Page 1

User's Guide
Acronis
®
True Image
for Microsoft Small
Business Server
Compute with confidence
www.acronis.com
Page 2

Copyright © Acronis, Inc., 2000-2008. All rights reserved.
“Acronis” and “Acronis Secure Zone” are registered trademarks of Acronis, Inc.
"Acronis Compute with Confidence", “Acronis Startup Recovery Manager”, “Acronis Activ e
restore” and the Acronis logo are trademarks of Acronis, Inc.
Linux is a registered trademark of Linus Torvalds.
Windows and MS-DOS are registered trademarks of Microsoft Corporation.
All other trademarks and copyrights referred to are the property of their respective
owners.
Distribution of substantively modified versions of this document is prohibited without t he
explicit permission of the copyright holder.
Distribution of this work or derivative work in any standard (paper) book form for
commercial purposes is prohibited unless prior permission is obtained fr om the copyright
holder.
DOCUMENTATION IS PROVIDED «AS IS» AND ALL EXPRESS OR IMPLIED CONDITIONS,
REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF
MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT,
ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE
LEGALLY INVALID.
2 Copyright © Acronis, Inc., 2000-2008
Page 3
ACRONIS, INC.
End User License Agreement (EULA)
BEFORE INSTALLING AND USING THE SOFTWARE PRODUCT WHICH EITHER YOU HAVE
DOWNLOADED OR IS CONTAINED ON THESE DISKS (“SOFTWARE”) YOU SHOULD CAREFULLY
READ THE FOLLOWING LICENSE AGREEMENT (“AGREEMENT”) THAT APPLIES TO THE
SOFTWARE. CLICK “ACCEPT” IF YOU FULLY ACCEPT AND AGREE TO ALL OF THE PROVISIONS OF
THIS AGREEMENT. OTHERWISE, CLICK “DO NOT ACCEPT.” CLICKING “ACCEPT” OR OTHERWISE
DOWNLOADING, INSTALLING AND OR USING THE SOFTWARE ESTABLISHES A BINDING
AGREEMENT BETWEEN YOU AS THE PERSON LICENSING THE SOFTWARE (THE "LICENSEE") AND
ACRONIS, INC. LOCATED AT: ACRONIS INTERNATIONAL GMBH VERWALTUNG EURO HAUS
RHEINWEG 5 SCHAFFHAUSEN, SWITZERLAND CH-8200, ("LICENSOR"). IF YOU DO NOT ACCEPT
ALL OF THE TERMS OF THIS AGREEMENT, YOU SHALL HAVE NOT RIGHT TO DOWNLOAD, INSTALL
AND/OR USE THE SOFTWARE AND MUST DELETE THE SOFTWARE AND ASSOCIATED FILES
IMMEDIATELY.
This Agreement applies to the Software, whether licensed under a Software License and/or an
Evaluation License, each as defined and described below:
purchase of a license to the Software, LICENSOR grants and LICENSEE accepts a nonexclusive, nontransferable,
Purchased License of Software
nonassignable license to use Software only for LICENSEE’s own internal use solely on the specific number of
Hardware (as defined below) licensed owned, leased or otherwise controlled by LICENSEE. LICENSEE may make
one copy of Software only for archival purposes, only in machine readable form, provided that such archival copy is
only used for archival purposes and never in a production environment and is marked with every notice on the
original Installation of Software is LICENSEE’s responsibility. The license described in this section shall be referred
to as a “Software License”).
. Subject to the terms and conditions of this Agreement, upon
Evaluation License of Software: The LICENSEE has the right to evaluate the Software for a period of
time not to exceed fifteen (15) days (the “Evaluation Period’) unless extended by LICENSOR. Software licensed
under this Evaluation License may not be used in a production environment. There will be no charge to the
LICENSEE for said evaluation of the Software under this Evaluation License. At the conclusion of the Evaluation
Period, unless a Software License to the Software is purchased, the LICENSEE will delete the Software from its
systems and have no further license or other rights with respect to the Software except as to the rights and
responsibilities in this Agreement. LICENSOR SHALL NOT BE LIABLE FOR ANY SPECIAL, DIRECT, INDIRECT,
PUNITIVE, OR CONSEQUENTIAL DAMAGES RESULTING FROM USE OF SOFTWARE UNDER THE
EVALUATION LICENSE UNDER ANY CONTRACT, NEGLIGENCE, STRICT LIABILITY OR OTHER THEORY.
THESE LIMITATIONS SHALL APPLY NOTWITHSTANDING ANY FAILURE OF ESSENTIAL PURPOSE OF ANY
LIMITED REMEDY. The following sections of this Agreement also apply to Evaluation License(s) of the Software:
Limitations, Confidentiality
Miscellaneous. The license described in this section shall be referred to as an “Evaluation License”).
, Disclaimer of Warranties, LICENSEE Indemnity, Law, Export Restrictions, and
Use Rights:
Assigning the License
that license to one of your PCs or Servers (depending upon the license you have purchased or are evaluating and
such purchase or evaluation is based upon the operating system on which that hardware operates, such PCs or
Servers shall be referred to as the “Hardware”). That Hardware is the licensed Hardware for that particular
Software license. You may assign other Software Licenses to the same Hardware, but you may not assign the same
Software License to more than one Hardware except as identified herein.
You may reassign a Software License if you retire the licensed Hardware due to permanent Hardware failure. If you
reassign a Software License, the Hardware to which you reassign the license becomes the new licensed Hardware
for that particular Software License.
. Before you run any instance of the Software under a Software License, you must assign
Running Instances of the Hardware Software. You have the rights to run the Software on one piece of
Hardware as defined above. Every Hardware creating an image and every Hardware to which an image is either
deployed to or restored from must have a valid license. In the case of Universal Deploy or Universal Restore, every
time an image is deployed or restored (as appropriate to either Universal Restore or Universal Deploy), to Hardware
that is dissimilar to the Hardware from which the image was originally created, a valid license of the Universal
Deploy or Universal Restore is required.
You have the rights below for each Software License you assign:
Standard Software license. A standard Software License is the general license that is available to LICENSEE.
Unless the Virtual Edition Software is purchased, you have purchased the standard Software License and may run
on the licensed Hardware, at any one time as follows:
Copyright © Acronis, Inc., 2000-2008 3
Page 4
• One (1) instance of the Hardware installed Software in one physical operating system environment; and
• Up to four (4) instances of the Hardware installed Software in virtual operating system environments (only
one (1) instance per virtual operating system environment).
If you run all five (5) permitted instances at the same time, the instance of the Hardware installed Software
running in the physical operating system environment may be used only to run hardware virtualization software
and to manage and service operating system environments on the licensed Hardware.
Virtual Edition. Virtual Edition (as identified by the product name (for example, True Image Virtual Edition)) is
licensed by physical Hardware. You may run on the licensed Hardware, at any one time as follows:
• One instance of the Hardware software in one physical operating system environment; and
• As many instances of the Hardware software in virtual operating system environments.
Support. If LICENSEE is under a current support contract with LICENSOR with respect to the Software and is
current in paying all amounts due thereunder, LICENSOR shall make available to LICENSEE the support described
in this paragraph (the “Support”) on a twenty four (24) hours a day, seven (7) days per week basis. Support shall
consist of: (i) supplying telephone or other electronic support, as determined by LICENSOR in its sole discretion, to
LICENSEE in order to help LICENSEE locate and, on its own, correct problems with the Software and (ii) supplying
all extensions, enhancements and other changes that LICENSOR, at its sole discretion, makes or adds to the
Software and which LICENSOR makes generally available, without additional charge, to other licensees of the
Software that are enrolled in Support. Upon mutual written agreement by both parties, LICENSOR may, but shall not
be required to: (i) supply code corrections to LICENSEE to correct Software malfunctions in order to bring such
Software into substantial conformity with the published operating specifications for the most current version of the
Software unless LICENSEE’s unauthorized modifications prohibit or hamper such corrections or cause the
malfunction; or (ii) supply code corrections to correct insubstantial problems at the next general release of the
Software.
Limitations. Notwithstanding any references to “purchase” , the Software is licensed and not sold pursuant to this
Agreement. This Agreement confers a limited license to the Software and does not constitute a transfer of title to or
sale of all or a portion of the Software, and LICENSOR retains ownership of all copies of the Software. LICENSEE
acknowledges that the Software contain trade secrets of LICENSOR, its suppliers or licensors, including but not
limited to the specific internal design and structure of individual programs and associated interface information.
Accordingly, except as otherwise expressly provided under this Agreement, LICENSEE shall have no right, and
LICENSEE specifically agrees not to: (i) transfer, assign or sublicense its license rights to any other person or entity,
or use the Software on ay equipment other than the Hardware, and LICENSEE acknowledges that any attempted
transfer, assignment, sublicense or use shall be void; (ii) make error corrections to or otherwise modify or adapt the
Software or create derivative works based upon the Software, or permit third parties to do the same; (iii) reverse
engineer or decompile, decrypt, disassemble or otherwise reduce the Software to human-readable form, except to
the extent otherwise expressly permitted under applicable law notwithstanding this restriction; (iv) use or permit the
Software to be used to perform services for third parties, whether on a service bureau or time sharing basis or
otherwise, without the express written authorization of LICENSEE; or (v) disclose, provide, or otherwise make
available trade secrets contained within the Software in any form to any third party without the prior written consent
of LICENSOR.
Confidentiality. The Software is a trade secret of LICENSOR and is proprietary to LICENSOR. LICENSEE shall
maintain Software in confidence and prevent disclosure of Software using at least the same degree of care it uses
for its own similar proprietary information, but in no event less than a reasonable degree of care. LICENSEE shall
not disclose Software or any part thereof to anyone for any purpose, other than to employees for the purpose of
exercising the rights expressly granted under this Agreement. License shall not, and shall not allow any third party
to, decompile, disassemble or otherwise, reverse engineer or attempt to reconstruct or discover any source code or
underlying ideas, algorithms, file formats or programming or interoperability interfaces of Software or of any files
contained or generated using Software by any means whatsoever. The obligations under this paragraph shall
survive any termination of the Agreement.
Disclaimer of Warranties. THE SOFTWARE IS PROVIDED “AS IS” AND LICENSOR DISCLAIMS ALL
WARRANTIES, EXPRESSED OR IMPLIED WITH RESPECT TO SOFTWARE INCLUDING ALL IMPLIED
WARRANTIES OF MERCHANTABILITY, TITLE, NON-INFRINGEMENT OF THIRD PARTIES’ RIGHTS, AND
FITNESS FOR A PARTICULAR USE. WITHOUT LIMITING THE FOREGOING, LICENSOR DOES NOT
WARRANT THAT THE FUNCTIONS CONTAINED IN SOFTWARE WILL OPERATE IN THE COMBINATION
LICENSEE SELECTS, THAT OPERATION OF SOFTWARE WILL BE UNINTERRUPTED OR ERROR-FREE
AND/OR THAT DEFECTS IN THE SOFTWARE WILL BE CORRECTED. THE ENTIRE RISK AS TO THE RESULTS
AND PERFORMANCE OF THE SOFTWARE IS ASSUMED BY LICENSEE. FURTHERMORE, LICENSOR DOES
NOT WARRANT OR MAKE ANY RE PRESENTATIONS REGARDING THE U SE OR THE RESULT S OF THE USE
OF THE SOFTWARE OR RELATED DOCUMENTATION IN TERMS OF THEIR CORRECTNESS, ACCURACY,
RELIABILITY, CURRENTNESS, OR OTHERWISE. NO ORAL OR WR ITTEN INFORMATION OR ADVICE GIVEN
4 Copyright © Acronis, Inc., 2000-2008
Page 5
BY LICENSOR SHALL CREATE A WARRANTY OR IN ANY WAY INCREASE THE SCOPE OF THIS WARRANTY.
Liability Limitations. LICENSOR SHALL NOT BE LIABLE FOR ANY SPECIAL, INDIRECT, PUNITIVE, OR
CONSEQUENTIAL DAMAGES RESULTING FROM USE OF SOFTWARE UNDER ANY CONTRACT,
NEGLIGENCE, STRICT LIABILITY OR OTHER THEORY. LICENSOR’S CUMULATIVE LIAB ILIT Y FOR DAMAGE S
HEREUNDER, WHETHER IN AN ACTION IN CONTRACT, WARRANTY, TORT, NEGLIGENCE, STRICT
LIABILITY, INDEMNITY, OR OTHERWISE, SHALL IN NO EVENT EXCEED THE AMOUNT OF LICENSE FEES
PAID BY THE LICENSEE FOR THE SOFTWARE LICENSED UNDER THIS AGREEMENT. THESE LIMITATIONS
SHALL APPLY NOTWITHSTANDING ANY FAILURE OF ESSENTIAL PURPOSE OF ANY LIMITED REMEDY.
LICENSEE Indemnity. LICENSEE agrees to indemnify and defend LICENSOR, and hold it harmless from all
costs, including attorney’s fees, arising from any claim that may be made against LICENSOR by any third party as a
direct or indirect result of any use by LICENSEE of the Software,
Termination. This Agreement and the license may be terminated without fee reduction (i) by LICENSEE without
cause on thirty (30) days notice; (ii) by LICENSOR, in addition to other remedies, if LICENSEE is in default and fails
to cure within ten (10) days following notice; (iii) on notice by either party hereto if the other party ceases to do
business in the normal course, becomes insolvent, or becomes subject to any bankruptcy, insolvency, or equivalent
proceedings. Upon termination for any reason, LICENSEE shall immediately return Software and all copies to
LICENSOR and delete all Software and all copies from the Hardware.
Law. This Agreement shall be governed by the laws of the Commonwealth of Massachusetts, exclusive of its
conflicts of laws provisions and without regard to the United Nations Convention on Contracts for the International
Sale of Goods, and any suit under this Agreement shall exclusively be brought in a federal or state court in
Massachusetts. Any action against LICENSOR under this Agreement must be commenced within one year after
such cause of action accrues.
Government End Users. This provision applies to all Software acquired directly or indirectly by or on behalf of the
United States Government. The Software is a commercial product, licensed on the open market at market prices,
and was developed entirely at private expense and without the use of any U.S. Government funds. If the Software is
supplied to the Department of Defense, the U.S. Government acquires only the license rights customarily provided to
the public and specified in this Agreement. If the Software is supplied to any unit or agency of the U.S. Government
other than the Department of Defense, the license to the U.S. Government is granted only with restricted rights. Use,
duplication, or disclosure by the U.S. Government is subject to the restrictions set forth in subparagraph (c) of the
Commercial Computer Software Restricted Rights clause of FAR 52.227-19.
Export Restriction. LICENSEE will not remove or export from the United States or the country originally shipped
to by LICENSOR (or re-export from anywhere) any part of the Software or any direct product thereof except in
compliance with applicable export laws and regulations, including without limitation, those of the U.S. Department of
Commerce.
Miscellaneous. This Agreement contains the entire understanding of the parties and supersedes all other
agreements, oral or written, including purchase orders submitted by LICENSEE, with respect to the subject matter
covered in this Agreement The delay or failure of either party to exercise any right provided in the Agreement shall
not be deemed a waiver. All notices must be in writing and shall be delivered by hand (effective when received) or
mailed by registered or certified mail (effective on the third day following the date of mailing). The notices addressed
to LICENSOR shall be sent to its address set out above. If any provision is held invalid, all others shall remain in
force. LICENSEE may not assign, pledge, or otherwise transfer this agreement, nor any rights or obligations
hereunder in whole or in part to any entity. Paragraph headings are for convenience and shall have no effect on
interpretation. In the event that it is necessary to undertake legal action to collect any amounts payable or to protect
or to defend against the unauthorized use, disclosure, distribution, of the Software hereunder and/or other violation
of this Agreement, LICENSOR shall be entitled to recover its costs and expenses including, without limitation,
reasonable attorneys' fees
.
Copyright © Acronis, Inc., 2000-2008 5
Page 6

Table of Contents
Chapter 1. Introduction ........................................................................................10
1.1 Acronis® True Image for Microsoft Small Business Server – a complete solution for
corporate users......................................................................................................................10
1.2 Acronis True Image for Microsoft Small Business Server components...................................12
1.3 New in Acronis for Microsoft Small Business Server.............................................................12
1.4 Supported file systems and storage media.........................................................................14
1.4.1 Supported file systems ..............................................................................................14
1.4.2 Supported storage media...........................................................................................14
1.5 License policy..................................................................................................................15
1.6 Technical support............................................................................................................15
Chapter 2. Acronis True Image for Microsoft Small Business Server installation
and startup .............................................................................................................16
2.1 System requirements.......................................................................................................16
2.1.1 Minimum hardware requirements ...............................................................................16
2.1.2 Supported operating systems.....................................................................................16
2.2 Security parameters.........................................................................................................16
2.2.1 Credentials...............................................................................................................16
2.2.2 Firewall setup...........................................................................................................17
2.2.3 Encrypted communication..........................................................................................17
2.2.4 Security parameters in Acronis Administrative Template...............................................18
2.3 Installing Acronis True Image for Microsoft Small Business Server components.....................19
2.3.1 Installation of Acronis True Image for Microsoft Small Business Server local version and
Acronis True Image Agent for Windows................................................................................20
2.3.2 Installation of Acronis Group Server............................................................................21
2.3.3 Acronis Backup Server installation and setup...............................................................21
2.3.4 Acronis Universal Restore installation..........................................................................25
2.4 Extracting Acronis True Image for Microsoft Small Business Server components....................25
2.5 Running Acronis True Image for Microsoft Small Business Server components......................25
2.5.1 Running Acronis True Image for Microsoft Small Business Server (local version).............25
2.5.2 Running Acronis True Image Management Console......................................................26
2.5.3 Running other Acronis components.............................................................................26
2.6 Removing Acronis True Image for Microsoft Small Business Server components....................26
Chapter 3. General information and proprietary Acronis technologies ................ 27
3.1 The difference between file archives and disk/partition images............................................27
3.2 Full, incremental and differential backups..........................................................................27
3.3 Acronis Secure Zone®......................................................................................................28
3.4 Acronis Startup Recovery Manager....................................................................................29
3.4.1 How it works ............................................................................................................29
3.4.2 How to use...............................................................................................................29
3.5 Acronis Backup Server .....................................................................................................30
3.5.1 Backup locations.......................................................................................................30
3.5.2 Quotas and time limits for computers and users...........................................................31
3.5.3 Administrators and Users...........................................................................................31
3.5.4 Operations with archives............................................................................................32
3.6 Acronis Active restore......................................................................................................32
3.6.1 Limitations in using Acronis Active restore...................................................................32
3.6.2 How it works ............................................................................................................32
3.6.3 How to use...............................................................................................................33
3.7 Acronis Universal Restore.................................................................................................33
3.7.1 Acronis Universal Restore purpose..............................................................................33
3.7.2 Acronis Universal Restore general principles................................................................34
3.7.3 Acronis Universal Restore and Microsoft Sysprep..........................................................34
3.7.4 Limitations in using Acronis Universal Restore..............................................................35
6 Copyright © Acronis, Inc., 2000-2008
Page 7

3.7.5 Getting Acronis Universal Restore...............................................................................35
3.8 Backing up to tape libraries and tape drives.......................................................................35
3.8.1 Understanding backup to tape devices........................................................................36
3.8.2 Backing up to a tape device through Acronis Backup Server..........................................38
3.8.3 Backing up to a locally attached tape device................................................................38
3.8.4 Restoring data from archives located on tape devices...................................................39
3.9 Viewing disk and partition information...............................................................................39
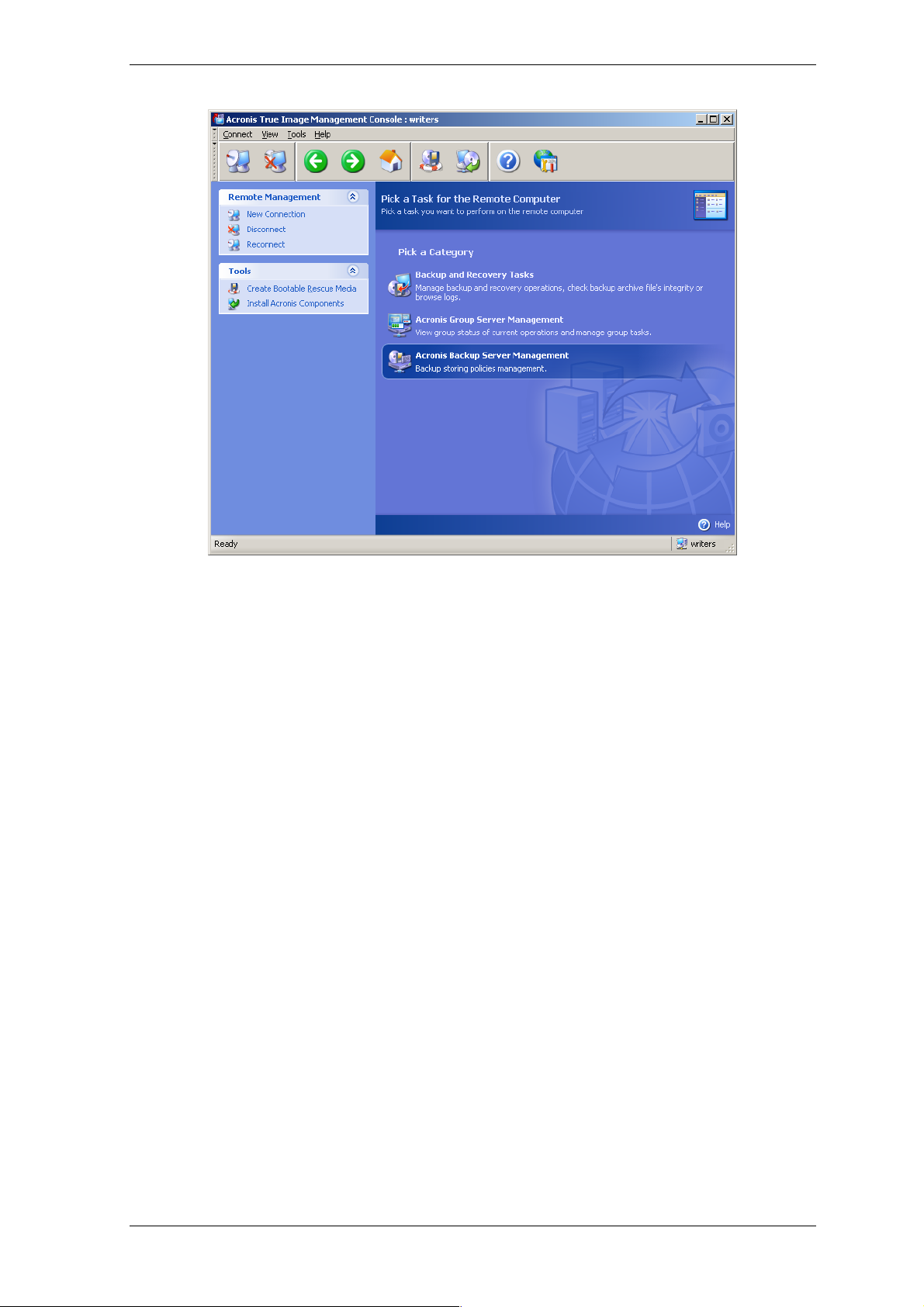
Chapter 4. Using Acronis True Image Management Console................................ 40
4.1 General information.........................................................................................................40
4.2 Installing/updating Acronis components on remote machines..............................................40
4.3 Managing a single remote computer..................................................................................43
4.3.1 Connecting to a remote computer ..............................................................................43
4.3.2 Backup and recovery tasks.........................................................................................44
4.4 Managing groups of computers.........................................................................................46
4.4.1 Group status display..................................................................................................46
4.4.2 Creating new group tasks ..........................................................................................48
4.4.3 Group tasks management..........................................................................................50
4.4.4 Acronis Group Server options.....................................................................................51
4.5 Managing backup server ..................................................................................................51
4.5.1 Default settings.........................................................................................................52
4.5.2 Set up Administrator profiles......................................................................................54
4.5.3 Adding Users and Administrators to the Acronis Backup Server database.......................55
4.5.4 Changing User profiles...............................................................................................57
4.5.5 Configuring Backup Locations.....................................................................................57
4.5.6 Managing Archives....................................................................................................58
4.5.7 Limiting access to Acronis Backup Server ....................................................................59
Chapter 5. Using Acronis True Image for Microsoft Small Business Server (local
version) ..................................................................................................................61
5.1 Main program window .....................................................................................................61
5.2 Managing a local computer...............................................................................................63
Chapter 6. Creating backup archives .................................................................... 66
6.1 Backing up files and folders (file backup)...........................................................................66
6.2 Backing up disks and partitions (image backup).................................................................70
6.3 Setting backup options.....................................................................................................72
6.3.1 Archive protection.....................................................................................................73
6.3.2 Source files exclusion ................................................................................................73
6.3.3 Pre/post commands ..................................................................................................74
6.3.4 Database support......................................................................................................74
6.3.5 Compression level.....................................................................................................75
6.3.6 Backup performance .................................................................................................76
6.3.7 Fast incremental/differential backup ...........................................................................77
6.3.8 Archive splitting........................................................................................................77
6.3.9 File-level security settings..........................................................................................77
6.3.10 Media components..................................................................................................78
6.3.11 Error handling.........................................................................................................79
6.3.12 Dual destination backup...........................................................................................79
6.3.13 Wake On LAN .........................................................................................................80
6.3.14 Additional settings...................................................................................................80
Chapter 7. Restoring the backup data ..................................................................82
7.1 Considerations before recovery.........................................................................................82
7.1.1 Restore under Windows or boot from CD?...................................................................82
7.1.2 Network settings in rescue mode................................................................................82
7.1.3 Recovering dynamic volumes.....................................................................................83
7.2 Restoring files and folders from file archives......................................................................84
Copyright © Acronis, Inc., 2000-2008 7
Page 8

