Comtrend AR-5312U User Manual

6.5 DNS
6.5.1 DNS Server
Select DNS Server Interface from available WAN interfaces OR enter static DNS
server IP addresses for the system. In ATM mode, if only a single PVC with IPoA or
static IPoE protocol is configured, Static DNS server IP addresses must be entered.
DNS Server Interfaces can have multiple WAN interfaces served as system dns
servers but only one will be used according to the priority with the first being the
highest and the last one the lowest priority if the WAN interface is connected.
Priority order can be changed by removing all and adding them back in again.
Click Apply/Save to save the new configuration.
NOTE: You must reboot the router to make the new configuration effective.
87
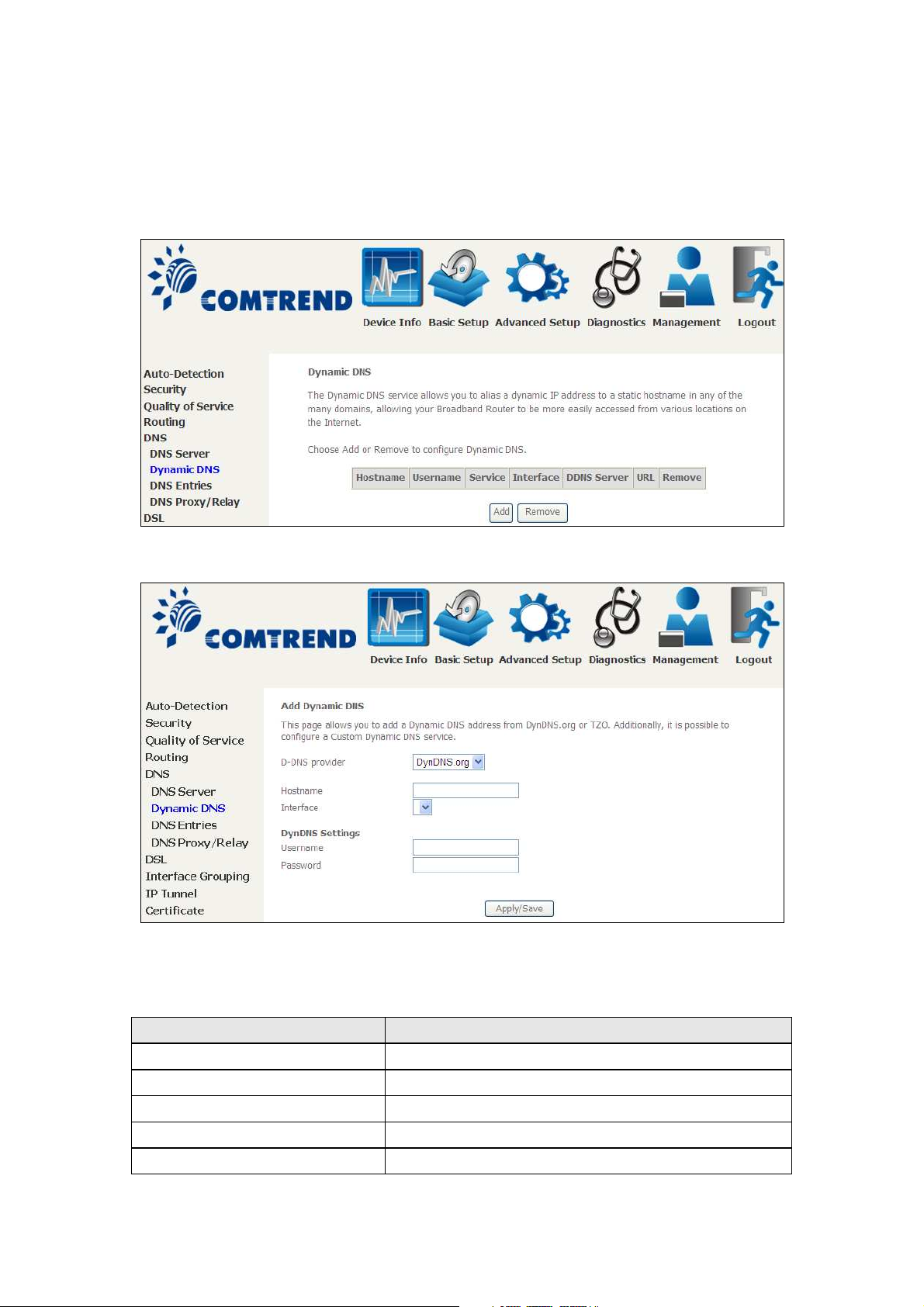
6.5.2 Dynamic DNS
The Dynamic DNS service allows you to map a dynamic IP address to a static
hostname in any of many domains, allowing the AR-5312u to be more easily
accessed from various locations on the Internet.
To add a dynamic DNS service, click Add. The following screen will display.
Click Apply/Save to save your settings.
Consult the table below for field descriptions.
Field Description
D-DNS provider Select a dynamic DNS provider from the list
Hostname Enter the name of the dynamic DNS server
Interface Select the interface from the list
Username Enter the username of the dynamic DNS server
Password Enter the password of the dynamic DNS server
88
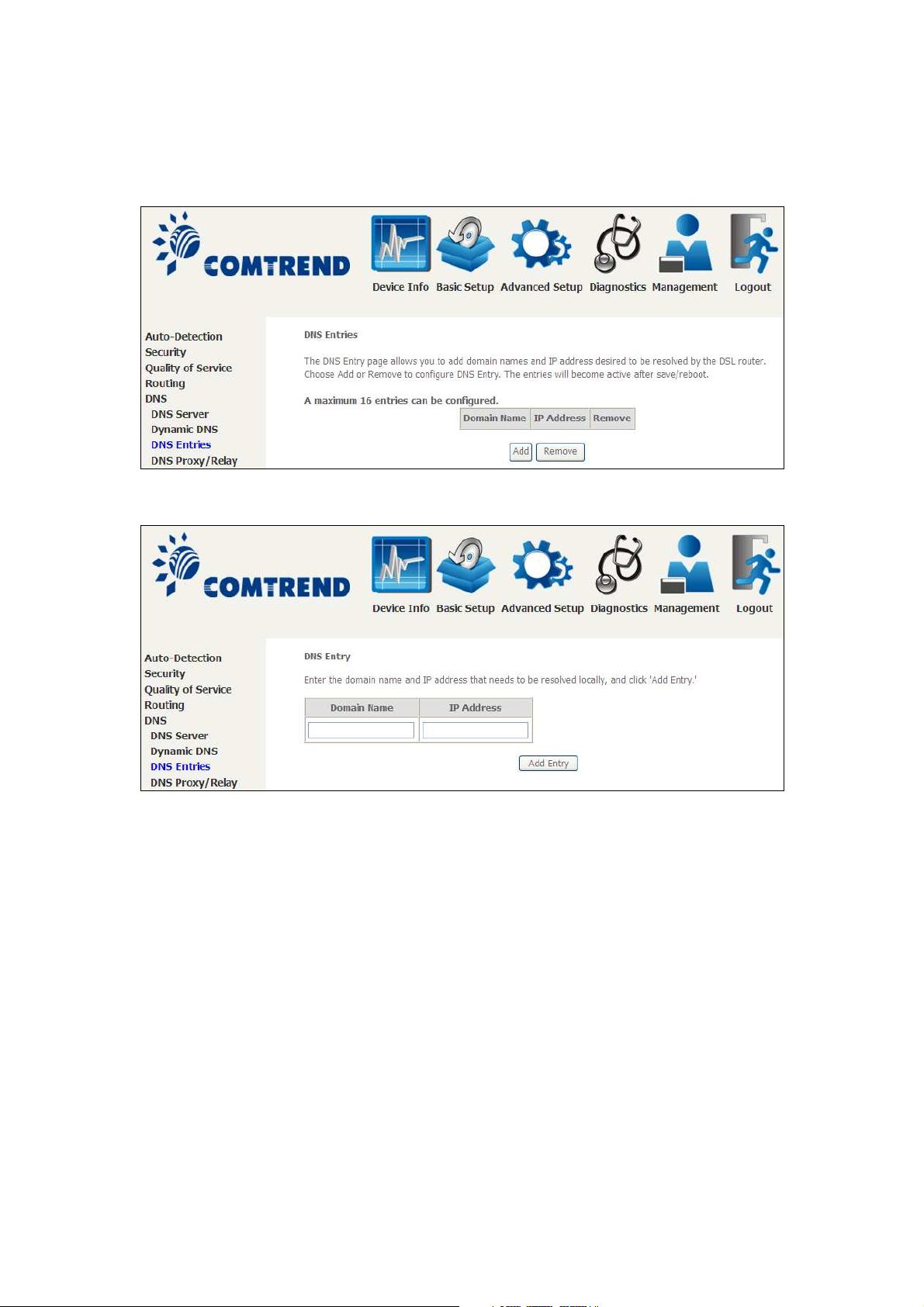
6.5.3 DNS Entries
The DNS Entry page allows you to add domain names and IP address desired to be
resolved by the DSL router.
Choose Add or Remove to configure DNS Entry. The entries will become active after
save/reboot.
Enter the domain name and IP address that needs to be resolved locally, and click
the Add Entry button.
89

6.5.4 DNS Proxy/Relay
DNS proxy receives DNS queries and forwards DNS queries to the Internet. After the
CPE gets answers from the DNS server, it replies to the LAN clients. Configure DNS
proxy with the default setting, when the PC gets an IP via DHCP, the domain name,
Home, will be added to PC’s DNS Suffix Search List, and the PC can access route with
“Comtrend.Home”.
90
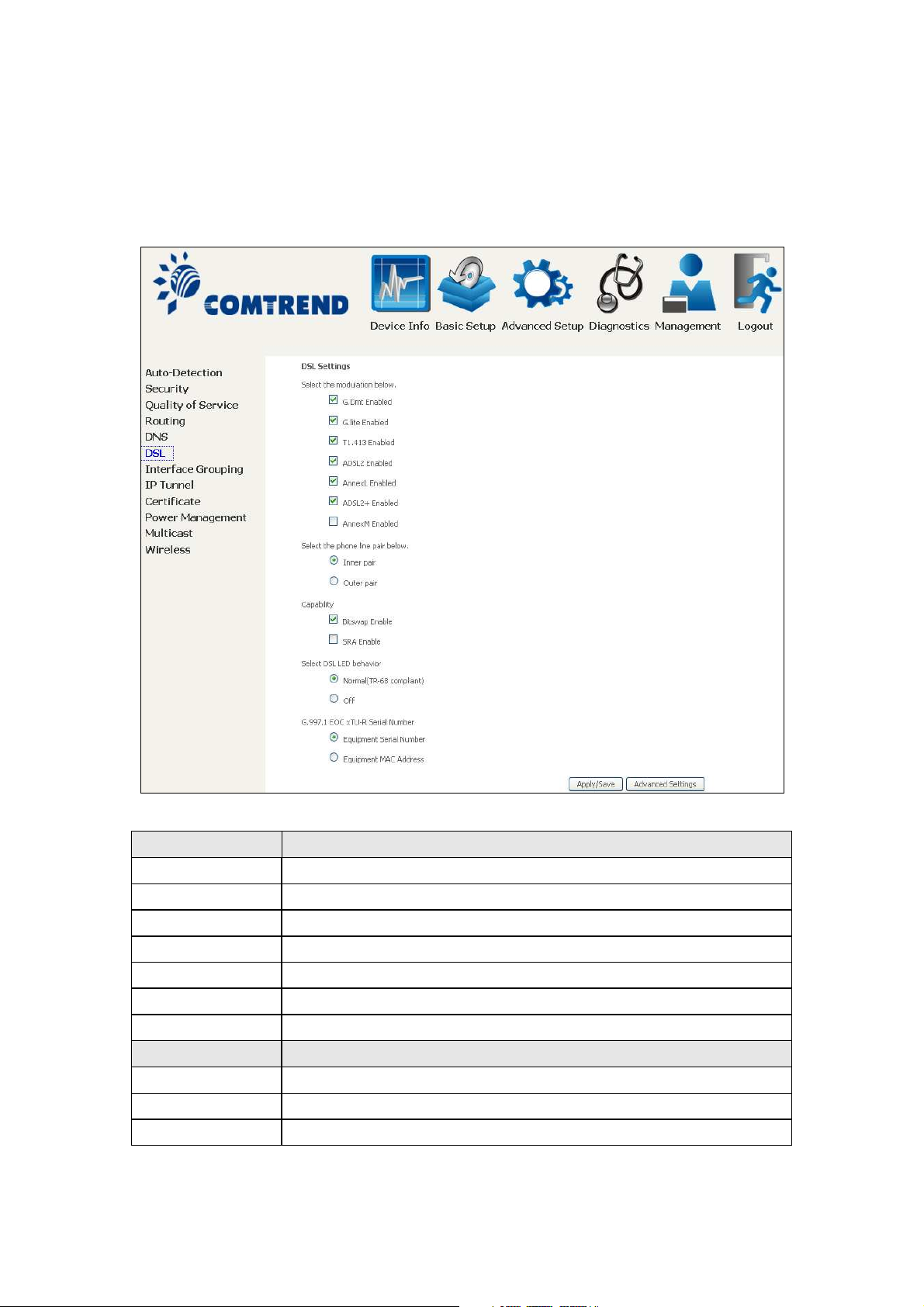
6.6 DSL
The DSL Settings screen allows for the selection of DSL modulation modes.
For optimum performance, the modes selected should match those of your ISP.
