Page 1
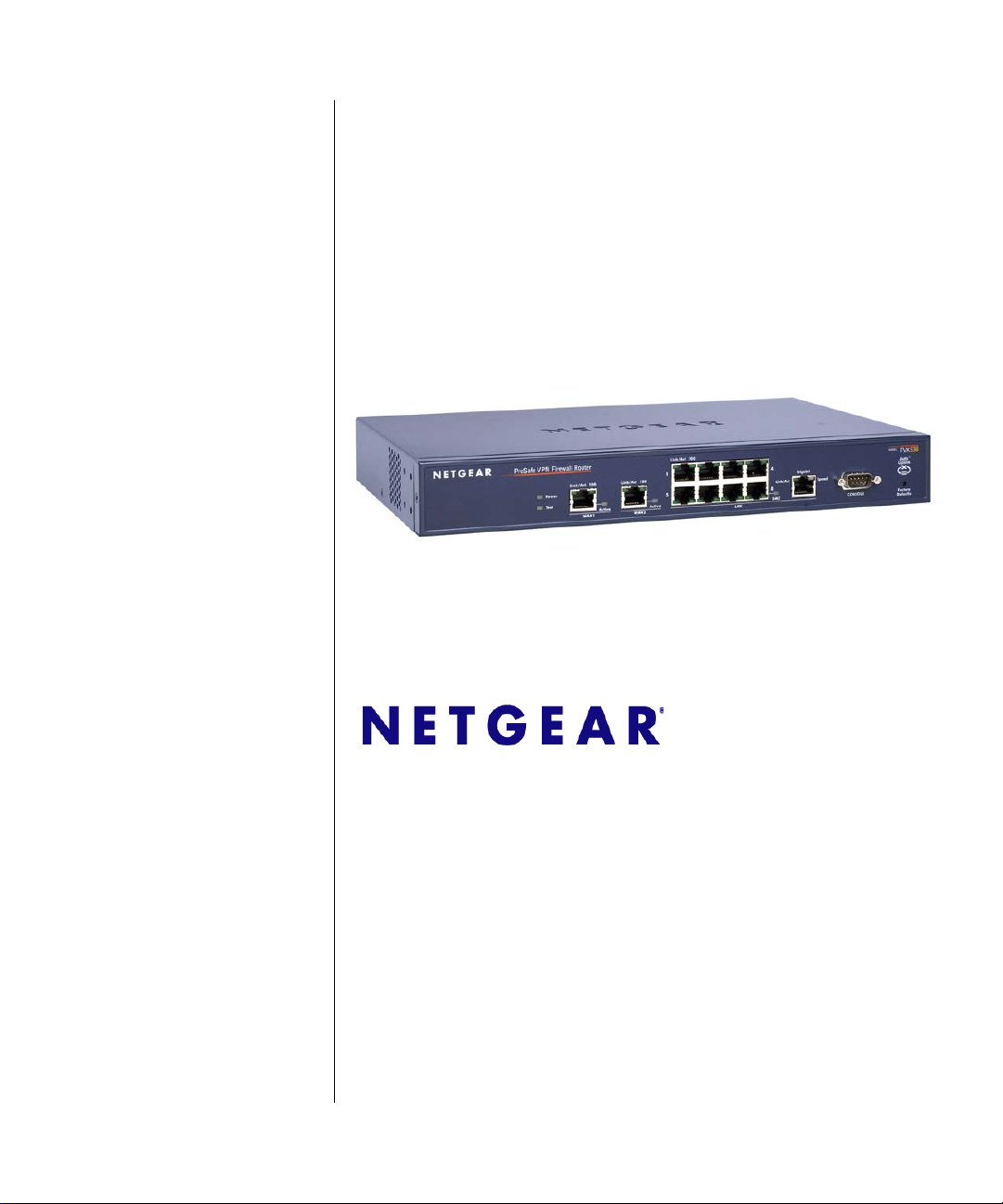
ProSafe VPN Firewall 200
FVX538 Reference
Manual
NETGEAR, Inc.
350 East Plumeria Drive
San Jose, CA 95134
202-10062-10
v1.0
January 2010
Page 2

© 2006–2010 by NETGEAR, Inc. All rights reserved.
Technical Support
Please refer to the support information card that shipped with your product. By registering your product at
http://www.netgear.com/register, we can provide you with faster expert technical support and timely notices of product
and software upgrades.
NETGEAR, INC. Support Information
Phone: 1-888-NETGEAR, for US & Canada only. For other countries, see your Support information card.
E-mail: support@netgear.com
North American NETGEAR website: http://www.netgear.com
Trademarks
NETGEAR and the NETGEAR logo are registered trademarks and ProSafe is a trademark of NETGEAR, Inc.
Microsoft, Windows, and Wi ndows NT are registered trademarks of Microsoft Corporation. Other brand and product
names are registered trademarks or trademarks of their respective holders.
Statement of Conditions
In the interest of improving internal design, operational function, and/or reliability, NETGEAR reserves the right to
make changes to the products described in this document without notice.
NETGEAR does not assume any liability that may occur due to the use or application of the product(s) or circuit
layout(s) described herein.
Federal Communications Commission (FCC) Compliance Notice: Radio Frequency
Notice
This equipment has been tested and found to comply with the limits for a Class B digital device, pursuant to
part 15 of the FCC Rules. These limits are designed to provide reasonable protection against harmful interference in a
residential installation. This equipment generates, uses, and can radiate radio frequency energy and, if not installed and
used in accordance with the instruct ions, may cause harmf ul interference to radio communications. However, there is no
guarantee that interference will not occur in a particular installation. If this equipment does cause harmful interference to
radio or television reception, which can be determined by turning the equipment off and on, the user is encouraged to try
to correct the interference by one or more of the following measures:
• Reorient or relocate the receiving antenna.
• Increase the separation between the equipment and receiver.
• Connect the equipment into an outlet on a circuit different from that to which the receiver is connected.
• Consult the dealer or an experienced radio/TV technician for help.
EU Regulatory Compliance Statement
The ProSafe VPN Firewall 200 is compliant with the following EU Council Directives: 89/336/EEC and LVD 73/23/
EEC. Compliance is verified by testing to the following standards: EN55022 Class B, EN55024 and EN60950-1.
ii
v1.0, January 2010
Page 3
Bestätigung des Herstellers/Importeurs
Es wird hiermit bestätigt, daß das ProSafe VPN Firewall 200 gemäß der im BMPT-AmtsblVfg 243/1991 und Vfg 46/
1992 aufgeführten Bestimmungen entstört ist. Das vorschriftsmäßige Betreiben einiger Geräte (z.B. Testsender) kann
jedoch gewissen Beschränkungen unterliegen. Lesen Sie dazu bitte die Anmerkungen in der Betriebsanleitung.
Das Bundesamt für Zulassungen in der Telekommunikation wurde davon unterrichtet, daß dieses Gerät auf den Markt
gebracht wurde und es ist berechtigt, die Serie auf die Erfüllung der Vorschriften hin zu überprüfen.
Certificate of the Manufacturer/Importer
It is hereby certified that the ProSafe VPN Firewall 200 has been suppressed in accordance with the conditions set out in
the BMPT-AmtsblVfg 243/1991 and Vfg 46/1992. The operation of some equipment (for example, test transmitters) in
accordance with the regulations may, however , be subject to certain restricti ons. Please refer to the notes in the operating
instructions.
Federal Office for Telecommunications Approvals has been notified of the placing of this equipment on the market
and has been granted the right to test the series for compliance with the regulations.
Voluntary Control Council for Interference (VCCI) Statement
This equipment is in the second category (information equipment to be used in a residential area or an adjacent area
thereto) and conforms to the standards set by the Voluntary Control Council for Interference by Data Processing
Equipment and Electronic Office Machines aimed at preventing radio interference in such residential areas.
When used near a radio or TV receiver , it may become the cause of radio interference.
Read instructions for correct handling.
Additional Copyrights
AES Copyright (c) 2001, Dr. Brian Gladman, brg@gladman.uk.net, Worcester, UK.
All rights reserved.
TERMS
Redistribution and use in source and binary forms, with or without modification, are permitted
subject to the following conditions:
1. Redistributions of source code must retain the above copyright notice, this list of
conditions, and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of
conditions, and the following disclaimer in the documentation and/or other materials
provided with the distribution.
3. The copyright holder’s name must not be used to endorse or promote any products
derived from this software without his specific prior written permission.
This software is provided “as is” with no express or implied warranties of correctness or fitness
for purpose.
v1.0, January 2010
iii
Page 4
Open SSL Copyright (c) 1998–2000 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted
provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice, this list of
conditions, and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of
conditions, and the following disclaimer in the documentation and/or other materials
provided with the distribution.
3. All advertising materials mentioning features or use of this software must display the
following acknowledgment: “This product includes software developed by the OpenSSL
Project for use in the OpenSSL Toolkit (
4. The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used to endorse or
promote products derived from this software without prior written permission. For written
permission, contact openssl-core@openssl.org.
5. Products derived from this software may not be called “OpenSSL” nor may “OpenSSL”
appear in their names without prior written permission of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment: “This
product includes software developed by the OpenSSL Project for use in the OpenSSL
Toolkit (
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS,” AND ANY
EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS
CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL,
EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO,
PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY
OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS
SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com). This
product includes software written by Tim Hudson (tjh@cryptsoft.com).
MD5 Copyright (C) 1990, RSA Data Security, Inc. All rights reserved.
License to copy and use this software is granted provided that it is identified as the “RSA Data
Security, Inc. MD5 Message-Digest Algorithm” in all material mentioning or referencing this
software or this function. License is also granted to make and use derivative works provided
that such works are identified as “derived from the RSA Data Security, Inc. MD5 MessageDigest Algorithm” in all material mentioning or referencing the derived work.
RSA Data Security, Inc. makes no representations concerning either the merchantability of
this software or the suitability of this software for any particular purpose. It is provided “as is”
without express or implied warranty of any kind.
These notices must be retained in any copies of any part of this documentation and/or
software.
http://www.openssl.org/).”
http://www.openssl.org/).”
iv
v1.0, January 2010
Page 5
PPP Copyright (c) 1989 Carnegie Mellon University. All rights reserved.
Redistribution and use in source and binary forms are permitted provided that the above
copyright notice and this paragraph are duplicated in all such forms and that any
documentation, advertising materials, and other materials related to such distribution and use
acknowledge that the software was developed by Carnegie Mellon University. The name of
the University may not be used to endor s e or promote products derived from this software
without specific prior written permission.
THIS SOFTWARE IS PROVIDED “AS IS” AND WITHOUT ANY EXPRESS OR IMPLIED
WARRANTIES, INCLUDING, WITHOUT LIMITATION, THE IMPLIED WARRANTIES OF
MERCHANTIBILITY AND FITNESS FOR A PARTICULAR PURPOSE.
Zlib zlib.h. Interface of the zlib general purpose compression library version 1.1.4, March 11th,
2002. Copyright (C) 1995–2002 Jean-loup Gailly and Mark Adler.
This software is provided “as is,” without any express or implied warranty. In no event will the
authors be held liable for any damages arising from the use of this software. Permission is
granted to anyone to use this software for any purpose, including commercial applications,
and to alter it and redistribute it freely, subject to the following restrictions:
1. The origin of this software must not be misrepresented; you must not claim that you wrote
the original software. If you use this software in a product, an acknowledgment in the
product documentation would be appreciated but is not required.
2. Altered source versions must be plainly marked as such, and must not be misrepresented
as being the original software.
3. This notice may not be removed or altered from any source distribution.
Jean-loup Gailly: jloup@gzip.org; Mark Adler: madler@alu mni.caltech.edu.
The data format used by the zlib library is described by RFCs (Request for Comments) 1950
to 1952 in the files
format), and rfc1952.txt (gzip format).
ftp://ds.internic.net/rfc/rfc1950.txt (zlib format), rfc1951.txt (deflate
Product and Publication Details
Model Number: FVX538
Publication Date: January 2010
Product Family: VPN Firewall
Product Name: ProSafe VPN Firewall 200
Home or Business Product: Business
Language: English
Publication Part Number: 202-10062-10
Publication Version Number 1.0
v1.0, January 2010
v
Page 6

vi
v1.0, January 2010
Page 7

Contents
ProSafe VPN Firewall 200 FVX538 Reference Manual
About This Manual
Conventions, Formats and Scope ...................................................................................xiii
How to Print This Manual ................................................................................................xiv
Revision History ..................... ... ... .... ... ... ... .......................................... .............................xiv
Chapter 1
Introduction
Key Features ..................................................................................................................1-1
Dual WAN Ports for Increased Reliability or Outbound Load Balancing ..................1-2
A Powerful, True Firewall with Content Filtering ......................................................1-2
Security Features .....................................................................................................1-3
Autosensing Ethernet Connections with Auto Uplink ...............................................1-3
Extensive Protocol Support ......................................................................................1-4
Easy Installation and Management ..........................................................................1-4
Maintenance and Support .................. .... ... ... ... .......................................... ... .... ... ... ..1-5
Package Contents ..........................................................................................................1-5
VPN Firewall Front and Rear Panels ..............................................................................1-6
Rack Mounting Hardware .........................................................................................1-8
The VPN Firewall’s IP Address, Login Name, and Password ........................................1-9
Qualified Web Browsers ...............................................................................................1-10
Chapter 2
Connecting the VPN Firewall to the Internet
Understanding the Connection Steps .............................................................................2-1
Logging into the VPN Firewall ................................................... ... ... ... ............................2-2
Configuring the Internet Connections to Your ISPs ........................................................2-2
Setting the VPN Firewall’s MAC Address ................................................................2-5
Manually Configuring Your Internet Connection .................................. .....................2-5
Configuring the WAN Mode (Required for Dual WAN) ................................................... 2-7
Setting Up Auto-Rollover Mode .......................... ....... ...... ....... ...... ....... ...... ....... ... .....2-9
v1.0, January 2010
vii
Page 8

ProSafe VPN Firewall 200 FVX538 Reference Manual
Setting Up Load Balancing .................................................................................. ...2-11
Configuring Dynamic DNS (Optional) ...........................................................................2-14
Configuring the Advanced WAN Options (Optional) ............................................... ...... 2-16
Additional WAN Related Configuration ..................................................................2-17
Chapter 3
LAN Configuration
Choosing the VPN Firewall DHCP Options ....................................................................3-1
Configuring the LAN Setup Options ...............................................................................3-2
Managing Groups and Hosts (LAN Groups) ...................................................................3-6
Creating the Network Database ...... ... .... ... ... ... ... .......................................... .... ... ... ..3-6
Viewing the Network Database ................................................................................3-7
Adding Devices to the Network Database ................................................................3-8
Changing Group Names in the LAN Groups Database ...........................................3-9
Setting Up DHCP Address Reservation ...................................................................3-9
Configuring Multi Home LAN IP Addresses ..................................................................3-10
Configuring and Enabling the DMZ Port .......................................................................3-11
Configuring Static Routes .............................................................................................3-14
Static Route Example .............................................................................................3-16
Configuring Routing Information Protocol (RIP) .... ... .... .......................................... ... ...3-16
Chapter 4
Firewall Protection and Content Filtering
About Firewall Protection and Content Filtering .............................................................4-1
Using Rules to Block or Allow Specific Kinds of Traffic ..................................................4-2
Services-Based Rules ........................................ .... ... ... ... .........................................4-3
Viewing Rules and Order of Precedence for Rules ................................ ................ ..4-7
Configuring LAN WAN Rules ...................................................................................4-9
Configuring DMZ WAN Rules ................................................................................4-12
Configuring LAN DMZ Rules ..................................................................................4-13
Inbound Rules Examples .......................................................................................4-15
Outbound Rules Example ................................................................ ... ... ... ... .... ... ...4-19
Configuring Other Firewall Features .............................................................................4-19
Attack Checks .............. ... ... ... .... ... ....................................... ... ... ... .... ... ... ... .............4-20
Setting Session Limits .. ... ... ... .... ... ... ... .... .......................................... ......................4-22
Managing the Application Level Gateway for SIP Sessions ..................................4-23
Creating Services, QoS Profiles, and Bandwidth Profiles ............................................4-24
viii Contents
v1.0, January 2010
Page 9

ProSafe VPN Firewall 200 FVX538 Reference Manual
Adding Customized Services .................................................................................4-24
Specifying Quality of Service (QoS) Priorities .................................. ... ... ... ... .... ... ...4-26
Creating Bandwidth Profiles ...... ... ... ....... ................................................................4-27
Setting a Schedule to Block or Allow Specific Traffic .......................... .... ... ... ................4-29
Blocking Internet Sites (Content Filtering) ....................................................................4-30
Configuring Source MAC Filtering ................................................................................4-33
Configuring IP/MAC Address Binding ...........................................................................4-35
Configuring Port Triggering ...........................................................................................4-37
E-Mail Notifications of Event Logs and Alerts ......................................... ......................4-40
Administrator Tips .........................................................................................................4-40
Chapter 5
Virtual Private Networking
Considerations for Dual WAN Port Systems ..................................................................5-1
Using the VPN Wizard for Client and Gateway Configurations ...................................... 5-3
Creating Gateway to Gateway VPN Tunnels with the Wizard .................................5-3
Creating a Client to Gateway VPN Tunnel ...............................................................5-6
Testing the Connections and Viewing Status Information ............................................. 5-12
NETGEAR VPN Client Status and Log Information ............................................... 5-12
VPN Firewall VPN Connection Status and Logs .... ... ... ... .... ... ... ... .... ... ... ... ... .... ... ...5-14
Managing VPN Policies .. .... ... ... ... .... ... ... ... .... ... ... ... ... .......................................... .... ... ...5-16
Configuring IKE Policies ............................... ... ... .... ... ... ... .... ... ... .............................5-16
Configuring VPN Policies .......................................................................................5-18
Managing Certificates ................................................................ ...................................5-19
Viewing and Loading CA Certificates .....................................................................5-21
Viewing Active Self Certificates ..............................................................................5-22
Obtaining a Self Certificate from a Certificate Authority ......................... ................5-22
Managing your Certificate Revocation List (CRL) .. ... ... ..........................................5-25
Extended Authentication (XAUTH) Configuration ............................ ................... ..........5-26
Configuring XAUTH for VPN Clients ......................................................................5-27
User Database Configuration .... ... ... ... .... .......................................... ... ... ... .............5-29
RADIUS Client Configuration .................................................................................5-30
Assigning IP Addresses to Remote Users (ModeConfig) .............................................5-32
Mode Config Operation ...... .......................................... ..........................................5-32
Configuring Mode Config Operation on the VPN Firewall ......................................5-33
Configuring the ProSafe VPN Client for ModeConfig .......................................... ...5-38
Contents ix
v1.0, January 2010
Page 10

ProSafe VPN Firewall 200 FVX538 Reference Manual
Configuring Keepalives and Dead Peer Detection .......................................................5-42
Configuring Keepalives ..........................................................................................5-42
Configuring Dead Peer Detection ..........................................................................5-43
Configuring NetBIOS Bridging with VPN ......................................................................5-44
Chapter 6
VPN Firewall and Network Management
Performance Management ................................. .......................................... ... ... .... ........ 6-1
Bandwidth Capacity .................. ... ... ... .... ... ... .......................................... ..................6-1
VPN Firewall Features That Reduce Traffic .............................................................6-2
VPN Firewall Features That Increase Traffic ...........................................................6-4
Using QoS to Shift the Traffic Mix ............................................................................6-7
Tools for Traffic Management ................................. ... ... ... .... ... ... ... ............................6-8
Configuring Users, Administrative Settings, and Remote Management .........................6-8
Changing Passwords and Settings ..........................................................................6-8
Adding External Users ........................... ... .............................................................6-10
Configuring an External Server for Authentication ................. ................................ 6-11
Enabling Remote Management Access .................................................................6-14
Using an SNMP Manager ......................................................................................6-16
Managing the Configuration File ............................................................................6-18
Configuring Date and Time Service .......................................................................6-21
Monitoring System Performance ..... ... ... ... .... ... ... ... ... .... ... ... ... .... ... ... ... .... ... ... ... .............6-23
Activating Notification of Events and Alerts ............................................................6-23
Viewing the Logs ....................................................................................................6-26
Enabling the Traffic Meter ......................................................................................6-27
Viewing the VPN Firewall Configuration and System Status .................................6-30
Monitoring VPN Firewall Statistics ......... ... ... ... ... .... .......................................... ... ...6-31
Monitoring WAN Ports Status ................. ... ... ... ... .... ... ... ..........................................6-32
Monitoring Attached Devices .................................................................................6-33
Monitoring VPN Tunnel Connection Status ............................ ... ... .... ... ... ... .............6-34
Viewing the VPN Logs ...........................................................................................6-35
Viewing the DHCP Log ..........................................................................................6-36
Viewing Port Triggering Status ...............................................................................6-36
Chapter 7
Troubleshooting
Basic Functions ..............................................................................................................7-1
x Contents
v1.0, January 2010
Page 11
ProSafe VPN Firewall 200 FVX538 Reference Manual
Power LED Not On ...................................................................................................7-2
LEDs Never Turn Off ................................................................................................7-2
LAN or Internet Port LEDs Not On ......... ... ... ... ... .... ... ... .......................................... ..7-2
Troubleshooting the Web Configuration Interface ..........................................................7-3
Troubleshooting the ISP Connection ..............................................................................7-4
Troubleshooting a TCP/IP Network Using a Ping Utility .................................................7-5
Testing the LAN Path to Your VPN Firewall .............................................................7-5
Testing the Path from Your PC to a Remote Device ................................................7-6
Restoring the Default Configuration and Password ............... .........................................7-7
Problems with Date and Time .........................................................................................7-7
Using the Diagnostics Utilities ........................................................................................7-8
Appendix A
Default Settings and Technical Specifications
Appendix B
Network Planning for Dual WAN Ports
What You Will Need to Do Before You Begin ................................................................ B-1
Cabling and Computer Hardware Requirements .................................................... B-3
Computer Network Configuration Requirements ......................... .... ... ... ... ... .... ... ... . B-3
Internet Configuration Requirements ...................................................................... B-3
Where Do I Get the Internet Configuration Parameters? ........................................ B-4
Internet Connection Information Form .................................................................... B-4
Overview of the Planning Process ................................................................................. B-5
Inbound Traffic ........................................................................................................ B-5
Virtual Private Networks (VPNs) ............................................................................. B-6
The Roll-over Case for Firewalls With Dual WAN Ports .......................................... B-6
The Load Balancing Case for Firewalls With Dual WAN Ports ............................... B-7
Inbound Traffic ............................................................................................................... B-7
Inbound Traffic to Single WAN Port (Reference Case) ........................................... B-7
Inbound Traffic to Dual WAN Port Systems ............................................................ B-8
Virtual Private Networks (VPNs) .................................................................................... B-9
VPN Road Warrior (Client-to-Gateway) .................................................................B-11
VPN Gateway-to-Gateway ........... ... ... .... ... ... ... ... .... ... ... ......................................... B-14
VPN Telecommuter (Client-to-Gateway Through a NAT Router) .......................... B-16
Contents xi
v1.0, January 2010
Page 12

