Page 1

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Reference Manual
April 2013
202-10536-05
350 East Plumeria Drive
San Jose, CA 95134
USA
Page 2
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Support
Thank you for selecting NETGEAR products.
After installing your device, locate the serial number on the label of your product and use it to register your product
at https://my.netgear.com. You must register your product before you can use NETGEAR telephone support.
NETGEAR recommends registering your product through the NETGEAR website. For product updates and web
support, visit http://support.netgear.com.
Phone (US & Canada only): 1-888-NETGEAR.
Phone (Other Countries): Check the list of phone numbers at
http://support.netgear.com/general/contact/default.aspx.
Trademarks
NETGEAR, the NETGEAR logo, and Connect with Innovation are trademarks and/or registered trademarks of
NETGEAR, Inc. and/or its subsidiaries in the United States and/or other countries. Information is subject to change
without notice. © NETGEAR, Inc. All rights reserved.
Revision History
Publication
Part Number
202-10536-05 – April 2013 Added the following features:
202-10536-04 1.0 July 2012 A major revision. Added the following features:
Version Publish Date Comments
• Auto-rollover support with failure detection for IPv6 WAN
interfaces (see Configure Auto-Rollover for IPv6 Interfaces
and Create an IPv6 Gateway-to-Gateway VPN Tunnel with
the Wizard)
• Multicast pass-through with alternate networks (see Configure
Multicast Pass-Through for IPv4 Traffic)
• SNMP access from the WAN and SNMP trap events (see Use
a Simple Network Management Protocol Manager)
• Option to define what constitutes a UCP flood attack (see
Attack Checks)
• Authentication and encryption for the PPTP server (see
Configure the PPTP Server)
• Authentication for the L2TP server (see Configure the L2TP
Server)
• Option to select a gateway when you ping or send a trace
packet and option to select a VPN policy when you ping or
send a trace packet through a VPN tunnel (see Send a Ping
Packet and Trace a Route)
• Support for IPv6 with multiple IPv6 features, including a new
general menu structure that provides both IPv4 and IPv6
radio buttons (very extensive revisions throughout the
manual)
• IPSec VPN autoinitiate support (see Manually Add or Edit a
VPN Policy)
• SNMPv3 support (see Use a Simple Network Management
Protocol Manager)
• Option to reboot with a different firmware version (see Select
the Firmware and Reboot the VPN Firewall)
• Extensive list of factory default settings (see Appendix A,
Default Settings and Technical Specifications)
2
Page 3
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
202-10536-03 1.0 November 2011 Incorporated nontechnical edits only (there are no feature
changes).
202-10536-02 1.0 July 2011 Added new features that are documented in the following
sections:
• Configure WAN QoS Profiles
• Inbound Rules (Port Forwarding) and Create LAN WAN
Inbound Service Rules
• Attack Checks
• Set Limits for IPv4 Sessions
• Create IP Groups
• Use the NETGEAR VPN Client Wizard to Create a Secure
Connection
• Manually Create a Secure Connection Using the NETGEAR
VPN Client
• Configure the ProSafe VPN Client for Mode Config Operation
• Configure Date and Time Service
• Configure and Enable the LAN Traffic Meter
202-10536-01 1.0 April 2010 Initial publication of this reference manual.
3
Page 4

Contents
Chapter 1 Introduction
What Is the ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308? .12
Key Features and Capabilities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .12
Quad-WAN Ports for Increased Reliability and Load Balancing. . . . . . .13
Advanced VPN Support for Both IPSec and SSL. . . . . . . . . . . . . . . . . .14
A Powerful, True Firewall with Content Filtering. . . . . . . . . . . . . . . . . . .14
Security Features . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .15
Autosensing Ethernet Connections with Auto Uplink . . . . . . . . . . . . . . .15
Extensive Protocol Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .15
Easy Installation and Management . . . . . . . . . . . . . . . . . . . . . . . . . . . .16
Maintenance and Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .17
Package Contents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .17
Hardware Features. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .17
Front Panel. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .17
Rear Panel . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .19
Bottom Panel with Product Label . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .20
Choose a Location for the VPN Firewall. . . . . . . . . . . . . . . . . . . . . . . . . . .20
Use the Rack-Mounting Kit. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .21
Log In to the VPN Firewall . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .21
Web Management Interface Menu Layout . . . . . . . . . . . . . . . . . . . . . . . . .23
Requirements for Entering IP Addresses. . . . . . . . . . . . . . . . . . . . . . . . . .25
IPv4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .25
IPv6 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .25
Chapter 2 IPv4 and IPv6 Internet and WAN Settings
Internet and WAN Configuration Tasks . . . . . . . . . . . . . . . . . . . . . . . . . . .27
Roadmap to Setting Up IPv4 Internet Connections to Your ISPs. . . . . .27
Roadmap to Setting Up IPv6 Internet Connections to Your ISPs. . . . . .28
Configure the IPv4 Internet Connection and WAN Settings. . . . . . . . . . . .29
Configure the IPv4 WAN Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .29
Let the VPN Firewall Automatically Detect and
Configure an IPv4 Internet Connection . . . . . . . . . . . . . . . . . . . . . . . . .31
Manually Configure an IPv4 Internet Connection. . . . . . . . . . . . . . . . . .34
Configure Load Balancing or Auto-Rollover for IPv4 Interfaces. . . . . . .40
Configure Secondary WAN Addresses . . . . . . . . . . . . . . . . . . . . . . . . .47
Configure Dynamic DNS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .49
Configure the IPv6 Internet Connection and WAN Settings. . . . . . . . . . . .52
Configure the IPv6 Routing Mode . . . . . . . . . . . . . . . . . . . . . . . . . . . . .53
Use a DHCPv6 Server to Configure an IPv6 Internet Connection . . . . .55
4
Page 5

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure a Static IPv6 Internet Connection. . . . . . . . . . . . . . . . . . . . . .58
Configure a PPPoE IPv6 Internet Connection . . . . . . . . . . . . . . . . . . . .61
Configure 6to4 Automatic Tunneling . . . . . . . . . . . . . . . . . . . . . . . . . . .64
Configure ISATAP Automatic Tunneling. . . . . . . . . . . . . . . . . . . . . . . . .65
View the Tunnel Status and IPv6 Addresses . . . . . . . . . . . . . . . . . . . . .67
Configure Stateless IP/ICMP Translation. . . . . . . . . . . . . . . . . . . . . . . .67
Configure Auto-Rollover for IPv6 Interfaces. . . . . . . . . . . . . . . . . . . . . .68
Configure Advanced WAN Options and Other Tasks. . . . . . . . . . . . . . . . .71
Configure WAN QoS Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .76
Additional WAN-Related Configuration Tasks . . . . . . . . . . . . . . . . . . . . . .82
Verify the Connection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .82
What to Do Next. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .82
Chapter 3 LAN Configuration
Manage IPv4 Virtual LANs and DHCP Options . . . . . . . . . . . . . . . . . . . . .84
Port-Based VLANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .85
Assign and Manage VLAN Profiles. . . . . . . . . . . . . . . . . . . . . . . . . . . . .86
VLAN DHCP Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .87
Configure a VLAN Profile . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .88
Configure VLAN MAC Addresses and LAN Advanced Settings. . . . . . .93
Configure IPv4 Multihome LAN IP Addresses on the Default VLAN . . . . .94
Manage IPv4 Groups and Hosts (IPv4 LAN Groups). . . . . . . . . . . . . . . . .96
Manage the Network Database . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .97
Change Group Names in the Network Database . . . . . . . . . . . . . . . . .100
Set Up DHCP Address Reservation. . . . . . . . . . . . . . . . . . . . . . . . . . .101
Manage the IPv6 LAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .102
DHCPv6 Server Options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .103
Configure the IPv6 LAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .104
Configure the IPv6 Router Advertisement Daemon and
Advertisement Prefixes for the LAN . . . . . . . . . . . . . . . . . . . . . . . . . . .109
Configure IPv6 Multihome LAN IP Addresses on the Default VLAN . . . .113
Enable and Configure the DMZ Port for IPv4 and IPv6 Traffic. . . . . . . . .114
DMZ Port for IPv4 Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .115
DMZ Port for IPv6 Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .118
Configure the IPv6 Router Advertisement Daemon and
Advertisement Prefixes for the DMZ. . . . . . . . . . . . . . . . . . . . . . . . . . .122
Manage Static IPv4 Routing. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .127
Configure Static IPv4 Routes . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .127
Configure the Routing Information Protocol . . . . . . . . . . . . . . . . . . . . .129
IPv4 Static Route Example. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .131
Manage Static IPv6 Routing. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .132
Chapter 4 Firewall Protection
About Firewall Protection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .135
Administrator Tips. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .135
Overview of Rules to Block or Allow Specific Kinds of Traffic . . . . . . . . .136
Outbound Rules (Service Blocking) . . . . . . . . . . . . . . . . . . . . . . . . . . .137
5
Page 6

