Page 1

USER GUIDE
SMC2552W-G2
EliteConnectTM Universal
802.11g 2.4GHz Wireless Access Point
Page 2

EliteConnect™ SMC2552W-G2
2.4GHz Wireless Access Point
The easy way to make all your network connections
20 Mason
Irvine, CA 92618
Phone: (949) 679-8000
September 2008
Pub.# 149100034100E
F4.3.2.2 E092008-AP-R03
Page 3

Information furnished by SMC Networks, Inc. (SMC) is believed to be accurate and
reliable. However, no responsibility is assumed by SMC for its use, nor for any
infringements of patents or other rights of third parties which may result from its use. No
license is granted by implication or otherwise under any patent or patent rights of SMC.
SMC reserves the right to change specifications at any time without notice.
Copyright © 2008 by
SMC Networks, Inc.
20 Mason
Irvine, CA 92618
All rights reserved. Printed in Taiwan
Trademarks:
SMC is a registered trademark; and EZ Switch, TigerStack and TigerSwitch are
trademarks of SMC Networks, Inc. Other product and company names are trademarks or
registered trademarks of their respective holders.
Page 4
Limited Warranty
Limited Warranty Statement: SMC Networks, Inc. (“SMC”) warrants its products to be
free from defects in workmanship and materials, under normal use and service, for the
applicable warranty term. All SMC products carry a standard 90-day limited warranty from
the date of purchase from SMC or its Authorized Reseller. SMC may, at its own discretion,
repair or replace any product not operating as warranted with a similar or functionally
equivalent product, during the applicable warranty term. SMC will endeavor to repair or
replace any product returned under warranty within 30 days of receipt of the product.
The standard limited warranty can be upgraded to a Limited Lifetime* warranty by
registering new products within 30 days of purchase from SMC or its Authorized Reseller.
Registration can be accomplished via the enclosed product registration card or online via
the SMC Web site. Failure to register will not affect the standard limited warranty. The
Limited Lifetime warranty covers a product during the Life of that Product, which is
defined as the period of time during which the product is an “Active” SMC product. A
product is considered to be “Active” while it is listed on the current SMC price list. As new
technologies emerge, older technologies become obsolete and SMC will, at its discretion,
replace an older product in its product line with one that incorporates these newer
technologies. At that point, the obsolete product is discontinued and is no longer an
“Active” SMC product. A list of discontinued products with their respective dates of
discontinuance can be found at:
http://www.smc.com/index.cfm?action=customer_service_warranty.
All products that are replaced become the property of SMC. Replacement products may
be either new or reconditioned. Any replaced or repaired product carries either a 30-day
limited warranty or the remainder of the initial warranty, whichever is longer. SMC is not
responsible for any custom software or firmware, configuration information, or memory
data of Customer contained in, stored on, or integrated with any products returned to
SMC pursuant to any warranty. Products returned to SMC should have any
customer-installed accessory or add-on components, such as expansion modules,
removed prior to returning the product for replacement. SMC is not responsible for these
items if they are returned with the product.
Customers must contact SMC for a Return Material Authorization number prior to
returning any product to SMC. Proof of purchase may be required. Any product returned
to SMC without a valid Return Material Authorization (RMA) number clearly marked on
the outside of the package will be returned to customer at customer’s expense. For
warranty claims within North America, please call our toll-free customer support number
at (800) 762-4968. Customers are responsible for all shipping charges from their facility to
SMC. SMC is responsible for return shipping charges from SMC to customer.
WARRANTIES EXCLUSIVE: IF AN SMC PRODUCT DOES NOT OPERATE AS
WARRANTED ABOVE, CUSTOMER’S SOLE REMEDY SHALL BE REPAIR OR
REPLACEMENT OF THE PRODUCT IN QUESTION, AT SMC’S OPTION. THE
FOREGOING WARRANTIES AND REMEDIES ARE EXCLUSIVE AND ARE IN LIEU OF
ALL OTHER WARRANTIES OR CONDITIONS, EXPRESS OR IMPLIED, EITHER IN
FACT OR BY OPERATION OF LAW, STATUTORY OR OTHERWISE, INCLUDING
WARRANTIES OR CONDITIONS OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE. SMC NEITHER ASSUMES NOR AUTHORIZES ANY OTHER
PERSON TO ASSUME FOR IT ANY OTHER LIABILITY IN CONNECTION WITH THE
SALE, INSTALLATION, MAINTENANCE OR USE OF ITS PRODUCTS. SMC SHALL
iv
Page 5

NOT BE LIABLE UNDER THIS WARRANTY IF ITS TESTING AND EXAMINATION
DISCLOSE THE ALLEGED DEFECT IN THE PRODUCT DOES NOT EXIST OR WAS
CAUSED BY CUSTOMER’S OR ANY THIRD PERSON’S MISUSE, NEGLECT,
IMPROPER INSTALLATION OR TESTING, UNAUTHORIZED ATTEMPTS TO REPAIR,
OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDED USE, OR BY
ACCIDENT, FIRE, LIGHTNING, OR OTHER HAZARD.
LIMITATION OF LIABILITY: IN NO EVENT, WHETHER BASED IN CONTRACT OR
TORT (INCLUDING NEGLIGENCE), SHALL SMC BE LIABLE FOR INCIDENTAL,
CONSEQUENTIAL, INDIRECT, SPECIAL, OR PUNITIVE DAMAGES OF ANY KIND, OR
FOR LOSS OF REVENUE, LOSS OF BUSINESS, OR OTHER FINANCIAL LOSS
ARISING OUT OF OR IN CONNECTION WITH THE SALE, INSTALLATION,
MAINTENANCE, USE, PERFORMANCE, FAILURE, OR INTERRUPTION OF ITS
PRODUCTS, EVEN IF SMC OR ITS AUTHORIZED RESELLER HAS BEEN ADVISED
OF THE POSSIBILITY OF SUCH DAMAGES.
SOME STATES DO NOT ALLOW THE EXCLUSION OF IMPLIED WARRANTIES OR
THE LIMITATION OF INCIDENTAL OR CONSEQUENTIAL DAMAGES FOR
CONSUMER PRODUCTS, SO THE ABOVE LIMITATIONS AND EXCLUSIONS MAY
NOT APPLY TO YOU. THIS WARRANTY GIVES YOU SPECIFIC LEGAL RIGHTS,
WHICH MAY VARY FROM STATE TO STATE. NOTHING IN THIS WARRANTY SHALL
BE TAKEN TO AFFECT YOUR STATUTORY RIGHTS.
* SMC will provide warranty service for one year following discontinuance from the active
SMC price list. Under the limited lifetime warranty, internal and external power supplies,
fans, and cables are covered by a standard one-year warranty from date of purchase.
SMC Networks, Inc.
20 Mason
Irvine, CA 92618
v
Page 6

vi
Page 7

COMPLIANCES
Federal Communication Commission Interference
Statement
This equipment has been tested and found to comply with the limits for a Class B
digital device, pursuant to Part 15 of the FCC Rules. These limits are designed to
provide reasonable protection against harmful interference in a residential
installation. This equipment generates, uses and can radiate radio frequency
energy and, if not installed and used in accordance with the instructions, may
cause harmful interference to radio communications. However, there is no
guarantee that interference will not occur in a particular installation. If this
equipment does cause harmful interference to radio or television reception, which
can be determined by turning the equipment off and on, the user is encouraged to
try to correct the interference by one of the following measures:
• Reorient or relocate the receiving antenna
• Increase the separation between the equipment and receiver
• Connect the equipment into an outlet on a circuit different from that to which the
receiver is connected
• Consult the dealer or an experienced radio/TV technician for help
FCC Caution: Any changes or modifications not expressly approved by the party
responsible for compliance could void the user's authority to operate this
equipment. This device complies with Part 15 of the FCC Rules. Operation is
subject to the following two conditions: (1) This device may not cause harmful
interference, and (2) this device must accept any interference received, including
interference that may cause undesired operation.
IMPORTANT NOTE:
FCC Radiation Exposure Statement
This equipment complies with FCC radiation exposure limits set forth for an
uncontrolled environment. This equipment should be installed and operated with a
minimum distance of 20 centimeters (8 inches) between the radiator and your
body. This transmitter must not be co-located or operating in conjunction with any
other antenna or transmitter.
i
Page 8
COMPLIANCES
Industry Canada - Class B
This digital apparatus does not exceed the Class B limits for radio noise emissions
from digital apparatus as set out in the interference-causing equipment standard
entitled “Digital Apparatus,” ICES-003 of Industry Canada.
Cet appareil numérique respecte les limites de bruits radioélectriques applicables
aux appareils numériques de Classe B prescrites dans la norme sur le matérial
brouilleur: “Appareils Numériques,” NMB-003 édictée par l’Industrie.
Taiwan DGT
Japan VCCI Class B
Australia/New Zealand AS/NZS 4771
N11846
ii
Page 9

C
OMPLIANCES
EC Conformance Declaration
Marking by the above symbol indicates compliance with the Essential
Requirements of the R&TTE Directive of the European Union (1999/5/
EC). This equipment meets the following conformance standards:
• EN 60950-1 (IEC 60950-1) - Product Safety
• EN 300 328 - Technical requirements for 2.4 GHz radio equipment
• EN 301 489-1 / EN 301 489-17 - EMC requirements for radio equipment
Countries of Operation & Conditions of Use in the European
Community
This device is intended to be operated in all countries of the European
Community. Requirements for indoor vs. outdoor operation, license
requirements and allowed channels of operation apply in some countries
as described below:
Note: The user must use the configuration utility provided with this
product to ensure the channels of operation are in conformance
with the spectrum usage rules for European Community countries
as described below.
• This device requires that the user or installer properly enter the current
country of operation in the command line interface as described in the
user guide, before operating this device.
• This device will automatically limit the allowable channels determined
by the current country of operation. Incorrectly entering the country of
operation may result in illegal operation and may cause harmful
interference to other systems. The user is obligated to ensure the
device is operating according to the channel limitations, indoor/outdoor
restrictions and license requirements for each European Community
country as described in this document.
• This device may be operated indoors or outdoors in all countries of the
European Community using the 2.4 GHz band: Channels 1 - 13, except
where noted below.
- In Italy the end-user must apply for a license from the national
spectrum authority to operate this device outdoors.
- In Belgium outdoor operation is only permitted using the 2.46 -
2.4835 GHz band: Channel 13.
- In France outdoor operation is only permitted using the 2.4 - 2.454
GHz band: Channels 1 - 7.
iii
Page 10
COMPLIANCES
Declaration of Conformity in Languages of the European
Community
English Hereby, SMC, declares that this Radio LAN device is in
Finnish Valmistaja SMC vakuuttaa täten että Radio LAN device tyyppinen
Dutch Hierbij verklaart SMC dat het toestel Radio LAN device in
French Par la présente SMC déclare que l'appareil Radio LAN device est
Swedish Härmed intygar SMC att denna Radio LAN device står I
Danish Undertegnede SMC erklærer herved, at følgende udstyr Radio
German Hiermit erklärt SMC, dass sich dieser/diese/dieses Radio LAN
Greek ΜΕ ΤΗΝ ΠΑΡΟΥΣΑ SMC ΔΗΛΩΝΕΙ ΟΤΙ radio LAN device
Italian Con la presente SMC dichiara che questo Radio LAN device è
compliance with the essential requirements and other relevant
provisions of Directive 1999/5/EC.
laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä
koskevien direktiivin muiden ehtojen mukainen.
overeenstemming is met de essentiële eisen en de andere
relevante bepalingen van richtlijn 1999/5/EG
Bij deze SMC dat deze Radio LAN device voldoet aan de
essentiële eisen en aan de overige relevante bepalingen van
Richtlijn 1999/5/EC.
conforme aux exigences essentielles et aux autres dispositions
pertinentes de la directive 1999/5/CE
överensstämmelse med de väsentliga egenskapskrav och övriga
relevanta bestämmelser som framgår av direktiv 1999/5/EG.
LAN device overholder de væsentlige krav og øvrige relevante
krav i direktiv 1999/5/EF
device in Übereinstimmung mit den grundlegenden
Anforderungen und den anderen relevanten Vorschriften der
Richtlinie 1999/5/EG befindet". (BMWi)
Hiermit erklärt SMC die Übereinstimmung des Gerätes Radio
LAN device mit den grundlegenden Anforderungen und den
anderen relevanten Festlegungen der Richtlinie 1999/5/EG.
(Wien)
ΣΥΜΜΟΡΦΩ ΝΕΤΑ Ι ΠΡΟΣ ΤΙ Σ ΟΥ Σ Ι Ω ΔΕΙ Σ ΑΠΑΙΤΗΣΕΙΣ ΚΑ Ι ΤΙ Σ ΛΟΙ Π ΕΣ
Σ Χ ΕΤΙ Κ ΕΣ ΔΙΑΤΑΞΕΙΣ ΤΗΣ ΟΔ Η Γ Ι Α Σ 1999/5/ΕΚ
conforme ai requisiti essenziali ed alle altre disposizioni pertinenti
stabilite dalla direttiva 1999/5/CE.
iv
Page 11
C
OMPLIANCES
Spanish Por medio de la presente Manufacturer declara que el Radio LAN
Portuguese Manufacturer declara que este Radio LAN device está conforme
device cumple con los requisitos esenciales y cualesquiera otras
disposiciones aplicables o exigibles de la Directiva 1999/5/CE
com os requisitos essenciais e outras disposições da Directiva
1999/5/CE.
Safety Compliance
Power Cord Safety
Please read the following safety information carefully before installing the access
point:
WARNING: Installation and removal of the unit must be carried out by qualified
personnel only.
• The unit must be connected to an earthed (grounded) outlet to comply with
international safety standards.
• Do not connect the unit to an A.C. outlet (power supply) without an earth
(ground) connection.
• The appliance coupler (the connector to the unit and not the wall plug) must have
a configuration for mating with an EN 60320/IEC 320 appliance inlet.
• The socket outlet must be near to the unit and easily accessible. You can only
remove power from the unit by disconnecting the power cord from the outlet.
• This unit operates under SELV (Safety Extra Low Voltage) conditions according
to IEC 60950. The conditions are only maintained if the equipment to which it is
connected also operates under SELV conditions.
• The PoE (Power over Ethernet), which is to be interconnected with other
equipment that must be contained within the same building including the
interconnected equipment’s associated LAN connections.
France and Peru only
This unit cannot be powered from IT
unit must be powered by 230 V (2P+T) via an isolation transformer ratio 1:1, with
the secondary connection point labelled Neutral, connected directly to earth
(ground).
†
Impédance à la terre
†
supplies. If your supplies are of IT type, this
v
Page 12
COMPLIANCES
Important! Before making connections, make sure you have the correct cord set.
Check it (read the label on the cable) against the following:
Power Cord Set
U.S.A. and
Canada
Denmark The supply plug must comply with Section 107-2-D1,
Switzerland The supply plug must comply with SEV/ASE 1011.
U.K. The supply plug must comply with BS1363 (3-pin 13 A) and
Europe The supply plug must comply with CEE7/7 (“SCHUKO”).
The cord set must be UL-approved and CSA certified.
The minimum specifications for the flexible cord are:
- No. 18 AWG - not longer than 2 meters, or 16 AWG.
- Type SV or SJ
- 3-conductor
The cord set must have a rated current capacity of at least
10 A
The attachment plug must be an earth-grounding type with
NEMA 5-15P (15 A, 125 V) or NEMA 6-15P (15 A, 250 V)
configuration.
Standard DK2-1a or DK2-5a.
be fitted with a 5 A fuse which complies with BS1362.
The mains cord must be <HAR> or <BASEC> marked and
be of type HO3VVF3GO.75 (minimum).
The mains cord must be <HAR> or <BASEC> marked and
be of type HO3VVF3GO.75 (minimum).
IEC-320 receptacle.
vi
Page 13
C
OMPLIANCES
Veuillez lire à fond l'information de la sécurité suivante avant
d'installer le access point:
AVERTISSEMENT: L’installation et la dépose de ce groupe doivent être confiés à un
personnel qualifié.
• Ne branchez pas votre appareil sur une prise secteur (alimentation électrique)
lorsqu'il n'y a pas de connexion de mise à la terre (mise à la masse).
• Vous devez raccorder ce groupe à une sortie mise à la terre (mise à la masse) afin
de respecter les normes internationales de sécurité.
• Le coupleur d’appareil (le connecteur du groupe et non pas la prise murale) doit
respecter une configuration qui permet un branchement sur une entrée d’appareil
EN 60320/IEC 320.
• La prise secteur doit se trouver à proximité de l’appareil et son accès doit être
facile. Vous ne pouvez mettre l’appareil hors circuit qu’en débranchant son cordon
électrique au niveau de cette prise.
• L’appareil fonctionne à une tension extrêmement basse de sécurité qui est
conforme à la norme IEC 60950. Ces conditions ne sont maintenues que si
l’équipement auquel il est raccordé fonctionne dans les mêmes conditions.
France et Pérou uniquement:
Ce groupe ne peut pas être alimenté par un dispositif à impédance à la terre. Si vos
alimentations sont du type impédance à la terre, ce groupe doit être alimenté par
une tension de 230 V (2 P+T) par le biais d’un transformateur d’isolement à rapport
1:1, avec un point secondaire de connexion portant l’appellation Neutre et avec
raccordement direct à la terre (masse).
Cordon électrique - Il doit être agréé dans le pays d’utilisation
Etats-Unis et
Canada:
Danemark: La prise mâle d’alimentation doit respecter la section 107-2
Le cordon doit avoir reçu l’homologation des UL et un
certificat de la CSA.
Les spécifications minimales pour un cable flexible sont
AWG No. 18, ou AWG No. 16 pour un cable de longueur
inférieure à 2 mètres.
- type SV ou SJ
- 3 conducteurs
Le cordon doit être en mesure d’acheminer un courant
nominal d’au moins 10 A.
La prise femelle de branchement doit être du type à mise à
la terre (mise à la masse) et respecter la configuration NEMA
5-15P (15 A, 125 V) ou NEMA 6-15P (15 A, 250 V).
D1 de la norme DK2 1a ou DK2 5a.
vii
Page 14
COMPLIANCES
Cordon électrique - Il doit être agréé dans le pays d’utilisation
Suisse: La prise mâle d’alimentation doit respecter la norme SEV/
Europe La prise secteur doit être conforme aux normes CEE 7/7
Bitte unbedingt vor dem Einbauen des Access Point die folgenden
Sicherheitsanweisungen durchlesen
WARNUNG: Die Installation und der Ausbau des Geräts darf nur durch
Fachpersonal erfolgen.
• Das Gerät sollte nicht an eine ungeerdete Wechselstromsteckdose
angeschlossen werden.
• Das Gerät muß an eine geerdete Steckdose angeschlossen werden, welche die
internationalen Sicherheitsnormen erfüllt.
• Der Gerätestecker (der Anschluß an das Gerät, nicht der
Wandsteckdosenstecker) muß einen gemäß EN 60320/IEC 320 konfigurierten
Geräteeingang haben.
• Die Netzsteckdose muß in der Nähe des Geräts und leicht zugänglich sein. Die
Stromversorgung des Geräts kann nur durch Herausziehen des
Gerätenetzkabels aus der Netzsteckdose unterbrochen werden.
• Der Betrieb dieses Geräts erfolgt unter den SELV-Bedingungen
(Sicherheitskleinstspannung) gemäß IEC 60950. Diese Bedingungen sind nur
gegeben, wenn auch die an das Gerät angeschlossenen Geräte unter
•
SELV-Bedingungen betrieben werden.
ASE 1011.
(“SCHUKO”)
LE cordon secteur doit porter la mention <HAR> ou
<BASEC> et doit être de type HO3VVF3GO.75 (minimum).
(Germany):
viii
Page 15
C
OMPLIANCES
Stromkabel. Dies muss von dem Land, in dem es benutzt wird geprüft werden:
U.S.A und
Kanada
Danemark Dieser Stromstecker muß die ebene 107-2-D1, der
Schweiz Dieser Stromstecker muß die SEV/ASE
Europe Das Netzkabel muß vom Typ HO3VVF3GO.75
Der Cord muß das UL gepruft und war das CSA
beglaubigt.
Das Minimum spezifikation fur der Cord sind:
- Nu. 18 AWG - nicht mehr als 2 meter, oder 16 AWG.
- Der typ SV oder SJ
- 3-Leiter
Der Cord muß haben eine strombelastbarkeit aus
wenigstens 10 A
Dieser Stromstecker muß hat einer erdschluss mit der typ
NEMA 5-15P (15A, 125V) oder NEMA 6-15P (15A, 250V)
konfiguration.
standard DK2-1a oder DK2-5a Bestimmungen einhalten.
1011Bestimmungen einhalten.
(Mindestanforderung) sein und die Aufschrift <HAR> oder
<BASEC> tragen.
Der Netzstecker muß die Norm CEE 7/7 erfüllen
(”SCHUKO”).
ix
Page 16