ProSafe VPN Firewall 200 FVX538 Reference Manual
Appendix C
System Logs and Error Messages
System Log Messages .................................................................................................. C-1
System Startup ............................. ... ... .... ... ... ... ... ....................................... ... .... ... ... . C-1
Reboot ....................................... ... ... ....................................... ... ... .... ... ... ... ... .... .......C-2
NTP .................................... ................................................................. .................... C-2
Login/Logout ........................................................................................................... C-3
Firewall Restart .......................................................................................................C-3
IPSec Restart ........ ... .... ... ... ... .... ...................................... .... ... ... ... .... ... ... .................C-4
WAN Status .................. ... ... ... ....................................... ... .... ... ... ... ........................... C-4
Web Filtering and Content Filtering Logs ................................................................ C-7
Traffic Metering Logs ........................................................................ ... ... ... ... ...........C-9
Unicast Logs ......................... .... ... ... ... .... ... ... ....................................... ... ... ... .... ... ... . C-9
FTP Logging ................................. ... ... .... ... .......................................... ..................C-10
Invalid Packet Logging ....... ... .... ... ... ... .... ... ... ... ... .... ... ... ... ...................................... C-10
Routing Logs ............................................................................................................... C-13
LAN to WAN Logs ................................................................................................. C-14
LAN to DMZ Logs .................................................................................................. C-14
DMZ to WAN Logs ................................................................................................C-14
WAN to LAN Logs ................................................................................................. C-14
DMZ to LAN Logs .................................................................................................. C-15
WAN to DMZ Logs ................................................................................................C-15
Appendix D
Two Factor Authentication
Why do I need Two-Factor Authentication? ...................................................................D-1
What are the benefits of Two-Factor Authentication? ............................................. D-1
What is Two-Factor Authentication ......................................................................... D-2
NETGEAR Two-Factor Authentication Solutions ....................................................... ... . D-2
Appendix E
Related Documents
Index
xii Contents
v1.0, January 2010
Page 13
About This Manual
The NETGEAR® ProSafe™ VPN Firewall 200 describes how to install, configure and
troubleshoot the ProSafe VPN Firewall 200. The information in this manual is intended for readers
with intermediate computer and Internet skills.
Conventions, Formats and Scope
The conventions, formats, and scope of this manual are described in the following paragraphs.
• Typographical Conventions. This manual uses the following typographical conventions:
Italics Emphasis, books, CDs, file and server names, extensions
Bold User input, IP addresses, GUI screen text
Fixed Command prompt, CLI text, code
italics URL links
• Formats. This manual uses the following formats to highlight special messages:
Note: This format is used to highlight information of importance or special interest.
Tip: This format is used to highlight a procedure that will save time or resources.
Warning: Ignoring this type of note may result in a malfunction or damage to the
equipment.
Danger: This is a safety warning. Failure to take heed of this notice may result in
personal injury or death.
v1.0, January 2010
xiii
Page 14
ProSafe VPN Firewall 200 FVX538 Reference Manual
• Scope. This manual is written for the VPN firewall according to these specifications.
Product Version ProSafe VPN Firewall 200
Manual Publication Date January 2010
For more information about network, Internet, firewall, and VPN technologies, see the links to the
NETGEAR website in Appendix E, “Related Documents.”
Note: Product updates are available on the NETGEAR, Inc. website at
http://kb.netgear.com/app/home.
How to Print This Manual
T o print this manual, your computer must have the free Adobe Acrobat reader installed in order to
view and print PDF files. The Acrobat reader is available on the Adobe websit e at
http://www.adobe.com.
Tip: If your printer supports printing two pages on a single sheet of paper, you can save
paper and printer ink by selecting this feature.
Revision History
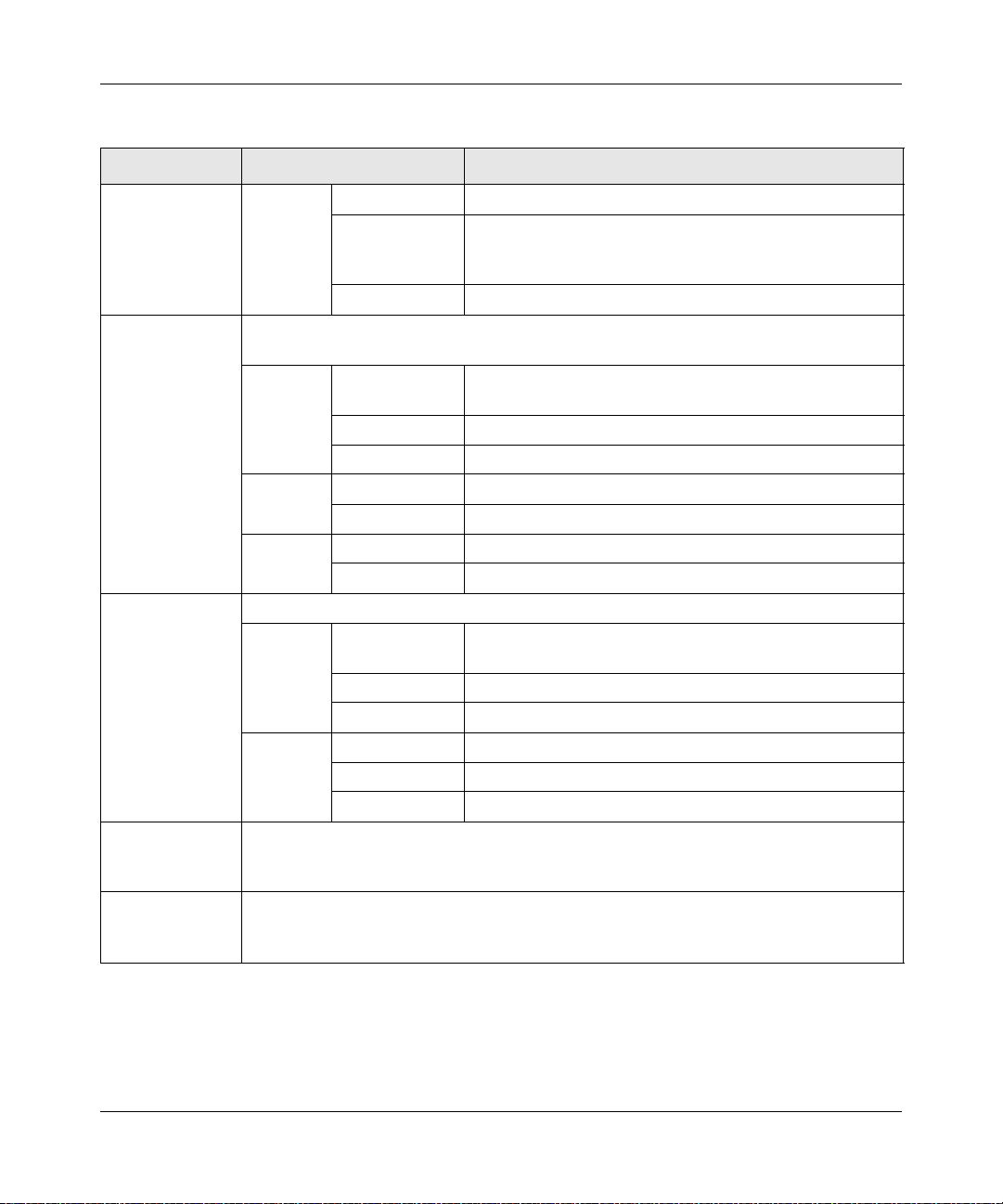
Part Number
202-10062-04 1.0 Aug. 2006 Product update: New firmware and a new user interface.
202-10062-05 1.0 Jan. 2007 Remove Trend Micro
202-10062-06 1.0 Jul. 2007 New features: IP/MAC Binding; Bandwidth Limits; Session Limits;
202-10062-06 1.1 Oct. 2007 Document corrections
202-10062-06 1.2 Oct. 2007 Document additions to Appendix C
202-10062-07 1.0 Mar. 08 Maintenance release
xiv About This Manual
Version
Number
Date Description
IKE Keep Alive; Dead Peer Detection; Oray Support
v1.0, January 2010
Page 15
ProSafe VPN Firewall 200 FVX538 Reference Manual
202-10062-09 1.0 Mar. 09 Adds these corrections and topics for the March 2009 firmware
maintenance release:
• WIKID 2 factor authentication
• SIP ALG support
• DHCP Relay support
• Update VPN configuration procedure topics
• Update the Certificate management topic
• Correct the firewall scheduling topic
202-10062-10 1.0 January
2010
Added the following new features for the January 2010 firmware
maintenance release:
• Connection reset and delay options on the WAN ISP Settings
screen (see “Manually Configuring Your Internet Connection”).
• Support for DNS 3322 in the Dynamic DNS submenu (see
“Configuring Dynamic DNS (Optional)”).
• Support for an address range for inbound LAN rules on the Add
LAN WAN Inbound Service screen (see “Inbound Rules (Port
Forwarding)” and “Inbound Rules Examples”).
• Support for new log options such as Resolved DNS Names and
VPN on the Firewall Logs & E-mail screen (see “Activating
Notification of Events and Alerts”).
In addition, made the following substantial changes to the book:
• Resized all screen captures for better viewing.
• Added qualified Web browser information in the “Qualified Web
Browsers” and “Computer Network Configuration Requirements”
sections.
• Updated the WAN1 ISP Settings screen (Figure 2-1) and the ISP
Type options in the
Connection” section.
• Updated the Dynamic DNS Configuration screen (Figure 2-6)
and the DDNS providers in the ““Configuring Dynamic DNS
(Optional)” section.
• Revised the “Enabling the Traffic Meter” section and moved this
section from the “Connecting the VPN Firewall to the Internet”
chapter to the “VPN Firewall and Network Management” chapter.
• Added the “Additional WAN Related Configuration“ section.
• Updated the LAN Setup screen (Figure 3-1), added LDAP
information and the Enable ARP Broadcast paragraph to the
“Configuring the LAN Setup Options” section, and revised this
section for more clarity.
• Updated the LAN Groups screen (Figure 3-2) and the Network
Database Group Name screen (Figure 3-3 ), and revised the
“Managing Groups and Hosts (LAN Groups)” section for more
clarity.
”“Manually Configuring Your Internet
About This Manual xv
v1.0, January 2010
Page 16
ProSafe VPN Firewall 200 FVX538 Reference Manual
202-10062-10
(continued)
1.0 January
2010
(continued)
• Updated the LAN Multi-homing screen (Figure 3-4) and revised
the “Configuring Multi Home LAN IP Addresses” section for more
clarity.
• Revised the “Configuring and Enabling the DMZ Port” section for
more clarity.
• Updated the RIP Configuration screen (Figure 3-8).
• Revised the “Viewing Rules and Order of Precedence for Rules”
section and updated the LAN WAN Rules screen (Figure 4-2).
• Updated the Add LAN WAN Inbound Service screen
(Figure 4-3), related screens in the “Inbound Rules Examples”
section, and the Inbound Rules table (Table 4-3) to show that a
range of IP addresses can be selected for the Send to LAN
Server field.
• Updated the sections and screens in the “Configuring Other
Firewall Features” section and added the “Managing the
Application Level Gateway for SIP Sessions” section.
• Updated the following sections and screens in the “Firewall
Protection and Content Filtering” chapter to show the current
user interface:
* “Creating Services, QoS Profiles, and Bandwidth Profiles”
* “Setting a Schedule to Block or Allow Specific Traffic”
* “Blocking Internet Sites (Content Filtering)”
* “Configuring Source MAC Filtering”
* “Configuring IP/MAC Address Binding”
* “Configuring Port Triggering”
• Moved the procedures and screens from the “E-Mail
Notifications of Event Logs and Alerts” section in the “Firewall
Protection and Content Filtering” chapter to the “Activating
Notification of Events and Alerts” section in the ”“VPN Firewall
and Network Management” chapter.
• Updated all FVX538 screens and made various corrections and
clarifications in the “Virtual Private Networking” chapter.
• Revised the “Managing Certificates” section and added the
following sections to the “Virtual Private Networking” chapter:
* “Configuring Keepalives and Dead Peer Detection”
* “Configuring NetBIOS Bridging with VPN”
• Revised the following sections in the “VPN Firewall and Network
Management” chapter and updated all screens in these sections:
* “Configuring Users, Administrative Settings, and Remote
Management”
* “Monitoring System Performance”
• Moved the “Using the Diagnostics Utilities” section from the
“VPN Firewall and Network Management” chapter to the
“Troubleshooting” chapter.
xvi About This Manual
v1.0, January 2010
Page 17

Chapter 1
Introduction
The ProSafe VPN Firewall 200 FVX538 with eight 1 0/100 ports and one 1/100/1000 port connects
your local area network (LAN) to the Internet through an external access device such as a cable
modem or DSL modem.
The FVX538 is a complete security solution that protects your network from attacks and
intrusions. For example, the FVX538 provides support for Stateful Packet Inspection, Denial of
Service (DoS) attack protection and multi-NAT support. The VPN firewall supports multiple W eb
content filtering options, plus browsing activity reporting and instant alerts—both via e-mail.
Network administrators can establish restricted access policies based on time-of-day, Website
addresses and address keywords.
The FVX538 is a plug-and-play device that can be installed and configured within minutes.
This chapter contains the following sections:
• “Key Features” on this page
• “Package Contents” on page 1-5
• “VPN Firewall Front and Rear Panels” on page 1-6
• “The VPN Firewall’s IP Address, Login Name, and Password” on page 1-9
• “Qualified Web Browsers” on page 1-10
Key Features
The VPN firewall provides the following features:
• Dual 10/100 Mbps Ethernet WAN ports for load balancing or failover protection, providing
increased system reliability and load balancing. The WAN ports do not respond at all to
unsolicited traffic (stealth mode).
• Support for up to 200 simultaneous IPSec VPN tunnels.
• Support for up to 400 internal LAN users (and 50K connections ) .
• Bundled with the 5-user license of the NETGEAR ProSafe VPN Client software (VPN05L)
• Quality of Service (QoS) and SIP 2.0 support for traffic prioritization, voice, and multimedia.
• Built-in 10/100 Mbps ports plus 1 Gigabit Switch port.
1-1
v1.0, January 2010
Page 18

ProSafe VPN Firewall 200 FVX538 Reference Manual
• One console port for local management.
• SNMP Manageable, optimized for the NETGEAR ProSafe Network Management Software
(NMS100).
• Easy, web-based setup for installation and management.
• Advanced SPI Firewall and Multi-NAT support.
• Extensive Protocol Support.
• Login capability.
• Front panel LEDs for easy monitoring of status and activity.
• Flash memory for firmware upgrade.
• One U Rack mountable.
Dual WAN Ports for Increased Reliability or Outbound Load Balancing
The FVX538 has two broadband WAN ports, WAN1 and WAN2, each capable of operating
independently at speeds of either 10 Mbps or 100 Mbps. The two WAN ports let you connect a
second broadband Internet line that can be configured on a mutually-exclusive basis to:
• Provide backup and rollover if one line is inoperable, ensuring you are never disconnected.
• Load balance, or use both Internet lines simultaneously for the outgoing traffic. The VPN
firewall balances users between the two lines for maximum bandwidth efficiency.
See “Network Planning for Dual WAN Ports” on page B-1 for the planning factors to consider
when implementing the following capabilities with dual WAN port gateways:
• Single or multiple exposed hosts
• V irtual private networks
A Powerful, True Firewall with Content Filtering
Unlike simple Internet sharing NAT routers, the FVX538 is a true firewall, using stateful packet
inspection to defend against hacker attacks. Its firewall features include:
• DoS protection. Automatically detects and thwarts DoS attacks such as Ping of Death, SYN
Flood, LAND Attack, and IP Spoofing.
• Secure Firewall. Blocks unwanted traffic from the Internet to your LAN.
• Block Sites. Blocks access from your LAN to Internet locations or services that you specify as
off-limits.
1-2 Introduction
v1.0, January 2010
Page 19
ProSafe VPN Firewall 200 FVX538 Reference Manual
• Logs security incidents. The FVX538 will log security events such as blocked incoming
traffic, port scans, attacks, and administrator logins. You can configure the VPN firewall to
e-mail the log to you at specified intervals. You can also configure the VPN firewall to send
immediate alert messages to your e-mail address or e-mail pager whenever a significant event
occurs.
• Keyword Filtering. With its URL keyword filtering feature, the FVX538 prevents
objectionable content from reaching your PCs. The VPN firewall allows you to control access
to Internet content by screening for keywords within Web addresses. You can configure the
VPN firewall to log and report attempts to access objectionable Internet sites.
Security Features
The FVX538 is equipped with several features designed to maintain security, as described in this
section.
• PCs Hidden by NAT. NAT opens a temporary path to the Internet for requests originating
from the local network. Requests originating from outside the LAN are discarded, preventing
users outside the LAN from finding and directly accessing the PCs on the LAN.
• Port Forwarding with NAT. Although NAT prevents Internet locations from directly
accessing the PCs on the LAN, the VPN firewall allows you to direct incoming traffic to
specific PCs based on the service port number of the incoming request. You can specify
forwarding of single ports or ranges of ports.
• DMZ port. Incoming traffic from the Internet is normally discarded by the VPN firewall
unless the traffic is a response to one of your local computers or a service for which you have
configured an inbound rule. Instead of discarding this traffic, you can have it forwarded to one
computer on your network.
Autosensing Ethernet Connections with Auto Uplink
With its internal 8-port 10/100 switch, the FVX538 can connect to either a 10 Mbps standard
Ethernet network or a 100 Mbps Fast Ethernet network. Both the LAN and WAN interfaces are
autosensing and capable of full-duplex or half-duplex operation.
The VPN firewall incorporates Auto Uplink
sense whether the Ethernet cable plugged into the port should have a ‘normal’ connection such as
to a PC or an ‘uplink’ connection such as to a switch or hub. That port will then configure itself to
the correct configuration. This feature also eliminates the need to worry about crossover cables, as
Auto Uplink will accommodate either type of cable to make the right connection.
Introduction 1-3
TM
technology. Each Ethernet port will automatically
v1.0, January 2010
Page 20

ProSafe VPN Firewall 200 FVX538 Reference Manual
Extensive Protocol Support
The FVX538 supports the Transmission Control Protocol/Internet Protocol (TCP/IP) and Routing
Information Protocol
Basics” document that you can access from the link in “Related Documents” in Appendix E.
• IP Address Sharing by NAT. The VPN firewall allows several networked PCs to share an
Internet account using only a single IP address, which may be statically or dynamically
assigned by your Internet service provider (ISP). This technique, known as NAT, allows the
use of an inexpensive single-user ISP account.
• Automatic Configuration of Attached PCs by DHCP. The VPN firewall dynamic ally
assigns network configuration information, including IP, gateway, and domain name server
(DNS) addresses, to attached PCs on the LAN using the Dynamic Host Configuration Protocol
(DHCP). This feature greatly simplifies configuration of PCs on your local network.
• DNS Proxy. When DHCP is enabled and no DNS addresses are specified, the VPN firewall
provides its own address as a DNS server to the attached PCs. The VPN firewall obtains actual
DNS addresses from the ISP during connection setup and forwards DNS requests from the
LAN.
• PPP over Ethernet (PPPoE). PPPoE is a protocol for connecting remote hosts to the Internet
over a DSL connection by simulating a dial-up connection. This feature eliminates the need to
run a login program such as EnterNet or WinPOET on your PC.
(RIP). For further information about TCP/IP, see the “TCP/IP Networking
Easy Installation and Management
You can install, configure, and operate the FVX538 within minutes after connecting it to the
network. The following features simplify installation and management tasks:
• Browser-Based Management. Browser-based configuration allows you to easily configure
your VPN firewall from almost any type of personal computer, such as Windows, Macintosh,
or Linux. A user-friendly Setup W izard is provided and online help documentation is built into
the browser-based Web Management Interface.
• Auto Detect. The VPN firewall automatically senses the type of Internet connection, asking
you only for the information required for your type of ISP account.
• VPN Wizard. The VPN firewall includes the NETGEAR VPN Wizard to easily configure
VPN tunnels according to the recommendations of the Virtual Private Network Consortium
(VPNC) to ensure the VPN tunnels are interoperable with other VPNC-compliant VPN routers
and clients.
1-4 Introduction
v1.0, January 2010
Page 21
ProSafe VPN Firewall 200 FVX538 Reference Manual
• SNMP. The VPN firewall supports the Simple Network Management Protocol (SNMP) to let
you monitor and manage log resources from an SNMP-compliant system manager. The SNMP
system configuration lets you change the system variables for MIB2.
• Diagnostic Functions. The VPN firewall incorporates built-in diagnostic functions such as
Ping, Trace Route, DNS lookup, and remote reboot.
• Remote Management. The VPN firewall allows you to login to the Web Management
Interface from a remote location on the Internet. For security, you can limit remote
management access to a specified remote IP address or range of addresses, and you can choose
a nonstandard port number.
• Visual monitoring. The VPN firewall’s front panel LEDs provide an easy way to monitor its
status and activity.
Maintenance and Support
NETGEAR offers the following features to help you maximize your use of the FVX538:
• Flash memory for firmware upgrade
• Technical support seven days a week, 24 hours a day, according to the terms identified in the
Warranty and Support information card provided with your product.
Package Contents
The product package should contain the following items:
• FVX538 ProSafe VPN Firewall 200.
• AC power cable.
• 19-inch rack mounting hardware and rubber feet.
• Category 5 (Cat5) Ethernet cable.
• Installation Guide, FVX538 ProSafe VPN Firewall 200
• Resource CD, including:
– Application Notes and other helpful information.
– ProSafe VPN Client Software – five user licenses.
• Warranty and Support Information Card.
If any of the parts are incorrect, missing, or damaged, contact your NETGEAR dealer. Keep the
carton, including the original packing materials, in case you need to return the VPN firewall for
repair.
Introduction 1-5
v1.0, January 2010
Page 22

