Nortel Secure Network Access Switch
Using the Command Line
Interface
Release: 2.0
Document Revision: 03.01
www.nortel.com
NN47230-100
.
320818-D

Nortel Secure Network Access Switch
Release: 2.0
Publication: NN47230-100
Document status: Standard
Document release date: 28 July 2008
Copyright © 2007, 2008 Nortel Networks
All Rights Reserved.
Sourced in Canada, the United States of America, and India
LEGAL NOTICE
While the information in this document is believed to be accurate and reliable, except as otherwise expressly
agreed to in writing NORTEL PROVIDES THIS DOCUMENT "AS IS "WITHOUT WARRANTY OR CONDITION OF
ANY KIND, EITHER EXPRESS OR IMPLIED. The information and/or products described in this document are
subject to change without notice.
Nortel, the Nortel logo, and the Globemark are trademarks of Nortel Networks.
All other trademarks are the property of their respective owners.
.
.
Contents
Software license 11
New in this release 15
Features 15
Other changes 16
Introduction 17
Before you begin 18
Text conventions 18
Related information 20
How to get help 21
Overview 23
The Nortel SNAS 24
Nortel SNAS configuration and management tools 36
Nortel SNAS configuration roadmap 37
3
Publications 20
Online 21
Elements of the Nortel SNAS 25
Supported users 25
Supporting additional users with the software license file 26
Role of the Nortel SNAS 27
Nortel SNAS clusters 35
Interface configuration 35
Initial setup 41
Before you begin 41
About the IP addresses 42
Initial setup 43
Setting up a single Nortel SNAS device or the first in a cluster 43
Adding a Nortel SNAS device to a cluster 50
Next steps 54
Applying and saving the configuration 55
Managing the network access devices 57
Before you begin 57
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
4
Managing network access devices 58
Roadmap of domain switch commands 58
Adding a network access devices 60
Deleting a network access devices 64
Configuring the network access devices 64
Mapping the VLANs 66
Managing SSH keys 68
Monitoring switch health 73
Controlling communication with the network access devices 74
Configuring SSCPLite 74
Configuring SNMP Profiles 75
Configuring SNMP Versions 76
Configuring SSCPLite Community 77
Configuring SNMP Templates 77
Configuring the domain 79
Configuring the domain 79
Roadmap of domain commands 81
Creating a domain 83
Deleting a domain 89
Configuring domain parameters 89
Configuring the Nortel Health Agent check 92
Configuring the SSL server 97
Configuring HTTP redirect 107
Browser-Based Management Configuration 108
Browser-Based Management Configuration with SSL 108
Configuring advanced settings 109
Configuring RADIUS accounting 110
Configuring local DHCP services 115
Creation of the location 123
Configuring Lumension PatchLink integration 124
Configuration of the RADIUS server 127
Overview of RADIUS server 127
802.1x functionality 127
Roadmap of RADIUS server configuration commands 128
Configuration of the RADIUS server 129
Configuration of the client 130
Configuration of the realms 131
Configuration of the dictionary 133
Configuration of the RADIUS accounting 134
Configuration of the RADIUS authentication methods 134
Configuration of the EAP authentication methods 136
Select the server certificate 137
Select the CA certificate 138
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
Configuration of Microsoft NAP Interoperability 139
Roadmap of NAP configuration commands 139
Configuration of NAP Interoperability 140
Probation Settings 141
Remote Network Policy Servers 142
System Health Validators 143
Configuration of Windows System Health Validator 144
Configuring groups and profiles 149
Overview 149
Groups 150
Linksets 151
SRS rule 151
Extended profiles 151
Before you begin 152
Configuring groups and extended profiles 153
Roadmap of group and profile commands 153
Configuring groups 156
Configuring client filters 162
Configuring extended profiles 164
Creating RADIUS attributes to a group 166
Mapping linksets to a group or profile 167
Creating a default group 169
5
Configuring authentication 171
Overview 171
Before you begin 172
Configuring authentication 174
Roadmap of authentication commands 174
Configuring authentication methods 177
Configuring advanced settings 179
Configuring RADIUS authentication 180
Configuring LDAP authentication 187
Configuring local database authentication 200
Specifying authentication fallback order 209
Managing system users and groups 211
User rights and group membership 211
Managing system users and groups 212
Roadmap of system user management commands 212
Managing user accounts and passwords 213
Managing user settings 216
Managing user groups 217
CLI configuration examples 218
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
6
Customizing the portal and user logon 227
Overview 227
Captive portal and Exclude List 228
Portal display 230
Managing the end user experience 237
Customizing the portal and logon 238
Roadmap of portal and logon configuration commands 238
Configuring the captive portal 240
Configuring the Exclude List 240
Changing the portal language 241
Configuring the portal display 244
Changing the portal colors 249
Configuring custom content 250
Configuring linksets 251
Configuring links 253
Configuring system settings 257
Configuring the cluster 257
Roadmap of system commands 258
Configuring system settings 262
Configuring the Nortel SNAS host 264
Configuring host interfaces 268
Configuring static routes 270
Configuring host ports 271
Managing interface ports 272
Configuring the Access List 273
Configuring date and time settings 274
Configuring DNS servers and settings 276
Configuring RSA servers 279
Configuring syslog servers 279
Configuring administrative settings 281
Enabling TunnelGuard SRS administration 284
Configuring Nortel SNAS host SSH keys 284
Configuring RADIUS auditing 286
Configuring authentication of system users 290
Configuration of auto blacklisting 293
Configuration of harden password 295
Managing certificates 297
Overview 297
Key and certificate formats 298
Creating certificates 299
Installing certificates and keys 299
Saving or exporting certificates and keys 300
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
Updating certificates 300
Managing private keys and certificates 301
Roadmap of certificate management commands 301
Managing and viewing certificates and keys 302
Generating and submitting a CSR 305
Adding a certificate to the Nortel SNAS 310
Adding a private key to the Nortel SNAS 312
Importing certificates and keys into the Nortel SNAS 314
Displaying or saving a certificate and key 316
Exporting a certificate and key from the Nortel SNAS 318
Generating a test certificate 320
Configuring SNMP 323
Configuring SNMP 324
Roadmap of SNMP commands 324
Configuring SNMP settings 325
Configuring the SNMP v2 MIB 326
Configuring the SNMP community 327
Configuring SNMPv3 users 328
Configuring SNMP notification targets 331
Configuring SNMP events 332
7
Viewing system information and performance statistics 337
Viewing system information and performance statistics 337
Roadmap of information and statistics commands 337
Viewing system information 339
Viewing alarm events 344
Viewing log files 345
Viewing AAA statistics 346
Viewing all statistics 348
Kicking by username or address 349
Nortel SNAS TPS Interface 349
Maintaining and managing the system 351
Managing and maintaining the system 352
Roadmap of maintenance and boot commands 352
Performing maintenance 353
Backing up or restoring the configuration 356
Configuring the Nortel SNAS scheduler 359
Managing Nortel SNAS devices 361
Managing software for a Nortel SNAS device 363
Upgrading or reinstalling the software 367
Upgrading the Nortel SNAS 367
Performing minor and major release upgrades 368
Activating the software upgrade package 369
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
8
Reinstalling the software 372
Before you begin 372
Reinstalling the software from an external file server 373
Reinstalling the software from a CD 375
The Command Line Interface 377
Connecting to the Nortel SNAS 378
Establishing a console connection 378
Establishing a Telnet connection 379
Establishing a connection using SSH 380
Accessing the Nortel SNAS cluster 381
CLI Main Menu or Setup 383
Command line history and editing 383
Idle timeout 383
Configuration example 385
Scenario 385
Steps 387
Configure the network DNS server 388
Configure the network DHCP server 388
Configure the network core router 392
Configure the Ethernet Routing Switch 8300 393
Configure the Ethernet Routing Switch 5510 395
Configure the Nortel SNAS 397
Troubleshooting 403
Troubleshooting tips 403
Cannot connect to the Nortel SNAS using Telnet or SSH 403
Cannot add the Nortel SNAS to a cluster 405
Cannot contact the MIP 406
The Nortel SNAS stops responding 407
A user password is lost 408
A user fails to connect to the Nortel SNAS domain 409
Trace tools 409
System diagnostics 410
Installed certificates 410
Network diagnostics 410
Active alarms and the events log file 412
Error log files 412
Using the CLI 413
Global commands 414
Command line history and editing 416
CLI shortcuts 417
Using slashes and spaces in commands 419
IP address and network mask formats 420
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Variables 420
CLI Main Menu 421
CLI command reference 422
Information menu 422
Statistics menu 423
Configuration menu 424
Boot menu 448
Maintenance menu 449
Syslog messages by message type 451
Operating system (OS) messages 452
System Control Process messages 453
Traffic Processing Subsystem messages 457
Start-up messages 461
AAA subsystem messages 461
NSNAS subsystem messages 463
Syslog messages in alphabetical order 465
Supported MIBs 477
Supported traps 481
485
Install All Administrative Tools (Windows 2000 Server) 485
Register the Schema Management dll (Windows Server 2003) 485
Add the Active Directory Schema Snap-in (Windows 2000 Server and Windows
Server 2003) 486
Permit write operations to the schema (Windows 2000 Server) 488
Create a new attribute(Windows 2000 Server and Windows Server 2003) 489
Create the new class 489
Configuring IP Phone auto-configuration 494
Creating the DHCP options 494
Configuring the Call Server Information and VLAN Information options 497
Setting up the IP Phone 500
Configuring the logon script 501
Creating a logon script 502
Creating the script as a batch file 502
Creating the script as a VBScript file 503
Assigning the logon script 503
9
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

10
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
Software license
This section contains the Nortel Networks software license.
Nortel Networks software license agreement
This Software License Agreement ("License Agreement") is between
you, the end-user ("Customer") and Nortel Networks Corporation and
its subsidiaries and affiliates ("Nortel Networks"). PLEASE READ THE
FOLLOWING CAREFULLY. YOU MUST ACCEPT THESE LICENSE
TERMS IN ORDER TO DOWNLOAD AND/OR USE THE SOFTWARE.
USE OF THE SOFTWARE CONSTITUTES YOUR ACCEPTANCE OF
THIS LICENSE AGREEMENT. If you do not accept these terms and
conditions, return the Software, unused and in the original shipping
container, within 30 days of purchase to obtain a credit for the full
purchase price.
"Software" is owned or licensed by Nortel Networks, its parent or one of
its subsidiaries or affiliates, and is copyrighted and licensed, not sold.
Software consists of machine-readable instructions, its components, data,
audio-visual content (such as images, text, recordings or pictures) and
related licensed materials including all whole or partial copies. Nortel
Networks grants you a license to use the Software only in the country
where you acquired the Software. You obtain no rights other than those
granted to you under this License Agreement. You are responsible for the
selection of the Software and for the installation of, use of, and results
obtained from the Software.
11
1. Licensed Use of Software. Nortel Networks grants Customer a
nonexclusive license to use a copy of the Software on only one
machine at any one time or to the extent of the activation or authorized
usage level, whichever is applicable. To the extent Software is
furnished for use with designated hardware or Customer furnished
equipment ("CFE"), Customer is granted a nonexclusive license to
use Software only on such hardware or CFE, as applicable. Software
contains trade secrets and Customer agrees to treat Software as
confidential information using the same care and discretion Customer
uses with its own similar information that it does not wish to disclose,
publish or disseminate. Customer will ensure that anyone who
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

12 Software license
2. Warranty. Except as may be otherwise expressly agreed to in
uses the Software does so only in compliance with the terms of this
Agreement. Customer shall not a) use, copy, modify, transfer or
distribute the Software except as expressly authorized; b) reverse
assemble, reverse compile, reverse engineer or otherwise translate the
Software; c) create derivative works or modifications unless expressly
authorized; or d) sublicense, rent or lease the Software. Licensors
of intellectual property to Nortel Networks are beneficiaries of this
provision. Upon termination or breach of the license by Customer or in
the event designated hardware or CFE is no longer in use, Customer
will promptly return the Software to Nortel Networks or certify its
destruction. Nortel Networks may audit by remote polling or other
reasonable means to determine Customer’s Software activation or
usage levels. If suppliers of third party software included in Software
require Nortel Networks to include additional or different terms,
Customer agrees to abide by such terms provided by Nortel Networks
with respect to such third party software.
writing between Nortel Networks and Customer, Software is provided
"AS IS" without any warranties (conditions) of any kind. NORTEL
NETWORKS DISCLAIMS ALL WARRANTIES (CONDITIONS)
FOR THE SOFTWARE, EITHER EXPRESS OR IMPLIED,
INCLUDING, BUT NOT LIMITED TO THE IMPLIED WARRANTIES OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
AND ANY WARRANTY OF NON-INFRINGEMENT. Nortel Networks is
not obligated to provide support of any kind for the Software. Some
jurisdictions do not allow exclusion of implied warranties, and, in such
event, the above exclusions may not apply.
3.
Limitation of Remedies. IN NO EVENT SHALL NORTEL
NETWORKS OR ITS AGENTS OR SUPPLIERS BE LIABLE FOR ANY
OF THE FOLLOWING: a) DAMAGES BASED ON ANY THIRD PARTY
CLAIM; b) LOSS OF, OR DAMAGE TO, CUSTOMER’S RECORDS,
FILES OR DATA; OR c) DIRECT, INDIRECT, SPECIAL, INCIDENTAL,
PUNITIVE, OR CONSEQUENTIAL DAMAGES (INCLUDING LOST
PROFITS OR SAVINGS), WHETHER IN CONTRACT, TORT OR
OTHERWISE (INCLUDING NEGLIGENCE) ARISING OUT OF
YOUR USE OF THE SOFTWARE, EVEN IF NORTEL NETWORKS,
ITS AGENTS OR SUPPLIERS HAVE BEEN ADVISED OF THEIR
POSSIBILITY. The foregoing limitations of remedies also apply to any
developer and/or supplier of the Software. Such developer and/or
supplier is an intended beneficiary of this Section. Some jurisdictions
do not allow these limitations or exclusions and, in such event, they
may not apply.
4. General
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Nortel Networks software license agreement 13
a. If Customer is the United States Government, the following
paragraph shall apply: All Nortel Networks Software available
under this License Agreement is commercial computer software
and commercial computer software documentation and, in the
event Software is licensed for or on behalf of the United States
Government, the respective rights to the software and software
documentation are governed by Nortel Networks standard
commercial license in accordance with U.S. Federal Regulations
at 48 C.F.R. Sections 12.212 (for non-DoD entities) and 48 C.F.R.
227.7202 (for DoD entities).
b. Customer may terminate the license at any time. Nortel Networks
may terminate the license if Customer fails to comply with the terms
and conditions of this license. In either event, upon termination,
Customer must either return the Software to Nortel Networks or
certify its destruction.
c. Customer is responsible for payment of any taxes, including
personal property taxes, resulting from Customer’s use of the
Software. Customer agrees to comply with all applicable laws
including all applicable export and import laws and regulations.
d.
Neither party may bring an action, regardless of form, more than
two years after the cause of the action arose.
e.
The terms and conditions of this License Agreement form the
complete and exclusive agreement between Customer and Nortel
Networks.
f.
This License Agreement is governed by the laws of the country in
which Customer acquires the Software. If the Software is acquired
in the United States, then this License Agreement is governed by
the laws of the state of New York.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

14 Software license
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
New in this release
The following sections detail what’s new in Nortel Secure Network Access
Using the Command Line Interface, (NN47230-100) for Release 2.0.
•
“Features” (page 15)
•
“Other changes” (page 16)
Features
This is the second standard release of the document. See the following
sections for information, which are added in this Release.
•
“Configuring SSCPLite” (page 74)
•
“Configuring SNMP Profiles” (page 75)
• “Creation of the location” (page 123)
•
“Configuring Lumension PatchLink integration ” (page 124)
15
•
“Creation of the location” (page 123)
•
“Configuration of the RADIUS server” (page 127)
• “Configuration of Microsoft NAP Interoperability” (page 139)
•
“Configuration of auto blacklisting” (page 293)
•
“Configuration of harden password” (page 295)
•
“Kicking by username or address” (page 349)
• “Nortel SNAS TPS Interface” (page 349)
• “Self service portal” (page 233)
• “Configuring the Nortel SNAS scheduler” (page 359)
On-the-fly SRS Policy Change—When a security policy is modified
on the SNAS using the administrative tool the policy is updated on the
Nortel Health Agent running on the logged in operating systems. For more
information, See the “Configuring the Nortel Health Agent check” (page
92).
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