7.3 Restoring disks/partitions or files from images ...................................................................86
7.3.1 Starting the Restore Data Wizard................................................................................87
7.3.2 Archive selection.......................................................................................................87
7.3.3 Restoration type selection..........................................................................................88
7.3.4 Selecting a disk/partition to restore ............................................................................89
7.3.5 Selecting a target disk/partition..................................................................................89
7.3.6 Changing the restored partition type...........................................................................90
7.3.7 Changing the restored partition file system..................................................................91
7.3.8 Changing the restored partition size and location.........................................................91
7.3.9 Assigning a letter to the restored partition...................................................................92
7.3.10 Restoring several disks or partitions at once..............................................................92
7.3.11 Using Acronis Universal Restore................................................................................92
7.3.12 Setting restore options.............................................................................................93
7.3.13 Restoration summary and executing restoration.........................................................93
7.4 Setting restore options.....................................................................................................93
7.4.1 Files to exclude from restoration.................................................................................94
7.4.2 Files overwriting mode...............................................................................................94
7.4.3 Pre/post commands ..................................................................................................94
7.4.4 Restoration priority....................................................................................................95
7.4.5 File-level security settings..........................................................................................95
7.4.6 Specifying mass storage drivers..................................................................................95
7.4.7 Additional settings.....................................................................................................96
7.4.8 Error handling...........................................................................................................96
7.5 Creating dynamic disks and volumes.................................................................................97
7.5.1 Creating dynamic volumes.........................................................................................97
Chapter 8. Scheduling tasks................................................................................100
8.1 Creating scheduled tasks................................................................................................100
8.1.1 Setting up daily execution........................................................................................102
8.1.2 Setting up weekly execution.....................................................................................103
8.1.3 Setting up monthly execution...................................................................................104
8.1.4 Setting up one-time execution..................................................................................104
8.1.5 Setting up event-driven execution ............................................................................105
8.2 Managing scheduled tasks..............................................................................................105
Chapter 9. Managing the Acronis Secure Zone ...................................................106
9.1 Creating Acronis Secure Zone......................................................................................... 106
9.2 Resizing the Acronis Secure Zone....................................................................................108
9.3 Changing the password for Acronis Secure Zone..............................................................109
9.4 Deleting Acronis Secure Zone.........................................................................................109
Chapter 10. Creating bootable media ................................................................. 110
10.1 Creating Acronis rescue media...................................................................................... 110
10.2 Creating a Win PE ISO with Acronis True Image for Microsoft Small Business Server .........112
Chapter 11. Operations with archives.................................................................114
11.1 Validating backup archives ...........................................................................................114
11.2 Exploring archives and mounting images ....................................................................... 114
11.2.1 Exploring an archive..............................................................................................115
11.2.2 Mounting an image................................................................................................116
11.2.3 Unmounting an image ...........................................................................................118
11.3 Consolidating backups..................................................................................................118
Chapter 12. Notifications and event tracing .......................................................122
12.1 Email notification.........................................................................................................122
12.2 WinPopup notification..................................................................................................123
12.3 Viewing logs................................................................................................................123
12.4 Event tracing...............................................................................................................124
8 Copyright © Acronis, Inc., 2000-2008
Page 9

12.4.1 Windows event log................................................................................................124
12.4.2 SNMP notifications.................................................................................................125
12.5 Managing System Restore............................................................................................125
Chapter 13. Working with a virtual environment ...............................................127
13.1 Backing up data on virtual machines .............................................................................127
13.2 Recovering data on virtual machines.............................................................................127
13.3 Using the disk conversion feature..................................................................................128
13.3.1 Recover data on the VM.........................................................................................128
13.3.2 Recover both data and the VM ...............................................................................128
13.3.3 Physical to virtual migration ...................................................................................128
13.3.4 Converting workloads............................................................................................129
13. 4 Converting disk images to virtual disks ......................................................................... 129
Chapter 14. Transferring the system to a new disk............................................131
14.1 General information.....................................................................................................131
14.2 Security......................................................................................................................132
14.3 Executing transfers......................................................................................................132
14.3.1 Selecting Clone mode............................................................................................ 132
14.3.2 Selecting source disk.............................................................................................132
14.3.3 Selecting destination disk.......................................................................................133
14.3.4 Partitioned destination disk ....................................................................................134
14.3.5 Old and new disk partition layout............................................................................134
14.3.6 Old disk data ........................................................................................................134
14.3.7 Destroying the old disk data...................................................................................135
14.3.8 Selecting partition transfer method.........................................................................136
14.3.9 Partitioning the old disk .........................................................................................137
14.3.10 Old and new disk partition layouts ........................................................................137
14.3.11 Cloning summary.................................................................................................138
14.4 Cloning with manual partitioning...................................................................................138
14.4.1 Old and new disk partition layouts..........................................................................138
Chapter 15. Adding a new hard disk ...................................................................140
15.1 Selecting a hard disk....................................................................................................140
15.2 Creating new partitions................................................................................................140
15.3 Disk add summary....................................................................................................... 141
Chapter 16. Command-line mode and scripting .................................................142
16.1 Working in the command-line mode..............................................................................142
16.1.1 Supported commands............................................................................................142
16.1.2 Common options (options common for most trueimagecmd commands) ....................145
16.1.3 Specific options (options specific for individual trueimagecmd commands)..................146
16.1.4 trueimagecmd.exe usage examples.........................................................................151
16.1.5 Command-line mode usage under DOS...................................................................155
16.2 Scripting.....................................................................................................................156
16.2.1 Script execution parameters...................................................................................156
16.2.2 Script structure .....................................................................................................156
16.2.3 Script usage examples...........................................................................................157
Copyright © Acronis, Inc., 2000-2008 9
Page 10

Chapter 1. Introduction
1.1 Acronis® True Image for Microsoft Small Business Server – a complete solution for corporate users
Acronis True Image for Microsoft Small Business Server is a comprehensive backup and
recovery solution for heterogeneous computer infrastructure that may include any
combination of physical and virtual, networked and standalone, Windows- and Linuxbased servers.
Acronis True Image for Microsoft Small Business Server creates a transportable image,
independent of the hardware platform that can be restored directly to and from any
virtual or physical environment.
Minimizes downtime
Acronis True Image for Microsoft Small Business Server enables you to restore systems in
minutes, not hours or days. An entire system can be restored from an image that includes
everything the system needs to run: the operating system , applications, databases, and
configurations. it is not necessary to reinstall software or reconfigure your system or
network settings. The complete system restoration can be performed to an existing
system, to a new system with different hardware, or to virtual machines. With the Acronis
Active restore feature, users can access the server and be gin working during the restore
process, further decreasing downtime. File-level backups provide you with the flexibility to
only backup specific, critical files.
Eases Administration
Wizards guide users through backup and recovery tasks, ensuring the product can be
implemented with minimal user training. A central management console provides remote
administration, ensuring that all systems in the network, regardless of the domain or
workgroup structure, can be managed from one location. Complete, unattended restores
from remote locations are supported with a remote bootable agent.
Automates Backup
With the scheduling capability in Acronis True Image for Microsoft Small Business Server,
you simply create backup tasks, tailored by group, or certain times or events.
To ensure that backups have occurred, or if user intervention is required, you can r equest
notifications via email or Windows Pop-up. You can view Acronis events in the Win dows
Application Events Log or Acronis own log files. Log messages can be automatically sent
out to SNMP clients.
The product also supports the creation of custom comman ds before and after backups.
For example, users can automatically run anti-virus products before an image is created
and verify the validity of backups after the image has been created. And because these
tasks can be scheduled, you need not recreate the script to run the pre- and post-event
tasks each time; you can set the scheduled events once and they will run each time
automatically.
Ensures 24 X 7 Uptime
With Acronis’ patented drive snapshot technology, systems can be imaged while they are
in use, ensuring 24-by-7 system availability. This technology enables the product to
backup and image critical operating system files, the master boot record and any
partition-based boot records without requiring a reboot. A CPU allocation feature allows
10 Copyright © Acronis, Inc., 2000-2008
Page 11

you to limit the amount of CPU usage for the application to maximize the CPU’s
availability for mission critical applications. Additionally, users can control hard disk drive
writing speeds and control network bandwidth used during backups, allowing minimal
disruption of business operations.
A feature that allows you to suspend database activity for several seconds is provided so
that you can create a valid image of mission-critical applications such as Microsoft
Exchange Server, Microsoft SQL Server and Oracle. This database suspension process
supports Microsoft’s Volume Shadow Copy Service (VSS). If your database or operating
system does not support VSS, Acronis True Image for Microsoft Small Business Server will
execute your custom commands to execute database suspension.
Supports Leading Edge Technology
Businesses today are moving to leverage the latest technologies, includ ing dual-core, 64bit processors and 64-bit operating systems. With Acronis True Image for Microsoft Small
Business Server, you can protect these new machines, as well as legacy servers, running
a single application with a common interface.
Leverages Existing Technology Investments
The product can leverage your current storage infrastru cture by supporting a variety of
storage media, so you can avoid costly hardware purchases to implement the solution.
The product supports key storage technologies such as: Direct Attached Storage ( DAS),
Network Attached Storage (NAS), Storage Area Networks (SAN), Redundant Arrays of
Independent Disks (RAID), tapes, USB and IEEE-1394 (FireWire) compliant storage
devices, CDs, DVDs, removable drives (Floppy, Zip, etc.) and shared storage. Mor eover,
the product ensures that you maximize the space on these reso urces with four levels of
compression.
Disk cloning and new disk deployment
Acronis True Image for Microsoft Small Business Server can be used to clone an image
onto multiple servers. For example, let’s say a company purchased several servers and
needs similar environments on each of them. Traditionally, the IT manager would install
the operating system and programs on every server. With Acronis True Image for
Microsoft Small Business Server, the IT manager would configure a single server, then
create a disk image of the system. That image can then be duplicated onto multiple
servers.
If you need to upgrade the server hard disk drive, Acronis True Image for Microsoft Small
Business Server simplifies the task to few mouse clicks creating the exact copy of your old
disk to a new one and adjusting partitions size to fit a new hard disk.
Volumes conversion
Acronis True Image for Microsoft Small Business Server can back up and recover dynamic
volumes.
Dynamic volume as is can be recovered over the same volume or unallocated space of a
dynamic group. Acronis True Image for Microsoft Small Business Server has necessary
tools for any-to-any disks conversion in terms of basic disks and dynamic volumes of any
type (simple, spanned, striped, mirrored or RAID 5). The tools are available in bootable
program version as well. Having booted the Acronis environment, you can easily prepare
the desired dynamic group on bare metal or a computer with non-Windows operating
system.
Copyright © Acronis, Inc., 2000-2008 11
Page 12
1.2 Acronis True Image for Microsoft Small Business Server components
Acronis True Image for Microsoft Small Business Server includes the following
components.
1. Acronis True Image Management Console is a tool for remote access to Acroni s
components. Administrator uses the console to install, configure and control the
components from remote.
2. Acronis True Image Agent is an application that resides on client computers and
performs Acronis operations such as data backup or restore.
3. Acronis Group Server is a management tool that provides ability to schedule,
monitor and manage group backup tasks. It deploys group tasks to the ag ents, polls the
agents for the status of running tasks and provides the administrator with the summary
tasks state display over the network.
4. Acronis Backup Server is an application for centralized storage and management of
enterprise backup archives.
The administrator can set space quotas and backup schemes, schedule check tasks that
consolidate backups in case of quota violati on, perform one-time backups consolidation.
This ensures optimal usage of the storage capacity . Acronis Backup Server also enables
users to access a tape library, connected to the server.
5. Acronis True Image for Microsoft Small Business Server (local version) is a
locally controlled server management tool with additional functionality as compared to
Acronis True Image Agent. The local version supports, besides backup and recovery
operations, exploring archives, mounting images as virtual drives, cloning hard disk s data
and formatting partitions on new hard disks, creating dynamic volumes, command-line
mode and scripts execution.
6. Acronis Universal Restore is an add-on to Acronis True Image for Microsoft Small
Business Server that automatically configures Windows drivers in a system, recovered on
dissimilar hardware. This enables the seamless system start and operation.
7. Acronis Bootable Rescue Media Builder - creates bootable media, its ISO image or
the RIS package thus enabling data recovery over bare metal, non-Windows or corrupted
operating systems.
1.3 New in Acronis for Microsoft Small Business Server
Management console
Reconnect (last connect) option
Centralized installation and update of Acronis components on multiple computers
Group server
Import and export computers through txt/csv files
Run, stop, restart, edit, check group tasks
Group validation tasks
Set how often to check the computers state (status refresh rate)
Wake on LAN for backup
12 Copyright © Acronis, Inc., 2000-2008
Page 13

Backup server
Import/export archives from external locations
Limit number of connections
Limit bandwidth used per connection
Access to tape library for every user
Backup
Backup and restore of 2+TB volumes
Encrypting backups with industry-standard AES cryptographic algorithm (key size 128,
192, 256 bit)
Multi-volume snapshot for databases spread on several disks
Control network bandwidth usage when backing up to FTP
Error handling: ignore bad sectors, silent mode (no pop-ups, continue on all errors)
Dual destination backup: Acronis Secure Zone + network share
Support for VMware Consolidated backup
Archive bit reset (file-level backup only)
Generating time-based names for bac kup files
Recovery
Recovery of dynamic volumes
Recovery of system dynamic volumes on dissimilar hardware using Acronis Universal
Restore or Acronis Active restore
Scheduling
Schedule archive validation
Start every N hours within daily schedule
Start on free disk space change by the specified amount
Cloning a task
Notification via e-mail
Multiple e-mail addresses
From and Subject fields
Logon to incoming mail server
Operations with archives
Convert disk images to virtual disks for VMware, Microsoft, XenServer and Parallels virtual
machines
Consolidate backup files (create a consistent copy of archive while deleting selected
backups)
Explore archives (open in read-only mode any image or file-level backup)
Operations with hard disks
Convert basic disk to dynamic
Copyright © Acronis, Inc., 2000-2008 13
Page 14

Create dynamic volumes
CLI features
MBR restore
Backup to FTP server
Allow logs on net share
Merge unallocated space by moving partitions and create Acronis Secure Zone on the
space
Security
Encrypted (SSL) communication between Acronis True Image for Microsoft Small Business
Server components
1.4 Supported file systems and storage media
1.4.1 Supported file systems
FAT16/32
NTFS
Ext2/Ext3
ReiserFS
Reiser4
Linux SWAP
XFS
JFS
DFS
If a file system is not supported or is corrupted, Acronis True Image for Microsoft Small
Business Server can copy data using a sector-by-sector approach.
For XFS and JFS file systems the partition resizing feature is not supported.
1.4.2 Supported storage media
Hard disk drives
Networked storage devices such as Storage Area Networks (SANs) and Network Attached
Storage (NAS)
Tape libraries, autoloaders, SCSI tape drives
IDE and SCSI RAID controllers of any level
FTP-servers*
CD-R/RW, DVD-R/RW, DVD+R (including double-layer DVD+R), DVD+RW, DVD-RAM**
USB 1.0 / 2.0, FireWire (IEEE-1394) and PC card storage devices
®
ZIP
, Jaz® and other removable media
14 Copyright © Acronis, Inc., 2000-2008
Page 15

* - an FTP-server must allow passive mode for file transfers. Data recovery directly from
FTP-server requires the archive to consist of files no more than 2GB in size. It is
recommended that you change the source computer firewall settings to open ports 20
and 21 for both TCP and UDP protocols and disable the Routing and Remote Access
Windows service.
** - Burned rewritable discs cannot be read in Linux without kernel patch.
1.5 License policy
Acronis True Image for Microsoft Small Business Server licensing is based on number of
servers on which Acronis True Image Agent and/or Acronis True Image for Microsoft
Small Business Server local version are to be installed. This means you need one license
for each server you are going to backup, whether you will control it on-site (with the local
program version) or remotely (using Acronis True Image Agent), or use both ways of
control. The number of Acronis True Image Management Console, Acr onis Group Server
and Acronis Backup Server installations is not counted.
Acronis Universal Restore is an option to Acronis True Image for Microsoft Small Business
Server and has its own serial number.
1.6 Technical support
As part of a purchased annual Support charge you are entitled to Technical Support as
follows: to the extent that electronic services are available , you may electronically access
at no additional charge, Support services for the Software, which Acronis shall endeavor
to make available twenty four (24) hours a day, seven (7) days per week. Such electronic
services may include, but are not limited to: user forums; software-specifi c information;
hints and tips; bug fix retrieval via the internet; software maintenance and demonstration
code retrieval via a WAN-accessible FTP server; and access to a problem resolution
database via Acronis customer support system.
Support shall consist of supplying telephone or other electronic support to you in or der to
help you locate and, on its own, correct problems with the Software and supplying
patches, updates and other changes that Acronis, at its sole discretion, makes or adds to
the Software and which Acronis makes generally available , without additional char ge, to
other licensees of the Software that are enrolled in Support. Upon mutual agre ement by
both parties, Acronis shall: (i) supply code corrections to you to correct Software
malfunctions in order to bring such Software into substantial conformity with the
published operating specifications for the most current version of the Software unless
your unauthorized modifications prohibit or hamper such corrections or cause the
malfunction; or (ii) supply code corrections to correct insubstantial problems at the next
general release of the Software.
More information about contacting Acronis Technical Support is available at the following
link: http://www.acronis.com/enterprise/support/
Copyright © Acronis, Inc., 2000-2008 15
Page 16

Chapter 2. Acronis True Image for Microsoft Small Business Server installation and startup
2.1 System requirements
2.1.1 Minimum hardware requirements
Acronis True Image for Microsoft Small Business Server requires the following hardware:
Pentium processor or higher
256MB RAM
FDD or CD-RW drive for bootable media creation
Mouse (recommended).
2.1.2 Supported operating systems
Acronis True Image Management Console
Windows Small Business Server 2003
Windows Professional 2000 SP4/XP Professional SP2
Windows Server 2000/Advanced Server 2000/Server 2003
Windows XP Professional x64 Edition, Windows Server 2003 x64 Editions
Windows Vista all Editions (except for installation of Acronis components on remote
machines running Vista)
Acronis True Image Agent for Windows
Acronis True Image for Microsoft Small Business Server
Acronis Backup Server
Acronis Group Server
Acronis Universal Restore (optional)
Windows Small Business Server 2003
Acronis True Image for Microsoft Small Business Server bootable version enables disk-
level backup and recovery on a computer running any PC-based operating system.
2.2 Security parameters
2.2.1 Credentials
Acronis True Image for Microsoft Small Business Server fully supports all security
standards used in Windows.
To install Acronis components on a computer, the user must be a member of the
Administrators group on the computer.
To get access to Acronis True Image Agent, installed on a computer, the user must be a
member of the Administrators or Backup operators group on the computer.
16 Copyright © Acronis, Inc., 2000-2008
Page 17

