Page 1
AP-7131N-FGR Access Point
Product Reference Guide
Page 2
Zebra and the Zebra head graphic are registered trademarks of ZIH Corp. The Symbol logo is a registered
trademark of Symbol Technologies, Inc., a Zebra Technologies company.
© 2015 Symbol Technologies, Inc.
Page 3

Contents
Chapter 1.
Introduction
New Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-2
IP Filtering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
MU Rate Limiting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
Per Radio MU Limit. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-3
Power Setting Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-4
AMSDU Transmission Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-4
IPSec VPN Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5
Feature Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-5
802.11n Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6
Sensor Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-6
Mesh Roaming Client . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9
Dual Mode Radio Options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9
Separate LAN and WAN Ports . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-9
Multiple Mounting Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Antenna Support for 2.4 GHz and 5 GHz Radios . . . . . . . . . . . . . . . . . . . . . . 1-10
Sixteen Configurable WLANs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Support for 4 BSSIDs per Radio . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-10
Quality of Service (QoS) Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-11
Industry Leading Data Security. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-11
EAP Authentication. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-12
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . WPA2-CCMP (802.11i) Encryption1-12
Firewall Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-13
Page 4

2
AP-7131N-FGR Access Point Product Reference Guide
VPN Tunnels. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-13
Content Filtering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-13
VLAN Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-14
Multiple Management Accessibility Options . . . . . . . . . . . . . . . . . . . . . . . . . 1-14
Updatable Firmware. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-14
Programmable SNMP v3 Trap Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-15
Power-over-Ethernet Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-15
MU-MU Transmission Disallow. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1-16
Voice Prioritization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-16
Support for CAM and PSP MUs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-17
Statistical Displays . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-17
Transmit Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-17
Advanced Event Logging Capability. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-18
Configuration File Import/Export Functionality . . . . . . . . . . . . . . . . . . . . . . . . 1-18
Default Configuration Restoration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-18
DHCP Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-18
Mesh Networking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-19
Additional LAN Subnet . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-20
On-board Radius Server Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-20
Hotspot Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-20
Routing Information Protocol (RIP). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-21
Manual Date and Time Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-21
Dynamic DNS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-21
Auto Negotiation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-22
Adaptive AP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-22
Rogue AP Enhancements. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-22
Radius Time-Based Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-22
QBSS Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-23
Theory of Operations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-23
Wireless Coverage. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-24
MAC Layer Bridging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-25
Media Types. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-25
Direct-Sequence Spread Spectrum . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-26
MU Association Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-26
Operating Modes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-27
Management Access Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-28
MAC Address Assignment. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .1-29
Page 5

Chapter 2.
Hardware Installation
Precautions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-2
Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Package Contents. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-2
Access Point Placement. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-3
Site Surveys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-4
Antenna Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-4
Power Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-6
Power Injector System . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-6
Installing the Power Injector . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-8
Preparing for Site Installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-8
Cabling the Power Injector . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-9
Mounting an AP-7131N-FGR . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-10
Wall Mounted Installations. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-10
Suspended Ceiling T-Bar Installations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-13
Above the Ceiling (Plenum) Installations. . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-15
LED Indicators . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-18
Dual Radio (2.4/5 GHz) LEDs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-20
Rear LED. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2-21
Setting Up MUs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-21
Legacy MUs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-21
802.11n MUs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .2-22
3
Chapter 3. Getting Started
Installing the Access Point. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-1
Configuration Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3-2
Initially Connecting to the Access Point . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-3
Connecting to the Access Point using the WAN Port . . . . . . . . . . . . . . . . . . . . 3-3
Connecting to the Access Point using the LAN Port . . . . . . . . . . . . . . . . . . . . . 3-3
Basic Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-4
Configuring Your Browser for AP-7131N-FGR Support . . . . . . . . . . . . . . . . . . .3-4
Accessing the AP-7131N-FGR Using Internet Explorer . . . . . . . . . . . . . . . 3-4
Accessing the AP-7131N-FGR Using Mozilla Firefox . . . . . . . . . . . . . . . . 3-5
Configuring the Access Point. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-5
Configuring Device Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3-8
Page 6

4
AP-7131N-FGR Access Point Product Reference Guide
Configuring Basic WLAN Security Settings . . . . . . . . . . . . . . . . . . . . . .3-15
Testing Connectivity. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3-17
Where to Go from Here? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3-18
Chapter 4.
System Configuration
Configuring System Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-2
Configuring Power Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-6
Adaptive AP Setup . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-11
Configuring Data Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-14
Managing Certificate Authority (CA) Certificates . . . . . . . . . . . . . . . . . . . . . . . . . .4-18
Importing a CA Certificate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-18
Creating Self Certificates. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-20
Creating a Certificate for Onboard RADIUS Authentication . . . . . . . . . . . . . .4-23
Configuring SNMP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-27
Configuring SNMP Access Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-33
Enabling SNMP Traps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-34
Configuring Specific SNMP Traps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-36
Configuring SNMP RF Trap Thresholds. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-39
Configuring Network Time Protocol (NTP) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-41
Logging Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-45
Importing/Exporting Configurations. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-47
Updating Device Firmware. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-51
Key Zeroisation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4-53
Key Zeroisation Process. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 4-54
Chapter 5. Network Management
Configuring the LAN Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-1
Configuring VLAN Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-5
Configuring LAN1 and LAN2 Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-8
Configuring Advanced DHCP Server Settings . . . . . . . . . . . . . . . . . . . . .5-12
Setting the Type Filter Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . .5-13
Configuring WAN Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-15
Configuring Network Address Translation (NAT) Settings . . . . . . . . . . . . . . .5-21
Configuring Port Forwarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-22
Configuring Dynamic DNS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-24
Page 7

Enabling Wireless LANs (WLANs). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-25
Creating/Editing Individual WLANs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-28
Configuring WLAN Security Policies. . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-33
Configuring a WLAN Access Control List (ACL) . . . . . . . . . . . . . . . . . . .5-34
Setting the WLAN Quality of Service (QoS) Policy . . . . . . . . . . . . . . . . .5-37
Configuring WLAN Hotspot Support . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-43
Setting the WLAN’s Radio Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-49
Configuring the 802.11a/n or 802.11b/g/n Radio . . . . . . . . . . . . . . . . . .5-54
Configuring MU Rate Limiting. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 5-65
Configuring Router Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-66
Setting the RIP Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-69
Configuring IP Filtering. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5-71
Applying a Filter to LAN1, LAN2 or a WLAN (1-16) . . . . . . . . . . . . . . . . . . . .5-74
Chapter 6. Configuring Access Point Security
Configuring Security Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-2
Setting Passwords . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-2
Resetting the Access Point Password . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-4
Enabling Authentication and Encryption Schemes . . . . . . . . . . . . . . . . . . . . . . . . . . 6-4
Configuring 802.1x EAP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-6
Configuring WPA2-CCMP (802.11i) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-11
Configuring Firewall Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-13
Configuring LAN to WAN Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-15
Available Protocols . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-17
Configuring Advanced Subnet Access. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-18
Configuring VPN Tunnels. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-22
Creating a VPN Tunnel between Two Access Points . . . . . . . . . . . . . . . . . . . 6-25
Configuring Manual Key Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-27
Configuring Auto Key Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-31
Configuring IKE Key Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-33
Viewing VPN Status. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-35
Configuring Content Filtering Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-38
Configuring Rogue AP Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-41
Moving Rogue APs to the Allowed AP List . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-45
Displaying Rogue AP Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-47
Using MUs to Detect Rogue Devices . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-49
5
Page 8

6
AP-7131N-FGR Access Point Product Reference Guide
Configuring User Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-51
Configuring the Radius Server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 6-51
Configuring LDAP Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-55
Configuring a Proxy Radius Server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-57
Managing the Local User Database . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-59
Wireless Users. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-59
Management Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-61
Mapping Users to Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-63
Defining User Access Permissions by Group. . . . . . . . . . . . . . . . . . . . . . . . . .6-65
Editing Group Access Permissions . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6-67
Chapter 7. Monitoring Statistics
Viewing WAN Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-2
Viewing LAN Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-6
Viewing a LAN’s STP Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-9
Viewing Wireless Statistics. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-11
Viewing WLAN Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-14
Viewing Radio Statistics Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-17
Viewing Radio Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 7-19
Retry Histogram . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-23
Viewing MU Statistics Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-24
Viewing MU Details. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-26
Pinging Individual MUs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-28
MU Authentication Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-29
Viewing the Mesh Statistics Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-30
Viewing Known Access Point Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .7-32
Chapter 8. CLI Reference
Connecting to the CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-2
Accessing the CLI through the Serial Port. . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-2
Accessing the CLI via SSH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-2
Admin and Common Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-3
Network Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-11
Network LAN Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-12
Network LAN, Bridge Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-17
Network LAN, WLAN-Mapping Commands . . . . . . . . . . . . . . . . . . . . . .8-20
Page 9

Network LAN, DHCP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-29
Network Type Filter Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-35
Network WAN Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-40
Network WAN NAT Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-43
Network WAN, VPN Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-49
Network WAN, Dynamic DNS Commands . . . . . . . . . . . . . . . . . . . . . . . 8-62
Network Wireless Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-66
Network WLAN Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-67
Network Security Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-80
Network ACL Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-87
Network Radio Configuration Commands . . . . . . . . . . . . . . . . . . . . . . . . 8-92
Network Quality of Service (QoS) Commands. . . . . . . . . . . . . . . . . . . . 8-123
Network Rate Limiting Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-128
Network Rogue-AP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-131
WIPS Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-141
Network MU Locationing Commands . . . . . . . . . . . . . . . . . . . . . . . . . .8-144
Network Firewall Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-147
Network Router Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-152
System Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-159
Power Setup Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-164
Adaptive AP Setup Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-167
System Access Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-171
System Certificate Management Commands . . . . . . . . . . . . . . . . . . . . . . . . 8-175
System SNMP Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-188
System SNMP Access Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-189
System SNMP Traps Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-194
System User Database Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 8-200
System Radius Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-218
System Network Time Protocol (NTP) Commands . . . . . . . . . . . . . . . . . . . . 8-241
System Log Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-246
System Configuration-Update Commands . . . . . . . . . . . . . . . . . . . . . . . . . . 8-253
Firmware Update Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-261
FIPS Test Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-266
Statistics Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .8-271
7
Page 10

8
AP-7131N-FGR Access Point Product Reference Guide
Chapter 9. Configuring Mesh Networking
Mesh Networking Overview. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-1
The Client Bridge Association Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-3
Client Bridge Configuration Process Example . . . . . . . . . . . . . . . . . . . . . .9-4
Spanning Tree Protocol (STP). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-4
Defining the Mesh Topology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-4
Mesh Networking and the Access Point’s Two Subnets. . . . . . . . . . . . . . . . . .9-5
Normal Operation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-5
Impact of Importing/Exporting Configurations to a Mesh Network . . . . . . . . .9-5
Configuring Mesh Networking Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-7
Setting the LAN Configuration for Mesh Networking Support . . . . . . . . . . . . .9-7
Configuring a WLAN for Mesh Networking Support . . . . . . . . . . . . . . . . . . . . .9-9
Configuring the Access Point Radio for Mesh Support . . . . . . . . . . . . . . . . . .9-13
Mesh Network Deployment - Quick Setup. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-20
Scenario 1 - Two Base Bridges and One Client Bridge . . . . . . . . . . . . . . . . . .9-20
Configuring AP#1:. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-21
Configuring AP#2 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-24
Configuring AP#3 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-25
Verifying Mesh Network Functionality for Scenario #1. . . . . . . . . . . . . .9-27
Scenario 2 - Two Hop Mesh Network with a Base Bridge Repeater and a Client Bridge9-
27
Configuring AP#1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-27
Configuring AP#2 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-28
Configuring AP#3 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .9-29
Verifying Mesh Network Functionality for Scenario #2. . . . . . . . . . . . . .9-31
Mesh Networking Frequently Asked Questions. . . . . . . . . . . . . . . . . . . . . . . . . . . .9-32
Chapter 10.
Adaptive AP
Adaptive AP Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-1
Where to Go From Here . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-2
Adaptive AP Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-3
Licensing. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-3
Switch Discovery . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-3
Manual Adoption Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-3
Securing a Configuration Channel Between Switch and AP . . . . . . . . . . . . . .10-4
Page 11

Adaptive AP WLAN Topology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-4
Configuration Updates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-4
Securing Data Tunnels between the Switch and AAP . . . . . . . . . . . . . . . . . .10-5
Adaptive AP Switch Failure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-5
Remote Site Survivability (RSS) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-6
Adaptive Mesh Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-6
Supported Adaptive AP Topologies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-7
Topology Deployment Considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-7
Extended WLANs Only . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-8
Independent WLANs Only . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-8
Extended WLANs with Independent WLANs . . . . . . . . . . . . . . . . . . . . . . . . .10-8
Extended WLAN with Mesh Networking. . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-9
How the AP Receives its Adaptive Configuration . . . . . . . . . . . . . . . . . . . . . . . . . .10-9
Establishing Basic Adaptive AP Connectivity. . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-11
Adaptive AP Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-11
Adopting an Adaptive AP Manually. . . . . . . . . . . . . . . . . . . . . . . . . . . .10-11
Adopting an Adaptive AP Using a Configuration File . . . . . . . . . . . . . .10-13
Switch Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .10-13
Adaptive AP Deployment Considerations . . . . . . . . . . . . . . . . . . . . . . . . . . .10-15
Sample Switch Configuration File for IPSec and Independent WLAN . . . . .10-16
9
Appendix A. Technical Specifications
Physical Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-2
Electrical Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-2
Radio Characteristics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-3
Country Codes. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . A-4
Appendix B. Usage Scenarios
Configuring an IPSEC Tunnel and VPN FAQs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . B-2
Configuring a VPN Tunnel Between Two Access Points . . . . . . . . . . . . . . . . . B-2
Configuring a Cisco VPN Device . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . B-5
Frequently Asked VPN Questions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . B-6
Appendix C. Zebra Support
Page 12

10
AP-7131N-FGR Access Point Product Reference Guide
Page 13
About This Guide
Introduction
This guide provides configuration and setup information for the AP-7131N-FGR model access
point.
Document Conventions
The following document conventions are used in this document:
NOTE Indicate tips or special requirements.
CAUTION Indicates conditions that can cause equipment damage or data
loss.
WARNING! Indicates a condition or procedure that could result in personal
injury or equipment damage.
Page 14

viii
AP-7131N-FGR Access Point Product Reference Guide
Notational Conventions
The following notational conventions are used in this document:
• Italics are used to highlight specific items in the general text, and to identify chapters and
sections in this and related documents.
• Bullets (•) indicate:
• action items
• lists of alternatives
• lists of required steps that are not necessarily sequential
• Sequential lists (those describing step-by-step procedures) appear as numbered lists.
Service Information
If a problem is encountered with the access point, contact Zebra Support. Refer to
Appendix C, Zebra Support for contact information. Before calling, have the model and serial number
on hand.
Page 15

1
Introduction
As a standalone access point, an AP-7131N-FGR provides small and medium-sized businesses with
a consolidated wired and wireless networking infrastructure, all in a single device. The integrated
router, gateway, firewall, DHCP and Power-over-Ethernet (PoE) simplify and reduce the costs
associated with networking by eliminating the need to purchase and manage multiple devices.
The access point is also designed to meet the needs of large, distributed enterprises by converging
the functionality of a thick access point and thin access port into a single device. This mode enables
the deployment of a fully featured intelligent access point that can be centrally configured and
managed via a wireless switch in either corporate headquarters or a network operations center
(NOC). In the event the connection between the access point and the wireless switch is lost, a Remote
Site Survivability (RSS) feature ensures the delivery of uninterrupted wireless services at the local or
remote site. All traffic between the adaptive access points and the wireless switch is secured though
an IPSec tunnel. Additionally, compatibility with The RF Management Suite (RFMS) allows you to
centrally plan, deploy, monitor and secure large deployments.
If you are new to using an access point for managing your network, refer to Theory of Operations on
page 1-23 for an overview on wireless networking fundamentals.
Page 16
1-2
AP-7131N-FGR Access Point Product Reference Guide
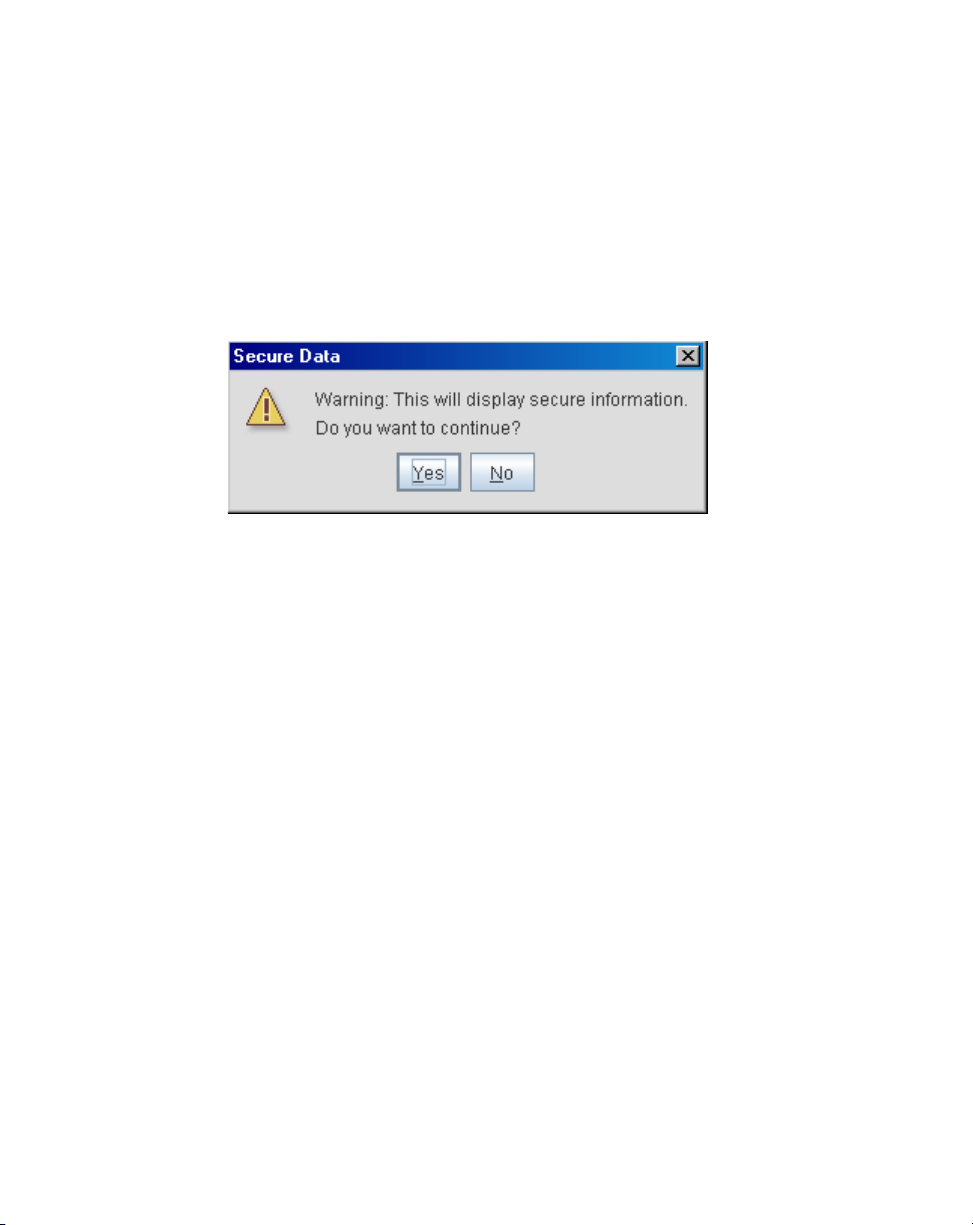
Beginning with the 4.x access point firmware baseline, the AP-7131N-FGR model access point has
been introduced as a compliment to the existing AP-7131 access point family. The new AP-7131NFGR access point supports the same feature set as existing AP-7131and AP-7131N model access
points. Unlike the AP-7131 and AP-7131N models however, an AP-7131N-FGR has specialized data
protection mechanisms and prompts the user when secure information is displayed within the access
point GUI applet.
The AP-7131N-FGR enables you to configure one radio for 802.11a/n support, and the other for
802.11b/g/n support.
The two models available to the AP-7131N-FGR series include:
• AP-7131N-66040-FGR (802.11an and 802.11bgn capable)
• AP-7131N-44040-FGR (802.11a and 802.11bg capable)
1.1 New Features
The following features are now available with the introduction of the new 4.0 access point hardware
and firmware baseline:
• IP Filtering
• MU Rate Limiting
• Per Radio MU Limit
• Power Setting Configuration
• AMSDU Transmission Support
• IPSec VPN Support
Page 17

