Dell M6220 Configuration manual

Dell™ PowerConnect™ M6220
Configuration Guide
Model M6220
www.dell.com | support.dell.com
Notes, Notices, and Cautions
NOTE: A NOTE indicates important information that helps you make better use of your computer.
NOTICE: A NOTICE indicates either potential damage to hardware or loss of data and tells you how to avoid the
problem.
CAUTION: A CAUTION indicates a potential for property damage, personal injury, or death.
____________________
Information in this document is subject to change without notice.
© 2008 Dell Inc. All rights reserved.
Reproduction in any manner whatsoever without the written permission of Dell Inc. is strictly forbidden.
Trademarks used in this text: Dell, Dell OpenManage, the DELL logo, Inspiron, Dell Precision, Dimension, OptiPlex, PowerConnect,
PowerApp, PowerVault, Axim, DellNet, and Latitude are trademarks of Dell Inc.; Microsoft, Windows, and Windows Vista are either trademarks
or registered trademarks of Microsoft Corporation in the United States and/or other countries. Procomm Plus is a registered trademark of
Symantec Corporation or its affiliates in the U.S. and other countries.
Other trademarks and trade names may be used in this document to refer to either the entities claiming the marks and names or their products.
Dell Inc. disclaims any proprietary interest in trademarks and trade names other than its own.
Model M6220
September 2008 Rev. A02

Contents
1 About this Document . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Organization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
Additional Documentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 9
2 System Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Traceroute . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
CLI Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 12
Configuration Scripting
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Considerations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
Outbound Telnet . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
Overview
CLI Examples
Simple Network Time Protocol (SNTP)
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Syslog
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
Port Description . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
CLI Example
Storm Control. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
CLI Example
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 16
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
. . . . . . . . . . . . . . . . . . . . . 17
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Cable Test for Copper Ports . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
CLI Example
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
3

3 Switching Configuration. . . . . . . . . . . . . . . . . . . . . . . . . 25
Virtual LANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 25
VLAN Configuration Example . . . . . . . . . . . . . . . . . . . . . . . . 26
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 26
Web Interface
IP Subnet and MAC-Based VLANs . . . . . . . . . . . . . . . . . . . . . 28
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
Private Edge VLANs
CLI Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
IGMP Snooping
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
IGMP Snooping Querier . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
CLI Examples
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 32
Link Aggregation/Port Channels . . . . . . . . . . . . . . . . . . . . . . . . . 33
CLI Example
Web Interface Configuration: LAGs/Port-channels
Port Mirroring
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
. . . . . . . . . . . . 36
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Port Security
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Operation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
CLI Examples
Link Layer Discovery Protocol
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
. . . . . . . . . . . . . . . . . . . . . . . . . . 39
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Denial of Service Attack Protection
. . . . . . . . . . . . . . . . . . . . . . . 41
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
DHCP Filtering
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Limitations. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
CLI Examples
Port Aggregator
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
4

Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 49
Simple Switch Mode Supported CLI Commands
. . . . . . . . . . . . . . 54
4 Routing Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . 61
VLAN Routing. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Using the Web Interface to Configure VLAN Routing . . . . . . . . . . . 63
Virtual Router Redundancy Protocol
. . . . . . . . . . . . . . . . . . . . . . 64
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64
Using the Web Interface to Configure VRRP . . . . . . . . . . . . . . . . 66
Proxy Address Resolution Protocol (ARP). . . . . . . . . . . . . . . . . . . . 66
Overview
CLI Examples
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
OSPF
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
OSPF Concepts and Terms . . . . . . . . . . . . . . . . . . . . . . . . . 67
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 69
Routing Information Protocol
. . . . . . . . . . . . . . . . . . . . . . . . . . 77
RIP Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78
Using the Web Interface to Configure RIP
Route Preferences
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 80
. . . . . . . . . . . . . . . . . 79
Assigning Administrative Preferences to Routing Protocols. . . . . . . . 80
Using Equal Cost Multipath . . . . . . . . . . . . . . . . . . . . . . . . . 81
Loopback Interfaces
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
5 Device Security. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
802.1x Network Access Control . . . . . . . . . . . . . . . . . . . . . . . . . 85
802.1x Network Access Control Examples
. . . . . . . . . . . . . . . . . 86
802.1X Authentication and VLANs . . . . . . . . . . . . . . . . . . . . . . . . 88
Authenticated and Unauthenticated VLANs
Guest VLAN
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89
. . . . . . . . . . . . . . . . 88
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89
5