16 New in this release
Multi-OS Applet Support—The Nortel Health captive portal applet
supports Windows and non-Windows operating systems. For
non-Windows operating systems the applet supports collecting operating
systems information and VLAN transition. for more information, see the
“Multi-OS Applet Support” (page 32).
Other changes
No changes.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
Introduction
Nortel* Secure Network Access (Nortel SNAS ) is a clientless solution that
provides seamless, secure access to the corporate network from inside
or outside that network. The Nortel SNAS combines multiple hardware
devices and software components to support the following features:
•
partitions the network resources into access zones (authentication,
remediation, and full access)
•
provides continual device integrity checking using Nortel Health Agent
•
supports both dynamic and static IP clients
The Nortel Secure Network Access Switch 4050or 4070 (Nortel SNAS
4050 or 4070) controls operation of the Nortel SNAS.
This user guide covers the process of implementing the Nortel SNAS using
the Nortel SNAS 4050 or 4070 for Nortel Secure Network Access Switch
Software Release 2.0. The document includes the following information:
17
•
overview of the role of the Nortel SNAS 4050 or 4070 in the Nortel
SNAS
•
initial setup
•
configuring authentication, authorization, and accounting (AAA)
features
•
managing system users
• customizing the portal
• upgrading the software
• logging and monitoring
• troubleshooting installation and operation
The document provides instructions for initializing and customizing the
features using the Command Line Interface (CLI). To learn the basic
structure and operation of the Nortel SNAS CLI, refer to “CLI reference”
(page 413). This reference guide provides links to where the function
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
18 Introduction
and syntax of each CLI command are described in the document. For
information on accessing the CLI, see “The Command Line Interface”
(page 377).
BBI is a graphical user interface (GUI) that runs in an online, interactive
mode. BBI allows the management of multiple devices (for example, the
Nortel SNAS) from one application. For information about using BBI to
configure and manage Nortel SNAS, see
Switch Configuration — Using the BBI, (NN47230-500).
Before you begin
This guide is intended for network administrators who have the following
background:
•
basic knowledge of networks, Ethernet bridging, and IP routing
• familiarity with networking concepts and terminology
•
experience with windowing systems or GUIs
•
basic knowledge of network topologies
Nortel Secure Network Access
Before using this guide, you must complete the following procedures. For
a new switch:
Step Action
1 Install the switch.
2 Connect the switch to the network.
Ensure that you are running the latest version of Nortel SNAS software.
For information about upgrading the Nortel SNAS, see “Upgrading or
reinstalling the software” (page 367).
Text conventions
This guide uses the following text conventions:
For installation instructions, see Nortel Secure Network Access
Switch 4050 Installation Guide , (NN47230-300).
For more information, see “The Command Line Interface” (page
377).
--End--
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Text conventions 19
angle brackets (< >)
Enter text based on the description inside the
brackets. Do not type the brackets when entering
the command.
Example: If the command syntax is
ping <ip_address>, you enter
ping 192.32.10.12
bold text Objects such as window names, dialog box names,
and icons, as well as user interface objects such
as buttons, tabs, and menu items.
bold Courier text
Command names, options, and text that you must
enter.
Example: Use the dinfo command.
Example: Enter show ip {alerts|routes}.
braces ({})
Required elements in syntax descriptions where
there is more than one option. You must choose
only one of the options. Do not type the braces
when entering the command.
Example: If the command syntax is
show ip {alerts|routes}, you must enter
either show ip alerts or show ip routes, but
not both.
brackets ([ ])
ellipsis points (. . . )
Copyright © 2007, 2008 Nortel Networks
Optional elements in syntax descriptions. Do not
type the brackets when entering the command.
Example: If the command syntax is
show ip interfaces [-alerts], you can enter
either show ip interfaces or
show ip interfaces -alerts.
Repeat the last element of the command as
needed.
Example: If the command syntax is
ethernet/2/1 [ <parameter> <value> ]...,
you enter ethernet/2/1 and as many
parameter-value pairs as needed.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

20 Introduction
italic text
plain Courier text
separator ( > )
vertical line ( | ) Options for command keywords and arguments.
Variables in command syntax descriptions. Also
indicates new terms and book titles. Where a
variable is two or more words, the words are
connected by an underscore.
Example: If the command syntax is
show at <valid_route>,
valid_route is one variable and you substitute
one value for it.
Command syntax and system output, for example,
prompts and system messages.
Example: Set Trap Monitor Filters
Menu paths.
Example: Protocols > IP identifies the IP
command on the Protocols menu.
Enter only one of the options. Do not type the
vertical line when entering the command.
Example: If the command syntax is
show ip {alerts|routes}, you enter either
show ip alerts or show ip routes, but not
both.
Related information
This section lists information sources that relate to this document.
Publications
Refer to the following publications for information on the Nortel SNAS:
• Nortel Secure Network Access Solution Guide, (NN47230-200)
•
Nortel Secure Network Access Switch 4050 Installation Guide ,
(NN47230-300).
• Nortel Secure Network Access Switch 4050 User Guide for the CLI
(NN47230-100),
• Installing and Using the Security,
• Release Notes for Nortel Ethernet Routing Switch 5500 Series,
Software Release 5.0.1,
• Release Notes for the Ethernet Routing Switch 8300, Software
Release 2.2.8 ,
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
Online
How to get help 21
• Release Notes for the Nortel Secure Network Access Solution,
Software Release 1.6.1 (NN47230-400),
• Release Notes for Enterprise Switch Manager (ESM), Software
Release 5.2 (209960-H),
• Using Enterprise Switch Manager Release 5.1 (208963-F),
• Nortel Secure Network Access Switch Configuration — Using the BBI,
(NN47230-500).
To access Nortel technical documentation online, go to the Nortel web site:
ttp://www.nortel.com/support
h
You can download current versions of technical documentation. To locate
documents, browse by category or search using the product name or
number.
You can print the technical manuals and release notes free, directly from
the Internet. Use Adobe* Reader* to open the manuals and release
notes, search for the sections you need, and print them on most standard
printers. Go to the Adobe Systems site at h
download a free copy of Adobe Reader.
ttp://www.adobe.com to
How to get help
If you purchased a service contract for your Nortel product from a
distributor or authorized reseller, contact the technical support staff for that
distributor or reseller for assistance.
If you purchased a Nortel service program, use the h
elp web page to locate information to contact Nortel for assistance:
•
• To call a Nortel Technical Solutions Center for assistance, click the
An Express Routing Code (ERC) is available for many Nortel products and
services. When you use an ERC, your call is routed to a technical support
person who specializes in supporting that product or service. To locate the
ERC for your product or service, go to the h
page and follow these links:
ttp://www.nortel.com/h
To obtain Nortel Technical Support contact information, click the
CONTACT US link on the left side of the page.
CALL US link on the left side of the page to find the telephone number
for your region.
ttp://www.nortel.com/helpweb
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
22 Introduction
Step Action
1 Click CONTACT US on the left side of the HELP web page.
2 Click Technical Support on the CONTACT US web page.
3 Click Express Routing Codes on the TECHNICAL SUPPORT
web page.
--End--
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.
Overview
The Nortel Secure Network Access Solution Release 2.0 features are
mapped to the relevant section(s) in this guide in the following table. For
information on the Nortel SNAS Release 1.6.1 see
Nortel Secure Network Access Solution Release 1.6.1, NN47230-400,
(formerly 320850).
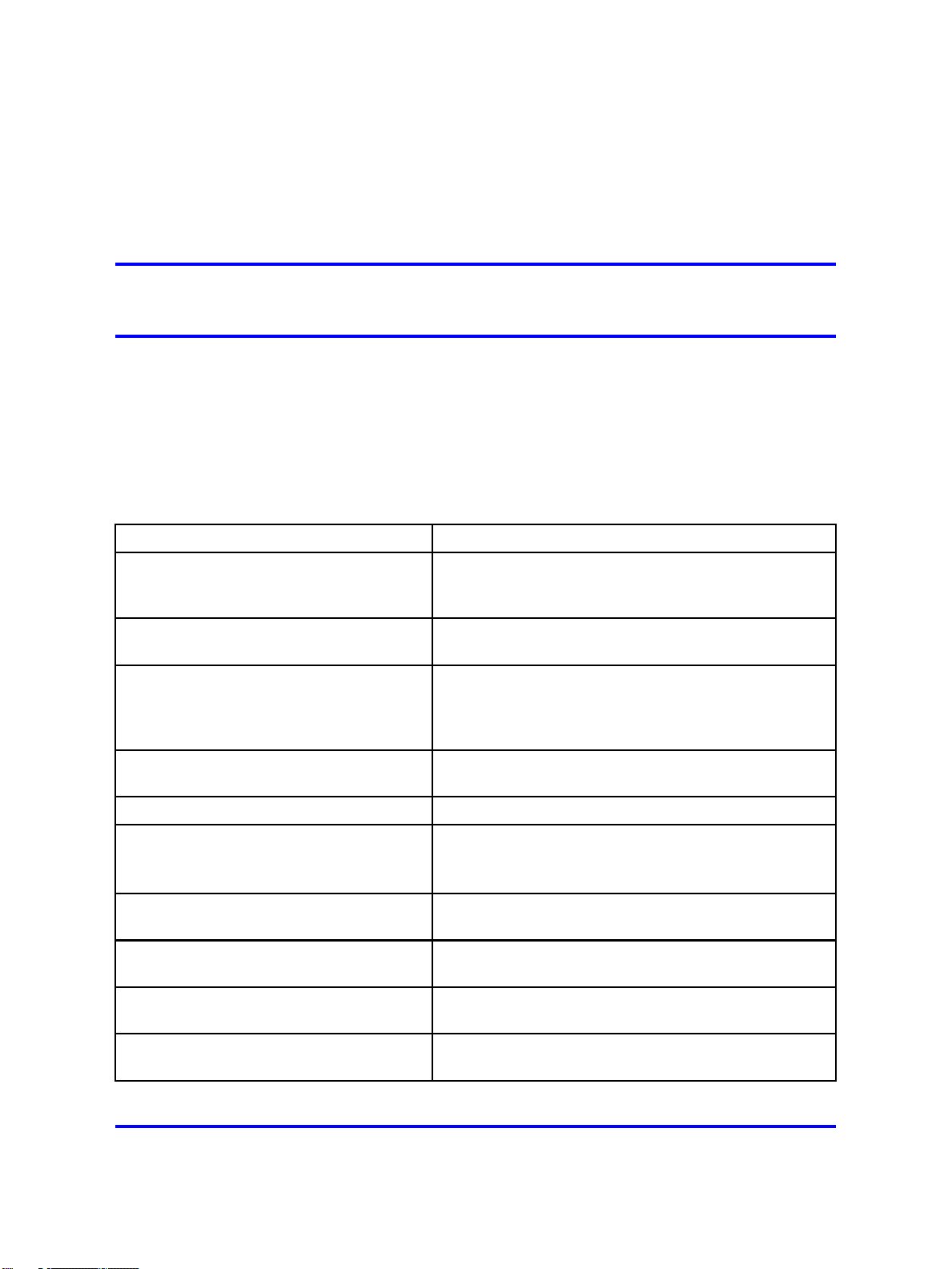
Table 1
Features on NSNA
23
Release Notes for
Feature
Performance and scalability
enhancements: 20,000 concurrent
users
Support for hubs “Configuring local DHCP services” (page 115), “Hub
Support for Nortel Ethernet Switch models
- 325 / 425 / 450 / 470 and 2500 series
and Ethernet Routing Switch models 4500 series, 5500 series, 8300 and 8600.
Support for WLAN Controller “Configuring local DHCP services” (page 115), “Hub
Support of RADIUS server “Configuration of the RADIUS server” (page 127)
Support of Microsoft NAP Interoperability “Configuration of Microsoft NAP Interoperability” (page
Nortel Health Agent Run-Once,
Continuous and Never modes
Support for MAC OSX, Linux OS, and
non-interactive devices
MAC address policy services “Configuring groups” (page 156), “Managing the local
Section
Not applicable.
DHCP subnet type” (page 118)
“Configuring local DHCP services” (page 115), “Hub
DHCP subnet type” (page 118)
DHCP subnet type” (page 118)
139)
“Configuring groups” (page 156), “Managing the local
MAC database” (page 206)
“Configuring groups” (page 156)
MAC database” (page 206)
Flexible deployment: Filter only and VLAN
and filters deployment
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
.
“Nortel SNAS enforcement types” (page 28),
“Configuring groups” (page 156)
28 July 2008
24 Overview
ATTENTION
Switches that support the Switch to Nortel SNAS Communication Protocol
(SSCP) are referred to as NSNA network access devices in this document.
Generally, NSNA network access devices are the Ethernet Routing Switch
5500 Series and the Ethernet Routing Switch 8300. Specifically, Release 1.6.1
features are supported by the Ethernet Routing Switch 5500 Series, Release
5.0.2 and later.
ATTENTION
The character combination "<" appears instead of the character "<" in several
command strings in this document. For example, <DN> rather than <DN>.
Resolution is under investigation.
This chapter includes the following topics:
Topic
“The Nortel SNAS ” (page 24)
“Elements of the Nortel SNAS ” (page 25)
“Supported users” (page 25)
“Role of the Nortel SNAS ” (page 27)
“Nortel SNAS configuration and management tools” (page 36)
“Nortel SNAS configuration roadmap” (page 37)
The Nortel SNAS
Nortel Secure Network Access Solution (Nortel SNAS ) is a protective
framework to completely secure the network from endpoint vulnerability.
The Nortel SNAS addresses endpoint security and enforces policy
compliance. Nortel SNAS delivers endpoint security by enabling only
trusted, role-based access privileges premised on the security level of the
device, user identity, and session context. Nortel SNAS enforces policy
compliance, such as for Sarbanes-Oxley and COBIT, ensuring that the
required anti-virus applications or software patches are installed before
users are granted network access.
For Nortel, success is delivering technologies providing secure access
to your information using security-compliant systems. Your success
is measured by increased employee productivity and lower network
operations costs. Nortel’s solutions provide your organization with the
network intelligence required for success.
“Nortel SNAS clusters” (page 35)
“Interface configuration” (page 35)
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
Elements of the Nortel SNAS
The following devices are essential elements of the Nortel SNAS:
•
Nortel Secure Network Access Switch 4050or 4070 (Nortel SNAS 4050
or 4070), which acts as the Policy Decision Point
• network access devices, which acts as the Policy Enforcement Point
—
Ethernet Routing Switch 8300
— Ethernet Routing Switch 4500, 5510, 5520, or 5530
ATTENTION
NSNA Release 1.6.1 does not currently support the Ethernet Routing Switch
8300 as a Policy Enforcement Point.
• RADIUS, DHCP, and DNS servers
The following devices are additional, optional elements of the Nortel
SNAS:
•
remediation server
•
corporate authentication services such as LDAP or RADIUS services
The Nortel SNAS 25
Each Nortel SNAS device can support up to five network access devices.
Supported users
The Nortel SNAS supports the following types of users:
•
PCs using the following operating systems:
— Windows 2000 SP4
—
Windows XP SP2
—
Linux
—
MAC OS
—
Vista
The Nortel SNAS supports the following browsers:
—
Internet Explorer version 6.0 or later
— Netscape Navigator version 7.3 or later
— Mozilla Firefox version 1.0.6 or later
Java Runtime Environment (JRE) for all browsers:
— JRE 1.6.0_04 or later
• VoIP phones
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
26 Overview
Supporting additional users with the software license file
— Nortel IP Phone 2002
—
Nortel IP Phone 2004
—
Nortel IP Phone 2007
See Release Notes for the Nortel Secure Network Access Solution,
Software Release 1.6.1 (NN47230-400), for the minimum firmware
versions required for the IP Phones operating with different call
servers.
Each Nortel SNAS -enabled port on a network access devices can support
one PC (untagged traffic) and one IP Phone (tagged traffic). Softphone
traffic is considered to be the same as PC traffic (untagged).
ATTENTION
Where there is both an IP Phone and a PC, the PC must be connected through
the 3-port switch on the IP Phone.
The standard Nortel SNAS 4050 implementation can support up to 200
authenticated user sessions. To support additional users on your Nortel
SNAS 4050 switch, you must obtain a Nortel SNA software license
file. The software license file contains a software license key that you
must enter into the Nortel SNAS 4050 switch to activate support for the
additional users. The file can support an additional 100, 250, 500, or 1000
users.
ATTENTION
An authenticated IP Phone is considered to be a licensed user.
Your unique software license key is based on your switch MAC address.
Before you obtain your software license file, first record the MAC address
for the Nortel Secure Network Access Switch to be upgraded. To find the
MAC address in the Command Line Interface, use the
command.
To obtain your software license file, contact Nortel to order the Nortel SNA
Software License Certificate. Follow the instructions on this certificate to
obtain your software license file.
After you obtain the software license file from Nortel, you must copy
the entire license key to the switch using the CLI or the BBI. When you
copy the license key, ensure you include the BEGIN LICENSE and END
LICENSE lines.
To copy the license key using the CLI, use the following command:
/cfg/sys/host <host ID> license <key>
/info/local
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

The Nortel SNAS 27
The following shows a sample display of the CLI interface when copying
the license key:
>> Main# cfg/sys/host
Enter Host number: 1
>> iSD host 1# license
Paste the license, press Enter to create a new line,
and then type "..." (without the quotation marks)
to terminate.
> -----BEGIN LICENSE----> U4GsdGVkX36AJpnd8KL4iImtRzBvZy+iANDzxog22+vq6Qx4aawSl4FVQo
> lXYlsNNFJpYW/vl3osvNPXhzcLV2E9hNHlqirkzc5aLDJ+2xYpK/BRDrMZ
> 86OQvdBMyer53xgq8Kk/5BvoFcQYvEC/yWrFyrmZr4XPtAr3qmuZ8UxLqJ
> 0x7PUrp6tVI=
> -----END LICENSE----> ...
License loaded
For more information, see “Configuring the Nortel SNAS host” (page 264).
To copy the license key using the BBI, use the Install New License screen
(System > Hosts > host > Install New License).
To view the license using BBI, in the cluster select Cluster > Hosts >
License from the menu. For more information, see Nortel Secure Network
Access Switch Configuration — Using the BBI, (NN47230-500).
Role of the Nortel SNAS
The Nortel SNAS helps protect the network by ensuring endpoint
compliance for devices that connect to the network.
Before allowing a device to have full network access, the Nortel SNAS
checks user credentials and host integrity against predefined corporate
policy criteria. Through tight integration with network access devices, the
Nortel SNAS can:
• dynamically move the user into a quarantine VLAN
• dynamically grant the user full or limited network access
• dynamically apply per port firewall rules that apply to a device’s
connection
Once a device has been granted network access, the Nortel SNAS
continually monitors the health status of the device to ensure continued
compliance. If a device falls out of compliance, the Nortel SNAS can
dynamically move the device into a quarantine or remediation VLAN.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

