Page 1

USER GUIDE
BARRICADE™ N
150Mbps 4-Port Wireless Broadband Router
SMCWBR14S-N5
Page 2

Wireless Broadband Router
User Guide
No. 1, Creation Road III,
Hsinchu Science Park,
30077, Taiwan, R.O.C.
TEL: +886 3 5638888
Fax: +886 3 6686111
E012013-AP-R06
Page 3

Information furnished by SMC Networks, Inc. (SMC) is believed to be accurate and reliable.
However, no responsibility is assumed by SMC for its use, nor for any infringements of patents or
other rights of third parties which may result from its use. No license is granted by implication or
otherwise under any patent or patent rights of SMC. SMC reserves the right to change specifications
at any time without notice.
Copyright © 2012 by
SMC Networks, Inc.
No. 1 Creation Road III,
Hsinchu Science Park,
30077, Taiwan, R.O.C.
All rights reserved
Tradem arks :
SMC is a registered trademark; and Barricade, EZ Switch, TigerStack, TigerSwitch, and TigerAccess
are trademarks of SMC Networks, Inc. Other product and company names are trademarks or
registered trademarks of their respective holders.
Page 4

WARRANTY AND PRODUCT REGISTRATION
To register SMC products and to review the detailed warranty statement,
please refer to the Support Section of the SMC Website at http://
www.smc.com.
– 4 –
Page 5

COMPLIANCES
FEDERAL COMMUNICATION COMMISSION INTERFERENCE STATEMENT
This equipment has been tested and found to comply with the limits for a
Class B digital device, pursuant to part 15 of the FCC Rules. These limits
are designed to provide reasonable protection against harmful interference
in a residential installation. This equipment generates, uses and can
radiate radio frequency energy and, if not installed and used in accordance
with the instructions, may cause harmful interference to radio
communications. However, there is no guarantee that interference will not
occur in a particular installation. If this equipment does cause harmful
interference to radio or television reception, which can be determined by
turning the equipment off and on, the user is encouraged to try to correct
the interference by one or more of the following measures:
◆ Reorient or relocate the receiving antenna
◆ Increase the separation between the equipment and receiver
◆ Connect the equipment into an outlet on a circuit different from that to
which the receiver is connected
◆ Consult the dealer or an experienced radio/TV technician for help
This device complies with Part 15 of the FCC Rules. Operation is subject to
the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received,
including interference that may cause undesired operation.
FCC Caution: Any changes or modifications not expressly approved by the
party responsible for compliance could void the user's authority to operate
this equipment.
N
OTE
:
The manufacturer is not responsible for any radio or TV interference
caused by unauthorized modifications to this equipment. Such
modifications could void the user’s authority to operate the equipment.
IMPORTANT NOTE:
FCC RADIATION EXPOSURE STATEMENT
This equipment complies with FCC RF radiation exposure limits set forth for
an uncontrolled environment. This device and its antenna must not be colocated or operating in conjunction with any other antenna or transmitter.
– 5 –
Page 6
“To comply with FCC RF exposure compliance requirements, this grant is
applicable to only Mobile Configurations. The antennas used for this
transmitter must be installed to provide a separation distance of at least 20
cm from all persons and must not be co-located or operating in conjunction
with any other antenna or transmitter.”
TAIWAN NCC
根據國家通信傳播委員會低功率電波輻射性電機管理辦法規定:
第十二條 經型式認證合格之低功率射頻電機,非經許可,公司、商號或使用者均不得擅自變更
頻率、加大功率或變更原設計之特性及功能。
第十四條 低功率射頻電機之使用不得影響飛航安全及干擾合法通信;經發現有干擾現象時,應
立即停用,並改善至無干擾時方得繼續使用。前項合法通信,指依電信法規定作業之
無線電通信。低功率射頻電機須忍受合法通信或工業、科學及醫療用電波輻射性電機
設備之干擾。
本機限在不干擾合法電台與不受被干擾保障條件下於室內使用。
減少電磁波影響,請妥適使用。
安全諮詢及注意事項
◆ 請使用原裝電源供應器或只能按照本產品注明的電源類型使用本產品。
◆ 清潔本產品之前請先拔掉電源線。請勿使用液體、噴霧清潔劑或濕布進行清潔。
◆ 注意防潮,請勿將水或其他液體潑灑到本產品上。
◆ 插槽與開口供通風使用,以確保本產品的操作可靠並防止過熱,請勿堵塞或覆蓋開口。
CE MARK WARNING
This is a class B product. In a domestic environment, this product may
cause radio interference, in which case the user may be required to take
adequate measures.
NATIONAL RESTRICTIONS
This device is intended for home and office use in all EU countries (and
other countries following the EU directive 1999/5/EC) without any
limitation except for the countries mentioned below:
Country Restriction Reason/Remark
Bulgaria None General authorization required for outdoor use and
France Outdoor use
italy None If used outside of own premises, general
Luxembourg None General authorization required for network and
limited to 10 mW
e.i.r.p. within the
band 2454-2483.5
MHz
public service
Military Radiolocation use. Refarming of the 2.4 GHz
band has been ongoing in recent years to allow
current relaxed regulation. Full implementation
planned 2012
authorization is required
service supply(not for spectrum)
– 6 –
Page 7
Country Restriction Reason/Remark
Norway Implemented This subsection does not apply for the geographical
Russian
Federation
N
OTE
:
Do not use the product outdoors in France.
None Only for indoor applications
area within a radius of 20 km from the centre of NyÅlesund
EUROPE - EU DECLARATION OF CONFORMITY
This device complies with the essential requirements of the R&TTE
Directive 1999/5/EC. The following test methods have been applied in
order to prove presumption of conformity with the essential requirements
of the R&TTE Directive 1999/5/EC:
◆ EN 60950-1:2006 + A11: 2009
Safety of Information Technology Equipment.
◆ EN 300 328 V1.7.1: 2006-10
Electromagnetic compatibility and Radio spectrum Matters (ERM);
Wideband transmission systems; Data transmission equipment
operating in the 2,4 GHz ISM band and using wide band modulation
techniques; Harmonized EN covering essential requirements under
article 3.2 of the R&TTE Directive.
◆ EN 301 489-17 V1.8.1/ 2008-04
EN 301 489-17 V2.1.1/ 2009-05
Electromagnetic compatibility and Radio spectrum Matters (ERM);
Electromagnetic Compatibility (EMC) standard for radio equipment and
services; Part 17: Specific conditions for 2.4 GHz wideband
transmission systems and 5 GHz high performance RLAN equipment.
◆ EN 55022: 2006 + A1: 2007
Limits and methods of measurement of radio disturbance
characteristics of information technology equipment.
◆ EN 55024: 1998 + A1: 2001 + A2: 2003
Information technology equipment immunity characteristics limits and
methods of measurement.
◆ EN 62311: 2008
Assessment of electronic and electrical equipment related to human
exposure restrictions for electromagnetic fields (0 Hz - 300 GHz).
This device is a 2.4 GHz wideband transmission system (transceiver),
intended for use in all EU member states and EFTA countries, except in
France and Italy where restrictive use applies.
– 7 –
Page 8

In Italy the end-user should apply for a license at the national spectrum
authorities in order to obtain authorization to use the device for setting up
outdoor radio links and/or for supplying public access to
telecommunications and/or network services.
This device may not be used for setting up outdoor radio links in France
and in some areas the RF output power may be limited to 10 mW EIRP in
the frequency range of 2454 - 2483.5 MHz. For detailed information the
end-user should contact the national spectrum authority in France.
This equipment may be operated in:
The official CE certificate of conformity can be downloaded by selecting the
relevant model/ part number from www.smc.com -> support -> download.
Bulgarian
Български
Czech
Česky
Danish
Dansk
Dutch
Nederlands
English Hereby, SMC Networks, declares that this Radio LAN device is in compliance with the
Estonian
Eesti
Finnish
Suomi
French
Français
С настоящето, SMC Networks декларира, че това безжично устройство е в
съответствие със съществените изисквания и другите приложими разпоредби на
Директива 1999/5/EC.
SMC Networks tímto prohlašuje, že tento Radio LAN device je ve shodě se základními
požadavky a dalšími příslušnými ustanoveními směrnice 1999/5/ES.
Undertegnede SMC Networks erklærer herved, at følgende udstyr Radio LAN device
overholder de væsentlige krav og øvrige relevante krav i direktiv 1999/5/EF
Hierbij verklaart SMC Networks dat het toestel Radio LAN device in overeenstemming is
met de essentiële eisen en de andere relevante bepalingen van richtlijn 1999/5/EG
Bij deze SMC Networks dat deze Radio LAN device voldoet aan de essentiële eisen en
aan de overige relevante bepalingen van Richtlijn 1999/5/EC.
essential requirements and other relevant provisions of Directive 1999/5/EC.
Käesolevaga kinnitab SMC Networks seadme Radio LAN device vastavust direktiivi
1999/5/EÜ põhinõuetele ja nimetatud direktiivist tulenevatele teistele asjakohastele
sätetele.
Valmistaja SMC Networks vakuuttaa täten että Radio LAN device tyyppinen laite on
direktiivin 1999/5/EY oleellisten vaatimusten ja sitä koskevien direktiivin muiden ehtojen
mukainen.
Par la présente SMC Networks déclare que l'appareil Radio LAN device est conforme aux
exigences essentielles et aux autres dispositions pertinentes de la directive 1999/5/CE
– 8 –
Page 9
German
Deutsch
Greek
Ελληνική
Hungarian
Magyar
Italian
Italiano
Latvian
Latviski
Lithuanian
Lietuvių
Maltese
Malti
Polish
Polski
Portuguese
Português
Romanian
Romană
Slovak
Slovensky
Slovenian
Slovensko
Spanish
Español
Swedish
Svenska
Turkish
Turk
Hiermit erklärt SMC Networks, dass sich dieser/diese/dieses Radio LAN device in
Übereinstimmung mit den grundlegenden Anforderungen und den anderen relevanten
Vorschriften der Richtlinie 1999/5/EG befindet". (BMWi)
Hiermit erklärt SMC Networks die Übereinstimmung des Gerätes Radio LAN device mit
den grundlegenden Anforderungen und den anderen relevanten Festlegungen der
Richtlinie 1999/5/EG. (Wien)
με την παρουσα SMC Networks δηλωνει οτι radio LAN device συμμορφωνεται προσ τισ
ουσιωδεισ απαιτησεισ και τισ λοιπεσ σχετικεσ διαταξεισ τησ οδηγιασ 1999/5/εκ.
Alulírott, SMC Networks nyilatkozom, hogy a Radio LAN device megfelel a vonatkozó
alapvetõ követelményeknek és az 1999/5/EC irányelv egyéb elõírásainak.
Con la presente SMC Networks dichiara che questo Radio LAN device è conforme ai
requisiti essenziali ed alle altre disposizioni pertinenti stabilite dalla direttiva 1999/5/CE.
Ar šo SMC Networks deklarē, ka Radio LAN device atbilst Direktīvas 1999/5/EK
būtiskajām prasībām un citiem ar to saistītajiem noteikumiem.
Šiuo SMC Networks deklaruoja, kad šis Radio LAN device atitinka esminius reikalavimus
ir kitas 1999/5/EB Direktyvos nuostatas.
Hawnhekk, SMC Networks, jiddikjara li dan Radio LAN device jikkonforma mal-ħtiġijiet
essenzjali u ma provvedimenti oħrajn relevanti li hemm fid-Dirrettiva 1999/5/EC.
Niniejszym SMC Networks o
wymogami oraz pozostałymi stosownymi postanowieniami Dyrektywy 1999/5/EC.
SMC Networks declara que este Radio LAN device está conforme com os requisitos
essenciais e outras disposições da Directiva 1999/5/CE.
SMC Networks declară că acest dispozitiv fără fir respectă cerinţele esenţiale precum şi
alte dispoziţii relevante ale Directivei 1999/5/EC.
SMC Networks týmto vyhlasuje, že Radio LAN device spĺňa základné požiadavky a
všetky príslušné ustanovenia Smernice 1999/5/ES.
SMC Networks izjavlja, da je ta radio LAN device v skladu z bistvenimi zahtevami in
ostalimi relevantnimi določili direktive 1999/5/ES.
Por medio de la presente SMC Networks declara que el Radio LAN device cumple con
los requisitos esenciales y cualesquiera otras disposiciones aplicables o exigibles de la
Directiva 1999/5/CE
Härmed intygar SMC Networks att denna Radio LAN device står I överensstämmelse
med de väsentliga egenskapskrav och övriga relevanta bestämmelser som framgår av
direktiv 1999/5/EG.
SMC Networks bu kablosuz cihazın temel gereksinimleri ve 1999/5/EC yonergesindeki
ilgili koşulları karşıladığını beyan eder.
świadcza, że Radio LAN device jest zgodny z zasadniczymi
SAFETY PRECAUTIONS
Read the following information carefully before operating the device. Please
follow the following precaution items to protect the device from risks and
damage caused by fire and electric power:
◆ Use the power adapter that is included with the device package.
◆ Pay attention to the power load of the outlet or prolonged lines. An
overburdened power outlet or damaged cords and plugs may cause
electric shock or fire. Check the power cords regularly, if you find any
damage, replace it at once.
– 9 –
Page 10

◆ Proper space for heat dissipation is necessary to avoid any damage
caused by device overheating. The ventilation holes on the device are
designed for heat dissipation to ensure that the device works normally.
Do not cover these ventilation holes.
◆ Do not put this device close to a place where a heat source exits or high
temperature occurs. Avoid placing the device in direct sunshine.
◆ Do not put this device close to a place which is damp or wet. Do not
spill any fluid on this device.
◆ Please follow the instructions in the user manual/quick install guide
carefully to connect the device to your PC or other electronic product.
Any invalid connection may cause a power or fire risk.
◆ Do not place this device on an unstable surface or support.
PRÉCAUTIONS DE SÉCURITÉ
Lisez attentivement les informations suivantes avant d’utiliser votre
appareil. Respectez toutes les précautions afin de protéger l’appareil des
risques et dégâts provoqués par un incendie et l’alimentation électrique :
◆ Utilisez exclusivement l’adaptateur d’alimentation fourni avec cet
appareil.
◆ Faites attention à la puissance de charge de la prise de courant ou des
rallonges électriques. Une prise surchargée ou des cordons et des
fiches endommagés peuvent provoquer une électrocution ou un
incendie. Vérifiez régulièrement votre câble électrique. Si vous
constatiez le moindre défaut, remplacez-le immédiatement.
◆ Il est primordial de laisser suffisamment d’espace autour de l’appareil
pour permettre la dissipation de la chaleur et éviter les dégâts
provoqués par une surchauffe de l’appareil. Les orifices de ventilation
de l’appareil sont conçus pour permettre la dissipation thermique et
garantir le bon fonctionnement de l’appareil. Ne couvrez jamais ces
orifices.
◆ Ne placez pas cet appareil à proximité d’une source de chaleur ou dans
un endroit exposé à des températures élevées. Evitez également de
l’exposer à la lumière directe du soleil.
◆ Ne placez pas cet appareil à proximité d’un lieu humide ou mouillé.
Prenez garde à ne renverser aucun liquide sur cet appareil.
◆ Merci de suivre les instructions du manuel d'utilisateur / guide
d’installation rapide attentivement pour connecter l'appareil à votre PC
ou à tout autre produit électronique. Toute connexion non valide peut
provoquer un problème électrique ou un risque d'incendie.
◆ Ne placez pas cet appareil sur une surface ou un support instable.
– 10 –
Page 11