Authentication Server Filter Assignment . . . . . . . . . . . . . . . . . . . . 90
Access Control Lists (ACLs)
. . . . . . . . . . . . . . . . . . . . . . . . . . . 90
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 90
MAC ACLs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 92
IP ACLs
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93
ACL Configuration Process . . . . . . . . . . . . . . . . . . . . . . . . . 93
IP ACL CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93
MAC ACL CLI Examples
RADIUS
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
. . . . . . . . . . . . . . . . . . . . . . . . . . . 95
RADIUS Configuration Examples . . . . . . . . . . . . . . . . . . . . . . 98
TAC ACS+
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 100
TACACS+ Configuration Example. . . . . . . . . . . . . . . . . . . . . 100
6IPv6 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 103
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 103
Interface Configuration
CLI Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 104
DHCPv6
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 107
. . . . . . . . . . . . . . . . . . . . . . . . . . . . 103
7 Quality of Service . . . . . . . . . . . . . . . . . . . . . . . . . . . . 109
Class of Service Queuing . . . . . . . . . . . . . . . . . . . . . . . . . . . 109
Ingress Port Configuration . . . . . . . . . . . . . . . . . . . . . . . . 109
Egress Port Configuration—Traffic Shaping . . . . . . . . . . . . . . . 110
Queue configuration
Queue Management Type . . . . . . . . . . . . . . . . . . . . . . . . 110
CLI Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 110
Differentiated Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . 113
CLI Example
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 114
DiffServ for VoIP Configuration Example
6
. . . . . . . . . . . . . . . . . . . . . . . . . . . 110
. . . . . . . . . . . . . . . . . 116

8 Multicast . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
IGMP Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 119
CLI Example
IGMP Proxy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 120
CLI Examples
DVMRP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 122
CLI Example
PIM . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 123
PIM-SM
PIM-DM
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 120
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 120
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 122
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 123
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 124
7
8


About this Document
This configuration guide provides examples of how to use the Dell™PowerConnect™ 6200 Series
switch in a typical network. It describes the advantages of specific functions the PowerConnect 6200
Series switch provides and includes information about configuring those functions using the
command line interface (CLI).
Organization
This document is organized as follows:
• "System Configuration" on page 11 describes how to configure basic system and port settings, use
system interfaces and utilities, and create and use CLI scripts.
• "Switching Configuration" on page 25 provides configuration scenarios for layer 2 switching,
including creating virtual local area networks (VLANs) and Internet Group Management Protocol
(IGMP) snooping interfaces, and enabling port security.
• "Routing Configuration" on page 61 provides configuration scenarios for layer 3 features such as
VLAN routing, Open Shortest Path First (OSPF), and Routing Information Protocol (RIP).
1
• "Device Security" on page 85 provides information on creating access control lists and configuring
RADIUS and TACACS+ servers.
• "IPv6" on page 103 describes configuring and using IPv6-enabled interfaces in a mixed IPv6/IPv4
network.
• "Quality of Service" on page 109 provides configuration scenarios for class-of-service (CoS)
queueing and differentiated services (DiffServ).
• "Multicast" on page 119 describes how to configure IGMP, IGMP proxy, Distance Vector Multicast
Routing Protocol (DVMRP), and Protocol Independent Multicast (PIM) on the switch.
Additional Documentation
The following documentation provides additional information about PowerConnect 6200 Series
software:
About this Document 9

•The
CLI Command Reference
from the command-line interface (CLI) for managing, monitoring, and configuring the switch.
for your Dell PowerConnect switch describes the commands available
•The
•The
• Release notes for your Dell PowerConnect product detail the platform-specific functionality of the
User’s Guide
described in this document can be fully configured using the Web interface. This guide also provides
initial system setup and configuration instructions.
Getting Started Guide
configure, and operate the system.
software packages, including issues and workarounds.
for your Dell PowerConnect switch describes the Web GUI. Many of the scenarios
for your Dell PowerConnect switch provides basic information to install,
10 About this Document
System Configuration
This section provides configuration scenarios for the following features:
•"Traceroute" on page11
• "Configuration Scripting" on page 13
• "Outbound Telnet" on page 16
• "Simple Network Time Protocol (SNTP)" on page 17
• "Syslog" on page 19
• "Port Description" on page 21
• "Storm Control" on page 22
• "Cable Test for Copper Ports" on page 23
2
NOTE: For information on setting up the hardware and serial or TFTP connection, refer to the
for your system.
Guide
Getting Started
Traceroute
Use Traceroute to discover the routes that packets take when traveling on a hop-by-hop basis to their
destination through the network.
• Maps network routes by sending packets with small Time-to-Live (TTL) values and watches the
ICMP time-out announcements
• Command displays all L3 devices
• Can be used to detect issues on the network
•Tracks up to 20 hops
• Default UDP port uses 33434 unless modified in the traceroute command
System Configuration 11

