to 31 alphanumeric
encrypted-password
which you can copy from another switch’s configuration file.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
User Guidelines
If both the user name (password) and user name (secret) are defined, only
—— An MD5 encrypted password with fixed length,
the latest configured password will take effect.
Example
Add and enable a new admin user named “tplink”, of which the password is
“admin”. The password will be displayed in the encrypted form.
T2500G-10TS(config)#user name tplink privilege admin secret 0 admin
3.3 show user account-list
Description
The show user account-list command is used to display the information of
the current users.
Syntax
show user account-list
26
Page 47

Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the information of the current users:
T2500G-10TS(config)# show user account-list
3.4 show user configuration
Description
The show user configuration command is used to display the security
configuration information of the users, including access-control, max-number
and the idle-timeout, etc.
Syntax
show user configuration
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the security configuration information of the users:
T2500G-10TS(config)# show user configuration
27
Page 48

Chapter 4 System Configuration Commands
System Commands can be used to configure the System information and System IP, reboot
and reset the switch, upgrade the switch system and other operations.
4.1 system-time manual
Description
The system-time manual command is used to configure the system time
manually.
Syntax
system-time manual
time
Parameter
time
—— Set the date and time manually, MM/DD/YYYY-HH:MM:SS. The valid
value of the year ranges from 2000 to 2037.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the system mode as manual, and the time is 12/20/2010 17:30:35
T2500G-10TS(config)# system-time manual 12/20/2010-17:30:35
4.2 system-time ntp
Description
The system-time ntp command is used to configure the time zone and the IP
address for the NTP Server. The switch will get UTC automatically if it has
connected to an NTP Server.
Syntax
system-time ntp {
fetching-rate
{
Parameter
timezone
UTC+13:00.
timezone
}
—— Your local time-zone, and it ranges from UTC-12:00 to
28
} {
ntp-server
} {
backup-ntp-server
}
Page 49

The detailed information that each time-zone means are displayed as follow:
UTC-12:00 —— TimeZone for International Date Line West.
UTC-11:00 —— TimeZone for Coordinated Universal Time-11.
UTC-10:00 —— TimeZone for Hawaii.
UTC-09:00 —— TimeZone for Alaska.
UTC-08:00 —— TimeZone for Pacific Time(US Canada).
UTC-07:00 —— TimeZone for Mountain Time(US Canada).
UTC-06:00 —— TimeZone for Central Time(US Canada).
UTC-05:00 —— TimeZone for Eastern Time(US Canada).
UTC-04:30 —— TimeZone for Caracas.
UTC-04:00 —— TimeZone for Atlantic Time(Canada).
UTC-03:30 —— TimeZone for Newfoundland.
UTC-03:00 —— TimeZone for Buenos Aires, Salvador, Brasilia.
UTC-02:00 —— TimeZone for Mid-Atlantic.
UTC-01:00 —— TimeZone for Azores, Cape Verde Is.
UTC —— TimeZone for Dublin, Edinburgh, Lisbon, London.
UTC+01:00 —— TimeZone for Amsterdam, Berlin, Bern, Rome, Stockholm,
Vienna.
UTC+02:00 —— TimeZone for Cairo, Athens, Bucharest, Amman, Beirut,
Jerusalem.
UTC+03:00 —— TimeZone for Kuwait, Riyadh, Baghdad.
UTC+03:30 —— TimeZone for Tehran.
UTC+04:00 —— TimeZone for Moscow, St.Petersburg, Volgograd, Tbilisi,
Port Louis.
UTC+04:30 —— TimeZone for Kabul.
UTC+05:00 —— TimeZone for Islamabad, Karachi, Tashkent.
UTC+05:30 —— TimeZone for Chennai, Kolkata, Mumbai, New Delhi.
UTC+05:45 —— TimeZone for Kathmandu.
UTC+06:00 —— TimeZone for Dhaka,Astana, Ekaterinburg.
UTC+06:30 —— TimeZone for Yangon (Rangoon).
UTC+07:00 —— TimeZone for Novosibrisk, Bangkok, Hanoi, Jakarta.
UTC+08:00—— TimeZone for Beijing, Chongqing, Hong Kong, Urumqi,
Singapore.
UTC+09:00 —— TimeZone for Seoul, Irkutsk, Osaka, Sapporo, Tokyo.
UTC+09:30 —— TimeZone for Darwin, Adelaide.
UTC+10:00 —— TimeZone for Canberra, Melbourne, Sydney, Brisbane.
UTC+11:00 —— TimeZone for Solomon Is., New Caledonia, Vladivostok.
UTC+12:00 —— TimeZone for Fiji, Magadan, Auckland, Welington.
UTC+13:00 —— TimeZone for Nuku'alofa, Samoa.
ntp-server
—— The IP address for the Primary NTP Server.
29
Page 50

backup-ntp-server
fetching-rate
—— Specify the rate fetching time from NTP server.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the system time mode as NTP, the time zone is UTC-12:00, the
primary NTP server is 133.100.9.2 and the secondary NTP server is
139.78.100.163, the fetching-rate is 11 hours:
T2500G-10TS(config)# system-time ntp UTC-12:00 133.100.9.2
139.79.100.163 11
—— The IP address for the Secondary NTP Server.
4.3 system-time dst predefined
Description
The system-time dst predefined command is used to select a daylight
saving time configuration from the predefined mode. The configuration can
be used recurrently. To disable DST function, please use no system-time dst
command.
Syntax
system-time dst predefined [ USA
no system-time dst
Parameter
USA
There are 4 options which are USA, Australia, Europe and New-Zealand
respectively. The default value is Europe.
Following are the time ranges of each option:
|
Australia | Europe | New-Zealand —— The mode of daylight saving time.
|
Australia | Europe | New-Zealand ]
USA —— Second Sunday in March, 02:00 ~ First Sunday in November, 02:00.
Australia —— First Sunday in October, 02:00 ~ First Sunday in April, 03:00.
Europe —— Last Sunday in March, 01:00 ~ Last Sunday in October, 01:00.
New Zealand —— Last Sunday in September, 02:00 ~ First Sunday in April,
03:00.
30
Page 51

Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the daylight saving time as USA standard:
T2500G-10TS(config)#system-time dst predefined USA
4.4 system-time dst date
Description
The system-time dst date command is used to configure the one-off
daylight saving time. The start date is in the current year by default. The time
range of the daylight saving time must shorter than one year, but you can
configure it spanning years. To disable DST function, please use no
system-time dst command.
Syntax
system-time dst date {
{
etime
no system-time dst
Parameter
smonth
showing as follows: Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
sday
you should show special attention to February and the differences between a
solar month and a lunar month.
stime
syear
smonth
} {
eyear }[offset ]
——The start month of the daylight saving time. There are 12 values
—— The start day of the daylight saving time, ranging from 1 to 31. Here
—— The start moment of the daylight saving time, HH:MM.
—— The start year of the daylight saving time.
} {
sday
} {
stime
} {
syear
} {
emonth
} {
eday
}
emonth
showing as follows: Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
eday
you should show special attention to February and the differences between a
solar month and a lunar month.
etime
eyear
—— The end month of the daylight saving time. There are 12 values
—— The end day of the daylight saving time, ranging from q to 31. Here
—— The end moment of the daylight saving time, HH:MM.
—— The end year of the daylight saving time.
31
Page 52

offset
—— The number of minutes to add during the daylight saving time. It is
60 minutes by default.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the daylight saving time from zero clock, Apr 1st to zero clock Oct
1st and the offset is 30 minutes in 2015:
T2500G-10TS(config)# system-time dst date Apr 1 00:00 2015 Oct 1 00:00
2015 30
4.5 system-time dst recurring
Description
The system-time dst recurring command is used to configure the recurring
daylight saving time. It can be configured spanning years. To disable DST
function, please use no system-time dst command.
Syntax
system-time dst recurring {
{
emonth
no system-time dst
Parameter
sweek
showing as follows: first, second, third, fourth, last.
sday
showing as follows: Sun, Mon, Tue, Wed, Thu, Fri, Sat.
smonth
showing as follows: Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov, Dec.
sweek
} {
etime
} [
offset
]
——The start week of the daylight saving time. There are 5 values
—— The start day of the daylight saving time. There are 7 values
—— The start month of the daylight saving time. There are 12 values
} {
sday
} {
smonth
} {
stime
} {
eweek
} {
eday}
stime
—— The start moment of the daylight saving time, HH:MM.
eweek
showing as follows: first, second, third, fourth, last.
eday
showing as follows: Sun, Mon, Tue, Wed, Thu, Fri, Sat.
——The end week of the daylight saving time. There are 5 values
—— The end day of the daylight saving time. There are 5 values
32
Page 53

emonth
showing as following: Jan, Feb, Mar, Apr, May, Jun, Jul, Aug, Sep, Oct, Nov,
Dec.
etime
offset
60 minutes by default.
—— The end month of the daylight saving time. There are 12 values
—— The end moment of the daylight saving time, HH:MM.
—— The number of minutes to add during the daylight saving time. It is
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the daylight saving time from 2:00am, the first Sunday of May to
2:00am, the last Sunday of Oct and the offset is 45 minutes:
T2500G-10TS(config)# system-time dst recurring first Sun May 02:00 last
Sun Oct 02:00 45
4.6 hostname
Description
The hostname command is used to configure the system name. To clear the
system name information, please use no hostname command.
Syntax
hostname [
no hostname
Parameter
hostname
characters. By default, it is the device name, for example “T2500G-10TS”.
Command Mode
—— System Name. The length of the name ranges from 1 to 32
hostname
]
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
33
Page 54

Example
Configure the system name as TPLINK:
T2500G-10TS(config)# hostname TPLINK
4.7 location
Description
The location command is used to configure the system location. To clear the
system location information, please use no location command.
Syntax
location [
no location
location
Parameter
location
most. It is “SHENZHEN” by default.
—— Device Location. It consists of 32 characters at
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the system location as SHENZHEN:
T2500G-10TS(config)# location SHENZHEN
]
4.8 contact-info
Description
The contact-info command is used to configure the system contact
information. To clear the system contact information, please use no
contact-info command.
Syntax
contact-info [
no contact-info
contact_info
]
34
Page 55

Parameter
contact_info
is “www.tp-link.com” by default.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the system contact information as www.tp-link.com:
T2500G-10TS(config)# contact-info www.tp-link.com
4.9 ip address
Description
This ip address command is used to configure the IP address and IP subnet
—— Contact Information. It consists of 32 characters at most. It
mask for the management interface manually.
Syntax
ip address {
no ip address [
ip-addr
ip-addr
Parameter
ip-addr
mask
default-gateway
gateway is the IP address to which the packet should be sent next.
—— The IP address of the management interface.
—— The subnet mask of the management interface.
—— Specify the interface’s default gateway. The default
Command Mode
Interface Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
} {
mask
] [
mask
} gateway {
]
default-gateway
}
35
Page 56

Example
Enter the management VLAN 1 and configure the IP address of the
management interface as 192.168.0.150/24 and default gateway as
192.168.0.10:
T2500G-10TS(config)# interface vlan 1
T2500G-10TS(config-if)# ip address 192.168.0.150 255.255.255.0 gateway
192.168.0.10
4.10 ip management-vlan
Description
This ip management-vlan command is used to specify the management vlan.
Only the user in the specified vlan can access to the switch
Syntax
ip management-vlan {
no management-vlan {
Parameter
Vlan-id
—— The ID of the management VLAN.
Command Mode
Global Configuration Mode
Example
Set VLAN 2 as the management vlan:
T2500G-10TS(config)# ip management-vlan 2
4.11 ip address-alloc
Description
vlan-id }
vlan-id
}
The IP address-alloc command is used to enable the DHCP Client function or
the BOOTP Protocol. When this function is enabled, the management
interface will obtain IP from DHCP Server or BOOTP server. To disable the IP
obtaining function on the interface, please use the no ip address command.
36
Page 57