Introduction
1.1.1 IP Filtering
IP filtering determines which IP packets are processed normally and which are discarded. If discarded,
the packet is deleted and completely ignored (as if never received). Optionally apply different criteria
to better refine which packets to filter.
IP filtering supports the creation of up to 20 filter rules enforced at layer 3. Once defined (using the
access point’s SNMP, GUI or CLI), filtering rules can be enforced on the access point’s LAN1, LAN2
and WLAN interfaces. An additional default action is also available denying traffic when the filter
rules fail. Lastly, imported and exported configurations retain their defined IP filtering configurations.
For information on configuring the access point’s IP filtering functionality, see Configuring IP Filtering
on page 5-71.
1.1.2 MU Rate Limiting
MU rate limiting enables an administrator to determine how much radio bandwidth is allocated to
each MU within any one of the 16 supported WLANs.
Before this 4.0 baseline release, access points supported bandwidth management on a per-WLAN
basis. Each WLAN could be configured to receive (at most) a certain percentage of the total available
downstream bandwidth. The new rate limiting feature is a replacement of the bandwidth
management feature allowing for better MU radio bandwidth allotments on a per WLAN basis.
1-3
To globally enable or disable the MU rate limit and assess the WLANs in which it’s currently invoked,
see Configuring MU Rate Limiting on page 5-65.
To define the actual MU rate limit (maximum downstream bandwidth allocation in kbps), see
Creating/Editing Individual WLANs on page 5-28.
1.1.3 Per Radio MU Limit
Prior to this new 4.0 AP firmware baseline, an access point allowed a total of 127 MU associations,
regardless of the number of radios on the AP. With a dual-radio AP, if there were already 127 MUs
associated to one radio, that were no slots available for a MU to associate with another radio.
With the new 4.0 firmware, an AP can reserve slots on each radio so MUs of one radio type (11a/n
or 11bg/n) have better chances for AP association. Therefore, the total number of MUs allowed to
associate remains at 127, but you can now strategically distribute the 127 MU associations between
the data radios.
Page 18

1-4
AP-7131N-FGR Access Point Product Reference Guide
For information on setting the number of MU associations on a specific radio, see Configuring the
802.11a/n or 802.11b/g/n Radio on page 5-54.
1.1.4 Power Setting Configuration
The access point’s power management functionality automatically configures the AP's operational
mode so it safely operates within available power. The power setting feature enables the user to
select one of three power operating modes, 3af, 3at and full power. When an access point is
operating in either 3af or 3at mode, the transmit power is always lower than the full power setting.
With the introduction of the AP-7131N-FGR model access point, the power options available for dual
radio model access points has never been more diverse, and careful consideration must be made
before deploying the access point.
The AP’s hardware design uses a complex programmable logic device (CPLD). When an AP is powered
on (or performing a cold reset), the CPLD determines the maximum power available to the AP by a
POE device. Once an operational power configuration is defined, the AP firmware can read the power
setting and configure operating characteristics based on the AP’s SKU and power configuration. If the
POE cannot provide sufficient power (with all interfaces enabled), the following interfaces could be
disabled or modified:
• Radio transmit power could be reduced due to lack of sufficient power or the radio can be
disabled
• The WAN port configuration could be changed (enabled or disabled)
For information on configuring the access point’s power configuration, see Configuring Power
Settings on page 4-6.
1.1.5 AMSDU Transmission Support
Aggregate MAC Service Data Unit (AMSDU) is an 802.11n specific MAC feature which enhances the
transmission of multiple MSDU contents wrapped within a single preamble/packet infrastructure.
The AMSDU transmission limit is set to 3839 bites by default.
For information on configuring AMSDU support for an access point radio, see Configuring the
802.11a/n or 802.11b/g/n Radio on page 5-54. AMSDU support can be defined by selecting the Set
Aggregation button within the Network Configuration -> Wireless -> Radio Configuration ->
Radio1 screen.
Page 19

Introduction
1.1.6 IPSec VPN Support
A VPN ensures data privacy between two end points, even while using a communication medium
which is itself insecure (like the Internet). VPNs create a secure tunnel between two end points as if
they are directly connected over a secure connection. Traffic is secured using a robust IPSec
encryption technique.
You can get the safety of a VPN in a WLAN by hosting the VPN server at the access point, and the
VPN client software on the MU. For that reason, a VPN provides secure WLAN access to MUs. A VPN
solution was more common before 802.11i was introduced, but is not as common now, since 802.11i/
WPA2 is considered more secure.
For information on configuring VPN support, see Configuring VPN Tunnels on page 6-22. For
instructions on configuring a IPSec VPN tunnel using two access points, see Creating a VPN Tunnel
between Two Access Points on page 6-25.
1.2 Feature Overview
The following legacy features have been carried forward into the 4.x firmware baseline:
• 802.11n Support
• Sensor Support
• Mesh Roaming Client
• Dual Mode Radio Options
• Separate LAN and WAN Ports
• Multiple Mounting Options
• Antenna Support for 2.4 GHz and 5 GHz Radios
• Sixteen Configurable WLANs
• Support for 4 BSSIDs per Radio
• Quality of Service (QoS) Support
• Industry Leading Data Security
• VLAN Support
• Multiple Management Accessibility Options
• Updatable Firmware
• Programmable SNMP v3 Trap Support
• Power-over-Ethernet Support
1-5
Page 20

1-6
AP-7131N-FGR Access Point Product Reference Guide
• MU-MU Transmission Disallow
• Voice Prioritization
• Support for CAM and PSP MUs
• Statistical Displays
• Transmit Power Control
• Advanced Event Logging Capability
• Configuration File Import/Export Functionality
• Default Configuration Restoration
• DHCP Support
• Mesh Networking
• Additional LAN Subnet
• On-board Radius Server Authentication
• Hotspot Support
• Routing Information Protocol (RIP)
• Manual Date and Time Settings
• Dynamic DNS
• Auto Negotiation
• Adaptive AP
• Rogue AP Enhancements
• Radius Time-Based Authentication
• QBSS Support
1.2.1 802.11n Support
Full life-cycle support is provided for either a new or existing 802.11n mobility deployment, from
network design to day-to-day support. For information on deploying your 802.11n radio, see
Configuring the 802.11a/n or 802.11b/g/n Radio on page 5-54.
1.2.2 Sensor Support
The Wireless Intrusion Protection System (WIPS) protects your wireless network, mobile devices and
traffic from attacks and unauthorized access. WIPS provides tools for standards compliance and
around-the-clock 802.11a/b/g wireless network security in a distributed environment. WIPS allows
administrators to identify and accurately locate attacks, rogue devices and network vulnerabilities in
Page 21
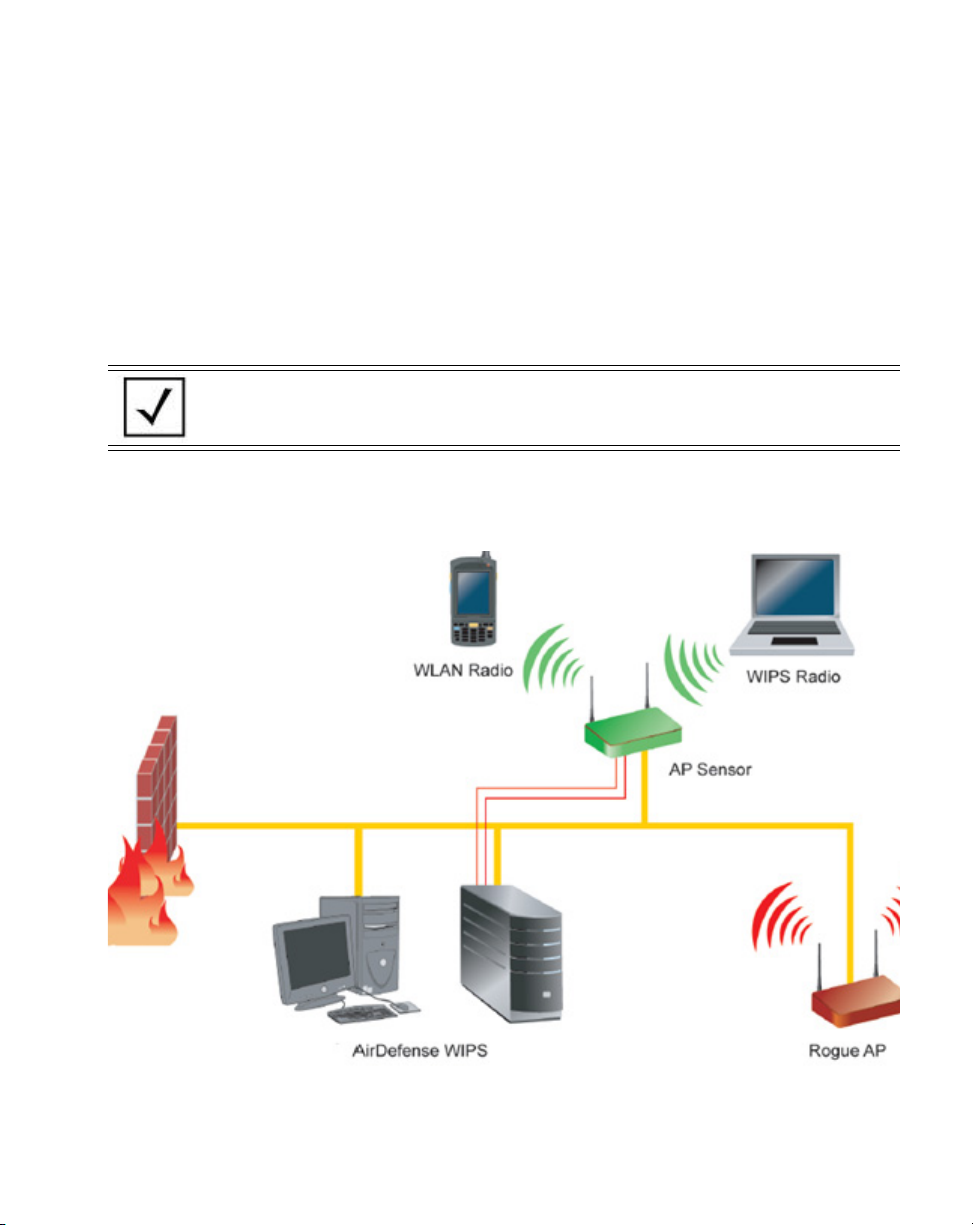
Introduction
real time and permits both a wired and wireless lockdown of wireless device connections upon
acknowledgement of a threat.
An access point radio can function as a sensor and upload sensor mode operation information to a
dedicated WIPS server. WIPS is not supported on a WLAN basis, rather sensor functionality is
supported on the access point radio(s) available to each WLAN. When an access point radio is
functioning as a WIPS sensor, it is able to scan in sensor mode across all channels within the 2.4 and
5.0 GHz bands.
NOTE Sensor support requires an AirDefense WIPS Server on the network.
Sensor functionality is not provided by the access point alone. The access
point works in conjunction with a dedicated WIPS server.
The following is a network topology illustrating how a sensor functions within an access point
supported wireless network:
1-7
Page 22
1-8
AP-7131N-FGR Access Point Product Reference Guide
A radio in sensor mode supports three basic features:
NOTE The functions described below are conducted on the WIPS server side,
not on the access point.
• Wireless Termination - The access point attempts to force an unwanted (or unauthorized)
connection to disconnect.
• Wireless Sniffing - All received frames are reported to the WIPS server. This feature
provides the WIPS server with visibility into the activity on the wireless network. The WIPS
server processes the received traffic and provides the IT administrator with useful
information about the 802.11 RF activities in the enterprise.
• Spectrum Analysis - The data needed to provide the current RF Spectrum is provided to the
WIPS server. The access point does not display the data, but it is available to the WIPS
server. Spectrum analysis can operate only when there are no WLAN radios configured. The
WIPS daemon and server are responsible for limiting operation only when there is no radio
in WLAN mode. When a configuration change is made at the AP, the Spectrum Analysis
operation stops.
• Live View- The WIPS application provides a live view of the sensors, APs and MUs operating
in a WLAN. Live view support exists throughout the WIPS application, wherever a device
icon appears in an information panel or navigation tree. Access Live View by right-clicking
on the device, which automatically limits the data to the specific device your choose.
Sensor radios can be tuned to channels in both the 2.4GHz and 5.0 GHz band. The channels in use by
a given radio are defined by the WIPS application. There is no need to explicitly set a band for a
sensor radio. Instead, select either default values or specific channels. Specific channels can be in
either band.
CAUTION Users cannot define a radio as a sensor when one of the access point
radios is functioning as a rogue AP detector. To use one of the radios
as a WIPS sensor, you must disable its current detector method(s)
first, then set the radio for WIPS sensor support. For information on
disabling rogue AP detection, see Configuring Rogue AP Detection on
page 6-41.
With this most recent 4.0 release of the access point firmware, WIPS functionality is no longer
configured within a designated WIPS screen. WIPS functionality is now defined as part of the access
point’s quick setup procedure. For information on using the access point’s Quick Setup screen to
Page 23

Introduction
define how WIPS can be supported on an access point radio, see Configuring Device Settings on page
3-8.
1.2.3 Mesh Roaming Client
Enable the Mesh Roaming Client feature (using the access point’s CLI) to allow a client bridge to
associate in the same manner as a regular mesh client bridge. After an initial (single) association, the
client bridge will not attempt additional associations. Since STP will be disabled, the association
forwards data as soon as the association attempt is successful. When Mesh Roaming Client is
enabled, base bridge mode is not supported to avoid a loop within the mesh topology. Thus, the Mesh
Roaming Client is always an end point (by design) within the mesh wireless topology. The base bridge
will need STP disabled to immediately begin forwarding data when a roaming client bridge
associates.
1.2.4 Dual Mode Radio Options
When the access pointAP-5131 is manufactured as a dual-radio access point, as is the case with the
AP-7131N-FGR, theAP-5131 access point enables you to configure one radio for 802.11a/n support,
and the other for 802.11b/g/n support.
1-9
The two models available to the AP-7131N-FGR series include:
• AP-7131N-66040-FGR (802.11an and 802.11bgn capable)
• AP-7131N-44040-FGR (802.11a and 802.11bg capable)
For detailed informationAP-5131, see Setting the WLAN’s Radio Configuration on page 5-49.
1.2.5 Separate LAN and WAN Ports
The access pointAP-5131 has one LAN (GE1/POE) port and one WAN (GE2) port, each with their own
MAC address. The access point must manage all data traffic over the LAN connection carefully as
either a DHCP client, BOOTP client, DHCP server or using a static IP address. The access point can
only use a Power-over-Ethernet device when connected to the LAN port.
For detailed information on configuring the AP-5131 LAN port, see Configuring the LAN Interface on
page 5-1.
A Wide Area Network (WAN) is a widely dispersed telecommunications network. In a corporate
environment, the WAN port might connect to a larger corporate network. For a small business, the
WAN port might connect to a DSL or cable modem to access the Internet. Regardless, network
address information must be configured for the access pointAP-5131’s intended mode of operation.
Page 24

