
Image Controller IC-402
User’s Guide
[Network Scanner Operations]
[Copier Network Functions]
Introduction
Introduction
Thank you for choosing this machine.
This User’s Guide contains descriptions of the network scanning functions
and operations that can be used from optional C450/C351 image controller
IC-402 and the network functions that can be used from the copier when the
IC-402 is installed. To ensure the best possible performance and most effective use of the machine, read this manual thoroughly. After reading this User’s Guide, store it in the designated holder for quick reference when
problems or questions arise during operation.
Views of the actual equipment may be slightly different from the illustrations
used in this manual.
IC-402 x-1

Trademarks and Registered Trademarks
KONICA MINOLTA and the KONICA MINOLTA logo are trademarks of Konica Minolta Holdings, Inc.
PageScope is a registered trademark of Konica Minolta Business Technologies, Inc.
Apple and Macintosh are registered trademarks of Apple Computer, Inc.
Ethernet is a registered trademark of Xerox Corporation.
Microsoft, Windows and Windows NT are registered trademarks of Microsoft
Corporation.
PostScript is a registered trademark of Adobe Systems, Inc.
EFI, Fiery and the Fiery logo are registered trademarks of Electronics for Imaging, Inc. and are legally registered in the United States and other countries.
The Electronics for Imaging logo, Fiery Remote Scan, Fiery WebScan, and
Fiery WebTools are trademarks of Electronics for Imaging, Inc.
OpenSSL Statement
OpenSSL License
Copyright © 1998-2000 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must
display the following acknowledgment:
“This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit. (http://www.openssl.org/)”
4. The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used
to endorse or promote products derived from this software without prior
written permission. For written permission, please contact opensslcore@openssl.org.
5. Products derived from this software may not be called “OpenSSL” nor
may “OpenSSL” appear in their names without prior written permission
of the OpenSSL Project.
Introduction
x-2 IC-402

Introduction
6. Redistributions of any form whatsoever must retain the following ac-
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS” AND
ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR
ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON
ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young
(eay@crypt-Soft.com). This product includes software written by Tim Hudson (tjh@cryptsoft.com).
Original SSLeay License
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are aheared to. The following conditions apply to all code
found in this distribution, be it the RC4, RSA, Ihash, DES, etc., code; not just
the SSL code.
The SSL documentation included with this distribution is covered by the
same copyright terms except that the holder is Tim Hudson (tjh@cryptsoft.com).
Copyright remains Eric Young’s, and as such any Copyright notices in the
code are not to be removed. If this package is used in a product, Eric Young
should be given attribution as the author of the parts of the library used. This
can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the copyright notice, this list
2. Redistributions in binary form must reproduce the above copyright no-
knowledgment:
“This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit (http://www.openssl.org/)”
of conditions and the following disclaimer.
tice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
IC-402 x-3

Introduction
3. All advertising materials mentioning features or use of this software must
display the following acknowledgement:
“This product includes cryptographic software written by Eric Young
(eay@crypt-soft.com)”
The word ‘cryptographic’ can be left out if the rouines from the library being used are not cryptographic related :-).
4. If you include any Windows specific code (or a derivative thereof) from
the apps directory (application code) you must include an acknowledgement:
“This product includes software written by Tin Hudson (tjh@cryptsoft.com)”
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO,
THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES
(INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution licence [including the GNU Public
Licence.]
All other product names are either trademarks or registered trademarks of
their respective companies.
Copyright © 2005 KONICA MINOLTA BUSINESS TECHNOLOGIES, INC.
In order to incorporate improvements in the product, the content of this manual is subject to change without notice.
x-4 IC-402

Introduction
Contents
Introduction
Trademarks and Registered Trademarks ...................................... x-2
Contents ............................................................................................ x-5
About This Manual .......................................................................... x-12
Structure of the Manual ................................................................x-12
Notation .........................................................................................x-12
Explanation of Manual Conventions ............................................. x-14
1 Before Using the Scan Functions
1.1 Environment Required for Using the Scan Functions ................... 1-3
1.2 Available Scanning Functions ......................................................... 1-4
Sending the Scanned Data in an E-Mail Message ......................... 1-4
Sending the Scanned Data as Files (FTP) ...................................... 1-5
Sending the Scanned Data to a Computer on the Network
(SMB) ............................................................................................. 1-6
Saving Scanned Data in Boxes on the Hard Disk
(Save in Mailbox) ............................................................................ 1-7
1.3 Settings for Using Network/Scanning Functions .......................... 1-8
Specifying Network Settings .......................................................... 1-8
Registering Destinations and Specifying Their Settings ................ 1-8
Registering Mailboxes (for Save in Mailbox Operations) ............... 1-9
1.4 Settings for Scanning ..................................................................... 1-10
Specifying the Scan Settings ....................................................... 1-10
Specifying the Destination ........................................................... 1-10
1.5 Connecting to the Network ........................................................... 1-11
Network Connection .................................................................... 1-11
Turning On the System ................................................................ 1-11
1.6 Flow Chart of Setup and Scanning Operations ........................... 1-12
1.7 Frequently Used Screens ............................................................... 1-13
To display the Scan screen .......................................................... 1-13
To display the User Setting screen .............................................. 1-15
To display the Administrator Setting screen ................................ 1-16
IC-402 x-5

2 Scanning Documents
2.1 Control Panel .....................................................................................2-3
2.2 Displaying the Scan Screen ..............................................................2-6
2.3 Sending Data in an E-Mail Message (Scan to E-Mail) ....................2-7
Scan to E-Mail ................................................................................2-7
Using Programs ..............................................................................2-7
Selecting Group Addresses ..........................................................2-10
Selecting Destinations From the Address Book ...........................2-13
Performing an LDAP Search .........................................................2-16
Entering the Addresses Directly ...................................................2-17
2.4 Sending Data to a Server (Scan to FTP) ........................................2-20
Scan to FTP ..................................................................................2-20
Using Programs ............................................................................2-20
Selecting Group Addresses ..........................................................2-22
Selecting Destinations From the Address Book ...........................2-25
Entering the Addresses Directly ...................................................2-28
2.5 Sending Data to a PC on the Network (Scan to SMB) .................2-32
Scan to SMB .................................................................................2-32
Using Programs ............................................................................2-32
Selecting Group Addresses ..........................................................2-34
Selecting Destinations From the Address Book ...........................2-36
Entering the Addresses Directly ...................................................2-39
2.6 Saving Data on the Hard Disk (Save in Mailbox) ..........................2-42
Save in Mailbox .............................................................................2-42
Types of Mailboxes .......................................................................2-42
Using Programs ............................................................................2-43
Selecting Group Addresses ..........................................................2-45
Selecting Destinations From the Address Book ...........................2-47
To save data to the specified mailbox ..........................................2-50
2.7 Specifying the Scan Settings ..........................................................2-53
Available Settings .........................................................................2-53
File Type ........................................................................................2-54
To specify the File Type settings ..................................................2-56
Resolution .....................................................................................2-57
Simplex/Duplex .............................................................................2-58
To specify the Simplex/Duplex setting .........................................2-58
Color .............................................................................................2-59
To specify the Color setting ..........................................................2-60
Scan Size ......................................................................................2-61
To specify the Scan Size setting ...................................................2-61
Brightness .....................................................................................2-63
Background Removal ...................................................................2-63
Original Setting .............................................................................2-65
Introduction
x-6 IC-402

Introduction
To specify the Original Settings ................................................... 2-65
Book Scanning (Application) ........................................................ 2-67
To use the “Book Scan” function ................................................. 2-68
Frame Erase (Application) ............................................................ 2-69
Separate Scan .............................................................................. 2-71
2.8 Checking the Settings .................................................................... 2-72
Checking the Settings .................................................................. 2-72
To check a job .............................................................................. 2-73
Deleting Unneeded Destinations ................................................. 2-77
Changing the File Name and Other Settings ............................... 2-79
To change the e-mail settings ...................................................... 2-80
2.9 Checking the Scan Job List ........................................................... 2-81
Displaying the Job List for Scan to E-mail, Scan to FTP and
Scan to SMB Operations ............................................................. 2-81
Checking the Box Job List ........................................................... 2-82
Displayed Information .................................................................. 2-83
3 Registering Destinations (Recipients) for Network
Scanning
3.1 Registering Abbreviated Destinations ............................................ 3-3
E-Mail Destinations ........................................................................ 3-3
FTP Destinations ............................................................................ 3-6
SMB Destinations ........................................................................ 3-10
Mailbox Destinations .................................................................... 3-14
3.2 Registering Group Destinations .................................................... 3-17
To register a group destination .................................................... 3-17
3.3 Registering Program Destinations ................................................ 3-19
To register a program destination ................................................ 3-19
4 Other Network Scanning Settings
4.1 Specifying E-Mail Settings ............................................................... 4-3
Subject ........................................................................................... 4-3
Text ................................................................................................ 4-5
4.2 Setting the Main Scan Mode Screen .............................................. 4-7
Default Tab ..................................................................................... 4-7
Program Default ............................................................................. 4-8
4.3 Setting the Save Format of the Data to Be Scanned .................... 4-9
JPEG Compression Level .............................................................. 4-9
To specify the compression level ................................................... 4-9
IC-402 x-7
4.4 Prefix/Suffix Settings ......................................................................4-11
Prefix/Suffix Parameters ...............................................................4-11
To specify the prefix/suffix settings ..............................................4-11
Prefix/Suffix Setting ......................................................................4-13
4.5 Authentication Function ..................................................................4-16
User Authentication/Account Track and Scan Functions .............4-16
Authentication Method and Fiery Remote Scan Software ...........4-16
5 Specifying Network Scanning Settings
5.1 Available Settings ..............................................................................5-3
5.2 Entering the Image Controller Setup Screen ..................................5-5
Displaying the Setup Screen ..........................................................5-5
5.3 Specifying Settings for E-Mail Transmissions ................................5-6
Checking Copier E-Mail Transmission Settings .............................5-6
To check the e-mail transmission setting .......................................5-6
Checking TCP/IP Settings ..............................................................5-6
E-Mail Transmission Settings .........................................................5-6
URL Notification E-Mail Messages .................................................5-7
5.4 Specifying Settings for Save in Mailbox Operations ......................5-8
Checking TCP/IP Settings ..............................................................5-8
Allowing Mailbox Passwords ..........................................................5-8
Creating a Mailbox ..........................................................................5-8
Downloading the Image Data to the Computer ............................5-10
5.5 Specifying Settings for FTP File Transmissions ...........................5-11
Checking TCP/IP Settings ............................................................5-11
Enabling the FTP Transfer Function .............................................5-11
Proxy Settings ...............................................................................5-11
5.6 Specifying Settings for SMB Server Transmissions .....................5-13
Checking Copier SMB Settings ....................................................5-13
To check the SMB setting ............................................................5-13
Checking TCP/IP Settings ............................................................5-13
5.7 Setting the Error Notification Destination .....................................5-14
To set the error notification destination ........................................5-14
5.8 Setting the Sender (From) Address ...............................................5-15
To set the sender (from) address ..................................................5-15
5.9 Hold Period of the Image Data .......................................................5-16
To specify the hold period of the image data ...............................5-16
Introduction
x-8 IC-402

Introduction
6 Copier Network Functions
6.1 Copier Network Settings .................................................................. 6-3
6.2 TCP/IP Settings ................................................................................. 6-6
Items To Be Specified .................................................................... 6-6
To specify TCP/IP settings ............................................................. 6-7
6.3 NetWare Settings .............................................................................. 6-9
NetWare Parameters ...................................................................... 6-9
To specify NetWare settings .......................................................... 6-9
6.4 FTP Settings .................................................................................... 6-10
FTP Parameters ........................................................................... 6-10
To specify FTP settings ................................................................ 6-10
6.5 SMB Settings ................................................................................... 6-11
SMB Parameters .......................................................................... 6-11
To specify SMB settings .............................................................. 6-12
6.6 Enabling LDAP Settings ................................................................. 6-13
Enabling LDAP Parameters .......................................................... 6-13
To specify Enabling LDAP settings .............................................. 6-13
Initial Setting for Search Details ................................................... 6-15
6.7 Setting Up LDAP Settings .............................................................. 6-17
LDAP Server Registration Parameters ......................................... 6-17
To specify Setting Up LDAP settings ........................................... 6-19
General Settings ........................................................................... 6-21
To specify the authentication method ......................................... 6-21
6.8 E-Mail TX (SMTP) Settings ............................................................. 6-22
E-Mail TX (SMTP) Parameters ...................................................... 6-22
To specify E-Mail TX (SMTP) settings .......................................... 6-23
SMTP Server Address .................................................................. 6-26
SMTP Authentication ................................................................... 6-27
6.9 E-Mail RX (POP) Settings ............................................................... 6-29
E-Mail RX (POP) Parameters ........................................................ 6-29
To specify E-Mail RX (POP) settings ............................................ 6-30
POP Server Address .................................................................... 6-31
6.10 MAC Address .................................................................................. 6-32
Device Parameters ....................................................................... 6-32
To check the MAC address ......................................................... 6-32
6.11 Time Adjustment Settings ............................................................. 6-33
Time Adjustment Parameters ....................................................... 6-33
To specify time adjustment settings ............................................ 6-33
NTP Server Address ..................................................................... 6-34
IC-402 x-9

