Page 1
Media Flow Controller™ Administrator’s Guide and CLI Command Reference
Release
2.0.4
Published: 2010-9-17
Copyright © 2010, Juniper Networks, Inc.
Page 2

Media Flow Controller Administrator’s Guide
Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered
trademarks of Juniper Networks, Inc. in the United States and other countries. The Juniper
Networks Logo, the Junos logo, and JunosE a re trademarks of Junip er Networks, Inc. All other
trademarks, service marks, registered trademarks, or registered service marks are the
property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper
Networks reserves the right to change, modify, transfer, or otherwise revise this publication
without notice.
Products made or sold by Juniper Networks or components thereof might be covered by one
or more of the following patents that are owned by or licensed to Juniper Networks: U.S.
Patent Nos. 5,473,599, 5,905,725, 5,909,440, 6,192,051, 6,333,650, 6,359,479, 6,406,312,
6,429,706, 6,459,579, 6,493,347, 6,538,518, 6,538,899, 6,552,918, 6,567,902, 6,578,186,
and 6,590,785.
II Copyright © 2010, Juniper Networks, Inc.
Page 3
Media Flow Controller Administrator’s Guide
End User License Agreement
READ THIS END USER LICENSE AGREEMENT (“AGREEMENT”) BEFORE DOWNLOADING, INSTALLING, OR USING THE SOFTWARE. BY
DOWNLOADING, INSTALLING, OR USING THE SOFTWARE OR OTHERWISE EXPRESSING YOUR AGREEMENT TO THE TERMS CONTAINED
HEREIN, YOU (AS CUSTOMER OR IF YOU ARE NOT THE CUSTOMER, AS A REPRESENTATIVE/AGENT AUTHORIZED TO BIND THE CUSTOMER)
CONSENT TO BE BOUND BY THIS AGREEMENT. IF YOU DO NOT OR CANNOT AGREE TO THE TERMS CONTAINED HEREIN, THEN (A) DO NOT
DOWNLOAD, INSTALL, OR USE THE SOFTWARE, AND (B) YOU MAY CONTACT JUNIPER NETWORKS REGARDING LICENSE TERMS.
1. The Parties. The parties to this Agreement are (i) Juniper Networks, Inc. (if the Customer’s principal office is located in the Americas) or Juniper Networks
(Cayman) Limited (if the Customer’s principal office is located outside the Americas) (such applicable entity being referred to herein as “Juniper”), and (ii) the
person or organization that originally purchased from Juniper or an authorized Juniper reseller the applicable license(s) for use of the Software (“Customer”)
(collectively, the “Parties”).
2. The Software. In this Agreement, “Software” means the program modules and features of the Juniper or Juniper-supplied software, for which Customer has paid
the applicable license or support fees to Juniper or an authorized Juniper reseller, or which was embedded by Juniper in equipment which Customer purch as ed
from Juniper or an authorized Juniper reseller. “Software” also includes updates, upgrades and new releases of such software. “Embedded Software” means
Software which Juniper has embedded in or loaded onto the Juniper equipment and any updates, upgrades, additions or replacements which are subsequently
embedded in or loaded onto the equipment.
3. License Grant. Subject to payment of the applicable fees and the limitations and restrictions set forth herein, Juniper grants to Customer a non-exclusive and
non-transferable license, without right to sublicense, to use the Software, in executable form only, subject to the following use restrictions:
a. Customer shall use Embedded Software solely as embedded in, and for execution on, Juniper equipment originally purchased by Customer from Juniper or
an authorized Juniper reseller.
b. Customer shall use the Software on a single hardware chassis having a single processing unit, or as many chassis or processing units for which Customer
has paid the applicable license fees; provid ed, however, with respect to the Steel-Belted or Odyssey Access Client software only, Customer shall use such
Software on a single computer containing a single physical random access memory space and containing any number of processors. Use of the Steel-Belted
or IMS AAA software on multiple computers or virtual machines (e.g., Solaris zones) requires multiple licenses, regardless of whether such computers or
virtualizations are physically contained on a single chassis.
c. Product purchase documents, paper or electronic user documentation, and/or the particular licenses purchased by Customer may specify limits to
Customer’s use of the Software. Such limits may restrict use to a maximum number of seats, registered endpoints, concurrent users, sessions, calls,
connections, subscribers, clusters, nodes, realms, devices, links, ports or transactions, or require the purchase of separate licenses to use particular features,
functionalities, services, applications, operations, or capabilities, or provide throughput, performance, configuration, bandwidth, interface, processing,
temporal, or geographical limits. In addition, such limits may restrict the use of the Software to managing certain kinds of networks or require the Software
to be used only in conjunction with other specific Software. Customer’s use of the Software shall be subject to all such limitations and purchase of all
applicable licenses.
d. For any trial copy of the Software, Customer’s right to use the Software expires 30 days after download, installation or use of the Software. Customer may
operate the Software after the 30-day trial period only if Customer pays for a license to do so. Customer may not extend or cre
by re-installing the Software after the 30-day trial period.
e. The Global Enterprise Edition of the Steel-Belted software may be used by Customer only to manage access to Customer’s enterprise network.
Specifically, service provider customers are expressly prohibited from using the Global Enterprise Edition of the Steel-Belted software to support any
commercial network access services.
The foregoing license is not transferable or assignable by Customer. No license is granted herein to any user who did not originally purchase the applicable
license(s) for the Software from Juniper or an authorized Juniper reseller.
4. Use Prohibitions. Notwithstanding the foregoing, the license provided herein does not permit the Customer to, and Customer agrees not to and shall not: (a)
modify, unbundle, reverse engineer, or create derivative works based on the Software; (b) make unauthorized copies of the Software (except as necessary for
backup purposes); (c) rent, sell, transfer, or grant any rights in and to any copy of the Software, in any form, to any third party; (d) remove any proprietary notices,
labels, or marks on or in any copy of the Software or any product in which the Software is embedded; (e) distribute any copy of the Software to any third party,
including as may be embedded in Juniper equipment sold in the secondhand market; (f) use any ‘locked’ or key-restricted feature, function, service, application,
operation, or capability without first purchasing the applicable license(s) and obtaining a valid key from Juniper, even if such feature, function, service,
application, operation, or capability is enabled without a key; (g) distribute any key for the Software provided by Juniper to any third party; (h) use the Software
in any manner that extends or is broader than the uses purchased by Customer from Juniper or an authorized Juniper reseller; (i) use Embedded Software on nonJuniper equipment; (j) use Embedded Software (or make it available for use) on Juniper equipment that the Customer did not originally purchase from Juniper or
an authorized Juniper reseller; (k) disclose the results of testing or benchmarking of the Software to any third party without the prior written consent of Juniper;
or (l) use the Software in any manner other than as expressly provided herein.
5. Audit. Customer shall maintain accurate records as necessary to verify compliance with this Agreement. Upon request by Juniper, Customer shall furnish such
records to Juniper and certify its compliance with this Agreement.
6. Confidentiality. The Parties agree that aspects of the Software and associated documentation are the confidential property of Juniper. As such, Customer shall
exercise all reasonable commercial ef forts t o mai nta in t he Soft ware a nd associat e d docume ntati on in conf idence , which at a mini mum i ncludes res tri cti ng acce ss
to the Software to Customer employees and contractors having a need to use the Software for Customer’s internal business purposes.
7. Ownership. Juniper and Juniper’s licensors, respectively, retain ownership of all right, title, and interest (including copyright) in and to the Software, associated
documentation, and all copies of the Software. Nothing in this Agreement constitutes a transfer or conveyance of any right, title, or interest in the Software or
associated documentation, or a sale of the Software, associated documentation, or copies of the Software.
8. Warranty, Limitation of Liability, Disclaimer of Warranty. The warranty applicable to the Software shall be as set forth in the warranty statement that
accompanies the Software (the “Warranty Statement”). Nothing in this Agreement shall give rise to any obligation to support the Software. Support services may
be purchased separately. Any such support shall be governed by a separate, written support services agreement. TO THE MAXIMUM EXTENT PERMITTED
BY LAW, JUNIPER SHALL NOT BE LIABLE FOR ANY LOST PROFITS, LOSS OF DATA, OR COSTS OR PROCUREMENT OF SUBSTITUTE GOODS
ate an additional trial period
III
Page 4

Media Flow Controller Administrator’s Guide
OR SERVICES, OR FOR ANY SPECIAL, INDIRECT, OR CONSEQUENTIAL DAMAGES ARISING OUT OF THIS AGREEMENT, THE SOFTWARE, OR
ANY JUNIPER OR JUNIPER-SUPPLIED SOFTWARE. IN NO EVENT SHALL JUNIPER BE LIABLE FOR DAMAGES ARISING FROM
UNAUTHORIZED OR IMPROPER USE OF ANY JUNIPER OR JUNIPER-SUPPLIED SOFTWARE. EXCEPT AS EXPRESSLY PROVIDED IN THE
WARRANTY STATEMENT TO THE EXTENT PERMITTED BY LAW, JUNIPER DISCLAIMS ANY AND ALL WARRANTIES IN AND TO THE
SOFTWARE (WHETHER EXPRESS, IMPLIED, STATUTORY, OR OTHERWISE), INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE, OR NONINFRINGEMENT. IN NO EVENT DOES JUNIPER WARRANT THAT THE SOFTWARE, OR ANY
EQUIPMENT OR NETWORK RUNNING THE SOFTWARE, WILL OPERATE WITHOUT ERROR OR INTERRUPTION, OR WILL BE FREE OF
VULNERABILITY TO INTRUSION OR ATTACK. In no event shall Juniper’s or its suppliers’ or licensors’ liability to Customer, whether in contract, tort
(including negligence), breach of warranty, or otherwise, exceed the price paid by Customer for the Software that gave rise to the claim, or if the Software is
embedded in another Juniper product, the price paid by Customer for such other product. Customer acknowledges and agrees that Juniper has set its prices and
entered into this Agreement in reliance upon the disclaimers of warranty and the limitations of liability set forth herein, that the same reflect an allocation of risk
between the Parties (including the risk that a contract remedy may fail of its essential purpose and cause consequential loss), and that the same form an essential
basis of the bargain between the Parties.
9. Termination. Any breach of this Agreement or failure by Customer to pay any applicable fees due shall result in automatic termination of the license granted
herein. Upon such termination, Customer shall destroy or return to Juniper all copies of the Software and related documentation in Customer’s possession or
control.
10. Taxes. All license fees payable under this agreement are exclusive of tax. Customer shall be responsible for paying Taxes arising from the purchase of the
license, or importation or use of the Software. If applicable, valid exemption documentation for each taxing jurisdiction shall be provided to Juniper prior to
invoicing, and Customer shall promptly notify Juniper if their exemption is revoked or modified. All payments made by Customer shall be net of any applicable
withholding tax. Customer will provide reasonable assistance to Juniper in connection with such withholding taxes by promptly: providing Juniper with valid
tax receipts and other required documentation showing Customer’s payment of any withholding taxes; completing appropriate applications that would reduce the
amount of withholding tax to be paid; and notifying and assisting Juniper in any audit or tax proceeding related to transactions hereunder. Customer shall comply
with all applicable tax laws and regulations, and Customer will promptly pay or reimburse Juniper for all costs and damages related to any liability incurred by
Juniper as a result of Customer’s non-compliance or delay with its responsibilities herein. Customer’s obligations under this Section sha ll surv iv e te rm in at ion or
expiration of this Agreement.
11. Export. Customer agrees to comply with all applicable export laws and restrictions and regulations of any United States and any applicable foreign agency or
authority, and not to export or re-export the Software or any direct product thereof in violation of any such restrictions, laws or regulations, or without all
necessary approvals. Customer shall be liable for any such violations. The version of the Software supplied to Customer may contain encryption or other
capabilities restricting Customer’s ability to export the Software without an export license.
12. Commercial Computer Software. The Software is “commercial computer software” and is provided with restricted rights. Use, duplication, or disclosure by the
United States government is subject to restrictions set forth in this Agreement and as provided in DFARS 227.7201 through 227.7202-4, FAR 12.212, FAR
27.405(b)(2), FAR 52.227-19, or FAR 52.227-14(ALT III) as applicable.
13. Interface Information
information needed to achieve interoperability between the Software and another independently created program, on payment of applicable fee, if any. Customer
shall observe strict obligations of confidentiality with respect to such information and shall use such information in compliance with any applicable terms and
conditions upon which Juniper makes such information available.
14. Third Party Software. Any licensor of Juniper whose software is embedded in the Software and any supplier of Juniper whose products or technology are
embedded in (or services are accessed by) the Software shall be a third party beneficiary with respect to this Agreement, and such licensor or vendor shall have
the right to enforce this Agreement in its own name as if it were Juniper. In addition, certain third party software may be provided with the Software and is subject
to the accompanying license(s), if any, of its respective owner(s). To the extent portions of the Software are distributed under and subject to open source licenses
obligating Juniper to make the source code for such portions publicly available (such as the GNU General Public License (“GPL”) or the GNU Library General
Public License (“LGPL”)), Juniper will make such source code portions (including Juniper modifications, as appropriate) available upon request for a period of
up to three years from the date of distribution. Such request can be made in writing to Juniper Networks, Inc., 1194 N. Mathilda Ave., Sunnyvale, CA 94089,
ATTN: General Counsel. You may obtain a copy of the GPL at http://www.gnu.org/licenses/gpl.html, and a copy of the LGPL at http://www.gnu.org/licenses/
lgpl.html.
15. Miscellaneous. This Agreement shall be governed by the laws of the State of California without reference to its conflicts of laws principles. The provisions of the
U.N. Convention for the International Sale of Goods shall not apply to this Agreement. For any disputes arising under this Agreement, the Parties hereby consent
to the personal and exclusive jurisdiction of, and venue in, the state and federal courts within Santa Clara County, California. This Agreement constitutes the
entire and sole agreement between Juniper and the Customer with respect to the Software, and supersedes all prior and contemporaneous agreements relating to
the Software, whether oral or written (including any inconsistent terms contained in a purchase order), except that the terms of a separate written agreement
executed by an authorized Juniper representative and Customer shall govern to the extent such terms are inconsistent or conflict with terms contained herein. No
modification to this Agreement nor any waiver of any rights hereunder shall be effective unless expressly assented to in writing by the party to be charged. If any
portion of this Agreement is held invalid, the Parties agree that such invalidity shall not affect the validity of the remainder of this Agreement. This Agreement
and associated documentation has been written in the English language, and the Parties agree that the English version will govern. (For Canada: Les parties aux
présentés confirment leur volonté que cette convention de même que tous les documents y compris tout avis qui s'y rattaché, soient redigés en langue anglaise.
(Translation: The parties confirm that this Agreement and all related documentation is and will be in the English language)).
. To the extent required by applicable law, and at Customer's written request, Juniper shall provide Customer with the interface
IV Copyright © 2010, Juniper Networks, Inc.
Page 5
Media Flow Controller Administrator’s Guide
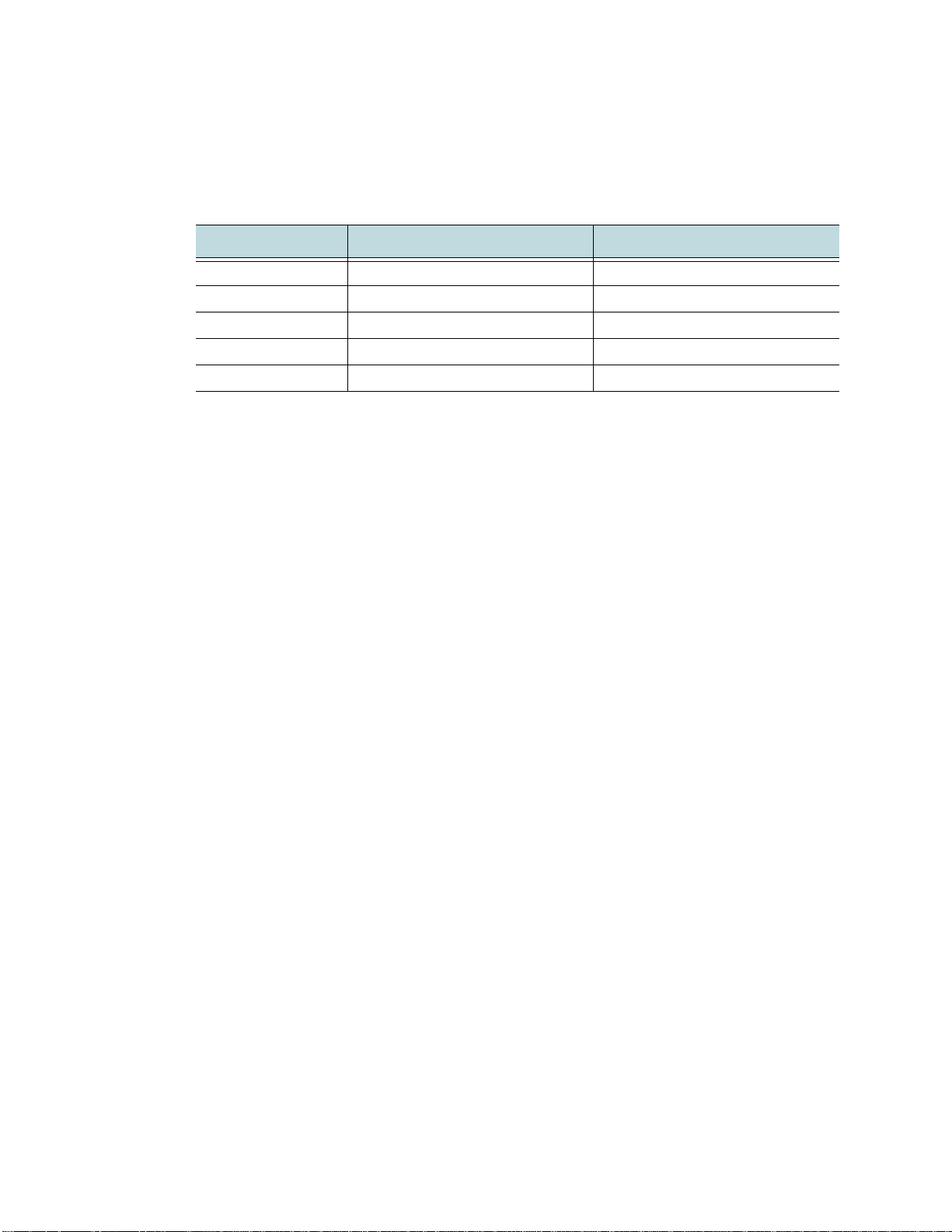
Document History
Date Media Flow Controller Version Comments
2010-4-27 Release 2.0 Document Version 2.0
2010-5-14 Release 2.0.1 Document Version 2.0a
2010-6-17 Release 2.0.2 Document Version 2.0b
2010-7-21 Release 2.0.3 Document Version 2.0c
2010-9-17 Release 2.0.4 Document Version 2.0d
V
Page 6

Media Flow Controller Administrator’s Guide
VI Copyright © 2010, Juniper Networks, Inc.
Page 7

TABLE OF CONTENTS
End User License Agreement..................................................................... III
Document History ........................................................................................V
1
Preface ...................................................................................................1.27
What’s New in Release 2.0.4...................................................................................... 1.27
PXE Installation Enhancements......................................................................................... 1.27
Installations on Non-Centos Linux Drives........................................................................... 1.27
Logging Enhancements...................................................................................................... 1.28
Media Cache ...................................................................................................................... 1.28
Hardware Support .............................................................................................................. 1.28
Guide to This Document............................................................................................. 1.28
Documentation and Release Notes............................................................................ 1.29
Text and Syntax Conventions..................................................................................... 1.29
Terminology................................................................................................................ 1.30
Documentation Feedback........................................................................................... 1.34
Requesting Technical Support.................................................................................... 1.34
Self-Help Online Tools and Resources .............................................................................. 1.35
Opening a Case with JTAC................................................................................................ 1.35
PART 1
Media Flow Controller Administration
2
Media Flow Controller Overview ............................................................2.39
Media Flow Controller Overview................................................................................. 2.39
Environment................................................................................................................2.40
Copyright © 2010, Juniper Networks, Inc. VII
Page 8

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
System and Hardware Overview ................................................................................ 2.40
System Requirements........................................................................................................ 2.40
Delivery Network Link Aggregation ....................................................................................2.41
Installation Requirements................................................................................................... 2.41
Console Port....................................................... ..................................... ........................... 2.41
Management Interfaces Overview.............................................................................. 2.41
Command Line Interface (CLI)................... .................................... ... ................................. 2.42
Web Interface (Management Console)............................................................................... 2.42
SNMP Interface to Network Management System............................................................. 2.42
Email and Email2SMS Alerts.............................................................................................. 2.43
How Media Flow Controller Works.............................................................................. 2.43
Media Flow Controller Functions Overview ................................................................ 2.45
Media Flow Controller Delivery Methods.................................................................... 2.45
Streaming with HTTP ......................................................................................................... 2.46
Streaming with RTSP......................................................................................................... 2.47
Connection Pooling......................................... ... ..................................... ........................... 2.48
Consistent Hash-Based Clustering and Origin Escalation ................................................. 2.48
Media Flow Controller Hierarchical Caching............................................................... 2.49
Media Flow Controller AssuredFlow........................................................................... 2.50
Admission Control............................................................................. .................................2.50
Media Flow Controller SmoothFlow............................................................................ 2.51
How SmoothFlow Works........................................................ .................................... ........ 2.52
Media Flow Controller Network Connection................................................................ 2.53
Media Flow Controller Namespace Functions............................................................ 2.53
Media Flow Controller Virtual Player Functions.......................................................... 2.53
Type generic....................................................... ... ............................................................. 2.54
Type break........................... ...................................................................... ......................... 2.54
Type qss-streamlet................................................ ... ..........................................................2.54
Type yahoo...................................................... ... ................................................................ 2.54
Type smoothflow ............................................. ... ..................................... ...........................2.55
Type youtube...................................................... ... ............................................................. 2.55
Type smoothstream-pub.............................................................. ....................................... 2.55
Encoding Schemes............................................................................................................. 2.56
Media Flow Controller Media Flow Manager Functions.............................................. 2.56
VIII Copyright © 2010, Juniper Networks, Inc.
Page 9

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
3
Media Flow Controller Configuration Tasks (CLI) ..................................3.57
Before You Configure Media Flow Controller ............................................................. 3.58
About the Media Flow Controller CLI.......................................................................... 3.58
Connecting and Logging In................................. ..................................... .. ......................... 3.59
Using the Command Modes............................................................................................... 3.59
Prompt and Response Conventions................................................................ ................... 3.60
CLI Options......................................................................................................................... 3.60
Logging In to Media Flow Controller for the First Time (CLI)...................................... 3.61
Media Flow Controller System Configuration Overview.............................................. 3.61
Configuring Interfaces, Hostname, Domain List, DNS, and Default Gateway (CLI)... 3.61
Cutting and Pasting an Interface Configuration (CLI)......................................................... 3.62
Example: Media Flow Controller Interface Configuration............................................ 3.63
Configuring Media Flow Controller System Clock and Banners (CLI)........................ 3.64
Creating and Configuring Link Bonding and Static Routes (CLI)................................ 3.65
Load Balancing (LB) Direct Server Return (DSR) Guidelines ............................................ 3.65
Configuring Link Bonding and Static Routes (CLI)............................................................. 3.66
Authentication / Authorization and Users Options ...................................................... 3.67
About MD5, SHA1, AES-128, and DES ............................................................................. 3.67
User Account Defaults and States...................................................................................... 3.68
Configuring Media Flow Controller User Accounts (CLI)............................................ 3.69
Enabling Media Flow Controller CMC Client Rendezvous (CLI)................................. 3.70
Applying the Media Flow Controller License (CLI)...................................................... 3.71
Media Flow Controller Policy Configurations Overview.............................................. 3.72
Setting Network Connection Options (CLI)................................................................. 3.72
Using Network Connection Assured Flow.......................................................................... 3.72
Configuring Network Connections (CLI)............................................................................. 3.72
Configuring Media Flow Controller Delivery Protocol (CLI) ........................................ 3.73
Creating and Configuring Virtual Players (CLI)........................................................... 3.74
Using query-string-parm..................................................................................................... 3.75
Using hash-verify................................................................................................................ 3.76
Using virtual-player type qss-streamlet rate-map............................................................... 3.76
Using Virtual Player Type youtube..................................................................................... 3.77
Example: Configuring generic Virtual Player (CLI).............................................................3.78
IX
Page 10

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
Creating and Configuring Server-Maps (CLI) ............................................................. 3.79
Using server-map to Create a Consistent Hash Cluster.....................................................3.79
Using server-map for Origin Escalation.............................................................................. 3.80
Configuring Media Flow Controller Server Maps (CLI).......................................................3.80
Creating a Namespace and Setting Namespace Options (CLI) ................................. 3.81
Using namespace cache-inherit......................................................................................... 3.82
Using namespace domain regex........................................................................................ 3.82
Using namespace domain <FQDN:Port>........................................................................... 3.83
Using namespace match uri regex..................................................................................... 3.84
Using namespace match <criteria> precedence................................................................ 3.84
Using namespace delivery protocol <protocol> origin-fetch cache-age............................. 3.85
Using namespace object delete | list.................................................................................. 3.86
Using namespace for Live Streaming Delivery Without Caching ....................................... 3.86
Using namespace for Live Streaming Delivery With Caching............................................ 3.87
Using namespace for Proxy Configurations....................................................................... 3.87
Example: Transparent Proxy Namespace Configuration ................................................... 3.88
Using namespace match virtual-host ................................................................................. 3.89
Configuring Media Flow Controller Namespaces (CLI) ...................................................... 3.89
Managing the Media Flow Controller Disk Cache (CLI).............................................. 3.92
Analyzing the Disk Cache...................................................................................................3.93
Disk Cache Problems......................................................................................................... 3.94
Replacing Bad Disks.......................................... ..................................... ........................... 3.95
Inserting New Disks into a VXA Series Media Flow Engine............................................... 3.95
Installing and Using FMS in Media Flow Controller (CLI)........................................... 3.97
Installing FMS on Media Flow Controller (CLI)...................................................................3.97
Modifying and Restarting the FMS Service (CLI)............................................................... 3.99
Configuring the FMS Admin Console—First Time (CLI)...................................................3.100
Configuring FMS on Media Flow Controller for Video On Demand (CLI)......................... 3.100
Using Video Directories for FMS......................................................................................3.103
Applying the Adobe Full-Function FMS Server License (CLI).......................................... 3.103
Administering Media Flow Controller Overview (CLI)............................................... 3.104
Saving and Applying Configurations, Resetting Factory Defaults (CLI).................... 3.104
Rebooting Media Flow Controller (CLI)..................................................................... 3.105
Upgrading Media Flow Controller (CLI) .................................................................... 3.105
Configuring the Web Interface (CLI)......................................................................... 3.106
Configuring the Web Interface Proxy (CLI)............................................................... 3.107
X Copyright © 2010, Juniper Networks, Inc.
Page 11

