Page 1

FortiGate 50A
Administration Guide
FortiGate-50A Administration Guide
STATUS
PWR
A
Version 2.80 MR6
5 November 2004
01-28006-0001-20041105
INTERNAL EXTERNAL
LINK 100 LINK 100
Page 2

© Copyright 2004 Fortinet Inc. All rights reserved.
No part of this publication including text, examples, diagrams or illustrations may be reproduced,
transmitted, or translated in any form or by any means, electronic, mechanical, manual, optical or
otherwise, for any purpose, without prior written permission of Fortinet Inc.
FortiGate-50A Administration Guide
Version 2.80 MR6
5 November 2004
01-28006-0001-20041105
Trademarks
Products mentioned in this document are trademarks or registered trademarks of their respective
holders.
Regulatory Compliance
FCC Class A Part 15 CSA/CUS
CAUTION: RISK OF EXPLOSION IF BATTERY IS REPLACED BY AN INCORRECT TYPE.
DISPOSE OF USED BATTERIES ACCORDING TO THE INSTRUCTIONS.
For technical support, please visit http://www.fortinet.com.
Send information about errors or omissions in this document or any Fortinet technical documentation to
techdoc@fortinet.com.
Page 3

Table of Contents
Introduction.......................................................................................................... 13
About FortiGate Antivirus Firewalls................................................................................... 13
Antivirus protection ....................................................................................................... 14
Web content filtering ..................................................................................................... 14
Spam filtering ................................................................................................................ 15
Firewall.......................................................................................................................... 15
VLANs and virtual domains........................................................................................... 16
Intrusion Prevention System (IPS)................................................................................ 16
VPN............................................................................................................................... 17
Secure installation, configuration, and management .................................................... 17
Document conventions ..................................................................................................... 19
FortiGate documentation .................................................................................................. 20
Comments on Fortinet technical documentation........................................................... 20
Related documentation ..................................................................................................... 21
FortiManager documentation ........................................................................................ 21
FortiClient documentation ............................................................................................. 21
FortiMail documentation................................................................................................ 21
FortiLog documentation ................................................................................................ 22
Customer service and technical support........................................................................... 23
Contents
System status....................................................................................................... 25
Console access................................................................................................................. 25
Status................................................................................................................................ 26
Viewing system status .................................................................................................. 26
Changing unit information ............................................................................................. 29
Session list........................................................................................................................ 31
Changing the FortiGate firmware...................................................................................... 32
Upgrading to a new firmware version ........................................................................... 32
Reverting to a previous firmware version...................................................................... 34
Installing firmware images from a system reboot using the CLI ................................... 37
Testing a new firmware image before installing it ......................................................... 40
System network ................................................................................................... 43
Interface............................................................................................................................ 43
Interface settings........................................................................................................... 44
Configuring interfaces ................................................................................................... 49
Zone.................................................................................................................................. 53
Zone settings ................................................................................................................ 54
Management..................................................................................................................... 55
DNS .................................................................................................................................. 56
FortiGate-50A Administration Guide 01-28006-0001-20041105 3
Page 4

Contents
Routing table (Transparent Mode).................................................................................... 57
Routing table list ........................................................................................................... 57
Transparent mode route settings .................................................................................. 58
Configuring the modem interface...................................................................................... 59
Connecting a modem to the FortiGate unit ................................................................... 59
Configuring modem settings ......................................................................................... 60
Connecting and disconnecting the modem................................................................... 61
Backup mode configuration .......................................................................................... 61
Standalone mode configuration .................................................................................... 62
Adding firewall policies for modem connections ........................................................... 63
VLAN overview ................................................................................................................. 63
FortiGate units and VLANs ........................................................................................... 64
VLANs in NAT/Route mode .............................................................................................. 64
Rules for VLAN IDs....................................................................................................... 65
Rules for VLAN IP addresses ....................................................................................... 65
Adding VLAN subinterfaces .......................................................................................... 66
VLANs in Transparent mode............................................................................................. 67
Rules for VLAN IDs....................................................................................................... 69
Transparent mode virtual domains and VLANs ............................................................ 69
Transparent mode VLAN list......................................................................................... 70
Transparent mode VLAN settings................................................................................. 70
FortiGate IPv6 support...................................................................................................... 72
System DHCP ....................................................................................................... 73
Service.............................................................................................................................. 73
DHCP service settings .................................................................................................. 74
Server ............................................................................................................................... 75
DHCP server settings ................................................................................................... 76
Exclude range................................................................................................................... 77
DHCP exclude range settings....................................................................................... 78
IP/MAC binding................................................................................................................. 78
DHCP IP/MAC binding settings .................................................................................... 79
Dynamic IP........................................................................................................................ 79
System config ...................................................................................................... 81
System time ...................................................................................................................... 81
Options.............................................................................................................................. 82
SNMP................................................................................................................................ 84
Configuring SNMP ........................................................................................................ 85
SNMP community ......................................................................................................... 85
FortiGate MIBs.............................................................................................................. 88
FortiGate traps .............................................................................................................. 88
Fortinet MIB fields ......................................................................................................... 90
4 01-28006-0001-20041105 Fortinet Inc.
Page 5

Replacement messages ................................................................................................... 92
Replacement messages list .......................................................................................... 93
Changing replacement messages ................................................................................ 94
FortiManager..................................................................................................................... 95
System administration ........................................................................................ 97
Administrators................................................................................................................... 97
Administrators list.......................................................................................................... 98
Administrators options .................................................................................................. 98
Access profiles.................................................................................................................. 99
Access profile list ........................................................................................................ 100
Access profile options ................................................................................................. 100
System maintenance ......................................................................................... 103
Backup and restore......................................................................................................... 103
Backing up and Restoring........................................................................................... 104
Update center ................................................................................................................. 106
Updating antivirus and attack definitions .................................................................... 108
Enabling push updates ............................................................................................... 111
Support ........................................................................................................................... 113
Sending a bug report .................................................................................................. 114
Registering a FortiGate unit ........................................................................................ 115
Shutdown........................................................................................................................ 117
Contents
System virtual domain....................................................................................... 119
Virtual domain properties................................................................................................ 120
Exclusive virtual domain properties ............................................................................ 120
Shared configuration settings ..................................................................................... 121
Administration and management ................................................................................ 122
Virtual domains ............................................................................................................... 122
Adding a virtual domain .............................................................................................. 123
Selecting a virtual domain........................................................................................... 123
Selecting a management virtual domain..................................................................... 123
Configuring virtual domains ............................................................................................ 124
Adding interfaces, VLAN subinterfaces, and zones to a virtual domain ..................... 124
Configuring routing for a virtual domain ...................................................................... 126
Configuring firewall policies for a virtual domain......................................................... 126
Configuring IPSec VPN for a virtual domain ............................................................... 128
Router ................................................................................................................. 129
Static............................................................................................................................... 129
Static route list ............................................................................................................ 131
Static route options ..................................................................................................... 132
FortiGate-50A Administration Guide 01-28006-0001-20041105 5
Page 6

Contents
Policy .............................................................................................................................. 133
Policy route list............................................................................................................ 133
Policy route options..................................................................................................... 134
RIP.................................................................................................................................. 134
General ....................................................................................................................... 135
Networks list................................................................................................................ 136
Networks options ........................................................................................................ 137
Interface list................................................................................................................. 137
Interface options ......................................................................................................... 138
Distribute list ............................................................................................................... 139
Distribute list options................................................................................................... 140
Offset list ..................................................................................................................... 141
Offset list options ........................................................................................................ 141
Router objects................................................................................................................. 142
Access list ................................................................................................................... 142
New access list ........................................................................................................... 142
New access list entry .................................................................................................. 143
Prefix list ..................................................................................................................... 143
New Prefix list ............................................................................................................. 144
New prefix list entry..................................................................................................... 145
Route-map list............................................................................................................. 145
New Route-map .......................................................................................................... 146
Route-map list entry.................................................................................................... 147
Key chain list............................................................................................................... 148
New key chain............................................................................................................. 148
Key chain list entry...................................................................................................... 149
Monitor............................................................................................................................ 150
Routing monitor list ..................................................................................................... 150
CLI configuration............................................................................................................. 151
get router info ospf ...................................................................................................... 151
get router info protocols .............................................................................................. 151
get router info rip......................................................................................................... 152
config router ospf ....................................................................................................... 152
config router static6..................................................................................................... 175
Firewall................................................................................................................ 177
Policy .............................................................................................................................. 178
How policy matching works......................................................................................... 178
Policy list ..................................................................................................................... 179
Policy options.............................................................................................................. 179
Advanced policy options ............................................................................................. 182
Configuring firewall policies ........................................................................................ 184
Policy CLI configuration .............................................................................................. 185
6 01-28006-0001-20041105 Fortinet Inc.
Page 7
Address........................................................................................................................... 186
Address list ................................................................................................................. 187
Address options .......................................................................................................... 187
Configuring addresses ................................................................................................ 188
Address group list ....................................................................................................... 189
Address group options ................................................................................................ 189
Configuring address groups........................................................................................ 190
Service............................................................................................................................ 190
Predefined service list................................................................................................. 191
Custom service list...................................................................................................... 194
Custom service options............................................................................................... 194
Configuring custom services....................................................................................... 195
Service group list ........................................................................................................ 197
Service group options ................................................................................................. 197
Configuring service groups ......................................................................................... 198
Schedule......................................................................................................................... 198
One-time schedule list ................................................................................................ 199
One-time schedule options ......................................................................................... 199
Configuring one-time schedules ................................................................................. 199
Recurring schedule list................................................................................................ 200
Recurring schedule options ........................................................................................ 201
Configuring recurring schedules ................................................................................. 201
Virtual IP ......................................................................................................................... 202
Virtual IP list ................................................................................................................ 203
Virtual IP options......................................................................................................... 203
Configuring virtual IPs................................................................................................. 204
IP pool............................................................................................................................. 206
IP pool list ................................................................................................................... 207
IP pool options ............................................................................................................ 207
Configuring IP pools.................................................................................................... 208
IP Pools for firewall policies that use fixed ports ......................................................... 208
IP pools and dynamic NAT ......................................................................................... 208
Protection profile............................................................................................................. 209
Protection profile list.................................................................................................... 209
Default protection profiles ........................................................................................... 210
Protection profile options ............................................................................................ 210
Configuring protection profiles .................................................................................... 214
CLI configuration......................................................................................................... 215
Contents
Users and authentication .................................................................................. 221
Setting authentication timeout......................................................................................... 222
Local ............................................................................................................................... 222
Local user list .............................................................................................................. 222
Local user options....................................................................................................... 222
FortiGate-50A Administration Guide 01-28006-0001-20041105 7
Page 8

Contents
RADIUS .......................................................................................................................... 223
RADIUS server list ...................................................................................................... 223
RADIUS server options............................................................................................... 224
LDAP............................................................................................................................... 225
LDAP server list .......................................................................................................... 225
LDAP server options ................................................................................................... 225
User group ...................................................................................................................... 227
User group list............................................................................................................. 227
User group options...................................................................................................... 228
CLI configuration............................................................................................................. 229
peer............................................................................................................................. 229
peergrp........................................................................................................................ 230
VPN...................................................................................................................... 233
Phase 1........................................................................................................................... 234
Phase 1 list ................................................................................................................. 234
Phase 1 basic settings ................................................................................................ 235
Phase 1 advanced options.......................................................................................... 236
Configuring XAuth....................................................................................................... 237
Phase 2........................................................................................................................... 238
Phase 2 list ................................................................................................................. 238
Phase 2 basic settings ................................................................................................ 239
Phase 2 advanced options.......................................................................................... 240
Manual key...................................................................................................................... 241
Manual key list ............................................................................................................ 242
Manual key options ..................................................................................................... 242
Concentrator ................................................................................................................... 243
Concentrator list.......................................................................................................... 243
Concentrator options................................................................................................... 244
Ping Generator................................................................................................................ 244
Ping generator options................................................................................................ 245
Monitor............................................................................................................................ 245
Dialup monitor............................................................................................................. 246
Static IP and dynamic DNS monitor............................................................................ 246
PPTP............................................................................................................................... 247
Setting up a PPTP-based VPN ................................................................................... 247
Enabling PPTP and specifying a PPTP range ............................................................ 248
Configuring a Windows 2000 client for PPTP ............................................................. 249
Configuring a Windows XP client for PPTP ................................................................ 249
PPTP passthrough...................................................................................................... 250
8 01-28006-0001-20041105 Fortinet Inc.
Page 9

L2TP .............................................................................................................................. 251
Setting up a L2TP-based VPN.................................................................................... 252
Enabling L2TP and specifying an L2TP range............................................................ 252
Configuring a Windows 2000 client for L2TP.............................................................. 253
Configuring a Windows XP client for L2TP ................................................................. 254
Certificates...................................................................................................................... 256
Viewing the certificate list............................................................................................ 257
Generating a certificate request.................................................................................. 257
Installing a signed certificate ...................................................................................... 259
Enabling VPN access for specific certificate holders ................................................. 260
CLI configuration............................................................................................................. 261
ipsec phase1............................................................................................................... 261
ipsec phase2............................................................................................................... 263
ipsec vip ...................................................................................................................... 264
Authenticating peers with preshared keys ...................................................................... 266
Gateway-to-gateway VPN............................................................................................... 266
Dialup VPN ..................................................................................................................... 267
Dynamic DNS VPN......................................................................................................... 267
Manual key IPSec VPN................................................................................................... 268
Adding firewall policies for IPSec VPN tunnels............................................................... 268
Setting the encryption policy direction ........................................................................ 268
Setting the source address for encrypted traffic ......................................................... 268
Setting the destination address for encrypted traffic................................................... 269
Adding an IPSec firewall encryption policy ................................................................. 269
Internet browsing through a VPN tunnel......................................................................... 269
Configuring Internet browsing through a VPN tunnel.................................................. 270
IPSec VPN in Transparent mode.................................................................................... 271
Special rules ............................................................................................................... 271
Hub and spoke VPNs...................................................................................................... 272
Configuring the hub..................................................................................................... 272
Configuring spokes ..................................................................................................... 274
Redundant IPSec VPNs.................................................................................................. 275
Configuring redundant IPSec VPNs............................................................................ 275
Configuring IPSec virtual IP addresses .......................................................................... 276
Troubleshooting .............................................................................................................. 278
Contents
IPS ....................................................................................................................... 279
Signature......................................................................................................................... 280
Predefined................................................................................................................... 280
Custom........................................................................................................................ 284
Anomaly.......................................................................................................................... 286
Anomaly CLI configuration.......................................................................................... 289
Configuring IPS logging and alert email.......................................................................... 290
Default fail open setting .................................................................................................. 290
FortiGate-50A Administration Guide 01-28006-0001-20041105 9
Page 10

Contents
Antivirus ............................................................................................................. 291
File block......................................................................................................................... 292
File block list ............................................................................................................... 293
Configuring the file block list ....................................................................................... 294
Quarantine ...................................................................................................................... 294
Quarantined files list ................................................................................................... 294
Quarantined files list options....................................................................................... 295
AutoSubmit list ............................................................................................................ 296
AutoSubmit list options ............................................................................................... 296
Configuring the AutoSubmit list................................................................................... 296
Config.......................................................................................................................... 297
Config.............................................................................................................................. 298
Virus list ...................................................................................................................... 298
Config.......................................................................................................................... 298
Grayware .................................................................................................................... 299
Grayware options........................................................................................................ 299
CLI configuration............................................................................................................. 300
heuristic....................................................................................................................... 300
quarantine ................................................................................................................... 301
service http.................................................................................................................. 302
service ftp.................................................................................................................... 303
service pop3................................................................................................................ 304
service imap................................................................................................................ 305
service smtp................................................................................................................ 306
Web filter............................................................................................................. 309
Content block.................................................................................................................. 310
Web content block list ................................................................................................. 311
Web content block options.......................................................................................... 311
Configuring the web content block list ........................................................................ 312
URL block ....................................................................................................................... 312
Web URL block list...................................................................................................... 313
Web URL block options .............................................................................................. 313
Configuring the web URL block list ............................................................................. 313
Web pattern block list.................................................................................................. 314
Web pattern block options .......................................................................................... 315
Configuring web pattern block .................................................................................... 315
URL exempt.................................................................................................................... 315
URL exempt list........................................................................................................... 316
URL exempt list options .............................................................................................. 316
Configuring URL exempt............................................................................................. 316
10 01-28006-0001-20041105 Fortinet Inc.
Page 11

Category block................................................................................................................ 317
FortiGuard managed web filtering service .................................................................. 317
Category block configuration options.......................................................................... 318
Configuring web category block.................................................................................. 319
Category block reports................................................................................................ 319
Category block reports options ................................................................................... 320
Generating a category block report............................................................................. 320
Category block CLI configuration................................................................................ 320
Script filter....................................................................................................................... 321
Web script filter options............................................................................................... 322
Spam filter .......................................................................................................... 323
IP address....................................................................................................................... 326
IP address list ............................................................................................................. 326
IP address options ...................................................................................................... 326
Configuring the IP address list .................................................................................... 327
RBL & ORDBL ................................................................................................................ 327
RBL & ORDBL list....................................................................................................... 328
RBL & ORDBL options................................................................................................ 328
Configuring the RBL & ORDBL list ............................................................................. 328
Email address ................................................................................................................. 329
Email address list........................................................................................................ 329
Email address options................................................................................................. 329
Configuring the email address list............................................................................... 330
MIME headers................................................................................................................. 330
MIME headers list ....................................................................................................... 331
MIME headers options ................................................................................................ 331
Configuring the MIME headers list.............................................................................. 331
Banned word................................................................................................................... 332
Banned word list ......................................................................................................... 332
Banned word options .................................................................................................. 333
Configuring the banned word list ................................................................................ 334
Using Perl regular expressions....................................................................................... 334
Contents
Log & Report ...................................................................................................... 337
Log config ....................................................................................................................... 338
Log Setting options ..................................................................................................... 338
Alert E-mail options..................................................................................................... 342
Log filter options.......................................................................................................... 343
Configuring log filters .................................................................................................. 346
Enabling traffic logging................................................................................................ 346
Log access...................................................................................................................... 347
Viewing log messages ................................................................................................ 347
Searching log messages............................................................................................. 349
FortiGate-50A Administration Guide 01-28006-0001-20041105 11
Page 12
Contents
CLI configuration............................................................................................................. 350
fortilog setting.............................................................................................................. 350
syslogd setting ............................................................................................................ 351
FortiGuard categories ....................................................................................... 355
FortiGate maximum values ............................................................................... 361
Glossary ............................................................................................................. 365
Index .................................................................................................................... 369
12 01-28006-0001-20041105 Fortinet Inc.
Page 13

FortiGate-50A Administration Guide Version 2.80 MR6
Introduction
FortiGate Antivirus Firewalls support network-based deployment of application-level
services, including antivirus protection and full-scan content filtering. FortiGate
Antivirus Firewalls improve network security, reduce network misuse and abuse, and
help you use communications resources more efficiently without compromising the
performance of your network. FortiGate Antivirus Firewalls are ICSA-certified for
firewall, IPSec, and antivirus services.
This chapter introduces you to FortiGate Antivirus Firewalls and the following topics:
• About FortiGate Antivirus Firewalls
• Document conventions
• FortiGate documentation
• Related documentation
• Customer service and technical support
About FortiGate Antivirus Firewalls
The FortiGate Antivirus Firewall is a dedicated easily managed security device that
delivers a full suite of capabilities that include:
• application-level services such as virus protection and content filtering,
• network-level services such as firewall, intrusion detection, VPN, and traffic
shaping.
The FortiGate Antivirus Firewall uses Fortinet’s Accelerated Behavior and Content
Analysis System (ABACAS™) technology, which leverages breakthroughs in chip
design, networking, security, and content analysis. The unique ASIC-based
architecture analyzes content and behavior in real-time, enabling key applications to
be deployed right at the network edge, where they are most effective at protecting
your networks. The FortiGate series complements existing solutions, such as hostbased antivirus protection, and enables new applications and services while greatly
lowering costs for equipment, administration, and maintenance.
The FortiGate-50A model is designed for
telecommuters and small remote offices with 10
or fewer employees. The FortiGate-50A
provides complete real-time network protection
through a combination of network-based
antivirus, web and email content filtering, firewall, VPN, network-based intrusion
detection and prevention, and traffic shaping.
PWR
STATUS
A
INTERNAL EXTERNAL
LINK 100 LINK 100
FortiGate-50A Administration Guide 01-28006-0001-20041105 13
Page 14

