Avaya AP-3 User Manual
Wireless AP-3 User’s Guide
For Software Release 2.5.2
Document No. 21-300403
Issue 1
October 2004
Copyright 2004, Avaya Inc.
All Rights Reserved
Notice
Every effort was made to ensure that the information in this document
was complete and accurate at the time of printing. However, information
is subject to change.
Warr ant y
Avaya Inc. provides a limited warranty on this product. Refer to your
sales agreement to establish the terms of the limited warranty. In
addition, Avaya’s standard warranty language as well as information
regarding support for this product, while under warranty, is available
through the following Web site: http://www.avaya.com/support
Preventing Toll Fraud
“Toll fraud” is the unauthorized use of your telecommunications system
by an unauthorized party (for example, a person who is not a corporate
employee, agent, subcontractor, or is not working on your company's
behalf). Be aware that there may be a risk of toll fraud associated with
your system and that, if toll fraud occurs, it can result in substantial
additional charges for your telecommunications services.
Avaya Fraud Intervention
If you suspect that you are being victimized by toll fraud and you need
technical assistance or support, in the United States and Canada, call the
Technical Service Center's Toll Fraud Intervention Hotline at
1-800-643-2353.
Disclaimer
Avaya is not responsible for any modifications, additions or deletions to
the original published version of this documentation unless such
modifications, additions or deletions were performed by Avaya. Customer
and/or End User agree to indemnify and hold harmless Avaya, Avaya's
agents, servants and employees against all claims, lawsuits, demands
and judgments arising out of, or in connection with, subsequent
modifications, additions or deletions to this documentation to the extent
made by the Customer or End User.
How to Get Help
For additional support telephone numbers, go to the Avaya support Web
site: http://www.avaya.com/support
• Within the United States, click the Escalation Contacts link.
Then click the appropriate link for the type of support you
need.
• Outside the United States, click the Escalation Contacts link.
Then click the International Services link that includes
telephone numbers for the international Centers of
Excellence.
Providing Telecommunications Security
Telecommunications security (of voice, data, and/or video
communications) is the prevention of any type of intrusion to (that is,
either unauthorized or malicious access to or use of) your company's
telecommunications equipment by some party.
Your company's “telecommunications equipment” includes both this
Avaya product and any other voice/data/video equipment that could be
accessed via this Avaya product (that is, “networked equipment”).
An “outside party” is anyone who is not a corporate employee, agent,
subcontractor, or is not working on your company's behalf. Whereas, a
“malicious party” is anyone (including someone who may be otherwise
authorized) who accesses your telecommunications equipment with
either malicious or mischievous intent.
Such intrusions may be either to/through synchronous (time-multiplexed
and/or circuit-based), or asynchronous (character-, message-, or
packet-based) equipment, or interfaces for reasons of:
• Utilization (of capabilities special to the accessed equipment)
• Theft (such as, of intellectual property, financial assets, or toll
facility access)
• Eavesdropping (privacy invasions to humans)
• Mischief (troubling, but apparently innocuous, tampering)
• Harm (such as harmful tampering, data loss or alteration,
Be aware that there may be a risk of unauthorized intrusions associated
with your system and/or its networked equipment. Also realize that, if
such an intrusion should occur, it could result in a variety of losses to your
company (including but not limited to, human/data privacy, intellectual
property, material assets, financial resources, labor costs, and/or legal
costs).
regardless of motive or intent)
. If you are:
.
Responsibility for Your Company’s Telecommunications Security
The final responsibility for securing both this system and its networked
equipment rests with you - Avaya’s customer system administrator, your
telecommunications peers, and your managers. Base the fulfillment of
your responsibility on acquired knowledge and resources from a variety
of sources including but not limited to:
• Installation documents
• System administration documents
• Security documents
• Hardware-/software-based security tools
• Shared information between you and your peers
• Telecommunications security experts
To prevent intrusions to your telecommunications equipment, you and
your peers should carefully program and configure:
• Your Avaya-provided telecommunications systems and their
interfaces
• Your Avaya-provided software applications, as well as their
underlying hardware/software platforms and interfaces
• Any other equipment networked to your Avaya products
TCP/IP Facilities
Customers may experience differences in product performance, reliability
and security depending upon network configurations/design and
topologies, even when the product performs as warranted.
Standards Compliance
Avaya Inc. is not responsible for any radio or television interference
caused by unauthorized modifications of this equipment or the
substitution or attachment of connecting cables and equipment other
than those specified by Avaya Inc. The correction of interference caused
by such unauthorized modifications, substitution or attachment will be the
responsibility of the user. Pursuant to Part 15 of the Federal
Communications Commission (FCC) Rules, the user is cautioned that
changes or modifications not expressly approved by Avaya Inc. could
void the user’s authority to operate this equipment.
Product Safety Standards
This product complies with and conforms to the following international
Product Safety standards as applicable:
Safety of Information Technology Equipment, IEC 60950, 3rd Edition, or
IEC 60950-1, 1st Edition, including all relevant national deviations as
listed in Compliance with IEC for Electrical Equipment (IECEE) CB-96A.
Safety of Information Technology Equipment, CAN/CSA-C22.2
No. 60950-00 / UL 60950, 3rd Edition, or CAN/CSA-C22.2 No.
60950-1-03 / UL 60950-1.
Safety Requirements for Customer Equipment, ACA Technical Standard
(TS) 001 - 1997.
One or more of the following Mexican national standards, as applicable:
NOM 001 SCFI 1993, NOM SCFI 016 1993, NOM 019 SCFI 1998.
The equipment described in this document may contain Class 1 LASER
Device(s). These devices comply with the following standards:
• EN 60825-1, Edition 1.1, 1998-01
• 21 CFR 1040.10 and CFR 1040.11.
The LASER devices used in Avaya equipment typically operate within the
following parameters:
Typical Center Wavelength Maximum Output Power
830 nm - 860 nm -1.5 dBm
1270 nm - 1360 nm -3.0 dBm
1540 nm - 1570 nm 5.0 dBm
Luokan 1 Laserlaite
Klass 1 Laser Apparat
Use of controls or adjustments or performance of procedures other than
those specified herein may result in hazardous radiation exposures.
Contact your Avaya representative for more laser product information.
Electromagnetic Compatibility (EMC) Standards
This product complies with and conforms to the following international
EMC standards and all relevant national deviations:
Limits and Methods of Measurement of Radio Interference of Information
Technology Equipment, CISPR 22:1997 and EN55022:1998.
Information Technology Equipment - Immunity Characteristics - Limits
and Methods of Measurement, CISPR 24:1997 and EN55024:1998,
including:
• Electrostatic Discharge (ESD) IEC 61000-4-2
• Radiated Immunity IEC 61000-4-3
• Electrical Fast Transient IEC 61000-4-4
• Lightning Effects IEC 61000-4-5
• Conducted Immunity IEC 61000-4-6
• Mains Frequency Magnetic Field IEC 61000-4-8
• Voltage Dips and Variations IEC 61000-4-11
Power Line Emissions, IEC 61000-3-2: Electromagnetic compatibility
(EMC) - Part 3-2: Limits - Limits for harmonic current emissions.
Power Line Emissions, IEC 61000-3-3: Electromagnetic compatibility
(EMC) - Part 3-3: Limits - Limitation of voltage changes, voltage
fluctuations and flicker in public low-voltage supply systems.
Federal Communications Commission Statement
Part 15:
Note: This equipment has been tested and found to comply with
the limits for a Class A digital device, pursuant to Part 15 of the
FCC Rules. These limits are designed to provide reasonable
protection against harmful interference when the equipment is
operated in a commercial environment. This equipment
generates, uses, and can radiate radio frequency energy and, if
not installed and used in accordance with the instruction
manual, may cause harmful interference to radio
communications. Operation of this equipment in a residential
area is likely to cause harmful interference in which case the
user will be required to correct the interference at his own
expense.
Means of Connection
Connection of this equipment to the telephone network is shown in the
following tables.
For MCC1, SCC1, CMC1, G600, and G650 Media Gateways:
Manufacturer’s Port
Identifier
Off premises station OL13C 9.0F RJ2GX,
DID trunk 02RV2-T 0.0B RJ2GX,
CO trunk 02GS2 0.3A RJ21X
Tie trunk TL31M 9.0F RJ2GX
Basic Rate Interface 02IS5 6.0F, 6.0Y RJ49C
1.544 digital interface 04DU9-BN 6.0F RJ48C,
120A4 channel service
unit
FIC Code SOC/
02LS2 0.3A RJ21X
04DU9-IKN 6.0F RJ48C,
04DU9-ISN 6.0F RJ48C,
04DU9-DN 6.0Y RJ48C
REN/
A.S. Code
Network
Jacks
RJ21X,
RJ11C
RJ21X
RJ48M
RJ48M
RJ48M
Part 68: Answer-Supervision Signaling
Allowing this equipment to be operated in a manner that does not provide
proper answer-supervision signaling is in violation of Part 68 rules. This
equipment returns answer-supervision signals to the public switched
network when:
• answered by the called station,
• answered by the attendant, or
• routed to a recorded announcement that can be administered
by the customer premises equipment (CPE) user.
This equipment returns answer-supervision signals on all direct inward
dialed (DID) calls forwarded back to the public switched telephone
network. Permissible exceptions are:
• A call is unanswered.
• A busy tone is received.
• A reorder tone is received.
Avaya attests that this registered equipment is capable of providing users
access to interstate providers of operator services through the use of
access codes. Modification of this equipment by call aggregators to block
access dialing codes is a violation of the Telephone Operator Consumers
Act of 1990.
REN Number
For MCC1, SCC1, CMC1, G600, and G650 Media Gateways:
This equipment complies with Part 68 of the FCC rules. On either the
rear or inside the front cover of this equipment is a label that contains,
among other information, the FCC registration number, and ringer
equivalence number (REN) for this equipment. If requested, this
information must be provided to the telephone company.
For G350 and G700 Media Gateways:
This equipment complies with Part 68 of the FCC rules and the
requirements adopted by the ACTA. On the rear of this equipment is a
label that contains, among other information, a product identifier in the
format US:AAAEQ##TXXXX. The digits represented by ## are the ringer
equivalence number (REN) without a decimal point (for example, 03 is a
REN of 0.3). If requested, this number must be provided to the telephone
company.
For all media gateways:
The REN is used to determine the quantity of devices that may be
connected to the telephone line. Excessive RENs on the telephone line
may result in devices not ringing in response to an incoming call. In most,
but not all areas, the sum of RENs should not exceed 5.0. To be certain
of the number of devices that may be connected to a line, as determined
by the total RENs, contact the local telephone company.
REN is not required for some types of analog or digital facilities.
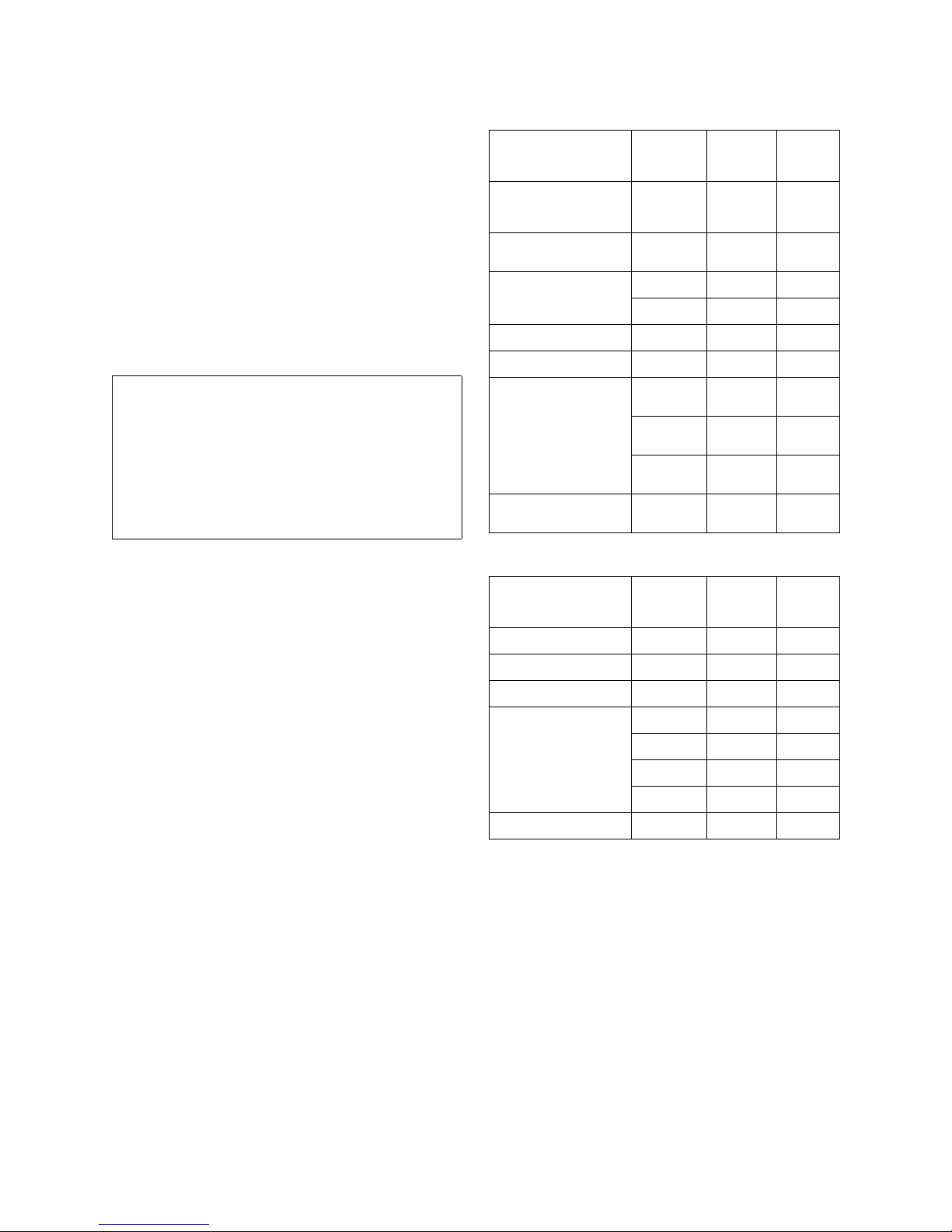
For G350 and G700 Media Gateways:
Manufacturer’s Port
Identifier
Ground Start CO trunk 02GS2 1.0A RJ11C
DID trunk 02RV2-T AS.0 RJ11C
Loop Start CO trunk 02LS2 0.5A RJ11C
1.544 digital interface 04DU9-BN 6.0Y RJ48C
Basic Rate Interface 02IS5 6.0F RJ49C
For all media gateways:
If the terminal equipment (for example, the media server or media
gateway) causes harm to the telephone network, the telephone company
will notify you in advance that temporary discontinuance of service may
be required. But if advance notice is not practical, the telephone
company will notify the customer as soon as possible. Also, you will be
advised of your right to file a complaint with the FCC if you believe it is
necessary.
The telephone company may make changes in its facilities, equipment,
operations or procedures that could affect the operation of the
equipment. If this happens, the telephone company will provide advance
notice in order for you to make necessary modifications to maintain
uninterrupted service.
If trouble is experienced with this equipment, for repair or warranty
information, please contact the Technical Service Center at
1-800-242- 2121 or contact your local Avaya representative. If the
equipment is causing harm to the telephone network, the telephone
company may request that you disconnect the equipment until the
problem is resolved.
FIC Code SOC/
04DU9-DN 6.0Y RJ48C
04DU9-IKN 6.0Y RJ48C
04DU9-ISN 6.0Y RJ48C
REN/
A.S. Code
Network
Jacks
A plug and jack used to connect this equipment to the premises wiring
and telephone network must comply with the applicable FCC Part 68
rules and requirements adopted by the ACTA. A compliant telephone
cord and modular plug is provided with this product. It is designed to be
connected to a compatible modular jack that is also compliant. It is
recommended that repairs be performed by Avaya certified technicians.
The equipment cannot be used on public coin phone service provided by
the telephone company. Connection to party line service is subject to
state tariffs. Contact the state public utility commission, public service
commission or corporation commission for information.
This equipment, if it uses a telephone receiver, is hearing aid compatible.
Canadian Department of Communications (DOC) Interference
Information
This Class A digital apparatus complies with Canadian ICES-003.
Cet appareil numérique de la classe A est conforme à la norme
NMB-003 du Canada.
This equipment meets the applicable Industry Canada Terminal
Equipment Technical Specifications. This is confirmed by the registration
number. The abbreviation, IC, before the registration number signifies
that registration was performed based on a Declaration of Conformity
indicating that Industry Canada technical specifications were met. It does
not imply that Industry Canada approved the equipment.
Installation and Repairs
Before installing this equipment, users should ensure that it is
permissible to be connected to the facilities of the local
telecommunications company. The equipment must also be installed
using an acceptable method of connection. The customer should be
aware that compliance with the above conditions may not prevent
degradation of service in some situations.
Repairs to certified equipment should be coordinated by a representative
designated by the supplier. Any repairs or alterations made by the user to
this equipment, or equipment malfunctions, may give the
telecommunications company cause to request the user to disconnect
the equipment.
Declarations of Conformity
United States FCC Part 68 Supplier’s Declaration of Conformity (SDoC)
Avaya Inc. in the United States of America hereby certifies that the
equipment described in this document and bearing a TIA TSB-168 label
identification number complies with the FCC’s Rules and Regulations 47
CFR Part 68, and the Administrative Council on Terminal Attachments
(ACTA) adopted technical criteria.
Avaya further asserts that Avaya handset-equipped terminal equipment
described in this document complies with Paragraph 68.316 of the FCC
Rules and Regulations defining Hearing Aid Compatibility and is deemed
compatible with hearing aids.
Copies of SDoCs signed by the Responsible Party in the U. S. can be
obtained by contacting your local sales representative and are available
on the following Web site: http://www.avaya.com/support
All Avaya media servers and media gateways are compliant with FCC
Part 68, but many have been registered with the FCC before the SDoC
process was available. A list of all Avaya registered products may be
found at: http://www.part68.org
manufacturer.
European Union Declarations of Conformity
by conducting a search using “Avaya” as
.
To order copies of this and other documents:
Call: Avaya Publications Center
Voice 1.800.457.1235 or 1.207.866.6701
FAX 1.800.457.1764 or 1.207.626.7269
Write: Globalware Solutions
200 Ward Hill Avenue
Haverhill, MA 01835 USA
Attention: Avaya Account Management
E-mail: totalware@gwsmail.com
For the most current versions of documentation, go to the Avaya support
Web site: http://www.avaya.com/support
.
Avaya Inc. declares that the equipment specified in this document
bearing the “CE” (Conformité Europeénne) mark conforms to the
European Union Radio and Telecommunications Terminal Equipment
Directive (1999/5/EC), including the Electromagnetic Compatibility
Directive (89/336/EEC) and Low Voltage Directive (73/23/EEC).
Copies of these Declarations of Conformity (DoCs) can be obtained by
contacting your local sales representative and are available on the
following Web site: http://www.avaya.com/support
Japan
This is a Class A product based on the standard of the Voluntary Control
Council for Interference by Information Technology Equipment (VCCI). If
this equipment is used in a domestic environment, radio disturbance may
occur, in which case, the user may be required to take corrective actions.
.

