Page 1

Aruba 3000, 6000/M3 and Dell
W-3000, W-6000M3
Controllers with ArubaOS FIPS
Firmware Non-Proprietary Security
Policy FIPS 140-2 Level 2 Release
Supplement
Page 2

Copyright
© 2011 Aruba Networks, Inc. Aruba Networks trademarks include , Aruba Networks
registered Aruba the Mobile Edge Company logo, Aruba Mobility Management System
Networks Must Follow®, RFProtect®, Green Island®. All rights reserved. All other trademarks are the property of their respective owners.
Open Source Code
Certain Aruba products include Open Source software code developed by third parties, including software code subject to the GNU
General Public License (GPL), GNU Lesser General Public License (LGPL), or other Open Source Licenses. The Open Source code used
can be found at this site:
®
, Mobile Edge Architecture®, People Move.
®
, Aruba Wireless Networks®, the
http://www.arubanetworks.com/open_source
Legal Notice
The use of Aruba Networks, Inc. switching platforms and software, by all individuals or corporations, to terminate other vendors’ VPN
client devices constitutes complete acceptance of liability by that individual or corporation for this action and indemnifies, in full, Aruba
Networks, Inc. from any and all legal actions that might be taken against it with respect to infringement of copyright on behalf of those
vendors.
Warranty
This hardware product is protected by the standard Aruba warranty of one year parts/labor. For more information, refer to the
ARUBACARE SERVICE AND SUPPORT TERMS AND CONDITIONS.
Altering this device (such as painting it) voids the warranty.
Copyright
© 2011 Aruba Networks, Inc. Aruba Networks trademarks include , Aruba Networks®, Aruba Wireless Networks®,the registered Aruba
the Mobile Edge Company logo, and Aruba Mobility Management System®. Dell™, the DELL™ logo, andPowerConnect™ are trademarks
of Dell Inc.
www.arubanetworks.com
1344 Crossman Avenue
Sunnyvale, California 94089
Phone: 408.227.4500
Fax 408.227.4550
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement 0510541-16 | October 2011
Page 3
Contents
Preface...................................................................................................................................5
Purpose of this Document.....................................................................................5
Aruba Dell Relationship................................................................................... 5
Related Documents ...............................................................................................6
Additional Product Information .......................................................................6
Chapter 1 The Aruba 3000 and 6000/M3 Controllers.............................................7
Overview................................................................................................................7
Physical Description .............................................................................................. 8
Dimensions .....................................................................................................8
Cryptographic Module Boundaries .................................................................8
Chassis............................................................................................................9
Chapter 2 FIPS 140-2 Level 2 Features .................................................................11
Intended Level of Security...................................................................................11
Physical Security .................................................................................................11
Operational Environment .....................................................................................12
Logical Interfaces ................................................................................................12
Roles and Services..............................................................................................13
Crypto Officer Role .......................................................................................13
User Role ......................................................................................................15
Authentication Mechanisms..........................................................................16
Unauthenticated Services .............................................................................16
Cryptographic Key Management.........................................................................17
Implemented Algorithms ...............................................................................17
Revision C4............................................................................................. 17
Revision B2.............................................................................................17
Non-FIPS Approved Algorithms....................................................................18
Critical Security Parameters..........................................................................18
Self-Tests.............................................................................................................21
Alternating Bypass State ..................................................................................... 22
Mitigation of Other Attacks..................................................................................23
XSec..............................................................................................................23
Wireless Intrusion Detection ......................................................................... 23
Unique Station and User Classification ..................................................23
Detecting and Disabling Rogue APs ......................................................24
Denial of Service and Impersonation Protection...........................................24
Man-in-the-Middle Protection.......................................................................24
Policy Definition and Enforcement ................................................................24
Using Wireless to Protect your Wired Network.............................................24
Using Wireless to Protect your Existing Wireless Network........................... 24
Chapter 3 Installing the Controller.........................................................................25
Pre-Installation Checklist..................................................................................... 25
Precautions.......................................................................................................... 25
The Security Kit ...................................................................................................26
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement | 3
Page 4

Product Examination.....................................................................................26
Package Contents.........................................................................................26
Minimum Configuration for the Aruba 6000..................................................26
Tamper-Evident Labels .......................................................................................27
Reading TELs................................................................................................27
Required TEL Locations................................................................................27
To Detect Opening the Chassis Cover ...................................................27
To Detect the Removal of Any Module or Cover Plate...........................27
To Detect Access to Restricted Ports .................................................... 28
To Detect Access to Restricted Port ......................................................28
To Detect Opening the Chassis Cover ...................................................28
Applying TELs ...............................................................................................28
Chapter 4 Ongoing Management........................................................................... 29
Crypto Officer Management ................................................................................29
User Guidance.....................................................................................................29
Chapter 5 Setup and Configuration....................................................................... 31
Setting Up Your Controller ..................................................................................31
Enabling FIPS Mode............................................................................................31
Enabling FIPS with the Setup Wizard ...........................................................31
Enabling FIPS with the WebUI ......................................................................31
Disallowed FIPS Mode Configurations................................................................32
4 | Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 5
Preface
NOTE
This security policy document can be copied and distributed freely.
Purpose of this Document
This release supplement provides information regarding the Aruba 3000 and 6000/M3 Controller and Dell W3000 and W-6000 M3 controllers with FIPS 140-2 Level 2 validation from Aruba Networks. The material in
this supplement modifies the general Aruba hardware and firmware documentation included with this
product and should be kept with your Aruba product documentation.
This supplement primarily covers the non-proprietary Cryptographic Module Security Policy for the Aruba
Controller. This security policy describes how the switch meets the security requirements of FIPS 140-2
Level 2 and how to place and maintain the switch in a secure FIPS 140-2 mode. This policy was prepared as
part of the FIPS 140-2 Level 2 validation of the product.
FIPS 140-2 (Federal Information Processing Standards Publication 140-2, Security Requirements for
Cryptographic Modules) details the U.S. Government requirements for cryptographic modules. More
information about the FIPS 140-2 standard and validation program is available on the National Institute of
Standards and Technology (NIST) Web-site at:
http://csrc.nist.gov/groups/STM/cmvp/index.html
Aruba Dell Relationship
Aruba Networks is the OEM for the Dell PowerConnect W line of products. Dell products are identical to
the Aruba products other than branding and Dell software is identical to Aruba software other than
branding.
Table 1 Aruba and Dell Part Numbers
Aruba Part Number Corresponding Dell Part Number
3200-USF1 W-3200-USF1
3400-USF1 W-3400-USF1
3600-USF1 W-3600-USF1
3200-F1 W-3200-F1
3400-F1 W-3400-F1
3600-F1 W-3600-F1
6000-400-F1 W-6000-400-F1
6000-400-USF1 W-6000-400-USF1
M3mk1-S-F1 W-6000M3
LC-2G-1 N/A
LC-2G24F-1 N/A
LC-2G24FP-1 N/A
Aruba part numbers have two XLR processor version varieties, which includes the use of the XLR Rev. B2
processor and the XLR Rev C4 processor. The XLR Rev. B2 processor is no longer sold. A B2 unit can be identified
by a serial number beginning with an A and a C4 unit has a serial number beginning with AK or BG.
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement Preface | 5
Page 6