1-10
AP-7131N-FGR Access Point Product Reference Guide
For detailed information on configuring the AP-5131access point’s WAN port, see Configuring WAN
Settings on page 5-15.
The LAN and WAN port MAC addresses can be located within the LAN and WAN Stats screens.
For detailed information on locating the access point’s MAC addresses, see Viewing WAN Statistics
on page 7-2 and Viewing LAN Statistics on page 7-6. For information on access point MAC address
assignments, see MAC Address Assignment on page 1-29.
1.2.6 Multiple Mounting Options
The accAP-5131ess point attaches to a wall, mounts under a ceiling or above a ceiling (attic). Choose
a mounting option based on the physical environment of the coverage area. Do not mount the access
pointAP-5131 in a location that has not been approved in a radio coverage site survey.
For detailed information on the mounting options available AP-5131, see Mounting an AP-7131N-FGR
on page 2-10.
1.2.7 Antenna Support for 2.4 GHz and 5 GHz Radios
The AP-5131access point supports several 802.11a/n and 802.11b/g/n radio antennas. Select the
antenna best suited to the radio transmission requirements of your coverage area.
1.2.8 Sixteen Configurable WLANs
A Wireless Local Area Network (WLAN) is a data-communications system that flexibly extends the
functionalities of a wired LAN. A WLAN does not require lining up devices for line-of-sight
transmission, and are thus, desirable for wireless networking. Roaming users can be handed off from
one access pointAP-5131 to another like a cellular phone system. WLANs can therefore be configured
around the needs of specific groups of users, even when they are not in physical proximity. Sixteen
WLANs are configurable on each access pointAP-5131.
To enable and configure WLANs on an access pointAP-5131 radio, see Click Undo Changes (if
necessary) to undo any changes made. Undo Changes reverts the settings displayed on the screen to
the last saved configuration. on page 5-25.
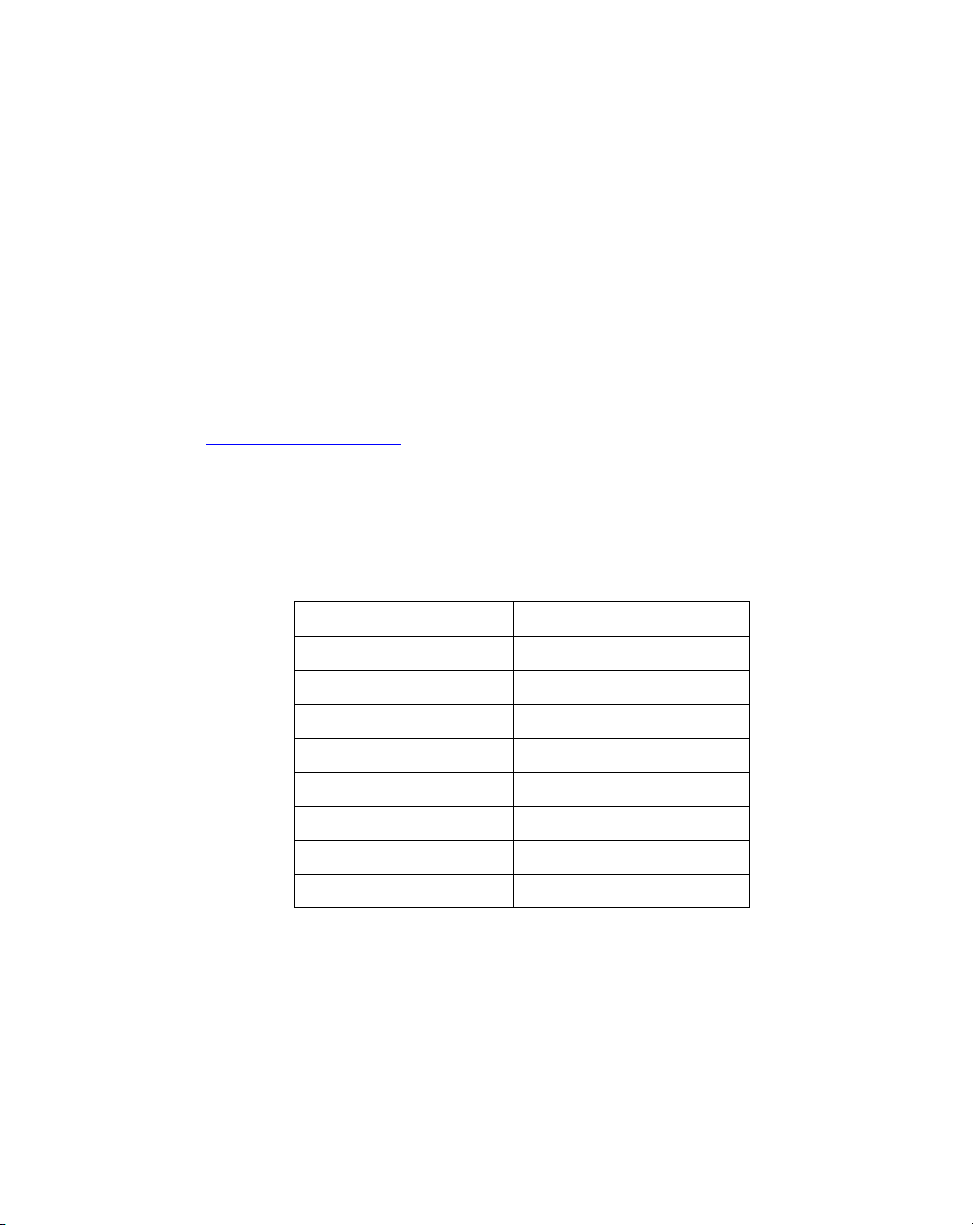
1.2.9 Support for 4 BSSIDs per Radio
The access point supports four BSSIDs per radio. Each BSSID has a corresponding MAC address. The
first MAC address corresponds to BSSID #1. The MAC addresses for the other three BSSIDs (BSSIDs
#2, #3, #4) are derived by adding 1, 2, 3, respectively, to the radio MAC address.
Page 25

Introduction
If the radio MAC address displayed on the Radio Settings screen is 00:23:68:72:20:DC, then the
BSSIDs for that radio will have the following MAC addresses:
BSSID MAC Address Hexadecimal Addition
BSSID #1 00:23:68:72:20:DC Same as Radio MAC address
BSSID #2 00:23:68:72:20:DD Radio MAC address +1
BSSID #3 00:23:68:72:20:DE Radio MAC address +2
BSSID #4 00:23:68:72:20:DF Radio MAC address +3
For detailed information on strategically mapping BSSIDs to WLANs, see Configuring the 802.11a/n
or 802.11b/g/n Radio on page 5-54. For information on access point MAC address assignments, see
MAC Address Assignment on page 1-29.
1.2.10 Quality of Service (QoS) Support
The AP-5131QoS implementation provides applications running on different wireless devices a
variety of priority levels to transmit data to and from the access pointAP-5131. Equal data
transmission priority is fine for data traffic from applications such as Web browsers, file transfers or
email, but is inadequate for multimedia applications.
1-11
Voice over Internet Protocol (VoIP), video streaming and interactive gaming are highly sensitive to
latency increases and throughput reductions. These forms of higher priority data traffic can
significantly benefit from the AP-5131 QoS implementation.The WiFi Multimedia QOS Extensions
(WMM) implementation used by the AP-5131 shortens the time between transmitting higher priority
data traffic and is thus desirable for multimedia applications. In addition, U-APSD (WMM Power
Save) is also supported.
WMM defines four access categories—voice, video, best effort and background—to prioritize traffic
for enhanced multimedia support.
For detailed information on configuring QoS supportAP-5131, see Setting the WLAN Quality of
Service (QoS) Policy on page 5-37.
1.2.11 Industry Leading Data Security
The AP-5131AP-7131N-FGR a unique set of encryption and authentication techniques to protect the
data transmitting on the WLAN.
The following authentication techniques are supported:
Page 26

1-12
AP-7131N-FGR Access Point Product Reference Guide
• EAP Authentication
The following encryption techniques are supportedAP-5131:
• WPA2-CCMP (802.11i) Encryption
In addition, the AP-5131access point supports the following additional security features:
• Firewall Security
• VPN Tunnels
• Content Filtering
For an overview on the encryption and authentication schemes available AP-5131, refer to
Configuring Access Point Security on page 6-1.
1.2.11.1 EAP Authentication
The Extensible Authentication Protocol (EAP) feature provides access points and their associated
MUs an additional measure of security for data transmitted over the wireless network. Using EAP,
authentication between devices is achieved through the exchange and verification of certificates.
EAP is a mutual authentication method whereby both the MU and AP are required to prove their
identities. Using EAP, the user loses device authentication if the server cannot provide proof of device
identification.
Using EAP, a user requests connection to a WLAN through the access pointAP-5131. The access point
AP-5131then requests the identity of the user and transmits that identity to an authentication server.
The server prompts the AP for proof of identity (supplied to the AP-5131 by the user) and then
transmits the user data back to the server to complete the authentication process.
An MU is not able to access the network if not authenticated. When configured for EAP support, the
access point displays the MU as an EAP station.
EAP is only supported on mobile devices running Windows XP, Windows 2000 (using Service Pack #4)
and Windows Mobile 2003. Refer to the system administrator for information on configuring a Radius
Server for EAP (802.1x) support.
For detailed information on EAP configurations, see Configuring 802.1x EAP Settings on page 6-6.
1.2.11.2 WPA2-CCMP (802.11i) Encryption
WPA2 is a newer 802.11i standard that provides even stronger wireless security than Wi-Fi Protected
Access (WPA) and WEP. Counter-mode/CBC-MAC Protocol (CCMP) is the security standard used by
Page 27

Introduction
the Advanced Encryption Standard (AES). CCMP computes a Message Integrity Check (MIC) using the
proven Cipher Block Message Authentication Code (CBC-MAC) technique. Changing just one bit in a
message produces a totally different result.
WPA2-CCMP is based on the concept of a Robust Security Network (RSN), which defines a hierarchy
of keys with a limited lifetime . Messages are encrypted using a 128-bit secret key and a 128-bit block
of data. The end result is an encryption scheme as secure as any the access pointAP-5131 provides.
For detailed information on WPA2-CCMP, see Configuring WPA2-CCMP (802.11i) on page 6-11.
1.2.11.3 Firewall Security
A firewall keeps personal data in and hackers out. The AP-5131access point’s firewall prevents
suspicious Internet traffic from proliferating the access pointAP-5131 managed network. The
AP-5131access point performs Network Address Translation (NAT) on packets passing to and from
the WAN port. This combination provides enhanced security by monitoring communication with the
wired network.
For detailed information on configuring the access point’s AP-5131firewall, see Configuring Firewall
Settings on page 6-13.
1.2.11.4 VPN Tunnels
1-13
Virtual Private Networks (VPNs) are IP-based networks using encryption and tunneling providing
users remote access to a secure LAN. In essence, the trust relationship is extended from one LAN
across the public network to another LAN, without sacrificing security. A VPN behaves like a private
network; however, because the data travels through the public network, it needs several layers of
security. The AP-5131access point can function as a robust VPN gateway.
For detailed information on configuring VPN security support, see Configuring VPN Tunnels on page
6-22.
1.2.11.5 Content Filtering
Content filtering allows system administrators to block specific commands and URL extensions from
going out through theAP-5131 WAN port. Therefore, content filtering affords system administrators
selective control on the content proliferating the network and is a powerful screening tool. Content
filtering allows the blocking of up to 10 files or URL extensions and allows blocking of specific
outbound requests.
For detailed information on configuring content filtering support, see Configuring Content Filtering
Settings on page 6-38.
Page 28

1-14
AP-7131N-FGR Access Point Product Reference Guide
1.2.12 VLAN Support
A Virtual Local Area Network (VLAN) can electronically separate data on the same AP from a single
broadcast domain into separate broadcast domains. By using a VLAN, you can group by logical
function instead of physical location. There are 16 VLANs supported on the access pointAP-5131. An
administrator can map up to 16 WLANs to 16 VLANs and enable or disable dynamic VLAN
assignment. In addition to these 16 VLANs, the access point supports dynamic, user-based, VLANs
when using EAP authentication.
VLANs enable organizations to share network resources in various network segments within large
areas (airports, shopping malls, etc.). A VLAN is a group of clients with a common set of requirements
independent of their physical location. VLANs have the same attributes as physical LANs, but they
enable administrators to group clients even when they are not members of the same network
segment.
For detailed information on configuring VLAN support, see Configuring VLAN Support on page 5-5.
1.2.13 Multiple Management Accessibility Options
The access pointAP-5131 can be accessed and configured using one of the following:
• Java-Based Web UI
• Human readable config file (imported via SFTP)
• MIB (Management Information Base)
• Command Line Interface (CLI) accessed via RS-232 . Use the access point’sAP-5131 DB-9
serial port for direct access to the command-line interface from a PC. Use a Null-Modem
cable (Part No. 25-632878-0) for the best fitting connection.
1.2.14 Updatable Firmware
Updated versions of device firmware are periodically released to the Zebra Web site. If the AP-5131
firmware version displayed on the System Settings screen (see Configuring System Settings on page
4-2) is older than the version on the Web site, update the access pointAP-5131 to the latest firmware
version for full feature functionality.
For detailed information on updating the AP-5131 firmware using SFTP, see Updating Device
Firmware on page 4-51.
Page 29
Introduction
1.2.15 Programmable SNMP v3 Trap Support
Simple Network Management Protocol (SNMP) facilitates the exchange of management information
between network devices. SNMP uses Management Information Bases (MIBs) to manage the device
configuration and monitor Internet devices in remote locations. MIB information accessed via SNMP
is defined by a set of managed objects called Object Identifiers (OIDs). An OID is used to uniquely
identify each object variable of a MIB.
SNMP allows a network administrator to configure the access point, manage network performance,
find and solve network problems, and plan network growth. The access pointAP-5131 supports SNMP
management functions for gathering information from its network components. The MIB files are
available at www.zebra.com/support
more information refer Appendix C, Zebra Support
Few acronyms used in the MIB files:
Portal Radio of an AP
MIB Management Information Base
LAN Local Area Network
. The user should serach for “AP7131N-GR MIBS 4.0.4.0”. For
Table 1.1 Acronyms
1-15
WAN Wide Area Network
POE Power Over Ethernet
WLAN Wireless LAN
AP Access Point
Switch RFS7000-GR
MU Mobile Unit
The AP-5131access point’s SNMP agent functions as a command responder and is a multilingual
agent responding to SNMP v3 managers (command generators). For detailed information on
configuring SNMP traps, see Configuring SNMP Settings on page 4-27.
1.2.16 Power-over-Ethernet Support
When users purchase a WLAN solution, they often need to place access points in obscure locations.
In the past, a dedicated power source was required for each access point in addition to the Ethernet
Page 30

1-16
AP-7131N-FGR Access Point Product Reference Guide
infrastructure. This often required an electrical contractor to install power drops at each access point
location.
An approved Power Injector solution merges power and Ethernet into one cable, reducing the burden
of installation and allows optimal access pointAP-5131 placement in respect to the intended radio
coverage area. The access point can only use a Power-over-Ethernet device when connected to the
access point’s LAN (GE1/POE) port. The access point can also support 3af/3at compliant products
from other vendors.
The Power Injector (Part No. AP-PSBIAS-1P3-AFR) is a single-port Power over Ethernet hub combining
low-voltage DC with Ethernet data in a single cable connecting to the access pointAP-5131. The
Power Injector’s single DC and Ethernet data cable creates a modified Ethernet cabling environment
on the AP-5131access point’s LAN port eliminating the need for separate Ethernet and power cables.
For detailed information on using the Power Injector, see Power Injector System on page 2-6.
1.2.17 MU-MU Transmission Disallow
The access point’s MU-MU Disallow feature prohibits MUs from communicating with each other even
if on the same WLAN, assuming one of the WLAN’s is configured to disallow MU-MU
communication. Therefore, if an MU’s WLAN is configured for MU-MU disallow, it will not be able to
communicate with any other MUs connected to this access point.
For detailed information on configuring an AP-5131 WLAN to disallow MU to MU communications,
see Creating/Editing Individual WLANs on page 5-28.
1.2.18 Voice Prioritization
Each AP-5131access point WLAN has the capability of having its QoS policy configured to prioritize
the network traffic requirements for associated MUs. A WLAN QoS page is available for each
enabled WLAN on either the AP-5131802.11a/n or 802.11b/g/n radio.
Use the QoS page to enable voice prioritization for devices to receive the transmission priority they
may not normally receive over other data traffic. Voice prioritization allows the access pointAP-5131
to assign priority to voice traffic over data traffic, and (if necessary) assign legacy voice supported
devices (non WMM supported voice devices) additional priority.
For detailed information on configuring voice prioritization over other voice enabled devices, see
Setting the WLAN Quality of Service (QoS) Policy on page 5-37.
Page 31

Introduction
1.2.19 Support for CAM and PSP MUs
The access pointAP-5131 supports both CAM and PSP powered MUs. CAM (Continuously Aware
Mode) MUs leave their radios on continuously to hear every beacon and message transmitted. These
systems operate without any adjustments by the access pointAP-5131.
A beacon is a uniframe system packet broadcast by the AP to keep the network synchronized. A
beacon includes the ESSID, AP-5131 MAC address, Broadcast destination addresses, a time stamp,
a DTIM (Delivery Traffic Indication Message) and the TIM (Traffic Indication Map).
PSP (Power Save Polling) MUs power off their radios for short periods. When a MU in PSP mode
associates with an access pointAP-5131, it notifies the AP-5131access point of its activity status. The
access point AP-5131 responds by buffering packets received for the MU. PSP mode is used to extend
an MU’s battery life by enabling the MU to “sleep” during periods of inactivity.
1.2.20 Statistical Displays
The access pointAP-5131 can display robust transmit and receive statistics for the WAN and LAN
ports. WLAN stats can be displayed collectively and individually for enabled WLANs. Transmit and
receive statistics are available for the AP-5131access point’s 802.11a/n and 802.11b/g/n radios. An
advanced radio statistics page is also available to display retry histograms for specific data packet
retry information.
1-17
Associated MU stats can be displayed collectively and individually for specific MUs. An echo (ping)
test is also available to ping specific MUs to assess association strength. Finally, the access
pointAP-5131 can detect and display the properties of other APs detected within its radio coverage
area. The type of AP detected can be displayed as well as the properties of individual APs.
For detailed information on available AP-5131access point statistical displays and the values they
represent, see Monitoring Statistics on page 7-1.
1.2.21 Transmit Power Control
The access pointAP-5131 has a configurable power level for each radio. This enables the network
administrator to define the antenna’s transmission power level in respect to the access point’s
placement or network requirements as defined in the AP-5131 site survey.
For detailed information on setting the radio transmit power level, see Configuring the 802.11a/n or
802.11b/g/n Radio on page 5-54.
Page 32

