Page 1

BioStation 2
USER GUIDE
Version 1.38
English
EN 102.00.BS2 V1.38A
Page 2

Contents
Safety Instructions ................................................................................. 4
Getting Started ....................................................................................... 6
Components ................................................................................................................................................... 6
Parts ................................................................................................................................................................ 7
Cables and connectors ........................................................................................................................... 9
How to Enroll a Fingerprint ...................................................................................................................... 11
Choose Ideal Fingers to Enroll .............................................................................................................. 11
How to Enroll Fingerprints .................................................................................................................. 11
Administrator Menus ........................................................................... 12
Full Menu ..................................................................................................................................................... 12
Quick Menu .................................................................................................................................................. 12
User Management ................................................................................ 13
Add User Information................................................................................................................................. 13
Edit User Information ................................................................................................................................. 14
Delete All Users .......................................................................................................................................... 14
Check User Usage ....................................................................................................................................... 14
Authentication Configuration ............................................................... 15
Finger ............................................................................................................................................................ 15
Card ............................................................................................................................................................... 15
ID ................................................................................................................................................................... 16
T&A Mode .................................................................................................................................................... 16
Fingerprint .................................................................................................................................................... 17
System Setup ....................................................................................... 18
Display & Sound ......................................................................................................................................... 18
Device ........................................................................................................................................................... 19
Date & Time........................................................................................................................................... 19
Daylight Saving Time ............................................................................................................................. 19
User ID Type .......................................................................................................................................... 20
USB Memory .......................................................................................................................................... 20
Restart Device ........................................................................................................................................ 21
Restore Default ...................................................................................................................................... 21
More Settings ......................................................................................................................................... 21
Network ........................................................................................................................................................ 23
TCP/IP Settings ...................................................................................................................................... 23
Server Settings ...................................................................................................................................... 23
RS-485 Settings ..................................................................................................................................... 24
Check Event Log .................................................................................. 25
Search Logs .................................................................................................................................................. 25
Delete All Logs ............................................................................................................................................ 25
Check Log Usage ........................................................................................................................................ 26
Troubleshooting .................................................................................... 27
Checklist Before Requesting Service ........................................................................................................ 27
Product Specifications ......................................................................... 28
Dimensions ................................................................................................................................................... 29
FCC Compliance Information ............................................................... 30
2
Page 3
Appendices ........................................................................................... 31
Disclaimers ................................................................................................................................................... 31