DSL Mode Data Transmission Rate - Mbps (Megabits per second)
G.Dmt Downstream: 12 Mbps Upstream: 1.3 Mbps
G.lite Downstream: 4 Mbps Upstream: 0.5 Mbps
T1.413 Downstream: 8 Mbps Upstream: 1.0 Mbps
ADSL2 Downstream: 12 Mbps Upstream: 1.0 Mbps
AnnexL Supports longer loops but with reduced transmission rates
ADSL2+ Downstream: 24 Mbps Upstream: 1.0 Mbps
AnnexM Downstream: 24 Mbps Upstream: 3.5 Mbps
Options Description
Inner/Outer Pair Select the inner or outer pins of the twisted pair (RJ11 cable)
Bitswap Enable Enables adaptive handshaking functionality
SRA Enable Enables Seamless Rate Adaptation (SRA)
91
DSL Mode Data Transmission Rate - Mbps (Megabits per second)
Select DSL LED
behavior
G997.1 EOC
xTU-R Serial
Number
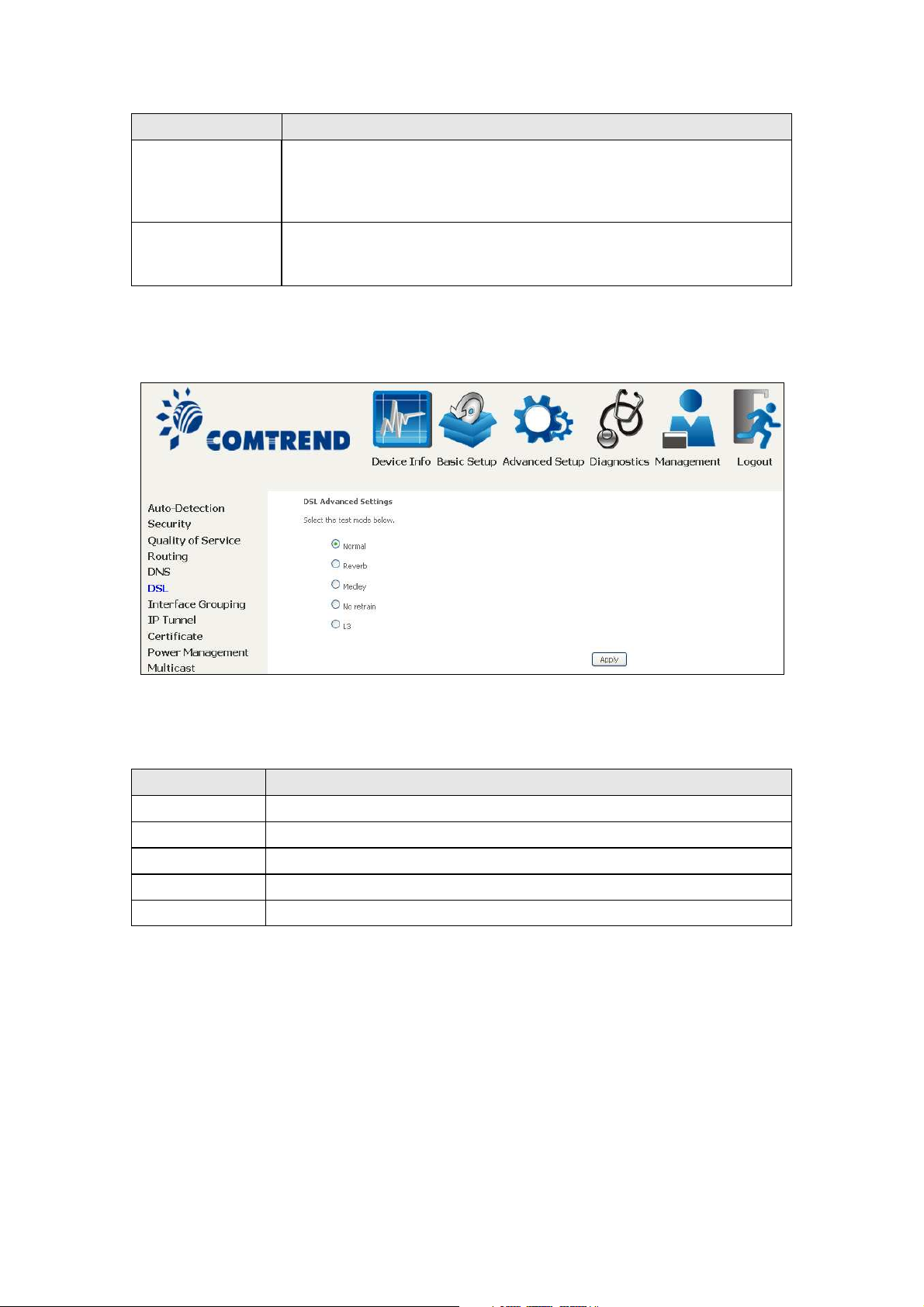
Advanced DSL Settings
Click Advanced Settings to reveal additional options.
Normal (TR-68 compliant): Select this option for DSL LED to
operate normally (See menu 2.2 LED Indicator)
Off:DSL LED will always be OFF
Select Equipment Serial Number or Equipment MAC Address to
use router’s serial number or MAC address in ADSL EOC
messages
On this screen you select the required test mode, then click the Apply button.
Field Description
Normal DSL line signal is detected and sent normally
Reverb DSL line signal is sent continuously in reverb mode
Medley DSL line signal is sent continuously in medley mode
No Retrain DSL line signal will always be on even when DSL line is unplugged
L3 DSL line is set in L3 power mode
92

6.7 Interface Grouping
Interface Grouping supports multiple ports to PVC and bridging groups. Each group
performs as an independent network. To use this feature, you must create mapping
groups with appropriate LAN and WAN interfaces using the Add button.
The Remove button removes mapping groups, returning the ungrouped interfaces
to the Default group. Only the default group has an IP interface.
To add an Interface Group, click the Add button. The following screen will appear.
It lists the available and grouped interfaces. Follow the instructions shown
onscreen.
93
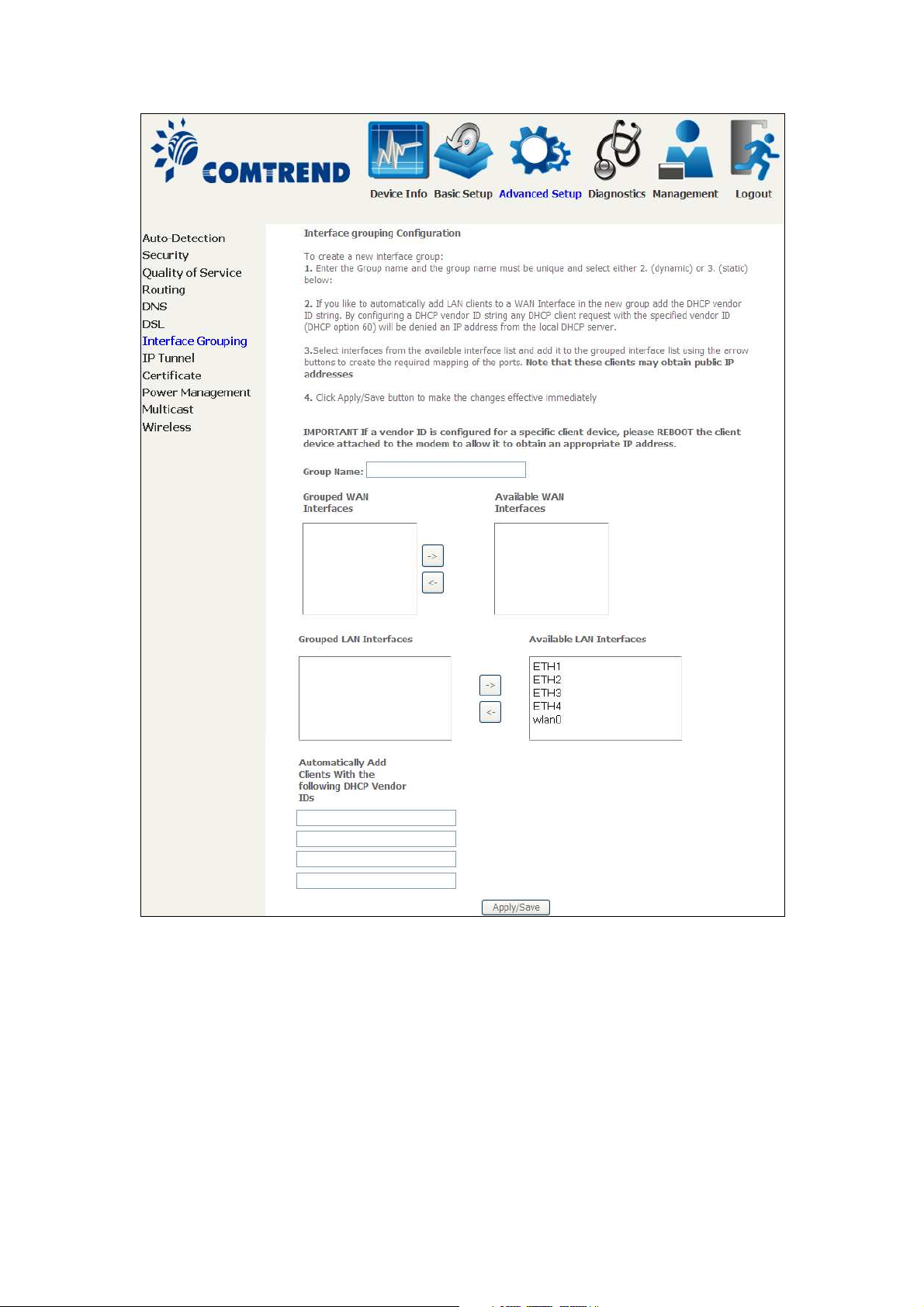
Automatically Add Clients With Following DHCP Vendor IDs:
Add support to automatically map LAN interfaces to PVC's using DHCP vendor ID
(option 60). The local DHCP server will decline and send the requests to a remote
DHCP server by mapping the appropriate LAN interface. This will be turned on when
Interface Grouping is enabled.
For example, imagine there are 4 PVCs (0/33, 0/36, 0/37, 0/38). VPI/VCI=0/33 is
for PPPoE while the other PVCs are for IP set-top box (video). The LAN interfaces are
ETH1, ETH2, ETH3, and ETH4.
The Interface Grouping configuration will be:
94

1. Default: ETH1, ETH2, ETH3, and ETH4.
2. Video: nas_0_36, nas_0_37, and nas_0_38. The DHCP vendor ID is "Video".
If the onboard DHCP server is running on "Default" and the remote DHCP server is
running on PVC 0/36 (i.e. for set-top box use only). LAN side clients can get IP
addresses from the CPE's DHCP server and access the Internet via PPPoE (0/33).
If a set-top box is connected to ETH1 and sends a DHCP request with vendor ID
"Video", the local DHCP server will forward this request to the remote DHCP server.
The Interface Grouping configuration will automatically change to the following:
1. Default: ETH2, ETH3, and ETH4
2. Video: nas_0_36, nas_0_37, nas_0_38, and ETH1
95
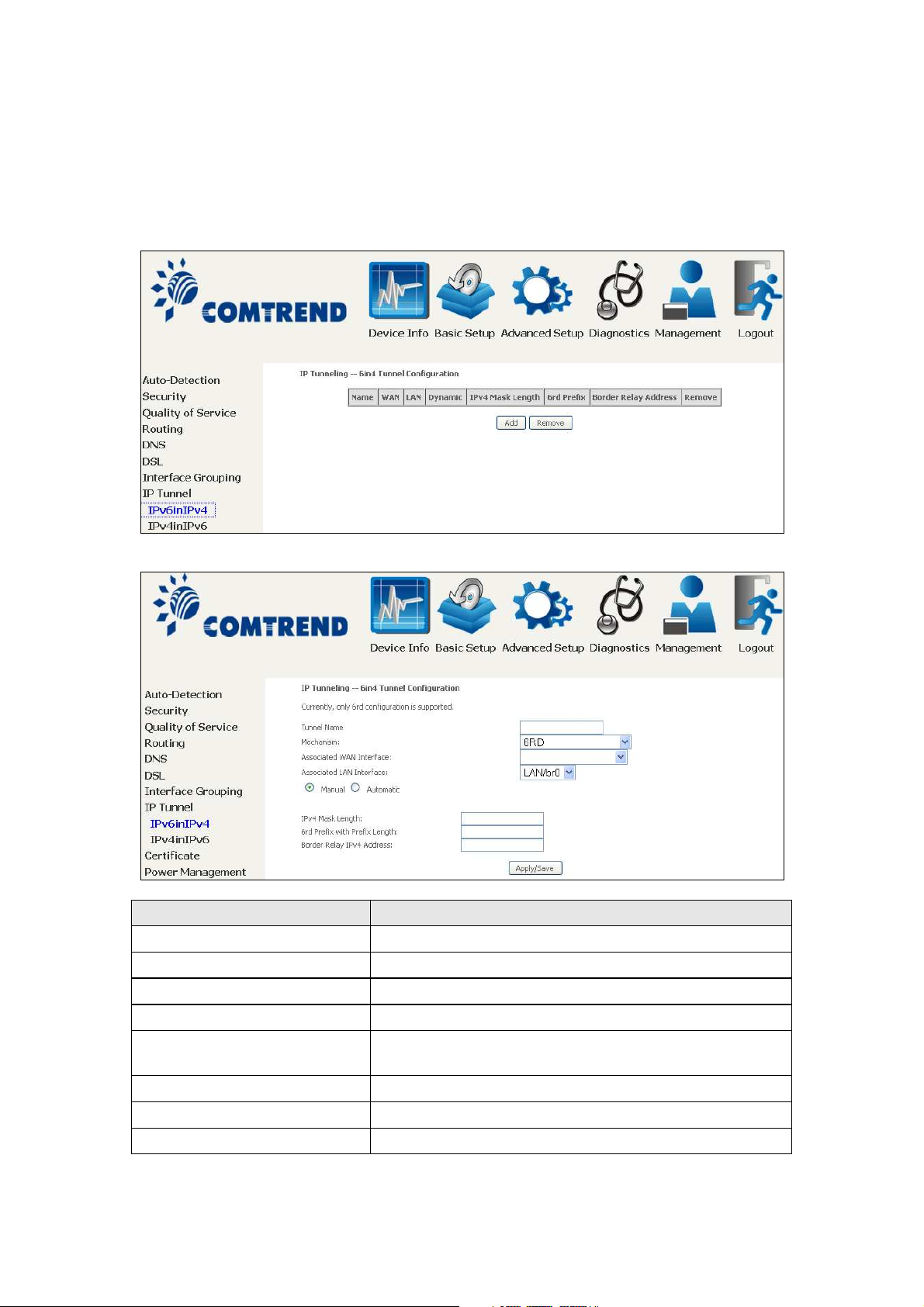
6.8 IP Tunnel
6.8.1 IPv6inIPv4
Configure 6in4 tunneling to encapsulate IPv6 traffic over explicitly-configured IPv4
links.