About FortiGate Antivirus Firewalls Introduction
Antivirus protection
FortiGate ICSA-certified antivirus protection scans web (HTTP), file transfer (FTP),
and email (SMTP, POP3, and IMAP) content as it passes through the FortiGate unit.
FortiGate antivirus protection uses pattern matching and heuristics to find viruses. If a
virus is found, antivirus protection removes the file containing the virus from the
content stream and forwards a replacement message to the intended recipient.
For extra protection, you can configure antivirus protection to block specified file types
from passing through the FortiGate unit. You can use the feature to stop files that
might contain new viruses.
FortiGate antivirus protection can also identify and remove known grayware
programs. Grayware programs are usually unsolicited commercial software programs
that get installed on PCs, often without the user’s consent or knowledge. Grayware
programs are generally considered an annoyance, but these programs can cause
system performance problems or be used for malicious means.
If the FortiGate unit contains a hard disk, infected or blocked files and grayware files
can be quarantined. The FortiGate administrator can download quarantined files so
that they can be virus scanned, cleaned, and forwarded to the intended recipient. You
can also configure the FortiGate unit to automatically delete quarantined files after a
specified time.
The FortiGate unit can send email alerts to system administrators when it detects and
removes a virus from a content stream. The web and email content can be in normal
network traffic or encrypted IPSec VPN traffic.
ICSA Labs has certified that FortiGate Antivirus Firewalls:
• detect 100% of the viruses listed in the current In The Wild List (www.wildlist.org),
• detect viruses in compressed files using the PKZip format,
• detect viruses in email that has been encoded using uuencode format,
• detect viruses in email that has been encoded using MIME encoding,
• log all actions taken while scanning.
Web content filtering
FortiGate web content filtering can scan all HTTP content protocol streams for URLs,
URL patterns, and web page content. If there is a match between a URL on the URL
block list, or a web page contains a word or phrase that is in the content block list, the
FortiGate unit blocks the web page. The blocked web page is replaced with a
message that you can edit using the FortiGate web-based manager.
FortiGate web content filtering also supports FortiGuard web category blocking. Using
web category blocking you can restrict or allow access to web pages based on
content ratings of web pages.
You can configure URL blocking to block all or some of the pages on a web site. Using
this feature, you can deny access to parts of a web site without denying access to it
completely.
To prevent unintentionally blocking legitimate web pages, you can add URLs to an
exempt list that overrides the URL blocking and content blocking lists. The exempt list
also exempts web traffic this address from virus scanning.
14 01-28006-0001-20041105 Fortinet Inc.
Page 15

Introduction About FortiGate Antivirus Firewalls
Web content filtering also includes a script filter feature that can block unsecure web
content such as Java applets, cookies, and ActiveX.
Spam filtering
FortiGate spam filtering can scan all POP3, SMTP, and IMAP email content for spam.
You can configure spam filtering to filter mail according to IP address, email address,
mime headers, and content. Mail messages can be identified as spam or clear.
You can also add the names of known Real-time Blackhole List (RBL) and Open
Relay Database List (ORDBL) servers. These services contain lists of known spam
sources.
If an email message is found to be spam, the FortiGate adds an email tag to the
subject line of the email. The recipient can use the mail client software to filter
messages based on the email tag. Spam filtering can also be configured to delete
SMTP email messages identified as spam.
Firewall
The FortiGate ICSA-certified firewall protects your computer networks from Internet
threats. ICSA has granted FortiGate firewalls version 4.0 firewall certification,
providing assurance that FortiGate firewalls successfully screen and secure corporate
networks against a range of threats from public or other untrusted networks.
After basic installation of the FortiGate unit, the firewall allows users on the protected
network to access the Internet while blocking Internet access to internal networks. You
can configure the firewall to put controls on access to the Internet from the protected
networks and to allow controlled access to internal networks.
FortiGate policies include a range of options that:
• control all incoming and outgoing network traffic,
• control encrypted VPN traffic,
• apply antivirus protection and web content filtering,
• block or allow access for all policy options,
• control when individual policies are in effect,
• accept or deny traffic to and from individual addresses,
• control standard and user defined network services individually or in groups,
• require users to authenticate before gaining access,
• include traffic shaping to set access priorities and guarantee or limit bandwidth for
each policy,
• include logging to track connections for individual policies,
• include Network Address Translation (NAT) mode and Route mode policies,
• include mixed NAT and Route mode policies.
The FortiGate firewall can operate in NAT/Route mode or Transparent mode.
NAT/Route mode
In NAT/Route mode, the FortiGate unit is a Layer 3 device. This means that each of its
interfaces is associated with a different IP subnet and that it appears to other devices
as a router. This is how a firewall is normally deployed.
FortiGate-50A Administration Guide 01-28006-0001-20041105 15
Page 16

About FortiGate Antivirus Firewalls Introduction
In NAT/Route mode, you can create NAT mode policies and Route mode policies.
• NAT mode policies use network address translation to hide the addresses in a
more secure network from users in a less secure network.
• Route mode policies accept or deny connections between networks without
performing address translation.
Transparent mode
In Transparent mode, the FortiGate unit does not change the Layer 3 topology. This
means that all of its interfaces are on the same IP subnet and that it appears to other
devices as a bridge. Typically, the FortiGate unit is deployed in Transparent mode to
provide antivirus and content filtering behind an existing firewall solution.
Transparent mode provides the same basic firewall protection as NAT mode. The
FortiGate unit passes or blocks the packets it receives according to firewall policies.
The FortiGate unit can be inserted in the network at any point without having to make
changes to your network or its components. However, some advanced firewall
features are available only in NAT/Route mode.
VLANs and virtual domains
Fortigate Antivirus Firewalls support IEEE 802.1Q-compliant virtual LAN (VLAN) tags.
Using VLAN technology, a single FortiGate unit can provide security services to, and
control connections between, multiple security domains according to the VLAN IDs
added to VLAN packets. The FortiGate unit can recognize VLAN IDs and apply
security policies to secure network and IPSec VPN traffic between each security
domain. The FortiGate unit can also apply authentication, content filtering, and
antivirus protection to VLAN-tagged network and VPN traffic.
The FortiGate unit supports VLANs in NAT/Route and Transparent mode. In
NAT/Route mode, you enter VLAN subinterfaces to receive and send VLAN packets.
FortiGate virtual domains provide multiple logical firewalls and routers in a single
FortiGate unit. Using virtual domains, one FortiGate unit can provide exclusive firewall
and routing services to multiple networks so that traffic from each network is
effectively separated from every other network.
You can develop and manage interfaces, VLAN subinterfaces, zones, firewall policies,
routing, and VPN configuration for each virtual domain separately. For these
configuration settings, each virtual domain is functionally similar to a single FortiGate
unit. This separation simplifies configuration because you do not have to manage as
many routes or firewall policies at one time.
Intrusion Prevention System (IPS)
The FortiGate Intrusion Prevention System (IPS) combines signature and anomaly
based intrusion detection and prevention. The FortiGate unit can record suspicious
traffic in logs, can send alert email to system administrators, and can log, pass, drop,
reset, or clear suspicious packets or sessions. Both the IPS predefined signatures and
the IPS engine are upgradeable through the FortiProtect Distribution Network (FDN).
You can also create custom signatures.
16 01-28006-0001-20041105 Fortinet Inc.
Page 17

Introduction About FortiGate Antivirus Firewalls
VPN
Using FortiGate virtual private networking (VPN), you can provide a secure
connection between widely separated office networks or securely link telecommuters
or travellers to an office network.
FortiGate VPN features include the following:
• Industry standard and ICSA-certified IPSec VPN, including:
• IPSec VPN in NAT/Route and Transparent mode,
• IPSec, ESP security in tunnel mode,
• DES, 3DES (triple-DES), and AES hardware accelerated encryption,
• HMAC MD5 and HMAC SHA1 authentication and data integrity,
• AutoIKE key based on pre-shared key tunnels,
• IPSec VPN using local or CA certificates,
• Manual Keys tunnels,
• Diffie-Hellman groups 1, 2, and 5,
• Aggressive and Main Mode,
• Replay Detection,
• Perfect Forward Secrecy,
• XAuth authentication,
• Dead peer detection,
• DHCP over IPSec,
• Secure Internet browsing.
• PPTP for easy connectivity with the VPN standard supported by the most popular
operating systems.
• L2TP for easy connectivity with a more secure VPN standard, also supported by
many popular operating systems.
• Firewall policy based control of IPSec VPN traffic.
• IPSec NAT traversal so that remote IPSec VPN gateways or clients behind a NAT
can connect to an IPSec VPN tunnel.
• VPN hub and spoke using a VPN concentrator to allow VPN traffic to pass from
one tunnel to another through the FortiGate unit.
• IPSec Redundancy to create a redundant AutoIKE key IPSec VPN connection to a
remote network.
Secure installation, configuration, and management
The first time you power on the FortiGate unit, it is already configured with default IP
addresses and security policies. Connect to the web-based manager, set the
operating mode, and use the Setup wizard to customize FortiGate IP addresses for
your network, and the FortiGate unit is ready to protect your network. You can then
use the web-based manager to customize advanced FortiGate features.
Web-based manager
Using HTTP or a secure HTTPS connection from any computer running Internet
Explorer, you can configure and manage the FortiGate unit. The web-based manager
supports multiple languages. You can configure the FortiGate unit for HTTP and
HTTPS administration from any FortiGate interface.
FortiGate-50A Administration Guide 01-28006-0001-20041105 17
Page 18

About FortiGate Antivirus Firewalls Introduction
You can use the web-based manager to configure most FortiGate settings. You can
also use the web-based manager to monitor the status of the FortiGate unit.
Configuration changes made using the web-based manager are effective immediately
without resetting the firewall or interrupting service. Once you are satisfied with a
configuration, you can download and save it. The saved configuration can be restored
at any time.
Command line interface
You can access the FortiGate command line interface (CLI) by connecting a
management computer serial port to the FortiGate RS-232 serial console connector.
You can also use Telnet or a secure SSH connection to connect to the CLI from any
network that is connected to the FortiGate unit, including the Internet.
The CLI supports the same configuration and monitoring functionality as the
web-based manager. In addition, you can use the CLI for advanced configuration
options that are not available from the web-based manager.
This Administration Guide contains information about basic and advanced CLI
commands. For a more complete description about connecting to and using the
FortiGate CLI, see the FortiGate CLI Reference Guide.
Logging and reporting
The FortiGate unit supports logging for various categories of traffic and configuration
changes. You can configure logging to:
• report traffic that connects to the firewall,
• report network services used,
• report traffic that was permitted by firewall policies,
• report traffic that was denied by firewall policies,
• report events such as configuration changes and other management events, IPSec
tunnel negotiation, virus detection, attacks, and web page blocking,
• report attacks detected by the IPS,
• send alert email to system administrators to report virus incidents, intrusions, and
firewall or VPN events or violations.
Logs can be sent to a remote syslog server or a WebTrends NetIQ Security Reporting
Center and Firewall Suite server using the WebTrends enhanced log format. Some
models can also save logs to an optional internal hard drive. If a hard drive is not
installed, you can configure most FortiGate units to log the most recent events and
attacks detected by the IPS to the system memory.
18 01-28006-0001-20041105 Fortinet Inc.
Page 19

Introduction Document conventions
Document conventions
This guide uses the following conventions to describe CLI command syntax.
• Angle brackets < > to indicate variables.
For example:
execute restore config <filename_str>
You enter:
execute restore config myfile.bak
<xxx_str> indicates an ASCII string that does not contain new-lines or carriage
returns.
<xxx_integer> indicates an integer string that is a decimal (base 10) number.
<xxx_octet> indicates a hexadecimal string that uses the digits 0-9 and letters
A-F.
<xxx_ipv4> indicates a dotted decimal IPv4 address.
<xxx_v4mask> indicates a dotted decimal IPv4 netmask.
<xxx_ipv4mask> indicates a dotted decimal IPv4 address followed by a dotted
decimal IPv4 netmask.
<xxx_ipv6> indicates a dotted decimal IPv6 address.
<xxx_v6mask> indicates a dotted decimal IPv6 netmask.
<xxx_ipv6mask> indicates a dotted decimal IPv6 address followed by a dotted
decimal IPv6 netmask.
• Vertical bar and curly brackets {|} to separate alternative, mutually exclusive
required keywords.
For example:
set opmode {nat | transparent}
You can enter set opmode nat or set opmode transparent.
• Square brackets [ ] to indicate that a keyword or variable is optional.
For example:
show system interface [<name_str>]
To show the settings for all interfaces, you can enter show system interface.
To show the settings for the internal interface, you can enter show system
interface internal.
• A space to separate options that can be entered in any combination and must be
separated by spaces.
For example:
set allowaccess {ping https ssh snmp http telnet}
You can enter any of the following:
set allowaccess ping
set allowaccess ping https ssh
set allowaccess https ping ssh
FortiGate-50A Administration Guide 01-28006-0001-20041105 19
Page 20

FortiGate documentation Introduction
set allowaccess snmp
In most cases to make changes to lists that contain options separated by spaces,
you need to retype the whole list including all the options you want to apply and
excluding all the options you want to remove.
FortiGate documentation
Information about FortiGate products is available from the following guides:
• FortiGate QuickStart Guide
Provides basic information about connecting and installing a FortiGate unit.
• FortiGate Installation Guide
Describes how to install a FortiGate unit. Includes a hardware reference, default
configuration information, installation procedures, connection procedures, and
basic configuration procedures. Choose the guide for your product model number.
• FortiGate Administration Guide
Provides basic information about how to configure a FortiGate unit, including how
to define FortiGate protection profiles and firewall policies; how to apply intrusion
prevention, antivirus protection, web content filtering, and spam filtering; and how
to configure a VPN.
• FortiGate online help
Provides a context-sensitive and searchable version of the Administration Guide in
HTML format. You can access online help from the web-based manager as you
work.
• FortiGate CLI Reference Guide
Describes how to use the FortiGate CLI and contains a reference to all FortiGate
CLI commands.
• FortiGate Log Message Reference Guide
Describes the structure of FortiGate log messages and provides information about
the log messages that are generated by FortiGate units.
• FortiGate High Availability Guide
Contains in-depth information about the FortiGate high availability feature and the
FortiGate clustering protocol.
Comments on Fortinet technical documentation
Please send information about any errors or omissions in this document, or any
Fortinet technical documentation, to techdoc@fortinet.com.
20 01-28006-0001-20041105 Fortinet Inc.
Page 21

Introduction Related documentation
Related documentation
Additional information about Fortinet products is available from the following related
documentation.
FortiManager documentation
• FortiManager QuickStart Guide
Explains how to install the FortiManager Console, set up the FortiManager Server,
and configure basic settings.
• FortiManager System Administration Guide
Describes how to use the FortiManager System to manage FortiGate devices.
• FortiManager System online help
Provides a searchable version of the Administration Guide in HTML format. You
can access online help from the FortiManager Console as you work.
FortiClient documentation
• FortiClient Host Security User Guide
Describes how to use FortiClient Host Security software to set up a VPN
connection from your computer to remote networks, scan your computer for
viruses, and restrict access to your computer and applications by setting up firewall
policies.
• FortiClient Host Security online help
Provides information and procedures for using and configuring the FortiClient
software.
FortiMail documentation
• FortiMail Administration Guide
Describes how to install, configure, and manage a FortiMail unit in gateway mode
and server mode, including how to configure the unit; create profiles and policies;
configure antispam and antivirus filters; create user accounts; and set up logging
and reporting.
• FortiMail online help
Provides a searchable version of the Administration Guide in HTML format. You
can access online help from the web-based manager as you work.
• FortiMail Web Mail Online Help
Describes how to use the FortiMail web-based email client, including how to send
and receive email; how to add, import, and export addresses; and how to configure
message display preferences.
FortiGate-50A Administration Guide 01-28006-0001-20041105 21
Page 22

Related documentation Introduction
FortiLog documentation
• FortiLog Administration Guide
Describes how to install and configure a FortiLog unit to collect FortiGate and
FortiMail log files. It also describes how to view FortiGate and FortiMail log files,
generate and view log reports, and use the FortiLog unit as a NAS server.
• FortiLog online help
Provides a searchable version of the Administration Guide in HTML format. You
can access online help from the web-based manager as you work.
22 01-28006-0001-20041105 Fortinet Inc.
Page 23

Introduction Customer service and technical support
Customer service and technical support
For antivirus and attack definition updates, firmware updates, updated product
documentation, technical support information, and other resources, please visit the
Fortinet Technical Support web site at http://support.fortinet.com.
You can also register Fortinet products and service contracts from
http://support.fortinet.com and change your registration information at any time.
Technical support is available through email from any of the following addresses.
Choose the email address for your region:
amer_support@fortinet.com For customers in the United States, Canada, Mexico, Latin
apac_support@fortinet.com For customers in Japan, Korea, China, Hong Kong, Singapore,
eu_support@fortinet.com For customers in the United Kingdom, Scandinavia, Mainland
America and South America.
Malaysia, all other Asian countries, and Australia.
Europe, Africa, and the Middle East.
For information about our priority support hotline (live support), see
http://support.fortinet.com.
When requesting technical support, please provide the following information:
• your name
• your company’s name and location
• your email address
• your telephone number
• your support contract number (if applicable)
• the product name and model number
• the product serial number (if applicable)
• the software or firmware version number
• a detailed description of the problem
FortiGate-50A Administration Guide 01-28006-0001-20041105 23
Page 24