COMPLIANCES
x
Page 17
Table of Contents
Chapter 1: Introduction 1-1
Package Checklist 1-2
Hardware Description 1-2
Antennas 1-3
LED Indicators 1-3
Security Slot 1-4
Console Port 1-4
Ethernet Port 1-4
Reset Button 1-5
Power Connector 1-5
Features and Benefits 1-5
System Defaults 1-6
Chapter 2: Hardware Installation 2-1
Chapter 3: Network Configuration 3-1
Network Topologies 3-2
Ad Hoc Wireless LAN (no Access Point) 3-2
Infrastructure Wireless LAN 3-3
Infrastructure Wireless LAN for Roaming Wireless PCs 3-4
Infrastructure Wireless Bridge 3-5
Infrastructure Wireless Repeater 3-6
Chapter 4: Initial Configuration 4-1
Initial Setup through the CLI 4-1
Required Connections 4-1
Initial Configuration Steps 4-2
Logging In 4-3
Chapter 5: System Configuration 5-1
Advanced Configuration 5-2
System Identification 5-3
TCP / IP Settings 5-5
RADIUS 5-7
SSH Settings 5-11
xi
Page 18
Contents
Authentication 5-12
Filter Control 5-17
VLAN 5-19
WDS Settings 5-21
AP Management 5-27
Administration 5-28
System Log 5-33
SNMP 5-37
Configuring SNMP and Trap Message Parameters 5-38
Configuring SNMPv3 Users 5-43
Configuring SNMPv3 Trap Filters 5-45
Configuring SNMPv3 Targets 5-47
Radio Interface 5-49
Security 5-66
Status Information 5-85
Access Point Status 5-85
Station Status 5-88
Event Logs 5-91
Chapter 6: Command Line Interface 6-1
Using the Command Line Interface 6-1
Accessing the CLI 6-1
Console Connection 6-1
Telnet Connection 6-1
Entering Commands 6-2
Keywords and Arguments 6-2
Minimum Abbreviation 6-3
Command Completion 6-3
Getting Help on Commands 6-3
Partial Keyword Lookup 6-4
Negating the Effect of Commands 6-4
Using Command History 6-4
Understanding Command Modes 6-4
Exec Commands 6-5
Configuration Commands 6-5
Command Line Processing 6-6
Command Groups 6-6
General Commands 6-7
configure 6-8
end 6-8
exit 6-8
ping 6-9
reset 6-10
show history 6-10
xii
Page 19

Contents
show line 6-11
System Management Commands 6-11
country 6-12
prompt 6-14
system name 6-14
username 6-15
password 6-15
ip ssh-server enable 6-16
ip ssh-server port 6-16
ip telnet-server enable 6-17
ip http port 6-17
ip http server 6-18
ip https port 6-18
ip https server 6-19
APmgmtIP 6-20
APmgmtUI 6-21
show apmagement 6-21
show system 6-22
show version 6-23
show config 6-23
show hardware 6-27
System Logging Commands 6-27
logging on 6-28
logging host 6-28
logging console 6-29
logging level 6-29
logging facility-type 6-30
logging clear 6-31
show logging 6-31
show event-log 6-32
System Clock Commands 6-32
sntp-server ip 6-33
sntp-server enable 6-33
sntp-server date-time 6-34
sntp-server daylight-saving 6-35
sntp-server timezone 6-35
show sntp 6-36
DHCP Relay Commands 6-37
dhcp-relay enable 6-37
dhcp-relay 6-38
show dhcp-relay 6-38
SNMP Commands 6-39
snmp-server community 6-40
snmp-server contact 6-40
snmp-server location 6-41
xiii
Page 20

Contents
snmp-server enable server 6-41
snmp-server host 6-42
snmp-server trap 6-43
snmp-server engine-id 6-45
snmp-server user 6-45
snmp-server targets 6-47
snmp-server filter 6-48
snmp-server filter-assignments 6-49
show snmp groups 6-49
show snmp users 6-50
show snmp group-assignments 6-50
show snmp target 6-51
show snmp filter 6-51
show snmp filter-assignments 6-52
show snmp 6-53
Flash/File Commands 6-54
bootfile 6-54
copy 6-55
delete 6-56
dir 6-57
show bootfile 6-57
RADIUS Client 6-58
radius-server address 6-58
radius-server port 6-59
radius-server key 6-59
radius-server retransmit 6-60
radius-server timeout 6-60
radius-server port-accounting 6-61
radius-server timeout-interim 6-61
radius-server radius-mac-format 6-62
radius-server vlan-format 6-62
show radius 6-63
802.1X Authentication 6-64
802.1x 6-64
802.1x broadcast-key-refresh-rate 6-65
802.1x session-key-refresh-rate 6-66
802.1x session-timeout 6-66
802.1x-supplicant enable 6-67
802.1x-supplicant user 6-67
show authentication 6-68
MAC Address Authentication 6-69
address filter default 6-69
address filter entry 6-70
address filter delete 6-70
mac-authentication server 6-71
xiv
Page 21

Contents
mac-authentication session-timeout 6-71
Filtering Commands 6-72
filter local-bridge 6-72
filter ap-manage 6-73
filter uplink enable 6-73
filter uplink 6-74
filter ethernet-type enable 6-74
filter ethernet-type protocol 6-75
show filters 6-76
WDS Bridge Commands 6-76
bridge role (WDS) 6-77
bridge-link parent 6-77
bridge-link child 6-78
bridge dynamic-entry age-time 6-79
show bridge aging-time 6-79
show bridge filter-entry 6-80
show bridge link 6-80
Spanning Tree Commands 6-82
bridge stp enable 6-82
bridge stp forwarding-delay 6-83
bridge stp hello-time 6-83
bridge stp max-age 6-84
bridge stp priority 6-84
bridge-link path-cost 6-85
bridge-link port-priority 6-85
show bridge stp 6-86
Ethernet Interface Commands 6-87
interface ethernet 6-87
dns server 6-88
ip address 6-88
ip dhcp 6-89
speed-duplex 6-90
shutdown 6-91
show interface ethernet 6-91
Wireless Interface Commands 6-92
interface wireless 6-94
vap 6-94
speed 6-95
multicast-data-rate 6-95
channel 6-96
transmit-power 6-96
radio-mode 6-97
preamble 6-98
antenna control 6-98
antenna id 6-99
xv
Page 22

Contents
antenna location 6-100
beacon-interval 6-100
dtim-period 6-101
fragmentation-length 6-101
rts-threshold 6-102
super-g 6-103
description 6-103
ssid 6-104
closed-system 6-104
max-association 6-105
assoc-timeout-interval 6-105
auth-timeout-value 6-105
shutdown 6-106
show interface wireless 6-107
show station 6-108
Rogue AP Detection Commands 6-108
rogue-ap enable 6-109
rogue-ap authenticate 6-110
rogue-ap duration 6-110
rogue-ap interval 6-111
rogue-ap scan 6-112
show rogue-ap 6-112
Wireless Security Commands 6-113
auth 6-113
encryption 6-115
key 6-116
transmit-key 6-117
cipher-suite 6-118
mic_mode 6-119
wpa-pre-shared-key 6-120
pmksa-lifetime 6-120
pre-authentication 6-121
Link Integrity Commands 6-122
link-integrity ping-detect 6-123
link-integrity ping-host 6-123
link-integrity ping-interval 6-124
link-integrity ping-fail-retry 6-124
link-integrity ethernet-detect 6-124
show link-integrity 6-125
IAPP Commands 6-126
iapp 6-126
VLAN Commands 6-127
vlan 6-127
management-vlanid 6-128
vlan-id 6-128
xvi
Page 23
Contents
WMM Commands 6-129
wmm 6-130
wmm-acknowledge-policy 6-130
wmmparam 6-131
Appendix A: Troubleshooting A-1
Appendix B: Cables and Pinouts B-1
Twisted-Pair Cable Assignments B-1
10/100BASE-TX Pin Assignments B-1
Straight-Through Wiring B-2
Crossover Wiring B-3
Console Port Pin Assignments B-3
Wiring Map for Serial Cable B-4
Appendix C: Specifications C-1
General Specifications C-1
Sensitivity C-3
Transmit Power C-3
Operating Range C-5
Glossary
Index
xvii
Page 24

Contents
xviii
Page 25

Chapter 1: Introduction
The 2.4 GHz Wireless Access Point is an IEEE 802.11b/g access point that provides
transparent, wireless high-speed data communications between the wired LAN and
fixed or mobile devices equipped with an 802.11b, or 802.11g wireless adapter.
This solution offers fast, reliable wireless connectivity with considerable cost savings
over wired LANs (which include long-term maintenance overhead for cabling). Using
802.11b and 802.11g technology, this access point can easily replace a 10 Mbps
Ethernet connection or seamlessly integrate into a 10/100 Mbps Ethernet LAN.
The access point supports up to eight Virtual Access Points. This allows traffic to be
separated for different user groups using an access point that services one area. For
each VAP, different security settings, VLAN assignments, and other parameters can
be applied.
Each radio interface on the access point can operate in one of four modes:
• Access Point – Providing conectivity to wireless clients in the service area.
• Repeater – Providing an extended link to a remote access point from the wired
LAN. In this mode, the access point does not have a cable connection to the wired
Ethernet LAN.
• Bridge – Providing links to access points operating in “Bridge” or “Root Bridge”
mode and thereby connecting other wired LAN segments.
• Root Bridge – Providing links to other access points operating in “Bridge” mode
and thereby connecting other wired LAN segments. Only one unit in the wireless
bridge network can be set to “Root Bridge” mode.
In addition, the access point offers full network management capabilities through an
easy to configure web interface, a command line interface for initial configuration
and troubleshooting, and support for Simple Network Management Protocol tools.
Radio Characteristics – The IEEE 802.11b/g standard uses a radio modulation
technique known as Orthogonal Frequency Division Multiplexing (OFDM), and a
shared collision domain (CSMA/CA). It operates at the 2.4 GHz Unlicensed National
Information Infrastructure (UNII) band for connections to 802.11g clients.
IEEE 802.11g includes backward compatibility with the IEEE 802.11b standard.
IEEE 802.11b also operates at 2.4 GHz, but uses Direct Sequence Spread
Spectrum (DSSS) and Complementary Code Keying (CCK) modulation technology
to achieve a communication rate of up to 11 Mbps.
The access point supports a 54 Mbps half-duplex connection to Ethernet networks
for each active channel.
1-1
Page 26
Introduction
1
Package Checklist
The 2.4 GHz Wireless Access Point package includes:
• One 2.4 GHz Wireless Access Point
• One Category 5 network cable
• One RS-232 console cable
• One AC power adapter and power cord
• Four rubber feet
• User Guide CD
Inform your dealer if there are any incorrect, missing or damaged parts. If possible,
retain the carton, including the original packing materials. Use them again to repack
the product in case there is a need to return it.
Hardware Description
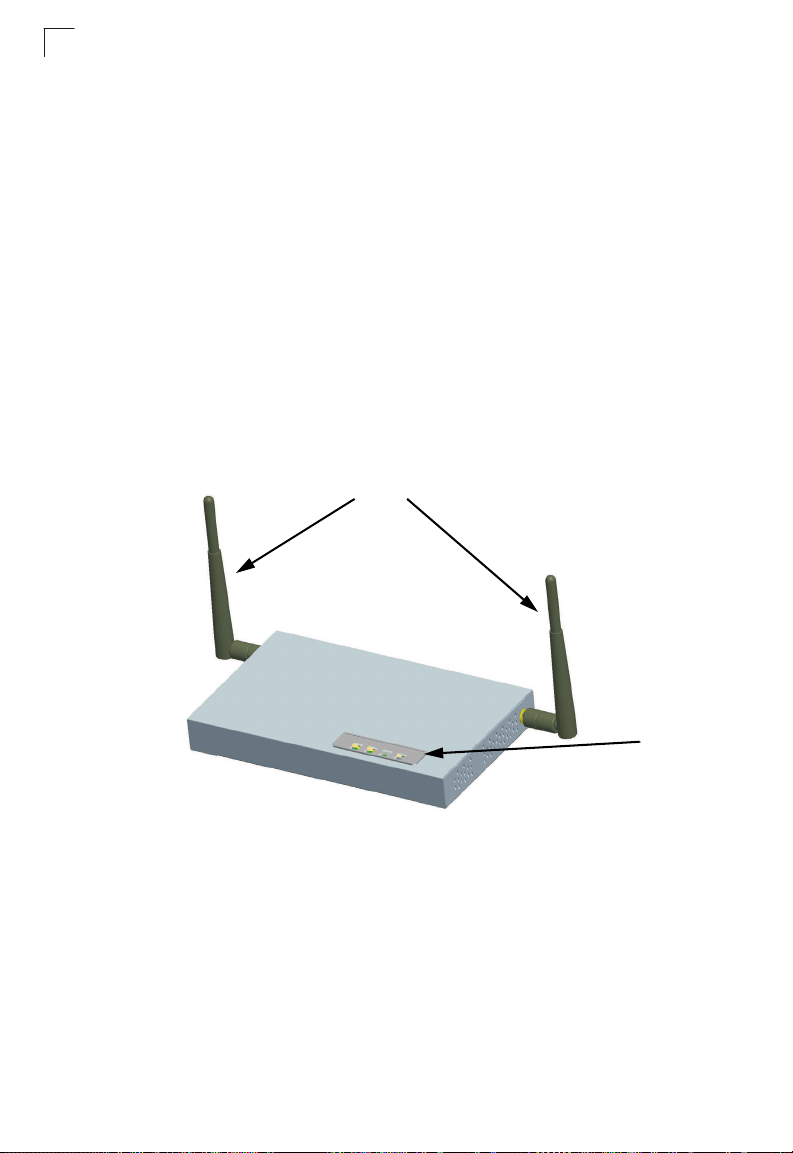
Top P a nel
Antennas
LED
Indicators
1-2
Page 27
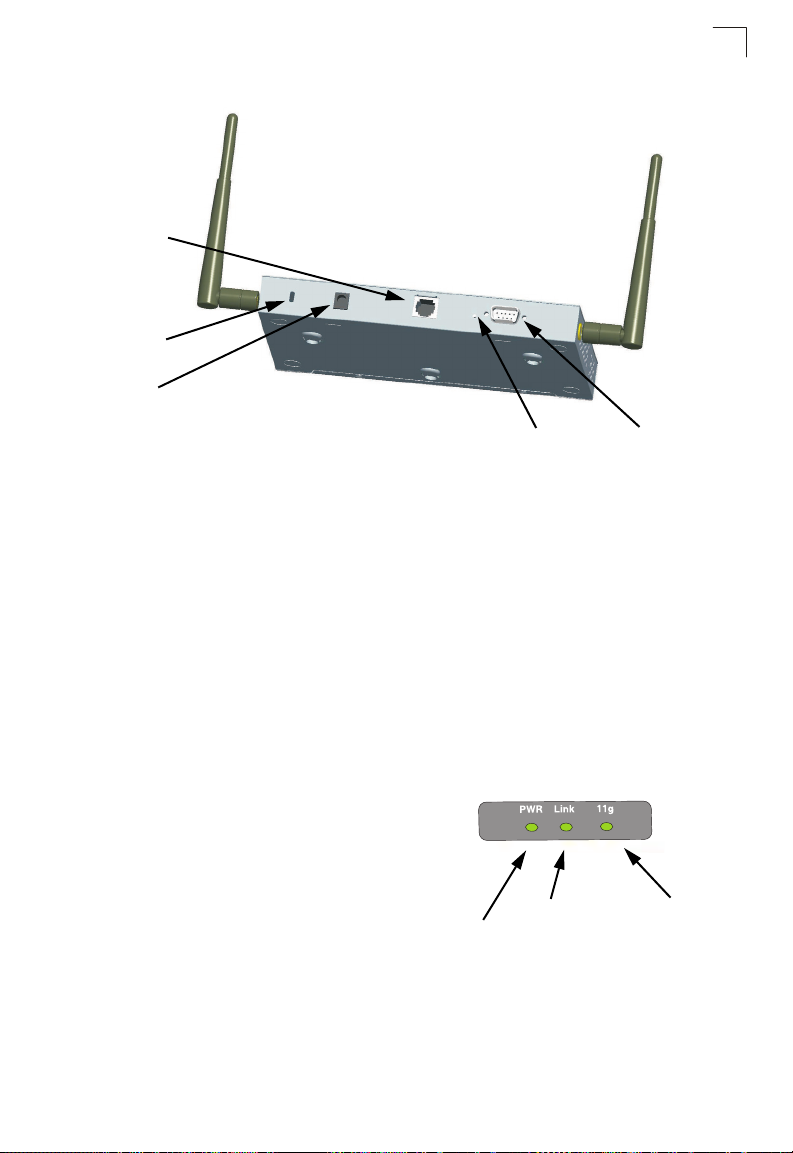
Hardware Description
Rear Panel
RJ-45 Port
Security Slot
5 VDC
Power Socket
Reset
Button
Console
Port
Antennas
The access point includes integrated diversity antennas for wireless
communications. A diversity antenna system uses two identical antennas to receive
and transmit signals, helping to avoid multipath fading effects. When receiving, the
access point checks both antennas and selects the one with the strongest signal.
When transmitting, it will continue to use the antenna previously selected for
receiving. The access point never transmits from both antennas at the same time.
The antennas transmit the outgoing signal as a toroidal sphere (doughnut shaped),
with the coverage extending most in a direction perpendicular to the antenna. The
antenna should be adjusted to an angle that provides the appropriate coverage for
the service area. For further information, see “Positioning the Antennas” on 2-2.
1
LED Indicators
The access point includes three status
LED indicators, as described in the
following figure and table.
Power
Ethernet
Link/Activity
802.11b/g
Wireless
Link/Activity
1-3
Page 28
Introduction
1
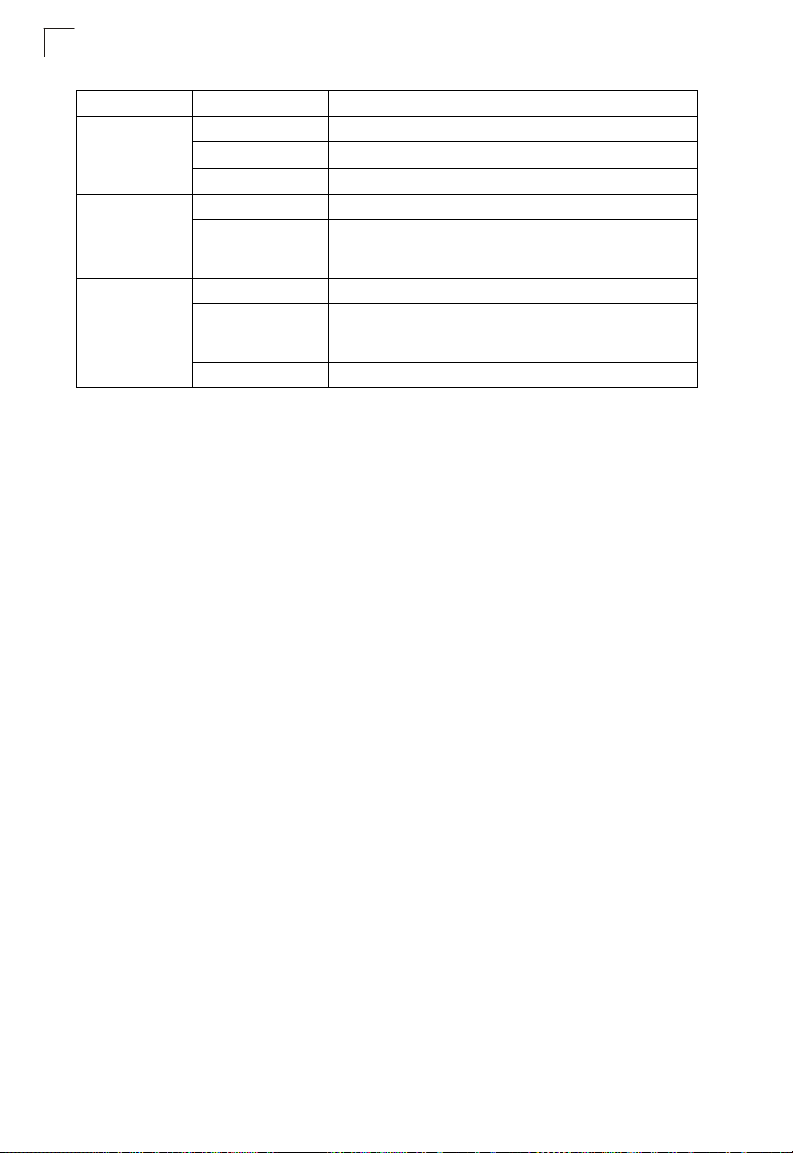
LED Status Description
PWR On Indicates that the system is working normally.
Flashing Indicates running a self-test or loading the software program.
Flashing (Prolonged) Indicates system errors.
Link On Indicates a valid 10/100 Mbps Ethernet cable link.
Flashing Indicates that the access point is transmitting or receiving data
11g On Indicates that the 802.11b/g radio is enabled.
Flashing Indicates that the access point is transmitting or receiving data
Off Indicates that the 802.11b/g radio is disabled.
on a 10/100 Mbps Ethernet LAN. Flashing rate is proportional
to network activity.
through wireless links. Flashing rate is proportional to network
activity.
Security Slot
The access point includes a Kensington security slot on the rear panel. You can
prevent unauthorized removal of the access point by wrapping the Kensington
security cable (not provided) around an unmovable object, inserting the lock into the
slot, and turning the key.
Console Port
This port is used to connect a console device to the access point through a serial
cable. This connection is described under “Console Port Pin Assignments” on page
B-3. The console device can be a PC or workstation running a VT-100 terminal
emulator, or a VT-100 terminal.
Ethernet Port
The access point has one 10BASE-T/100BASE-TX RJ-45 port that can be attached
directly to 10BASE-T/100BASE-TX LAN segments. These segments must conform
to the IEEE 802.3 or 802.3u specifications.
This port supports automatic MDI/MDI-X operation, so you can use straight-through
cables for all network connections to PCs, switches, or hubs.
The access point appears as an Ethernet node and performs a bridging function by
moving packets from the wired LAN to remote workstations on the wireless
infrastructure.
Note: The RJ-45 port also supports Power over Ethernet (PoE) based on the IEEE
802.3af standard. Refer to the description for the “Power Connector” for
information on supplying power to the access point’s network port from a network
device, such as a switch, that provides Power over Ethernet (PoE).
1-4
Page 29