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
4
Media Flow Controller Configuration Tasks (Web Interface) ............... 4.109
About the Media Flow Controller Web Interface....................................................... 4.110
Connecting and Logging In................................. ... .................................... ... .................... 4.110
Logging In to Media Flow Controller for the First Time (Web Interface)................... 4.111
Configuring Media Flow Controller for the First Time (Web Interface)...................... 4.111
Setting the System Hostname (EZconfig)........................................................................ 4.113
Setting Network Parameters (EZconfig).......................................................................... 4.113
Creating a Virtual Player (EZconfig)................................................................................ 4.113
Adding a Namespace (EZconfig).......................... ... ........................................................ 4.114
Enabling Interfaces (EZconfig).................. ... ................................................................... 4.114
Restarting Services (EZconfig)........................................................................................ 4.114
Monitoring Media Flow Controller Statistics (Web Interface)....................................4.115
Summary Page................................................................................................................. 4.115
Viewing Media Flow Controller Statistics.......................................................................... 4.115
Viewing Media Flow Controller Bandwidth Usage..................................... ... .................... 4.116
Viewing Media Flow Controller Namespace Counters..................................................... 4.117
Viewing Media Flow Controller CPU Load ......................................................... .............. 4.117
Viewing Network Usage................................................................................................... 4.118
Viewing Memory Utilization.............................................................................................. 4.119
Media Flow Controller System Configuration Overview............................................ 4.119
Configuring Interfaces, Default Gateway, Static Routes, DNS and Domain Names,
Hostname and Banners (Web Interface) ..................................................................4.119
Configuring Interfaces (Web Interface)............................................................................. 4.119
Setting the Default Gateway and Static Routes (Web Interface)...................................... 4.122
Configuring DNS and Domain Names (Web Interface).................................................... 4.124
Setting Hostnames and Banners (Web Interface)............................................................ 4.127
Configuring Static Hosts and ARP (Web Interface).................................................. 4.129
Configuring Static Hosts................................................................................................... 4.129
Configuring ARP (Web Interface).....................................................................................4.130
Configuring Date, Time, and NTP (Web Interface)................................................... 4.131
Configuring the System Date and Time (Web Interface).................................................. 4.131
Configuring NTP (Web Interface).....................................................................................4.132
Configuring RADIUS, TACACS+, and SSH (Web Interface).................................... 4.134
Configuring RADIUS (Web Interface)............................................................................... 4.134
Configuring TACACS+ (Web Interface)............................................................................ 4.136
Configuring SSH (Web Interface).....................................................................................4.138
Configuring Users and AAA (Web Interface)............................................................ 4.139
Configuring Users (Web Interface)...................................................................................4.140
Configuring AAA (Web Interface)..................................................................................... 4.142
XI
Page 12

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
Configuring SNMP, Faults, and Logging (Web Interface)......................................... 4.143
Configuring SNMP (Web Interface)..................................................................................4.143
Configuring Fault Reporting (Web Interface).................................................................... 4.145
Configuring System Logging (Web Interface)................................................................... 4.148
Administering Media Flow Controller Overview........................................................ 4.152
Managing Configuration Files (Web Interface) ......................................................... 4.152
Installing Licenses (Web Interface)........................................................................... 4.155
Upgrading the System (Web Interface).....................................................................4.156
Rebooting the System (Web Interface)..................................................................... 4.157
Configuring the Web Interface (Web Interface) ....................................................... 4.158
Configuring the Web Interface Proxy (Web Interface).............................................. 4.159
Configuring Central Management Console Access (Web Interface) ........................ 4.160
Configuring CMC Client Access (Web Interface) ............................................................. 4.160
Service Configurations Overview.............................................................................. 4.162
Configuring the Delivery Network (Web Interface).................................................... 4.163
Network Connection......................................................................................................... 4.163
Configuring Delivery Protocols (Web Interface)........................................................ 4.164
Set HTTP Listen Port........................................................................................................ 4.166
Configure Rate Control..................................................................................................... 4.166
Configure/Add Selected HTTP Listen Interfaces.............................................................. 4.166
HTTP Listen Interfaces.......................................................................................... ........... 4.166
HTTP Listen Ports....................................................... .. ..................................... ... ........... 4.166
Configuring Virtual Players (Web Interface).............................................................. 4.167
Add Virtual Player.............................................................................................................4.167
Configure, Show, or Remove Virtual Players................................................................... 4.167
Virtual Player generic Type Configuration........................................................................ 4.168
Virtual Player break Type Configuration........................................................................... 4.170
Virtual Player qss-streamlet Type Configuration.............................................................. 4.171
Example: Rate Map Configuration.................................................................................... 4.173
Virtual Player yahoo Type Configuration.......................................................................... 4.173
Virtual Player smoothflow Type Configuration............................. ..................................... 4.175
Virtual Player youtube Type Configuration....................................................................... 4.177
Virtual Player smoothstream-pub Type Configuration...................................................... 4.179
Configuring NameSpaces (Web Interface)............................................................... 4.179
Add Namespace............................................................................................................... 4.180
Configuration List..............................................................................................................4.180
Namespace Configuration................................................................................................ 4.180
Managing the Media-Cache (Web Interface)............................................................ 4.186
Disk Name........................................................................................................................ 4.186
XII Copyright © 2010, Juniper Networks, Inc.
Page 13

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
Configuring Service Logging (Web Interface)........................................................... 4.187
Access Log Configuration.............................. ................................................................... 4.187
Access Log Copy/Auto Download Configuration.............................................................. 4.187
Stream Log Configuration.................................................................. ... ............................ 4.188
Stream Log Copy/Auto Download Configuration.............................................................. 4.189
Viewing Logs Overview.............................................................................................4.189
Viewing the System Log (Web Interface)......................................................................... 4.189
Viewing the Service Log (Web Interface)......................................................................... 4.190
Viewing the Cache Log (Web Interface)........................................................................... 4.190
Viewing the Trace Log (Web Interface)............................................................................ 4.191
Viewing the Stream Log (Web Interface).......................................................................... 4.191
Viewing the FMSConnector Log (Web Interface)............................................................. 4.191
Viewing the FMSAccess Log (Web Interface).................................................................. 4.191
Viewing the FMSEdge Log (Web Interface)..................................................................... 4.192
Viewing the Dashboard.............................................................................................4.192
Viewing Reports (Interface Statistics)....................................................................... 4.195
5
Media Flow Controller Common Configuration Tasks (CLI) ................ 5.197
Configuring Caching All Contents for a Website (CLI).............................................. 5.197
Configuring YouTube Video Caching (CLI)............................................................... 5.199
Configuring NFS Fetch for Images (CLI) ..................................................................5.200
Configuring HTTP Fetch for Videos (CLI)................................................................. 5.201
Configuring RTSP Fetch for Videos (CLI)................................................................. 5.201
Configuring SmoothFlow Restricted by File Path (CLI) ............................................ 5.202
Configuring the SNMP Agent (CLI)........................................................................... 5.203
Pre-Staging Content with FTP (CLI)......................................................................... 5.203
Configuring Media Flow Controller Mid-Tier Proxy (CLI).......................................... 5.203
Configuring Media Flow Controller for SmoothFlow (CLI) ........................................ 5.204
Configuring SmoothFlow Virtual Player (CLI)...................................................................5.204
Configuring SmoothFlow Namespaces (CLI)................................................................... 5.206
Using SSH in Automated Scripts (CLI)..................................................................... 5.208
Example: SSH Configuration for a Trusted User (CLI).....................................................5.208
XIII
Page 14

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
6
Configuring and Using Media Flow Controller Logs and Alarms ......... 6.209
Log Codes and Sub-Codes....................................................................................... 6.210
Status/Error Codes........................................................................................................... 6.210
Status/Error Sub-Codes ................................................................................................... 6.211
Service Log (accesslog)............................................................................................ 6.212
Accesslog CLI Commands............................................................................................... 6.212
Viewing the Accesslog...................................................................................................... 6.213
Reading the Accesslog..................................................................................................... 6.213
Cache Log (cachelog)...............................................................................................6.214
Viewing the Cache Log..................................................................................................... 6.215
Error Log (errorlog)................................................................................................... 6.215
Viewing the Errorlog......................................................................................................... 6.217
FMSAccess Log (fmsaccesslog)............................................................................... 6.217
Viewing the FMSAccess Log............................................................................................6.218
FMSEdge Log (fmsedgelog)..................................................................................... 6.218
Viewing the FMSEdge Log............................................................................................... 6.219
FMSConnector Log / fuselog.................................................................................... 6.219
Viewing the FMSConnector Log....................................................................................... 6.220
Stream Log (streamlog)............................................................................................ 6.220
Viewing the Stream Log................................................................................................... 6.220
System Log............................................................................................................... 6.220
System Baseline and Health ............................................................................................ 6.221
Viewing the System Log................................................................................................... 6.222
Tech-Support Log.....................................................................................................6.222
Viewing the Tech-Support Output .................................................................................... 6.223
Trace Log (tracelog).................................................................................................. 6.223
Viewing the Trace Log......................................................................................................6.226
About Log Rotation...................................................................................................6.226
Configuring Media Flow Controller Service Logs (CLI)............................................. 6.226
Media Flow Controller System Logging Overview.................................................... 6.228
System Log Severity Levels and Classes........................................................................ 6.228
Configuring Media Flow Controller System Logging (CLI) ............................................... 6.229
Configuring Log Statistics Thresholds (CLI) .............................................................6.231
Stats Reports Names Options.......................................................................................... 6.232
Stats Measurement Counters................................................................................... 6.233
XIV Copyright © 2010, Juniper Networks, Inc.
Page 15

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
Stats Alarms..............................................................................................................6.234
Configuring stats alarm Noti fic ations................................................................................ 6.236
SNMP Alarms ........................................................................................................... 6.237
SNMP............................................................................................................................... 6.237
Configuring Media Flow Controller Fault Notifications (CLI).....................................6.240
7
Server Map Configuration ....................................................................7.243
Server Map Overview ............................................................................................... 7.243
Server Map Format Types........................................................................................ 7.243
Creating the host-origin-map XML File..................................................................... 7.244
Example: host-origin-map DTD........................................................................................ 7.245
Validating With the DTD.................... ... ..................................... .................................... ...7.245
Creating the cluster-map XML File ........................................................................... 7.245
Example: cluster-map DTD.............................................................................................. 7.246
Creating the origin-escalation-map XML File............................................................ 7.247
Example origin-escalation-map DTD................................................................................ 7.248
nfs-map XML File......................................................................................................7.248
Configuring Server Maps (CLI)................................................................................. 7.249
8
SmoothFlow Deployment ..................................................................... 8.251
SmoothFlow Deployment Overview.......................................................................... 8.251
Evaluating Your Needs.............................................................................................8.252
Encoding Requirements................................................................................................... 8.252
Creating SmoothFlow Media Assets.........................................................................8.253
Creating Assets Using an SaaS................................................................................ 8.253
Requirements for Creating Assets Using an SaaS...........................................................8.254
Steps for Creating Assets Using an SaaS........................................................................ 8.255
Scripts for Creating Assets Using an SaaS...................................................................... 8.255
Initiate Encoding Using an SaaS...................................................................................... 8.256
Verify that Encoding has Completed.................. .............................................................. 8.259
Prepare Media Flow Controller for Assets Created Using an SaaS................................. 8.260
Logs for Assets Created Using an SaaS.......................................................................... 8.261
XV
Page 16

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
Creating On-Demand Assets.................................................................................... 8.262
Steps for Creating On-Demand Assets............................................................................ 8.263
Requirements and Files for Creating On-Demand Assets ............................................... 8.263
Bitrate Profiles Naming Conventions for On-Demand Assets.......................................... 8.263
Create AssetDescription.dat File for On-Demand Assets ................................................ 8.264
Pre-Stage On-Demand Assets.........................................................................................8.265
Initiate SmoothFlow Processing for On-Demand Assets.................................................. 8.265
Deploying the SmoothFlow Reference Client Player................................................ 8.267
Troubleshooting........................................................................................................ 8.268
Deployment Checklist............................................................................................... 8.269
9
Media Flow Controller Troubleshooting ...............................................9.271
Displaying Information Using Show Commands....................................................... 9.271
Testing Network Connectivity ...................................................................................9.275
Testing Media Flow Controller Delivery Functions.................................................... 9.276
Testing HTTP Origin Fetch............................................................................................... 9.277
Testing NFS Origin Fetch................................................................................................. 9.279
Testing a Specific Transaction ......................................................................................... 9.281
Enabling Debug Operations......................................................................................9.281
Common Media Flow Controller Configuration Errors.............................................. 9.282
Media Flow Controller Licenses Invalid............................................................................ 9.282
Namespace Match Uri Configuration................................................................................ 9.283
Namespace Domain Configuration................................................................................... 9.283
File Not Getting Cached................................................ ..................................... .............. 9.283
Cache Promotion Not Happening..................................................................................... 9.283
Incoming Requests’ URL Length...................................................................................... 9.283
PART 2
Media Flow Controller Command and MIB Reference
10
Media Flow Controller CLI Commands .............................................. 10.287
aaa.......................................................................................................................... 10.289
aaa (authentication)................................................................................................ 10.289
aaa (authorization).................................................................................................. 10.289
accesslog................................................................................................................10.290
XVI Copyright © 2010, Juniper Networks, Inc.
Page 17

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
accesslog format Options .......................................................................................10.291
analytics.................................................................................................................. 10.292
application...............................................................................................................10.293
arp. .......................................................................................................................... 10.293
banner.....................................................................................................................10.294
bond........................................................................................................................ 10.294
boot......................................................................................................................... 10.295
cachelog..................................................................................................................10.295
clear........................................................................................................................10.296
cli.............................................................................................................................10.296
clock........................................................................................................................10.298
cmc ......................................................................................................................... 10.299
cmc auth ................................................................................................................. 10.299
cmc client................................................................................................................ 10.300
cmc rendezvous...................................................................................................... 10.302
collect counters....................................................................................................... 10.303
configuration ........................................................................................................... 10.304
configuration text.....................................................................................................10.306
configure.................................................................................................................10.308
debug...................................................................................................................... 10.308
delivery....................................................................................................................10.308
email ....................................................................................................................... 10.310
email event name Options...................................................... .................................... ... .10.312
email class Options ..................................................... ................................................... 10.312
enable.....................................................................................................................10.313
errorlog....................................................................................................................10.313
errorlog level Options ....................................................... ... ........................................... 10.314
errorlog module Options................................................................................................. 10.314
exit .......................................................................................................................... 10.316
file ........................................................................................................................... 10.316
fmsaccesslog..........................................................................................................10.317
fmsedgelog ............................................................................................................. 10.318
fuselog .................................................................................................................... 10.319
hostname................................................................................................................10.320
XVII
Page 18

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
image......................................................................................................................10.320
interface..................................................................................................................10.321
ip.............................................................................................................................10.323
ip filter chain rule arguments................................................................................... 10.325
ldap.........................................................................................................................10.327
license.....................................................................................................................10.328
logging .................................................................................................................... 10.328
logging severity level...................................................................................................... 10.331
management........................................................................................................... 10.332
media-cache ........................................................................................................... 10.332
mfdlog..................................................................................................................... 10.334
namespace ............................................................................................................. 10.335
(namespace) delivery protocol {http | rtsp} origin-fetch........................................... 10.339
(namespace) delivery protocol http origin-request.................................................. 10.340
(namespace) origin-server...................................................................................... 10.341
(namespace) object list | delete | revalidate............................................................ 10.343
network ................................................................................................................... 10.344
ntp........................................................................................................................... 10.346
ntpdate.................................................................................................................... 10.346
ping.........................................................................................................................10.347
radius-server...........................................................................................................10.347
ram-cache............................................................................................................... 10.348
reload...................................................................................................................... 10.348
reset........................................................................................................................ 10.349
server-map.............................................................................................................. 10.349
server-map Example for NFS Origin ................................................. ... .......................... 10.350
server-map Example for HTTP Origin................... ......................................................... 10.351
service.....................................................................................................................10.351
show........................................................................................................................10.352
slogin.......................................................................................................................10.353
snmp-server............................................................................................................ 10.353
snmp traps...................................................................................................................... 10.354
snmp traps events.................................................... .................................... .................. 10.354
ssh .......................................................................................................................... 10.355
XVIII Copyright © 2010, Juniper Networks, Inc.
Page 19

Media Flow Controller Administrator’s Guide TABLE OF CONTENTS
ssh client.................................................................................................................10.355
ssh server ............................................................................................................... 10.357
stats ........................................................................................................................ 10.358
stats alarms.............................................................................................................10.360
stats alarm States........................................................................................................... 10.360
stats alarm rate-limit count............................................................................................. 10.360
stats CHDs..............................................................................................................10.362
stats samples.......................................................................................................... 10.364
streamlog................................................................................................................10.365
streamlog format Options............................................................................................... 10.366
tacacs-server .......................................................................................................... 10.368
tcpdump..................................................................................................................10.369
tech-support............................................................................................................ 10.369
telnet.......................................................................................................................10.369
telnet-server............................................................................................................ 10.369
terminal...................................................................................................................10.370
tracelog...................................................................................................................10.370
traceroute................................................................................................................10.371
upload..................................................................................................................... 10.371
username................................................................................................................ 10.371
virtual-player ........................................................................................................... 10.373
virtual-player type generic....................................................................................... 10.374
virtual-player type break.......................................................................................... 10.375
virtual-player type qss-streamlet............................................................................. 10.376
virtual-player type yahoo.........................................................................................10.377
virtual-player type smoothflow ................................................................................10.378
virtual-player type youtube......................................................................................10.380
virtual-player type smoothstream-pub..................................................................... 10.381
web ......................................................................................................................... 10.381
web proxy................................................................................................................10.382
write ........................................................................................................................ 10.383
XIX
Page 20

TABLE OF CONTENTS Media Flow Controller Administrator’s Guide
11
Media Flow Controller MIB Definitions ...............................................11.385
Variables................................................................................................................. 11.385
NOTIFICATIONS....................................................................................................11.388
INDEX .................................................................................................IX.391
XX Copyright © 2010, Juniper Networks, Inc.
Page 21

LIST OF FIGURES
Figure 1 Juniper Networks Media Flow Controller Operations (reverse proxy deployment) ...... 2.44
Figure 2 Media Flow Controller Ingest and Delivery Options.....................................................2.46
Figure 3 Media Flow Controller Cache Ingest and Promotion Process...................................... 2.49
Figure 4 SmoothFlow™ Deployment Overview..........................................................................2.52
Figure 5 Example Connectivity.......................................................... .. ..................................... ..3.64
Figure 6 Direct Server Return................................................................. ... ................................. 3.66
Figure 7 Media Flow Controller Login Page.............................................................................4.110
Figure 8 EZ Config Tab Page Detail (missing Enable Interfaces and Service Restar t areas) . 4.112
Figure 9 Monitoring > Bandwidth Usage (Last Hour) Chart Example ............................... ... ...4.116
Figure 10 Monitoring > CPU Load Page Detail .........................................................................4.117
Figure 11 Monitoring > Network Usage (Last Hour) Page Detail........................................ ......4.118
Figure 12 Network Interfaces Page Detail (eth0 state and eth0 configuration)..........................4.120
Figure 13 Network Interfaces Page Detail (DHCP Primary Interface)........................................4.121
Figure 14 Network Interfaces Page Detail (Add new interface alias)......................................... 4.122
Figure 15 IP Routing Page....................................................................... .................................. 4.123
Figure 16 DNS Page Detail (Add or Modify Name Servers)....................................................... 4.125
Figure 17 Hostname and Banners Page Detail (more Banners options at bottom of page) ...... 4.127
Figure 18 Static Hosts Page....................................................................................................... 4.129
Figure 19 Address Resolution Page...........................................................................................4.130
Figure 20 System Config > Date and Time Page Detail (Date and Time)..................................4.131
Figure 21 NTP Page.......................................... ... .................................... .................................. 4.132
Figure 22 RADIUS Page ......................................................... ..................................... ... ...........4.135
Figure 23 TACACS+ Page ..................................................................................... ....................4.137
Figure 24 SSH Page............................................. .................................... .................................. 4.139
Figure 25 Users Page Detail (additional Password areas are displayed for each user) ............ 4.140
Figure 26 AAA Page.......................................... .................................... ..................................... 4.142
Figure 27 System Config > SNMP Page............................ ........................................................4.144
Figure 28 Faults Page.......................................... .................................... ... ...............................4.146
Figure 29 Logging Page Detail (does not show Log Format area).............................................4.149
Copyright © 2010, Juniper Networks, Inc. XXI
Page 22

LIST OF FIGURES
Figure 30 Logging Page Detail (Log Format)............................................................................. 4.151
Figure 31 System Config > Configurations Page Detail (Configuration Files)............................4.152
Figure 32 System Config > Configurations Page Detail (Configuration Files)............................4.154
Figure 33 System Config > Configurations Page Detail (Configuration Files)............................4.154
Figure 34 System Config > Configurations Page Detail (Import Configuration)......................... 4.155
Figure 35 System Config > License Page Detail (Installed Licenses)........................................4.155
Figure 36 System Config > Upgrade Page Detail (Installed Images)............. ... .........................4.156
Figure 37 System Config > Reboot Page Detail.........................................................................4.157
Figure 38 Web Settings Page Detail (Web UI Configuration).....................................................4.159
Figure 39 Web Settings Page Detail (Web Proxy Configuration)...............................................4.160
Figure 40 CMC Clients Page................................................. .. ..................................... ..............4.161
Figure 41 CMC Clients Page Detail (Enable Configuration Changes) ....................................... 4.161
Figure 42 Delivery Network Page...............................................................................................4.163
Figure 43 Delivery Protocol Configuration Page ........................................................................4.165
Figure 44 Virtual Player Page.................................................. ..................................... ... ...........4.167
Figure 45 Virtual Player Type generic Configuration Page ........................................................4.168
Figure 46 Virtual Player Type break Configuration Page ...........................................................4.170
Figure 47 Virtual Player Type qss-streamlet Configuration Page................................. ..............4.172
Figure 48 Virtual Player Type yahoo Configuration Page ..........................................................4.174
Figure 49 Virtual Player Type smoothflow Configuration Page..................................................4.176
Figure 50 Virtual Player Type youtube Configuration Page .......................................................4.178
Figure 51 Service Config > Namespace Page Detail (Add Namespace) ...................................4.180
Figure 52 Service Config > Namespace Page Detail (Configuration List)..................................4.180
Figure 53 Service Config > Namespace Configure Pa ge Detail (Origin Server Configuration) . 4.182
Figure 54 Service Config > Namespace Configure Pa ge Detail (Match Details) .......................4.183
Figure 55 Service Config > Namespace Configure Pa ge Detail (Parameters) ..........................4.184
Figure 56 Service Config > Namespace Configure Pa ge (Pre-Stage User Configuration)........4.184
Figure 57 Service Config > Namespace Configure Pa ge (HTTP Origin Fetch Configuration)... 4.185
Figure 58 Service Config > Namespace Configure Page (RTSP Origin Fetch Configuration)... 4.186
Figure 59 Service Config > Media-Cache Page Detail...............................................................4.186
Figure 60 Log Configuration Page Detail (Access Log Configuration).......................................4.187
Figure 61 Log Configuration Page Detail (Access Log Copy/Auto Upload Configuration)......... 4.188
Figure 62 Log Configuration Page Detail (Str eam Log Configuration).......................................4.188
Figure 63 Log Configuration Page Detail (Str eam Log Copy/Auto Upload Configuration)......... 4.189
Figure 64 Media Flow Controller Example Current Log .............................................................4.190
Figure 65 Media Flow Controller Dashboard Example............................................................... 4.193
Figure 66 Media Flow Controller Disk Cache Graph Example...................................................4.194
XXII Copyright © 2010, Juniper Networks, Inc.
Page 23

LIST OF FIGURES
Figure 67 Publishing Workflow, Typical Steps ...........................................................................8.254
Figure 68 On-Demand Workflow, Typical Steps ........................................................................8.263
Figure 69 wget Test for Media Flow Controller HTTP Delivery and Cache................................9.277
XXIII
Page 24