Contents
Chapter 1: Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Document Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
Introduction to Wireless Networking . . . . . . . . . . . . . . . . . . . . . . . . . 20
Site Survey . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
Guidelines for Roaming . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Wireless Standard Support . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Network Names . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Security Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Cell Coverage . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Data Rates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Channels . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
IEEE 802.11 Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
802.11b . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
802.11a . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
802.11g . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Management and Monitoring Capabilities . . . . . . . . . . . . . . . . . . . . . . 23
HTTP/HTTPS Interface. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 23
Command Line Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
How To Access the CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
SNMP Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 24
SNMPv3 Secure Management. . . . . . . . . . . . . . . . . . . . . . . . . 25
Chapter 2: Getting Started . . . . . . . . . . . . . . . . . . . . . . . . . 27
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Prerequisites . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 27
Product Package. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 29
5 GHz Antenna Adapter or AP-3 11a Upgrade Kit . . . . . . . . . . . . . . . . 29
System Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 30
Hardware Installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
AP-3 with Active Ethernet . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
AP-3 with Power Supply. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
5 GHz or AP-3 11a Upgrade Kit . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Initialization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
ScanTool . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Default IP Address . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
ScanTool Instructions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 40
Setup Wizard . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Setup Wizard Instructions. . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Issue 1 October 2004 5