6.12 Status Notification Settings ............................................................6-36
Status Notification Parameters .....................................................6-36
To specify status notification settings ..........................................6-36
Notification Item Setting ...............................................................6-37
6.13 PING Confirmation ..........................................................................6-38
PING Confirmation Parameters ....................................................6-38
To specify PING confirmation settings .........................................6-38
PING TX Address ..........................................................................6-40
6.14 IS OpenAPI Settings ........................................................................6-41
Access Setting ..............................................................................6-41
Port No. .........................................................................................6-42
SSL ...............................................................................................6-42
Authentication ...............................................................................6-44
7 Using PageScope Web Connection
7.1 System Requirements .......................................................................7-3
Computer ........................................................................................7-3
7.2 Accessing PageScope Web Connection .........................................7-4
To access PageScope Web Connection ........................................7-4
Page Structure ................................................................................7-5
Administrator Modes ......................................................................7-6
Logging On to Administrator Mode ................................................7-7
Logging On to the Image Controller’s Administrator Mode ............7-7
Logging On to the Copier’s Administrator Mode ............................7-8
Changing the Administrator Password ...........................................7-9
Changing the Image Controller’s Administrator Password ............7-9
Changing the Copier’s Administrator Password ............................7-9
7.3 User Mode .......................................................................................7-10
System tab ....................................................................................7-10
Job tab ..........................................................................................7-11
User Box tab .................................................................................7-12
Print tab ........................................................................................7-13
Scan Tab .......................................................................................7-14
“Address Book” Menu ..................................................................7-14
To register new destinations in the address book ........................7-16
“Group” Menu ...............................................................................7-17
To register new “Group” ...............................................................7-17
“Program” Menu ...........................................................................7-19
To register new destinations .........................................................7-25
“Temporary One-Touch” Menu ....................................................7-27
“Subject” Menu .............................................................................7-29
“Text” Menu ..................................................................................7-30
Introduction
x-10 IC-402

Introduction
7.4 Image Controller Administrator Mode .......................................... 7-32
System Tab .................................................................................. 7-32
“Device Information” Menu .......................................................... 7-32
“Online Assistance” Menu ........................................................... 7-33
User Box Tab ............................................................................... 7-34
“Mailbox” Menu ........................................................................... 7-34
7.5 Copier Administrator Mode ........................................................... 7-36
System tab ................................................................................... 7-36
User Box tab ................................................................................ 7-37
Scan Tab ...................................................................................... 7-38
“Prefix/Suffix” Menu ..................................................................... 7-38
“Import/Export” Menu .................................................................. 7-39
Importing ...................................................................................... 7-39
Exporting ...................................................................................... 7-39
“Other” Menu ............................................................................... 7-40
Network Tab ................................................................................. 7-40
“TCP/IP” Menu ............................................................................. 7-41
“NetWare” Menu .......................................................................... 7-42
“FTP” — “Server” Menu ............................................................... 7-43
“SMB” — “Scan” Menu ............................................................... 7-44
“LDAP” Menu ............................................................................... 7-45
“E-Mail” — “E-Mail Receive” Menu ............................................. 7-47
“E-Mail” — “E-Mail Transmission” Menu ..................................... 7-48
“SSL/TLS” Menu .......................................................................... 7-50
SSL/TLS Setting ........................................................................... 7-52
To create a certificate .................................................................. 7-53
SSL/TLS Setting — Install a Certificate ....................................... 7-55
“Authentication” — “Auto Logout” Menu .................................... 7-56
“IS OpenAPI” Menu ..................................................................... 7-57
8 Appendix
8.1 Entering Text ..................................................................................... 8-3
To type text .................................................................................... 8-6
List of Available Characters ........................................................... 8-6
Number of Characters That Can Be Entered ................................. 8-7
8.2 Glossary ............................................................................................. 8-8
8.3 Index ................................................................................................ 8-12
IC-402 x-11
About This Manual
This User’s Guide provides descriptions of the network scanning functions
available with IC-402 (the optional image controller for C450/C351). In addition, supplementary descriptions are provided in chapter 6 for the network
functions that can be used from the copier when IC-402 is installed.
This section introduces the structure of the manual and the notations used
for product names, etc.
This manual is intended for users who understand the basic operations of
computers and this machine. For operating procedures of the Windows or
Macintosh operating system and software applications, refer to the corresponding manuals.
Structure of the Manual
This manual consists of the following chapters.
Chapter 1 Before Using the Scan Functions
Chapter 2 Scanning Documents
Chapter 3 Registering Destinations (Recipients) for Network Scanning
Chapter 4 Other Network Scanning Settings
Chapter 5 Specifying Network Scanning Settings
Chapter 6 Copier Network Functions
Chapter 7 Using PageScope Web Connection
Chapter 8 Appendix
Lists the characters that can be entered from the control panel.
Introduction
Notation
Product Name Notation in the Manual
bizhub C450 Copier, C450
bizhub C351 Copier, C351
IC-402 Image Controller Image Controller
Microsoft Windows 98 Windows 98
Microsoft Windows Me Windows Me
Microsoft Windows NT 4.0 Windows NT 4.0
Microsoft Windows 2000 Windows 2000
Microsoft Windows XP Windows XP
Microsoft Windows Server 2003 Windows Server 2003
x-12 IC-402
Introduction
Product Name Notation in the Manual
When the operating systems above are written
together
Windows 95/98/Me
Windows NT 4.0/2000/XP/Server 2003
Windows 95/98/Me/NT 4.0/2000/XP/Server
2003
IC-402 x-13
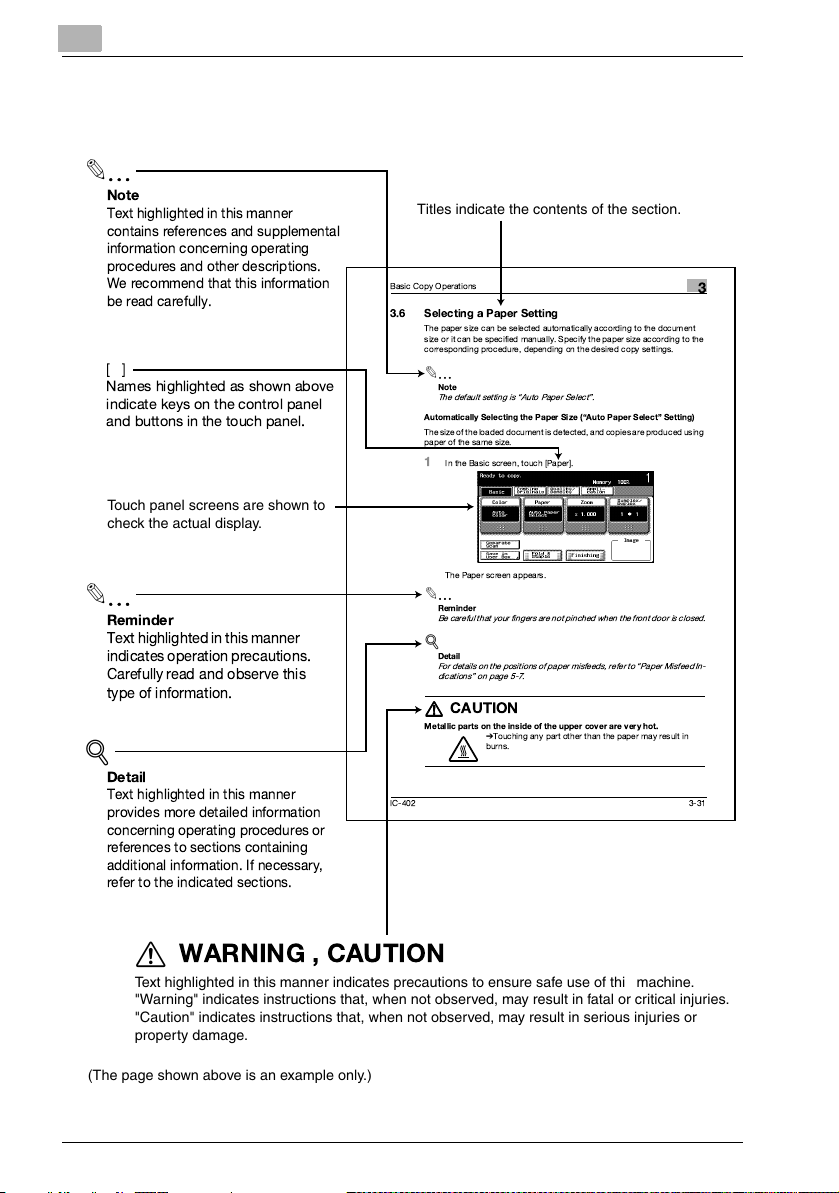
Explanation of Manual Conventions
2
Note
Text highlighted in this manner
contains references and supplemental
information concerning operating
procedures and other descriptions.
We recommend that this information
be read carefully.
[]
Names highlighted as shown above
indicate keys on the control panel
and buttons in the touch panel.
Touch panel screens are shown to
check the actual display.
2
Reminder
Text highlightedin this manner
indicates operationprecautions.
Carefully read and observe this
type of information.
Titles indicate the contents of the section.
Basic Copy Operations
3.6 Selecting a Paper Setting
The paper size can be selected automatically according to the document
size or it can be specified manually. Specify the paper size acc ording to the
corresponding procedure, depending on the desired copy settings.
2
Note
The default setting is Auto Paper Select.
Automatically Selecting the Paper Size (Auto Paper Select Setting)
The size of the loadeddocument is detected, an d copies are prod uced using
paper of the same size.
1
In the Basic screen, touch [Paper].
The Paper screen appears.
2
Reminder
Be careful that your fingers are n ot pinched whenthe frontdoor is closed.
!
Detail
For details on the positions of paper misfeeds, refer toPaper Misfeed In-
dications on page 5-7.
7
7
7 7
Metallic parts on the inside of the upper cover are very hot.
!
Detail
Text highlighted in this manner
provides more detailed information
concerning operating procedures or
references to sections containing
additional information. If necessary,
refer to the indicated sections.
IC-402 3-31
CAUTION
%
Touching any part other than the paper may result in
burns.
Introduction
3
WARNING , CAUTION
7
Text highlighted in this manner indicates precautions to ensure safe use of this machine.
"Warning" indicates instructions that, when not observed, may result in fatal or critical injuries.
"Caution" indicates instructions that, when not observed, may result in serious injuries or
property damage.
(The page shown above is an example only.)
x-14 IC-402

