Page 1

FortiExtender 20D, 40D
QuickStart Guide
Page 2

July 17, 2019
Copyright © 2018 Fortinet, Inc. All rights reserved. Fortinet®, FortiGate®,
FortiCare® and FortiGuard®, and certain other marks are registered
trademarks of Fortinet, Inc., in the U.S. and other jurisdictions, and
other Fortinet names herein may also be registered and/or common
law trademarks of Fortinet. All other product or company names may
be trademarks of their respective owners. Performance and other
metrics contained herein were attained in internal lab tests under ideal
conditions, and actual performance and other results may vary. Network
variables, different network environments and other conditions may affect
performance results. Nothing herein represents any binding commitment by
Fortinet, and Fortinet disclaims all warranties, whether express or implied,
except to the extent Fortinet enters a binding written contract, signed by
Fortinet’s General Counsel, with a purchaser that expressly warrants that
the identified product will perform according to certain expressly-identified
performance metrics and, in such event, only the specific performance
metrics expressly identified in such binding written contract shall be
binding on Fortinet. For absolute clarity, any such warranty will be limited
to performance in the same ideal conditions as in Fortinet’s internal lab
tests. In no event does Fortinet make any commitment related to future
deliverables, features or development, and circumstances may change
such that any forward-looking statements herein are not accurate. Fortinet
disclaims in full any covenants, representations, and guarantees pursuant
hereto, whether express or implied. Fortinet reserves the right to change,
modify, transfer, or otherwise revise this publication without notice, and the
most current version of the publication shall be applicable.
Register for Support
Register your Fortinet product to receive:
• Technical Support
• New product features
• Protection from new threats
Vous devez enregistrer le produit pour recevoir:
• Support technique
• Nouvelles fonctionnalitées du produit
• Protection contre de nouvelles menaces
La reistrazione ti permette di usufruire di:
• Supporto Tecnico
• Nuove funzionalita
• Proteezione dalle ultime minaccce
Debe registrar el producto para recibir:
• Apoyo técnico
• Nuevas funcionalidades del producto
• Protección contra ataques
登録のお願い
本日、フォーティネット製品の登録をしてください。
登録すると次のメリットがあります。
テクニカルサポート • 新機能の追加 • 新しい脅威への防御
请马上注册
您的飞塔产品
您在注册以后才能得到技术支持、新产品特点信息、最新威胁防护
https://support.fortinet.com
Toll free: 1 866 648 4638
Phone: 1 408 486 7899
Fax: 1 408 235 7737
Email: register@fortinet.com
QuickStart Guide
Page 3
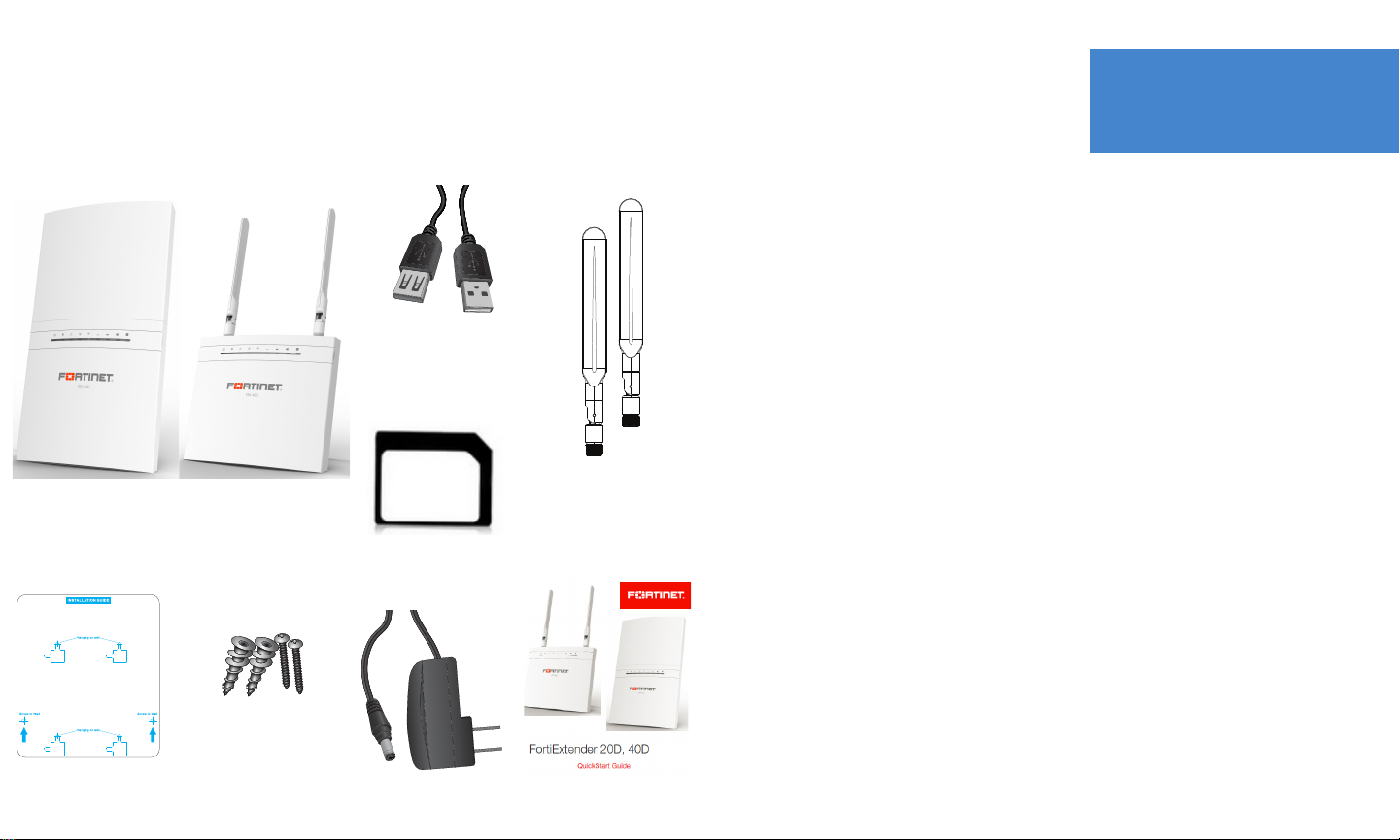
Box Includes
Device Guide
FEX-20D or FEX-40D
Mount Kit
1 Drill template
2 Self-tap anchors and long screws
2 Small assembly screws (FEX-20D)
USB Extension Cable
(FEX-20D only)
2 Micro/Nano to Mini
SIM card adapter sets
(FEX-40D only)
Power Adapter
(Optional Accessory)
Antennas
(FEX-40D only)
Initial Setup and Installation
1. Connect the device to the network.
2. Assemble the hardware.
3. Configure the device.
4. Mount the device.
QuickStart Guide
* Images are a representation of items in the box.
4
5
Page 4
1
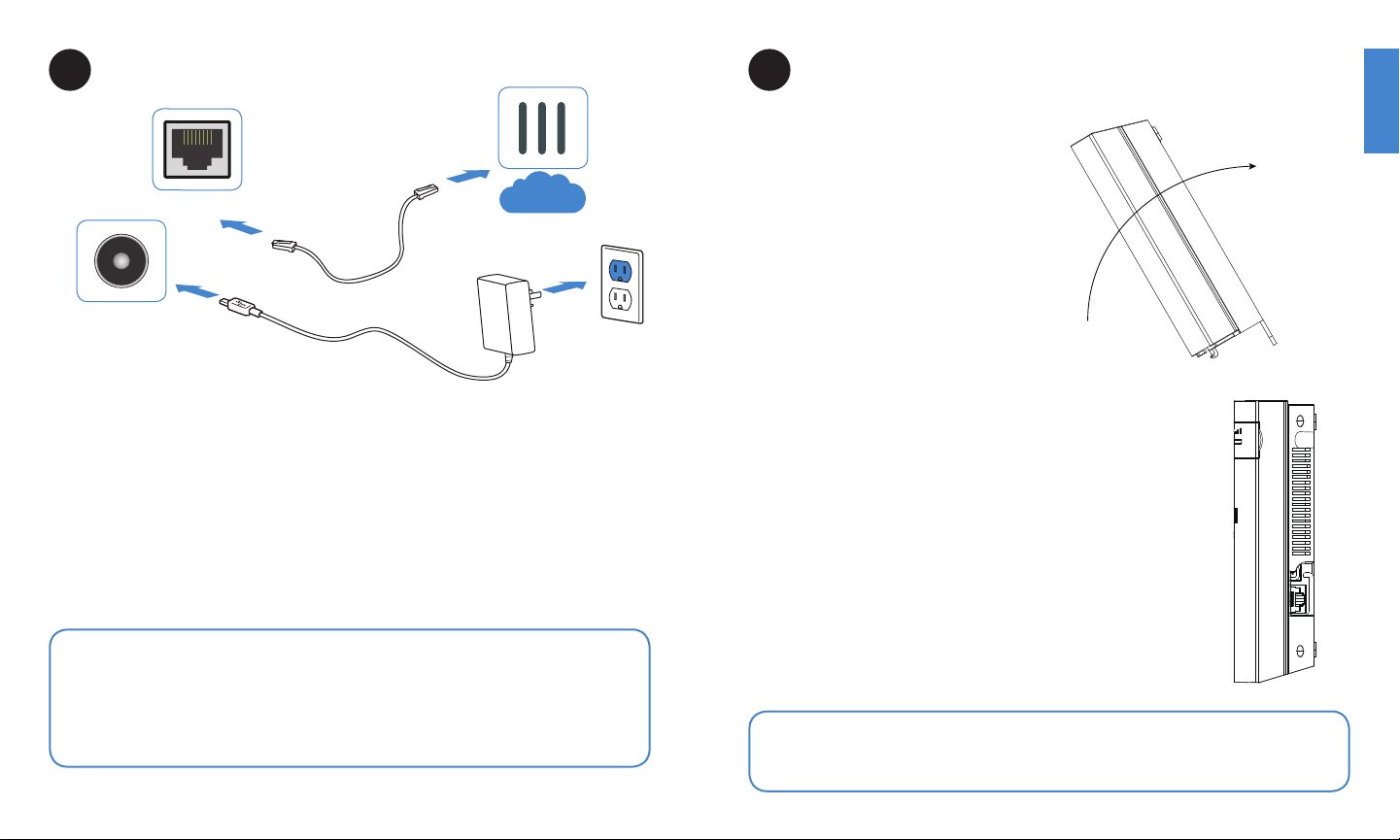
Basic Connections
LAN/POE
Optional Power
Connection
1. Connect the modem or SIM card:
FEX-20D: Insert your 3G/4G modem into the USB port on the device either directly or
using the provided USB extension adapter.
