Page 1
Ethernet Routing Switch
8600
Engineering
> Technical Configuration Guide
for SNMP
Enterprise Network Engineering
Document Date: December 15, 2006
Document Version: 2.0
Page 2

Technical Configuration Guide for SNMP v2.0 December 2006
Nortel is a recognized leader in delivering communications capabilities that enhance the human
experience, ignite and power global commerce, and secure and protect the world’s most critical
information. Serving both service provider and enterprise customers, Nortel delivers innovative
technology solutions encompassing end-to-end broadband, Voice over IP, multimedia services
and applications, and wireless broadband designed to help people solve the world’s greatest
challenges. Nortel does business in more than 150 countries. For more information, visit Nortel
on the Web at nortel.com.
NORTEL NETWORKS CONFIDENTIAL: This document contains material considered to be
proprietary to Nortel. No part of it shall be disclosed to a third party for any reason except after
receiving express written permission from Nortel and only after securing agreement from the third
party not to disclose any part of this document. Receipt of this document does not confer any
type of license to make, sell or use any device based upon the teachings of the document.
Receipt of the document does not constitute a publication of any part hereof and Nortel explicitly
retains exclusive ownership rights to all proprietary material contained herein. This restriction
does not limit the right to use information contained herein if it is obtained from any other source
without restriction.
Nortel Business Made Simple, Nortel, the Nortel logo, and the Globemark are trademarks of
Nortel Networks.
All other trademarks are the property of their owners.
Copyright © 2006
Nortel Networks. All rights reserved. Information in this document is subject to
change without notice. Nortel assumes no responsibility for any errors that may appear in this
document.
Disclaimer
This engineering d ocument contains the best inform ation available at the t ime of publication in
terms of supporting the application and engineering of Nortel products in the customer
environment. They are solely for use by Nortel customers and meant as a guide for network
engineers and planners from a network engineering perspective. All information is subject to
interpretation based on internal Norte l test methodol ogies which wer e used to derive th e various
capacity and equipment performance criteria and should be reviewed with Nortel engineering
primes prior to implementation in a live environment.
______________________________________________________________________________________________________
NORTEL External Distribution
1
Page 3

Technical Configuration Guide for SNMP v2.0 December 2006
Abstract
This document provi des an overvie w on how to config ure SNMP on the Norte l Ethernet Routin g
Switch (ERS) 8600.
______________________________________________________________________________________________________
NORTEL External Distribution
2
Page 4

Technical Configuration Guide for SNMP v2.0 December 2006
Table of Contents
1. SNMPV3 OVERVIEW..............................................................................................................5
2. SNMP UPGRADE CONSIDERATIONS..................................................................................6
2.1 H
IDDEN FILE DETAILS.........................................................................................................6
3. BLOCKING SNMP...................................................................................................................7
3.1 B
3.2 B
3.3 SNMP
3.4 N
LOCKING SNMPV1/2 ONLY...............................................................................................7
LOCKING SNMP VIA AN ACCESS POLICY – PRIOR TO SOFTWARE RELEASE 3.7.9 OR 4.1...... 7
GROUP ACCESS POLICY – RELEASE 3.7.9, 4.1 OR HIGHER.......................................9
EW DEFAULT COMMUNITY STRINGS IN HIGH SECURE (HSECURE) MODE...........................19
4. SNMP SETTINGS..................................................................................................................20
5. SNMP WITH RADIUS AUTHENTICATION AND ACCOUNTING........................................22
6. CONFIGURING SNMPV3......................................................................................................23
6.1 L
6.2 A
6.3 A
6.4 A
6.5 A
6.6 C
OADING THE DES OR AES ENCRYPTION MODULE............................................................23
DDING A NEW SNMPV3 USER TO USM TABLE................................................................ 23
SSIGN USM USER TO USM GROUP................................................................................24
SSIGNING THE USM GROUP ACCESS LEVEL.................................................................... 25
SSIGNING THE MIB VIEW TO THE USM GROUP................................................................26
REATING A MIB VIEW .....................................................................................................27
7. CONFIGURATION EXAMPLE: CHANGING SNMP COMMUNITIES..................................28
7.1 C
7.2 C
ONFIGURATION EXAMPLE: SNMP COMMUNITIES WITH RELEASE 3.5.................................28
ONFIGURATION EXAMPLE: CHANGING THE DEFAULT SNMP COMMUNITY NAME WITH
RELEASE 3.7 OR 4.1.....................................................................................................................29
7.3 C
ONFIGURATION EXAMPLE: ADDING A NEW SNMP COMMUNITY TO AN EXISTING SNMP
GROUP MEMBER..........................................................................................................................29
7.4 T
7.5 C
ESTING SNMP USING DEVICE MANAGER ........................................................................32
ONFIGURATION EXAMPLE: CHANGING THE MIB VIEW FOR AN SNMPV1/2 COMMUNITY......32
8. CONFIGURATION EXAMPLE USING SNMPV3.................................................................. 34
8.1 T
ESTING SNMPV3 USING DEVICE MANAGER ....................................................................35
9. SOFTWARE BASELINE: ...................................................................................................... 36
10. REFERENCE DOCUMENTATION:...................................................................................37
11. APPENDIX A: CONFIGURATION FILES.........................................................................38
11.1 F
11.2 F
ROM CONFIGURATION EXAMPLE 7.5................................................................................38
ROM CONFIGURATION EXAMPLE 8...................................................................................38
______________________________________________________________________________________________________
NORTEL External Distribution
3
Page 5

Technical Configuration Guide for SNMP v2.0 December 2006
List of Figures
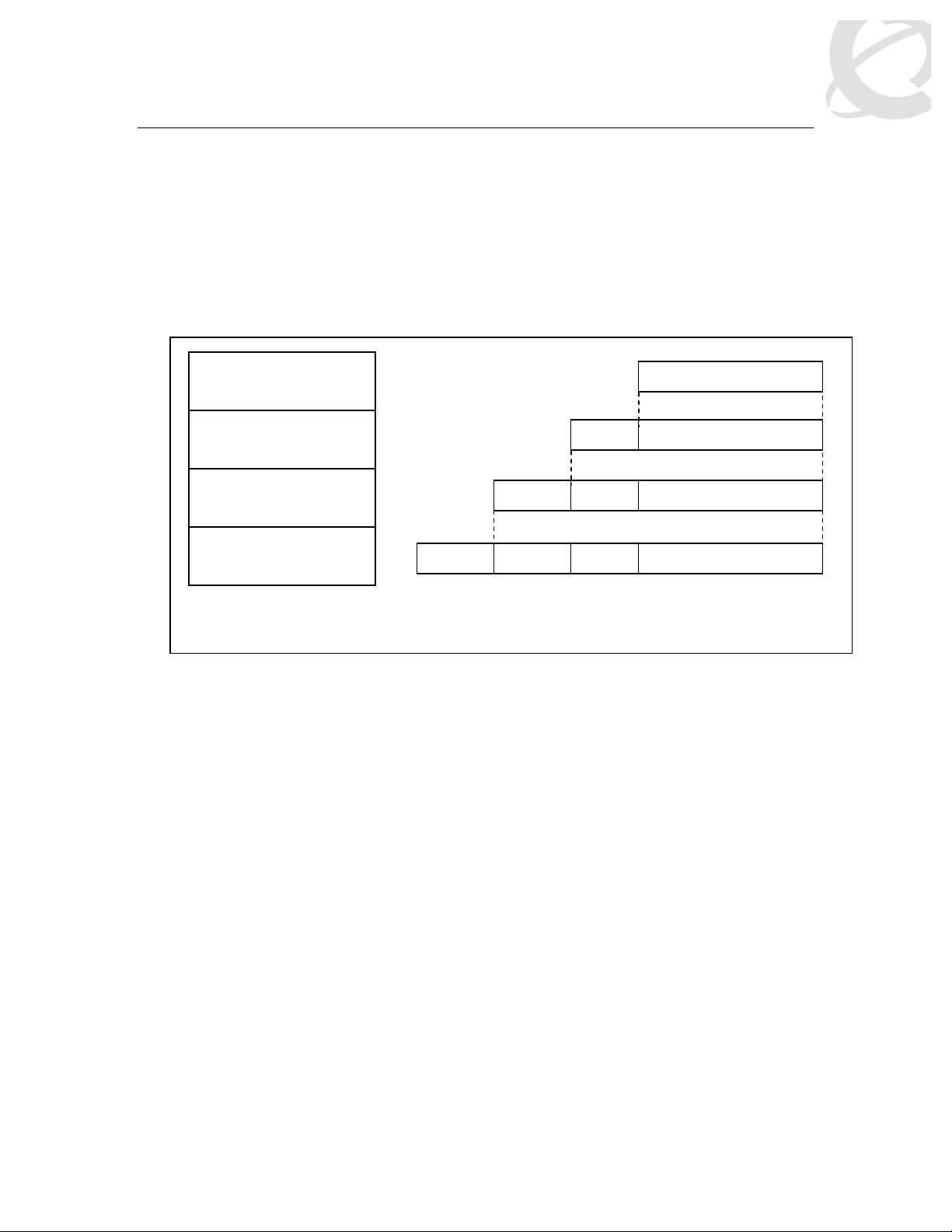
Figure 1: SNMPv3 USM................................................................................................................... 5
Figure 2: MIB Structure.................................................................................................................. 27
List of Tables
Table 1: New Default Password Settings ......................................................................................19
Table 2: New Default Community Settings....................................................................................19
______________________________________________________________________________________________________
NORTEL External Distribution
4
Page 6
Technical Configuration Guide for SNMP v2.0 December 2006
1. SNMPv3 Overvie w
SNMPv3 is the third version of the Internet-Standard Management Framework and is derived
from and builds u pon b oth the original Internet-Standard M ana gement Framework ( SNM Pv 1) a nd
the second Internet-Stan dard Managem ent Fram ework (SNMPv2). SNM Pv3 is not a s tand-alone
replacement for SNM Pv1 and/or SNMv2. It d efines se curity capab ilities to be used in c onjuncti on
with SNMPv2 (preferr ed) or SNMPv 1. As shown in the Figure 1 belo w, SNMPv3 s pecif ies a User
Security Model (U SM) that uses a payload of either a SNMPv1 or a SNMPv2 protocol dat a unit
(PDU).
PDU Processing
(SNMPv1 or SNMPv2)
Message Processing
(SNMPv3 USM)
UDP
UDP-H
V3-MH
V3-MH
SNMP PDU
SNMP PDU
SNMP PDU
PDU = Protocol Data Unit
USM = User Based Security
IP
IP-H
UDP-H
V3-MH
IP-H = IP header
UDP-H = UDP header
V3-MH = SNMPv3 message header
SNMP PDU
Figure 1: SNMPv3 USM
Authentication with in the User-based Secur ity Model (USM) allows t he recipient of the mes sage
to verify whom the message is from and whether the message has been altered. As per RFC
2574, if authentication is used, the entire message is checked for the integrity. Authentication
uses a secret key to produc e a fingerpr int of the m essage, which is incl uded in th e mes sage. T he
receiving entity uses the same secret key to validate the fingerprint. Currently there are 2
authentication protocols defined, HMAC-MD5 and HMAC-SHA-96 for use with USM.
While the USM provides the user-name/password authentication and privacy services, control
access to management information (MIB) must be defined. The View-based Access Control
Module (VACM) is used to define a set of services that an application can use for checking
access rights (read, wr ite, notify) to a par ticular object. V ACM uses the ASN.1 n otation (3.6.1.4)
or the name of the SNM P MIB branch, i.e. Org. Dod.In ternet. Privat e. T he adm inist rator can def in e
a MIB group view for a us er to allow access to an ap propriate portion of the MIB matched to an
approved security level. The three security levels are:
• NoAuthNoPriv-Communication without authentication and privacy
• AuthNoPriv-Communication with authentication (MD5 or SHA) and without privacy
• AuthPriv-Communication with authentication (MD5 or SHA) and privacy (DES or AES)
NOTE: Please refer to the Ether net Ro uti ng S witc h 86 00 4.1 re le as e not es ( Part number 317177D Rev 01) regarding im portant inf orm ation r egardin g SNMP v3. Spec ial c onsider ati ons nee d to be
considered regarding hidden and encrypted that contains community table information.
______________________________________________________________________________________________________
NORTEL External Distribution
5
Page 7

