ZyXEL ZyWALL 10, ZyWALL 10 II, ZyWALL 50 User Manual
ZyWALL 10/10 II/50
Internet Security Gateway
User’s Guide
Version 3.50
June 2002

ZYWALL 10/10 II/50 Internet Security Gateway
Copyright
Copyright © 2002 by ZyXEL Communications Corporation.
The contents of this publication may not be reproduced in any part or as a whole, transcribed, stored in a
retrieval system, translated into any language, or transmitted in any form or by any means, electronic,
mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise, without the prior written
permission of ZyXEL Communications Corporation.
Published by ZyXEL Communications Corporation. All rights reserved.
Disclaimer
ZyXEL does not assume any liability arising out of the application or use of any products, or software
described herein. Neither does it convey any license under its patent rights nor the patent rights of others.
ZyXEL further reserves the right to make changes in any products described herein without notice. This
publication is subject to change without notice.
Trademarks
ZyNOS (ZyXEL Network Operating System) is a registered trademark of ZyXEL Communications, Inc.
Other trademarks mentioned in this publication are used for identification purposes only and may be
properties of their respective owners.
ii Copyright

ZYWALL 10/10 II/50 Internet Security Gateway
Federal Communications Commission
(FCC) Interference Statement
This device complies with Part 15 of FCC rules. Operation is subject to the following two conditions:
• This device may not cause harmful interference.
• This device must accept any interference received, including interference that may cause undesired
operations.
This equipment has been tested and found to comply with the limits for a Class B digital device pursuant to
Part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful
interference in a commercial environment. This equipment generates, uses, and can radiate radio frequency
energy, and if not installed and used in accordance with the instructions, may cause harmful interference to
radio communications.
If this equipment does cause harmful interference to radio/television reception, which can be determined by
turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of
the following measures:
1. Reorient or relocate the receiving antenna.
2. Increase the separation between the equipment and the receiver.
3. Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
4. Consult the dealer or an experienced radio/TV technician for help.
Notice 1
Changes or modifications not expressly approved by the party responsible for compliance could void the
user's authority to operate the equipment.
FCC iii