Click the Add button to display the following.
Options Description
Tunnel Name Input a name for the tunnel
Mechanism Mechanism used by the tunnel deployment
Associated WAN Interface Select the WAN interface to be used by the tunnel
Associated LAN Interface Select the LAN interface to be included in the tunnel
Manual/Automatic Select automatic for point-to-multipoint tunneling /
manual for point-to-point tunneling
IPv4 Mask Length The subnet mask length used for the IPv4 interface
6rd Prefix with Prefix Length Prefix and prefix length used for the IPv6 interface
Border Relay IPv4 Address Input the IPv4 address of the other device
96
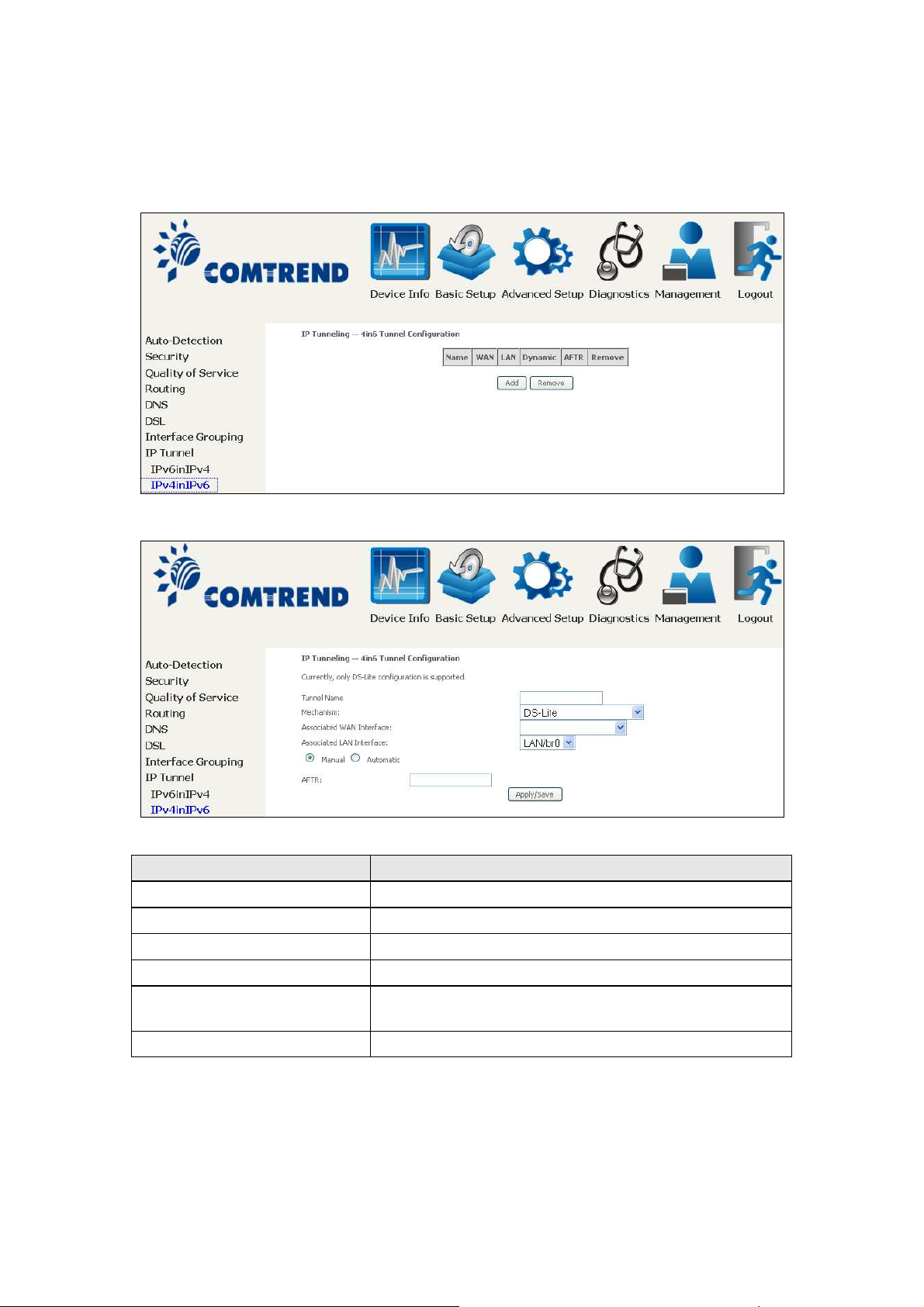
6.8.2 IPv4inIPv6
ġġġġ
Configure 4in6 tunneling to encapsulate IPv4 traffic over an IPv6-only environment.
Click the Add button to display the following.
Options Description
Tunnel Name Input a name for the tunnel
Mechanism Mechanism used by the tunnel deployment
Associated WAN Interface Select the WAN interface to be used by the tunnel
Associated LAN Interface Select the LAN interface to be included in the tunnel
Manual/Automatic Select automatic for point-to-multipoint tunneling /
manual for point-to-point tunneling
AFTR Address of Address Family Translation Router
97
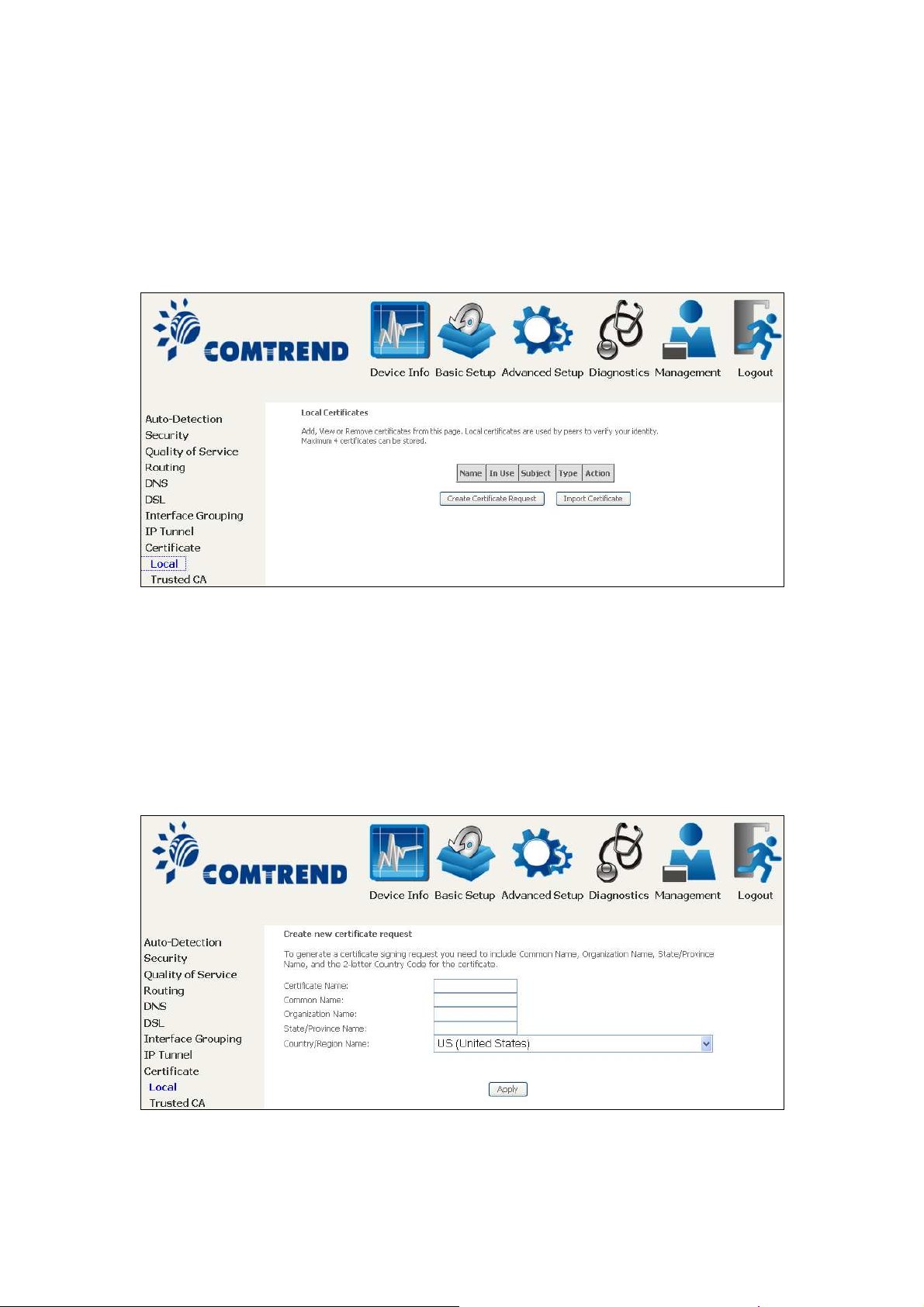
6.9 Certificate
A certificate is a public key, attached with its owner’s information (company name,
server name, personal real name, contact e-mail, postal address, etc) and digital
signatures. There will be one or more digital signatures attached to the certificate,
indicating that these entities have verified that this certificate is valid.
6.9.1 Local
CREATE CERTIFICATE REQUEST
Click Create Certificate Request to generate a certificate-signing request.
The certificate-signing request can be submitted to the vendor/ISP/ITSP to apply for
a certificate. Some information must be included in the certificate-signing request.
Your vendor/ISP/ITSP will ask you to provide the information they require and to
provide the information in the format they regulate. Enter the required information
and click Apply to generate a private key and a certificate-signing request.
The following table is provided for your reference.
98
Field Description
T
Certificate Name A user-defined name for the certificate.
Common Name Usually, the fully qualified domain name for the machine.
Organization Name The exact legal name of your organization.
Do not abbreviate.
State/Province Name
Country/Region Name The two-letter ISO abbreviation for your country.
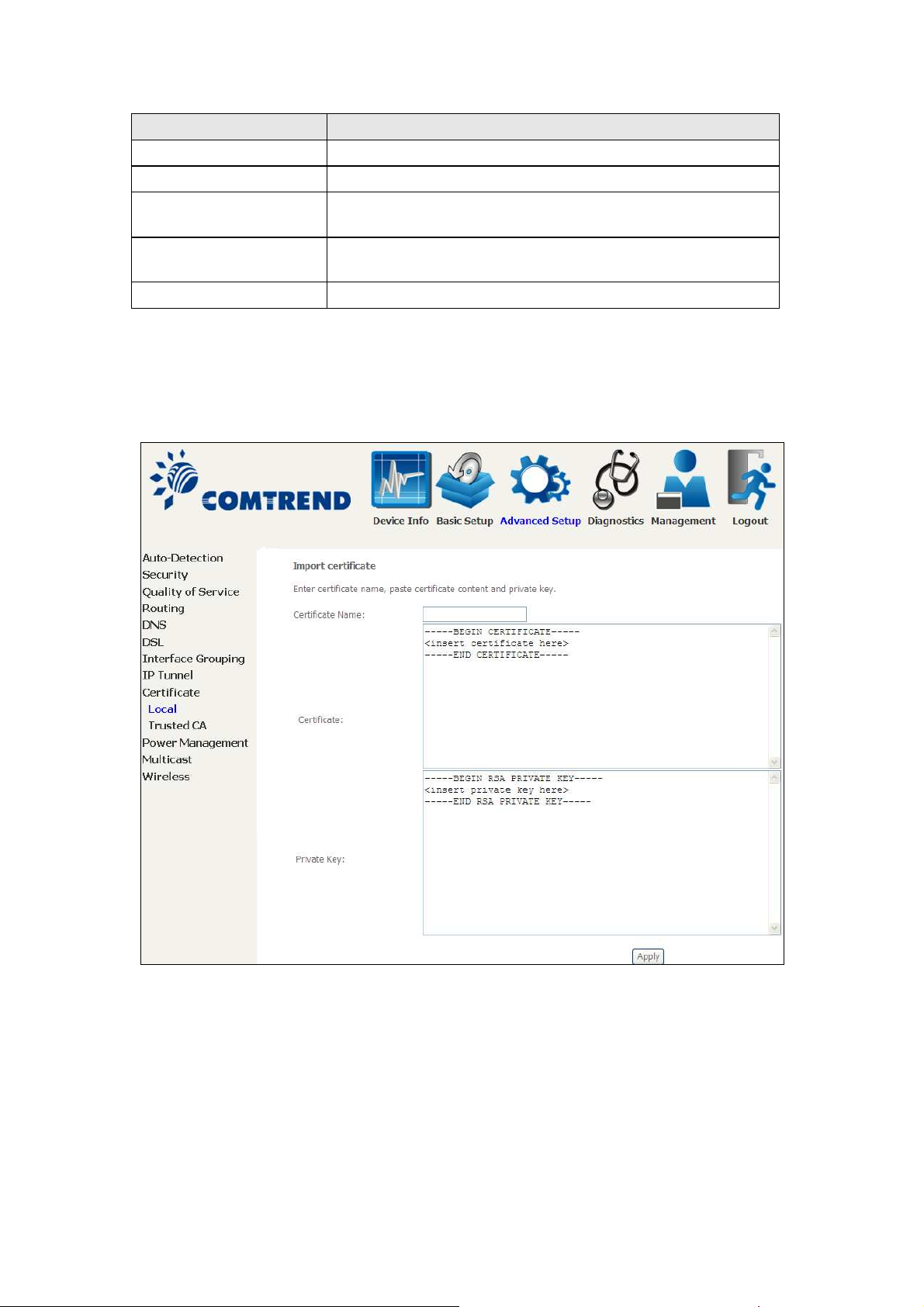
IMPORT CERTIFICATE
Click Import Certificate to paste the certificate content and the private key
provided by your vendor/ISP/ITSP into the corresponding boxes shown below.
he state or province where your organization is located.
