Page 1
Wireless-G Notebook Adapter
19
Instant Wireless®Series
18
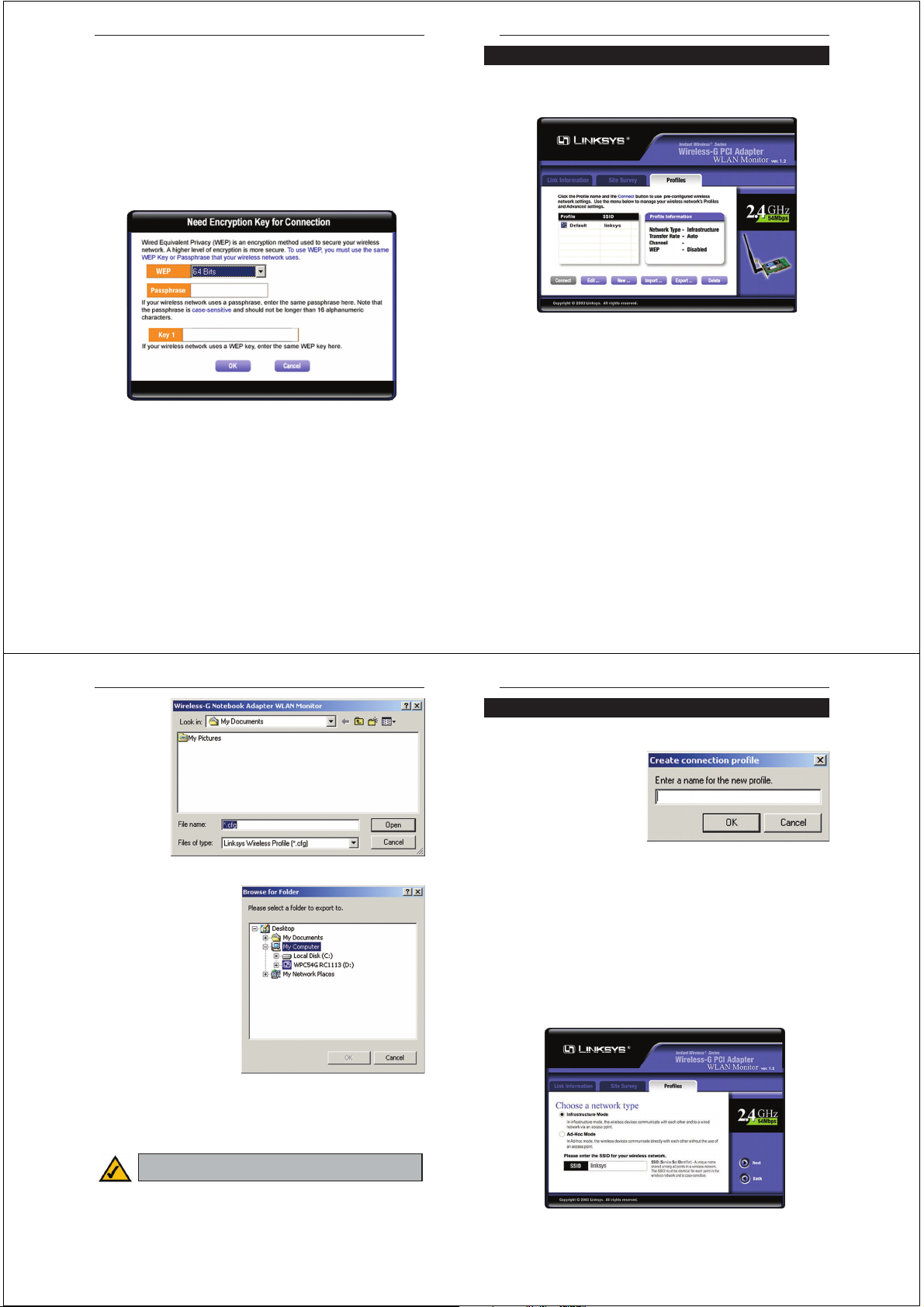
The Profiles screen (Figure 7-6) lets you save different configuration profiles
for different network setups. You can also import or export profiles. The default
profile holds the initial conf iguration saved when you ran the Setup Wizard.
Profile - Name of the connection profile.