CLI Example
The following shows an example of using the traceroute command to determine how many hops there
are to the destination. The command output shows each IP address the packet passes through and how
long it takes to get there. In this example, the packet takes 16 hops to reach its destination.
console#traceroute ?
ipv6 Use keyword 'ipv6' if entering IPv6 Address.
<cr> Press enter to execute the command.
<ip-address|hostname> Enter IP Address or Host Name.console#traceroute
console#traceroute 72.14.253.99
Tracing route over a maximum of 20 hops
1 10.131.10.1 <10 ms <10 ms <10 ms
2 210.210.108.193 <10 ms 10 ms <10 ms
3 192.168.81.1 <10 ms 10 ms <10 ms
4 210.214.5.161 <10 ms 10 ms 10 ms
5 210.214.5.169 <10 ms <10 ms 10 ms
6 124.7.202.2 10 ms <10 ms <10 ms
7 210.18.7.166 40 ms 30 ms 30 ms
8 202.144.2.193 30 ms 30 ms 30 ms
9 202.144.113.151 30 ms 40 ms 30 ms
10 72.14.196.97 40 ms 30 ms 100 ms
11 216.239.43.216 40 ms 40 ms 30 ms
12 216.239.43.209 60 ms 40 ms 40 ms
13 216.239.43.222 40 ms 50 ms 50 ms
14 216.239.43.221 100 ms 110 ms 100 ms
15 209.85.250.88 130 ms 130 ms 120 ms
16 209.85.250.105 130 ms 120 ms 130 ms
17 209.85.250.91 160 ms 160 ms 160 ms
18 216.239.47.237 290 ms 240 ms 250 ms
19 216.239.46.211 240 ms 270 ms 250 ms
--More-- or (q)uit
20 64.233.174.99 250 ms 240 ms 250 ms
console#traceroute
Switch-traceroute> Enter the ip-address|hostname : 10.27.64.141
Switch-traceroute> Packet size (default: 40 bytes): 60
Switch-traceroute> Max ttl value (default: 20): 30
Switch-traceroute> Number of probes to send at each level (default 3): 4
12 System Configuration
Switch-traceroute> Timeout (default: 3 seconds): 5
Switch-traceroute> Source ip-address (default to select best interface address):
Switch-traceroute> Type of service byte (default) :
Tracing route over a maximum of 20 hops
1 10.27.64.141 0 ms 0 ms 0 ms
Configuration Scripting
Configuration scripting allows you to generate a text-formatted script file that shows the current system
configuration. You can generate multiple scripts and upload and apply them to more than one switch.
Overview
Configuration scripting:
• Provides scripts that can be uploaded and downloaded to the system.
• Provides flexibility to create command configuration scripts.
• Can be applied to several switches.
• Can save up to ten scripts up to a maximum size of 2 MB of memory.
• Provides List, Delete, Apply, Upload, Download.
• Provides script format of one CLI command per line.
NOTE: The startup-config and backup-config scripts are not bound by the 2 MB memory limit.
Considerations
When you use configuration scripting, keep the following considerations in mind:
• The total number of scripts stored on the system is limited by NVRAM/FLASH size.
• The application of scripts is partial if the script fails. For example, if the script executes five of ten
commands and the script fails, the script stops at five.
• Scripts cannot be modified or deleted while being applied.
• Validation of scripts checks for syntax errors only. It does not validate that the script will run.
CLI Examples
The following are examples of the commands used for configurations scripting.
Example #1: Viewing the Script Options
console#script ?
System Configuration 13

apply Applies configuration script to the switch.
delete Deletes a configuration script file from the switch.
list Lists all configuration script files present on the switch.
show Displays the contents of configuration script.
validate Validate the commands of configuration script.
Example #2: Viewing and Deleting Existing Scripts
console#script list
Configuration Script Name Size(Bytes)
-------------------------------- ----------abc.scr 360
running-config.scr 360
startup-config 796
test.scr 360
4 configuration script(s) found.
2046 Kbytes free.
console#script delete test.scr
Are you sure you want to delete the configuration script(s)? (y/n)y
1 configuration script(s) deleted.
Example #3: Applying a Script to the Active Configuration
console#script apply abc.scr
Are you sure you want to apply the configuration script? (y/n)y
.....
....
Configuration script 'abc.scr' applied.
Example #4: Copying the Active Configuration into a Script
Use this command to capture the running configuration into a script.
console#show running-config running-config.scr
Config script created successfully.
Example #5: Uploading a Configuration Script to the TFTP Server
Use this command to upload a configuration script to the TFTP server.
14 System Configuration

console#copy script abc.scr tftp://10.27.64.141/abc.scr
Mode........................................... TFTP
Set TFTP Server IP............................. 10.27.64.141
TFTP Path...................................... ./
TFTP Filename.................................. abc.scr
Data Type...................................... Config Script
Source Filename................................ abc.scr
Management access will be blocked for the duration of the transfer
Are you sure you want to start? (y/n) y
267 bytes transferred
File transfer operation completed successfully.
Example #6: Downloading a Configuration Script to the TFTP Server
Use this command to download a configuration script from the TFTP server to the switch.
console#copy tftp://10.27.64.141/abc.scr script abc.scr
Mode........................................... TFTP
Set TFTP Server IP............................. 10.27.64.141
TFTP Path...................................... ./
TFTP Filename.................................. abc.scr
Data Type...................................... Config Script
Destination Filename........................... abc.scr
Management access will be blocked for the duration of the transfer
Are you sure you want to start? (y/n) y
193 bytes transferred
Validating configuration script...
configure
exit
configure
logging web-session
bridge aging-time 100
exit
Configuration script validated.
File transfer operation completed successfully.
Example #7: Validating a Script
console#script validate abc.scr
System Configuration 15