FEX-40D: Insert your 3G/4G LTE SIM card(s) into the ports labeled SIM1 and SIM2.
2. Insert the provided Ethernet cable into the LAN/POE port on the device.
3. Insert the other end of the Ethernet cable into the PoE LAN port on your FortiGate
appliance. FortiGate and FortiExtender must be on the same subnet.
4. Optionally, if you are not using PoE, connect the device to a power outlet using the
optional power adapter.
Internet
2
Assembly
FEX-20D
1. Insert a supported 3G/4G modem
into the USB port on the device either
directly or using the provided USB
extension adapter.
2. Attach the cover:
a. Insert the front tabs.
b. Align the front lip.
c. Tilt back and secure the cover with
two machine screws.
Warning: Adequate grounding must be provided to the PoE injector of the
FortiExtender unit if required, in compliance with your local electrical code or
regulations.
This device complies with IEEE 802.3af PoE specification. Do not use a PoE injector
that is not IEEE 802.3af compliant as it might damage your device.
6
Note: For the latest FortiExtender USB modem compatibility matrix please visit:
http://docs.fortinet.com/d/modem-compatibility-matrix
7
Page 5
FEX-40D
1. Remove the dust cover that protects the SIM ports and fits over the antenna posts.
2. Insert your 3G/4G LTE SIM card(s) into the SIM ports. A Micro/Nano to Mini SIM card
adapter is provided. Observe these guidelines:
• If you install one SIM card, it can be inserted in either SIM port.
• If you install two SIM cards, SIM1 is the primary port and SIM2 is the secondary.
3. Press the SIM card in slot 1 as primary and slot 2 for backup link. Press again to
remove.
4. Reattach the cover and then attach the antennas.
Step 1
3
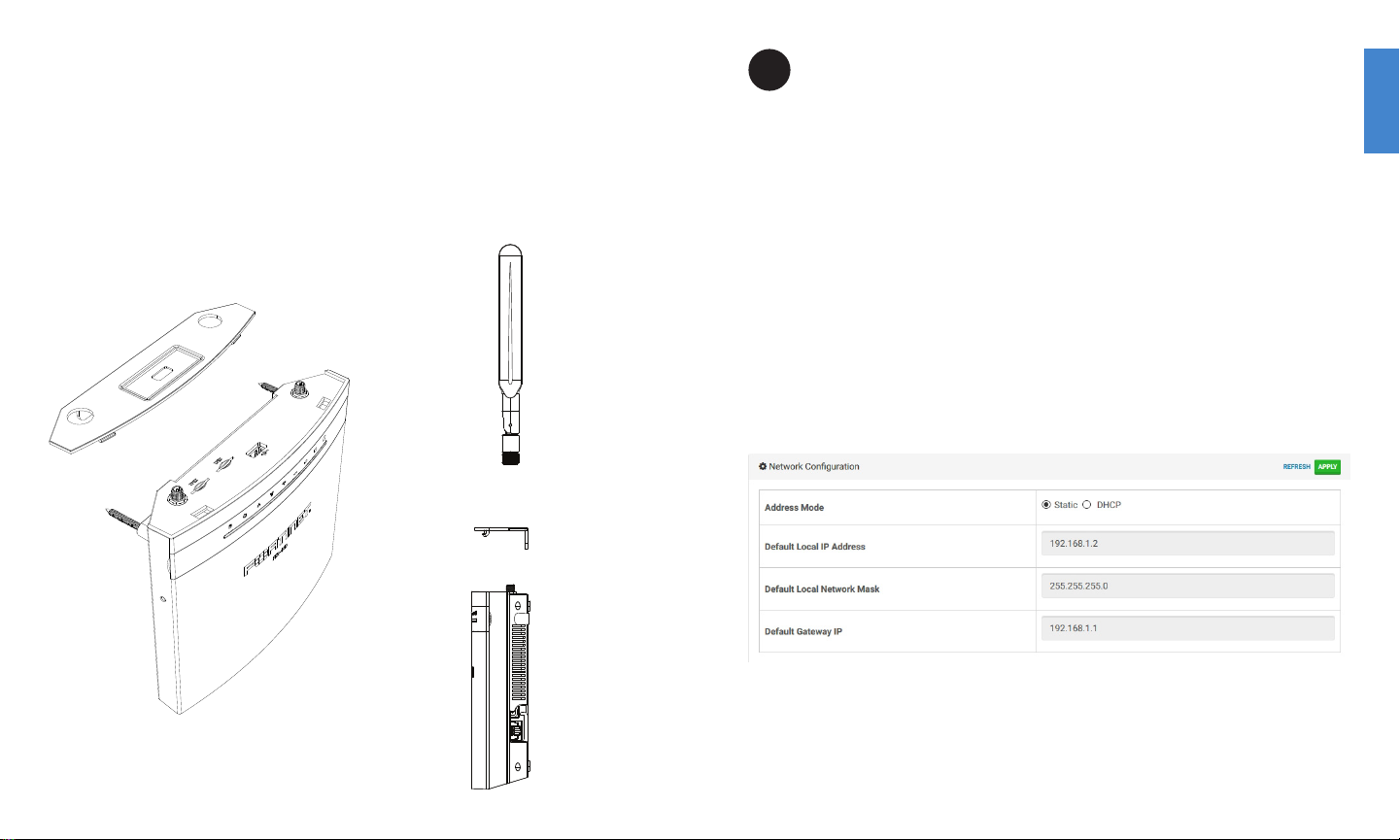
Configuration
Conguring an IP address
After you have connected the FortiExtender network interfaces, the device automatically
attempts to obtain an IP address from a DHCP server. If you do not use DHCP, you can
configure a static IP address.
To configure a static IP address:
1. Use a network cable to connect the FortiExtender WAN/POE port to the Ethernet port
of your laptop.
2. Configure the laptop to be on the same subnet as FortiExtender by changing the
laptop IP address to 192.168.1.1 and the netmask to 255.255.255.0.
3. Open the laptop web browser to the default FortiExtender web UI address
http://192.168.1.2.