Copyright Notice ......................................................................................................................................... 31
Open Source License .................................................................................................................................... 31
GNU General Public License ................................................................................................................ 31
GNU Lesser General Public License .................................................................................................... 37
OpenSSL License ................................................................................................................................... 39
Original SSLeay License ....................................................................................................................... 39
3
Page 4
Safety Instructions
Safety Instructions
Please read the following instructions carefully before using the product. This information is important for ensuring the safety of
the user and for preventing damage to the user's property.
Warning
Failure to follow the instructions may cause serious injury or death.
Installation Instructions
Do not install the product in direct sunlight or in a location that is damp or dusty.
• This can cause a fire or electric shock.
Do not install the product near any heat source such as electric heaters.
• This can cause a fire from overheating or electric shock.
Install the product in a dry place.
• Moisture can cause product damage or electric shock.
Install the product in a place where there is no electromagnetic interference.
• This can cause product damage or electric shock.
Have qualified service professionals install or repair the product.
• Otherwise, it can cause a fire, electric shock, or injury.
• If the product is damaged due to a user's unauthorized installation or dismantling of the product, a service fee will be charged
for repair.
Operating Instructions
Be careful not to spill any liquid such as water, drinks, or chemicals inside the product.
• This can cause fire, electric shock, or product damage.
Caution
Ignoring these instructions may result in minor injuries or damage to the product.
Installation Instructions
Protect the power cord from being walked on or pinched.
• This can cause product damage or injury.
Keep the product away from strong magnetic objects such as magnets, TVs, monitors (especially CRT monitors), or speakers.
• This can cause a failure.
Only use a DC 12V power adapter that provides a current of at least 500mA.
• This device does not work if the proper power source is not used.
After all the cables are properly installed, apply the liquid silicone underneath and above the cables within the groove ap
proximately 10mm wide. The cable cover must be installed to ensure the IP65 rating.
• Non-proper installation of the cable cover may cause device malfunction or damage from water and dust.
If installing the product outside where the product is completely exposed, it is recommended to install the product together with
the enclosure.
Use a separate power supply for Secure I/O 2, electric lock and BioStation 2 respectively.
• If connecting and using the power supply to these devices together, the devices may malfunction.
4
Page 5
Safety Instructions
Operating Instructions
Do not drop the product or subject it to shock or impact during use.
• This can cause a failure.
Keep the password secret from others and change it periodically.
• Failure to do so may lead to an illegal intrusion.
Do not press the buttons on the product with excessive force or with a sharp tool.
• This can cause a failure.
Be careful not to contaminate or damage the fingerprint reader with dirty hands or materials.
• This can decrease performance or cause failures to read fingerprints.
Clean the product with a soft, dry cloth. Do not use alcohol, benzene, or water.
• This can cause a product failure.
BioStation 2 uses the capacitive button. If there is much moisture (humidity) like a rainy weather or on the product, wipe with a
soft and dry cloth.
There is a risk of fire if batteries are replaced by an incorrect type.
Dispose of batteries in accordance with local and national disposal regulations.
5
Page 6
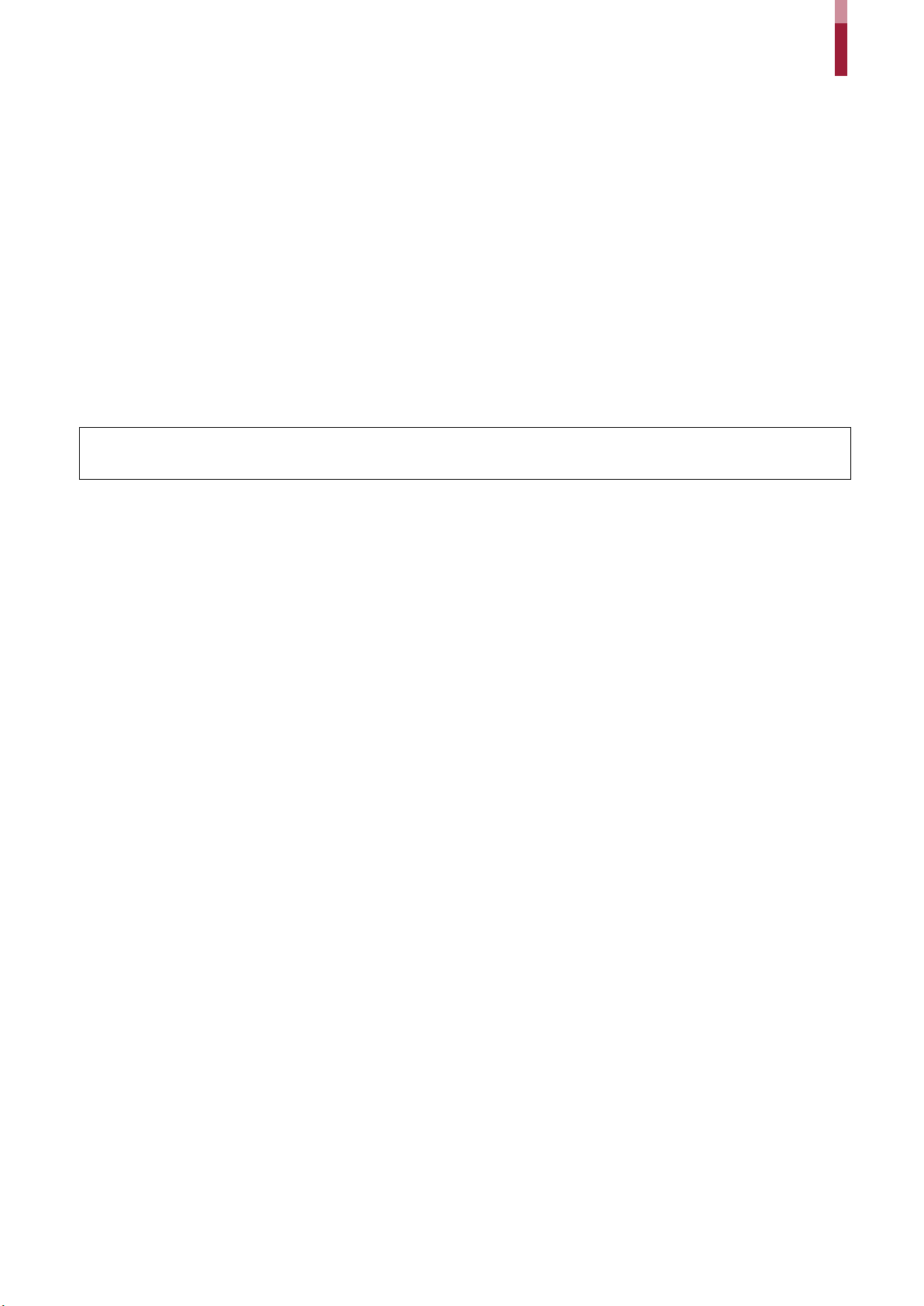
Getting Started
BioStation 2
Wall Bracket
Fixing Screws x4
PVC Anchors x4
Diode
Cable Cover
Connector Cables
Ferrite Core
Drilling Template
Quick Guide
Bracket Fixing Screw
Open Source Software
Components
Getting Started
(1x2-pin, 1x3-pin, 3x4-pin, 1x5-pin)
(Star Shaped)
NOTE
• The components may differ depending on where the product is installed.
• When assembling the product with the bracket, you can use the included bracket fixing screw(Star Shaped) instead of the
• For more information on installation, visit the Suprema website (www.supremainc.com) to see the installation guide.
product fixing screw for enhanced security.
Guide
6
Page 7
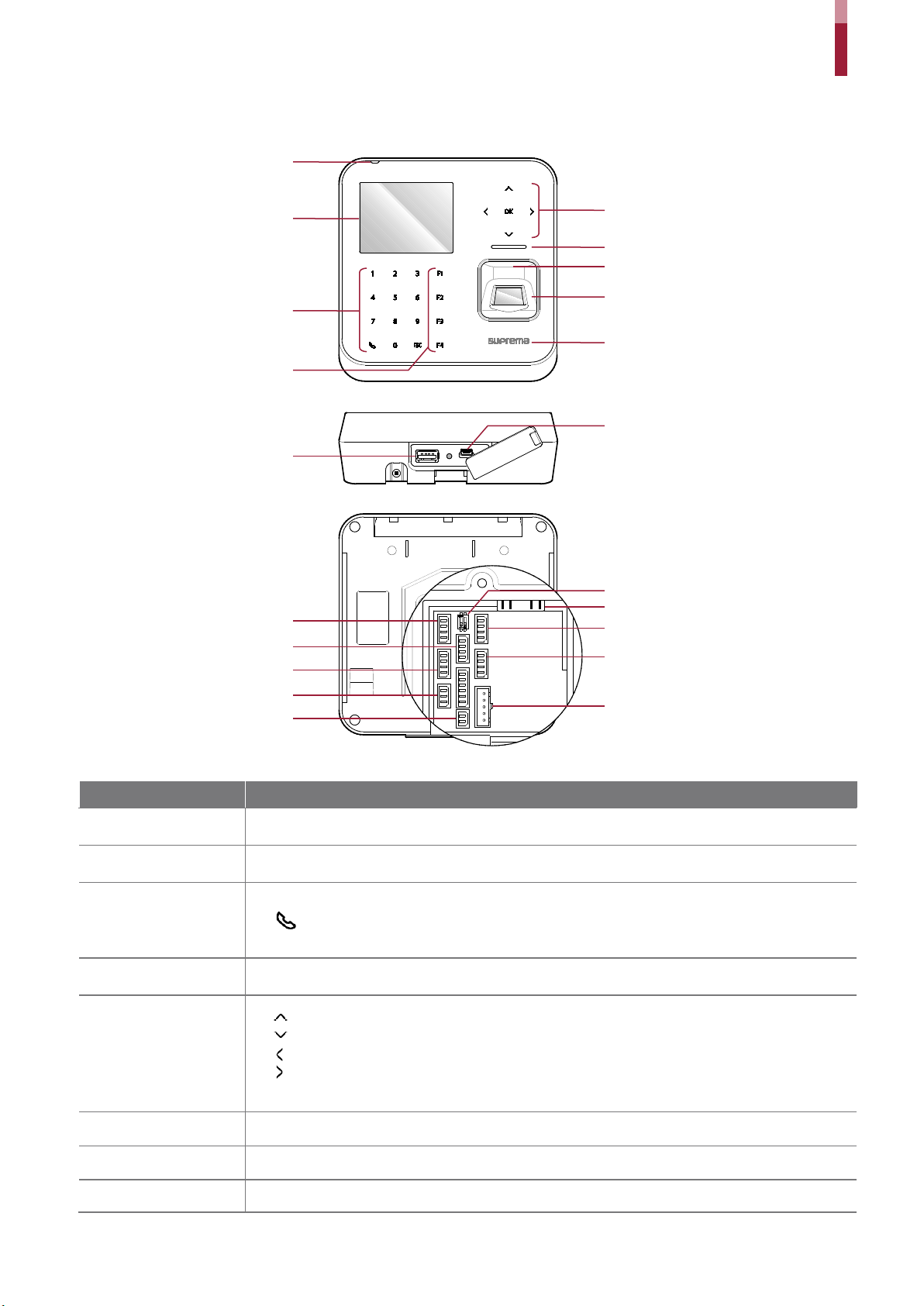
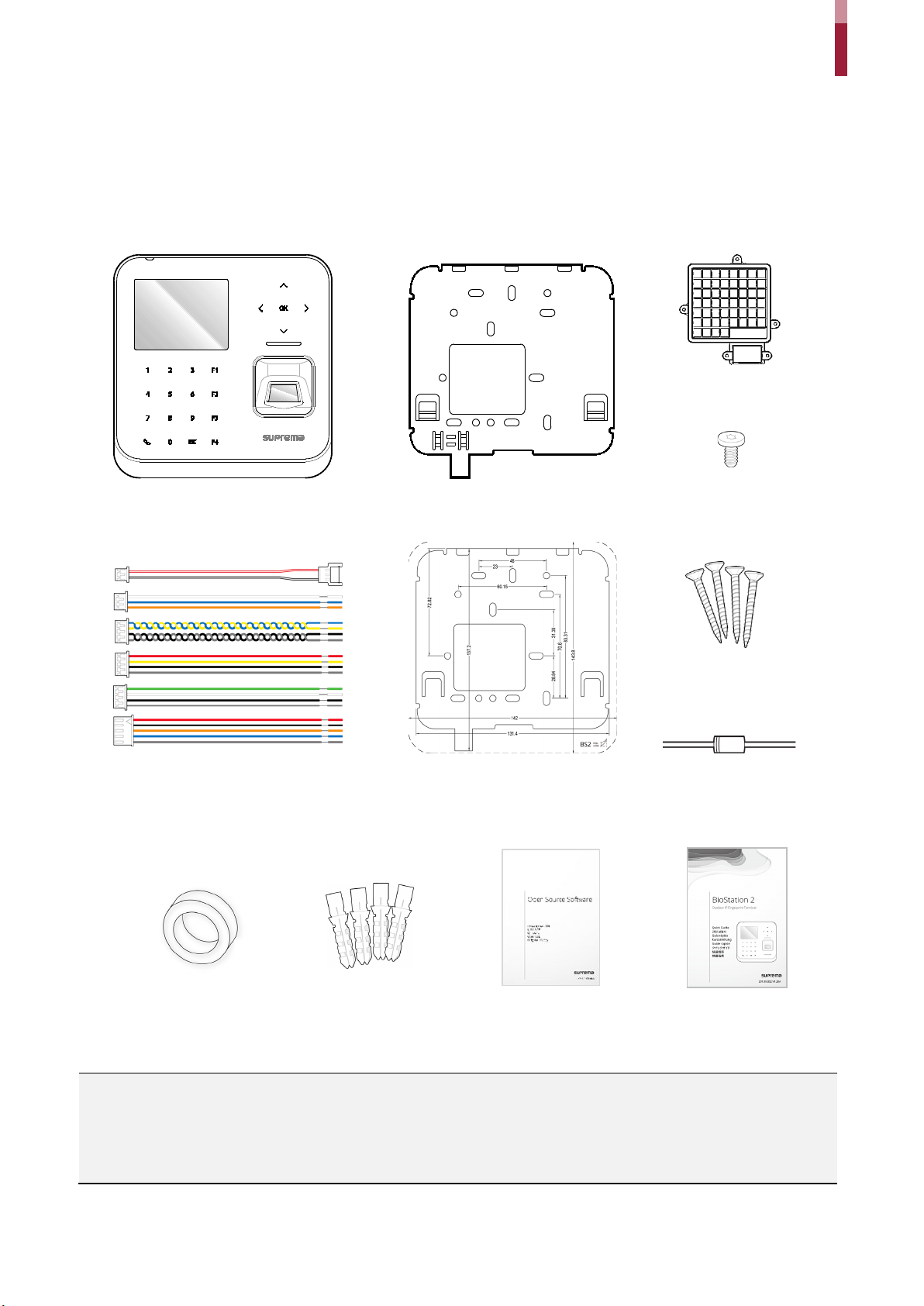
Parts
Fingerprint sensor
Arrow keys/OK button
Numpad/Intercom/ESC
Function buttons
LED lamp
Microphone
LCD screen
USB memory port
TTL input (4-pin)
Power (2-pin)
RS-485 (4-pin)
TTL output (4-pin)
DIP switches
Ethernet
Wiegand input (4-pin)
Wiegand output (4-pin)
Intercom (5-pin)
Relay (3-pin)
RF card reader
Mini-USB cable port
Speaker
Getting Started
button
Name Description
Microphone Transmits the user's voice to the intercom.
LCD screen Displays various information or settings.
Numpad/Intercom/ESC
button
Function buttons Serves as T&A function key or selects a sub-menu item.
Arrow keys/OK button
Speaker Makes a sound.
LED lamp Shows the status of the product with different colors.
Fingerprint sensor Reads fingerprints.
• 1 to 9: Enters numbers/characters or selects a menu item.
• : Connects to the intercom.
• ESC: Opens the menu, moves back to the previous screen, or cancels input
• : Changes the character type.
• : Changes the character type or selects a T&A event.
• : Deletes numbers/characters.
• : Inserts symbols or configures an item.
• OK: Selects an item or saves the settings.
7
Page 8
RF card reader Reads RF cards.
USB memory port Connects a USB memory stick.
Mini-USB cable port To be supported later.
TTL input (4-pin) Connects a TTL input/output cable.
RS-485 (4-pin) Connects an RS-485 cable.
TTL output (4-pin) Connects a TTL input/output cable.
Relay (3-pin) Connects a relay cable.
Power (2-pin) Connects the power cable.
Getting Started
DIP switch
Ethernet Connects an Ethernet cable.
Wiegand input (4-pin) Connects a Wiegand input/output cable.
Wiegand output (4-pin) Connects a Wiegand input/output cable.
Intercom (5-pin) Connects the intercom cable.