1
Before Using the Scan
Functions


Before Using the Scan Functions
1 Before Using the Scan Functions
1.1 Environment Required for Using the Scan Functions
The following conditions are required to use the network and scanning functions.
- The machine is connected to the network.
The functions can be used over a TCP/IP network.
– For details on connecting the network cable, refer to “Connecting to the
Network” on page 1-11.
– In order to use this machine on a network, settings such as the IP address
of the image controller must be specified. For details, refer to “Settings
for Using Network/Scanning Functions” on page 1-8.
1
IC-402 1-3
1
1.2 Available Scanning Functions
“Scanning” refers to the operation of reading the image of a document fed
through the automatic document feeder or placed on the original glass of the
copier. The scanning functions can be used to send scanned data in an email message over a network or upload the data to a file server.
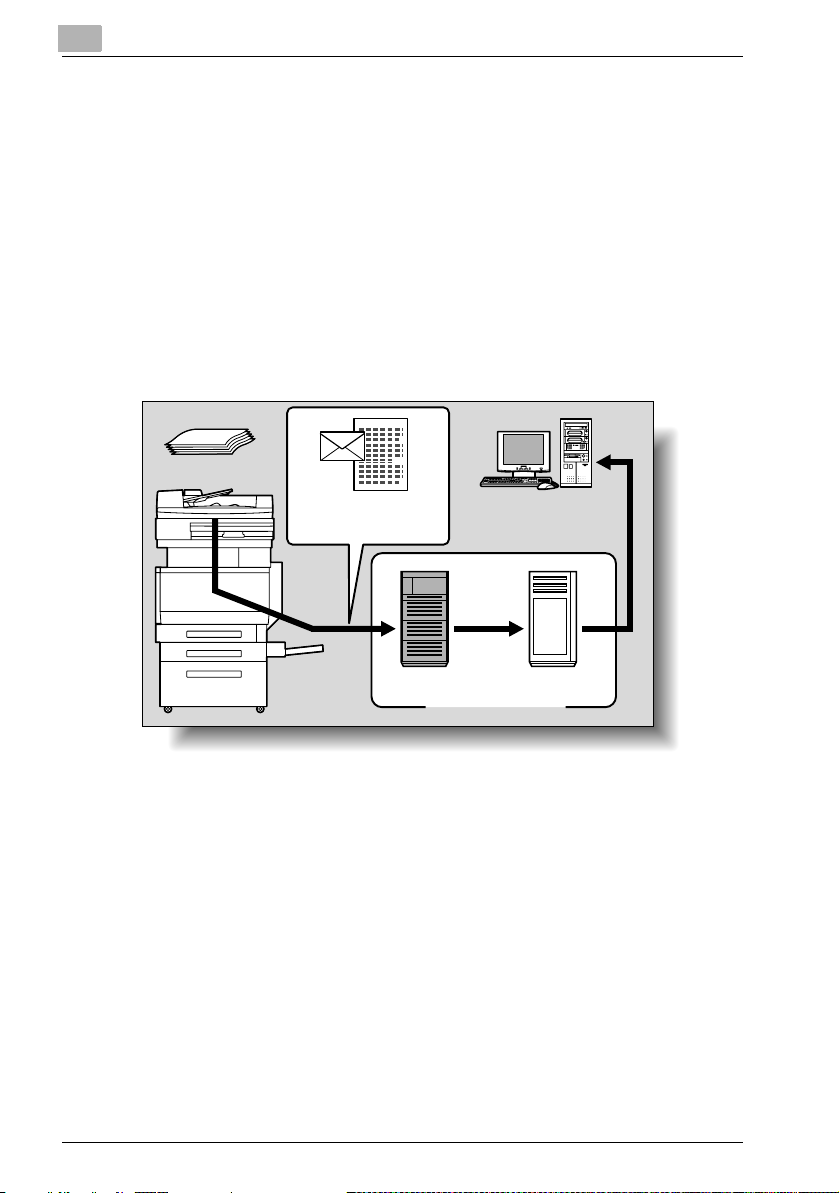
Sending the Scanned Data in an E-Mail Message
The scanned data can be sent to a specified e-mail address. The destination
is specified from the touch panel of this copier, and the scanned data is sent
as an e-mail attachment.
For details, refer to “Sending Data in an E-Mail Message (Scan to E-Mail)” on
page 2-7.
Original
Copier
Before Using the Scan Functions
E-mail and scan data
SMTP server POP server
E-mail reception
Internet
1-4 IC-402
Before Using the Scan Functions
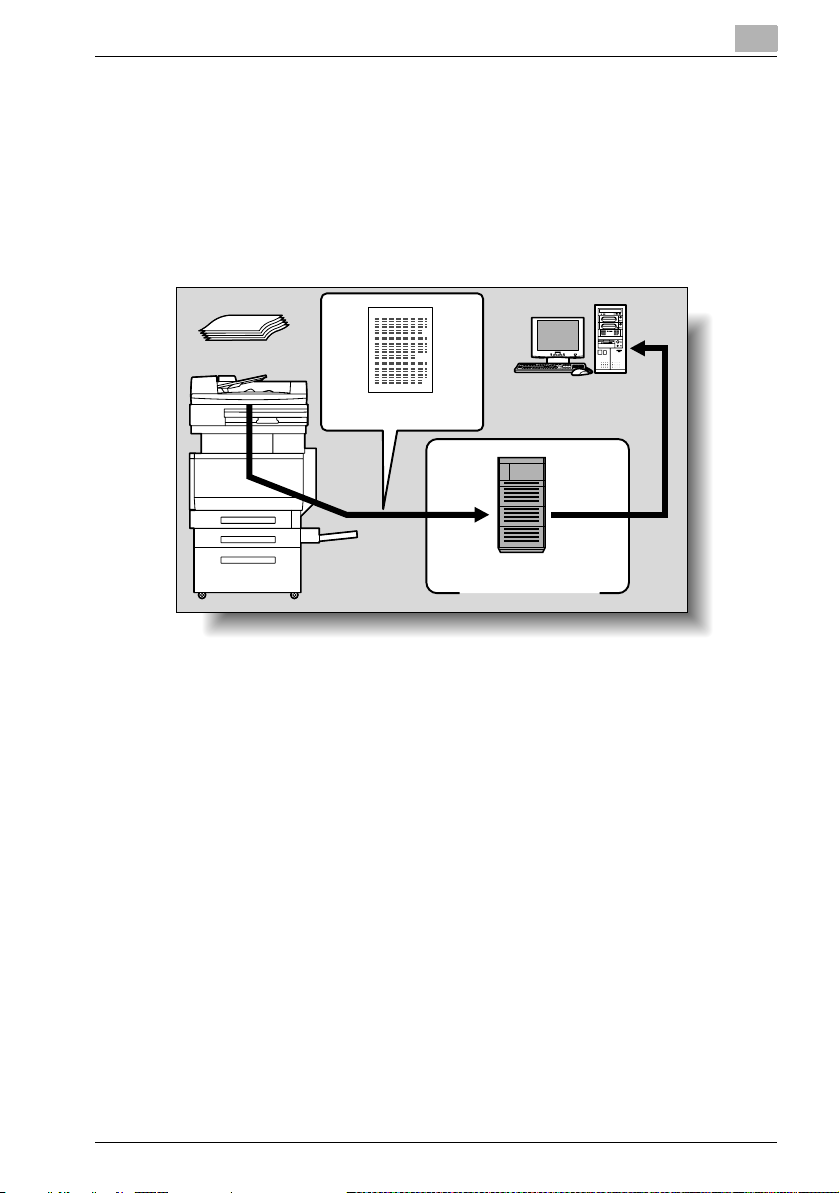
Sending the Scanned Data as Files (FTP)
The scanned data is uploaded to a specified FTP server. The FTP server address, login password, and other information are entered from the touch
panel of this copier.
The data files uploaded to the FTP server can be downloaded from a computer on the network.
For details, refer to “Sending Data to a Server (Scan to FTP)” on page 2-20.
Original
Copier
1
Scan data
Download
FTP server
Internet
IC-402 1-5
1
Before Using the Scan Functions
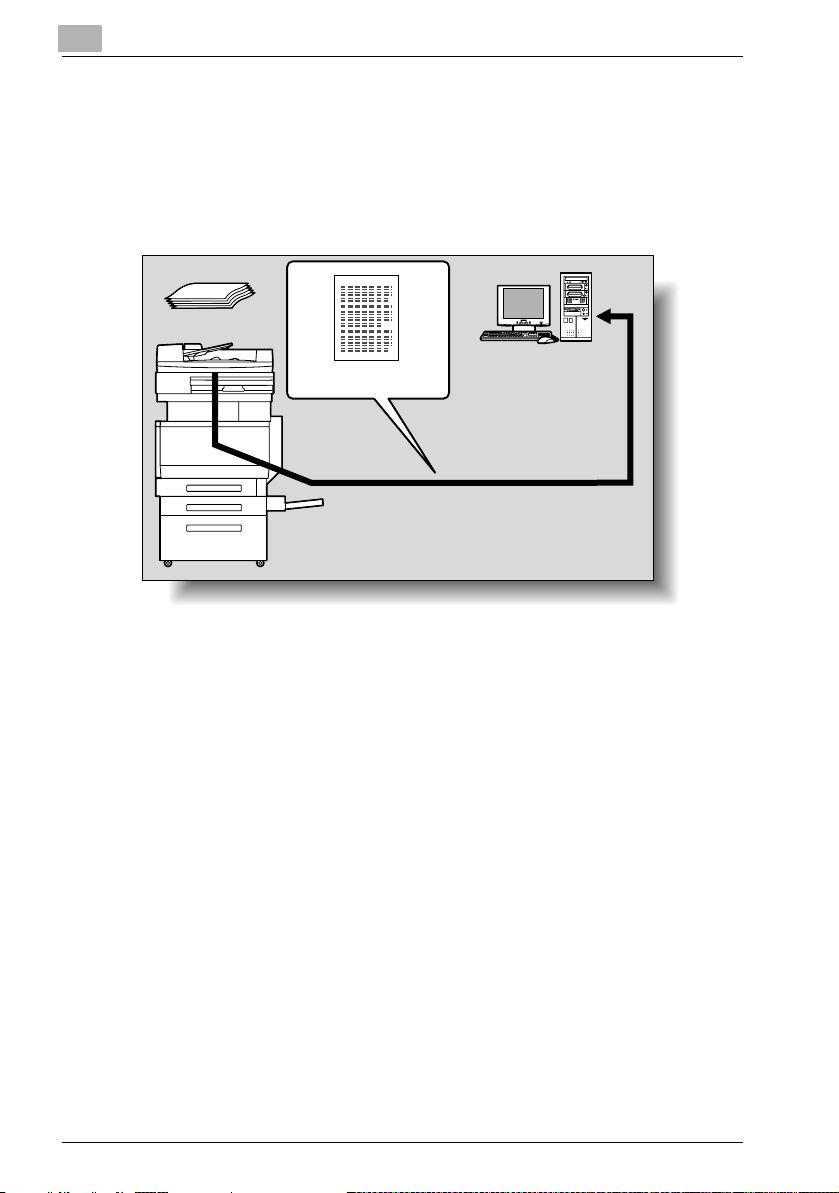
Sending the Scanned Data to a Computer on the Network (SMB)
The scanned data can be sent to a shared folder on a specified computer.
The name of the destination computer, login password, and other information are entered from the touch panel of this copier.
For details, refer to “Sending Data to a PC on the Network (Scan to SMB)”
on page 2-32.
Original
Copier
Scan data
Save to a shared folder
1-6 IC-402
Before Using the Scan Functions
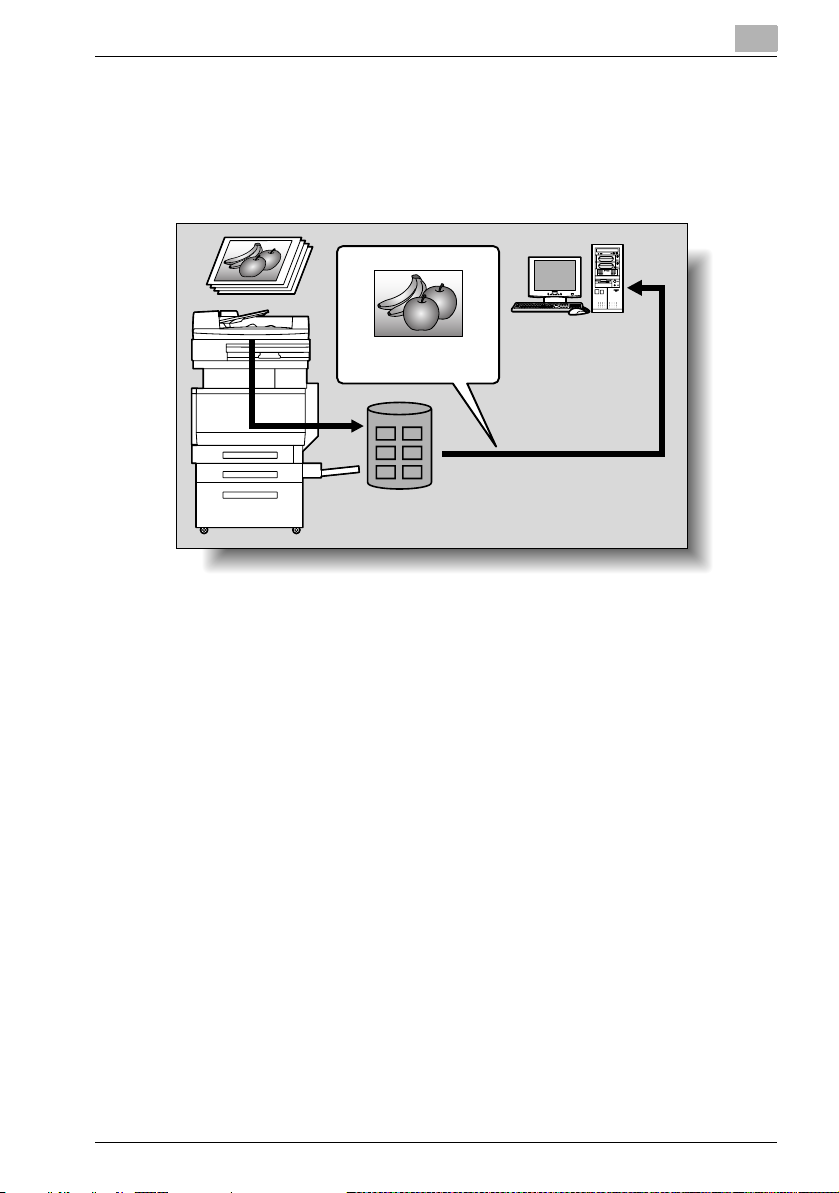
Saving Scanned Data in Boxes on the Hard Disk (Save in Mailbox)
The scanned data can be saved in a mailbox created on the hard disk of the
image controller, and the saved data can be downloaded from a computer
on the network. For details, refer to “Saving Data on the Hard Disk (Save in
Mailbox)” on page 2-42.
1
Scan data
Image controller
IC-402 1-7
1
Before Using the Scan Functions
1.3 Settings for Using Network/Scanning Functions
It is recommended that the settings described below be specified before using the network/scanning functions. The network settings described in
“Specifying Network Settings” must be specified first. Set other items as
necessary.
Specifying Network Settings
In order to use this machine on a network, the network settings for the image
controller must be specified.
Specify the network settings from the image controller screen, which appears in the control panel of the copier.
!
Detail
For details on specifying network settings and using the control panel of
the image controller, refer to “5 Specifying Network Scanning Settings”.
Registering Destinations and Specifying Their Settings
The destinations (recipients) of scanned data must be registered.
The following registration methods are available.
- Register from the touch panel of the copier.
- Use PageScope Web Connection from a PC on the network.
- Use PageScope Data Administrator from a PC on the network.
The three types of destinations described below can be registered.
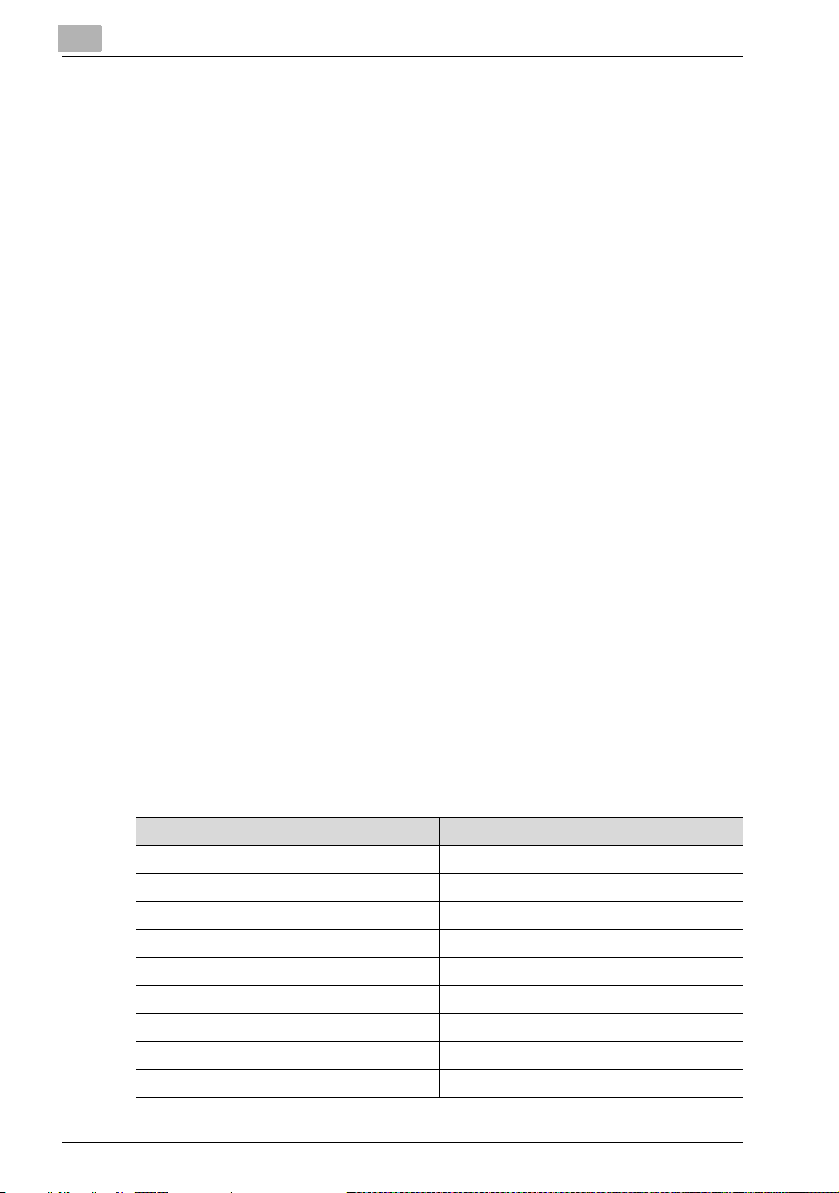
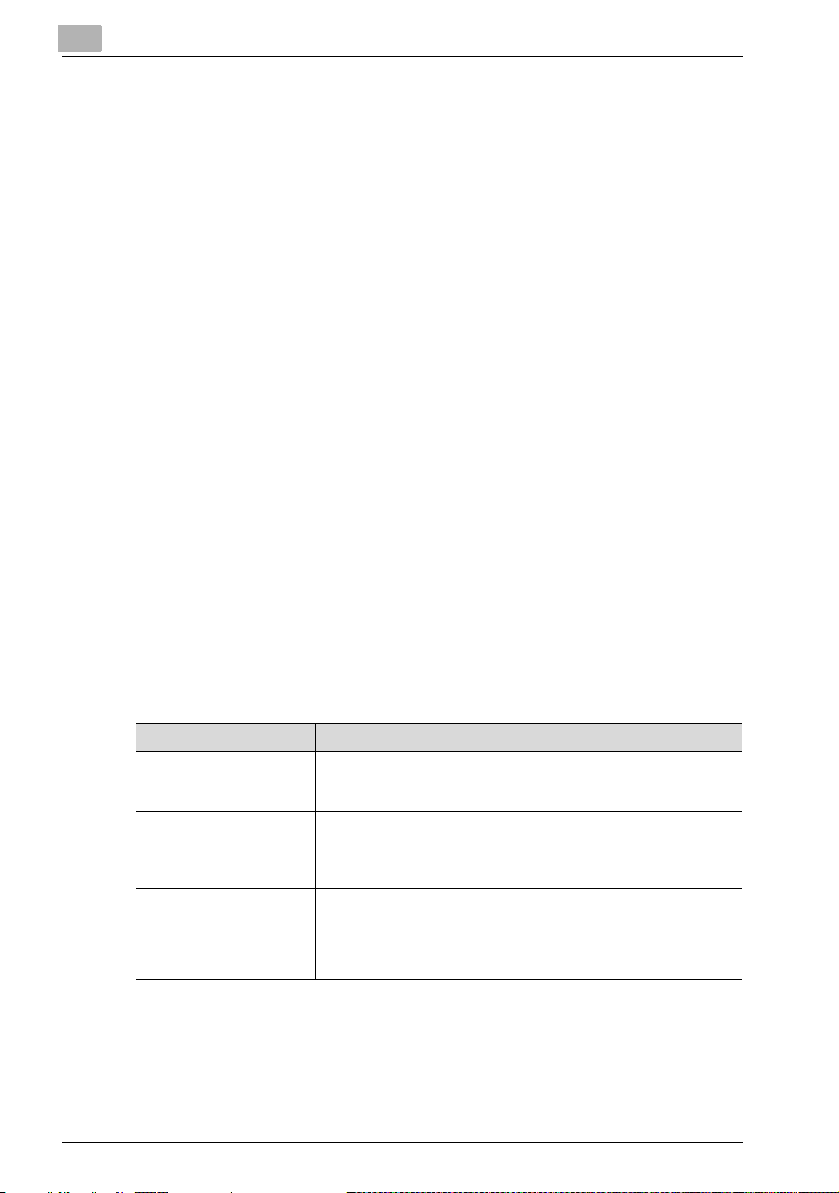
Destination (Recipient) Characteristics
Abbreviated Destination The destination can be selected with one button. The registered
Group Multiple destinations can be registered in groups. E-mail, FTP,
Program The destination and scan settings can be registered together as a
destinations are displayed by press the [Scan] key, then touching
[Address Book].
SMB, and mailbox destinations can be registered together in a
single group. The registered destinations are displayed by press
the [Scan] key, then touching [Group].
single program. This is convenient for frequently scanning documents and sending data under the same conditions. The registered
destinations are displayed by press the [Scan] key, then touching
[Program].
1-8 IC-402