4. In both the username and password fields, type admin and press Enter.
5. Go to Network Configuration.
6. For address mode, select Static.
7. Specify the IP address, netmask, and gateway; and then click APPLY.
Step 4
8 9
Page 6
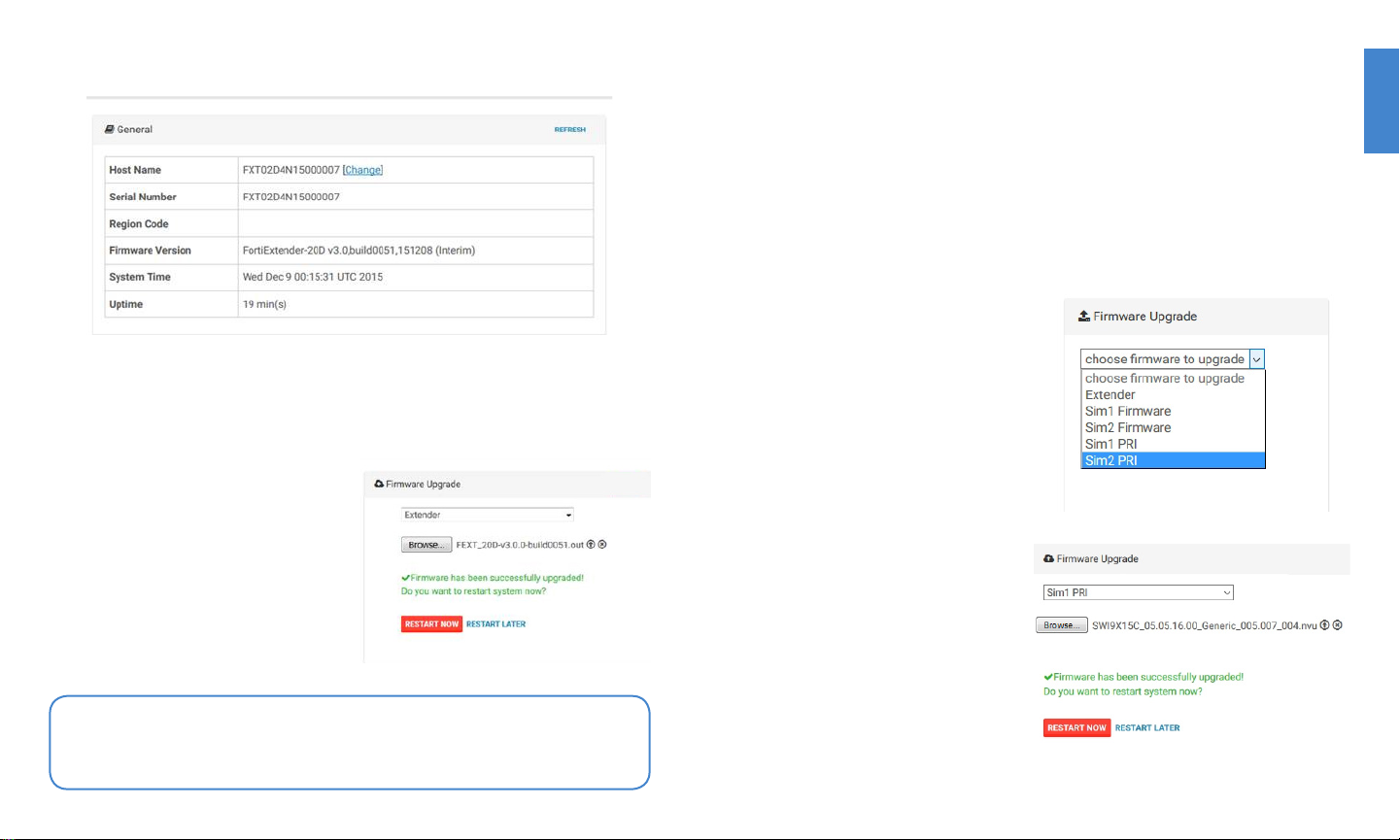
Updating FortiExtender rmware
You can find the version of the installed firmware on the FortiExtender web UI home page.
Fortinet periodically updates FortiExtender firmware. Check the Fortinet Customer Service
& Support website at https://support.fortinet.com to see if updates are available. If the
support site firmware download page shows a newer version than the one displayed on
the FortiExtender web UI home page, read the release notes and download the firmware.
To install and boot the new firmware:
1. Go to Firmware Upgrade.
2. Select Extender.
3. Use the controls to browse, select, and
upload the firmware file.
When you click the upload icon (up arrow),
the file is uploaded and the upgrade is
initiated. A green success message is
displayed when the process is complete.
4. Click RESTART NOW to boot the newly
installed firmware.
Updating SIM rmware (FEX-40D)
The firmware installed in the factory supports AT&T and Verizon 3G/4G LTE SIM cards.
If you have a SIM card for a different ISP, you can use the FortiExtender CLI or web UI to
update the firmware. Check the Fortinet Customer Service & Support website to see if a
firmware package is available for your ISP’s SIM card.
Before you begin:
You must download the appropriate firmware to your laptop. Depending on the package
you download and the instructions from your ISP, you might need to install a firmware file,
a carrier provisioning file (PRI), or both.
To install and boot the new firmware:
1. Go to Firmware Upgrade.
2. Select SIM1 Firmware or SIM2
Firmware to update the firmware for
respective slot.
3. Use the controls to browse, select,
and upload the firmware file.
When you click the upload icon (up
arrow), the file is uploaded and the
upgrade is initiated. A green success
message is displayed when the
process is complete.
4. Select SIM1 PRI or SIM2 PRI to
upload the carrier provisioning file for
the respective slot.
5. Click RESTART NOW to boot the
newly installed firmware.
Note: You can also use the CLI to upgrade FortiExtender firmware, or you can
upgrade a FortiGate-managed FortiExtender unit from the FortiGate management
web UI. For details, see the FortiExtender release notes.
10 11
Page 7

Managing the FortiExtender device with FortiGate
FortiExtender requires no user configuration in most networks. Once linked, FortiGate can
automatically control the FortiExtender device and its modem via a CAPWAP tunnel.
To manage the FortiExtender device with FortiGate:
1. By default, configuration options for FortiExtender are hidden in the FortiGate web UI.
Use the following commands to enable it:
cong system global
set fortiextender enable
set wireless-controller enable
end
2. Use the following commands to allow CAPWAP on the port to which the FortExtender
unit is connected:
cong system interface
edit [port]
set allowaccess capwap
end
3. In the FortiGate web UI, go to System > Network > FortiExtender to display the status
and configuration page.
4. In the Administrative Status row, click Authorize.
5. After the device has been authorized, you can use FortiGate to monitor its status and
configure its settings. For details, see the FortiOS Handbook.
4
Mounting
The unit is designed for placement near a window (desk or wall mount) to achieve the
best 3G/4G signal.
Wall mounting holes
(long screws).
Mounting holes
can be used with the
desk mount stand or
wall mounting
(bear claw screws).
To use the stand
1. Attach the stand bracket to the mounting holes on the back of the FortiExtender unit.
2. Set the unit upright.
12 13
Page 8

To hang on a wall with screws
1. Tape the drill template sticker to the wall in the desired location.
2. Use the template to mark and drill the pilot
holes.
3. Insert the anchors into the holes.
4. Insert the screws into the anchors and
tighten, but not all the way—leave around
a 5mm gap between the screw head and
the wall.
5. Position the device so the
mounting holes line up with the
screws.
6. Place the mounting slots over the
screws and slide the device down
until the screws fit into slots.
To screw to a wall with long screws
1. Tape the drill template sticker to the wall in the desired location.
2. Use the template to mark and drill the pilot holes.
3. Insert the anchors into the holes.
4. Snap off the plastic cover over the
LEDs on the front to reveal the long
screw holes.
5. Insert the long screws through the
device from front to back.
Tip: Use bear claw screws. The screw heads of bear claw screws have a built-in
gap that fits well with the hanging holes. You can purchase bear claw screws from a
local or online hardware store.
14 15
Page 9

6. Insert the long screws into
the anchors on the wall and
tighten.
7. Replace the plastic cover over
the LEDs on the front.
1
1. USB
USB-A port for 3G/4G
modem.
2. Reset Button
Press and hold to reset
the system to the factory
defaults
3. Power
12V DC, 2A power
adapter connection.
Optional.
4. LAN/POE
RJ-45 port, 10/100/1000
Ethernet, PoE-PD
enabled, 802.3af/at
compliant, (15.4W).
5. Console
RJ-45 port.
2
3
4
5
FEX-20D
16 17
Page 10

1. SIM1, SIM2
PCIe ports for primary and
secondary 3G/4G LTE SIM cards.
2. USB
Reserved for future use.
3. Reset Button
Press and hold to reset
the system to the factory
1
2
3
4
defaults
4. Power
12V DC, 2A power
adapter connection.
Optional.
5. LAN/POE
RJ-45 port, 10/100/1000
Ethernet, PoE-PD
enabled, 802.3af/at
compliant, (15.4W).
Status
On: System running
Flashing: System booting up
Off: System error
Power
On
Off
LAN
On: Connected
Flashing: Activity
Off: Not connected
LTE/WiFI
On: Connected
Flashing: Activity
Off: Not connected
Signal Strength
1 LED: Weak signal
2 or 3 LEDs: Moderate signal
4 LEDs: Strong signal
5
6. Console
RJ-45 port
6
FEX-40D
18 19
Page 11

Cautions and Warnings (FEX-20D)
Environmental specications
Ambient operating temperature: 40°C
Refer to specific Product Model Data Sheet for Environmental
Specifications (Operating Temperature, Storage Temperature, Humidity,
and Altitude).
Référez à la Fiche Technique de ce produit pour les caractéristiques
environnementales (Température de fonctionnement, température de
stockage, humidité et l’altitude).
Safety
Caution: This equipment is to be used in a Network Environment 0 per
IECTR 62101. This product is connected only to PoE networks without
routing to the outside plant.
Attention: Ce matériel doit être utilisé dans un Environnement Réseau
0 par IECTR 62101. Ce produit est uniquement connecté aux réseaux
PoE sans installation externe de routage.
This product is intended to be supplied by a Listed Direct Plug-In Power
Unit marked LPS or Class 2 and rated 12 Vdc, 2 A or by 48 Vdc from
PoE source.
Le produit doit être alimenté par un bloc d’alimentation à courant
continu homologué UL de 12 Vdc, 2 A nominal marqué LPS ou Class 2
ou par une source d’alimentation par Ethernet de 48 Vdc (PoE).