ZYWALL 10/10 II/50 Internet Security Gateway
Information for Canadian Users
The Industry Canada label identifies certified equipment. This certification means that the equipment meets
certain telecommunications network protective operation and safety requirements. The Industry Canada
label does not guarantee that the equipment will operate to a user's satisfaction.
Before installing this equipment, users should ensure that it is permissible to be connected to the facilities
of the local telecommunications company. The equipment must also be installed using an acceptable
method of connection. In some cases, the company's inside wiring associated with a single line individual
service may be extended by means of a certified connector assembly. The customer should be aware that
compliance with the above conditions may not prevent degradation of service in some situations.
Repairs to certified equipment should be made by an authorized Canadian maintenance facility designated
by the supplier. Any repairs or alterations made by the user to this equipment, or equipment malfunctions,
may give the telecommunications company cause to request the user to disconnect the equipment.
For their own protection, users should ensure that the electrical ground connections of the power utility,
telephone lines, and internal metallic water pipe system, if present, are connected together. This precaution
may be particularly important in rural areas.
Caution
Users should not attempt to make such connections themselves, but should contact the appropriate electrical
inspection authority, or electrician, as appropriate.
Note
This digital apparatus does not exceed the Class A limits for radio noise emissions from digital apparatus
set out in the radio interference regulations of Industry Canada.
iv Information for Canadian Users
Standard
• EN 55022
• EN 61000-3-2
• EN 61000-3-3
• EN 61000-4-2
• EN 61000-4-3
• EN 61000-4-4
• EN 61000-4-5
• EN 61000-4-6
• EN 61000-4-8
• EN 61000-4-11
ZYWALL 10/10 II/50 Internet Security Gateway
Declaration of Conformity
We, the Manufacturer/Importer,
ZyXEL Communications Corp.
No. 6, Innovation Rd. II,
Science-Based Industrial Park,
Hsinchu, Taiwan, 300 R.O.C
declare that the product
ZYWALL 10/10 II/50
is in conformity with
(reference to the specification under which conformity is declared)
Standard Item
Radio disturbance characteristics — Limits and method of
measurement.
Disturbance in supply system caused by household appliances
and similar electrical equipment “Harmonics”.
Disturbance in supply system caused by household appliances
and similar electrical equipment “Voltage fluctuations”.
Electrostatic discharge immunity test — Basic EMC Publication 1995
Radiated, radio-frequency, electromagnetic field immunity test 1996
Electrical fast transient / burst immunity test - Basic EMC
Publication
Surge immunity test 1995
Immunity to conducted disturbances, induced by radio-frequency
fields
1993
Voltage dips, short interruptions and voltage variations immunity
tests
Version
1994
1995
1995
1995
1996
1994
Certifications
Refer to the product page at www.zyxel.com
.
Declaration of Conformity v
ZYWALL 10/10 II/50 Internet Security Gateway
ZyXEL Limited Warranty
ZyXEL warrants to the original end user (purchaser) that this product is free from any defects in materials or
workmanship for a period of up to two years from the date of purchase. During the warranty period, and upon
proof of purchase, should the product have indications of failure due to faulty workmanship and/or materials,
ZyXEL will, at its discretion, repair or replace the defective products or components without charge for
either parts or labor, and to whatever extent it shall deem necessary to restore the product or components to
proper operating condition. Any replacement will consist of a new or re-manufactured functionally
equivalent product of equal value, and will be solely at the discretion of ZyXEL. This warranty shall not
apply if the product is modified, misused, tampered with, damaged by an act of God, or subjected to
abnormal working conditions.
Note
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This
warranty is in lieu of all other warranties, express or implied, including any implied warranty of
merchantability or fitness for a particular use or purpose. ZyXEL shall in no event be held liable for indirect
or consequential damages of any kind of character to the purchaser.
To obtain the services of this warranty, contact ZyXEL's Service Center for your Return Material
Authorization number (RMA). Products must be returned Postage Prepaid. It is recommended that the unit be
insured when shipped. Any returned products without proof of purchase or those with an out-dated warranty
will be repaired or replaced (at the discretion of ZyXEL) and the customer will be billed for parts and labor.
All repaired or replaced products will be shipped by ZyXEL to the corresponding return address, Postage
Paid. This warranty gives you specific legal rights, and you may also have other rights that vary from country
to country.
Online Registration
Register online at www.zyxel.com
vi ZyXEL Limited Warranty
for free future product updates and information.
ZYWALL 10/10 II/50 Internet Security Gateway
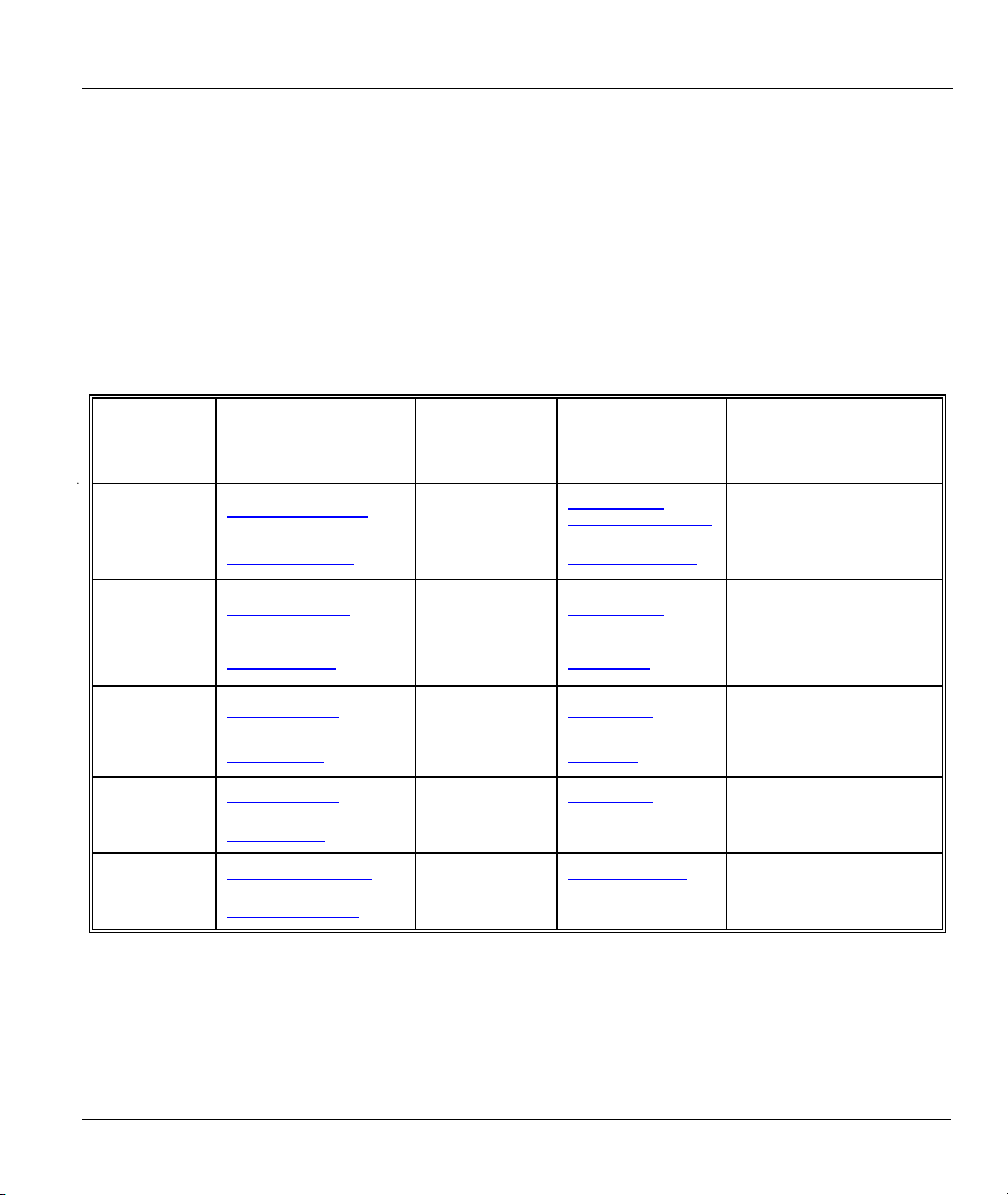
Customer Support
Please have the following information ready when you contact customer support.
• Product model and serial number.
• Information in Menu 24.2.1 – System Information.
• Warranty Information.
• Date that you received your device.
• Brief description of the problem and the steps you took to solve it.
METHOD
LOCATION
E-MAIL
SUPPORT/SALES
TELEPHONE/FAX WEB SITE/ FTP SITE REGULAR MAIL
WORLDWIDE
NORTH
AMERICA
SCANDINAVIA
GERMANY
MALAYSIA
support@zyxel.com.tw +886-3-578-3942
sales@zyxel.com.tw
support@zyxel.com
sales@zyxel.com
support@zyxel.dk +45-3955-0700 www.zyxel.dk
sales@zyxel.dk
support@zyxel.de +49-2405-6909-0 www.zyxel.de
sales@zyxel.de
support@zyxel.com.my +603-795-44-688 www.zyxel.com.my
sales@zyxel.com.my
+886-3-578-2439 ftp.europe.zyxel.com
+1-714-632-0882
800-255-4101
+1-714-632-0858 ftp.zyxel.com
+45-3955-0707 ftp.zyxel.dk
+49-2405-6909-99
+603-795-34-407
www.zyxel.com
www.europe.zyxel.com
www.zyxel.com
ZyXEL Communications Corp.,
6 Innovation Road II, ScienceBased Industrial Park, Hsinchu
300, Taiwan
ZyXEL Communications Inc.,
1650 Miraloma Avenue,
Placentia, CA 92870, U.S.A.
ZyXEL Communications A/S,
Columbusvej 5, 2860 Soeborg,
Denmark
ZyXEL Deutschland GmbH.
Adenauerstr. 20/A4 D-52146
Wuerselen, Germany
Lot B2-06, PJ Industrial Park,
Section 13, Jalan Kemajuan,
46200 Petaling Jaya Selangor
Darul Ehasn, Malaysia
Customer Support vii