Before Using the Scan Functions
2
Note
The destination can also be entered from the copier’s control panel before scanning, even if no destination has been registered in advance.
The destination can also be entered before scanning. This is called “direct input”. For details, refer to “Entering the Addresses Directly” on
page 2-17.
!
Detail
For details on registering destinations and specifying settings, refer to the
sections listed below.
“Registering Abbreviated Destinations” on page 3-3
“Registering Group Destinations” on page 3-17
“Registering Program Destinations” on page 3-19
Registering Mailboxes (for Save in Mailbox Operations)
Mailboxes must be registered only when using Save in Mailbox operations.
!
Detail
For details on registering mailboxes, refer to the following section.
“Specifying Settings for Save in Mailbox Operations” on page 5-8.
1
IC-402 1-9
1
1.4 Settings for Scanning
Specifying the Scan Settings
The following scan settings can be specifying when scanning a document.
These settings are specified from the touch panel of the copier.
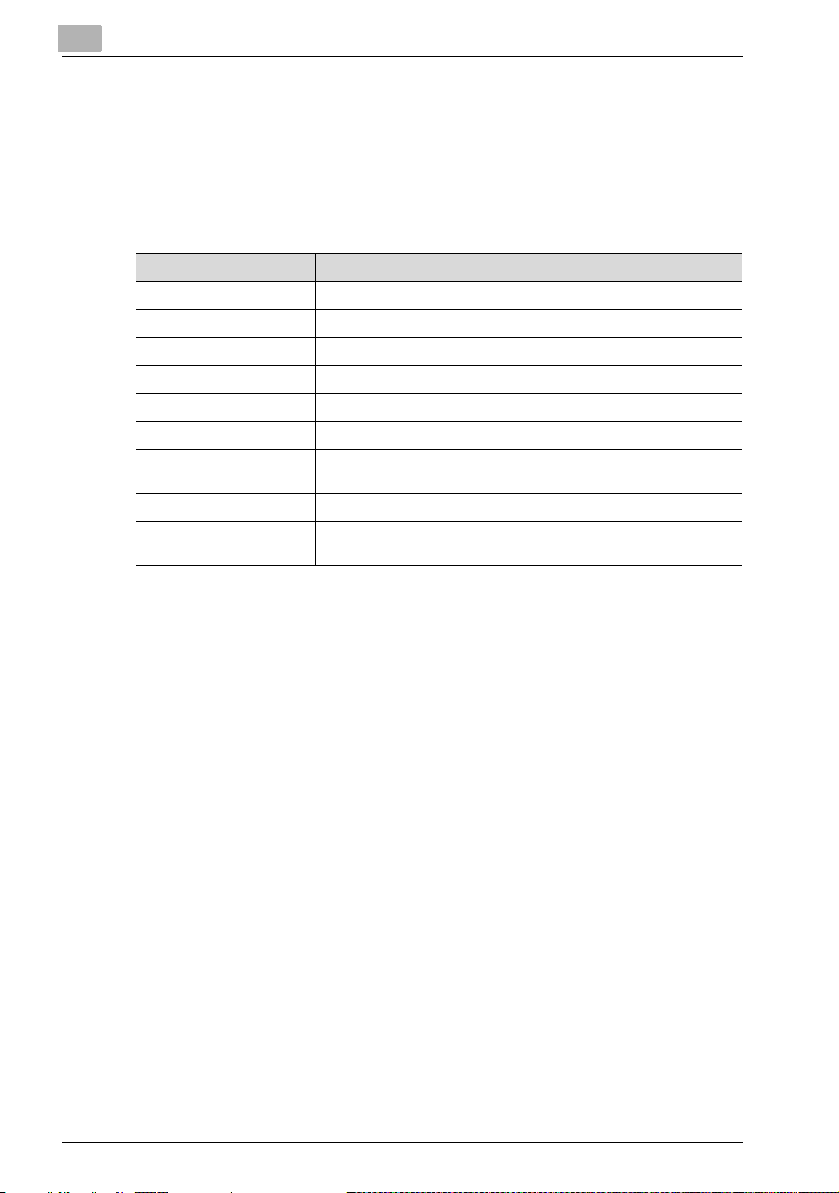
Item Description
File Type Sets the file type to be saved.
Resolution Sets the scan resolution.
Simplex/Duplex Selects whether to scan one side of the document or both sides.
Scan Size Sets the size to be scanned.
Color Sets the color of the scanned document.
Brightness Adjusts the brightness of the document.
Background Removal Adjusts the density of the background (blank areas) of the docu-
ment.
Original Setting Specifies the type and characteristics of the loaded document.
Application Provides functions for adjusting the print image, for example, for
scanning books and for erasing the surrounding area.
!
Detail
For details on the scan settings, refer to “Specifying the Scan Settings”
on page 2-53.
Before Using the Scan Functions
Specifying the Destination
Specify the destination (recipient) for the scan data. If the destination has
been registered in advance, select a destination from those that are already
registered. If the destination has not been registered, specify the destination
through direct input.
1-10 IC-402
Before Using the Scan Functions
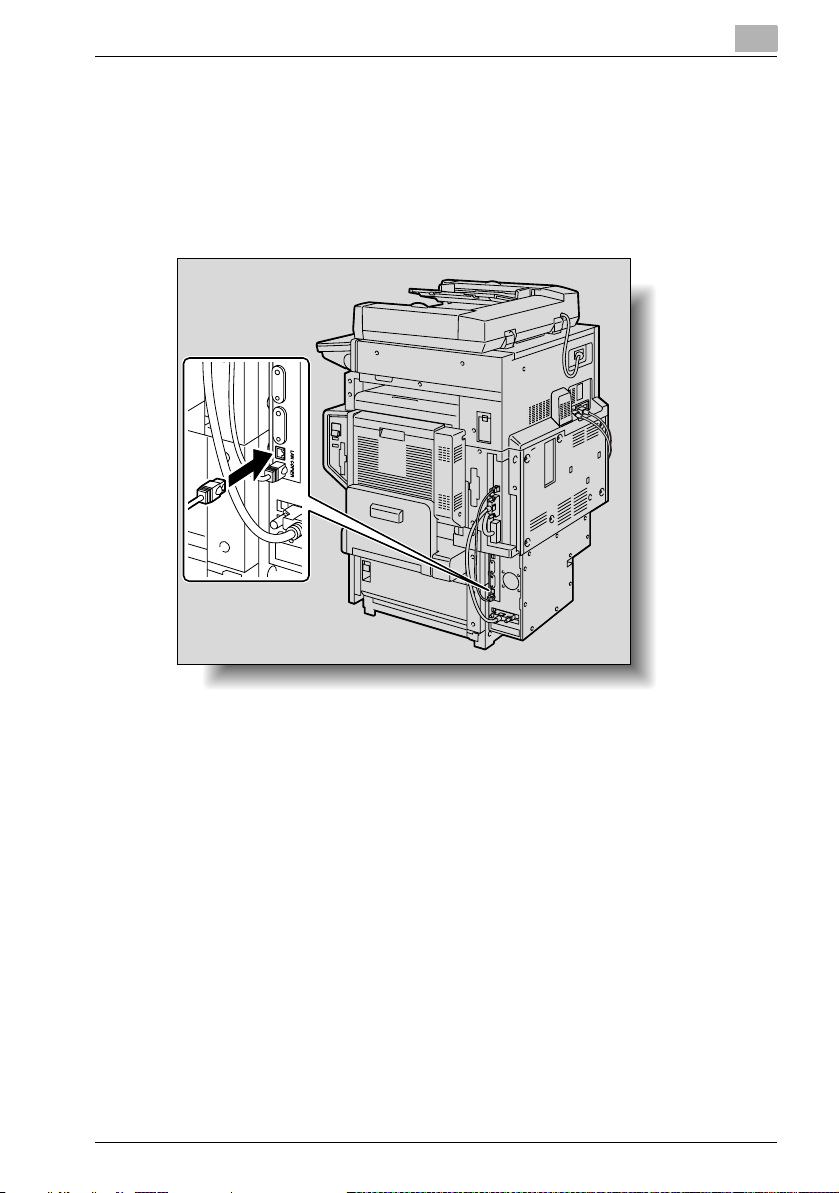
1.5 Connecting to the Network
The image controller can be connected to the network.
Network Connection