configure
stack
member 1 2
exit
exit
configure
stack
exit
ip address dhcp
username "admin" password 16d7a4fca7442dda3ad93c9a726597e4 level 15 encrypted
exit
Configuration script 'abc' validated.
console#script apply abc.scr
Are you sure you want to apply the configuration script? (y/n)y
configure
stack
member 1 2
Switch 1 already exists!
exit
exit
configure
stack
exit
ip address dhcp
username "admin" password 16d7a4fca7442dda3ad93c9a726597e4 level 15 encrypted
exit
Configuration script 'abc.scr' applied.
Outbound Telnet
Overview
Outbound telnet:
• Establishes an outbound telnet connection between a device and a remote host.
• When a telnet connection is initiated, each side of the connection is assumed to originate and
terminate at a “Network Virtual Terminal” (NVT).
• Server and user hosts do not maintain information about the characteristics of each other’s terminals
and terminal handling conventions.
• Must use a valid IP address.
16 System Configuration

CLI Examples
The following are examples of the commands used in the outbound telnet feature.
Example #1: Connecting to Another System by Using Telnet
console#telnet 192.168.77.151
Trying 192.168.77.151...
console#
User:admin
Password:
(Dell PC62XX Routing) >enable
Password:
console#show ip interface
Management Interface:
IP Address..................................... 10.27.65.89
Subnet Mask.................................... 255.255.254.0
Default Gateway................................ 10.27.64.1
Burned In MAC Address.......................... 00FF.F2A3.6688
Network Configuration Protocol Current......... DHCP
Management VLAN ID............................. 4022
Routing Interfaces:
Netdir Multi
Interface IP Address IP Mask Bcast CastFwd
---------- --------------- --------------- -------- --------
Simple Network Time Protocol (SNTP)
Overview
The SNTP implementation has the following features:
• Used for synchronizing network resources
•Adaptation of NTP
• Provides synchronized network timestamp
• Can be used in broadcast or unicast mode
• SNTP client implemented over UDP that listens on port 123
CLI Examples
The following are examples of the commands used in the SNTP feature.
System Configuration 17

Example #1: Viewing SNTP Options
(Dell PC62XX Routing)(Config) #sntp ?
console(config)#sntp ?
authenticate Require authentication for received Network Time
Protocol (NTP) traffic from servers.
authentication-key
broadcast Configure SNTP client broadcast parameters.
client Configure the SNTP client parameters.
server Configure SNTP server parameters.
trusted-key Authenticate the identity of a system to which
unicast Configure SNTP client unicast parameters.
Define an authentication key for Simple Network
Protocol (SNTP).
SNTP will synchronize.
Time
Example #2: Configuring the SNTP Server
console(config)#sntp server ?
<ipaddress/domain-name> Enter SNTP server address or the domain name.
console(config)#sntp server 192.168.10.25 ?
key Authentication key to use when sending packets to
this peer.
poll Enable/Disable SNTP server polling.
priority Configure SNTP server priority.
<cr> Press enter to execute the command.
console(config)#sntp server 192.168.10.25
Example #3: Viewing SNTP Information
console#show sntp ?
configuration Show the configuration of the Simple Network Time
Protocol (SNTP).
status To show the status of the Simple Network Time
Protocol (SNTP).
console#show sntp configuration
Polling interval: 512 seconds
MD5 Authentication keys:
Authentication is not required for synchronization.
Trusted keys:
No trusted keys.
Unicast clients: Disable
18 System Configuration
Unicast servers:
Server Key Polling
--------- ----------- -----------
192.168.10.25 Disabled Enabled
console#show sntp status
Unicast servers:
Server Status Last response
--------- ----------- --------------------------
192.168.10.25 Unknown 00:00:00 Jan 1 1970
Syslog
Overview
Syslog:
• Allows you to store system messages and/or errors.
• Can store to local files on the switch or a remote server running a syslog daemon.
• Provides a method of collecting message logs from many systems.
Interpreting Log Files
Figure 2-1 describes the information that displays in log messages.
<130> JAN 01 00:00:06 0.0.0.0-1 UNKN [0x800023]: bootos.c(386) 4 %% Event (0xaaaaaa
AB
A. Priority
B. Timestamp
C. Stack ID
D. Component Name
E. Thread ID
F. File Name
G. Line Number
H Sequence Number
I. Message
C
DEF GH I
aa)
System Configuration 19