SSID - The wireless network’s unique name, as set in the connection profile.
Profile Information
Network Type - The mode of the wireless network currently in use.
Transfer Rate - The data transfer rate of the current connection. (In Auto
mode, the Adapter dynamically shifts to the fastest data transfer rate possible
at any given time.)
Channel - The channel to which the wireless network devices are set.
WEP - The status of the WEP encryption security feature.
Connect - To connect to a wireless network using a specific prof ile, select the
profile, and click the Connect button.
Edit - Select a profile, and click the Edit button to change an existing prof ile.
New - Click the New button to create a new profile. See the next section,
“Creating a New Profile,” for detailed instructions.
Figure 7-6
Profiles
Site Information
Wireless Mode - The mode of the wireless network currently in use.
Channel - The channel to which the wireless network devices are set.
WEP - The status of the WEP encryption security feature.
MAC - The MAC address of the wireless network’s access point.
Surveyed at - The time at which the wireless network was scanned.
Refresh - Click the Refresh button to perform a new search for wireless
devices.
Connect - To connect to one of the networks on the list, select the wireless network, and click the Connect button. If the wireless network has WEP encryption enabled, you will see the screen shown in Figure 7-5.
In the WEP drop-down box, select the type of WEP encryption used by the
wireless network: 64-bit, or 128-bit WEP.
If the wireless network uses a passphrase, enter the passphrase in the
Passphrase f ield. If the wireless network uses a WEP key, enter the WEP key
in the Key 1 field.
Click the OK button to complete the network connection and return to the Site
Survey screen, or click the Cancel button to cancel the network connection and
return to the Site Survey screen.
On the Site Survey screen, click the X (Close) button in the upper right corner
to exit the WLAN Monitor.
Figure 7-5
Wireless-G Notebook Adapter
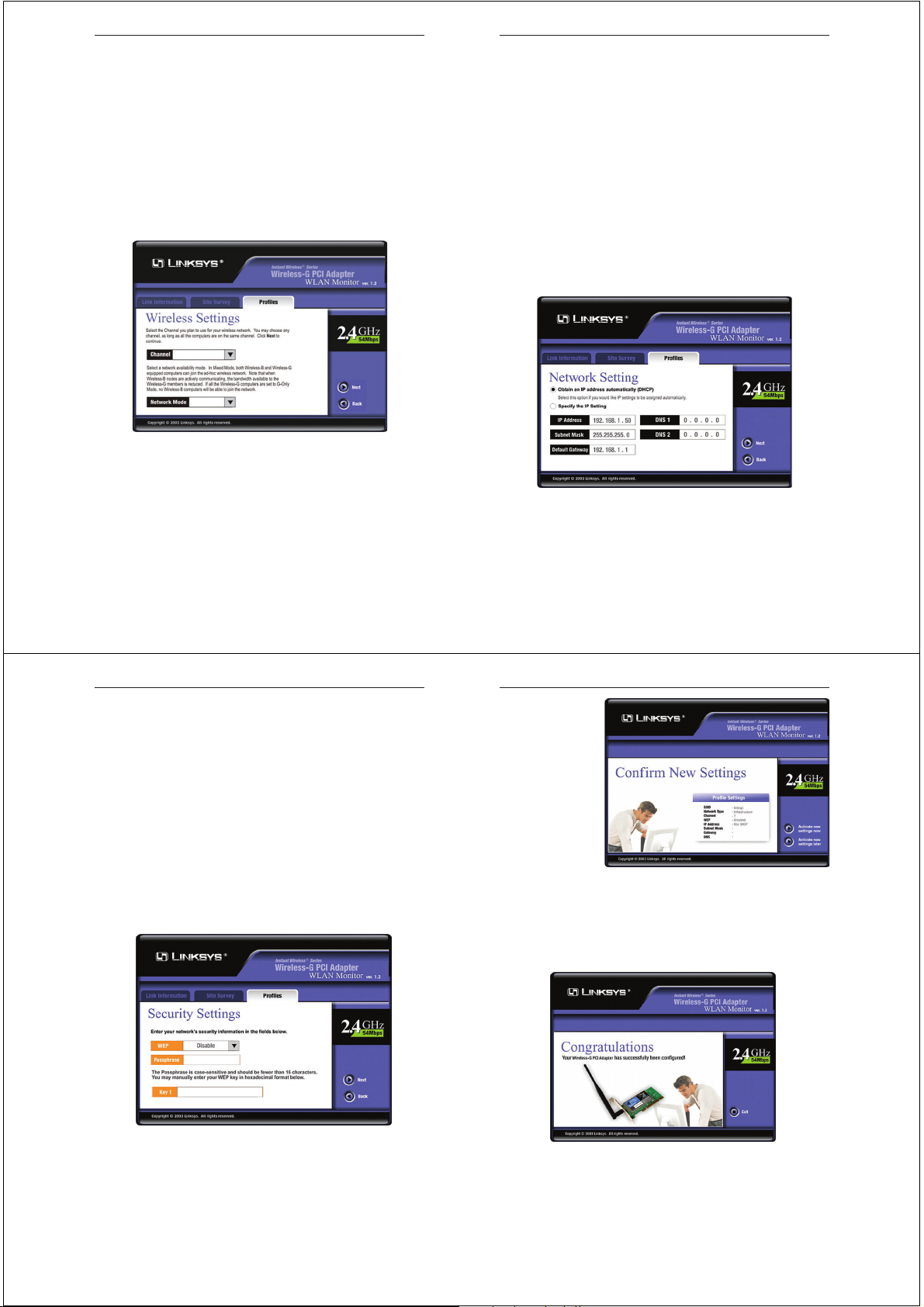
1. On the Profiles screen, shown in Figure 7-6, click the New button to create
a new profile.
2. When the Create connection
profile screen appears (Figure
7-9), enter a name for the new
profile. Click OK to save the
profile name or click Cancel
to return to the previous
screen.
3. The Choose a network type screen (Figure 7-10) shows a choice of two
wireless modes. Click the Infrastructure Mode radio button if you want
your wireless computers to communicate with computers on your wired
network via a wireless access point. Click the Ad-Hoc Mode radio button