Connect a UTP cable (category 5 recommended) from the network to the
Ethernet connector on the image controller.
1
Turning On the System
Follow the procedure described below to turn on the system.
1 Turn on the image controller.
2 Wait a little while and turn on the copier.
– If the network functions of the copier are operating correctly, turn
the copier off, then on.
!
Detail
If the copier is turned on before the image controller has finished starting
up and is ready to be used, the copier’s network functions may not operate correctly. Therefore, before turning on the copier, be sure to wait a
little while after turning on the image controller. For more details, refer to
“TCP/IP Settings” on page 6-6.
IC-402 1-11
1
Before Using the Scan Functions
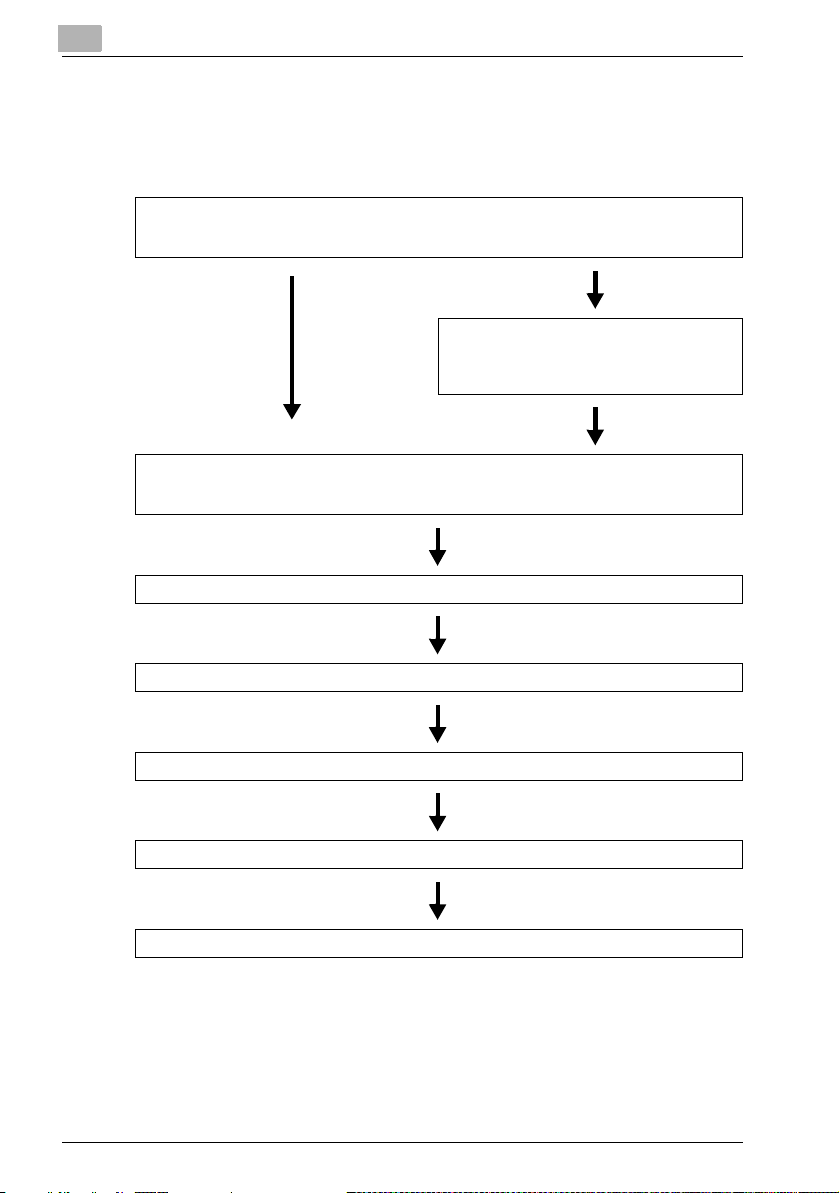
1.6 Flow Chart of Setup and Scanning Operations
The sequence from the setup operations required to use the scanning functions to the scanning operation is shown below.
Specify network settings.
* Specify settings in order to use the network scanning operations (refer to “5 Specifying Network Scanning Settings”).
Create mailboxes for saving documents.
*Specify settings for saving documents in mailboxes (refer to “Specifying Settings for Save in
Mailbox Operations” on page 5-8).
Register destinations.
* Register destinations (e-mail addresses, ftp servers and computer names).
(refer to “3 Registering Destinations (Recipients) for Network Scanning”).
Load the document.
Specify the destination.
Specify the scan settings (refer to page 2-53).
Press the [Start] key in the control panel.
The document is scanned, and the data is transmitted.
1-12 IC-402
Before Using the Scan Functions
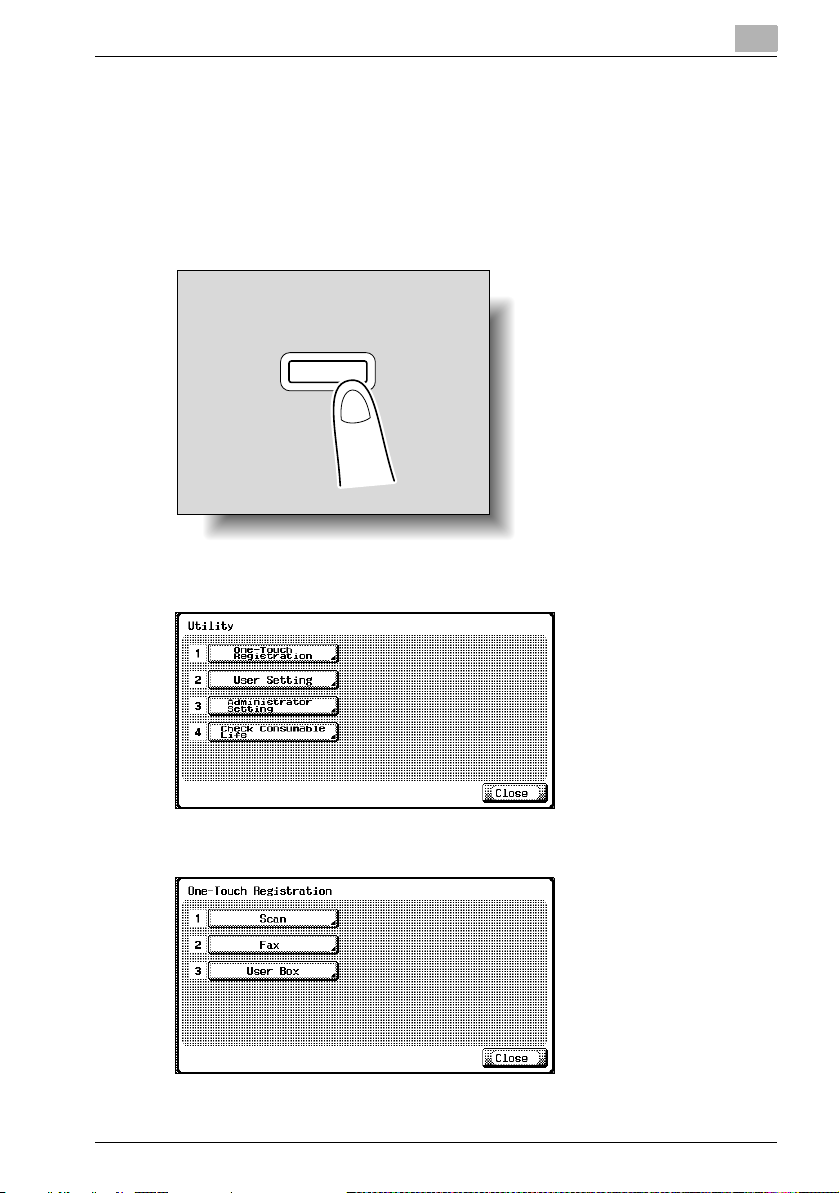
1.7 Frequently Used Screens
This section describes the copier’s control panel screens that are frequently
used for specifying network scanning settings.
To display the Scan screen
1 Press the [Utility/Counter] key.
Utility/
Counter
2 Touch [1 One-Touch Registration].
1
3 Touch [1 Scan].
IC-402 1-13
1
Before Using the Scan Functions
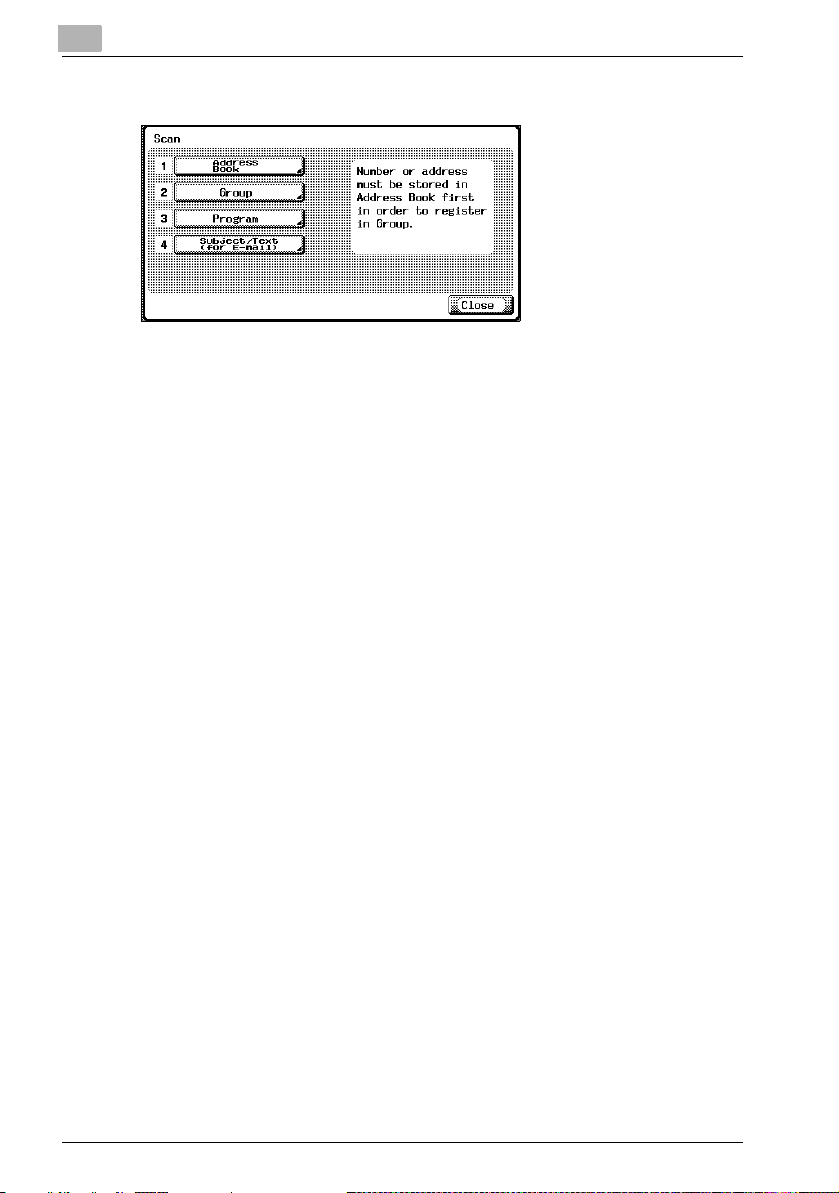
The Scan screen appears.
1-14 IC-402
Before Using the Scan Functions
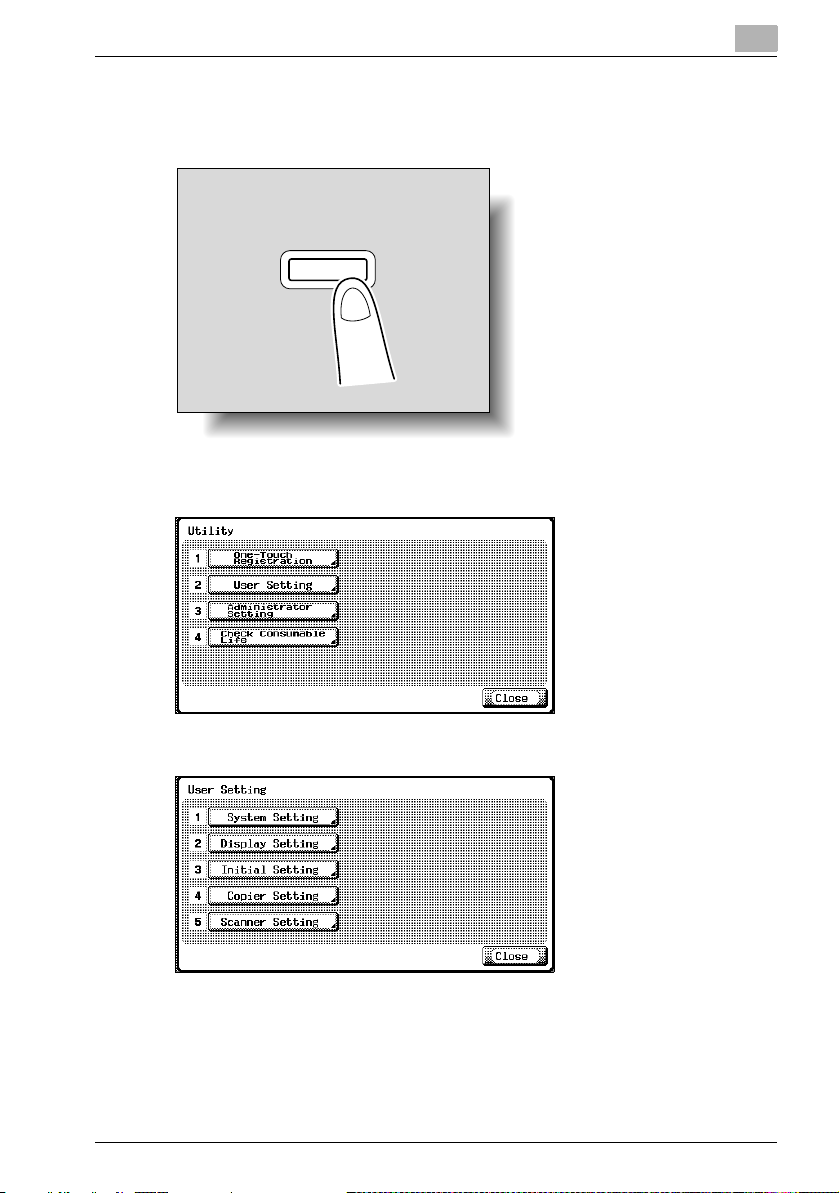
To display the User Setting screen
1 Press the [Utility/Counter] key.
Utility/
Counter
2 Touch [2 User Setting].
1
The User Setting screen appears.
IC-402 1-15