LIST OF FIGURES
XXIV Copyright © 2010, Juniper Networks, Inc.
Page 25

LIST OF TABLES
Table 1 Text and Syntax Conventions Used in This Book........................................................1.29
Table 2 Media Flow Controller System Requirements..............................................................2.40
Table 3 HTTP Methods.............................................................................................................2.46
Table 4 RTSP Methods.............................................................................................................2.47
Table 5 Container Types vs. Encoding Schemes.....................................................................2.56
Table 6 Example Machine Setup of Management and Traffic Ports........ ... ..............................3.63
Table 7 YouTube Formats.........................................................................................................3.77
Table 8 Example namespace domain regex entries .................................................................3.83
Table 9 Example namespace match uri regex entries .............................................................. 3.84
Table 10 Namespace origin-server and origin-request Dependencies per Proxy Deployment... 3.88
Table 11 Logging Status (%s) Codes........................................................................................6.210
Table 12 Logging Status Sub-Codes ........................................................................................6.211
Table 13 Error Log Modules......................................................................................................6.215
Table 14 Error Log Levels.........................................................................................................6.216
Table 15 Syslog Severity Levels...............................................................................................6.221
Table 16 Delivery Protocol HTTP Trace Points.........................................................................6.224
Table 17 Stats Samples............................................................................................................ 6.233
Table 18 Media Flow Controller Stats Alarms...........................................................................6.235
Table 19 SNMP Alarms, Possible Causes, and Recommended Actions..................................6.237
Table 20 SmoothFlow Implementation Tasks...........................................................................8.251
Table 21 Media Flow Controller Acceptable Containers and Codecs.......................................8.252
Table 22 setup.xml File Parameters..........................................................................................8.256
Table 23 asset.xml File Parameters..........................................................................................8.258
Table 24 jobid.xml File Parameters...........................................................................................8.259
Table 25 segment_config.xml Parameters................................................................................8.260
Table 26 Required Configurable Nodes and Parameters .........................................................8.267
Table 27 TCP/IP Diagnostic Utilities .........................................................................................9.276
Table 28 Accesslog Format Options....................................................................................... 10.291
Table 29 errorlog level Options...............................................................................................10.314
Table 30 errorlog module Options...........................................................................................10.314
Copyright © 2010, Juniper Networks, Inc. XXV
Page 26

LIST OF TABLES Media Flow Controller Administrator’s Guide
Table 31 Logging Severity Levels...........................................................................................10.331
Table 32 SNMP Traps Notify-able Events...............................................................................10.355
Table 33 Stats Alarms............................................................................................................. 10.361
Table 34 Stats CHDs............................................................................................................... 10.362
Table 35 Stats Samples..........................................................................................................10.364
Table 36 streamlog format Options.........................................................................................10.366
XXVI Copyright © 2010, Juniper Networks, Inc.
Page 27
Preface Media Flow Controller Administrator’s Guide
CHAPTER 1
Preface
This Administrator’s Guide is written for system and network administrators who plan,
implement, and manage video delivery environments. In addition to What’s New in Release
2.0.4, this preface includes these topics:
• Guide to This Document
• Documentation and Release Notes
• Text and Syntax Conventions
• Terminology
• Documentation Feedback
• Requesting Technical Support
What’s New in Release 2.0.4
Release 2.0.4 introduces minor feature enhancements and issue resolutions. This section
provides short descriptions of the feature enhancements in Release 2.0.4.
PXE Installation Enhancements
In Release 2.0.4, Media Flow Controller simplifies the PXE boot process by eliminating the
need for administrators to have an interactive console session to boot it. Administrators can
configure the PXE boot options at the PXE server, in the PXE configuration specification file
(PXE spec). The following new PXE boot functions are supported in Release 2.0.4:
• No need to specify an URL for PXE boot
• Option to pre-accept the End User License Agreement (EULA)
• Automatically mark the interface that was used for PXE-booting as eth0
• Ability to specify all installation options in the PXE spec so administrator does not have to
manually enter anything
See the Media Flow Controller and Media Flow Manager Installation Guide
Installations on Non-Centos Linux Drives
On fresh installations, any partition data on the drive is overwritten. Previously , if disk drives
had non-Centos data when doing a fresh installation, the installer responded with a partition
error.
for details.
Copyright © 2010, Juniper Networks, Inc. What’s New in Release 2.0.4 27
Page 28
Preface Media Flow Controller Administrator’s Guide
Logging Enhancements
The option to export log files at more frequent rates than every hour has been added. You ca n
now configure automatic log imports for every 5 minutes.
You can now keep log files on Media Flow Controller for up to 14 days.
Logs can now be uploaded via SFTP with SSH keys rather than sending the password in
cleartext.
Media Cache
You can now upload meta data to the media cache.
You can now list controllers on the media cache; currently 3ware controller only.
Hardware Support
Juniper Networks VXA Series Chassis
• Media Flow Controller Release 2.0.4 is qualified to run on Juniper Networks VXA Series
appliances.
• Supported models are VXA1001and VXA1002 chassis, and VXA2002 and VXA2010
NEBS-compliant chassis.
• Media Flow Controller Release 2.0.2 and higher numbered releases are the only
recommended releases for the VXA Series of products.
Other Hardware
• Support for Intel ET series of NIC based on Intel MAC controller 82576.
• Support for Intel 10GbE NIC
• Media Flow Controller Release 2.0.4 has been tested to run with Chelsio 10GbE NIC.
Guide to This Document
This document provides information on the following topics:
• “Media Flow Controller Overview” on page 39: Describes how Juniper Networks Media
Flow Controller fits into the network topology, and the basic working principals including
feature descriptions.
• “Media Flow Controller Configuration Tasks (CLI)” on page 57: Describes basic system
setup including initial logins and configuration methods, plus service configurations. Plus
how to reset the system to its factory configuration, reboot the system, and install
upgrades to the system.
• “Media Flow Controller Configuration Tasks (Web Interface)” on page 109: Describes
basic system setup including initial logins and configuration methods, plus service
configurations.
• “Media Flow Controller Common Configuration Tasks (CLI)” on page 197: Describes
several configuration scenarios with step-by-step procedures.
28 Guide to This Document Copyright © 2010, Juniper Networks, Inc.
Page 29
Media Flow Controller Administrator’s Guide Preface
• “Configuring and Using Media Flow Controller Logs and Alarms” on page 209: Describes
Media Flow Controller logs including fields, formats (where applicable), and configuration
options. Also describes how to configure SNMP alarms, logging, and event notifications.
• “Server Map Configuration” on page 243: Describes how to create the XML server map
file needed for the server-map command. All three server map types are described.
• “SmoothFlow Deployment” on page 251: Describes how to create SmoothFlow video
assets using an SaaS or independently.
• “Media Flow Controller Troubleshooting” on page 271: Provides details on available
diagnostic tools including displaying information with show commands. Includes Testing
Network Connectivity, Testing Media Flow Controller Namespace and Delivery, and
common configuration errors.
• “Media Flow Controller CLI Commands” on page 287: Alphabetical list of all commands
including keywords, arguments, and notes.
• “Media Flow Controller MIB Definitions” on page 385: Provides the base MIBs supporte d
by Media Flow Controller.
Documentation and Release Notes
To obtain the most current version of all Juniper Networks technical documentation, see the
product documentation page on the Juniper Networks website at
http://www.juniper.net/techpubs/
Juniper Networks supports a technical book program to publish books by Juniper Networks
engineers and subject matter experts with book publishers around the world. These books go
beyond the technical documentation to explore the nuances of network architecture,
deployment, and administration using Junos OS and Juniper Networks devices. In addition,
the Juniper Networks Technical Library, published in conjunction with O'Reilly Media, explores
improving network security, reliability, and availability using Junos OS configuration
techniques. All the books are for sale at technical bookstores and book outlets around the
world. The current list can be viewed at http://www.juniper.net/books
.
.
Text and Syntax Conventions
Table 1 Text and Syntax Conventions Used in This Book
Convention Description Example
Plain Text Ordinary text. The origin server organizes media content
hierarchically.
Bold Text Commands in running text, and screen
elements such as page titles, and option
labels.
Use the interface command to configure IP
addresses.
In the Management Console, use the
Setup > Date and time page.
Documentation and Release Notes 29
Page 30
Preface Media Flow Controller Administrator’s Guide
Table 1 Text and Syntax Conventions Used in This Book (Continued)
Convention Description Example
Italic Text Book titles, and emphasis. See the Juniper Networks Media Flow
Manager Administrator’s Guide and CLI
Command Reference
Syntax Conventions in the Command Reference Chapter
Fixed-width
Text
Fixed-width
Bold Text
< > (angle brackets) Text enclosed in angel brackets (< >) is
[ ] (box brackets) Optional commands. Anything not
{ } (braces) Represent a set of mutually exclusive
| (pipe symbol) Separates mutually exclusive options.
... (ellipsis) An ellipsis (...) indicates that the previous
Command keywords.
Text displayed online at a command line.
Command text that you type.
variable and must be replaced by whatever
it represents. In the example to the right,
the user would replace <file_name> with
the name of the specific file.
enclosed in brackets must be specified.
options, where one option is required.
Y ou can enter one of the options separated
by the vertical bar, but you cannot enter
multiple options in a singe use of the
command.
A vertical bar can be used to separate
optional or required options.
option can be repeated multiple times with
different values. It can be used inside or
outside of brackets.
interface <interface_name>
Please enter your IP address
interface eth0 ip address <IP
address>
show file <file_name>
web proxy host <IP_address>
[port <TCP_port>]
web proxy auth authtype
{none | basic}
analytics last-evict-time
diff <1 | seconds>
clock timezone <zone>
[<zone>] ...
Terminology
This section provides definitions for Media Flow Controller terms and industry-standard terms
that may be unfamiliar to the reader.
Absolute URL An absolute URL points to the exact location of a file or directory on the
Internet, by name. Contrast with Relative URL
AFR Assured Flow Rate. A Media Flow Controller option that, when enabled, ensures that
media content is delivered at a rate that is minimally needed for the video to play smoothly.
ARP Address Resolution Protocol; allows systems to map IP addresses to MAC addresses.
Bit-rate A data rate (the amount of data tran sf er re d in on e dir ect ion over a link divided by the
time taken to transfer it) expressed in bits per second. Juniper Networks notation examples:
Kbps (kilobits per second), KB/s (kilobytes per second). See also Profile (Bit-rate profile)
30 Terminology Copyright © 2010, Juniper Networks, Inc.
.
.
Page 31

Media Flow Controller Administrator’s Guide Preface
Broadcast A type of network routing scheme where data is sent to all possible destinations on
a network. Contrast with Multicast
and Unicast.
CDN Content Delivery Network. A system of computers networked together across the
Internet that cooperate transparently to deliver content most often for the p urpose of impro ving
performance, scalability, and cost efficiency, to end users.
CHD Computed Historical Datapoints; traffic samples that have been computed in some
manner, such as summation and averaging.
CLI Command Line Interface.
Client Node or software program (front-end device) that requests services from a server.
CMC Central Management Console, Juniper Networks management interface that allows you
to push configurations to a number of Media Flow Controllers from a central interface. In
Release 2.0.4, only client configuration is supported.
DHCP Dynamic Host Configuration Protocol.
DSR Direct Server Return. A method of handling TCP traffic in the context of utilizing a proxy.
Edge cache An appliance, placed between the Inte rnet and close to the end user, tha t caches
and delivers content (like Java Script, CSS, images, and so forth.) freeing up Web servers for
other processes. Media Flow Controller as an edge cache is effectively a “reverse proxy,” that
provides these benefits: reduces the load (network and CPU) on an origin server by servicing
previously retrieved content and enhances the user experience due to a decrease in latency.
FMS Flash Media Server.
Full Download An HTTP media delivery mode in which the entire media file is downloaded
before playback; contrast with Progressive Download (PDL)
.
HDD Hard Disk Drives.
“Hot” Content (Short Tail vs. Long Tail) When content is often requested it becomes “hot.”
Media Flow Controller caches content hierarchically based on hotness. Short tail videos are
those that are often requested: a few videos requested by many different clients. Long tail
videos are those that are seldom requested: many different videos requested by few clients.
Ingest Data placed on a Media Flow Controller, analyzed, and queued; contrast with Pre-
stage.
KB and KiB KB=1000 Kilo Bytes (networking), KiB=1024 Kilo Bytes (storage).
Local boot This refers to booting from the default boot partition on the system; for example,
when the reboot command is given.
MB, MiB, and Mbit MB=1,000,000 Mega Bytes (networking). MiB=1,048,576 (1024 x 1024)
Mega Bytes (storage). Mbit=1,000,000 x 8 Megabits (data transfer).
MTU Maximum transmission unit. The size (in bytes) of the largest packet or frame that a
given layer of a communications protocol can pass onwards.
Multicast A type of network routing scheme where data is sent to certain destinations based
on address. Contrast with Broadcast
, and Unicast.
Namespace A defined collection of delivery policies for different categories of content or
domains.
Network prefix An IPv4 network prefix specifying a network. Used in conjunction with a
netmask to determine which bits are significant. For example, "192.168.0.0".
Terminology 31
Page 32

Preface Media Flow Controller Administrator’s Guide
NFS (network file system) A protocol that allows a user on a client computer to access files
over a network similarly to how local storage is accessed.
NIC Network Interface Controller/Card.
NTP Network Time Protocol.
Origin library The source of media content, typically a server located at a data center.
Origin server The media content server. Juniper Networks Media Flow Controller can be
configured as an Origin server.
Player (media player software) Any media player for playing back digital video data from
files of appropriate formats such as MPEG, AVI, RealVideo, Flash, QuickTime, and so forth. In
addition to VCR-like functions such as playing, pausing, stopping, rewinding, and forwarding,
some common functions include zooming/full screen, audio channel selection, subtitle
selection, and frame capturing.
Pre-stage Data placed on a Media Flow Controller or origin server before an HTTP request
comes in for it. Contrast with Ingest
.
Profile (Bit-rate profile) A media “bit-rate profile” is the bit-rate encoding that allows optimal
downloads to different bandwidths.
Progressive Download (PDL) An HTTP media delivery mode in which the media file is
played while it is being downloaded; contrast with Full Download
.
Proxy (reverse, mid-tier, transparent, virtual) A reverse proxy is a server processing in-
bound traffic, installed in front of origin servers. Reverse proxies are used for scaling origin
servers, caching (serving commonly-accessed files), load balancing, and security (denying
requests, preventing direct origin server access, and so forth.). A mid-tier proxy sits between
the origin servers and the edge, and serves requests from the edge caches. Mid-tier proxies
improve response time for requests because content is closer to the user; and off-load origin
servers from repeat requests from the edge. A transparent proxy is a proxy that does not
modify the request or response beyond what is required for proxy authentication and
identification. Transparent proxies help optimize networks transparently (no client
configuration required, no modification of traffic done). A virtual proxy uses the HOST header
of the incoming request to derive origin; use this variant of a reverse proxy as an alternate to
providing a single origin-server. Media Flow Controller can be used in any of these capacities.
Publishing Point (live-pub-point) A way to distribute content to your users (live or
broadcast as live); either through a defined SDP (service delivery protocol) file, or a
namespace.
Pull vs. Push Pull refers to media fetches from the origin server initiated by Media Flow
Controller based on received requests. Push refers to scheduled media deliveries from the
origin server to Media Flow Controller.
PXE (Preboot eXecution Environment) boot A way to boot computers using a network
interface without needing a CDROM or USB drive; PXE must be properly installed first.
Remote Authentication Dial In User Service. A netwo rking protocol that provides centr alized
access, authorization and accounting management for people or computers to connect and
use a network service.
Regex An extended regular expression. Enclose all regex entries in single quotes; for
example, a regex for www.example.com plus example.com could be this:
‘^.*\example\.com’.
32 Terminology Copyright © 2010, Juniper Networks, Inc.
Page 33

Media Flow Controller Administrator’s Guide Preface
Relative URL A relative URL points to the location of a file from a point of reference, usually
the directory beneath. Preceded by two dots (../directory_path/file.txt) for the directory above;
one dot (./directory_path/file.txt) for the current directory. Contrast with Absolute URL
.
RTMP Real Time Messaging Protocol. A m ultimedia streaming and RPC (remote procedure
call) protocol primarily used in Adobe Flash. RTMP has three variations: The “plain” protocol
which works on top of TCP and uses port 1935, RTMPT which is encapsulated within HTTP
requests to traverse firewalls, RTMPS which works just like RTMPT but over a secure HTTPS
connection.
RTP Real-time Transport Protocol. A standardized packet format for delivering audio and
video over the Internet. It is used in conjunction with other protocols such as RTSP. The RTP
standard defines a pair of protocols, RTP and the Real-time Transport Control Protocol
(RTCP). RTP is used for transfer of multimedia data and RTCP is used to periodically send
control information and QoS (quality of service) parameters between the server and client.
RTSP Real Time Streaming Protocol. An application level protocol for the control of real-time
streaming data sent over RTP. Typic ally RTP data is sent over UDP, but it can also be sent
over the RTSP channel via an inter leave d me chan ism or over TCP v ia p ort 80 with HTTP -like
syntax and operations.
RU (Rack Unit) A unit of measurement of the height of a rack-mounted device.
RX A communications abbreviation for “receive.”
SAS Serial attached SCSI. A data transfer technology designed to move data to and from
computer storage devices such as hard drives and tape drives.
SATA Serial Advanced Technology Attachment. A computer bus technology primarily
designed for transfer of data to and from a hard disk.
SCP The SCP (secure channel protocol) pseudo-URL format is:
scp://<username>[:<password>]@<hostname>/<path>[</filename>]
The path is an absolute path. Paths relative to the user's home directory are not currently
supported. You must have an SCP server installed in order to SCP files to your machine.
SFTP The SFTP (secure file transfer protocol) pseudo-URL format is:
sftp://<username@<hostname>:<path>[</filename>]
The path is an absolute path. Paths relative to the user's home directory are not currently
supported. You must have FTP server installed in order to FTP or SFTP, respectively, files to
your machine. SFTP uses SSH.
SSD Solid-state drive, a storage device using solid-state memory to store persistent data.
Streaming Streaming is the process of playing a file while it is still being downloaded.
Streaming technology lets a user view and hear digitized content as it is being downloaded.
Tunneling When a payload protocol is incompatible with the delivery network, a tunneling
protocol can encapsulate it for delivery only; no polic es can be applie d.
Unicast A type of network routing scheme where data is sent to a single destination h ost on a
network. Contrast with Broadcast
, and Multicast.
UOL, URI, URL Uniform Object Locator, Uniform Resource Identifier, Uniform Resource
Locator (respectively). When shown as a command variable, for example <URL>, this
indicates a normal URL, using any protocol that WGET supports, including HTTP, HTTPS,
FTP, and TFTP; or a pseudo-URL specifying an SCP file transfer.
Terminology 33
Page 34

Preface Media Flow Controller Administrator’s Guide
uri-prefix This namespace argument refines what requests Media Flow Controller accepts.
In the URL shown, the uri-prefix could be defined as / (slash), /vod, or /vod/path1. If / (slash)
is used, all incoming requests to that domain are honored; if /vod, only requests containing “/
vod” (and any sub-directory of it) are honored; if /vod/path1, request s must include that prefix
and that sub-directory (sub-sub-directories of path1 need not be specified).
Virtu al Host A virtual host is a capability of some computers that can respond to different IP
addresses and offer different services appearing to be a distinct host on a distinct machine; a
single machine can supply several virtual hosts.
Virtual Player This term refers to the sever-side player provided by Media Flow Controller to
assist in media viewing. Media Flow Controller offers several types of virtual player for use in
different scenarios; for SmoothFlow, the Type 4 virtual player is used exclusively.
VOD Video On Demand.
Documentation Feedback
We encourage you to provide feedback, comments, and suggestions so that we can improve
the documentation. You can send your comments to
techpubs-comments@juniper.net, or fill out the documentation feedback form at
https://www.juniper.net/cgi-bin/docbugreport/
following information with your comments:
• Document or topic name
• URL or page number
• Software release version (if applicable)
Requesting Technical Support
Technical product support is available through the Juniper Networks Technical Assistance
Center (JTAC). If you are a custo mer with an a c tive J-Care or JNASC support contract, or are
covered under warranty, and need post-sales technical support, you can access our tools and
resources online or open a case with JTAC.
• JTAC Policies—For a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/customers/support/downloads/710059.pdf
• Product Warranties—For product warranty information, visit
http://www.juniper.net/support/warranty/
. If you are using e-mail, be sure to inc lude the
• JTAC Hours of Operation—The JTAC centers have resources available 24 hours a day,
7 days a week, 365 days a year.
34 Documentation Feedback Copyright © 2010, Juniper Networks, Inc.
Page 35

Media Flow Controller Administrator’s Guide Preface
Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online self-service
portal called the Customer Support Center (CSC) that provides you with the following features:
• Find CSC offerings:
http://www.juniper.net/customers/support/
• Search for known bugs:
http://www2.juniper.net/kb/
• Find product documentation:
http://www.juniper.net/techpubs/
• Find solutions and answer questions using our Knowledge Base:
http://kb.juniper.net/
• Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
• Search technical bulletins for relevant hardware and software notifications:
https://www.juniper.net/alerts/
• Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
• Open a case online in the CSC Case Manager:
http://www.juniper.net/cm/
To verify service entitlement by product serial number, use our Serial Number Entitlement
(SNE) Tool located at
https://tools.juniper.net/SerialNumberEntitlementSearch/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
• Use the Case Manager tool in the CSC at
http://www.juniper.net/cm/
• Call 1-888-314-JTAC
(1-888-314-5822 – toll free in the USA, Canada, and Mexico)
For international or direct-dial options in countries without toll-free numbers, visit
http://www.juniper.net/support/requesting-support.html
Requesting Technical Support 35
Page 36

Preface Media Flow Controller Administrator’s Guide
36 Requesting Technical Support Copyright © 2010, Juniper Networks, Inc.
Page 37

PART 1
Media Flow Controller Administration
Copyright © 2010, Juniper Networks, Inc. 37
Page 38

Media Flow Controller Administrator’s Guide
38 Copyright © 2010, Juniper Networks, Inc.
Page 39

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
CHAPTER 2
Media Flow Controller Overview
• “Media Flow Controller Overview” on page 39
• “Environment” on page 40
• “System and Hardware Overview” on page 40
• “Management Interfaces Overview” on page 41
• “How Media Flow Controller Works” on page 43
• “Media Flow Controller Functions Overview” on page 45
• “Media Flow Controller Delivery Methods” on page 45
• “Media Flow Controller Hierarchical Caching” on page 49
• “Media Flow Controller AssuredFlow” on page 50
• “Media Flow Controller SmoothFlow” on page 51
• “Media Flow Controller Network Connection” on page 53
• “Media Flow Controller Namespace Functions” on page 53
• “Media Flow Controller Virtual Player Functions” on page 53
• “Media Flow Controller Media Flow Manager Functions” on page 56
Media Flow Controller Overview
The Juniper Networks Media Flow Controller combines video intelligence, storage
organization, multi-tier caching, and network optimization to scale media throughput and
enhance end-user experience in a purpose-built appliance. Media Flow Controller can be
implemented as an end-to-end cache; an edge cache; an origin server; a mid-tier cache; or
used for storage or load balancing optimization; to cache, store, and serve content in one
appliance and is designed to:
• Facilitate progressive download of Web video.
• Deliver the highest quality video content that the viewing device/network can support at
that time.
• Combine media storage optimization, multi-tier caching, and rate-based delivery
mechanisms to deliver large numbers of concurrent media streams at different data rates
with an extremely high aggregate bandwidth.
Media Flow Controller is powered by the Juniper Networks Media Operating System
(NMoS™), a media-intelligent operating system designed to serve large numbers of sessions
and deliver high throughput by optimizing resource utilization and new media technologies.
Copyright © 2010, Juniper Networks, Inc. Media Flow Controller Overview 39
Page 40

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Environment
Media Flow Controller software can be deployed in any network that uses the TCP/IP protocol.
Media Flow Controller allows you to manage and deploy network bandwidth efficiently,
thereby ensuring the highest quality experience for your end users. Media Flow Controller is
compatible with the other tools, applications, and solutions that constitute your content
management and deployment environment.
• The Media Flow Controller open architecture enables it to integrate easily into existing
network and storage infrastructures without requiring disruptive chang es. Media Flow
Controller supports industry standard storage interfaces and devices.
• Media Flow Controller supports industry standard video players, including Flash,
QuickTime, SilverLight and Windows Media Player.
• Media Flow Controller runs on industry standard x86 64-bit server platforms.
Media Flow Controller uses deep media intelligence, identifying and understanding different
content type requirements, to store, distribute, and deliver content based on those
requirements. It creates an hierarchical caching solution that dynamically shifts content
between tiers. Via adaptive bit rate streaming, Media Flow Controller offers comprehensive
support for delivering differen t bit rates of media depending on variations in the network; both
native adaptive streaming and third-party techniques are supported.
System and Hardware Overview
This section provides a high-level overview of Media Flow Controller hardware specifications,
for the most up-to-date and complete information, see the Media Flow Controller With VXA
Series and Media Flow Manager datasheet.
• “System Requirements” on page 40
• “Delivery Network Link Aggregation” on page 41
• “Installation Requirements” on page 41
• “Console Port” on page 41
System Requirements
The following are either required or recommended for Media Flow Controller optimal
performance.
Table 2 Media Flow Controller System Require men ts
Hardware Description
Processor
•Juniper Networks VXA Series Media Flow Engine.
•One quad-core (2.0 GHz or higher) x86 64-bit processor (second quad-
core processor recommended for future capacity expansion).
RAM Minimum of 8GB. The actual amount of RAM depends on system
requirements like throughput sessions per seconds, and so forth.
40 Environment Copyright © 2010, Juniper Networks, Inc.
Page 41