Figure 2-1. Log Files Key
CLI Examples
The following are examples of the commands used in the Syslog feature.
Example #1: Viewing Logging Information
console#show logging
Logging is enabled
Console Logging: level warning. Console Messages: 230 Dropped.
Buffer Logging: level info. Buffer Messages: 230 Logged, 200 Max
File Logging: level notActive. File Messages: 0 Dropped.
CLI Command Logging : disabled
Web Session Logging : disabled
SNMP Set Command Logging : disabled
0 Messages were not logged.
Buffer Log:
<189> JAN 01 03:57:58 10.27.65.86-1 TRAPMGR[216282304]: traputil.c(908) 31 %%
Instance 0 has elected a new STP root: 8000:00ff:f2a3:8888
<189> JAN 01 03:57:58 10.27.65.86-1 TRAPMGR[216282304]: traputil.c(908) 32 %%
Instance 0 has elected a new STP root: 8000:0002:bc00:7e2c
<189> JAN 01 04:04:18 10.27.65.86-1 TRAPMGR[231781808]: traputil.c(908) 33 %% New
Spanning Tree Root: 0, Unit: 1
<189> JAN 01 04:04:18 10.27.65.86-1 TRAPMGR[216282304]: traputil.c(908) 34 %% The
unit 1 elected as the new STP root
Example #2: Viewing the Logging File
console#show logging file
Persistent Logging : disabled
Persistent Log Count : 0
Example #5: Configuring Syslog Server
console(config)#logging ?
buffered Buffered (In-Memory) Logging Configuration.
cli-command CLI Command Logging Configuration.
console Console Logging Configuration.
facility Syslog Facility Configuration.
file Configure logging file parameters.
on Enable logging to all supporting destinations.
snmp SNMP Set Command Logging Configuration.
web-session Web Session Logging Configuration.
<ip-address|hostname> Configure syslog server IP address.
20 System Configuration

console(config)#logging 192.168.10.65
console(Config-logging)#?
description Specify syslog server description.
exit To exit from the mode.
level Specify logging level.
port Specify UDP port (default is 514).
console(Config-logging)#level ?
alert Immediate action needed
critical Critical conditions
debug Debugging messages
emergency System is unusable
error Error conditions
info Informational messages
notice Normal but significant conditions
warning Warning conditions
console(Config-logging)#level critical
Port Description
The Port Description feature lets you specify an alphanumeric interface identifier that can be used for
SNMP network management.
CLI Example
Use the commands shown below for the Port Description feature.
Example #1: Enter a Description for a Port
This example specifies the name “Test” for port 1/g10:
console#configure
console(config)#interface ethernet 1/g2
console(config-if-1/g2)#description Test
console(config-if-1/g2)#exit
console(config)#exit
Example #2: Show the Port Description
console#show interfaces description ethernet 1/g2
Port Description
---- ---------------------------------------------------------1/g2 Test
System Configuration 21
Storm Control
A traffic storm is a condition that occurs when incoming packets flood the LAN, which creates
performance degradation in the network. The Storm Control feature protects against this condition.
The switch software provides broadcast, multicast, and unicast storm recovery for individual interfaces.
Unicast Storm Control protects against traffic whose MAC addresses are not known by the system.
For broadcast, multicast, and unicast storm control, if the rate of traffic ingressing on an interface
increases beyond the configured threshold for that type, the traffic is dropped.
To configure storm control, you will enable the feature for all interfaces or for individual interfaces, and
you will set the threshold (storm control level) beyond which the broadcast, multicast, or unicast traffic
will be dropped.
Configuring a storm-control level also enables that form of storm-control. Disabling a storm-control level
(using the “no” version of the command) sets the storm-control level back to default value and disables
that form of storm-control. Using the “no” version of the “storm-control” command (not stating a
“level”) disables that form of storm-control but maintains the configured “level” (to be active next time
that form of storm-control is enabled).
NOTE: The actual rate of ingress traffic required to activate storm-control is based on the size of incoming packets
and the hard-coded average packet size of 512 bytes - used to calculate a packet-per-second (pps) rate - as the
forwarding-plane requires pps versus an absolute rate kbps. For example, if the configured limit is 10%, this is
converted to ~25000 pps, and this pps limit is set in forwarding plane (hardware). You get the approximate desired
output when 512bytes packets are used.
CLI Example
The following examples show how to configure the storm control feature on port two, which is an
Ethernet interface. The interface number is 1/g2.
Example #1: Set Broadcast Storm Control for an Interface
console#configure
console(config)#interface ethernet 1/g2
console(config-if-1/g2)#storm-control broadcast ?
level Configure storm-control thresholds.
<cr> Press enter to execute the command.
console(config-if-1/g2)#storm-control broadcast level ?
<rate> Enter the storm-control threshold as percent of port
speed. Percent of port speed is converted to
PacketsPerSecond based on 512 byte average packet
size and applied to HW. Refer to documentation for
further details.
22 System Configuration
console(config-if-1/g2)#storm-control broadcast level 7
Example #2: Set Multicast Storm Control for an Interface
console(config-if-1/g2)#storm-control multicast level 8
Example #3: Set Unicast Storm Control for an Interface
console(config-if-1/g2)#storm-control unicast level 5
Cable Test for Copper Ports
The cable test feature enables you to determine the cable connection status on a selected port. The
switch uses Time Domain Reflectometry (TDR) technology to determine the quality and characteristics
of a copper cable attached to a port.
NOTE: The cable test feature is supported only for copper cable. it is not supported for optical fiber cable.
In privileged exec mode, enter test copper-port tdr unit/port to run the cable test on the
specified port. One of the following statuses are returned:
•
Normal
Open
•
•
Short
•
Cable Test Failed
: The cable is working correctly.
: The cable is disconnected or there is a faulty connector.
: There is an electrical short in the cable.
: The cable status could not be determined. The cable may in fact be working.
The command also returns a cable length estimate if this feature is supported by the PHY for the current
link speed. The length is displayed as the estimated length. Note that if the link is down and a cable is
attached to a 10/100 Ethernet adapter, then the cable status may display as Open or Short because some
Ethernet adapters leave unused wire pairs unterminated or grounded. Unknown is displayed if the cable
length could not be determined.
If the port has an active link while the cable test is run, the link can go down for the duration of the test.
The test may take several seconds to run.
To view cable status information for multiple ports, enter show copper-ports tdr. If the cable test
has not been run on a port, the results indicate that the test has not been performed.
CLI Example
console#test copper-port tdr 1/g1
Cable Status................................... Short
Cable Length................................... 5m
console#show copper-ports tdr
Port Result Length [meters] Date
------- ------ --------------- --------------------1/g1 Short 9 Jan 01 1970 18:03:23
1/g2 Test has not been performed
System Configuration 23
1/g3 Test has not been performed
1/g4 Test has not been performed
1/g5 Test has not been performed
--More-- or (q)uit
NOTE: You can also run a cable test using the Web Interface. In the navigation tree, click System > Diagnostics.
24 System Configuration

