Page 1

IFS NS2503-24P/2C User
Manual
P/N 1072568 • REV 00.07 • ISS 31JAN13
Page 2
Copyright
© 2013 UTC Fire & Security Americas Corporation, Inc.
Interlogix is part of UTC Climate Controls & Security, a unit of United
Technologies Corporation. All rights reserved.
Trademarks and patents
The IFS NS3601-24P/4S GE-DSSG-244 GE-DSSG-244-POE and logo
are trademarks of United Technologies.
Other trade names used in this document may be trademarks or
registered trademarks of the manufacturers or vendors of the respective
products.
Intended use
Use this product only for the purpose it was designed for; refer to the
data sheet and user documentation for details. For the latest product
information, contact your local supplier or visit us online at
www.interlogix.com.
Manufacturer
UTC Fire & Security Americas Corporation, Inc.
2955 Red Hill Avenue
Costa Mesa, CA 92626-5923, USA
EU authorized manufacturing representative:
UTC Fire & Security B.V., Kelvinstraat 7,
6003 DH Weert, The Netherlands
Certification
N4131
FCC compliance
This equipment has been tested and found to comply with the limits for a
Class A digital device, pursuant to part 15 of the FCC Rules. These limits
are designed to provide reasonable protection against harmful
interference when the equipment is operated in a commercial
environment. This equipment generates, uses, and can radiate radio
frequency energy and, if not installed and used in accordance with the
instruction manual, may cause harmful interference to radio
communications.
You are cautioned that any changes or modifications not expressly
approved by the party responsible for compliance could void the user's
authority to operate the equipment.
ACMA compliance Notice! This is a Class A product. In a domestic environment this
product may cause radio interference in which case the user may be
required to take adequate measures.
Canada
This Class A digital apparatus complies with Canadian ICES-003.
Cet appareil numérique de la classe A est conforme á la norme
NMB-003du Canada.
European Union directives 2004/108/EC (EMC Directive): Hereby, UTC Fire & Security Americas
Corporation, Inc. declares that this device is in compliance with the
essential requirements and other relevant provisions of Directive
2004/108/EC.
2002/96/EC (WEEE directive): Products marked with this symbol
cannot be disposed of as unsorted municipal waste in the European
Union. For proper recycling, return this product to your local supplier
upon the purchase of equivalent new equipment, or dispose of it at
designated collection points. For more information see:
www.recyclethis.info.
Contact information
Contact support
For contact information see our Web site: www.interlogix.com
www.interlogix.com/customer support
.
Page 3

NS2503-24P/2C User Manual
TABLE OF CONTENTS
IFS NS2503-24P/2C USER MANUAL..............................................................................1
INTRODUCTION
Package Contents......................................................................................................................................8
Product Description...................................................................................................................................8
How to Use This Manual......................................................................................................................... 10
Product Features..................................................................................................................................... 11
Product Specification............................................................................................................................. 13
..............................................................................................................8
INSTALLATION..............................................................................................................15
Hardware Description............................................................................................................................. 15
Switch Front Panel.............................................................................................................................. 15
LED Indications................................................................................................................................... 16
Switch Rear Panel .............................................................................................................................. 18
Install the Switch..................................................................................................................................... 19
Desktop Installation ............................................................................................................................ 19
Rack Mounting.................................................................................................................................... 20
Installing the SFP transceiver............................................................................................................. 21
SWITCH MANAGEMENT...............................................................................................23
Requirements .......................................................................................................................................... 23
Management Access Overview.............................................................................................................. 24
Web Management.................................................................................................................................... 25
SNMP-Based Network Management ..................................................................................................... 26
Administration Console.......................................................................................................................... 26
Protocols.................................................................................................................................................. 28
Virtual Terminal Protocols .................................................................................................................. 28
SNMP Protocol ................................................................................................................................... 28
Management Architecture .................................................................................................................. 28
WEB-BASED MANAGEMENT.......................................................................................29
About Web-based Management............................................................................................................. 29
Requirements ..................................................................................................................................... 30
Logging on the Managed Switch ........................................................................................................ 30
Main WEB PAGE................................................................................................................................ 32
System...................................................................................................................................................... 34
System Information............................................................................................................................. 35
IP Configuration .................................................................................................................................. 38
Console Port Info ................................................................................................................................ 40
3
Page 4
NS2503-24P/2C User Manual
SNMP Configuration........................................................................................................................... 41
Syslog Setting..................................................................................................................................... 49
System Log......................................................................................................................................... 50
SNTP Setting ...................................................................................................................................... 51
Firmware Upgrade.............................................................................................................................. 52
Configuration Backup ......................................................................................................................... 54
Factory Default ................................................................................................................................... 56
System Reboot ................................................................................................................................... 56
Port Configuration .................................................................................................................................. 57
Port Control......................................................................................................................................... 57
Rate Control........................................................................................................................................ 59
Port Status .......................................................................................................................................... 60
Port Statistics...................................................................................................................................... 61
Port Sniffer.......................................................................................................................................... 62
Protect Port......................................................................................................................................... 64
Remote Ping ....................................................................................................................................... 65
VLAN configuration ................................................................................................................................ 66
VLAN Overview .................................................................................................................................. 66
Static VLAN Configuration.................................................................................................................. 68
Port-based VLAN................................................................................................................................ 69
802.1Q VLAN...................................................................................................................................... 71
GVRP VLAN ....................................................................................................................................... 76
Q-in-Q VLAN....................................................................................................................................... 79
Trunking................................................................................................................................................... 82
Aggregator setting .............................................................................................................................. 83
Aggregator Information....................................................................................................................... 84
State Activity ....................................................................................................................................... 88
Forwarding and Filtering........................................................................................................................ 89
Dynamic MAC Table........................................................................................................................... 89
Static MAC Table................................................................................................................................ 90
MAC Filtering ...................................................................................................................................... 91
IGMP Snooping ....................................................................................................................................... 92
Theory................................................................................................................................................. 92
IGMP Configuration ............................................................................................................................ 96
Static Multicast Table.......................................................................................................................... 98
Spanning Tree Protocol........................................................................................................................ 100
Theory............................................................................................................................................... 100
Illustration of STP ............................................................................................................................. 103
STP Parameters ............................................................................................................................... 104
4
Page 5
NS2503-24P/2C User Manual
STP System Configuration ............................................................................................................... 105
Port Configuration............................................................................................................................. 109
DHCP Relay & Option 82...................................................................................................................... 111
LLDP....................................................................................................................................................... 113
Port Configuration............................................................................................................................. 113
Per Port Configuration ...................................................................................................................... 114
Access Control List .............................................................................................................................. 115
Users Configuration.............................................................................................................................. 118
MAC Limit............................................................................................................................................... 121
MAC Limit Configuration................................................................................................................... 121
MAC Limit Port Status ...................................................................................................................... 122
802.1X Configuration............................................................................................................................ 123
Understanding IEEE 802.1X Port-Based Authentication.................................................................. 123
System Configuration ....................................................................................................................... 125
802.1x Port Configuration................................................................................................................. 127
Misc Configuration ............................................................................................................................ 128
QoS Configuration ................................................................................................................................ 129
Understand QoS ............................................................................................................................... 129
QoS Configuration ............................................................................................................................ 130
TOS/DSCP ....................................................................................................................................... 133
Power over Ethernet............................................................................................................................. 136
Power over Ethernet Powered Device.............................................................................................. 136
NS2503-24P/2C Power Management .............................................................................................. 137
PoE Schedule ................................................................................................................................... 141
CONSOLE MANAGEMENT.........................................................................................143
Login in the Console Interface............................................................................................................. 143
Configure IP address............................................................................................................................ 144
Commands Level .................................................................................................................................. 146
COMMAND LINE INTERFACE
Operation Notice ................................................................................................................................... 147
System Commands............................................................................................................................... 148
....................................................................................147
Switch Static Configuration................................................................................................................. 149
Port Configuration and show status.................................................................................................. 149
Trunk Configuration.............................................................................................................................. 152
Trunking Commands ........................................................................................................................ 152
LACP Command............................................................................................................................... 152
VLAN Configuration.............................................................................................................................. 154
Virtual LANs...................................................................................................................................... 154
VLAN Mode: Port-based................................................................................................................... 155
5
Page 6

NS2503-24P/2C User Manual
Advanced 802.1Q VLAN Configuration............................................................................................ 156
Misc Configuration................................................................................................................................ 159
Administration Configuration.............................................................................................................. 159
Change Username / Password......................................................................................................... 159
IP Configuration ................................................................................................................................ 160
Reboot switch ................................................................................................................................... 161
Reset to Default ................................................................................................................................ 161
TFTP Update Firmware .................................................................................................................... 161
Restore Configure File...................................................................................................................... 162
Backup Configure File ...................................................................................................................... 162
MAC limit................................................................................................................................................ 162
Port Mirroring Configuration................................................................................................................ 163
Quality of Service.................................................................................................................................. 164
QoS Configuration ............................................................................................................................ 164
Per Port Priority ................................................................................................................................ 165
MAC Address Configuration................................................................................................................ 165
STP/MSTP Commands.......................................................................................................................... 167
SNMP...................................................................................................................................................... 172
System Options ................................................................................................................................ 172
Community Strings ........................................................................................................................... 172
Trap Managers ................................................................................................................................. 173
IGMP....................................................................................................................................................... 173
802.1x Protocol...................................................................................................................................... 175
Access Control List .............................................................................................................................. 177
Ipv4 ACL commands ........................................................................................................................ 177
Non-Ipv4 ACL commands ................................................................................................................ 178
Binding................................................................................................................................................... 179
SIP/SMAC binding commands ......................................................................................................... 179
Power over Ethernet Commands......................................................................................................... 180
Display System PoE status .............................................................................................................. 180
Configure PoE Over Temperature Protection .................................................................................. 181
Configure PoE -- System.................................................................................................................. 182
Configure PoE -- Port ....................................................................................................................... 185
SWITCH OPERATION .................................................................................................188
Address Table........................................................................................................................................ 188
Learning................................................................................................................................................. 188
Forwarding & Filtering.......................................................................................................................... 188
Store-and-Forward................................................................................................................................ 188
Auto-Negotiation................................................................................................................................... 188
6
Page 7

NS2503-24P/2C User Manual
POWER OVER ETHERNET OVERVIEW.....................................................................189
What is PoE? ......................................................................................................................................... 189
The PoE Provision Process ................................................................................................................. 190
Stages of powering up a PoE link..................................................................................................... 191
Line Detection................................................................................................................................... 191
Classification..................................................................................................................................... 191
Start-up ............................................................................................................................................. 191
Operation .......................................................................................................................................... 191
Power Disconnection Scenarios....................................................................................................... 191
TROUBLE SHOOTING ................................................................................................193
APPENDIX A—RJ-45 PIN ASSIGNMENT
Switch's RJ-45 Pin Assignments......................................................................................................... 194
10/100Mbps, 10/100Base-TX ................................................................................................................ 194
...................................................................194
APPENDIX B: LOCAL USER ACCESS LEVEL TABLE .............................................196
7
Page 8
NS2503-24P/2C User Manual
Introduction
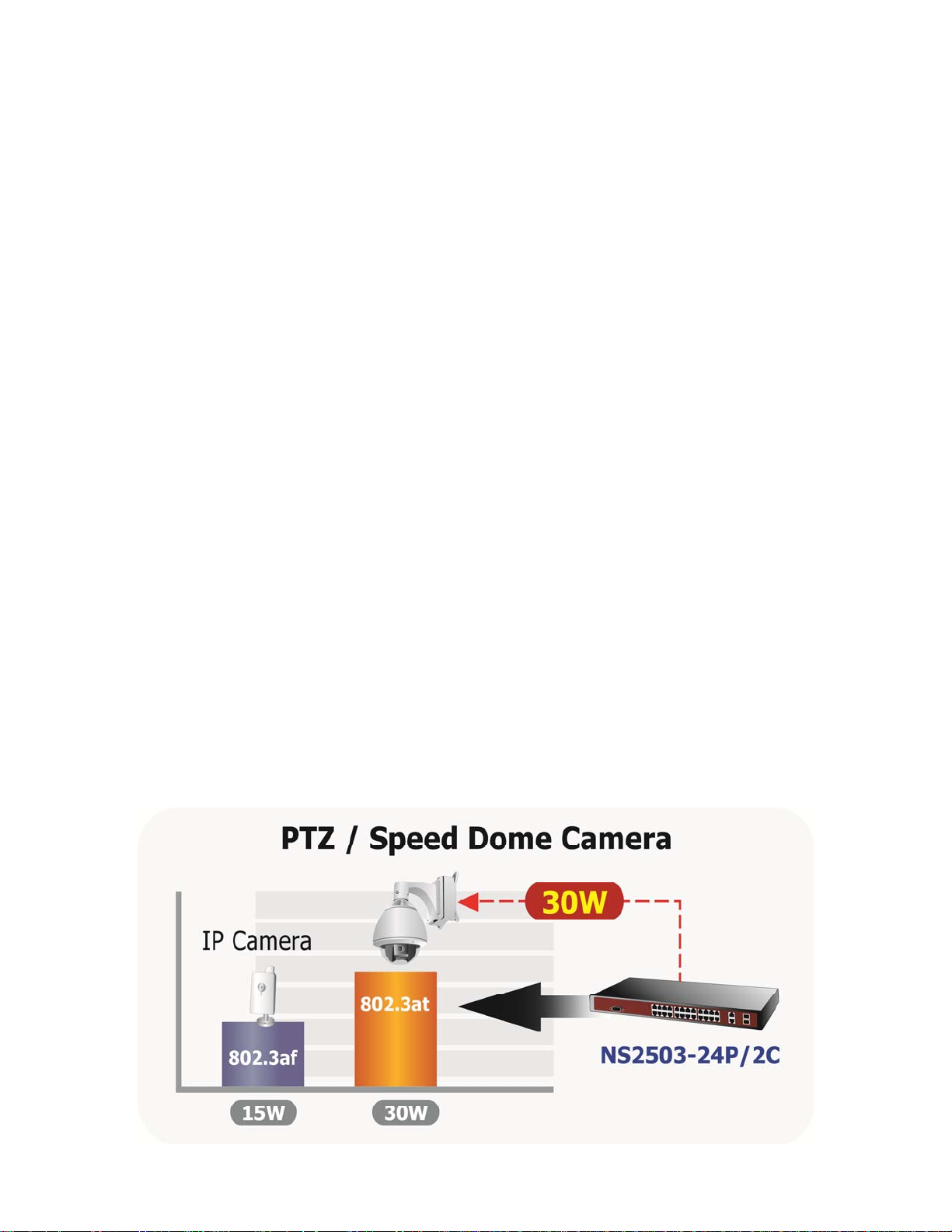
The IFS Layer 2 Managed Switch NS2503-24P/2C has 24 10/100Mbps 802.3at compliant PoE ports, with two Gigabit TP/SFP
fiber optical combo ports and robust layer 2 features. The NS2503-24P/2C also provides IEEE 802.3af / IEEE 802.3at Power
over Ethernet standards to meet requirements for various PoE applications.
Package Contents
Open the box of the Managed Switch and carefully unpack it. The box should contain the following items:
Check the contents of your package for following parts:
The Managed Switch
x1
Quick Installation Guide
User’s Manual CD
19” Rack mount Accessory Kit
Power Cord
Rubber Feet
RS-232 DB9 Male Console Cable
If any of these are missing or damaged, please contact your distributor or IFS sales rep immediately, if possible, retain the
original carton and packaging material in case you need to return the product for repair/replacement.
x1
x1
x1
x1
X4
x1
Product Description
Power over Ethernet
The PoE in-line power following the standard IEEE 802.3af and IEEE 802.3at enables the Managed Switch to power up to 24
IEEE 802.3af PoE devices or 11 IEEE 802.3at PoE devices at the distance of up to 100 meters through the 4-pair Cat 5/5e UTP
wire (assuming devices use max limits of these standards; i.e. 15W for 802.3af, and 30W for 802.3at).
Flexibile PoE System Management
Managed Switch not only provides more PoE management function than ever before but also provides better reliability. System
PoE Admin Mode feature offers user to switch PoE system mode between IEEE 802.3af and IEEE 802.3at easily and the
Temperature Threshold and PoE Usage Threshold provides more realiable control.
8
Page 9

NS2503-24P/2C User Manual
Cost-effective solution with SNMP mo nitor for Network deployment
Not only for catering to the need of easy WEB-based management but also the centralized SNMP application to monitor the
status of Managed Switch and traffic per port, the key features are as below:
802.3af / 802.3at PoE SNMP and 4 RMON groups
WEB / SSL / Telnet Access Control List
802.1Q / Q-in-Q VLAN IGMP Snooping
Multiple Spanning Tree Protocol
PoE Management / Alarm
High Performance Wire-Speed Switching
The Managed Switch is equipped with 24 10/100Mbps Fast Ethernet ports with 2 Gigabit TP/SFP combo ports (Port-25, 26).
The two Gigabit TP/SFP combo ports can be either 1000Base-T for 10/100/1000Mbps or 1000Base-SX/LX/BX through SFP
(Small Form-Factor Pluggable) interface. Managed Switch boasts a high performance switch architecture that is capable of
providing non-blocking switch fabric and wire-speed throughput as high as 8.8Gbps. Its two built-in GbE uplink ports also offer
incredible extensibility, flexibility and connectivity to the Core switch or Servers.
Remote and Centralize Management installation
With its built-in Web-based management, the Managed Switch offers an easy-to-use, platform-independent management and
configuration facility. The Managed Switch supports standard Simple Network Management Protocol (SNMP) and can be
monitored via any standard-based management software.
For efficient management, via WEB interface the Managed Switch can be programmed for basic switch management functions
such as port speed configuration, Port Trunking, VLAN, Port Mirroring, Rapid Spanning Tree and Misc Configuration.
Additionally, the firmware includes advanced features such as IGMP snooping, QoS (Quality of Service), broadcast storm and
bandwidth control, to enhance bandwidth utilization.
Powerful Security
The Managed Switch offers comprehensive Access Control List (ACL) for enforcing security to the edge. Its protection
mechanisms comprises of Port-based 802.1X user and device authentication. Moreover, the switch provides MAC filter and
Static MAC for enforcing security policies to the edge. The administrators can now construct highly secured corporate networks
with considerably less time and effort than before.
9
Page 10