The Acronis Group Server uses administrator’s credentials to perform data backup tasks
on the computers. You will be asked for the credentials during the Acronis Group Server
installation. The credentials you provide will be used for running the Acronis Group Server
service and also applied to all networked computers.
Therefore, it is recommended that you have a uniform account for all computers where
the Acronis True Image Agent is installed. Domain administrators can use the domain
administrator account. In a workgroup, it would make sense to create identical accounts
in the Administrators group on each computer with Acronis True Image Agent.
If you do not wish to create a uniform account, provide credentials for each computer
after Acronis Group Server installation as described in point 4 of
display
You can combine both methods, for example, to set up a uniform account for domain
members and set individual accounts for members of a workgroup.
.
4.4.1 Group status
2.2.2 Firewall setup
Acronis True Image for Microsoft Small Business Server uses the following ports and I P
addresses for remote operation:
server (Acronis True Image Agent) UDP port: 9876
server (Acronis True Image Agent) TCP port: 9876, if busy choose a port at random
client (Acronis True Image Management Console) UDP port: 9877, if busy choose a port
at random
IPv4 multicast address: 239.255.219.45
IPv6 multicast address: FF05::fAA5:741E.
You might have to set the appropriate firewall access options. Options for the Win dows
Firewall, included in Windows XP Service Pack 2 and Windows 2003 Server, are set
automatically during Acronis True Image for Microsoft Small Business Server components
installation. However, make sure that the option File and Printer Sharing in the
Control panel -> Windows Firewall -> Exceptions is enabled on the remote
computer, before the remote operation starts.
2.2.3 Encrypted communication
Acronis True Image for Microsoft Small Business Server provides capability to secure all
data transferred between Acronis components within local net and through DMZ,
including the backup stream.
Encryption starts on the first (earliest) stage of connection attempt, so all data transferred
on the next steps (including data required for client authentication) is encrypted.
Once Acronis True Image for Microsoft Small Business Server components are installed,
encrypted communication between the components is enabled automati cally.
The earlier versions of Acronis True Image Enterprise Server did not support encrypted
communication, therefore connection to such components, if they present on the
network, will not be encrypted. You have an option to completely disable non-encrypted
communication with some or all Acronis True Image for Microsoft Small Business Server
components. In this case, the components will not be able to communicate with
components of earlier versions. For how to disable non -encr ypted comm unication , s ee the
next section.
Copyright © Acronis, Inc., 2000-2008 17
Page 18
The earlier versions of Acronis True Image Management Console cannot communicate
with Acronis True Image for Microsoft Small Business Server agents. The console must be
upgraded to the Acronis True Image for Microsoft Small Business Server console.
Encryption is provided with Secure Socket Layer mechanism. There ar e two stakeholders
of the encryption operation:
Client application – the application that tries to establish (initiates) connection. This
could be the Acronis True Image Management Console or Acronis Group Server.
Acronis True Image for Microsoft Small Business Server local version can also be a
client when it performs backup to Acronis Backup Server.
Server application – the application to which the client tries to connect. This could be
Acronis True Image Agent, Acronis Group Server, Acronis Backup Server.
2.2.4 Security parameters in Acronis Administrative Template
As stated above, encryption generally does not require setting up. However, connecti on to
Acronis components of earlier versions will not be encrypted. To completely disable nonencrypted communication with some or all Acronis True Image for Microsoft Small
Business Server components, use the Administrative Template, provided by Acronis.
Through the Microsoft Group Policy mechanism, the template can be applied to a single
computer as well as to a domain.
How to apply Acronis Administrative Template
1. Run Windows Group Policy Objects Editor (\WINDOWS\system32\gpedit.msc).
2. Open the Group Policy object you want to edit, and in the console tree right-click
Administrative Templates.
3. Click Add/Remove Templates.
4. Click Add.
5. Browse to the Acronis Administrative Template
(\Program files\Common Files\Acronis\Agent \acronis_agent.adm or \Program
files\Acronis\TrueImageConsole\acronis_agent.adm), and click Open.
6. Once the template is added, open it and edit the desired settings.
For detailed information about Windows GPO Editor please see:
http://msdn2.microsoft.com/en-us/library/aa374163.aspx
For detailed information about Group Policies please see:
http://msdn2.microsoft.com/en-us/library/aa374177.aspx
The Acronis Administrative Template contains the following settings.
18 Copyright © Acronis, Inc., 2000-2008
Page 19

Encryption Options
Server Requires Encryption
This option defines the server behavior in case the client does not support encryption.
When enabled, connection to the client will be terminated. When disabled, the client will
be allowed to establish non-encrypted connection.
Client Requires Encryption
When connecting to server applications, the Acronis client applications always attempt to
establish an encrypted connection. The Client Requires Encryption option defines the
client behavior in case the server does not support encryption. When disabled, the nonencrypted connection will be established. When enabled, the connection will be
terminated.
After applying the template or editing the encryption options, you should restart the
Remote Agent(s).
2.3 Installing Acronis True Image for Microsoft Small Business Server components
To install Acronis True Image for Microsoft Small Business Server components, run the
Acronis True Image for Microsoft Small Business Server setup file.
If you have the trial version of Acronis True Image for Microsoft Small Business Server
installed on your system, you must uninstall it before installing the commercial version of
the product.
Select the program to install and follow instructions on the screen.
Copyright © Acronis, Inc., 2000-2008 19
Page 20

Acronis True Image for Microsoft Small Business Server Install Window
It is recommended that you install Acronis True Image Management Console first. After
that you will be able to install Acronis True Image for Microsoft Small Business Server
(local version) and Acronis True Image Agent for Windows remotely to networked
computers.
2.3.1 Installation of Acronis True Image for Microsoft Small Business Server local version and Acronis True Image Agent for Windows
For Acronis True Image for Microsoft Small Business Server and Acronis True Image
Agent for Windows, Typical, Custom and Complete installation is available. Having
pressed Custom, you can choose to install, besides the main component, Rescue Media
Builder and Bart PE plug-in for Acronis True Image for Microsoft Small Business
Server, or Acronis Secure Zone manager for Acronis True Image Agent.
With Rescue Media Builder you can create bootable rescue disks or RIS packages (see
details in
Chapter 10. Creating bootable media
Builder will allow you to create bootable media, its ISO image or a bootable RIS package
at any time from the main program window or running Bootable Rescue Media
Builder on its own.
The widely used Bart PE utility provides a Windows-like operating environment invoked
via removable bootable media. Applications are installed into Bart PE in the form of plugins. Choosing Bart PE plug-in installation (disabled by default) provides the ability to
include Acronis True Image for Microsoft Small Business Server into a Bart PE pl ug-in tab.
The plug-in files will be placed into the component installation folder along with other
program files.
). Installing the Bootable Rescue Media
Acronis Secure Zone manager lets you create, delete and resize a special hidden
partition for storing backup archives (see
When installed, Acronis True Image for Microsoft Small Business Server (local version)
creates a new device in the Device Manager list (Control Panel -> System ->
Hardware -> Device Manager -> Acronis Devices -> Acronis TrueImage
Backup Archive Explorer). Do not disable or uninstall this device, as it is necessary for
20 Copyright © Acronis, Inc., 2000-2008
3.3 Acronis Secure Zone
).
Page 21

connecting image backups as virtual disks (see
11.2.2 Mounting an image
).
2.3.2 Installation of Acronis Group Server
The Acronis Group Server only can be installed locally on a computer by running the setup
program.
When installing Acronis Group Server, you will be asked for credentials. The credentials
you provide are used for running the Acronis Group Server service and also appli ed to all
networked computers.
Enter the uniform account information discussed in
2.2.1 Credentials
. If you do not use a
uniform account, provide credentials for each computer after the Acronis Group Server
installation as described in point 4 of
4.4.1 Group status display
.
2.3.3 Acronis Backup Server installation and setup
The Acronis Backup Server only can be installed locally on a computer by running the
setup program.
Before starting installation of this component, please read section
Server
to get understanding of this component functionality and define the storage policy
advantageous to your network.
We suggest that you start using Acronis Backup Server as follows:
3.5 Acronis Backup
1. Set up a server with a system drive and a high capacity storage drive.
2. Install Acronis Backup Server on the system drive. Reboot on prompt.
In Windows XP SP2 or Windows 2003 Server, the option Control panel -> Windows
Firewall -> Exceptions -> File and Printer Sharing must be enabled. Otherwise
remote users will not be able to back up on the backup server.
3. Connect the console to Acronis Backup Server.
When connecting to a backup server inside a domain, mind whether your domain or
local account is saved on the backup server. If you used your local account to install the
backup server, and then logged in Windows on the console computer using your domain
account, enter the local user name along with the backup server name (for example,
Server1\username). Otherwise the name will be identified as a domain one.
Copyright © Acronis, Inc., 2000-2008 21
Page 22
4. Acronis Backup Server Management -> Specify Default Settings -> Set
Backup Location -> specify path to the storage drive. You can create a f older for the
backup location on the storage drive. To see the folder in the tree and add it to the path ,
collapse and expand the drive.
5. Click Back -> Configure Backup Locations -> make sure that the new default
location is created and delete the location in \Documents and Settings.
6. Set limitations to disk space and storage period for the location, if needed,
according to the selected policy.
To do so, select Configure Backup Locations -> select location -> Quotas and
time limits. The maximum backup location size can be set to the storage drive capacity
minus the estimated size of the largest backup (some space must be reserved for the
temporary file created at consolidation).
7. Set the default limitations for users/computers, if needed, according to the
selected policy.
To do so, select Acronis Backup Server Management -> Specify Default Settings
-> Set Quotas and time limits. The maximum disk space allowed for a user/computer
can be set as the max location size divided by total number of users and computers.
Generally, value of this setting can reach the maximum location size.
8. Read about administrators and users profiles in
3.5.3 Administrators and Users
.
Define if you need more than one administrator on the backup server. If yes, add
administrators as follows:
Add the person’s local or domain account to the AcronisBackupServerUsers group on the
backup server.
Click Set up User profiles -> Add.
Choose the user name.
22 Copyright © Acronis, Inc., 2000-2008
Page 23
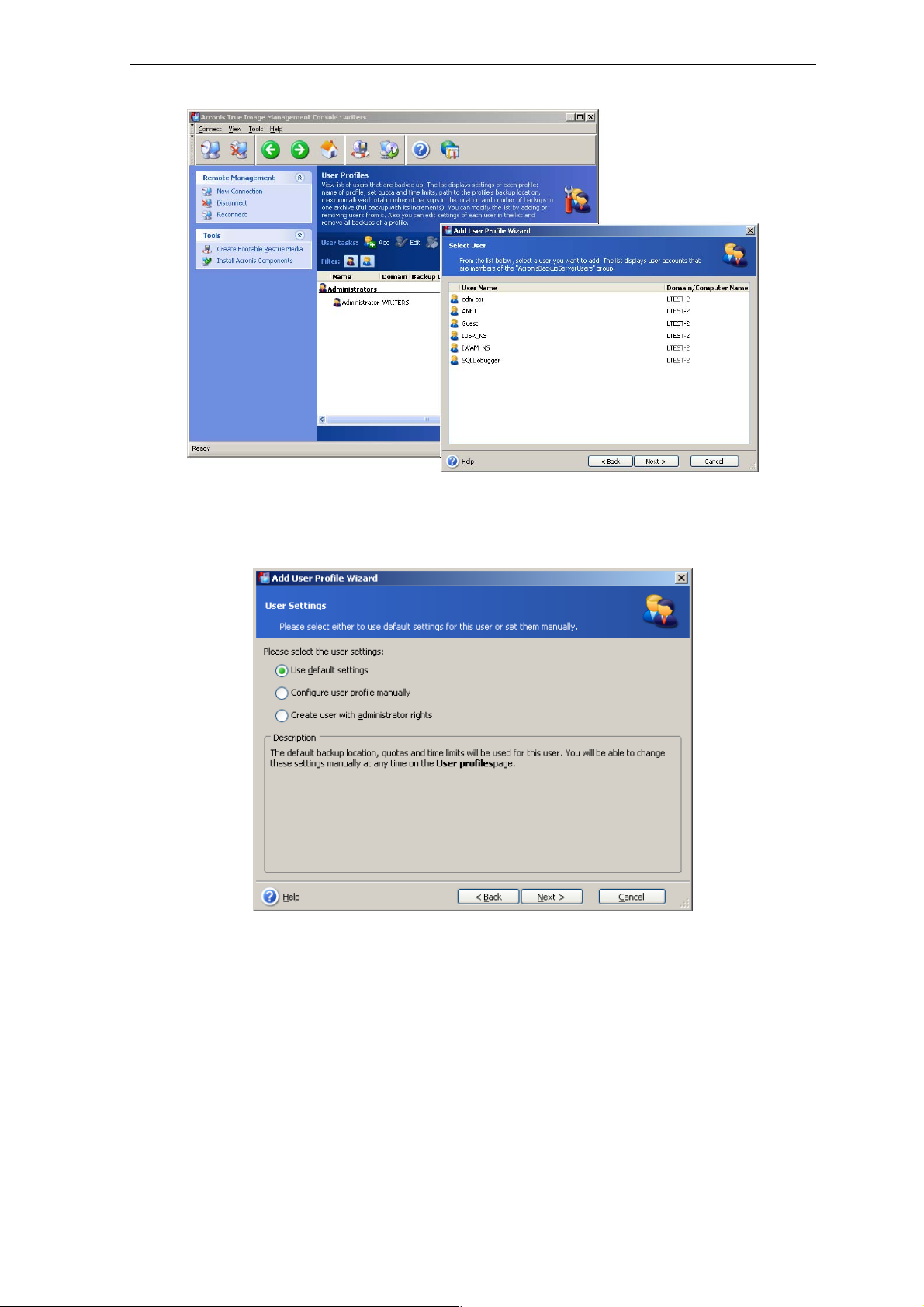
Select from the local backup server users or the domain users
Choose Create user with administrator’s rights.
Click Proceed.
User or administrator?
9. Define which users will be allowed to back up data on the backup server. Add the
users as follows:
Add the person’s local or domain account to the AcronisBackupServerUsers group on the
backup server.
Click Set up User profiles -> Add.
Choose the user name.
Choose Use default settings.
Click Proceed.
Copyright © Acronis, Inc., 2000-2008 23
Page 24
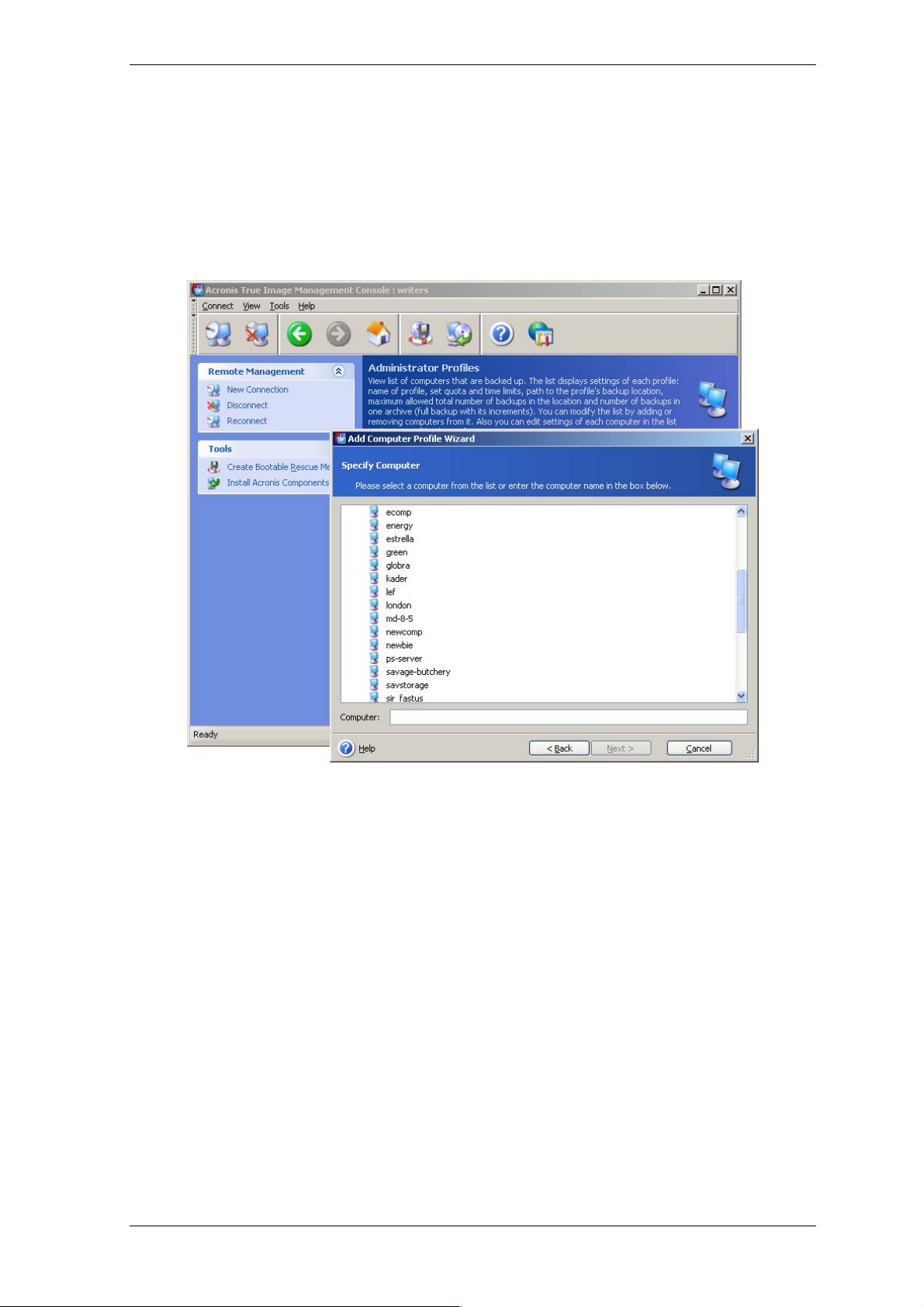
10. Define the computers which administrators will back up using Acronis True Image
Agents. Add the computers as follows.
Click Set up Administrator profiles -> Add.
Choose the computer or enter its name.
Choose Use default settings.
Click Proceed.
Adding a computer to the administrator profile
11. Schedule a check for exceeding the quotas and time limits, if needed according to
the selected policy.
To do so, select Acronis Backup Server Management -> Specify Default Settings
-> Schedule automatic consolidation and backup management.
Choose Periodically.
Choose Weekly.
Schedule check to be performed once a week during off-peak time.
Click Proceed.
The backup server is ready to work. To perform backup using the Administrator profile,
connect the console to the agent on a remote computer and create a standard backup
task while selecting Acronis Backup Servers -> backup server name -> Personal
Backup Location as backup destination. Or create a group task for several computers
with the same destination.
Users can back up their data with local program versions while selecting the same
destination.
24 Copyright © Acronis, Inc., 2000-2008
Page 25

2.3.4 Acronis Universal Restore installation
Acronis Universal Restore is an option for Acronis True Image for Microsoft Small Business
Server. It is included at no extra charge with Acronis True Image for Microsoft Small
Business Server and installed from a separate setup file. Acronis Universal Restore has its
own serial number that is required at installation.
Acronis Universal Restore can only be installed on a computer where at least one of the
following Acronis components is installed:
Acronis True Image Agent for Windows
Acronis True Image for Microsoft Small Business Server (local version)
Bootable Media Builder.
Acronis Universal Restore can be installed on a networked computer either locally, by
running the setup program, or remotely, using one of remote installation services such as
Systems Management Server (a component of Microsoft Windows NT BackOffice progra m
package). Remote installation of Acronis Universal Restore with Acronis True Image
Management Console is not supported.
After installation, Acronis Universal Restore automatically plugs in one or more of abov e
program components. Acronis True Image for Microsoft Small Business Server (local
version) name, displayed in its main window, changes to Acronis True Image for
Microsoft Small Business Server with Universal Restore.
2.4 Extracting Acronis True Image for Microsoft Small Business Server components
During Acronis True Image Management Console installation, all Acronis True Image for
Microsoft Small Business Server components’ setup (.msi) files will be placed to
C:\Program Files\Common Files\Acronis\RemoteInstall folder. Thus, you will be able to
remotely install, modify or repair the components using Acronis True Image Management
Console or msiexec.exe utility.
When installing Acronis True Image for Microsoft Small Business Server components on a
local computer, you can save setup files for each Acronis True Image for Microsoft Smal l
Business Server component separately on a local or network drive. This will help when
modifying or recovering the existing component installation on a local computer.
To save a component’s setup file:
run the Acronis True Image for Microsoft Small Business Server setup file
in the Install Menu, right-click on the component name and select Extract
select a location for the setup file and click Save.
2.5 Running Acronis True Image for Microsoft Small Business Server components
2.5.1 Running Acronis True Image for Microsoft Small Business Server (local version)
You can run Acronis True Image for Microsoft Small Business Server in Windows by
selecting Start -> Programs -> Acronis -> Acronis True Image for Microsoft
Small Business Server -> Acronis True Image for Microsoft Small Business
Server or clicking the appropriate shortcut on the desktop.
Copyright © Acronis, Inc., 2000-2008 25
Page 26

If your operating system fails to load, you can run Acronis Startup Recovery Manager.
prior
However, this must be activated
to learn more about this procedure. To run the program, press F11 during the server
bootup when you see a corresponding message that tells you to press that key. Acronis
True Image for Microsoft Small Business Server will be run in the standalone mode,
allowing you to recover the damaged partitions.
If your disk data is totally corrupted and you cannot boot (or if you have not activated
Acronis Startup Recovery Manager), load the standalone Acronis True Image for Microsoft
Small Business Server version from the bootable media (created by you using Rescue
Media Builder) or RIS-server. Then you will be able to restore the disk from a previously
created image.
to use; see
3.4 Acronis Startup Recovery Manager
2.5.2 Running Acronis True Image Management Console
To run Acronis True Image Management Console, select Start -> Programs -> Acronis
-> Acronis True Image Management Console -> Acronis True Image
Management Console.
2.5.3 Running other Acronis components
Acronis True Image Agents, Acronis Backup Server and Acronis Group Server run as
services immediately after installation and the consequent system re boot (if the latter is
required). Later on they will automatically launch at every system restart. You can stop
and start these programs in the same way as other services.
2.6 Removing Acronis True Image for Microsoft Small Business Server components
You can remove any Acronis True Image for Microsoft Small Business Server component
separately by selecting Control panel -> Add or remove programs -> <The
component name> -> Remove. Then follow instructions on the screen. You may have
to reboot your computer afterwards to complete the task.
In case you remove Acronis True Image Agent or Acronis True Image for Microsoft Small
Business Server local version from the system, there is an option to keep the Acronis
Secure Zone along with its contents (which will enable data recovery on booting from
bootable media) or remove Acronis Secure Zone.
26 Copyright © Acronis, Inc., 2000-2008
Page 27

