Page 1

Netopia® Software User Guide
Version 7.6
®
Netopia
April 2006
2200 and 3300 Series Gateways
Page 2

Copyright
Copyright © 2006 Netopia, Inc.
Netopia, the Netopia logo, and 3-D Reach are registered trademarks belonging to Netopia, Inc., registered U.S. Patent and Trademark
Office. Broadband Without Boundaries is a trademark belonging to Netopia, Inc. All other trademarks are the proper ty of their respective owners. All rights reserved.
Netopia, Inc. Part Number: 6161227-00-01
2
Page 3

Table of Contents
Table of Contents
Copyright . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 2
CHAPTER 1
CHAPTER 2
Introduction
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
What’s New in 7.6 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 13
About Netopia Documentation . . . . . . . . . . . . . . . . . . . . . . . . . 14
Intended Audience . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
Documentation Conventions . . . . . . . . . . . . . . . . . . . . . . . . . . 15
General . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Internal Web Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Command Line Interface . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Organization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 17
A Word About Example Screens . . . . . . . . . . . . . . . . . . . . . . . 17
Basic Mode Setup
Important Safety Instructions . . . . . . . . . . . . . . . . . . . . . . . . . . 20
POWER SUPPLY INSTALLATION . . . . . . . . . . . . . . . . . . . . . . . . . . . 20
TELECOMMUNICATION INSTALLATION. . . . . . . . . . . . . . . . . . . . . . 20
Wichtige Sicherheitshinweise . . . . . . . . . . . . . . . . . . . . . . . . . . 21
NETZTEIL INSTALLIEREN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
INSTALLATION DER TELEKOMMUNIKATION . . . . . . . . . . . . . . . . . 21
Setting up the Netopia Gateway . . . . . . . . . . . . . . . . . . . . . . . . 22
Microsoft Windows: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 22
Macintosh MacOS 8 or higher or Mac OS X: . . . . . . . . . . . . . . . 24
Configuring the Netopia Gateway . . . . . . . . . . . . . . . . . . . . . . 26
MiAVo VDSL and Ethernet WAN models Quickstart . . . . . . . . . . . . . . 27
PPPoE Quickstart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 28
Netopia Gateway Status Indicator Lights . . . . . . . . . . . . . . . . . 30
Home Page - Basic Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
Manage My Account . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 33
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 19
3
Page 4

Table of Contents
Status Details . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 34
Enable Remote Management. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 35
Expert Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 36
Update Firmware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 37
Factory Reset . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 38
CHAPTER 3
Expert Mode
Accessing the Expert Web Interface . . . . . . . . . . . . . . . . . . . . . 39
Open the Web Connection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
Home Page - Expert Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Home Page - Information . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Toolbar . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Navigating the Web Interface . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Breadcrumb Trail . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Restart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Alert Symbol . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Help . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
Configure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
Quickstart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 48
LAN. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 50
Wireless . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 53
Privacy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 54
Advanced . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 57
Multiple SSIDs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 62
Wireless MAC Authorization. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 63
WAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 68
Advanced . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 72
IP Static Routes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 73
IP Static ARP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75
IPMaps . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 82
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 39
How to Use the Quickstart Page . . . . . . . . . . . . . . . . . . . . . . . . . 48
Setup Your Gateway using a PPP Connection . . . . . . . . . . . . . . 48
About Closed System Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . 59
WPA Version Allowed . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 61
Use RADIUS Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 66
Configure Specific Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76
Planning for Your Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 76
Example: A LAN Requiring Three Pinholes . . . . . . . . . . . . . . . . . 76
Pinhole Configuration Procedure . . . . . . . . . . . . . . . . . . . . . . . . . 79
4
Page 5

Table of Contents
Configure the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
FAQs for the IPMaps Feature . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
What are IPMaps and how are they used? . . . . . . . . . . . . . . . . . 83
What types of servers are supported by IPMaps? . . . . . . . . . . . 83
Can I use IPMaps with my PPPoE or PPPoA connection? . . . . . 83
Will IPMaps allow IP addresses from different subnets to be assigned to my
Gateway? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 83
IPMaps Block Diagram. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84
Default Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
Configure a Default Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 85
Typical Network Diagram . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
NAT Combination Application . . . . . . . . . . . . . . . . . . . . . . . . . . . 86
IP-Passthrough . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 87
A restriction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 88
Differentiated Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 89
DNS. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 92
DHCP Server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 92
RADIUS Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 94
SNMP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 95
IGMP (Internet Group Management Protocol) . . . . . . . . . . . . . . . . . . 97
UPnP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 100
LAN Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 101
Advanced -> Ethernet Bridge . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 102
Configuring for Bridge Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 103
VLAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106
System. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 111
Syslog Parameters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 111
Log Event Messages. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .113
Internal Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
Software Hosting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 116
List of Supported Games and Software . . . . . . . . . . . . . . . . . . . 117
Rename a User(PC) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .119
Clear Options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 120
Time Zone . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 121
Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 122
Passwords. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 123
Create and Change Passwords . . . . . . . . . . . . . . . . . . . . . . . . 123
Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 125
Use a Netopia Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 125
BreakWater Basic Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . 125
Configuring for a BreakWater Setting . . . . . . . . . . . . . . . . . . . . 125
TIPS for making your BreakWater Basic Firewall Selection . . . 127
Basic Firewall Background. . . . . . . . . . . . . . . . . . . . . . . . . . . . . 127
IPSec. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 130
5
Page 6

Table of Contents
SafeHarbour IPSec VPN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 131
Configuring a SafeHarbour VPN . . . . . . . . . . . . . . . . . . . . . . . . 132
Parameter Descriptions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 136
Stateful Inspection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 140
Stateful Inspection Firewall installation procedure . . . . . . . . . . . . . . . 140
Exposed Addresses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 141
Stateful Inspection Options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 144
Open Ports in Default Stateful Inspection Installation . . . . . . . . . . . . 145
Firewall Tutorial . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 146
General firewall terms. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 146
Basic IP packet components . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 146
Basic protocol types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 147
Firewall design rules. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
Firewall Logic. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 148
Implied rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 149
Example filter set page . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 150
Filter basics. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Example network. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 151
Example filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
Example 1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
Example 2 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
Example 3 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 152
Example 4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 153
Example 5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 153
Packet Filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 154
What’s a filter and what’s a filter set? . . . . . . . . . . . . . . . . . . . . . . . . . 155
How filter sets work. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 155
Filter priority. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 156
How individual filters work . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 156
A filtering rule. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 157
Parts of a filter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 157
Port numbers. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 158
Port number comparisons . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 158
Other filter attributes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159
Putting the parts together . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 159
Filtering example #1 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 160
Filtering example #2 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 162
Design guidelines . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 163
An approach to using filters. . . . . . . . . . . . . . . . . . . . . . . . . . . . 163
Working with IP Filters and Filter Sets . . . . . . . . . . . . . . . . . . 164
Adding a filter set . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 164
Adding filters to a filter set . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 165
Viewing filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 169
6
Page 7

Table of Contents
Modifying filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
Deleting filters. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
Moving filters . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
Deleting a filter set. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 170
Associating a Filter Set with an Interface . . . . . . . . . . . . . . . . 171
Policy-based Routing using Filtersets . . . . . . . . . . . . . . . . . . 173
TOS field matching . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 173
Security Log. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 176
Using the Security Monitoring Log . . . . . . . . . . . . . . . . . . . . . . . 176
Timestamp Background . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 178
Install . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 179
Install Software . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 180
Updating Your Gateway’s Netopia Firmware Version . . . . . . . . 180
Step 1: Required Files. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 181
Step 2: Netopia firmware Image File . . . . . . . . . . . . . . . . . . . . . . . . . 181
Install Keys . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 184
Use Netopia Software Feature Keys . . . . . . . . . . . . . . . . . . . . . . . . . 184
Obtaining Software Feature Keys . . . . . . . . . . . . . . . . . . . . . . . 184
Procedure - Install a New Feature Key File . . . . . . . . . . . . . . . . 184
To check your installed features: . . . . . . . . . . . . . . . . . . . . . . . . 186
Install Certificate . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 188
CHAPTER 4
CHAPTER 5
Basic Troubleshooting
. . . . . . . . . . . . . . . . . . . . . . . . 191
Status Indicator Lights . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 192
LED Function Summary Matrix . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 201
Factory Reset Switch . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 203
Advanced Troubleshooting
Home Page . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 206
Expert Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 208
System Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 209
Ports: Ethernet. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 210
Ports: DSL . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 211
IP: Interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 212
DSL: Circuit Configuration. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 213
System Log: Entire . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 214
Diagnostics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 215
Network Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 216
. . . . . . . . . . . . . . . . . . . . . 205
7
Page 8

Table of Contents
CHAPTER 6
Command Line Interface
Overview . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 222
Starting and Ending a CLI Session . . . . . . . . . . . . . . . . . . . . . 224
Logging In. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 224
Ending a CLI Session . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 224
Saving Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 225
Using the CLI Help Facility . . . . . . . . . . . . . . . . . . . . . . . . . . . 225
About SHELL Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 225
SHELL Prompt . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 225
SHELL Command Shortcuts. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 225
SHELL Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 226
Common Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 226
WAN Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 236
About CONFIG Commands . . . . . . . . . . . . . . . . . . . . . . . . . . 237
CONFIG Mode Prompt . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
Navigating the CONFIG Hierarchy . . . . . . . . . . . . . . . . . . . . . . . . . . . 237
Entering Commands in CONFIG Mode . . . . . . . . . . . . . . . . . . . . . . . 239
Guidelines: CONFIG Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . 240
Displaying Current Gateway Settings. . . . . . . . . . . . . . . . . . . . . . . . . 240
Step Mode: A CLI Configuration Technique . . . . . . . . . . . . . . . . . . . . 240
Validating Your Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 241
CONFIG Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 242
DSL Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 242
ATM Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 242
Bridging Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
Common Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 244
DHCP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
Common Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 245
DMT Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 247
DSL Commands . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 247
Domain Name System Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 248
Common Commands. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 248
Dynamic DNS Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 248
IGMP Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 249
IP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
Common Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
ARP Timeout Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
DSL Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 250
Ethernet LAN Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 252
. . . . . . . . . . . . . . . . . . . . . . . 221
8
Page 9

Table of Contents
Default IP Gateway Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . 254
IP-over-PPP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 254
Static ARP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
IGMP Forwarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
IPsec Passthrough . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 257
IP Prioritization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 258
Differentiated Services (DiffServ). . . . . . . . . . . . . . . . . . . . . . . . 258
SIP Passthrough . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 260
Static Route Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 260
IPMaps Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 262
Network Address Translation (NAT) Default Settings . . . . . . . . . . . . 262
Network Address Translation (NAT) Pinhole Settings . . . . . . . . . . . . 263
PPPoE /PPPoA Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 264
Configuring Basic PPP Settings . . . . . . . . . . . . . . . . . . . . . . . . 264
Configuring Port Authentication . . . . . . . . . . . . . . . . . . . . . . . . 266
Ethernet Port Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 267
Command Line Interface Preference Settings . . . . . . . . . . . . . . . . . 267
Port Renumbering Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 269
Security Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 270
Firewall Settings (for BreakWater Firewall) . . . . . . . . . . . . . . . . 270
SafeHarbour IPSec Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . 270
Internet Key Exchange (IKE) Settings . . . . . . . . . . . . . . . . . . . . 275
Stateful Inspection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 276
Example: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 277
Packet Filtering Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 278
Example: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 281
SNMP Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 282
SNMP Notify Type Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . 283
System Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 283
Syslog . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 288
Default syslog installation procedure . . . . . . . . . . . . . . . . . . . . . 288
Wireless Settings (supported models). . . . . . . . . . . . . . . . . . . . . . . . 290
Wireless Privacy Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 293
Wireless MAC Address Authorization Settings . . . . . . . . . . . . . 296
RADIUS Server Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 296
VLAN Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 297
Example: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 297
UPnP settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 299
DSL Forum settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 299
TR-064 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 299
TR-069 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 300
VDSL Settings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 302
VDSL Parameter Defaults . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 303
VDSL Parameters Accepted Values . . . . . . . . . . . . . . . . . . . . . 304
9
Page 10

Table of Contents
CHAPTER 7
CHAPTER 8
Glossary
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 311
-----A----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 311
-----B----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 312
-----C----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 313
-----D----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 314
-----E----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 315
-----F----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 316
-----H----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 317
-----I----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 318
-----K----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 319
-----L-----. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 319
-----M----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 319
-----N----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 320
-----P----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 321
-----Q----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 322
-----R----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 322
-----S----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 323
-----T----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 325
-----U----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 325
-----V----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 325
-----W----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 326
-----X----- . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 326
Technical Specifications and Safety Information
. . . . . 327
10
Description . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Dimensions: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Communications interfaces: . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Power requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Environment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Operating temperature: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Storage temperature: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327
Relative storage humidity: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Software and protocols. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Software media: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Routing: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
WAN support: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Security: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Management/configuration methods: . . . . . . . . . . . . . . . . . . . . . 328
Diagnostics: . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 328
Agency approvals . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
North America . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
Page 11