Customer service and technical support Introduction
24 01-28006-0001-20041105 Fortinet Inc.
Page 25
FortiGate-50A Administration Guide Version 2.80 MR6
System status
You can connect to the web-based manager and view the current system status of the
FortiGate unit. The status information that is displayed includes the system status, unit
information, system resources, and session log.
This chapter includes:
• Console access
• Status
• Session list
• Changing the FortiGate firmware
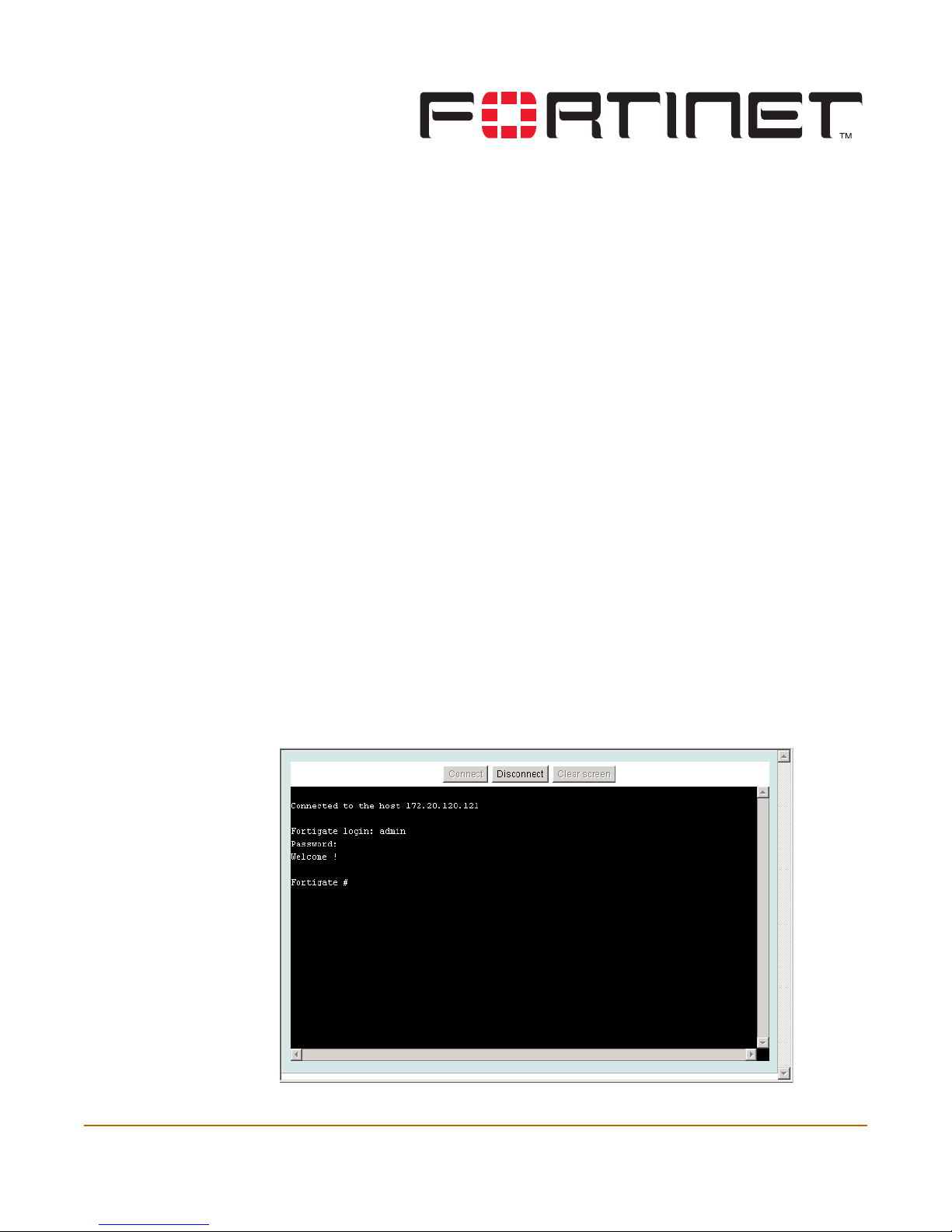
Console access
An alternative to the web-based manager discussed in this manual is text-based
Console Access, using the FortiGate command line interface (CLI). You can get
console access by selecting Console Access button in the upper right corner of the
web-based manager. The management computer must have Java version 1.3 or
higher installed.
For information on how to use the CLI, see the FortiGate CLI Reference Guide.
Figure 1: Console access
FortiGate-50A Administration Guide 01-28006-0001-20041105 25
Page 26
Status System status
Connect Select Connect to connect to the CLI.
Disconnect Select Disconnect to disconnect from the CLI.
Clear screen Select Clear screen to start a new page.
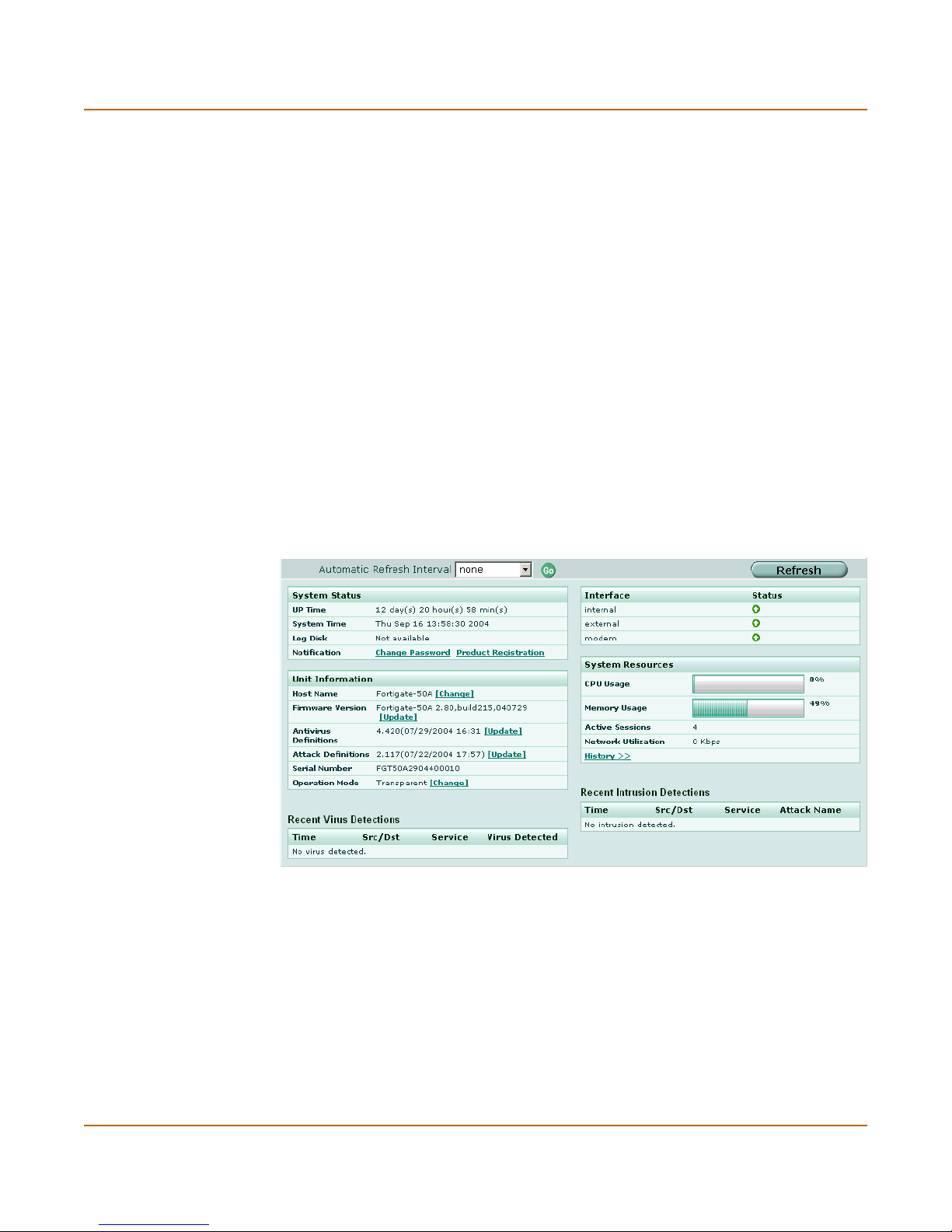
Status
View the system status page for a snap shot of the current operating status of the
FortiGate unit. All FortiGate administrators with read access to system configuration
can view system status information.
FortiGate administrators whose access profiles contain system configuration write
privileges can change or update FortiGate unit information. For information on access
profiles, see “Access profiles” on page 99.
• Viewing system status
• Changing unit information
Viewing system status
Figure 2: System status
Automatic Refresh
Interval
Go Select to set the selected automatic refresh interval.
Refresh Select to manually update the system status display.
System status
UP Time The time in days, hours, and minutes since the FortiGate unit was last
System Time The current time according to the FortiGate unit internal clock.
26 01-28006-0001-20041105 Fortinet Inc.
Select to control how often the web-based manager updates the system
status display.
started.
Page 27

System status Status
Log Disk Displays hard disk capacity and free space if the FortiGate unit contains a
Notification Contains reminders such as “Change Password” or “Product Registration”.
hard disk or Not Available if no hard disk is installed. The FortiGate unit uses
the hard disk to store log messages and quarantine files infected with a virus
or blocked by antivirus file blocking.
Select the reminder to see the detailed reminder message.
Unit Information
Admin users and administrators whose access profiles contain system configuration
read and write privileges can change or update the unit information. For information
on access profiles, see “Access profiles” on page 99.
Host Name The host name of the current FortiGate unit.
Firmware Version The version of the firmware installed on the current FortiGate unit.
Antivirus Definitions The current installed version of the FortiGate Antivirus Definitions.
Attack Definitions The current installed version of the FortiGate Attack Definitions used by
Serial Number The serial number of the current FortiGate unit.
the Intrusion Prevention System (IPS).
The serial number is
specific to the FortiGate unit and does not change with firmware
upgrades.
Operation Mode The operation mode of the current FortiGate unit.
Recent Virus Detections
Time The time at which the recent virus was detected.
Src / Dst The source and destination addresses of the virus.
Service The service from which the virus was delivered; HTTP, FTP, IMAP,
Virus Detected The name of the virus detected.
POP3, or SMTP.
Interface Status
All interfaces in the FortiGate unit are listed in the table.
Interface The name of the interface.
IP / Netmask The IP address and netmask of the interface (NAT/Route mode only).
Status The status of the interface; either up (green up arrow) or down (red
down arrow).
System Resources
CPU Usage The current CPU status. The web-based manager displays CPU usage
Memory Usage The current memory status. The web-based manager displays memory
FortiGate-50A Administration Guide 01-28006-0001-20041105 27
for core processes only. CPU usage for management processes (for
example, for HTTPS connections to the web-based manager) is
excluded.
usage for core processes only. Memory usage for management
processes (for example, for HTTPS connections to the web-based
manager) is excluded.
Page 28

Status System status
Hard Disk Usage The current hard disk (local disk) status. The web-based manager
Active Sessions The number of communications sessions being processed by the
Network Utilization The total network bandwidth being used through all FortiGate interfaces
History Select History to view a graphical representation of the last minute of
Figure 3: Sample system resources history
displays hard disk usage for core processes only. CPU usage for
management processes (for example, for HTTPS connections to the
web-based manager) is excluded.
FortiGate unit.
and the percentage of the maximum network bandwidth that can be
processed by the FortiGate unit.
CPU, memory, sessions, and network usage. This page also shows the
virus and intrusion detections over the last 20 hours.
History
The history page displays 6 graphs representing the following system resources and
protection:
CPU Usage History CPU usage for the previous minute.
Memory Usage History Memory usage for the previous minute.
Session History Session history for the previous minute.
Network Utilization
History
Virus History The virus detection history over the last 20 hours.
Intrusion History The intrusion detection history over the last 20 hours.
Network utilization for the previous minute.
Recent Intrusion Detections
Time The time at which the recent intrusion was detected.
Src / Dst The source and destination addresses of the attack.
Service The service from which the attack was delivered; HTTP, FTP, IMAP,
Attack Name The name of the attack.
POP3, or SMTP.
28 01-28006-0001-20041105 Fortinet Inc.
Page 29

System status Status
Changing unit information
Administrators with system configuration write access can use the unit information
area of the System Status page:
• To change FortiGate host name
• To update the firmware version
• To update the antivirus definitions manually
• To update the attack definitions manually
• To change to Transparent mode
• To change to NAT/Route mode
To change FortiGate host name
The FortiGate host name appears on the Status page and in the FortiGate CLI
prompt. The host name is also used as the SNMP system name. For information
about the SNMP system name, see “SNMP” on page 84.
The default host name is FortiGate-50.
1 Go to System > Status > Status.
2 In the Host Name field of the Unit Information section, select Change.
3 In the New Name field, type a new host name.
4 Select OK.
The new host name is displayed in the Host Name field, and in the CLI prompt, and is
added to the SNMP System Name.
To update the firmware version
For information on updating the firmware, see “Changing the FortiGate firmware” on
page 32.
To update the antivirus definitions manually
Note: For information about configuring the FortiGate unit for automatic antivirus definitions
updates, see “Update center” on page 106.
1 Download the latest antivirus definitions update file from Fortinet and copy it to the
computer that you use to connect to the web-based manager.
2 Start the web-based manager and go to System > Status > Status.
3 In the Antivirus Definitions field of the Unit Information section, select Update.
4 In the Update File field, type the path and filename for the antivirus definitions update
file, or select Browse and locate the antivirus definitions update file.
5 Select OK to copy the antivirus definitions update file to the FortiGate unit.
The FortiGate unit updates the antivirus definitions. This takes about 1 minute.
6 Go to System > Status to confirm that the Antivirus Definitions Version information
has updated.
FortiGate-50A Administration Guide 01-28006-0001-20041105 29
Page 30
Status System status
To update the attack definitions manually
Note: For information about configuring the FortiGate unit for automatic attack definitions
updates, see “Update center” on page 106.
1 Download the latest attack definitions update file from Fortinet and copy it to the
computer that you use to connect to the web-based manager.
2 Start the web-based manager and go to System > Status > Status.
3 In the Attack Definitions field of the Unit Information section, select Update.
The Intrusion Detection System Definitions Update dialog box appears.
4 In the Update File field, type the path and filename for the attack definitions update
file, or select Browse and locate the attack definitions update file.
5 Select OK to copy the attack definitions update file to the FortiGate unit.
The FortiGate unit updates the attack definitions. This takes about 1 minute.
6 Go to System > Status > Status to confirm that the Attack Definitions Version
information has updated.
To change to Transparent mode
After you change the FortiGate unit from the NAT/Route mode to Transparent mode,
most of the configuration resets to Transparent mode factory defaults.
To change to Transparent mode:
1 Go to System > Status > Status.
2 In the Operation Mode field of the Unit Information section, select Change.
3 In the Operation Mode field, select Transparent.
4 Select OK.
The FortiGate unit changes operation mode.
5 To reconnect to the web-based manager, connect to the interface configured for
Transparent mode management access and browse to https:// followed by the
Transparent mode management IP address.
By default in Transparent mode, you can connect to the internal interface. The default
Transparent mode management IP address is 10.10.10.1.
Note: If the web-based manager IP address was on a different subnet in NAT/Route mode, you
may have to change the IP address of your computer to the same subnet as the management
IP address.
To change to NAT/Route mode
After you change the FortiGate unit from the NAT/Route mode to Transparent mode,
most of the configuration resets to Transparent mode factory defaults.
To change to NAT/Route mode:
1 Go to System > Status > Status.
2 In the Operation Mode field of the Unit Information section, select Change.
3 In the Operation Mode field, select NAT/Route.
30 01-28006-0001-20041105 Fortinet Inc.
Page 31

System status Session list
4 Select OK.
The FortiGate unit changes operation mode.
5 To reconnect to the web-based manager, you must connect to the interface
configured by default for management access.
By default in NAT/Route mode, you can connect to the internal interface. The default
internal interface IP address is 192.168.1.99.
Note: If the management IP address was on a different subnet in Transparent mode, you may
have to change the IP address of your computer to the same subnet as the interface configured
for management access.
Session list
The session list displays information about the communications sessions currently
being processed by the FortiGate unit. You can use the session list to view current
sessions.
Figure 4: Sample session list
From IP Set source IP address for list filtering
From Port Set source port for list filtering
To IP Set destination IP address for list filtering
To Port Set destination port for list filtering
Apply Filter Select to filter session list
Virtual Domain Select a virtual domain to list the sessions being processed by that virtual
Total Number of
Sessions
Protocol The service protocol of the connection, for example, udp, tcp, or icmp.
From IP The source IP address of the connection.
From Port The source port of the connection.
To IP The destination IP address of the connection.
To Port The destination port of the connection.
Expire The time, in seconds, before the connection expires.
domain. Select All to view sessions being processed by all virtual domains.
Total number of sessions currently being conducted through the FortiGate
unit.
Refresh icon. Select to update the session list
Page up icon. Select to view previous page in the session list
Page down icon. Select to view the next page in the session list.
Delete icon. Select to stop an active communication session.
FortiGate-50A Administration Guide 01-28006-0001-20041105 31
Page 32

Changing the FortiGate firmware System status
To view the session list
1 Go to System > Status > Session.
The web-based manager displays the total number of active sessions in the FortiGate
unit session table and lists the top 16.
2 To navigate the list of sessions, select Page Up or Page Down.
3 Select Refresh to update the session list.
4 If you are logged in as an administrative user with read and write privileges or as the
admin user, you can select Clear to stop an active session.
Changing the FortiGate firmware
FortiGate administrators whose access profiles contain system configuration read and
write privileges and the FortiGate admin user can change the FortiGate firmware.
After you download a FortiGate firmware image from Fortinet, you can use the
procedures listed in Table 1 to install the firmware image on your FortiGate unit.
Table 1: Firmware upgrade procedures
Procedure Description
Upgrading to a new
firmware version
Reverting to a
previous firmware
version
Installing firmware
images from a system
reboot using the CLI
Testing a new
firmware image before
installing it
Use the web-based manager or CLI procedure to upgrade to a new
FortiOS firmware version or to a more recent build of the same
firmware version.
Use the web-based manager or CLI procedure to revert to a
previous firmware version. This procedure reverts the FortiGate
unit to its factory default configuration.
Use this procedure to install a new firmware version or revert to a
previous firmware version. To use this procedure you must connect
to the CLI using the FortiGate console port and a null-modem
cable. This procedure reverts the FortiGate unit to its factory
default configuration.
Use this procedure to test a new firmware image before installing it.
To use this procedure you must connect to the CLI using the
FortiGate console port and a null-modem cable. This procedure
temporarily installs a new firmware image using your current
configuration. You can test the firmware image before installing it
permanently. If the firmware image works correctly you can use
one of the other procedures listed in this table to install it
permanently.
Upgrading to a new firmware version
Use the following procedures to upgrade the FortiGate unit to a newer firmware
version.
Upgrading the firmware using the web-based manager
Note: Installing firmware replaces the current antivirus and attack definitions with the definitions
included with the firmware release that you are installing. After you install new firmware, use the
procedure “To update antivirus and attack definitions” on page 109 to make sure that antivirus
and attack definitions are up to date.
32 01-28006-0001-20041105 Fortinet Inc.
Page 33

System status Changing the FortiGate firmware
To upgrade the firmware using the web-based manager
1 Copy the firmware image file to your management computer.
2 Log into the web-based manager as the admin administrative user.
Note: To use this procedure you must login using the admin administrator account, or an
administrator account that has system configuration read and write privileges.
3 Go to System > Status.
4 Under Unit Information > Firmware Version, select Update.
5 Type the path and filename of the firmware image file, or select Browse and locate the
file.
6 Select OK.
The FortiGate unit uploads the firmware image file, upgrades to the new firmware
version, restarts, and displays the FortiGate login. This process takes a few minutes.
7 Log into the web-based manager.
8 Go to System > Status and check the Firmware Version to confirm that the firmware
upgrade is successfully installed.
9 Update antivirus and attack definitions. For information about updating antivirus and
attack definitions, see “Update center” on page 106.
Upgrading the firmware using the CLI
To use the following procedure you must have a TFTP server that the FortiGate unit
can connect to.
Note: Installing firmware replaces your current antivirus and attack definitions with the
definitions included with the firmware release that you are installing. After you install new
firmware, use the procedure “To update antivirus and attack definitions” on page 109 to make
sure that antivirus and attack definitions are up to date. You can also use the CLI command
execute update_now to update the antivirus and attack definitions.
To upgrade the firmware using the CLI
1 Make sure that the TFTP server is running.
2 Copy the new firmware image file to the root directory of the TFTP server.
3 Log into the CLI.
Note: To use this procedure you must login using the admin administrator account, or an
administrator account that has system configuration read and write privileges.
4 Make sure the FortiGate unit can connect to the TFTP server.
You can use the following command to ping the computer running the TFTP server.
For example, if the IP address of the TFTP server is 192.168.1.168:
execute ping 192.168.1.168
5 Enter the following command to copy the firmware image from the TFTP server to the
FortiGate unit:
execute restore image <name_str> <tftp_ipv4>
FortiGate-50A Administration Guide 01-28006-0001-20041105 33
Page 34