1
Before Using the Scan Functions
To display the Administrator Setting screen
1 Press the [Utility/Counter] key.
Utility/
Counter
2 Touch [3 Administrator Setting].
3 Type in the password, and then touch [OK].
1-16 IC-402

Before Using the Scan Functions
The Administrator Setting screen appears.
1
IC-402 1-17

1
Before Using the Scan Functions
1-18 IC-402

2
Scanning Documents


Scanning Documents
er Sa
Bo
Access
ABC
DEF
JKL
GHI
MNO
TUV
PQRS
WXYZ
Mode Memor
Mode Chec
Utility/
Counter
ax
Scan
Cop
Reset
Interr
upt
er
Stop
Proof Cop
Star
Data
Main P
er
Help
Accessibility
Enlarge Displa
Contr
ast
2 Scanning Documents
2.1 Control Panel
1234 5 6 7
2
Fax
x
24
23
22
Power Sa
ve
Help
Accessibility
Enlarge Displa
Contr
ast
Bo
Access
Mode Memor
y
y
Utility/
Counter
Mode Chec
k
Cop
y
Scan
ABC
DEF
JKL
GHI
MNO
Proof Cop
TUV
PQRS
WXYZ
Star
t
Data
Main P
17192021
13
15141618
No. Part Name Description
1 [Power Save] key Press to enter Power Save mode. While the
machine is in Power Save mode, the indicator on
the [Power Save] key lights up in green and the
touch panel goes off. To cancel Power Save mode,
press the [Power Save] key again.
2 Touch panel Displays various screens and messages.
Specify the various settings by directly touching the
panel.
3 [Access] key If user authentication or account track settings
have been applied, press this key after entering the
user name and password (for user authentication)
or the account name and password (for account
track) in order to use this machine.
This key is also used to log off.
4 [Box] key Press to enter Box mode.
While the machine is in Box mode, the indicator on
the [Box] key lights up in green. For details, refer to
the User’s Guide [Box Operations] included with
the copier.
5 [Fax] key Press to enter Fax mode.
While the machine is in Fax mode, the indicator on
the [Fax] key lights up in green.
For details, refer to the User’s Guide [Facsimile
Operations] included with the copier.
IC-402 2-3
Interr
y
Reset
Power
ower
Stop
8
upt
9
10
11
12

2
Scanning Documents
No. Part Name Description
6 [Scan] key Press to enter Scan mode. While the machine is in
7 [Copy] key Press to enter Copy mode. (As a default, the
8 [Reset] key Press to clear all settings (except programmed
9 [Interrupt] key Press to enter Interrupt mode. While the machine is
10 Auxiliary power button Press to turn on/off machine operations, for exam-
11 [Stop] key Press the [Stop] key during scanning to stop the
12 [Star t] key Press to start scanning . When this machine is ready
13 Main Power indicator Lights up in green when the copier is turned on with
14 Data indicator Flashes in green while a print job is being received.
15 [Proof Copy] key Press to print a single proof copy to be checked
16 Keypad Use to type in the number of copies to be
17 [C] (clear) key Press to erase a value (such as the number of
18 [Mode Check] key Press to display screens showing the specified
19 [Utility/Counter] key Press to display the Utility screen and Meter Count
20 [Mode Memory] key Press to register the desired copy settings as a pro-
21 Contrast dial Use to adjust the contrast of the touch panel.
Scan mode, the indicator on the [Scan] key lights
up in green.
For details, refer to this manual.
machine is in Copy mode.) While the machine is in
Copy mode, the indicator on the [Copy] key lights
up in green.
For details, refer to the User’s Guide [Copy Operations].
settings) entered in the control panel and touch
panel.
in Interrupt mode, the indicator on the [Interrupt]
key lights up in green and the message “Now in
Interrupt mode.” appears on the touch panel. To
cancel Interrupt mode, press the [Interrupt] key
again.
ple, for copying, printing or scanning. When turned
off, the machine enters a state where it conserves
energy.
scan operation.
to begin scanning, the indicator on the [Start] key
lights up in green. If the indicator on the [Start] key
lights up in orange, scanning cannot begin.
Press to restart a stopped job.
the auxiliary power button
Lights up in green when data is being printed.
before printing a large number of copies.
produced.
Use to type in the zoom ratio.
Use to type in the various settings.
copies, a zoom ratio, or a size) entered using the
keypad.
settings.
screen.
gram or to recall a registered copy program.
2-4 IC-402

Scanning Documents
No. Part Name Description
22 [Enlarge Display] key Press to enter Enlarge Display mode.
23 [Accessibility] key Press to display the screen for specifying user
24 [Help] key Press to display the Help Main Menu screen, where
7
7 CAUTION
7 7
To prevent damage to the touch panel, do not push down on the touch
panel with force.
% Also, do not push down on the touch panel using hard or sharp objects.
2
accessibility functions.
descriptions of the various functions and details of
operations can be displayed.
IC-402 2-5

2
2.2 Displaying the Scan Screen
Display the Scan mode screen in order to perform scanning operations.
Turn the machine on. When the machine is ready to make copies, the Basic
screen appears.
Press the [Scan] key in the control panel to display the Scan mode screen.
The displayed functions and modes can be selected by gently touching the
buttons that are displayed in the screen.
2 4 5 6 7 8 1093
1
No Name Description
1 Sub display area This area displays destinations, etc.
2 [Job List] button Displays jobs being performed and jobs being stored.
3 Date/Time display area Displays the current date/time.
4 Message display area Displays the machine status and details on operations
5 [Program] button Displays destinations that are registered in programs.
6 [Group] button Displays destinations that are registered in groups.
7 [Address Book] button Used to search for abbreviated destinations that are
8 [Direct Input] button Used to type in the destination when performing Scan to
9 Available memory display Shows the amount of space available on the copier’s
10 Address number display
area
11 [Scan Settings] button Used to specify scan settings.
Various commands for checking and managing jobs are
available.
that must be performed.
registered.
E-mail, Scan to FTP, or Scan to SMB operations or to select the mailbox where the job is to be stored.
This button does not appear if the [Manual Destination Input] on the Security Details screen (displayed by touching
[9 Security Setting] on the Administrator Setting screen)
is set to “Restrict”.
built-in memory.
Shows the number of specified addresses.
Scanning Documents
11
2-6 IC-402

Scanning Documents
2.3 Sending Data in an E-Mail Message (Scan to E-Mail)
Scan to E-Mail
The Scan to E-mail operation is used to send images scanned on this machine to an e-mail address as an attachment.
The methods described below are available for specifying the destination.
The methods can also be combined, for example, by selecting a group destination, then adding other destinations through direct input.
Using Programs
“Program” refers to a set of destination addresses and scan settings that are
registered together. This feature is convenient for frequently scanning documents and sending data under the same conditions. The following procedure
describes how to send data by selecting a program that has been registered
in advance.
For details on registering programs, refer to “Registering Program Destinations” on page 3-19.
1 Press the [Scan] key on the control panel.
2
Scan
The Scan mode screen appears.
IC-402 2-7

2
Scanning Documents
2 Touch [Program].
The selected destinations are listed under “Broadcast Destinations”.
Only the destinations that can be specified are displayed. For example,
fax destinations are not displayed.
3 Touch [Scan Settings] to check the specified scan settings. The set-
tings that appear in the main Scan mode screen can be specified in advance for each program. For details, refer to “Registering Program
Destinations” on page 3-19.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2-8 IC-402

Scanning Documents
4 After checking the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group], [Address Book] or [Direct Input] to specify or add other
destinations.
5 Load the document into the automatic document feeder or position it
on the original glass of the copier.
6 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2
IC-402 2-9

2
Scanning Documents
Selecting Group Addresses
“Group” refers to multiple destinations that are registered collectively. The
following procedure describes how to send data by selecting a group that
has been registered in advance.
For details on registering groups, refer to “Registering Group Destinations”
on page 3-17.
1 Press the [Scan] key on the control panel.
Scan
The Scan mode screen appears.
2 Touch [Group].
Touching the button for a group displays the list of members registered
in the group.
2-10 IC-402

Scanning Documents
3 Select the desired destinations, and then touch [OK].
The selected destinations are listed under “Broadcast Destinations”.
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Address Book] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
IC-402 2-11

2
Scanning Documents
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2-12 IC-402

Scanning Documents
Selecting Destinations From the Address Book
“Address book” refers to the collection of abbreviated destinations that have
been registered in advance and appear so that the desired destination can
be selected. The following procedure describes how to send data by selecting destinations from the address book. Multiple addresses can be specified
simultaneously from the address book.
For details on registering addresses in the address book, refer to “Registering Abbreviated Destinations” on page 3-3.
1 Press the [Scan] key on the control panel.
2
Scan
The Scan mode screen appears.
2 Touch [Address Book].
When the address book appears, touch an index button to display the
buttons for the abbreviated destinations registered in the selected index. The index for the abbreviated destinations can be specified when
the abbreviated destination is registered.
– Touch [Detail Search], and then type in the name of the destination
or part of the address to search for the corresponding address.
IC-402 2-13

2
Scanning Documents
– Touch [LDAP Search] to search the addresses registered on the
LDAP server for the address that corresponds to the specified conditions.
Why is [LDAP Search] not displayed on the Address Book tab?
?
% If the [Manual Destination Input] on the Security Details screen (dis-
played by touching [9 Security Setting] on the Administrator Setting
screen) is set to [Restrict], [LDAP Search] does not appear on the
Address Book tab. For details on LDAP searches, refer to “Performing an LDAP Search” on page 2-16.
3 Touch the button for a destination to select it.
The selected buttons are highlighted, and the selected destinations are
listed under “Broadcast Destinations”. Other destination addresses
can be added through direct input.
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2-14 IC-402