Turns on the termination resistor for the RS-485 interface
• To use the termination resistor, set DIP switch 1 to ON.
8
Page 9
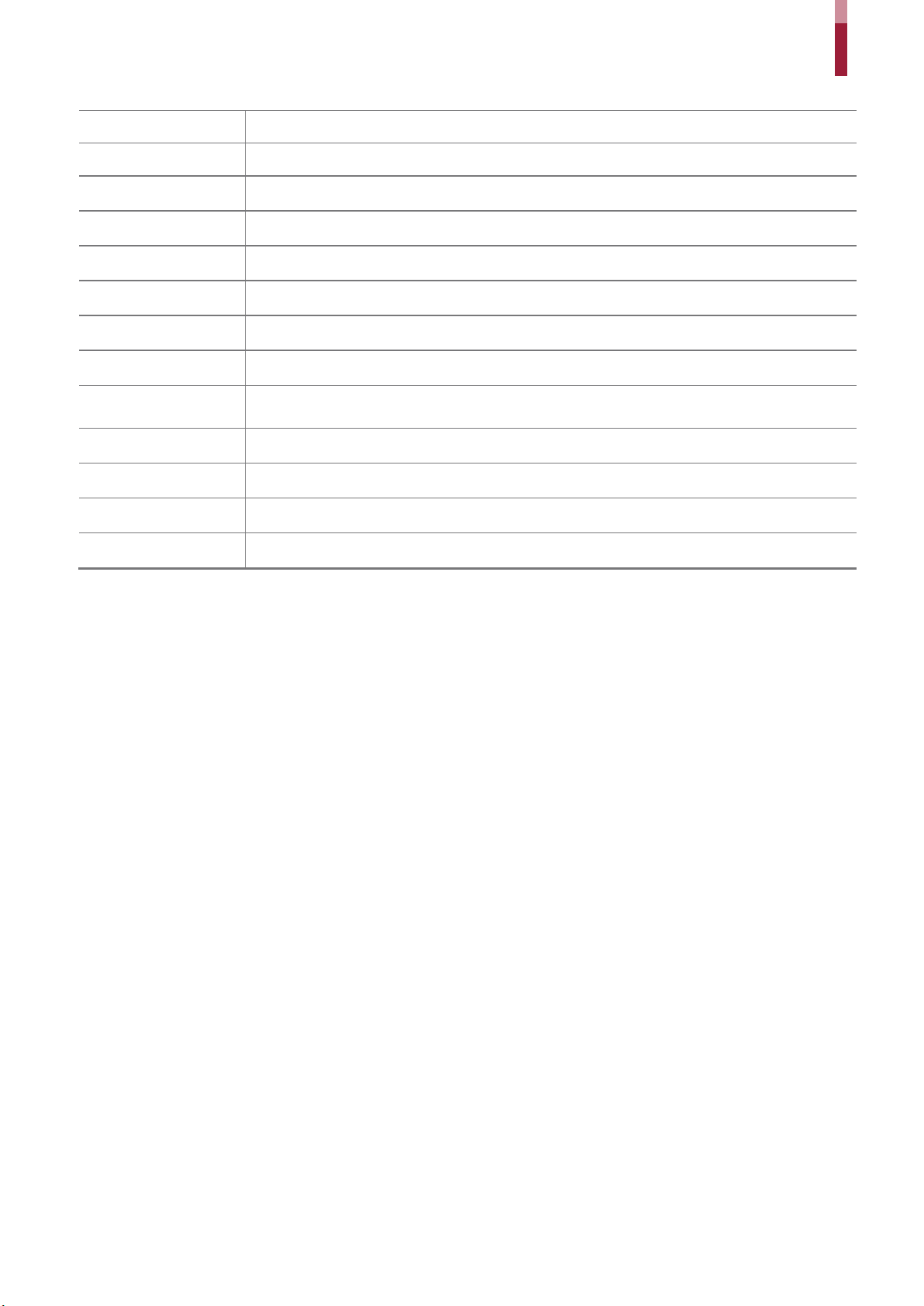
Cables and connectors
1
PWR +VDC
Red (White stripe)
2
PWR GND
Black (White stripe)
1
RLY N O
White
2
RLY C OM
Blue
3
RLY N C
Orange
1
485 TRXP
Blue
2
485 TRXN
Yellow
3
485 GND
Black
4
SH GND
Gray
1
TTL IN0 / OUT0
Red
2
TTL IN1 / OUT1
Yellow
3
TTL GND
Black
4
SH GND
Gray
1
WG IN0 / OUT0
Green
2
WG IN1 / OUT1
White
3
WG GND
Black
Power
Pin Name Color
Relay
Pin Name Color
Getting Started
RS-485
TTL input/output
Wiegand input/output
Pin Name Color
Pin Name Color
Pin Name Color
4 SH GND Gray
9
Page 10
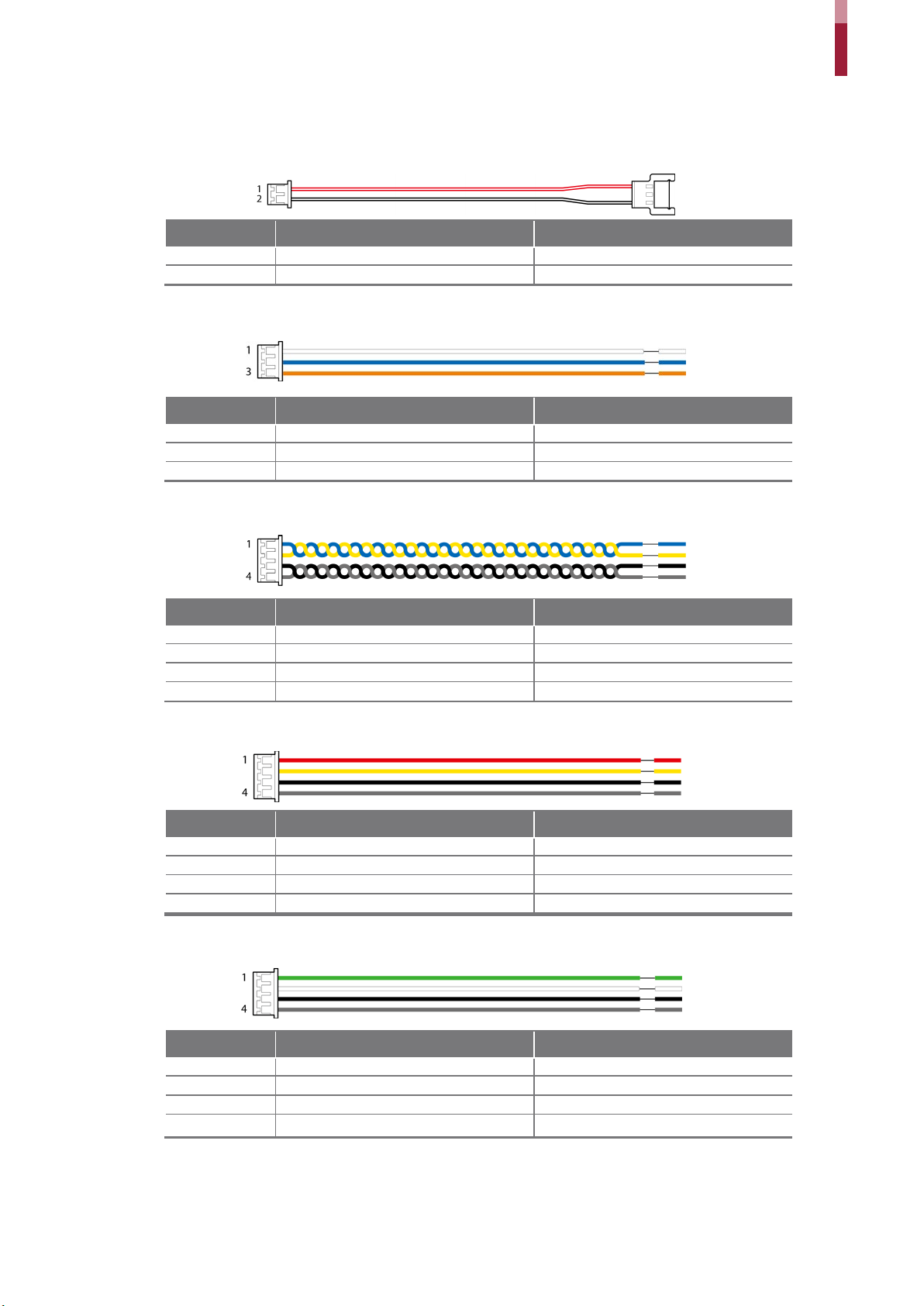
Intercom
1
INPH +VDC
Red
2
INPH GND
Black
3
INPH AUD
Orange
4
INPH DTA
Blue
5
SH GND
Gray
Getting Started
Pin Name Color
10
Page 11
Getting Started
• Each person can enroll up to ten fingerprints. If a finger is injured or scratched, it is
1
When enrolling a fingerprint, the “Scan 1st finger” message will appear on the LCD screen. Place a finger on the fingerprint
sensor, and then press softly in order to improve the recognition.
2
After a beep sounds, you will be notified to scan again then remove your finger and place it again to scan.
(You are required to scan the same finger twice for enrollment.)
How to Enroll a Fingerprint
Correct fingerprint enrollment is critical in improving fingerprint recognition. BioStation 2 is loaded with powerful fingerprint
algorithm which is capable of recognizing a fingerprint even when the angle or position of the finger on the reader is not optimal.
Nevertheless, enrolling a fingerprint with the following instructions can improve the recognition performance.
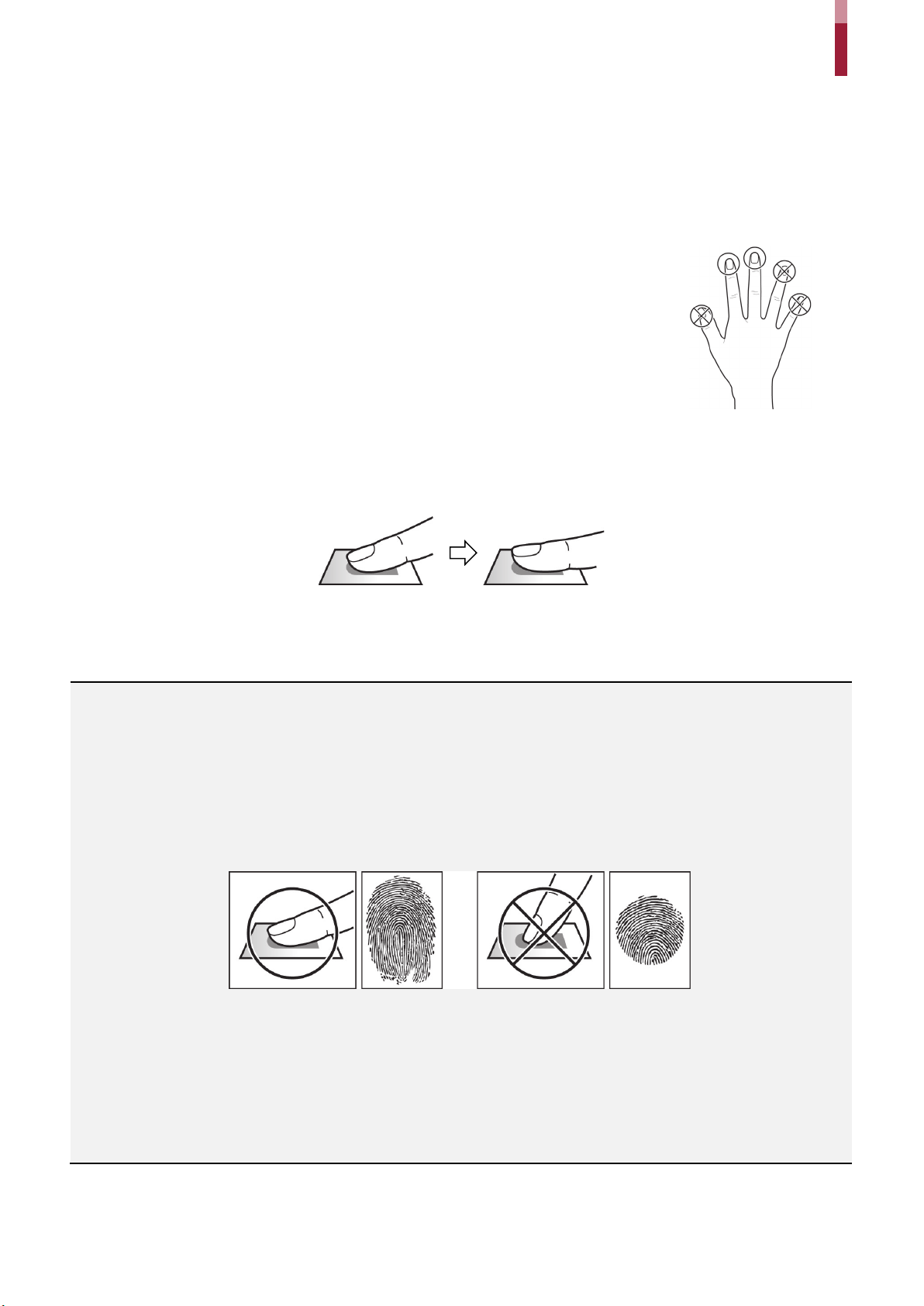
Choose Ideal Fingers to Enroll
recommended to use another finger.
• If the fingerprint recognition fails, you can enroll the same finger multiple times, which will
improves the recognition performance.
• If a finger is injured or the fingerprint is not clear, please enroll a different finger.
• The index finger and middle finger are preferred for enrolling fingerprints. Other fingers
may have a lower recognition rate because those fingers tend to have difficulty being
placed at the center of the fingerprint sensor.
How to Enroll Fingerprints
NOTE
Precautions for enrolling fingerprints
Enrolling fingerprints is the most important procedure because this device uses enrolled fingerprints to compare them with a scanned
fingerprint. Please ensure the following when enrolling fingerprints:
• Place the finger firmly on the fingerprint sensor for it to be read completely.
• The center of the fingerprint should be placed at the center of the fingerprint sensor.
• If a finger is injured or the fingerprint is not clear, please enroll another finger.
• Follow the instructions on the screen and place the finger correctly without movement when the finger is read.
• Place your finger to completely cover the sensor with maximum surface.
When the fingerprint recognition fails
BioStation 2 can read fingerprints regardless of the change in seasons or condition of the fingers. However, the external environment or the
finger's position can affect the recognition performance.
If the fingerprint recognition fails, the following actions are recommended.
• If there is water or sweat on the finger, please wipe it off before scanning the finger.
• If the finger is too dry, please blow softly on the fingertip before scanning the finger.
• If the finger is injured, please enroll another finger.
• If the fingerprint recognition failure persists, please follow ‘Precautions for enrolling fingerprints’ to re-enroll the fingerprint.
11
Page 12
Administrator Menus
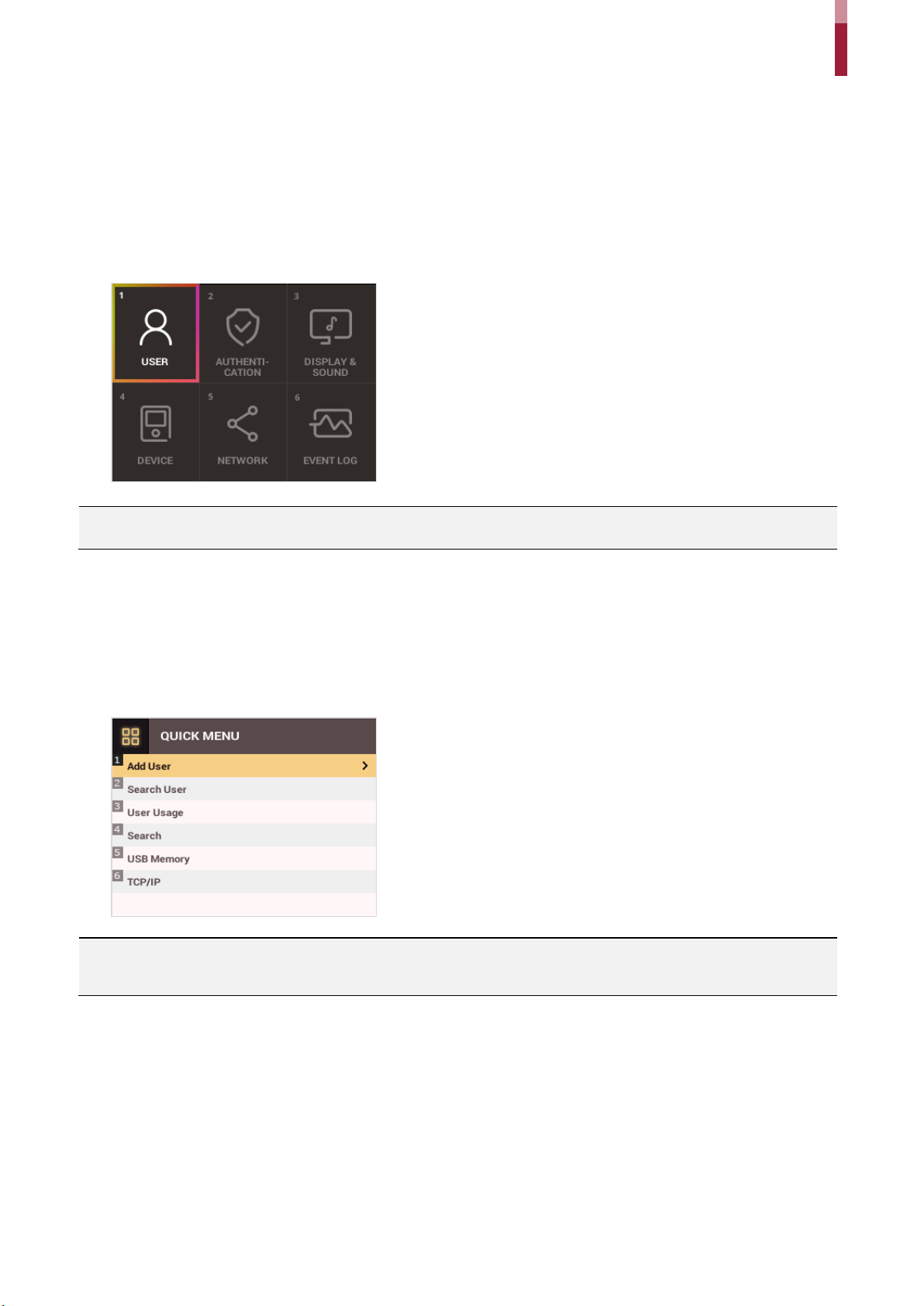
Full Menu
1 Press the ESC button then authenticate as an administrator.
2 Select the desired menu item.
NOTE
• If there is no administrator on the device, anyone can access the menu just by pressing the ESC button.
Administrator Menus
Quick Menu
1 Press and hold the ESC button for more than one second and then release the button. Next, authenticate yourself as an
administrator.
2 Select the desired menu item.
NOTE
• If there is no administrator on the device, anyone can access the quick menu just by pressing and holding the ESC button and then
releasing the button.
12
Page 13
User Management
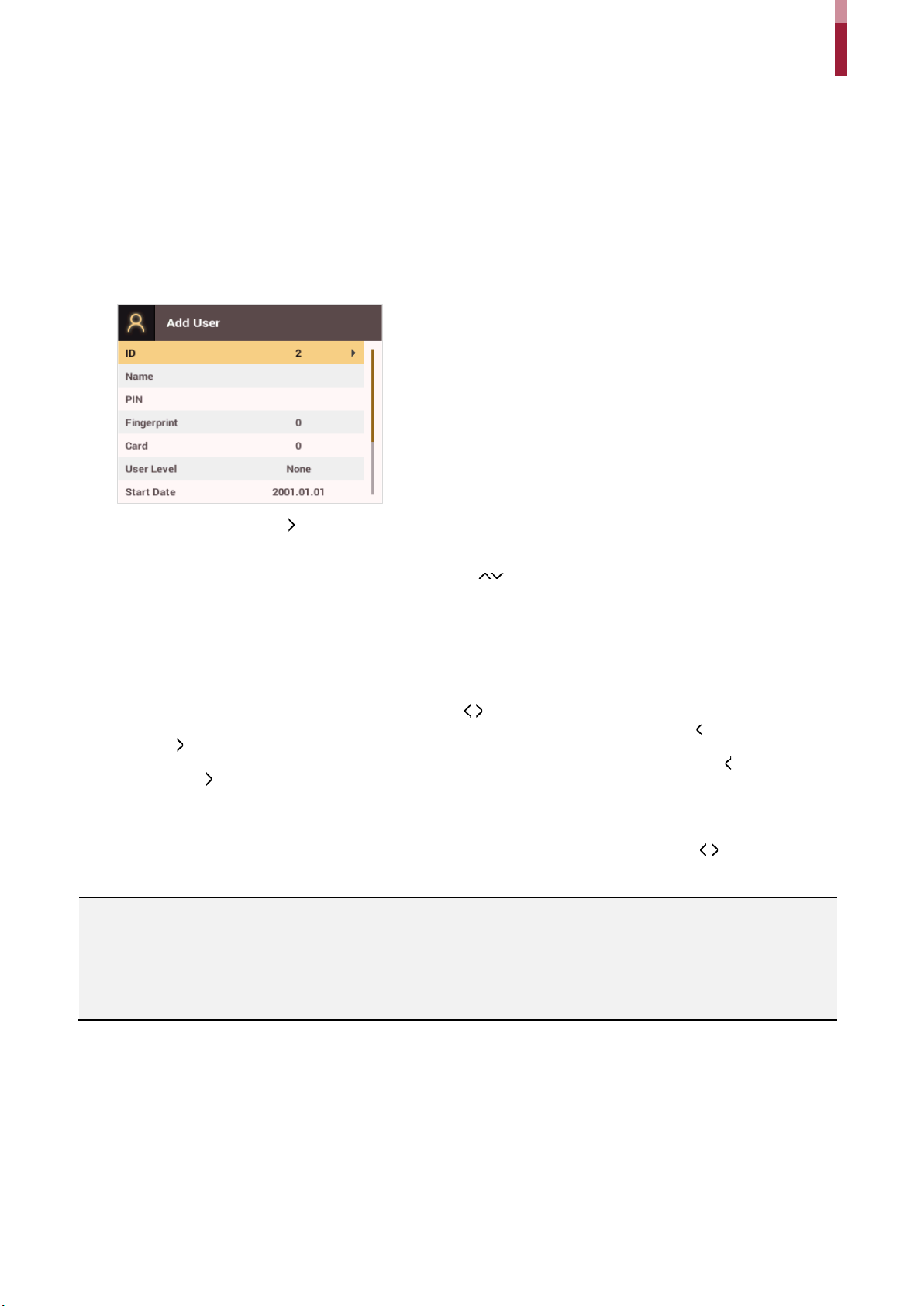
Add User Information
You can register the user information and fingerprints.
1 Press the ESC button then authenticate as an administrator.
2 Go to USER > Add User and press OK.
User Management
3 Select an item then press the button. Press OK after configuring the item to register the user information.
• ID: Enter a number between 1 and 429467295 to register as the user ID. If User ID Type set to Alphanumeric, a combination of
alphanumeric characters and symbols (_, -) can be used for the ID. Up to 32 characters can be input.
• Name: Enters the user name with the number buttons. Press the / buttons to switch between letters and numbers. Press F1/F2 to
show more letters.
• PIN: Enters a PIN. Enter the PIN and press OK. Enter the PIN again to confirm it, then press the OK button. PIN numbers must be 4 to 16
digits to prevent leaking of the PIN.
• Fingerprint: Enrolls fingerprints for user authentication. After scanning the fingerprint of the registered finger, the same finger should be
scanned one more time. Press the ESC button if you do not want to enroll a fingerprint.
• Card: Registers cards for user authentication. Scan the cards that you want to assign to users. Press the ESC button if you do not want
to register another card.
• User Level: Selects the privileges to assign to the user. Use the / buttons to select the user level.
• Start Date: Sets the start date for the user account. Press the number buttons to enter the date. Use the button to delete the date.
Use the button to enter a separator.
• Expiration Date: Sets the end date for the user account. Press the number buttons to enter the date. Use the button to delete the
date. Use the button to enter a separator.
• Security Level: Sets the security level for 1:1 Authentication.
• Duress: Selects the index of the fingerprints to be used as duress fingerprints. This is available only when there are two or more
registered fingerprints.
• Private Auth Mode: Changes the authentication mode for each user. Select a desired item and press the / buttons to change the
settings.
NOTE
The available menus vary depending on the selected user level.
• None: Indicates the level for normal users who cannot use the menu.
• Administrator: The user can use all menus.
• Configuration: The user can use AUTHENTICATION, DISPLAY & SOUND, DEVICE, NETWORK, and EVENT LOG menus.
• User Mgmt: The user can use USER and EVENT LOG menus.
13
Page 14