ProSafe VPN Firewall 200 FVX538 Reference Manual
12 3 4 5 6 7
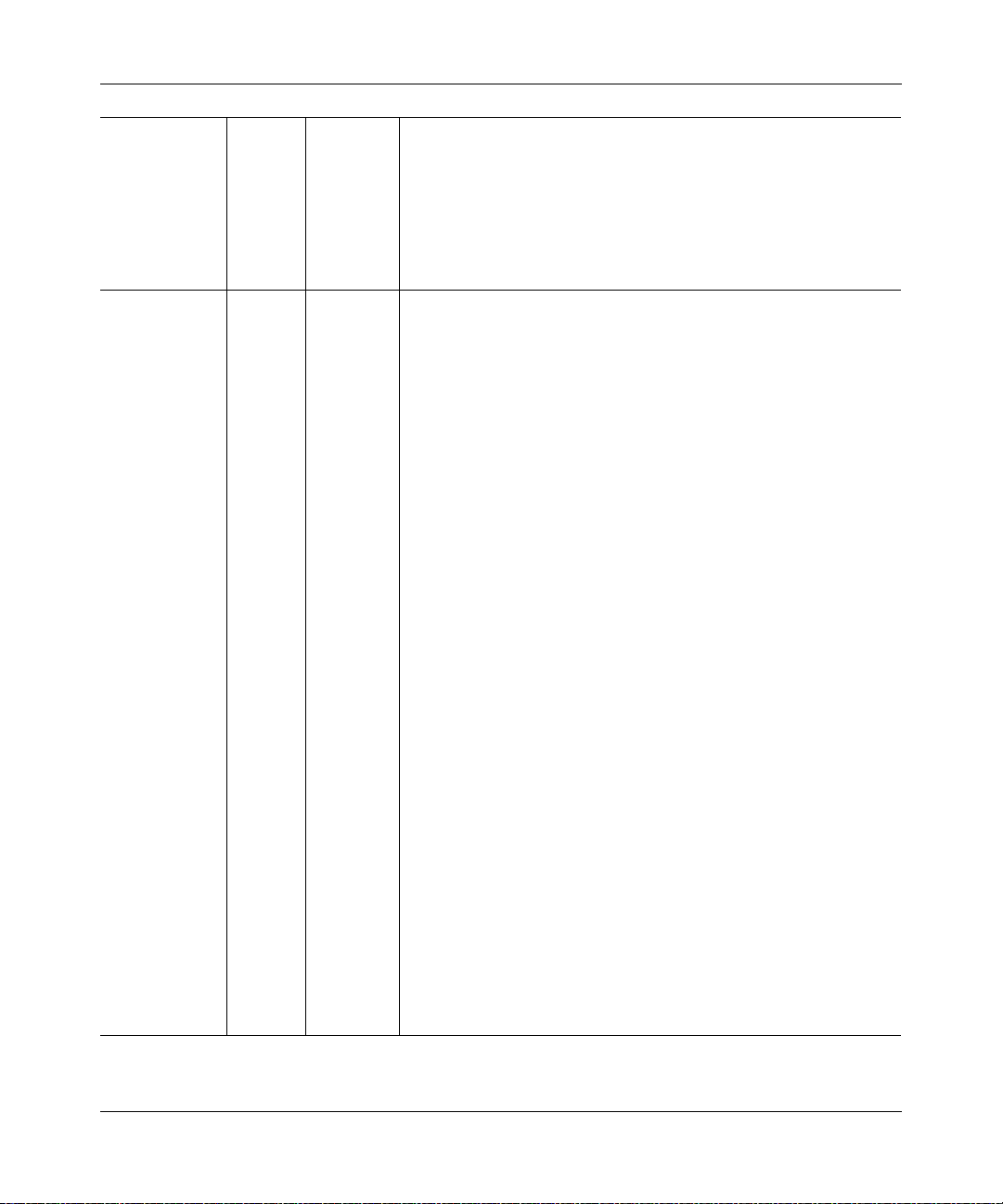
VPN Firewall Front and Rear Panels
The FVX538 front panel shown below contains the port connections, status LEDs, and the factory
defaults reset button.
Figure 1-1
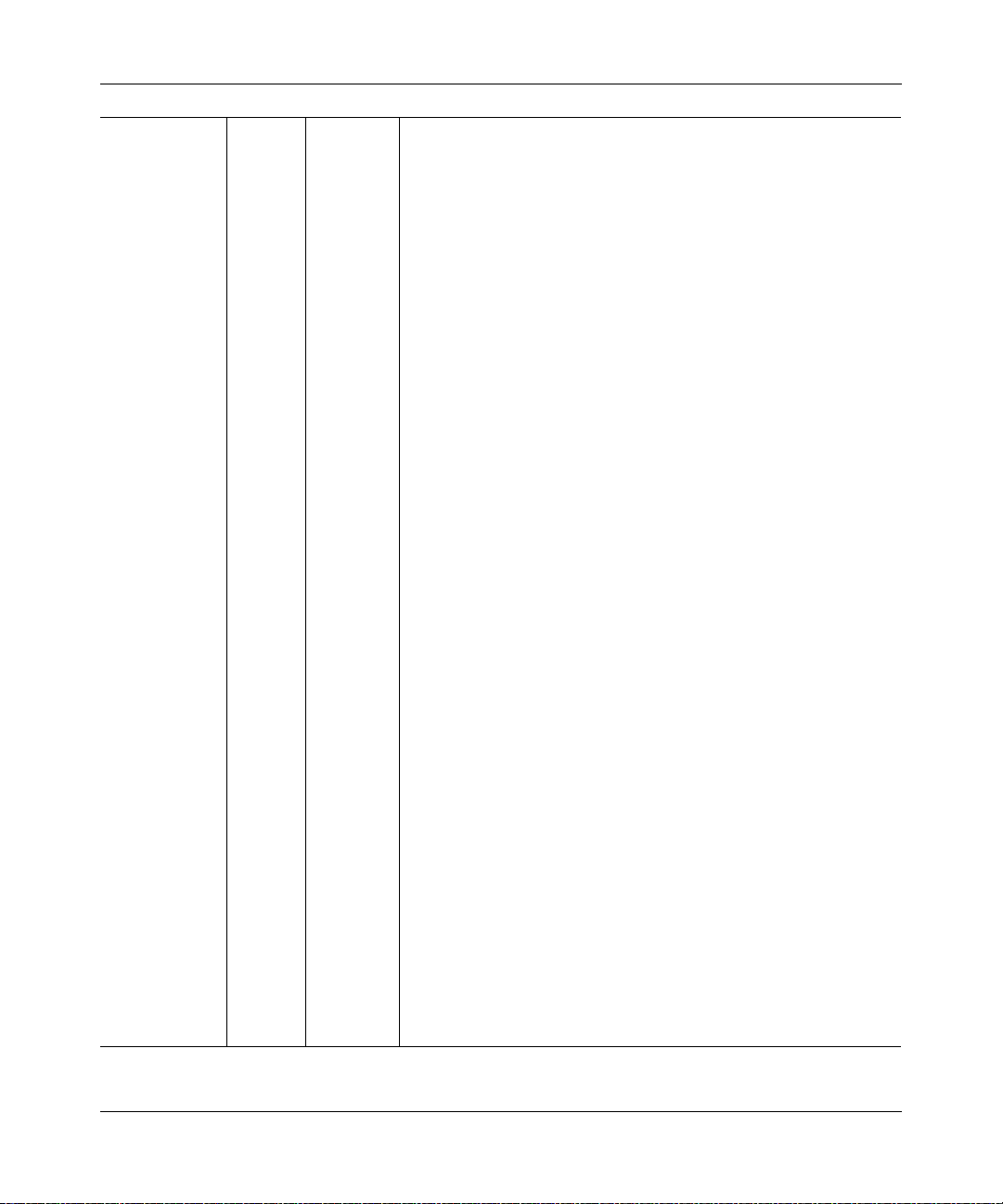
Table 1-1 describe s each item on the front panel and its operation.
Table 1-1. Object Descriptions
Object LED Activity Description
1.
Power LED
2.
Test LED
3,
WAN Ports and
LEDs
On (Green) Power is supplied to the VPN firewall.
Off Power is not supplied to the VPN firewall.
On (Amber) Test mode: The system is initializing or the initialization
has failed.
Blinking (Amber) Writing to Flash memory (during upgrading or resetting to
defaults).
Off The system has booted successfully.
Two RJ-45 WAN ports N-way automatic speed negotiation, Auto MDI/MDIX.
On (Green) The WAN port has detected a link with a connected
Link/Act
LED
100 LED
Blinking (Green) Data is being transmitted or received by the WAN port.
Off The WAN port has no link.
On (Green) The WAN port is operating at 100 Mbps.
Off The WAN port is operating at 10 Mbps.
Ethernet device.
1-6 Introduction
v1.0, January 2010
Page 23
ProSafe VPN Firewall 200 FVX538 Reference Manual
Table 1-1. Object Descriptions (continued)
Object LED Activity Description
On (Green) The WAN port has a valid Internet connection.
3,
WAN Ports and
LEDs
(continued)
4.
LAN Ports and
LEDs
5.
Gigabit Port and
LEDs
6.
Console Port
7.
Factory Defaults
Active
LED
8-port RJ-45 10/100 Mbps Fast Ethernet Switch N-way automatic speed negotiation,
auto MDI/MDIX.
Link/Act
LED
100 LED
DMZ LED
(port 8)
Gbit RJ-45 connector. Port for connecting to a Gigabit Ethernet device.
Link/Act
LED
Speed
LED
DB9 male connector.
Port for connecting to an optional console terminal. Default baud rate is 115.2K; pinouts:
(2) Tx, (3) Rx, (5) and (7) Gnd.
Push in with a sharp object
Factory Defaults reset push button (see Appendix A, “Default Settings and Technical
Specifications” for the factory defaults).
On (Amber) The Internet connection is down or not being used
because the port is available for failover in case the
connection on other WAN port fails.
Off The WAN port is either not enabled or has no link.
On (Green) The LAN port has detected a link with a connected
Ethernet device.
Blinking (Green) Data is being transmitted or received by the LAN port.
Off The LAN port has no link.
On (Green) The LAN port is operating at 100 Mbps.
Off The LAN port is operating at 10 Mbps.
On (Green) Port 8 is operating as a dedicated hardware DMZ port.
Off Port 8 is operating as a normal LAN port.
On (Green) The LAN port has detected a link with a connected
Ethernet device.
Blinking (Green) Data is being transmitted or received by the LAN port.
Off The LAN port has no link.
On (Green) The LAN port is operating at 1,000 Mbps.
On (Amber) The LAN port is operating at 100 Mbps.
Off The LAN port is operating at 10 Mbps.
Introduction 1-7
v1.0, January 2010
Page 24
ProSafe VPN Firewall 200 FVX538 Reference Manual
12
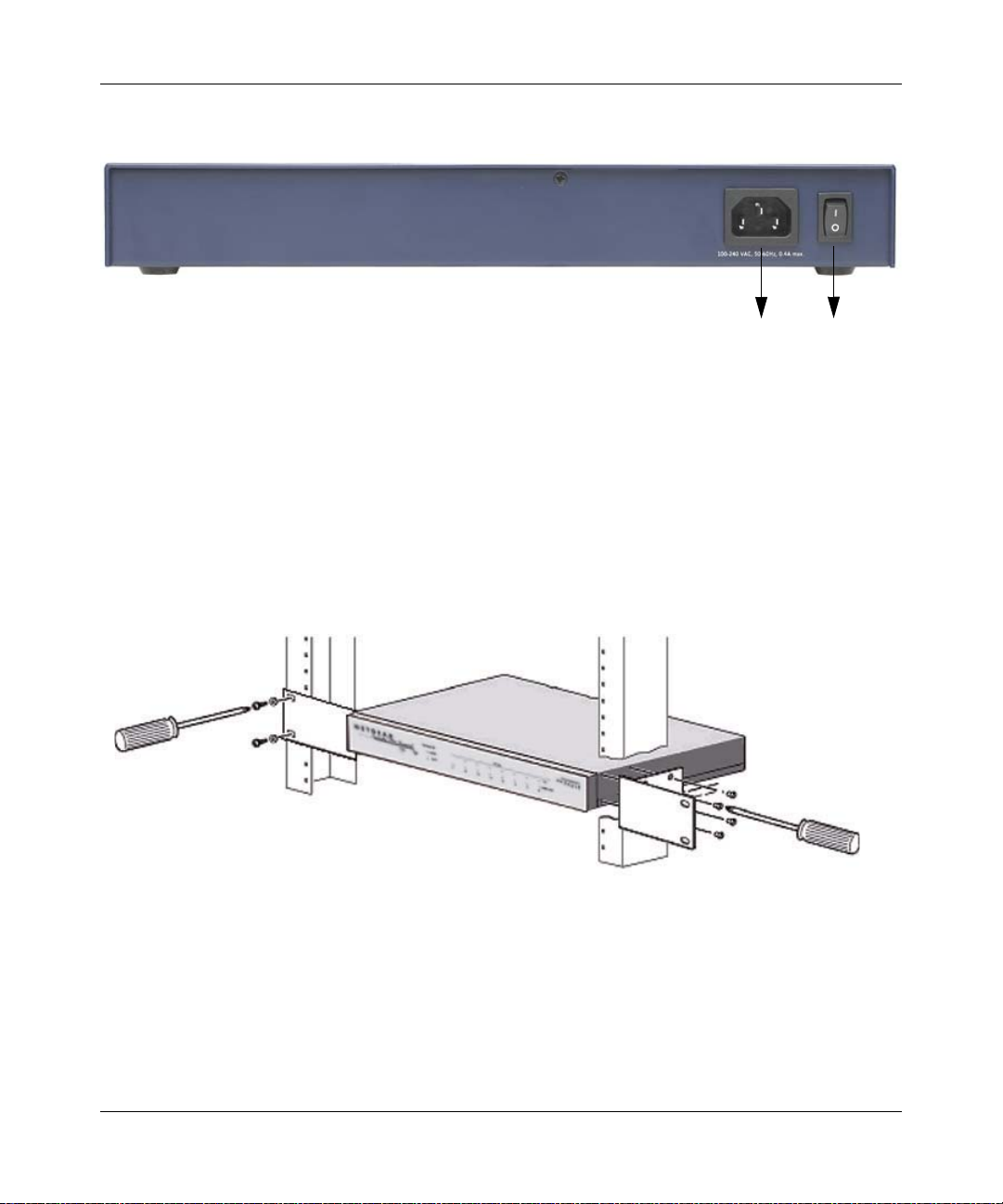
The rear panel of the FVX538 contains the On/Off switch and AC power connection.
Figure 1-2
Viewed from left to right, the rear panel contains the following elements:
1. AC power in
2. On/Off switch
Rack Mounting Hardware
The FVX538 can be mounted either on a desktop (using included rubber feet) or in a 19-inch rack
(using the included rack mounting hardware illustrated in Figure 1-3).
Figure 1-3
1-8 Introduction
v1.0, January 2010
Page 25
ProSafe VPN Firewall 200 FVX538 Reference Manual
LAN IP Address
User Name
Password
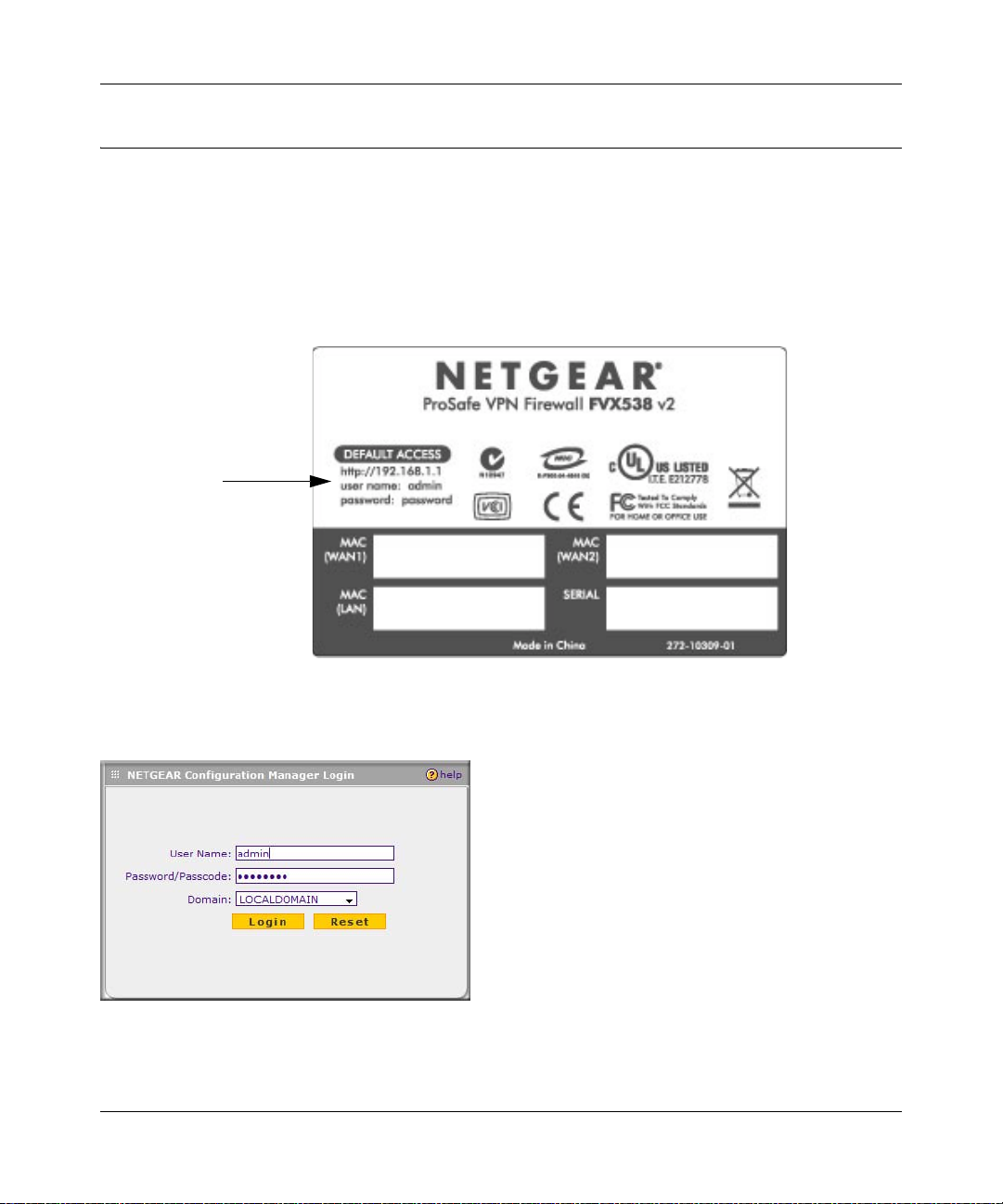
The VPN Firewall’s IP Address, Login Name, and Password
Check the label on the bottom of the FVX538’s enclosure if you forget the following factory
default information:
• IP Address: http://192.168.1.1 to reach the Web-based GUI from the LAN
• User name: admin
• Password: password
Figure 1-4
To log in to the FVX538 once it is connected, go to http://192.168.1.1.
Figure 1-5
Once the login screen displays, enter admin for the User Name and the password for Password.
Introduction 1-9
v1.0, January 2010
Page 26