28 Overview
Nortel SNAS functions
The Nortel SNAS performs the following functions:
•
Acts as a web server portal, which is accessed by users in clientless
mode for authentication and host integrity check and which sends
remediation instructions and guidelines to endpoint clients if they fail
the host integrity check.
•
Communicates with backend authentication servers to identify
authorized users and levels of access.
• Acts as a policy server, which communicates with the Nortel Health
Agent applet that verifies host integrity.
• Instructs the network access devices to move clients to the appropriate
enforcement zones.
• Can be a DNS proxy in the Red VLAN when the Nortel SNAS functions
as a captive portal
•
Supports the RADIUS server
•
Supports Microsoft NAP Interoperability.
•
Performs session management.
•
Monitors the health of clients and switches.
•
Performs logging and auditing functions.
•
Provides High Availability (HA) through IPmig protocol.
Nortel SNAS enforcement types
Nortel SNAS provides several enforcement types for restricting access
to the network.
• VLANs and filters uses a combination of VLANs and filters to provide
enforcement. It is available with NSNA network access devices; that is,
devices that support SSCP (Switch-SNAS Communication Protocol),
SSCP-Lite, and 802.1x switches.
• Filters only uses only filters to provide enforcement. It is available with
NSNA network access devices.
• NSNA network access devices including Nortel Ethernet Switch
models - 325, 425, 450, 470 and 2500 series and Ethernet Routing
Switch models - 4500 series, 5500 series, 8300 and 8600 as well as
third-party switches.
VLANs and filters
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
The Nortel SNAS 29
Four type of Layer 2 or Layer 3 VLANs are configured for VLANs and
filters enforcement:
•
Red—extremely restricted access. If the default filters are used, the
user can communicate only with the Nortel SNAS and the Windows
domain controller network. There is one Red VLAN for each network
access devices.
•
Yellow—restricted access for remediation purposes if the client PC fails
the host integrity check. Depending on the filters and Nortel Health
Agent rules configured for the network, the client may be directed to
a remediation server participating in the Yellow VLAN. There can be
up to five Yellow VLANs for each network access devices. Each user
group is associated with only one Yellow VLAN.
• Green—full access, in accordance with the user’s access privileges.
There can be up to five Green VLANs for each network access
devices.
•
VoIP—automatic access for VoIP traffic. The network access devices
places VoIP calls in a VoIP VLAN without submitting them to the Nortel
SNAS authentication and authorization process.
When a client attempts to connect to the network, the network access
devices places the client in its Red VLAN. The Nortel SNAS authenticates
the client. By default, the Nortel SNAS then downloads a Nortel Health
Agent applet to check the integrity of the client host. If the integrity check
fails, the Nortel SNAS instructs the network access devices to move the
client to a Yellow VLAN, with its associated filter. If the integrity check
succeeds, the Nortel SNAS instructs the network access devices to move
the client to a Green VLAN, with its associated filter. The network access
devices applies the filters when it changes the port membership.
The VoIP filters allow IP phone traffic into preconfigured VoIP VLANs, for
VoIP communication only.
The default filters can be modified to accommodate network requirements,
such as Quality of Service (QoS) or specific workstation boot processes
and network communications.
For information about configuring VLANs and filters on the network access
devices, see Release Notes for Nortel Ethernet Routing Switch 5500
Series, Software Release 5.0.1,orRelease Notes for the Ethernet Routing
Switch 8300, Software Release 2.2.8 ,.
To configure the Nortel SNAS for VLANs and filters enforcement, see
“Configuring groups” (page 156), enftype.
Filters only
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

30 Overview
Filters only enforcement uses two VLANs: Red and VoIP. A client
computer is placed in the Red VLAN where it is held pending successful
authentication. If successful, Nortel Health Agent integrity checking can be
used to determine if remediation is required. Filters are applied to direct
the client to the appropriate network resources but the client remains in
the same VLAN regardless of its status. This contrasts with VLANs and
filters where the client is moved to another VLAN in addition to applying
filters. Filters only handles IP phones in the same manner as VLANs
and filters.
With Filters only, there is less network configuration than with VLANs and
filters because there are only two VLANs (Red and VoIP) to configure.
However, the double layer of protection afforded with VLANs and filters
is not provided.
To configure the Nortel SNAS for Filters only enforcement, see
“Configuring groups” (page 156), enftype. Though configuring for Filters
only can result in higher DNS demands on the Nortel SNAS, using the
filter DHCP subnet type maintains these demands at the same level as
with VLANs and filters: for more information, see “Configuring local
DHCP services” (page 115).
DHCP hub subnet
DHCP hub subnet enforcement allows the Nortel SNAS to operate with
a broader range of Nortel ethernet switches as well as third party network
access devices. Unlike VLANs and filters and Filters only enforcement,
DHCP hub subnet enforcement does not require SSCP support on the
network access device.
The DHCP hub subnet configuration is an integral component of the
DHCP services provided by the Nortel SNAS. For more information, see
“Configuring local DHCP services” (page 115).
Groups and profiles
Users are organized in groups. In the user gorup we can specify Locaion
also. Group membership determines:
• user access rights
Within the group, extended profiles further refine access rights
depending on the outcome of the Nortel Health Agent checks.
• number of sessions allowed
• the Nortel Health Agent SRS rule to be applied
• what on the portal page after the user has been authenticated
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

The Nortel SNAS 31
For information about configuring groups and extended profiles on the
Nortel SNAS, see “Configuring groups and profiles” (page 149).
Authentication methods
You can configure more than one authentication method within a Nortel
SNAS domain. Nortel Secure Network Access Switch Software Release
2.0 supports the following authentication methods:
•
external database
—
Remote Authentication Dial-In User Service (RADIUS)
—
Lightweight Directory Access Protocol (LDAP)
The Nortel SNAS authenticates the user by sending a query to an
external RADIUS or LDAP server. This makes it possible to use
authentication databases already existing within the intranet. The
Nortel SNAS device includes username and password in the query and
requires the name of one or more access groups in return. The name
of the RADIUS and LDAP access group attribute is configurable.
•
local authentication databases
—
Portal authentication: The Nortel SNAS can store up to 1,000 user
authentication entries in its own portal database. Each entry in the
database specifies a username, password, and relevant access
group.
Use the local authentication method if no external authentication
databases exist, for testing purposes, for speedy deployment, or
as a fallback for external database queries. You can also use the
local database for authorization only, if an external server provides
authentication services but cannot be configured to return a list of
authorized groups.
— MAC authentication: The media access control (MAC) address of
the end point device can be used for authentication. The Nortel
SNAS 4050 can store over 10,000 MAC addresses and support
over 2,000 concurrent MAC sessions. Each entry in the database
specifies a MAC address, IP type, device type, and group name(s).
You can optionally specify a user name, IP address of the device,
comments, and the IP address, unit, and port of the switch to which
the device is attached.
You can populate the local authentication databases by manually
adding entries on the Nortel SNAS, or you can import a database from
a TFTP/FTP/SCP/SFTP server.
For information about configuring authentication on the Nortel SNAS, see
“Configuring authentication” (page 171).
For more information about the way Nortel SNAS controls network access,
see Nortel Secure Network Access Solution Guide, (NN47230-200).
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

32 Overview
Nortel Health Agent host integrity check
The Nortel Health Agent application checks client host integrity by verifying
that the components you have specified are required for the client’s
personal firewall (executables, DLLs, configuration files, and so on) are
installed and active on the client PC. You specify the required component
entities and engineering rules by configuring a Software Requirement Set
(SRS) rule and mapping the rule to a user group.
After a client gets authenticated, the Nortel SNAS downloads a Nortel
Health Agent as an applet to the client PC. The Nortel Health Agent applet
fetches the SRS rule applicable for the group to which the authenticated
user belongs, so that Nortel Health Agent can perform the appropriate host
integrity check. The Nortel Health Agent applet reports the result of the
host integrity check to the Nortel SNAS.
If the required components are present on the client machine, Nortel
Health Agent reports that the SRS rule check succeeded. The Nortel
SNAS then instructs the network access devices to permit access to
intranet resources in accordance with the user group’s access privileges.
The Nortel SNAS also requests the Nortel Health Agent applet to redo a
DHCP request in order to renew the client’s DHCP lease with the network
access devices.
If the required components are not present on the client machine, Nortel
Health Agent reports that the SRS rule check failed. You configure
behavior following host integrity check failure: The session can be torn
down, or the Nortel SNAS can instruct the network access devices to grant
the client restricted access to the network for remediation purposes.
The Nortel Health Agent applet repeats the host integrity check periodically
throughout the client session. If the check fails at any time, the client
is either evicted or quarantined, depending on the behavior you have
configured. The recheck interval is configurable.
For information about configuring the Nortel Health Agent host integrity
check, see “Configuring the Nortel Health Agent check” (page 92). For
information about configuring the SRS rules, see information about the
Nortel Health Agent SRS Builder in Nortel Secure Network Access Switch
4050 User Guide for the SREM (NN47230-101), . For information about
mapping an SRS rule to a group, see “Configuring groups” (page 156).
Multi-OS Applet Support
The Nortel Health captive portal applet supports Windows and
non-Windows operating systems. For non-Windows operating systems
the applet supports collecting operating systems information and VLAN
transition.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

The Nortel SNAS 33
The “Multi-OS Support" feature allows the Nortel Health Agent to identify
Linux operating system or Macintosh operating system users and collect
the necessary information. The Nortel Health Agent is allowed to identify
the operating system as Linux or Macintosh and collect the device specific
information and also performs additional compliance checks for those
operating systems.
The following types of Linux operating system are supported:
•
RedHat Enterprise Linux 4
• RedHat Enterprise Linux 3
• Fedora Core 6
• Fedora Core 5
•
SUSE Linux Enterprise 10
The following types of Macintosh operating system are supported:
• Mac OS X Server v10.5 Leopard
•
Mac OS X Server v10.4 Tiger
•
Mac OS X v10.3 Panther
•
Mac OS X v10.2
•
Mac OS 9
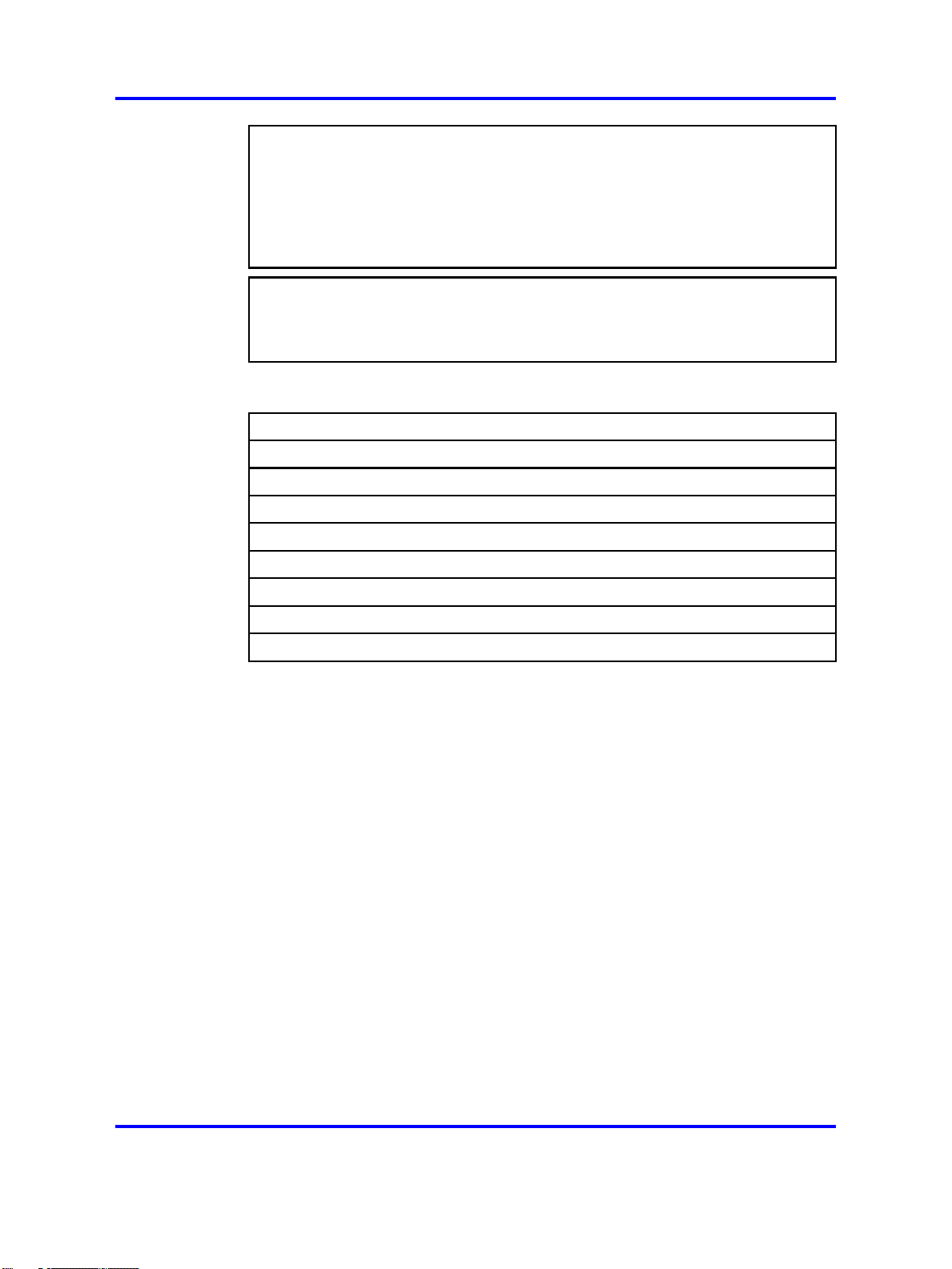
Communication channels
Communications between the Nortel SNAS and key elements of the Nortel
SNAS are secure and encrypted. Table 2 "Communication channels in the
Nortel SNAS network" (page 33) shows the communication channels in
the network.
Table 2
Communication channels in the Nortel SNAS network
Communication Communication protocol
Between Nortel SNAS and edge
switches
Between Nortel SNAS devices in a
cluster
Between Nortel SNAS and client PC
(Nortel Health Agent applet)
For Nortel SNAS BBI
SSH
TCP and UDP
SSL/TLS
From edge switch to EPM SNMPv3 Inform
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

34 Overview
Table 2
Communication channels in the Nortel SNAS network (cont’d.)
Communication Communication protocol
From EPM to edge switch Telnet over SSH
From authorized endpoint to DHCP
server
UDP
Telnet or SSH can be used for management communications between
remote PCs and the Nortel SNAS devices.
About SSH The Secure Shell (SSH) protocol provides secure and
encrypted communication between the Nortel SNAS and the network
access devices, and between Nortel SNAS devices and remote
management PCs not using Telnet.
SSH uses either password authentication or public key authentication.
With public key authentication, pairs of public/private SSH host keys
protect against "man in the middle" attacks by providing a mechanism for
the SSH client to authenticate the server. SSH clients keep track of the
public keys to be used to authenticate different SSH server hosts.
SSH clients in the Nortel SNAS network do not silently accept new keys
from previously unknown server hosts. Instead, they refuse the connection
if the key does not match their known hosts.
The Nortel SNAS supports the use of three different SSH host key types:
• RSA1
•
RSA
• DSA
SSH protocol version 1 always uses RSA1 keys. SSH protocol version
2 uses either RSA or DSA keys.
For management communications in the Nortel SNAS, the Nortel SNAS
can act both as SSH server (when a user connects to the CLI using an
SSH client) and as SSH client (when the Nortel SNAS initiates file or data
transfers using the SCP or SFTP protocols).
For information about managing SSH keys for communication between
the Nortel SNAS and the network access devices, see “Managing SSH
keys” (page 68).
For information about managing SSH keys for Nortel SNAS management
communications, see “Configuring Nortel SNAS host SSH keys” (page
284).
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Nortel SNAS clusters
For Release 1.6.1
A cluster is a group of Nortel SNAS 4050 devices that share the same
configuration parameters. Nortel Secure Network Access Switch Software
Release 1.6.1 supports four Nortel SNAS 4050 devices, or nodes, in a
cluster. A network can contain multiple clusters.
For Release 2.0
A cluster is a group of Nortel SNAS 4050 or 4070 devices that share the
same configuration parameters. Nortel Secure Network Access Switch
Software Release 2.0 supports a combination of four Nortel SNAS 4050
and 4070 devices, or nodes, in a cluster. A Nortel SNAS network can
contain multiple clusters.
Clustering offers the following benefits:
• manageability—The cluster is a single, seamless unit that automatically
pushes configuration changes to its members.
The Nortel SNAS 35
•
scalability—The Nortel SNAS nodes in a cluster share the burden
of resource-intensive operations. The cluster distributes control of
the network access devices between the Nortel SNAS nodes and
distributes handling of session logon. As a result, Nortel SNAS devices
in a cluster can control more switches and handle more user sessions.
•
fault tolerance—If a Nortel SNAS device fails, the failure is detected by
the other node in the cluster, which takes over the switch control and
session handling functions of the failed device. As long as there is one
running Nortel SNAS, no sessions will be lost.
The devices in the cluster can be located anywhere in the network and
do not have to be physically connected to each other. All the Nortel
SNAS devices in the cluster must be in the same subnet. The cluster is
created during initial setup of the second node, when you specify that
the setup is a join operation and you associate the node with an existing
Management IP address (MIP).
For more information about Nortel SNAS IP addresses, see “About the IP
addresses” (page 42). For information about adding a node to a cluster,
see “Adding a Nortel SNAS device to a cluster” (page 50).
Interface configuration
The Nortel SNAS must interface to two kinds of traffic: client and
management. The interface to the client side handles traffic between the
Nortel Health Agent applet on the client and the portal. The interface to
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