Regulatory Notices (FEX-20D)
Federal Communication Commission (FCC) – USA
This device complies with Part 15 of FCC Rules. Operation is subject to
the following two conditions:
(1) this device may not cause harmful interference, and
(2) this device must accept any interference received; including
interference that may cause undesired operation.
This equipment has been tested and found to comply with the limits for
a Class B digital device, pursuant to Part 15 of the FCC Rules. These
limits are designed to provide reasonable protection against harmful
interference in residential installation. This equipment generates, uses,
and can radiate radio frequency energy, and if it is not installed and
used in accordance with the instruction manual, it may cause harmful
interference to radio communications. However, there is no guarantee
that interference will not occur in a particular installation.
If this equipment does cause harmful interference to radio or television
reception, which can be determined by turning the equipment off and
on, the user is encouraged to try to correct the interference by one or
more of the following measures:
Reorient or relocate the receiving antenna.
Increase the separation between the equipment and receiver.
Connect the equipment into an outlet on a circuit different from
that to which the receiver is connected.
Consult the dealer or an experienced radio/TV technician
for help.
WARNING: Any changes or modifications to this unit not expressly
approved by the party responsible for compliance could void the user’s
authority to operate the equipment
Industry Canada Equipment Standard for Digital
Equipment (ICES) – Canada
CAN ICES-3 (B) / NMB-3 (B)
European Conformity (CE) – EU
This is a Class B product. In a domestic environment, this product may
cause radio interference, in which case the user may be required to take
adequate measures.
Cautions and Warnings (FEX-40D)
Environmental specications
Ambient operating temperature: 40°C
Refer to specific Product Model Data Sheet for Environmental
Specifications (Operating Temperature, Storage Temperature, Humidity,
and Altitude).
Référez à la Fiche Technique de ce produit pour les caractéristiques
environnementales (Température de fonctionnement, température de
stockage, humidité et l’altitude).
Safety
Caution: This equipment is to be used in a Network Environment 0 per
IECTR 62101. This product is connected only to PoE networks without
routing to the outside plant.
Attention: Ce matériel doit être utilisé dans un Environnement Réseau
0 par IECTR 62101. Ce produit est uniquement connecté aux réseaux
PoE sans installation externe de routage.
This product is intended to be supplied by a Listed Direct Plug-In Power
Unit marked LPS or Class 2 and rated 12 Vdc, 2 A or by 48 Vdc from
PoE source.
Le produit doit être alimenté par un bloc d’alimentation à courant
continu homologué UL de 12 Vdc, 2 A nominal marqué LPS ou Class 2
ou par une source d’alimentation par Ethernet de 48 Vdc (PoE).
Regulatory Notices (FEX-40D)
Federal Communication Commission (FCC) – USA
This device complies with Part 15 of FCC Rules. Operation is subject to
the following two conditions:
(1) this device may not cause harmful interference, and
(2) this device must accept any interference received; including
interference that may cause undesired operation.
This equipment has been tested and found to comply with the limits for
a Class B digital device, pursuant to Part 15 of the FCC Rules. These
limits are designed to provide reasonable protection against harmful
interference in residential installation. This equipment generates, uses,
and can radiate radio frequency energy, and if it is not installed and
used in accordance with the instruction manual, it may cause harmful
interference to radio communications. However, there is no guarantee
that interference will not occur in a particular installation.
If this equipment does cause harmful interference to radio or television
reception, which can be determined by turning the equipment off and
on, the user is encouraged to try to correct the interference by one or
more of the following measures:
Reorient or relocate the receiving antenna.
Increase the separation between the equipment and receiver.
Connect the equipment into an outlet on a circuit different from
that to which the receiver is connected.
Consult the dealer or an experienced radio/TV technician
for help.
WARNING: Any changes or modifications to this unit not expressly
approved by the party responsible for compliance could void the user’s
authority to operate the equipment
This equipment complies with FCC radiation exposure limits set forth
for an uncontrolled environment. This equipment should be installed
and operated with minimum distance 20cm between the radiator and
your body. This transmitter must not be co-located or operating in
conjunction with any other antenna or transmitter.
Industry Canada Equipment Standard for Digital
Equipment (ICES) – Canada
CAN ICES-3 (B) / NMB-3 (B)
Industry Canada (IC RSS) – Canada
This device complies with Industry Canada licence-exempt RSS
standard(s). Operation is subject to the following two conditions: (1) this
device may not cause interference, and (2) this device must accept any
interference, including interference that may cause undesired operation
of the device.
Le présent appareil est conforme aux CNR d’Industrie Canada
applicables aux appareils radio exempts de licence. L’exploitation est
autorisée aux deux conditions suivantes : (1) l’appareil ne doit pas
produire de brouillage, et (2) l’utilisateur de l’appareil doit accepter tout
brouillage radioélectrique subi, même si le brouillage est susceptible
d’en compromettre le fonctionnement.
This equipment complies with IC radiation exposure limits set forth
for an uncontrolled environment. This equipment should be installed
and operated with minimum distance 20cm between the radiator &
your body.
Page 12

Cet équipement est conforme aux limites d’exposition aux
rayonnements IC établies pour un environnement non contrôlé. Cet
équipement doit être installé et utilisé avec un minimum de 20cm de
distance entre la source de rayonnement et votre corps.
European Conformity (CE) – EU
This is a Class B product. In a domestic environment, this product may
cause radio interference, in which case the user may be required to take
adequate measures.
Simplied EU Declaration of Conformity
This declaration is only valid for Fortinet products (including,
combinations of software, firmware and hardware) provided by Fortinet
or Fortinet’s authorized partners to the end-customers directly for use
within the EU or countries that have implemented the EU Directives
and/or spectrum regulation. Any Fortinet products not obtained directly
from Fortinet or Fortinet’s authorized partners may not comply with EU
Directives and Fortinet makes no assurances for such products.
Български
Този продукт е в съответствие с Директива 2014/53/EC.
Česky
Tento produkt je v souladu se směrnicí 2014/53/EU.
Dansk
Dette produkt er i overensstemmelse med direktiv 2014/53/EU.
Deutsch
Dieses Produkt entspricht der Richtlinie 2014/53/EU.
Eesti
See toode vastab direktiivile 2014/53/EL.
English
This product is in compliance with Directive 2014/53/EU.
Español
Este producto cumple con la Directiva 2014/53/UE.
Ελληνική
Το προϊόν αυτό συμμορφώνεται με την Οδηγία 2014/53/EE.
Français
Ce produit est conforme à la Directive 2014/53/UE.
Hrvatski
Ovaj proizvod je u skladu s Direktivom 2014/53/EU.
Italiano
Questo prodotto è conforme alla Direttiva 2014/53/EU.
Latviski
Questo prodotto è conforme alla Direttiva 2014/53/EU.
Lietuvių
Šis gaminys atitinka direktyvą 2014/53/ES.
Malti
Dan il-prodott huwa konformi mad-Direttiva 2014/53/UE.
Magyar
Ez a termék megfelel a 2014/53/EU irányelvnek.
Nederlands
Dit product is in overeenstemming met Richtlijn 2014/53/EU.
Norsk
Dette produktet er i samsvar med direktiv 2014/53/EU.
Polski
Ten produkt jest zgodny z dyrektywą 2014/53/UE.
Português
Este produto está em conformidade com a Diretiva 2014/53/UE.
Rumunski
Acest produs este în conformitate cu Directiva 2014/53/UE.
Slovensky
Tento produkt je v súlade so smernicou 2014/53/EÚ.
Slovensko
Ta izdelek je v skladu z Direktivo 2014/53/EU.
Suomi
Tämä tuote on direktiivin 2014/53/EU mukainen.
Svenska
Denna produkt överensstämmer med direktiv 2014/53/EU.
Note: The full declaration of conformity for this product is available in
the link below:
https://site.fortinet.com/ProductRegulatory/EU
Fortinet Product License Agreement / EULA and Warranty Terms
Trademarks and Copyright Statement
Fortinet®, FortiGate®, and FortiGuard® are registered trademarks of Fortinet, Inc., and other Fortinet names may also be trademarks, registered or otherwise, of Fortinet.
All other product or company names may be trademarks of their respective owners. Copyright © 2016 Fortinet, Inc., All Rights reserved. Contents and terms are subject
to change by Fortinet without prior notice. No part of this publication may be reproduced in any form or by any means or used to make any derivative such as translation,
transformation, or adaptation without permission from Fortinet, Inc., as stipulated by the United States Copyright Act of 1976.
