Page 1

User’s Guide
Gateway desktop series
- 1
Page 2

TABLE OF CONTENTS
Starting your computer 4
Registration ........................................................ 4
Software installation ........................................... 5
Recovery ............................................................ 5
Having trouble? .................................................. 5
Computer Basics 7
Safety and comfort ............................................. 7
Safety precautions ...................................... 7
Health precautions .................................... 10
Setting up your computer 12
Arranging a comfortable work area.................. 12
Adjusting your chair .................................. 12
Positioning your PC .................................. 13
Positioning your monitor ........................... 14
Positioning your keyboard......................... 14
Positioning your mouse............................. 14
Using your computer 16
Connecting the computer ................................. 16
Connect your mouse and keyboard.......... 16
Connect a monitor..................................... 17
Connect to a broadband network.............. 17
Connect to power...................................... 17
Turning on your computer ................................ 18
Turning off your computer ................................ 18
Using the optical drive ...................................... 18
To insert a disc into your computer's
optical drive:.............................................. 19
Taking care of your optical discs .............. 19
Upgrading your computer 20
Expanding through options .............................. 20
Connectivity options.................................. 20
2 - Table of Contents
Software 25
Using Windows and your software .................. 25
Welcome Center ...................................... 25
Internet security offer ............................... 25
Productivity software................................ 26
Gateway Recovery Management............. 26
Playing multimedia files............................ 26
AutoPlay................................................... 28
Playing downloaded files.......................... 29
Playing DVD movies ................................ 30
Playing Blu-ray movies............................. 31
Internet 32
First steps on the net ....................................... 32
Protecting your computer ......................... 32
Choose an Internet Service Provider ....... 32
Network connections ................................ 34
Surf the Net! ............................................. 37
Security .................................................... 40
Helpdesk 53
Safe computing................................................ 53
Maintenance............................................. 53
Updates.................................................... 60
Windows Remote Assistance................... 62
Frequently asked questions 63
Recovery 66
Gateway Recovery Management .................... 66
Creating recovery discs............................ 66
Recovering your system .................................. 69
Types of recovery..................................... 71
Page 3
Regulatory information 77
Environment 89
Software license 92
Index 95
Copyright © 2012.
All Rights Reserved.
Gateway desktop series user’s guide
Original Issue: 22 March 2012
Visit registration.gateway.com and discover the benefits of being a customer of
Gateway.
Remark: All images are for reference purposes only. Actual configuration may vary.
Table of Contents - 3
Page 4
STARTING YOUR COMPUTER
Thank you for purchasing this Gateway computer!
This guide has been designed to introduce you to the features of your
computer and assist in your computing experience.
After setting up and starting your computer, as shown in the setup
instructions, it will ask you questions that will help you connect to the
Internet. Your computer will then configure installed software.
REGISTRATION
When using your computer for the first time, it is recommended that you
register it. This gives you access to some useful benefits, such as:
• Faster service from our trained representatives.
• Membership in the Gateway community: receive promotions and
participate in customer surveys.
• The latest news from Gateway.
How to register
During the initial startup of your computer, a window will invite you to
register. Please fill in the information and click Next. The second window
you'll see contains optional fields that will help us to provide you with a
more personable customer service experience.
4 - Starting your computer
Page 5
Another option
Another way to register your Gateway product is to visit our website at
registration.gateway.com. Choose your country and follow the simple
instructions.
After registering, you will be sent a confirmation email with important
information that you should keep in a safe place.
SOFTWARE INSTALLATION
Your computer will automatically install software and prepare your
computer for use. This may take some time, please do not turn off your
computer; wait until the installation has finished.
RECOVERY
You should create recovery discs as soon as you are able. The Gateway
Recovery Management program allow you to create recovery discs and
then to restore or reinstall applications and drivers provided by Gateway.
You will need a pack of writable DVDs.
HAVING TROUBLE?
Gateway provides several options to support your purchase.
Gateway support
Make sure you write down your computer serial number, date and place of
purchase and model name on the area provided in this guide; save your
proof of purchase. Before you call us, please write down any error
Starting your computer - 5
Page 6
message that accompanies the problem, and have the computer in front of
you and switched on if possible. Having these items to hand when
contacting us will ensure better and quicker service.
Gateway website
Remember to visit www.gateway.com - Check out the support section for
up-to-date information, help, drivers and downloads.
Warranty and contact information
You can find information about the warranty for your computer and how to
contact technical support in your computer’s Warranty.
6 - Starting your computer
Page 7
COMPUTER BASICS
SAFETY AND COMFORT
Safety precautions
Please follow the guidelines below to use your computer comfortably and
to avoid health problems.
Computer environment
Make sure that the computer:
• Is used on a stable surface, stand or table. A fall can seriously damage
the computer.
• Is not used on a surface that vibrates, or used when taking part in sport,
exercise or other activities in a dynamic environment. Vibration or
movement can loosen fastenings, damage internal components and
even cause battery leakage.
• Is away from direct sunlight and sources of heat.
• Is away from magnetic fields or any device generating static electricity.
• Is kept at least 30 centimetres (one foot) away from a mobile phone.
• Is not in a dusty or damp environment.
• Is not used near water. Never spill liquids of any kind on or into your
computer.
• Is not placed on a carpet or any other surface that may have an
electrical charge.
Computer Basics - 7
Page 8
Cables
Make sure that:
• Cables are not strained and that there is no risk of people walking or
tripping over them.
• Other devices do not crush the cables.
• The power cable is connected to the computer before connecting the
power cable to the AC power outlet.
• The power cable is unplugged from the power outlet before
disconnecting the power cable from the computer.
• Three-pin power cords are connected to a grounded power outlet.
• The power outlet is easily accessible and as close to the computer as
possible (do not overload it with too many adapters).
If your computer uses an external AC adapter:
• Do not cover or place objects on the AC adapter. Allow the adapter to
cool properly during use by keeping it clear of objects.
• Only use the AC adapter that is supplied with your computer. Although
other adapters may look similar, using them can damage your computer.
If a replacement is required, use only parts certified for use with your
computer.
Cleaning your computer
• Always unplug your computer from the power outlet before cleaning it.
• Do not use liquid or aerosol cleaners, use a damp cloth instead.
• Never spray cleaning product directly on the screen.
8 - Computer Basics
Page 9
• If dust has accumulated inside your computer, do not use a vacuum
cleaner to remove it.
• If you spill liquid on your computer or any device attached to it, switch it
off immediately, unplug the power cord and make sure it is completely
dry before switching it on again. Wait overnight if necessary.
Note: If your computer includes slots for memory cards or expansion
devices, plastic ’dummies’ may be installed in the card slots. Dummies
protect unused slots from dust, metal objects or other particles. Save
the dummies for use when no cards are in the slots.
Servicing your computer
Do not attempt to service your computer yourself, as opening or removing
covers may expose you to dangerous voltage or other risks. Refer all
servicing to qualified service personnel.
Unplug your computer from the wall outlet and refer servicing to qualified
service personnel when:
• the power cord or plug is damaged, cut or frayed,
• liquid was spilled into the product,
• the product was exposed to rain or water,
• the product has been dropped or the case has been damaged,
• the product exhibits a distinct change in performance,
• the product does not operate normally after following the operating
instructions
Computer Basics - 9
Page 10
Note: Adjust only those controls that are covered by the operating
instructions, since improper adjustment of other controls may result in
damage and will often require extensive work by a qualified technician
to restore the product to normal condition.
Health precautions
• The computer and accessories may contain small parts. Keep them out
of the reach of small children.
• If you work or play for hours at a time, then make sure you take regular
breaks. Look away from the computer's screen once in a while. Do not
use your computer if you are tired.
• To protect your hearing, when using speakers or headphones, increase
volume gradually until you can hear clearly and comfortably; do not
increase the volume level after your ears have adjusted. Do not listen to
high volumes for extended periods. Do not increase the volume to block
out noisy surroundings; decrease the volume if you cannot hear people
speaking near you.
• Ensure that the computer’s ventilation slots and openings are never
obstructed or covered. Do not place the computer on a soft surface
(such as a carpet, chair or bed) that may block ventilation slots.
• Do not push objects of any kind into ventilation or case slots as they
may touch dangerous voltage points or short-out parts that may result in
a fire or electric shock.
• Some disorders of the hands, wrists, arms, neck, shoulders, legs and
back may be associated with, or aggravated by certain repetitive
10 - Computer Basics
Page 11