Switching Configuration
This section provides configuration scenarios for the following features:
• "Virtual LANs" on page 25
• "IGMP Snooping" on page 30
• "IGMP Snooping Querier" on page 32
• "Link Aggregation/Port Channels" on page 33
• "Port Mirroring" on page 37
• "Port Security" on page 37
• "Link Layer Discovery Protocol" on page 39
• "Denial of Service Attack Protection" on page 41
• "DHCP Filtering" on page 43
• "Port Aggregator" on page 44
Virtual LANs
3
Adding Virtual LAN (VLAN) support to a Layer 2 switch offers some of the benefits of both bridging
and routing. Like a bridge, a VLAN switch forwards traffic based on the Layer 2 header, which is fast.
Like a router, it partitions the network into logical segments, which provides better administration,
security and management of multicast traffic.
A VLAN is a set of end stations and the switch ports that connect them. You can have many reasons
for the logical division, for example, department or project membership. The only physical
requirement is that the end station, and the port to which it is connected, both belong to the same
VLAN.
Each VLAN in a network has an associated VLAN ID, which appears in the IEEE 802.1Q tag in the
Layer 2 header of packets transmitted on a VLAN. An end station may omit the tag, or the VLAN
portion of the tag, in which case the first switch port to receive the packet may either reject it or
insert a tag using its default VLAN ID. A given port may handle traffic for more than one VLAN, but
it can only support one default VLAN ID.
Two features let you define packet filters that the switch uses as the matching criteria to determine if
a particular packet belongs to a particular VLAN.
• The IP-subnet Based VLAN feature lets you map IP addresses to VLANs by specifying a source IP
address, network mask, and the desired VLAN ID.
Switching Configuration 25
• The MAC-based VLAN feature let packets originating from end stations become part of a VLAN
according to source MAC address. To configure the feature, you specify a source MAC address and a
VLAN ID.
The Private Edge VLAN feature lets you set protection between ports located on the switch. This means
that a protected port cannot forward traffic to another protected port on the same switch.
The feature does not provide protection between ports located on different switches.
For information about authenticated, unauthenticated, and guest VLANs, see "802.1X Authentication
and VLANs" on page 88.
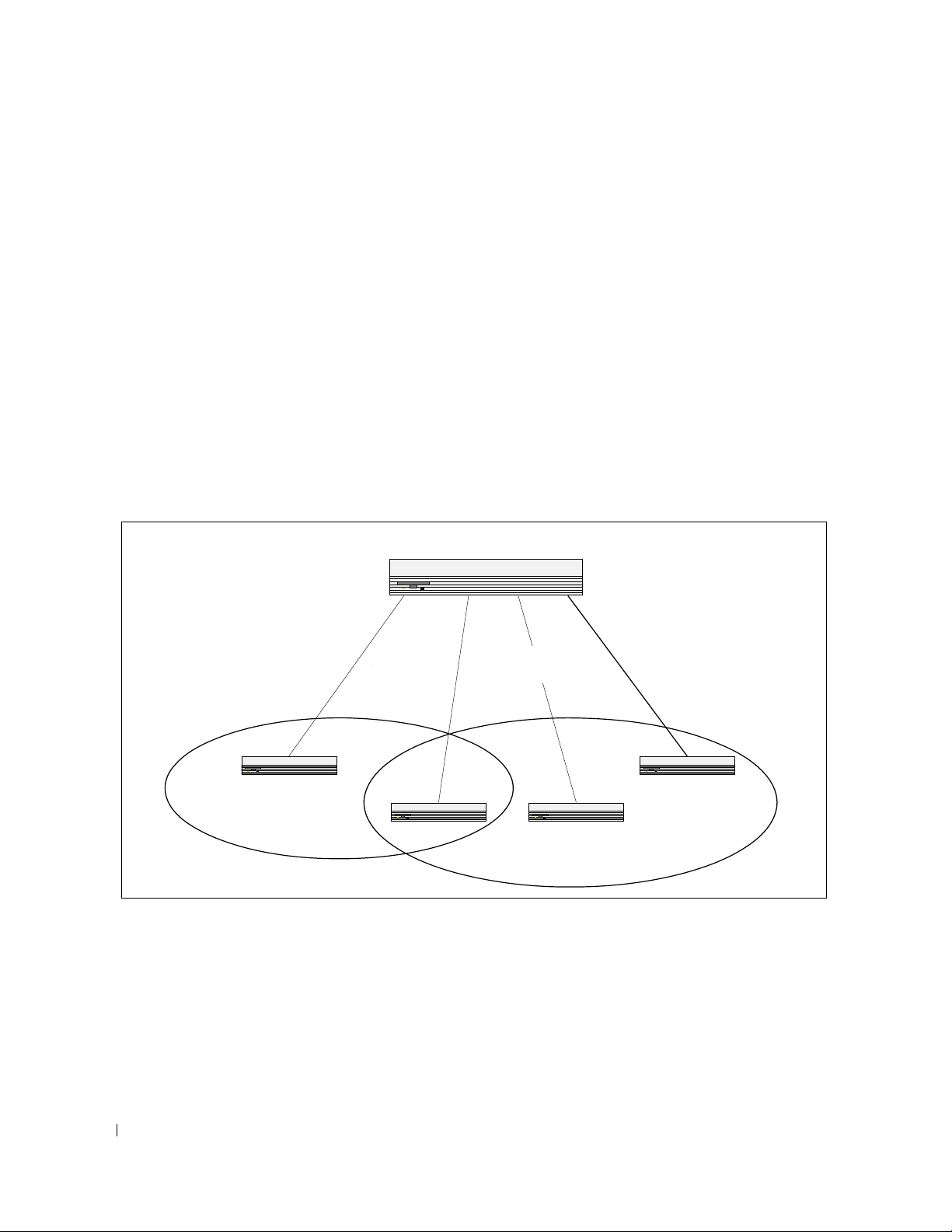
VLAN Configuration Example
The diagram in this section shows a switch with four ports configured to handle the traffic for two
VLANs. Port 1/g2 handles traffic for both VLANs, while port 1/g1 is a member of VLAN 2 only, and ports
1/g3 and 1/g4 are members of VLAN 3 only. The script following the diagram shows the commands you
would use to configure the switch as shown in the diagram.
Layer 3 Switch
Port 1/g4
Port 1/g1
Port 1/0/1
VLAN 2
VLAN 2
Port 1/g2
Port 1/0/2
VLANs 2 & 3
VLANs 2 & 3
Port 1/g3
Port 1/0/3
VLAN 3
VLAN 3
Port 1/0/4
VLAN 3
VLAN 3
VLAN 2
Figure 3-1. VLAN Example Network Diagram
VLAN 3
CLI Examples
The following examples show how to create VLANs, assign ports to the VLANs, and assign a VLAN as the
default VLAN to a port.
26 Switching Configuration

