Videoswitch Vi-C5101, Vi-C5102, Vi-C5112, Vi-C5105, Vi-C5109 User Manual
...
Vi-C5000 Series Network
Camera User Manual
Products covered by this manual
Vi-C5101, Vi-C5102, Vi-C5105, Vi-C5109,
Vi-C5111, Vi-C5112, Vi-C5113, Vi-C5114,
Vi-C5115, Vi-C5116, Vi-C5117, Vi-C5118
Document Reference Date
Vc608a.doc
24/02/15
Videoswitch
Telephone
01252-851510
Unit 15 Redfields Industrial Park
Fax
01252-851296
Redfields Lane, Church Crookham
Email
sales@videoswitch.co.uk
Hants GU52 0RD
Web
www.videoswitch.co.uk
User Manual of Network Camera
1
This manual applies to the network camera (V5.1.0).
Thank you for purchasing our product. If there are any questions, or requests, please
do not hesitate to contact the dealer.
This manual applies to Network Camera.
This manual may contain several technical incorrect places or printing errors, and the
content is subject to change without notice. The updates will be added to the new
version of this manual. We will readily improve or update the products or procedures
described in the manual.
DISCLAIMER STATEMENT
“Underwriters Laboratories Inc. (“UL”) has not tested the performance or reliability
of the security or signaling aspects of this product. UL has only tested for fire, shock
or casualty hazards as outlined in UL’s Standard(s) for Safety, UL60950-1. UL
Certification does not cover the performance or reliability of the security or signaling
aspects of this product. UL MAKES NO REPRESENTATIONS, WARRANTIES OR
CERTIFICATIONS WHATSOEVER REGARDING THE PERFORMANCE OR
RELIABILITY OF ANY SECURITY OR SIGNALING RELATED FUNCTIONS
OF THIS PRODUCT.
User Manual of Network Camera
2
Regulatory Information
FCC Information
FCC compliance: This equipment has been tested and found to comply with the
limits for a digital device, pursuant to part 15 of the FCC Rules. These limits are
designed to provide reasonable protection against harmful interference when the
equipment is operated in a commercial environment. This equipment generates, uses,
and can radiate radio frequency energy and, if not installed and used in accordance
with the instruction manual, may cause harmful interference to radio communications.
Operation of this equipment in a residential area is likely to cause harmful
interference in which case the user will be required to correct the interference at his
own expense.
FCC Conditions
This device complies with part 15 of the FCC Rules. Operation is subject to the
following two conditions:
1. This device may not cause harmful interference.
2. This device must accept any interference received, including interference that may
cause undesired operation.
EU Conformity Statement
This product and - if applicable - the supplied accessories too are
marked with "CE" and comply therefore with the applicable
harmonized European standards listed under the Low Voltage
Directive 2006/95/EC, the EMC Directive 2004/108/EC, the RoHS
Directive 2011/65/EU.
2012/19/EU (WEEE directive): Products marked with this symbol
cannot be disposed of as unsorted municipal waste in the European
Union. For proper recycling, return this product to your local
supplier upon the purchase of equivalent new equipment, or dispose
of it at designated collection points. For more information see:
www.recyclethis.info.
2006/66/EC (battery directive): This product contains a battery that
cannot be disposed of as unsorted municipal waste in the European
Union. See the product documentation for specific battery
information. The battery is marked with this symbol, which may
include lettering to indicate cadmium (Cd), lead (Pb), or mercury
(Hg). For proper recycling, return the battery to your supplier or to
a designated collection point. For more information see:
www.recyclethis.info.
User Manual of Network Camera
3
Safety Instruction
These instructions are intended to ensure that the user can use the product correctly to
avoid danger or property loss.
The precaution measure is divided into ‘Warnings’ and ‘Cautions’:
Warnings: Serious injury or death may be caused if any of these warnings are
neglected.
Cautions: Injury or equipment damage may be caused if any of these cautions are
neglected.
Warnings Follow these safeguards to
prevent serious injury or death.
Cautions Follow these precautions to
prevent potential injury or material
damage.
Warnings:
Please adopt the power adapter which can meet the safety extra low voltage
(SELV) standard. And source with 12 VDC or 24 VAC (depending on models)
according to the IEC60950-1 and Limited Power Source standard.
If the product does not work properly, please contact your dealer or the nearest
service center. Never attempt to disassemble the camera yourself. (We shall not
assume any responsibility for problems caused by unauthorized repair or
maintenance.)
To reduce the risk of fire or electrical shock, do not expose this product to rain or
moisture.
This installation should be made by a qualified service person and should conform
to all the local codes.
Please install blackouts equipment into the power supply circuit for convenient
supply interruption.
Please make sure that the ceiling can support more than 50(N) Newton gravities if
the camera is fixed to the ceiling.
If the product does not work properly, please contact your dealer or the nearest
service center. Never attempt to disassemble the camera yourself. (We shall not
assume any responsibility for problems caused by unauthorized repair or
maintenance.)
User Manual of Network Camera
4
Cautions:
Make sure the power supply voltage is correct before using the camera.
Do not drop the camera or subject it to physical shock.
Do not touch sensor modules with fingers. If cleaning is necessary, use a clean
cloth with a bit of ethanol and wipe it gently. If the camera will not be used for an
extended period of time, put on the lens cap to protect the sensor from dirt.
Do not aim the camera lens at the strong light such as sun or incandescent lamp.
The strong light can cause fatal damage to the camera.
The sensor may be burned out by a laser beam, so when any laser equipment is
being used, make sure that the surface of the sensor not be exposed to the laser
beam.
Do not place the camera in extremely hot, cold temperatures (the operating
temperature should be between -30°C ~ 60°C, or -40°C ~ 60°C if the camera
model has an “H” in its suffix), dusty or damp environment, and do not expose it
to high electromagnetic radiation.
To avoid heat accumulation, good ventilation is required for a proper operating
environment.
Keep the camera away from water and any liquid.
While shipping, the camera should be packed in its original packing.
Improper use or replacement of the battery may result in hazard of explosion.
Please use the manufacturer recommended battery type.
Notes:
For the dome camera that supports IR, you are required to pay attention to the
following precautions to prevent IR reflection:
Dust or grease on the dome cover will cause IR reflection. Please do not remove
the dome cover film until the installation is finished. If there is dust or grease on
the dome cover, clean the dome cover with clean soft cloth and isopropyl alcohol.
Make certain the installation location does not have reflective surfaces of objects
too close to the camera. The IR light from the camera may reflect back into the
lens causing reflection.
The foam ring around the lens must be seated flush against the inner surface of
the bubble to isolate the lens from the IR LEDS. Fasten the dome cover to camera
body so that the foam ring and the dome cover are attached seamlessly.

User Manual of Network Camera
5
Table of Contents
Chapter 1 System Requirement .............................................................................. 8
Chapter 2 Network Connection ............................................................................. 9
2.1 Setting the Network Camera over the LAN......................................................... 9
2.1.1 Wiring over the LAN ......................................................................................................... 9
2.1.2 Detecting and Changing the IP Address .......................................................................... 10
2.2 Setting the Network Camera over the WAN ....................................................... 11
2.2.1 Static IP Connection ........................................................................................................ 11
2.2.2 Dynamic IP Connection ................................................................................................... 12
Chapter 3 Access to the Network Camera ........................................................... 15
3.1 Accessing by Web Browsers ................................................................................ 15
3.2 Accessing by Client Software .............................................................................. 17
3.2.1 Accessing by Vi-Viewer4000. ......................................................................................... 17
3.2.2 Accessing by Vi-GUARDEXP Software ........................................................................ 18
Chapter 4 Wi-Fi Settings ...................................................................................... 19
4.1 Configuring Wi-Fi Connection in Manage and Ad-hoc Modes ....................... 19
4.2 Easy Wi-Fi Connection with WPS function ....................................................... 23
4.3 IP Property Settings for Wireless Network Connection ................................... 26
Chapter 5 Live View ............................................................................................. 27
5.1 Live View Page ..................................................................................................... 27
5.2 Starting Live View ................................................................................................ 28
5.3 Recording and Capturing Pictures Manually ................................................... 29
5.4 Operating PTZ Control ....................................................................................... 29
5.4.1 PTZ Control Panel . .......................................................................................................... 29
5.4.2 Setting / Calling a Preset. ................................................................................................. 30
Chapter 6 Network Camera Configuration ......................................................... 32
6.1 Configuring Local Parameters............................................................................ 32
6.2 Configuring Time Settings .................................................................................. 34
6.3 Configuring Network Settings ............................................................................ 36
6.3.1 Configuring TCP/IP Settings ........................................................................................... 36
6.3.2 Configuring Port Settings ................................................................................................ 37
6.3.3 Configuring PPPoE Settings ............................................................................................ 38
6.3.4 Configuring DDNS Settings ............................................................................................ 38
6.3.5 Configuring SNMP Settings ............................................................................................ 42
6.3.6 Configuring 802.1X Settings ........................................................................................... 43
6.3.7 Configuring QoS Settings ................................................................................................ 44

User Manual of Network Camera
6
6.3.8 Configuring UPnP™ Settings .......................................................................................... 45
6.3.9 Email Sending Triggered by Alarm ................................................................................. 46
6.3.10 Configuring NAT (Network Address Translation) Settings ....................................... 48
6.3.11 Configuring FTP Settings ........................................................................................... 48
6.4 Configuring Video and Audio Settings ............................................................... 50
6.4.1 Configuring Video Settings ............................................................................................. 50
6.4.2 Configuring Audio Settings . ............................................................................................ 52
6.4.3 Configuring ROI Encoding . ............................................................................................. 52
6.5 Configuring Image Parameters .......................................................................... 54
6.5.1 Configuring Display Settings .......................................................................................... 54
6.5.2 Configuring OSD Settings . .............................................................................................. 59
6.5.3 Configuring Text Overlay Settings .................................................................................. 61
6.5.4 Configuring Privacy Mask ............................................................................................... 61
6.5.5 Configuring Picture Overlay ............................................................................................ 62
6.6 Configuring and Handling Alarms ..................................................................... 63
6.6.1 Configuring Motion Detection......................................................................................... 64
6.6.2 Configuring Video Tampering Alarm .............................................................................. 70
6.6.3 Configuring Alarm Input ................................................................................................. 71
6.6.4 Configuring Alarm Output . .............................................................................................. 72
6.6.5 Handling Exception ......................................................................................................... 73
6.6.6 Configuring Face Detection ............................................................................................. 74
6.6.7 Configuring Audio Exception Detection ......................................................................... 75
6.6.8 Configuring Intrusion Detection ...................................................................................... 76
6.6.9 Configuring Defocus Detection ....................................................................................... 77
6.6.10 Configuring Scene Change Detection ......................................................................... 77
Chapter 7 Storage Settings ................................................................................... 79
7.1 Configuring NAS Settings ................................................................................... 79
7.2 Configuring Recording Schedule ........................................................................ 81
7.3 Configuring Snapshot Settings ........................................................................... 85
Chapter 8 Playback .............................................................................................. 88
Chapter 9 Log Searching ..................................................................................... 90
Chapter 10 Others .................................................................................................. 91
10.1 Managing User Accounts ..................................................................................... 91
10.2 Configuring RTSP Authentication ...................................................................... 93
10.3 Anonymous Visit .................................................................................................. 93
10.4 IP Address Filter ................................................................................................... 94
10.5 Viewing Device Information ................................................................................ 96
10.6 Maintenance ......................................................................................................... 97

User Manual of Network Camera
7
10.6.1 Rebooting the Camera................................................................................................ 97
10.6.2 Restoring Default Settings ......................................................................................... 97
10.6.3 Exporting / Importing Configuration File .................................................................. 98
10.6.4 Upgrading the System ................................................................................................ 99
10.7 RS-232 Settings ..................................................................................................... 99
10.8 RS-485 Settings ................................................................................................... 100
Appendix .................................................................................................................... 101
Appendix 1 SADP Software Introduction ..................................................................... 101
Appendix 2 Port Mapping .............................................................................................. 104

User Manual of Network Camera
8
Chapter 1 System Requirement
Operating System: Microsoft Windows XP SP1 and above version / Vista / Win7 /
Server 2003 / Server 2008 32bits
CPU: Intel Pentium IV 3.0 GHz or higher
RAM: 1G or higher
Display: 1024×768 resolution or higher
Web Browser: Internet Explorer 6.0 and above version, Safari 5.02 and above
version, Mozilla Firefox 3.5 and above version and Google Chrome8 and above
versions.