actions. To reduce your risk of developing these disorders, type with
your wrists straight and your hands and wrists floating above the
keyboard. If you experience periods of pain, tingling, numbness or other
discomfort, please contact your doctor.
• We advise that parents monitor the use of games by their children. If you
or your child experience any of the following symptoms: dizziness,
blurred vision, eye or muscle twitches, loss of consciousness,
disorientation, any involuntary movement or convulsion, IMMEDIATELY
discontinue use and consult your doctor. This may happen even if the
person has no medical history of epilepsy.
Computer Basics - 11
Page 12
SETTING UP YOUR COMPUTER
ARRANGING A COMFORTABLE WORK AREA
Working safely and comfortably begins with the arrangement of your work
space and the proper use of equipment. For this reason, it is very
important to take time and think about how you are going to arrange your
work area. Refer to the diagram on the following page as you set up your
system.
Here are some points to consider:
Adjusting your chair
Having the right kind of chair does not necessarily mean you'll be properly
supported. It is necessary to adjust your chair to fit your body. Proper body
posture will make you more comfortable and productive.
• Avoid tilting your chair. If you have a chair that tilts, lock the tilt knobs so
that your chair will not tilt forward or backward while you are using your
computer.
• Adjust your chair height in such a way that you can sit on it with your
thighs parallel to the floor and your feet resting flat on the floor.
• Rest your body on the chair back. Your torso works harder to maintain
balance if you do not rest your body on the chair back.
12 - Setting up your computer
Page 13
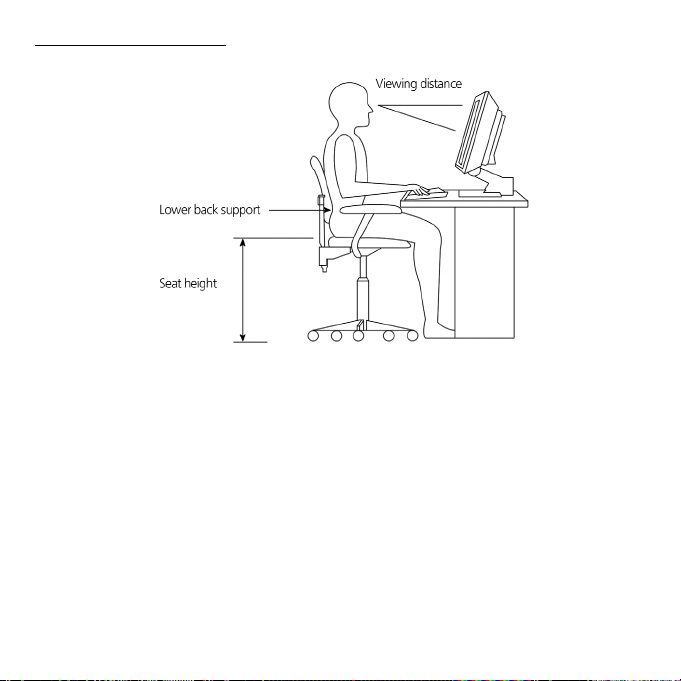
Positioning your PC
Take note of the following when selecting a location for your computer:
• Do not put your computer near any equipment that might cause
electromagnetic or radio frequency interference, such as radio
transmitters, televisions, copy machines or heating and air-conditioning
equipment.
• Avoid dusty areas and extremes of temperature and humidity.
• You may place your computer beside your desk or under your table, as
long as it does not block the space you need for working and moving.
Setting up your computer - 13
Page 14
Positioning your monitor
Place your monitor at a comfortable viewing distance, usually 50 to 60 cm
away. Adjust the display in such a way that the top of the screen is at or
slightly below eye level.
Positioning your keyboard
The location of the keyboard is a very important factor for your posture.
Placing it too far away will make your body lean forward, forcing you to sit
in an unnatural position. Placing it too high will add tension to your
shoulder muscles.
• The keyboard should be placed just above your lap. Adjust the keyboard
height by flipping the folding stands located under the keyboard.
• Keep your lower arms parallel to the floor as you type. Your upper arms
and shoulders should be relaxed. Then try typing with a light touch. If
you feel any shoulder or neck strain, stop for a while and check your
posture.
• Position your keyboard in front of your monitor. Putting your keyboard
beside your monitor will make you turn your head while you type which
could add tension to your neck muscles.
Positioning your mouse
• The mouse should be placed on the same surface as your keyboard so
that you can reach it with ease.
14 - Setting up your computer
Page 15
• Adjust its position to allow enough space for movement without making
you stretch or lean over.
• Use your arm to move the mouse. Do not rest your wrist on the table
when moving the mouse.
Setting up your computer - 15
Page 16
USING YOUR COMPUTER
CONNECTING THE COMPUTER
Setting up your computer is easy. For the most part, you only have four
things to connect: the mouse, the keyboard, the monitor, and the power
cable.
Note: The peripherals shown in the connections below are for your
reference only. Actual device models may vary.
Please follow the instructions provided on the setup guide.
Connect your mouse and keyboard
PS/2 interface
Plug the PS/2 mouse and keyboard cable into the PS/2 keyboard port
(purple port) and mouse port (green port) located on the rear panel of your
computer.
USB interface
You can also plug a USB mouse or a USB keyboard cable into any of the
USB ports located on the front and rear panels of your computer.
Wireless
Certain computers include a wireless mouse and keyboard. Please follow
the instructions provided on the setup guide.
16 - Using your computer
Page 17
Connect a monitor
To connect a monitor, simply plug the monitor cable into the appropriate
port located on the rear panel of your computer.
Note: The type of connection can vary. Use a cable that matches both
your monitor and your computer. Refer to the monitor manual for
additional instructions and information.
Connect to a broadband network
Individual network configuration
Connect one end of the network cable on the network port on the rear of
the computer, then connect the other end of the network cable into the
cable modem or network jack or hub on your network.
Note: Consult your operating system help files for information on how
to configure your network setup.
Connect to power
1. Plug the power cable into the power cable socket located on the rear
panel of your computer.
2. Plug the other end of the power cable into a power outlet.
Caution: Before you proceed, check the voltage range in your
area. Make sure that it matches your computer's voltage setting.
If they don't match, change your computer's voltage setting
according to your area's voltage range.
Using your computer - 17
Page 18
TURNING ON YOUR COMPUTER
After making sure that you have properly set up the system, applied
power, and connected all the necessary peripherals, you can now power
on the system.
Important: Make sure that the power cable is properly plugged into an
electrical outlet. If you are using a power strip or an AVR (AutoVoltage Regulator), make sure that it is plugged in and turned on.
TURNING OFF YOUR COMPUTER
1. On the Windows taskbar, click on the Start button, then click Shut Down.
2. Turn off all peripherals connected to your computer.
If you cannot shut down your computer normally, press and hold the
power button for at least four seconds. Quickly pressing the button may
put the computer in suspend mode only.
USING THE OPTICAL DRIVE
Your computer may come with an optical drive. This drive is located on the
front panel of your computer. The drive allows you to play all common CD,
DVDs, and optionally Blu-ray discs. You may also save information and
create your own CDs or DVDs with appropriate software and special
writable discs (e.g by using a CD-R, CD-RW, DVD-R or DVD-RW).
Optical discs are compact, lightweight and easy to carry around. However,
they are delicate and must be handled with care.
18 - Using your computer
Page 19
To insert a disc into your computer's optical drive:
1. Press the optical drive’s eject button.
2. When the disc tray slides open, place the disc gently on the tray. Make
sure that the label or title side of the disc is facing upward.
When holding a disc, hold it by the edges to avoid leaving smudges or
fingerprints.
3. Push the tray and it will close automatically or press the eject/load
button.
Taking care of your optical discs
• Keep your disc in its case when not in use to avoid scratches or other
damage. Any kind of dirt or damage can affect the data on the disc,
impair the disc lens reader on the optical drive, or stop the computer
from successfully reading the disc.
• When handling discs, always hold them by the edges to avoid smudges
or fingerprints.
• When cleaning discs, use a clean, dust-free cloth and wipe in a straight
line from the center to the edge. Do not wipe in a circular motion.
• Clean you optical drive periodically with a cleaning kit; cleaning kits may
be purchased at any computer or electronics shop.
Using your computer - 19
Page 20
UPGRADING YOUR COMPUTER
EXPANDING THROUGH OPTIONS
Your computer offers you many options for a complete computing
experience.
Connectivity options
Ports allow you to connect peripheral devices to your computer. For
instructions on how to connect different external devices to the computer,
read the following section.
Memory card reader
Memory cards are used in a wide selection of digital
cameras, PDAs, MP3 players and mobile phones.
Inserting a memory card
1. Align the card so that the connector points towards
the port, with the connectors facing down.
2. Carefully slide the card into the port. If you find you
need to use any force to insert the card, try reorientating the card
slightly.
3. Push the card until it clicks into place. A few millimetres of the card will
extend from beyond the slot.
20 - Upgrading your computer
Page 21
If the card contains some files, the Windows Auto Play window may
appear (this depends on the contents of the card) and ask you if you wish
to use a program to access the contents of the card. Select an option
here if it is appropriate, otherwise select Cancel. If the card contains no
files, or unknown files, a window will open showing the contents of the
card.
SD, SDHC and SDXC cards
Different types of SD cards cover different capacities, while using the
same overall design. SD cards contain up to 4 GB, SDHC cards contain
up to 32 GB, and SDXC cards can contain up to 2048 GB (2 TB). Your
computer provides an SDHC or SDXC compatible card reader.
Note: SDXC memory cards can only be used in an SDXC-compatible
reader; SD and SDHC cards can be used in either type.
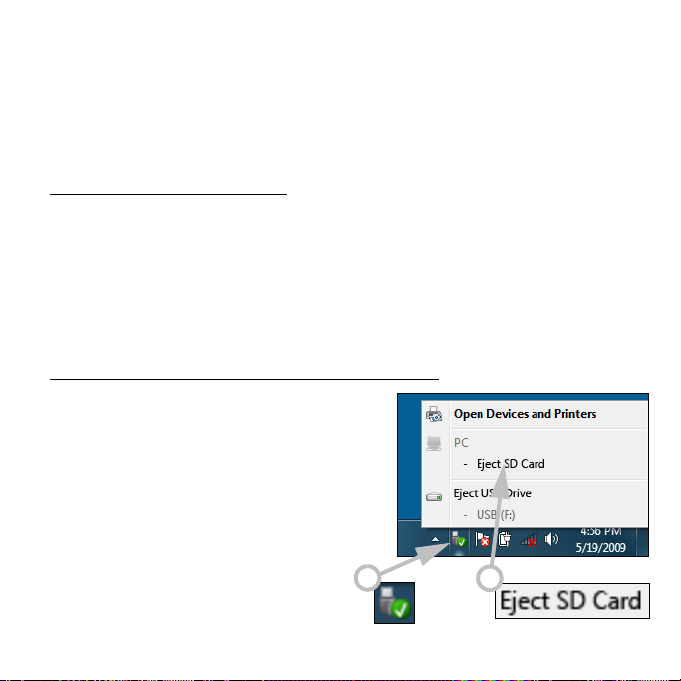
Removing a card from an memory card reader
1. Click on the Safely Remove
Hardware icon in the Notification
Area (next to the clock).
2. Click on Eject SD Card (or the
name of the device).
3. Wait until a Safe to Remove
Hardware message is displayed.
4. Remove the card.
1
2
Upgrading your computer - 21
Page 22
Built-in networking
The built-in networking allows you to connect your computer to an
Ethernet-based network.
Connect an Ethernet cable from the Ethernet (RJ-45) port on the
chassis of the computer to a network jack or hub on your network.
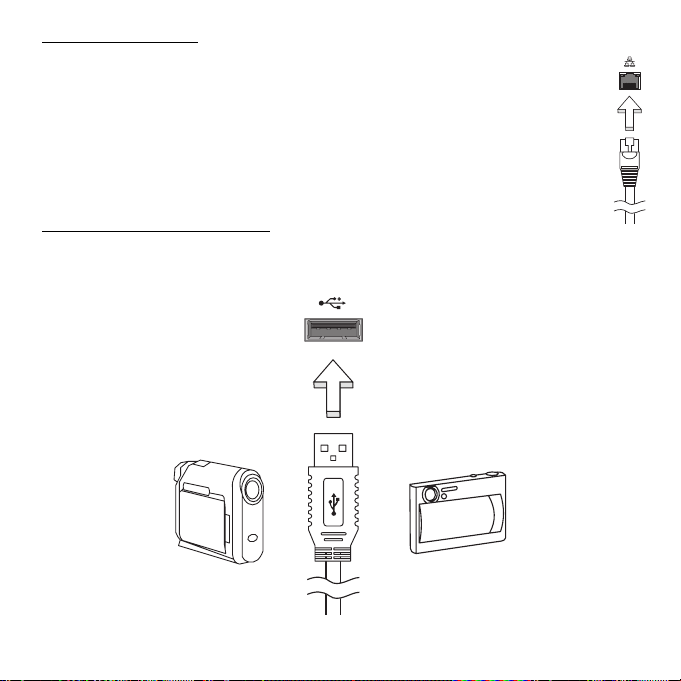
Universal Serial Bus (USB)
The USB port is a high-speed serial bus which allows you to connect USB
peripherals without taking up system resources.
22 - Upgrading your computer
Page 23
Certain computers may include one or more USB 3.0 ports. These
resemble standard USB ports, except they include additional internal
connections and are blue. You may use USB 3.0 compatible devices with
these ports to benefit from faster transfer speeds.
Video port
Connect to a monitor with a VGA or DVI port (the type of connection
supported depends on your computer’s configuration). The appropriate
cable is usually included with the monitor.
Follow these steps to connect an monitor to your computer:
1. Check that the computer is powered off and the monitor power switch is
turned off.
2. Attach the video cable to the monitor port on the computer. Secure the
cable connection with the screws provided.
3. Connect the monitor power cable and plug it into a properly grounded
wall outlet.
4. Follow any setup instructions in the monitor's user's guide.
5. Turn on power to the monitor, then the computer.
6. Make sure that the current resolution and refresh rate do not exceed the
specifications of the monitor. If necessary change the display settings
used by the computer.
Note: To access the display controls: Click on Start, Control Panel,
Appearance and Personalization. Click on the Display category,
then select Change Display Settings.
Upgrading your computer - 23
Page 24
High-Definition Multimedia Interface (only for certain models)
HDMI (High-Definition Multimedia Interface) is an industrysupported, uncompressed, all-digital audio/video interface.
HDMI provides an interface between any compatible digital
audio/video source, such as a set-top box, DVD player, and
A/V receiver and a compatible digital audio and/or video
monitor, such as a digital television (DTV), over a single
cable.
Use the HDMI port on your computer to connect with highend audio and video equipment. Single cable
implementation allows tidy setup and fast connection.
Headphones and microphone
These two ports allow you to connect audio devices. Use the headphone
port to plug in stereo headphones or powered speakers. Plugging an
audio device to the headphone port disables the built-in speakers. Use the
microphone port to connect an external microphone for mono recording;
plugging in an external microphone disables the built-in microphone.
24 - Upgrading your computer
Page 25
SOFTWARE
USING WINDOWS AND YOUR SOFTWARE
Gateway computers include software to help you use your computer; the
programs and categories available on your computer depend on the
model purchased. Most of this software is ’pre-installed’ and ready to be
used; however some software may be provided on a CD or DVD and must
first be installed if you wish to use it. To do so, insert the installation CD or
DVD. An installation wizard will start automatically and all you have to do
is follow the instructions on the screen.
Welcome Center
The first time you turn on your computer, the Welcome Center window
opens. The Welcome Center introduces you to the new features and tools
of Windows. You can access the Welcome Center later by clicking Start
> Getting Started.
Internet security offer
It is vital to protect your computer from viruses and attacks over the
Internet (see Security on page 40). An comprehensive Internet security
suite, including a free trial subscription period, is offered when you first
start your computer. You should activate this protection before connecting
to the Internet. This security suite protects your computer from the most
Software - 25
Page 26
recent online threats and protects your personal data (bank account
credentials, credit card numbers, passwords, and more).
Productivity software
Work Great with Microsoft® Office 2010 - Express your ideas, solve
problems and simplify everyday projects with Office 2010.
Photo editing - Easily edit and print your photos with Windows Live Photo
Gallery. Then share them on Facebook, YouTube™ or Windows Live.
Search & Decide with Bing™ - Find and organize the answers you need
using Bing™, so you can make faster, more informed decisions.
Gateway Recovery Management
To prepare your computer for system recovery options, you should create
a set of recovery discs as soon as possible. See page 66 for more
information.
Playing multimedia files
You may use the media software on your computer to play music, films or
photo slide-shows and watch television (if your computer has a TV tuner).
Other options allow you to create CDs or DVDs.
One or more media programs are installed on your computer, Windows
Media Player and optionally Windows Media Center are provided by
Microsoft. Other media programs may have been installed by Gateway to
provide an improved media experience.
26 - Software
Page 27
Windows Media Player
Windows Media Player may be used to play MP3 or WMA audio files, CDs
or most video files.
Note: It is not recommended that you use Windows Media Player to
play DVD movies. Other media players (such as Windows Media
Center) provide additional playback options.
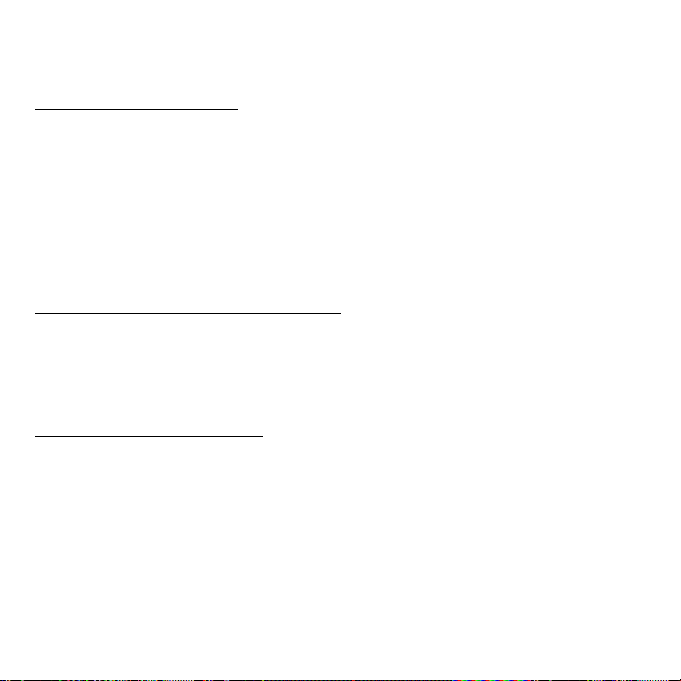
Windows Media Center (optional)
Certain computers include all-inone media ‘centers’ such as
Windows Media Center. These
programs can handle a variety of
multimedia content, presented with
simple menus that may be easily
controlled with a remote control.
You may watch live or recorded TV
(if your computer has a TV tuner),
listen to digital music, view pictures and personal videos, create CDs and
DVDs, or access content from online services.
To start the media program installed on your computer, click on Start >
Windows Media Center.
Setup
Caution: If your computer includes a remote control or TV tuner
they must be connected and active before starting the media
program for the first time.
Software - 27
Page 28
The first time you start the media program, it will start a setup wizard,
which will configure some basic settings. If available, select the Express
setup option, you may then configure additional options as needed.
Note: If you have an Internet connection, the Guide (Electronic
Program Guide) allows you to view a list of current TV shows. This
shows channel and network information, as well as the title,
description and scheduled broadcast time of shows.
Cyberlink PowerDVD (optional)
If your computer does not include Windows Media Center, or it is equipped
with a Blu-ray drive, you may watch movies with PowerDVD. You may
start PowerDVD by inserting a disc and waiting for the program to start
automatically.
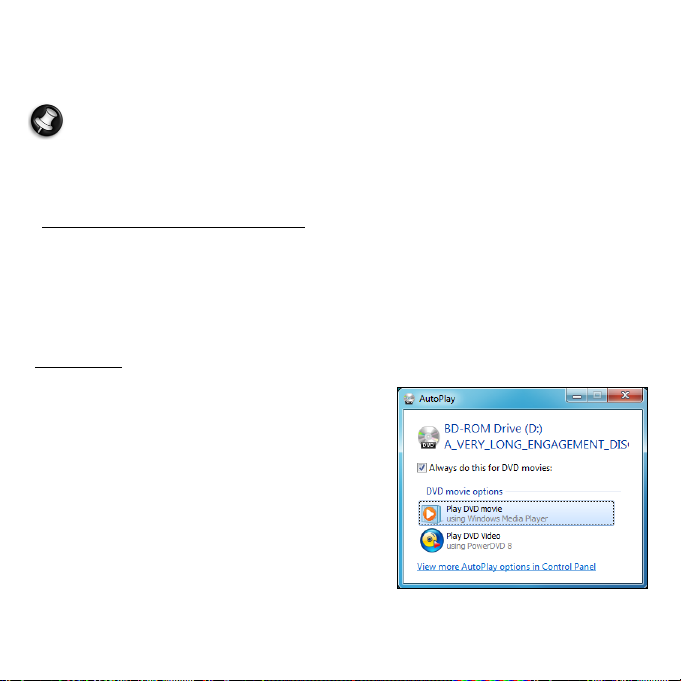
AutoPlay
The Windows AutoPlay function allows
you to choose the way Windows handles
media files on devices with removable
storage (digital camera, CD, DVD, etc).
If you have inserted a disk that contains
files (such as a DVD, USB key or memory
card), Windows will display a dialog box
and ask you to choose how you want to
open the files.
For example, if you have inserted an audio CD or a DVD movie, Windows
will automatically display a dialog box and ask you to choose how you
28 - Software
Page 29
want to play it. If Windows asks you to select a DVD player, we
recommend that you always choose the DVD player included with your
software collection (e.g. PowerDVD or Windows Media Player).
Playing downloaded files
Downloaded files may work with the media programs installed on your
computer, or may require specific programs. Files that include DRM
functions may only play in specific programs (e.g. iTunes, Windows Media
Player) or only on devices certified for use with the each type of file. Other
formats may require a specific audio or video codec that may not have
been installed on your computer.
Codecs
A codec is software that is used to compress or decompress a digital
media file, such as a song or video. Windows Media Player and other
programs use codecs to play and create digital media files.
For example, when you rip a song from an audio CD to your computer, the
player uses the Windows Media Audio codec to compress the song into a
compact WMA file. When you play that WMA file (or any WMA file that
might be streamed from a Web site), the media player uses the Windows
Media Audio codec to decompress the file so the music can be played
through your speakers.
Why do I get a message that says my computer is missing a codec?
If you get a message that says that your computer is missing a codec, it
may be because you are using a file that was compressed using a codec
Software - 29
Page 30
that Windows or the media player does not include by default. In many
cases, you can download and install the missing codec by clicking on the
Web Help button in the error message.
Please also see Windows Help and Support for more information.
Playing DVD movies
You can play DVD movies on your computer.
1. Insert the DVD.
Important! When you launch the DVD player for the first time, the
program asks you to enter the region code. DVD content is coded with
one of six regions. Please refer to the table below for DVD movie
region code information.
Once your DVD drive is set to a region code, it will play DVD discs
of that region only. You can set the region code a maximum of
five times (including the first time), after which the last region
code set will remain permanent. Recovering your hard disk does
not reset the number of times the region code has been set.
2. The DVD movie will automatically play after a few seconds.
Region code Country or region
1 USA, Canada
2 Europe, Middle East, South Africa, Japan
3 Southeast Asia, Taiwan, South Korea
4 Latin America, Australia, New Zealand
5 Former USSR, parts of Africa, India
30 - Software
Page 31