Chapter 3. General information and proprietary Acronis technologies
3.1 The difference between file archives and disk/partition images
A backup archive is a file or a group of files (also called in this guide “backups”), that
contains a copy of selected files/folders data or a copy of all information stored on
selected disks/partitions.
When you back up files and folders, only the data, along with the folder tree, is
compressed and stored.
Backing up disks and partitions is performed in a different way: A cronis True Image for
Microsoft Small Business Server saves a sector-based snapshot of the disk, which includes
the operating system, registry, drivers, software applications and data files, as well as
system areas hidden from the user. This procedure is calle d “creating a disk image,” and
the resulting backup archive is often called a disk/partitio n image.
Acronis True Image for Microsoft Small Business Server stores only those hard disk parts
that contain data (for supported file systems). Further, it does not back up swap file
information (pagefile.sys) and hiberfil.sys (a file that keeps RAM contents when the
computer goes into hibernation). This reduces image size and speeds up image creation
and restoration.
A partition image includes all files and folders independent of their attributes (including
hidden and system files), boot record, FAT (file allocation table), root and the zero track
of the hard disk with master boot record (MBR).
A disk image includes images of all disk partitions as well as the zero track with the
master boot record (MBR).
All Acronis True Image for Microsoft Small Business Server archives files have a “.tib”
extension by default.
It is important to note that you can restore files and folders not only from file archives,
but from disk/partition images, too. To do so, mount the image as a virtual disk (see
11.2.2 Mounting an image
files or folders.
) or start the image restoration and select Restore specified
3.2 Full, incremental and differential backups
Acronis True Image for Microsoft Small Business Server can create full , incremental and
differential backups.
A full backup contains all data at the moment of backup creation. It forms a base for
further incremental or differential backup or is used as a standalone archive. A full backup
has the shortest restore time as compared to incremental or differential ones.
An incremental backup only contains data changed since the last full or incremental
backup creation. Therefore, it is smaller and takes less time to create. However, since it
all
does not contain all data needed to restore an image,
and
backups
the initial full backup are required for restoration.
the previous incremental
A differential backup creates an independent file containing all changes since the last
full archive. Generally, data from a differential backup will be restored faster than an
Copyright © Acronis, Inc., 2000-2008 27
Page 28

incremental backup, as it does not have to process through a long chain of previous
backups.
A standalone, full backup could be an optimal solution if you often roll back the system to
the initial state (for example, systems in a gaming club or Interne t café where you need
to undo changes made by the guests). In this case, you need not re-create the initial full
image, so the backup time is not crucial and the restore time will be minimal.
Alternatively, if you are interested in saving only the most current data state to be able t o
restore it in case of system failure, consider the differential backup. It is particularly
effective if your data changes tend to be little as compared to the full data volume.
An incremental backup is most useful when you need frequent back ups and possibility to
roll back to any one of multiple stored states. For example, let’s say you create a full
backup once a month. If you then crea te an incremental backup each day of a month,
you will get the same result as if you created full backups every day. However, the cost in
time and disk space (or removable media usage) will be as little as one tenth as much.
It is important to note that the above arguments are just examples for your information.
Feel free to make up your own backup policy in accordance with your specific tasks and
conditions. Acronis True Image for Microsoft Small Business Server is flexible enough to
meet any real-life demands.
An incremental or differential backup created after a disk is defragmented might be
considerably larger than usual. This is because the defragmentation program changes file
locations on disk and the backups reflect these changes. Therefore, it is recommended
that you re-create a full backup after disk defragmentation.
3.3 Acronis Secure Zone®
The Acronis Secure Zone is a special, hidden partition for storing archives on the
computer system itself. For archive security purposes, ordinary applicati ons cannot access
it. In the Acronis True Image for Microsoft Small Business Server Wizards’ windows the
zone is listed along with all partitions available for storing archives. Acronis Secure Zone is
necessary for using Acronis Startup Recovery Manager and Acronis Active restore features
(see below). The three features, in combination, instantly make operational a system that
fails to boot.
A consistent external copy of archives, saved on Acronis Secure Zone, can be created on
a network share using dual destination backup feature. See details in
destination backup
.
Acronis Secure Zone is always available for archive creation as long as there is space for
the backup file. If there is not enough space, older archives will be deleted to create
space.
Acronis True Image for Microsoft Small Business Server uses the following approaches to
clear space in the Acronis Secure Zone:
6.3.12 Dual
If there is not enough free space in the zone to create a backup, t he program deletes the
oldest full backup with all subsequent incremental/differential backups.
If there is only one full backup (with subsequent incremental/differential backups) left and
a full backup is in progress, then the old full backup and incremental/differential
backups are deleted.
If there is only one full backup left, and an incremental or differential backup is in
progress, you will get an error message telling you there is a lack of available space.
28 Copyright © Acronis, Inc., 2000-2008
Page 29
In that case, you will have to either re-create the full backup or increase the size of
the Acronis Secure Zone.
You can back up data automatically on a schedule (see
Chapter 8. Scheduling tasks
), and
not worry about zone overflow issues. However, if you keep long chains of incremental
backups, it is a good practice to check the zone free space periodically. To do so, star t the
Manage Acronis Secure Zone wizard and see the zone free space that is displayed on
the wizard’s second page.
For information on how to create, resize or delete Acronis Secure Zone using this wizard,
Chapter 9. Managing the Acronis Secure Zone
see
.
In case you remove Acronis True Image Agent or Acronis True Image for Microsoft Small
Business Server local version from the system, there is an option to keep Acronis Secure
Zone along with its contents (which will enable data recovery on booting from bootable
media) or remove Acronis Secure Zone.
The Acronis Secure Zone should not be the only location where a backup is stored.
Should the disk have a physical failure, the Acronis Secure Zone could be lost. This is
particularly critical for backups of servers; the Acronis Secure Zone should only be one
part of an overall backup strategy.
3.4 Acronis Startup Recovery Manager
3.4.1 How it works
The Acronis Startup Recovery Manager enables starting Acronis True Image for Micros oft
Small Business Server on a local computer without loading the operating system. If the
operating system won't load, you can run Acronis True Image for Microsoft Small
Business Server by itself to restore damaged partitions. Unlike booting from the A cronis
removable media or RIS server, you will not need a separate media or network
connection to start Acronis True Image for Microsoft Small Business Server. It is especially
handy for mobile users who need to run a server operating system on their laptop.
3.4.2 How to use
To be able to use Acronis Startup Recovery Manager at boot time, prepare as follows (you
can do it either locally, using Acronis True Image for Microsoft Small Business Server local
version, or remotely, using Acronis True Image Management Console):
1. Install Acronis True Image for Microsoft Small Business Server local version or Acronis
True Image Agent on a computer.
2. Create Acronis Secure Zone on the computer hard disk (see
Acronis Secure Zone
).
3. Activate Acronis Startup Recovery Manager. To do so, click Activate Acronis Startup
Recovery Manager and follow the Wizard’s instructions.
If you try to activate Acronis Startup Recovery Manager while Acronis Secure Zone is
missing from the system, you will be prompted to create the zone,
Recovery Manager will be activated. Otherwise, Acronis Startup Recovery Manager will be
activated immediately.
When Acronis Startup Recovery Manager is activated, it overwrites the master boot
record (MBR) with its own boot code. If you have any third-party boot managers
installed, you will have to reactivate them after activating the Startup Recovery Manager.
For Linux loaders (e.g. LiLo and GRUB), you might consider installing them to a Linux
root (or boot) partition boot record instead of MBR before activating Acronis Startup
Chapter 9. Managing the
then Acronis Startup
Copyright © Acronis, Inc., 2000-2008 29
Page 30

Recovery Manager.
Here’s an example of how you would use this feature. If failure occurs on a computer,
turn on the computer and press F11 when you see the "Press F11 for Acronis Startup
Recovery Manager" message. This will run a standalone version of Acronis True Image for
Microsoft Small Business Server that only slightly differs from the complete version. For
information on restoring damaged partitions, see
Be careful! Disk letters in standalone Acronis True Image for Microsoft Small Business
Server might sometimes differ from the way Windows identifies drives. For example, the
D: drive identified in the standalone Acronis True Image might correspond to the E: drive
in Windows.
Chapter 7. Restoring the backup data
.
3.5 Acronis Backup Server
Acronis Backup Server is an application for centralized storage and management of
enterprise backup archives in accordance with the policies, set by an administrator. It
ensures optimal usage of storage resources us ed for backup archives. Outdated archives
will be automatically deleted; at the same time, the latest data recovery is always
possible. In addition, Acronis Backup Server facilitates creation and executing group
backup tasks.
For information on how to install and set up Acronis Backup Server, see
Backup Server installation and setup
Server, see
4.5 Managing backup server
. For information on how to manage Acronis Backup
.
2.3.3 Acronis
3.5.1 Backup locations
Backup server is a networked computer where Acronis Backup Server is installed. A
backup location is a storage area for backups on a local backup server hard drive.
At installation, Acronis Backup Server creates one (default) backup location. The location
has the following properties:
Path: C:\Documents and Settings\All Users\Application Data\Acronis\BackupServer\
Backups
Maximum backup location size: Unlimited
Maximum storage period (days): Unlimited
All backup data destined to the backup server will be saved in the default backup location.
Because it may not be practical or efficient for you to store all backup data in one
location, the backup server allows you to cr ea te as many locations as you need, each with
its own properties. The three basic rules are:
any location, except for the default one, must be assigned to at least one user or
computer
only one location can be assigned to a user or computer
the default location may not be assigned to a u ser or computer. There must be a default
backup location on a backup server though.
You can create a separate location for each user or comp uter while adding them to the
backup server, distribute the users/computers between several locations, or assign the
same location to all users/computers.
Maintaining multiple small backup locations on a single disk does not allow for tracking
changes in total disk space usage. At the same time, manual management of thousands
30 Copyright © Acronis, Inc., 2000-2008
Page 31

of archives in a location may be a serious problem. Practice is the best criterion for your
choice.
You can move, clear or delete existing backup locations or edit their size limitations and
storage period.
3.5.2 Quotas and time limits for computers and users
Individual quotas and time limits determine every computer’s or user’s quota on a backup
server. This include
1) maximum storage space, allocated to a user/computer, in MB, GB or TB
2) maximum number of backups
3) maximum number of incremental backups for each full backup
4) maximum storage period for the user’s/computer’s backups.
A storage period is the amount of time that is allotted for a user or the backup location to
maintain a file.
These values define how Acronis Backup Server itself will handle the backup archives.
At first backup of the computer/user’s data to the backup server, a full backup will be
created. The next backups will be incremental, until the maximum number of incremental
backups is reached. After that a full backup and a set of subsequent incremental backups
is created, then again a full backup and so on.
When backing up to backup server, a user cannot select backup mode (full, incremental,
differential). The backup mode will be set by Acronis Backup Server.
An attempt to direct user/computer backup data to the backup server while space or
number quota is exceeded will not succeed. Backup to the full location will also be
prohibited.
An administrator can schedule a check of meeting the limitations. All archives on the
backup server will be checked and, if the space quota is violated or the maximum number
of backups is exceeded, the backups will be processed as follows:
Acronis Backup Server will combine the first full backup with the next incremental one
into one full backup which will be dated the later backup date. Then, if necessary, this
backup will be combined with the next, until the occupied storage space (or number
of backups) decreases to the preset limit. Thus, the archive integrity will not be
affected, in spite of the fact that the oldest backups will be deleted. This procedure is
called automatic consolidation.
The actual number of backups can exceed the Maximum number of backups by one.
This enables the program to detect the fact of quota violation and start c ons olidation.
3.5.3 Administrators and Users
At installation, Acronis Backup Server creates the user group called
AcronisBackupServerUsers:
Control Panel -> Administrative Tools -> Computer Management -> Local Users and
Groups -> AcronisBackupServerUsers.
Copyright © Acronis, Inc., 2000-2008 31
Page 32

The person who installed the program becomes the administrator in this group. The
administrator is automatically registered on the backup server.
Generally, there are two types of profiles on the backup server: Administrators and Users.
The Administrators profiles are designed to p erform ba ckups on rem ote comp uters with
Acronis True Image Agents. Whatever computer the administrator backs up, backup data
will be sent to the same location, assigned to the computer. Administrators can also
manage archives on the backup server, including archives created via Users’ profiles.
The Users profiles are designed to back up data from computers with Acronis True
Image for Microsoft Small Business Server local version. Whatever computer the user
operates on, backup data will be sent to the same location assigned to that user.
3.5.4 Operations with archives
Acronis Backup Server can display a list of backups, stored on the backup server, and sort
the list by location or owners (users and computers).
An administrator, if need be, can consolidate any backup ( except for the oldest one in t he
archive) manually with the preceding backup file. This operation deletes the preceding
backup and sets concatenation between the backup being consolidated and the backup
before the deleted one. Thus, the archive integrity will not be affected, in spite of the fact
that one backup will be deleted. Data recovery from any of the remaining backups will be
possible.
An archive can be exported from Acronis Backup Server to a local har d drive or network
share or imported from external location to a computer’s or user’s backup location on the
backup server.
3.6 Acronis Active restore
With this feature you can boot the OS on a crashed computer before the system is
completely restored from an image and start work seconds after the restoration is
launched. The restoration will be continued in the background.
3.6.1 Limitations in using Acronis Active restore
1. Acronis Active restore is currently available for images located in the Acronis Secure
Zone only.
2. Acronis Active restore does not support images of Windows Vista. If any Vista edition is
detected in an image, the Active restore option will not appear.
3. Acronis Active restore does not work if the image contains dynamic disks and volumes.
4. Acronis Active restore cannot be used if the image contains no operating system (a
logical partition or disk image) or when restoring file archives.
3.6.2 How it works
When the restoration procedure is started, Acronis True Image for Microsoft Small
Business Server:
1. Finds the sectors in the image which contain system files, and restores these sectors
first. First the OS is restored and can be star ted very quickly. Having started the OS, th e
user sees the folder tree with files, though file contents still is not recovered.
Nevertheless, the user can start working.
32 Copyright © Acronis, Inc., 2000-2008
Page 33

2. Next, the application writes on the hard disk its own drivers, which intercept system
queries to the files. When the user attempts to open files or launch applications, the
drivers receive the system queries and restore the sectors that are necessary for the
requested operation.
3. At the same time, Acronis True Image for Microsoft Small Business Server proceeds
with the complete sector-by-sector image restoration in the background. However, the
requested sectors have the highest priority.
Finally, the image will be fully restored even if the user performs no actions at all. But if
you choose to start working as soon as possible after the system failure, you will gain at
least several minutes, considering that restoration of a 10-20GB image (most common
image size) takes about 10 minutes. The larger the image size, the more time you save.
3.6.3 How to use
To be able to use Acronis Active restore, prepare your system this way: (you can do it
either locally, using Acronis True Image for Microsoft Small Business Server local version,
or remotely using Acronis True Image Management Console):
1. Install Acronis True Image for Microsoft Small Business Server local version or Acronis
True Image Agent on the local computer.
2. Create the Acronis Secure Zone on the local computer hard disk (see
Managing the Acronis Secure Zone
3. Activate Acronis Startup Recovery manager (see
Manager
Microsoft Small Business Server (see
4. Back up (image) the local computer’s system disk to Acronis Secure Zone (see
Backing up disks and partitions (image backup)). You can back up other disks/partitions
as well, but the system image is mandatory.
If failure occurs, boot the local computer from th e bootable media, or RI S server, or using
F11. Start the recovery procedure (see
images
restore and in the next window click Proceed. In a few seconds the computer will
reboot to the restored system. Log in and start work – no additional reboots or other
actions are required.
You can perform Active restore running Acronis True Image for Micros oft Small Business
Server in Windows operating systems as well. However, it is mandatory to have bootable
media in case Windows cannot boot.
) and create bootable media or RIS package with Acronis True Image for
When performing Active restore, the current Acronis True Image for Microsoft Small
Business Server version always restores the entire system disk. Therefore, if your system
disk consists of several partitions, all of them must be included in the image. Any
partitions which are missing from the image will be lost.
), select the system disk image from Acronis Secure Zone, choose Use Active
).
3.4 Acronis Startup Recovery
Chapter 10. Creating bootable
7.3 Restoring disks/partitions or files from
media).
Chapter 9.
6.2
3.7 Acronis Universal Restore
3.7.1 Acronis Universal Restore purpose
A system disk image can be deployed easily on the hardware where it was created or to
identical hardware. However, if you change a motherboard or use another processor
version — a likely possibility in case of hardware failure — the restored system could be
unbootable. An attempt to transfer the system to a new, much more powerful computer
Copyright © Acronis, Inc., 2000-2008 33
Page 34

will usually produce the same unbootable result because the new hardware is
incompatible with the most critical drivers included in the image.
Using Microsoft System Preparation Tool (Sysprep) does not solve t his problem, because
Sysprep permits replacing drivers only for Plug-and-Play devices (sound cards, network
adapters, video cards etc.). As for system Hardware Abstraction Layer (HAL) and mass
storage device drivers, they must be identical on the source and the target computers
(see Microsoft Knowledge Base, articles 302577 and 216915).
Acronis Universal Restore technology provides an efficient solution for hardwareindependent system restoration by replacing the crucial Hardware Abstraction Layer (HAL)
and mass storage device drivers.
Acronis Universal Restore is applicable for:
1. Instant recovery of a failed system on different hardware
2. Hardware-independent cloning and deployment of operating systems
3. Real-to-virtual and virtual-to-real computer migration for system recovery, test and
other purposes.
3.7.2 Acronis Universal Restore general principles
1. Automatic HAL and mass storage drivers selection
Acronis Universal Restore searches the Windows default driver storage folders (in the
image being restored) for HAL and mass storage device drivers and installs drivers that
better fit the target hardware. You can specify a custom driver repository (a folder or
folders on a network drive or CD) which will also be used for drivers search.
The Windows default driver storage folder is determined in the registry key
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Current version\DevicePath. This
storage folder is usually WINDOWS/inf.
2. Manual selection of mass storage device driver
If the target hardware has a specific mass storage controller (such as a SCSI, RAID, or
Fibre Channel adapter) for the hard disk, you can install the appropriate driver manually,
bypassing the automatic driver search-and-install procedure.
3. Installing drivers for plug and play devices
Acronis Universal Restore relies on built-in plug and play discovery and configuration
process to handle hardware differences in devices that are not critical for the system
start, such as video, audio and USB. Windows takes control over this process during the
logon phase, and if some of the new hardware is not detected, you will have a chance to
install drivers for it later manually.
3.7.3 Acronis Universal Restore and Microsoft Sysprep
Acronis Universal Restore is
not
a system preparation tool. You can apply it to any s ystem
image created by Acronis products, including images prepared with Microsoft System
Preparation Tool (Sysprep). The following is an example of using both tools on the same
system.
Acronis Universal Restore does not strip security identifier (SID) and us er profile settings
in order to run the system immediately after recovery without re-joining the domain or remapping network user profiles. If you are going to change the above settings on a
34 Copyright © Acronis, Inc., 2000-2008
Page 35

recovered system, you can prepare the system with Sysprep, image it and restore, if need
be, using Acronis Universal Restore.
3.7.4 Limitations in using Acronis Universal Restore
1. The system recovered by Acronis Universal Restore might not start if the partition
structure in the image or the target disk partitioning does not coincide with that of th e
source disk. As a result, the loader, restored from the image, will point to the wrong
partition and the system will not boot or will malfunction.
Such might be the case if you:
- image only selected partitions but not the entire source disk
Keep in mind, that the source disk may have a hidden maintenance partition created by
the computer vendor. Therefore, if you check each partition for backup instead of
checking the disk, this hidden partition will not be included into the image.
- restore not the entire source disk, but only the selected partitions. In some cases,
especially if your system resides on a partition other than the first, this can confuse th e
loader and prevent the restored system from startup.
To avoid the problem, we recommend that you image and restore the entire system disk.
2. The Acronis Universal Restore option does not work if a computer is booted with
Acronis Startup Recovery Manager (using F11) or the backup image is located in Acronis
Secure Zone. This is because Acronis Startup Recovery Manager and Acronis Secure Zone
are primarily meant for instant data recovery on the same computer.
3.7.5 Getting Acronis Universal Restore
Acronis Universal Restore is an add-on to Acronis True Image for Microsoft Small Business
Server. It is included at no extra charge with with Acronis True Image for Microsoft Small
Business Server , has its own license, and is installed from a separate setup file.
Let’s assume for a moment that you own Acronis True Image for Microsoft Small Business
Server but have not purchased Acronis Universal Restore. When you create a task for
restoring a Windows system disk and select a target disk (either physical or virtual) in the
Restore Data Wizard, the program compares crucial for the system star t devices found in
the image registry and the target computer registry. If th e chipset, motherboard or mass
storage device are different, and therefore there is a risk that the system cannot boot,
you will be prompted whether you want to use Acronis Universal Restore. Follow the link
and Acronis Universal Restore will be added automatically for free.
If you already have Acronis Universal Restore, the prompt will not come up and you will
have an option to enable Acronis Universal Restore later in the Restore Data Wizard.
3.8 Backing up to tape libraries and tape drives
A tape library is a high-capacity storage device consisting of one or mor e tape drives and
a loader that automatically selects and loads multiple tape cartridges. Tape libraries with
only one drive and loader are known as autoloaders.
Acronis True Image for Microsoft Small Business Server supports tape libraries,
autoloaders, SCSI and USB tape drives as storage devices.
Tape libraries, autoloaders and tape drives are accessible through the Acronis Backup
Server or using Acronis True Image for Microsoft Small Business Server local version. The
Copyright © Acronis, Inc., 2000-2008 35
Page 36

following diagram illustrates ways of access to tape devices for networks with (I) and
without (II) backup server.
The devices must be locally attached to the servers and work through Windows
Removable Storage Management (RSM). Devices that use the N etwork Data Management
Protocol (NDMP) are not supported.
The following operations are available for backups stored on tape devices:
• validation
• data recovery
• converting an image to virtual disk.
Consolidation, mounting or exploring backups stored on tape devices is not supported.
Acronis True Image for Microsoft Small Business Server does not support tape devices
when working in preinstallation environment such as Win PE or Bart PE.
The bootable Acronis True Image for Microsoft Small Business Server version cannot
access archives created by the local version on locally attached tape devices.
To be able to access archives with bootable media, please back up to Acronis Backup
Server or back up to the local tape device using the bootable media.
3.8.1 Understanding backup to tape devices
Archives cataloguing
Acronis True Image for Microsoft Small Business Server creates a dedicated database for
archives and tapes cataloguing (\Program files\Common
Files\Acronis\Fomatik\tape_archives.fdb.)
Each tape of an RSM-managed device has its own GUID stored in the Windows registry.
Acronis True Image for Microsoft Small Business Server creates its own ID for each tape,
sets up the correspondence between this ID and the RSM GUID and stores that
information along with information about the archive in its own database. Additionally, the
program stores metadata on tape, so that identification infor m ation can be obtained when
mounting a tape that is not registered in the database.
If the database is lost or not available (say, you detach the tape device and a ttach it to
another computer or reinstall Windows) the necessary information is derived from the
36 Copyright © Acronis, Inc., 2000-2008
Page 37

metadata saved on the tape and the database will be recreated on the new host using the
new host RSM. This operation is performed at first access to the tape device while setting
up a backup, recovery or validation task. Therefore, under Windows the program knows
which tape should be mounted even if the data is recovered on another machine.
When booted from Acronis rescue media, Acronis True Image for Microsoft Small Business
Server uses another mechanism for access to tape devices since RSM is not available.
Moving tapes between tape devices
A tape that already has backups can be added to a tape device. When the tape device is
selected in the recovery or validation wizard, the newly added tape is scanned by the RSM
and then by Acronis and added to the Acronis database and the Acronis pool. The a ccess
to the archives on the tape becomes available.
However, Acronis will not scan the added tape for changes if the tape already is in the
Acronis database. If you eject a tape, back up another machine on this tape and ta ke the
tape back to the first tape device, the second machine archive will not be discovered by
Acronis and therefore cannot be restored by the first tape device. Please be awar e of this
limitation when using tapes between multiple computers.
Using RSM pools
At first backup to the tape device, Acronis True Image for Microsoft Small Business Server
takes a tape from the Free pool. The program creates the Acronis pool and puts th e 1st
tape in the pool. The tape stays mounted after writing a backup is completed. The next
backups, regardless of their contents, will be placed on the same tape, unless the tape
free space runs out.
When the 1st tape is full, the program looks for another cartridge in the Free pool and
uses it without user intervention. If the Free pool is empty, a cartridge from the Import
media pool is used through a prompt. (You have an option to disable prompts, see
6.3.14 Additional settings
.)
So, to fully automate changing tapes at backup, you must always have at least one tape
in the Free pool (or a tape in the Import media pool and the prompt disabled.)
Overwriting old archives
You can move tapes with outdated archives from the Acronis pool to the Free pool
periodically using the Removable storage snap-in. To do so:
1. Select Control panel -> Administrative tools -> Computer management -> Removable
storage -> Media pools -> Acronis.
2. Right click on the tape in the Acronis pool, deallocate the tape if it is mounted and
select Free from the context menu. The tape will be moved to the Free pool. After
putting a tape in the Free pool RSM and then Acronis will rescan it and record it to the
database with a new GUID.
A deleted archive is not necessarily deleted from the tape, it can be just marked as
deleted in the catalogue.
Saving a full backup to a new tape
You can enable saving a full backup on a new tape even if the currently mounted tape is
not full. To do so, deallocate the current tape and eject it, add a new t ape and move the
tape to the Free pool using RSM. Incremental or differential backups cannot be
performed in this way because access to the previous backups is required.
Copyright © Acronis, Inc., 2000-2008 37
Page 38