SICHERHEITSMAßNAHMEN
Lesen Sie vor der Inbetriebnahme des Gerätes aufmerksam die
nachstehenden Informationen. Bitte befolgen Sie die nachstehenden
Sicherheitsmaßnahmen, damit das Gerät nicht beschädigt wird oder
Gefahren durch Brand oder elektrische Energie entstehen:
◆ Verwenden Sie nur das beim Gerät mitgelieferte Netzteil.
◆ Achten Sie auf die Last der Steckdose oder des Verlängerungskabels.
Eine überlastete Steckdose oder beschädigte Kabel und Stecker können
Stromschläge und Brand verursachen. Prüfen Sie die Netzkabel
regelmäßig. Ersetzen Sie sie umgehend, falls sie beschädigt sind.
◆ Achten Sie zur Vermeidung von Geräteschäden aufgrund von
Überhitzung darauf, dass genügend Freiraum zur Wärmeabfuhr
vorhanden ist. Die Belüftungsöffnungen am Gerät dienen der
Wärmeabfuhr und damit der Gewährleistung eines normalen
Gerätebetriebs. Decken Sie diese Belüftungsöffnungen nicht ab.
◆ Stellen Sie dieses Gerät nicht in der Nähe von Wärmequellen oder an
Orten mit hohen Temperaturen auf. Platzieren Sie das Gerät nicht im
direkten Sonnenlicht.
◆ Stellen Sie dieses Gerät nicht an feuchten oder nassen Orten auf.
Achten Sie darauf, keine Flüssigkeiten über dem Gerät zu verschütten.
◆ Befolgen Sie die Hinweise im Benutzerhandbuch (bzw. in der
Kurzanleitung) zum Anschluß des Gerätes an einen PC oder ein anderes
Elektrogerät. Jegliche unzulässige Verbindung birgt die Gefahr von
Stromschlägen und Brandgefahr.
◆ Platzieren Sie dieses Gerät nicht auf einer instabilen Oberfläche oder
Halterung.
PRECAUCIONES DE SEGURIDAD
Lea la siguiente información detenidamente antes de utilizar el dispositivo.
Siga las indicaciones de precaución que se mencionan a continuación para
proteger el dispositivo contra riesgos y daños causados por el fuego y la
energía eléctrica:
◆ Utilice el adaptador de alimentación incluido en el paquete del
dispositivo.
◆ Preste atención a la carga de potencia de la toma de corriente o de los
alargadores. Una toma de corriente sobrecargada o líneas y enchufes
dañados pueden provocar descargas eléctricas o un incendio.
Compruebe los cables de alimentación con cierta frecuencia. Si detecta
algún daño, reemplácelos inmediatamente.
– 11 –
Page 12

◆ Deje un espacio adecuado para que se disipe el calor y evitar así
cualquier daño en el dispositivo causado por sobrecalentamiento. Los
orificios de ventilación del dispositivo están diseñados para disipar el
calor y garantizar que dicho dispositivo funciona con normalidad. No
tape estos orificios de ventilación.
◆ No coloque este dispositivo cerca de un lugar donde haya una fuente de
calor o temperaturas elevadas. Evite exponer el dispositivo a la luz
solar directa.
◆ No coloque este dispositivo junto a un lugar húmedo o mojado. No
derrame ningún fluido sobre el dispositivo.
◆ Por favor, siga cuidadosamente las instrucciones que figuran en el
manual/guía de instalación rápida para conectar el dispositivo a su PC o
a cualquier otro producto electrónico. Cualquier conexión no válida
podría causar riesgo de descarga o de incendio.
◆ No coloque este dispositivo en una superficie o soporte inestable.
PRECAUÇÕES DE SEGURANÇA
Leia atentamente as seguintes informações antes de utilizar o dispositivo.
Respeite as seguintes indicações de segurança para proteger o dispositivo
contra riscos e danos causados por fogo e energia eléctrica:
◆ Utilize o transformador incluído na embalagem do dispositivo.
◆ Respeite a potência da tomada eléctrica e das extensões. Uma tomada
eléctrica sobrecarregada ou cabos e fichas danificadas podem causar
choques eléctricos ou fogo. Verifique regularmente os cabos de
alimentação. Caso algum se encontre danificado, substitua-o
imediatamente.
◆ É necessário deixar algum espaço livre em volta do dispositivo para
dissipação de calor, de forma a evitar danos causados pelo
sobreaquecimento do dispositivo. Os orifícios de ventilação do
dispositivo foram concebidos para dissipar o calor e assegurar que o
mesmo funciona normalmente. Não bloqueie esses orifícios de
ventilação.
◆ Não coloque este dispositivo junto a fontes de calor ou em locais com
temperaturas elevadas. Evite colocar o dispositivo sob luz solar directa.
◆ Não coloque este dispositivo junto a locais molhados ou com humidade.
Não derrame líquidos sobre o dispositivo.
◆ Por favor siga atentamente as instruções do manual / guia de
instalação rápida para conectar o dispositivo ao seu PC ou a qualquer
outro dispositivo electrónico. Atenção que qualquer tipo de ligação
inválida pode originar risco de choque eléctrico ou de incêndio.
◆ Não coloque este dispositivo numa superfície ou suporte instáveis.
– 12 –
Page 13

BSMI NOTICE
在進行安裝及設定之前,建議您先閱讀以下注意事項:
1. 確認寬頻的線路是否正常:請先確認當 ADSL 或 Cable 或是對外的線路,直接結到您
的電腦時,是否能正常的連接到網際網路。
2. 移除撥號軟體:若您已經安裝 ISP 所提供的 ADSL 撥接(號)軟體,請先將其移除后
再開始進行連線設定。
3. 系統需求:本產品只需要使用網頁瀏覽器 (Browser)來進行設定安裝,不需要額
外安裝任何程式,在開始設定之前,建議您使用 Internet Explorer 6.0 或更新的
版本來進行安裝設定。
4. 設定時無需連上網際網路 (Internet),只需要透過區域連線 (LAN)即可進行設
定。 ※ 僅需從電腦端拉一條網路線連接至 SMCWBR14S-N5 的 LAN 埠,WAN 埠則先不
要連上 ISP 線路。此動作作用是用來確認您可以正常連到此設備。
5. SMCWBR14S-N5只需要設定一次,其餘要透過SMCWBR14S-N5 的電腦或者設備只需要做
相關的 TCP/IP 設定即可。
– 13 –
Page 14
ABOUT THIS GUIDE
PURPOSE This guide details the hardware features of the wireless router, including its
physical and performance-related characteristics, and how to install the
device and use its configuration software.
AUDIENCE This guide is for PC users with a working knowledge of computers. You
should be familiar with Windows operating system concepts.
CONVENTIONS The following conventions are used throughout this guide to show
information:
N
OTE
:
Emphasizes important information or calls your attention to related
features or instructions.
C
AUTION
damage the system or equipment.
W
ARNING
:
Alerts you to a potential hazard that could cause loss of data, or
:
Alerts you to a potential hazard that could cause personal injury.
RELATED PUBLICATIONS The following publication gives basic information on how to install and use
the wireless router.
Quick Installation Guide
Also, as part of the wireless router’s software, there is online help that
describes all configuration related features.
REVISION HISTORY This section summarizes the changes in each revision of this guide.
DECEMBER 2012 REVISION
This is the sixth revision of this guide. It includes the following change:
◆ Added Operation Mode Configuration.
OCTOBER 2012 REVISION
This is the fifth revision of this guide. It includes the following change:
– 14 –
Page 15

A
BOUT THIS GUIDE
◆ Add BSMI Notice to the Compliances section.
SEPTEMBER 2012 REVISION
This is the fourth revision of this guide. It includes the following change:
◆ Updated the Compliances section.
NOVEMBER 2011 REVISION
This is the third revision of this guide. It includes the following change:
◆ Updated the Compliances section.
SEPTEMBER 2011 REVISION
This is the second revision of this guide. It includes the following change:
◆ Updated the Compliances section.
JULY 2011 REVISION
This is the first revision of this guide.
– 15 –
Page 16
CONTENTS
WARRANTY AND PRODUCT REGISTRATION 4
C
OMPLIANCES 5
BOUT THIS GUIDE 14
A
C
ONTENTS 16
F
IGURES 19
ABLES 23
T
1I
NTRODUCTION 24
Overview of the Router 24
Main Features 25
Key Hardware Features 25
Package Contents 26
Front Panel 26
LED Indicators 26
WPS Button 27
Rear Panel 27
Wireless Antennas 27
Power 27
Ethernet WAN Port 28
Ethernet LAN Ports 28
2CONNECTING THE ROUTER 29
System Requirements 29
Installation Environment Requirements 29
Connecting the Router 29
Connecting the Router in Router Mode 29
Connecting the Router in Client Mode 30
3QUICK INSTALLATION GUIDE 32
TCP/IP Configuration 32
– 16 –
Page 17

C
ONTENTS
Quick Installation Guide 34
4CONFIGURING THE ROUTER 40
Login 40
Status 41
Quick Setup 42
WPS 42
Operation Mode 49
Network 50
LAN 50
WAN 51
MAC Clone
(Router Mode Only) 59
Wireless 59
Wireless Settings
(Router Mode) 60
Wireless Settings
(Client Mode) 62
Wireless Security 64
Wireless MAC Filtering 68
Wireless Advanced 70
Wireless Statistics 72
DHCP 72
DHCP Settings 73
DHCP Clients List 74
Address Reservation 74
Forwarding 76
Virtual Servers 76
Port Triggering 78
DMZ 80
UPnP 81
Security 82
Basic Security 82
Advanced Security 83
Local Management 85
Remote Management 85
Parental Control 86
Access Control 89
– 17 –
Page 18

C
ONTENTS
Rule 89
Host 92
Target 94
Schedule 97
Advanced Routing 99
Bandwidth Control 100
IP & MAC Binding 101
Binding Setting 102
ARP List 103
DDNS 104
System Tools 107
Time Settings 107
Diagnostic 109
Firmware Upgrade 110
Factory Defaults 111
Backup & Restore 112
Reboot 112
Password 113
System Log 114
Statistics 116
ACONFIGURING THE PC 118
Install TCP/IP Components 118
BFAQ 122
How do I configure the Router for Internet access by ADSL users? 122
How do I configure the Router for Internet access by Ethernet users? 123
I want to use Netmeeting, what do I need to do? 124
I want to build a WEB Server on the LAN, what should I do? 126
Wireless stations cannot connect to the Router 127
CSPECIFICATIONS 129
G
LOSSARY 131
I
NDEX 133
– 18 –
Page 19
FIGURES
Figure 1: Front Panel 26
Figure 2: Rear Panel 27
Figure 3: Router Mode 30
Figure 4: Client Router Mode 31
Figure 5: Success Result of a Ping Command 33
Figure 6: Failure of a Ping Command 33
Figure 7: Log in to the Router 34
Figure 8: Windows Login 34
Figure 9: Quick Setup 35
Figure 10: Operation Mode 35
Figure 11: Choose the WAN Connection Type 35
Figure 12: Quick Setup – PPPoE 36
Figure 13: Quick Setup - Static IP 36
Figure 14: Quick Setup – Wireless 37
Figure 15: Quick Setup – Finish 38
Figure 16: Quick Setup - Finish 39
Figure 17: The Main Menu 40
Figure 18: Status 41
Figure 19: WPS (Wi-Fi Protected Setup) 42
Figure 20: Front Panel 43
Figure 21: WPS Button 43
Figure 22: WPS-Wireless Configuration Completed 44
Figure 23: Front Panel 44
Figure 24: WPS-Push the button on my access point 45
Figure 25: WPS-Wireless Configuration Completed 45
Figure 26: Add A New Device 46
Figure 27: WPS-Push the button on my access point 46
Figure 28: WPS-Wireless Configuration Completed 47
Figure 29: Add Device 47
Figure 30: WPS-Enter a PIN into my access point 48
Figure 31: WPS-Enter a PIN from my access point 49
– 19 –
Page 20

C
ONTENTS
Figure 32: Operation Mode 49
Figure 33: The Network Menu 50
Figure 34: LAN 50
Figure 35: WAN-Dynamic IP 51
Figure 36: WAN-Static IP 52
Figure 37: WAN-PPPoE 53
Figure 38: WAN-PPPoE Advanced Settings 55
Figure 39: WAN-L2TP 56
Figure 40: WAN-PPTP 57
Figure 41: MAC Address Clone 59
Figure 42: Wireless Menu 60
Figure 43: Wireless Settings (Router Mode) 60
Figure 44: Note Dialog 61
Figure 45: Enable WDS 62
Figure 46: Wireless Settings (Client Router Mode) 63
Figure 47: Wireless Security 65
Figure 48: WEP 65
Figure 49: WPA/WPA2 67
Figure 50: WPA-PSK 67
Figure 51: Wireless MAC Address Filtering 68
Figure 52: Add or Modify Wireless MAC Address Filtering Entry 69
Figure 53: Filtering Rules 70
Figure 54: Wireless Advanced 70
Figure 55: Wireless Statistics 72
Figure 56: The DHCP Menu 72
Figure 57: DHCP Settings 73
Figure 58: DHCP Clients List 74
Figure 59: Address Reservation 75
Figure 60: Add or Modify an Address Reservation Entry 75
Figure 61: The Forwarding Menu 76
Figure 62: Virtual Servers 76
Figure 63: Add or Modify a Virtual Server Entry 77
Figure 64: Port Triggering 78
Figure 65: Add or Modify a Triggering Entry 79
Figure 66: DMZ 80
Figure 67: UPnP 81
– 20 –
Page 21