Region code Country or region
6 People's Republic of China
Note: To change region code, insert a DVD movie of a different region
into the DVD drive.
Playing Blu-ray movies
If your computer is equiped with a Blu-ray disc drive, you can play Blu-ray
movies on your computer.
Simply insert the disc into the optical drive, after a short delay Cyberlink
PowerDVD will start to play the movie. Use the media controls to control
playback.
Software - 31
Page 32

INTERNET
FIRST STEPS ON THE NET
Protecting your computer
It is vital to protect your computer from viruses and attacks over the
Internet (see Internet security offer on page 25 and Security on page 40).
A comprehensive Internet security program is offered when you first start
your computer. You should activate this protection as soon as possible,
certainly before you connect to the Internet.
Choose an Internet Service Provider
Using the Internet has become a natural part of daily
computing. Just a few simple steps can connect you to a
vast collection of knowledge and communication tools.
To accomplish these steps you should first select an
Internet Service Provider (ISP), which supplies the
connection between your computer and the Internet. You
should research the ISPs available in your region, not
forgetting to talk to friends and family about their experiences or to check
reviews and consumer reports. The ISP you select will provide instructions
on how to connect to the Internet (you may need additional software or a
special ‘box’ that connects to your phone line).
32 - Internet
Page 33

Connection types
Depending on your computer model, your location and your
communication needs, you have several ways to connect to the Internet.
Dial-up
Some computers include a telephone dial-up (‘modem’) connector. This
allows you to connect to the Internet using your telephone line. With a dialup connection, you cannot use the modem and the telephone
simultaneously on a single phone line. This type of connection is
recommended only if you have limited use of the Internet as the
connection speed is low and connection time is typically charged per hour.
DSL (e.g. ADSL)
DSL (Digital Subscriber Line) is an ‘always-on’ connection that runs over
the phone line. As DSL and phone do not use the same frequencies, you
can use your telephone at the same time you are connected to the Internet
(this requires a ‘micro-filter’ on each telephone socket to avoid
interference). To be eligible for DSL, you must be located near an DSLequipped phone exchange (service is sometimes unavailable in rural
areas). Connection speeds vary depending on your location, but DSL
generally provides very fast and reliable Internet connection. As the
connection is always-on, it is generally charged at fixed monthly rates.
Note: A DSL connection requires an appropriate modem. A modem is
usually provided by the ISP when you register. Many of these
modems include an ‘router’ that provides network and wi-fi access.
Internet - 33
Page 34

Cable
A cable connection provides fast and always-on Internet service via a
cable television line. This service is generally available in large cities. You
can use your telephone and watch cable TV at the same time you are
connected to the Internet.
Network connections
A LAN (Local Area Network) is a group of computers (for example, within
an office building or home) that share a common communications line and
resources. When you set up a network, you can share files, peripheral
devices (such as a printer) and an Internet connection. You can set up a
LAN using wired technologies (such as Ethernet) or wireless technologies
(such as WiFi or Bluetooth).
Wireless networks
A wireless LAN or WLAN is a wireless local area network, which may link
two or more computers without using wires. Setting up a wireless network
is easy and allows you to share files, peripheral devices and an Internet
connection.
What are benefits of a wireless network?
Mobility
Wireless LAN systems allow you and other users of your home network to
share access to files and devices connected to the network, for example a
printer or scanner.
34 - Internet
Page 35

Also you can share an internet connection with other computers in your
home.
Installation speed and simplicity
Installing a wireless LAN system can be fast and easy and eliminates the
need to pull cables through walls and ceilings.
Components of a wireless LAN
To set up your Wireless network at home you need to have the following:
Access point (router)
Access points (routers) are two-way transceivers that broadcast data into
the surrounding environment. Access points act as a mediator between
wired and wireless network. Most routers have a built-in DSL modem that
will allow you access to a high speed DSL internet connection. The ISP
(Internet Service Provider) you have chosen normally supplies a modem/
router with the subscription to their services. Read carefully the
documentation supplied with your Access point/router for detailed setup
instructions.
Network cable (RJ45)
A network cable (also called RJ45 cable) is used to connect the host
computer to the access point (see illustration below); this type of cable
may also be used to connect peripheral devices to the access point.
Internet - 35
Page 36

Wireless adapter
This is connected to the computer that
you wish to connect to your network,
there are different types of wireless
adapter available, the most common
are:
USB WiFi adapter: Connects to a free
USB port on your computer.
Wireless Expansion Card: This card is installed inside your computer in an
available expansion slot.
Diagram of a working network
1. Access point/router
2. Desktop computer
3. Modem
5
4
4. Printer
5. Portable computer
6. PDA/Smartphone
7. Network cables
1
3
7
2
(RJ45)
6
36 - Internet
Page 37

