Page 1
HP ProCurve Identity Driven Manager 3.0
User’s Guide
Page 2
© Copyright 2004, 2005, 2007, 2009 Hewlett-Packard Development
Company, LP.
All Rights Reserved.
Publication Number
5990-8851
May, 2009
Trademark Credits
Microsoft, Windows, Windows XP, are Windows Vista are
U.S. registered trademarks of Microsoft Corporation.
Intel and Pentium aretrademarks of Intel Corporation in the
U.S. and other countries.
Adobe is a trademark of Adobe Systems Incorporated.
Disclaimer
The information contained in this document is subject to
change without notice.
The only warranties for HP products and services are set
forth in the express warranty statement accompanying such
products and services. Nothing herein should be construed
as constituting an additional warranty. HP shall not be liable
for technical or editorial errors or omissions contained
herein.
Warranty
See the Customer Support/Warranty booklet included with
the product.
A copy of the specific warranty terms applicable to your
Hewlett-Packard products and replacement parts can be
obtained from your HP Sales and Service Office or autho-
rized dealer.
Hewlett-Packard Company
8000 Foothills Boulevard, m/s 5551
Roseville, California 95747-5551
http://www.procurve.com
Page 3
Contents
1 About ProCurve Identity Driven Manager
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
Why IDM? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
What’s New in IDM 3.0 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5
IDM Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-8
IDM Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Supported Devices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Operating Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Additional Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-11
Upgrading from Previous Versions of PCM and IDM . . . . . . . . . . . . . 1-11
Learning to Use ProCurve IDM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-13
Getting ProCurve Documentation From the Web . . . . . . . . . . . . . . . . 1-13
ProCurve Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-13
2 Getting Started
Before You Begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Installing the IDM Agent . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Using the IDM Auto-Discover Feature . . . . . . . . . . . . . . . . . . . . . . . . . . 2-5
IDM Configuration Process Overview . . . . . . . . . . . . . . . . . . . . . . . . . . 2-6
IDM Usage Strategies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-6
Understanding the IDM Model . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-8
IDM GUI Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-9
IDM Dashboard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-11
Using the Navigation Tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-12
Toolbars and Menus . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-18
Using IDM as a Monitoring Tool . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-19
Using IDM Reports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-20
Creating Report Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-24
Configuring a Policy Action to Generate Reports . . . . . . . . . . . . . . . . 2-24
IDM Session Cleanup Policy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-30
User Session Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-34
Finding a User . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-37
User Reports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-38
Show Mitigations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-39
i
Page 4

Contents
IDM Preferences . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-41
Using Active Directory Synchronization . . . . . . . . . . . . . . . . . . . . . . . 2-43
3 Using Identity Driven Manager
IDM Configuration Model . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-3
Configuration Process Review . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-3
Configuring Identity Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-4
Configuring Locations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-6
Adding a New Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-7
Modifying a Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-11
Deleting a Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-12
Configuring Times . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-13
Creating a New Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Modifying a Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Deleting a Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Configuring Network Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-18
Adding a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
Modifying a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-21
Deleting a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Configuring Access Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-23
Creating a New Access Profile . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24
Modifying an Access Profile . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-31
Defining Access Policy Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-33
Creating an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-34
Modifying an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-39
Deleting an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-39
Configuring User Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-40
Adding Users to an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . 3-41
Changing Access Policy Group Assignments . . . . . . . . . . . . . . . . . . . 3-42
Using Global Rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-43
Deploying Configurations to the Agent . . . . . . . . . . . . . . . . . . . . . . . . 3-46
Using Manual Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-47
Defining New Realms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-47
Modifying and Deleting Realms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-48
Adding RADIUS Clients . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-49
Deleting RADIUS Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-55
Adding New Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-56
Using the User Import Wizard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-59
Importing Users from Active Directory . . . . . . . . . . . . . . . . . . . . . . . . 3-60
Importing Users from an LDAP Server . . . . . . . . . . . . . . . . . . . . . . . . . 3-64
ii
Page 5

Contents
Importing Users from XML files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-74
4 Using the Secure Access Wizard
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-2
Supported Devices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-2
Using Secure Access Wizard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-3
5 Troubleshooting IDM
IDM Events . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-2
Pausing the Events Display . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-4
Using Event Filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-5
Viewing the Events Archive . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-7
Setting IDM Event Preferences . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-9
Using Activity Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-10
Using Decision Manager Tracing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-12
A Using ProCurve Network Access Controller with IDM
About ProCurve Network Access Controller 800 . . . . . . . . . . . . . . . A-1
Before You Begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-2
Using the NAC Tab Displays . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-3
Setting the ProCurve NAC GUI Login . . . . . . . . . . . . . . . . . . . . . . . . . . A-4
Using the NAC Home Tab . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-5
Using the NAC Monitor Tab . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-5
Using the NAC Configuration Tab . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-6
Using Local Authentication Directory on ProCurve NAC . . . . . . . A-8
Adding Locally Authenticated Users . . . . . . . . . . . . . . . . . . . . . . . . . . A-9
B IDM Technical Reference
Device Support for IDM Functionality . . . . . . . . . . . . . . . . . . . . . . . . . B-1
Support for Secure Access Wizard Feature . . . . . . . . . . . . . . . . . . . . . B-2
Best Practices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . B-3
Types of User Events . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . B-6
iii
Page 6

Contents
iv
Page 7
About ProCurve Identity Driven Manager
Chapter Contents
Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
Why IDM? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
What’s New in IDM 3.0 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5
IDM Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6
Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-8
IDM Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Supported Devices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Operating Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Additional Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-11
Upgrading from Previous Versions of PCM and IDM . . . . . . . . . . . . . 1-11
Learning to Use ProCurve IDM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-13
Getting ProCurve Documentation From the Web . . . . . . . . . . . . . . . . 1-13
ProCurve Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-13
1
1-1
Page 8
About ProCurve Identity Driven Manager
Introduction
Introduction
Network usage has skyrocketed with the expansion of the Internet, wireless,
and convergence technologies. This increases the burden on network managers working to control network usage. Also, the complexity of large networks
makes it difficult to control network access and usage by individual users.
ProCurve Identity Driven Manager (IDM) is an add-on module to the ProCurve
Manager Plus (PCM+) application that extends the functionality of PCM+ to
include authorization control features for edge devices in networks using
RADIUS servers and Web-Authentication, MAC-Authentication, or 802.1x
security protocols.
Using IDM simplifies user access configuration by automatically discovering
RADIUS Servers, Realms, and users. You can use IDM to monitor users on the
network, and to create and assign access policies that work to dynamically
configure edge devices (wired and wireless) and manage network resources
available to individual users. Using IDM, access rights, quality of service
(QoS), bandwidth throttling, ACLs, and VLAN enrollment are associated with
a user and applied at the point of entry or "edge" of the network.
1-2
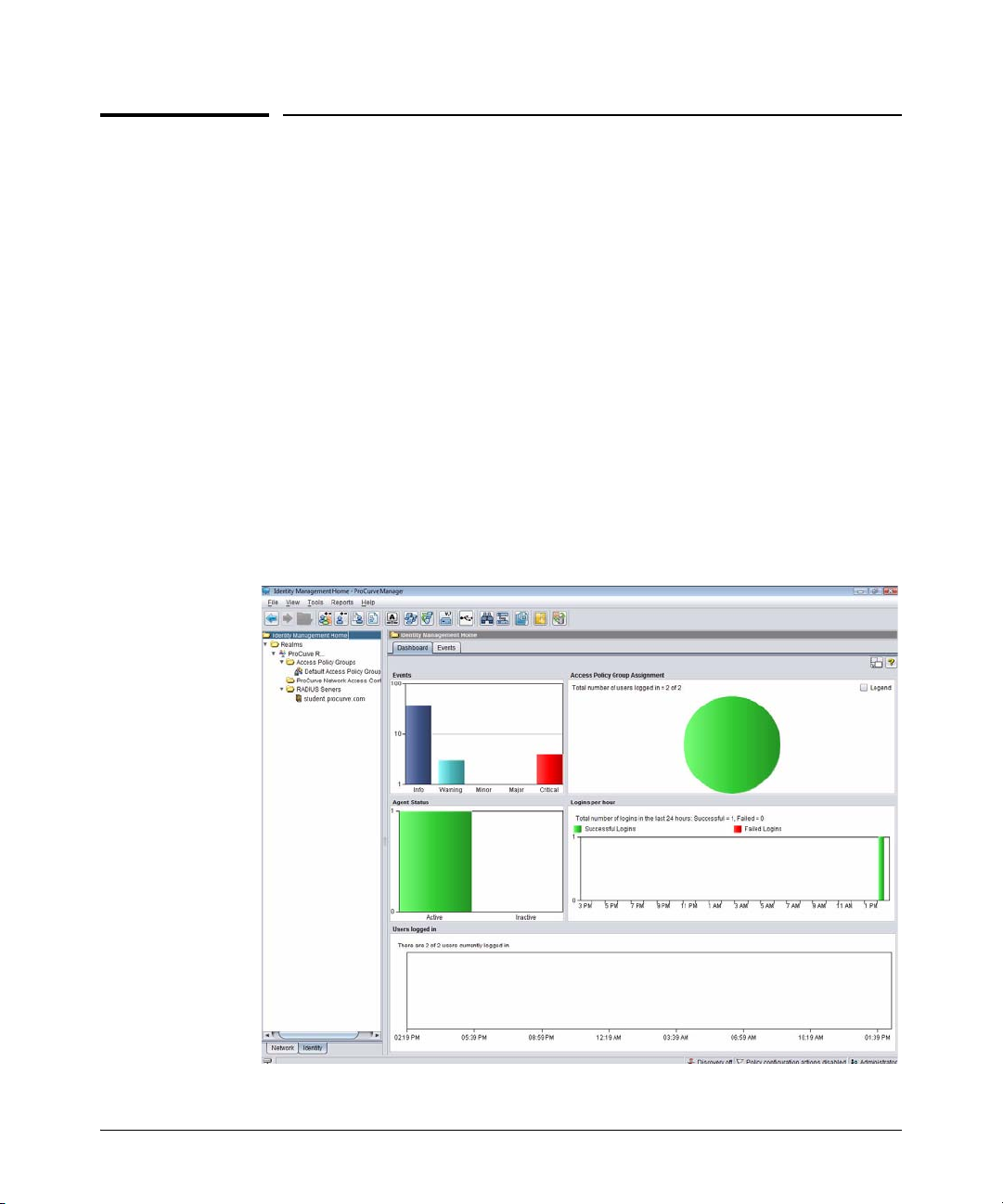
Figure 1-1. ProCurve Identity Driven Manager home
Page 9

About ProCurve Identity Driven Manager
Introduction
Why IDM?
Today, access control using a RADIUS system and ProCurve devices (switches
or wireless access points) is typically made up of several steps.
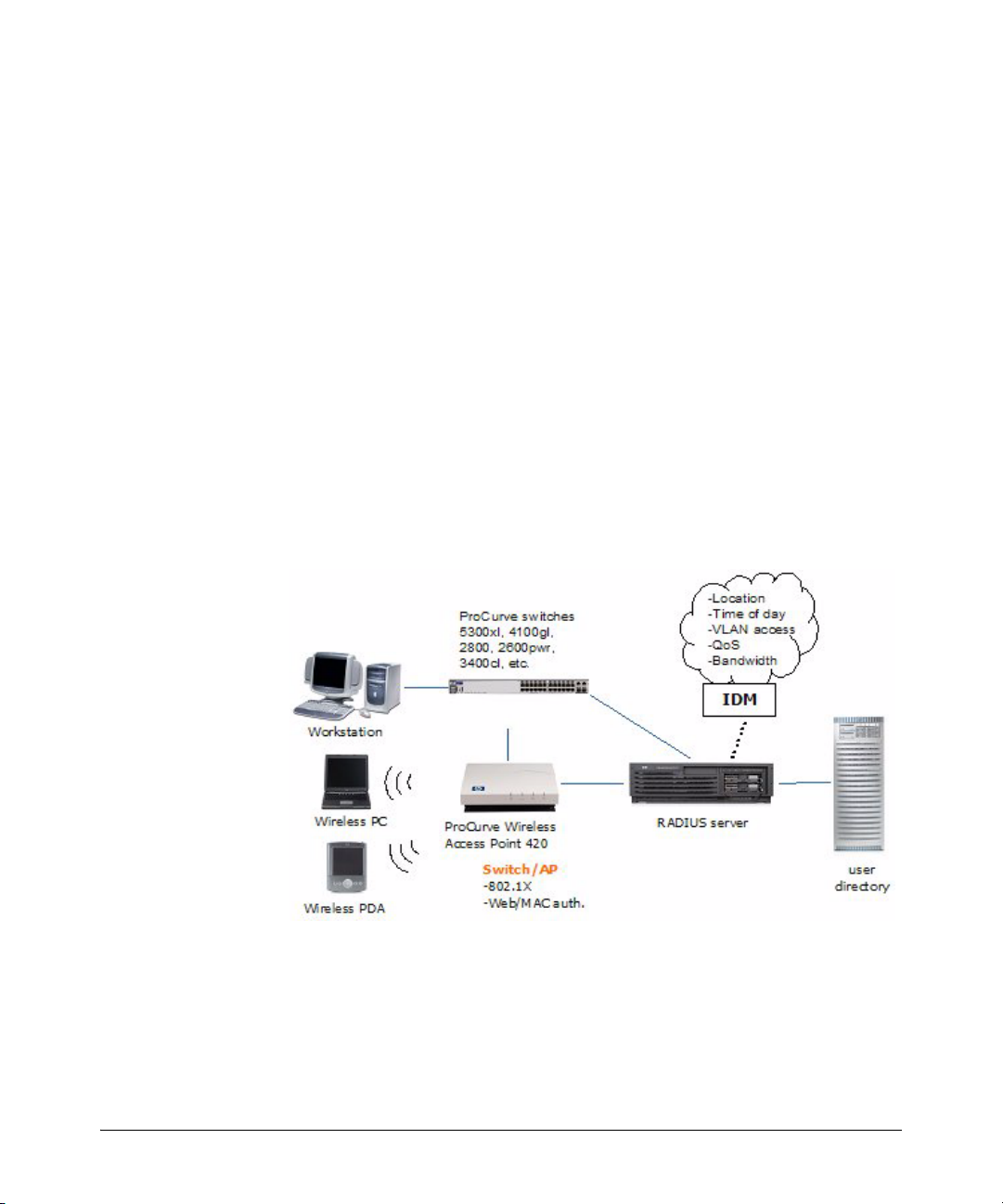
Figure 1-2. Current Access Control process
1. A client (user) attempts to connect to the network.
2. The edge device recognizes a connection state change, and requests
identifying information about the client. This can include MAC address,
username and password, or more complex information.
3. The switch forwards an access request, including the client information
to the authentication server (RADIUS).
4. The RADIUS server validates the user’s identity in the user directory,
which can be an Active Directory, database or flat file. Based on the
validation result received from the user directory, the authentication
server returns an accept or deny response to the switch.
5. If the user is authenticated, the ProCurve device grants the user access to
the network. If the user is not authenticated, access is denied.
For networks using IDM, access control is enhanced to include authorization
parameters along with the authentication response. IDM enhances existing
network security by adding network authorization information, with access
and resource usage parameters, to the existing authentication process. Using
IDM you can assign access rights and connection attributes at the network
switch, with dynamic configuration based on the time, place, and client that
is generating the access request.
1-3
Page 10
About ProCurve Identity Driven Manager
Introduction
When using IDM, the authentication process proceeds as described in the first
three steps, but from that point the process changes as follows:
4. The RADIUS server validates the user’s identity in the user directory.
Based on the validation result received from the user directory, the
authentication server returns an accept or deny response to the switch. If
the user is accepted (authenticated), the IDM Agent on the RADIUS server
processes the user information. IDM then inserts the network access
rights configured for the user into the Authentication response sent to the
switch.
5. If the user is authenticated, the switch grants the user access to the
network. The (IDM) authorization information included in the authentication response is used to configure VLAN access, QoS and Bandwidth
parameters for the user, and what network resources the user can access
based on time and location of the user’s login.
If the user is authenticated by the RADIUS server, but IDM’s authorization
data indicates that the user is attempting to access the network at the
wrong time, or from the wrong location or system, the user’s access
request is denied by IDM.
1-4
Figure 1-3. Access Control using IDM
If a user is authenticated in RADIUS, but is unknown to IDM, IDM will not
override RADIUS authentication and default switch settings, unless you
configure it to do so. You can create a "guest" profile in IDM to provide
limited access for unknown users.
Page 11