User Management
Edit User Information
Users with the user level of Administrator and User Mgmt can change user information. They can add fingerprints or a card for a
user, and also change PIN numbers and access levels.
1 Press the ESC button then authenticate as an administrator.
2 Go to USER > Search User and press OK.
3 Select a search method and press the button. You can search for users by ID, Name, Fingerprint, or Card.
• If you press OK without selecting a search method, a list of all users will be displayed.
4 Select the user you want to edit and press F2. Edit the information by referring to Adding User Information.
• Press F3 and then the OK button to delete a user.
NOTE
• Access Group can be registered in BioStar 2. For more information on registering access groups, see the BioStar 2 Administrator
Guide.
Delete All Users
You can delete all registered users.
1 Press the ESC button then authenticate as an administrator.
2 Go to USER > Delete User, then press OK.
3 If you press OK, all registered users will be deleted.
Check User Usage
Shows the numbers of registered users, fingerprints, and cards.
1 Press the ESC button then authenticate as an administrator.
2 Go to USER > User Usage, then press OK.
14
Page 15

Authentication Configuration
Finger
A schedule can be configured for each authentication method using fingerprints.
1 Press the ESC button then authenticate as an administrator.
2 Go to AUTHENTICATION > Finger, then press OK.
Authentication Configuration
3 Select an item and press the / buttons to set a schedule.
• : This mode only uses fingerprints.
• + : In this mode, a PIN must be entered after fingerprint authentication.
4 Press OK to save the settings.
NOTE
• You can configure a schedule in BioStar 2. You can select Never or Always if there is no configured schedule.
• For more information on configuring schedules, see the BioStar 2 Administrator Guide.
Card
A schedule can be configured for each authentication method using cards.
1 Press the ESC button then authenticate as an administrator.
2 Go to AUTHENTICATION > Card, then press OK.
3 Select an item and press the / buttons to set a schedule.
• : This mode only uses a card.
• + : In this mode, fingerprint authentication is required after card authentication.
• + : In this mode, a PIN must be entered after card authentication.
• + / : In this mode, fingerprint authentication or entering a PIN is required after card authentication.
• + + : In this mode, both fingerprint authentication and entering a PIN are required after card authentication.
4 Press OK to save the settings.
15
Page 16