Technical Configuration Guide for SNMP v2.0 December 2006
2. SNMP Upgrade Consider ations
Please note the following when upgra di ng sof t ware on the ERS8600.
Starting in software release 3.7 and continued to software release 4.1.x, the CLI command save
config creates a hidden and encrypted file that contains the SNMP community table information.
For security purposes, the save config command also removes reference to the existing SNMP
community strings in the newly created configuration file. Please note that if you only have one
CPU, and if you swap the CPU, you must backup all hidden files or else all the password and
SNMP references will be lost. If you do not backup the hidden files, you must reconfigure your
trap receivers and community strings every time you change the CPU.
The commands to change the SNMP Community strings and trap receivers in software release
3.3 have changed in software releases 3.5, 3.7, 4.0, and 4.1.x. However, even though software
releases 3.5, 3.7, 4.0, and 4.1.x use the same commands, in software release 3.7 and 4.1.x only,
the SNMP community strings and trap receivers are stored in a hidden and encrypted file and are
not found in the configuration file. This is similar with software releases 3.5 and 4.0; however the
files are stored in a hidden non-encrypted file. Upgrades from 3.7 to 4.1.x, all files are translated
as-is. Please see section 3.3.3 for more details.
2.1 Hidden File Details
Backup the following configuration files to either via FTP, a TFTP server or a PCMCIA card:
• shadov.txt
• snmp_usm.txt
• snmp_comm.txt
• password.txt
______________________________________________________________________________________________________
NORTEL External Distribution
6
Page 8

Technical Configuration Guide for SNMP v2.0 December 2006
3. Blocking SNMP
By default, SNMP access is enabled. You can disable SNMP; this includes SNMPv1/v2 and
SNMPv3, access to the ERS 8600 by using the following commands:
• ERS-8610:5# config bootconfig flags block-snmp true
• ERS-8610:5#save boot
• ERS-8610:5#boot -y
To re-enable SNMP access, type in the following command:
• ERS-8610:5# config bootconfig flags block-snmp false
3.1 Blocking SNMPv1/2 only
If you wish to allow only SNMPv3 access, you c an d isa ble SNMPv1/2 by configur ing the SNMPv3
MIB view. Portions of the MIB can be conf igured to either include or exclude access at an MIB
OID level. This is explained in section 5.5 . For SNMPv3, this can be done on a per-user bas ic.
For SNMPv1/v2, it can be d one o n a g lob al/c om munity basis. By defau lt, SNM Pv 1/ v2 is p er mitted
access to all MIB OIDs un der 1.3 in the MIB O ID tree with the except ion with sections r elated to
the SNMP USM, VACM, and Community MIBs. This cannot be altered, but, if an additional
exclusion statement is added, the entire usable MIB can be disabled through SNMPv1/v2.
Specifically, if the entire MIB tree under 1.3.6 (iso org dod) is excluded, none of the switches
public or private MIBs will b e acces s ibl e.
To disable SNMPv1/v2 only, enter the following command:
• PP8600-B:6# config snmp-v3 mib-view create v1v2only 1.3.6 type exclude
At this point, SNMPv1/v2 will be disabled and only SNMPv3 will be allowed.
3.2 Blocking SNMP via an Access Policy – prior to
software release 3.7.9 or 4.1
You can also ena ble or disable SN MP via an Acces s Policy. Over all, the Acces s Policy feature
on the ERS 8600 supports the following feature:
• Access level: Specifies th e access level of the trust ed as hostreadOnly (ro), readW rite
(rw), or readWriteAll (rwa)
• Mode: Indic ates whether a packet having a so urce IP address that matches t his entry
should be permitted to enter the device or denied access.
• Service: Indicates the protocol to whic h this entry should be a pplied. Choices ar e telnet,
snmp, tftp, ftp, http, rlogin, and/or ssh.
• Precedence: Indicates the precedence of the policy. T he lower the number, the higher
the precedence (1 to 128).
• Network Address and Network Mask: Indicates the source network IP address and
mask. An address of 0.0.0.0 specifies any address on the network.
• Host: Indicates the trusted IP addres s of the hos t perf or ming rlogin or rsh into the dev ic e.
Applies only to rlogin and rsh.
• Access-strict: Sets the access level strictly.
______________________________________________________________________________________________________
NORTEL External Distribution
7
Page 9

Technical Configuration Guide for SNMP v2.0 December 2006
To add an access polic y, you must first enable the ac cess policy feature gl obally by enter ing the
following command:
• ERS-8606:5# config sys access-policy enable <true/false>
After the access polic y feature has been en abled globa lly, to add a new acces s policy, enter the
following command:
a) Add a new policy
• ERS-8606:5# config sys access-policy policy <1..65535>
b) After entering the above command, enter the appropriate parameters:
• ERS-8606:5# config sys access-policy policy <1..65535> ?
Sub-Context: service
Current Context:
accesslevel <ro|rw|rwa>
access-strict <true|false>
create
delete
disable
enable
host <ipaddr>
info
mode <allow|deny>
name <name>
network <addr/mask>
precedence <precedence>
username <string>
c) Add the services to the newly created access policy:
• ERS-8606:5# config sys access-policy policy <1..65535> service ?
Sub-Context:
Current Context:
ftp <enable|disable>
http <enable|disable>
info
rlogin <enable|disable>
snmp <enable|disable>
ssh <enable|disable>
telnet <enable|disable>
tftp <enable|disable>
Please refer to p ublication number 314997-C titled I mportant Security Information for th e 8000
Series Switch for more details on Access Policies.
______________________________________________________________________________________________________
NORTEL External Distribution
8
Page 10