Features and Benefits
Reset Button
This button is used to reset the access point or restore the factory default
configuration. If you hold down the button for less than 5 seconds, the access point
will perform a hardware reset. If you hold down the button for 5 seconds or more,
any configuration changes you may have made are removed, and the factory default
configuration is restored to the access point.
Power Connector
The access point does not have a power switch. It is powered on when connected to
the AC power adapter, and the power adapter is connected to a power source. The
power adapter automatically adjusts to any voltage between 100-240 volts at 50 or
60 Hz. No voltage range settings are required.
The access point may also receive Power over Ethernet (PoE) from a switch or
other network device that supplies power over the network cable based on the IEEE
802.3af standard.
Note that if the access point is connected to a PoE source device and also
connected to a local power source through the AC power adapter, PoE will be
disabled.
Features and Benefits
• Local network connection via 10/100 Mbps Ethernet ports or 54 Mbps wireless
interface (supporting up to 128 mobile users)
• IEEE 802.11b and 802.11g compliant
• Interoperable with multiple vendors based on the IEEE 802.11f protocol
• Advanced security through 64/128/152-bit Wired Equivalent Protection (WEP)
encryption, IEEE 802.1X authentication via a RADIUS server, Wi-Fi Protected
Access (WPA), and MAC address filtering features to protect your sensitive data
and authenticate only authorized users to your network
• Provides seamless roaming within the IEEE 802.11b and 802.11g WLAN
environment
• Scans all available channels and selects the best channel for each client based on
the signal-to-noise ratio
• Allows the country of operation to be set to match regulatory requirements (for
countries outside of the United States)
1
1-5
Page 30
Introduction
1
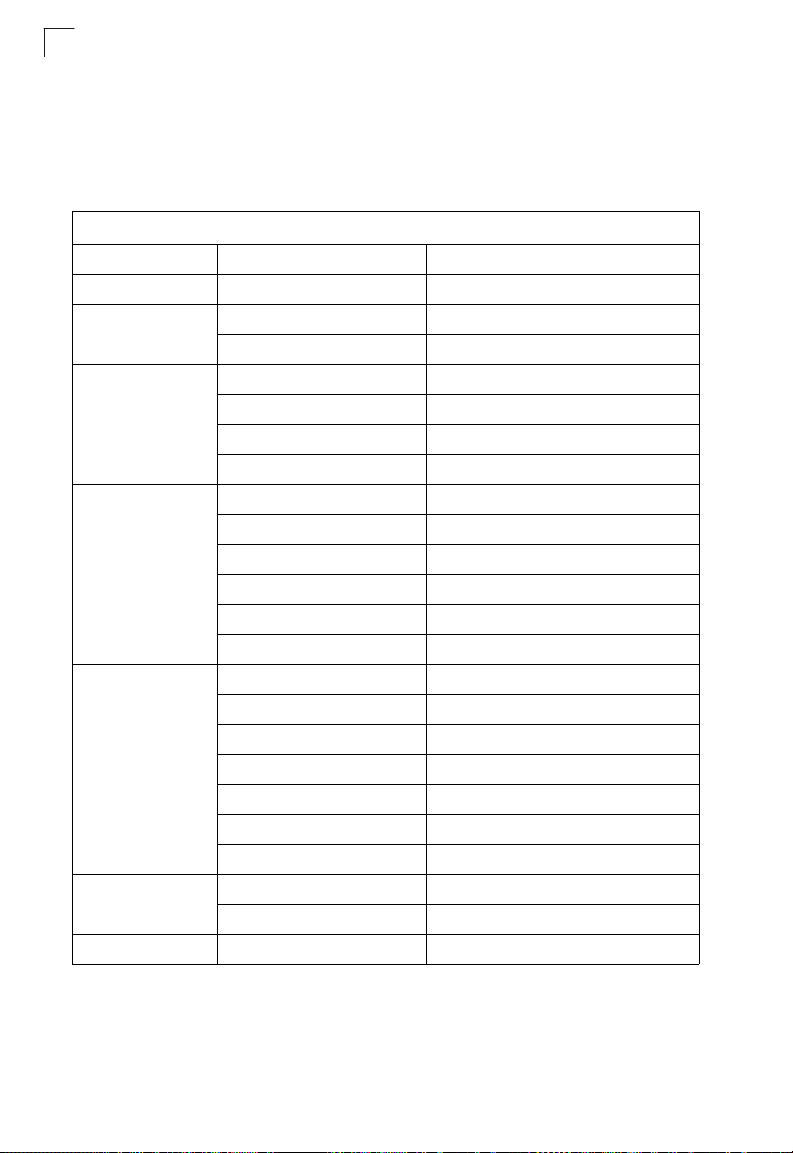
System Defaults
The following table lists some of the access point’s basic system defaults. To reset
the access point defaults, use the CLI command “reset configuration” from the Exec
level prompt.
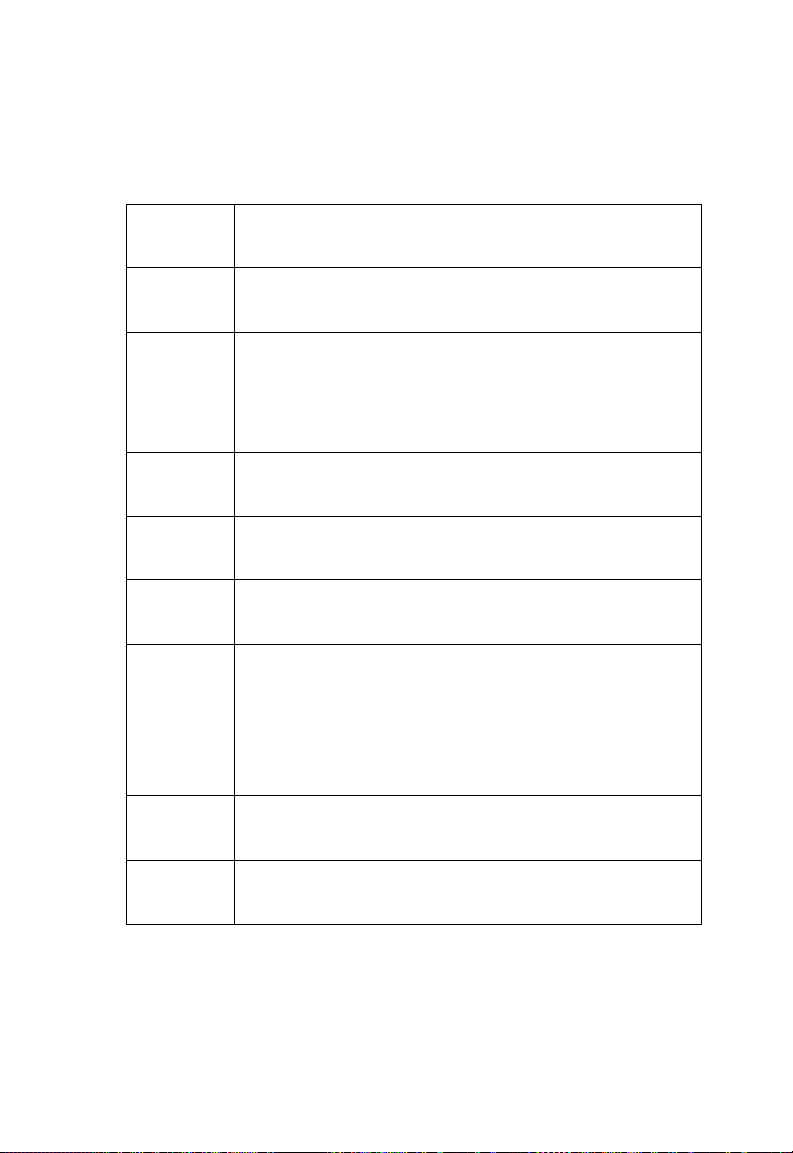
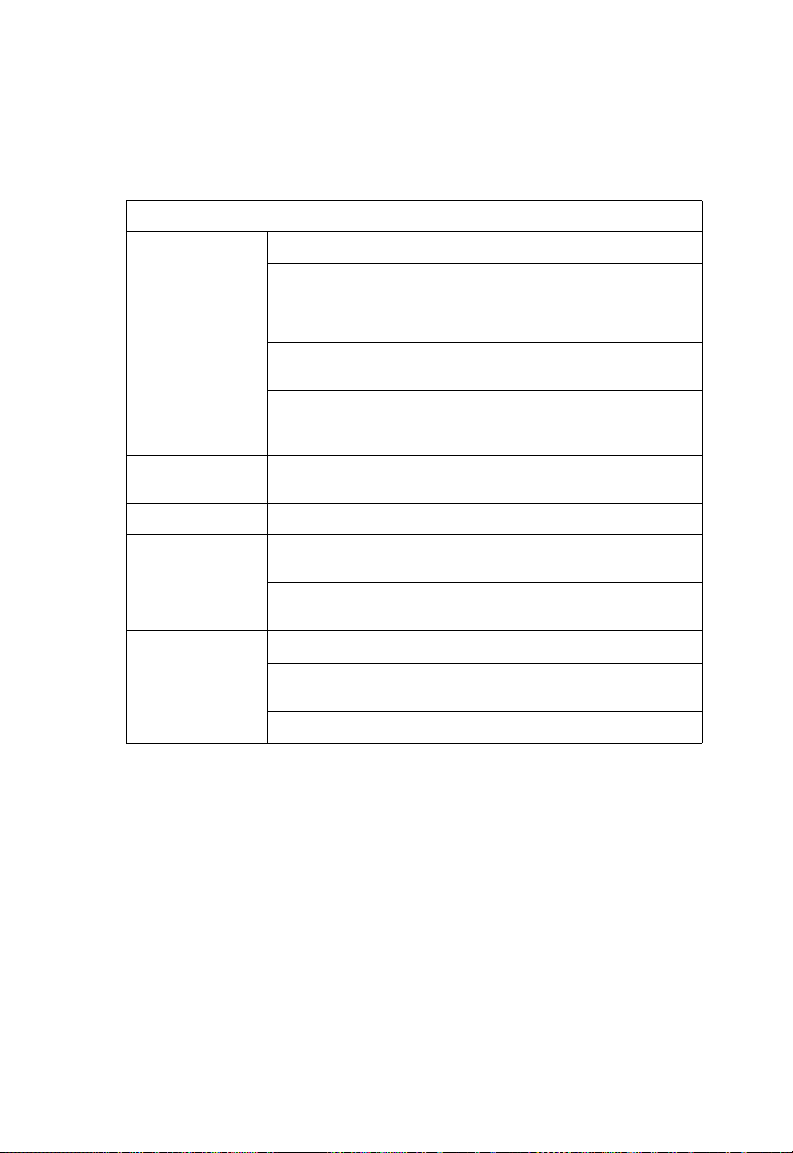
Table 1-1. System Defaults
Feature Parameter Default
Identification System Name SMC
Administration User Name admin
Password smcadmin
General
TCP/IP DHCP Enabled
RADIUS (Primary and
Secondary)
SSH Server Status Enabled
PPPoE PPPoE Status Disabled
HTTP Server Enabled
HTTP Server Port 80
HTTP Server Enabled
HTTP Server Port 443
IP Address 192.168.2.2
Subnet Mask 255.255.255.0
Default Gateway 0.0.0.0
Primary DNS IP 0.0.0.0
Secondary DNS IP 0.0.0.0
IP Address 0.0.0.0
Port 1812
Key DEFAULT
Timeout 5 seconds
Retransmit attempts 3
Accounting Port 0 (Disabled)
Interim Update Timeout 3600 seconds
Server Port 22
1-6
Page 31

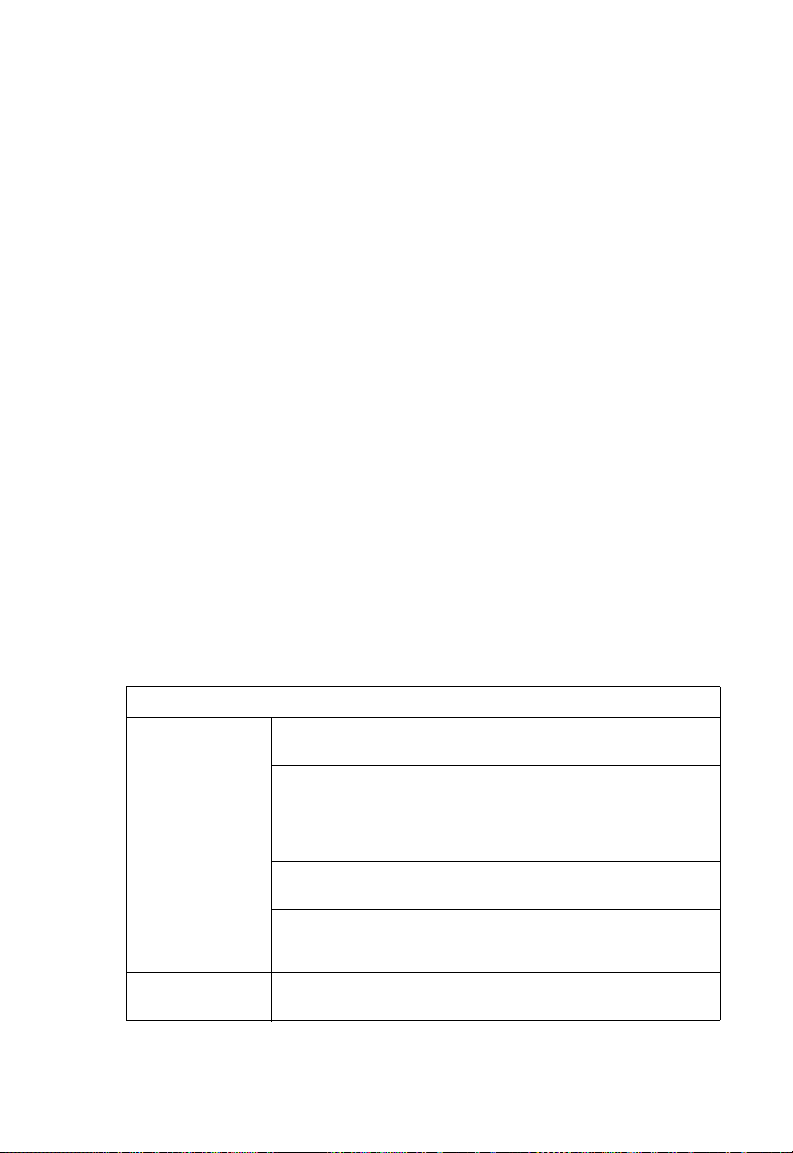
Table 1-1. System Defaults
Feature Parameter Default
MAC Authentication MAC Disabled
Authentication Session Timeout 0 minutes (disabled)
Local MAC System Default Allowed
Local MAC Permission Allowed
802.1X Authentication Status Disabled
Broadcast Key Refresh 0 minutes (disabled)
Session Key Refresh 0 minutes (disabled)
Reauthentication Refresh Rate 0 seconds (disabled)
Supplicant Disabled
VLAN Management VLAN ID 1
VLAN ID (VAP Interface) 1
VLAN Tag Support Disabled
QoS QoS Mode Off
SVP (SpectraLink Voice Priority) Disabled
Filter Control Local Bridge Disabled
AP Management Enabled
Ethernet Type Disabled
SNMP Status Enabled
Location null
Contact null
Community (Read Only) Public
Community
(Read/Write)
Traps Enabled
Trap Destination (1-4) Disabled
Trap Destination IP Address null
Trap Destination Community
Name
SNMP v3 Groups RO
SNMP v3 Users none
Private
Public
RWAuth
RWPriv
System Defaults
1
1-7
Page 32