Authentication Configuration
NOTE
• You can configure a schedule with BioStar 2. You can select Never or Always if there is no configured schedule.
• For more information on configuring schedules, see the BioStar 2 Administrator Guide.
ID
A schedule can be configured for each authentication method using IDs.
1 Press the ESC button then authenticate as an administrator.
2 Go to AUTHENTICATION > ID, then press OK.
3 Select an item and press the / buttons to set a schedule.
• + : In this mode, fingerprint authentication is required after entering an ID.
• + : In this mode, a PIN must be entered after entering an ID.
• + / : In this mode, fingerprint authentication or entering a PIN is required after entering an ID.
• + + : In this mode, both fingerprint authentication and entering a PIN are required after entering an ID.
4 Press OK to save the settings.
NOTE
• You can configure a schedule with BioStar 2. You can select Never or Always if there is no configured schedule.
• For more information on configuring schedules, see the BioStar 2 Administrator Guide.
T&A Mode
You can select registration options for the T&A Mode.
1 Press the ESC button then authenticate as an administrator.
2 Go to AUTHENTICATION > T&A Mode, then press OK.
3 Select an item and configure the settings.
• T&A Mode: Selects how to use the T&A Mode.
• T&A Event: Checks T&A Events.
• T&A Required: Selects the registration option for the T&A Mode. If Use is selected, you can set the T&A Event as a required option to
select during authentication.
16
Page 17

4 Press OK to save the settings.
Fingerprint
You can configure the fingerprint authentication settings.
1 Press the ESC button then authenticate as an administrator.
2 Go to AUTHENTICATION > Fingerprint, then press OK.
Authentication Configuration
3 Select an item and press the / buttons to change the settings.
• Security Level: Configures the security level for 1:N Authentication.
• Timeout: Sets a timeout period. If the authentication is not completed within the set time, the authentication fails.
• View Image: You can view the original image when a fingerprint is scanned.
• Sensor Sensitivity: Sets the sensitivity level of the fingerprint reader sensor. Set the sensor sensitivity high if you wish to use a higher
sensor sensitivity level and obtain more detailed fingerprint information.
• 1:N Fast Mode: Sets the fingerprint authentication speed. Select Auto On to have the authentication speed configured according to the
total fingerprint templates enrolled on the device.
• Template Format: Sets the fingerprint template format. The default format is SUPREMA. Be careful when changing the template format
as it can render all previously stored fingerprints unusable.
• Sensor Mode: If Auto On is selected, the fingerprint sensor detects if a finger is present. And the sensor is on while the finger is present
on the sensor. If Always On is selected, the fingerprint sensor is always on.
• Advanced Enrollment: You can check the quality of a scanned fingerprint to save high quality fingerprint data. If Enabled is selected, the
user will be notified when the fingerprint quality is low. This helps users to scan the fingerprints correctly.
• Duplicate Check: When registering fingerprints, you can check duplicates.
4 Press OK to save the settings.
NOTE
• Change the template type after deleting all user fingerprint information. If there is any user fingerprint information stored on the
device, the template type cannot be changed.
17
Page 18

System Setup
Display & Sound
You can configure the display and sound settings on the device.
1 Press the ESC button then authenticate as an administrator.
2 Go to DISPLAY & SOUND, then press OK.
System Setup
3 Select an item and press the / buttons to change the settings.
• Theme: Changes the style of the home screen.
• Background: Selects items to display on the home screen background.
• Server Private Msg.: Set whether or not to use a Private Message, which will be displayed on the screen when the user authenticates.
• Backlight Timeout: Configures how long (in seconds) the LCD screen light stays on.
• Menu Timeout: Configures the time (in seconds) for the menu screen to automatically disappear. If there is no button input for the
specified period, the display goes back to the home screen.
• Msg Timeout: Configures the time (in seconds) for the configuration completion message or notification message to automatically
disappear.
• Language: Selects the language to use.
• Voice Instruction: You can use voice instructions instead of beep.
• Volume: Adjusts the volume.
NOTE
• You can set the Server Private Msg. on the ser v er. If you have not set it on the server, the device does not display a message when
authentication is successful even if Server Private Msg. is enabled on the device.
4 Press OK to save the settings.
18
Page 19

System Setup
Device
Date & Time
You can configure the date and time settings. Be sure to correctly configure the settings to collect accurate log data.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Date & Time, then press OK.
3 Select an item and press the / buttons to change the settings.
• Date: Sets the current date. Press the number buttons to enter the date.
• Time: Sets the current time. Press the number buttons to enter the time.
• Time Zone: Sets the time zone for your area.
• Time Sync: Synchronizes the time with the server. To synchronize the time with the server, select Use.
• Date Format: Selects the date format. You can select from among the YYYY/MM/DD, MM/DD/YYYY, or DD/MM/YYYY formats.
• Time Format: Selects the time format. You can select from among the 24 hour or 12 hour (AM/PM) formats.
NOTE
• Press the number buttons to enter the date and time. Use the button to delete the values entered. Use the button to enter a
separator.
Daylight Saving Time
You can use the device by applying daylight saving time. Set the start and end time correctly.
1 Press ESC and authenticate with the Admin level credential.
2 Select DEVICE > Daylight Saving Time, then press OK.
3 Select an item and press the / buttons to change the settings.
4 To save settings, press OK.
19
Page 20

System Setup
User ID Type
You can set the type of user ID to be registered on the device to Number or Alphanumeric characters.
1 Press ESC and authenticate with the Admin level credential.
2 Select DEVICE > User ID Type, then press OK.
3 Press the / buttons to change the settings.
4 To save settings, press OK.
5 Press OK to save the settings.
USB Memory
By connecting a USB memory stick, you can import or export the log, data and configurations data to or from the USB memory
stick and upgrade the firmware.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > USB Memory, then press OK.
3 Select an item and change the settings.
• Export: Selects data to export to the connected USB memory stick. Press the / buttons to select an item and press OK.
• FW Upgrade: If there are firmware files stored on the USB memory stick, select the firmware file to use and press OK to upgrade the
firmware.
NOTE
Supported USB memory sticks are as follows. If you use other memory sticks, they may not work properly.
• Samsung Electronics: SUM-LSB 8 GB, SUM-PSB 8 GB, SUM-PSB 16 GB, and SUM-BSG 32 GB
• LG Electronics: XTICK J3 WINDY 8 GB, SMART USB MU1 White 8 GB, MU 1 USB 32 GB, MU28GBC 32 GB, XTICK MOBY J1 16 GB
• SanDisk: Cruzer 16 GB, Cruzer Blade CZ50 4 GB, Cruzer Blade CZ50 32 GB, CZ48 Ultra USB 3.0 64 GB, CZ80 USB3.0 64 GB, CZ52 64
GB, Cruzer Glide Z60 128 GB, Cruzer Force CZ71 32 GB
• Sony: Micro Vault Click 8 GB, MicroVault CLICK 16 GB, USM-SA1 32 GB
• Transcend: JetFlash 760 8 GB, JetFlash 760 32 GB, JetFlash 500 8 GB
• Memorette: MINI500 8 GB
• A-DATA: S102 PRO 8 GB
• TriGem: Pastel 8 GB
20
Page 21

Restart Device
The user can restart the device.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Restart Device, then press OK.
3 Press OK to restart the device. Press ESC to cancel.
Restore Default
System Setup
Device settings, network settings, and operator levels will be reset.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Restore Default, then press OK.
• Reset All Settings: You can reset all settings stored on the device. Press OK to reset all device settings. To cancel, press ESC.
• Reset without Network Settings: You can reset all settings except network settings. Press OK to reset all settings except netwo
rk settings. To cancel, press ESC.
• Factory Default: You can delete all the information saved in the device and the root certificate and restore default settings.
• Delete the Root Certificate: You can delete the root certificate saved in the device.
3 If you proceed to restore the defaults, the device will restart.
NOTE
• When you reset, the operator level will be reset as well. After resetting, make sure to set the operator level again.
• Language setting will not change after resetting.
• Factory Default menu can be used when the root certificate is saved in the device.
• Delete the Root Certificate menu can be used only when the root certificate is saved in the device and Administrator has been
designated.
More Settings
Relay
You can set the open time and the input port of the exit button in the device. This option is useful when the device is used as a
standalone.
1 Press ESC and authenticate with the Admin level credential.
2 Select DEVICE > Relay, then press OK.
• Relay: You can set whether relay is enabled or not. To set the open time and the input port of the exit button, set to Enabled.
• Open Time: Set the duration for the door to remain open when standard user authentication has been carried out.
• Exit Button: Select the input port where the exit button is connected.
3 To save settings, press OK.
21
Page 22

Intercom
You can select whether or not to use the intercom.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Interphone, then press OK.
3 When the intercom is connected, press the / buttons to select Enabled.
Secure Tamper
When the tamper is turned on, you can set to delete the entire user, the entire log, and the security key.
System Setup
1 Press ESC and authenticate with the Admin level credential. 2 Select DEVICE > Secure Tamper, then change the settings by pressing or . 3 To save settings, press OK.
Device Info
Shows the model name, device ID, FW version, and MAC address.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Device Info, then press OK.
• Shows the model name, device ID, HW / FW / Kernel versions and Ethernet/WiFi MAC addresses.
3 Check the device information and press OK.
Memory Info
Shows the memory usage status.
1 Press the ESC button then authenticate as an administrator.
2 Go to DEVICE > Memory Info, then press OK.
3 Check the memory information and press OK.
22
Page 23

Network
• Port: Enter the port number of the device.
the device.
• AP Search: Select the AP to connect to.
TCP/IP Settings
You can configure the network settings for the device.
1 Press the ESC button then authenticate as an administrator.
2 Go to NETWORK > TCP/IP then press OK.
3 Press the / buttons to select a Type then select an item. You can select Ethernet or Wireless.
System Setup
• DHCP: Select whether or not to use DHCP. If
Disabled is selected, the user can modify IP
Address, Gateway, and Subnet Mask.
• IP Address: Enter the IP address of the device.
• Gateway: Enter the gateway address of the
device.
• Subnet Mask: Enter the subnet mask address of
• Encryption: Shows the encryption method of the AP.
• Password: Enter the AP login password.
• Port: Enter the port number of the device.
• DHCP: Select whether or not to use DHCP. If Disabled is
selected, the user can modify the IP Address.
• IP Address: Enter the IP address of the device.
4 Press OK to save the settings.
NOTE
• Press the number buttons to enter the IP address, gateway address, and subnet mask address. Use the button to delete the
values entered. Use the button to enter a separator.
• To use Wireless, you need a wireless router. For more information on installing and configuring the wireless router, see the manual
of the wireless router.
Server Settings
1 Press the ESC button then authenticate as an administrator.
2 Go to NETWORK > Server then press OK.
3 Select an item and change the settings.
• Connection Mode: Select Device > Server to send the connect signal from the device directly to the server. If Server > Device is selected,
Server IP and Server Port address cannot be entered.
23
Page 24

System Setup
• Server URL: Enter the BioStar 2 server’s URL instead of Server IP. You can enter the values when Device > Server is selected for
Connection Mode.
• Server IP: Enter the IP address of the PC where BioStar 2 is installed. You can enter the values when Device > Server is selected for
Connection Mode.
• Server Port: Enter the port address of the PC with BioStar 2 installed. You can enter the values when Device > Server is selected for
Connection Mode.
4 Press OK to save the settings.
NOTE
• Press the number buttons to enter the values for Server IP and Server Port. Use the button to delete the values entered. Use the
button to enter a separator.
RS-485 Settings
1 Press the ESC button then authenticate as an administrator.
2 Go to NETWORK > RS-485 then press OK.
3 Select an item and press the / buttons to change the settings.
• Mode: Select RS-485 mode.
• Baud Rate: Select a baud rate.
4 Press OK to save the settings.
24
Page 25