Technical Configuration Guide for SNMP v2.0 December 2006
3.2.1 Configuration Example: Blocking SNMP via an Access Policy
In this example, we will create an access policy to not allo w SNMP for any user coming from
network 172.30.x.y/16.
a) Enable access policy globally:
• ERS-8606:5# config sys access-policy enable true
b) Add a ne w pol icy, in t his ex am ple, s ince it is the f irst p olic y, we will s im ply create polic y 2
and name it policy2:
• ERS-8606:5# config sys access-policy policy 2 create
• ERS-8606:5# config sys access-policy policy 2 name policy2
c) Add network 172.30.0.0/16 to policy 2:
• ERS-8606:5# config sys access-policy policy 2 network 172.30.0.0/16
d) Add read/write/all access level to policy 2:
• ERS-8606:5# config sys access-policy policy 2 accesslevel rwa
e) Disable SNMP service for policy 2:
• ERS-8606:5# config sys access-policy policy 2 service snmp disable
After the policy has been created, enter the following command to view policy 2:
• ERS-8606:5# show sys access-policy info policy2
AccessPolicyEnable: on
Id: 2
Name: policy2
PolicyEnable: true
Mode: allow
Service: http|telnet|ssh
Precedence: 128
NetAddr: 172.30.0.0
NetMask: 255.255.0.0
TrustedHostAddr: 0.0.0.0
TrustedHostUserName: none
AccessLevel: readWriteAll
AccessStrict: false
Usage: 337
3.3 SNMP Group Access Policy – Release 3.7.9, 4.1 or
higher
In release 3.7.9 or 4.1, a new policy enhancem ent was added that allows the administrator to
specify a group or groups for SNMPv3 access. With SNMPv3, the community name is not
mapped to an access level, but det ermined only thr ough VACM. T his allows the administrator to
create separate policies for SNMP users based on USM or community and associate them to
groups.
The following items where added high-lighted in red below.
ERS-8610:5# config sys access-policy policy 1 ?
______________________________________________________________________________________________________
NORTEL External Distribution
9
Page 11

Technical Configuration Guide for SNMP v2.0 December 2006
Sub-Context: service
Current Context:
accesslevel <level>
access-strict <true|false>
create
delete
disable
enable
host <ipaddr>
info
mode <mode>
name <name>
network <addr/mask>
precedence <precedence>
snmp-group-add <group name> <model>
snmp-group-del <group name> <model>
snmp-group-info
username <string>
ERS-8610:5# config sys access-policy policy 1 service ?
Sub-Context:
Current Context:
ftp <enable|disable>
http <enable|disable>
info
rlogin <enable|disable>
snmpv3 <enable|disable>
ssh <enable|disable>
telnet <enable|disable>
tftp <enable|disable>
3.3.1 SNMPv3 Group Access Policy: Configuration Example
For this example, we wish to create a policy for read-writ e-all access and only allow teln et and
SNMPv3 access onl y for SNMPv3 usm group named grou p_example. Please see Section 5 in
regards to how to configure SNMPv3.
a) Enable access policies globally
• ERS-8606:5# config sys access-policy enable true
b) Assuming no access policies have been created, we can start with policy 2 and nam e the
policy policy2.
• ERS-8606:5# config sys access-policy policy 2 create
• ERS-8606:5# config sys access-policy policy 2 name policy2
c) Add read/write/all access level to policy 2:
• ERS-8606:5# config sys access-policy policy 2 accesslevel rwa
d) Add the usm group ‘group_example’ to policy 2:
______________________________________________________________________________________________________
NORTEL External Distribution
10
Page 12

Technical Configuration Guide for SNMP v2.0 December 2006
• ERS-8610:5# config sys access-policy policy 2 snmp-group-add group_example
usm
e) Enable access strict enable
• ERS-8610:5# config sys access-policy policy 2 access-strict true
f) Enable telnet and SNMPv3 service:
• ERS-8610:5# config sys access-policy policy 2 service telnet enable
• ERS-8610:5# config sys access-policy policy 2 service snmpv3 enable
g) Enable policy 2:
• ERS-8610:5# config sys access-policy policy 2 enable
h) After the policy has been created, enter the following command to view policy 2:
• ERS-8606:5# show sys access-policy info policy2
AccessPolicyEnable: on
Id: 2
Name: policy2
PolicyEnable: true
Mode: allow
Service: telnet|snmpv3
Precedence: 10
NetAddr: 0.0.0.0
NetMask: 0.0.0.0
TrustedHostAddr: 0.0.0.0
TrustedHostUserName: none
AccessLevel: readWriteAll
AccessStrict: true
Usage: 3777
• ERS-8610:5# show sys access-policy snmp-group-info
snmpv3-groups :
Policy 1 snmpv3-groups :
Group Name Snmp-Model
Policy 2 snmpv3-groups :
Group Name Snmp-Model
group_example usm
3.3.2 SNMPv1/2 Group Access Policy: Configuration Example
As release 3.7 and 4.1 is based on the SNMPv3, you must add the SNMPv3 group name and
model for both SNMPv1 and SNMPv2 when setting up an access policy. To view the SNMPv3
group name and model, please use the following as shown below. Note that the items highlighted in red need to be added when setting up the access policy.
• ERS8610-B:5# show snmp-v3 group-access
=========================================================================
VACM Group Access Configuration
=========================================================================
______________________________________________________________________________________________________
NORTEL External Distribution
11
Page 13

Technical Configuration Guide for SNMP v2.0 December 2006
Group Prefix Model Level ReadV WriteV NotifyV
------------------------------------------------------------------------initial usm noAuthNoPriv root root root
initial usm authPriv root root root
readgrp snmpv1 noAuthNoPriv v1v2only org
readgrp snmpv2c noAuthNoPriv v1v2only org
v1v2grp snmpv1 noAuthNoPriv v1v2only v1v2only v1v2only
v1v2grp snmpv2c noAuthNoPriv v1v2only v1v2only v1v2only
esegroup usm authPriv org org
sBladeGrp snmpv1 noAuthNoPriv sBladeView sBladeView sBladeView
sBladeGrp snmpv2c noAuthNoPriv sBladeView sBladeView sBladeView
9 out of 9 Total entries displayed
-------------------------------------------------------------------------
The following example will add a new access policy that will allow SNMPv1/2 and telnet.
a) Enable access policies globally
• ERS-8606:5# config sys access-policy enable true
b) Assuming no access policies have been created, we can start with policy 2 and nam e the
policy policy2.
• ERS-8606:5# config sys access-policy policy 2 create
• ERS-8606:5# config sys access-policy policy 2 name policy2
c) Add read/write/all access level to policy 2:
• ERS-8606:5# config sys access-policy policy 2 accesslevel rwa
d) Add the SNMPv1/2 group name and models to policy 2:
• ERS-8610:5# config sys access-policy policy snmp-group-add readgrp snmpv1
• ERS-8610:5# config sys access-policy policy 2 snmp-group-add readgrp snmpv2c
ERS-8610:5# config sys access-policy policy snmp-group-add v1v2grp snmpv1
•
ERS-8610:5# config sys access-policy policy snmp-group-add v1v2grp snmpv2c
•
e) Enable telnet and SNMPv3 service:
• ERS-8610:5# config sys access-policy policy 2 service telnet enable
• ERS-8610:5# config sys access-policy policy 2 service snmpv3 enable
f) Enable policy 2:
• ERS-8610:5# config sys access-policy policy 2 enable
g) After the policy has been created, enter the following command to view policy 2:
• ERS-8606:5# show sys access-policy info policy2
AccessPolicyEnable: on
Id: 2
Name: policy2
PolicyEnable: true
Mode: allow
Service: telnet|snmpv3
Precedence: 10
NetAddrType: ipv4
NetAddr: 0.0.0.0
NetMask: 0.0.0.0
TrustedHostAddr: 47.133.58.69
______________________________________________________________________________________________________
NORTEL External Distribution
12
Page 14

Technical Configuration Guide for SNMP v2.0 December 2006
TrustedHostUserName: none
AccessLevel: readWriteAll
AccessStrict: false
Usage: 385
• ERS-8610:5# show sys access-policy snmp-group-info
snmpv3-groups :
Policy 1 snmpv3-groups:
Group Name Snmp-Model
Policy 2 snmpv3-groups:
Group Name Snmp-Model
readgrp snmpv1
readgrp snmpv2c
v1v2grp snmpv1
v1v2grp snmpv2c
3.3.3 SNMP Community Strings
For security reasons, the SNMP agent validates each request from an SNMP manager before
responding to the request. This is accomplis hed by verif ying that the manager belongs to a valid
SNMP communit y. An SNMP comm unity is a logical relationship between an S NMP agent and
one or more SNMP manager s ( the m anager sof t ware implements the protocols used to ex c hang e
data with SNMP agents). You define communities locally at the agent.
The agent establish es one comm unity for each com bination of au thenticatio n and access control
characteristics that you choose. You assign each c ommunity a un ique name ( community string),
and all members of a community have the same access privileges, either read-only or read-write:
• Read-only: members can view configuration and performance information.
• Read-write: members can view configuration and performance information, and also
change the configuration.
By defining a community, an agent limits access to its MIB to a selected set of management
stations. By using mor e than one c om munity, the agent can provide dif ferent levels of MIB acces s
to different management stations.
SNMP communit y strings are requ ired for access to the switch usi ng Device Manager or other
SNMP-based managem ent software. You set the SNMP c ommunity stri ngs using the CLI . If you
have read/write/all ac cess authority, you can m odify the SNMP community strin gs for access to
the device through Device Manager.
In the ERS 8000 Series switch software release 3.7, the CLI command save config creates a
hidden and encrypted file that contains the SNMP community table information. The SNMP
community strings are no t referenced in the ERS 8600 c onfiguration file. Please see publication
number 317177-A titled Re lease Notes for the ERS 8000 Seri es Switch Softw are Releas e 3.7 for
more details regarding upgrading SNMP to release 3.7.
Caution: For security reasons, Nortel Networks recommends that you set the passwords to
values other than the factory defaults.
______________________________________________________________________________________________________
NORTEL External Distribution
13
Page 15