ZYWALL 10/10 II/50 Internet Security Gateway
Table of Contents
Copyright .....................................................................................................................................................ii
Federal Communications Commission (FCC) Interference Statement .................................................iii
Information for Canadian Users ...............................................................................................................iv
ZyXEL Limited Warranty .........................................................................................................................vi
Customer Support .....................................................................................................................................vii
List of Figures ...........................................................................................................................................xvi
List of Tables ...........................................................................................................................................xxiii
List of Diagrams ....................................................................................................................................xxvii
Preface .....................................................................................................................................................xxix
GETTING STARTED...................................................................................................................................... I
Chapter 1 Getting to Know Your ZyWALL ...........................................................................................1-1
1.1 The ZyWALL 10/10 II/50 Internet Security Gateway ................................................................1-1
1.2 Features.......................................................................................................................................1-1
1.3 Applications ................................................................................................................................1-4
1.3.1 Secure Broadband Internet Access via Cable or DSL Modem ...........................................1-4
1.3.2 VPN Application.................................................................................................................1-5
Chapter 2 Hardware Installation ............................................................................................................2-1
2.1 Front Panel LEDs and Back Panel Ports .....................................................................................2-1
2.1.1 Front Panel LEDs................................................................................................................2-1
2.2 ZyWALL Rear Panel and Connections.......................................................................................2-2
2.3 Additional Installation Requirements..........................................................................................2-6
Chapter 3 Initial Setup.............................................................................................................................3-1
viii Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
3.1 Turning On Your ZyWALL ....................................................................................................... 3-1
3.1.1 Initial Screen....................................................................................................................... 3-1
3.1.2 Entering the Password ........................................................................................................ 3-1
3.2 Navigating the SMT Interface .................................................................................................... 3-2
3.2.1 Main Menu ......................................................................................................................... 3-3
3.2.2 System Management Terminal Interface Summary ........................................................... 3-3
3.2.3 SMT Menus at a Glance .....................................................................................................3-5
3.3 Changing the System Password.................................................................................................. 3-7
3.4 Resetting the ZyWALL .............................................................................................................. 3-8
3.4.1 Methods of Restoring Factory-Defaults ............................................................................. 3-8
3.4.2 Procedure To Use The Reset Button .................................................................................. 3-9
Chapter 4 General And WAN Setup....................................................................................................... 4-1
4.1 System Name.............................................................................................................................. 4-1
4.2 Dynamic DNS ............................................................................................................................ 4-1
4.2.1 DYNDNS Wildcard............................................................................................................ 4-2
4.3 General Setup ............................................................................................................................. 4-2
4.4 WAN Setup ................................................................................................................................ 4-5
Chapter 5 LAN Setup.............................................................................................................................. 5-1
5.1 Introduction ................................................................................................................................ 5-1
5.2 LAN Port Filter Setup ................................................................................................................ 5-1
5.3 TCP/IP and DHCP for LAN....................................................................................................... 5-1
5.3.1 Factory LAN Defaults ........................................................................................................ 5-2
5.3.2 DHCP Configuration .......................................................................................................... 5-2
5.3.3 IP Address and Subnet Mask.............................................................................................. 5-2
5.3.4 Private IP Addresses........................................................................................................... 5-3
5.3.5 RIP Setup............................................................................................................................ 5-4
5.3.6 IP Multicast ........................................................................................................................ 5-4
Table of Contents ix

ZYWALL 10/10 II/50 Internet Security Gateway
5.3.7 IP Alias................................................................................................................................5-5
5.4 TCP/IP and DHCP Ethernet Setup Menu....................................................................................5-5
5.4.1 IP Alias Setup......................................................................................................................5-7
Chapter 6 Internet Access ........................................................................................................................6-1
6.1 Internet Access Setup..................................................................................................................6-1
6.1.1 Ethernet Encapsulation........................................................................................................6-1
6.1.2 PPTP Encapsulation............................................................................................................6-2
6.1.3 Configuring the PPTP Client ..............................................................................................6-3
6.1.4 PPPoE Encapsulation..........................................................................................................6-3
6.2 Basic Setup Complete .................................................................................................................6-5
ADVANCED APPLICATIONS......................................................................................................................II
Chapter 7 Remote Node Setup ................................................................................................................7-1
7.1 Remote Node Profile...................................................................................................................7-1
7.1.1 Ethernet Encapsulation........................................................................................................7-1
7.1.3 PPTP Encapsulation............................................................................................................7-5
7.2 Editing TCP/IP Options (with Ethernet Encapsulation)..............................................................7-7
7.2.1 Editing TCP/IP Options (with PPTP Encapsulation) ..........................................................7-8
7.2.2 Editing TCP/IP Options (with PPPoE Encapsulation) ......................................................7-10
7.3 Remote Node Filter...................................................................................................................7-10
Chapter 8 IP Static Route Setup..............................................................................................................8-1
8.1 IP Static Route Setup ..................................................................................................................8-2
Chapter 9 Network Address Translation (NAT) ....................................................................................9-1
9.1 Introduction.................................................................................................................................9-1
9.1.1 NAT Definitions .................................................................................................................9-1
9.1.2 What NAT Does..................................................................................................................9-2
9.1.3 How NAT Works ................................................................................................................9-2
9.1.4 NAT Application.................................................................................................................9-3
x Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
9.1.5 NAT Mapping Types.......................................................................................................... 9-4
9.2 Using NAT ................................................................................................................................. 9-6
9.2.1 SUA (Single User Account) Versus NAT.......................................................................... 9-6
9.2.2 Applying NAT.................................................................................................................... 9-6
9.3 NAT Setup.................................................................................................................................. 9-8
9.3.1 Address Mapping Sets........................................................................................................ 9-8
9.4 NAT Server Sets – Port Forwarding......................................................................................... 9-13
9.4.1 Configuring a Server behind NAT ................................................................................... 9-14
9.5 General NAT Examples ........................................................................................................... 9-16
9.5.1 Internet Access Only ........................................................................................................ 9-16
9.5.2 Example 2: Internet Access with an Inside Server ........................................................... 9-17
9.5.3 Example 3: Multiple Public IP Addresses With Inside Servers........................................ 9-18
9.5.4 Example 4: NAT Unfriendly Application Programs........................................................ 9-22
FIREWALL AND CONTENT FILTERS ....................................................................................................III
Chapter 10 Firewalls.............................................................................................................................. 10-1
10.1 What Is a Firewall?............................................................................................................... 10-1
10.2 Types of Firewalls................................................................................................................ 10-1
10.2.1 Packet Filtering Firewalls ................................................................................................. 10-1
10.2.2 Application-level Firewalls ..............................................................................................10-1
10.2.3 Stateful Inspection Firewalls ............................................................................................10-2
10.3 Introduction to ZyXEL’s Firewall ........................................................................................ 10-2
10.4 Denial of Service.................................................................................................................. 10-3
10.4.1 Basics ............................................................................................................................... 10-3
10.4.2 Types of DoS Attacks....................................................................................................... 10-4
10.5 Stateful Inspection................................................................................................................ 10-7
10.5.1 Stateful Inspection Process............................................................................................... 10-8
10.5.2 Stateful Inspection and the ZyWALL............................................................................... 10-9
10.5.3 TCP Security .................................................................................................................. 10-10
Table of Contents xi