ProSafe VPN Firewall 200 FVX538 Reference Manual
Qualified Web Browsers
To configure the FVX538, you must use a Web browser such as Microsoft Internet Explorer 6 or
higher, Mozilla Firefox 3 or higher, or Apple Safari 3 or higher with JavaScript, cookies, and you
must have SSL enabled.
1-10 Introduction
v1.0, January 2010
Page 27
Chapter 2
Connecting the VPN Firewall to the Internet
This section provides instructions for connecting the ProSafe VPN Firewall 200 FVX538,
including these topics:
• “Understanding the Connection Steps” on this page
• “Logging into the VPN Firewall” on page 2-2
• “Configuring the Internet Connections to Your ISPs” on page 2-2
• “Configuring the WAN Mode (Required for Dual WAN)” on page 2-7
• “Configuring Dynamic DNS (Optional)” on page 2-14
• “Configuring the Advanced WAN Options (Optional)” on page 2-16
Setting up VPN tunnels is covered in Chapter 5, “Virtual Private Networking.”
Understanding the Connection S teps
Typically, six steps are required to complete the basic Internet connection of your VPN firewall.
1. Connect the VPN firewall physically to your network. Connect the cables and restart your
network according to the instructions in the installation guide. See the Installation Guide,
FVX538 ProSafe VPN Firewall 200 for complete steps. A PDF of the Installation Guide is on
the NETGEAR website at: http://kbserver.netgear.com.
2. Log in to the VPN Firewall. After logging in, you are ready to set up and configure your
VPN firewall. You can also change your password and enable remote management at this
time. See “Logging into the VPN Firewall” on page 2-2.
3. Configure the Internet connections to your ISP(s). During this phase, you will connect to
your ISPs. See “Configuring the Internet Connections to Your ISPs” on page 2-2.
4. Configure the WAN mode (required for dual WAN operation). Select either dedicated
(single WAN) mode, auto-rollover mode, or load balancing mode. For load balancing, you can
also select any necessary protocol bindings. See “Configuring the WAN Mode (Required for
Dual WAN)” on page 2-7.
2-1
v1.0, January 2010
Page 28
ProSafe VPN Firewall 200 FVX538 Reference Manual
5. Configure dynamic DNS on the WAN ports (optional). Configure your fully qualified
domain names during this phase (if required). See “Configuring Dynamic DNS (Optional)” on
page 2-14.
6. Configure the WAN options (optional). Optionally, you can enable each WAN port to
respond to a ping, and you can change the factory default MTU size and port speed. However ,
these are advanced features and changing them is not usually required. See “Configuring the
Advanced WAN Options (Optional)” on page 2-16.
Each of these tasks is detailed separately in this chapter. The configuration of firewall and VPN
features is described in later chapters.
Logging into the VPN Firewall
To connect to the VPN firewall, your computer needs to be configured to obtain an IP address
automatically via DHCP. If you need instructions on how to configure you computer for DHCP,
refer to the “Preparing Your Network” document that you can access from the link in Appendix E,
“Related Documents.”
To log in to the VPN firewall:
1. Connect to the VPN firewall by typing http://192.168.1.1 in the address field of your browser.
2. When prompted, enter admin for the VPN firewall user name and password for the VPN
firewall password, both in lower case letters. (The VPN firewall user name and password are
not the same as any user name or password you may use to log in to your Internet connection.)
3. Click Login.
Note: You might want to enable remote management at this time so that you can log
in remotely in the future to manage the VPN firewall (see “Configuring an
External Server for Authentication” on page 6-11). If you enable remote
management, you are strongly advised to change your password (see
“Changing Passwords and Settings” on page 6-8).
Configuring the Internet Connections to Your ISPs
You should first configure your Internet connections to your ISPs on WAN port 1, and then on
WAN port 2.
2-2 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 29
ProSafe VPN Firewall 200 FVX538 Reference Manual
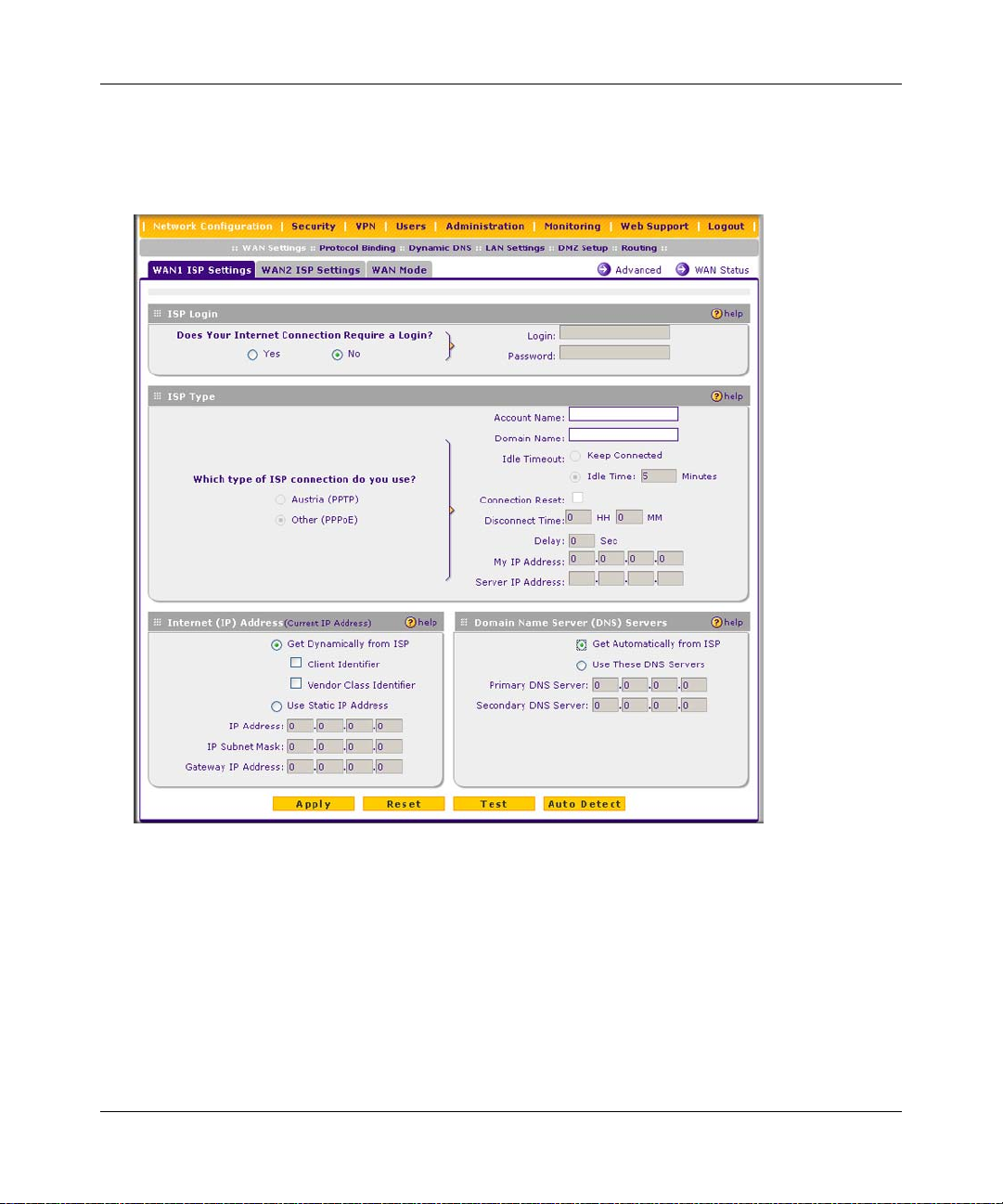
To automatically configure the WAN ports and connect to the Internet:
1. Select the primary menu option Network Configuration and the submenu option WAN
Settings. WAN1 ISP Settings screen will display.
Figure 2-1
2. Click Auto Detect at the bottom of the screen to automatically detect the type of Internet
connection provided by your ISP. Auto Detect will probe for different connection methods and
suggest one that your ISP will most likely support.
Connecting the VPN Firewall to the Internet 2-3
v1.0, January 2010
Page 30
ProSafe VPN Firewall 200 FVX538 Reference Manual
When Auto Detect successfully detects an active Internet service, it reports which connection
type it discovered. The options are described in Table 2-1.
Note: When you click Auto Detect while the WAN port already has a connection,
you might lose the connection because the VPN firewall will enter its
detection mode.
Table 2-1. Internet connection methods
Connection
Method
PPPoE Login (Username, Password); Account Name, Domain Name
PPTP Login (Username, Password), Account Name, Local IP address, and PPTP
DHCP (Dynamic IP) No data is required.
Fixed (Static) IP Static IP address, Subnet, and Gateway IP; and related data supplied by your
Data Required
Server IP address;
ISP.
If Auto Detect does not find a connection, you will be prompted to check the physical
connection between your VPN firewall and the cable or DSL line or to check your VPN
firewall’s MAC address (see “Setting the VPN Firewall’s MAC Address” on page 2-5).
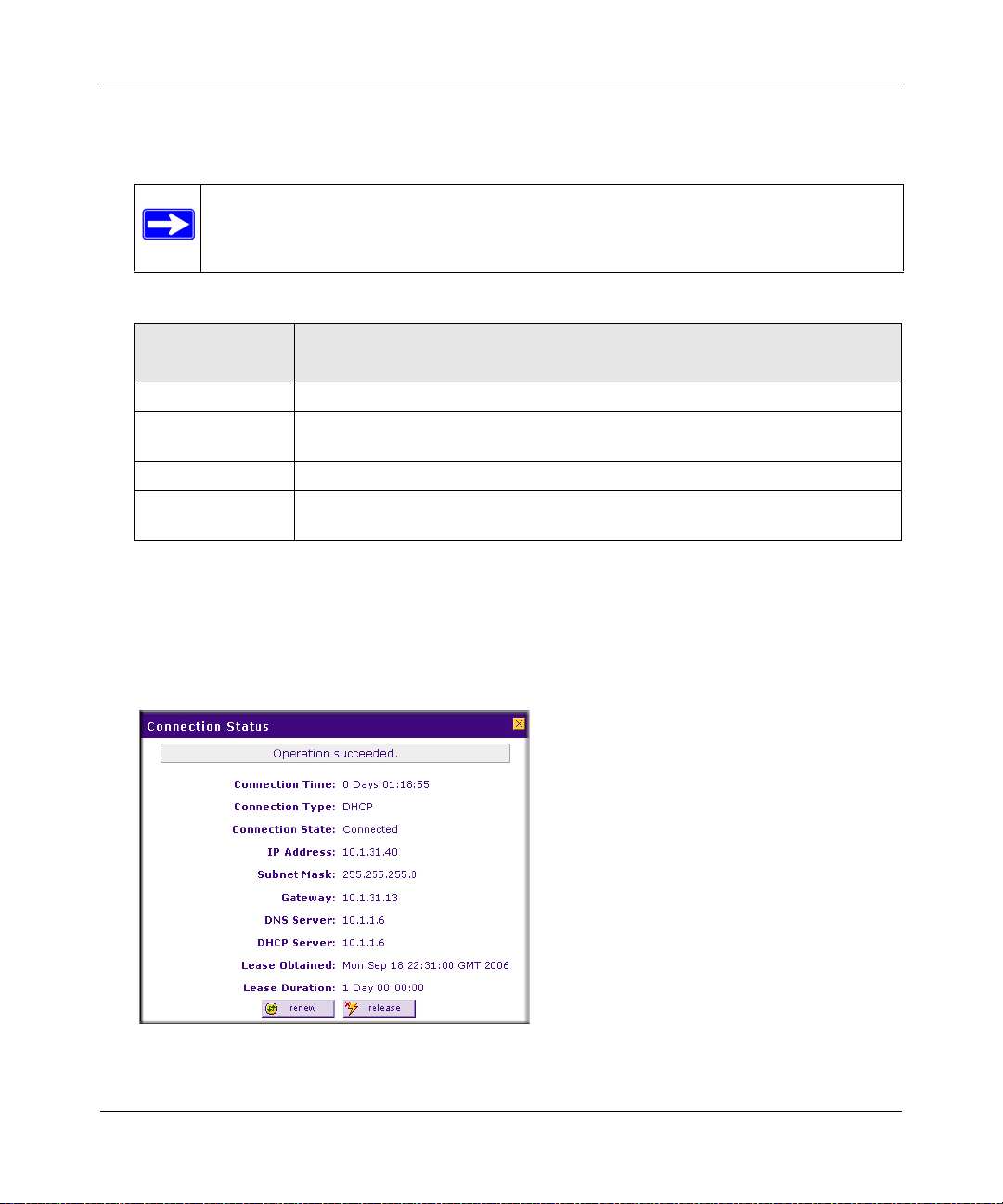
3. Click W AN Status at the top right of the screen to verify WAN Port 1 connection status. Click
Connect if there is no connection.
Figure 2-2
2-4 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 31

ProSafe VPN Firewall 200 FVX538 Reference Manual
4. Set up the traffic meter for WAN 1 ISP if desired. See “Enabling the Traffic Meter” on page 6-
27.
Note: At this point of the configuration process, you are now connected to the
Internet through WAN port 1. But you must continue with the configuration
process to get the complete functionality of the dual WAN interface.
The configure the WAN2 ISP settings:
1. Repeat the above steps to set up the para meters for WAN2 ISP. Start by selecting the WAN2
ISP Settings tab. Next click Auto Detect on the WAN2 ISP Settings screen and then verify
the connection by clicking the WAN Status link.
2. Set up the traffic meter for WAN2 ISP, if desired. See “Enabling the Traffic Meter” on page 6-
27.
Setting the VPN Firewall’s MAC Address
Each computer or router on your network has a unique 48-bit local Ethernet address. This is also
referred to as the computer's MAC (Media Access Control) address. The default is set to Use
Default Address. If your ISP requires MAC authentication and another MAC address has been
previously registered with your ISP, then you must enter that address. Setting the VPN firewall’s
MAC address is controlled through the Advanced options on the WAN1 ISP Settings and WAN2
ISP Settings screen (see“Configuring the Advanced WAN Options (Optional)” on page 2-16).
Manually Configuring Yo ur Internet Connection
If you know your ISP connection type, you can bypass the Auto Detect feature and connect your
VPN firewall manually . Ensure that you have all of the relevant connection information such as IP
Addresses, account information, type of ISP connection, etc., before you begin. Unless your ISP
automatically assigns your configuration automatically via DHCP, you will need the configuration
parameters from your ISP (see Figure 2-1 on page 2-3).
Note: To enable a WAN port to respond to a Ping from the Internet, use the Rules menu
(Figure 4-2 on page 4-9).
To manually configure your WAN1 ISP Settings:
1. Does your Internet connection require a login? If you need to enter login information every
time you connect to the Internet through your ISP, select Yes. Otherwise, select No.
Connecting the VPN Firewall to the Internet 2-5
v1.0, January 2010
Page 32

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. What type of IPS connection do you use? If your connection is PPPoE, PPTP or BigPond
Cable, then you must login. Check the Yes radio box. The text box fields that require data
entry will be highlighted, based on the connection that you selected. If your ISP has not
assigned any login information, then choose the No radio box and skip this section. For
example:
• PPTP: If your ISP is Austria Telecom or any other ISP that uses PPTP for login, select
this. Then, fill in the following highlighted fields:
– Account Name. (also known as Host Name or System Name): Enter the valid account
name for the PPTP connection (usually your e-mail “ID” assigned by your ISP). Some
ISPs require entering your full e-mail address here.
– Domain Name. Your domain name or workgroup name assigned by your ISP, or your
ISPs domain name. You may leave this field blank.
– Idle Timeout. Check the Keep Connected radio box to keep the connection always
on. To logout after the connection is idle for a period of time, select Idle Time and
enter the number of minutes to wait before disconnecting in the timeout field. This is
useful if your ISP charges you based on the amount of time you have logged in.
– My IP Address. IP address assigned by the ISP to make the connection with the ISP
server.
– Server IP Address. IP address of the PPTP server.
• Other (PPPoE): If you have installed login software such as WinPoET or Enternet, then
your connection type is PPPoE. Select this connection and configure the following fields:
– Account Name. Valid account name for the PPPoE connection
– Domain Name. Name of your ISPs domain or your domain name if your ISP has
assigned one. You may leave this field blank.
– Idle Timeout. Select Keep Connected, to keep the connection always on. To logout
after the connection is idle for a period of time, select Idle Time and enter the n umber
of minutes to wait before disconnecting, in the timeout field.
– Connection Reset. Select this checkbox to to specify a time when the PPPoE WAN
connection is reset, that is, the connection is disconnected momentarily and then reestablished. Enter the hour and minutes in the Disconnect Time fields to specify when
the connection should be disconnected. Enter the seconds in the Delay field to specify
the period after which the connection should be re-established.
2-6 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 33

ProSafe VPN Firewall 200 FVX538 Reference Manual
3. If your ISP has assigned a fixed (static or permanent) IP address, select the Use Static IP
Address radio box and fill in the following fields:
• IP Address. Static IP address assigned to you. This will i dentify the VPN firewal l to your
ISP.
• IP Subnet Mask. This is usually provided by the ISP or your network administrator.
• Gateway IP Address. IP address of the ISP’s gateway. This is usually provided by the ISP
or your network administrator.
If your ISP has not assigned a static IP address, select the Get Dynamically from ISP radio
box. The ISP will automatically assign an IP address to the VPN firewall using DHCP network
protocol.
4. If your ISP has not assigned any Domain Name Servers (DNS) addresses, select the Get
Automatically from ISP radio box. If your ISP has assigned DNS addresses, select the Use
These DNS Servers radio box. Ensure that you enter valid DNS server IP addresses in the
fields. Incorrect DNS entries may cause connectivity issues.
Note: Domain Name Servers (DNS) convert Internet names such as
www.google.com, www.netgear.com, etc. to Internet addresses called IP
addresses. Incorrect settings here will result in connectivity problems.
5. Click Apply to save the settings or click Reset to discard any changes and revert to the
previous settings.
6. Click Test to try and connect to the NE TGE AR website. If you connect successfully and your
settings work, then you may click Logout or go on and configure additional settings.
To configure your WAN2 ISP settings:
1. Select the WAN2 ISP Settings tab. The WAN2 ISP Settings screen will display.
2. Repeat steps 1 through 7 above.
Configuring the WAN Mode (Required for Dual WAN)
The dual WAN ports of the VPN firewall can be configured on a mutually exclusive basis for
either auto-rollover (for increased system reliability) or load balancing (for maximum bandwidth
efficiency).
Connecting the VPN Firewall to the Internet 2-7
v1.0, January 2010
Page 34

ProSafe VPN Firewall 200 FVX538 Reference Manual
The VPN firewall supports the following modes:
• Auto-Rollover Mode. In this mode, the selected WAN interface is made primary and the other
is the rollover link. As long as the primary link is up, all traffic is sent over the primary link.
Once the primary WAN interface goes down, the rollover link is brought up to send the traffic.
Traffic will automatically roll back to the original primary link once the original primary link
is back up and running again.
If you want to use a redundant ISP link for backup purposes, select the WAN port that will act
as the primary link for this mode. Ensure that the backup WAN port has also been configured
and that you configure the WAN Failure Detection Method to support Auto-Rollover.
• Load Balancing Mode. In this mode the VPN firewall distributes the outbound traffic equally
among the WAN interfaces that are functional.
Note: Scenarios could arise when load balancing needs to be bypassed for certain
traffic or applications. Here the traffic needs to go on a specific WAN
interface. This is done with the protocol binding rules of that WAN interface.
The rule should match the desired traffic.
For both alternatives, you must also set up Network Address Translation (NAT):
• NAT. NAT is the technology which allows all PCs on your LAN to share a single Internet IP
address. From the Internet, there is only a single device (the VPN firewall) and a single IP
address. PCs on your LAN can use any private IP address range, and these IP addresses are not
visible from the Internet.
– The VPN firewall uses NAT to select the correct PC (on your LAN) to receive any
incoming data.
– If you only have a single Internet IP address, you MUST use NAT.
NAT is the default setting.
• Classical Routing. In this mode, the VPN firewall performs routing, but without NAT . T o gain
Internet access, each PC on your LAN must have a valid Internet IP address.
If your ISP has allocated many IP addresses to you, and you have assigned one of these
addresses to each PC, you can choose Classical Routing. Or, you can use Classical Routing for
routing private IP addresses within a campus environment. Otherwise, selecting this method
will not allow Internet access through this VPN firewall.
To learn the status of the WAN ports, you can view the Router Status screen (see “Viewing the
VPN Firewall Configuration and System Status” on page 6-30) or look at the LEDs on the front
panel (see “VPN Firewall Front and Rear Panels” on page 1-6).
2-8 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 35

ProSafe VPN Firewall 200 FVX538 Reference Manual
Setting Up Auto-Rollover Mode
If you want to use a redundant ISP link for backup purposes, ensure that the backup WAN port has
already been configured. Then you select the WAN port that will act as the primary link for this
mode and configure the WAN Failure Detection Method to support Auto-Rollover.
When the VPN firewall is configured in Auto-Rollover mode, the VPN firewall uses the WAN
Failure Detection Method to check the connection of the primary link at regular intervals to
detect its status. Link failure is detected in one of the following ways:
• By using DNS queries to a DNS server, or
• By a Ping to an IP address.
For each WAN interfa ce, DNS queries or Ping requests are sent to the specified IP address. If
replies are not received, the corresponding WAN interface is considered down.
To configure the dual WAN ports for Auto-Rollover
1. Select Network Configuration from the primary menu and WAN Mode from the secondary
menu. The WAN Mode screen will display.
2. In the Port Mode section, check the Auto-Rollover Using WAN port radio box.
3. Selection the WAN port that will act as the primary link for this mode from the pull-down
menu.
4. From the WAN Failure detection Method section, select the detection failure method radio
box from one of the following choices:
• DNS lookup using configured DNS Servers (ISP DNS Servers). In this case, DNS
queries are sent to the DNS server configured on the WAN ISP screens (see “Configuring
the Internet Connections to Your ISPs” on page 2-2).
• DNS lookup using this DNS Server (for example, a public DNS Server). Enter any
public DNS server. DNS queries are sent to this server through the WAN interface being
monitored.
• Ping to this IP address. Enter a public IP address that will not reject the ping request or
will not consider the traffic abuse. Queries are sent to this server through the WAN
interface being monitored.
Connecting the VPN Firewall to the Internet 2-9
v1.0, January 2010
Page 36