Contents
Downloading the Latest Software . . . . . . . . . . . . . . . . . . . . . . . . . . 50
Setting Up your TFTP Server . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
Downloading Updates from a TFTP Server . . . . . . . . . . . . . . . . . . . 51
Additional Hardware Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
Installing the AP in a Plenum . . . . . . . . . . . . . . . . . . . . . . . . . . . 52
Installing/Removing the Metal Faceplate. . . . . . . . . . . . . . . . . . . 52
Active Ethernet. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
LED Indicators . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
Related Topics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 55
Chapter 3: Viewing Status Information. . . . . . . . . . . . . . . . . . . 57
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
Logging into the HTTP Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
System Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 58
Chapter 4: Performing Advanced Configuration . . . . . . . . . . . . . 61
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Configuring the AP Using the HTTP/HTTPS Interface. . . . . . . . . . . . . . . . 62
System Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64
Dynamic DNS Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 64
Access Point System Naming Convention. . . . . . . . . . . . . . . . . . 65
Network Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 65
IP Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
DHCP Server Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . 67
Link Integrity Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . 70
Interface Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
Operational Mode Configuration . . . . . . . . . . . . . . . . . . . . . . . . . 73
Wireless-A and Wireless-B Interface Configuration. . . . . . . . . . . . . . . 73
Wireless 802.11a Interface Configuration . . . . . . . . . . . . . . . . . . . . 74
Dynamic Frequency Selection (DFS) . . . . . . . . . . . . . . . . . . . . . 75
RTS/CTS Medium Reservation . . . . . . . . . . . . . . . . . . . . . . . . 76
Wireless Service Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77
Wireless 802.11b Interface Configuration . . . . . . . . . . . . . . . . . . . . 78
Distance Between APs . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81
Multicast Rate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
Wireless 802.11b/g Interface Configuration . . . . . . . . . . . . . . . . . . . 85
WDS Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 88
Bridging WDS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 88
WDS Setup Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89
6 Wireless AP-3 User’s Guide

