Page 1
USER GUIDE
Page 2
Abou
t This Guide
W
a
:
should
hy
add
add
.
s
add
b
dd
h
.
l
y
y
y
y
h
.
Icon Descriptions
hile reading through the User Guide you may see
various icons that call attention to specific items. Below is
description of these icons
NOTE: This check mark indicates that there is
a note of interest and is something that you
pay special attention to while using the
roduct.
WARNING: This exclamation point indicates
that there is a caution or warning and it is
omething that could damage your property or
product.
About This Guide
WEB: This globe icon indicates a notewort
website
ress or e-mail
ress
nline Resource
ebsite addresses in this document are listed without
ttp:// in front of the
rowsers do not require it. If you use an older web browser,
ou may have to a
Resource Website
inksys www.linksys.com
inksys Internationalwww.linksys.com/internationa
Glossar
etwork Securit
ress because most current we
ttp://in front of the web address
www.linksys.com/glossar
www.linksys.com/securit
Copyright and Trademarks
inksys, Cisco and the Cisco Logo are
registered trademarks or trademarks
f Cisco Systems, Inc. and/or its
affiliates in the U.S. and certain other
ountries. Copyright © 2008 Cisco
Systems, Inc. All rights reserved.
er brands and product names are
Ot
trademarks or registered trademarks
f their respective holders
i
Page 3

Table of Contents
Chapter 1: Product Overview 4
Front Panel..................................................4
Back Panel . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4
Bottom Panel . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4
Chapter 2: Wireless Security Checklist 5
General Network Security Guidelines .................................5
Additional Security Tips . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5
Chapter 3: Advanced Conguration 6
Setup > Basic Setup . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6
Setup > DDNS................................................ 9
Setup > MAC Address Clone.......................................10
Setup > Advanced Routing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10
Wireless > Basic Wireless Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .11
Wireless > Wireless Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .12
Wireless > Wireless MAC Filter......................................14
Wireless > Advanced Wireless Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .14
Security > Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .15
Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .16
Security > VPN Passthrough.......................................16
Access Restrictions > Internet Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .16
Applications and Gaming > Port Range Forward..........................17
Applications & Gaming > Port Triggering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .18
Applications and Gaming > DMZ . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .18
Applications and Gaming > QoS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .19
Administration > Management.....................................20
Administration > Log . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .20
Administration > Diagnostics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .21
Administration > Factory Defaults ...................................21
Administration > Upgrade Firmware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .21
Administration > Config Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
Status > Router . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
Status > Local Network . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .22
Status > Wireless . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .23
Appendix A: Troubleshooting 25
Appendix B: Specications 26
Appendix C: Warranty Information 27
Limited Warranty..............................................27
Appendix D: US Regulatory Information 29
FCC Statement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
FCC Radiation Exposure Statement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
ii
Page 4