36 Overview
the management side handles Nortel SNAS management traffic (traffic
connecting the Nortel SNAS to internal resources and configuring the
Nortel SNAS from a management station).
The Nortel SNAS supports what is known as an One armed configuration.
The following section describes this configuration type.
One armed configuration
In an one armed configuration, the Nortel SNAS has only one interface,
which acts as both the client portal interface and the management traffic
interface.
Figure 1 "One armed configuration" (page 36) illustrates a one-armed
configuration.
Figure 1
One armed configuration
Nortel SNAS configuration and management tools
You can use a number of device and network management tools to
configure and manage the Nortel SNAS:
• Command Line Interface (CLI)
You must use the CLI to perform initial setup on the Nortel SNAS and
to set up the Secure Shell (SSH) connection between the Nortel SNAS
and the network access devices, and between the Nortel SNAS and
the GUI management tool. You can then continue to use the CLI to
configure and manage the Nortel SNAS, or you can use the GUI.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
.
28 July 2008

Nortel SNAS configuration roadmap 37
The configuration chapters in this User Guide describe the specific CLI
commands used to configure the Nortel SNAS. For general information
about using the CLI, see “The Command Line Interface” (page 377).
•
Security & Routing Element Manager (SREM)
The SREM is a GUI application you can use to configure and manage
the Nortel SNAS.
For information about configuring the Nortel SNAS using the SREM,
Nortel Secure Network Access Switch 4050 User Guide for the
see
SREM (NN47230-101), . For general information about installing and
using the SREM, see Installing and Using the Security,.
• Browser Based Interface (BBI)
The BBI is a web browser application you can use to configure and
manage the Nortel SNAS.
For information about configuring the Nortel SNAS using the BBI, see
Nortel Secure Network Access Switch Configuration — Using the BBI
(NN47230-500).
•
Enterprise Policy Manager (EPM) release 4.2
Enterprise Policy Manager (EPM) is a security policy and quality
of service provisioning application. You can use EPM to provision
filters on the Nortel SNAS network access devices. EPM 4.2 supports
preconfiguration of Red, Yellow, and Green VLAN filters prior to
enabling the Nortel SNAS feature. In future releases of the Nortel
SNAS and EPM software, users will have the additional ability to add
and modify security and quality of service filters while Nortel SNAS is
enabled on the device.
For general information about installing and using EPM, see Installing
Nortel Enterprise Policy Manager (318389),.
•
Simple Network Management Protocol (SNMP) agent
For information about configuring SNMP for the Nortel SNAS, see
“Configuring SNMP” (page 323).
Nortel SNAS configuration roadmap
The following task list is an overview of the steps required to configure the
Nortel SNAS.
Step Action
1 Configure the network DNS server to create a forward lookup
zone for the Nortel SNAS domain.
For an example, see “Configuration example” (page 385).
2 Configure the network DHCP server.
For an example, see “Configuration example” (page 385).
For each VLAN:
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
28 July 2008
.

38 Overview
a Create a DHCP scope.
b Specify the IP address range and subnet mask for that
scope.
c Configure the following DHCP options:
• Specify the default gateway.
•
Specify the DNS server to be used by endpoints in that
scope.
• If desired, configure DHCP so that the IP Phones learn
their VLAN configuration data automatically from the
DHCP server. For more information, see “Configuring
DHCP to auto-configure IP Phones” (page 493).
ATTENTION
For the Red VLANs, the DNS server setting is one of the Nortel
SNAS portal Virtual IP addresses (pVIP).
While the endpoint is in the Red VLAN, there are limited DNS server
functions to be performed, and the Nortel SNAS itself acts as the
DNS server. When the endpoint is in one of the other VLANs, DNS
requests are forwarded to the corporate DNS servers.
The DNS server setting is required for the captive portal to work.
3 Configure the network core router:
a Create the Red, Yellow, Green, VoIP, and Nortel SNAS
management VLANs.
b If the edge switches are operating in Layer 2 mode, enable
802.1q tagging on the uplink ports to enable them to
participate in multiple VLANs, then add the ports to the
applicable VLANs.
ATTENTION
The uplink ports must participate in all the VLANs.
c Configure IP addresses for the VLANs.
These IP interfaces are the default gateways the DHCP
Relay will use.
d If the edge switches are operating in Layer 2 mode, configure
DHCP relay agents for the Red, Yellow, Green, and VoIP
VLANs.
Use the applicable show commands on the router to verify
that DHCP relay is activated to reach the correct scope for
each VLAN.
For more information about performing these general
configuration steps, see the regular documentation for the type
of router used in your network.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Nortel SNAS configuration roadmap 39
4 Configure the network access devices:
a Configure static routes to all the networks behind the core
router.
b Configure the switch management VLAN, if necessary.
c Configure and enable SSH on the switch.
d Configure the Nortel SNAS portal Virtual IP address
(pVIP)/subnet.
e Configure port tagging, if applicable.
For a Layer 2 switch, the uplink ports must be tagged to allow
them to participate in multiple VLANs.
f Create the port-based VLANs.
These VLANs are configured as VoIP, Red, Yellow, and
Green VLANs in step i and step j.
g Configure DHCP relay and IP routing if the switch is used in
Layer 3 mode.
h (Optional) Configure the Red, Yellow, Green, and VoIP filters.
The filters are configured automatically as predefined defaults
when you configure the Red, Yellow, and Green VLANs (step
j). Configure the filters manually only if your particular system
setup requires you to modify the default filters. You can
modify the filters after Nortel SNAS is enabled.
i Configure the VoIP VLANs.
j Configure the Red, Yellow, and Green VLANs, associating
each with the applicable filters.
k Configure the Nortel SNAS ports.
Identify switch ports as either uplink or dynamic. When you
configure the uplink ports, you associate the Nortel SNAS
VLANs with those ports. Clients are connected on the
dynamic ports. You can configure Nortel SNAS ports (both
dynamic and uplink) after Nortel SNAS is enabled globally.
l Enable Nortel SNAS globally.
For more information about configuring an Ethernet Routing
Switch 5510, 5520, or 5530 in a Nortel SNAS network, see
Release Notes for Nortel Ethernet Routing Switch 5500 Series,
Software Release 5.0.1,.
For more information about configuring an Ethernet Routing
Switch 8300 in a Nortel SNAS network, see Release Notes for
the Ethernet Routing Switch 8300, Software Release 2.2.8 ,.
For an example of the commands used to create a Nortel SNAS
configuration, see “Configuration example” (page 385).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

40 Overview
5 Perform the initial setup on the Nortel SNAS (see “Initial setup”
(page 43)). Nortel recommends running the quick setup wizard
during initial setup, in order to create and configure basic
settings for a fully functional portal.
6 Enable SSH and SRS Admin to allow communication with the
SREM (see “Configuring administrative settings” (page 281)).
7 Generate and activate the SSH key for communication
between the Nortel SNAS and the network access devices (see
“Managing SSH keys” (page 68)).
8 Specify the Software Requirement Set (SRS) rule for the default
nhauser group (see “Configuring groups” (page 156)).
9 Add the network access devices and export the SSH key (see
“Adding a network access devices ” (page 60)).
10 Specify the VLAN mappings (see “Mapping the VLANs” (page
66)).
11 Test Nortel SNAS connectivity by using the /maint/chkcfg
command (see “Performing maintenance” (page 353)).
12 Configure groups (see “Configuring groups and profiles” (page
149)).
13 Configure client filters (see “Configuring client filters” (page
162)).
14 Configure extended profiles (see “Configuring extended profiles”
(page 164) ).
15 Specify the authentication mechanisms (see “Configuring
authentication” (page 171)).
16 Configure system users (see “Managing system users and
groups” (page 211)).
17 Configure the end user experience (see “Customizing the portal
and user logon” (page 227)).
--End--
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

.
Initial setup
This chapter includes the following topics:
Topic
“Before you begin” (page 41)
“About the IP addresses” (page 42)
“Initial setup” (page 43)
“Setting up a single Nortel SNAS device or the first in a cluster” (page 43)
“Adding a Nortel SNAS device to a cluster” (page 50)
“Next steps” (page 54)
“Applying and saving the configuration” (page 55)
Before you begin
Before you can set up the Nortel SNAS, you must complete the following
tasks:
41
Step Action
1 Plan the network. For more information, see Nortel Secure
Network Access Solution Guide, (NN47230-200).
In order to configure the Nortel SNAS, you require the following
information:
• IP addresses
Copyright © 2007, 2008 Nortel Networks
— Nortel SNAS Management IP address (MIP), portal Virtual
IP address (pVIP), Real IP address (RIP)
— default gateway
— DNS server
— NTP server (if applicable)
— external authentication servers (if applicable)
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

42 Initial setup
— network access devices
— remediation server (if applicable)
For more information about the Nortel SNAS MIP, pVIP, and
RIP, see “About the IP addresses” (page 42).
•
VLAN IDs
— Nortel SNAS management VLAN
— Red VLANs
— Yellow VLANs
— Green VLANs
— VoIP VLANs (optional)
• Groups and profiles to be configured
2 Configure the network DNS server, DHCP server, core router,
and network access devices, as described in “Nortel SNAS
configuration roadmap” (page 37), steps 1 through 4.
3 Install the Nortel SNAS device. For more information, see
Nortel Secure Network Access Switch 4050 Installation Guide
, (NN47230-300).
4 Establish a console connection to the Nortel SNAS (see
“Establishing a console connection” (page 378)).
About the IP addresses
Management IP address
The Management IP address (MIP) identifies the Nortel SNAS in the
network. In a multi-Nortel SNAS solution, the MIP is an IP alias to one
of the Nortel SNAS devices in the cluster and identifies the cluster. The
MIP always resides on a master Nortel SNAS device. If the master Nortel
SNAS that currently holds the MIP fails, the MIP automatically migrates to
a functional master Nortel SNAS. In order to configure the Nortel SNAS or
Nortel SNAS cluster remotely, you connect to the MIP using Telnet (for the
CLI) or SSH (for the CLI, the SREM or the BBI).
Portal Virtual IP address
The portal Virtual IP address (pVIP) is the address assigned to the Nortel
SNAS device’s web portal server. The pVIP is the address to which clients
connect in order to access the Nortel SNAS network. While the client is in
the Red VLAN and the Nortel SNAS is acting as DNS server, the pVIP is
the DNS server IP address. Although it is possible to assign more than
one pVIP to a Nortel SNAS device, Nortel recommends that each Nortel
SNAS have only one pVIP. When the Nortel SNAS portal is configured as
a captive portal, the pVIP is used to load balance logon requests.
--End--
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Initial setup
Initial setup 43
Real IP address
The Real IP address (RIP) is the Nortel SNAS device host IP address for
network connectivity. The RIP is the IP address used for communication
between Nortel SNAS devices in a cluster. The RIP must be unique on the
network and must be within the same subnet as the MIP.
ATTENTION
Nortel recommends that you always use the MIP for remote configuration, even
though it is possible to configure the Nortel SNAS device remotely by connecting
to its RIP. Connecting to the MIP allows you to access all the Nortel SNAS
devices in a cluster. The MIP is always up, even if one of the Nortel SNAS
devices is down and therefore not reachable at its RIP.
ATTENTION
If an IP address — MIP, VIP, RIP, or gateway — is changed, the Nortel SNAS
must be rebooted for the change to take effect.
The initial setup is a guided process that launches automatically the first
time you power up the Nortel SNAS and log on. You must use a console
connection in order to perform the initial setup.
• For a standalone Nortel SNAS or the first Nortel SNAS in a cluster, see
“Setting up a single Nortel SNAS device or the first in a cluster” (page
43).
•
To add a Nortel SNAS to a cluster, see “Adding a Nortel SNAS device
to a cluster” (page 50).
Setting up a single Nortel SNAS device or the first in a cluster
Step Action
1 Log on using the following username and password:
login: admin
Password: admin
The Setup Menu appears.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

44 Initial setup
Alteon iSD NSNAS
Hardware platform: 4050
Software version: x.x
---------------------------------------------------
---[Setup Menu]
join - Join an existing cluster
new - Initialize host as a new installation
boot - Boot menu
info - Information menu
exit - Exit [global command, always available]
>> Setup#
2 Select the option for a new installation.
>> Setup# new
Setup will guide you through the initial configuration.
3 Specify the management interface port number. This port will be
assigned to Interface 1.
Enter port number for the management interface [1-4]:
<port>
In an one-armed configuration, you are specifying the port you
want to use for all network connectivity, since Interface 1 is used
for both management traffic (Nortel SNAS management and
connections to intranet resources) and client portal traffic (traffic
between the Nortel Health Agent applet on the client and the
portal).
4 Specify the RIP for this device. This IP address will be assigned
to Interface 1.
Enter IP address for this machine (on management
interface): <IPaddr>
The RIP must be unique on the network and must be within the
same subnet as the MIP.
5 Specify the network mask for the RIP on Interface 1.
Enter network mask [255.255.255.0]: <mask>
6 If the core router attaches VLAN tag IDs to incoming packets,
specify the VLAN tag ID used.
Enter VLAN tag id (or zero for no VLAN) [0]:
If you do not specify a VLAN tag id (in other words, you accept
the default value of zero), the traffic will not be VLAN tagged.
When configuring the network access devices in Layer 2
configurations, ensure that you add the uplink ports to the Nortel
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

SNAS management VLAN, for traffic between the Nortel SNAS
and the network access device.
7 Specify the default gateway IP address.
Enter default gateway IP address (or blank to skip):
<IPaddr>
The default gateway is the IP address of the interface on the
core router that will be used if no other interface is specified. The
default gateway IP address must be within the same network
address range as the RIP.
8 Specify the MIP for this device or cluster.
Enter the Management IP (MIP) address: <IPaddr>
Making sure the MIP does not exist...ok
Trying to contact gateway...ok
The MIP must be unique on the network and must be within the
same subnet as the RIP and the default gateway for Interface 1.
WARNING
If you receive an error message that the iSD (the
Nortel SNAS device) cannot contact the gateway,
verify your settings on the core router. Do not
proceed with the initial setup until the connectivity test
succeeds.
Initial setup 45
9 Configure the interface for client portal traffic (Interface 2).
a Specify a port number for the client portal interface. This port
will be assigned to Interface 2. The port number must not be
the same as the port number for the management interface
(Interface 1).
b Specify the RIP for Interface 2.
c Specify the network mask for the RIP on Interface 2.
d If the core router attaches VLAN tag IDs to incoming packets,
specify the VLAN tag ID used.
e Specify the default gateway IP address for Interface 2. The
default gateway is the IP address of the interface on the core
router that will be used if no other interface is specified. The
default gateway IP address on Interface 2 must be within the
same subnet as the RIP for Interface 2.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

46 Initial setup
Enter port number for the traffic interface [1-4]:
<port>
Enter IP address for this machine (on traffic
interface): <IPaddr>
Enter network mask [255.255.255.0]: <mask>
Enter VLAN tag id (or zero for no VLAN) [0]:
Enter default gateway IP address (on the traffic
interface): <IPaddr>
10 Specify the time zone.
Enter a timezone or ’select’ [select]: <timezone>
If you do not know the time zone you need, press <CR> to
access the selection menus:
Select a continent or ocean: <Continent or ocean by
number>
Select a country: <Country by number>
Select a region: <Region by number, if applicable>
Selected timezone: <Suggested timezone, based on your
selections>
11 Enter the current date settings.
Enter the current date (YYYY-MM-DD) [2008-03-10]:
12 Enter the current time settings.
Enter the current time (HH:MM:SS) [00:04:10]:
13 Specify the NTP server, if applicable.
Enter NTP server address (or blank to skip): <IPaddr>
ATTENTION
If you do not have access to an NTP server at this point, you
can configure this item after the initial setup is completed. See
“Configuring date and time settings” (page 274).
14 Specify the DNS server.
Enter DNS server address (or blank to skip): <IPaddr>
15 Generate the new SSH host keys for secure management and
maintenance communication from and to Nortel SNAS devices.
Generate new SSH host keys (yes/no) [yes]:
This may take a few seconds...ok
If you do not generate the SSH host keys at this stage, generate
them later when you configure the system (see “Configuring
Nortel SNAS host SSH keys” (page 284)).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Initial setup 47
For communication between the Nortel SNAS and the network
access devices, generate the SSH key after you have completed
the initial setup (see “Managing SSH keys” (page 68)).
16 Change the admin user password, if desired.
Enter a password for the "admin" user:
Re-enter to confirm:
Make sure you remember the password you define for the admin
user. You will need to provide the correct admin user password
when logging in to the Nortel SNAS (or the Nortel SNAS cluster)
for configuration purposes.
17 Run the Nortel SNAS quick setup wizard. This creates all the
settings required to enable a fully functional portal, which you
can customize later (see “Configuring the domain” (page 79)).
For information about the default settings created by the wizard,
see “Settings created by the quick setup wizard” (page 49).
18 Start the quick setup wizard.
Run NSNAS quick setup wizard [yes]:
Creating default networks under /cfg/doamin #/aaa/
network
yes
19 Specify the portal virtual IP address (pvip) of the Nortel SNAS
device.
Enter NSNAS Portal Virtual IP address(pvip): <IPaddr>
20 Specify a name for the Nortel SNAS domain.
Enter NSNAS Domain name: <name>
21 Specify any domain names you wish to add to the DNS search
list, as a convenience to clients. If the domain name is in the
DNS search list, clients can use a shortened form of the domain
name in the address fields on the Nortel SNAS portal.
Enter comma separated DNS search list
(eg company.com,intranet.company.com):
For example, if you entered company.com in the DNS search
list, users can type nsnas to connect to nsnas.company.com
from the portal page.
22 If you want to enable HTTP to HTTPS redirection, create a
redirect server.
Create http to https redirect server [yes]:
23 Specify the action to be performed when an SRS rule check fails.
The options are:
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