Ethernet Interface Configuration . . . . . . . . . . . . . . . . . . . . . . . . . 92
Management Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 92
Password Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 93
IP Access Table Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . 94
Services Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 95
Secure Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
SNMP Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
HTTP Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97
HTTPS Access (SSL) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 98
Telnet Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 99
SSH Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 99
Serial Port Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 102
RADIUS-Based Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . 103
Automatic Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 104
Hardware Configuration Reset . . . . . . . . . . . . . . . . . . . . . . . . . . 108
Configuration Reset via Serial Port During Bootup . . . . . . . . . . . . . 108
Configuring Hardware Configuration Reset . . . . . . . . . . . . . . . . . 109
Resetting the Configuration via the Serial Interface. . . . . . . . . . . . . 110
Filtering Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 110
Ethernet Protocol Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 110
Static MAC Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 111
Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 112
Configuring Static MAC Filter Entries . . . . . . . . . . . . . . . . . . . . 113
Static MAC Filter Examples . . . . . . . . . . . . . . . . . . . . . . . . . . 113
Advanced Filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 115
TCP/UDP Port Filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
Adding TCP/UDP Port Filters . . . . . . . . . . . . . . . . . . . . . . . . . 116
Editing TCP/UDP Port Filters . . . . . . . . . . . . . . . . . . . . . . . . . 117
Alarm Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 117
Alarm Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 117
Severity Levels. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 123
Alarm Host Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 124
Adding an Entry or Enabling the AP to Send Traps . . . . . . . . . . . . . 124
Editing or Deleting an Entry. . . . . . . . . . . . . . . . . . . . . . . . . . 124
Syslog . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 124
Setting Syslog Event Notifications . . . . . . . . . . . . . . . . . . . . . . 125
Configuring Syslog Event Notifications . . . . . . . . . . . . . . . . . . . 125
Syslog Messages . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 126
RAD . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 127
RAD Configuration Requirements . . . . . . . . . . . . . . . . . . . . . . 128
Contents
Issue 1 October 2004 7

Contents
Configuring RAD . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 129
Bridge Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130
Spanning Tree . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130
Storm Threshold . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 131
Intra BSS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 131
Packet Forwarding. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 132
Configuring Interfaces for Packet Forwarding. . . . . . . . . . . . . . . . 132
QoS (Quality of Service). . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 132
RADIUS Profile Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . 133
RADIUS Servers per Authentication Mode and per VLAN . . . . . . . . . . . 134
RADIUS-based VLAN Assignment . . . . . . . . . . . . . . . . . . . . . . 135
RADIUS Servers Enforcing VLAN Access Control . . . . . . . . . . . . . 135
Configuring RADIUS Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . 135
Configuring a RADIUS Server Profile. . . . . . . . . . . . . . . . . . . . . 136
MAC Access Control by Means of RADIUS Authentication. . . . . . . . . . . 139
802.1x Authentication using RADIUS . . . . . . . . . . . . . . . . . . . . . . 139
RADIUS Accounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
Session Length . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
Security Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
Management VLAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
VLAN Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
Enabling or Disabling the VLAN Protocol . . . . . . . . . . . . . . . . . . 144
MAC Access . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 145
Configuring MAC Access Control . . . . . . . . . . . . . . . . . . . . . . 146
Security Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 147
WEP Encryption . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
802.1x Authentication . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
Wi-Fi Protected Access (WPA) . . . . . . . . . . . . . . . . . . . . . . . . 150
Authentication Protocol Hierarchy . . . . . . . . . . . . . . . . . . . . . . 152
VLANs and Security Profiles . . . . . . . . . . . . . . . . . . . . . . . . . 152
Configuring Security Profiles . . . . . . . . . . . . . . . . . . . . . . . . . 152
Wireless-A and Wireless-B . . . . . . . . . . . . . . . . . . . . . . . . . . . . 156
Adding or Modifying an SSID/VLAN with VLAN Protocol Disabled . . . . 156
Adding or Modifying an SSID/VLAN with VLAN Protocol Enabled . . . . . 160
Broadcast SSID and Closed System . . . . . . . . . . . . . . . . . . . . . 164
Chapter 5: Monitoring the AP-3. . . . . . . . . . . . . . . . . . . . . . . 167
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 167
Logging into the HTTP Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . 167
Version . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 169
8 Wireless AP-3 User’s Guide

ICMP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 171
IP/ARP Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 172
Learn Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 173
IAPP. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 174
RADIUS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 175
Interfaces. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 176
Station Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 177
Enabling and Viewing Station Statistics . . . . . . . . . . . . . . . . . . . . . 177
Refreshing Station Statistics . . . . . . . . . . . . . . . . . . . . . . . . . . . 178
Description of Station Statistics . . . . . . . . . . . . . . . . . . . . . . . 178
Chapter 6: Performing Commands . . . . . . . . . . . . . . . . . . . . . 179
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 179
Logging into the HTTP Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . 179
Introduction to File Transfer by TFTP or HTTP . . . . . . . . . . . . . . . . . . . 181
TFTP File Transfer Guidelines . . . . . . . . . . . . . . . . . . . . . . . . . . 182
HTTP File Transfer Guidelines . . . . . . . . . . . . . . . . . . . . . . . . . . 182
Image Error Checking during File Transfer . . . . . . . . . . . . . . . . . . . 182
Contents
Updating the AP by Using TFTP . . . . . . . . . . . . . . . . . . . . . . . . . . . 183
Updating the AP by Using HTTP . . . . . . . . . . . . . . . . . . . . . . . . . . . 184
Uploading AP Files by Using TFTP. . . . . . . . . . . . . . . . . . . . . . . . . . 186
Uploading AP Files by Using HTTP. . . . . . . . . . . . . . . . . . . . . . . . . . 188
Rebooting the AP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 190
Resetting the AP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 191
Help Link . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 191
Chapter 7: Troubleshooting the AP-3 . . . . . . . . . . . . . . . . . . . 193
In This Chapter. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 193
Troubleshooting Concepts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 193
Symptoms and Solutions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 194
Connectivity Issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 194
AP Unit Will Not Boot - No LED Activity . . . . . . . . . . . . . . . . . . . 194
Serial Link Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . . . 195
Ethernet Link Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . . 195
Basic Software Setup and Configuration Problems. . . . . . . . . . . . . . . 195
Lost AP, Telnet, or SNMP Password . . . . . . . . . . . . . . . . . . . . . 196
Client Computer Cannot Connect . . . . . . . . . . . . . . . . . . . . . . 196
AP Has Incorrect IP Address . . . . . . . . . . . . . . . . . . . . . . . . . 196
Issue 1 October 2004 9