Introduction
1
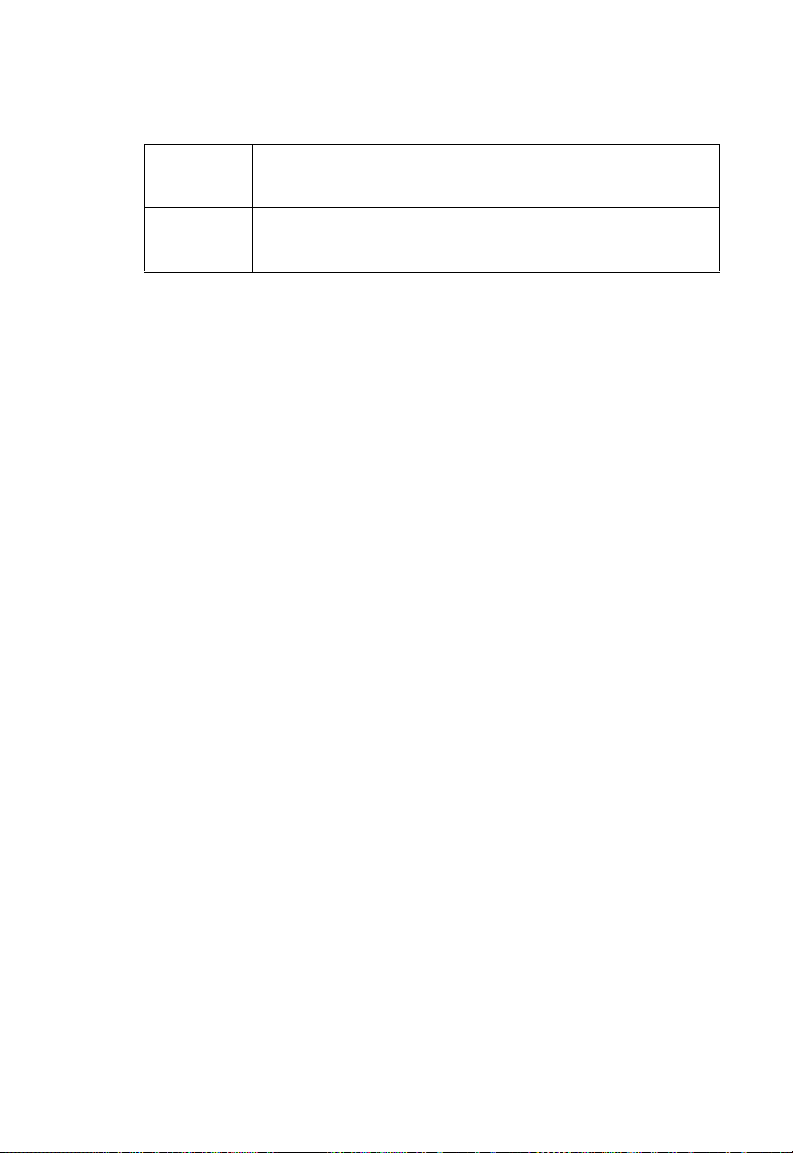
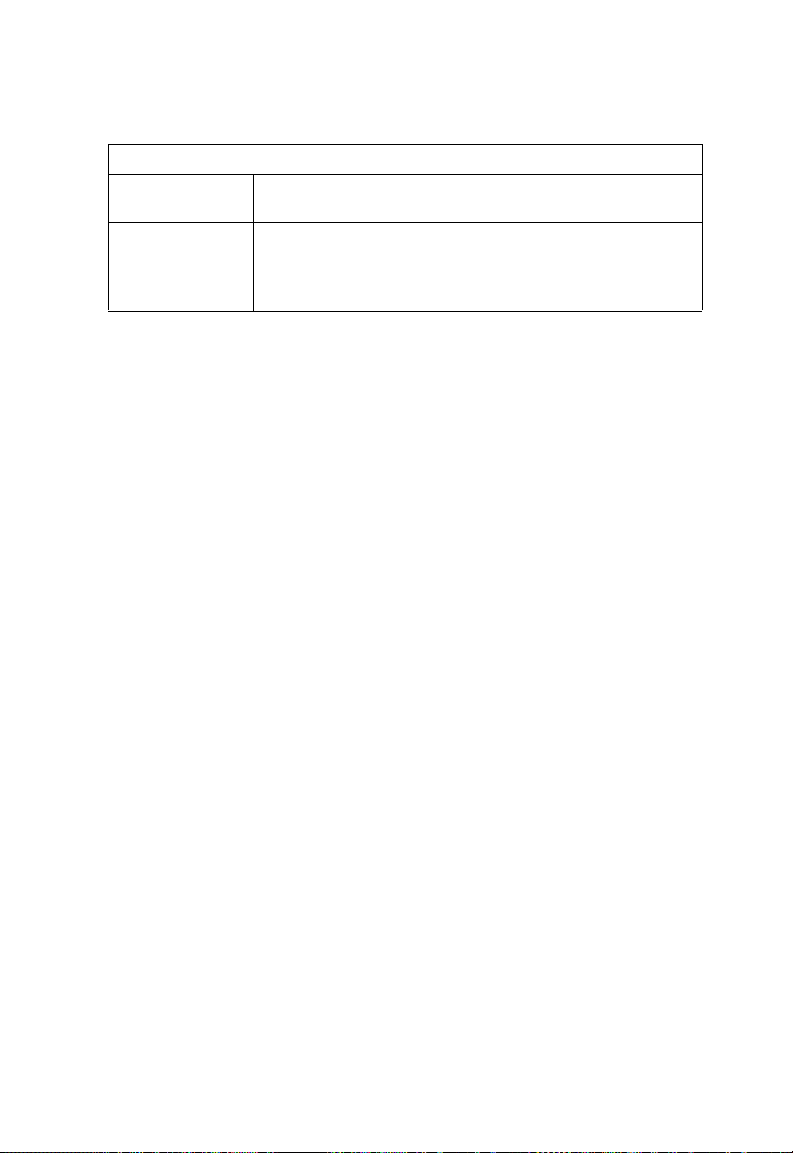
Table 1-1. System Defaults
Feature Parameter Default
System Logging Syslog Disabled
Logging Host Disabled
Logging Console Disabled
IP Address / Host Name 0.0.0.0
Logging Level Informational
Logging Facility Type 16
System Clock SNTP Server Status Enabled
SNTP Server 1 IP 137.92.140.80
SNTP Server 2 IP 192.43.244.18
Date and Time 00:00, Jan 1, 1970 (when there is no time
Daylight Saving Time Disabled
Time Zone GMT-5 (Eastern Time, US and Canada)
Ethernet Interface Speed and Duplex Auto
Wireless Interface
802.11b/g
IAPP Enabled
SSID SMC
Radio Mode b+g
Status Disabled
Auto Channel Select Enabled
Closed System Disabled
Transmit Power Full
Max Station Data Rate 54 Mbps
Multicast Data Rate 5.5 Mbps
Preamble Length Long
Beacon Interval 100 TUs
Data Beacon Rate (DTIM Interval) 1 beacon
RTS Threshold 2347 bytes
Association Timeout Interval 30 minutes
Authentication Timeout Interval 60 minutes
Rogue AP Detection Disabled
Antenna Control Method Diversity
server)
1-8
Page 33

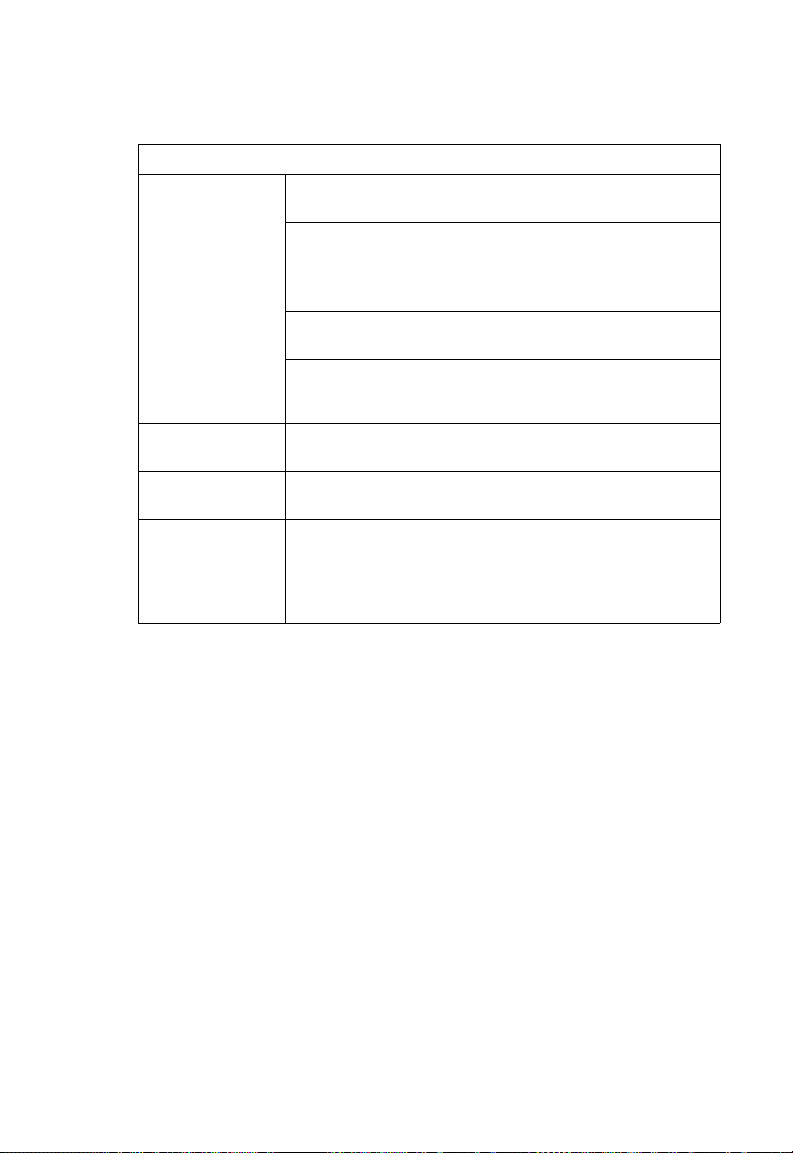
Table 1-1. System Defaults
Feature Parameter Default
Wireless Interface
802.11b/g (contd.)
Wireless Security
802.11b/g
Link Integrity Status Disabled
Antenna ID 0x0000
Antenna Location Indoor
Authentication Type Open System
Data Encryption Disabled
WEP Key Length 128 bits
WEP Key Type Hexadecimal
WEP Transmit Key Number 1
WEP Keys null
WPA Configuration Mode WEP Only (Disabled)
WPA Key Management WPA Pre-shared Key
WPA PSK Type Alphanumeric
Multicast Cipher WEP
Ping Interval 30 seconds
Fail Retry Count 6
System Defaults
1
1-9
Page 34

1
Introduction
1-10
Page 35

Chapter 2: Hardware Installation
1. Select a Site – Choose a proper place for the access point. In general, the best
location is at the center of your wireless coverage area, within line of sight of all
wireless devices. Try to place the access point in a position that can best cover
its Basic Service Set (refer to “Infrastructure Wireless LAN” on page 3-3). For
optimum performance, consider these points:
• Mount the access point as high as possible above any obstructions in the
coverage area.
• Avoid mounting next to or near building support columns or other obstructions
that may cause reduced signal or null zones in parts of the coverage area.
• Mount away from any signal absorbing or reflecting structures (such as those
containing metal).
2. Mount the Access Point – The access point can be mounted on any
horizontal surface.
Mounting on a horizontal surface – To keep the access point from sliding on the
surface, attach the four rubber feet provided in the accessory kit to the marked
circles on the bottom of the access point.
3. Lock the Access Point in Place – To prevent unauthorized removal of the
access point, you can use a Kensington Slim MicroSaver security cable (not
included) to attach the access point to a fixed object.
2-1
Page 36

Hardware Installation
2
4. Connect the Power Cord – Connect the power adapter to the access point,
and the power cord to an AC power outlet.
Otherwise, the access point can derive its operating power directly from the
RJ-45 port when connected to a device that provides IEEE 802.3af compliant
Power over Ethernet (PoE).
Note: If the access point is connected to both a PoE source device and an AC power
source, AC power will be disabled.
Caution: Use ONLY the power adapter supplied with this access point. Otherwise, the
product may be damaged.
5. Observe the Self Test – When you power on the access point, verify that the
PWR indicator stops flashing and remains on, and that the other indicators start
functioning as described under “LED Indicators” on page 1-3. If the PWR LED
does not stop flashing, the self test has not completed correctly. Refer to
“Troubleshooting” on page A-1.
6. Connect the Ethernet Cable – The access point can be wired to a 10/100
Mbps Ethernet through a network device such as a hub or a switch. Connect
your network to the RJ-45 port on the back panel with category 3, 4, or 5 UTP
Ethernet cable. When the access point and the connected device are powered
on, the Ethernet Link LED should light indicating a valid network connection. If
this LED fails to turn on refer to “Troubleshooting” on page A-1.
Note: The RJ-45 port on the access point supports auto=MDI/MDI-X operation, so you
can use either straight-through or crossover cable to connect to switches or PCs.
7. Position the Antennas – Each antenna emits a radiation pattern that is
toroidal (doughnut shaped), with the coverage extending most in the direction
perpendicular to the antenna. Therefore, the antennas should be oriented so
that the radio coverage pattern fills the intended horizontal space. Also, the
diversity antennas should both be positioned along the same axes, providing
the same coverage area. For example, if the access point is mounted on a
horizontal surface, both antennas should be positioned pointing vertically up to
provide optimum coverage.
8. Connect the Console Port – Connect the console cable (included) to the
RS-232 console port for accessing the command-line interface. You can
manage the access point using the console port (Chapter 6), the web interface
(Chapter 5), or SNMP management software such as SMC’s EliteView.
2-2
Page 37

Chapter 3: Network Configuration
Wireless networks support a stand-alone configuration as well as an integrated
configuration with 10/100 Mbps Ethernet LANs. The 2.4 GHz Wireless Access Point
also provides repeater and bridging services.
Access points can be deployed to support wireless clients and connect wired LANs
in the following configurations:
• Ad hoc for departmental, SOHO or enterprise LANs
• Infrastructure for wireless LANs
• Infrastructure wireless LAN for roaming wireless PCs
• Infrastructure wireless bridge to connect wired LANs
• Infrastructure wireless repeater for extended range
The 802.11b and 802.11g frequency band which operates at 2.4 GHz can easily
encounter interference from other 2.4 GHz devices, such as other 802.11b or g
wireless devices, cordless phones and microwave ovens. If you experience poor
wireless LAN performance, try the following measures:
• Limit any possible sources of radio interference within the service area
• Increase the distance between neighboring access points
• Decrease the signal strength of neighboring access points
• Increase the channel separation of neighboring access points (e.g. up to 5
channels of separation for 802.11b and 802.11g)
3-1
Page 38

Network Configuration
3
Network Topologies
Ad Hoc Wireless LAN (no Access Point)
An ad hoc wireless LAN consists of a group of computers, each equipped with a
wireless adapter, connected via radio signals as an independent wireless LAN.
Computers in a specific ad hoc wireless LAN must therefore be configured to the
same radio channel. An ad hoc wireless LAN can be used for a branch office or
SOHO operation.
Ad Hoc Wireless LAN
Notebook with
Wireless USB Adapter
Notebook with
Wireless PC Card
PC with Wireless
PCI Adapter
3-2
Page 39

Network Topologies
Infrastructure Wireless LAN
The access point also provides access to a wired LAN for wireless workstations. An
integrated wired/wireless LAN is called an Infrastructure configuration. A Basic
Service Set (BSS) consists of a group of wireless PC users, and an access point
that is directly connected to the wired LAN. Each wireless PC in this BSS can talk to
any computer in its wireless group via a radio link, or access other computers or
network resources in the wired LAN infrastructure via the access point.
The infrastructure configuration not only extends the accessibility of wireless PCs to
the wired LAN, but also increases the effective wireless transmission range for
wireless PCs by passing their signal through one or more access points.
A wireless infrastructure can be used for access to a central database, or for
connection between mobile workers, as shown in the following figure.
Wired LAN Extension
to Wireless Clients
Server
3
Desktop PC
Switch
Access Point
Notebook PC
Desktop PC
3-3
Page 40

Network Configuration
3
Infrastructure Wireless LAN for Roaming Wireless PCs
The Basic Service Set (BSS) defines the communications domain for each access
point and its associated wireless clients. The BSS ID is a 48-bit binary number
based on the access point’s wireless MAC address, and is set automatically and
transparently as clients associate with the access point. The BSS ID is used in
frames sent between the access point and its clients to identify traffic in the service
area.
The BSS ID is only set by the access point, never by its clients. The clients only
need to set the Service Set Identifier (SSID) that identifies the service set provided
by one or more access points. The SSID can be manually configured by the clients,
can be detected in an access point’s beacon, or can be obtained by querying for the
identity of the nearest access point. For clients that do not need to roam, set the
SSID for the wireless card to that used by the access point to which you want to
connect.
A wireless infrastructure can also support roaming for mobile workers. More than
one access point can be configured to create an Extended Service Set (ESS). By
placing the access points so that a continuous coverage area is created, wireless
users within this ESS can roam freely. All wireless network cards and adapters and
wireless access points within a specific ESS must be configured with the same
SSID.
Seamless Roaming
Between Access Points
3-4
Desktop PC
Switch
Access Point
Desktop PC
Server
Notebook PC
<BSS 1>
Switch
Access Point
Notebook PC
<BSS 2>
<ESS>
Page 41

Network Topologies
Infrastructure Wireless Bridge
The IEEE 802.11 standard defines a WIreless Distribution System (WDS) for bridge
connections between BSS areas (access points). The access point uses WDS to
forward traffic on links between units.
The access point supports WDS bridge links on the 2.4 GHz (802.11b/g) band and
can be used with various external antennas to offer flexible deployment options.
Up to six WDS bridge links can be specified for each unit in the wireless bridge
network. One unit only must be configured as the “root bridge” in the wireless
network. The root bridge should be the unit connected to the main core of the wired
LAN. Other bridges must configure one “parent” link to the root bridge or to a bridge
connected to the root bridge. The other five available WDS links can be specified as
“child” links to other bridges. This forms a tiered-star topology for the wireless bridge
network.
When set to WDS bridging mode, only other units set to bridge mode can associate
to the access point. The access point cannot support wireless clients and bridging at
the same time.
3
Network
Core
Bridge
Root Bridge
Radio
Bridge Link
Wireless Bridge Links
Between Access Points
Radio
Bridge Link
Radio
Bridge Link
Bridge
Bridge
3-5
Page 42

Network Configuration
3
Infrastructure Wireless Repeater
The access point can also operate in a bridge “repeater” mode to extend the range
of links to wireless clients. The access point uses WDS to forward traffic between
the repeater bridge and the root bridge. The access point supports up to six WDS
repeater links.
In repeater mode, the access point does not support an Ethernet link to a wired LAN.
Note that when the access point operates in this mode only half the normal
throughput is possible. This is because the access point has to receive and then
re-transmit all data on the same channel.
Network
Core
Wireless Repeater Links
Between Access Points
Root Bridge
802.11g Radio
802.11g Radio
Repeater Link
Repeater Link
3-6
802.11g Radio
AP Link
Repeater
802.11g Radio
AP Link
Repeater
Page 43