About ProCurve Identity Driven Manager
Introduction
What’s New in IDM 3.0
ProCurve Identity Driven Manager version 3.0 includes the following new
features and enhancements:
■ Support for PCM’s new architecture
The new architecture in PCM 3.0 lets you logically divide the network and
manage devices on remote segments of large networks connected by WAN
links that might or might not be behind a NAT firewall. For additional
information, see the HP ProCurve Manager Network Administrator’s
Guide.
■ Configuring RADIUS clients
RADIUS clients can now be added and updated on supported RADIUS
servers.
■ Support for tagged VLANs
Tagged VLANs can now be dynamically assigned to devices that support
RFC 4675 by IDM. During the 802.1X authentication process, IDM evaluates a set of administrator-defined rules to categorize the user/device and
select the Access Profile used to govern the session.
■ NIM user mitigations
NIM mitigations (actions taken in response to security threats) for users
can now be displayed and deleted in IDM.
■ IDM Agent auto updates
Software updates to IDM Agents on all platforms can now be downloaded
and installed via PCM’s auto update component.
■ Enhanced Secure Access Wizard
• Added RADIUS client selection
• Enhancements to Save Settings and Save Templates
1-5
Page 12
About ProCurve Identity Driven Manager
Introduction
IDM Architecture
In IDM, when a user attempts to connect to the network through an edge
switch, the user is authenticated via the RADIUS Server and user directory.
Then, IDM is used to return the user’s "access profile" along with the authentication response from RADIUS to the switch. The IDM information is used to
dynamically configure the edge switch to provide the appropriate authorizations to the user, that is, what VLAN the user can access, and what resources
(QoS, bandwidth) the user gets.
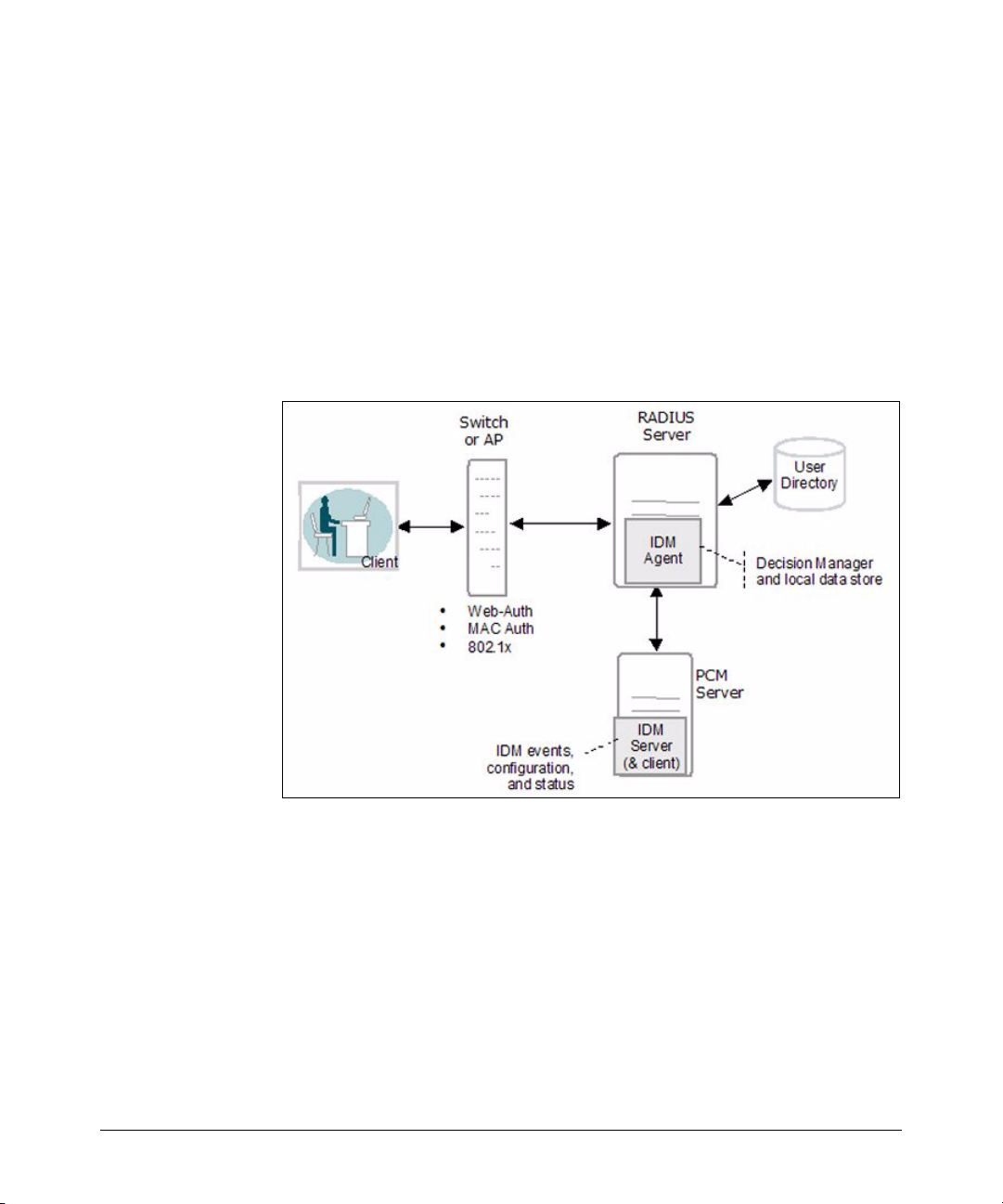
The following figure illustrates the IDM architecture and how it fits in with
RADIUS.
1-6
Figure 1-4. IDM Architecture
IDM consists of an IDM Agent that is co-resident on the RADIUS server, and
an IDM Server that is co-resident with PCM+. Configuration and access
management tasks are handled via the IDM GUI on the PCM+ management
workstation.
The IDM agent includes:
• A RADIUS interface that captures user authentication information
from the RADIUS server and passes the applicable user data (username, location, time of request) to the IDM Decision Manager. The
interface also passes user access parameters from IDM to the RADIUS
server.
Page 13

About ProCurve Identity Driven Manager
Introduction
• A Decision Manager that receives the user data and checks it against
user data in the local IDM data store. Based on the parameters defined
in the data store for the user data received, the Decision Manager
outputs access parameters for VLAN, QoS, bandwidth, and network
resource access to the RADIUS interface component.
• A Local Data Store that contains information on Users and the Access
Policy Groups to which the user belongs. The Access Policy Group
defines the rules that determine the user’s access rights.
The IDM Server provides configuration and monitoring of Identity Driven
Manager. It operates as an add-on module to PCM+, using the PCM model
database to store IDM data, and a Windows GUI (client) to provide access to
configuration and monitoring tools for IDM.
You use the IDM GUI to monitor IDM Agent status and users logged into the
network, and to manage IDM configuration, including:
• Defining access parameters for the network, such as locations, times,
network resources, and access profiles.
• Creating access profiles that define the network resources and attri-
butes (VLAN, QoS, bandwidth) assigned to users in an Access Policy
Group.
• Creating Access Policy Groups with rules (access policies) that will
be assigned to users in that Group.
• Assigning users to Access Policy Groups.
• Deploying IDM configuration data to the IDM Agent on the RADIUS
server.
1-7
Page 14
About ProCurve Identity Driven Manager
Terminology
Terminology
Access Policy
Group
Access Profile An IDM access profile sets the VLAN, quality of service, and bandwidth (rate-
Authentication The process of proving the user’s identity. In networks this involves the use
Authentication
Server
Authorization The process that determines what an authenticated user can do. It establishes
Bandwidth Amount of network resources available. Generally used to define the amount
Client An end-node device such as a management station, workstation, or mobile PC
An IDM access policy group consists of one or more rules that govern the login
times, devices, quality of service, bandwidth, and VLANs for users assigned to
the access policy group.
limits) applied when a user logs in and is authenticated on the network.
of usernames and passwords, network cards (smartcards, token cards, etc.),
and a device’s MAC address to determine who and/or what the "user" is.
Authentication servers are responsible for granting or denying access to the
network. Also referred to as RADIUS servers because most current authentication servers implement the RADIUS protocol.
what network resources the user is, or is not permitted to use.
of network resources a specific user can consume at any given time. Also
referred to as rate-limiting.
attempting to access the network. Clients are linked to the switch through a
point-to-point LAN link, either wired or wireless.
Directory Name Directory Name (DN) is an identifier that uniquely represents an object in the
X.500 Directory Information Tree (DIT) [X501]. (See: domain name.) A DN is
a set of attribute values that identify the path leading from the base of the DIT
to the object that is named. An X.509 public-key certificate or CRL contains a
DN that identifies its issuer, and an X.509 attribute certificate contains a DN
or other form of name that identifies its subject.
Domain A domain is a group of computers and devices on a network that are admin-
istered as a unit with common rules and procedures. Within the internet,
domains are defined by the IP Address. All devices sharing a common part of
the IP address are said to be in the same domain.
Edge Device A network device (switch or wireless access point) that connects the user to
the rest of the network. The edge devices can be engaged in the process of
granting user access and assigning a user’s access rights and restrictions.
1-8
Page 15

About ProCurve Identity Driven Manager
Terminology
Endpoint Integrity Also referred to as "Host Integrity," this refers to the use of applications that
check hosts attempting to connect to the network to ensure they meet
requirements for configuration and security. Generally to make sure that virus
checking and spyware applications are in place and up to date.
IDM Agent The IDM Agent resides on the RADIUS server. It inspects incoming authenti-
cation requests, and inserts appropriate authorization information (IDM
Access Profiles) into the outgoing authentication reply.
QoS Quality of Service, relates to the priority given to outbound traffic sent from
the user to the rest of the network.
RADIUS Remote Authentication Dial-in User Service, (though it also applies to authen-
tication service in non-dial-in environments)
RADIUS Server A server running the RADIUS application on your network. This server
receives user connection requests from the switch, authenticates users, and
then returns all necessary information to the edge device.
Realm A Realm is similar to an Active Directory Domain, but it works across non-
Windows (Linux, etc.) systems. Generally specified in User-name as
"user@realm."
VLAN A port-based Virtual LAN configured on the switch. When the client connec-
tion terminates, the port drops its membership in the VLAN.
1-9
Page 16
About ProCurve Identity Driven Manager
IDM Specifications
IDM Specifications
Supported Devices
ProCurve Identity Driven Manager (IDM) supports authorization control functions on the following ProCurve devices*:
ProCurve Switches:
6400cl Series
6200 Series
5400 Series
5300xl Series
4200 Series
3500 Series
3400cl Series
4100gl Series
2800 Series
2600 Series (PWR included)
6100 Series
2500 Series
ProCurve Wireless (420, 520wl, 530)
Wireless Edge Services Module (WESM)
9300
9400
2900 Series
6600
8212zl
1-10
* Not all devices support all features of IDM. Refer to Appendix A for details.
Operating Requirements
The system requirements for IDM (Server and Client installation) are:
■ Minimum Processor: 2.0 GHz Intel Pentium, or equivalent
■ Recommended Processor: 3.0 GHz Intel Pentium, or equivalent
■ Minimum Memory: 1 GB RAM
■ Recommended Memory: 2 GB RAM
■ Disk Space: 500 MB free hard disk space minimum. (A total of 1 GB
will be required for PCM+ and IDM.)
■ Implementation of one of the following RADIUS servers. The IDM
agent and will be installed on this system.
Page 17
About ProCurve Identity Driven Manager
IDM Specifications
• Microsoft Network Policy Server on Windows Server 2008 (32-bit)
• Microsoft Internet Authentication Service (IAS) on Windows Server
2003 (32-bit)
• FreeRADIUS supplied with Red Hat Enterprise Linux (4.7 and 5.2)
• FreeRADIUS supplied with SuSE Enterprise Linux (9.3 and 10.2)
• RADIUS on the ProCurve Network Access Controller 800
■ ProCurve Manager Plus software must be installed for IDM to operate.
The IDM software cannot be installed as a separate component. PCM
system requirements are provided in the HP ProCurve Network
Management Installation and Getting Started Guide.
Additional processing power and additional disk space may be required for
larger networks.
Additional Requirements
■ Implementation of an access control method, using either MAC-auth,
Web-auth, or an 802.1x supplicant application.
For assistance with implementation of RADIUS and access control methods for use with ProCurve switches, refer to the Access Security Guide
that came with your switch. All ProCurve Switch manuals can also be
downloaded from the ProCurve web site.
For assistance with using RADIUS and 802.1x access control methods,
contact the ProCurve Elite Partner nearest you that can provide ProCurve
Access Control Security solutions.
on the Find a Partner link at http://www.procurve.com
■ If you plan to restrict user access to specific network segments, you
You can find ProCurve Direct Elite partners
.
will need to configure VLANs within your network. For information
on using VLANs, refer to the HP ProCurve Manager Network Admin-
istrator’s Guide, or the configuration guides that came with your
switch.
Upgrading from Previous Versions of PCM and IDM
The installation package for PCM 3.0 contains the IDM 3.0 installation files. If
you are running earlier versions of IDM, you must select the IDM option during
the PCM 3.0 install process. This is required to support changes made in the
underlying PCM and IDM databases.
1-11
Page 18

About ProCurve Identity Driven Manager
IDM Specifications
If you want to test the IDM 3.0 functionality using the 60-day trial provided
with the PCM 3.0 Auto-update package, you need to install the software on a
separate system that has no previous IDM version installed or in use.
When you upgrade to IDM 3.0, you need to manually install the IDM Agent
upgrade on each of your RADIUS Servers. Refer to “Installing the IDM Agent”
on page 2-2 for detailed instructions.
1-12
Page 19
About ProCurve Identity Driven Manager
Learning to Use ProCurve IDM
Learning to Use ProCurve IDM
The following information is available for learning to use ProCurve Identity
Driven Manager (IDM):
■ This User’s Guide—helps you become familiar with using the appli-
cation tools for access control management.
■ Online help information—provides information through Help buttons
in the application GUI that provide context-sensitive help, and a table
of contents with hypertext links to additional procedures and reference information.
■ HP ProCurve Network Management Installation and Getting
Started Guide—provides details on installing the application and
licensing, and an overview of ProCurve Manager functionality.
■ For additional information on configuring your network, refer to the
documentation that came with your switches.
Getting ProCurve Documentation From the Web
IDM manuals can be downloaded from:
http://www.hp.com/rnd/support/manuals/IDM.htm
ProCurve Support
Product support is available on the Web at: http://www.procurve.com
Click on the Customer Care tab. The information available at this site includes:
• Product Manuals
• Software updates
• Links to Additional Support information.
You can also call your HP Authorized Dealer or the nearest HP Sales and
Support Office, or contact the ProCurve Elite Partner nearest you for information on ProCurve Access Control Security solutions.
You can find ProCurve Elite partners on the
http://www.procurve.com.
Find a Partner link at
1-13
Page 20