Table of Contents
Safety Notices................................................29
Industry Canada Statement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
Avis d’Industrie Canada..........................................30
Wireless Disclaimer . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .30
Avis de non-responsabilité concernant les appareils sans fil . . . . . . . . . . . . . . . . . .30
User Information for Consumer Products Covered by EU Directive 2002/96/EC on Waste
Electric and Electronic Equipment (WEEE) ..............................31
Appendix E: EU Regulatory Information 35
FCC Statement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .35
Safety Notices................................................35
Industry Canada Statement . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .35
Avis d’Industrie Canada..........................................35
Wireless Disclaimer . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .36
Avis de non-responsabilité concernant les appareils sans fil . . . . . . . . . . . . . . . . . .36
Declaration of Conformity with Regard to EU Directive 1999/5/EC (R&TTE Directive) . .37
Wireless Equipment (Wireless-N/G/A/B Products) . . . . . . . . . . . . . . . . . . . . . . . . .38
CE Marking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .38
National Restrictions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .38
Product Usage Restrictions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .39
Technical Documents on www.linksys.com/international . . . . . . . . . . . . . . . . . . . .39
User Information for Consumer Products Covered by EU Directive 2002/96/EC on Waste
Electric and Electronic Equipment (WEEE) ..............................40
Appendix F: Software License Agreement 44
Software in Linksys Products . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .44
Software Licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .44
iii
Page 5
Chapter 1
T
.
.
)
T
f-
dly lit.
.
ll
.
ll
.
l
T
T
.
y.
Product Overview
apter 1:
roduct Overview
hank you for choosing the Linksys Compact Wireless-G
Broadband Router. The Compact Wireless-G Broadband
Router will allow you to network wirelessly better than
ever, sharing Internet access, files and fun, easily and
securely.
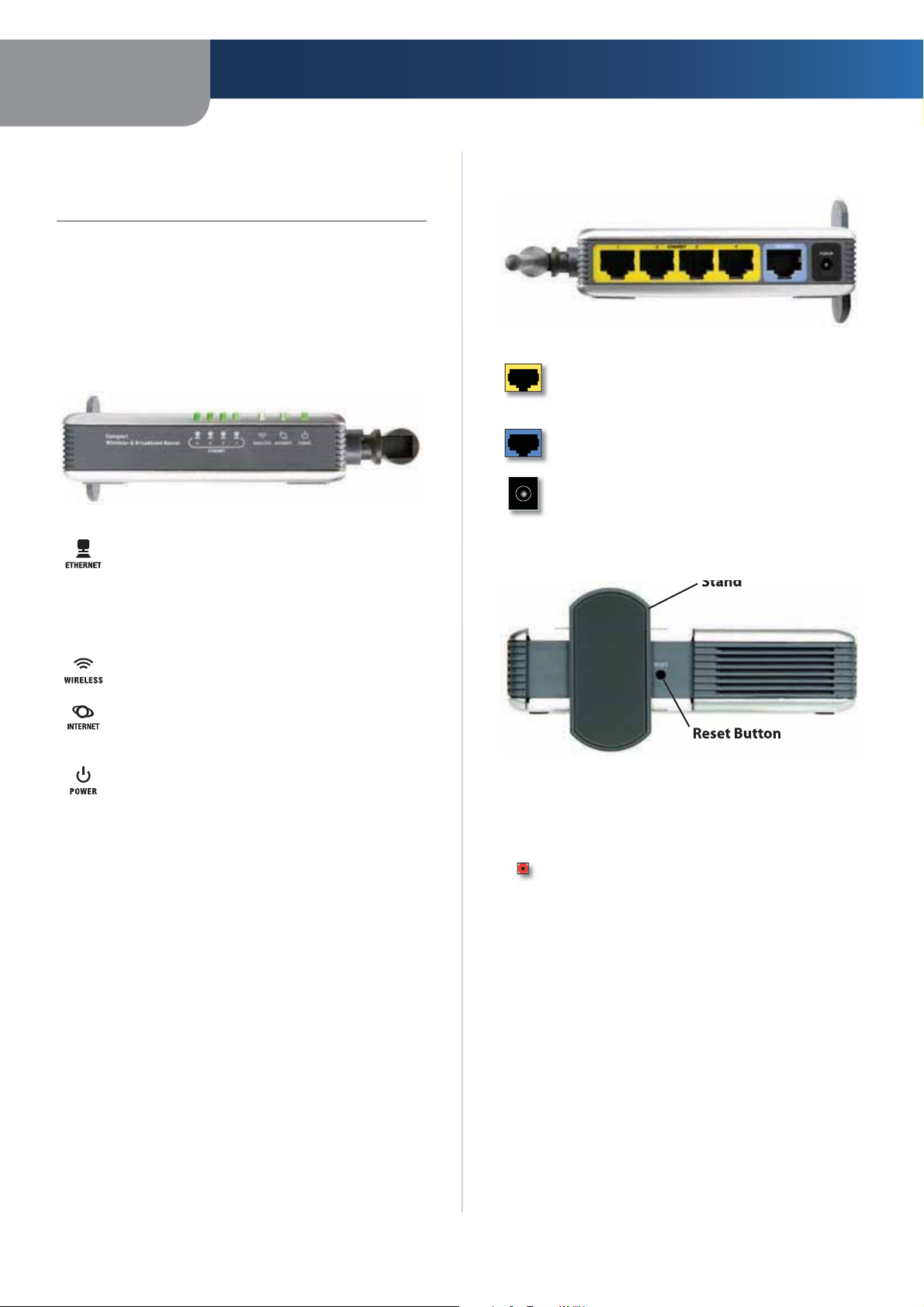
Front Panel
Ethernet 1-4 (Green) These numbered LEDs,
orresponding with the numbered ports on the
Router’s back panel, serve two purposes. If the
LED is continuously lit, the Router is connected
o a device through that port. A flashing LED
ndicates network activity over that port
Wireless
hen there is a successful wireless connection
Green) The WIRELESS LED flashes
Back Panel
Ethernet 1-4These ports connect the Router
o your networked PCs and other Ethernet
network devices
InternetThe Internet port is where you wi
onnect your broadband Internet connection
PowerThe Power port is where you wi
onnect the power adapter
Bottom Pane
Internet (Green) The INTERNET LED lights up
hen there is a connection through the Internet
port.
Power
nd will stay on while the Router is powered
LED will flash. When the diagnostic is complete,
Green
n. When the Router goes through its sel
iagnostic mode during every boot-up, this
e LED will be soli
he POWER LED lights up
he Router’s Reset button is located on the bottom panel.
o access the button, turn the stand perpendicular to
the Router. Use a sharp object like a pencil to push in the
utton
Reset There are two ways to reset the Router’s
actory defaults. Either press the RESET button,
for approximately eight seconds, or restore the
efaults from Administration > Factory Defaults
in the Router’s Web-based Utilit
4
Page 6
Chapter 2
.
g
y
d
.
s
.
.
s
y
.
T
.
g
o
Wireless Security Checklist
apter 2:
Wireless Security Checklist
ireless networks are convenient and easy to install, so
homes with high-speed Internet access are adopting them
t a rapid pace. Because wireless networking operates by
sending information over radio waves, it can be more
vulnerable to intruders than a traditional wired network
Like signals from your cellular or cordless phones, signals
rom your wireless network can also be intercepted. Since
ou cannot physically prevent someone from connecting
to your wireless network, you need to take some additional
steps to keep your network secure.
1. Change the default wireless
network name or SSID
ireless devices have a default wireless network name
or Service Set Identifier (SSID) set by the factory. This
s the name of your wireless network, and can be up
to 32 characters in length. Linksys wireless products
inksys as the default wireless network name. You
should change the wireless network name to somethin
nique to distinguish your wireless network from other
wireless networks that may exist around you, but do not
se personal information (such as your Social Securit
umber) because this information may be available for
nyone to see when browsing for wireless networks.
2. Change the default password
For wireless products such as access points, routers, an
gateways, you will be asked for a password when you
want to change their settings. These devices have a default
assword set by the factory. The Linksys default password
min. Hackers know these defaults and may try to
se them to access your wireless device and change your
etwork settings. To thwart any unauthorized changes,
customize the device’s password so it will be hard to
guess.
4. Enable encryption
Encryption protects data transmitted over a wireless
etwork. Wi-Fi Protected Access (WPA/WPA2) and Wired
Equivalency Privacy (WEP) offer different levels of security
or wireless communication
network encrypted with WPA/WPA2 is more secure
than a network encrypted with WEP, because WPA/WPA2
ses dynamic key encryption. To protect the information
s it passes over the airwaves, you should enable the
highest level of encryption supported by your network
equipment.
EP is an older encryption standard and may be the
only option available on some older devices that do not
support WPA.
General Network Security Guideline
ireless network security is useless if the underlying
etwork is not secure.
Password protect all computers on the network and
ndividually password protect sensitive files
Change passwords on a regular basis
Install anti-virus software and personal firewall
software.
Disable file sharing (peer-to-peer). Some applications
ay open file sharing without your consent and/or
knowledge.
Additional Security Tip
Keep wireless routers, access points, or gateways awa
rom exterior walls and windows
urn wireless routers, access points, or gateways
off when they are not being used (at night, during
vacations)
Use strong passphrases that are at least eight characters
n length. Combine letters and numbers to avoid usin
standard words that can be found in the dictionary.
3. Enable MAC address filtering
Linksys routers and gateways give you the ability to
enable Media Access Control (MAC) address filtering. The
MAC address is a unique series of numbers and letters
ssigned to every networking device. With MAC address
iltering enabled, wireless network access is provided
solely for wireless devices with specific MAC addresses.
For example, you can specify the MAC address of each
computer in your home so that only those computers can
ccess your wireless network.
WEB: F
security, visit www.linksys.com/security
r more information on wireless
5
Page 7
Chapter 3
h
.
T
ll
.
y.
y
T
68.1.1
ess
f
screen.) Click
.
n
p
T
Basic Setup
p
T
.
e
:
P
oE
P
)
P
apter 3:
dvanced Configuration
ter setting up the Router with the Setup Wizard (located
on the CD-ROM), the Router will be ready for use. However,
f you’d like to change its advanced settings, use the
Router’s web-based utility. This chapter describes eac
web page of the utility and each page’s key functions. You
can access the utility via a web browser on a computer
connected to the Router
he web-based utility has these main tabs: Setup,
ireless, Security, Access Restrictions, Applications &
Gaming, Administration, and Status. Additional tabs wi
e available after you click one of the main tabs
NOTE: When first installing the Router, you
ould use the Setup Wizard on the Setup
CD-ROM. If you want to configure advanced
ettings, use this chapter to learn about the
web-based utilit
Advanced Configuration
>
Internet Setu
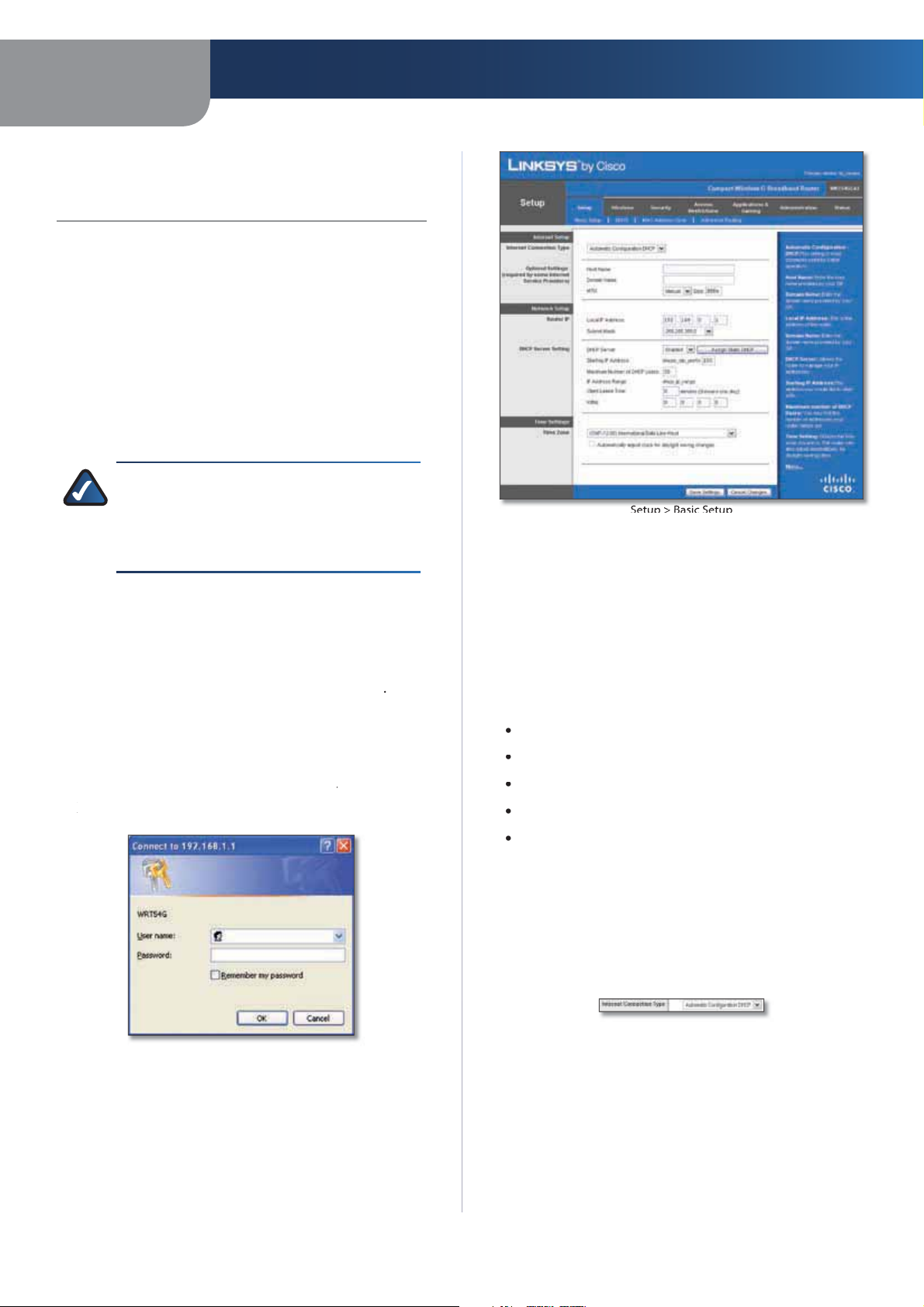
How to Access the Web-Based Utilit
o access the web-based utility, launch the web browser on
our computer, and enter the Router’s default IP address,
192.1
password request screen will appear. (Non-Windows XP
sers will see a similar screen.) Leave the
lank. The first time you open the Web-based utility, use
the default password
rom the Administration tab’s
to continue
in the Addr
ield. Then, press Enter
ser name field
min. (You can set a new password
assword Scree
he Internet Setup section configures the Router to your
Internet connection. Most of this information can be
obtained through your ISP
nternet Connection Typ
elect the type of Internet connection your ISP provides
rom the drop-down menu. The available types are
utomatic Configuration - DHCP
tatic I
PPP
Automatic Configuration - DHC
By default, the Router’s Internet Connection Type is set
toutomatic Configuration - DHCP, which should be
kept only if your ISP supports DHCP or you are connecting
through a dynamic IP address. (This option usually applies
to cable connections.
Internet Connection Type > Automatic Configuration - DHC
etup > Basic Setu
he first screen that appears is the
ows you to change the Router’s general settings.
asic Setup screen. This
6
Page 8
Chapter 3
P
.
ll
.
.
.
l
abl
oE
E
d
ect
.
lly
ll
lly
od
field,
.
.
.
k.
y
.
d
.
lly
.
od
field, you specify how often
.
ly.
Advanced Configuration
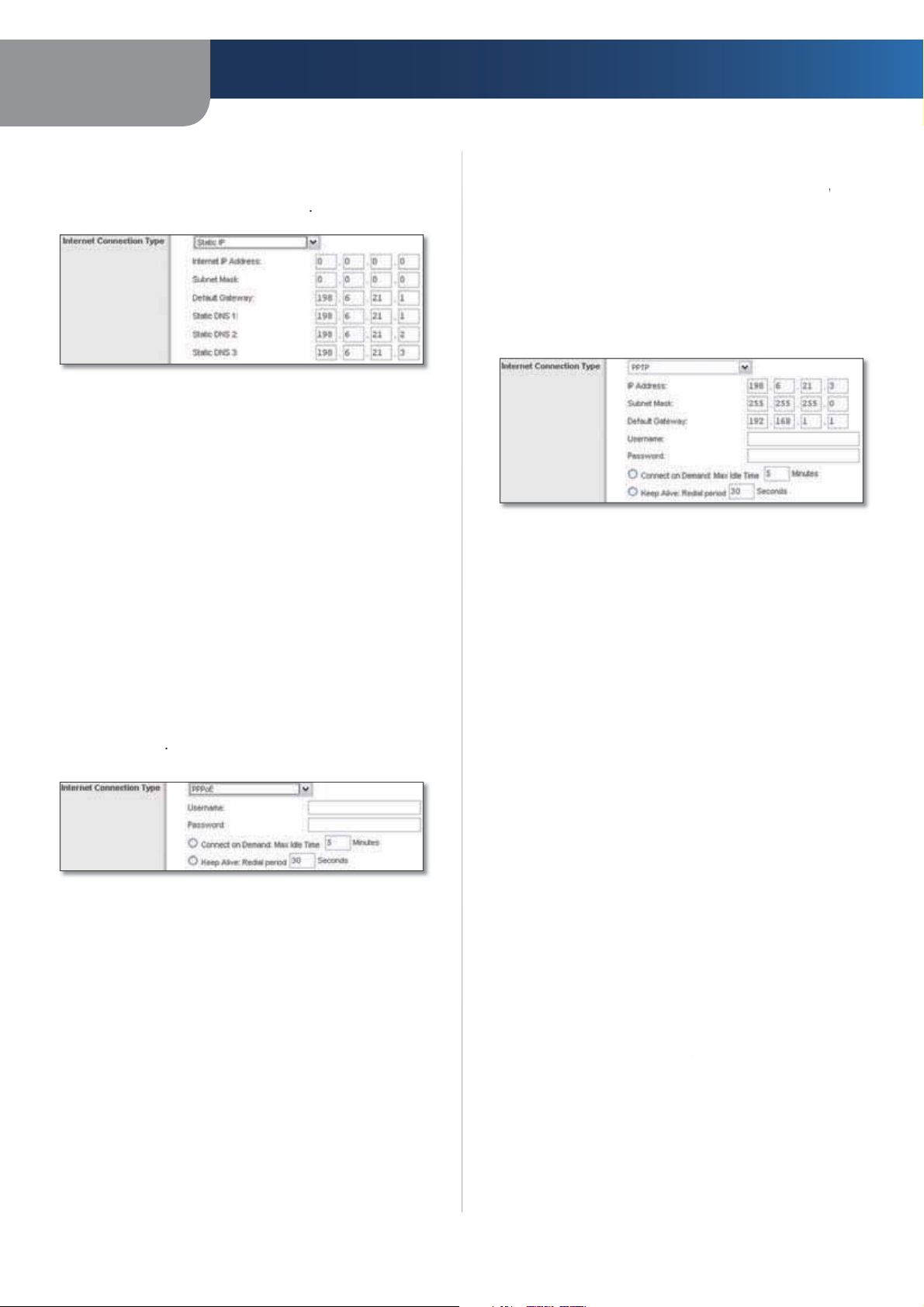
tatic I
If you are required to use a permanent IP address to
connect to the Internet, select
nternet Connection Type > Static IP
Internet IP AddressThis is the Router’s IP address, when
seen from the Internet. Your ISP will provide you with the
IP Address you need to specify here
Subnet Mask This is the Router’s Subnet Mask, as seen
users on the Internet (including your ISP). Your ISP wi
rovide you with the Subnet Mask
Gateway
ress, which is the ISP server’s IP address
DNS
(Domain Name System) Server IP Address
our ISP will provide you with the Gateway
our ISP will provide you with at least one DNS
tatic IP
oE
ome DSL-based ISPs use PPPoE (Point-to-Point Protoco
over Ethernet) to establish Internet connections. If you are
connected to the Internet through a DSL line, check with
your ISP to see if they use PPPoE. If they do, you will have
to en
e
PP
connection. If you are disconnected, then the Router
automatica
wi
this option, select
you specify how often you want the Router to check
the Internet connection. The default Redial Period is
seconds
re-establish your connection. To use
eep Alive In the Redial Peri
PPTP
Point-to-Point Tunneling Protocol (PPTP) is a service that
pplies to connections in Europe only
Internet Connection Type > PPTP
Internet IP Address This is the Router’s IP address, as
seen from the Internet. Your ISP will provide you with the
IP Address you need to specify here
Subnet Mask This is the Router’s Subnet Mask, as seen
users on the Internet (including your ISP). Your ISP will
rovide you with the Subnet Mas
Gateway
ress
User Name and Password Enter the User Name an
Password provided by your ISP
our ISP will provide you with the Gatewa
nternet Connection Type > PPPo
User Name and Password Enter the User Name an
Password provided by your ISP.
Connect on Demand: Max Idle Time You can configure
the Router to cut the Internet connection after it has been
nactive for a specified period of time (Max Idle Time). If
our Internet connection has been terminated due to
nactivity, Connect on Demand enables the Router to
utomatically re-establish your connection as soon as you
ttempt to access the Internet again. To use this option,
l
nnect on Demand In the
enter the number of minutes you want to have elapsed
efore your Internet connection terminates. The default
Max Idle Time is
Keep Alive: Redial Period If you select this option,
the Router will periodica
minutes
check your Internet
x Idle Timefield,
Connect on Demand: Max Idle Time You can configure
the Router to cut the Internet connection after it has been
nactive for a specified period of time (Max Idle Time). If
our Internet connection has been terminated due to
nactivity, Connect on Demand enables the Router to
utomatica
ttempt to access the Internet again. To use this option,
enter the number of minutes you want to have elapsed
efore your Internet connection terminates. The default
Max Idle Time is
Keep Alive: Redial Period
Router will periodically check your Internet connection. If
ou are disconnected, then the Router will automatically
e-establish your connection. To use this option, select
Keep Alive In the
ou want the Router to check the Internet connection. The
default value is 30seconds
L2TP is a service that applies to connections in Israel on
re-establish your connection as soon as you
onnect on Demand. In the
minutes
If you select this option, the
ial Peri
ax Idle Timefield,
7
Page 9
Chapter 3
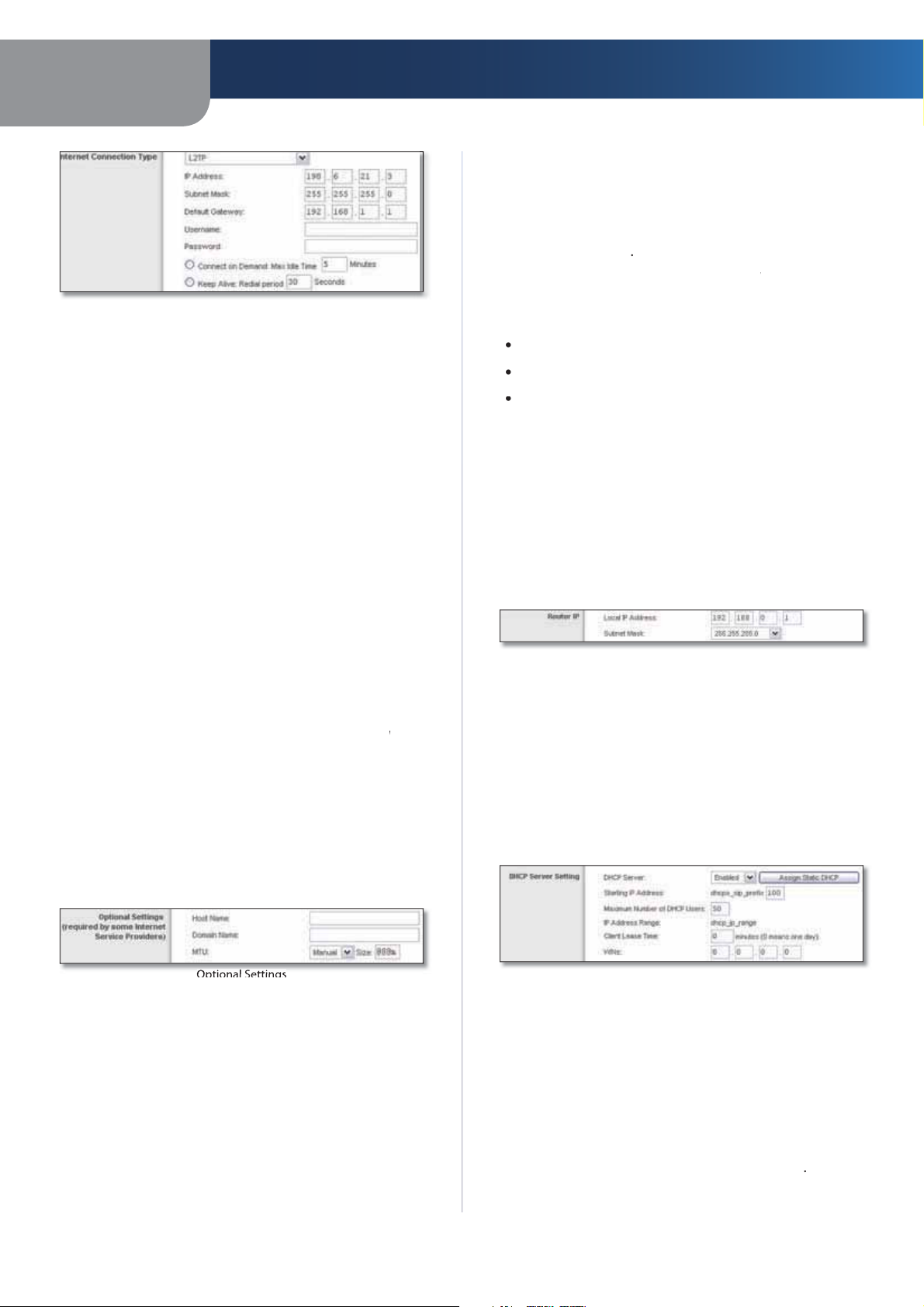
L2TP
d
.
add
.
.
lly
s
lly
od
field,
fau
.
s
.
Settings
.
ual
field, this option
:
00
60
p
T
.
P
T
.
Add
s
)
T
Add
(DHCP)
.
92.168.1.100
Advanced Configuration
MTU MTU is the Maximum Transmission Unit. It specifies
the largest packet size permitted for Internet transmission.
elect Manual if you want to manually enter the largest
acket size that is transmitted. To have the Router select
the best MTU for your Internet connection, keep the
default setting, Auto
nternet Connection Type >
User Name and Password Enter the User Name an
Password provided by your ISP
L2TP ServerThis is the IP
Your ISP will provide you with the IP Address you need to
specify here
Connect on Demand: Max Idle Time You can configure
the Router to cut the Internet connection after it has been
nactive for a specified period of time (Max Idle Time). If
your Internet connection has been terminated due to
nactivity, Connect on Demand enables the Router to
utomatica
ttempt to access the Internet again. To use this option,
select
enter the number of minutes you want to have elapsed
efore your Internet connection terminates. The default
Max Idle Time is
Keep Alive: Redial Period If you select this option,
the Router will periodically check your Internet
connection. If you are disconnected, then the Router
will automatica
this option, select
you specify how often you want the Router to check
the Internet connection. The de
seconds
re-establish your connection as soon as you
onnect on Demand. In the
minute
re-establish your connection. To use
eep Alive In the Redial Peri
ress of the L2TP Server
ax Idle Timefield,
lt Redial Period is
Optional Setting
ome of these settings may be required by your ISP. Verify
with your ISP before making any changes
Size
s enabled. Leave this value in the 1200 to 1500 range. The
default size depends on the Internet Connection Type
en Man
DHCP, Static IP, or Telstra:
PPPoE:
1492
TP or L2TP:14
is selected in the
5
Network Setu
he Network Setup section changes the settings on the
etwork connected to the Router’s Ethernet ports. Wireless
etup is performed through the Wireless tab
ter I
his presents both the Router’s IP Address and Subnet
Mask as seen by your network
ter IP
etwork Address Server Settings (DHCP
he settings allow you to configure the Router’s Dynamic
Host Configuration Protocol (DHCP) server function. The
Router can be used as a DHCP server for your network. A
DHCP server automatically assigns an IP address to each
computer on your network. If you choose to enable the
Router’s DHCP server option, make sure there is no other
DHCP server on your network.
res
Router Name
9 characters to represent the Router.
Host Name/Domain NameThese fields allow you to
supply a host and domain name for the Router. Some ISPs,
sually cable ISPs, require these names as identification.
You may have to check with your ISP to see if your
roadband Internet service has been configured with a
host and domain name. In most cases, leaving these fields
lank will work
n this field, you can enter a name of up to
DHCP Server DHCP is enabled by factory default. If you
ready have a DHCP server on your network, or you don’t
want a DHCP server, then select
eatures will be available)
Starting IP Address
start with when issuing IP addresses. Because the Router’s
efault IP address is 192.168.1.1, the Starting IP Address must
e 192.168.1.2 or greater, but smaller than 192.168.1.253.
The default Starting IP Address is 1
etwork
ress Server Settings
isable (no other DHCP
nter a value for the DHCP server to
8
Page 10
Chapter 3
T
y.
y
)
Ti
tting
.
T
abl
S
T
.
e
ce
ect
m
T
g
DDNS > DynDNS
.
.
add
.
.
m
DDNS > TZ O
.
Advanced Configuration
Maximum Number of DHCP Users
umber of PCs that you want the DHCP server to assign
IP addresses to. This number cannot be greater than 253.
he default is
Client Lease TimeThe Client Lease Time is the amount
time a network user will be allowed connection to the
Router with their current dynamic IP address. Enter the
mount of time, in minutes, that the user will be “leased”
this dynamic IP address. After the time is up, the user will
e automatically assigned a new dynamic IP address. The
default is 0 minutes, which means one da
Static DNS (1-3)
he Internet translates domain or website names into
nternet addresses or URLs. Your ISP will provide you with at
east one DNS Server IP Address. If you wish to use another,
enter that IP Address in one of these fields. You can enter up
o three DNS Server IP Addresses here. The Router will use
hese for quicker access to functioning DNS servers
WINS The Windows Internet Naming Service (WINS)
anages each PC’s interaction with the Internet. If you
se a WINS server, enter that server’s IP Address here.
therwise, leave this blank.
The Domain Name System (DNS) is how
nter the maximum
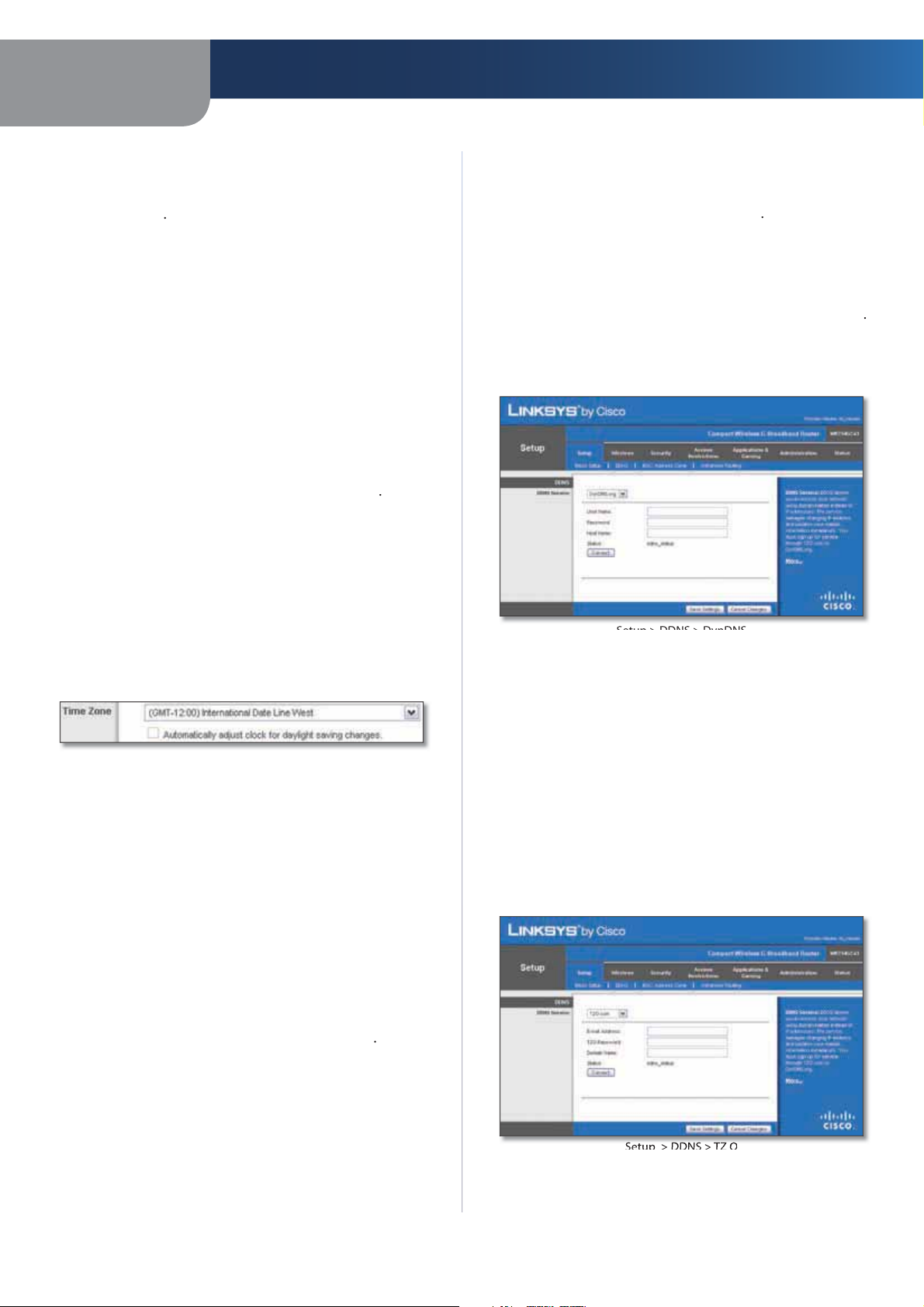
Time Setting
elect the time zone in which your network functions
rom this drop-down menu. (You can even automaticall
djust for daylight saving time.
Before you can use this feature, you need to sign up for
DDNS service at one of two DDNS service providers,
DynDNS.org or TZO.com. If you do not want to use this
eature, keep the default setting, Disabl
DNS Servi
If your DDNS service is provided by DynDNS.org, then
l
ynDNS.org from the drop-down menu. If your
DDNS service is provided by TZO, then select TZO.co
he features available on the DDNS screen will vary,
depending on which DDNS service provider you use.
DynDNS.or
>
User Name Enter the User Name for your DDNS account
Password
nter the Password for your DDNS account
me Se
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
etup > DDNS
he Router offers a Dynamic Domain Name System (DDNS)
eature. DDNS lets you assign a fixed host and domain
ame to a dynamic Internet IP address. It is useful when
you are hosting your own website, FTP server, or other
server behind the Router.
Before you can use this feature, you need to sign
for DDNS service with a DDNS service provider,
www.dyndns.org or www.TZO.com. If you do not want to
se this feature, keep the default setting,
DDN
he Router offers a Dynamic Domain Name System (DDNS)
eature. DDNS lets you assign a fixed host and domain
ame to a dynamic Internet IP address. It is useful when
ou are hosting your own website, FTP server, or other
server behind the Router
is
e
Host NameThe is the DDNS URL assigned by the DDNS
service.
Internet IP Address The Router’s Internet IP
displayed here. Because it is dynamic, it will change
Status The status of the DDNS service connection is
displayed here.
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
ress is
ZO.co
>
E-mail Address, TZO Key, and Domain Name
settings of the account you set up with TZO
nter the
9
Page 11
Chapter 3
.
.
ly
.
MAC Address Clone
e
ble
.
.
.
g
T
g
lly ad
.
Advanced Routing (Gateway)
Advanced Routing (Router )
.
g
y
,
)
Internet IP Address The Router’s Internet IP address is
isplayed here. Because it is dynamic, it will change
Status The status of the DDNS service connection is
displayed here.
lick
ave Settingsto apply your changes, or click Cancel
hangesto cancel your changes
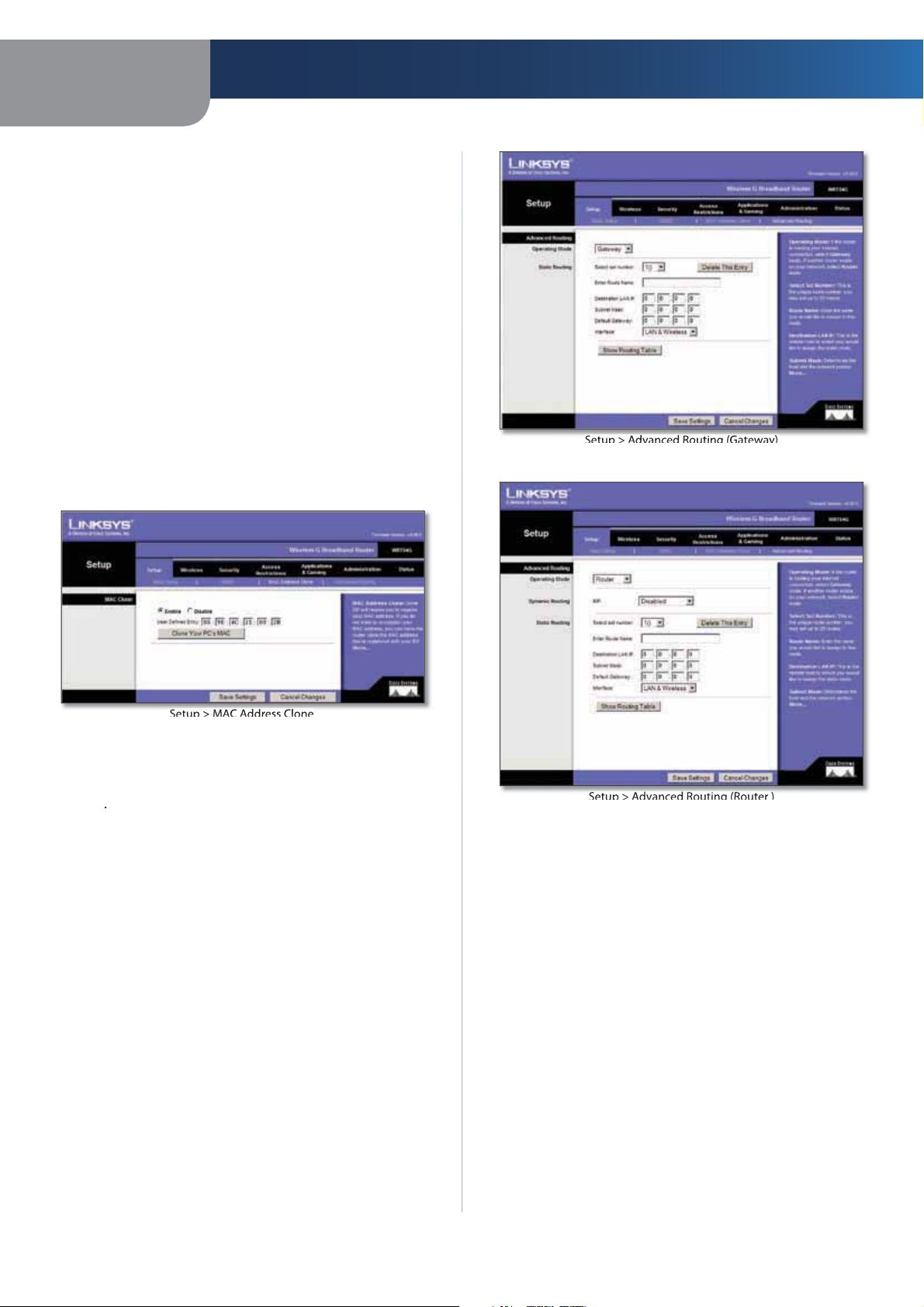
etup > MAC Address Clone
MAC address is a 12-digit code assigned to a unique
iece of hardware for identification. Some ISPs will require
ou to register a MAC address in order to access the
Internet. If you do not wish to re-register the MAC address
with your ISP, you may assign the MAC address you have
current
MAC Address Clone feature
registered with your ISP to the Router with the
Advanced Configuration
>
>
MAC Address Clon
Enable/DisableTo have the MAC Address cloned, select
Ena
User Defined Entry
with your ISP here
Clone Your PC’s MAC
MAC address of the computer you are using
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
nter the MAC Address registered
icking this button will clone the
etup > Advanced Routin
his screen is used to set up the Router’s advanced routin
unctions. NAT routes the host Router ‘s network connection
to the Internet. Dynamic Routing automatica
how packets travel on your network. Static Routing sets
p a fixed route to another network destination
justs
>
Advanced Routing
Operating Mode
will function. If this Router is hosting your network’s
connection to the Internet, select
Router exists on your network, select
Router is chosen,Dynamic Routingwill be available as
n option
ynamic Routin
RIPThis feature enables the Router to automaticall
djust to physical changes in the network’s layout and
exchange routing tables with the other router(s). The
Router determines the network packets’ route based on
the fewest number of hops between the source and the
destination. This feature is Disabled by default. From the
drop-down menu, you can also select
which performs dynamic routing over your Ethernet and
wireless networks. You can also select WAN (Internet
which performs dynamic routing with data coming from
elect the mode in which this Router
ateway. If another
ter When
AN & Wireless
10
Page 12
Chapter 3
.
-
)
.
.
h
.
)
.
l
Table
.
T
k
T
e
T
.
ll
y
e
y
k.
Advanced Configuration
the Internet. Finally, selecting
outing for both networks, as well as data from the
Internet
Select set number To set up a static route between the
Router and another network, select a number from the
tatic Routing drop-down list. (A static route is a pre
determined pathway that network information must travel
to reach a specific host or network.) Enter the information
described below to set up a new static route. (Click the
Delete This Entry button to delete a static route.
Enter Route Name Enter a name for the Route here,
sing a maximum of 25 alphanumeric characters
Destination LAN IPThe Destination LAN IP is the address
of the remote network or host to which you want to assign
static route
Subnet Mask The Subnet Mask determines whic
ortion of a Destination LAN IP address is the network
ortion, and which portion is the host portion.
Default GatewayThis is the IP address of the gateway
device that allows for contact between the Router and the
emote network or host
InterfaceThis interface tells you whether the Destination
IP Address is on the LAN & Wireless (Ethernet and wireless
etworks) or the
Delete This EntryTo delete a route, select its number
rom the drop-down menu, and click this button
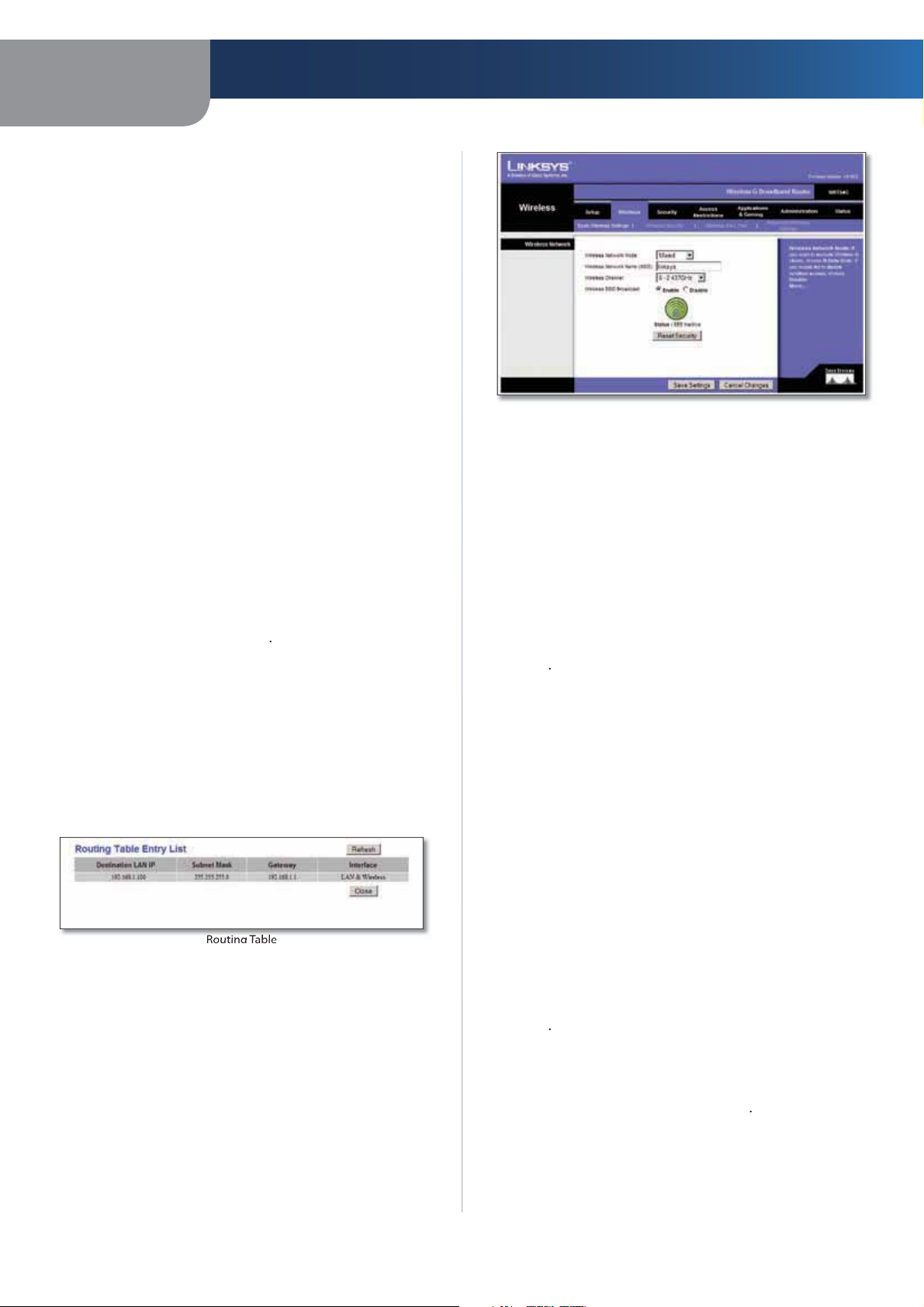
Show Routing Table
screen displaying how data is routed through your loca
etwork. For each route, the Destination LAN IP address,
ubnet Mask, Gateway, and Interface are displayed. Click
Refresh to update the information. Click Close to exit this
Internet
lick Show Routing Table to open
oth enables dynamic
Basic Wireless Settings
Wireless Networ
he basic settings for wireless networking are set on this
Wireless Network Mode From this drop-down menu,
you can select the wireless standards running on your
etwork. If you have both 802.11g and 802.11b devices
n your network, keep the default setting, Mixed If you
have only 802.11g devices, select
only 802.11b devices, select B-Only If you do not have
ny 802.11g and 802.11b devices in your network, select
Disabl
Wireless Network Name (SSID)The SSID is the network
ame shared among all devices in a wireless network.
he SSID must be identical for all devices in the wireless
etwork. It is case-sensitive and must not exceed 32
characters (use any of the characters on the keyboard).
Make sure this setting is the same for all devices in your
wireless network. For added security, you should change
the default SSID (inksys
to a unique name
-Only If you have
Wireless Channel
rovided to correspond with your network settings. A
evices in your wireless network must be broadcast on
the same channel in order to function correctly.
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
Wireless > Basic Wireless Settings
he basic settings for wireless networking are set on this
Wireless SSID Broadcast When wireless clients survey
the local area for wireless networks to associate with, the
will detect the SSID broadcast by the Router. To broadcast
the Router’s SSID, keep the default setting,
o not want to broadcast the Router’s SSID, then select
Disabl
SecureEasySetup If you did not utilize this network
connection feature during the Setup Wizard, you may use
t here by clicking the green logo. When you are prompted
to start the push button setup, click OK
Reset Security Use this button to reset the securit
settings on your network. You will need to run
ecureEasySetup again on each device on your network
to re-associate it to your networ
elect the channel from the list
nable
If you
11
Page 13