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
Table 2 Media Flow Controller System Require m en ts (Continue d)
Hardware Description
Direct Attached Storage
(DAS)
•Up to 16 DAS drives (SSD, SA TA, or SAS), depending on server model
and amount of cache.
•72 GB minimum for boot drive.
•32 GB minimum recommended for additional drives (used for cache
only).
Network Attached Storage NFS (Network File System) supported for handling cache misses.
Network Interfaces Up to ten 1GbE ports or two 10GbE ports for content delivery.
Management Interface Dedicated 1GbE port. Network ports on the motherboard use lower
performance controllers adequate for a management interface that
typically does not require the full GbE capacity.
Delivery Network Link Aggregation
Media Flow Controller supports LACP (Link Aggregation Control Protocol) to provide
redundancy and conserve IP addresses. A part of IEEE specification 802.3ad, LACP controls
the bundling of several physical ports together to form a single logical channel. LACP allows a
network device to negotiate an automatic bundling of links by sending LACP packets to the
peer (directly connected device that also implements LACP).
Installation Requirements
Media Flow Controller supports local boot from CD-ROM or USB flash drive, or Net Boot (PXE
Boot) for installation. Media Flow Controller runs from the local HDD (hard disk drive).
Console Port
Media Flow Controller provides a serial console port, USB, DB-9 serial, or VGA (video
graphics array), for configuration.
Management Interfaces Overview
Media Flow Controller can be remotely configured and managed.
• “Command Line Interface (CLI)” on page 42
• “Web Interface (Management Console)” on page 42
• “SNMP Interface to Network Management System” on page 42
• “Email and Email2SMS Alerts” on page 43
In addition to these management interfaces, multiple Media Flow Controllers deployed in a
network can be configured and managed from a centralized location using Juniper Networks
Media Flow Manager.
Management Interfaces Overview 41
Page 42

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Command Line Interface (CLI)
You can log in to the Media Flow Controller server via the command line interface (CLI) by
invoking a SSH session. The CLI allows all aspects of system configuration and management.
Web Interface (Management Console)
You can log in to the Media Flow Controller Web interface, also referred to as the
Management Console, from a Web browser using HTTP and port 8080 (for example, http://
Media Flow Controller-Hostname:8080/) . HTTPS can also be used if SSH certificates are se t
up properly. The Web interface ma kes it easy to configure an d manage the system fro m any
remote location. The Web interface provides a powerful dashboard that displays real-time
performance data such as number of concurrent connections, cache-hit ration, bandwidth
served, and CPU/memory/disk utilization.
SNMP Interface to Network Management System
The Simple Network Management Protocol (SNMP) is used by network management systems
(NMS) to communicate with properly configured network elements. Media Flow Controller can
be integrated with 3rd party network management systems via its built-in SNMP agent. The
Media Flow Controller SNMP agent provides the follo win g fu nct ion s:
• Supports SNMP MIBs that can be queried to retrieve system status, and system counters
• Generates SNMPv2 traps in case of system failures, that can be sent to higher-level
network management systems
SNMP Messages (TRAPs, GETs, and SETs)
SNMP messages may be initiated by either the network management system (NMS) or by the
Media Flow Controller. An SNMP TRAP is a message initiated by a Media Flow Controller an d
sent to the NMS; for example, a message that one of its redundant power supplies failed. An
SNMP GET is a message initiated by the NMS when it wants to retrieve some data from a
network element; for example, the network management system might query a Media Flow
Controller for the utilization on a WAN link every 5 minutes. It could then create graphs from
that data, or warn the administrator when the link was overutilized. An SNMP SET is a
message initiated by the NMS when it wants to change data on a network element (for
example, alter a static route); in Release 2.0.4 Media Flow Controller does not support SNMP
SET.
The SNMP MIB
The SNMP MIB, or Management Information Base, is a collection of variables shar ed between
the NMS and the Media Flow Controller. See Chapter 11, “
Definitions” for details.
SNMP Community Strings
The most basic form of SNMP security is the Community String. SNMP Community Strings
are like passwords for network e lements. Most often, there is on e community string which is
used for read-only (ro) access to a Media Flow Controller. The default value for this
community string is public. Using this community string like a password, the NMS can retrieve
data from Media Flow Controllers. In Release 2.0.4 only SNMP ro (Read-Only) is supported.
Media Flow Controller MIB
42 Management Interfaces Overview Copyright © 2010, Juniper Networks, Inc.
Page 43

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
Email and Email2SMS Alerts
Media Flow Controller allows you to be notified via email during events such as high CPU/
Memory utilization, Interface up/down, threshold crossing on statistics or counters. Media Flow
Controller uses SMTP protocol to send emails to the administrators. You can use the
Email2SMS facility provided by mobile network operators to configure Media Flow Controller
to send SMS notifications.
Example:
From: "System Administrator" <do-not-reply@mfc.example.com>
Date: December 28, 2009 9:40:47 AM PST
To: admin@example.com
Subject: System event on mfc.example.com: Process exit: ftpd
Hostname: mfc.example.com
Date: 2009/12/28 17:40:47
Description: Unexpected exit of process ftpd.
Uptime: 1h 15m 34.860s
Version: mfc-1.2.0
How Media Flow Controller Works
A single Media Flow Controller can sustain up to 40,000 simultaneous connections for
different media streams and operate in three different proxy modes: reverse proxy,
transparent proxy, and mid-tier proxy. Media Flow Controller consolidates all streaming
protocols (HTTP, RTSP, RTMP) into a single server, reducing the number of servers required
to deliver video over multiple protocols.
Media Flow Controller is able to get co ntent from origin servers or origin st orages once, and
serve it to several users simultaneously.
When a request for content is received, Media Flow Controller identifies the content to be
served, and does a resource check to verify that the content can be delivered in an acceptab le
manner for that session. After the delivery session is admitted, AssuredFlow can guarantee
certain resources throughout the life of that session: if Media Flow Controller does not have
enough resources, it rejects the request.
Media Flow Controller then checks its hierarchical caches to minimize the cost of serving this
media object. If no copy exists in any cache (also known as “cache miss”), Media Flow
Controller posts a request to the target origin server, fetches the content, and serves it to the
user. Then Media Flow Controller decides if that content is cache-worthy. Media Flow
Controller decides the cache-worthiness based on its intelligent Analytical Engine and
customer-configured policies. When objects become “hot” (downloaded at a high rate), Media
Flow Controller promotes them to a cache tier that supports faster delivery. Promotion in
Media Flow Controller can happen startin g from the lowest tier; for example, SATA to SAS,
SSD, and RAM. This allows Media Flow Controller to scale throughput and meet increased
demand.
The Analytical Engine determines th e “hotness” of content based on frequency of download
requests. As requests for a particular video increase, the hotness of that video increases and
the Analytical Engine moves that video up in the cache hierarchy. Likewise, as requests for a
video fall off, the Analytical Engine moves that video down in the cache hierarchy.
How Media Flow Controller Works 43
Page 44

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
A caching structure that starts with RAM and incorporates a flexible hierarchy of cache
devices ensures that objects are placed and migrated across the hierarchies based on
dynamic load characteristics.
Cache tiers are implemented as an extendable framework, making it easy to add new types of
caching devices and origin storage. The caching system is agnostic to the delivery protocol,
allowing multiple delivery protocols to share the cached content. See Figure 1
.
User
Media Flow Controller 1
VXA Series
Media Flow Engine
User User
Internet
1
Switch
Load Balancer (optional)
Gigabit Ethernet
traffic ports
Origin library
Media Flow Controller 2
(optional)
VXA Series
Media Flow Engine
2
Eth0 HTTP (8080) LO HTTP (80)
Management VLAN
Internal
Network
3
Management station
Internal
Network
NFS
g015412
Figure 1 Juniper Networks Media Flow Controller Operations (reverse proxy deployment)
Figure 1
illustrates the relations between Media Flow Controller and other network
components in the media delivery optimization operation.
1. Requests come in from the Internet via HTTP, to (typically) an Ethernet switch or Load
Balancer that redirects the request to Media Flow Controller. Media Flow Controller does
certain basic checks, such as URL validation, and parses the URL query string, and
header fields to identify the content and any associated policies. Media Flow Controller
44 How Media Flow Controller Works Copyright © 2010, Juniper Networks, Inc.
Page 45

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
then (optionally) calculates the AFR needed to deliver this content, and does a resource
check to verify that the content can be delivered in an acceptable manner for that session
2. Upon a cache-miss (the content is not already in the cache), Media Flow Controller
obtains the content from origin, serves it, and caches a copy. Subsequent requests are
served directly from the Media Flow Controller cache.
3. Management interfaces monitor activity and allow configuration changes.
Media Flow Controller Functions Overview
Juniper Networks Media Flow Controller provides several highly specialized functions for
optimizing the delivery and storage of media content.
• “Media Flow Controller Delivery Methods” on page 45
• “Media Flow Controller Hierarchical Caching” on page 49
• “Media Flow Controller AssuredFlow” on page 50
• “Media Flow Controller SmoothFlow” on page 51
• “Media Flow Controller Network Connection” on page 53
• “Media Flow Controller Namespace Functions” on page 53
• “Media Flow Controller Virtual Player Functions” on page 53
• “Media Flow Controller Media Flow Manager Functions” on page 56
Media Flow Controller Delivery Methods
Media Flow Controller can deliver content simultaneously to a large audience across 3
screens (PCs, TVs and Mobile devices), by supporting a wide range of delivery protocols and
container formats.
Media Flow Controller dynamically adapts to the change in traffic pattern across 3-screens
without re-provisioning.
Media Flow Controller supports on-demand and live streaming of videos and consolidates
multiple delivery protocols such as HTTP, RTSP and RTMP. See Figure 2
• Efficiently caches objects of all sizes, ranging from small objects (thumbnails) to the
largest objects (videos and software downloads)
• Supports delivery via HTTP, RTSP and RTMP
• Supports various formats required for delivery to different screen
• Supports multi-tenancy to host multiple hostnames
Media Flow Controller supports the entire spectrum of adaptive streaming methods for ondemand and live streaming such as Apple iPhone Streaming, Microsoft Smooth Streaming,
Move Adaptive Streaming and Adobe Dynamic RTMP streaming.
Media Flow Controller supports SmoothFlow™ for on-demand streaming.
Media Flow Controller supports HTTP Progressive Download (PDL), RTSP/RTP streaming,
and RTMP.
, for illustration.
Media Flow Controller Functions Overview 45
Page 46

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
User
User User
Media Flow Controller
Internet
g015413
Flash media server
HTTPRTSP
RTMP
HTTPHTTP
RTSP
RTMP
RTMP RTSP
RTMP
NFS
Media
Flow
Controller
Flash
media
server
Live
sources
Streaming
server
File server Web server
RTSP/RTP
Delivery
Ingest
Figure 2 Media Flow Controller Ingest and Delivery Options
Streaming with HTTP
A standard Web server streams media data with HTTP on top of TCP, which handles the data
transfers. TCP is optimized for delivering non-real-time applications such as file transfers and
tries to maximize the data transfer rate while ensuring stability and high throughput. One of the
ways TCP achieves reliable data transfer is by re-transmitting lost packets; however, it cannot
ensure that all re-transmitted packets arrive in time to be played in the media stream.
Table 3 describes the HTTP methods supported for Media Flow Controller in Release 2.0.4.
Table 3 HTTP Methods
CONNECT Reserved for proxy use.
DELETE Request to delete a resource.
GET Retrieve the resource identified by the Request-URI. Responses are
HEAD Obtain meta-information. Identical to GET except content is not returned.
Method Description
Responses not cacheable.
cacheable.
Responses are cacheable.
46 Media Flow Controller Delivery Methods Copyright © 2010, Juniper Networks, Inc.
Page 47

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
Table 3 HTTP Methods (Continued)
Method Description
OPTIONS Get available request/response options. Responses are not cacheable.
POST Request server action:
•annotate an existing resource
•post a message
•accept a block of data
•append data in a database
Responses are not cacheable without the Cache-Control or Expires header.
PUT Request to store or create a resource.
Responses not cacheable.
TRACE Invoke a loop-back of the request, for testing or diagnosis. Not cacheable.
Streaming with RTSP
Streaming media servers can use the HTTP/TCP protocols as well as specialized protocols
such as the User Datagram Protocol (UDP). UDP does not do re-transmission or data-rate
management functionality, making it ideal for transmitting real-time audio and video data,
which can tolerate some lost packets. Streaming media servers can use an intelligent
retransmission scheme to ensure that only lost packets that can be sent to the client in time to
get played are retransmitted.
A compressed media file is produced and copied to a specialized streaming media server
instead of a Web server. Data is sent to the client at the exact rate associated with the
compressed audio and video streams, rather than at a set rate. The server and the client
communicate during the delivery process allowing additional services to be applied.
RTSP/RTP can dynamically respond to client feedb ac k, ad justin g de live ry rate s ap p ropr iat ely,
increasing the likelihood of uninterrupted viewing. Advanced features such as detailed
reporting of streams played, VCR controls (seek, fast-forward, re wind), live video delivery, and
delivery of multiple streams to the client are available.
Because Web server streaming typically creates a local cached copy of every media file played,
there is no way to prevent end users from keeping the media. With an RTSP/RTP delivery
scheme, users can only stream data and cannot download a media file to their hard disk.
Table 4 describes the RT SP methods supported for Media Flow Controller in Release 2.0.4.,
where C stands for Client, and S stands for server.
Table 4 RTSP Methods
Method Direction Requirement Description
DESCRIBE C --> S REQUIRED Get description of media object
OPTION C --> S, S --> C Recommended Get available request/response options
PAUSE C --> S Recommended Halt delivery but keep state
PLAY C --> S REQUIRED Start playback via the transport
mechanism established with SETUP
SETUP C --> S REQUIR ED Establish transport mechanism
TEARDOWN C --> S REQUIRED Remove state
Media Flow Controller Delivery Methods 47
Page 48

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Connection Pooling
A connection pool is a list of origin-side open connections maintained so they can be reused
for additional data requests. Connection pools enhance the performance of executing
requests made to a dynamic database-driven Website application. In connection pooling,
connections from Media Flow Controller to origin are placed in a pool and used over again so
that a new connection does not have to be established from Media Flow Co ntroller to origin for
each client request for content not in cache. If all the origin-side connections are being used, a
new connection is made and is also added to the po ol. This cuts d own on the amount o f time a
user must wait to establish a connection. You use the delivery protocol CLI commands to
control connection pooling.
Consistent Hash-Based Clustering and Origin Escalation
Media Flow Controller provides a configuration to use a consistent hashing scheme to bind
objects to nodes using an XML file server map. Additionally, you can create an origin-server
node map for origin escalation: if the target origin-server fails, another configur ed origin- server
is automatically chosen. Both of these configurations are achieved through the creation of a
server-map (format-type cluster-map and format-type origin-escalation-map) that is then
associated with a namespace.
Note! The hash scheme and origin server data distribution must be pre-configured.
A consistent hash scheme is used by the Media Flow Controller with the cluster-map node
definitions (and, optionally namespace cluster-hash configuration) to map to the target
origins. In the case where no origins exist due to network connectivity issues, an alternative
set of origin servers can be consulted via an origin-escalation-map, or another cluster-map,
to resolve the request. Consistent hash-based cluster prop erties are as follows:
• No inter-cache communication required.
• Ability to identify the target node via strict computation.
• Uniform distribution amongst the nodes.
• Object stickiness after cluster re-configuration.
• After a node deletion, existing entries map to the same node and objects associated
with the deleted node are uniformly distributed amongst the remaining nodes.
• After an addition of a preexisting node, entries map to the same nodes as observed
prior to the node deletion.
• After an addition of a new node, an equal portion of the address space is remapped to
the new node resulting in a uniform distribution amongst the nodes. Existing entries
may be moved to the new node.
Origin escalation is a configuration consisting of <N> origin servers which are logically viewed
as one, where requests are sequentially initiated to specific origin servers (based upon a
configured weight), until the request is satisfied or all known available origin servers at
request initiation time have been tried. An origin server request is re-initiated to the next
configured origin server (escalation) when network connectivity errors are received or when a
specific, configured, origin server response code is received (for example, HTTP 404).
You can use these two server-map type s together to create a server hierarchy of server-maps
consisting of multiple instances of cluster-map and origin-escalation The order of in wh ich
the maps are added to the namespace denotes the order in which they are read.
See Chapter 7, “
Server Map Configuration,” for more details including requirements.
48 Media Flow Controller Delivery Methods Copyright © 2010, Juniper Networks, Inc.
Page 49

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
Media Flow Controller Hierarchical Caching
When Media Flow Controller fetches data from origin upon cache miss, it caches the data in its
local disks. Media Flow Controller implements an hierarchical caching mechanism that allows
it to serve up to 10Gbps of data with just 16GB of RAM and a combination of SSD, SAS, and
SATA storage. Media Flow Controller has its own optimized storage sub-system in which data
is placed intelligently so it can be read back for very fast delivery to end-users.
Media Flow Controller organizes data in a hierarch ical fashion us ing a cache tier manag er that
dynamically calculates the “hotness” of the data and places it in the right cache tier (see “
Content (Short Tail vs. Long Ta il)” on page 31 for explanation of hotness). RAM is the highest
tier, followed by SSD, SAS, and SATA, in that order.
Disk speeds are calculated and assigned to a tier in the cache hierarchy as part of the
initialization of Media Flow Controller. When data is accessed from origin, it is stored in the
lowest cache tier, and promoted to higher cache tier s as the hotness of the data increases. All
this is done automatically by Media Flow Controller.
Additionally, Media Flow Controller allows you to configure cache ingestion and promotion
parameters (cache-ingest size-threshold and cache-promotion hotness-threshold) via
the analytics command to create policies for when to ingest, or promote, hot objects to cache
or the next highest cache tier, respectively. See “
“ingest.”
See Figure 3
, for an illustration.
Terminology” on page 30 for definition of
“Hot”
Figure 3 Media Flow Controller Cache Ingest and Promotion Process
Media Flow Controller Hierarchical Caching 49
Page 50

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Media Flow Controller AssuredFlow
The AssuredFlow feature assures that Media Flow Controller provides the required ban dwidth
for a connection so that media encoded at different bit-rates are delivered at appr oximately the
encoded bit-rate rather than the fastest possible. This helps optimize use of the available
bandwidth per session along with contri buting to the viewing experience of the end user.
It also may be tied to the end-user’s service level agreement (SLA). This ensures that
bandwidth is not wasted by sending data at a rate higher than the rate at which it is being
consumed (decoded) by the client. Furthermore, it ensures sufficient bandwidth is available
(reserved) for clients that need higher bit rate video. Examples include:
• Full-screen mode clients (higher bit rate) versus small window client (lower bit rate).
• Premium content (higher bit rate) versus free content (lower bit rate).
• Content delivery to a primary site visitor with higher bit rate versus content delivered to a
viewer redirected from a partner site.
Assured-flow rate (AFR) is the parameter through which Media Flow Controller provides
customer control of the AssuredFlow feature. AFR is specified in Kbps, and its intent is to
ensure that Media Flow Controller reserves at least the configured rate in bandwidth for each
delivery session. Clearly, the sum of AFR cannot exceed the aggregate bandwidth of the
server. To be more specific, if an interface, say, GbE, has “n” sessions, AssuredFlow can
guarantee that the sum of AFR assigned to each active session does not exceed the capacity
of the GbE port, or 1Gbps. An active se ssion is one that is sending data at any one particular
instance. We recommend that the sum of AFR be configured to 80 to 90 percent of the link
speed, for best performance. Further, the configured AFR should reflect the average
bandwidth the target origin server is set to deliver media. For example, if a portal delivers
video to users at an average rate of 750 Kbps, AFR should be configured to reflect this value
(for example, 750 Kbps). Assured-flow rate can be configured globally or through a virtual
player configuration. Traffic is served at the configured AFR, or the dynamic AFR set by the
virtual player, up to the configured maximum session bandwidth.
It is not uncommon to have portals set the logic in their player to signal the AFR on each
session. In that case, the signaled AFR overrides the configured AFR. AFR is disabled by
default, which means Media Flow Controller does not assure a delivery rate. When AFR is
disabled in Media Flow Controller, player-signaled AFR is still effective.
Admission Control
Session admission control provides a mechanism to avoid bandwidth overload; this is an
important part of AssuredFlow. Before a new session is admitted, a series of checks across
various resources determines whether the session can be admitted. A new session is defined
as the first GET request received within a new network connection. Existing sessions are not
subject to this control. The following are the various checks that can reject a new session.
1. A new connection is rejected if the incoming interface is already serving at its bandwidth
limit.
2. After a new connection is accepted, the first GET request can be rejected (with an HTTP
error code) during various stages of processing:
50 Media Flow Controller AssuredFlow Copyright © 2010, Juniper Networks, Inc.
Page 51

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
a. The AFR for the request is based on the URL along with other query parameters and
Media Flow Controller can determine that this AFR cannot be serviced given the
existing bandwidth being served on that port.
b. Media Flow Controller can refuse to create the delivery task if it is out of processing
resources.
c. Media Flow Controller can return an error if it is out of memory resources.
d. Media Flow Controller can return an error if meeting this request would exceed the
capacity of the internal caches or origin libraries.
Logging and statistics for which Media Flow Controller module refused session admission are
provided in the errorlog.
Media Flow Controller SmoothFlow
SmoothFlow™ refers to the Quality of Experience (QoE) feature that Juniper Networks Media
Flow Controller can provide to viewers for uninterrupted video viewing.
Last-mile bandwidth fluctuations can cause buffering, or long pauses. Juniper Networks
SmoothFlow technology provide s viewers a TV-like video viewing experien ce irrespective of
last-mile bandwidth fluctuations, by dynamically detecting available bandwidth and seamlessly
switching the bit-rate of a video being progressively downloaded over HTTP.
Viewers with high bandwidth connections receive videos at higher quality resolutions while
viewers with lower bandwidth connectio ns receive videos enco ded at bit-rates matchi ng their
available bandwidth. Media Flow Controller always sends video data at the bit-rate that is
appropriate to the available bandwidth between the server and client at any point of time.
Media Flow Controller SmoothFlow receives client-side signals fr om the client player providin g
information about real-time resource utilization (for example, if the viewer starts a CPUintensive application while watching a video).
In addition to SmoothFlow, such signals enable Media Flow Controller to allow viewers to
control their media playback experie nce using flow commands such as fast forward, rewind,
frame step, pause, and so forth, on a video that is currently being downloaded.
Media Flow Controller server-side intelligence, coupled with player feedback, allows Juniper
Networks Media Flow Controller to deliver a really high quality of viewing experience tailored
specifically to each viewer. Figure 4
“SmoothFlow Deployment,” for more information.
, illustrates a SmoothFlow deployment. See Chapter 8,
Media Flow Controller SmoothFlow 51
Page 52

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Internet
Origin library
NFS or HTTP
2
4
Client
players
Media Flow Controller Edge
Seattle
Client
players
Media Flow Controller Edge
Chicago
Client
players
Media Flow Controller Edge
Boston
3
Media Flow Controller
Origin server with
SmoothFlow processing
Publishing system
Multi bit-rate
videos
1
FTP push
SmoothFlow
processing
request
Figure 4 SmoothFlow™ Deployment Overview
How SmoothFlow Works
SmoothFlow is based on a dual channel approach where one channel is used for video
delivery, and the other for control purposes to signal to Media Flow Controller adaptation
points for responding to bandwidth fluctuations. SmoothFlow technology is delivered via
progressive download over HTTP, providing the additional benefit that the consumer does not
need to download a custom player. As shown in Figure 4
1. Content providers decide how many bit-rate profiles (differently encoded versions) of any
one video they want to create. Each set of encoded bit-rate profiles must include a
metadata file describing ho w many bit-rate pr ofiles a video has and wher e they are stored;
this file may be created by the provider, or auto-created, depending on the encoding
procedure used. Together, the bit-rate profiles and the description file are the “asset.” Af ter
the assets are created, they are pre-staged to an origin server, typically via FTP.
2. Next the publisher or encoder sends a properly configured Media Flow Controller a
SmoothFlow processing request for the asset. This may be done with a script, depending
on the encoding procedure used.
3. SmoothFlow reads the data file given in the processing request, obtains the video files,
and processes them for delivery; this includes chunking the different bit-rate profiles,
creating the internal metadata file for Media Flow Controller, and queuing the assets on
the origin server.
4. Assets are delivered to the edge either upon cache miss or via a SmoothFlow virtual
player. As the assets are delivered to the client players over the delivery channel,
feedback hints to SmoothFlow are sent over the control channel telling Media Flow
Controller when to switch to a different bit-rate profile.
:
52 Media Flow Controller SmoothFlow Copyright © 2010, Juniper Networks, Inc.
Page 53

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
Media Flow Controller Network Connection
The network connection CLI commands let you specify how requests are handle d. These
are global values and may be overridden by namespace custom virtual-player settings. You
can specify an assured-flow-rate, how many concurrent sessions to allow (Media Flow
Controller can support up to 40,000 concurrent sessions), the idle timeout for a connection,
and max-bandwidth (the maximum allowable bandwidth) for any o ne gi ven session. If you d o
not use a customized virtual player in your namespace, these values are used.
Media Flow Controller Namespace Functions
The namespace feature allows you to classify different types of traffic based on a combination
of URL and FQDN, and apply se parate deliver y policies to each type of classified traffic. This
gives you a way to separate your video delivery traffic characteristics based on any given
variable in the stream/request being received by Media Flow Controller from the client. You
can create up to 256 namespaces in one Media Flow Controller
At a minimum, namespace configuration requires a domain (only one per namespace) , an
origin-server (one per namespace unless using server-map), and a match criteria (to refine
delivery of incoming requests). Additional parameters for origin-fetch, cache options, and so
forth, are optional. You can further define control by assigning a configured virtual-player
(overrides network connection global defaults). The namespace is referenced via the URL in
the HTTP request directed to Media Flow Controller. For example; if you are serving content
through Media Flow Controller for media under the following directories from your origin
library...
• example.com/videos/trg
• example.com/videos/UGC
• example.com/videos/premiumcontent
... you might create three namespaces: TRG, UGC, and Premium each with a different set of
delivery policies.
Media Flow Controller Virtual Player Functions
Media Flow Controller provides a virtual player function that assists in media viewing
optimization. You can create any number of virtual players; they are utilized when assigned to
a namespace. Namespaces that are not assigned a virtual-player use the values configured
under network connection for the same functions. Virtual players let you implement custom
delivery policies. There are five types of virtual players, described in this section. Type
generic has a super-set of delivery options includ ing hash verification of da ta; Type break has
a subset of Type 0 delivery options, Type qss-streamlet lets you create an assured flow rate
map to apply different delivery rates per URI; Type yahoo provides a subset of delivery
options plus special health and hash verification options; Type smoothflow provides
SmoothFlow options and is required for SmoothFlow delivery; Type youtube provides a
subset of delivery options and YouTube-specific options.
Media Flow Controller Network Connection 53
Page 54