Syntax
ip address-alloc { dhcp | bootp }
no ip address
Parameter
dhcp —— Specify the management interface to obtain IP address from the
DHCP Server.
bootp
—— Specify the management interface to obtain IP address from the
BOOTP Server.
Command Mode
Interface Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Enter the management VLAN 1 and enable the DHCP Client function on the
management interface:
T2500G-10TS(config)# interface vlan 1
T2500G-10TS(config-if)# ip address-alloc dhcp
Disable the IP address obtaining function on the VLAN interface 1:
T2500G-10TS(config)# interface vlan 1
T2500G-10TS(config-if)# no ip address
4.12 reset
Description
The reset command is used to reset the switch’s software. After resetting, all
configuration of the switch will restore to the factory defaults and your
current settings will be lost.
Syntax
reset
Command Mode
Privileged EXEC Mode
37
Page 58

Privilege Requirement
Only Admin level users have access to these commands.
Example
Reset the software of the switch:
T2500G-10TS# reset
4.13 reboot
Description
The reboot command is used to reboot the Switch. To avoid damage, please
don’t turn off the device while rebooting.
Syntax
reboot
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Reboot the switch:
T2500G-10TS# reboot
4.14 reboot-schedule
Description
This reboot-schedule command is used to configure the switch to reboot at
a certain time point. To delete the reboot schedule settings, please use the
reboot-schedule cancel command.
Syntax
reboot-schedule at
reboot-schedule in
reboot-schedule cancel
time [ date
interval
] [ save_before_reboot ]
[ save_before_reboot ]
38
Page 59
Parameter
time
—— Specify the time point for the switch to reboot, in the format of
hh:mm.
date
—— Specify the date for the switch to reboot, in the format of
DD:MM:YYYY. The date should be within 30 days.
save_before_reboot
interval
from 1 to 43200 minutes.
cancel —— Delete the reboot schedule settings.
—— Specify a time period after which the switch reboots. It ranges
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
User Guidelines
In the command reboot-schedule at
no date is specified and the time you set here is later than the time that this
command is executed, the switch will reboot later that day; otherwise the
switch will reboot at the time point the next day.
—— Save the configuration file before the switch
reboots.
time [ date
] [ save_before_reboot ], if
Example
Specify the switch to save the configuration files and reboot in 200 minutes,:
T2500G-10TS(config)# reboot-schedule in 200 save_before_reboot
4.15 copy running-config startup-config
Description
The copy running-config startup-config command is used to save the
current settings.
Syntax
copy running-config startup-config
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
39
Page 60

Example
Save current settings:
T2500G-10TS# copy running-config startup-config
4.16 copy startup-config tftp
Description
The copy startup-config tftp command is used to backup the configuration
file to TFTP server.
Syntax
copy startup-config tftp ip-address
Parameter
ip-addr
supported, for example 192.168.0.1 or fe80::1234.
name
—— IP Address of the TFTP server. Both IPv4 and IPv6 addresses are
—— Specify the name for the configuration file which would be backup.
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Backup the configuration files to TFTP server with the IP 192.168.0.148 and
name this file config.cfg:
T2500G-10TS# copy startup-config tftp ip-address 192.168.0.148 filename
config
ip-addr
filename
name
Backup the configuration files to TFTP server with the IP fe80::1234 and name
this file config.cfg:
T2500G-10TS# copy startup-config tftp ip-address fe80::1234 filename
config
4.17 copy tftp startup-config
Description
The copy tftp startup-config command is used to download the
configuration file to the switch from TFTP server.
40
Page 61

Syntax
copy tftp startup-config ip-address
Parameter
ip-addr
supported, for example 192.168.0.1 or fe80::1234.
name
downloaded.
—— IP Address of the TFTP server. Both IPv4 and IPv6 addresses are
—— Specify the name for the configuration file which would be
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Download the configuration file named as config.cfg to the switch from TFTP
server with the IP 192.168.0.148:
T2500G-10TS# copy tftp startup-config ip-address 192.168.0.148 filename
ip-addr
filename
name
config
Download the configuration file named as config.cfg to the switch from TFTP
server with the IP fe80::1234
T2500G-10TS# copy tftp startup-config ip-address fe80::1234 filename
config
4.18 copy backup-config tftp
Description
The copy backup-config tftp command is used to export the backup
configuration file of the switch to TFTP server.
Syntax
copy backup-config tftp ip-address
Parameter
ip-addr
filename
name
ip-addr
supported, for example 192.168.0.1 or fe80::1234.
name
—— IP Address of the TFTP server. Both IPv4 and IPv6 addresses are
—— Specify the name for the configuration file which would be exported.
41
Page 62

Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Export the backup configuration file of the switch to the TFTP server with the
IP 192.168.0.148 and name the file config.cfg:
T2500G-10TS# copy backup-config tftp ip-address 192.168.0.148 filename
config
4.19 copy backup-config startup-config
Description
The copy backup-config startup-config command is used to replace the
startup configuration file using the backup configuration file.
Syntax
copy backup-config startup-config
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Replace the startup configuration file using the backup configuration file.:
T2500G-10TS# copy backup-config startup-config
4.20 copy running-config backup-config
Description
The copy running-config backup-config tftp command is used to save the
current running configuration as the backup configuration file.
Syntax
copy running-config backup-config
42
Page 63

Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Save the current running configuration as the backup configuration file.
T2500G-10TS# copy running-config backup-config
4.21 copy tftp backup-config
Description
The copy tftp backup-config command is used to download the backup
configuration file from a TFTP server.
Syntax
Copy tftp backup-config ip-address
Parameter
ip-addr
supported, for example 192.168.0.1 or fe80::1234.
name
downloaded.
—— IP Address of the TFTP server. Both IPv4 and IPv6 addresses are
—— Specify the name for the configuration file which would be
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Download the configuration file named config.cfg from the TFTP server with
the IP 192.168.0.148:
ip-addr
filename
name
T2500G-10TS# copy tftp backup-config ip-address 192.168.0.148 filename
config
43
Page 64

4.22 boot application
Description
The boot application command is used to configure the image file as startup
image or backup image.
Syntax
boot application filename { image1 | image 2 } { startup | backup }
no boot application
Parameter
image1 | image2 —— Specify the image file to be configured. By default, the
image1.bin is the startup image and the image2.bin is the backup image.
startup | backup —— Specify the property of the image, either startup image
or backup image.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Configure the image2.bin as the startup image:
T2500G-10TS(config)# boot application filename image2 startup
4.23 boot config
Description
The boot config command is used to configure the configuration file as
startup configuration or backup configuration.
Syntax
boot config filename { config1 | config 2 } { startup | backup }
no boot application
44
Page 65

Parameter
config1 | config2 —— Specify the configuration file to be configured. By
default, the config1.cfg is the startup image and the config2.cfg is the backup
image.
startup | backup—— Specify the property of the configuration.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Configure the config2.cfg as the startup image:
T2500G-10TS(config)# boot config filename config2 startup
4.24 remove backup-image
Description
The remove backup-image command is used to delete the backup-image.
Syntax
remove backup-image
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Delete the backup image file:
T2500G-10TS# remove backup-image
45
Page 66

4.25 firmware upgrade
Description
The firmware upgrade command is used to upgrade the switch’s backup
iamge file via the TFTP server. The uploaded firmware file will take place of
the Backup Image, and user can chose whether to reboot the switch will the
Backup Image.
Syntax
firmware upgrade ip-address
Parameter
ip-addr
supported, for example 192.168.0.1 or fe80::1234.
name
—— IP Address of the TFTP server. Both IPv4 and IPv6 addresses are
—— Specify the name for the firmware file.
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Upgrade the switch’s backup iamge file with the file firmware.bin in the TFTP
server with the IP address 192.168.0.148, and reboot the switch with this
firmware:
T2500G-10TS# firmware upgrade ip-address 192.168.0.148 filename
ip-addr
filename
name
firmware.bin
It will only upgrade the backup image. Continue? (Y/N):y
Operation OK!
Reboot with the backup image? (Y/N): y
Upgrade the switch’s backup iamge file with the file firmware.bin in the TFTP
server with the IP address fe80::1234, but do not reboot the switch:
T2500G-10TS# firmware upgrade ip-address fe80::1234 filename
firmware.bin
It will only upgrade the backup image. Continue? (Y/N):y
Operation OK!
Reboot with the backup image? (Y/N): n
46
Page 67

4.26 ping
Description
The ping command is used to test the connectivity between the switch and
one node of the network.
Syntax
ping [ ip | ipv6 ] {
Parameter
ip
—— The type of the IP address for ping test should be IPv4.
ipv6
—— The type of the IP address for ping test should be IPv6.
ip_addr
parameter ip/ipv6 is not selected, both IPv4 and IPv6 addresses are
supported, for example 192.168.0.100 or fe80::1234.
-n
ranges from 1 to 10. By default, this value is 4.
-l
1500 bytes. By default, this value is 64.
-i
to 1000 milliseconds. By default, this value is 1000.
—— The IP address of the destination node for ping test. If the
count
—— The amount of times to send test data during Ping testing. It
size
—— The size of the sending data during ping testing. It ranges from 1 to
interval
—— The interval to send ICMP request packets. It ranges from 100
Command Mode
Privileged EXEC Mode
ip_addr
} [ -n
count
] [ -l
size
] [ -i
interval
]
Privilege Requirement
None.
Example
To test the connectivity between the switch and the network device with the
IP 192.168.0.131, please specify the
1000 milliseconds. If there is not any response after 8 times’ Ping test, the
connection between the switch and the network device is failed to establish:
T2500G-10TS# ping 192.168.0.131 –n 8 –l 512
To test the connectivity between the switch and the network device with the
IP fe80::1234, please specify the
milliseconds. If there is not any response after 8 times’ Ping test, the
connection between the switch and the network device is failed to establish:
T2500G-10TS# ping fe80::1234 –n 8 –l 512
count
(-l) as 512 bytes and
count
(-l) as 512 bytes and
count
count
(-i) as
(-i) as 1000
47
Page 68

4.27 tracert
Description
The tracert command is used to test the connectivity of the gateways during
its journey from the source to destination of the test data.
Syntax
tracert [ ip | ipv6 ]
Parameter
ip —— The type of the IP address for tracert test should be IPv4.
ipv6 —— The type of the IP address for tracert test should be IPv6.
ip_addr
is not selected, both IPv4 and IPv6 addresses are supported, for example
192.168.0.100 or fe80::1234.
maxHops
though. It ranges from 1 to 30. By default, this value is 4.
—— The IP address of the destination device. If the parameter ip/ipv6
—— The maximum number of the route hops the test data can pass
Command Mode
Privileged EXEC Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
ip_addr [ maxHops
]
Example
Test the connectivity between the switch and the network device with the IP
192.168.0.131. If the destination device has not been found after 20
maxHops,
failed to establish:
T2500G-10TS# tracert 192.168.0.131 20
Test the connectivity between the switch and the network device with the IP
fe80::1234. If the destination device has not been found after 20
the connection between the switch and the destination device is failed to
establish:
T2500G-10TS# tracert fe80::1234 20
the connection between the switch and the destination device is
maxHops,
48
Page 69