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Inbound Rules (Port Forwarding) . . . . . . . . . . . . . . . . . . . . . . . . . . . . .140
Order of Precedence for Rules. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .144
Configure LAN WAN Rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .145
Create LAN WAN Outbound Service Rules . . . . . . . . . . . . . . . . . . . . .147
Create LAN WAN Inbound Service Rules . . . . . . . . . . . . . . . . . . . . . .149
Configure DMZ WAN Rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .152
Create DMZ WAN Outbound Service Rules. . . . . . . . . . . . . . . . . . . . .154
Create DMZ WAN Inbound Service Rules . . . . . . . . . . . . . . . . . . . . . .156
Configure LAN DMZ Rules. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .158
Create LAN DMZ Outbound Service Rules . . . . . . . . . . . . . . . . . . . . .160
Create LAN DMZ Inbound Service Rules. . . . . . . . . . . . . . . . . . . . . . .162
Examples of Firewall Rules . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .164
Examples of Inbound Firewall Rules . . . . . . . . . . . . . . . . . . . . . . . . . .164
Examples of Outbound Firewall Rules . . . . . . . . . . . . . . . . . . . . . . . . .168
Configure Other Firewall Features. . . . . . . . . . . . . . . . . . . . . . . . . . . . . .170
Attack Checks. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .170
Set Limits for IPv4 Sessions. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .173
Configure Multicast Pass-Through for IPv4 Traffic. . . . . . . . . . . . . . . .174
Manage the Application Level Gateway for SIP Sessions . . . . . . . . . .176
Services, Bandwidth Profiles, and QoS Profiles. . . . . . . . . . . . . . . . . . . .176
Add Customized Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .177
Create IP Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .179
Create Bandwidth Profiles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .181
Create Quality of Service Profiles for IPv4 Firewall Rules . . . . . . . . . .184
Quality of Service Priorities for IPv6 Firewall Rules . . . . . . . . . . . . . . .186
Configure Content Filtering . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .186
Set a Schedule to Block or Allow Specific Traffic. . . . . . . . . . . . . . . . . . .189
Enable Source MAC Filtering. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .190
Set Up IP/MAC Bindings . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .192
Configure Port Triggering. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .197
Configure Universal Plug and Play. . . . . . . . . . . . . . . . . . . . . . . . . . . . . .199
Chapter 5 Virtual Private Networking Using
IPSec and L2TP Connections
Considerations for Dual WAN Port Systems . . . . . . . . . . . . . . . . . . . . . .202
Use the IPSec VPN Wizard for Client and Gateway Configurations . . . .203
Create an IPv4 Gateway-to-Gateway VPN Tunnel with the Wizard. . .204
Create an IPv6 Gateway-to-Gateway VPN Tunnel with the Wizard. . .208
Create an IPv4 Client-to-Gateway VPN Tunnel with the Wizard . . . . .212
Test the Connection and View Connection and Status Information. . . . .227
Test the NETGEAR VPN Client Connection . . . . . . . . . . . . . . . . . . . .227
NETGEAR VPN Client Status and Log Information . . . . . . . . . . . . . . .229
View the VPN Firewall IPSec VPN Connection Status. . . . . . . . . . . . .229
View the VPN Firewall IPSec VPN Log . . . . . . . . . . . . . . . . . . . . . . . .230
Manage IPSec VPN Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .231
Manage IKE Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .231
Manage VPN Policies. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .238
6
Page 7

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure Extended Authentication (XAUTH) . . . . . . . . . . . . . . . . . . . . .245
Configure XAUTH for VPN Clients . . . . . . . . . . . . . . . . . . . . . . . . . . . .246
User Database Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .247
RADIUS Client and Server Configuration. . . . . . . . . . . . . . . . . . . . . . .247
Assign IPv4 Addresses to Remote Users (Mode Config). . . . . . . . . . . . .250
Mode Config Operation. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .250
Configure Mode Config Operation on the VPN Firewall. . . . . . . . . . . .250
Configure the ProSafe VPN Client for Mode Config Operation . . . . . .257
Test the Mode Config Connection . . . . . . . . . . . . . . . . . . . . . . . . . . . .264
Modify or Delete a Mode Config Record. . . . . . . . . . . . . . . . . . . . . . . .265
Configure Keep-Alives and Dead Peer Detection . . . . . . . . . . . . . . . . . .265
Configure Keep-Alives . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .266
Configure Dead Peer Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .267
Configure NetBIOS Bridging with IPSec VPN . . . . . . . . . . . . . . . . . . . . .268
Configure the PPTP Server . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .269
View the Active PPTP Users . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .271
Configure the L2TP Server. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .272
View the Active L2TP Users. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .273
Chapter 6 Virtual Private Networking Using
SSL Connections
SSL VPN Portal Options. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .276
Overview of the SSL Configuration Process . . . . . . . . . . . . . . . . . . . . . .276
Create the Portal Layout. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .277
Configure Domains, Groups, and Users. . . . . . . . . . . . . . . . . . . . . . . . . .281
Configure Applications for Port Forwarding . . . . . . . . . . . . . . . . . . . . . . .282
Add Servers and Port Numbers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .282
Add a New Host Name. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .283
Configure the SSL VPN Client . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .284
Configure the Client IP Address Range . . . . . . . . . . . . . . . . . . . . . . . .285
Add Routes for VPN Tunnel Clients . . . . . . . . . . . . . . . . . . . . . . . . . . .287
Use Network Resource Objects to Simplify Policies . . . . . . . . . . . . . . . .288
Add New Network Resources. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .288
Edit Network Resources to Specify Addresses . . . . . . . . . . . . . . . . . .289
Configure User, Group, and Global Policies. . . . . . . . . . . . . . . . . . . . . . .291
View Policies. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .292
Add an IPv4 or IPv6 SSL VPN Policy. . . . . . . . . . . . . . . . . . . . . . . . . .293
Access the New SSL Portal Login Screen . . . . . . . . . . . . . . . . . . . . . . . .297
View the SSL VPN Connection Status and SSL VPN Log. . . . . . . . . . . .299
Chapter 7 Manage Users, Authentication, and VPN Certificates
The VPN Firewall’s Authentication Process and Options. . . . . . . . . . . . .302
Configure Authentication Domains, Groups, and Users. . . . . . . . . . . . . .303
Configure Domains. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .303
Configure Groups . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .307
Configure User Accounts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .310
Set User Login Policies. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .313
7
Page 8

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Change Passwords and Other User Settings. . . . . . . . . . . . . . . . . . . .318
Manage Digital Certificates for VPN Connections . . . . . . . . . . . . . . . . . .320
VPN Certificates Screen. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .321
Manage VPN CA Certificates. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .322
Manage VPN Self-Signed Certificates . . . . . . . . . . . . . . . . . . . . . . . . .323
Manage the VPN Certificate Revocation List . . . . . . . . . . . . . . . . . . . .326
Chapter 8 Network and System Management
Performance Management. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .329
Bandwidth Capacity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .329
Features That Reduce Traffic. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .330
Features That Increase Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .332
Use QoS and Bandwidth Assignment to Shift the Traffic Mix. . . . . . . .335
Monitoring Tools for Traffic Management. . . . . . . . . . . . . . . . . . . . . . .336
System Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .336
Change Passwords and Administrator and Guest Settings . . . . . . . . .336
Configure Remote Management Access . . . . . . . . . . . . . . . . . . . . . . .338
Use the Command-Line Interface. . . . . . . . . . . . . . . . . . . . . . . . . . . . .342
Use a Simple Network Management Protocol Manager. . . . . . . . . . . .342
Manage the Configuration File . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .347
Configure Date and Time Service . . . . . . . . . . . . . . . . . . . . . . . . . . . .352
Chapter 9 Monitor System Access and Performance
Configure and Enable the WAN Traffic Meter . . . . . . . . . . . . . . . . . . . . .356
Configure and Enable the LAN Traffic Meter . . . . . . . . . . . . . . . . . . . . . .359
Configure Logging, Alerts, and Event Notifications . . . . . . . . . . . . . . . . .362
How to Send Syslogs over a VPN Tunnel between Sites . . . . . . . . . .367
View Status Screens . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .369
View the System Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .369
View the VPN Connection Status, L2TP Users, and PPTP Users. . . .378
View the VPN Logs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .380
View the Port Triggering Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .381
View the WAN Port Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .382
View the Attached Devices and the DHCP Log . . . . . . . . . . . . . . . . . .385
Diagnostics Utilities . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .388
Send a Ping Packet . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .389
Trace a Route. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .390
Look Up a DNS Address . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .390
Display the Routing Tables. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .390
Capture Packets in Real Time . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .391
Reboot the VPN Firewall Remotely . . . . . . . . . . . . . . . . . . . . . . . . . . .391
Chapter 10 Troubleshooting
Basic Functioning. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .393
Power LED Not On. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .393
Test LED Never Turns Off . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .393
8
Page 9