ZYWALL 10/10 II/50 Internet Security Gateway
10.5.4 UDP/ICMP Security .......................................................................................................10-10
10.5.5 Upper Layer Protocols ....................................................................................................10-11
10.6 Guidelines For Enhancing Security With Your Firewall ....................................................10-11
10.6.1 Security In General .........................................................................................................10-12
10.7 Packet Filtering Vs Firewall................................................................................................10-12
10.7.1 Packet Filtering: ..............................................................................................................10-13
10.7.2 Firewall ...........................................................................................................................10-13
Chapter 11 Introducing the ZyWALL Firewall....................................................................................11-1
11.1 Remote Management and the Firewall..................................................................................11-1
11.2 Access Methods ....................................................................................................................11-1
11.3 Using ZyWALL SMT Menus ...............................................................................................11-1
11.3.1 Activating the Firewall......................................................................................................11-1
11.3.2 Viewing the Firewall Log .................................................................................................11-2
Chapter 12 Using the ZyWALL Web Configurator.............................................................................12-1
12.1 Web Configurator Login and Main Menu Screens ...............................................................12-1
12.2 Enabling the Firewall............................................................................................................12-2
12.3 E-mail....................................................................................................................................12-2
12.3.1 Alerts.................................................................................................................................12-2
12.3.2 Logs...................................................................................................................................12-3
12.3.3 SMTP Error Messages ......................................................................................................12-5
12.3.4 Example E-mail Log .........................................................................................................12-5
12.4 Attack Alert...........................................................................................................................12-6
12.4.1 Threshold Values ..............................................................................................................12-6
12.4.2 Half-Open Sessions...........................................................................................................12-7
Chapter 13 Creating Custom Rules ......................................................................................................13-1
13.1 Rules Overview.....................................................................................................................13-1
13.2 Rule Logic Overview............................................................................................................13-1
xii Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
13.2.1 Rule Checklist .................................................................................................................. 13-1
13.2.2 Security Ramifications ..................................................................................................... 13-2
13.2.3 Key Fields For Configuring Rules.................................................................................... 13-2
13.3 Connection Direction............................................................................................................ 13-3
13.3.1 LAN to WAN Rules .........................................................................................................13-3
13.3.2 WAN to LAN Rules .........................................................................................................13-4
13.4 Rule Summary...................................................................................................................... 13-4
13.5 Predefined Services .............................................................................................................. 13-7
13.5.1 Creating/Editing Firewall Rules ..................................................................................... 13-10
13.5.2 Source and Destination Addresses.................................................................................. 13-11
13.6 Timeout .............................................................................................................................. 13-13
13.6.1 Factors Influencing Choices for Timeout Values........................................................... 13-13
Chapter 14 Custom Ports...................................................................................................................... 14-1
14.1 Introduction .......................................................................................................................... 14-1
14.2 Creating/Editing A Custom Port........................................................................................... 14-3
Chapter 15 Logs ..................................................................................................................................... 15-1
15.1 Log Screen............................................................................................................................ 15-1
Chapter 16 Example Firewall Rules..................................................................................................... 16-1
16.1 Examples .............................................................................................................................. 16-1
16.1.1 Example 1: Firewall Rule To Allow Web Service From The Internet ............................. 16-1
16.1.2 Example 2: Small Office With Mail, FTP and Web Servers ............................................ 16-6
16.1.3 Example 3: DHCP Negotiation and Syslog Connection from the Internet..................... 16-12
Chapter 17 Content Filtering................................................................................................................ 17-1
17.1 Categories............................................................................................................................. 17-1
17.1.1 Restrict Web Features....................................................................................................... 17-1
17.1.2 Filter List .......................................................................................................................... 17-1
17.1.3 Time of Day...................................................................................................................... 17-1
Table of Contents xiii

ZYWALL 10/10 II/50 Internet Security Gateway
17.2 List Update............................................................................................................................17-1
17.3 Exempt Computers................................................................................................................17-1
17.4 Customizing ..........................................................................................................................17-2
17.5 Keywords ..............................................................................................................................17-2
17.6 Logs.......................................................................................................................................17-2
ADVANCED MANAGEMENT ................................................................................................................... IV
Chapter 18 Filter Configuration ...........................................................................................................18-1
18.1 About Filtering......................................................................................................................18-1
18.1.1 The Filter Structure of the ZyWALL ................................................................................18-2
18.2 Configuring a Filter Set.........................................................................................................18-4
18.2.1 Filter Rules Summary Menu .............................................................................................18-6
18.2.2 Configuring a Filter Rule ..................................................................................................18-7
18.2.3 TCP/IP Filter Rule ............................................................................................................18-7
18.2.4 Generic Filter Rule..........................................................................................................18-12
18.3 Example Filter.....................................................................................................................18-14
18.4 Filter Types and NAT .........................................................................................................18-17
18.5 Firewall ...............................................................................................................................18-17
18.6 Applying a Filter and Factory Defaults...............................................................................18-18
18.6.1 LAN traffic......................................................................................................................18-18
18.6.2 Remote Node Filters .......................................................................................................18-18
Chapter 19 SNMP Configuration..........................................................................................................19-1
19.1 About SNMP.........................................................................................................................19-1
19.2 Supported MIBs ....................................................................................................................19-3
19.3 Configuring SNMP ...............................................................................................................19-3
19.4 SNMP Traps..........................................................................................................................19-5
xiv Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
Chapter 20 System Information & Diagnosis...................................................................................... 20-1
20.1 System Status ....................................................................................................................... 20-1
20.2 System Information and Console Port Speed ....................................................................... 20-3
20.2.1 System Information .......................................................................................................... 20-4
20.2.2 Console Port Speed........................................................................................................... 20-5
20.3 Log and Trace....................................................................................................................... 20-5
20.3.1 Viewing Error Log ........................................................................................................... 20-5
20.3.2 UNIX Syslog .................................................................................................................... 20-7
20.3.3 Call-Triggering Packet ................................................................................................... 20-10
20.4 Diagnostic........................................................................................................................... 20-11
20.4.1 WAN DHCP................................................................................................................... 20-12
Chapter 21 Firmware and Configuration Maintenance ..................................................................... 21-1
21.1 Filename Conventions.......................................................................................................... 21-1
21.2 Backup Configuration .......................................................................................................... 21-2
21.2.1 Backup Configuration ...................................................................................................... 21-2
21.2.2 Using the FTP Command from the Command Line......................................................... 21-3
21.2.3 Example of FTP Commands from the Command Line .................................................... 21-3
21.2.4 GUI-Based FTP Clients....................................................................................................21-4
21.2.5 TFTP and FTP over WAN Will Not Work When ............................................................ 21-4
21.2.6 Backup Configuration Using TFTP.................................................................................. 21-5
21.2.7 TFTP Command Example ................................................................................................ 21-5
21.2.8 GUI-Based TFTP Clients ................................................................................................. 21-6
21.2.9 Backup Via Console Port ................................................................................................. 21-6
21.3 Restore Configuration .......................................................................................................... 21-7
21.3.1 Restore Using FTP or TFTP ............................................................................................. 21-8
21.3.2 Procedure To Restore Using FTP..................................................................................... 21-8
21.3.3 Restore Using FTP Session Example ............................................................................... 21-9
21.3.4 Restore Via Console Port .................................................................................................21-9
21.4 Uploading Firmware and Configuration Files .................................................................... 21-10
Table of Contents xv