Changing the FortiGate firmware System status
Where <name_str> is the name of the firmware image file and <tftp_ip> is the IP
address of the TFTP server. For example, if the firmware image file name is
FGT_300-v280-build183-FORTINET.out and the IP address of the TFTP server
is 192.168.1.168, enter:
execute restore image FGT_300-v280-build183-FORTINET.out
192.168.1.168
The FortiGate unit responds with the message:
This operation will replace the current firmware version!
Do you want to continue? (y/n)
6 Type y.
The FortiGate unit uploads the firmware image file, upgrades to the new firmware
version, and restarts. This process takes a few minutes.
7 Reconnect to the CLI.
8 To confirm that the new firmware image is successfully installed, enter:
get system status
9 Use the procedure “To update antivirus and attack definitions” on page 109 to update
antivirus and attack definitions, or from the CLI, enter:
execute update_now
Reverting to a previous firmware version
Use the following procedures to revert your FortiGate unit to a previous firmware
version.
Reverting to a previous firmware version using the web-based
manager
The following procedures revert the FortiGate unit to its factory default configuration
and deletes IPS custom signatures, web content lists, email filtering lists, and changes
to replacement messages.
Before beginning this procedure you can:
• Back up the FortiGate unit configuration.
• Back up the IPS custom signatures.
• Back up web content and email filtering lists.
For information, see “Backing up and Restoring” on page 104.
If you are reverting to a previous FortiOS version (for example, reverting from FortiOS
v2.80 to FortiOS v2.50), you might not be able to restore the previous configuration
from the backup configuration file.
Note: Installing firmware replaces the current antivirus and attack definitions with the definitions
included with the firmware release that you are installing. After you install new firmware, use the
procedure “To update antivirus and attack definitions” on page 109 to make sure that antivirus
and attack definitions are up to date.
34 01-28006-0001-20041105 Fortinet Inc.
Page 35

System status Changing the FortiGate firmware
To revert to a previous firmware version using the web-based manager
1 Copy the firmware image file to the management computer.
2 Log into the FortiGate web-based manager.
Note: To use this procedure you must login using the admin administrator account, or an
administrator account that has system configuration read and write privileges.
3 Go to System > Status.
4 Under Unit Information > Firmware Version, select Update.
5 Type the path and filename of the firmware image file, or select Browse and locate the
file.
6 Select OK.
The FortiGate unit uploads the firmware image file, reverts to the old firmware version,
resets the configuration, restarts, and displays the FortiGate login. This process takes
a few minutes.
7 Log into the web-based manager.
8 Go to System > Status and check the Firmware Version to confirm that the firmware
is successfully installed.
9 Restore your configuration.
For information about restoring your configuration, see “Backup and restore” on
page 103.
10 Update antivirus and attack definitions.
For information about antivirus and attack definitions, see “To update antivirus and
attack definitions” on page 109.
Reverting to a previous firmware version using the CLI
This procedure reverts the FortiGate unit to its factory default configuration and
deletes IPS custom signatures, web content lists, email filtering lists, and changes to
replacement messages.
Before beginning this procedure you can:
• Back up the FortiGate unit system configuration using the command execute
backup config.
• Back up the IPS custom signatures using the command execute backup
ipsuserdefsig
• Back up web content and email filtering lists.
For information, see “Backing up and Restoring” on page 104.
If you are reverting to a previous FortiOS version (for example, reverting from FortiOS
v2.80 to FortiOS v2.50), you might not be able to restore your previous configuration
from the backup configuration file.
FortiGate-50A Administration Guide 01-28006-0001-20041105 35
Page 36

Changing the FortiGate firmware System status
Note: Installing firmware replaces the current antivirus and attack definitions with the definitions
included with the firmware release that you are installing. After you install new firmware, use the
procedure “To update antivirus and attack definitions” on page 109 to make sure that antivirus
and attack definitions are up to date. You can also use the CLI command execute
update_now
to update the antivirus and attack definitions.
To use the following procedure you must have a TFTP server that the FortiGate unit
can connect to.
To revert to a previous firmware version using the CLI
1 Make sure that the TFTP server is running.
2 Copy the firmware image file to the root directory of the TFTP server.
3 Log into the FortiGate CLI.
Note: To use this procedure you must login using the admin administrator account, or an
administrator account that has system configuration read and write privileges.
4 Make sure the FortiGate unit can connect to the TFTP server.
You can use the following command to ping the computer running the TFTP server.
For example, if the TFTP server's IP address is 192.168.1.168:
execute ping 192.168.1.168
5 Enter the following command to copy the firmware image from the TFTP server to the
FortiGate unit:
execute restore image <name_str> <tftp_ipv4>
Where <name_str> is the name of the firmware image file and <tftp_ip> is the IP
address of the TFTP server. For example, if the firmware image file name is
FGT_300-v280-build158-FORTINET.out and the IP address of the TFTP server
is 192.168.1.168, enter:
execute restore image FGT_300-v280-build158-FORTINET.out
192.168.1.168
The FortiGate unit responds with the message:
This operation will replace the current firmware version!
Do you want to continue? (y/n)
6 Type y.
The FortiGate unit uploads the firmware image file. After the file uploads, a message
similar to the following is displayed:
Get image from tftp server OK.
Check image OK.
This operation will downgrade the current firmware version!
Do you want to continue? (y/n)
7 Type y.
The FortiGate unit reverts to the old firmware version, resets the configuration to
factory defaults, and restarts. This process takes a few minutes.
8 Reconnect to the CLI.
36 01-28006-0001-20041105 Fortinet Inc.
Page 37

System status Changing the FortiGate firmware
9 To confirm that the new firmware image has been loaded, enter:
get system status
10 To restore your previous configuration if needed, use the command:
execute restore config <name_str> <tftp_ipv4>
11 Update antivirus and attack definitions.
For information, see “To update antivirus and attack definitions” on page 109, or from
the CLI, enter:
execute update_now
Installing firmware images from a system reboot using the CLI
This procedure installs a specified firmware image and resets the FortiGate unit to
default settings. You can use this procedure to upgrade to a new firmware version,
revert to an older firmware version, or re-install the current firmware version.
Note: This procedure varies for different FortiGate BIOS versions. These variations are
explained in the procedure steps that are affected. The version of the BIOS running on the
FortiGate unit is displayed when you restart the FortiGate unit using the CLI through a console
connection.
For this procedure you:
• access the CLI by connecting to the FortiGate console port using a null-modem
cable,
• install a TFTP server that you can connect to from the FortiGate internal interface.
The TFTP server should be on the same subnet as the internal interface.
Before beginning this procedure you can:
• Back up the FortiGate unit configuration.
For information, see “Backing up and Restoring” on page 104.
• Back up the IPS custom signatures.
For information, see “Backing up and restoring custom signature files” on
page 285.
• Back up web content and email filtering lists.
For information, see “Web filter” on page 309 and “Spam filter” on page 323.
If you are reverting to a previous FortiOS version (for example, reverting from FortiOS
v2.80 to FortiOS v2.50), you might not be able to restore your previous configuration
from the backup configuration file.
Note: Installing firmware replaces the current antivirus and attack definitions with the definitions
included with the firmware release that you are installing. After you install new firmware, use the
procedure “To update antivirus and attack definitions” on page 109 to make sure that antivirus
and attack definitions are up to date.
To install firmware from a system reboot
1 Connect to the CLI using the null-modem cable and FortiGate console port.
2 Make sure that the TFTP server is running.
3 Copy the new firmware image file to the root directory of the TFTP server.
FortiGate-50A Administration Guide 01-28006-0001-20041105 37
Page 38

Changing the FortiGate firmware System status
4 Make sure that the internal interface is connected to the same network as the TFTP
server.
5 To confirm that the FortiGate unit can connect to the TFTP server, use the following
command to ping the computer running the TFTP server. For example, if the IP
address of the TFTP server is 192.168.1.168, enter:
execute ping 192.168.1.168
6 Enter the following command to restart the FortiGate unit:
execute reboot
The FortiGate unit responds with the following message:
This operation will reboot the system !
Do you want to continue? (y/n)
7 Type y.
As the FortiGate units starts, a series of system startup messages is displayed.
When one of the following messages appears:
• FortiGate unit running v2.x BIOS
Press Any Key To Download Boot Image.
...
• FortiGate unit running v3.x BIOS
Press any key to display configuration menu.....
......
Immediately press any key to interrupt the system startup.
Note: You have only 3 seconds to press any key. If you do not press a key soon enough, the
FortiGate unit reboots and you must log in and repeat the execute reboot command.
If you successfully interrupt the startup process, one of the following messages
appears:
• FortiGate unit running v2.x BIOS
Enter TFTP Server Address [192.168.1.168]:
Go to step 9.
• FortiGate unit running v3.x BIOS
[G]: Get firmware image from TFTP server.
[F]: Format boot device.
[B]: Boot with backup firmware and set as default.
[Q]: Quit menu and continue to boot with default firmware.
[H]: Display this list of options.
Enter G,F,B,Q,or H:
8 Type G to get the new firmware image from the TFTP server.
The following message appears:
Enter TFTP server address [192.168.1.168]:
9 Type the address of the TFTP server and press Enter.
The following message appears:
Enter Local Address [192.168.1.188]:
38 01-28006-0001-20041105 Fortinet Inc.
Page 39

System status Changing the FortiGate firmware
10 Type an IP address that the FortiGate unit can use to connect to the TFTP server.
The IP address can be any IP address that is valid for the network that the interface is
connected to. Make sure you do not enter the IP address of another device on this
network.
The following message appears:
Enter File Name [image.out]:
11 Enter the firmware image filename and press Enter.
The TFTP server uploads the firmware image file to the FortiGate unit and messages
similar to the following are displayed:
• FortiGate unit running v2.x BIOS
Do You Want To Save The Image? [Y/n]
Type Y.
• FortiGate unit running v3.x BIOS
Save as Default firmware/Run image without saving:[D/R]
or
Save as Default firmware/Backup firmware/Run image without
saving:[D/B/R]
12 Type D.
The FortiGate unit installs the new firmware image and restarts. The installation might
take a few minutes to complete.
Restoring the previous configuration
Change the internal interface address if required. You can do this from the CLI using
the command:
config system interface
edit internal
set ip <address_ipv4mask>
set allowaccess {ping https ssh telnet http}
end
After changing the interface address, you can access the FortiGate unit from the
web-based manager and restore the configuration.
• To restore the FortiGate unit configuration, see “Backup and restore” on page 103.
• To restore IPS custom signatures, see “Backing up and restoring custom signature
files” on page 285.
• To restore web content filtering lists, see “Backup and restore” on page 103.
• To restore email filtering lists, see “Backup and restore” on page 103.
• To update the virus and attack definitions to the most recent version, see
“Updating antivirus and attack definitions” on page 108.
If you are reverting to a previous firmware version (for example, reverting from
FortiOS v2.80 to FortiOS v2.50), you might not be able to restore your previous
configuration from the backup up configuration file.
FortiGate-50A Administration Guide 01-28006-0001-20041105 39
Page 40

Changing the FortiGate firmware System status
Testing a new firmware image before installing it
You can test a new firmware image by installing the firmware image from a system
reboot and saving it to system memory. After completing this procedure the FortiGate
unit operates using the new firmware image with the current configuration. This new
firmware image is not permanently installed. The next time the FortiGate unit restarts,
it operates with the originally installed firmware image using the current configuration.
If the new firmware image operates successfully, you can install it permanently using
the procedure “Upgrading to a new firmware version” on page 32.
For this procedure you:
• access the CLI by connecting to the FortiGate console port using a null-modem
cable,
• install a TFTP server that you can connect to from the FortiGate internal interface.
The TFTP server should be on the same subnet as the internal interface.
To test a new firmware image
1 Connect to the CLI using a null-modem cable and FortiGate console port.
2 Make sure the TFTP server is running.
3 Copy the new firmware image file to the root directory of the TFTP server.
4 Make sure that the internal interface is connected to the same network as the TFTP
server.
You can use the following command to ping the computer running the TFTP server.
For example, if the TFTP server's IP address is 192.168.1.168:
execute ping 192.168.1.168
5 Enter the following command to restart the FortiGate unit:
execute reboot
6 As the FortiGate unit reboots, press any key to interrupt the system startup.
As the FortiGate units starts, a series of system startup messages are displayed.
When one of the following messages appears:
• FortiGate unit running v2.x BIOS
Press Any Key To Download Boot Image.
...
• FortiGate unit running v3.x BIOS
Press any key to display configuration menu.....
......
7 Immediately press any key to interrupt the system startup.
Note: You have only 3 seconds to press any key. If you do not press a key soon enough, the
FortiGate unit reboots and you must log in and repeat the execute reboot command.
40 01-28006-0001-20041105 Fortinet Inc.
Page 41

System status Changing the FortiGate firmware
If you successfully interrupt the startup process, one of the following messages
appears:
• FortiGate unit running v2.x BIOS
Enter TFTP Server Address [192.168.1.168]:
Go to step 9.
• FortiGate unit running v3.x BIOS
[G]: Get firmware image from TFTP server.
[F]: Format boot device.
[Q]: Quit menu and continue to boot with default firmware.
[H]: Display this list of options.
Enter G,F,Q,or H:
8 Type G to get the new firmware image from the TFTP server.
The following message appears:
Enter TFTP server address [192.168.1.168]:
9 Type the address of the TFTP server and press Enter.
The following message appears:
Enter Local Address [192.168.1.188]:
10 Type an IP address that can be used by the FortiGate unit to connect to the FTP
server.
The IP address must be on the same network as the TFTP server, but make sure you
do not use the IP address of another device on this network.
The following message appears:
Enter File Name [image.out]:
11 Enter the firmware image file name and press Enter.
The TFTP server uploads the firmware image file to the FortiGate unit and messages
similar to the following appear.
• FortiGate unit running v2.x BIOS
Do You Want To Save The Image? [Y/n]
Type N.
• FortiGate unit running v3.x BIOS
Save as Default firmware/Run image without saving:[D/R]
or
Save as Default firmware/Backup firmware/Run image without
saving:[D/B/R]
12 Type R.
The FortiGate image is installed to system memory and the FortiGate unit starts
running the new firmware image but with its current configuration.
13 You can log into the CLI or the web-based manager using any administrative account.
14 To confirm that the new firmware image has been loaded, from the CLI enter:
get system status
You can test the new firmware image as required.
FortiGate-50A Administration Guide 01-28006-0001-20041105 41
Page 42

Changing the FortiGate firmware System status
42 01-28006-0001-20041105 Fortinet Inc.
Page 43

FortiGate-50A Administration Guide Version 2.80 MR6
System network
System network settings control how the FortiGate unit connects to and interacts with
your network. Basic network settings start with configuring FortiGate interfaces to
connect to your network and configuring the FortiGate DNS settings.
More advanced network settings include adding VLAN subinterfaces and zones to the
FortiGate network configuration.
• Interface
• Zone
• Management
• DNS
• Routing table (Transparent Mode)
• Configuring the modem interface
• VLAN overview
• VLANs in NAT/Route mode
• VLANs in Transparent mode
• FortiGate IPv6 support
Interface
In NAT/Route mode, go to System > Network > Interface to configure FortiGate
interfaces and to add and configure VLAN subinterfaces.
Note: Unless stated otherwise, in this section the term interface can refer to a physical
FortiGate interface or to a FortiGate VLAN subinterface.
• For information about VLANs in NAT/Route mode, see “VLANs in NAT/Route
mode” on page 64.
• For information about VLANs in Transparent mode, see “VLANs in Transparent
mode” on page 67.
FortiGate-50A Administration Guide 01-28006-0001-20041105 43
Page 44

Interface System network
Figure 5: Interface list
Create New Select Create New to create a VLAN.
Virtual Domain Select a virtual domain to display the interfaces added to this virtual domain.
Name The names of the physical interfaces available to your FortiGate unit.
IP The current IP address of the interface.
Netmask The netmask of the interface.
Access The administrative access configuration for the interface.
Status The administrative status for the interface.
Only available if you have added a virtual domain.
• Interface names indicate the default function of the interface (for
example, internal and external)
• The modem interface is available if a modem is connected to the USB
port (see “Configuring the modem interface” on page 59)
If you have added VLAN subinterfaces, they also appear in the name list,
below the physical interface that they have been added to. See “VLAN
overview” on page 63.
See “To control administrative access to an interface” on page 52 for
information about administrative access options.
If the administrative status is a green arrow, the interface is up and can
accept network traffic. If the administrative status is a red arrow, the
interface is administratively down and cannot accept traffic. To change the
administrative status, select Bring Down or Bring Up. For more information,
see “To bring down an interface that is administratively up” on page 50 and
“To start up an interface that is administratively down” on page 50.
Delete, edit, and view icons.
Interface settings
Interface settings displays the current configuration of a selected FortiGate interface
or VLAN subinterface. Use interface settings to configure a new VLAN subinterface or
to change the configuration of a FortiGate interface or VLAN subinterface.
44 01-28006-0001-20041105 Fortinet Inc.
Page 45

System network Interface
Figure 6: Interface settings
See the following procedures for configuring interfaces:
• To bring down an interface that is administratively up
• To start up an interface that is administratively down
• To add interfaces to a zone
• To add an interface to a virtual domain
• To change the static IP address of an interface
• To configure an interface for DHCP
• To configure an interface for PPPoE
• To add a secondary IP address
• To add a ping server to an interface
• To control administrative access to an interface
• To change the MTU size of the packets leaving an interface
• To configure traffic logging for connections to an interface
Name
The name of the Interface.
Interface
Select the name of the physical interface to add the VLAN subinterface to. All VLAN
subinterfaces must be associated with a physical interface. Once created, the VLAN is
listed below its physical interface in the Interface list.
VLAN ID
Enter the VLAN ID that matches the VLAN ID of the packets to be received by this
VLAN subinterface. You cannot change the VLAN ID of an existing VLAN
subinterface.
FortiGate-50A Administration Guide 01-28006-0001-20041105 45
Page 46

Interface System network
The VLAN ID can be any number between 1 and 4096 and must match the VLAN ID
added by the IEEE 802.1Q-compliant router or switch connected to the VLAN
subinterface.
For more information on VLANs, see “VLAN overview” on page 63.
Virtual Domain
Select a virtual domain to add the interface or VLAN subinterface to this virtual
domain. Virtual domain is only available if you have added a virtual domain.
For more information on virtual domains, see “System virtual domain” on page 119.
Addressing mode
Select Manual, DHCP, or PPPoE to set the addressing mode for this interface.
Manual
Select Manual and enter an IP address and netmask for the interface. The IP address
of the interface must be on the same subnet as the network the interface is connecting
to.
Note: Where you can enter both an IP address and a netmask in the same field, you can use
the short form of the netmask. For example, 192.168.1.100/255.255.255.0 can also be entered
as 192.168.1.100/24.
Two interfaces cannot have the same IP address and cannot have IP addresses on
the same subnet.
DHCP
If you configure the interface to use DHCP, the FortiGate unit automatically
broadcasts a DHCP request. You can disable Connect to server if you are configuring
the FortiGate unit offline and you do not want the FortiGate unit to send the DHCP
request.
Distance Enter the administrative distance for the default gateway retrieved from
Retrieve default
gateway from server
Override internal DNS Enable Override internal DNS to use the DNS addresses retrieved
Connect to server Enable Connect to Server so that the interface automatically attempts
Status Displays DHCP status messages as the FortiGate unit connects to the
initializing No activity.
the DHCP server. The administrative distance, an integer from 1-255,
specifies the relative priority of a route when there are multiple routes
to the same destination. A lower administrative distance indicates a
more preferred route. The default distance for the default gateway is 1.
Enable Retrieve default gateway from server to retrieve a default
gateway IP address from the DHCP server. The default gateway is
added to the static routing table.
from the DHCP server instead of the DNS server IP addresses on the
DNS page.
to connect to a DHCP server. Disable this option if you are configuring
the interface offline.
DHCP server and gets addressing information. Select Status to refresh
the addressing mode status message.
46 01-28006-0001-20041105 Fortinet Inc.
Page 47