Technical Configuration Guide for SNMP v2.0 December 2006
3.3.3.1 Setting the SNMP Community String and Trap Receivers with Software Release
3.3
In the ERS 8000 Series Sw itch Release 3.3, SNMP comm unity strings and traps are added by
using the two commands shown below. In the 3.3 release, these commands appear in the
configuration file.
• ERS-8606:5# config sys set snmp community < ro|rw|l2|l3|rwa> <commstring>
• ERS-8606:5# config sys set snmp trap-recv <ipaddr> v2c public
Where:
• ro|rw|l2|l3|rwa is the c hoice of community. ro is read-onl y, rw is read/writ e, l2 is
layer 2 read/write, l3 is layer 3 (and layer 2) read/write, and rwa is read/write/all.
• commstr is the input community string up to 1024 characters.
3.3.3.2 Setting the SNMP Community String and Trap Receivers with Software Release
3.5, 4.0, 3.7 and 4.1
The two commands shown above in section 3.3.3.1 are now obsolete. To set the ERS 8600
community strings, enter the following command:
• ERS-8606:5# config snmp-v3 community create <Comm Idx> <name> <security>
[tag <value>]
Where:
config snmp-v3 community create
followed by:
Comm Idx
The unique index value of a row in this table. The
range is 1-32 characters.
name
The community string for which a row in this table
represents a configuration
security
Maps community string to the security name in the
VACM Group Member Table.
tag <value>
(optional)
The transport tag name in the table. The range is 1-32
characters.
In release 3.7 or 4.1, after you save the configuration, infor mation regarding SNMP comm unity
strings are stored in a s eparate file and will not be found in t he configuration fil e. This is not the
case for software release 3.5.
______________________________________________________________________________________________________
NORTEL External Distribution
14
Page 16

Technical Configuration Guide for SNMP v2.0 December 2006
3.3.4 Modifying and/or adding community strings
Initially, there are 4 communities: first, second, index1 and index2. first represents the default
read-only access ( public) and second repres ents the default read- write access (private) create d
by the SNMPv3 engine. T he access rights ar e determined by the Secur ity Name from the VACM
table.
Previously existing default communities prior to software upgrade to release 3.7 appear as
index1 (private) and index2 (public). They can be modified or deleted. If you had other
communities defined, they will appear converted as index3, index4, etc…
You can modify or delete those, but you can not delete the default communities first and second,
however, you can change the community strings for them.
• ERS-8606:5# config snmp-v3 community info
================================================================================
Community Table
================================================================================
Index Name Security Name Transport Tag
-------------------------------------------------------------------------------first ******** readview
index1 ******** initialview
index2 ******** readview
second ******** initialview
4 out of 4 Total entries displayed
--------------------------------------------------------------------------------
Please note that in software release 3.5, the community name is displayed as shown below.
• ERS8600G:3# config snmp-v3 community info
==========================================================================
Community Table
==========================================================================
INDEX NAME SECURITYNAME
-------------------------------------------------------------------------first public initialview
second private initialview
2 out of 2 Total entries displayed
--------------------------------------------------------------------------
To change the def ault communities, for example, the index named first with a new community
name of readonly a nd the index nam ed second with a ne w community nam e of readwrite, enter
the following commands:
• ERS-8606:5# config snmp-v3 community commname first new-commname
readonly
• ERS-8606:5# config snmp-v3 community commname second new-commname
readwrite
You will now not be able to access the switch with the def ault com munities public and private; you
will need to use readonly and readwrite instead.
Note: You will not be ab le t o see those new c omm unities as th ey are now enc r ypted and hidde n.
However, you can still always modify them.
If you wish to change or create further comm unities, alter the exist ing comm unities, c reate a ne w
community or delet e a com m unit y (for exam ple, in cas e you ha ve for gotten t he co mm unity stri ng,
which is now encrypted and hidden).
______________________________________________________________________________________________________
NORTEL External Distribution
15
Page 17

Technical Configuration Guide for SNMP v2.0 December 2006
For example, assum ing we have upgraded to release 3.7 an d now wish to delete communit y’s
index1 and index2:
• ERS-8606:5# config snmp-v3 community delete index1
• ERS-8606:5# config snmp-v3 community delete index2
A new SNMP community can be added by using the following command:
• ERS-8606:5# config s nmp-v3 community create <Com m Idx> <name> <security> [tag
<value>]
where:
Parameter
Comm Idx
name
security
tag <value>
(optional)
Description
The unique index value of a row in this table. The range is 1-32
characters.
The community string for which a row in this table represents a
configuration
Maps community string to the security name in the VACM Group
Member Table.
The transport tag name in the table. The range is 1-32 characters.
For example, to ad d a new community with a com munity index named third with a comm unity
name of readonly, and a community index named forth with a community name of readwrite,
enter the following:
• ERS-8606:5# config snmp-v3 community create third readonly readview
• ERS-8606:5# config snmp-v3 community create forth readwrite initialview
• ERS-8606:5# config snmp-v3 community info
==============================================================
Community Table
==============================================================
Index Name Security Name Transport Tag
-------------------------------------------------------------first ******** readview
forth ******** initialview
second ******** initialview
third ******** readview
4 out of 4 Total entries displayed
--------------------------------------------------------------
Please see section 7 for more details in regards to configuring SNMP communities.
______________________________________________________________________________________________________
NORTEL External Distribution
16
Page 18

Technical Configuration Guide for SNMP v2.0 December 2006
3.3.5 Creating or deleting trap receivers with Software release 3.7 or 4.1
With software release 3.7 or 4.1, you create tr ap rec eivers by creating SNMP- v3 trap not ific ations
and then specifying the target address where you wish to send the notifications along with
specific target parameters.
By default, the ERS8600 has a default trap notification of “trapTag”. You can use this default
notification when s etting up the SNMP tr ap target address or if you wish, you c an create a new
trap notification using the following command:
• ERS-8606:5# config snmp-v3 notify ?
Sub-Context:
Current Context:
create <Notify Name> [tag <value>] [type <value>]
delete <Notify Name>
info
tag <Notify Name> new-tag <value>
type <Notify Name> new-type <value>
For example, to create a n ew trap notification n amed “Trap2” with a t ag value of “T rap2”, please
enter the following command
• ERS-8606:5# config snmp-v3 notify create Trap2 tag trapTag2 type trap
You can view the notification table by using the following command:
• ERS-8606:5# show snmp-v3 notify info
===========================================================================
Notify Configuration
===========================================================================
Notify Name Tag Type
--------------------------------------------------------------------------Inform informTag inform
Trap trapTag trap
Trap2 trapTag2 trap
The SNMP target address is configured using the following command:
• ERS-8606:5# config snmp-v3 target-addr ?
Sub-Context:
Current Context:
create <Target Name> <Ip addr:port> <Target parm> [timeout
<value>] [retry <value>] [taglist <value>] [mask <value>] [mms <value>]
delete <Target Name>
info
address <Target Name> new-addr <value>
mask <Target Name> new-mask <value>
mms <Target Name> new-mms <value>
parms <Target Name> new-parms <value>
retry <Target Name> new-retry <value>
taglist <Target Name> new-taglist <value>
timeout <Target Name> new-timeout <value>
______________________________________________________________________________________________________
NORTEL External Distribution
17
Page 19

Technical Configuration Guide for SNMP v2.0 December 2006
For example, to add a SNMPv1 trap-receiver , enter the following as suming the Target Nam e is
TAddr1 and assuming you are using the default trap notify of trapTag and the default targetparam of TparamV1 for SNMPv1 traps:
• ERS-8606:5# config snmp-v3 target-addr create TAddr1 X.X.X.X:162 TparamV1
timeout 1500 retry 3 taglist trapTag mask 0xff:ff:00:00:00:00 mms 484
Where X.X.X.X is the IP-Address of your trap-receiver. Enter TparamV1 for SNMPv1 and
TparamV2 for SNMP v2c . F or each s ubs e que nt tr a p re c eiv er that you add, you mus t gi ve it a ne w
target address, for example TAddr2, mgmtstation, etc.
The following is an example of adding an SN MP target addres s of 10.10.1.1 02 using th e default
notification tag “trapTag” for SNMPv1 traps.
• ERS-8606:5# config snmp-v3 target-addr create TAddr1 10.10.1.102:162 TparamV1
timeout 1500 retry 3 taglist trapTag mask 0xff:ff:00:00:00:00 mms 484
NOTE: If you wish, you can also manua lly set the sourc e IP address for al l trap mess ages sent
by the ERS 8600. For exa mple, you could creat e a circuit-less IP address and us e this address
as the source IP for all traps generated. Please see section 4 for more details.
NOTE: You also configure the E RS 8600 to send aut hentication traps. Please s ee section 4 for
more details.
To delete a trap receiver, delete the target name, for example:
• ERS-8606:5# config snmp-v3 target-addr delete TAddr1
To view the trap receiver table, enter the following command:
• ERS-8606:5# config snmp-v3 target-addr info
================================================================================
Target Address Configuration
================================================================================
Target Name TDomain TAddress TMask
-------------------------------------------------------------------------------TAddr1 ipv4 10.10.1.102:162 0xff:ff:00:0
0:00:00
================================================================================
Target Address Configuration
================================================================================
Target Name Timeout Retry TagList
Params MMS
-------------------------------------------------------------------------------TAddr1 1500 3 trapTag
TparamV1 484
To view the SNMPv3 target parameters, enter the following command:
• ERS-8610:5# config snmp-v3 target-param info
================================================================================
Target Params Configuration
================================================================================
Target Name MP Model Security Name Sec
Level
-------------------------------------------------------------------------------TparamV1 snmpv1 readview noAu
thNoPriv
TparamV2 snmpv2c readview noAu
thNoPriv
______________________________________________________________________________________________________
NORTEL External Distribution
18
Page 20