Table of Contents
International . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
Regulatory notices. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
European Community. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 329
Manufacturer’s Declaration of Conformance . . . . . . . . . . . . . 330
United States . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 330
Service requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 330
Canada . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 331
Declaration for Canadian users . . . . . . . . . . . . . . . . . . . . . . . . . 331
Caution. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 331
Important Safety Instructions . . . . . . . . . . . . . . . . . . . . . . . . . 332
Australian Safety Information . . . . . . . . . . . . . . . . . . . . . . . . . . . 332
Caution. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 332
Caution. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 332
Telecommunication installation cautions . . . . . . . . . . . . . . . . . . 332
47 CFR Part 68 Information . . . . . . . . . . . . . . . . . . . . . . . . . . 333
FCC Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 333
FCC Statements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 333
Electrical Safety Advisory . . . . . . . . . . . . . . . . . . . . . . . . . . . . 334
CHAPTER 9
Overview of Major Capabilities
Wide Area Network Termination . . . . . . . . . . . . . . . . . . . . . . . 336
PPPoE/PPPoA (Point-to-Point Protocol over Ethernet/ATM) . . . . . . 336
Instant-On PPP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 336
Simplified Local Area Network Setup . . . . . . . . . . . . . . . . . . . 337
DHCP (Dynamic Host Configuration Protocol) Server . . . . . . . . . . . 337
DNS Proxy. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 337
Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 338
Embedded Web Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 338
Diagnostics. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 338
Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 339
Remote Access Control. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 339
Password Protection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 339
Network Address Translation (NAT). . . . . . . . . . . . . . . . . . . . . . 339
Netopia Advanced Features for NAT . . . . . . . . . . . . . . . . . . . . . 341
Internal Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 341
Pinholes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 341
Default Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 342
Combination NAT Bypass Configuration . . . . . . . . . . . . . . . . . . 342
IP-Passthrough. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 343
. . . . . . . . . . . . . . . . . . 335
11
Page 12

Table of Contents
VPN IPSec Pass Through . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 343
VPN IPSec Tunnel Termination. . . . . . . . . . . . . . . . . . . . . . . . . 344
Stateful Inspection Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . 344
SSL Certificate Support. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 344
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .345
12
Page 13

What’s New in 7.6
CHAPTER 1 Introduction
What’s New in 7.6
New in Netopia Firmware Version 7.6 are the following features:
TR-069 CLI Enhancements. See “TR-069” on page 300.
•
•
Variable wireless transmission power control CLI command. See page 293.
Wireless WPA Version 2 support for wireless models. See “WPA Version Allowed” on
•
page 61.
•
Added web UI management control for IGMP Snooping. See “IGMP (Internet Group Man-
agement Protocol)” on page 97.
Changes and improvements that require no user inter vention include:
•
Automatically purge old, disassociated entries in the SNMP association table.
•
Onboard Access Controls removed; replaced by Netopia Parental Controls service.
13
Page 14
About Netopia Documentation
☛
Netopia, Inc. provides a suite of technical information for its 2200- and 3300-series family
of intelligent enterprise and consumer Gateways. It consists of:
Software User Guide
•
•
Dedicated Quickstart guides
Specific White Papers
•
The documents are available in electronic form as Por table Document Format (PDF) files.
They are viewed (and printed) from Adobe Acrobat Reader, Exchange, or any other application that supports PDF files.
They are downloadable from Netopia’s website:
http://www.netopia.com/
NOTE:
This guide describes the wide variety of features and functionality of the Netopia Gateway, when used in Router mode. The Netopia Gateway may also be
delivered in Bridge mode. In Bridge mode, the Gateway acts as a pass-through
device and allows the workstations on your LAN to have public addresses
directly on the Internet.
14
Intended Audience
This guide is targeted primarily to residential ser vice subscribers.
Expert Mode sections may also be of use to the support staffs of broadband ser vice providers and advanced residential service subscribers.
See “Expert Mode” on page 39.
Page 15
Documentation Conventions
Documentation Conventions
General
This manual uses the following conventions to present information:
Convention (Typeface) Description
bold italic
monospaced
bold italic sans serif
terminal
bold terminal
Italic Italic type indicates the complete titles of
Internal Web Interface
Menu commands
Web GUI page links and button names
Computer display text
User-entered text
manuals.
Convention (Graphics) Description
blue rectangle or line
Denotes an “excerpt” from a Web page or
the visual truncation of a Web page
Denotes an area of emphasis on a Web
page
solid rounded rectangle
with an arrow
Command Line Interface
Syntax conventions for the Netopia Gateway command line interface are as follows:
Convention Description
straight ([ ]) brackets in cmd line Optional command arguments
15
Page 16

curly ({ }) brackets, with values separated with vertical bars (|).
bold terminal type
face
italic terminal
type face
Alternative values for an argument are presented in curly ({ }) brackets, with values
separated with vertical bars (|).
User-entered text
Variables for which you supply your own values
16
Page 17
Organization
Organization
This guide consists of nine chapters, including a glossary, and an index. It is organized as
follows:
• Chapter 1, “Introduction” — Describes the Netopia document suite, the purpose of,
the audience for, and structure of this guide. It gives a table of conventions.
• Chapter 2, “Basic Mode Setup” — Describes how to get up and running with your
Netopia Gateway.
• Chapter 3, “Expert Mode” — Focuses on the “Expert Mode” Web-based user inter-
face for advanced users. It is organized in the same way as the Web UI is organized. As
you go through each section, functions and procedures are discussed in detail.
• Chapter 4, “Basic Troubleshooting” — Gives some simple suggestions for trouble-
shooting problems with your Gateway’s initial configuration.
• Chapter 5, “Advanced Troubleshooting” — Gives suggestions and descriptions of
expert tools to use to troubleshoot your Gateway’s configuration.
• Chapter 6, “Command Line Interface” — Describes all the current text-based com-
mands for both the SHELL and CONFIG modes. A summary table and individual command examples for each mode is provided.
• Chapter 7, “Glossary”
• Chapter 8, “Technical Specifications and Safety Information”
• Chapter 9, “Overview of Major Capabilities” — Presents a product description sum-
mary.
• Index
A Word About Example Screens
This manual contains many example screen illustrations. Since Netopia 2200- and 3300
Series Gateways offer a wide variety of features and functionality, the example screens
shown may not appear exactly the same for your particular Gateway or setup as they
appear in this manual. The example screens are for illustrative and explanator y purposes,
and should not be construed to represent your own unique environment.
17
Page 18