Product License Agreement
The parties to this agreement are you, the end customer, and either (i) where you have purchased your Product within the Americas, Fortinet, Inc., or (ii) where you have purchased your Product outside of the Americas, Fortinet Singapore Private Limited (each referred to herein as “Fortinet”). CAREFULLY READ THE FOLLOWING LEGAL AGREEMENT
(THE OR THIS “AGREEMENT” OR “EULA”). USE OR INSTALLATION OF FORTINET PRODUCT(S) AND ANY UPDATES THERETO, INCLUDING HARDWARE APPLIANCE PRODUCTS,
SOFTWARE AND FIRMWARE INCLUDED THEREIN BY FORTINET, AND STAND-ALONE SOFTWARE PRODUCTS SOLD BY FORTINET (TOGETHER, THE “PRODUCTS”) CONSTITUTES
ACCEPTANCE BY YOU OF THE TERMS IN THIS AGREEMENT, AS AMENDED OR UPDATED FROM TIME TO TIME IN FORTINET’S DISCRETION BY FORTINET PUBLISHING AN
AMENDED OR UPDATED VERSION. FORTINET SHALL NOT BE BOUND BY ANY ADDITIONAL AND/OR CONFLICTING PROVISIONS IN ANY ORDER, RELEASE, ACCEPTANCE OR
OTHER WRITTEN CORRESPONDENCE OR OTHER WRITTEN OR VERBAL COMMUNICATION UNLESS EXPRESSLY AGREED TO IN A WRITING SIGNED BY THE GENERAL COUNSEL OF
FORTINET. IF YOU DO NOT AGREE TO ALL OF THE TERMS OF THIS AGREEMENT, DO NOT START THE INSTALLATION PROCESS OR USE THE PRODUCTS. IF YOU DO NOT AGREE TO
THE TERMS OF THIS AGREEMENT, YOU SHOULD IMMEDIATELY, AND IN NO EVENT LATER THAN FIVE (5) CALENDAR DAYS AFTER YOUR RECEIPT OF THE PRODUCT IMMEDIATELY
NOTIFY THE FORTINET LEGAL TEAM IN WRITING AT LEGAL@FORTINET.COM OF REQUESTED CHANGES TO THIS AGREEMENT.
1. License Grant.
This is a license, not a sales agreement, between you and Fortinet. The term “Software”, as used throughout this Agreement, includes all Fortinet and third party rmware
and software provided to you with, or incorporated into, Fortinet appliances and any stand-alone software provided to you by Fortinet, with the exception of any open source
software contained in Fortinet’s Products which is discussed in detail in section 15 below, and the term “Software” includes any accompanying documentation, any updates
and enhancements of the software or rmware provided to you by Fortinet, at its option. Fortinet grants to you a non-transferable (except as provided in section 5 (“Transfer”)
and section 15 (“Open Source Software”) below), non-exclusive, revocable (in the event of your failure to comply with these terms or in the event Fortinet is not properly paid
for the applicable Product) license to use the Software solely for your internal business purposes (provided, if a substantial portion of your business is to provide managed
service provider services to your end-customers, you may use the Software embedded in FortiGate and supporting hardware appliances to provide those services, subject to
the other restrictions in this Agreement), in accordance with the terms set forth in this Agreement and subject to any further restrictions in Fortinet documentation, and solely
on the Fortinet appliance, or, in the case of blades, CPUs or databases, on the single blade, CPU or database on which Fortinet installed the Software or, for stand-alone Software, solely on a single computer running a validly licensed copy of the operating system for which the Software was designed unless and except set forth in the published
documentation otherwise, or, in the case of blades, CPUs or databases, on a single blade, CPU or database. For clarity, notwithstanding anything to the contrary, all licenses of
Software to be installed on blades, CPUs or databases are licensed on a per single blade, solely for one blade and not for multiple blades that may be installed in a chassis, per
single CPU or per single database basis, as applicable. The Software is “in use” on any Fortinet appliances when it is loaded into temporary memory (i.e. RAM). You agree that,
except for the limited, specic license rights granted in this section 1, you receive no license rights to the Software.
2. Limitation on Use.
You may not attempt to, and, if you are a corporation, you are responsible to prevent your employees and contractors from attempting to, (a) modify, translate, reverse
engineer, decompile, disassemble, create derivative works based on, sublicense, or distribute the Software; (b) rent or lease any rights in the Software in any form to any third
party or make the Software available or accessible to third parties in any other manner; (c) except as provided in section 5, transfer assign or sublicense right to any other
person or entity, (d) remove any proprietary notice, labels, or marks on the Software, Products, and containers, or (e) use the Software for third-party training, commercial
time-sharing or service bureau use or use the Software to provide services to third parties except as expressly set forth in this Agreement.
3. Proprietary Rights.
All rights, title, interest, and all copyrights to the Software and any copy made thereof by you and to any Product remain with Fortinet. You acknowledge that no title to the
intellectual property in the Software or other Products is transferred to you and you will not acquire any rights to the Software or other Products except for the specic license
as expressly set forth in section 1 (“License Grant”) above. You expressly agree and acknowledge that Fortinet owns and shall retain all intellectual property rights in and
to, and you have no intellectual property rights in and to, the Products and the Software other than the License Grant. You agree to keep condential all Fortinet condential
information and only to use such information for the purposes for which Fortinet disclosed it.
4. Term and Termination.
Except for evaluation and beta licenses or other licenses, such as subscription licenses, where the term of the license is limited per the evaluation/beta or other agreement,
in the ordering documents or otherwise, the term of the license is for the duration of Fortinet’s copyright in the Software. Fortinet may terminate this Agreement, and the
licenses and other rights herein, immediately without notice if you breach or fail to comply with any of the terms and conditions of this Agreement or for other reasons as
stated in Fortinet’s other documentation. You agree that, upon such termination, you will cease using the Software and any Product and either destroy all copies of the Fortinet
documentation or return all materials to Fortinet.
5. Transfer.
If you are a Fortinet contracted and authorized reseller or distributor of Products, you may transfer (not rent or lease unless specically agreed to in writing by Fortinet) the
Software to one end user on a permanent basis, provided that: (i) you ensure that your customer and the end user receives a copy of this Agreement, is bound by its terms
and conditions, and, by selling the Product or Software, you hereby agree to enforce the terms in this Agreement against such end user, (ii) you at all times comply with all
applicable United States export control laws and regulations, and (iii) you agree to refund any fees paid to you by an end user who purchased Product(s) from you but does not
agree to the terms contained in this Agreement and therefore wishes to return the Product(s) as provided for in this Agreement. Further, if you are a non-authorized reseller
of Products, you are not authorized to sell Product(s) or Software, but, regardless, by selling Product(s) or Software, you hereby agree you are bound by the restrictions and
obligations herein and are bound to: (i) ensure that your customer and the end user receive a copy of this Agreement and are bound in full by all restrictions and obligations
herein (ii) enforce the restrictions and obligations in this Agreement against such customer and/or end user, (iii) comply with all applicable United States export control laws
and regulations and all other applicable laws, and (iv) refund any fees paid to you by a customer and/or end user who purchased Product(s) from you but does not agree to
the restrictions and obligations contained in this Agreement and therefore wishes to return the Product(s) as provided for in this Agreement. Notwithstanding anything to the
contrary, distributors, resellers and other Fortinet partners (a) are not agents of Fortinet and (b) are not authorized to bind Fortinet in any way.
6. Limited Warranty.
Fortinet provides this limited warranty for its product only to the single end-user person or entity that originally purchased the Product from Fortinet or its authorized reseller or
distributor and paid for such Product. The warranty is only valid for Products which are properly registered on Fortinet’s Support Website, https://support.fortinet.com, or such
other website as provided by Fortinet, or for which the warranty otherwise starts according to Fortinet’s policies. The warranty periods discussed below will start according to
Page 13

Fortinet’s policies posted at http://www.fortinet.com/aboutus/legal.html or such other website as provided by Fortinet. It is the Fortinet distributor’s and reseller’s responsibility
to make clear to the end user the date the product was originally shipped from Fortinet, and it is the end user’s responsibility to understand the original ship date from the
party from which the end user purchased the product. All warranty claims must be submitted in writing to Fortinet before the expiration of the warranty term or such claims
are waived in full. Fortinet provides no warranty for any beta, donation or evaluation Products, for any spare parts not purchased directly from Fortinet by the end-user, for
any accessories, or for any stand-alone software. Fortinet warrants that the hardware portion of the Products, including spare parts unless noted otherwise (“Hardware”) will
be free from material defects in workmanship as compared to the functional specications for the period set forth as follows and applicable to the Product type (“Hardware
Warranty Period”): a three hundred sixty-ve (365) day limited warranty for the Hardware excluding spare parts, power supplies, and accessories (provided, solely with respect
to FortiAP and Meru AP indoor Wi-Fi access point Hardware appliance products and FortiSwitch Hardware appliance products other than the FortiSwitch-5000 series (for both
excluding spare parts, power supplies, and accessories), the warranty herein shall last from the start of the warranty period as discussed above until ve (5) years following
the product announced end-of-life date), and, for spare parts, power supplies, and accessories, solely a ninety (90) days limited warranty. Fortinet’s sole obligation shall be
to repair or offer replacement Hardware for the defective Hardware at no charge to the original owner. This obligation is exclusive of transport fees, labor, de-installation,
installation, reconguration, or return shipment and handling fees and costs, and Fortinet shall have no obligation related thereto. Such repair or replacement will be rendered
by Fortinet at an authorized Fortinet service facility as determined by Fortinet. The replacement Hardware need not be new or of an identical make, model, or part; Fortinet
may, in its discretion, replace the defective Hardware (or any part thereof) with any reconditioned Product that Fortinet reasonably determines is substantially equivalent (or
superior) in all material respects to the defective Hardware. The Hardware Warranty Period for the repaired or replacement Hardware shall be for the greater of the remaining
Hardware Warranty Period or ninety days from the delivery of the repaired or replacement Hardware. If Fortinet determines in its reasonable discretion that a material defect
is incapable of correction or that it is not practical to repair or replace defective Hardware, the price paid by the original purchaser for the defective Hardware will be refunded
by Fortinet upon return to Fortinet of the defective Hardware. All Hardware (or part thereof) that is replaced by Fortinet, or for which the purchase price is refunded, shall
become the property of Fortinet upon replacement or refund. Fortinet warrants that the software as initially shipped with the Hardware Products will substantially conform to
Fortinet’s then current functional specications for the Software, as set forth in the applicable documentation for a period of ninety (90) days (“Software Warranty Period”), if
the Software is properly installed on approved Hardware and operated as contemplated in its documentation. Fortinet’s sole obligation shall be to repair or offer replacement
Software for the non-conforming Software with software that substantially conforms to Fortinet’s functional specications. This obligation is exclusive of transport fees, labor,
de-installation, installation, reconguration, or return shipment and handling fees and costs, and Fortinet shall have no obligation related thereto. Except as otherwise agreed
by Fortinet in writing, the warranty replacement Software is provided only to the original licensee, and is subject to the terms and conditions of the license granted by Fortinet
for the Software. The Software Warranty Period shall extend for an additional ninety (90) days after any warranty replacement software is delivered. If Fortinet determines in
its reasonable discretion that a material non-conformance is incapable of correction or that it is not practical to repair or replace the non-conforming Software, the price paid
by the original licensee for the non-conforming Software will be refunded by Fortinet; provided that the non-conforming Software (and all copies thereof) is rst returned to
Fortinet. The license granted respecting any Software for which a refund is given automatically terminates immediately upon refund. For purpose of the above hardware and
software warranties, the term “functional specications” means solely those specications authorized and published by Fortinet that expressly state in such specications
that they are the functional specications referred to in this section 6 of this Agreement, and, in the event no such specications are provided to you with the Software or
Hardware, there shall be no warranty on such Software.