Contents
HTTP (browser) or Telnet Interface Does Not Work . . . . . . . . . . . . . 197
HTML Help Files Do Not Appear . . . . . . . . . . . . . . . . . . . . . . . 197
Telnet CLI Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . . . . 197
TFTP Server Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . . 198
Client Connection Problems . . . . . . . . . . . . . . . . . . . . . . . . . . . 198
Client Software Finds No Connection . . . . . . . . . . . . . . . . . . . . 198
Client PC Card Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . 198
Intermittent Loss of Connection . . . . . . . . . . . . . . . . . . . . . . . 198
Client Does Not Receive an IP Address - Cannot Connect to Internet . . . 199
VLAN Operation Issues . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 199
Verifying Proper Operation of the VLAN Feature . . . . . . . . . . . . . . 199
VLAN Workgroups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
Active Ethernet (AE) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
The AP Does Not Work . . . . . . . . . . . . . . . . . . . . . . . . . . . . 200
There Is No Data Link . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 201
“Overload” Indications . . . . . . . . . . . . . . . . . . . . . . . . . . . . 201
Recovery Procedures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 201
Reset to Factory Default Procedure . . . . . . . . . . . . . . . . . . . . . . . 202
Forced Reload Procedure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 203
Download a New Image Using ScanTool. . . . . . . . . . . . . . . . . . . 203
Download a New Image Using the Bootloader CLI . . . . . . . . . . . . . 205
Setting IP Address using Serial Port . . . . . . . . . . . . . . . . . . . . . . . 207
Hardware and Software Requirements . . . . . . . . . . . . . . . . . . . . 207
Attaching the Serial Port Cable . . . . . . . . . . . . . . . . . . . . . . . . 207
Initializing the IP Address using CLI . . . . . . . . . . . . . . . . . . . . . 207
Related Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 209
RADIUS Authentication Server . . . . . . . . . . . . . . . . . . . . . . . . . . 209
TFTP Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 209
Appendix A: The Command Line Interface . . . . . . . . . . . . . . . . 211
In This Appendix. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
General Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
Prerequisite Skills and Knowledge . . . . . . . . . . . . . . . . . . . . . . . . 213
Notation Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
Important Terminology . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
Navigation and Special Keys . . . . . . . . . . . . . . . . . . . . . . . . . . . 214
CLI Error Messages . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Bootloader CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 216
CLI Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 217
Command Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 218
10 Wireless AP-3 User’s Guide

Entering Text Strings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 219
CLI Help . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 219
The Question Mark. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 220
Example 1. Displaying the command list. . . . . . . . . . . . . . . . . . . 220
Example 2. Displaying specific commands . . . . . . . . . . . . . . . . . 221
Example 3. Displaying parameters for set and show commands . . . . . 221
Example 4. Displaying prompts for successive parameters . . . . . . . . 223
The Help Command . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 223
Accessing the AP CLI . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 224
Using HyperTerminal to Log in to the AP . . . . . . . . . . . . . . . . . . . . 225
Using Telnet to Log in to the AP . . . . . . . . . . . . . . . . . . . . . . . . . 225
CLI Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 226
done . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 226
download . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 227
Syntax . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 227
Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 227
exit . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 227
help . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 227
Syntax . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 228
Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 228
history . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 229
passwd . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 229
quit . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 229
reboot. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 229
search . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
set. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
Syntax . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 230
Configuring Objects that Require Reboot . . . . . . . . . . . . . . . . . . 230
Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 231
show . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 232
Syntax . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 232
Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 233
upload . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 234
Syntax . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
Contents
Parameter Tables . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 235
Auto Configuration Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . 236
Auto Configuration Parameters. . . . . . . . . . . . . . . . . . . . . . . . . . 236
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 236
Issue 1 October 2004 11

Contents
DHCP Server Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
DHCP Server Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
IP Address Pool Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 238
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 238
DNS Client Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 239
DNS Client for RADIUS Name Resolution Parameters . . . . . . . . . . . . . 239
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 239
Ethernet Interface Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 240
Ethernet Interface Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . 240
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 240
Filtering Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 241
Ethernet Protocol Filtering Parameters . . . . . . . . . . . . . . . . . . . . . 241
Ethernet Protocol Filtering Table Parameters . . . . . . . . . . . . . . . . . . 242
Static MAC Address Filter Table . . . . . . . . . . . . . . . . . . . . . . . . . 242
Proxy ARP Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 243
IP ARP Filtering Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
Broadcast Filtering Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
TCP/UDP Port Filtering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
TCP/UDP Port Filtering Table . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
Hardware Configuration Reset Commands . . . . . . . . . . . . . . . . . . . . . 246
Hardware Configuration Reset Parameters . . . . . . . . . . . . . . . . . . . 247
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 247
HTTP and HTTPS Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 248
HTTP (Web browser) Parameters . . . . . . . . . . . . . . . . . . . . . . . . . 248
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 249
Change HTTP Interface Password . . . . . . . . . . . . . . . . . . . . . . 249
Configure Management Interfaces . . . . . . . . . . . . . . . . . . . . . . 249
Set TCP Port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 249
Configure Secure Socket Layer (HTTPS). . . . . . . . . . . . . . . . . . . 249
IAPP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
IAPP Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
Intra BSS Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Intra BSS Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Syntax Example . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 251
Inventory Management Commands . . . . . . . . . . . . . . . . . . . . . . . . . 252
Inventory Management Parameters . . . . . . . . . . . . . . . . . . . . . . . 252
IP Access Table Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
IP Access Table Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 253
12 Wireless AP-3 User’s Guide

Edit Management IP Access Table . . . . . . . . . . . . . . . . . . . . . . 253
IP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 253
IP Configuration Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 253
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 254
Link Integrity Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 255
Link Integrity Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 255
IP Target Table Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . 255
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 256
MAC Access Control Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . 256
MAC Access Control Parameters. . . . . . . . . . . . . . . . . . . . . . . . . 256
MAC Access Control Table Parameters . . . . . . . . . . . . . . . . . . . . . 257
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
Setup MAC (Address) Access Control . . . . . . . . . . . . . . . . . . . . 257
Add an Entry to the MAC Access Control Table. . . . . . . . . . . . . . . 257
Disable or Delete an Entry in the MAC Access Control Table . . . . . . . 257
Monitoring Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 258
Packet Forwarding Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 259
Packet Forwarding Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . 259
RAD Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 259
RAD Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 260
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 260
Contents
RADIUS Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 261
General RADIUS Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 261
RADIUS Server Configuration Parameters. . . . . . . . . . . . . . . . . . . . 261
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 262
Configure RADIUS Authentication servers . . . . . . . . . . . . . . . . . 262
RADIUS-Based Management Access Commands . . . . . . . . . . . . . . . . . . 265
RADIUS-Based Management Access Parameters . . . . . . . . . . . . . . . . 266
Secure Management Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . 266
Secure Management Parameters . . . . . . . . . . . . . . . . . . . . . . . . . 266
Security Profile Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 266
Security Profile Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 266
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 268
Configure a Security Profile with Non Secure Security Mode . . . . . . . 268
Configure a Security Profile with WEP Security Mode . . . . . . . . . . . 268
Configure a Security Profile with 802.1x Security Mode . . . . . . . . . . 268
Configure a Security Profile with WPA Security Mode . . . . . . . . . . . 268
Configure a Security Profile with WPA-PSK Security Mode . . . . . . . . 268
Configure a Security Profile with 802.11i Security Mode . . . . . . . . . . 269
Issue 1 October 2004 13
Contents
Configuring a Security Profile with 802.11i-PSK Security Mode . . . . . . 269
Serial Port Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 269
Serial Port Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 269
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 270
SNMP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 271
SNMP Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 271
SNMP Trap Host Table Parameters. . . . . . . . . . . . . . . . . . . . . . . . 272
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 272
Change SNMP Passwords. . . . . . . . . . . . . . . . . . . . . . . . . . . 272
Configure Management Interfaces . . . . . . . . . . . . . . . . . . . . . . 273
Spanning Tree Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 273
Spanning Tree Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . 273
Spanning Tree Priority and Path Cost Table. . . . . . . . . . . . . . . . . . . 274
SpectraLink VoIP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 275
SpectraLink VoIP Parameters (802.11b and b/g Modes Only) . . . . . . . . . 275
SSH Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 276
SSH Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 276
Storm Threshold Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 277
Storm Threshold Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . 277
Storm Threshold Table . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 277
Syslog Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 278
Syslog Parameters. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 278
Syslog Host Table Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . 279
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 279
System Information Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . 280
System Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 280
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 281
Telnet Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 282
Telnet Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 282
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 282
Configure Management Interfaces . . . . . . . . . . . . . . . . . . . . . . 282
Set TCP Port . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 283
Set Telnet Session Timeouts . . . . . . . . . . . . . . . . . . . . . . . . . 283
TFTP Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 283
TFTP Server Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 283
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 284
Download an AP Configuration File from a TFTP Server . . . . . . . . . . 284
Backup your AP Configuration File to a TFTP Server . . . . . . . . . . . . 285
WDS Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 285
14 Wireless AP-3 User’s Guide