Check Event Log
Search Logs
You can search logs after setting the condition.
1 Press the ESC button then authenticate as an administrator.
2 Go to EVENT LOG > Search then press OK.
Check Event Log
3 Select an item and press the / buttons to change the condition. If you press OK, matching logs will be displayed on the
screen.
4 Press ESC to return to the previous screen.
Delete All Logs
You can delete all logs stored on the device.
1 Press the ESC button then authenticate as an administrator.
2 Go to EVENT LOG > Delete All then press OK.
3 Press OK to delete all logs. Press ESC to cancel.
25
Page 26

Check Log Usage
Shows the status of the log usage.
1 Press the ESC button then authenticate as an administrator.
2 Go to EVENT LOG > Log Usage then press OK.
3 Press OK after checking the log usage.
Check Event Log
26
Page 27

Troubleshooting
• Refer to ‘How to Register Fingerprints’, and then enroll the fingerprint
finger.
On.
The lock does not work when
the door is closed.
Checklist Before Requesting Service
Category Problem Possible Causes & Remedy
Troubleshooting
Power
PIN
Fingerprint
Power is supplied to the
device, but the device does
not work.
I've lost my PIN.
I cannot open a locked door
when I enter a PIN and then
press the OK button.
A fingerprint is enrolled
successfully, but the
fingerprint recognition fails
too often.
The fingerprint recognition
does not work.
The fingerprint sensor does
not turn on.
• If the terminal is apart from the bracket, it may not work due to the tamper
switch.
• Check the adapter or power connection cable.
• For a normal user's PIN, contact your administrator and then enter the PIN
again.
• If an administration's PIN is lost, contact your installer.
• Check whether the registered PIN is entered correctly.
• Check whether the PIN has recently been changed.
• If you cannot find the PIN, contact your administrator to change the PIN.
again.
• Since there are variations in recognition rates due to the different
characteristics of each fingerprint, please try to enroll another fingerprint.
• If there are many number of enrolled fingerprints, change the Matching
Timeout setting and then try again.
• If a finger is injured, the finger may be recognized as another person's
• Check whether the finger or the fingerprint sensor has sweat, water, or
dust on it, and then wipe it clear.
• Try again after clearing the finger and the fingerprint sensor with a dry
cloth.
• If the finger is too dry, try again after blowing gently on the finger.
• When Sensor Mode set to Auto On, the fingerprint sensor detects if a
finger is present. And the sensor is on while the finger is present on the
sensor. If you want to keep the fingerprint sensor on, go to
AUTHENTICATION > Fingerprint > Sensor Mode and then select Always
Door lock
Time
Administrator
Connection
The time displayed on the
device is not correct.
The administrator mode
cannot be accessed due to
losing the administrator PIN.
• The electric lock may have a problem. Ask your installer to examine it.
• Even though BioStation 2 includes an internal battery, the time could
become incorrect due to the discharge of the internal battery if power has
not been applied to the system for a long time. Refer to Date & Time to
adjust the time.
• Since BioStation 2 administrators are in charge of permitting the right of
entrance, only the administrators can access the menu.
• If the administrator menu cannot be accessed, it is possible to get a PIN
issued in accordance with a predefined procedure. Ask your installer
about the procedure to issue a password.
27
Page 28

Product Specifications
• BS2-OMPW: 13.56Mhz MIFARE, MIFARE Plus, DESFire/EV1, FeliCa,
BS2-OEPW: 125kHz EM
Category Feature Specification
Biometric Fingerprint
IP Rating IP 65
Product Specifications
Main
Capacity
Interface
Relay
NFC
RF Option*
Max. User (1:1) 500,000
Max. User (1:N) 20,000
Max. Template (1:1) 1,000,000 (Two templates per finger)
Max. Template (1:N) 40,000 (Two templates per finger)
M ax . Te xt Lo g 3,000,000
Wi-Fi Yes
TCP/IP Yes
RS-485 1ch Host or Slave (Selectable)
Wiegand 1ch Input, 1ch Output
TTL Input 2ch Inputs, 2ch Outputs
Relay 1 Relay
USB USB 2.0 (Host)
Voltage Max. 24VDC
Current 0.5A, Max. 1.A
• BS2-OIPW: 13.56MHz iCLASS SE/SR/Seos, NFC
• BS2-OHPW: 125kHz HID Prox
•
CPU 1.0 GHz
Memory 8GB Flash + 256 MB RAM
LCD 2.8” QVGA Color LCD
LED Multi-Color
Sound 16-bit Hi-Fi
Hardware
* For detailed information on our supported card list, contact Suprema technical support team at support.supremainc.com.
Operating Temp. -20°C ~ 50°C
Tamper Yes
Power 9V ~ 18V
PoE Optional
Dimensions (W x H x D mm) 142 x 144 x 45(38)
Certificates CE, FCC, KC, RoHS, REACH, WEEE
28
Page 29

Dimensions
Product Specifications
(Unit: mm)
29
Page 30

FCC Compliance Information
FCC Compliance Information
This device complies with Part 15 of the FCC Rules.
Operation is subject to the following two conditions:
(1) This device may not cause harmful interference, and
(2) This device must accept any interference received, including interference that may cause undesired operation.
Note: This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to Part 15 of the
FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a residential installation.
This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the
instructions, may cause harmful interference to radio communications. However, there is no guarantee that interference will not
occur in a particular installation. If this equipment does cause harmful interference to radio or television reception, which can be
determined by turning the equipment off and on, the user is encouraged to try to correct the interference by one or more of the
following measures:
• Reorient or relocate the receiving antenna.
• Increase the separation between the equipment and the receiver.
• Connect the equipment into an outlet different from that to which the receiver is connected.
• Consult the dealer or an experienced radio/TV technician for help.
Any changes or modifications of the product not expressly approved by the manufacturer could void the user’s authority to
operate the equipment according to the FCC Rules.
This appliance and its antenna must not be co-located or operation in conjunction with any other antenna or transmitter.
A minimum separation distance of 20 cm must be maintained between the antenna and the person for this appliance to satisfy
the RF exposure requirements.
30
Page 31

Appendices
Appendices
Disclaimers
• The information contained in this Guide is provided in regard to the Suprema product.
• Your right of usage is recognized only for products included in sales agreements and conditions guaranteed by Suprema. No
license rights over other intellectual properties mentioned in this Guide are recognized.
• Suprema makes no representations or warranties concerning infringement of patents, copyrights or other intellectual
property rights as well as merchantability and fitness of the product for a particular purpose in regard to the sale or use of the
Suprema product.
• Do not use the Suprema product in medical, life-saving and life-sustaining situations or in situations where malfunction of
the product could lead to personal injury or loss of life. However, if an accident occurs while the purchaser is using the
product in any of the situations stated above, even if shortcomings are discovered in the design or production process of the
product and are claimed as a point of major negligence, employees, subsidiaries, branches, affiliates, or distributors of
Suprema shall not be liable and shall not make reimbursements for any direct or indirect costs or expenses associated,
including lawyer fees.
• Suprema may change the product standards and specifications at any time without any adequate notice for improvements
in stability, performance or design of the product. Designers should keep in mind that features or descriptions marked as "to
be implemented" or "to be defined" are always subject to change. Suprema will implement or define such features or
descriptions in the near future and shall not be liable for any consequential problems, including problems of compatibility.
• If you wish to obtain the latest specification documentation before you place an order for the product, please contact
Suprema, a sales agent of Suprema, or a regional distributor.
Copyright Notice
Suprema owns the copyright for this document. The rights of other product names, brands, and trademarks belong to the
individuals or organizations who own them.
Open Source License
• The software of this product is based on "Linux Kernel 3.x", which is licensed under GPL. As for GPL, please refer to the GNU
General Public License in this manual.
• This product uses the "glibc" library, which is licensed under LGPL. As for LGPL, please refer to the GNU Lesser General Public
License in this manual.
• This product uses the "QT" library, which is licensed under LGPL. As for LGPL, please refer to the GNU Lesser General Public
License in this manual.
• This product uses the "OpenSSL", which is licensed under the OpenSSL and Original SSLeay licenses. As for the OpenSSL
and Original SSLeay licenses, please refer to OpenSSL License and Original SSLeay License in this manual.
• To request the modified source code based on Linux Kernel 3.x and the source code of glibc and QT libraries, which are
included in this product, please contact us at tech@supremainc.com.
GNU General Public License
Version 3, 29 June 2007
Copyright © 2007 Free Software Foundation, Inc. <http://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
Preamble
The GNU General Public License is a free, copyleft license for software and other kinds of works.
The licenses for most software and other practical works are designed to take away your freedom to share and change the
works. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change all versions of a
program--to make sure it remains free software for all its users. We, the Free Software Foundation, use the GNU General Public
License for most of our software; it applies also to any other work released this way by its authors. You can apply it to your
programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure
31
Page 32

Appendices
that you have the freedom to distribute copies of free software (and charge for them if you wish), that you receive source code or
can get it if you want it, that you can change the software or use pieces of it in new free programs, and that you know you can do
these things.
To protect your rights, we need to prevent others from denying you these rights or asking you to surrender the rights. Therefore,
you have certain responsibilities if you distribute copies of the software, or if you modify it: responsibilities to respect the
freedom of others.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must pass on to the recipients the same
freedoms that you received. You must make sure that they, too, receive or can get the source code. And you must show them
these terms so they know their rights.
Developers that use the GNU GPL protect your rights with two steps: (1) assert copyright on the software, and (2) offer you this
License giving you legal permission to copy, distribute and/or modify it.
For the developers' and authors' protection, the GPL clearly explains that there is no warranty for this free software. For both
users' and authors' sake, the GPL requires that modified versions be marked as changed, so that their problems will not be
attributed erroneously to authors of previous versions.
Some devices are designed to deny users access to install or run modified versions of the software inside them, although the
manufacturer can do so. This is fundamentally incompatible with the aim of protecting users' freedom to change the software.
The systematic pattern of such abuse occurs in the area of products for individuals to use, which is precisely where it is most
unacceptable. Therefore, we have designed this version of the GPL to prohibit the practice for those products. If such problems
arise substantially in other domains, we stand ready to extend this provision to those domains in future versions of the GPL, as
needed to protect the freedom of users.
Finally, every program is threatened constantly by software patents. States should not allow patents to restrict development and
use of software on general-purpose computers, but in those that do, we wish to avoid the special danger that patents applied to
a free program could make it effectively proprietary. To prevent this, the GPL assures that patents cannot be used to render the
program non-free.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS
0. Definitions.
“This License” refers to version 3 of the GNU General Public License.
“Copyright” also means copyright-like laws that apply to other kinds of works, such as semiconductor masks.
“The Program” refers to any copyrightable work licensed under this License. Each licensee is addressed as “you”. “Licensees”
and “recipients” may be individuals or organizations.
To “modify” a work means to copy from or adapt all or part of the work in a fashion requiring copyright permission, other than the
making of an exact copy. The resulting work is called a “modified version” of the earlier work or a work “based on” the earlier
work.
A “covered work” means either the unmodified Program or a work based on the Program.
To “propagate” a work means to do anything with it that, without permission, would make you directly or secondarily liable for
infringement under applicable copyright law, except executing it on a computer or modifying a private copy. Propagation
includes copying, distribution (with or without modification), making available to the public, and in some countries other
activities as well.
To “convey” a work means any kind of propagation that enables other parties to make or receive copies. Mere interaction with a
user through a computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays “Appropriate Legal Notices” to the extent that it includes a convenient and prominently
visible feature that (1) displays an appropriate copyright notice, and (2) tells the user that there is no warranty for the work
(except to the extent that warranties are provided), that licensees may convey the work under this License, and how to view a
copy of this License. If the interface presents a list of user commands or options, such as a menu, a prominent item in the list
meets this criterion.
1. Source Code.
The “source code” for a work means the preferred form of the work for making modifications to it. “Object code” means any nonsource form of a work.
A “Standard Interface” means an interface that either is an official standard defined by a recognized standards body, or, in the
case of interfaces specified for a particular programming language, one that is widely used among developers working in that
32
Page 33