3.8.2 Backing up to a tape device through Acronis Backup Server
To enable backup to a tape device in the local network:
1. Install Acronis Backup Server on a server accessible to all users.
2. Attach the tape device to that server.
3. Move tapes from the Unrecognized or Import media pool to the Free pool using
the Removable storage snap-in (Control panel -> Administrative tools -> Computer
management -> Removable storage -> Media pools.)
4. Create local accounts on that server for all users who will back up their data to the
autoloader. Accounts must belong to the Backup Operators group and be the real
accounts with which users log in Windows.
5. When creating backup tasks (if logged in Windows with the above accounts), users of
local Acronis True Image for Microsoft Small Business Server version will be able to select
the tape device from the list of destination devices.
The backup server administrator can create group or individual tasks for computers to
back up their data to the tape device using Acronis True Image Management Console.
Filenames for backups are not needed when backing up to tape.
Archives, created on tape devices through Acronis Backup Server, can be accessed by
Acronis True Image for Microsoft Small Business Server local and bootable versions and
agents for validation, data recovery and converting images to virtual disks.
You can attach the tape device to another Acronis Backup Server, if need be (say, the
current backup server is down.) Before doing so, delete the Acronis database for tape
devices on that server, if there is one (\Program files\Common
Files\Acronis\Fomatik\tape_archives.fdb.) This will allow the backup server to create the
database for the newly attached tape device using metadata contained on tapes.
Acronis Backup Server does not allow for creating manageable backup locations on tape
devices. This means that you cannot limit the number of backups or the period while the
archives are stored on tape devices. This functionality is supported only on the backup
server internal hard drives.
3.8.3 Backing up to a locally attached tape device
Backup to a locally attached tape device can be performed using either Acronis True
Image for Microsoft Small Business Server local version or bootable media.
The bootable Acronis True Image for Microsoft Small Business Server version cannot
access archives created by the local version on locally attached tape devices.
To be able to access archives with bootable media, please back up to Acronis Backup
Server or back up to the local tape device using the bootable media.
To enable backup to a locally attached tape device with A cronis True Image for Microsoft
Small Business Server local version:
1. Install Acronis True Image for Microsoft Small Business Server local version.
2. Attach the tape device to the computer.
3. Move cartridges from the Unrecognized or Import media pool to the Free pool
using the Removable storage snap-in (Control panel -> Administrative tools -> Computer
management -> Removable storage -> Media pools.)
38 Copyright © Acronis, Inc., 2000-2008
Page 39

4. If the tape contains data, its contents will be overwritten on prompt. You have an
option to disable prompts, see
5. When creating a backup task, you will be able to select the tape device from the list of
destination devices. Filenames for backups are not needed when backing up to tape.
6. [Tape drive] As soon as the tape is full, a dialog window with a request to insert a new
tape will appear.
[Tape library or autoloader] As soon as the tape is full, the program automatically draws a
tape from the Free or Import media pool. The above request will appear if no tapes are
found in either of these pools.
You might experience short pauses that are required to rewind the ta pe. Low-quality or
old tape, as well as dirt on the magnetic head, might lead to pauses that can last up to
several minutes.
6.3.14 Additional settings
.
3.8.4 Restoring data from archives located on tape devices
Data recovery from archives located on tape devices is performed in the same way as
with other storage devices.
When recovering, you start the restore wizard, select the local tape device or tap e device
under the backup server, select the archive and the backup to restore data from.
[Tape drive] You will be prompted to insert tapes required for restoring data from the
selected backup.
[Tape library or autoloader] The program finds the tapes and inserts them automatically
in the right order. A prompt comes up if the required tape is not found.
3.9 Viewing disk and partition information
You can change the way data is represented in all schemes you see in various wizards.
To the right are three icons: Arrange Icons by, Choose Details and i (Display the
properties of the selected item), the last duplicated in the context menu invoked by
right-clicking objects.
To sort messages by a particular column, click the header (another click will switch the
messages to the opposite order) or Arrange Icons by button and select the column.
To select columns to view, right-click the headers line or left-cli ck the Choose Details
button. Then flag the columns you want to display.
If you click the i (Display the properties of the selected item) button, you will see
the selected partition or disk properties window.
This window contains two panels. The left panel contains the properties tree and the right
describes the selected property in detail. The disk information includes its physical
parameters (connection type, device type, size, etc.); partition information includes both
physical (sectors, location, etc.), and logical (file system, fr ee space, assigned letter , etc.)
parameters.
You can change the width of a column by dragging its borders with the mouse.
Copyright © Acronis, Inc., 2000-2008 39
Page 40

Chapter 4. Using Acronis True Image Management Console
4.1 General information
Acronis True Image Management Console is the primary tool for managing data
backup/restore on remote computers where Acronis True Image Agent is installed. The
console allows for the managing of computer groups and corporate backup archives using
Group and Backup Servers, as well as managing individual backup/restore tasks for ever y
computer.
Acronis True Image Management Console main window
4.2 Installing/updating Acronis components on remote machines
Acronis True Image Management Console allows for group installation and updates of
Acronis True Image for Microsoft Small Business Server (local version) and Acronis True
Image Agent for Windows on remote computers. To perform any of these oper ations, you
will need administrator rights on the target machines.
Installation of Acronis components onto remote machines running all Windows Vista
editions is not possible. You will have to install the components locally on such
computers.
If the remote computer runs Windows XP, the option Control panel -> Folder options
-> View -> Use simple file sharing must be disabled on that computer.
If the remote computer runs Windows XP with Service Pack 2 or Windows 2003 Server,
the option Control panel -> Windows Firewall -> Exceptions -> File and Printer
Sharing must be enabled on that computer.
40 Copyright © Acronis, Inc., 2000-2008
Page 41

To install Acronis components:
1. Click Install Acronis components to a remote computer in the center of Acronis
True Image Management Console main window, on the toolbar or the sidebar, or select
the same item from the Tools menu.
2. Select the installer location from the list (Registered Components, Search
removable media or Specify location). The default selection Registered
Components will use setup files from the default C:\Program Files\Common
Files\Acronis\RemoteInstall folder.
3. Select the Acronis component and specify the component features y ou want to install
(for custom component features see
Business
Server components.)
2.3 Installing Acronis True Image for Microsoft Small
4. Select computers on which the Acronis component is to be installed. This can be done
by:
- browsing the network. When browsing the network, you can select entire workgroups or
domains
- typing the computers names or addresses (click Next then add computers to the list)
- importing the computers list from .txt or .csv files.
Copyright © Acronis, Inc., 2000-2008 41
Page 42

5. Provide administrator username and password for each computer. If there is a
universal administrator account on the network, enter the account credentials for one
computer and set the option to apply it to all computers that you select. Domain
administrator credentials and universal credentials for wor kgroups can be applied in this
way.
If you do not specify credentials for all machines involved, or if the credentials are not
valid for some machines, you will have an option to provide credentials during installation
(there is an option Other user in the username/password error prompt.)
Most Acronis components require the system restart on their installation. To allow
immediate remote computer reboot, check th e Reboot the remote computer box. This
option also can be applied to all computers or set to each machine individually.
6. The summary window displays a list of computers where the Acronis component will be
installed.
42 Copyright © Acronis, Inc., 2000-2008
Page 43

7. Once the installation starts, the program displays the oper ation progress and the name
of the computer on which the component is being installed.
To update an Acronis component on a remote computer, perform the same procedure.
4.3 Managing a single remote computer
To perform any operation on a single remote computer, you must first connect to it.
4.3.1 Connecting to a remote computer
To establish a remote connection:
1. Click Connect to a remote computer in the center of Acronis True Image
Management Console main window or on the toolbar, or select New connection from
the sidebar or the Connect menu.
2. Enter the computer network name, IP address or select it using Browse… button.
Browse… will open a list, including all computers controllable with Acronis True Image
Management Console.
3. Enter administrator or backup operator username and password.
When connecting to a backup server inside a domain, mind whether your domain or
local account is registered on the backup server. If you entered Windows on a network
computer using your domain account while your local account is registered, enter the
local user name along with the backup server name (for example, Server1\username).
Otherwise the name will be identified as a domain one.
After a connection is established, you will see a list of operations available in the central
part of Acronis True Image Management Console main window:
Main window of Acronis True Image Management Console when connected to a remote
computer
Copyright © Acronis, Inc., 2000-2008 43
Page 44

The task list content depends on the programs installed on the connected computer. The
most populated list will include managing Backup and Recovery Tasks (using the
Acronis True Image Agent), Acronis Group Server Management and Acronis
Backup Server Management.
While you are operating on a remote computer, the computer could reboot or the
connection to the computer could be broken for other reasons. This will result in
operations failure, such as hiding of the remote computer file system in wizards, or
operation may hang. Use Reconnect on the sidebar to test whether the computer is
available again or eliminate any malfunction that persists.
The console automatically attempts to reconnect to the last connected machine every 30
sec. To change the time interval between the attempts, select Tools -> Options ->
Network -> Reconnect options.
When the console is disconnected, Reconnect provides a handy one-click connection to
the most recently accessed machine.
4.3.2 Backup and recovery tasks
After clicking on Backup and Recovery Tasks, the program window will appear like the
graphic below:
You can perform the following operations on the remote computer.
Operation How to access
Back up and Recover
Back up and restore data, including system
disks/partitions
44 Copyright © Acronis, Inc., 2000-2008
Click Backup or Recovery, then follow the
Wizard’s instructions. See details in
6. Creating backup archives
Restoring the backup data.
and
Chapter
Chapter 7.
Page 45

Browse logs of Acronis True Image Agent
operation
Set up default backup or restore options,
such as system/network resources usage,
before/after backup commands, etc.
Set up default parameters for sending
notifications about Acronis True Image for
Microsoft Small Business Server operation
and tracing this operation in the Windows
Application Event Log
Scheduling Tasks
Schedule backup and archive validation
operations
Run, stop, edit, clone, rename, delete
backup and archive validation tasks
Click Show Log. See details in
Viewing logs
.
12.3
Click Remote Computer Options, select
Default backup options or Default
restoration options and make settings.
See details in
7.4 Setting restore options.
and
6.3 Setting backup options
Click Remote Computer Options, select
Notifications or Event tracing and make
settings. See details in
Notifications and event tracing.
Chapter 12.
Click Show tasks to navigate to the
Manage Computer Tasks window. Click
Create then follow the wizard’s
instructions. See details in
Scheduling tasks
.
Chapter 8.
Click Show tasks to navigate to the
Manage Computer Tasks window. See
details in
8.2 Managing scheduled tasks
.
Archives Management
Validate backup archives wherever they
reside, be it local, network or removable
media
Consolidate backup files in an archive
Convert disk images to virtual disk files of
the type you select (.vmdk, .vhd, .hdd)
Click Validate Backup Archive, then
follow the wizard’s instructions. See details
in
11.1 Validating backup archives
.
Click Consolidate archive, then follow the
Wizard’s instructions. See details in
11.3
Consolidating backup.
Click Convert backup to Virtual Disk
and follow the wizard’s instructions. See
details in
virtual disks
13. 4 Converting disk images to
Hard Disk Management
Manage Acronis Secure Zone (create,
delete, resize, remove or change password)
Click Manage Acronis Secure Zone, then
follow the wizard’s instructions. See details
in
Chapter 9. Managing the Acronis Secure
.
Zone
Activate Acronis Startup Recovery Manager Click Activate Acronis Startup Recovery
Manager, then follow the wizard’s
instructions. See details in
Startup Recovery Manager
3.4 Acronis
.
Copyright © Acronis, Inc., 2000-2008 45
Page 46

Other Tools
Create bootable rescue media, its ISO or
See
Chapter 10. Creating bootable media
.
RIS package
Update the remote agent Click Update the remote agent, then
follow the Wizard’s instructions. The
procedure is the same as described in
4.2
Installing/updating Acronis components on
remote machine
After you perform all necessary operations on the remote computer, select Disconnect
or New connection on the toolbar, sidebar or the Connect menu.
4.4 Managing groups of computers
4.4.1 Group status display
When connected to a computer where Acronis Group Server is installed, click Acronis
Group Server management to display the following window.
Here you can monitor states of Acronis True Image for Microsoft Small Business Server
tasks (backup, restore, validating backup archives) on all networked computers:
Ready – the remote computer is available for the next task
Prepare - preparations are being made on a remote machine for the task execution
(analyzing partitions, preparing backup scripts, etc.)
Running – a task is being executed on the remote computer
Paused – the task is paused and waiting for user input on the remote computer
Failed – the task could not be completed because of an error
Finished – the task has been completed successfully
46 Copyright © Acronis, Inc., 2000-2008
Page 47

Cancelled – the task has been cancelled on the remote computer
Offline - the remote computer is not connected to the netw ork or is switched of f
Inaccessible - the remote computer is not accessible due to lack of access rights,
firewall and security settings, etc.
Unmanaged - the Acronis True Image Agent is not installed on the remote machine.
Use Search to find a computer in the list quickly.
To see details of the computer in brief (the computer role, operating system and IP
address), click the computer name. The details are displayed on the sidebar.
To see details of the group task being executed on a remote computer, mouse over the
computer name.
In this window you can also:
1. Filter out from the list offline, inaccessible or unmanaged computers or filter out
online computers to see those that cannot be managed (use buttons in the Filter group).
2. Import computers into the group server in case they are not discovered
automatically due to network behavior. It makes sense to i nstall Acronis components on
these computers first so that you will be able to create tasks for these computers.
To add a single computer:
click Add on the toolbar
type in the computer name or IP address.
To add computers from Active directory:
click Add on the toolbar
type in the name of the domain controller
when the active directory is expanded, tick off the desired computers or the entire
directory.
To add multiple computers from a file:
prepare a .txt or .csv file, listing semicolon-separated computers names and IP addresses
as follows: Name1; IP1; Name2; IP2;…
click Add on the toolbar
specify path to the above file.
3. Export computers from the group server to a .txt or .csv file that can be used by
other application or new versions of Acronis Group Server. To do so:
click Export on the toolbar
specify name of the file and a path to a folder where you want to create it.
4. Set and test credentials for access to each computer. To do so, select th e computer,
then select on the sidebar Computer details -> Credentials: Set, type username and
password and click Test connection. The program will display the test result. Key icons
for successfully tested connections are colored gold.
5. Set (or change) the MAC address for each computer. To do s o, select the computer,
then select on the sidebar Computer details -> MAC address: Set or Change and type
the hex MAC address as XXXXXXXXXXXX or XX-XX-XX-XX-XX. The program will test the
MAC address for validity and display the test result.
Copyright © Acronis, Inc., 2000-2008 47
Page 48

6. Hide computers that you do not wish to browse or make a hidden computer visible. To
hide a computer, select it, then select on the sidebar Computer details -> Visibility:
Hide. To make a hidden computer visible (and monitored), enable Show hidden
computers in the Filter group, select the hidden computer, then select on the sidebar
Computer details -> Visibility: Unhide.
7. Create a group backup task for several remote computers at once (see
Creating new group tasks
8. Connect to a remote computer to see the operation log, start or edit tasks for this
computer etc. (see
and click Connect.
9. Switch to the Group tasks management window for managing group tasks.
).
4.3 Managing a single remote computer
). To do so, select a computer
4.4.2
4.4.2 Creating new group tasks
You can create a disk/partition backup task or a rchive validation task for several remote
computers at once. File-level backup for groups of computers is unavailable.
1. In Group status or Group tasks management window, select New Group Task
on the toolbar. The Create Group Task Wizard starts to guide you through the task
creation procedure.
2. Select the type of the task: backup or validation.
3. Form a group for the current task: check computers in the list of remote computers.
4. For the backup task only: Select disks/partitions to backup. You can select any
combination of hard disks (by number, according to Windows numeration) and partitions
(by letter); or All hard disks. This setting is applied to every computer in the group, so
having a standard (similar) disks/partitions layout on remote computers would be a plus.
5. Specify the paths for the backup archiv es. To place ever y archiv e on it s local comp uter,
specify Local path or select Acronis Secure Zone, if there is such a zone on every
remote computer. For more information about the Acronis Secure Zone see
Secure Zone
folder and specify the username and password for access to the network drive. When
48 Copyright © Acronis, Inc., 2000-2008
. To place backups on the network, check Network path, select the target
3.3 Acronis
Page 49

backing up to a backup server, choose Personal Backup Location or tape drive and
enter backup server administrator’s credentials. For more information about backup
servers see
3.5 Acronis Backup Server
.
You should also provide the archive name for each computer, unless the archives are
targeted to Acronis Secure Zones or a backup server. Pressing the button to the right of
the name input field will assign to each archive the respective computer’s name.
6. For the backup task only: Specify the usual backup settings: backup mode (full,
incremental or differential), a password for the backup archive (if ne cessary), default or
custom backup options and comment. For more information see
backup archives
.
Chapter 6. Creating
7. Provide a name for the group task. The name will be displayed in the Group Tasks
Management window (see below) to allow quick task identification.
8. Select when you would like the task to be started. The scheduling procedure is almost
the same for individual and group tasks, see
Chapter 8. Scheduling tasks
for details.
9. If, for any reason (traffic limitation, for example), you do not want the task to start on
all computers simultaneously, set the Start time shift parameter. The task will start on
all computers in turn, with the time shift you specify. As soon as you select time shift, the
resulting task start time for the first and the last computer will be displayed.
10. Now enter the username and password. It is assumed that accounts with the same
username and password exist on all computers of the group. In this case, the task will be
automatically distributed to the computers. Otherwise, you will be asked for the username
and password for every computer during the task distribution.
11. At the final step, the group task summary is displayed. Up to this point, you can clic k
Back to make changes in the created task.
12. After you click Proceed, Acronis True Image Management Console connects to ever y
computer of the group in turn to distribute the task. If a remote computer is inaccessible
(shut down, for example), a dialog box appears. In this box, choose Ignore to exclude
the computer from the group or Cancel to cancel the entire task.
Copyright © Acronis, Inc., 2000-2008 49
Page 50

When distribution is complete, the group task appears in Group Tasks Management
window. If you connect to any computer included into the group, you will see its
individual task, based on the group task you successfully created.
4.4.3 Group tasks management
The Group Tasks Management window displays the list of group tasks.
To see details of a group task, mouse over the task name.
To create new or delete existing backup task, use the New and Delete items on the
Group tasks toolbar.
To edit a task, select it and click Edit. Editing is performed in the same way as creation,
however, the earlier selected options will be set, so you have to enter only the changes.
Deleting or editing a task does not affect the current tas k execution. A task, that has been
edited or deleted while running, will come to an end without any changes. The changes
you made will be applied when execution is completed.
In addition to editing tasks for groups, you can edit individual tasks produced by the
group task on each computer involved. To do so, connect the console to the desired
computer. For details, see
8.2 Managing scheduled tasks
.
To stop or restart the task execution, use the Stop or Restart toolbar items. The task
schedule, if created, remains valid.
For a group task that is not currently being executed on either computer, the follo wing
operations are also available:
Run now - an instant task start command. The task schedule, if created, remains valid.
Check – the group server will connect in turn to all computers involved in the group task
and check if the child tasks are intact on the computers so that the group task can run
effectively. The result will be displayed.
50 Copyright © Acronis, Inc., 2000-2008
Page 51

When managing a group task, enter the same username and password you entered when
created the task.
4.4.4 Acronis Group Server options
Acronis Group Server regularly polls computers included in its database for their status
(Ready, Offline and so on, according to
between enquires is 2 seconds. You have an option to set the status re fresh rate based
on your network requirements.
There is usually no need to refresh the view at all when the cons ole is disconnected from
the group server. A separate option allows you to disable the polling on console
disconnection or set a wider interval between packets.
There is also an option to stop scanning network for newly connected computers. This
can speed up operations with the computers already discovered. After the scanning is
disabled, Acronis Group Server stops sending the packets, bu t the response may come to
the packets already sent. Therefore, some computers may be added to the computer list
after scanning is disabled. This is not a malfunction.
4.4.1 Group status display.
) The default interval
To adjust the status refresh rate, connect the console to the computer where Acronis
Group Server is installed and select Tools -> Options -> Network -> Status check
interval.
4.5 Managing backup server
Before you start managing the backup server, be sure to r ead secti on
Server
When connected to a computer where Acronis Backup Server is installed, click Acronis
Backup Server management to display the following window.
Copyright © Acronis, Inc., 2000-2008 51
stating the basic operating principles of this application.
3.5 Acronis Backup
Page 52

When connecting to a backup server inside a domain, be aware whether your domain
or local account is registered on the backup server. If you entered Windows on a network
computer using your domain account while your local account is registered, enter the
local user name along with the backup server name (for example, Server1\username).
Otherwise the name will be identified as a domain one.
4.5.1 Default settings
Each user or computer, added to Acronis Backup Serv er database, is associated with the
default backup location and the default user/computer quotas and time limits.
When installed on a computer (which becomes a backup server from this point on),
Acronis Backup Server creates the following folder:
C:\Documents and Settings\All Users\Application Data\Acronis\BackupServer.
This folder is a default backup location.
You can change the default backup location and its quotas/time limits by selecting
Specify Default Settings -> Set backup location and entering the desired location
and values. Changing the default backup location will direct backups of newly added
users/computers to another folder, while users/computers associated with old default
backup location will continue back up to the old place.
52 Copyright © Acronis, Inc., 2000-2008
Page 53

The default quotas/time limits are preset to Unlimited, except for Maximum number
of incremental backups for each full backup, which is set to 5 (the largest value of
this parameter is not limited, but it is recommended that you do not set unreasonably
large values).
You can change the default user/computer quotas/time limits by selecting Specify
Default Settings -> Set Quotas/Time limits and entering the desired values.
To enable Acronis Backup Server to process archives, schedule quotas/time limits check
task. Select Specify Default Settings -> Schedule Automatic Consolidation and
Backup Management and schedule one-time, daily, weekly or monthly check of all
user’s/computers archives on the backup server for meeting limitations. If the check
reveals that some of quotas/time limits are exceeded, the archive process ing described in
3.5.2 Quotas and time limits for computers and users
Copyright © Acronis, Inc., 2000-2008 53
will be executed.
Page 54

Please take note of the fact that checking limitations makes no sense if you have not
changed at least one of the preset Unlimited values for quotas/time limits.
The actual number of backups created in a backup location can exceed the Maximum
number of backups by one. This enables the program to detect the fact of exceeding
and start consolidation. Backup to the full location will be prohibited until the
consolidation takes place.
4.5.2 Set up Administrator profiles
Add a remote computer to Acronis Backup Server database if you want to be able to
remotely back up data from that networked computer where Acronis True Image Agent is
installed. Click Set up Administrator profiles -> Add, select the computer and specify
backup location, quotas and time limits for this computer in Add Computer Profile
Wizard windows.
You can use the default backup location, quotas and time limits or make particular
settings for the new computer. If you specify a new path to backup location for the new
computer, a new backup location will be created.
You might need to change a computer profile already set. To do so, sel ect the computer
and click Edit. The Edit Computer Profile Wizard will guide you through the same
selections, as the Add Computer Profile Wizard.
Changing the computer backup location will move all existing and redirect future backups
of this computer to another folder (device etc.). As moving files may take a lot of time
and system resources, it is recommended that you schedule this operation for the time
when the backup server computing load will be minimal. You can do this in the Start
Parameters window. To complete configuring the profile, click Finish in the final
summary window.
54 Copyright © Acronis, Inc., 2000-2008
Page 55