C
ONTENTS
Figure 68: The Security Menu 82
Figure 69: Basic Security 82
Figure 70: Advanced Security 83
Figure 71: Local Management 85
Figure 72: Remote Management 85
Figure 73: Parental Control Settings 86
Figure 74: Add or Modify Parental Control Entry 88
Figure 75: Parental Control Settings 89
Figure 76: Access Control 89
Figure 77: Access Control Rule Management 90
Figure 78: Add or Modity Internet Access Control Entry 91
Figure 79: Host Settings 92
Figure 80: Add or Modify an IP Host Entry 93
Figure 81: Add or Modify a MAC Host Entry 93
Figure 82: Target Settings 94
Figure 83: Add or Modify an IP Access Target Entry 95
Figure 84: Add or Modify a Domain Name Access Target Entry 96
Figure 85: Target Setting 96
Figure 86: Schedule Settings 97
Figure 87: Advanced Schedule Settings 98
Figure 88: Static Routing 99
Figure 89: Add or Modify a Static Route Entry 99
Figure 90: Bandwidth Control 100
Figure 91: The IP & MAC Binding Menu 101
Figure 92: Binding Setting 102
Figure 93: IP & MAC Binding Setting (Add & Modify) 102
Figure 94: Find IP & MAC Binding Entry 103
Figure 95: ARP List 103
Figure 96: Dyndns.org DDNS Settings 105
Figure 97: No-ip.com DDNS Settings 105
Figure 98: Comexe.cn DDNS Settings 106
Figure 99: The System Tools Menu 107
Figure 100: Time Settings 107
Figure 101: Diagnostic Tools 109
Figure 102: Diagnostic Results 110
Figure 103: Firmware Upgrade 110
– 21 –
Page 22

C
ONTENTS
Figure 104: Restore Factory Default 111
Figure 105: Backup & Restore Configuration 112
Figure 106: Reboot 112
Figure 107: Password 113
Figure 108: System Log 114
Figure 109: Mail Account Settings 115
Figure 110: Statistics 116
Figure 111: TCP/IP 118
Figure 112: Internet Protocol 119
Figure 113: Internet Protocol Properties 120
Figure 114: Setting the IP Address Manually 121
Figure 115: PPPoE Connection Type 122
Figure 116: PPPoE Connection Mode 122
Figure 117: MAC Clone 123
Figure 118: Virtual Servers 124
Figure 119: Add or Modify a Virtual Server Entry 124
Figure 120: DMZ 125
Figure 121: Basic Security 126
Figure 122: Remote Management 126
Figure 123: Virtual Servers 127
Figure 124: Add or Modify a Virtual Server Entry 127
– 22 –
Page 23

TABLES
Table 1: Key Hardware Features 25
Table 2: LED Behavior 26
– 23 –
Page 24
1 INTRODUCTION
OVERVIEW OF THE ROUTER
The Barricade™ SMCWBR14S-N5 150Mbps 4-Port Wireless Broadband
Router delivers exceptional range and speed, which can fully meet the
needs of Small Office/Home Office (SOHO) networks and users demanding
higher network performance. The router integrates a 4-port switch,
firewall, NAT router, and wireless access point (AP).
INCREDIBLE SPEED
The SMCWBR14S-N5 provides up to 150 Mbps wireless connections with
other 802.11n wireless clients, and the speed makes the routers ideal for
handling multiple data streams at the same time, which ensures your
network remains stable and smooth. The routers are compatible with all
IEEE 802.11g and IEEE 802.11b products.
MULTIPLE SECURITY PROTECTIONS
With multiple protection measures, including SSID broadcast control, 64/
128/152-bit WEP encryption, Wi-Fi protected Access (WPA2-PSK, WPAPSK), as well as advanced firewall protection, the routers provide complete
data privacy.
FLEXIBLE ACCESS CONTROL
The routers provide flexible access control, so that parents or network
administrators can establish restricted access policies for children or staff.
It also supports Virtual Server and DMZ host for Port Triggering, and then
the network administrators can manage and monitor the network in real
time with the remote management function.
SIMPLE INSTALLATION
Since the routers are compatible with all major operating systems, it is
easy to manage. A Quick Setup Wizard is supported and detailed step-bystep instructions are provided in this User Guide. Before installing the
router, read through this guide to understand all the router’s features.
– 24 –
Page 25
MAIN FEATURES
C
HAPTER
1
| Introduction
Main Features
◆ IEEE 802.11n wireless technology provides a wireless data rate of up to
150 Mbps.
◆ One 10/100 Mbps Auto-Negotiation RJ-45 WAN port, four 10/100 Mbps
Auto-Negotiation RJ-45 LAN ports, supporting Auto MDI/MDIX.
◆ Provides WPA/WPA2, WPA-PSK/WPA2-PSK authentication, TKIP/AES
encryption security.
◆ Shares data and Internet access for users, supporting dynamic IP/static
IP/PPPoE Internet access.
◆ Supports Virtual Server, Forwarding, and DMZ host.
◆ Supports UPnP, DDNS, Static Routing.
◆ Provides automatic and scheduled connection to the Internet.
◆ Connects to the Internet on demand, and disconnects from the Internet
when idle for PPPoE.
◆ Built-in NAT and DHCP server supporting static IP address assignment.
◆ Supports Stateful Packet Inspection.
◆ Supports VPN Passthrough.
◆ Supports Parental Control and Access Control.
◆ Provides 64/128/152-bit WEP encryption security and wireless LAN ACL
(Access Control List).
◆ Supports Flow Statistics.
◆ Supports firmware upgrade and Web management.
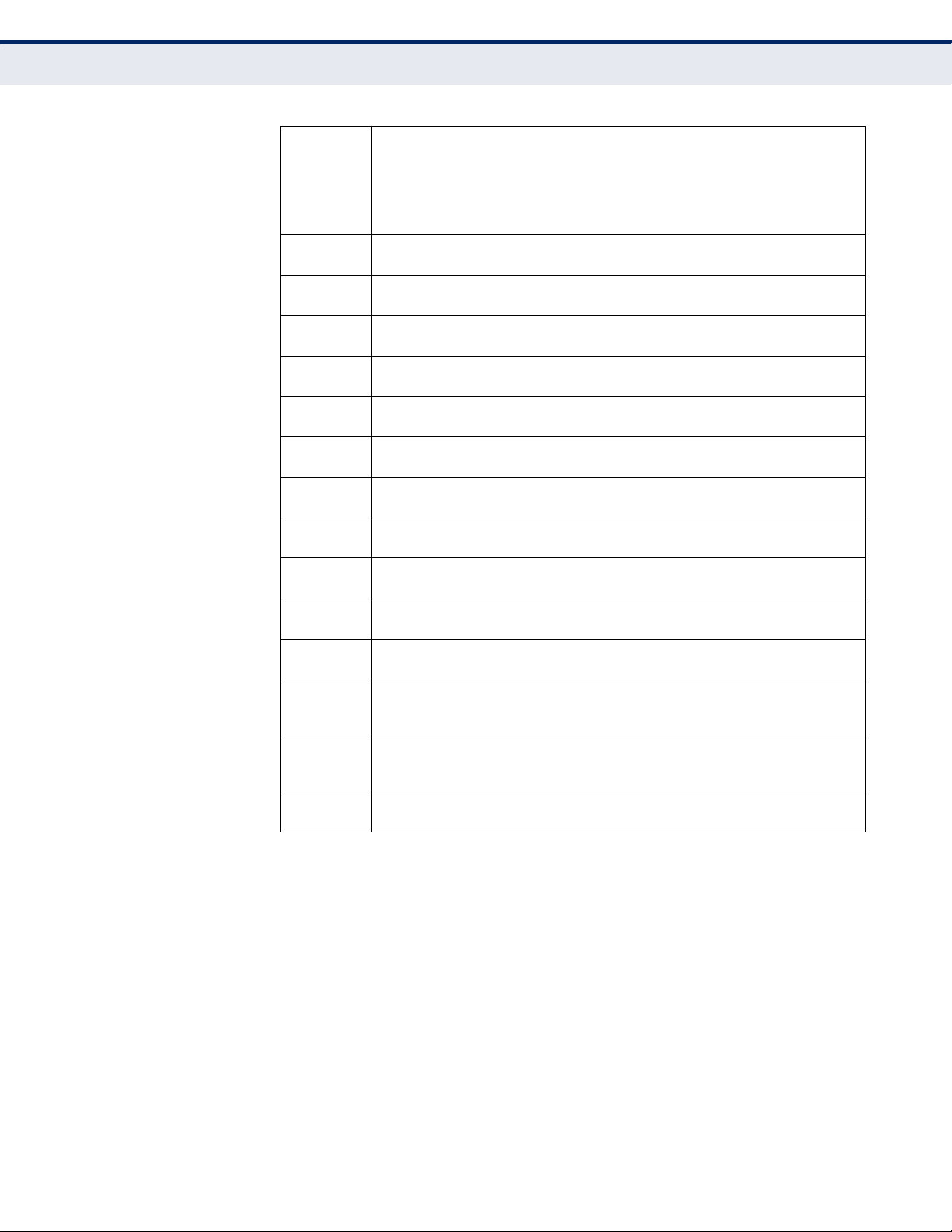
KEY HARDWARE FEATURES
The following table describes the main hardware features of the Router.
Table 1: Key Hardware Features
Feature Description
WAN Port One 100BASE-TX RJ-45 port for connecting to the Internet.
LAN Port Four 100BASE-TX RJ-45 ports for local network connections.
WPS Button For WPS security and resetting the unit.
LEDs Provides LED indicators for Power, WAN port, LAN port, and WLAN
status.
– 25 –
Page 26

PACKAGE CONTENTS
C
HAPTER
1
| Introduction
Package Contents
The following items should be found in your package:
◆ SMCWBR14S-N5 150Mbps 4-Port Wireless Broadband Router,
◆ AC Power Adapter
◆ Quick Installation Guide
◆ Resource CD, including:
◆ This Guide
◆ Other Helpful Information
N
OTE
:
Make sure that the package contains the above items. If any of the
listed items are damaged or missing, please contact with your distributor.
FRONT PANEL
LED INDICATORS The
Figure 1: Front Panel
Router
includes eight status LED indicators, as described in the
following table.
Table 2: LED Behavior
LED Status Description
Power On The unit is receiving power and is operating normally.
Off There is no power currently being supplied to the
System On The Router is initializing or may have a system error.
Blinking The Router is working properly.
Off The Router has a system error.
WLAN On/Blinking The Wireless function is enabled.
Off The Wireless function is disabled.
unit.
– 26 –
Page 27

C
HAPTER
Table 2: LED Behavior (Continued)
LED Status Description
WAN
LAN (1-4)
WPS On A wireless device has been successfully added to the
On There is a device linked to the corresponding port, but
Blinking There is an active device linked to the corresponding
Off There is no device linked to the corresponding port.
Slow Blinking A wireless device is connecting to the network by
Off WPS is not in progress.
there is no activity.
port.
network by WPS. The LED will remain on for about 5
minutes.
WPS. This process lasts for about 2 minutes.
1
| Introduction
Rear Panel
WPS BUTTON Push this button to start WPS authentication of a wireless device. Push and
hold down this button for more than 5 seconds to reset the unit.
N
OTE
:
After a device is successfully added to the network by WPS, the WPS
LED will remain on for about 5 minutes and then turn off. When press and
hold the WPS Button for more than 5 seconds, you will reset the router.
REAR PANEL
Figure 2: Rear Panel
The following items are located on the rear panel (from left to right).
WIRELESS ANTENNAS Receives and transmits wireless data.
POWER The Power socket is where you connect the power adapter. Use the power
adapter provided with the Router.
– 27 –
Page 28

C
HAPTER
ETHERNET WAN PORT This WAN port is where you connect the DSL/cable Modem.
1
| Introduction
Rear Panel
ETHERNET LAN
PORTS
LAN1,2,3,4: These ports (1, 2, 3, 4) connect the Router to local PCs.
– 28 –
Page 29
2 CONNECTING THE ROUTER
SYSTEM REQUIREMENTS
You must meet the following minimum requirements:
◆ Broadband Internet Access Service (DSL/Cable/Ethernet)
◆ One DSL/Cable Modem that has an RJ-45 connector.
◆ PCs with working Ethernet adapters and Ethernet cables with RJ-45
connectors.
◆ TCP/IP protocol on each PC.
◆ Web browser, such as Microsoft Internet Explorer, Mozilla Firefox, or
Apple Safari.
INSTALLATION ENVIRONMENT REQUIREMENTS
◆ Place the Router in a well ventilated place far from any heater or
heating vent
◆ Avoid direct exposure to any strong light (such as sunlight)
◆ Keep at least 2 inches (5 cm) of clear space around the Router
◆ Operating Temperature: 0 °C ~ 40 °C (32 °F ~ 104 °F)
◆ Operating Humidity: 10% ~ 90% RH, Non-condensing
CONNECTING THE ROUTER
Before installing the Router, make sure your PC is successfullyconnected to
the Internet through the broadband service. If there are any problems,
first contact your ISP. After that, install the Router according to the
following steps.
CONNECTING THE
ROUTER IN ROUTER
MODE
1. Power off your PC, Cable/DSL Modem, and the Router.
– 29 –
Page 30

C
PCNoteboook
Cable Modem
HAPTER
2
| Connecting the Router
Connecting the Router
2. Locate an optimum location for the Router. The best place is usually at
the center of your network. The place must meet the Installation
Environment Requirements.
3. Adjust the direction of the antennas. Normally, upright is the best
direction.
4. Connect PCs and any switch in your LAN to the LAN Ports on the Router,
as shown in Figure 3.
5. Connect the DSL/Cable Modem to the WAN port on the Router, as
shown in Figure 3.
6. Connect the AC power adapter to the power socket on the Router, and
the other end into an electrical outlet. The Router will start to work
automatically.
7. Power on your PC and Cable/DSL Modem.
Figure 3: Router Mode
CONNECTING THE
ROUTER IN CLIENT
MODE
1. Power off your PC, Cable/DSL Modem, and the Router.
2. Locate an optimum location for the Router. The best place is usually at
the center of your network. The place must meet the Installation
Environment Requirements.
3. Adjust the direction of the antennas. Normally, upright is the best
direction.
4. Connect PCs and any switch in your LAN to the LAN Ports on the Router,
as shown in Figure 4.
5. Connect the AC power adapter to the power socket on the Router, and
the other end into an electrical outlet. The Router will start to work
automatically.
– 30 –
Page 31

Figure 4: Client Router Mode
WISP Signal
Noteboook PC
C
HAPTER
2
| Connecting the Router
Connecting the Router
– 31 –
Page 32