NOTE
References to Aruba, ArubaOS, Aruba 6000 series, Aruba 3000 series and Aruba 6000/M3 series apply to both the
Aruba and Dell versions of these products and documentation. There is no Dell equivalent for the LC-2G-1, LC2G24F-1, or LC-2G24FP-1.
Related Documents
The following items are part of the complete installation and operations documentation included with this
product:
Aruba 6000 Mobility Controller Installation Guide
Aruba 3000-series Mobility Controller Installation Guide
ArubaOS 6.1 User Guide
ArubaOS 6.1 CLI Reference Guide
ArubaOS 6.1 Quick Start Guide
ArubaOS 6.1 Upgrade Guide
Aruba AP Installation Guides
Additional Product Information
More information is available from the following sources:
The Aruba Networks Web-site contains information on the full line of products from Aruba Networks:
http://www.arubanetworks.com
The Dell Web site contains information on the full line of products from Dell.
http://www.dell.com/
The NIST Validated Modules Web-site contains contact information for answers to technical or sales-
related questions for the product:
http://csrc.nist.gov/groups/STM/cmvp/index.html
6 | Preface Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 7
Chapter 1
The Aruba 3000 and 6000/M3
Controllers
This chapter introduces the Aruba 3000 and 6000/M3 Controllers with FIPS 140-2 Level 2 validation. It
describes the purpose of the controller, its physical attributes, and its interfaces.
Overview
Aruba Networks has developed a purpose-built Wireless LAN voice and data switching solution designed to
specifically address the needs of large-scale WiFi network deployments for Government agencies and
global enterprises. The Aruba Controller solution provides advanced security and management of the
corporate RF environment and enforces User security and service policies to both wired and wireless users.
The Aruba Wireless FIPS 140-2 Level 2 validated Controlling platform serves value-add high speed data and
QoS assured voice services to thousands of mobile wireless users simultaneously from a single, cost
effective, redundant and scalable solution that performs centralized functionality for:
Uncompromised User security, authentication and encryption
Stateful LAN-speed firewalling
VPN termination
Wireless intrusion detection, prevention and rogue containment
RF Air monitoring
Powerful packet processing switching
Mobility management
Advanced RF management
Advanced User and network service / element management
The Aruba FIPS 140-2 Level 2 validated Controller solution is a highly available, modular and upgradeable
switching platform which connects, controls, secures, and intelligently integrates wireless Access Points
and Air Monitors into the wired LAN, serving as a gateway between a wireless network and the wired
network. The wireless network traffic from the APs is securely tunneled over a L2/L3 network and is
terminated centrally on the switch via 10/100/1000 Ethernet physical interfaces where it is authenticated,
assigned the appropriate security policies and VLAN assignments and up-linked onto the wired network.
The Aruba Controller solution consists of the three major components:
Aruba Controller. This is an enterprise-class switch into which multiple Access Points (APs) and Air
Monitors (AMs) may be directly or in-directly (tunneled over a L2/L3 network) connected and
controlled.
Aruba Wireless Access Point. This is a next-generation wireless transceiver which functions as an AP
or AM. Although third-party APs can be used with the Aruba WLAN system, the Aruba AP provides
the most comprehensive features and simpler integration.
Aruba ArubaOS Switch firmware. This firmware intelligently integrates the Controller and APs to
provide load balancing, rate limiting, self healing, authentication, mobility, security, firewalls,
encryption, and centralization for monitoring and upgrades.
The Aruba switch configurations tested during the cryptographic module testing included:
Aruba 3200 Revision B2
Aruba 3200 Revision C4
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement The Aruba 3000 and 6000/M3 Controllers | 7
Page 8

Aruba 3400 Revision B2
Aruba 3400 Revision C4
Aruba 3600 Revision B2
Aruba 3600 Revision C4
Aruba 6000 Revision B2 with [(minimum one: LC-2G-1, LC-2G24F-1, or LC-2G24FP-1) and (one or
two: M3mk1-G10X-10G2X)] (no more than four total).
Aruba 6000 Revision C4 with [(minimum one: LC-2G-1, LC-2G24F-1, or LC-2G24FP-1) and (one or
two: M3mk1-G10X-10G2X Revision C4)] (no more than four total).
The exact firmware versions tested were ArubaOS_MMC_6.1.2.3-FIPS and Dell_PCW_MMC_6.1.2.3-
FIPS
Physical Description
Dimensions
The Aruba 6000 Controller has the following physical dimensions:
3 RU chassis is designed to fit in a standard 19" rack. A separate mounting kit is needed for a 23" rack.
Size:
Width 17.4" (19" rack width)
Height 5.25" (3 RU)—3.5" for the card slots plus 1 RU for the power supply slots
Depth 14"
Maximum weight: Up to 58 lbs (26.5 kg)
The Aruba 3200 Controller has the following physical dimensions:
1 RU chassis is designed to fit in a standard 19" rack with the included mounting kit. A separate
mounting kit is needed for a 23" rack.
Size:
Width 13.8"
Height 1.75" (1 RU)
Depth 11.7"
Maximum weight: Up to 7.1 lbs (3.2 kg)
The Aruba 3400 and 3600 Controllers have the following physical dimensions:
1 RU chassis is designed to fit in a standard 19" rack with the included mounting kit. A separate
mounting kit is needed for a 23" rack.
Size:
Width 13.8"
Height 1.75" (1 RU)
Depth 11.7"
Maximum weight: Up to 7.4 lbs (3.4 kg)
Cryptographic Module Boundaries
For FIPS 140-2 Level 2 validation, the Controller has been validated as a multi-chip standalone
cryptographic module. The steel chassis physically encloses the complete set of hardware and firmware
components and represents the cryptographic boundary of the switch. The cryptographic boundary is
defined as encompassing the top, front, left, right, rear, and bottom surfaces of the case.
8 | The Aruba 3000 and 6000/M3 Controllers Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 9
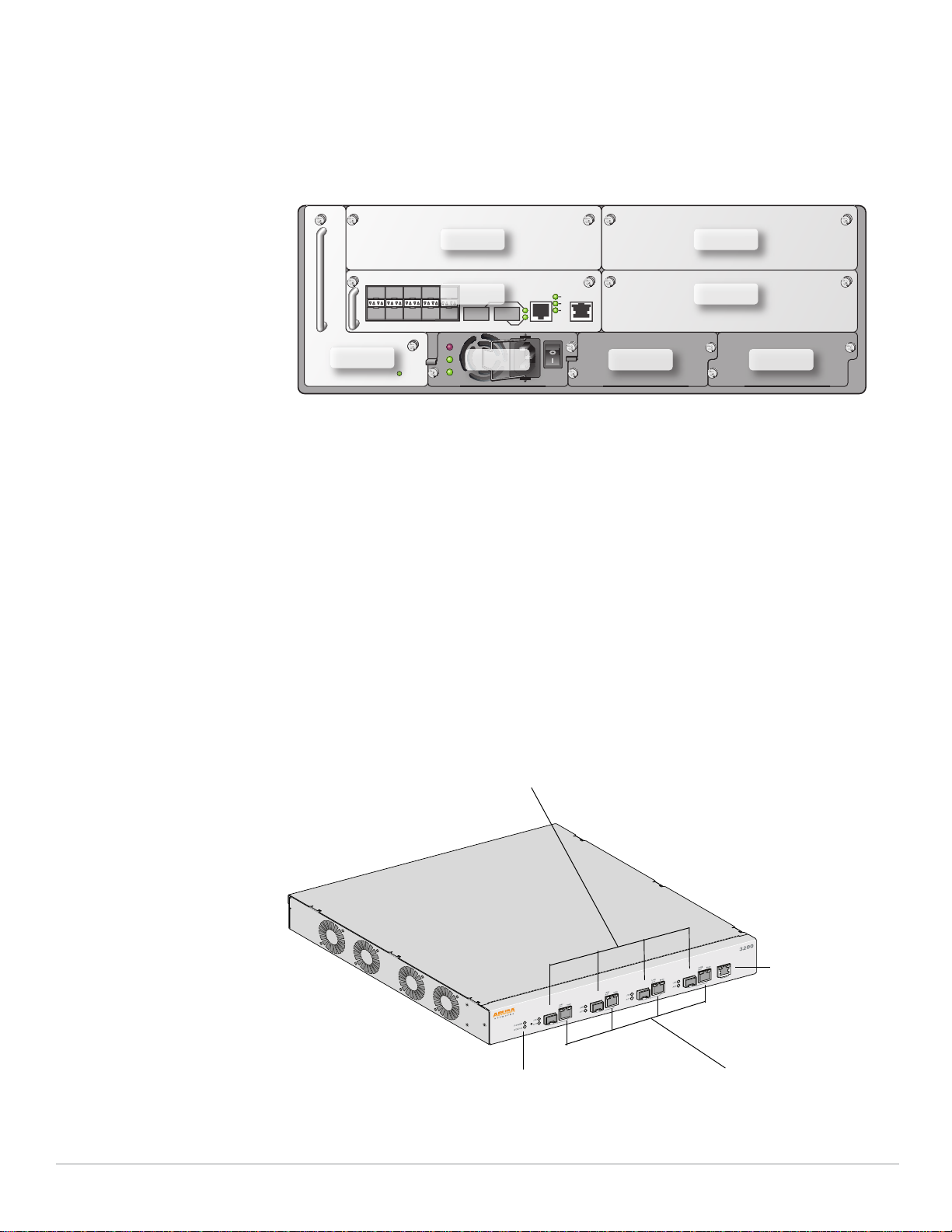
Chassis
arun_0118A
Slot 2
Slot 0
Slot 3
Slot 1
Fan Tray
PS1 PS2 PS3
Optional 1000Base-X ports
Serial Console Port
System indicator LEDs
Gigabit Ethernet ports
The Aruba 6000 Controller chassis is designed to be modular. All of the modular components, consisting of
the switching supervisor and network line cards, the fan tray, and the power supplies, are accessible from
the front of the chassis and are field replaceable and hot-swappable.
Figure 1 The Aruba 6000 Controller with M3 Mark I
Figure 1 shows the front of the Aruba 6000 Controller, and illustrates the following:
Slots 2 and 3 are for optional Line Card modules to provide extra port capacity.
Slots 0 and 1 are for one or two Multi-service Mobility Modules (M3), which combine the Supervisor
Card and Line Card functionality in a single module. Note that this validation covers only configurations
with one or two M3s.
M3 indicator LEDs indicate power state, status of the device, and link activity.
The hot-swappable fan tray cools the switch. The fan tray pulls air from right to left, as viewed from the
front of the chassis, across the installed cards.
PS1, PS2, and PS3 are for Power Supply modules. The number of power supplies required for the system
depends on the number and type of Line Cards installed, and whether to include redundancy for fault
tolerance.
The Aruba 3000-series Controller chassis is a 1U not-modular chassis.
Figure 2 The Aruba 3000-series Controller Chassis
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement The Aruba 3000 and 6000/M3 Controllers | 9
Page 10