About ProCurve Identity Driven Manager
Learning to Use ProCurve IDM
1-14
Page 21
Getting Started
Chapter Contents
Before You Begin . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Installing the IDM Agent . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Using the IDM Auto-Discover Feature . . . . . . . . . . . . . . . . . . . . . . . . . . 2-5
IDM Configuration Process Overview . . . . . . . . . . . . . . . . . . . . . . . . . . 2-6
IDM Usage Strategies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-6
Understanding the IDM Model . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-8
IDM GUI Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-9
IDM Dashboard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-11
Using the Navigation Tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-12
Toolbars and Menus . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-18
Using IDM as a Monitoring Tool . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-19
Using IDM Reports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-20
Creating Report Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-24
Configuring a Policy Action to Generate Reports . . . . . . . . . . . . . . . . 2-24
IDM Session Cleanup Policy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-30
User Session Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-34
Finding a User . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-37
User Reports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-38
Show Mitigations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-39
IDM Preferences . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-41
Using Active Directory Synchronization . . . . . . . . . . . . . . . . . . . . . . . 2-43
2
2-1
Page 22
Getting Started
Before You Begin
Before You Begin
If you have not already done so, please review the list of supported devices
and operating requirements under “IDM Specifications” on page 1-10.
If you intend to restrict user access to specific areas of the network using
VLANs, make sure you have set up your network for use of VLANs. For details
on configuring VLANs, refer to the HP ProCurve Manager Network Admin-
istrator’s Guide, or the Advanced Traffic Management Guide for your ProCurve switch.
The IDM Client is included with the PCM Plus software. To install a remote
PCM/IDM Client, download the PCM Client to a remote PC using the same
process as for installing the IDM Agent, just select the PCM Client option from
the PCM server. For detailed instructions, see the HP ProCurve Network
Management Installation and Getting Started Guide.
Installing the IDM Agent
The IDM application components are installed on your system when you select
the IDM option during PCM+ software installation. The IDM Agent can be
installed on a RADIUS server, a supported Linux system, or a ProCurve
Network Access Controller.
2-2
If the PCM software is not on the same system as the IDM Agent, you must
configure "Client/Server" access permissions on the PCM server to allow
communication. This is done by adding the IP address of the RADIUS server,
Linux system, or ProCurve Network Access Controller to the access.txt file on
the PCM server. For details, refer to the HP ProCurve Network Management
Installation and Getting Started Guide.
On a RADIUS Server
During the installation process, you will be prompted to enter the IP address of the
PCM Server. This is needed to establish communication between the IDM Agent on the
RADIUS server, and the IDM application on the PCM Server.
The IDM Agent can only be installed on a system with the RADIUS server configured.
If the RADIUS server is not found on the system, the IDM Agent installation displays
an error message, and the installation process is aborted.
1. Start a web browser on the computer where the IDM Agent will be installed, and
type the IP address of the PCM server computer followed by a colon and the port
ID 8040. For example, if the IP address of the server computer is 10.15.20.25, enter
the following URL:
Page 23
Getting Started
Before You Begin
http://10.15.20.25:8040
2. Click the Download the Windows PCM/IDM agent link, and click Save to download
the file.
3. Once the download completes, close the Download window and the web browser.
4. Open the downloaded procurve-agent-setup.exe file by double-clicking on it. The
Agent Installation Wizard will then guide you through the installation.
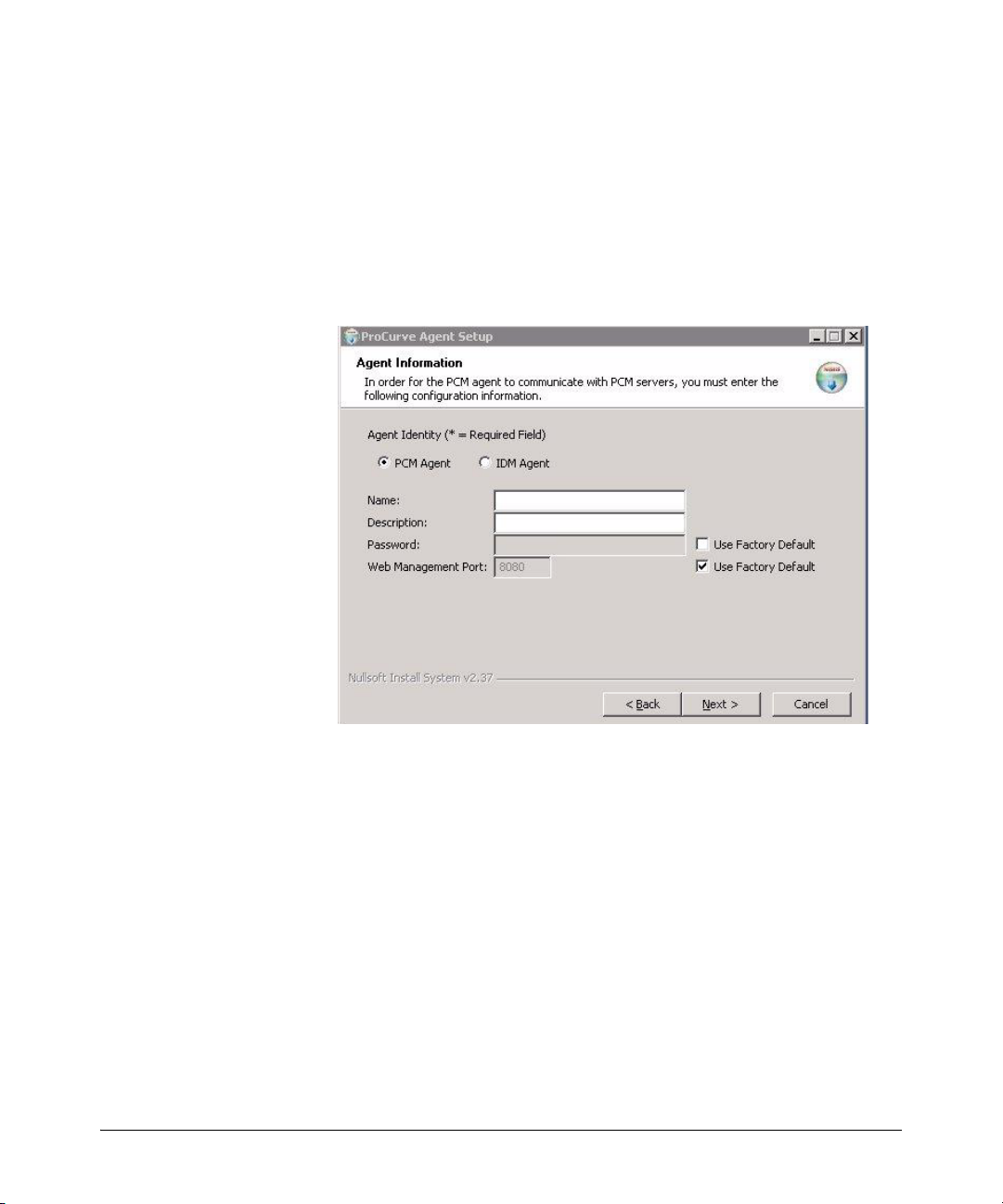
5. On the Agent Information window of the Agent Installation Wizard:
Figure 2-1. Agent Information
a. Select IDM Agent.
b. Type a Name and, optionally, a Description for the Agent.
c. Enter a unique password or check the Use Factory Default check box to use
the default password of “procurve”. This password is used for authenticating
with the PCM server.
d. If you do not want to use the default Web Management Port 8081, uncheck
the Use Factory Default check box and enter the web management port that
will be used to authenticate with the PCM server.
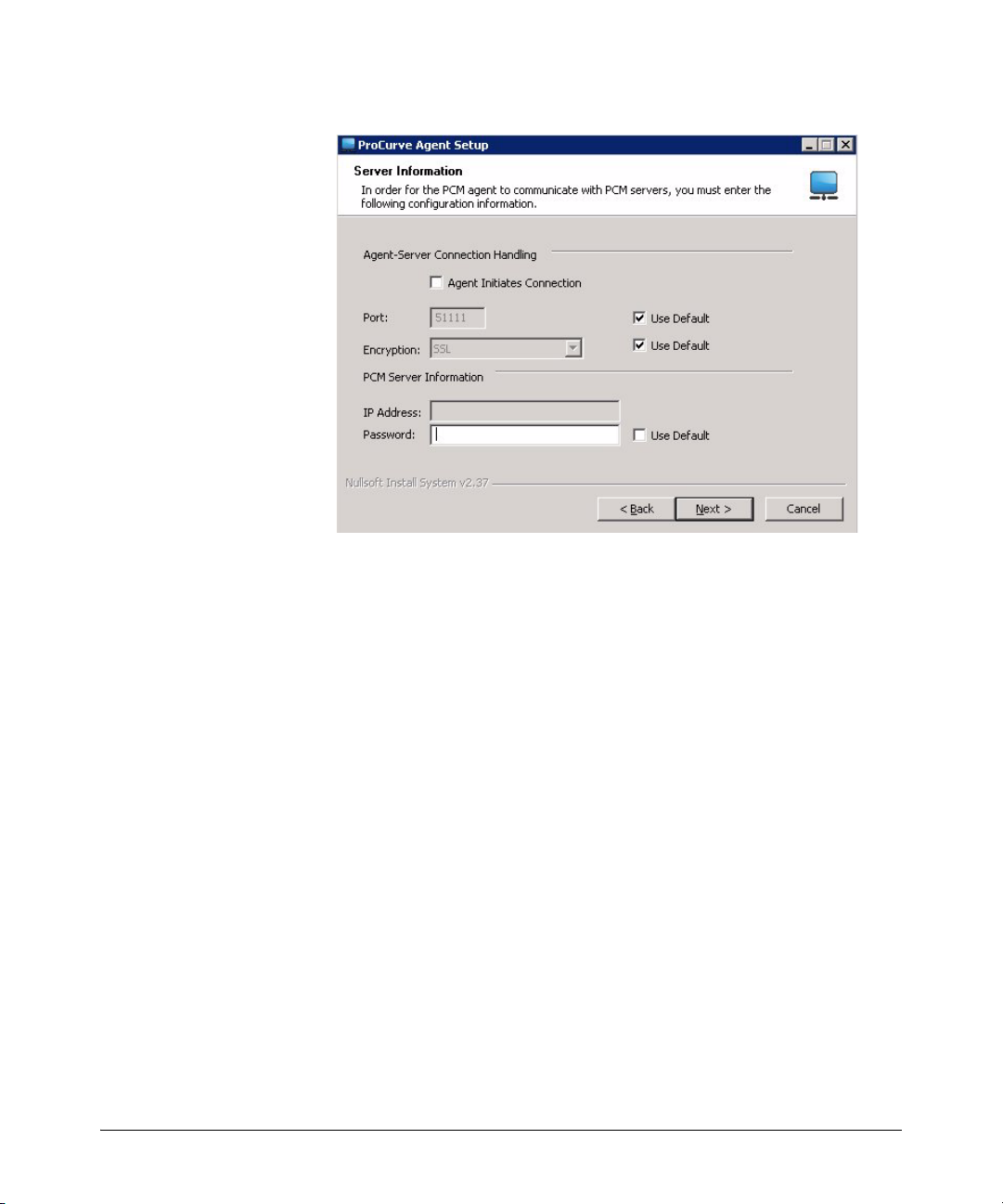
6. On the Server Information window, configure the Agent-server connection
settings and any required server information:
2-3
Page 24
Getting Started
Before You Begin
Figure 2-2. Server Information
For the Agent to communicate with the PCM server, these values MUST MATCH
the values set on the PCM server for this Agent.
a. If the Agent will initiate connection to the PCM server, check the Agent
Initiates Connection check box. If the PCM server will initiate a connection to
the Agent, ensure this check box is unchecked.
All Agent that initiate connection to the PCM server must use the same port
number and encryption type as configured in the Agent Manager Server Setup
tab.
b. To change the default Port that the Agent will use to communicate with the
PCM server, uncheck the related Use Default check box and type the desired
port. The default PCM server port is 51111, which can be changed to any
unused port during PCM server installation or at the PCM server.
c. If you do not want to encrypt data s ent to the PCM server, uncheck the related
Use Default check box and select Plain Text from the Encryption drop-down list.
The default encryption method is SSL. If the PCM server is behind a firewall,
we recommend using SSL encryption.
d. In the IP Address field, type the IP address of the PCM server if the Agent is
initiating the connection to the PCM server.
e. To change the default Password that the Agent will use to communicate with
the PCM server, uncheck the related
desired port (any number of alphanumeric characters). The default password is “procurve”. This must match the password set on the Agent Manager
Server Setup tab.
Use Default check box and type the
2-4
Page 25

Getting Started
Before You Begin
Once installed the IDM Agent begins collecting User, Realm, and RADIUS data.
On a Linux System or ProCurve Network Access Controller
To install the IDM Agent on a supported Linux system or ProCurve Network Access
Controller:
1. Start a web browser, and type the IP address of the PCM server computer followed
by a colon and the port ID 8040. For example, if the IP address of the server
computer is 10.15.20.25, enter the following URL:
http://10.15.20.25:8040
2. Click the Download the IDM FreeRADIUS Agent link, and click Save to download the
file.
3. Once the download completes, move the file to a location accessible by the target
Agent system, if necessary.
4. Extract the downloaded HpIdmLinuxAgentInstaller-<version>.tar.gz file to a
temporary location on the RADIUS server.
5. Change to the HpIdmLinuxAgentInstaller-<version> directory, run install.sh as
root, and then follow the prompts.
Using the IDM Auto-Discover Feature
You can manually configure the RADIUS server, Realms, and Users in IDM, or
you can let IDM do the hard work for you. And, you have two options for
automatically discovering users. Either enable Active Directory synchronization to import users from the Active Directory, or install the IDM Agent on the
system with the RADIUS Server, then let it run to collect the information as
users log into the network. Even after you begin creating configurations in
IDM, both options continue to collect information on users and Realms
(domains in Active Directory) and pass that information to the IDM server.
If you are using multiple RADIUS servers, you need to install an IDM Agent
on each of the servers. The IDM Agent collects information only on the system
where it is installed. The IDM client can display information for all RADIUS
servers where the IDM Agent is installed.
When you start the IDM Client and expand the navigation tree in the IDM
Dashboard tab, you will see any discovered or defined Realms found on the
RADIUS server, along with the IP address for the RADIUS Server(s).
2-5
Page 26

Getting Started
Before You Begin
IDM Configuration Process Overview
To configure IDM to provide access control on your network, first let IDM run
long enough to "discover" the Realms, RADIUS servers, and users on your
network. Once IDM has performed these tasks for you, your configuration
process would be as follows:
1. If you intend to use them, define "locations" from which users will access
the network. A location may relate to port-based VLANS, or to all ports
on a device. (See page 3-7)
2. If you intend to use them, define "times" at which users are allowed or
denied access. This can be by day, week or even hour. (See page 3-14)
3. Define any network resources (systems and applications) that you want
to specifically allow or restrict users from accessing.
4. If you intend to restrict a user access to specific systems, you need to set
the User profile to include the MAC address for each system that the user
is allowed to login on. (See page 3-57.)
5. Create the Access Profiles, to set the VLAN, QoS, rate-limits (bandwidth)
attributes, and the network resources that are available, to users in an
Access Policy Group. (See page 3-24.)
6. Create an Access Policy Group, with rules containing the Location, Time,
System, and Access Profile that is applied to users when they login. (See
page 3-34.)
OR
If using Active Directory synchronization, add rules and Access Profiles
to the Access Policy Groups automatically created by Active Directory
synchronization.
7. If Active Directory synchronization is not used, assign Users to the
appropriate Access Policy Group. (See page 3-41).
8. If automatic deployment is disabled, deploy the configuration policies to
the IDM Agent on the RADIUS server. (See page 3-46)
IDM Usage Strategies
You can use IDM to simply monitor user activity on the network, or to apply
user authentication rules to improve network security and performance. The
following table identifies the IDM configuration for various deployment and
usage strategies for IDM.
2-6
Page 27

Authenticate Authorize Strategy Description
Getting Started
Before You Begin
VLAN QoS Rate-
x
xx
xx
xxx
xxxxx
Limit
Network
Resources
Monitor and report user activity.
Enhance normal RADIUS authentication with
Location, Time, and System rules
Provide rudimentary VLAN segregation
(Unknown Users, Guests, Visitors, Contractors)
Provide complete VLAN placement for all
Users
Provide QoS and Rate-limits per User
VLAN, QoS, and Rate-limit attributes, and
accessibility of defined Network Resources for
all users, based on Location, Time, and System
Table 2-1: IDM Deployment and Usage Strategies
2-7
Page 28

Getting Started
Before You Begin
Understanding the IDM Model
The first thing to understand, is that IDM works within the general concept of
‘domains’ or ‘realms’. Basically, realms are very large organizational units;
every user belongs to one, and only one, realm. While it is possible to have
multiple realms, most organizations have only one, for example, hp.com or
csuchico.edu.
The basic operational model of IDM involves Users and Groups. Every User
belongs to a Group – in IDM these are called Access Policy Groups (APGs).
Each APG has an Access Policy defined for it, which governs the access rights
that are applied to its Users as they enter the network.
In the IDM GUI, the top level of the navigation tree is the Realm, with all other
information for APGs, and RADIUS Servers beneath the Realm in the navigation tree. Users are linked to the Realm to which they belong, and the Access
Policy Group to which they are assigned.
The IDM configuration tools are available at the top level. The definition of
times, locations, network resources, and access profiles is independent of
individual Realms or Groups. You can define multiple locations, times, and
network resources, then create multiple access profiles to be applied to any
Access Policy Group, in any Realm that exists within IDM.
2-8
Page 29
Getting Started
IDM GUI Overview
IDM GUI Overview
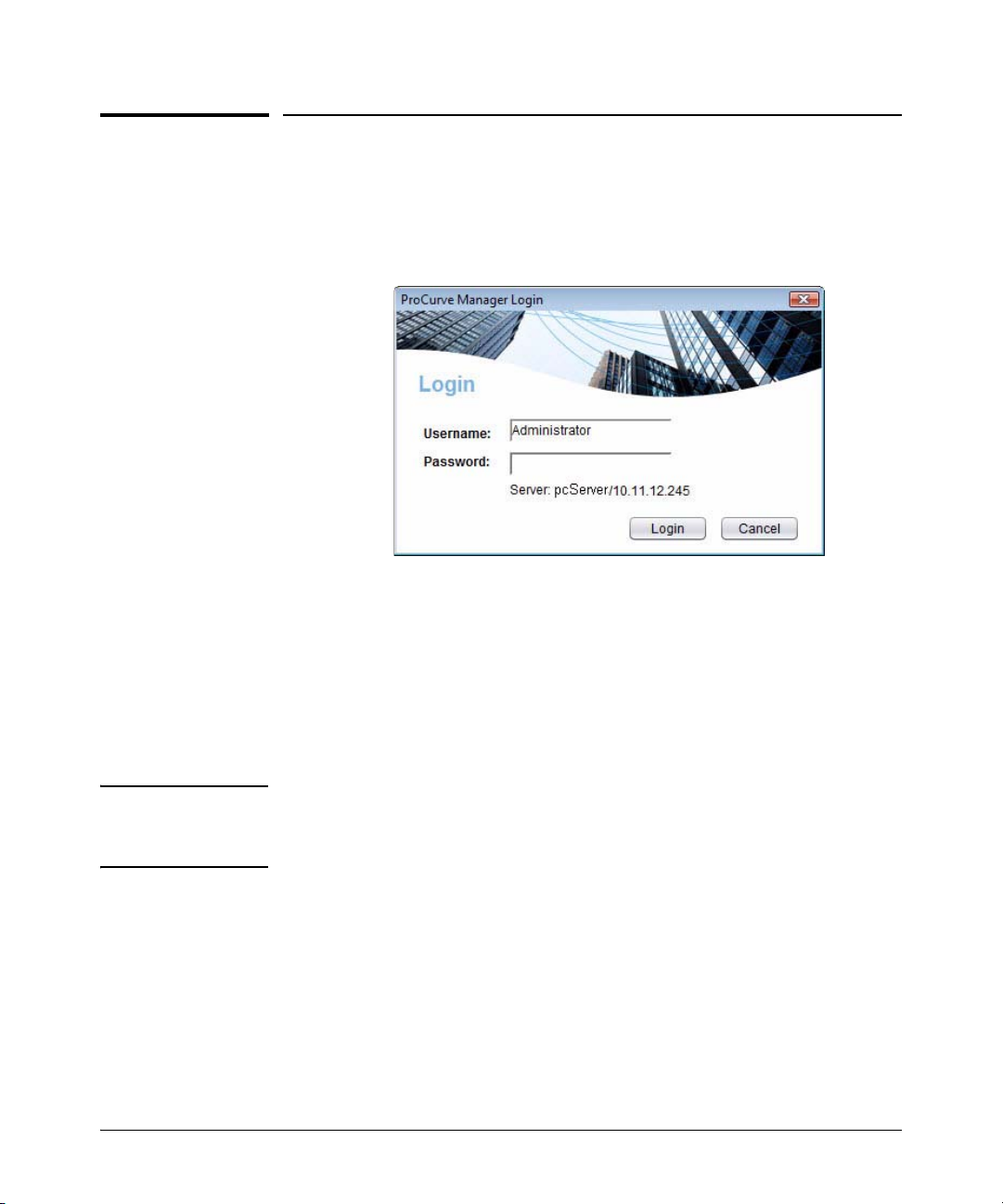
To use the IDM client, launch the PCM Client on your PC. Select the ProCurve
Manager option from the Windows Program menu to launch the PCM Client.
The PCM Client will start up and the Login dialogue is launched.
Figure 2-3. PCM Login
If you did not enter a Username or Password during install, type in the default
Username, Administrator, then Click Login to complete the login and startup.
For additional information on using the PCM Client, refer to the HP ProCurve
Manager Network Administrator’s Guide.
Select the Identity tab at the bottom left of the PCM window to display the
IDM Dashboard.
Note: You can also access the IDM Dashboard by selecting the Network Manage-
ment Home node in the PCM navigation tree and clicking the Identity-driven
Manager tab at the top of the right pane.
2-9
Page 30
Getting Started
IDM GUI Overview
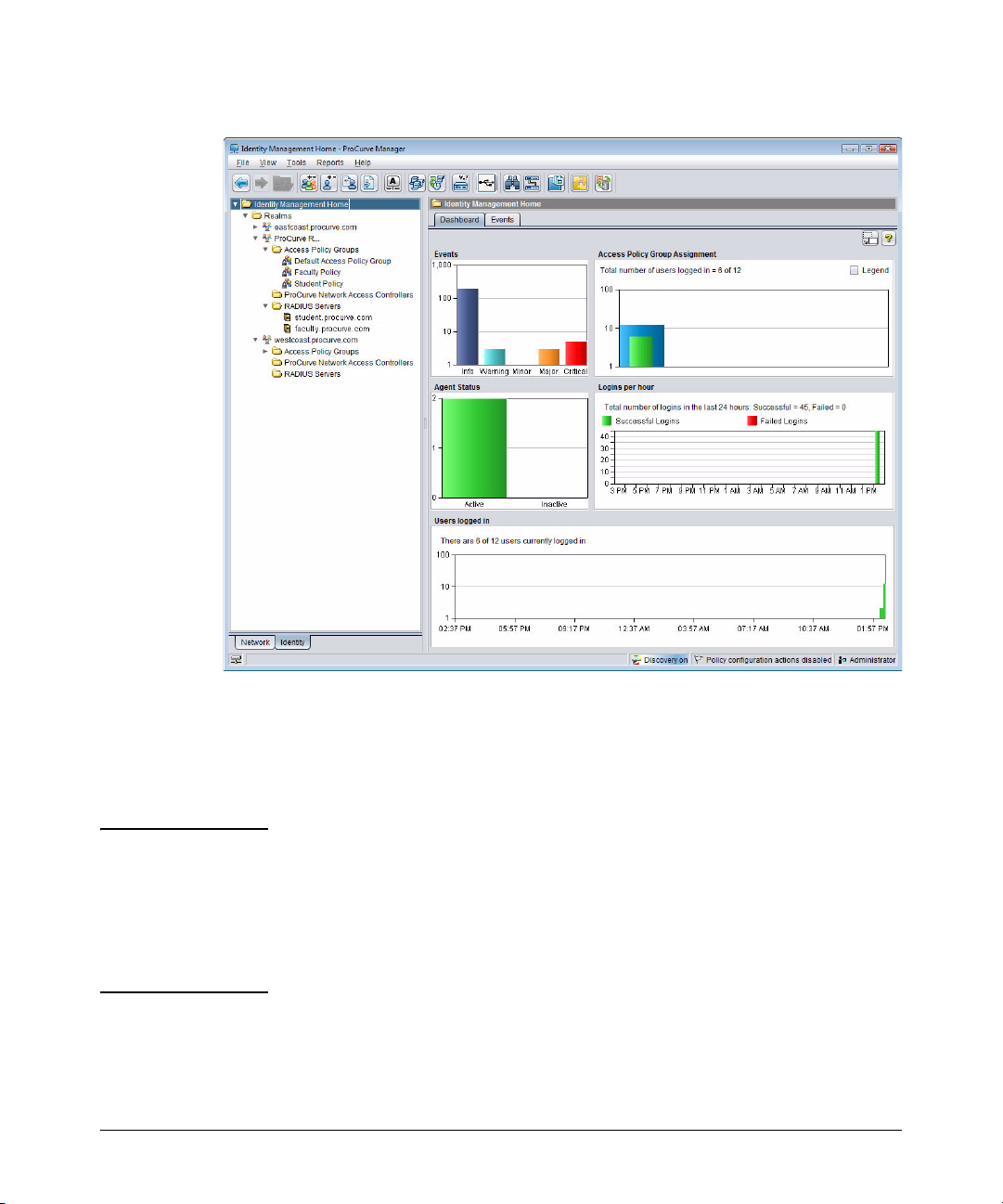
Figure 2-4. IDM Dashboard
The IDM initial display provides a quick view of IDM status in the Dashboard
tab, along with an Events tab, navigation tree, and access to menu and toolbar
functions. You can resize the entire window, and/or resize the panes (subwindows) within the Identity Management Home window frame.
NOTE: If the IDM Dashboard shows the IDM Agent Status as inactive, and the
Inventory and Logins panes show no data:
■ Check the PCM Events tab for the following entry:
"PCM remote client authentication failure: <ip address>"
■ Check for IDM application events related to devices "supporting" or
"not supporting" the configuration.
2-10
Page 31