3 QUICK INSTALLATION GUIDE
This chapter shows you how to quickly configure the basic functions of your
Router using the Quick Setup Wizard.
TCP/IP CONFIGURATION
The default IP address of the Router is 192.168.2.1. And the default
Subnet Mask is 255.255.255.0. These values can be changed as you
desire. In this guide, all the default values are used for descriptions.
Connect local PCs to the LAN ports of the Router. And then you can
configure the IP address for your PC in the following two ways.
CONFIGURE THE IP ADDRESS MANUALLY
1. Set up the TCP/IP Protocol for your PC. If you need instructions on how
to do this, refer to Appendix A: “Configuring the PC” on page 118.
2. Configure the network parameters. The IP address is 192.168.2.xxx
(“xxx” is any number from 2 to 254), Subnet Mask is 255.255.255.0,
and Gateway is 192.168.2.1 (the Router's default IP address).
OBTAIN AN IP ADDRESS AUTOMATICALLY
1. Set the TCP/IP Protocol to “Obtain an IP address automatically” mode
on your PC. If you need instructions as to how to do this, refer to
Appendix A: “Configuring the PC” on page 118.
2. Then the built-in DHCP server will assign IP address for the PC.
Now you can run the Ping command at the command prompt to verify the
network connection between your PC and the Router. The following
example is for Windows 2000.
Open a command prompt and type “ping 192.168.2.1”, and then press
Enter.
If the result displayed is similar to the Figure 5 on page 33, it means a
connection between your PC and the Router has been established.
– 32 –
Page 33

C
HAPTER
Figure 5: Success Result of a Ping Command
3
| Quick Installation Guide
TCP/IP Configuration
If the result displayed is similar to Figure 6, it means the connection
between your PC and the Router has failed.
Figure 6: Failure of a Ping Command
Follow these steps to check the connection:
1. Is the connection between your PC and the Router correct?
The LAN port LED on the Router and the LED on your PC's adapter
should be on.
2. Is the TCP/IP configuration for your PC correct?
– 33 –
Page 34

If the Router's IP address is 192.168.2.1, your PC's IP address must be
within the range of 192.168.2.2 ~ 192.168.2.254.
QUICK INSTALLATION GUIDE
Using the Web-based utility, it is easy to configure and manage the Router.
The Web-based utility can be used on any Windows, Macintosh, or UNIX
system with a Web browser, such as Microsoft Internet Explorer, Mozilla
Firefox, or Apple Safari.
1. To access the configuration utility, open a web-browser and type in the
default address http://192.168.2.1 in the address field of the browser.
Figure 7: Log in to the Router
C
HAPTER
3
| Quick Installation Guide
Quick Installation Guide
After a moment, a login window appears similar to Figure 8. Enter “admin”
for the User Name and “smcadmin” for the Password, both in lower case
letters. Then click the OK button or press the Enter key.
Figure 8: Windows Login
N
OTE
:
If the above screen does not display, it means that your Webbrowser has been set to a proxy. Go to Tools menu>Internet
Options>Connections>LAN Settings, and in the screen that displays,
cancel the “Using Proxy” checkbox, and click OK.
2. After successfully logging in, click “Quick Setup” to quickly configure
your Router.
– 34 –
Page 35

C
HAPTER
Figure 9: Quick Setup
3
| Quick Installation Guide
Quick Installation Guide
3. After successfully logging in, click “Quick Setup” to quickly configure
your Router. Select Wireless Router mode for an Internet connection
through a DSL/cable modem connected to the WAN port. Select
Wireless Client Router mode for an Internet connection through a
wireless service provider.
Figure 10: Operation Mode
4. Click Next. The WAN Connection Type page will appear, as shown in
Figure 11.
Figure 11: Choose the WAN Connection Type
The Router supports three popular ways (PPPoE, Dynamic IP, and Static IP)
to connect to the Internet. It is recommended that you make use of the
auto-detect function. If you are sure of what kind of connection type your
ISP provides, you can select the type and click Next to go on configuring.
a. If the connection type detected is PPPoE, the screen shown in
Figure 12 will display.
– 35 –
Page 36

C
HAPTER
3
| Quick Installation Guide
Quick Installation Guide
Figure 12: Quick Setup – PPPoE
●
User Name and Password — Enter the User Name and
Password provided by your ISP. These fields are case sensitive.
If you have difficulty with this process, contact your ISP.
b. If the connection type detected is Dynamic IP, the screen shown in
Figure 14 will display. You can then continue with the wireless
configuration.
c. If the connection type detected is Static IP, the screen shown in
Figure 13 will display.
Figure 13: Quick Setup - Static IP
●
IP Address - This is the WAN IP address as seen by external
users on the Internet (including your ISP). Enter the IP address
into the field.
●
Subnet Mask - The Subnet Mask is used for the WAN IP
address, it is usually 255.255.255.0.
●
Default Gateway - Enter the gateway IP address into the box,
if required.
●
Primary DNS - Enter the DNS Server IP address into the box, if
required.
●
Secondary DNS - If your ISP provides another DNS server,
enter it into this field.
5. Click Next to continue. The Wireless settings page will appear, as shown
in Figure 14.
– 36 –
Page 37

Figure 14: Quick Setup – Wireless
C
HAPTER
3
| Quick Installation Guide
Quick Installation Guide
■
Wireless Radio - Enable or disable the wireless radio choosing
from the pull-down list.
■
SSID - Enter a value of up to 32 characters. The same name of
SSID (Service Set Identification) must be assigned to all wireless
devices in your network. Considering your wireless network
security, the default SSID is set to “SMC”. This value is casesensitive. For example, “TEST” is NOT the same as “test”.
■
Region - Select your region from the pull-down list. This field
specifies the region where the wireless function of the Router can be
used. It may be illegal to use the wireless function of the Router in a
region other than one of those specified in this field. If your country
or region is not listed, contact your local government agency for
assistance.
■
Channel - This field determines which operating frequency will be
used. The default channel is set to Auto, so the AP will choose the
best channel automatically. It is not necessary to change the
wireless channel unless you notice interference problems with
another nearby access point.
■
Mode - This field determines the wireless mode in which the Router
works.
■
Channel Width - Select any channel width from the pull-down list.
The default setting is automatic, which can adjust the channel width
for your clients automatically.
■
Disable Security - The wireless security function can be enabled or
disabled. If disabled, the wireless stations will be able to connect
– 37 –
Page 38

C
HAPTER
3
| Quick Installation Guide
Quick Installation Guide
the Router without encryption. It is recommended strongly that you
choose one of following options to enable security.
■
WPA-PSK/WPA2-PSK - Select WPA based on pre-shared
passphrase.
●
PSK Password - You can enter ASCII or Hexadecimal characters.
For ASCII, the key can be made up of any numbers 0 to 9 and
any letters A to Z, the length should be between 8 and 63
characters.
For Hexadecimal, the key can be made up of any numbers 0 to
9 and letters A to F, the length should be between 8 and 64
characters.
Please also note the key is case sensitive, this means that upper
and lower case keys will affect the outcome. It would also be a
good idea to write down the key and all related wireless security
settings.
■
No Change - If you chose this option, wireless security
configuration will not change.
These settings are only for basic wireless parameters. For advanced
settings, please refer to “Wireless” on page 59.
6. Click the Next button. You will then see the Finish page.
If you don’t make any changes on the Wireless page, you will see the
Finish page, as shown in Figure 15. Click the Finish button to finish
the Quick Setup.
Figure 15: Quick Setup – Finish
If there is something changed on the Wireless page, you will see the
Finish page as shown in Figure 16. Click the Reboot button to make
your wireless configuration to take effect and finish the Quick Setup.
– 38 –
Page 39

Figure 16: Quick Setup - Finish
C
HAPTER
3
| Quick Installation Guide
Quick Installation Guide
– 39 –
Page 40

4 CONFIGURING THE ROUTER
This chapter shows each Web page's key functions and the configuration
method.
LOGIN
After successful login, you see the main menu on the left of the Web page.
On the right, there are the corresponding explanations and instructions.
Figure 17: The Main Menu
The detailed explanations for each Web page’s key functions are listed
below.
– 40 –
Page 41

STATUS
C
HAPTER
4
| Configuring the Router
Status
The Status page provides the current status information about the Router.
All information is read-only.
Figure 18: Status
– 41 –
Page 42

QUICK SETUP
WPS
C
HAPTER
4
| Configuring the Router
Quick Setup
Refer to “Quick Installation Guide” on page 32.
This section shows how to quickly add a new wireless device to an existing
network using WPS (Wi-Fi Protected Setup).
1. Select WPS from the menu. You will see the next screen, as shown in
Figure 19.
Figure 19: WPS (Wi-Fi Protected Setup)
■
WPS Status - Enable or disable the WPS function here.
■
Current PIN - The current value of the Router's PIN is displayed
here. The default PIN of the Router can be found in the label or User
Guide.
■
Restore PIN - Restore the PIN of the Router to its default.
■
Gen New PIN - Click this button, and then you can get a new
random value for the Router's PIN. You can ensure the network
security by generating a new PIN.
■
Add device - You can add a new device to the existing network
manually by clicking this button.
TO ADD A NEW DEVICE:
If the wireless adapter supports Wi-Fi Protected Setup (WPS), you can
establish a wireless connection between wireless adapter and Router using
either Push Button Configuration (PBC) method or PIN method.
N
OTE
:
To make a successful connection using WPS, you should also
perform the corresponding WPS configuration on the new device.
– 42 –
Page 43

C
HAPTER
4
| Configuring the Router
WPS
For the configuration of a new device, this example uses an SMC Wireless
Adapter.
BY PBC
If the wireless adapter supports Wi-Fi Protected Setup and the Push Button
Configuration (PBC) method, you can add it to the network by PBC with the
following two methods.
Method One:
1. Enable the WPS function from Web management page.
2. Press the WPS button on the front panel of the Router.
Figure 20: Front Panel
3. Press and hold the WPS button of the wireless client for 2 or 3 seconds.
Figure 21: WPS Button
4. Wait until the next screen appears. Click Finish to complete the WPS
configuration.
– 43 –
Page 44

C
HAPTER
Figure 22: WPS-Wireless Configuration Completed
4
| Configuring the Router
WPS
Method Two:
1. Enable the WPS function from Web management page.
2. Press the WPS button on the front panel of the Router.
Figure 23: Front Panel
3. For the configuration of the wireless adapter, select “Push the button
on my access point” in the WPS configuration, as below, and click
Next.
– 44 –
Page 45

C
HAPTER
Figure 24: WPS-Push the button on my access point
4
| Configuring the Router
WPS
4. Wait until the next screen appears. Click Finish to complete the WPS
configuration.
Figure 25: WPS-Wireless Configuration Completed
Method Three:
1. Keep the default WPS Status as Enabled and click the “Add device”
button in Figure 26, then the following screen will appear.
– 45 –
Page 46

C
HAPTER
Figure 26: Add A New Device
4
| Configuring the Router
WPS
2. Select “Press the button of the new device in two minutes” and click
Connect.
3. For the configuration of the wireless adapter, select “Push the button on
my access point” in the WPS configuration utility, as below, and click
Next.
Figure 27: WPS-Push the button on my access point
4. Wait until the next screen appears. Click Finish to complete the WPS
configuration.
– 46 –
Page 47

C
HAPTER
Figure 28: WPS-Wireless Configuration Completed
4
| Configuring the Router
WPS
BY PIN
If the new device supports Wi-Fi Protected Setup and the PIN method, you
can add it to the network by PIN with the following two methods.
Method One: Enter the PIN into my Router.
1. Keep the default WPS Status as Enabled and click the “Add device”
button in Figure 29, then the following screen will appear.
Figure 29: Add Device
2. Select “Enter the new device's PIN” and enter the PIN code of the
wireless adapter in the field after PIN, as shown in the figure above.
Then click Connect.
N
OTE
:
The PIN code of the adapter is always displayed on the WPS
configuration screen.
– 47 –
Page 48

C
HAPTER
4
| Configuring the Router
WPS
3. For the configuration of the wireless adapter, selected “Enter a PIN into
my access point or a registrar” in the WPS configuration, as below, and
click Next.
Figure 30: WPS-Enter a PIN into my access point
N
OTE
:
In this example, the default PIN code of the adapter is 16952898, as
shown in the above figure.
Method Two: Enter the PIN from my Router.
1. Read the Current PIN code of the Router in Figure 26 (each Router has
its unique PIN code. This example has the Router PIN code 12345670).
2. For the configuration of the wireless adapter, select “Enter a PIN from
my access point” in the WPS configuration utility, as below, and enter
the PIN code of the Router into the field after “Access Point PIN”. Then
click Next.
– 48 –
Page 49

C
HAPTER
Figure 31: WPS-Enter a PIN from my access point
4
| Configuring the Router
Operation Mode
OPERATION MODE
N
OTE
:
The default PIN code of the Router can be found on its label, or in
the WPS configuration screen, as shown in Figure 26.
Then the new device successfully connected to the network.
N
OTE
:
The WPS LED on the Router will turn on green for five minutes when
a device has been successfully added to the network.
N
OTE
:
The WPS function cannot be configured if the wireless function of the
Router is disabled. Make sure the wireless function is enabled before
configuring WPS.
The Router supports two operation mode types: Wireless Router and
Wireless Client Router mode. Click Save to save your choice, which is
shown as Figure 32.
Figure 32: Operation Mode
– 49 –
Page 50

NETWORK
C
HAPTER
4
| Configuring the Router
Network
◆ Wireless Router - In this mode, the device enables multiple users to
share a single Internet connection through a DSL/cable modem. All
wireless client users share the same Internet connection through the
Ethernet WAN port as LAN port users.
◆ Wireless Client Router - In this mode, the device enables multiple
users to share a single Internet connection from a wireless Internet
service provider (WISP). The LAN port devices share the WISP
connection, where the wireless port operates as a WAN port in wireless
client mode.
There are three submenus under the Network menu (shown in Figure 33):
LAN,WAN and MAC Clone. Click any of them to configure the
corresponding function.
Figure 33: The Network Menu
LAN Choose menu “Network-> LAN”, you can configure the IP parameters of
the LAN on the screen as below.
Figure 34: LAN
◆ MAC Address - The physical address of the Router, as seen from the
LAN. The value cannot be changed.
◆ IP Address - Enter the IP address of your Router or reset it in dotted-
decimal notation (factory default: 192.168.2.1).
◆ Subnet Mask - An address code that determines the size of the
network. Normally use 255.255.255.0 as the subnet mask.
– 50 –
Page 51

C
HAPTER
N
OTE
:
If you change the IP Address of LAN, you must use the new IP
4
| Configuring the Router
Network
Address to login the Router.
N
OTE
:
If the new LAN IP Address you set is not in the same subnet, the IP
Address pool of the DHCP server will change accordingly at the same time,
while the Virtual Server and DMZ Host will not take effect until they are reconfigured.
WAN Select “Network>WAN”, you can configure the IP parameters of the WAN
on the screen below.
1. If your ISP provides the DHCP service, choose Dynamic IP, and the
Router will automatically receive IP parameters from your ISP. You can
see the page as follows (Figure 35).
Figure 35: WAN-Dynamic IP
This page displays the WAN IP parameters assigned dynamically by your
ISP, including IP address, Subnet Mask, Default Gateway, etc. Click the
Renew button to renew the IP parameters from your ISP. Click the Release
button to release the IP parameters.
◆ MTU Size - The normal MTU (Maximum Transmission Unit) value for
most Ethernet networks is 1500 Bytes. It is not recommended that you
change the default MTU Size unless required by your ISP.
– 51 –
Page 52