Figure 2 shows the front of the Aruba 3000-series Controller, and illustrates the following:
System indicator LEDs indicate power state and status of the device.
Four Gigabit Ethernet ports provide network connectivity.
Optional 1000Base-X fiber optic ports provide network connectivity.
Serial Console port is for connecting to a local management console.
10 | The Aruba 3000 and 6000/M3 Controllers Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 11

Chapter 2
FIPS 140-2 Level 2 Features
Intended Level of Security
The Aruba 3000 and 6000/M3 Controllers and associated modules are intended to meet overall FIPS 140-2
Level 2 requirements as shown in Table 2.
Table 2 Intended Level of Security
Section Section Title Level
1 Cryptographic Module Specification 2
2 Cryptographic Module Ports and Interfaces 2
3 Roles, Services, and Authentication 2
4 Finite State Model 2
5 Physical Security 2
6 Operational Environment N/A
7 Cryptographic Key Management 2
8 EMI/EMC 2
9Self-tests 2
10 Design Assurance 2
11 Mitigation of Other Attacks 2
Physical Security
The Aruba Controller is a scalable, multi-processor standalone network device and is enclosed in a robust
steel housing. The switch enclosure is resistant to probing and is opaque within the visible spectrum. The
enclosure of the switch has been designed to satisfy FIPS 140-2 Level 2 physical security requirements.
For the Aruba 6000 the left, top, right, and bottom surfaces are irremovable. The rear panel can be removed
by unscrewing fifteen screws. The switch has a number of hot-swappable components at front side,
including four slots for supervisor and line cards, one fan tray, and three power supplies. Each of the
components is attached with two screws.
For the Aruba 3000-series the left, right, front, rear, and bottom surfaces are irremovable. The top panel can
be removed by unscrewing two screws. A metallic opaque shield is installed at the factory during
manufacturing and can not be removed by the User.
For physical security, the Aruba 6000 switch requires Tamper-Evident Labels (TELs) to allow the detection
of the opening of the chassis covers; the removal or replacement of any module or cover plate, and to block
the Serial console port.
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 11
Page 12

The Aruba 3000-series Controllers require Tamper-Evident Labels (TELs) to allow the detection of the
opening of the chassis cover and to block the Serial console port.
To protect the Aruba 3000 and 6000/M3 Controllers from any tampering with the product, TELs should be
applied by the Crypto Officer as covered under “Tamper-Evident Labels” on page27.
Operational Environment
The operational environment is non-modifiable. The control plane Operating System (OS) is Linux, a realtime, multi-threaded operating system that supports memory protection between processes. Access to the
underlying Linux implementation is not provided directly. Only Aruba Networks provided interfaces are
used, and the CLI is a restricted command set.
Logical Interfaces
All of these physical interfaces are separated into logical interfaces defined by FIPS 140-2, as described in
the following table.
Table 3 FIPS 140-2 Logical Interfaces
FIPS 140-2 Logical Interface Module Physical Interface
Data Input Interface 10/100 Mbps Ethernet port
10/100/1000 Mbps Ethernet ports
Data Output Interface 10/100 Mbps Ethernet port
10/100/1000 Mbps Ethernet ports
Control Input Interface Power switch (Aruba 6000 only)
Reset button (Aruba 6000 only)
10/100 Mbps Ethernet port
10/100/1000 Mbps Ethernet ports
Serial console port (disabled)
Status Output Interface 10/100 Mbps Ethernet port
10/100/1000 Mbps Ethernet ports
LEDs
Serial console port (disabled)
Power Interface Power Supply
POE (Aruba 6000 only)
Data input and output, control input, status output, and power interfaces are defined as follows:
Data input and output are the packets that use the firewall, VPN, and routing functionality of the
modules.
Control input consists of manual control inputs for power and reset through the power and reset switch.
It also consists of all of the data that is entered into the switch while using the management interfaces.
Status output consists of the status indicators displayed through the LEDs, the status data that is output
from the switch while using the management interfaces, and the log file.
LEDs indicate the physical state of the module, such as power-up (or rebooting), utilization level,
activation state (including fan, ports, and power). The log file records the results of self-tests,
configuration errors, and monitoring data.
12 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 13
A power supply is used to connect the electric power cable. Operating power is also provided (Aruba
6000 only) to a compatible Power Over Ethernet (POE) device when connected. The power is provided
through the connected Ethernet cable.
The switch distinguishes between different forms of data, control, and status traffic over the network ports
by analyzing the packets header information and contents.
Roles and Services
The Aruba Controller supports role-based authentication. There are two roles in the switch (as required by
FIPS 140-2 Level 2) that operators may assume: a Crypto Officer role and a User role. The Administrator
maps to the Crypto-Officer role and the client Users map to the User role.
Crypto Officer Role
The Crypto Officer role has the ability to configure, manage, and monitor the switch. Three management
interfaces can be used for this purpose:
CLI
The Crypto Officer can use the CLI to perform non-security-sensitive and security-sensitive monitoring
and configuration. The CLI can be accessed remotely by using the SSHv2 secured management session
over the Ethernet ports or locally over the serial port. In FIPS mode, the serial port is disabled.
Web Interface
The Crypto Officer can use the Web Interface as an alternative to the CLI. The Web Interface provides a
highly intuitive, graphical interface for a comprehensive set of switch management tools. The Web
Interface can be accessed from a TLS-enabled Web browser using HTTPS (HTTP with Secure Socket
Layer) on logical port 4343.
Bootrom Monitor Mode
In Bootrom monitor mode, the Crypto Officer can reboot, update the Bootrom, issue file system-related
commands, modify network parameters, and issue various show commands. The Crypto Officer can
only enter this mode by pressing any key during the first four seconds of initialization. Bootrom Monitor
Mode is disabled in FIPS mode.
The Crypto Officer can also use SNMPv1/2c/3 to remotely perform non-security-sensitive monitoring and
use get and getnext commands. See the table below for descriptions of the services available to the Crypto
Officer role.
Table 4 Crypto-Officer Services
Service Description Input Output CSP Access
SSH Provide authenticated and
encrypted remote management
sessions while using the CLI
SSH key agreement
parameters, SSH
inputs, and data
SSH outputs and
data
Diffie-Hellman key pair
(read/ write access), session
key for SSH (read/write
access), RNG keys (read
access); Crypto Officer's
password (read access)
IKEv1/IKEv2-IPSec Provide authenticated and
encrypted remote management
sessions to access the CLI
functionality
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 13
IKEv1/IKEv2 inputs and
data; IPSec inputs,
commands, and data
IKEv1/IKEv2
outputs, status,
and data; IPSec
outputs, status,
and data
RSA or ECDSA key pair for
IKEv1/IKEv2 (read access),
Diffie-Hellman or Elliptic
curve Diffie-Hellman key pair
for IKEv1/IKEv2 (read/write
access), pre- shared keys
for IKEv1/IKEv2 (read
access); Session keys for
IPSec (read/write access)
Page 14