Getting Started
IDM GUI Overview
IDM Dashboard
The IDM Dashboard is a monitoring tool that provides a quick summary view
of IDM users, RADIUS servers, and events. The Dashboard can be viewed:
• From within PCM by selecting Network Management Home and
clicking the Identity Driven Manager tab.
• By clicking the Identity tab at the bottom of the PCM navigation tree.
The Dashboard tab contains the following panes of status information:
Events: The Events pane shows the total number of outstanding IDM events
and the number of IDM events in each state. Clicking anywhere in the IDM
events pane or clicking the Events tab displays the IDM Events window, which
contains detailed information about each event.
Agent Status: The Agent Status pane contains a color-coded graph showing
the number of currently active and inactive IDM agents installed on RADIUS
servers.
Access Policy Group Assignment: The Access Policy Group Assignment
pane contains a pie chart showing the number of users assigned to each Access
Policy Group. Mousing over a section of this chart displays information for
the group and its users.
Logins per Hour: The Logins per Hour pane is a scrolling 24-hour display
that summarizes the total number of successful and failed IDM user logins at
any given time during the past 24 hours. Information in this panel is updated
every minute.
Users Logged In: The Users Logged In pane is a scrolling 24-hour display that
shows the total number of users logged in at any given time during the past 24
hours. Information in this panel is updated every minute.
2-11
Page 32

Getting Started
IDM GUI Overview
Using the Navigation Tree
The navigation tree in the left pane of the IDM window provides access to IDM
features using the standard Windows file navigation system. Click the nodes
to expand the list and change the display in the right window panel.
Figure 2-5. IDM Navigation Tree
Realms
2-12
The top level of the tree lists each of the Realms that have been discovered by
an IDM Agent or defined manually. Clicking on the Realms node in the tree
displays the Realms List in the right panel of the window. Expanding the node
displays each Realm name in the tree, and Unassigned RADIUS Servers if they
exist.
Figure 2-6. Realms List tab
Realm
Expanding the Realms node and clicking a realm in the tree displays the
Dashboard tab in the right pane, along with the Properties, Global Rules, and Users
tabs.
Page 33

Getting Started
IDM GUI Overview
Figure 2-7. Realm Dashboard tab
Realm Dashboard: The Realm Dashboard is a monitoring tool that provides
a quick summary view of IDM users and Agents. The Dashboard tab is similar
to the IDM Dashboard but contains statistics for the selected realm only.
The Agent Status pane contains a color-coded graph showing the number of
currently active and inactive IDM agents installed on RADIUS servers for the
selected realm.
The Successful Logins per Access Policy Group pane contains a pie chart
showing the number of successful and failed IDM user logins to each Access
Policy Group during the selected time period. Use the drop-down list in this
pane to select the time period reflected in the chart. Mousing over a section
of this chart displays information for the group and its users. You can also hide
the legend for the chart by unchecking the Legend check box.
The Access Policy Group Assignment pane shows the number of users
assigned to each Access Policy Group in the realm and the total number of
those users that are currently logged in. You can hide the legend for this pane
by unchecking the Legend check box.
2-13
Page 34
Getting Started
IDM GUI Overview
The Top Talkers pane displays input octets (bytes), output octets, or both. Use
the drop-down list in this pane to select whether to display input octets, output
octets, or both. You can hide the legend for this pane by unchecking the Legend
check box.
The Logins per Hour pane is a scrolling 24-hour display that summarizes the
total number of successful and failed IDM user logins for the selected realm
at any given time during the past 24 hours. Information in this panel is updated
every minute.
The Users Logged In pane is a scrolling 24-hour display that shows the total
number of users logged in at any given time during the past 24 hours. Information in this panel is updated every minute.
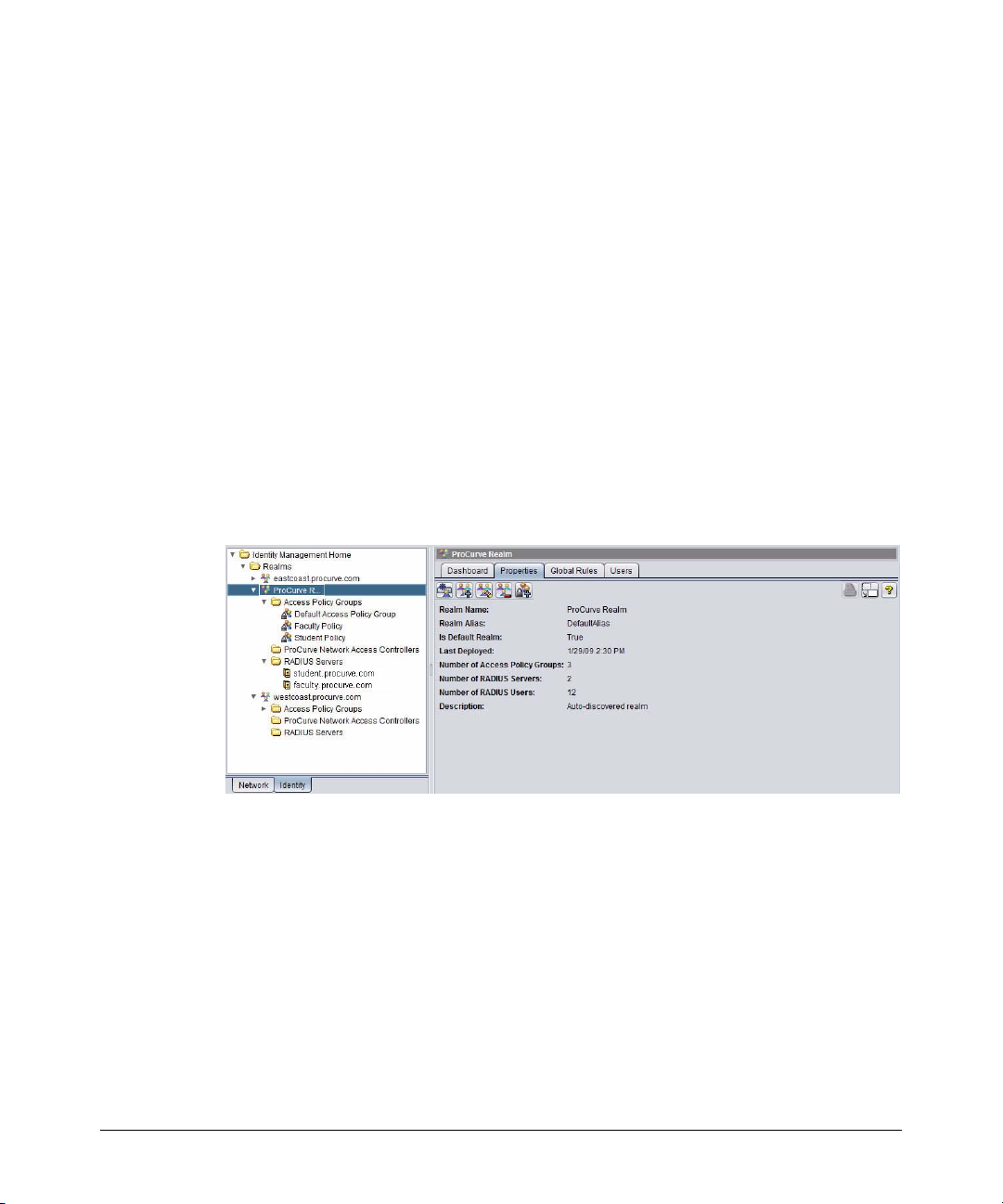
Realm Properties tab: Selecting an individual realm in the tree and then
clicking the Properties tab displays summary information about a Realm and its
assignments. It also shows when the Realm was last deployed, which is
especially useful when you've made recent changes or are investigating IDM
events.
2-14
Figure 2-8. Realm Properties tab
Page 35

IDM GUI Overview
The following information is shown on the Realm Properties tab:
Realm Name Name used to identify the Realm
Realm Alias Alternate name for the Realm (usually the NETBIOS name)
Getting Started
Is Default Realm Whether the Realm is set as the default Realm: true means this Realm
Last Deployed Date and time the policy was last deployed. Use this field to ensure
Number of Access
Policy Groups
Number of RADIUS
Servers
Number of RADIUS
Users
Description Brief description of the Realm
is the default Realm and false means it is not. The default Realm is
used when IDM cannot determine the Realm for a RADIUS server or
user login.
that the current Realm attributes have been deployed.
Total number of Access Policy Groups currently assigned to the Realm
Total number of RADIUS servers assigned to the Realm
Total number of users assigned to Access Policy Groups used for the
Realm and currently logged in
Realm Global Rules tab: Click the Global Rules tab to view rules that over-
ride Access Policy Group rules and provides functions to configure and
prioritize global rules. See “Using Global Rules” on page 3-43 for more information.
Realm Users tab: Click the Users tab to view a list of users in the Realm that
were discovered by the IDM Agent, or defined manually.
Figure 2-9. Realm Users tab
Expanding the Realm node in the tree will display the Access Policy Groups
and RADIUS server nodes for the Realm.
2-15
Page 36

Getting Started
IDM GUI Overview
Access Policy Groups: Click the Access Policy Group node to display the Access
Policy Groups tab with a list of currently configured groups. You can also expand
the node to view the APGs in the tree.
Figure 2-10. Access Policy Groups tab
Click the individual group node in the tree to display the group’s Dashboard,
Properties, and Users tabs. The Dashboard tab is similar to the IDM Dashboard
but contains statistics for the selected access policy group only. The Users tab
contains the list of users currently assigned to the Access Policy Group. The
Properties tab shows the attributes of the group.
2-16
Figure 2-11. Access Policy Group Properties tab
Page 37

Getting Started
IDM GUI Overview
RADIUS Servers: Clicking the RADIUS Servers node displays the RADIUS List tab,
with status and configuration information for each RADIUS Server in the
Realm that has an IDM Agent installed, or that is manually defined.
Figure 2-12. RADIUS List tab
You can expand the RADIUS Servers node to view the servers in the tree. Click
the individual server to display the RADIUS Server Properties.
Figure 2-13. RADIUS Server Properties tab
The Activity Log tab underneath the properties display contains a listing of IDM
application events for that RADIUS server such as server startup, server
connections, user logins, IDM configuration deployment, etc.
2-17
Page 38

Getting Started
IDM GUI Overview
Toolbars and Menus
Because IDM is a module within PCM, it uses the same Main Menu and Global
toolbar functions. Individual tabs or windows within the IDM module also
include separate component toolbars.
The functions available in the component toolbar vary based on applicable
functions for that component. Toolbar icons for disabled functions are grayed
out. The component toolbar options are described under the process they
support in the next chapter. You can hover with the mouse to display "Tooltips"
for each icon.
Using Right-Click Menus
You can also access most of the functions provided with IDM via the "rightclick" menus. To use the right-click menu, select an object (node) in the
navigation tree on the left of the screen, then right-click your mouse to display
the menu. You can also access the right-click menus when an item is selected
in a list on the tab window displays.
2-18
Figure 2-14. IDM Right-click menu
The options available in the right-click menu will vary based on the node or
list item you have selected. Disabled functions are grayed out.
Page 39

Using IDM as a Monitoring Tool
Getting Started
Using IDM as a Monitoring Tool
Whether or not you configure and apply access and authorization parameters
using IDM, you can use IDM to monitor user sessions on the network and
generate usage reports. You can use the monitoring features along with the
IDM Reports to track usage patterns, user session statistics, bandwidth usage,
top users, and so on. The User session information can also be used to track
current user sessions and modify the User’s access to network resources if
needed.
NOTE: Session accounting must be enabled on the switch, and in IDM, for the
monitoring and User session accounting in IDM to work. Refer to the section
on "Radius Authentication and Accounting" in the Access and Security Guide
provided with the ProCurve switch for details on enabling session accounting.
You can enable or disable IDM monitoring using the IDM Preferences. Using
the IDM Preferences, you can also configure IDM to work with existing
"Endpoint Integrity" applications used to determine the compliance of the
authenticating clients to rules and requirements (for firewalls, anti-virus, etc.)
that have been set up in the domain.
NOTE: If you are using Web-Auth or MAC-Auth for user authentication, user session
statistics are unavailable from the switch and cannot be collected, unless you
are using a version of firmware on the switch that supports accounting for
Web-Auth and MAC-Auth sessions. Not all switch software versions support
this. Check the ProCurve web site for updates.
2-19
Page 40

Getting Started
Using IDM Reports
Using IDM Reports
IDM provides reports designed to help you monitor and analyze usage patterns
for network resources. The report options are available from the Reports>User
Access Control menu at the top of the window.
Figure 2-15. IDM Reports Menu
The Report wizard screens and report parameters vary, depending on the type
of report selected. When you select a report using the Reports>User Access
Control drop-down list, the Report wizard is launched. Use the wizard to set
filter options, and selectable data elements. When you click Finish, the report
is generated and displayed, similar to the following example:
Figure 2-16. IDM Configuration Report
2-20
Page 41

Getting Started
Using IDM Reports
You can save the report to a file, or print the report. To apply customized
Report Header information for your company, use the Reports option in the
global preferences (Tools> Preferences> Reports). You can also schedule reports
to be created at recurring intervals by creating a policy with PCM’s policy
manager, as described in “Creating Report Policies” on page 2-24.
Each of the available reports is summarized below, along with the report filter
options, and configurable report parameters, if applicable.
Note: You must have the Enable user session accounting option selected in the IDM
Preferences in order to collect Bandwidth and other user session data for
reports.
By default, all user history is reset and all session history is deleted by the
predefined IDM Session Cleanup policy on the first day of each month at
midnight. However, the IDM Session Cleanup policy can be modified to fit
your needs.
Configuration Report: The Configuration Report provides detailed information
for every Realm, RADIUS server, Access Policy Group, and, optionally, user
that the IDM agent has learned or that have been defined in IDM. Realm
information includes the most recent deployment date and number of
assigned users and RADIUS servers.
The RADIUS server section includes the server name, whether the server is
currently active, number of successful and failed logins since midnight of the
current day, and number of Realms defined on the server (similar to that
shown on the RADIUS Server Properties window).
The Access Policy Group section includes the Access Policy Group name,
number of Realms to which the Access Policy Group is assigned, and number
of users assigned to the Access Policy Group.
The Users section shows the Realm and Access Policy Group to which the
user is assigned, username, date and time of last login, and input, output, and
total bytes used during the reporting period.
To collect report data, ensure the Identity Management Preferences are set to
enable user session accounting.
Endpoint Integrity Report: The Endpoint Integrity Report shows whether
a computer used to login is in compliance with corporate standards monitored
by a third-party endpoint integrity solution. If the RADIUS server used to
2-21
Page 42

Getting Started
Using IDM Reports
authenticate the user has a endpoint integrity solution, the computer where
the user logged in may be checked for integrity criteria such as up-to-date antivirus software and an authorized operating system. This report is especially
helpful in identifying computers that require anti-virus, operating system, or
other software installations/updates.
IDM Statistics: The IDM Statistics report shows the total hourly and daily logins
and bandwidth usage during the reporting period. This report is especially
helpful in identifying access profiles that require bandwidth adjustment and
hardware components that require maintenance.
Session History Details: The Session History Details Report shows the detailed
information about all login attempts, whether successful or failed. This report
is especially helpful in identifying login failures and whether an access profile,
location, or user needs to be modified in PCM.
Once the initial report dates and filters are set, you can also configure what
columns you want to include in the report. The available column headings
include:
RADIUS Server IP Location
MAC Address Device
Device Port VLAN
QOS Endpoint Integrity State
BW (Bandwidth)
2-22
Unsuccessful Login Report: The Unsuccessful Login Report lists failed system
logins, which can be filtered by date. The report includes the following
information for each failed login
User Bandwidth Usage Report: The Bandwidth Usage Report summarizes system usage by users. This report can include all users or be limited to only the
top bandwidth users during the reporting period. This report is especially
helpful in identifying candidates for throttling.
User MAC Addresses: The User MAC Addresses shows the MAC address of
every computer from which the user logged in during the report period. This
report is especially helpful when setting up login restrictions and for accounting purposes.
User Report: The User Report lists information for recent sessions in which the
user participated, similar to the Session History report.
Page 43
Getting Started
Using IDM Reports
To display the User Report select a username in the Users tab of the Access
Policy Group or RADIUS Server window, and then click the User Report icon
in the toolbar.
2-23
Page 44