ProSafe VPN Firewall 200 FVX538 Reference Manual
5. Enter a Test Period in seconds. DNS query is sent periodically after every test period. The
default test period is 30 seconds.
Figure 2-3
6. Enter the Maximum Fa ilover amount. The WAN interface is considered down after the
configured number of queries have failed to elicit a reply. The rollover link is brought up after
this. The Failover default is 4 failures.
The default time to roll over after the primary WAN interface fails is 2 minutes (a 30-second
minimum test period, times a minimum of 4 tests).
7. Click Apply to save your settings.
8. Click Reset to revert to the previous settings.
Once a rollover occurs, an alert will be generated (see “Activating Notification of Events and
Alerts” on page 6-23). When notified that the failed WAN interface has been restored, you can
force traffic back on the original primary WAN interface by reapplying the Auto-Rollover settings
in the WAN Port Mode menu.
2-10 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 37

ProSafe VPN Firewall 200 FVX538 Reference Manual
Setting Up Load Balancing
To use multiple ISP links simultaneously, select Load Balancing. In Load Balancing mode, both
links will carry data for the protocols that are bound to them. For example, if the HTTP protocol is
bound to WAN1 and the FTP protocol is bound to WAN2, then the VPN firewall will
automatically channel FTP data from and to the computers on the LAN through the WAN2 port.
All HTTP traffic will be routed through the WAN1 port.
Note: NETGEAR recommends that all specific traffic (for example, HTTP) be
configured for the WAN2 port. The only way to make certain traffic goes out one
port and all other traffic goes out the other port is to use WAN2 for specified
traffic.
Load Balancing can be used to segregat e traf fic betwee n links that ar e not of the same speed. High
volume traffic can be routed through the port connected to a high speed link and low volume
traffic can be routed through the port connected to the low speed link.
To configure the dual WAN ports for load balancing with protocol binding:
1. Check the Load Balancing radio button on the WAN Mode screen shown in Figure 2-3 on
page 2-10.
2. Click view protocol bindings (if protocol binding is needed). The WAN1 Protocol Bindings
screen will display.
Figure 2-4
Connecting the VPN Firewall to the Internet 2-11
v1.0, January 2010
Page 38

ProSafe VPN Firewall 200 FVX538 Reference Manual
3. Enter the following data in the Add Protocol Binding section:
a. Service – From the pu ll-down menu, select the desired Services or applications to be
covered by this rule. If the desired service or application does not appear in the list, you
must define it using the Services menu (see “Services-Based Rules” on page 4-3).
b. Destination Network – These settings determine which Internet locations are covered by
the rule, based on their IP address. Select the desired option:
• Any. All Internet IP address are covered by this rule.
• Single address. Enter the required address in the start fields.
• Address range. If this option is selected, you must enter the start and finish fields.
c. Source Network. These settings determine which computers on your network are affected
by this rule. Select the desired options:
• Any. All PCs and devices on your LAN.
• Single address. Enter the required address and the rule will be applied to that
particular PC.
• Address range. If this option is selected, you must enter the start and finish fields.
• Group 1-Group 8. If this option is selected, the devices assigned to this group will be
affected. (You may also assign a customized name to the group. See Edit Group
Names on the Groups and Hosts menu in the LAN Groups submenu.)
4. Click Add in the Add column adjacent to the rule. The new Protocol Binding Rule will be
enabled and added to the Protocol Binding Table for the WAN1 port.
Select the WAN2 Protocol Bindings tab, and repeat steps 1 through 9, to set protocol bindings
for the WAN2 port.
To Edit or Add additional Protocol Binding settings:
1. Select Network Configuration from the main menu and Protocol Binding from the
submenu. The WAN1 Protocol Bindings screen will display.
You can add or edit protocol bindings to either the WAN1 port or click the WAN2 Protocol
Bindings tab to access the WAN2 Protocol Bindings screen. To add a new protocol binding,
following the preceding procedure.
2. Check the radio button adjacent to the protocol binding rule you want to modify. Click Edit in
the Action column adjacent to the rule. The Edit Protocol Binding screen will display (see
Figure 2-5 on page 2-13).
2-12 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 39

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 2-5
3. Modify the parameters for the protocol binding service you selected.
4. Click Apply. The modified rule will be enabled and appear in the Protocol Binding table.
5. Click Reset to return to the previously configured settings.
Connecting the VPN Firewall to the Internet 2-13
v1.0, January 2010
Page 40

ProSafe VPN Firewall 200 FVX538 Reference Manual
Configuring Dynamic DNS (Optional)
Dynamic DNS (DDNS) is an Internet service that allows routers with varying public IP addresses
to be located using Internet domain names. To use DDNS, you must setup an account with a
DDNS provider such as DynDNS.org, TZO.com, Oray.net, or 3322.org. Links to DynDNS, TZO,
Oray, and 3322 are provided for your convenience on the Dynamic DNS Configuration screen.
The VPN firewall firmware includes software that notifies dynamic DNS servers of changes in the
WAN IP address, so that the services running on this network can be accessed by others on the
Internet.
If your network has a permanently assigned IP address, you can register a domain name and have
that name linked with your IP address by public Domain Name Servers (DNS). However, if your
Internet account uses a dynamically assigned IP address, you will not know in advance what your
IP address will be, and the address can change frequently—hence, the need for a commercial
DDNS service, which allows you to register an extension to its domain, and restores DNS requests
for the resulting FQDN to your frequently-changing IP address.
After you have configured your account information in the VPN firewall, whenever your
ISP-assigned IP address changes, your VPN firewall will automatically contact your DDNS
service provider, log in to your account, and register your new IP address.
• For auto-rollover mode, you will need a fully qualified domain name (FQDN) to implement
features such as exposed hosts and virtual private networks regardless of whether you have a
fixed or dynamic IP address.
• For load balancing mode, you may still need a fully qualified domain name (FQDN) either for
convenience or if you have a dynamic IP address.
Note: If your ISP assigns a private WAN IP address such as 192.168.x.x or 10.x.x.x, the
dynamic DNS service will not work because private addresses will not be routed
on the Internet.
To configure Dynamic DNS:
1. Select Network Configuration from the primary menu and Dynamic DNS from the
submenu. The Dynamic DNS Configuration screen will display (see Figure 2-6 on page 2-15).
The WAN Mode section displays the currently configured WAN mode (for example, Single
Port WAN1, Load Balancing or Auto Rollover). Only those options that match the configured
WAN Mode will be access ible.
2-14 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 41

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 2-6
2. Click the tab of the Dynamic DNS Service you want to enable. Each DNS service provider
requires registration and you then configure its parameters on the corresponding screen.
3. Access the website of one of the DDNS service providers and set up an account. A link to each
DDNS provider is to the right of the tabs.
4. After setting up your account, return to the Dynamic DNS Configuration screen and fill in the
required fields for the DDNS service you selected:
a. In the Host and Domain Name field, enter the entire FQDN name that your dynamic DNS
service provider gave you (for example: <yourname>.dyndns.org).
b. Enter the user name, user e-mail address, or account name requested by the DDNS Service
to identify you when logging into your DDNS account.
c. Enter the Password, or User Key, for your DDNS account.
Connecting the VPN Firewall to the Internet 2-15
v1.0, January 2010
Page 42

ProSafe VPN Firewall 200 FVX538 Reference Manual
d. If your dynamic DNS provider allows the use of wild cards in resolving your URL, you
may check the Use wildcards radio box to activate this feature.
For example, the wildcard feature will cause
the same IP address as
yourhost.dyndns.org
*.yourhost.dyndns.org to be aliased to
5. Click Apply to save your configuration.
6. Click Reset to return to the previous settings.
Configuring the Advanced WAN Options (Optional)
To configure the advanced WAN options:
1. Select Network Configuration from the primary menu and W AN Settings from the submenu.
The WAN Settings screen will display.
2. Click Advanced to access the WAN1 Advanced Options screen.
Figure 2-7
2-16 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 43

ProSafe VPN Firewall 200 FVX538 Reference Manual
3. Edit the default information you want to change.
• MTU Size. The normal MTU (Maximum Transmit Unit) value for most Ethernet
networks is 1500 Bytes, or 1492 Bytes for PPPoE connections. For some ISPs you may
have to reduce the MTU. But this is rarely required, and should not be done unless you are
sure it is necessary for your ISP connection.
• Port Speed. In most cases, your VPN firewall can automatically determine the connection
speed of the Internet (WAN) port. If you cannot establish an Internet connection and the
Internet LED blinks continuously, you may have to manually select the port speed.
AutoSense is the default.
If you know that the Ethernet port on your broadband modem supports 100BaseT, select
100BaseT Half_Duplex; otherwise, select 10BaseT Half_Duplex. Use the half-duplex
settings unless you are sure you need full duplex.
• Router's MAC Address. Each computer or router on your network has a unique 32-bit
local Ethernet address. This is also referred to as the computer's MAC (Media Access
Control) address. The default is Use Default Address. However, if your ISP requires
MAC authentication, then select either
– Use this Computer’s MAC address to enable the VPN firewall to use the MAC
address of the computer you are now using, or
– Use This MAC Address to manually type in the MAC address that your ISP expects.
The format for the MAC address is XX:XX:XX:XX:XX:XX (numbers 0-9 and either
uppercase or lowercase letters A-F). If you select Use This MAC Address and then type
in a MAC address, your entry will be overwritten.
Additional WAN Related Configuration
• If you want the ability to manage the VPN firewalll remotely, enable remote management at
this time (see “Enabling Remote Management Access” on page 6-14). If you enable remote
management, NETGEAR strongly recommends that you change your password (see
“Changing Passwords and Settings” on page 6-8).
• At this point, you can set up the traffic meter for each WAN, if desired. See “Enabling the
Traffic Meter” on page 6-27.
Connecting the VPN Firewall to the Internet 2-17
v1.0, January 2010
Page 44

ProSafe VPN Firewall 200 FVX538 Reference Manual
2-18 Connecting the VPN Firewall to the Internet
v1.0, January 2010
Page 45

Chapter 3
LAN Configuration
This chapter describes how to configure the advanced LAN features of your ProSafe VPN Firewall
200 FVX538, including the following sections:
• “Choosing the VPN Firewall DHCP Options” on this page
• “Managing Groups and Hosts (LAN Groups)” on page 3-6
• “Managing Groups and Hosts (LAN Groups)” on page 3-6
• “Configuring Multi Home LAN IP Addresses” on page 3-10
• “Configuring and Enabling the DMZ Port” on page 3-11
• “Configuring Static Routes” on page 3-14
• “Configuring Routing Information Protocol (RIP)” on page 3-16
Choosing the VPN Firewall DHCP Options
By default, the VPN firewall will function as a DHCP (Dynamic Host Configuration Protocol)
server, allowing it to assign IP, DNS server, WINS Server, and default gateway addresses to all
computers connected to the VPN firewall LAN. The assigned default gateway address is the LAN
address of the VPN firewall. IP addresses will be assigned to the attached PCs from a pool of
addresses that you must specify. Each pool address is tested before it is assigned to avoid duplicate
addresses on the LAN. The DHCP options are available for both the LAN and DMZ settings.
For most applications, the default DHCP and TCP/IP settings of the VPN firewall are satisfactory.
See the link to “TCP/IP Networking Basics” in Appendix E, “Related Documents for an
explanation of DHCP and information about how to assign IP addresses for your network.
If another device on your network will be the DHCP server, or if you will manually configure the
network settings of all of your computers, clear the Enable DHCP server radio box by selecting
the Disable DHCP Server radio box. Otherwise, leave it checked.
Specify the pool of IP addresses to be assigned by setting the starting IP address and ending IP
address. These addresses should be part of the same IP address subnet as the VPN firewall’s LAN
IP address. Using the default addressing scheme, you should define a range between 192.168.1.2
and 192.168.1.100, although you may wish to save part of the range for devices with fixed
addresses.
3-1
v1.0, January 2010
Page 46

ProSafe VPN Firewall 200 FVX538 Reference Manual
The VPN firewall will deliver the following parameters to any LAN device that requests DHCP:
• An IP address from the range that you have defined.
• Subnet mask.
• Gateway IP address (the VPN firewall’s LAN IP address).
• Primary DNS server (the VPN firewall’s LAN IP address).
• WINS server (if you entered a WINS server address in the DHCP section of the LAN Setup
screen).
• Lease time (date obtained and duration of lease).
DHCP Relay options allow you to make the VPN firewall a DHCP relay agent. The DHCP Relay
Agent makes it possible for DHCP broadcast messages to be sent over routers that do not support
forwarding of these types of messages. The DHCP Relay Agent is therefore the routing protocol
that enables DHCP clients to obtain IP addresses from a DHCP server on a remote subnet, or
which is not located on the local subnet. If you have no configured DHCP Relay Agent, your
clients would only be able to obtain IP addresses from the DHCP server which is on the same
subnet. T o enable clients to obtain IP addresses from a DHCP server on a remote subnet, you have
to configure the DHCP Relay Agent on the subnet that contains the remote clients, so that it can
relay DHCP broadcast messages to your DHCP server.
When the DNS Proxy option is enabled, the VPN firewallwill act as a proxy for all DNS requests
and communicate with the ISP’s DNS servers (as configured in the WAN settings screen). All
DHCP clients will receive the Primary/Secondary DNS IP along with the IP address where the
DNS proxy is running, that is, the VPN firewall’s LAN IP address. When disabled, all DHCP
clients will receive the DNS IP addresses of the ISP excluding the DNS proxy IP address. The
feature is particularly useful in Auto Rollover mode. For example, if the DNS servers for each
connection are different, then a link failure may render the DNS servers inaccessible. However,
when the DNS proxy is enabled, then clients can make requests to the VPN firewall and the VPN
firewall, in turn, sends those requests to the DNS servers of the active connection.
Configuring the LAN Setup Options
The LAN Setup screen allows configuration of LAN IP services such as DHCP and allows you to
configure a secondary or “multi-home” LAN IP setup in the LAN. The default values are suitable
for most users and situations. Disable the DNS Proxy if you are using a dual WAN co nfiguration
with route diversity and failover. These are advanced settings most usually configured by a
network administrator.
3-2 LAN Configuration
v1.0, January 2010
Page 47

ProSafe VPN Firewall 200 FVX538 Reference Manual
Note: If you enable the DNS Relay feature, you will not use the VPN firewall as a DHCP
server but rather as a DHCP relay agent for a DHCP server somewhere else on
your network.
To configure the LAN Setup options:
1. Select Network Configuration from the primary menu and LAN Settings from the submenu.
The LAN Setup screen will display .
Figure 3-1
2. In the LAN TCP/IP Setup section, configure the following settings:
• IP Address. The LAN address of your VPN firewall (factory default: 192.168.1.1).
LAN Configuration 3-3
v1.0, January 2010
Page 48

ProSafe VPN Firewall 200 FVX538 Reference Manual
Note: If you change the LAN IP address of the VPN firewall while connected
through the browser, you will be disconnected. You must then open a new
connection to the new IP address and log in again. For example, if you
change the default IP address 192.168.1.1 to 10.0.0.1, you must now enter
https://10.0.0.1 in your browser to reconnect to the Web Configuration
Manager.
• IP Subnet Mask. The subnet mask specifies the network number portion of an IP address.
Your VPN firewall will automatically calculate the subnet mask based on the IP address
that you assign. Unless you are implementing subnetting, use 255.255.255.0 as the subnet
mask. (Always make sure that the LAN Port IP address and DMZ port IP address are in
different subnets.)
3. In the DHCP section, select Disable DHCP Server, Enable DHCP Server, or DHCP Relay.
By default, the VPN firewall will function as a DHCP server, providing TCP/IP configuration
settings for all computers connected to the VPN firewall’s LAN. If another device on your
network will be the DHCP server, or if you will manually configure all devices, click Disable
DHCP Server. If the VPN firewall will function as a DHCP relay agent, select DHCP Relay
and enter the IP address of the DHCP relay gateway in the Relay Gateway field.
If the DHCP server is enabled, enter the following parameters:
• Domain Name. (Optional) The DHCP will assign the entered domain to DHCP clients.
• Starting IP Address. Specifies the first of the contiguous addresses in the IP address pool.
Any new DHCP client joining the LAN will be assigned an IP address between this
address and the Ending IP Address. The IP address 192.168.1.2 is the default start address.
• Ending IP Address. Specifies the last of the contiguous addresses in the IP address pool.
The IP address 192.168.1.100 is the default ending address.
Note: The starting and ending DHCP addresses should be in the same subnet as
the LAN IP address of the VPN firewall (the IP address that is configured
in the LAN TCP/IP Setup section of the LAN Setup screen).
• Primary DNS Server. (Optional) If an IP address is specified, the VPN firewall will
provide this address as the primary DNS server IP address. If no address is specified, the
VPN firewall will provide its own LAN IP address as the primary DNS server IP address.
• Secondary DNS Server. (Optional) If an IP address is specified, the VPN firewall will
provide this address as the secondary DNS server IP address.
3-4 LAN Configuration
v1.0, January 2010
Page 49

ProSafe VPN Firewall 200 FVX538 Reference Manual
• WINS Server. (Optional) Specifies the IP address of a local Windows NetBIOS Server if
one is present in your network.
• Lease Time. This specifies the duration for which IP addresses will be leased to clients.
If you will use a Lightweight Directory Access Protocol (LDAP) authentication server for
network-validated domain-based authentication, select Enable LDAP Information to enable
the DHCP server to provide LDAP server information. Enter the following parameters:
• LDAP Server. Specifies the name or the IP address of the device that hosts the LDAP
server.
• Search Base. Specifies the distinguished name (dn) at which to start the search, specified
as a sequence of relative distinguished names (rdn), connected with commas and without
any blank spaces. For most users, the search base is a variation of the domain name. For
example, if your domain is yourcompany.com, your search base dn might be as follows:
dc=yourcompany,dc=com.
• port. Specifies the port number that the LDAP server is using. Leave this field blank for
the default port.
4. In the Advanced Settings section, configure the following settings:
• Enable DNS Proxy. If the DNS proxy is enabled (which is the default setting), the DHCP
server will provide the VPN firewall’s LAN IP address as the DNS server for address
name resolution. If this box is unchecked, the DHCP server will provide the ISP’s DNS
server IP addresses. The VPN firewall will still service DNS requests sent to its LAN IP
address unless you disable DNS Proxy in the VPN firewall settings (see “Attack Checks”
on page 4-20).
• Enable ARP Broadcast. If ARP broadcast is enabled (which is the default setting), the
Address Resolution Protocol (ARP) is broadcasted on the LAN so that IP addresses can be
mapped to physical addresses (that is, MAC addresses).
5. Click Apply to save your settings or click Reset to discard any changes and revert to the
previous configuration.
Note: Once you have completed the LAN IP setup, all outbound traffic is allowed
and all inbound traffic is discarded. To change these traffic rules, refer to
Chapter 4, “Firewall Protection and Content Filtering.”
LAN Configuration 3-5
v1.0, January 2010
Page 50

ProSafe VPN Firewall 200 FVX538 Reference Manual
Managing Groups and Hosts (LAN Groups)
The Known PCs and Devices table on the Groups and Hosts screen contains a list of all known
PCs and network devices, as well as hosts, that are assigned dynamic IP addresses by this VPN
firewall. Collectively, these entries make up the Network Database.
The Network Database is updated by these methods:
• DHCP Client Requests. By default, the DHCP server in this VPN firewall is enabled, and
will accept and respond to DHCP client requests from PCs and other network devices. These
requests also generate an entry in the Network Database. Because of this, leaving the DHCP
Server feature (on the LAN screen) enabled is strongly recommended.
• Scanning the Network. The local network is scanned using standard methods such as ARP.
This will detect active devices which are not DHCP clients. However, sometimes the name of
the PC or device cannot be accurately determined, and will be shown as Unknown.
• Manual Entry. You can manually enter information about a network device.
Creating the Network Database
Some advantages of the Network Database are:
• Generally, you do not need to enter either IP address or MAC addresses. Instead, you can just
select the desired PC or device.
• No need to reserve an IP address for a PC in the DHCP Server. All IP address assignments
made by the DHCP Server will be maintained until the PC or device is removed from the
database, either by expiry (inactive for a long time) or by you.
• No need to use a fixed IP address on PCs. Because the address allocated by the DHCP Server
will never change, you do not need to assign a fixed IP address to a PC to ensure it always has
the same IP address.
• MAC level control over PCs. The Network Database uses the MAC address to identify each
PC or device. So changing a PC’s IP address does not affect any restrictions on that PC.
• Group and individual control over PCs.
– You can assign PCs to groups and apply restrictions to each group using the Firewall
Rules screen (see “Using Rules to Block or Allow Specific Kinds of Traffic” on page 4-2).
– You can also select the groups to be covered by the Block Sites feature (see “Blocking
Internet Sites (Content Filtering)” on page 4-30).
3-6 LAN Configuration
v1.0, January 2010
Page 51

ProSafe VPN Firewall 200 FVX538 Reference Manual
– If necessary, you can also create firewall rules to apply to a single PC (see “Configuring
Source MAC Filtering” on page 4-33). Because the MAC address is used to identify each
PC, users cannot avoid these restrictions by changing their IP address.
• A computer is identified by its MAC address—not its IP address. Hence, changing a
computer’s IP address does not affect any restrictions applied to that PC.
Viewing the Network Database
To view the Network Database, follow these steps:
1. Select Network Configuration from the primary menu and LAN Settings from the submenu.
The LAN Setup screen will display .
2. Click the LAN Groups tab. The LAN Groups screen will display.
Figure 3-2
The Known PCs and Devices table lists the entries in the Network Database. For each computer
or device, the following fields are displayed:
• Name. The name of the computer or device. Computers that do not support the NetBIOS
protocol will be listed as Unknown. In this case, the name can be edited manually for easier
management. If the computer was assigned an IP address by the DHCP server, then an asterisk
is be appended to the name.
• IP Address. The current IP address of the computer. For DHCP clients of the VPN firewall,
this IP address will not change. If a computer is assigned a static IP address, you must to
update this entry manually when the IP address of the computer changes.
LAN Configuration 3-7
v1.0, January 2010
Page 52