Table 4 Crypto-Officer Services
Service Description Input Output CSP Access
Configuring
Network
Management
Configuring the
module Platform
Configuring
Hardware
Controllers
Configuring the
Internet Protocol
Configuring Quality
of Service (QoS)
Configuring the
VPN
Create management Users and
set their password and privilege
level; configure the SNMP agent
Define the platform subsystem
firmware of the module by
entering Bootrom Monitor Mode,
File System, fault report, message
logging, and other platform
related commands
Define synchronization features
for module
Set IP functionality Commands and
Configure QOS values for module Commands and
Configure Public Key
Infrastructure (PKI); configure the
Internet Key Exchange (IKEv1/
IKEv2) Security Protocol;
configure the IPSec protocol
Commands and
configuration data
Commands and
configuration data
Commands and
configuration data
configuration data
configuration data
Commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
Crypto Officer's password
for CLI (read/write access)
None
None
None
None
RSA and ECDSA keys pair
(read/write access), Preshared key (read/write
access)
Configuring DHCP Configure DHCP on module Commands and
configuration data
Configuring
Security
HTTPS over TLS Secure browser connection over
IPSec tunnel
establishment for
RADIUS protection
Self-test Run Power On Self-Tests and
Configuring
Bypass Operation
Define security features for
module, including Access List,
AAA, and firewall functionality
Transport Layer Security acting as
a Crypto Officer service (web
management interface)
Provided authenticated/
encrypted channel to RADIUS
server
Conditional Tests
Configure bypass operation on
the module
Commands and
configuration data
TLS inputs, commands,
and data
IKEv1/IKEv2 inputs and
data; IPSec inputs,
commands, and data
None Error messages
Commands and
configuration data
Status of
commands and
configuration data
Status of
commands and
configuration data
TLS outputs,
status, and data
IKEv1/IKEv2
outputs, status,
and data; IPSec
outputs, status,
and data
logged if a failure
occurs
Status of
commands and
configuration data
None
AAA User password (read/
write access), RADIUS
password (read/ write
access)
RSA key pair for TLS; TLS
Session Key
Preshared key/RSA private
key for IKEv1/IKEv2 (read
access), Diffie-Hellman and
Elliptic curve Diffie-Hellman
key pair for IKEv1/IKEv2
(read/write access), Session
keys for IPSec (read/write
access)
None
None
14 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 15
Table 4 Crypto-Officer Services
Service Description Input Output CSP Access
Updating Firmware Updating firmware on the module Commands and
Configuring OCSP
Responder
Configuring
Control Plane
Security (CPSec)
Configuring OCSP responder
functionality
Configuring Control Plane
Security mode to protect
communication with APs using
IPSec and issue self signed
certificates to APs
configuration data
OCSP inputs,
commands, and data
Commands and
configuration data,
IKEv1/IKEv2 inputs and
data; IPSec inputs,
commands, and data
Status of
commands and
configuration data
OCSP outputs,
status, and data
Status of
commands, IKEv1/
IKEv2 outputs,
status, and data;
IPSec outputs,
status, and data
and configuration
data, self signed
certificates
None
RSA/ECDSA key pair for
signing OCSP responses
RSA private key for IKEv1/
IKEv2 and certificate signing
(read access), Diffie-Hellman
key pair for IKEv1/IKEv2
(read/write access), Session
keys for IPSec (read/write
access)
User Role
The User role can access the switch’s IPSec and IKEv1/IKEv2 services. Service descriptions and inputs/
outputs are listed in the following table:
Table 5 User Service
Service Description Input Output CSP Access
IKEv1/IKEv2-IPSec Access the module's IPSec
services in order to secure
network traffic
HTTPS over TLS Access the module’s TLS
services in order to secure
network traffic
EAP-TLS
termination
802.11i Shared
Key Mode
802.11i with EAPTLS
Provide EAP-TLS termination EAP-TLS inputs,
Access the module’s 802.11i
services in order to secure
network traffic
Access the module’s 802.11i
services in order to secure
network traffic
IPSec inputs,
commands, and data
TLS inputs, commands,
and data
commands and data
802.11i inputs,
commands and data
802.11i inputs,
commands and data
IPSec outputs,
status, and data
TLS outputs,
status, and data
EAP-TLS outputs,
status and data
802.11i outputs,
status and data
802.11i outputs,
status, and data
RSA and ECDSA key pair for
IKEv1/IKEv2 (read access);
Diffie-Hellman and Elliptic
curve Diffie-Hellman key pair
for IKEv1/IKEv2 (read and
write access); pre-shared
keys for IKEv1/IKEv2 (read
access)
RSA key pair for TLS; TLS
Session Key
EAP-TLS RSA private key
(read)
EAP-TLS ECDSA private key
(read)
802.11i Pre-Shared Key
(read)
802.11i Session key (read/
write)
EAP-TLS RSA private key
(read)
EAP-TLS ECDSA private key
(read) 802.11i
Pair-Wise Master Key (read/
write) 802.11i
Session key (read/write)
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 15
Page 16

Table 5 User Service
Service Description Input Output CSP Access
Data link (Layer 2)
Encryption
Access the module’s Layer 2
encrypted tunnel services to
secure network trafficData link
encryption inputs, commands
and data
Data link encryption
inputs, commands and
data
Data link
encryption, status,
and data
Data link encryption AES
key (read)
Authentication Mechanisms
The Aruba Controller supports role-based authentication. Role-based authentication is performed before
the Crypto Officer enters privileged mode using admin password via Web Interface or SSH or by entering
enable command and password in console. Role-based authentication is also performed for User
authentication.
This includes password and RSA/ECDSA-based authentication mechanisms. The strength of each
authentication mechanism is described below.
Table 6 Estimated Strength of Authentication Mechanisms
Authentication Type Role Strength
Password-based authentication
(CLI and Web Interface)
Crypto Officer Passwords are required to be at least six characters long.
Numeric, alphabetic (upper and lowercase), and keyboard
and extended characters can be used, which gives a total of
95 characters to choose from. Therefore, the number of
potential six-character passwords is 956 (735091890625).
RSA-based authentication
(IKEv1/IKEv2)
Pre-shared key-based
authentication (IKEv1/IKEv2)
Pre-shared key based
authentication (802.11i)
EAP-TLS authentication User 1024 and 2048 bit RSA keys correspond to effective strength
ECDSA-based authentication
(IKEv1/IKEv2)
User RSA signing and verification is used to authenticate to the
User Pre-shared keys must be at least six characters long and up
User 1024 and 2048 bit RSA keys correspond to effective strength
User ECDSA signing and verification is used to authenticate to the
module during IKEv1/IKEv2. This mechanism is as strong as
the RSA algorithm using a 1024 or 2048 bit key pair.
to 64 bytes long. Even if only uppercase letters were used
without repetition for a six character pre-shared key, the
probability of randomly guessing the correct sequence is one
in 165,765,600.
80
of 2
80
of 2
module during IKEv1/IKEv2. Both P-256 and P-384 keys are
supported. ECDSA P-256 provides 128 bits of equivalent
security, and P-384 provides 192 bits of equivalent security.
and 2
and 2
112
respectively.
112
respectively.
Unauthenticated Services
The Aruba Controller can perform SNMP management, VLAN, bridging, firewall, routing, and forwarding
functionality without authentication. These services do not involve any cryptographic processing.
Additional unauthenticated services include performance of the power-on self test and system status
indication via LEDs.
16 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 17

Cryptographic Key Management
Implemented Algorithms
FIPS-approved cryptographic algorithms have been implemented in firmware and hardware.
The firmware supports the following cryptographic implemetations.
ArubaOS OpenSSL Module implements the following FIPS-approved algorithms:
AES (Cert. #1854)
Triple-DES (Cert. #1201)
SHA (Cert. #1631)
RNG (Cert. #972)
RSA (Cert. #937)
HMAC (Cert. #1101)
ECDSA (#258)
ArubaOS Crypto Module implementation supports the following FIPS ApprovedAlgorithms:
AES (Cert. #1850)
Triple-DES (Cert. #1198)
SHA (Cert. #1627)
RNG (Cert. #969)
RSA (Cert. #933)
HMAC (Cert. #1098)
ECDSA (Cert. #257)
ArubaOS UBOOT Bootloader implements the following FIPS-approved algorithms:
RSA (Cert. #935)
SHA-1 (Cert. #1629)
The hardware supports the following cryptographic implemetations.
Revision C4
Hardware encryption acceleration is provided for bulk cryptographic operations for the following FIPS
approved algorithms:
AES (Cert. #762) - CBC; 128,192,256 bits - CCM; 128 bits - GCM; 128, 192, 256 bits, Assoc. Data Len Range:
15 - 30, Payload Length Range: 0 - 32, Nonce Length(s): 13, Tag Length(s): 8
Triple-DES (Cert. #667) - CBC; 192 bits (168 used)/1,2,3 keys keying option
SHS (Cert. #769) - SHA-1, SHA-256, SHA-384, SHA-512 - BYTE oriented
HMAC (Cert. #417) - HMAC-SHA-1, HMAC-SHA-256, HMAC -SHA384, and HMA-SHA512
Revision B2
Hardware encryption acceleration is provided for bulk cryptographic operations for the following FIPS
approved algorithms:
AES (Cert. #465) - CBC; 128,192,256 bits - CCM
Triple-DES (Cert. #482) - CBC; 192 bits (168 used)/1,2,3 keys keying option
SHA (Cert. #768) - SHA-1, SHA-256 - BYTE oriented
HMAC (Cert.#416) - HMAC-SHA-1, HMAC-SHA-256
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 17
Page 18