if you want multiple wireless computers to communicate directly with each
other. Click the Next button to continue or the Back button to return to the
previous screen.
Infrastructure Mode - This mode allows wireless and wired networks to
communicate through an access point.
Ad-Hoc Mode - This mode allows wireless-equipped computers to communicate directly with each other. No access point is used.
21
Instant Wireless®Series
20
Figure 7-10
Figure 7-9
Creating a New Profile
Import - Click
the Import button to import a
profile that has
been saved in
another location.
From the screen
that appears
(shown in Figure
7-7), select the
appropriate file,
and click the
Open button.
Export - To save the profile(s) in
a different location, click the
Export button. On the screen that
appears (Figure 7-8), direct
Windows to the appropriate folder and click the OK button.
Delete - Click the Delete button to delete a prof ile.
Click the X (Close) button in the upper right corner to exit the WLAN Monitor.
Figure 7-7
Figure 7-8
Note: If you have more than one profile, all profiles will be automatically selected and exported to the same folder.
Page 2
Wireless-G Notebook Adapter
23
Instant Wireless®Series
4. The Wireless Settings screen (Figure 7-11) will appear. If you chose
Infrastructure Mode, go to Step 5 now. If you chose Ad-Hoc Mode, select
the correct operating channel for your network from the Channel drop-
down menu. Then, select the Network Mode from the drop-down menu.
Click the Next button, and go to Step 5. Click the Back button to change
any settings.
Channel - The channel you choose should match the channel set on the
other devices in your wireless network. If you are unsure about which channel to use, select the default channel (Channel 6).
Network Mode - Select Mixed Mode, and both Wireless-G and Wireless-
B computers will be allowed on the network, but the speed will be reduced.
Select G-Only Mode for maximum speed, but no Wireless-B users will be
allowed on the network.
5. The Network Setting screen (Figure 7-12) will appear.
If your network has a DHCP server, click the radio button next to Obtain
an IP address automatically (DHCP). Click the Next button to continue,
or click the Back button to return to the previous screen.
22
If your network does not have a DHCP server, click the radio button next to
Specify the IP address. Enter an IP Address, Subnet Mask, Default
Gateway, and DNS appropriate for your network. Enter each address in this
format: xxx.xxx.xxx.xxx (the x’s represent the numbers that make up each
address). You must specify the IP Address and Subnet Mask on this screen.