1-18
AP-7131N-FGR Access Point Product Reference Guide
1.2.22 Advanced Event Logging Capability
The access pointAP-5131 periodically logs system events. Logging events is useful in assessing the
throughput and performance of the access pointAP-5131 or troubleshooting problems on the
AP-5131access point managed Local Area Network (LAN).
For detailed information on access pointAP-5131 events, see Logging Configuration on page 4-45.
1.2.23 Configuration File Import/Export Functionality
Configuration settings for an access pointAP-5131 can be downloaded from the current configuration
of another access pointAP-5131. This affords the administrator the ability to save the current
configuration before making significant changes or restoring a default configuration. A configuration
file from a dual radio AP-7131N-FGR can be imported to another dual radio model AP-7131N-FGR.
For detailed information on importing or exporting configuration files, see Importing/Exporting
Configurations on page 4-47.
1.2.24 Default Configuration Restoration
The access pointAP-5131 can restore its default configuration or a partial default configuration (with
the exception of current WAN and SNMP settings). Restoring the default configuration is a good way
to create new WLANs if the MUs the AP-5131access point supports have been moved to different
radio coverage areas.
For detailed information on restoring a default or partial default configuration, see Configuring
System Settings on page 4-2.
1.2.25 DHCP Support
The access pointAP-5131 can use Dynamic Host Configuration Protocol (DHCP) to obtain a leased IP
address and configuration information from a remote server. DHCP is based on the BOOTP protocol
and can coexist or interoperate with BOOTP. Configure the access pointAP-5131 to send out a DHCP
request searching for a DHCP/BOOTP server to acquire HTML, firmware or network configuration files
when the AP-5131access point boots. Because BOOTP and DHCP interoperate, whichever responds
first becomes the server that allocates information.
The access pointAP-5131 can be set to only accept replies from DHCP or BOOTP servers or both (this
is the default setting). Disabling DHCP disables BOOTP and DHCP and requires network settings to
be set manually. If running both DHCP and BOOTP, do not select BOOTP Only. BOOTP should only be
used when the server is running BOOTP exclusively.
Page 33

Introduction
The DHCP client automatically sends a DHCP request at an interval specified by the DHCP server to
renew the IP address lease as long as the AP-5131access point is running (this parameter is
programmed at the DHCP server). For example: Windows 2000 servers typically are set for 3 days.
1.2.26 Mesh Networking
Utilize the new mesh networking functionality to allow the access point to function as a bridge to
connect two Ethernet networks or as a repeater to extend your network’s coverage area without
additional cabling. Mesh networking is configurable in two modes. It can be set in a wireless client
bridge mode and/or a wireless base bridge mode (which accepts connections from client bridges).
These two modes are not mutually exclusive.
In client bridge mode, the access point scans to find other access points using the selected WLAN’s
ESSID. The access point must go through the association and authentication process to establish a
wireless connection. The mesh networking association process is identical to the access point’s MU
association process. Once the association/authentication process is complete, the wireless client
adds the connection as a port on its bridge module. This causes the access point (in client bridge
mode) to begin forwarding configuration packets to the base bridge. An access point in base bridge
mode allows the access point radio to accept client bridge connections.
The two bridges communicate using the Spanning Tree Protocol (STP). The spanning tree determines
the path to the root and detects if the current connection is part of a network loop with another
connection. Once the spanning tree converges, both access points begin learning which destinations
reside on which side of the network. This allows them to forward traffic intelligently.
1-19
After the access point (in client bridge mode) establishes at least one wireless connection, it will
begin beaconing and accepting wireless connections (if configured to support mobile users). If the
access point is configured as both a client bridge and a base bridge, it begins accepting client bridge
connections. In this way, the mesh network builds itself over time and distance.
Once the access point (in client bridge mode) establishes at least one wireless connection, it
establishes other wireless connections in the background as they become available. In this way, the
access point can establish simultaneous redundant links. An access point (in client bridge mode) can
establish up to 3 simultaneous wireless connections with other access points. A client bridge always
initiates the connections and the base bridge is always the acceptor of the mesh network data
proliferating the network.
Since each access point can establish up to 3 simultaneous wireless connections, some of these
connections may be redundant. In that case, the STP algorithm determines which links are the
redundant links and disables the links from forwarding.
Page 34

1-20
AP-7131N-FGR Access Point Product Reference Guide
For an overview on mesh networking as well as details on configuring the access point’s mesh
networking functionality, see Configuring Mesh Networking on page 9-1.
1.2.27 Additional LAN Subnet
In a typical retail or small office environment (wherein a wireless network is available along with a
production WLAN) it is often necessary to segment a LAN into two subnets. Consequently, a second
LAN is required to “segregate” wireless traffic.
The access point has a second LAN subnet enabling administrators to segment the access point’s
LAN connection into two separate networks. The main access point LAN screen now allows the user
to select either LAN1 or LAN2 as the active LAN over the access point’s Ethernet port. Both LANs can
still be active at any given time, but only one can transmit over the access point’s physical LAN
connection. Each LAN has a separate configuration screen (called LAN 1 and LAN 2 by default)
accessible under the main LAN screen. The user can rename each LAN as necessary. Additionally,
each LAN can have its own Ethernet Type Filter configuration, and subnet access (SSH, SNMP)
configuration.
For detailed information on configuring the access point for additional LAN subnet support, see
Configuring the LAN Interface on page 5-1.
1.2.28 On-board Radius Server Authentication
The access point can function as a RADIUS Server to provide user database information and user
authentication. Several new screens have been added to the access point’s menu tree to configure
RADIUS server authentication and configure the local user database and access policies. The new
RADIUS Server functionality allows an administrator to define the data source, authentication type
and associate digital certificates with the authentication scheme. The LDAP screen allows the
administrator to configure an external LDAP Server for use with the access point. A new Access Policy
screen enables the administrator to set WLAN access based on user groups defined within the User
Database screen. Each user is authorized based on the access policies applicable to that user. Access
policies allow an administrator to control access to a user groups based on the WLAN configurations.
For detailed information on configuring the access point for AAA RADIUS Server support, see
Configuring User Authentication on page 6-51.
1.2.29 Hotspot Support
The access point allows hotspot operators to provide user authentication and accounting without a
special client application. The access point uses a traditional Internet browser as a secure
Page 35

Introduction
authentication device. The access point issues an IP address to the user using a DHCP Server,
authenticates the user and grants the user to access the Internet.
If a tourist visits a public hotspot and wants to browse a Web page, they boot their laptop and
associate with a local Wi-Fi network by entering a valid SSID. They start a browser, and the hotspot’s
access controller forces the un-authenticated user to a Welcome page (from the hotspot operator)
that allows the user to login with a username and password. In order to send a redirected page (a
login page), a TCP termination exists locally on the access point. Once the login page displays, the
user enters their credentials. The access point connects to the RADIUS server and determines the
identity of the connected wireless user. Thus, allowing the user to access the Internet once
successfully authenticated.
For detailed information on configuring the access point for Hotspot support, see Configuring WLAN
Hotspot Support on page 5-43.
1.2.30 Routing Information Protocol (RIP)
RIP is an interior gateway protocol that specifies how routers exchange routing-table information.
The parent Router screen also allows the administrator to select the type of RIP and the type of RIP
authentication used.
1-21
For detailed information on configuring RIP functionality as part of the access point’s Router
functionality, see Setting the RIP Configuration on page 5-69.
1.2.31 Manual Date and Time Settings
As an alternative to defining a NTP server to provide access point system time, the access point can
now have its date and time set manually. A new Manual Date/Time Setting screen can be used to set
the time using a Year-Month-Day HH:MM:SS format.
For detailed information on manually setting the access point’s system time, see Configuring Network
Time Protocol (NTP) on page 4-41.
1.2.32 Dynamic DNS
The access point supports the Dynamic DNS service. Dynamic DNS (or DynDNS) is a feature offered
by www.dyndns.com
When the dynamically assigned IP address of a client changes, the new IP address is sent to the
DynDNS service and traffic for the specified domain(s) is routed to the new IP address. For
information on configuring Dynamic DNS, see Configuring Dynamic DNS on page 5-24.
allowing the mapping of domain names to dynamically assigned IP addresses.
Page 36

1-22
AP-7131N-FGR Access Point Product Reference Guide
1.2.33 Auto Negotiation
Auto negotiation enables the access point to automatically exchange information about data
transmission speed and duplex capabilities. Auto negotiation is helpful when using the access point
in an environment where different devices are connected and disconnected on a regular basis. For
information on configuring the auto negotiation feature, see Configuring the LAN Interface on page
5-1 or Configuring WAN Settings on page 5-15.
1.2.34 Adaptive AP
An adaptive AP (AAP) is an access point that can adopt like an AP300 (L3). The management of an
AAP is conducted by a switch, once the access point connects to a RFS7000 model switch and
receives its AAP configuration.
An AAP provides:
• local 802.11 traffic termination
• local encryption/decryption
• local traffic bridging
• the tunneling of centralized traffic to the wireless switch
For a information overview of the adaptive AP feature as well as how to configure it, refer to
Adaptive AP on page 10-1.
1.2.35 Rogue AP Enhancements
The access point can scan for rogues over all channels on both of the access point’s radio bands. The
switching of radio bands is based on a timer with no user intervention required.
For information on configuring the access point for Rogue AP support, see Configuring Rogue AP
Detection on page 6-41.
1.2.36 Radius Time-Based Authentication
An AAA server maintains a users and groups database used by the access point for access
permissions. Various kinds of access policies can be applied to each group. Individual groups can be
configured with their own time-based access policy. Each group’s policy has a user defined interval
defining the days and hours access is permitted. Authentication requests for users belonging to the
group are honored only during these defined hourly intervals.
Page 37

Introduction
For more information on defining access point access policies by group, see Defining User Access
Permissions by Group on page 6-65.
1.2.37 QBSS Support
Each access point radio can be configured to optionally allow the access point to communicate
channel usage data to associated devices and define the beacon interval used for channel utilization
transmissions. The QBSS load represents the percentage of time the channel is in use by the access
point and the access point’s station count. This information is very helpful in assessing the access
point’s overall load on a channel, its availability for additional device associations and multi media
traffic support.
For information on enabling QBSS and defining the channel utilization transmission interval, see
Configuring the 802.11a/n or 802.11b/g/n Radio on page 5-54.
1.3 Theory of Operations
To understand AP-5131access point management and performance alternatives, users need
familiarity with AP-5131 functionality and configuration options. The AP-5131access point includes
features for different interface connections and network management.
1-23
The AP-5131access point uses electromagnetic waves to transmit and receive electric signals
without wires. Users communicate with the network by establishing radio links between mobile units
(MUs) and access points.
The access pointAP-5131 uses DSSS (direct sequence spread spectrum) to transmit digital data from
one device to another. A radio signal begins with a carrier signal that provides the base or center
frequency. The digital data signal is encoded onto carriers using a DSSS chipping algorithm. The
AP-5131 radio signal propagates into the air as electromagnetic waves. A receiving antenna (on the
MU) in the path of the waves absorbs the waves as electrical signals. The receiving MU interprets
(demodulates) the signal by reapplying the direct sequence chipping code. This demodulation results
in the original digital data.
The access pointAP-5131 uses its environment (the air and certain objects) as the transmission
medium.The AP-5131 access point can either transmit in the 2.4 to 2.5-GHz frequency range (802.11b/
g/n radio) or the
5 GHz frequency range (802.11a/n radio), the actual range is country-dependent. Devices have
unique, hardware encoded Media Access Control (MAC) or IEEE addresses. MAC addresses
determine the device sending or receiving data. A MAC address is a
Page 38

1-24
AP-7131N-FGR Access Point Product Reference Guide
48-bit number written as six hexadecimal bytes separated by colons. For example: 00:A0:F8:24:9A:C8
Also see the following:
• Wireless Coverage
• MAC Layer Bridging
• Content Filtering
• DHCP Support
• Media Types
• Direct-Sequence Spread Spectrum
• MU Association Process
• Operating Modes
• Management Access Options
• MAC Address Assignment
1.3.1 Wireless Coverage
An access pointAP-5131 establishes an average communication range with MUs called a Basic
Service Set (BSS) or cell. When in a particular cell, the MU associates and communicates with the
AP-5131access point supporting the radio coverage area of that cell. Adding AP-5131access points
to a single LAN establishes more cells to extend the range of the network. Configuring the same
ESSID (Extended Service Set Identifier) on all access pointAP-5131s makes them part of the same
Wireless LAN.
AP-5131Access points with the same ESSID define a coverage area. A valid ESSID is an
alphanumeric, case-sensitive identifier up to 32 characters. An MU searches for an access
pointAP-5131 with a matching ESSID and synchronizes (associates) to establish communications.
This device association allows MUs within the coverage area to move about or roam. As the MU
roams from cell to cell, it associates with a different access pointAP-5131. The roam occurs when the
MU analyzes the reception quality at a location and determines a different AP-5131 provides better
signal strength and lower MU load distribution.
If the MU does not find an AP-5131access point with a workable signal, it can perform a scan to find
any AP. As MUs switch APs, the AP updates its association statistics.
The user can configure the ESSID to correspond to up to 16 WLANs on each 802.11a/n or
802.11b/g/n radio. A Wireless Local Area Network (WLAN) is a data-communications system that
flexibly extends the functionalities of a wired LAN. A WLAN does not require lining up devices for
line-of-sight transmission, and are thus, desirable. Within the WLAN, roaming users can be handed
Page 39

Introduction
off from one AP-5131 access point to another like a phone system. WLANs can therefore be
configured around the needs of specific groups of users, even when they are not in physical proximity.
1.3.2 MAC Layer Bridging
The access pointAP-5131 provides MAC layer bridging between its interfaces. The AP-5131access
point monitors traffic from its interfaces and, based on frame address, forwards the frames to the
proper destination. The access point tracks source and destination addresses to provide intelligent
bridging as MUs roam or network topologies change. The access pointAP-5131 also handles
broadcast and multicast messages and responds to MU association requests.
The access pointAP-5131 listens to all packets on its LAN and WAN interfaces and builds an address
database using MAC addresses. An address in the database includes the interface media that the
device uses to associate with the AP-5131access point. The access pointAP-5131 uses the database
to forward packets from one interface to another. The bridge forwards packets addressed to unknown
systems to the Default Interface (Ethernet).
The access pointAP-5131 internal stack interface handles all messages directed to the access
pointAP-5131. Each AP-5131 stores information on destinations and their interfaces to facilitate
forwarding. When a user sends an ARP (Address Resolution Protocol) request packet, the access
pointAP-5131 forwards it over all enabled interfaces except over the interface the ARP request packet
was received.
1-25
On receiving the ARP response packet, the access pointAP-5131 database keeps a record of the
destination address along with the receiving interface. With this information, the access
pointAP-5131 forwards any directed packet to the correct destination. Transmitted ARP request
packets echo back to other MUs. The access point removes from its database the destination or
interface information not used for a specified time. The AP refreshes its database when it transmits
or receives data from these destinations and interfaces.
1.3.3 Media Types
The access pointAP-5131 radio interface conforms to IEEE 802.11 specifications. The AP-5131access
point supports multiple-cell operations with fast roaming between cells. Within a direct-sequence
system, each cell can operates independently. Adding cells to the network provides an increased
coverage area and total system capacity.
The serial port provides a Command Line Interface (CLI) connection. The serial link supports a direct
serial connection. The AP-5131access point is a Data Terminal Equipment (DTE) device with male pin
Page 40

1-26
AP-7131N-FGR Access Point Product Reference Guide
connectors for the RS-232 port. Connecting the AP-5131access point to a PC requires a null modem
serial cable.
1.3.4 Direct-Sequence Spread Spectrum
Spread spectrum (broadband) uses a narrowband signal to spread the transmission over a segment
of the radio frequency band or spectrum. Direct-sequence is a spread spectrum technique where the
transmitted signal is spread over a particular frequency range. The access point uses
Direct-Sequence Spread Spectrum (DSSS) for radio communication.
Direct-sequence systems communicate by continuously transmitting a redundant pattern of bits
called a chipping sequence. Each bit of transmitted data is mapped into chips by the access
pointAP-5131 and rearranged into a pseudorandom spreading code to form the chipping sequence.
The chipping sequence is combined with a transmitted data stream to produce the output signal.
MUs receiving a direct-sequence transmission use the spreading code to map the chips within the
chipping sequence back into bits to recreate the original data transmitted by the access
pointAP-5131. Intercepting and decoding a direct-sequence transmission requires a predefined
algorithm to associate the spreading code used by the transmitting access pointAP-5131 to the
receiving MU. This algorithm is established by IEEE 802.11b specifications. The bit redundancy within
the chipping sequence enables the receiving MU to recreate the original data pattern, even if bits in
the chipping sequence are corrupted by interference.
The ratio of chips per bit is called the spreading ratio. A high spreading ratio increases the resistance
of the signal to interference. A low spreading ratio increases the bandwidth available to the user. The
access pointAP-5131 uses different modulation schemes to encode more bits per chip at higher data
rates.
1.3.5 MU Association Process
An AP-5131access point recognizes MUs as they begin the association process. An AP-5131access
point keeps a list of the MUs it services. MUs associate with an access pointAP-5131 based on the
following conditions:
• Signal strength between the AP-5131and MU
• Number of MUs currently associated with the AP-5131access point
• MUs encryption and authentication capabilities
• MUs supported data rate
Page 41

Introduction
MUs perform pre-emptive roaming by intermittently scanning for AP-5131’s and associating with the
best available access pointAP-5131. Before roaming and associating, MUs perform full or partial
scans to collect AP-5131 statistics and determine the direct-sequence channel used by the
AP-5131access point.
Scanning is a periodic process where the MU sends out probe messages on all channels defined by
the country code. The statistics enable an MU to reassociate by synchronizing its channel to the
access pointAP-5131. The MU continues communicating with that AP-5131 until it needs to switch
cells or roam.
MUs perform partial scans at programmed intervals, when missing expected beacons or after
excessive transmission retries. In a partial scan, the MU scans access points classified as proximate
on the AP-5131access point table. For each channel, the MU tests for Clear Channel Assessment
(CCA). The MU broadcasts a probe with the ESSID and broadcast BSS_ID when the channel is
transmission-free. It sends an ACK to a directed probe response from the access pointAP-5131 and
updates the table.
An MU can roam within a coverage area by switching AP-5131access points. Roaming occurs when:
• Unassociated MU attempts to associate or reassociate with an available AP-5131access
point
• Supported rate changes or the MU finds a better transmit rate with another AP-5131access
point
• RSSI (received signal strength indicator) of a potential access pointAP-5131 exceeds the
current access pointAP-5131
• Ratio of good-transmitted packets to attempted-transmitted packets that fall below a
threshold.
1-27
An MU selects the best available access pointAP-5131 and adjusts itself to the access pointAP-5131
direct-sequence channel to begin association. Once associated, the AP-5131access point begins
forwarding frames addressed to the target MU. Each frame contains fields for the current directsequence channel. The MU uses these fields to resynchronize to the AP-5131access point.
The scanning and association process continues for active MUs. This process allows MUs to find new
AP-5131access points and discard out-of-range or deactivated AP-5131access points. By testing the
airwaves, MUs can choose the best network connection available.
1.3.6 Operating Modes
The AP-5131access point can operate in a couple of configurations.
Page 42