7. Disclaimer of Other Warranties and Restrictions.
EXCEPT FOR THE LIMITED WARRANTY SPECIFIED IN SECTION 6 ABOVE, THE PRODUCT AND SOFTWARE ARE PROVIDED “AS-IS” WITHOUT ANY WARRANTY OF ANY KIND INCLUDING, WITHOUT LIMITATION, ANY IMPLIED WARRANTY, IMPLIED OR EXPRESS WARRANTY OF MERCHANTABILITY, OR WARRANTY FOR FITNESS FOR A PARTICULAR PURPOSE
AND NON-INFRINGEMENT. IF ANY IMPLIED WARRANTY CANNOT BE DISCLAIMED IN ANY TERRITORY WHERE A PRODUCT IS SOLD, THE DURATION OF SUCH IMPLIED WARRANTY
SHALL BE LIMITED TO NINETY (90) DAYS FROM THE DATE OF ORIGINAL SHIPMENT FROM FORTINET. EXCEPT AS EXPRESSLY COVERED UNDER THE LIMITED WARRANTY
PROVIDED HEREIN, THE ENTIRE RISK AS TO THE QUALITY, SELECTION AND PERFORMANCE OF THE PRODUCT IS WITH THE PURCHASER OF THE PRODUCT. NOTWITHSTANDING
ANYTHING TO THE CONTRARY, THE HARDWARE WARRANTY PERIOD DISCUSSED ABOVE DOES NOT APPLY TO CERTAIN FORTINET PRODUCTS, INCLUDING FORTITOKEN WHICH
HAS A 365 DAY WARRANTY FROM THE DATE OF SHIPMENT FROM FORTINET’S FACILITIES, AND THE SOFTWARE WARRANTY DOES NOT APPLY TO CERTAIN FORTINET PRODUCTS, INCLUDING FORTIGATE-ONE AND VDOM SOFTWARE. YOU HEREBY ACKNOWLEDGE AND AGREE THAT NO VENDOR CAN ASSURE COMPLETE SECURITY AND NOTHING
HEREIN OR ELSEWHERE SHALL BE DEEMED TO IMPLY A SECURITY GUARANTEE OR ASSURANCE.
The warranty in Section 6 above does not apply if the Software, Product or any other equipment upon which the Software is authorized to be used (a) has been altered, except
by Fortinet or its authorized representative, (b) has not been installed, operated, repaired, updated to the latest version, or maintained in accordance with instructions supplied
by Fortinet, (c) has been subjected to abnormal physical or electrical stress, misuse, negligence, or accident; (d) is licensed for beta, evaluation, donation, testing or demonstration purposes or for which Fortinet does not charge a purchase price or license fee. In the case of beta, testing, evaluation, donation or free Software or Product, the end
user acknowledges and agrees that such Software or Product may contain bugs or errors and could cause system failures, data loss and other issues, and the end user agrees
that such Software or Product is provided “as-is” without any warranty whatsoever, and Fortinet disclaims any warranty or liability whatsoever. An end user’s use of evaluation
or beta Software or Product is limited to thirty (30) days from original shipment unless otherwise agreed in writing by Fortinet.
8. Governing Law.
Any disputes arising out of this Agreement or Fortinet’s limited warranty shall be governed by the laws of the state of California, without regard to the conict of laws
principles. In the event of any disputes arising out of this Agreement or Fortinet’s limited warranty, the parties submit to the jurisdiction of the federal and state courts located
in Santa Clara County, California, as applicable.
9. Limitation of Liability.
TO THE MAXIMUM EXTENT PERMITTED BY LAW AND NOTWITHSTANDING ANYTHING TO THE CONTRARY, FORTINET IS NOT LIABLE UNDER ANY CONTRACT, NEGLIGENCE,
TORT, STRICT LIABILITY, INFRINGEMENT OR OTHER LEGAL OR EQUITABLE THEORY FOR ANY LOSS OF USE OF THE PRODUCT OR SERVICE OR ANY DAMAGES OF ANY KIND
WHATSOEVER, WHETHER DIRECT, SPECIAL, INCIDENTAL OR CONSEQUENTIAL (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF GOODWILL, LOSS OF PROFIT, LOSS
OF OPPORTUNITY, LOSS OR DAMAGE RELATED TO USE OF THE PRODUCT OR SERVICE IN CONNECTION WITH HIGH RISK ACTIVITIES, DE-INSTALLATION AND INSTALLATION
FEES AND COSTS, DAMAGE TO PERSONAL OR REAL PROPERTY, WORK STOPPAGE, COMPUTER FAILURE OR MALFUNCTION, COMPUTER SECURITY BREACH, COMPUTER VIRUS
INFECTION, LOSS OF INFORMATION OR DATA CONTAINED IN, STORED ON, OR INTEGRATED WITH ANY PRODUCT INCLUDING ANY PRODUCT RETURNED TO FORTINET FOR
WARRANTY SERVICE) RESULTING FROM THE USE OF THE PRODUCT, RELATING TO WARRANTY SERVICE, OR ARISING OUT OF ANY BREACH OF THE LIMITED WARRANTY IN
SECTION 6 ABOVE, EVEN IF FORTINET HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. THE SOLE REMEDY FOR A BREACH OF THE LIMITED WARRANTY IS REPAIR,
REPLACEMENT OR REFUND OF THE DEFECTIVE OR NON-CONFORMING PRODUCT AS SPECIFICALLY STATED IN SECTION 6 ABOVE.
10. Import / Export Requirements; FCPA Compliance.
You are advised that the Products may be subject to the United States Export Administration Regulations and other import and export laws; diversion contrary to United States
law and regulation is prohibited. You agree to comply with all applicable international and national laws that apply to the Products as well as end user, end-use, and destination
restrictions issued by U.S. and other governments. For additional information on U.S. export controls see www.bis.doc.gov. Fortinet assumes no responsibility or liability for
your failure to obtain any necessary import and export approvals, and Fortinet reserves the right to terminate or suspend shipments, services and support in the event Fortinet
has a reasonable basis to suspect any import or export violation. You represent that neither the United States Bureau of Industry and Security nor any other governmental
agency has issued sanctions against you or otherwise suspended, revoked or denied your export privileges. You agree not to use or transfer the Products for any use relating
to nuclear, chemical or biological weapons, or missile technology, unless authorized by the United States Government by regulation or specic written license. Additionally,
you agree not to directly or indirectly export, import or transmit the Products contrary to the laws or regulations of any other governmental entity that has jurisdiction over
such export, import, transmission or use. Furthermore, you represent that you understand, and you hereby agree to comply with, all requirements of the U.S. Foreign Corrupt
Practices Act and all other applicable laws. For beta, testing, evaluation, donation or free Products and/or related services, you hereby agree, represent and warrant to Fortinet
that (a) receipt of the Products and/or services comply with all policies and you have obtained all necessary approvals for such Products and/or services, (b) the Products
and/or services are not provided in exchange for Fortinet maintaining current business or for new business opportunities, and (c) the Products and/or services are not being
received for the benet of, and are not being transferred to, any government entity, representative or afliate.