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Type generic
The type generic (formerly type 0) virtual player provides options for nearly all virtual player
functions.
• assured-flow—Assure that content is delivered at the specified rate (AFR), but no more
than the configured connection max-bandwidth. AFR is defined in a kilobits per second
rate, auto (auto-calculate), or signaled with a query param.
• connection max-bandwidth—Maximum allowable bandwidth for a session. The actual
session bandwidth used does not exceed this value, even if there is available bandwidth in
the link. When it is a full download, Media Flow Controller tries to allocate this value to the
session.
• fast-start—Deliver the 1st set of kilobytes at either the configured maximum session
speed or the detected available bandwidth; or by a value determined by one of the faststart options: either a static size value, a static time value, or a query-string-parm name.
• full-download—Allow the delivery to download at the fastest possible speed, up to the
configured connection max-bandwidth and possibly exceeding the configured assuredflow rate.
• hash-verify—Verify the authorization hash value specified in the URL query string.
• seek—Implement seek (currently only for FLV media files) based on the value of query-
string-parm. This function allows the client player to seek a specific part of the media
content; for example, to jump ahead a few minutes or go back a few minutes in the video.
Type break
The type break (formerly type 1) virtual player offers a subset of Media Flow Controller
delivery options: assured-flow, connection max-bandwidth, fast-start, hash-verify, and
seek options (see Type generic for details).
Type qss-streamlet
The type qss-streamlet (former ly type 2) virtual player includes connection max -bandwidth
(see Type generic for details) and AssuredFlow via a special rate-map attribute. The rate-
map rate argument extracts the value from the URL to calculate the assured flow rate needed
for each HTTP request. By default, the match string (length must be 2 bytes) is extracted by
going to the end of the URL and skipping 12 Bytes from the end. The value in that location is
mapped to the configured rate in kbps. Example:
http://video.example.com/public/BBB87026/xy_750_1938344/
AC60E15B2A7C4A45AC4C1472E2AC0816_030000003F.flv
In the URL, the value 03 (12 Bytes from the end of the URL) is extracted, and the
corresponding assured flow rate (1000Kbps) is applied.
Type yahoo
The type yahoo (formerly type 3) virtual player includes assured-flow, connection max-
bandwidth, and seek options (see T ype generic for details) as well as these special options:
54 Media Flow Controller Virtual Player Functions Copyright © 2010, Juniper Networks, Inc.
Page 55

Media Flow Controller Administrator’s Guide Media Flow Controller Overview
• health-probe—Configure an external server to do health checks by making Media Flow
Controller fetch data from origin and play it to the server initiating the he a lth chec k. Th e
signal that a given HTTP request is for a health probe is the health-probe query-string-
parm name. If that name value matches the following <string> value, the GET request is
treated as a health probe. When servicing health probes, Media Flow Controller does not
cache the data into disk or in buffer. Use virtual player <name> type 3 no health-probe
to disable.
• req-auth—Compute MD-5 hash of query string parameters representing stream-id,
auth-id, a configured shared-secret, and time-interval; and match the computed value
with the specified match query-string-parm <string>. The HTTP GET proceeds if the
computed MD-5 hash matches; if there is no match, the session is rejected. Use virtual
player <name> type 3 no req-auth to disable.
Type smoothflow
The type smoothflow (formerly type 4) virtual player configures SmoothFlow. It is a
requirement of SmoothFlow that this virtual player be configured and used through a
configured namespace. The Type 4 virtual player includes connection max-bandwidth,
hash-verify, and seek options (see Type generic for details) as well as thes e special options:
• control-point—Specify either server or player for smooth flow signaling. If server,
then Media Flow Controller detects the bandwidth variations at the client side and adjusts
the bit-rate of the video accordingly. If player, then the player at the client side explicitly
signals the bandwidth changes and Media Flow Controller adjusts the bit-rate of the video
accordingly.
• signals—Configure triggers for delivery functions; use virtual player <name> type 4 no
signals to disable.
session-id query-string-parm—Specify a query-string-parm name to set the
•
session ID; default is sid. Session ID is the way you bind the control session that
signals the bandwidth change with the data channel.
•
state query-string-parm—Specify a query-string-parm name to set
SmoothFlow state; default is sf. The values this query param take signal various
function calls to SmoothFlow.
•
profile query-string-parm—Specify a query param name to set the media
bit-rate profile; default is pf.
Type youtube
The type youtube (formerly type 5) virtual p layer is designed for Yo uTube and offers a subset
of Media Flow Controller delivery options: assured-flow, connection max-bandwidth, fast-
start, seek (see Type generic for details), and YouTube-specific options for identifying the
requested video, video-id, and its format, format-tag.
Type smoothstream-pub
The type smoothstream-pub virtual player supports Smoothstream functionality for Internet
Information Se4rvices (IIS) for Windows® Server.
Media Flow Controller Virtual Player Functions 55
Page 56

Media Flow Controller Overview Media Flow Controller Administrator’s Guide
Encoding Schemes
Media Flow Controller supports the formats and encoding schemes shown in Table 5.
Table 5 Container Types vs. Encoding Schemes
Container Type/Extension Encoding Schemes
FLV Sorenson, H.263, H.264, VP6, VP7
MP4 MPEG-1, MPEG-2, MPEG-4 (A)SP, H.264, VC-1/WMV
QuickTime (.MOV) MPEG-1, MPEG-2, MPEG-4 (A)SP, H.264, VC-1/WMV, Theora
Media Flow Controller Media Flow Manager Functions
Media Flow Controller can be managed by Media Flow Manager; to configure this you use the
Web-based Management Console interface or the cmc commands at the CLI.
Using Media Flow Manager, you can remotely manage individual Media Flow Controllers, or
you can group Media Flow Controllers, and remotely apply saved configurations, called
“profiles.” For details, see the Media Flow Manager™ Administrator’s Guide and CLI
Command Reference.
56 Media Flow Controller Media Flow Manager Functions Copyright © 2010, Juniper Networks, Inc.
Page 57

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
CHAPTER 3
Media Flow Controller Configuration Tasks (CLI)
• “Before You Configure Media Flow Controller” on page 58
• “About the Media Flow Controller CLI” on page 58
• “Logging In to Media Flow Controller for the First Time (CLI)” on page 61
• “Media Flow Controller System Configuration Overview” on page 61
• “Configuring Interfaces, Hostname, Domain List, DNS, and Default Gateway (CLI)” on
page 61
• “Configuring Media Flow Controller System Clock and Banners (CLI)” on page 64
• “Creating and Configuring Link Bonding and Static Routes (CLI)” on page 65
• “Authentication / Authorization and Users Options” on page 67
• “Configuring Media Flow Controller User Accounts (CLI)” on page 69
• “Enabling Media Flow Controller CMC Client Rendezvous (CLI)” on page 70
• “Applying the Media Flow Controller License (CLI)” on page 71
• “Media Flow Controller Policy Configurations Overview” on page 72
• “Setting Network Connection Options (CLI)” on page 72
• “Configuring Media Flow Controller Delivery Protocol (CLI)” on page 73
• “Creating and Configuring Virtual Players (CLI)” on page 74
• “Creating and Configuring Server-Maps (CLI)” on page 79
• “Creating a Namespace and Setting Namespace Options (CLI)” on page 81
• “Managing the Media Flow Controller Disk Cache (CLI)” on page 92
• “Installing and Using FMS in Media Flow Controller (CLI)” on page 97
• “Administering Media Flow Controller Overview (CLI)” on page 104
• “Saving and Applying Configurations, Resetting Factory Defaults (CLI)” on page 104
• “Rebooting Media Flow Controller (CLI)” on page 105
• “Upgrading Media Flow Controller (CLI)” on page 105
• “Configuring the Web Interface (CLI)” on page 106
• “Configuring the Web Interface Proxy (CLI)” on page 107
Copyright © 2010, Juniper Networks, Inc. 57
Page 58

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Before You Configure Media Flow Controller
Media Flow Controller is a network appliance a nd the network p arame ters must be configured
first, as any network appliance. Before you begin, you will need to know:
• Hostnames/IP addresses (including but not limited to, Subnet Mask, Default Gateway,
DNS servers, and NTP servers) for the Media Flow Controller traffic and management
ports (eth0 is default management port, eth1 is the recommended origin-fetch interface).
• Hostnames/IP addresses for external servers such as origin servers/libraries, logging,
SNMP, SSH, or storage servers. In order to configure the (required) namesp ace, you must
know the uri-prefix (see uri-prefix
(fully qualified domain name) or IP address, at a minimum. This information tells Media
Flow Controller where to fetch media from and how to handle it.
• Domain names for the Media Flow Controller to resolve unqualified hostnames.
• The users you want to be able to administer or monitor Media Flow Controller, their email
addresses (for event email notifications), an d the authentication / authorization schemes
you want to use; these schemes can be complicated and should be prepared by an
expert.
• The query parameters that you use in URLs to pass information, if you expect to configure
a virtual player (not required). Many content delivery networks (CDNs) have proprietary
query params already defined.
for definition), domain name, and origin server FQDN
• The types of content that you serve and their optimal delivery rates, the protocols that you
use for delivery, and the general bandwidths of delivery connections that you want to
maintain.
Related Topics
• “How Media Flow Controller Works” on page 43
• “Media Flow Controller Functions Overview” on page 45
About the Media Flow Controller CLI
The Juniper Networks Media Flow Controller™command line interface (CLI) supports
industry-standard commands for configuration and management as well as Media Flow
Controller specific commands.
The CLI supports command-line editing: press the up arrow to repeat previous lines, and the
left arrow to edit the current line. The CLI also supports command completion when you press
the Tab key. Commands must terminate with CRLF (carriage return followed by newline).
• “Connecting and Logging In” on page 59
• “Using the Command Modes” on page 59
• “Prompt and Response Conventions” on page 60
• “CLI Options” on page 60
58 Before You Configure Media Flow Controller Copyright © 2010, Juniper Networks, Inc.
Page 59

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Connecting and Logging In
You can connect to the CLI with SSH, Telnet (after enabled; Telnet is disabled by default), or
serial console using the IP address of your Media Flow Controller. The Media Flow Controller
responds with a login prompt. Enter admin as the user; there is no default password. After you
have connected, you must enter enable and then configure terminal in order to begin
configuring Media Flow Controller.
Likewise, you can log in to the Web-based interface by entering the IP address in a browser
window and using admin as the login name. The Management Console has a subset of the
CLI commands, but is good for simple or First Day configurations.
Each user account has at least one privilege level that determines which commands they can
issue and what CLI modes they can access:
• Administrator (admin): Full privileges. Can enter Enable mode and Config mode.
• Monitor (monitor): Can read all data and perform all actions, but not change any
configuration. Can enter Enable mode from Standard mode but cannot change
configurations.
• Unprivileged (unpriv): Can issue a small subset of commands including debugging and
show commands. Can log in to Standard mode only.
Using the Command Modes
When you log into the management shell over SSH (or optionally TELNET, if enabled; this is
not recommended) you are in the lowest tier, St andard mode; only show, help, diagnost ic
commands and a few others can be entered. You get into Enable mode by issuing the enable
command. In Enable mode you can view current configurations but not make configurations.
You need to enter Configure mode to make any changes. The CLI can be in one of three
modes, which determine which set of commands are available.
• Standard mode—When the CLI is launched, it begins in Standard mode. This is the most
restrictive mode and only has commands to query a restricted set of state information. You
cannot take any actions that would directly affect the system, you cannot change settings.
• Enable mode—The enable command moves you to Enable mode. This has commands
to view all state information, and take certain kinds of actions like rebooting the system,
but does not allow any configuration to be changed. It s commands are a superset of th ose
in Standard mode. Enter disable to exit Enable mode.
• Configure mode—The configure terminal command moves you to Configure mode.
This has a full unrestricted set of commands to view anything, take any action, or change
any configuration. Its commands are a superset of those in Enable mode. Enter exit to
leave Configure mode.
• Prefix mode—Some commands have a prefix mode; that is, when you enter a keyword,
you enter a mode for that configuration . Fo r exam p le:
test-vos (config) # accesslog
test-vos (config accesslog) #
When in the prefix mode, you can only make configurations for that command set and
typing ? (question mark) shows you only the options for those configurations. To leave the
prefix mode, type exit.
About the Media Flow Controller CLI 59
Page 60

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Example:
test-vos > enable
test-vos # configure terminal
test-vos (config) # namespace test
test-vos (config namespace test) # exit
test-vos (config) # exit
test-vos # disable
test-vos >
Prompt and Response Conventions
The prompt always begins with the hostname of the system. What follows depends on what
command mode you are in. To demonstrate by example, say the hostname is "test-vos". The
prompts for each of the modes would be:
test-vos > Standard mode
test-vos # Enable mode
test-vos (config) # Configure mode
Commands that succeed in doing what was asked do not print any response. The next thing
you see after pressing Enter is the command prompt. If an error is encountered in executing a
command, the response begins with % (percent sign), followed by some text describing the
error.
Note! All CLI commands allow completion with TAB. For example, typing en and then
pressing TAB completes the en command out to enable. Completion (hitting TAB) also shows
all commands following the typed letters; for example, typing e (in Standard mode) and then
pressing TAB shows enable and exit as the available commands starting with e.
CLI Options
There are four groups of commands relating to the CLI itself:
• cli session commands change a setting only for the current CLI session. They do not
• cli default commands change the defaults for the specified setting for all future CLI
• Other cli commands that take one-time actions, rather than change a setting, and thus do
• terminal commands are clones of a subset of the cli session commands, and are only
See cli for CLI command details.
Note! Some settings, such as the terminal length and width, are inherently session-specific,
and there are no corresponding commands to set defaults. Also, some commands are only
available in default form.
affect any other sessions, and can be performed by any user at any time.
sessions of all users. They also change the setting for the current session from which they
were executed, but not for any other currently active sessions. Since they change
configuration, the user must be in configuration mode to run them, so they can only be run
by admin privilege user.
not fall under the session or default umbrellas. For example, cli clear-history.
present for ease-of-use.
60 About the Media Flow Controller CLI Copyright © 2010, Juniper Networks, Inc.
Page 61

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Logging In to Media Flow Controller for the First T ime (CLI)
Before you log in to Media Flow Controller for the first time, see “Before You Configure Media
Flow Controller” on page 58.
To log into the system command line interface (CLI) for the first time, you need the IP address
assigned the management interface.
1. Open an SSH session and enter the Media Flow Controller management IP address or
hostname, or open a serial console session with the console server IP address and port,
to connect.
2. Log in with these default credentials (there is no default password).
User: admin
To log into the Management Console (Web UI), just navigate to the configured Media Flow
Controller IP address, specify the management port (:8080), and use the same login
credentials. The Management Console has a subset of the CLI commands, but is good for
simple or First Day configurations. Example:
http://192.168.1.100:8080.
Media Flow Controller System Configuration Overview
You can configure many basic system settings using the Media Flow Controller CLI.
Note! Some of these configurations may have already been done at installation.
Important! Save your settings after each configuration by typing write memory.
To configure system settings:
• “Configuring Interfaces, Hostname, Domain List, DNS, and Default Gateway (CLI)” on
page 61
• “Configuring Media Flow Controller System Clock and Banners (CLI)” on page 64
• “Creating and Configuring Link Bonding and Static Routes (CLI)” on page 65
• “Authentication / Authorization and Users Options” on page 67
• “Configuring Media Flow Controller User Accounts (CLI)” on page 69
• “Enabling Media Flow Controller CMC Client Rendezvous (CLI)” on page 70
• “Applying the Media Flow Controller License (CLI)” on page 71
Configuring Interfaces, Hostname, Domain List, DNS, and Default Gateway (CLI)
Before you configure Media Flow Controller interfaces, see “Before You Configure Media Flow
Controller” on page 58.
Tip! You may want to temporarily change the CLI default logout time (900 = 15 minutes); to do
this, use this command:
cli session auto-logout <seconds>
Logging In to Media Flow Controller for the First Time (CLI) 61
Page 62

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
To configure Media Flow Controller interfaces, hostname, domain list, DNS, and default g ateway:
1. Configure interface IP addresses for management (eth0), and origin fetch (eth1). Later,
use the delivery protocol commands to configure traffic in terfaces as needed (described
in “
Media Flow Controller Policy Configurations Overview”). It is important to keep the
traffic ports separate from the origin fetch ports for proper function ing of assured-flow, if
used. Use show interfaces to verify.
interface <interface_name> ip address <mangagement_IP_address>
<netmask_or_length>
2. Enable or disable (with no) use of DHCP on the specified interface. When enab led, DHCP
gets the IP address and netmask, so those settings are ignored. Conversely, setting the IP
address and netmask disables DHCP implicitly. Use renew to force a restart on the DHCP
client for the specified interface. Default is disabled.
interface <interface_name> dhcp
3.
Configure the system hostname.
hostname <name_for_the_appliance>
Use show hosts to verify.
4. Since delivery changes have been made, restart the delivery service (mod-delivery).
service restart mod-delivery
5.
Configure domain list (to resolve unqualified hostnames), and name server (DNS).
Use show
hosts to verify.
ip domain-list <domain_name_for_resolving_hostnames> ...
ip name-server <DNS_server_IP_address>
6. Configure the default gateway. Use show ip default-gateway to verify.
ip default-gateway <default_gateway_IP_address>
Sample configuration from unconfigured login prompt:
mfc-unconfigured-8a4990 login: admin
mfc-unconfigured-8a4990 > enable
mfc-unconfigured-8a4990 # configure terminal
mfc-unconfigured-8a4990 (config) # interface eth0 ip address 123.45.10.9 /
24
mfc-unconfigured-8a4990 (config) # hostname test-vos
test-vos (config) # ip domain-list example.local
test-vos (config) # ip name-server 172.19.172.1
test-vos (config) # ip default-gateway 123.45.10.1
test-vos (config) # service restart mod-delivery
Cutting and Pasting an Interface Configuration (CLI)
You can copy this series of comma nds, plug in your variable s, and save them to a file to reuse as needed.
enable
configure terminal
interface eth0 ip address <IP_address> {<netmask> | <mask_length>}
hostname <name>
ip domain-list <domain_name_for_resolving_hostnames> ...
ip name-server <IP_address>
ip default-gateway <IP_address>
service restart mod-delivery
write memory
62 Configuring Interfaces, Hostname, Domain List, DNS, and Default Gateway (CLI) Copyright © 2010, Juniper
Page 63

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Example: Media Flow Controller Interface Configuration
When Media Flow Controller initializes, the on-board Ethernet interfaces are numbered Eth0,
Eth1, and so on. When a NIC, dual- or qu ad - por t, is attached to the server, the 1st NIC (goes
by PCI channel number) gets interface names Eth10, Eth11, and so on to Eth19. Second NIC
gets the names Eth20, Eth21, and so on to Eth29; it is assumed that only up to 10 Ethernet
interfaces per NIC exist.
See Table 6, “
Important! For VXA Series Media Flow Engine appliances, do not ever change the eth name
mappings, all interface assignments are handled automatically during manufacturing.
Example Machine Setup of Management and Traffic Ports," for details.
In Table 6 on page 63, and Fi g ur e 5 on page 64
, example, the wiring logic is:
• Eth 0: Running SNMP, sending analytics to another machine, Web management, SSH,
and Telnet; connected to your internal network.
• Eth 1: Upstream fetching content from origin; connected to the network that connects to
the origin server.
• Eth 2 - 5: Service traffic; connected to the public Internet. These interfaces must have IP
addresses.
Table 6 Example Machine Setup of Management and Traffic Ports
Interface Connectivity IP Address
Eth 0 onboard 192.168.1.100 255.255.255.0 8080, 22 yes Management
Eth 1 onboard 172.20.46.10* 255.255.255.0 80 yes Origin fetch
Eth 2 PCIe card 10.1.1.11 255.255.255.0 80 not
Eth 3 PCIe card 10.1.2.11 255.255.255.0 80 not
Subnet
Mask
Open
Ports
Internet
Access
applicable
applicable
Purpose
Traffic
Traffic
Eth 4 PCIe card 10.1.3.11 255.255.255.0 80 not
applicable
Eth 5 PCIe card 10.1.4.11 255.255.255.0 80 not
applicable
*Eth0 AND Eth1 can be on the same subnet; this e xamples indicates they are not.
Example: Media Flow Controller Interface Configuration 63
Traffic
Traffic
Page 64

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Switch
User
User User
Internet
g015428
Origin
Server
Terminal server console
Switch
Intranet/
Internet
Origin
Server
Management station
Management VLAN
Media Flow Controller
traffic
Eth 2, 3, 4...
HTTP (80)
origin fetch
Eth 1
HTTP (80)
management
Eth0
HTTP (8080)
SSH (22)
HTTP
NFS
Figure 5 Example Connectivity
Configuring Media Flow Controller System Clock and Banners (CLI)
Note! Eth0 and Eth, typically the first two interf aces you us e, are usua lly the first two network
ports built into the system—either part of the system board, or the first add-in card or module.
Note! Lights Out management (also known as "out-of-band") involves the use of a dedicated
management channel for device maintenance. It allows you to monitor and manage servers
and other network equipment by remote control regardless of whether th e machine is powe red
on. You can configure out-of-band management through the BIOS.
Important! Media Flow Controller does not support RAID arrays.
Before you configure Media Flow Controller system clock and banners, see “Before You
Configure Media Flow Controller” on page 58. Proper time configuration is required for
accurate functioning. To configure an NTP (network time protocol) server OR system clock
and timezone:
1. Configure NTP server. Use show ntp to verify.
ntp server 123.45.10.8
Example:
test-vos (config) # ntp server 123.45.10.7
Alternately, configure the system clock, and timezone. Use show clock to verify.
clock set <hh:mm:ss> [<yyyy/mm/dd>]
clock timezone <zone> [<zone_word>] [<zone_word>] ...
Example:
test-vos (config) # clock set 15:51:30
64 Configuring Media Flow Controller System Clock and Banners (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 65

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
test-vos (config) # clock
2. Optionally, configure banne rs. There are two configu rable banners: motd (message of the
day) and login. In the CLI, both are displayed at the command line when you log in; in the
Management Console, only the login message is displayed, on the login page. M ulti-word
messages must be surrounded by quotes. Use show host and show banner to verif y.
banner [login <message_string>] [banner motd <message_string>]
Example:
test-vos (config) # banner login “Welcome to Media Flow Controller”
test-vos (config) # banner motd “Please note new link bonding commands”
timezone America North United_States Pacific
Creating and Configuring Link Bonding and Static Routes (CLI)
Media Flow Controller supports three bonding modes:
• balance-rr—”Round robin” mode. Sends TCP/IP packets belonging to the same
session across multiple links. Out-of-order TCP packets coming through di fferen t links are
retransmitted; supports load balancing and failover.
• balance-xor-layer3+4— Traffic to a particular network peer goes across multiple links,
although packets belonging to a single connection/session do not span multiple links;
supports load balancing and failover. Link selection based on TCP port + IP address.
• link-agg-layer3+4—Link Aggregation Control Protocol (LACP). Allows the automatic
negotiation of port bundling to form a single log ical cha nnel between LACP-ena bled links;
supports load balancing and failover.
Load Balancing (LB) Direct Server Return (DSR) Guidelines
In order to implement DSR in Media Flow Controller, the following configurations are required.
• Server load balancer (SLB) and Media Flow Controller must be Layer 2 adjacent.
• Media Flow Contro ller mus t ha ve th e de stin a tio n virtual IP address (VIP) configured on a
loopback or a network interface that will not broadcast that IP address on the network.
• Media Flow Controller must not GARP (gratuitous address resolution protocol) the VIP
address with its own MAC (media access control) address. You can disable ARP on a
Media Flow Controller interface with interface <interface_name> arp disable.
• The return response from Media Flow Controller must bypass the SLB.
• Response from Media Flow Controller routed to host not Layer 2 adjacent, via configured
route or gateway.
Examples:
• L4 LB + DSR: This is one of the most popular modes as it allows deployment with an
inexpensive load balancer. DSR allows the return data (response) to go from Media Flow
Controller to the client directly. This allows scaling from to 10Gbps with a relatively
inexpensive LB. The LB itself need not scale to 10Gbps; as long as it has enough
bandwidth to handle the rate of incoming requests, this provides a good solution.
• L7 LB: DSR does not work in this case. The LB has to match the sum of the capacity of all
the Media Flow Controllers to which the LB is load-balancing. However, rich L7 policies
based on URI, header , and so forth. can be built on LB, and traffic steering can be done in
a more flexible way.
Creating and Configuring Link Bonding and Static Routes (CLI) 65
Page 66