Turning on/off a wireless network connection
If your computer has wireless access, but does not feature a
Communication button, you may turn your wireless network on or off, or
control what is shared over the network with the network management
options. Click on Start > Control Panel > Network and Internet >
Network and Sharing Center.
Surf the Net!
To surf the Internet, you need a program called an
Internet browser. Internet Explorer provides an easy and
secure web browsing experience. As soon as you have
your Internet access installed and you are connected,
click on the Internet Explorer shortcut located on the
Windows desktop and take your Internet experience to a
new level!
Internet - 37
Page 38

Internet Explorer features
The image below shows the Internet Explorer browser’s start page. A brief
description of some key aspects of the browser are listed below.
6543
87
9
2
1
1. Bing Bar: Search the web and use Bing tools to alert you of news, fill
forms automatically, stay safe online and more.
2. Back and Forward buttons: Navigate through pages you have already
visited.
3. Address bar: Type in an Internet address (e.g. www.gateway.com) and
press the Enter key on your keyboard, this will take you directly to the
address you typed.
4. Refresh: Reload the selected page.
38 - Internet
Page 39

5. Search Box: Search the web without having to open a new page.
6. Tabs: Each tab displays a web page. The tabs allow you to instantly
switch from one site to another.
7. New tab: Open a new tab with links to your most popular sites.
8. Reduce, maximize or close the window.
9. Home, Favorites and Tools: Open the home page; manage your favorite
websites, feeds and history; and access browser tools, such as Print,
Safety or Options.
Caution: Internet Explorer includes a Phishing Filter that warns
you about and helps to protect you from potential or known
fraudulent websites (sites that look legitimate but actually are
designed to capture your personal information). The address bar
will turn yellow and a warning message will be displayed if you
visit a suspected phishing site.
Gateway website
To get you started why not visit our website, www.gateway.com.
Gateway is dedicated to provide you with on-going personalized support.
Check out our Support section to get help tailored to your needs.
www.gateway.com is your portal to a world of online activities and
services: visit us regularly for the latest information and downloads!
Internet - 39
Page 40

Security
You are probably eager to explore everything the Internet has to offer. In
order for you to be safe online, Gateway has pre-installed Symantec’s
award-winning Norton Internet Security™ on your computer.
Norton Internet Security runs quietly in the background to block today’s
complex threats and protect your identity when you shop, bank, or browse
online.
Norton Internet Security blocks online identity theft, detects and eliminates
spyware, removes viruses and Internet worms, protects against hackers.
Definitions
What is a virus?
Malicious software, typically called ‘viruses’, are programs designed to
infect and damage computers. Most viruses are transmitted over the
Internet, emails or malicious Web sites. A typical virus will replicate and
pass itself undetected to multiple computers. Other forms of nuisance,
such as Trojan horses, worms or spam can infect your computer in various
ways, using up resources or clogging up a network.
Note: Gateway guarantees that your computer was 100% virus free
at the time of purchase and does not cover damages due to viruses.
What is spyware?
Spyware refers to generally unwanted programs that are downloaded onto
your computer while connected to the Internet, often without you knowing
it. Once it has infected your computer, it can snoop on your browsing
40 - Internet
Page 41

activity, collect personal information, cause pop-up ads to appear, or even
change the configuration of your computer. Spyware consumes resources
on your computer; it can slow down your Internet connection or entire
computer system, and even cause crashes.
Spyware is sometimes used by unscrupulous companies to monitor and
track the sites you visit on the Internet so as to determine your web-surfing
habits and display targeted pop-up ads on your screen. However, some
kinds of spyware go beyond simple tracking and actually monitor
keystrokes and capture passwords, posing a serious security risk.
What is malware?
Malicious software, also known as malware, is software designed to
deliberately harm your computer. For example, viruses, worms, and
Trojan horses are malicious software. To help protect your computer
against malware, make sure it is using up-to-date antivirus and antimalware software.
What is a personal firewall?
A personal firewall is a software program designed to prevent
unauthorized access to or from a private network. It acts as a shield to
protect your Internet connection from unwanted connections, some of
which may attempt to take control of your computer to install or redistribute viruses or malicious programs. Each connection to your
computer is monitored - programs that attempt to receive information
without your permission are detected and the firewall will display an alert.
You can then decide if you will allow the connection, if the connection is to
a program you are currently using then normally you would allow it (i.e. a
Internet - 41
Page 42

game connecting to a multi-player server or an encyclopaedia making a
content update).
How to protect your computer
Cybercrime prevention can be straight-forward - when armed with a little
technical advice and common sense, many attacks can be avoided. In
general, online criminals are trying to make their money as quickly and
easily as possible. The more difficult you make their job, the more likely
they are to leave you alone and move on to an easier target. The tips
below provide basic information on how you can prevent online fraud.
Keep your computer current with the latest patches and updates
One of the best ways to keep attackers away from your computer is to
apply patches and other software fixes when they become available. By
regularly updating your computer, you block attackers from being able to
take advantage of software flaws (vulnerabilities) that they could otherwise
use to break into your system.
While keeping your computer up-to-date will not protect you from all
attacks, it makes it much more difficult for hackers to gain access to your
system, blocks many basic and automated attacks completely, and might
be enough to discourage less-determined attackers, so they will give up
and look for a more vulnerable computer elsewhere.
More recent versions of Microsoft Windows and other popular software
can be configured to download and apply updates automatically so that
you do not have to remember to check for the latest software. Taking
advantage of auto-update features in your software is a great start toward
keeping yourself safe online.
42 - Internet
Page 43

Protect your computer with security software
Several types of security software are necessary for basic online security.
Security software essentials include firewall and antivirus programs. A
firewall is usually your computer's first line of defense-it controls who and
what can communicate with your computer online. You could think of a
firewall as a sort of "policeman" that watches all the data attempting to
flow in and out of your computer on the Internet, allowing communications
that it knows are safe and blocking "bad" traffic such as attacks from ever
reaching your computer.
The next line of defense many times is your antivirus software, which
monitors all online activities such as email messages and Web browsing
and protects an individual from viruses, worms, Trojan horse and other
types of malicious programs. Your antivirus and antispyware software
should be configured to update itself, and it should do so every time you
connect to the Internet.
Integrated security suites such as Norton Internet Security, which combine
firewall, antivirus, antispyware with other features such as antispam and
parental controls, have become popular as they offer all the security
software needed for online protection in a single package. Many people
find using a comprehensive security suite an attractive alternative to
installing, configuring and updating several different types of security
software.
A complete version of Norton Internet Security™ is pre-installed on
your Gateway system. It includes a free trial subscription to
protection updates. Make sure you Activate it!
Internet - 43
Page 44

Choose strong passwords and keep them safe
Passwords are a fact of life on the Internet today; we use them for
everything from ordering flowers and online banking to logging into our
favorite airline Web site to see how many miles we have accumulated.
The following tips can help make your online experiences secure:
• Selecting a password that cannot be easily guessed is the first step
toward keeping passwords secure and out of the wrong hands. Strong
passwords have eight characters or more and use a combination of
letters, numbers and symbols (e.g., # $ % ! ?). Avoid using any of the
following as your password: your login name, anything based on your
personal information such as your last name, and words that can be
found in the dictionary, especially "password". Try to select especially
strong, unique passwords for protecting activities like online banking.
• Keep your passwords in a safe place and try not to use the same
password for every service you use online.
• Change passwords on a regular basis, at least every 90 days. This can
limit the damage caused by someone who has already gained access to
your account. If you notice something suspicious with one of your online
accounts, one of the first steps you can take is to change your
password.
Protect your personal information
Exercise caution when sharing personal information such as your name,
home address, phone number, and email address online. To take
advantage of many online services, you will inevitably have to provide
personal information in order to handle billing and shipping of purchased
44 - Internet
Page 45

goods. Since not divulging any personal information is rarely possible, the
following list contains some advice for how to share personal information
safely online:
• Keep an eye out for phony email messages. Things that indicate a
message may be fraudulent are misspellings, poor grammar, odd
phrasing, Web site addresses with strange extensions, Web site
addresses that are entirely numbers where there are normally words,
and anything else out of the ordinary. Additionally, phishing messages
will often tell you that you have to act quickly to keep your account open,
update your security, or urge you to provide information immediately or
else something bad will happen. Don't take the bait.
• Don't respond to email messages that ask for personal
information. Legitimate companies will not use email messages to ask
for your personal information. When in doubt, contact the company by
phone or by typing in the company Web address into your Web browser.
Don't click on the links in these messages as they make take you to
fraudulent, malicious Web sites.
• Steer clear of fraudulent Web sites used to steal personal
information. When visiting a Web site, type the address (URL) directly
into the Web browser rather than following a link within an email or
instant message. Fraudsters often forge these links to make them look
convincing.
A shopping, banking or any other Web site where sensitive information
should have an "S" after the letters "http". The "s" stands for secure and
should appear when you are in an area requesting you to login or
provide other sensitive data. Another sign that you have a secure
Internet - 45
Page 46

connection is the small lock icon in the bottom of your web browser
(usually the right-hand corner).
• Pay attention to privacy policies on Web sites and in software. It is
important to understand how an organization might collect and use your
personal information before you share it with them.
• Guard your email address. Spammers and "phishers" sometimes send
millions of messages to email addresses that may or may not exist in
hopes of finding a potential victim. Responding to these messages or
even downloading images ensures you will be added to their lists for
more of the same messages in the future. Also be careful when posting
your email address online in newsgroups, blogs or online communities.
Online offers that look too good to be true usually are
The old saying "there's no such thing as a free lunch" still rings true today.
Supposedly "free" software such as screen savers or smileys, secret
investment tricks sure to make you untold fortunes, and contests that
you've surprisingly won without entering are the enticing hooks used by
companies to grab your attention.
While you may not directly pay for the software or service with money, the
free software or service you asked for may have been bundled with
advertising software ("adware") that tracks your behavior and displays
unwanted advertisements. You may have to divulge personal information
or purchase something else in order to claim your supposed content
winnings. If an offer looks so good it's hard to believe, ask for someone
else's opinion, read the fine print, or even better, simply ignore it.
46 - Internet
Page 47

Review bank and credit card statements regularly
The impact of identity theft and online crimes can be greatly reduced if you
can catch it shortly after your data is stolen or when the first use of your
information is attempted. One of the easiest ways to get the tip-off that
something has gone wrong is by reviewing the monthly statements
provided by your bank and credit card companies for anything out of the
ordinary.
Additionally, many banks and services use fraud prevention systems that
call out unusual purchasing behavior (i.e. if you live in Texas and all of the
sudden start buying refrigerators in Budapest). In order to confirm these
out of the ordinary purchases, they might call you and ask you to confirm
them. Don't take these calls lightly; this is your hint that something bad
may have happened and you should take necessary action.
Protect your computer with Windows security tools
Windows provides a variety of protection applications.
Windows Action Center
Windows provides a central area from where you can control the security
settings of your computer, helping you to protect it from Internet attacks
and ensuring that the latest security updates have been downloaded and
installed on your computer.
To open the Action Center, click on Start > Control Panel > System
and Security > Action Center.
Internet - 47
Page 48

Alternatively, if a security alert
has been reported (in the
Notification Area, next to the
clock) then you can click on the
notification balloon or double-click
on the small Security Alert icon.
The Action Center indicates the
status and settings used for
important applications that protect
your computer. In addition
Windows Firewall, Windows
Defender and Windows Automatic Updates are provided by Microsoft as
part of a comprehensive system to defend your computer. The antivirus
application varies according to the program installed on your computer.
Windows Firewall
Windows has a firewall that protects your computer when connected to the
Internet. It stops programs from accessing the Internet without your
permission.
48 - Internet
Page 49

Certain programs need access
to the Internet to function
properly, or even to function at
all. If this is the case, you will
usually be asked to allow
access when you install a
program, or the first time you
use it. To check firewall
settings, click on Start >
Control Panel > System and
Security > Windows Firewall.
Note: When you first start to use a Firewall it is in a ‘Learning mode’,
you may see pop-up windows alerting you that certain programs you
know and trust wish to access the internet. After a period of time the
Firewall will know your list of trusted programs and won’t ask for
permission the next time the program tries to connect to the internet.
The Firewall also protects your computer from programs from the
internet trying to access your computer; this sometimes is necessary
to allow access for program updates, downloads, etc.
Caution: Please note that most security software suites provide
similar functionality and will disable Windows Firewall in order to
improve system performance.
Windows Updates
If you have an active Internet connection, Windows can check for
important updates for your computer and install them automatically. These
Internet - 49
Page 50

updates include security patches and program updates that can improve
your computing experience and help protect your computer against new
viruses and attacks.
Windows Defender
Windows Defender helps protect
your computer against malicious
and unwanted software, such as
spyware and adware. Windows
Defender is installed and turned
on by default.
To help protect your privacy and
your computer, Windows
Defender includes real-time
protection options. Real-time
protection alerts you when
spyware and other potentially
unwanted software attempt to install themselves or run on your computer.
You are also alerted if programs attempt to change important Windows
settings.
Note: Windows Defender works with your Windows Update settings
to automatically install the latest definitions.
Caution: Please note that most security software suites provide
similar functionality and will disable Windows Defender in order
to improve system performance.
50 - Internet
Page 51