System network Interface
connecting The interface is attempting to connect to the DHCP server.
connected The interface retrieves an IP address, netmask, and other settings
failed The interface was unable to retrieve an IP address and other
from the DHCP server.
information from the DHCP server.
PPPoE
If you configure the interface to use PPPoE, the FortiGate unit automatically
broadcasts a PPPoE request. You can disable connect to server if you are configuring
the FortiGate unit offline and you do not want the FortiGate unit to send the PPPoE
request.
FortiGate units support many of the PPPoE RFC features (RFC 2516) including
unnumbered IPs, initial discovery timeout that times and PPPoE Active Discovery
Terminate (PADT).
Figure 7: PPPoE settings
User Name The PPPoE account user name.
Password The PPPoE account password.
Unnumbered IP Specify the IP address for the interface. If your ISP has assigned you a
Initial Disc
Timeout
Initial PADT
timeout
Distance Enter the administrative distance for the default gateway retrieved from the
Retrieve default
gateway from
server
Override internal
DNS
block of IP addresses, use one of them. Otherwise, this IP address can be
the same as the IP address of another interface or can be any IP address.
Initial discovery timeout. The time to wait before retrying to start a PPPoE
discovery. Set Initial Disc to 0 to disable.
Initial PPPoE Active Discovery Terminate (PADT) timeout in seconds. Use
this timeout to shut down the PPPoE session if it is idle for this number of
seconds. PADT must be supported by your ISP. Set initial PADT timeout to
0 to disable.
PPPoE server. The administrative distance, an integer from 1-255,
specifies the relative priority of a route when there are multiple routes to the
same destination. A lower administrative distance indicates a more
preferred route. The default distance for the default gateway is 1.
Enable Retrieve default gateway from server to retrieve a default gateway
IP address from a PPPoE server. The default gateway is added to the static
routing table.
Enable Override internal DNS to replace the DNS server IP addresses on
the DNS page with the DNS addresses retrieved from the PPPoE server.
FortiGate-50A Administration Guide 01-28006-0001-20041105 47
Page 48

Interface System network
Connect to server Enable Connect to Server so that the interface automatically attempts to
Status Displays PPPoE status messages as the FortiGate unit connects to the
initializing No activity.
connecting The interface is attempting to connect to the PPPoE server.
connected The interface retrieves an IP address, netmask, and other settings from the
failed The interface was unable to retrieve an IP address and other information
connect to a PPPoE server. Disable this option if you are configuring the
interface offline.
PPPoE server and gets addressing information. Select Status to refresh the
addressing mode status message.
PPPoE server.
from the PPPoE server.
DDNS
Enable or disable updates to a Dynamic DNS (DDNS) service. When the FortiGate
unit has a static domain name and a dynamic public IP address, select DDNS Enable
to force the unit to update the DDNS server each time the address changes. In turn,
the DDNS service updates Internet DNS servers with the new IP address for the
domain.
Dynamic DNS is available only in NAT/Route mode.
Server Select a DDNS server to use. The client software for these services is built into the
Domain The domain name to use for the DDNS service.
Username The user name to use when connecting to the DDNS server.
Password The password to use when connecting to the DDNS server.
FortiGate firmware. The FortiGate unit can only connect automatically to a DDNS
server for the supported clients.
Ping server
Add a ping server to an interface if you want the FortiGate unit to confirm connectivity
with the next hop router on the network connected to the interface. Adding a ping
server is required for routing failover. See “To add or edit a static route” on page 132.
The FortiGate unit uses dead gateway detection to ping the Ping Server IP address to
make sure that the FortiGate unit can connect to this IP address. To configure dead
gateway detection, see “To modify the dead gateway detection settings” on page 84.
Administrative access
Configure administrative access to an interface to control how administrators access
the FortiGate unit and the FortiGate interfaces to which administrators can connect.
You can select the following administrative access options:
HTTPS To allow secure HTTPS connections to the web-based manager through this
PING If you want this interface to respond to pings. Use this setting to verify your
HTTP To allow HTTP connections to the web-based manager through this interface.
interface.
installation and for testing.
HTTP connections are not secure and can be intercepted by a third party.
48 01-28006-0001-20041105 Fortinet Inc.
Page 49

System network Interface
SSH To allow SSH connections to the CLI through this interface.
SNMP To allow a remote SNMP manager to request SNMP information by connecting to
TELNET To allow Telnet connections to the CLI through this interface. Telnet connections
this interface. See “Configuring SNMP” on page 85.
are not secure and can be intercepted by a third party.
MTU
To improve network performance, you can change the maximum transmission unit
(MTU) of the packets that the FortiGate unit transmits from any interface. Ideally, this
MTU should be the same as the smallest MTU of all the networks between the
FortiGate unit and the destination of the packets. If the packets that the FortiGate unit
sends are larger, they are broken up or fragmented, which slows down transmission.
Experiment by lowering the MTU to find an MTU size for best network performance.
To change the MTU, select Override default MTU value (1500) and enter the
maximum packet size. For manual and DHCP addressing mode the MTU size can be
from 576 to 1500 bytes. For PPPoE addressing mode the MTU size can be from 576
to 1492 bytes.
Note: In Transparent mode, if you change the MTU of an interface, you must change the MTU
of all interfaces to match the new MTU.
Log
Select Log to record logs for any traffic to or from the interface. To record logs you
must also enable traffic log for a logging location and set the logging severity level to
Notification or lower. Go to Log & Report > Log Config to configure logging locations
and types. For information about logging see “Log & Report” on page 337.
Configuring interfaces
Use the following procedures to configure FortiGate interfaces and VLAN
subinterfaces.
You cannot use the following procedures for the modem interface.
• To bring down an interface that is administratively up
• To add interfaces to a zone
• To add an interface to a virtual domain
• To change the static IP address of an interface
• To configure an interface for DHCP
• To configure an interface for PPPoE
• To add a secondary IP address
• To add a ping server to an interface
• To control administrative access to an interface
• To change the MTU size of the packets leaving an interface
• To configure traffic logging for connections to an interface
FortiGate-50A Administration Guide 01-28006-0001-20041105 49
Page 50

Interface System network
To add a VLAN subinterface
See “To add a VLAN subinterface in NAT/Route mode” on page 66.
To bring down an interface that is administratively up
You can bring down physical interfaces or VLAN subinterfaces. Bringing down a
physical interface also brings down the VLAN subinterfaces associated with it.
1 Go to System > Network > Interface.
The interface list is displayed.
2 Select Bring Down for the interface that you want to stop.
To start up an interface that is administratively down
You can start up physical interfaces and VLAN subinterfaces. Starting a physical
interface does not start the VLAN subinterfaces added to it.
1 Go to System > Network > Interface.
The interface list is displayed.
2 Select Bring Up for the interface that you want to start.
To add interfaces to a zone
If you have added zones to the FortiGate unit, you can use this procedure to add
interfaces or VLAN subinterfaces to the zone. To add a zone, see “To add a zone” on
page 54. You cannot add an interface to a zone if you have added firewall policies for
the interface. Delete firewall policies for the interface and then add the interface to the
zone.
1 Go to System > Network > Zone.
2 Choose the zone to add the interface or VLAN subinterface to and select Edit.
3 Select the names of the interfaces or VLAN subinterfaces to add to the zone.
4 Select OK to save the changes.
To add an interface to a virtual domain
If you have added virtual domains to the FortiGate unit, you can use this procedure to
add an interface or VLAN subinterface to a virtual domain. To add a virtual domain,
see “To add a virtual domain” on page 123. You cannot add an interface to a virtual
domain if you have added firewall policies for the interface. Delete firewall policies for
the interface and then add the interface to the virtual domain.
1 Go to System > Network > Interface.
2 Choose the interface or VLAN subinterface to add to a virtual domain and select Edit.
3 From the Virtual Domain list, select the virtual domain that you want to add the
interface to.
4 Select OK to save the changes.
5 Repeat these steps to add more interfaces or VLAN subinterfaces to virtual domains.
50 01-28006-0001-20041105 Fortinet Inc.
Page 51

System network Interface
To change the static IP address of an interface
You can change the static IP address of any FortiGate interface.
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 Set Addressing Mode to Manual.
4 Change the IP address and Netmask as required.
5 Select OK to save your changes.
If you changed the IP address of the interface to which you are connecting to manage
the FortiGate unit, you must reconnect to the web-based manager using the new
interface IP address.
To configure an interface for DHCP
You can configure any FortiGate interface to use DHCP.
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 In the Addressing Mode section, select DHCP.
4 Select the Retrieve default gateway and DNS from server check box if you want the
FortiGate unit to obtain a default gateway IP address and DNS server IP addresses
from the DHCP server.
5 Select the Connect to Server check box if you want the FortiGate unit to connect to
the DHCP server.
6 Select Apply.
The FortiGate unit attempts to contact the DHCP server from the interface to set the
IP address, netmask, and optionally the default gateway IP address, and DNS server
IP addresses.
7 Select Status to refresh the addressing mode status message.
8 Select OK.
To configure an interface for PPPoE
Use this procedure to configure any FortiGate interface to use PPPoE. See “PPPoE”
on page 47 for information on PPPoE settings.
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 In the Addressing Mode section, select PPPoE.
4 Enter your PPPoE account User Name and Password.
5 Enter an Unnumbered IP if required by your PPPoE service.
6 Set the Initial Disc Timeout and Initial PADT Timeout if supported by your ISP.
7 Select the Retrieve default gateway from server check box if you want the FortiGate
unit to obtain a default gateway IP address from the PPPoE server.
8 Select the Override Internal DNS check box if you want the FortiGate unit to obtain a
DNS server IP address from the PPPoE server.
FortiGate-50A Administration Guide 01-28006-0001-20041105 51
Page 52

Interface System network
9 Select the Connect to Server check box if you want the FortiGate unit to connect to
the PPPoE server.
10 Select Apply.
The FortiGate unit attempts to contact the PPPoE server from the interface to set the
IP address, netmask, and optionally default gateway IP address and DNS server IP
addresses.
11 Select Status to refresh the addressing mode status message.
12 Select OK.
To add a secondary IP address
You can use the CLI to add a secondary IP address to any FortiGate interface. The
secondary IP address cannot be the same as the primary IP address but it can be on
the same subnet.
From the FortiGate CLI, enter the following commands:
config system interface
edit <intf_str>
config secondaryip
edit 0
set ip <second_ip> <netmask_ip>
Optionally, you can also configure management access and add a ping server to the
secondary IP address:
set allowaccess ping https ssh snmp http telnet
set gwdetect enable
Save the changes:
end
To add a ping server to an interface
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 Set Ping Server to the IP address of the next hop router on the network connected to
the interface.
4 Select the Enable check box.
5 Select OK to save the changes.
To control administrative access to an interface
For a FortiGate unit running in NAT/Route mode, you can control administrative
access to an interface to control how administrators access the FortiGate unit and the
FortiGate interfaces to which administrators can connect.
52 01-28006-0001-20041105 Fortinet Inc.
Page 53

System network Zone
Controlling administrative access for an interface connected to the Internet allows
remote administration of the FortiGate unit from any location on the Internet. However,
allowing remote administration from the Internet could compromise the security of
your FortiGate unit. You should avoid allowing administrative access for an interface
connected to the Internet unless this is required for your configuration. To improve the
security of a FortiGate unit that allows remote administration from the Internet:
• Use secure administrative user passwords,
• Change these passwords regularly,
• Enable secure administrative access to this interface using only HTTPS or SSH,
• Do not change the system idle timeout from the default value of 5 minutes (see “To
set the system idle timeout” on page 83).
To configure administrative access in Transparent mode, see “To configure the
management interface” on page 56.
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 Select the Administrative Access methods for the interface.
4 Select OK to save the changes.
To change the MTU size of the packets leaving an interface
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
Zone
3 Select Override default MTU value (1500).
4 Set the MTU size.
Note: You cannot set the MTU of a VLAN larger than the MTU of its physical interface. Nor can
you set the MTU of a physical interface smaller than the MTU of any VLAN on that interface.
To configure traffic logging for connections to an interface
1 Go to System > Network > Interface.
2 Choose an interface and select Edit.
3 Select the Log check box to record log messages whenever a firewall policy accepts a
connection to this interface.
4 Select OK to save the changes.
You can use zones to group related interfaces and VLAN subinterfaces. Grouping
interfaces and VLAN subinterfaces into zones simplifies policy creation. If you group
interfaces and VLAN subinterfaces into a zone, you can configure policies for
connections to and from this zone, rather than to and from each interface and VLAN
subinterface.
FortiGate-50A Administration Guide 01-28006-0001-20041105 53
Page 54

Zone System network
You can add zones, rename and edit zones, and delete zones from the zone list.
When you add a zone, you select the names of the interfaces and VLAN subinterfaces
to add to the zone.
Zones are added to virtual domains. If you have added multiple virtual domains to
your FortiGate configuration, make sure you are configuring the correct virtual domain
before adding or editing zones.
Figure 8: Zone list
Create New Select Create New to create a zone.
Name The names of the zones that you have added.
Block intra-zone
traffic
Interface Members The names of the interfaces added to the zone.
Displays Yes if traffic between interfaces in the same zone is blocked and
No if traffic between interfaces in the same zone is not blocked.
Edit/View icons. Select to edit or view a zone.
Delete icon. Select to remove a zone.
Zone settings
1 If you have added a virtual domain, go to System > Virtual Domain > Current
2 Go to System > Network > Zone.
3 Select Create New.
Figure 9: Zone options
Name Enter the name to identify the zone.
Block intra-zone
traffic
Interface members Enable check boxes to select the interfaces that are part of this zone.
Select Block intra-zone traffic to block traffic between interfaces or VLAN
subinterfaces in the same zone.
To add a zone
Virtual Domain and select the virtual domain to which you want to add the zone.
4 In the New Zone dialog box, type a name for the zone.
54 01-28006-0001-20041105 Fortinet Inc.
Page 55

System network Management
5 Select the Block intra-zone traffic check box if you want to block traffic between
interfaces or VLAN subinterfaces in the same zone.
6 Select the names of the interfaces or VLAN subinterfaces to add to the zone.
7 Select OK.
To delete a zone
You can only delete zones that have the Delete icon beside them in the zone list.
1 If you have added a virtual domain, go to System > Virtual Domain > Current
Virtual Domain and select the virtual domain from which to delete the zone.
2 Go to System > Network > Zone.
3 Select Delete to remove a zone from the list.
4 Select OK to delete the zone.
To edit a zone
1 If you have added a virtual domain, go to System > Virtual Domain > Current
Virtual Domain and select the virtual domain in which to edit the zone.
2 Go to System > Network > Zone.
3 Select Edit to modify a zone.
4 Select or deselect Block intra-zone traffic.
5 Select the names of the interfaces or VLAN subinterfaces to add to the zone.
Management
6 Clear the check box for the names of the interfaces or VLAN subinterfaces to remove
from the zone.
7 Select OK.
Configure the management interface in Transparent mode to set the management IP
address of the FortiGate unit. Administrators connect to this IP address to administer
the FortiGate unit. The FortiGate also uses this IP address to connect to the FDN for
virus and attack updates (see “Update center” on page 106).
You can also configure interfaces to control how administrators connect to the
FortiGate unit for administration. See “To control administrative access to an
interface” on page 52.
FortiGate-50A Administration Guide 01-28006-0001-20041105 55
Page 56

DNS System network
Controlling administrative access to a FortiGate interface connected to the Internet
allows remote administration of the FortiGate unit from any location on the Internet.
However, allowing remote administration from the Internet could compromise the
security of the FortiGate unit. You should avoid allowing administrative access for an
interface connected to the Internet unless this is required for your configuration. To
improve the security of a FortiGate unit that allows remote administration from the
Internet:
• Use secure administrative user passwords,
• Change these passwords regularly,
• Enable secure administrative access to this interface using only HTTPS or SSH,
• Do not change the system idle timeout from the default value of 5 minutes (see “To
set the system idle timeout” on page 83).
Figure 10: Management
DNS
Management
IP/Netmask
Default
Gateway
Management
Virtual Domain
Enter the management IP address and netmask. This must be a valid IP
address for the network that you want to manage the FortiGate unit
from.
Enter the default gateway address.
Select the virtual domain from which you want to perform system
management.
To configure the management interface
1 Go to System > Network > Management.
2 Enter the Management IP/Netmask.
3 Enter the Default Gateway.
4 Select the Management Virtual Domain.
5 Select Apply.
The FortiGate unit displays the following message:
Management IP address was changed. Click here to redirect.
6 Click on the message to connect to the new Management IP.
Several FortiGate functions, including Alert E-mail and URL blocking, use DNS. You
can add the IP addresses of the DNS servers to which your FortiGate unit can
connect. DNS server IP addresses are usually supplied by your ISP.
56 01-28006-0001-20041105 Fortinet Inc.
Page 57

System network Routing table (Transparent Mode)
You can configure primary and secondary DNS server addresses, or you can
configure the FortiGate unit to obtain DNS server addresses automatically. To obtain
addresses automatically, at least one interface must use the DHCP or PPPoE
addressing mode. See “DHCP” on page 46. See “PPPoE” on page 47.
If you enable DNS Forwarding on an interface, hosts on the attached network can use
the interface IP address as their DNS server. DNS requests sent to the interface are
forwarded to the DNS server addresses you configured or that the FortiGate unit
obtained automatically.
Figure 11: DNS
Obtain DNS server
address automatically
Primary DNS Server Enter the primary DNS server IP address.
Secondary DNS Server Enter the secondary DNS server IP address.
Enable DNS
forwarding from
When DHCP is used on an interface, also obtain the DNS server IP
address. Available only in NAT/Route mode.
Enable the check boxes of the interfaces to which DNS Forwarding
applies. Available only in NAT/Route mode.
To add DNS server IP addresses
1 Go to System > Network > DNS.
2 Change the primary and secondary DNS server IP addresses as required.
3 Select Apply to save the changes.
Routing table (Transparent Mode)
In Transparent mode, you can configure routing to add static routes from the
FortiGate unit to local routers.
Routing table list
Figure 12: Routing table
FortiGate-50A Administration Guide 01-28006-0001-20041105 57
Page 58

Routing table (Transparent Mode) System network
Create New Select Create New to add a new route.
# Route number.
IP The destination IP address for this route.
Mask The netmask for this route.
Gateway The IP address of the next hop router to which this route directs traffic.
Distance The the relative preferability of this route. 1 is most preferred.
Delete icon. Select to remove a route.
View/edit icon. Select to view or edit a route.
Move To icon. Select to change the order of a route in the list.
Transparent mode route settings
Figure 13: Transparent mode route options
Destination IP
/Mask
Gateway Enter the IP address of the next hop router to which this route directs traffic
Distance The the relative preferability of this route. 1 is most preferred.
Enter the destination IP address and netmask for this route.
To add a Transparent mode route
1 Go to System > Network > Routing Table.
2 Select Create New to add a new route.
3 Set the Destination IP and Mask to 0.0.0.0.
For the default route, set the Destination IP and Mask to 0.0.0.0.
Note: Only one default route can be active at a time. If two default routes are added to the
routing table, only the default route closest to the top of the routing table is active.
4 Set Gateway to the IP address of the next hop routing gateway.
For an Internet connection, the next hop routing gateway routes traffic to the Internet.
5 Select OK to save the route.
58 01-28006-0001-20041105 Fortinet Inc.
Page 59