Chapter 4: Initial Configuration
The 2.4 GHz Wireless Access Point offers a variety of management options,
including a web-based interface, a direct connection to the console port, Telnet,
Secure Shell (SSH), or using SNMP software.
The initial configuration steps can be made through the web browser interface or
CLI. The access point requests an IP address via DHCP by default. If no response is
received from the DHCP server, then the access point uses the default address
192.168.2.2. If this address is not compatible with your network, you can first use the
command line interface (CLI) as described below to configure a valid address.
Note: Units sold in countries outside the United States are not configured with a specific
country code. You must use the CLI to set the country code and enable wireless
operation (page 4-3).
Initial Setup through the CLI
Required Connections
The access point provides an RS-232 serial port that enables a connection to a PC
or terminal for monitoring and configuration. Attach a VT100-compatible terminal, or
a PC running a terminal emulation program to the access point. You can use the
console cable provided with this package, or use a cable that complies with the
wiring assignments shown on page B-3.
To connect to the console port, complete the following steps:
1. Connect the console cable to the serial port on a terminal, or a PC running
terminal emulation software, and tighten the captive retaining screws on the
DB-9 connector.
2. Connect the other end of the cable to the RS-232 serial port on the access
point.
3. Make sure the terminal emulation software is set as follows:
• Select the appropriate serial port (COM port 1 or 2).
• Set the data rate to 9600 baud.
• Set the data format to 8 data bits, 1 stop bit, and no parity.
• Set flow control to none.
• Set the emulation mode to VT100.
• When using HyperTerminal, select Terminal keys, not Windows keys.
4. Once you have set up the terminal correctly, press the [Enter] key to initiate the
console connection. The console login screen will be displayed.
4-1
Page 44

Initial Configuration
4
For a description of how to use the CLI, see “Using the Command Line Interface” on
page 6-1. For a list of all the CLI commands and detailed information on using the
CLI, refer to “Command Groups” on page 6-6.
Initial Configuration Steps
Logging In – Enter “admin” for the user name, and “smcadmin” for the password.
The CLI prompt appears displaying the access point’s name.
Username: admin
Password: smcadmin
Enterprise AP#
Setting the IP Address – By default, the access point is configured to obtain IP
address settings from a DHCP server. If a DHCP server is not available, the IP
address defaults to 192.168.2.2, which may not be compatible with your network.
You will therefore have to use the command line interface (CLI) to assign an IP
address that is compatible with your network.
Type “configure” to enter configuration mode, then type “interface ethernet” to
access the Ethernet interface-configuration mode.
Enterprise AP#configure
Enterprise AP(config)#interface ethernet
Enterprise AP(config-if)#
Type “no ip dhcp” to disable DHCP client mode. Then type “ip address ip-address
netmask gateway,” where “ip-address” is the access point’s IP address, “netmask” is
the network mask for the network, and “gateway” is the default gateway router.
Check with your system administrator to obtain an IP address that is compatible with
your network.
Enterprise AP(if-ethernet)#no ip dhcp
Enterprise AP(if-ethernet)#ip address 192.168.2.2
255.255.255.0 192.168.2.254
Enterprise AP(if-ethernet)#
After configuring the access point’s IP parameters, you can access the management
interface from anywhere within the attached network. The command line interface
can also be accessed using Telnet from any computer attached to the network.
4-2
Page 45

Logging In
Setting the Country Code – Units sold in the United States are configured by
default to use only radio channels 1-11 in 802.11b or 802.11g mode as defined by
FCC regulations. Units sold in other countries are configured by default without a
country code (i.e., 99). You must use the CLI to set the country code. Setting the
country code restricts operation of the access point to the radio channels and
transmit power levels permitted for wireless networks in the specified country.
Type “exit” to leave configuration mode. Then type “country ?” to display the list of
countries. Select the code for your country, and enter the country command again,
following by your country code (e.g., tw for Taiwan).
Enterprise AP#country tw
Enterprise AP#
Note: The CLI examples shown later in this manual abbreviate the console prompt to
just "AP." The console prompt can be configured using the "prompt" command
(page 6-14).
Logging In
There are only a few basic steps you need to complete to connect the access point
to your corporate network, and provide network access to wireless clients.
The access point can be managed by any computer using a web browser (Internet
Explorer 5.0 or above, or Netscape 6.2 or above). Enter the default IP address: http:/
/192.168.2.2
4
Logging In – Enter the username “admin,” and password “smcadmin” then click
LOGIN. For information on configuring a user name and password, see page 5-28.
4-3
Page 46

Initial Configuration
4
The home page displays the Main Menu.
4-4
Page 47

Chapter 5: System Configuration
Before continuing with advanced configuration, first complete the initial configuration
steps described in Chapter 4 to set up an IP address for the access point.
The access point can be managed by any computer using a web browser (Internet
Explorer 5.0 or above, or Netscape 6.2 or above). Enter the configured IP address of
the access point, or use the default address: http://192.168.2.2
To log into the access point, enter the default user name “admin” and the password
“smcadmin”, then press “LOGIN”. When the home page displays, click on Advanced
Setup. The following page will display.
The information in this chapter is organized to reflect the structure of the web
screens for easy reference. However, it is recommended that you configure a user
name and password as the first step under “Administration” to control management
access to this device (page 5-28).
5-1
Page 48

System Configuration
5
Advanced Configuration
The Advanced Configuration pages include the following options.
Table 5-2. Menu
Menu Description Page
System Configures basic administrative and client access 5-3
Identification Specifies the host name 5-3
TCP / IP Settings Configures the IP address, subnet mask, gateway, and domain
RADIUS Configures the RADIUS server for wireless client authentication
SSH Settings Configures Secure Shell management access 5-11
Authentication Configures 802.1X client authentication, with an option for MAC
Filter Control Filters communications between wireless clients, access to the
VLAN Enables VLAN support and sets the management VLAN ID 5-19
WDS Settings Configures bridge or repeater modes for each radio interface and
AP Management Configures access to management interfaces 5-27
Administration Configures user name and password for management
System Log Controls logging of error messages; sets the system clock via
SNMP Configures SNMP settings 5-37
SNMP Controls access to this access point from management stations
SNMP Trap Filters Defines trap filters for SNMPv3 users 5-45
SNMP Targets Specifies SNMPv3 users that will receive trap messages 5-47
Radio Interface G Configures the IEEE 802.11g interface 5-49
Radio Settings Configures common radio signal parameters and other settings for
Security Enables each VAP interface, sets the SSID, and configures
Status Displays information about the access point and wireless clients 5-85
AP Status Displays configuration settings for the basic system and the
name servers
and accounting
address authentication
management interface from wireless clients, and traffic matching
specific Ethernet protocol types
sets spanning tree parameters
upgrades software from local file, FTP or TFTP server;
configuration settings to factory defaults; and resets the access
point
SNTP server or manual configuration
using SNMP, as well as the hosts that will receive trap messages
each VAP interface
wireless security
wireless interface
access;
resets
5-5
5-7
5-12
5-17
5-21
5-28
5-33
5-37
5-49
5-66
5-85
5-2
Page 49

Advanced Configuration
Table 5-2. Menu
Menu Description Page
Station Station Shows the wireless clients currently associated with the access
Event Logs Shows log messages stored in memory 5-91
point
5-88
System Identification
The system name for the access point can be left at its default setting. However,
modifying this parameter can help you to more easily distinguish different devices in
your network.
5
System Name – An alias for the access point, enabling the device to be uniquely
identified on the network. (Default: Enterprise Wireless AP; Range: 1-32 characters)
5-3
Page 50

System Configuration
5
CLI Commands for System Identification – Enter the global configuration mode, and
use the system name command to specify a new system name. Then return to the
Exec mode, and use the show system command to display the changes to the
system identification settings.
Enterprise AP#config
Enterprise AP(config)#system name R&D 6-14
Enterprise AP(config)#end 6-87
Enterprise AP#show system 6-22
Enterprise AP#config 6-8
Enter configuration commands, one per line.
Enterprise AP(config)#system name R&D 6-14
Enterprise AP(config)#end 6-87
Enterprise AP#show system 6-22
System Information
==============================================================
Serial Number :
System Up time : 0 days, 0 hours, 32 minutes, 22 seconds
System Name : R&D
System Location :
System Contact : Contact
System Country Code : US - UNITED STATES
MAC Address : 00-12-CF-12-34-60
Radio A MAC Address : 00-12-CF-12-34-61
Radio G MAC Address : 00-12-CF-12-34-65
IP Address : 192.168.2.2
Subnet Mask : 255.255.255.0
Default Gateway : 0.0.0.0
VLAN State : DISABLED
Management VLAN ID(AP): 1
IAPP State : ENABLED
DHCP Client : ENABLED
HTTP Server : ENABLED
HTTP Server Port : 80
HTTPS Server : ENABLED
HTTPS Server Port : 443
Slot Status : Single band(b/g)
Boot Rom Version : v1.1.5
Software Version : v5.0.0.0
SSH Server : ENABLED
SSH Server Port : 22
Telnet Server : ENABLED
DHCP Relay : DISABLED
==============================================================
Enterprise AP#
5-4
Page 51

Advanced Configuration
TCP / IP Settings
Configuring the access point with an IP address expands your ability to manage the
access point. A number of access point features depend on IP addressing to
operate.
Note: You can use the web browser interface to access IP addressing only if the access
point already has an IP address that is reachable through your network.
By default, the access point will be automatically configured with IP settings from a
Dynamic Host Configuration Protocol (DHCP) server. However, if you are not using
a DHCP server to configure IP addressing, use the CLI to manually configure the
initial IP values (see page 4-2). After you have network access to the access point,
you can use the web browser interface to modify the initial IP configuration, if
needed.
Note: If there is no DHCP server on your network, or DHCP fails, the access point will
automatically start up with a default IP address of 192.168.2.2.
5
DHCP Client (Enable) – Select this option to obtain the IP settings for the access
point from a DHCP (Dynamic Host Configuration Protocol) server. The IP address,
subnet mask, default gateway, and Domain Name Server (DNS) address are
dynamically assigned to the access point by the network DHCP server.
(Default: Enabled)
DHCP Client (Disable) – Select this option to manually configure a static address for
the access point.
• IP Address: The IP address of the access point. Valid IP addresses consist of four
decimal numbers, 0 to 255, separated by periods.
5-5
Page 52

System Configuration
5
• Subnet Mask: The mask that identifies the host address bits used for routing to
specific subnets.
• Default Gateway: The default gateway is the IP address of the router for the access
point, which is used if the requested destination address is not on the local subnet.
If you have management stations, DNS, RADIUS, or other network servers
located on another subnet, type the IP address of the default gateway router in the
text field provided. Otherwise, leave the address as all zeros (0.0.0.0).
• Primary and Secondary DNS Address: The IP address of Domain Name Servers
on the network. A DNS maps numerical IP addresses to domain names and can
be used to identify network hosts by familiar names instead of the IP addresses.
If you have one or more DNS servers located on the local network, type the IP
addresses in the text fields provided. Otherwise, leave the addresses as all zeros
(0.0.0.0).
CLI Commands for TCP/IP Settings – From the global configuration mode, enter the
interface configuration mode with the interface ethernet command. Use the ip
dhcp command to enable the DHCP client, or no ip dhcp to disable it. To manually
configure an address, specify the new IP address, subnet mask, and default
gateway using the ip address command. To specify DNS server addresses use the
dns server command. Then use the show interface ethernet command from the
Exec mode to display the current IP settings.
Enterprise AP(config)#interface ethernet 6-87
Enter Ethernet configuration commands, one per line.
Enterprise AP(if-ethernet)#no ip dhcp 6-89
Enterprise AP(if-ethernet)#ip address 192.168.1.2
255.255.255.0 192.168.1.253 6-88
Enterprise AP(if-ethernet)#dns primary-server 192.168.1.556-88
Enterprise AP(if-ethernet)#dns secondary-server 10.1.0.556-88
Enterprise AP(config)#end 6-8
Enterprise AP#show interface ethernet 6-91
Ethernet Interface Information
========================================
IP Address : 192.168.1.2
Subnet Mask : 255.255.255.0
Default Gateway : 192.168.1.253
Primary DNS : 192.168.1.55
Secondary DNS : 10.1.0.55
Speed-duplex : 100Base-TX Full Duplex
Admin status : Up
Operational status : Up
========================================
Enterprise AP#
5-6
Page 53

Advanced Configuration
RADIUS
Remote Authentication Dial-in User Service (RADIUS) is an authentication protocol
that uses software running on a central server to control access to RADIUS-aware
devices on the network. An authentication server contains a database of user
credentials for each user that requires access to the network.
A primary RADIUS server must be specified for the access point to implement IEEE
802.1X network access control and Wi-Fi Protected Access (WPA) wireless security.
A secondary RADIUS server may also be specified as a backup should the primary
server fail or become inaccessible.
In addition, the configured RADIUS server can also act as a RADIUS Accounting
server and receive user-session accounting information from the access point.
RADIUS Accounting can be used to provide valuable information on user activity in
the network.
Note: This guide assumes that you have already configured RADIUS server(s) to
support the access point. Configuration of RADIUS server software is beyond the
scope of this guide, refer to the documentation provided with the RADIUS server
software.
5
5-7
Page 54

System Configuration
5
5-8
Page 55

Advanced Configuration
MAC Address Format – MAC addresses can be specified in one of four formats,
using no delimeter, with a single dash delimeter, with multiple dash delimeters, and
with multiple colon delimeters.
VLAN ID Format – A VLAN ID (a number between 1 and 4094) can be assigned to
each client after successful authentication using IEEE 802.1X and a central RADIUS
server. The user VLAN IDs must be configured on the RADIUS server for each user
authorized to access the network. VLAN IDs can be entered as hexadecimal
numbers or as ASCII strings.
Primary Radius Server Setup – Configure the following settings to use RADIUS
authentication on the access point.
• IP Address: Specifies the IP address or host name of the RADIUS server.
• Port: The UDP port number used by the RADIUS server for authentication
messages. (Range: 1024-65535; Default: 1812)
• Key: A shared text string used to encrypt messages between the access point and
the RADIUS server. Be sure that the same text string is specified on the RADIUS
server. Do not use blank spaces in the string. (Maximum length: 255 characters)
• Timeout: Number of seconds the access point waits for a reply from the RADIUS
server before resending a request. (Range: 1-60 seconds; Default: 5)
• Retransmit attempts: The number of times the access point tries to resend a
request to the RADIUS server before authentication fails. (Range: 1-30; Default: 3)
• Accounting Port: The RADIUS Accounting server UDP port used for accounting
messages. (Range: 0 or 1024-65535; Default: 0, disabled)
• Interim Update Timeout: The interval between transmitting accounting updates to
the RADIUS server. (Range: 60-86400; Default: 3600 seconds)
Note: For the Timeout and Retransmit attempts fields, accept the default values unless
you experience problems connecting to the RADIUS server over the network.
5
Secondary Radius Server Setup – Configure a secondary RADIUS server to provide
a backup in case the primary server fails. The access point uses the secondary
server if the primary server fails or becomes inaccessible. Once the access point
switches over to the secondary server, it periodically attempts to establish
communication again with primary server. If communication with the primary server
is re-established, the secondary server reverts to a backup role.
5-9
Page 56

System Configuration
5
CLI Commands for RADIUS – From the global configuration mode, use the
radius-server address command to specify the address of the primary or
secondary RADIUS servers. (The following example configures the settings for the
primary RADIUS server.) Configure the other parameters for the RADIUS server.
Then use the show show radius command from the Exec mode to display the
current settings for the primary and secondary RADIUS servers.
Enterprise AP(config)#radius-server address 192.168.1.256-58
Enterprise AP(config)#radius-server port 181 6-59
Enterprise AP(config)#radius-server key green 6-59
Enterprise AP(config)#radius-server timeout 10 6-60
Enterprise AP(config)#radius-server retransmit 5 6-60
Enterprise AP(config)#radius-server port-accounting 18136-61
Enterprise AP(config)#radius-server timeout-interim 5006-61
Enterprise AP(config)#exit
Enterprise AP#show radius 6-63
Radius Server Information
========================================
IP : 192.168.1.25
Port : 181
Key : *****
Retransmit : 5
Timeout : 10
Radius MAC format : no-delimiter
Radius VLAN format : HEX
========================================
Radius Secondary Server Information
========================================
IP : 0.0.0.0
Port : 1812
Key : *****
Retransmit : 3
Timeout : 5
Radius MAC format : no-delimiter
Radius VLAN format : HEX
========================================
Enterprise AP#
5-10
Page 57

Advanced Configuration
SSH Settings
Telnet is a remote management tool that can be used to configure the access point
from anywhere in the network. However, Telnet is not secure from hostile attacks.
The Secure Shell (SSH) can act as a secure replacement for Telnet. The SSH
protocol uses generated public keys to encrypt all data transfers passing between
the access point and SSH-enabled management station clients and ensures that
data traveling over the network arrives unaltered. Clients can then securely use the
local user name and password for access authentication.
Note that SSH client software needs to be installed on the management station to
access the access point for management via the SSH protocol.
Notes: 1. The access point supports only SSH version 2.0.
2. After boot up, the SSH server needs about two minutes to generate host
encryption keys. The SSH server is disabled while the keys are being
generated.
5
SSH Settings
• Telnet Server Status: Enables or disables the Telnet server. (Default: Enabled)
• SSH Server Status: Enables or disables the SSH server. (Default: Enabled)
• SSH Server Port: Sets the UDP port for the SSH server. (Range: 1-65535;
Default: 22)
5-11
Page 58

System Configuration
5
CLI Commands for SSH – To enable the SSH server, use the ip ssh-server enable
command from the CLI Ethernet interface configuration mode. To set the SSH
server UDP port, use the ip ssh-server port command. To view the current settings,
use the show system command from the CLI Exec mode (not shown in the
following example).
Enterprise AP(if-ethernet)#no ip telnet-server 6-17
Enterprise AP(if-ethernet)#ip ssh-server enable 6-16
Enterprise AP(if-ethernet)#ip ssh-server port 1124 6-16
Enterprise AP(if-ethernet)#exit
Enterprise AP(if-ethernet)#configure
Authentication
Wireless clients can be authenticated for network access by checking their MAC
address against the local database configured on the access point, or by using a
database configured on a central RADIUS server. Alternatively, authentication can
be implemented using the IEEE 802.1X network access control protocol.
A client’s MAC address provides relatively weak user authentication, since MAC
addresses can be easily captured and used by another station to break into the
network. Using 802.1X provides more robust user authentication using user names
and passwords or digital certificates. You can configure the access point to use both
MAC address and 802.1X authentication, with client station MAC authentication
occurring prior to IEEE 802.1X authentication. However, it is better to choose one or
the other, as appropriate.
Take note of the following points before configuring MAC address or 802.1X
authentication:
• Use MAC address authentication for a small network with a limited number of
users. MAC addresses can be manually configured on the access point itself
without the need to set up a RADIUS server, but managing a large number of MAC
addresses across many access points is very cumbersome. A RADIUS server can
be used to centrally manage a larger database of user MAC addresses.
• Use IEEE 802.1X authentication for networks with a larger number of users and
where security is the most important issue. When using 802.1X authentication, a
RADIUS server is required in the wired network to centrally manage the credentials
of the wireless clients. It also provides a mechanism for enhanced network security
using dynamic encryption key rotation or W-Fi Protected Access (WPA).
Note: If you configure RADIUS MAC authentication together with 802.1X, RADIUS MAC
address authentication is performed prior to 802.1X authentication. If RADIUS
MAC authentication succeeds, then 802.1X authentication is performed. If
RADIUS MAC authentication fails, 802.1X authentication is not performed.
5-12
Page 59