ProSafe VPN Firewall 200 FVX538 Reference Manual
• MAC Address. The MAC address of the computer’s network interface.
• Group. Each PC or device can be assigned to a single group. By default, a computer is
assigned to the first group (Group 1). To change the group assignment by selecting the Edit
link in the Action column.
• Action/Edit. Allows modification of the selected entry.
Adding Devices to the Network Database
To add devices manually to the Network Database:
1. To add computers to the network database manually, fill in the following fields:
• Name: The name of the PC or device.
• IP Address Type. From the pull-down menu, choose how this device receives its IP
address:
– Select Fixed (Set on PC) if the IP address is statically assigned on the computer.
– Select Reserved (DHCP Client) to direct the VPN firewall to reserve the IP address
for allocation by the DHCP server (see “Setting Up DHCP Address Reservation” on
page 3-9).
Note: When assigning a reserved IP address to a client, the IP address selected
must be outside the range of addresses allocated to the DHCP server pool.
• IP Address. The IP address that this computer or device is assigned. If the IP Address
Type is Reserved (DHCP Client), the VPN firewall will reserve the IP address for the
associated MAC address.
• MAC Address. The MAC address of the computer’s network interface. The MAC
address format is six colon-separated pairs of hexadecimal characters (0-9 and A-F), such
as 01:23:45:67:89:AB.
• Group. The group to which the computer has to be assigned. (Group 1 is the default
group.)
2. Click Add to add the new entry to the network database.
3. As an optional step: To enable DHCP address reservation for the entry that you just added to
the Known PCs and Devices table, select the checkbox for the table entry and click Save
Binding to bind the IP address to the MAC address for DHCP assignment.
3-8 LAN Configuration
v1.0, January 2010
Page 53

ProSafe VPN Firewall 200 FVX538 Reference Manual
Changing Group Names in the LAN Groups Database
By default, the LAN Groups are named Group1 through Group8. You can rename these group
names to be more descriptive, such as Engineering or Marketing.
To edit the names of any of the eight available groups:
1. From the LAN Groups screen, click the Edit Group Names link to the right of the tabs. The
Network Database Group Names screen appears.
Figure 3-3
2. Select the radio button next to any group name to make that name active for editing.
3. Type a new name in the field.
4. Select and edit other group names if desired.
5. Click Apply to save your settings.
Setting Up DHCP Address Reservation
When you specify a reserved IP address for a device on the LAN (based on the MAC address of
the device), that computer or device will always receive the same IP address each time it accesses
the VPN firewall’s DHCP server. Reserve d IP addresses should be assigned to servers or access
points that require permanent IP settings. The Reserved IP address that you select must be outside
of the DHCP Server pool.
LAN Configuration 3-9
v1.0, January 2010
Page 54

ProSafe VPN Firewall 200 FVX538 Reference Manual
To reserve an IP address, manually enter the device on the LAN Groups screen, specifying
Reserved (DHCP Client), as described in “Adding Devices to the Network Database” on page 3-
8.
Note: The reserved address will not be assigned until the next time the PC contacts the
VPN firewall's DHCP server. Reboot the PC or access its IP configuration and
force a DHCP release and renew.
Configuring Multi Home LAN IP Addresses
If you have computers on your LAN using different IP address ranges (for example, 172.16.2.0 or
10.0.0.0), you can add “aliases” to the LAN port, giving computers on those networks access to the
Internet through the VPN firewall. This allows the VPN firewall to act as a gateway to additional
logical subnets on your LAN. You can assign the VPN firewall an IP address on each additional
logical subnet.
To add a secondary LAN IP address:
1. Select Network Configuration from the primary menu and LAN Settings from the submenu.
The LAN Setup screen will display .
2. Click the LAN Multi-homing tab. The LAN Multi-homing screen will display.
Figure 3-4
The Available Secondary LAN IPs table lists the secondary LAN IP addresses added to the
VPN firewall.
3-10 LAN Configuration
v1.0, January 2010
Page 55

ProSafe VPN Firewall 200 FVX538 Reference Manual
• IP Address. The IP address alias added to the LAN port of the VPN firewall. This is the
gateway for computers that need to access the Internet.
• Subnet Mask. IPv4 Subnet Mask.
• Action. The Edit link allows you to make changes to the selected entry.
• Select All. Selects all the entries in the Available Secondary LAN IPs table.
• Delete. Deletes selected entries from the Available Secondary LAN IPs table.
3. Type in the IP Address and the Subnet Mask in the respective text fields.
4. Click Add. The Secondary LAN IP address will be added to the Secondary LAN IPs table.
Note: Additional IP addresses cannot be configured in the DHCP server. The hosts on the
secondary subnets must be manually configured with the IP addresses, gateway IP
and DNS server IPs.
Warning: Make sure the secondary IP addresses are different from the LAN, WAN,
DMZ, and any other subnet attached to this VPN firewall.
For example:
WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0
WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0
DMZ IP address: 192.168.10.1 with subnet 255.255.255.0
LAN IP address: 192.168.1.1 with subnet 255.255.255.0
Secondary LAN IP: 192.168.20.1 with subnet 255.255.255.0
Configuring and Enabling the DMZ Port
The De-Militarized Zone (DMZ) is a network which, when compared to the LAN, has fewer
firewall restrictions, by default. This zone can be used to host servers (such as a web server, ftp
server, or e-mail server, for example) and give public access to them. The eighth LAN port on the
VPN firewall can be dedicated as a hardware DMZ port for safely providing services to the
Internet, without compromising security on your LAN.
The DMZ port feature is also helpful when using some online games and videoconferencing
applications that are incompatible with NAT. The VPN firewall is programmed to recognize some
of these applications and to work properly with them, but there are other applications that may not
function well. In some cases, local PCs can run the application properly if those PCs are used on
the DMZ port.
LAN Configuration 3-11
v1.0, January 2010
Page 56

ProSafe VPN Firewall 200 FVX538 Reference Manual
Note: A separate firewall security profile is provided for the DMZ port that is hardware
independent of the standard firewall security used for the LAN.
The DMZ Setup screen allows you to set up the DMZ port. It permits you to enable or disable the
hardware DMZ port (LAN port 8, see “VPN Firewall Front and Rear Panels” on page 1-6) and
configure an IP address and Mask for the DMZ port.
To enable and configure the DMZ port:
1. From the main menu, select Network Configuration and then select DMZ Setup from the
submenu. The DMZ Setup screen will display.
2. Check the Do you want to enable DMA Port? radio box.
3. Enter an IP address and the subnet mask for the DMZ port. Make sure that the DMZ port IP
address and LAN Port IP address are in different subnets (for example, an address outside the
LAN Address pool, such as 192.168.1.101).
Figure 3-5
3-12 LAN Configuration
v1.0, January 2010
Page 57

ProSafe VPN Firewall 200 FVX538 Reference Manual
If desired, select Enable DHCP Server, which will provide TCP/IP configuration for all
computers connected to the VPN firewall’s DMZ network. If another device on your DMZ
network will be the DHCP server, or if you will manually configure all devices, leave the
Disable DHCP Server radio box selected, which is the default setting.
If the DHCP server is enabled, enter the following parameters:
• Domain Name. (Optional) The DHCP will assign the entered domain to DHCP clients.
• Starting IP Address. Specifies the first of the contiguous addresses in the IP address pool.
Any new DHCP client joining the LAN will be assigned an IP address between this
address and the Ending IP Address. The IP address 192.168.1.2 is the default start address.
• Ending IP Address. Specifies the last of the contiguous addresses in the IP address pool.
The IP address 192.168.1.100 is the default ending address.
Note: The Starting and Ending DHCP addresses should be in the same subnet as
the LAN IP address of the VPN firewall (the IP Address configured in the
LAN TCP/IP Setup section).
• Primary DNS Server. (Optional) If an IP address is specified, the VPN firewall will
provide this address as the primary DNS server IP address. If no address is specified, the
VPN firewall will provide its own LAN IP address as the primary DNS server IP address.
• Secondary DNS Server. (Optional) If an IP address is specified, the VPN firewall will
provide this address as the secondary DNS server IP address.
• WINS Server. (Optional) Specifies the IP address of a local Windows NetBIOS Server if
one is present in your network.
• Lease Time. This specifies the duration for which IP addresses will be leased to clients.
If you will use a Lightweight Directory Access Protocol (LDAP) authentication server for
network-validated domain-based authentication, select Enable LDAP Information to enable
the DHCP server to provide LDAP server information. Enter the following parameters:
• LDAP Server. Specifies the name or the IP address of the device that hosts the LDAP
server.
• Search Base. Specifies the distinguished name (dn) at which to start the search, specified
as a sequence of relative distinguished names (rdn), connected with commas and without
any blank spaces. For most users, the search base is a variation of the domain name. For
example, if your domain is yourcompany.com, your search base dn might be as follows:
dc=yourcompany,dc=com.
LAN Configuration 3-13
v1.0, January 2010
Page 58

ProSafe VPN Firewall 200 FVX538 Reference Manual
• port. Specifies the port number that the LDAP server is using. Leave this field blank for
the default port.
4. In the Advanced Settings section, select Enable DNS Proxy if you want to enabled the DNS
proxy , which is the default setting. The DHCP server will provide the VPN firewall’s LAN IP
address as the DNS server for address name resolution. If this box is unchecked, the DHCP
server will provide the ISP’s DNS server IP addresses. The VPN firewall will still service
DNS requests sent to its LAN IP address unless you disable DNS Proxy in the VPN firewall’s
settings (see “Attack Checks” on page 4-20).
5. Click Apply to save your settings or click Reset to discard any changes and revert to the
previous configuration. The DMZ LED next to LAN port 8 (see “VPN Firewall Front and
Rear Panels” on page 1-6) will light up indicating that the DMZ port has been enabled.
To define the DMZ WAN Rules and LAN DMZ Rules, see “Configuring DMZ WAN Rules” on
page 4-12 and “Configuring LAN DMZ Rules” on page 4-13, respectively.
Configuring Static Routes
Static Routes provide additional routing information to your VPN firewall. Under normal
circumstances, the VPN firewall has adequate routing information after it has been configured for
Internet access, and you do not need to configure additional static routes. You should configure
static routes only for unusual cases such as multiple firewalls or multiple IP subnets located on
your network.
To add or edit a static route:
1. Select Network Configuration from the main menu and Routing from the submenu. The
Routing screen will display.
Figure 3-6
3-14 LAN Configuration
v1.0, January 2010
Page 59

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. Click Add. The Add Static Route screen will display.
Figure 3-7
3. Enter a route name for this static route in the Route Name field (for identification and
management).
4. Select Active to make this route effective.
5. Select Private if you want to limit access to the LAN only. The static route will not be
advertised in RIP.
6. Enter the destination IP Address to the host or network to which the route leads.
7. Enter the IP subnet mask for this destination. If the destination is a single host, enter
255.255.255.255.
8. Select the ph ysical network interface (WAN1, WAN2, or LAN) through which this route is
accessible.
9. Enter the gateway IP a ddress through which the destination host or network can be reached
(must be a device on the same LAN segment as the VPN firewall).
10. Enter the metric priority for this route. If multiple routes to the same destination exit, the route
with the lowest metric is chosen. (value must be between 1 and 15),
11. Click Reset to discard any changes and revert to the previous settings or click Apply to save
your settings.
The new static route will be added to Static Routes table.
You can edit the route’s settings by clicking Edit in the Action column adjacent to the route.
LAN Configuration 3-15
v1.0, January 2010
Page 60

ProSafe VPN Firewall 200 FVX538 Reference Manual
Static Route Example
For example, you may require a static route if:
• You r primary Internet access is through a cable modem to an ISP.
• You have an ISDN firewall on your home network for connecting to the company where you
are employed. This firewall’s address on your LAN is 192.168.1.100.
• You r company’s network is 134.177.0.0.
When you first configured your VPN firewall, two implicit static routes were created. A default
route was created with your ISP as the gateway, and a second static route was created to your local
network for all 192.168.1.x addresses. With this configuration, if you attempt to access a device on
the 134.177.0.0 network, your VPN firewall will forward your request to the ISP. The ISP
forwards your request to the company where you are employed, and the request will likely be
denied by the company’s firewall.
In this case you must define a static route, telling your VPN firewall that 134.177.0.0 should be
accessed through the ISDN firewall at 192.168.1.100.
In this example:
• The Destination IP Address and IP Subnet Mask fields specify that this static route applies to
all 134.177.x.x addresses.
• The Gateway IP Address fields specifies that all traffic for these addresses should be
forwarded to the ISDN firewall at 192.168.1.100.
• A Metric value of 1 will work since the ISDN firewall is on the LAN.
• Private is selected only as a precautionary security measure in case RIP is activated.
Configuring Routing Information Protocol (RIP)
RIP (Routing Information Protocol, RFC 2453) is an Interior Gateway Protocol (IGP) that is
commonly used in internal networks (LANs). It allows a router to exchange its routing information
automatically with other routers, and allows it to dynamically adjust its routing tables and adapt to
changes in the network. RIP is disabled by default.
To configure RIP:
1. Select Network Configuration from the main menu and Routing from the submenu. The
Routing screen will display (see Figure 3-6 on page 3-14).
3-16 LAN Configuration
v1.0, January 2010
Page 61

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. Click RIP Configuration link to the right of the Routing tab. The RIP Configuration screen
will display.
Figure 3-8
3. From the RIP Direction pull-down menu, select the direction in which the VPN firewall will
send and receives RIP packets. The choices are:
• None. The VPN firewall neither broadcasts its route table nor does it accept any RIP
packets from other routers. This effectively disables RIP.
• Both. The VPN firewall broadcasts its routing table and also processes RIP information
received from other routers.
• Out Only. The VPN firewall broadcasts its routing table periodically but does not accept
RIP information from other routers.
• In Only. The VPN firewall accepts RIP information from other routers, but does not
broadcast its routing table.
4. From the RIP Version pull-down menu, select the version:
• Disabled. The default section disables RIP versions.
• RIP-1. A class-based routing that does not include subnet information. This is the most
commonly supported version.
LAN Configuration 3-17
v1.0, January 2010
Page 62

ProSafe VPN Firewall 200 FVX538 Reference Manual
• RIP-2. This includes all the functionality of RIPv1 plus it supports subnet information.
Though the data is sent in RIP-2 format for both RIP-2B and RIP-2M, the modes in which
packets are sent are different.
– RIP-2B. Sends the routing data in RIP-2 format and uses subnet broadcasting.
– RIP-2M. Sends the routing data in RIP-2 format and uses multicasting.
5. Authentication for RIP2B/2M required? If you selected RIP-2B or RIP-2M, check the Yes
radio box to enable authentication, and enter the MD-5 keys to authenticate between devices in
the First Key Parameters and Second Key Parameters sections on the screen.
6. Click Reset to discard any changes and revert to the previous settings or click Apply to save
your settings.
3-18 LAN Configuration
v1.0, January 2010
Page 63

Chapter 4
Firewall Protection and Content Filtering
This chapter describes how to use the content filtering features of the ProSafe VPN Firewall 200
FVX538 to protect your network.
This chapter includes the following sections:
• “About Firewall Protection and Content Filtering” on this page
• “Using Rules to Block or Allow Specific Kinds of Traffic” on page 4-2
• “Configuring Other Firewall Features” on page 4-19
• “Creating Services, QoS Profiles, and Bandwidth Profiles” on page 4-24
• “Setting a Schedule to Block or Allow Specific Traffic” on page 4-29
• “Blocking Internet Sites (Content Filtering)” on page 4-30
• “Configuring Source MAC Filtering” on page 4-33
• “Configuring IP/MAC Address Binding” on page 4-35
• “Configuring Port Triggering” on page 4-37
• “Administrator Tips” on page 4-40
About Firewall Protection and Content Filtering
The VPN firewall provides you with Web content filtering options, plus browsing activity
reporting and instant alerts via e-mail. Parents and network administrators can establish restricted
access policies based on time-of-day, Web addresses and Web address keywords. You can also
block Internet access by applications and services, such as chat or games.
A firewall is a special category of router that protects one network (the “trusted” network, such as
your LAN) from another (the untrusted network, such as the Internet), while allowing
communication between the two. You can further segment keyword blocking to certain known
groups (see “Managing Groups and Hosts (LAN Groups)” on page 3-6 to set up LAN Groups).
A firewall incorporates the functions of a NAT (Network Address Translation) router, while
adding features for dealing with a hacker intrusion or attack, and for controlling the types of traffic
that can flow between the two networks. Unlike simple Internet sharing NAT routers, a firewall
uses a process called stateful packet inspection to protect your network from attacks and
4-1
v1.0, January 2010
Page 64

ProSafe VPN Firewall 200 FVX538 Reference Manual
intrusions. NAT performs a very limited stateful inspection in that it considers whether the
incoming packet is in response to an outgoing request, but true Stateful Packet Inspection goes far
beyond NAT.
Using Rules to Block or Allow Specific Kinds of Traffic
This section includes the following topics:
• “Services-Based Rules” on this page
• “Viewing Rules and Order of Precedence for Rules” on page 4-7
• “Configuring LAN WAN Rules” on page 4-9
• “Configuring DMZ WAN Rules” on page 4-12
• “Configuring LAN DMZ Rules” on page 4-13
• “Inbound Rules Examples” on page 4-15
• “Outbound Rules Example” on page 4-19
Firewall rules are used to block or allow specific traffic passing through from one side to the other.
You can configure up to 600 rules on the VPN firewall. Inbound rules (WAN to LAN) restrict
access by outsiders to private resources, selectively allowing only specific outside users to access
specific resources. Outbound rules (LAN to WAN) determine what outside resources local users
can have access to.
A firewall has two default rules, one for inbound traffic and one for outbound. The default rules of
the VPN firewall are:
• Inbound. Block all access from outside except responses to requests from the LAN side.
• Outbound. Allow all access from the LAN side to the outside.
The firewall rules for blocking/allowing traffic on the VPN firewall can be applied to LAN/WAN
traffic, DMZ/WAN traffic and LAN/DMZ traffic.
Table 4-1. Supported FIrewall Rule Configurations
Traffic Rule Outbound Rules Inboun d Ru les
LAN WAN 50 50
DMZ WAN 50 50
LAN DMZ 50 50
4-2 Firewall Protection and Content Filtering
v1.0, January 2010
Page 65

ProSafe VPN Firewall 200 FVX538 Reference Manual
Services-Based Rules
The rules to block traffic are based on the traffic’s category of service.
• Outbound Rules (service blocking). Outbound traffic is normally allowed unless the VPN
firewall is configured to disallow it.
• Inbound Rules (port forwarding). Inbound traffic is normally blocked by the VPN firewall
unless the traffic is in response to a request from the LAN side. The VPN firewall can be
configured to allow this otherwise blocked traffic.
• Customized Services. Additional services can be added to the list of services in the factory
default list. These added services can then have rules defined for them to either allow or block
that traffic (see “Adding Customized Services” on page 4-24).
• Quality of Service (QoS) priorities. Each service has its own native priority that impacts its
quality of performance and tolerance for jitter or delays. You can change the QoS priority
which will change the traffic mix through the system (see “Specifying Quality of Service
(QoS) Priorities” on page 4-26).
Outbound Rules (Service Blocking)
The VPN firewall allows you to block the use of certain Internet services by PCs on your network.
This is called service blocking or port filtering.
Note: See “Configuring Source MAC Filtering” on page 4-33 for yet another way to
block outbound traffic from selected PCs that would otherwise be allowed by the
VPN firewall.
Table 4-2. Outbound Rules
Item Description
Service Select the desired service or application to be covered by this rule. If the desired service
or application does not appear in the list, you must define it using the Services menu (see
“Adding Customized Services” on page 4-24).
Action Select the desired action for outgoing connections covered by this rule:
• BLOCK always
• BLOCK by schedule, otherwise Allow
• ALLOW always
• ALLOW by schedule, otherwise Block
Note: Any outbound traffic that is not blocked by rules you create will be allowed by the
default rule.
ALLOW rules are only useful if the traffic is already covered by a BLOCK rule. That is,
you wish to allow a subset of traffic that is currently blocked by another rule.
Firewall Protection and Content Filtering 4-3
v1.0, January 2010
Page 66

ProSafe VPN Firewall 200 FVX538 Reference Manual
Table 4-2. Outbound Rules (continued)
Item Description
Select Schedule Select the desired time schedule (Schedule1, Schedule2, or Schedule3) that will be used
by this rule.
• This pull-down menu gets activated only when “BLOCK by schedule, otherwise Allow”
or “ALLOW by schedule, otherwise Block” is selected as Action.
• Use schedule screen to configure the time schedules (see “Setting a Schedule to Block
or Allow Specific Traffic” on page 4-29).
LAN Users These settings determine which computers on your network are affected by this rule.
Select the desired options:
• Any – All PCs and devices on your LAN.
• Single address – Enter the required address and the rule will be applied to that
particular PC.
• Address range – If this option is selected, you must enter the start and finish fields.
• Groups – Select the Group to which this rule will apply. Use the LAN Groups screen
(under Network Configuration) to assign PCs to Groups. See “Managing Groups and
Hosts (LAN Groups)” on page 3-6.
WAN Users These settings determine which Internet locations are covered by the rule, based on their
IP address. Select the desired option:
• Any – All Internet IP address are covered by this rule.
• Single address – Enter the required address in the start field.
• Address range – If this option is selected, you must enter the start and end fields.
DMZ Users These settings determine which DMZ computers on the DMZ network are affected by this
rule. Select the desired options.
• Any – All PCs and devices on your DMZ network.
• Single address – Enter the required address and the rule will be applied to that
particular PC on the DMZ network.
• Address range – If this option is selected, you must enter the start and finish fields of
the DMZ computers.
QoS Priority Specifies the priority of a service which, in turn, determines the quality of that service for
the traffic passing through the VPN firewall. By default, the priority shown is that of the
selected service. The user can change it accordingly. If the user does not make a
selection (leaves it as Normal-Service), then the native priority of the service will be
applied to the policy. See “Specifying Quality of Service (QoS) Priorities” on page 4-26.
Log This determines whether packets covered by this rule are logged. Select the desired
action:
• Always – always log traffic considered by this rule, whether it matches or not. This is
useful when debugging your rules.
• Never – never log traffic considered by this rule, whether it matches or not.
4-4 Firewall Protection and Content Filtering
v1.0, January 2010
Page 67