User Account Control
The User Accounts control panel can help prevent unauthorized changes
to your computer. User Accounts will ask you for permission or an
administrator password before performing actions that could potentially
affect your computer's operation or that change settings that affect other
users. When you see a User Account message, read it carefully, and then
make sure the name of the action or program that's about to start is one
that you intended to start.
By verifying these actions before they start, User Account settings can
help prevent malicious software (malware) and spyware from installing or
making changes to your computer without permission.
To access User Account settings, click on Start > Control Panel >
User Accounts and Family Safety > User Accounts.
Note: You may turn off the User Account Control Messages (not
recommended) in the User Account Control settings window.
Internet - 51
Page 52

Internet Explorer security settings
Internet sites use small files called cookies to keep track of user
preferences and information. You can adjust your Internet browser's
security settings to determine how much -or how little- information you are
willing to accept from a Web site.
To access Internet Explorer security settings:
1. In Internet Explorer, click on Tools > Internet Options.
2. In the Privacy tab, move the slider up or down to select a setting.
How do I know when my computer is at risk?
If the Action Center reports an alert, or if your computer behaves
erratically, crashes unexpectedly or if some of your programs do not work
correctly, your computer may be infected by malicious software. However,
do not blame every computer problem on a virus! If you suspect your
computer is infected, the first thing to do is update, if you have not already
done so, and run your antivirus and anti-spyware software.
52 - Internet
Page 53

HELPDESK
SAFE COMPUTING
To make the most of your new computer and ensure it runs smoothly for a
long time, you should use the programs below and regularly perform the
actions described in this guide.
Maintenance
Recommended maintenance tasks
There are several tasks you should perform periodically (about once per
month) to ensure your computer stays in good health:
Error checking
Using the Check Disk tool regularly prevents your system from getting
unreliable and information getting lost. It checks and repairs two types of
errors:
• file system errors, such as fragmented files that were not deleted and
files with invalid sizes or dates;
• physical errors, which may occur on your hard disk as it wears out over
time.
1. Click on Start > Computer. Right-click on the Gateway (C:) icon
and select Properties.
2. Click on Tools and Check Now in the Error-checking section.
Helpdesk - 53
Page 54

3. Tick Automatically fix file system errors in the options area. If you tick
Scan for and attempt recovery of bad sectors, your computer will
carry out the physical error checking when you next restart your
computer. Click on Start to proceed.
Disk Cleanup
The Disk Cleanup Wizard helps
free up space on your disk drive. It
searches your drive and displays
unused files, such as temporary
Internet files, files in the Recycle
Bin and other temporary files that
you may safely delete.
1. Click on Start > Computer.
Right-click on the Gateway icon
and select Properties.
2. Select the General tab and click
on the Disk Cleanup button
(next to the diagram of the disk
drive.
3. Tick each category in the Files to
delete area you wish to delete
and click on OK.
54 - Helpdesk
Page 55

Disk Defragmenter
With the creation and deletion of files over time, scattering occurs all over
the hard disk area and affects performance. The Disk Defragmenter helps
you rearrange the items stored on your hard drive to make your computer
run faster and more efficiently.
Running the Disk Defragmenter once a month (depending on computer
usage) will decrease wear and tear on your hard drive and thus decrease
the chance of a fault developing at a later date.
1. Perform a Disk Cleanup and
close all open programs.
2. Click on Start > Computer.
Right-click on the Gateway icon
and select Properties.
3. Click on Tools and Defragment
now....
4. Click on the volume you want to
defragment and click on
Defragment to start. The whole
process may take several hours
to complete. It is best not to use your computer while running the Disk
Defragmenter as any changes on your system may cause the process
to restart. If your hard disk is divided into several partitions you should
perform the same action for each partition.
Helpdesk - 55
Page 56

Manage your hard disk drive (HDD)
Check the remaining free space on your hard disk drive
1. Click on Start > Computer.
2. Right-click on the Gateway icon and select
Properties.
3. The Hard Disk Properties window displays the
amount of used space and free space on your
hard disk. If your hard disk is almost full (less
than 200 MB remaining), you should consider
freeing some space.
To see easily how much space is used and how
much is left, simply place your pointer over the
hard disk drive icon. The information will
automatically appear.
Free some Space on your hard disk drive
1. Empty the Recycle Bin: When you delete a file
from your computer, Windows places it in the
Recycle Bin. All the deleted files remain there until
you decide to permanently delete them from your
computer or to restore them to their original
location. Double-click on the Recycle Bin on the
Windows desktop and click on Empty Recycle
Bin or select only the items you want to delete. Items deleted from
external devices, such as memory cards, do not go to the Recycle Bin,
they are permanently deleted.
56 - Helpdesk
Page 57

2. Uninstall the programs you no longer use:
Click on Start > Control Panel > Programs > Programs and
Features.
3. Archive files on an external hard disk drive, recordable CDs or DVDs (if
your computer is equipped with a CD or DVD writer) and delete them
from the hard disk.
Run Windows System Tools
Windows includes some convenient tools to keep your computer in good
shape. Use these tools on a regular basis to maintain a reliable and
speedy system! To make it easier, System Tools includes a Scheduled
Tasks utility, which you can customize to run specific tasks regularly.
To access the list of System Tools, click Start > All Programs, then
the Accessories folder in the list of programs and finally select System
Tools.
Helpdesk - 57
Page 58

Windows System Restore.
System Restore monitors changes to your computer and automatically
creates restore points that store your computer’s configuration each time a
major change occurs (such as installing programs). It can undo harmful
changes to your computer and restore settings and performance without
removing your personal data files (such as documents, browsing history,
photos, favorites, or emails).
Note: If you only need to uninstall a program, do not use System
Restore. To uninstall a program use Programs and Features in the
Control Panel.
To start System Restore from the Windows desktop:
Click Start > All Programs > Accessories > System Tools >
System Restore.
58 - Helpdesk
Page 59

If you cannot access the Windows desktop:
1. Press the Alt+F10 key upon start-up when the Gateway logo appears.
This will open the Recovery Program.
2. Select Windows System Restore and click Next. Your computer will
automatically restart and open System Restore.
System Restore options
Restore your computer to an earlier time
This option will return to your computer to how it was on an earlier date,
without affecting your personal documents or emails (it will not restore lost
documents either). By default Windows saves snapshots of itself when
major changes are made to the Operating System (e.g. driver installations
or specific software). This is useful when a driver installation failed, or
when you changed a system setting, and it did not work.
1. Click Next.
2. Select from the list the date when the restore point was created and
click Next.
3. In the confirmation screen, click on Finish to restore the computer to the
selected date and time.
Helpdesk - 59
Page 60

Create a Restore Point
Windows creates restore points automatically at regularly scheduled times
or before certain programs or drivers are installed. This option allows you
to create your own restore points when you need to.
1. Click Start > Control Panel > System and Security > System.
Click on System protection in the sidebar and then click the Create...
button.
2. Enter a description to identify this restore point. System Restore
automatically adds the date and time to this name.
3. To finish, click on Create.
Undo the last restoration
If the system fails after restoring the computer to a certain date, you can
use this option to undo the restoration.
Alternately, you can use Last Known Good Configuration to restore the
system to your most recent settings that worked.
1. Restart the computer, press F8 to access advanced startup options.
2. Use the arrow keys to highlight Last Known Good Configuration and
press Enter.
Updates
As new viruses, worms, and other threats are discovered every day,
keeping your security applications and operating system up-to-date is
crucial.
To keep your computer safe and reliable:
60 - Helpdesk
Page 61

• Perform updates when prompted by Windows Action Center.
• Use Microsoft Windows Automatic Updates.
• Run Windows Update.
Internet security
Norton Internet Security, combined with other security applications can
protect your computer from Internet attacks and ensure that the latest
security updates have been downloaded and installed on your computer.
Norton Internet Security performs automatic updates through Live Update.
You can also start a manual update from the main interface of Norton
Internet Security and the Live Update link.
Operating system, software and drivers
Windows Update can help you
keep your computer up-to-date. It
allows you to choose and download
updates for your computer's
operating system, software, and
hardware.
New content is added to Windows
Update regularly, so you can
always get the most recent updates
and solutions to protect your
computer and keep it running smoothly.
• Start > Control Panel > System and Security > Windows Update.
Helpdesk - 61
Page 62

Windows Remote Assistance
Remote Assistance allows a Windows user to temporarily take over a
remote Windows computer over a network or the internet to resolve
issues. Remote Assistance makes it possible to diagnose and repair
problems with a computer without personally visiting it.
You can access Remote Assistance by clicking on Start > All
Programs > Maintenance > Windows Remote Assistance. Upon
launching Remote Assistance, you will see a screen giving you the choice
of either inviting someone to help you or offering to help someone.
62 - Helpdesk
Page 63

FREQUENTLY ASKED QUESTIONS
The following questions indicate possible situations that may arise during
the use of your computer and each is followed by easy answers and
solutions.
I pressed the power button but the system did not boot up.
Check the LED on the power button.
If the LED is not lit, no power is being applied to the system. Try the
following:
• Check if you properly plugged the power cable into an electrical outlet.
• If you are using a power strip, make sure it is plugged in and turned on.
If the LED is lit, check the following:
• The operating system files may be damaged or missing. Insert the
startup disc you created during Windows setup into the ODD and press
<Ctrl> + <Alt> + <Del> to restart your computer. This will automatically
diagnose your system and make necessary fixes. However, if the
diagnostic utility still reports a problem, then you may have to perform
the recovery process to restore your system to its original default factory
settings.
Nothing appears on the screen.
Your computer's power management function automatically blanks the
screen to save power. Press any key to turn the display back on.
Frequently asked questions - 63
Page 64

If pressing a key does not work, you can restart your computer.
If there is still nothing on the screen, check cables and connections:
• Make sure the monitor is connected to a power outlet and that it is
turned on.
• Make sure that the monitor is correctly connected to the computer.
If these steps do not work, contact your dealer or technical support center
for assistance.
The printer does not work.
Do the following:
• Make sure the printer is connected to a power outlet and that it is turned
on.
• Make sure the printer is correctly connected to the computer.
• For additional information concerning the printer, refer to the printer's
documentation.
No sound comes out from the computer.
Check the following:
• The volume may be muted. Look for the Volume icon on the taskbar. If it
is crossed-out, click on the icon and deselect the Mute option. You can
also press the volume control/mute knob on your USB keyboard to
toggle from mute to sound on.
• If headphones, earphones or external speakers are connected to the
line-out jack of your computer, the internal or built-in speakers are
automatically turned off.
64 - Frequently asked questions
Page 65

System cannot read hard disk or optical disc drive information.
Check the following:
• Make sure you are using the correct type of disk.
• Make sure the disc is inserted into the drive correctly.
• Check if the disc is clean and unscratched.
• Check your drive by using a good (undamaged) disc. If your drive can
not read the information on the good disc there may be a problem with
the drive. Contact your dealer or technical support center for assistance.
System cannot write data on the hard disk or disc.
Check the following:
Make sure the disk is not write-protected.
Make sure you are using the correct type of disc.
Frequently asked questions - 65
Page 66

RECOVERY
GATEWAY RECOVERY MANAGEMENT
Gateway Recovery Management is only available with a preinstalled
Windows operating system.
If your computer experiences problems that are not recoverable by other
methods, you may need to reinstall the Windows operating system and
factory-loaded software and drivers. To ensure you can recover your
computer when needed, you should create a recovery backup as soon as
possible.
Creating recovery discs
To reinstall using discs, you must create a set of recovery discs
beforehand. Throughout the process, you will be guided by on-screen
instructions. Please read them carefully!
1. Click on Start > All Programs > Gateway, then click on Gateway
Recovery Management.
66 - Recovery
Page 67