48 Initial setup
• restricted. The session remains intact, but access is
restricted in accordance with the rights specified in the
access rules for the group.
•
teardown. The SSL session is torn down.
The default is restricted.
Use restricted (teardown/restricted) action for Nortel
Health Agent check failure? [yes]:
24 Create the default user and group.
The action to be performed when the Nortel Health Agent check
fails depends on your selection in step f.
Using ’restricted’ action for Nortel Health Agent check
failure.
Setting up user account policies...
Create default user account [yes]:
User name: nha
User password: nha
Creating SRS rule ’srs-rule-test’ for compliancy
check.
This rule check for the presence of the file
C:\tunnelguard\tg.txt
Creating client filter ’nha_passed’.
Creating client filter ’nha_failed’.
Creating linkset ’nha_passed’.
Creating linkset ’nha_failed’.
Creating group ’nhauser’ with secure access.
Associating group ’nhauser’ with srs rule ’srs-rule-te
st’.
Creating extended profile, full access when
nha_passed
Enter green vlan id [110]: <VID>
Creating extended profile, remediation access when
nha_failed
Enter yellow vlan id [120]: <VID>
Creating user ’nha’ in group ’nhauser’.
Setting up system account policies...
Create default system account [yes]:
System account name: sys
System account password: sys
Creating client filter ’nha_passed’.
Creating client filter ’nha_system_failed’.
Creating SRS rule ’srs-rule-syscred-test’ for
compliancy check.
This rule check for the presence of the file
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Initial setup 49
C:\tunnelguard\tg.txt
Creating linkset ’nha_system_passed’.
Creating linkset ’nha_system_failed’.
Creating group ’nhauser’ with secure access.
Associating group ’nhasystem’ with srs rule
’srs-rule-syscred-test’.
Creating extended profile, full access when
nha_system_passed
Enter system green vlan id [115]:
Creating extended profile, remediation access when
nha_system_failed
Enter yellow vlan id [120]: <VID>
Creating system account ’nha’ in group ’nhasystem’.
Setting activation date to 2008 03 10 0:03.
Setting earliest push date to 2008 03 09 23:59.
Setting system credentials in group ’nhasystem’.
Would you like to enable the Nortel Desktop Agent?
[yes]:
Enabling Nortel Desktop Agent login on the captive
portal.
Enable secure web based configuration management
[yes]:
Enabling configuration management to https://192.168.
0.62:4443
Loading default radius dictionaries. Initializing
system......ok
Setup successful. Relogin to configure.
<VID>
Settings created by the quick setup wizard
The quick setup wizard creates the following basic Nortel SNAS settings:
Step Action
1 A Nortel SNAS domain (Doamin 1). A Nortel SNAS domain
encompasses all switches, authentication servers, and
remediation servers associated with the Nortel SNAS.
2 A virtual SSL server. A portal IP address, or pVIP, is assigned to
the virtual SSL server. Clients connect to the pVIP in order to
access the portal.
3 A test certificate is installed and mapped to the Nortel SNAS
portal.
4 The authentication method is set to Local database.
Copyright © 2007, 2008 Nortel Networks
--End--
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

50 Initial setup
5 One test user is configured. You were prompted to set a user
name and password during the quick setup wizard (in this
example, user name and password are both set to
nha). The
test user belongs to a group called nhauser. There are two
profiles within the group: nha_passed and nha_failed. Each
profile is associated with a client filter and a linkset. The profiles
determine the VLAN to which the user is allocated. Table 3
"Extended profile details" (page 50) shows the extended profiles
that have been created.
Table 3
Extended profile details
Index
1
2
Client filter name
nha_failed yellow nha_failed
nha_passed
6 One or several domain names have been added to the DNS
search list, depending on what you specified at the prompt in the
quick setup wizard. This means that the client can enter a short
name in the portal’s various address fields (for example, inside
instead of inside.example.com if example.com was added
to the search list).
7 If you selected the option to enable http to https redirection, an
HTTP server was created to redirect requests made with http to
https, since the Nortel SNAS portal requires an SSL connection.
Adding a Nortel SNAS device to a cluster
After you have installed the first Nortel SNAS in a cluster (see “Setting
up a single Nortel SNAS device or the first in a cluster” (page 43)), you
can add another Nortel SNAS to the cluster by configuring the second
Nortel SNAS setup to use the same MIP. When you set up the Nortel
SNAS to join an existing cluster, the second Nortel SNAS gets most of its
configuration from the existing Nortel SNAS device in the cluster. The
amount of configuration you need to do at setup is minimal.
VLAN ID Linkset name
green
--End--
nha_passed
You can later modify settings for the cluster, the device, and the interfaces
using the /cfg/sys/[host <host ID> /interface] commands.
Before you begin
Log on to the existing Nortel SNAS device to check the software version
and system settings. Use the /boot/software/cur command to
check the currently installed software version (for more information, see
“Managing software for a Nortel SNAS device” (page 363)). Use the
/cfg/sys/accesslist/list command to view settings for the Access
List (for more information, see “Configuring the Access List” (page 273)).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Initial setup 51
Do not proceed with the join operation until the following requirements are
met.
•
Verify that the IP addresses you will assign to the new Nortel SNAS
device conform to Nortel SNAS network requirements. For more
information, see “About the IP addresses” (page 42) and “Interface
configuration” (page 35).
•
The Access List is updated, if necessary.
The Access List is a system-wide list of IP addresses for hosts
authorized to access the Nortel SNAS devices by Telnet and SSH.
/info/sys command executed on the existing Nortel SNAS
If the
shows no items configured for the Access List, no action is required.
However, if the Access List is not empty before the new Nortel SNAS
joins the cluster, you must add to the Access List the cluster’s MIP, the
existing Nortel SNAS RIP on Interface 1, and the new Nortel SNAS
RIP on Interface 1. You must do this before you perform the join
operation, or the devices will not be able to communicate with each
other.
For information about adding entries to the Access List, see
“Configuring the Access List” (page 273).
• The existing Nortel SNAS and the new Nortel SNAS must run the
same version of software. If the versions are different, decide which
version you want to use and then do one of the following:
— To change the version on the new NSNAS, download the desired
software image and reinstall the software (see “Reinstalling the
software” (page 372)).
—
To change the version on the existing Nortel SNAS, download the
desired software image and upgrade the software on the existing
cluster (see “Upgrading the Nortel SNAS ” (page 367)).
ATTENTION
Nortel recommends always using the most recent software version.
Joining a cluster
Step Action
1 Log on using the following username and password:
login: admin
Password: admin
The Setup Menu appears.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

52 Initial setup
Alteon iSD NSNAS
Hardware platform: 4050
Software version: x.x
---------------------------------------------------
---[Setup Menu]
join - Join an existing cluster
new - Initialize host as a new installation
boot - Boot menu
info - Information menu
exit - Exit [global command, always available]
>> Setup#
2 Select the option to join an existing cluster.
>> Setup# join
Setup will guide you through the initial configuration.
3 Specify the management interface port number. This port will be
assigned to Interface 1.
Enter port number for the management interface [1-4]:
<port>
In a one-armed configuration, you are specifying the port you
want to use for all network connectivity, since Interface 1 is used
for both management traffic (Nortel SNAS management and
connections to intranet resources) and client portal traffic (traffic
between the Nortel Health Agent applet on the client and the
portal).
ATTENTION
For consistency, Nortel recommends that you specify the same
port number for the management interface port on all Nortel SNAS
devices in the cluster.
4 Specify the RIP for this device. This IP address will be assigned
to Interface 1.
Enter IP address for this machine (on management
interface): <IPaddr>
The RIP must be unique on the network and must be within the
same subnet as the MIP.
5 Specify the network mask for the RIP on Interface 1.
Enter network mask [255.255.255.0]: <mask>
6 If the core router attaches VLAN tag IDs to incoming packets,
specify the VLAN tag ID used.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Initial setup 53
Enter VLAN tag id (or zero for no VLAN) [0]:
7 Configure the interface for client portal traffic (Interface 2).
a Specify a port number for the client portal interface. This port
will be assigned to Interface 2. The port number must not be
the same as the port number for the management interface
(Interface 1).
b Specify the RIP for Interface 2.
c Specify the network mask for the RIP on Interface 2.
d If the core router attaches VLAN tag IDs to incoming packets,
specify the VLAN tag ID used.
Enter port number for the traffic interface [1-4]:
<port>
Enter IP address for this machine (on traffic
interface): <IPaddr>
Enter network mask [255.255.255.0]: <mask>
Enter VLAN tag id (or zero for no VLAN) [0]:
8 Specify the MIP of the existing cluster.
The system is initialized by connecting to the
management server on an existing iSD, which must be
operational and initialized.
Enter the Management IP (MIP) address: <IPaddr>
9 Specify the default gateway IP address for Interface 2. The
default gateway is the IP address of the interface on the core
router that will be used if no other interface is specified. The
default gateway IP address on Interface 2 must be within the
same subnet as the RIP for Interface 2.
Enter default gateway IP address (on the traffic
interface): <IPaddr>
10 Provide the correct admin user password configured for the
existing cluster.
Enter the existing admin user password: <password>
11 Wait while the setup utility finishes processing. When processing
is complete, you will see Setup successful.
The new Nortel SNAS automatically picks up all other required
configuration data from the existing Nortel SNAS in the cluster.
After a short while, you receive the login prompt.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

54 Initial setup
Next steps
Setup successful.
login:
--End--
Step Action
1 To enable the SREM connection to the Nortel SNAS:
a Use the /cfg/sys/adm/ssh on command to enable
SSH access to the Nortel SNAS (for more information, see
“Configuring administrative settings” (page 281)).
b Use the /cfg/sys/adm/srsadmin ena command to
enable SRS administration (for more information, see
“Enabling TunnelGuard SRS administration” (page 284)).
This is automatically enabled at the time of quick wizard as a
part of configuration management enable.
ATTENTION
For greater security, you may want to restrict access to the Nortel
SNAS to those machines specified in an Access List. In this case,
ensure that you add an IP address for the BBI to the Access List. For
more information about using the Access List to control Telnet and
SSH access, see “Configuring the Access List” (page 273).
From this point on, you can configure the Nortel SNAS using
either the CLI or the BBI.
2 To enable remote management using Telnet, use the
/cfg/sys/adm/telnet on command to enable Telnet access
to the Nortel SNAS (for more information, see “Configuring
administrative settings” (page 281)).
3 To finish connecting the Nortel SNAS to the rest of the network,
complete the following tasks:
a Generate and activate the SSH keys for communication
between the Nortel SNAS and the network access devices
(see “Managing SSH keys” (page 68)).
b Specify the SRS rule for the nhauser group (see “Configuring
groups” (page 156)).
c Add the network access devices (see “Adding a network
access devices ” (page 60)).
d Specify the VLAN mappings (see “Mapping the VLANs” (page
Copyright © 2007, 2008 Nortel Networks
.
66)).
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

e If you did not run the quick setup wizard during the initial
setup, configure the following:
• Create the domain (see “Creating a domain” (page 83)).
•
Create at least one group.
• Specify the VLANs to be used when the Nortel Health
Agent check succeeds and when it fails (see “Configuring
extended profiles” (page 164)).
4 Save the configuration (see “Applying and saving the
configuration” (page 55)).
Applying and saving the configuration
You must enter explicit commands in order to make configuration changes
permanent and in order to create a backup configuration file.
If you have not already done so after each sequence of configuration
steps, confirm your changes using the apply command.
Applying and saving the configuration 55
--End--
To view your configuration on the screen, for copy and paste into a text
file, use the following command:
/cfg/dump
To save your configuration to a TFTP, FTP, SCP, or SFTP server, use the
following command:
/cfg/ptcfg
For more information, see “Backing up or restoring the configuration” (page
356).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

56 Initial setup
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

.
Managing the network access devices
This chapter includes the following topics:
Topic
“Before you begin” (page 57)
“Managing network access devices ” (page 58)
“Roadmap of domain switch commands” (page 58)
“Adding a network access devices ” (page 60)
“Deleting a network access devices ” (page 64)
“Configuring the network access devices ” (page 64)
“Mapping the VLANs” (page 66)
“Managing SSH keys” (page 68)
“Monitoring switch health” (page 73)
“Controlling communication with the network access devices ” (page 74)
57
Before you begin
In Trusted Computing Group (TCG) terminology, the edge switches in a
Nortel SNAS function as the Policy Enforcement Point. In this document,
the term network access devices is used to refer to the edge switch once it
is configured for the Nortel SNAS network.
The following edge switches can function as network access devices in
the Nortel SNAS:
• Ethernet Routing Switch 8300
• Ethernet Routing Switch 5510, 5520, and 5530
Before you can configure the edge switches as network access devices in
the Nortel SNAS domain, you must complete the following:
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

58 Managing the network access devices
• Create the domain, if applicable. If you ran the quick setup wizard
during initial setup, Domain 1 is created. For more information about
creating a domain, see “Configuring the domain” (page 79).
•
Configure the edge switches for Nortel SNAS (see “Nortel SNAS
configuration roadmap” (page 37), step 4). For detailed information
about configuring the edge switches for Nortel SNAS, see Release
Notes for the Ethernet Routing Switch 8300, Software Release 2.2.8
,orRelease Notes for Nortel Ethernet Routing Switch 5500 Series,
Software Release 5.0.1,.
For secure communication between the Nortel SNAS and the network
access devices, each must have knowledge of the other’s public SSH key.
After you have added the network access devices to the Nortel SNAS
domain, you must exchange the necessary SSH keys (see “Managing
SSH keys” (page 68)).
You require the following information for each network access devices:
•
IP address of the switch
•
VLAN names and VLAN IDs for the Red, Yellow, and Green VLANs
•
the TCP port to be used for Nortel SNAS communication
• for Ethernet Routing Switch 8300 switches, a valid rwa user name
Managing network access devices
The Nortel SNAS starts communicating with the network access devices
as soon as you enable the switch on the Nortel SNAS by using the
/cfg/domain #/switch #/ena command.
You cannot configure the VLAN mappings for a network access devices in
the Nortel SNAS domain if the switch is enabled. When you add a network
access devices to the domain, it is disabled by default. Do not enable the
network access devices until you have completed the configuration. To
reconfigure the VLAN mappings for an existing network access devices,
first disable it by using the /cfg/domain #/switch #/dis command.
Roadmap of domain switch commands
The following roadmap lists the CLI commands to configure the network
access devices in a Nortel SNAS deployment. Use this list as a quick
reference or click on any entry for more information:
Command
/cfg/domain #/switch <switch ID>
/cfg/domain #/switch #/delete
Parameter
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 59
Command
Parameter
/cfg/domain #/switch <switch ID> name <name>
type ERS8300|ERS5500
ip <IPaddr>
mgmtproto <sscp|sscplite>
port <port>
rvid <VLAN ID>
reset
ena
dis
delete
/cfg/domain #/vlan add <name> <VLAN ID>
del <index>
list
/cfg/domain #/switch #/vlan add <name> <VLAN ID>
del <index>
list
/cfg/domain #/sshkey generate
show
export
/cfg/domain #/switch #/sshkey import
add
del
show
export
user <user>
/cfg/domain #/switch #/hlthchk interval <interval>
deadcnt <count>
sq-int <interval>
/cfg/domain #/switch #/dis
/cfg/domain #/switch #/ena
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