C
HAPTER
4
| Configuring the Router
Network
◆ Use These DNS Servers - If your ISP gives you one or two DNS
addresses, select Use These DNS Servers and enter the primary and
secondary addresses into the correct fields. Otherwise, the DNS servers
will be assigned dynamically from your ISP.
N
OTE
:
If you find an error when you go to a Web site after entering the
DNS addresses, it is likely that your DNS servers are set up improperly. You
should contact your ISP to check the DNS server addresses.
◆ Get IP with Unicast DHCP - Some ISP DHCP servers do not support
broadcast applications. If you cannot get the IP Address normally, you
can choose this option. (It is rarely required.)
Click the Save button to save your settings.
2. If your ISP provides a static or fixed IP Address, Subnet Mask, Gateway
and DNS setting, select Static IP. The Static IP settings page will
appear, shown in Figure 36.
Figure 36: WAN-Static IP
◆ IP Address - Enter the IP address in dotted-decimal notation provided
by your ISP.
◆ Subnet Mask - Enter the subnet Mask in dotted-decimal notation
provided by your ISP, usually is 255.255.255.0.
◆ Default Gateway - Enter the gateway IP address in dotted-decimal
notation provided by your ISP.
◆ MTU Size - The normal MTU (Maximum Transmission Unit) value for
most Ethernet networks is 1500 Bytes. It is not recommended that you
change the default MTU Size unless required by your ISP.
– 52 –
Page 53

C
HAPTER
4
| Configuring the Router
Network
◆ Primary/Secondary DNS - (Optional) Enter one or two DNS
addresses in dotted-decimal notation provided by your ISP.
Click the Save button to save your settings.
3. If your ISP provides a PPPoE connection, select PPPoE option. And you
should enter the following parameters (Figure 37):
Figure 37: WAN-PPPoE
◆ User Name/Password - Enter the User Name and Password provided
by your ISP. These fields are case-sensitive.
◆ Secondary Connection - It is available only for PPPoE Connection. If
your ISP provides an extra Connection type such as Dynamic/Static IP
to connect to a local area network, then you can check the radio button
of Dynamic/Static IP to activate this secondary connection.
■
Disabled - The Secondary Connection is disabled by default, so
there is PPPoE connection only. This is recommended.
■
Dynamic IP - You can check this radio button to use Dynamic IP as
the secondary connection to connect to the local area network
provided by ISP.
■
Static IP - You can check this radio button to use Static IP as the
secondary connection to connect to the local area network provided
by ISP.
– 53 –
Page 54

C
HAPTER
4
| Configuring the Router
Network
◆ Connect on Demand - In this mode, the Internet connection can be
terminated automatically after a specified inactivity period (Max Idle
Time) and be re-established when you attempt to access the Internet
again. If you want your Internet connection keeps active all the time,
please enter “0” in the Max Idle Time field. Otherwise, enter the
number of minutes you want to have elapsed before your Internet
access disconnects.
◆ Connect Automatically - The connection can be re-established
automatically when it was down.
◆ Time-based Connecting - The connection will only be established in
the period from the start time to the end time (both are in HH:MM
format).
N
OTE
:
Only when you have configured the system time on System Tools ->
Time page, will the Time-based Connecting function can take effect.
◆ Connect Manually - You can click the Connect/ Disconnect button to
connect/disconnect immediately. This mode also supports the Max Idle
Time function as Connect on Demand mode. The Internet connection
can be disconnected automatically after a specified inactivity period and
re-established when you attempt to access the Internet again.
C
AUTION
:
Sometimes the connection cannot be terminated although you
specify a time to Max Idle Time, since some applications are visiting the
Internet continually in the background.
4. If you want to do some advanced configurations, please click the
Advanced button, and the page shown in Figure 38 will then appear:
– 54 –
Page 55

C
Figure 38: WAN-PPPoE Advanced Settings
HAPTER
4
| Configuring the Router
Network
◆ MTU Size - The default MTU size is “1480” bytes, which is usually fine.
It is not recommended that you change the default MTU Size unless
required by your ISP.
◆ Service Name/AC Name - The service name and AC (Access
Concentrator) name, which should not be configured unless you are
sure it is necessary for your ISP. In most cases, leaving these fields
blank will work.
◆ ISP Specified IP Address - If your ISP does not automatically assign
IP addresses to the Router during login, please click “Use IP address
specified by ISP” check box and enter the IP address provided by your
ISP in dotted-decimal notation.
◆ Detect Online Interval - The Router will detect Access Concentrator
online at every interval. The default value is “0”. You can input the
value between “0”and “120”. The value “0” means no detect.
◆ DNS IP address - If your ISP does not automatically assign DNS
addresses to the Router during login, please click “Use the following
DNS servers” check box and enter the IP address in dotted-decimal
notation of your ISP’s primary DNS server. If a secondary DNS server
address is available, enter it as well.
Click the Save button to save your settings.
5. If your ISP provides L2TP connection, please select L2TP option. And
you should enter the following parameters (Figure 39):
– 55 –
Page 56

Figure 39: WAN-L2TP
C
HAPTER
4
| Configuring the Router
Network
◆ User Name/Password - Enter the User Name and Password provided
by your ISP. These fields are case-sensitive.
◆ Dynamic IP/ Static IP - Choose either as you are given by your ISP.
Click the Connect button to connect immediately. Click the Disconnect
button to disconnect immediately.
◆ Connect on Demand - You can configure the Router to disconnect
from your Internet connection after a specified period of inactivity
(Max Idle Time). If your Internet connection has been terminated due
to inactivity, Connect on Demand enables the Router to automatically
re-establish your connection as soon as you attempt to access the
Internet again. If you wish to activate Connect on Demand, click the
radio button. If you want your Internet connection to remain active at
all times, enter 0 in the Max Idle Time field. Otherwise, enter the
number of minutes you want to have elapsed before your Internet
connection terminates.
◆ Connect Automatically - Connect automatically after the Router is
disconnected. To use this option, click the radio button.
– 56 –
Page 57

C
HAPTER
4
| Configuring the Router
Network
◆ Connect Manually - You can configure the Router to make it connect
or disconnect manually. After a specified period of inactivity (Max Idle
Time), the Router will disconnect from your Internet connection, and
you will not be able to re-establish your connection automatically as
soon as you attempt to access the Internet again. To use this option,
click the radio button. If you want your Internet connection to remain
active at all times, enter "0" in the Max Idle Time field. Otherwise,
enter the number in minutes that you wish to have the Internet
connecting last unless a new link is requested.
C
AUTION
:
Sometimes the connection cannot be disconnected although you
specify a time to Max Idle Time, since some applications is visiting the
Internet continually in the background.
6. If your ISP provides PPTP connection, please select PPTP option. And
you should enter the following parameters (Figure 40):
Figure 40: WAN-PPTP
◆ User Name/Password - Enter the User Name and Password provided
by your ISP. These fields are case-sensitive.
– 57 –
Page 58

C
HAPTER
4
| Configuring the Router
Network
◆ Dynamic IP/ Static IP - Choose either as you are given by your ISP
and enter the ISP’s IP address or the domain name. If you choose static
IP and enter the domain name, you should also enter the DNS assigned
by your ISP. And click the Save button. Click the Connect button to
connect immediately. Click the Disconnect button to disconnect
immediately.
◆ Connect on Demand - You can configure the Router to disconnect
from your Internet connection after a specified period of inactivity (Max
Idle Time). If your Internet connection has been terminated due to
inactivity, Connect on Demand enables the Router to automatically reestablish your connection as soon as you attempt to access the Internet
again. If you wish to activate Connect on Demand, click the radio
button. If you want your Internet connection to remain active at all
times, enter 0 in the Max Idle Time field. Otherwise, enter the number
of minutes you want to have elapsed before your Internet connection
terminates.
◆ Connect Automatically - Connect automatically after the Router is
disconnected. To use this option, click the radio button.
◆ Connect Manually - You can configure the Router to make it connect
or disconnect manually. After a specified period of inactivity (Max Idle
Time), the Router will disconnect from your Internet connection, and
you will not be able to re-establish your connection automatically as
soon as you attempt to access the Internet again. To use this option,
click the radio button. If you want your Internet connection to remain
active at all times, enter "0" in the Max Idle Time field. Otherwise,
enter the number in minutes that you wish to have the Internet
connecting last unless a new link is requested.
C
AUTION
:
Sometimes the connection cannot be disconnected although you
specify a time to Max Idle Time, since some applications are visiting the
Internet continually in the background.
N
OTE
:
If you do not know how to choose the appropriate connection type,
click the Detect button to allow the Router to automatically search your
Internet connection for servers and protocols. The connection type will be
reported when an active Internet service is successfully detected by the
Router. This report is for your reference only. To make sure the connection
type your ISP provides, please refer to the ISP. The various types of
Internet connections that the Router can detect are as follows:
■
PPPoE - Connections which use PPPoE that requires a user name
and password.
■
Dynamic IP - Connections which use dynamic IP address
assignment.
■
Static IP - Connections which use static IP address assignment.
– 58 –
Page 59

C
HAPTER
4
| Configuring the Router
Wireless
The Router can not detect PPTP/L2TP/BigPond connections with your ISP. If
your ISP uses one of these protocols, then you must configure your
connection manually.
MAC CLONE
(ROUTER MODE ONLY)
Choose menu “Network->MAC Clone”, you can configure the MAC
address of the WAN on the screen below, Figure 41:
Figure 41: MAC Address Clone
Some ISPs require that you register the MAC Address of your adapter.
Changes are rarely needed here.
◆ WAN MAC Address - This field displays the current MAC address of
the WAN port. If your ISP requires you to register the MAC address,
please enter the correct MAC address into this field in XX-XX-XX-XX-XXXX format (X is any hexadecimal digit).
◆ Your PC's MAC Address - This field displays the MAC address of the
PC that is managing the Router. If the MAC address is required, you can
click the Clone MAC Address To button and this MAC address will fill in
the WAN MAC Address field.
WIRELESS
Click Restore Factory MAC to restore the MAC address of WAN port to the
factory default value.
Click the Save button to save your settings.
N
OTE
:
Only the PC on your LAN can use the MAC Address Clone function.
There are five submenus under the Wireless menu (shown in Figure 42):
Wireless Settings, Wireless Security, Wireless MAC Filtering,
Wireless Advanced, and Wireless Statistics. Click any of them, and you
will be able to configure the corresponding function.
– 59 –
Page 60

Figure 42: Wireless Menu
C
HAPTER
4
| Configuring the Router
Wireless
WIRELESS SETTINGS
(ROUTER MODE)
Choose menu Wireless -> Wireless Setting; you can configure the basic
settings for the wireless network on this page.
The wireless settings section displays configuration settings for the access
point functionality of the Wireless AP/router. It includes the following
sections:
Figure 43: Wireless Settings (Router Mode)
◆ SSID - Enter a value of up to 32 characters. The same SSID (Service
Set Identification) must be assigned to all wireless devices in your
network. The default SSID is set to be “SMC”. This value is casesensitive. For example, “TEST” is NOT the same as “test”.
◆ SSID (2-4) - Up to four SSIDs for each BSS can be set, the names can
be up to 32 characters. The multi-SSID function is available only when
Enable is checked.
◆ Region - Select your region from the pull-down list. This field specifies
the region where the wireless function of the Router can be used. It
may be illegal to use the wireless function of the Router in a region
– 60 –
Page 61

C
HAPTER
4
| Configuring the Router
other than one of those specified in this field. If your country or region
is not listed, please contact your local government agency for
assistance.
When you select your local region from the pull-down list, click the
Save button, then the Note Dialog appears. Click OK.
Figure 44: Note Dialog
N
OTE
:
Limited by local law regulations, the version for North America does
not have a region selection option.
Wireless
◆ Channel - This field determines which operating frequency will be used
for wireless operation. The default setting is Auto, so the AP will choose
the best channel automatically. It is not necessary to change the
wireless channel unless you notice interference problems with another
nearby access point.
◆ Mode - Select the operating mode. The default is 11b/g/n mixed.
■
11b only - Select if all of your wireless clients are 802.11b.
11g only - Select if all of your wireless clients are 802.11g.
11n only- Select only if all of your wireless clients are 802.11n.
11b/g mixed - Select if you are using both 802.11b and 802.11g
wireless clients.
11b/g/n mixed - Select if you are using a mix of 802.11b, 11g,
and 11n wireless clients.
When 802.11g mode is selected, only 802.11g wireless stations can
connect to the Router. When 802.11n mode is selected, only
802.11n wireless stations can connect to the Router. It is strongly
recommended to set the mode to 11b/g/n mixed, then all 802.11b,
802.11g, and 802.11n wireless stations can connect to the Router.
◆ Channel width - Select any channel width from the pull-down list. The
default setting is automatic, which can adjust the channel width for
your clients automatically.
N
OTE
:
If 11b only, 11g only, or 11bg mixed is selected in the Mode field,
the Channel Width selecting field will turn grey and the value will become
20M, which cannot be changed.
– 61 –
Page 62

C
HAPTER
4
| Configuring the Router
Wireless
◆ Max Tx Rate - You can limit the maximum transmit rate of the Router
through this field.
◆ Enable Wireless Router Radio - The wireless radio of this Router can
be enabled or disabled to allow wireless stations access.
◆ Enable SSID Broadcast - When wireless clients survey the local area
for wireless networks to associate with, they will detect the SSID
broadcast by the Router. If you select the Enable SSID Broadcast
checkbox, the Wireless Router will broadcast its name (SSID) on the
air.
◆ Enable WDS - Check this box to enable WDS. With this function, the
Router can bridge two or more WLANs. If this checkbox is selected, you
will have to set the following parameters as shown in Figure 45. Make
sure the following settings are correct.
Figure 45: Enable WDS
WIRELESS SETTINGS
(CLIENT MODE)
Choose menu Wireless -> Wireless Setting; you can configure the basic
settings for the wireless network on this page.
The wireless settings section displays configuration settings for the access
point functionality of the Wireless AP/router. It includes the following
sections:
– 62 –
Page 63