18
Page 19
CHAPTER 2 Basic Mode Setup
Most users will find that the basic Quickstart configuration is all that they ever need to use.
This section may be all that you ever need to configure and use your Netopia Gateway. The
following instructions cover installation in Router Mode.
This section covers:
• “Impor tant Safety Instructions” on page 20
• “Wichtige Sicherheitshinweise” on page 21 (German)
• “Setting up the Netopia Gateway” on page 22
• “Configuring the Netopia Gateway” on page 26
• “Netopia Gateway Status Indicator Lights” on page 30
• “Home Page - Basic Mode” on page 31
19
Page 20
Important Safety Instructions
POWER SUPPLY INSTALLATION
Connect the power supply cord to the power jack on the Netopia Gateway. Plug the power
supply into an appropriate electrical outlet.
☛ CAUTION:
Depending on the power supply provided with the product, either the direct
plug-in power supply blades, power supply cord plug or the appliance coupler
serves as the mains power disconnect. It is important that the direct plug-in
power supply, socket-outlet or appliance coupler be located so it is readily
accessible.
(Sweden) Apparaten skall anslutas till jordat uttag när den ansluts till ett
nätverk
(Norway) Apparatet må kun tilkoples jordet stikkontakt.
USB-powered models: For Use with Listed I.T.E. Only
TELECOMMUNICATION INSTALLATION
When using your telephone equipment, basic safety precautions should always be followed
to reduce the risk of fire, electric shock and injur y to persons, including the following:
• Do not use this product near water, for example, near a bathtub, wash bowl, kitchen
sink or laundry tub, in a wet basement or near a swimming pool.
• Avoid using a telephone (other than a cordless type) during an electrical storm. There
may be a remote risk of electrical shock from lightning.
• Do not use the telephone to report a gas leak in the vicinity of the leak.
20
SAVE THESE INSTRUCTIONS
Page 21
Wichtige Sicherheitshinweise
Wichtige Sicherheitshinweise
NETZTEIL INSTALLIEREN
Verbinden Sie das Kabel vom Netzteil mit dem Power-Anschluss an dem Netopia Gateway.
Stecken Sie dann das Netzteil in eine Netzsteckdose.
☛ Achtung:
Abhängig von dem mit dem Produkt gelieferten Netzteil, entweder die direkten
Steckernetzgeräte, Stecker vom Netzkabel oder der Gerätekoppler dienen als
Hauptspannungsunterbrechung. Es ist wichtig, dass das Steckernetzgerät,
Steckdose oder Gerätekoppler frei zugänglich sind.
(Sweden) Apparaten skall anslutas till jordat uttag när den ansluts till ett
nätverk
(Norway) Apparatet må kun tilkoples jordet stikkontakt.
USB-powered models: For Use with Listed I.T.E. Only
INSTALLATION DER TELEKOMMUNIKATION
Wenn Ihre Telefonausrüstung verwendet wird, sollten grundlegende Sicherheitsanweisungen immer befolgt werden, um die Gefahr eines Feuers, eines elektrischen Schlages und
die Verletzung von Personen, zu verringern. Beachten Sie diese weiteren Hinweise:
• Benutzen Sie dieses Produkt nicht in Wassernähe wie z.B. nahe einer Badewanne,
Waschschüssel, Küchenspüle, in einem nassen Keller oder an einem Swimmingpool.
• Vermeiden Sie das Telefonieren (gilt nicht für schnurlose Telefone) während eines Gewit-
ters. Es besteht die Gefahr eines elektrischen Schlages durch einen Blitz.
• Nicht das Telefon benutzen um eine Gasleckstelle zu Melden, wenn Sie sich in der Nähe
der Leckstelle befinden.
Bewahren Sie diese Anweisungen auf
21
Page 22
Setting up the Netopia Gateway
Refer to your Quickstart Guide for instructions on how to connect your Netopia gateway to
your power source, PC or local area network, and your Internet access point, whether it is a
dedicated DSL outlet or a DSL or cable modem. Different Netopia Gateway models are
supplied for any of these connections. Be sure to enable Dynamic Addressing on your PC.
Perform the following:
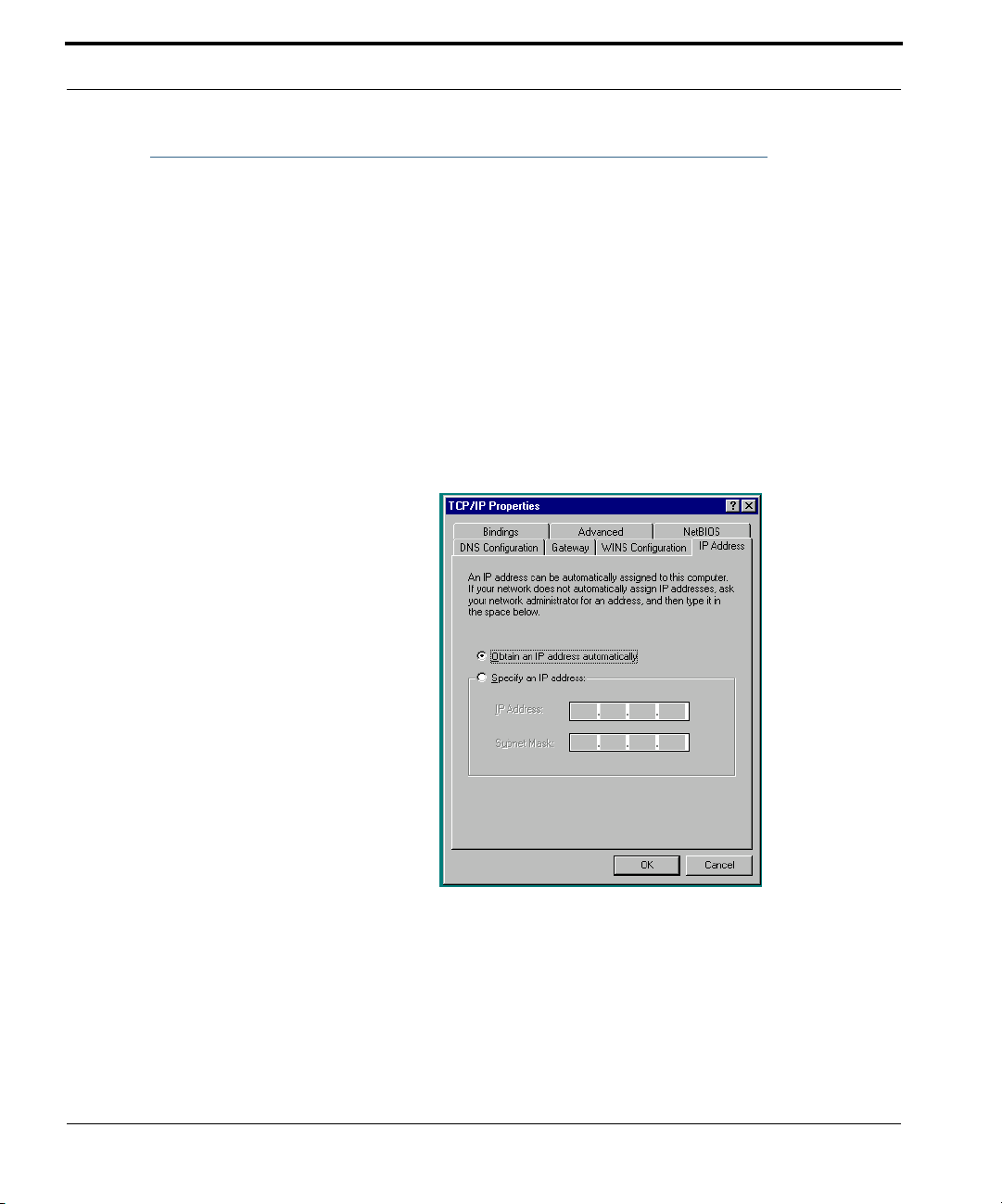
Microsoft Windows:
Step 1. Navigate to the TCP/IP Properties Control Panel.
a. Some Windows
versions follow a
path like this:
Start menu -> Settings -> Control Panel -> Network (or Network and
Dial-up Connections -> Local Area Connection -> Properties) -> TCP/
IP [your_network_card] or Internet Protocol [TCP/IP] -> Properties
22
Page 23
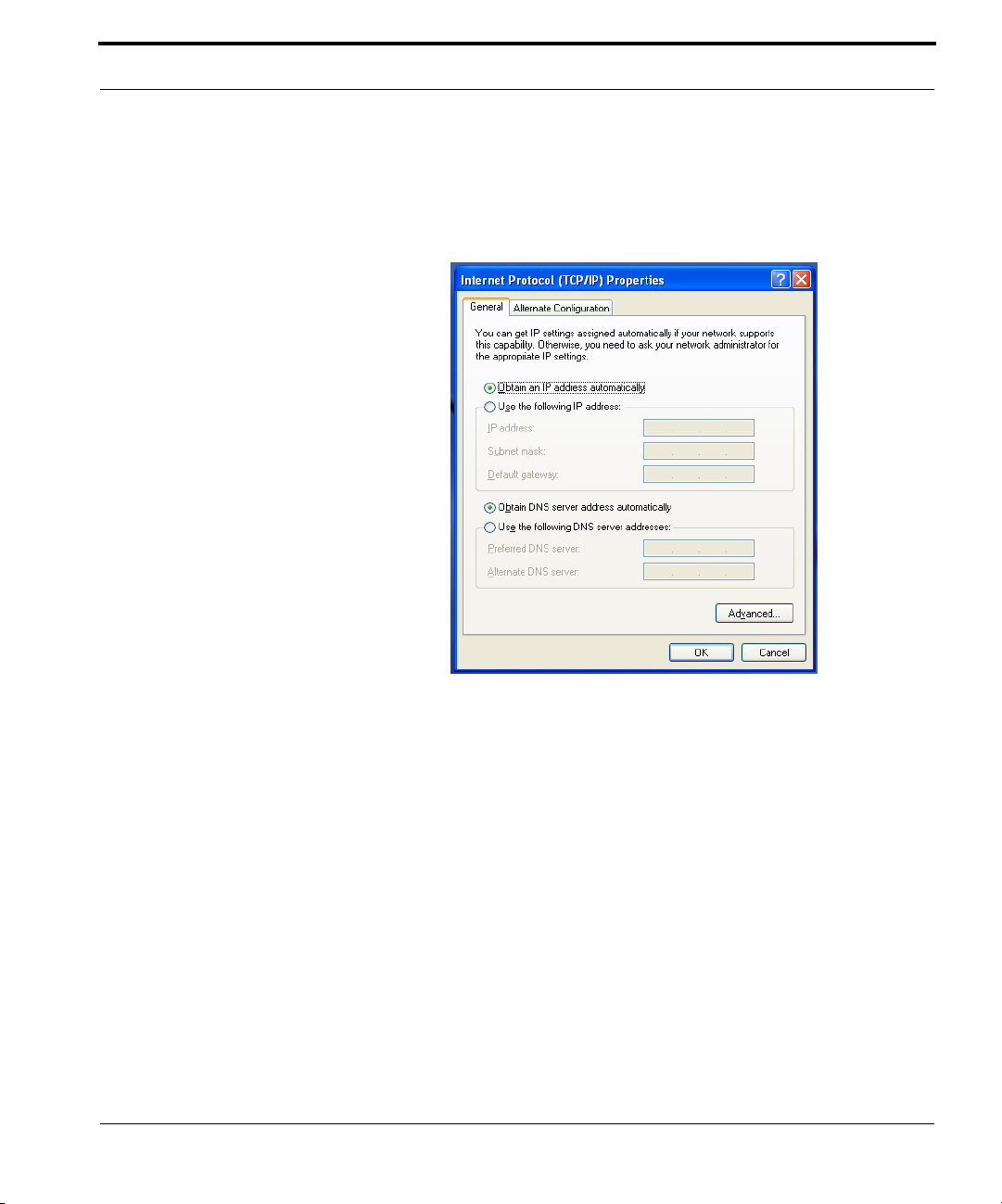
Setting up the Netopia Gateway
b. Some Windows
versions follow a
path like this:
Then go to Step 2.
Start menu -> Control Panel -> Network and Internet Connections ->
Network Connections -> Local Area Connection -> Properties -> Internet Protocol [TCP/IP] -> Proper ties
Step 2. Select Obtain an IP address automatically.
Step 3. Select Obtain DNS server address automatically, if available.
Step 4. Remove any previously configured Gateways, if available.
Step 5. OK the settings. Restart if prompted.
23
Page 24
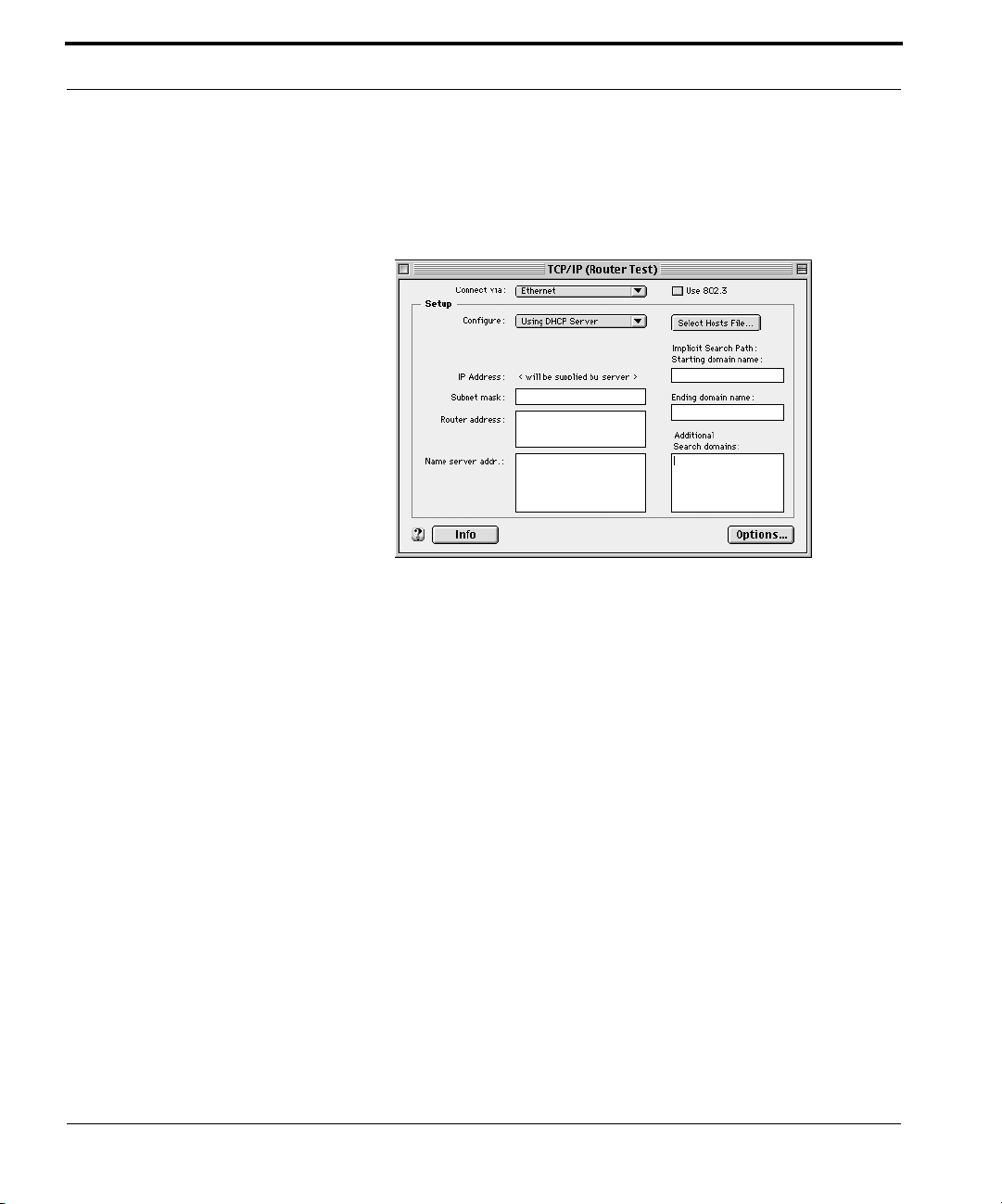
Macintosh MacOS 8 or higher or Mac OS X:
Step 1. Access the TCP/IP or Network control panel.
a. MacOS follows a
path like this:
Apple Menu -> Control Panels -> TCP/IP Control Panel
24
Page 25
Setting up the Netopia Gateway
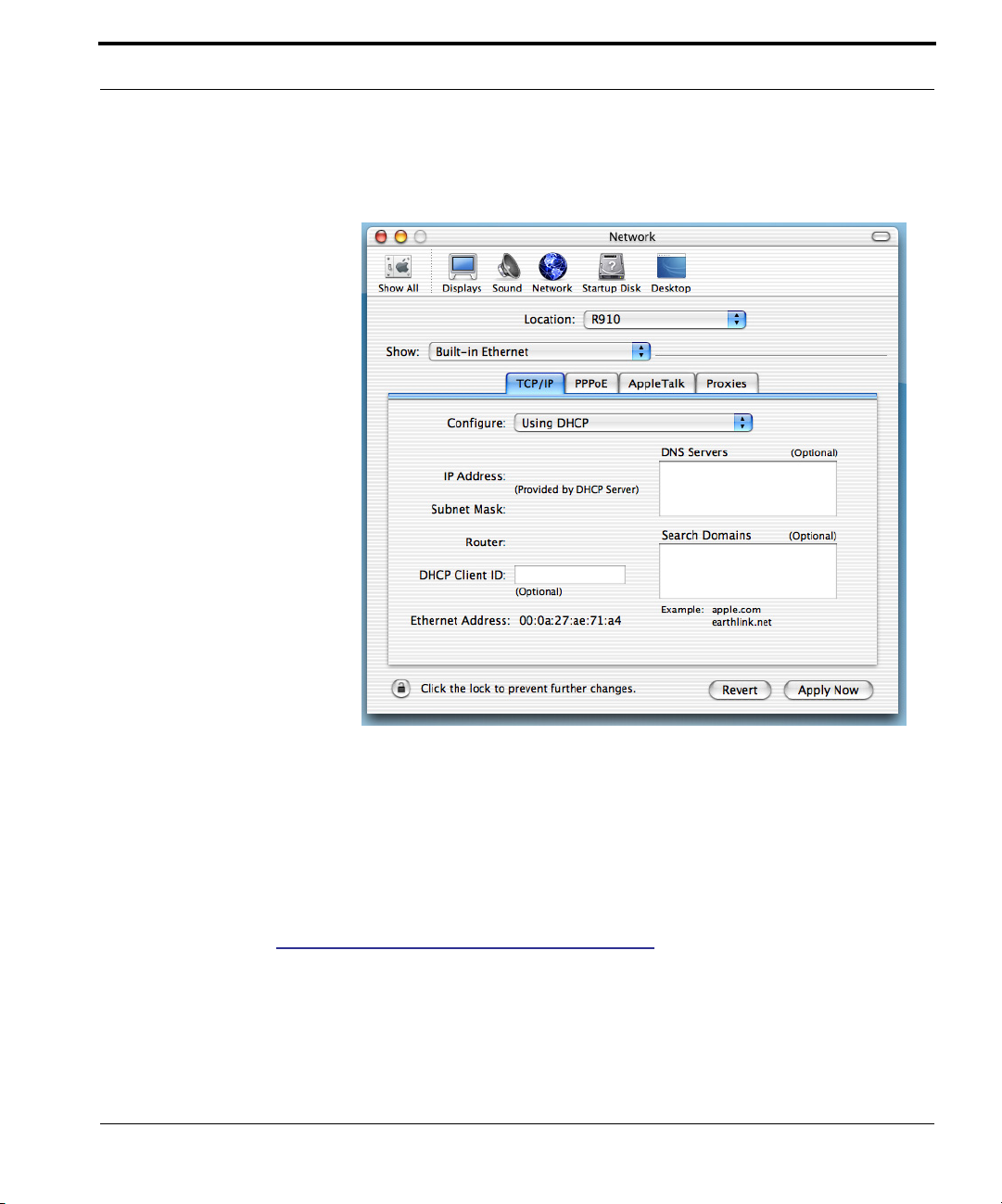
b. Mac OS X follows
a path like this:
Apple Menu -> System Preferences -> Network
Then go to Step 2.
Step 2. Select Built-in Ethernet
Step 3. Select Configure Using DHCP
Step 4. Close and Save, if prompted.
Proceed to “Configuring the Netopia Gateway” on page 26.
25
Page 26
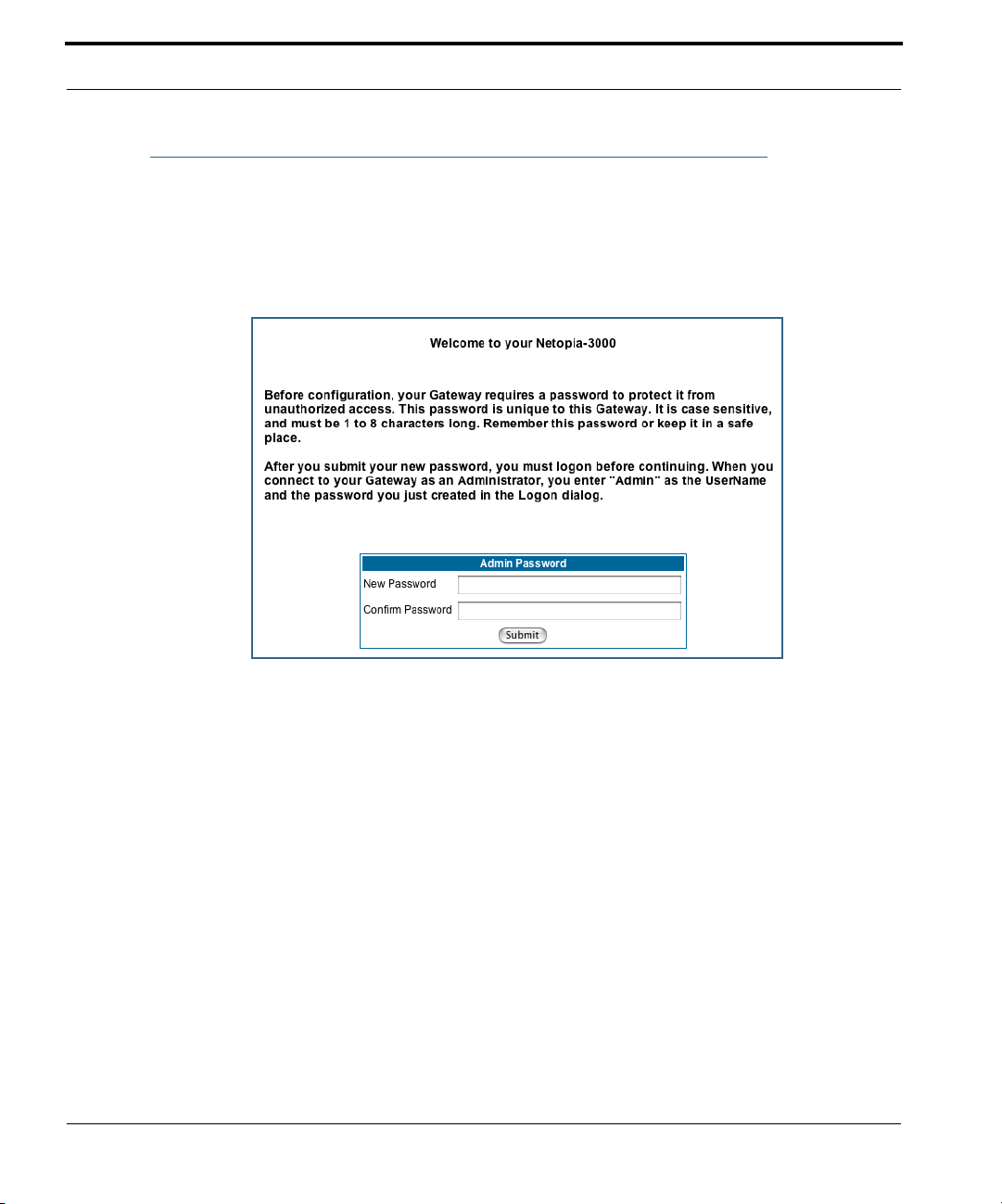
Configuring the Netopia Gateway
1. Run your Web browser application, such as Firefox or Microsoft Internet
Explorer, from the computer connected to the Netopia Gateway.
Enter http://192.168.1.254 in the Location text box.
The Admin Password page appears.
Access to your Netopia device can be controlled through two access control accounts,
Admin or User.
• The Admin, or administrative user, performs all configuration, management or mainte-
nance operations on the Gateway.
• The User account provides monitor capability only.
A user may NOT change the configuration, perform upgrades or invoke maintenance
functions.
For the security of your connection, an Admin password must be set on the Netopia
unit.
26
Page 27