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
LAN or WAN Port LEDs Not On . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .394
Troubleshoot the Web Management Interface. . . . . . . . . . . . . . . . . . . . .394
When You Enter a URL or IP Address, a Time-Out Error Occurs . . . . . .395
Troubleshoot the ISP Connection. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .396
Troubleshooting the IPv6 Connection . . . . . . . . . . . . . . . . . . . . . . . . . . .397
Troubleshoot a TCP/IP Network Using a Ping Utility . . . . . . . . . . . . . . . .400
Test the LAN Path to Your VPN Firewall . . . . . . . . . . . . . . . . . . . . . . .400
Test the Path from Your Computer to a Remote Device . . . . . . . . . . .401
Restore the Default Configuration and Password . . . . . . . . . . . . . . . . . .401
Address Problems with Date and Time . . . . . . . . . . . . . . . . . . . . . . . . . .403
Access the Knowledge Base and Documentation . . . . . . . . . . . . . . . . . .403
Appendix A Default Settings and Technical Specifications
Factory Default Settings. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .405
Physical and Technical Specifications . . . . . . . . . . . . . . . . . . . . . . . . . . .410
Appendix B Network Planning for Multiple WAN Ports
What to Consider Before You Begin. . . . . . . . . . . . . . . . . . . . . . . . . . . . .414
Cabling and Computer Hardware Requirements . . . . . . . . . . . . . . . . .415
Computer Network Configuration Requirements . . . . . . . . . . . . . . . . .415
Internet Configuration Requirements . . . . . . . . . . . . . . . . . . . . . . . . . .416
Overview of the Planning Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .418
Inbound Traffic . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .419
Inbound Traffic to a Single WAN Port System . . . . . . . . . . . . . . . . . . .419
Inbound Traffic to a Dual WAN Port System . . . . . . . . . . . . . . . . . . . .420
Virtual Private Networks. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .421
VPN Road Warrior (Client-to-Gateway) . . . . . . . . . . . . . . . . . . . . . . . .422
VPN Gateway-to-Gateway . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .425
VPN Telecommuter (Client-to-Gateway through a NAT Router) . . . . .427
Appendix C System Logs and Error Messages
Log Message Terms. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .431
System Log Messages. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .431
NTP. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .432
Login/Logout. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .432
System Startup. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .433
Reboot . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .433
Firewall Restart. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .433
IPSec Restart . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .434
Unicast, Multicast, and Broadcast Logs . . . . . . . . . . . . . . . . . . . . . . . .434
WAN Status . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .435
Resolved DNS Names . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .438
VPN Log Messages . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .439
Traffic Meter Logs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .444
Routing Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .444
LAN to WAN Logs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .445
9
Page 10

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
LAN to DMZ Logs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .445
DMZ to WAN Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .445
WAN to LAN Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .445
DMZ to LAN Logs. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .446
WAN to DMZ Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .446
Other Event Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .446
Session Limit Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .446
Source MAC Filter Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .447
Bandwidth Limit Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .447
DHCP Logs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .447
Appendix D Two-Factor Authentication
Why Do I Need Two-Factor Authentication? . . . . . . . . . . . . . . . . . . . . . .450
What Are the Benefits of Two-Factor Authentication? . . . . . . . . . . . . .450
What Is Two-Factor Authentication? . . . . . . . . . . . . . . . . . . . . . . . . . .450
NETGEAR Two-Factor Authentication Solutions. . . . . . . . . . . . . . . . . . .451
Appendix E Notification of Compliance
Index
10
Page 11
1. Introduction
This chapter provides an overview of the features and capabilities of the ProSAFE Gigabit Quad
WAN SSL VPN Firewall SRX5308 and explains how to log in to the device and use its web
management interface. The chapter contains the following sections:
• What Is the ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308?
• Key Features and Capabilities
• Package Contents
• Hardware Features
• Choose a Location for the VPN Firewall
• Log In to the VPN Firewall
• Web Management Interface Menu Layout
• Requirements for Entering IP Addresses
1
Note: For more information about the topics covered in this manual, visit
the support website at http://support.netgear.com.
Note: Firmware updates with new features and bug fixes are made
available from time to time on downloadcenter.netgear.com. Some
products can regularly check the site and download new firmware,
or you can check for and download new firmware manually
features or behavior of your product do not match what is described
in this guide, you might need to update your firmware.
. If the
11
Page 12

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
What Is the ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308?
The ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308, hereafter referred to as the
VPN firewall, connects your local area network (LAN) to the Internet through up to four
external broadband access devices such as cable or DSL modems or satellite or wireless
Internet dishes. Four wide area network (WAN) ports allow you to increase effective data rate
to the Internet by utilizing all WAN ports to carry session traffic or to maintain backup
connections in case of failure of your primary Internet connection.
The VPN firewall routes both IPv4 and IPv6 traffic. A powerful, flexible firewall protects your
IPv4 and IPv6 networks from denial of service (DoS) attacks, unwanted traf
objectionable content. IPv6 traffic is supported through 6to4 and Intra-Site Automatic Tunnel
Addressing Protocol (ISATAP) tunnels.
The VPN firewall is a security solution that protects your network from attacks and intrusions.
For example, the VPN firewall provides support for stateful packet inspection (SPI), denial of
service (DoS) attack protection, and multi-NAT support.
web content filtering options, plus browsing activity reporting and instant alerts—both through
email. Network administrators can establish restricted access policies based on time of day,
website addresses, and address keywords.
The VPN firewall supports multiple
fic, and traf
fic with
The VPN firewall provides advanced IPSec and SSL VPN technologies for secure and simple
remote connections.
transfer speeds.
The VPN firewall is a plug-and-play device that can be installed and configured within
minutes.
The use of Gigabit Ethernet LAN and W
AN ports ensures high data
Key Features and Capabilities
• Quad-WAN Ports for Increased Reliability and Load Balancing
• Advanced VPN Support for Both IPSec and SSL
• A Powerful, True Firewall with Content Filtering
• Security Features
• Autosensing Ethernet Connections with Auto Uplink
• Extensive Protocol Support
• Easy Installation and Management
• Maintenance and Support
Introduction
12
Page 13

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The VPN firewall provides the following key features and capabilities:
• Four 10/100/1000 Mbps Gigabit Ethernet WAN ports for load balancing and failover
protection of your Internet connection, providing increased data rate and increased
system reliability.
• Built-in four-port 10/100/1000 Mbps Gigabit Ethernet LAN switch for fast data transfer
between local network resources and support for up to 200,000 internal or external
connections.
• Both IPv4 and IPv6 support
• Advanced IPSec VPN and SSL VPN support with support for up to 125 concurrent IPSec
VPN tunnels and up to 50 concurrent SSL VPN tunnels.
• Bundled with a single-user license of the NETGEAR ProSafe VPN Client software
(VPN01L).
• L2TP tunnel and PPTP tunnel support
• Advanced stateful packet inspection (SPI) firewall with multi-NA
• Quality of Service (QoS) and SIP 2.0 support for traffic prioritization, voice, and
multimedia.
• Extensive protocol support.
• One console port for local management.
• SNMP support with SNMPv1, SNMPv2c, and SNMPv3, and management optimized for
the NETGEAR ProSafe Network Management Software (NMS200) over a LAN
connection.
• Front panel LEDs for easy monitoring of status and activity
• Flash memory for firmware upgrade.
• Internal universal switching power supply
• Rack-mounting kit for 1U rackmounting.
.
T support.
.
Quad-WAN Ports for Increased Reliability and Load Balancing
The VPN firewall provides four broadband WAN ports. These WAN ports allow you to
connect additional broadband Internet lines that can be configured to:
• Load-balance outbound traffic between up to four lines for maximum bandwidth
efficiency.
• Provide backup and rollover if one line is inoperable, ensuring that you are never
disconnected.
See Appendix B, Network Planning for Multiple WAN Ports for the planning factors to
consider when implementing the following capabilities with multiple WAN port gateways:
• Single or multiple exposed hosts.
• V
irtual private networks (VPNs).
Introduction
13
Page 14