User Manual of Network Camera
9
Chapter 2 Network Connection
Before you start:
If you want to set the network camera via a LAN (Local Area Network), please
refer to Section 2.1 Setting the Network Camera over the LAN.
If you want to set the network camera via a WAN (Wide Area Network), please
refer to Section 2.2 Setting the Network Camera over the WAN.
2.1 Setting the Network Camera over the LAN
Purpose:
To view and configure the camera via a LAN, you need to connect the network
camera in the same subnet with your computer, and install the SADP or iVMS-4200
software to search and change the IP of the network camera.
Note: For the detailed introduction of SADP, please refer to Appendix 1.
2.1.1 Wiring over the LAN
The following figures show the two ways of cable connection of a network camera
and a computer:
Purpose:
To test the network camera, you can directly connect the network camera to the
computer with a network cable as shown in Figure 2-1.
Refer to the Figure 2-2 to set network camera over the LAN via a switch or a
router.
Figure 2-1 Connecting Directly

User Manual of Network Camera
10
Figure 2-2 Connecting via a Switch or a Router
2.1.2 Detecting and Changing the IP Address
You need the IP address to visit the network camera.
Steps:
1. To get the IP address, you can choose either of the following methods:
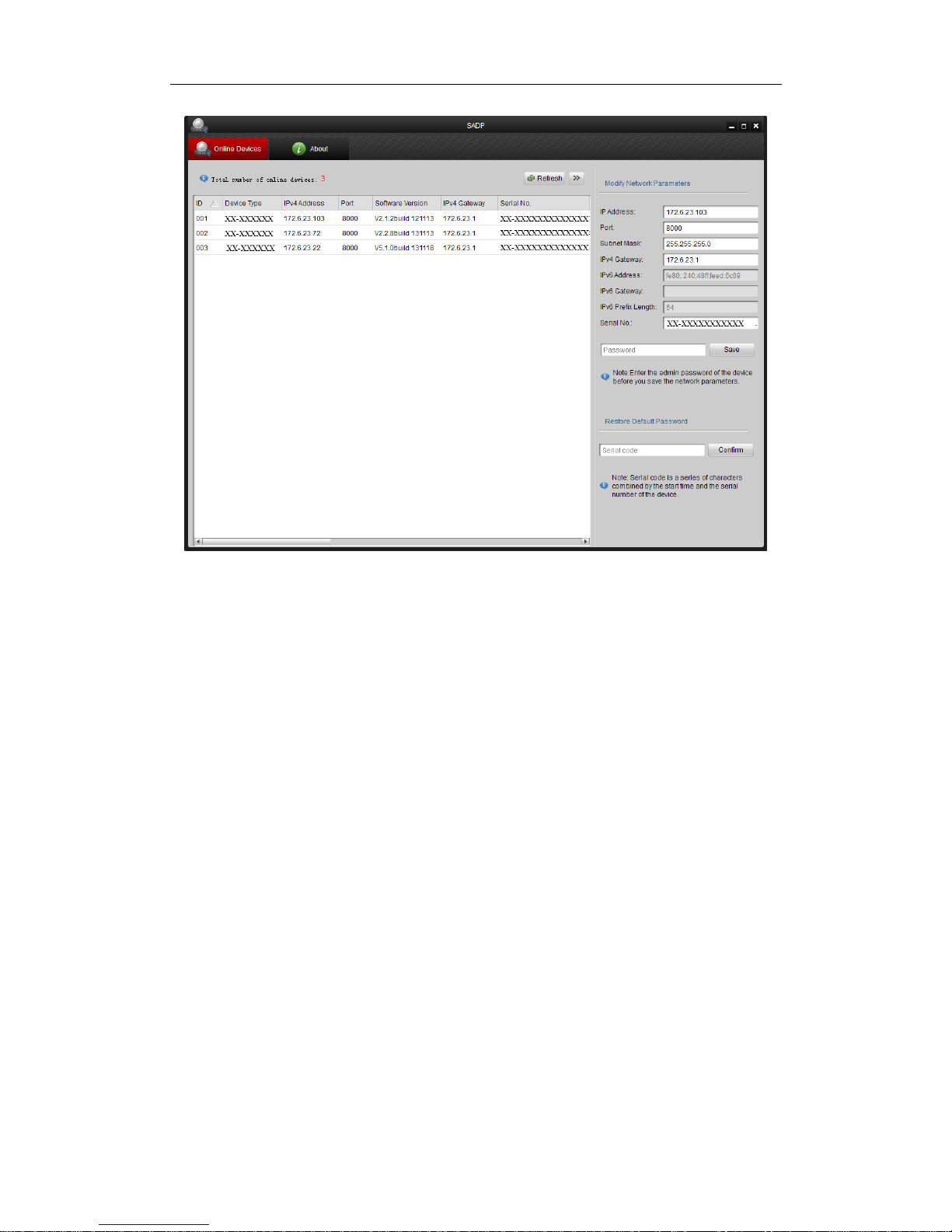
Use SADP, a software tool which can automatically detect the online
network cameras in the LAN and list the device information including IP
address, subnet mask, port number, device serial number, device version, etc.,
shown in Figure 2-3.
Use the Vi-Viewer4000 client software to list the online devices. Please
refer to the user manual of Vi-Viewer4000 client software for detailed
information.
2. Change the IP address and subnet mask to the same subnet as that of your
computer.
3. Enter the IP address of network camera in the address field of the web browser to
view the live video.
Notes:
The default IP address is 192.0.0.64 and the port number is 8000. The default user
name is admin, and password is 12345.
For accessing the network camera from different subnets, please set the gateway
for the network camera after you logged in. For detailed information, please refer
to Section 6.3.1 Configuring TCP/IP Settings.
User Manual of Network Camera
11
Figure 2-3 SADP Interface
2.2 Setting the Network Camera over the WAN
Purpose:
This section explains how to connect the network camera to the WAN with a static IP
or a dynamic IP.
2.2.1 Static IP Connection
Before you start:
Please apply a static IP from an ISP (Internet Service Provider). With the static IP
address, you can connect the network camera via a router or connect it to the WAN
directly.
Connecting the network camera via a router
Steps:
1. Connect the network camera to the router.

User Manual of Network Camera
12
2. Assign a LAN IP address, the subnet mask and the gateway. Refer to Section 2.1.2
Detecting and Changing the IP Address for detailed IP address configuration of
the camera.
3. Save the static IP in the router.
4. Set port mapping, e.g., 80, 8000, and 554 ports. The steps for port mapping vary
according to the different routers. Please call the router manufacturer for
assistance with port mapping.
Note: Refer to Appendix 2 for detailed information about port mapping.
5. Visit the network camera through a web browser or the client software over the
internet.
Figure 2-4 Accessing the Camera through Router with Static IP
Connecting the network camera with static IP directly
You can also save the static IP in the camera and directly connect it to the internet
without using a router. Refer to Section 2.1.2 Detecting and Changing the IP Address
for detailed IP address configuration of the camera.