Technical Configuration Guide for SNMP v2.0 December 2006
3.4 New Default Community Strings in High Secure
(hsecure) Mode
If the ERS 8600 has been configured for high security mode (config bootconfig flags hsecure
true) after a factory default setting, the software will change the default password and SNMP
communities. All new passwords must be at least 8 characters and in release 4.1, all new
passwords must be at least 10 characters. All o ld passwords less than 8 or 10 (for release 4.1)
characters are no longer valid and you will be prompted to change the password to the
mandatory character length.
To enable or disable hsecure, enter the following commands:
• ERS-8606:5# config bootconfig flags hsecure {false|true}
• ERS-8606:5# save boot
• ERS-8606:5# boot –y
From a previous default factory setting, without changes made to the password or SNMP
community strings, the following tables display the default hsecure settings.
Table 1: New Default Password Settings
User ID New Default Password
rwa rwarwarrw
rw rwrwrwrw
ro rorororo
l3 l3l3l3l3
l2 l2l2l2l2
l1 l1l1l1l1
l4admin l4adminl
slbadmin slbadmin
oper operoper
l4oper l4operl4
slboper slbopers
ssladmin ssladmin
Table 2: New Default Community Settings
User ID New Default Password
ro publiconly
l1 privateonly
l2 privateonly
l3 privateonly
rw privateonly
rwa secretonly
______________________________________________________________________________________________________
NORTEL External Distribution
19
Page 21

Technical Configuration Guide for SNMP v2.0 December 2006
4. SNMP Settings
To configure the SNMP settings, enter the following command:
• ERS-8606:5# config sys set snmp ?
Sub-Context:
Current Context:
force-iphdr-sender <true|false>
force-trap-sender <true|false>
info
sender-ip <ipaddr> <ipaddr>
Where:
config sys set snmp
followed by:
force-iphdr-sender
<true|false>
force-trap-sender
<true|false>
info
sender-ip
<target_address>
<source_address>
If set to true, the configured source address is sent in the
IP header of the notification message as the source
address.
If set to true, the configured source address is sent in the
notification message as the sender network.
Displays the current SNMP settings.
Configures a source IP address which is set in the
notification sent to the target. The source IP add`ress
should be a circuitless IP address.
For example, assume we have an ERS 8600 switch with software release 4.1 and we wish to
send SNMPv2 traps using the circuitless IP address. For this example, let’s assume the trap
receiver IP address is 10.1.50.10, the circuitless IP address is 1.1.1.1/32, and OSPF is used as
the IGP.
1. First, add the circuitless IP address and enable OSPF
• ERS-8606:5# config ip circuitless-ip-int 1 create 1.1.1.1/32
• ERS-8606:5# config ip circuitless-ip-int 1 ospf enable
2. Add the SNMP trap target address using the default trap notification “trapTag”
• ERS-8606:5# config snmp-v3 target-addr create TAddr1 10.1.50.10:162 TparamV2
timeout 1500 retry 3 taglist trapTag mask 0xff:ff:00:00:00:00 mms 484
3. Finally, set the SNMP sender IP address using the CLIP address
• ERS-8606:5# config sys set snmp sender-ip 10.1.50.10 1.1.1.1
• ERS-8606:5# config sys set snmp force-iphdr-sender true
• ERS-8606:5# config sys set snmp force-trap-sender true
Also, you can enable authentication traps by entering the following command:
• ERS-8606:5# config sys set sendAuthenticationTrap true
______________________________________________________________________________________________________
NORTEL External Distribution
20
Page 22

Technical Configuration Guide for SNMP v2.0 December 2006
After the ERS 8600 has been configured, the trap receiver should display traps from the ERS
8600 with a source IP address of 1.1.1.1 as shown below using Enterprise Switch Manager.
______________________________________________________________________________________________________
NORTEL External Distribution
21
Page 23

Technical Configuration Guide for SNMP v2.0 December 2006
5. SNMP with RADIUS Authentication and
Accounting
Radius-SNMP authentication and accounting is supported in release 3.5 for SNMPv1 and
SNMPv2. Radius-SNMP authentication operates by passing the community string to a RADIUS
server. The RADIUS server will in return will send an integer value indicating the level of access
allowed or no access at all.
Please note that software releases 3.7 and 4.1.x do not support this feature.
______________________________________________________________________________________________________
NORTEL External Distribution
22
Page 24

Technical Configuration Guide for SNMP v2.0 December 2006
6. Configuring SNMPv3
The following are the configuration steps required to enable SNMPv3:
• Load the DES or AES (release 4.1 only) Encryption Module
• Adding a SNMP Use r USM
• Assigning the USM as a member to a SNMPv3 USM group
• Assigning the USM group access level of either authPriv, authNoPriv, or noAuthNoPriv
• Assigning a MIB view to the USM group
6.1 Loading the DES or AES Encryption Module
Prior to configuring SNMPv3 on the ERS 8600, the DES or AES encryption module must be
loaded. Note that Adva nced Encryption Standard (AES) is suppor ted only release 4.1. T he DES
or AES module is req uired in order to pr ovide secure communications b etween the user an d the
ERS 8600.
The AES standard is the c urrent encr yption stand ard (FIPS- 197) int ended to be us ed by the U.S.
Government organi zations to protect sens itive inform ation. It is also becom ing a global standar d
for commercial software and hardware that uses encryption or other security features.
Once the DES or AES enc ryption m odule is uplo aded to the ER S 8600 (the f ile ends with a .des
or .aes extension, i.e. p80c3700.des or p80c4100. aes), it can be loaded b y typing the following
command:
For single DES:
• ERS-8610:5# config load-encryption-module DES /flash/<filename>.des
For single 3DES:
• ERS-8610:5# config load-encryption-module 3DES /flash/<filename>.des
For AES:
• ERS-8610:5# config load-encryption-module AES /flash/<filename>.aes
6.2 Adding a New SNMPv3 User to USM Table
After the DES or AES module has been loaded, the switch is now ready for SNMPv3
configuration. T he first step is to add a user to the US M (User-based Sec urity Model) tab le. You
can add a new user to the USM table by typing in the following command:
• ERS-8610:5# config snmp-v3 usm create [User Name<1-32>] [authentication
protocol <md5|sha>] auth [authentication password<1-32>] [priv-protocol
<des|aes>] priv [privacy password<1-32>]
In release 4.1, there is one additional change to support AES:
• ERS-8610:5# config snmp-v3 usm create [User Name<1-32>] [authentication
protocol <md5|sha>] auth [authentication password<1-32>] priv [privacy
password<1-32>]
For example, the follo wing will create a ne w user named “user1”, set the authentication protoc ol
to MD5 with a password of “user1234” and a privilege password of userpriv:
______________________________________________________________________________________________________
NORTEL External Distribution
23
Page 25

Technical Configuration Guide for SNMP v2.0 December 2006
For release 3.7, the command will be:
• ERS-8610:5# config snmp-v3 usm create user1 md5 auth user1234 priv userpriv
For release 4.1, if using AES, the command will be:
• ERS-8610:5# config snmp-v3 usm create user1 md5 auth user1234 priv-prot aes
priv userpriv
After the user has been installed, you can view the users in the USM table by typing in the
following command:
• ERS-8610:5# config snmp-v3 usm info
Engine ID = 80:00:08:E0:03:00:E0:7B:82:9C:00
============================================================================
USM Configuration
============================================================================
User/Security Name Engine Id Protocol
---------------------------------------------------------------------------user1 800008E00300E07B829C00 HMAC_MD5, DES PRIVACY
1 out of 1 Total entries displayed
----------------------------------------------------------------------------
6.3 Assign USM User to USM Group
The next step is to ass ign t he user to a USM gr oup. T he USM gr oup is used t o def ine the ac cess
level and MIB vi e w giv en t o a us er . T he USM access level and MIB view will be added in the next
two steps.
You can add a new USM Group by entering the following command:
• ERS-8610:5# config snmp-v3 group-member create <user name> usm <group
name>
Example: the following example adds the user ‘user1’ created above to a USM group named
‘group_example’:
• ERS-8610:5# config snmp-v3 group-member create user1 usm group_example
To view the USM group, enter the following command:
• ERS-8610-C:5# config snmp-v3 group-member info
================================================================================
VACM Group Membership Configuration
================================================================================
Sec Model Security Name Group Name
-------------------------------------------------------------------------------snmpv1 readview readgrp
snmpv1 sBladeUser sBladeGrp
snmpv1 initialview v1v2grp
snmpv2c readview readgrp
snmpv2c sBladeUser sBladeGrp
snmpv2c initialview v1v2grp
usm user1 group_example
usm initial initial
usm OpsQosPolicyUser OpsQosPolicyUser
9 out of 9 Total entries displayed
--------------------------------------------------------------------------------
______________________________________________________________________________________________________
NORTEL External Distribution
24
Page 26