Getting Started
Creating Report Policies
Creating Report Policies
You can also use the Policy Manager feature to schedule reports to be created
at regular intervals, or in response to an event. For complete details on
creating policies, refer to “Configuring Policies” in the HP ProCurve Manager
Network Administrator’s Guide.
The basic process for creating a Report Policy is:
■ Configure the Time periods when the report policy can be executed. If
no time is specified, the policy can execute at any time.
■ Alerts - Use the Scheduled Alert option to set a recurring schedule for a
report to be generated. Alerts serve as the trigger used to launch an
Action. Alerts can be event-driven, or scheduled to occur at a specified time.
■ Action - Configure the Report Manager:GenerateReport type(s) for the
policy. The following section describes the Report action types and
configurable parameters and filters for each report type.
You do not need to configure the Sources or Targets for a report, Policy as you
will select the device groups the policy applies to in the Report Action.
Configuring a Policy Action to Generate Reports
To configure a Policy Action to run the Security History report:
1. Click the
Manager
2. Click the Actions node in the Policy Manager window to display the
Manage Actions panel.
Policy Manager icon in the toolbar to launch the Poli cy Configuration
window.
2-24
Page 45

Creating Report Policies
Getting Started
Figure 2-17. Policy Manager, Actions
The Manage Actions window displays the list of defined Actions.
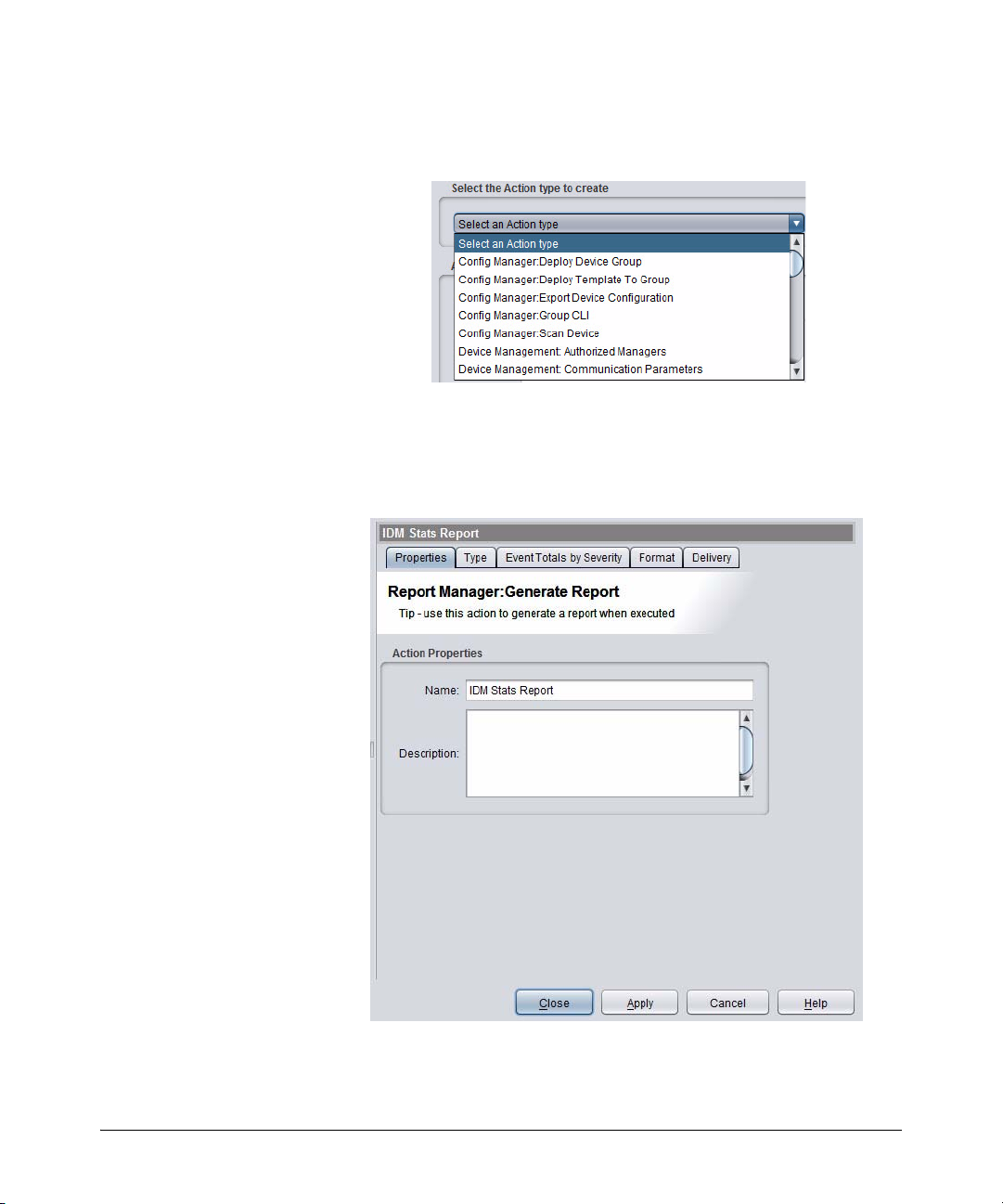
3. Click
Figure 2-18. Policy Manager, Create Action
New... to launch the Create Action dialog:
2-25
Page 46
Getting Started
Creating Report Policies
4. Select the Report Manager:Generate Report Action type from the pull-down
menu.
Figure 2-19. Policy Manager, Select Action
5. Type a Name for the Action (required) and a brief Description (optional)
6. Click
OK to save the Action and display the Action Properties tab.
The properties you set in the previous step should appear.
2-26
Figure 2-20. Policy Manager: Report Manager Action configuration
Page 47
Creating Report Policies
Getting Started
At this point the other tabs displayed are:
Typ e: Lets you select the Report type you want to generate. As soon as
you select a report type, additional tabs may appear in the window
depending on the filter criteria for the report.
Format: Lets you set the report output format
Delivery: lets you select where the report will be sent (to file, e-mail,
etc.)
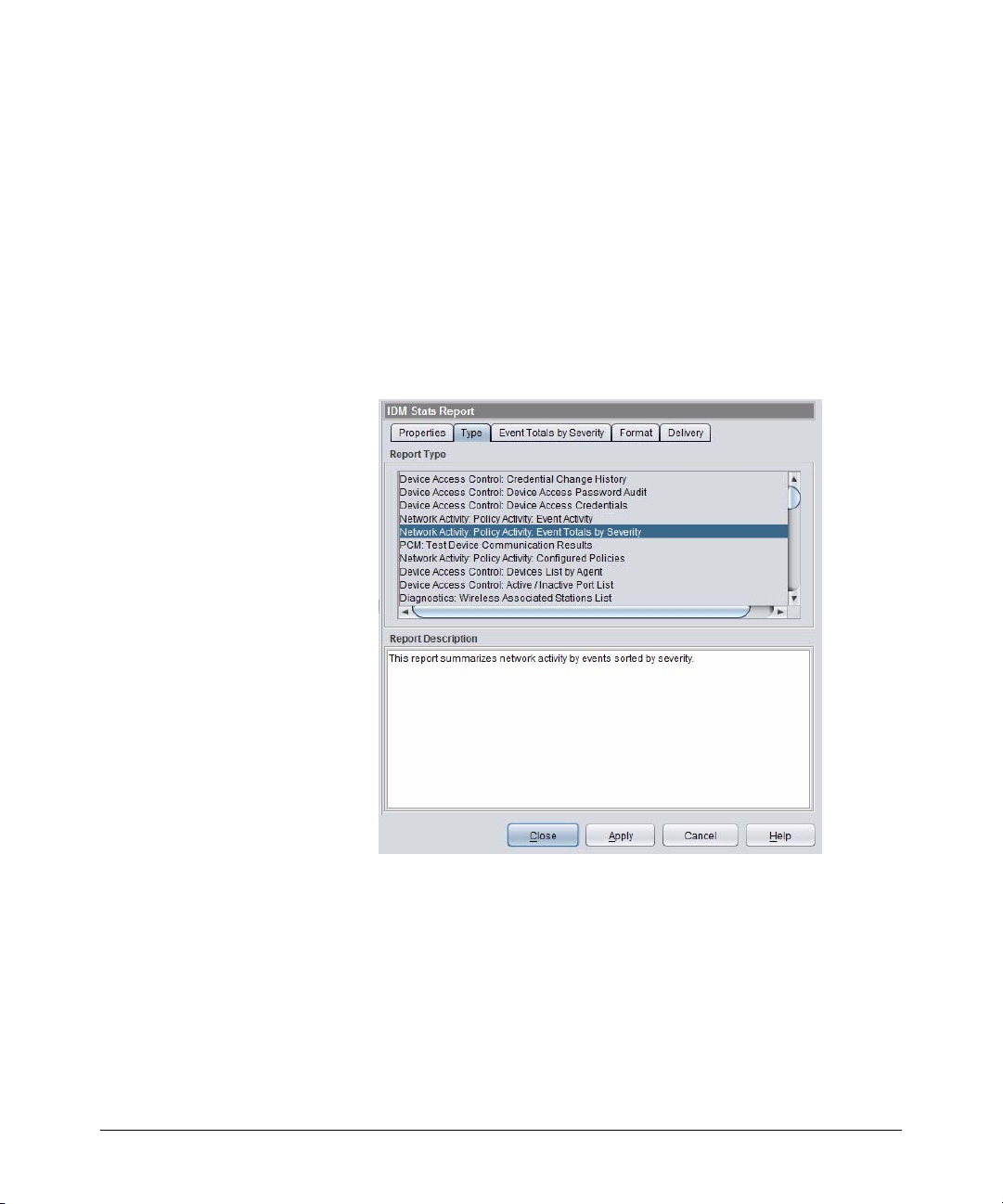
7. Click the Type tab and select the IDM Report type you want included in the
action. In this example, the IDM Statistics report is selected, and the Report
Filter tab is added in the window.
Figure 2-21. Report Manager Action, Report Type selection
8. Click the Report Filter tab to select the report criteria:
Report Filter: Lets you select the filter criteria to be applied when generating
the report. The filter options will vary based on the selected report.
9. Click the Format tab to set the report output style you want to generate.
2-27
Page 48

Getting Started
Creating Report Policies
Figure 2-22. Report Manager Action: Report format selection
• PDF Produce the report in .pdf format. To view this file format, you
will need Adobe Acrobat Reader, which can be downloaded free
from http://get.adobe.com/reader.
• HTML Produce the report in .html format, which can be viewed with
any Web browser.
• CSV Produce the report using comma separated values with double
quotes. This report can be viewed using WordPad, Notepad, or
imported into other spreadsheet programs, such as Excel.
• ODT Produce the report in .odt format, which is a zipped .xml file.
• XLS Produce the report in .xls format, which can be viewed in MS
Excel spreadsheets.
• RTF Produce the report in .rtf format, which can be viewed in most
word processing applications.
2-28
10. Click the Delivery tab to configure the method used to deliver the report.
Page 49

Creating Report Policies
Figure 2-23. Report Manager Action: Report Delivery method
Getting Started
E-mail is the default method. It will e-mail the report to the address
specified. It also requires that you have an SMTP profile for the e-mail
address. See “Creating SMTP Profiles” in the HP ProCurve Manager
Network Administrator’s Guide for details.
Use the pull-down menu to select a different delivery method.
Figure 2-24. Report Manager Action: Select Delivery Method
Selecting FTP as the delivery method lets you save the report on an FTP
site. However, proxy support is not provided.
a. In the FTP Server field, type the IP address of the FTP site where you
want to save the report.
b. In the Path field, type the complete path to the server location where
you want to save the report.
c. In the Filename field, type the filename you want to assign to the report.
You can automatically add a timestamp to the filename in the Filename conventions pane.
d. In the Username field, type the username used to access the FTP site.
2-29
Page 50

Getting Started
Creating Report Policies
e. In the Password field, type the password used to access the FTP site.
f. Select the Filename conventions to use:
– No timestamp in file name: Name the file exactly as entered in the
Filename field.
– Prepend timestamp to file name: Add the timestamp at the beginning
of the filename entered in the Filename field
– Append timestamp to file name: Add the timestamp at the end of the
filename entered in the Filename field.
Selecting File as the delivery method lets you save the report in a file on
the PCM server.
a. In the Path field, type the complete path to the server location where
you want to save the report.
The path is relative to the server (not to the client). To save the report
on the client, there must be a path from the server to the client. For
example, use UNC paths, since the server runs as a service and cannot
be set up easily to use mapped drives.
b. In the Filename field, type the filename you want to assign to the
report.
c. Select the Filename conventions to use, as described above for FTP files.
11. Click Apply to save the Action Configuration.
12. Click Close to exit the Policy Manager window.
If you click Close before you click Apply, you will be prompted to save, or
discard the configuration.
NOTE: Report output is limited to 40 pages. Therefore, to create a report on many
(1000+) items, you need to create separate reports to generate all the data.
You can access User Reports by right-clicking on the user in the Users tab
display in IDM, then select the report option.
IDM Session Cleanup Policy
The IDM Session Cleanup Policy is included in the PCM+ policies by default
when you install IDM. The report statistics IDM reports are cleared by the
Session Statistics Cleanup policy (in PCM) on the first day of each month. A
special IDM Session Cleanup alert is used to define the schedule for the policy.
You can edit the policy (alert) if you want to change the cleanup recurrence
schedule.
2-30
Page 51

Creating Report Policies
Getting Started
To modify the IDM Session Cleanup Alert:
1. Click the Policies icon in the global (PCM and IDM) toolbar at the top of
the window to display the Policy Manager window.
2. Click the Alerts node in the navigation tree to display the Manage Alerts
panel.
Figure 2-25. Manage Alerts: IDM Session Cleanup selection
3. Select the IDM Session Cleanup Policy and click the Edit... button to display
the properties.
Figure 2-26. IDM Session Cleanup Schedule properties
2-31
Page 52

Getting Started
Creating Report Policies
4. Click the Schedule tab to review and edit the schedule parameters.
Figure 2-27. IDM Session Cleanup Schedule, alert configuration
2-32
5. Set the Start Date for enforcement of the policy. The default is the start
date and time for IDM.
You can type in a new date and time, or use the arrows to increase or
decrease the date and time entries. Note that the time clock uses 24 hour
format; thus a time of 22:00 is used to indicate a start time of 10:00 pm.
To trigger the IDM Session Cleanup policy to run immediately, click the
checkbox for Run at first opportunity if schedule missed.
6. You can change the session cleanup interval using the Recurrence pattern
options:
If you select... The action is...
Never No further action is required (Policy definition is saved, but will not
be enforced).
One time No further action is required (the currently scheduled time is used
with no recurrences).
Hourly Type the number of hours and minutes to wait between session
cleanup. If you do not want the policy enforced on Saturdays and
Sundays, check the Skip weekend checkbox.
Daily Type the number of days to wait between session cleanups. If you
do not want the policy enforced on Saturdays and Sundays, check
the Skip weekend checkbox.
Page 53

Creating Report Policies
Weekly Check the boxes for the days of the week you want to enforce the
policy.
Monthly Click the Last day of the month button to enforce the schedule on
the last day of the month.
OR
Click the Day button and use the up or down arrows to select the
day of the month.
Getting Started
7. Click the radio button to select No end date, End by, or Maximum occurrences to
identify when the schedule should end.
• If you select No end date, the schedule will run at the selected intervals
until the policy is changed or deleted.
• If you selected End by, click the up and down arrows in the End by field
until the desired end date and time are shown.
• If you selected Maximum occurrences, type the number of times the policy
should be enforced before it is disabled automatically.
8. Click Apply to save the changes, then Close to exit the alert configuration.
2-33
Page 54

Getting Started
User Session Information
User Session Information
You can use IDM to just monitor the network, and receive detailed information
about user's access to the network. The User Session information provides
statistics about exactly *how* the network is being used (when the user logged
in and out, where a user logged in from, and how much bandwidth they
consumed, for example). Based on the User Session information, you can
adjust access rights for users, further restricting or providing additional
network resources and access attributes as needed.
To review user session information,
1. Navigate to the Realm the user belongs to, and display the Users tab.
2. Click the Show User’s session status button in the Users tab toolbar to display
the Session Information window.
2-34
Figure 2-28. IDM Session Cleanup Schedule, alert configuration
Page 55

User Session Information
Getting Started
The Session List provides a listing of recent sessions, including the following
information:
Active True if the user is currently logged in for this session or False
Login Time Date and time the user logged in
Login Successful True if the user logged in successfully or False if login failed
Location Name of the location where the user logged in
Access Profile Access profile assigned to the access policy group
if the session has ended
governing the user’s permissions during the session
The User Properties tab of the User Status window contains the following
information:
Realm Realm to which the user is currently assigned.
Username Username used to login
Friendly Name Name of the user to which the username is assigned
MAC Address MAC address of the computer where the user logged in
Last login time Date and time of the most recent user login
Login Count Total number of times the user logged in during the report
period.
The Session Information tab of the User Status window contains the following
information:
Is Active True if the user is currently logged in for this session or False
RADIUS Server IP address of the RADIUS server that authenticated the user
Login was successful True if the user logged in successfully or False if login failed
Reason login was
unsuccessful
Session start Date and time the user logged in
Session end time Date and time the user logged out or the session was ended
Termination cause Reason the RADIUS server ended the session (e.g., user
if the session has ended
If the login was unsuccessful, the reason the RADIUS server
or IDM denied the login (e.g., access policy group not found
for user or username/password incorrect)
logout, connection interruption, or idle timer expiration)
2-35
Page 56

Getting Started
User Session Information
Input octets Bytes received by the user during the session
Output octets Bytes sent by the user during the session
To track the user’s login location information for the session, click the Location
Information tab. The Location Information tab of the User Status window contains the
following information:
Location name Name of the location where the user logged in
Device address IP address of the device used to login
Ethernet port Port on the device used for the session
BSSID MAC address used for wireless device
Click the Disable port or Enable port links to disable or re-enable the port used
for the session. For example, if you want to prevent the user from logging in
at a specific device or force the user to re-authenticate, you would use the
Disable port function. If you need to re-enable the port so the user can resume
the session, use the Enable port function.
Click the Access Information tab to display details about the access attributes
applied to the user session. The Access Information tab of the User Status window
contains the following information:
2-36
Access Policy Group Access policy group that governs user permissions for the
session.
Access Profile Access profile assigned to the access policy group.
QoS assigned Quality of service or priority for outbound traffic. QoS ranges
from lowest to highest.
Ingress Rate limit Maximum bandwidth for inbound traffic to allocated to user
by the access profile.
Egress Rate Limit Maximum bandwidth for outbound traffic to allocated to
user by the access profile
Untagged VLAN The untagged VLAN to which access is given.
DEFAULT_VLAN(1) is equivalent to allowing access on the
entire network.
Tagged VLANs The tagged VLAN to which access is given.
ACL The access control rules that were applied to the user's
session on the switch or access point.
Page 57