Chapter 3
.
y
T
y
”
y
de
d
al
.
Mode > WPA Personal
T
o
)
d
.
h
00
e
T
Mode > WPA Enterprise
T
)
.
2
.
T
.
l
Mode > WPA2 Personal
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
Advanced Configuration
keys. The default Group Key Renewal period is
seconds.
6
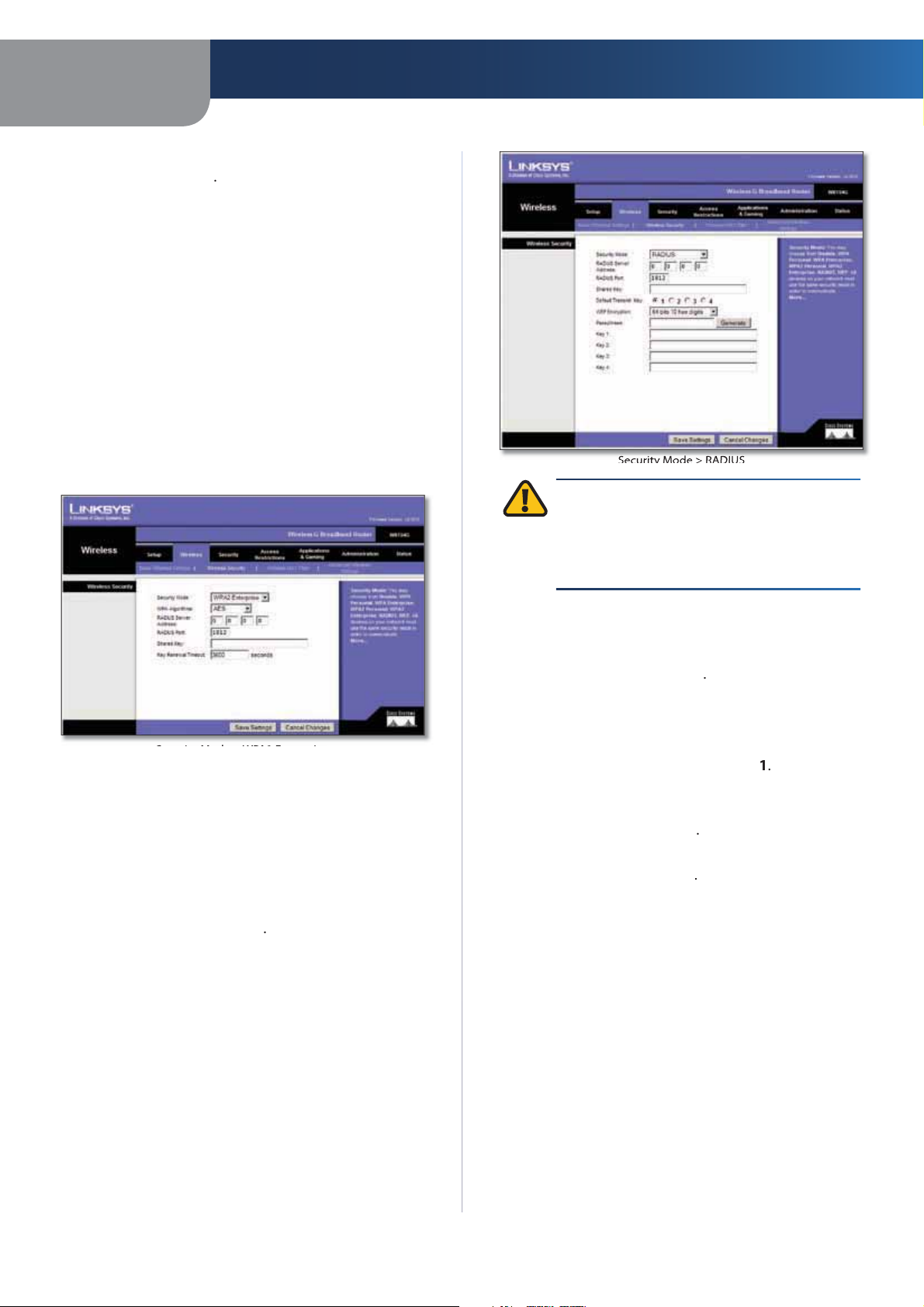
Wireless > Wireless Securit
he Wireless Security settings configure the security of
our wireless network. There are six wireless securit
ode options supported by the Router: WPA Personal,
PA Enterprise, WPA2 Personal, WPA2 Enterprise, RADIUS,
nd WEP. (WPA stands for Wi-Fi Protected Access, which is
security standard stronger than WEP encryption. WPA2
s a more advanced, more secure version of WPA. WEP
stands for Wired Equivalent Privacy, and RADIUS stands
or Remote Authentication Dial-In User Service.) These
six are briefly discussed here. For detailed instructions
on configuring wireless security for the Router, refer to
Chapter 2: Wireless Security.
Wireless Securit
ecurity Mo
elect the security method for your wireless network. If
you do not want to use wireless security, keep the default,
Disable
PA Person
NOTE: If you are using WPA, always remember
that each device in your wireless network MUST
se the same WPA method and shared key, or
else the network will not function properly
A Enterpris
his option features WPA used in coordination with a
RADIUS server. (This should only be used when a RADIUS
server is connected to the Router.)
WPA Algorithm
KIP and AES, with dynamic encryption keys. Select
the type of algorithm,
encryption method than TKIP.
RADIUS Server Address
RADIUS server
RADIUS Port Enter the port number of the RADIUS
server. The default value is
PA supports two encryption m ethods,
KIP or
ES (AES is a stronger
nter the IP Address of the
1
WPA Algorithm WPA supports two encryption methods,
KIP and AES, with dynamic encryption keys. Select
the type of algorithm,
encryption method than TKIP.
WPA Shared Key Enter the key shared by the Router an
your other network devices. It must have 8-63 characters
Group Key Renewal Enter a Key Renewal period, whic
tells the Router how often it should change the encryption
r AES. (AES is a stronger
Shared Key Enter the key shared between the Router
nd the server
Key Renewal Timeout Enter a Key Renewal Timeout
eriod, which instructs the Router how often it should
change the encryption keys. The default Key Renewal
imeout period is
seconds
PA2 Persona
WPA Algorithm WPA2 supports two encryption
ethods, TKIP and AES, with dynamic encryption keys.
12
Page 14
Chapter 3
S
.
.
e
T
)
Mode > WPA2 Enterprise
fau
S
.
2
.
T
.
S
T
)
Mode > RADIUS
.
2
.
y
s
or
fau
e
.
P
Advanced Configuration
elect the type of algorithm, AES or
default selection is AE
WPA Shared Key
characters
Group Key Renewal Enter a Group Key Renewal period,
which instructs the Router how often it should change the
encryption keys. The default Group Key Renewal period is
600seconds
nter a WPA Shared Key of 8-63
AES. The
A2 Enterpris
his option features WPA2 used in coordination with a
RADIUS server. (This should only be used when a RADIUS
server is connected to the Router.
IMPORTANT: If you are using WEP encryption,
lways remember that each device in your
ireless network MUST use the same WEP
encryption method and encryption key, or else
our wireless network will not function properly.
WPA Algorithm WPA2 supports two encryption
ethods, TKIP and AES, with dynamic encryption keys.
elect the type of algorithm, AES or
e
lt selection is AE
RADIUS Server Address
RADIUS server
RADIUS Port Enter the port number of the RADIUS
server. The default value is
Shared Key Enter the key shared between the Router
nd the server
Key Renewal Timeout Enter a Key Renewal Timeout
eriod, which instructs the Router how often it should
change the encryption keys. The default Key Renewal
imeout period is
nter the IP Address of the
1
seconds
KIP+AES. The
RADIUS Server Address
RADIUS server
RADIUS Port Enter the port number of the RADIUS
server. The default value is
Shared Key Enter the key shared between the Router
nd the server
Default Transmit Key Select a Default Transmit Ke
(choose which Key to use). The default is
WEP Encryption
64 bits 10 hex digit
e
lt is
4 bits 10 hex digits
Passphrase
EP keys. Then click
Key 1-4
key(s) manually
you did not enter a Passphrase, enter the WEP
elect a level of WEP encryption,
nter a Passphrase to automatically generate
nter the IP Address of the
81
128 bits 26 hex digits. The
enerat
E
EP is a basic encryption method, which is not as secure
s WPA.
RADIU
his option features WEP used in coordination with a
RADIUS server. (This should only be used when a RADIUS
server is connected to the Router.
13
Page 15
Chapter 3
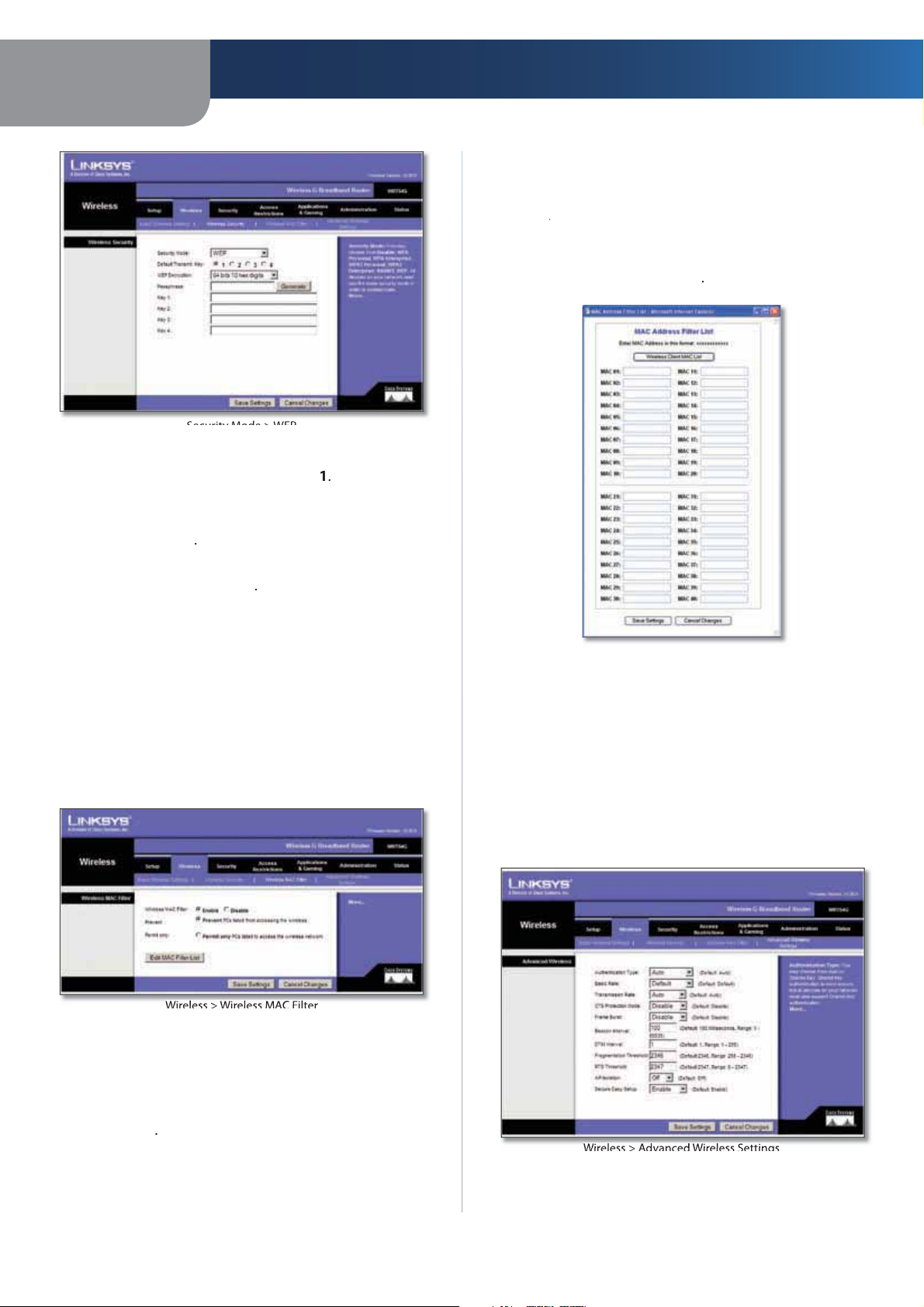
Mode > WEP
s
s
o
s
lly
e
lly.
.
eless
eless
lte
.
Wireless MAC Filter
ess
ter
e
ect this
.
.
ess
t
screen. On this screen, you can list users, by MAC
eless Client
s
Add
Fil
t
l
.
gs
Th
d
.
Advanced Wireless Settings
Advanced Configuration
Default Transmit Key Select a Default Transmit Key
(choose which Key to use). The default is
WEP Encryption
10 hex digit
64 bits 10 hex digit
Passphrase
EP keys. Then click
elect a level of WEP encryption,
r
28 bits 26 hex digits The default is
nter a Passphrase to automatica
enerat
it
generate
Permit Only
Address. This button is not selected by default
Edit MAC Filter List
ilter Lis
ress, to whom you wish to provide or block access. For
easy reference, click Wir
of network users by MAC Addres
elect this to allow wireless access by MAC
lick this to open the MAC Addr
MAC List to display a list
Key 1-4
ey(s) manua
lick
hangesto cancel your changes
Wir
Wireless access can be filtered by using the MAC addresses of
the wireless devices transmitting within your network’s radius
Wirel
f you did not enter a Passphrase, enter the WEP
ave Settingsto apply your changes, or click Cancel
> Wir
MAC Fi
>
r
MAC Fil
ress
ter Lis
Clickave Settingsto apply your changes, or click Cance
hangesto cancel your changes
Wireless > Advanced Wireless Settin
is Wireless > Advanced Wireless Settings screen is use
to set up the Router’s advanced wireless functions. These
settings should only be adjusted by an expert administrator
s incorrect settings can reduce wireless performance
Wireless MAC Filter
ither permitting or blocking access, click Enable If you do
not wish to filter users by MAC Address, keep the default
etting, Disabl
Prevent
Address. This button is selected by default
l
To filter wireless users by MAC Address,
o block wireless access by MAC
>
14
Page 16

Chapter 3
s
fau
.
fault
.
lly
fau
o
ly
.
ble
ble
fau
alu
.
g
oadca
y
T
fau
6
ll
T
f
by default.
o
.
.
ll
The
screen is used to configure a firewall
.
l
Advanced Configuration
Advanced Wireles
Authentication Type The de
llows either Open System or Shared Key authentication
o be used. With
nd the recipient do NOT use a WEP key for authentication.
ith Shared Key authentication, the sender and recipient
se a WEP key for authentication
Basic Rate The Basic Rate setting is not actually one rate
of transmission but a series of rates at which the Router
can transmit. The Router will advertise its Basic Rate to the
other wireless devices in your network, so they know which
ates will be used. The Router will also advertise that it will
utomatically select the best rate for transmission. The
default setting is De
t all standard wireless rates (1-2Mbps, 5.5Mbps, 11Mbps,
8Mbps, and 24Mbps). Other options are
se with older wireless technology, and
Router can transmit at all wireless rates. The Basic Rate
s not the actual rate of data transmission. If you want to
specify the Router’s rate of data transmission, configure
the Transmission Rate setting
Transmission Rate The rate of data transmission should
e set depending on the speed of your wireless network.
You can select from a range of transmission speeds, or you
can select
astest possible data rate and enable the Auto-Fallback
eature. Auto-Fallback will negotiate the best possible
connection speed between the Router and a wireless
client. The de
CTS Protection Mode CTS (Clear-To-Send) Protection
Mode should remain disabled unless you are having severe
roblems with your Wireless-G products not being able
to transmit to the Router in an environment with heavy
802.11b traffic. This function boosts the Router’s ability
to catch all Wireless-G transmissions but will severe
decrease performance
Frame Burst Enabling this option should provide your
etwork with greater performance, depending on the
anufacturer of your wireless products. To turn on the
Frame Burst option, select Ena
pen Systemauthentication, the sender
, when the Router can transmit
utoto have the Router automatica
lt value is
lt is set toAuto, which
-2Mbps for
when the
t
. The default is
use the
isa
hear the beacons and awaken to receive the br
nd multicast messages. The default value is
Fragmentation Threshold This value specifies the
aximum size for a packet before data is fragmented
nto multiple packets. If you experience a high packet
error rate,
hreshold. Setting the Fragmentation Threshold too low
ay result in poor network performance. Only minor
eduction of the de
cases, it should remain at its default value of
RTS Threshold
low, only minor reduction of the default value, 2347, is
ecommended. If a network packet is smaller than the
reset RTS threshold size, the RTS/CTS mechanism wi
ot be enabled. The Router sends Request to Send (RTS)
rames to a particular receiving station and negotiates
the sending of a data frame. After receiving an RTS, the
wireless station responds with a Clear to Send (CTS) frame
to acknowledge the right to begin transmission. The RTS
hreshold value should remain at its default value of
47
AP Isolation This isolates all wireless clients and wireless
devices on your network from each other. Wireless devices
will be able to communicate with the Router but not with
each other. To use this function, select
turned Of
SecureEasySetupThis feature allows you to enable or
disable the SecureEasySetup feature. Select Disabled t
disable the feature and turn off the button’s light. The
eature is Enabledby default
lick
hanges to cancel your changes
ou may slightly increase the Fragmentation
lt value is recommended. In most
4
ould you encounter inconsistent data
AP Isolation is
ave Settingsto apply your changes, or click Cancel
ecurity > Firewa
that can filter out various types of unwanted traffic on the
Router’s local network
st
Beacon IntervalThe de
etween 1 and 65,535 milliseconds. The Beacon Interval
alue indicates the frequency interval of the beacon. A
eacon is a packet broadcast by the Router to synchronize
the wireless network
DTIM Interval This value, between 1 and 255, indicates
the interval of the Delivery Traffic Indication Message
(DTIM). A DTIM field is a countdown field informin
clients of the next window for listening to broadcast
and multicast messages. When the Router has buffered
roadcast or multicast messages for associated clients, it
ends the next DTIM with a DTIM Interval value. Its clients
lt value is
Enter a v
e
Security > Firewal
15
Page 17

Chapter 3
l
ect
s
.
lte
.
T
.
.
h
The
.
VPN Passthrough
V
gh
hod used to
abl
l
.
The
Access Restrictions
ccess
.
Restrictions > Internet Access
s
ete
screen by
elete
o
Advanced Configuration
Firewal
Firewall Protection To use firewall protection, keep the
default selection, Enable. To turn off firewall protection,
l
Disable
ock WAN Request
Block Anonymous Internet Requests This feature
kes it more difficult for outside users to work their
way into your network. This feature is selectedby default.
Deselect the feature to allow anonymous Internet
equests
Filter Multicast
transmissions to specific recipients at the same time. If
ulticasting is permitted, then the Router will allow IP
ulticast packets to be forwarded to the appropriate
computers. This feature is selected by default. Deselect
this feature to disable it
Filter Internet NAT Redirection This feature uses
ort forwarding to block access to local servers from
local networked computers. Select Fi
Redirection to filter Internet NAT redirection. This feature
s not selected by default
ulticasting allows for multiple
r Internet NAT
PPTP Passthrough
(PPTP) allows the Point-to-Point Protocol (PPP) to be
tunneled through an IP network. To allow PPTP tunnels to
ass through the Router, keep the default,
L2TP Passthrough Layer 2 Tunneling Protocol is the
et
Internet on the Layer 2 level. To allow L2TP tunnels to pass
through the Router, keep the default,
Clickave Settingsto apply your changes, or click Cance
hangesto cancel your changes
oint-to-Point Tunneling Protocol
en
e Point-to-Point sessions via the
nable
nable
Access Restrictions > Internet Access
to block or allow specific kinds of Internet usage and
traffic, such as Internet access, designated services, and
websites during specific days and times
> Internet A
screen allows you
Filter IDENT (Port 113)This feature keeps port 113 from
eing scanned by devices outside of your local network.
his feature is selected by default. Deselect this feature to
isable it
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
ecurity > VPN Passthroug
Security > VPN Passthrough screen allows you to enable
VPN tunnels using IPSec, PPTP, or L2TP protocols to pass
hrough the Router’s firewall
>
PN Passthrou
IPSec Passthrough Internet Protocol Security (IPSec) is
suite of protocols used to implement secure exchange
of packets at the IP layer. To allow IPSec tunnels to pass
through the Router, keep the default,
nable
nternet Acces
Internet Access Policy Access can be managed by a
olicy. Use the settings on this screen to establish an
ccess policy (after Save Settings is clicked). Selecting a
olicy from the drop-down menu will display that policy’s
settings. To delete a policy, select that policy’s number
nd click
Policies can be deleted from the
selecting the policy or policies and clicking D
eturn to the Internet Access tab, click Close
l
. To view all the policies, click
ummary
T
16
Page 18

Chapter 3
y
abl
:
drop-
u.
T
.
y
orAllo
s
s
.
k
.
.
s
ces
.
.
T
l
drop-
ge
f
.
Then click
T
T
cklete
s
e
s
d
d
.
d
The
Applications & Gaming > Port Range Forward
scree
nternet Policy Summar
Status
select the policy number from the drop-down menu, and
select
olicies are disabled by default. To enable a policy,
n
e
o create an Internet Access policy
elect a number from the
wn men
o enable this policy, select2
Enter a Policy Name in the field provided.
lick
Edit List of PCs to select which PCs will be affected
y the policy. The
elect a PC by MAC Address or IP Address. You can also
enter a range of IP Addresses if you want this policy
o affect a group of PCs. After making your changes,
clickSave Settings to apply your changes or Cancel
Changes to cancel your changes. Then click Close
ist of PCs screen appears. You can
nable
Advanced Configuration
locked Service
You can filter access to various services accessed over the
Internet, such as FTP or telnet, by selecting services from
the drop-down menus next to Blocked Servi
lock up to 20 services.) Then enter the range of ports you
want to filter
If the service you want to block is not listed or you want to
edit a service’s settings, then click
thePort Servicesscreen will appear
Port Services
o add a service, enter the service’s name in the Service
ame field. Select its protocol from the Protoco
down menu, and enter its range in the
Add
o modify a service, select it from the list on the right.
Change its name, protocol setting, or port range. Then
lickModify
dd/Edit Service. Then
ort Ran
(You can
ields
st of PCs
elect the appropriate option,
depending on whether you want to block or allow
Internet access for the PCs you listed on the List of PC
Decide which days and what times you want this policy
to be enforced. Select the individual days during which
the policy will be in effect, or select
enter a range of hours and minutes during which the
olicy will be in effect, or select
elect any Blocked Services or Website Blocking you
wish to use
Clic
8
Save Settingsto save the policy’s settings, or
clickCancel Changesto cancel the policy’s settings
en
veryday Then
4 Hour
o delete a service, select it from the list on the right. Then
li
hen you are finished making changes on the
ervicesscreen, click
want to cancel your changes, click
Port Services screen and return to the Access Restriction
screen, click
os
pplyto save the changes. If you
ncel To close the
ort
Website Blocking by URL Address
If you want to block websites with specific URL addresses,
w
enter each URL in a separate field next to Website Blocking
URL Addres
Website Blocking by Keywor
If you want to block websites using specific keywords,
enter each keyword in a separate field next to
ocking by Keywor
lick
ave Settingsto apply your changes, or click Cancel
hangesto cancel your changes
ebsite
Applications and Gaming > Port Range
Forwar
n
allows you to set up public services on your network, such as
web servers, ftp servers, e-mail servers, or other specialized
Internet applications. (Specialized Internet applications are
17
Page 19

Chapter 3
)
and Gaming > Port Range Forward
d
To f
.
.
.
h
.
ble
.
.
g
The
.
and Gaming > Port Triggering
g
.
ge
.
.
ect
ppl
.
l
.
T
any applications that use Internet access to perform functions
uch as videoconferencing or online gaming. Some Internet
applications may not require any forwarding.
Port Triggerin
Application
Advanced Configuration
nter the application name of the trigger
Port Range Forwar
orward a port, enter the information on each line for
the criteria required
Application
the application. Each name can be up to 12 characters
Start/End This is the port range. Enter the number that
starts the port range in the Start column and the number
that ends the range in the End column
Protocol Select the protocol used for this application,
eitherTCPor
IP Address
the PC running the specific application
Enable Select Ena
elevant application
lick
ave Settingsto apply your changes, or click Cancel
angesto cancel your changes
n this field, enter the name you wish to give
DP
orot
or each application, enter the IP Address of
to enable port forwarding for the
Applications & Gaming > Port Triggerin
Applications & Gaming > Port Triggeringscreen allows
the Router to watch outgoing data for specific port
umbers. The IP address of the computer that sends the
atching data is remembered by the Router, so that when
the requested data returns through the Router, the data is
ulled back to the proper computer by way of IP address
nd port mapping rules
Triggered Range
For each application, list the triggered port number range.
Check with the Internet application documentation for
the port number(s) needed.
Start Port
Range.
End Port Enter the ending port number of the Triggered
ange.
nter the starting port number of the Triggered
orwarded Ran
For each application, list the forwarded port number
ange. Check with the Internet application documentation
or the port number(s) needed
Start Port
Forwarded Range
End Port Enter the ending port number of the Forwarded
Range.
Enable
icable a
Clickave Settingsto apply your changes, or click Cance
hangesto cancel your changes
nter the starting port number of the
l
Enable to enable port triggering for the
ication
Applications and Gaming > DMZ
he DMZ feature allows one network computer to be
exposed to the Internet for use of a special-purpose
service such as Internet gaming or videoconferencing.
DMZ hosting forwards all the ports at the same time to
one PC. The Port Range Forward feature is more secure
ecause it only opens the ports you want to have opened,
18
Page 20

Chapter 3
and Gaming > DMZ
Z
.
T
ble
ost
ess
.
l
.
y
T
.
.
o
orManual
fro
.
and Gaming > QoS
y
e
y
.
ect
gh
o
.
y
.
lly all
while DMZ hosting opens all the ports of one computer,
exposing the computer to the Internet.
M
ny PC whose port is being forwarded must have its DHCP
client function disabled and should have a new static IP
ress assigned to it because its IP address may change
when using the DHCP function
Advanced Configuration
o expose one PC, select Ena
computer’s IP address in the DMZ H
eature is disabled by default
Clickave Settingsto apply your changes, or click Cance
angesto cancel your changes
. Then, enter the
IP Addr
field. This
Applications and Gaming > QoS
Quality of Service (QoS) ensures better service to
high-priority types of network traffic, which ma
nvolve demanding, real-time applications, such as
videoconferencing.
here are three types of QoS available: Device Priority,
Ethernet Port Priority, and Application Priority
oS
Enable/DisableTo enable QoS, select
elect
isable
QoS is disabled by default
Upstream Bandwidth
the drop-down menu. Manual allows you to specify the
aximum outgoing bandwidth that applications can
tilize
elect Aut
nable
Otherwise,
m
evice Priorit
Enter the name of your network device in the
ield, enter its MAC Address, and then select its priority
rom the drop-down menu.
vice nam
thernet Port Priorit
Ethernet Port Priority QoS allows you to prioritize
erformance for the Router’s four ports, LAN Ports 1-4. For
each port, select the priority and flow control setting
Priority
Router’s four ports have been assigned low priority by
default.
Flow Control If you want the Router to control the
transmission of data between network devices, select
Enabled To disable this feature, select
Port Priority QoS does not require support from your ISP
ecause the prioritized ports LAN ports 1-4 are in your
etwork. This feature is enabled by default
l
Hi
r
w in the Priority column. The
isabled. Ethernet
pplication Priorit
pplication Priority QoS manages information as it is
transmitted and received. Depending on the settings of
theoS screen, this feature will assign information a high
or low priority for the applications that you specify
Optimize Gaming Applications Select this to
utomatica
ow common game application ports
19
Page 21