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Advanced VPN Support for Both IPSec and SSL
The VPN firewall supports IPSec and SSL virtual private network (VPN) connections:
• IPSec VPN delivers full network access between a central office and branch of
between a central office and telecommuters. Remote access by telecommuters requires
the installation of VPN client software on the remote computer.
- IPSec VPN with broad protocol support for secure connection to other IPSec
gateways and clients.
- Up to 125 simultaneous IPSec VPN connections.
- Bundled with a 30-day trial license for the ProSafe VPN Client software (VPN01L).
• SSL VPN provides remote access for mobile users to selected corporate resources
without requiring a preinstalled VPN client on their computers.
- Uses the familiar Secure Sockets Layer (SSL) protocol, commonly used for
e-commerce transactions, to provide client-free access with customizable user portals
and support for a wide variety of user repositories.
- Up to 50 simultaneous SSL VPN connections.
- Allows browser-based, platform-independent remote access through a number of
popular browsers, such as Microsoft Internet Explorer
Safari.
- Provides granular access to corporate resources based on user type or group
membership.
, Mozilla Firefox, and
fices, or
Apple
A Powerful, True Firewall with Content Filtering
Unlike simple NA T routers, the VPN firewall is a true firewall, using stateful packet inspection
(SPI) to defend against hacker attacks. Its firewall features have the following capabilities:
• DoS protection. Automatically detects and thwarts denial of service (DoS) attacks such
as Ping of Death and SYN flood.
• Secure firewall. Blocks unwanted traffic from the Internet to your LAN.
• Content filtering
can control access to Internet content by screening for web services, web addresses, and
keywords within web addresses.
• Schedule policies. Permits scheduling of firewall policies by day and time.
• Logs security incidents. Logs security events such as logins and secure logins.
configure the firewall to email the log to you at specified intervals. You can also configure
the VPN firewall to send immediate alert messages to your email address or email pager
when a significant event occurs.
. Prevents objectionable content from reaching your computers. Y
Y
ou
ou can
Introduction
14
Page 15

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Security Features
The VPN firewall is equipped with several features designed to maintain security:
• Computers hidden by NAT. NA
originating from the local network. Requests originating from outside the LAN are
discarded, preventing users outside the LAN from finding and directly accessing the
computers on the LAN.
• Port forwarding with NA
accessing the computers on the LAN, the VPN firewall allows you to direct incoming
traffic to specific computers based on the service port number of the incoming request.
• DMZ port. Incoming traffic from the Internet is usually discarded by the VPN firewall
unless the traf
have configured an inbound rule. Instead of discarding this traffic, you can use the
dedicated demilitarized zone (DMZ) port to forward the traffic to one computer on your
network.
fic is a response to one of your local computers or a service for which you
T.
T opens a temporary path to the Internet for requests
Although NAT prevents Internet locations from directly
Autosensing Ethernet Connections with Auto Uplink
With its internal four-port 10/100/1000 Mbps switch and four 10/100/1000 WAN ports, the
VPN firewall can connect to a 10-Mbps standard Ethernet network, a 100-Mbps Fast
Ethernet network, a 1000-Mbps Gigabit Ethernet network, or a combination of these
networks. All LAN and WAN interfaces are autosensing and capable of full-duplex or
half-duplex operation.
TM
The VPN firewall incorporates Auto Uplink
senses whether the Ethernet cable plugged into the port should have a normal connection
such as to a computer or an uplink connection such as to a switch or hub. That port then
configures itself correctly. This feature eliminates the need for you to think about crossover
cables, as Auto Uplink accommodates either type of cable to make the right connection.
technology. Each Ethernet port automatically
Extensive Protocol Support
The VPN firewall supports the Transmission Control Protocol/Internet Protocol (TCP/IP) and
Routing Information Protocol (RIP). The VPN firewall provides the following protocol support:
• IP address sharing by NAT. The VPN firewall allows many networked computers to
share an Internet account using only a single IP address, which might be statically or
dynamically assigned by your Internet service provider (ISP). This technique, known as
Network Address Translation (NAT), allows the use of an inexpensive single-user ISP
account.
• Automatic configuration of attached computers by DHCP.
dynamically assigns network configuration information, including IP
Domain Name Server (DNS) addresses, to attached computers on the LAN using the
Dynamic Host Configuration Protocol (DHCP). This feature greatly simplifies
configuration of computers on your local network.
Introduction
15
The VPN firewall
, gateway, and
Page 16

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• DNS proxy. When DHCP is enabled and no DNS addresses are specified, the VPN
firewall provides its own address as a DNS server to the attached computers. The firewall
obtains actual DNS addresses from the ISP during connection setup and forwards DNS
requests from the LAN.
• PPP over Ethernet (PPPoE). PPPoE is a protocol for connecting remote hosts to the
Internet over a DSL connection by simulating a dial-up connection.
• Quality of Service (QoS).
and traffic classification with Type of Service (ToS) and Differentiated Services Code
Point (DSCP) marking.
• Layer 2 Tunneling Protocol (L2TP)
private networks (VPNs).
• Point to Point Tunneling Protocol (PPTP).
support VPNs.
The VPN firewall supports QoS, including traf
. A tunneling protocol that is used to support virtual
Another tunneling protocol that is used to
fic prioritization
Easy Installation and Management
You can install, configure, and operate the VPN firewall within minutes after connecting it to
the network. The following features simplify installation and management tasks:
• Browser-based management. Browser-based configuration allows you to easily
configure the VPN firewall from almost any type of operating system, such as Windows,
Macintosh, or Linux. Online help documentation is built into the browser-based web
management interface.
• Auto-detection of ISP.
connection, asking you only for the information required for your type of ISP account.
• IPSec VPN Wizard
can easily configure IPSec VPN tunnels according to the recommendations of the Virtual
Private Network Consortium (VPNC). This ensures that the IPSec VPN tunnels are
interoperable with other VPNC-compliant VPN routers and clients.
• SNMP.
let you monitor and manage log resources from an SNMP-compliant system manager
The SNMP system configuration lets you change the system variables for MIB2.
• Diagnostic functions. The VPN firewall incorporates built-in diagnostic functions such
as ping, traceroute, DNS lookup, and remote reboot.
• Remote management
interface from a remote location on the Internet. For security
management access to a specified remote IP address or range of addresses.
• Visual monitoring. The VPN firewall’s front panel LEDs provide an easy way to monitor
its status and activity
The VPN firewall supports the Simple Network Management Protocol (SNMP) to
The VPN firewall automatically senses the type of Internet
. The VPN firewall includes the NETGEAR IPSec VPN Wizard so you
.
. The VPN firewall allows you to log in to the web management
, you can limit remote
.
Introduction
16
Page 17