It cannot be abbreviated.
Enter a certificate name and click the Apply button to import the certificate and its
private key.
99
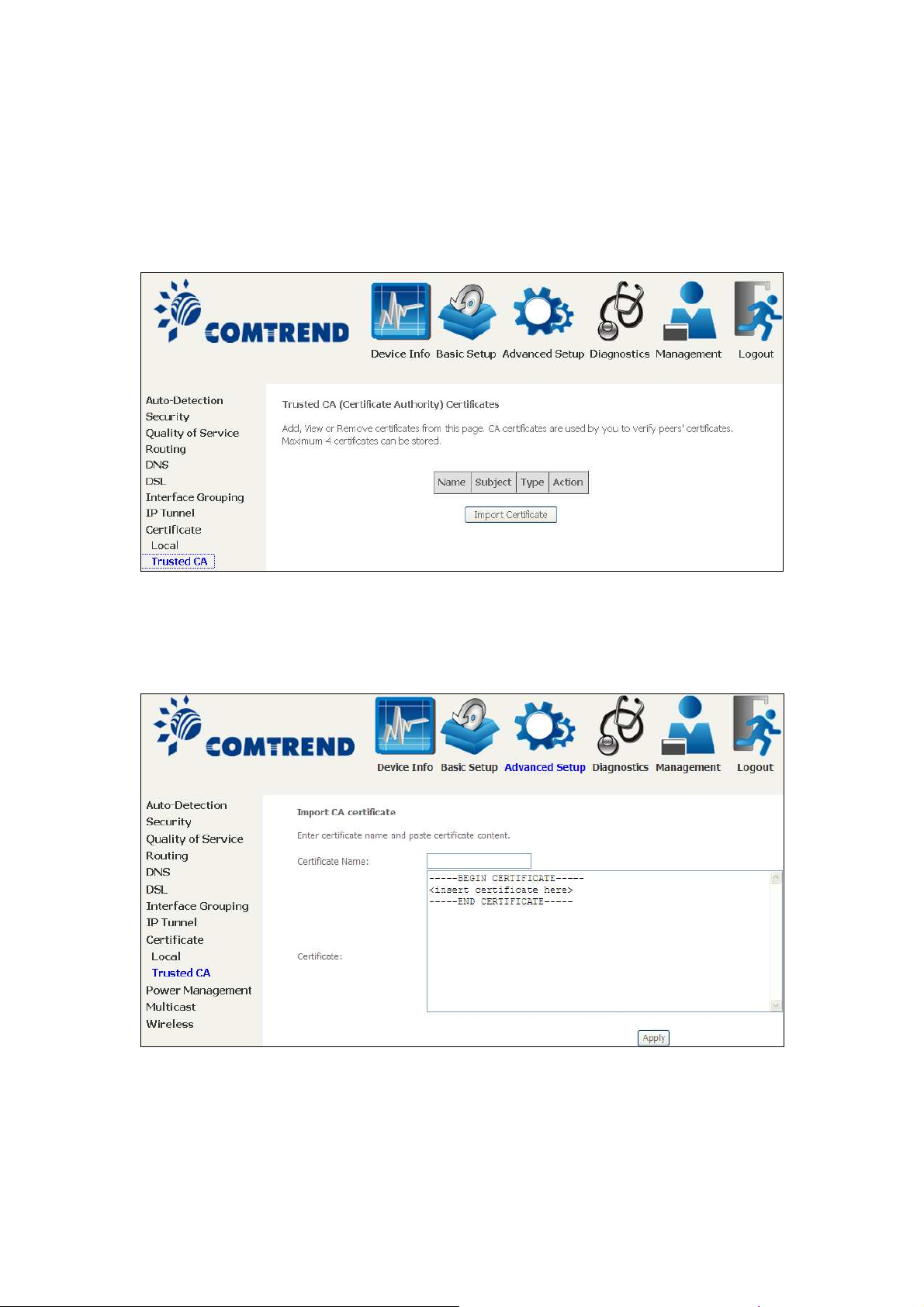
6.9.2 Trusted CA
CA is an abbreviation for Certificate Authority, which is a part of the X.509 system.
It is itself a certificate, attached with the owner information of this certificate
authority; but its purpose is not encryption/decryption. Its purpose is to sign and
issue certificates, in order to prove that these certificates are valid.
Click Import Certificate to paste the certificate content of your trusted CA. The
CA certificate content will be provided by your vendor/ISP/ITSP and is used to
authenticate the Auto-Configuration Server (ACS) that the CPE will connect to.
Enter a certificate name and click Apply to import the CA certificate.
100
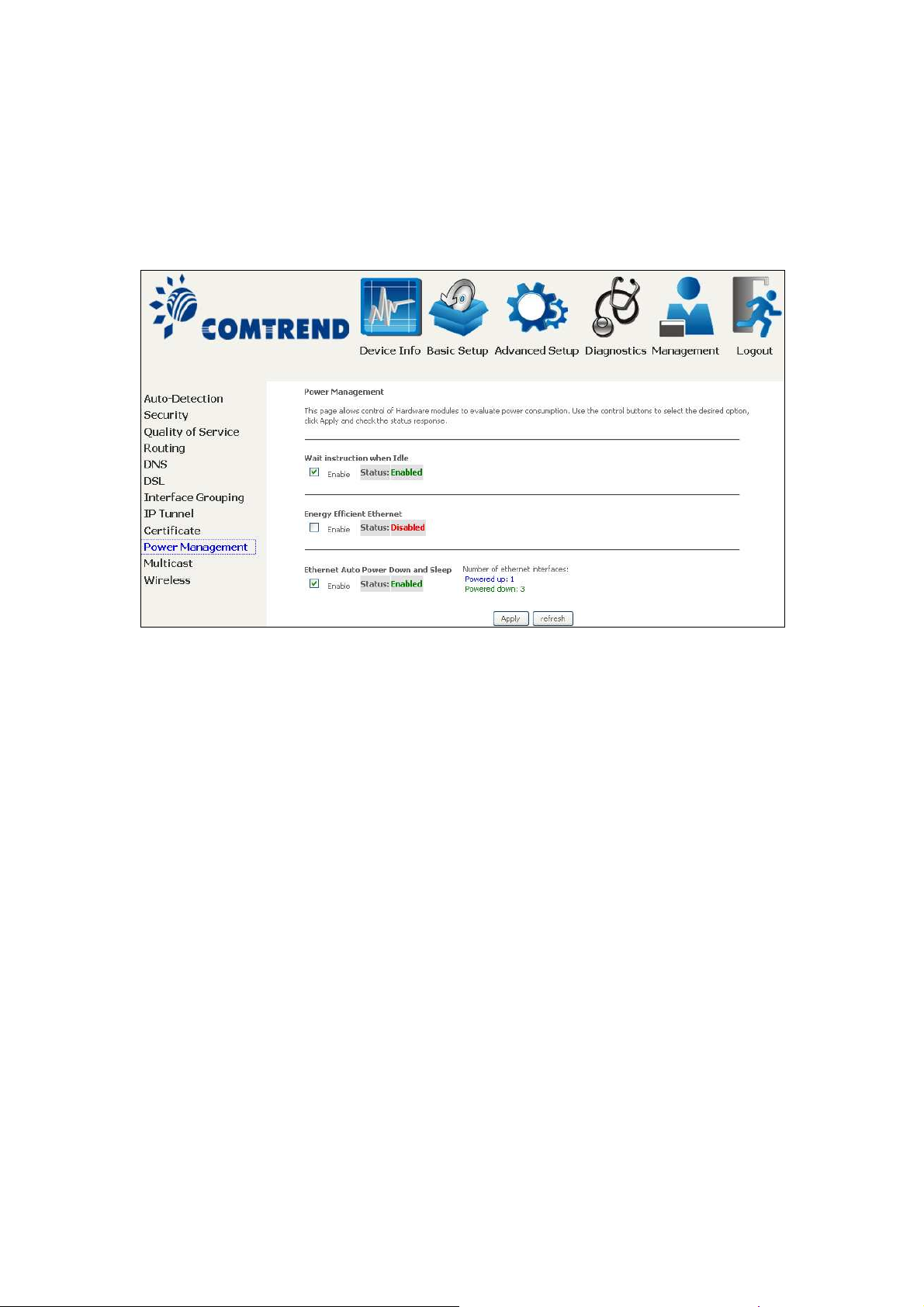
6.10 Power Management
This screen allows for control of hardware modules to evaluate power consumption.
Use the buttons to select the desired option, click Apply and check the response.
101
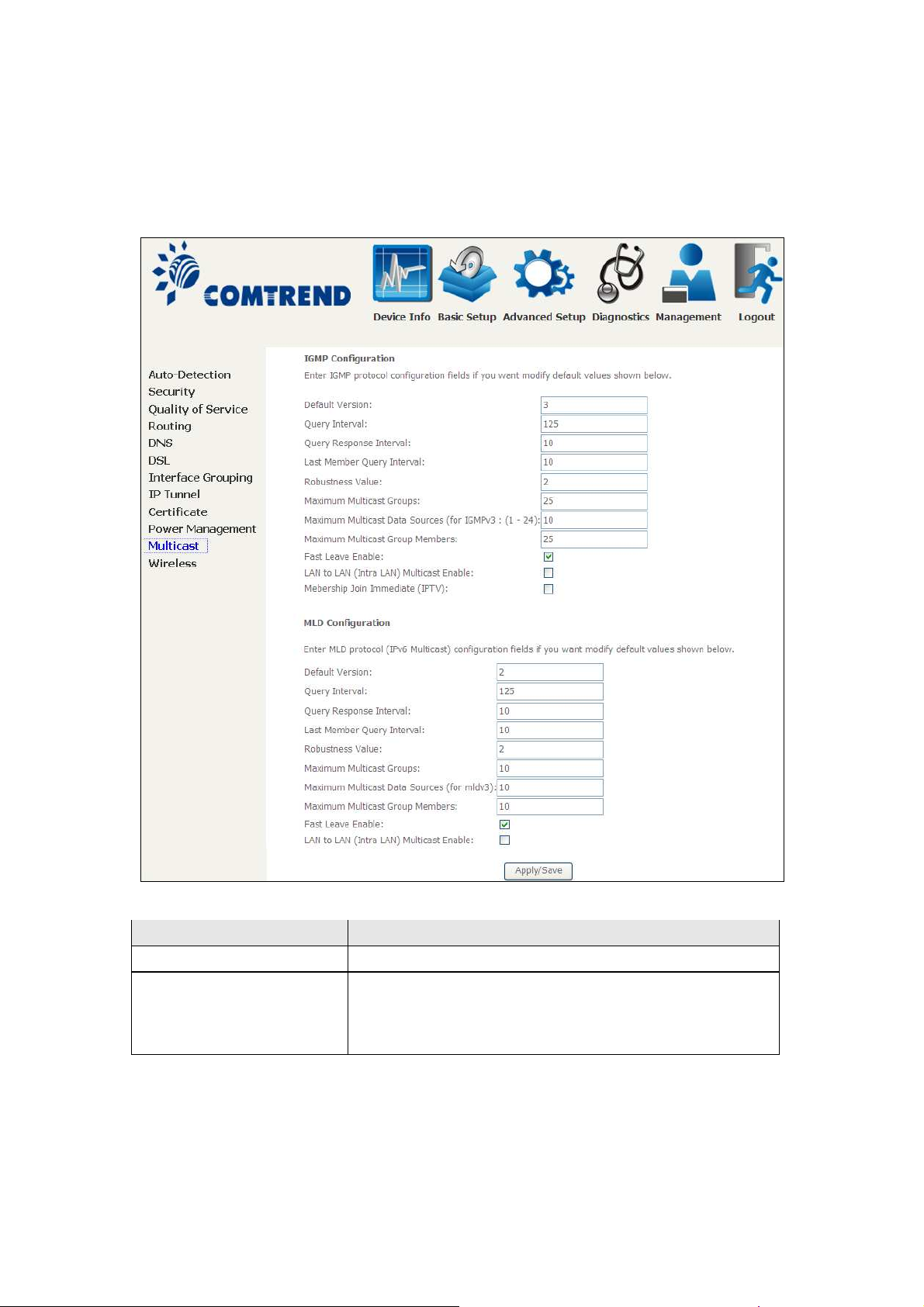
6.11 Multicast
Input new IGMP or MLD protocol configuration fields if you want modify default
values shown. Then click Apply/Save.
Field Description
Default Version Define IGMP using version with video server.
Query Interval The query interval is the amount of time in seconds
between IGMP General Query messages sent by the
router (if the router is the querier on this subnet). The
default query interval is 125 seconds.
102
Field Description
Query Response Interval The query response interval is the maximum amount
of time in seconds that the IGMP router waits to
receive a response to a General Query message. The
query response interval is the Maximum Response
Time field in the IGMP v2 Host Membership Query
message header. The default query response interval
is 10 seconds and must be less than the query
interval.