Non-FIPS Approved Algorithms
The cryptographic module implements the following non-approved algorithms that are not permitted for
use in the FIPS 140-2 mode of operations:
DES
HMAC-MD5
MD5
RC4
In addition, withing the FIPS Approved mode of operation, the module supports the following allowed key
establishment schemes:
Diffie-Hellman (key agreement; key establishment methodology provides between 80 bits of encryption
strength; non-compliant less than 80-bits of encryption strength)
EC Diffie-Hellman (key agreement; key establishment methodology provides between 128 and 192 bits
of encryption strength)
RSA (key wrapping; key establishment methodology provides 80 bits of encryption strength)
Critical Security Parameters
The following are the Critical Security Parameters (CSPs) used in the switch.
Table 7 CSPs Used in Aruba Controllers
CSPs CSPs type Generation Storage and Zeroization Use
Key Encryption Key
(KEK)
IKEv1/IKEv2 Pre-shared
key
RADIUS server shared
secret
Enable secret 6-64 character
IPSec session
encryption keys
Triple-DES 168-bit key Hard Coded Stored in Flash and zeroized
by using the CLI command
wipe out flash
64 character preshared key
CO configured Stored encrypted in Flash
with the KEK. Zeroized by
changing (updating) the preshared key through the User
interface.
6-128 character shared
secret
CO configured Stored encrypted in Flash
with the KEK. Zeroized by
changing (updating) the preshared key through the User
interface.
CO configured Store in ciphertext in flash.
password
Zeroized by changing
(updating) through the user
interface.
168-bit Triple-DES or
128/192/256-bit AESCBC or 128/256-bit
Established during the
Diffie-Hellman key
agreement
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
AES-GCM keys
Encrypts IKEv1/IKEv2
Pre-shared key,
RADIUS server shared
secret, RSA private key,
ECDSA private key,
802.11i pre-shared key
and Passwords.
User and module
authentication during
IKEv1, IKEv2
Module and RADIUS
server authentication
Administrator
authentication
Secure IPSec traffic
IPSec session
authentication keys
HMAC SHA-1 key Established during the
Diffie-Hellman key
agreement
18 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
User authentication
Page 19

Table 7 CSPs Used in Aruba Controllers
CSPs CSPs type Generation Storage and Zeroization Use
SSH Diffie-Hellman
shared secret
IKEv1/IKEv2 DiffieHellman private key
IKEv1/IKEv2 DiffieHellman shared secret
IKEv1/IKEv2 session
authentication key
IKEv1/IKEv2 session
encryption key
128-octet intermediate
value used for key
derivation
768/1024-bit (MODP
group) or 256/384-bit
(Elliptic curve group)
Diffie-Hellman private
key.
Note: Key size 768 bits
is not allowed in FIPS
mode.
128 octet or 32/48
octet (Elliptic curve
Diffie Hellman)
intermediate value
used for cryptographic
key derivation
160-bit HMAC-SHA1or
256 byte HMAC-SHA256-128 or 384 byte
HMAC-SHA-384-192
key
168-bit Triple-DES or
128/192/256-bit AESCBC key
Established during the
SSH Diffie-Hellman
key agreement
Generated internally
during IKEv1/IKEv2
negotiations
Established during the
Diffie-Hellman Key
Agreement
Established as a result
of Diffie-Hellman key
agreement.
Established as a result
of Diffie-Hellman key
agreement.
Stored in plain text in volatile
memory, Zeroized when
session is closed.
Stored in the volatile memory.
Zeroized after the session is
closed.
Stored in plaintext in volatile
memory. Zeroized when
session is closed.
Stored in plaintext in volatile
memory. Zeroized when
session is closed.
Stored in plaintext in volatile
memory. Zeroized when
session is closed.
Key agreement in SSH
Used in establishing the
session key for an
IPSec session
Key agreement in
IKEv1/IKEv2
IKEv1/IKEv2 payload
integrity verification
IKEv1/IKEv2 payload
encryption
SSH session keys 168-bit Triple-DES or
128/192/256-bit AES
keys
SSH session
authentication key
SSH Diffie-Hellman
Private Key
TLS pre-master secret 48 byte secret Externally generated Stored in plaintext in volatile
TLS session encryption
key
TLS session
authentication key
160-bit HMAC-SHA-1 Established during the
768/1024-bit DiffieHellman private key.
Note: Key size 768 bits
is not allowed in FIPS
mode.
AES 128, 192, 256 Generated in the
160-bit HMAC-SHA1
key
Established during the
SSH key exchange
using the DiffieHellman key
agreement
SSH key exchange
using the DiffieHellman key
agreement
Generated internally
during the SSH
session negotiations
module
Generated in the
module
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
Stored in the volatile memory.
Zeroized after the session is
closed.
memory. Zeroized when the
session is closed.
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
Stored in plaintext in volatile
memory. Zeroized when the
session is closed.
Secure SSH traffic
Secure SSH traffic
Used in establishing the
session key for an SSH
session.
Key agreement during
TLS
Key agreement during
802.1x connection
Key agreement during
802.1x connection
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 19
Page 20

Table 7 CSPs Used in Aruba Controllers
CSPs CSPs type Generation Storage and Zeroization Use
RSA Private Key RSA 1024/2048 bit key Generated in the
ECDSA Private Key ECDSA suite B P-256
and P-384 curves
skeyid Intermediate 160-bit/
256-byte/384-byte
value used in key
derivation
skeyid_d Intermediate 160-bit/
802.11i Pre-Shared Key
(PSK)
256-byte/384-byte
value used in key
derivation
802.11i pre-shared
secret key (256-bit)
module
Generated in the
module
Established during the
Diffie-Hellman Key
Agreement
Established during the
Diffie-Hellman Key
Agreement
CO configured Stored in flash memory
Stored in flash memory
encrypted with KEK. Zeroized
by the CO command write
erase all.
Stored in flash memory
encrypted with KEK. Zeroized
by the CO command write
erase all.
Stored in plaintext in volatile
memory. Zeroized when
session is closed.
Stored in plaintext in volatile
memory. Zeroized when
session is closed.
encrypted with KEK. Zeroized
by the CO command write
erase all.
Used by TLS and EAPTLS/PEAP protocols
during the handshake,
used for signing OCSP
responses, and used by
IKEv1/IKEv2 for device
authentication and for
signing certificates
Used by TLS and EAPTLS/PEAP protocols
during the handshake.
Key agreement in
IKEv1/IKEv2
Key agreement in
IKEv1/IKEv2
Used by the 802.11i
protocol
802.11i Pair-Wise
Master key (PMK)
802.11i session key AES-CCM key (128
Data link (Layer 2)
encryption key
Data link (Layer 2)
integrity key
Passwords 6-character password CO configured Stored encrypted in Flash
ArubaOS OpenSSL RNG
Seed for FIPS compliant
ANSI X9.31, Appendix
A2.4 using AES-128 key
algorithm
802.11i secret key
(256-bit)
bit), AES-GCM key
(128/256-bit)
AES key (256 bit) Derived during the
HMAC-SHA1 key (160bit)
Seed (16 bytes) Derived using NON-
Derived during the
EAP-TLS/PEAP
handshake
Derived from 802.11
PMK
EAP-TLS handshake
Derived during EAPTLS handshake
storage and
zeroization: Stored in
plaintext in volatile
memory
FIPS approved HW
RNG (/dev/urandom)
Stored in the volatile memory.
Zeroized on reboot.
Stored in plaintext in volatile
memory. Zeroized on reboot.
Stored in plaintext in volatile
memory. Zeroized on reboot.
Stored in plaintext in volatile
memory. Zeroized on reboot.
with KEK. Zeroized by either
deleting the password
configuration file or by
overwriting the password
with a new one.
Stored in plaintext in volatile
memory only. Zeroized on
reboot.
Used by the 802.11i
protocol
Used for 802.11i
encryption
Used to encrypt
tunneled Layer 2 frames
Used to integrityprotect tunneled Layer
2 frames
Authentication for
accessing the
management
interfaces, RADIUS
authentication
Seed ANSI X9.31 RNG
20 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 21

Table 7 CSPs Used in Aruba Controllers
CSPs CSPs type Generation Storage and Zeroization Use
ArubaOS OpenSSL RNG
Seed key for FIPS
compliant ANSI X9.31,
Appendix A2.4 using
AES-128 key algorithm
ArubaOS cryptographic
Module RNG seed for
FIPS compliant 186-2
General purpose (xchange Notice); SHA-1
RNG
ArubaOS cryptographic
Module RNG seed key
for FIPS compliant 1862 General purpose (xchange Notice); SHA-1
RNG
Self-Tests
The Aruba Controller performs both power-up and conditional self-tests. In the event any self-test fails, the
switch will enter an error state, log the error, and reboot automatically.
The following self-tests are performed:
Seed key (16 bytes,
AES-128 key
algorithm)
Derived using NONFIPS approved HW
RNG (/dev/urandom)
Seed (64 bytes) Derived using NON-
FIPS approved HW
RNG (/dev/urandom)
Seed key (64 bytes) Derived using NON-
FIPS approved HW
RNG (/dev/urandom)
Stored in plaintext in volatile
memory only. Zeroized on
reboot.
Stored in plaintext in volatile
memory. Zeroized on reboot.
Stored in plaintext in volatile
memory. Zeroized on reboot.
Seed ANSI X9.31 RNG
Seed 186-2 General
purpose (x-change
Notice); SHA-1 RNG
Seed 186-2 General
purpose (x-change
Notice); SHA-1 RNG
ArubaOS OpenSSL Module:
AES KAT
Triple-DES KAT
RNG KAT
RSA KAT
ECDSA (sign/verify)
SHA (SHA1, SHA256 and SHA384) KAT
HMAC (HMAC-SHA1, HMAC-SHA256 and HMAC-SHA384) KAT
ArubaOS Cryptographic Module
AES KAT
Triple-DES KAT
SHA (SHA1, SHA256, SHA384 and SHA512) KAT
HMAC (HMAC-SHA1, HMAC-SHA256, HMAC-SHA384 and HMAC-SHA512) KAT
RSA (sign/verify)
ECDSA (sign/verify)
FIPS 186-2 RNG KAT
ArubaOS Uboot BootLoader Module
Firmware Integrity Test: RSA 2048-bit Signature Validation
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 21
Page 22