60 Managing the network access devices
Adding a network access devices
You can add a network access devices to the configuration in two ways.
You must repeat the steps for each switch that you want to add to the
domain configuration.
•
“Using the quick switch setup wizard” (page 60)
•
“Manually adding a switch” (page 62)
Using the quick switch setup wizard
To add a network access devices to the Nortel SNAS domain using the
quick switch setup wizard, use the following command:
/cfg/doamin #/quick
You can later modify all settings created by the quick switch setup wizard
(see “Configuring the network access devices ” (page 64)).
Step Action
1 Launch the quick switch setup wizard.
>> Main# /cfg/domain #/quick
2 Specify the IP address of the network access devices.
IP address of Switch: <IPaddr>
3 Specify the SNMP profile of the network access devices.
If the quick setup of your domain is not completed in this case
most likely there is no SNMP profile to select. See “Configuring
SNMP Profiles” (page 75) for more information.
SNMP profile:
4 It searches for the SNMP settings for the switch.
You will receive an error message and be prompted to use the
sscp or sscplite.
Starting auto discovery........
Using default SNMP Profile for auto discovery.........
.
Error: Auto Discovery Failed !! Please check the SNMP
settings in the Switch
Do you want to use sscp or sscplite <sscp/sscplite>
[sscp]:
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 61
ATTENTION
Based on the discovery result, the wizard asks for switch ports, switch
uplinks port (in case of sscplite switch) or NSNA communication port
(in case of sscp switch).
5 Specify the VLAN ID of the Red VLAN, as configured on the
network access devices. The network access devices in the
domain can share a common Red VLAN or can each have a
separate Red VLAN.
Red vlan id of Switch: <VLAN ID>
6 Specify the type of switch. Valid options are:
ERS8300 (for an Ethernet Routing Switch 8300), ERS5500 or
ERS55 (for an Ethernet Routing Switch 5510, 5520, or 5530),
and ERS4500.
The default is ERS8300.
ATTENTION
The input is case sensitive.
Enter the type of the switch (ERS8300/ERS5500/ERS4500)
[ERS8300]:
7 Specify the TCP port for communication between the Nortel
SNAS and the network access devices. The default is port 5000.
NSNA communication port[5000]:
8 The SSH fingerprint of the switch is automatically picked up if the
switch is reachable. If the fingerprint is successfully retrieved,
go to step 7.
If the fingerprint is not successfully retrieved, you will receive an
error message and be prompted to add the SSH key.
Trying to retrieve fingerprint...failed.
Error: "Failed to retrieve host key"
Do you want to add ssh key? (yes/no) [no]:
Choose one of the following:
a To paste in a public key you have downloaded from the
switch, enter Yes.Gotostep 6.
b To continue adding the switch to the configuration without
adding its public SSH key at this time, press Enter to accept
the default value (no). After you have added the switch, add
or import the SSH public key for the switch (see “Managing
SSH keys for Nortel SNAS communication” (page 71)).
Go to step 7.
9 To add the switch public key:
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

62 Managing the network access devices
a At the prompt to add the SSH key, enter Yes.
b When prompted, paste in the key from a text file, then press
Enter.
c Enter an ellipsis (...) to signal the end of the key.
d To continue, go to step 7.
Do you want to add ssh key? (yes/no) [no]: yes
Paste the key, press Enter to create a new line,
and then type "..." (without the quotation marks)
to terminate.
> 47.80.18.98 ssh-dss
AAAAB3NzaC1kc3MAAABRAJfEJJvYic9yOrejtZ88prdWdRWBF8Q
km9iJz3I6t6O1nzymt1Z1DVMXxCSb2InPcjq3o7WfPKa3VnUNUg
TpESrFlH7ooK+Zys8iEUbmJ3kpAAAAFQCUE/74fr6ACaxJpMcz0
TlWwahdzwAAAFEAgPWVrk0VOOXQmfLhutwaTrxltIDkJzOEIXPf
AIEpvDsvnlNkFE/i2vVdq/GTKmAghfN3BYjRIQT0PAwUKOS5gky
fLG9I5rKqJ/hFWJThR4YAAABQI9yJG5Q7q+2Pnk+tx1Kd44nCD6
/9j7L4RIkIEnrDbgsVxvMcsNdI+HLnN+vmBR5wd+vrW5Bq/ToMv
PspwI+WbV8TjycWeC7nk/Tg++X53hc=
> ...
10 Wait while the wizard completes processing to add the network
access devices, then enter Apply to activate the changes. The
system automatically assigns the lowest available switch ID to
the network access devices.
The switch is disabled when it is first added to the configuration.
Do not enable the switch until you have completed configuring
the system. For more information, see “Configuring the network
access devices ” (page 64).
Creating Switch 1
Use apply to activate the new Switch.
>> domain #
--End--
Manually adding a switch
To add a network access devices and configure it manually, use the
following command:
/cfg/domain #/switch <switch ID>
where
switch ID is an integer in the range 1 to 255 that
uniquely identifies the network access devices
in the Nortel SNAS domain.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 63
When you first add the network access devices, you are prompted to enter
the following information:
•
switch name—a string that identifies the switch on the Nortel SNAS.
The maximum length of the string is 255 characters. After you have
defined a name for the switch, you can use either the switch name or
the switch ID to access the
•
type of switch—valid options are ERS8300, ERS5500, and ERS4500.
The input is case sensitive.
Switch menu.
• IP address of the switch.
• NSNA communication port—the TCP port for communication between
the Nortel SNAS and the network access devices. The default is port
5000.
• Red VLAN ID—the VLAN ID of the Red VLAN configured on the
switch.
•
username—the user name for an rwa user on the switch (required for
Ethernet Routing Switch 8300 only).
The SSH fingerprint of the switch is automatically picked up if the switch
is reachable. If the fingerprint is not successfully retrieved, you receive an
error message (Error: Failed to retrieve host key). After you
have added the switch, you must add or import the SSH public key for the
switch (see “Managing SSH keys for Nortel SNAS communication” (page
71)).
The Switch menu appears.
Figure 2 "Adding a switch manually" (page 64) shows sample output for
the /cfg/domain #/switch command and commands on the Switch
menu. For more information about the Switch menu commands, see
“Configuring the network access devices ” (page 64).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

64 Managing the network access devices
Figure 2
Adding a switch manually
Deleting a network access devices
To remove a network access devices from the domain configuration, first
disable the switch then delete it. Use the following commands:
/cfg/domain #/switch #/dis
/cfg/domain/switch/delete
The disable and delete commands log out all clients connected
through the switch.
The delete command removes the current switch from the control of the
Nortel SNAS cluster.
Configuring the network access devices
When you first add a network access devices to the Nortel SNAS domain,
the switch is disabled by default. Do not enable the switch until you have
completed configuring it. In particular, do not enable the switch until you
have mapped the VLANs (see “Mapping the VLANs” (page 66)) and
exchanged the necessary SSH keys (see “Managing SSH keys” (page
68)).
If you want to reconfigure the VLAN mappings or delete a VLAN for an
existing network access devices, use the /cfg/domain/switch/dis
command to disable the switch first.
ATTENTION
Remember to enable the network access devices after completing the
configuration in order to activate the network access devices in the Nortel SNAS
network.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 65
To configure a network access devices in the Nortel SNAS domain, use
the following command:
/cfg/domain #/switch <switch ID>
where
switch ID is the ID or name of the switch you want to
configure.
The Switch menu appears.
The Switch menu includes the following options:
/cfg/domain #/switch <switch ID>
followed by:
name <name> Names or renames the switch. After you have
defined a name for the switch, you can use
either the switch name or the switch ID to
access the Switch menu.
type ERS8300|ERS5500
mgmtproto<mgmtproto>
ip <IPaddr>
port <port>
hlthchk
vlan
• name is a string that must be unique in the
domain. The maximum length of the string
is 255 characters.
Specifies the type of network access devices.
Valid options are:
•
ERS8300—an Ethernet Routing Switch
8300
• ERS5500—an Ethernet Routing Switch
5510, 5520, or 5530
The default is ERS8300.
Sets the Switch Management Protocol.
Specifies the IP address of the switch.
Specifies the TCP port used for Nortel SNAS
communication. The default is port 5000.
Accesses the Healthcheck menu, in order
to configure settings for the Nortel SNAS
to monitor the health of the switch (see
“Monitoring switch health” (page 73)).
Accesses the Switch Vlan menu, in order to
map the Green and Yellow VLANs configured
on switch (see “Mapping the VLANs” (page
66)).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

66 Managing the network access devices
/cfg/domain #/switch <switch ID>
followed by:
rvid <VLAN ID> Identifies the Red VLAN for the network access
sshkey
reset
ena
dis
delete
devices.
• VLAN ID is the ID of the Red VLAN, as
configured on the switch
Accesses the SSH Key menu, in order
to manage the exchange of public keys
between the switch and the Nortel SNAS
(see “Managing SSH keys for Nortel SNAS
communication” (page 71))
Resets all the Nortel SNAS -enabled ports on
the switch. Clients connected to the ports are
moved into the Red VLAN.
Enables the network access devices. As soon
as you enable the switch, the Nortel SNAS
begins communicating with the switch and
controlling its Nortel SNAS clients.
Disables the switch for Nortel SNAS operation.
Removes the switch from the Nortel SNAS
domain configuration.
Mapping the VLANs
The VLANs are configured on the network access devices. You specify the
Red VLAN for each network access devices when you add the switch (see
“Adding a network access devices ” (page 60)). After adding the switch,
you must identify the Yellow and Green VLANs to the Nortel SNAS.
You can perform the VLAN mapping in two ways:
•
for all switches in a domain (by using the /cfg/domain #/vlan/add
command)
• switch by switch (by using the /cfg/domain #/switch #/vlan/add
command)
Nortel recommends mapping the VLANs by domain. In this way, if you
later add switches which use the same VLAN IDs, their VLAN mappings
will automatically be picked up.
If you map the VLANs by domain, you can modify the mapping for
a particular network access devices by using the switch-level vlan
command. Switch-level settings override domain settings.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 67
To manage the VLAN mappings for all the network access devices in the
Nortel SNAS domain, first disable all the switches in the domain, then use
the following command:
/cfg/domain #/vlan
To manage the VLAN mappings for a specific network access devices, first
disable the switch in the domain, then use the following command:
/cfg/domain #/switch #/vlan
The Nortel SNAS maintains separate maps for the domain and the switch.
If you add a VLAN from the domain-level vlan command, you must use
the domain-level command for all future management of that mapping.
Similarly, if you add a VLAN from the switch-level vlan command, you
must use the switch-level command for all future management of that
mapping.
The Domain vlan or Switch vlan menu appears.
The Domain vlan or Switch vlan menu includes the following options:
/cfg/domain #[/switch #]/vlan
followed by:
add <name> <VLAN ID>
Adds the specified VLAN to the domain or
switch VLAN map. You are prompted to
enter the required parameters if you do not
include them in the command.
• name is the name of the VLAN, as
configured on the switch
• VLAN ID is the ID of the VLAN, as
configured on the switch
The system automatically assigns an index
number to the VLAN entry when you add
it. If you are executing the command from
the Domain vlan menu, the index number
indicates the position of the new entry in
the domain map. If you are executing the
command from the Switch vlan menu, the
index number indicates the position of the
new entry in the switch map.
Copyright © 2007, 2008 Nortel Networks
.
Repeat this command for each Green and
Yellow VLAN configured on the network
access devices.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

68 Managing the network access devices
/cfg/domain #[/switch #]/vlan
followed by:
del <index>
list
Managing SSH keys
The Nortel SNAS and the network access devices controlled by the
Nortel SNAS domain exchange public keys so that they can authenticate
themselves to each other in future SSH communications.
Removes the specified VLAN entry from the
applicable VLAN map.
•
index is an integer indicating the index
number automatically assigned to the
VLAN mapping when you created it
The index numbers of the remaining entries
adjust accordingly.
To view the index numbers for all VLAN
entries in the map, use the /cfg/domain
#[/switch #]/vlan/list command.
The index number, name, and VLAN ID for
all VLAN entries in the map.
To enable secure communication between the Nortel SNAS and the
network access devices, do the following:
Step Action
1 Generate an SSH public key for the Nortel SNAS domain (see
“Generating SSH keys for the domain” (page 70)), if necessary.
Apply the change immediately.
If you created the domain manually, the SSH key was generated
automatically (see “Manually creating a domain” (page 83)).
ATTENTION
The SSH key for the Nortel SNAS domain is not the same as the
SSH key generated during initial setup for all Nortel SNAS hosts in
the cluster (see “Initial setup” (page 41), step 15).
2 Export the Nortel SNAS public key to each network access
devices.
• For an Ethernet Routing Switch 8300:
Use the /cfg/domain #/switch #/sshkey/export
command to export the key directly to the switch (see
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Managing network access devices 69
“Managing SSH keys for Nortel SNAS communication” (page
71)).
• For an Ethernet Routing Switch 5510, 5520, or 5530:
Use the /cfg/domain #/sshkey/export command to
upload the key to a TFTP server, for manual retrieval from
the switch (see “Generating SSH keys for the domain” (page
70)). For information about downloading the key from the
server to the switch, see Release Notes for Nortel Ethernet
Routing Switch 5500 Series, Software Release 5.0.1,.
If you regenerate the key at any time, you must re-export the
key to each network access devices.
ATTENTION
If you export the key after the network access devices are
enabled, you may need to disable and re-enable the switch in
order to activate the change.
3 For each network access devices, import its public key into the
Nortel SNAS domain, if necessary (see “Managing SSH keys for
Nortel SNAS communication” (page 71)).
• For an Ethernet Routing Switch 8300, you can retrieve the
key in two ways:
— Use the /cfg/domain #/switch #/sshkey/import
command to import the key directly from the network
access devices.
— Use the /cfg/domain #/switch #/sshkey/add
command to paste in the key.
•
For an Ethernet Routing Switch 5510, 5520, or 5530:
— Use the /cfg/domain #/switch #/sshkey/import
command to import the key directly from the network
access devices.
If the network access devices was reachable when you added
it to the domain configuration, the SSH key was automatically
retrieved.
If the network access devices defaults, it generates a new public
key. You must reimport the key whenever the switch generates
a new public key (see “Reimporting the network access devices
SSH key” (page 72)).
ATTENTION
In general, enter Apply to apply the changes immediately after you
execute any of the SSH commands.
Copyright © 2007, 2008 Nortel Networks
.
--End--
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

70 Managing the network access devices
Generating SSH keys for the domain
To generate, view, and export the public SSH key for the domain, use the
following command:
/cfg/domain #/sshkey
The NSNAS SSH key menu appears.
The NSNAS SSH key menu includes the following options:
/cfg/domain #/sshkey
followed by:
generate
show
export
Generates an SSH public key for the domain.
There can be only one key in effect for the Nortel
SNAS domain at any one time. If a key already
exists, you are prompted to confirm that you want
to replace it.
Enter Apply to apply the change immediately and
create the key.
The SSH public key generated for the domain.
Exports the Nortel SNAS domain public key to a
file exchange server. You are prompted to enter
the following information:
Copyright © 2007, 2008 Nortel Networks
• protocol—options are tftp|ftp|scp|sftp.
The default is tftp.
ATTENTION
Use TFTP to export to an Ethernet Routing
Switch 5500 Series switch. Ethernet Routing
Switch 5500 Series switches do not support
the other protocols.
•
host name or IP address of the server
• file name of the key (file type .pub) you are
exporting
• for FTP, SCP, and SFTP, user name and
password to access the file exchange server
To export the key directly to an Ethernet Routing
Switch 8300, use the /cfg/domain #/switch
#/sshkey/export command (see “Managing
SSH keys for Nortel SNAS communication” (page
71)).
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Managing network access devices 71
Figure 3 "Generating an SSH key for the domain" (page 71) shows sample
output for the /cfg/domain #/sshkey command.
Figure 3
Generating an SSH key for the domain
Managing SSH keys for Nortel SNAS communication
To retrieve the public key for the network access devices and export the
public key for the domain, use the following command:
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

72 Managing the network access devices
/cfg/domain #/switch #/sshkey
The SSH Key menu appears.
The SSH Key menu includes the following options:
/cfg/domain #/switch #/sshkey
followed by:
import
add
del
show
export
Retrieves the SSH public key from the network
access devices, if it is reachable.
Allows you to paste in the contents of a key
file you have downloaded from the Ethernet
Routing Switch 8300 network access devices.
When prompted, paste in the key, then press
Enter. Enter an elllipsis (...) to signal the end
of the key.
Deletes the SSH public key for the network
access devices in the domain.
The SSH public key type and fingerprint for the
network access devices.
Exports the SSH public key for the Nortel
SNAS domain to the network access devices.
ATTENTION
You cannot use this command to export
the key to an Ethernet Routing Switch
5500 series switch. Instead, use the
/cfg/domain#1/sshkey/export
command to upload the key to a file
exchange server.
user <user>
Specifies the user name for the network
access devices (required for Ethernet Routing
Switch 8300 only).
• user is the user name of an administrative
user (rwa) on the switch.
Reimporting the network access devices SSH key
Whenever the network access devices generates a new public SSH key,
you must import the new key into the Nortel SNAS domain.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Step Action
1 Use the /cfg/domain #/switch #/sshkey/del command to
delete the original key.
2 Enter Apply to apply the change immediately.
3 Use the /cfg/domain #/switch #/sshkey/import
command to import the new key.
4 Enter Apply to apply the change immediately.
Monitoring switch health
The Nortel SNAS continually monitors the health of the network access
devices. At specified intervals, a health check daemon sends queries
and responses to the switch as a heartbeat mechanism. If no activity
(heartbeat) is detected, the daemon will retry the health check for a
specified number of times (the dead count). If there is still no heartbeat,
then after a further interval (the status-quo interval) the network access
devices moves all its clients into the Red VLAN. When connectivity is
re-established, the Nortel SNAS synchronizes sessions with the network
access devices.
Managing network access devices 73
--End--
The health check interval, dead count, and status-quo interval are
configurable.
To configure the interval and dead count parameters for the Nortel SNAS
health checks and status-quo mode, use the following command:
/cfg/domain #/switch #/hlthchk
The HealthCheck menu appears.
The HealthCheck menu includes the following options:
/cfg/domain #/switch #/hlthchk
followed by:
interval <interval>
Sets the time interval between checks for
switch activity.
• interval is an integer that indicates the
time interval in seconds (s), minutes (m), or
hours (h). The valid range is 60s (1m) to
64800s (18h). The default is 1m (1 minute).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