Last Member Query
Interval
Robustness Value The robustness variable is a way of indicating how
Maximum Multicast
Groups
Maximum Multicast Data
Sources (for IGMPv3)
Maximum Multicast
Group Members
Fast Leave Enable When you enable IGMP fast-leave processing, the
The last member query interval is the amount of time
in seconds that the IGMP router waits to receive a
response to a Group-Specific Query message. The last
member query interval is also the amount of time in
seconds between successive Group-Specific Query
messages. The default last member query interval is
10 seconds.
susceptible the subnet is to lost packets. IGMP can
recover from robustness variable minus 1 lost IGMP
packets. The robustness variable should be set to a
value of 2 or greater. The default robustness variable
value is 2.
Setting the maximum number of Multicast groups.
Define the maximum multicast video stream number.
Setting the maximum number of groups that ports
can accept.
switch immediately removes a port when it detects an
IGMP version 2 leave message on that port.
LAN to LAN (Intra LAN)
Multicast Enable
Membership to join
Immediate (IPTV)
103
This will activate IGMP snooping for cases where
multicast data source and player are all located on the
LAN side.
Enable IGMP immediate join feature for multicast
membership group.
6.12 Wireless
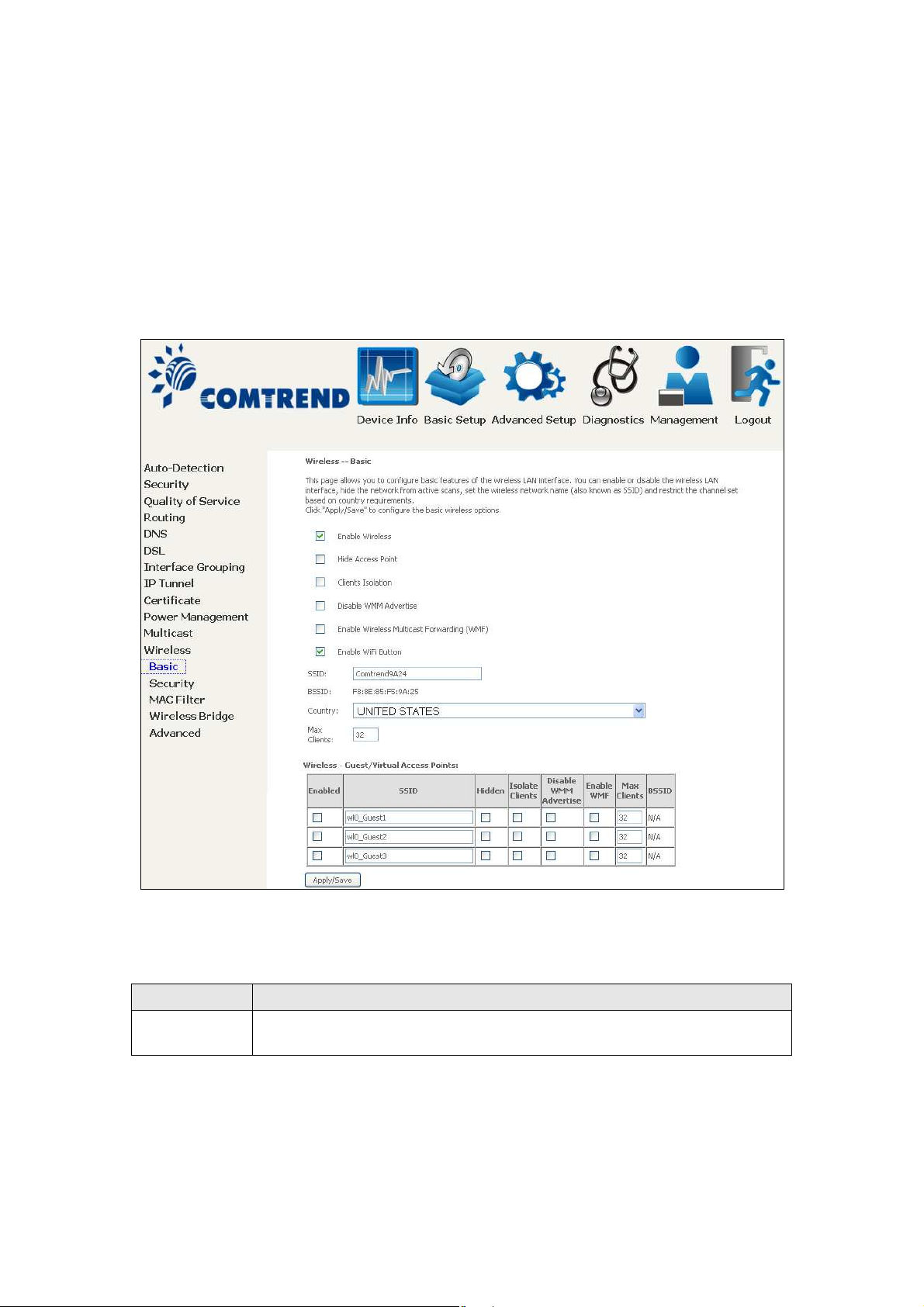
6.12.1 Basic
The Basic option allows you to configure basic features of the wireless LAN interface.
Among other things, you can enable or disable the wireless LAN interface, hide the
network from active scans, set the wireless network name (also known as SSID)
and restrict the channel set based on country requirements.
Click Apply/Save to apply the selected wireless options.
Consult the table below for descriptions of these options.
Option Description
Enable
Wireless
104
A checkbox that enables or disables the wireless LAN interface.
When selected, a set of basic wireless options will appear.
Option Description
Hide Access
Point
Select Hide Access Point to protect the access point from detection
by wireless active scans. To check AP status in Windows XP, open
Network Connections from the start Menu and select View
Available Network Connections. If the access point is hidden, it
will not be listed there. To connect a client to a hidden access point,
the station must add the access point manually to its wireless
configuration.
Clients
Isolation
When enabled, it prevents client PCs from seeing one another in My
Network Places or Network Neighborhood. Also, prevents one
wireless client communicating with another wireless client.
Disable WMM
Advertise
Stops the router from ‘advertising’ its Wireless Multimedia (WMM)
functionality, which provides basic quality of service for
time-sensitive applications (e.g. VoIP, Video).
Enable
Select the checkbox to enable this function.
Wireless
Multicast
Forwarding
Enable WiFi
Select the checkbox to enable the WiFi button.
Button
SSID
[1-32
characters]
Sets the wireless network name. SSID stands for Service Set
Identifier. All stations must be configured with the correct SSID to
access the WLAN. If the SSID does not match, that user will not be
granted access.
BSSID The BSSID is a 48-bit identity used to identify a particular BSS
(Basic Service Set) within an area. In Infrastructure BSS
networks, the BSSID is the MAC (Media Access Control) address of
the AP (Access Point); and in Independent BSS or ad hoc networks,
the BSSID is generated randomly.
Country A drop-down menu that permits worldwide and specific national
settings. Local regulations limit channel range:
US= worldwide, Japan=1-14, Jordan= 10-13, Israel= 1-13
Max Clients The maximum number of clients that can access the router.
Wireless Guest /
Virtual
Access Points
This router supports multiple SSIDs called Guest SSIDs or Virtual
Access Points. To enable one or more Guest SSIDs select the
checkboxes in the Enabled column. To hide a Guest SSID select
its checkbox in the Hidden column.
Do the same for Isolate Clients and Disable WMM Advertise.
For a description of these two functions, see the previous entries for
“Clients Isolation” and “Disable WMM Advertise”. Similarly, for
Enable WMF, Max Clients and BSSID, consult the matching
entries in this table.
NOTE: Remote wireless hosts cannot scan Guest SSIDs.
105
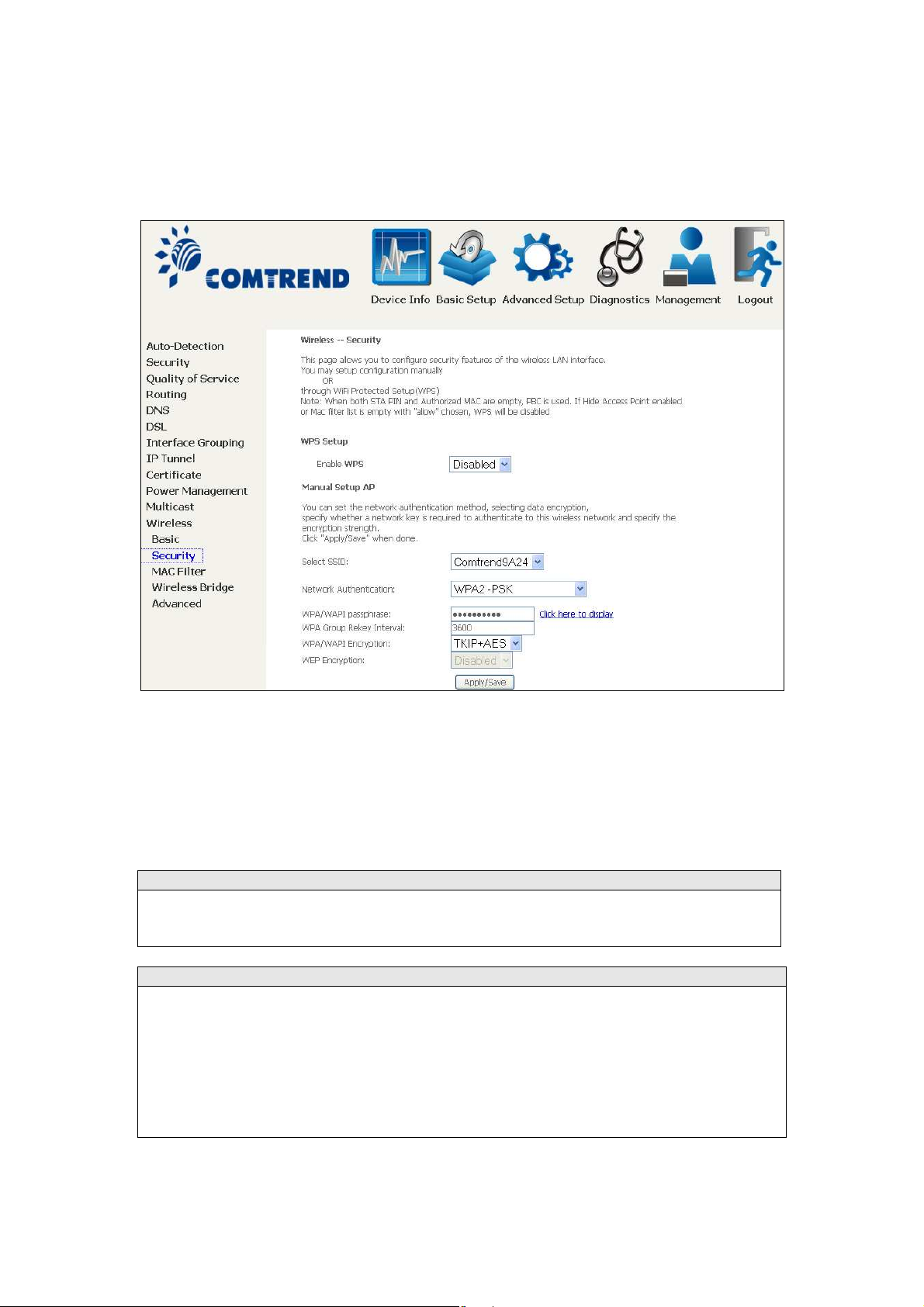
6.12.2 Security
g
The following screen appears when Wireless Security is selected. The options shown
here allow you to configure security features of the wireless LAN interface.
Click Apply/Save to implement new configuration settings.
WIRELESS SECURITY
Setup requires that the user configure these settings using the Web User Interface
(see the table below).
Select SSID
Select the wireless network name from the drop-down box. SSID stands for Service
Set Identifier. All stations must be confi
WLAN. If the SSID does not match, that client will not be granted access.
Network Authentication
This option specifies whether a network key is used for authentication to the
wireless network. If network authentication is set to Open, then no authentication
is provided. Despite this, the identity of the client is still verified.