Wireless Distribution System (WDS) Parameters . . . . . . . . . . . . . . . . 285
Wireless Distribution System (WDS) Security Table Parameters . . . . . . . 286
802.11a Wireless Interface Commands. . . . . . . . . . . . . . . . . . . . . . . . 286
802.11a Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 286
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 288
Network Name (SSID) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 288
Operational Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 289
TX Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 289
Autochannel Select (ACS). . . . . . . . . . . . . . . . . . . . . . . . . . . 289
Enable/Disable Closed System . . . . . . . . . . . . . . . . . . . . . . . . 289
Shutdown/Resume Wireless Service . . . . . . . . . . . . . . . . . . . . . 290
802.11b Wireless Interface Commands. . . . . . . . . . . . . . . . . . . . . . . . 290
802.11b Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 290
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 292
Network Name (SSID) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 292
Operational Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 292
TX Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 293
Autochannel Select (ACS). . . . . . . . . . . . . . . . . . . . . . . . . . . 293
Enable/Disable Closed System . . . . . . . . . . . . . . . . . . . . . . . . 293
Shutdown/Resume Wireless Service . . . . . . . . . . . . . . . . . . . . . 293
Enable/Disable Interference Robustness (802.11b Only) . . . . . . . . . . 294
Enable/Disable Load Balancing (802.11b Only) . . . . . . . . . . . . . . . 294
Enable/Disable Medium Density Distribution (802.11b Only) . . . . . . . . 294
Set the Distance Between APs (802.11b Only). . . . . . . . . . . . . . . . 294
Set the Multicast Rate (802.11b Only) . . . . . . . . . . . . . . . . . . . . 294
802.11b/g Wireless Interface Commands . . . . . . . . . . . . . . . . . . . . . . 295
802.11b/g Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 295
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
Network Name (SSID) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
Operational Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
TX Power Control . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 298
Autochannel Select (ACS). . . . . . . . . . . . . . . . . . . . . . . . . . . 299
Enable/Disable Closed System . . . . . . . . . . . . . . . . . . . . . . . . 299
Shutdown/Resume Wireless Service . . . . . . . . . . . . . . . . . . . . . 299
Contents
Wireless Interface SSID/VLAN/Profile Commands . . . . . . . . . . . . . . . . . 300
Wireless Interface SSID Table Parameters. . . . . . . . . . . . . . . . . . . . 300
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 301
VLAN/SSID Pair Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 302
VLAN/SSID Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 302
Syntax Examples . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 302
Issue 1 October 2004 15

Contents
Enable VLAN Management . . . . . . . . . . . . . . . . . . . . . . . . . . 302
Disable VLAN Management . . . . . . . . . . . . . . . . . . . . . . . . . . 302
CLI Batch File . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 303
Auto Configuration and the CLI Batch File . . . . . . . . . . . . . . . . . . . 303
CLI Batch File Format and Syntax . . . . . . . . . . . . . . . . . . . . . . . . 303
Sample CLI Batch File . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 304
Reboot Behavior . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 304
CLI Batch File Error Log. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 304
Appendix B: ASCII Character Chart . . . . . . . . . . . . . . . . . . . . 307
Description . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 307
Character Chart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 307
Appendix C: Specifications . . . . . . . . . . . . . . . . . . . . . . . . . 309
In This Appendix. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Software Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Number of Stations per BSS . . . . . . . . . . . . . . . . . . . . . . . . . . . 309
Management Functions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 310
Advanced Bridging Functions . . . . . . . . . . . . . . . . . . . . . . . . . . 310
Medium Access Control (MAC) Functions . . . . . . . . . . . . . . . . . . . . 311
Security Functions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 312
Network Functions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 313
Advanced Wireless Functions . . . . . . . . . . . . . . . . . . . . . . . . . . 314
Hardware Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 314
Physical Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
AP-3 Unit . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
802.11a Antenna Adapter . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
Electrical Specifications. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
Without Active Ethernet Module . . . . . . . . . . . . . . . . . . . . . . . 315
With Active Ethernet Module . . . . . . . . . . . . . . . . . . . . . . . . . 315
Environmental Specifications. . . . . . . . . . . . . . . . . . . . . . . . . . . 315
AP-3 Unit . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
802.11a Antenna Adapter . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
Ethernet Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
Serial Port Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
Active Ethernet Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
HTTP Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
Radio Specifications. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
802.11a Channel Frequencies. . . . . . . . . . . . . . . . . . . . . . . . . . . 317
802.11b Channel Frequencies . . . . . . . . . . . . . . . . . . . . . . . . . . 319
16 Wireless AP-3 User’s Guide

802.11g Channel Frequencies . . . . . . . . . . . . . . . . . . . . . . . . . . 320
Wireless Communication Range . . . . . . . . . . . . . . . . . . . . . . . . . 321
802.11b Wireless Communication Ranges. . . . . . . . . . . . . . . . . . 322
802.11a (5 GHz Upgrade Kit) Wireless Communication Ranges . . . . . . 323
802.11a (11a Upgrade Kit) Wireless Communication Ranges . . . . . . . 323
802.11b/g Wireless Communication Ranges. . . . . . . . . . . . . . . . . 324
Appendix D: Technical Support . . . . . . . . . . . . . . . . . . . . . . 325
Before You Seek Help . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 325
Contents
Issue 1 October 2004 17

Contents
18 Wireless AP-3 User’s Guide
Chapter 1: Introduction
In This Chapter
The following topics are covered in this section:
● Document Conventions on page 19
● Introduction to Wireless Networking on page 20
● IEEE 802.11 Specifications on page 22
● Management and Monitoring Capabilities on page 23
Document Conventions
● The term, AP, refers to an Access Point.
● The term, 802.11, is used to describe features that apply to the 802.11a, 802.11b, and
802.11g wireless standards.
● A Dual-radio AP is an Access Point that includes two radios; it can support one or two
IEEE radio standards (depending on the type of radios installed). The AP-3 is a Dual-radio
AP.
● An 802.11a AP is an Access Point that supports the IEEE 802.11a standard.
● An 802.11b AP is an Access Point that supports the IEEE 802.11b standard.
● An 802.11b/g AP is an Access Point that supports the IEEE 802.11g standard.
● Blue text indicates a link to a topic or Web address. If you are viewing this documentation
on your computer, click the blue text to jump to the linked item.
Note:
Note: A Note indicates important information that helps you make better use of your
computer.
!
CAUTION:
CAUTION: A Caution indicates either potential damage to hardware or loss of data and tells
you how to avoid the problem.
Issue 1 October 2004 19