4.28 show system-info
Description
The show system-info command is used to display System Description,
Device Name, Device Location, System Contact, Hardware Version, Firmware
Version, System Time, Run Time and so on.
Syntax
show system-info
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the system information:
T2500G-10TS# show system-info
4.29 show image-info
Description
The show image-info command is used to display the information of image
files in the system.
Syntax
show image-info
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the system image files’ information:
T2500G-10TS# show image-info
49
Page 70

4.30 show boot
Description
The show boot command is used to display the boot configuration of the
system.
Syntax
show boot
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the system boot configuration information:
T2500G-10TS# show boot
4.31 show running-config
Description
The show running-config command is used to display the current operating
configuration of the system or of a specified port.
Syntax
show running-config
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the system current operating configuration:
T2500G-10TS# show running-config
50
Page 71

4.32 show startup-config
Description
The show startup-config command is used to display the current
configuration saved in the switch. These configuration settings will not be lost
the next time you reboot the switch.
Syntax
show startup-config
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the saved configuration:
T2500G-10TS# show startup-config
4.33 show system-time
Description
The show system-time command is used to display the time information of
the switch.
Syntax
show system-time
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the time information of the switch
T2500G-10TS# show system-time
51
Page 72

4.34 show system-time dst
Description
The show system-time dst command is used to display the DST information
of the switch.
Syntax
show system-time dst
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the DST information of the switch
T2500G-10TS# show system-time dst
4.35 show system-time ntp
Description
The show system-time ntp command is used to display the NTP mode
configuration information.
Syntax
show system-time ntp
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the NTP mode configuration information of the switch:
T2500G-10TS# show system-time ntp
52
Page 73

4.36 show cable-diagnostics interface
Description
The show cable-diagnostics interface command is used to display the cable
diagnostics of the connected Ethernet Port., which facilitates you to check
the connection status of the cable connected to the switch, locate and
diagnose the trouble spot of the network.
Syntax
show cable-diagnostics interface { fastEthernet
| ten-gigabitEthernet
port
}
Parameter
port
—— The number of the port which is selected for Cable test.
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Show the cable-diagnostics of port 3:
T2500G-10TS# show cable-diagnostics interface gigabitEthernet 1/0/3
4.37 show cpu-utilization
port
| gigabitEthernet
port
Description
The show cpu-utilization command is used to display the system’s CPU
utilization in the last 5 seconds/1minute/5minutes.
Syntax
show cpu-utilization
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
53
Page 74

Example
Display the CPU utilization information of the switch:
T2500G-10TS# show cpu-utilization
4.38 show memory-utilization
Description
The show memory-utilization command is used to display the current
system’s memory utilization in the last 5 seconds/1minute/5minutes.
Syntax
show memory-utilization
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the memory utilization information of the switch:
T2500G-10TS# show memory-utilization
54
Page 75

Chapter 5 EEE Configuration Commands
EEE (Energy Efficient Ethernet) is used to save power consumption of the switch during periods
of low data activity. You can simply enable this feature on ports to allow power reduction.
5.1 eee
Description
The eee command is used to enable EEE on the port. To disable EEE on the
port, please use no eee command.
Syntax
eee
no eee
Command Mode
Interface Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Enable EEE on port 1/0/1:
T2500G-10TS(config)#interface gigabitEthernet 1/0/1
T2500G-10TS(config-if)#eee
5.2 show interface eee
Description
The show interface eee command is used to display the EEE configuration
on each port.
Syntax
show interface eee [ fastEthernet
Command Mode
Privileged EXEC Mode and Any Configuration Mode
55
port
| gigabitEthernet
port
]
Page 76

Privilege Requirement
None.
Example
Display the EEE configuration of each port
T2500G-10TS# show interface eee
56
Page 77

Chapter 6 SDM Template Commands
This chapter describes how to configure the Switch Database Management (SDM) templates to
allocate hardware resources on the switch for different uses.
6.1 sdm prefer
Description
The sdm prefer command is used to configure the SDM template. The SDM
template is used to allocate system resources to best support the features
being used in your application. To return to use the default template, please
use the sdm prefer default command. The template change will takes effect
after a reboot.
Syntax
sdm prefer { default | enterpriseV4 | enterpriseV6 }
Parameter
default —— Specify the SDM template used in the switch as “default”.
enterpriseV4
“enterpriseV4”.
enterpriseV6
“enterpriseV6”.
—— Specify the SDM template used in the switch as
—— Specify the SDM template used in the switch as
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Specify the SDM template as enterpriseV4:
T2500G-10TS(config)# sdm prefer enterpriseV4
57
Page 78

6.2 show sdm prefer
Description
The show sdm prefer command is used to display resource allocation of the
current SDM template in use, or the SDM templates that can be used.
Syntax
show sdm prefer { used | default | enterpriseV4 | enterpriseV6 }
Parameter
used —— Display the resource allocation of the template currently in use, and
the template that will become active after a reboot.
default
enterpriseV4
template. enterpriseV6
enterpriseV6 template.
—— Display the resource allocation of the default template.
—— Display the resource allocation of the enterpriseV4
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin level users have access to these commands.
Example
Display the resource allocation of the template currently in use, and the
—— Display the resource allocation of the
template that will become active after a reboot:
T2500G-10TS(config)#show sdm prefer used
58
Page 79

Chapter 7 Time Range Commands
With this feature, you can configure a time range and bind it to an ACL rule.
7.1 time-range
Description
The time-range command is used to create time-range entry for the switch
and enter Time-range Create Configuration Mode. After a time-range entry is
created, you need to specify the date and time. A time-range can implement
multiple time-ranges simultaneously as long as they do not conflict with each
other. To delete the corresponding time-range configuration, please use no
time-range command.
Syntax
time-range
no time-range
Command Mode
Global Configuration Mode
Parameter
name
—— The time-range name, ranging from 1 to 16 characters.
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Create a time-range named “tRange1” for the switch:
T2500G-10TS(config)# time-range tRange1
7.2 absolute
name
name
Description
The absolute command is used to create an absolute time-range for the
time-range of the switch. To delete the corresponding absolute time-range
configuration, please use no absolute command.
59
Page 80