How to Use This Manual
This User Manual is structured as follows:
Section 2, INSTALLATION
The section explains the functions of the Switch and how to physically install the Managed Switch.
Section 3, SWITCH MANAGEMENT
The section contains the information about the software function of the Managed Switch.
Section 4, WEB CONFIGURATION
The section explains how to manage the Managed Switch by Web interface.
Section 5, CONSOLE MANAGEMENT
The section describes how to use the Console management interface.
Section 6, COMMAND LINE INTERFACE
The section explains how to manage the Managed Switch by Command Line interface.
Section 7, SWITCH OPERATION
The chapter explains how to does the switch operation of the Managed Switch.
NS2503-24P/2C User Manual
Section 8, POWER OVER ETHERNET OVERVIEW
The chapter introduce the IEEE 802.3af / IEEE 802.3at PoE standard and PoE provision of the Managed Switch.
Section 9, TROUBSHOOTING
The chapter explains how to trouble shooting of the Managed Switch.
Appendix A
The section contains cable information of the Managed Switch.
10
Page 11
Product Features
Physical Port
24-Port 10/100Base-TX Fast Ethernet ports with IEEE 802.3af / IEEE 802.3at PoE injector
2 10/100/1000Base-T TP combo interfaces
2 1000Base-X mini-GBIC/SFP slots, shared with Port-25 and Port-26
Reset button for system management
1 RS-232 male DB9 console interface for Switch basic management and setup
Power over Ethernet
Complies with IEEE 802.3af / IEEE 802.3at Power over Ethernet End-Span PSE
Up to 24 IEEE 802.3af devices powered
Up to 11 IEEE 802.3at devices powered
Support PoE Power up to 15.4 Watts / 30 Watts for each PoE port
Auto detect powered device (PD)
Circuit protection to prevent power interference between ports
Remote power feeding up to 100m
PoE Management
IEEE 802.3af and IEEE 802.3at mode switch control
Total PoE power budget control
Per port PoE function enable/disable
PoE Admin-mode control
PoE Port Power feeding priority
PD classification detection
Over Temperature Protection function
Temperature Threshold Control
PoE Usage Threshold Control
NS2503-24P/2C User Manual
Layer 2 Features
Prevents packet loss Flow Control:
- IEEE 802.3x PAUSE Frame flow control for Full-Duplex mode
- Back-Pressure Flow Control in Half-Duplex mode
High performance of Store-and-Forward architecture, runt/CRC filtering eliminate erroneous packets to optimize the
network bandwidth
Broadcast / Multicast / Unicast storm control
8K MAC address table, automatic source address learning and ageing
Supports VLAN
- IEEE 802.1Q Tag-based VLAN
- Port-Based VLAN
- Q-in-Q tunneling
- GVRP for dynamic VLAN Management
- Private VLAN Edge (PVE / Protect Port )
Supports Link Aggregation
up to 13 trunk groups
up to 8 ports per trunk group with 1.6Gbps bandwidth (Full Duplex Mode)
IEEE 802.3ad LACP (Link Aggregation Control Protocol)
11
Page 12

Cisco ether-channel (Static Trunk)
Spanning Tree Protocol
- STP, IEEE 802.1D (Classic Spanning Tree Protocol)
- MSTP, IEEE 802.1s (Multiple Spanning Tree Protocol, spanning tree by VLAN)
Port Mirroring to monitor the incoming or outgoing traffic on a particular port
Quality of Service
4 priority queues on all switch ports
Traffic classification:
- IEEE 802.1p CoS
- IP TOS / DSCP to 802.1p priority mapping
- Port-Based priority
Strict priority and Weighted Round Robin (WRR) CoS policies
Supports QoS and In/Out bandwidth control on each port
In/Out rate limit control on each port
Multicast
Supports IGMP Snooping v1 and v2
IGMP Snooping v2 fast leave
Querier mode support
NS2503-24P/2C User Manual
Security
IEEE 802.1x Port-Based network access control protocol
RADIUS users access authentication
L3 / L4 Access Control List (ACL)
Source IP-MAC / Port-Binding
Port Security for Source MAC address entries filtering
Management
Switch Management Interface
- Telnet Command Line Interface
- Web switch management
- SNMP v1, v2c, v3 switch management
- SSL switch management
Three user privilege levels control (Admin, Operator, viewer)
DHCP client for IP address assignment
DHCP Option82 and DHCP Relay
Link Layer Discovery Protocol (LLDP) for easy network management
Built-in Trivial File Transfer Protocol (TFTP) client
Firmware upgrade via TFTP or HTTP
Configuration restore / backup via TFTP or HTTP
Event message logging to remote Syslog server
Alarm records extractable in standard CSV format for post processing
Four RMON groups 1, 2, 3, 9 (history, statistics, alarms, and events)
SNMP trap / E-Mail Alarm for interface Link Up and Link Down notification
Supports Ping function
Supports Simple Network Protocol (SNTP)
12
Page 13
Product Specification
NS2503-24P/2C User Manual
Product
Hardware Specification
10/100Mbps Copper Ports 24 10/ 100Base-TX RJ-45 Auto-MDI/MDI-X ports
1000Mbps Copper Ports 2 10/100/1000Mbps RJ-45 Auto-MDI/MDI-X ports
SFP/mini-GBIC Slots 2 1000Base-SX/LX/BX, shared with Port-25~Port-26
Switch Architecture Store-and-Forward
Switch Fabric 8.8Gbps / non-blocking
Switch Throughput 6.547Mpps @64Bytes
Address Table 8K entries
Share Data Buffer 512Kbytes
Flash 4MB
DRAM 32MB
Maximum Frame Size 9K Bytes
Flow Control
LED
Dimensions ( W x D x H) 440 x 300 x 44.5mm, 1U height
Weight 4.6kg
Power Requirement 100 - 240VAC, 50 - 60Hz, Auto-sensing.
Power Consumption
Operating Temperature 0°C ~ 50°C Degree C
Operating Humidity 10% ~ 95% (non-condensing)
Storage Temperature -20°C ~ 70 Degree C
Storage Humidity 10% ~ 95% (non-condensing)
Reset Button
Power over Ethernet
PoE Standard IEEE 802.3af / IEEE 802.3at Power over Ethernet / PSE
PoE Power Supply Type End-Span
PoE Power Output
Power Pin Assignment 1/2(+), 3/6(-)
PoE Power Budget 360 Watts (Port 1 to port 12: 180 Watts, port 13 to port 24: 180 Watts)
Max. number of Class 1 PD 24
Max. number of Class 2 PD 24
Max. number of Class 3 PD 24
Max. number of Class 0, 4 PD 11
Layer 2 Function
Management Interface Console, Telnet, Web Browser, SSL, SNMPv1, v2c, v3
Port Configuration Port disable/enable
NS2503-24P/2C
24-Port 10/100Mbps + 2 Gigabit TP / SFP Managed 802.3at PoE Switch
Back pressure for Half-Duplex
IEEE 802.3x Pause Frame for Full-Duplex
Power, PoE Power, FAN Alert
Link/Activity (Green)
PoE In-Use (Amber)
1000 LNK / ACT(Green)
10/100 LNK / ACT(Green)
System: 110V: 29 Watts / 98BTU, 220V: 31 Watts / 105BTU
Ethernet Full Loading: 110V: 34 Watts / 116BTU, 220V: 35 Watts / 119BTU
PoE Full Loading: 110V: 360 Watts / 1228BTU, 220V: 360 Watts / 1228BTU
< 5 sec: System reboot
> 10 sec: Factory Default
Per Port 52V DC, 350mA . Max.15.4 Watts (IEEE 802.3af)
Per Port 52V DC, 590mA. Max. 30 Watts (IEEE 802.3at)
13
Page 14
Auto-negotiation
10/100/1000Mbps full and half duplex mode selection
Flow Control disable / enable
Port Status
Port Mirroring
Bandwidth Control
VLAN
Link Aggregation
QoS
IGMP Snooping IGMP (v1/v2) Snooping, up to 256 multicast Groups
Access Control List
SNMP MIBs
Standards Conformance
Standards Compliance
* With total PoE power output be limited at 360 Watts
Display each port’s speed duplex mode, link status and Flow control status.
Auto negotiation status, trunk status.
TX / RX / Both
1 to 1 monitor
Ingress / Egress Rate Control
Allow to configure per 128Kbps
IEEE 802.1Q Tag-based VLAN, up to 255 VLANs groups, out of 4041 VLAN IDs
Port-based VLAN
Q-in-Q tunneling
GVRP for VLAN Management, up to 128 dynamic VLAN entries
Private VLAN Edge(PVE / Protected port) with two protected port groups
Static Port Trunk
IEEE 802.3ad LACP (Link Aggregation Control Protocol)
Supports 13 groups of 8-Port trunk support
4 priority queue
Traffic classification based on:
- Port priority
- 802.1p priority
- DSCP/TOS field in IP Packet
IP-Based Layer 3 / Layer 4 ACL
Up to 200 ACL rule entries
RFC-1213 MIB-II
RFC-2863 Interface MIB
RFC-2665 EtherLike MIB
RFC-1493 Bridge MIB
RFC-2819 RMON MIB (Group 1, 2, 3,9)
RFC-2737 Entity MIB
POWER-ETHERNET-MIB
IEEE 802.3
IEEE 802.3u
IEEE 802.3z
IEEE 802.3ab
IEEE 802.3x
IEEE 802.3ad
IEEE 802.1D
IEEE 802.1s
IEEE 802.1p
IEEE 802.1Q
IEEE 802.1x
IEEE 802.3af
IEEE 802.3at
RFC 768
RFC 793
RFC 791
RFC 792
RFC 2068
RFC 1112
RFC 2236
10Base-T
100Base-TX
1000Base-SX/LX/BX
1000Base-T
Flow Control and Back pressure
Port trunk with LACP
Spanning Tree Protocol
Multiple Spanning Tree Protocol
Class of Service
VLAN Tagging
Port Authentication Network Control
Power over Ethernet
Power over Ethernet (Pre-Standard)
UDP
TFTP
IP
ICMP
HTTP
IGMP version 1
IGMP version 2
NS2503-24P/2C User Manual
14
Page 15

NS2503-24P/2C User Manual
INSTALLATION
This section describes the hardware features and installation of the Managed Switch on the desktop or rack mount. For easier
management and control of the Managed Switch, familiarize yourself with its LED indicators, and ports. Front panel illustrations
in this chapter describe the functions of the LED indicators. Before connecting any network device to the Managed Switch,
please read this chapter completely.
Hardware Description
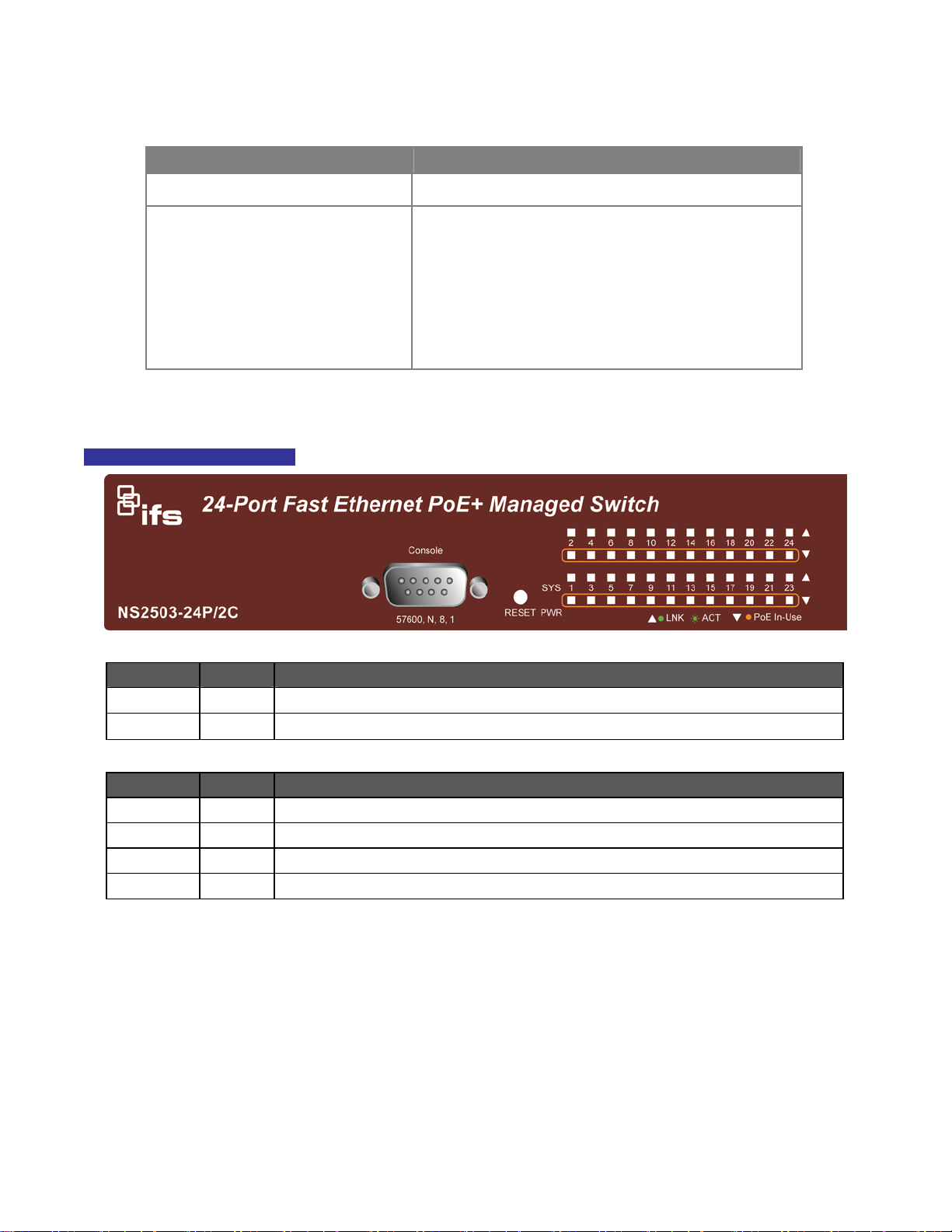
Switch Front Panel
The unit front panel provides a simple interface monitoring the switch. Figure 2-1 shows the front panel of the Managed Switch.
NS2503-24P/2C Front Panel
Figure 2-1:NS2503-24P/2C Front Panel
■ 10/100Mbps TP Interface
Port-1~Port-24: 10/100Base-TX Copper, RJ-45 Twist-Pair: Up to 100 meters.
■ Gigabit TP Interface
Port-25, Port-26: 10/100/1000Base-T Copper, RJ-45 Twist-Pair: up to 100 meters.
■ Gigabit SFP Slots
Port-25, Port-26: 1000Base-SX/LX/BX mini-GBIC slot, SFP (Small Factor Pluggable) transceiver module: From 550 meters
(Multi-mode fiber), up to 10/20/30/40/50/70 kilometers (Single-mode fiber).
■ Console Port
The console port is a DB9, RS-232 male serial port connector. It is an interface for connecting to a terminal directly.
Through the console port, it provides rich diagnostic information including IP Address settings, factory reset, port
management, link status and system settings. Users can use the attached RS-232 cable in the package and connect to the
console port on the device. After the connection, users can run any terminal emulation program (Hyper Terminal, ProComm
Plus, Telix, Winterm, etc.) to enter the startup screen of the device.
15
Page 16
NS2503-24P/2C User Manual
■ Reset button
On the left side of the front panel, the reset button is designed for rebooting the Managed Switch without a power cycle.
The following is the summary table of Reset button functions:
Reset Button Pressed and Released Function
About 5 seconds Reboot the Managed Switch.
Reset the Managed Switch to Factory Default configuration.
The Managed Switch will then reboot and load the default
settings as below:
About 10 seconds
。 Default Password: admin
。 Default IP address: 192.168.0.100
。 Subnet mask: 255.255.255.0
。 Default Gateway: 192.168.0.254
LED Indications
The front panel LEDs indicates instant status of port links, data activity and system power.
NS2503-24P/2C LED indicators
Figure 2-2:NS2503-24P/2C LED Panel
System
LED Color Function
PWR Green Illuminates to indicate that the Switch has power.
SYS Green Illuminates to indicate the system is on.
Alert
LED Color Function
PWR Alert Green
FAN1 Green
FAN2 Green
FAN3 Green
Illuminates to indicate that the PoE power supply has failed.
Illuminates to indicate that the FAN1 has failed.
Illuminates to indicate that the FAN2 has failed.
Illuminates to indicate that the FAN3 has failed.
16
Page 17
Per 10/100Mbps port, PoE interfaces (Port-1 to Por-24)
LED Color Function
Illuminates:
LNK/ACT Green
PoE In-Use Orange
Per 10/100/1000Base-T port / SFP interfaces
LED Color Function
1000
LNK/ACT
10/100
LNK/ACT
Green
Green
Blink:
Illuminates:
Off:
Illuminates:
Blink:
Off:
Illuminates:
Blink:
Off:
To indicate the link through that port is successfully established.
To indicate that the Switch is actively sending or receiving data over that port.
To indicate the port is providing 52V DC in-line power.
To indicate the connected device is not a PoE Powered Device (PD).
To indicate the link through that port is successfully established with speed
1000Mbps.
To indicate that the Switch is actively sending or receiving data over that port.
If 10/100 LNK/ACT LED is light, it indicates that the port is operating at
10Mbps or 100Mbps. If LNK/ACT LED is Off, it indicates that the port is link
down.
To indicate the link through that port is successfully established with speed
10Mbps or 100Mbps.
To indicate that the Switch is actively sending or receiving data over that port.
If 1000 LNK/ACT LED is ON, it indicates that the port is operating at
1000Mbps.
If 1000 LNK/ACT LED is Off, it indicates that the port is link down.
NS2503-24P/2C User Manual
1. Press the RESET button for 5 seconds to reboot the Managed Switch.
2. Press the RESET button for 10 seconds to restore the Managed Switch back to the factory default
settings. The entire configuration will be reset to default after this function.
3. The 2 Gigabit TP/SFP combo ports are shared with port 25/26 of the Managed Switch. Either of these
ports can operate at the same time.
17
Page 18
NS2503-24P/2C User Manual
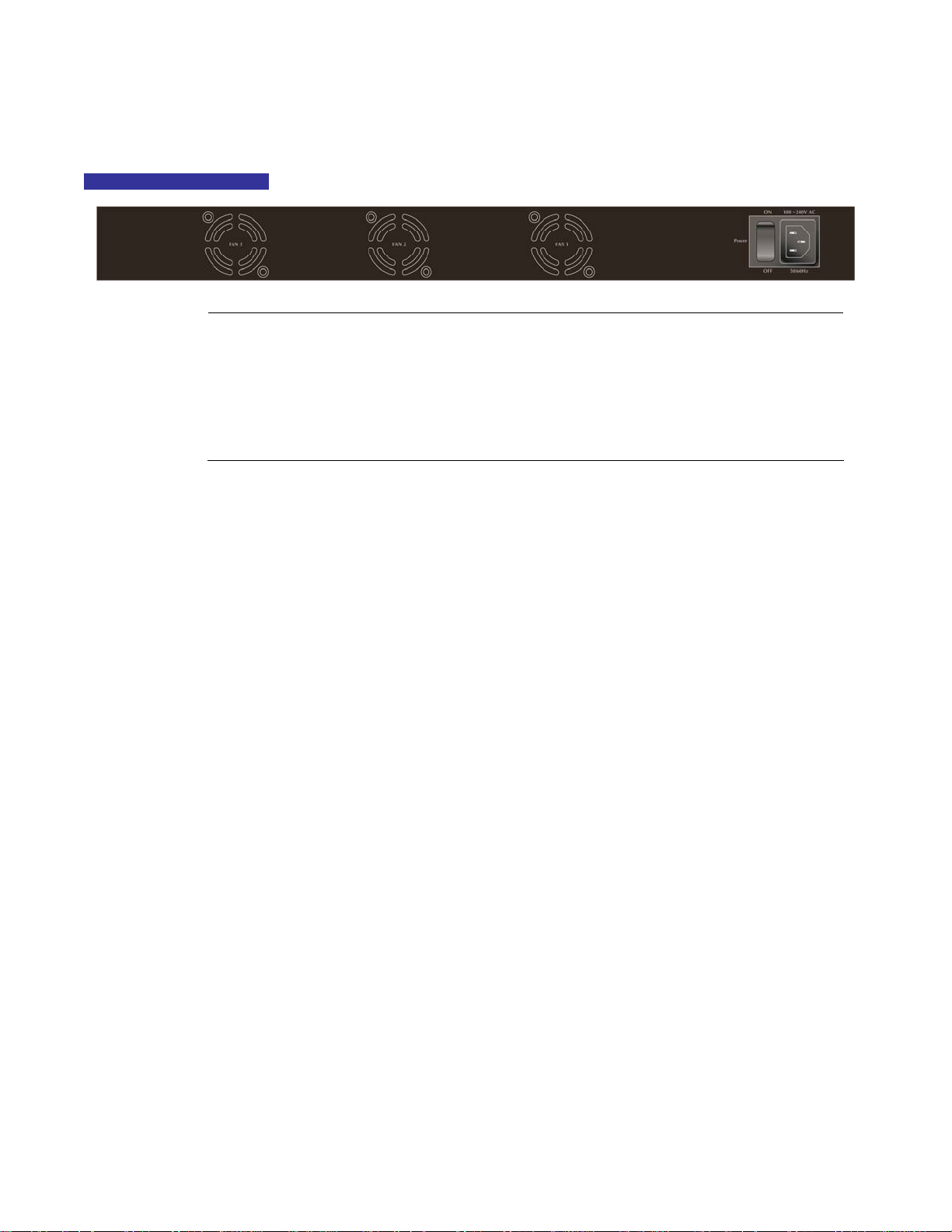
Switch Rear Panel
The rear panel of the Managed Switch indicates an AC inlet power socket, which works with an input power range from 100 to
240V AC, 50-60Hz. Figure 2-3 shows the rear panel of the Managed Switch.
NS2503-24P/2C Rear Panel
Power Notice:
Figure 2-3: NS2503-24P/2C Rear Panel.
1. The device requires a power connection to operate. To ensure network reliability and to reduce
the possibility of data loss, we recommend that a UPS (Uninterruptable Power Supply) be
installed as a part of your installation.
2. For additional protection against unregulated voltage or current surges, you may also want to
consider surge suppression as part of your installation.
18
Page 19