Aruba Hardware Known Answer Tests for Revision C4:
AES KAT
AES-CCM KAT
AES-GCM KAT
Triple DES KAT
HMAC (HMAC-SHA1, HMAC-SHA256, HMAC-SHA384 and HMAC-SHA512) KAT
Aruba Hardware Known Answer Tests Revision B2:
AES KAT
AES-CCM KAT
Triple DES KAT
HMAC (HMAC-SHA1, HMAC-SHA256) KAT
Following Conditional Self-tests are performed in the switch:
Continuous Random Number Generator Test—This test is run upon generation of random data by the
switch’s random number generators to detect failure to a constant value. The module stores the first
random number for subsequent comparison, and the module compares the value of the new random
number with the random number generated in the previous round and enters an error state if the
comparison is successful. The test is performed for approved as well as non-approved RNGs.
Bypass test
RSA Pairwise Consistency test
ECDSA Pairwise Consistency test
Firmware Load Test
Self-test results are logged in a log file. Upon successful completion of the power-up self tests, the module
logs a KATS: passed message into a log file. Confirm the file update by checking the associated time of the
file.
In the event of a hardware KATs failure, the log file records one of the following messages depending on the
algorith being tested:
AES256 HMAC-SHA1 hash failed
AES256 Encrypt failed
AES256 Decrypt Failed
3DES HMAC-SHA1 hash failed
3DES Encrypt failed
3DES Decrypt Failed
DES HMAC-SHA1 hash failed
DES Encrypt failed
DES Decrypt Failed
HW KAT test failed for AESCCM CTR. Rebooting
AESCCM Encrypt Failed
This text is followed by this message:
The POST Test failed!!!!
Rebooting…
Alternating Bypass State
The controller implements an alternating bypass state when:
a port is configured in trusted mode to provide unauthenticated services
22 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 23

a configuration provides wireless access without encryption
The alternating bypass status can be identified by retrieving the port configuration or the wireless network
configuration.
Mitigation of Other Attacks
ArubaOS includes two modules that provide protection from attacks. These are:
XSec
Wireless Intrusion Protection
XSec
xSec is a highly secure data link layer (Layer 2) protocol that provides a unified framework for securing all
wired and wireless connections using strong encryption and authentication. xSec provides greater security
than Layer 3 encryption technologies through the use of FIPS-validated encryption algorithms (AES-CBC256 with HMAC-SHA1) to secure Layer 2 traffic, as well as the encryption of Layer 2 header information
including MAC addresses. xSec was jointly developed by Aruba Networks and Funk Software.
Many government agencies and commercial entities that transmit highly sensitive information over wireless
networks mandate that strong Layer 2 encryption technologies be deployed to ensure absolute data privacy.
U.S. DoD Directive 8100.2 requires that all data transmitted using commercial wireless devices be encrypted
at Layer 2 or Layer 3. The U.S. Navy and Army are requiring Layer 2 encryption, and cryptographic engines
used for all sensitive government communications must be validated as meeting FIPS 140-2 requirements.
xSec has been designed to address this requirement and to provide a number of additional benefits.
Wireless Intrusion Detection
Aruba’s Wireless Intrusion Protection (WIP) module eliminates the need for a separate system of RF
sensors and security appliances. The WIP module provides extraordinary capabilities to Aruba’s enterprise
mobility system, giving administrators visibility into the network, along with the power to thwart malicious
wireless attacks, impersonations and unauthorized intrusions.
Wireless intrusion detection is only the first step in securing the corporate environment from unwanted
wireless access. Without adequate measures to quickly shut down intrusions, detection is almost worthless.
Without accurate classification of APs and stations (e.g., valid, rogue, or neighbor), providing an automated
response to possible intrusion is impossible.
Aruba access points constantly scan all channels of the RF spectrum, capturing all 802.11 traffic and locally
examining the captured data. Only policy violations are sent to the central controller to ensure minimal
impact on wired network performance. While scanning the environment, the Aruba system learns about all
wireless APs and stations and classifies these devices based on traffic flows seen on the wire and in the air.
This traffic is collected and correlated on the controller.
Aruba’s WIP module provides both detection and prevention capabilities. Users and devices are detected
and classified so administrators can react to both unintentional and malicious WLAN access. No other
system on the market provides such capabilities.
Unique Station and User Classification
Aruba’s patent-pending classification system automatically identifies and classifies all APs and stations
connected to the network. The system works by comparing traffic seen in the air with traffic seen on the
wire. When a match is found, it is known with certainty that the device belongs to the local network rather
than a neighboring network. This avoids false alarms for the administrator, because only true rogue devices
are classified as such.
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement FIPS 140-2 Level 2 Features | 23
Page 24

Detecting and Disabling Rogue APs
Aruba’s classification algorithms allow the system to accurately determine who is a threat and who is not.
Once classified as rogue, these APs can be automatically disabled. Administrators are also notified of the
presence of rogue devices, along with their precise physical location on a floorplan, so that they may be
removed from the network.
Denial of Service and Impersonation Protection
Wireless networks, by their nature, make an attractive target for denial of service attacks. Such attacks
include software that floods the network with association requests, attacks that make a laptop look like
thousands of APs, and deauthentication floods. Aruba controllers equipped with the Aruba WIP module
maintain signatures of many different wireless attacks and are able to block them so service is not
disrupted.
Advanced Denial of Service (DoS) protection keeps enterprises safe against a variety of wireless attacks,
including association and de-authentication floods, honeypots and AP and station impersonations. Based on
location signatures and client classification, Aruba access points will drop illegal requests and generate
alerts to notify administrators of the attack.
Man-in-the-Middle Protection
One of the common attacks possible in wireless networks is the “man-in-the-middle” attack. During a manin-the-middle attack, a hacker masquerades as a legitimate AP. Then, acting as a relay point, this man-in-themiddle fools users and other APs into sending data through the unauthorized device. An attacker can then
modify or corrupt data or conduct password-cracking routines.
Aruba access points monitor the air to detect other wireless stations masquerading as valid APs. When such
masquerading is detected, appropriate defense mechanisms are put into place. Aruba controllers also track
unique “signatures” for each wireless client in the network. If a new station is introduced claiming to be a
particular client, but without the proper signature, a station impersonation attack is detected.
Policy Definition and Enforcement
Aruba WIP provides a number of policies that can be configured to take automatic action when a policy is
violated. Examples of wireless policies include weak WEP implementation detection, AP misconfiguration
protection, ad-hoc network detection and protection, unauthorized NIC type detection, wireless bridge
detection and more.
Using Wireless to Protect your Wired Network
Even if wireless LANs are not sanctioned at this time, no security conscious company can afford to do
nothing. Aruba’s WIP will keep wireless traffic from working its way into the wired network through rogue
APs unknowingly attached to a network port. With Aruba’s mobility system equipped with WIP, the
enterprise network is protected against wireless security holes. And when the enterprise is ready to deploy
wireless LANs, the Aruba system can be easily reconfigured to provide a scalable and secure wireless LAN
infrastructure.
Using Wireless to Protect your Existing Wireless Network
Aruba’s mobility system with WIP delivers the detection and protection necessary to keep your existing
wireless network safe from undesirable wireless access. ArubaOS WIP complements and enhances any
existing WLAN deployment, including Cisco deployments, by providing advanced RF security and control
features not found in first-generation wireless products.
24 | FIPS 140-2 Level 2 Features Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 25

Chapter 3
Installing the Controller
This chapter covers the physical installation of the Aruba 3000 and 6000/M3 Controllers with FIPS 140-2
Level 2 validation. The Crypto Officer is responsible for ensuring that the following procedures are used to
place the switch in a FIPS-approved mode of operation.
This chapter covers the following installation topics:
Precautions to be observed during installation
Requirements for the switch components and rack mounting gear
Selecting a proper environment for the switch
Mounting the switch in a rack
Connecting power to the switch
Pre-Installation Checklist
You will need the following during installation:
Aruba 3000 and 6000/M3 Controller components.
Aruba 3000 and 6000/M3 rack mounting kit.
Phillips or cross-head screwdriver.
19-inch equipment rack, or equivalent.
3U rack space for the Aruba 6000 and 1U rack space for the Aruba 3000-Series with 10 cm (4 inches)
clearance to the left, right, front, and rear of the rack.
Another person to help position the switch.
Aruba power cord for each power supply, rated to at least 10 A with IEC320 connector.
Adequate power supplies and electrical power.
Cool, non-condensing air 0 to 40 ºC (32 to 104 ºF). May require air conditioning.
Management Station (PC) with 10/100 Mbps Ethernet port and SSH software.
A 4- or 8-conductor Category 5 UTP Ethernet cable.
Precautions
Installation should be performed only by a trained technician.
Dangerous voltage in excess of 240 VAC is always present while the Aruba power supply is plugged into
an electrical outlet. Remove all rings, jewelry, and other potentially conductive material before working
with this product.
Never insert foreign objects into the chassis, the power supply, or any other component, even when the
power supplies have been turned off, unplugged, or removed.
Main power is fully disconnected from the switch only by unplugging all power cords from their power
outlets. For safety reasons, make sure the power outlets and plugs are within easy reach of the operator.
Do not handle electrical cables that are not insulated. This includes any network cables.
Keep water and other fluids away from the product.
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement Installing the Controller | 25
Page 26