Introduction
Introduction to Wireless Networking
An AP extends the capability of an existing Ethernet network to devices on a wireless network.
Wireless devices can
● connect to a single Access Point, or
● move between multiple Access Points located within the same vicinity. As wireless clients
move from one coverage cell to another, the devices maintain network connectivity.
Site Survey
To determine the best location for an Access Point, Avaya recommends conducting a Site
Survey before placing the device in its final location. For information about how to conduct a
Site Survey, contact your local reseller.
Before an Access Point can be configured for your specific networking requirements, it must
first be initialized. See Chapter 2:
Getting Started for details.
Figure 1: Typical wireless network access infrastructure
20 Wireless AP-3 User’s Guide

Once initialized, the network administrator can configure each unit according to the network’s
requirements. The AP functions as a wireless network access point to data networks. An AP
network provides:
● Seamless client roaming
● Easy installation and operation
● Over-the-air encryption of data
● High speed network links
To be fully operational, the AP-3 needs at least one wireless card installed.
Guidelines for Roaming
Wireless Standard Support
An AP can only communicate with client devices that support its wireless standard. For
example, an 802.11a client cannot communicate with an 802.11b AP and an 802.11b client
cannot communicate with an 802.11a AP. However, both 802.11b and 802.11g clients can
communicate with an 802.11b/g AP.
Introduction to Wireless Networking
Network Names
● All Access Points must have the same Network Name to support client roaming.
● All workstations with an 802.11 client adapter installed must use either a Network Name of
“any” or the same Network Name as the Access Points that they will roam between. If an
AP has Closed System enabled, a client must have the same Network Name as the
Access Point to communicate (see Interface Configuration
Security Settings
All Access Points and clients must have the same security settings to communicate.
Cell Coverage
● The Access Points’ cells must overlap to ensure that there are no gaps in coverage and to
ensure that the roaming client will always have a connection available.
● The coverage area of an 802.11b or 802.11b/g AP is larger than the coverage area of an
802.11a AP. The 802.11b and 802.11b/g APs operate in the 2.4 GHz frequency band; the
802.11a AP operates in the 5 GHz band. Products that operate in the 2.4 GHz band offer
greater range than products that operate in the 5 GHz band.
on page 72).
Issue 1 October 2004 21
Introduction
Data Rates
An 802.11a or 802.11b/g AP operates at faster data rates than the 802.11b AP. 802.11a and
802.11g products operate at speeds of up to 54 Mbits/sec; 802.11b products operate at speeds
of up to 11 Mbits/sec.
Channels
● All Access Points in the same vicinity should use a unique, independent Channel. By
default, the AP automatically scans for available Channels during boot-up but you can also
set the Channel manually (see Interface Configuration
● Access Points that use the same Channel should be installed as far away from each other
as possible to reduce potential interference.
IEEE 802.11 Specifications
on page 72 for details).
In 1997, the Institute of Electrical and Electronics Engineers (IEEE) adopted the 802.11
standard for wireless devices operating in the 2.4 GHz frequency band. This standard includes
provisions for three radio technologies: direct sequence spread spectrum, frequency hopping
spread spectrum, and infrared. Devices that comply with the 802.11 standard operate at a data
rate of either 1 or 2 Megabits per second (Mbits/sec).
802.11b
In 1999, the IEEE modified the 802.11 standard to support direct sequence devices that can
operate at speeds of up to 11 Mbits/sec. The IEEE ratified this standard as 802.11b. 802.11b
devices are backwards compatible with 2.4 GHz 802.11 direct sequence devices (that operate
at 1 or 2 Mbits/sec). Available Frequency Channels vary by regulatory domain and/or country.
See 802.11b Channel Frequencies
802.11a
Also in 1999, the IEEE modified the 802.11 standard to support devices operating in the 5 GHz
frequency band. This standard is referred to as 802.11a. 802.11a devices are not compatible
with 2.4 GHz 802.11 or 802.11b devices. 802.11a radios use a radio technology called
Orthogonal Frequency Division Multiplexing (OFDM) to achieve data rates of up to 54 Mbits/
sec. Available Frequency Channels vary by regulatory domain and/or country. See 802.11a
Channel Frequencies on page 317 for details.
on page 319 for details.
22 Wireless AP-3 User’s Guide
Management and Monitoring Capabilities
802.11g
In 2003, the IEEE introduced the 802.11g standard. 802.11g devices operate in the 2.4 GHz
frequency band using OFDM to achieve data rates of up to 54 Mbits/sec. In addition, 802.11g
devices are backwards compatible with 802.11b devices. Available Frequency Channels vary
by regulatory domain and/or country. See 802.11g Channel Frequencies
details.
Management and Monitoring Capabilities
There are three management and monitoring interfaces available to the network administrator
to configure and manage an AP on the network:
● HTTP/HTTPS Interface on page 23
● Command Line Interface on page 24
on page 320 for
● SNMP Management on page 24
HTTP/HTTPS Interface
The HTTP Interface (also known as the Web browser Interface) provides easy access to
configuration settings and network statistics from any computer on the network. You can access
the HTTP Interface:
● over your LAN (switch, hub, etc.),
● over the Internet, or
● with a “crossover” Ethernet cable connected directly to your computer’s Ethernet Port.
HTTPS provides an HTTP connection over a Secure Socket Layer. HTTPS is one of two
available secure management options on the AP; the other secure management option is
SNMPv3. Enabling HTTPS makes it possible for you to access the AP in a secure fashion by
using Secure Socket Layer (SSL) over port 443. The AP supports SSLv3 with a 128-bit
encryption certificate maintained by the AP for secure communications between the AP and the
HTTP client. All communications are encrypted using the server and the client-side certificate.
The AP comes preinstalled with all required SSL files: default certificate, private key and SSL
Certificate Passphrase.
Issue 1 October 2004 23
Introduction
Command Line Interface
The Command Line Interface (CLI) is a text-based configuration utility that supports a set of
keyboard commands and parameters to configure and manage an AP.
Users enter Command Statements, composed of CLI Commands and their associated
parameters. Statements may be issued from the keyboard for real time control, or from scripts
that automate configuration.
For example, when downloading a file, administrators enter the download CLI Command along
with IP Address, file name, and file type parameters.
How To Access the CLI
You access the CLI over a HyperTerminal serial connection or via Telnet.
During initial configuration, you can use the CLI over a serial port connection to configure an
Access Point’s IP address.
When accessing the CLI via Telnet, you can communicate with the Access Point from over your
LAN (switch, hub, etc.), from over the Internet, or with a “crossover” Ethernet cable connected
directly to your computer’s Ethernet Port.
See Appendix A:
The Command Line Interface for more information on the CLI and for a list of
CLI commands and parameters.
SNMP Management
You can also manage and configure an AP using the Simple Network Management Protocol
(SNMP).
Note:
Note: This requires an SNMP manager program, like HP Openview or Castlerock’s
SNMPc.
The AP supports several Management Information Base (MIB) files that describe the
parameters that can be viewed and/or configured over SNMP:
● MIB-II (RFC 1213)
● Bridge MIB (RFC 1493)
● Ethernet-like MIB (RFC 1643)
● 802.11 MIB
● Avaya Wireless Enterprise MIB
24 Wireless AP-3 User’s Guide