Figure 2-5 Accessing the Camera with Static IP Directly
2.2.2 Dynamic IP Connection
Before you start:
Please apply a dynamic IP from an ISP. With the dynamic IP address, you can connect
the network camera to a modem or a router.
Connecting the network camera via a router
Steps:

User Manual of Network Camera
13
1. Connect the network camera to the router.
2. In the camera, assign a LAN IP address, the subnet mask and the gateway. Refer
to Section 2.1.2 Detecting and Changing the IP Address for detailed LAN
configuration.
3. In the router, set the PPPoE user name, password and confirm the password.
4. Set port mapping. E.g. 80, 8000, and 554 ports. The steps for port mapping vary
depending on different routers. Please call the router manufacturer for assistance
with port mapping.
Note: Refer to Appendix 2 for detailed information about port mapping.
5. Apply a domain name from a domain name provider.
6. Configure the DDNS settings in the setting interface of the router.
7. Visit the camera via the applied domain name.
Connecting the network camera via a modem
Purpose:
This camera supports the PPPoE auto dial-up function. The camera gets a public IP
address by ADSL dial-up after the camera is connected to a modem. You need to
configure the PPPoE parameters of the network camera. Refer to Section 5.3.3
Configuring PPPoE Settings for detailed configuration.
Figure 2-6 Accessing the Camera with Dynamic IP
Note: The obtained IP address is dynamically assigned via PPPoE, so the IP address
always changes after rebooting the camera. To solve the inconvenience of the
dynamic IP, you need to get a domain name from the DDNS provider (E.g.
DynDns.com). Please follow the steps below for normal domain name resolution and
private domain name resolution to solve the problem.
Normal Domain Name Resolution

User Manual of Network Camera
14
Figure 2-7 Normal Domain Name Resolution
Steps:
1. Apply a domain name from a domain name provider.
2. Configure the DDNS settings in the DDNS Settings interface of the network
camera. Refer to Section 6.3.4 Configuring DDNS Settings for detailed
configuration.
3. Visit the camera via the applied domain name.
Private Domain Name Resolution
Figure 2-8 Private Domain Name Resolution
Steps:
1. Install and run the IP Server software in a computer with a static IP.
2. Access the network camera through the LAN with a web browser or the client
software.
3. Enable DDNS and select IP Server as the protocol type. Refer to Section 6.3.4
Configuring DDNS Settings for detailed configuration.
User Manual of Network Camera
15
Chapter 3 Access to the Network
Camera
3.1 Accessing by Web Browsers
Steps:
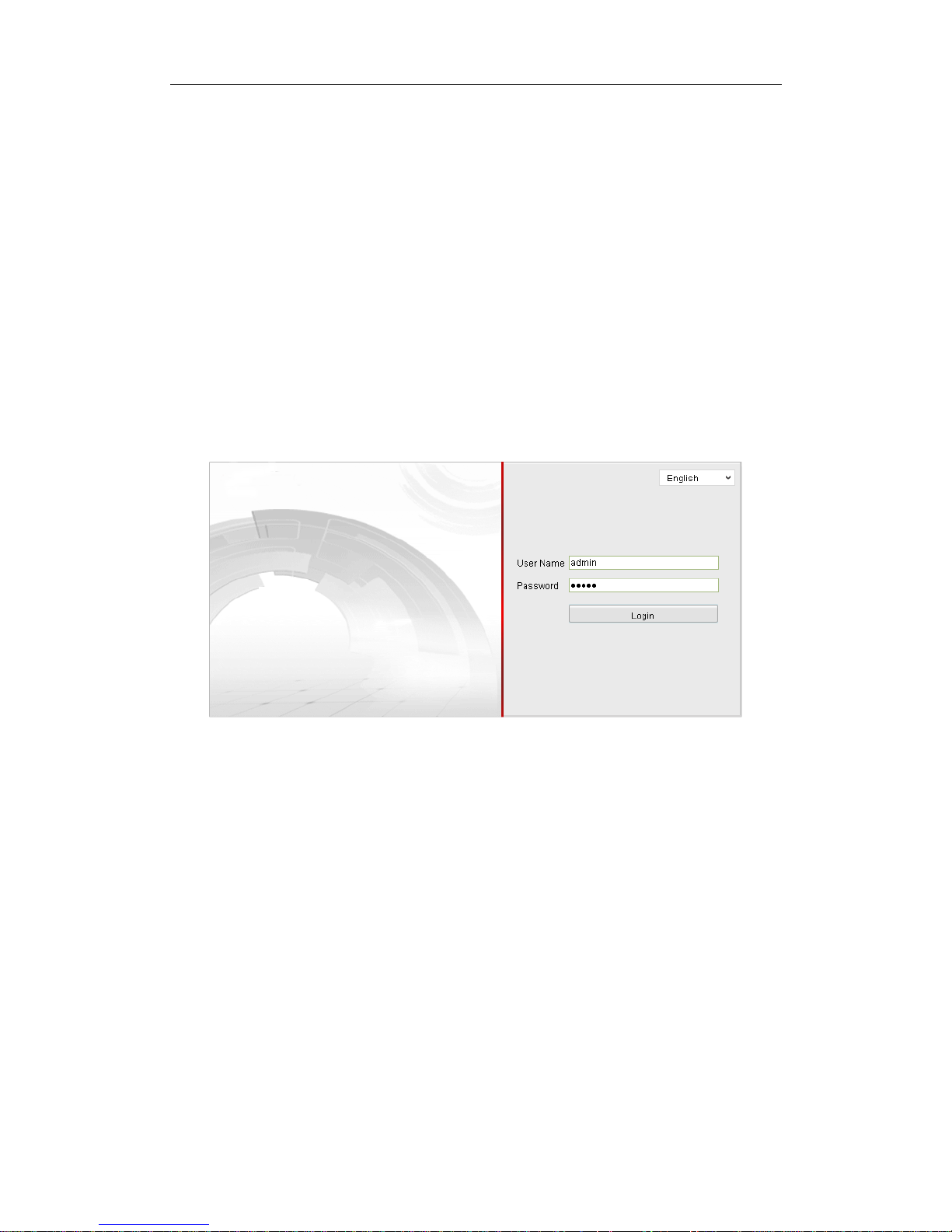
1. Open the web browser.
2. Input the IP address of the network camera in the address bar, e.g., 192.0.0.64 and
press the Enter key to enter the login interface.
3. Input the user name and password and click Login.
Figure 3-1 Login Interface
Notes:
The default user name is admin, and the default password is 12345.
Multi-language is supported. English, Simplified Chinese, Traditional Chinese,
Russian, Turkish, Japanese, Korean, Thai, Vietnamese, Estonian, Bulgarian,
Hungarian, Czech, Slovak, French, Italian, German, Spanish, Portuguese, Polish,
Greek, Dutch, etc.
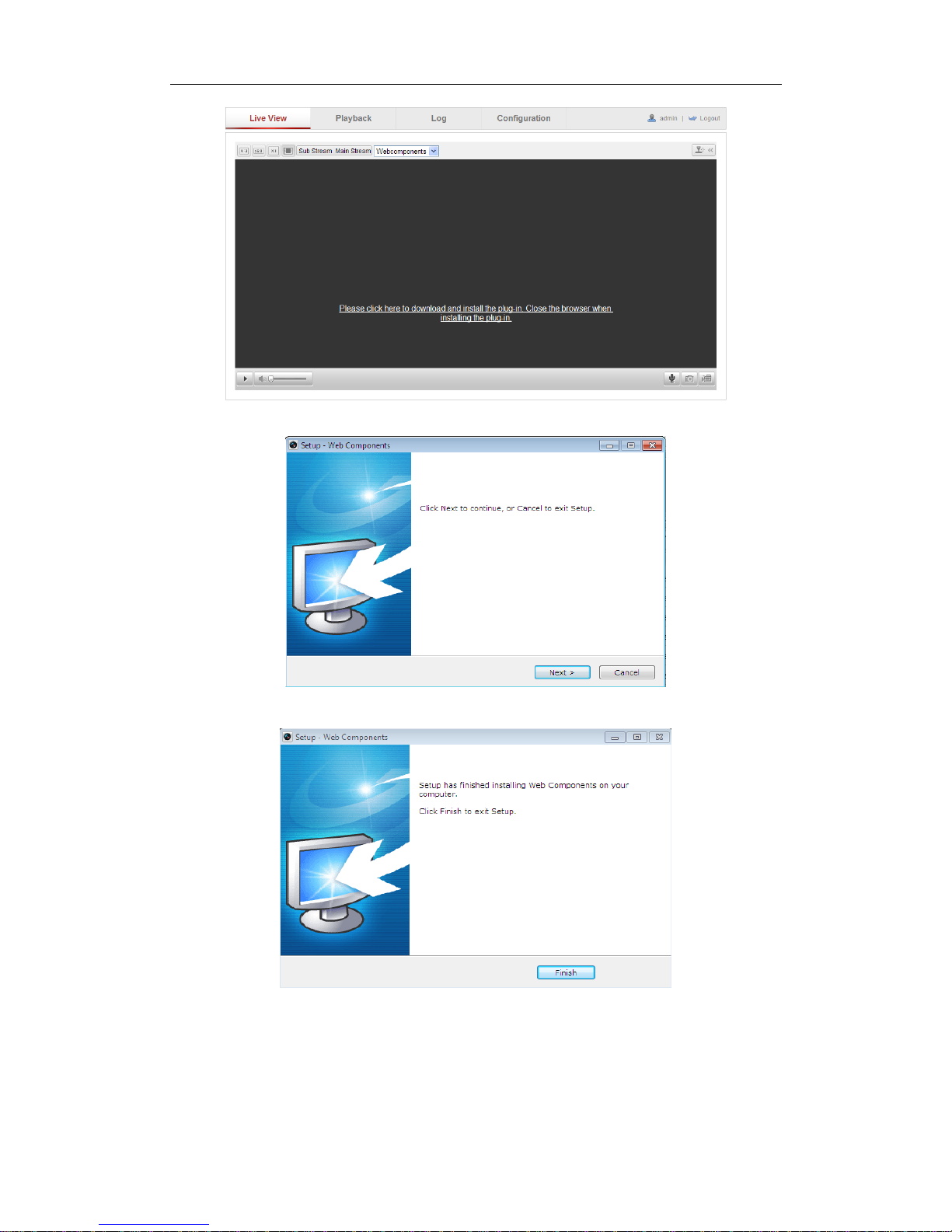
4. Install the plug-in before viewing the live video and operating the camera. Please
follow the installation prompts to install the plug-in.