Each authentication type has its own settings. For example, selecting 802.1X
authentication will reveal the RADIUS Server IP address, Port and Key fields. WEP
Encryption will also be enabled as shown below.
ured with the correct SSID to access the
106
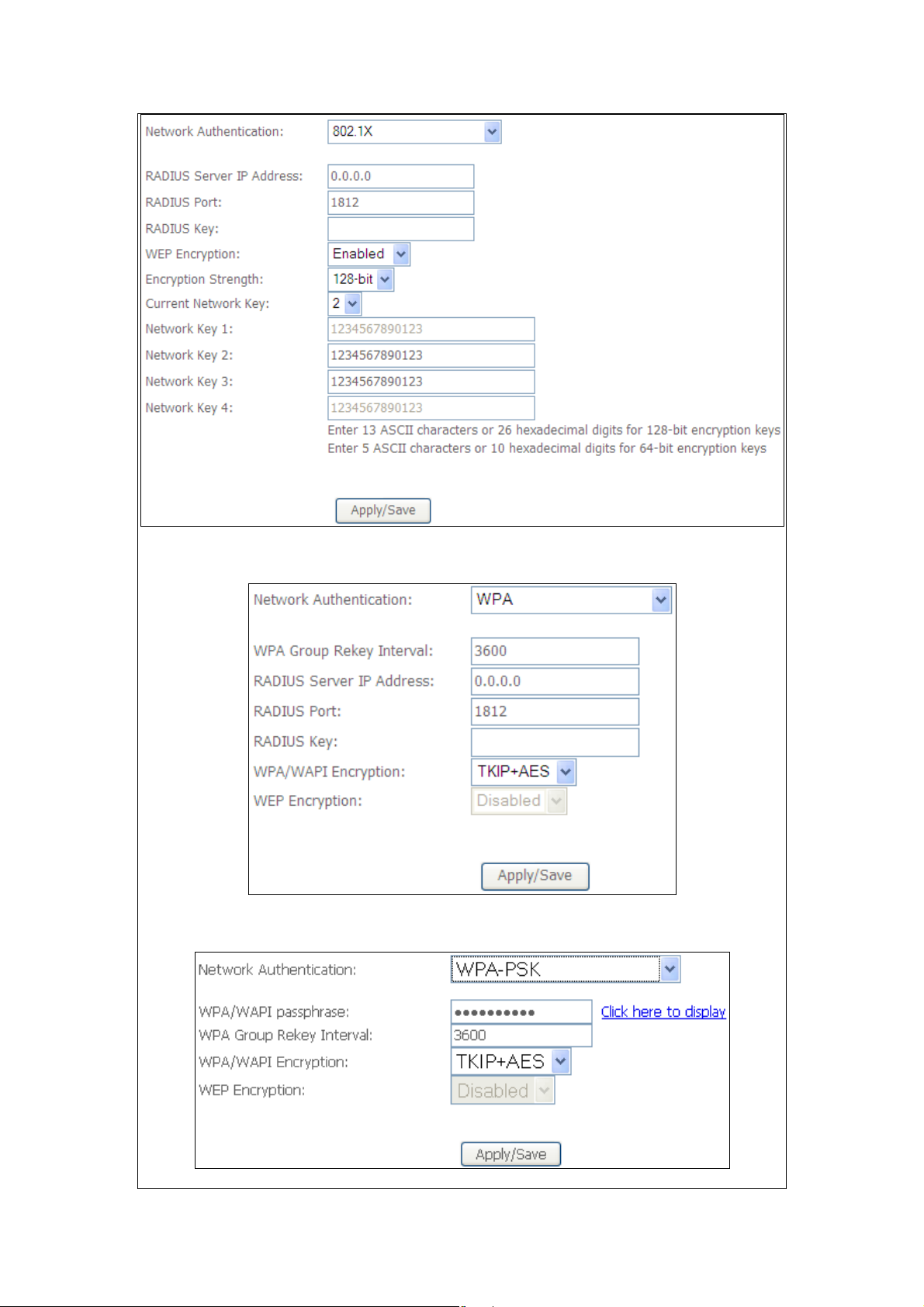
The settings for WPA authentication are shown below.
The settings for WPA-PSK authentication are shown next.
107
WEP Encryption
g
g
g
g
This option specifies whether data sent over the network is encrypted. The same
network key is used for data encryption and network authentication. Four network
keys can be defined althou
Network Key list box to select the appropriate network key.
Security options include authentication and encryption services based on the wired
equivalent privacy (WEP) algorithm. WEP is a set of security services used to
protect 802.11 networks from unauthorized access, such as eavesdroppin
case, the capture of wireless network traffic.
When data encryption is enabled, secret shared encryption keys are
used by the source station and the destination station to alter frame bits, thus
avoiding disclosure to eavesdroppers.
Under shared key authentication, each wireless station is assumed to have received
a secret shared key over a secure channel that is independent from the 802.11
wireless network communications channel.
Encryption Strength
This drop-down list box will display when WEP Encryption is enabled. The key
strength is proportional to the number of binary bits comprising the key. This
means that keys with a
are considerably more difficult to crack. Encryption strength can be set to either
64-bit or 128-bit. A 64-bit key is equivalent to 5 ASCII characters or 10
hexadecimal numbers. A 128-bit key contains 13 ASCII characters or 26
hexadecimal numbers. Each key contains a 24-bit header (an initiation vector)
which enables parallel decoding of multiple streams of encrypted data.
h only one can be used at any one time. Use the Current
; in this
enerated and
reater number of bits have a greater degree of security and
108
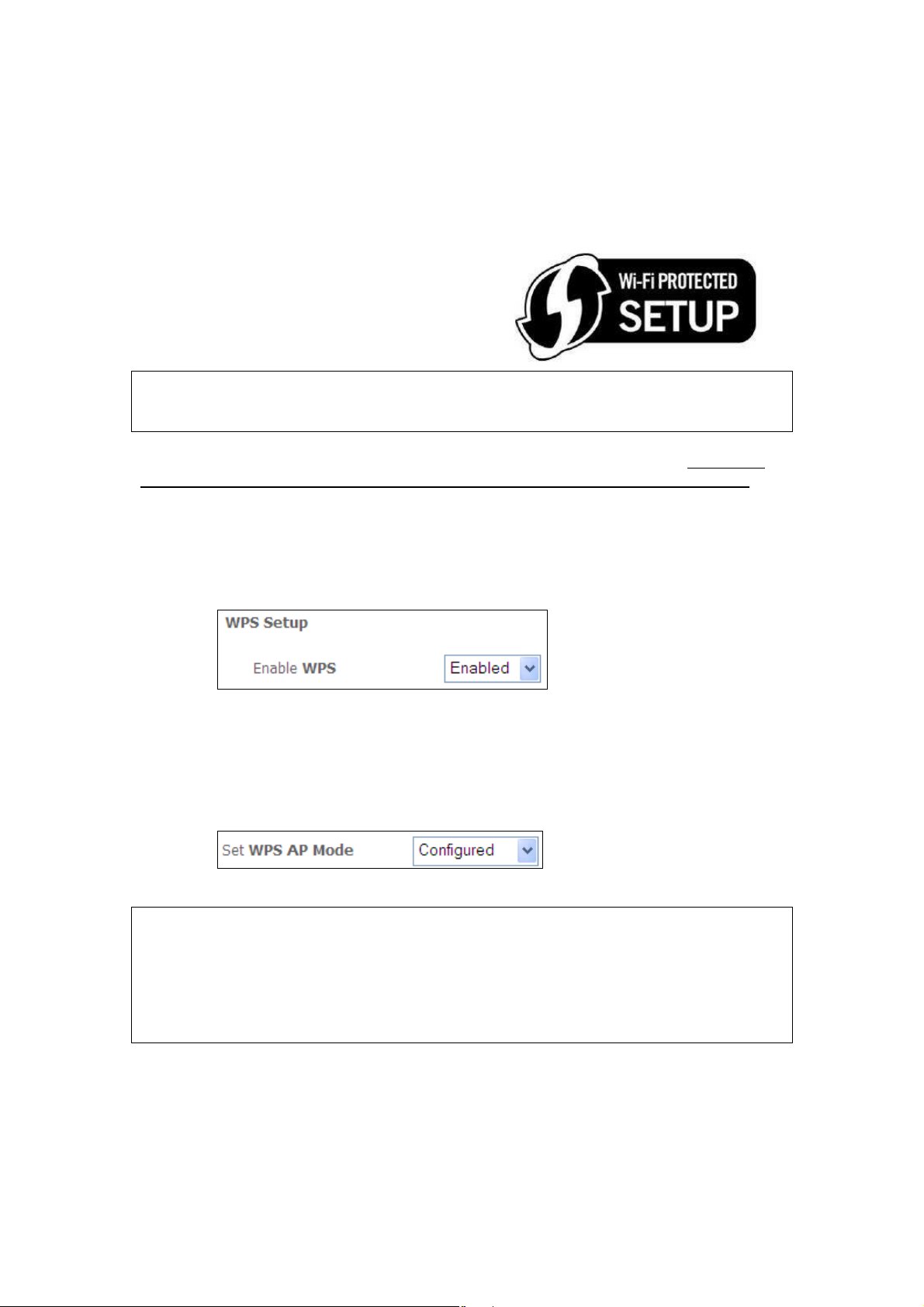
6.12.3 WPS
Wi-Fi Protected Setup (WPS) is an industry standard that simplifies wireless security
setup for certified network devices. Every WPS certified device has both a PIN
number and a push button, located on the device or accessed through device
software. The AR-5312u has a WPS button on the device.
Devices with the WPS logo (shown here)
support WPS. If the WPS logo is not present
on your device it still may support WPS, in
this case, check the device documentation
for the phrase “Wi-Fi Protected Setup”.
NOTE: WPS is only available in Open, WPA-PSK, WPA2-PSK and Mixed
WPA2/WPA-PSK network authentication modes. Other authentication
modes do not use WPS so they must be configured manually.
To configure security settings with WPS, follow the procedures below. You must
choose either the Push-Button or PIN configuration method for Steps 6 and 7.
I. Setup
Step 1: Enable WPS by selecting Enabled from the drop down list box shown.
Step 2: Set the WPS AP Mode. Configured is used when the AR-5312u will assign
security settings to clients. Unconfigured is used when an external
client assigns security settings to the AR-5312u.
NOTES: You r client may or may not have the ability to provide security settings to
the AR-5312u. If it does not, then you must set the WPS AP mode to
Configured. Consult the device documentation to check its capabilities.
In addition, using Windows 7, you can add an external registrar using the
Config AP button (Appendix F - WPS OPERATION has detailed
instructions).
109
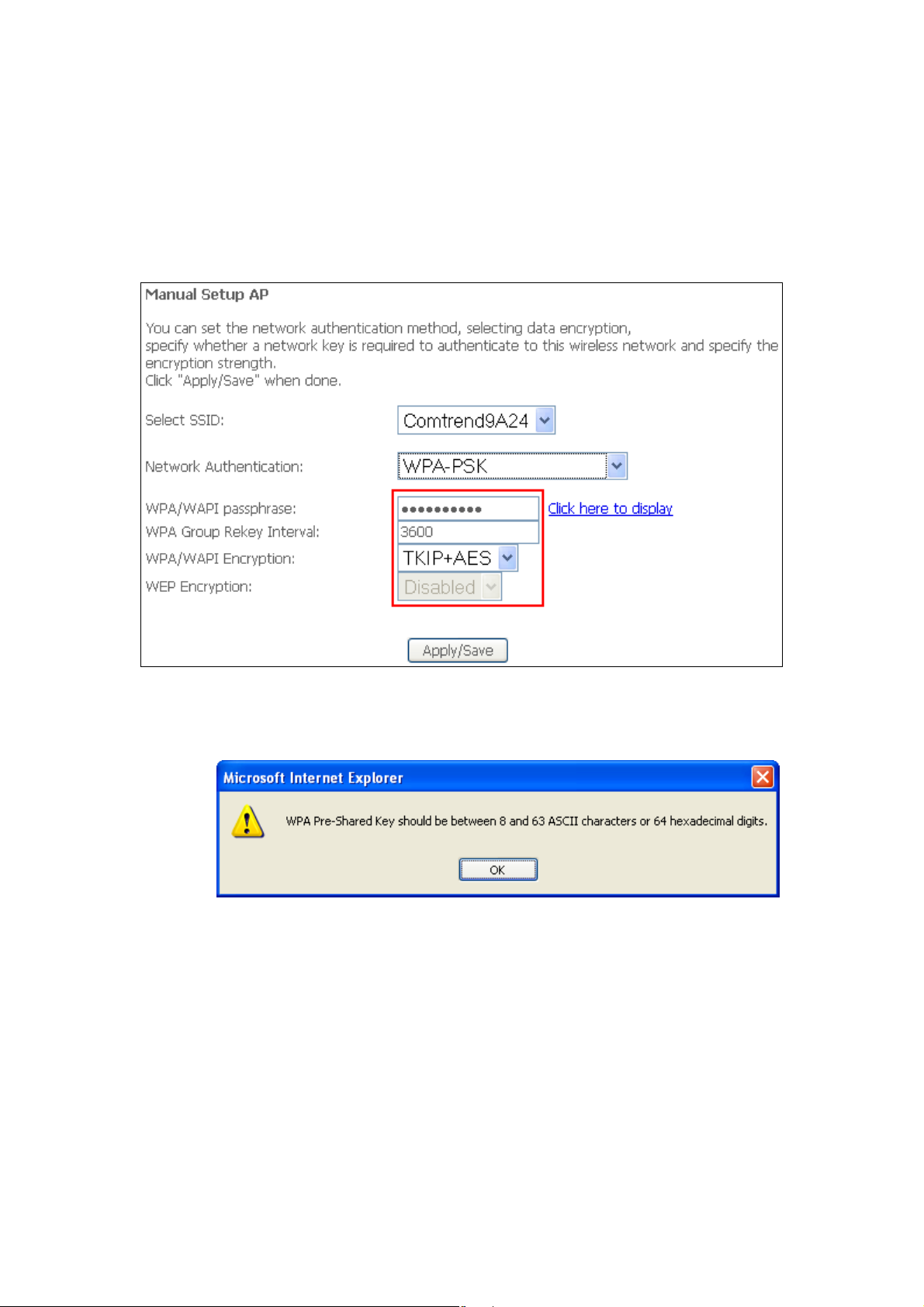
II. NETWORK AUTHENTICATION
Step 3: Select Open, WPA-PSK, WPA2-PSK, or Mixed WPA2/WPA-PSK network
authentication mode from the Manual Setup AP section of the Wireless
Security screen. The example below shows WPA2-PSK mode.
Step 4: For the Pre-Shared Key (PSK) modes, enter a WPA Pre-Shared Key. You
will see the following dialog box if the Key is too short or too long.
Step 5: Click the Apply/Save button at the bottom of the screen.
IIIa. PUSH-BUTTON CONFIGURATION
The WPS push-button configuration provides a semi-automated configuration
method. The WPS button on the rear panel of the router can be used for this
purpose or the Web User Interface (WUI) can be used exclusively.
The WPS push-button configuration is described in the procedure below. It is
assumed that the Wireless function is Enabled and that the router is configured as
the Wireless Access Point (AP) of your WLAN. In addition, the wireless client must
also be configured correctly and turned on, with WPS function enabled.
110
NOTE: The wireless AP on the router searches for 2 minutes. If the router stops
searching before you complete Step 7, return to Step 6.