User Session Information
Getting Started
Finding a User
The Find User feature lets you search for and display information about a user
by name or MAC address. The displayed information is similar to User Session
Status information.
To find information for a user or MAC address:
1. In the IDM navigation tree, right-click the Realms or Access Policy Groups
folder to which the user or computer is assigned. Select Find User from the
right-click menu.
This launches the Find User window.
Figure 2-29. Find User
2. In the Username field, type the complete user name of the user you want
to find and display information (This field is not case-sensitive.),
OR
In the MAC address field, type the MAC address of the computer for which
you want to find and display information. The MAC address can be
separated by a vertical bar (|), hyphen, or colon or typed with no spaces.
3. Click the Only show active sessions checkbox to get only the information
on active sessions for the user.
4. Click Find to display information for the specified user or computer.
5. Click Close to exit the window.
2-37
Page 58

Getting Started
User Session Information
User Reports
To review information for multiple sessions, run the User Report.
1. Select a username in the Users tab of the Access Policy Group or RADIUS Server
window.
2. Click the User Report icon in the toolbar. This launches the Report Wizard,
Report Filter window.
2-38
Figure 2-30. Report Wizard, Report Filter
3. To report a specific time range, uncheck the All Dates check box and select
the Start Date and End Date. Click Next to select the report contents.
Page 59

User Session Information
Getting Started
Figure 2-31. Report Wizard, Columns to Include
4. Click the check boxes to select the data columns.
If wireless settings are enabled the WLAN and BSSID options also appear.
5. Click Finish to run the report.
The report is displayed in a separate window on the IDM Client.
Show Mitigations
The Show Mitigations window lists all NIM mitigations (actions taken to
resolve security threats) for the selected user and is used to delete NIM
mitigation rules. Mitigation can include prohibiting user login or limiting user
capabilities by VLAN restrictions, rate limiting, Quality of Service (QoS), etc.
Rules can also be rolled back with NIM mitigation policies. However, if a
rollback timer has not been defined for the policy, the IDM mitigation rules
are permanent and must be deleted through the Mitigations window.
2-39
Page 60

Getting Started
User Session Information
Figure 2-32. Show Mitigations
To show or delete mitigations:
1. In the IDM Users tab, right-click a mitigated user and choose Show
Mitigations to display the Mitigations window. This function is selectable
for mitigated users only. Mitigated users are identified by one of the
following icons:
User successfully logged in, but the session was mitigated in some
way (e.g., VLAN, rate limit, QoS)
User login was prohibited by NIM mitigation action
The Mitigations window lists each rule associated with the selected user
and all MAC addresses where the user has logged in.
2. To delete a single rule, select the rules to delete and click Revoke.
3. To delete all rules, click Select All and then click Revoke.
2-40
Page 61
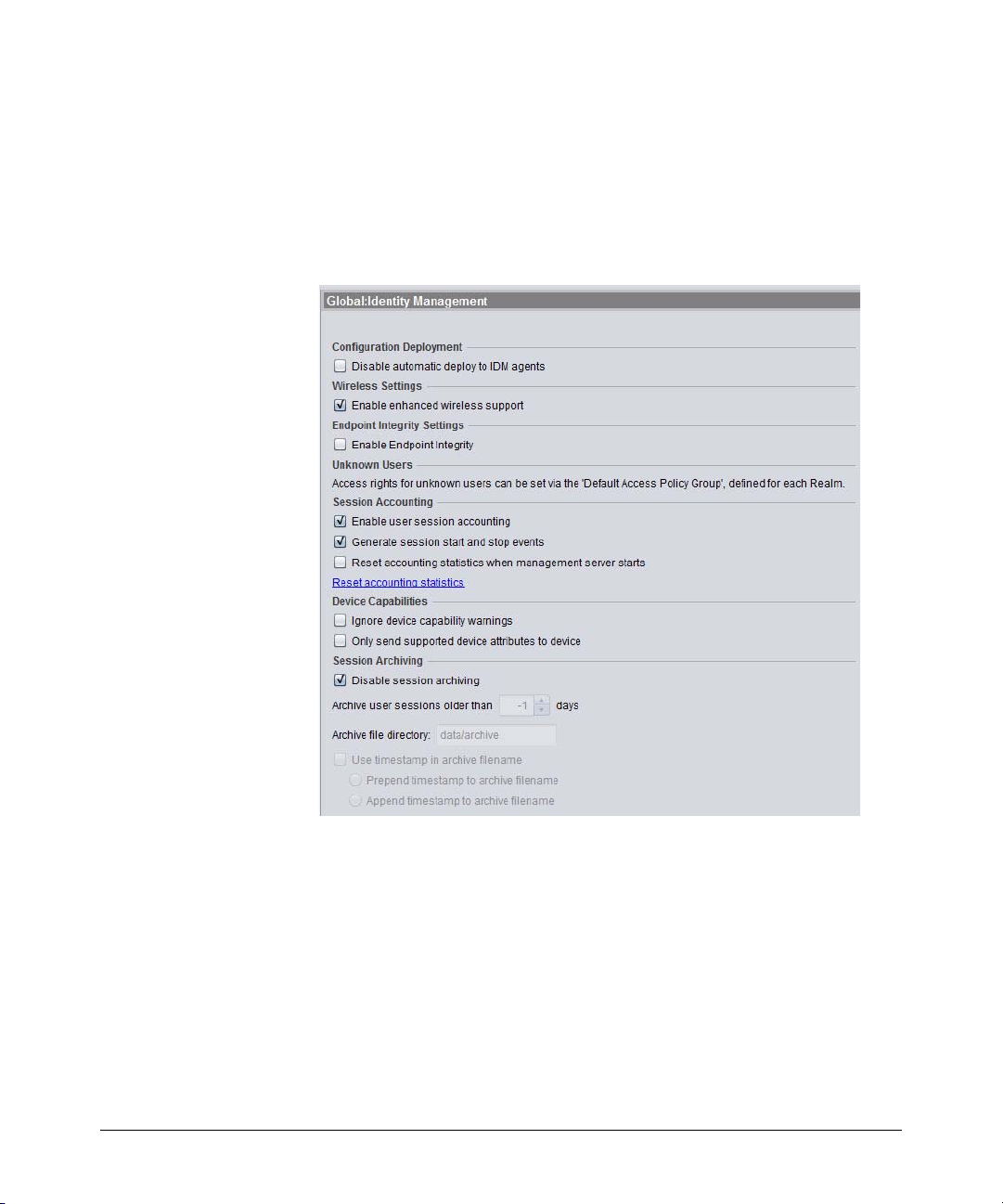
User Session Information
Getting Started
IDM Preferences
The IDM Preferences window is used to set up global attributes for session
accounting and archiving, as well as enabling the Endpoint Integrity option.
Click the Tools menu and select Identity Management to display the Preferences,
Global:Identity Management window.
Figure 2-33. Global Preferences for IDM
Click on the option check boxes to select (check) or deselect (blank) the
option.
1. The Configuration Deployment option is used to automatically deploy
IDM configuration settings (Access Profiles, Locations, Times, Network
Resources) to the IDM agent. The default preference is to allow automatic
configuration deployment.
2-41
Page 62

Getting Started
User Session Information
Click to select the Disable automatic deploy to IDM agents option if you do
not want to use automatic IDM configuration deployment.
If you "disable" the Configuration Deployment option. in order for IDM
configuration changes to take affect you will need to manually deploy the
configuration to the IDM agent(s).
2. The Wireless Settings option is used to allow configuration of Identity
Management features for select ProCurve wireless devices. The default
preference has the Enable enhanced wireless support option selected.
When this option is deselected (no check mark), wireless configuration
options will not be visible and will not be applicable in rule evaluation
3. To enable Endpoint integrity, check the Enable Endpoint Integrity checkbox.
This will enable the Endpoint Integrity option in the Access Rules definitions, and you can configure an Access Rule with one of the Endpoint
Integrity options (Pass, Fail or ANY). When you enable Endpoint Integrity
and set the attribute in a Global Access Rule or Access Policy Group rule,
the IDM agent will look for the RADIUS attribute in the supplicant’s
authentication request and act accordingly, applying the defined access
rule based on the endpoint integrity system response.
4. To collect information about user logins and logouts, check the Enable
User session accounting checkbox. This box must be checked if you want
to collect data for user logins and bandwidth usage, which is used for the
Bandwidth, Session, and User reports.
2-42
5. To generate user session start and stop events and display them in the IDM
Events list, check the Generate Session Start and Stop Events box. This
option does not affect accounting or collection of session history and
statistical information. Turning this option off will reduce the load on your
IDM server and the GUI by eliminating two-thirds of the events created
for every user login and logout.
6. To reset all session accounting information whenever the server is
restarted, check the Reset accounting statistics when the management server
starts box. When this option is selected, IDM closes any open sessions and
resets the RADIUS Server totals to zero when the server restarts.
If the status of users—logged on or off—seems incorrect, it is possible
that the session accounting is out of sync. Use the Reset accounting
statistics option to correct the problem. This immediately closes any open
sessions (this has no effect on the user, only on the IDM accounting), and
resets user login counts on the RADIUS server to zero.
Existing accounting records are not removed by the Reset procedures, the
only effect is that currently open sessions are closed.
Page 63

User Session Information
7. To ignore capability override warnings generated by switches that don't
support certain capabilities (e.g., VLAN, QoS, Bandwidth, and ACL overrides), check the Ignore device capability warnings checkbox.
8. To send only those attributes supported by the device, check the Only send
supported device attributes to device checkbox.
9. If you wish to archive accounting records older than a specified time
period, uncheck the Disable session archiving box, and set the desired
archival time period in the Archive user sessions older than x days field.
10. To archive the user session archive file in a location other than the default
IDM data archive directory, type the desired path in the Archive file directory
field. The default path is:
C:\Program Files\Hewlett-Packard\PNM\server\idm\data
11. If you do not want to add a timestamp to the archive filename, uncheck
the Use timestamp in archive filename option.
If a timestamp is not used in the archive filename, the existing archive file
is overwritten each time user sessions are archived.
a. To insert a timestamp in the front of the archive filename, check the
Prepend timestamp to archive filename option.
b. To add a timestamp to the end of the archive filename, check the
Append timestamp to archive filename option.
Getting Started
12. Click Ok to save your changes and exit the window.
Click Apply to save your changes and leave the Preferences window open.
Click Cancel to close the window without saving changes.
Using Active Directory Synchronization
The Active Directory Synchronization (AD Sync) feature provides the ability
to receive change notifications from the active directory server for the domain
the management server is logged into. The Active Directory Synchronization
will automatically update the IDM database with changes made in your Active
Directory, including new users, changes to existing users, and deletion of
users.
To enable automatic synchronization from Active Directory to IDM, navigate
to the Tools -> Preferences-> Identity Management -> User Directory Settings window.
2-43
Page 64

Getting Started
User Session Information
Figure 2-34. Identity Management Preferences: User Directory Settings.
1. Check the Enable automatic Active Directory synchronization check box,
which enables the remaining fields and displays the current status of the
connection between IDM and Active Directory (AD Status) at the bottom
of the window.
2. In the Username field, type the Username for the Active Directory. Active
Directory credentials (username, domain, and password) must be for a
domain administrator.
3. Optionally, in the Password field, type the password for the Active Directory.
4. If displayed, select the Groups to synchronize.
2-44
Page 65

User Session Information
Getting Started
5. To Add a group to the "Groups to Synchronize" list, click Add or Remove
Groups... to display the Add or Remove Groups dialog.
Figure 2-35. Active Directory Synchronization: Add or Remove Groups
The Active Directory is queried for all groups in the domain and the groups
are displayed in the "Groups in Active Directory" list.
NOTE: When adding or removing groups remember that synchronization
includes all users who are indirect members of a group via intervening
nested group relationships. In addition, users belonging to more than one
AD group are added to the IDM group with the higher priority. For
example, User 1 in the following example is imported into Group ALL if
IDM synchronizes on Group ALL. Or, if IDM synchronizes on Group A or
Group B, User 1 is imported into the group with the higher priority. If IDM
synchronizes on Group d or Group y, the User 1 is not imported.
2-45
Page 66

Getting Started
User Session Information
6. Select the Active Directory Groups you want to Synchronize to IDM, then
click the >> button to move the groups to the "Groups to Synchronize" list.
Use the Filter field to locate a group easily.
To remove groups from the synchronization, select the group in the
"Groups to Synchronize" and click the << button to move it to the "Groups
in Active Directory" list.
7. Click OK to save the Groups to Synchronize and return to the User
Directory Settings window.
8. To accommodate users who are members of multiple groups, ensure the
listed groups are in the desired order. To reorder a group, select the group
and click the Move up or Move down button.
A user can belong to only one Access Policy Group. IDM associates users
with the first group in the group list that the user is a member of.
Therefore, order is important.
9. Click Apply to save the settings without exiting the window.
Click OK to save the settings and close the window.
An Access Policy Group is created for each selected Active Directory
group, and all users that belong to the selected groups will be imported
from the Active Directory server. into the appropriate Access Policy
Group. Changes to users in the selected groups will be imported (synchronized) as long as the Active Directory Synchronization is enabled.
2-46
Operating Notes:
■ If a user belongs to more than one Active Directory group, the user is
imported into the IDM Access Policy Group with the highest priority
(set in User Directory Settings Preferences).
■ If an Active Directory group is deleted while Active Directory
synchronization is enabled, the associated Access Policy Group is
deleted. If that group is the priority IDM Access Policy Group for a
user who belongs to more than one Active Directory group, the user
is automatically reassigned to the next highest priority Access Policy
Group. Users who do not belong to more than one Active Directory
group are reassigned to the default Access Policy Group for the
Realm.
■ If an Active Directory group is deleted while Active Directory
synchronization is disabled, the associated Access Policy Group is
NOT deleted when synchronization is enabled. However, all users will
be reassigned to other groups (next highest priority or default Access
Policy Group for the Realm) as part of the resynchronization process.
Page 67

User Session Information
■ Users deleted from Active Directory while synchronization is
Getting Started
disabled are assigned to the default Access Policy group during the
resynchronization process (instead of being deleted). This prevents
users who were added by another method from being deleted.
■ Within a Realm, Access Policy Group names must be unique. If Access
Policy Groups are being created manually within the same Realm, use
naming conventions to ensure these names do not conflict with Active
Directory group names.
■ Performance for the import from Active Directory to IDM varies
depending on your environment. Using a 1.86 GHz processor with
2GB RAM, importing 20,000 Active Directory users in 75 groups takes
approximately 65 minutes. A similar test that imported 10,000 of
20,000 users by selecting 2 of the 75 groups completed in 30 minutes.
■ Once the initial synchronization is completed, IDM monitors all
changes to the Active Directory which much less system resources.
If Active Directory synchronization is disabled or IDM is restarted, all
groups must be resynchronized.
■ Importing only relevant groups can reduce the import time signifi-
cantly. Selecting only groups of users for which access policies are
defined instead of selecting the Domain Users group (which includes
all users in the domain) can significantly reduce the amount of
information that must be maintained in IDM and synchronized with
Active Directory.
■ When Active Directory is queried for the "Add or Remove Groups"
function in IDM, it may take several seconds to display the list of
available groups. An hourglass is displayed when such an extended
process is occurring. Performance will vary depending on your environment. Using a 1.86 GHz Intel Core2 Duo processor with 2GB RAM
takes approximately 30 seconds to present a list of 20,000 groups.
■ If an error occurs while attempting to read the Active Directory, an
entry is made in the IDM events log, and IDM attempts to reconnect
to Active Directory once per minute.
2-47
Page 68

Getting Started
User Session Information
2-48
Page 69

Using Identity Driven Manager
Chapter Contents
IDM Configuration Model . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-3
Configuration Process Review . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-3
Configuring Identity Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-4
Configuring Locations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-6
Adding a New Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-7
Modifying a Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-11
Deleting a Location . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-12
Configuring Times . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-13
Creating a New Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-14
Modifying a Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Deleting a Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-16
Configuring Network Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-18
Adding a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-20
Modifying a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-21
Deleting a Network Resource . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-22
Configuring Access Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-23
Creating a New Access Profile . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-24
Modifying an Access Profile . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-31
Defining Access Policy Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-33
Creating an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-34
Modifying an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-39
Deleting an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-39
Configuring User Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-40
Adding Users to an Access Policy Group . . . . . . . . . . . . . . . . . . . . . . . 3-41
Changing Access Policy Group Assignments . . . . . . . . . . . . . . . . . . . 3-42
Using Global Rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-43
Deploying Configurations to the Agent . . . . . . . . . . . . . . . . . . . . . . . . 3-46
Using Manual Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-47
Defining New Realms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-47
Modifying and Deleting Realms . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-48
3
3-1
Page 70

Using Identity Driven Manager
Adding RADIUS Clients . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-49
Using the User Import Wizard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-59
Deleting RADIUS Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-55
Adding New Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-56
Importing Users from Active Directory . . . . . . . . . . . . . . . . . . . . . . . . 3-60
Importing Users from an LDAP Server . . . . . . . . . . . . . . . . . . . . . . . . . 3-64
Importing Users from XML files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-74
3-2
Page 71

Using Identity Driven Manager
IDM Configuration Model
IDM Configuration Model
As described in the IDM model on page 2-8, everything relates to the top level,
or Realm. Each User in the Realm belongs to an Access Policy Group (APG).
The APG has an Access Policy defined for it that governs the access rights that
are applied to its Users as they enter the network.
The Access Policy is defined using a set of Access Rules. These rules take four
inputs:
• Location (where is the user accessing the network from?)
• Time (what time is the user accessing the network?)
• System (from what system is the user accessing the network?)
Using these input parameters, IDM evaluates each of the rules. When a
matching rule is found, then the access rights (called an Access Profile)
associated with that rule are applied to the user. The Access Profile defines
access provided to the network once the user is authenticated, including:
• VLAN—what VLANs the user can access.
• QoS—Quality of Service, from lowest to highest.
• Rate-limits—bandwidth that is available for the user.
• Network Resources—resources the user can access, by IP address
and/or protocol. These resources must be defined, similarly to the
Locations and Times used in the access rules.
Thus, based on the rules defined in the APG, the user gets the appropriate level
of access to the network.
In summary, for identity driven management each user in a Realm belongs to
one Access Policy Group. The Access Policy Group defines the rules that are
evaluated to determine the access policies that are applied at the switch when
the user connects to the network.
Configuration Process Review
Assuming that you opted to enable Active Directory synchronization or let
IDM run long enough to discover the Realm, users, and RADIUS server, your
configuration process will be:
1. Define "locations" (optional) from which users access the network. The
location may relate to port-based VLANS, or to all ports on a switch.
3-3
Page 72