Advanced Configuration
• The access point can also operate in a 802.1X supplicant mode. This enables the
access point itself to be authenticated with a RADIUS server using a configured
MD5 user name and password. This prevents rogue access points from gaining
access to the network.
5
MAC Authentication – You can configure a list of the MAC addresses for wireless
clients that are authorized to access the network. This provides a basic level of
authentication for wireless clients attempting to gain access to the network. A
database of authorized MAC addresses can be stored locally on the access point or
remotely on a central RADIUS server.
(Default: Disabled)
• Disabled: No checks are performed on an associating station’s MAC address.
• Local MAC: The MAC address of the associating station is compared against the
local database stored on the access point. Use the Local MAC Authentication
section of this web page to set up the local database, and configure all access
points in the wireless network service area with the same MAC address database.
5-13
Page 60

System Configuration
5
• Radius MAC: The MAC address of the associating station is sent to a configured
RADIUS server for authentication. When using a RADIUS authentication server for
MAC address authentication, the server must first be configured in the Radius
window (see “RADIUS” on page 5-7). The database of MAC addresses and
filtering policy must be defined in the RADIUS server.
Note: MAC addresses on the RADIUS server can be entered in four different formats
(see “RADIUS” on page 5-7).
802.1X Supplicant – The access point can also operate in a 802.1X supplicant
mode. This enables the access point itself to be authenticated with a RADIUS server
using a configured MD5 user name and password. This prevents rogue access
points from gaining access to the network.
Local MAC Authentication – Configures the local MAC authentication database. The
MAC database provides a mechanism to take certain actions based on a wireless
client’s MAC address. The MAC list can be configured to allow or deny network
access to specific clients.
• System Default: Specifies a default action for all unknown MAC addresses (that is,
those not listed in the local MAC database).
• Deny: Blocks access for all MAC addresses except those listed in the local
database as “Allow.”
• Allow: Permits access for all MAC addresses except those listed in the local
database as “Deny.”
• MAC Authentication Settings: Enters specified MAC addresses and permissions
into the local MAC database.
• MAC Address: Physical address of a client. Enter six pairs of hexadecimal digits
separated by hyphens; for example, 00-90-D1-12-AB-89.
• Permission: Select Allow to permit access or Deny to block access. If Delete is
selected, the specified MAC address entry is removed from the database.
• Update: Enters the specified MAC address and permission setting into the local
database.
• MAC Authentication Table: Displays current entries in the local MAC database.
5-14
Page 61

Advanced Configuration
CLI Commands for Local MAC Authentication – Use the mac-authentication
server command from the global configuration mode to enable local MAC
authentication. Use the mac-authentication session-timeout command to set the
authentication interval. Set the default action for MAC addresses not in the local
table using the address filter default command, then enter MAC addresses in the
local table using the address filter entry command. To remove an entry from the
table, use the address filter delete command. To display the current settings, use
the show authentication command from the Exec mode.
Enterprise AP(config)#mac-authentication server local 6-71
Enterprise AP(config)#mac-authentication session-timeout 5 6-71
Enterprise AP(config)#address filter default denied 6-69
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1a denied 6-70
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1b allowed
Enterprise AP(config)#address filter entry
00-70-50-cc-99-1c allowed
Enterprise AP(config)#address filter delete
00-70-50-cc-99-1c 6-70
Enterprise AP(config)#exit
Enterprise AP#show authentication 6-67
Authentication Information
===========================================================
MAC Authentication Server : LOCAL
MAC Auth Session Timeout Value : 0 min
802.1x supplicant : DISABLED
802.1x supplicant user : EMPTY
802.1x supplicant password : EMPTY
Address Filtering : DENIED
5
System Default : ALLOW addresses not found in filter table.
Filter Table
MAC Address Status
----------------- ---------00-70-50-cc-99-1a DENIED
00-70-50-cc-99-1b ALLOWED
=========================================================
Enterprise AP#
5-15
Page 62

System Configuration
5
CLI Commands for RADIUS MAC Authentication – Use the mac-authentication
server command from the global configuration mode to enable remote MAC
authentication. Set the timeout value for re-authentication using the macauthentication session-timeout command. Be sure to also configure connection
settings for the RADIUS server (not shown in the following example). To display the
current settings, use the show authentication command from the Exec mode.
Enterprise AP(config)#mac-authentication server remote6-71
Enterprise AP(config)#mac-authentication
session-timeout 300 6-71
Enterprise AP(config)#exit
Enterprise AP#show authentication 6-67
Authentication Information
===========================================================
MAC Authentication Server : REMOTE
MAC Auth Session Timeout Value : 300 min
802.1x supplicant : DISABLED
802.1x supplicant user : EMPTY
802.1x supplicant password : EMPTY
Address Filtering : DENIED
System Default : DENY addresses not found in filter table.
Filter Table
MAC Address Status
----------------- ---------00-70-50-cc-99-1a DENIED
00-70-50-cc-99-1b ALLOWED
=========================================================
Enterprise AP#
CLI Command for 802.1x Supplicant – To configure the access point to operate as a
802.1X supplicant, first use the 802.1X supplicant user command to set a user
name and password for the access point, then use the 802.1X supplicant command
to enable the feature. To display the current settings, use the show authentication
command from the Exec mode (not shown in the following example)
Enterprise AP(config)#802.1X supplicant user SMC2555W dot1xpass
6-67
Enterprise AP(config)#802.1X supplicant 6-67
Enterprise AP(config)#
5-16
Page 63

Advanced Configuration
Filter Control
The access point can employ network traffic frame filtering to control access to
network resources and increase security. You can prevent communications between
wireless clients and prevent access point management from wireless clients. Also,
you can block specific Ethernet traffic from being forwarded by the access point.
5
Inter Client STAs Communication Filter – Sets the global mode for
wireless-to-wireless communications between clients associated to Virtual AP (VAP)
interfaces on the access point. (Default: Prevent Inter and Intra VAP client
Communication)
• Disabled: All clients can communicate with each other through the access point.
• Prevent Intra VAP client communication: When enabled, clients associated with a
specific VAP interface cannot establish wireless communications with each other.
Clients can communicate with clients associated to other VAP interfaces.
• Prevent Inter and Intra VAP client communication: When enabled, clients cannot
establish wireless communications with any other client, either those associated to
the same VAP interface or any other VAP interface.
AP Management Filter – Controls management access to the access point from
wireless clients. Management interfaces include the web, Telnet, or SNMP.
(Default: Disabled)
• Disabled: Allows management access from wireless clients.
• Enabled: Blocks management access from wireless clients.
Uplink Port MAC Address Filtering Status – Prevents traffic with specified source
MAC addresses from being forwarded to wireless clients through the access point.
You can add a maximum of eight MAC addresses to the filter table. (Default:
Disabled)
5-17
Page 64

System Configuration
5
• MAC Address: Specifies a MAC address to filter, in the form xx-xx-xx-xx-xx-xx.
• Permission: Adds or deletes a MAC address from the filtering table.
Ethernet Type Filter – Controls checks on the Ethernet type of all incoming and
outgoing Ethernet packets against the protocol filtering table. (Default: Disabled)
• Disabled: Access point does not filter Ethernet protocol types.
• Enabled: Access point filters Ethernet protocol types based on the configuration of
protocol types in the filter table. If the status of a protocol is set to “ON,” the protocol
is filtered from the access point.
Note: Ethernet protocol types not listed in the filtering table are always forwarded by the
access point.
CLI Commands for Bridge Filtering – Use the filter local-bridge command from the
global configuration mode to prevent wireless-to-wireless communications through
the access point. Use the filter ap-manage command to restrict management
access from wireless clients. To configure Ethernet protocol filtering, use the filter
ethernet-type enable command to enable filtering and the filter ethernet-type
protocol command to define the protocols that you want to filter. To remove an entry
from the table, use the address filter delete command. To display the current
settings, use the show filters command from the Exec mode.
Enterprise AP(config)#filter local-bridge 6-72
Enterprise AP(config)#filter ap-manage 6-73
Enterprise AP(config)#filter uplink enable 6-73
Enterprise AP(config)#filter uplink add 00-12-34-56-78-9a6-74
Enterprise AP(config)#filter ethernet-type enable 7-74
Enterprise AP(config)#filter ethernet-type protocol ARP6-75
Enterprise AP(config)#exit
Enterprise AP#show filters 6-76
Protocol Filter Information
=========================================================
Local Bridge :ENABLED
AP Management :ENABLED
Ethernet Type Filter :ENABLED
Enabled Protocol Filters
--------------------------------------------------------Protocol: ARP ISO: 0x0806
=========================================================
Enterprise AP#
5-18
Page 65

Advanced Configuration
VLAN
The access point can employ VLAN tagging support to control access to network
resources and increase security. VLANs separate traffic passing between the
access point, associated clients, and the wired network. There can be a VLAN
assigned to each associated client, a default VLAN for each VAP (Virtual Access
Point) interface, and a management VLAN for the access point.
Note the following points about the access point’s VLAN support:
• The management VLAN is for managing the access point through remote
management tools, such as the web interface, SSH, SNMP, or Telnet. The access
point only accepts management traffic that is tagged with the specified
management VLAN ID.
• All wireless clients associated to the access point are assigned to a VLAN. If IEEE
802.1X is being used to authenticate wireless clients, specific VLAN IDs can be
configured on the RADIUS server to be assigned to each client. If a client is not
assigned to a specific VLAN or if 802.1X is not used, the client is assigned to the
default VLAN for the VAP interface with which it is associated. The access point
only allows traffic tagged with assigned VLAN IDs or default VLAN IDs to access
clients associated on each VAP interface.
• When VLAN support is enabled on the access point, traffic passed to the wired
network is tagged with the appropriate VLAN ID, either an assigned client VLAN
ID, default VLAN ID, or the management VLAN ID. Traffic received from the wired
network must also be tagged with one of these known VLAN IDs. Received traffic
that has an unknown VLAN ID or no VLAN tag is dropped.
• When VLAN support is disabled, the access point does not tag traffic passed to the
wired network and ignores the VLAN tags on any received frames.
Note: Before enabling VLAN tagging on the access point, be sure to configure the
attached network switch port to support tagged VLAN frames from the access
point’s management VLAN ID, default VLAN IDs, and other client VLAN IDs.
Otherwise, connectivity to the access point will be lost when you enable the VLAN
feature.
5
Using IEEE 802.1X and a central RADIUS server, up to 64 VLAN IDs can be
mapped to specific wireless clients, allowing users to remain within the same VLAN
as they move around a campus site. This feature can also be used to control access
to network resources from clients, thereby improving security.
A VLAN ID (1-4094) can be assigned to a client after successful IEEE 802.1X
authentication. The client VLAN IDs must be configured on the RADIUS server for
each user authorized to access the network. If a client does not have a configured
VLAN ID on the RADIUS server, the access point assigns the client to the
configured default VLAN ID for the VAP interface.
Note: When using IEEE 802.1X to dynamically assign VLAN IDs, the access point must
have 802.1X authentication enabled and a RADIUS server configured. Wireless
clients must also support 802.1X client software.
5-19
Page 66

System Configuration
5
When setting up VLAN IDs for each user on the RADIUS server, be sure to use the
RADIUS attributes and values as indicated in the following table.
Number RADIUS Attribute Value
64 Tunnel-Type VLAN (13)
65 Tunnel-Medium-Type 802
81 Tunnel-Private-Group-ID VLANID
VLAN IDs on the RADIUS server can be entered as hexadecimal digits or a string
(see “radius-server vlan-format” on page 6-62).
Note: The specific configuration of RADIUS server software is beyond the scope of this
guide. Refer to the documentation provided with the RADIUS server software.
(1 to 4094 as hexadecimal or string)
VLAN Classification – Enables or disables VLAN tagging support on the access
point.
Native VLAN ID – The VLAN ID that traffic must have to be able to manage the
access point. (Range 1-4094; Default: 1)
5-20
Page 67

Advanced Configuration
WDS Settings
Each access point radio interface can be configured to operate in a bridge or
repeater mode, which allows it to forward traffic directly to other access point units.
To set up bridge links between access point units, you must configure the wireless
Distribution System (WDS) forwarding table by specifying the wireless MAC address
of all units to which you want to forward traffic. Up to six WDS bridge or repeater
links can be specified for each unit in the wireless bridge network.
The Spanning Tree Protocol (STP) can be used to detect and disable network loops,
and to provide backup links between bridges. This allows a wireless bridge to
interact with other bridging devices (that is, an STP-compliant switch, bridge or
router) in your network to ensure that only one route exists between any two stations
on the network, and provide backup links which automatically take over when a
primary link goes down.
WDS Bridge – Up to six WDS bridge or repeater links (MAC addresses) can be
specified for each unit in the wireless bridge network. One unit only must be
configured as the “root bridge” in the wireless network. The root bridge is the unit
connected to the main core of the wired LAN. Other bridges need to specify one
“Parent” link to the root bridge or to a bridge connected to the root bridge. The other
five WDS links are available as “Child” links to other bridges.
• Bridge Role – Sets the radio to operate in one of the following four modes: (Default:
AP)
• AP (Access Point): Operates as an access point for wireless clients, providing
connectivity to a wired LAN.
• Bridge: Operates as a bridge to other access points. The “Parent” link to the root
bridge must be configured. Up to five other ”Child” links are available to other
bridges.
• Repeater: Operates as a wireless repeater, extending the range for remote
wireless clients and connecting them to the root bridge. The “Parent” link to the
root bridge must be configured. In this mode, traffic is not forwarded to the
Ethernet port from the radio interface.
• Root Bridge: Operates as the root bridge in the wireless bridge network. Up to
six ”Child” links are available to other bridges in the network.
• Bridge Parent – The physical layer address of the root bridge unit or the bridge unit
connected to the root bridge. (12 hexadecimal digits in the form
“xx-xx-xx-xx-xx-xx”)
• Bridge Child – The physical layer address of other bridge units for which this unit
serves as the bridge parent or the root bridge. Note that the first entry under the list
of child nodes is reserved for the root bridge, and can only be configured if the role
is set to “Root Bridge.” (12 hexadecimal digits in the form “xx-xx-xx-xx-xx-xx”)
5
5-21
Page 68

System Configuration
5
Spanning Tree Protocol – STP uses a distributed algorithm to select a bridging
device (STP-compliant switch, bridge or router) that serves as the root of the
spanning tree network. It selects a root port on each bridging device (except for the
root device) which incurs the lowest path cost when forwarding a packet from that
device to the root device. Then it selects a designated bridging device from each
LAN which incurs the lowest path cost when forwarding a packet from that LAN to
the root device. All ports connected to designated bridging devices are assigned as
5-22
Page 69

Advanced Configuration
designated ports. After determining the lowest cost spanning tree, it enables all root
ports and designated ports, and disables all other ports. Network packets are
therefore only forwarded between root ports and designated ports, eliminating any
possible network loops.
Once a stable network topology has been established, all bridges listen for Hello
BPDUs (Bridge Protocol Data Units) transmitted from the root bridge. If a bridge
does not get a Hello BPDU after a predefined interval (Maximum Age), the bridge
assumes that the link to the root bridge is down. This bridge will then initiate
negotiations with other bridges to reconfigure the network to reestablish a valid
network topology.
• Bridge – Enables/disables STP on the wireless bridge or repeater.
(Default: Disabled)
• Bridge Priority – Used in selecting the root device, root port, and designated port.
The device with the highest priority becomes the STP root device. However, if all
devices have the same priority, the device with the lowest MAC address will then
become the root device. (Note that lower numeric values indicate higher priority.)
• Range: 0-65535
• Default: 32768
• Bridge Max Age – The maximum time (in seconds) a device can wait without
receiving a configuration message before attempting to reconfigure. All device
ports (except for designated ports) should receive configuration messages at
regular intervals. Any port that ages out STP information (provided in the last
configuration message) becomes the designated port for the attached LAN. If it is
a root port, a new root port is selected from among the device ports attached to the
network. (Range: 6-40 seconds)
• Default: 20
• Minimum: The higher of 6 or [2 x (Hello Time + 1)].
• Maximum: The lower of 40 or [2 x (Forward Delay - 1)]
• Bridge Hello Time – Interval (in seconds) at which the root device transmits a
configuration message. (Range: 1-10 seconds)
• Default: 2
•Minimum: 1
• Maximum: The lower of 10 or [(Max. Message Age / 2) -1]
• Bridge Forwarding Delay – The maximum time (in seconds) this device waits
before changing states (i.e., discarding to learning to forwarding). This delay is
required because every device must receive information about topology changes
before it starts to forward frames. In addition, each port needs time to listen for
conflicting information that would make it return to a discarding state; otherwise,
temporary data loops might result. (Range: 4-30 seconds)
• Default: 15
• Minimum: The higher of 4 or [(Max. Message Age / 2) + 1]
• Maximum: 30
5
5-23
Page 70

System Configuration
5
• Link Path Cost – This parameter is used by the STP to determine the best path
between devices. Therefore, lower values should be assigned to ports attached to
faster media, and higher values assigned to ports with slower media. (Path cost
takes precedence over port priority.)
• Range: 1-65535
• Default: Ethernet interface: 19; Wireless interface: 40
• Link Port Priority – Defines the priority used for this port in the Spanning Tree
Protocol. If the path cost for all ports on a switch are the same, the port with the
highest priority (i.e., lowest value) will be configured as an active link in the
spanning tree. This makes a port with higher priority less likely to be blocked if the
Spanning Tree Protocol is detecting network loops. Where more than one port is
assigned the highest priority, the port with lowest numeric identifier will be enabled.
• Default: 128
• Range: 0-240, in steps of 16
CLI Commands for WDS Settings – To set the role of the access point radio
interface, use the bridge role command from the CLI wireless interface
configuration mode. If the role of the radio interface is set to “Bridge” or “Repeater,”
the MAC address of the parent node must also be configured using the bridge-link
parent command. If the role is set to anything other than “Access Point,” then you
should also configure the MAC addresses of the child nodes using the bridge-link
child command. To view the current bridge link settings, use the show bridge link
command.
5-24
Page 71

Advanced Configuration
Enterprise AP(if-wireless g)#bridge role bridge 6-96
Enterprise AP(if-wireless g)#bridge-link child 2
00-08-3e-84-bc-6d 6-98
Enterprise AP(if-wireless g)#bridge-link child 3
00-08-3e-85-13-f2
Enterprise AP(if-wireless g)#bridge-link child 4
00-08-3e-84-79-31
Enterprise AP(if-wireless g)#bridge-link parent
00-08-2d-69-3a-51 6-97
Enterprise AP(if-wireless g)#exit
Enterprise AP#show bridge link wireless g 6-101
Interface Wireless G WDS Information
====================================
AP Role: Bridge
Parent: 00-08-2d-69-3a-51
Child:
Child 2: 00-08-3e-84-bc-6d
Child 3: 00-08-3e-85-13-f2
Child 4: 00-08-3e-84-79-31
Child 5: 00-00-00-00-00-00
Child 6: 00-00-00-00-00-00
STAs:
No WDS Stations.
Enterprise AP#
5
5-25
Page 72