Comply with electrical grounding standards during all phases of installation and operation of the
NOTE
NOTE
product. Do not allow the switch chassis, network ports, power supplies, or mounting brackets to
contact any device, cable, object, or person attached to a different electrical ground. Also, never connect
the device to external storm grounding sources.
Installation or removal of the chassis or any module must be performed in a static-free environment. The
proper use of anti-static body straps and mats is strongly recommended.
Keep modules in anti-static packaging when not installed in the chassis.
Do not ship or store this product near strong electromagnetic, electrostatic, magnetic or radioactive
fields.
Do not disassemble chassis or modules. They have no internal user-serviceable parts. When service or
repair is needed, contact Aruba Networks.
The Security Kit
The Aruba Controller FIPS 140-2 Level 2 Security Kit modifies the standard Aruba Controller hardware,
firmware, and documentation to assure FIPS 140-2 Level 2 validation.
Product Examination
The Crypto Officer receives the switch in a carton. The Crypto Officer should examine the carton for
evidence of tampering. Tamper-evidence includes tears, scratches, and other irregularities in the packaging.
Package Contents
The product carton should include the following:
Aruba 3000 and 6000/M3 Controller
Rack mounting kit
Aruba User Documentation CD
Tamper-Evident Labels
Minimum Configuration for the Aruba 6000
The Aruba 6000 Controller must include the following basic components:
One modular switch chassis
One fan tray
One Aruba M3 card in slot 0
Power Supply
The number and type of power supplies required depends on the number and type of line cards installed in
the chassis (refer to the Aruba 6000 Mobility Controller Installation Guide.
The switch is shipped with all required modules installed.
The Aruba 3000 series do not have minimum configurations, as they are fixed configuration chassis.
26 | Installing the Controller Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 27
Tamper-Evident Labels
NOTE
1
2
5
11
6
34
7
9 10
8
arun_0118B
After testing, the Crypto Officer must apply Tamper-Evident Labels (TELs) to the switch. When applied
properly, the TELs allow the Crypto Officer to detect the opening of the chassis cover, the removal or
replacement of modules or cover plates, or physical access to restricted ports. Vendor provides FIPS 140
designated TELs which have met the physical security testing requirements for tamper evident labels under
the FIPS 140-2 Standard. TELs are not endorsed by the Cryptographic Module Validation Program (CMVP).
The tamper-evident labels shall be installed for the module to operate in a FIPS Approved mode of
operation.
Reading TELs
Once applied, the TELs included with the switch cannot be surreptitiously broken, removed, or reapplied
without an obvious change in appearance:
Figure 3 Tamper-Evident Labels
Each TELs also has a unique serial number to prevent replacement with similar labels.
Required TEL Locations
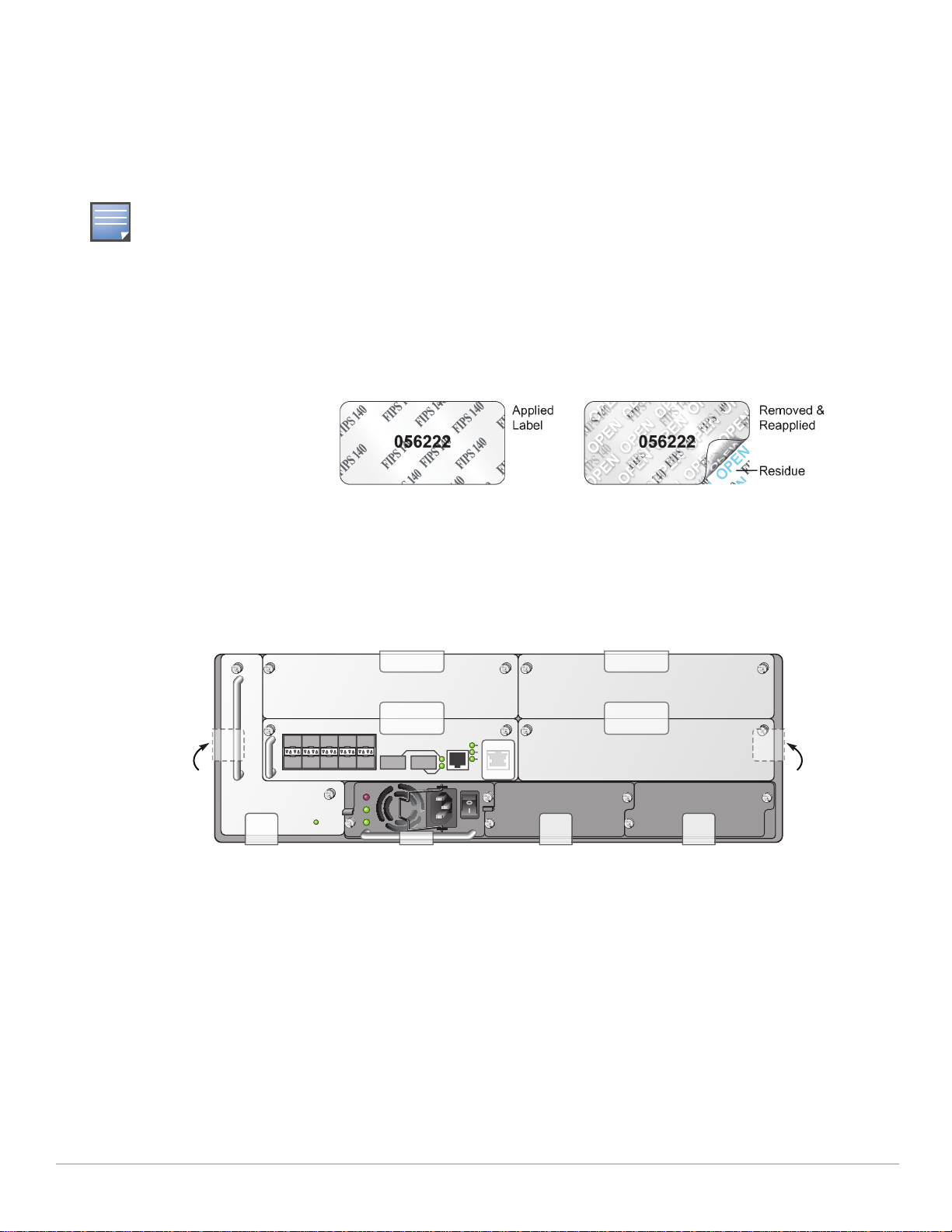
The Aruba 6000 Controller requires a minimum of 11 TELs to be applied as follows:
Figure 4 Required TELs for the Aruba 6000 Mobility Controller
To Detect Opening the Chassis Cover
1. Spanning the left side and rear of the chassis
2. Spanning the right side and rear of the chassis
To Detect the Removal of Any Module or Cover Plate
3. Spanning the Slot 2 faceplate or blank and the top of the chassis
4. Spanning the Slot 3 faceplate or blank and the top of the chassis
5. Spanning the Slot 0 faceplate or blank and the Slot 2 faceplate or blank
6. Spanning the Slot 1 faceplate or blank and the Slot 3 faceplate or blank
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement Installing the Controller | 27
Page 28
7. Spanning the fan tray faceplate and the bottom of the chassis
arun_0120A
3
1
2
8. Spanning the PS1 handle (or blank faceplate) and the bottom of the chassis
9. Spanning the PS2 handle (or blank faceplate) and the bottom of the chassis
10. Spanning the PS3 handle (or blank faceplate) and the bottom of the chassis
To Detect Access to Restricted Ports
11. Spanning the Serial port on the M3
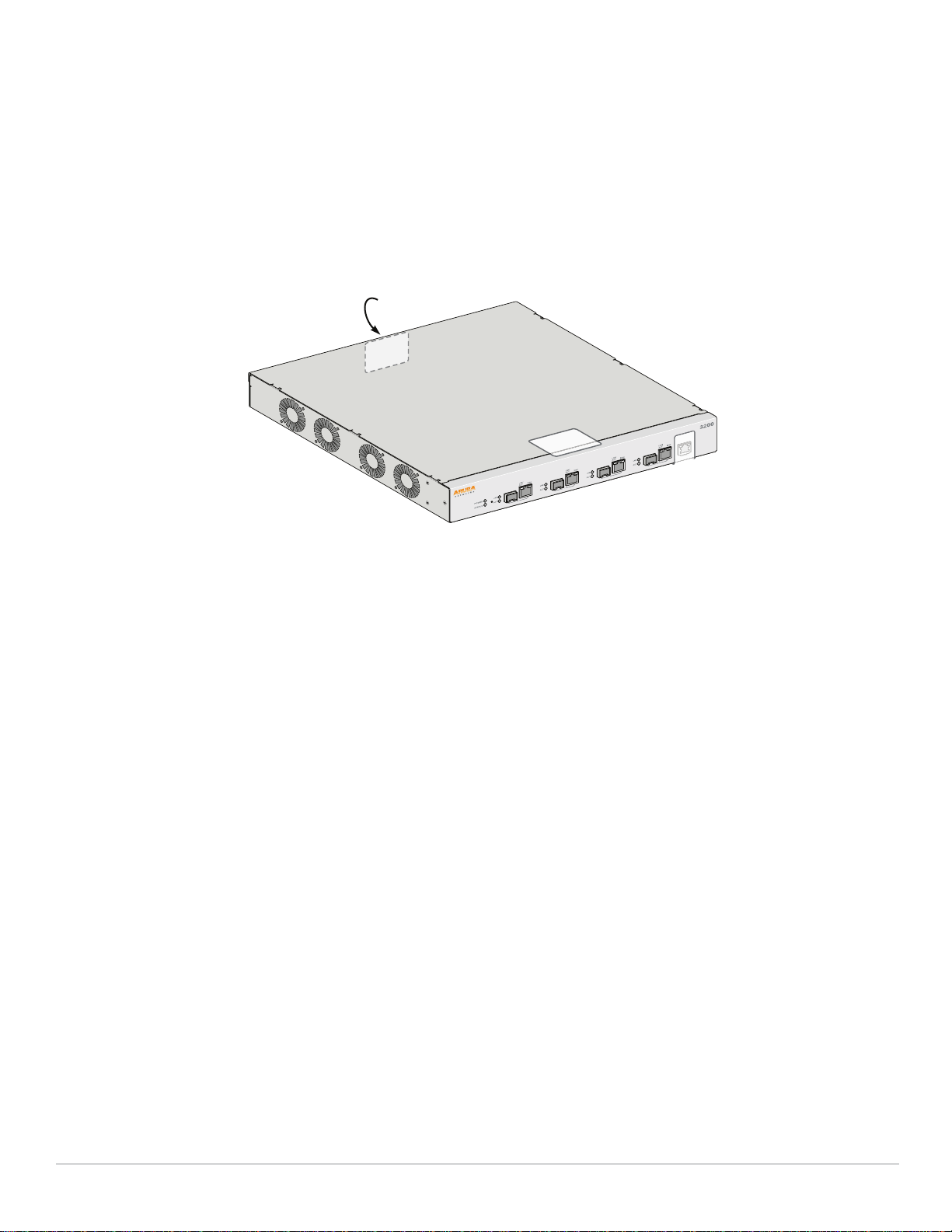
The Aruba 3000 series Controller require a minimum of 3 TELs to be applied as follows:
Figure 5 Required TELs for the Aruba 3000-series Controller
To Detect Access to Restricted Port
1. Spanning the Serial port
To Detect Opening the Chassis Cover
2. Spanning the top of the faceplate and top of the chassis
3. Spanning the back and top of the chassis
Applying TELs
The Crypto Officer should employ TELs as follows:
Before applying a TEL, make sure the target surfaces are clean and dry.
Do not cut, trim, punch, or otherwise alter the TEL.
Apply the wholly intact TEL firmly and completely to the target surfaces.
Ensure that TEL placement is not defeated by simultaneous removal of multiple modules.
Allow 24 hours for the TEL adhesive seal to completely cure.
Record the position and serial number of each applied TEL in a security log.
Once the TELs are applied, the Crypto Officer (CO) should perform initial setup and configuration as
described in the next chapter.
28 | Installing the Controller Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 29
Chapter 4
Ongoing Management
The Aruba 3000 and 6000/M3 Controllers meet FIPS 140-2 Level 2 requirements. The information below
describe how to keep the switch in FIPS-approved mode of operation. The Crypto Officer must ensure that
the switch is kept in a FIPS-approved mode of operation.
Crypto Officer Management
The Crypto Officer must ensure that the switch is always operating in a FIPS-approved mode of operation.
This can be achieved by ensuring the following:
FIPS mode must be enabled on the switch before Users are permitted to use the switch (see “Enabling
FIPS Mode” on page31)
The admin role must be root.
Passwords must be at least six characters long.
VPN services can only be provided by IPsec or L2TP over IPsec.
Access to the switch Web Interface is permitted only using HTTPS over a TLS tunnel. Basic HTTP and
HTTPS over SSL are not permitted.
Only SNMP read-only may be enabled.
Only FIPS-approved algorithms can be used for cryptographic services (such as HTTPS, L2, AES-CBC,
SSH, and IKEv1/IKEv2-IPSec), which include AES, Triple-DES, SHA-1, HMAC SHA-1, and RSA signature
and verification.
TFTP can only be used to load backup and restore files. These files are: Configuration files (system
setup configuration), the WMS database (radio network configuration), and log files. (FTP and TFTP
over IPsec can be used to transfer configuration files.)
The switch logs must be monitored. If a strange activity is found, the Crypto Officer should take the
switch off line and investigate.
The Tamper-Evident Labels (TELs) must be regularly examined for signs of tampering.
When installing expansion or replacement modules for the Aruba 6000, use only FIPS-approved
modules, replace TELs affected by the change, and record the reason for the change, along with the new
TEL locations and serial numbers, in the security log.
The Crypto Officer shall not configure the Diffie-Hellman algorithm with 768-bits (Group 1) in FIPS
mode for IKEv1/IKEv2-IPSec and SSH.
User Guidance
The User accesses the switch VPN functionality as an IPsec client. The user can also access the switch
802.11i functionality as an 802.11 client. Although outside the boundary of the switch, the User should be
directed to be careful not to provide authentication information and session keys to others parties.
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement Ongoing Management | 29
Page 30