2. To create recovery discs for the hard drive’s entire original contents,
including Windows and all factory-loaded software and drivers, click
Create Factory Default Disc.
- OR To create recovery discs for only the factory-loaded software and drivers,
click Create Drivers and Applications Backup Disc.
Important: We recommend that you create each type of recovery
disc as soon as possible.
Recovery - 67
Page 68

The Create Factory Default Backup dialog box opens.
This dialog box tells you the number of blank, recordable discs you will
need to complete the recovery discs. Make sure that you have the
required number of identical, blank discs ready before continuing.
68 - Recovery
Page 69

3. Insert a blank disc into the drive indicated in the Backup to list, then click
Next. You will be shown the backup progress on the screen.
The drive ejects each disc as it completes burning it.
4. Remove the disc from the drive and mark it with a permanent marker.
Important: Write a unique, descriptive label on each disc, such as
‘Windows Recovery Disc 1 of 2’ or ‘Apps/Drivers Recovery disc’.
Make sure you keep the discs in a safe place that you will
remember.
5. If multiple discs are required, insert a new disc when prompted, then
click OK. Continue until the process is complete.
RECOVERING YOUR SYSTEM
If Gateway support did not help fix your problem, you can use the
Gateway Recovery Management program. This will restore your computer
Recovery - 69
Page 70
to the same state as when you purchased it, while giving you an option to
retain all settings and personal data for later retrieval.
To recover your system:
1. Perform minor fixes.
If only one or two items of software or hardware have stopped working
correctly, the problem may be solved by reinstalling the software or the
device drivers.
To recover software and drivers that were pre-installed at the factory, see
“Recovering pre-installed software and drivers” on page 71.
For instructions on reinstalling software and drivers that were not preinstalled, see that product’s documentation or technical support Web
site.
2. Revert to a previous system condition.
If reinstalling software or drivers does not help, then the problem may be
solved by returning your system to a previous state when everything was
working correctly.
For instructions, see “Returning to a previous system condition” on page
72.
3. Reset your system to its factory condition.
If nothing else has solved the problem and you want to reset your system
to factory condition, see “Returning your system to its factory condition”
on page 73.
70 - Recovery
Page 71

Types of recovery
Recovering pre-installed software and drivers
As a troubleshooting step, you may need to reinstall the software and
device drivers that came pre-installed on your computer from the factory.
You can recover using either your hard drive or the backup you have
created.
• New software - If you need to recover software that did not come pre-
installed on your computer, you need to follow that software’s installation
instructions.
• New device drivers - If you need to recover device drivers that did not
come pre-installed on your computer, follow the instructions provided
with the device.
To recover your pre-installed software and drivers:
1. Click on Start > All Programs > Gateway, then click on Gateway
Recovery Management. Gateway Recovery Management opens.
- OR If you are recovering from your driver and application recovery backup,
insert it into the disc drive, then go to Step 3 after the Gateway Application
Recovery main menu opens.
2. Click on the Restore tab, then click Reinstall Drivers or Applications.
The Gateway Application Recovery main menu opens.
Recovery - 71
Page 72

3. Click on Contents. A list of software and device drivers opens.
4. Click on the install icon for the item you want to install, then follow the
on-screen prompts to complete the installation. Repeat this step for
each item you want to reinstall.
Returning to a previous system condition
Microsoft System Restore periodically takes ’snapshots’ of your system
settings and saves them as restore points. In most cases of hard-toresolve software problems, you can return to one of these restore points to
get your system running again.
Windows automatically creates an additional restore point each day, and
also each time you install software or device drivers.
72 - Recovery
Page 73

Help: For more information about using Microsoft System Restore,
click Start, then click Help and Support. Type windows system
restore in the Search Help box, then press Enter.
To return to a restore point:
1. Click on Start > Control Panel > System and Security > Action
Center, then click on Recovery.
2. Click on Open System Restore, then Next.
3. Click on he restore point you want, click on Next, then Finish. A
confirmation message box appears.
4. Click on Yes. Your system is restored using the restore point you
specified. This process may take several minutes, and may restart your
computer.
Returning your system to its factory condition
If your computer experiences problems that are not recoverable by other
methods, you may need to reinstall everything to return your system to its
factory condition. You can reinstall using either your hard drive or the
recovery discs you have created.
Caution: This complete recovery deletes everything on your hard
drive, then reinstalls Windows and all software and drivers that
were pre-installed on your system. If you can access important
files on your hard drive, back them up now.
• If you can still run Windows, see “Recovering from within Windows”
below.
Recovery - 73
Page 74

• If you cannot run Windows and your original hard drive is still working,
see “Recovering from the hard drive during startup” on page 75.
• If you cannot run Windows and your original hard drive has been
completely re-formatted or you have installed a replacement hard drive,
see “Recovering from your recovery discs” on page 75.
Recovering from within Windows
To reinstall Windows and all pre-installed software and drivers:
1. Click on Start > All Programs > Gateway, then click on Gateway
Recovery Management. Gateway Recovery Management opens.
2. Click on the Restore tab, then Restore system to factory default. The
Confirm Restoration dialog box opens.
3. Click on Yes, then Start. A dialog box displays information about the
hard drive that the operating system will be recovered to.
Caution: Continuing the process will erase all files on your hard
drive.
4. Click on OK. The recovery process begins by restarting your computer,
then continues by copying files to your hard drive. This process may
take a while, but a Gateway Recovery Management screen shows you
its progress.
When the recovery has finished, a dialog box prompts you to restart your
computer.
5. Click on OK. Your computer restarts.
6. Follow the on-screen prompts for first-time system setup.
74 - Recovery
Page 75

Recovering from the hard drive during startup
To reinstall Windows and all pre-installed software and drivers:
1. Turn on your computer, then press Alt+F10 during startup. Gateway
Recovery Management opens.
2. Click on Restore system from factory default.
Caution: Continuing the process will erase all files on your hard
drive.
3. Click on Next. Your hard drive’s original, factory-loaded contents are
recovered. This process will take several minutes.
Recovering from your recovery discs
To reinstall Windows and all pre-installed software and drivers:
1. Turn on your computer, insert the first system recovery disc into your
optical disc drive, then restart your computer.
Caution: Continuing the process will erase all files on your hard
drive.
2. If it is not already enabled, you must enable the F12 Boot Menu:
1. Press F2 when starting your computer.
2. Use the left or right arrow keys to select the Main menu.
3. Press the down key until F12 Boot Menu is selected, press F5 to
change this setting to Enabled.
4. Use the left or right arrow keys to select the Exit menu.
5. Select Save Changes and Exit and press Enter. Select OK to
confirm.
Recovery - 75
Page 76

6. Your computer will restart.
3. During startup, press F12 to open the boot menu. The boot menu allows
you to select which device to start from, such as the hard drive or an
optical disc.
4. Use your arrow keys to select the line CDROM/DVD (this line may start
with ’IDE 1...’), then press Enter. Windows installs from the recovery
disc you inserted.
5. Insert the second recovery disc when prompted, then follow the onscreen prompts to complete the recovery.
76 - Recovery
Page 77

REGULATORY INFORMATION
PREVENTION OF HEARING LOSS
- Caution: Permanent hearing loss may occur if earphones or headphones are used
at high volume for prolonged periods of time.
This device have been tested to comply with the Sound Pressure Level
requirement laid down in the applicable EN 50332-1 and/or EN 50332-2 standards.
Note:
For France, mobile headphones or earphones for this device have
been tested to comply with the Sound Pressure requirement laid down in the
applicable NF EN 50332-1:2000 and/or NF EN 50332-2:2003 standards as required
by French Article L. 5232-1.
- A pleine puissance, l’écoute prolongée du baladeur peut endommager l’oreille de
l’utilisateur.
CAUTION when listening
To protect your hearing, follow these instructions.
- Increase the volume gradually until you can hear clearly and comfortably.
- Do not increase the volume level after your ears have adjusted.
- Do not listen to music at high volumes for extended periods.
- Do not increase the volume to block out noisy surroundings.
- Decrease the volume if you can’t hear people speaking near you.
IRELESS DEVICES
W
Caution: Wireless devices are not user-serviceable. Do not modify them in
any way. Modification to a wireless device will void the authorization to use
it. Contact Gateway for service information.
Caution: The transmitting device embedded in this computer may not be
used with any antenna other than the one provided with the computer.
Regulatory information - 77
Page 78

Warning: Using wireless devices while flying in aircraft is prohibited. Switch
off all devices before boarding an aircraft; they may be dangerous to the
operation of the aircraft, disrupt communications, and even be illegal.
F
EDERAL COMMUNICATIONS COMMISSION (FCC) INTENTIONAL EMITTER PER FCC PART 15
Low power, Radio transmitter type devices (radio frequency (RF) wireless communication
devices), operating in the 2.4 GHz band and/or 5.15 – 5.35 GHz band, may be present
(embedded) in your computer system. This section is only applicable if these devices are
present. Refer to the system label to verify the presence of wireless devices.
Wireless devices that may be in your system are only qualified for use in the United States
of America if an FCC ID number is on the system label.
Operation of this device is subject to the following two conditions: (1) This device may not
cause harmful interference, and (2) this device must accept any interference received,
including interference that may cause undesired operation of the device.
U
NINTENTIONAL EMITTER PER FCC PART 15
This device has been tested and found to comply with the limits for a Class B digital
device, pursuant to Part 15 of the FCC rules. These limits are designed to provide
reasonable protection against harmful interference in a residential installation. This
equipment generates, uses, and can radiate radio frequency energy and, if not installed
and used in accordance with the instructions, may cause harmful interference to radio or
television reception. However, there is no guarantee that interference will not occur in a
particular installation. If this equipment does cause interference to radio and television
reception, which can be determined by turning the equipment off and on, the user is
encouraged to try to correct the interference by one or more of the following measures:
- Reorient or relocate the receiving antenna.
- Increase the separation between the equipment and receiver.
- Connect the equipment into an outlet on a circuit different from that to which the
receiver is connected.
Consult the dealer or an experienced radio/TV technician for help.
78 - Regulatory information
Page 79

RADIO DEVICE REGULATORY NOTICE
-
Note:
Regulatory information below is for models with wireless LAN and/or Bluetooth
only.
General
This product complies with the radio frequency and safety standards of any country or
region in which it has been approved for wireless use. Depending on configuration, this
product may or may not contain wireless radio devices (such as wireless LAN and/or
Bluetooth modules). Information below is for products with such devices.
Wireless operation channels for different domains
N. America 2.412-2.462 GHz Ch01 through Ch11
Japan 2.412-2.484 GHz Ch01 through Ch14
Europe ETSI 2.412-2.472 GHz Ch01 through Ch13
This equipment is in compliance with the essential requirements and other relevant
provisions of Directive 1999/5/EC.
France: Restricted wireless frequency bands
Some areas of France have a restricted frequency band. The worst case maximum
authorized power indoors is:
- 10 mW for the entire 2.4 GHz band (2400 MHz - 2483.5 MHz)
- 100 mW for frequencies between 2446.5 MHz and 2483.5 MHz
- Note: Channels 10 through 13 inclusive operate in the band 2446.6 MHz to 2483.5
MHz.
There are few possibilities for outdoor use: On private property or on the private property
of public persons, use is subject to a preliminary authorization procedure by the Ministry
of Defense, with maximum authorized power of 100 mW in the 2446.5 - 2483.5 MHz band.
Use outdoors on public property is not permitted.
In the departments listed below, for the entire 2.4 GHz band:
- Maximum authorized power indoors is 100 mW
- Maximum authorized power outdoors is 10 mW
Regulatory information - 79
Page 80