Configuring the Netopia Gateway
MiAVo VDSL and Ethernet WAN models Quickstart
The browser then displays the Quickstart page.
2. Click the
Once a connection is established, your browser is redirected to your ser vice provider’s
home page or a registration page on the Internet.
Connect to the Internet
button.
☛
For MiAVo Series models, your configuration is complete. You can skip to
“Home Page - Basic Mode” on page 31.
27
Page 28
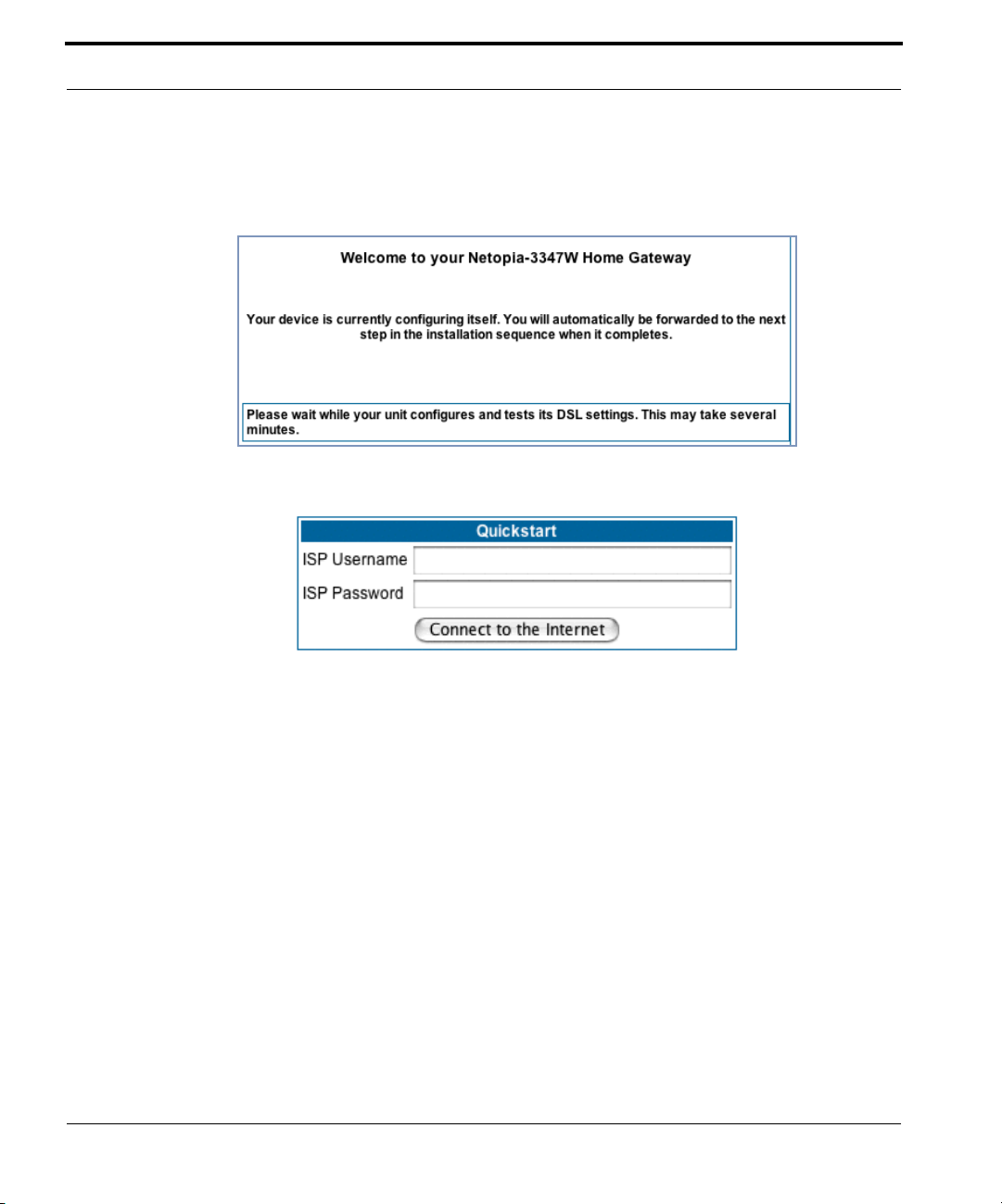
PPPoE Quickstart
For a PPPoE connection, your browser will display a different series of web pages:
The browser then displays the Quickstart web page.
3. Enter the username and password supplied by your Internet Service Pro-
vider. Click the
Once you enter your username and password here, you will no longer need to enter
them whenever you access the Internet. The Netopia Gateway stores this information
and automatically connects you to the Internet.
The Gateway displays a message while it configures itself.
Connect to the Internet
button.
28
Page 29

Configuring the Netopia Gateway
4. When the connection succeeds, your browser will display a success
message.
Once a connection is established, your browser is redirected to your ser vice provider’s
home page or a registration page on the Internet.
5. Congratulations! Your installation is complete. You can now surf to your
favorite Web sites by typing an URL in your browser’s location box or by
selecting one of your favorite Internet bookmarks.
29
Page 30
Netopia Gateway Status Indicator Lights
Colored LEDs on your Netopia Gateway indicate the status of various port activity. Different
Gateway models have different ports for your connections and different indicator LEDs.
The Quickstart Guide accompanying your Netopia Gateway describes the behavior of the
various indicator LEDs.
Example status indicator lights
Status Indicator Lights (LEDs)
netopia
30
Page 31

Home Page - Basic Mode
Home Page - Basic Mode
After you have performed the basic Quickstar t configuration, any time you log in to your
Netopia Gateway you will access the Netopia Gateway Home Page.
You access the Home Page by typing
tion box.
The Basic Mode Home Page appears.
http://192.168.1.254
in your Web browser’s loca-
31
Page 32

The Home Page displays the following information in the center section:
Item Description
Serial Number
Software
Release
Warranty Date
Status of DSL
Status of
Connection
Local WAN IP
Address
Remote
Gateway
Address
Primary DNS
Secondary
DNS
ISP Username
This is the unique serial number of your Gateway.
This is the version number of the current embedded software in your Gateway.
This is the date that your Gateway was installed and enabled.
DSL connection (Internet) is either Up or Down
‘Waiting for DSL’ is displayed while the Gateway is training. This should
change to ‘Up’ within two minutes.
‘Up’ is displayed when the ADSL line is synched and the PPPoE session is
established.
‘Down’ indicates inability to establish a connection; possible line failure.
This is the negotiated address of the Gateway’s WAN interface. This
address is usually dynamically assigned.
This is the negotiated address of the remote router to which this Gateway
is connected.
These are the negotiated DNS addresses.
This is your PPPoE username as assigned by your service provider.
32
Ethernet
Status
USB Status
Date & Time
The links in the left-hand column on this page allow you to manage or configure several features of your Gateway. Each link is described in its own section.
(if so equipped) Local Area Network (Ethernet) is either Up or
Down
If your Gateway is so equipped, Local Area Network (USB) is
either Up or Down
This is the current UTC time; blank if this is not available due to lack of a
network connection.
Page 33

Home Page - Basic Mode
Link: Manage My Account
You can change your ISP account information for the Netopia Gateway. You can also manage other aspects of your account on your service provider’s account management Web
site.
Click on the
If you have a PPPoE account, enter your username, and then your new password. Confirm
your new password. For security, your actual passwords are not displayed on the screen as
you type. You must enter the new password twice to be sure you have typed it correctly.
Click the
Manage My Account
Submit
button.
link. The Manage My Account page appears.
If you have a non-PPPoE account, click the OK button.
You will be taken to your service provider’s Web site account management page.
33
Page 34

Link: Status Details
If you need to diagnose any problems with your Netopia Gateway or its connection to the
Internet, you can run a sophisticated diagnostic tool. It checks several aspects of your
physical and electronic connection and repor ts its results on-screen. This can be useful for
troubleshooting, or when speaking with a technical support technician.
Click on the
Click the
of these tests, see “Diagnostics” on page 215.
Status Details
Run Diagnostics
link. The Diagnostics page appears.
button to run your diagnostic tests. For a detailed description
34
Page 35

Home Page - Basic Mode
Link: Enable Remote Management
This link allows you to authorize a remotely-located person, such as a support technician,
to directly access your Netopia Gateway. This is useful for fixing configuration problems
when you need expert help. You can limit the amount of time such a person will have
access to your Gateway. This will prevent unauthorized individuals from gaining access
after the time limit has expired.
Click the
Since you’ve already has entered an Admin password, you can use that Admin password or
enter a new password. If you enter a new password, it becomes the temporar y Admin password. After the time-out period has expired, the Admin password rever ts to the original
Admin password you entered.
Enter a temporary password for the person you want to authorize, and confirm it by typing it
again. You can select a time-out period for this password, from 5 to 30 minutes, from the
pull-down menu. Be sure to tell the authorized person what the password is, and for how
long the time-out is set. Click the
Enable Rmt Mgmt
link. The Enable Remote Management page appears.
Submit
button.
35
Page 36

Link: Expert Mode
Most users will find that the basic Quickstart configuration is all that they ever need to use.
Some users, however, may want to do more advanced configuration. The Netopia Gateway
has many advanced features that can be accessed and configured through the Exper t
Mode pages.
Click the
You should carefully consider any configuration changes you want to make, and be sure
that your service provider suppor ts them.
Once you click the OK button you will be taken to the Expert Mode Home Page.
The Expert Mode Home Page is the main access point for configuring and managing the
advanced features of your Gateway. See “Expert Mode” on page 39 for information.
Expert Mode
link to display the Expert Mode Confirmation page.
36
Page 37