Technical Configuration Guide for SNMP v2.0 December 2006
6.4 Assigning the USM Group Access Level
The next step is to assi gn the access level to the USM G roup. One of the following thr ee USM
access levels must be configured:
• NoAuthNoPriv-Communication without authentication and privacy
• AuthNoPriv-Communication with authentication (MD5 or SHA) and without privacy
• AuthPriv-C ommunication with authent ication (MD5 or SHA) and privac y (DES or AES in
release 4.1)
The ERS 8600 has a number of default grou ps, with one default USM group na med ‘initial’. The
default groups can be examined by typing in the following command:
• ERS-8610:5# config snmp-v3 group-access info
================================================================================
VACM Group Access Configuration
================================================================================
Group Prefix Model Level ReadV WriteV NotifyV
-------------------------------------------------------------------------------Group Prefix Model Level ReadV WriteV NotifyV
-------------------------------------------------------------------------------initial usm noAuthNoPriv root root root
initial usm authPriv root root root
readgrp snmpv1 noAuthNoPriv v1v2only org
readgrp snmpv2c noAuthNoPriv v1v2only org
v1v2grp snmpv1 noAuthNoPriv v1v2only v1v2only v1v2only
v1v2grp snmpv2c noAuthNoPriv v1v2only v1v2only v1v2only
sBladeGrp snmpv1 noAuthNoPriv sBladeView sBladeView sBladeView
sBladeGrp snmpv2c noAuthNoPriv sBladeView sBladeView sBladeView
OpsQosPolicyUser usm noAuthNoPriv org org org
9 out of 9 Total entries displayed------------------------------------------------
The default USM l evel, nam ed ‘initial’, has both authentica tion and encr yption (auth Priv) with ful l
read-write views. You can use this gro up for initial SN MPv3 access to the ERS 8600. The nam e
of the read-write view starts at ‘org’ – please see next step in regards to setting up the MIB view.
To set the SNMP USM security level, type in the following command:
• ERS-8610:5# config snmp-v3 group-access create [group name <0-32>] [prefix <0-
32>] usm [noAuthNoPriv|authNoPriv|authPriv]
Example: the following will add USM security level of ‘authPriv’ to the USM group named
‘group_example’:
• ERS-8610:5# config snmp-v3 group-access create group_exa mple "" usm authPriv
NOTE: The prefix entered above is en tered using d ouble quotes . If you wish, you can def ine the
‘exact’ context m atch that shou ld be m atched against the contex t of the inc oming PDU; i.e. exact
prefix match of r ead or write. There is no read or write view associated with the group yet. This
will be defined in the next step.
______________________________________________________________________________________________________
NORTEL External Distribution
25
Page 27

Technical Configuration Guide for SNMP v2.0 December 2006
6.5 Assigning the MIB View to the USM Group
We can assign the USM group to e ither an existin g MIB view or cr eate a new MIB vie w fist (next
step) and then ass ign it to the USM group. T he next s ection will describe how to add a n ew MIB
view.
To view the default MIB views, enter the following command:
• ERS-8610:5# config snmp-v3 mib-view info
===============================================================================
MIB View
===============================================================================
View Name Subtree Mask Type
-------------------------------------------------------------------------------org 1 include
root 1 include
snmp 1.3.6.1.6.3 include
snmp 1.3.6.1.2.1.1 include
layer1 1.3 exclude
. . .
. . .
sBladeView 1.3.6.1.4.1.1872 include
50 out of 50 Total entries displayed---------------------------------------------
To associate the USM group to a MIB view, enter the following command:
• ERS-8610:5# config snmp-v3 group-access view <group name> <prefix> usm
<noAuthNoPriv|authNoPriv|authPriv> read <value> write <value>
Example: to assign both read and write view to the existing view of ‘org’ to the group
‘group_example’ created earlier, enter the following command:
• ERS-8610:5# config snmp-v3 group-access view group_example "" usm authPriv
read org write org
You can view the Group Access MIB view table by entering the following command:
• ERS-8610:5# config snmp-v3 group-access info
================================================================================
VACM Group Access Configuration
================================================================================
Group Prefix Model Level ReadV WriteV NotifyV
-------------------------------------------------------------------------------initial usm noAuthNoPriv root root root
initial usm authPriv root root root
readgrp snmpv1 noAuthNoPriv v1v2only org
readgrp snmpv2c noAuthNoPriv v1v2only org
v1v2grp snmpv1 noAuthNoPriv v1v2only v1v2only v1v2only
v1v2grp snmpv2c noAuthNoPriv v1v2only v1v2only v1v2only
sBladeGrp snmpv1 noAuthNoPriv sBladeView sBladeView sBladeView
sBladeGrp snmpv2c noAuthNoPriv sBladeView sBladeView sBladeView
group_example usm authPriv org org
OpsQosPolicyUser usm noAuthNoPriv org org org
10 out of 10 Total entries displayed
--------------------------------------------------------------------------------
______________________________________________________________________________________________________
NORTEL External Distribution
26
Page 28

Technical Configuration Guide for SNMP v2.0 December 2006
6.6 Creating a MIB View
As mentioned in the previous step, the ERS 8 600 has a number of def ault MIB views. The MIB
view configures the branches of the SNMP MIB tree that are permitted or not permitted for a
particular user or group . T he ERS 860 0 MIB tree f ollo ws the ASN.1 hier archic al struc ture f or both
private and enterprise (priv ate) MIBs .
Iso (1)
Ccitt (0)
Ccitt (0)
Directory (1) Security (5) SnmpV2 (6)Experimental (3) Mail (7)
Directory (1) Security (5) SnmpV2 (6)Experimental (3) Mail (7)
Mgmt (2)
Mgmt (2)
Mgmt (2)
Mib-2 (1)
Mib-2 (1)
Standard MIBSStandard MIBS
Iso (1)
Org(3)
Org(3)
Dod (6)
Dod (6)
Internet (1)
Internet (1)
Rapid City (227 2 )
Joint-iso-ccitt(2)
Joint-iso-ccitt(2)
Private (4)
Private (4)
Enterprises (1)
Nortel (562)
Synoptics(45)
Wellfleet (18)
Enterprise MIBS
Figure 2: MIB Structure
To create a new MIB view, enter the following command:
• ERS-8610:5# config snmp-v3 mib-view create [view name<1..32>] <subtree oid>
mask <value in hex> type <include|exclude>
Example: to add a new MIB view named ‘ro_private’ to exclude the Private branch, enter the
following command:
• ERS-8606:5# config snmp-v3 mib-view create ro_private 1.3.6.1.4 type exclude
• ERS-8610:5# config snmp-v3 mib-view info
===============================================================================
MIB View
===============================================================================
View Name Subtree Mask Type
-------------------------------------------------------------------------------org 1 include
root 1 include
snmp 1.3.6.1.6.3 include
. . .
. . .
. . .
v1v2only 1.3.6.1.6.3.16 exclude
v1v2only 1.3.6.1.6.3.18 exclude
sBladeView 1.3.6.1.4.1.1872 include
50 out of 50 Total entries displayed
40 out of 40 Total entries displayed
--------------------------------------------------------------------------------
______________________________________________________________________________________________________
NORTEL External Distribution
27
Page 29

Technical Configuration Guide for SNMP v2.0 December 2006
7. Configuration Example: Changing SNMP
Communities
7.1 Configuration Example: SNMP Communities with
Release 3.5
PP8600
CLIP = 1.1.1.1/32
Core
Network
SNMP NMS Server
10.1.30.10
In this configuration example, we wish to accomplish the following:
• Change the ‘rwa’ community string to rwa123pp8600
• Change the ‘ro’ community string to ro567pp8600
• Add a trap receiver using the IP address of the SNMP NMS server
To accomplish the above, please complete the following steps:
A) Add the new rwa community string
• ERS-8606:5# config sys set snmp community rwa rwa123pp8600
B) Add the new ro communit y string
• ERS-8606:5# config sys set snmp community ro ro567pp8600
C) Add the SN MP trap rec e iver
• ERS-8606:5# config sys set snmp trap-recv 10.1.30.10 v1 puplic
NOTE: The Circuit-less IP (C LIP) can be used as the Source IP addr ess for the SNMP traps. If
you wish to use the CLIP address, assum ing the CLIP address is 1.1.1.1/32, enter the f ollowing
commands:
• ERS-8606:5# config sys set snmp trap-recv 10.1.30.10 v1 puplic 1.1.1.1
• ERS-8606:5# config sys set snmp force-trap-sender true
To view the SNMP communities, enter the following commands:
• ERS-8606:5# show sys community
Community String
ro ********
l1 ********
l2 ********
l3 ********
rw ********
rwa ********
______________________________________________________________________________________________________
NORTEL External Distribution
28
Page 30