Step 6: Press WPS button
Press the WPS button on the front panel of the router. The WPS LED will
blink to show that the router has begun searching for the client.
Step 7: Go to your WPS wireless client and activate the push-button function.
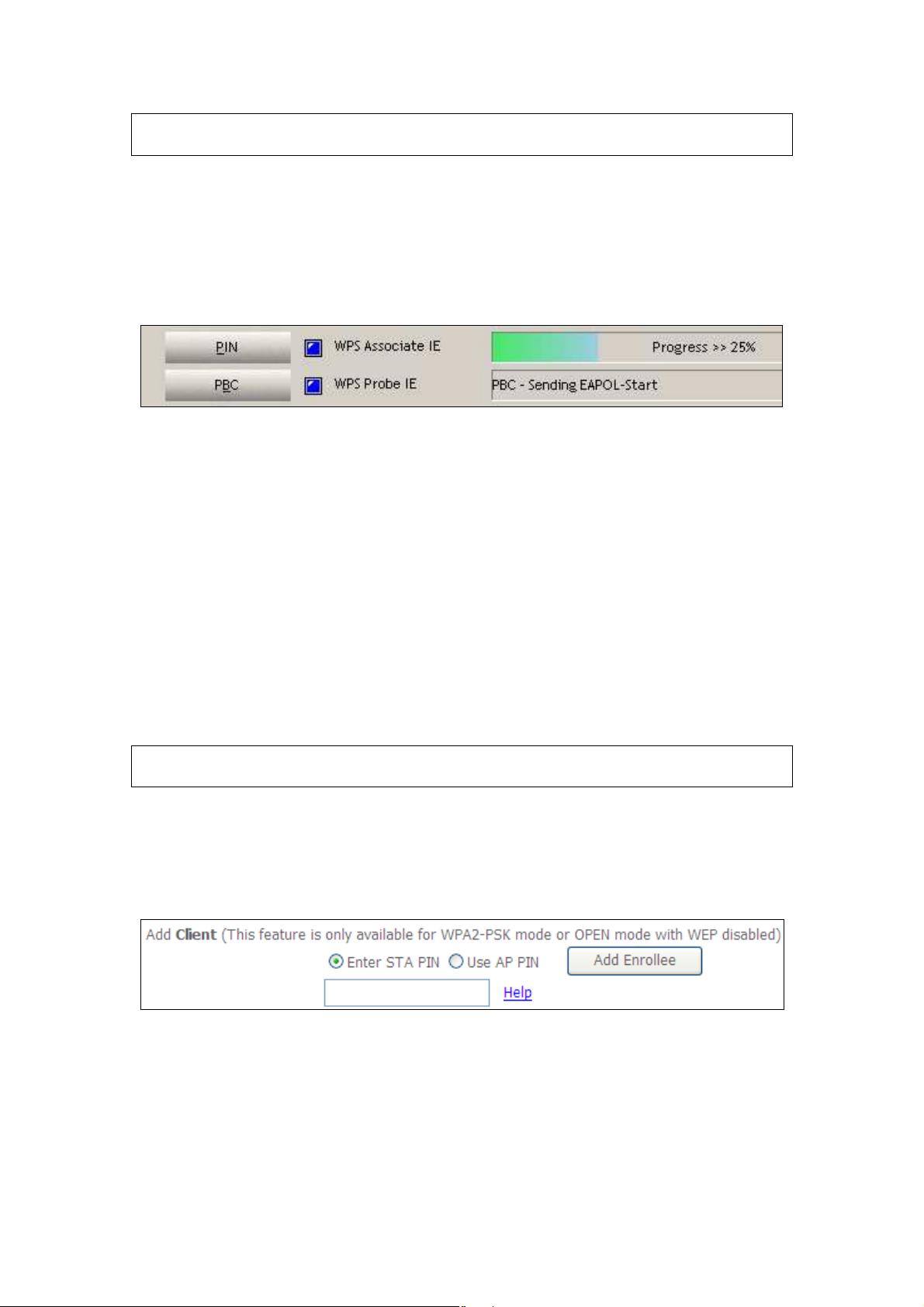
A typical WPS client screenshot is shown below as an example.
Now go to Step 8 (part IV. Check Connection) to check the WPS connection.
IIIb. WPS – PIN CONFIGURATION
Using this method, security settings are configured with a personal identification
number (PIN). The PIN can be found on the device itself or within the software.
The PIN may be generated randomly in the latter case. To obtain a PIN number for
your client, check the device documentation for specific instructions.
The WPS PIN configuration is described in the procedure below. It is assumed that
the Wireless function is Enabled and that the router is configured as the Wireless
Access Point (AP) of your wireless LAN. In addition, the wireless client must also be
configured correctly and turned on, with WPS function enabled.
NOTE: Unlike the push-button method, the pin method has no set time limit.
This means that the router will continue searching until it finds a client.
Step 6: Select the PIN radio button in the WSC Setup section of the Wireless
Security screen, as shown in A or B below, and then click the appropriate
button based on the WSC AP mode selected in step 2.
A - For Configured mode, click the Add Enrollee button.
Enter STA PIN: a Personal Identification Number (PIN) has to be read from either
a sticker or the display on the new wireless device. This PIN must then be inputted
at representing the network, usually the Access Point of the network.
B - For Unconfigured mode, click the Config AP button.
111
Step 7: Activate the PIN function on the wireless client. For Configured mode,
the client must be configured as an Enrollee. For Unconfigured mode,
the client must be configured as the Registrar. This is different from the
External Registrar function provided in Windows Vista.
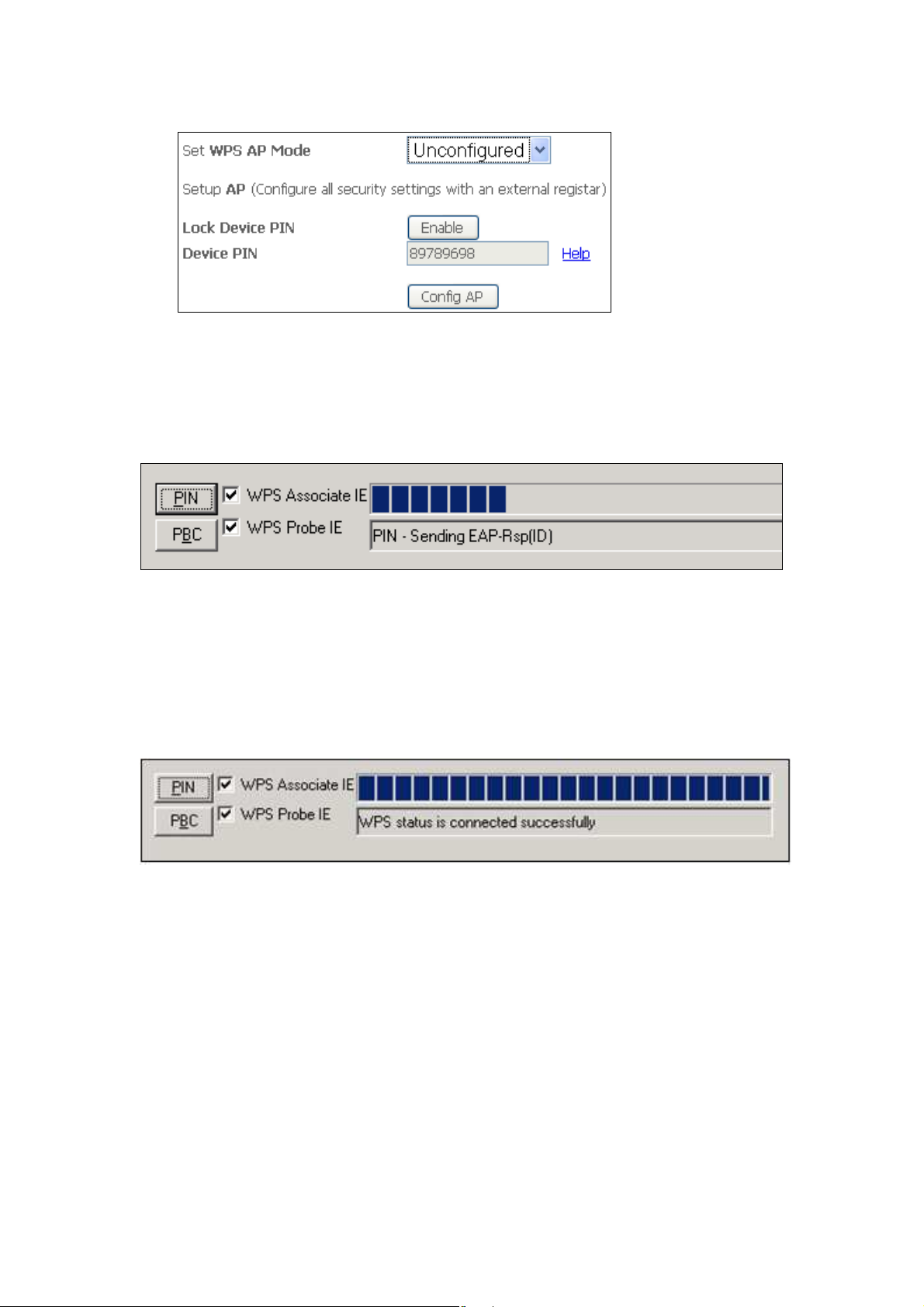
The figure below provides an example of a WPS client PIN function in-progress.
Now go to Step 8 (part IV. Check Connection) to check the WPS connection.
IV. CHECK CONNECTION
Step 8: If the WPS setup method was successful, you will be able access the
wireless AP from the client. The client software should show the status.
The example below shows that the connection established successfully.
You can also double-click the Wireless Network Connection icon from the
Network Connections window (or the system tray) to confirm the status of
the new connection.
112
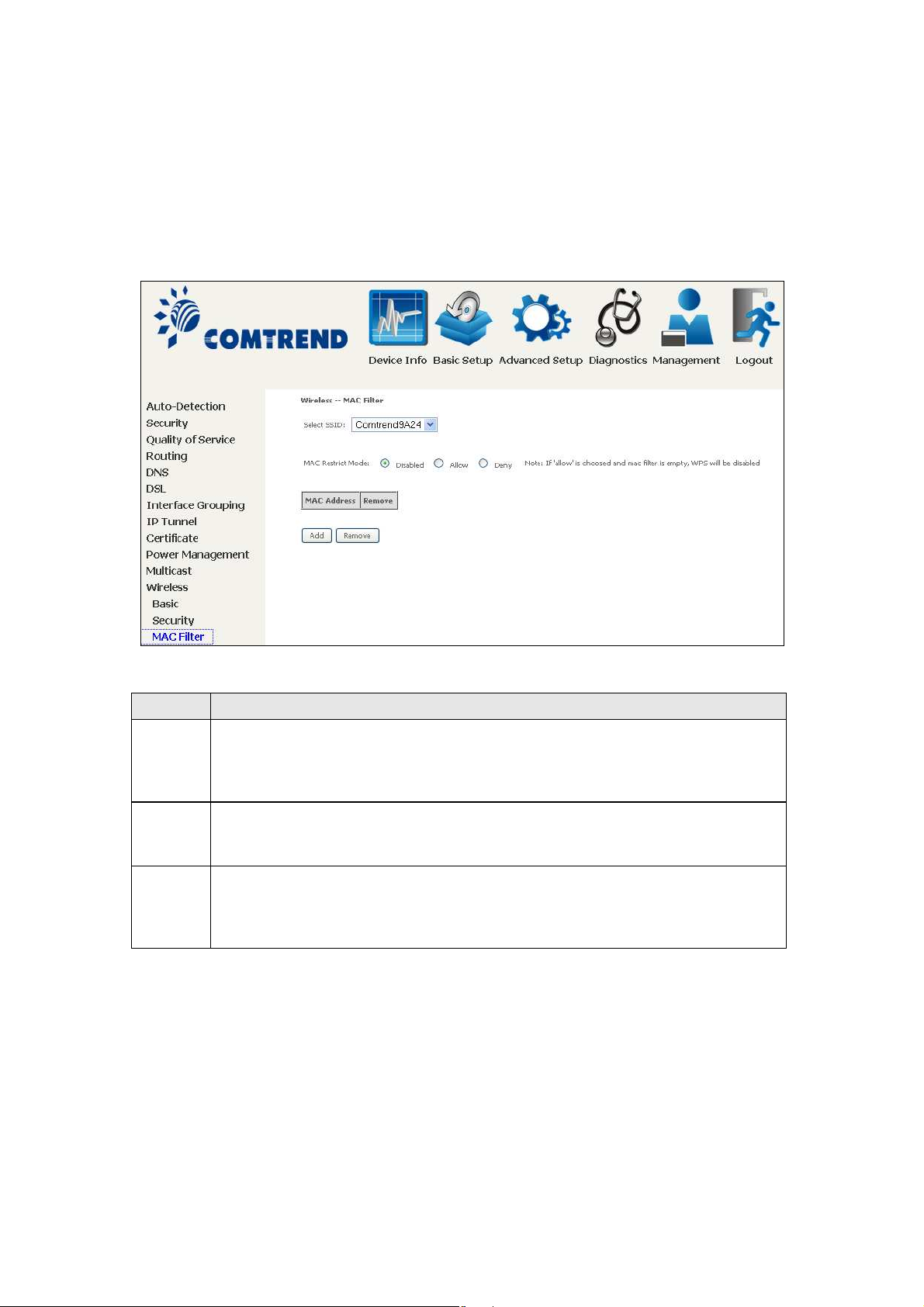
6.12.4 MAC Filter
This option allows access to the router to be restricted based upon MAC addresses.
To add a MAC Address filter, click the Add button shown below. To delete a filter,
select it from the MAC Address table below and click the Remove button.
Option Description
Select
SSID
MAC
Restrict
Mode
MAC
Address
After clicking the Add button, the following screen appears.