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
2
1
g015415
Client
Internet
Media
Flow
Controller
Client requests video over IP address
Server load balancer
makes LB decision.
Forwards to available
Media Flow Controller.
3
Media Flow Controller responds
directly to client. (Direct Server Return)
Server
load
balancer
Media
Flow
Controller
See Figure 6, “Direct Server Return,” for illustration.
Figure 6 Direct Server Return
Configuring Link Bonding and Static Routes (CLI)
Bond interfaces to create a port-channel or aggregated link for load distribution across links
and increased link availability. Example shows bonding interfaces eth10 and eth11 as a
named bonded interface “0”. In this way, layer 2 packets are distributed across the defined
links for load distribution; if one of the links fail, the other links take over the media delivery.
After you have created the bonded interface, you can use the delivery protocol command to
assign it as a traffic interface and configure its listen port, if needed.
1. Create the bond interface with a name and specify a mode. Note! The CLI lists several
options for bond <bond_interface> mode that are not supported. Only balance-rr
(“round robin”), balance-xor-layer3+4 (Non-LACP), and link-agg-layer3+4 (LACP) are
supported modes.
bond <name_for_virtual_interface> mode <bond_mode>
2. Add interfaces to bond; repeat as needed.
interface <interface_name> <virtual_interface_name>
3. Assign the new bonded interface as a traffic interface and set non-default (80) listen ports,
if needed; up to 64 port s can be assig ned. Note! Af ter you assign a traffic interface, Media
Flow Controller accepts traffic only on those assigned interfaces (up to 10); by default,
Media Flow Controller accepts traffic on all interfaces.
delivery protocol http interface <bonded_interface_name>
delivery protocol http listen port <port> <port> <port>
Example:
test-vos (config) # bond 0 mode balance-rr
test-vos (config) # interface eth10 bond 0
test-vos (config) # interface eth11 bond 0
test-vos (config) # delivery protocol http interface bond 0 eth12 eth13
test-vos (config) # delivery protocol http listen port 80 81 82
test-vos (config) # show bonds
Bonded Interface 0:
Enabled: yes
Mode: balance-rr
66 Creating and Configuring Link Bonding and Static Routes (CLI) Copyright © 2010, Juniper Networks, Inc.
Link Monitor Time: 100
Interfaces:
eth10
eth11
Page 67

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
4. Configure the IP address for the bonded interface.
test-vos (config) # interface 0 <IP_address>
5. Optionally, configure static routes and ensure a static host mapping for the defined
hostname. The ip route command only works on devices that already have an IP address
assigned. Use show ip route to verify.
ip route <network_prefix> {<netmask> | <mask_length>} {next_hop_IP_address
| interface_name>}
ip map-hostname
Example:
test-vos (config) # ip route 123.45.10.0 /24 eth0
6. Since delivery changes have been made, restart the delivery service.
service restart mod-delivery
Note! Bonded interfaces show Speed and Duplex as UNKNOWN in show interfaces output;
this is not an error condition.
Related Topics
• “Load Balancing (LB) Direct Server Return (DSR) Guidelines” on page 65
Authentication / Authorization and Users Options
Several configurations or tasks can use an already configured authentication / authorization
scheme (AAA, namespace pre-staging, users, file transfers, and so forth.). Authentication
schemes can be complex to configure—this section does not attempt to guide you through the
configuration steps for setting authentication or AAA options, but provides references to the
CLI commands. Before configuring any authentication / authorization schemes, you must have
this information: the hostname o r I P ad dr e ss of the authenticating server, and a shared secret
for authentication.
• “About MD5, SHA1, AES-128, and DES” on page 67
• “User Account Defaults and States” on page 68
About MD5, SHA1, AES-128, and DES
The first two, md5 and sha1 are cryptographic hash algor it hms .
• md5—Message-Digest algorithm 5. Considered somewhat faster but less secure than
sha1, but still supported for legacy systems. Generates a 128-bit (16 byte) hash.
• sha1—Secure Hash algorithm 1. Considered more secure than md5 but still vulnerable to
collision attacks. Generates a 160-bit (20 byte) hash.
The second two, AES-128 and DES are encryption standards used to encrypt and un-encyrpt
data.
• AES-128—Advanced Encryption Standard; 128 is a specific “block cipher.” AES is a
newer standard than DES and considered much more secure. Generates a 128 bit
encryption key . AES is an asymmetric encryption algorithm which means the sender uses
Authentication / Authorization and Users Options 67
Page 68

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
the public key of the receiver to encrypt the message an d the receiver uses it's private key
to decrypt the message.
• DES—Data Encryption Standard. This standard is older than AES-128 and considered
less secure than AES-128 but still supported for legacy systems using it. Generates 56
bits encryption key. DES is a symmetric encryption algorithm which means that you use
the same key to encrypt and decrypt the message.
User Account Defaults and States
The system comes initially with three accounts already created:
• admin—Full privileges to do any th ing on the system.
• juniper_probe_ftpuser—The auto-created user for CMC probes.
• cmcrendv—Default CMC user.
• monitor—Privileges to read almost everything on the system, and perform some actions,
but cannot modify configurations.
These accounts are both enabled, and by default have no password required for login (except
cmcrendv, a new account/capability not fully supported in Release 2.0.4)
There are five states an account may be in:
• “Account disabled” (not listed in /etc/passwd). The admin account cannot be disabled.
username foo disable
• “Local password login disab led ” (h a she d password se t to "*" ). Th e re is no locally-
configured password to permit the user to log in. The user may still log in using an SSH
authorized key if one is installed, or remote authentication (for example, RADIUS or
TACACS+). The admin account may not be in this state unless it has an SSH authorized
key installed.
username foo disable password
• “All password login disabled” (hashed password set to "!!"). No CLI command for this; the
hashed password must be set to “!!”. Same as "Local password login disabled" except that
the user cannot be remotely authenticated (for example, by a RADIUS or TACACS+
server). The user may still log in using an SSH authorized key if one is installed. The
admin account may not be in this state unless it has an SSH authorized key installed.
• “Local password set”. The user can log in by typing the password whose hashed version
we have stored. This is not necessary if an SSH authorized key is installed, or if a remote
auth server comes earlier in the authentication order.
username foo password mypassword
• “No password required for login” (hashed password set to ""). Anyone can log into this
account without providing authentic at ion . Th e ad min and monitor accounts begin in this
state (unless overridden by configured defaults), but should be changed for better
security.
username foo nopassword
68 Authentication / Authorization and Users Options Copyright © 2010, Juniper Networks, Inc.
Page 69

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Configuring Media Flow Controller User Accounts (CLI)
Before you configure Media Flow Controller user accounts, see “Before You Configure Media
Flow Controller” on page 58.
You may want to configure user accounts to allow multiple administrators to make
configuration changes, or to allow certain people to view or monitor the appliance.
To configure users with the CLI:
1. Configure authentication / authorization: see radius-server and tacacs-server for CLI
details.
2. After your authentication set tin gs ar e m ade, configure authentication and authorization
parameters such as setting the default login authentication order and default authorization
mapping for local and remote users. See aaa for CLI details.
3. Configure users. Media Flow Controller provides three capability sets for users: admin
(full privileges), monitor (can view configurations but make no changes), and unpriv
(very limited command access); see username for CLI details. In addition to the
capabilities, you can configure password options and disable a user account. Use show
usernames to verify.
a. Add a user and specify the capability; users are added with admin privileges.
username <username> capability <capability>
b. Delete a user.
no username <username>
c. Disable a user’s password; this does not remove the user or the password.
username <username> disable password
d. For a defined user, allow no password.
username <username> nopassword
e. For a defined user, configure a password. If no password is specified the user logs in
with no password; if 0 is specified, enter a password in cleartext (the system encrypts
it using the DES algorithm) and the user logs in with that password; if 7 is specified,
you must enter the previously-created, DES encrypted password for that user at the
command line. Important! Media F low Controller default admin user does not have a
default password; set an admin password to secure and restrict administration.
username password [ 0 <cleartext_password> | 7 <encrypted_password> |
<cleartext_password>]
Example:
test-vos (config) # username joe capability unpriv
test-vos (config) # username joe password 12345
test-vos (config) # username joe disable password
test-vos (config) # username joe nopassword
Related Topics
• “Authentication / Authorization and Users Options” on page 67
Configuring Media Flow Controller User Accounts (CLI) 69
Page 70

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Enabling Media Flow Controller CMC Client Rendezvous (CLI)
Media Flow Controller has the ability to be managed by a Media Flow Manager Central
Management Console (CMC), which makes the Media Flow Controller a client of the CMC.
CMC allows you to manage Media Flow Controllers remotely, configure profiles (lists of CLI
commands) that can be pushed to individual appliances, and create groups of Media Flow
Controllers that can be managed as a unit. The rendezvous feature is a mechanism by which
properly configured Media Flow Controllers can find a Media Flo w Manager and request
management. For rendezvous to work, it must be configured on the client (the Media Flow
Controller) and on the CMC server (the Media Flow Manager).
Before you configure Media Flow Controller CMC client rendezvous, see “
Configure Media Flow Controller” on page 58.
To enable CMC client rendezvous:
1. Enter the address of the CMC server that will manage this Media Flow Controller:
cmc rendezvous client server-addr <hostname_or_IP_address>
2. (Optional) Set an existing authentication method for client-server rendezvous or set a
password; to have the client prompted for the password, do not enter a password after the
password password keywords:
cmc rendezvous client auth <auth_type>
cmc rendezvous client auth password password [<password>]
3. Enable automatic rendezvous for the client:
cmc rendezvous client auto
4. (Optional) Set an initial retry delay in case you do not want the Media Flow Controller to
attempt rendezvous immediately :
To change the default initial retry delay (first time, or after a boot or a disconnect) from 30
seconds:
cmc rendezvous client auto initial-delay <seconds>
5. (Optional) Set rendezvous intervals:
To change the default interval-long (after a sucessful rendezvous, in case the server has
lost the information) from 86400 seconds (one day):
cmc rendezvous client auto interval-long <seconds>
To change the default interval-short (after an unsucessful rendezvous) from 300 seconds
(five minutes):
cmc rendezvous client auto interval-short <seconds>
6. To force a rendezvous attempt:
cmc rendezvous client force
7. To verify CMC settings for this Media Flow Controller and to check rendezvous status:
show cmc
show cmc rendezvous
8. All Media Flow Controlle rs ar e en a ble d fo r CMC man a gem en t by de fa u lt. To disable this
and ensure that this Media Flow Controller cannot be managed by CMC:
no cmc client enable
Before You
70 Enabling Media Flow Controller CMC Client Rendezvous (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 71

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Applying the Media Flow Controller License (CLI)
Media Flow Controller comes unlicensed and by default can only support 10 connections at
200Kbps each; it is a 40Mbps delivery system. Neither the number of sessions or the session
rate (network connection parameters) is configurable without the Media Flow Controller
license.
After you install Media Flow Controller, contact Juniper Networks to obtain the Media Flow
Controller license for normal operations. You need to provide the node ID, which is the MAC
address of Eth0 interface; use show interface eth0 to find the hardware (HW MAC) address.
Based on this Juniper Networks will provide you a license key. After installing the license you
get full feature capability. See license for CLI details.
To apply the Media Flow Controller license:
1. Install a license.
license install <license_key>
2. Delete a license
license delete <license_key>
3. View installed licenses, including expiration dates.
show licenses
Example:
test-vos (config) # show license
No licenses have been configured.
test-vos-cl65 (config) # show network
Network time out (seconds) : 60
Maximum concurrent sessions : 10
Per Session assured flow rate (Kbits/sec) : 0
Per Session Maximum bandwidth (Kbits/sec) : 200
test-vos (config) # license install LK2-MFC-413E-5N42-3EE6-4381-GLL8-CE98
test-vos (config) # show license
License 1: LK2-MFC-413E-5N42-3EE6-4381-GLL8-CE98
Feature: Media Flow Controller
Valid: yes
Start date: 2009/03/15 (ok)
End date: 2009/06/30 (ok)
Tied to MAC addr: 00:1E:C9:FF:0C:FA (ok)
Active: yes
test-vos-cl65 (config) # show network
Network time out (seconds) : 60
Maximum concurrent sessions : 5000
Per Session assured flow rate (Kbits/sec) : 0
Per Session Maximum bandwidth (Kbits/sec) : 0
test-vos-cl65 (config) #
Applying the Media Flow Controller License (CLI) 71
Page 72

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Media Flow Controller Policy Configurations Overview
After you have your appliance network connections and basic settings configured, you are
ready to start configuring Media Flow Controller policy settings.
Important! For namespaces, you must configure domain, match, origin-server, and status
activation, at a minimum. For CLI details see Chapter 10, “
Commands.”
Note! Any time network configuration changes are made the delivery service (mod-delivery)
must be restarted with service restart mod-delivery. This includes initial configurations after
installation. In the Management Console, do this on the EZconfig page.
Important! Save your settings after each configuration by typing write memory in the CLI; in
the Management Console, click Save in the upper right corner of each page.
• “Setting Network Connection Options (CLI)” on page 72
• “Configuring Media Flow Controller Delivery Protocol (CLI)” on page 73
• “Creating and Configuring Virtual Players (CLI)” on page 74
• “Creating a Namespace and Setting Namespace Options (CLI)” on page 81
• “Managing the Media Flow Controller Disk Cache (CLI)” on page 92
Media Flow Controller CLI
Setting Network Connection Options (CLI)
Before you configure Media Flow Controller network connection options, see “Before You
Configure Media Flow Controller” on page 58.
Configure network connection settings (global Media Flow Controller defaults). The assured-
flow-rate and max-bandwidth options are available in virtual-player configurations, which
override network connection configurations.
Using Network Connection Assured Flow
Assured Flow™ is a function using the values configured for max-bandwidth, concurrent
session, and assured-flow rate (AFR). AFR is the rate that Media Flow Controller provisions
at the network level. For example, if a video encoded at 800 Kbps needs to be transferred over
HTTP that uses TCP/IP over Ethernet, you must account for the overheads of the HTTP, TCP,
IP, and Ethernet protocols. Usually, HTTP + TCP + IP + Ethernet overheads amount to 10 to
15%. With this in mind, AFR for a video encoded at 800 Kbps should be set to 900Kbps or
slightly higher. See “
See network for CLI details.
Configuring Network Connections (CLI)
To configure network connections with the CLI:
1. Configure global network assured-flow-rate (minimum rate for a given session); default, 0
(zero), means assured flow is disabled (no minimum rate is pr ovisioned). See “
Controller AssuredFlow” on page 50 for detailed description.
network connection assured-flow-rate {0 | <kbps>}
Media Flow Controller AssuredFlow” on page 50 for more information.
Media Flow
72 Media Flow Controller Policy Configurations Overview Copyright © 2010, Juniper Networks, In c.
Page 73

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
2. Important! Configure global network concurrent session limit; default is 10 (without Media
Flow Controller license), 5000 (with Media Flow Controller license). The Media Flow
Controller license changes the default.
network connection concurrent session {5000 | <integer>}
3. Configure global network socket idled-out time in seconds; this is the time the network
waits before closing a connection when there is no dat a in se ssion ; de fault is 60 seconds.
network connection idle timeout <seconds>
4. Configure global network maximum allowed bandwidth (burst rate); even if there is
available bandwidth in the link, Media Flow Controller does not allocate more than this
value for a session. When there is a full download, Media Flow Controller tries to allocate
this value to the session; default is 200 without Media Flow Controller license, 0 kbps
(unbounded) with Media Flow Controller license. The Media Flow Controller license
changes the default.
network connection max-bandwidth {0 | <kbps>}
5. T o verify configurations.
show network
6. Save configuration settings.
write memory
Example:
test-vos (config) # network connection assured-flow-rate 2000
test-vos (config) # network connection concurrent session 4000
test-vos (config) # network connection idle timeout 900
test-vos (config) # network connection max-bandwidth 2000
test-vos (config) # show network
Network time out (seconds) : 900
Maximum concurrent sessions : 4000
Per Session assured flow rate (Kbits/sec): 2000
Per Session Maximum bandwidth (Kbits/sec): 2000
Network Access-Control PERMIT list: NONE
Network Access-Control DENY list: NONE
Configuring Media Flow Controller Delivery Protocol (CLI)
These are the ports on the Media Flow Controller that receive and deliver media. These ports
typically have Internet access, and should be connected with highest-quality cables. See
Table 6, “
The delivery protocol command lets you specify what protoc ols to use for media de livery and
manipulate headers; in Release 2.0.4 http and rtsp are allowed values. By default, Media
Flow Controller listens on all interfaces; if you set specific traffic interfaces, only those are
used for traffic. See delivery for CLI details.
Before you configure Media Flow Controller delivery protocol options, see “
Configure Media Flow Controller” on page 58.
To configure delivery protocol options with the CLI:
1. Media Flow Controller supports known HTTP methods (GET, POST, TRACE, CONNECT,
Example Machine Setup of Management and Tra ffic Ports for an example.
Before You
OPTIONS, DELETE, PUT) always. T o add support for http request methods, use allow-
req and specify up to 16 custom request methods. Use all to permit Media Flow Controller
Configuring Media Flow Controller Delivery Protocol (CLI) 73
Page 74

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
to tunnel any request. Default is none, only the known methods listed are allowe d. Use no
to remove the specified method or methods.
delivery protocol http allow-req all
2. Optionally, disable/enable connectio n pooling (enabled by default) and configure
parameters; for delivery protocol http only.
delivery protocol http conn-pool origin {enable | disable}
a. Use max-conn to limit the maximum allowed pooled connection; default is 256,
maximum allowed is 2048.
b. Use timeout to configure a pooled connection timeout; default is 300 seconds,
maximum allowed is 86,4000 seconds (24 hours).
3. Optionally, configure interfaces for Media Flow Controller traffic; after configured, Media
Flow Controller accepts traffic on those interfaces only. Applies to both http and rtsp
delivery protocols. Up to 10 interfaces can be specified.
delivery protocol [http | rtsp] interface <interface_name>...
4. Optionally, configure listen ports for the traffic interfaces as needed; default is port 80 for
http, port 554 for rtsp. By default, Media Flow Controller listens on port 80 for HTTP and
port 554 for RTSP on all interfaces.
delivery protocol http listen port <port>
5. Optionally, set the maximum request length (domain + URI + Query Params + Headers),
in characters/bytes, for incoming requests (http delivery protocol only). Default is 16384
bytes; maximum allowed value is 32768. Incoming requests with lengths exceeding the
configured value are rejected.
delivery protocol http req-length maximum <bytes>
6. Since delivery changes have been made (steps 3 and 4), restart the delivery service
(mod-delivery).
service restart mod-delivery
7. T o verify configurations.
show delivery protocol http
8. Save configuration settings.
write memory
Example:
test-vos (config) # delivery protocol http conn-pool origin max-conn 200
test-vos (config) # delivery protocol http interface eth11 eth12 eth13
test-vos (config) # delivery protocol http listen port 80
test-vos (config) # delivery protocol http req-length maximum 23576
test-vos (config) # service restart mod-delivery
test-vos (config) # write memory
Creating and Configuring Virtual Players (CLI)
Create virtual players to customize how videos are delivered; after created, they are assigned
to a namespace. This is optional; if a namespace does not have a defined virtual player
assigned to it, it uses the network connection settings.
You may want to create a virtual player for each type of video you deliver; for example, if you
deliver YouTube® videos, create a type youtube virtual-player for use in the corresponding
namespace. Media Flow Controller virtual players support and complement client-side video
74 Creating and Configuring Virtual Players (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 75

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
players. Whereas namespaces allow you to define what gets fetched from where and how,
virtual players let you fine-tune video delivery.
There are five types of virtual players: Type generic virtual player offers all generic virtual
player options; Type break players are a su b-se t of Type generic, Type qss-streamlet virtual
players allow multiple settings of assured flow via a rate-map, Type yahoo players are for
YouTube™ videos and include a health-probe option and a special authentication option.
Type smoothflow players for SmoothFlow are documented after this section. Type youtube
players are for YouTube media. A sixth player type, smoothstream-pub is not supported in
Release 2.0.4.
• “Using query-string-parm” on page 75
• “Using hash-verify” on page 76
• “Using virtual-player type qss-streamlet rate-map” on page 76
• “Using Virtual Player Type youtube” on page 77
• “Example: Configuring generic Virtual Player (CLI)” on page 78
• “Configuring YouTube Video Caching (CLI)” on page 199
Note! Media Flow Controller provides an API you can use to create custom virtual pla yers. For
more information, contact Juniper Networks Customer Support; see “
Technical Support” on page 34.
Note! In Release 2.0.4, the show options command ? (question mark), lists all virtual player
options no matter what virtual player type you are configuring; however, if you try to set an
option that does not apply to that player type, an error is displayed.
Requesting
Using query-string-parm
The query-string-parm argument, used extensively in virtual player configurations, allows
you to use query params. Query params, a string with an associated value, are a way of
passing information through a URL. The query pa ram part of the URL is designated with a
question mark (?) followed by defined query params. The query param is a name that is
associated with a pre-defined value. Additional queries in the URL are separated by
ampersand signs (&). Query params are composed of a name and value pair. For example, a
request for a query param for assured-flow-rate could be shown in a URL like this:
http://xyz.com/test.flv?afr=100
In the example, the query-string-parm <string> is afr and its value is 100. The namespace
for this connection tells Media Flow Controller that when it finds afr in the query params part of
the URL it is to use the value following it for that function. So, if the URL has ?afr=100 Media
Flow Controller knows (through the URL’s defined namespace and associated virtual player or
configured network connection properties) to use 100 Kbps for the assured-flow rate.
In the Media Flow Controller CLI, you can only specify the query param <string> and should
know the units of the value for that query parameter as query params can be defined to mean
many different things and are used to signal the start or value of assured flow, fast-start, fulldownload, seek, and smooth flow functions, and the match value for hash-verify and rate-
map.
Important! The virtual player query-string-parm values you configure in your Media Flow
Controller origin must match the corresponding query-string-parm values configured in your
Media Flow Controller edge.
Creating and Configuring Virtual Players (CLI) 75
Page 76

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Using hash-verify
Media Flow Controller computes an md-5 hash of an incoming URL by combining a specified
part of the URL along with a pre-shared secret value (configured via Media Flow Controller
CLI). The computed hash digest value is then compared with the hash value provided in the
incoming URL via a pre-specified match query-string-parm (configured via Media Flow
Controller CLI). If a match between the computed and provided hash values is unsuccessful,
then the incoming request is denied.
Example URL showing match query-string-parm h (configured in Media Flow Controller):
http://video.example.com/public/2010/
qwerty.flv?fs=5000&ri=300&rs=1234567&h=<128-bit-md-5-hash>
If Media Flow Controller encounters this URL, it takes the entire URL (shown in blue), until it
encounters the provided match query-string-parm; for example, h (shown in red).
The hash value is then computed by either appending or prefixing to the URL the configured
shared-secret value as specified in the CLI, and comparing the computed value with the
value provided via the match query-string-parm (shown in green).
Example if shared-secret is appended:
Computed hash value = MD5(http://video.example.com/public/2010/
qwerty.flv?fs=5000&ri=300&rs=1234567 + shared-secret)
Example if shared-secret is prefixed:
Computed hash value = MD5(shared-secret + http://video.example.com/public/
2010/qwerty.flv?fs=5000&ri=300&rs=1234567)
Note! The secret key is called a shared-secret key, because the same key is also used by
the browser/video player that generates the request for the object, to compute the hash value
which is present in the pre-specified query parameter for comparison.
Note! Types 1 and 4 virtual-players have a default match query- string-par m of h, this can be
changed in the CLI.
Using virtual-player type qss-streamlet rate-map
Virtual player type qss-streamlet allows you to configure a rate-map to ensure a specified
delivery rate is applied to certain requests. The configuration calls for you to specify a match
<string> to a rate <kbps>; when the request arrives the match <string> is extracted from the
URL and its corresponding rate (in kbps) is used for the delivery rate.
By default, the match string (length must be 2 bytes; for example, 01) is extracted by going to
the end of the URL and skipping 12 Bytes from the end; the value in that location is map ped to
the configured rate in kbps. Example:
http://video.example.com/public/BBB87026/xy_750_1938344/
AC60E15B2A7C4A45AC4C1472E2AC0816_030000003F.flv
In the URL, the value 03 (12 Bytes from the end of the URL) is extracted, and the
corresponding assured flow rate (1000Kbps) is applied.
The configured CLI looks like this:
virtual-player my_virtual_player type qss-streamlet
rate-map match 01 rate 300
rate-map match 02 rate 500
rate-map match 03 rate 1000
76 Creating and Configuring Virtual Players (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 77

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
In this way, URLs containing 01 in the corr ect pl ace (12 bytes from the end) map to an
assured flow rate of 300; with 02 the assured flow rate is 500; and so on. Defaults are:
Match: 00 Rate: 150 kbps
Match: 01 Rate: 180 kbps
Match: 02 Rate: 270 kbps
Match: 03 Rate: 330 kbps
Match: 04 Rate: 420 kbps
Match: 05 Rate: 470 kbps
Match: 06 Rate: 520 kbps
Match: 07 Rate: 575 kbps
Match: 08 Rate: 700 kbps
Match: 09 Rate: 800 kbps
Match: 0A Rate: 900 kbps
Match: 0B Rate: 1300 kbps
Match: 0C Rate: 1750 kbps
Match: 0D Rate: 1920 kbps
Important! Media Flow Controller checks for an un der sco re ( _ ) befor e the 14th byte; if th e
underscore is missing, the URI does not map correctly.
Using Virtual Player Type youtube
YouTube encodes media content using industry standard video and audio compression
schemes such as H.264/AVC for video and AAC for audio. It stores the encoded bit streams
using either FLV, MP4 or 3GP containers, depending on the spatial resolution of the video.
Currently, YouTube supports the following different formats as outlined in Table 7.
Associations to one of these formats is signaled through a request originating from the player
via a query parameter typically of the type fmt or itag
Table 7 YouTube Formats
Media Types Standard Medium High 720p 1080P Mobile
Format/Tag Values
(fmt, itag)
Container Types FLV MP4 FL V MP4 MP4 3GPP
Video Codec H.264/AVC H.264/AVC H.264/AVC H.264/AVC H.264/AVC MPEG-4 Part 2
Audio Codec AAC AAC AAC AAC AAC AAC
Spatial Resolution 320x240
34 18 35 22 37 17
640x480
480x360
480x270
854x480 1280x720 1920x1080 176x144
Requests originating from a YouTube player for a video asset have been observed to typically
come in the following two forms (underlining
(a)GET “http://www.youtube.com/get_video?video_id=fBE7y6Uba5M&t=
vjVQa1PpcFPfHDFKYQ1s_RIHTM-GxADM8vFGLxxc_rs=&el=detailpage&ps=&fmt=34
noflv=1”
highlights important details):
&asv=2&
(b)GET “http://v8.nonxt7.c.YouTube.com/
videoplayback?ip=0.0.0.0&sparams=id%2Cexpire%2Cip%2Cipbits%2Citag%2Calgorith
m%2Cburst%2Cfactor&fexp=904405&algorithm=throttle-factor&itag=34
Creating and Configuring Virtual Players (CLI) 77
&ipbits=0&bu
Page 78