NS2503-24P/2C User Manual
Install the Switch
This section describes how to install the Managed Switch and make connections to it. Please read the following topics and
perform the procedures in the order being presented.
Desktop Installation
To install the Managed Switch on desktop or shelf, please follows these steps:
Step1: Attach the rubber feet to the recessed areas on the bottom of the Managed Switch.
Step2: Place the Managed Switch on the desktop or the shelf near an AC power source.
Figure 2-4: Place the Managed Switch on the desktop
Step3: Keep enough ventilation space between the Managed Switch and the surrounding objects.
When choosing a location, please keep in mind the environmental restrictions discussed in
Chapter 1, Section 4, in Product Specification.
Step4: Connect the Managed Switch to network devices.
A. Connect one end of a standard network cable to the 10/100/1000 RJ-45 ports on the front of the Managed Switch
B. Connect the other end of the cable to the network devices such as printer servers, workstations or routers…etc.
Connection to the Managed Switch requires UTP Category 5 network cabling with RJ-45
tips. For more information, please see the Cabling Specification in Appendix A.
Step5: Supply power to the Managed Switch.
A. Connect one end of the power cable to the Managed Switch.
B. Connect the power plug of the power cable to a standard wall outlet.
When the Managed Switch receives power, the Power LED should remain solid Green.
19
Page 20
NS2503-24P/2C User Manual
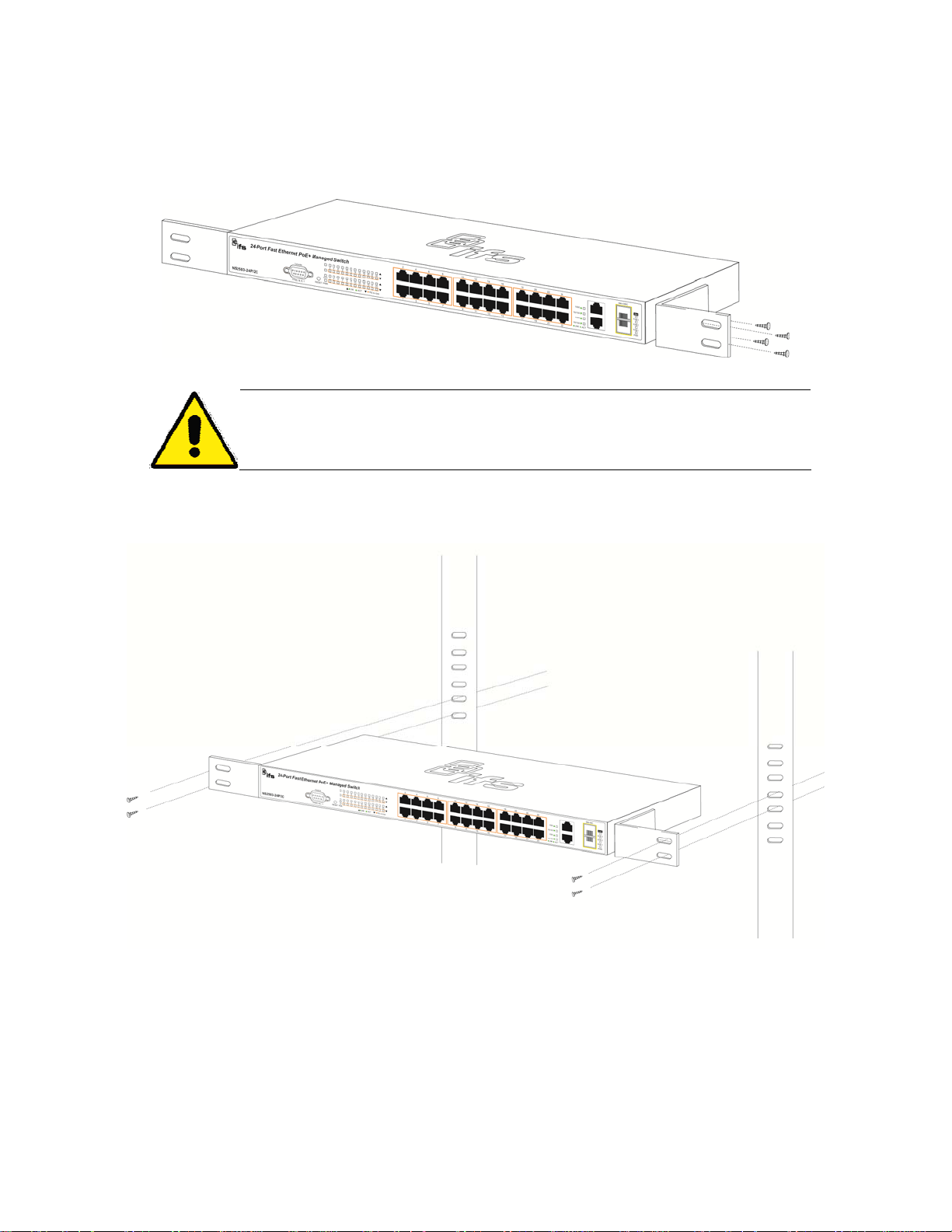
Rack Mounting
To install the Managed Switch in a 19-inch standard rack, please follows the instructions described below.
Step1: Place the Managed Switch on a flat surface, with the front panel positioned towards the front side.
Step2: Attach the rack-mount bracket to each side of the Managed Switch with the supplied screws included in the package.
Figure 2-5 shows how to attach brackets to one side of the Managed Switch.
Figure 2-5: Attach brackets to the Managed Switch
You must use the screws supplied with the mounting brackets. Damage caused to the parts
by using incorrect screws would invalidate the warranty.
Step3: Secure the brackets tightly.
Step4: Follow the same steps to attach the second bracket to the opposite side.
Step5: After the brackets are attached to the Managed Switch, use matching screws to securely attach the brackets to the rack,
as shown in Figure 2-6.
Figure 2-6: Mounting the Switch in a Rack
Step6: Proceed with the step 4 and step 5 of section 2.2.1. Desktop Installation to connect the network cabling and supply
power to the Managed Switch.
20
Page 21
NS2503-24P/2C User Manual
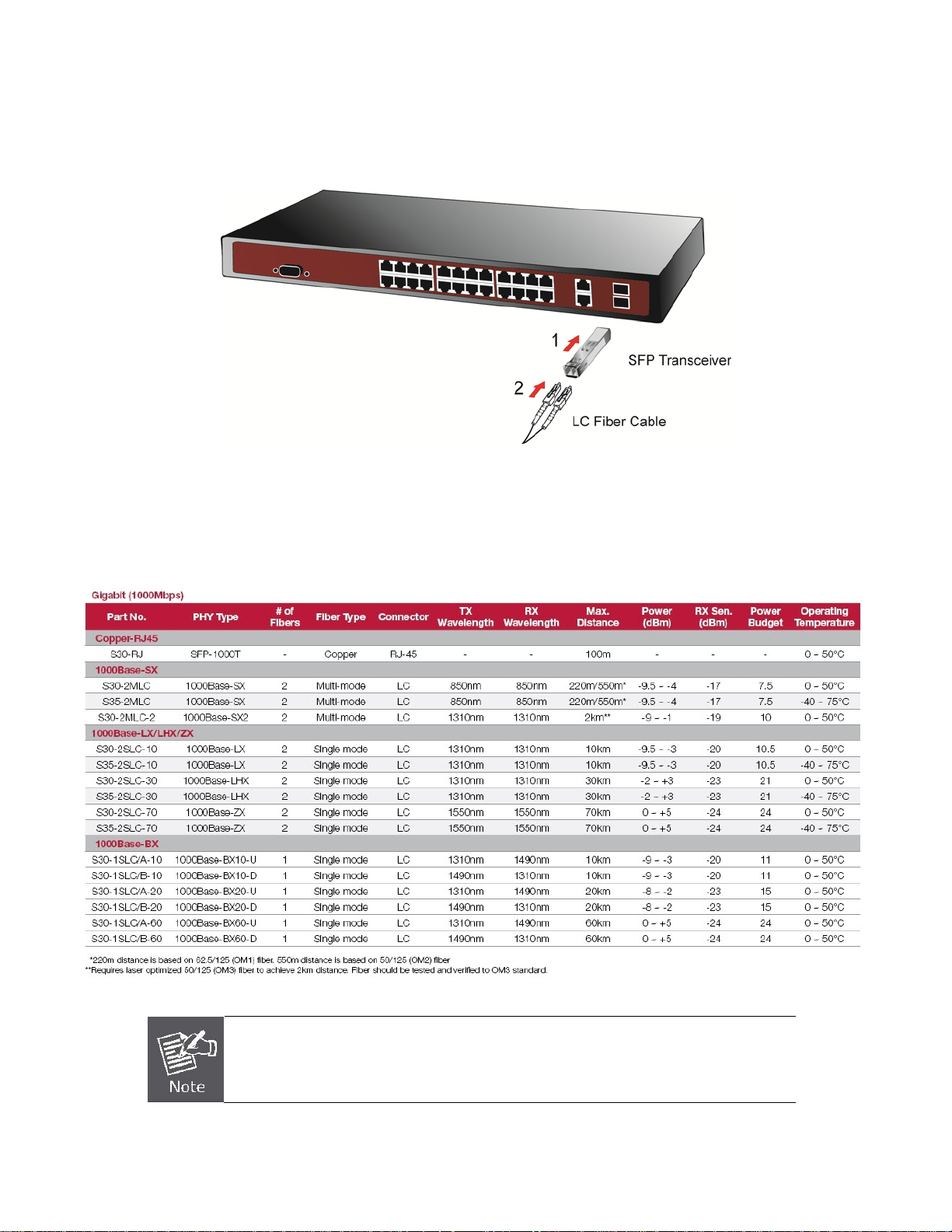
Installing the SFP transceiver
This section describes how to plug-in an SFP transceiver into an SFP slot.
The SFP transceivers are hot-swappable. You can plug-in and out the transceiver to/from any SFP port without a need to shut
down the Managed Switch.
Figure 2-7: Plug-in the SFP transceiver
Approved IFS SFP Transceivers
IFS Managed switches support both single mode and multi mode SFP transceivers. Please refer to below chart, as well as IFS
website for latest compatible SFP modules.
1000Base-SX/LX SFP transceiver:
It recommends using IFS SFPs on the Switch. If you insert a SFP transceiver that is not
supported, the Managed Switch will not recognize it.
21
Page 22