Chapter 3
ke
s
fau
.
e
f
d.
ect
w
.
S
f
ect
abled
abled
ect
abled
l
.
Th
Administration > Management
screen allows the
.
Management
d
s
.
ect
P
or
fau
P
abl
y.
Rou
.
.
l
.
g
T
Log
Advanced Configuration
to have a higher priority. These games include, but are
ot limited to:
setting is unselected
Application Name Enter the name you wish to give the
pplication in theApplication Nam
Priority
pplication. The default selection is
Specific Port #
lication
ounter-Stri
uake2/uake3, and
l
High or
ow to assign priority to the
nter the port number for the
alf-LifeAge of Empire
iablo II The de
iel
o
Wireless Qo
WMM Support
nown as Wireless Multimedia Extensions (WME), is
Wi-Fi Alliance certified feature, based on the IEEE
802.11e standard. This feature provides QoS to wireless
etworks. It is especially suitable for voice, music and
video applications;
streaming, and interactive gaming. If you have other
evices on your wireless network that support WMM,
l
n
No Acknowledgement This feature prevents the Router
rom re-sending data if an error occurs. To use this feature,
l
En
Disabled
Clickave Settingsto apply your changes, or click Cance
angesto cancel your changes
i-Fi Multimedia (WMM), formerly
or example, Voice over IP (VoIP), video
Otherwise, keep the default, Dis
Otherwise, keep the default setting,
Router Passwor
lt
cal Router Acces
Router Password Enter a new Password for the Router
Re-enter to confirm
nter the Password again to confirm.
Web Access
Access Server
the communications protocol used to connect to servers
on the World Wide Web. HTTPS uses SSL (Secured Socket
Layer) to encrypt data transmitted for higher security.
l
HTT
Wireless Access Web If you are using the Router in
public domain where you are giving wireless access
to your guests, you can disable wireless access to the
Router’s web-based utility. You will only be able to access
the web-based utility via a wired connection if you disable
the setting. Keep the default,
ccess to the Router’s web-based utility, or select
to disable wireless access to the utilit
emote
Remote Management To access the Router remotely,
rom outside the network, select
Management Port Enter the port number that will be
open to outside access. You will need to enter the Router’s
assword when accessing the Router this way, as usual
TTP (HyperText Transport Protocol) is
TTPS. The de
lt selection is HTT
n
e
to enable wireless
ter Access
nable
isable
Administration > Management
e
etwork’s administrator to manage specific Router
unctions for access and security
>
Use httpsTo require the use of HTTPS for remote access,
select this feature
PnP
UPnP
eature; otherwise, select
eep the default, Enableto enable the UPnP
isable
lick
ave Settingsto apply your changes, or click Cance
hangesto cancel your changes
Administration > Lo
he Router can keep logs of all traffic for your Internet
connection.
>
20
Page 22

Chapter 3
g
o
.
l
.
The d
.
Diagnostics
screen. Enter the address
g
t
screen will show if the test was successful. To stop the
.
The Ping T
screen. Enter
screen will show
screen.
The T
t
s
Th
f
s
.
Factory Defaults
T
Advanced Configuration
Log
Log To disable the Log function, keep the default setting,
Disable To monitor traffic between the network and the
Internet, select
hen you wish to view the logs, click
utgoing Log, depending on which you wish to view
Clickave Settingsto apply your changes, or click Cance
hangesto cancel your changes
nable
ncoming Lo
Administration > Diagnostics
iagnostic tests (Ping and Traceroute) allow you to
check the connections of your network components
>
nd click
f the test was successful. To stop the test, click
lear Log to clear the screen. Click
iagnostics
r
raceroute
The
top Click
loseto return to the
raceroute Tes
Administration > Factory Default
e Administration > Factory Defaultsscreen allows you
to restore the Router’s con
settings.
Factory Default
Restore Factory Defaults To reset the Router’s settings
to the default values, select
Settings Any settings you have saved will be lost when
the default settings are restored
iguration to its factory default
es and then click
ave
Ping Test
PingThe Ping test checks the status of a connection.
Clickng to open the
of the PC whose connection you wish to test and how
any times you wish to test it. Then, click
es
test, click
loseto return to the
top Click Clear Log to clear the screen. Click
iagnostics screen
est
ing The
in
raceroute Test
>
Administration > Upgrade Firmware
heAdministration > UpgradeFirmwarecreen allows you
o upgrade the Router’s firmware. Do not upgrade the
firmware unless you are experiencing problems with the
outer or the new firmware has a feature you want to use.
TracerouteTo test the performance of a connection,
clickracerouteto open the
the address of the PC whose connection you wish to test
21
Page 23

Chapter 3
Upgrade Firmware
.
.
e
de
.
Th
.
Config Management
T
p
T
.
n
e
r
The
outer
screen displays the Router’s current
Router
n
.
b.
.
b.
t
e
T
screen.
esh
.
Th
k
screen displays the status of
Advanced Configuration
>
Before upgrading the firmware, download the Router’s
irmware upgrade file from the Linksys website, www
linksys.com. Then extract the file
Upgrade Firmwar
Please select a file to upgrade
the extracted firmware upgrade file. Then cickpgra
nd follow the on-screen instructions
ickrowse and select
Administration > Config Management
is screen is used to back up or restore the Router’s
configuration file
>
Router Informatio
Firmware Version This is the Router’s current firmware
Current Time This shows the time, as you set on the
etup tab.
MAC Address This is the Router’s MAC Address, as seen
your ISP.
Router Name This is the specific name for the Router,
which you set on the Setup ta
Host Name
entered on the Setup tab
Domain Name If required by your ISP, this would have
een entered on the Setup ta
required by your ISP, this would have been
>
Backup Configuration
o back up the Router’s configuration file, click Backu
hen follow the on-screen instructions
Restore Configuratio
Please select a file to restore
the configuration file. Then click
lickrowseand select
estor
tatus > Route
> R
status.
Interne
Configuration Typ
his section shows the current network information
stored in the Router. The information varies depending on
the Internet connection type selected on the Setup > Basic
etup
lick Refr
to update the on-screen information
tatus > Local Network
e Status > Local Networ
your network.
22
Page 24

Chapter 3
Local Network
.
k.
g
.
.
.
e
button.
Clients Tabl
.
Th
.
Wireless
.
-
.
.
ess
ess
.
ess
screen, this displays the status of the
.
.
Advanced Configuration
tatus > Wireless
e Status > Wirelessscreen displays the status of your
wireless network
>
Local Network
MAC Address This is the Router’s MAC Address, as seen
on your local, Ethernet network
IP Address This shows the Router’s IP Address, as it
ppears on your local, Ethernet networ
Subnet Mask This shows the current subnet mask bein
configured for your local network
DHCP Server If you are using the Router as a DHCP server,
that will be displayed here
Start IP Address
devices on your local, Ethernet network, the beginning of
that range is shown here
End IP Address
devices on your local, Ethernet network, the end of that
ange is shown here.
DHCP Clients Table Clicking this button will open a
screen to show you which PCs are utilizing the Router as a
DHCP server. You can delete PCs from that list, and sever
their connections, by checking a
theelet
or the range of IP Addresses used by
or the range of IP Addresses used by
elete box and clicking
>
Wireless
MAC Address This is the Router’s MAC Address, as seen
on your local, wireless network
Mode As selected from the Wireless > Basic Wireless
ettings screen, this displays the wireless mode (Mixed, G
Only, or Disabled) used by the network
SSID As entered on the
screen, this displays the wireless network name or SSID
DHCP Server The status of the DHCP server function is
isplayed here.
Channel
Settings screen, this displays the channel on which your
wireless network is broadcasting
Encryption Function As selected on the
outer’s wireless security
Click
s entered on the Wirel
efresh to update the on-screen information
ireless > Basic Wireless Settings
> Basic Wirel
irel
>
ClickRefreshto update the on-screen information
e
23
Page 25

Chapter 3
Advanced Configuration
24
Page 26

Appendix A
y
:
g.
ld
.
.
T
p
.
.
y
lly.
.
Th
d
.
.
):
ect
.
ect
ection.
T
.
.
y
.
68.1.1
.
m
Troubleshooting
ppendix A:
Troubleshooting
our computer cannot connect to the Internet.
Follow these instructions until
to the Internet
Make sure that the Router is powered on. The Power
LED should be green and not flashin
If the Power LED is flashing, then power off all of
our network devices, including the modem, Router,
nd computers. Then power on each device in the
ollowing order:
Cable or DSL modem
ter
Computer
Check the cable connections. The computer shou
e connected to one of the ports numbered 1-4 on
the Router, and the modem must be connected to the
Internet port on the Router
The modem does not have an Ethernet port
he modem is a dial-up modem for traditional dial-u
service. To use the Router, you need a cable/DSL modem
nd high-speed Internet connection
ou cannot use the DSL service to connect manually to
the Internet
ter you have installed the Router, it will automaticall
connect to your Internet Service Provider (ISP), so you no
onger need to connect manua
our computer can connect
When you double-click the web browser, you are
prompted for a username and password. If you want to
et rid of the prompt, follow these instructions
Launch the web browser and perform the following steps
(these steps are specific to Internet Explorer but are similar
or other browsers
l
Tools
ick the2
l
lick
The Router does not have a coaxial port for the cable
nn
he Router does not replace your modem. You still need
our cable modem in order to use the Router. Connect
our cable connection to the cable modem, and then
nsert the setup CD into your computer. Click Setup and
ollow the on
The computer cannot connect wirelessly to the network
Make sure the wireless network name or SSID is the same
on both the computer and the Router. If you have enabled
wireless security, then make sure the same securit
ethod and key are used by both the computer and the
Router.
ou need to modify the settings on the Router
Open the web browser (for example, Internet Explorer or
Firefox), and enter the Router’s IP address in the address
ield (the default IP address is
rompted, enter the password to the Router (the default is
admin). Click the appropriate tab to change the settings
Internet Options
onnections tab.
ever dial a connection
creen instructions
1
. When
The DSL telephone line does not t into the Router’s
nternet port
e Router does not replace your modem. You still nee
our DSL modem in order to use the Router. Connect the
telephone line to the DSL modem, and then insert the
setup CD into your computer. Click
screen instructions
etup and follow the
WEB: If your questions are not addressed here,
refer to the Linksys website,
ww.linksys.co
25
Page 27

Appendix B
l
G
ds
)
t
p
e
5
p
t
m
s
y
y
g
s
”
)
ht
)
r
A
M
.
)
)
g
y
g
ppendix B:
ecifications
Specifications
Mode
tandar
Channels
Ports Internet: One 10/100 RJ-45 Port
tton Reset, SecureEasySetu
Cabling Typ
LEDs Power, DMZ, WLAN, LAN (1-4),
RF Power Outpu
UPnP able/cert
ecurity Feature
ireless Securit
RT54
1 Channels (US, Canada)
3 Channels (Europe, Japan
LAN: Four 10/100 RJ-45 Switched
Ports
ne Power Por
AT
Internet, SecureEasySetu
8
B
tateful Packet Inspection (SPI)
Firewall, Internet Polic
i-Fi Protected Access™2 (WPA2),
EP, Wireless MAC Filterin
Environmental
Dimension
eig
Powe
Certifications FCC, IC-03, CE, Wi-Fi (802.11b,
perating Temp
torage Temp. -4 to 158ºF (-20 to 70ºC
Operating Humidity0 to 85%, Noncondensin
torage Humidit
7.32” x 1.89” x 6.06
186 x 48 x 154 mm
1.2 oz (317 g
External, 12V DC, 0.5
802.11g), WPA2, WM
2 to 104ºF (0 to 40ºC
to 90%, Noncondensin
Specifications are subject to change without notice.
26
Page 28

Appendix C
y
:
t
t
T
dy
y
.
s
T
.
T
f
y
TO
,
,
by
j
.
T
T
O
T
y
.
e
ypp
T
y
T
Warranty Information
ppendix C:
Warranty Information
Limited Warrant
Linksys warrants this Linksys hardware product against
defects in materials and workmanship under normal
se for the Warranty Period, which begins on the date of
urchase by the original end-user purchaser and lasts for
the period specified below
One (1) year for new produc
Ninety (90) days for refurbished produc
his limited warranty is non-transferable and extends only
to the original end-user purchaser. Your exclusive reme
nd Linksys’ entire liability under this limited warrant
will be for Linksys, at its option, to (a) repair the product
with new or refurbished parts, (b) replace the product
with a reasonably available equivalent new or refurbished
Linksys product, or (c) refund the purchase price of the
roduct less any rebates. Any repaired or replacement
roducts will be warranted for the remainder of the
original Warranty Period or thirty (30) days, whichever is
onger. All products and parts that are replaced become
the property of Linksys
Exclusions and Limitation
his limited warranty does not apply if: (a) the product
ssembly seal has been removed or damaged, (b) the
roduct has been altered or modified, except by Linksys, (c)
the product damage was caused by use with non-Linksys
roducts, (d) the product has not been installed, operated,
epaired, or maintained in accordance with instructions
supplied by Linksys, (e) the product has been subjected to
bnormal physical or electrical stress, misuse, negligence,
or accident, (f) the serial number on the Product has been
ltered, defaced, or removed, or (g) the product is supplied
or licensed for beta, evaluation, testing or demonstration
urposes for which Linksys does not charge a purchase
rice or license fee
LL SOFTWARE PROVIDED BY LINKSYS WITH THE
PRODUCT, WHETHER FACTORY LOADED ON THE
PRODUCT OR CONTAINED ON MEDIA ACCOMPANYING
HE PRODUCT, IS PROVIDED “AS IS” WITHOUT WARRANTY
OF ANY KIND. Without limiting the
ot warrant that the operation of the product or software
will be uninterrupted or error free. Also, due to the
continual development of new techniques for intruding
pon and attacking networks, Linksys does not warrant
that the product, software or any equipment, system or
etwork on which the product or software is used will be
ree of vulnerability to intrusion or attack. The product
ay include or be bundled with third party software or
oregoing, Linksys does
service offerings. This limited warranty shall not apply to
such third party software or service offerings. This limited
warranty does not guarantee any continued availabilit
of a third party’s service for which this product’s use or
operation may require.
THE EXTENT NOT PROHIBITED BY LAW, ALL IMPLIED
ARRANTIES AND CONDITIONS OF MERCHANTABILITY
ATISFACTORY QUALITY OR FITNESS FOR A PARTICULAR
PURPOSE ARE LIMITED TO THE DURATION OF THE
ARRANTY PERIOD. ALL OTHER EXPRESS OR IMPLIED
CONDITIONS, REPRESENTATIONS AND WARRANTIES
INCLUDING, BUT NOT LIMITED TO, ANY IMPLIED
ARRANTY OF NON-INFRINGEMENT, ARE DISCLAIMED.
ome jurisdictions do not allow limitations on how long
n implied warranty lasts, so the above limitation may not
pply to you. This limited warranty gives you specific legal
ights, and you may also have other rights which vary
urisdiction
O THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT
ILL LINKSYS BE LIABLE FOR ANY LOST DATA, REVENUE
R PROFIT, OR FOR SPECIAL, INDIRECT, CONSEQUENTIAL,
INCIDENTAL OR PUNITIVE DAMAGES, REGARDLESS OF THE
HEORY OF LIABILITY (INCLUDING NEGLIGENCE), ARISING
T OF OR RELATED TO THE USE OF OR INABILITY T
USE THE PRODUCT (INCLUDING ANY SOFTWARE), EVEN
IF LINKSYS HAS BEEN ADVISED OF THE POSSIBILITY OF
CH DAMAGES. IN NO EVENT WILL LINKSYS’ LIABILITY
EXCEED THE AMOUNT PAID BY YOU FOR THE PRODUCT.
he foregoing limitations will apply even if any warrant
or remedy provided under this limited warranty fails of
ts essential purpose. Some jurisdictions do not allow
the exclusion or limitation of incidental or consequential
damages, so the above limitation or exclusion may not
pply to you
taining Warranty Servic
If you have a question about your product or experience a
roblem with it, please go to
where you will find a variety of online support tools and
nformation to assist you with your product. If the product
roves defective during the Warranty Period, contact
Linksys Technical Support for instructions on how to
obtain warranty service. The telephone number for Linksys
echnical Support in your area can be found in the product
ser Guide and at
serial number and proof of purchase on hand when calling.
DATED PROOF OF ORIGINAL PURCHASE IS REQUIRED
O PROCESS WARRANTY CLAIMS. If you are requested to
eturn your product, you will be given a Return Materials
uthorization (RMA) number. You are responsible for
roperly packaging and shipping your product to Linksys
t your cost and risk. You must include the RMA number
nd a copy of your dated proof of original purchase when
eturning your product. Products received without a RMA
umber and dated proof of original purchase will be
. Have your product
27
Page 29

Appendix C
ll
.
t
T
ypp
T
j
.
.
ejected. Do not include any other items with the product
ou are returning to Linksys. Defective product covered
this limited warranty will be repaired or replaced and
eturned to you without charge. Customers outside of
the United States of America and Canada are responsible
or all shipping and handling charges, custom duties,
VAT and other associated taxes and charges. Repairs or
eplacements not covered under this limited warranty wi
e subject to charge at Linksys’ then-current rates
echnical Suppor
his limited warranty is neither a service nor a support
contract. Information about Linksys’ current technical
support offerings and policies (including any fees for
support services) can be found at:
his limited warranty is governed by the laws of the
urisdiction in which the Product was purchased by you
Please direct all inquiries to: Linksys, P.O. Box 18558, Irvine,
A 92623
Warranty Information
28
Page 30

Appendix D
t
T
T
.
Th
y
.
y
:
a
s
e
y
.
T
h
Th
.
s
.
l.
T
.
g.
Th
003 and
0.
:
T
d
T
.
h
.
T
:
Th
.
Th
.
Regulatory Information
ppendix D:
S Regulatory Information
FCC Statemen
his device complies with Part 15 of the FCC Rules.
Operation is subject to the following two conditions: (1)
his device may not cause harmful interference, and (2) this
device must accept any interference received, including
nterference that may cause undesired operation
is product has been tested and complies with the
specifications for a Class B digital device, pursuant to Part
5 of the FCC Rules. These limits are designed to provide
easonable protection against harmful interference in
residential installation. This equipment generates,
ses, and can radiate radio frequency energy and, if not
nstalled and used according to the instructions, ma
cause harmful interference to radio communications
However, there is no guarantee that interference will not
occur in a particular installation. If this equipment does
cause harmful interference to radio or television reception,
which is found by turning the equipment off and on, the
ser is encouraged to try to correct the interference b
one or more of the following measures
Reorient or relocate the receiving antenn
Increase the separation between the equipment or
evice
Connect the equipment to an outlet other than the
eceiver’s
Consult a dealer or an experienced radio/TV technician
or assistanc
FCC Caution: Any changes or modifications not expressl
pproved by the party responsible for compliance could
void the user’s authority to operate this equipment
FCC Radiation Exposure Statement
his equipment complies with FCC radiation exposure
limits set forth for an uncontrolled environment. This
equipment should be installed and operated wit
inimum distance 20cm between the radiator and your
ody.
afety Notice
Caution: To reduce the risk of fire, use only No.26 AWG
or larger telecommunication line cord
Do not use this product near water, for example, in a
wet basement or near a swimming poo
void using this product during an electrical storm.
here may be a remote risk of electric shock from
ightning
WARNING: This product contains lead, known
to the State of California to cause cancer, and
irth defects or other reproductive harm. Wash
hands after handlin
Industry Canada Statement
is Class B digital apparatus complies with Canadian
ICES-
Operation is subject to the following two conditions
his device may not cause interference an
his device must accept any interference, including2
nterference that may cause undesired operation of the
evice. This device has been designed to operate wit
n antenna having a maximum gain of 2dBi. Antenna
having a higher gain is strictly prohibited per regulations
of Industry Canada. The required antenna impedance
s 50 ohms
o reduce potential radio interference to other users,
the antenna type and its gain should be so chosen
that the EIRP is not more than required for successful
communication.
Industry Canada Radiation Exposure Statement
is equipment complies with IC radiation exposure limits
set forth for an uncontrolled environment. This equipment
should be installed and operated with minimum distance
20cm between the radiator & your body
is transmitter must not be co-located or operating in
conjunction with any other antenna or transmitter
RSS21
is transmitter must not be co-located or operating in
conjunction with any other antenna or transmitter. IEEE
802.11b or 802.11g operation of this product in the USA is
irmware-limited to channels 1 through 11
Footer
29
Page 31

Appendix D
003
ada.
:
.
:
r
T
.
.
Regulatory Information
Avis d’Industrie Canada
Cet appareil numérique de la classe B est conforme aux
rmes NMB-
L’utilisation de ce dispositif est autorisée seulement aux
conditions suivantes
l ne doit pas produire de brouillage et
l doit accepter tout brouillage radioélectrique reçu,
ême si ce brouillage est susceptible de compromettre
le fonctionnement du dispositif. Le dispositif a été
conçu pour fonctionner avec une antenne ayant un gain
aximum de 2 dBi. Les règlements d’Industrie Canada
nterdisent strictement l’utilisation d’antennes dont le
gain est supérieur à cette limite. L’impédance requise
e l’antenne est de 50 ohms.
in de réduire le risque d’interférence aux autres
tilisateurs, le type d’antenne et son gain doivent
être choisis de façon à ce que la puissance isotrope
ayonnée équivalente (p.i.r.e.) ne soit pas supérieure
u niveau requis pour obtenir une communication
satisfaisante
Avis d’Industrie Canada concernant l’exposition
ux radiofréquences
et RSS210 du Can
Avis de non-responsabilité concernant les
ppareils sans fil
Les performances maximales pour les réseaux sans fil
sont tirées des spécifications de la norme IEEE 802.11.
Les performances réelles peuvent varier, notamment
en fonction de la capacité du réseau sans fil, du débit
de la transmission de données, de la portée et de la
couverture. Les performances dépendent de facteurs,
conditions et variables multiples, en particulier de la
distance par rapport au point d’accès, du volume du trafic
éseau, des matériaux utilisés dans le bâtiment et du
type de construction, du système d’exploitation et de la
combinaison de produits sans fil utilisés, des interférences
et de toute autre condition défavorable
Ce matériel est conforme aux limites établies par IC
en matière d’exposition aux radiofréquences dans un
environnement non contrôlé. Ce matériel doit être installé
et utilisé à une distance d’au moins 20 cm entre l’antenne
et le corps de l’utilisateur.
L’émetteur ne doit pas être placé près d’une autre antenne
ou d’un autre émetteur, ou fonctionner avec une autre
ntenne ou un autre émetteur.
Wireless Disclaime
he maximum performance for wireless is derived from
IEEE Standard 802.11 specifications. Actual performance
can vary, including lower wireless network capacity,
data throughput rate, range and coverage. Performance
depends on many factors, conditions and variables,
ncluding distance from the access point, volume of
etwork traffic, building materials and construction,
operating system used, mix of wireless products used,
nterference and other adverse conditions
Footer
30
Page 32

Appendix D
)
T
:
)
e
U
ff
lek
n
Regulatory Information
User Information for Consumer Products
Covered by EU Directive 2002/96/EC on
Waste Electric and Electronic Equipment
WEEE
his document contains important information for users
with regards to the proper disposal and recycling of
Linksys products. Consumers are required to comply with
this notice for all electronic products bearing the following
symbol
English - Environmental Information for Customers in
he European Union
European Directive 2002/96/EC requires that the equipment
bearing this symbol on the product and/or its packaging must
ot be disposed of with unsorted municipal waste. The symbol
ndicates that this product should be disposed of separately
rom regular household waste streams. It is your responsibility to
ispose of this and other electric and electronic equipment via
esignated collection facilities appointed by the government or
ocal authorities. Correct disposal and recycling will help prevent
otential negative consequences to the environment and
uman health. For more detailed information about the disposal
f your old equipment, please contact your local authorities,
aste disposal service, or the shop where you purchased the
roduct.
Български (Bulgarian) - Информация относно
пазването на околната среда за потребители в
Европейския съюз
Европейска директива 2002/96/EC изисква уредите, носещи
този символ върху изделието и/или опаковката му, да не
се изхвърля т с несортирани битови отпадъци. Символът
обозначава, че изделието трябва да се изхвърля отделно от
сметосъбирането на обикновените битови отпадъци. Ваша
е отговорността този и другите електрически и електронни
реди да се изхвърлят в предварително определени от
държавните или общински органи специализирани пунктове
за събиране. Правилното изхвърляне и рециклиране
ще спомогнат да се предотвратят евентуални вредни за
околната среда и здравето на населението последствия. За
по-подробна информация относно изхвърлянето на вашите
стари уреди се обърнете към местните власти, службите за
сметосъбиране или магазина, от който сте закупили уреда.
eština (Czech
nformace o ochraně životního
prostředí pro zákazníky v zemích Evropské uni
Evropská směrnice 2002/96/ES zakazuje, aby zařízení označené
tímto symbolem na produktu anebo na obalu bylo likvidováno
netříděným komunálním odpadem. Tento symbol udává,
e daný produkt musí být likvidován odděleně od běžného
omunálního odpadu. Odpovídáte za likvidaci tohoto produktu
dalších elektrických a elektronických zařízení prostřednictvím
rčených sběrných míst stanovených vládou nebo místními
řady. Správná likvidace a recyklace pomáhá předcházet
otenciálním negativním dopadům na životní prostředí a lidské
draví. Podrobnější informace o likvidaci starého vybavení si
askavě vyžádejte od místních úřadů, podniku zabývajícího se
ikvidací komunálních odpadů nebo obchodu, kde jste produkt
akoupili.
Dansk (Danish) - Miljøinformation for kunder i E
EU-direktiv 2002/96/EF kræver, at udstyr der bærer dette symbol
på produktet og/eller emballagen ikke må bortskaffes som
usorteret kommunalt a
skal bortskaffes adskilt fra det almindelige husholdningsaffald.
Det er dit ansvar at bortskaffe dette og andet elektrisk og
tronisk udstyr via bestemte indsamlingssteder udpeget
e
af staten eller de lokale myndigheder. Korrekt bortskaffelse
og genvinding vil hjælpe med til at undgå mulige skader for
miljøet og menneskers sundhed. Kontakt venligst de lokale
myndigheder, renovationstjenesten eller den butik, hvor du
har købt produktet, angående mere detaljeret information om
bortskaffelse af dit gamle udstyr.
ald. Symbolet betyder, at dette produkt
Deutsch (German) - Umweltinformation für Kunden
innerhalb der Europäischen Unio
Die Europäische Richtlinie 2002/96/EC verlangt, dass technische
Ausrüstung, die direkt am Gerät und/oder an der Verpackung mit
iesem Symbol versehen ist
emeindeabfall entsorgt werden darf. Das Symbol weist darauf
in, dass das Produkt von regulärem Haushaltmüll getrennt
ntsorgt werden sollte. Es liegt in Ihrer Verantwortung, dieses
erät und andere elektrische und elektronische Geräte über
ie dafür zuständigen und von der Regierung oder örtlichen
ehörden dazu bestimmten Sammelstellen zu entsorgen.
rdnungsgemäßes Entsorgen und Recyceln trägt dazu bei,
otentielle negative Folgen für Umwelt und die menschliche
esundheit zu vermeiden. Wenn Sie weitere Informationen zur
ntsorgung Ihrer Altgeräte benötigen, wenden Sie sich bitte an
ie örtlichen Behörden oder städtischen Entsorgungsdienste
er an den Händler, bei dem Sie das Produkt erworben haben.
nicht zusammen mit unsortiertem
Footer
31
Page 33