Home Page - Basic Mode
Link: Update Firmware
(This link is not available on the 3342/3352 models, since firmware updates must be
upgraded via the USB host driver.)
Periodically, the embedded firmware in your Gateway may be updated to improve the operation or add new features. Your gateway includes its own onboard installation capability.
Your service provider may inform you when new firmware is available, or you can check for
yourself.
Click the
If you click the
latest firmware revision. If a newer version is found, your firmware will be automatically
updated once you confirm the installation.
Update Firmware
Continue
button, the Gateway will check a remote Firmware Ser ver for the
link. The Firmware Update Confirmation page appears.
37
Page 38

Link: Factory Reset
In some cases, you may need to clear all the configuration settings and start over again to
program the Netopia Gateway. You can perform a factor y reset to do this.
Click on
Factory Reset
☛ NOTE:
Exercise caution before per forming a Factory Reset. This will erase any configuration changes that you may have made and allow you to reprogram your
Gateway.
to reset the Gateway back to its original factory default settings.
38
Page 39

Accessing the Expert Web Interface
CHAPTER 3 Expert Mode
Using the Expert Mode Web-based user interface for the Netopia 2200- and 3300-series
Gateway you can configure, troubleshoot, and monitor the status of your Gateway.
Accessing the Expert Web Interface
Open the Web Connection
Once your Gateway is powered up, you can use any recent version of the best-known web
browsers such as Netscape Navigator or Microsoft Internet Explorer from any LAN-attached
PC or workstation. The procedure is:
1. Enter the name or IP address of your Netopia Gateway in the Web
browser's window and press Return.
For example, you would enter
2. If an administrator or user password has been assigned to the Netopia
Gateway, enter
word and click
The Basic Mode Home Page opens.
Admin
OK
.
http://192.168.1.254
or
User
as the username and the appropriate pass-
.
39
Page 40

40
3. Click on the
You are challenged to confirm your choice.
Click OK.
The Home Page opens in Expert Mode.
Expert Mode
link in the left-hand column of links.
Page 41

Accessing the Expert Web Interface
Home Page - Expert Mode
The Home Page is the summary page for your Netopia Gateway. The toolbar at the top provides links to controlling, configuring, and monitoring pages. Critical configuration and operational status is displayed in the center section.
41
Page 42

Home Page - Information
The Home page’s center section contains a summary of the Gateway’s configuration settings and operational status.
Summary Information
Field Status and/or Description
General Information
Hardware Model number and summary specification
Serial Number Unique serial number, located on label attached to bottom of unit
Software Version Release and build number of running Netopia Operating System.
Product ID Refers to internal circuit board series; useful in determining which software
upgrade applies to your hardware type.
Date & Time This is the current UTC time; blank if this is not available due to lack of a
network connection.
Breakwater Firewall If the optional feature key is installed: Status of the Breakwater Firewall:
ClearSailing, SilentRunning, or LANdLocked.
Safe Harbour If the optional feature key is installed: SafeHarbour VPN IPsec Tunnel option
(if installed): either On or Off.
WAN
Status Wide Area Network may be Waiting for DSL (or other waiting status), Up or
Down
Data Rate (Kbps) Once connected, displays DSL speed rate, Downstream and Upstream
Local Address IP address assigned to the WAN port.
Peer Address The IP address of the gateway to which the connection defaults. If doing
DHCP, this info will be acquired. If doing PPP, this info will be negotiated.
Connection Type May be either Instant On or Always On.
NAT On or Off. ON if using Network Address Translation to share the IP address
across many LAN users.
WAN Users Displays the number of users allotted and the total number available for
use.
LAN
IP Address Internal IP address of the Netopia Gateway.
Netmask Defines the IP subnet for the LAN
Default is 255.255.255.0 for a Class C device
42
Page 43

Accessing the Expert Web Interface
DHCP Server On or Off. ON if using DHCP to get IP addresses for your LAN client
machines.
DHCP Leases A “lease” is held by each LAN client that has obtained an IP address through
DHCP.
Ethernet (or USB)
Status
Status of your Ethernet network connection (if supported). Up or Down.
43
Page 44

Toolbar
The toolbar is the dark blue bar at the top of the page containing the major navigation buttons. These buttons are available from almost ever y page, allowing you to move freely
about the site.
Home Configure Troubleshoot Security Install Restart Help
Quickstart System Status Passwords Install Keys
LAN Network Tools Firewall Install Software
WAN Diagnostics IPSec Install Certificate
Advanced Stateful Inspection
Packet Filter
Security Log
Navigating the Web Interface
Link: Breadcrumb Trail
The breadcrumb trail is built in the light brown area beneath the toolbar. As you navigate
down a path within the site, the trail is built from left to right. To return anywhere along the
path from which you came, click on one of the links.
44
Page 45

Restart
Restart
Button: Restart
The Restart button on the toolbar allows you to restar t the Gateway at any time. You will be
prompted to confirm the restar t before any action is taken. The Restart Confirmation message explains the consequences of and reasons for restarting the Gateway.
45
Page 46

Link: Alert Symbol
The Alert symbol appears in the upper right corner if you make a database change; one in
which a change is made to the Gateway’s configuration. The Alert serves as a reminder
that you must Save the changes and Restart the Gateway before the change will take
effect. You can make many changes on various pages, and even leave the browser for up
to 5 minutes, but if the Gateway is restarted before the changes are applied, they will be
lost. When you click on the Alert symbol, the Save Changes page appears. Here you can
select various options to save or discard these changes.
If more than one Alert is triggered, you will need to take action to clear the first Aler t before
you can see the second Alert.
46
Page 47

Help
Help
Button: Help
Context-sensitive Help is provided in your Gateway. The page shown here is displayed when
you are on the Home page or other transitional pages. To see a context help page example,
go to
Security -> Passwords
, then click
Help
.
47
Page 48

Configure
Button: Configure
The Configuration options are presented in the order of likelihood you will need to use
them. Quickstart is typically accessed during the hardware installation and initial configuration phase. Often, these settings should be changed only in accordance with infor-
mation from your Service Provider. LAN and WAN settings are available to fine-tune
your system. Advanced provides some special capabilities typically used for gaming or
small office environments, or where LAN-side ser vers are involved.
☛ This button will not be available if you log on as User.
Link: Quickstart
How to Use the Quickstart Page. Quickstart is normally used immediately after
the new hardware is installed. When you are first configuring your Gateway, Quickstart
appears first.
48
(Once you have configured your Gateway, logging on displays the Home page. Thereafter, if
you need to use Quickstart, choose it from the Exper t Mode Configure menu.)
Setup Your Gateway using a PPP Connection.
This example screen is the for a PPP Quickstart configuration. Your gateway authenticates with the Service Provider equipment using the ISP Username and Password. These
values are given to you by your Service Provider.
1. Enter your ISP Username and ISP Password.
Page 49

Configure
2. Click
Connect to the Internet
.
A brief message is displayed while the Gateway attempts to establish a connection.
3. When the connection succeeds, your browser will display your Service
Provider’s home page.
If you encounter any problems connecting, refer to the chapters “Basic Troubleshooting”
on page 191 or “Advanced Troubleshooting” on page 205.
49
Page 50

Link: LAN
* Enable Interface: Enables all LAN-connected computers to share resources and to connect to the WAN. The Interface should always be enabled unless you are instructed to disable it by your Service Provider during troubleshooting.
* IP Address: The LAN IP Address of the Gateway. The IP Address you assign to your LAN
interface must not be used by another device on your LAN network.
50
* IP Netmask: Specifies the subnet mask for the TCP/IP network connected to the virtual
circuit. The subnet mask specifies which bits of the 32-bit binary IP address represent network information. The default subnet mask for most networks is 255.255.255.0 (Class C
subnet mask.)
* Restrictions: Specifies whether an administrator can open a Web Administrator or Telnet
connection to the Gateway over the LAN interface in order to monitor and configure the
Gateway. On the LAN Interface, you can enable or disable administrator access. By default,
administrative restrictions are turned of f, meaning an administrator can open a Web
Administrator or Telnet connection through the LAN Inter face.
Page 51

Configure
• Advanced: Clicking on the Advanced link displays the Advanced LAN IP Interface page.
• IGMP Forwarding: The default setting is Disabled. If you check this option, it will
enable Internet Group Management Protocol (IGMP) multicast for warding. IGMP allows
a router to determine which host groups have members on a given network segment.
• RIP Send Mode: Specifies whether the gateway should use Routing Information Proto-
col (RIP) broadcasts to advertise its routing tables to other routers on your network. You
may choose from the following protocols:
• RIP-1: Routing Information Protocol version 1
• RIP-2: RIP Version 2 is an extension of the original Routing Information Protocol (RIP-
1) that expands the amount of useful information in the RIP packets. While RIP-1 and
RIP-2 share the same basic algorithms, RIP-2 supports several new features, including
inclusion of subnet masks in RIP packets and implementation of multicasting instead of
broadcasting (which reduces the load on hosts which do not suppor t routing protocols.
• RIP-1 compatibility: Compatible with RIP version 1
• RIP-2 with MD5: MD5 authentication is an extension of RIP-2 that increases security
by requiring an authentication key when routes are adver tised.
• RIP MD5 Key: Secret password when using RIP-2 with MD5.
• RIP Receive Mode: Specifies whether the Gateway should use Routing Information
Protocol (RIP) broadcasts to update its routing tables with information received from
other routers on your network. The protocol choices are the same as for the RIP send
mode.
• Proxy ARP: Specifies whether you want the Gateway to respond when it receives an
address resolution protocol for devices behind it. This is a way to make a computer that
is physically located on one network appear to be part of a different physical network
connected to the same Gateway. It allows you to hide a computer with a public IP
address on a private network behind your Gateway, and still have the computer appear
to be on the public network “in front of” the Gateway.
51
Page 52

• Static Client Address Translation: If you check this checkbox, this feature allows a
statically addressed computer whose IP address falls outside of the LAN subnet(s) to
simply plug in and get online without any manual configuration on either the host or the
Netopia Gateway. If enabled, statically addressed LAN hosts that have an address outside of LAN subnets will be able to communicate via the Router’s WAN interface to the
Internet. Supported static IP address values must fall outside of the Router's LAN subnet(s).
• DHCP Server: Your Gateway can provide network configuration information to computers
on your LAN, using the Dynamic Host Configuration Protocol (DHCP).
If you already have a DHCP server on your
LAN, you should turn this service of f.
If you want the Gateway to provide this service, click the
choose Server, then configure the range of IP
addresses that you would like the Gateway to
hand out to your computers.
You can also specify the length of time the computers can use the configuration information; DHCP calls this period the lease time.
Server Mode
pull-down menu,
52
Your Service Provider may, for certain ser vices, want to provide configuration from its
DHCP servers to the computers on your LANs. In this case, the Gateway will relay the
DHCP requests from your computers to a DHCP ser ver in the Ser vice Provider's network.
Click the relay-agent and enter the IP address of the Ser vice Provider's DHCP ser ver in the
Server Address field. This address is furnished by the Service Provider.
☛ NOTE:
The Relay-agent option only works when NAT is off and the Gateway is in
router mode.
Page 53

Configure
Wireless
(supported models)
If your Gateway is a wireless model (such as a 3347W) you can enable or disable the wireless LAN (WLAN) by clicking the
Wireless functionality is enabled by default.
Wireless
link.
If you uncheck the Enable Wireless checkbox, the Wireless Options are disabled, and the
Gateway will not provide or broadcast any wireless LAN ser vices.
SSID (Network ID): The SSID is preset to a number that is unique to your unit. You can
either leave it as is, or change it by entering a freeform name of up to 32 characters, for
example “Ed’s Wireless LAN”. On client PCs’ software, this might also be called the Net-
work Name. The SSID is used to identify this particular wireless LAN. Depending on their
operating system or client wireless card, users must either:
• select from a list of available wireless LANs that appear in a scanned list on their client
• or, if you are in Closed System Mode (see Enable Closed System Mode below), enter
this name on their clients in order to join this wireless LAN.
The pull-down menu for enabling Privacy offers four settings: WPA-802.1x, WPA-PSK,
WEP - Automatic, and Off - No Privacy. WEP-Manual is also available on the Advanced
Configuration Options page. See “
Privacy” on page 54.
53
Page 54

☛ NOTE:
On the 2200-Series Gateways, WEP-Manual privacy is enabled by default.
Use the Netopia Installation Wizard on the accompanying Netopia CD to generate WEP keys for connecting wireless client computers.
Privacy
54
• Off - No Privacy provides no encr yption on your wireless LAN data.
• WPA-802.1x provides RADIUS server authentication suppor t.
• WPA-PSK provides Wireless Protected Access, the most secure option for your wire-
less network. This mechanism provides the best data protection and access control.
Page 55

Configure
The Pre Shared Key is a passphrase shared between the Router and the clients and is
used to generate dynamically changing keys. The passphrase can be 8-63 characters or
up to 64 hex characters. It is recommended to use at least 20 characters for best security.
• WEP - Automatic is a passphrase generator. You enter a passphrase that you choose
in the Passphrase field. The passphrase can be any string of words or numbers.
You can provide a level of data security by enabling WEP (Wired Equivalent Privacy) for
encryption of network data. You can enable 40-, 128-, or 256-bit WEP Encryption
(depending on the capability of your client wireless card) for IP traffic on your LAN.
You select a single key for encryption of outbound traffic. The WEP-enabled client must
have an identical key of the same length, in the identical slot (1 – 4) as the Gateway, in
order to successfully receive and decr ypt the traf fic. Similarly, the client also has a
‘default’ key that it uses to encrypt its transmissions. In order for the Gateway to
receive the client’s data, it must likewise have the identical key of the same length, in
the same slot. For simplicity, a Gateway and its clients need only enter, share, and use
the first key.
55
Page 56