NS2503-24P/2C User Manual
Before connecting the other switches, workstation or Media Converter:
1. Make sure both sides use the same SFP transceiver, for example: 1000Base-SX to 1000Base-SX, 1000Base-LX to
1000Base-LX.
2. make sure the fiber-optic cable type match the SFP transceiver model.
To connect to 1000Base-SX SFP transceiver, use the multi-mode fiber cable- with one side must be male duplex LC
connector type.
To connect to 1000Base-LX SFP transceiver, use the single-mode fiber cable-with one side must be male duplex
LC connector type.
Connect the fiber cable
1. Attach the duplex LC connector on the network cable into the SFP transceiver.
2. Connect the other end of the cable to a device – switches with SFP installed, fiber NIC on a workstation or a Media
Converter.
3. Check the LNK/ACT LED of the SFP slot on the front of the Managed Switch. Ensure that the SFP transceiver is operating
correctly.
4. Check the Link mode of the SFP port if the link failed.
Remove the transceiver module
1. Make sure there is no network activity. Use the management interface of the switch to disable the port in advance.
2. Remove the Fiber Optic Cable gently.
3. Turn the handle of the MGB module to the horizontal position.
4. Pull out the module gently with the handle.
5.
Figure 2-8: Pull out the SFP transceiver
Never pull out the module without using the handle or the push bolts on the module.
Forcfully pulling out the module may damage the module and SFP module slot of the
Managed Switch.
22
Page 23
NS2503-24P/2C User Manual
SWITCH MANAGEMENT
This chapter explains the methods that you can use to configure management access to the Managed Switch. It describes the
types of management applications and the communication and management protocols that deliver data between your
management device (work-station or personal computer) and the system. It also contains information about port connection
options.
This chapter covers the following topics:
Requirements
Management Access Overview
Administration Console Access
Web Management Access
SNMP Access
Standards, Protocols, and Related Reading
Requirements
The operating system of the workstation running Windows XP/2003, Vista, Windows 7, MAC OS X , Linux, Fedora,
Ubuntu or other platform compatible with TCP/IP protocols.
Workstation installed with Ethernet NIC (Network Interface Card)
Ethernet Port connection
Network cables - Use standard network (UTP) cables with RJ45 connectors.
Above Workstation installed with WEB Browser and JAVA runtime environment Plug-in
Serial Port connection
Above PC with COM Port (DB-9 / RS-232) or USB-to-RS-232 converter
It is recommended to use Internet Explore 6.0 or above to access Managed Switch.
23
Page 24
NS2503-24P/2C User Manual
Management Access Overview
The Managed Switch gives you the flexibility to access and manage it using any or all of the following methods:
Web browser interface
An external SNMP-based netw ork management application
An administration console
The administration console and Web browser interface support are embedded in the Managed Switch software and are
available for immediate use. Each of these management methods has their own advantages. Table 3-1 compares the three
management methods.
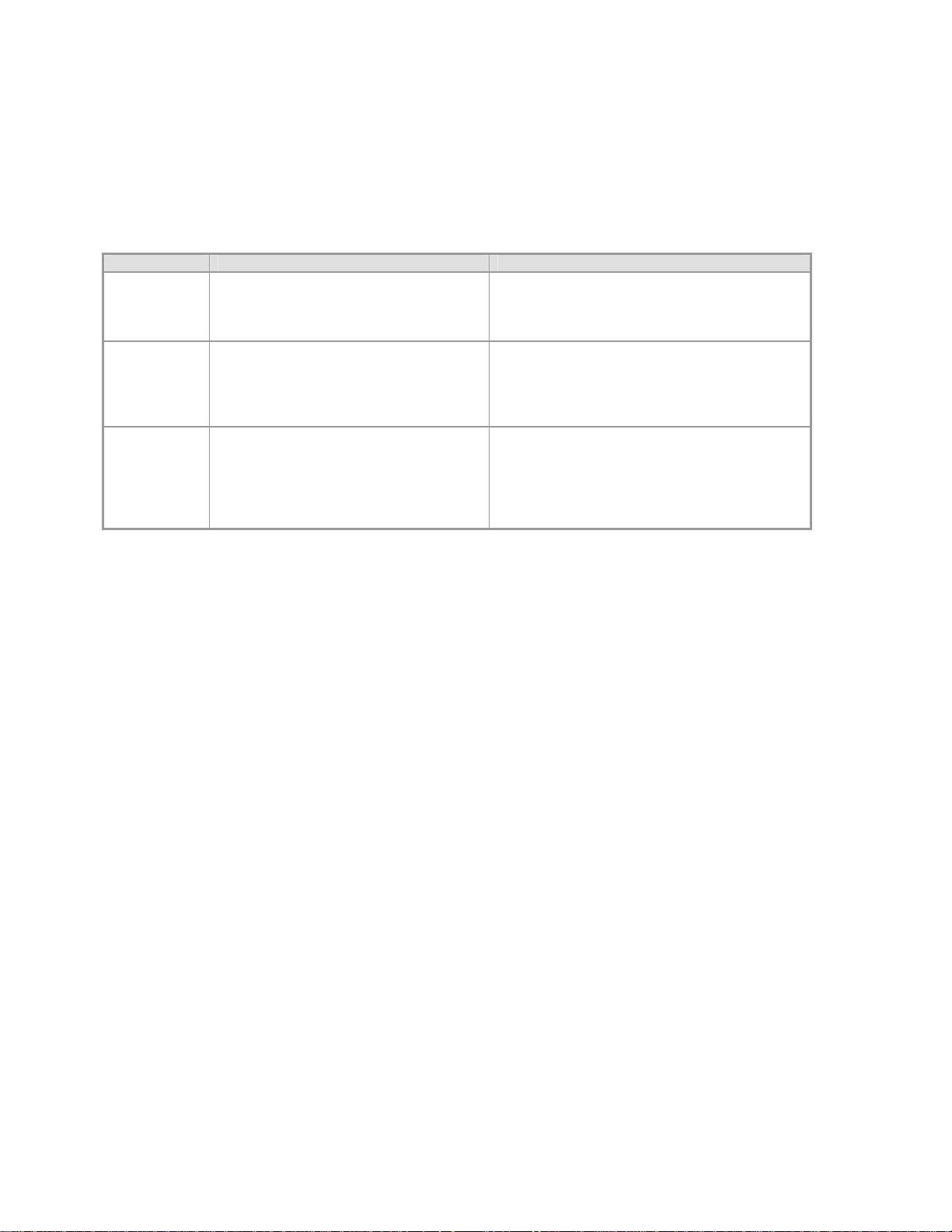
Method Advantages Disadvantages
Web Browser
SNMP Agent
Console
Ideal for configuring the switch remotely
Compatible with all popular browsers
Can be accessed from any location
user friendly GUI
Communicates with switch functions at
the MIB level
Based on open standards
No IP address or subnet needed
Text-based
HyperTerminal built into Windows
XP/2003/Vista/ Windows 7 operating
systems
Secure
Table 3-1: Management Methods Comparison
Security can be compromised (hackers need
only know the IP address and subnet mask)
May encounter lag times on poor connections
Requires SNMP manager software
Least visually appealing of all three methods
Some settings require calculations
Security can be compromised (hackers need
only know the community name)
Must be near switch or use dial-up connection
Not convenient for remote users
Modem connection may prove to be unreliable
or slow
24
Page 25

NS2503-24P/2C User Manual
Web Management
The Managed Switch offers management features that allow users to manage the Managed Switch from anywhere on the
network through a standard browser such as Microsoft Internet Explorer. After you set up your IP address for the switch, you
can access the Managed Switch's Web interface applications directly in your Web browser by entering the IP address of the
Managed Switch.
Figure 3-1: Web Management Diagram
You can then use your Web browser to list and manage the Managed Switch configuration parameters from one central location,
just as if you were directly connected to the Managed Switch's console port. Web Management requires either Microsoft
Internet Explorer 6.0 or later, Safari or Mozilla Firefox 3.0 or later.
Figure 3-2: Web Main Screen of Managed Switch
25
Page 26
NS2503-24P/2C User Manual
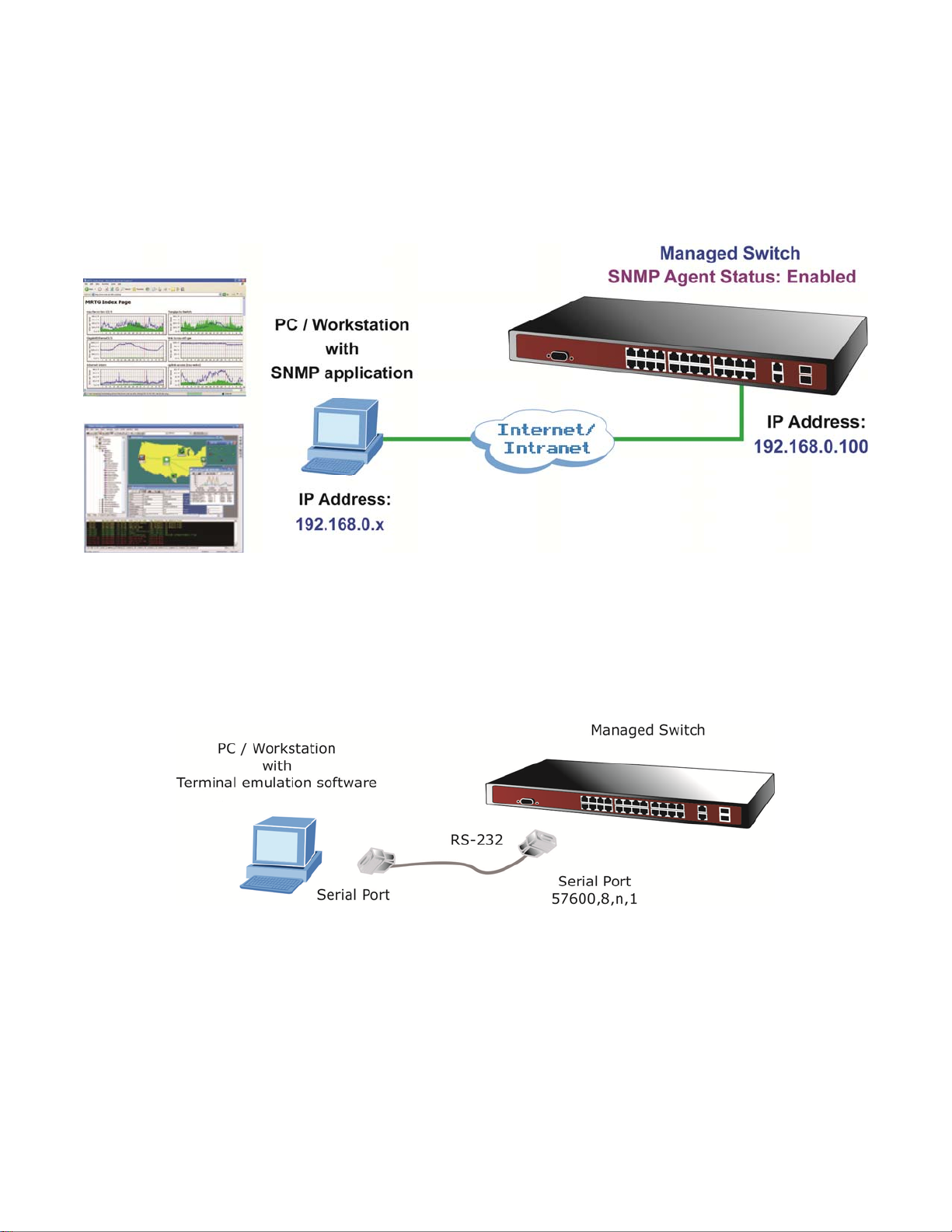
SNMP-Based Network Management
You can use an external SNMP-based application to configure and manage the Managed Switch, such as SNMPc Network
Manager, HP Openview Network Node Management (NNM) or What’sup Gold. This management method requires the SNMP
agent on the switch and the SNMP Network Management Station to use the same community string. This management
method, in fact, uses two community strings: the get community string and the set community string. If the SNMP Network
management Station only knows the set community string, it can read and write to the MIBs. However, if it only knows the get
community string, it can only read MIBs. The default get and set community strings for the Managed Switch are public.
Figure 3-3: SNMP Management Diagram
Administration Console
The administration console is an internal, character-oriented, and command line user interface for performing system
administration such as displaying statistics or changing option settings. Using this method, you can view the administration
console from a terminal, personal computer, Apple Macintosh, or workstation connected to the switch's console (serial) port.
There are two ways to use this management method: via direct access or modem port access. The following sections describe
these methods. For more information about using the console, refer to Chapter 5 Console Management.
Figure 3-4: Console Management Diagram
Direct Access
Direct access to the administration console is achieved by directly connecting a terminal or a PC equipped with a
terminal-emulation program (such as HyperTerminal) to the Managed Switch console (serial) port.
When using this management method, a straight DB9 RS-232 cable is required to connect the switch to the PC. After
making this connection, configure the terminal-emulation program and use the following parameters:
The default parameters are:
57600 bps
8 data bits
No parity
1 stop bit
26
Page 27
NS2503-24P/2C User Manual
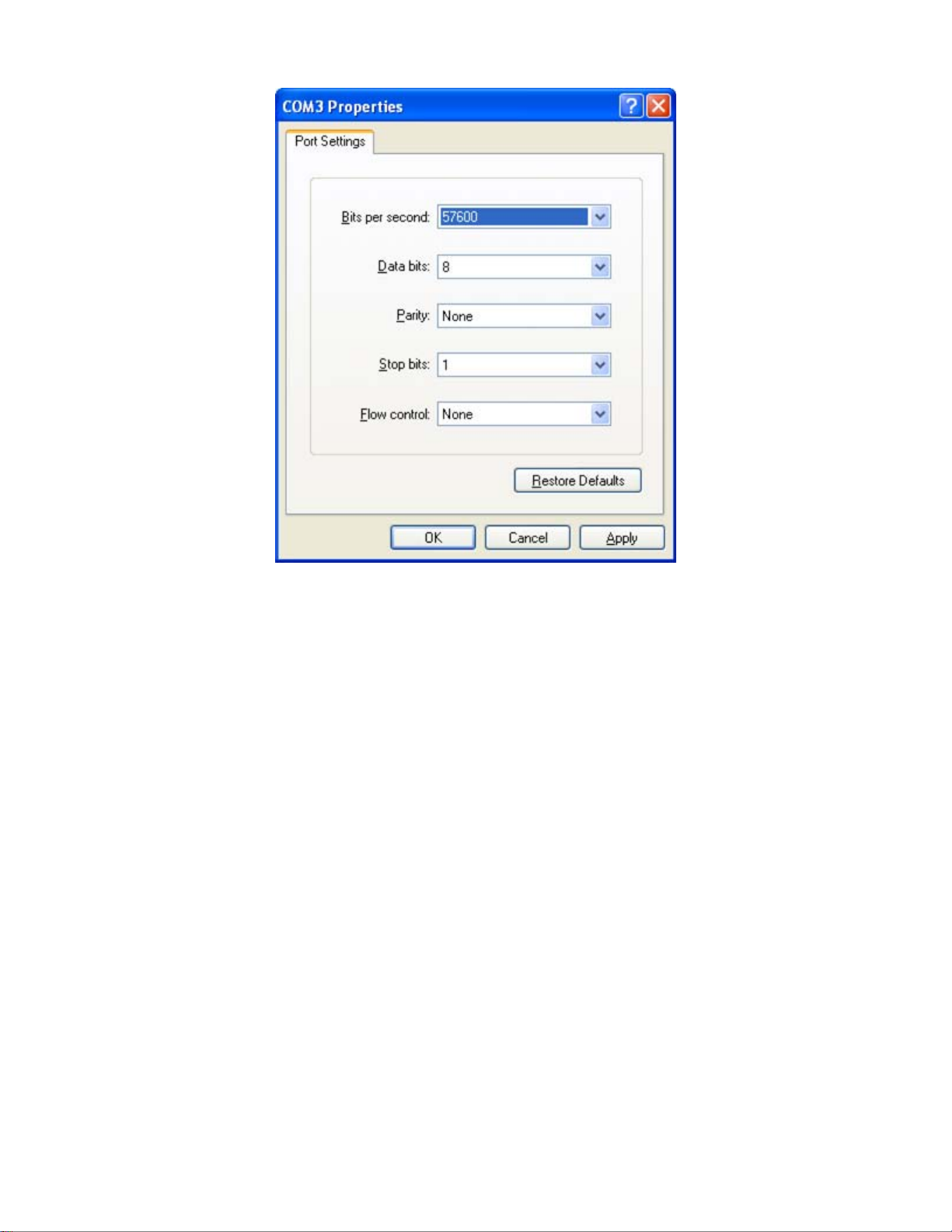
Figure 3-5: Terminal Parameter Settings
You can change these settings, if desired, after you log on. This management method is often preferred because you can
remain connected and monitor the system during system reboots. Also, certain error messages are sent to the serial port,
regardless of the interface through which the associated action was initiated. A Macintosh or PC attachment can use any
terminal-emulation program for connecting to the terminal serial port. A workstation attachment under UNIX can use an
emulator such as TIP.
27
Page 28
NS2503-24P/2C User Manual
Protocols
The Managed Switch supports the following protocols:
Virtual terminal protocols, such as Telnet
Simple Network Management Protocol (SNMP)
Virtual Terminal Protocols
A virtual terminal protocol is a software program, such as Telnet, that allows you to establish a management session from a
Macintosh, a PC, or a UNIX workstation. Because Telnet runs over TCP/IP, you must have at least one IP address configured
on the Managed Switch before you can establish access to it with a virtual terminal protocol.
Terminal emulation differs from a virtual terminal protocol in that you must connect a terminal directly
to the console (serial) port.
To access the Managed Switch through a Telnet session:
1. Make sure that the Managed Switch is configured with an IP address and the Managed Switch is reachable from a
PC.
2. Start the Telnet program on a PC and connect to the Managed Switch.
The management interface is exactly the same with RS-232 console management.
SNMP Protocol
Simple Network Management Protocol (SNMP) is the standard management protocol for multi-vendor IP networks. SNMP
supports transaction-based queries that allow the protocol to format messages and to transmit information between reporting
devices and data-collection programs. SNMP runs on top of the User Datagram Protocol (UDP), offering a
connectionless-mode service.
Management Architecture
All of the management application modules use the same Messaging Application Programming Interface (MAPI). By unifying
management methods with a single MAPI, configuration parameters set using one method i.e console port, can immediately be
displayed by the other management methods (for example, SNMP agent of Web browser).
The management architecture of the switch adheres to the IEEE open standard. This compliance assures customers that the
Managed Switch is compatible with, and will interoperate with other solutions that adhere to the same open standard.
28
Page 29