30 | Ongoing Management Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
Page 31
Chapter 5
Setup and Configuration
The Aruba 3000 and 6000/M3 Controllers meet FIPS 140-2 Level 2 requirements. The sections below
describe how to place and keep the switch in FIPS-approved mode of operation. The Crypto Officer (CO)
must ensure that the switch is kept in a FIPS-approved mode of operation.
The switch can operate in two modes: the FIPS-approved mode, and the standard non-FIPS mode. By
default, the switch operates in non-FIPS mode.
Setting Up Your Controller
To set up your controller:
1. Make sure that the controller is not connected to any device on your network.
2. Boot up the controller.
3. Connect your PC or workstation to a line port on the controller.
For further details, see the ArubaOS 6.1 Quick Start Guide.
Enabling FIPS Mode
For FIPS compliance, users cannot be allowed to access the switch until the CO changes the mode of
operation to FIPS mode. There are two ways to enable FIPS mode:
Use the WebUI
Use the Setup Wizard
Enabling FIPS with the Setup Wizard
The Setup Wizard allows you to configure access to the controller, install software licenses, and configure
wireless local area networks (WLANs) for internal or guest users.
The Setup Wizard is available the first time you connect to and log into the controller or whenever the
controller is reset to its factory default configuration. After you complete the Setup Wizard, the controller
reboots using the new configuration information you entered.
For details on running the Setup Wizard, see the ArubaOS 6.1 Quick Start Guide.
Enabling FIPS with the WebUI
The default IP address of the controller is 172.16.0.254. When you connect a PC or workstation to a line port
on the controller, you can connect to this IP address through a Web browser. The system must be
configured to either obtain its IP address via DHCP or have a static IP address on the 172.16.0.0/24
subnetwork.
To log in with the WebUI:
1. Open a Web browser and connect to http://172.16.0.254.
2. Log in.
3. Go to the Configuration > Network > Controller > System Settings page (the default page when
you click the Configuration tab).
Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement Setup and Configuration | 31
Page 32

4. Click the FIPS Mode for Controller Enable checkbox.
If you need to enable FIPS mode on a controller that is no longer in the factory default configuration, you
can either:
Log in through the WebUI as described previously
Enable FIPS on the Configuration > Wizards > Controller Wizard page
Disallowed FIPS Mode Configurations
When you enable FIPS mode, the following configuration options are disallowed:
All WEP features
WPA
TKIP mixed mode
Any combination of DES, MD5, and PPTP
32 | Setup and Configuration Aruba 3000, 6000/M3 and Dell W-3000, W-6000M3 | FIPS 140-2 Level 2 Release Supplement
 Loading...
Loading...