Table 4-2. Outbound Rules (continued)
Item Description
ProSafe VPN Firewall 200 FVX538 Reference Manual
Bandwidth
Profile
NAT IP Specifies whether the source IP address of the outgoing packets should be the WAN
NAT Single IP Is
On (interface)
Bandwidth Limiting determines the way in which the data is sent to/from your host. The
purpose of bandwidth limiting is to provide a solution for limiting the outgoing/incoming
traffic, thus preventing the LAN users for consuming all the bandwidth of our internet link.
Bandwidth Limiting for outbound traffic will be done on the available WAN interface in the
single port and Auto-Failover modes. The limiting will be done on the user-specified
interface in Load Balancing mode. The bandwidth limiting for inbound traffic will be done
on the LAN interface for all WAN modes. Bandwidth Limiting will not apply to the DMZ
interface. See “Creating Bandwidth Profiles” on page 4-27.
interface address or a specified address, which should belong to the WAN subnet.
Specifies to which WAN interface the NAT IP address belongs. All outgoing packets will
be routed through the specified WAN interface only.
Inbound Rules (Port Forwarding)
Because the VPN firewall uses Network Address Translation (NAT), your network presents only
one IP address to the Internet and outside users cannot directly address any of your local
computers. However, by defining an inboun d rule you can make a local server (for example, a Web
server or game server) visible and available to the Internet. The rule tells the VPN firewall to direct
inbound traffic for a particular service to one local server based on the destination port number.
This is also known as port forwarding.
Whether or not DHCP is enabled, how the PCs will access the server’s LAN address impacts the
inbound rules. For example:
• If your external IP address is assigned dynamically by your ISP (DHCP enabled), the IP
address may change periodically as the DHCP lease expires. Consider using dynamic DNS so
that external users can always find your network (see “Configuring Dynamic DNS (Optional)”
on page 2-14).
• If the IP address of the local server PC is assigned by DHCP, it may change when the PC is
rebooted. To avoid this, use the Reserved IP address feature to keep the PC’s IP address
constant (see “Setting Up DHCP Address Reservation” on page 3-9).
• Local PCs must access the local server using the PCs’ local LAN address. Attempts by local
PCs to access the server using the external WAN IP address will fail.
Note: See “Configuring Port Triggering” on page 4-37 for yet another way to allow
certain types of inbound traffic that would otherwise be blocked by the VPN
firewall.
Firewall Protection and Content Filtering 4-5
v1.0, January 2010
Page 68

ProSafe VPN Firewall 200 FVX538 Reference Manual
Table 4-3. Inbound Rules
Item Description
Services Select the desired service or application to be covered by this rule. If the desired service
or application does not appear in the list, you must define it using the Services screen
(see “Adding Customized Services” on page 4-24).
Action Select the desired action for packets covered by this rule:
• BLOCK always
• BLOCK by schedule, otherwise Allow
• ALLOW always
• ALLOW by schedule, otherwise Block
Note: Any inbound traffic which is not allowed by rules you create will be blocked by the
Default rule.
Select Schedule Select the desired time schedule (that is, Schedule1, Schedule2, or Schedule3) that will
be used by this rule (see “Setting a Schedule to Block or Allow Specific Traffic” on page 4-
29).
• This pull-down menu gets activated only when “BLOCK by schedule, otherwise Allow”
or “ALLOW by schedule, otherwise Block” is selected as Action.
• Use the schedule screen to configure the time schedules.
Send to LAN
Server
Send to DMZ
Server
Translate to Port
Number
WAN
Destination IP
Address
LAN Users These settings determine which computers on your network are affected by this rule.
WAN Users These settings determine which Internet locations are covered by the rule, based on their
This field appears only with NAT routing (not classical routing). This LAN address or
range of LAN addresses determines which computer or computers on your network are
hosting this service rule. (You can also translate these addresses to a port number.)
The DMZ server address determines which computer on your network is hosting this
service rule. (You can also translate this address to a port number.)
Check the “Translate to Port Number” and enter a port number if you want to assign the
LAN Server to a specific port.
This setting determines the destination IP address applicable to incoming traffic.
This is the public IP address that will map to the internal LAN server; it can either be the
address of the WAN1 or WAN2 ports or another public IP address
Select the desired options:
• Any – All PCs and devices on your LAN.
• Single address – Enter the required address and the rule will be applied to that
particular PC.
• Address range – If this option is selected, you must enter the start and finish fields.
• Groups – Select the Group to which this rule will apply. Use the LAN Groups screen
(under Network Configuration) to assign PCs to Groups. See “Managing Groups and
Hosts (LAN Groups)” on page 3-6.
IP addresses. Select the desired option:
• Any – All Internet IP address are covered by this rule.
• Single address – Enter the required address in the start field.
• Address range – If this option is selected, you must enter the start and end fields.
.
4-6 Firewall Protection and Content Filtering
v1.0, January 2010
Page 69

ProSafe VPN Firewall 200 FVX538 Reference Manual
Table 4-3. Inbound Rules (continued)
Item Description
Log This determines whether packets covered by this rule are logged. Select the desired
action:
• Always – Always log traffic considered by this rule, whether it matches or not. This is
useful when debugging your rules.
• Never – Never log traffic considered by this rule, whether it matches or not.
Bandwidth
Profile
Bandwidth Limiting determines the way in which the data is sent to/from your host. The
purpose of bandwidth limiting is to provide a solution for limiting the outgoing/incoming
traffic, thus preventing the LAN users for consuming all the bandwidth of our internet link.
Bandwidth Limiting for outbound traffic will be done on the available WAN interface in the
single port and Auto-Failover modes. The limiting will be done on the user-specified
interface in Load Balancing mode. The bandwidth limiting for inbound traffic will be done
on the LAN interface for all WAN modes. Bandwidth Limiting will not apply to the DMZ
interface. See “Creating Bandwidth Profiles” on page 4-27.
Note: Some residential broadband ISP accounts do not allow you to run any server
processes (such as a Web or FTP server) from your location. Your ISP may
periodically check for servers and may suspend your account if it discovers any
active services at your location. If you are unsure, refer to the Acceptable Use
Policy of your ISP.
Remember that allowing inbound services opens holes in your VPN firewall. Only enable those
ports that are necessary for your network. It is also advisable to turn on the server application
security and invoke the user password or privilege levels, if provided.
Viewing Rules and Order of Precedence for Rules
To view the firewall rules, select Security from the main menu and Firewall from the submenu.
The LAN WAN Rules screen appears (Figure 4-1 on page 4-8 shows some examples). As you
define new rules, they are added to the tables in the Rules menu as the last item in the list.
Firewall Protection and Content Filtering 4-7
v1.0, January 2010
Page 70

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-1
For LAN WAN rules, DMZ WAN rules, and LAN DMZ rules, for any traffic attempting to pass
through the VPN firewall, the packet information is subjected to the rules in the order shown in the
Outbound Services and Inbound Services rules tables rules tables, beginning at the top and
proceeding to the bottom. In some cases, the order of precedence of two or more rules may be
important in determining the disposition of a packet. For example, you should place the most strict
rules at the top (those with the most specific services or addresses). The up and down button
allows you to relocate a defined rule to a new position in the table (see below).
To make changes to an existing outbound or inbound service rule on the the LAN WAN Rules,
DMZ WAN Rules, or LAN DMZ Rules screen, in the Action column to the right of to the rule,
click on of the following table buttons:
• edit. Allows you to make any changes to the rule definition of an existing rule. Depending on
your selection, either an Edit Outbound Service screen or Edit Inbound Service screen
displays, containing the data for the selected rule.
• up. Moves the rule up one position in the table rank.
• down. Moves the rule down one position in the table rank.
To enable, disable, or delete one or more rules on the LAN WAN Rules, DMZ WAN Rules, or
LAN DMZ Rules screen:
1. Select the checkbox to the left of the rule that you want to delete or disable or click the select
all table button to select all rules.
4-8 Firewall Protection and Content Filtering
v1.0, January 2010
Page 71

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. Click one of the following table buttons:
• enable. Enables the rule or rules. The “!” status icon changes from a grey circle to a green
circle, indicating that the rule is or rules are enabled. (By default, when a rule is added to
the table, it is automatically enabled.)
• disable. Disables the rule or rules. The “!” status icon changes from a green circle to a
grey circle, indicating that the rule is or rules are disabled.
• delete. Deletes the rule or rules.
To add a new rule, click Add. For more information, see “Configuring LAN WAN Rules” on this
page, “Configuring DMZ WAN Rules” on page 4-12, and “Configuring LAN DMZ Rules” on
page 4-13.
Configuring LAN WAN Rules
The default outbound policy is to allow all traffic to the Internet to pass through. Firewall rules can
then be applied to block specific types of traffic from going out from the LAN to the Internet
(outbound). The default policy of Allow Always can be changed to block all outbound traffic
which then allows you to enable only specific services to pass through the VPN firewall.
To change the default outbound policy:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
Figure 4-2
2. Change the Default Outbound Policy by selecting Block Always from the pull-down menu.
Firewall Protection and Content Filtering 4-9
v1.0, January 2010
Page 72

ProSafe VPN Firewall 200 FVX538 Reference Manual
3. Click Apply.
LAN WAN Outbound Services Rules
You may define rules that will specify exceptions to the default rules. By adding custom rules, you
can block or allow access based on the service or application, source or destination IP addresses,
and time of day. The outbound rule will block the selected application from any internal IP LAN
address to any external WAN IP address according to the schedule created in the Schedule menu.
You can also tailor these rules to your specific needs (see “Administrator Tips” on page 4-40).
Note: This feature is for advanced administrators only! Incorrect configuration will cause
serious problems.
To create a new LAN WAN outbound service rule:
1. In the LAN WAN Rules screen, click Add under the Outbound Services table. The A dd LAN
WAN Outbound Service screen will display...
Figure 4-3
2. Configure the parameters based on the descriptions in Table 4-2 on page 4-3.
4-10 Firewall Protection and Content Filtering
v1.0, January 2010
Page 73

ProSafe VPN Firewall 200 FVX538 Reference Manual
3. Click Apply to save your changes and reset the fields on this screen. The new rule will be
listed in the Outbound Services table.
LAN WAN Inbound Services Rules
This Inbound Services table lists all existing rules for inbound traf fic. If you have not defined any
rules, no rules will be listed. By default, all inbound traffic is blocked. Remember that allowing
inbound services opens holes in your VPN firewall. Only enable those ports that are necessary for
your network.
To create a new LAN WAN inbound service rule:
1. In the LAN WAN Rules screen, click Add under the Inbound Services table. The Add LAN
WAN Inbound Service screen will display.
Figure 4-4
2. Configure the parameters based on the descriptions in Table 4-3 on page 4-6.
3. Click Apply to save your changes and reset the fields on this screen. The new rule will be
listed in the Inbound Services table.
Firewall Protection and Content Filtering 4-11
v1.0, January 2010
Page 74

ProSafe VPN Firewall 200 FVX538 Reference Manual
Configuring DMZ WAN Rules
The firewall rules for traffic between the DMZ and the WAN/Internet are configured on the DMZ
WAN Rules screen. The Default Outbound Policy is to allow all traffic from and to the Internet to
pass through. Firewall rules can then be applied to block specific types of traffic from either going
out from the DMZ to the Internet (outbound) or coming in from the Internet to the DMZ
(inbound). The default outbound policy can be changed to block all outbound traffic and enable
only specific services to pass through the VPN firewall by adding an outbound services rule.
To create a new DMZ WAN outbound service policy:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
2. Select the DMZ WAN Rules tab. The DMZ WAN Rules screen will display.
Figure 4-5
3. Click Add under the Outbound Services table. The Add DMZ WAN Outbound Services
screen will display (see Figure 4-6 on page 4-13).
4-12 Firewall Protection and Content Filtering
v1.0, January 2010
Page 75

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-6
4. Configure the parameters based on the descriptions in Table 4-2 on page 4-3.
5. Click Apply. The new rule will appear in the Outbound Services table. The rule is
automatically enabled.
The procedure to add a new DMZ WAN inbound service policy is similar to the procedure
described above with the exception that you click Add under the Inbound Services table, you
configure the parameters based on the descriptions in Table 4-3 on page 4-6, and the policy is
added to the Inbound Services table.
Configuring LAN DMZ Rules
The LAN DMZ Rules screen allows you to create rules that define the movement of traffic
between the LAN and the DMZ. The Default Outbound and Inbound Policies is to allow all traffic
between the local LAN and DMZ network. Firewall rules can then be applied to block specific
types of traffic from either going out from the LAN to the DMZ (outbound) or coming in from the
DMZ to the LAN (inbound).
To create a new LAN DMZ outbound service policy:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
Firewall Protection and Content Filtering 4-13
v1.0, January 2010
Page 76

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. Select the LAN DMZ Rules tab. The LAN DMZ Rules screen will display.
Figure 4-7
3. Click Add under the Outbound Services Table. The Add LAN DMZ Outb ound Service screen
will display.
Figure 4-8
4. Configure the parameters based on the descriptions in Table 4-2 on page 4-3.
5. Click Apply. The new rule will appear in the Outbound Services table. The rule is
automatically enabled.
4-14 Firewall Protection and Content Filtering
v1.0, January 2010
Page 77

ProSafe VPN Firewall 200 FVX538 Reference Manual
The procedure to add a new LAN DMZ inbound service policy is sim ilar to the procedure
described above with the exception that you click Add under the Inbound Services table, you
configure the parameters based on the descriptions in Table 4-3 on page 4-6, and the policy is
added to the Inbound Services table.
Inbound Rules Examples
LAN WAN Inbound Rule: Hosting a Local Public Web Server
If you host a public W eb ser ver on your local network, you can define a rule to allow inbound Web
(HTTP) requests from any outside IP address to the IP address of your Web server at any time of
day.
Figure 4-9
Firewall Protection and Content Filtering 4-15
v1.0, January 2010
Page 78

ProSafe VPN Firewall 200 FVX538 Reference Manual
LAN WAN Inbound Rule: Allowing Videoconference from Restricted Addresses
If you want to allow incoming videoconferencing to be initiated from a restricted range of outside
IP addresses, such as from a branch office, you can create an inbound rule.
Figure 4-10
In the example, CU-SeeMe connections are allowed only from a specified range of external IP
addresses.
LAN WAN or DMZ WAN Inbound Rule: Setting Up One-to-One NAT Mapping
If you arrange with your ISP to have more than one public IP address for your use, you can use the
additional public IP addresses to map to servers on your LAN or DMZ. One of these public IP
addresses will be used as the primary IP address of the VPN firewall. This address will be used to
provide Internet access to your LAN PCs through NAT. The other addresses are available to map
to your servers.
In the example shown in Figure 4-11 on page 4-17, we have configured multi-NAT to support
multiple public IP addresses on one WAN interface. The inbound rule instructs the VPN firewall
to host an additional public IP address (10.1.0.5) and to associate this address with the W eb server
on the LAN (at 192.168.1.1). We also instruct the VPN firewall to translate the incoming HTTP
port number (port 80) to a different port number (port 8080).
4-16 Firewall Protection and Content Filtering
v1.0, January 2010
Page 79

Figure 4-11
ProSafe VPN Firewall 200 FVX538 Reference Manual
The following addressing scheme is used in this example:
• VPN firewall FVX538
– WAN1 primary public IP address: 10.1.0.1
– WAN1 additional public IP address: 10.1.0.5
– LAN IP address 192.168.1.1
• Web server PC on the VPN firewall’s LAN
– LAN IP address: 192.168.1.11
– Port number for Web service: 8080
To test the connection from a PC on the WAN side, type http://10.1.0.5. The home page of the
Web server should appear.
LAN WAN or DMZ WAN Inbound Rule: Specifying an Exposed Host
Specifying an exposed host allows you to set up a computer or server that is available to anyone on
the Internet for services that you have not yet defined.
Firewall Protection and Content Filtering 4-17
v1.0, January 2010
Page 80

ProSafe VPN Firewall 200 FVX538 Reference Manual
1. Select Any and Allow Always (or Allow by Schedule)
2. Place rule below all other inbound rules
To expose one of the PCs on your LAN or DMZ as this host:
1. Create an inbound rule that allows all protocols.
2. Place the rule below all other inbound rules.
Note: For security, NETGEAR strongly recommends that you avoid creating an exposed
host. When a computer is designated as the exposed host, it loses much of the
protection of the firewall and is exposed to many exploits from the Internet. If
compromised, the computer can be used to attack your network.
Figure 4-12
4-18 Firewall Protection and Content Filtering
v1.0, January 2010
Page 81

ProSafe VPN Firewall 200 FVX538 Reference Manual
Outbound Rules Example
Outbound rules let you prevent users from using applications such as Instant Messenger, Real
Audio or other non-essential sites.
LAN WAN Outbound Rule: Blocking Instant Messenger
If you want to block Instant Messenger usage by employees during working hours, you can create
an outbound rule to block that application from any internal IP address to any external address
according to the schedule that you have created in the Schedule menu.
Figure 4-13
You can also have the VPN firewall log any attempt to use Instant Messenger during that blocked
period.
Configuring Other Firewall Features
You can configure attack checks, set session limits, and manage the Application Level Gateway
(ALG) for SIP sessions.
Firewall Protection and Content Filtering 4-19
v1.0, January 2010
Page 82

ProSafe VPN Firewall 200 FVX538 Reference Manual
Attack Checks
The Attack Checks screen allows you to specify whether or not the VPN firewall should be
protected against common attacks in the DMZ, LAN and WAN networks. To enable the
appropriate attack checks for your environment:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
2. Click the Attack Checks tab. The Attack Checks screen will display.
Figure 4-14
3. Check the boxes for the Attack Checks you wish to monitor. The various types of attack
checks are listed and defined below.
4. Click Apply to save your settings.
The various types of attack checks listed on the Attack Checks screen are:
• WAN Security Checks
– Respond To Ping On Internet Ports. By default, the VPN firewall responds to an ICMP
Echo (ping) packet coming from the Internet or WAN side. Responding to a ping can be a
useful diagnostic tool when there are connectivity problems. If the ping option is enabled,
you can allow either any IP address or a specific IP address only to respond to a ping. You
can disable the ping option to prevent hackers from easily discovering the VPN firewall
via a ping.
4-20 Firewall Protection and Content Filtering
v1.0, January 2010
Page 83

ProSafe VPN Firewall 200 FVX538 Reference Manual
– Enable Stealth Mode. In stealth mode, the VPN firewall will not respond to port scans
from the WAN or Internet, which makes it less susceptible to discovery and attacks.
– Block TCP Flood. A SYN flood is a form of denial of service attack in which an attacker
sends a succession of SYN requests to a target system. When the system responds, the
attacker does not complete the connection, thus saturating the server with half-open
connections. No legitimate connections can then be made.
When blocking is enabled, the VPN firewall will limit the lifetime of partial connections
and will be protected from a SYN flood attack.
• LAN Security Checks
– Block UDP flood. A UDP flood is a form of denial of service attack in which the
attacking machine sends a large number of UDP packets to random ports to the victim
host. As a result, the victim host will check for the application listening at that port, see
that no application is listening at that port, and reply with an ICMP Destination
Unreachable packet.
When the victimized system is flooded, it is forced to send many ICMP packets,
eventually making it unreachable by other clients. The attacker may also spoof the IP
address of the UDP packets, ensuring that the excessive ICMP return packets do not reach
him, making the attacker’s network location anonymous.
If flood checking is enabled, the VPN firewall will not accept more than 20 simultaneous,
active UDP connections from a single computer on the LAN.
– Disable Ping Reply on LAN Ports. To prevent the VPN firewall from responding to ping
requests from the LAN, click this checkbox.
• VPN Pass through. When the VPN firewall functions in NAT mode, all packets going to the
Remote VPN Gateway are first filtered through NAT and then encrypted per the VPN policy.
If a VPN client or gateway on the LAN side of the VPN firewall wants to connect to another
VPN endpoint on the WAN, with the VPN firewall between the two VPN end points, all
encrypted packets will be sent to the VPN firewall. Since the VPN firewall filters the
encrypted packets through NAT, the packets become invalid.
IPSec, PPTP, and L2TP represent different types of VPN tunnels that can pass through the
VPN firewall. T o allow the VPN traffic to pass through without filtering, enable those options
for the type of tunnel(s) that will pass through the VPN firewall.
Firewall Protection and Content Filtering 4-21
v1.0, January 2010
Page 84

ProSafe VPN Firewall 200 FVX538 Reference Manual
Setting Session Limits
Session Limit allows you to specify the total number of sessions allowed, per user, over an IP
(Internet Protocol) connection across the VPN firewall. This feature is enabled on the Session
Limit screen and shown below in Figure 4-15. Session Limit is disabled by default.
To set session limits:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
2. Click the Session Limit tab. The Session Limit screen will display..
Figure 4-15
3. Click the Yes radio button under Do you want to enable Session Limit?
4. From the User Limit Parameter pull-down menu, define the maximum number of sessions
per IP either as a percentage of maximum sessions or as an absolute.
The percentage is computed on the total connection capacity of the device.
5. Enter the User Limit. If the User Limit Parameter is set to Percentage of Max Sessions, this
is the maximum number of sessions allowed from a single source machine as a percentage of
the total connection capacity. (Session Limit is per machine based.) Otherwise, if the User
Limit Parameter is set to Number of Sessions, the user limit is an absolute value.
4-22 Firewall Protection and Content Filtering
v1.0, January 2010
Page 85