Using Identity Driven Manager
IDM Configuration Model
2. Define "times" (optional) at which users will be allowed or denied access.
3. If you intend to restrict a user’s access to specific systems, based on the
4. Define the Network Resources that users will have access to, or will be
5. Create the Access Profiles to set the VLAN, QoS, rate-limits (Bandwidth),
6. If you don’t use Active Directory synchronization, create the Access
7. If you do not use Active Directory synchronization, assign Users to the
This can be by day, week or even hour.
system they use to access the network, you need to modify the User profile
to include the MAC address for each system from which the user is
allowed to login.
denied from using, if applicable.
and network resources that are applied to users in Access Policy Groups.
Policy Groups, with rules containing the Location, Time, System, and
Access Profile that will be applied to users when they login.
OR
If using Active Directory synchronization, add rules and access profiles
to the Access Policy Groups that were created by Active Directory synchronization.
appropriate Access Policy Group.
8. If you do not use automatic deployment, deploy the configuration to the
IDM Agent on the RADIUS Server. The authorization controls can then be
applied when IDM detects an authenticated user login. If you do not use
automatic deployment and do not manually deploy the IDM configuration
to the Agent on the RADIUS server, the configuration will not be applied
NOTE: If you want to modify or delete an Access Policy Group, or the locations, times,
or access profiles used in the Access Policy Group, make sure your changes
will not adversely affect users assigned to that group.
Configuring Identity Management
All of the elements described for configuring user access in IDM are available
in the Identity Management Configuration window.
To launch the Identity Management Configuration window:
1. Right-click on the Identity Management navigation tree, and select the
Configure Identity Management... option from the menu, or
3-4
Page 73

Using Identity Driven Manager
IDM Configuration Model
2. Click the Configure Identity Management icon in the Realms window
toolbar.
The Identity Management Configuration default display is the Access Profiles
pane with the Default Access Profile.
Figure 3-1. Identity Management Configuration, default display
Click the node in the navigation tree to display the defined configuration
parameters and add or edit new configuration parameters, as described in the
following sections.
3-5
Page 74
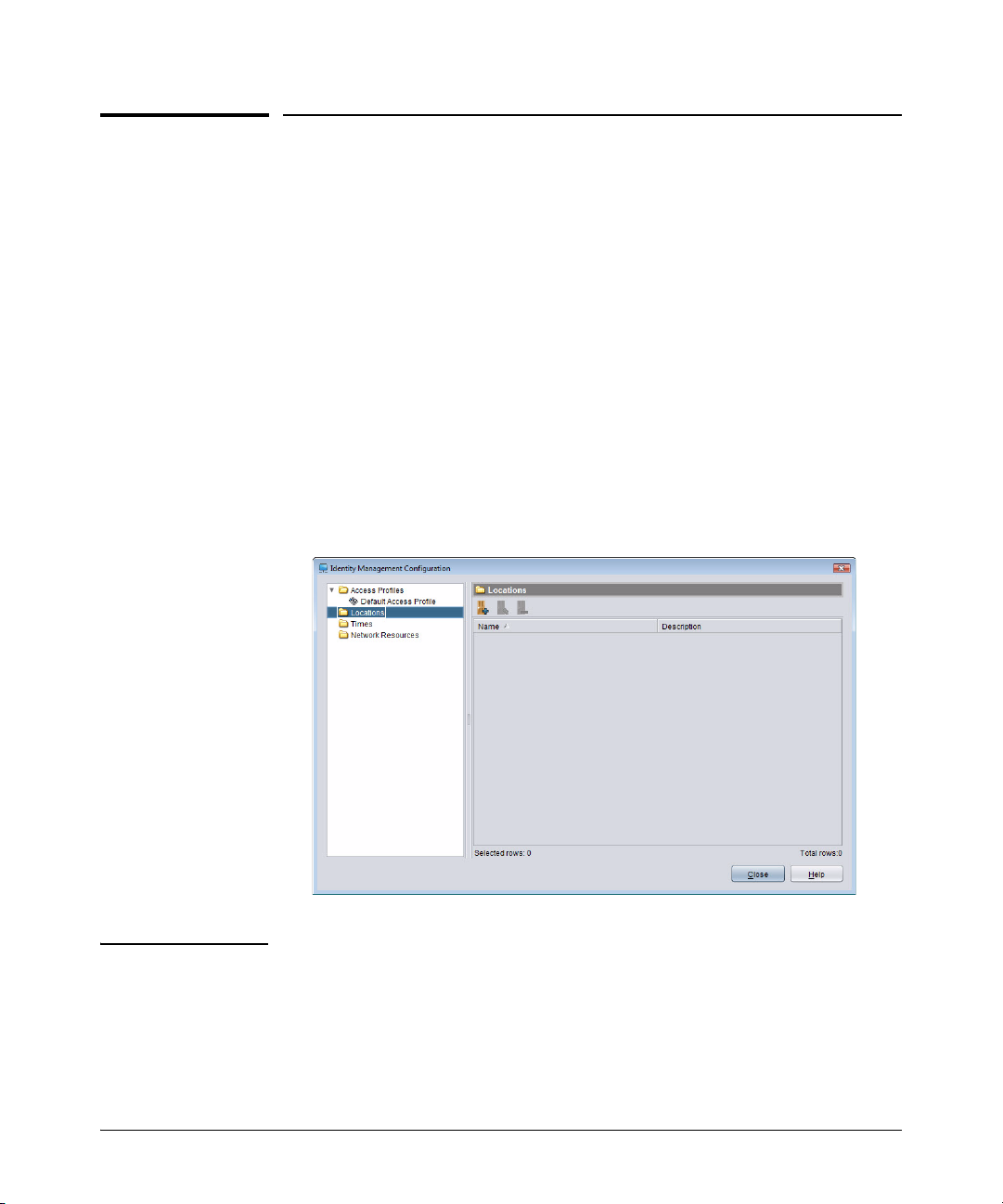
Using Identity Driven Manager
Configuring Locations
Configuring Locations
Locations in IDM identify the switch and/or ports on the switch and wireless
access points where users connect to the network. Users generally are allowed
to log in to the network from a variety of locations, IDM allows you to create
customized locations to match specific environments.
For example, a generalized company "location" may include all of the ports on
a switch, or multiple switches through which users can connect to the network. You can define a lobby location as a single switch, or a single port on
the switch, in order to restrict access to the network for visitors attaching to
the network in the lobby.
To configure a location:
Click the
to display the Locations panel.
Figure 3-2. Locations panel
Locations node in the Identity Management Configura tion navigation tree
Tip: IDM also lets you include wireless devices in the location configuration. The
"Enable Enhanced Wireless Support" option in IDM Preferences add a wireless
devices tab to the Create a new Locations window.
3-6
Page 75

Adding a New Location
To create a new location:
Using Identity Driven Manager
Configuring Locations
1. Click the
window.
Figure 3-3. Create a New Location display
New Location icon in the toolbar to display the new locations
2. Type in a Name for the location.
3. Type in a Description for the location.
To add wired devices to the location:
4. Click Add device... to open the New Device window, and define the devices
and/or port combinations that will be included in the location.
See “To Add a Wireless Device to a Location” on page 3-9 for details on support
for wireless locations.
3-7
Page 76

Using Identity Driven Manager
Configuring Locations
Figure 3-4. New Device window
5. Use the Select Device Group drop-down list to select the Agent and device
model that will be allocated to users logging in from the associated
location.
6. Enter the Device to be added using the Device Selection pull-downs, or
select the Manually enter device address option.
Using the
Device Selection option:
a. Select a device group using the pull-down menu. This will enable the
Select Device pull-down menu in the next field.
b. Select a device from the pull-down list of available devices. The list
is populated with the IP address or DNS name for all (PCM managed)
devices in the selected group.
Using the
Manually enter device address option:
a. Click the check box to enable the data entry field below it.
b. Type in the IP address or DNS name of the device to be added.
Note: If PMM is licensed, this dialog will not show wireless device. You must add
wireless devices from the "Wireless Devices" tab on the "New Location Dialog"
If PMM is not licensed, wireless devices will appear in this dialog. However,
you will not be able to select any ports, the only option will be "Any port"
3-8
Page 77

Using Identity Driven Manager
Configuring Locations
7. Use the Port Selection to define the ports on the device that will be
associated with the location.
• Click to select Any port on the switch, or
• Click Select ports, then use the pull down lists to select the Begin and
End ports on the device that will be associated with the new location.
If you manually entered the device address, the
Begin port and End port
pull-down menus are disabled, and you must manually enter the ports.
8. Click Ok to save the New Device settings to the Location, and close the
window.
NOTE: If a switch in the device list is not configured to authenticate with the RADIUS
server, the settings in IDM will have no affect.
You can type in an IP address for non-ProCurve devices and if the device uses
industry standard RADIUS protocols, the settings should work; however, HP
does not provide support for IDM configurations with non-ProCurve devices.
9. The Device address and ports information is displayed in the
window.
10. Repeat steps 4 through 7 to add additional devices to the Location, or click
OK to save the new Location and close the window.
To Add a Wireless Device to a Location:
11. Click the Wireless devices tab:
New Location
3-9
Page 78

Using Identity Driven Manager
Configuring Locations
Figure 3-5. Create a New Location, Wireless Devices
12. Click Add Device... to display the Wireless Devices Selection dialog.
Figure 3-6. Select Wireless Device for a location
13. All discovered Radios and radio ports are displayed.
3-10
Page 79

Using Identity Driven Manager
Configuring Locations
Click the check box to select the radio ports to be included in the location,
and then click OK to save the selection and return to the Create a new
Location (Wireless Devices tab) window.
14. Click OK in the Create a new Location window to save and exit, or repeat
the steps to add additional devices to the location.
Modifying a Location
To edit the information for an existing Location:
1. Click the
Locations node in the Identity Management Co nfiguration navigation
tree to display the Locations panel, with the list of defined locations.
2. Double-click on a location in the navigation tree, or in the
Locations list to
open the (modify) location panel.
You can also select the location in the list, then click the
Edit Location icon
in the toolbar to display the Location in edit mode
3. Edit the location Name and Description as needed.
4. To edit the device configuration for the location
• To Modify the device settings, select the device in the list, then click
Edit device... to display the
Modify Device window.
The Modify Device window contains the same fields as the New
Device window. You can edit the ports associated with the location,
or you can choose a different device and reset the ports for the new
device. Click OK to save your changes and close the window.
The changes are displayed in the Location panel.
• To add another device, click Add Device.
• To delete a device, select the device in the list, then click Delete Device
5. Click OK to save the location changes and close the Locations window.
Click
Cancel to close the window without saving the changes. The original
location configuration will be maintained.
.
NOTE: When modifying Locations, make sure all devices for the location are config-
ured with the appropriate VLANs. If you Modify a Location that is part of a
VLAN (subnet) and that Location is currently used in an Access Policy Group
rule, IDM will check to make sure that the VLAN exists. If not, an error message
is displayed.
3-11
Page 80

Using Identity Driven Manager
Configuring Locations
Deleting a Location
To remove an existing Location:
1. Click the
tree to display the Locations panel, with the list of defined locations.
2. Click on a location in the list to select it.
3. Click on the
The first time you use the Delete Location option, a warning pop-up is
displayed. Click Ok to continue, or
4. The location is removed from the Locations list.
Locations node in the Identity Management Co nfiguration navigation
Delete Location icon in the toolbar to remove the location.
Cancel to stop the delete process.
NOTE: If you modify or delete a Location, check to make sure that the changes do
not adversely affect users in Access Policy Groups where the Location is used.
3-12
Page 81

Using Identity Driven Manager
Configuring Times
Configuring Times
Times are used to define the hours and days when a user can connect to the
network. When included in the Access Policy Group rules, the time can be
used to allow or deny access from specific locations at specific time. For
example, students might be allowed network access from the "Classroom"
location during weekdays, from 9:00 am to 5:00 pm, but denied access from
the Classroom at any other time.
To configure a Time:
1. Click the Times node in the Identity Management Configuration navigation tree to display the Times panel.
Figure 3-7. Identity Management Configuration, Times panel
The Times window lists the name and description of defined times. Doubleclick the time in the list, or select the time in the navigation tree to display the
Time’s properties, including:
Name Name used to identify the time
Description Brief description of the time
Tim e Time of day when the access policy group is active.
Days of week Days of the week when the access policy group is
Range Dates during which the "Time" will be in effect. A start
active
date must be specified.
3-13
Page 82

Using Identity Driven Manager
Configuring Times
Figure 3-8. Times Properties
Creating a New Time
To configure a Time:
1. Click the
tree to display the
2. Click the
window.
Times node in the Identity Management Configuration navigation
Times panel.
Add New Time toolbar icon to display the Create a new Time
3-14
Page 83

Using Identity Driven Manager
Configuring Times
Figure 3-9. Create a New Time
3. Define the properties for the new time.
Name Name used to identify the time
Description Brief description of the time
Tim e Time of day when user will be accepted on the network. To allow
Days of week Days of the week that a user will be accepted or rejected on the
Range Dates during which the time will be in effect. Select the Start Date and
access the entire day, click the All day radio button.
To restrict access to specific hours of the day, click the From radio
button and type the beginning and ending times. The ending time must
be later than the beginning time. AM or PM must be specified.
network. Click the radio button next to the desired days. Click the
Custom radio button to enable the day(s) of the week check boxes.
then click the No End Date radio button, or select the End Date.
Table 3-1. IDM Time parameters
4. Click Ok to save the new "Time" and close the panel.
The new time appears in the Times window.
3-15
Page 84

Using Identity Driven Manager
Configuring Times
Modifying a Time
1. Click the Times node in the Identity Management Configuration navigation
tree to display the Times panel.
2. Click on a
mode, similar to the
You can also select the
Time in the navigation tree to display the Time details in edit
Create a new Time panel.
Time in the list then click the Modify Time icon in
the toolbar to display the modify panel.
3. Modify the time parameters, as described in Table 3-1 on page 3-15.
4. Click Ok to save your changes and close the window
NOTE: If you modify or delete a Time, check to make sure that the changes do not
adversely affect users in Access Policy Groups where the Time is used.
Deleting a Time
To remove an existing Time:
1. Click the
tree to display the Times panel with the list of defined Times.
2. Click on a
3. Click on the
The first time you use the Delete Time option, a warning pop-up is
displayed. Click Ok to continue, or
Times node in the Identity Management Configuration navigation
Time in the list to select it.
Delete Time icon in the toolbar to remove the location.
Cancel to stop the delete process.
3-16
4. The Time is removed from the
Times list.
Page 85
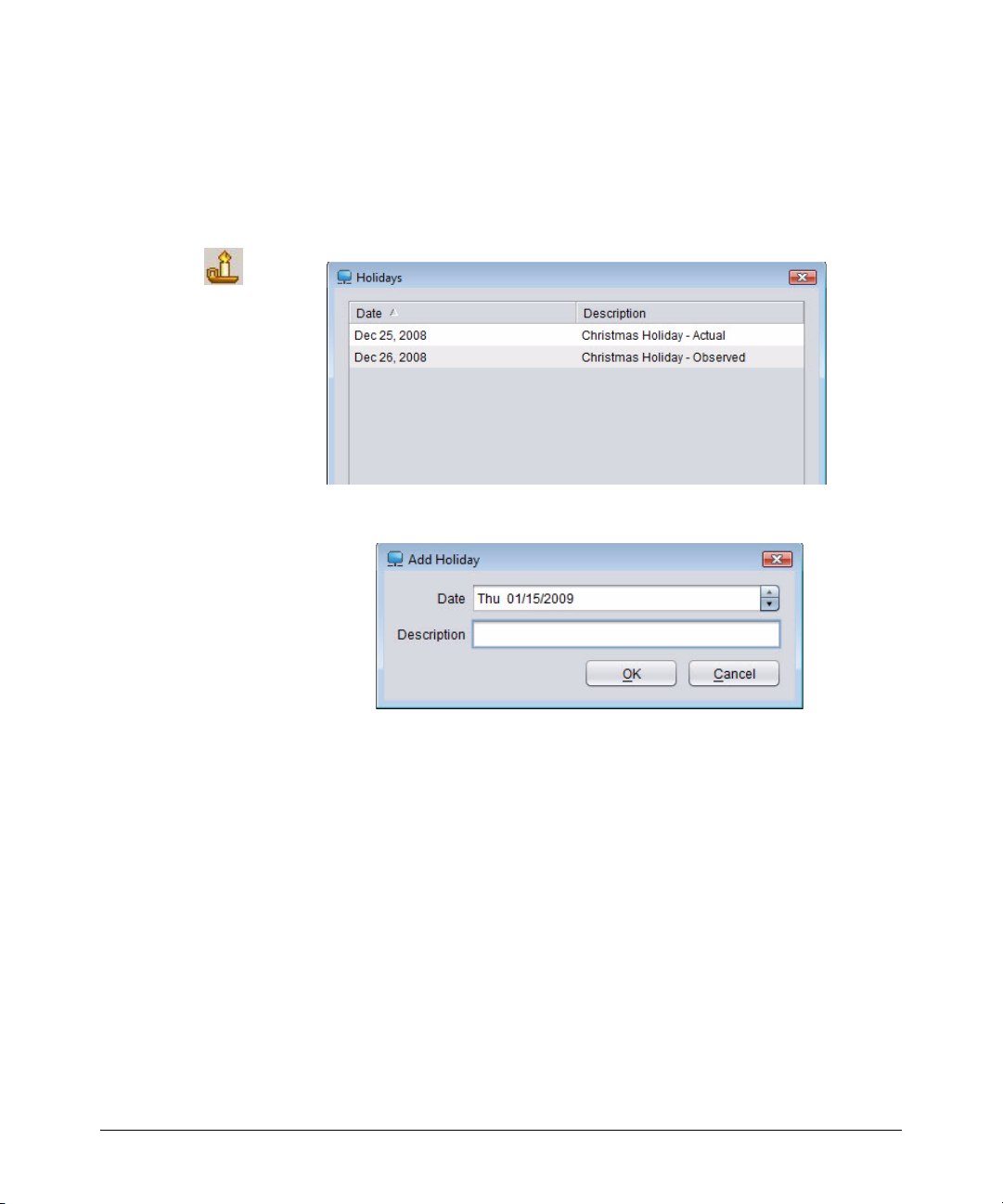
Using Identity Driven Manager
Defining Holidays
To add holidays for use when defining Times in IDM:
Configuring Times
1. Click the
Times node in the Identity Management Configuration navigation
tree to display the Times panel.
2. Click the Holidays icon in the toolbar to launch the
Figure 3-10. Holidays window
3. Click Add. to launch the
Add Holidays window.
Figure 3-11. Add Holiday
Holidays window.
4. The Date field defaults to the current date. You can use the field buttons
to increase or decrease the date. You can also type in a new date.
5. In the Description field, enter the text that will identify the holiday in the
Holidays list.
6. Click OK to save the holiday and close the window. The new holiday
appears in the
Holidays list.
To edit a Holiday, select it in the Holidays list, then click Edit... This launches
the
Edit Holiday window, similar to the Add Holiday window.
To delete a Holiday, select it in the Holidays list, then click Delete... Click Ye s
in the confirmation pop-up to complete the process.
3-17
Page 86