To change a computer backup location within the same device, you must have at least as
much free space on the device as the computer archives occupy because the archives will
first be copied to the new location and then deleted from the old folder.
If you select a computer and click Clear, all archives of this computer data will be
deleted.
Deleting a computer profile will disable backup to backup server for this computer and
delete its existing archives. This operation can be time-consuming so schedule it for the
off-peak period.
4.5.3 Adding Users and Administrators to the Acronis Backup Server database
Acronis Backup Server creates a user group named AcronisBackupServerUsers (see
Control Panel -> Administrative Tools -> Computer Management -> Local
Users and Groups) on the backup server when it is installed. At this point, the group
contains the only user who installed the program.
By default, this user has administrator’s rights on the backup server and is able to
manage the backup server and perform backups using computer profiles.
To enable any other user to back up data from any networked computer where Acronis
True Image for Microsoft Small Business Server local version is installed to backup server,
an administrator should add this user to Acronis Backup Server database.
To do so, first, add this person’s local or domain account to the AcronisBackupServerUsers
group. Then click Set up User profiles -> Add User.
The Add User Profile Wizard will offer you a choice of adding the new user name from
the list of domain users, or entering it manually. In some cases, when the list of domain
users is excessively big, the manual way of entering the new user name will prove
quicker, but you have to know the exact user name.
If you click Next, you will go to the window where you can enter the user name
manually, if you don’t know the correct user name, you will be able to return to the
previous window and pick the other option.
Copyright © Acronis, Inc., 2000-2008 55
Page 56

If you opted for picking the user name out of the domain user list, you will skip the above
window and proceed to the other windows where you will select the user name and
specify backup location, quotas and time limits for this user in Add User Profile Wizard
windows. Use the default backup location, quotas and time limits or make specific settings
for the new user. If you specify a new path to backup location for the new user, a new
backup location will be created.
To add another administrator, first add this person’s local or domain account to the
AcronisBackupServerUsers group. Then click Set up User profiles -> Add, select the
user name and choose Create user with administrator’s rights on the next page.
An administrator can manage all archives on the backup server regardless of their owner,
while a common user can only backup or restore his data from the backup server. An
administrator has no user profile, in other words, the administrator is not assigned a
56 Copyright © Acronis, Inc., 2000-2008
Page 57

backup location, quotas and time limits like common us ers are and uses the administrator
profile for both remotely and locally controlled backups.
4.5.4 Changing User profiles
You might need to change a user profile that is already set. To do so, select the user and
click Edit. The Edit User Profile Wizard will guide you through the same selections, as
the Add User Profile Wizard, except administrator’s or user’s rights. To change the
rights, you will have to delete the user profile and then add the user again with the new
rights.
Changing the user’s backup location will move all existing and redirect future backups,
performed by the user, to another folder (device, etc). As moving files can take a lot of
time and system resources, it is recommended that you schedule this operation for the
time when the backup server computing load will be minimal. You can do it in the Start
Parameters window. To complete configuring the profile, click Finish in the final
summary window.
To change a user’s backup location within the same device, you must have at least as
much free space on the device as the user’s archives occupy because the archives will
first be copied to the new location and then deleted from the old place.
If you select a user profile and click Clear, all archives created by this user will be
deleted. However, this operation will not work for the administrators’ profiles.
If you select a user profile and click Delete, this will disable backup to the backup server
for this user and his existing archives will be deleted. This operation might also be timeconsuming, so you can schedule it for the off-peak period.
Deleting an administrator profile will not result in deleting any archives. The person
whose profile is deleted just loses the right to back up to the backup server and to
manage the backup server.
There must be at least one administrator on a backup server. Therefore, deleting the last
administrator profile is not possible. The maximum number of administrators is not
limited.
4.5.5 Configuring Backup Locations
To display a full list of backup locations, click Configure Backup Locations.
Copyright © Acronis, Inc., 2000-2008 57
Page 58

To edit limitations for a backup location, select the backup location, click Quotas and
Time Limits and enter the new values in the appearing window.
To move a backup location along with all archives existing on it, select the backup
location and click Move to. The Move Backup Location Wizard will display all users
and computers associated with the selected backup location so you coul d make sure your
choice is right. Then select the new location for the archives.
As moving files can take a lot of time and system resources, it is recommended that you
schedule this operation for the time when the backup server computing load will be
minimal. You can do it in the Start Parameters window. To complete configuring the
operation, click Finish in the final summary window.
To move a backup location within the same device, you must have at least as much free
space on the device as all the archives in the backup location occupy, because the
archives will first be copied to the new place, and then deleted from the old place.
To delete all archives stored in a backup location, select the location and click Clear.
To delete a backup location, select the location and click Delete. This will delete all
archives stored in this location and redirect the associated co mputer/ user’s backups to the
default backup location.
The default backup location cannot be deleted. If you try to do so, the program will clean
the default backup location and issue an appropriate message. To delete the location
completely, first reassign the default backup location by selecting Specify Default
Settings -> Set backup location.
Cleaning and deleting backup locations might be time-consuming operations, so you can
schedule them for the off-peak period.
4.5.6 Managing Archives
To display a full list of backups, stored on the backup server, click Manage Backup
Archives.
58 Copyright © Acronis, Inc., 2000-2008
Page 59

You can:
1. Sort the list by Location or Owners (users and computers) by clicking on the
respective item above the list.
2. Filter out from the list all user’s or all computer’s backups (use buttons in the Filter
group).
3. Consolidate any backup (ex cept for the oldest one in the archive) wi th the preceding
backup file. This operation deletes the preceding backup and sets concatenation between
the backup being consolidated and the backup befor e the deleted one. Thus, the archive
integrity will not be affected, in spite of the fact that one backup will be deleted. Data
recovery from any of the remaining backups will be possible.
4. Export an archive from Acronis Backup Server to a local hard drive or network share.
To do so, select any backup belonging to the archive and click Export. Then provide
name for the archive copy and a path to the location where the copy will be created.
5. Import an archive from external location to a computer’s or user’s backup location on
the backup server. To do so, use Import on the tool bar.
Editing images, mounted in R/W mode, results in creating incremental backups, that are
a kind of offshoots of the incremental chain. Such backups are always excluded from the
archive being imported.
4.5.7 Limiting access to Acronis Backup Server
To access the Acronis Backup Server options, connect the console to the backup server
and select Tools -> Options from the menu.
1. Maximum number of connections
This comes in handy when you want to back up a group of computers quickly and not
allow users to access the backup server at the time. Generally, limiting number of tasks
simultaneously processed by Acronis Backup Server may speed up each taken separately
backup procedure at the expense of its possible delay.
Copyright © Acronis, Inc., 2000-2008 59
Page 60

If maximum number of connections is set, then some agents or local Acronis True Image
for Microsoft Small Business Server versions may be unable to access the server
immediately after starting their task. They will be trying to connect to the server every 5
seconds until the connection is allowed. Therefore, the real backup start time may differ
from the scheduled one. If it is not practical or efficient for you, be aware of this se tting
when creating group tasks so that number of computers in the group does not exceed the
limit you set.
By default, the number of connections is unlimited. This corresponds to setting “0”. The
console connection to Acronis Backup Server is not counted.
2. Limit bandwidth for a connection to:
Limiting bandwidth for each connection helps equalize the server usage among
simultaneously running tasks. Practice is the best way to determine the correct limit. In
most cases you can leave it as is.
By default, bandwidth per connection is not limited. This corresponds to setting “0”.
60 Copyright © Acronis, Inc., 2000-2008
Page 61

Chapter 5. Using Acronis True Image for Microsoft Small Business Server (local version)
Acronis True Image for Microsoft Small Business Server (local version) supports the GUI
mode, the command-line mode, and can be used to execute XML scripts. Here we
describe the operations available in the GUI mode, which provides the widest
functionality. For console commands and scripting please see
mode and scripting
.
5.1 Main program window
The main program window contains the menu, the toolbar, the sidebar and the main
area. The sidebar features a pane for selecting task category, the Tools and Help panes.
The main area displays operation icons or tasks depending on the category selected.
Chapter 16. Command-line
By default, the program displays operations included in the Backup and Recovery
category. Operation icons are divided into three groups.
The Task group contains the following operations:
Backup – create a backup archive
Recovery – restore data from a previously created archive
The Manage Tasks group contains the following operations:
Tasks – schedule backup or archive validation tasks on your computer and manage them
Logs – open the Log Viewer window
The Tools group contains the following items:
Copyright © Acronis, Inc., 2000-2008 61
Page 62

Explore and Validate Backup Archives – explore file-level archives, mount
disk/partition images as virtual drives, run the archive integrity checking procedure
Manage Hard Disks – clone disk (i.e. transfer the OS, applications and data from the
old disk to the new one) or mark out partitions on a new hard disk added for data
storage with the OS and applications kept on the old one, convert basic disks to
dynamic and create dynamic volumes
Activate Acronis Startup Recovery Manager – activate the b oot restoration manager (F11
key)
Manage System Restore – turn on/off Microsoft Windows System Restore tool and set
its options directly from Acronis True Image for Microsoft Small Business Server
Create Bootable Rescue Media – run the bootable media creation procedure
Program menu
The program menu bar features the Operations, View, Tools and Help items.
The Operations menu contains a list of the available operations, including scheduling
tasks.
The View menu contains items for managing the program window look:
Toolbars – contains commands that control toolbar icons
Common Task Bar – enables/disables the sidebar
Status Bar – enables/disables the status bar
The Tools menu contains the following items:
Manage Acronis Secure Zone – create, delete and resize a special hidden partiti on for
storing archives (Acronis Secure Zone)
Activate Acronis Startup Recovery Manager – activate the b oot restoration manager (F11
key)
Explore Backup Archive – explore file-level archives or mount disk/partition imag es as
virtual drives
Validate Backup Archive – run the archive integrity checking procedure
Consolidate archive – applicable for archives containing more than one backup s. This
will create a consistent copy of the archive with an option to exclude backups that are
no more needed
Convert Backup to Virtual Disk - convert a disk image, created with the program
(.tib), to a virtual disk file of the type you select (.vmdk, .vhd, .hdd)
Create Bootable Rescue Media – run the bootable media creation procedure
Dynamic Volume Creation Wizard – create dynamic volumes on basic or dynamic
disks
Show Log – open the Log Viewer window
Options – open a window for editing default backup/restore options, setting text
appearance (fonts), configuring e-mail or Windows pop-up notifications etc.
The Help menu is used to view help and obtain information about Acronis True Image for
Microsoft Small Business Server.
62 Copyright © Acronis, Inc., 2000-2008
Page 63

Most of the operations are represented two or even three times in different window areas,
providing several ways to select them for more convenience. For example, you can start
the necessary operation or tool by clicking its icon in the main area or by selecting the
same item from the Operations or Tools menu.
Status bar
There is a status bar divided into two parts at the bottom of th e main window. The left
side briefly describes the selected operation; the right side indicates operation progress
and results. If you double-click on the operation results, you will see the log window.
Taskbar notification area icon
During most of the operations, a special indicator icon appears in the Windows taskbar
notification area. If you mouse over the icon, you will see a tool tip indicating the
operation’s progress. This icon doesn’t depend on the main program window b eing open.
It is present for background execution of scheduled tasks as well.
5.2 Managing a local computer
You can perform the following operations on the local computer.
Operation How to access
Back up and Recover
Back up and restore data, including system
disks/partitions
Browse logs of Acronis True Image for
Microsoft Small Business Server operation
Set up default backup or restore options,
such as system/network resources usage,
before/after backup commands etc.
Set up default parameters for sending
notifications about Acronis True Image for
Microsoft Small Business Server operation
and tracing this operation in Windows
Application Event Log
Click Backup or Recovery, then follow the
wizard’s instructions. See details in
6. Creating backup archives
Restoring the backup data.
Click Logs in the Manage Tasks group or
select the Show Log tool on the sidebar to
navigate to the Event Log window. See
details in
Select Tools -> Options -> Default
backup options or Default restoration
options and make settings. See details in
12.3 Viewing logs
6.3 Setting backup options
restore options.
Select Tools -> Options -> Notifications
or Event tracing and make settings. See
details in
event tracing
Chapter 12. Notifications and
.
and
.
and
Chapter
Chapter 7.
7.4 Setting
Scheduling Tasks
Schedule backup and archive validation
operations
Copyright © Acronis, Inc., 2000-2008 63
Click Tasks in the Manage Tasks group
or select the Task Scheduling category
on the sidebar to navigate to the Scheduled
Tasks window. Then click the Create
button on the toolbar and follow the
wizard’s instructions. See details in
8. Scheduling tasks
.
Chapter
Page 64

Run, stop, edit, clone, rename, delete
backup and archive validation tasks
Click Tasks in the Manage Tasks group
or select the Task Scheduling category
on the sidebar to navigate to the Scheduled
Tasks window. See details in
scheduled tasks
.
8.2 Managing
Archives Management
Explore any archive’s contents and restore
individual files from any archive
Validate backup archives wherever they
reside, be it local, network or removable
media
Select Tools -> Explore Backup Archive
and follow the wizard’s instructions. See
details in
11.2.1 Exploring an archive
Select Tools -> Validate Backup
Archive, then follow the wizard’s
instructions. See details in
backup archives
.
11.1 Validating
Consolidate backup files inside an archive Select Tools -> Consolidate archive,
then follow the Wizard’s instructions. See
Convert disk images to virtual disk files of
the type you select (.vmdk, .vhd, .hdd)
details in
Select Tools -> Convert backup to
Virtual Disk and follow the wizard’s
instructions. See details in
Converting disk images to virtual disks
11.3 Consolidating backup.
13. 4
Mount partitions’ images to explore and
modify their contents, or to restore
individual files
Unmount previously mounted partition
images
Select Operations -> Mount Image and
follow the wizard’s instructions. See details
11.2.2 Mounting an image.
in
Select Operations -> Unmount Image
and follow the wizard’s instructions. See
details in
11.2.3 Unmounting an image
.
Hard Disk Management
Manage Acronis Secure Zone (create,
delete, resize, remove or change password)
Click Manage Acronis Secure Zone, then
follow the wizard’s instructions. See details
in
Chapter 9. Managing the Acronis Secure
.
Zone
Activate Acronis Startup Recovery Manager Click Activate Acronis Startup Recovery
Manager, then follow the wizard’s
instructions. See details in
Startup Recovery Manager
3.4 Acronis
.
Create a dynamic volume Select Tools -> Dynamic volume
creation wizard, then follow the Wizard’s
instructions. See details in
dynamic volumes.
7.5.1 Creating
Transfer the system to a new hard disk See
Format partitions on a new hard disk See
64 Copyright © Acronis, Inc., 2000-2008
Chapter 14. Transferring the system to
a new disk
.
Chapter 15. Adding a new hard disk
.
Page 65

Other Tools
Create bootable rescue media, its ISO or
RIS package
Turn on/off Windows System Restore tool See
See
Chapter 10. Creating bootable media
12.5 Managing System Restore
.
.
Some of the above operations can be executed in command-line mode. For more
information on Acronis True Image for Microsoft Small Business Server command-line
mode see
16.1 Working in the command-line mode
.
Copyright © Acronis, Inc., 2000-2008 65
Page 66

Chapter 6. Creating backup archives
To be able to restore the lost data or roll back your system t o a predetermined state, you
should first create a data or entire system backup file.
If you are not concerned about restoration of your operating system along with all
settings and applications, but plan to keep safe only certain data (the current project, for
example), choose file/folder backup. This will reduce the archive size, thus saving disk
space and possibly reducing removable media costs.
Backing up the entire system disk (creating a disk image) takes more disk space but
enables you to restore the system in minutes in case of severe data damage or hardware
failure. Moreover, the imaging procedure is much faster than copying files, and may
significantly speed the backup process when it comes to backing up large volumes of data
(see details in
3.1 The difference between file archives and disk/partition images
6.1 Backing up files and folders (file backup)
1. Start the Create Backup Wizard by clicking on the backup operation icon in the main
program window.
).
2. Select My Data.
3. From the tree pane, select files and folders to back up. You can select a random set of
files, folders, partitions, disks and even computers.
In order to restore your operating system, you must image the system disk or partition; a
file-based backup is not sufficient for the operating system restore.
4. You can exclude specific files from a backup by setting filters for the types of files you
do not wish to back up. For example, you may want to exclude hi dden and system files
and folders or files with .~, .tmp and .bak extensions.
66 Copyright © Acronis, Inc., 2000-2008
Page 67

You can also apply custom filters, using the common Windows masking rules. For
example, to exclude all files with extension .exe, add *.exe. My???.exe will exclude all
.exe files with names consisting of five symbols and starting with “my”.
All of these settings will take effect for the current task. For information on how to set the
default filters that will be called each time you create a file backup task, see
files exclusion.
6.3.2 Source
5. Select the name and location of the archive.
If you are going to create a full backup, type the file name in the File Name line, or use
the file name generator (a button to the right of the line). If you select an existing full
backup, it will be overwritten.
Including [date] in the backup file name will add to the name the time and date of the
backup creation formatted as <DD-Month-YYYY HH:MM:SS>. Example:
C:\MyBackup[date].tib.
If you are going to create an incremental backup (see
differential backup
In fact, if all incremental backup files are stored together with the basic full backup, it
doesn't matter which one you select, as the program will recognize them as a single
archive. If you stored the files on several removable disks, you must provide the latest
archive file; otherwise, restoration problems might occur.
), select the latest full or incremental backup you have.
3.2 Full, incremental and
If you are going to create a differential backup, select the full backup which will be a
base, or any of the existing differential backups. Either way, the program will create a
new differential backup.
Copyright © Acronis, Inc., 2000-2008 67
Page 68

The “farther” you store the archive from the original folders, the safer it will be in case of
data damage. For example, saving the archive to another hard disk will protect your data
if the primary disk is damaged, but won’t be useful if the computer is destroyed in a fire
or flood. Data saved to a network disk, ftp server or removable media will survive even if
all your local hard disks are down. You can also use Acronis Secure Zone (see details in
3.3 Acronis Secure Zone
Server
) for storing backups. In those cases, you need not provide the file name.
) or Acronis Backup Server (see details in
3.5 Acronis Backup
When backing up to Acronis Secure Zone, you have an option of dual destination backup.
If enabled, the program will automatically place a copy of your backup archives on a local
drive or network share as well as Acronis Secure Zone. See details in
destination backup
.
6.3.12 Dual
Dynamic volumes are fully supported as a backup destination place. Acronis True Image
for Microsoft Small Business Server can access backup archives, created on dynamic
volumes, in standalone (rescue) mode as well as under Windows control.
See notes and recommendations for using the FTP server in
.
media
1.4.2 Supported storage
6. If your choice was not Acronis Backup Server, select whether you want to create a full,
incremental or differential backup. If you have not backed up the selected files/folders
yet, or the full archive seems too old to append incremental changes to it, choose full
backup. Otherwise it is recommended that you create an incremental or differential
backup (see
3.2 Full, incremental and differential backup
).
68 Copyright © Acronis, Inc., 2000-2008
Page 69

7. Select the backup options (that is, backup file splitting, compression level, password
protection, pre/post backup commands etc.). You may select Use default options or
Set the options manually. If the latter is the case, the settings will be applied only to
the current backup task. Alternatively, you can edit the default options from the current
screen. Then your settings will be saved as the defaults. See
6.3 Setting backup options
for more information.
8. Provide a comment for the archive. This can help prevent you from restoring the wrong
files. However, you can choose not to make any notes. The backup file size and creation
date are automatically appended to the description, so you do not need to enter this
information.
9. At the final step, the backup task summary is displayed. Up to this point, you can click
Back to make changes in the created task. Clicking Proceed will launch the task.
10. (For Acronis True Image for Microsoft Small Business Server local version only) The
task progress will be shown in a special window. You can stop the procedure by clicking
Cancel.
You can also close the progress window by clicking Hide. The backup creation will
continue, but you will be able to start another operation or close the main program
window. In the latter case, the program will continue working in the background and will
automatically close once the backup archive is ready. If you prepare some more backup
operations, they will be queued after the current one.
Copyright © Acronis, Inc., 2000-2008 69
Page 70

You can adjust the backup process priority. To do so, click on the process icon in the
System Tray and select Low, Normal, or High priority from the menu that appears. For
information on how to set the default priority, see
6.3.6 Backup performance
.
11. You may want to see the log when the task is completed. To view the log, click the
Show Operation Logs button on the toolbar.
If you burn an archive to multiple removable media, be sure to number them, since you
will have to insert them in order during the restoration.
6.2 Backing up disks and partitions (image backup)
1. Start the Create Backup Wizard by clicking on the backup operation icon in the main
program window.
2. Select My Computer.
3. Select disks, partitions or dynamic volumes to ba ck up. You can sel ect a random set of
disks, partitions and dynamic volumes.
70 Copyright © Acronis, Inc., 2000-2008
Page 71

4. Select the name and location of the archive.
If you are going to create a full backup, type the file name in the File Name line, or use
the file name generator (a button to the right of the line). If you select an existing full
backup, it will be overwritten.
Including [date] in the backup file name will add to the name the time and date of the
backup creation formatted as <DD-Month-YYYY HH:MM:SS>. Example:
C:\MyBackup[date].tib.
If you are going to create an incremental backup (see
differential backup
In fact, if all incremental backup files are stored together with the basic full backup, it
doesn't matter which one you select, as the program will recognize them as a single
archive. If you stored the files on several removable disks, you must provide the latest
archive file; otherwise, restoration problems might occur.
), select the latest full or incremental backup you have.
3.2 Full, incremental and
If you are going to create a differential backup, select the full backup which will be a
base, or any of the existing differential backups. Either way, the program will create a
new differential backup.
The “farther” you store the archive from the original partition, the safer it will be in case
of data damage. For example, saving the archive to another hard disk will protect your
data if your primary disk is damaged. Data saved to a network disk, ftp server or
removable media will survive even if all your local hard disks are down. You can also use
Acronis Secure Zone (see details in
(see details in
3.5 Acronis Backup Server
3.3 Acronis Secure Zone
) for storing backups. In those cases, you need
) or Acronis Backup Server
not provide the file name.
When backing up to Acronis Secure Zone, you have an option of dual destination backup.
If enabled, the program will automatically place a copy of your backup archives on a local
drive or network share. See details in
6.3.12 Dual destination backup.
Dynamic volumes are fully supported as a backup destination place. Acronis True Image
for Microsoft Small Business Server can access backup archives, created on dynamic
volumes, in standalone (rescue) mode as well as under Windows control.
Copyright © Acronis, Inc., 2000-2008 71
Page 72