User Manual of Network Camera
16
Figure 3-2 Download and Install Plug-in
Figure 3-3 Install Plug-in (1)
Figure 3-4 Install Plug-in (2)
Note: You may have to close the web browser to install the plug-in. Please reopen the
web browser and log in again after installing the plug-in.
User Manual of Network Camera
17
3.2 Accessing by Client Software
3.2.1 Accessing by Vi-Viewer4000
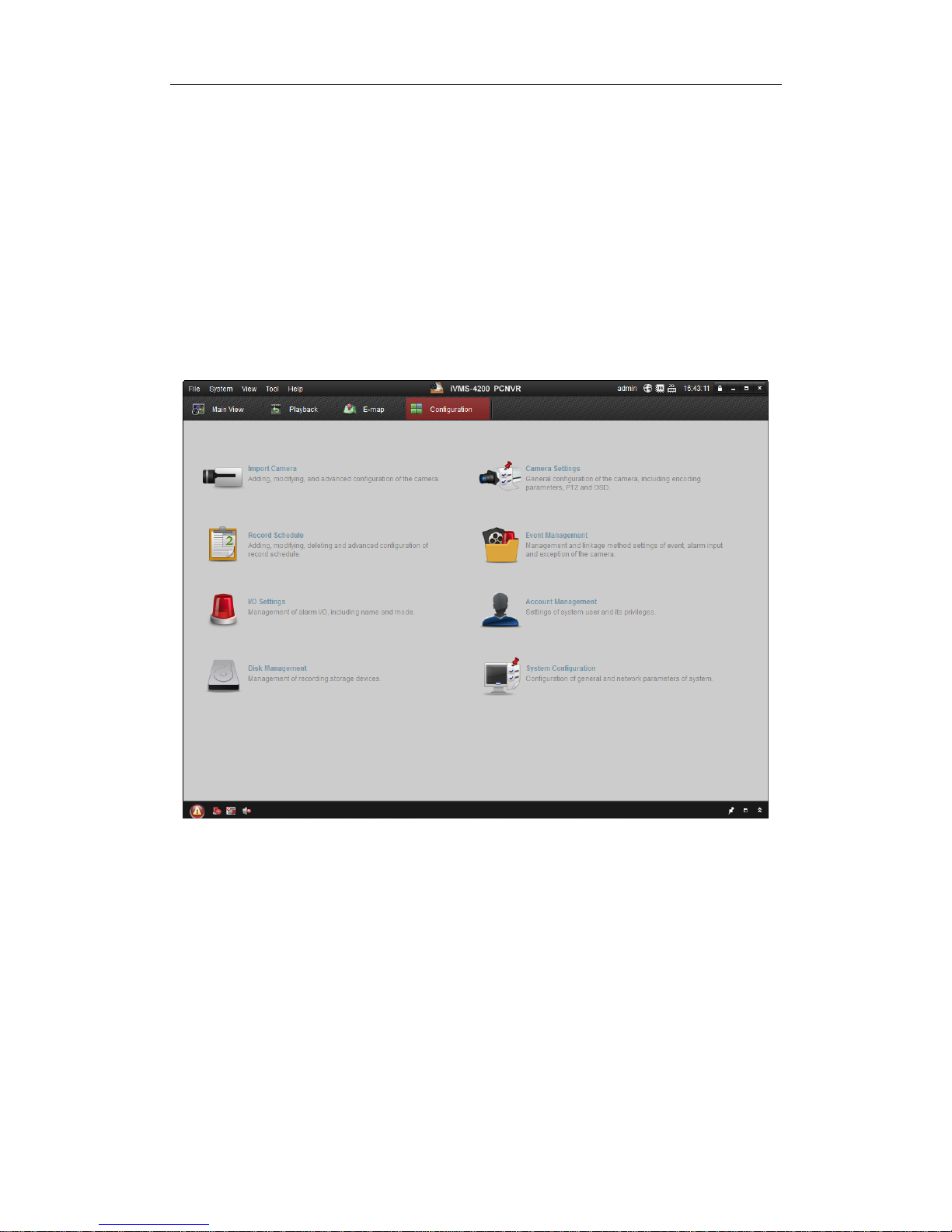
The product CD contains the Vi-Viewer4000. You can view the live video and
manage the camera with the software.
Follow the installation prompts to install the software. The control panel and live view
interface of Vi-Viewer4000 are shown as bellow.
Figure 3-5 Vi-Viewer4000 Control Panel
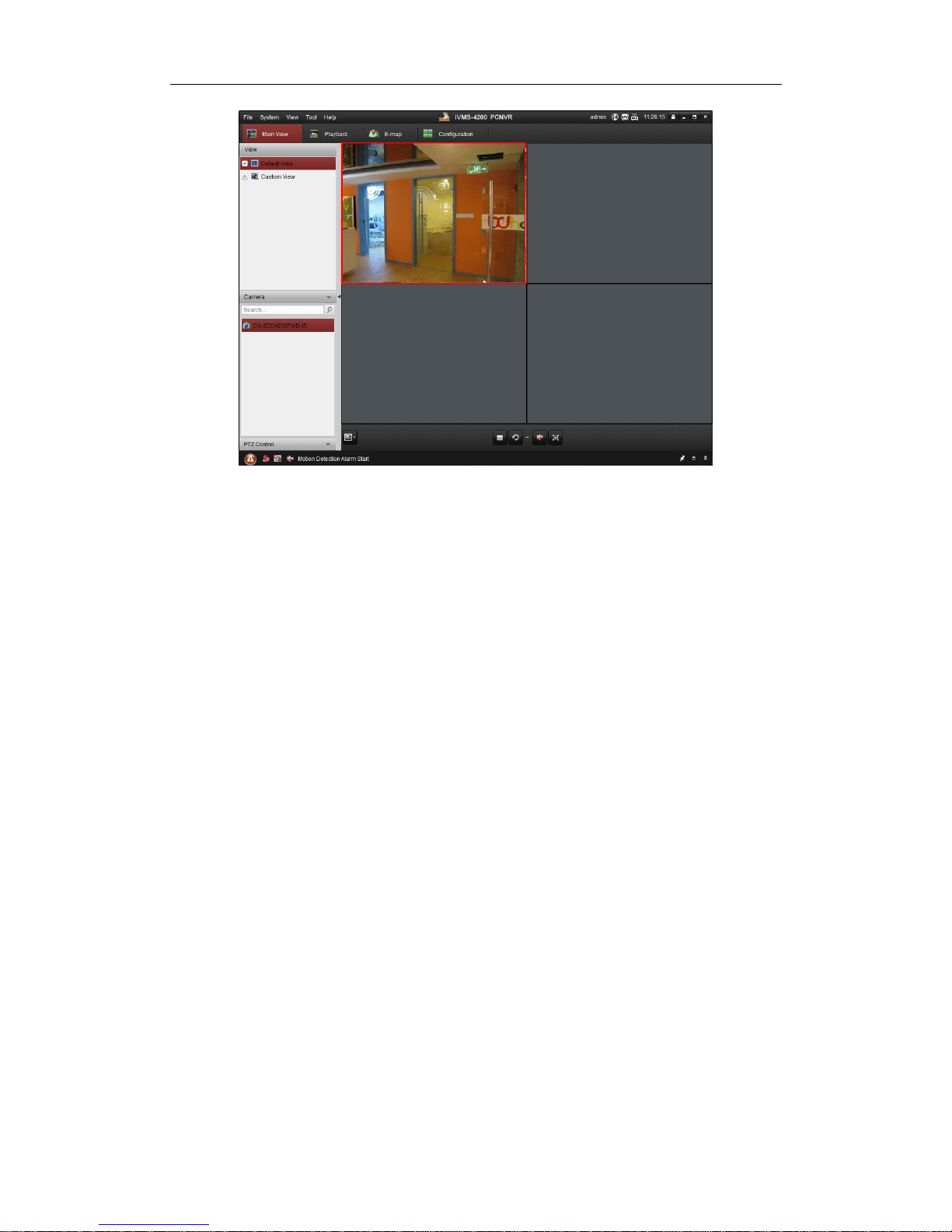
User Manual of Network Camera
18
Figure 3-6 iVMS-4200 Configuration Panel
Note: For detailed information about the software, please refer to the user manual of
the Vi-Viewer4000.
3.2.2 Accessing by Vi-GUARDEXP Software
To view the camera with a mobile phone, you can just install the Vi-GUARDEXP
client software in your mobile phone. The software can be downloaded from apps
store. Note: For detailed information about Vi-GUARDEXP client software, please
refer to the user manual of Vi-GUARDEXP.
User Manual of Network Camera
19
Chapter 4 Wi-Fi Settings
Purpose:
By connecting to the wireless network, you don’t need to use cable of any kind for
network connection, which is very convenient for the actual surveillance application.
Note: This chapter is only applicable for the cameras with the built-in Wi-Fi module.