C
HAPTER
Figure 46: Wireless Settings (Client Router Mode)
4
| Configuring the Router
Wireless
◆ SSID - The SSID of the AP your Router is going to connect to as a
client. You can also use the survey function to select the SSID to join.
◆ BSSID - The BSSID of the AP your Router is going to connect to as a
client. You can also use the survey function to select the BSSID to join.
◆ Survey - Click the Survey button to search the AP which runs in the
current channel.
◆ Key type - This option should be chosen according to the AP's security
configuration. It is recommended that the security type is the same as
your AP's security type. (Options: None, WEP (ASCII), WEP (HEX) and
WPA-PSK/WPA2-PSK)
◆ WEP Index - Sets WEP key values. Each WEP key has an index
number. Enter key values that match the key type and length settings.
Enter 5 alphanumeric characters or 10 hexadecimal digits for 64-bit
keys, or enter 13 alphanumeric characters or 26 hexadecimal digits for
128-bit keys.
◆ Auth type - When choose WEP security, select Open System or
Shared-Key authentication type automatically based on the wireless
station's capability and request.
◆ Password - If the AP your Router is going to connect needs password,
you need to fill the password in this blank.
– 63 –
Page 64

C
HAPTER
4
| Configuring the Router
Wireless
◆ SSID - Enter a value of up to 32 characters. The same SSID (Service
Set Identification) must be assigned to all wireless devices in your
network. The default SSID is set to be “SMC”. This value is casesensitive. For example, “TEST” is NOT the same as “test”.
◆ Enable Wireless Router Radio - The wireless radio of this Router can
be enabled or disabled to allow wireless stations access.
◆ Enable SSID Broadcast - When wireless clients survey the local area
for wireless networks to associate with, they will detect the SSID
broadcast by the Router. If you select the Enable SSID Broadcast
checkbox, the Wireless Router will broadcast its name (SSID) on the
air.
WIRELESS SECURITY Choose menu “Wireless->Wireless Security”; you can then configure
the security settings of your wireless network.
There are five wireless security modes supported by the Router: WEP
(Wired Equivalent Privacy), WPA (Wi-Fi Protected Access), WPA2 (Wi-Fi
Protected Access 2), WPA2-PSK (Pre-Shared Key), and WPA-PSK (PreShared Key).
– 64 –
Page 65

Figure 47: Wireless Security
C
HAPTER
4
| Configuring the Router
Wireless
◆ Disable Security - If you do not want to use wireless security, select
this check box. However, it is strongly recommended to choose one of
the following modes to enable security.
◆ WEP - This security is based on the IEEE 802.11 standard. If you select
this check box, you will find a notice in red, as shown in Figure 48.
Figure 48: WEP
– 65 –
Page 66

C
HAPTER
■
Type - you can choose the type for the WEP security on the pull-
4
| Configuring the Router
down list. The default setting is Automatic, which can select Open
System or Shared-Key authentication type automatically based on
the wireless station's capability and request.
■
WEP Key Format - Hexadecimal and ASCII formats are provided.
Hexadecimal format stands for any combination of hexadecimal
digits (0-9, a-f, A-F) in the specified length. ASCII format stands for
any combination of keyboard characters in the specified length.
■
WEP Key- Select which of the four keys will be used and enter the
matching WEP key that you create. Make sure these values are
identical on all wireless stations in your network.
■
Key Type - You can select the WEP key length (64-bit, or 128-bit,
or 152-bit.) for encryption. "Disabled" means this WEP key entry is
invalid.
●
64-bit - You can enter 10 hexadecimal digits (any combination
of 0-9, a-f, A-F, zero key is not promoted) or 5 ASCII characters.
128-bit - You can enter 26 hexadecimal digits (any combination
of 0-9, a-f, A-F, zero key is not promoted) or 13 ASCII
characters.
152-bit - You can enter 32 hexadecimal digits (any combination
of 0-9, a-f, A-F, zero key is not promoted) or 16 ASCII
characters.
Wireless
N
OTE
:
If you do not set the key, the wireless security function is still
disabled even if you have selected Shared Key as the Authentication Type.
◆ WPA /WPA2 - Authentication that uses a RADIUS Server.
■
Version - you can choose the version of the WPA security on the
pull-down list. The default setting is Automatic, which can select
WPA (Wi-Fi Protected Access) or WPA2 (WPA version 2)
automatically based on the wireless station's capability and request.
■
Encryption - You can select either Automatic, TKIP, or AES.
N
OTE
:
If you check the WPA/WPA2 radio button and choose TKIP
encryption, you will find a notice in red, as shown in Figure 49.
– 66 –
Page 67

Figure 49: WPA/WPA2
■
Radius Server IP - Enter the IP address of the RADIUS Server.
■
Radius Port - Enter the port that the RADIUS service uses.
■
Radius Password - Enter the password for the RADIUS server.
■
Group Key Update Period - Specify the group key update interval
in seconds. The value should be 30 or above. Enter 0 to disable the
update.
C
HAPTER
4
| Configuring the Router
Wireless
◆ WPA-PSK/WPA2-PSK - The WPA/WPA2 authentication type based on
a pre-shared passphrase.
■
Version - You can choose the version of the WPA-PSK security from
the drop-down list. The default setting is Automatic, which can
select WPA-PSK (Pre-shared key of WPA) or WPA2-PSK (Pre-shared
key of WPA2) automatically based on the wireless station's
capability and request.
■
Encryption - When WPA-PSK or WPA is set as the Authentication
Type, you can select either Automatic, TKIP, or AES as the
encryption type.
N
OTE
:
If you check the WPA-PSK/WPA2-PSK radio button and choose TKIP
encryption, you will find a notice in red, as shown in Figure 50.
Figure 50: WPA-PSK
■
PSK Passphrase - You can enter between 8 and 63 ASCII
characters, or 8 to 64 Hexadecimal characters.
– 67 –
Page 68

C
HAPTER
■
Group Key Update Period - Specify the group key update interval
4
| Configuring the Router
in seconds. The value should be 30 or above. Enter 0 to disable the
update.
Be sure to click the Save button to save your settings on this page.
Wireless
WIRELESS MAC
FILTERING
Choose Wireless -> MAC Filtering from the menu; you can then control
wireless access by configuring the Wireless MAC Address Filtering function,
as shown in Figure 51.
Figure 51: Wireless MAC Address Filtering
To filter wireless users by MAC Address, click Enable. The default setting is
Disable.
◆ MAC Address - The wireless station's MAC address that you want to
filter.
◆ Status - The status of this entry, either Enabled or Disabled.
◆ Description - A simple description of the wireless station.
To Add a Wireless MAC Address filtering entry, click the “Add New” button.
The "Add or Modify Wireless MAC Address Filtering entry" page will appear,
as shown in Figure 52:
– 68 –
Page 69

C
HAPTER
Figure 52: Add or Modify Wireless MAC Address Filtering Entry
To add or modify a MAC Address Filtering entry, follow these instructions:
4
| Configuring the Router
Wireless
1. Enter the appropriate MAC Address into the MAC Address field. The
format of the MAC Address is XX-XX-XX-XX-XX-XX (X is any
hexadecimal digit). For example: 00-0A-EB-00-07-8A.
2. Provide a simple description of the wireless station in the Description
field. For example: Wireless station A.
3. Select Enabled or Disabled for this entry on the Status pull-down list.
4. Click the Save button to save this entry.
To modify or delete an existing entry:
1. Click the Modify in the entry you want to modify. If you want to delete
the entry, click the Delete button.
2. Modify the information.
3. Click the Save button.
Click the Enable All button to make all entries enabled.
Click the Disabled All button to make all entries disabled.
Click the Delete All button to delete all entries.
Click the Next button to go to the next page.
Click the Previous button to return to the previous page.
For example: If you want wireless station A (MAC address 00-0A-EB-0007-8A) and wireless station B (MAC address 00-0A-EB-00-23-11) to be
able to access the Router, but not all the other wireless stations, you can
configure the Wireless MAC Address Filtering list as follows:
1. Click the Enable button to enable this function.
2. Select the radio button: Deny the stations not specified by any enabled
entries in the list to access for Filtering Rules.
– 69 –
Page 70

C
HAPTER
4
| Configuring the Router
Wireless
3. Delete all or disable all entries if there are any entries already.
4. Click the Add New button.
a. Enter the MAC address 00-0A-EB-00-07-8A /00-0A-EB-00-23-11 in
the MAC Address field.
b. Enter wireless station A/B in the Description field.
c. Select Enabled in the Status pull-down list.
d. Click the Save Button.
e. Click the Back button.
The filtering rules that are configured should look similar to the following
list:
Figure 53: Filtering Rules
WIRELESS ADVANCED Choose Wireless -> Wireless Advanced from the menu; you can then
configure the advanced settings of your wireless network.
Figure 54: Wireless Advanced
– 70 –
Page 71

C
HAPTER
4
| Configuring the Router
Wireless
◆ Transmit Power - Here you can specify the transmit power of the
Router. You can select High, Middle, or Low. High is the default setting
and is recommended.
◆ Beacon Interval - Enter a value between 20-1000 milliseconds for the
Beacon Interval. The beacons are packets sent by the router to
synchronize a wireless network. The Beacon Interval value determines
the time interval of beacons. The default value is 100.
◆ RTS Threshold - Specifies the RTS (Request to Send) Threshold. If a
packet is larger than the specified RTS Threshold size, the router will
send RTS frames to a particular receiving station and negotiate the
sending of a data frame. The default value is 2346.
◆ Fragmentation Threshold - This value determines the maximum size
before packets are fragmented. Setting the Fragmentation Threshold
too low may result in poor network performance since excessive
packets may be sent. The default setting is 2346 and is recommended.
◆ DTIM Interval - This value determines the interval of the Delivery
Traffic Indication Message (DTIM). A DTIM field is a countdown field
informing clients of the next window for listening to broadcast and
multicast messages. When the Router has buffered broadcast or
multicast messages for associated clients, it sends the next DTIM with a
DTIM Interval value. You can specify the value between 1-255 Beacon
Intervals. The default value is 1, which indicates the DTIM Interval is
the same as Beacon Interval.
◆ Enable WMM - The WMM function guarantees that packets with high-
priority messages are transmitted before other packets. It is strongly
recommended to enable this feature.
◆ Enable Short GI - This function is recommended, since it increases
the data capacity by reducing the guard interval time.
◆ Enabled AP Isolation - This function can isolate wireless stations on
your network from each other. Wireless devices will be able to
communicate with the Router, but not with each other. To use this
function, check this box. AP Isolation is disabled by default.
N
OTE
:
If you are not familiar with the settings on this page, it is strongly
recommended to keep the default values; otherwise it may result in lower
wireless network performance.
– 71 –
Page 72

C
HAPTER
4
| Configuring the Router
DHCP
WIRELESS STATISTICS Select Wireless -> Wireless Statistics from the menu; you can see the
MAC Address, Current Status, Received Packets, and Sent Packets for each
connected wireless station.
Figure 55: Wireless Statistics
◆ MAC Address - The connected wireless station's MAC address.
◆ Current Status - The connected wireless station's running status, one
of STA-AUTH / STA-ASSOC / STA-JOINED / WPA / WPA-PSK / WPA2 /
WPA2-PSK / AP-UP / AP-DOWN / Disconnected.
DHCP
◆ Received Packets - Packets received by the station.
◆ Sent Packets - Packets sent by the station.
You cannot change any of the values on this page. To update this page and
to show the current connected wireless stations, click on the Refresh
button.
If the numbers of connected wireless stations go beyond one page, click
the Next button to go to the next page, and click the Previous button to
return the previous page.
N
OTE
:
This page will be refreshed automatically every 5 seconds.
There are three submenus under the DHCP menu (shown in Figure 56):
DHCP Settings, DHCP Clients List, and Address Reservation. Click
any of them, and you will be able to configure the corresponding function.
Figure 56: The DHCP Menu
– 72 –
Page 73

C
HAPTER
4
| Configuring the Router
DHCP
DHCP SETTINGS Select DHCP -> DHCP Settings from the menu. You can configure the
DHCP Server on the page, as shown in Figure 57. The Router is set up by
default as a DHCP (Dynamic Host Configuration Protocol) server, which
provides the TCP/IP configuration for all the PCs that are connected to the
Router on the LAN.
Figure 57: DHCP Settings
◆ DHCP Server - Enable or Disable the DHCP server. If you disable the
Server, you must have another DHCP server in your network or you
must configure computers manually.
◆ Start IP Address - Specify an IP address for the DHCP Server to start
with when assigning IP addresses. 192.168.2.100 is the default start
address.
◆ End IP Address - Specify an IP address for the DHCP Server to end
with when assigning IP addresses. 192.168.2.199 is the default end
address.
◆ Address Lease Time - The amount of time a network user will be
allowed connection to the Router with their current dynamic IP Address.
Enter the amount of time in minutes and the user will be “leased” this
dynamic IP Address. After the time is up, the user will be automatically
assigned a new dynamic IP address. The range of the time is 1 ~ 2880
minutes. The default value is 120 minutes.
◆ Default Gateway - (Optional.) Suggest to input the IP address of the
LAN port of the Router, default value is 192.168.2.1
◆ Default Domain - (Optional.) Input the domain name of your network.
◆ Primary DNS - (Optional.) Input the DNS IP address provided by your
ISP. Or consult your ISP.
◆ Secondary DNS - (Optional.) Input the IP address of another DNS
server if your ISP provides two DNS servers.
– 73 –
Page 74

C
HAPTER
N
OTE
:
To use the DHCP server function of the Router, you must configure
4
| Configuring the Router
all computers on the LAN as "Obtain an IP Address automatically" mode.
DHCP CLIENTS LIST Select DHCP -> DHCP Clients List from the menu; you can view the
information about the clients attached to the Router in the next screen
(shown in Figure 58).
Figure 58: DHCP Clients List
DHCP
ADDRESS
RESERVATION
◆ ID - The index of the DHCP Client.
◆ Client Name - The name of the DHCP client.
◆ MAC Address - The MAC address of the DHCP client.
◆ Assigned IP - The IP address that the Router has allocated to the
DHCP client.
◆ Lease Time - The time of the DHCP client leased. After the dynamic IP
address has expired, a new dynamic IP address will be automatically
assigned to the user.
You cannot change any of the values on this page. To update this page and
to show the current attached devices, click the Refresh button.
Select DHCP -> Address Reservation from the menu; you can view and
add reserved addresses for clients from the next screen (shown in
Figure 59). When you specify a reserved IP address for a PC on the LAN,
that PC will always receive the same IP address each time when it accesses
the DHCP server. Reserved IP addresses should be assigned to servers that
require permanent IP settings.
– 74 –
Page 75

C
HAPTER
Figure 59: Address Reservation
4
| Configuring the Router
◆ MAC Address - The MAC address of the PC for which you want to
reserve an IP address.
◆ Assigned IP Address - The reserved IP address for the PC.
◆ Status - The status of this entry either Enabled or Disabled.
DHCP
To Reserve IP addresses:
1. Click the “Add New” button (as shown in Figure 60).
2. Enter the MAC address (in XX-XX-XX-XX-XX-XX format.) and IP address
in dotted-decimal notation of the computer you wish to add.
3. Click the Save button when finished.
Figure 60: Add or Modify an Address Reservation Entry
To modify or delete an existing entry:
1. Click Modify in the entry you want to modify. If you want to delete the
entry, click the Delete.
2. Modify the information.
3. Click the Save button.
4. Click the Enable/Disable All button to enable/disable all entries.
– 75 –
Page 76