11. U.S. Government End Users.
The Software and accompanying documentation are deemed to be “commercial computer software” and “commercial computer software documentation,” respectively, pursuant to DFAR Section 227.7202 and FAR Section 12.212, as applicable. Any use, modication, reproduction, release, performance, display or disclosure of the Software and
accompanying documentation by the United States Government shall be governed solely by the terms of this Agreement and shall be prohibited except to the extent expressly
permitted by the terms of this Agreement and its successors.
12. Tax Liability.
You agree to be responsible for payment of any sales or use taxes imposed at any time on this transaction.
13. General Provisions.
Except as specically permitted and required in section 5 (“Transfer”) above, you agree not to assign this Agreement or transfer any of the rights or obligations under this
Agreement without the prior written consent of Fortinet. This Agreement shall be binding upon, and inure to the benet of, the successors and permitted assigns of the parties.
The United Nations Convention on Contracts for the International Sales of Goods is expressly excluded. This Agreement and other Fortinet agreements may be amended or
supplemented only by a writing that refers explicitly to the agreement signed on behalf of both parties, or, for this Agreement, as otherwise expressly provided in the lead-in
above Section 1 above, provided, notwithstanding anything to the contrary and except for this Agreement which may be amended or updated as expressly provided in the
lead-in above Section 1 above, for any amendment or other agreement to be binding on Fortinet, such amendment or other agreement must be signed by Fortinet’s General
Counsel. No waiver will be implied from conduct or failure to enforce rights nor effective unless in a writing signed on behalf of the party against whom the waiver is asserted.
If any part of this Agreement is found unenforceable, that part will be enforced to the maximum extent permitted and the remainder shall continue in full force and effect. You
acknowledge that you have read this Agreement, understand it, and agree to be bound by its terms and conditions.
14. Privacy.
Fortinet’s collection, use, protection and transfer of your personal information is governed by the Fortinet privacy policy on the Fortinet web site (http://www.fortinet.com/
aboutus/privacy.html).
15. Open Source Software.
Fortinet’s products may include software modules that are licensed (or sublicensed) to the user under the GNU General Public License, Version 2, of June 1991 (“GPL”) or
GNU Lesser General Public License, Version 2.1, of February 1999 (“LGPL”) or other open source software licenses which, among other rights, permit the user touse, copy,
modify and redistribute modules, or portions thereof, and may also require attribution disclosures and access to the source code (“Open Source Software”). The GPL requires
that for any Open Source Software covered under the GPL, which is distributed to someone in an executable binary format, that the source code also be made available to
those users. For any Open Source Software covered under the GPL, the source code is made available on this CD or download package. If any Open Source Software licenses
require that Fortinet provide rights to use, copy or modify a Open Source Software program that are broader than the rights granted in this agreement, then such rights shall
take precedence over the rights and restrictions herein. Fortinet will provide, for a charge reecting our standard distribution costs, the complete machine-readable copy of the
modied software modules. To obtain a complete machine-readable copy, please send your written request, along with a check in the amount of US $25.00, to General Public
License Source Code Request, Fortinet, Inc., 899 Kifer Rd, Sunnyvale, CA 94086 USA. In order to receive the modied software modules, you must also include the following
information: (a) Name, (b) Address, (c) Telephone number, (d) E-mail Address, (e) Product purchased (if applicable), (f) Product Serial Number (if applicable). All open source
software modules are licensed free of charge. There is no warranty for these modules, to the extent permitted by applicable law. The copyright holders provide these software
modules “AS-IS” without warranty of any kind, either expressed or implied. In no event will the copyright holder for the open source software be liable to you for damages,
including any special, incidental or consequential damages arising out of the use or inability to use the software modules, even if such holder has been advised of the possibility of such damages. A full copy of this license, including additional open source software license disclosures and third party license disclosures applicable to certain Fortinet
products, may obtained by contacting Fortinet’s Legal Department at legal@fortinet.com.
GNU GENERAL PUBLIC LICENSE GNU GENERAL PUBLIC LICENSE
Copyright (C) 1989, 1991 Free Software Foundation, Inc.
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
This License applies to any program or other work which contains a notice placed by the copyright holder saying it may be distributed under the terms of this General Public
License. The “Program”, below, refers to any such program or work, and a “work based on the Program” means either the Program or any derivative work under copyright
law: that is to say, a work containing the Program or a portion of it, either verbatim or with modications and/or translated into another language. (Hereinafter, translation is
included without limitation in the term “modication”.) Each licensee is addressed as “you”.
Activities other than copying, distribution and modication are not covered by this License; they are outside its scope. The act of running the Program is not restricted, and the
output from the Program is covered only if its contents constitute a work based on the Program (independent of having been made by running the Program). Whether that is
true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program’s source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on
each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and give any
other recipients of the Program a copy of this License along with the Program. You may charge a fee for the physical act of transferring a copy, and you may at your option
offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion of it, thus forming a work based on the Program, and copy and distribute such modications or work
under the terms of Section 1 above, provided that you also meet all of these conditions:
a) You must cause the modied les to carry prominent notices stating that you changed the les and the date of any change.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
Version 2, June 1991
Page 14

b) You must cause any work that you distribute or publish, that in whole or in part contains or is derived from the Program or any part thereof, to be licensed as a whole at no
charge to all third parties under the terms of this License.
c) If the modied program normally reads commands interactively when run, you must cause it, when started running for such interactive use in the most ordinary way, to print
or display an announcement including an appropriate copyright notice and a notice that there is no warranty (or else, saying that you provide a warranty) and that users may
redistribute the program under these conditions, and telling the user how to view a copy of this License. (Exception: if the Program itself is interactive but does not normally
print such an announcement, your work based on the Program is not required to print an announcement.)
These requirements apply to the modied work as a whole. If identiable sections of that work are not derived from the Program, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute
the same sections as part of a whole which is a work based on the Program, the distribution of the whole must be on the terms of this License, whose permissions for other
licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.. Thus, it is not the intent of this section to claim rights or contest your rights
to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Program. In addition, mere
aggregation of another work not based on the Program with the Program (or with a work based on the Program) on a volume of a storage or distribution medium does not
bring the other work under the scope of this License.
3. You may copy and distribute the Program (or a work based on it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above provided that
you also do one of the following:
a) Accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections1 and 2 above on a medium
customarily used for software interchange; or,
b) Accompany it with a written offer, valid for at least three years, to give any third party, for a charge no more than your cost of physically performing source distribution, a
complete machine-readable copy of the corresponding source code, to be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software
interchange; or,
c) Accompany it with the information you received as to the offer to distribute corresponding source code. (This alternative is allowed only for noncommercial distribution and
only if you received the program in object code or executable form with such an offer, in accord with Subsection b above.)
Source code for a work means the preferred form of the work for making modications to it. For an executable work, complete source code means all the source code for
all modules it contains, plus any associated interface denition les, plus the scripts used to control compilation and installation of the executable. However, as a special
exception, the source code distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler, kernel, and
so on) of the operating system on which the executable runs, unless that component itself accompanies the executable. If distribution of executable or object code is made by
offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place counts as distribution of the source code, even
though third parties are not compelled to copy the source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense or dis-
tribute the Program is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License
will not have their licenses terminated so long as such parties remain in full compliance.
5. You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Program or its derivative
works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Program (or any work based on the Program), you
indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the Program), the recipient automatically receives a license from the original licensor to copy, distribute or
modify the Program subject to these terms and conditions. You may not impose any further restrictions on the recipients’ exercise of the rights granted herein. You are not
responsible for enforcing compliance by third parties to this License.
7. If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether
by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so
as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Program at all. For
example, if a patent license would not permit royalty-free redistribution of the Program by all those who receive copies directly or indirectly through you, then the only way you
could satisfy both it and this License would be to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply and the section as a whole is
intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole
purpose of protecting the integrity of the free software distribution system, which is implemented by public license practices. Many people have made generous contributions
to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is willing to
distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the
Program under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not
thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions of the General Public License from time to time. Such new versions will be similar in spirit to the
present version, but may differ in detail to address new problems or concerns. Each version is given a distinguishing version number. If the Program species a version number
of this License which applies to it and “any later version”, you have the option of following the terms and conditions either of that version or of any later version published by
the Free Software Foundation. If the Program does not specify a version number of this License, you may choose any version ever published by the Free Software Foundation.
10. If you wish to incorporate parts of the Program into other free programs whose distribution conditions are different, write to the author to ask for permission. For software
which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided by the two
goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally.
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN
OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED
OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE
QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR
OR CORRECTION.
NO WARRANTY
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES
ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES
SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN
ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
GNU LESSER GENERAL PUBLIC LICENSE
Version 2.1, February 1999
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
59 Temple Place, Suite 330, Boston, MA 02111-1307 USA
0. This License Agreement applies to any software library or other program which contains a notice placed by the copyright holder or other authorized party saying it may be
distributed under the terms of this Lesser General Public License (also called “this License”). Each licensee is addressed as “you”.
A “library” means a collection of software functions and/or data prepared so as to be conveniently linked with application programs (which use some of those functions and
data) to form executables.