System network Configuring the modem interface
Configuring the modem interface
You can connect a modem to the FortiGate unit and use it as either a backup interface
or standalone interface in NAT/Route mode.
• In backup mode, the modem interface automatically takes over from a selected
ethernet interface when that ethernet interface is unavailable.
• In standalone mode, the modem interface is the connection from the FortiGate unit
to the Internet.
When connecting to the ISP, in either configuration, the FortiGate unit modem can
automatically dial up to three dialup accounts until the modem connects to an ISP.
• Connecting a modem to the FortiGate unit
• Configuring modem settings
• Connecting and disconnecting the modem
• Backup mode configuration
• Standalone mode configuration
• Adding firewall policies for modem connections
Figure 14: Example modem interface network connection
FortiGate-60
External modem
V.9 2
PWR STATUS
USB connector
USB-to-serial
converter
serial connector
Connecting a modem to the FortiGate unit
INTERNAL
LINK 100 LINK 100 LINK 100 LINK 100 LINK 100 LINK 100 LINK 100
DMZ4321
WAN1 WAN2
Internet
The FortiGate unit can operate with most standard external serial interface modems
that support standard Hayes AT commands. To connect, install a USB-to-serial
converter between one of the two USB ports on the FortiGate unit and the serial port
on the modem. The FortiGate unit does not support a direct USB connection between
the two devices.
FortiGate-50A Administration Guide 01-28006-0001-20041105 59
Page 60

Configuring the modem interface System network
Configuring modem settings
Configure modem settings so that the FortiGate unit uses the modem to connect to
your ISP dialup accounts. You can configure the modem to connect to up to three
dialup accounts. You can also enable and disable FortiGate modem support,
configure how the modem dials, and select the FortiGate interface that the modem is
redundant for.
Figure 15: Modem settings
Enable USB
Modem
Dial Up/Hang UpSelect Dial Up to manually connect to a dialup account. If the modem is
Redial Limit The maximum number of times (1-10) that the FortiGate unit dials the ISP to
Holddown
Timer
Redundant for To associate the modem interface with the ethernet interface that you want to
Dialup Account Configure up to three dialup accounts. The FortiGate unit try connecting to
Phone Number The phone number required to connect to the dialup account. Do not add
User Name The user name (maximum 63 characters) sent to the ISP.
Password The password sent to the ISP.
Select to enable the FortiGate modem. When the modem is dialing modem
status shows whether the modem is active or not active.
connected, you can select Hang Up to manually disconnect the modem.
restore an active connection on the modem interface. The default redial limit
is 1. Select None to allow the modem to never stop redialing.
For backup configurations. The time (1-60 seconds) that the FortiGate unit
waits before switching from the modem interface to the primary interface,
after the primary interface has been restored. The default is 1 second.
Configure a higher value if you find the FortiGate unit switching repeatedly
between the primary interface and the modem interface.
either back up (backup configuration) or replace (standalone configuration).
each account in order until a connection can be established.
spaces to the phone number. Make sure to include standard special
characters for pauses, country codes, and other functions as required by
your modem to connect to your dialup account.
60 01-28006-0001-20041105 Fortinet Inc.
Page 61

System network Configuring the modem interface
To configure modem settings
You can configure and use the modem in NAT/Route mode only.
1 Go to System > Network > Modem.
2 Select Enable USB Modem.
3 Change any of the following dialup connection settings:
4 Enter the following Dialup Account 1 settings:
5 If you have multiple dialup accounts, enter Phone Number, User Name, and
Password for Dialup Account 2 and Dialup Account 3.
6 Select Apply.
Connecting and disconnecting the modem
To connect to a dialup account
1 Go to System > Network > Modem.
2 Select Enable USB Modem.
3 Make sure there is correct information in one or more Dialup Accounts.
4 Select Apply if you make any configuration changes.
5 Select Dial Up.
The FortiGate unit initiates dialing into each dialup account in turn until the modem
connects to an ISP.
To disconnect the modem
Use the following procedure to disconnect the modem from a dialup account.
1 Go to System > Network > Modem.
2 Select Hang Up if you want to disconnect from the dialup account.
To disconnect the modem
1 Go to System > Network > Modem.
Modem status is one of the following:
not active The modem interface is not connected to the ISP.
active The modem interface is attempting to connect to the ISP, or is connected to
A green check mark indicates the active dialup account.
The IP address and netmask assigned to the modem interface appears on the System
Network Interface page of the web-based manager.
Backup mode configuration
The modem interface in backup mode backs up a selected ethernet interface. If that
ethernet interface disconnects from its network, the modem automatically dials the
configured dialup accounts. When the modem connects to a dialup account, the
FortiGate unit routes IP packets normally destined for the selected ethernet interface
to the modem interface.
the ISP.
FortiGate-50A Administration Guide 01-28006-0001-20041105 61
Page 62

Configuring the modem interface System network
The FortiGate unit disconnects the modem interface and switches back to the
ethernet interface when the ethernet interface can again connect to its network.
For the FortiGate unit to be able to switch from an ethernet interface to the modem
you must select the name of the interface in the modem configuration and configure a
ping server for that interface. You must also configure firewall policies for connections
between the modem interface and other FortiGate interfaces.
Note: Do not add policies for connections between the modem interface and the interface that
the modem is backing up.
To configure backup mode
1 Go to System > Network > Modem.
2 From the Redundant for list, select the ethernet interface that you want the modem to
back up.
3 Configure other modem settings as required.
See “Configuring modem settings” on page 60.
4 Configure a ping server for the ethernet interface selected in step 2.
See “To add a ping server to an interface” on page 52.
5 Configure firewall policies for connections to the modem interface.
See “Adding firewall policies for modem connections” on page 63.
Standalone mode configuration
In standalone mode, you manually connect the modem to a dialup account. The
modem interface operates as the primary connection to the Internet. The FortiGate
unit routes traffic through the modem interface, which remains permanently connected
to the dialup account.
If the connection to the dialup account fails, the FortiGate unit redials the modem. The
modem redials the number of times specified by the redial limit, or until it connects to a
dialup account.
In standalone mode the modem interface replaces the WAN1 or WAN2 ethernet
interface. When configuring the modem, you must set Redundant for to the name of
the ethernet interface that the modem interface replaces. You must also configure
firewall policies for connections between the modem interface and other FortiGate
interfaces.
Note: Do not add a default route to the ethernet interface that the modem interface replaces.
Note: Do not add firewall policies for connections between the ethernet interface that the
modem replaces and other interfaces.
To operate in standalone mode
1 Go to System > Network > Modem.
2 From the Redundant for list, select the ethernet interface that the modem is replacing.
62 01-28006-0001-20041105 Fortinet Inc.
Page 63

System network VLAN overview
3 Configure other modem settings as required.
See “Configuring modem settings” on page 60.
Make sure there is correct information in one or more Dialup Accounts.
4 Select Dial Up.
The FortiGate unit initiates dialing into each dialup account in turn until the modem
connects to an ISP.
5 Configure firewall policies for connections to the modem interface.
See “Adding firewall policies for modem connections” on page 63.
Adding firewall policies for modem connections
The modem interface requires firewall addresses and policies. You can add one or
more addresses to the modem interface. For information about adding addresses, see
“To add an address” on page 188. When you add addresses, the modem interface
appears on the policy grid.
You can configure firewall policies to control the flow of packets between the modem
interface and the other interfaces on the FortiGate unit. For information about adding
firewall policies, see “To add a firewall policy” on page 184.
VLAN overview
A VLAN is group of PCs, servers, and other network devices that communicate as if
they were on the same LAN segment, even though they may not be. For example, the
workstations and servers for an accounting department could be scattered throughout
an office, connected to numerous network segments, but they can still belong to the
same VLAN.
A VLAN segregates devices logically instead of physically. Each VLAN is treated as a
broadcast domain. Devices in VLAN 1 can connect with other devices in VLAN 1, but
cannot connect with devices in other VLANs. The communication among devices on a
VLAN is independent of the physical network.
A VLAN segregates devices by adding 802.1Q VLAN tags to all of the packets sent
and received by the devices in the VLAN. VLAN tags are 4-byte frame extensions that
contain a VLAN identifier as well as other information.
VLANs allow highly flexible, efficient network segmentation, enabling users and
resources to be grouped logically, regardless of physical locations.
FortiGate-50A Administration Guide 01-28006-0001-20041105 63
Page 64

VLANs in NAT/Route mode System network
Figure 16: Basic VLAN topology
Internet
Untagged
packets
Esc Enter
VLAN trunk
VLAN 1
VLAN 2
Firewall or
Router
VLAN 1 network VLAN 2 network
FortiGate units and VLANs
In a typical VLAN configuration, 802.1Q-compliant VLAN layer-2 switches or layer-3
routers or firewalls add VLAN tags to packets. Packets passing between devices in
the same VLAN can be handled by layer 2 switches. Packets passing between
devices in different VLANs must be handled by a layer 3 device such as router,
firewall, or layer 3 switch.
Using VLANs, a single FortiGate unit can provide security services and control
connections between multiple security domains. Traffic from each security domain is
given a different VLAN ID. The FortiGate unit can recognize VLAN IDs and apply
security policies to secure network and IPSec VPN traffic between security domains.
The FortiGate unit can also apply authentication, protection profiles, and other firewall
policy features for network and VPN traffic that is allowed to pass between security
domains.
POWER
VLAN 1
VLAN Switch or router
VLAN 2
VLANs in NAT/Route mode
Operating in NAT/Route mode, the FortiGate unit functions as a layer 3 device to
control the flow of packets between VLANs. The FortiGate unit can also remove VLAN
tags from incoming VLAN packets and forward untagged packets to other networks,
such as the Internet.
64 01-28006-0001-20041105 Fortinet Inc.
Page 65

System network VLANs in NAT/Route mode
In NAT/Route mode, the FortiGate units support VLANs for constructing VLAN trunks
between an IEEE 802.1Q-compliant switch (or router) and the FortiGate unit. Normally
the FortiGate unit internal interface connects to a VLAN trunk on an internal switch,
and the external interface connects to an upstream Internet router untagged. The
FortiGate unit can then apply different policies for traffic on each VLAN that connects
to the internal interface.
In this configuration, you add VLAN subinterfaces to the FortiGate internal interface
that have VLAN IDs that match the VLAN IDs of packets in the VLAN trunk. The
FortiGate unit directs packets with VLAN IDs, to subinterfaces with matching VLAN
IDs.
You can also define VLAN subinterfaces on all FortiGate interfaces. The FortiGate
unit can add VLAN tags to packets leaving a VLAN subinterface or remove VLAN tags
from incoming packets and add a different VLAN tags to outgoing packets.
Rules for VLAN IDs
In NAT/Route mode, two VLAN subinterfaces added to the same physical interface
cannot have the same VLAN ID. However, you can add two or more VLAN
subinterfaces with the same VLAN IDs to different physical interfaces. There is no
internal connection or link between two VLAN subinterfaces with same VLAN ID. Their
relationship is the same as the relationship between any two FortiGate network
interfaces.
Rules for VLAN IP addresses
IP addresses of all FortiGate interfaces cannot overlap. That is, the IP addresses of all
interfaces must be on different subnets. This rule applies to both physical interfaces
and to VLAN subinterfaces.
Note: If you are unable to change your existing configurations to prevent IP overlap, enter the
CLI command config system global and set ip-overlap enable to allow IP address
overlap. If you enter this command, multiple VLAN interfaces can have an IP address that is
part of a subnet used by another interface. This command is recommended for advanced users
only.
Figure 17 shows a simplified NAT/Route mode VLAN configuration. In this example,
FortiGate internal interface connects to a VLAN switch using an 802.1Q trunk and is
configured with two VLAN subinterfaces (VLAN 100 and VLAN 200). The external
interface connects to the Internet. The external interface is not configured with VLAN
subinterfaces.
When the VLAN switch receives packets from VLAN 100 and VLAN 200, it applies
VLAN tags and forwards the packets to local ports and across the trunk to the
FortiGate unit. The FortiGate unit is configured with policies that allow traffic to flow
between the VLANs and from the VLANs to the external network.
FortiGate-50A Administration Guide 01-28006-0001-20041105 65
Page 66

VLANs in NAT/Route mode System network
Figure 17: FortiGate unit in Nat/Route mode
POWER
Fa0/3 Fa0/9 Fa0/24
VLAN 100 VLAN 200
VLAN switch
802.1Q Trunk
FortiGate
Esc Enter
Internal
192.168.110.126
External
172.16.21.2
VLAN 100 network
10.1.1.0
10.1.1.2
Adding VLAN subinterfaces
The VLAN ID of each VLAN subinterface must match the VLAN ID added by the IEEE
802.1Q-compliant router. The VLAN ID can be any number between 1 and 4096.
Each VLAN subinterface must also be configured with its own IP address and
netmask.
Note: A VLAN must not have the same name as a virtual domain or zone.
You add VLAN subinterfaces to the physical interface that receives VLAN-tagged
packets.
To add a VLAN subinterface in NAT/Route mode
1 Go to System > Network > Interface.
2 Select Create New to add a VLAN subinterface.
3 Enter a Name to identify the VLAN subinterface.
4 Select the physical interface that receives the VLAN packets intended for this VLAN
subinterface.
5 Enter the VLAN ID that matches the VLAN ID of the packets to be received by this
VLAN subinterface.
VLAN 200 network
10.1.2.0
10.1.2.2
Internet
6 Select the virtual domain to which to add this VLAN subinterface.
See “System virtual domain” on page 119 for information about virtual domains.
7 Select the name of a zone if you want this VLAN subinterface to belong to a zone.
You can only select a zone that has been added to the virtual domain selected in the
previous step. See “Zone” on page 53 for information about zones.
8 Configure the VLAN subinterface settings as you would for any FortiGate interface.
See “Interface settings” on page 44.
9 Select OK to save your changes.
The FortiGate unit adds the new VLAN subinterface to the interface that you selected
in step 4.
66 01-28006-0001-20041105 Fortinet Inc.
Page 67

System network VLANs in Transparent mode
To add firewall policies for VLAN subinterfaces
Once you have added VLAN subinterfaces you can add firewall policies for
connections between VLAN subinterfaces or from a VLAN subinterface to a physical
interface.
1 Go to Firewall > Address.
2 Select Create New to add firewall addresses that match the source and destination IP
addresses of VLAN packets.
See “Address” on page 186.
3 Go to Firewall > Policy.
4 Add firewall policies as required.
VLANs in Transparent mode
In Transparent mode, the FortiGate unit can apply firewall policies and services, such
as authentication, protection profiles, and other firewall features, to traffic on an IEEE
802.1 VLAN trunk. You can insert the FortiGate unit operating in Transparent mode
into the trunk without making changes to your network. In a typical configuration, the
FortiGate internal interface accepts VLAN packets on a VLAN trunk from a VLAN
switch or router connected to internal VLANs. The FortiGate external interface
forwards tagged packets through the trunk to an external VLAN switch or router which
could be connected to the Internet. The FortiGate unit can be configured to apply
different policies for traffic on each VLAN in the trunk.
For VLAN traffic to be able to pass between the FortiGate Internal and external
interface you would add a VLAN subinterface to the internal interface and another
VLAN subinterface to the external interface. If these VLAN subinterfaces have the
same VLAN IDs, the FortiGate unit applies firewall policies to the traffic on this VLAN.
If these VLAN subinterfaces have different VLAN IDs, or if you add more than two
VLAN subinterfaces, you can also use firewall policies to control connections between
VLANs.
If the network uses IEEE 802.1 VLAN tags to segment your network traffic, you can
configure a FortiGate unit operating in Transparent mode to provide security for
network traffic passing between different VLANs. To support VLAN traffic in
Transparent mode, you add virtual domains to the FortiGate unit configuration. A
virtual domain consists of two or more VLAN subinterfaces or zones. In a virtual
domain, a zone can contain one or more VLAN subinterfaces.
When the FortiGate unit receives a VLAN tagged packet at an interface, the packet is
directed to the VLAN subinterface with matching VLAN ID. The VLAN subinterface
removes the VLAN tag and assigns a destination interface to the packet based on its
destination MAC address. The firewall policies for this source and destination VLAN
subinterface pair are applied to the packet. If the packet is accepted by the firewall,
the FortiGate unit forwards the packet to the destination VLAN subinterface. The
destination VLAN ID is added to the packet by the FortiGate unit and the packet is
sent to the VLAN trunk.
FortiGate-50A Administration Guide 01-28006-0001-20041105 67
Page 68

VLANs in Transparent mode System network
Figure 18: FortiGate unit with two virtual domains in Transparent mode
VLAN Switch or router
FortiGate unit
VLAN1
External
VLAN trunk
VLAN1
VLAN2
VLAN3
VLAN Switch
or router
Internet
VLAN2
VLAN3
Internal
VLAN1
VLAN2
VLAN3
VLAN trunk
root virtual domain
VLAN1
New virtual domain
VLAN2
VLAN3
VLAN1
VLAN2
VLAN3
Figure 19 shows a FortiGate unit operating in Transparent mode and configured with
three VLAN subinterfaces. In this configuration the FortiGate unit could be added to
this network to provide virus scanning, web content filtering, and other services to
each VLAN.
68 01-28006-0001-20041105 Fortinet Inc.
Page 69

System network VLANs in Transparent mode
Figure 19: FortiGate unit in Transparent mode
VLAN 1
VLAN ID = 100
FortiGate unit
operating in
Transparent mode
VLAN
switch
VLAN 2
VLAN ID = 200
POWER
Esc Enter
VLAN
switch
POWER
VLAN
Trunk
Internal
External
VLAN 1
VLAN 2
VLAN 3
VLAN
Trunk
Untagged
packets
Router
VLAN 3
VLAN ID = 300
VLAN 1
VLAN 2
VLAN 3
Internet
Rules for VLAN IDs
In Transparent mode two VLAN subinterfaces added to the same physical interface
cannot have the same VLAN ID. However, you can add two or more VLAN
subinterfaces with the same VLAN IDs to different physical interfaces. There is no
internal connection or link between two VLAN subinterfaces with same VLAN ID. Their
relationship is the same as the relationship between any two FortiGate network
interfaces.
Transparent mode virtual domains and VLANs
VLAN subinterfaces are added to and associated with virtual domains. By default the
FortiGate configuration includes one virtual domain, named root, and you can add as
many VLAN subinterfaces as you require to this virtual domain.
You can add more virtual domains if you want to separate groups of VLAN
subinterfaces into virtual domains. For information on adding and configuring virtual
domains, see “System virtual domain” on page 119
FortiGate-50A Administration Guide 01-28006-0001-20041105 69
Page 70

VLANs in Transparent mode System network
Transparent mode VLAN list
In Transparent mode, go to System > Network > Interface to add VLAN
subinterfaces.
Figure 20: Sample Transparent mode VLAN list
Create New Select Create New to add a VLAN subinterface to a FortiGate interface.
Virtual Domain Select a virtual domain to display the VLAN interfaces added to this virtual
Name The name of the interface or VLAN subinterface.
Access The administrative access configuration for the interface. See “To control
Status The administrative status for the interface.
domain.
administrative access to an interface” on page 52 for information about
administrative access options.
If the administrative status is a green arrow, the interface is up and can accept
network traffic. If the administrative status is a red arrow, the interface is
administratively down and cannot accept traffic. To change the administrative
status, see “To bring down an interface that is administratively up” on page 50
and “To start up an interface that is administratively down” on page 50.
Delete icon. Select to delete a VLAN subinterface.
View/Edit icon. Select to view or edit an interface or VLAN subinterface.
Transparent mode VLAN settings
VLAN settings displays the current configuration of a selected FortiGate interface or
VLAN subinterface. Use VLAN settings to configure a new VLAN subinterface or to
change the configuration of a FortiGate interface or VLAN subinterface.
Figure 21: VLAN settings
See “Interface settings” on page 44 for descriptions of all VLAN settings.
70 01-28006-0001-20041105 Fortinet Inc.
Page 71