Click the
Submit
button. The Alert icon appears.
56
Click the Alert icon, and then the
Save and Restart
link.
Page 57

Advanced
If you click the
Configure
Advanced
link, the advanced 802.11 Wireless Settings page appears.
Note: This page displays different options depending on which form of Privacy or other
57
Page 58

options you have enabled.
You can then configure:
Operating Mode: The pull-down menu allows you to select and lock the Gateway into the
wireless transmission mode you want. For compatibility with clients using 802.11b (up to
11 Mbps transmission) and 802.11g (up to 20+ Mbps), select Normal (802.11b + g). To
limit your wireless LAN to one mode or the other, select 802.11b Only, or 802.11g Only.
☛ NOTE:
If you choose to limit the operating mode to 802.11b or 802.11g only, clients
using the mode you excluded will not be able to connect.
Default Channel: on which the network will broadcast. This is a frequency range within the
2.4Ghz band. Channel selection depends on government regulated radio frequencies that
vary from region to region. The widest range available is from 1 to 14. However, in North
America only 1 to 11 may be selected. Europe, France, Spain and Japan will differ. Channel
selection can have a significant impact on performance, depending on other wireless activity close to this Gateway. Channel selection is not necessary at the client computers; the
clients will scan the available channels seeking access points using the same SSID as the
client.
AutoChannel Setting: For 802.11G models, AutoChannel is a feature that allows the
Netopia Gateway to determine the best channel to broadcast automatically.
58
Three settings are available from the pull-down menu: Off-Use default, At Startup, and
Continuous.
• Off-Use default is the default setting; the Netopia Gateway will use the configured
default channel selected from the previous pull-down menu.
• At Startup causes the Netopia Gateway at startup to briefly initialize on the default
channel, then perform a full two- to three-second scan, and switch to the best channel
it can find, remaining on that channel until the next reboot.
• Continuous per forms the at-startup scan, and will continuously monitor the current
channel for any other Access Point beacons. If an Access Point beacon is detected on
the same channel, the Netopia Gateway will initiate a three- to four-minute scan of the
channels, locate a better one, and switch. Once it has switched, it will remain on this
channel for at least 30 minutes before switching again if another Access Point is
detected.
Page 59

Configure
Enable Closed System Mode: If enabled, Closed System Mode hides the wireless network from the scanning features of wireless client computers. Unless both the wireless clients and the Gateway share the same SSID in Closed System mode, the Gateway’s
wireless LAN will not appear as an available network when scanned for by wireless-enabled
computers. Members of the Closed System WLAN must log onto the Gateway’s wireless
network with the identical SSID as that configured in the router.
Closed System mode is an ideal way to increase wireless security and to prevent casual
detection by unwanted neighbors, office users, or malicious users such as hackers.
If you do not enable Closed System Mode, it is more convenient, but potentially less
secure, for clients to access your WLAN by scanning available access points. You must
decide based on your own network requirements.
About Closed System Mode
Enabling Closed System Mode on your wireless Gateway provides another level of security,
since your wireless LAN will no longer appear as an available access point to client PCs
that are casually scanning for one.
Your own wireless network clients, however, must log into the wireless LAN by using the
exact SSID of the Netopia Gateway.
In addition, if you have enabled WEP encryption on the Netopia Gateway, your network clients must also have WEP encryption enabled, and must have the same WEP encryption
key as the Netopia Gateway.
Once the Netopia Gateway is located by a client computer, by setting the client to a matching SSID, the client can connect immediately if WEP is not enabled. If WEP is enabled then
the client must also have WEP enabled and a matching WEP key.
Wireless client cards from dif ferent manufacturers and different operating systems accomplish connecting to a wireless LAN and enabling WEP in a variety of ways. Consult the documentation for your particular wireless card and/or operating system.
☛ NOTE:
While clients may also have a passphrase feature, these are vendor-specific
and may not necessarily create the same keys. You can passphrase generate
a set of keys on one, and manually enter them on the other to get around this.
59
Page 60

Block Wireless Bridging: Check the checkbox to block wireless clients from communicating with other wireless clients on the LAN side of the Gateway.
• WEP - Manual allows you to enter your own encr yption keys manually. This is a difficult
process, but only needs to be done once. Avoid the temptation to enter all the same
characters.
60
Encryption Key Size #1 – #4: Selects the length of each encryption key. The longer the
key, the stronger the encryption and the more dif ficult it is to break the encryption.
Page 61

Configure
Encryption Key #1 – #4: The encryption keys. You enter keys using hexadecimal digits.
For 40/64bit encryption, you need ten digits; 26 digits for 128bit, and 58 digits for 256bit
WEP. Hexadecimal characters are 0 – 9, and a – f.
Examples:
• 40bit: 02468ACE02
• 128bit: 0123456789ABCDEF0123456789
• 256bit: 592CA140F0A238B0C61AE162F592CA140F0A238B0C61AE162F21A09C
Use WEP encryption key (1 – 4) #: Specifies which key the Gateway will use to encrypt
transmitted traffic. The default is key #1.
You disable the wireless LAN by unchecking the Enable Wireless checkbox, clicking the
Submit
WPA Version Allowed
If you select either WPA-802.1x or WPA-PSK as your privacy setting, the WPA Version
Allowed pull-down menu appears to allow you to select the WPA version(s) that will be
required for client connections. Choices are:
button, followed by the
Save and Restart
link.
• WPA Version 1 and 2, for maximum interoperability,
• WPA Version 1 Only, for backward compatibility,
• WPA Version 2 Only, for maximum security.
All clients must support the version(s) selected in order to successfully connect.
61
Page 62

Multiple SSIDs
The Multiple Wireless SSIDs feature allows you to add additional network identifiers
(SSIDs or Network Names) for your wireless network.
To enable Multiple Wireless SSIDs, click the
When the Multiple Wireless SSIDs screen appears, check the Enable SSID checkbox for
each SSID you want to enable.
The screen expands to allow you to name each additional Wireless ID, and specify a Privacy mode for each one.
Multiple SSIDs
link.
62
Page 63

Configure
Privacy modes available from the pull-down menu for the multiple SSIDs are: WPA-PSK,
WPA-802.1x, or Off-No Privacy. WEP can also be selected on the additional SSIDs as
long as it is not used on the primary SSID. WEP can only be used on one SSID, so any others will not have WEP available.
These additional Wireless IDs are “Closed System Mode” Wireless IDs that will not be
shown by a client scan, and therefore must be manually configured at the client. In addition, wireless bridging between clients is disabled for all members of these additional network IDs.
Click the
After your first entry, the Alert icon will appear in the upper right corner of your screen.
When you are finished adding SSIDs, click the Alert icon, and Save your changes and
restart the Gateway.
Submit
button.
Wireless MAC Authorization
Wireless MAC Authorization allows you to specify which client PCs are allowed to join
the wireless LAN by specific hardware address. Once it is enabled, only entered MAC
addresses that have been set to Allow will be accepted onto the wireless LAN. All unlisted
addresses will be blocked, in addition to the listed addresses with Allow disabled.
63
Page 64

To enable Wireless MAC Authentication, click the
When the Wireless MAC Authentication screen appears, check the Enable Wireless MAC
Authorization checkbox:
The screen expands as follows:
MAC Authorization
link.
64
Click the
Add
button. The Authorized Wireless MAC Address Entry screen appears.
Page 65

Configure
Enter the MAC (hardware) address of the client PC you want to authorize for access to your
wireless LAN. The Allow Access? checkbox is enabled by default. Unchecking this checkbox specifically denies access from this MAC address. Click the
Submit
button.
☛ Note:
When MAC Authorization is enabled, all wireless clients are blocked until their
MAC addresses are added to the Authorized list.
Your entry will be added to a list of up to 32 authorized addresses as shown:
You can continue to
buttons.
After your first entry, the Alert icon will appear in the upper right corner of your
screen. When you are finished adding addresses to the list, click the Aler t icon, and Save
your changes and restart the Gateway.
Add, Edit
, or
Delete
addresses to the list by clicking the respective
65
Page 66

Use RADIUS Server
RADIUS servers allow external authentication of users by means of a remote authentication database. The remote authentication database is maintained by a Remote Authentication Dial-In User Service (RADIUS) server. In conjunction with Wireless User Authentication,
you can use a RADIUS server database to authenticate users seeking access to the wireless services, as well as the authorized user list maintained locally within the Gateway.
If you click the
information.
RADIUS
link, the screen expands to allow you to enter your RADIUS server
• RADIUS Server Addr/Name: The default RADIUS ser ver name or IP address that you
want to use.
• RADIUS Server Secret: The RADIUS secret key used by this server. The shared secret
should have the same characteristics as a normal password.
• RADIUS Server Port: The por t on which the RADIUS ser ver is listening, typically, the
default 1812.
66
Click the
You can also configure alternate RADIUS servers from the Advanced Network Configuration
page, by clicking the
Submit
button.
Advanced
link.
Page 67

Configure
The Advanced Network Configuration page appears.
You access the RADIUS Server configuration screen from the Advanced Network Configuration web page, by clicking the
RADIUS Server
link.
67
Page 68

Link: WAN
WAN IP Interfaces
Your IP interfaces are listed. Click on an inter face to configure it.
IP Gateway
Enable Gateway: You can configure the Gateway to send packets to a default gateway
if it does not know how to reach the destination host.
Interface Type: If you have PPPoE enabled, you can specify that packets destined for
unknown hosts will be sent to the gateway being used by the remote PPP peer. If you
select ip-address, you must enter the IP address of a host on a local or remote network
to receive the traffic.
Default Gateway: The IP Address of the default gateway.
68
Other WAN Options
PPPoE: You can enable or disable PPPoE. This link also allows configuration of NAT,
admin restrictions, PPPoE username/password, and connection type.
Page 69

Configure
ATM Circuits: You can configure the ATM circuits and the number of Sessions. The IP
Interface(s) should be reconfigured after making changes here.
Available Encapsulation types: Available Multiplexing types:
PPP over Ethernet (PPPoE) LLC/SNAP
PPP over ATM (PPPoA) VC muxed
RFC-1483 Bridged Ethernet
RFC-1483 Routed IP
None
Netopia Firmware Version 7 supports VPI/VCI autodetection by default. If VPI/VCI autodetection is enabled, the ATM Circuits page displays VPI/VCI = 0. If you configure a new
ATM VPI/VCI pair, upon saving and restarting, autodetection is disabled and only the
new VPI/VCI pair configuration will be enabled.
VPI/VCI Autodetection consists of eight static VPI/VCI pair configurations. These are 0/
35, 8/35, 0/32, 8/32, 1/35, 1/1, 1/32, 2/32. These eight VPI/VCI pairs will be created if the Gateway is configured for autodetection. the Gateway does not establish a
circuit using any of these preconfigured VPI/VCI pairs, then you can manually enter a
VPI/VCI pair in the ATM Circuits page.
ATM Traffic Shaping: You can prioritize delay-sensitive data by configuring the Quality
of Service (QoS) characteristics of the virtual circuit. Click the
ATM Traffic Shaping
link.
69
Page 70

You can choose UBR (Unspecified Bit Rate), CBR (Constant Bit Rate), or VBR (Variable
Bit Rate) from the pull-down menu and set the Peak Cell Rate (PCR) in the editable field.
UBR (Unspecified Bit Rate) guarantees no minimum transmission rate. Cells are
transmitted on a “best effort” basis. However, there is a cap on the maximum transmission rate for UBR VCs. In a practical situation:
• UBR VCs should be transmitted at a priority lower than CBR.
• Bandwidth should be shared equally among UBR VCs.
UBR applications are non-real-time traffic such as IP data traffic.
CBR (Constant Bit Rate) guarantees a certain transmission rate (although the appli-
cation may underutilize this bandwidth). A Peak Cell Rate (PCR) characterizes CBR. CBR
is most suited for real time applications such as real time voice / video, although it can
be used for other applications.
VBR (Variable Bit Rate) This class is characterized by:
• a Peak Cell Rate (PCR), which is a temporary burst, not a sustained rate, and
• a Sustained Cell Rate (SCR),
• a Burst Tolerance (BT), specified in terms of Maximum Burst Size (MBS). The MBS
is the maximum number of cells that can be transmitted at the peak cell rate and
should be less than, or equal to the Peak Cell Rate, which should be less than, or equal
to the line rate.
VBR has two sub-classes:
a. VBR non-real-time (VBR-nrt): Typical applications are non-real-time traf fic, such as IP
data traffic. This class yields a fair amount of Cell Delay Variation (CDV).
b. VBR real time (VBR-rt): Typical applications are real-time traf fic, such as compressed
voice over IP and video conferencing. This class transmits cells with a more tightly
bounded Cell Delay Variation. The applications follow CBR.
70
Page 71

Configure
☛ Note:
The difference between VBR-rt and VBR-nr t is the tolerated Cell Delay Variation range and the provisioned Maximum Burst Size.
Class PCR SCR MBS Transmit Priority Comments
UBR X N/A N/A Low PCR is a cap
CBR X N/A N/A High PCR is a guaranteed rate
VBR X X X High PCR > SCR.
SCR is a guaranteed rate.
PCR is a cap.
71
Page 72