ZYWALL 10/10 II/50 Internet Security Gateway
21.4.1 Firmware File Upload .....................................................................................................21-11
21.4.2 Configuration File Upload ..............................................................................................21-11
21.4.3 FTP File Upload Command from the Command Line Example.....................................21-12
21.4.4 FTP Session Example of Firmware File Upload.............................................................21-13
21.4.5 TFTP File Upload ...........................................................................................................21-13
21.4.6 TFTP Upload Command Example..................................................................................21-14
21.4.7 Uploading Via Console Port ...........................................................................................21-14
21.4.8 Uploading a Firmware File Via Console Port .................................................................21-14
21.4.9 Example Xmodem Firmware Upload Using HyperTerminal..........................................21-15
21.4.10 Uploading a Configuration File Via Console Port ......................................................21-16
21.4.11 Example Xmodem Configuration Upload Using HyperTerminal...............................21-16
Chapter 22 System Maintenance & Information.................................................................................22-1
22.1 Command Interpreter Mode..................................................................................................22-1
22.2 Call Control Support .............................................................................................................22-2
22.2.1 Budget Management .........................................................................................................22-3
22.2.2 Call History .......................................................................................................................22-4
22.3 Time and Date Setting...........................................................................................................22-4
22.3.1 Resetting the Time ............................................................................................................22-6
Chapter 23 Remote Management..........................................................................................................23-1
23.1 Telnet ....................................................................................................................................23-1
23.2 FTP........................................................................................................................................23-1
23.3 Web.......................................................................................................................................23-2
23.4 Remote Management ............................................................................................................23-2
23.4.1 Remote Management Limitations .....................................................................................23-4
23.5 Remote Management and NAT.............................................................................................23-4
23.6 System Timeout ....................................................................................................................23-5
CALL SCHEDULING AND VPN/IPSEC..................................................................................................... V
xvi Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
Chapter 24 Call Scheduling .................................................................................................................. 24-1
24.1 Introduction .......................................................................................................................... 24-1
Chapter 25 Introduction to IPSec ......................................................................................................... 25-1
25.1 Introduction .......................................................................................................................... 25-1
25.1.1 VPN.................................................................................................................................. 25-1
25.1.2 IPSec................................................................................................................................. 25-1
25.1.3 Security Association......................................................................................................... 25-1
25.1.4 Other Terminology ........................................................................................................... 25-1
25.1.5 VPN Applications............................................................................................................. 25-2
25.2 IPSec Architecture................................................................................................................ 25-3
25.2.1 IPSec Algorithms.............................................................................................................. 25-4
25.2.2 Key Management.............................................................................................................. 25-4
25.3 Encapsulation .......................................................................................................................25-5
25.3.1 Transport Mode ................................................................................................................ 25-5
25.3.2 Tunnel Mode ....................................................................................................................25-5
25.4 IPSec and NAT..................................................................................................................... 25-5
Chapter 26 VPN/IPSec Setup................................................................................................................ 26-1
26.1 VPN/IPSec Setup ................................................................................................................. 26-1
26.2 IPSec Algorithms.................................................................................................................. 26-2
26.2.1 AH (Authentication Header) Protocol .............................................................................. 26-2
26.2.2 ESP (Encapsulating Security Payload) Protocol ..............................................................26-2
26.3 IPSec Summary.................................................................................................................... 26-3
26.3.1 My IP Address .................................................................................................................. 26-4
26.3.2 Secure Gateway Address .................................................................................................. 26-4
26.4 IPSec Setup........................................................................................................................... 26-9
26.5 IKE Setup ........................................................................................................................... 26-12
26.5.1 IKE Phases ..................................................................................................................... 26-12
Table of Contents xvii

ZYWALL 10/10 II/50 Internet Security Gateway
26.5.2 Negotiation Mode ...........................................................................................................26-13
26.5.3 Pre-Shared Key ...............................................................................................................26-14
26.5.4 Diffie-Hellman (DH) Key Groups ..................................................................................26-14
26.5.5 Perfect Forward Secrecy (PFS) .......................................................................................26-14
26.6 Manual Setup ......................................................................................................................26-17
26.6.1 Active Protocol ...............................................................................................................26-17
26.6.2 Security Parameter Index (SPI).......................................................................................26-17
Chapter 27 SA Monitor ..........................................................................................................................27-1
1.1. Introduction...............................................................................................................................27-1
27.1 Using SA Monitor.................................................................................................................27-1
Chapter 28 IPSec Log.............................................................................................................................28-1
28.1 VPN Initiator IPSec Log .......................................................................................................28-1
28.2 VPN Responder IPSec Log...................................................................................................28-2
TROUBLESHOOTING, APPENDICES AND INDEX ............................................................................. VI
Chapter 29 Troubleshooting ..................................................................................................................29-1
29.1 Problems Starting Up the ZyWALL .....................................................................................29-1
29.2 Problems with the LAN Interface .........................................................................................29-2
29.3 Problems with the WAN interface ........................................................................................29-2
29.4 Problems with Internet Access ..............................................................................................29-3
29.5 Problems with the Password .................................................................................................29-3
29.6 Problems with Remote Management ....................................................................................29-3
Appendix A The Big Picture ......................................................................................................................A
Appendix B PPPoE..................................................................................................................................... C
Appendix C PPTP....................................................................................................................................... E
Appendix D Hardware Specifications.......................................................................................................H
xviii Table of Contents

ZYWALL 10/10 II/50 Internet Security Gateway
Appendix E Important Safety Instructions ............................................................................................... I
Appendix F Boot Commands..................................................................................................................... J
Appendix G Command Interpreter........................................................................................................... L
Appendix H Firewall Commands .............................................................................................................M
Appendix I NetBIOS Filter Commands.................................................................................................... S
Appendix J NetBIOS Filter Commands....................................................................................................Z
Index..........................................................................................................................................................CC
Table of Contents xix

ZYWALL 10/10 II/50 Internet Security Gateway
List of Figures
Figure 1-1 Secure Internet Access via Cable ..................................................................................................1-4
Figure 1-2 Secure Internet Access via DSL....................................................................................................1-4
Figure 1-3 VPN Application ...........................................................................................................................1-5
Figure 2-1 Front Panel ....................................................................................................................................2-1
Figure 2-2 ZyWALL 10 Rear Panel and Connections ....................................................................................2-3
Figure 2-3 ZyWALL 10 II/50 Rear Panel and Connections............................................................................2-4
Figure 3-1 Initial Screen .................................................................................................................................3-1
Figure 3-2 Password Screen ...........................................................................................................................3-2
Figure 3-3 ZyWALL Main Menu....................................................................................................................3-3
Figure 3-4 Getting Started and Advanced Applications SMT Menus.............................................................3-5
Figure 3-5 Advanced Management SMT Menus ............................................................................................3-6
Figure 3-6 IPSec VPN Configuration SMT Menus ........................................................................................3-7
Figure 3-7 Menu 23 — System Password ......................................................................................................3-7
Figure 4-1 Menu 1 — General Setup..............................................................................................................4-2
Figure 4-2 Configure Dynamic DNS..............................................................................................................4-3
Figure 4-3 Menu 2 — WAN Setup .................................................................................................................4-5
Figure 5-1 Menu 3 — LAN Setup..................................................................................................................5-1
Figure 5-2 Menu 3.1 — LAN Port Filter Setup..............................................................................................5-1
Figure 5-3 Physical Network .......................................................................................................................... 5-5
Figure 5-4 Partitioned Logical Networks .......................................................................................................5-5
Figure 5-5 Menu 3 — TCP/IP and DHCP Setup ............................................................................................5-5
Figure 5-6 Menu 3.2 — TCP/IP and DHCP Ethernet Setup...........................................................................5-6
Figure 5-7 Menu 3.2.1 — IP Alias Setup........................................................................................................5-8
Figure 6-1 Menu 4 — Internet Access Setup (Ethernet).................................................................................6-1
Figure 6-2 Internet Access Setup (PPTP) .......................................................................................................6-3
xx List of Figures