Appendix D
le
bol
l
f
i
a
q
ada sob
ης
τ
ηψη
e
ball
bol
l
f
.
a
ā
Regulatory Information
Eesti (Estonian) - Keskkonnaalane informatsioon
Euroopa Liidus asuvatele klientide
Euroopa Liidu direktiivi 2002/96/EÜ nõuete kohaselt on
seadmeid, millel on tootel või pakendil käesolev sümbol
eelatud kõrvaldada koos sorteerimata olmejäätmetega. See
näitab, et toode tuleks kõrvaldada eraldi tavalistest
süm
olmejäätmevoogudest. Olete kohustatud kõrvaldama käesoleva
ja ka muud elektri- ja elektroonikaseadmed riigi või kohalike
ametiasutuste poolt ette nähtud kogumispunktide kaudu.
Seadmete korrektne kõrvaldamine ja ringlussevõtt aitab vältida
võimalikke negatiivseid tagajärgi keskkonnale ning inimeste
e. Vanade seadmete kõrvaldamise kohta täpsema
tervise
in
ormatsiooni saamiseks võtke palun ühendust kohalike
ametiasutustega, jäätmekäitlusfirmaga või kauplusega, kust te
toote osts
te.
Español (Spanish) - Información medioambiental para
lientes de la Unión Europe
La Directiva 2002/96/CE de la UE exige que los equipos que
lleven este símbolo en el propio aparato y/o en su embalaje
no deben eliminarse junto con otros residuos urbanos no
seleccionados. El símbolo indica
debe separarse de los residuos domésticos convencionales con
vistas a su eliminación. Es responsabilidad suya desechar este y
cualesquiera otros aparatos eléctricos y electrónicos a través de
los puntos de recogida que ponen a su disposición el gobierno y
las autoridades locales. Al desechar y reciclar correctamente estos
aparatos estará contribuyendo a evitar posibles consecuencias
negativas para el medio ambiente y la salud de las personas. Si
esea obtener información más detall
segura de su aparato usado, consulte a las autoridades locales,
al servicio de recogida y eliminación de residuos de su zona o
pregunte en la tienda donde adquirió el producto.
ue el producto en cuestión
re la eliminación
λληνικά (Greek) - Στοιχεία περιβαλλοντικής
προστασίας για πελάτες εντός της Ευρωπαϊκής
Ένωσ
Η Κοινοτική Οδηγία 2002/96/EC απαιτεί ότι ο εξοπλισμός ο οποίος
έρει αυτό το σύμβολο στο προϊόν και/ή στη συσκευασία
ου δεν πρέπει να απορρίπτεται μαζί με τα μικτά κοινοτικά
πορρίμματα. Το σύμβολο υποδεικνύει ότι αυτό το προϊόν θα
ρέπει να απορρίπτεται ξεχωριστά από τα συνήθη οικιακά
πορρίμματα. Είστε υπεύθυνος για την απόρριψη του παρόντος
αι άλλου ηλεκτρικού και ηλεκτρονικού εξοπλισμού μέσω των
αθορισμένων εγκαταστάσεων συγκέντρωσης απορριμμάτων οι
ποίες παρέχονται από το κράτος ή τις αρμόδιες τοπικές αρχές.
σωστή απόρριψη και ανακύκλωση συμβάλλει στην πρόλ
ιθανών αρνητικών συνεπειών για το περιβάλλον και την υγεία.
ια περισσότερες πληροφορίες σχετικά με την απόρριψη του
αλιού σας εξοπλισμού, παρακαλώ επικοινωνήστε με τις τοπικές
ρχές, τις υπηρεσίες απόρριψης ή το κατάστημα από το οποίο
οράσατε το προϊόν.
Français (French) - Informations environnementales
pour les clients de l’Union européenn
La directive européenne 2002/96/CE exige que l’équipement
sur lequel est apposé ce symbole sur le produit et/ou son
age ne soit pas jeté avec les autres ordures ménagères. Ce
em
sym
e indique que le produit doit être éliminé dans un circuit
istinct de celui pour les déchets des ménages. Il est de votre
responsabilité de jeter ce matériel ainsi que tout autre matériel
ectrique ou électronique par les moyens de collecte indiqués
é
par le gouvernement et les pouvoirs publics des collectivités
territoriales. L’élimination et le recyclage en bonne et due forme
ont pour but de lutter contre l’impact néfaste potentiel de ce
type de produits sur l’environnement et la santé publique. Pour
plus d’in
équipement, veuillez prendre contact avec les pouvoirs publics
ocaux, le service de traitement des déchets, ou l’e ndroit où vous
avez acheté le produit
ormations sur le mode d’élimination de votre ancien
Italiano (Italian) - Informazioni relative all’ambiente
er i clienti residenti nell’Unione Europe
La direttiva europea 2002/96/EC richiede che le apparecchiature
contrassegnate con questo simbolo sul prodotto e/o
ull’imballaggio non siano smaltite insieme ai rifiuti urbani
on differenziati. Il simbolo indica che questo prodotto non
eve essere smaltito insieme ai normali rifiuti domestici. È
esponsabilità del proprietario smaltire sia questi prodotti sia
e altre apparecchiature elettriche ed elettroniche mediante
e specifiche strutture di raccolta indicate dal governo o dagli
nti pubblici locali. Il corretto smaltimento ed il riciclaggio
iuteranno a prevenire conseguenze potenzialmente negative
er l’ambiente e per la salute dell’essere umano. Per ricevere
nformazioni più dettagliate circa lo smaltimento delle vecchie
pparecchiature in Vostro possesso, Vi invitiamo a contattare gli
nti pubblici di competenza, il servizio di smaltimento rifiuti o il
egozio nel quale avete acquistato il prodotto.
Latviešu valoda (Latvian) - Ekoloģiska informācija
lientiem Eiropas Savienības jurisdikcij
Direktīvā 2002/96/EK ir prasība, ka aprīkojumu, kam pievienota
zīme uz paša izstrādājuma vai uz tā iesaiņojuma, nedrīkst
zmest nešķirotā veidā kopā ar komunālajiem atkritumiem
tiem, ko rada vietēji iedzīvotāji un uzņēmumi). Šī zīme nozīmē
o, ka šī ierīce ir jāizmet atkritumos tā, lai tā nenonāktu kopā ar
arastiem mājsaimniecības atkritumiem. Jūsu pienākums ir šo
n citas elektriskas un elektroniskas ierīces izmest atkritumos,
zmantojot īpašus atkritumu savākšanas veidus un līdzekļus, ko
odrošina valsts un pašvaldību iestādes. Ja izmešana atkritumos
n pārstrāde tiek veikta pareizi, tad mazinās iespējamais
aitējums dabai un cilvēku veselībai. Sīkākas ziņas par
ovecojuša aprīkojuma izmešanu atkritumos jūs varat saņemt
ietējā pašvaldībā, atkritumu savākšanas dienestā, kā arī veikalā,
ur iegādājāties šo izstrādājumu.
Footer
32
Page 34

Appendix D
s
l
Š
k
a
j
a
Ö
l
e
d
f
f
f af
U
f
duk
y
odo
ka
b
Regulatory Information
Lietuvškai (Lithuanian) - Aplinkosaugos informacija,
irta Europos Sąjungos vartotojam
Europos direktyva 2002/96/EC numato, kad įrangos, kuri ir
urios pakuotė yra pažymėta šiuo simboliu (įveskite simbolį),
ima šalinti kartu su nerūšiuotomis komunalinėmis
nega
atliekomis.
nuo bendro buitinių atliekų srauto. Jūs privalote užtikrinti, kad
ši ir kita elektros ar elektroninė įranga būtų šalinama per tam
ras nacionalinės ar vietinės valdžios nustatytas atliekų rinkimo
ti
sistemas. Tinkamai šalinant ir perdirbant atliekas, bus išvengta
galimos žalos aplinkai ir žmonių sveikatai. Daugiau informacijos
apie jūsų senos įrangos šalinimą gali pateikti vietinės valdžios
institucijos, atliekų šalinimo tarnybos arba parduotuvės, kuriose
sigijote tą gaminį.
is simbolis rodo, kad gaminį reikia šalinti atskirai
alti (Maltese) - Informazzjoni Ambjentali għal Klijenti
l-Unjoni Ewrope
Id-Direttiva Ewropea 2002/96/KE titlob li t-tagħmir li jkun fih issimbolufuq il-prodott u/jew fuq l-ippakkjar ma jistax jintrema
a’ skart muniċipali li ma ġiex isseparat. Is-simbolu jindika
i dan il-prodott għandu jintrema separatament minn ma’ lskart domestiku regolari. Hija responsabbiltà tiegħek li tarmi
an it-tagħmir u kull tagħmir ieħor ta’ l-elettriku u elettroniku
ermezz ta’ faċilitajiet ta’ ġbir appuntati apposta mill-gvern jew
ill-awtoritajiet lokali. Ir-rimi b’mod korrett u r-riċiklaġġ jgħin
ipprevjeni konsegwenzi negattivi potenzjali għall-ambjent u
ħas-saħħa tal-bniedem. Għal aktar informazzjoni dettaljata
war ir-rimi tat-tagħmir antik tiegħek, jekk jogħġbok ikkuntattja
ill-awtoritajiet lokali tiegħek, is-servizzi għar-rimi ta’ l-iskart, jew
l-ħanut minn fejn xtrajt il-prodott.
Nederlands (Dutch) - Milieu-informatie voor klanten
in de Europese Uni
De Europese Richtlijn 2002/96/EC schrijft voor dat apparatuur die
is voorzien van dit symbool op het product of de verpakking,
niet mag wor
a
val. Dit symbool geeft aan dat het product apart moet worden
ingezameld. U bent zelf verantwoordelijk voor de vernietiging
van deze en andere elektrische en elektronische apparatuur via de
daarvoor door de landelijke o
inzamelingskanalen. De juiste vernietiging en recycling van
eze apparatuur voorkomt mogelijke negatieve gevolgen voor
het milieu en de gezondheid. Voor meer informatie over het
vernietigen van uw oude apparatuur neemt u contact op met
de plaatselijke autoriteiten o
winkel waar u het product hebt aangeschaft.
en ingezameld met niet-gescheiden huishoudelijk
plaatselijke overheid aangewezen
valverwerkingsdienst, of met de
Norsk (Norwegian) - Miljøinformasjon for kunder i E
EU-direktiv 2002/96/EF krever at utstyr med følgende symbol
avbildet på produktet og/eller pakningen, ikke må kastes
sammen med usortert av
produktet skal håndteres atskilt fra ordinær avfallsinnsamling
for husholdningsavfall. Det er ditt ansvar å kvitte deg med
ette produktet og annet elektrisk og elektronisk avfall via egne
innsamlingsordninger slik myndighetene eller kommunene
bestemmer. Korrekt avfallshåndtering og gjenvinning vil
være med på å forhindre mulige negative konsekvenser for
miljø og helse. For nærmere informasjon om håndtering av
et kasserte utstyret ditt, kan du ta kontakt med kommunen,
en innsamlingsstasjon for avfall eller butikken der du kjøpte
tet.
pro
all. Symbolet indikerer at dette
agyar (Hungarian) - Környezetvédelmi információ az
urópai uniós vásárlók számár
A 2002/96/EC számú európai uniós irányelv megkívánja, hogy
azokat a termékeket, amelyeken, és/vagy amelyek csomagolásán
az alábbi címke megjelenik, tilos a többi szelektálatlan lakossági
ulladékkal együtt kidobni. A címke azt jelöli, hogy az adott
termék kidobásakor a szokványos háztartási hulladékelszállítási
rendszerektõl elkülönített eljárást kell alkalmazni. Az
elelõssége, hogy ezt, és más elektromos és elektronikus
erendezéseit a kormányzati vagy a helyi hatóságok által
kijelölt gyűjtõredszereken keresztül számolja fel. A megfelelõ
hulladékfeldolgozás segít a környezetre és az emberi egészségre
potenciá
elavult berendezéseinek felszámolásához további részletes
információra van szüksége, kérjük, lépjen kapcsolatba a helyi
hatóságokkal, a hulladékfeldolgozási szolgálattal, vagy azzal
üzlettel, ahol a terméket vásárolta.
isan ártalmas negatív hatások megelõzésében. Ha
n
Polski (Polish) - Informacja dla klientów w Unii
Europejskiej o przepisach dotyczących ochron
r
wis
Dyrektywa Europejska 2002/96/EC wymaga, aby sprzęt
oznaczony symbolem znajdującym się na produkcie i/lub jego
pakowaniu nie był wyrzucany razem z innymi niesortowanymi
dpadami komunalnymi. Symbol ten wskazuje, że produkt
nie powinien
ospodarstw domowych. Na Państwu spoczywa obowiązek
yrzucania tego i innych urządzeń elektrycznych oraz
ektronicznych w punktach odbioru wyznaczonych przez władze
rajowe lub lokalne. Pozbywanie się sprzętu we właściwy sposób
jego recykling pomogą zapobiec potencjalnie negatywnym
onsekwencjom dla środowiska i zdrowia ludzkiego. W celu
zyskania szczegółowych informacji o usuwaniu starego sprzętu,
prosimy zwrócić się do lokalnych władz, służb oczyszczania
miasta lub sklepu, w którym produkt został nabyty.
yć usuwany razem ze zwykłymi odpadami z
Footer
33
Page 35

Appendix D
l
d
l
bel
ă
ţ
ţ
ţ
i
i
b
delek od
.
-
y
j
y
.
Regulatory Information
Português (Portuguese) - Informação ambiental para
ientes da União Europeia
A Directiva Europeia 2002/96/CE exige que o equipamento
que exibe este símbolo no produto e/ou na sua embalagem
não seja e
separa
eliminado separadamente dos resíduos domésticos regulares.
da sua responsabilidade eliminar este e qualquer outro
equipamento e
e recolha designadas pelas autoridades governamentais ou
ocais. A eliminação e reciclagem correctas ajudarão a prevenir
as consequências negativas para o ambiente e para a saúde
humana. Para obter informações mais detalhadas sobre a
orma de eliminar o seu equipamento antigo, contacte as
autoridades locais, os serviços de eliminação de resíduos ou o
esta
iminado junto com os resíduos municipais não
os. O símbolo indica que este produto deve ser
éctrico e electrónico através das instalações
ecimento comercial onde adquiriu o produto.
Română (Romanian) - Informaţii de mediu pentru
lienţii din Uniunea European
Directiva europeană 2002/96/CE impune ca echipamentele care
rezintă acest simbol pe produs şi/sau pe ambalajul acestuia să
nu fie casate împreună cu gunoiul menajer municipal. Simbolul
indică faptul că acest produs trebuie să fie casat separat de
gunoiul menajer obişnuit. Este responsabilitatea dvs. să casaţi
acest produs şi alte echipamente electrice şi electronice prin
intermediul unită
sau de autorită
la prevenirea poten
mediului şi a oamenilor. Pentru mai multe informaţii detaliate
cu privire la casarea acestui echipament vechi, contactaţi
autorităţile locale, serviciul de salubrizare sau magazinul de la
care aţi achiziţionat produsul.
ilor de colectare special desemnate de guvern
ile locale. Casarea şi reciclarea corecte vor ajuta
ialelor consecinţe negative asupra sănătăţii
Slovenčina (Slovak) - Informácie o ochrane životného
prostredia pre zákazníkov v Európskej úni
Podľa európskej smernice 2002/96/ES zariadenie s týmto
symbolom na produkte a/alebo jeho balení nesmie byť
ikvidované spolu s netriedeným komunálnym odpadom.
ymbol znamená, že produkt by sa mal likvidovať oddelene
d bežného odpadu z domácností. Je vašou povinnosťou
ikvidovať toto i ostatné elektrické a elektronické zariadenia
rostredníctvom špecializovaných zberných zariadení určených
ádou alebo miestnymi orgánmi. Správna likvidácia a recyklácia
omôže zabrániť prípadným negatívnym dopadom na životné
rostredie a zdravie ľudí. Ak máte záujem o podrobnejšie
nformácie o likvidácii starého zariadenia, obráťte sa, prosím, na
iestne orgány, organizácie zaoberajúce sa likvidáciou odpadov
ebo obchod, v ktorom ste si produkt zakúpili.
Slovenčina (Slovene) - Okoljske informacije za stranke
v Evropski unij
Evropska direktiva 2002/96/EC prepoveduje odlaganje opreme,
označene s tem simbolom – na izdelku in/ali na embalaži – med
ičajne, nerazvrščene odpadke. Ta simbol opozarja, da je treba
o
iz
Vaša odgovornost je, da to in preostalo električno in elektronsko
opremo odnesete na posebna zbirališča, ki jih določijo
ržavne ustanove ali lokalna uprava. S pravilnim odlaganjem
in recikliranjem boste preprečili morebitne škodljive vplive na
okolje in zdravje ljudi. Če želite izvedeti več o odlaganju stare
opreme, se obrnite na lokalno upravo, odpad ali trgovino, kjer
ste izdelek kupili
vreči ločeno od preostalih gospodinjskih odpadkov.
Suomi (Finnish) - Ympäristöä koskevia tietoja EU
alueen asiakkaille
EU-direktiivi 2002/96/EY edellyttää, että jos laitteistossa on tämä
symboli itse tuotteessa ja/tai sen pakkauksessa, laitteistoa
ei saa hävittää lajittelemattoman yhdyskuntajätteen mukana.
mboli merkitsee sitä, että tämä tuote on hävitettävä erillään
S
tavallisesta kotitalous
tämä elektroniikkatuote ja muut vastaavat elektroniikkatuotteet
viemällä tuote tai tuotteet viranomaisten määräämään
spisteeseen. Laitteiston oikea hävittäminen estää
kerä
mahdolliset kielteiset vaikutukset ympäristöön ja ihmisten
terveyteen. Lisätietoja vanhan laitteiston oikeasta hävitystavasta
saa paikallisilta viranomaisilta, jätteenhävityspalvelusta tai siitä
myymälästä, josta ostit tuotteen.
ätteestä. Sinun vastuullasi on hävittää
Svenska (Swedish) - Miljöinformation för kunder i
Europeiska unionen
Det europeiska direktivet 2002/96/EC kräver att utrustning med
enna symbol på produkten och/eller förpackningen inte får
astas med osorterat kommunalt avfall. Symbolen visar att denna
produkt bör kastas efter att den avskiljts från vanligt hushållsavfall.
et faller på ditt ansvar att kasta denna och annan elektrisk och
lektronisk utrustning på fastställda insamlingsplatser utsedda
av regeringen eller lokala myndigheter. Korrekt kassering och
tervinning skyddar mot eventuella negativa konsekvenser
ör miljön och personhälsa. För mer detaljerad information om
assering av din gamla utrustning kontaktar du dina lokala
myndigheter, avfallshanteringen eller butiken där du köpte
produkten
WEB: For additional information, please visit
www.linksys.com
Footer
YMMDDVVNC-WI
34
Page 36

Appendix E
n
t
T
y
f
y
:
a
s
s
e
t
Th
s
.
l.
T
.
Th
003 and
0.
:
T
d
T
T
t
T
.
Th
.
003
ada.
:
.
s
p
.
Regulatory Information
ppendix E:
U Regulatory Informatio
FCC Statemen
his product has been tested and complies with the
specifications for a Class B digital device, pursuant to Part
5 of the FCC Rules. These limits are designed to provide
easonable protection against harmful interference in
residential installation. This equipment generates,
ses, and can radiate radio frequency energy and, if not
nstalled and used according to the instructions, ma
cause harmful interference to radio communications.
However, there is no guarantee that inter
occur in a particular installation. If this equipment does
cause harmful interference to radio or television reception,
which is found by turning the equipment off and on, the
ser is encouraged to try to correct the interference b
one or more of the following measures
Reorient or relocate the receiving antenn
Increase the separation between the equipment or
device
Connect the equipment to an outlet other than the
iver’
Consult a dealer or an experienced radio/TV technician
or assistanc
FCC Radiation Exposure Statemen
is equipment complies with FCC radiation exposure
limits set forth for an uncontrolled environment. This
equipment should be installed and operated with
inimum distance 20 cm between the radiator and your
ody.
afety Notice
Caution: To reduce the risk of fire, use only No.26 AWG
or larger telecommunication line cord
erence will not
Industry Canada Statement
is Class B digital apparatus complies with Canadian
ICES-
Operation is subject to the following two conditions
his device may not cause interference an
his device must accept any interference, including
nterference that may cause undesired operation
of the device.
o reduce potential radio interference to other users,
the antenna type and its gain should be so chosen
that the EIRP is not more than required for successful
communication.
RSS21
Industry Canada Radiation Exposure Statemen
his equipment complies with IC radiation exposure limits
set forth for an uncontrolled environment. This equipment
should be installed and operated with minimum distance
20 cm between the radiator & your body
is transmitter must not be co-located or operating in
conjunction with any other antenna or transmitter
Avis d’Industrie Canada
Cet appareil numérique de la classe B est conforme aux
rmes NMB-
L’utilisation de ce dispositif est autorisée seulement aux
conditions suivantes
l ne doit pas produire de brouillage et
l doit accepter tout brouillage radioélectrique reçu,
ême si ce brouillage est susceptible de compromettre le
onctionnement du dispositif.
fin de réduire le risque d’interférence aux autres
tilisateurs, le type d’antenne et son gain doivent
être choisis de façon à ce que la puissance isotrope
ayonnée équivalente (p.i.r.e.) ne soit pas supérieure
u niveau requis pour obtenir une communication
satisfaisante
et RSS210 du Can
Do not use this product near water, for example, in a
wet basement or near a swimming poo
void using this product during an electrical storm.
here may be a remote risk of electric shock from
ightning
Avis d’Industrie Canada concernant l’exposition
ux radiofréquence
Ce matériel est conforme aux limites établies par IC
en matière d’exposition aux radiofréquences dans un
environnement non contrôlé. Ce matériel doit être installé
et utilisé à une distance d’au moins 20 cm entre l’antenne
et le corps de l’utilisateur.
L’émetteur ne doit
ou d’un autre émetteur, ou fonctionner avec une autre
ntenne ou un autre émetteur
as être placé près d’une autre antenne
35
Page 37

Appendix E
r
T
.
.
Wireless Disclaime
he maximum performance for wireless is derived from
IEEE Standard 802.11 specifications. Actual performance
can vary, including lower wireless network capacity,
data throughput rate, range and coverage. Performance
depends on many factors, conditions and variables,
ncluding distance from the access point, volume of
etwork traffic, building materials and construction,
operating system used, mix of wireless products used,
nterference and other adverse conditions
Avis de non-responsabilité concernant les
areils sans fil
Les performances maximales pour les réseaux sans fil
sont tirées des spécifications de la norme IEEE 802.11.
Les performances réelles peuvent varier, notamment
en fonction de la capacité du réseau sans fil, du débit
e la transmission de données, de la portée et de la
couverture. Les performances dépendent de facteurs,
conditions et variables multiples, en particulier de la
distance par rapport au point d’accès, du volume du trafic
éseau, des matériaux utilisés dans le bâtiment et du
type de construction, du système d’exploitation et de la
combinaison de produits sans fil utilisés, des interférences
et de toute autre condition défavorable
Regulatory Information
36
Page 38