1-28
AP-7131N-FGR Access Point Product Reference Guide
• Access Point - As an Access Point, the AP-5131access point functions as a layer 2 bridge.
The wired uplink can operate as a trunk and support multiple VLANs. Up to 16 WLANs can
be defined and mapped to access pointAP-5131 WLANs. Each WLAN can be configured to
be broadcast by one or both AP-5131access point radios. An AP-7131N-FGR can operate in
both an access point mode and Wireless Gateway/Router mode simultaneously. The
network architecture and access point configuration define how the Access Point and
Wireless Gateway/Router mode are negotiated.
• Wireless Gateway/Router - If operating as a Wireless Gateway/Router, the access point
functions as a router between two layer 2 networks: the WAN uplink (the ethernet port) and
the Wireless side. The following options are available providing a solution for single-cell
deployment:
• PPPoE - The WAN interface can terminate a PPPoE connection, thus enabling the access
point to operate in conjunction with a DSL or Cable modem to provide WAN connectivity.
• NAT - (Network Address Translation) on the Wireless interface. Using NAT, the
AP-5131router is able to manage a private IP scheme. NAT allows translation of private
addresses to the WAN IP address.
• DHCP - The access pointAP-5131 can assign private IP addresses.
• Firewall - A Firewall protects against a number of known attacks.
1.3.7 Management Access Options
Managing the AP-5131access point includes viewing network statistics and setting configuration
options. Statistics track the network activity of associated MUs and data transfers on the AP
interfaces.
The AP-5131access point requires one of the following connection methods to perform a custom
installation and manage the network:
• Secure Java-Based WEB UI - (use Sun Microsystems’ JRE 1.6 available from Sun’s Web site
and be sure to disable Microsoft’s Java Virtual Machine if installed)
• Command Line Interface (CLI) via Serial, and SSH
• Config file - Human-readable; Importable/Exportable via SFTP
MIB (Management Information Base) accessing the access pointAP-5131 SNMP function using a MIB
Browser. The MIB files are available at www.zebra.com/support
“AP7131N-GR MIBS 4.0.4.0”. For more information refer Appendix C, Zebra Support
. The user should serach for
Page 43

Introduction
Few acronyms used in the MIB files:
Table 1.2 Acronyms
Portal Radio of an AP
MIB Management Information Base
LAN Local Area Network
WAN Wide Area Network
POE Power Over Ethernet
WLAN Wireless LAN
AP Access Point
Switch RFS7000-GR
MU Mobile Unit
Make configuration changes to access pointAP-5131’s individually. Optionally, use the access
pointAP-5131
import/export configuration function to download settings to other access points.
1-29
For detailed information, see Importing/Exporting Configurations on page 4-47.
1.3.8 MAC Address Assignment
MAC address assignments are as follows:
• LAN (GE1) - The access point MAC address can be found underneath the access point
chassis.
• WAN (GE2) - WAN MAC address + 1.
• LAN2 - A virtual LAN not mapped to the LAN Ethernet port. This address is the lowest of the
two radio MAC addresses.
• Radio1 (802.11b/g/n) - Random address located on the Web UI, CLI and SNMP interfaces.
• Radio2 (802.11a/n) - Random address located on the Web UI, CLI and SNMP interfaces.
The access point’s BSS (virtual AP) MAC addresses are calculated as follows:
• BSS1 - The same as the corresponding base radio’s MAC address.
• BSS2 - Base radio MAC address +1
• BSS3 - Base radio MAC address +2
Page 44

1-30
AP-7131N-FGR Access Point Product Reference Guide
• BSS4 - Base radio MAC address +3
Page 45

2
Hardware Installation
An AP-7131N-FGR access point installation includes mounting the access point, connecting the
access point to the network, connecting antennae and applying power. Installation procedures vary
for different environments. See the following sections for more details:
• Precautions
• Requirements
• Package Contents
• Access Point Placement
• Power Options
• Power Injector System
• Mounting an AP-7131N-FGR
• LED Indicators
• Setting Up MUs
Page 46

2-2
AP-7131N-FGR Access Point Product Reference Guide
CAUTION Conduct a radio site survey prior to installing an access point. A site
survey is an excellent method of documenting areas of radio
interference and providing a tool for device placement.
2.1 Precautions
Before installing an AP-7131N-FGR model access point, verify the following:
• Do not install in wet or dusty areas without additional protection.
• Verify the environment has a continuous temperature range between -20° C to 50° C.
2.2 Requirements
The minimum installation requirements for a single-cell, peer-to-peer network:
• An AP-7131N-FGR model access point (in
either of its two available dual-radio
models)
• 48 Volt Power Supply Part No. 50-14000-247R or Power Injector
(Part No. AP-PSBIAS-1P3-AFR))
• A power outlet
• Dual-band antennae or an antenna specifically supporting the AP’s 2.4 or 5 GHz band
!
2.3 Package Contents
Check package contents for the correct model and accessories. Each available configuration (at a
minimum), contains:
• AP-7131N-FGR access point (accessories dependent on SKU ordered)
• AP-7131N-FGR Install Guide
• China ROHS compliance addendum
• Wall mount screw and anchor kit
• Accessories Bag (4 rubber feet and a LED light pipe and badge with label for above the
ceiling installations)
Contact Zebra Support to report missing or improperly functioning items.
Page 47

NOTE The access point façade with 6 Element Antenna (Part No.
ML-2452-PTA2M3X3-1) is separately orderable and provides an
integrated antenna option. The facade connects to the access point as
illustrated. Once attached, the LEDs continue to illuminate through the
facade.
Hardware Installation
2-3
2.4 Access Point Placement
For optimal performance, install the access point away from transformers, heavy-duty motors,
fluorescent lights, microwave ovens, refrigerators and other industrial equipment. Signal loss can
occur when metal, concrete, walls or floors block transmission. Install the access point in an open
area or add access points as needed to improve coverage.
Antenna coverage is analogous to lighting. Users might find an area lit from far away to be not bright
enough. An area lit sharply might minimize coverage and create dark areas. Uniform antenna
placement in an area (like even placement of a light bulb) provides even, efficient coverage.
Place the access point using the following guidelines:
• Install the access point at an ideal height of 10 feet from the ground.
• Orient the access point antennas vertically for best reception.
Page 48

2-4
AP-7131N-FGR Access Point Product Reference Guide
• Point the access point antennas downward if attaching to the ceiling.
To maximize the access point’s radio coverage area, Conduct a site survey to define and document
radio interference obstacles before installing the access point.
2.4.1 Site Surveys
A site survey analyzes the installation environment and provides users with recommendations for
equipment and placement. The optimum placement of 802.11a/n access points differs from
802.11b/g/n access points, because the locations and number of access points required are different
to support the radio coverage area.
Conduct a new site survey and developing a new coverage area floor plan when switching from
legacy access points to a new AP-7131N-FGR model, as the device placement requirements could be
significantly different.
2.4.2 Antenna Options
Two antenna suites are supported for AP-7131N-FGR. One antenna suite supporting the 2.4 GHz band
and another antenna suite supporting the 5 GHz band. Select an antenna model best suited to the
intended operational environment of your access point.
NOTE On dual-radio model AP-7131N-FGR access points, Radio 1 refers to the
2.4 GHz radio and Radio 2 refers to the 5 GHz radio. However, there could
be some cases where a dual-radio access point is performing a Rogue AP
detector function. In this scenario, the access point is receiving in either
2.4 GHz or 5 GHz over the Radio 1 or Radio 2 antennae depending on
which radio is selected for the scan.
Page 49

Hardware Installation
R1 defines the access point’s radio 1 antenna connectors and R2 defines radio 2 antenna connectors.
2-5
The 2.4 GHz antenna suite includes the following models:
Part No. Antenna Type Approximate Gain (dBi)
ML-2499-11PNA2-01R Wide Angle Directional 8.5
ML-2499-HPA3-01R Omni-Directional Antenna 3.3
ML-2499-BYGA2-01R Yagi Antenna 13.9
ML-2452-APA2-01 Dual-Band 3/4
ML-2452-PTA2M3X3-1 Facade with 6 Element
Antenna Module
ML-2452-PTA3M3-036 3 Port MIMO Antenna 4.75/5.5
NOTE An additional adapter is required to use ML-2499-11PNA2-01 and
ML-2499-BYGA2-01 model antennae.
3/5
Page 50

2-6
AP-7131N-FGR Access Point Product Reference Guide
The 5 GHz antenna suite includes the following models:
Part No. Antenna Type Approximate Gain (dBi)
ML-5299-WPNA1-01R Panel Antenna 13
ML-5299-HPA1-01R Wide-Band Omni-Directional
Antenna
ML-2452-APA2-01 Dual-Band 3/4
ML-2452-PTA2M3X3-1 Facade with 6 Element Antenna
Module
ML-2452-PTA3M3-036 3 Port MIMO Antenna 5/5
ML-2452-APA6J-01 Dipole 2.4GHz Peak Gain: -5.76dBi
5.0
4.75/5.5
5GHz Peak Gain:
band 1: -3.77dBi
band 2: -3.38dBi
band 3: -2.84dBi
band 4: -2.94dBi
2.5 Power Options
The power options for an AP-7131N-FGR include:
• 48-Volt Power Supply (Part No. 50-14000-247R)
• Power Injector (Part No. AP-PSBIAS-1P3-AFR)
CAUTION An AP-7131N-FGR and must use the 48-Volt Power Supply designed
specifically for use with the AP-7131N-FGR (Part No. 50-14000-247R).
Additionally, a single-port Power of Ethernet Power Injector is
available for use with the AP-7131N-FGR a (Part No. AP-PSBIAS-1P3AFR). Only these two powering solutions should be used with the AP7131N-FGR.
2.6 Power Injector System
An AP-7131N-FGR can receive power via an Ethernet cable connected to the GE1/POE (LAN) port.
Page 51

Hardware Installation
When users purchase a WLAN solution, they often need to place access points in obscure locations.
In the past, a dedicated power source was required for each access point in addition to the Ethernet
infrastructure. This often required an electrical contractor to install power drops at each access point
location. The Power Injector merges power and Ethernet into one cable, reducing the burden of
installation and allowing optimal access point placement in respect to the intended coverage area.
The Power Injector (Part No. AP-PSBIAS-1P3-AFR) is a high power POE Injector delivering up to 30
watts. The access point can only use a Power Injector when connecting the unit to the GE1/POE port.
The Power Injector is a separately ordered component and not shipped with an existing access point
SKU. A separate Power Injector is required for each access point comprising the network.
An AP-7131 and AP-7131N can also be used with the 3af power injector (AP-PSBIAS-1P2-AFR).
However, AP functionality is limited when powered by an AP-PSBIAS-1P2-AFR, since the AP has
Ethernet connectivity limited to only the GE1 port.
The access point Power Supply (Part No. 50-14000-247R) is not included with the access point and is
orderable separately as an accessory. If the access point is provided both POE power over the GE1/
POE connection, as well as the 50-14000-247R power supply concurrently, the access point will
source power from the 50-14000-247R supply only. Disconnecting AC power from the 50-14000247R, causes the AP to re-boot before sourcing power from the POE power injector. If the AP is
operating using injector supplied power, the AP will not automatically reboot if an AC adapter is
connected. The AP continues to operate with power supplied from the AC adapter without change to
the AP operating configuration. If using AC adapter supplied power and a change to the AP’s
operating configuration is warranted (for example, if needing to access the GE2 port), the AP needs
to be manually rebooted by the customer.
2-7
Page 52

2-8
AP-7131N-FGR Access Point Product Reference Guide
CAUTION The access point supports any standards-based compliant power
source. However, using the wrong solution (including a POE system
used on a legacy access point) could either limit functionality or
severely damage the access point and void the product warranty.
2.6.1 Installing the Power Injector
Refer to the following sections for information on planning, installing, and validating the installation:
• Preparing for Site Installation
• Cabling the Power Injector
2.6.1.1 Preparing for Site Installation
The Power Injector can be installed free standing, on an even horizontal surface or wall mounted
using the unit’s wall mounting key holes. The following guidelines should be adhered to before
cabling the Power Injector to an Ethernet source and access point:
• Do not block or cover airflow to the Power Injector
• Keep the unit away from excessive heat, humidity, vibration and dust.
Page 53

Hardware Installation
• The Power Injector is not a repeater, and does not amplify the Ethernet data signal. For
optimal performance, ensure the unit is placed as close as possible to the network data port.
CAUTION To avoid problematic performance and restarts, disable POE from a
wired switch port connected to an access point if mid-span power
sourcing equipment (PSE) is used between the two, regardless of the
manufacturer of the switch.
2.6.1.2 Cabling the Power Injector
To install a Power Injector to an Ethernet data source and an access point:
CAUTION Ensure AC power is supplied to the Power Injector using an AC cable
with an appropriate ground connection approved for the country of
operation.
1. Connect an RJ-45 Ethernet cable between the network data supply (host) and the Power
Injector’s Data In connector.
2. Connect an RJ-45 Ethernet cable between the Power Injector’s Data & Power Out
connector and the access point’s GE1/POE port.
2-9
CAUTION Cabling the Power Injector to WAN port (GE2) renders the AP non-
operational. Only use a AP-PSBIAS-1P3-AFR (or AP-PSBIAS-1P2-AFR)
Power Injector with the access point’s GE1/POE (LAN) port.
Ensure the cable length from the Ethernet source (host) to the Power Injector and access
point does not exceed 100 meters (333 ft). The Power Injector has no On/Off power switch.
The Power Injector receives power and is ready for access point connection and operation
as soon as AC power is applied. Refer to the Installation Guide shipped with the Power
Injector for a description of the device’s LED behavior.
3. Verify all cable connections are complete before supplying power to the access point.
Page 54

2-10
AP-7131N-FGR Access Point Product Reference Guide
2.7 Mounting an AP-7131N-FGR
An AP-7131N-FGR can attach to a wall, mount under a suspended T-Bar or above a ceiling (plenum
or attic) following the same installation instructions. Choose one of the following mounting options
based on the physical environment of the coverage area. Do not mount the access point in a location
that has not been approved in a site survey.
Refer to the following, depending on how you intend to mount the access point:
• Wall Mounted Installations
• Suspended Ceiling T-Bar Installations
• Above the Ceiling (Plenum) Installations
2.7.1 Wall Mounted Installations
Wall mounting requires hanging the access point along its width (or length) using the pair of slots on
the bottom of the unit and using the access point mounting template for the screws.
CAUTION An access point should be wall mounted to concrete or plaster-wall-
board (dry wall) only. Do not wall mount an access point to
combustible surfaces.
The hardware and tools (customer provided) required to install the access point on a wall consists of:
• Two Phillips pan head self-tapping screws (ANSI Standard) #6-18 X 0.875in. Type A or AB
Self-Tapping screw, or (ANSI Standard Metric) M3.5 X 0.6 X 20mm Type D Self-Tapping
screw
• Two wall anchors
• Wall mount template (included on next page)
• Security cable (optional third part provided accessory)
1. To mount the access point on a wall using the provided template:
Page 55

Hardware Installation
2-11
Page 56

2-12
AP-7131N-FGR Access Point Product Reference Guide
Xerox copy the template (on the previous page) to a blank piece of paper. Do not reduce or
enlarge the scale of the template.
CAUTION If printing the mounting template (on the previous page) from an
electronic PDF, dimensionally confirm the template by measuring each
value for accuracy.
2. Tape the template to the wall mounting surface.
• If the installation requires the antenna be positioned vertically, the centerline reference
(of the template) needs to be positioned vertically. The cabling shall exit the access point
in a vertical direction.
• If the installation requires the antenna be positioned horizontally, the vertical centerline
(of the template) needs to be positioned horizontally. The cabling shall exit the access
point in a horizontal direction.
3. At mounting targets A and B, mark the mounting surface through the template at the target
center.
4. Discard the mounting template.
5. At each point, drill a hole in the wall, insert an anchor, screw into the anchor the wall
mounting screw and stop when there is 1mm between the screw head and the wall.
If pre-drilling a hole, the recommended hole size is 2.8mm (0.11in.) if the screws are going
directly into the wall and 6mm (0.23in.) if wall anchors are being used.
6. If required, install and attach a security cable to the access point’s lock port.
7. Attach the antennas to their correct connectors.
For more information on available antennas, see Antenna Options on page 2-4.
8. Place the large center opening of each of the mount slots over the screw heads.
9. Slide the access point down along the mounting surface to hang the mount slots on the
screw heads.
CAUTION Ensure you are placing the antennas on the correct connectors
(depending on your dual-radio model and frequency used) to ensure
the successful operation of the access point.
NOTE It is recommended the access point be mounted with the RJ45 cable
connector oriented upwards or downwards to ensure proper operation.
Page 57

Hardware Installation
10. Cable the access point using either the Power Injector solution or an approved line cord and
power supply.
For Power Injector installations:
a. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the Power Injector Data In connector.
b. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the Power Injector Data &
Power Out connector and the access point’s GE1/POE port.
c. Ensure the cable length from the Ethernet source to the Power Injector and access point
does not exceed 100 meters (333 ft). The Power Injector has no On/Off power switch.
The Power Injector receives power as soon as AC power is applied. For more information
on using the Power Injector, see Power Injector System on page 2-6.
For standard 48-Volt Power Adapter (Part No. 50-14000-247R) and line cord installations:
a. Connect RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the access point’s GE1/POE port.
b. Verify the power adapter is correctly rated according the country of operation.
c. Connect the power supply line cord to the power adapter.
d. Attach the power adapter cable into the power connector on the access point.
e. Plug the power adapter into an outlet.
11. Verify the behavior of the access point’s LEDs. For more information, see LED Indicators on
page 2-18.
The access point is ready to configure. For information on an access point default
configuration, see Getting Started on page 3-1. For specific details on system
configurations, see System Configuration on page 4-1.
2-13
2.7.2 Suspended Ceiling T-Bar Installations
A suspended ceiling mount requires holding the access point up against the T-bar of a suspended
ceiling grid, and twisting the chassis onto the T-bar.
The mounting tools (customer provided) and hardware required to install the access point on a ceiling
T-bar consists of:
• Safety wire (recommended and customer supplied)
• Security cable (and customer supplied)
Page 58