System network VLANs in Transparent mode
To add a VLAN subinterface in Transparent mode
The VLAN ID of each VLAN subinterface must match the VLAN ID added by the IEEE
802.1Q-compliant router or switch. The VLAN ID can be any number between 1 and
4096. You add VLAN subinterfaces to the physical interface that receives VLAN-
tagged packets.
Note: A VLAN must not have the same name as a virtual domain or zone.
1 Go to System > Network > Interface.
2 Select Create New to add a VLAN subinterface.
3 Enter a Name to identify the VLAN subinterface.
4 Select the physical interface that receives the VLAN packets intended for this VLAN
subinterface.
5 Enter the VLAN ID that matches the VLAN ID of the packets to be received by this
VLAN subinterface.
6 Select the virtual domain to which to add this VLAN subinterface.
See “System virtual domain” on page 119 for information about virtual domains.
7 Enable or disable using a Dynamic DNS service (DDNS). If the FortiGate unit uses a
dynamic IP address, you can arrange with a DDNS service provider to use a domain
name to provide redirection of traffic to your network whenever the IP address
changes.
8 Configure the administrative access, MTU, and log settings as you would for any
FortiGate interface.
See “Interface settings” on page 44 for more descriptions of these settings.
9 Select OK to save your changes.
The FortiGate unit adds the new subinterface to the interface that you selected.
10 Select Bring up to start the VLAN subinterface.
To add firewall policies for VLAN subinterfaces
Once you have added VLAN subinterfaces you can add firewall policies for
connections between VLAN subinterfaces or from a VLAN subinterface to a physical
interface.
1 Go to Firewall > Address.
2 Select Create New to add firewall addresses that match the source and destination IP
addresses of VLAN packets.
See “Address” on page 186.
3 Go to Firewall > Policy.
4 Add firewall policies as required.
FortiGate-50A Administration Guide 01-28006-0001-20041105 71
Page 72

FortiGate IPv6 support System network
FortiGate IPv6 support
You can assign both an IPv4 and an IPv6 address to any interface on a FortiGate unit.
The interface functions as two interfaces, one for IPv4-addressed packets and
another for IPv6-addressed packets.
FortiGate units support static routing, periodic router advertisements, and tunneling of
IPv6-addressed traffic over an IPv4-addressed network. All of these features must be
configured through the Command Line Interface (CLI). See the FortiGate CLI
Reference Guide for information on the following commands:
Table 2: IPv6 CLI commands
Feature CLI Command
Interface configuration, including periodic
router advertisements
Static routing config router static6
IPv6 tunneling config system ipv6_tunnel
config system interface
See the keywords beginning with “ip6”.
config ip6-prefix-list
72 01-28006-0001-20041105 Fortinet Inc.
Page 73

FortiGate-50A Administration Guide Version 2.80 MR6
System DHCP
You can configure DHCP server or DHCP relay agent functionality on any FortiGate
interface or VLAN subinterface.
A FortiGate interface can act as either a DHCP server or as a DHCP relay agent. An
interface cannot provide both functions at the same time.
Note: To configure DHCP server or DHCP relay functionality on an interface, the FortiGate unit
must be in NAT/Route mode and the interface must have a static IP address.
This section describes:
• Service
• Server
• Exclude range
• IP/MAC binding
• Dynamic IP
Service
Go to System > DHCP > Service to configure the DHCP service provided by each
FortiGate interface. You can configure each interface to be a DHCP relay or a DHCP
server or you can turn off DHCP services.
Figure 22: DHCP service list
FortiGate-50A Administration Guide 01-28006-0001-20041105 73
Page 74

Service System DHCP
Interface List of FortiGate interfaces.
Service The DHCP service provided by the interface (none, DHCP Relay, or DHCP
Server).
Edit/View icon. Select to view or modify the DHCP service configuration for
an interface.
DHCP service settings
Go to System > DHCP > Service and select an edit or view icon to view to modify the
DHCP service configuration for an interface.
Figure 23: View or edit DHCP service settings for an interface
Interface The name of the interface.
None No DHCP services provided by the interface.
DHCP Relay Agent Select to configure the interface to be a DHCP relay agent.
Type Select the type of DHCP relay agent.
Regular Configure the interface to be a DHCP relay agent for computers on the
IPSEC Configure the interface to be a DHCP relay agent only for remote VPN
DHCP Server IP If you select DHCP Relay Agent, enter the IP address of the DHCP server
DHCP Server Select DHCP Server if you want the FortiGate unit to be the DHCP server.
network connected to this interface. See “To configure an interface as a
regular DHCP relay agent” on page 74.
clients with an IPSec VPN connection to this interface that uses DHCP
over IPSec.
used by the computers on the network connected to the interface.
See “To configure an interface to be a DHCP server” on page 75.
To configure an interface as a regular DHCP relay agent
In a DHCP relay configuration, the FortiGate interface configured for DHCP relay
forwards DHCP requests from DHCP clients through the FortiGate unit to a DHCP
server. The FortiGate unit also returns responses from the DHCP server to the DHCP
clients. The DHCP server must have a route to the FortiGate unit that is configured as
the DHCP relay so that the packets sent by the DHCP server to the DHCP client arrive
at the FortiGate performing DHCP relay.
1 Go to System > DHCP > Service.
2 Select Edit for the interface that you want to be a DHCP relay agent.
3 Select DHCP Relay Agent.
74 01-28006-0001-20041105 Fortinet Inc.
Page 75

System DHCP Server
4 Set type to Regular.
5 Enter the DHCP Server IP address.
6 Select OK.
To configure an interface to be a DHCP server
You can configure a DHCP server for any FortiGate interface. As a DHCP server, the
interface dynamically assigns IP addresses to hosts on the network connected to the
interface. You can also configure a DHCP server for more than one FortiGate
interface.
1 Go to System > DHCP > Service.
2 Select Edit beside the interface to which you want to add a DHCP server.
3 Select DHCP Server.
4 Select OK.
5 Add a DHCP server configuration for this interface.
See “To configure a DHCP server for an interface” on page 76.
Server
You can configure one or more DHCP servers for any FortiGate interface. As a DHCP
server, the interface dynamically assigns IP addresses to hosts on a network
connected to the interface.
You can add more than one DHCP server to a single interface to be able to provide
DHCP services to multiple networks. For more information, see “To configure multiple
DHCP servers for an interface” on page 77.
Figure 24: DHCP Server list
Create New Add a new DHCP server.
Name Name of the DHCP server.
Interface The interface for which the DHCP server is configured.
Default Gateway The DHCP server configuration default gateway
Delete Delete a DHCP server configuration.
Edit/View icon View or modify a DHCP server configuration.
FortiGate-50A Administration Guide 01-28006-0001-20041105 75
Page 76

Server System DHCP
DHCP server settings
Figure 25: Server options
Name Enter a name for the DHCP server configuration.
Interface Select the interface for which to configure the DHCP server.
Domain Enter the domain that the DHCP server assigns to DHCP clients.
Default Gateway Enter the IP address of the default gateway that the DHCP server
IP Range Enter the starting IP and ending IP for the range of IP addresses that this
Network Mask Enter the netmask that the DHCP server assigns to DHCP clients.
Lease Time Select Unlimited for an unlimited lease time or enter the interval in days,
DNS Server Enter the IP addresses of up to 3 DNS servers that the DHCP server
WINS Server Add the IP addresses of one or two WINS servers that the DHCP server
Option Up to three custom DHCP options that can be sent by the DHCP server.
assigns to DHCP clients.
DHCP server assigns to DHCP clients.
hours, and minutes after which a DHCP client must ask the DHCP server
for new settings. The lease time can range from 5 minutes to 100 days.
assigns to DHCP clients.
assigns to DHCP clients.
Code is the DHCP option code in the range 1 to 255. Option is an even
number of hexadecimal characters and is not required for some option
codes. For detailed information about DHCP options, see RFC 2132,
DHCP Options and BOOTP Vendor Extensions.
To configure a DHCP server for an interface
After configuring an interface to be a DHCP server (using the procedure “To configure
an interface to be a DHCP server” on page 75), you must configure a DHCP server for
the interface.
1 Go to System > DHCP > Server.
2 Select Create New.
76 01-28006-0001-20041105 Fortinet Inc.
Page 77

System DHCP Exclude range
3 Add a name for the DHCP server.
4 Select the interface
5 Configure the DHCP server.
The IP range must match the subnet address of the network from which the DHCP
request was received. Usually this would be the subnet connected to the interface for
which you are added the DHCP server.
6 Select OK to save the DHCP server configuration.
To configure multiple DHCP servers for an interface
If an interface is connected to a network that includes routers connected to different
subnets, you can:
1 Configure computers on the subnets to get their IP configuration using DHCP.
The IP range of each DHCP server must match the subnet addresses.
2 Configure the routers for DHCP relay.
3 Add multiple DHCP servers to the interface, one for each subnet.
When a computer on one of the connected subnets sends a DHCP request it is
relayed to the FortiGate interface by the router, using DHCP relay. The FortiGate unit
selects the DHCP server configuration with an IP range that matches the subnet
address from which the DHCP request was received and uses this DHCP server to
assign an IP configuration to the computer that made the DHCP request. The DHCP
configuration packets are sent back to the router and the router relays them to the
DHCP client.
Exclude range
Add up to 16 exclude ranges of IP addresses that FortiGate DHCP servers cannot
assign to DHCP clients. Exclude ranges apply to all FortiGate DHCP servers.
Figure 26: Exclude range list
Create New Select Create New to add an exclude range.
# The ID number of each exclude range. ID numbers are assigned
sequentially by the web-based manager. When you add or edit exclude
ranges from the CLI you must specify the ID number.
Starting IP The starting IP of the exclude range.
Ending IP The ending IP of the exclude range.
Delete Delete an exclude range.
Edit/View icon View or modify an exclude range.
FortiGate-50A Administration Guide 01-28006-0001-20041105 77
Page 78

IP/MAC binding System DHCP
DHCP exclude range settings
The range cannot exceed 65536 IP addresses.
Figure 27: Exclude range settings
Starting IP Enter the starting IP of an exclude range.
Ending IP Enter the ending IP of an exclude range.
To add an exclusion range
1 Go to System > DHCP > Exclude Range.
2 Select Create New.
3 Add the starting IP and ending IP.
4 Select OK to save the exclusion range.
IP/MAC binding
If you have added DHCP servers, you can use DHCP IP/MAC binding to reserve an
IP address for a particular device on the network according to the MAC address of the
device. When you add the MAC address and an IP address to the IP/MAC binding list,
the DHCP server always assigns this IP address to the MAC address. IP/MAC binding
pairs apply to all FortiGate DHCP servers.
Figure 28: IP/MAC binding list
Create New Select Create New to add a DHCP IP/MAC binding pair.
Name The name for the IP and MAC address pair.
IP Address The IP address for the IP and MAC address pair. The IP address must be
within the configured IP range.
MAC Address The MAC address of the device.
Delete icon. Delete an IP/MAC binding pair.
Edit/View icon. View or modify an IP/MAC binding pair.
78 01-28006-0001-20041105 Fortinet Inc.
Page 79

System DHCP Dynamic IP
DHCP IP/MAC binding settings
Figure 29: IP/MAC binding options
Name Enter a name for the IP/MAC address pair.
IP Address Enter the IP address for the IP and MAC address pair. The IP address must
MAC Address Enter the MAC address of the device.
To add a DHCP IP/MAC binding pair
1 Go to System > DHCP > IP/MAC Binding.
2 Select Create New.
3 Add a name for the IP/MAC pair.
4 Add the IP address and MAC address.
5 Select OK to save the IP/MAC pair.
be within the configured IP range.
Dynamic IP
You can view the list of IP addresses that the DHCP server has assigned, their
corresponding MAC addresses, and the expiry time and date for these addresses.
Interface Select to display its dynamic IP list.
IP The IP addresses that the DHCP server has assigned.
MAC The corresponding MAC addresses for the dynamic IP addresses.
Expire The expiry time and date for the dynamic IP addresses and their corresponding
MAC addresses.
To view the dynamic IP list
1 Go to System > DHCP > Dynamic IP.
2 Select the interface for which you want to view the list.
FortiGate-50A Administration Guide 01-28006-0001-20041105 79
Page 80

Dynamic IP System DHCP
80 01-28006-0001-20041105 Fortinet Inc.
Page 81

FortiGate-50A Administration Guide Version 2.80 MR6
System config
Use the System Config page to make any of the following changes to the FortiGate
system configuration:
• System time
• Options
• SNMP
• Replacement messages
• FortiManager
System time
Go to System > Config > Time to set the FortiGate system time.
For effective scheduling and logging, the FortiGate system time must be accurate.
You can either manually set the FortiGate system time or you can configure the
FortiGate unit to automatically keep its system time correct by synchronizing with a
Network Time Protocol (NTP) server.
Figure 30: System time
System Time The current FortiGate system date and time.
Refresh Select Refresh to update the display of the current FortiGate system date
Time Zone Select the current FortiGate system time zone.
and time.
FortiGate-50A Administration Guide 01-28006-0001-20041105 81
Page 82

Options System config
Automatically
adjust clock for
daylight saving
changes
Set Time Select Set Time to set the FortiGate system date and time to the correct
Synchronize with
NTP Server
Server Enter the IP address or domain name of the NTP server that the
Syn Interval Specify how often the FortiGate unit should synchronize its time with the
Select the Automatically adjust clock for daylight saving changes check
box if you want the FortiGate system clock to be adjusted automatically
when your time zone changes to daylight saving time and back to
standard time.
date and time.
Select Synchronize with NTP Server to configure the FortiGate unit to
use NTP to automatically set the system date and time. For more
information about NTP and to find the IP address of an NTP server that
you can use, see http://www.ntp.org.
FortiGate unit can use to set its time and date.
NTP server. A typical Syn Interval would be 1440 minutes for the
FortiGate unit to synchronize its time once a day.
To manually set the FortiGate date and time
1 Go to System > Config > Time.
2 Select Refresh to display the current FortiGate system date and time.
3 Select your Time Zone from the list.
4 Optionally, select Automatically adjust clock for daylight saving changes check box.
5 Select Set Time and set the FortiGate system date and time.
6 Set the hour, minute, second, month, day, and year as required.
7 Select Apply.
Options
To use NTP to set the FortiGate date and time
1 Go to System > Config > Time.
2 Select Synchronize with NTP Server to configure the FortiGate unit to use NTP to
automatically set the system time and date.
3 Enter the IP address or domain name of the NTP server that the FortiGate unit can
use to set its time and date.
4 Specify how often the FortiGate unit should synchronize its time with the NTP server.
5 Select Apply.
Go to System > Config > Options to set the following options:
• Timeout settings including the idle timeout and authentication timeout
• The language displayed by the web-based manager
• Dead gateway detection interval and failover detection
82 01-28006-0001-20041105 Fortinet Inc.
Page 83

System config Options
Figure 31: System config options
Idle Timeout Set the idle time out to control the amount of inactive time before the
Auth Timeout Set the firewall user authentication timeout to control how long an
Language Select a language for the web-based manager to use. Choose from
Detection Interval Set the dead gateway detection failover interval. Enter a number in
Fail-over Detection Set the ping server dead gateway detection failover number. Enter the
administrator must log in again. The maximum admintimeout is 480
minutes (8 hours). To improve security keep the idle timeout at the default
value of 5 minutes.
authenticated connection can be idle before the user must authenticate
again. The maximum authtimeout is 480 minutes (8 hours). The
default Auth Timeout is 15 minutes.
For more information, see “Setting authentication timeout” on page 222.
English, Simplified Chinese, Japanese, Korean, or French.
seconds to specify how often the FortiGate unit pings the target.
number of times that ping fails before the FortiGate unit assumes that the
gateway is no longer functioning.
To set the system idle timeout
1 Go to System > Config > Options.
2 For Idle Timeout, type a number in minutes.
3 Select Apply.
To set the Auth timeout
1 Go to System > Config > Options.
2 For Auth Timeout, type a number in minutes.
3 Select Apply.
To select a language for the web-based manager
1 Go to System > Config > Options.
2 From the Languages list, select a language for the web-based manager to use.
3 Select Apply.
FortiGate-50A Administration Guide 01-28006-0001-20041105 83
Page 84

SNMP System config
Note: You should select the language that the management computer operating system uses.
To modify the dead gateway detection settings
Modify dead gateway detection to control how the FortiGate unit confirms connectivity
with a ping server added to an interface configuration. For information about adding a
ping server to an interface, see “To add a ping server to an interface” on page 52.
1 Go to System > Config > Options.
2 For Detection Interval, type a number in seconds to specify how often the FortiGate
unit tests the connection to the ping target.
3 For Fail-over Detection, type a number of times that the connection test fails before
the FortiGate unit assumes that the gateway is no longer functioning.
4 Select Apply.
SNMP
You can configure the FortiGate SNMP agent to report system information and send
traps (alarms or event messages) to SNMP managers. Using an SNMP manager, you
can access SNMP traps and data from any FortiGate interface or VLAN subinterface
configured for SNMP management access.
The FortiGate SNMP implementation is read-only. SNMP v1 and v2c compliant SNMP
managers have read-only access to FortiGate system information and can receive
FortiGate traps. To monitor FortiGate system information and receive FortiGate traps
you must compile Fortinet proprietary MIBs as well as Fortinet-supported standard
MIBs into your SNMP manager.
RFC support includes support for most of RFC 2665 (Ethernet-like MIB) and most of
RFC 1213 (MIB II) (for more information, see “FortiGate MIBs” on page 88).
This section describes:
• Configuring SNMP
• SNMP community
• FortiGate MIBs
• FortiGate traps
• Fortinet MIB fields
84 01-28006-0001-20041105 Fortinet Inc.
Page 85

System config SNMP
Configuring SNMP
Go to System > Config > SNMP v1/v2c to configure the SNMP agent.
Figure 32: Configuring SNMP
SNMP Agent Enable the FortiGate SNMP agent.
Description Enter descriptive information about the FortiGate unit. The description
Location Enter the physical location of the FortiGate unit. The system location
Contact Enter the contact information for the person responsible for this FortiGate
Apply Save changes made to the description, location, and contact information.
Create New Select Create New to add a new SNMP community.
Communities The list of SNMP communities added to the FortiGate configuration. You
Name The name of the SNMP community.
Queries The status of SNMP queries for each SNMP community. The query
Traps The status of SNMP traps for each SNMP community. The trap status
Enable Select Enable to activate an SNMP community.
Delete icon Select Delete to remove an SNMP community.
Edit/View icon View or modify an SNMP community.
can be up to 35 characters long.
description can be up to 35 characters long.
unit. The contact information can be up to 35 characters long.
can add up to 3 communities.
status can be enabled or disabled.
can be enabled or disabled.
SNMP community
An SNMP community is a grouping of equipment for network administration purposes.
Add SNMP communities so that SNMP managers can connect to the FortiGate unit to
view system information and receive SNMP traps. You can add up to three SNMP
communities. Each community can have a different configuration for SNMP queries
and traps. Each community can be configured to monitor the FortiGate unit for a
different set of events. You can also add the IP addresses of up to 8 SNMP managers
to each community.
FortiGate-50A Administration Guide 01-28006-0001-20041105 85
Page 86