Departments in which the use of the 2400 - 2483.5 MHz band is permitted with an EIRP
of less than 100 mW indoors and less than 10 mW outdoors:
01 Ain Orientales
02 Aisne
03 Allier
05 Hautes Alpes
08 Ardennes
09 Ariege
11 A ud e
12 Aveyron
16 Charente
24 Dordogne
25 Doubs
26 Drome
32 Gers
36 Indre
37 Indre et Loire
41 Loir et Cher
45 Loret
50 Manche
55 Meuse
58 Nievre
59 Nord
60 Oise
61 Orne
63 Puy Du Dome
64 Pyrenees Atlantique
66 Pyrenees
67 Bas Rhin
68 Haut Rhin
70 Haute Saone
71 Saone et Loire
75 Paris
82 Tarn et Garonne
84 Vaucluse
88 Vosges
89 Yonne
90 Territoire de Belfort
94 Val de Marne
This requirement is likely to change over time, allowing you to use your wireless LAN card
in more areas within France.
Please check with ART for the latest information (www.art-telecom.fr).
-
Note:
Your WLAN Card transmits less than 100 mW, but more than 10 mW.
List of National Codes
This equipment may be operated in the following countries:
Country
Austria AT Germany DE Malta MT United Kingdom GB
Belgium BE Greece GR Netherlands NT Iceland IS
Cyprus CY Hungary HU Poland PL Liechtenstein LI
Czech Republic CZ Ireland IE Portugal PT Norway NO
Denmark DK Italy IT Slovakia SK Switzerland CH
Estonia EE Latvia LV Slovenia SL Bulgaria BG
Finland FI Lithuania LT Spain ES Romania RO
France FR Luxembourg LU Sweden SE Turkey TR
80 - Regulatory information
ISO 3166
2 letter
code
Country
ISO 3166
2 letter
code
Country
ISO 3166
2 letter
code
Country
ISO 3166
2 letter
code
Page 81

Compliance accessories
The accessories associated with this equipment are: shielded video cable when an
external monitor is connected. These accessories are required to be used in order to
ensure compliance with FCC rules.
ALIFORNIA PROPOSITION 65 WARNING
C
This product contains chemicals known to the State of California to cause cancer, birth
defects, and/or other reproductive harm. For additional information regarding this product
warning, go to www.gateway.com/prop65.
M
ERCURY WARNING
THE LAMP IN THIS DISPLAY CONTAINS MERCURY. DISPOSE ACCORDING
TO LOCAL, STATE, AND FEDERAL LAW.
TELECOMMUNICATIONS PER PART 68 OF THE CODE OF FEDERAL REGULATIONS (CFR 47)
(APPLICABLE TO PRODUCTS FITTED WITH USA MODEMS)
Your modem complies with Part 68 of the Code of Federal Regulations (CFR 47) rules.
On the computer or modem card is a label that contains the FCC registration number and
Ringer Equivalence Number (REN) for this device. If requested, this information must be
provided to the telephone company.
A telephone line cord with a modular plug is required for use with this device. The modem
is designed to be connected to the telephone network or premises wiring using a
compatible modular jack which is Part 68-compliant. See installation instructions for
details.
The Ringer Equivalence Number (REN) is used to determine the number of devices which
may be connected to the telephone line. Excessive RENs on a telephone line may result
in the devices not ringing in response to an incoming call. In most areas, the sum of RENs
should not exceed five (5). To be certain of the number of devices that may be connected
to a line, as determined by the total RENs, contact the local telephone company.
If this device causes harm to the telephone network, the telephone company will notify you
in advance that temporary discontinuance of service may be required. The telephone
company may request that you disconnect the equipment until the problem is resolved.
Regulatory information - 81
Page 82

The telephone company may make changes in its facilities, equipment, operations, or
procedures that could affect the operation of this equipment. If this happens, the
telephone company will provide advance notice in order for you to make necessary
modifications to maintain uninterrupted service.
This equipment cannot be used on telephone company-provided coin service. Connection
to party line service is subject to state tariffs. Contact the state public utility commission or
public service commission for information.
When programming or making test calls to emergency numbers:
- Remain on the line and briefly explain to the dispatcher the reason for the call.
- Perform such activities in the off-peak hours such as early morning or late evenings.
The United States Telephone Consumer Protection Act of 1991 makes it unlawful for any
person to use a computer or other electronic device to send any message via a telephone
fax machine unless such message clearly contains, in a margin at the top or bottom of
each transmitted page or on the first page of the transmission, the date and time it is sent,
an identification of the business, other entity, or other individual sending the message, and
the telephone number of the sending machine or such business, other entity, or individual.
Refer to your fax communication software documentation for details on how to comply
with the fax-branding requirement.
I
NDUSTRY CANADA (IC) INTENTIONAL EMITTER PER RSS 210
Caution: To prevent radio interference to licensed service or co-channel
Mobile Satellite systems, this device is intended to be operated indoors and
away from windows to provide maximum shielding. Equipment (or its
transmit antenna) that is installed outdoors is subject to licensing.
Low power, Radio transmitter type devices (radio frequency (RF) wireless communication
devices), operating in the 2.4 GHz band and/or 5.15 – 5.35 GHz band, may be present
(embedded) in your computer system. This section is only applicable if these devices are
present. Refer to the system label to verify the presence of wireless devices.
Wireless devices that may be in your system are only qualified for use in Canada if an
Industry Canada ID number is on the system label.
82 - Regulatory information
Page 83

Operation of this device is subject to the following two conditions: (1) This device may not
cause harmful interference, and (2) this device must accept any interference received,
including interference that may cause undesired operation of the device.
U
NINTENTIONAL EMITTER PER ICES-003
This digital apparatus does not exceed the Class B limits for radio noise emissions from
digital apparatus as set out in the radio interference regulations of Industry Canada.
Le présent appareil numérique n’émet pas de bruits radioélectriques dépassant les limites
applicables aux appareils numériques de Classe B prescrites dans le règlement sur le
brouillage radioélectrique édicté par Industrie Canada.
T
ELECOMMUNICATIONS PER INDUSTRY CANADA CS-03 (FOR PRODUCTS FITTED WITH AN IC-
COMPLIANT MODEM)
The Industry Canada label identifies certified equipment. This certification means that the
equipment meets certain telecommunications network protective, operation, and safety
requirements. The Department does not guarantee the equipment will operate to the
users’ satisfaction.
Before installing this equipment, users should make sure that it is permissible to be
connected to the facilities of the local telecommunications company. The equipment must
also be installed using an acceptable method of connection. In some cases, the inside
wiring associated with a single-line individual service may be extended by means of a
certified connector assembly. The customer should be aware that compliance with the
above conditions may not prevent degradation of service in some situations.
Repairs to certified equipment should be made by an authorized Canadian maintenance
facility designated by the supplier. Any repairs or alterations made by the user to this
equipment, or equipment malfunctions, may give the telecommunications company cause
to request the user to disconnect the equipment.
Warning: To avoid electrical shock or equipment malfunction do not attempt
to make electrical ground connections by yourself. Contact the appropriate
inspection authority or an electrician, as appropriate.
Regulatory information - 83
Page 84

Users should make sure, for their own protection, that the electrical ground connections
of the power utility, telephone lines, and internal metallic water pipe system, if present, are
connected together. This precaution may be particularly important in rural areas.
The Ringer Equivalence Number (REN) assigned to each terminal device provides an
indication of the maximum number of terminals allowed to be connected to a telephone
interface. The termination on an interface may consist of any combination of devices
subject only to the requirement that the sum of the Ringer Equivalence Numbers of all the
devices does not exceed 5.
日本
(JAPAN)
本装置は、第二種情報装置(住宅地域またはその隣接した地域において使用されるべき
情報装置)デ住宅地域での電波障害防止を目的とした情報装置等電波障害自主規制協議
会(VCCI)基準に適合しております。
しかし、本装置をラジオ、テレビジョン受信機に、近接してご使用になると、受信障害
の原因となることがあります。本書の説明にしたがって正しい取り扱いをしてくださ
い。
Japanese modem notice
本製品を日本で使用する場合は必ず日本国モードでご使用ください。他国のモードをご
使用になると電気通信事業法(技術基準)に違反す行為となります。なお、ご購入時は
初期値が日本国モードとなっておりますので、そのままご利用ください。
CE
COMPLIANCE REQUIREMENT
Products with the CE marking comply with both the Electromagnetic
Compatibility Directive (2004/108/EC) and the Low Voltage Directive (2006/95/
EC) issued by the Council of the European Communities.
Compliance with these directives implies conformity to the following European Standards:
EN55022: Radio disturbance characteristics
EN55024: Immunity characteristics
EN61000-3-2: Limitation of harmonic current emissions
EN61000-3-3: Limitation of voltage fluctuation and flicker in low-voltage supply system
84 - Regulatory information
Page 85

EN60950-1: Product Safety. If your computer includes a telecommunication network
board, the input/output socket is classified as Telecommunication Network Voltage (TNV-
3).
Note for computers equipped with wireless controllers and wired modems:
Hereby, Gateway, declares that the wireless devices provided with this
computer include a low power radio transmitter in full compliance with the
essential requirements and other relevant provisions of Directive 1999/
05/EC for Low Voltage, EMC and RF of the R&TTE.
List of applicable countries
This product must be used in strict accordance with the regulations and constraints in the
country of use. For further information, contact the local office in the country of use.
Please see http://ec.europa.eu/enterprise/rtte/implem.htm for the latest country list.
M
ODIFICATIONS TO THE PRODUCT
CE Marking
Gateway cannot be held responsible for unauthorized modifications made by the user and
the consequences thereof, which may alter the conformity of the product with the CE
Marking.
Radio frequency interference
The manufacturer is not responsible for any radio or TV interference caused by
unauthorised modifications to this equipment.
ONNECTIONS AND REMOTE EARTHS
C
PELV (Protected Extra Low Voltage)
To ensure the extra-low voltage integrity of the equipment, only connect equipment with
mains-protected electrically-compatible circuits to the external ports.
SELV (Safety Extra Low Voltage)
Every input and output of this product is classified as Safety Extra Low Voltage.
Regulatory information - 85
Page 86

Remote earths
To prevent electrical shock, connect all local (individual office) computers and computer
support equipment to the same electrical circuit of the building wiring. If you are unsure,
check the building wiring to avoid remote earth conditions.
Building supply
Only connect the equipment to a building supply that is in accordance with current wiring
regulations in your country. In the U.K., these are the IEE regulations.
OWER SUPPLY AND CABLES
P
Power supply
The power supply socket-inlet and socket-outlet (if equipped) are classified as Hazardous
Voltage.
You must unplug the power supply cord to disconnect the equipment from the power
supply. In that aim, the socket-outlet should be installed near to the equipment and should
be easily accessible.
Under no circumstances should the user attempt to disassemble the power supply. The
power supply has no user-replaceable parts. Inside the power supply are hazardous
voltages that can cause serious personal injury.
A defective power supply must be returned to your dealer.
Power cables and plug
This Product requires a three-wire grounded power cord and plug. The plug only fits in a
grounded power outlet. Make sure the power outlet is properly grounded before inserting
the plug. Do not insert the plug into a non-grounded power outlet. Contact your electrician
for details.
The cord length must not exceed 2.5 metres. To prevent electrical hazards, do not remove
or disable the ground contact on the power cord. Replace the power cord if it gets
damaged. Contact your dealer for an exact replacement. In Europe, the plug must be
rated for 250 VAC, 10 amp minimum. The plug must display an international agency
86 - Regulatory information
Page 87

approval marking. The cord must be suitable for use in the end-user country. Consult your
dealer or the local electrical authorities if you are unsure of the type of power cord to use
in your country.
Cables
For cables which are not delivered with the Product in the computer's packaging:
The EMC performance of the system is guaranteed only if the cable and interface use
efficient shielding.
The use of shielded interface cable is required for USB, IEEE1394, serial, printer, game,
analog or digital audio/ video, PS2, TV or FM antennas, and generally all high-speed
cable interfaces.
Use only UL Listed No. 26AWG or larger telecommunication cords.
Only Ethernet LAN or RTC modem cable can have length exceeding 3 metres.
Gateway recommends that you add a ferrite core round clip to each cable connecting your
computer to a hardware device that was not included with your computer.
- Ferrite reference: 28A-2029 from Steward (two loops)
During product certification, Gateway used the following cable quality:
- USB2.0 Certified Cables from Hama 46778
- IEEE1394 shielded FireWire from Hama 50011
- RCA-RCA shielded Audio/Video Cables from Thomson KHC001M, KHC012M,
KHC028M
- Stereo Jack shielded Audio cables from Hama 43330H, 42714H
HASSIS COVER REMOVAL AND REPLACEMENT
C
Before removing the chassis cover to service or modify the equipment, you must
disconnect all power and modem cords.
- Caution: Some components inside the computer can become hot after prolonged
use.
You then must close the chassis before you plug in and switch on the equipment.
Regulatory information - 87
Page 88