See notes and recommendations for using the FTP server in
.
media
1.4.2 Supported storage
5. If your choice was not Acronis Backup Server, select whether you want to create a full
or incremental backup. If you have not backed up the selected disks/pa rtitions yet, or the
full archive seems too old to append incremental changes to it, choose full backup.
Otherwise it is recommended that you create an incremen tal or differential backup (see
3.2 Full, incremental and differential backup
).
6. Select the backup options (that is, backup file splitting, compression level, password
protection, pre/post backup commands etc.). You may Use default options or Set the
options manually. If the latter is the case, the settings will be applied only to the
current backup task. Alternatively, you can edit the default options from the current
screen. Then your settings will be saved as the defaults. See
6.3 Setting backup options
for more information.
7. Provide a comment for the archive. This can help prevent you from restoring the wrong
disk or partition. However, you also can choose not to make any notes. The backup file
size and creation date are automatically appended to the description, so you do not need
to enter this information.
8. At the final step, the backup task summary is displayed. Up to this point, you can click
Back to make changes in the created task. Clicking Proceed will launch the task.
9. (For Acronis True Image for Microsoft Small Business Server local version only) The
task progress will be shown in a special window. You can stop the procedure by clicking
Cancel.
You can also close the progress window by clicking Hide. The backup creation will
continue, but you will be able to start another operation or close the main program
window. In the latter case, the program will continue working in the background and will
automatically close once the backup archive is ready. If you prepare some more backup
operations, they will be queued after the current.
You can adjust the backup process priority. To do so, click on the process icon in the
System Tray and select Low, Normal, or High priority from the menu that appears. For
information on how to set the default priority, see
6.3.6 Backup performance
.
10. You may want to see the log when the task is completed. To view the log, click the
Show Operation Logs button on the toolbar.
If you burn an archive to multiple removable media, be sure to number them, since you
will have to insert them in order during the restoration.
6.3 Setting backup options
To view or edit the default backup options in Acronis True Image for Microsoft Small
Business Server local version, select Tools -> Options -> Default Backup Options
from the main program menu.
To do the same remotely, connect Acronis True Image Management Console to the
remote computer, click Remote Computer Options and select Default backup
options.
You can edit the default (or set the tempor ary) backup options while creating a backup
task as well.
72 Copyright © Acronis, Inc., 2000-2008
Page 73

6.3.1 Archive protection
Password
The preset is no password.
An archive can be protected with a password. To protect the archive data from being
accessed by anybody except you, enter a password and its confirmation into the text
fields. A password should consist of at least eight symbols and contain both letters (in the
upper and lower cases preferably) and numbers to make it more difficult to guess.
If you try to restore data from a password-protected archive, or append an
incremental/differential backup to such an archive, Acronis True Image for Microsoft Small
Business Server will ask for the password in a special window, allowing access only to
authorized users.
Passwords cannot be set for archives created in the Acronis Secure Zone. To protect such
archives, set a password for the zone itself.
Encryption
The preset is 128 bit.
Once the password has been set, you can choose to encrypt the backup for advanced
security with industry-standard AES cryptographic algorithm. The password is used to
generate a key which may differ in length. There are 4 choices: no encryption , 128, 192
and 256-bit encryption. The more the k ey size, the longer time to cipher and the greater
is your data security.
6.3.2 Source files exclusion
By default, all files from the selected folders will be included in the archive.
You can set default filters for the specific types of files you do not wish to back up. For
example, you may want hidden and system files and folders, as well as files with .~,
.tmp and .bak extensions, not to be stored in the archive.
Copyright © Acronis, Inc., 2000-2008 73
Page 74

You can also apply custom filters, using the common Windows masking rules. For
example, to exclude all files with extension .exe, add *.exe. My???.exe will exclude all
.exe files with names consisting of five symbols and starting with “my”.
This option is effective for file/folders backup only. When creating a dis k/partition image,
you cannot filter out any files.
6.3.3 Pre/post commands
You can specify commands or batch files to be automatically executed before and aft er
the
backup procedure
disk before starting backup or configure a third-party a ntivirus product to be starte d each
time before the backup starts. Click Edit to open the Edit Command window where you
can easily input the command, its arguments and worki ng directory or browse folders to
find a batch file.
The program does not support interactive commands, i.e. commands that require user
input (for example, “pause”.)
The backup process will run concurrently with your commands if you uncheck the Do not
perform operations until the commands execution is complete box, which is
checked by default.
. For example, you may want to remove some tmp files from the
6.3.4 Database support
Database servers, such as MS SQL Server and MS Exchange, can be problematic to
backup, partially due to open files and indexes and partially due to ra pid data changes.
Therefore it is usually recommended that the database be suspended just before the
backup (data capture). You can suspend th e database and clear all cac hes to ensure that
all transactions are completed at the moment of data capture. If it become necessary to
restore a damaged database, it will be restored completely and be ready to access after
recovery.
1. Volume Shadow Copy Service
Microsoft Volume Shadow Copy Service (VSS) provides the infrastructure for
backup on running systems by keeping up coordination between user applications that
update data on disk and backup applications. VSS is available in Microsoft Windows XP
and Microsoft Windows Server 2003 operating systems.
If your database is compatible with Microsoft Volume Shadow Copy Service (VSS), then
checking the Enable VSS support box in Database support window will ensure
completion of all transactions before the backup process starts. The examples of VSSaware databases are Exchange, Oracle, SQL Server.
2. Before/after data capture commands
However, VSS is not available in server operation systems older than Windows 2003
Server, and not all databases support VSS. In these cases, the transactions completion
can be ensured by executing batch files or scripts that pause the appropriate Windows
services and automatically resume them after data capture.
An example of a batch file, suspending the Windows services for MS Exchange:
net stop msexchangesa /y /y
net stop “Microsoft Exchange Routing Engine”
An example of a batch file, resuming the Windows services for MS Exchange:
net start “Microsoft Exchange System Attendant”
74 Copyright © Acronis, Inc., 2000-2008
Page 75

net start “Microsoft Exchange Event”
net start “Microsoft Exchange IMAP4”
net start “Microsoft Exchange MTA Stacks”
net start “Microsoft Exchange POP3”
net start “Microsoft Exchange Routing Engine”
Create batch files in any text editor (for example, name it
resume_services.bat
). Use Edit buttons to the right of Before data capture command
pause_services.bat
and
and After data capture command fields, to open the Edit Command window where
you can browse folders to find the respective batch files or scripts. A single command can
be specified in the same window along with its arguments and working directory.
It is critical to note that these commands, as opposed to Pre/post commands above,
will be executed before and after the
data capture
process, which takes seconds, while
the entire backup procedure may take much longer, dep ending on the amount of data to
be imaged. Therefore, the database idle time will be minimal.
Before/after data capture commands can also be used for other purposes, especially
if VSS support is enabled. You may want to suspend an application other than a database,
for example. The commands execution and the VSS actions will be sequenced as follows:
“before” commands -> VSS Suspend -> data capture -> VSS Resume -> “after”
commands.
The backup process will run concurrently with your commands if you uncheck the Do not
perform operations until the commands execution is complete box, which is
checked by default.
3. Multi-volume snapshot
The preset is disabled.
Enable the Multi-volume snapshot feature if you are going to back up data loca ted on
multiple volumes and you must preserve its consistency (such as a database spanned
across the volumes). In this case, a single snapshot for all volumes is created, which will
be used for backup creation. When disabled, snapshots for volumes will be taken one by
one.
6.3.5 Compression level
The preset is Normal.
The data will be copied without any compression, which may significantly increase the
backup file size, if you select None as the compression level. However, if you select
Maximum compression, the backup will take longer to create.
The optimal data compression level depends on the type of files stored in the archive. For
example, even maximum compression will not significantly reduce the archive size if the
archive contains essentially compressed files, such as .jpg, .pdf or .mp3. However,
formats such as .doc or .xls will compress more than other file types.
Generally, it is recommended that you use the default Normal compression level. You
might want to select Maximum compression for removable media to reduce the number
of blank disks required.
Copyright © Acronis, Inc., 2000-2008 75
Page 76

6.3.6 Backup performance
The three options below might have a more or less noticeable effect on the backup
process speed. This depends on overall system configuration and physical characteristics
of devices.
1. Backup process priority
The preset is Low.
The priority of any process running in a system determines the amount of CPU usag e and
system resources allocated to that process. Decreasing the backup priority will free more
resources for other CPU tasks. Increasing the backup priority may speed up the backup
process due to taking resources from the other currently running processes. The effect
will depend on total CPU usage and other factors.
2. HDD writing speed
The preset is Maximum.
Backing up in the background to an internal hard disk (for example, to the Acronis Secure
Zone) may slow other programs’ performance because of the large amounts of data
transferred to the disk. You can limit the hard disk usage by Acronis True Image for
Microsoft Small Business Server to the desired level . To set the d esired HDD writing speed
for data being backed up, drag the slider or enter the writing speed in kilobytes per
second.
3. Network connection speed
The preset is Maximum.
If you frequently backup data to network drives, thi nk of limiting the networ k usage used
by Acronis True Image for Microsoft Small Business Server. To set the desired data
transfer speed, drag the slider or enter the bandwidth limit for transferri ng backup data in
kilobytes per second. This setting is also applied to an FTP connection, if an FTP server is
selected as backup destination device.
76 Copyright © Acronis, Inc., 2000-2008
Page 77

6.3.7 Fast incremental/differential backup
The preset is Use fast incremental/differential backup.
Incremental/differential backup captures only changes in data occurred since the last
backup. To speed up the backup process, Acronis True Image for Microsoft Small
Business Server determines whether the file has changed by file size and the date/tim e
when the file was last saved. Disabling this feature will make the program compare the
entire file contents to that stored in the archive.
This option relates only to disk/partition (image) backup.
6.3.8 Archive splitting
Sizeable backups can be split into several files that together make the original backup. A
backup file can be split for burning to removable media or saving on a n FTP server (data
recovery directly from an FTP server requires the archive to be split into files no more
than 2GB in size).
The preset is Automatic. With this setting, Acronis True Image for Microsoft Small
Business Server will act as follows:
When backing up to the hard disk:
The program will create a single archive file if the
selected disk has enough space and its file system allows the estimated file size.
The program will automatically split the backup into several files if the storage disk has
enough space, but its file system does not allow the estimated file size.
FAT16 and FAT32 file systems have a 4GB file size limit. However, the existing hard
drive’s capacity can reach as much as 2TB. Therefore, an archive file might easily exceed
this limit if you are going to back up the entire disk.
If you do not have enough space to store the backup on your hard disk, the program will
warn you and wait for your decision as to how you plan to fix the problem. You can try to
free some additional space and continue or click Back and select another disk.
When backing up to a diskette, CD-R/RW or DVD+R/RW:
Acronis True Image for
Microsoft Small Business Server will ask you to insert a new disk when the previous one is
full.
Alternatively, you can select Fixed size and enter the desired file size or select it from
the drop-down list. The backup will then be split into multiple files of the specified size.
That comes in handy when backing up to a hard disk with a view to burning the archive
to CD-R/RW or DVD+
Creating a backup directly on CD-R/RW or DVD+R/RW generally will take considerably
more time than it would on a hard disk.
R/RW later on.
6.3.9 File-level security settings
Preserve files’ security settings in archives
By default, files and folders are saved in the archive with their original Windows security
settings (i.e. permissions for read, write, execute and so on for each user or user group,
set in file Properties -> Security). If you restore a secured file/folder on a computer
without the user account, specified in the permissions, you may not be able to read or
modify this file.
Copyright © Acronis, Inc., 2000-2008 77
Page 78

You can disable preserving the files’ security settings in archives to completely elim inate
this kind of problem. Then the restored files/folders will always inherit the permissions
from the folder to which they are restored (parent folder or disk, if restored to the root).
Alternatively, you can disable files’ security settings during restoration, even if they are
available in the archive (see
7.4.5 File-level security settings
below). The result will be
the same - the files will inherit the permissions from the parent folder.
In archives, store encrypted files in decrypted state
The preset is disabled.
Simply ignore this option if you do not use the encryption feature available in Windows
2003 Server and Windows XP operating systems. (Files/folders encryption is set in
Properties -> General -> Advanced Attributes -> Encrypt contents to secure
data).
Check the option if there are encrypted files in the backup and you want them to be
accessed by any user after restore. Otherwise, only the user who encrypted the
files/folders will be able to read them. Decryption may also be useful if you are going to
restore encrypted files on another computer.
These options relate only to file/folders backup.
6.3.10 Media components
The preset is disabled.
When backing up to removable media, you can make this media bootable by writing to it
additional components. As a result, you will not need a separate rescue disk.
Choose the basic components necessary for boot and restoring data on the General tab.
The Acronis One-Click Restore is a minimal addition to the image archive, stored o n
removable media, allowing one-click disk recovery from this archive. This means that a t
boot from the media and clicking “restore” all the data contained in the image will be
silently restored.
Because the one-click approach does not presume user selections, such as selecting
partitions to restore, Acronis One-Click Restore always restores the entire disk. Therefore,
if your disk consists of several partitions and you are planning to use Acronis One-Click
Restore, all the partitions must be included in the image. Any partitions missing from the
image will be lost.
If you want more functionality during restoration, write a standalone version of Acronis
True Image for Microsoft Small Business Server to the rescue disk. Then you will be
able to configure the restore task using Restore Data Wizard, use A cronis Active restore
or Acronis Universal Restore.
The Advanced tab lets you select full, safe or both Acronis True Image for Microsoft
Small Business Server loader versions. The safe version does not have USB, PC card or
SCSI drivers and is useful only in cases where the full version does not load. If you want
the computer, booted from the media to be accessible for remote control with Acronis
True Image Management Console, add Acronis Bootable Agent to the media. If you
have other Acronis products, such as Acronis Disk Director Suite, installed on your
computer, the bootable versions of these programs’ components will be offered as
Advanced as well.
78 Copyright © Acronis, Inc., 2000-2008
Page 79

6.3.11 Error handling
1. Ignore bad sectors
The preset is disabled.
With the default setting, the program will display a pop-up window each time it comes
across a bad sector and ask for user decision whether to continue or stop the backup
procedure. In order to back up the valid information on a rapidly dying disk, enable
ignoring bad sectors. The rest of the data will be backed up and you will be able to mount
the image and extract valid files to another disk.
2. Do not show messages and dialogs while processing (“silent” mode)
The preset is disabled.
Corporate administrators need an option to continue a back up despite any errors that
might occur without the system popping up an error box. Details of the operation,
including errors, if any, could be found in the operation log.
With the silent mode enabled, the program will not display interactive windows. Instead,
it will automatically handle situations requiring user intervention such as running out disk
space (except for handling bad sectors, which is defined as a separate option.) No
prompts will be displayed, including those for removable media or overwriting data on a
tape. If an operation cannot continue without user action, it will fail.
Therefore, enable this feature if you do not want unattended backup operations hang on
pop-ups and errors.
3. If an error occurs, re-attempt in (minutes)
The preset is enabled.
When the backup destination location on the network is not available or not reachable,
the program will attempt to reach the location at the specified time interval.
6.3.12 Dual destination backup
The preset is disabled. The option is available
Acronis Secure Zone.
If enabled, the program will automatically place a copy of each backup being created in
Acronis Secure Zone on a local drive or network share. The consistency of the external
archive copy is maintained automatically. After a backup is saved to the Acronis Secure
Zone, the program compares the updated archive contents to the copy contents, and if
some backups are missing from the copy, they will be copied to the external location
along with the new backup.
In addition to enhancing the archive security provided with replication, this feature allows
traveling users to keep a consistent copy of the laptop data both on the laptop an d the
corporate server. When the network is not available, the program will back up data to
Acronis Secure Zone alone. When connected again, all changes made to the archive will
be transferred to the copy during the first backup operation.
only
if the backup is destined for the
The feature provides quick backup to the internal drive as an intermediate step before
saving the ready backup on the network on stationary servers. This comes in handy in
cases of slow or busy networks and time-consuming backup procedures. Disconnection
during the copy transfer will not affect the backup procedure as opposed to backing up
directly to the remote location.
Copyright © Acronis, Inc., 2000-2008 79
Page 80

Even if a password is set for the Acronis Secure Zone, the copy archive will not be
protected with the password.
6.3.13 Wake On LAN
This option is available only for tasks created by the Acronis Group Server.
The preset is Enable Wake On LAN.
With this setting, Acronis Group Server will send a magic packet to the remote computer
network interface card (NIC) before starting backup. (A magic packet is a packet that
contains 16 contiguous copies of the receiving NIC's Ethernet address.) This will power on
the computer for running the backup task. Once the backup procedure is over, the
computer can go to sleep if it times out.
Before using the feature, make sure that Wake On LAN is enabled both on the computers
that you intend to back up and the Acronis Group Server.
To enable the Wake On LAN feature on a computer to be backed up:
1. Enter the computer BIOS and set Power -> Wake On PCI PME -> Power On.
2. Set the NIC properties on the computer as follows.
Control Panel -> System -> Device Manager -> Network adapters -> select the NIC ->
Properties -> Advanced:
Enable PME -> Enabled
Wake On Link Settings -> OS Controlled
Wake On Settings -> Wake On Magic Packet.
3. Find out the computer MAC address (Local Area Connection -> Status -> Support ->
Details -> Physical Address.)
4. Repeat steps 1-3 for all computers you wish to wake on LAN.
To enable the Wake On LAN option on the Acronis Group Server:
1. Find the computer to be backed up in the list of computers.
2. Select the computer and enter its MAC address in the Acronis Group Server (sidebar ->
Computer details -> MAC address: Set -> type the hex MAC address as XXXXXXXXXXXX
or XX-XX-XX-XX-XX -> click OK). The program will test the MAC address for validity and
display the test result.
3. Repeat steps 1-2 for all computers you wish to wake on LAN.
4. Schedule a group backup task for the above computers. When setting the backup
options, ensure that the Wake On LAN option is enabled. An y computer that is asleep as
the task starts will be powered on for running the task.
6.3.14 Additional settings
1. Validate backup archive upon operation completion
The preset is disabled.
The program will check integrity of the just created or supplemented archive immediately
after backup when enabled.
80 Copyright © Acronis, Inc., 2000-2008
Page 81

To check archive data integrity, you must have all incremental and differential backups
belonging to the archive and the initial full backup. If any of successive backups is
missing, validation is not possible.
2. Overwrite data on a tape without user confirmation
The preset is enabled.
A full backup, when created on a tape drive, overwrites all data stored on the tape (see
Archives cataloguing
for more information). In this situation, Acronis True Image for
Microsoft Small Business Server will warn that you are about to lose data on the tape. To
disable this warning, check the middle box.
3. Ask for first media while creating backup archives on removable media
The preset is enabled.
You can choose whether to display the Insert First Media prompt when backing up to
removable media. With the default setting, backing up to removable media may be not
possible if the user is away, because the program will wait for someone to press OK in
the prompt box. Therefore, you should disable the prompt when scheduling a backup to
removable media. Then, if the removable media is available (for example, CD-R/RW
inserted), the task can run unattended.
4. Reset archive bit
The preset is disabled. The option relates only to file-level backup.
In Windows operating systems, each file has an attribute File is ready for archiving,
available at selecting file -> Properties -> General -> Advanced -> Archive and
Index attributes. This attribute, also known as archive bit, is set by the operating
system each time the file is changed and can be reset by backup applications each tim e
they include the file in a backup copy. Archive bit value is used by various applications
such as databases.
With Reset archive bit enabled, Acronis True Image for Microsoft Small Business Server
will reset archive bits of all files being backed up. Acronis True Image for Microsoft Small
Business Server itself does not use the archive bit value. When performing incremental or
differential backup, it determines whether a file has changed by the file size and the
date/time when the file was last saved.
Copyright © Acronis, Inc., 2000-2008 81
Page 82

Chapter 7. Restoring the backup data
7.1 Considerations before recovery
7.1.1 Restore under Windows or boot from CD?
As mentioned above (see
Server
in several ways. We recommend that you first try to restore data running Acronis True
Image for Microsoft Small Business Server under Windows because this method provides
more functionality. Boot from the bootable media or use the Startup Recovery Manag er
(see
The boot CD from which you loaded the program does not keep you from using other CDs
with backups. Acronis True Image for Microsoft Small Business Server is loaded entirely
into RAM, so you can remove the bootable CD to insert the archive disk.
(local version)), Acronis True Image for Microsoft Small Business Server can be run
3.4 Acronis Startup Recovery Manager)
Be careful! Disk letters in standalone Acronis True Image for Microsoft Small Business
Server might sometimes differ from the way Windows identifies drives. For example, the
D: drive identified in the standalone Acronis True Image for Microsoft Small Business
Server might correspond to the E: drive in Windows.
If a backup image is located on bootable media, you might have a choice of using Acronis
One-Click Restore. This operation always restores the entire physical disk. Therefore, if
your disk consists of several partitions, the partitions that are missing from the image will
be lost. Please make sure that the image contains all disk partitions or you do not need
the partitions that are not imaged before using Acronis One-Click Restore. For more
information on Acronis One-Click Restore, see
2.5.1 Running Acronis True Image for Microsoft Small Business
only if Windows does not load.
6.3.10 Media components
.
7.1.2 Network settings in rescue mode
When booted from removable media, RIS server or by Startup Recovery Manager, Acronis
True Image for Microsoft Small Business Server may not detect the network. This can
occur if there is no DHCP server in your network or if your computer address was not
identified automatically for some reason.
To enable a network connection, specify network settings manually in the window
available at Tools -> Options -> Network adapters.
82 Copyright © Acronis, Inc., 2000-2008
Page 83

7.1.3 Recovering dynamic volumes
Dynamic volumes are volumes located on dynamic disks, i.e. disks managed by Windows
Logical Disk Manager (LDM). For more information on dynamic disks, please refer to your
Windows documentation.
Acronis True Image for Microsoft Small Business Server can back up and recover dynamic
volumes.
A dynamic volume can be recovered over the same volume or unallocated space of a
dynamic group. If recovered over another volume, the target volume’s contents will be
overwritten with the image contents, but the type or other properties of the target
volume will not be changed.
To restore a dynamic volume exactly as it is, prepare a target dynamic group without
volumes. In case you want to restore a dynamic volume in place of s ome volumes already
existing on the target disks, delete the original volumes using third-party tools, such as
the Windows Disk Management tool.
Dynamic volume contents alone can be recovered onto a basic or dynamic volume
without changing the target volume type. Acronis True Image for Microsoft Small
Business Server local version has the Create dynamic volume tool so that you be able
to prepare the desired volumes on the target disks.
Backward conversion of dynamic volume to basic disks can be performed, if need be,
using the Add new disk operation (see
Chapter 15. Adding a new hard disk
).
With these tools, anywhere-to-anywhere data recovery becomes available, in terms of
basic disks and dynamic volumes of any type (simple, spanned, striped, mirrored or RAID
5). The tools are available in bootable program version. Having booted the Acronis
environment, you can easily prepare the desired dynamic group on bare metal or a
computer with non-Windows operating system.
For how to use the above tools see
Copyright © Acronis, Inc., 2000-2008 83
7.5 Creating dynamic disks and volumes.
Page 84