If you are unsure about the Default Gateway and DNS addresses, then leave
these fields alone.
IP Address - This IP Address must be unique to your network.
Subnet Mask - The Adapter’s Subnet Mask must be the same as your wired
network’s Subnet Mask.
Default Gateway - Enter the IP address of your network’s Gateway here.
DNS - Enter the DNS addresses of your Ethernet (wired) network here.
Click the Next button to continue or the Back button to return to the previous screen.
6. The Security Settings screen (Figure 7-13) will appear. Enable or disable
Wired Equivalent Privacy (WEP) encryption for your wireless network. If
you enable WEP, enter a Passphrase or WEP key. Click the Next button to
continue or the Back button to return to the previous screen.
Figure 7-12
Figure 7-11
Wireless-G Notebook Adapter
25
Instant Wireless®Series
WEP (Disabled/64 bits WEP/128 bits WEP) - If you do not want to use
WEP encryption, choose Disabled. To use WEP encryption (recommended
to increase network security), select 64 bits or 128 bits WEP from the
drop-down menu, and enter either a Passphrase or WEP key.
Passphrase - Instead of manually entering WEP keys, you can enter a
Passphrase, so that a WEP key is automatically generated. It is case-sensitive and should not be longer than 16 alphanumeric characters. This
passphrase must match the passphrase of your wireless network and is compatible with other Linksys wireless products only. (If you have any nonLinksys wireless products, enter the WEP key(s) manually on those products.)
Key 1 - This WEP key must match the WEP key of your wireless network.
If you are using 64-bit WEP encryption, then the key must consist of exactly 10 hexadecimal characters. If you are using 128-bit WEP encryption,
then the key must consist of exactly 26 hexadecimal characters. Valid hexadecimal characters are “0” to “9” and “A” to “F”.
24
7. The Conf irm New
Settings screen
(Figure 7-14) will
appear. To save the
new settings, click
the Ye s button. To
cancel the settings
and return to the
Profiles screen,
click the No button.
To edit the new settings, click the
Back button.
8. The Congratulations screen (Figure 7-15) will appear next. Click Activate
new settings now to implement the new settings immediately and return to
the Link Information screen. Click Activate new settings later to keep the
current settings active, and return to the Profiles screen so that you can edit
your profile or create another profile.
You have successfully created a connection profile. Click the X (Close) but-
ton in the upper right corner to exit the WLAN Monitor.
Figure 7-14
Figure 7-15
Figure 7-13
Page 3

Wireless-G Notebook Adapter
Can I play computer games with other members of the wireless network?
Yes, as long as the game supports multiple players over a LAN (local area network). Refer to the game’s user guide for more information.
What is the IEEE 802.11b standard?
It is one of the IEEE standards for wireless networks. The 802.11b standard
allows wireless networking hardware from different manufacturers to communicate, provided that the hardware complies with the 802.11b standard. The
802.11b standard states a maximum data transfer rate of 11Mbps and an oper-
ating frequency of 2.4GHz.
What IEEE 802.11b features are supported?
The product supports the following IEEE 802.11b functions:
• CSMA/CA plus Acknowledge protocol
• Multi-Channel Roaming
• Automatic Rate Selection
• RTS/CTS feature
• Fragmentation
• Power Management
What is ad-hoc mode?
When a wireless network is set to ad-hoc mode, the wireless-equipped computers are configured to communicate directly with each other. The ad-hoc
wireless network will not communicate with any wired network.
What is infrastructure mode?
When a wireless network is set to infrastructure mode, the wireless network is
configured to communicate with a wired network through a wireless access
point.
What is roaming?
Roaming is the ability of a portable computer user to communicate continuously while moving freely throughout an area greater than that covered by a single access point. Before using the roaming function, the workstation must make
sure that it is the same channel number with the access point of dedicated coverage area.
27
Instant Wireless®Series
Appendix A: Troubleshooting
This chapter provides solutions to problems that may occur during the installation and operation of the Wireless-G PCI Adapter. Read the descriptions below
to solve your problems. If you can’t find an answer here, check the Linksys
website at www.linksys.com.