NS2503-24P/2C User Manual
Web-Based Management
This section introduces the configuration and functions of the Web-Based management.
About Web-based Management
The Managed Switch offers management features that allow users to manage the Managed Switch from anywhere on the
network through a standard browser such as Microsoft Internet Explorer.
The Web-Based Management supports Internet Explorer 6.0. It is based on Java Applets with an aim to reduce network
bandwidth consumption, enhance access speed and present an easy viewing screen.
By default, IE6.0 or later version does not allow Java Applets to open sockets. The user has to
explicitly modify the browser setting to enable Java Applets to use network ports.
The Managed Switch can be configured through an Ethernet connection, make sure the manager PC must be set on same the
IP subnet address with the Managed Switch.
For example, the default IP address of the Managed Switch is 192.168.0.100, then the manager PC should be set at
192.168.0.x (where x is a number between 1 and 254, except 100), and the default subnet mask is 255.255.255.0.
If you have changed the default IP address of the Managed Switch to 192.168.1.1 with subnet mask 255.255.255.0 via console,
then the manager PC should be set at 192.168.1.x (where x is a number between 2 and 254) to do the relative configuration on
manager PC.
29
Page 30
NS2503-24P/2C User Manual
Requirements
The operating system of subscriber PC: Windows XP/2003, Vista, Windows 7, MAC OS X , Linux, Fedora, Ubuntu or other
platform compatible with TCP/IP protocols.
Workstation installed with Ethernet NIC (Network Card).
Ethernet Port connection
Network cables - Use standard network (UTP) cables with RJ45 connectors.
Above PC installed with WEB Browser and JAVA runtime environment Plug-in.
It is recommended to use Internet Explore 6.0 or above to access the Managed Switch.
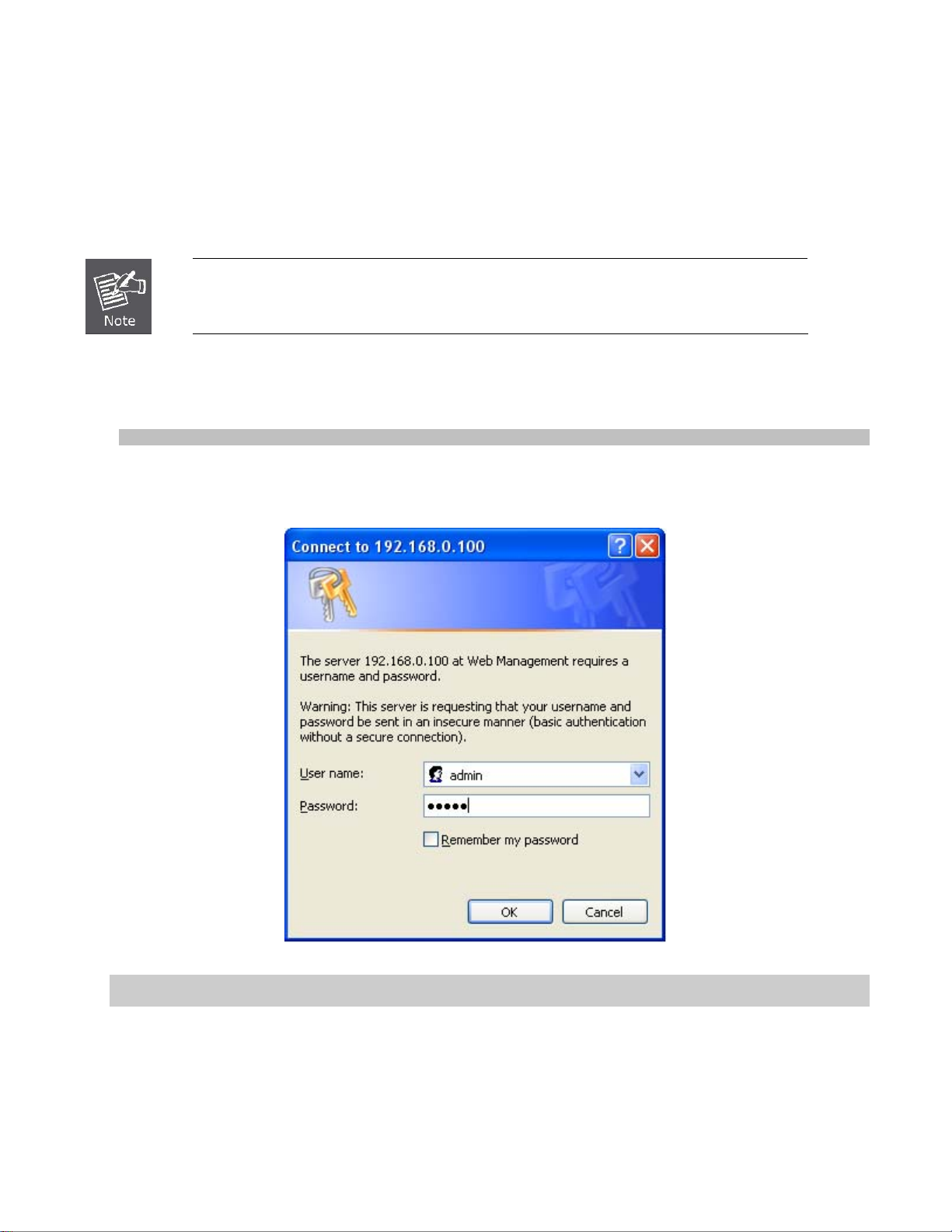
Logging on the Managed Switch
1. Use Internet Explorer 6.0 or above Web browser. Enter the factory-default IP address to access the Web interface. The
factory-default IP Address as following:
http://192.168.0.100
2. When the following login screen appears, please enter the default username “admin” with password “admin” (or the
username/password you have changed via console) to login the main screen of Managed Switch. The login screen in
Figure 4-1-1 appears.
Figure 4-1-1: Login Screen
Default User name: admin
Default Password: admin
1. After entering the username and password, the main screen appears as Figure 4-1-2.
30
Page 31

NS2503-24P/2C User Manual
Figure 4-1-2: Web Main Page Screenshot
2. The Switch Menu on the left of the Web page let you access all the management parameters that the Switch provides.
1. We recommend using Internet Explore 6.0 or above to access Managed Switch.
2. If the IP address of the switch is changed, the change will take effect immediately after you
have clicked on the Apply button, Therefore you need to use the new IP address to access
the Web interface.
3. For security reasons, please change and memorize the new password after the first setup.
4. The Switch accepts commands in lowercase letters on the web interface.
31
Page 32

NS2503-24P/2C User Manual
Main WEB PAGE
The Managed Switch provides a Web-based browser interface for configuring and managing it. This interface allows you to
access the Managed Switch using the Web browser of your choice. This chapter describes how to use the Managed Switch’s
Web browser interface to configure and manage it.
Copper Port Link Status
SFP Port Link Status
Main Screen
Main Functions Menu
Panel Display
The web agent displays an image of the Managed Switch’s ports. The Mode can be set to display different information for the
ports, including Link up or Link down. Clicking on the image of a port opens the Port Statistics page.
The port status is illustrated as follows:
Main Menu
Using the onboard web agent, you can define system parameters, manage and control the Managed Switch, and all its ports, or
monitor network conditions. Via the Web-Management, the administrator can setup the Managed Switch by selecting the
functions those listed in the Main Function. The screen in Figure 4-1-4 appears.
Figure 4-1-3: Web Main Page Allocation Screenshot
State Disabled Down Link
RJ-45 Ports
SFP Ports
PoE Ports
32
Page 33

NS2503-24P/2C User Manual
Figure 4-1-4: Managed Switch Main Functions Menu Screenshot
33
Page 34

NS2503-24P/2C User Manual
System
Use the System menu items to display and configure basic administrative details of the Managed Switch. Under System the
following topics are provided to configure and view the system information: This section has the following items:
■ System Information Provides basic system description, including contact information.
■ IP Configuration Sets the IP address for management access.
■ Console Port Info Provides console port connection information.
■ SNMP Configuration Configures SNMP agent and SNMP Trap.
■ Syslog Setting Configures system log function.
■ System Log Provides system log information.
■ SNTP Setting Configures SNTP function.
■ Firmware Upgrade Upgrades the firmware via TFTP server or Web Browser file transfer.
■ Configuration Backup Save/view the Managed Switch configuration to remote host.
Uploads the switch configuration from remote host.
■ Factory Default Resets the configuration of the Managed Switch.
■ System Reboot Restarts the Managed Switch.
34
Page 35

NS2503-24P/2C User Manual
System Information
In System information, it has two parts of setting – Basic and Misc Config. We will describe the configure detail in following.
Basic
The Basic System Info page provides information for the current device information. Basic System Info page helps a switch
administrator to identify the model name, firmware / hardware version and MAC address. The screen in Figure 4-2-1 appears.
The page includes the following fields:
Object Description
Model Name:
Description:
MAC Address:
Firmware Version:
Hardware Version:
Figure 4-2-1: Basic System Information Screenshot
Display the system name of the Managed Switch.
Describes the Managed Switch.
Displays the unique hardware address assigned by manufacturer (default).
Displays the Managed Switch’s firmware version.
Displays the current hardware version.
35
Page 36

NS2503-24P/2C User Manual
Misc Config
Choose Misc Config from System Information of Managed Switch, the screen in Figure 4-2-2 appears.
Figure 4-2-2: Switch Misc Config Screenshot
36
Page 37

The page includes the following fields:
Object Description
MAC Address Age-out
Time
Port Interval
Broadcast Storm Filter
Mode
Broadcast Storm Filter
Packets Select
Collision Retry Forever
Hash Algorithm
NS2503-24P/2C User Manual
Type the number of seconds that an inactive MAC address remains in the
switch’s address table. The value is a multiple of 6.
Default is 300 seconds.
Type the number of seconds that an interval time between turning off and turning
on port for flooding CPU port. Default is 0 seconds.
To configure broadcast storm control, enable it and set the upper threshold for
individual ports. The threshold is the percentage of the port’s total bandwidth
used by broadcast traffic. When broadcast traffic for a port rises above the
threshold you set, broadcast storm control becomes active.
The valid threshold values are 1/2, 1/4, 1/8, 1/16 and OFF.
Default is “OFF”.
To select broadcast storm Filter Packets type. If no packets type by selected,
mean can not filter any packets .The Broadcast Storm Filter Mode will show OFF.
The selectable items as below:
Broadcast Packets
IP Multicast
Control Packets
Flooded Unicast / Multicast Packets
Provide Collision Retry Forever function”Disable” or 16, 32, 48 collision numbers
on Managed Switch. If this function is disabled, when a packet meet a collision,
the Managed Switch will retry 6 times before discard the packets. Otherwise, the
Managed Switch will retry until the packet is successfully sent.
Default value is 16.
Provide MAC address table Hashing setting on Managed Switch; available
options are CRC Hash and Direct Map.
Default mode is CRC-Hash.
IP/MAC Binding Enable / disable IP MAC Binding function.
802.1x protocol Enable / disable 802.1x protocols.
Apply button
Press the button to complete the configuration.
37
Page 38

NS2503-24P/2C User Manual
IP Configuration
The Managed Switch is a network device which needs to be assigned an IP address for being identified on the network. Users
have to decide on an IP address for the Managed Switch.
IP address overview
What is an IP address?
Each device (such as a computer) which participates in an IP network needs a unique "address" on the network. It's similar to
having a US mail address so other people have a known way to send you messages. An IP address is a four byte number,
which is usually written in "dot notation" - each of the bytes' decimal value is written as a number, and the numbers are
separated by "dots" (aka periods). An example: 199.25.123.1
How do I get one for this box?
The IP addresses on most modern corporate networks are assigned by an employee called a "Network Administrator", or
"System Administrator". This person assigns IP addresses and is responsible for making sure that IP addresses are not
duplicated - If this happens one or both machines with a duplicate address will stop working.
Another possibility is getting your address assigned to you automatically over the net via DHCP protocol. Enable DHCP function,
and reset the machine. If your network is set up for this service, you will get an IP address assigned over the network. If you
don't get an address in about 30 seconds, you probably don't have DHCP set up in your network.
IP Configuration
The IP Configuration includes the IP Address, Subnet Mask and Gateway. The Configured column is used to view or change the
IP configuration. Fill up the IP Address, Subnet Mask and Gateway for the device. The screen in Figure 4-2-3 appears.
Figure 4-2-3: IP configuration Interface Screenshot
38
Page 39

The page includes the following fields:
Object Description
DHCP
IP Address
NS2503-24P/2C User Manual
Enable or disable the DHCP client function.
When DHCP function is enabled, the Managed Switch will be assigned an IP
address from the network DHCP server. The default IP address will be replaced
by the assigned IP address on DHCP server. After the user clicks Apply, a
popup dialog shows up to inform the user that when the DHCP client is enabled,
the current IP will lose and user should find the new IP on the DHCP server.
Assign the IP address that the network is using.
If DHCP client function is enabled, this switch is configured as a DHCP client.
The network DHCP server will assign the IP address to the switch and display it
in this column.
The default IP is 192.168.0.100 or the user has to assign an IP address
manually when DHCP Client is disabled.
Assign the subnet mask to the IP address.
Subnet Mask
Gateway
If DHCP client function is disabled, the user has to assign the subnet mask in
this column field.
Assign the network gateway for the switch.
If DHCP client function is disabled, the user has to assign the gateway in this
column field.
The default gateway is 192.168.0.254.
39
Page 40

NS2503-24P/2C User Manual
Console Port Info
The Managed Switch provide local console interface for switch command line management, console port info contains console
baud rate information and the screen in Figure 4-2-4 appears.
The page includes the following fields:
Object Description
Baudrate (bits / sec) Provide Baudrate information.
Data Bits
Parity Check
Stop Bits
Flow Control
Help
Figure 4-2-4: Console Information Screenshot
Provide Data Bits information.
Provide Parity Check information.
Provide Stop Bits information.
Provide Flow Control information.
Provide Console Setting Help information.
40
Page 41

NS2503-24P/2C User Manual
SNMP Configuration
SNMP Overview
The Simple Network Management Protocol (SNMP) is an application layer protocol that facilitates the exchange of
management information between network devices. It is part of the Transmission Control Protocol/Internet Protocol (TCP/IP)
suite. SNMP enables network administrators to manage network performance, find and solve network problems, and plan for
network growth.
Figure 4-2-5: SNMP Configuration Interface Screenshot
An SNMP-managed network consists of three key components: Network management stations (NMSs), SNMP agents,
Management information base (MIB) and network-management protocol:
Network management stations (NMSs) : Sometimes called consoles, these devices execute management
applications that monitor and control network elements. Physically, NMSs are usually engineering workstation-caliber
computers with fast CPUs, megapixel color displays, substantial memory, and abundant disk space. At least one NMS
must be present in each managed environment.
Agents:Agents are software modules that reside in network elements. They collect and store management
information such as the number of error packets received by a network element.
Management information base (MIB) :A MIB is a collection of managed objects residing in a virtual information store.
Collections of related managed objects are defined in specific MIB modules.
network-management protocol:A management protocol is used to convey management information between
agents and NMSs. SNMP is the Internet community's de facto standard management protocol.
SNMP Operations
SNMP itself is a simple request/response protocol. NMSs can send multiple requests without receiving a response.
Get -- Allows the NMS to retrieve an object instance from the agent.
Set -- Allows the NMS to set values for object instances within an agent.
Trap -- Used by the agent to asynchronously inform the NMS of some event. The SNMPv2 trap message is designed
to replace the SNMPv1 trap message.
41
Page 42

NS2503-24P/2C User Manual
SNMP community
An SNMP community is the group that devices and management stations running SNMP belong to. It helps define where
information is sent. The community name is used to identify the group. A SNMP device or agent may belong to more than one
SNMP community. It will not respond to requests from management stations that do not belong to one of its communities.
SNMP default communities are:
Write = private
Read = public
System Options
Use this page to define management stations. You can also define a name, location, and contact person for the Managed
Switch.
Figure 4-2-6: SNMP Configuration Interface Screenshot
The page includes the following fields:
Object Description
System Name
System Location
System Contact
SNMP Status
An administratively assigned name for this managed node. By convention, this is
the node's fully-qualified domain name. A domain name is a text string drawn
from the alphabet (A-Za-z), digits (0-9), minus sign (-). No space characters are
permitted as part of a name. The first character must be an alpha character. And
the first or last character must not be a minus sign.
The allowed string length is 0 to 255.
The physical location of this node (e.g., telephone closet, 3rd floor).
The textual identification of the contact person for this managed node, together
with information on how to contact this person.
Indicates the SNMP mode operation. Possible modes are:
Enabled: Enable SNMP mode operation.
Disabled: Disable SNMP mode operation.
Default mode is disable.
Community Strings
Community strings serve as passwords and can be entered as one of the following:
Figure 4-2-7: Community Strings Interface Screenshot
42
Page 43

The page includes the following fields:
A
Object Description
Community Strings: Here you can define the new community string set and remove the unwanted
dd
button
Remove
button
NS2503-24P/2C User Manual
community string.
String: Fill the name string.
RO: Read only. Enables requests accompanied by this community string to
display MIB-object information.
RW: Read/write. Enables requests accompanied by this community string to
display MIB-object information and to set MIB objects.
Press the button to add the management SNMP community strings on the
Managed Switch.
Press the button to remove the management SNMP community strings that you
defined before on the Managed Switch.
43
Page 44