74 Managing the network access devices
/cfg/domain #/switch #/hlthchk
followed by:
deadcnt <count>
sq-int <interval>
Specifies the number of times the Nortel SNAS
will repeat the check for switch activity when
no heartbeat is detected.
•
count is an integer in the range 1–65535
that indicates the number of retries. The
default is 3.
If no heartbeat is detected after the specified
number of retries, the Nortel SNAS enters
status-quo mode.
Sets the time interval for status-quo mode,
after which the network access devices moves
all clients into the Red VLAN.
•
interval is an integer that indicates the
time interval in seconds (s), minutes (m), or
hours (h). The valid range is 0 to 64800s
(18h). The default is 1m (1 minute).
Controlling communication with the network access devices
To stop communication between the Nortel SNAS and a network access
devices, use the following command:
/cfg/domain #/switch #/dis
Enter apply to apply the change immediately.
ATTENTION
If the switch is not going to be used in the Nortel SNAS network, Nortel
recommends deleting the switch from the Nortel SNAS domain, rather than just
disabling it.
To restart communication between the Nortel SNAS and a network access
devices, use the following command:
/cfg/domain #/switch #/ena
Enter apply to apply the change immediately.
Configuring SSCPLite
SSCPLite is a SNAS enforcement protocol that uses SNMP to restrict a
users network access using dynamically provisioned VLAN’s based on
users credentials and device health assessment. SSCPLite supports
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Configuring SNMP Profiles 75
Nortel ES 325, 425, 450, 460, BPS, 470, and ERS 2500, 4500, 5500,
8300, and 8600. In addition, SSCPLite supports Cisco 2900, 3500, and
3700 series Ethernet switches.
• SSCPLite uses the SNMP Protocol
• Switches does not support Dynamic Host Control Protocol
• Switches may not support the DHCP signature based identification for
VOIP phones
• Nortel SNAS should use MAC Authentication
• Multiple PCs connected using hub to the switch port are not supported.
To configure the sscplite, access the menu by using the following
command.
cfg/domain #/switch #/mgmtproto
Configuration of switch menu are modified to include different
communication protocols (sscp, sscplite). SSCP is selected by default.
Usage: mgmtproto <sscp/sscplite>
SSCP SSCPLite
The sscplite includes the following option:
/cfg/domain #/switch #/sscplite
followed by:
profile Set SNMP profile to use
Configuring SNMP Profiles
To configure the snmp profiles, use the following command:
cfg/domain #/snmp-profile
Enter the SNMP profile number. Creates the SNMP profile #.
Enter the name of this SNMP profile.
Enter the version supported for the SNMP profile. Values are v1, v2c, and
v3.
Enter the SNMP port to communicate.
Enter the data refresh interval in seconds.
Enter the CLI user name.
Enter the CLI user password.
Reconfirm the password.
Enter the CLI login type. Values are ssh and telnet.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

76 Managing the network access devices
The SNMPProfile # menu appears.
The snmp profile menu includes the following options:
/cfg/domain #/snmp-profile
followed by
<name> Set the name of the profile.
<versions> Set the supported SNMP versions.
<community> SNMP community menu appears.
<port> Set SNMP port to communicate.
refresh Set the data refresh rate interval.
<cli-user> Set the CLI login user name.
<cli-passwd> Set the CLI login password.
<cli-logint> Set the CLI login type.
del Deletes the SNMP profile.
Configuring SNMP Versions
For configuring SNMP versions, use the following command:
/cfg/domain #/snmp-profile #/versions
The different versions of SNMP are the SNMPv1, SNMPv2c, and
SNMPv3.
• SNMPv1 is the standard version of SNMP. SNMPv1 framework
distinguishes between application entities and protocol entities.
• The SNMPv2c was created as an update of SNMPv1 with several
features. The key enhancements of SNMPv2c are focused on the SMI,
Manager-to-manager capability, and protocol operations.
• SNMPv3 defines the secure version of the SNMP. In SNMPv3,
the concept of an authentication service is expanded to include
other services, such as privacy. SNMPv3 also facilitates remote
configuration of the SNMP entities. SNMPv3 was formed mainly to
address the deficiencies related to security and administration.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Configuring SSCPLite Community
To configure SSCPLite Community, use the following command
/cfg/domain #/snmp-profile #/community
•
SNMP community is the group that devices and manages stations
running SNMP. An SNMP device or agent may belong to more
than one SNMP community. It will not respond to requests from
management stations that do not belong to one of its communities.
•
SNMP can be protected from the internet with a firewall. When
a device receives an authentication that fails, a trap is sent to a
management station.
The SSCPLite Community menu appears.
The SSCPLite Community menu includes the following options:
/cfg/domain #/snmp-profile #/community
followed by:
Configuring SNMP Templates 77
read Set Read Community string
Read = Public
write Set Write Community string
Write = Private
trap
Set Trap Community string.
trap = trap
Configuring SNMP Templates
To configure the SNMP templates, use the following commands:
/cfg/device
The SNMP templates includes the following options:
/cfg/device
followed by
list Lists the templates being used.
show Shows the detailed information in the template.
import Imports new switch Templates to the SNAS.
This will add one more switch type in the
domain Menu.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
28 July 2008
.

78 Managing the network access devices
export Export new switch Templates to the Tftp
servers.
clear Delete command will delete the template entry
from the list and can delete the whole list of
Templates.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

.
Configuring the domain
This chapter includes the following topics:
Topic
“Configuring the domain” (page 79)
“Roadmap of domain commands” (page 81)
“Creating a domain” (page 83)
“Deleting a domain” (page 89)
“Configuring domain parameters” (page 89)
“Configuring the Nortel Health Agent check” (page 92)
“Configuring the SSL server” (page 97)
“Configuring HTTP redirect” (page 107)
“Configuring advanced settings” (page 109)
“Configuring RADIUS accounting” (page 110)
79
“Configuring local DHCP services” (page 115)
A Nortel SNAS domain encompasses all the switches, authentication
servers, and remediation servers associated with that Nortel SNAS cluster.
If you ran the quick setup wizard during initial setup, Domain 1 is created.
If you did not run the quick setup wizard, you must create at least one
domain. For information about creating a domain, see “Creating a domain”
(page 83).
To delete a domain, see “Deleting a domain” (page 89).
ATTENTION
With Nortel Secure Network Access Switch Software Release 1.6.1, you cannot
configure the Nortel SNAS to have more than one domain.
Configuring the domain
To configure the domain, access the Domain menu by using the following
command:
Nortel Secure Network Access Switch
Copyright © 2007, 2008 Nortel Networks
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

80 Configuring the domain
/cfg/domain
From the Domain menu, you can configure and manage the following:
•
domain parameters such as name and portal IP address (pVIP) (see
“Configuring domain parameters” (page 89))
• Authentication, Authorization, and Accounting (AAA) features
—
— for authorization, see “Configuring groups and profiles” (page
— for accounting, see “Configuring RADIUS accounting” (page 110)
•
SNMP profile ( see “Configuring SNMP Profiles” (page 75)
•
PatchLink (see “Configuring Lumension PatchLink integration ” (page
124))
• RADIUS server (see “Configuration of the RADIUS server” (page 127))
•
NAP Interoperability (see “Configuration of Microsoft NAP
Interoperability” (page 139))
for authentication, see “Configuring authentication” (page 171)
149) and “Configuring the Nortel Health Agent check” (page 92)
•
Location based security (see “Creation of the location” (page 123))
• the SSL server used for the domain portal (see “Configuring the SSL
server” (page 97))
—
SSL trace commands
—
SSL settings
—
logging traffic with syslog messages
•
portal settings (see “Customizing the portal and user logon” (page
227))
—
captive portal
—
portal look and feel
—
linksets
•
the network access devices (see “Managing the network access
devices ” (page 57))
• the Nortel SNAS VLANs (see “Managing the network access devices ”
(page 57))
• SSH keys for the domain (see “Managing SSH keys” (page 68))
• HTTP redirect settings (see “Configuring HTTP redirect” (page 107))
• advanced settings such as a backend interface and logging options
(see “Configuring advanced settings” (page 109))
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Roadmap of domain commands
The following roadmap lists the CLI commands to configure the domain in
a Nortel SNAS deployment. Use this list as a quick reference or click on
any entry for more information:
Configuring the domain 81
Command
/cfg/domain <domain ID>
/cfg/quick
/cfg/domain #/del
/cfg/domain <domain ID> name <name>
/cfg/domain #/aaa/nha recheck <interval>
Parameter
pvips <IPaddr>
heartbeat <interval>
hbretrycnt <count>
hbretrycnt <count>
status-quo on|off
onflysrs on|off
desktopnam Desktop agent shortcut
name
action teardown | restricted
list
details on|off
custscript
on|off
persistoob
on|off
loglevel fatal | error | warning | info
| debug
/cfg/domain #/aaa/nha/quick
cfg/domain #/aaa/nha/desktopagent
/cfg/domain #/server port <port>
/cfg/domain #/server/trace ssldump
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
Copyright © 2007, 2008 Nortel Networks
Usage: desktopagent <on|off|auto>
interface <interface ID>
dnsname <name>
tcpdump
ping <host>
dnslookup <host>
traceroute <host>
.

82 Configuring the domain
Command
Parameter
/cfg/domain #/server/ssl cert <certificate index>
cachesize <sessions>
cachettl <ttl>
cacerts <certificate index>
cachain <certificate index list>
protocol ssl2 | ssl3 | ssl23 | tls1
ciphers <cipher list>
ena
dis
/cfg/domain #/server/adv/traflog sysloghost <IPaddr>
udpport <port>
protocol ssl2 | ssl3 | ssl23 | tls1
priority debug | info | notice
facility auth | authpriv | daemon |
local0-7
ena
dis
/cfg/domain #/httpredir port <port>
redir on | off
/cfg/domain #/adv interface <interface ID>
log
/cfg/domain #/aaa/radacct ena
dis
/cfg/domain #/aaa/radacct/servers list <ip> <port> <secret>
del <index number>
add <ip> <port> <secret>
insert <position> <ip> <port>
<secret>
move <index number value> <new index
number value>
/cfg/domain #/aaa/radacct/domainattr vendorid
vendortype
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
28 July 2008
.

Creating a domain
You can create a domain in two ways:
•
“Manually creating a domain” (page 83)
•
“Using the Nortel SNAS domain quick setup wizard in the CLI” (page
84)
Manually creating a domain
To create and configure a domain manually, use the following command:
/cfg/domain <domain ID>
where
domain ID is an integer in the range 1 to 256 that
uniquely identifies the domain in the Nortel
SNAS cluster.
When you first create the domain, you are prompted to enter the following
parameters:
Configuring the domain 83
•
domain name—a string that identifies the domain on the Nortel
SNAS, as a mnemonic aid. The maximum length of the string is 255
characters.
•
portal Virtual IP address (pVIP)—the IP address of the Nortel SNAS
portal. You can have more than one pVIP for a domain. To specify
more than one pVIP, use a comma separator. The pVIP is the address
to which the client connects for authentication and host integrity check.
For more information, see “About the IP addresses” (page 42).
The Domain menu appears.
Figure 4 "Creating a domain" (page 84) shows sample output for the
/cfg/domain <domain ID> command and commands on the Domain
menu. For more information about the Domain menu commands, see
“Configuring domain parameters” (page 89).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

84 Configuring the domain
Figure 4
Creating a domain
Using the Nortel SNAS domain quick setup wizard in the CLI
To create a domain using the Nortel SNAS quick setup wizard, use the
following command:
/cfg/quick
The NSNAS quick setup wizard is similar to the quick setup wizard
available during initial setup.
Depending on the options you select in connection with certificates and
creating a test user, the two wizards also create similar default settings
(see “Settings created by the quick setup wizard” (page 49)).
You can later modify all settings created by the domain quick setup wizard
(see “Configuring domain parameters” (page 89)).
Copyright © 2007, 2008 Nortel Networks
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Configuring the domain 85
Step Action
1 Launch the domain quick setup wizard.
>> Main# cfg/quick
2 Specify the pVIP of the Nortel SNAS domain.
You can configure additional pVIPs later (see “Configuring
domain parameters” (page 89)).
IP address of domain portal: <IPaddr>
3 Specify a name for the Nortel SNAS domain, as a mnemonic aid.
Name of the domain: <name>
4 Specify the port on which the portal web server listens for SSL
communications. The default for HTTPS communications is port
443.
Listen port of domain portal [443]:
5 Specify the certificate to be used by the portal server.
Use existing certificate (no/1) [no]:
If certificates exist on the system, the certificate numbers will be
offered as valid input options. Choose one of the following:
a To create a new certificate by pasting in the contents of a
certificate file from a text editor, press Enter to accept the
default value (no). Go to step 6.
b To create a test certificate, press Enter to accept the default
value (no). Go to step 7.
c To use an existing certificate, enter the applicable certificate
number. Go to Step 8.
Use the /info/certs command to view the main attributes of
all configured certificates. The certificate number is shown in the
Certificate Menu line (for example, Certificate Menu 1:).
For more information about certificates and keys, see “Managing
certificates” (page 297).
6 To create a new certificate:
a At the prompt to create a test certificate, enter No.
b When prompted, paste in the certificate and key from a text
file, then press Enter.
c Enter an ellipsis (...) to signal the end of the certificate.
d To continue, go to Step 8.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

86 Configuring the domain
7 To create a test certificate:
Use existing certificate (no/1) [no]:
Create a test certificate? (yes/no): no
Enter server certificate.
Paste the certificate and key, press Enter to create a
new line, and then type "..." (without the quotation
marks) to terminate.
>
a At the prompt to create a test certificate, enter Yes.
b When prompted, enter the required certificate information.
For more information, see “Generating and submitting a CSR”
(page 305).
c To continue, go to Step 8.
Use existing certificate (no/1) [no]:
Create a test certificate? (yes/no): yes
The combined length of the following parameters may not
exceed 225 bytes.
Country Name (2 letter code):
State or Province Name (full name):
Locality Name (eg, city):
Organization Name (eg, company):
Organizational Unit Name (eg, section):
Common Name (eg, your name or your server’s hostname):
Email Address:
Subject alternative name (blank or comma separated
list of URI:<uri>, DNS:<fqdn>, IP:<ip-address>,
email:<email-address>):
Valid for days [365]:
Key size (512/1024/2048/4096) [1024]:
8 Specify whether the SSL server uses chain certificates.
Do you require chain certificates (yes/no) [no]:
9 If you want to enable HTTP to HTTPS redirection, create a
redirect server.
Do you want an http to https redirect server (yes/no)
[no]:
10 Specify whether you want to add a network access devices to
the domain.
Do you want to configure a switch? (yes/no) [no]:
If you do want to add a network access devices, enter yes to
launch the quick switch wizard. Go to step 11.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Configuring the domain 87
If you do not want to add a network access devices at this time,
press Enter to accept the default value (no). Go to step 12.
11 To add a network access devices, enter the required information
when prompted. For more information, see “Using the quick
switch setup wizard” (page 60).
Do you want to configure a switch? (yes/no) [no]: yes
Enter the type of the switch (ERS8300/ERS5500)
[ERS8300]: IP address of Switch:
NSNA communication port[5000]:
Red vlan id of Switch:
To continue, go to step 12.
12 Specify the action to be performed when an SRS rule check fails.
The options are:
•
restricted—the session remains intact, but access is
restricted in accordance with the rights specified in the
access rules for the group
•
teardown—the SSL session is torn down
The default is restricted.
In the event that the Nortel health Agent checks fails
on a client, the session can be teardown, or left in
restricted mode with limited access.
Which action do you want to use for Health Agent check
failure? (teardown/restricted) [restricted]:
13 Specify whether you want to create a test local user (nha) in the
default nhauser group.
Do you want to create a test local user? (yes/no)
[yes]:
If you do want to create a test user, press Enter to accept the
default value (yes). The wizard will create a test user named
nha, with password nha, in the default nhauser group.
If you do not want to create a test user, enter no.
14 Specify whether you want to create a test user for system
authentication.
Do you want to create a test user for system
authentication? (yes/no) [yes]:
15 Wait while the wizard completes processing to create the
domain, then enter Apply to activate the changes.
The wizard assigns the following default VLAN IDs:
• Green VLAN = VLAN ID 110
• Yellow VLAN = VLAN ID 120
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