4.1 Configuring Wi-Fi Connection in Manage and
Ad-hoc Modes
Before you start:
A wireless network must be configured.
Wireless Connection in Manage Mode
Steps:
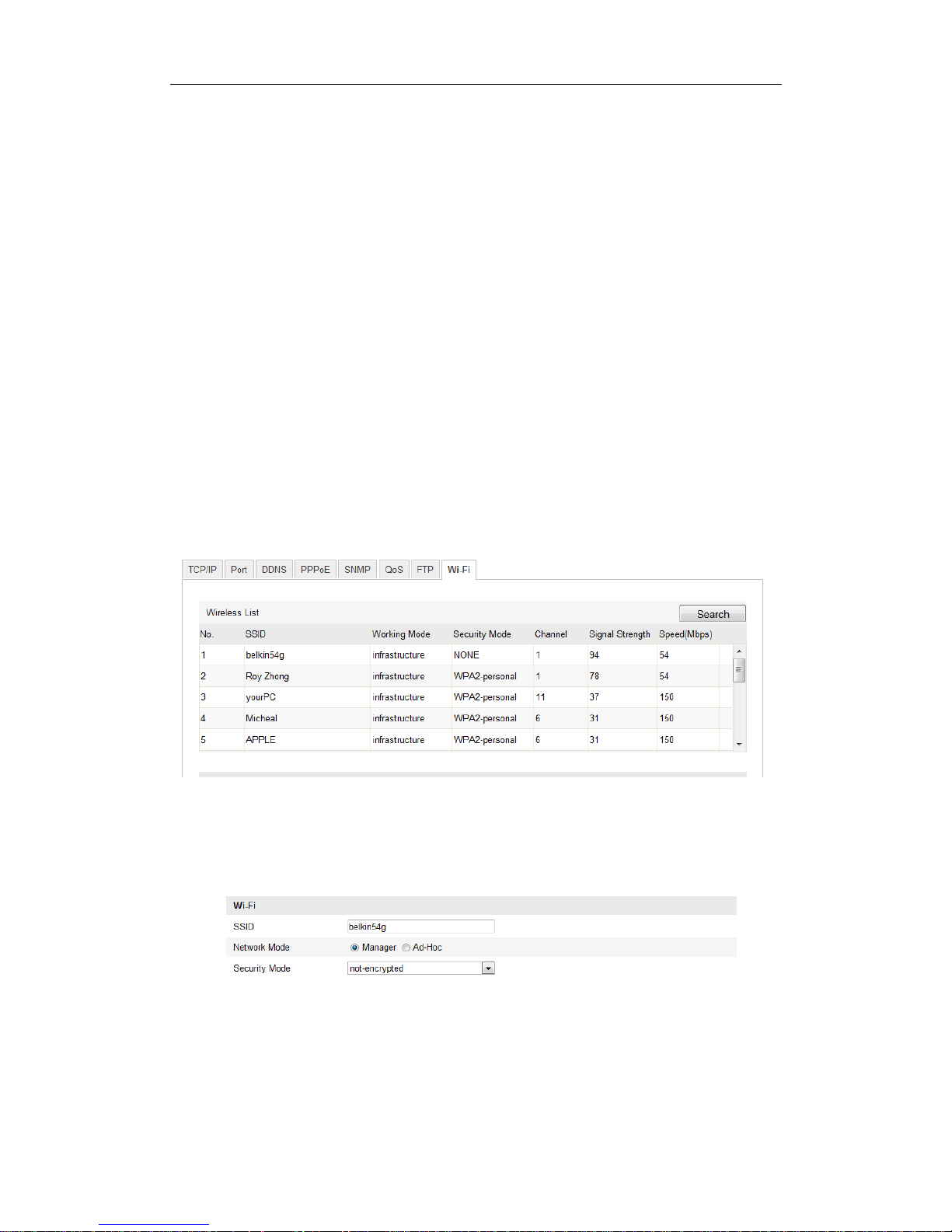
1. Enter the Wi-Fi configuration interface.
Configuration> Advanced Configuration> Network> Wi-Fi
Figure 4-1 Wireless Network List
2. Click Search to search the online wireless connections.
3. Click to choose a wireless connection on the list.
Figure 4-2 Wi-Fi Setting- Manage Mode
User Manual of Network Camera
20
4. Check the checkbox to select the Network mode as Manage, and the Security
mode of the network is automatically shown when you select the wireless
network, please don’t change it manually.
Note: These parameters are exactly identical with those of the router.
5. Enter the key to connect the wireless network. The key should be that of the
wireless network connection you set on the router.
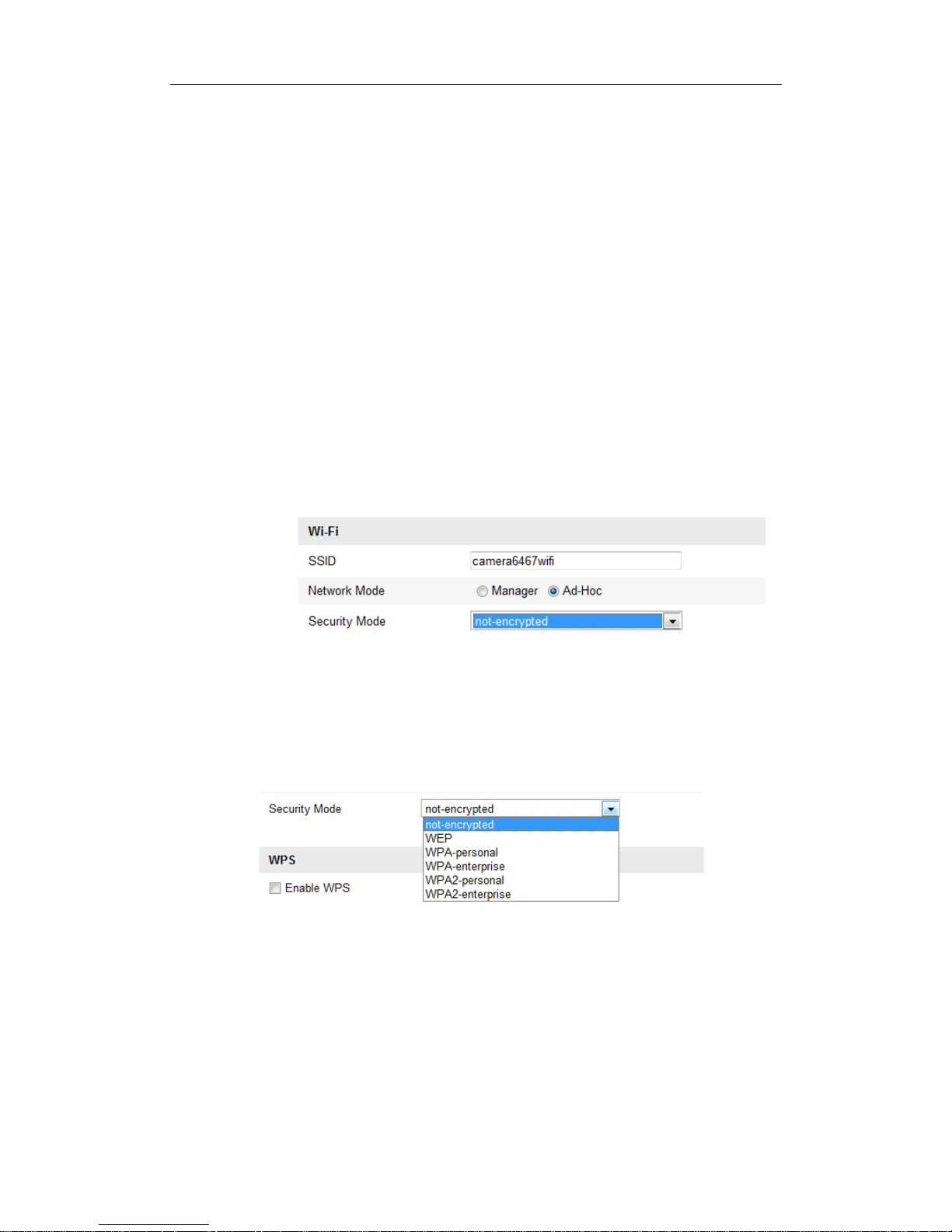
Wireless Connection in Ad-hoc Mode
If you choose the Ad-hoc mode, you don’t need to connect the wireless camera via a
router. The scenario is the same as you connect the camera and the PC directly with a
network cable.
Steps:
1. Choose Ad-hoc mode.
Figure 4-3 Wi-Fi Setting- Ad-hoc
2. Customize a SSID for the camera.
3. Choose the Security Mode of the wireless connection.
Figure 4-4 Security Mode- Ad-hoc Mode
4. Enable the wireless connection function for your PC.
5. On the PC side, search the network and you can see the SSID of the camera
listed.

User Manual of Network Camera
21
Figure 4-5 Ad-hoc Connection Point
6. Choose the SSID and connect.
Security Mode Description:
Figure 4-6 Security Mode
You can choose the Security Mode as not-encrypted, WEP, WPA-personal,
WPA-enterprise, WPA2-personal, and WPA2-enterprise.
WEP mode:
Figure 4-7 WEP Mode
Authentication - Select Open or Shared Key System Authentication, depending on
User Manual of Network Camera
22
the method used by your access point. Not all access points have this option, in
which case they probably use Open System, which is sometimes known as SSID
Authentication.
Key length - This sets the length of the key used for the wireless encryption, 64 or
128 bit. The encryption key length can sometimes be shown as 40/64 and
104/128.
Key type - The key types available depend on the access point being used. The
following options are available:
HEX - Allows you to manually enter the hex key.