NS2503-24P/2C User Manual
Trap Managers
A trap manager is a management station that receives the trap messages generated by the switch. If no trap manager is defined,
no traps will be issued. To define a management station as a trap manager, assign an IP address, enter the SNMP community
strings, and select the SNMP trap version.
Figure 4-2-8: Trap Managers Interface Screenshot
The page includes the following fields:
Object Description
IP Address:
Community:
Enter the IP address of the trap manager.
Enter the community string for the trap station.
SNMPv3 Groups
Configure SNMPv3 groups table on this page. The entry index keys are Security Model and Security Name.
The SNMPv3 Groups Configuration screen in Figure 4-2-9 appears.
Figure 4-2-9: SNMP Configuration Interface Screenshot
44
Page 45

NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
Group Name:
V1 | V2c | USM
Security Name:
Remove
A string identifying the group name that this entry should belong to.
The allowed string length is 1 to 15.
Indicates the security model that this entry should belong to. Possible security
models are:
v1: Reserved for SNMPv1.
v2c: Reserved for SNMPv2c.
usm: User-based Security Model (USM).
A string identifying the security name that this entry should belong to.
The allowed string length is 1 to 15.
Check to delete the entry. It will be deleted during the next save.
SNMPv3 View
Configure SNMPv3 views table on this page. The entry index keys are View Name and OID Subtree.
The SNMPv3 Views Configuration screen in Figure 4-2-10 appears.
Figure 4-2-10: SNMP Configuration Interface Screenshot
45
Page 46

NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
View N ame:
Included | Excluded:
View Subtree
View Mask(Hexadecimal
Digits):
A string identifying the view name that this entry should belong to.
The allowed string length is 1 to 15.
Indicates the view type that this entry should belong to. Possible view type are:
included: An optional flag to indicate that this view subtree should be
included.
excluded: An optional flag to indicate that this view subtree should be
excluded.
The OID defining the root of the subtree to add to the named view. The allowed
OID length is 1 to 128. The allowed string content is digital number or asterisk(*)
View mask is defined in order to reduce the amount of configuration information
required when fine-grained access control is required (e.g., access control at
the object instance level)
SNMPv3 Access
Configure SNMPv3 access table on this page. The entry index keys are Group Name, Security Model and Security Level.
The SNMPv3 Access Configuration screen in Figure 4-2-11 appears.
Figure 4-2-11: SNMP Configuration Interface Screenshot
46
Page 47

The page includes the following fields:
Object Description
Group Name:
V1 | V2c | USM:
SNMP Access:
Read View:
Write View:
NS2503-24P/2C User Manual
A string identifying the group name that this entry should belong to.
The allowed string length is 1 to 15.
Indicates the security model that this entry should belong to. Possible security
models are:
v1: Reserved for SNMPv1.
v2c: Reserved for SNMPv2c.
usm: User-based Security Model (USM)
Indicates the security model that this entry should belong to. Possible security
models are:
NoAuth: No authentication and no privacy.
Auth: Authentication and no privacy.
Authpriv: Authentication and privacy.
The name of the MIB views defining the MIB objects for which this request may
request the current values.
The allowed string length is 1 to 16.
The name of the MIB views defining the MIB objects for which this request may
potentially SET new values.
The allowed string length is 1 to 16.
Notify View:
Set up the notify view.
Remove Check to delete the selected entry. It will be deleted during the next save.
47
Page 48

NS2503-24P/2C User Manual
SNMP V3 usm-user
Configure SNMPv3 users table on this page. The entry index keys are Engine ID and User Name. The SNMPv3 Users
Configuration screen in Figure 4-2-12 appears.
Figure 4-2-12: SNMP Configuration Interface Screenshot
The page includes the following fields:
Object Description
SNMP User Name:
Auth Type:
Auth Key(8~32):
Private Key(8~32):
Remove Check to delete the selected entry. It will be deleted during the next save.
A string identifying the user name that this entry should belong to. The allowed
string length is 1 to 15.
Indicates the authentication protocol that this entry should belong to. Possible
authentication protocols are:
None: No authentication protocol.
MD5: An optional flag to indicate that this user using MD5 authentication
protocol.
The value of security level cannot be modified if the entry already exists. That
means you must first ensure that the value is set correctly.
A string identifying the authentication pass phrase.
For MD5 authentication protocol, the allowed string length is 8 to 32.
A string identifying the privacy pass phrase.
The allowed string length is 8 to 32.
48
Page 49

NS2503-24P/2C User Manual
Syslog Setting
The Syslog Setting page allows you to configure the logging of messages that are sent to remote syslog servers or other
management stations. You can also limit the event messages sent to only those messages below a specified level.
Figure 4-2-13: Syslog Setting Screenshot
The page includes the following fields:
Object Description
Syslog Server IP
Log level None: No syslog message sent to the syslog server, and Max Age
Apply
Help
IP address of syslog server.
parameters of the root bridge, regardless of how it is configured.
Major: only send major syslog to syslog server, eg: link up/down, system
warm/cold start
All: send all syslog messages to syslog server.
Press this button for the changes to take affect.
Press this button for System Log information.
49
Page 50

NS2503-24P/2C User Manual
System Log
It provides the functions allowing the user to update the switch firmware via the Trivial File Transfer Protocol (TFTP) server.
Before updating, make sure the TFTP server is ready and the firmware image is located on the TFTP server.
The page includes the following fields:
Object Description
System Log Mode:
Log level:
Apply
Help
Figure 4-2-14: System Log Screenshot
Enable or disable the System Log Mode function.
None: No syslog message sent to the syslog server, and Max Age
parameters of the root bridge, regardless of how it is configured.
Major: only send major syslog to syslog server, eg: link up/down, system
warm/cold start
All: send all syslog messages to syslog server.
Press this button to take affect.
Press this button for System Log information.
50
Page 51

NS2503-24P/2C User Manual
SNTP Setting
Network Time Protocol (NTP) is a networking protocol for time synchronization between computer systems over Networks.
The page includes the following fields:
Object Description
SNTP:
SNTP server IP:
UTC Type: Provide “Before-UTC” and “After-UTC” options for UTV Type.
Time Range (0~24):
Time:
Apply
Help
Figure 4-2-15: SNTP Setting Screenshot
Provide Disable or enable SNTP function.
Provide input the SNTP server IP address.
Provide input the time range and the available range is 0 to 24.
Provide SNTP Time display.
Press this button for the changes to take affect.
Press this button for SNTP Setting information.
51
Page 52

NS2503-24P/2C User Manual
Firmware Upgrade
It provides the functions allowing the user to update the switch firmware via the Trivial File Transfer Protocol (TFTP) server.
Before updating, make sure the TFTP server is ready and the firmware image is located on the TFTP server.
TFTP Firmware Upgrade
The Firmware Upgrade page provides the functions to allow a user to update the Managed Switch firmware from the TFTP
server in the network. Before updating, make sure you have your TFTP server ready and the firmware image is on the TFTP
server. The screen in Figure 4-2-16 appears.
Use this menu to download a file from specified TFTP server to the Managed Switch.
Figure 4-2-16: Firmware Upgrade Interface Screenshot
The page includes the following fields:
Object Description
TFTP Server IP Address: Type in your TFTP server IP.
Firmware File Name: Type in the name of the firmware image file to be updated.
Apply
Help
Press this button for the changes to take affect.
Press this button for Firmware Upgrade information.
52
Page 53

NS2503-24P/2C User Manual
HTTP Firmware Upgrade
The HTTP Firmware Upgrade page contains fields for downloading system image files from the Local File browser to the
device. The Web Firmware Upgrade screen in Figure 4-2-17 appears.
Figure 4-2-17: HTTP Firmware Upgrade Interface Screenshot
To open Firmware Upgrade screen perform the following:
1. Click System -> Web Firmware Upgrade.
2. The Firmware Upgrade screen is displayed as in Figure 4-2-18.
3. Click the “Browse” button of the main page, the system would pop up the file selection menu to choose firmware.
4.
Figure 4-2-18: Firmware Location Screenshot
5. Select on the firmware then click “Upload”, the Software Upload Progress would show the file upload status.
Firmware upgrade needs several minutes. Please wait a while, and then manually
refresh the webpage.
53
Page 54

NS2503-24P/2C User Manual
Configuration Backup
TFTP Restore Configuration
You can restore a previous backup configuration from the TFTP server to recover the settings. Before doing that, you must
locate the image file on the TFTP server first and the Managed Switch will download back the flash image.
Figure 4-2-19: Configuration Restore Interface Screenshot
The page includes the following fields:
Object Description
TFTP Server IP Address:
Restore File Name:
Apply
Help
Type in the TFTP server IP.
Type in the correct file name for restoring.
Press this button for the changes to take affect.
Press this button for Configuration Restore information.
54
Page 55

NS2503-24P/2C User Manual
TFTP Backup Configuration
You can back up the current configuration from flash ROM to the TFTP server for the purpose of recovering the configuration
later. It helps you to avoid wasting time on configuring the settings by backing up the configuration.
Figure 4-2-20: Configuration Backup Interface Screenshot
The page includes the following fields:
Object Description
TFTP Server IP Address:
Backup File Name:
Apply
Help
Save config except IP
Address
Type in the TFTP server IP.
Type in the file name.
Press this button for the changes to take affect.
Press this button for Configuration Backup information.
Press this button to save the configuration except the IP address.
55
Page 56

NS2503-24P/2C User Manual
Factory Default
Reset switch to default configuration. Click the RESET button to reset all configurations to the default value.
Figure 4-2-21: Factory Default Interface Screenshot
System Reboot
Reboot the switch in software reset. Click the REBOOT button to reboot the system.
Figure 4-2-22: System Reboot Interface Screenshot
56
Page 57

NS2503-24P/2C User Manual
Port Configuration
Use the Port Configuration Menu to display or configure the Managed Switch's ports. This section has the following items:
Port Control
Port Status
Port Statistics
Port Sniffer
Port Control
In Port control you can configure the settings of each port to control the connection parameters, and the status of each port is
listed beneath.
Configures port connection settings
Display the current Port link status and speed etc.
Lists Ethernet and RMON port statistics
Sets the source and target ports for mirroring
Figure 4-3-1: Port Control Interface Screenshot
57
Page 58

The page includes the following fields:
Object Description
Port:
Description: User add per port description for indication, the available range is 16 letters.
NS2503-24P/2C User Manual
Use the scroll bar and click on the port number to choose the port to be
configured.
State:
Link: Indicate per port link up and link down status.
Negotiation:
Speed:
Duplex:
Flow Control:
Current port state. The port can be set to disable or enable mode. If the port state
is set as ‘Disable’, it will not receive or transmit any packet.
Auto and Force. if set as Auto, the speed and duplex mode are negotiated
automatically. When you set it as Force, you have to set the speed and duplex
mode manually.
It is available for selecting when the Negotiation column is set as Force. When
the Negotiation column is set as Auto, this column is read-only.
It is available for selecting when the Negotiation column is set as Force. When
the Negotiation column is set as Auto, this column is read-only.
Whether or not the receiving node sends feedback to the sending node is
determined by this item. When enabled, once the device exceeds the input data
rate of another device, the receiving device will send a PAUSE frame which halts
the transmission of the sender for a specified period of time. When disabled, the
receiving device will drop the packet if too much to process.
A port in security mode will be “locked” without permission of address learning.
Only the incoming packets with SMAC already existing in the address table can
Security:
BSF:
Jumbo Frame:
be forwarded normally.
User can disable the port from learning any new MAC addresses, then use the
static MAC addresses screen to define a list of MAC addresses that can use the
secure port. Enter the settings, then click Apply button to change on this page.
User can disable/Enable port broadcast storm filtering option by port.
The filter mode and filter packets type can be select in the Managed Switch
Setting > Misc Config
User can disable/Enable port jumbo frame option by port. When port jumbo
frame is enable, the port forwards the jumbo frame packet.
page.
58
Page 59

NS2503-24P/2C User Manual
Rate Control
This page provides rate control on each port - it contains Ingress and Egress items and the unit is 128Kbps. The rate control
screen is displayed as in Figure 4-3-2.
The page includes the following fields:
Object Description
Rate Control:
(Unit: 128KBbps)
Port
Ingress
Egress
Figure 4-3-2: Rate Control Interface Screenshot
Port-1 ~ Port-24, supports by-port ingress and egress rate control.
For example, assume port 1 is 10Mbps, users can set its effective egress rate at
1Mbps and ingress rate at 500Kbps. Device will perform flow control or
backpressure to confine the ingress rate to meet the specified rate.
Allows user to choose which port will be limited rate speed.
Type the port effective ingress rate.
The valid range is 0 ~ 8000. The unit is 128K.
0: disable rate control.
1 ~ 8000: valid rate value
Type the port effective egress rate.
The valid range is 0 ~ 8000. The unit is 128K.
0: disable rate control.
1 ~8000: valid rate value.
59
Page 60

NS2503-24P/2C User Manual
Port Status
This page displays current port configurations and operating status. Via the summary table, status of each port is provided
clearly for details such as port description, Port Link Up/Link Down status, negotiation, Link Speed, Duplex mode and Flow
Control, security, jumbo frame.
Figure 4-3-3: Port Status Interface Screenshot
60
Page 61

NS2503-24P/2C User Manual
Port Statistics
The following chart provides the current statistic information which displays the real-time packet transfer status for each port.
The user might use the information to plan and implement the network, or check and find the problems when the collision or
heavy traffic occurs.
Figure 4-3-4: Port Statistics Interface Screenshot
The page includes the following fields:
Object Description
Port: The port number.
State:
Link: The status of linking—‘Up’ or ‘Down’.
Tx Good Packet: The counts of transmitting good packets via this port.
Tx Bad Packet:
Rx Good Packet: The counts of receiving good packets via this port.
Rx Bad Packet:
Tx Abort Packet: The aborted packet while transmitting.
Packet Collision: The counts of collision packet.
Packet Dropped: The counts of dropped packet.
Reset: To clear current per port counters.
It’s set by Port Control. When the state is disabled, the port will not transmit or
receive any packet.
The counts of transmitting bad packets (including undersize [less than 64 octets],
oversize, CRC Align errors, fragments and jabbers packets) via this port.
The counts of receiving good packets (including undersize [less than 64 octets],
oversize, CRC error, fragments and jabbers) via this port.
61
Page 62

NS2503-24P/2C User Manual
Port Sniffer
The Port Sniffer (mirroring) is a method for monitor traffic in switched networks. Traffic through a port can be monitored by one
specific port. This is done by duplicating the traffic through the monitored port on another (sniffer) port.
Figure 4-3-5: Port Mirror application
Configuring the port mirroring by assigning a source port from which to copy all packets and a destination port where those
packets will be sent.
62
Page 63

NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
Select a sniffer mode:
Sniffer Type:
Analysis (Monitoring) Port:
Monitor Port:
1 When the Mirror Mode is set to RX or TX and the Analysis Port is selected, the
packets to and from the Analysis Port will not be transmitted. The Analysis Port will
accept only copied packets from the Monitored Port.
2 If you want to disable this function, you must set the monitor port to none.
It means the Analysis port can be used to see the traffic on another port you want
to monitor. You can connect Analysis port to LAN analyzer or packet sniffer.
The port you want to monitor. The monitor port traffic will be copied to Analysis
port. You can select one monitor port in the switch. User can choose which port
they want to monitor in only one sniffer type.
Figure 4-3-6: Port Sniffer Interface Screenshot
Disable
Rx
Tx
Both
63
Page 64

NS2503-24P/2C User Manual
Protect Port
There are two protected port groups; ports in different groups can't communicate.
In the same group, protected ports can't communicate with each other, but can communicate with unprotected ports.
Unprotected ports can communicate with any port, including protected ports.
Figure 4-3-7: Protected Port Setting Web Interface Screenshot
The page includes the following fields:
Object Description
Port ID Identify the Managed Switch interface.
Enable the Protected function on the selected port.
Protected
Group 1
Group 2
If the check box is not shown as
communicate with any port - including protected ports
Set the protected port to bea Group 1 member.
Set the protected port to be a Group 2 member.
, then this port is an unprotected port and it can
64
Page 65

Remote Ping
The Remote Ping allows user to check the device connection status via the ping function.
NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
Remote IP Address
Ping Size
Ping
Result
Save
Reset
Clear
Figure 4-3-8: Remote Ping interface
Allows user to define the IP address of remote device.
Allows user to define ping packet size. Generally, the size should be 64.
Click “Ping” button to start ping to remote device.
Shows ping action result.
If the ping successful, it will be showed “Ping Ok, Send 5 Packet, I 5 Packet”.
If the ping failed, it will showed “Ping Failed”
Click the “Save” button to save the Remote Ping configuration. A User can use the
ping function even when the configuration is not saved. When the configuration is
not saved, and the WEB page is refreshed, the
configuration is cleared.
Clicking the “Reset” button will reset all Remote Ping configuration and save
automatically.
Click “Clear” button will clear result message.
65
Page 66