Scanning Documents
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2
IC-402 2-15

2
Scanning Documents
Performing an LDAP Search
Searches the address that meets the conditions from the addresses registered on the LDAP server.
A “Basic Search” in which a keyword is entered and a “Advanced Search” in
which multiple conditions are used to narrow down the search are available.
Basic Search
Advanced Search
2-16 IC-402

Scanning Documents
Entering the Addresses Directly
“Direct input” refers to the operation of directly entering the destination address from the copier’s control panel.
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2 Touch [Direct Input], then [Scan to E-Mail].
2
Scan
A screen for entering the destination address appears.
Why is the Direct Input tab not displayed?
?
% If the [Manual Destination Input] on the Security Details screen (dis-
played by touching [9 Security Setting] on the Administrator Setting
screen) is set to [Restrict], the Direct Input tab does not appear.
IC-402 2-17

2
Scanning Documents
3 Enter the destination address, and then touch [OK].
– To specify an additional address, touch [Next Dest.], and then
specify the address.
– Frequently entered user names and domain names can be regis-
tered to be recalled and used again. First, prefixes and suffixes
must be registered in Administrator mode.
The addresses that were entered are listed under “Broadcast Destinations”.
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2-18 IC-402

Scanning Documents
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Address Book] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2
IC-402 2-19

2
2.4 Sending Data to a Server (Scan to FTP)
Scan to FTP
The Scan to FTP operation can be used in a network environment with an
FTP server. The scanned data is sent to a specified folder in an FTP server
on the network.
This function is suitable for sending data of a large size such as high-resolution images.
The methods described below are available for specifying the destination.
The methods can also be combined, for example, by selecting a group destination, then adding other destinations through direct input.
Transmission may not be possible if the destination server has placed limitations on the document name. Because the document name becomes the file
name at the time of transmission, consult your network administrator when
specifying the document name.
2
Note
If a mail server is available on the network, the e-mail notification function
can be used to send an e-mail message containing notification of the
storage location of the scan data. For details on the e-mail notification
function, refer to “Checking the Settings” on page 2-72.
Scanning Documents
Using Programs
“Program” refers to a set of destination FTP servers and scan settings that
are registered together. The following procedure describes how to send data
by selecting a program that has been registered in advance.
If a proxy server is available on the network, FTP servers on the Internet can
be accessed via a proxy server. For details on the proxy settings, refer to
“Specifying Settings for FTP File Transmissions” on page 5-11.
For details on registering programs, refer to “Registering Program Destinations” on page 3-19.
2-20 IC-402

Scanning Documents
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2 Touch [Program].
The selected destinations are listed under “Broadcast Destinations”.
Only the destinations that can be specified are displayed. For example,
fax destinations are not displayed.
2
Scan
3 Touch [Scan Settings] to check the specified scan settings. The set-
tings that appear in the main Scan mode screen can be specified in advance for each program. For details, refer to “Registering Program
Destinations” on page 3-19.
IC-402 2-21

2
Scanning Documents
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
4 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group], [Address Book] or [Direct Input] to specify or add other
destinations.
5 Load the document into the automatic document feeder or position it
on the original glass of the copier.
6 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
Selecting Group Addresses
“Group” refers to multiple destinations that are registered collectively. The
following procedure describes how to send data by selecting a group that
has been registered in advance.
For details on registering groups, refer to “Registering Group Destinations”
on page 3-17.
2-22 IC-402

Scanning Documents
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2 Touch [Group].
Touching the button for a group displays the list of members registered
in the group. Other destination addresses can be added using the address book or through direct input.
2
Scan
3 Select the desired destination, and then touch [OK].
The selected destinations are listed under “Broadcast Destinations”.
IC-402 2-23

2
Scanning Documents
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Address Book] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2-24 IC-402

Scanning Documents
Selecting Destinations From the Address Book
“Address book” refers to the collection of abbreviated destinations that have
been registered in advance and appear so that the desired destination can
be selected. The following procedure describes how to send data by selecting destinations from the address book. Multiple addresses can be specified
simultaneously from the address book.
For details on registering addresses in the address book, refer to “Registering Abbreviated Destinations” on page 3-3.
1 Press the [Scan] key on the control panel.
2
Scan
The Scan mode screen appears.
IC-402 2-25

2
Scanning Documents
2 Touch [Address Book].
When the address book appears, touch an index button to display the
buttons for the abbreviated destinations registered in the selected index. The index for the abbreviated destinations can be specified when
the abbreviated destination is registered.
How can the address book be searched for the desired address?
?
% Touch [Detail Search] to search for addresses. The address book
can be searched for names or addresses.
3 Touch the button for a destination to select it.
The buttons are highlighted, and the selected destinations are listed
under “Broadcast Destinations”. Other destinations can be added
through direct input.
2-26 IC-402

Scanning Documents
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
2
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
IC-402 2-27

2
Scanning Documents
Entering the Addresses Directly
“Direct input” refers to the operation of directly inputting the destination address from the copier’s control panel.
The following procedure describes how to directly specify an address.
1 Press the [Scan] key on the control panel.
Scan
The Scan mode screen appears.
2 Touch [Direct Input], then [Scan to FTP].
A screen for entering the destination host name, destination folder, and
other information appears.
Why is the Direct Input tab not displayed?
?
% If the [Manual Destination Input] on the Security Details screen (dis-
played by touching [9 Security Setting] on the Administrator Setting
screen) is set to [Restrict], the Direct Input tab does not appear.
2-28 IC-402

Scanning Documents
3 Enter the host name, destination folder, user name, and password.
– Host Name: Use the keyboard that appears in the touch panel to
specify the destination host name or IP address, and then touch
[OK].
– In order to specify an FTP destination as a host address, the DNS
setting must have been specified in the image controller’s setup
screen. In the setup screen for the image controller, select [Network
Setup] – [Protocol Setup] – [TCP/IP Setup] – [DNS Setup] to specify
the setting. For details on displaying the image controller’s setup
screen, refer to “Displaying the Setup Screen” on page 5-5.
– Destination Folder: Use the keyboard that appears in the touch
panel to specify the path to the destination folder, and then touch
[OK].
– User Name: Use the keyboard that appears in the touch panel to
specify the login user name, and then touch [OK].
– Password: Use the keyboard that appears in the touch panel to
specify the password, and then touch [OK].
2
4 Touch [Detail Setting], and then specify detailed FTP settings.
– Port Number: Check the port number.
– PASV mode: Select whether the PASV (passive) mode is used.
Touch [Yes] or [No].
– Proxy: Select whether a proxy server is used. Touch [Yes] or [No].
5 Touch [OK].
IC-402 2-29

2
Scanning Documents
6 Enter the destination Information, and then touch [OK].
– To specify an additional address, touch [Next Dest.], and then
specify the address.
The addresses that were entered are listed under “Broadcast Destinations”.
7 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2-30 IC-402

Scanning Documents
8 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Address Book] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
9 Load the document into the automatic document feeder or position it
on the original glass of the copier.
10 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2
IC-402 2-31

2
Scanning Documents
2.5 Sending Data to a PC on the Network (Scan to SMB)
Scan to SMB
The Scan to SMB operation can be used to directly send the scanned data
to a specific computer on the network.
To use the Scan to File (SMB) function, specify the Windows shared file setting on the PC that is to receive the data in advance.
Using Programs
“Program” refers to a set of destination computers and scan settings that are
registered together. The following procedure describes how to send data by
selecting a program that has been registered in advance.
For details on registering programs, refer to “Registering Program Destinations” on page 3-19.
1 Press the [Scan] key on the control panel.
Scan
The Scan mode screen appears.
2-32 IC-402

Scanning Documents
2 Touch [Program].
The selected destinations are listed under “Broadcast Destinations”.
Only the destinations that can be specified are displayed. For example,
fax destinations are not displayed.
3 Touch [Scan Settings] to check the specified scan settings. The set-
tings that appear in the main Scan mode screen can be specified in advance for each program. For details, refer to “Registering Program
Destinations” on page 3-19.
2
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
4 After checking the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group], [Address Book] or [Direct Input] to specify or add other
destinations.
IC-402 2-33

2
Scanning Documents
5 Load the document into the automatic document feeder or position it
on the original glass of the copier.
6 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
Selecting Group Addresses
“Group” refers to multiple destinations that are registered collectively. The
following procedure describes how to send data by selecting a group that
has been registered in advance.
For details on registering groups, refer to “Registering Group Destinations”
on page 3-17.
1 Press the [Scan] key on the control panel.
Scan
The Scan mode screen appears.
2 Touch [Group].
Touching the button for a group displays the list of members registered
in the group. Other destination addresses can be added using the address book or through direct input.
2-34 IC-402

Scanning Documents
3 Select the desired destinations, and then touch [OK].
The selected destinations are listed under “Broadcast Destinations”.
4 Touch [Scan Settings], and then specify the scan settings.
2
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Address Book] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
IC-402 2-35

2
Scanning Documents
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
Selecting Destinations From the Address Book
“Address book” refers to the collection of abbreviated destinations that have
been registered in advance and appear so that the desired destination can
be selected. The following procedure describes how to send data by selecting destinations from the address book. Multiple addresses can be specified
simultaneously from the address book.
For details on registering addresses in the address book, refer to “Registering Abbreviated Destinations” on page 3-3.
1 Press the [Scan] key on the control panel.
Scan
The Scan mode screen appears.
2-36 IC-402

Scanning Documents
2 Touch [Address Book].
When the address book appears, touch an index button to display the
buttons for the abbreviated destinations registered in the selected index. The index for the abbreviated destinations can be specified when
the abbreviated destination is registered.
How can the address book be searched for the desired address?
?
% Touch [Detail Search] to search for addresses. The address book
can be searched for names or addresses.
2
3 Touch the button for a destination to select it.
The selected buttons are highlighted, and the selected destinations are
listed under “Broadcast Destinations”. Other destinations can be added through direct input.
IC-402 2-37

2
Scanning Documents
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
5 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Direct Input] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
2-38 IC-402

Scanning Documents
Entering the Addresses Directly
“Direct input” refers to the operation of directly inputting the destination address from the copier’s control panel.
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2 Touch [Direct Input], then [Scan to SMB].
2
Scan
A screen for entering the destination host name, destination folder, and
other information appears.
Why is the Direct Input tab not displayed?
?
% If the [Manual Destination Input] on the Security Details screen (dis-
played by touching [9 Security Setting] on the Administrator Setting
screen) is set to [Restrict], the Direct Input tab does not appear.
IC-402 2-39

2
Scanning Documents
3 Enter the destination information.
– Host Name: Use the keyboard that appears in the touch panel to
specify the destination host name or IP address, and then touch
[OK].
– Destination Folder: Enter the path to the destination folder.
– User Name: Use the keyboard that appears in the touch panel to
specify the login user name, and then touch [OK].
– Password: Use the keyboard that appears in the touch panel to
specify the password, and then touch [OK].
– In order to send scan data to a folder that can only be accessed by
user accounts belonging to the domain, the user ID must be en-
tered in either of the following formats.
1 user_ID>@<domain_name>
2 <domain_name>\<user_ID>
(Note: In format 2, use the backslash (\). If the slash (/) is used, the
data will not be sent correctly.)
– To specify an additional address, touch [Next Dest.], and then
specify the address.
4 Touch [OK].
The specified addresses are listed under “Broadcast Destinations”.
2-40 IC-402

Scanning Documents
5 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
6 After specifying the settings, touch [OK].
– To send the data to another destination at the same time, touch
[Group] or [Address Book] to specify or add other destinations.
– If a destination registered in a program is added, the scan settings
registered in the program are given priority, and the scan data is
sent with the scan settings registered in the program.
2
7 Load the document into the automatic document feeder or position it
on the original glass of the copier.
8 Press the [Start] key on the control panel.
The document is scanned, and the data is sent.
IC-402 2-41

2
Scanning Documents
2.6 Saving Data on the Hard Disk (Save in Mailbox)
Save in Mailbox
The Save in Mailbox operation can be used to save document data on the
hard disk of the image controller. The saved data can be imported from a
computer.
Types of Mailboxes
17 mailboxes can be added to the default “admin”, “operator” and “guest”
mailboxes.
If “Enable Mailbox Password” from the setup screen of the image controller
is set to “No”, a password is not required to access the “admin”, “operator”,
“guest” boxes and other added boxes.
- Default mailboxes
As a default, three mailboxes (“admin”, “operator”, and “guest”) have
been created. The image controller administrator password is required to
access the “admin” mailbox. However, the “operator” and “guest” mailboxes do not require a password for access.
- Added mailboxes
Mailboxes can be added by the user. Personal mailboxes can be protected with a password. If a password has been specified, access to the
mailbox is permitted only if the correct password is entered.
2-42 IC-402