ASCII - In this method the string must be exactly 5 characters for 64-bit WEP
and 13 characters for 128-bit WEP.
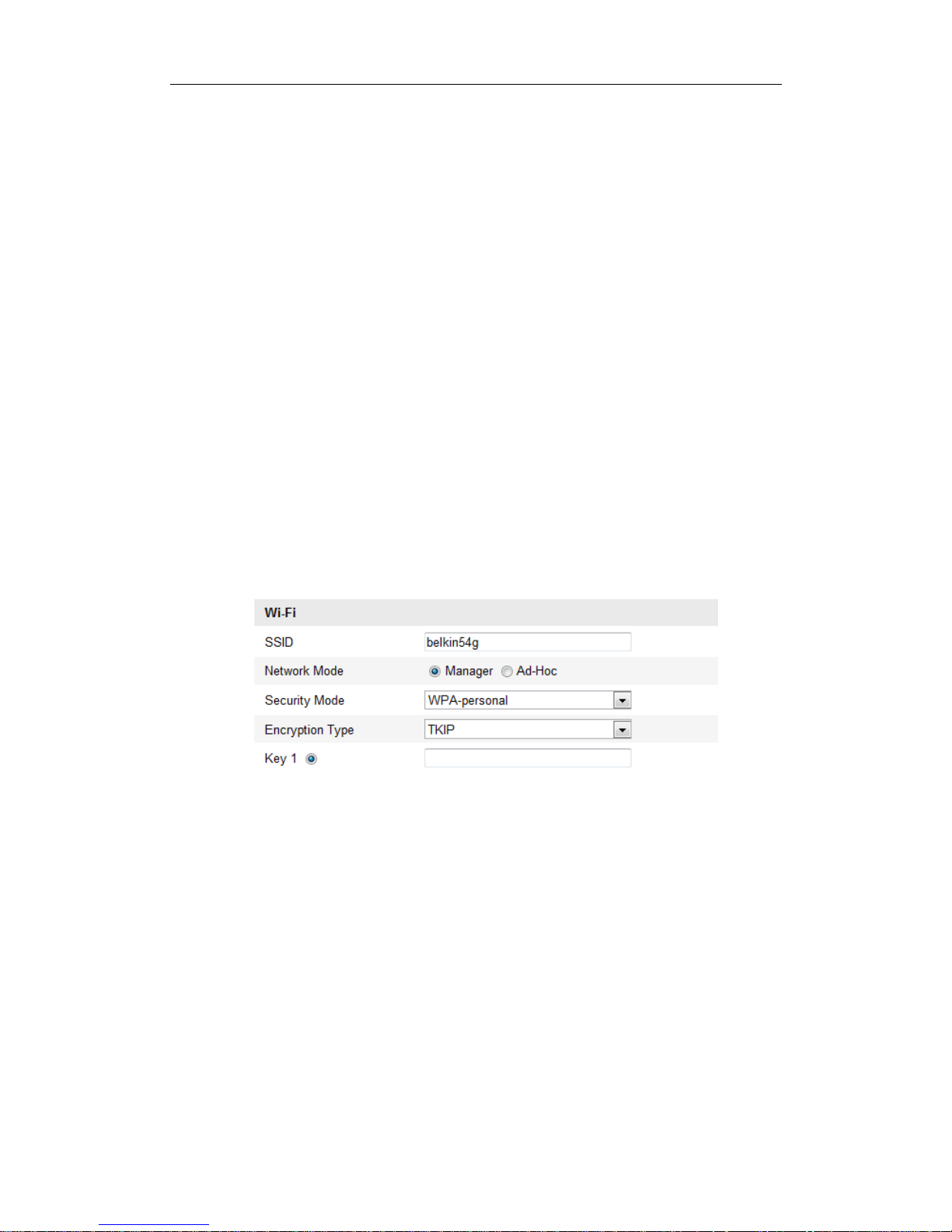
WPA-personal and WPA2-personal Mode:
Enter the required Pre-shared Key for the access point, which can be a hexadecimal
number or a passphrase.
Figure 4-8 Security Mode- WPA-personal
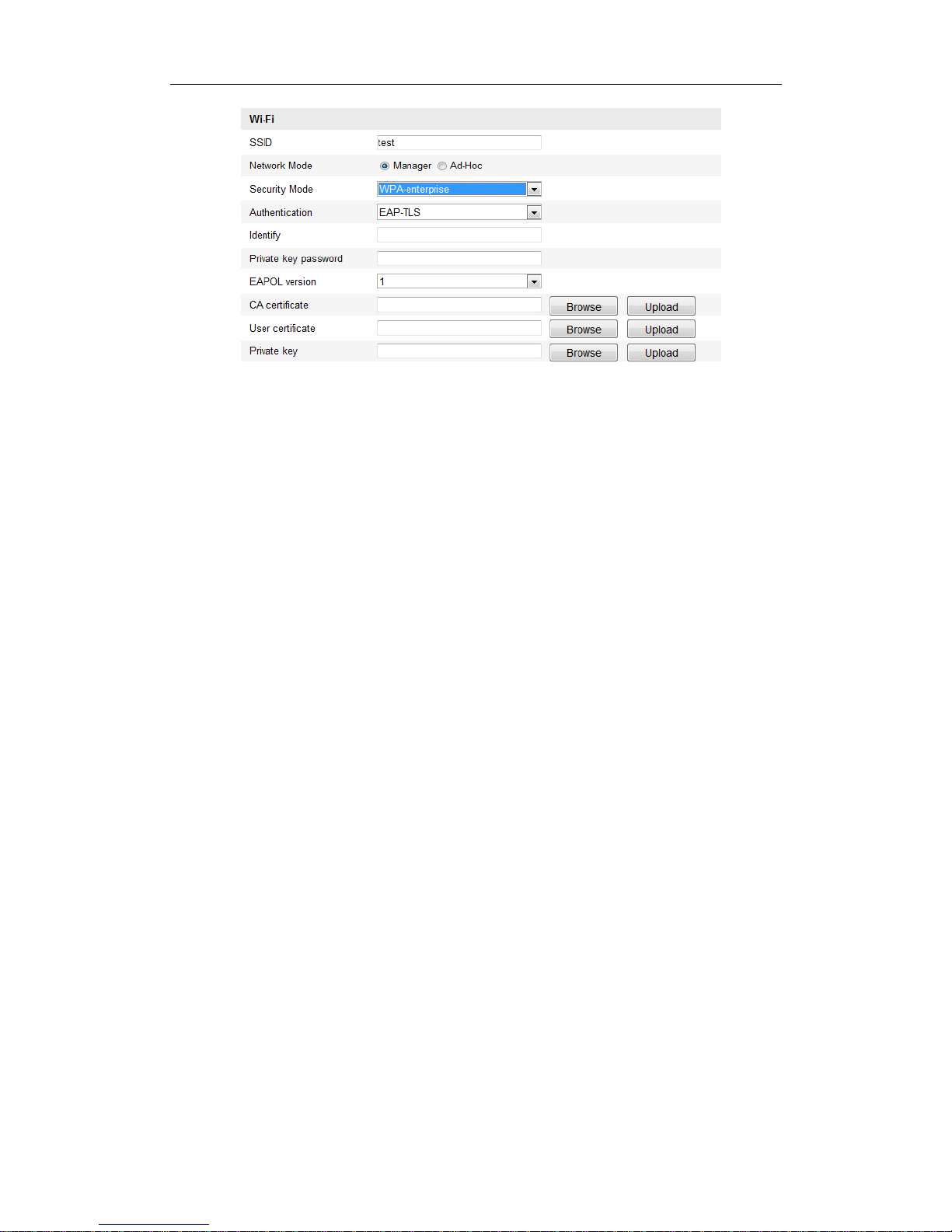
WPA- enterprise and WPA2-enterprise Mode:
Choose the type of client/server authentication being used by the access point;
EAP-TLS or EAP-PEAP.
EAP-TLS
User Manual of Network Camera
23
Figure 4-9 EAP-TLS
Identity - Enter the user ID to present to the network.
Private key password – Enter the password for your user ID.
EAPOL version - Select the version used (1 or 2) in your access point.
CA Certificates - Upload a CA certificate to present to the access point for
authentication.
EAP-PEAP:
User Name - Enter the user name to present to the network
Password - Enter the password of the network
PEAP Version - Select the PEAP version used at the access point.
Label - Select the label used by the access point.
EAPOL version - Select version (1 or 2) depending on the version used at the
access point
CA Certificates - Upload a CA certificate to present to the access point for
authentication
4.2 Easy Wi-Fi Connection with WPS function
Purpose:
The setting of the wireless network connection is never easy. To avoid the complex
setting of the wireless connection you can enable the WPS function.

User Manual of Network Camera
24
WPS (Wi-Fi Protected Setup) refers to the easy configuration of the encrypted
connection between the device and the wireless router. The WPS makes it easy to add
new devices to an existing network without entering long passphrases. There are two
modes of the WPS connection, the PBC mode and the PIN mode.
Note: If you enable the WPS function, you do not need to configure the parameters
such as the encryption type and you don’t need to know the key of the wireless
connection.
Steps:
Figure 4-10 Wi-Fi Settings - WPS
PBC Mode:
PBC refers to the Push-Button-Configuration, in which the user simply has to push a
button, either an actual or virtual one (as the button on the configuration
interface of the IE browser), on both the Access Point (and a registrar of the network)
and the new wireless client device.
1. Check the checkbox of to enable WPS.
2. Choose the connection mode as PBC.
Note: Support of this mode is mandatory for both the Access Points and the
connecting devices.
3. Check on the Wi-Fi router to see if there is a WPS button. If yes push the button
and you can see the indicator near the button start flashing, which means the WPS
function of the router is enabled. For detailed operation, please see the user guide of
the router.