SNMP System config
Figure 33: SNMP community options (part 1)
Figure 34: SNMP community options (part 2)
Community Name Enter a name to identify the SNMP community.
Hosts Identify the SNMP managers that can use the settings in this SNMP
IP Address The IP address of an SNMP manager than can use the settings in this
Interface Optionally select the name of the interface that this SNMP manager uses
Add Select Add to add more SNMP managers. You can add up to 8 SNMP
86 01-28006-0001-20041105 Fortinet Inc.
community to monitor the FortiGate unit.
SNMP community to monitor the FortiGate unit. You can also set the IP
address to 0.0.0.0 to so that any SNMP manager can use this SNMP
community.
to connect to the FortiGate unit. You only have to select the interface if
the SNMP manager is not on the same subnet as the FortiGate unit. This
can occur if the SNMP manager is on the Internet or behind a router.
managers to a single community. Select the Delete icon to remove an
SNMP manager.
Page 87

System config SNMP
Queries Enter the Port number (161 by default) that the SNMP managers in this
Traps Enter the Local and Remote port numbers (162 by default) that the
SNMP Event Enable each SNMP event for which the FortiGate unit should send traps
community use for SNMP v1 and SNMP v2c queries to receive
configuration information from the FortiGate unit. Select the Enable
check box to activate queries for each SNMP version.
FortiGate unit uses to send SNMP v1 and SNMP v2c traps to the SNMP
managers in this community. Select the Enable check box to activate
traps for each SNMP version.
to the SNMP managers in this community.
To configure SNMP access to an interface in NAT/Route mode
Before a remote SNMP manager can connect to the FortiGate agent, you must
configure one or more FortiGate interfaces to accept SNMP connections. See “To
control administrative access to an interface” on page 52.
1 Go to System > Network > Interface.
2 Choose an interface that an SNMP manager connects to and select Edit.
3 For Administrative Access, select SNMP.
4 Select OK.
To configure SNMP access to an interface in Transparent mode
Before a remote SNMP manager can connect to the FortiGate agent, you must
configure one or more FortiGate interfaces to accept SNMP connections. See “To
configure the management interface” on page 56.
1 Go to System > Network > Management.
2 Choose an interface that the SNMP manager connects to and select SNMP.
3 Select Apply.
To enable SNMP and configure basic SNMP settings
1 Go to System > Config > SNMP v1/v2c.
2 Select the Enable check box to enable the FortiGate SNMP Agent.
3 Configure the following SNMP settings: Description, Location, and Contact.
4 Select Apply.
5 Add one or more SNMP communities.
To add an SNMP community
1 Go to System > Config > SNMP v1/v2c.
2 Select Create New.
3 Enter a Community Name to identify the SNMP community.
4 Configure Hosts, Queries, Traps, and SNMP Events.
5 Select OK.
FortiGate-50A Administration Guide 01-28006-0001-20041105 87
Page 88

SNMP System config
FortiGate MIBs
The FortiGate SNMP agent supports FortiGate proprietary MIBs as well as standard
RFC 1213 and RFC 2665 MIBs. RFC support includes support for the parts of RFC
2665 (Ethernet-like MIB) and the parts of RFC 1213 (MIB II) that apply to FortiGate
unit configuration.
The FortiGate MIBs are listed in Table 3. You can obtain these MIB files from Fortinet
technical support. To be able to communicate with the SNMP agent, you must
compile all of these MIBs into your SNMP manager.
Your SNMP manager might already include standard and private MIBs in a compiled
database that is ready to use. You must add the Fortinet proprietary MIBs to this
database. If the standard MIBs used by the Fortinet SNMP agent are already
compiled into your SNMP manager you do not have to compile them again.
Table 3: FortiGate MIBs
MIB file name or RFC Description
fortinet.2.80.mib The Fortinet MIB is a proprietary MIB that includes detailed FortiGate
fortinet.trap.2.80.mib The Fortinet trap MIB is a proprietary MIB that is required for your
RFC-1213 (MIB II) The FortiGate SNMP agent supports MIB II groups with the following
RFC-2665 (Ethernetlike MIB)
system configuration information. Add this MIB to your SNMP
manager to monitor all FortiGate configuration settings. For more
information about FortiGate MIB fields, see “FortiGate MIBs” on
page 88.
SNMP manager to receive traps from the FortiGate SNMP agent. For
more information about FortiGate traps, see “FortiGate traps” on
page 88.
exceptions.
No support for the EGP group from MIB II (RFC 1213, section 3.11
and 6.10).
Protocol statistics returned for MIB II groups (IP/ICMP/TCP/UDP/etc.)
do not accurately capture all FortiGate traffic activity. More accurate
information can be obtained from the information reported by the
Fortinet MIB.
The FortiGate SNMP agent supports Ethernet-like MIB information
with the following exception.
No support for the dot3Tests and dot3Errors groups.
FortiGate traps
The FortiGate agent can send traps to SNMP managers that you have added to
SNMP communities. For SNMP managers to receive traps, you must load and
compile the Fortinet trap MIB (file name fortinet.trap.2.80.mib) onto the SNMP
manager.
All traps include the trap message as well as the FortiGate unit serial number.
88 01-28006-0001-20041105 Fortinet Inc.
Page 89

System config SNMP
Table 4: Generic FortiGate traps
Trap message Description
ColdStart
Standard traps as described in RFC 1215.
WarmStart
LinkUp
LinkDown
Table 5: FortiGate system traps
Trap message Description
CPU usage high
CPU usage exceeds 90%.
(SysCpuHigh)
Disk low On a FortiGate unit with a hard drive, hard drive usage exceeds
90%.
<FortiGate_serial_no>
<interface_name>
The configuration of an interface of a FortiGate unit changes. The
trap message includes the name of the interface and the serial
number of the FortiGate unit.
HA state HA state changes. The trap message includes the previous state, the
new state and a flag indicating whether the unit is the master.
HA switch The primary unit in an HA cluster fails and is replaced with a new
primary unit.
Memory low
Memory usage exceeds 90%.
(SysMemLow)
The <interface_name>
Interface IP is changed
to <new_IP>
(Serial No.:
<FortiGate_serial_no>)
The IP address of an interface of a FortiGate unit changes. The trap
message includes the name of the interface, the new IP address of
the interface, and the serial number of the FortiGate unit. This trap
can be used to track interface IP address changes for interfaces
configured with dynamic IP addresses set using DHCP or PPPoE.
(IntfIpChange)
Table 6: FortiGate VPN traps
Trap message Description
VPN tunnel is up
(VpnTunnelUp)
VPN tunnel down
An IPSec VPN tunnel starts up and begins processing network
traffic.
An IPSec VPN tunnel shuts down.
(VpnTunnelDown)
Table 7: FortiGate IPS traps
Trap message Description
Syn flood attack.
(IdsSynFlood)
Port scan attack.
(IdsPortScan)
NIDS attack prevention detects and provides protection from a
syn flood attack.
NIDS attack prevention detects and provides protection from a
port scan attack.
FortiGate-50A Administration Guide 01-28006-0001-20041105 89
Page 90

SNMP System config
Table 8: FortiGate antivirus traps
Trap message Description
Virus detected
(AvVirus)
Table 9: FortiGate logging traps
Trap message Description
Log full
(SysLogFull)
Table 10: FortiGate HA traps
Trap message Description
Primary unit
switch
(HaSwitch)
The FortiGate unit detects a virus and removes the infected file from an
HTTP or FTP download or from an email message.
On a FortiGate unit with a hard drive, hard drive usage exceeds 90%. On a
FortiGate unit without a hard drive, log to memory usage has exceeds 90%.
The different unit in the HA cluster became the primary unit.
Fortinet MIB fields
The Fortinet MIB contains fields reporting current FortiGate unit status information.
The tables below list the names of the MIB fields and describe the status information
available for each one. You can view more details about the information available
from all Fortinet MIB fields by compiling the fortinet.2.80.mib file into your SNMP
manager and browsing the Fortinet MIB fields.
Table 11: System MIB fields
MIB field Description
model FortiGate model number, for example, 400 for the FortiGate-400.
serial FortiGate unit serial number.
version The firmware version currently running on the FortiGate unit.
versionAv The antivirus definition version installed on the FortiGate unit.
versionNids The attack definition version installed on the FortiGate unit.
haMode The current FortiGate High-Availability (HA) mode (standalone, A-A, A-P)
opMode The FortiGate unit operation mode (NAT or Transparent).
cpuUsage The current CPU usage (as a percent).
memUsage The current memory utilization (in MB).
sesCount The current IP session count.
90 01-28006-0001-20041105 Fortinet Inc.
Page 91

System config SNMP
Table 12: HA MIB fields
MIB field Description
groupId HA group ID.
priority The clustering priority of the individual FortiGate unit in a cluster.
override The master-override setting (enable or disable) for an individual FortiGate unit in
a cluster.
autoSync Auto config synchronization flag.
schedule Load balancing schedule for A-A mode.
stats Statistics for all of the units in the HA cluster.
index The index number of the FortiGate unit.
serial The FortiGate unit serial number.
cpuUsage The current FortiGate unit CPU usage as a percent.
memUsage The current FortiGate unit memory usage (in MB).
netUsage The current FortiGate unit network utilization (in Mbps).
sesCount The number of active sessions being processed by the FortiGate
unit.
pktCount The number of packets processed by the FortiGate unit.
byteCount The number of bytes processed by the FortiGate unit
idsCount The number of attacks detected by the IPS running on the
FortiGate unit in the last 20 hours.
avCount The number of viruses detected by the antivirus system running
on the FortiGate unit in the last 20 hours.
Table 13: Administrator accounts
MIB field Description
index The index number of the administrator account added to the FortiGate unit.
name The user name of an administrator account added to the FortiGate unit.
addr Up to three trusted host IP addresses for the administrator account.
mask Up to three trusted host netmasks for the administrator account.
perm The access profile assigned to the account.
Table 14: Local users
MIB field Description
index The index number of the local user added to the FortiGate unit.
name The user name of the local user added to the FortiGate unit.
auth The authentication type of for the local user. Can be password, LDAP, or
RADIUS.
state Whether the local user is enabled or disable.
FortiGate-50A Administration Guide 01-28006-0001-20041105 91
Page 92

Replacement messages System config
Table 15: Virtual domains
MIB field Description
index The index number virtual domain added to the FortiGate unit.
name The name of the virtual domain added to the FortiGate unit. Each FortiGate
auth The authentication type of for the local user. Can be password, LDAP, or
state Whether the local user is enabled or disable.
Table 16: Active IP sessions
MIB field Description
index The index number of the active IP session.
proto The IP protocol (TCP, UDP, ICMP, and so on) of the IP session.
fromAddr The source IP address of the active IP session.
fromPort The source port of the active IP session.
toPort The destination IP address of the active IP session.
toAddr The destination port of the active IP session.
expiry The expiry time or time-to-live in seconds for the session.
unit includes at least one virtual domain named root.
RADIUS.
Replacement messages
Change replacement messages to customize alert email and information that the
FortiGate unit adds to content streams such as email messages, web pages, and FTP
sessions. The FortiGate unit adds replacement messages to a variety of content
streams. For example, if a virus is found in an email message, the file is removed from
the email and replaced with a replacement message. The same applies to pages
blocked by web filtering and email blocked by spam filtering.
92 01-28006-0001-20041105 Fortinet Inc.
Page 93

System config Replacement messages
Replacement messages list
Figure 35: Replacement messages list
Name The type of replacement message. You can change messages added to email,
Description Description of the replacement message type. The web-based manager
web pages in http traffic, messages that are displayed to ftp users, alert mail
messages, messages added to smtp email, and messages added to web
pages blocked by web filter category blocking.
describes where each replacement message is used by the FortiGate unit.
Edit/View icon. Select to change a replacement message.
To change a replacement message
1 Go to System > Config > Replacement Messages.
2 Select the category of replacement message to edit by clicking on the blue triangle for
that category.
3 For the replacement message that you want to change, select Edit.
4 Edit the content of the message.
FortiGate-50A Administration Guide 01-28006-0001-20041105 93
Page 94

Replacement messages System config
Changing replacement messages
Figure 36: Sample HTTP virus replacement message
Replacement messages can be text or HTML messages. You can add HTML code to
HTML messages. In addition, replacement messages can include replacement
message tags. When users receive the replacement message, the replacement
message tag is replaced with content relevant to the message. Table 17 lists the
replacement message tags that you can add.
Table 17: Replacement message tags
Tag Description
%%FILE%% The name of a file that has been removed from a content stream.
%%VIRUS%% The name of a virus that was found in a file by the antivirus system.
%%QUARFILENAME%% The name of a file that has been removed from a content stream
%%URL%% The URL of a web page. This can be a web page that is blocked by
%%CRITICAL_EVENT%% Added to alert email critical event email messages.
%%PROTOCOL%% The protocol (http, ftp, pop3, imap, or smtp) in which a virus was
%%SOURCE_IP%% The IP address of the request originator who would have received
%%DEST_IP%% The IP address of the request destination from which a virus was
This could be a file that contained a virus or was blocked by
antivirus file blocking. %%FILE%% can be used in virus and file block
messages.
%%VIRUS%% can be used virus messages
and added to the quarantine. This could be a file that contained a
virus or was blocked by antivirus file blocking.
%%QUARFILENAME%% can be used in virus and file block messages.
Quarantining is only available on FortiGate units with a local disk.
web filter content or URL blocking. %%URL%% can also be used in
http virus and file block messages to be the URL of the web page
from which a user attempted to download a file that is blocked.
%%CRITICAL_EVENT%% is replaced with the critical event message
that triggered the alert email.
detected. %%PROTOCOL%% is added to alert email virus messages.
the blocked file. For email this is the IP address of the user’s
computer that attempted to download the message from which the
file was removed.
received. For email this is the IP address of the email server that
sent the email containing the virus. For HTTP this is the IP address
of web page that sent the virus.
94 01-28006-0001-20041105 Fortinet Inc.
Page 95

System config FortiManager
Table 17: Replacement message tags (Continued)
Tag Description
%%EMAIL_FROM%% The email address of the sender of the message from which the file
%%EMAIL_TO%% The email address of the intended receiver of the message from
%%NIDSEVENT%% The IPS attack message. %%NIDSEVENT%% is added to alert email
%%SERVICE%% The name of the web filtering service.
%%CATEGORY%% The name of the content category of the web site.
%%FORTINET%% The Fortinet logo.
was removed.
which the file was removed.
intrusion messages.
FortiManager
Configure the FortiGate unit for IPSec communication between the FortiGate unit and
a FortiManager server. When you enable this feature, all communication between the
FortiGate unit and the FortiManager server takes place using VPN.
Figure 37: FortiManager configuration
Enable FortiManager Enable secure IPSec VPN communication between the FortiGate unit
FortiManager ID The remote ID of the FortiManager IPSec tunnel.
FortiManager IP The IP Address of the FortiManager Server.
and a FortiManager Server.
FortiGate-50A Administration Guide 01-28006-0001-20041105 95
Page 96

FortiManager System config
96 01-28006-0001-20041105 Fortinet Inc.
Page 97

FortiGate-50A Administration Guide Version 2.80 MR6
System administration
When the FortiGate unit is first installed, it is configured with a single administrator
account with the user name admin. From this administrator account, you can add and
edit administrator accounts. You can also control the access level of each of these
administrator accounts and control the IP address from which the administrator
account can connect to the FortiGate unit.
Each administrator account belongs to an access profile. You can create access
profiles that deny access to or allow read only, write only, or both read and write
access to the following FortiGate features.
Administrators
System
Configuration
Log & Report Can access the log setting, and log message features.
Security Policy Can access the firewall, VPN, IPS, and antivirus features.
Auth Users Can access the authorized users feature.
Admin Users Can access the administrative users feature.
FortiProtect
Update
System
Shutdown
This chapter describes:
• Administrators
• Access profiles
Use the admin account or an account with system configuration read and write
privileges to add new administrator accounts and control their permission levels.
Can access the system status, interface, virtual domain, HA, routing, option,
SNMP, time, and replacement message features.
Can access the update options feature.
Can access the system shutdown, and system reboot functions.
FortiGate-50A Administration Guide 01-28006-0001-20041105 97
Page 98

Administrators System administration
Administrators list
Figure 38: Administrators list
Create New Add an administrator account.
Name The login name for an administrator account.
Trusted hosts The trusted host IP address and netmask from which the administrator can log
Permission The permission profile for the administrator.
in.
The Delete, Edit/View, or Change Password icon.
The admin administrator account cannot be deleted.
Administrators options
Figure 39: Administrator account configuration
Administrator Enter the login name for the administrator account.
Password Type a password for the administrator account.
For improved security, the password should be at least 6 characters long.
Confirm
Password
Trusted Host #1
Trusted Host #2
Trusted Host #3
Access Profile The access profile for the administrator. For more information on access
Type the password for the administrator account a second time to confirm
that you have typed it correctly.
Optionally, type the trusted host IP address and netmask from which the
administrator can log in to the FortiGate unit. You can specify up to three
trusted hosts.
Setting trusted hosts for all of your administrators can enhance the security of
your system. For more information, see “Using trusted hosts” on page 99.
profiles, see “Access profile list” on page 100.
To configure an administrator account
1 Go to System > Admin > Administrators.
2 Select Create New to add an administrator account or select the Edit icon to make
changes to an existing administrator account.
98 01-28006-0001-20041105 Fortinet Inc.
Page 99

System administration Access profiles
3 Type a login name for the administrator account.
4 Type and confirm a password for the administrator account.
5 Optionally type a Trusted Host IP address and netmask from which the administrator
can log into the web-based manager.
6 Select the access profile for the administrator.
7 Select OK.
Figure 40: Change an administrator password
To change an administrator password
1 Go to System > Admin > Administrators.
2 Select the Change Password icon next to the administrator account you want to
change the password for.
3 Enter and confirm the new password.
4 Select OK.
Access profiles
Using trusted hosts
Setting trusted hosts for all of your administrators increases the security of your
network by further restricting administrative access. In addition to knowing the
password, an administrator must connect only through the subnet or subnets you
specify. You can even restrict an administrator to a single IP address if you define only
one trusted host IP address with a netmask of 255.255.255.255.
When you set trusted hosts for all administrators, the FortiGate unit does not respond
to administrative access attempts from any other hosts. This provides the highest
security. If you leave even one administrator unrestricted, the unit accepts
administrative access attempts on any interface that has administrative access
enabled, potentially exposing the unit to attempts to gain unauthorized access.
The trusted hosts you define apply both to the web-based manager and to the CLI
when accessed through telnet or SSH. CLI access through the console connector is
not affected.
Go to System > Admin > Access Profile to add access profiles for FortiGate
administrators. Each administrator account belongs to an access profile. You can
create access profiles that deny access to or allow read only, write only, or both read
and write access to FortiGate features.
FortiGate-50A Administration Guide 01-28006-0001-20041105 99
Page 100

Access profiles System administration
Access profile list
Figure 41: Access profile list
Create New Add a new access profile.
Profile Name The name of the access profile.
The Delete, and Edit icons.
You cannot delete the prof_admin access profile.
Access profile options
Figure 42: Access profile option
Profile Name Enter the name of the access profile.
Access Control Access Control lists the items that can be controlled by the access profile.
Allow Read All Select Allow Read All to give an administrator read privilege on all the items
Allow Write All Select Allow Write All to give an administrator write privilege on all the items
System
Configuration
Log & Report Allow or deny access to the log setting, log access, and alert email features.
Security Policy Allow or deny access to the firewall, VPN, IPS, and antivirus features.
Auth Users Allow or deny access to the authorized users feature.
Admin Users Allow or deny access to the administrative users feature.
FortiProtect
Update
System
Shutdown
under Access Control.
under Access Control.
Allow or deny access to the system status, interface, virtual domain, HA,
routing, option, SNMP, time, and replacement message features.
Allow or deny access to the FortiProtect Distribution Network update feature.
Allow or deny access to the system shutdown and reboot functionality.
100 01-28006-0001-20041105 Fortinet Inc.
 Loading...
Loading...