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
rst=40&sver=3&expire=1266310800&key=yt1&signature=66222E9350B9BB5AC68297F12A
C1DCB4C53AAFDE.55B33FFFA04EBF001AF39A4F316E657FC318E0E5&factor=1.25&id=efa3a
0434887fdc0&redirect_counter=1”
It is observed that these two request formats do not have an explicit association or reference
to the media object, and the URI themselves are not cache friendly. The association to the
media object is provided using a combination of an id and format tag.
For case (a) this association is provided by the video_id and fmt query parameters.
For case (b) this association is provided by the id and itag query parameters.
Media Flow Controller uses a combination of these query parameters to generate an internal
cache name for the media object. YouTube videos in Media Flow Controller are cached with a
cache name format as:
yt_video_id_efa3a0434887fdc0_fmt_34
Media Flow Controller also supports random access via seek/scrub for YouTube videos.
YouTube signals a seek point via a query parameter, begin, with units of milliseconds. Media
Flow Controller translates this seek point to the correct position in the video file for both the
FLV or MP4 container formats and data that is delivered to the player is from the seek point
onwards to the end of the file.
Example: Configuring generic Virtual Player (CLI)
The generic virtual player can be used to cache most Web content.
To configure the type generic (formerly Type 0) virtual player:
1. Configure a virtual player with a name and type generic (enters you to virtual-player
configuration mode). Use no virtual-player <name> to delete; use virtual- player <name
no <option> to make changes to configurations (either reset default or remove setting).
virtual-player <name> type generic
2. Configure hash verification options. Note! In Release 2.0.4, only md-5 digest is
supported. Configure a shared secret value to be appended or prefixed to the URL as
specified, for matching against the hash value provided in the URL and indicated by the
match query-string-parm you configure.
hash-verify
query-string-parm <string>
digest md-5
shared-secret <string> {append | prefix} match
3. Configure download parameters for delivering files at the fastest possible speed. If you
choose always, then file downloads are always delivered at the fastest possible speed;
otherwise, you must have either a query param or a header name that indicate that a full
download should be processed.
full-download {always | match <string> {query-string-parm <string> |
header <header_name>}}
4. Optionally, configure assured-flow delivery optimization. Note! The auto option is not
supported in Release 2.0.4. A query param can be used or define a static rate value in
kbps, a value of 0 (zero) means no throughput at all. After a value is entered, this
parameter is enabled. See “
Media Flow Controller AssuredFlow” on page 50 for more
information.
assured-flow {auto | query-string-parm <string> | rate <kbps>}
78 Creating and Configuring Virtual Players (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 79

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
5. Optionally, configure connec tion max-bandwidth delivery optimization. Default is 0
(unbounded) with the Media Flow Controller license, 200 kbps without it; you must have
the license to change the unlicensed default. Use no connection to reset default.
connection max-bandwidth {0 | <kbps>}
6. Optionally, configure fast-start delivery optimization.
fast-start {query-string-parm <string> | size <KB> | time <seconds>}
7. Optionally, configure seek de livery optimization specifying a query param for when seek
should start and how long it should last. Query params must be used.
seek query-string-parm <string> [seek-length query-string-parm <string>]
8. Optionally, configure smooth-flow delivery optimization. A query param must be used.
See “
Media Flow Controller SmoothFlow” on page 51 for detailed descriptions.
smooth-flow query-string-parm <string>
9. Type exit to leave virtual-player configuration mode.
Example:
test-vos (config) # virtual-player test type generic
test-vos (config virtual-player test) # hash-verify digest md-5 match
query-string-parm h shared-secret zpzp prefix
test-vos (config virtual-player test) # assured-flow query-string-parm afr
test-vos (config virtual-player test) # full-download always
test-vos (config virtual-player test) # connection max-bandwidth 0
test-vos (config virtual-player test) # fast-start time 90
test-vos (config virtual-player test) # seek query-string-parm sk
test-vos (config virtual-player test) # smooth-flow query-string-parm sf
test-vos (config virtual-player test) # exit
test-vos (config) #
10. Verify configurations with show virtual-player <name>.
Creating and Configuring Server-Maps (CLI)
Media Flow Controller server-map allows you to define the origin server or servers to which
Media Flow Controller goes in case of a cache-miss. To use this feature, you define an XML
file with the origin server parameters, such as host, protocol, and port number, described in
detail in Chapter 7, “
including the file-url (which is immediately validated) using the server-map command and,
finally, you add the server-map to a configured namespace. See Chapter 7, “
Configuration,” for XML file formatting. See server-map for CLI details.
• “Using server-map to Create a Consistent Hash Cluster” on page 79
• “Using server-map for Origin Escalation” on page 80
• “Configuring Media Flow Controller Server Maps (CLI)” on page 80
Using server-map to Create a Consistent Hash Cluster
The cluster-map server map lets you to define a consistent hashing sch eme to bind objects to
nodes. See “
overview, server-map for CLI details, and Creating the cluster-map XML File in Chapter 7,
Consistent Hash-Based Clustering and Origin Escalation” on page 48 for an
Server Map Configuration,”. After the file is defined, you set parameters,
Creating and Configuring Server-Maps (CLI) 79
Server Map
Page 80

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
“Server Map Configuration,” for details on clustering and creating the XML file for cluster-
map.
Consistent hash cluster requirements:
• A cluster is one Level 1 node and >= one Level 2 nodes.
• Level 1 node must be a Media Flow Controller operating as a reverse proxy.
Example server-map cluster-map configuration:
server-map sm2
format-type cluster-map
file-url http://mapfile.nokeena.com/nfs/path/cluster.xml refresh-interval 60
Using server-map for Origin Escalation
The server-map format-type origin-escalation-map allows you to specify a set of originservers that are sequentially (in the order defined in the XML server map file) tried until a
request is fulfilled or all defined origins have been tried; if no origin can fulfill the request a 404
(file not found) error is given. See “
on page 48 for an overview, server-map for CLI details, and Creating the origin-escalation-
map XML File in Chapter 7, “
for origin-escalation-map.
Origin escalation requirements:
Consistent Hash-Based Clustering and Origin Escalation”
Server Map Configuration,” for details on creating the XML file
• All origin servers are viewed as a single entity where any origin server is capable of
resolving a miss or handling a validate request.
• All origin servers are monitored via a periodic heartbeat (HTTP request) insuring that
escalation only occurs to currently online members.
• Origin server HTTP response codes resulting in escalation are configurable on a per origin
server basis.
• Applicable only to a Media Flow Controller reverse proxy configuration.
Example server-map origin-escalation-map configuration:
server-map sm3
format-type origin-escalation-map
file-url http://mapfile.nokeena.com/nfs/path/originescalation.xml refreshinterval 60
Configuring Media Flow Controller Server Maps (CLI)
Use server maps to configure multiple origin servers for a namespace.
To configure a server-map for either HTTP or NFS origin server:
1. First, create the server-map with a <name> and format-type. To map the incoming
(target origin) HOST header value to a specified origin server, set format-type host-
origin-map. To use consistent hashing to determine the origin server, set format-type
cluster-map. To allow origin escalation (try another defined origin if the first fails), set
format-type origin-escalation-map. To use NFS publishing points for origin, set format-
type nfs-map. For cluster-map and origin-escalation-map only , you can define and add
80 Creating and Configuring Server-Maps (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 81

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
any number and combination of these two to a namespace; the order of in which the
maps are added to the namespace denotes the order in which they are read.
server-map <name> [format-type <type>]
2. Set a URL for the server-map; this tells Media Flow Controller where to fetch the XML
mapping file. Also, set a refresh interval (how often Media Flow Controller refreshes the
XML file). The default refresh-interval is 0 (zero), wh ich means no re fr esh after the initial
fetch. When you set the file-url Media Flow Controller immediately initiates an HTTP GET,
retrieves the file, and executes MapXML to convert the data to binary. From server-map
prefix mode:
file-url <URL> refresh-interval <time>
3. The final step is to add a server-map (or, potentially, multiple server-maps in the case of
cluster-map and origin-escalation-map) to a namespace origin-server configuration.
When the server map is added, Media Flow Controller starts the heartbeat (cluster-map
and origin-escalation-map only) to the defined nodes (10 beats/second).
namespace<name> origin-server <protocol> server-map <name>
Example (for NFS origin):
test-vos (config) # server-map newMap
test-vos (config server-map newMap) # file-url http://example.com/nfs/
maps/ refresh-interval 9000
test-vos (config server-map newMap) # exit
test-vos (config) # show server-map
Server-map : newMap
Format-Type :
Map File : http://example.com/nfs/maps/
Refresh Interval : 9000
test-vos (config) #
namespace newTest origin-server nf s ser ver -m ap ne wM ap
Creating a Namespace and Setting Namespace Options (CLI)
Before you configure Media Flow Controller namespaces, see “Before You Configure Me dia
Flow Controller” on page 58.
Create namespaces to define fine-grained delivery policies, including optionally adding a
custom virtual player . You must create a namespace for each origin server and delivery criteria
scheme you use. You can create up to 256 namespaces in one Media Flow Controller. See
namespace for CLI details.
• Using namespace cache-inherit
• Using namespace domain regex
• Using namespace domain <FQDN:Port>
• Using namespace match uri regex
• Using namespace match <criteria> precedence
• Using namespace delivery protocol <protocol> origin-fetch cache-age
• Using namespace object delete | list
• Using namespace for Live Streaming Delivery Without Caching
• Using namespace for Live Streaming Delivery With Caching
Creating a Namespace and Setting Namespace Options (CLI) 81
Page 82

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
• Using namespace for Proxy Configurations
• Example: Transparent Proxy Namespace Configuration
• Using namespace match virtual-host
• Configuring Media Flow Controller Namespaces (CLI)
See “Common Media Flow Controller Configuration Errors” on page 282 for additional
namespace tips.
Using namespace cache-inherit
Use the namespace cache-inherit option to add an existing namespace’s cache and UUID to
a new one; the contents are not duplicated, but the new namespace uses the inherited cache
rather than creating a new one. When a namespace is created, the system assigns it a Unique
ID (UUID). There is no option in the CLI to configure the UUID; but it can be set indirectly using
the cache-inherit subcommand that sets a new namespace to inherit the cache of an existing
namespace. This is useful under the following situations:
• You add a new namespace and want it to share the UUID with an existing namespace;
sharing the UUID allows the two namespaces to have a common cache.
• You delete an existing namespace, rename it, and want to use the data cached under it.
• You delete a namespace by accident and want to recreate it and you do not want it given
a new UUID. In this case, you dump the namespace and its associated UUID, and force
the UUID of an existing namespace for the one you are creating. You would do this by:
1. Issue show namespace list to gather the list of "Currently defined" and "Deleted/nonexisting" (but whose cache content still exists) namespaces and their associated UUIDs.
2. Then issue namespace <name> cache-inherit <existing or non-existing namespace
integer>.
Example: show namespace list (namespace test2 inherited namespace test cache):
show namespace list
Currently defined namespaces :
Name : UID
new_ns : /new_ns:b3ad64a8 (inactive)
test2 : /test:1250bcac (active)
testIE : /testIE:b911b24 (inactive)
-------------------------
List of unmapped/deleted namespace UIDs (if any)
non-exsiting1: /test3:954ef8aa
Using namespace domain regex
This section provides some examples of namespace domain regex use. Change specifics
accordingly. Note! Regex entries do not contain spaces; also, enclose all regex entries in
single quotes (not shown in examples). See Table 8.
82 Creating a Namespace and Setting Namespace Options (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 83

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Table 8 Example namespace domain regex entries
Regex Matches
www.example.com|example.com
.*example.com
^[a-f,0-9]{8}\.(origin\.|cdn\.)?cms\.example\.com:80$
^cms[0-9]{3}\.(dc2|qcg7)\.example\.com:80$
^orig.(sv1|qcg1|qcg5)\.example\.com:80$
^(cms[0-9]{3}).*(qcg[0-9]+|sv1|ch1|dc2|af1)\.example\.com:80$ cms123.x.y.qcg0.example.com:80
www.example.com
example.com
abcdef02.origin.cms.example.com:80
abcdef02.cdn.cms.example.com:80
abcdef02.cms.example.com:80
cms123.dc2.example.com:80
cms123.qcg7.example.com:80
orig.sv1.example.com:80
orig.qcg1.example.com:80
orig.qcg5.example.com:80
cms123.x.y.qcg01.example.com:80
cms123.x.y.sv1.example.com:80
cms123.x.y.ch1.example.com:80
cms123.x.y.dc2.example.com:80
cms123.x.y.af1.example.com:80
Using namespace domain <FQDN:Port>
Media Flow Controller can listen for requests on multiple TCP ports, up to 64; default is port 80
for HTTP, port 554 for RTSP. In order to map incoming requests to the correct namespace,
especially on a non-default port, the namespace domain MUST be set properly with port
number included. Media Flow Controller maps an incoming URL to a namespace by extracting
the value against the HOST header and matching it to the value configured for the
namespace domain.
When non-default port numbers are used you MUST ensure that the HOST header has the
port number coded correctly in the incoming URL and also in the namespace domain.
Example: If Media Flow Controller listens on port 80, 8080, and 4040 for incoming HTTP
requests; and the requests on port 80 must go to namespace ns80, those coming in on port
4040 must go to namespace ns4040, and those on port 5050 must go to namespace ns5050,
then the configuration would be as follows:
namespace ns80
domain video.example.com
namespace ns8080
domain video.example.com:4040
namespace ns4040
domain video.example.com:5050
For requests to match ns80, domain/HOST: header must be video.example.com.
For requests to match ns4040, domain/HOST: header must be video.example.com:4040.
For requests to match ns5050, domain/HOST: header must be video.example.com:5050.
Creating a Namespace and Setting Namespace Options (CLI) 83
Page 84

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Using namespace match uri regex
This section provides some examp les of namespace match uri regex use. Change specifics
accordingly. Note! Regex entries do not contain spaces; also, enclose all regex entries in
single quotes (not shown in examples). See Table 9.
For namespace match uri <uri-prefix>, the regex is written against the ab so lute path p ortion
of the URL. For example, given the following URL: http://abc.com:8080/index.html,
/index.html would be the absolute path portion of the URI.
Table 9 Example namespace match uri regex entries
Regex Matches
'\/A\/b\/c\/d\/index\.html'
'\/A\/b\/c\/d\/index\..*'
'\/A\/b\/.*\/d\/index\..*'
Using namespace match <criteria> precedence
Use namespace <name> match <crite ria> pr ecedence to set unambiguous mapping of
incoming GET requests in the case of match <criteria> overlap; precedence can be set on
all match <criteria>. The lower the number, the h igher the preference for that namespace;
values 0 (highest precedence) - 10 (lowest precedence) can be used. All na mespaces have a
default precedence of 0. For example, consider three URLs and namespaces as follows:
1. http://a.com/abc/def/file1.flv
2. http://a.com/abc/file2.flv
3. http://a.com/pqr/file3.flv
namespace ns1
domain a.com
match uri /abc/def
origin-server http o1.com
status active
namespace ns2
domain a.com
match uri /abc
origin-server http o2.com
status active
namespace ns3
domain a.com
match uri / precedence 3
origin-server http o3.com
status active
All three URLs match namespace ns3 set domain (a.com) and match uri / (slash). In order to
ensure that match uri #1 (/abc/def) maps to ns1 and not ns3, set the precedence value.
precedence 1
precedence 2
/A/b/c/d/index.html
/A/b/c/d/index.html
/A/b/c/d/index.html
/A/b/x/d/index.html
/A/b/xx/d/index.html
/A/b/abc/d/index.html
84 Creating a Namespace and Setting Namespace Options (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 85

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Same as the case with match uri #2 (/abc), to map to ns2. Only match uri 3 ( / )should be
mapped to ns3 with the precedence value configured as shown.
Note! Excessive use of precedence has performance impact as precedence allows for
longest prefix matching. If possible, namespaces should be configure d in such a way tha t they
have no overlaps in the domain and match <criteria> combination, which are used for
mapping the incoming HTTP GET to a namespace.
Using namespace delivery protocol <protocol> origin-fetch cache-age
The namespace <name> delivery protocol <protocol> origin-fetch cache-age argument
allows you to set granular cache aging policies based on content type, as well as a default
cache age. The cache-age for each content-type must be specified separately with positive
integers. Examples:
• cache-age content-type-any 28800
Irrespective of content-type, override your configured cache-age-default or , if cache-age-
default is unconfigured, set the max-age for any content-type to 28800 seconds. If the
content request does not specify a max-age, set it to max-age 28800.
• cache-age content-type application/flv 2880
cache-age-default 57900
When content-type is application/flv, set max-age to 2880 seconds. For all other content-
types use default configuration (57900 seconds in the example). If the received max-age
is set, use that value.
• cache-age content-type application/flv 28800
cache-age content-type application/mov 2880
cache-age content-type application/3gp 288
cache-age content-type application/f4v 28
cache-age-default 57900
When content-type is application/flv, set max-age to 28800 seconds; for application/
mov, set max-age to 2880 seconds; for application/3gp, set max-age to 288; and for
application/f4v, set max-age to 28. For all other content-types use default configuration
(57900 seconds in the example). If the received max-age is set, use that value.
• cache-age content-type application/qmx 60
cache-age content-type application/qss 288000
When content-type is application/qmx, set cache-age to 60 seconds, for application/
qss, set cache-age to 288000 seconds. For all other content-types use default
configuration: if max-age is not set in the data coming from origin, set it to the configured
default value (28800 if unspecified). If the received max-age is set, use that value.
Creating a Namespace and Setting Namespace Options (CLI) 85
Page 86

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Using namespace object delete | list
List or delete contents in a namespace. The comman d takes in the name of a namesp ace and
applies a list or delete operation to the objects matching the given pattern.
namespace <name> object {list |delete} {all | <URI> | pattern}
For example, with this namespace and a URL of http://example.com/abc/def/file.flv:
namespace ns1
domain example.com
match uri /abc
1. To list an object and get its characteristics:
namespace ns1 object list /abc/def/file.flv
2. To delete an object with the same URL:
namespace ns1 object delete /abc/def/file.flv
3. To delete all the objects in that namespace’s disk cache with the same URL:
namespace ns1 object delete all
4. List all the first 50 objects in that disk cache and create a file named with the UUID of the
namespace listing all cached objects for that namespace. In the example, if the
namespace had a UUID of 80213A2C, the file containing the list is 80213A2C.lst.
Note! Only the first 50 cached objects are listed; if there are more than 50, use the upload
command. See “
namespace ns1 object list all
upload object list <namespace> <SCP>
5. You can also list and delete based on patterns. For example; you can specify *.flv as a
pattern. Media Flow Controller does not support a full Regular Expression for deleting or
listing. The command namespace ns1 object list all is equivalent to namespace ns1
object list /abc/def/*.
Terminology” on page 30 for the scp URL format).
Using namespace for Live Streaming Delivery Without Caching
An example namespace configuration to deliver live streaming objects without caching is
given; the delivery protocol and live-pub-point commands both enter you to prefix mode.
namespace <name>
match uri <uri-prefix>
origin-server rtsp <IP_address | hostname> [port]
status active
delivery protocol rtsp
exit
live-pub-point <pp_ name>
receive-mode on-demand
status active
exit
exit
86 Creating a Namespace and Setting Namespace Options (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 87

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Using namespace for Live Streaming Delivery With Caching
An example namespace configuration to deliver live streaming objects with caching is given;
the delivery protocol and live-pub-point commands both enter you to prefix mode.
namespace <name>
match uri <uri-prefix>
origin-server rtsp <IP_address | hostname> [port]
status active
delivery protocol rtsp
exit
live-pub-point <pp_ name>
receive-mode on-demand
status active
caching enable
exit
exit
Using namespace for Proxy Configurations
You can use namespace settings to configure Media Flow Controller to operate as a proxy in
various ways.
• Reverse Proxy—Setting namespace origin-server to <FQDN> or server-map implies a
reverse proxy configuration. Media Flow Controller as an edge cache is effectively a
reverse proxy that reduces network and CPU load on an origin server by serving
previously-retrieved content, and enhances user experience by decreasing latency.
• Mid-Tier Proxy—Setting namespace origin-server to absolute-url implies a mid-tier
proxy configuration. As a mid-tier proxy, Media Flow Controller must be explicitly
configured in the browser to intercept all requests. After Media Flow Controller receives
traffic from the client, it separates the traffic; cacheable requests are sent via Media Flow
Controller for performance enhanced delivery. Non-cacheable requests are tunnelled. See
also “
Configuring Media Flow Controller Mid-Tier Proxy (CLI)” on page 203.
• Transparent Proxy—Setting namespace origin-server to follow header HOST or X-
NKN or follow dest-ip (with or without the use-client-ip argument) implies a transparent
proxy configuration. A transparent proxy is one that requires no browser configuration and
is not readily visible to end-users. As a transparent proxy where origin-server access is
derived from the HOST header, the X-NKN header, or the destination IP address given in
the incoming request, explicit origin-server configuration is disallowed. Use this as an
alternate to providing a single origin server address. Be sure that delivery protocol http
allow-req is set to all (default). See also Example: Transparent Proxy Namespace
Configuration, after Table 10.
Creating a Namespace and Setting Namespace Options (CLI) 87
Page 88

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Table 10, gives details on the configurations and defaults per proxy deployment.
Table 10 Namespace origin-server and origin-request Dependencies per Proxy Deployment
origin-server setting
Proxy Mode
default for origin-request
For origin...
host header inherit incoming-req
Reverse http <FQDN> Specified
deny
Reverse http server-map Server-map
deny
Reverse nfs <FQDN:path> NFS mount
permit
Reverse nfs server-map Server-map
permit
Mid-Tier http absolute-url Client request
permit
Transparent
(origin based on
HOST header)
Transparent (origin
based on X-NKN
or custom header)
Transparent (origin
based on client
destination IP)
Transparent http follow dest-ip use-client-ip Client request
http follow header HOST HOST header
permit
http follow header <name> use-client-ip Specified
permit
http follow dest-ip Client request
permit
permit
FQDN
HTTP mount
point
point
NFS mount
point
absolute URL
value
header
destination IP
destination IP
Source IP for
Cache Miss
Media Flow
Controller IP
address
Media Flow
Controller IP
address
None
(NFS mounted)
None
(NFS mounted)
Media Flow
Controller IP
address
Media Flow
Controller IP
address
Client IP address DNS resolved IP address of
Media Flow
Controller IP
address
Client IP address No DNS resolution. Origin IP
Destination IP for
Cache Miss
DNS resolved IP address of
FQDN
DNS resolved IP address of
server-map origin-server
None (NFS mounted)
None (NFS mounted)
DNS resolved IP address of
origin-server chosen from
the client request
DNS resolved IP address of
the origin-server from the
HOST header
the origin-server from the
given header
No DNS resolution. Origin IP
is client destination IP
is client destination IP
Important! If a non-default origin-request host header inherit incoming-req value is
configured against an origin-server setting, the behavior is undefined and no error or warning
is issued. For example, if origin-server http absolute-url is set (Mid-Tier proxy), and you set
origin-request host-header inherit incoming-req deny, the behavior is undefined.
Example: Transparent Proxy Namespace Configuration
In Release 2.0.4, some namespace configurations are required for a transparent proxy;
specifically, you must set proxy-mode transparent on-ip. Note! The non-default delivery
protocol http origin-request option values given are set automatically when proxy-mode
transparent on-ip is configured. The value shown for origin-fetch content-store media
object-size is only a recommendation; default value is 0 (zero).
namespace tproxy
match uri / precedence 1
origin-server http follow dest-ip use-client-ip
88 Creating a Namespace and Setting Namespace Options (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 89

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
proxy-mode transparent on-ip <IP_address_of_your_interface>
delivery protocol http
origin-request x-forwarded-for disable
origin-request host-header inherit incoming-req permit
origin-fetch content-store media object-size 32768
status active
exit
exit
Using namespace match virtual-host
You can specify a virtual host for the namespace match criteria; see Virtu al Host for
definition. To do this, enter the IP address of the virtual host and, optionally, a port number;
you can also set a precedence, if needed. In this configuration, the incoming session's
destination IP is used to find the match to the namespace. In order for the match to be based
only on destination IP you should set domain to any. In that way, the incoming session's
destination IP and destination port (if given) are used to match to the namespace. Examples,
from namespace prefix mode:
• Match all sessions whose destination IP is 10.1.1.1 to the namespace:
match virtual-host 10.1.1.1
• Match all incoming HTTP REQ with destination IP 10.1.1.1 and port 8080 to this
namespace:
match virtual-host 10.1.1.1:8080
• M at ch all inc om in g RE Q on de stin at ion por t 80 80 to this nam esp ace:
match virtual-host 0.0.0.0:8080
Configuring Media Flow Controller Namespaces (CLI)
Configure namespaces to set fine-grained delivery policies; every Media Flow Controller
deployment must have at least one namespace, and usually several.
To configure a namespace:
1. Configure a namespace with a name (enters you to namespace configuration mode, use
exit when finished); optionally inherit another namespace’s cache or UUID. Use show
namespace list to find namespace UUIDs. See namespace for CLI details.
namespace <name> [cache-inherit <namespace:UUID>]
2. Configure domain settings (default is any). Note! The domain you enter should match
whatever you have configured as HOST header, unless using regex; you may append a
port number as well if needed (and used in HOST header). See “
domain regex” on page 82 and “Using namespace domain <FQDN:Port>” on page 83 for
details.
domain {any | <FQDN> | regex <regex>}
3. Configure origin-server settings (example uses http); multiple origin servers can be
configured with the server-map option; port specification is optional. See “
Configuring Server-Maps (CLI)” on page 79, for more information. See (namespace)
origin-server for CLI details.
origin-server
http {absolute-url | follow {header <header> [use-client-ip] | dest-ip
[use-client-ip]} | server-map <map_name> | <FQDN/path> [<port>]}
Using namespace
Creating and
Creating a Namespace and Setting Namespace Options (CLI) 89
Page 90