Syntax
absolute from
no absolute [
start-date
index
Parameter
start-date
MM/DD/YYYY.
end-date
MM/DD/YYYY.
—— The start date in Absoluteness Mode, in the format of
—— The end date in Absoluteness Mode, in the format of
Command Mode
Time-range Create Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Create an absolute time-range for the switch and specify the date extending
from May 5th, 2017 through Oct. 5th, 2017:
to
end-date
]
T2500G-10TS(config)#time-range tRange1
T2500G-10TS(config-time-range)#absolute from 05/05/2017 to
10/05/2017
7.3 periodic
Description
The periodic command is used to create a periodic mode time-range for the
time-range of the switch. To delete the corresponding periodic mode
time-range configuration, please use no periodic command.
Syntax
periodic start
no periodic [
Parameter
start-time
index
]
end
end-time
day-of-the-week
week-day
start-time
end-time
week-day
numbers 1-7 respectively represent Monday, Tuesday, Wednesday,
Thursday, Friday, Saturday and Sunday.
——Specify the start time in the format of HH:MM
——Specify the end time in the format of HH:MM
——Specify the days of a week in the format of 1-3, 7. The
60
Page 81

Command Mode
Time-range Create Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Configure the time-range named “tRange2” as a periodic time-range and
specify the date and time as 8:30 to 12:00 on weekends:
T2500G-10TS(config)#time-range tRange2
T2500G-10TS(config -time-range)#periodic start 08:30 end 12:00
day-of-the-week 6-7
7.4 holiday (time-range mode)
Description
The holiday command is used to create holiday mode time-range for the
time-range of the switch. When the holiday which is excluded from
time-range occurs, the switch will not supply power.
Syntax
holiday { exclude | include }
Parameter
exclude
include
——The time range will not take effect on holiday.
—— The time range will take effect on holiday.
Command Mode
Time-range Create Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Create a time-range entry named “tRange3” and configure time-range to
exclude the holiday:
T2500G-10TS(config)#time-range tRange3
T2500G-10TS(config-time-range)#holiday exclude
61
Page 82

7.5 holiday
Description
The holiday command is used to create holiday for the switch. To delete the
corresponding holiday configuration, please use no holiday command.
Syntax
holiday
no holiday
name
name
start-date
Parameter
name
—— The holiday name, ranging from 1 to 16 characters.
start-date
instance, 05/01.
end-date
instance, 05/01.
—— The start date of the holiday, in the format of MM/DD, for
——The end date of the holiday, in the format of MM/DD, for
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
start-date
end-date
end-date
Create a holiday named “holiday1” and configure the start date as October
1st and the end date as October 3rd:
T2500G-10TS(config)# holiday holiday1 start-date 10/01 end-date 10/03
7.6 show holiday
Description
The show holiday command is used to display the defined holiday.
Syntax
show holiday
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
62
Page 83

Example
Display the defined holiday:
T2500G-10TS# show holiday
7.7 show time-range
Description
The show time-range command is used to display the defined time-range.
Syntax
show time-range [
Parameter
time-range-name
characters.
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the defined time-range:
T2500G-10TS# show time-range
time-range-name
—— The time-range name, ranging from 1 to 16
]
63
Page 84

Chapter 8 Port Configuration Commands
Port Configuration Commands can be used to configure the Bandwidth Control, Negotiation
Mode and Storm Control for Ethernet ports.
8.1 interface gigabitEthernet
Description
The interface gigabitEthernet command is used to enter the Interface
gigabitEthernet Configuration Mode and configure the corresponding Gigabit
Ethernet port.
Syntax
interface gigabitEthernet
Parameter
port
—— The Ethernet port number.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
To enter the Interface gigabitEthernet Configuration Mode and configure port
2:
T2500G-10TS(config)# interface gigabitEthernet 1/0/2
port
8.2 interface range gigabitEthernet
Description
The interface range gigabitEthernet command is used to enter the interface
range gigabitEthernet Configuration Mode and configure multiple Gigabit
Ethernet ports at the same time.
64
Page 85

Syntax
interface range gigabitEthernet
Parameter
port-list
—— The list of Ethernet ports.
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
User Guidelines
Command in the Interface Range gigabitEthernet Mode is executed
independently on all ports in the range. It does not affect the execution on the
other ports at all if the command results in an error on one port.
Example
port-list
To enter the Interface range gigabitEthernet Configuration Mode, and
configure ports 1, 2, 3, 6, 7 and 9 at the same time by adding them to one
port-list:
T2500G-10TS(config)# interface range gigabitEthernet
1/0/1-3,1/0/6-7,1/0/9
8.3 description
Description
The description command is used to add a description to the Ethernet port.
To clear the description of the corresponding port, please use no
description command.
Syntax
description
string
no description
Parameter
string
—— Content of a port description, ranging from 1 to 16 characters.
65
Page 86

Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Add a description Port_5 to port 1/0/5:
T2500G-10TS(config)# interface gigabitEthernet 1/0/5
T2500G-10TS(config-if)# description Port_5
8.4 shutdown
Description
The shutdown command is used to disable an Ethernet port. To enable this
port again, please use no shutdown command.
Syntax
shutdown
no shutdown
Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Disable port 1/0/3:
T2500G-10TS(config)# interface gigabitEthernet 1/0/3
T2500G-10TS(config-if)# shutdown
66
Page 87

8.5 flow-control
Description
The flow-control command is used to enable the flow-control function for a
port. To disable the flow-control function for this corresponding port, please
use no flow-control command. With the flow-control function enabled, the
Ingress Rate and Egress Rate can be synchronized to avoid packet loss in the
network.
Syntax
flow-control
no flow-control
Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Enable the flow-control function for port 1/0/3:
T2500G-10TS(config)# interface gigabitEthernet 1/0/3
T2500G-10TS(config-if)# flow-control
8.6 duplex
Description
The duplex command is used to configure the Duplex Mode for an Ethernet
port. To return to the default configuration, please use no duplex command.
Syntax
duplex { auto | full | half }
no duplex
67
Page 88