Using Identity Driven Manager
Configuring Network Resources
Configuring Network Resources
The Network Resources in IDM are used to permit or deny traffic to and from
specified sources and destination. This is done by configuring an IP-based
filter based on either:
■ The IP address (individual address or subnet address) of the source
or destination, or
■ The protocol (IP, ICMP, VRRP, etc.)
■ The TCP or UDP port (i.e., based on protocol and application, such
as Telnet or HTTP)
For example, you can create a Network Resource to restrict "guest accounts"
so that they only have access to the external Internet, and no access to internal
resources. Or you can define a resource that allows HR employees to access
the payroll systems, and denies access to all other employees.
Note: Network Resource features can be used only for switches that support IDM-
based ACLs. To date, this includes only the 5300 version E.10.02 and greater;
check the ProCurve web site (www.procurve.com) for more information.
3-18
To configure a Network Resource:
1. Click the
navigation tree to display the
Network Resources node in the Identity Management Configuration
Network Resources panel.
Figure 3-12. Network Resources
Page 87

Using Identity Driven Manager
Configuring Network Resources
The Network Resources window lists the name and parameters for defined
resources, including:
Name Name used to identify the resource
IP Address IP Address for the switch associated with the resource ("any" if the
Network Mask The subnet mask for the IP Address.
Ports Device port(s) associated with the resource or Any if the resource is
Protocol The Protocol (UDP, TCP, or IP) used to filter access to the resource.
resource is being filtered by protocol).
being filtered by protocol.
Ports can be selected by number, or friendly port name. Refer to the
section on "Using Friendly (Optional) Port Names" in the Management
and Configuration Guide for your switch for details.
Double-click the Network Resource in the list, or select it in the navigation
tree on the left to display individual Network Resource configuration details.
Figure 3-13. Network Resource Configuration Details
Note that when you open the window, it is in "Edit" mode. You can modify the
entries in the display fields, and the changes are automatically saved when
you click Close. For details on the field entries, refer to the definitions under
“Adding a Network Resource” on the next page.
3-19
Page 88

Using Identity Driven Manager
Configuring Network Resources
Adding a Network Resource
To define a Network Resource:
1. Click the
Network Resources node in the Identity Management Configuration
navigation tree to display the
2. Click the
Resource
Add Network Resource toolbar icon to display the Define Network
window.
Figure 3-14. Define Network Resource
Network Resources panel.
3-20
3. Define the properties for the network resource.
Name Name used to identify the network resource
Description Brief description of the network resource (optional)
Resource Attributes:
IP Address: To filter by device address, uncheck the Any Address checkbox and
Mask: The subnet mask for the IP Address (if used). Use the up/down buttons
type the IP address for the switch associated with the resource in the
IP Address field.
Use the Any address option if you will be filtering by Protocol and
application port only, and not by specific device or port.
[
▲, ▼] to set the mask number.
Table 3-2. IDM Network Resource parameters
Page 89

Using Identity Driven Manager
Configuring Network Resources
Protocol: Select UDP, TCP, or IP to identify the protocol used to filter access to
the resource. Protocol can be used alone or with an IP address and
port parameters to define the network resource access.
To use a custom protocol number for a network resource, check the
Enter protocol number checkbox and type the protocol number (0-137)
Port: Any port is selected by default, which means all ports associated to
the IP address are included in the network resource definition. To
specify a port for the network resource, click the Any port checkbox
to de-select it and enable the Port field. Enter the port number, or
friendly port name* used for the resource.
Table 3-2. IDM Network Resource parameters
* Valid Friendly port names supported in IDM include: ftp, syslog,
ldap, http, imap4, imap3, nntp, pop2, pop3, smtp, ssl, telnet, bootpc,
bootps, ssh, dhcp, ntp, radius, rip, snmpsnmp-trap, tftp.
Note: If you are setting a resource to represent an application port such as "dhcp" or
smtp" or "http", you must make sure that you set the correct protocol, either
"
TCP or UDP. If you do not set the correct protocol, the rule will not operate as
intended at the switch or access point.
4. Click Ok to save the Network Resource definition and close the window.
All entries are saved immediately upon entry. This allows you to configure
several IDM features without closing and reopening the Configure Identity
Management window
Click
Cancel to close the window without saving your changes.
Modifying a Network Resource
To edit a Network Resource:
1. Click the
tion navigation tree to display the
2. Click in the list to select the network resource to edit, then click the
Network Resource
dow.
3. Edit the properties as needed. Refer to “Adding a Network Resource” on
the previous page for definitions.
4. Click Ok to save the Network Resource definition and close the window.
Network Resources node in the Identity Management Configura-
Network Resources panel.
Edit
toolbar icon to display the Define Network Resource win-
3-21
Page 90

Using Identity Driven Manager
Configuring Network Resources
Deleting a Network Resource
To delete a Network Resource:
1. Click the
navigation tree to display the
Network Resources node in the Identity Management Configuration
Network Resources panel.
2. Click in the list to select the network resource to edit, then click the
Network Resource
toolbar icon.
3. Click Yes in the confirmation pop-up to complete the process.
The selected network resource is removed from the
Network Resources list
display.
Delete
3-22
Page 91

Using Identity Driven Manager
Configuring Access Profiles
Configuring Access Profiles
IDM uses an Access Profile to set the VLAN, QoS, Bandwidth (rate-limits) and
Network Resource access rules that are applied to the user when they are
authenticated on the network. This is where the real benefits of "access
control" are realized. When users log in, the Access Profile dynamically
configures the switch or wireless access point settings to provide the proper
network access and resources for the user.
To begin, click the
Access Profiles node in the Identit y Management Config uration
navigation tree to display the Access Profiles window.
Figure 3-15. Access Profiles window
The Access Profiles window lists defined Access Profiles, including:
Name Name used to identify the profile
Untagged VLAN Name of untagged VLAN to which users in the group
are assigned when they log in
QoS The "Quality of Service" setting
Ingress Rate Limit Maximum amount of traffic (in Kbps) allowed from
Egress Rate Limit Maximum amount of traffic (in Kbps) allowed to user
user
The Access Profile tells the switch to override any local settings for the port
the user is accessing with the settings specified in IDM.
3-23
Page 92

Using Identity Driven Manager
Configuring Access Profiles
Click the Access Profile node in the navigation tree, or double-click on a profile
in the list to display the details of the selected profile.The
and
Network Resources section lists the Network Resources included in the profile:
Name, Description,
Access Attributes are the same as defined in the Access Profiles list. The
Priority The order in which the network resource rules are evaluated;
Action Indicates if access to the Network Resource is allowed or
Resource The defined network resource name.
Accounting Tells the switch to count the number of hits using this rule.
the first one to match each incoming packet is applied
denied.
Creating a New Access Profile
1. Click the Access Profiles node in the Identity Management Configuration
navigation tree to display the Access Profiles window.
2. Click the
Access Profile
Add Access Profile icon in the toolbar to display the Create a new
window.
3-24
Figure 3-16. Create Access Profile
Page 93

3. Define the attributes for the Access Profile:
Name Name used to identify the Access Profile
Description Brief description of the Access Profile
Using Identity Driven Manager
Configuring Access Profiles
Untagged VLAN or
Tagged VLANs
QoS The Quality of Service, or "priority" given to outbound traffic under
Ingress rate-limit
Egress rate-limit
Select the type of VLAN used for the access profile.
To select an untagged VLAN, check the Untagged VLAN check
box and select the VLAN that can be accessed from the dropdown list. Selecting a VLAN from the list grants the user access
to that network segment only.
To select a tagged VLAN, check the Tagged VLAN check box and
click Edit. When the VLAN Selection window appears, select the
tagged VLANs to be accessed from the Available VLANs list and
click >> to select them. When all tagged VLANS that can be
accessed are displayed in the Selected VLANs list, click OK to
close the window and return to the Identity Management
Configuration window.
Keep the following in mind when selecting VLANs:
• The list of VLANs is derived from the VLANs that PCM discovers.
Therefore, you should run Discovery to populate the VLAN list
before creating a new Access Profile.
• Untagged VLANs and tagged VLANs are mutually exclusive,
meaning the customer cannot select the same VLAN for
untagged and tagged.
• The VLAN set for a user overrides the statically configured
VLAN, as well as the auth-vid that may have been configured
for that port.
• If an unauth-vid is set and the user is rejected by IDM for any
reason, the port is opened and the VLAN is set to the unauth-vid.
this profile. Select the setting from the pull-down menu.
The rate-limits applied for this profile. Use the up-down arrows to
increase or decrease the bandwidth setting. The default setting
is 1000 Kbps (1 Mbps) AP1
NOTE: This is translated to a percentage of bandwidth at the
switch.
NOTE: If you are assigning any VLAN other than the default VLAN, ensure that the
VLAN is configured correctly on the all switches to which this access profile
will be applied before defining the access profile.
The VLAN that gets set for a user will override the statically configured VLAN,
as well as the
that if an
port is opened and the VLAN is set to the
auth-vid which may have been configured for that port. Note also
unauth-vid is set and the user is rejected by IDM for any reason, the
unauth-vid.
3-25
Page 94

Using Identity Driven Manager
Configuring Access Profiles
4. If you want the IDM QoS attributes to override the switch attributes, use
5. In the Ingress rate-limit field, click the drop-down arrow and select the
6. In the Egress rate-limit field, click the drop-down arrow and select the
the QoS drop-down list to select the quality of service or priority for
outbound traffic of users in groups associated with the access profile. QoS
ranges from lowest to highest, with Normal being the default.
maximum bandwidth or rate limit allocated for traffic from users assigned
to the Access Policy Group using the Access Profile. The default setting
is 1000 Kbps (1 Mbps), which is translated to a percentage of bandwidth
at the switch.
maximum bandwidth or rate limit allocated for traffic to users assigned
to the Access Policy Group using the Access Profile. The default setting
is 1000 Kbps (1 Mbps), which is translated to a percentage of bandwidth
at the switch.
7. To assign the Network Resources, click Edit... This launches the
Resource Assignment
Wizard.
Network
Figure 3-17. Network Resource Assignment Wizard
8. Click Next to continue to the Allowed Network Resources window.
3-26
Page 95
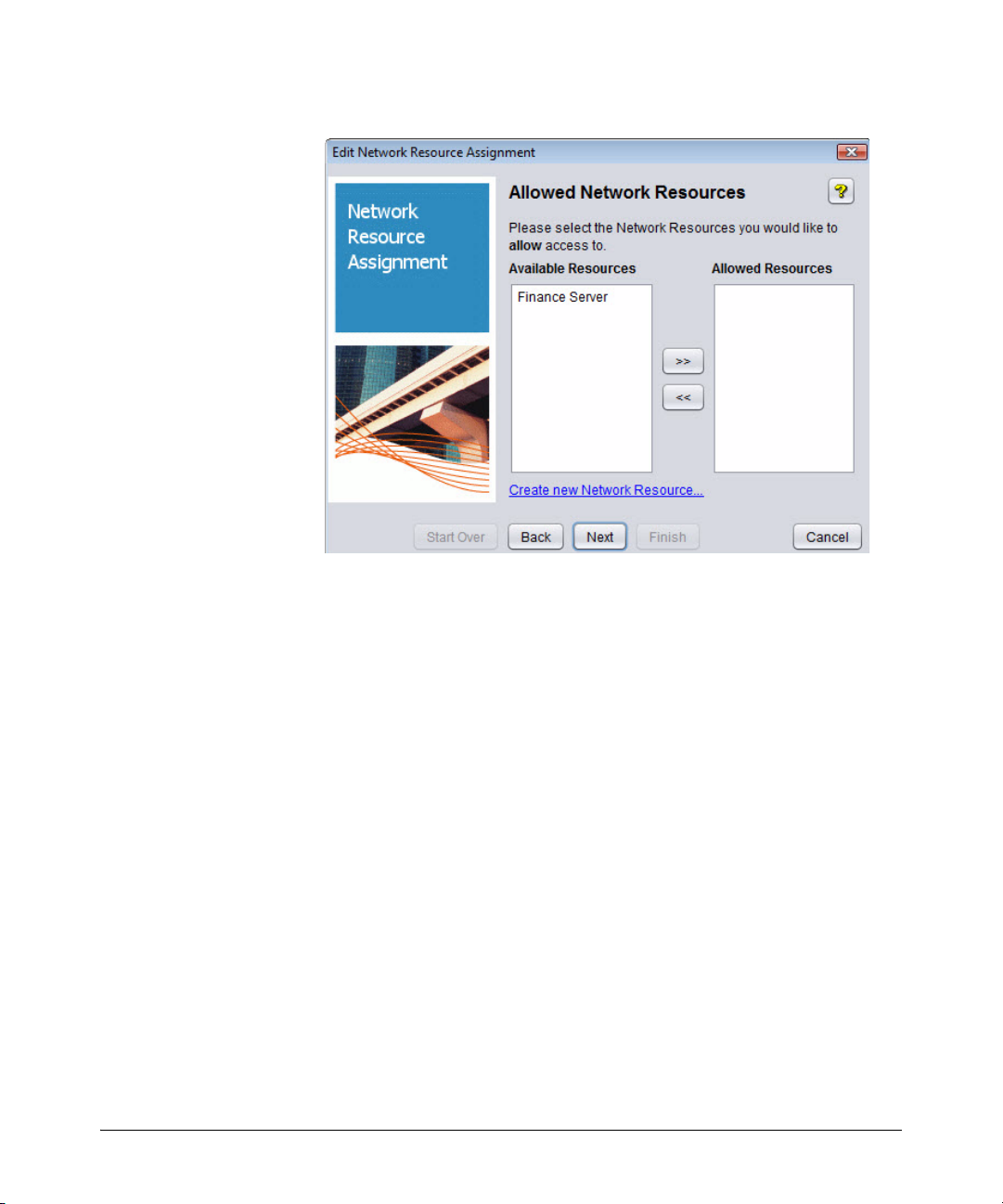
Using Identity Driven Manager
Configuring Access Profiles
Figure 3-18. Network Resource Assignment Wizard, Allowed Network Resources
9. To permit access to Network Resources:
a. Select the Resource in the
Available Resources list. Use shift-click to
select multiple resources.
b. Move the
Available Resource(s) to the Allowed Resources list
(click >>)
c. Click Next to continue to the Denied Resources window.
3-27
Page 96

Using Identity Driven Manager
Configuring Access Profiles
Figure 3-19. Network Resource Assignment Wizard, Denied Network Resources
10. To deny access to Network Resources:
a. Select the Resource in the
Available Resources list. Use shift-click to
select multiple resources.
b. Move the
Available Resource(s) to the Denied Resources list
(click >>)
c. Click Next to continue to the Priority Assignment window.
3-28
Page 97

Using Identity Driven Manager
Configuring Access Profiles
Figure 3-20. Network Resource Assignment Wizard, Priority Assignment
11. Set the priority (order of evaluation) for the Network Resources. To
change the priority, click the Resource in the list, then click Move down
or Move up. The first rule to match is the one that will be applied.
12. Click Next to continue to the Default Access window.
Figure 3-21. Network Resource Assignment Wizard, Default Access
3-29
Page 98

Using Identity Driven Manager
Configuring Access Profiles
13. Select the option to tell IDM what to do if there are no matches found in
14. Click Next to continue to the Resource Accounting window.
the network resource access rules.
3-30
Figure 3-22. Network Resource Assignment Wizard, Resource Accounting
15. Click the check box to enable the Accounting function (optional).
This enables tracking of hits on this resource on the switch or access
point. Use CLI on the switch to review the hits.
16. Click Next to continue to the Summary window.
Page 99

Using Identity Driven Manager
Configuring Access Profiles
Figure 3-23. Network Resource Assignment Wizard, Summary
17. Click Finish to save the Network Resource Assignments to the Access
Profile and close the wizard.
Click
Back to return to a previous window to change the assignment, or
Click
Cancel to close the wizard without saving the changes.
Click
Start Over to return to the start of the Network Assignment Wizard.
Modifying an Access Profile
To modify an existing Access Profile:
1. Click the
navigation tree to display the Access Profiles window.
2. Click on an Access Profile in the list to select it.
3. Click the
Profile
Profile, similar to the
4. Modify the access profile parameters, as described for creating a new
profile. Click the
ments using the wizard.
5. Click Ok to save your changes and close the window
Access Profiles node in the Identity Management Configuration
Modify Access Profile icon in the toolbar to display the Modify Access
window. The Modify window shows the details of the Access
Create a new Access Profile window.
Edit... button to change the Network Resource Assign-
3-31
Page 100

Using Identity Driven Manager
Configuring Access Profiles
The changes are displayed in the Access Profiles list.
NOTE: When modifying Access Profiles, make sure the appropriate VLANs are con-
figured on the network and at the switch. If you Modify the VLAN attribute in
an Access Profile that is currently used in an Access Policy Group rule, IDM
will check that the VLAN exists. If not, an error message is displayed.
Deleting an Access Profile
To remove an existing Access Profile:
1. Click the
Access Profiles node in the Identity Management Configuration
navigation tree to display the Access Profiles window.
2. Click on an Access Profile in the list to select it.
3. Click on the
Delete Access Profile icon in the toolbar to remove it.
The first time you use the Delete option, a warning pop-up is displayed.
Click Ok to continue, or
Cancel to stop the delete process.
NOTE: Before you modify or delete an Access Profile, make sure that your changes
will not adversely affect users in Access Policy Groups where the profile is
used.
3-32
 Loading...
Loading...