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
nfs {<FQDN:export_path> [<port>] | server-map <name>}
rtsp {<FQDN> [<port#>]} [alternate <string> [<port#>]]
4. Configure match criteria options (determines the URI to cache). All match options may
utilize the precedence argument to break ties when namespaces are defined with the
same match criteria. See “
Using namespace match <criteria> precedence” on page 84,
for details.
match
header {<header> | regex <regex>} [precedence <number>]
query-string {<name> | regex <regex>} [precedence <number>]
uri <uri-prefix> | regex <regex>} [precedence <number>]
virtual-host <IP_address> [<port>] [precedence <number>]
• header— (http only) A header name and value; can also be a regex. Optionally , set a
precedence.
• query-string—(http only) A defined query param; can also be a regex. Optionally,
set a precedence.
• uri—A <uri-prefix>; can als o be a regex. See “
uri-prefix” on page 34 for uri-prefix
definition and usage details. Optionally, set a precedence.
• virtual-host—The IP address must be a /32 address; it can take a special value of
0.0.0.0, which means any IP address. Port number specification is optional. To map
requests by TCP port number only, set the IP address to 0.0.0.0 and configure the port
number. If you set the domain to any, configure virtual-host IP to 0.0.0.0, then
requests can be assigned to a namespace based solely on the port number on which
the request comes in to Media Flow Controller. Optionally, set a precedence.
Note! All regex values should be enclosed in single quotes; for example, a regex for
www.example.com plus example.com could be this: ‘^.*\example\.com’.
5. Configure delivery protocol options; only origin-fetch options are available for rtsp.
Note! To enable delivery protocol rtsp, press enter after rtsp; then set RTSP options.
• client-request [cookie | query-string]—(http only) Optionally, set an action,
whether or not to cache (default), for cookies or objects with a query-string (such
objects are typically dynamic and often not ap propriate for caching). F or query-string
you can also opt to not cache the query-string itself.
client-request [cookie | query-string] action {cache [exclude-querystring] | no-cache}
• client-response—(http only) Optionally, configure client-response header actions.
Up to sixteen client-response headers and actions may be specified.
client-response header <name> [<value>] action {add | delete}
• origin-fetch—Optionally, configure origin-fetch parameters for data fetched from
origin, including managing the cache, and modifying the Date header. See
(namespace) delivery protocol {http | rtsp} origin-fetch for CLI details.
origin-fetch
cache-age {content-type<string> <seconds> | content-type-
any<seconds>}
cache-age-default <seconds>
cache-directive no-cache {follow | override}
content-store media [cache-age-threshold<seconds>] [object-
size<bytes>]
date-header modify {deny | permit}
• origin-request—(http only) Optionally, configure param eters for dat a requeste d from
origin. See (namespace) delivery protocol http origin-request for CLI details.
90 Creating a Namespace and Setting Namespace Options (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 91

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Note! Set origin-request host-header inherit incoming-req in accordance with the
origin-server setting; see Table 10, “
Namespace origin-server and origin-request
Dependencies per Proxy Deployment for CLI details. Use x-forwarded-for to allow
(with enable) or disallow (with disable) setting the X-Forwarded-For header to the
client IP address; default is enable.
origin-request
cache-revalidation {deny | permit}
header <name> [<value>] action add ...
host-header inherit incoming-req {deny | permit}
x-forwarded-for {disable | enable}
Example:
test-vos (config) #
test-vos (config namespace test)
test-vos (config namespace test)
test-vos (config namespace test) # match uri / precedence 3
test-vos (config namespace test)
test-vos (config namespace test delivery protocol http) #
action no-cache
test-vos (config namespace test delivery protocol http) #
Location action delete
test-vos (config namespace test
cache-age-default 14400
test-vos (config namespace test
forwarded-for enable
test-vos (config namespace test
test-vos (config namespace test) # exit
namespace test
#
domain any
#
origin-server http example.com/video
#
delivery protocol http
client-request cookie
client-response header
delivery protocol http
delivery protocol http
delivery protocol http
) # origin-fetch
) # origin-request x-
) # exit
6. Optionally, make live-pub-point settings if needed for live streaming.
• caching—Enable caching for this service (default is disabled).
• receive-mode—Set a method for receiving live streaming:
• on-demand—When a request is received.
• sdp-name <URL>—Use an SDP (service delivery protocol) file to set the live
publishing point. The URL can be scp://... or http://... only. After Media Flow
Controller encounters this, it pulls in the file from the specified location, and saves
it in the file system (not disk cache) so it is available for RTP/RTSP. Optionally,
choose immediate, to start as soon as the file is retrieved or enter a start-time
and, optionally, an end-time. See “
format).
• status—Make active or inactive the live-pub-point.
7. Set parameters for pre-staging content from origin; authentication schemes must be preconfigured to be used. See namespace for CLI details. The ftp user is auto-generated as
<namespace>_ftpuser, without a password (login disallowed). Set the password here;
this entry overrides a user <namespace>_ftpuser password setting. Verify with show
usernames. Remove set password with no pre-stage ftp user <user_name>.
pre-stage ftp user <name> password {RADIUS | TACACS | <password>
[encrypt]}
Example:
test-vos (config namespace test) # domain any
test-vos (config namespace test) # origin-server http example.com/video
test-vos (config namespace test) # pre-stage ftp user test_ftpuser
password 678
Terminology” on page 30 for the scp URL
Creating a Namespace and Setting Namespace Options (CLI) 91
Page 92

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
test-vos (config namespace test) # show usernames
USERNAME FULL NAME CAPABILITY ACCOUNT STATUS
admin System Administrator admin No password required for login
cmcrendv CMC Rendezvous User cmcrendv Local password login disabled
monitor System Monitor monitor No password required for login
test_ftpuser ftpuser Password set
test-vos (config namespace test) # no pre-stage ftp user test_ftpuser
test-vos (config namespace test) # show usernames
USERNAME FULL NAME CAPABILITY ACCOUNT STATUS
admin System Administrator admin No password required for login
cmcrendv CMC Rendezvous User cmcrendv Local password login disabled
monitor System Monitor monitor No password required for login
test_ftpuser ftpuser
Local password login disabled
8. Also optional, add an existing virtual-player to the new namespace.
virtual-player <name>
9. Activate the namespace. Verify configurations with show namespace <name>.
status active
10. Type exit to leave namespace configuration mode.
Example:
test-vos (config namespace test) # virtual-player test
test-vos (config namespace test) # status active
test-vos (config namespace test) # exit
Note! Configuration changes, including a namespace deletion, may not be updated for up to
30 seconds. This is due to a deferred update scheme that requires an HTTP request. An
internal probe ensures that such a request occurs at least every 30 seconds.
Managing the Media Flow Controller Disk Cache (CLI)
The media caches/disks are active and enabled by defau lt and typically require no config uring.
However, you must deactivate and disable disks and caching to change disks. Before you
activate or enable a cache, run show media-cache disk list and get the name assigned to
the disk to use in configuration. See media-cache for CLI details.
Media Flow Controller supports 3 cache tiers corresponding to SSD (tier 1), SAS HDD (tier 2),
and SATA HDD (tier 3). "Hot" content generally stays in tier1 (the highest). Media Flow
Controller promotes contents between the cache tiers based on content hotness (see “
Content (Short Tail vs. Long Tail)” on page 31 for definition). As content gets hotter, it is
promoted to the next higher tier. 1st time content is always put in the lowest cache tier. The
default values are: tier1 weight = 6, tier2 weight = 2, tier3 weight = 1. So, any content
requested once is cached in Tier 3; requested twice and it is promoted to Tier2; and, if
requested 6 times, it is promoted to Tier1.
• “Analyzing the Disk Cache” on page 93
• “Disk Cache Problems” on page 94
• “Replacing Bad Disks” on page 95
92 Managing the Media Flow Controller Disk Cache (CLI) Copyright © 2010, Junipe r Networks, Inc.
“Hot”
Page 93

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Analyzing the Disk Cache
When Media Flow Controller is having caching issues, you want to check the disk cache. To
analyze the media disk cache:
1. Get system-assigned disk names to use in configuration. Use list to view all disk drives,
their names, physical location, seri al number, type, and capacity. Use cache_name to
view information on the specified cache.
show media-cache disk {list |<cache_name>}
show media-cache disk list
Example:
test-vos (config) # show media-cache disk list
show media-cache disk list
Device Type Tier Active Cache Free Space State
------ ---- ---- ------ ----- ---------- ----dc_1 SATA Tier-3 yes yes 38890 MiB cache running
dc_2 SATA Tier-3 yes yes 68668 MiB cache running
Total Free Space: 107486 MiB
test-vos-cl66 (config) # show media-cache disk dc_1
Disk Cache Configuration & Status:
Device Name/Type: dc_1/SATA
Cache Tier: Tier-3
Activated: yes
Cache Enabled: yes
Free Space: 2304 MiB
Disk State : cache running
-------------------------------------
2. Determine the fre e block th re sh old s of th e disk cache s.
show media-cache free-block threshold
3. Disable a disk if you need to pull the disk for any maintenance purposes; for example, to
upgrade to a higher capacity disk, replace a SATA disk with a SAS disk, replace a failed
disk, reformat the disk, or if contents should not be cached.
media-cache disk <cache_name> cache disable
4. Deactivate a disk cache. Media Flow Controller allows OIR (On-line Insertion and
Removal) of HDD (Hard Disk Drives). However, the HDD MUST be made inactive to be
removed. When a new HDD is in the disk, it must be made active and (if so decided)
enabled for caching.
media-cache disk <cache_name> status inactive
5. Put in a new drive and mount it.
media-cache disk mount-new
6. Find the new (inactive) disk’s name.
show media-cache disk list
7. Activate or re-activate a media-cache disk.
media-cache disk <cache_name> status active
8. Format the disk if it is newly inserted and empty or you do not want to use its contents. Do
this after you issue the mount command.
media-cache disk <cache_name> format
Managing the Media Flow Controller Disk Cache (CLI) 93
Page 94

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
9. Enable or re-enable a disk for caching.
media-cache disk <cache_name> cache enable
Example:
test-vos (config) # show media-cache disk list
Device Type Tier Active Cache Free Space State
------ ---- ---- ------ ----- ---------- ----dc_1 SATA Tier-3 yes yes 38890 MiB cache running
dc_2 SATA Tier-3 yes yes 68668 MiB cache running
Total Free Space: 107486 MiB
test-vos (config) # media-cache disk dc_2 cache disable
Disk Cache Disabled
test-vos (config) # media-cache disk dc_2 status inactive
Disk Deactivated
test-vos (config) # media-cache disk mount-new
Message sent to detect for new disks
Please check disk state for status
test-vos (config) # show media-cache disk list
Device Type Tier Active Cache Free Space State
------ ---- ---- ------ ----- ---------- ----dc_1 SATA Tier-3 yes yes 38890 MiB cache running
dc_2 SATA Tier-3 no no - disk has been deac
tivated
Total Free Space: 107486 MiB
test-vos (config) # media-cache disk dc_2 status active
Disk Activated
test-vos (config) # media-cache disk dc_2 format
Disk Formatted
test-vos (config) # media-cache disk dc_2 cache enable
Disk Cache Enabled
test-vos (config) # show media-cache disk list
Device Type Tier Active Cache Free Space State
------ ---- ---- ------ ----- ---------- ----dc_1 SATA Tier-3 yes yes 38890 MiB cache running
dc_2 SATA Tier-3 yes yes 68668 MiB cache running
Total Free Space: 107486 MiB
Disk Cache Problems
These are the disk state messages you might get when managing the media-cache disk.
DM2_MGMT_STATE_CACHEABLE = "disk cacheable, but cache not enabled"
DM2_MGMT_STATE_INVAL_FORMAT_BEFORE_MOUNT and
DM2_MGMT_STATE_FORMAT_UNKNOWN_AFTER_MOUNT = "disk has wrong format
hence not cacheable"
DM2_MGMT_STATE_DEACTIVATED = "disk has been deactivated";
DM2_MGMT_STATE_ACTIVATED = "disk has been activated";
94 Managing the Media Flow Controller Disk Cache (CLI) Copyright © 2010, Junipe r Networks, Inc.
Page 95

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
DM2_MGMT_STATE_IMPROPER_UNMOUNT and
DM2_MGMT_STATE_IMPROPER_MOUNT = "soft disk error, try to clear"
DM2_MGMT_STATE_CACHE_RUNNING = "cache running";
DM2_MUST_FORMAT = “Disk Cache Enable Failed - Disk Cache must be form atted before
enabling”
DEFAULT = "unknown state, please try again a little later";
When a disk cache error is displayed, a first step to take is bringing down the disk and bringing
it back up; to do, first find cache names, then act on the problem cache:
show media-cache disk list
media-cache disk <cache_name> status inactive
media-cache disk <cache_name> status active
media-cache disk <cache_name> enable
Replacing Bad Disks
In order to replace a bad disk, first disable and inactivate the disk, and then add a new disk.
This procedure uses dc_bad for the disk name; replace appropriately.
1. Discover the bad disk’s name.
show media disk list
2. Disable the bad disk by name.
media-cache disk dc_bad cache disable
3. Make the bad disk inactive.
media-cache disk dc_bad status inactive
4. Pull the drive, put in a new drive and mount the new disk.
media-cache disk mount-new
5. Find the inactive disk’s name.
show media-cache disk list
6. Activate the new disk .
media-cache disk dc_new status active
7. Format the new disk ; takes approximately five minutes.
media-cache disk dc_new format
8. Enable the new disk .
media-cache disk dc_new cache enable
Important! This procedure will not work when adding a new disk or disks to a Juniper
Networks VXA Series to a slot that was never configured. In such a case, please follow the
instructions in the VXA Series hardware guides for adding a new disk using the Adaptec Utility
or see “
Inserting New Disks into a VXA Series Media Flow Engine” on page 95.
Inserting New Disks into a VXA Series Media Flow Engine
The task “Replacing Bad Disks” on page 95 is incorrect for VXA Series hardware when adding
one or more new disks to a slot that was never used (configured) before because Media Flow
Controller only searches for new disks at manufacture time. Use this procedure instead.
Managing the Media Flow Controller Disk Cache (CLI) 95
Page 96

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
To add a disk, or disks, on a VXA Series Media Flow Engine to an unconfigured slot:
1. From Enable or Configuration mode in the CLI, check the current drive list; you may
want to note the drives you have installed:
show media-cache disk list
2. Insert the new disks and reboot:
reload
3. When you are prompted to open the Adaptec Utility, press Ctrl+a to open the utility.
The Adaptec Utility menu is displayed.
4. Select Array Configuration Utility.
The Configuration Change confirmation window is displayed.
5. Select Accept.
The Configuration Utility Main menu is displayed.
6. Use the arrow keys to select Initialize Drives, and press Enter.
A list of discovered drives is displayed.
7. Select the drive or drives that you added, and press Enter.
A warning message is displayed.
If you are unsure which drives to select, you can use the Esc key to exit to the
Adaptec Utility menu and use the Disk Utilities function to identify the drives.
8. Enter Yes.
An Initializing is Done message is displayed.
9. Press any key to continue.
The Configuration Utility Main menu is displayed.
10. Select Create JBOD, and press Enter.
A drives list is displayed.
11. Select the new drives, and press Enter.
A confirmation window is displayed.
12. Enter Yes.
The Adaptec Utility menu is displayed.
13. Press Esc to exit the Adaptec Utility.
The system reboots automatically.
14. Using the Media Flow Controller CLI, mount the new disks and activate them:
media-cache disk mount-new
show media-cache disk list
media-cache disk <disk_name> activate
15. Verify the new disks are properly mounted:
show media-cache disk list
Note! The documented disk replacement procedure for replacing a bad disk on VXA Series
works correctly provided that Media Flow Controller can still identify the disk (show mediacache disk list).
96 Managing the Media Flow Controller Disk Cache (CLI) Copyright © 2010, Junipe r Networks, Inc.
Page 97

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Installing and Using FMS in Media Flow Controller (CLI)
Before you configure FMS in Media Flow Controller, see “Before You Configure Media Flow
Controller” on page 58.
Media Flow Controller has the ability to work with Adobe Flash Media Server (FMS) to stream
Flash videos over Real Time Messaging Protocol™ (RTMP).
FMS RTMP delivery service listens on Transmission Control Protocol (TCP) port 1935; the
FMS administration service listens on TCP port 1111. RTMP is a proprietary protocol
developed by Adobe Systems for streaming audio, video and data over the Internet, between
a Flash player and a server.
• “Installing FMS on Media Flow Controller (CLI)” on page 97
• “Modifying and Restarting the FMS Service (CLI)” on page 99
• “Configuring the FMS Admin Console—First Time (CLI)” on page 100
• “Configuring FMS on Media Flow Controller for Video On Demand (CLI)” on page 100
• “Applying the Adobe Full-Function FMS Server License (CLI)” on page 103
Installing FMS on Media Flow Controller (CLI)
To install FMS, you must first download the image; you can do this directly from Adobe (the
“Development Server” version, available for free, is adequate for this procedure, but it is
limited to 10 simultaneous streams). First download the image to a Web or F TP/SCP serv er to
which you have access. Use these CLI commands at the (config) # prompt (must have adm in
privileges and enter enable and then configure terminal first):
application fms download <URL_of_FMS_image>
application fms install <name_of_FMS_image>
The download command downloads the image given in the URL (SCP, HTTP, or FTP) to the
directory /nkn/adobe/downloads directory that is visible in th e FMS shell. See “
on page 30 for the scp URL format).
The install command shows files in the FMS download directory and, when the install image
is given, interactively installs FMS.
Important! It is critical that a few of the installation questions are answered with the correct
values; be sure to use these values as indicated in the following step procedure.
1. Accept the license agreement and enter your FMS server serial number or leave blank
and press Enter to install the FMS Development Server. The FMS Development Server is
free, but limited to 10 simultaneous streams.
Do you agree with the license agreement? (y/n): y
Please enter your Flash Media Server 3.5 serial number.
You have not entered a serial number. Falling back to the Adobe Flash
Media Development Server!
Would you like to try again? y/n: Default [n]: n
Adobe Flash Media Server 3.5 requires approximately 200MB of disk space.
2. Enter the correct directory for the installation, /nkn/adobe/fms.
Terminology”
The installer will install Adobe Flash Media Server 3.5 in the following
directory. Default [/opt/adobe/fms]: /nkn/adobe/fms
Installing and Using FMS in Media Flow Controller (CLI) 97
Page 98

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
3. If you get a previous installation warning, overwrite it.
WARNING: The installer has detected a previous installation.
Do you want the installer to overwrite the previous installation with this
installation or quit this installer? (y/q) Default [y]: y
4. Enter the port on which the FMS is to communicate, 1935.
The Adobe Flash Media Server communicates on the IANA-assigned port of
1935, which is the port most Flash applications expect, and can also
communicate on port 80, both for tunneling Flash over HTTP, and for
proxying HTTP to a webserver.
Please enter the Adobe Flash Media Server port(s), comma-separated Defaul t
[1935,80]: 1935
5. Enter the port on which the FMS Admin service is to run, 1111.
Please enter the port to use for the Admin service. You can only specify
one admin port. Default [1111]: 1111
6. Enter credentials for using the FMS Admin Console. Example uses admin / admin.
The administrative user name and password you provide here is required to
use the Adobe Flash Media Server Management Console for administration,
monitoring, and debugging.
Please enter the administrative username: admin
Please enter the administrative password:
Please do not enter a blank password.
Please enter the administrative password: *****
Confirm password: *****
7. Enter a username for the user the FMS is to run as; Media Flow Controller requires this to
be admin.
When the Adobe Flash Media Server service is started, the service can be
run as a user other than "root". The server would change to this user when
the server is started and has acquired its ports.
Please enter the user that the Adobe Flash Media Server service will run
as Default user [nobody]: admin
8. Enter a group for the FMS service user; Media Flow Controller requires this to be admin.
Please enter a valid user group for the "admin" user: Default group
[admin]: admin
9. Decline Apache installation.
Do you want to install apache? (y/n) Default [y]: n
10. Decline FM S ru nn ing as a da em o n.
Do you want the Adobe Flash Media Server service to run as a daemon? (y/n)
Default [y]: n
11 . Decline starting FMS after this installation.
Do you want to start the Adobe Flash Media Server after the installation
is done? (y/n) Default [y]: n
----------- Install Action Summary ----------WARNING: You have chosen to overwrite a previous installation.
Installation directory = /nkn/adobe/fms
Flash Media Server Port = 1935
98 Installing and Using FMS in Media Flow Controller (CLI) Copyright © 2010, Juniper Networks, Inc.
Page 99

Media Flow Controller Administrator’s Guide Media Flow Controller Configuration Tasks (CLI)
Flash Media Admin Server Port = 1111
Administrative username = admin
Administrative password = (suppressed)
service owner = admin
service user = admin
service group = admin
12. Finish the installation.
Proceed with the installation? (y/n/q): y
Modifying and Restarting the FMS Service (CLI)
You must manually configure two FMS files. If any configuration changes are made to FMS,
including installation, the FMS services need to be restarted.
1. Modify the FMS server and adminserver files using vi. To do this, first log in to the FMS
shell from the CLI config mode in Media Flow Controller:
application fms shell
2. Locate the server and adminserver files and edit them as indicated; for this line:
if [ "X$USERID" != "Xroot" ]; then
Change to:
if [ "X$USERID" != "Xadmin" ]; then
Example:
test-vos # enable
test-vos # configure terminal
test-vos (config) # application fms shell
BusyBox v1.00 (2008.12.21-08:07+0000) Built-in shell (ash)
Enter 'help' for a list of built-in commands.
# ls
fms lib bin
# cd fms
# ls
documentation tcSrvMsg fmsadmin.pid
applications uninstallFMS modules
auto_fms_start_enabled fmsmgr tools
shmrd logo.gif dh1024.pem
fmsmaster.pid logs scriptlib
licenses conf fmscore
fmsmaster fmsadmin libasneu.so.1
server webroot readme.htm
License.htm samples dh512.pem
touch tmp adminserver
License.txt fmsedge
3. Exit the FMS shell by typing exit; the window closes and you must open a new session to
Media Flow Controller.
4. In the new Media Flow Controller session, enter config mode and restart FMS:
service restart mod-rtmp-admin
service restart mod-rtmp-fms
Installing and Using FMS in Media Flow Controller (CLI) 99
Page 100

Media Flow Controller Configuration Tasks (CLI) Media Flow Controller Administrator’s Guide
Configuring the FMS Admin Console—First Time (CLI)
The FMS Admin Console allows you to monitor and manage FMS activity, including the
current FMS user sessions, streams, and performance. The Media Flow Controller Webbased Management Console lets you monitor only the delivery of the files configured under
VOD.
Note! Do not use your Media Flow Controller as a Web server for the FMS Admin Console.
To use the FMS Admin Console to monitor FMS activity, you need to copy three files under
the FMS installation directory to the doc root of your origin-server; We recommend placing
these files in a directory separate from your FMS video files directory.
1. To obtain the three files, you can download the FMS Development Server to your originserver and unpack it.
2. You can locate the thr ee files you need in the fms/webroot dire ctory of the unpacked FMS
Development Server tarball:
/fms_adminConsole.htm
/resources/AC_RunActiveContent.js
/swfs/fms_adminConsole.swf
Copy these three files to your doc root (/var/www/ht ml ) in a directo ry yo u cre a te ; for
example fmsAdmin.
3. Open a browser to your Media Flow Controller using this URL (example uses fmsAdmin):
http://<IP_address_of_origin-server>/fmsAdmin/fms_adminConsole.htm
4. Login with the FMS Admin Console credentials you configured in step 6 of “Installing FMS
on Media Flow Controller (CLI)” on page 97 and the IP address of your Media Flow
Controller for Server Address.
5. Complete FMS setup on Media Flow Controller by following the instructions given in
“
Configuring FMS on Media Flow Controller for Video On Demand (CLI) .”
The advantage to installing the FMS Admin Console before FMS configuration is complete is
that, when FMS configuration on Media Flow Controller is complete, you can immediately
check the installation via the FMS Admin Console. Otherwise, you must send appropriately
defined traffic and verify FMS processing through the Media Flow Controller. You can do this
either by looking at the logs and graphs in the Media Flow Controlle r Web-based Mana gement
Console or by using show counters at the CLI to observe FMS traffic.
Configuring FMS on Media Flow Controller for Video On Demand (CLI)
To configure FMS for video on demand (VOD), log in to the FMS shell from the CLI config
mode in Media Flow Controller:
application fms shell
This CLI command takes you to the FMS installation directory and from there, all FMS
configuration changes can be done. The configuration entails creating a Media Flow Controller
FMS directory and namespace or namespaces.
When an RTMP request comes to FMS, it scans the configuration file in the application
directory /fms/applications to find the requested file. You configure Media Flow Controller
namespace to correspond with the configuration of VOD_DIR.
100 Installing and Using FMS in Media Flow Controller (CLI) Copyright © 2010, Juniper Networks, Inc.
 Loading...
Loading...