1. The Wireless-G PCI Adapter does not work properly.
• Reinser t the Wireless-G PCI Adapter into your PC’s PCI slot.
• Right click on My Computer and select Properties. Select the device
manager and click on the Network Adapter. You will find the Wireless-G
PCI Adapter if it is installed successfully. If you see the yellow exclamation mark, the resources are conflicting. You will see the status of the
Wireless-G PCI Adapter. If there is a yellow question mark, please check
the following:
• Make sure that your PC has a free IRQ (Interr upt ReQuest, a hardware
interrupt on a PC.)
• Make sure that you have inserted the right adapter and installed the proper driver.
If the Wireless-G PCI Adapter does not function after attempting the above
steps, remove the adapter and do the following:
• Uninstall the driver software from your PC.
• Restar t your PC and repeat the hardware and software installation as
specified in this User Guide.
2. I cannot communicate with the other computers linked via Ethernet in the
Infrastructure configuration.
• Make sure that the PC to which the Wireless-G PCI Adapter is associated
is powered on.
• Make sure that your Wireless-G PCI Adapter is conf igured on the same
channel and with the same security options as with the other computers in
the Infrastructure configuration.
Can I run an application from a remote computer over the wireless network?
This will depend on whether or not the application is designed to be used over
a network. Consult the application’s user guide to determine if it supports operation over a network.
26
Common Problems and Solutions
Frequently Asked Questions
Wireless-G Notebook Adapter
29
Instant Wireless®Series
28
an unintended receiver, FHSS appears to be short-duration impulse noise.
Direct-Sequence Spread-Spectrum (DSSS) generates a redundant bit pattern
for each bit to be transmitted. This bit pattern is called a chip (or chipping
code). The longer the chip, the greater the probability that the original data can
be recovered. Even if one or more bits in the chip are damaged during transmission, statistical techniques embedded in the radio can recover the original
data without the need for retransmission. To an unintended receiver, DSSS
appears as low power wideband noise and is rejected (ignored) by most narrowband receivers.
Would the information be intercepted while transmitting on air?
WLAN features two-fold protection in security. On the hardware side, as with
Direct Sequence Spread Spectrum technology, it has the inherent security feature of scrambling. On the software side, WLAN offers the encryption function
(WEP) to enhance security and access control.
What is WEP?
WEP is Wired Equivalent Privacy, a data privacy mechanism based on a 64-bit
or 128-bit shared key algorithm, as described in the IEEE 802.11 standard.
To achieve true seamless connectivity, the wireless LAN must incorporate a
number of different functions. Each node and access point, for example, must
always acknowledge receipt of each message. Each node must maintain contact
with the wireless network even when not actually transmitting data. Achieving
these functions simultaneously requires a dynamic RF networking technology
that links access points and nodes. In such a system, the user’s end node undertakes a search for the best possible access to the system. First, it evaluates such
factors as signal strength and quality, as well as the message load currently
being carried by each access point and the distance of each access point to the
wired backbone. Based on that information, the node next selects the right
access point and registers its address. Communications between end node and
host computer can then be transmitted up and down the backbone.
As the user moves on, the end node’s RF transmitter regularly checks the system to determine whether it is in touch with the original access point or whether
it should seek a new one. When a node no longer receives acknowledgment
from its original access point, it undertakes a new search. Upon finding a new
access point, it then re-registers, and the communication process continues.
What is ISM band?
The FCC and their counterparts outside of the U.S. have set aside bandwidth
for unlicensed use in the ISM (Industrial, Scientific and Medical) band.
Spectrum in the vicinity of 2.4 GHz, in particular, is being made available
worldwide. This presents a truly revolutionary opportunity to place convenient
high-speed wireless capabilities in the hands of users around the globe.
What is Spread Spectrum?
Spread Spectrum technology is a wideband radio frequency technique developed by the military for use in reliable, secure, mission-critical communications systems. It is designed to trade off bandwidth efficiency for reliability,
integrity, and security. In other words, more bandwidth is consumed than in the
case of narrowband transmission, but the trade-off produces a signal that is, in
effect, louder and thus easier to detect, provided that the receiver knows the
parameters of the spread-spectrum signal being broadcast. If a receiver is not
tuned to the right frequency, a spread-spectrum signal looks like background
noise. There are two main alternatives, Direct Sequence Spread Spectrum
(DSSS) and Frequency Hopping Spread Spectrum (FHSS).