The “Library”, below, refers to any such software library or work which has been distributed under these terms. A “work based on the Library” means either the Library or any
derivative work under copyright law: that is to say, a work containing the Library or a portion of it, either verbatim or with modications and/or translated straightforwardly into
another language. (Hereinafter, translation is included without limitation in the term “modication”.)
“Source code” for a work means the preferred form of the work for making modications to it. For a library, complete source code means all the source code for all modules it
contains, plus any associated interface denition les, plus the scripts used to control compilation and installation of the library.
Activities other than copying, distribution and modication are not covered by this License; they are outside its scope. The act of running a program using the Library is not
restricted, and output from such a program is covered only if its contents constitute a work based on the Library (independent of the use of the Library in a tool for writing it).
Whether that is true depends on what the Library does and what the program that uses the Library does.
1. You may copy and distribute verbatim copies of the Library’s complete source code as you receive it, in any medium, provided that you conspicuously and appropriately
publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and
distribute a copy of this License along with the Library. You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection
in exchange for a fee.
2. You may modify your copy or copies of the Library or any portion of it, thus forming a work based on the Library, and copy and distribute such modications or work under
the terms of Section 1 above, provided that you also meet all of these conditions:
a) The modied work must itself be a software library.
b) You must cause the les modied to carry prominent notices stating that you changed the les and the date of any change.
c) You must cause the whole of the work to be licensed at no charge to all third parties under the terms of this License.
d) If a facility in the modied Library refers to a function or a table of data to be supplied by an application program that uses the facility, other than as an argument passed
when the facility is invoked, then you must make a good faith effort to ensure that, in the event an application does not supply such function or table, the facility still operates,
and performs whatever part of its purpose remains meaningful.
These requirements apply to the modied work as a whole. If identiable sections of that work are not derived from the Library, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute
the same sections as part of a whole which is a work based on the Library, the distribution of the whole must be on the terms of this License, whose permissions for other
licensees extend to the entire whole, and thus to each and every part regardless of who wrote it. Thus, it is not the intent of this section to claim rights or contest your rights
to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Library. In addition, mere
aggregation of another work not based on the Library with the Library (or with a work based on the Library) on a volume of a storage or distribution medium does not bring the
other work under the scope of this License.
3. You may opt to apply the terms of the ordinary GNU General Public License instead of this License to a given copy of the Library. To do this, you must alter all the notices that
refer to this License, so that they refer to the ordinary GNU General Public License, version 2 instead of to this License. (If a newer version than version 2 of the ordinary GNU
General Public License has appeared, then you can specify that version instead if you wish.) Do not make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy, so the ordinary GNU General Public License applies to all subsequent copies and derivative works
made from that copy. This option is useful when you wish to copy part of the code of the Library into a program that is not a library.
4. You may copy and distribute the Library (or a portion or derivative of it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above
provided that you accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on a
medium customarily used for software interchange.
If distribution of object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place satises
the requirement to distribute the source code, even though third parties are not compelled to copy the source along with the object code.
5. A program that contains no derivative of any portion of the Library, but is designed to work with the Library by being compiled or linked with it, is called a “work that uses
the Library”. Such a work, in isolation, is not a derivative work of the Library, and therefore falls outside the scope of this License.
However, linking a “work that uses the Library” with the Library creates an executable that is a derivative of the Library (because it contains portions of the Library), rather
than a “work that uses the library”. The executable is therefore covered by this License. Section 6 states terms for distribution of such executables.
When a “work that uses the Library” uses material from a header le that is part of the Library, the object code for the work may be a derivative work of the Library even
though the source code is not.
Whether this is true is especially signicant if the work can be linked without the Library, or if the work is itself a library. The threshold for this to be true is not precisely
dened by law.
If such an object le uses only numerical parameters, data structure layouts and accessors, and small macros and small inline functions (ten lines or less in length), then the
use of the object le is unrestricted, regardless of whether it is legally a derivative work. (Executables containing this object code plus portions of the Library will still fall under
Section 6.) Otherwise, if the work is a derivative of the Library, you may distribute the object code for the work under the terms of Section 6. Any executables containing that
work also fall under Section 6, whether or not they are linked directly with the Library itself.
6. As an exception to the Sections above, you may also combine or link a “work that uses the Library” with the Library to produce a work containing portions of the Library,
and distribute that work under terms of your choice, provided that the terms permit modication of the work for your own use and reverse engineering for debugging such
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
Page 15

modications. You must give prominent notice with each copy of the work that the Library is used in it and that the Library and its use are covered by this License. You must
supply a copy of this License. If the work during execution displays copyright notices, you must include the copyright notice for the Library among them, as well as a reference
directing the user to the copy of this License. Also, you must do one of these things:
a) Accompany the work with the complete corresponding machine-readable source code for the Library including whatever changes were used in the work (which must be
distributed under Sections 1 and 2 above); and, if the work is an executable linked with the Library, with the complete machine-readable “work that uses the Library”, as
object code and/or source code, so that the user can modify the Library and then relink to produce a modied executable containing the modied Library. (It is understood that
the user who changes the contents of denitions les in the Library will not necessarily be able to recompile the application to use the modied denitions.)
b) Use a suitable shared library mechanism for linking with the Library. A suitable mechanism is one that (1) uses at run time a copy of the library already present on the user’s
computer system, rather than copying library functions into the executable, and (2) will operate properly with a modied version of the library, if the user installs one, as long
as the modied version is interface-compatible with the version that the work was made with.
c) Accompany the work with a written offer, valid for at least three years, to give the same user the materials specied in Subsection 6a, above, for a charge no more than the
cost of performing this distribution.
d) If distribution of the work is made by offering access to copy from a designated place, offer equivalent access to copy the above specied materials from the same place.
e) Verify that the user has already received a copy of these materials or that you have already sent this user a copy.
For an executable, the required form of the “work that uses the Library” must include any data and utility programs needed for reproducing the executable from it. However, as
a special exception, the materials to be distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler,
kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable. It may happen that this requirement
contradicts the license restrictions of other proprietary libraries that do not normally accompany the operating system. Such a contradiction means you cannot use both them
and the Library together in an executable that you distribute.
7. You may place library facilities that are a work based on the Library side-by-side in a single library together with other library facilities not covered by this License, and
distribute such a combined library, provided that the separate distribution of the work based on the Library and of the other library facilities is otherwise permitted, and
provided that you do these two things:
a) Accompany the combined library with a copy of the same work based on the Library, uncombined with any other library facilities. This must be distributed under the terms
of the Sections above.
b) Give prominent notice with the combined library of the fact that part of it is a work based on the Library, and explaining where to nd the accompanying uncombined form
of the same work.
8. You may not copy, modify, sublicense, link with, or distribute the Library except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense,
link with, or distribute the Library is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such parties remain in full compliance.
9. You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Library or its derivative
works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Library (or any work based on the Library), you indicate
your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Library or works based on it.
10. Each time you redistribute the Library (or any work based on the Library), the recipient automatically receives a license from the original licensor to copy, distribute, link
with or modify the Library subject to these terms and conditions. You may not impose any further restrictions on the recipients’ exercise of the rights granted herein. You are
not responsible for enforcing compliance by third parties with this License.
11. If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether
by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so as
to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Library at all. For example,
if a patent license would not permit royalty-free redistribution of the Library by all those who receive copies directly or indirectly through you, then the only way you could
satisfy both it and this License would be to refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply, and the section as a whole is
intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole
purpose of protecting the integrity of the free software distribution system which is implemented by public license practices. Many people have made generous contributions
to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is
willing to distribute software through any other system and a licensee cannot impose that choice. This section is intended to make thoroughly clear what is believed to be a
consequence of the rest of this License.
12. If the distribution and/or use of the Library is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the
Library under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not
thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
13. The Free Software Foundation may publish revised and/or new versions of the Lesser General Public License from time to time. Such new versions will be similar in spirit
to the present version, but may differ in detail to address new problems or concerns. Each version is given a distinguishing version number. If the Library species a version
number of this License which applies to it and “any later version”, you have the option of following the terms and conditions either of that version or of any later version published by the Free Software Foundation. If the Library does not specify a license version number, you may choose any version ever published by the Free Software Foundation.
14. If you wish to incorporate parts of the Library into other free programs whose distribution conditions are incompatible with these, write to the author to ask for permission.
For software which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided
by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally.
15. The warranty disclaimer contained in Sections 11 and 12 of the preceding GPL License is incorporated herein.
Page 16

Page 17

Fortinet Customer Service & Support
Create a support account, register and manage your products,
download updates, firmware images and release notes, and create
technical support tickets.
https://support.fortinet.com
Fortinet Document Library
Up-to-date versions of Fortinet publications for the entire family of
Fortinet products.
http://docs.fortinet.com
Training Services
Course descriptions, availability, schedules, and location of training
programs in your area.
http://www.fortinet.com/training
Technical Discussion Forums
Communicate with other customers and Fortinet partners about
Fortinet products, services, and configuration issues.
https://support.fortinet.com/forum
FortiGuard Threat Research and Response
Up-to-date information on vulnerabilities and threats, includes a
virus scanner, IP signature look-up, and web filtering tools.
http://www.fortiguard.com
Fortinet.com
 Loading...
Loading...