Appendices
language.
The “System Libraries” of an executable work include anything, other than the work as a whole, that (a) is included in the normal
form of packaging a Major Component, but which is not part of that Major Component, and (b) serves only to enable use of the
work with that Major Component, or to implement a Standard Interface for which an implementation is available to the public in
source code form. A “Major Component”, in this context, means a major essential component (kernel, window system, and so on)
of the specific operating system (if any) on which the executable work runs, or a compiler used to produce the work, or an object
code interpreter used to run it.
The “Corresponding Source” for a work in object code form means all the source code needed to generate, install, and (for an
executable work) run the object code and to modify the work, including scripts to control those activities. However, it does not
include the work's System Libraries, or general-purpose tools or generally available free programs which are used unmodified in
performing those activities but which are not part of the work. For example, Corresponding Source includes interface definition
files associated with source files for the work, and the source code for shared libraries and dynamically linked subprograms that
the work is specifically designed to require, such as by intimate data communication or control flow between those subprograms
and other parts of the work.
The Corresponding Source need not include anything that users can regenerate automatically from other parts of the
Corresponding Source.
The Corresponding Source for a work in source code form is that same work.
2. Basic Permissions.
All rights granted under this License are granted for the term of copyright on the Program, and are irrevocable provided the
stated conditions are met. This License explicitly affirms your unlimited permission to run the unmodified Program. The output
from running a covered work is covered by this License only if the output, given its content, constitutes a covered work. This
License acknowledges your rights of fair use or other equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not convey, without conditions so long as your license otherwise
remains in force. You may convey covered works to others for the sole purpose of having them make modifications exclusively
for you, or provide you with facilities for running those works, provided that you comply with the terms of this License in
conveying all material for which you do not control copyright. Those thus making or running the covered works for you must do
so exclusively on your behalf, under your direction and control, on terms that prohibit them from making any copies of your
copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under the conditions stated below. Sublicensing is not allowed;
section 10 makes it unnecessary.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological measure under any applicable law fulfilling obligations under
article 11 of the WIPO copyright treaty adopted on 20 December 1996, or similar laws prohibiting or restricting circumvention of
such measures.
When you convey a covered work, you waive any legal power to forbid circumvention of technological measures to the extent
such circumvention is effected by exercising rights under this License with respect to the covered work, and you disclaim any
intention to limit operation or modification of the work as a means of enforcing, against the work's users, your or third parties'
legal rights to forbid circumvention of technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program's source code as you receive it, in any medium, provided that you
conspicuously and appropriately publish on each copy an appropriate copyright notice; keep intact all notices stating that this
License and any non-permissive terms added in accord with section 7 apply to the code; keep intact all notices of the absence of
any warranty; and give all recipients a copy of this License along with the Program.
You may charge any price or no price for each copy that you convey, and you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to produce it from the Program, in the form of source code
under the terms of section 4, provided that you also meet all of these conditions:
• a) The work must carry prominent notices stating that you modified it, and giving a relevant date.
• b) The work must carry prominent notices stating that it is released under this License and any conditions added under
section 7. This requirement modifies the requirement in section 4 to “keep intact all notices”.
• c) You must license the entire work, as a whole, under this License to anyone who comes into possession of a copy. This
License will therefore apply, along with any applicable section 7 additional terms, to the whole of the work, and all its parts,
regardless of how they are packaged. This License gives no permission to license the work in any other way, but it does not
33
Page 34

Appendices
invalidate such permission if you have separately received it.
• d) If the work has interactive user interfaces, each must display Appropriate Legal Notices; however, if the Program has
interactive interfaces that do not display Appropriate Legal Notices, your work need not make them do so.
A compilation of a covered work with other separate and independent works, which are not by their nature extensions of the
covered work, and which are not combined with it such as to form a larger program, in or on a volume of a storage or distribution
medium, is called an “aggregate” if the compilation and its resulting copyright are not used to limit the access or legal rights of
the compilation's users beyond what the individual works permit. Inclusion of a covered work in an aggregate does not cause
this License to apply to the other parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms of sections 4 and 5, provided that you also convey the
machine-readable Corresponding Source under the terms of this License, in one of these ways:
• a) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied
by the Corresponding Source fixed on a durable physical medium customarily used for software interchange.
• b) Convey the object code in, or embodied in, a physical product (including a physical distribution medium), accompanied
by a written offer, valid for at least three years and valid for as long as you offer spare parts or customer support for that
product model, to give anyone who possesses the object code either (1) a copy of the Corresponding Source for all the
software in the product that is covered by this License, on a durable physical medium customarily used for software
interchange, for a price no more than your reasonable cost of physically performing this conveying of source, or (2) access
to copy the Corresponding Source from a network server at no charge.
• c) Convey individual copies of the object code with a copy of the written offer to provide the Corresponding Source. This
alternative is allowed only occasionally and noncommercially, and only if you received the object code with such an offer, in
accord with subsection 6b.
• d) Convey the object code by offering access from a designated place (gratis or for a charge), and offer equivalent access to
the Corresponding Source in the same way through the same place at no further charge. You need not require recipients to
copy the Corresponding Source along with the object code. If the place to copy the object code is a network server, the
Corresponding Source may be on a different server (operated by you or a third party) that supports equivalent copying
facilities, provided you maintain clear directions next to the object code saying where to find the Corresponding Source.
Regardless of what server hosts the Corresponding Source, you remain obligated to ensure that it is available for as long as
needed to satisfy these requirements.
• e) Convey the object code using peer-to-peer transmission, provided you inform other peers where the object code and
Corresponding Source of the work are being offered to the general public at no charge under subsection 6d.
A separable portion of the object code, whose source code is excluded from the Corresponding Source as a System Library, need
not be included in conveying the object code work.
A “User Product” is either (1) a “consumer product”, which means any tangible personal property which is normally used for
personal, family, or household purposes, or (2) anything designed or sold for incorporation into a dwelling. In determining
whether a product is a consumer product, doubtful cases shall be resolved in favor of coverage. For a particular product received
by a particular user, “normally used” refers to a typical or common use of that class of product, regardless of the status of the
particular user or of the way in which the particular user actually uses, or expects or is expected to use, the product. A product is
a consumer product regardless of whether the product has substantial commercial, industrial or non-consumer uses, unless
such uses represent the only significant mode of use of the product.
“Installation Information” for a User Product means any methods, procedures, authorization keys, or other information required
to install and execute modified versions of a covered work in that User Product from a modified version of its Corresponding
Source. The information must suffice to ensure that the continued functioning of the modified object code is in no case
prevented or interfered with solely because modification has been made.
If you convey an object code work under this section in, or with, or specifically for use in, a User Product, and the conveying
occurs as part of a transaction in which the right of possession and use of the User Product is transferred to the recipient in
perpetuity or for a fixed term (regardless of how the transaction is characterized), the Corresponding Source conveyed under this
section must be accompanied by the Installation Information. But this requirement does not apply if neither you nor any third
party retains the ability to install modified object code on the User Product (for example, the work has been installed in ROM).
The requirement to provide Installation Information does not include a requirement to continue to provide support service,
warranty, or updates for a work that has been modified or installed by the recipient, or for the User Product in which it has been
modified or installed. Access to a network may be denied when the modification itself materially and adversely affects the
operation of the network or violates the rules and protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided, in accord with this section must be in a format that is
publicly documented (and with an implementation available to the public in source code form), and must require no special
password or key for unpacking, reading or copying.
7. Additional Terms.
34
Page 35

Appendices
“Additional permissions” are terms that supplement the terms of this License by making exceptions from one or more of its
conditions. Additional permissions that are applicable to the entire Program shall be treated as though they were included in this
License, to the extent that they are valid under applicable law. If additional permissions apply only to part of the Program, that
part may be used separately under those permissions, but the entire Program remains governed by this License without regard
to the additional permissions.
When you convey a copy of a covered work, you may at your option remove any additional permissions from that copy, or from
any part of it. (Additional permissions may be written to require their own removal in certain cases when you modify the work.)
You may place additional permissions on material, added by you to a covered work, for which you have or can give appropriate
copyright permission.
Notwithstanding any other provision of this License, for material you add to a covered work, you may (if authorized by the
copyright holders of that material) supplement the terms of this License with terms:
• a) Disclaiming warranty or limiting liability differently from the terms of sections 15 and 16 of this License; or
• b) Requiring preservation of specified reasonable legal notices or author attributions in that material or in the Appropriate
Legal Notices displayed by works containing it; or
• c) Prohibiting misrepresentation of the origin of that material, or requiring that modified versions of such material be
marked in reasonable ways as different from the original version; or
• d) Limiting the use for publicity purposes of names of licensors or authors of the material; or
• e) Declining to grant rights under trademark law for use of some trade names, trademarks, or service marks; or
• f) Requiring indemnification of licensors and authors of that material by anyone who conveys the material (or modified
versions of it) with contractual assumptions of liability to the recipient, for any liability that these contractual assumptions
directly impose on those licensors and authors.
All other non-permissive additional terms are considered “further restrictions” within the meaning of section 10. If the Program
as you received it, or any part of it, contains a notice stating that it is governed by this License along with a term that is a further
restriction, you may remove that term. If a license document contains a further restriction but permits relicensing or conveying
under this License, you may add to a covered work material governed by the terms of that license document, provided that the
further restriction does not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you must place, in the relevant source files, a statement of the
additional terms that apply to those files, or a notice indicating where to find the applicable terms.
Additional terms, permissive or non-permissive, may be stated in the form of a separately written license, or stated as exceptions;
the above requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly provided under this License. Any attempt otherwise to
propagate or modify it is void, and will automatically terminate your rights under this License (including any patent licenses
granted under the third paragraph of section 11).
However, if you cease all violation of this License, then your license from a particular copyright holder is reinstated (a)
provisionally, unless and until the copyright holder explicitly and finally terminates your license, and (b) permanently, if the
copyright holder fails to notify you of the violation by some reasonable means prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is reinstated permanently if the copyright holder notifies you of the
violation by some reasonable means, this is the first time you have received notice of violation of this License (for any work) from
that copyright holder, and you cure the violation prior to 30 days after your receipt of the notice.
Termination of your rights under this section does not terminate the licenses of parties who have received copies or rights from
you under this License. If your rights have been terminated and not permanently reinstated, you do not qualify to receive new
licenses for the same material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or run a copy of the Program. Ancillary propagation of a covered
work occurring solely as a consequence of using peer-to-peer transmission to receive a copy likewise does not require
acceptance. However, nothing other than this License grants you permission to propagate or modify any covered work. These
actions infringe copyright if you do not accept this License. Therefore, by modifying or propagating a covered work, you indicate
your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically receives a license from the original licensors, to run, modify
and propagate that work, subject to this License. You are not responsible for enforcing compliance by third parties with this
License.
An “entity transaction” is a transaction transferring control of an organization, or substantially all assets of one, or subdividing an
organization, or merging organizations. If propagation of a covered work results from an entity transaction, each party to that
35
Page 36