Parameter
auto | full | half —— The duplex mode of the Ethernet port. There are three
options: auto-negotiation mode, full-duplex mode and half-duplex mode. By
default the Gigabit Ethernet port is auto-negotiation mode.
Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the Duplex Mode as full-duplex for port 1/0/3:
T2500G-10TS(config)# interface gigabitEthernet 1/0/3
T2500G-10TS(config-if)# duplex full
8.7 jumbo-size
Description
The jumbo-size command is used to specify the size of jumbo frames.
Syntax
jumbo-size
Parameter
size
—— The value of jumbo frames. It ranges from 1518 to 9216 bytes, and
the default is 1518 bytes.
Command Mode
Global Configuration Mode
size
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Globally configure the size of jumbo frames as 9216:
T2500G-10TS(config)# jumbo-size 9216
68
Page 89

8.8 speed
Description
The speed command is used to configure the Speed Mode for an Ethernet
port. To return to the default configuration, please use no speed command.
Syntax
speed { 10 | 100 | 1000 | auto }
no speed
Parameter
10 | 100 | 1000 | auto —— The speed mode of the Ethernet port. There are
four options: 10Mbps, 100Mbps, 1000Mbps and Auto negotiation mode
(default).
Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Configure the Speed Mode as 100Mbps for port 1/0/3:
T2500G-10TS(config)# interface gigabitEthernet 1/0/3
T2500G-10TS(config-if)# speed 100
8.9 clear counters
Description
The clear counters command is used to clear the statistics information of all
the Ethernet ports and port channels.
Syntax
clear counters
clear counters interface [ gigabitEthernet
port-channel-id
Parameter
port
—— The Ethernet port number.
]
69
port
] [ port-channel
Page 90

port-channel-id
—— The ID of the port channel.
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
Only Admin and Operator level users have access to these commands.
Example
Clear the statistic information of all ports and port channels:
T2500G-10TS(config)# clear counters
8.10 show interface status
Description
The show interface status command is used to display the connection
status of the Ethernet port/port channel.
Syntax
show interface status [fastEthernet
port-channel
Parameter
port
port-channel-id
—— The Ethernet port number.
port-channel-id ]
—— The ID of the port channel..
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the connection status of all ports and port channels:
T2500G-10TS(config)# show interface status
Display the connection status of port 1/0/1:
port
| gigabitEthernet
port
|
T2500G-10TS(config)# show interface status gigabitEthernet 1/0/1
70
Page 91

8.11 show interface counters
Description
The show interface counters command is used to display the statistics
information of all ports/port channels.
Syntax
show interface counters [fastEthernet
port-channel
Parameter
port
port-channel-id
—— The Ethernet port number.
port-channel-id ]
—— The ID of the port channel.
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the statistics information of all Ethernet ports and port channels:
T2500G-10TS(config)# show interface counters
Display the statistics information of port 1/0/2:
T2500G-10TS(config)# show interface counters gigabitEthernet 1/0/2
port
| gigabitEthernet
port
|
8.12 show interface configuration
Description
The show interface configuration command is used to display the
configurations of all ports and port channels, including Port-status, Flow
Control, Negotiation Mode and Port-description.
Syntax
show interface configuration [fastEthernet
port-channel
Parameter
port
—— The Ethernet port number.
port-channel-id
Command Mode
Privileged EXEC Mode and Any Configuration Mode
port-channel-id ]
—— The ID of the port channel.
71
port
| gigabitEthernet
port
|
Page 92

Privilege Requirement
None.
Example
Display the configurations of all Ethernet ports and port channels:
T2500G-10TS(config)# show interface configuration
Display the configurations of port 1/0/2:
T2500G-10TS(config)# show interface configuration gigabitEthernet 1/0/2
72
Page 93

Chapter 9 Port Isolation Commands
Port Isolation provides a method of restricting traffic flow to improve the network security by
forbidding the port to forward packets to the ports that are not on its forwarding port list.
9.1 port isolation
Description
The port isolation command is used to configure the forward port/port
channel list of a port/port channel, so that this port/port channel can only
communicate with the ports/port channels on its list. To delete the
corresponding configuration, please use no port isolation command.
Syntax
port isolation { [ fa-forward-list
gi-forward-list
te-forward-list
no port isolation
] [ po-forward-list
] }
Parameter
fa-forward-list / gi-forward-list / te-forward-list
po
-forward-list —— The list of port channels.
Command Mode
Interface Configuration Mode (interface fastEthernet / interface range
fastEthernet / interface fastEthernet / interface range fastEthernet /interface
gigabitEthernet / interface range gigabitEthernet / interface port-channel /
interface range port-channel)
Privilege Requirement
Only Admin and Operator level users have access to these commands.
fa-forward-list
po-forward-list
—— The list of Ethernet ports.
] [ gi-forward-list
] [ te-forward-list
Example
Set port 1, 2, 4 and port channel 2 to the forward list of port 1/0/5:
T2500G-10TS(config)# interface gigabitEthernet 1/0/5
T2500G-10TS(config-if)# port isolation gi-forward-list 1/0/1-2,1/0/4
po-forward-list 2
Set all Ethernet ports and port channels to forward list of port 1/0/2, namely
restore to the default setting:
73
Page 94