FORWARDING
C
HAPTER
4
| Configuring the Router
Forwarding
5. Click the Delete All button to delete all entries.
6. Click the Next button to go to the next page and click the Previous
button to return the previous page.
There are four submenus under the Forwarding Application menu (shown in Figure 61): Virtual Servers, Port Triggering, DMZ, and UPnP. Click any of them and you will be able to configure the corresponding function.
Figure 61: The Forwarding Menu
VIRTUAL SERVERS Select Forwarding->Virtual Servers from the menu; you can view and
add virtual servers in the next screen (as shown in Figure 62). Virtual
servers can be used for setting up public services on your LAN, such as
DNS, Email and FTP. A virtual server is defined as a service port, and all
requests from the Internet to this service port will be redirected to the
computer specified by the server IP. Any PC that was used for a virtual
server must have a static or reserved IP Address because its IP Address
may be changed when using the DHCP function.
Figure 62: Virtual Servers
◆ Service Port - The number of an external port. You can type a service
port or a range of service ports (in XXX – YYY format, XXX is the start
port number, YYY is the end port number).
◆ IP Address - The IP Address of the PC providing the service
application.
◆ Protocol - The protocol used for this application, either TCP, UDP, or All
(all protocols supported by the Router).
– 76 –
Page 77

C
HAPTER
◆ Status - The status of this entry either Enabled or Disabled.
To setup a virtual server entry:
4
| Configuring the Router
Forwarding
1. Click the Add New… button. (Figure 63)
2. Select the service you want to use from the Common Service Port
list. If the Common Service Port list does not have the service that
you want to use, type the number of the service port or service port
range in the Service Port box.
3. Type the IP Address of the computer in the IP Address box.
4. Select the protocol used for this application, either TCP, UDP, or All.
5. Select the Enable check box to enable the virtual server.
6. Click the Save button.
Figure 63: Add or Modify a Virtual Server Entry
N
OTE
:
If your computer or server has more than one type of available
service, please select another service, and enter the same IP Address for
that computer or server.
To modify or delete an existing entry:
1. Click Modify for the entry you want to modify. If you want to delete the
entry, click Delete.
2. Modify the information.
3. Click the Save button.
4. Click the Enable/Disable All button to enable/disable all entries.
5. Click the Delete All button to delete all entries.
– 77 –
Page 78

C
HAPTER
4
| Configuring the Router
Forwarding
6. Click the Next button to go to the next page and click the Previous
button to return the previous page.
N
OTE
:
If you set the service port of the virtual server as 80, you must set
the Web management port on “Security –> Remote Management” page
to be any other value except 80, such as 8080. Otherwise there will be a
conflict, which will disable the virtual server.
PORT TRIGGERING Select Forwarding -> Port Triggering from the menu; you can view and
add port triggering in the next screen (shown in Figure 64). Some
applications require multiple connections, like Internet games, video
conferencing, Internet calling and so on. These applications cannot work
with a pure NAT Router. Port Triggering is used for some of these
applications that can work with a NAT Router.
Figure 64: Port Triggering
Once the Router is configured, the operation is as follows:
1. A local host makes an outgoing connection using a destination port
number defined in the Trigger Port field.
2. The Router records this connection, opens the incoming port or ports
associated with this entry in the Port Triggering table, and associates
them with the local host.
3. When necessary the external host will be able to connect to the local
host using one of the ports defined in the Incoming Ports field.
◆ Trigger Port - The port for outgoing traffic. An outgoing connection
using this port will "Trigger" this rule.
◆ Trigger Protocol - The protocol used for Trigger Ports, either TCP,
UDP, or All (all protocols supported by the Router).
– 78 –
Page 79

C
HAPTER
◆ Incoming Ports Range - The port or port range used by the remote
system when it responds to the outgoing request. A response using one
of these ports will be forwarded to the PC that triggered this rule. You
can input at most 5 groups of ports (or port section). Every group of
ports must be set apart with ",". For example, 2000-2038, 2050-2051,
2085, 3010-3030.
◆ Incoming Protocol - The protocol used for Incoming Ports Range,
either TCP or UDP, or ALL (all protocols supported by the Router).
◆ Status - The status of this entry either Enabled or Disabled.
To add a new rule, follow the steps below.
4
| Configuring the Router
Forwarding
1. Click the “Add New” button, the next screen will pop-up as shown in
Figure 65.
2. Select a common application from the Common Applications drop-down
list, then the Trigger Port field and the Incoming Ports field will be
automatically filled. If the Common Applications do not have the
application you need, enter the Trigger Port and the Incoming Ports
manually.
3. Select the protocol used for Trigger Port from the Trigger Protocol drop-
down list, either TCP, UDP, or All.
4. Select the protocol used for Incoming Ports from the Incoming Protocol
drop-down list, either TCP or UDP, or All.
5. Select Enable in Status field.
6. Click the Save button to save the new rule.
Figure 65: Add or Modify a Triggering Entry
To modify or delete an existing entry:
1. Click Modify in the entry you want to modify. If you want to delete the
entry, click Delete.
– 79 –
Page 80

C
HAPTER
4
| Configuring the Router
2. Modify the information.
3. Click the Save button.
4. Click the Enable All button to make all entries enabled
5. Click the Disabled All button to make all entries disabled.
6. Click the Delete All button to delete all entries
N
OTE
:
When the trigger connection is released, the according opening ports
will be closed.
N
OTE
:
Each rule allowed to be used only by one host on LAN synchronously.
The trigger connection of other hosts on LAN will be refused.
N
OTE
:
Incoming Port Ranges cannot overlap each other.
Forwarding
DMZ Select Forwarding -> DMZ from the menu; you can view and configure
the DMZ host in the screen (shown in Figure 66).The DMZ host feature
allows one local host to be exposed to the Internet for a special-purpose
service such as Internet gaming or videoconferencing. DMZ host forwards
all the ports at the same time. Any PC whose port is being forwarded must
have its DHCP client function disabled and should have a new static IP
Address assigned to it because its IP Address may be changed when using
the DHCP function.
Figure 66: DMZ
To assign a computer or server to be a DMZ server:
1. Click the Enable radio button
2. Enter the local host IP Address in the DMZ Host IP Address field
3. Click the Save button.
N
OTE
:
After you set the DMZ host, the firewall related to the host will not
work.
– 80 –
Page 81

C
HAPTER
4
| Configuring the Router
UPNP Select Forwarding -> UPnP from the menu; you can view the
information about UPnP (Universal Plug and Play) in the screen (shown in
Figure 67). The UPnP feature allows devices, such as Internet computers,
to access the local host resources or devices as needed. UPnP devices can
be automatically discovered by the UPnP service application on the LAN.
Figure 67: UPnP
Forwarding
◆ Current UPnP Status - UPnP can be enabled or disabled by clicking
the Enable or Disable button. As allowing this may present a risk to
security, this feature is enabled by default.
◆ Current UPnP Settings List - This table displays the current UPnP
information.
■
App Description - The description provided by the application in
the UPnP request
■
External Port - External port, which the router opened for the
application.
■
Protocol - Shows which type of protocol is opened.
■
Internal Port - Internal port, which the router opened for local
host.
■
IP Address - The UPnP device that is currently accessing the
router.
■
Status - The port’s status displayed here. “Enabled” means that
port is still active. Otherwise, the port is inactive.
Click Refresh to update the Current UPnP Settings List.
– 81 –
Page 82

SECURITY
BASIC SECURITY Select Security -> Basic Security from the menu; you can configure the
C
HAPTER
4
| Configuring the Router
Security
There are four submenus under the Security menu as shown in Figure 88:
Basic Security, Advanced Security, Local Management and Remote Management. Click any of them, and you will be able to configure the
corresponding function.
Figure 68: The Security Menu
basic security in the screen as shown in Figure 69.
Figure 69: Basic Security
◆ VPN - VPN Passthrough must be enabled if you want to allow VPN
tunnels using IPSec, PPTP, or L2TP protocols to pass through the
Router’s firewall.
■
PPTP Passthrough - Point-to-Point Tunneling Protocol (PPTP)
allows the Point-to-Point Protocol (PPP) to be tunneled through an
IP network. To allow PPTP tunnels to pass through the Router, keep
the default, Enabled.
■
L2TP Passthrough - Layer 2 Tunneling Protocol (L2TP) is the
method used to enable Point-to-Point sessions via the Internet on
the Layer 2 level. To allow L2TP tunnels to pass through the Router,
keep the default, Enabled.
– 82 –
Page 83

C
HAPTER
■
IPSec Passthrough - Internet Protocol Security (IPSec) is a suite
4
| Configuring the Router
Security
of protocols for ensuring private, secure communications over
Internet Protocol (IP) networks, through the use of cryptographic
security services. To allow IPSec tunnels to pass through the Router,
keep the default, Enabled.
◆ ALG - It is recommended to enable Application Layer Gateway (ALG)
because ALG allows customized Network Address Translation (NAT)
traversal filters to be plugged into the gateway to support address and
port translation for certain application layer "control/data" protocols
such as FTP, TFTP, H323 etc.
■
FTP ALG - To allow FTP clients and servers to transfer data across
NAT, keep the default Enable.
■
TFTP ALG - To allow TFTP clients and servers to transfer data
across NAT, keep the default Enable.
■
H323 ALG - To allow Microsoft NetMeeting clients to communicate
across NAT, keep the default Enable.
Click the Save button to save your settings.
ADVANCED SECURITY Select Security -> Advanced Security from the menu; you can protect
the Router from being attacked by TCP-SYN Flood, UDP Flood and ICMPFlood in the screen, as shown in Figure 70.
Figure 70: Advanced Security
– 83 –
Page 84

C
HAPTER
4
| Configuring the Router
Security
◆ Packets Statistics Interval (5~60) - The default value is 10. Select
a value between 5 and 60 seconds from the drop-down list. The Packets
Statistics Interval value indicates the time section of the packets
statistics. The result of the statistics is used for analysis by SYN Flood,
UDP Flood and ICMP-Flood.
◆ DoS Protection - Denial of Service protection. Check the Enable or
Disable button to enable or disable the DoS protection function. Only
when it is enabled, will the flood filters be enabled.
N
OTE
:
Dos Protection will take effect only when the Traffic Statistics in
“System Tool > Traffic Statistics” is enabled.
◆ Enable ICMP-FLOOD Attack Filtering - Enable or Disable the ICMP-
FLOOD Attack Filtering.
◆ ICMP-FLOOD Packets Threshold (5~3600) - The default value is
50. Enter a value between 5 ~ 3600. When the current ICMP-FLOOD
Packets number is beyond the set value, the Router will startup the
blocking function immediately.
◆ Enable UDP-FLOOD Filtering - Enable or Disable the UDP-FLOOD
Filtering.
◆ UDP-FLOOD Packets Threshold (5~3600) - The default value is
500. Enter a value between 5 ~ 3600. When the current UPD-FLOOD
Packets number is beyond the set value, the Router will startup the
blocking function immediately.
◆ Enable TCP-SYN-FLOOD Attack Filtering - Enable or Disable the
TCP-SYN-FLOOD Attack Filtering.
◆ TCP-SYN-FLOOD Packets Threshold (5~3600) - The default value
is 50. Enter a value between 5 ~ 3600. When the current TCP-SYNFLOOD Packets numbers is beyond the set value, the Router will startup
the blocking function immediately.
◆ Ignore Ping Packet From WAN Port - Enable or Disable Ignore Ping
Packet From WAN Port. The default setting is disabled. If enabled, the
ping packet from the Internet cannot access the Router.
◆ Forbid Ping Packet From LAN Port - Enable or Disable Forbid Ping
Packet From LAN Port. The default setting is disabled. If enabled, the
ping packet from LAN cannot access the Router. This function can be
used to defend against some viruses.
Click the Save button to save the settings.
◆ Click the Blocked DoS Host List button to display the DoS host table
by blocking.
– 84 –
Page 85

C
HAPTER
4
| Configuring the Router
Security
LOCAL MANAGEMENT Select Security->Local Management from the menu; you can configure
the management rules in the screen, as shown in Figure 71. The
management feature allows you to deny computers in the LAN from
accessing the Router.
Figure 71: Local Management
REMOTE
MANAGEMENT
By default, the radio button “All the PCs on the LAN are allowed to access
the Router's Web-Based Utility” is checked. If you want to allow PCs with
specific MAC Addresses to access the Setup page of the Router's WebBased Utility locally from inside the network, check the radio button “Only
the PCs listed can browse the built-in web pages to perform Administrator
tasks”, and then enter each MAC Address in a separate field. The format for
the MAC Address is XX-XX-XX-XX-XX-XX (X is any hexadecimal digit). Only
the PCs with MAC address listed can use the password to browse the builtin web pages to perform Administrator tasks while all the others will be
blocked.
After click the Add button, your PC's MAC Address will be placed in the list
above.
Click the Save button to save your settings.
Select Security->Remote Management from the menu; you can
configure the Remote Management function in the screen, as shown in
Figure 72. This feature allows you to manage your Router from a remote
location via the Internet.
Figure 72: Remote Management
– 85 –
Page 86

C
HAPTER
4
| Configuring the Router
Parental Control
◆ Web Management Port - Web browser access normally uses the
standard HTTP service port 80. This Router's default remote
management web port number is 80. For greater security, you can
change the remote management web port to a custom port by entering
that number in the box provided. Choose a number between 1 and
65534, but do not use the number of any common service port.
◆ Remote Management IP Address - This is the current address you
will use when accessing your Router from the Internet. This function is
disabled when the IP address is set to the default value of 0.0.0.0. To
enable this function change 0.0.0.0 to a valid IP address. If set to
255.255.255.255, then all the hosts can access the Router from
internet.
N
OTE
:
To access the Router, you should type your Router's WAN IP address
into your browser's address (in IE) or Location (in Navigator) box, followed
by a colon and the custom port number. For example, if your Router's WAN
address is 202.96.12.8, and the port number used is 8080, please enter
http://202.96.12.8:8080 in your browser. Later, you may be asked for the
Router's password. After successfully entering the username and
password, you will be able to access the Router's web-based utility.
N
OTE
:
Be sure to change the Router's default password to a very secure
password.
PARENTAL CONTROL
Select Parental Control from the menu; you can then configure the
parental control in the displayed page, as shown in Figure 73. The Parental
Control function can be used to limit children’s access to certain websites
and restrict the time of surfing.
Figure 73: Parental Control Settings
– 86 –
Page 87