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Maintenance and Support
NETGEAR offers the following features to help you maximize your use of the VPN firewall:
• Flash memory for firmware upgrades.
• T
echnical support seven days a week, 24 hours a day. Information about support is
available on the NETGEAR website at
http://support.netgear
.com/app/answers/detail/a_id/212.
Package Contents
The VPN firewall product package contains the following items:
• ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• One
• One Category 5 (Cat 5) Ethernet cable
• One rack-mounting kit
• ProSAFE Gigabit Quad W
• Resource CD, including:
AC power cable
AN SSL VPN Firewall SRX5308 Installation Guide
- Application Notes and other helpful information
- ProSafe VPN Client software (VPN01L)
If any of the parts are incorrect, missing, or damaged, contact your NETGEAR dealer. Keep
the carton, including the original packing materials, in case you need to return the product for
repair
.
Hardware Features
• Front Panel
• Rear Panel
• Bottom Panel with Product Label
The front panel ports and LEDs, rear panel ports, and bottom label of the VPN firewall are
described in the following sections.
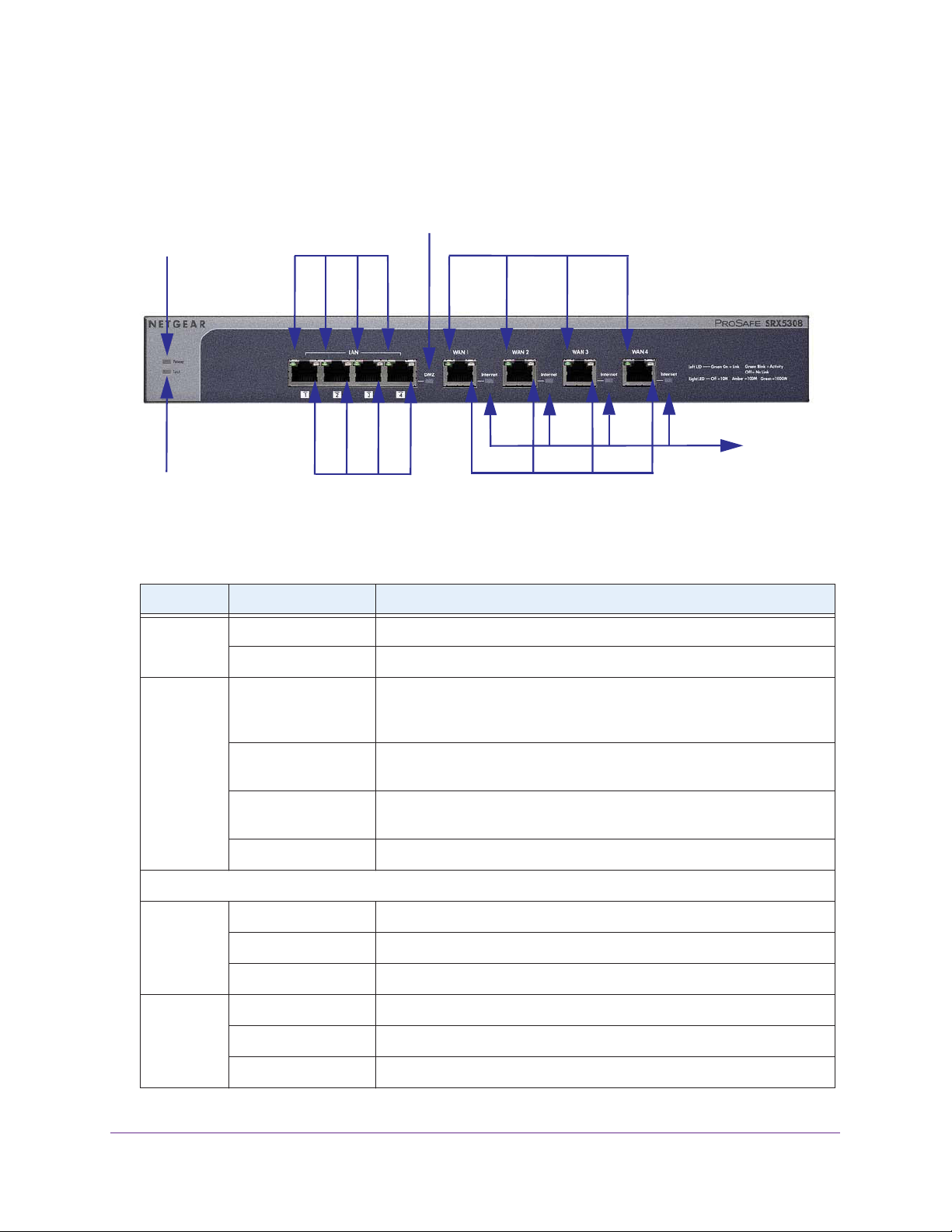
Front Panel
Viewed from left to right, the VPN firewall front panel contains the following ports (see the
following figure).
• LAN Ethernet ports. Four switched N-way automatic speed negotiating, Auto MDI/MDIX,
Gigabit Ethernet ports with RJ-45 connectors
• WAN Ethernet ports. Four independent N-way automatic speed negotiating, Auto
MDI/MDIX, Gigabit Ethernet ports with RJ-45 connectors
Introduction
17
Page 18
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The front panel also contains three groups of status indicator light-emitting diodes (LEDs),
including Power and Test LEDs, LAN LEDs, and WAN LEDs, all of which are described in the
following table.
DMZ LED
Power LED
Left LAN LEDs
Left WAN LEDs
Internet
LEDs
Test LED
Right LAN LEDs
Right WAN LEDs
Figure 1.
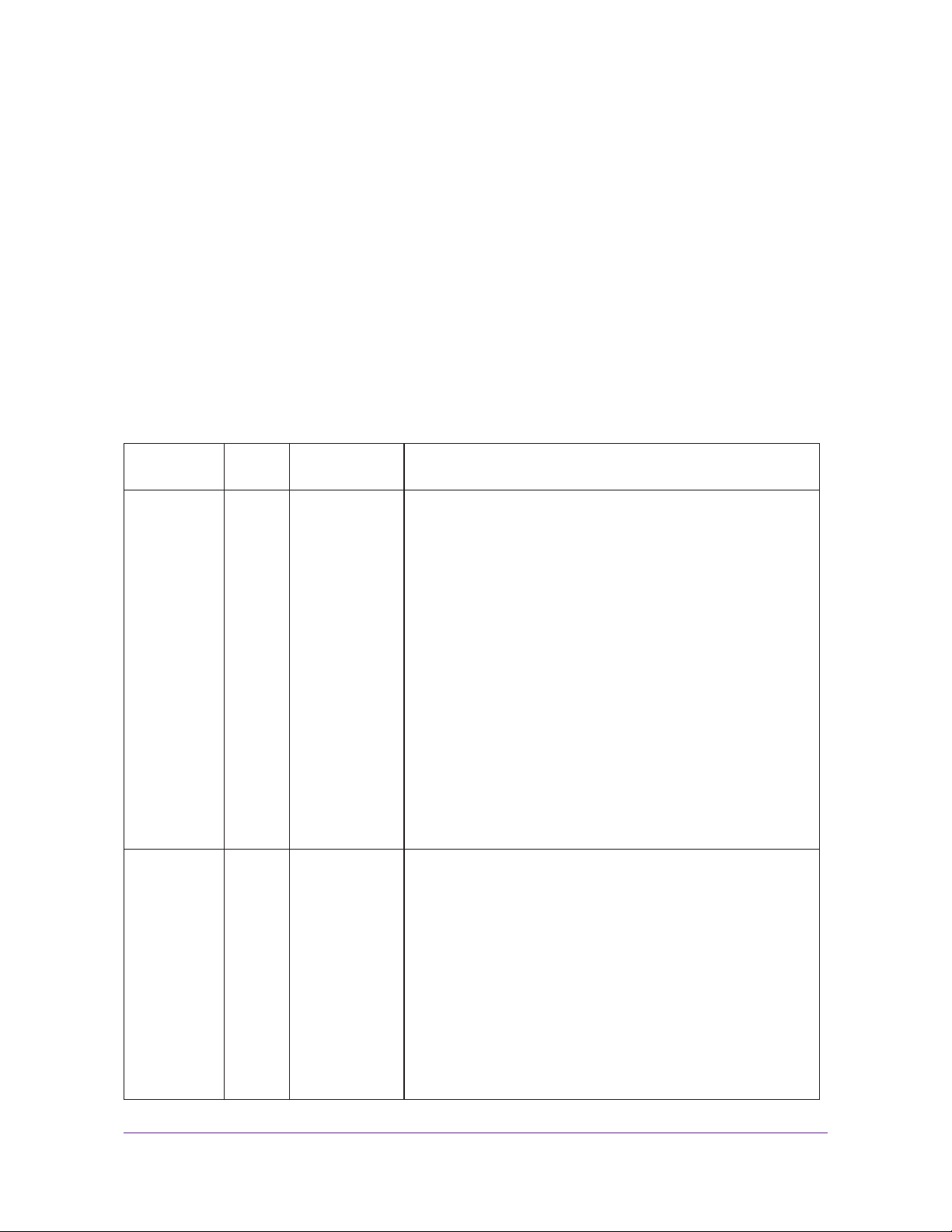
Table 1. LED descriptions
LED Activity Description