System Configuration
5
CLI Commands for STP Settings – If the role of a radio interface is set to Repeater,
Bridge or Root Bridge, STP can be enabled on the access point to maintain a valid
network topology. To globally enable STP, use the bridge stp enable command
from the CLI configuration mode. Then configure the other global STP parameters
for the bridge. The path cost and priority for each bridge link can be set using the
bridge-link path-cost and bridge-link port-priority command from the Wireless
Interface configuration mode. The path cost and priority can also be set for the
Ethernet port from the Ethernet Interface configuration mode. To view the current
STP settings, use the show bridge stp command.
Enterprise AP(config)#bridge stp enable 6-104
Enterprise AP(config)#bridge stp forwarding-delay 25006-105
Enterprise AP(config)#bridge stp hello-time 500 6-106
Enterprise AP(config)#bridge stp max-age 4000 6-107
Enterprise AP(config)#bridge stp priority 40000 6-108
Enterprise AP(config)#interface wireless g
Enterprise AP(if-wireless g)#bridge-link path-cost 2 406-109
Enterprise AP(if-wireless g)#bridge-link port-priority 2 64
6-110
Enterprise AP(if-wireless g)#exit
Enterprise AP#show bridge stp 6-111
Bridge MAC : 00:30:F1:F0:9A:9C
Status : Disabled
priority : 32768
desiginated-root : priority = 0, MAC = 00:00:00:00:00:00
root-path-cost : 0
root-Port-no : 0
Hold Time : 0 Seconds
Hello Time : 0 Seconds
Maximum Age : 0 Seconds
Forward Delay : 0 Seconds
bridge Hello Time : 2 Seconds
bridge Maximum Age : 20 Seconds
bridge Forward Delay : 5 Seconds
time-since-top-change: 3168 Seconds
topology-change-count: 0
Enterprise AP#
5-26
Page 73

Advanced Configuration
AP Management
The Web, Telnet, and SNMP management interfaces are enabled and open to all IP
addresses by default. To provide more security for management access to the
access point, specific interfaces can be disabled and management restricted to a
single IP address or a limited range of IP addresses.
Once you specify an IP address or range of addresses, access to management
interfaces is restricted to the specified addresses. If anyone tries to access a
management interface from an unauthorized address, the access point will reject the
connection.
5
UI Management – Enables or disables management access through Telnet, the Web
(HTTP), or SNMP interfaces. (Default: Enabled)
Note: Secure Web (HTTPS) connections are not affected by the UI Management or IP
Management settings.
IP Management – Restricts management access to Telnet, Web, and SNMP
interfaces to specified IP addresses. (Default: Any IP)
• Any IP: Indicates that any IP address is allowed management access.
• Single IP: Specifies a single IP address that is allowed management access.
• Multiple IP: Specifies an address range as defined by the entered IP address and
subnet mask. For example, IP address 192.168.1.6 and subnet mask
255.255.255.0, defines all IP addresses from 192.168.1.1 to 192.168.1.254.
5-27
Page 74

System Configuration
5
CLI Commands for AP Management features.
Enterprise AP(config)#apmgmtip multiple 192.168.1.50
255.255.255.0 6-20
Enterprise AP(config)#apmgmtui SNMP enable 6-21
Administration
Changing the Password
Management access to the web and CLI interface on the access point is controlled
through a single user name and password. You can also gain additional access
security by using control filters (see “Filter Control” on page 5-17).
To protect access to the management interface, you need to configure an
Administrator’s user name and password as soon as possible. If the user name and
password are not configured, then anyone having access to the access point may
be able to compromise access point and network security. Once a new Administrator
has been configured, you can delete the default “admin” user name from the system.
Note: Pressing the Reset button on the back of the access point for more than five
seconds resets the user name and password to the factory defaults. For this
reason, we recommend that you protect the access point from physical access by
unauthorized persons.
Username – The name of the user. The default name is “admin.” (Length: 3-16
characters, case sensitive)
New Password – The password for management access. (Length: 3-16 characters,
case sensitive)
Confirm New Password – Enter the password again for verification.
5-28
Page 75

Advanced Configuration
CLI Commands for the Administrator’s User Name and Password – Use the
username and password commands from the CLI configuration mode.
Enterprise AP(config)#username bob 6-15
Enterprise AP(config)#password admin 6-15
Enterprise AP#
Upgrading Firmware
You can upgrade new access point software from a local file on the management
workstation, or from an FTP or TFTP server. New software may be provided
periodically from your distributor.
After upgrading new software, you must reboot the access point to implement the
new code. Until a reboot occurs, the access point will continue to run the software it
was using before the upgrade started. Also note that new software that is
incompatible with the current configuration automatically restores the access point to
the factory default settings when first activated after a reboot.
5
5-29
Page 76

System Configuration
5
Before upgrading new software, verify that the access point is connected to the
network and has been configured with a compatible IP address and subnet mask.
If you need to download from an FTP or TFTP server, take the following additional
steps:
• Obtain the IP address of the FTP or TFTP server where the access point software
is stored.
• If upgrading from an FTP server, be sure that you have an account configured on
the server with a user name and password.
• If VLANs are configured on the access point, determine the VLAN ID with which
the FTP or TFTP server is associated, and then configure the management station,
or the network port to which it is attached, with the same VLAN ID. If you are
5-30
Page 77

Advanced Configuration
managing the access point from a wireless client, the VLAN ID for the wireless
client must be configured on a RADIUS server.
Current version – Version number of runtime code.
Firmware Upgrade Local – Downloads an operation code image file from the web
management station to the access point using HTTP. Use the Browse button to
locate the image file locally on the management station and click Start Upgrade to
proceed.
• New firmware file: Specifies the name of the code file on the server. The new
firmware file name should not contain slashes (\ or /), the leading letter of the file
name should not be a period (.), and the maximum length for file names is 32
characters for files on the access point. (Valid characters: A-Z, a-z, 0-9, “.”, “-”, “_”)
Firmware Upgrade Remote – Downloads an operation code image file from a
specified remote FTP or TFTP server. After filling in the following fields, click Start
Upgrade to proceed.
• New firmware file: Specifies the name of the code file on the server.
firmware file name should not contain slashes (\ or /),
name should not be a period (.), and the maximum length for file names on the
FTP/TFTP server is 255 characters or 32 characters for files on the access point.
(Valid characters: A-Z, a-z, 0-9, “.”, “-”, “_”)
• IP Address: IP address or host name of FTP or TFTP server.
• Username: The user ID used for login on an FTP server.
• Password: The password used for login on an FTP server.
Restore Factory Settings – Click the Restore button to reset the configuration
settings for the access point to the factory defaults and reboot the system. Note that
all user configured information will be lost. You will have to re-enter the default user
name (admin) to re-gain management access to this device.
Reboot Access Point – Click the Reset button to reboot the system.
Note: If you have upgraded system software, then you must reboot the access point to
implement the new operation code. New software that is incompatible with the
current configuration automatically restores the access point to default values
when first activated after a reboot.
the leading letter of the file
The new
5
5-31
Page 78

System Configuration
5
CLI Commands for Downloading Software from a TFTP Server – Use the copy tftp
file command from the Exec mode and then specify the file type, name, and IP
address of the TFTP server. When the download is complete, the dir command can
be used to check that the new file is present in the access point file system. To run
the new software, use the reset board command to reboot the access point.
Enterprise AP#copy tftp file 6-55
1. Application image
2. Config file
3. Boot block image
Select the type of download<1,2,3>: [1]:1
TFTP Source file name:img.bin
TFTP Server IP:192.168.2.29
Enterprise AP#dir 6-57
File Name Type File Size
-------------------------- ---- ----------dflt-img.bin 2 1319939
img.bin 2 1629577
syscfg 5 17776
syscfg_bak 5 17776
262144 byte(s) available
Enterprise AP#reset board 6-10
Reboot system now? <y/n>: y
5-32
Page 79

Advanced Configuration
System Log
The access point can be configured to send event and error messages to a System
Log Server. The system clock can also be synchronized with a time server, so that
all the messages sent to the Syslog server are stamped with the correct time and
date.
5
Enabling System Logging
The access point supports a logging process that can control error messages saved
to memory or sent to a Syslog server. The logged messages serve as a valuable tool
for isolating access point and network problems.
System Log Setup – Enables the logging of error messages. (Default: Disable)
Server (1-4) – Enables the sending of log messages to a Syslog server host. Up to
four Syslog servers are supported on the access point. (Default: Disable)
Server Name/IP – The IP address or name of a Syslog server. (Default: 0.0.0.0)
UDP Port – The UDP port used by a Syslog server. (Range: 514 or 11024-65535;
Default: 514)
Logging Console – Enables the logging of error messages to the console.
(Default: Disable)
5-33
Page 80

System Configuration
5
Logging Level – Sets the minimum severity level for event logging.
(Default: Informational)
The system allows you to limit the messages that are logged by specifying a
minimum severity level. The following table lists the error message levels from the
most severe (Emergency) to least severe (Debug). The message levels that are
logged include the specified minimum level up to the Emergency level.
Error Level Description
Emergency System unusable
Alerts Immediate action needed
Critical Critical conditions (e.g., memory allocation, or free memory error - resource
Error Error conditions (e.g., invalid input, default used)
Warning Warning conditions (e.g., return false, unexpected return)
Notice Normal but significant condition, such as cold start
Informational Informational messages only
Debug Debugging messages
Note: The access point error log can be viewed using the Event Logs window in the
Status section (page 5-91). The Event Logs window displays the last 128
messages logged in chronological order, from the newest to the oldest. Log
messages saved in the access point’s memory are erased when the device is
rebooted.
exhausted)
Logging Facility Type – Sets the facility type for remote logging of syslog messages.
The command specifies the facility type tag sent in syslog messages. (See RFC
3164.) This type has no effect on the kind of messages reported by the switch.
However, it may be used by the syslog server to sort messages or to store
messages in the corresponding database. (Range: 16-23; Default: 16)
5-34
Page 81

Advanced Configuration
CLI Commands for System Logging – To enable logging on the access point, use
the logging on command from the global configuration mode. The logging level
command sets the minimum level of message to log. Use the logging console
command to enable logging to the console. Use the logging host command to
specify up to four Syslog servers. The CLI also allows the logging facility-type
command to set the facility-type number to use on the Syslog server. To view the
current logging settings, use the show logging command.
Enterprise AP(config)#logging on 6-28
Enterprise AP(config)#logging level alert 6-29
Enterprise AP(config)#logging console 6-29
Enterprise AP(config)#logging host 1 IP 10.1.0.3 514 6-28
Enterprise AP(config)#logging host 1 Port 514 6-28
Enterprise AP(config)#logging facility-type 19 6-30
Enterprise AP(config)#exit
Enterprise AP#show logging 6-31
Logging Information
============================================
Syslog State : Enabled
Logging Console State : Enabled
Logging Level : Alert
Logging Facility Type : 19
Servers
1: 10.1.0.3, UDP Port: 514, State: Enabled
2: 0.0.0.0, UDP Port: 514, State: Disabled
3: 0.0.0.0, UDP Port: 514, State: Disabled
4: 0.0.0.0, UDP Port: 514, State: Disabled
=============================================
5
Enterprise AP#
Configuring SNTP
Simple Network Time Protocol (SNTP) allows the access point to set its internal
clock based on periodic updates from a time server (SNTP or NTP). Maintaining an
accurate time on the access point enables the system log to record meaningful
dates and times for event entries. If the clock is not set, the access point will only
record the time from the factory default set at the last bootup.
The access point acts as an SNTP client, periodically sending time synchronization
requests to specific time servers. You can configure up to two time server IP
addresses. The access point will attempt to poll each server in the configured
sequence.
SNTP Server – Configures the access point to operate as an SNTP client. When
enabled, at least one time server IP address must be specified.
5-35
Page 82

System Configuration
5
• Primary Server: The IP address of an SNTP or NTP time server that the access
point attempts to poll for a time update.
• Secondary Server: The IP address of a secondary SNTP or NTP time server. The
access point first attempts to update the time from the primary server; if this fails it
attempts an update from the secondary server.
Note: The access point also allows you to disable SNTP and set the system clock
manually.
Set Time Zone – SNTP uses Coordinated Universal Time (or UTC, formerly
Greenwich Mean Time, or GMT) based on the time at the Earth’s prime meridian,
zero degrees longitude. To display a time corresponding to your local time, you must
indicate the number of hours your time zone is located before (east) or after (west)
UTC.
Enable Daylight Saving – The access point provides a way to automatically adjust
the system clock for Daylight Savings Time changes. To use this feature you must
define the month and date to begin and to end the change from standard time.
During this period the system clock is set back by one hour.
CLI Commands for SNTP – To enable SNTP support on the access point, from the
global configuration mode specify SNTP server IP addresses using the sntp-server
ip command, then use the sntp-server enable command to enable the service. Use
the sntp-server timezone command to set the time zone for your location, and the
sntp-server daylight-saving command to set daylight savings. To view the current
SNTP settings, use the show sntp command.
Enterprise AP(config)#sntp-server ip 1 10.1.0.19 6-33
Enterprise AP(config)#sntp-server enable 6-33
Enterprise AP(config)#sntp-server timezone +8 6-35
Enterprise AP(config)#sntp-server daylight-saving 6-35
Enter Daylight saving from which month<1-12>: 3
and which day<1-31>: 31
Enter Daylight saving end to which month<1-12>: 10
and which day<1-31>: 31
Enterprise AP(config)#exit
Enterprise AP#show sntp 6-36
SNTP Information
=========================================================
Service State : Enabled
SNTP (server 1) IP : 10.1.10.19
SNTP (server 2) IP : 192.43.244.18
Current Time : 19 : 35, Oct 10th, 2003
Time Zone : +8 (TAIPEI, BEIJING)
Daylight Saving : Enabled, from Mar, 31st to Oct, 31st
=========================================================
Enterprise AP#
5-36
Page 83

SNMP
CLI Commands for the System Clock – The following example shows how to
manually set the system time when SNTP server support is disabled on the access
point.
Enterprise AP(config)#no sntp-server enable 6-33
Enterprise AP(config)#sntp-server date-time 6-34
Enter Year<1970-2100>: 2003
Enter Month<1-12>: 10
Enter Day<1-31>: 10
Enter Hour<0-23>: 18
Enter Min<0-59>: 35
Enterprise AP(config)#
SNMP
Simple Network Management Protocol (SNMP) is a communication protocol
designed specifically for managing devices on a network. Equipment commonly
managed with SNMP includes switches, routers and host computers. SNMP is
typically used to configure these devices for proper operation in a network
environment, as well as to monitor them to evaluate performance or detect potential
problems.
Managed devices supporting SNMP contain software, which runs locally on the
device and is referred to as an agent. A defined set of variables, known as managed
objects, is maintained by the SNMP agent and used to manage the device. These
objects are defined in a Management Information Base (MIB) that provides a
standard presentation of the information controlled by the agent. SNMP defines both
the format of the MIB specifications and the protocol used to access this information
over the network.
The access point includes an onboard agent that supports SNMP versions 1, 2c,
and 3 clients. This agent continuously monitors the status of the access point, as
well as the traffic passing to and from wireless clients. A network management
station can access this information using SNMP management software that is
compliant with MIB II. To implement SNMP management, the access point must first
have an IP address and subnet mask, configured either manually or dynamically.
Access to the onboard agent using SNMP v1 and v2c is controlled by community
strings. To communicate with the access point, the management station must first
submit a valid community string for authentication.
Access to the access point using SNMP v3 provides additional security features that
cover message integrity, authentication, and encryption; as well as controlling
notifications that are sent to specified user targets.
5
5-37
Page 84

System Configuration
5
Configuring SNMP and Trap Message Parameters
The access point SNMP agent must be enabled to function (for versions 1, 2c, and
3 clients). Management access using SNMP v1 and v2c also requires community
strings to be configured for authentication. Trap notifications can be enabled and
sent to up to four management stations.
SNMP – Enables or disables SNMP management access and also enables the
access point to send SNMP traps (notifications). (Default: Disable)
Location – A text string that describes the system location. (Maximum length: 255
characters)
Contact – A text string that describes the system contact. (Maximum length: 255
characters)
Community Name (Read Only) – Defines the SNMP community access string that
has read-only access. Authorized management stations are only able to retrieve
MIB objects. (Maximum length: 23 characters, case sensitive; Default: public)
5-38
Page 85

SNMP
Community Name (Read/Write) – Defines the SNMP community access string that
has read/write access. Authorized management stations are able to both retrieve
and modify MIB objects. (Maximum length: 23 characters, case sensitive;
Default: private)
Trap Destination (1 to 4) – Enables recipients (up to four) of SNMP notifications.
• Trap Destination IP Address – Specifies the recipient of SNMP notifications. Enter
the IP address or the host name. (Host Name: 1 to 63 characters, case sensitive)
• Trap Destination Community Name – The community string sent with the
notification operation. (Maximum length: 23 characters, case sensitive;
Default: public)
Engine ID – Sets the engine identifier for the SNMPv3 agent that resides on the
access point. This engine protects against message replay, delay, and redirection.
The engine ID is also used in combination with user passwords to generate the
security keys for authenticating and encrypting SNMPv3 packets. A default engine
ID is automatically generated that is unique to the access point. (Range: 10 to 64
hexadecimal characters)
Note: If the local engine ID is deleted or changed, all SNMP users will be cleared. All
existing users will need to be re-configured. If you want to change the default
engine ID, change it first before configuring other SNMP v3 parameters.
5
5-39
Page 86

System Configuration
5
Trap Configuration – Allows selection of specific SNMP notifications to send. The
following items are available:
• sysSystemUp - The access point is up and running.
• sysSystemDown - The access point is about to shutdown and reboot.
• sysRadiusServerChanged - The access point has changed from the primary
RADIUS server to the secondary, or from the secondary to the primary.
• sysConfigFileVersionChanged - The access point’s configuration file has been
changed.
• dot11StationAssociation - A client station has successfully associated with the
access point.
• dot11StationReAssociation - A client station has successfully re-associated with
the access point.
• dot11StationAuthentication - A client station has been successfully authenticated.
• dot11StationRequestFail - A client station has failed association, re-association, or
authentication.
• dot11InterfaceBFail - The 802.11b interface has failed.
• dot1xMacAddrAuthSuccess - A client station has successfully authenticated its
MAC address with the RADIUS server.
• dot1xMacAddrAuthFail - A client station has failed MAC address authentication
with the RADIUS server.
• dot1xAuthNotInitiated - A client station did not initiate 802.1X authentication.
• dot1xAuthSuccess - A 802.1X client station has been successfully authenticated
by the RADIUS server.
• dot1xAuthFail - A 802.1X client station has failed RADIUS authentication.
• dot1xSuppAuthenticated - A supplicant station has been successfully
authenticated by the RADIUS server
• localMacAddrAuthSuccess - A client station has successfully authenticated its
MAC address with the local database on the access point.
• localMacAddrAuthFail - A client station has failed authentication with the local MAC
address database on the access point.
• iappStationRoamedFrom - A client station has roamed from another access point
(identified by its IP address).
• iappStationRoamedTo - A client station has roamed to another access point
(identified by its IP address).
• iappContextDataSent - A client station’s Context Data has been sent to another
access point with which the station has associated.
• sntpServerFail - The access point has failed to set the time from the configured
SNTP server.
• wirelessExternalAntenna - An external antenna has been enabled.
• dot11WirelessStationDeauthenticate - A client station has de-authenticated from
the network.
• dot11StationDisassociate - A client station no longer associates with the network.
5-40
Page 87