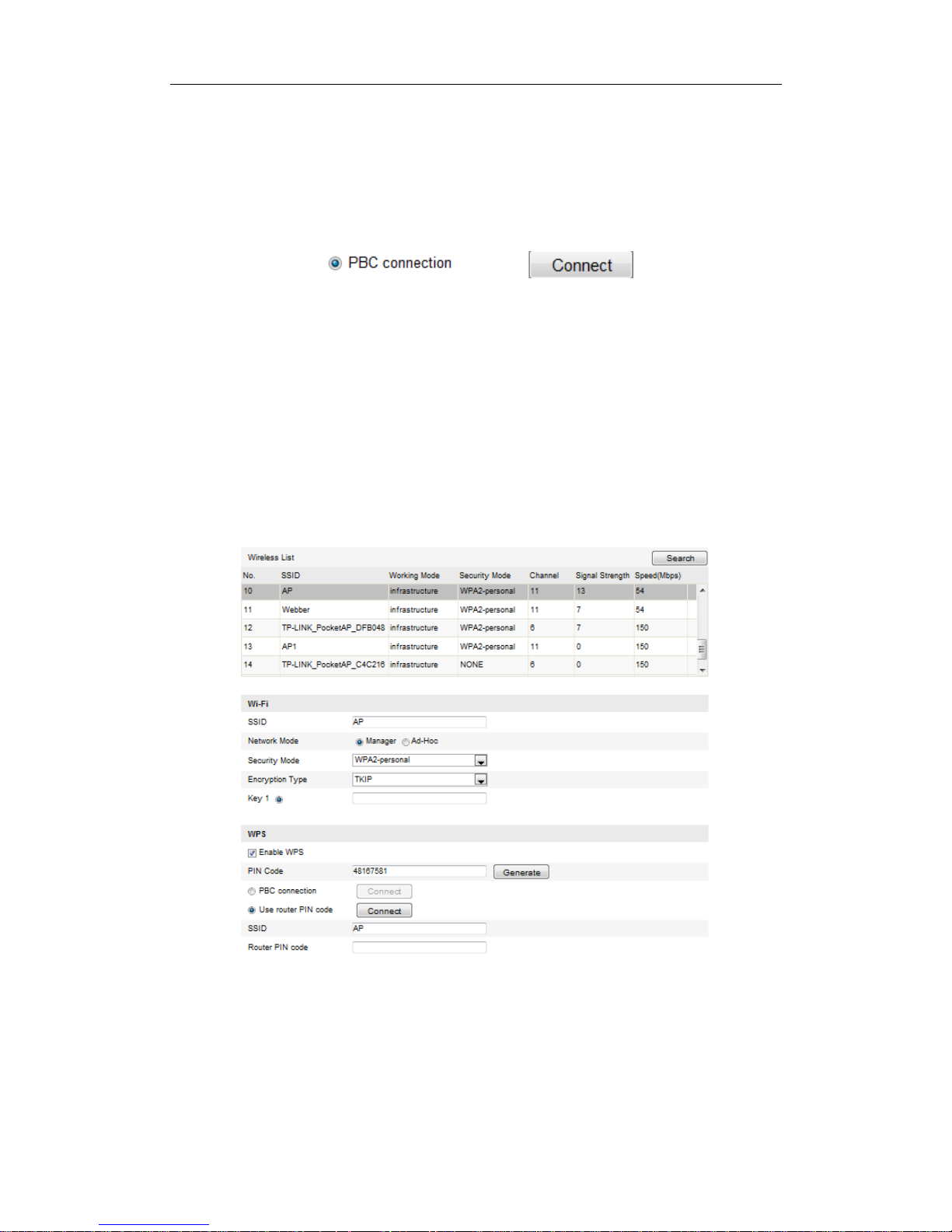
User Manual of Network Camera
25
4. Push the WPS button to enable the function on the camera.
If there is not a WPS button on the camera, you can also click the virtual button to
enable the PBC function on the web interface.
5. Click Connect button.
When the PBC mode is both enabled in the router and the camera, the camera and the
wireless network is connected automatically.
PIN Mode:
The PIN mode requires a Personal Identification Number (PIN) to be read from either
a sticker or the display on the new wireless device. This PIN must then be entered to
connect the network, usually the Access Point of the network.
Steps:
1. Choose a wireless connection on the list and the SSID is shown.
Figure 4-11 Wi-Fi Settings – WPS PIN Mode
2. Choose Use route PIN code.
If the PIN code is generated from the router side, you should enter the PIN code you
get from the router side in the Router PIN code field.
User Manual of Network Camera
26
3. Click Connect.
Or
You can generate the PIN code on the camera side. And the expired time for the PIN
code is 120 seconds.
1. Click Generate.
2. Enter the code to the router, in the example, enter 48167581 to the router.
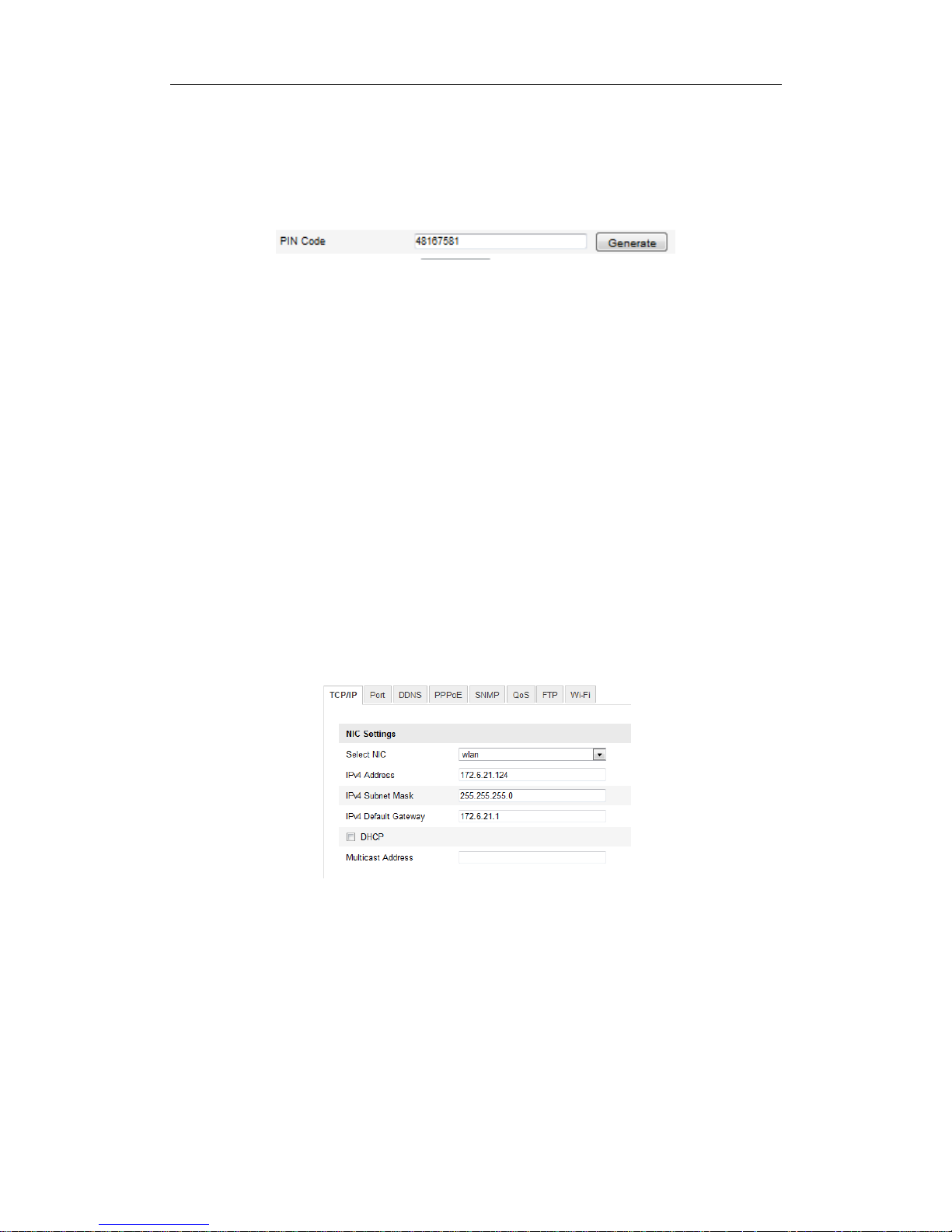
4.3 IP Property Settings for Wireless Network
Connection
The default IP address of wireless network interface controller is 192.168.1.64. When
you connect the wireless network you can change the default IP.
Steps:
1. Enter the TCP/IP configuration interface.
Configuration> Advanced Configuration> Network> TCP/IP
or
Configuration> Basic Configuration> Network> TCP/IP
Figure 4-12 TCP/IP Settings
2. Select the NIC as wlan.
3. Customize the IPv4 address, the IPv4 Subnet Mask and the Default Gateway.
The setting procedure is the same with that of LAN.
If you want to be assigned the IP address you can check the checkbox to enable the
DHCP.

User Manual of Network Camera
27
Chapter 5 Live View
5.1 Live View Page
Purpose:
The live view page allows you to view the real-time video, capture images, realize
PTZ control, set/call presets and configure video parameters.
Log in the network camera to enter the live view page, or you can click Live View on
the menu bar of the main page to enter the live view page.
Descriptions of the live view page:
Figure 5-1 Live View Page
Menu Bar:
Click each tab to enter Live View, Playback, Log and Configuration page
respectively.
Display Control:
Click each tab to adjust the layout and the stream type of the live view. And you can
click the drop-down to select the plug-in. For IE (internet explorer) user,
webcomponents and quick time are selectable. And for Non-IE user, webcomponents,
quick time, VLC or MJPEG is selectable if they are supported by the web browser.