Technical Configuration Guide for SNMP v2.0 December 2006
7.2 Configuration Example: Changing the Default
SNMP Community Name with Release 3.7 or 4.1
By default, the ERS 8600 public and private communities are c onfigured using the names first
and second respectively. You can view the SNMP community table by using the following
command. Notice the community names, public and private by default, are asterisk out.
• ERS-8606:5# config snmp-v3 community info
========================================================================
Community Table
========================================================================
Index Name Security Name Transport Tag
-----------------------------------------------------------------------first ******** readview
second ******** initialview
3 out of 3 Total entries displayed
------------------------------------------------------------------------
To change the def ault public/private SNMPv1, SN MPv2, and SNMPv3 comm unity name, enter
the following command:
• To c hange th e def au lt pu bl i c c ommunity name, in this example to ro567pp8600, e nter the
following command:
o ERS-8606:5# config snmp-v3 community commname first new-commname
ro567pp8600
• To change the default pri vate communit y name, in this exam ple to rwa123pp8600, enter
the following command:
o ERS-8606:5# config snmp-v3 community commname second new-commname
rwa123pp8600
7.3 Configuration Example: Adding a New SNMP
Community to an Existing SNMP Group Member
If you use an existing group m ember in the VCAM table, a ne w comm unity can b e sim ply added.
To view the SNMP VACM and MIB view, the following commands can be used
• To view the VACM Membership configuration, enter the following command:
o ERS-8610-C:5# config snmp-v3 group-member info
• To view the VCAM Group Access configuration, enter the following command:
o ERS-8610-C:5# config snmp-v3 group-access info
• To view the SNMP MIB View, enter the following command:
o ERS-8610-C:5# config snmp-v3 mib-view info
For example, if you wish to add a new community named pp8600579 with read/write access,
enter the following command:
• ERS-8610-C:5# config snmp-v3 community create third pp8600579 initialview
______________________________________________________________________________________________________
NORTEL External Distribution
29
Page 31

Technical Configuration Guide for SNMP v2.0 December 2006
After the community has been added, you can view the SNMP community table by using the
following command:
• ERS-8610-C:5# config snmp-v3 community info
========================================================================
Community Table
========================================================================
Index Name Security Name Transport Tag
-----------------------------------------------------------------------OpsQosPolicyUser ******** OpsQosPolicyUser OpsQosPolicyUser
first ******** readview
second ******** initialview
third ******** initialview
4 out of 4 Total entries displayed
------------------------------------------------------------------------
NOTE: Notice that we mapped the ne w community string to an existing security name named
‘initialview’. You c an v iew t he VAC M group m em ber conf igurat ion by using the c omm ands shown
below.
• ERS-8610-C:5# config snmp-v3 group-member info
========================================================================
VACM Group Membership Configuration
========================================================================
Sec Model Security Name Group Name
-----------------------------------------------------------------------snmpv1 readview readgrp
snmpv1 sBladeUser sBladeGrp
snmpv1 initialview v1v2grp
snmpv2c readview readgrp
snmpv2c sBladeUser sBladeGrp
snmpv2c initialview v1v2grp
usm initial initial
usm OpsQosPolicyUser OpsQosPolicyUser
8 out of 8 Total entries displayed
• ERS-8610-C:5# config snmp-v3 group-access info
========================================================================
VACM Group Access Configuration
========================================================================
Group Prefix Model Level ReadV WriteV NotifyV
-----------------------------------------------------------------------initial usm noAuthNoPriv root root root
initial usm authPriv root root root
readgrp snmpv1 noAuthNoPriv v1v2only org
readgrp snmpv2c noAuthNoPriv v1v2only org
v1v2grp snmpv1 noAuthNoPriv v1v2only v1v2only v1v2only
v1v2grp snmpv2c noAuthNoPriv v1v2only v1v2only v1v2only
sBladeGrp snmpv1 noAuthNoPriv sBladeView sBladeView sBladeView
sBladeGrp snmpv2c noAuthNoPriv sBladeView sBladeView sBladeView
OpsQosPolicyUser usm noAuthNoPriv org org org
OpsQosPolicyUser usm authNoPriv org org org
10 out of 10 Total entries displayed
______________________________________________________________________________________________________
NORTEL External Distribution
30
Page 32

Technical Configuration Guide for SNMP v2.0 December 2006
• ERS-8610-C:5# config snmp-v3 mib-view info
================================================================================
MIB View
================================================================================
View Name Subtree Mask Type
-------------------------------------------------------------------------------org 1.3 include
root 1 include
snmp 1.3.6.1.6.3 include
snmp 1.3.6.1.2.1.1 include
layer1 1.3 exclude
layer1 1.3.6.1.2.1.2.2.1.7 include
layer1 1.3.6.1.4.1.2272.1.1.8 include
layer1 1.3.6.1.4.1.2272.1.26.2 include
layer1 1.3.6.1.4.1.2272.1.4.11.2 include
layer1 1.3.6.1.4.1.2272.1.4.10.1.1.11 include
layer1 1.3.6.1.4.1.2272.1.4.10.1.1.12 include
layer1 1.3.6.1.4.1.2272.1.4.10.1.1.14 include
layer1 1.3.6.1.4.1.2272.1.4.10.1.1.50 include
layer2 1.3 include
layer2 1.3.6.1.4.1.2272.1.8 exclude
layer2 1.3.6.1.4.1.2272.1.9 exclude
layer2 1.3.6.1.4.1.2272.1.19 exclude
layer2 1.3.6.1.4.1.2272.1.24 exclude
layer2 1.3.6.1.4.1.2272.1.29 exclude
layer2 1.3.6.1.4.1.2272.1.31 exclude
layer2 1.3.6.1.4.1.2272.1.34 exclude
layer2 1.3.6.1.4.1.2272.1.51 exclude
layer2 1.3.6.1.4.1.2272.1.23.15 exclude
layer2 1.3.6.1.4.1.2272.1.30.9 exclude
layer2 1.3.6.1.4.1.2272.1.30.10 exclude
layer2 1.3.6.1.4.1.2272.1.100.2 exclude
layer3 1.3 include
layer3 1.3.6.1.4.1.2272.1.19 exclude
layer3 1.3.6.1.4.1.2272.1.29 exclude
layer3 1.3.6.1.4.1.2272.1.31 exclude
layer3 1.3.6.1.4.1.2272.1.33 exclude
layer3 1.3.6.1.4.1.2272.1.34 exclude
v1v2only 1.0 include
v1v2only 1.2 include
v1v2only 1.3 include
v1v2only 1.3.6.1.6.3.15 exclude
v1v2only 1.3.6.1.6.3.16 exclude
v1v2only 1.3.6.1.6.3.18 exclude
sBladeView 1.3.6.1.4.1.1872 include
39 out of 39 Total entries displayed
--------------------------------------------------------------------------------
______________________________________________________________________________________________________
NORTEL External Distribution
31
Page 33

Community
Technical Configuration Guide for SNMP v2.0 December 2006
7.4 Testing SNMP Using Device Manager
Now that you have changed the read and write communities, you can test the configuration by
using Device Manager . The window shown below displa ys the parameters entered for the read
and write communities.
Enter ro567pp8600 for the Read
Community
Enter rwa123pp8600 for the Write
7.5 Configuration E xample: Changing the MIB View for
an SNMPv1/2 Community
In software release 3.7 or 4.1, you can create a new MIB vie w and apply it to a specific SNMP
community. This allows you, for example, to restrict write access to the ERS 8600 private MIB.
In this configuratio n example, we will create a new MIB vie w named private_rest rict and appl y it
to a new community named no_private_comm. To accomplish these tasks, please enter the
following commands:
A) Create a new MIB vie w named private_restrict. N ote, as shown in section 6.6, the ERS
8600 Private OID is 1.3.6.1.4.
• ERS-8610:5# config snmp-v3 mib-view create private_restrict 1.3.6.1.4 type
exclude
B) Create a new SNMP group access named no_private:
1. Add SNMP group access with a secur ity level of noAuthNoPriv for SNMP v1 with writ e
restrict assigned to the MIB view ‘private_restrict’ create in step A above:
• ERS-8610:5# config snmp-v3 group-access create no_private "" snmpv1
noAuthNoPriv
• ERS-8610-C:5# config snmp-v3 group-access view no_private "" snmpv1
noAuthNoPriv read org write private_restrict notify org
2. Add SNM P group access with s ecurity leve l of noAuthNoPriv f or SNMPv2 with write
restrict assigned to the MIB view ‘private_restrict’ create in step A above:
______________________________________________________________________________________________________
NORTEL External Distribution
32
Page 34

Technical Configuration Guide for SNMP v2.0 December 2006
• ERS-8610:5# config snmp-v3 group-access create no_private "" snmpv2
noAuthNoPriv
• ERS-8610-C:5# config snmp-v3 group-access view no_private "" snmpv2
noAuthNoPriv read org write private_restrict notify org
C) Create a new SNMP group member named “private” for SNMPv1/2 and add group
access “no_private” created in step 2 above
1. In this example, we will add a new MIB vie w nam ed ‘private ’ to exc lude acc ess to the
SNMP Private MIB
• ERS-8610:5# config snmp-v3 group-member create private snmpv1
no_private
• ERS-8610:5# config snmp-v3 group-member create private snmpv2
no_private
D) Create a new SNMP community named ‘forth’ with a community name of
‘no_private_comm’ and add group member ‘private’ created in step C above:
1. Assign to usm group ‘group_1’ read view to ‘org and write MIB view to ‘private’:
• ERS-8610:5# config snmp-v3 community create forth no_private_comm
private
______________________________________________________________________________________________________
NORTEL External Distribution
33
Page 35