Select the wireless network name from the drop-down box. SSID stands
for Service Set Identifier. All stations must be configured with the correct
SSID to access the WLAN. If the SSID does not match, that user will not
be granted access.
Disabled: MAC filtering is disabled.
Allow: Permits access for the specified MAC addresses.
Deny: Rejects access for the specified MAC addresses.
Lists the MAC addresses subject to the MAC Restrict Mode. A maximum
of 60 MAC addresses can be added. Every network device has a unique
48-bit MAC address. This is usually shown as xx.xx.xx.xx.xx.xx, where
xx are hexadecimal numbers.
113
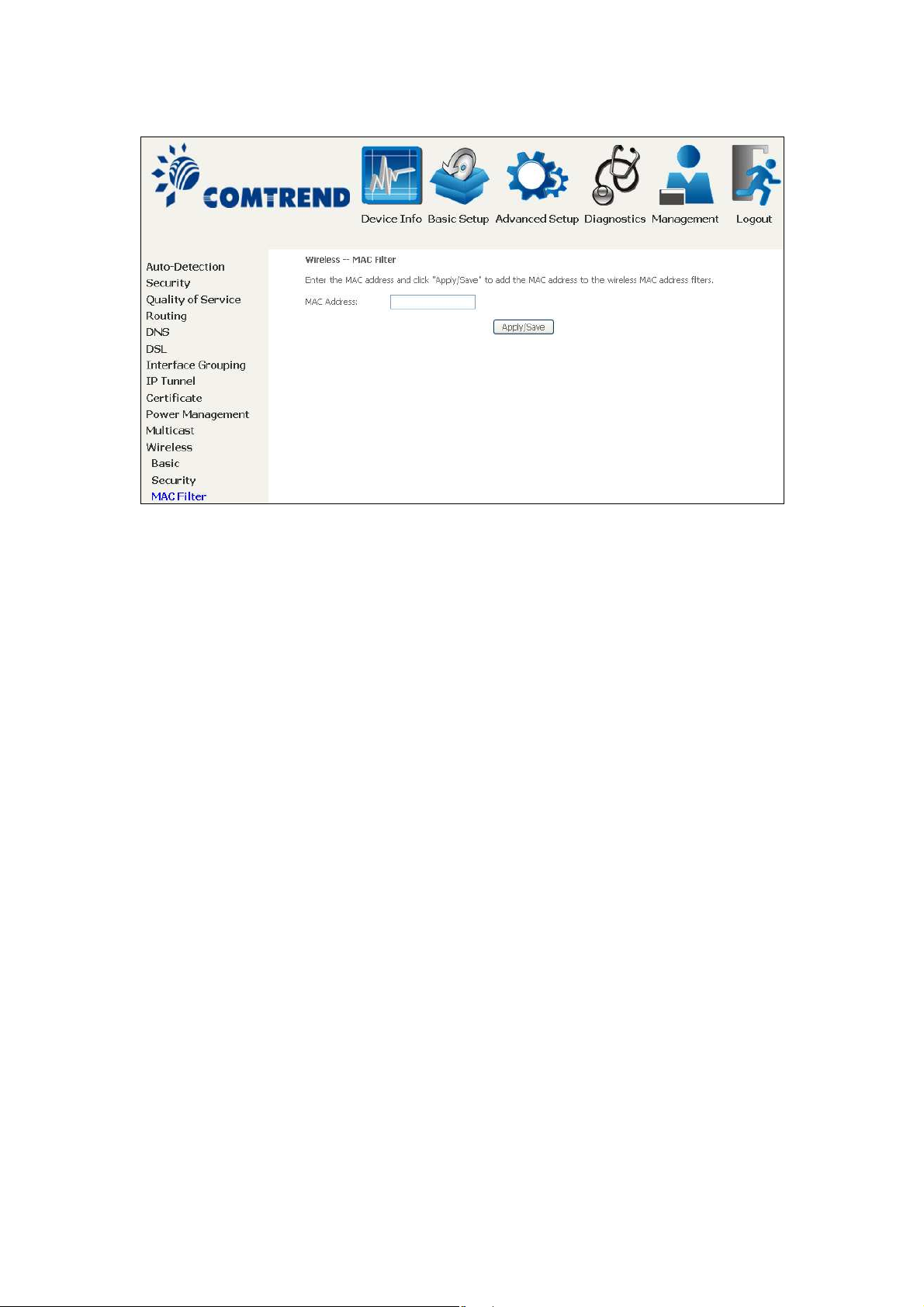
Enter the MAC address in the box provided and click Apply/Save.
114
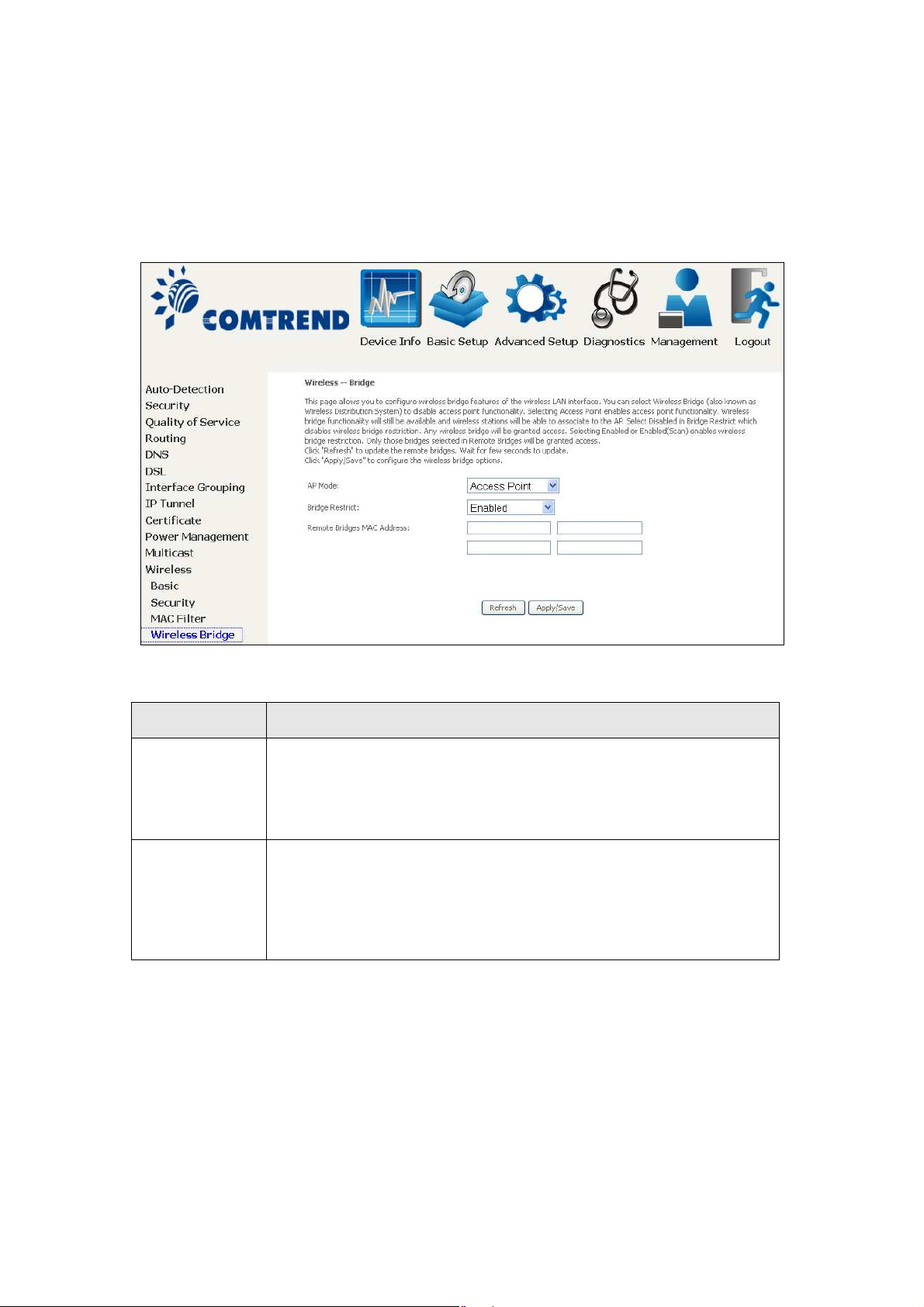
6.12.5 Wireless Bridge
This screen allows for the configuration of wireless bridge features of the WIFI
interface. See the table beneath for detailed explanations of the various options.
Click Apply/Save to implement new configuration settings.
Feature Description
AP Mode Selecting Wireless Bridge (aka Wireless Distribution System)
disables Access Point (AP) functionality, while selecting Access
Point enables AP functionality. In Access Point mode, wireless
bridge functionality will still be available and wireless stations
will be able to associate to the AP.
Bridge Restrict Selecting Disabled disables wireless bridge restriction, which
means that any wireless bridge will be granted access.
Selecting Enabled or Enabled (Scan) enables wireless bridge
restriction. Only those bridges selected in the Remote Bridges
list will be granted access. Click Refresh to update the station
list when Bridge Restrict is enabled.
115
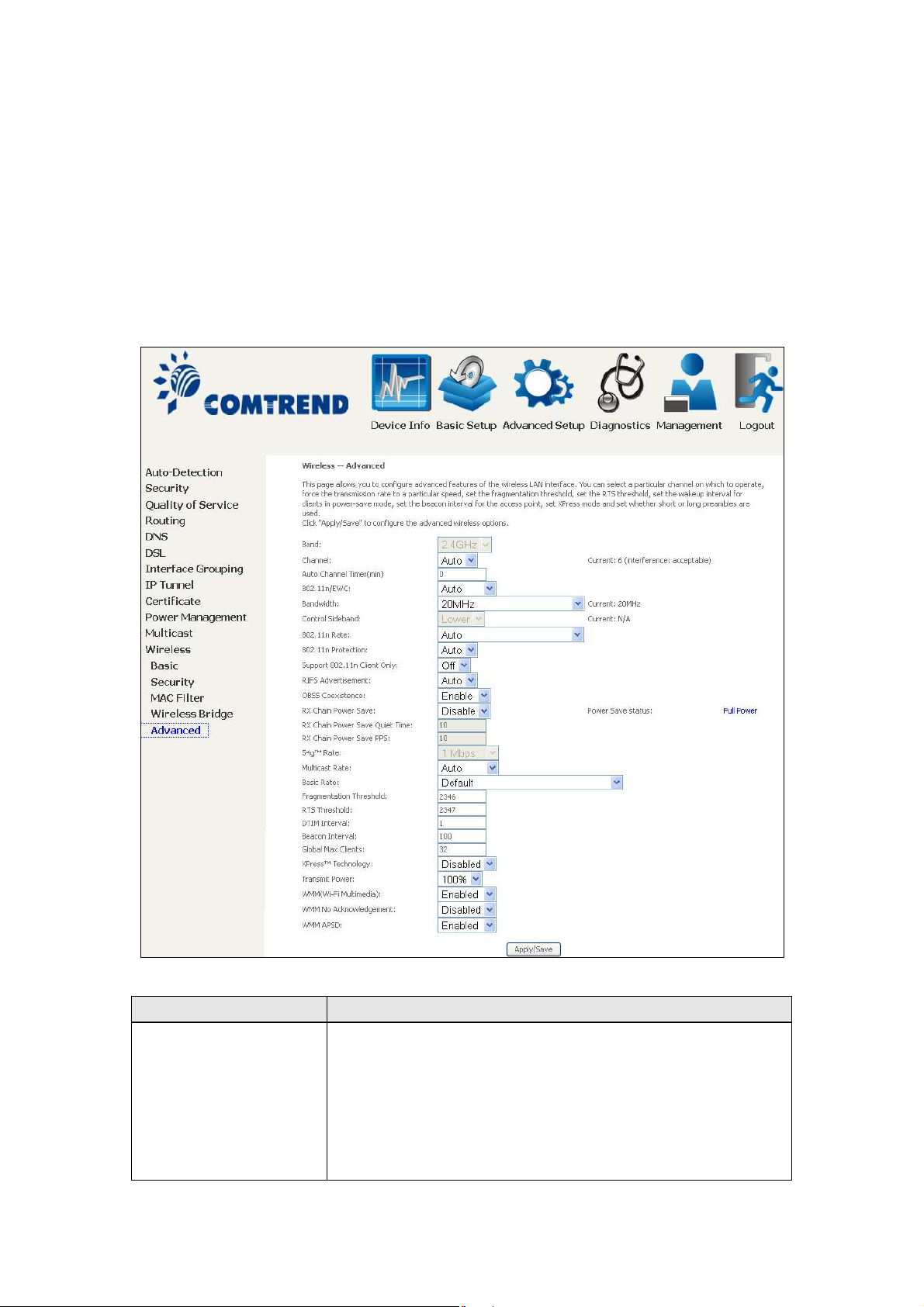
6.12.6 Advanced
The Advanced screen allows you to configure advanced features of the wireless LAN
interface. You can select a particular channel on which to operate, force the
transmission rate to a particular speed, set the fragmentation threshold, set the RTS
threshold, set the wakeup interval for clients in power-save mode, set the beacon
interval for the access point, set XPress mode and set whether short or long
preambles are used. Click Apply/Save to set new advanced wireless options.
Field Description
Band Set to 2.4 GHz for compatibility with IEEE 802.11x
standards. The new amendment allows IEEE 802.11n
units to fall back to slower speeds so that legacy IEEE
802.11x devices can coexist in the same network. IEEE
802.11g creates data-rate parity at 2.4 GHz with the IEEE
802.11a standard, which has a 54 Mbps rate at 5 GHz.
(IEEE 802.11a has other differences compared to IEEE
802.11b or g, such as offering more channels.)
116
 Loading...
Loading...