Example #1: Create Two VLANs
Use the following commands to create two VLANs and to assign the VLAN IDs while leaving the names
blank.
console(config)#vlan database
console(config-vlan)#vlan 2
console(config-vlan)#vlan 3
console(config-vlan)#exit
Example #2: Assign Ports to VLAN2
This sequence shows how to assign ports to VLAN2, specify that frames will always be transmitted
tagged from all member ports, and that untagged frames will be rejected on receipt.
console(config)#interface ethernet 1/g1
console(config-if-1/g1)#switchport mode general
console(config-if-1/g1)#switchport general allowed vlan add 2
console(config-if-1/g1)#
console(config-if-1/g1)#exit
console(config)#interface ethernet 1/g2
console(config-if-1/g2)#switchport mode general
console(config-if-1/g2)#switchport general allowed vlan add 2
console(config-if-1/g2)#
console(config-if-1/g2)#exit
switchport general acceptable-frame-type tagged-only
switchport general acceptable-frame-type tagged-only
Example #3: Assign Ports to VLAN3
This example shows how to assign the ports that will belong to VLAN 3. Untagged frames will be
accepted on ports 1/g3 and 1/g4.
Note that port 1/g2 belongs to both VLANs and that port 1/g1 can never belong to VLAN 3.
console(config)#interface ethernet 1/g2
cconsole(config-if-1/g2)#switchport general allowed vlan add 3
console(config-if-1/g2)#exit
console(config)#interface ethernet 1/g3
console(config-if-1/g3)#switchport general allowed vlan add 3
console(config-if-1/g3)#exit
console(config)#interface ethernet 1/g4
console(config-if-1/g4)#switchport general allowed vlan add 3
Example #4: Assign VLAN3 as the Default VLAN
This example shows how to assign VLAN 3 as the default VLAN for port 1/g2.
console(config)#interface ethernet 1/g2
console(config-if-1/g2)#switchport general pvid 3
Switching Configuration 27