Link: Advanced
Selected Advanced options are discussed in the pages that follow. Many are self-explanatory or are dictated by your ser vice provider.
The following are links under Configure -> Advanced:
72
Page 73

Configure
Link: IP Static Routes
A static route identifies a manually configured pathway to a remote network. Unlike
dynamic routes, which are acquired and confirmed periodically from other routers, static
routes do not time out. Consequently, static routes are useful when working with PPP,
since an intermittent PPP link may make maintenance of dynamic routes problematic.
When you click the
You can configure as many as 32 static IP routes for the Gateway. To add a static route,
click the
The IP Static Route Entry page appears.
Add
Static Routes
button.
link, the IP Static Routes page appears.
• Destination Network: Enter the IP address of the static route. It may not be 0.0.0.0.
• Netmask: Enter the subnet mask for the IP network at the other end of the static route.
The subnet mask associated with the destination network must represent the same
network class (A, B, or C) or a lower class (such as a class C subnet mask or class B
network number) to be valid.
73
Page 74

• Interface Type: Choose PPP (vcc1) – depending on the interface; typically vcc1 for
DSL – or IP Address from the pull-down menu to specify whether the static route is
accessible through PPP or IP address.
• Gateway: Enter the IP address of the gateway for the static route. The default gateway
must be located on a network connected to your Netopia Gateway configured interface.
• Metric: Specifies the hop count for the static route. Enter a number from 1 to 15 to indi-
cate the number of routes (actual or best guess) a packet must traverse to reach the
remote network. Some metric or a value of 1 will be used to indicate:
• The remote network is one router away and the static route is the best way to
reach it.
• The remote network is more than one router away but the static route should not
be replaced by a dynamic route, even if the dynamic route is more ef ficient.
• RIP Advertise: From the pull-down menu, choose how the static route should be adver-
tised via RIP:
• Split Horizon: Do not advertise route if the gateway is on the same subnet.
• Always: Advertise route in all RIP messages.
• Never: Do not advertise route.
Click the
Save Changes page, when you are finished.
Once you save your changes, you will be returned to the IP Static Routes entr y screen.
Submit
button. The Alert icon will appear, so that you can switch to the
• You can continue to Add, Edit, or Delete Static Routes from this screen.
74
Page 75

Configure
When you are finished, click the Alert icon , switch to the Save Changes page, and
click the
Save Changes
link.
Link: IP Static ARP
Your Gateway maintains a dynamic Address Resolution Protocol (ARP) table to map IP
addresses to Ethernet (MAC) addresses. It populates this ARP table dynamically, by retrieving IP address/MAC address pairs only when it needs them. Optionally, you can define
static ARP entries to map IP addresses to their corresponding Ethernet MAC addresses.
Unlike dynamic ARP table entries, static ARP table entries do not time out. The IP address
cannot be 0.0.0.0. The Ethernet MAC address entr y is in nn-nn-nn-nn-nn-nn (hexadecimal)
format.
Link: Pinholes
Pinholes allow you to transparently route selected types of network traffic, such as FTP
requests or HTTP (Web) connections, to a specific host behind the Gateway. Creating a pinhole allows access traffic originating from a remote connection (WAN) to be sent to the
internal computer (LAN) that is specified in the Pinhole page.
Pinholes are common for applications like multiplayer online games. Refer to software
manufacturer application documentation for specific traffic types and port numbers.
75
Page 76

Configure Specific Pinholes. Planning for Your Pinholes. Determine if any
of the service applications that you want to provide on your LAN stations use TCP or UDP
protocols. If an application does, then you must configure a pinhole to implement por t forwarding. This is accessed from the Advanced -> Pinholes page.
Example: A LAN Requiring Three Pinholes . The procedure on the following
pages describes how you set up your NAT-enabled Netopia Gateway to support three separate applications. This requires passing three kinds of specific IP traffic through to your
LAN.
Application 1
and would like users on the Internet to have access to it. With NAT “On”, the only externally
visible IP address on your network is the Gateway’s WAN IP (supplied by your Service Provider). All traffic intended for that LAN Web server must be directed to that IP address.
Application 2
email for all of the LAN users.
Application 3
want this specific LAN station to be dedicated to games.
A sample table to plan the desired pinholes is:
For this example, Internet protocols TCP and UDP must be passed through the NAT security
feature and the Gateway’s embedded Web (HTTP) port must be re-assigned by configuring
new settings on the Internal Servers page.
: You have a Web server located on your LAN behind your Netopia Gateway
: You want one of your LAN stations to act as the “central repository” for all
: One of your LAN stations is specially configured for game applications. You
WAN Traffic Type Protocol Pinhole Name
Web TCP my-webserver 192.168.1.1
Email TCP my-mailserver 192.168.1.2
Games UDP my-games 192.168.1.3
LAN Internal IP
Address
76
Page 77

Configure
☛ TIPS for making Pinhole Entries:
1. If the port forwarding feature is required for Web services, ensure that the
embedded Web server’s port number is re-assigned PRIOR to any Pinhole
data entry.
2. Enter data for one Pinhole at a time.
3. Use a unique name for each Pinhole. If you choose a duplicate name, it will
overwrite the previous information without warning.
77
Page 78

A diagram of this LAN example is:
Internet
WAN
Ethernet
Interface
210.219.41.20
Gateway
my-webserver
192.168.1.1
LAN
Ethernet
Interface
NAT
Embedded
NAT Pinholes
Web Server
210.219.41.20:8100
You can also use the LAN-side address of the Gateway, 192.168.1.x:8100 to access the
web and 192.168.1.x:23 to access the telnet server.
my-mailserver
192.168.1.2
my-games
192.168.1.3
78
Page 79

Configure
Pinhole Configuration Procedure. Use the following steps:
1. From the
Servers
Since Port Forwarding is required for this example, the Netopia embedded Web server
is configured first.
Configure
link.
toolbar button ->
Advanced
link, select the
Internal
☛ NOTE:
The two text boxes, Web (HTTP) Server Port and Telnet Server Port, on this
page refer to the port numbers of the Netopia Gateway’s embedded admin-
istration ports.
To pass Web traffic through to your LAN station(s), select a Web (HTTP) Port number that is
greater than 1024. In this example, you choose 8100.
2. Type
8100
in the Web (HTTP) Server Port text box.
3. Click the
4. Click
Advanced
Submit
button.
. Select the
Pinholes
link to go to the Pinhole page.
79
Page 80

5. Click
page. Click
Add
. Type your specific data into the Pinhole Entries table of this
Submit
.
6. Click on the
Add or Edit more Pinholes
link. Click the
next Pinhole. Type the specific data for the second Pinhole.
Add
button. Add the
80
Page 81

Configure
7. Click on the
next Pinhole. Type the specific data for the third Pinhole.
Add or Edit more Pinholes
link. Click the
☛ NOTE:
Note the following parameters for the “my-games” Pinhole:
1. The Protocol ID is UDP.
2. The external port is specified as a range.
3. The Internal port is specified as the lower range entr y.
Add
button. Add the
8. Click on the
sure they are correct.
9. Click the
Add or Edit more Pinholes
Alert
button.
link. Review your entries to be
81
Page 82

10. Select the
task and ensure that the parameters are properly saved.
Save and Restart
link to complete the entire Pinhole creation
☛ NOTE:
REMEMBER: When you have re-assigned the port address for the embedded
Web server, you can still access this facility.
Use the Gateway’s WAN address plus the new port number.
In this example it would be
<WAN Gateway address>:<new port number> or, in this case,
210.219.41.20:8100
You can also use the LAN-side address of the Gateway, 192.168.1.x:8100 to
access the web and 192.168.1.x:23 to access the telnet server.
Link: IPMaps
IPMaps supports one-to-one Network Address Translation (NAT) for IP addresses assigned
to servers, hosts, or specific computers on the LAN side of the Netopia Gateway.
A single static or dynamic (DHCP) WAN IP address must be assigned to support other
devices on the LAN. These devices utilize Netopia’s default NAT/PAT capabilities.
82
Page 83

Configure
Configure the IPMaps Feature
FAQs for the IPMaps Feature
Before configuring an example of an IPMaps-enabled network, review these frequently
asked questions.
What are IPMaps and how are they used? The IPMaps feature allows multi-
ple static WAN IP addresses to be assigned to the Netopia Gateway.
Static WAN IP addresses are used to support specific services, like a web ser ver, mail
server, or DNS server. This is accomplished by mapping a separate static WAN IP address
to a specific internal LAN IP address. All traffic arriving at the Gateway intended for the
static IP address is transferred to the internal device. All outbound traffic from the internal
device appears to originate from the static IP address.
Locally hosted servers are suppor ted by a public IP address while LAN users behind the
NAT-enabled IP address are protected.
IPMaps is compatible with the use of NAT, with either a statically assigned IP address or
DHCP/PPP served IP address for the NAT table.
What types of servers are supported by IPMaps? IPMaps allows a Netopia
Gateway to support servers behind the Gateway, for example, web, mail, FTP, or DNS servers. VPN servers are not suppor ted at this time.
Can I use IPMaps with my PPPoE or PPPoA connection? Yes. IPMaps
can be assigned to the WAN interface provided they are on the same subnet. Service
providers will need to ensure proper routing to all IP addresses assigned to your WAN interface.
Will IPMaps allow IP addresses from different subnets to be assigned
to my Gateway?
same subnet.
WAN IP addresses from different subnets are not supported.
IPMap will support statically assigned WAN IP addresses from the
83
Page 84

IPMaps Block Diagram
The following diagram shows the IPMaps principle in conjunction with existing Netopia NAT
operations:
Netopia Gateway
Static IP Addresses
for IPMaps Applications
143.137.50.37
143.137.50.36
143.137.50.35
Static IP Addresses
or
DHCP/PPP Served IP Address
for Netopia’s default NAT/PAT
Capabilities
WAN Interface LAN Interface
IPMaps:
One-to-One
Multiple Address Mapping
NAT/PAT Table
143.137.50.37
143.137.50.36
143.137.50.35
LAN stations with WAN IP traffic
forwarded by Netopia’s IPMaps
LAN stations with WAN IP traffic
forwarded by Netopia’s NAT function.
...
192.168.1.1
192.168.1.2
192.168.1.3
...
192.168.1.n
192.168.1.1
192.168.1.2
192.168.1.3
.
.
.
192.168.1.n
84
Page 85

Configure
Link: Default Server
This feature allows you to:
• Direct your Gateway to forward all externally initiated IP traf fic (TCP and UDP protocols
only) to a default host on the LAN.
• Enable it for cer tain situations:
– Where you cannot anticipate what port number or packet protocol an in-bound application might use. For example, some network games select arbitrary port numbers
when a connection is opened.
– When you want all unsolicited traffic to go to a specific LAN host.
• Configure for IP Passthrough.
Configure a Default Server. This feature allows you to direct unsolicited or non-
specific traffic to a designated LAN station. With NAT “On” in the Gateway, these packets
normally would be discarded.
For instance, this could be application traffic where you don’t know (in advance) the port or
protocol that will be used. Some game applications fit this profile.
Use the following steps to setup a NAT default server to receive this information:
1. Select the
Server
2. From the pull-down menu, select
Configure
link.
toolbar button, then
Default-Server
Advanced
. The NAT Server IP
, then the
Default
Address field appears.
3. Determine the IP address of the LAN computer you have chosen to
receive the unexpected or unknown traffic.
Enter this address in the NAT Server IP Address field.
4. Click the
5. Click the
6. Click the
Submit
Alert
button.
button.
Save and Restart
link to confirm.
85
Page 86

Typical Network Diagram. A typical network using the NAT Default Server looks like
this:
Internet
Gateway
LAN STN #3
192.168.1.3
WAN
Ethernet
Interface
210.219.41.20
LAN
Ethernet
Interface
86
NAT
Embedded
Web Server
210.219.41.20
(Port 80 default)
You can also use the LAN-side address of the Gateway, 192.168.1.x to access the web
and telnet server.
NAT Default
Server
LAN STN #2
192.168.1.2
NAT protected
NAT Default Server
192.168.1.1
NAT Combination Application. Netopia’s NAT security feature allows you to con-
figure a sophisticated LAN layout that uses both the Pinhole and Default Server capabilities.
Page 87

Configure
With this topology, you configure the embedded administration ports as a first task, followed by the Pinholes and, finally, the NAT Default Server.
When using both NAT pinholes and NAT Default Server the Gateway works with the following rules (in sequence) to for ward traffic from the Internet to the LAN:
1. If the packet is a response to an existing connection created by outbound
traffic from a LAN PC, forward to that station.
2. If not, check for a match with a pinhole configuration and, if one is found,
forward the packet according to the pinhole rule.
3. If there’s no pinhole, the packet is forwarded to the Default Server.
IP-Passthrough. Your Gateway offers an IP passthrough feature. The IP passthrough
feature allows a single PC on the LAN to have the Gateway’s public address assigned to it.
It also provides PAT (NAPT) via the same public IP address for all other hosts on the private
LAN subnet. Using IP passthrough:
• The public WAN IP is used to provide IP address translation for private LAN computers.
• The public WAN IP is assigned and reused on a LAN computer.
• DHCP address serving can automatically serve the WAN IP address to a LAN computer.
When DHCP is used for addressing the designated passthrough PC, the acquired or
configured WAN address is passed to DHCP, which will dynamically configure a singleservable-address subnet, and reser ve the address for the configured MAC address.
This dynamic subnet configuration is based on the local and remote WAN address and
subnet mask. If the WAN interface does not have a suitable subnet mask that is
usable, for example when using PPP or PPPoE, the DHCP subnet configuration will
default to a class C subnet mask.
• If you want to manually assign the WAN address to a LAN PC, do not check the DHCP
Enable checkbox.
• If you check the DHCP Enable checkbox, the screen expands.
87
Page 88