Power On (green) Power is supplied to the VPN firewall.
Off Power is not supplied to the VPN firewall.
T
est On (amber) during
startup.
On (amber) during
any other time
Blinking (amber) The VPN firewall is writing to flash memory (during upgrading or resetting
Off The system has booted successfully.
LAN Ports
Left LED On (green) The LAN port has detected a link with a connected Ethernet device.
Test mode: The VPN firewall is initializing. After approximately 2 minutes,
when the VPN firewall has completed its initialization, the Test LED goes
off.
The initialization has failed, or a hardware failure has occurred.
to defaults).
Blinking (green)
Of
f The LAN port has no link.
Right LED On (green) The LAN port operates at 1000 Mbps.
On (amber) The LAN port operates at 100 Mbps.
Off The LAN port operates at 10 Mbps.
The LAN port receives or transmits data.
Introduction
18
Page 19
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
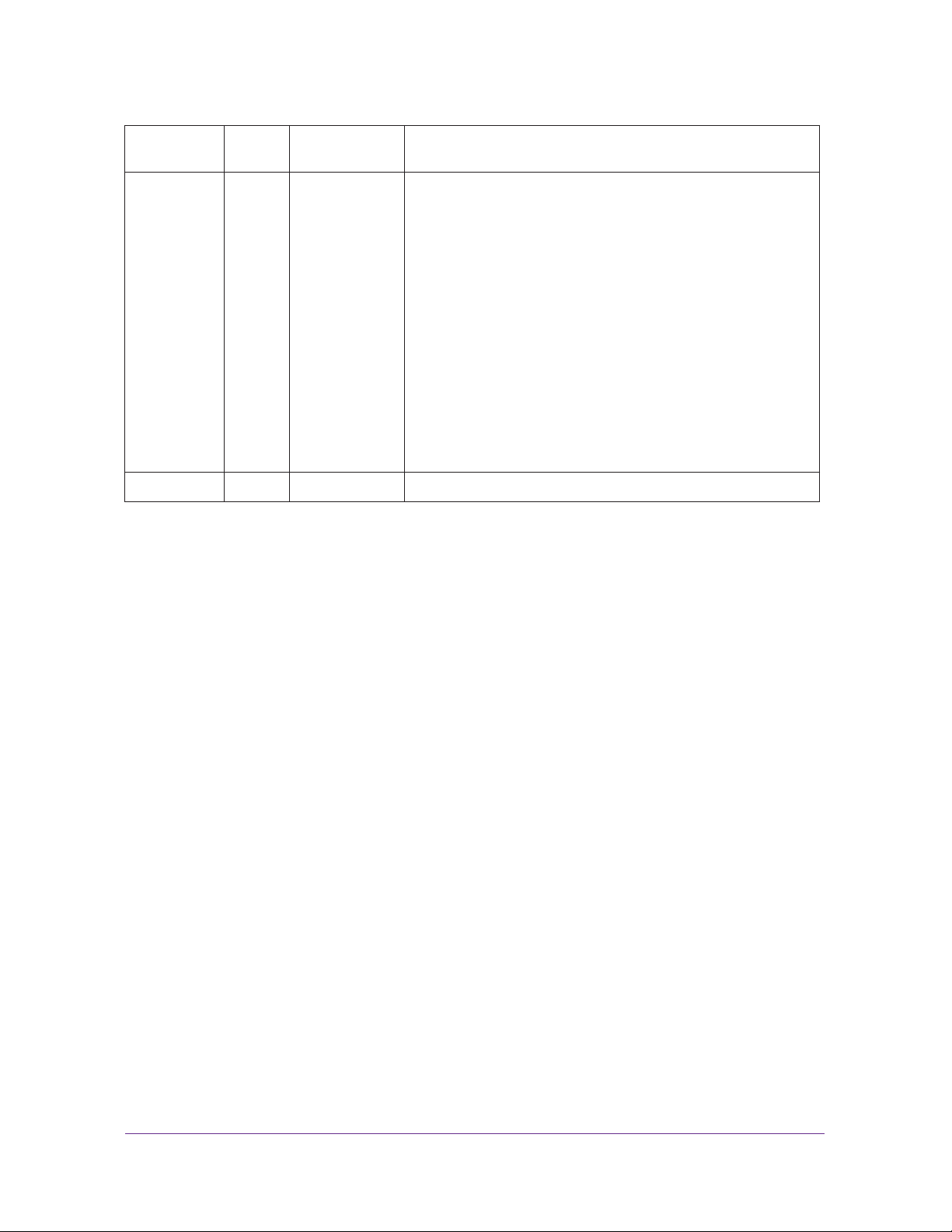
Table 1. LED descriptions (continued)
LED Activity Description
DMZ LED On (green) Port 4 operates as a dedicated hardware DMZ port.
Off Port 4 operates as a normal LAN port.
WAN Ports
Left LED On (green) The WAN port has a valid connection with a device that provides an
Internet connection.
Blinking (green) The WAN port receives or transmits data.
Off The WAN port has no physical link, that is, no Ethernet cable is plugged
into the VPN firewall.
Right LED On (green) The WAN port operates at 1000 Mbps.
On (amber) The WAN port operates at 100 Mbps.
Off The WAN port operates at 10 Mbps.
Internet LED On (green) The WAN port has a valid Internet connection.
Off The WAN port is either not enabled or has no link to the Internet.
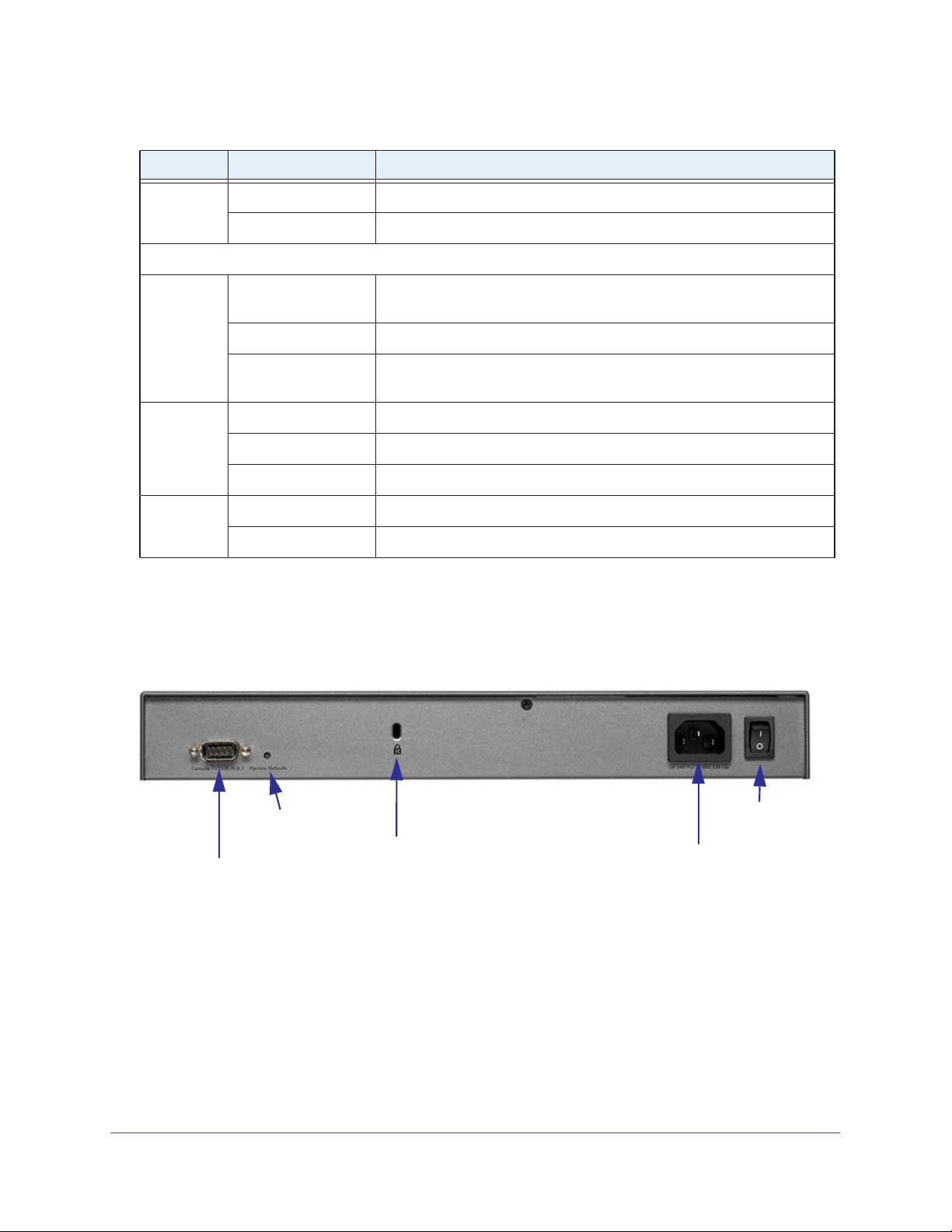
Rear Panel
The rear panel of the VPN firewall includes a console port, a Factory Defaults Reset button, a
cable lock receptacle, an AC power connection, and a power switch.
Factory Defaults
Reset button
Console port
Figure 2.
Security lock
receptacle
AC power
receptacle
Viewed from left to right, the rear panel contains the following components:
• Cable security lock receptacle.
• Console port. Port for connecting to an optional console terminal.
male connector
. The default baud rate is 1 15200 K. The pinouts are (2) Tx, (3) Rx, (5) and
The port has a DB9
(7) Gnd. For information about accessing the command-line interface (CLI) using the
console port, see Use the Command-Line Interface on page 342.
Power
switch
Introduction
19
Page 20
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• Factory Defaults Reset button. Using a sharp object, press and hold this button for about
8 seconds until the front panel Test LED flashes to reset the VPN firewall to factory
default settings. All configuration settings are lost, and the default password is restored.
• AC power receptacle. Universal AC input (100–240 V
• A power on/off switch.
AC, 50–60 Hz).
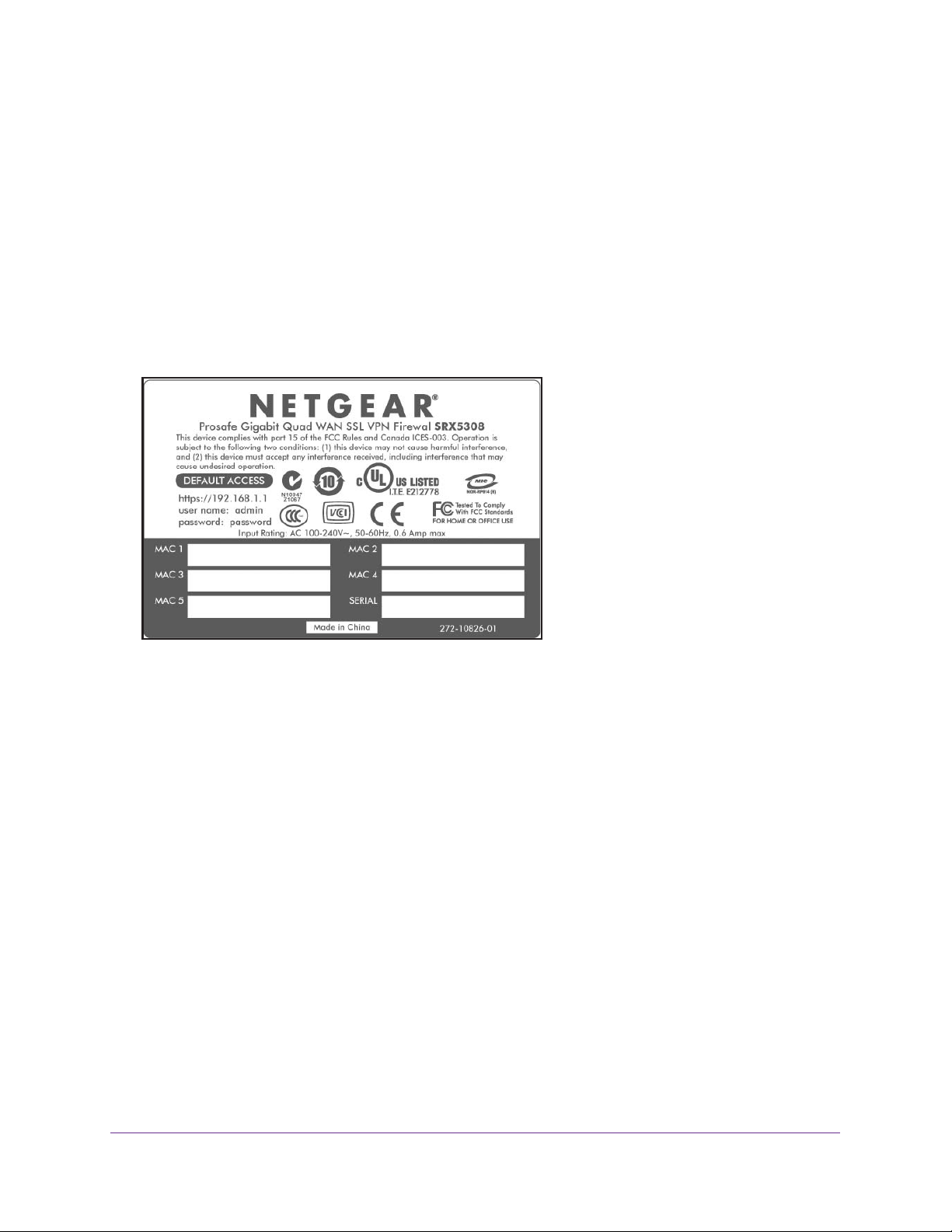
Bottom Panel with Product Label
The product label on the bottom of the VPN firewall’s enclosure displays factory default
settings, regulatory compliance, and other information.
Figure 3.
Choose a Location for the VPN Firewall
The VPN firewall is suitable for use in an office environment where it can be freestanding (on
its runner feet) or mounted into a standard 19-inch equipment rack. Alternatively, you can
rack-mount the VPN firewall in a wiring closet or equipment room.
Consider the following when deciding where to position the VPN firewall:
• The unit is accessible, and cables can be connected easily.
• Cabling is away from sources of electrical noise. These include lift shafts, microwave
ovens, and air-conditioning units.
• Water or moisture cannot enter the case of the unit.
• Airflow around the unit and through the vents in the side of the case is not restricted.
Provide a minimum of 25 mm or 1-inch clearance.
• The air is as free of dust as possible.
• T
emperature operating limits are not likely to be exceeded. Install the unit in a clean,
air-conditioned environment. For information about the recommended operating
temperatures for the VPN firewall, see
Specifications.
Appendix A, Default Settings and Technical
Introduction
20
Page 21