ProSafe VPN Firewall 200 FVX538 Reference Manual
Note: Some protocols (such as FTP or RSTP) create two sessions per connection
which should be considered when configuring Session Limiting.
The Total Number of Packets Dropped due to Session Limit field shows total number of
packets dropped when session limit is reached.
6. In the Session Timeout section, modify the TCP, UDP and ICMP timeout values as you
require. A session will expire if no data for the session is received for the duration of the
timeout value. The default timeout values are 1200 seconds for TCP sessions, 180 seconds for
UDP sessions, and 8 seconds for ICMP sessions.
7. Click Apply to save your settings.
Managing the Application Level Gateway for SIP Sessions
The Application Level Gateway (ALG) facilitates multimedia sessions such as voice over IP
(VoIP) sessions that use the Session Initiation Protocol (SIP) across the firewall and provides
support for multiple SIP clients. ALG support for SIP is disabled by default.
To enable ALG for SIP:
1. Select Security from the main menu and Firewall Rules from the submenu. The LAN WAN
Rules screen will display.
2. Click the Advanced tab. The Advanced screen will display.
Figure 4-16
3. Select the Enable SIP ALG checkbox.
4. Click Apply to save your settings.
Firewall Protection and Content Filtering 4-23
v1.0, January 2010
Page 86

ProSafe VPN Firewall 200 FVX538 Reference Manual
Creating Services, QoS Profiles, and Bandwidth Profiles
When you create inbound and outbound firewall rules, you use firewall objects such as services,
QoS profiles, bandwidth profiles, and schedules to narrow down the firewall rules:
• Services. A service narrows down the firewall rule to an application and a port number. For
information about adding services, see “Adding Customized Services” on page 4-24.
• QoS profiles. A quality of service (QoS) profile defines the relative priority of an IP packet
for traffic that matches the firewall rule. For information about creating QoS profiles, see
“Specifying Quality of Service (QoS) Priorities” on page 4-26.
• Bandwidth Profiles. A bandwidth profile allocates and limits traffic bandwidth for the LAN
users to which a firewall rule is applied. For information about creating bandwidth profiles,
see “Creating Bandwidth Profiles” on page 4-27.
Note: A schedule narrows down the period during which a firewall rule is applied. For
information about specifying schedules, see “Setting a Schedule to Block or Allow
Specific Traffic” on page 4-29.
Adding Customized Services
Services are functions performed by server computers at the request of client computers. You can
configure up to 125 custom services.
For example, Web servers serve Web pages, time servers serve time and date information, and
game hosts serve data about other players’ moves. When a computer on the Internet sends a
request for service to a server computer, the requested service is identified by a service or port
number. This number appears as the destination port number in the transmitted IP packets. For
example, a packet that is sent with destination port number 80 is an HTTP (Web server) request.
The service numbers for many common protocols are defined by the Internet Engineering Task
Force (IETF) and published in RFC1700, “Assigned Numbers.” Service numbers for other
applications are typically chosen from the range 1024 to 65535 by the authors of the application.
Although the VPN firewall already holds a list of many service port numbers, you are not limited
to these choices. Use the Services screen to add additional services and applications to the list for
use in defining firewall rules. The Services screen shows a list of services that you have defined, as
shown in Figure 4-17 on page 4-25.
4-24 Firewall Protection and Content Filtering
v1.0, January 2010
Page 87

ProSafe VPN Firewall 200 FVX538 Reference Manual
To define a new service, first you must determine which port number or range of numbers is used
by the application. This information can usually be determined by contacting the publisher of the
application or from user groups of newsgroups. When you have the port number information, you
can enter it on the Services screen.
To add a customized service:
1. Select Security from the main menu and Services from the submenu. The Services screen will
display.
Figure 4-17
2. In the Add Custom Service table, enter a descriptive name for the service (this is for your
convenience).
3. Select the Layer 3 Protocol that the service uses as its transport protocol. It can be TCP, UDP
or ICMP.
4. Enter the first TCP or UDP port of the range that the service uses. If the service uses only one
port, then the Start Port and the Finish Port will be the same.
5. Enter the last port of the range that the service uses. If the service only uses a single port
number, enter the same number in both fields.
6. Click Add. The new custom service will be added to the Custom Services Table.
Firewall Protection and Content Filtering 4-25
v1.0, January 2010
Page 88

ProSafe VPN Firewall 200 FVX538 Reference Manual
Modifying a Service
To edit the parameters of a service:
1. In the Custom Services Table, click the Edit icon adjacent to the service you want to edit. The
Edit Service screen will display.
Figure 4-18
2. Modify the parameters you wish to change.
3. Click Reset to cancel the changes and restore the previous settings or click Apply to confirm
your changes. The modified service will display in the Custom Services Table.
Specifying Quality of Service (QoS) Priorities
The Quality of Service (QoS) Priorities setting determines the priority of a service, which in turn,
determines the quality of that service for the traffic passing through the firewall. The user can
change this priority
• On the Services screen in the Custom Services Table for customized services (see
Figure 4-17).
• On the Add LAN WAN Outbound Services screen (see Figure 4-3 o n page 4-10).
• On the Add DMZ WAN Outbound Services screen (see Figure 4-6 on page 4-13).
The QoS priority definition for a service determines the queue that is used for the traffic passing
through the VPN firewall. A priority is assigned to IP packets using this service. Priorities are
defined by the “Type of Service (ToS) in the Internet Protocol Suite” standards, RFC 1349.
4-26 Firewall Protection and Content Filtering
v1.0, January 2010
Page 89

ProSafe VPN Firewall 200 FVX538 Reference Manual
A ToS priority for traffic passing through th e VPN firewall is one of the following:
• Normal-Service. No special priority given to the traffic. The IP packets for services with this
priority are marked with a ToS value of 0.
• Minimize-Cost. Used when data has to be transferred over a link that has a lower “cost”. The
IP packets for services with this priority are marked with a ToS value of 1.
• Maximize-Reliability. Used when data needs to travel to the destination over a reliable link
and with little or no retransmission. The IP packets for services with this priority are marked
with a ToS value of 2.
• Maximize-Throughput. Used when the volume of data transferred during an interval is
important even if the latency over the link is high. The IP packets for services with this priority
are marked with a ToS value of 4.
• Minimize-Delay. Used when the time required (latency) for the packet to reach the destination
must be low. The IP packets for services with this priority are marked with a ToS value of 8.
Creating Bandwidth Profiles
Bandwidth limiting determines the way in which data is communicated with your host. The
purpose of bandwidth limiting is to provide a method for limiting traffic, thus preventing LAN
users from consuming all the bandwidth on your WAN link.
• Bandwidth limiting is done on the available WAN interface in both the single port and AutoFailover modes. Bandwidth limiting is handled on the user-specified interface in Load
Balancing mode.
• Bandwidth limiting does not apply to the DMZ interface.
For example, when a new connection is established by a device, the device will locate the firewall
rule corresponding to the connection.
• If the rule has a bandwidth profile specification, then the device will create a bandwidth class
in the kernel.
• If multiple connections correspond to the same firewall rule, they will share the same class.
An exception occurs for an individual bandwidth profile if the classes are per source IP . The source
IP is the IP of the first packet of the connection:
The class is deleted when all the connections using the class expire.
To add a bandwidth profile:
1. Select Security from the main menu and Bandwidth Profile from the submenu. The
Bandwidth Profile screen will display (see Figure 4-19 on page 4-28).
Firewall Protection and Content Filtering 4-27
v1.0, January 2010
Page 90

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-19
2. Click Add to add a new bandwidth profile. The Add New Bandwidth Profile screen displays.
Figure 4-20
3. Enter the following information:
a. Enter a Profile Name. This name will become available in the firewall rules definition
menus.
b. From the Direction pull-down box, select whether the profile will apply to outbound,
inbound, or both outbound and inbound traffic.
4-28 Firewall Protection and Content Filtering
v1.0, January 2010
Page 91

ProSafe VPN Firewall 200 FVX538 Reference Manual
c. Depending on the direction that you selected, enter the minimum and maximum
bandwidths to be allowed:
• Enter the Outbound Minimum Bandwidth and Outbound Maximum Bandwidth
in Kbps.
• Enter the Inbound Minimum Bandwidth and Inbound Maximum Bandwidth in
Kbps.
The minimum bandwidth can range from 0 Kbps to the maximum bandwidt h that you
specify. The maximum bandwidth can range from 100 Kbps to 100,000 Kbps.
d. From the Type pull-down box, select whether the profile will apply to a group or
individual.
e. From the WAN pull-down box, specify the WAN interface (if in Load Balancing Mode)
for the profile.
• Click Apply. The new bandwidth profile will be added to the List of Bandwidth Pr ofiles
table.
To edit a bandwidth profile:
1. Click the Edit link adjacent to the profile you want to edit. The Edit Bandwidth Profile screen
is displayed. (This screen shows the same fields as the Add New Bandwidth Profile screen.)
2. Modify the settings that you wish to change.
3. Click Apply. Your modified profile will display in the Bandwidth Profile table.
To remove an entry from the table, select the profile and click delete.
To remove all the profiles, click select All and then click delete.
Setting a Schedule to Block or Allow Specific Traffic
Schedules define the timeframes under which firewall rules may be applied.
Three schedules, Schedule 1, Schedule 2 and Schedule3 can be defined, and any one of these can
be selected when defining firewall rules.
To invoke rules based on a schedule, follow these steps:
1. Select Security from the main menu and Schedule from the submenu. The Schedule 1 screen
will display (see Figure 4-21 on page 4-30).
Firewall Protection and Content Filtering 4-29
v1.0, January 2010
Page 92

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-21
2. Check the radio button for All Days or Specific Days. If you chose Specific Days, check the
radio button for each day you want the schedule to be in effect.
3. Check the radio button to schedule the time of day: All Day, or Specific Times. If you chose
Specific Times, enter the Start Time and End Time fields (Hour, Minute, AM/PM), which
will limit access during certain times for the selected days.
4. Click Apply to save your settings to Schedule 1.
Repeat these steps to set to a schedule for Schedule 2 and Schedule 3.
Blocking Internet Sites (Content Filtering)
If you want to restrict internal LAN users from access to certain sites on the Internet, you can use
the VPN firewall’s Content Fi ltering and Web Components filtering. By default, these features are
disabled; all requested traffic from any website is allowed. If you enable one or more of these
features and users try to access a blocked site, they will see a “Blocked by NETGEAR” message.
4-30 Firewall Protection and Content Filtering
v1.0, January 2010
Page 93

ProSafe VPN Firewall 200 FVX538 Reference Manual
Several types of blocking are available:
• Web Components blocking. You can block the following Web component types: Proxy, Java,
ActiveX, and Cookies. Some of these components are can be used by malicious Websites to
infect computers that access them. Even sites on the Trusted Domains list will be subject to
Web Components blocking when the blocking of a particular Web component is enabled.
– Proxy. A proxy server (or simply, proxy) allows computers to route connections to other
computers through the proxy, thus circumventing certain firewall rules. For example, if
connections to a specific IP address are blocked by a firewall rule, the requests can be
routed through a proxy that is not blocked by the rule, rendering the restriction ineffective.
Enabling this feature blocks proxy servers.
– Java. Blocks java applets from being downloaded from pages that contain them. Java
applets are small programs embedded in web pages that enable dynamic functionality of
the page. A malicious applet can be used to compromise or infect computers. Enabling this
setting blocks Java applets from being downloaded.
– ActiveX. Similar to Java applets, ActiveX controls install on a Windows computer
running Internet Explorer. A malicious ActiveX control can be used to compromise or
infect computers. Enabling this setting blocks ActiveX applets from being downloaded.
– Cookies. Cookies are used to store session information by websites that usually require
login. However, several websites use cookies to store tracking information and browsing
habits. Enabling this option filters out cookies from being created by a website..
Note: Many websites require that cookies be accepted in order for the site to be
accessed properly. Blocking cookies may interfere with useful functions
provided by these websites.
• Keyword Blocking (Domain Name Blocking). You can specify up to 32 words that, should
they appear in the website name (URL) or in a newsgroup name, will cause that site or
newsgroup to be blocked by the VPN firewall.
You can apply the keywords to one or more groups. Requests from the PCs in the groups for
which keyword blocking has been enabled will be blocked. Blocking does not occur for the
PCs that are in the groups for which keyword blocking has not been enabled.
You can bypass keyword blocking for trusted domains by adding the exact matching domain
to the list of Trusted Domains. Access to the domains or keywords on this list by PCs, even
those in the groups for which keyword blocking has been enabled, will still be allowed without
any blocking.
Firewall Protection and Content Filtering 4-31
v1.0, January 2010
Page 94

ProSafe VPN Firewall 200 FVX538 Reference Manual
Keyword application examples:
• If the keyword “XXX” is specified, the URL <http://www.badstuff.com/xxx.html> is blocked,
as is the newsgroup alt.pictures.XXX.
• If the keyword “.com” is specified, only Web sites with other domain suffixes (such as .edu or
.gov) can be viewed.
• If you wish to block all Internet browsing access, enter the keyword “.”.
To enable Content Filtering:
1. Select Security from the main menu and Block Sites from the submenu. The Block Sites
screen will display.
Figure 4-22
4-32 Firewall Protection and Content Filtering
v1.0, January 2010
Page 95

ProSafe VPN Firewall 200 FVX538 Reference Manual
2. Check the Yes radio button to enable content filtering.
3. Click Apply to activate the screen controls.
4. Check the radio boxes of any web components you wish to block.
5. Check the radio buttons of the groups to which you wish to apply keyword blocking. Click
Enable to activate keyword blocking (or disable to deactivate keyword blocking).
6. Build your list of blocked keywords or domain names in the Blocked Keyword fields. After
each entry , click Add. The keyword or domain name will be added to the Blocked Keywords
table. (You can also edit an entry by clicking Edit in the Action column adjacent to the entry.)
7. Build a list of trusted domains in the Trusted Domains fields. After each entry, click Add.
The trusted domain will appear in the T rusted Domains table. (You can also edit any entry by
clicking Edit in the Action column adjacent to the entry.)
Configuring Source MAC Filtering
Source MAC filtering allows you to filter out traffic coming from certain known machines or
devices.
• By default, the source MAC address filter is disabled. All the traffic received from PCs with
any MAC address is allowed.
• When enabled, traffic will be dropped coming from any computers or devices whose MAC
addresses are listed in Available MAC Addresses to be Blocked table.
Note: For additional ways of restricting outbound traffic, see “Outbound Rules (Service
Blocking)” on page 4-3.
To enable MAC filtering and add MAC addresses to be blocked:
1. Select Security from the main menu and Addr ess Filter from the submenu. The Source MAC
Filter screen will display (see Figure 4-23 on page 4-34).
Firewall Protection and Content Filtering 4-33
v1.0, January 2010
Page 96

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-23
2. Check the Yes radio box in the MAC Filtering Enable section.
3. Select the action to be taken on outbound traffic from the listed MAC addresses:
• Block this list and permit all other MAC addresses.
• Permit this list and block all other MAC addresses.
4. Enter a MAC Address in the Add Source MAC Address checkbox and click Add. The MAC
address will appear in the MAC Addresses table. Repeat this process to add additional MAC
addresses.
A valid MAC address is six colon-separated pairs of hexadecimal digits (0 to 9 and a to f). For
example: 01:23:45:ab:cd:ef.
5. Click Reset to cancel a MAC address entry before adding it to the table or click Apply to save
your settings.
You can edit the MAC address by clicking Edit in the Action column adjacent to the MAC
Address.
To remove an entry from the table, select the MAC address entry and click Delete.
T o select all the list of MAC addresses, click Select All. A checkmark will appear in the box to the
left of each MAC address in the MAC Addresses table
4-34 Firewall Protection and Content Filtering
.
v1.0, January 2010
Page 97

ProSafe VPN Firewall 200 FVX538 Reference Manual
Configuring IP/MAC Address Binding
IP/MAC binding allows you to bind an IP address to a MAC address and the other way around.
Some devices are configured with static addresses. To prevent users from changing their static IP
addresses, IP/MAC binding must be enabled on the VPN firewall. If the VPN firewall detects
packets with a matching IP address, but with the inconsistent MAC address (or the other way
around), it will drop these packets. If users have enabled the logging option for IP/MAC binding,
these packets will be logged before they are dropped. The VPN firewallwill then display the total
number of dropped packets that violated either the IP-to-MAC binding or the MAC-to-IP binding.
Following is an example:
Assume that three computers on the LAN are set up as follows:
• Host1: MAC address (00:01:02:03:04:05) and IP address (192.168.10.10)
• Host2: MAC address (00:01:02:03:04:06) and IP address (192.168.10.11)
• Host3: MAC address (00:01:02:03:04:07) and IP address (192.168.10.12)
If all the above host entries are added to the IP/MAC Binding table, the following scenarios
indicate the possible outcome.
• Host1: Matching IP address and MAC address in the IP/MAC Bindings table.
• Host2: Matching IP address but inconsistent MAC address in the IP/MAC Bindings table.
• Host3: Matching MAC address but inconsistent IP address in the IP/MAC Bindings table.
The VPN firewall will block the traffic coming from Host2 and Host3, but allow the traf fic coming
from Host1 to any external network. The total count of dropped packets will be displayed.
To enable IP/MAC Binding and add IP and MAC address for binding:
1. Select Security from the main menu and Address Filter from the submenu.
2. Select the IP/MAC Binding tab. The IP/MAC Binding screen will display (see Figure 4-24 on
page 4-36).
Firewall Protection and Content Filtering 4-35
v1.0, January 2010
Page 98

ProSafe VPN Firewall 200 FVX538 Reference Manual
Figure 4-24
3. Select the Yes radio box and click Apply. Make sure that you have enabled the e-maling of
logs (see “Activating Notification of Events and Alerts” on page 6-23).
4. Add an IP/MAC Bind rule by entering:
a. Name. Specify an easily identifiable name for this rule.
b. MAC Address. Specify the MAC Address for this rule.
c. IP Addresses. Specify the IP Address for this rule.
d. Log Dropped Packets. Select the logging option for this rule from the pull-down menu.
5. Click Add. The new IP/MAC rule will be appear the IP/MAC Binding table.
The IP/MAC Binding Table lists the currently defined IP/MAC Bind rules:
• Name. Displays the user-defined name for this rule.
• MAC Addresses. Displays the MAC Addresses for this rule.
• IP Addresses. Displays the IP Addresses for this rule.
• Log Dropped Packets. Displays the logging option for this rule.
4-36 Firewall Protection and Content Filtering
v1.0, January 2010
Page 99

ProSafe VPN Firewall 200 FVX538 Reference Manual
To edit an IP/MAC Bind rule, click Edit adjacent to the entry. The following fields of an existing
IP/MAC Bind rule can be modified:
• MAC Address. Specify the MAC Address for this rule.
• IP Addresses. Specify the IP Address for this rule.
• Log Dropped Packets. Specify the logging option for this rule.
To remove an entry from the table, select the IP/MAC Bind entry and click Delete.
To see the counter that shows the packets that were dropped because of IP-MAC binding
violations and to set the poll interval, click the Set Poll Interval link at the top of the IP/MAC
Binding screen.
Configuring Port Triggering
Port triggering allows some applications to function correctly that would otherwise be partially
blocked by the VPN firewall when it functions in NAT mode. Some applications require that when
external devices connect to them, they receive data on a specific port or range of ports. The VPN
firewall must send all incoming data for that application only on the required port or range of
ports. Using this feature requires that you know the port numbers used by the application.
Port triggering allows computers on the private network (LAN) to request that one or more ports
be forwarded to them. Unlike basic port forwarding which forwards ports to only one
preconfigured IP address, port triggering waits for an outbound request from the private network
on one of the defined outgoing ports. It then automatically sets up forwarding to the IP address that
sent the request. When the application ceases to transmit data over the port, the VPN firewall waits
for a timeout interval and then closes the port or range of ports, making them available to other
computers on the private network.
Once configured, port triggering operates as follows:
1. A PC makes an outgoing connection using a port number defined in the Port T riggering table.
2. The VPN firewall records this connection, opens the additional incoming port or ports
associated with this entry in the Port Triggering table, and associates them with the PC.
3. The remote system receives the PCs request and responds using the different port numbers that
you have now opened.
4. The VPN firewall matches the response to the previous request, and forwards the response to
the PC.
Without port triggering, this response would be treated as a new connection request rather than a
response. As such, it would be handled in accordance with the port forwarding rules.
Firewall Protection and Content Filtering 4-37
v1.0, January 2010
Page 100

ProSafe VPN Firewall 200 FVX538 Reference Manual
Note these restrictions with port triggering:
• Only one PC can use a port triggering application at any time.
• After a PC has finished using a port triggering application, there is a time-out period before the
application can be used by another PC. This is required because the VPN firewall cannot
detect when the application has terminated.
Note: For additional ways of allowing inbound traffic, see “Inbound Rules (Port
Forwarding)” on page 4-5.
To add a port triggering Rule:
1. Select Security from the main menu and Port Triggering from the submenu. The Port
Triggering screen will display.
Figure 4-25
2. Enter a user-defined name for this rule in the Name field.
3. From the Enable pull-down menu, indicate if the rule is enabled or disabled.
4. From the Protocol pull-down menu, select either the TCP or UDP protocol.
5. In the Outgoing (Trigger) Port Range fields:
a. Enter the Start Port range (1 - 65534).
b. Enter the End Port range (1 - 65534).
4-38 Firewall Protection and Content Filtering
v1.0, January 2010
 Loading...
Loading...