SNMP
• dot11StationAuthenticateFail - A client station has tried and failed to authenticate
to the network.
• Enable All Traps - Click the button to enable all the available traps.
• Disable All Traps - Click the button to disable all the available traps.
CLI Commands for SNMP and Trap Configuration – Use the snmp-server enable
server command from the global configuration mode to enable the SNMP agent.
Use the snmp-server location and snmp-server contact commands to indicate
the physical location of the access point and define a system contact. To set the
read-only and read/write community names, use the snmp-server community
command. Use the snmp-server host command to define a trap receiver host and
the snmp-server trap command to enable or disable specific traps.
Enterprise AP(config)#snmp-server enable server 6-41
Enterprise AP(config)#snmp-server community alpha rw 6-40
Enterprise AP(config)#snmp-server community beta ro
Enterprise AP(config)#snmp-server location WC-19 6-41
Enterprise AP(config)#snmp-server contact Paul 6-40
Enterprise AP(config)#snmp-server host 192.168.1.9 alpha6-42
Enterprise AP(config)#snmp-server trap dot11StationAssociation
6-43
Enterprise AP(config)#
5
5-41
Page 88

System Configuration
5
To view the current SNMP settings, use the show snmp command.
Enterprise AP#show snmp 6-53
SNMP Information
==============================================
Service State : Enable
Community (ro) : *****
Community (rw) : *****
Location : WC-19
Contact : Paul
EngineId :80:00:07:e5:80:00:00:2e:62:00:00:00:18
EngineBoots:1
Trap Destinations:
1: 192.168.1.9, Community: *****, State: Enabled
2: 0.0.0.0, Community: *****, State: Disabled
3: 0.0.0.0, Community: *****, State: Disabled
4: 0.0.0.0, Community: *****, State: Disabled
dot11InterfaceAGFail Enabled dot11InterfaceBFail Enabled
dot11StationAssociation Enabled dot11StationAuthentication
Enabled
dot11StationReAssociation Enabled dot11StationRequestFail
Enabled
dot1xAuthFail Enabled dot1xAuthNotInitiated Enabled
dot1xAuthSuccess Enabled dot1xMacAddrAuthFail Enabled
dot1xMacAddrAuthSuccess Enabled iappContextDataSent
Enabled
iappStationRoamedFrom Enabled iappStationRoamedTo
Enabled
localMacAddrAuthFail Enabled localMacAddrAuthSuccess
Enabled
iappContextDataSent Enabled dot1XSuppAuthenticated
Enabled
wirelessExternalAntenna Enabled dot11InterfaceAFail
Enabled
dot11InterfaceGFail Enabled
pppLogonFail Enabled sntpServerFail Enabled
configFileVersionChanged Enabled radiusServerChanged
Enabled
systemDown Enabled systemUp Enabled
=============================================
Enterprise AP#
5-42
Page 89

SNMP
Configuring SNMPv3 Users
The access point allows up to 10 SNMP v3 users to be configured. Each user must
be defined by a unique name, assigned to one of three pre-defined security groups,
and configured with specific authentication and encryption settings.
User – The SNMPv3 user name. (32 characters maximum)
Group – The SNMPv3 group name. (Options: RO, RWAuth, or RWPriv; Default: RO)
• RO – Read-only access.
• RWAuth – Read/write access with user authentication.
• RWPriv – Read/write access with both user authentication and data encryption.
Auth Type – The authentication type used for the SNMP user; either MD5 or none.
When MD5 is selected, enter a password in the corresponding Passphrase field.
Priv Type – The data encryption type used for the SNMP user; either DES or none.
When DES is selected, enter a key in the corresponding Passphrase field.
Passphrase – The password or key associated with the authentication and privacy
settings. A minimum of eight plain text characters is required.
Action – Click the Add button to add a new user to the list. Click the edit button to
change details of an existing user. Click the Del button to remove a user from the list.
Note: Users must be assigned to groups that have the same security levels. For
example, a user who has “Auth Type” and “Priv Type” configured to MD5 and
DES respectively (that it, uses both authentication and data encryption) must be
assigned to the RWPriv group. If this same user were instead assigned to the
read-only (RO) group, the user would not be able to access the database.
5
5-43
Page 90

System Configuration
5
CLI Commands for Configuring SNMPv3 Users – Use the snmp-server engine-id
command to define the SNMP v3 engine before assigning users to groups. Use the
snmp-server user command to assign users to one of the three groups and set the
appropriate authentication and encryption types to be used. To view the current
SNMP v3 engine ID, use the show snmp command. To view SNMP users and
group settings, use the show snmp users or show snmp group-assignments
commands.
Enterprise AP(config)#snmp-server engine-id 1a:2b:3c:4d:00:ff
6-45
Enterprise AP(config)#snmp-server user 6-45
User Name<1-32> :chris
Group Name<1-32> :RWPriv
Authtype(md5,<cr>none):md5
Passphrase<8-32>:a good secret
Privacy(des,<cr>none) :des
Passphrase<8-32>:a very good secret
Enterprise AP(config)#exit
Enterprise AP#show snmp users 6-50
=============================================
UserName :chris
GroupName :RWPriv
AuthType :MD5
Passphrase:****************
PrivType :DES
Passphrase:****************
=============================================
Enterprise AP#show snmp group-assignments 6-50
GroupName :RWPriv
UserName :chris
Enterprise AP#
5-44
Page 91

SNMP
Configuring SNMPv3 Trap Filters
SNMP v3 users can be configured to receive notification messages from the access
point. An SNMP Target ID is created that specifies the SNMP v3 user, IP address,
and UDP port. A user-defined notification filter can be created so that specific
notifications can be prevented from being sent to particular targets.
The access point allows up to 10 notification filters to be created. Each filter can be
defined by up to 20 MIB subtree ID entries.
To configure a new notification filter, click the New button. A new page opens to
configure the filter (see below). To edit an existing filter, select the radio button next
to the entry in the table and then click the Edit button. To delete a filter, select the
radio button next to the entry in the table and then click the Delete button.
When you click on the New button in the SNMP Trap Filters page, a new page
opens where the filter parameters are configured. Define a filter name and subtree
ID to be filtered. Select the filter type, include or exclude, from the drop-down list.
Click Apply to create the filter.
5
To add more subtree IDs to the filter, return to the SNMP Trap Filters page and click
the Edit button. In the Edit page, click the New button to access the Add SNMP
Notification Subtree page and configure a new subtree ID to be filtered.
5-45
Page 92

System Configuration
5
Note: Only the New Filter page allows the Filter ID to be configured.
Filter ID – A user-defined name that identifies the filter. (Maximum length: 32
characters)
Subtree OID – Specifies MIB subtree to be filtered. The MIB subtree must be
defined in the form “.1.3.6.1” and always start with a “.”.
Filter Type – Indicates if the filter is to “include” or “exclude” the MIB subtree objects
from the filter. Note that MIB objects included in the filter are not sent to the receiving
target and objects excluded are sent. By default all traps are sent, so you can first
use an “include” filter entry for all trap objects. Then use “exclude” entries for the
required trap objects to send to the target. Note that the filter entries are applied in
the sequence that they are defined.
CLI Commands for Configuring SNMPv3 Trap Filters – To create a notification filter,
use the snmp-server filter command from the CLI configuration mode. Use the
command more than once with the same filter ID to build a filter that includes or
excludes multiple MIB objects. To view the current SNMP filters, use the show
snmp filter command from the CLI Exec mode.
Enterprise AP(config)#snmp-server filter trapfilter
include .1 6-48
Enterprise AP(config)#snmp-server filter trapfilter
exclude .1.3.6.1.2.1.2.2.1.1.23
Enterprise AP(config)#exit
Enterprise AP#show snmp filter 6-51
Filter: trapfilter
Type: include
Subtree: iso
Type: exclude
Subtree: iso.3.6.1.2.1.2.2.1.1.23
=============================
Enterprise AP#
5-46
Page 93

SNMP
Configuring SNMPv3 Targets
An SNMP v3 notification Target ID is specified by the SNMP v3 user, IP address,
and UDP port. A user-defined filter can also be assigned to specific targets to limit
the notifications received to specific MIB objects. (Note that the filter must first be
configured. see “Configuring SNMPv3 Trap Filters” on page 5-45)
To configure a new notification receiver target, click the New button. A new page
opens to configure the settings (see below). To edit an existing target, select the
radio button next to the entry in the table and then click the Edit button. To delete
targets, select the radio button next to the entry in the table and then click the Delete
button.
When you click on the New or Edit button in the SNMP Targets page, a new page
opens where the target parameters are configured. Define the parameters and
select a filter, if required. Note that the SNMP v3 user name must first be defined
(see “Configuring SNMPv3 Users” on page 5-43). Click Apply.
Note: The Target ID cannot be changed in the Edit Target page. Only the New Target
page allows the Target ID to be configured.
5
5-47
Page 94

System Configuration
5
Target ID – A user-defined name that identifies a receiver of notifications. The
access point supports up to 10 target IDs. (Maximum length: 32 characters)
IP Address – Specifies the IP address of the receiving management station.
UDP Port – The UDP port that is used on the receiving management station for
notification messages.
SNMP User – The defined SNMP v3 user that is to receive notification messages.
Assigned Filter – The name of a user-defined notification filter that is applied to the
target.
CLI Commands for Configuring SNMPv3 Targets – To create a notification target,
use the snmp-server targets command from the CLI configuration mode. To assign
a filter to a target, use the snmp-server filter-assignment command. To view the
current SNMP targets, use the show snmp target command from the CLI Exec
mode. To view filter assignment to targets, use the show snmp filter-assignments
command.
5-48
Page 95

Radio Interface
Enterprise AP(config)#snmp-server targets mytraps
192.168.1.33 chris 6-47
Enterprise AP(config)#snmp-server filter-assignment
mytraps trapfilter 6-49
Enterprise AP(config)#exit
Enterprise AP#show snmp target 6-51
Host ID : mytraps
User : chris
IP Address : 192.168.1.33
UDP Port : 162
=============================
Enterprise AP#show snmp filter-assignments 6-52
HostID FilterID
mytraps trapfilter
Enterprise AP#
Radio Interface
The IEEE 802.11b/g interface includes configuration options for radio signal
characteristics and wireless security features.
The IEEE 802.11g standard operates within the 2.4 GHz band at up to 54 Mbps.
Also note that because the IEEE 802.11g standard is an extension of the IEEE
802.11b standard, it allows clients with 802.11b wireless network cards to associate
to an 802.11g access point.
The access point can operate in three modes, IEEE 802.11b only, 802.11g only, or a
mixed 802.11b/g mode. Also note that 802.11g is backward compatible with
802.11b.
Each radio supports up to eight virtual access point (VAP) interfaces numbered 0 to
7. Each VAP functions as a separate access point, and can be configured with its
own Service Set Identification (SSID) and security settings. However, most radio
signal parameters apply to all eight VAP interfaces.
The VAPs function similar to a VLAN, with each VAP mapped to its own VLAN ID.
Traffic to specific VAPs can be segregated based on user groups or application
traffic. Each VAP can have up to 64 wireless clients, whereby the clients associate
with these VAPs the same as they would with a physical access point.
Note: The radio channel settings for the access point are limited by local regulations,
which determine the number of channels that are available. Refer to “General
Specifications” on page C-1 for additional information on the maximum number
channels available.
Note: You must first enable VAP interface 0 before the other interfaces can be enabled.
5
5-49
Page 96

System Configuration
5
Radio Channel – The radio channel that the access point uses to communicate with
wireless clients. When multiple access points are deployed in the same area, set the
channel on neighboring access points at least five channels apart to avoid
interference with each other. For example, in the United States you can deploy up to
three access points in the same area (e.g., channels 1, 6, 11). Also note that the
channel for wireless clients is automatically set to the same as that used by the
access point to which it is linked. (Range: 1-11; Default: 1)
Auto Channel Select – Enables the access point to automatically select an
unoccupied radio channel. (Default: Enabled)
Transmit Power – Adjusts the power of the radio signals transmitted from the access
point. The higher the transmission power, the farther the transmission range. Power
selection is not just a trade off between coverage area and maximum supported
clients. You also have to ensure that high-power signals do not interfere with the
operation of other radio devices in the service area. (Options: 100%, 50%, 25%,
12%, minimum; Default: 100%)
Note: When operating the access point using 5 GHz channels in a European
Community country, the end user and installer are obligated to operate the device
in accordance with European regulatory requirements for Transmit Power Control
(TPC).
5-50
Page 97

Radio Interface
Maximum Station Data Rate – The maximum data rate at which the access
point transmits unicast packets on the wireless interface. The maximum
transmission distance is affected by the data rate. The lower the data rate,
the longer the transmission distance. (Default: 54 Mbps)
Maximum Associated Clients – Sets the maximum number of clients that can
be associated with a VAP interface at the same time. (Range: 1-64 per VAP
interface: Default: 64)
Antenna ID – Selects the antenna to be used by the access point; either the
integrated diversity antennas (the "Default Antenna") or an optional external
antenna. The optional external antennas (if any) that are certified for use
with the access point are listed in the drop-down menu. Selecting the correct
antenna ID ensures that the access point's radio transmissions are within regulatory
power limits for the country of operation. (Default: Default Antenna)
Note: The Antenna ID must be selected in conjunction with the Antenna Control Method
to configure proper use of any of the antenna options. This access point does not
support optional external antennas.
Antenna Control Method - Selects the use of both fixed antennas operating in
diversity mode or a single antenna. (Default: Diversity)
• Diversity: The radio uses both antennas in a diversity system. Select this method
when the Antenna ID is set to "Default Antenna" to use the access point's
integrated antennas.
• Right: The radio only uses the antenna on the right side (the side closest to the
access point LEDs). Select this method when using an optional external antenna
that is connected to the right antenna connector.
• Left: The radio only uses the antenna on the left side (the side farthest from the
access point LEDs). Select this method when using an optional external antenna
that is connected to the left antenna connector.
Antenna Location – Selects the mounting location of the antenna in use; either
“Indoor” or “Outdoor.” Selecting the correct location ensures that the access point
only uses radio channels that are permitted in the country of operation.
(Default: Indoor)
MIC Mode – The Michael Integrity Check (MIC) is part of the Temporal Key Integrity
Protocol (TKIP) encryption used in Wi-Fi Protected Access (WPA) security. The MIC
calculation is performed in the access point for each transmitted packet and this can
impact throughput and performance. The access point supports a choice of software
or hardware MIC calculation. The performance of the access point can be improved
by selecting the best method for the specific deployment. (Default: Software)
• Hardware: Provides best performance when the number of supported clients is
less than 27.
• Software: Provides the best performance for a large number of clients on one radio
interface. Throughput may be reduced when the 802.11g interface is supporting a
high number of clients simultaneously.
5
5-51
Page 98

System Configuration
5
Super G – The Atheros proprietary Super G performance enhancements
are supported by the access point. These enhancements include bursting,
compression, fast frames and dynamic turbo. Maximum throughput ranges between
40 to 60 Mbps for connections to Atheros-compatible clients. (Default: Disabled)
Radio Mode – Selects the operating mode for the 802.11g wireless interface.
(Default: 802.11b+g)
• 802.11b+g: Both 802.11b and 802.11g clients can communicate with the access
point (up to 54 Mbps).
• 802.11b only: Both 802.11b and 802.11g clients can communicate with the access
point, but 802.11g clients can only transfer data at 802.11b standard rates (up to
11 Mbps).
• 802.11g only: Only 802.11g clients can communicate with the access point (up to
54 Mbps).
Preamble – Sets the length of the signal preamble that is used at the start of a data
transmission. (Default: Long)
• Long: Sets the preamble to long (192 microseconds). Using a long preamble
ensures the access point can support all 802.11b and 802.11g clients.
• Short or Long: Sets the preamble according to the capability of clients that are
currently asscociated. Uses a short preamble (96 microseconds) if all associated
clients can support it, otherwise a long preamble is used. The access point can
increase data throughput when using a short preamble, but will only use a short
preamble if it determines that all associated clients support it.
Beacon Interval – The rate at which beacon signals are transmitted from the access
point. The beacon signals allow wireless clients to maintain contact with the access
point. They may also carry power-management information.
(Range: 20-1000 TUs; Default: 100 TUs)
Data Beacon Rate – The rate at which stations in sleep mode must wake up to
receive broadcast/multicast transmissions.
Known also as the Delivery Traffic Indication Map (DTIM) interval, it indicates how
often the MAC layer forwards broadcast/multicast traffic, which is necessary to wake
up stations that are using Power Save mode. The default value of 2 indicates that
the access point will save all broadcast/multicast frames for the Basic Service Set
(BSS) and forward them after every second beacon. Using smaller DTIM intervals
delivers broadcast/multicast frames in a more timely manner, causing stations in
Power Save mode to wake up more often and drain power faster. Using higher DTIM
values reduces the power used by stations in Power Save mode, but delays the
transmission of broadcast/multicast frames.
(Range: 1-255 beacons; Default: 1 beacon)
Multicast Data Rate – The maximum data rate at which the access point transmits
multicast and broadcast packets on the wireless interface. (Options: 24, 12, 6
Mbps; Default: 6 Mbps)
5-52
Page 99

Radio Interface
Fragmentation Length – Configures the minimum packet size that can be
fragmented when passing through the access point. Fragmentation of the PDUs
(Package Data Unit) can increase the reliability of transmissions because it
increases the probability of a successful transmission due to smaller frame size. If
there is significant interference present, or collisions due to high network utilization,
try setting the fragment size to send smaller fragments. This will speed up the
retransmission of smaller frames. However, it is more efficient to set the fragment
size larger if very little or no interference is present because it requires overhead to
send multiple frames. (Range: 256-2346 bytes; Default: 2346 bytes)
RTS Threshold – Sets the packet size threshold at which a Request to Send (RTS)
signal must be sent to a receiving station prior to the sending station starting
communications. The access point sends RTS frames to a receiving station to
negotiate the sending of a data frame. After receiving an RTS frame, the station
sends a CTS (clear to send) frame to notify the sending station that it can start
sending data.
If the RTS threshold is set to 0, the access point always sends RTS signals. If set to
2347, the access point never sends RTS signals. If set to any other value, and the
packet size equals or exceeds the RTS threshold, the RTS/CTS (Request to Send /
Clear to Send) mechanism will be enabled.
The access points contending for the medium may not be aware of each other. The
RTS/CTS mechanism can solve this “Hidden Node Problem.” (Range: 0-2347 bytes:
Default: 2347 bytes)
5
5-53
Page 100

System Configuration
5
CLI Commands for Radio Settings – From the global configuration mode, enter the
interface wireless g command to access the 802.11g radio interface. From the
802.11g interface mode, you can access radio settings that apply to all VAP
interfaces. Use the turbo command to enable this feature before setting the radio
channel with the channel command. Set any other radio setting as required before
enabling the VAP interface (with the no shutdown command). To view the current
802.11g radio settings for the VAP interface, use the show interface wireless g
[0~7] command as shown on 6-94.
Enterprise AP(config)#interface wireless g 6-87
Enter Wireless configuration commands, one per line.
Enterprise AP(if-wireless g)#super-g 6-103
Enterprise AP(if-wireless g)#channel 42 6-96
Enterprise AP(if-wireless g)#transmit-power full 6-96
Enterprise AP(if-wireless g)#speed 9 6-95
Enterprise AP(if-wireless g)#antenna id 0000 6-99
Enterprise AP(if-wireless g)#antenna control right 6-98
Enterprise AP(if-wireless g)#antenna location indoor 6-100
Enterprise AP(if-wireless g)#mic_mode hardware 6-119
Enterprise AP(if-wireless g)#super-g 7-104
Enterprise AP(if-wireless g)#beacon-interval 150 6-100
Enterprise AP(if-wireless g)#beacon-interval 150 6-100
Enterprise AP(if-wireless g)#dtim-period 5 6-101
Enterprise AP(if-wireless g)#multicast-data-rate 6 6-95
Enterprise AP(if-wireless g)#fragmentation-length 512 6-101
Enterprise AP(if-wireless g)#rts-threshold 256 6-102
Enterprise AP(if-wireless g)#
5-54
 Loading...
Loading...