Appendix E
ess
)
Т
T
k
i
Th
l
τ
k
]
T
T
T
.
.
.
.
Regulatory Information
Declaration of Conformity with Regard to
EU Directive 1999/5/EC (R&TTE Directive)
omplian
Products Relevant to the EU and Other Countries Following
the EU Directive 1999/5/EC (R&TTE Directive
ългарски
Bulgarian]
esky
Czech]:
ans
Danish]:
eutsch
German]:
Eest
Estonian]:
tion
ова оборудване отговаря на съществените
зисквания и приложими клаузи на
иректива 1999/5/ЕС.
oto zařízení je v souladu se základními
ožadavky a ostatními odpovídajícími
stanoveními Směrnice 1999/5/EC.
ette udstyr er i overensstemmelse med
e væsentlige krav og andre relevante
estemmelser i Direktiv 1999/5/EF.
ieses Gerät entspricht den grundlegenden
nforderungen und den weiteren
ntsprechenden Vorgaben der Richtlinie
999/5/EU.
ee seade vastab direktiivi 1999/5/EÜ olulistele
õuetele ja teistele asjakohastele sätetele.
,4-
zW
l
ederlands
Dutch]:
alti
Maltese]:
agyar
Hungarian]:
ors
Norwegian]:
olski
Polish]:
ortuguês
Portuguese]:
omână
Romanian
it apparaat voldoet aan de essentiele eisen
n andere van toepassing zijnde bepalingen
an de Richtlijn 1999/5/EC.
an l-apparat huwa konformi mal-ħtiġiet
ssenzjali u l-provedimenti l-oħra rilevanti
ad-Direttiva 1999/5/EC.
z a készülék teljesíti az alapvető
övetelményeket és más 1999/5/EK
rányelvben meghatározott vonatkozó
endelkezéseket.
ette utstyret er i samsvar med de
runnleggende krav og andre relevante
estemmelser i EU-direktiv 1999/5/EF.
rządzenie jest zgodne z ogólnymi
ymaganiami oraz szczególnymi warunkami
reślonymi Dyrektywą UE: 1999/5/EC.
ste equipamento está em conformidade com
s requisitos essenciais e outras provisões
elevantes da Directiva 1999/5/EC.
cest echipament este in conformitate
u cerintele esentiale si cu alte prevederi
elevante ale Directivei 1999/5/EC.
nglish:
spaño
Spanish]:
ηνική
Greek]:
rançais
French]:
slenska
Icelandic]:
taliano
Italian]:
atviski
Latvian]:
etuvių
Lithuanian]:
is equipment is in compliance with the
ssential requirements and other relevant
rovisions of Directive 1999/5/EC.
ste equipo cumple con los requisitos
senciales asi como con otras disposiciones
e la Directiva 1999/5/CE.
υτός ο εξοπλισµός είναι σε συµµόρφωση µε
ις ουσιώδεις απαιτήσεις και άλλες σχετικές
ιατάξεις της Οδηγίας 1999/5/EC.
et appareil est conforme aux exigences
ssentielles et aux autres dispositions
ertinentes de la Directive 1999/5/EC.
etta tæki er samkvæmt grunnkröfum og
rum viðeigandi ákvæðum Tilskipunar
999/5/EC.
uesto apparato é conforme ai requisiti
ssenziali ed agli altri principi sanciti dalla
irettiva 1999/5/CE.
ī iekārta atbilst Direktīvas 1999/5/EK
ūtiskajām prasībām un citiem ar to
aistītajiem noteikumiem.
is įrenginys tenkina 1999/5/EB Direktyvos
sminius reikalavimus ir kitas šios direktyvos
uostatas.
ovensko
Slovenian]:
ovensky
Slovak]:
uomi
Finnish]:
venska
Swedish]:
a naprava je skladna z bistvenimi zahtevami
n ostalimi relevantnimi pogoji Direktive
999/5/EC.
oto zariadenie je v zhode so základnými
ožiadavkami a inými príslušnými nariadeniami
irektív: 1999/5/EC.
ämä laite täyttää direktiivin 1999/5/EY
ennaiset vaatimukset ja on siinä asetettujen
uiden laitetta koskevien määräysten
ukainen.
enna utrustning är i överensstämmelse med
e väsentliga kraven och andra relevanta
estämmelser i Direktiv 1999/5/EC.
For all products, the Declaration of Conformity (DofC) is
vailable through one or more of these options:
pdf file is included on the product’s CD
print copy is included with the product
pdf file is available on the product’s webpage.
Visitww.linksys.com/international and select your
country or region. Then select your product
If you need any other technical documentation, see the
Technical Documents on www.linksys.com/international”
section, as shown later in this appendix
37
Page 39

Appendix E
)
T
:
300 328 and
1
).
g
.
.
Th
:
-
:
:
bleabeled
l
i
y
d
.
T
T
Regulatory Information
Wireless Equipment
Wireless-N/G/A/B Products
he following standards were applied during the
ssessment of the product against the requirements of
the Directive 1999/5/EC
io: EN
EMC: EN 301 489-1, EN 301 489-17
a
EN 60950 and either EN 50385 or EN 5037
DFS: The equipment meets the DFS requirements as
defined in ETSI EN 301 893. This feature is required by
the regulations to avoid interference with Radio Location
ervices (radars
CE Markin
For the Linksys Wireless-N, -G, -B, and/or -A products,
the following CE mark, notified body number (where
licable), and class 2 identifier are added to the
equipment
National Restrictions
is product may be used in all EU countries (and other
countries following the EU directive 1999/5/EC) without
ny limitation except for the countries mentioned below
Ce produit peut être utilisé dans tous les pays de l’UE (et dans
tous les pays ayant transposés la directive 1999/5/CE) sans
aucune limitation, excepté pour les pays mentionnés ci
essous
Questo prodotto è utilizzabile in tutte i paesi EU (ed in tutti
gli altri paesi che seguono le direttive EU 1999/5/EC) senza
nessuna limitazione, eccetto per i paesi menzionati di
seguito
as Produkt kann in allen EU Staaten ohne Einschränkungen
ingesetzt werden (sowie in anderen Staaten die der EU
irektive 1999/5/CE folgen) mit Außnahme der folgenden
aufgeführten Staaten:
In the majority of the EU and other European countries,
the 2,4- bands
or the use of wireless local area networks (LANs). The
ta
ireless LANs” provides an overview of the regulator
equi
mets applicable
Later in this document you will find an overview of
countries in which additional restrictions or requirements
or both are applicable
he requirements for any country may evolve. Linksys
ecommends that you check with the local authorities for
the latest status of their national regulations for both the
2,4-G
wiess LAN
e been made
iew of
egu
qu
ban
ilable
s
Check the CE label on the product to find out which
otified body was involved during the assessment
Overview of Regulatory Requirements for Wireless LANs
Frequency
Band (MHz)
400-2483.5
he following countries have restrictions and/or
equirements in addition to those given in the table
labeled “Overview of Regulatory Requirements for
ireless LANs”:
Max Power Level
(EIRP) (mW)
Indoor
ONLY
Indoor &
Outdoor
38
Page 40

Appendix E
.
p
.
)
5
)
r
4
5
)
ly
T
y
.
2
.
ia
T
.
2
.
.
T
.
T
.
s
T
.
T
.
:
.
.
.
y.
y.
.
l
Regulatory Information
France
For 2,4 GHz, the product should not be used outdoors
n the band 2454 - 2483,5 MHz. There are no restrictions
when used in other parts of the 2,4 GHz band when used
ndoors. Check http://www.arcep.fr/ for more details
Pour la bande 2,4 GHz, l’ équipement ne doit pas être utilisé
n extérieur dans la bande 2454 - 2483,5 MHz. Il n’y a pas de
restrictions pour des utilisations en intérieur dans d’autres
arties de la bande 2,4GHz. Consultez http://www.arcep.fr/
pour de plus amples détails
licable Power Levels in France
Location
Indoor
No restrictions
Outdoo
Frequency
Range (MHz)
400-2483.
400-245
454-2483.
Power (EIRP)
100 mW (20 dBm
100 mW (20 dBm)
10 mW (10 dBm
Ita
Product Usage Restrictions
his product is designed for indoor usage only. Outdoor
sage is not recommended, unless otherwise noted
2,4 GHz Restriction
his product is designed for use with the standard, integral
or dedicated (external) antenna(s) that is/are shipped
together with the equipment. However, some applications
ay require the antenna(s), if removable, to be separated
rom the product and installed remotely from the device
using extension cables. For these applications, Linksys
ers an RSMA extension cable (AC9SMA) and an R-TNC
extension cable (AC9TNC). Both of these cables are 9
eters long and have a cable loss (attenuation) of 5 dB. To
compensate for the attenuation, Linksys also offers higher
gain antennas, the HGA7S (with R-SMA connector) and
HGA7T (with R-TNC connector). These antennas have a
gain of 7 dBi and may only be used with either the R-SMA
or R-TNC extension cable
Combinations of extension cables and antennas resulting
n a radiated power level exceeding 100 mW EIRP are
llegal.
his product meets the National Radio Interface and
he requirements specified in the National Frequenc
llocation Table for Italy. Unless this 2,4-GHz wireless LAN
roduct is operating within the boundaries of the owner’s
roperty, its use requires a “general authorization”. Please
check http://www.comunicazioni.it/it/ for more details
Questo prodotto è conforme alla specifiche di Interfaccia
Radio Nazionali e rispetta il Piano Nazionale di ripartizione
elle frequenze in Italia. Se non viene installato all’interno
el proprio fondo, l’utilizzo di prodotti Wireless LAN a
,4 GHz richiede una “Autorizzazione Generale”. Consultare
http://www.comunicazioni.it/it/ per maggiori dettagli
Latv
he outdoor usage of the 2,4 GHz band requires an
uthorization from the Electronic Communications Office.
Please check http://www.esd.lv for more details
,4 GHz frekveču joslas izmantošanai ārpus telpām
nepieciešama atļauja no Elektronisko sakaru direkcijas.
Vairāk informācijas: http://www.esd.lv
Notes:
though Norway, Switzerland and Liechtenstein are
ot EU member states, the EU Directive 1999/5/EC has
lso been implemented in those countries
he regulatory limits for maximum output power are
specified in EIRP. The EIRP level of a device can be
calculated by adding the gain of the antenna used
(specified in dBi) to the output power available at the
connector (specified in dBm)
hird-Party Software or Firmware
he use of software or firmware not supported/provided
Linksys may result that the equipment is no longer
compliant with the regulatory requirements
Technical Documents on
ww.linksys.com/international
Follow these steps to access technical documents
Enter http://www.linksys.com/international in your
eb browser
elect the country or region in which you live
lick theProductstab
elect the appropriate product categor
elect the product sub-category, if necessar
elect the product.
elect the type of documentation you want from the7
More Information section. The document will open
n PDF format if you have Adobe Acrobat installed on
our computer.
NOTE: If you have questions regarding
the compliance of this product or you
cannot find the information you need,
lease contact your local sales office or visit
www.linksys.com/internationa
39
Page 41

Appendix E
)
T
:
)
e
U
ff
lek
n
Regulatory Information
User Information for Consumer Products
Covered by EU Directive 2002/96/EC on
Waste Electric and Electronic Equipment
WEEE
his document contains important information for users
with regards to the proper disposal and recycling of
Linksys products. Consumers are required to comply with
this notice for all electronic products bearing the following
symbol
English - Environmental Information for Customers in
he European Union
European Directive 2002/96/EC requires that the equipment
bearing this symbol on the product and/or its packaging must
ot be disposed of with unsorted municipal waste. The symbol
ndicates that this product should be disposed of separately
rom regular household waste streams. It is your responsibility to
ispose of this and other electric and electronic equipment via
esignated collection facilities appointed by the government or
ocal authorities. Correct disposal and recycling will help prevent
otential negative consequences to the environment and
uman health. For more detailed information about the disposal
f your old equipment, please contact your local authorities,
aste disposal service, or the shop where you purchased the
roduct.
Български (Bulgarian) - Информация относно
пазването на околната среда за потребители в
Европейския съюз
Европейска директива 2002/96/EC изисква уредите, носещи
този символ върху изделието и/или опаковката му, да не
се изхвърля т с несортирани битови отпадъци. Символът
обозначава, че изделието трябва да се изхвърля отделно от
сметосъбирането на обикновените битови отпадъци. Ваша
е отговорността този и другите електрически и електронни
реди да се изхвърлят в предварително определени от
държавните или общински органи специализирани пунктове
за събиране. Правилното изхвърляне и рециклиране
ще спомогнат да се предотвратят евентуални вредни за
околната среда и здравето на населението последствия. За
по-подробна информация относно изхвърлянето на вашите
стари уреди се обърнете към местните власти, службите за
сметосъбиране или магазина, от който сте закупили уреда.
eština (Czech
nformace o ochraně životního
prostředí pro zákazníky v zemích Evropské uni
Evropská směrnice 2002/96/ES zakazuje, aby zařízení označené
tímto symbolem na produktu anebo na obalu bylo likvidováno
netříděným komunálním odpadem. Tento symbol udává,
e daný produkt musí být likvidován odděleně od běžného
omunálního odpadu. Odpovídáte za likvidaci tohoto produktu
dalších elektrických a elektronických zařízení prostřednictvím
rčených sběrných míst stanovených vládou nebo místními
řady. Správná likvidace a recyklace pomáhá předcházet
otenciálním negativním dopadům na životní prostředí a lidské
draví. Podrobnější informace o likvidaci starého vybavení si
askavě vyžádejte od místních úřadů, podniku zabývajícího se
ikvidací komunálních odpadů nebo obchodu, kde jste produkt
akoupili.
Dansk (Danish) - Miljøinformation for kunder i E
EU-direktiv 2002/96/EF kræver, at udstyr der bærer dette symbol
på produktet og/eller emballagen ikke må bortskaffes som
usorteret kommunalt a
skal bortskaffes adskilt fra det almindelige husholdningsaffald.
Det er dit ansvar at bortskaffe dette og andet elektrisk og
tronisk udstyr via bestemte indsamlingssteder udpeget
e
af staten eller de lokale myndigheder. Korrekt bortskaffelse
og genvinding vil hjælpe med til at undgå mulige skader for
miljøet og menneskers sundhed. Kontakt venligst de lokale
myndigheder, renovationstjenesten eller den butik, hvor du
har købt produktet, angående mere detaljeret information om
bortskaffelse af dit gamle udstyr.
ald. Symbolet betyder, at dette produkt
Deutsch (German) - Umweltinformation für Kunden
innerhalb der Europäischen Unio
Die Europäische Richtlinie 2002/96/EC verlangt, dass technische
Ausrüstung, die direkt am Gerät und/oder an der Verpackung mit
iesem Symbol versehen ist
emeindeabfall entsorgt werden darf. Das Symbol weist darauf
in, dass das Produkt von regulärem Haushaltmüll getrennt
ntsorgt werden sollte. Es liegt in Ihrer Verantwortung, dieses
erät und andere elektrische und elektronische Geräte über
ie dafür zuständigen und von der Regierung oder örtlichen
ehörden dazu bestimmten Sammelstellen zu entsorgen.
rdnungsgemäßes Entsorgen und Recyceln trägt dazu bei,
otentielle negative Folgen für Umwelt und die menschliche
esundheit zu vermeiden. Wenn Sie weitere Informationen zur
ntsorgung Ihrer Altgeräte benötigen, wenden Sie sich bitte an
ie örtlichen Behörden oder städtischen Entsorgungsdienste
er an den Händler, bei dem Sie das Produkt erworben haben.
nicht zusammen mit unsortiertem
40
Page 42

Appendix E
le
bol
l
f
a
bolo
j
y
ada sob
g
y
g
ης
τ
ηψη
e
ball
bol
l
f
.
a
ā
Regulatory Information
Eesti (Estonian) - Keskkonnaalane informatsioon
Euroopa Liidus asuvatele klientide
Euroopa Liidu direktiivi 2002/96/EÜ nõuete kohaselt on
seadmeid, millel on tootel või pakendil käesolev sümbol
eelatud kõrvaldada koos sorteerimata olmejäätmetega. See
süm
näitab, et toode tuleks kõrvaldada eraldi tavalistest
olmejäätmevoogudest. Olete kohustatud kõrvaldama käesoleva
ja ka muud elektri- ja elektroonikaseadmed riigi või kohalike
ametiasutuste poo
Seadmete korrektne kõrvaldamine ja ringlussevõtt aitab vältida
võimalikke negatiivseid tagajärgi keskkonnale ning inimeste
tervisele. Vanade seadmete kõrvaldamise kohta täpsema
informatsiooni saamiseks võtke palun ühendust kohalike
ametiasutustega, jäätmekäitlus
toote ostsite.
t ette nähtud kogumispunktide kaudu.
irmaga või kauplusega, kust te
Español (Spanish) - Información medioambiental para
lientes de la Unión Europe
La Directiva 2002/96/CE de la UE exige que los equipos que
lleven este sím
no deben eliminarse
seleccionados. El símbolo indica que el producto en cuestión
debe separarse de los residuos domésticos convencionales con
vistas a su eliminación. Es responsabilidad su
cualesquiera otros aparatos eléctricos y electrónicos a través de
los puntos de recogida que ponen a su disposición el gobierno y
las autoridades locales. Al desechar y reciclar correctamente estos
aparatos estará contribuyendo a evitar posibles consecuencias
negativas para el medio ambiente y la salud de las personas. Si
esea obtener información más detall
ura de su aparato usado, consulte a las autoridades locales,
se
al servicio de recogida
unte en la tienda donde adquirió el producto.
pre
en el propio aparato y/o en su embalaje
unto con otros residuos urbanos no
a desechar este y
re la eliminación
eliminación de residuos de su zona o
λληνικά (Greek) - Στοιχεία περιβαλλοντικής
προστασίας για πελάτες εντός της Ευρωπαϊκής
Ένωσ
Η Κοινοτική Οδηγία 2002/96/EC απαιτεί ότι ο εξοπλισμός ο οποίος
έρει αυτό το σύμβολο στο προϊόν και/ή στη συσκευασία
ου δεν πρέπει να απορρίπτεται μαζί με τα μικτά κοινοτικά
πορρίμματα. Το σύμβολο υποδεικνύει ότι αυτό το προϊόν θα
ρέπει να απορρίπτεται ξεχωριστά από τα συνήθη οικιακά
πορρίμματα. Είστε υπεύθυνος για την απόρριψη του παρόντος
αι άλλου ηλεκτρικού και ηλεκτρονικού εξοπλισμού μέσω των
αθορισμένων εγκαταστάσεων συγκέντρωσης απορριμμάτων οι
ποίες παρέχονται από το κράτος ή τις αρμόδιες τοπικές αρχές.
σωστή απόρριψη και ανακύκλωση συμβάλλει στην πρόλ
ιθανών αρνητικών συνεπειών για το περιβάλλον και την υγεία.
ια περισσότερες πληροφορίες σχετικά με την απόρριψη του
αλιού σας εξοπλισμού, παρακαλώ επικοινωνήστε με τις τοπικές
ρχές, τις υπηρεσίες απόρριψης ή το κατάστημα από το οποίο
οράσατε το προϊόν.
Français (French) - Informations environnementales
pour les clients de l’Union européenn
La directive européenne 2002/96/CE exige que l’équipement
sur lequel est apposé ce symbole sur le produit et/ou son
age ne soit pas jeté avec les autres ordures ménagères. Ce
em
sym
e indique que le produit doit être éliminé dans un circuit
istinct de celui pour les déchets des ménages. Il est de votre
responsabilité de jeter ce matériel ainsi que tout autre matériel
ectrique ou électronique par les moyens de collecte indiqués
é
par le gouvernement et les pouvoirs publics des collectivités
territoriales. L’élimination et le recyclage en bonne et due forme
ont pour but de lutter contre l’impact néfaste potentiel de ce
type de produits sur l’environnement et la santé publique. Pour
plus d’in
équipement, veuillez prendre contact avec les pouvoirs publics
ocaux, le service de traitement des déchets, ou l’e ndroit où vous
avez acheté le produit
ormations sur le mode d’élimination de votre ancien
Italiano (Italian) - Informazioni relative all’ambiente
er i clienti residenti nell’Unione Europe
La direttiva europea 2002/96/EC richiede che le apparecchiature
contrassegnate con questo simbolo sul prodotto e/o
ull’imballaggio non siano smaltite insieme ai rifiuti urbani
on differenziati. Il simbolo indica che questo prodotto non
eve essere smaltito insieme ai normali rifiuti domestici. È
esponsabilità del proprietario smaltire sia questi prodotti sia
e altre apparecchiature elettriche ed elettroniche mediante
e specifiche strutture di raccolta indicate dal governo o dagli
nti pubblici locali. Il corretto smaltimento ed il riciclaggio
iuteranno a prevenire conseguenze potenzialmente negative
er l’ambiente e per la salute dell’essere umano. Per ricevere
nformazioni più dettagliate circa lo smaltimento delle vecchie
pparecchiature in Vostro possesso, Vi invitiamo a contattare gli
nti pubblici di competenza, il servizio di smaltimento rifiuti o il
egozio nel quale avete acquistato il prodotto.
Latviešu valoda (Latvian) - Ekoloģiska informācija
lientiem Eiropas Savienības jurisdikcij
Direktīvā 2002/96/EK ir prasība, ka aprīkojumu, kam pievienota
zīme uz paša izstrādājuma vai uz tā iesaiņojuma, nedrīkst
zmest nešķirotā veidā kopā ar komunālajiem atkritumiem
tiem, ko rada vietēji iedzīvotāji un uzņēmumi). Šī zīme nozīmē
o, ka šī ierīce ir jāizmet atkritumos tā, lai tā nenonāktu kopā ar
arastiem mājsaimniecības atkritumiem. Jūsu pienākums ir šo
n citas elektriskas un elektroniskas ierīces izmest atkritumos,
zmantojot īpašus atkritumu savākšanas veidus un līdzekļus, ko
odrošina valsts un pašvaldību iestādes. Ja izmešana atkritumos
n pārstrāde tiek veikta pareizi, tad mazinās iespējamais
aitējums dabai un cilvēku veselībai. Sīkākas ziņas par
ovecojuša aprīkojuma izmešanu atkritumos jūs varat saņemt
ietējā pašvaldībā, atkritumu savākšanas dienestā, kā arī veikalā,
ur iegādājāties šo izstrādājumu.
41
Page 43

Appendix E
s
l
Š
k
a
j
a
Ö
l
e
d
f
f
f af
U
f
duk
y
odo
ka
b
Regulatory Information
Lietuvškai (Lithuanian) - Aplinkosaugos informacija,
irta Europos Sąjungos vartotojam
Europos direktyva 2002/96/EC numato, kad įrangos, kuri ir
urios pakuotė yra pažymėta šiuo simboliu (įveskite simbolį),
ima šalinti kartu su nerūšiuotomis komunalinėmis
nega
atliekomis.
nuo bendro buitinių atliekų srauto. Jūs privalote užtikrinti, kad
ši ir kita elektros ar elektroninė įranga būtų šalinama per tam
ras nacionalinės ar vietinės valdžios nustatytas atliekų rinkimo
ti
sistemas. Tinkamai šalinant ir perdirbant atliekas, bus išvengta
galimos žalos aplinkai ir žmonių sveikatai. Daugiau informacijos
apie jūsų senos įrangos šalinimą gali pateikti vietinės valdžios
institucijos, atliekų šalinimo tarnybos arba parduotuvės, kuriose
sigijote tą gaminį.
is simbolis rodo, kad gaminį reikia šalinti atskirai
alti (Maltese) - Informazzjoni Ambjentali għal Klijenti
l-Unjoni Ewrope
Id-Direttiva Ewropea 2002/96/KE titlob li t-tagħmir li jkun fih issimbolufuq il-prodott u/jew fuq l-ippakkjar ma jistax jintrema
a’ skart muniċipali li ma ġiex isseparat. Is-simbolu jindika
i dan il-prodott għandu jintrema separatament minn ma’ lskart domestiku regolari. Hija responsabbiltà tiegħek li tarmi
an it-tagħmir u kull tagħmir ieħor ta’ l-elettriku u elettroniku
ermezz ta’ faċilitajiet ta’ ġbir appuntati apposta mill-gvern jew
ill-awtoritajiet lokali. Ir-rimi b’mod korrett u r-riċiklaġġ jgħin
ipprevjeni konsegwenzi negattivi potenzjali għall-ambjent u
ħas-saħħa tal-bniedem. Għal aktar informazzjoni dettaljata
war ir-rimi tat-tagħmir antik tiegħek, jekk jogħġbok ikkuntattja
ill-awtoritajiet lokali tiegħek, is-servizzi għar-rimi ta’ l-iskart, jew
l-ħanut minn fejn xtrajt il-prodott.
Nederlands (Dutch) - Milieu-informatie voor klanten
in de Europese Uni
De Europese Richtlijn 2002/96/EC schrijft voor dat apparatuur die
is voorzien van dit symbool op het product of de verpakking,
niet mag wor
a
val. Dit symbool geeft aan dat het product apart moet worden
ingezameld. U bent zelf verantwoordelijk voor de vernietiging
van deze en andere elektrische en elektronische apparatuur via de
daarvoor door de landelijke o
inzamelingskanalen. De juiste vernietiging en recycling van
eze apparatuur voorkomt mogelijke negatieve gevolgen voor
het milieu en de gezondheid. Voor meer informatie over het
vernietigen van uw oude apparatuur neemt u contact op met
de plaatselijke autoriteiten o
winkel waar u het product hebt aangeschaft.
en ingezameld met niet-gescheiden huishoudelijk
plaatselijke overheid aangewezen
valverwerkingsdienst, of met de
Norsk (Norwegian) - Miljøinformasjon for kunder i E
EU-direktiv 2002/96/EF krever at utstyr med følgende symbol
avbildet på produktet og/eller pakningen, ikke må kastes
sammen med usortert av
produktet skal håndteres atskilt fra ordinær avfallsinnsamling
for husholdningsavfall. Det er ditt ansvar å kvitte deg med
ette produktet og annet elektrisk og elektronisk avfall via egne
innsamlingsordninger slik myndighetene eller kommunene
bestemmer. Korrekt avfallshåndtering og gjenvinning vil
være med på å forhindre mulige negative konsekvenser for
miljø og helse. For nærmere informasjon om håndtering av
et kasserte utstyret ditt, kan du ta kontakt med kommunen,
en innsamlingsstasjon for avfall eller butikken der du kjøpte
tet.
pro
all. Symbolet indikerer at dette
agyar (Hungarian) - Környezetvédelmi információ az
urópai uniós vásárlók számár
A 2002/96/EC számú európai uniós irányelv megkívánja, hogy
azokat a termékeket, amelyeken, és/vagy amelyek csomagolásán
az alábbi címke megjelenik, tilos a többi szelektálatlan lakossági
ulladékkal együtt kidobni. A címke azt jelöli, hogy az adott
termék kidobásakor a szokványos háztartási hulladékelszállítási
rendszerektõl elkülönített eljárást kell alkalmazni. Az
elelõssége, hogy ezt, és más elektromos és elektronikus
erendezéseit a kormányzati vagy a helyi hatóságok által
kijelölt gyűjtõredszereken keresztül számolja fel. A megfelelõ
hulladékfeldolgozás segít a környezetre és az emberi egészségre
potenciá
elavult berendezéseinek felszámolásához további részletes
információra van szüksége, kérjük, lépjen kapcsolatba a helyi
hatóságokkal, a hulladékfeldolgozási szolgálattal, vagy azzal
üzlettel, ahol a terméket vásárolta.
isan ártalmas negatív hatások megelõzésében. Ha
n
Polski (Polish) - Informacja dla klientów w Unii
Europejskiej o przepisach dotyczących ochron
r
wis
Dyrektywa Europejska 2002/96/EC wymaga, aby sprzęt
oznaczony symbolem znajdującym się na produkcie i/lub jego
pakowaniu nie był wyrzucany razem z innymi niesortowanymi
dpadami komunalnymi. Symbol ten wskazuje, że produkt
nie powinien
ospodarstw domowych. Na Państwu spoczywa obowiązek
yrzucania tego i innych urządzeń elektrycznych oraz
ektronicznych w punktach odbioru wyznaczonych przez władze
rajowe lub lokalne. Pozbywanie się sprzętu we właściwy sposób
jego recykling pomogą zapobiec potencjalnie negatywnym
onsekwencjom dla środowiska i zdrowia ludzkiego. W celu
zyskania szczegółowych informacji o usuwaniu starego sprzętu,
prosimy zwrócić się do lokalnych władz, służb oczyszczania
miasta lub sklepu, w którym produkt został nabyty.
yć usuwany razem ze zwykłymi odpadami z
42
Page 44