2-14
AP-7131N-FGR Access Point Product Reference Guide
To install the access point on a ceiling T-bar:
1. You should loop a safety wire—with a diameter of at least 1.01 mm (.04 in.), but no more
than 0.158 mm (.0625 in.) —through the tie post (above the console connector) and secure
the loop.
2. If desired, install and attach a security cable to the access point’s lock port.
3. Attach the radio antennas to their correct connectors.
For more information on available antennas, see Antenna Options on page 2-4.
4. Cable the access point using either the Power Injector or an approved power supply.
CAUTION Do not supply power to the access point until the cabling of the unit is
complete.
For Power Injector installations:
a. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the Power Injector Data In connector.
b. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the Power Injector Data &
Power Out connector and the access point’s GE1/POE port.
c. Ensure the cable length from the Ethernet source to the Power Injector and access point
does not exceed 100 meters (333 ft). The Power Injector has no On/Off power switch.
The Power Injector receives power as soon as AC power is applied. For more information
on using the Power Injector, see Power Injector System on page 2-6.
For standard 48-Volt Power Adapter (Part No. 50-14000-247R) and line cord installations:
a. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the access point’s GE1/POE port.
b. Verify the power adapter is correctly rated according the country of operation.
c. Connect the power supply line cord to the power adapter.
d. Attach the power adapter cable into the power connector on the access point.
e. Plug the power adapter into an outlet.
5. Verify the behavior of the LEDs. For more information, see LED Indicators on page 2-18.
6. Align the bottom of the ceiling T-bar with the back of the access point.
7. Orient the access point’s chassis by its length and the length of the ceiling T-bar.
8. Rotate the access point chassis 45 degrees clockwise.
Page 59

Hardware Installation
9. Push the back of the access point chassis on to the bottom of the ceiling T-bar.
CAUTION Ensure the safety wire and cabling used in the T-Bar installation is
securely fastened to the building structure in order to provide a safe
operating environment.
10. Rotate the access point chassis 45 degrees counter-clockwise. The clips click as they fasten
to the T-bar.
2-15
11. The access point is ready to configure. For information on an access point default
configuration, see Getting Started on page 3-1. For specific details on access point system
configurations, see System Configuration on page 4-1.
2.7.3 Above the Ceiling (Plenum) Installations
An above the ceiling installation requires placing the access point above a suspended ceiling and
installing the provided light pipe under the ceiling tile for viewing the rear panel status LEDs of the
unit. An above the ceiling installation enables installations compliant with drop ceilings, suspended
ceilings and industry standard tiles from .625 to .75 inches thick.
Page 60

2-16
AP-7131N-FGR Access Point Product Reference Guide
NOTE The AP-7131N-FGR is Plenum rated to UL2043 and NEC1999 to support
above the ceiling installations.
CAUTION Do not mount the access point directly to any suspended ceiling tile
with a thickness less than 12.7mm (0.5in.) or a suspended ceiling tile
with an unsupported span greater than 660mm (26in.). Fit the access
point with a safety wire suitable for supporting the weight of the
device. The safety wire should be a standard ceiling suspension cable
or equivalent steel wire between 1.59mm (.062in.) and 2.5mm (.10in.)
in diameter.
The mounting hardware required to install the access point above a ceiling consists of:
• Light pipe
• Badge for light pipe
• Decal for badge
• Safety wire (strongly recommended)
• Security cable (optional)
To install the access point above a ceiling:
1. If possible, remove the adjacent ceiling tile from its frame and place it aside.
2. Install a safety wire, between 1.5mm (.06in.) and 2.5mm (.10in.) in diameter, in the ceiling
space.
3. If required, install and attach a security cable to the access point’s lock port.
4. Mark a point on the finished side of the tile where the light pipe is to be located.
5. Create a light pipe path hole in the target position on the ceiling tile.
6. Use a drill to make a hole in the tile the approximate size of the LED light pipe.
CAUTION Care should be taken not to damage the finished surface of the ceiling
tile when creating the light pipe hole and installing the light pipe.
7. Remove the light pipe’s rubber stopper before installing the light pipe.
8. Connect the light pipe to the bottom of the access point. Align the tabs and rotate
approximately 90 degrees. Do not over tighten
Page 61

Hardware Installation
9. Fit the light pipe into hole in the tile from its unfinished side.
10. Place the decal on the back of the badge and slide the badge onto the light pipe from the
finished side of the tile.
11. Attach the radio antennas to their correct connectors. For more information on available
antennas, see Antenna Options on page 2-4.
12. Attach safety wire to the access point’s safety wire tie point or security cable (if used) to the
access point’s lock port.
13. Align the ceiling tile into its former ceiling space.
14. Cable the access point using either a Power Injector or approved line cord and power supply.
2-17
CAUTION Do not supply power to the access point until the cabling of the unit is
complete.
For Power Injector installations:
a. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the Power Injector Data In connector.
b. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the Power Injector Data &
Power Out connector and the access point’s GE1/POE port.
c. Ensure the cable length from the Ethernet source to the Power Injector and access point
does not exceed 100 meters (333 ft). The Power Injector has no On/Off power switch.
The Power Injector receives power as soon as AC power is applied. For more information
on using the Power Injector, see Power Injector System on page 2-6.
Page 62
2-18
AP-7131N-FGR Access Point Product Reference Guide
For standard 48-Volt Power Adapter (Part No. 50-14000-247R) and line cord installations:
a. Connect a RJ-45 CAT5e (or CAT6) Ethernet cable between the network data supply (host)
and the access point’s GE1/POE port.
b. Verify the power adapter is correctly rated according the country of operation.
c. Connect the power supply line cord to the power adapter.
d. Attach the power adapter cable into the power connector on the access point.
e. Plug the power adapter into an outlet.
15. Verify the behavior of the LEDs. For more information, see LED Indicators on page 2-18.
16. Place the ceiling tile back in its frame and verify it is secure.
The access point is ready to configure. For information on an access point default
configuration, see Getting Started on page 3-1. For specific details on system
configurations, see System Configuration on page 4-1.
2.8 LED Indicators
An AP-7131N-FGR model access point has six LEDs on the top of the access point housing, and one
optional LED light pipe at the bottom of the unit. However, an AP-7131N-FGR model access point does
not use LED 6, as no third radio is available. Five LEDs illuminate (on top of the housing) for dual radios
models.
The access point utilizes two (different colored) lights below each LED. Only one light displays within
a LED at any given time. Every light within each LED is exercised during startup to allow the user to
see if an LED is non-functional. The LEDs turn on and off while rotating around in a circle. Since two
LEDs feed each light pipe, the pattern is from left to right, then right to left.
NOTE LED blink rate is proportional to activity. The busiest traffic corresponds
to the fastest blink, while the slowest traffic corresponds to slowest
blink.
Page 63

Hardware Installation
NOTE Depending on how the 5 GHz and 2.4 GHz radios are configured, the LEDs
will blink at different intervals between amber and yellow (5 GHz radio)
and emerald and yellow (2.4 GHz radio).
2-19
The LEDs on the top housing of the access point are clearly visible in wall and below ceiling
installations. The top housing LEDs have the following display and functionality:
Page 64

2-20
AP-7131N-FGR Access Point Product Reference Guide
2.8.1 Dual Radio (2.4/5 GHz) LEDs
A dual radio (2.4/5 Ghz) model access point has the following unique LED behavior:
LED 1 LED 2 (LAN) LED 3 (WAN) LED 4 - 5 GHz LED 5 - 2.4 GHz LED 6
Blinking Red
indicates
booting.Solid
Red defines
the diagnostic
mode.
White
defines
normal
operation.
Green
defines
normal GE1
operation.
Green
defines
normal GE2
operation.
Blinking
Amber
indicates
802.11a
activity.
A 5 second
Amber and
Yellow blink
rate defines
802.11an
activity.
A 2 second
Amber and
Yellow blink
rate defines
802.11an
(40 MHz)
activity.
When
functioning as
a sensor, LED
alternates
between
Amber and
Yellow.
The blink
interval is 0.5
seconds. It’s 1
second when
no Server is
connected.
Blinking
Emerald
indicates
802.11bg
activity.
A 5 second
Emerald and
Yellow blink
rate defines
802.11bgn
activity.
A 2 second
Emerald and
Yellow blink
rate defines
802.11bgn
(40 MHz)
activity.
When
functioning as
a sensor, LED
alternates
between
Emerald and
Yellow.
The blink
interval is 0.5
seconds. It’s 1
second when
no Server is
connected.
Not used
Page 65

Hardware Installation
2.8.2 Rear LED
The LED on the rear (bottom) of the access point is optionally viewed using a single (customer
installed) extended light pipe, adjusted as required to suit above the ceiling installations. The LED
light pipe has the following color display and functionality:
LED 7
Blinking Red (160 msec) indicates a failure condition.
Solid Red defines the diagnostic mode.
White defines normal operation.
2.9 Setting Up MUs
2.9.1 Legacy MUs
For a discussion of how to initially test the access point to ensure it can interoperate with the MUs
intended for its operational environment, see Basic Configuration on page 3-4 and specifically Tes ting
Connectivity on page 3-17.
2-21
Refer to the LA-5030 & LA-5033 Wireless Networker PC Card and PCI Adapter Users Guide, available
from the Zebra Web site, for installing drivers and client software if operating in an 802.11a/g
network environment.
Refer to the Spectrum24 LA-4121 PC Card, LA-4123 PCI Adapter & LA-4137 Wireless Networker User
Guide, available from the Zebra Web site, for installing drivers and client software if operating in an
802.11b network environment.
Use the default values for the ESSID and other configuration parameters until the network connection
is verified. MUs attach to the network and interact with the AP transparently.
Page 66

2-22
AP-7131N-FGR Access Point Product Reference Guide
2.9.2 802.11n MUs
Third-party 802.11n clients can connect to the access point using default settings with no additional
user intervention. However, there could be instances where the specific (high-performance) 802.11n
settings cannot be sustained due to adverse radio traffic conditions within the network. When this
occurs, change the Windows XP settings so the adapter can use settings defined for legacy (802.11a/
bg) adapter operation. Once network conditions improve, use Windows XP to re-enable the adapter
for 802.11n support.
To change the access point’s settings to support legacy 802.11a/bg operation (using Windows XP):
1. Select My Network Places.
2. Right-click and select Properties. The Network Connections screen displays.
3. Select (right-click on) the adapter supporting 802.11n operation with the access point and
select Properties.
4. Click on the Configure button.
The Network Connection screen displays supporting the 802.11n adapter.
5. Select the Advanced tab.
6. Select 802.11n Network from the Property field and select either Enable or Disable from
the Value drop-down menu.
Select Disable when the 802.11n rate settings and performance values defined on the
access point cannot be sustained (due to network congestion or interference). Once network
conditions improve to the point where 802.11n traffic can be sustained, enable the 802.11n
Network parameter once again.
Page 67

Hardware Installation
2-23
NOTE If re-enabling the adapter for 802.11 support, ensure additional 802.11n
settings (Aggregation, Channel Width, Guard Interval etc.) are also
enabled to ensure optimal operation.
7. Click OK to save the updates to the adapter’s configuration.
Page 68

2-24
AP-7131N-FGR Access Point Product Reference Guide
Page 69

3
Getting Started
The access point should be installed in an area tested for radio coverage using one of the site survey
tools available to the field service technician. Once an installation site has been identified, the
installer should carefully follow the hardware precautions, requirements, mounting guidelines and
power options outlined in Hardware Installation.
See the following sections for more details:
• Installing the Access Point
• Configuration Options
• Basic Configuration
3.1 Installing the Access Point
Make the required cable and power connections before mounting the access point in its final
operating position. Test the access point with an associated MU before mounting and securing the
access point. Carefully follow the mounting instructions in one of the following sections to ensure the
access point is installed correctly:
Page 70

3-2
AP-7131N-FGR Access Point Product Reference Guide
• For instructions on mounting the access point to a wall, see Wall Mounted Installations on
page 2-10.
• For instructions on mounting an access point to a ceiling T-bar, see Suspended Ceiling T-Bar
Installations on page 2-13.
• For instructions on installing the access point in an above the ceiling attic space, see Above
the Ceiling (Plenum) Installations on page 2-15.
For information on the antenna suite available to the AP-7131N-FGR, see Antenna Options on page
2-4. For more information on using a Power Injector to combine Ethernet and power in one cable to
an access point, see Power Injector System on page 2-6. To verify LED behavior once installed, see
LED Indicators on page 2-18.
3.2 Configuration Options
Once installed and powered, the access point can be configured using one of several connection
techniques. Managing the AP-5131 includes viewing network statistics and setting configuration
options. The AP-5131 requires one of the following connection methods to manage the network:
• Secure Java-Based WEB UI - (use Sun Microsystems’ JRE 1.6 available from Sun’s Web site.
Disable Microsoft’s Java Virtual Machine if installed). For information on using the Web UI
to set AP-5131 default configuration, see Basic Configuration on page 3-4 or chapters 4
through 7 of this guide.
• Command Line Interface (CLI) via Serial, and SSH. The access point CLI is accessed through
the RS232 port, via SSH. The CLI follows the same configuration conventions as the device
user interface with a few documented exceptions. For details on using the CLI to manage
the access point, see Connecting to the CLI on page 8-2.
• Config file - Readable text file; Importable/Exportable via SFTP. Configuration settings for an
access point can be downloaded from the current configuration of another access point
meeting the import/export requirements. For information on importing or exporting
configuration files, see Importing/Exporting Configurations on page 4-47.
MIB (Management Information Base) accessing the AP-5131 SNMP functions using a MIB Browser.
The MIB files are available atwww.zebra.com/support
MIBS 4.0.4.0”. For more information refer Appendix C, Zebra Support.
. The user should serach for “AP7131N-GR
Page 71

Getting Started
3.3 Initially Connecting to the Access Point
NOTE The procedures described below assume this is the first time you are
connecting to an AP-7131N-FGR model access point.
NOTE The computer being used should be configured to use the same IP address
and subnet mask as the access point.
3.3.1 Connecting to the Access Point using the WAN Port
To initially connect to the access point using the access point’s WAN port:
1. Connect AC power to the access point, as Power-Over-Ether support is not available on the
access point’s WAN (or GE2) port.
2. Start a browser and enter the access point’s static IP address (10.1.1.1). The default
password is “admin123.”
3. Refer to Basic Configuration on page 3-4 for instructions on the initial (basic) configuration
of the access point.
3-3
3.3.2 Connecting to the Access Point using the LAN Port
To initially connect to the access point using the access point’s LAN port:
1. The LAN (or GE1/POE) port has a default static IP address of 192.168.0.1/24.
2. To view the IP address, connect one end of a null modem serial cable to the access point and
the other end to the serial port of a computer running HyperTerminal or similar emulation
program.
3. Configure the following settings:
• Baud Rate - 19200
• Data Bits - 8
• Stop Bits - 1
• No Parity
• No Flow Control
4. Press <ESC> or <Enter> to access the access point CLI.
5. Enter the default username of “admin” and the default password of “admin123.”
Page 72

3-4
AP-7131N-FGR Access Point Product Reference Guide
As this is the first time you are logging into the access point, you are prompted to enter a
new password and set the county code. Refer to Country Codes on page A-4 for a list of each
available countries two digit country code.
6. At the CLI prompt (admin>), type “summary.”
The access point’s LAN IP address will display.
7. Using a Web browser, use the access point’s IP address to access the access point.
8. Refer to Basic Configuration on page 3-4 for instructions on the initial (basic) configuration
of the access point.
3.4 Basic Configuration
3.4.1 Configuring Your Browser for AP-7131N-FGR Support
An AP-7131N-FGR model access point is compliant with the FIPS140-2 standard. The AP-7131N-FGR
is only accessible using browsers that support the TLS 1.0 protocol. The AP-7131N-FGR is not
accessible by browsers supporting the SSL 2.0 or SSL 3.0 protocols. Additionally, ensure JRE (version
1.6) is installed on the computer accessing the AP-7131N-FGR GUI applet. The following sections
describe how to change your browser settings using either Internet Explorer or Mozilla Firefox in order
to correctly launch and display the AP-7131N-FGR GUI applet. Without these browser modifications,
you will not be able to access the AP-7131N-FGR GUI applet.
CAUTION With both the Internet Explorer and Mozilla Firefox browser
configurations, screens may display stating Website certificates
cannot be validated or have been certified by an unknown
authority. Do not exit the browser configuration, as these
messages will occur with only the initial AP-7131N-FGR browser
configuration.
3.4.1.1 Accessing the AP-7131N-FGR Using Internet Explorer
To define the browser settings needed to access the AP-7131N-FGR using Windows Internet Explorer:
1. Open the Internet Explorer browser and open the Too ls > Internet Options menu.
2. Select the Advanced tab.
3. Scroll down to the bottom of the Advanced tab and ensure the Use TLS 1.0 option is
selected. Remember, the AP-7131N-FGR does not support SSL 2.0 or SSL 3.0.
Page 73