T2500G-10TS(config)# interface gigabitEthernet 1/0/2
T2500G-10TS(config-if)# no port isolation
9.2 show port isolation interface
Description
The show port isolation interface command is used to display the forward
port list of a port/port channel.
Syntax
show port isolation interface [fastEthernet
ten-gigabitEthernet
Parameter
port ——
in the format of 1/0/2.
port-channel-id ——
list, ranging from 1 to 6.
The number of Ethernet port you want to show its forward port list,
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the forward-list of port 1/0/2:
T2500G-10TS# show port isolation interface gigabitEthernet 1/0/2
port
| gigabitEthernet
port
| port-channel
The ID of port channel you want to show its forward port
port-channel-id ]
port
|
Display the forward-list of all Ethernet ports and port channels:
T2500G-10TS# show port isolation interface
74
Page 95

Chapter 10 Loopback Detection Commands
With loopback detection feature enabled, the switch can detect loops using loopback
detection packets. When a loop is detected, the switch will display an alert or further block the
corresponding port according to the configuration.
10.1 loopback-detection (global)
Description
The loopback-detection command is used to enable the loopback detection
function globally. To disable it, please use no loopback detection command.
Syntax
loopback-detection
no loopback-detection
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Enable the loopback detection function globally:
T2500G-10TS(config)# loopback-detection
10.2 loopback-detection interval
Description
The loopback-detection interval command is used to define the interval of
sending loopback detection packets from switch ports to network, aiming at
detecting network loops periodically.
Syntax
loopback-detection interval
Parameter
interval-time
ranges from 1 to 1000 seconds. By default, this value is 30.
interval-time
—— The interval of sending loopback detection packets. It
75
Page 96

Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Specify the interval-time as 50 seconds:
T2500G-10TS(config)# loopback-detection interval 50
10.3 loopback-detection recovery-time
Description
The loopback-detection recovery-time command is used to configure the
time after which the blocked port would automatically recover to normal
status.
Syntax
loopback-detection recovery-time
Parameter
recovery-time
recover to normal status, and the loopback detection would restart. It ranges
from 2 to 1000000 seconds. By default, this value is 90.
—— The time after which the blocked port would automatically
Command Mode
Global Configuration Mode
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Configure the recovery-time as 70 seconds:
recovery-time
T2500G-10TS(config)# loopback-detection recovery-time 70
76
Page 97

10.4 loopback-detection (interface)
Description
The loopback-detection command is used to enable the loopback
detection function of the specified port. To disable it, please use no
loopback-detection command.
Syntax
loopback-detection
no loopback-detection
Command Mode
Interface Configuration Mode (interface fastEthernet | interface range
fastEthernet | interface gigabitEthernet | interface range gigabitEthernet |
interface port-channel | interface range port-channel )
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Enable the loopback detection function of ports 1-3:
T2500G-10TS(config)# interface range gigabitEthernet 1/0/1-3
T2500G-10TS(Config-if-range)# loopback-detection
10.5 loopback-detection config process-mode
Description
The loopback-detection config process-mode command is used to
configure the process-mode for the ports by which the switch copes with the
detected loops. You also need to configure the recovery mode to remove the
block status of the port or VLAN when the process-mode is Port Based or
VLAN Based.
Syntax
loopback-detection config process-mode { alert | port-based | vlan-based }
recovery-mode { auto | manual }
Parameter
alert
generate an entry on the log file. It is the default setting
——
When a loop is detected, the switch will send a trap message and
.
77
Page 98

——
port-based
and generate an entry on the log file. In addition, the switch will block the port
on which the loop is detected and no packets can pass through the port.
When a loop is detected, the switch will send a trap message
vlan-based
and generate an entry on the log file. In addition, the switch will block the
VLAN in which the loop is detected and only the packets of the blocked VLAN
cannot pass through the port.
auto —— Block status can be automatically removed after recovery time.
manual —— Block status can only be removed manually.
——
When a loop is detected, the switch will send a trap message
Command Mode
Interface Configuration Mode (interface fastEthernet | interface range
fastEthernet | interface gigabitEthernet | interface range gigabitEthernet |
interface port-channel | interface range port-channel )
Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Configure the loopback detection process-mode as port-based, and
configure the recovery mode as manual for port 2:
T2500G-10TS(config)# interface gigabitEthernet 1/0/2
T2500G-10TS(config-if)# loopback-detection config process-mode
port-based recovery-mode manual
10.6 loopback-detection recover
Description
The loopback-detection recover command is used to remove the block
status of selected ports, recovering the blocked ports to normal status,
Syntax
loopback-detection recover
Command Mode
Interface Configuration Mode (interface fastEthernet | interface range
fastEthernet | interface gigabitEthernet | interface range gigabitEthernet |
interface port-channel | interface range port-channel )
78
Page 99

Privilege Requirement
Only Admin, Operator and Power User level users have access to these
commands.
Example
Recover the blocked port 1/0/2 to normal status:
T2500G-10TS(config)# interface gigabitEthernet 1/0/2
T2500G-10TS(config-if)# loopback-detection recover
10.7 show loopback-detection global
Description
The show loopback-detection global command is used to display the global
configuration of loopback detection function such as loopback detection
global status, loopback detection interval and loopback detection recovery
time.
Syntax
show loopback-detection global
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the global configuration of loopback detection function:
T2500G-10TS# show loopback-detection global
10.8 show loopback-detection interface
Description
Syntax
The show loopback-detection interface command is used to display the
configuration of loopback detection function and the status of the specified
Ethernet port.
show loopback-detection interface [ gigabitEthernet
lagid
] [ detail ]
79
port |
port-channel
Page 100

Parameter
port
—— The Ethernet port number.
lagid
—— The number of LAG, ranging from 1 to 14.
detail
—— Displays the loop status and block status of the VLAN which the
specified port belongs to.
Command Mode
Privileged EXEC Mode and Any Configuration Mode
Privilege Requirement
None.
Example
Display the configuration of loopback detection function and the status of all
ports:
T2500G-10TS# show loopback-detection interface
Display the configuration of loopback detection function and the status of
port 5:
T2500G-10TS# show loopback-detection interface gigabitEthernet 1/0/5
80
 Loading...
Loading...