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 6-3 Internet Access Setup (PPPoE)..................................................................................................... 6-4
Figure 7-1 Menu 11.1 — Remote Node Profile for Ethernet Encapsulation ................................................. 7-2
Figure 7-2 Menu 11.1 — Remote Node Profile for PPPoE Encapsulation .................................................... 7-4
Figure 7-3 Menu 11.1 — Remote Node Profile for PPTP Encapsulation ...................................................... 7-6
Figure 7-4 Menu 11.3 — Remote Node Network Layer Options .................................................................. 7-7
Figure 7-5 Menu 11.3 — Remote Node Network Layer Options .................................................................. 7-9
Figure 7-6 Menu 11.5 — Remote Node Filter (Ethernet Encapsulation)...............................7-11
Figure 7-7 Menu 11.5 — Remote Node Filter (PPPoE or PPTP Encapsulation)..........................................7-11
Figure 8-1 Example of Static Routing Topology............................................................................................ 8-1
Figure 8-2 Menu 12 — IP Static Route Setup................................................................................................ 8-2
Figure 8-3 Menu 12. 1 — Edit IP Static Route .............................................................................................. 8-2
Figure 9-1 How NAT Works.......................................................................................................................... 9-3
Figure 9-2 NAT Application With IP Alias .................................................................................................... 9-4
Figure 9-3 Menu 4 — Applying NAT for Internet Access ............................................................................. 9-6
Figure 9-4 Menu 11.3 — Applying NAT to the Remote Node ...................................................................... 9-7
Figure 9-5 Menu 15 — NAT Setup................................................................................................................ 9-8
Figure 9-6 Menu 15.1 — Address Mapping Sets ........................................................................................... 9-8
Figure 9-7 Menu 15.1.1 — SUA Address Mapping Rules............................................................................. 9-9
Figure 9-8 Menu 15.1.1 — First Set .............................................................................................................9-11
Figure 9-9 Menu 15.1.1.1 — Editing/Configuring an Individual Rule in a Set........................................... 9-12
Figure 9-10 Menu 15.2 — NAT Server Setup.............................................................................................. 9-15
Figure 9-11 Multiple Servers Behind NAT Example ................................................................................... 9-16
Figure 9-12 NAT Example 1........................................................................................................................ 9-17
Figure 9-13 Menu 4 — Internet Access & NAT Example ........................................................................... 9-17
Figure 9-14 NAT Example 2........................................................................................................................ 9-18
Figure 9-15 Menu 15.2 — Specifying an Inside Server............................................................................... 9-19
Figure 9-16 NAT Example 3........................................................................................................................ 9-20
List of Figures xxi

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 9-17 Example 3: Menu 11.3 ..............................................................................................................9-21
Figure 9-18 Example 3: Menu 15.1.1.1........................................................................................................9-21
Figure 9-19 Example 3: Final Menu 15.1.1 ..................................................................................................9-22
Figure 9-20 Example 3: Menu 15.2..............................................................................................................9-22
Figure 9-21 NAT Example 4.........................................................................................................................9-23
Figure 9-22 Example 4: Menu 15.1.1.1 — Address Mapping Rule..............................................................9-24
Figure 9-23 Example 4: Menu 15.1.1 — Address Mapping Rules ............................................................... 9-24
Figure 10-1 ZyWALL Firewall Application .................................................................................................10-3
Figure 10-2 Three-Way Handshake ..............................................................................................................10-5
Figure 10-3 SYN Flood ................................................................................................................................10-5
Figure 10-4 Smurf Attack .............................................................................................................................10-6
Figure 10-5 Stateful Inspection.....................................................................................................................10-8
Figure 11-1 Menu 21 — Filter and Firewall Setup.......................................................................................11-1
Figure 11-2 Menu 21.2 — Firewall Setup.................................................................................................... 11-2
Figure 11-3 Example Firewall Log ...............................................................................................................11-2
Figure 12-1 Enabling the Firewall ................................................................................................................ 12-2
Figure 12-2 E-mail Screen............................................................................................................................12-3
Figure 12-3 E-mail Log ................................................................................................................................12-6
Figure 12-4 Attack Alert ...............................................................................................................................12-8
Figure 13-1 LAN to WAN Traffic.................................................................................................................13-3
Figure 13-2 WAN to LAN Traffic.................................................................................................................13-4
Figure 13-3 Firewall Rules Summary — First Screen..................................................................................13-5
Figure 13-4 Creating/Editing A Firewall Rule............................................................................................13-10
Figure 13-5 Adding/Editing Source and Destination Addresses .................................................................13-12
Figure 13-6 Timeout Screen .......................................................................................................................13-14
Figure 14-1 Custom Ports.............................................................................................................................14-1
Figure 14-2 Creating/Editing A Custom Port................................................................................................14-3
xxii List of Figures

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 15-1 Log Screen................................................................................................................................ 15-1
Figure 16-1 Activate the Firewall ................................................................................................................ 16-2
Figure 16-2 Example 1: E-Mail Screen........................................................................................................ 16-3
Figure 16-3 Example 1: Configuring a Rule................................................................................................ 16-4
Figure 16-4 Example 1: Destination Address for Traffic Originating from the Internet .............................. 16-5
Figure 16-5 Example 1: Rule Summary Screen ........................................................................................... 16-6
Figure 16-6 Send Alerts When Attacked...................................................................................................... 16-7
Figure 16-7 Configuring A POP Custom Port.............................................................................................. 16-8
Figure 16-8 Example 2: Local Network Rule 1 Configuration.................................................................... 16-9
Figure 16-9 Example 2: Local Network Rule Summary............................................................................ 16-10
Figure 16-10 Example: Internet to Local Network Rule Summary ............................................................16-11
Figure 16-11 Custom Port for Syslog......................................................................................................... 16-12
Figure 16-12 Syslog Rule Configuration ................................................................................................... 16-13
Figure 16-13 Example 3: Rule Summary................................................................................................... 16-14
Figure 18-1 Outgoing Packet Filtering Process ........................................................................................... 18-2
Figure 18-2 Filter Rule Process.................................................................................................................... 18-3
Figure 18-3 Menu 21 — Filter and Firewall Setup...................................................................................... 18-4
Figure 18-4 Menu 21.1 — Filter Set Configuration..................................................................................... 18-5
Figure 18-5 NetBIOS_WAN Filter Rules Summary ....................................................................................18-5
Figure 18-6 Menu 21.1.1.1 — TCP/IP Filter Rule....................................................................................... 18-8
Figure 18-7 Executing an IP Filter..............................................................................................................18-11
Figure 18-8 Menu 21.4.1.1 — Generic Filter Rule.................................................................................... 18-12
Figure 18-9 Telnet Filter Example ............................................................................................................. 18-14
Figure 18-10 Example Filter — Menu 21.1.3.1......................................................................................... 18-15
Figure 18-11 Example Filter Rules Summary — Menu 21.1.3.................................................................. 18-16
Figure 18-12 Protocol and Device Filter Sets ............................................................................................ 18-17
Figure 18-13 Filtering LAN Traffic ........................................................................................................... 18-18
List of Figures xxiii