Avaya provides these MIB files on the CD included with each Access Point. You need to
compile one or more of the above MIBs into your SNMP program’s database before you can
manage an Access Point using SNMP. See the documentation that came with your SNMP
manager for instructions on how to compile MIBs.
The Enterprise MIB defines the read and read-write objects that can be viewed or configured
using SNMP. These objects correspond to most of the settings and statistics that are available
with the other management interfaces. See the Enterprise MIB for more information; the MIB
can be opened with any text editor, such as Microsoft Word, Notepad, or WordPad.
SNMPv3 Secure Management
SNMPv3 is one of two available secure management options on the AP; the other secure
management option is HTTPS (HTTP connection over Secure Socket Layer). SNMPv3 is based
on the existing SNMP framework, but addresses security requirements for device and network
management.
The security threats addressed by secure management are:
● Modification of information: An entity could alter an in-transit message generated by an
authorized user so as to perform unauthorized management operations, including the
setting of object values.The essence of this threat is that an unauthorized entity could
change any management parameter, including those related to configuration, operations,
and accounting.
Management and Monitoring Capabilities
● Masquerade: An entity could attempt to perform management operations for which it is not
authorized by assuming the identity of an entity who is authorized to perform the operation.
● Message stream modification: SNMP is designed to operate over a connectionless
transport protocol. An entity could reorder, delay or replay (duplicate) SNMP messages to
perform unauthorized management operations. For example, a message to reboot a
device could be copied and replayed later.
● Disclosure: An entity could observe exchanges between a manager and an agent and
learn the values of managed objects and learn of notifiable events. For example, an entity
could learn new user passwords by observing set commands that change passwords.
To address the these security threats, SNMPv3 provides the following features when secure
management is enabled:
● Authentication: Provides data integrity and authentication of data origin (user
authentication).
● Privacy (a.k.a Encryption): Protects against disclosure of message payload.
● Access Control: Controls and authorizes access to managed objects
Issue 1 October 2004 25

Introduction
The default SNMPv3 username is administrator, with SHA authentication, and DES privacy
protocol.
Note: The remainder of this guide describes how to configure an AP using the HTTP
Note:
Web interface or the CLI interface. For information on how to manage devices
using SNMP, see the documentation that came with your SNMP program. Also,
see the MIB files for information on the parameters available via SNMP.
26 Wireless AP-3 User’s Guide
Chapter 2: Getting Started
In This Chapter
● Prerequisites on page 27
● Product Package on page 29
● System Requirements on page 30
● Hardware Installation on page 31
● Initialization on page 39
● Downloading the Latest Software on page 50
● Additional Hardware Features on page 52
Prerequisites
Before installing an AP, you need to gather certain network information. Tab le 1 identifies the
information you need.
Note:
Note: Passwords must be configured with at least 6 characters in length.
Table 1: Required Network Information 1 of 2
Required Information Explanation
Network Name (SSID of the
wireless cards)
Assign the Access Point a Primary Network Name before
wireless users can communicate with it. The clients also need
the same Network Name. This is not the same as the System
Name, which applies only to the Access Point. The network
administrator typically provides the Network Name.
AP’s IP Address If you do not have a DHCP server on your network, then you
need to assign the Access Point an IP address that is valid on
your network.
HTTP (Web) Interface
Password
Each Access Point requires a read/write password to access
the Web interface. The default password is “public”.
1 of 2
Issue 1 October 2004 27
Getting Started
Table 1: Required Network Information 2 of 2
Required Information Explanation
CLI Interface Password Each Access Point requires a read/write password to access
SNMP Read Password Each Access Point requires a password to allow get requests
the CLI interface. The default password is “public”.
from an SNMP manager. The default password is “public”.
SNMP Read-Write
Password
Each Access Point requires a password to allow get and set
requests from an SNMP manager. The default password is
“public”. This password must be at least 6 characters in length.
SNMPv3 Authentication
Password
If Secure Management is enabled, each Access Point requires
a password for sending authenticated SNMPv3 messages.
The default password is “public”.
The default SNMPv3 username is administrator, with SHA
authentication, and DES privacy protocol.
SNMPv3 Privacy Password If Secure Management is enabled, each Access Point requires
a password when sending encrypted SNMPv3 data. The
default password is “public”.
Security Settings You need to determine what security features you will enable
on the Access Point.
Authentication Method A primary authentication server may be configured; a backup
authentication server is optional. The network administrator
typically provides this information.
Authentication Server
Shared Secret
This is a password shared between the Access Point and the
RADIUS authentication server (so both passwords must be
the same), and is typically provided by the network
administrator.
Authentication Server
Authentication Port
This is a port number (default is 1812) and is typically provided
by the network administrator.
Client IP Address Pool
Allocation Scheme
DNS Server IP Address The network administrator typically provides this IP Address.
28 Wireless AP-3 User’s Guide
The Access Point can automatically provide IP addresses to
clients as they sign on. The network administrator typically
provides the IP Pool range.
2 of 2
Product Package
Each Dual-radio AP comes with the following:
● One ceiling or wall mounting plate
● Mounting hardware
● Metal faceplate for APs mounted in a plenum environment
● AP cover
● Processor module (with integrated Active Ethernet, if applicable)
● Power supply (not provided with Active Ethernet unit)
● AC power cord (not provided with Active Ethernet unit)
● 802.11b PC Card or 802.11b/g AP Card
● One Installation CD-ROM that contains the following:
- Software Installation Wizard
Product Package
- ScanTool
- Solarwinds TFTP software
- HTML Help
- This user’s guide in PDF format
● One Access Point Quick Start Guide
If any of these items are missing or damaged, please contact your reseller or Technical Support
(see Appendix D:
Technical Support for contact information).
5 GHz Antenna Adapter or AP-3 11a Upgrade Kit
The 5 GHz Antenna Adapter or 11a Upgrade Kit can be used in the Access Point. Because
802.11a requires an antenna adapter, only one 5 GHz radio can be installed in the AP. The
second slot can be populated with an 802.11b or 802.11b/g card.
Issue 1 October 2004 29
Getting Started
System Requirements
The following are the minimum requirements to begin using an AP:
● A 10Base-T Ethernet or 100Base-TX Fast Ethernet switch or hub
● At least one radio card designed for the AP:
- an 802.11b PC Card,
- 802.11b/g Card,
- 5 GHz Antenna Adapter Kit, or
- 11a Upgrade Kit
● At least one of the following IEEE 802.11-compliant devices:
You will need an: If you have an:
802.11a client device 802.11a AP
802.11b or 802.11b/g client device 802.11b AP
802.11b/g client device 802.11b/g AP
● A computer that is connected to the same IP network as the AP and has one of the
following Web browsers installed:
- Microsoft Internet Explorer 6 with Service Pack 1 or later and patch Q323308
- Netscape 6.1 or later
(The computer is required to configure the AP using the Web interface.)
30 Wireless AP-3 User’s Guide
 Loading...
Loading...