Scanning Documents
Using Programs
“Program” refers to a destination mailbox and scan settings that are registered together. The following procedure describes how to save data by selecting a program that has been registered in advance.
For details on registering programs, refer to “Registering Program Destinations” on page 3-19.
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2
Scan
2 Touch [Program].
The selected destinations are listed under “Broadcast Destinations”.
Only the destinations that can be specified are displayed. For example,
fax destinations are not displayed.
IC-402 2-43

2
Scanning Documents
3 Touch [Scan Settings] to check the specified scan settings. The set-
tings that appear in the main Scan mode screen can be specified in advance for each program. For details, refer to “Registering Program
Destinations” on page 3-19.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
4 After checking the settings, touch [OK].
5 Load the document into the automatic document feeder or position it
on the original glass of the copier.
6 Press the [Start] key on the control panel.
The document is scanned, and the document data is saved in the mailbox.
2-44 IC-402

Scanning Documents
Selecting Group Addresses
“Group” refers to multiple destinations that are registered collectively. The
following procedure describes how to save data by selecting a destination
from a group that has been registered in advance.
For details on registering groups, refer to “Registering Group Destinations”
on page 3-17.
1 Press the [Scan] key on the control panel.
The Scan mode screen appears.
2
Scan
2 Touch [Group].
Touching the button for a group displays the list of members registered
in the group.
IC-402 2-45

2
Scanning Documents
3 Select the desired destination, and then touch [OK].
The selected destinations are listed under “Broadcast Destinations”.
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
5 After specifying the settings, touch [OK].
6 Load the document into the automatic document feeder or position it
on the original glass of the copier.
7 Press the [Start] key on the control panel.
The document is scanned, and the document data is saved in the mailbox.
2-46 IC-402

Scanning Documents
Selecting Destinations From the Address Book
“Address book” refers to the collection of abbreviated destinations that have
been registered in advance and appear so that the desired destination can
be selected. The following procedure describes how to save data by selecting destinations from the address book. Multiple addresses can be specified
simultaneously from the address book.
For details on registering addresses in the address book, refer to “Registering Abbreviated Destinations” on page 3-3.
1 Press the [Scan] key in the control panel.
2
Scan
The Scan mode screen appears.
2 Touch [Address Book].
When the address book appears, touch an index button to display the
buttons for the abbreviated destinations registered in the selected index. The index for the abbreviated destinations can be specified when
the abbreviated destination is registered.
IC-402 2-47

2
Scanning Documents
How can the address book be searched for the desired address?
?
% Touch [Detail Search] to search for addresses. The address book
can be searched for names or addresses.
3 Touch the button for the mailbox where the data is to be saved.
The selected destinations are listed under “Broadcast Destinations”.
Why is [LDAP Search] not displayed on the Address Book tab?
?
% If the “Manual Destination Input” parameter on the Security Details
screen (displayed by touching [9 Security Setting] on the Adminis-
trator Setting screen) is set to “Restrict”, [LDAP Search] does not
appear on the Address Book tab.
4 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
2-48 IC-402

Scanning Documents
5 After specifying the settings, touch [OK].
6 Load the document into the reverse automatic document feeder or
place it on the original glass of the copier.
7 Press the [Start] key in the control panel.
The document is scanned and the document data is saved.
2
IC-402 2-49

2
Scanning Documents
To save data to the specified mailbox
Specifying the mailbox where the data is to be saved directly from the copier’s control panel is called “direct input”.
1 Press the [Scan] key in the control panel.
Scan
The Scan mode screen appears.
2 Touch [Direct Input], then [Save in User Box].
A screen appears, allowing you to enter the mailbox name.
Why is the Direct Input tab not displayed?
?
% If the “Manual Destination Input” parameter on the Security Details
screen (displayed by touching [9 Security Setting] on the Adminis-
trator Setting screen) is set to “Restrict”, the Direct Input tab does
not appear.
2-50 IC-402

Scanning Documents
3 Type in the name of the mailbox where the data is to be saved.
– Enter the name of the mailbox created on the hard disk of the image
controller.
– Correctly type in the mailbox name using uppercase and lowercase
letters.
4 Touch [OK].
The selected destinations are listed under “Broadcast Destinations”.
2
5 Touch [Scan Settings], and then specify the scan settings.
– For details on the scan settings, refer to “Specifying the Scan Set-
tings” on page 2-53.
IC-402 2-51

2
Scanning Documents
6 After specifying the settings, touch [OK].
7 Load the document into the reverse automatic document feeder or
place it on the original glass of the copier.
8 Press the [Start] key in the control panel.
The document is scanned, and the document data is saved in the mailbox.
!
Detail
For details on the scan settings, refer to “Specifying the Scan Settings”
on page 2-53.
For details on specifying the settings of the main Scan mode screen in
advance, refer to “Setting the Main Scan Mode Screen” on page 4-7.
2-52 IC-402

Scanning Documents
2.7 Specifying the Scan Settings
Available Settings
Detailed scan settings can be specified by touching [Scan Settings] in the
Scan mode screen.
The settings that can be specified are as follows:
Item Description Reference
File Type Selects the file type for saving the
Resolution Selects the scan resolution. “Resolution” on page 2-57
Simplex/Duplex Selects whether to scan one side of
Scan Size Sets the paper size to be scanned. “Scan Size” on page 2-61
Color Sets whether to scan in color or
Brightness Adjusts the brightness of the docu-
Background
Removal
Original Setting Specifies the type of document that
Application Provides functions for adjusting the
scanned data.
the document or both sides.
black and white.
ment.
Adjusts the density of the
background (blank areas) of the
document.
is loaded, for example, if it contains
mixed sizes or is a thick document.
print image, for example, for
scanning books and for erasing the
surrounding area.
“File Type” on page 2-54
“Simplex/Duplex” on page 2-58
“Color” on page 2-59
“Brightness” on page 2-63
“Background Removal” on
page 2-63
“Original Setting” on page 2-65
“Book Scanning (Application)” on
page 2-67
“Frame Erase (Application)” on
page 2-69
2
IC-402 2-53

2
Scanning Documents
Item Description Reference
Separate Scan The scan operation can be divided
into several sessions when all pages
of a document cannot be loaded
into the automatic document feeder
or when placing the document on
the original glass. In addition, the
documents can be scanned separately according to their type, such
as when single-sided documents
are mixed with double-sided documents.
“Separate Scan” on page 2-71
File Type
Select the file type for saving the scanned data. The following three file types
are available.
File type
Item Description
PDF Saves to the PDF format.
TIFF Saves to the TIFF format.
JPEG Saves to the JPEG format.
Some file types may not be available depending on the selected Color setting. The possible combinations of the File Type and Color settings are
shown below.
!
Detail
For details on the Color settings, refer to “Color” on page 2-59.
Auto Full Color Gray
PDF Yes Yes Yes Yes
TIFF No No No Yes
JPEG Yes Yes Yes No
Scale
Also, grouping of the saved data can be specified.
2-54 IC-402
Black

Scanning Documents
Scan Setting
Item Description
Single Page A file is created for each page of the document. When a
Multi-Page The entire scanned document is saved to a single file. This
double-sided document is scanned, a file is created from
every two pages that are scanned. This setting is not
selectable when [File Type] is PDF.
setting is not selectable when [File Type] is JPEG.
2
IC-402 2-55

2
Scanning Documents
To specify the File Type settings
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [File Type].
3 Select the file type.
4 Select the scan setting.
5 Touch [OK], and then touch [OK] in the next screen that appears.
2-56 IC-402

Scanning Documents
Resolution
Set the scanning resolution to 200 dpi, 300 dpi, 400 dpi, or 600 dpi.
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Resolution].
3 Select the resolution.
2
4 Touch [OK], and then touch [OK] in the next screen that appears.
IC-402 2-57

2
Scanning Documents
Simplex/Duplex
Select whether to scan one side of the document or both sides.
Item Description
1-Sided Scans one side of the document.
2-Sided Scans both sides of the document.
To specify the Simplex/Duplex setting
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Simplex/Duplex].
3 Select the scan type.
4 Touch [OK], and then touch [OK] in the next screen that appears.
2-58 IC-402

Scanning Documents
Color
Set whether to scan in color or black and white. Select from the following four
types.
Item Description
Auto Automatically detects the color of the document and scans
Full Color Scans at full color.
Gray Scale Select this setting when the document is full of halftone colors
Black Select this setting when the white and black boundaries are
Some color settings may not be available depending on the selected File
Type setting. The possible combinations of the File Type and Color settings
are shown below.
!
Detail
For details on the File Type settings, refer to “File Type” on page 2-54.
2
accordingly.
such as in a black-and-white photo.
distinct such as in a line drawing.
Auto Full Color Gray
Scale
PDF Yes Yes Yes Yes
TIFF No No No Yes
JPEG Yes Yes Yes No
Black
IC-402 2-59

2
Scanning Documents
To specify the Color setting
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Color].
3 Select the color type.
4 Touch [OK], and then touch [OK] in the next screen that appears.
2-60 IC-402

Scanning Documents
Scan Size
Set the paper size to be scanned.
The available scan sizes are as follows:
Item Description
Auto Detects the size of the first page of the loaded document.
Standard sizes Select a standard size and direction.
Custom Size Use to enter the dimensions of a custom size not available as
Photo Size Use to select the photo size.
To specify the Scan Size setting
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Scan Size].
a standard size.
The lengths in the X and Y directions can be set within the
ranges of 2 in. to 17 in. (30 mm - 432 mm) and 2 in. to 11-11/
16 in. (30 mm - 297 mm), respectively.
2
3 Select the size and direction.
IC-402 2-61

2
Scanning Documents
– Select the size and direction of the paper to be scanned.
– Touch [Custom Size] to display a screen for specifying the size.
Use the keypad or touch [-] and [+] to specify the size. Touch [⇔]
to switch between the integer and the fraction. The integer can be
specified in increments of 1 inch, and the fraction can be specified
in increments of 1/16 in. Touch [OK].
– Touch [Photo Size] to display a screen for specifying the size. Se-
lect the size and direction of the photo to be Scanned, and then
touch [OK].
4 Touch [OK], and then touch [OK] in the next screen that appears.
2-62 IC-402

Scanning Documents
Brightness
Adjust the brightness of the document during scanning.
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Brightness].
3 Specify the adjustment amount.
2
4 Touch [OK], and then touch [OK] in the next screen that appears.
Background Removal
Adjust the background density of the document during scanning. When
scanning a document on colored paper, the background may be dark in the
scan. In such cases, the background density can be adjusted.
1 Touch [Scan Settings] in the Scan mode screen.
IC-402 2-63

2
Scanning Documents
2 Touch [Background Removal].
– Touch [Auto] to adjust the background density automatically.
– To select a specific density, touch [Lighter] or [Darker].
– Touch [Std.] to select the default setting.
3 Touch [OK], and then touch [OK] in the next screen that appears.
2-64 IC-402

Scanning Documents
Original Setting
Specify the type of document that is loaded, for example, if it contains mixed
sizes or is a thick document.
2
Note
These functions can be combined.
Item Description
Mixed Original Select this setting when documents of different sizes are
Thick Original Select this setting when Scanning a thick document.
Original Direction Specifies the orientation of the document. The data is
Bind Specifies the binding position for punched holes and staples.
loaded into the automatic document feeder. The scan speed
is decreased since the size of each page is detected before it
is scanned.
processed so that the top and bottom ends are correctly
positioned when the document is scanned.
This function adjusts the binding position so that it is not reversed when a double-sided document is scanned.
Left: A document with a bind on the left side.
Top: A document with a bind on the top side.
Auto: If the length is 11-3/4 in. or less, the binding position is
along the long side of the paper. If the length is more than
11-3/4 in., the binding position is along the short side of the
paper.
2
To specify the Original Settings
1 Touch [Scan Settings] in the Scan mode screen.
2 Touch [Original Setting].
IC-402 2-65

2
Scanning Documents
3 Specify the original settings.
– If “Original Direction” is selected, a screen for selecting the direc-
tion appears. Select the direction, and then touch [OK].
– To select the default settings, touch [Reset].
– If “Bind” is selected, a screen for selecting the document binding
position appears. Select the binding position, and then touch [OK].
4 Touch [OK], and then touch [OK] in the next screen that appears.
2-66 IC-402

Scanning Documents
Book Scanning (Application)
Select this function when scanning page spreads. The four scanning methods listed below are available. In addition, frame erasing and center erasing
can be specified.
Item Description
Book Spread Scans a spread as one page.
Book Separation Scans a spread as separate left and right pages (2 pages).
Specify the spread document size for the scan size.
Shadows that occur from scanning page spreads can be erased from the
scans.
Item Description
Erase Erases the perimeter of the document. The width to be erased
Center Erase Erases the shadow along the center binding. The width can be
The left side is the first page, and the right side is the second
page.
can also be specified separately for the top, left, right, and
bottom sides within the range of 1/16 in. to 2 in (0.1 mm 50 mm).
set within the range of 1/16 in. to 1-3/6 in (0.1 mm - 30 mm).
2
2
Note
If the width to be erased is specified using the Book Erase functions in
the Book Scanning screen, the same value is set for the “Erase” function
on the Application screen.
IC-402 2-67
 Loading...
Loading...