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 18-14 Filtering Remote Node Traffic ..............................................................................................18-19
Figure 19-1 SNMP Management Model.......................................................................................................19-2
Figure 19-2 Menu 22 — SNMP Configuration ............................................................................................19-4
Figure 20-1 Menu 24 — System Maintenance.............................................................................................20-1
Figure 20-2 Menu 24.1 — System Maintenance — Status...........................................................................20-2
Figure 20-3 Menu 24.2 — System Information and Console Port Speed.....................................................20-4
Figure 20-4 Menu 24.2.1 — System Maintenance — Information .............................................................20-4
Figure 20-5 Menu 24.2.2 — System Maintenance — Change Console Port Speed .................................... 20-5
Figure 20-6 Menu 24.3 — System Maintenance — Log and Trace .............................................................20-6
Figure 20-7 Examples of Error and Information Messages ..........................................................................20-6
Figure 20-8 Menu 24.3.2 — System Maintenance — UNIX Syslog ...........................................................20-7
Figure 20-9 Call-Triggering Packet Example.............................................................................................20-11
Figure 20-10 Menu 24.4 — System Maintenance — Diagnostic...............................................................20-12
Figure 20-11 WAN & LAN DHCP.............................................................................................................20-13
Figure 21-1 Telnet into Menu 24.5 ...............................................................................................................21-3
Figure 21-2 FTP Session Example................................................................................................................21-4
Figure 21-3 System Maintenance — Backup Configuration........................................................................21-6
Figure 21-4 System Maintenance — Starting Xmodem Download Screen..................................................21-7
Figure 21-5 Backup Configuration Example................................................................................................21-7
Figure 21-6 Successful Backup Confirmation Screen .................................................................................. 21-7
Figure 21-7 Telnet into Menu 24.6 ...............................................................................................................21-8
Figure 21-8 Restore Using FTP or TFTP Session Example..........................................................................21-9
Figure 21-9 System Maintenance — Restore Configuration........................................................................ 21-9
Figure 21-10 System Maintenance — Starting Xmodem Download Screen..............................................21-10
Figure 21-11 Restore Configuration Example ............................................................................................21-10
Figure 21-12 Successful Restoration Confirmation Screen........................................................................21-10
Figure 21-13 Telnet into Menu 24.7.1 — Upload System Firmware.......................................................... 21-11
xxiv List of Figures

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 21-14 Telnet into Menu 24.7.2 — System Maintenance................................................................. 21-12
Figure 21-15 FTP Session Example of Firmware File Upload .................................................................. 21-13
Figure 21-16 Menu 24.7.1 Using the Console Port.................................................................................... 21-15
Figure 21-17 Example Xmodem Upload ................................................................................................... 21-15
Figure 21-18 Menu 24.7.2 Using the Console Port.................................................................................... 21-16
Figure 21-19 Example Xmodem Upload ................................................................................................... 21-17
Figure 22-1 Command Mode in Menu 24.................................................................................................... 22-1
Figure 22-2 Valid Commands ...................................................................................................................... 22-2
Figure 22-3 Call Control.............................................................................................................................. 22-2
Figure 22-4 Budget Management................................................................................................................. 22-3
Figure 22-5 Call History .............................................................................................................................. 22-4
Figure 22-6 Menu 24 — System Maintenance ............................................................................................ 22-5
Figure 22-7 Menu 24.10 System Maintenance — Time and Date Setting................................................... 22-5
Figure 23-1 Telnet Configuration on a TCP/IP Network ............................................................................. 23-1
Figure 23-2 Menu 24.11 – Remote Management Control............................................................................ 23-3
Figure 24-1 Menu 26 - Schedule Setup........................................................................................................ 24-1
Figure 24-2 Schedule Set Setup ................................................................................................................... 24-2
Figure 24-3 Applying Schedule Set(s) to a Remote Node (PPPoE)............................................................. 24-4
Figure 24-4 Applying Schedule Set(s) to a Remote Node (PPTP)............................................................... 24-4
Figure 25-1 Encryption and Decryption....................................................................................................... 25-2
Figure 25-2 VPN Application ...................................................................................................................... 25-3
Figure 25-3 IPSec Architecture .................................................................................................................... 25-4
Figure 25-4 Transport and Tunnel Mode IPSec Encapsulation.................................................................... 25-5
Figure 26-1 VPN SMT Menu Tree............................................................................................................... 26-1
Figure 26-2 Menu 27 — VPN/IPSec Setup ................................................................................................. 26-2
Figure 26-3 IPSec Summary Fields ............................................................................................................. 26-3
Figure 26-4 Telecommuter’s ZyWALL Configuration.................................................................................26-5
List of Figures xxv

ZYWALL 10/10 II/50 Internet Security Gateway
Figure 26-5 Headquarters ZyWALL Configuration...................................................................................... 26-5
Figure 26-6 Menu 27.1 — IPSec Summary..................................................................................................26-6
Figure 26-7 Menu 27.1.1 — IPSec Setup.....................................................................................................26-9
Figure 26-8 Two Phases to set up the IPSec SA .........................................................................................26-13
Figure 26-9 Menu 27.1.1.1 — IKE Setup.......................................................................................................26-15
Figure 26-10 Menu 27.1.1.2 — Manual Setup ...........................................................................................26-18
Figure 27-1 Menu 27.2 — SA Monitor ........................................................................................................27-1
Figure 28-1 Example VPN Initiator IPSec Log ............................................................................................28-1
Figure 28-2 Example VPN Responder IPSec Log........................................................................................28-2
xxvi List of Figures