Example #5: Assign IP Addresses to VLAN 2
In order for the VLAN to function as a routing interface, you must enable routing on the VLAN and on
the switch. Routing is only permitted on VLAN interfaces. Routing on physical interfaces is not
supported.
console#configure
console(config)#interface vlan 2
console(config-if-vlan2)#ip address 192.168.10.33 255.255.255.0
console(config-if-vlan2)#routing
console(config-if-vlan2)#exit
console(config)#ip routing
Example #6: View Information About VLAN 2
console#show ip interface vlan 2
Primary IP Address............................ 192.168.10.33/255.255.255.0
Routing Mode.................................. Enable
Administrative Mode........................... Enable
Forward Net Directed Broadcasts............... Disable
Proxy ARP..................................... Enable
Local Proxy ARP............................... Disable
Active State.................................. Inactive
Link Speed Data Rate.......................... 10 Half
MAC Address................................... 00FF.F2A3.888A
Encapsulation Type............................ Ethernet
IP MTU........................................ 1500
Web Interface
Use the following screens to perform the same configuration using the Web Interface:
•
Switching > VLAN > Membership
•
Switching > VLAN > Port Settings.
. To create VLANs and specify port participation.
To specify the PVID and mode for the port.
IP Subnet and MAC-Based VLANs
In addition to port-based VLANs, the switch also supports VLANs that are based on the IP address or
MAC address of a host. With IP subnet and MAC-based VLANs, the VLAN membership is determined
by the address of the host rather than the port to which the host is attached.
CLI Examples
The following examples show how to associate an IP subnet with a VLAN, a specific IP address with a
VLAN, and a MAC address with a VLAN.
28 Switching Configuration

Example #1: Associate an IP Subnet with a VLAN
This example shows how to configure the switch so that all hosts with IP addresses in the 192.168.25.0/24
network are members of VLAN 10.
console#configure
console(config)#vlan database
console(config-vlan)#vlan association subnet 192.168.25.0 255.255.255.0 10
Example #2: Associate an IP Address with a VLAN
This example shows how to configure the switch so a host with an IP addresses of 192.168.1.11 is a
member of VLAN 10.
console#configure
console(config)#vlan database
console(config-vlan)#vlan association subnet 192.168.1.11 255.255.255.255 10
Example #3: Associate a MAC Address with a VLAN
This example shows how to configure the switch so a host with a MAC address of 00:ff:f2:a3:88:86 is a
member of VLAN 10.
console#configure
console(config)#vlan database
console(config-vlan)#vlan association mac 00:ff:f2:a3:88:86 10
Example #4: Viewing IP Subnet and MAC-Based VLAN Associations
console#show vlan association mac
MAC Address VLAN ID
----------------- ------00FF.F2A3.8886 10
console#show vlan association subnet
IP Subnet IP Mask VLAN ID
---------------- ---------------- -------
192.168.25.0 255.255.255.0 10
192.168.1.11 255.255.255.255 10
Private Edge VLANs
Use the Private Edge VLAN feature to prevent ports on the switch from forwarding traffic to each other
even if they are on the same VLAN.
• Protected ports cannot forward traffic to other protected ports in the same group, even if they have the
same VLAN membership. Protected ports can forward traffic to unprotected ports.
• Unprotected ports can forward traffic to both protected and unprotected ports.
Switching Configuration 29

You can also configure groups of protected ports, but unprotected ports are independent and cannot be
added to a group. Each group’s configuration consists of a name and a mask of ports. A port can belong
to only one set of protected ports, but an unprotected port can be added to a group as a protected port.
The group name is configurable by the network administrator.
Use the switchport protected command to designate a port as protected. Use the show
switchport protected command to display a listing of the protected ports.
CLI Example
Example #1: Configuring a Protected Port
The commands in this example name the protected port group 1 “PP_Test” and assign ports 1 and 2 to
the group.
console(config)#switchport protected 1 name PP_Test
console(config)#interface ethernet 1/g1
console(config-if-1/g1)#switchport protected 1
console(config-if-1/g1)#exit
console(config)#interface ethernet 1/g2
console(config-if-1/g2)#switchport protected 1
console(config-if-1/g2)#exit
console(config)#exit
Example #2: Viewing Protected Port Group 1
console#show switchport protected 1
Name......................................... "PP_Test"
1/g1, 1/g2
IGMP Snooping
This section describes the Internet Group Management Protocol (IGMP) Snooping feature. IGMP
Snooping enables the switch to monitor IGMP transactions between hosts and routers. It can help
conserve bandwidth by allowing the switch to forward IP multicast traffic only to connected hosts that
request multicast traffic.
Overview
The IGMP feature:
•Uses Version 3 of IGMP
• Includes snooping, which can be enabled per VLAN
30 Switching Configuration
 Loading...
Loading...