Technical Configuration Guide for SNMP v2.0 December 2006
8. Configuration Example Using SNMPv3
SNMPv3
User 1
User 2
For this configuration example, we wish to accomplish the following:
• Add User 1 to USM table with authentication protocol of MD5 and privacy protocol of
DES, i.e. authPriv)
• Allow User 1 full MIB views with full permission starting the existing view “org”
Access
• Add User 2 to USM table authentication protocol of MD5 with no privacy protocol, i.e.
authNoPriv
• Allow User 2 full MIB read perm ission starting from the exiting “org” level, but exclude
write permission from all Private Enterprise MIB’s
To accomplish the above, please follow the steps below.
A) Load the DES module:
1. Assuming the DES module has been installed on the ERS 8600 switch, enter the
following command:
• ERS-8610:5# config load-encryption-module DES /flash/p80c3700.des
B) Add User 1 to USM ta ble. In this example, we wi ll use a user name of ‘user1 ’, a MD5
password of ‘user1234’, and a DES privacy password of ‘userpriv’
• ERS-8610:5# config snmp-v3 usm create user1 md5 auth user1234 priv
userpriv
Or via 4.1.1
• ERS-8610:5# config snmp-v3 usm create user1 md5 auth user1234 priv-prot
des priv userpriv
C) Add User 1 to USM group. In this configuration example, we will add ‘user1’ to USM
group named “group_1”
1. Add ‘user1’ to group ‘group_1’:
• ERS-8610:5# config snmp-v3 group-member create user1 usm group_1
D) Assign Access Level to USM group:
1. Assign access level of ‘authPriv’ to USM group ‘group_1’
• ERS-8610:5# config snmp-v3 group-access create group_1 "" usm authPriv
E) Assign the Read and Write view to the USM group:
1. Assign to usm group ‘group_1’ read and write view to ‘org’:
______________________________________________________________________________________________________
NORTEL External Distribution
34
Page 36

Technical Configuration Guide for SNMP v2.0 December 2006
• ERS-8610:5# config snmp-v3 group-access view group_1 "" usm authPriv
read org write org
F) Add User 2 to USM tab le. I n th is ex ample, we will use a user n ame of ‘user2’, and a MD 5
password of ‘user2abcd.
• ERS-8610:5# config snmp-v3 usm create user2 md5 auth user2abcd
G) Add User 2 to USM group. We will add User 2 to the group named ‘group_1’ created
above.
1. Add ‘user2’ to group ‘group_1’:
• ERS-8610:5# config snmp-v3 group-member create user2 usm group_1
H) Assign Access Level to USM group:
1. Assign access level of ‘authNoPriv’ to usm group ‘group_1’
• ERS-8610:5# config snmp-v3 group-access create group_1 "" usm
authNoPriv
I) Create a new MIB view to exclude the private MIB for User 2
1. In this example, we will add a new MIB vie w nam ed ‘private ’ to exc lude acc ess to the
SNMP Private MIB
• ERS-8610:5# config snmp-v3 mib-view create private 1.3.6.1.4 type exclude
J) Assign the Read and Write view to the usm group:
1. Assign to usm group ‘group_1’ read view to ‘org and write MIB view to ‘private’:
• ERS-8610:5# config snmp-v3 group-access view group_1 "" usm
authNoPriv read org write private
8.1 Testing SNMPv3 Using Device Manager
Now that you have created two new users, you can test the configuration by using Device
Manager. The window shown below displays the parameters entered for user1.
Enter user1 for User Name
Select MD5 for Authentication Protocol
Enter user1234 for Authentication Password
Select DES for Privacy Protocol
Enter userpriv for Privacy Password
______________________________________________________________________________________________________
NORTEL External Distribution
35
Page 37

Technical Configuration Guide for SNMP v2.0 December 2006
9. Software Baseline
All configuration ex amples are based o n the ERS 8600 3.7 rel ease with updated inf ormation
release to AES support for release 4.1.
______________________________________________________________________________________________________
NORTEL External Distribution
36
Page 38

Technical Configuration Guide for SNMP v2.0 December 2006
10. Reference Documentation
(Identify reference documentation such as Technical Pubs and Engineering Guidelines).
Document Title Publication
Number
Configuring and Managin g
Security
Configuring Network
Management
Important Security Information
for the 8000 Series Switch
Release Notes for the
Ethernet Routing Switch 8600
Configuring and Managin g
Security
Configuring Network
Management
314724-C Passport 8000 Series Software
314723-C Passport 8000 Series Software
314997-C Passport 8000 Series Software
317177-D Rev 01 Release 4.1.0
314724-E Rev 00 Ethernet Routing Switch 8600 Software
314723-E Rev 00 Ethernet Routing Switch 8600 Software
Description
Release 3.7
Release 3.7
Release 3.7
Release 4.1
Release 4.1
______________________________________________________________________________________________________
NORTEL External Distribution
37
Page 39

Technical Configuration Guide for SNMP v2.0 December 2006
11. Appendix A: Configuration Files
11.1 From Configuration Example 7.5
#
# SNMP V3 GROUP MEMBERSHIP CONFIGURATION
#
snmp-v3 group-member create private snmpv1 no_private
snmp-v3 group-member create private snmpv2c no_private
snmp-v3 group-member create user1 usm group_1
snmp-v3 group-member create user2 usm group_1
#
# SNMP V3 GROUP ACCESS CONFIGURATION
#
snmp-v3 group-access create group_1 "" usm authNoPriv
snmp-v3 group-access view group_1 "" usm authNoPriv read "org" write "pri vate" notify ""
snmp-v3 group-access create group_1 "" usm authPriv
snmp-v3 group-access view group_1 "" usm authPriv read "org" write "org" notify ""
snmp-v3 group-access create no_private "" snmpv1 noAuthNoPriv
snmp-v3 group-access view no_private "" snmpv1 noAuthNoPriv read "org" write "private_restrict" notify "org"
snmp-v3 group-access create no_private "" snmpv2c noAuthNoP ri v
snmp-v3 group-access view no_private "" snmpv2c noAuthNoPriv read "org" write "private_restrict" notify "org"
snmp-v3 group-access create OpsQosPolicyUser "" usm authNoPriv
snmp-v3 group-access view OpsQosPolicyUser "" usm authNoPriv read "org" write "org" notify "org"
#
# SNMP V3 MIB VIEW CONFIGURATION
#
snmp-v3 mib-view create private_restrict 1.3.6.1.4 type exclude
11.2 From Configuration Example 8
#
# SNMP V3 GROUP MEMBERSHIP CONFIGURATION
#
snmp-v3 group-member create user1 usm group_1
snmp-v3 group-member create user2 usm group_1
snmp-v3 group-member create OpsQosPolicyUser usm OpsQosPolicyUser
#
# SNMP V3 GROUP ACCESS CONFIGURATION
#
snmp-v3 group-access create group_1 "" usm authNoPriv
snmp-v3 group-access view group_1 "" usm authNoPriv read "org" write "private" n
otify ""
snmp-v3 group-access create group_1 "" usm authPriv
snmp-v3 group-access view group_1 "" usm authPriv read "org" write "org" notify
""
snmp-v3 group-access create OpsQosPolicyUser "" usm authNoPriv
snmp-v3 group-access view OpsQosPolicyUser "" usm authNoPriv read "org" write "o
rg" notify "org"
#
# SNMP V3 MIB VIEW CONFIGURATION
#
______________________________________________________________________________________________________
NORTEL External Distribution
38
Page 40

Technical Configuration Guide for SNMP v2.0 December 2006
snmp-v3 mib-view create private 1.3.6.1.4 type exclude
#
# SNMP V3 NOTIFY CONFIGURATION
#
#
# SNMP V3 TARGET ADDRESS CONFIGURATION
#
snmp-v3 target-addr create OpsQosPolicyUser 47.133.56.105:8162 OpsQosPolicyUser
timeout 1500 retry 3 taglist OpsQosPolicyUser mms 484
#
# SNMP V3 TARGET PARAMS CONFIGURATION
#
snmp-v3 target-param create OpsQosPolicyUser mp-model usm sec-level authNoPriv s
ec-name OpsQosPolicyUser
snmp-v3 target-param create TparamV1 mp-model snmpv1 sec-level noAuthNoPriv secname readview
snmp-v3 target-param create TparamV2 mp-model snmpv2c sec-level noAuthNoPriv sec
-name readview
#
# SNMP V3 NOTIFY FILTER CONFIGURATION
#
snmp-v3 ntfy-filter create OpsQosPolicyUser 1.3.6.1.4.1.562.42.5.1.3 type includ
e
#
# SNMP V3 NOTIFY FILTER PROFILE CONFIGURATION
#
snmp-v3 ntfy-profile create OpsQosPolicyUser profile OpsQosPolicyUser
______________________________________________________________________________________________________
NORTEL External Distribution
39
Page 41

Technical Configuration Guide for SNMP v2.0 December 2006
Contact us
If you purchased a service contract for your Nortel product from a distributor or authorized
reseller, contact the technical support staff for that distributor or reseller for assistance.
If you purchased a Nortel Networks service program, contact Nortel Technical Support. To obtain
contact information online, go to www.nortel.com/contactus
From the Technical Support page, you can open a Customer Service Request online or find the
telephone number for the nearest Technical Solutions Center. If you are not connected to the
Internet, call 1-800-4NORTEL (1-800-466-7835) to learn the telephone number for the nearest
Technical Solutions Center.
An Express Routing Code (ERC) is available for many Nortel products and services. When you
use an ERC, your call is routed to a technical support person who specializes in supporting that
product or service. To locate an ERC for your product or service, go to www.nortel.com/erc
.
.
______________________________________________________________________________________________________
NORTEL External Distribution
40
 Loading...
Loading...