Appendix E
l
d
l
bel
ă
ţ
ţ
ţ
i
i
b
delek od
.
-
y
j
y
.
l
Regulatory Information
Português (Portuguese) - Informação ambiental para
ientes da União Europeia
A Directiva Europeia 2002/96/CE exige que o equipamento
que exibe este símbolo no produto e/ou na sua embalagem
não seja e
separa
eliminado separadamente dos resíduos domésticos regulares.
da sua responsabilidade eliminar este e qualquer outro
equipamento e
e recolha designadas pelas autoridades governamentais ou
ocais. A eliminação e reciclagem correctas ajudarão a prevenir
as consequências negativas para o ambiente e para a saúde
humana. Para obter informações mais detalhadas sobre a
orma de eliminar o seu equipamento antigo, contacte as
autoridades locais, os serviços de eliminação de resíduos ou o
esta
iminado junto com os resíduos municipais não
os. O símbolo indica que este produto deve ser
éctrico e electrónico através das instalações
ecimento comercial onde adquiriu o produto.
Română (Romanian) - Informaţii de mediu pentru
lienţii din Uniunea European
Directiva europeană 2002/96/CE impune ca echipamentele care
rezintă acest simbol pe produs şi/sau pe ambalajul acestuia să
nu fie casate împreună cu gunoiul menajer municipal. Simbolul
indică faptul că acest produs trebuie să fie casat separat de
gunoiul menajer obişnuit. Este responsabilitatea dvs. să casaţi
acest produs şi alte echipamente electrice şi electronice prin
intermediul unită
sau de autorită
la prevenirea poten
mediului şi a oamenilor. Pentru mai multe informaţii detaliate
cu privire la casarea acestui echipament vechi, contactaţi
autorităţile locale, serviciul de salubrizare sau magazinul de la
care aţi achiziţionat produsul.
ilor de colectare special desemnate de guvern
ile locale. Casarea şi reciclarea corecte vor ajuta
ialelor consecinţe negative asupra sănătăţii
Slovenčina (Slovak) - Informácie o ochrane životného
prostredia pre zákazníkov v Európskej úni
Podľa európskej smernice 2002/96/ES zariadenie s týmto
symbolom na produkte a/alebo jeho balení nesmie byť
ikvidované spolu s netriedeným komunálnym odpadom.
ymbol znamená, že produkt by sa mal likvidovať oddelene
d bežného odpadu z domácností. Je vašou povinnosťou
ikvidovať toto i ostatné elektrické a elektronické zariadenia
rostredníctvom špecializovaných zberných zariadení určených
ádou alebo miestnymi orgánmi. Správna likvidácia a recyklácia
omôže zabrániť prípadným negatívnym dopadom na životné
rostredie a zdravie ľudí. Ak máte záujem o podrobnejšie
nformácie o likvidácii starého zariadenia, obráťte sa, prosím, na
iestne orgány, organizácie zaoberajúce sa likvidáciou odpadov
ebo obchod, v ktorom ste si produkt zakúpili.
Slovenčina (Slovene) - Okoljske informacije za stranke
v Evropski unij
Evropska direktiva 2002/96/EC prepoveduje odlaganje opreme,
označene s tem simbolom – na izdelku in/ali na embalaži – med
ičajne, nerazvrščene odpadke. Ta simbol opozarja, da je treba
o
iz
Vaša odgovornost je, da to in preostalo električno in elektronsko
opremo odnesete na posebna zbirališča, ki jih določijo
ržavne ustanove ali lokalna uprava. S pravilnim odlaganjem
in recikliranjem boste preprečili morebitne škodljive vplive na
okolje in zdravje ljudi. Če želite izvedeti več o odlaganju stare
opreme, se obrnite na lokalno upravo, odpad ali trgovino, kjer
ste izdelek kupili
vreči ločeno od preostalih gospodinjskih odpadkov.
Suomi (Finnish) - Ympäristöä koskevia tietoja EU
alueen asiakkaille
EU-direktiivi 2002/96/EY edellyttää, että jos laitteistossa on tämä
symboli itse tuotteessa ja/tai sen pakkauksessa, laitteistoa
ei saa hävittää lajittelemattoman yhdyskuntajätteen mukana.
mboli merkitsee sitä, että tämä tuote on hävitettävä erillään
S
tavallisesta kotitalous
tämä elektroniikkatuote ja muut vastaavat elektroniikkatuotteet
viemällä tuote tai tuotteet viranomaisten määräämään
spisteeseen. Laitteiston oikea hävittäminen estää
kerä
mahdolliset kielteiset vaikutukset ympäristöön ja ihmisten
terveyteen. Lisätietoja vanhan laitteiston oikeasta hävitystavasta
saa paikallisilta viranomaisilta, jätteenhävityspalvelusta tai siitä
myymälästä, josta ostit tuotteen.
ätteestä. Sinun vastuullasi on hävittää
Svenska (Swedish) - Miljöinformation för kunder i
Europeiska unionen
Det europeiska direktivet 2002/96/EC kräver att utrustning med
enna symbol på produkten och/eller förpackningen inte får
astas med osorterat kommunalt avfall. Symbolen visar att denna
produkt bör kastas efter att den avskiljts från vanligt hushållsavfall.
et faller på ditt ansvar att kasta denna och annan elektrisk och
lektronisk utrustning på fastställda insamlingsplatser utsedda
av regeringen eller lokala myndigheter. Korrekt kassering och
tervinning skyddar mot eventuella negativa konsekvenser
ör miljön och personhälsa. För mer detaljerad information om
assering av din gamla utrustning kontaktar du dina lokala
myndigheter, avfallshanteringen eller butiken där du köpte
produkten
WEB: For additional information, please visit
www.linksys.com/internationa
43
Page 45

Appendix F
t
s
T
-
e
ygp
as
.
oad fro
ygp
ygp
or
.
,
O
)
.
T
y
.
t
T
T
T
T
T
T
O
T
.
icense
T
.
y
y
d
y
.
/
Software License Agreement
ppendix F: Software
cense Agreemen
oftware in Linksys Product
his product from Cisco-Linksys LLC or from one of its
ffiliates Cisco Systems-Linksys (Asia) Pte Ltd. or Cisco
Linksys K.K. (“Linksys”) contains software (including
irmware) originating from Linksys and its suppliers
nd may also contain software from the open source
community. Any software originating from Linksys and its
suppliers is licensed under the Linksys Software License
greement contained at Schedule 1 below. You may also
e prompted to review and accept that Linksys Software
License Agreement upon installation of the softwar
ny software from the open source community is licensed
nder the specific license terms applicable to that software
ade available by Linksys at
rovided for in Schedules 2, 3 and 4 below
here such specific license terms entitle you to the source
code of such software, that source code is upon request
vailable at cost from Linksys for at least three years
rom the purchase date of this product and may also be
vailable for downl
detailed license terms and additional information on
open source software in Linksys products please look at
the Linksys public web site at:
chedules 2, 3 or 4 below as applicable
BY DOWNLOADING OR INSTALLING THE SOFTWARE
R USING THE PRODUCT CONTAINING THE SOFTWARE,
YOU ARE CONSENTING TO BE BOUND BY THE SOFTWARE
LICENSE AGREEMENTS BELOW. IF YOU DO NOT AGREE T
LL OF THESE TERMS, THEN YOU MAY NOT DOWNLOAD,
INSTALL OR USE THE SOFTWARE. YOU MAY RETURN
UNUSED SOFTWARE (OR, IF THE SOFTWARE IS SUPPLIED
S PART OF ANOTHER PRODUCT, THE UNUSED PRODUCT
FOR A FULL REFUND UP TO 30 DAYS AFTER ORIGINAL
PURCHASE, SUBJECT TO THE RETURN PROCESS AND
POLICIES OF THE PARTY FROM WHICH YOU PURCHASED
UCH PRODUCT OR SOFTWARE
m
oftware Licenses
he software Licenses applicable to software from Linksys
re made available at the Linksys public web site at:
. For your convenience of reference, a
copy of the Linksys Software License Agreement and the
ain open source code licenses used by Linksys in its
roducts are contained in the Schedules below
or
For
Schedule 1 - Linksys Software License Agreemen
HIS LICENSE AGREEMENT IS BETWEEN YOU AND
CISCO-LINKSYS LLC OR ONE OF ITS AFFILIATES CISCO
YSTEMS-LINKSYS (ASIA) PTE LTD. OR CISCO-LINKSYS
K.K. (“LINKSYS”) LICENSING THE SOFTWARE INSTEAD OF
CISCO-LINKSYS LLC. BY DOWNLOADING OR INSTALLING
HE SOFTWARE, OR USING THE PRODUCT CONTAINING
HE SOFTWARE, YOU ARE CONSENTING TO BE BOUND BY
HIS AGREEMENT. IF YOU DO NOT AGREE TO ALL OF THESE
ERMS, THEN YOU MAY NOT DOWNLOAD, INSTALL OR USE
HE SOFTWARE. YOU MAY RETURN UNUSED SOFTWARE
(OR, IF THE SOFTWARE IS SUPPLIED AS PART OF ANOTHER
PRODUCT, THE UNUSED PRODUCT) FOR A FULL REFUND
UP TO 30 DAYS AFTER ORIGINAL PURCHASE, SUBJECT T
HE RETURN PROCESS AND POLICIES OF THE PARTY FROM
HICH YOU PURCHASED SUCH PRODUCT OR SOFTWARE
L
of the Linksys product containing the Software (“You”)
embedded in or (where authorized in the applicable
documentation) for communication with such product.
except to a person or entity to which you transfer
ownership of the complete Linksys product containing
the Software, provided you permanently transfer all rights
copies of the Software, and the recipient agrees to the
terms of this Agreement
with the applicable Linksys product, excluding technolog
or an authorized reseller, provided you already hold a
valid license to the original software and have paid an
Protection of Information. The Software and
or modify the Software or decompile, decrypt, reverse
engineer or disassemble the Software (except to the
extent expressly permitted by law notwithstanding this
such trade secrets or copyrighted material in any form
to any third party. Title to and ownership of the Software
solely with Linksys or its suppliers
Collection and Processing of Information. You agree that
Linksys and/or its affiliates may, from time to time, collect
or the Software and/or your use of either in order (i) to
enable Linksys to offer you Upgrades; (ii) to ensure that
. Subject to the terms and conditions of this
greement, Linksys grants the original end user purchaser
nonexclusive license to use the Software solely as
his license may not be sublicensed, and is not transferable
nder this Agreement and do not retain any full or partial
Software” includes, and this Agreement will apply to
a)the software of Linksys or its suppliers provided in or
rom the open source community, and (b) any upgrades,
pdates, bug fixes or modified versions (“Upgrades”) or
ackup copies of the Software supplied to You by Linksys
pplicable fee for the Upgrade.
ocumentation contain trade secrets and/or copyrighte
aterials of Linksys or its suppliers. You will not cop
rovision), and You will not disclose or make available
nd documentation and any portion thereof, will remain
nd process information about your Linksys product and
44
Page 46

Appendix F
f
/
,
.
lly
lly
h
ly.
pygp
y
.
.
.
,
T
y
.
Users.
.
d
T
.
dule 2
pggpygp
E
A
.
T
y
Software License Agreement
your Linksys product and/or the Software is being used in
ccordance with the terms of this Agreement; (iii) to provide
mprovements to the way Linksys delivers technology to
you and to other Linksys customers; (iv) to enable Linksys
to comply with the terms of any agreements it has with
ny third parties regarding your Linksys product and/or
oftware and/or (v) to enable Linksys to comply with all
pplicable laws and/or regulations, or the requirements
o
any regulatory authority or government agency.
Linksys and/ or its affiliates may collect and process
this information provided that it does not identify you
ersonally. Your use of your Linksys product and/or the
oftware constitutes this consent by you to Linksys and
or its affiliates’ collection and use of such information and
or EEA customers, to the transfer of such information to a
location outside the EEA
Software Upgrades etc.If the Software enables you to
eceive Upgrades, you may elect at any time to receive
these Upgrades either automatically or manually. If you
elect to receive Upgrades manua
elect not to receive or be notified of any Upgrades, you
ay expose your Linksys product and/or the Software
to serious security threats and/or some features within
our Linksys product and/or Software may become
naccessible. There may be circumstances where we
pply an Upgrade automatica
changes in legislation, legal or regulatory requirements
or as a result of requirements to comply with the terms
of any agreements Linksys has with any third parties
egarding your Linksys product and/or the Software. You
will always be notified of any Upgrades being delivered
to you. The terms of this license will apply to any such
Upgrade unless the Upgrade in question is accompanied
y a separate license, in which event the terms of that
icense will app
Open Source Software.The GPL or other open source
code incorporated into the Software and the open source
license for such source code are available for free download
t
of the GPL or other open source code in this Software on a
CD, Linksys will mail to You a CD with such code for $9.99
lus the cost of shipping, upon request
Term and Termination. You may terminate this License
t any time by destroying all copies of the Software
nd documentation. Your rights under this License will
terminate immediately without notice from Linksys if You
ail to comply with any provision of this Agreement
Limited Warranty. The warranty terms and period
specified in the applicable Linksys Product User Guide
shall also apply to the Software
Disclaimer of Liabilities. IN NO EVENT WILL LINKSYS OR
ITS SUPPLIERS BE LIABLE FOR ANY LOST DATA, REVENUE
R PROFIT, OR FOR SPECIAL, INDIRECT, CONSEQUENTIAL
INCIDENTAL OR PUNITIVE DAMAGES, REGARDLESS OF
CAUSE (INCLUDING NEGLIGENCE), ARISING OUT OF
or you otherwise
in order to comply wit
. If You would like a cop
OR RELATED TO THE USE OF OR INABILITY TO USE THE
FTWARE, EVEN IF LINKSYS HAS BEEN ADVISED OF
HE POSSIBILITY OF SUCH DAMAGES. IN NO EVENT WILL
LINKSYS’ LIABILITY EXCEED THE AMOUNT PAID BY YOU
FOR THE PRODUCT. The foregoing limitations will appl
even if any warranty or remedy under this Agreement fails
of its essential purpose. Some jurisdictions do not allow
the exclusion or limitation of incidental or consequential
damages, so the above limitation or exclusion may not
pply to You.
xport. Software, including technical data, may be subject
to U.S. export control laws and regulations and/or export
or import regulations in other countries. You agree to
comply strictly with all such laws and regulations
.S. Government
qualify as “commercial items” as defined at 48 C.F.R. 2.101
nd 48 C.F.R. 12.212. All Government users acquire the
oftware and documentation with only those rights
herein that apply to non-governmental customers
General Terms. This Agreement will be governed by an
construed in accordance with the laws of the State of
California, without reference to conflict of laws principles.
he United Nations Convention on Contracts for the
International Sale of Goods will not apply. If any portion
of this Agreement is found to be void or unenforceable,
the remaining provisions will remain in full force and
effect. This Agreement constitutes the entire agreement
etween the parties with respect to the Software and
supersedes any conflicting or additional terms contained
n any purchase order or elsewhere
END OF SCHEDULE 1
The Software and documentation
Sche
If this Linksys product contains open source software
licensed under Version 2 of the “GNU General Public
License” then the license terms below in this Schedule 2
will apply to that open source software. The license terms
elow in this Schedule 2 are from the public web site at
GNU GENERAL PUBLIC LICENS
Version 2, June 1991
Copyright © 1989, 1991 Free Software Foundation, Inc.
1 Franklin Street, Fifth Floor, Boston, MA 02110-1301,
US
Everyone is permitted to copy and distribute verbatim
copies of this license document, but changing it is not
llowed
reamble
he licenses for most software are designed to take awa
our freedom to share and change it. By contrast, the
45
Page 47

Appendix F
g
T
y
T
T
.
ON
T
/
d
y
y
y
y
Software License Agreement
GNU General Public License is intended to guarantee your
reedom to share and change free software–to make sure
the software is free for all its users. This General Public
License applies to most of the Free Software Foundation’s
software and to any other program whose authors
commit to usin
software is covered by the GNU Lesser General Public
License instead.) You can apply it to your programs, too.
hen we speak of free software, we are referring to
reedom, not price. Our General Public Licenses are
designed to make sure that you have the freedom to
distribute copies of free software (and charge for this
service if you wish), that you receive source code or can
get it if you want it, that you can change the software or
se pieces of it in new free programs; and that you know
you can do these things.
o protect your rights, we need to make restrictions that
orbid anyone to deny you these rights or to ask you to
surrender the rights. These restrictions translate to certain
esponsibilities for you if you distribute copies of the
software, or if you modify it.
For example, if you distribute copies of such a program,
whether gratis or for a fee, you must give the recipients
ll the rights that you have. You must make sure that they,
too, receive or can get the source code. And you must
show them these terms so they know their rights.
e protect your rights with two steps: (1) copyright the
software, and (2) offer you this license which gives you
legal permission to copy, distribute and/or modify the
software.
lso, for each author’s protection and ours, we want to
ake certain that everyone understands that there is no
warranty for this free software. If the software is modified
y someone else and passed on, we want its recipients
to know that what they have is not the original, so that
ny problems introduced by others will not reflect on the
original authors’ reputations.
Finally, any free program is threatened constantly b
software patents. We wish to avoid the danger that
edistributors of a free program will individually obtain
atent licenses, in effect making the program proprietary.
o prevent this, we have made it clear that any patent must
e licensed for everyone’s free use or not licensed at all.
he precise terms and conditions for copying, distribution
nd modification follow
it. (Some other Free Software Foundation
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND
DIFICATI
his License applies to any program or other work
which contains a notice placed by the copyright
holder saying it may be distributed under the terms
of this General Public License. The “Program”, below,
efers to any such program or work, and a “work
ased on the Program” means either the Program
or any derivative work under copyright law: that is
to say, a work containing the Program or a portion
of it, either verbatim or with modifications and
or translated into another language. (Hereinafter,
translation is included without limitation in the term
modification”.) Each licensee is addressed as “you”.
ctivities other than copying, distribution an
odification are not covered by this License; the
re outside its scope. The act of running the Program
s not restricted, and the output from the Program is
covered only if its contents constitute a work based on
the Program (independent of having been made by
unning the Program). Whether that is true depends
on what the Program does.
You may copy and distribute verbatim copies of the
Program’s source code as you receive it, in any medium,
rovided that you conspicuously and appropriatel
ublish on each copy an appropriate copyright
otice and disclaimer of warranty; keep intact all the
tices that refer to this License and to the absence
of any warranty; and give any other recipients of the
Program a copy of this License along with the Program.
You may charge a fee for the physical act of transferring
copy, and you may at your option offer warrant
rotection in exchange for a fee.
You may modify your copy or copies of the Program
or any portion of it, thus forming a work based on the
Program, and copy and distribute such modifications
or work under the terms of Section 1 above, provided
that you also meet all of these conditions:
You must cause the modified files to carr
rominent notices stating that you changed the
iles and the date of any change.
You must cause any work that you distribute or
ublish, that in whole or in part contains or is
derived from the Program or any part thereof, to be
licensed as a whole at no charge to all third parties
nder the terms of this License.
46
Page 48

Appendix F
d
lly
T
T
ff
T
.
lly
Software License Agreement
If the modified program normally reads commandsc.
nteractively when run, you must cause it, when
started running for such interactive use in the most
ordinary way, to print or display an announcement
ncluding an appropriate copyright notice an
notice that there is no warranty (or else, saying
that you provide a warranty) and that users may
edistribute the program under these conditions,
nd telling the user how to view a copy of
this License. (Exception: if the Program itself is
nteractive but does not norma
nnouncement, your work based on the Program
s not required to print an announcement.)
hese requirements apply to the modified work as
whole. If identifiable sections of that work are not
derived from the Program, and can be reasonably
considered independent and separate works in
themselves, then this License, and its terms, do not
pply to those sections when you distribute them as
separate works. But when you distribute the same
sections as part of a whole which is a work based on
the Program, the distribution of the whole must be on
the terms of this License, whose permissions for other
licensees extend to the entire whole, and thus to each
nd every part regardless of who wrote it.
hus, it is not the intent of this section to claim rights
or contest your rights to work written entirely by you;
ather, the intent is to exercise the right to control the
distribution of derivative or collective works based on
the Program.
In addition, mere aggregation of another work not
ased on the Program with the Program (or with a
work based on the Program) on a volume of a storage
or distribution medium does not bring the other work
nder the scope of this License.
You may copy and distribute the Program (or a
work based on it, under Section 2) in object code or
executable form under the terms of Sections 1 and 2
bove provided that you also do one of the following:
ccompany it with the complete corresponding
.
achine-readable source code, which must be
istributed under the terms of Sections 1 and 2
bove on a medium customarily used for software
nterchange; or,
ccompany it with a written offer, valid for at least
three years, to give any third party, for a charge
o more than your cost of physically performing
source distribution, a complete machine-readable
copy of the corresponding source code, to be
distributed under the terms of Sections 1 and 2
bove on a medium customarily used for software
nterchange; or,
print such an
ccompany it with the information you received asc.
to the offer to distribute corresponding source code.
(This alternative is allowed only for noncommercial
distribution and only if you received the program
n object code or executable form with such an
er, in accord with Subsection b above.)
o
he source code for a work means the preferred form
of the work for making modifications to it. For an
executable work, complete source code means all
the source code for all modules it contains, plus any
ssociated interface definition files, plus the scripts
sed to control compilation and installation of the
executable. However, as a special exception, the source
code distributed need not include anything that is
ormally distributed (in either source or binary form)
with the major components (compiler, kernel, and so
on) of the operating system on which the executable
uns, unless that component itself accompanies the
executable.
If distribution of executable or object code is made
offering access to copy from a designated place,
then offering equivalent access to copy the source
code from the same place counts as distribution of
the source code, even though third parties are not
compelled to copy the source along with the object
code.
You may not copy, modify, sublicense, or distribute
the Program except as expressly provided under
this License. Any attempt otherwise to copy, modify,
sublicense or distribute the Program is void, and will
utomatically terminate your rights under this License.
However, parties who have received copies, or rights,
rom you under this License will not have their licenses
terminated so long as such parties remain in full
compliance.
You are not required to accept this License, since you
have not signed it. However, nothing else grants you
ermission to modify or distribute the Program or its
derivative works. These actions are prohibited by law if
you do not accept this License. Therefore, by modifying
or distributing the Program (or any work based on the
Program), you indicate your acceptance of this License
to do so, and all its terms and conditions for copying,
distributing or modifying the Program or works based
n it
Each time you redistribute the Program (or any work
ased on the Program), the recipient automatica
eceives a license from the original licensor to copy,
distribute or modify the Program subject to these
terms and conditions. You may not impose any further
estrictions on the recipients’ exercise of the rights
granted herein. You are not responsible for enforcing
compliance by third parties to this License.
47
Page 49

Appendix F
.
T
ly
p
T
h
f f
.
,
.
T
O
,
,
,
O
S
2
3
pgg gp
Software License Agreement
If, as a consequence of a court judgment or allegation7
of patent infringement or for any other reason (not
limited to patent issues), conditions are imposed on
you (whether by court order, agreement or otherwise)
that contradict the conditions of this License, they do
ot excuse you from the conditions of this License. If
you cannot distribute so as to satisfy simultaneously
our obligations under this License and any other
ertinent obligations, then as a consequence you
ay not distribute the Program at all. For example,
a patent license would not permit royalty-free
edistribution of the Program by all those who receive
copies directly or indirectly through you, then the only
way you could satisfy both it and this License would be
to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or
nenforceable under any particular circumstance,
the balance of the section is intended to apply and
the section as a whole is intended to apply in other
circumstances.
It is not the purpose of this section to induce you to
nfringe any patents or other property right claims or
to contest validity of any such claims; this section has
the sole purpose of protecting the integrity of the free
software distribution system, which is implemented
public license practices. Many people have
ade generous contributions to the wide range of
software distributed through that system in reliance
on consistent application of that system; it is up to
the author/donor to decide if he or she is willing to
distribute software through any other system and a
icensee cannot impose that choice.
his section is intended to make thoroughly clear
what is believed to be a consequence of the rest of this
License.
If the distribution and/or use of the Program is
estricted in certain countries either by patents or by
copyrighted interfaces, the original copyright holder
who places the Program under this License may add an
explicit geographical distribution limitation excluding
those countries, so that distribution is permitted on
n or among countries not thus excluded. In such case,
this License incor
the body of this License.
he Free Software Foundation may publish revised
nd/or new versions of the General Public License
rom time to time. Such new versions will be similar in
spirit to the present version, but may differ in detail to
ddress new problems or concerns.
version is given a distinguishing version number.
Eac
If the Program specifies a version number of this
License which applies to it and “any later version”, you
have the option o
either of that version or of any later version published
y the Free Software Foundation. If the Program does
orates the limitation as if written in
ollowing the terms and conditions
ot specify a version number of this License, you
ay choose any version ever published by the Free
tware Foundation
If you wish to incorporate parts of the Program into
other free programs whose distribution conditions are
different, write to the author to ask for permission. For
software which is copyrighted by the Free Software
Foundation, write to the Free Software Foundation; we
sometimes make exceptions for this. Our decision will
e guided by the two goals of preserving the free status
of all derivatives of our free software and of promoting
the sharing and reuse of software generally.
WARRANTY
BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE
1
HERE IS NO WARRANTY FOR THE PROGRAM, TO THE
EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT
HEN OTHERWISE STATED IN WRITING THE COPYRIGHT
HOLDERS AND/OR OTHER PARTIES PROVIDE THE
GRAM “AS IS” WITHOUT WARRANTY OF ANY
PR
KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING
BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE PROGRAM IS WITH YOU.
HOULD THE PROGRAM PROVE DEFECTIVE, YOU
SSUME THE COST OF ALL NECESSARY SERVICING
REPAIR OR CORRECTION.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR
GREED TO IN WRITING WILL ANY COPYRIGHT HOLDER
R ANY OTHER PARTY WHO MAY MODIFY AND/OR
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE,
BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL
DAMAGES ARISING OUT OF THE USE OR INABILITY T
USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO
LOSS OF DATA OR DATA BEING RENDERED INACCURATE
R LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR
FAILURE OF THE PROGRAM TO OPERATE WITH ANY
OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER
PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
UCH DAMAGES.
END OF TERMS AND CONDITION
END OF SCHEDULE
Schedule
If this Linksys product contains open source software
licensed under Version 2.1 of the “GNU Lesser General Public
License” then the license terms below in this Schedule 3
will apply to that open source software. The license terms
elow in this Schedule 3 are from the public web site at
48
Page 50