Getting Started
4. Enter the IP address of the AP-7131N-FGR 4.0 within Internet Explorer. Select the Continue
to this Website (not recommended) option. The default IP address is 10.1.1.1.
At this point in the browser configuration, a screen displays stating the Web site’s certificate
cannot be verified.
5. Click Yes to continue. The access point’s login screen displays.
6. Log in using admin as the default User ID and admin123 as the default password. If the
default login is successful, the Change Admin Password window displays. You need to
immediately change the password for security.
7. For more information, see Configuring the Access Point on page 3-5.
3.4.1.2 Accessing the AP-7131N-FGR Using Mozilla Firefox
To define the browser settings needed to access the AP-7131N-FGR using Mozilla Firefox:
1. Open the Mozilla Firefox browser and open the Too ls > Options menu.
2. Select the Advanced tab, then select either the Encryption or Security tab (they differ
depending on the version of Firefox used).
3. Within the Protocols field, ensure the Use TLS 1.0 option is selected. Remember, the
AP-7131N-FGR does not support SSL 2.0 or SSL 3.0.
3-5
A Website Certified by an Unknown Authority screen displays stating Firefox is unable
to define a trusted site.
4. Select either the Accept this certificate permanently or Accept this certificate
temporarily for this session. Click the OK button to continue.
A Security Error: Domain Name Mismatch screen could display. Click OK to continue.
At this point in the browser configuration, a screen displays stating the Web site’s certificate
cannot be verified.
5. Click Yes to continue. The access point’s login screen displays.
6. Log in using admin as the default User ID and admin123 as the default password. If the
default login is successful, the Change Admin Password window displays. You need to
immediately change the password for security. For more information, see Configuring the
Access Point on page 3-5.
3.4.2 Configuring the Access Point
For the basic setup described in this section, the Java-based Web UI will be used to configure the
access point.To access the access point via the GE1/POE port,the GE1/POE port is statically assigned
Page 74
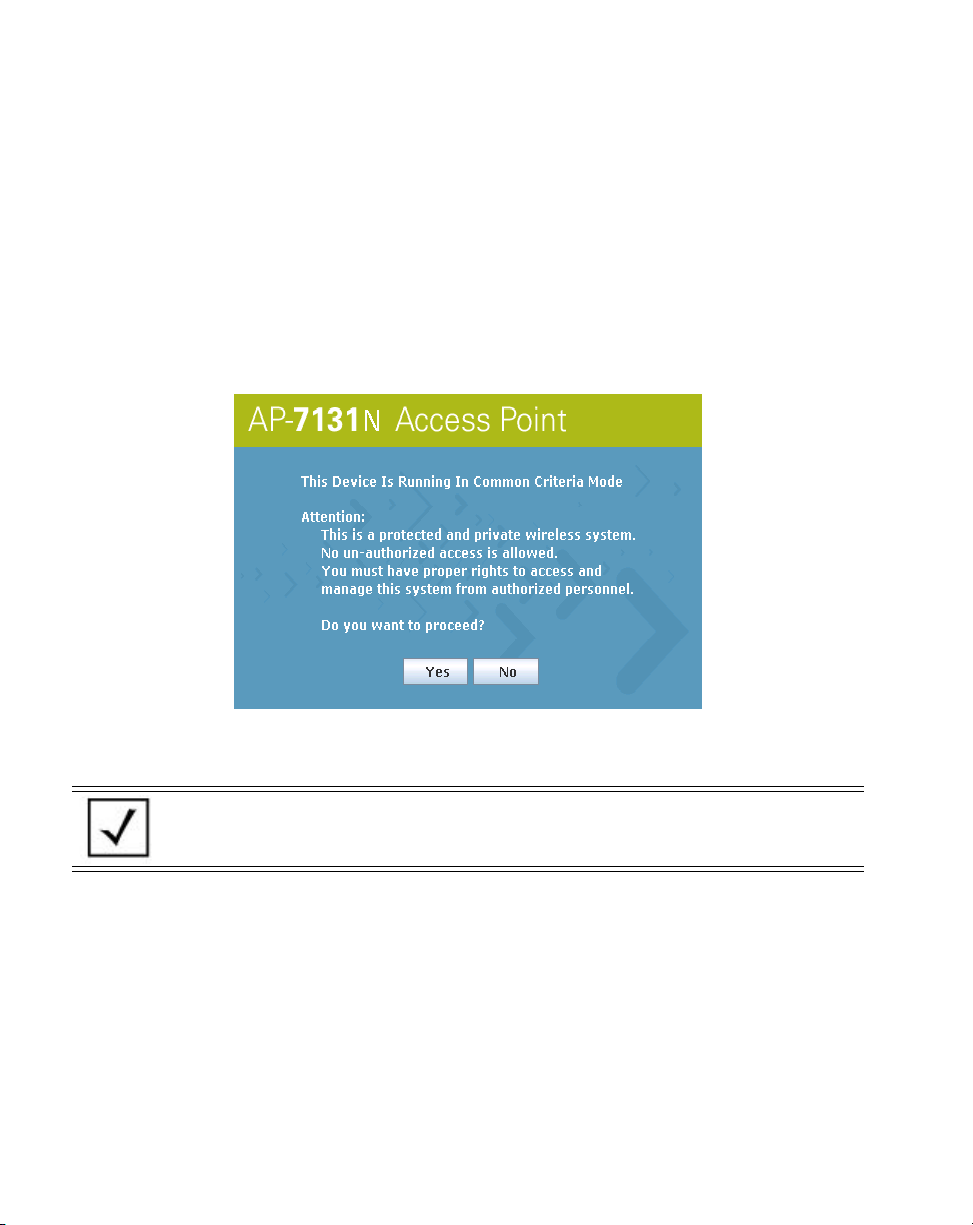
3-6
AP-7131N-FGR Access Point Product Reference Guide
default IP address of 192.168.0.1. The default WAN IP address for GE2 port is set to 10.1.1.1. For this
example, the access point’s LAN interface (GE1 port) will be used to connect to the access point.For
optimal viewing of the Web UI, the screen resolution should be set to 1024 x 768 pixels or greater.
Remember, Internet Explorer and Mozilla Firefox require unique settings be defined in order for the
browser to access the AP-7131N-FGR GUI applet. For instructions on configuring these browser
settings, see Configuring Your Browser for AP-7131N-FGR Support on page 3-4.
1. Start a browser and enter the following IP address in the address field:
https://192.168.0.1
2. Log in using admin as the default Username and admin123 as the default Password. Use
your new password if it has been updated from default.
NOTE For optimum compatibility, use Sun Microsystems’ JRE 1.6 (available from
Sun’s Website), and be sure to disable Microsoft’s Java Virtual Machine if
installed.
Page 75

Getting Started
3. If the default login is successful, the Change Admin Password window displays. Change
the 8-19 character password to ensure the AP-7131N-FGR is using a secure password
different from the default password.
Enter the current password and a new admin password in fields provided. Click Apply. Once
the admin password has been updated, a warning message displays stating the access point
must be set to a country. Proceed to Configuring Device Settings on page 3-8 to validate the
country setting.
3-7
The export function will always export the encrypted Admin User password. The import
function will import the Admin Password only if the access point is set to factory default. If
the access point is not configured to factory default settings, the Admin User password WILL
NOT get imported.
NOTE Though the AP-5131 can have its basic settings defined using a number of
different screens, Use the AP-5131 Quick Setup screen to set the correct
country of operation and define its minimum required configuration from
one convenient location.
Page 76

3-8
AP-7131N-FGR Access Point Product Reference Guide
3.4.3 Configuring Device Settings
Configure a set of minimum required device settings within the Quick Setup screen. The values
(LAN, WAN etc.) can often be defined in other locations within the menu tree. When you change the
settings in the Quick Setup screen, the values also change within the screen where these parameters
also exist. Additionally, if the values are updated in these other screens, the values initially set within
the Quick Setup screen will be updated.
NOTE Beginning with the 4.0 release of the access point firmware, a new
scheme for radio configuration and WIPS server management has been
implemented within the Quick Setup GUI applet. These radio buttons
define how WLAN and sensor functionality are supported amongst the
radios available to the access point. The options available depend on the
SKU supported (and are described within this section).
To define a basic access point configuration:
1. Select System Configuration -> Quick Setup from the menu tree, if the Quick Setup
screen is not already displayed.
2. Select the System Configuration tab to define the access point’s system, WIPS server and
radio configuration.
NOTE Beginning with the 4.0 release of the access point firmware, sensor
functionality is no longer configured within a designated WIPS screen.
The WIPS Server designation and radio configuration is now defined as
part of the access point’s quick setup. For a description of sensor
functionality and how it relates to access point operation, see Sensor
Support on page 1-6.
Page 77

Getting Started
3-9
3. Refer to the AP-71xx System Settings field to define the following parameters:
System Name Assign a System Name to define a title for this access point. The
System Name is useful if multiple devices are being administered.
Country Select the Country for the AP-5131’s country of operation. The access
point prompts for the correct country code on the first login. A warning
message also displays stating an incorrect country setting may result in
illegal radio operation. Selecting the correct country is central to legally
operating the access point. Each country has its own regulatory
restrictions concerning electromagnetic emissions and the maximum RF
signal strength that can be transmitted. To ensure compliance with
national and local laws, set the country accurately. CLI and MIB users
cannot configure their access point until a two character country code
(for example, United States - us) is set. Refer to Country Codes on page
A-4 for the two character country codes.
Page 78

3-10
AP-7131N-FGR Access Point Product Reference Guide
Time Server Optionally enter the IP address of the server used to provide system time
to the AP-5131 within the Time Server field. Once the IP address is
entered, the AP-5131’s Network Time Protocol (NTP) functionality is
engaged automatically. Refer to Configuring Network Time Protocol
(NTP) on page 4-41 (if necessary) for information on setting alternate
time servers and setting a synchronization interval for the AP-5131 to
adjust its displayed time.
WIPS Servers Define a primary and alternate WIPS server IP Address for WIPS Server
1 and 2. These are the addresses of the primary and secondary WIPS
console server. WIPS support requires an AirDefense WIPS Server on
the network. WIPS functionality is not provided by the access point
alone. The access point works in conjunction with the dedicated WIPS
server(s).
NOTE The System Name and Country are also configurable within the System
Settings screen. Refer to Configuring System Settings on page 4-2 (if
necessary) to set a system location and admin email address for the
AP-5131 or to view other default settings.
4. Refer to the new Radio Configuration field to define how WLAN and WIPS are supported
by the access point’s radio(s). Remember, the options available depend on the radio model
SKU deployed.
A dual radio model access point displays 7 configuration options. Refer to the following
table for the options available to dual radio models.
Radio Button AP-7131N-FGR Dual Radio SKU
2.4 GHz WLAN,
& Sensor
5.0 GHz WLAN
& Sensor
2.4 GHz WLAN &
5.0 GHz WLAN only - no Sensor
Radio1 WLAN,
Radio 2 WIPS
Radio 1 WIPS,
Radio 2 WLAN
Radio 1 WLAN,
Radio 2 WLAN
Page 79

Getting Started
3-11
Sensor only Spectrum Analysis
mode
Radio 1 WIPS,
Radio 2 WIPS
(no WLAN)
2.4 GHz WLAN - no Sensor Radio1 WLAN,
Radio 2 Disabled
5.0 GHz WLAN - no Sensor Radio1 Disabled,
Radio 2 WLAN
Radios Off Radios 1 and 2 Disabled
5. Select the Quick Setup screen’s Network Configuration tab to define a minimum set of
WAN or LAN configuration values. The WAN tab displays by default.
Set a minimum set of parameters for using the WAN interface.
a. Select the Enable WAN Interface checkbox to enable a connection between the
AP-5131 and a larger network or outside world through the WAN port. Disable this
option to effectively isolate the AP-5131’s WAN connection. No connections to a larger
Page 80

3-12
AP-7131N-FGR Access Point Product Reference Guide
network or the Internet will be possible. MUs cannot communicate beyond the
configured subnets.
b. Select the This Interface is a DHCP Client checkbox to enable DHCP for the AP-5131’s
WAN connection. This is useful, if the larger corporate network or Internet Service
Provider (ISP) uses DHCP. DHCP is a protocol that includes mechanisms for IP address
allocation and delivery of host-specific configuration parameters from a DHCP server to
a host. Some of these parameters are IP address, network mask, and gateway.
NOTE The WAN and LAN ports should not be configured as DHCP clients at the
same time.
c. Specify an IP address for the AP-5131’s WAN connection. An IP address uses a series
of four numbers expressed in dot notation, for example, 190.188.12.1 (no DNS names
supported).
d. Specify a Subnet Mask for the AP-5131’s WAN connection. This number is available
from the ISP for a DSL or cable-modem connection, or from an administrator if the
AP-5131 connects to a larger network. A subnet mask uses a series of four numbers
expressed in dot notation. For example, 255.255.255.0 is a valid subnet mask.
e. Define a Default Gateway address for the AP-5131’s WAN connection. The ISP or a
network administrator provides this address.
f. Specify the address of a Primary DNS Server. The ISP or a network administrator
provides this address.
g. Optionally, use the Enable PPP over Ethernet checkbox to enable Point-to-Point
Protocol over Ethernet (PPPoE) for a high-speed connection that supports this protocol.
Most DSL providers are currently using or deploying this protocol. PPPoE is a data-link
protocol for dialup connections. PPPoE will allow the access point to use a broadband
modem (DSL, cable modem, etc.) for access to high-speed data networks.
h. Select the Keep Alive checkbox to enable occasional communications over the WAN
port even when client communications to the WAN are idle. Some ISPs terminate
inactive connections, while others do not. In either case, enabling Keep-Alive maintains
the WAN connection, even when there is no traffic. If the ISP drops the connection after
the idle time, the AP-5131 automatically reestablishes the connection to the ISP.
i. Specify the Username entered when connecting to the ISP. When the Internet session
begins, the ISP authenticates the username.
Page 81

j. Specify the Password entered when connecting to the ISP. When the Internet session
starts, the ISP authenticates the password.
For additional AP-5131 WAN port configuration options, see Configuring WAN Settings on
page 5-15.
6. Select the LAN#1 tab to set a minimum set of parameters to use the LAN#1 interface.
a. Select the Enable LAN Interface checkbox to forward data traffic over the AP-5131’s
LAN connection. The LAN connection is enabled by default.
b. Use the This Interface drop-down menu to specify how network address information
is defined over the LAN connection. Select DHCP Client if the larger corporate network
uses DHCP. DHCP is a protocol that includes mechanisms for IP address allocation and
delivery of host-specific configuration parameters from a DHCP server to a host. Some
of these parameters are IP address, network mask, and gateway. Select DHCP Server
to use the AP-5131 as a DHCP server over the LAN connection. Select the Bootp client
option to enable a diskless system to discover its own IP address.
.
NOTE The WAN and LAN ports should not both be configured as DHCP clients.
Getting Started
3-13
c. Enter the network-assigned IP Address of the AP-5131.
NOTE DNS names are not supported as a valid IP address for the AP-5131. The
user is required to enter a numerical IP address.
d. The Subnet Mask defines the size of the subnet. The first two sets of numbers specify
the network domain, the next set specifies the subset of hosts within a larger network.
These values help divide a network into subnetworks and simplify routing and data
transmission.
e. If using the static or DHCP Server option, enter a Default Gateway to define the
numerical IP address of a router the AP-5131 uses on the Ethernet as its default gateway.
f. If using the static or DHCP Server option, enter the Primary DNS Server numerical IP
address.
g. If using the DHCP Server option, use the Address Assignment Range parameter to
specify a range of IP address reserved for mapping clients to IP addresses. If a manually
(static) mapped IP address is within the IP address range specified, that IP address could
Page 82

3-14
AP-7131N-FGR Access Point Product Reference Guide
still be assigned to another client. To avoid this, ensure all statically mapped IP
addresses are outside of the IP address range assigned to the DHCP server.
For additional AP-5131 LAN port configuration options, see Configuring the LAN Interface
on page 5-1.
7. Select the WLAN #1 tab (WLANs 1 - 4 are available within the Quick Setup screen) to define
its ESSID and security scheme for basic operation.
NOTE A maximum of 16 WLANs are configurable within the Wireless
Configuration screen. The limitation of 16 WLANs.
a. Enter the Extended Services Set Identification (ESSID) and name associated with the
WLAN. For additional information on creating and editing up to 16 WLANs per AP-5131,
see Creating/Editing Individual WLANs on page 5-28.
b. Use the Available On checkboxes to define whether the target WLAN is operating in
the 2.4 or 5 GHz radio band. Ensure the radio selected has been enabled (see step 8).
8. Once the WLAN’s radio designations have been made, the radio must be configured in
respect to intended 2.4 or 5 GHz radio traffic and the antennas used. Refer to
Network Configuration -> Wireless -> Radio Configuration -> Radio1 (or Radio2),
and configure the Radio Settings field (at a minimum). If you know the radio’s Properties,
Performance and Beacon Settings, those fields can also be defined at this time.
Define the Channel Settings, Power Level and 802.11 mode in respect to the 2.4 or 5 GHz
802.11b/g/n or 802.11a/n radio traffic and anticipated gain of the antennas.
CAUTION Only a qualified wireless network administrator should set the
access point radio configuration. Refer to Configuring the
802.11a/n or 802.11b/g/n Radio on page 5-54 for an
understanding of additional radio values and their implications.
NOTE Even an access point configured with minimal values must protect its data
against theft and corruption. A security policy should be configured for
WLAN1 as part of the basic configuration outlined in this guide. A security
policy can be configured for the WLAN from within the Quick Setup
screen. Policies can be defined over time and saved to be used as needed
as security requirements change. You should familiarize yourself with the
security options available on the access point before defining a security
policy. Refer to Configuring Basic WLAN Security Settings on page 3-15.
Page 83

Getting Started
9. Click Apply to save any changes to the AP-5131 Quick Setup screen. Navigating away from
the screen without clicking Apply results in all changes to the screens being lost.
10. Click Undo Changes (if necessary) to undo any changes made. Undo Changes reverts the
settings displayed on the AP-5131 Quick Setup screen to the last saved configuration.
3.4.3.1 Configuring Basic WLAN Security Settings
To configure a basic security policy for a WLAN:
1. From the Quick Setup screen, click the Create button to the right of the Security Policy item.
At a minimum, a basic security scheme (in this case WPA2/CCMP) is recommended in a
network environment where sensitive data is transmitted.
NOTE For information on configuring the other encryption and authentication
options available to the AP-5131, see Configuring Security Options on
page 6-2.
2. Ensure the Name of the security policy entered suits the intended configuration or function
of the policy.
Multiple WLANs can share the same security policy, so be careful not to name security
policies after specific WLANs or risk defining a WLAN to single policy. You should name the
policy after the attributes of the authentication or encryption type selected.
3. Select the WPA2/CCMP (802.11i) checkbox.
3-15
Page 84

3-16
AP-7131N-FGR Access Point Product Reference Guide
4. Configure the Key Rotation Settings as required to set Broadcast Key Rotation and the
update interval.
Broadcast Key
Rotation
Select the Broadcast Key Rotation checkbox to enable or
disable broadcast key rotation. When enabled, the key
indices used for encrypting/decrypting broadcast traffic will
be alternatively rotated on every interval specified in the
Broadcast Key Rotation Interval. Enabling broadcast key
rotation enhances the broadcast traffic security on the
WLAN. This value is disabled by default.
Update broadcast
keys every (30604800 seconds)
Specify a time period in seconds to rotate the key index used
for the broadcast key. Set the interval to a shorter duration
like 3600 seconds for tighter broadcast traffic security on the
wireless LAN. Set the interval to a longer duration like 86400
seconds for less broadcast traffic security requirements.
Default value is 86400 secs.
Page 85