What is DSSS? What is FHSS? And what are their differences?
Frequency-Hopping Spread-Spectrum (FHSS) uses a narrowband carrier that
changes frequency in a pattern that is known to both transmitter and receiver.
Properly synchronized, the net effect is to maintain a single logical channel. To
Page 4

Wireless-G Notebook Adapter
31
Instant Wireless®Series
30
CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) - In local
area networking, this is the CSMA technique that combines slotted time-division multiplexing with carrier sense multiple access/collision detection
(CSMA/CD) to avoid having collisions occur a second time. This works best if
the time allocated is short compared to packet length and if the number of situations is small.
CTS (Clear To Send) - An RS-232 signal sent from the receiving station to the
transmitting station that indicates it is ready to accept data.
Default Gateway - The routing device used to forward all traffic that is not
addressed to a station within the local subnet.
DHCP (Dynamic Host Conf iguration Protocol) - A protocol that lets network
administrators manage centrally and automate the assignment of Internet
Protocol (IP) addresses in an organization's network. Using the Internet's set of
protocol (TCP/IP), each machine that can connect to the Internet needs a
unique IP address. When an organization sets up its computer users with a connection to the Internet, an IP address must be assigned to each machine.
Without DHCP, the IP address must be entered manually at each computer and,
if computers move to another location in another part of the network, a new IP
address must be entered. DHCP lets a network administrator supervise and distribute IP addresses from a central point and automatically sends a new IP
address when a computer is plugged into a different place in the network.
DHCP uses the concept of a "lease" or amount of time that a given IP address
will be valid for a computer. The lease time can vary depending on how long a
user is likely to require the Internet connection at a particular location. It's especially useful in education and other environments where users change frequently. Using very short leases, DHCP can dynamically reconfigure networks
in which there are more computers than there are available IP addresses.
DHCP supports static addresses for computers containing Web servers that
need a permanent IP address.
DNS - The domain name system (DNS) is the way that Internet domain name
are located and translated into Internet Protocol (IP) addresses. A domain name
is a meaningful and easy-to-remember "handle" for an Internet address.
Domain - A subnetwork comprised of a group of clients and servers under the
control of one security database. Dividing LANs into domains improves performance and security.
Appendix B: Glossary
802.11b - One of the IEEE standards for wireless networking hardware.
Products that adhere to a specific IEEE standard will work with each other,
even if they are manufactured by different companies. The 802.11b standard
specifies a maximum data transfer rate of 11Mbps, an operating frequency of
2.4GHz, and WEP encryption for security. 802.11b networks are also referred
to as Wi-Fi networks.
802.11g - A proposed, but as yet unratified extension of the IEEE 802.11 stan-
dard for wireless networking hardware. The draft 802.11g specifications used
by Linksys specify a maximum data transfer rate of 54Mbps using OFDM
modulation, an operating frequency of 2.4GHz, backward compatibility with
IEEE 802.11b devices, and WEP encryption for security.
Adapter - Printed circuit board that plugs into a PC to add to capabilities or
connectivity to a PC. In a networked environment, a network interface card is
the typical adapter that allows the PC or server to connect to the intranet and/or
Internet.
Ad-hoc Network - An ad-hoc network is a group of computers, each with a
wireless adapter, connected as an independent 802.11 wireless LAN. Ad-hoc
wireless computers operate on a peer-to-peer basis, communicating directly
with each other without the use of an access point. Ad-hoc mode is also
referred to as an Independent Basic Service Set (IBSS) or as peer-to-peer
mode, and is useful at a departmental scale or SOHO operation.
Backbone - The part of a network that connects most of the systems and networks together and handles the most data.
Bandwidth - The transmission capacity of a given facility, in terms of how
much data the facility can transmit in a fixed amount of time; expressed in bits
per second (bps).
Bit - A binary digit. The value - 0 or 1-used in the binary numbering system.
Also, the smallest form of data.
BSS (Basic Service Set) - An infrastructure network connecting wireless
devices to a wired network using a single access point.
 Loading...
Loading...