The Host Hardware Address field displays. Here you enter the MAC address of the designated IP-Passthrough computer.
• If this MAC address is not all zeroes, then it will use DHCP to set the LAN host's
address to the (configured or acquired) WAN IP address.
The MAC address must be six colon-delimited or dash-delimited sets of hex digits ('0' –
'FF').
• If the MAC address is all zeroes, then the LAN host will have to be configured manually.
Once configured, the passthrough host's DHCP leases will be shor tened to two minutes.
This allows for timely updates of the host's IP address, which will be a private IP address
before the WAN connection is established. After the WAN connection is established and
has an address, the passthrough host can renew its DHCP address binding to acquire the
WAN IP address.
A restriction. Since both the Gateway and the passthrough host will use the same IP
address, new sessions that conflict with existing sessions will be rejected by the Gateway.
For example, suppose you are a teleworker using an IPSec tunnel from the Gateway and
from the passthrough host. Both tunnels go to the same remote endpoint, such as the VPN
access concentrator at your employer’s office. In this case, the first one to start the IPSec
traffic will be allowed; the second one – since, from the WAN, it's indistinguishable – will
fail.
88
Page 89

Configure
Link: Differentiated Services
When you click the
tion screen appears.
Netopia Firmware Version 7.6 offers Dif ferentiated Services (Diffserv) enhancements.
These enhancements allow your Gateway to make Quality of Service (QoS) decisions about
what path Internet traffic, such as Voice over IP (VoIP), should travel across your network.
For example, you may want streaming video conferencing to use high quality, but more
restrictive, connections, or, you might want e-mail to use less restrictive, but less reliable,
connections.
Differentiated Services
link, the Differentiated Services configura-
• To enable Differentiated Ser vices, check the Enable checkbox.
• Enter a value from 60 to 100 (percent) in the Low-High Priority Ratio field. The
default is 92.
Differentiated Services uses the low-to-high priority queue ratio to regulate traf fic flow.
For example, to provide the least possible latency and highest possible throughput for
high priority traffic, you could set the ratio to 100(%). This would cause the gateway to
forward low priority data only after the high priority queue is completely empty. In practice, you should set it to something less than 100%, since the low priority traffic might
have to wait too long to be passed, and consequently be subject to time-outs.
Click the
Submit
button.
89
Page 90

You can then define Custom Flows. If your applications do not provide Quality of Service
(QoS) control, Custom Flows allows you to define streams for some protocols, por t ranges,
and between specific end point addresses.
• To define a custom flow, click the
The Custom Flow Entry screen appears.
• Inside IP Address/Netmask – For outbound flows, specify an IP address on your LAN.
For inbound flows, this setting is ignored. This setting marks packets from this LAN IP
host/network based on the address and netmask information. For outbound flows, the
Inside IP Address/Netmask is the source address. If you enter a zero IP address
(0.0.0.0), the IP address/netmask fields will be ignored.
• Outside IP Address/Netmask – If you want traffic destined for and originating from a
certain WAN IP address to be controlled, enter the IP address and subnet mask here. If
you leave the default all-zeroes, the outside address check is ignored.
For outbound flows, the outside address is the destination IP address for traffic; for
inbound packets, the outside address is the source IP address.
Note:
When setting the Inside/Outside IP Address/Netmask settings, note that a netmask
value can be used to configure for a network rather than a single IP address.
Add
button.
• Name – Enter a name in this field to
label the flow.
• Protocol – Select the protocol from the
pull-down menu: TCP (default), UDP, ICMP,
or Other. “Other” is appropriate for setting up flows on protocols with non-standard port definitions. IPSEC and PPTP are
common examples.
• Numerical Protocol – If you select
“Other” protocol, this field appears for
you to provide its actual protocol number,
with a range of 0 – 255.
• Direction – Choose Outbound (default),
Inbound, or Both from the pull-down
menu.
• Start Port – For TCP or UDP protocols,
you can optionally specify a range of
ports. Enter the starting por t here.
• End Port – Enter the ending port here.
90
Page 91

Configure
• Quality of Service (QoS) – This is the Quality of Service setting for the flow, based
on the TOS bit information. Select Expedite, Assure, or Of f (default) from the pull-down
menu. The following table outlines the TOS bit settings and behavior:
QoS Setting TOS Bit Value Behavior
Off TOS=000 This custom flow is disabled. You can activate
it by selecting one of the two settings below.
This setting allows you to pre-define flows without actually activating them.
Assure TOS=001 Use normal queuing and throughput rules, but
do not drop packets if possible. Appropriate
for applications with no guaranteed delivery
mechanism.
Expedite TOS=101 Use minimum delay. Appropriate for VoIP and
video applications.
91
Page 92

Link: DNS
Your Service Provider may maintain a Domain Name server. If you have the information for
the DNS servers, enter it on the DNS page. If your Gateway is configured to use DHCP to
obtain its WAN IP address, the DNS information is automatically obtained from that same
DHCP Server.
92
Link: DHCP Server
Your Gateway can provide network configuration information to computers on your LAN,
using the Dynamic Host Configuration Protocol (DHCP).
If you already have a DHCP server on your LAN, you should turn this ser vice off.
If you want the Gateway to provide this service, click the
then configure the range of IP addresses that you would like the Gateway to hand out to
your computers.
You can also specify the length of time the computers can use the configuration information; DHCP calls this period the lease time.
Server Mode
pull-down menu,
Page 93

Configure
Your Service Provider may, for certain ser vices, want to provide configuration from its
DHCP servers to the computers on your LANs. In this case, the Gateway will relay the
DHCP requests from your computers to a DHCP ser ver in the Ser vice Provider's network.
Click the relay-agent and enter the IP address of the Ser vice Provider's DHCP ser ver in the
Server Address field. This address is furnished by the Service Provider.
☛ NOTE:
The relay-agent option only works when NAT is off and the Gateway is in router
mode.
93
Page 94

Link: RADIUS Server
RADIUS servers allow external authentication of users by means of a remote authentication database. The remote authentication database is maintained by a Remote Authentication Dial-In User Service (RADIUS) server. In conjunction with Wireless User Authentication,
you can use a RADIUS server database to authenticate users seeking access to the wireless services, as well as the authorized user list maintained locally within the Gateway.
If you click the
RADIUS
link, the RADIUS Servers screen appears.
• RADIUS Server Addr/Name: The default RADIUS ser ver name or IP address that you
want to use.
• RADIUS Server Secret: The RADIUS secret key used by this server. The shared secret
should have the same characteristics as a normal password.
• RADIUS Server Port: The por t on which the RADIUS ser ver is listening, typically, the
default 1812.
Click the
Submit
button.
94
You can also configure alternate RADIUS servers from the Wireless Configuration pages.
See “Use RADIUS Server” on page 66 for more inormation.
Page 95

Link: SNMP
Configure
When you click the
SNMP
link, the SNMP configuration page appears.
The Simple Network Management Protocol (SNMP) lets a network administrator monitor
problems on a network by retrieving settings on remote network devices. The network
administrator typically runs an SNMP management station program on a local host to
obtain information from an SNMP agent. In this case, the Netopia Gateway is an SNMP
agent. Your Gateway supports SNMP-V1, with the exception of most sets (read-only and
traps), and SNMP-V2. (For certain parts of the NPAV2TRAP.MIB – parameters under resNat-
Params, resDslParams, resSecParams – set is supported.)
You enter SNMP configuration information on this page. Your network administrator furnishes the SNMP parameters.
95
Page 96

☛ WARNING:
SNMP presents you with a security issue. The community facility of
SNMP behaves somewhat like a password. The community “public” is a
well-known community name. It could be used to examine the configuration of your Gateway by your service provider or an uninvited
reviewer. The information can be read from the Gateway.
If you are strongly concerned about security, you may leave the “public”
community blank.
The Notification Type pull-down menu allows you to configure the type of SNMP notifications that will be generated:
• v1 Trap – This selection will generate notifications containing an SNMPv1 Trap Protocol
Data Unit (PDU)
• v2 Trap – This selection will generate notifications containing an SNMPv2 Trap PDU
• Inform – This selection will generate notifications containing an SNMPv2 InformRe-
quest PDU.
96
To send SNMP traps, you must add IP addresses for each trap receiver you want to have.
Click the
Add
button.
Page 97

Configure
The IP Trap Entry screen appears.
Enter an IP Trap Entry IP address. This is the destination for SNMP trap messages, the IP
address of the host acting as an SNMP console.
Click the
and Restart
Submit
link.
button. Click the Alert icon, and in the resulting page, click the
Save
Link: IGMP (Internet Group Management Protocol)
Multicasting is a method for transmitting large amounts of information to many, but not all,
computers over an internet. One common use is to distribute real time voice, video, and
data services to the set of computers which have joined a distributed conference. Other
uses include: updating the address books of mobile computer users in the field or sending
out company newsletters to a distribution list.
Since a router should not be used as a passive forwarding device, Netopia Routers use a
protocol for forwarding multicasting: Internet Group Management Protocol (IGMP). Netopia
Routers can use either IGMP Version 1 or Version 2.
IGMP “Snooping” is a feature of Ethernet layer 2 switches that “listens in” on the IGMP
conversation between computers and multicast routers. Through this process, it builds a
database of where the multicast routers reside by noting IGMP general queries used in the
querier selection process and by listening to other router protocols.
From the host point of view, the snooping function listens at a port level for an IGMP
report. The switch then processes the IGMP repor t and starts forwarding the relevant multicast stream onto the host's port. When the switch receives an IGMP leave message, it
processes the leave message, and if appropriate stops the multicast stream to that par ticular port. Basically, customer IGMP messages although processed by the switch are also
sent to the multicast routers.
97
Page 98

To configure the IGMP options available in Netopia Gateways, click the
The IGMP page appears.
IGMP
link.
98
You can set the following options:
• IGMP Snooping – checking this checkbox enables the Netopia Gateway to “listen in”
to IGMP traffic. The Gateway discovers multicast group membership for the purpose of
restricting multicast transmissions to only those ports which have requested them. This
helps to reduce overall network traffic from streaming media and other bandwidth-intensive IP multicast applications.
• Robustness – a way of indicating how sensitive to lost packets the network is. IGMP
can recover from robustness minus 1 lost IGMP packet. The default value is 2.
• Query Interval– the amount of time in seconds between IGMP General Query mes-
sages sent by the querier gateway. The default query inter val is 125 seconds.
• Query Response Interval – the maximum amount of time in tenths of a second that
the IGMP router waits to receive a response to a General Quer y message. The default
query response inter val is 10 seconds and must be less than the quer y interval.
Page 99

Configure
• Unsolicited Report Interval – the amount of time in seconds between repetitions of a
particular computer’s initial repor t of membership in a group. The default unsolicited
report inter val is 10 seconds.
• Querier Version – select a version of the IGMP Querier from the pull-down menu: v1 or
v2. If you know you will be communicating with other hosts that are limited to v1, for
backward compatibility, select v1; otherwise, allow the default v2.
☛ NOTE:
IGMP Querier version is relevant only if the router is configured for IGMP forwarding. If any IGMP v1 routers are present on the subnet, the querier must
use IGMP v1. The use of IGMP v1 must be administratively configured, since
there is no reliable way of dynamically determining whether IGMP v1 routers
are present on a network. IGMP for warding is enabled per IP Profile and WAN
Connection Profile.
• Last Member Query Interval – the amount of time in tenths of a second that the IGMP
gateway waits to receive a response to a Group-Specific Quer y message. The last member query interval is also the amount of time in seconds between successive GroupSpecific Query messages. The default last member query inter val is 1 second (10 deciseconds).
• Last Member Query Count – the number of Group-Specific Query messages sent
before the gateway assumes that there are no members of the host group being queried on this interface. The default last member quer y count is 2.
• Fast Leave – Checking this checkbox enables a non-standard expedited leave mecha-
nism. The querier keeps track of which client is requesting which channel by IP address.
When a leave message is received, the querier can check its internal table to see if
there are any more clients on this group. If there are none, it immediately sends an
IGMP leave message to the upstream querier. By default, Fast Leave is set to Off.
Click the
Submit
and Restart
button. Click the Alert icon, and in the resulting page, click the
link.
Save
99
Page 100

Link: UPnP
Universal Plug and Play (UPnP™) is a set of protocols that allows a PC to automatically discover other UPnP devices (anything from an internet gateway device to a light switch),
retrieve an XML description of the device and its services, control the device, and subscribe to real-time event notification.
By default, UPnP is enabled on the Netopia Gateway.
For Windows XP users, the automatic discovery feature places an
icon representing the Netopia Gateway automatically in the “My
Network Places” folder. Double-clicking this icon opens the Gateway’s web UI.
PCs using UPnP can retrieve the Gateway’s WAN IP address, and automatically create NAT
port maps. This means that applications that support UPnP, and are used with a UPnPenabled Netopia Gateway, will not need application layer gateway support on the Netopia
Gateway to work through NAT.
You can disable UPnP, if you are not using any UPnP devices or applications.
100
• Uncheck the
UPnP Enabled
checkbox, and click the
Submit
button.
• The Aler t icon will appear in the upper right corner of the web page. Click the Alert icon,
and when prompted, click the
Save and Restart
link.
 Loading...
Loading...