ZYWALL 10/10 II/50 Internet Security Gateway
List of Tables
Table 2-1 LED Descriptions........................................................................................................................... 2-1
Table 3-1 Main Menu Commands.................................................................................................................. 3-2
Table 3-2 Main Menu Summary ....................................................................................................................3-3
Table 4-1 General Setup Menu Field ............................................................................................................. 4-2
Table 4-2 Configure Dynamic DNS Menu Fields.......................................................................................... 4-3
Table 4-3 WAN Setup Menu Fields ............................................................................................................... 4-5
Table 5-1 Example of Network Properties for LAN Servers with Fixed IP Addresses.................................. 5-2
Table 5-2 Private IP Address Ranges ............................................................................................................. 5-3
Table 5-3 DHCP Ethernet Setup Menu Fields................................................................................................5-6
Table 5-4 LAN TCP/IP Setup Menu Fields.................................................................................................... 5-7
Table 5-5 IP Alias Setup Menu Fields............................................................................................................ 5-8
Table 6-1 Internet Access Setup Menu Fields ................................................................................................ 6-1
Table 6-2 New Fields in Menu 4 (PPTP) screen ............................................................................................ 6-3
Table 6-3 New Fields in Menu 4 (PPPoE) screen .......................................................................................... 6-4
Table 7-1 Fields in Menu 11.1........................................................................................................................ 7-2
Table 7-2 Fields in Menu 11.1 (PPPoE Encapsulation Specific) ...................................................................7-5
Table 7-3 Fields in Menu 11.1 (PPTP Encapsulation)....................................................................................7-6
Table 7-4 Remote Node Network Layer Options Menu Fields...................................................................... 7-7
Table 7-5 Remote Node Network Layer Options Menu Fields...................................................................... 7-9
Table 8-1 IP Static Route Menu Fields........................................................................................................... 8-3
Table 9-1 NAT Definitions............................................................................................................................. 9-1
Table 9-2 NAT Mapping Types...................................................................................................................... 9-5
Table 9-3 Applying NAT in Menus 4 & 11.3 ................................................................................................. 9-7
Table 9-4 SUA Address Mapping Rules......................................................................................................... 9-9
Table 9-5 Fields in Menu 15.1.1 .................................................................................................................. 9-11
List of Tables xxvii

ZYWALL 10/10 II/50 Internet Security Gateway
Table 9-6 Menu 15.1.1.1 — Editing/Configuring an Individual Rule in a Set ............................................ 9-13
Table 9-7 Services & Port Numbers ............................................................................................................ 9-14
Table 10-1 Common IP Ports....................................................................................................................... 10-4
Table 10-2 ICMP Commands That Trigger Alerts....................................................................................... 10-6
Table 10-3 Legal NetBIOS Commands ....................................................................................................... 10-7
Table 10-4 Legal SMTP Commands............................................................................................................ 10-7
Table 11-1 View Firewall Log ......................................................................................................................11-2
Table 12-1 E-mail ........................................................................................................................................ 12-4
Table 12-2 SMTP Error Messages............................................................................................................... 12-5
Table 12-3 Attack Alert................................................................................................................................ 12-8
Table 13-1 Firewall Rules Summary — First Screen .................................................................................. 13-5
Table 13-2 Predefined Services ................................................................................................................... 13-7
Table 13-3 Creating/Editing A Firewall Rule ............................................................................................ 13-10
Table 13-4 Adding/Editing Source and Destination Addresses ................................................................. 13-13
Table 13-5 Timeout Menu.......................................................................................................................... 13-15
Table 14-1 Custom Ports.............................................................................................................................. 14-2
Table 14-2 Creating/Editing A Custom Port ................................................................................................ 14-4
Table 15-1 Log Screen ................................................................................................................................. 15-2
Table 18-1 Abbreviations Used in the Filter Rules Summary Menu ........................................................... 18-6
Table 18-2 Rule Abbreviations Used........................................................................................................... 18-6
Table 18-3 TCP/IP Filter Rule Menu Fields ................................................................................................ 18-8
Table 18-4 Generic Filter Rule Menu Fields ............................................................................................. 18-13
Table 19-1 General SNMP Commands........................................................................................................ 19-3
Table 19-2 SNMP Configuration Menu Fields ............................................................................................ 19-4
Table 19-3 SNMP Traps............................................................................................................................... 19-5
Table 20-1 System Maintenance — Status Menu Fields ............................................................................. 20-2
Table 20-2 Fields in System Maintenance — Information .......................................................................... 20-4
xxviii List of Tables

ZYWALL 10/10 II/50 Internet Security Gateway
Table 20-3 System Maintenance Menu Syslog Parameters.......................................................................... 20-7
Table 20-4 System Maintenance Menu Diagnostic.................................................................................... 20-13
Table 21-1 Filename Conventions................................................................................................................ 21-2
Table 21-2 General Commands for GUI-Based FTP Clients....................................................................... 21-4
Table 21-3 General Commands for GUI-Based TFTP Clients..................................................................... 21-6
Table 22-1 Budget Management .................................................................................................................. 22-3
Table 22-2 Call History Fields .....................................................................................................................22-4
Table 22-3 Time and Date Setting Fields..................................................................................................... 22-6
Table 23-1 Menu 24.11 – Remote Management Control ............................................................................. 23-3
Table 24-1 Schedule Set Setup Fields .......................................................................................................... 24-2
Table 25-1 VPN and NAT ............................................................................................................................ 25-6
Table 26-1 AH and ESP ............................................................................................................................... 26-3
Table 26-2 Telecommuter and Headquarters Configuration Example ......................................................... 26-4
Table 26-3 Menu 27.1 — IPSec Summary................................................................................................... 26-6
Table 26-4 Menu 27.1.1 — IPSec Setup ...................................................................................................... 26-9
Table 26-5 Menu 27.1.1.1 — IKE Setup........................................................................................................ 26-15
Table 26-6 Active Protocol — Encapsulation and Security Protocol......................................................... 26-17
Table 26-7 Menu 27.1.1.2 — Manual Setup ..............................................................................................26-18
Table 27-1 Menu 27.2 — SA Monitor .........................................................................................................27-2
Table 28-1 Sample IKE Key Exchange Logs............................................................................................... 28-2
Table 28-2 Sample IPSec Logs During Packet Transmission ...................................................................... 28-4
Table 28-3 RFC-2408 ISAKMP Payload Types........................................................................................... 28-4
Table 29-1 Troubleshooting the Start-Up of your ZyWALL ........................................................................ 29-1
Table 29-2 Troubleshooting the LAN Interface ........................................................................................... 29-2
Table 29-3 Troubleshooting the WAN interface........................................................................................... 29-2
Table 29-4 Troubleshooting Internet Access................................................................................................ 29-3
Table 29-5 Troubleshooting the Password ................................................................................................... 29-3
List of Tables xxix

ZYWALL 10/10 II/50 Internet Security Gateway
Table 29-6 Troubleshooting Remote Management...................................................................................... 29-3
xxx List of Tables
 Loading...
Loading...