Appendices
transaction who receives a copy of the work also receives whatever licenses to the work the party's predecessor in interest had
or could give under the previous paragraph, plus a right to possession of the Corresponding Source of the work from the
predecessor in interest, if the predecessor has it or can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the rights granted or affirmed under this License. For example,
you may not impose a license fee, royalty, or other charge for exercise of rights granted under this License, and you may not
initiate litigation (including a cross-claim or counterclaim in a lawsuit) alleging that any patent claim is infringed by making,
using, selling, offering for sale, or importing the Program or any portion of it.
11. Patents.
A “contributor” is a copyright holder who authorizes use under this License of the Program or a work on which the Program is
based. The work thus licensed is called the contributor's “contributor version”.
A contributor's “essential patent claims” are all patent claims owned or controlled by the contributor, whether already acquired or
hereafter acquired, that would be infringed by some manner, permitted by this License, of making, using, or selling its contributor
version, but do not include claims that would be infringed only as a consequence of further modification of the contributor
version. For purposes of this definition, “control” includes the right to grant patent sublicenses in a manner consistent with the
requirements of this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free patent license under the contributor's essential patent
claims, to make, use, sell, offer for sale, import and otherwise run, modify and propagate the contents of its contributor version.
In the following three paragraphs, a “patent license” is any express agreement or commitment, however denominated, not to
enforce a patent (such as an express permission to practice a patent or covenant not to sue for patent infringement). To “grant”
such a patent license to a party means to make such an agreement or commitment not to enforce a patent against the party.
If you convey a covered work, knowingly relying on a patent license, and the Corresponding Source of the work is not available
for anyone to copy, free of charge and under the terms of this License, through a publicly available network server or other readily
accessible means, then you must either (1) cause the Corresponding Source to be so available, or (2) arrange to deprive yourself
of the benefit of the patent license for this particular work, or (3) arrange, in a manner consistent with the requirements of this
License, to extend the patent license to downstream recipients. “Knowingly relying” means you have actual knowledge that, but
for the patent license, your conveying the covered work in a country, or your recipient's use of the covered work in a country,
would infringe one or more identifiable patents in that country that you have reason to believe are valid.
If, pursuant to or in connection with a single transaction or arrangement, you convey, or propagate by procuring conveyance of, a
covered work, and grant a patent license to some of the parties receiving the covered work authorizing them to use, propagate,
modify or convey a specific copy of the covered work, then the patent license you grant is automatically extended to all
recipients of the covered work and works based on it.
A patent license is “discriminatory” if it does not include within the scope of its coverage, prohibits the exercise of, or is
conditioned on the non-exercise of one or more of the rights that are specifically granted under this License. You may not
convey a covered work if you are a party to an arrangement with a third party that is in the business of distributing software,
under which you make payment to the third party based on the extent of your activity of conveying the work, and under which the
third party grants, to any of the parties who would receive the covered work from you, a discriminatory patent license (a) in
connection with copies of the covered work conveyed by you (or copies made from those copies), or (b) primarily for and in
connection with specific products or compilations that contain the covered work, unless you entered into that arrangement, or
that patent license was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting any implied license or other defenses to infringement that may
otherwise be available to you under applicable patent law.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License,
they do not excuse you from the conditions of this License. If you cannot convey a covered work so as to satisfy simultaneously
your obligations under this License and any other pertinent obligations, then as a consequence you may not convey it at all. For
example, if you agree to terms that obligate you to collect a royalty for further conveying from those to whom you convey the
Program, the only way you could satisfy both those terms and this License would be to refrain entirely from conveying the
Program.
13. Use with the GNU Affero General Public License.
Notwithstanding any other provision of this License, you have permission to link or combine any covered work with a work
licensed under version 3 of the GNU Affero General Public License into a single combined work, and to convey the resulting work.
The terms of this License will continue to apply to the part which is the covered work, but the special requirements of the GNU
Affero General Public License, section 13, concerning interaction through a network will apply to the combination as such.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions of the GNU General Public License from time to time.
36
Page 37

Appendices
Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies that a certain numbered version of the GNU
General Public License “or any later version” applies to it, you have the option of following the terms and conditions either of that
numbered version or of any later version published by the Free Software Foundation. If the Program does not specify a version
number of the GNU General Public License, you may choose any version ever published by the Free Software Foundation.
If the Program specifies that a proxy can decide which future versions of the GNU General Public License can be used, that
proxy's public statement of acceptance of a version permanently authorizes you to choose that version for the Program.
Later license versions may give you additional or different permissions. However, no additional obligations are imposed on any
author or copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE
STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT
WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE
OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY
SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY
OTHER PARTY WHO MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES,
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO
USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES
SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN
IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided above cannot be given local legal effect according to their terms,
reviewing courts shall apply local law that most closely approximates an absolute waiver of all civil liability in connection with
the Program, unless a warranty or assumption of liability accompanies a copy of the Program in return for a fee.
END OF TERMS AND CONDITIONS
GNU Lesser General Public License
Version 3, 29 June 2007
Copyright © 2007 Free Software Foundation, Inc. <http://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
This version of the GNU Lesser General Public License incorporates the terms and conditions of version 3 of the GNU General
Public License, supplemented by the additional permissions listed below.
0. Additional Definitions.
As used herein, “this License” refers to version 3 of the GNU Lesser General Public License, and the “GNU GPL” refers to version 3
of the GNU General Public License.
“The Library” refers to a covered work governed by this License, other than an Application or a Combined Work as defined below.
An “Application” is any work that makes use of an interface provided by the Library, but which is not otherwise based on the
Library. Defining a subclass of a class defined by the Library is deemed a mode of using an interface provided by the Library.
A “Combined Work” is a work produced by combining or linking an Application with the Library. The particular version of the
Library with which the Combined Work was made is also called the “Linked Version”.
The “Minimal Corresponding Source” for a Combined Work means the Corresponding Source for the Combined Work, excluding
any source code for portions of the Combined Work that, considered in isolation, are based on the Application, and not on the
Linked Version.
The “Corresponding Application Code” for a Combined Work means the object code and/or source code for the Application,
including any data and utility programs needed for reproducing the Combined Work from the Application, but excluding the
System Libraries of the Combined Work.
1. Exception to Section 3 of the GNU GPL.
37
Page 38

Appendices
You may convey a covered work under sections 3 and 4 of this License without being bound by section 3 of the GNU GPL.
2. Conveying Modified Versions.
If you modify a copy of the Library, and, in your modifications, a facility refers to a function or data to be supplied by an
Application that uses the facility (other than as an argument passed when the facility is invoked), then you may convey a copy of
the modified version:
• a) under this License, provided that you make a good faith effort to ensure that, in the event an Application does not supply
the function or data, the facility still operates, and performs whatever part of its purpose remains meaningful, or
• b) under the GNU GPL, with none of the additional permissions of this License applicable to that copy.
3. Object Code Incorporating Material from Library Header Files.
The object code form of an Application may incorporate material from a header file that is part of the Library. You may convey
such object code under terms of your choice, provided that, if the incorporated material is not limited to numerical parameters,
data structure layouts and accessors, or small macros, inline functions and templates (ten or fewer lines in length), you do both
of the following:
• a) Give prominent notice with each copy of the object code that the Library is used in it and that the Library and its use are
covered by this License.
• b) Accompany the object code with a copy of the GNU GPL and this license document.
4. Combined Works.
You may convey a Combined Work under terms of your choice that, taken together, effectively do not restrict modification of the
portions of the Library contained in the Combined Work and reverse engineering for debugging such modifications, if you also do
each of the following:
• a) Give prominent notice with each copy of the Combined Work that the Library is used in it and that the Library and its use
are covered by this License.
• b) Accompany the Combined Work with a copy of the GNU GPL and this license document.
• c) For a Combined Work that displays copyright notices during execution, include the copyright notice for the Library
among these notices, as well as a reference directing the user to the copies of the GNU GPL and this license document.
• d) Do one of the following:
- 0) Convey the Minimal Corresponding Source under the terms of this License, and the Corresponding Application Code
in a form suitable for, and under terms that permit, the user to recombine or relink the Application with a modified
version of the Linked Version to produce a modified Combined Work, in the manner specified by section 6 of the GNU
GPL for conveying Corresponding Source.
- 1) Use a suitable shared library mechanism for linking with the Library. A suitable mechanism is one that (a) uses at
run time a copy of the Library already present on the user's computer system, and (b) will operate properly with a
modified version of the Library that is interface-compatible with the Linked Version.
• e) Provide Installation Information, but only if you would otherwise be required to provide such information under section 6
of the GNU GPL, and only to the extent that such information is necessary to install and execute a modified version of the
Combined Work produced by recombining or relinking the Application with a modified version of the Linked Version. (If you
use option 4d0, the Installation Information must accompany the Minimal Corresponding Source and Corresponding
Application Code. If you use option 4d1, you must provide the Installation Information in the manner specified by section 6
of the GNU GPL for conveying Corresponding Source.)
5. Combined Libraries.
You may place library facilities that are a work based on the Library side by side in a single library together with other library
facilities that are not Applications and are not covered by this License, and convey such a combined library under terms of your
choice, if you do both of the following:
• a) Accompany the combined library with a copy of the same work based on the Library, uncombined with any other library
facilities, conveyed under the terms of this License.
• b) Give prominent notice with the combined library that part of it is a work based on the Library, and explaining where to find
the accompanying uncombined form of the same work.
6. Revised Versions of the GNU Lesser General Public License.
The Free Software Foundation may publish revised and/or new versions of the GNU Lesser General Public License from time to
time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or
concerns.
Each version is given a distinguishing version number. If the Library as you received it specifies that a certain numbered version
of the GNU Lesser General Public License “or any later version” applies to it, you have the option of following the terms and
conditions either of that published version or of any later version published by the Free Software Foundation. If the Library as you
received it does not specify a version number of the GNU Lesser General Public License, you may choose any version of the GNU
Lesser General Public License ever published by the Free Software Foundation.
If the Library as you received it specifies that a proxy can decide whether future versions of the GNU Lesser General Public
License shall apply, that proxy's public statement of acceptance of any version is permanent authorization for you to choose that
version for the Library.
38
Page 39

Appendices
OpenSSL License
Copyright (c) 1998-2017 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following
conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following
disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgment: "This
product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org/)"
4. The names "OpenSSL Toolkit" and "OpenSSL Project" must not be used to endorse or promote products derived from this
software without prior written permission. For written permission, please contact openssl-core@openssl.org.
5. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their names without prior
written permission of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment: "This product includes software
developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/)"
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY EXPRESSED OR IMPLIED WARRANTIES,
INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY
DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This product includes software
written by Tim Hudson (tjh@cryptsoft.com).
Original SSLeay License
Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com). The implementation was written so as to
conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are aheared to. The following
conditions apply to all code found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just the SSL code. The SSL
documentation included with this distribution is covered by the same copyright terms except that the holder is Tim Hudson
(tjh@cryptsoft.com).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If this package is used in a
product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual
message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following
conditions are met:
1. Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer
in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the following acknowledgement: "This
product includes cryptographic software written by Eric Young (eay@cryptsoft.com)" The word 'cryptographic' can be left
out if the rouines from the library being used are not cryptographic related :-).
4. If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must
include an acknowledgement: "This product includes software written by Tim Hudson (tjh@cryptsoft.com)"
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT
LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED.
IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR
SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF
LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
39
Page 40

Appendices
WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code
cannot simply be copied and put under another distribution licence [including the GNU Public Licence.]
40
Page 41

Suprema Inc.
17F Parkview Tower, 248, Jeongjail-ro, Bundang- gu, Seongnam-si, Gyeonggi-do, 13554, Rep. of KOREA
Tel: +82 31 783 4502 I Fax: +82 31 783 4503 I Inquiry: sales@supremainc.com
©2019
Suprema Inc. Suprema and identifying product names and numbers herein are registered trade marks of Suprema, Inc. All non-Suprema brands and product names are
trademarks or registered trademarks of their respective companies. Product appearance, build status and/or specifications are subject to change without notice.
 Loading...
Loading...