7.2 Restoring files and folders from file archives
Here we describe how to restore files/folders from a file backup archive. You can restore
the desired files/folders from a disk/partition image as well. To do so, mount the image
11.2.2 Mounting an image
(see
specified files or folders (see
1. Start the Restore Data Wizard by clicking on the restore operation icon in the main
program window.
2. Select the archive. If the archive is located in Acronis Secure Zone, select it to choose
the archive on the next step.
) or start the image restoration and select Restore
7.3 Restoring disks/partitions or files from images
).
If the archive is located on removable media, e.g. CD, first insert the last CD and then
insert disks in reverse order when Restore Data Wizard prompts.
Data recovery directly from an FTP server requires the archive to consist of files no more
than 2GB in size. If you suspect that some of the files may be larger, first copy the entire
archive (along with the initial full backup) to a local hard disk or network share disk. See
notes and recommendations for supporting FTP server in
.
media
1.4.2 Supported storage
If you added a comment to the archive, it will be displayed to the right of the drives tree.
If the archive was protected with a password, Acronis True Image for Microsoft Small
Business Server will ask for it. The comment and the Next button will be unavailable until
you enter the correct password.
3. If the selected archive contains incremental backups, A cronis True Image for Microsoft
Small Business Server will suggest that you select one of successive incremental backups
by its creation date/time. Thus, you can return the files/folders to a specific time and
date.
To restore data from an incremental backup, you must have all previous incremental
backups and the initial full backup. If any of successive backups is missing, restoration is
not possible.
To restore data from a differential backup, you must have the initial full backup as well.
84 Copyright © Acronis, Inc., 2000-2008
Page 85

4. Select a folder on your computer where you want to restore sel ected folders/files (a
target folder). You can restore data to their original location or choose another folder, if
necessary.
5. Select files and folders to restore. You can choose to restore all data or browse the
archive contents and select the desired folders or files.
6. Select the options for the restoration process (that is, pre/post restoration commands,
restoration process priority, file-level security settings etc.). You may Use default
options or Set the options manually. If you set options manually, the settings will be
applied only to the current restore task. Alternatively, you can edit the default options
from the current screen. Then your settings will be saved as default. See
restore options
for more information.
7.4 Setting
Copyright © Acronis, Inc., 2000-2008 85
Page 86

7. Set filters for the specific types of files that are not t o be restored. For example, you
may want hidden and system files and folders, as well as files with .~, .tmp and .bak
extensions, not to be restored from the archive.
You can also apply custom filters, using the common Windows masking rules. For
example, to exclude all files with extension .exe, add *.exe. My???.exe will reject all
.exe files with names consisting of five symbols and starting with “my”.
All of these settings will take effect for the current task. How to set the default filters that
will be called each time you restore data, see
7.4.1 Files to exclude from restoration
.
8. The next selection allows you to keep useful data changes made since the selected
backup was created. Choose what to do if the program finds in the target folder a file
with the same name as in the archive.
Overwrite existing file – this will give the archived file unconditional priority over the
file on the hard disk.
Overwrite existing file if it is older – this will give the priority to the most recent file
modification, whether it be in the archive or on the disk
Do not overwrite existing file – this will give the file on the hard disk unconditional
priority over the archived file.
9. At the final step, the restoration summary is displayed. Up to this point, you can click
Back to make changes in the created task. Clicking Proceed will launch the task.
10. (For Acronis True Image for Microsoft Small Business Server local or bootable version)
The task progress will be shown in a special window. You can stop the procedure by
clicking Cancel. Please keep in mind that the aborted procedure still may caus e changes
in the destination folder.
7.3 Restoring disks/partitions or files from images
To restore a partition (disk) from an image, Acronis True Image for Microsoft Small
Business Server must obtain exclusive access to the target partition (disk). This means
no other applications can access it at that time. If you receive a message stating that the
partition (disk) can not be blocked, close applications that use this partition (disk) and
86 Copyright © Acronis, Inc., 2000-2008
Page 87

start over. If you can not determine which applications use the partition (disk), close them
all.
7.3.1 Starting the Restore Data Wizard
Start the Restore Data Wizard by clicking on the restore operation icon in the main
program window.
7.3.2 Archive selection
1. Select the archive. If the archive is located in Acronis Secure Zone, select it to choose
the archive at the next step.
If the archive is located on removable media, e.g. CD, first insert the last CD and then
insert disks in reverse order when Restore Data Wizard prompts.
Data recovery directly from an FTP server requires the archive to be split into files no
more than 2GB in size. If you suspect that some of the files may be larger, first copy the
entire archive (along with the initial full backup) to a local hard disk or network share
disk. See notes and recommendations for supporting FTP server in
storage media
.
1.4.2 Supported
If you added a comment to the archive, it will be displayed to the right of the drives tree.
If the archive was protected with a password, Acronis True Image for Microsoft Small
Business Server will ask for it. The partitions layout, the comment and the Next button
will be unavailable until you enter the correct password.
2. If the selected archive contains incremental backups, A cronis True Image for Microsoft
Small Business Server will suggest that you select one of successive incremental backups
by its creation date/time. Thus, you can return the disk data to a certain moment.
To restore data from an incremental backup, you must have all previous incremental
backups and the initial full backup. If any of successive backups is missing, restoration is
not possible.
To restore data from a differential backup, you must have the initial full backup as well.
Copyright © Acronis, Inc., 2000-2008 87
Page 88

7.3.3 Restoration type selection
Select what you want to restore:
Restore specified files or folders
With this selection, you will be further offered to select where to restore selected
folders/files (original or new location), choose files/folders to be restored and so on.
These steps look like those in file archive restore. However, watch your selection; if you
want to restore files instead of disk/partition, uncheck the unnecessary folders. Otherwise
you will restore a lot of extra files. Then you will be taken directly to Restoration
Summary screen (
7.3.13 Restoration summary and executing restoration)
Restore disks or partitions
Having selected a usual way of disks/partitions recovery, you will have to make all
settings described below.
Using Active restore
When restoring a system disk/partition image (except for Windows Vista images) from
Acronis Secure Zone, you will have the third choice – to use Acronis Active restore.
Having selected this option, you will proceed directly to the summary window (
Restoration summary and executing restoration
). A few seconds after pressing Proceed,
7.3.13
the computer will reboot to the restored system. Log in and start work – no more reboots
or other actions are required. For more about Acronis Active restore, see
Active restore
.
3.6 Acronis
When performing Active restore, the Acronis True Image for Microsoft Small Business
Server always restores the entire system disk. Therefore, if your disk consists of several
partitions, the partitions which are missing from the image will be lost. Please make sure
that the image contains all disk partitions or you do not need the partitions that are not
imaged before using Acronis Active restore.
However, you can choose an ordinary way of restoration for that image. This will allow
you to make changes to the restored partition that would not be possible when using
Acronis Active restore.
88 Copyright © Acronis, Inc., 2000-2008
Page 89

Finally, if you are not going to recover the system, but only want to repair damaged files,
select Restore specified files or folders.
7.3.4 Selecting a disk/partition to restore
The selected backup can contain images of several partitions or even disks. Sel ect which
disk/partition to restore.
Disks and partitions images contain a copy of track 0 along with the MBR (Master Boot
Record). It appears in this window in a separate line. You can choose whether to restore
MBR and track 0 by checking the respective box. R estore the MBR if it is critical to your
system boot.
7.3.5 Selecting a target disk/partition
1. Select a target disk or partition where you want to deploy the sel ected image. You can
restore data to its initial location, to another disk/partition or to a n un allocat ed space. The
target partition should be at least the same size as the uncompressed image data.
All the data stored on the target partition will be replaced by the image data, so be
careful and watch for non-backed-up data that you might need.
When restoring a Windows system disk and select a target disk, the program compares
critical for the system start devices, found in the image registry and the target co mputer
registry.
If the chipset, motherboard or mass storage d evice are different, there is a risk that the
system will not be able to boot. Then you will be prompted whether you want to use
Acronis Universal Restore. To find out more about this option, see
Universal Restore
. To get the option, follow the link.
3.7 Acronis
If you already have Acronis Universal Restore, the prompt will not come up and you will
have an option to enable Acronis Universal Restore later in the Restore Data Wizard.
2. When restoring an entire disk, the program will analyze the target disk structure to see
if the disk is free.
Copyright © Acronis, Inc., 2000-2008 89
Page 90

If there are partitions on the target disk, you will be prompted by the Nonempty
Destination Hard Disk Drive window stating that the destination disk contains
partitions, perhaps with data.
You will have to select between:
Yes, I want to delete all the partitions on the destination hard disk before restoring – all
existing partitions will be deleted and all their data will be lost.
No, I do not want to delete partitions – no existing partition will be deleted,
discontinuing the recovery operation. You will be able to cancel the operation or
return to select another disk.
Note that no real changes or data destruction will be performed at this time! For now, the
program will just map out the procedure. All changes will be implemented only when you
click Proceed in the wizard’s final window.
To continue, select the first choice and click Next. You will be taken directly to step
7.3.10 Restoring several disks or partitions at once
.
7.3.6 Changing the restored partition type
When restoring a partition, you can change its type, though it is not required in most
cases.
To illustrate why you might need to do this, let’s imagine that both the operating system
and data were stored on the same primary partition on a damaged disk.
If you are restoring a system partition to the new (or the same) disk and want to load an
operating system from it, you will select Active.
If you restore a system partition to another hard disk with its own partitions and OS, most
likely you will need only the data. In this case, you can restore the partition as Logical to
access the data only.
By default, the original partition type is selected.
90 Copyright © Acronis, Inc., 2000-2008
Page 91

Selecting Active for a partition without an installed operating system could prevent your
server from booting.
7.3.7 Changing the restored partition file system
You can change the partition file system during its restoration, although it is seldom
required. Acronis True Image for Microsoft Small Business Server can make the foll owing
file system conversions: FAT 16 -> FAT 32 and Ext2 -> Ext3. For partitions with other
native file systems, this option is not available.
Let us imagine you are to restore a partition from an old, low-capacity FAT16 disk to a
newer disk. FAT16 would not be effective and might even be impossible to set on the
high-capacity hard disk. That's because FAT16 supports partitions up to 4GB, so you will
not be able to restore a 4GB FAT16 partition to a partition that exceeds that limit without
changing the file system. It would make sense here to change the file system from FAT16
to FAT32.
However, keep in mind that not all operating systems support FAT32. MS-DOS, Windows
95 and Windows NT 3.x, 4.x do not support FAT32 and will not be operable after you
restore a partition and change its file system. These can be normally restored on a FAT16
partition only.
7.3.8 Changing the restored partition size and location
You can resize and relocate a partition by dragging it or its borders wit h a mouse or by
entering corresponding values in the appropriate fields.
Using this feature, you can redistribute the disk space between partitions being restored.
In this case, you will have to restore the partition to be reduced first.
These changes might be useful if you are to copy your hard disk to a new, high-capacity
one by creating its image and restoring it to a new disk with larger partitions.
Copyright © Acronis, Inc., 2000-2008 91
Page 92

7.3.9 Assigning a letter to the restored partition
Acronis True Image for Microsoft Small Business Server will assign an unused letter to a
restored partition. You can select the desired letter from a drop-down list. If you s et the
switch to No, no letters will be assigned to the restored partition, hiding it from OS.
You should not assign letters to partitions inaccessible to Windows, such as to those other
than FAT and NTFS.
7.3.10 Restoring several disks or partitions at once
During a single session, you can restore several partitions or disks, one by one, by
selecting one disk and setting its parameters first and then repeating these actions for
every partition or disk to be restored.
If you want to restore another disk (partition), select Yes, I want to restore another
partition or hard disk drive. Then you will return to the partition selection window
(7.3.4) again and will have to repeat the above steps. Otherwise, do not set this switch.
7.3.11 Using Acronis Universal Restore
Acronis Universal Restore is an add-on to Acronis True Image for Microsoft Small Business
Server. It is included at no extra charge with with Acronis True Image for Microsoft Small
Business Server and installed from a separate setup file. The following is true for Acronis
True Image for Microsoft Small Business Server installations including Acronis Universal
Restore.
1. Using Acronis Universal Restore will help you create a bootable system clone on
different hardware (for more information see
when restoring a system disk to a computer with a dissimilar processor, different
motherboard or other mass storage device than in the imaged system.
3.7 Acronis Universal Restore
). Choose this
2. If the target hardware has a specific mass storage controller (such as a SCSI, RAID, or
Fibre Channel adapter) for the hard disk, you can install the appropriate driver manually,
bypassing the automatic driver search-and-install procedure.
Use this option only if the automatic search-and-install procedure was unsuccessful.
92 Copyright © Acronis, Inc., 2000-2008
Page 93

Acronis Universal Restore uses three sources for drivers:
- the driver repository - a folder or folders on a netw ork drive or CD specified in restore
options. If you have not specified the driver repository in advance, you can do it at next
step.
- the mass storage device driver specified by the user at the current step
- the Windows default driver storage folders (in the image being restored).
The program will find the most suitable drivers of all available drivers and install them into
the restored system. However, the driver defined by the user, will have the priority. It will
be installed, with appropriate warnings, even if the program finds the better driver.
When restoring the system to a virtual machine that uses SCSI hard drive controller, be
sure to specify SCSI drivers for virtual environment in the Specifying Mass Storage
Drivers window. Use drivers bundled with your virtual machine software or download
the latest drivers versions from the software manufacturer website.
7.3.12 Setting restore options
Select the options for the restoration process (that is, pre/post restoration commands,
restoration process priority etc.). You may Use default options or Set the options
manually. If you set the options manually, the settings will be applied only to the current
restore task. Alternatively, you can edit the def ault options from the current screen. Then
your settings will be saved as default. See
information.
7.4 Setting restore options
for more
7.3.13 Restoration summary and executing restoration
1. At the final step, the restoration summary is displayed. Up to this point, you can click
Back to make changes in the created task. If you click Cancel, no changes will be made
to disk(s). Clicking Proceed will launch the task execution.
2. (For Acronis True Image for Microsoft Small Business Server local or standalone
version) The task progress will be shown in a special window.
You can stop the procedure by clicking Cancel. However, it is critical to note that the
target partition will be deleted and its space unallocated – the same result you will get if
the restoration is unsuccessful. To recover the “lost” partition, you will have to restore it
from the image again.
If Acronis Universal Restore finds no Hardware Abstraction Layer (HAL) or mass storage
devices drivers compatible with the new hardware in all available sources, you will be
prompted to browse to a network share drive or insert a floppy disk or CD with the
necessary drivers. Upon starting Windows, it will initialize the standard procedure for
installing new hardware. At this point, you will be able to specify drivers for devices if
Windows cannot find them automatically.
7.4 Setting restore options
To view or edit the default restore options in Acronis True Image for Microsoft Small
Business Server local version, select Tools -> Options -> Default Restoration
Options from the main program menu.
To do the same remotely, connect the Acronis True Image Management Console to the
remote computer, click Remote Computer Options and select Default Restoration
options.
Copyright © Acronis, Inc., 2000-2008 93
Page 94

You can edit the default (or set the temporary) restore options while creating a restor e
task as well.
7.4.1 Files to exclude from restoration
The preset is Restore all files.
You can set the default filters for the specific types of files that are not to be restored.
Use the common Windows masking rules. For example, to exclude all files with extension
.exe, add *.exe. My???.exe will exclude all .exe files with names, consisting of five
symbols and starting with “my”.
This option is effective only when restoring files from file/folders archives. When restoring
files from a disk/partition image, you cannot filter out any files.
7.4.2 Files overwriting mode
This option allows you to keep useful data changes made since the backup being restored
was done. Choose what to do if the program finds in the target folder a file with the same
name as in the archive.
Overwrite existing file – this will give the archived file unconditional priority over the
file on the hard disk.
Overwrite existing file if it is older – this will give the priority to the most recent file
modification, whether it be in the archive or on the disk.
Do not overwrite existing file – this will give the file on the hard disk unconditional
priority over the archived file.
This option is effective only when restoring files from file/folders archives.
7.4.3 Pre/post commands
You can specify commands or batch files to be automatically executed before and aft er
the restore procedure. Click Edit to open the Edit Command window where you can
easily input the command, its arguments and working directory or browse folders to find a
batch file.
94 Copyright © Acronis, Inc., 2000-2008
Page 95

The program does not support interactive commands, i.e. commands that require user
input (for example, “pause”.)
The backup process will run concurrently with your commands if you uncheck the Do not
perform operations until the commands execution is complete box, which is
checked by default.
7.4.4 Restoration priority
The default setting – Low.
The priority of any process running in a system determines the amount of CPU usag e and
system resources allocated to that process. Decreasing the restoration priority will free
more resources for other CPU tasks. Increasing of restoration priority may speed up the
restore process due to taking resources from the other currently running processes. The
effect will depend on total CPU usage and other factors.
7.4.5 File-level security settings
The preset is Restore files with their security settings.
If the files’ security settings were preserved during backup (see
settings
), you can choose whether to restore files’ security settings or let the files inherit
6.3.9 File-level security
the security settings of the folder where they will be restored.
This option is effective only when restoring files from file/folders archives.
7.4.6 Specifying mass storage drivers
This option appears only in those computers’ options, where Acronis Universal Restore is
installed.
Acronis Universal Restore is an option to Acronis True Image for Microsoft Small Business
Server. It should be included at no extra charge with with Acronis True Image for
Microsoft Small Business Server and installed from a separate setup file. For more
information see
3.7 Acronis Universal Restore
.
Copyright © Acronis, Inc., 2000-2008 95
Page 96

Here you can specify a path to the driver repository on a network drive or CD where
Acronis Universal Restore will search for drivers at restoring a system disk on dissimilar
hardware. If several paths are specified, the program will scan all locations and choose
the most suitable driver.
7.4.7 Additional settings
1. You can choose whether to restore files’ date and time from the archive or assign the
files the current date and time.
2. Before data is restored from the archive, Acronis True Imag
Business
corrupte
3. Having restored a disk/par
Business
system
Server can check its integrity. If you suspect that the archive might have been
d, select Validate backup archive before restoration.
To check archive data integrity you must have all incremental and differential backups
belonging to the archive and the initial full backup. If any of successive backups is
missing, validation is not possible.
tition from an image, Acronis True Image for Microsoft Small
Server can check the integrity of the file system. To do so, select Check file
after restoration.
Verification of the file system is available only when restoring disk/partitions under
Windows and for FAT16/32 and NTFS file system
s.
4. Restore file and fold
ers without full path
The preset is disabled.
When enabled, files and folders are restore
target folder. When disabled, the full path to the
d directly to the folder that you specified as a
files and folders that exists in the backup
will be reproduced within the target folder.
5. Change SID after restoration is finished
The preset is disabled.
e for Microsoft Small
Acronis True Image for Microsoft Small Business Server can generate a unique security
identifier (SID) for the restored system. You do not need a new SID when restoring a
system on the same computer where the image was taken from or when c
reating a full
duplicate that will replace the original system. Generate a new SID if the original and the
restored systems will work concurrently in the same workgroup or domain.
6. The bootable Acronis True Image for Microsoft Small Business Server version has also
an option that after the restoration is finished, the compute r reboots and starts the newly
restored OS without any us
er interaction. If this option is set, post operation com mands
will not be executed. Include the reboot command in your batch file if you need these
commands to be executed.
7.4.8 Error handling
1. Do not show messages and d
The preset is disabled.
With the silent mode enabled, the program will not display interactive windows. Instead,
it will automatically handle situations requiring user intervention. No prompts will be
displayed, including those for inserting remo
ialogs while processing (“silent” mode)
vable media or the next tape. If an operation
96 Copyright © Acronis, Inc., 2000-2008
Page 97

cannot continue without user action, it will fail. Details of the operation, including errors,
if any, could be found in the operation log.
2. If an error occurs, re-attempt in (minutes)
The preset is enabled.
When the backup location on the network is not available or not reachable, th e program
will attempt to reach the location at the specified time interval.
7.5 Creating dynamic disks and volumes
Acronis True Imag
e for Microsoft Small Business Server must obtain exclusive access to
the disks to perform operations with disks and volumes. This means no other applications
can access it at that time. Please close all
other applications that use the disks (such as
Windows Disk Management) before starting the disk conversion and dynamic volume
creation wizards.
7.5.1 Creating dynamic volumes
This operation is available only in Acronis True Image for Microsoft Small Business Server
local version, including bootable version of this component. Having booted to the Acronis
environment, you can eas
compute
The operati
be conv ted to dynamic.
r with a non-Windows operating system.
on supports both dynamic disks and MBR or GPT basic disks. Basic disks will
er
All data contained on the basic disk and the basic disk partitioning will be lost. On
dynamic disks, only unallocated space will be used for the new volume.
An MBR basic disk must have at least 1MB of free space at the end of the disk
dynamic disk database.
To create a dynamic volume:
ily prepare the desired dynamic group on bare metal or a
for the
1. Close all applications that use the disk(s) on which the volume is to be created.
2. Start the Dynamic Volume Creation Wizard by selecting Tools -> Create Dynamic
Volume in th
e main program menu.
3. Select basic, dynamic or newly connected disks on which the dynamic volume will be
created. Dynamic disks are selected by default. You can d eselect any, if need be, later in
the wizard.
If you tick off disks other than dynamic, these will be converted to dynamic disks and
included in the dynamic group. However, this will be done when the operation starts.
While you are using the wizard, no changes are made to disks.
Copyright © Acronis, Inc., 2000-2008 97
Page 98

4. Select the type of dynamic volume that will be created: simple/spanned, striped,
mirrored or RAID 5.
5. Specify amount of space that the dynamic volume will occupy on each of the selected
disks. The value you set is adjusted to the selected volume type.
For a spanned volume, amount of space on each disk is selected independently. If only
one disk is selected, a simple volume is created.
Striped, mirrored and RAID 5 volumes imply even distribution of data between disks.
Therefore, the volume must occupy the same space on each disk. If you set different
values, your latest setting will be applied to all the disks. If the set value is more than
unallocated space on any disk, the minimal available space amount will be applied to all
the disks. The resulting volume size is displayed under the disk selection field.
At this step, you can deselect disks that you do not want to be included in the volume.
6. Click Proceed in the summary window.
98 Copyright © Acronis, Inc., 2000-2008
Page 99

On completion of operations, the dynamic volumes are unformatted an d have no letters
assigned. You will be able to assign the letters using Windows Disk Management tool after
restoring Windows on the created volumes.
Copyright © Acronis, Inc., 2000-2008 99
Page 100

Chapter 8. Scheduling tasks
Acronis True Image for Microsoft Small Business Server allows you to schedule periodic
backup and archive validation tasks. Doing so will give you peace of mind, knowing that
your data are safe.
You can create more than one independently scheduled task. For example, you can back
up your current project daily and back up the application disk once a week.
All the scheduled tasks appear in the Scheduled Tasks window, where you can start,
stop, edit, delete and rename them. To navigate to the Scheduled Tasks window, click
Tasks in the Manage Tasks group or select the Task Scheduling category on the
sidebar.
8.1 Creating scheduled tasks
1. To start the Schedule Task Wizard, click Create on the Scheduled Tasks window
toolbar or select Operations -> Schedule Task from the main menu.
2. Choose the Backup or Validate operation. If the latter is the cas e, choos e the ar chiv e
in the next window and you will be taken straight to step 4.
3. If backup is your choice, configure a backup task in the usual way (see
Creating backup archives
enter a user name and a password for the drive access.
4. Set the task execution periodicity.
). If you choose to create the backup archive on a network drive,
Chapter 6.
100 Copyright © Acronis, Inc., 2000-2008
 Loading...
Loading...