NS2503-24P/2C User Manual
VLAN configuration
VLAN Overview
A Virtual Local Area Network (VLAN) is a network topology configured according to a logical scheme rather than the physical
layout. VLAN can be used to combine any collection of LAN segments into an autonomous user group that appears as a single
LAN. VLAN also logically segment the network into different broadcast domains so that packets are forwarded only between
ports within the VLAN. Typically, a VLAN corresponds to a particular subnet, although not necessarily.
VLAN can enhance performance by conserving bandwidth, and improve security by limiting traffic to specific domains.
A VLAN is a collection of end nodes grouped by logic instead of physical location. End nodes that frequently communicate with
each other are assigned to the same VLAN, regardless of where they are physically on the network. Logically, a VLAN can be
equated to a broadcast domain, because broadcast packets are forwarded to only members of the VLAN on which the
broadcast was initiated.
1. No matter what basis is used to uniquely identify end nodes and assign these nodes VLAN
membership, packets cannot cross VLAN without a network device performing a routing
function between the VLAN.
2. The Managed Switch supports IEEE 802.1Q VLAN. The port untagging function can be used
to remove the 802.1 tag from packet headers to maintain compatibility with devices that are
tag-unaware.
The Managed Switch supports IEEE 802.1Q (tagged-based) and Port-Base VLAN setting in web management page. In the
default configuration, VLAN support is “802.1Q”.
Port-based VLAN
Port-based VLAN limit traffic that flows into and out of switch ports. Thus, all devices connected to a port are members of the
VLAN(s) the port belongs to, whether there is a single computer directly connected to a switch, or an entire department.
On port-based VLAN, NICs do not need to be able to identify 802.1Q tags in packet headers. NIC send and receive normal
Ethernet packets. If the packet's destination lies on the same segment, communications take place using normal Ethernet
protocols. Even though this is always the case, when the destination for a packet lies on another switch port, VLAN
considerations come into play to decide if the packet is dropped by the Managed Switch or delivered.
IEEE 802.1Q VLANs
IEEE 802.1Q (tagged) VLAN are implemented on the Managed Switch. 802.1Q VLAN require tagging, which enables them to
span the entire network (assuming all switches on the network are IEEE 802.1Q-compliant).
VLAN allows a network to be segmented in order to reduce the size of broadcast domains. All packets entering a VLAN will only
be forwarded to the stations (over IEEE 802.1Q enabled switches) that are members of that VLAN, and this includes broadcast,
multicast and unicast packets from unknown sources.
VLAN can also provide a level of security to your network. IEEE 802.1Q VLAN will only deliver packets between stations that
are members of the VLAN. Any port can be configured as either tagging or untagging. The untagging feature of IEEE 802.1Q
VLAN allows VLAN to work with legacy switches that don't recognize VLAN tags in packet headers. The tagging feature allows
VLAN to span multiple 802.1Q-compliant switches through a single physical connection and allows Spanning Tree to be
enabled on all ports and work normally.
Some relevant terms:
- Tagging - The act of putting 802.1Q VLAN information into the header of a packet.
- Untagging - The act of stripping 802.1Q VLAN information out of the packet header.
802.1Q VLAN Tags
The figure below shows the 802.1Q VLAN tag. There are four additional octets inserted after the source MAC address. Their
presence is indicated by a value of 0x8100 in the Ether Type field. When a packet's Ether Type field is equal to 0x8100, the
packet carries the IEEE 802.1Q/802.1p tag. The tag is contained in the following two octets and consists of 3 bits of user priority,
1 bit of Canonical Format Identifier (CFI - used for encapsulating Token Ring packets so they can be carried across Ethernet
backbones), and 12 bits of VLAN ID (VID). The 3 bits of user priority are used by 802.1p. The VID is the VLAN identifier and is
used by the 802.1Q standard. Because the VID is 12 bits long, 4094 unique VLAN can be identified.
The tag is inserted into the packet header making the entire packet longer by 4 octets. All of the information originally contained
in the packet is retained.
66
Page 67

NS2503-24P/2C User Manual
802.1Q Tag
User Priority CFI VLAN ID (VID)
3 bits 1 bits 12 bits
TPID (Tag Protocol Identifier) TCI (Tag Control Information)
2 bytes 2 bytes
Preamble
Destination
Address
6 bytes 6 bytes 4 bytes 2 bytes 46-1517 bytes 4 bytes
The Ether Type and VLAN ID are inserted after the MAC source address, but before the original Ether Type/Length or Logical
Link Control. Because the packet is now a bit longer than it was originally, the Cyclic Redundancy Check (CRC) must be
recalculated.
Adding an IEEE802.1Q Tag
Dest. Addr. Src. Addr. Length/E. type Data Old CRC
Dest. Addr. Src. Addr. E. type Tag Length/E. type Data New CRC
Source
Address
VLAN TAG
Ethernet
Type
Data FCS
Original Ethernet
Priority CFI VLAN ID
New Tagged Packet
Port VLAN ID
Packets that are tagged (are carrying the 802.1Q VID information) can be transmitted from one 802.1Q compliant network
device to another with the VLAN information intact. This allows 802.1Q VLAN to span network devices (and indeed, the entire
network – if all network devices are 802.1Q compliant).
Every physical port on a switch has a PVID. 802.1Q ports are also assigned a PVID, for use within the switch. If no VLAN are
defined on the switch, all ports are then assigned to a default VLAN with a PVID equal to 1. Untagged packets are assigned the
PVID of the port on which they were received. Forwarding decisions are based upon this PVID, in so far as VLAN are
concerned. Tagged packets are forwarded according to the VID contained within the tag. Tagged packets are also assigned a
PVID, but the PVID is not used to make packet forwarding decisions, the VID is.
Tag-aware switches must keep a table to relate PVID within the switch to VID on the network. The switch will compare the VID
of a packet to be transmitted to the VID of the port that is to transmit the packet. If the two VID are different the switch will drop
the packet. Because of the existence of the PVID for untagged packets and the VID for tagged packets, tag-aware and
tag-unaware network devices can coexist on the same network.
A switch port can have only one PVID, but can have as many VID as the switch has memory in its VLAN table to store them.
Because some devices on a network may be tag-unaware, a decision must be made at each port on a tag-aware device before
packets are transmitted – should the packet to be transmitted have a tag or not? If the transmitting port is connected to a
tag-unaware device, the packet should be untagged. If the transmitting port is connected to a tag-aware device, the packet
should be tagged.
Default VLANs
The Managed Switch initially configures one VLAN, VID = 1, called "default." The factory default setting assigns all ports on the
Switch to the "default". As new VLAN are configured in Port-based mode, their respective member ports are removed from the
"default."
VLAN and Link aggregation Groups
In order to use VLAN segmentation in conjunction with port link aggregation groups, you can first set the port link aggregation
group(s), and then you may configure VLAN settings. If you wish to change the port link aggregation grouping with VLAN
already in place, you will not need to reconfigure the VLAN settings after changing the port link aggregation group settings.
VLAN settings will automatically change in conjunction with the change of the port link aggregation group settings.
67
Page 68

NS2503-24P/2C User Manual
Static VLAN Configuration
A Virtual LAN (VLAN) is a logical network grouping that limits the broadcast domain. It allows you to isolate network traffic so
only members of the VLAN receive traffic from the same VLAN members. Basically, creating a VLAN from a switch is logically
equivalent of reconnecting a group of network devices to another Layer 2 switch. However, all the network devices are still plug
into the same switch physically.
The Managed Switch supports Port-based and 802.1Q (Tagged-based) VLAN in web management page. In the default
configuration, VLAN support is “802.1Q”.
Figure 4-4-1: Static VLAN Interface Screenshot
1 No matter what basis is used to uniquely identify end nodes and assign these nodes
VLAN membership, packets cannot cross VLAN without a network device performing a
routing function between the VLAN.
2 The Managed Switch supports Port-based VLAN and IEEE 802.1Q VLAN. The port
untagging function can be used to remove the 802.1 tag from packet headers to
maintain compatibility with devices that are tag-unaware.
68
Page 69

NS2503-24P/2C User Manual
Port-based VLAN
Packets can go among only members of the same VLAN group. Note all unselected ports are treated as belonging to another
single VLAN. If the port-based VLAN enabled, the VLAN-tagging is ignored.
In order for an end station to send packets to different VLANs, it has to be either capable of tagging packets it sends with VLAN
tags or attached to a VLAN-aware bridge that is capable of classifying and tagging the packet with different VLAN ID based on
not only default PVID, but also other information about the packet, such as the protocol.
Figure 4-4-2: Port-based VLAN Interface Screenshot
Create a VLAN and add member ports to it
1. Click the hyperlink "VLAN” \ “Static VLAN" to enter the VLAN configuration interface.
2. Select “Port Based VLAN” at the VLAN Operation Mode, to enable the port-based VLAN function.
3. Click “Add “to create a new VLAN group. Then the following Figure 4-4-3 appears.
4. Type a name and Group ID for the new VLAN, the available range is 2-4094.
5. From the Available ports box, select ports to add to the Managed Switch and click “Add”.
6. Click Apply.
7. You will see that the VLAN Group displays.
8. If the port-based VLAN groups list over one page, please click “Next Page” to view other VLAN groups on other page.
9. Use “Delete” button to delete unwanted port-based VLAN groups
10. Use “Edit” button to modify existing port-based VLAN groups.
69
Page 70

By adding ports to the VLAN you have created one port-based VLAN group completely.
NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
Use this optional field to specify a name for the VLAN. It can be up to 16
VLAN Name
Group ID
Port
Member
All unselected ports are treated as belonging to another single VLAN. If the port-based
VLAN is enabled, then the VLAN-tagging is ignored.
alphanumeric characters long, including blanks.
You can configure the ID number of the VLAN by this item. This field is used to add
VLANs one at a time. The VLAN group ID and available range is 2-4094.
Indicate port 1 to port 26.
Add
Remove
Figure 4-4-3: Static VLAN Interface Screenshot
Defines the interface as a Port-Based member of a VLAN.
Forbidden ports are not included in the VLAN.
70
Page 71

NS2503-24P/2C User Manual
802.1Q VLAN
Tagged-based VLAN is an IEEE 802.1Q specification standard. Therefore, it is possible to create a VLAN across devices from
different switch vendors. IEEE 802.1Q VLAN uses a technique to insert a "tag" into the Ethernet frames. Tag contains a VLAN
Identifier (VID) that indicates the VLAN numbers.
You can create and delete Tag-based VLAN. There are a total of 256 VLAN groups that can be configured. Once 802.1Q VLAN
is enabled, all ports belong to the default VLAN with the default VID defined as 1. The default VLAN can’t be deleted.
Understand nomenclature of the Switch
■ IEEE 802.1Q Tagged and Untagged
Every port on an 802.1Q compliant switch can be configured as tagged or untagged.
Tagged
Untgged
Frame Leave
Ports with tagging enabled will put the VID number, priority and other VLAN information into the
header of all packets that flow into those ports. If a packet has previously been tagged, the port
will not alter the packet, thus keeping the VLAN information intact. The VLAN information in the
tag can then be used by other 802.1Q compliant devices on the network to make
packet-forwarding decisions.
Ports with untagging enabled will strip the 802.1Q tag from all packets that flow into those
ports. If the packet doesn't have an 802.1Q VLAN tag, the port will not alter the packet. Thus,
all packets received by and forwarded by an untagging port will have no 802.1Q VLAN
information. (Remember that the PVID is only used internally within the Switch). Untagging is
used to send packets from an 802.1Q-compliant network device to a non-compliant network
device.
Frame Income
Income Frame is tagged Income Frame is untagged
Leave port is tagged Frame remains tagged Tag is inserted
Leave port is untagged Tag is removed Frame remain untagged
71
Page 72

VLAN Group Configuration
VLAN Group Configuration
NS2503-24P/2C User Manual
Figure 4-4-4: VLAN Group Configuration Interface Screenshot
1. Click the hyperlink "VLAN” \ “Static VLAN" to enter the VLAN configuration interface.
2. Select “802.1Q” at the VLAN Operation Mode, to enable the 802.1Q VLAN function.
3. Click Add to create a new VLAN group or Edit to manage the existing VLAN groups. Then the VLAN Group column
appears.
4. Define a VLAN group ID. Available range is 2-4094.
72
Page 73

NS2503-24P/2C User Manual
Figure 4-4-5: VLAN Group Configuration Interface Screenshot
5. Select specific port as member port and the screen in Figure 4-4-6 appears.
6. After setup completed, press “Apply” button to take effect.
7. Press “Back” for return to VLAN configuration screen to add other VLAN group, the screen in Figure 4-33 appears.
8. If there are many groups exceeding the limit of one page, you can click Next to view other VLAN groups.
9. Use Delete button to delete unwanted VLAN.
10. Use Edit button to modify existing VLAN group.
73
Page 74

NS2503-24P/2C User Manual
Figure 4-4-6: 802.1Q VLAN Setting Interface Screenshot
The page includes the following fields:
Object Description
VLAN Name
VLAN ID
Port
UnTag Member
Once 802.1Q VLAN is enabled, all ports belong to the default VLAN with the default VID
defined as 1.
Use this optional field to specify a name for the VLAN. It can be up to 16
alphanumeric characters long, including blanks.
You can configure the ID number of the VLAN by this item. This field is used to
add VLANs one at a time.
The VLAN group ID and available range is 2-4094.
Indicate port 1 to port 10.
Untag
Tag
Packets forwarded by the interface are untagged.
Defines the interface as a tagged member of a VLAN. All packets
forwarded by the interface are tagged. The packets contain VLAN
information.
74
Page 75

NS2503-24P/2C User Manual
VLAN Filter
802.1Q VLAN Port Configuration
This page is used for configuring the Switch port VLAN. The VLAN per Port Configuration page contains fields for managing
ports that are part of a VLAN. The port default VLAN ID (PVID) is configured on the VLAN Port Configuration page. All untagged
packets arriving to the device are tagged by the ports PVID.
This section provides 802.1Q Ingress Filter of each port from the Switch, The screen displays as shown in Figure 4-4-7.
Figure 4-4-7: 802.1Q Ingress Filter Interface Screenshot
75
Page 76

The page includes the following fields:
Object Description
NO
Indicate port 1 to port 10.
NS2503-24P/2C User Manual
PVID
Ingress Filtering 1
Ingress Filtering 2
Apply button
Set the port VLAN ID that will be assigned to untagged traffic on a given port.
This feature is useful for accommodating devices that you want to participate in
the VLAN but that don’t support tagging.
Each port allows user to set one VLAN ID, the range being 1~255, and the
default VLAN ID is 1.
The VLAN ID must be the as same as the VLAN ID of the group the port belongs
to, otherwise the untagged traffic will be dropped.
Ingress filtering lets frames belonging to a specific VLAN to be forwarded if the
port belongs to that VLAN.
Enable: Forward only packets with VID matching this port’s configured VID.
Disable: Disable Ingress filter function.
Drop untagged frame.
Disable: Accepts all Packets.
Enable: Only packet with a matching VLAN ID can be allowed to go through the
port.
Press the button to save the configuration.
GVRP VLAN
GVRP (GARP VLAN Registration Protocol or Generic VLAN Registration Protocol) is a protocol that facilitates control of
virtual local area networks (VLANs) within a larger network. GVRP conforms to the IEEE 802.1Q specification, which defines a
method of tagging frames with VLAN configuration data. This allows network devices to dynamically exchange VLAN
configuration information with other devices.
76
Page 77

GVRP Setting
To configure GVRP
Enable global GVRP function: select GVRP enable "Enable".
Enable port GVRP function: select GVRP checkbox for special port.
NS2503-24P/2C User Manual
Figure 4-4-8: GVRP Configuration Interface Screenshot
The page includes the following fields:
Object Description
GVRP:
Port:
Port GVRP:
Enable global GVRP function.
Indicate port 1 to port 26.
Enable selected port GVRP function
77
Page 78

GVRP Table
The GVRP Table can be used to display dynamic VLANs from being learned via GVRP.
NS2503-24P/2C User Manual
The page includes the following fields:
Object Description
VLAN ID:
Port Members:
Display the learned VLANs via GVRP protocol on GVRP enabled ports.
The Managed Switch allows displaying up to 128 dynamic VLAN entries.
Identify the GVRP enabled port that dynamic VLAN is learned from.
Figure 4-4-9: GVRP Table Interface Screenshot
78
Page 79

NS2503-24P/2C User Manual
Q-in-Q VLAN
■ IEEE 802.1Q Tunneling (Q-in-Q)
IEEE 802.1Q Tunneling (QinQ) is designed for service providers carrying traffic for multiple customers across their networks.
QinQ tunneling is used to maintain customer-specific VLAN and Layer 2 protocol configurations even when different customers
use the same internal VLAN IDs. This is accomplished by inserting Service Provider VLAN (SPVLAN) tags into the customer’s
frames when they enter the service provider’s network, and then stripping the tags when the frames leave the network.
A service provider’s customers may have specific requirements for their internal VLAN IDs and number of VLANs supported.
VLAN ranges required by different customers in the same service-provider network might easily overlap, and traffic passing
through the infrastructure might be mixed. Assigning a unique range of VLAN IDs to each customer would restrict customer
configurations, require intensive processing of VLAN mapping tables, and could easily exceed the maximum VLAN limit of
4096.
The Managed Switch supports multiple VLAN tags and can therefore be used in MAN applications as a provider bridge,
aggregating traffic from numerous independent customer LANs into the MAN (Metro Access Network) space. One of the
purposes of the provider bridge is to recognize and use VLAN tags so that the VLANs in the MAN space can be used
independent of the customers’ VLANs. This is accomplished by adding a VLAN tag with a MAN-related VID for frames entering
the MAN. When leaving the MAN, the tag is stripped and the original VLAN tag with the customer-related VID is again available.
This provides a tunneling mechanism to connect remote costumer VLANs through a common MAN space without interfering
with the VLAN tags. All tags use Ether Type 0x8100 or 0x88A8, where 0x8100 is used for customer tags and 0x88A8 are used
for service provider tags.
In cases where a given service VLAN only has two member ports on the switch, the learning can be disabled for the particular
VLAN and can therefore rely on flooding as the forwarding mechanism between the two ports. This way, the MAC table
requirements is reduced.
79
Page 80