88 Configuring the domain
Creating Domain 1
Creating Certificate 1
Creating Client Filter 1
Name: nha_passed
Creating Client Filter 2
Name: nha_failed
Creating Client Filter 3
Name: nha_system_passed
Creating Client Filter 4
Name: nha_system_failed
Creating Linkset 1
Name: nha_passed
This Linkset just prints the Health Agent result
Creating Linkset 2
Name: nha_failed
This Linkset just prints the Health Agent result
Creating Linkset 3
Name: nha_system_passed
This Linkset just prints the Health Agent result
Creating Linkset 4
Name: nha_system_failed
This Linkset just prints the Health Agent result
Creating Group 1
Name: nhauser
Creating Extended Profile 1
Giving full access when health check passed
Creating "green" vlan with id 110
Creating Access rule 1
Giving remediation access when health check failed
Creating Extended Profile 2
Not using SRS rule for user compliancy:
Creating Authentication 1
Adding user ’nha’ with password ’nha’
Creating Group 2
You can change the VLAN mappings when you add or modify
the network access devices (see “Configuring the network
access devices ” (page 64)). You specify the Red VLAN when
you add the network access devices to the domain.
The components created by the wizard depend on the selections
you made in the preceding steps. For example, the sample
output illustrates the following options:
•
an existing certificate (Certificate 1) is being used
•
no network access devices is being added
•
the test user is being created
--End--
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Group for system policies
Name: nhasystem
Creating Extended Profile 1
Giving system access when system health checks passed
Creating "green_system" vlan with id 115
Creating Extended Profile 2
Giving remediation access when system health checks failed
Creating "yellow" vlan with id 120
Not using SRS rule for system compliancy
2008 03 10 00:46
2008 03 10 00:14
Setting Activation and Earliest Push Date
Enable System Credentials
Adding user ’nhasystem’ with password ’nhasystem’ Use apply to
activate the new domain.
>> Configuration# apply
Changes applied successfully.
Deleting a domain
To delete a domain, use the following command:
Configuring the domain 89
/cfg/domain #/del
This command removes the current domain from the system configuration,
including all settings in menus and submenus for the portal, groups,
authentication services, linksets, and network access devices configured
for that domain.
Configuring domain parameters
To configure the domain, use the following command:
/cfg/domain <domain ID>
where
domain ID is an integer in the range 1 to 256 that
uniquely identifies the domain in the Nortel
SNAS cluster.
The Domain menu appears.
The Domain menu includes the following options:
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

90 Configuring the domain
Table 4
Configuring domain parameters
/cfg/domain <domain ID>
followed by:
name<name> Names or renames the domain.
pvips <IPaddr> Sets the pVIP for the domain. The pVIP is the
aaa
• name is a string that must be unique in the
domain. The maximum length of the string
is 255 characters.
The name is a mnemonic aid only and is not
used by other functions.
portal address to which clients connect in order
to access the Nortel SNAS network. For more
information, see “About the IP addresses”
(page 42).
A domain can have more than one pVIP. To
configure multiple IP addresses for the portal,
use a comma to separate the IP address
entries.
Accesses the AAA menu, in order to configure
authentication, authorization, and accounting
features.
location
patchlink
server
Copyright © 2007, 2008 Nortel Networks
•
For authentication, see “Configuring
authentication” (page 171).
• For authorization, see “Configuring groups
and profiles” (page 149) and .“Configuring
the Nortel Health Agent check” (page 92)
•
For accounting, see “Configuring RADIUS
accounting” (page 110).
Accesses the Location menu for the location
based security. (see “Creation of the location”
(page 123))
Accesses the PatchLink Servers menu. (see
“Configuring Lumension PatchLink integration
” (page 124))
Accesses the Server menu, in order
to configure the portal SSL server (see
“Configuring the SSL server” (page 97)).
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Table 4
Configuring domain parameters (cont’d.)
/cfg/domain <domain ID>
followed by:
portal
linkset
switch
snmp-profi
vlan
dhcp
Configuring the domain 91
Accesses the Portal menu, in order to
customize the portal page that in the client’s
web browser (see “Customizing the portal and
user logon” (page 227)).
Accesses the Linkset menu, in order to
configure the linksets to display on the portal
Home tab (see “Configuring linksets” (page
251)).
Accesses the Switch menu, in order to
configure the network access devices
controlled by the Nortel SNAS domain (see
“Managing network access devices ” (page
58)).
Accesses the SNMPProfile menu.
(see“Configuring SNMP Profiles” (page
75))
Accesses the Domain vlan menu, in order to
manage VLAN mappings on the Nortel SNAS
domain (see “Mapping the VLANs” (page 66)).
Accesses the DHCP menu.
sshkey
dnscapt
httpredir
radius
Copyright © 2007, 2008 Nortel Networks
Accesses the NSNAS SSH key menu, in order
to generate and show the public SSH key for
the Nortel SNAS domain (see “Generating
SSH keys for the domain” (page 70)).
Accesses the DNS capture menu, in order
to set the Nortel SNAS domain portal as a
captive portal and to configure the Exclude
List (see “Configuring the captive portal” (page
240)).
Accesses the HTTP Redir menu, in order to
configure HTTP to HTTPS redirect settings
(see “Configuring HTTP redirect” (page 107)).
Accesses the RADIUS menu to configure
RADIUS server. (see“Configuration of the
RADIUS server” (page 127))
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

92 Configuring the domain
Table 4
Configuring domain parameters (cont’d.)
/cfg/domain <domain ID>
followed by:
nap
quick
syslog
adv
del
Accesses the NAP menu to configure the
NAP. (see“Configuration of Microsoft NAP
Interoperability” (page 139))
Launches the quick switch setup wizard, in
order to add network access devices to the
Nortel SNAS domain (see “Using the quick
switch setup wizard” (page 60)).
Accesses the Syslog Servers menu.
Accesses the Advanced menu, in order to
configure a backend interface for the Nortel
SNAS domain and specify the log settings for
syslog messages (see “Configuring advanced
settings” (page 109)).
Removes the current domain from the system
configuration, including all settings in menus
and submenus.
Configuring the Nortel Health Agent check
Before an authenticated client is allowed into the network, the Nortel
Health Agent application checks client host integrity by verifying that the
components required for the client’s personal firewall (executables, DLLs,
configuration files, and so on) are installed and active on the client PC. For
more information about how the Nortel Health Agent check operates in the
Nortel SNAS, see “Nortel Health Agent host integrity check” (page 32).
If you ran the quick setup wizard during the initial setup or to create the
domain, the Nortel Health Agent check has been configured with default
settings and the check result you selected (teardown or restricted). You
can rerun the Nortel Health Agent portion of the quick setup wizard at any
time by using the
“Using the quick Nortel Health Agent setup wizard in the CLI” (page 96)).
To configure settings for the Nortel Health Agent host integrity check and
the check result, use the following command:
/cfg/domain #/aaa/nha
The Nortel Health Agent menu appears.
The Nortel Health Agent menu includes the following options:
/cfg/domain #/aaa/nha/quick command (see
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Table 5
Configuring the Nortel Health Agent
/cfg/domain #/aaa/nha
followed by:
quick
recheck <interval>
Launches the Quick Nortel Health Agent
setup wizard, in order to configure default
Nortel Health Agent check settings and the
check result (see “Using the quick Nortel
Health Agent setup wizard in the CLI” (page
96)).
Sets the time interval between SRS rule
rechecks made by the Nortel Health Agent
applet on the client machine.
•
Configuring the domain 93
interval is an integer that indicates the
time interval in seconds (s), minutes (m),
hours (h), or days (d). The valid range is
60s (1m) to 86400s (1d). The default is
15m (15 minutes).
heartbeat <interval>
hbretrycnt <count>
If a recheck fails, the Nortel SNAS performs
the action specified in the action command
(see "action teardown|restricted" (page 94) ).
Sets the time interval between checks for
client activity.
•
interval is an integer that indicates the
time interval in seconds (s), minutes (m),
hours (h), or days (d). The valid range is
60s (1m) to 86400s (1d). The default is
1m (1 minute).
Specifies the number of times the Nortel
SNAS repeats the check for client activity
when no heartbeat is detected.
• count is an integer in the range 1–65535
that indicates the number of retries. The
default is 3.
If no heartbeat is detected after the specified
number of retries (the inactivity interval),
the Nortel SNAS default behavior is to
terminate the session (see /cfg/domain
#/aaa/nha/status-quo).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

94 Configuring the domain
Table 5
Configuring the Nortel Health Agent (cont’d.)
/cfg/domain #/aaa/nha
followed by:
status-quo on|off
onflysrs
desktopage
desktopnam
Specifies whether the Nortel SNAS domain
operates in status-quo mode. Status-quo
mode determines the behavior of the
Nortel SNAS if no client activity is detected
after the inactivity interval (
hbretrycnt). The options are:
•
on—the client session continues
indefinitely
•
off—the Nortel SNAS terminates the
session immediately
The default is off.
Enables or disables the on-the-fly-srs-update-
mode.
When a security policy is modified on the
SNAS using the administrative tool the policy
is updated on the Nortel Health Agent running
on the logged in operating systems.
Values: on and off
default: off
Enables or disables the desktop agent name.
Values: on, off, and auto
default: off
Specifies the desktop agent shortcut name.
heartbeat x
action teardown|restric
ted
Copyright © 2007, 2008 Nortel Networks
Specifies the action to be performed if the
client fails the Nortel Health Agent SRS rule
check. The options are:
•
restricted—the session remains intact,
but access is restricted in accordance with
the rights specified in the access rules for
the group
• teardown—the SSL session is torn down
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
.

Table 5
Configuring the Nortel Health Agent (cont’d.)
/cfg/domain #/aaa/nha
followed by:
list
Configuring the domain 95
Lists the SRS rules configured for the
domain.
For information about creating SRS rules,
see the information about the Nortel Health
Agent SRS Rule Builder in Nortel Secure
Network Access Switch 4050 User Guide for
the SREM (NN47230-101),.
The Nortel Health Agent applet can apply
different SRS rules for different groups.
For information about specifying the SRS
rule to use for the Nortel Health Agent, see
“Configuring groups” (page 156).
details on|off
custscript
persistoob
loglevel fatal|error|war
ning| info|debug
Specifies whether SRS failure details can be
displayed on the portal page.
Valid options are:
• on—details will be displayed
•
off—details will not be displayed
The default is off.
If set to on, the client can click on the Nortel
Health Agent icon on the portal page to
display details about which elements of the
SRS rule check failed.
Allows the client script customization.
Values: on and off
Persists the out-of-bound connections.
Values: on and off
Sets the log level for the Nortel Health Agent
applet. The options are:
• fatal—fatal errors only
Copyright © 2007, 2008 Nortel Networks
.
• error—all errors
• warning—warning information about
conditions that are not error conditions
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

96 Configuring the domain
Table 5
Configuring the Nortel Health Agent (cont’d.)
/cfg/domain #/aaa/nha
followed by:
Using the quick Nortel Health Agent setup wizard in the CLI
To configure the settings for the SRS rule check using the Nortel Health
Agent quick setup wizard, use the following command:
•
info—high-level information about
processes
•
debug—detailed information about all
processes
The default is info.
The information in the client’s Java Console
window. You can use the information to track
errors in the Nortel Health Agent SRS rules.
/cfg/domain #/aaa/nha/quick
The Nortel Health Agent quick setup wizard is similar to the last few steps
of the Nortel SNAS domain quick setup wizard. The wizard prompts you
for the following information:
•
the action to be performed if the Nortel Health Agent check fails (see
step 12)
•
whether you want to create a test user (see step 13)
The Nortel Health Agent quick setup wizard creates a default SRS rule
(srs-rule-test). This rule checks for the presence of a text file on the
client’s machine (C:\tunnelguard\tg.txt).
The following table shows the sample output for the Nortel Health Agent
quick setup wizard.
>> Main# /cfg/domain #/aaa/nha/quick
In the event that the Nortel Health Agent checks fails on a client, the session
can be teardown, or left in restricted mode with limited access.
Which action do you want to use for Nortel Health Agent check failure?
(teardown/restricted) [restricted]:
Do you want to create a test user for system authentication? (yes/no) [yes]:
Do you want to create a test local user? (yes/no) [yes]:
User policy configuration...
Creating Client Filter 1
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Configuring the domain 97
Name: nha_passed
Creating Client Filter 2
Name: nha_failed
Using existing nha_passed linkset
Using existing nha_failed linkset
Using existing SRS Rule srs-rule-test
Creating Group 1
Group for user policies
Name: nhauser
Creating Extended Profile 1
Giving full access when health check passed
Using existing green vlan
Creating Extended Profile 2
Giving remediation access when health check failed
Using existing yellow vlan
Using SRS rule for user compliancy: srs-rule-test
Adding user ’nha’ with password ’nha’
System policy configuration...
Creating Client Filter 3
Name: nha_system_passed
Creating Client Filter 4
Name: nha_system_failed
Using existing nha_system_passed linkset
Using existing nha_system_failed linkset
Using existing SRS Rule srs-rule-syscred-test
Creating Group 2
Group for system policies
Name: nhasystem
Creating Extended Profile 1
Giving system access when system health passed
Using existing green_system vlan
Creating Extended Profile 2
Giving remediation access when system health failed
Using existing yellow vlan
Using SRS rule for system compliancy: srs-rule-syscred-test
2008 03 10 00:50
2008 03 10 00:18
Setting Activation and Earliest Push Date
Enable System Credentials
Adding system account ’sys’ with password ’sys’
Use ’diff’ to view pending changes, and ’apply’ to commit
>> Nortel Health Agent# apply Changes applied successfully.
Configuring the SSL server
The server number assigned to the portal server configured for the domain
is server 1001.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
Copyright © 2007, 2008 Nortel Networks
28 July 2008
.

98 Configuring the domain
To configure the portal server used in the domain, use the following
command:
/cfg/domain #/server
The Server 1001 menu appears.
The Server 1001 menu includes the following options:
Table 6
Configuring SSL server
/cfg/domain #/server
followed by:
port <port> Specifies the port to which the portal server listens
interface <interface
ID>
dnsname <name>
for HTTPS communications.
• port is an integer in the range 1–65534 that
indicates the TCP port number. The default is
443.
Specifies the backend interface used by the server.
• interface ID is an integer that indicates the
interface number. The default is 0.
Assigns a DNS name to the portal IP address.
trace
•
name is the fully qualified domain name (FQDN)
of the pVIP (for example, nsnas.example.com).
Generally, you need to specify a DNS name only
if your corporate DNS server is unable to perform
reverse lookups of the portal IP address.
When you press Enter after specifying the DNS
name, the system performs a check against the
DNS server included in the system configuration
(see /cfg/sys/dns) to verify that:
• the FQDN is registered in DNS
• the resolved IP address corresponds to the
pVIP
Accesses the Trace menu, in order to capture
and analyze SSL and TCP traffic between clients
and the portal server. For more information, see
“Tracing SSL traffic” (page 99).
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

Table 6
Configuring SSL server (cont’d.)
/cfg/domain #/server
followed by:
ssl
adv
Tracing SSL traffic
To verify connectivity and to capture information about SSL and TCP traffic
between clients and the portal server, use the following command:
/cfg/domain #/server/trace
The Trace menu appears.
Configuring the domain 99
Accesses the SSL Settings menu, in order to
configure SSL settings for the portal server (see
“Configuring SSL settings” (page 102)).
Accesses the Advance settings menu, in order
to configure traffic log settings for a syslog server
(see “Configuring traffic log settings” (page 105)).
The Trace menu includes the following options:
Table 7
Tracing SSL traffic
/cfg/domain #/server/trace
followed by:
ssldump
Creates a dump of the SSL traffic flowing
between clients and the portal server. You are
prompted to enter the following information:
• ssldump flags and ssldump
filter—for more information about
the flags and filter expressions available for
SSLDUMP using UNIX, see h
ump.org/tcpdump_man.html.
• output mode
Options for the output mode are:
• interactive—captured information
decrypted on the screen. SSLDUMP
cannot decrypt any traffic if it is started after
the browser. SSLDUMP must be running
during the initial SSL handshake.
ttp://www.tcpd
Copyright © 2007, 2008 Nortel Networks
.
• tftp|ftp|sftp—the dump will be saved
as a file to the file exchange server you
specify, using a destination file name you
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008

100 Configuring the domain
/cfg/domain #/server/trace
followed by:
tcpdump
specify. You are prompted to enter the
required information. You can specify the
file exchange server using either the host
name or the IP address.
For TFTP, the number of files sent depends
on the amount of captured information. A
sequence number is appended to the file
name given in the CLI, starting at 1 and
incremented automatically for additional
files.
For ftp and sftp, you will also be
prompted to specify a user name and
password valid on the file exchange server.
The default output mode is interactive.
Creates a dump of the TCP traffic flowing
between clients and the virtual SSL server.
You are prompted to enter the following
information:
• tcpdump flags and tcpdump
filter—for more information about
the flags and filter expressions available for
TCPDUMP using UNIX, see h
dump.org/tcpdump_man.html.
•
output mode
Options for the output mode are:
•
interactive—captured information on
the screen
ttp://www.tcp
• tftp|ftp|sftp—the dump will be saved
as a file to the file exchange server you
specify, using a destination file name you
specify. You are prompted to enter the
required information. You can specify the
file exchange server using either the host
name or the IP address.
For TFTP, the number of files sent depends
on the amount of captured information. A
sequence number is appended to the file
name given in the CLI, starting at 1 and
incremented automatically for additional
files.
For ftp and sftp, you will also be
prompted to specify a user name and
password valid on the file exchange server.
Copyright © 2007, 2008 Nortel Networks
.
Nortel Secure Network Access Switch
Using the Command Line Interface
NN47230-100 03.01 Standard
28 July 2008
 Loading...
Loading...