Getting Started
5. Configure the Key Settings as needed.
256-bit Key To use a hexadecimal value (and not an ASCII passphrase),
select the checkbox and enter 16 hexadecimal characters
into each of the four fields displayed.
Default (hexadecimal) 256-bit keys for WP2A/CCMP include:
1011121314151617
18191A1B1C1D1E1F
2021222324252627
28292A2B2C2D2E2F
6. Configure the Fast Roaming (802.1x only) field as required to enable additional AP-5131
roaming and key caching options. This feature is applicable only when using 802.1x EAP
authentication with WPA2/CCMP.
Pre-Authentication Selecting this option enables an associated MU to carry out
an 802.1x authentication with another AP-5131 before it
roams to it. The AP-5131 caches the keying information of
the client until it roams to the other AP-5131. This enables
the roaming client to start sending and receiving data sooner
by not having to do 802.1x authentication after it roams. This
feature is only supported when 802.1x EAP authentication is
enabled.
3-17
NOTE PMK key caching is enabled internally by default when 802.1x EAP
authentication is enabled.
7. Click the Apply button to save the security policy and return to the Quick Setup screen.
At this point, you can test the AP-5131 for MU interoperability.
3.4.4 Testing Connectivity
Verify the access point’s link with an MU by sending Wireless Network Management Protocol
(WNMP) ping packets to the associated MU. Use the Echo Test screen to specify a target MU and
Page 86

3-18
AP-7131N-FGR Access Point Product Reference Guide
configure the parameters of the test. The WNMP ping test only works with Zebra MUs. Only use a
Zebra MU to test access point connectivity using WNMP.
NOTE Before testing for connectivity, the target MU needs to be set to the same
ESSID as the access point. Since WPA2/CCMP has been configured for
the access point, the MU also needs to be configured for WPA2/CCMP
and use the same keys. Ensure the MU is associated with the access point
before testing for connectivity.
To ping a specific MU to assess its connection with an access point:
1. Select Status and Statistics -> MU Stats from the menu tree.
2. Select the Echo Test button from within the MU Stats Summary screen.
3. Define the following parameters for the test.
Station Address The station address is the IP address of the target MU.
Refer to the MU Stats Summary screen for associated MU
IP address information.
Number of pings Defines the number of packets to be transmitted to the
MU. The default is 100.
Packet Length Specifies the length of each packet transmitted to the MU
during the test. The default length is 100 bytes.
4. Click the Ping button to begin transmitting packets to the specified MU address.
Refer to the Number of Responses value to assess the number of responses from the MU
versus the number of ping packets transmitted by the access point. Use the ratio of packets
sent versus the number of packets received the link quality between the MU and the access
point.
Click the OK button to exit the Echo Test screen and return to the MU Stats Summary screen.
3.4.5 Where to Go from Here?
Once basic connectivity has been verified, the AP-5131 can be fully configured to meet the needs of
the network and the users it supports. Refer to the following:
• For detailed information on AP-5131 device access, SNMP settings, network time,
importing/exporting device configurations and device firmware updates, see
Chapter 4, System Configuration on page 4-1.
Page 87

Getting Started
• For detailed information on configuring AP-5131 LAN interface (subnet) and WAN interface
see, Chapter 5, Network Management on page 5-1.
• For detailed information on configuring specific encryption and authentication security
schemes for individual AP-5131 WLANs, see
Chapter 6, Configuring Access Point Security on page 6-1.
• To view detailed statistics on the AP-5131 and its associated MUs, see
Chapter 7, Monitoring Statistics on page 7-1.
3-19
Page 88

3-20
AP-7131N-FGR Access Point Product Reference Guide
Page 89

4
System Configuration
The access point contains a built-in browser interface for system configuration and remote
management using a standard Web browser such as Microsoft Internet Explorer, Netscape Navigator
or Mozilla Firefox (version 0.8 or higher is recommended). The browser interface also allows for
system monitoring of the access point.
Web management of the AP-5131 requires either Microsoft Internet Explorer 5.0 or later or Netscape
Navigator 6.0 or later.
NOTE For optimum compatibility, use Sun Microsystems’ JRE 1.6 (available from
Sun’s Web site), and be sure to disable Microsoft’s Java Virtual Machine
if installed.
To connect to the access point, an IP address is required. If connected to the access point using the
WAN port, the default static IP address is 10.1.1.1. The default password is “
to the access point using the LAN port, the default static IP addrees is 192.168.0.1/24. The user is
required to know the IP address to connect to the access point using a Web browser.
admin123.” If connected
Page 90

4-2
AP-7131N-FGR Access Point Product Reference Guide
System configuration topics include:
• Configuring System Settings
• Configuring Power Settings
• Adaptive AP Setup
• Configuring Data Access
• Managing Certificate Authority (CA) Certificates
• Configuring SNMP Settings
• Configuring Network Time Protocol (NTP)
• Logging Configuration
• Importing/Exporting Configurations
• Updating Device Firmware
• Key Zeroisation
4.1 Configuring System Settings
Use the System Settings screen to specify the name and location of the AP-5131, assign an e-mail
address for the network administrator, restore the AP’s default configuration or restart the AP.
To configure System Settings for the AP-5131:
CAUTION The access point’s country of operation is set from within the System
Settings screen. If the country code is changed, the access point’s
power level, primary channel and secondary channel return to their
default values. If changing the country code, be aware these values
will require modification to their previous settings.
1. Select System Configuration -> System Settings from the AP-5131 menu tree.
Page 91

System Configuration
2. Configure the AP-5131 System Settings field to assign a system name and location, set
the country of operation and view device version information.
4-3
System Name Specify a device name for the AP-5131. Select a name serving as a
reminder of the user base the AP-5131 supports (engineering,
retail, etc.). This name will appear in the WIPS server when one of
the radios is configured as a sensor and the WIPS functionality
connects to the WIPS server. The WIPS module only accepts names
with up to 20 characters, keep that if intending to use this AP as a
sensor.
System Location Enter the location of the AP-5131. The System Location
parameter acts as a reminder of where the AP can be found. Use
the System Name field as a specific identifier of device location.
Use the System Name and System Location fields together to
optionally define the AP name by the radio coverage it supports and
specific physical location. For example, “second floor engineering”
Admin Email Address Specify the AP administrator's e-mail address.
Page 92

4-4
AP-7131N-FGR Access Point Product Reference Guide
Country The AP-5131 prompts the user for the correct country code after the
first login. A warning message also displays stating that an
incorrect country setting will lead to an illegal use of the access
point. Use the pull-down menu to select the country of operation.
Selecting the correct country is extremely important. Each country
has its own regulatory restrictions concerning electromagnetic
emissions (channel range) and the maximum RF signal strength
transmitted. To ensure compliance with national and local laws, be
sure to set the Country field correctly.
If using the AP-5131 configuration file, CLI or MIB to configure the
AP-5131’s country code, see Country Codes on page A-4.
Version The displayed number is the current version of the device firmware.
Use this information to determine if the access point is running the
most recent firmware. Use the Firmware Update screen to keep
the AP’s firmware up to date. For more information, see Updating
Device Firmware on page 4-51.
System Uptime Displays the current uptime of the AP-5131 defined in the System
Name field. System Uptime is the cumulative time since the
AP-5131 was last rebooted or lost power.
Serial Number Displays the AP-5131 Media Access Control (MAC) address. The
AP-5131 MAC address is hard coded at the factory and cannot be
modified. The LAN and WAN port MAC addresses can be located
within the LAN and WAN Stats screens. For information on
locating the access point MAC addresses, see Viewing WAN
Statistics on page 7-2 and Viewing LAN Statistics on page 7-6.
AP Mode Displays the access point’s mode of operation to convey whether
the access point is functioning as a standalone access point
(Independent mode) or in Adaptive (thin AP) mode. If in Adaptive
mode, the access point attempts to discover a switch through one
or more of several mechanisms: DNS, DHCP, ICMP, CAPWAP or a
statically programmed IP address. For information on adaptive AP,
see, Adaptive AP on page 10-1.
Enable DNS-Relay By default DNS-Relay-Mode is enabled.
3. Refer to the Factory Defaults field to restore either a full or partial default configuration.
Page 93

System Configuration
CAUTION Restoring the access point’s configuration back to default settings
changes the administrative password back to “admin123.” If restoring
the configuration back to default settings, be sure you change the
administrative password accordingly.
4-5
Restore Default
Configuration
Restore Partial
Default Configuration
Select the Restore Default Configuration button to reset the
AP’s configuration to factory default settings. If selected, a
message displays warning the user the current configuration will
be lost if the default configuration is restored. Before using this
feature, use the Config Import/Export screen to export the
current configuration for safekeeping, see Importing/Exporting
Configurations on page 4-47.
Select the Restore Partial Default Configuration button to
restore a default configuration with the exception of the current
LAN, WAN, SNMP settings and IP address used to launch the
browser. If selected, a message displays warning the user all
current configuration settings will be lost with the exception of
WAN and SNMP settings. Before using this feature, use the
Config Import/Export screen to export the current configuration
for safekeeping, see Importing/Exporting Configurations on page 4-
47.
4. Use the Reset Keys field to zeroise the key values (if necessary).
Reset Keys to Zero In AP7131N, key zeroisation function zeroises all Cryptographic
Keys and Critical Security Parameters (CSP) by overwriting the
storage area three times with an alternating pattern (i.e, three
different patterns).
5. Refer to the Self Test field to run self tests and view self test logs.
Run Self Test Select the Run Self Test button to run self tests. The AP-7131N-
FGR access points run a series of self tests. If one of the self test
fails, the device transitions into an error state where all data output
and cryptographic operations are disabled.
Show Self Test Logs Select the Show Self Test Logs
to view the self test logs.
6. Use the Restart field to restart the AP (if necessary).
Page 94

4-6
AP-7131N-FGR Access Point Product Reference Guide
Restart Click the Restart button to reboot the AP-7131N-FGR. Restarting
the AP-7131N-FGR resets all data collection values to zero. Do not
restart the AP-7131N-FGR during significant system uptime or data
collection activities.
CAUTION After a reboot, static route entries disappear from the AP Route Table
if a LAN Interface is set to DHCP Client. The entries can be retrieved
(once the reboot is done) by performing an Apply operation from the
WEB UI or a save operation from the CLI.
7. Click Apply to save any changes to the System Settings screen. Navigating away from the
screen without clicking the Apply button results in all changes to the screen being lost.
NOTE The Apply button is not needed for restoring the AP-5131 default
configuration or restarting the AP-5131.
8. Click Undo Changes (if necessary) to undo any changes made. Undo Changes reverts the
settings displayed on the System Settings screen to the last saved configuration.
9. Click Logout to securely exit the AP-5131 applet. A prompt displays confirming the logout
before the applet is closed.
4.2 Configuring Power Settings
Use the Power Setting screen to select one of two power modes, 3af or Auto. When automatic is
selected, the access point safely operates within available power. Once the power configuration is
determined, the access point configures its operating power characteristics based on its SKU and
power configuration.
The access point uses a complex programmable logic device (CPLD). The CPLD determines proper
supply sequencing, the maximum power available and other status information. One of the primary
functions of the CPLD is to determine the access point’s maximum power budget. When the AP is
powered on (or performing a cold reset), the CPLD determines the maximum power provided by the
POE device and the budget available to the access point. The CPLD also determines the access point
hardware SKU and the number of radios. If the access point’s POE resource cannot provide sufficient
power to run the access point (with all intended interfaces enabled), some of the following interfaces
could be disabled or modified:
Page 95

System Configuration
• The access point’s transmit and receive algorithms could be negatively impacted
• The access point’s transmit power could be reduced due to insufficient power
• The access point’s WAN port configuration could be changed (either enabled or disabled)
Automatic is the default mode. When Auto is selected, the CPLD determines how much power is
available at startup (3af, 3at or Full Power for an AP-7131N-FGR model).
NOTE An AP-7131N-FGR model uses 22 watts when its power status is 3af,
23 - 26 watts when its power status is 3at and 27 watts when its power
status is Full Power.
CAUTION The power modes described in the section are only obtainable using
the 48-Volt Power Supply (Part No. 50-14000-247R) designed for an
AP-7131N-FGR or using the single-port Power Injector (Part No.
AP-PSBIAS-1P3-AFR).
NOTE Radio transmit power is not used as one of the factors to determine the
available power budget. If an external power supply is used, it is assumed
it will provide full power. When operating using full power, each radio has
3x3 antenna mode support and its intended transmit power budget.
4-7
Radios at Full Power
The table below describes the maximum transmit power available to each radio (at varying data rates)
when the access point is receiving full DC power and is not compromised in its power budget. These
values should be viewed as the safe limit for the access point’s radio at full power and should not be
exceeded.
Maximum
Transmit Power
Rates (Mbps) MCS Indices EVM Bandwidth
1 -9 20MHz 23 NA
2 -9 20MHz 23 NA
5.5 -9 20MHz 23 NA
11 -9 20MHz 23 NA
6 -5 20MHz 23 20
2.4 GHz
Maximum
Transmit Power
5 GHz
Page 96

4-8
AP-7131N-FGR Access Point Product Reference Guide
Maximum
Transmit Power
Rates (Mbps) MCS Indices EVM Bandwidth
9 -8 20MHz 23 20
12 -10 20MHz 23 20
18 -13 20MHz 23 20
24 -16 20MHz 22 20
36 -19 20MHz 22 19
48 -22 20MHz 21 18
54 -25 20MHz 20 17
MCS0/MCS8 -5 HT20/40 23 20
MCS1/MCS9 -10 HT20/40 23 20
MCS2/MCS10 -13 HT20/40 23 20
MCS3/MCS11 -16 HT20/40 23 19
MCS4/MCS12 -19 HT20/40 22 19
MCS5/MCS13 -22 HT20/40 22 18
MCS6/MCS14 -25 HT20/40 21 17
2.4 GHz
Maximum
Transmit Power
5 GHz
MCS7/MCS15 -28 HT20/40 20 17
Radios at Low Power
The table below describes the maximum transmit power available to each radio (at varying data rates)
when the access point is receiving low DC power in either af or at mode.
CAUTION Exceeding the limits listed below can cause damage to the access
point or cause the radio to operate unpredictably. Thus, these values
should be viewed as the safe limit for the access point’s radio and
should not be exceeded in either af or at mode.
Page 97

System Configuration
4-9
Maximum
Transmit Power
Rates (Mbps) MCS Indices EVM Bandwidth
1 -9 20MHz 20 NA
2 -9 20MHz 20 NA
5.5 -9 20MHz 20 NA
11 -9 20MHz 20 NA
6 -5 20MHz 22 19
9 -8 20MHz 22 19
12 -10 20MHz 22 19
18 -13 20MHz 22 18
24 -16 20MHz 21 18
36 -19 20MHz 20 17
48 -22 20MHz 18 15
54 -25 20MHz 17 13
MCS0/MCS8 -5 HT20/40 22 19
MCS1/MCS9 -10 HT20/40 22 19
2.4 GHz
Maximum
Transmit Power
5 GH
MCS2/MCS10 -13 HT20/40 21 18
MCS3/MCS11 -16 HT20/40 21 17
MCS4/MCS12 -19 HT20/40 20 17
MCS5/MCS13 -22 HT20/40 19 16
MCS6/MCS14 -25 HT20/40 18 15
MCS7/MCS15 -28 HT20/40 17 15
NOTE The access point could allow the operation of only one radio depending on
the POE power level provided. When only one radio is operational, it is
configured as either a WIPS or WLAN radio. Consequently, if the access
point transitions from dual to single radio operation, a WIPS radio might
not be available.
Page 98

4-10
AP-7131N-FGR Access Point Product Reference Guide
To define the access point’s power setting:
1. Select System Configuration -> Power Settings from the menu tree.
2. Refer to the following to assess the access point’s current power state. Once known,
determine how available power resources are applied to the access point’s radios.
a
NOTE Within the Power Settings field, an installation professional selects a
power mode as auto or 3af.
Contact Zebra Support if unsure of your access point’s optimal power
management settings.
Page 99

System Configuration
Power Mode When the access point is powered on for the first time, the system
determines the power budget available to the access point. Using
the Auto setting (default setting), the access point automatically
determines the best power configuration based on the available
power budget.
If 3af is selected, the AP assumes 12.95 watts are available. If the
mode is changed, the access point requires a reset to implement
the change.
Power Status Refer to the (read-only) power status field to review the power
available to the AP. For an AP-7131N-FGR model, the options are:
3at, 3af, or Full Power.
3. Click Apply to save any changes to the Power Settings screen. Navigating away from the
screen without clicking the Apply button results in all changes to the screen being lost.
4. Click Undo Changes (if necessary) to undo any changes made. Undo Changes reverts the
settings displayed on the Power Settings screen to the last saved configuration.
5. Click Logout to securely exit the access point applet. A prompt displays confirming the
logout before the applet is closed.
4-11
4.3 Adaptive AP Setup
An access point needs settings defined to discover (and adopt) an available switch and establish a
connection and data tunnel. It’s through this switch adoption that the access point receives its
adaptive AP (AAP) configuration. The access point has a screen to define the mechanisms used to
adopt a switch and route AAP configuration information
NOTE For an AAP overview and a theoretical discussion of how an access point
discovers a switch to creates a secure data tunnel for adaptive AP
operation, see Adaptive AP on page 10-1.
NOTE AAP functionality is only supported on a switch running firmware version
4.0 or higher and a RFS7000 model switch (running firmware version 4.0
or higher).
NOTE The Adaptive AP Setup screen does not display the AAP’s adoption status
or adopted switch. This information is available using the access point’s
CLI. To review AAP adoption status and adopted switch information, see
AP7131N>admin(system.aap-setup)>show on page 8-168.
.
Page 100

4-12
AP-7131N-FGR Access Point Product Reference Guide
To configure the access point’s switch discovery method and connection medium:
1. Select System Configuration -> Adaptive AP Setup from the menu tree.
2. Define the following to prioritize a switch connection scheme and AP interface used to adopt
to the switch.
Control Port Define the port used by the switch FQDN to transmit and receive
with the AAP. The default control port is 24576.
Switch FQDN Add a complete switch fully qualified domain name (FQDN) to add
a switch to the 12 available switch IP addresses available for
connection. The access point resolves the name to one or more IP
addresses if a DNS IP address is present. This method is used when
the access point fails to obtain an IP address using DHCP.
PSK Before the access point sends a packet requesting its mode and
configuration, the switch and the access point require a secure link
using a pre-shared key.
 Loading...
Loading...