Q-in-Q Port Setting
The QinQ VLAN \ QinQ Port Setting screen in Figure 4-4-10 appears.
NS2503-24P/2C User Manual
Figure 4-4-10: Q-in-Q Port Setting Interface Screenshot
The page includes the following fields:
Object Description
Enable: Sets the Managed Switch to QinQ mode, and allows the QinQ tunnel port to
QinQ
QinQ TPID
Port QinQ
QinQ Uplink
Disable:
The default is for the Managed Switch to function in Disable mode.
The Tag Protocol Identifier (TPID) specifies the ethertype of incoming packets on a
tunnel access port.
802.1Q Tag: 8100
vMAN Tag: 88A8
Default: 802.1Q Tag.
Check: Sets the Port to QinQ mode. Or the port operates in its normal VLAN mode.
Default: Un-check.
Check:
Cancel:
be configured.
The Managed Switch operates in its normal VLAN mode.
Configures IEEE 802.1Q tunneling (QinQ) for an uplink port to another device
within the service provider network.
Configures IEEE 802.1Q tunneling (QinQ) for a client access port to segregate
and preserve customer VLAN IDs for traffic crossing the service provider
network.
80
Page 81

NS2503-24P/2C User Manual
Q-in-Q Tunnel Setting
Business customers of service providers often have specific requirements for VLAN IDs and the number of VLANs to be
supported. The VLAN ranges required by different customers in the same service-provider network might overlap, and traffic of
customers through the infrastructure might be mixed. Assigning a unique range of VLAN IDs to each customer would restrict
customer configurations and could easily exceed the VLAN limit (4096) of the IEEE 802.1Q specification.
Using the QinQ feature, service providers can use a single VLAN to support customers who have multiple VLANs. Customer
VLAN IDs are preserved, and traffic from different customers is segregated within the service-provider network, even when they
appear to be in the same VLAN. Using QinQ expands VLAN space by using a VLAN-in-VLAN hierarchy and retagging the
tagged packets. A port configured to support QinQ is called a QinQ user-port. A port configured to support QinQ Uplink is called
a QinQ uplink-port.
Figure 4-4-11: Q-in-Q Tunnel Setting Interface Screenshot
To configure QinQ Port
1. Enable global QinQ function: select QinQ enable "Enable".
2. Fill QinQ Tpid.
3. Enable port QinQ function: select QinQ checkbox for special port.
4. Enable port QinQ Uplink function: select QinQ Uplink checkbox for special port.
81
Page 82

NS2503-24P/2C User Manual
Trunking
Port trunking is the combination of several ports or network cables to expand the connection speed beyond the limits of any one
single port or network cable. The Managed Switch supports two types of port trunk technology:
Static Trunk
LACP
The Link Aggregation Control Protocol (LACP) provides a standardized means for exchanging information between Partner
Systems on a link to allow their Link Aggregation Control instances to reach agreement on the identity of the Link Aggregation
Group to which the link belongs, move the link to that Link Aggregation Group, and enable its transmission and reception
functions in an orderly manner. Link aggregation lets you group up to eight consecutive ports into a single dedicated connection.
This feature can expand bandwidth to a device on the network. LACP operation requires full-duplex mode. For more detail
information refer to the IEEE 802.3ad standard.
82
Page 83

NS2503-24P/2C User Manual
Aggregator setting
This section provides Port Trunk-Aggregator Setting of each port from the Managed Switch, the screen in Figure 4-5-1 appears.
Figure 4-5-1: Port Trunk—Aggregator Setting Interface (two ports are added to the left field with LACP enabled)
The page includes the following fields:
Object Description
System Priority:
Group ID:
LACP:
A value which is used to identify the active LACP. The Managed Switch with the
lowest value has the highest priority and is selected as the active LACP peer of
the trunk group.
There are 13 trunk groups to be selected. Assign the "Group ID" to the trunk
group.
Enabled, the trunk group is using LACP. A port which joins an LACP trunk
group has to make an agreement with its member ports first.
Disabled, the trunk group is a static trunk group. The advantage of having
the LACP disabled is that a port joins the trunk group without any
handshaking with its member ports; but member ports won’t know that they
should be aggregated together to form a logic trunk group.
83
Page 84

NS2503-24P/2C User Manual
This column field allows the user to type in the total number of active port up to
four. With LACP static trunk group, e.g. you assign four ports to be the
Work ports:
Please notice that a trunk group, including member ports split between two switches, has to enable the
LACP function of the two switches.
members of a trunk group whose work ports column field is set as two; the
excess ports are standby/redundant ports and can be aggregated if working ports
fail. If it is a static trunk group (non-LACP), the number of work ports must be
equal to the total number of group member ports.
Aggregator Information
When you had setup the LACP aggregator, you will see relation information in here.
LACP disabled
Having set up the aggregator setting with LACP disabled, you will see the local static trunk group information on the tab of
Aggregator Information.
Figure 4-5-2: Assigning 2 ports to a Trunk Group with LACP Disabled Screenshot
84
Page 85

Figure 4-5-3: Static Trunking Group Information Screenshot
The page includes the following fields:
Object Description
NS2503-24P/2C User Manual
Group Key:
Port Member:
This is a read-only column field that displays the trunk group ID.
This is a read-only column field that displays the members of this static trunk
group.
LACP enabled
Having set up the aggregator setting with LACP enabled, you will see the trunking group information between two switches on
the tab of Aggregator Information.
Switch 1 configuration
1. Set System Priority of the trunk group. The default is 32768.
2. Select a trunk group ID by pull down the drop-down menu bar.
3. Enable LACP.
4. Include the member ports by clicking the Add button after selecting the port number and the column field of Work
Ports changes automatically.
85
Page 86

NS2503-24P/2C User Manual
Figure 4-5-4: Aggregation Information of Switch 1 Screenshot
5. Click on the tab of Aggregator Information to check the trunked group information as the illustration shown above
after the two switches configured.
Switch 2 configuration
1. Set System Priority of the trunk group. For example: 1.
2, Select a trunk group ID by pull down the drop-down menu bar.
3. Enable LACP.
4. Include the member ports by clicking the Add button after selecting the port number and the column field of Work Ports
changes automatically.
86
Page 87

NS2503-24P/2C User Manual
Figure 4-5-5: Swit ch 2 Configuration Interface Screenshot
5. Click on the tab of Aggregator Information to check the trunked group information as the illustration shown above
after the two switches configured.
Figure 4-5-6: Switch 1 Aggregator Information Screenshot
87
Page 88

NS2503-24P/2C User Manual
State Activity
Having the set up the LACP aggregator the tab of Aggregator Setting, you can configure the state activity for the members of
the LACP trunk group by selecting the checkbox beside the state label. When you remove the check mark of the port and
Apply
click
, the port state activity will change to
Passive
.
The page includes the following fields:
Object Description
Active: The port automatically sends LACP protocol packets.
Passive:
A link having two passive LACP nodes will not perform dynamic LACP trunk because both
ports are waiting for an LACP protocol packet from the other device.
Figure 4-5-7: State Activity of Switch 1 Screenshot
The port does not send LACP protocol packets automatically, and responds only
if it receives LACP protocol packets from the other device.
88
Page 89

NS2503-24P/2C User Manual
Forwarding and Filtering
The frames of Ethernet Packets contain a MAC address (SMAC address), which shows the MAC address of the equipment
sending the frame. The SMAC address is used by the switch to automatically update the MAC table with these dynamic MAC
addresses. Dynamic entries are removed from the MAC table if no frames with the corresponding SMAC address have been
seen after a configurable age time.
Dynamic MAC Table
Entries in the MAC Table are shown on this page. The Dynamic MAC Table contains up to 8192 entries, and is sorted first by
VLAN ID, then by MAC address. You can view all of the dynamic MAC addresses learned by the listed port.
MAC Table Columns
Object Description
NO
MAC
PORT
VID
Type
Click “
Clear”
Figure 4-6-1: Dynamic MAC Address Interface Screenshot
The MAC address index entry.
The MAC address of the entry.
The ports that are members of the entry.
The VLAN ID of the entry.
Indicates whether the entry is a static or dynamic entry.
to clear the dynamic MAC addresses information of the current port shown on the screen.
89
Page 90

NS2503-24P/2C User Manual
Static MAC Table
You can add a static MAC address that remains in the switch's address table regardless of whether the device is physically
connected to the switch. This saves the switch from having to re-learn a device's MAC address when the disconnected or
powered-off device is active on the network again. Via this interface, you can add / modify / delete a static MAC address.
Add the Static MAC Address
You can add static MAC address in the switch MAC table here.
Figure 4-6-2: Static MAC Addresses Interface Screenshot
The page includes the following fields:
Object Description
MAC Address:
Enter the MAC address of the port that should permanently forward traffic,
regardless of the device network activity.
Port num.:
VLAN ID:
Pull down the selection menu to select the port number.
The VLAN ID for the entry.
90
Page 91

NS2503-24P/2C User Manual
MAC Filtering
By filtering MAC address, the switch can easily filter the pre-configured MAC address and reduce the un-safety. You can add
and delete filtering MAC address.
The page includes the following fields:
Object Description
MAC Address:
VLAN ID:
Figure 4-6-3: MAC Filtering Interface Screenshot
Enter the MAC address that you want to filter.
The VLAN ID for the entry.
91
Page 92

NS2503-24P/2C User Manual
IGMP Snooping
Theory
The Internet Group Management Protocol (IGMP) lets host and routers share information about multicast groups
memberships. IGMP snooping is a switch feature that monitors the exchange of IGMP messages and copies them to the CPU
for feature processing. The overall purpose of IGMP Snooping is to limit the forwarding of multicast frames to only ports that are
a member of the multicast group.
About the Internet Group Management Protocol (IGMP) Snooping
Computers and network devices that want to receive multicast transmissions need to inform nearby routers that they will
become members of a multicast group. The Internet Group Management Protocol (IGMP) is used to communicate this
information. IGMP is also used to periodically check the multicast group for members that are no longer active. In the case
where there is more than one multicast router on a sub network, one router is elected as the querier. This router then keeps
track of the membership of the multicast groups that have active members. The information received from IGMP is then used to
determine if multicast packets should be forwarded to a given sub network or not. The router can check, using IGMP, to see if
there is at least one member of a multicast group on a given subnet work. If there are no members on a sub network, packets
will not be forwarded to that sub network.
Figure 4-7-1: Multicast Service
92
Page 93

NS2503-24P/2C User Manual
Figure 4-7-2: Multicast Flooding
Figure 4-7-3: IGMP Snooping Multicast Stream Control
93
Page 94

NS2503-24P/2C User Manual
IGMP Versions 1 and 2
Multicast groups allow members to join or leave at any time. IGMP provides the method for members and multicast routers to
communicate when joining or leaving a multicast group.
IGMP version 1 is defined in RFC 1112. It has a fixed packet size and no optional data.
The format of an IGMP packet is shown below:
IGMP Message Format
Octets
0 8 16 31
Type Response Time Checksum
Group Address (all zeros if this is a query).
The IGMP Type codes are shown below:
Type Meaning
0x11
0x11
0x16 Membership Report (version 2).
0x17 Leave a Group (version 2).
0x12 Membership Report (version 1).
IGMP packets enable multicast routers to keep track of the membership of multicast groups, on their respective sub networks.
The following outlines what is communicated between a multicast router and a multicast group member using IGMP.
A host sends an IGMP “report” to join a group.
A host will never send a report when it wants to leave a group (for version 1).
A host will send a “leave” report when it wants to leave a group (for version 2).
Multicast routers send IGMP queries (to the all-hosts group address: 224.0.0.1) periodically to see whether any group members
exist on their sub networks. If there is no response from a particular group, the router assumes that there are no group members
on the network.
The Time-to-Live (TTL) field of query messages is set to 1 so that the queries will not be forwarded to other sub networks.
IGMP version 2 introduces some enhancements such as a method to elect a multicast queried for each LAN, an explicit leave
message, and query messages that are specific to a given group.
The states a computer will go through to join or to leave a multicast group are shown below:
Membership Query (if Group Address is 0.0.0.0).
Specific Group Membership Query (if Group Address is
Present).
94
Page 95

NS2503-24P/2C User Manual
Figure 4-7-4: IGMP State Transitions
IGMP Querier
A router, or multicast-enabled switch, can periodically ask their hosts if they want to receive multicast traffic. If there is more
than one router/switch on the LAN performing IP multicasting, one of these devices is elected “querier” and assumes the
role of querying the LAN for group members. It then propagates the service requests on to any upstream multicast
switch/router to ensure that it will continue to receive the multicast service.
Multicast routers use this information, along with a multicast routing protocol such as
DVMRP or PIM, to support IP multicasting across the Internet.
95
Page 96

NS2503-24P/2C User Manual
IGMP Configuration
The Managed Switch support IP multicast, can enable IGMP protocol on web management’s switch setting advanced page, to
display the IGMP snooping information. IP multicast addresses range is from 224.0.0.0 to 239.255.255.255.
Figure 4-7-5: IGMP Configuration Interface Screenshot
The page includes the following fields:
Object Description
IGMP Protocol:
Enable or disable the IGMP protocol.
96
Page 97

NS2503-24P/2C User Manual
IGMP Fast leave:
IGMP Querier:
IGMP Router Port:
Fast Leave:
The Managed Switch can be configured to immediately delete a member port of a multicast service if a
leave packet is received at that port and the fast leave function is enabled for the parent VLAN. This allows
the Managed switch to remove a port from the multicast forwarding table without first having to send an
IGMP group-specific query to that interface.
Enable or disable Fast Leave on the port.
Enable or disable the IGMP query function. The IGMP query information will be
displayed in IGMP status section.
Allows user choosing three IGMP router port modes as follows:
a. Auto: Dynamic IGMP router port mode, where the system detects
multicast source then set the port to router port automatically.
b. Static: System will be forced to forward IGMP Join or Leave control
packet to another switch via an indicate port.
c. Forbidden: Allows user to set port as a non-router port.
97
Page 98

NS2503-24P/2C User Manual
Static Multicast Table
Static Multicast Table is a feature for user to force steaming multicast stream to indicate port. When you add a static multicast
address, it remains in the multicast group table, regardless of whether the multicast stream has been joined or hasn’t been
joined. The static multicast group will be saved to the switch and it will not be released unless user deletes it.
To delete static multicast group, user has to input the multicast address, port and VID, and then press Delete button.
Figure 4-7-6: Static Multicast Table Interface
98
Page 99

The page includes the following fields:
Object Description
NS2503-24P/2C User Manual
IP Address:
VLAN ID:
Allows user to input multicast address group.
Allows multicast streaming to indicate port.
Remove multicast streaming from indicate port.
Allows user to input VLAN ID for streaming multicast packet.
Allows user to add static multicast information to IGMP Snooping table.
Allows user to delete static multicast information from IGMP Snooping table.
Click this button shows help description
99
Page 100

NS2503-24P/2C User Manual
Spanning Tree Protocol
Theory
The Spanning Tree protocol can be used to detect and disable network loops, and to provide backup links between switches,
bridges or routers. This allows the switch to interact with other bridging devices in your network to ensure that only one route
exists between any two stations on the network, and provide backup links which automatically take over when a primary link
goes down. The spanning tree algorithms supported by this Managed Switch include these versions:
STP – Spanning Tree Protocol (IEEE 802.1D)
MSTP – Multiple Spanning Tree Protocol (IEEE 802.1s)
STP - The Spanning Tree Protocol (STP) is a standardized method (IEEE 802.1D) for avoiding loops in switching networks.
Enable STP to ensure that only one path at a time is active between any two nodes on the network.
MSTP - The Multiple Spanning Tree Protocol (MSTP) is a standardized method (IEEE 802.1S) for providing simple and full
connectivity for frames assigned to any given VLAN throughout a Bridged Local Area Network comprising arbitrarily
interconnected Bridges, each operating MSTP, STP , or RSTP. MSTP allows frames assigned to different VLANs to follow
separate paths, each based on an independent Multiple Spanning Tree Instance (MSTI), within Multiple Spanning Tree
(MST) Regions composed of LANs and or MST Bridges. These Regions and the other Bridges and LANs are connected into a
single Common Spanning Tree (CST).
The IEEE 802.1D Spanning Tree Protocol and IEEE 802.1s Multiple Spanning Tree Protocol allow the blocking of links
between switches that form loops within the network. When multiple links between switches are detected, a primary link is
established. Duplicated links are blocked from use and become standby links. The protocol allows for the duplicate links to be
used in the event of a failure of the primary link. Once the Spanning Tree Protocol is configured and enabled, primary links are
established and duplicated links are blocked automatically. The reactivation of the blocked links (at the time of a primary link
failure) is also accomplished automatically without operator intervention.
This automatic network reconfiguration provides maximum uptime to network users. However, the concepts of the Spanning
Tree Algorithm and protocol are a complicated and complex subject and must be fully researched and understood. It is possible
to cause serious degradation of the performance of the network if the Spanning Tree is incorrectly configured. Please read the
following before making any changes from the default values.
The Switch STP performs the following functions:
Creates a single spanning tree from any combination of switching or bridging elements.
Creates multiple spanning trees – from any combination of ports contained within a single switch, in user specified
groups.
Automatically reconfigures the spanning tree to compensate for the failure, addition, or removal of any element in
the tree.
Reconfigures the spanning tree without operator intervention.
100
 Loading...
Loading...