LASER COMPLIANCE STATEMENT
The optical devices are tested and certified to be compliant with International
Electrotechnical Commission IEC60825-1 and European EN60825-1 standards for Class
1 laser products.
Class 1 laser products are not considered hazardous. The optical devices are designed
such that there is never human access to laser radiation above a Class 1 level during
normal operation or prescribed maintenance conditions.
The optical devices installed in your computer are designed for use solely as components
of such electronic product and therefore do not comply with the appropriate requirements
of Code of Federal Regulation Sec. 1040.10 and Sec. 1040.11 for COMPLETE laser
products.
Because exposure to laser radiation is extremely hazardous, under no circumstances
should the user attempt to disassemble the laser device.
P
ACKAGING
The packaging of this product is compliant with the European Environmental Directive 94/
62/EC from December 20 th 1994 and its equivalent in the French Legislation by the
Decree 98-638 from july 20 th 1998.
C
OMPLIANT WITH RUSSIAN / UKRAINE REGULATORY CERTIFICATION
88 - Regulatory information
Page 89

ENVIRONMENT
ENVIRONMENT
Temperature:
- Operating: 5 ºC to 35 ºC
- Non-operating: -20 ºC to 65 ºC
Humidity (non-condensing):
- Operating: 20% to 80%
- Non-operating: 20% to 80%
UR COMMITMENT TO ENVIRONMENTAL PROTECTION
O
Environment has been at the heart of our products.
Gateway is committed to limit the environmental impact of its products during product life
cycle.
Starting at design phase, with a very strict procurement policy, maximum attention is given
to electronic components in order to limit their weight in heavy metals such as lead,
cadmium, chromium, mercury, etc. Suppliers are asked, for each part of any product, to
respect all regulations.
As far as end-of-life products are concerned, measures have been taken to anticipate and
facilitate the recycling of all our products. Thus, all plastic parts heavier than 25 grams
used in Gateway products are labelled ISO 11469. This label allows a quick recognition
of the material and eases its valorisation. Likewise, desktop computers are designed to
be easily dismantled, with screws being replaced by clips.
Environment - 89
Page 90
PRODUCT DISPOSAL
The 2002/96/EC Directive, known as Waste Electrical and Electronic
Equipment (WEEE) Directive, requires that used electrical and electronic
products must be disposed of separately from normal household waste in
order to promote reuse, recycling and other forms of recovery and to
reduce the quantity of waste to be eliminated with a view to reducing
landfill and incineration. The crossed-out dustbin logo is there to remind
you that these products must be sorted separately for disposal. These
rules concern all Gateway products and also all accessories, such as keyboard, mouse,
speakers, remote control, etc. When you have to dispose of such products, make sure
that they are correctly recycled by checking with your local authority, or by returning your
old equipment to your retailer if you are replacing it. For information, visit
www.gateway.com/about/corp_responsibility/environment.php.
Battery disposal (when applicable)
Before disposing of your equipment ensure that you have removed any batteries that may
be fitted in the equipment. European law states that batteries must be collected for
disposal separately from household waste. Do not throw your used batteries in the
dustbin. Dispose of your used batteries via a battery collection scheme where available,
or ask your distributor or local authority what infrastructures you can use. Your efforts will
enable the safe collection, recycling and destruction of used batteries and will help protect
the environment and reduce health hazards.
- Caution: Risk of explosion if battery is replaced by an incorrect type. Dispose of
used batteries according to the instructions.
Mercury advisory
For electronic products containing a non-LED-backlit LCD/CRT monitor or
display: Lamp(s) inside this product contain mercury and must be recycled or
disposed of according to local, state or federal laws. For more information,
contact the Electronic Industries Alliance at www.eiae.org. for lamp-specific
disposal information, check www.lamprecycle.org.
90 - Environment
Page 91

ENERGY STAR
Gateway's ENERGY STAR qualified products save your money by
reducing energy cost and protecting the environment without sacrificing
features or performance. Gateway is proud to offer our customers
products with the ENERGY STAR mark.
What is ENERGY STAR?
Products that are ENERGY STAR qualified use less energy and prevent greenhouse gas
emissions by meeting strict energy efficiency guidelines set by the U.S. Environmental
Protection Agency. Gateway is committed to offering products and services worldwide
that help customers save money, conserve energy and improve the quality of our
environment. The more energy we can save through higher energy efficiency, the more
we reduce greenhouse gases and the risks of climate change. More information refers to
www.energystar.gov or www.energystar.gov/powermanagement.
- Note: The statement above is applicable only to Gateway system with an ENERGY
STAR sticker.
Gateway ENERGY STAR qualified products:
- Produce less heat and reduce cooling loads in warmer climates.
- The display is configured to go into sleep mode after less than 10 minutes of user
inactivity. The computer is configured to go into sleep mode after less than 30
minutes of user inactivity.
- Wake the computer from sleep mode by pushing keyboard or moving mouse.
- Computers will save more than 80% energy at "sleep" mode.
ENERGY STAR and the ENERGY STAR mark are registered U.S. marks.
Environment - 91
Page 92

SOFTWARE LICENSE
- Note: Most of the software applications are already preinstalled on your Gateway
computer. They are ready to use or to set up. However, some titles require a CD or
DVD to run. You will find these discs in your computer's packaging.
Gateway License Agreement (CD and/or DVD Products). This copy of the original is your
proof of license. Please treat it as valuable property.
Important!
Read carefully before installing the software.
The following License Agreement applies to you. This is a legal agreement between you
(either individual or an entity) and Gateway By installing the software you are agreeing to
be bound by the terms of this Agreement. If you do not agree to the terms of this
Agreement, promptly return your entire computer system, the unopened software
packet(s), if any, as well as the accompanying terms (including written materials or other
container(s)) in the place you obtained them for a full refund.
G
ATEWAY SOFTWARE LICENSE
1. Grant of License
This Gateway License Agreement (“License”) permits you to use one copy of the specified
version of the Gateway SOFTWARE identified above (which may include at least one CD
or DVD disc) on any single computer, provided the SOFTWARE is in use on only one
computer at any time. If you have multiple Licenses for the SOFTWARE, then at any time
you may have as many copies of the SOFTWARE in use as you have Licenses. The
SOFTWARE is “in use” on a computer when it is loaded into the temporary memory (i.e.
RAM) or installed in the permanent memory (e.g. hard disk, CD and/or DVD, or other
storage device of that computer, except that a copy installed on a network server for the
sole purpose of distribution of other computer is not “in use.” If the anticipated number of
users of the SOFTWARE will exceed the number of applicable Licenses, then you must
have a reasonable mechanism or process in place to assure that the number of persons
92 - Software license
Page 93

using the SOFTWARE concurrently does no exceed the number of Licenses. If the
SOFTWARE is permanently installed on the hard disk or the storage device of a computer
(other than a network server) and one person uses that computer more than 80% of the
time it is in use, then that person may also use the SOFTWARE on a portable or home
computer.
2. Copyright
The SOFTWARE is owned by Gateway or its suppliers and is protected by United States
copyright laws and international treaty provision. Therefore, you must treat the
SOFTWARE like any other copyrighted material (e.g. a book or musical recording) except
that you may transfer the CD and/or DVD disc portion of the SOFTWARE, if any, to a
single hard disk provided you keep the original solely for backup or archival purposes. You
may not copy the CD and/or DVD disc portion of the SOFTWARE or the written materials
accompanying the SOFTWARE.
3. Other restrictions
You may not rent or lease the SOFTWARE, but you may transfer the SOFTWARE and
accompanying written materials on a permanent basis provided you retain no copies and
the recipient agrees to the terms of this Agreement. You may not reverse engineer,
decompile or disassemble the SOFTWARE. Any transfer of the SOFTWARE must include
the most recent update and all prior versions.
T
HIRD PARTY SOFTWARE OR FREE SOFTWARE LICENSE INFORMATION
Software pre-loaded, embedded or otherwise distributed with the products provided by
Gateway does contain free or third party software programs (the “Free Software”), which
are licensed under the terms GNU General Public License (the “GPL”). The Free Software
is marked as such. Your copying, distribution and/or modification of the Free Software
shall be subject to the terms of the GPL.
The Free Software is distributed in the hope that, but it will be useful WITHOUT ANY
WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS
FOR A PARTICULAR PURPOSE. The provisions of the GNU General Public License
shall always apply. You may access http://www.gnu.org directly to obtain a copy of the
Software license - 93
Page 94

GPL or write to the free Software Foundation, Inc. and request a copy. The address of the
Free Software Foundation, Inc is: 59 Temple Place - Suite 330, Boston, MA, 02111-1307,
USA.
For a period of three (3) years as commencing from your receipt of this software, you may
obtain a complete machine-readable copy of the source code for the Free Software under
the terms of the GPL without charge except for the cost of media, shipping, and handling,
upon a written request to us.
Contact us if you have any further questions. Our mailing address is 8F, 88, Sec. 1, Hsin
Tai Wu Rd., Hsichih, New Taipei City 221, Taiwan.
94 - Software license
Page 95

INDEX
A
Audio CDs.............................................. 27 Autoplay................................................. 28
B
Batteries................................................. 90
battery disposal...................................... 90
Cables................................................ 8, 86
Cleaning your computer ........................... 8
Codec..................................................... 29
Disk Cleanup.......................................... 54
Disk Defragmenter ................................. 55
disk drives
taking care of discs .......................... 19
Download ............................................... 29
Electronic Program Guide ...................... 28
Environment........................................... 89
Firewall............................................. 41, 48
Frequently-asked questions................... 63
blank screen .................................... 63
no audio ........................................... 64
Blu-ray ............................................. 28, 31
Browser.................................................. 37
C
Computer environment ............................ 7
connections
network............................................ 22
D
Drives
Memory card reader ........................ 20
DSL........................................................ 33
DVD ....................................................... 30
DVD movies........................................... 30
playing............................................. 30
E
Epilepsy warning.................................... 11
Error checking........................................ 53
F
no sound.......................................... 64
printer not working........................... 64
system cannot read disk.................. 65
system cannot write to disk ............. 65
Index - 95
Page 96

system did not boot up..................... 63
G
Gateway
Recovery Management Program..... 26
H
HDD (Hard Disk Drive)
Free space....................................... 54
Management.................................... 56
Health precautions................................. 10
Helpdesk................................................ 53
I
Interference............................................ 85
Internet
Connection................................. 32, 33
Firewall ...................................... 41, 48
Internet Service Provider (ISP) .............. 32
L
LAN (Local Area Network) ..................... 34 Last Known Good Configuration............ 60
M
Maintenance
HDD management ........................... 56
Recovery Management Program..... 26
System tools .................................... 57
Malware ................................................. 41
Memory card reader .............................. 20
Modem................................................... 33
Multimedia files...................................... 26
N
network................................................... 22
Network connections.............................. 34
Norton Internet Security................... 40, 43
O
optical drive............................................ 18 optical drives
inserting a disc ................................ 19
96 - Index
Page 97

P
ports ....................................................... 20
Power cords ............................................. 8
PowerDVD............................................. 28
R
Recovery
Recovery Management Program..... 26
System Restore ............................... 58
Regulatory Information..................... 77, 89
Removable media devices..................... 21
Removing hardware............................... 21
Removing software ................................ 56
Restore points........................................ 60
S
Safe Computing ..................................... 53
Safety precautions ................................... 7
Security
Antivirus ........................................... 42
Updates ..................................... 49, 60
Windows Action Center ............. 47, 61
setting up computer................................ 12
area.................................................. 12
broadband network .......................... 17
chair ................................................. 12
keyboard .......................................... 14
monitor............................................. 14
mouse.............................................. 14
power cable ..................................... 17
Software
Removing software.......................... 56
Software License............................. 92
Spyware................................................. 40
System Restore ..................................... 58
System tools
Disk Cleanup ................................... 54
Disk Defragmenter .......................... 55
Error checking ................................. 53
Windows System Restore ............... 58
T
turning off computer ............................... 18
software shutdown........................... 18
suspend mode ................................. 18
turning on computer ............................... 18
power button.................................... 18
power switch.................................... 18
TV tuner................................................. 26
U
Uninstalling hardware............................. 21 universal serial bus................................ 22
Index - 97
Page 98

Update
Windows automatic updates...... 49, 61
Warranty................................................... 6
Welcome Center .................................... 25
WiFi........................................................ 34
Windows
System Restore ............................... 58
Using Windows ................................ 25
Welcome Center .............................. 25
User Account Control............................. 51
W
Windows Action Center ............. 47, 61
Windows automatic updates ..... 49, 61
Windows Defender .......................... 50
Windows Media Center ............. 26, 27
Windows Media Player.............. 26, 27
Windows Remote Assistance.......... 62
V12A2
98 - Index
 Loading...
Loading...