Appendix F
E
9
A
.
]
T
y
.
T
y
y
y
f f
.
T
.
h
.
/
.
T
ff
y
.
y.
.
l
j
.
-
.
Software License Agreement
GNU LESSER GENERAL PUBLIC LICENS
Version 2.1, February 199
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
1 Franklin Street, Fifth Floor, Boston, MA 02110-1301,
US
Everyone is permitted to copy and distribute verbatim
copies of this license document, but changing it is not
llowed
This is the first released version of the Lesser GPL. It also
counts as the successor of the GNU Library Public License,
version 2, hence the version number 2.1.
reamble
he licenses for most software are designed to take awa
our freedom to share and change it. By contrast, the GNU
General Public Licenses are intended to guarantee your
reedom to share and change free software—to make
sure the software is free for all its users
his license, the Lesser General Public License, applies to
some specially designated software packages—typicall
libraries—of the Free Software Foundation and other
uthors who decide to use it. You can use it too, but we
suggest
or the ordinary General Public License is the better strateg
to use in any particular case, based on the explanations
elow.
hen we speak of free software, we are referring to
reedom of use, not price. Our General Public Licenses
re designed to make sure that you have the freedom
to distribute copies o
service if you wish); that you receive source code or can
get it if you want it; that you can change the software and
se pieces of it in new free programs; and that you are
nformed that you can do these things
o protect your rights, we need to make restrictions that
orbid distributors to deny you these rights or to ask you
to surrender these rights. These restrictions translate to
certain responsibilities for you if you distribute copies of
the library or if you modify it
For example, if you distribute copies of the library,
whether gratis or for a fee, you must give the recipients
ll the rights that we gave you. You must make sure that
they, too, receive or can get the source code. If you link
ot
object files to the recipients, so that they can relink them
with the library after making changes to the library and
ecompiling it. And you must show them these terms so
they know their rights
e protect your rights with a two-step method: (1) we
copyright the library, and (2) we offer you this license,
which gives you legal permission to copy, distribute and
or modify the library
ou first think carefully about whether this license
ree software (and charge for this
er code with the library, you must provide complete
o protect each distributor, we want to make it very clear
that there is no warranty for the free library. Also, if the
library is modified by someone else and passed on, the
ecipients should know that what they have is not the
original version, so that the original author’s reputation
will not be a
y others.
Finall
existence of any free program. We wish to make sure
that a company cannot effectively restrict the users of
free program by obtaining a restrictive license from a
atent holder. Therefore, we insist that any patent license
obtained for a version of the library must be consistent
with the full freedom of use specified in this license
Most GNU software, including some libraries, is covered
y the ordinary GNU General Public License. This license,
the GNU Lesser General Public License, applies to certain
designated libraries, and is quite different from the
ordinary General Public License. We use this license for
certain libraries in order to permit linking those libraries
nto non-free programs.
hen a program is linked with a library, whether
statically or using a shared library, the combination of
the two is legally speaking a combined work, a derivative
of the original library. The ordinary General Public
License therefore permits such linking only if the entire
combination fits its criteria of freedom. The Lesser General
Public License permits more lax criteria for linking other
code with the librar
e call this license the “Lesser” General Public License
ecause it does Less to protect the user’s freedom than
the ordinary General Public License. It also provides
other free software developers Less of an advantage over
competing non-free programs. These disadvantages are
the reason we use the ordinary General Public License
or many libraries. However, the Lesser license provides
dvantages in certain special circumstances
For example, on rare occasions, there may be a specia
eed to encourage the widest possible use of a certain
library, so that it becomes a de-facto standard. To achieve
this, non-free programs must be allowed to use the library.
more frequent case is that a free library does the same
ob as widely used non-free libraries. In this case, there is
little to gain by limiting the free library to free software
only, so we use the Lesser General Public License
In other cases, permission to use a particular library in non
ree programs enables a greater number of people to use
large body of free software. For example, permission to
se the GNU C Library in non-free programs enables many
ore people to use the whole GNU operating system, as
well as its variant, the GNU/Linux operating system
lthough the Lesser General Public License is Less
rotective of the users’ freedom, it does ensure that the
ser of a program that is linked with the Library has the
ected by problems that might be introduced
, software patents pose a constant threat to the
49
Page 51

Appendix F
y.
T
.
SE
ON
T
y
.
T
y
)
y.
g
.
o
y.
.
:
T
.
)
.
)
ll-
-
y
)
T
y
.
Software License Agreement
reedom and the wherewithal to run that program using a
odified version of the Librar
he precise terms and conditions for copying, distribution
nd modification follow. Pay close attention to the
difference between a “work based on the library” and a
work that uses the library”. The former contains code
derived from the library, whereas the latter must be
combined with the library in order to run
NU LESSER GENERAL PUBLIC LICEN
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND
DIFICATI
his License Agreement applies to any software librar
or other program which contains a notice placed by
the copyright holder or other authorized party saying
t may be distributed under the terms of this Lesser
General Public License (also called “this License”). Each
icensee is addressed as “you”.
“library” means a collection of software functions
nd/or data prepared so as to be conveniently linked
with application programs (which use some of those
unctions and data) to form executables
he “Library”, below, refers to any such software library
or work which has been distributed under these terms.
“work based on the Library” means either the Librar
or any derivative work under copyright law: that is to
say, a work containing the Library or a portion of it,
either verbatim or with modifications and/or translated
straightforwardly into another language. (Hereinafter,
translation is included without limitation in the term
modification”.
Source code” for a work means the preferred form of
the work for making modifications to it. For a library,
complete source code means all the source code for
ll modules it contains, plus any associated interface
definition files, plus the scripts used to control
compilation and installation of the librar
ctivities other than copying, distribution and
odification are not covered by this License; they are
outside its scope. The act of running a program usin
the Library is not restricted, and output from such a
rogram is covered only if its contents constitute a
work based on the Library (independent of the use
of the Library in a tool for writing it). Whether that is
true depends on what the Library does and what the
rogram that uses the Library does
You may copy and distribute verbatim copies of the
Library’s complete source code as you receive it, in
ny medium, provided that you conspicuously and
ppropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep
ntact all the notices that refer to this License and t
the absence of any warranty; and distribute a copy of
this License along with the Librar
You may charge a fee for the physical act of transferring
copy, and you may at your option offer warranty
rotection in exchange for a fee
You may modify your copy or copies of the Library or
ny portion of it, thus forming a work based on the
Library, and copy and distribute such modifications
or work under the terms of Section 1 above, provided
that you also meet all of these conditions
he modified work must itself be a software
library.
)
You must cause the files modified to carry
rominent notices stating that you changed the
iles and the date of any change
You must cause the whole of the work to bec
icensed at no charge to all third parties under the
terms of this License
If a facility in the modified Library refers to a functiond
or a table of data to be supplied by an application
rogram that uses the facility, other than as an
rgument passed when the facility is invoked, then
ou must make a good faith effort to ensure that,
n the event an application does not supply such
unction or table, the facility still operates, and
erforms whatever part of its purpose remains
eaningful.
(For example, a function in a library to compute
square roots has a purpose that is entirely we
defined independent of the application. Therefore,
ubsection 2d requires that any application
supplied function or table used by this function
ust be optional: if the application does not suppl
t, the square root function must still compute
square roots.
hese requirements apply to the modified work as
whole. If identifiable sections of that work are not
derived from the Library, and can be reasonabl
considered independent and separate works in
themselves, then this License, and its terms, do
ot apply to those sections when you distribute
them as separate works. But when you distribute
the same sections as part of a whole which is a
work based on the Library, the distribution of the
whole must be on the terms of this License, whose
ermissions for other licensees extend to the entire
whole, and thus to each and every part regardless
who wrote it
50
Page 52

Appendix F
T
ly
y.
.
a
.
d
y.
T
y.
.
.
.
.
y
.
y
)
f.
.
:
)
Software License Agreement
hus, it is not the intent of this section to claim
ights or contest your rights to work written entire
you; rather, the intent is to exercise the right to
control the distribution of derivative or collective
works based on the Librar
In addition, mere aggregation of another work
ot based on the Library with the Library (or with
work based on the Library) on a volume of a
storage or distribution medium does not bring the
other work under the scope of this License
You may opt to apply the terms of the ordinary GNU
General Public License instead of this License to
given copy of the Library. To do this, you must alter all
the notices that refer to this License, so that they refer
to the ordinary GNU General Public License, version
2, instead of to this License. (If a newer version than
version 2 of the ordinary GNU General Public License
has appeared, then you can specify that version
nstead if you wish.) Do not make any other change in
these notices
Once this change is made in a given copy, it is
rreversible for that copy, so the ordinary GNU General
Public License applies to all subsequent copies an
derivative works made from that cop
his option is useful when you wish to copy part of the
code of the Library into a program that is not a librar
You may copy and distribute the Library (or a portion
or derivative of it, under Section 2) in object code or
executable form under the terms of Sections 1 and
2 above provided that you accompany it with the
complete corresponding machine-readable source
code, which must be distributed under the terms of
ections 1 and 2 above on a medium customarily used
or software interchange
If distribution of object code is made by offering
ccess to copy from a designated place, then offering
equivalent access to copy the source code from the
same place satisfies the requirement to distribute
the source code, even though third parties are not
compelled to copy the source along with the object
code
program that contains no derivative of any portion
of the Library, but is designed to work with the Library
being compiled or linked with it, is called a “work
that uses the Library”. Such a work, in isolation, is not
derivative work of the Library, and therefore falls
outside the scope of this License
However, linking a “work that uses the Library” with
the Library creates an executable that is a derivative
of the Library (because it contains portions of the
Library), rather than a “work that uses the library”. The
executable is therefore covered by this License. Section
states terms for distribution of such executables
hen a “work that uses the Library” uses material from
header file that is part of the Library, the object code
or the work may be a derivative work of the Librar
even though the source code is not. Whether this is
true is especially significant if the work can be linked
without the Library, or if the work is itself a library. The
threshold for this to be true is not precisely defined by
aw
If such an object file uses only numerical parameters,
data structure layouts and accessors, and small macros
nd small inline functions (ten lines or less in length),
then the use of the object file is unrestricted, regardless
of whether it is legally a derivative work. (Executables
containing this object code plus portions of the Librar
will still fall under Section 6.
Otherwise, if the work is a derivative of the Library, you
ay distribute the object code for the work under the
terms of Section 6. Any executables containing that
work also fall under Section 6, whether or not they are
linked directly with the Library itsel
s an exception to the Sections above, you may also
combine or link a “work that uses the Library” with the
Library to produce a work containing portions of the
Library, and distribute that work under terms of your
choice, provided that the terms permit modification
of the work for the customer’s own use and reverse
engineering for debugging such modifications
You must give prominent notice with each copy of
the work that the Library is used in it and that the
Library and its use are covered by this License. You
ust supply a copy of this License. If the work during
execution displays copyright notices, you must include
the copyright notice for the Library among them, as
well as a reference directing the user to the copy of this
License. Also, you must do one of these things
ccompany the work with the complete
corresponding machine-readable source code
or the Library including whatever changes were
sed in the work (which must be distributed
nder Sections 1 and 2 above); and, if the work
s an executable linked with the Library, with the
complete machine-readable “work that uses the
Library”, as object code and/or source code, so that
the user can modify the Library and then relink
to produce a modified executable containing the
odified Library. (It is understood that the user
who changes the contents of definitions files in the
Library will not necessarily be able to recompile the
lication to use the modified definitions.
51
Page 53

Appendix F
y
y
o
.
)
.
)
)
y.
y
lly
.
.
.
:
above.
.
d
lly
.
.
.
y
.
.
y
ld
.
u
.
Use a suitable shared library mechanism for linking
)
with the Library. A suitable mechanism is one that
(1) uses at run time a copy of the library alread
resent on the user’s computer system, rather than
copying library functions into the executable, and
(2) will operate properl
the library, if the user installs one, as long as the
odified version is interface-compatible with the
versi
n that the work was made with
ccompany the work with a written offer, validc
or at least three years, to give the same user the
aterials specified in Subsection 6a, above, for a
charge no more than the cost of performing this
istribution
If distribution of the work is made by offering accessd
to copy from a designated place, offer equivalent
ccess to copy the above specified materials from
the same place.
Verify that the user has already received a copy of e
these materials or that you have already sent this
ser a cop
For an executable, the required form of the “work that
ses the Library” must include any data and utilit
rograms needed for reproducing the executable from
t. However, as a special exception, the materials to be
istributed need not include anything that is norma
distributed (in either source or binary form) with the
ajor components (compiler, kernel, and so on) of the
operating system on which the executable runs, unless
that component itself accompanies the executable
It may happen that this requirement contradicts the
license restrictions of other proprietary libraries that
do not normally accompany the operating system.
uch a contradiction means you cannot use both
them and the Library together in an executable that
ou distribute
You may place library facilities that are a work based7
on the Library side-by-side in a single library together
with other library facilities not covered by this License,
nd distribute such a combined library, provided that
the separate distribution of the work based on the
Library and of the other library facilities is otherwise
ermitted, and provided that you do these two
things
ccompany the combined library with a copy of the
same work based on the Library, uncombined with
ny other library facilities. This must be distributed
nder the terms of the Sections
Give prominent notice with the combined library of
)
the fact that part of it is a work based on the Library,
nd explaining where to find the accompanying
ncombined form of the same work
with a modified version of
Software License Agreement
You may not copy, modify, sublicense, link with, or
istribute the Library except as expressly provide
nder this License. Any attempt otherwise to copy,
odify, sublicense, link with, or distribute the Library
s void, and will automatica
nder this License. However, parties who have received
copies, or rights, from you under this License will not
ave their licenses terminated so long as such parties
emain in full compliance
You are not required to accept this License, since you
ave not signed it. However, nothing else grants you
ermission to modify or distribute the Library or its
derivative works. These actions are prohibited by law if
ou do not accept this License. Therefore, by modifying
or distributing the Library (or any work based on the
Library), you indicate your acceptance of this License
to do so, and all its terms and conditions for copying,
distributing or modifying the Library or works based
on it
Each time you redistribute the Library (or any work
0
ased on the Library), the recipient automaticall
eceives a license from the original licensor to copy,
distribute, link with or modify the Library subject
to these terms and conditions. You may not impose
ny further restrictions on the recipients’ exercise of
the rights granted herein. You are not responsible
or enforcing compliance by third parties with this
License
If, as a consequence of a court judgment or allegation
1
of patent infringement or for any other reason (not
limited to patent issues), conditions are imposed on
ou (whether by court order, agreement or otherwise)
that contradict the conditions of this License, they do
ot excuse you from the conditions of this License. If
ou cannot distribute so as to satisfy simultaneousl
our obligations under this License and any other
ertinent obligations, then as a consequence you may
ot distribute the Library at all. For example, if a patent
license would not permit royalty-free redistribution of
the Library by all those who receive copies directly or
ndirectly through you, then the only way you cou
satisfy both it and this License would be to refrain
entirely from distribution of the Library
If any portion of this section is held invalid or
nenforceable under any particular circumstance,
the balance of the section is intended to apply, and
the section as a whole is intended to apply in other
circ
mstances
It is not the purpose of this section to induce you to
nfringe any patents or other property right claims or
to contest validity of any such claims; this section has
the sole purpose of protecting the integrity of the free
software distribution system which is implemented
public license practices. Many people have
ade generous contributions to the wide range of
terminate your rights
52
Page 54

Appendix F
.
T
.
.
T
f
h
.
.
Y
,
.
T
,
O
T
.
,
T
.
S
3
:
T
ppg
T
y
.
T
.
ll
ppg
T
.
Software License Agreement
software distributed through that system in reliance
on consistent application of that system; it is up to
the author/donor to decide if he or she is willing to
distribute software through any other system and a
icensee cannot impose that choice
his section is intended to make thoroughly clear
what is believed to be a consequence of the rest of this
License
If the distribution and/or use of the Library is restricted
n certain countries either by patents or by copyrighted
nterfaces, the original copyright holder who places
the Library under this License may add an explicit
geographical distribution limitation excluding those
countries, so that distribution is permitted only in or
mong countries not thus excluded. In such case, this
License incorporates the limitation as if written in the
ody of this License
he Free Software Foundation may publish revised
nd/or new versions of the Lesser General Public
License
similar in spirit to the present version, but may differ in
detail to address new problems or concerns.
Eac
If the Library specifies a version number of this License
which applies to it and “any later version”, you have the
option of following the terms and conditions either of
that version or of any later version published by the Free
oftware Foundation. If the Library does not specify a
icense version number, you may choose any version
ever published by the Free Software Foundation
rom time to time. Such new versions will be
version is given a distinguishing version number.
BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE
5
HERE IS NO WARRANTY FOR THE LIBRARY, TO THE
EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT
HEN OTHERWISE STATED IN WRITING THE COPYRIGHT
HOLDERS AND/OR OTHER PARTIES PROVIDE THE
LIBRARY “AS IS” WITHOUT WARRANTY OF ANY KIND,
EITHER EXPRESSED OR IMPLIED
NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS F
PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND
PERFORMANCE OF THE LIBRARY IS WITH YOU. SHOULD
HE LIBRARY PROVE DEFECTIVE, YOU ASSUME THE
COST OF ALL NECESSARY SERVICING, REPAIR OR
CORRECTION
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW
OR AGREED TO IN WRITING WILL ANY COPYRIGHT
HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY
ND/OR REDISTRIBUTE THE LIBRARY AS PERMITTED
BOVE, BE LIABLE TO YOU FOR DAMAGES
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE
USE OR INABILITY TO USE THE LIBRARY (INCLUDING
BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING
RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE LIBRARY
O OPERATE WITH ANY OTHER SOFTWARE), EVEN IF
CH HOLDER OR OTHER PARTY HAS BEEN ADVISED
OF THE POSSIBILITY OF SUCH DAMAGES
END OF TERMS AND CONDITION
END OF SCHEDULE
INCLUDING, BUT
R A PARTICULAR
If you wish to incorporate parts of the Library into
4
other free programs whose distribution conditions are
ncompatible with these, write to the author to ask for
ermission. For software which is copyrighted by the
Free Software Foundation, write to the Free Software
Foundation; we sometimes make exceptions for
this. Our decision will be guided by the two goals of
reserving the free status of all derivatives of our free
software and of promoting the sharing and reuse of
software generally.
NO WARRANT
Schedule 4
If this Linksys product contains open source software
licensed under the OpenSSL license
his product includes software developed by the
OpenSSL Project for use in the OpenSSL Toolkit.
his product includes cryptographic software written b
Eric Young (eay@cryptsoft.com)
his product includes software written by Tim Hudson
(tjh@cryptsoft.com)
In addition, if this Linksys product contains open
source software licensed under the OpenSSL license
then the license terms below in this Schedule 3 wi
pply to that open source software. The license terms
elow in this Schedule 3 are from the public web site at
he OpenSSL toolkit stays under a dual license, i.e. both
the conditions of the OpenSSL License and the original
SLeay license apply to the toolkit. See below for the
ctual license texts. Actually both licenses are BSD-style
Open Source licenses. In case of any license issues related
to OpenSSL please contact openssl-core@openssl.org
53
Page 55

Appendix F
.
:
.
.
.
p
(
ppg
Th
g.
.
(
ppg
T
,
O
,
,
T
.
T
.
Th
.
T
T
T
j
.
.
d.
y
.
:
.
.
”
T
@
T
Software License Agreement
enSSL License
Copyright © 1998-2007 The OpenSSL Project. All rights
eserved
Redistribution and use in source and binary forms, with
or without modification, are permitted provided that the
ollowing conditions are met
Redistributions of source code must retain the above
copyright notice, this list of conditions and the
ollowing disclaimer
Redistributions in binary form must reproduce the2
bove copyright notice, this list of conditions and the
ollowing disclaimer in the documentation and/or
other materials provided with the distribution
ll advertising materials mentioning features or
se of this software must display the following
cknowledgment: “This product includes software
developed by the OpenSSL Project for use in the
enSSL Toolkit.
O
e names “OpenSSL Toolkit” and “OpenSSL Project”
ust not be used to endorse or promote products
derived from this software without prior written
ermission. For written permission, please contact
openssl-core@openssl.or
Products derived from this software may not be called
OpenSSL” nor may “OpenSSL” appear in their names
without prior written permission of the OpenSSL
roject
Redistributions of any form whatsoever must retain
the following acknowledgment: “ This product includes
software developed by the OpenSSL Project for use in
the OpenSSL Toolkit
HIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT
AS IS” AND ANY EXPRESSED OR IMPLIED WARRANTIES
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED
ARRANTIES OF MERCHANTABILITY AND FITNESS FOR
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
HALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE
LIABLE F
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING
BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS;
OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND
N ANY THEORY OF LIABILITY, WHETHER IN CONTRACT
TRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR
OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF
HIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
CH DAMAGE
his product includes cryptographic software written by
Eric Young (eay@cryptsoft.com). This product includes
software written by Tim Hudson (tjh@cryptsoft.com)
R ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
”
”
riginal SSLeay License
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com)All
ights reserved.
is package is an SSL implementation written by Eric
Young (eay@cryptsoft.com)
he implementation was written so as to conform with
Netscape’s SSL.
his library is free for commercial and non-commercial
se as long as the following conditions are adhered to.
he following conditions apply to all code found in this
distribution, be it the RC4, RSA, lhash, DES, etc., code; not
ust the SSL code. The SSL documentation included with
this distribution is covered by the same copyright terms
except that the holder is Tim Hudson (tjh@cryptsoft
com)
Copyright remains Eric Young’s, and as such any Copyright
tices in the code are not to be remove
If this package is used in a product, Eric Young should be
given attribution as the author of the parts of the librar
sed. This can be in the form of a textual message at
rogram startup or in documentation (online or textual)
rovided with the package
Redistribution and use in source and binary forms, with
or without modification, are permitted provided that the
ollowing conditions are met
Redistributions of source code must retain the
copyright notice, this list of conditions and the
ollowing disclaimer
Redistributions in binary form must reproduce the
bove copyright notice, this list of conditions and the
ollowing disclaimer in the documentation and/or
other materials provided with the distribution
ll advertising materials mentioning features or
se of this software must display the following
cknowledgement:
This product includes cryptographic software written
Eric Young (eay@cryptsoft.com)
he word ‘cryptographic’ can be left out if the routines
rom the library being used are not cryptographic
elated.
If you include any Windows specific code (or a derivative
thereof) from the apps directory (application code)
ou must include an acknowledgement: “This product
ncludes software written by Tim Hudson (tjh
cryptsoft.com)”
HIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND
NY EXPRESS OR IMPLIED WARRANTIES, INCLUDING,
BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE
UTHOR OR CONTRIBUTORS BE LIABLE FOR ANY
54
Page 56

Appendix F
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY,
OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT
LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY
OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE,
EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The license and distribution terms for any publicly available
version or derivative of this code cannot be changed. i.e.
this code cannot simply be copied and put under another
distribution license [including the GNU Public License.]
END OF SCHEDULE 4
Software License Agreement
RSS-GEN 7.1.4:
User Manual for Transmitters with Detachable Antennas
The user manual of transmitter devices equipped with detachable antennas shall contain the following
information in a conspicuous location:
This device has been designed to operate with the antennas listed below, and having a maximum
gain of [2.4] dB. Antennas not included in this list or having a gain greater than [2.4] dB are strictly
prohibited for use with this device. The required antenna impedance is [50] ohms.
RSS-GEN 7.1.5
To reduce potential radio interference to other users, the antenna type and its gain should be so
chosen that the equivalent isotropically radiated power (e.i.r.p.) is not more than that permitted
for successful communication.
You are cautioned that changes or modifications not expressly approved by the party responsible for compliance could void your
authority to operate the equipment.
FCC RF Radiation Exposure Statement:
1. This Transmitter must not be co-located or operating in conjunction with any other antenna or transmitter.
REMARK
˜˘˘˘ʳˋ˃˅ˁ˄˄˵ʳʳˋ˃˅ˁ˄˄˺ʳ˸˴˼ʳ˹ʳ˻˼ʳ˷˶ʳ˼ʳ˻˸ʳ˨ˁ˦ˁ˔ˁʳ˼ʳ˹˼˴˸ˀ˿˼˼˸˷ʳʳ˶˻˴˸˿ʳ˄ʳ˻˺˻ʳ˄˄ˁ
ϘOperation is subject to the following two conditions:(1) this device may not cause
interference, and (2) this device must accept any interference, including interference
that may cause undesired operation of the device.”
REMARK
˜˘˘˘ʳˋ˃˅ˁ˄˄˵ʳʳˋ˃˅ˁ˄˄˺ʳ˸˴˼ʳ˹ʳ˻˼ʳ˷˶ʳ˼ʳ˻˸ʳ˖˴˴˷˴ʳ˼ʳ˹˼˴˸ˀ˿˼˼˸˷ʳʳ˶˻˴˸˿ʳ˄ʳ˻˺˻ʳ˄˄ˁ
55
 Loading...
Loading...