Live View Window:
Display the live video.
User Manual of Network Camera
28
Toolbar:
Operations on the live view page, e.g., live view, capture, record, audio on/off,
two-way audio, etc.
PTZ Control:
Panning, tilting and zooming actions of the camera and the lighter and wiper control
(if it supports PTZ function or an external pan/tilt unit has been installed).
Preset Setting/Calling:
Set and call the preset for the camera (if supports PTZ function or an external pan/tilt
unit has been installed).
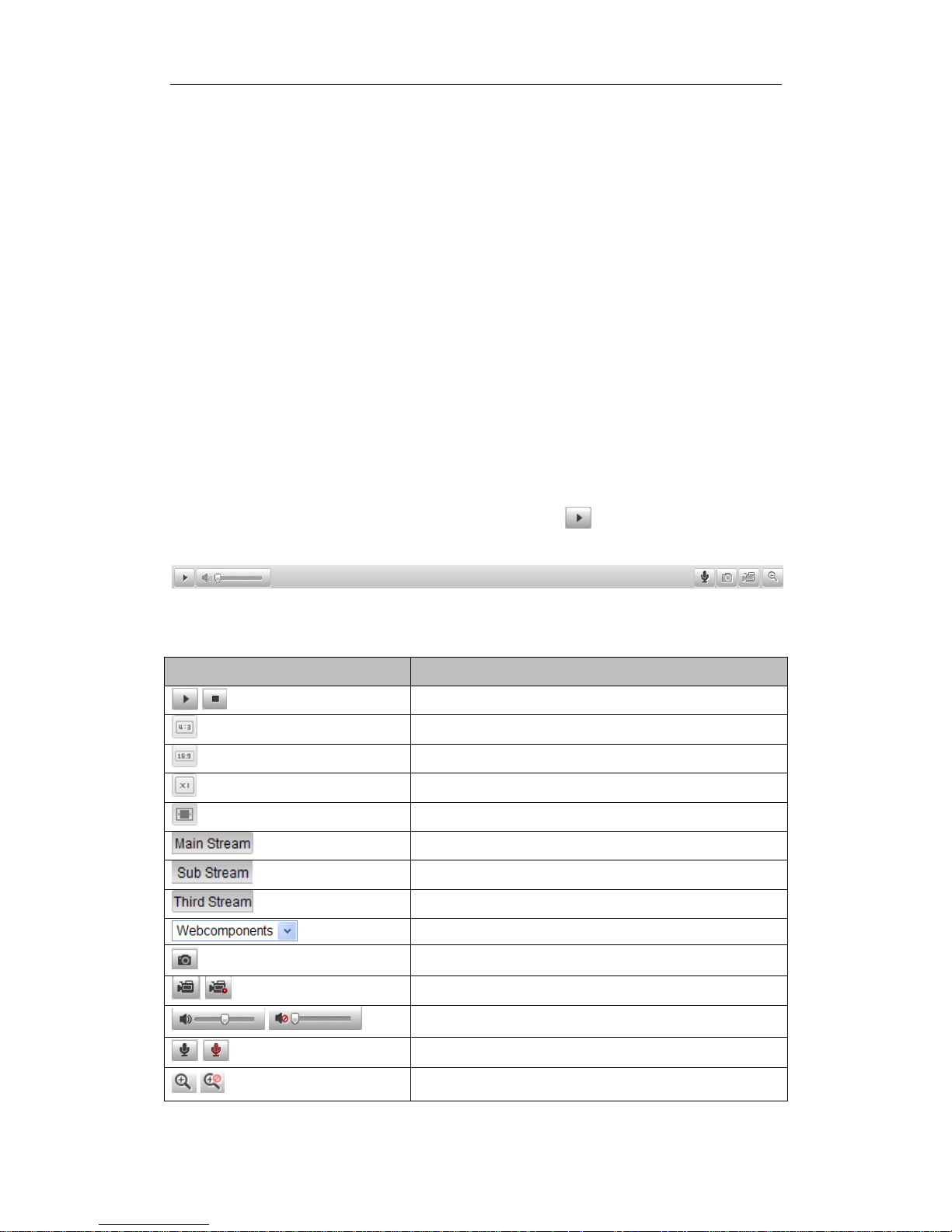
5.2 Starting Live View
In the live view window as shown in Figure 5-2, click on the toolbar to start the
live view of the camera.
Figure 5-2 Live View Toolbar
Table 5-1 Descriptions of the Toolbar
Icon
Description
/
Start/Stop live view.
The window size is 4:3.
The window size is 16:9.
The original widow size.
Self-adaptive window size.
Live view with the main stream.
Live view with the sub stream.
Live view with the third stream.
Click to select the third-party plug-in.
Manually capture the picture.
/
Manually start/stop recording.
/
Audio on and adjust volume /Mute.
/
Turn on/off microphone.
/
Turn on/off 3D zooming function.
User Manual of Network Camera
29
5.3 Recording and Capturing Pictures Manually
In the live view interface, click on the toolbar to capture the live pictures or
click to record the live view. The saving paths of the captured pictures and clips
can be set on the Configuration > Local Configuration page. To configure remote
scheduled recording, please refer to Section 7.2.
Note: The captured image will be saved as JPEG file or BMP file in your computer.
5.4 Operating PTZ Control
Purpose:
In the live view interface, you can use the PTZ control buttons to realize pan/tilt/zoom
control of the camera.
Before you start:
To realize PTZ control, the camera connected to the network must support the PTZ
function or a pan/tilt unit has been installed to the camera. Please properly set the PTZ
parameters on RS-485 settings page referring to Section 10.8 RS-485 Settings.
5.4.1 PTZ Control Panel
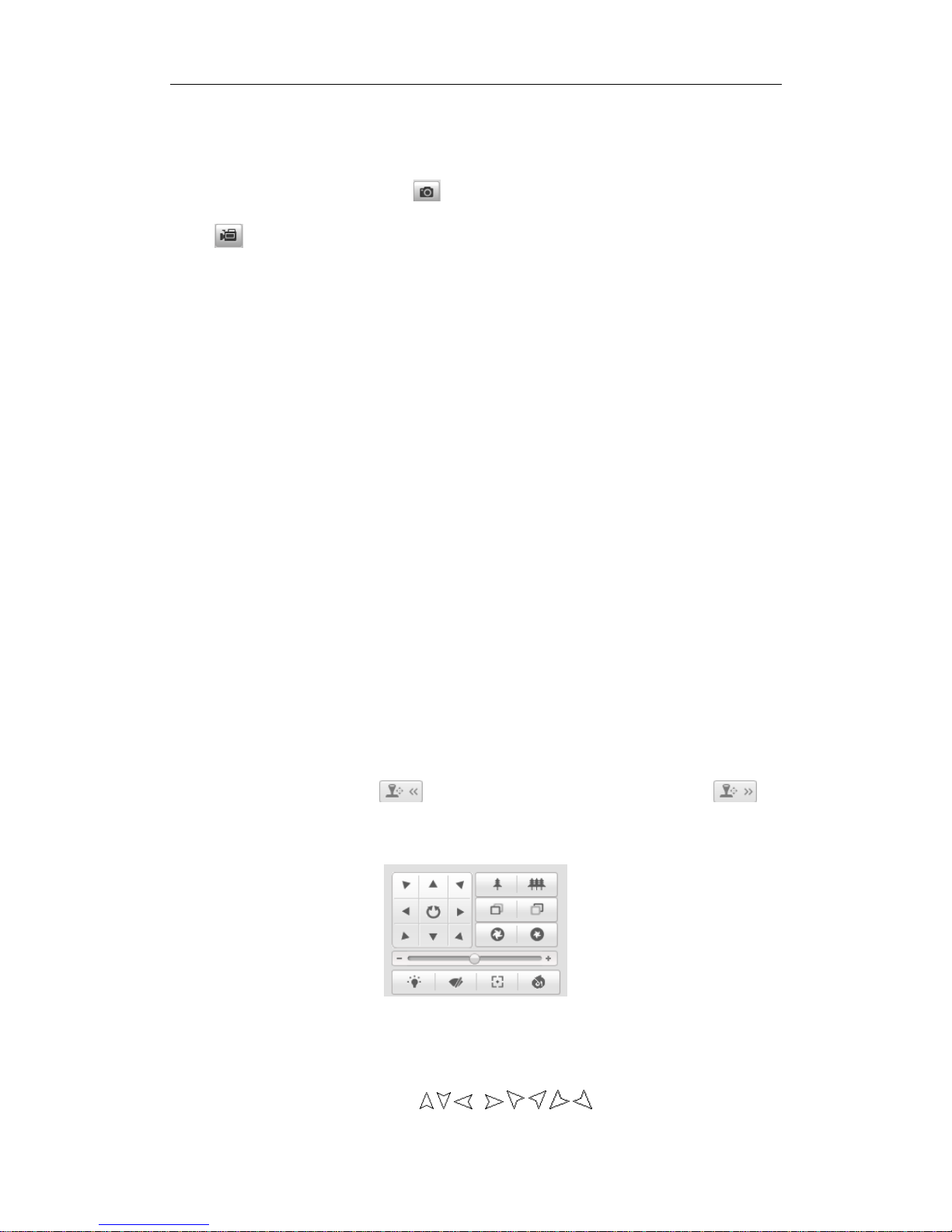
On the live view page, click to show the PTZ control panel or click to
hide it.
Click the direction buttons to control the pan/tilt movements.
Figure 5-3 PTZ Control Panel
Click the zoom/iris/focus buttons to realize lens control.
Notes:
There are 8 direction arrows ( , , , , , , , ) in the live view window
 Loading...
Loading...