C
HAPTER
◆ Parental Control - Check Enable if you want this function to take
effect, otherwise check Disable.
◆ MAC Address of Parental PC - In this field, enter the MAC address of
the controlling PC, or you can make use of the “Copy To Above” button
below.
◆ MAC Address of Your PC - This field displays the MAC address of the
PC that is managing this Router. If the MAC Address of your adapter is
registered, you can click the “Copy To Above” button to fill this address
to the MAC Address of Parental PC field above.
◆ Website Description - Description of the allowed website for the child
PC.
◆ Schedule - The time period allowed for the PC controlled to access the
Internet. For detailed information, please go to “Access Control ->
Schedule”.
◆ Modify - Here you can edit or delete an existing entry.
4
| Configuring the Router
Parental Control
To add a new entry, please follow the steps below.
1. Click the “Add New” button and the next screen will pop-up, as shown
in Figure 74.
2. Enter the MAC address of the PC (e.g. 00-11-22-33-44-AA) you want to
control in the “MAC Address of Child PC” field. Or you can choose the
MAC address from the “All Address in Current LAN” drop-down list.
3. Give a description (e.g. Allow Google) for the website allowed to be
accessed in the Website Description field.
4. Enter the allowed domain name of the website, either the full name or
the keywords (e.g. google) in the Allowed Domain Name field. Any
domain name with keywords in it (www.google.com.cn) will be allowed.
5. Select from the “Effective Time” drop-down list the schedule (e.g.
Schedule_1) you want the entry to take effect. If there are not suitable
schedules for you, click the Schedule in red below to go to the Advance
Schedule Settings page and create the schedule you need.
6. In the Status field, you can select Enabled or Disabled to enable or
disable your entry.
7. Click the Save button.
Click the Enable All button to enable all the rules in the list.
Click the Disable All button to disable all the rules in the list.
Click the Delete All button to delete all the entries in the table.
Click the Next button to go to the next page, or click the Previous
button return to the previous page.
– 87 –
Page 88

C
HAPTER
Figure 74: Add or Modify Parental Control Entry
4
| Configuring the Router
Parental Control
For example: If you desire that the child PC with MAC address 00-11-2233-44-AA can access www.google.com on Saturday only while the parent
PC with MAC address 00-11-22-33-44-BB is without any restriction, you
should follow the settings below.
1. Click Parental Control on the menu to enter the Parental Control
Settings page. Check Enable and enter the MAC address 00-11-22-3344-BB in the “MAC Address of Parental PC” field.
2. Click Access Control -> Schedule on the left to enter the Schedule
Settings page. Click the “Add New” button to create a new schedule
with Schedule Description “Schedule_1,” Day is “Sat” and Time is all
day-24 hours.
3. Click “Parental Control” menu on the left to go back to the Add or
Modify Parental Control Entry page:
■
Click the “Add New” button.
■
Enter 00-11-22-33-44-AA in the MAC Address of Child PC field.
■
Enter “Allow Google” in the Website Description field.
■
Enter “www.google.com” in the Allowed Domain Name field.
■
Select “Schedule_1” you create just now from the Effective Time
drop-down list.
■
In Status field, select Enable.
– 88 –
Page 89

C
HAPTER
4
| Configuring the Router
Access Control
4. Click Save to complete the settings.
Then you will go back to the Parental Control Settings page and see the
following list, as shown in Figure 75.
Figure 75: Parental Control Settings
ACCESS CONTROL
RULE Select Access Control->Rule from the menu; you can view and set
There are four submenus under the Access Control menu as shown in
Figure 76: Rule, Host, Target, and Schedule. Click any of them, and you
will be able to configure the corresponding function.
Figure 76: Access Control
access control rules in the screen, as shown in Figure 77.
– 89 –
Page 90

C
HAPTER
Figure 77: Access Control Rule Management
4
| Configuring the Router
Access Control
◆ Enable Internet Access Control - Select the check box to enable the
Internet Access Control function, so the Default Filter Policy can take
effect.
◆ Rule Name - Here displays the name of the rule and this name is
unique.
◆ Host - Here displays the host selected in the corresponding rule.
◆ Target - Here displays the target selected in the corresponding rule.
◆ Schedule - Here displays the schedule selected in the corresponding
rule.
◆ Action - Here displays the action the Router takes to deal with the
packets. It could be Allow or Deny. Allow means that the Router permits
the packets to go through the Router. Deny means that the Router
rejects the packets to go through the Router.
◆ Status - This field displays the status of the rule. Enabled means the
rule will take effect, Disabled means the rule will not take effect.
◆ Modify - Here you can edit or delete an existing rule.
To add a new rule, please follow the steps below.
1. Click the “Add New” button and the next screen will pop-up, as shown
in Figure 78.
2. Give a name (e.g. Rule_1) for the rule in the Rule Name field.
– 90 –
Page 91

C
HAPTER
4
| Configuring the Router
Access Control
3. Select a host from the Host drop-down list or choose “Click Here To Add
New Host List”.
4. Select a target from the Target drop-sown list or choose “Click Here To
Add New Target List”.
5. Select a schedule from the Schedule drop-down list or choose “Click
Here To Add New Schedule”.
6. In the Action field, select Deny or Allow.
7. In the Status field, select Enabled or Disabled to enable or disable your
entry.
Click the Save button.
Click the Enable All button to enable all the rules in the list.
Click the Disable All button to disable all the rules in the list.
Click the Delete All button to delete all the entries in the table.
You can change the entry’s order as desired. Fore entries are before hind
entries. Enter the ID number in the first box you want to move and another
ID number in second box you want to move to, and then click the Move
button to change the entry’s order.
Click the Next button to go to the next page, or click the Previous button
return to the previous page.
Figure 78: Add or Modity Internet Access Control Entry
For example: If you desire to allow the host with MAC address 00-11-2233-44-AA to access www.google.com only from 18:00 to 20:00 on
Saturday and Sunday, and forbid other hosts in the LAN to access the
Internet, you should follow the settings below:
1. Click “Access Control->Host” in the left to enter the Host Settings page.
Add a new entry with the Host Description is Host_1 and MAC Address
is 00-11-22-33-44-AA.
– 91 –
Page 92

C
HAPTER
4
| Configuring the Router
Access Control
2. Click “Access Control->Target” in the left to enter the Target Settings
page. Add a new entry with the Target Description is Target_1 and
Domain Name is www.google.com.
3. Click “Access Control->Schedule” in the left to enter the Schedule
Settings page. Add a new entry with the Schedule Description is
Schedule_1, Day is Sat and Sun, Start Time is 1800 and Stop Time is
2000.
4. Click “Access Control->Rule” in the left to return to the Access Control
Rule Management page. Select “Enable Internet Access Control” and
choose "Deny the packets not specified by any access control policy to
pass through the Router".
5. Click the “Add New” button to add a new rule as follows:
■
In Rule Name field, create a name for the rule. Note that this name
should be unique, for example Rule_1.
■
In Host field, select Host_1.
■
In Target field, select Target_1.
■
In Schedule field, select Schedule_1.
■
In Action field, select Allow.
■
In Status field, select Enable.
■
Click Save to complete the settings.
Then you will go back to the Access Control Rule Management page and
see the following list.
HOST Select Access Control->Host from the menu; you can view and set a
Host list in the screen, as shown in Figure 79. The host list is necessary for
the Access Control Rule.
Figure 79: Host Settings
◆ Host Description - Displays the description of the host and this
description is unique.
– 92 –
Page 93

C
HAPTER
4
| Configuring the Router
Access Control
◆ Information - Displays the information about the host. It can be IP or
MAC.
◆ Modify - To modify or delete an existing entry.
To add a new entry, please follow the steps below.
1. Click the “Add New” button.
2. In the Mode field, select IP Address or MAC Address.
■
If you select IP Address, the screen in Figure 80 is displayed.
●
In the Host Description field, create a unique description for the
host (e.g. Host_1).
●
In LAN IP Address field, enter the IP address.
■
If you select MAC Address, the screen in Figure 81 is displayed.
●
In Host Description field, create a unique description for the host
(e.g. Host_1).
●
In MAC Address field, enter the MAC address.
3. Click the Save button to complete the settings.
Click the Delete All button to delete all the entries in the table.
Click the Next button to go to the next page, or click the Previous button
return to the previous page.
Figure 80: Add or Modify an IP Host Entry
Figure 81: Add or Modify a MAC Host Entry
– 93 –
Page 94

C
HAPTER
4
| Configuring the Router
Access Control
For example: If you desire to restrict the internet activities of host with
MAC address 00-11-22-33-44-AA, you should first follow the settings
below:
1. Click “Add New” button in Figure 79 to enter the “Add or Modify a Host
Entry” page.
2. In Mode field, select MAC Address from the drop-down list.
3. In Host Description field, create a unique description for the host (e.g.
Host_1).
4. In MAC Address field, enter 00-11-22-33-44-AA.
5. Click Save to complete the settings.
Then you will go back to the Host Settings page and see the following list.
TARGET Select Access Control -> Target from the menu; you can view and set a
Target list in the screen, as shown in Figure 82. The target list is necessary
for Access Control Rules.
Figure 82: Target Settings
◆ Target Description - Here displays the description about the target
and this description is unique.
◆ Information - The target can be IP address, port, or domain name.
◆ Modify - To modify or delete an existing entry.
To add a new entry, follow the steps below.
1. Click the “Add New” button.
2. In Mode field, select IP Address or Domain Name.
a. If you select IP Address, the screen in Figure 83 is shown.
●
In Target Description field, create a unique description for the
target (e.g. Target_1).
– 94 –
Page 95

C
HAPTER
●
In IP Address field, enter the IP address of the target.
●
Select a common service from Common Service Port drop-down
4
| Configuring the Router
Access Control
list, so that the Target Port will be automatically filled. If the
Common Service Port drop-down list doesn’t have the service
you want, specify the Target Port manually.
●
In Protocol field, select TCP, UDP, ICMP or ALL.
b. If you select Domain Name, the screen in Figure 84 is shown.
●
In Target Description field, create a unique description for the
target (e.g. Target_1).
●
In Domain Name field, enter the domain name, either the full
name or the keywords (for example google) in the blank. Any
domain name with keywords in it (www.google.com,
www.google.cn) will be blocked or allowed. You can enter 4
domain names.
3. Click the Save button.
Click the Delete All button to delete all the entries in the table.
Click the Next button to go to the next page, or click the Previous button
return to the previous page.
Figure 83: Add or Modify an IP Access Target Entry
– 95 –
Page 96

C
HAPTER
Figure 84: Add or Modify a Domain Name Access Target Entry
4
| Configuring the Router
Access Control
For example: If you desire to restrict the internet activities of a host with
MAC address 00-11-22-33-44-AA in the LAN to access www.google.com
only, you should first follow the settings below:
1. Click the “Add New” button in Figure 82 to enter the Add or Modify an
Access Target Entry page.
2. In Mode field, select Domain Name from the drop-down list.
3. In Target Description field, create a unique description for the target
(e.g. Target_1).
4. In Domain Name field, enter www.google.com.
5. Click Save to complete the settings.
Then you will go back to the Target Settings page and see the following list.
Figure 85: Target Setting
– 96 –
Page 97

C
HAPTER
4
| Configuring the Router
Access Control
SCHEDULE Select Access Control -> Schedule from the menu; you can view and set
a schedule list in the next screen, as shown in Figure 86. The schedule list
is necessary for Access Control Rules.
Figure 86: Schedule Settings
◆ Schedule Description - Here displays the description of the schedule
and this description is unique.
◆ Day - Here displays the day(s) in a week.
◆ Time - Here displays the time period in a day.
◆ Modify - Here you can edit or delete an existing schedule.
To add a new schedule, follow the steps below.
1. Click the “Add New” button shown in Figure 86 and the next screen will
pop-up as shown in Figure 87.
2. In Schedule Description field, create a unique description for the
schedule (e.g. Schedule_1).
3. In Day field, select the day or days you need.
4. In Time field, you can select all day-24 hours or you may enter the
Start Time and Stop Time in the corresponding field.
5. Click Save to complete the settings.
Click the Delete All button to delete all the entries in the table.
Click the Next button to go to the next page, or click the Previous button
return to the previous page.
– 97 –
Page 98

C
HAPTER
Figure 87: Advanced Schedule Settings
4
| Configuring the Router
Access Control
For example: If you desire to restrict the internet activities of host with
MAC address 00-11-22-33-44-AA to access www.google.com only from
18:00 to 20:00 on Saturday and Sunday, you should first follow the
settings below:
1. Click the “Add New” button shown in Figure 87 to enter the Advanced
Schedule Settings page.
2. In Schedule Description field, create a unique description for the
schedule (e.g. Schedule_1).
3. In Day field, check the Select Days radio button and then select Sat and
Sun.
4. In Time field, enter 1800 in Start Time field and 2000 in Stop Time
field.
5. Click Save to complete the settings.
Then you will go back to the Schedule Settings page and see the following
list.
– 98 –
Page 99

ADVANCED ROUTING
C
HAPTER
Select static routing list from the menu; you can configure the static
route in the next screen (Figure 88). A static route is a pre-determined
path that network information must travel to reach a specific host or
network.
Figure 88: Static Routing
4
| Configuring the Router
Advanced Routing
To add static routing entries:
1. Click Add New.
Figure 89: Add or Modify a Static Route Entry
2. Enter the following data:
◆ Destination IP Address - The Destination IP Address is the address
of the network or host that you want to assign to a static route.
◆ Subnet Mask - The Subnet Mask determines which portion of an IP
Address is the network portion, and which portion is the host portion.
◆ Gateway - This is the IP Address of the gateway device that allows for
contact between the Router and the network or host.
3. Select Enabled or Disabled for this entry on the Status pull-down list.
4. Click the Save button to make the entry take effect.
– 99 –
Page 100

BANDWIDTH CONTROL
C
HAPTER
4
| Configuring the Router
Bandwidth Control
Other configurations for the entries:
Click the Delete button to delete the entry.
Click the Enable All button to enable all the entries.
Click the Disable All button to disable all the entries.
Click the Delete All button to delete all the entries.
Click the Previous button to view the information in the previous screen.
Click the Next button to view the information in the next screen.
Figure 90: Bandwidth Control
◆ Enable IP QoS - Enable or disable the function of IP QoS.
◆ Choose BandWidth Type - Select the network connection type from
the drop-down list.
◆ Bandwidth Apply - The bandwidth you get. If you are not clear about
that, please contact with your ISP for help.
◆ IP Range - IP range of this entry.
◆ Mode - There are two types of mode: Minimum Bandwidth Guarantee
and Maximum Bandwidth Limit.
◆ Bandwidth - The bandwidth you supply to this entry.
◆ Description - The description for this entry.
– 100 –
 Loading...
Loading...