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Use the Rack-Mounting Kit
Use the mounting kit for the VPN firewall to install the appliance in a rack. Attach the
mounting brackets using the hardware that is supplied with the mounting kit.
Figure 4.
Before mounting the VPN firewall in a rack, verify that:
• You have the correct screws (supplied with the installation kit).
• The rack onto which you plan to mount the VPN firewall is suitably located.
Log In to the VPN Firewall
Note: To connect the VPN firewall physically to your network, connect the
cables and restart your network according to the instructions in the
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Installation Guide. A PDF of this guide is on the NETGEAR support
website at http://kb.netgear.com/app/products/model/a_id/13568.
To configure the VPN firewall, you need to use a web browser such as Microsoft Internet
Explorer 7.0 or later, Mozilla Firefox 4.0 or later, or Apple Safari 3.0 or later with JavaScript,
cookies, and SSL enabled.
Although these web browsers are qualified for use with the VPN firewall’s web management
interface, SSL VPN users should choose a browser that supports JavaScript, Java, cookies,
SSL, and ActiveX to take advantage of the full suite of applications. Note that Java is required
only for the SSL VPN portal, not for the web management interface.
To log in to the VPN firewall:
1. Start any of the qualified web browsers.
2. In the address field, enter https://192.168.1.1. The
screen displays in the browser.
NETGEAR
Configuration Manager Login
Introduction
21
Page 22
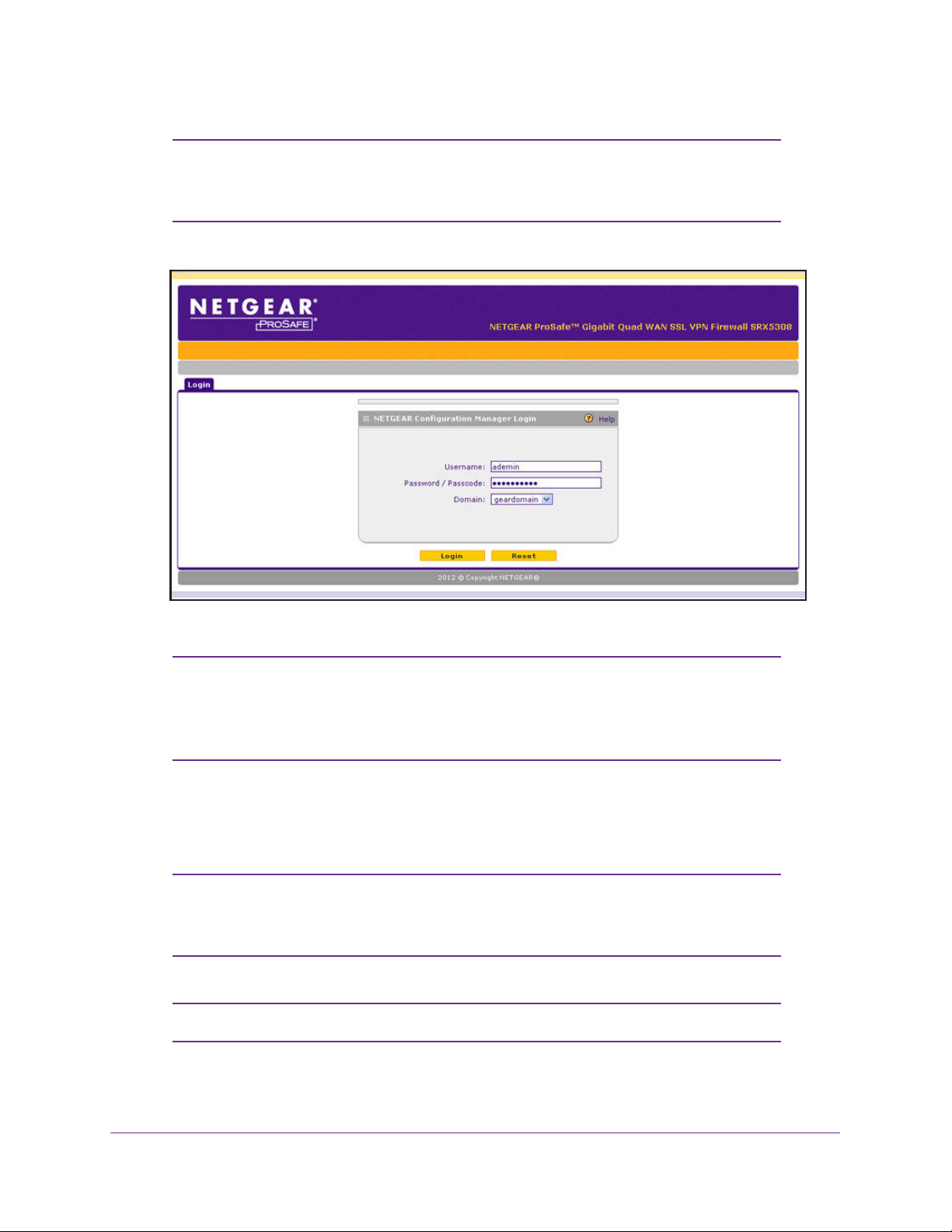
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: The VPN firewall factory default IP address is 192.168.1.1. If you
change the IP address, you need to use the IP address that you
assigned to the VPN firewall to log in to the VPN firewall.
Figure 5.
Note: The first time that you remotely connect to the VPN firewall with a
browser through an SSL connection, you might get a warning
message regarding the SSL certificate. Follow the directions of your
browser to accept the SSL certificate.
3. In the User Name field, type admin. Use lowercase letters.
4. In the Password / Passcode field, type password. Here, too, use lowercase letters.
Note: The VPN firewall user name and password are not the same as any
user name or password you might use to log in to your Internet
connection.
Note: Leave the domain as it is (geardomain).
Introduction
22
Page 23
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
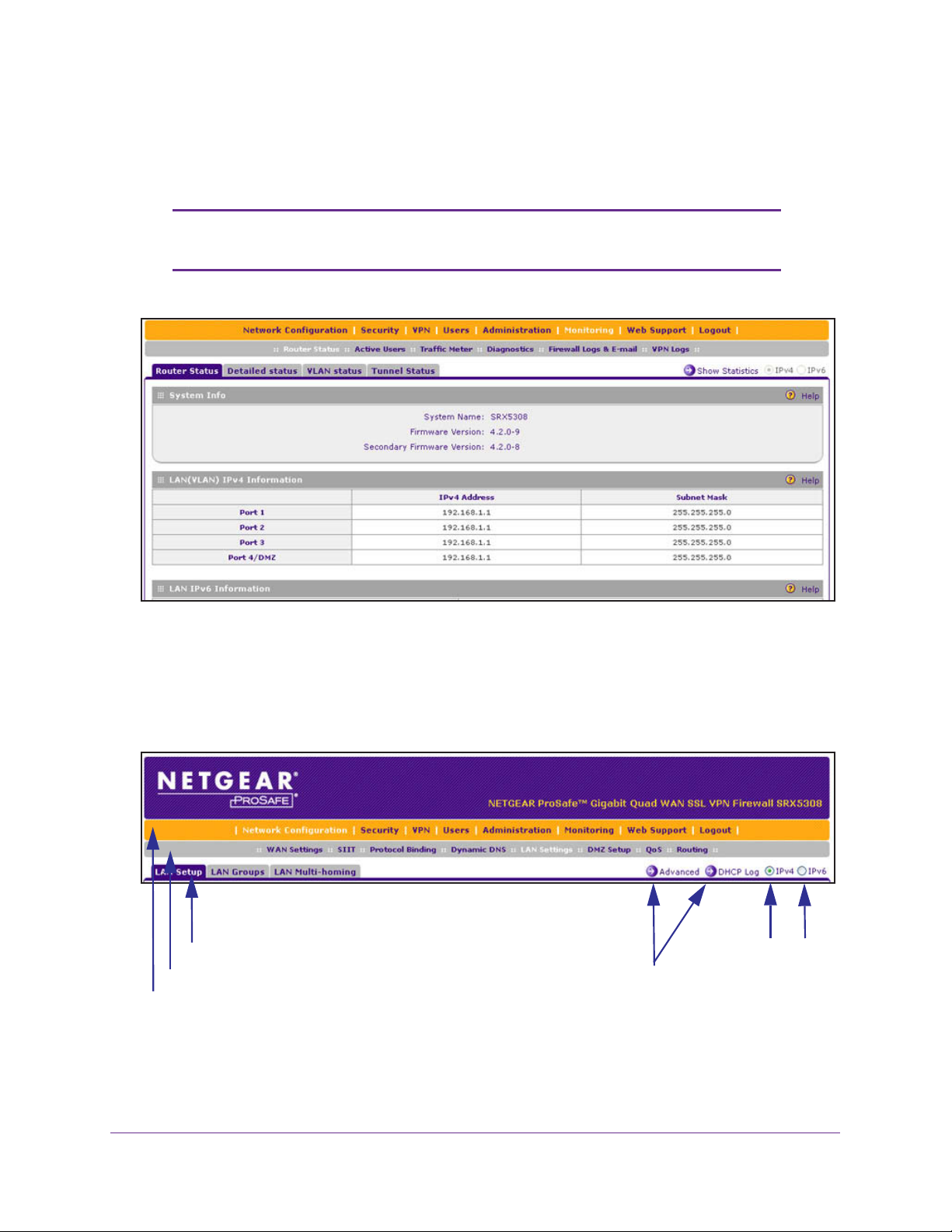
5. Click Login. The web management interface displays, showing the Router Status screen.
The following figure shows the top part of the Router Status screen. For more information,
see View the System Status on page 369.
Note: After 5 minutes of inactivity (the default login time-out), you are
automatically logged out.
Figure 6.
Web Management Interface Menu Layout
The following figure shows the menu at the top the web management interface:
3rd level: Submenu tab (blue)
2nd level: Configuration menu link (gray)
1st level: Main navigation menu link (orange)
Figure 7.
Option arrows: Additional screen for submenu item
IP radio buttons
Introduction
23
Page 24
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The web management interface menu consists of the following components:
• 1st level: Main navigation menu links. The main navigation menu in the orange bar
across the top of the web management interface provides access to all the configuration
functions of the VPN firewall, and remains constant. When you select a main navigation
menu link, the letters are displayed in white against an orange background.
• 2nd level: Configuration menu links.
The configuration menu links in the gray bar
(immediately below the main navigation menu bar) change according to the main
navigation menu link that you select. When you select a configuration menu link, the
letters are displayed in white against a gray background.
• 3rd level: Submenu tabs. Each configuration menu item has one or more submenu tabs
that are listed below the gray menu bar
. When you select a submenu tab, the text is
displayed in white against a blue background.
• Option arrows. If there are additional screens for the submenu item, links to the screens
display on the right side in blue letters against a white background, preceded by a white
arrow in a blue circle.
• IP radio buttons
feature to be configured onscreen.
. The IPv4 and IPv6 radio buttons let you select the IP version for the
There are four options:
- Both buttons are operational. You can configure the feature onscreen
for IPv4 functionality or for IPv6 functionality. After you have correctly configured the
feature for both IP versions, the feature can function with both IP versions
simultaneously.
- The IPv4 button is operational but the IPv6 button is disabled
. You
can configure the feature onscreen for IPv4 functionality only.
- The IPv6 button is operational but the IPv4 button is disabled. You
can configure the feature onscreen for IPv6 functionality only.
- Both buttons are disabled. IP functionality does not apply.
The bottom of each screen provides action buttons. The nature of the screen determines
which action buttons are shown.
Figure 8.
The following figure shows an example:
Any of the following action buttons might display onscreen (this list might not be complete):
• Apply. Save and apply the configuration.
• Reset. Reset the configuration to the previously saved configuration.
• T
est.
Test the configuration.
• Auto Detect. Enable the VPN firewall to detect the configuration automatically and
suggest values for the configuration.
• Cancel. Cancel the operation.
Introduction
24
Page 25
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
When a screen includes a table, table buttons display to let you configure the table entries.
The nature of the screen determines which table buttons are shown. The following figure
shows an example:
Figure 9.
Any of the following table buttons might display onscreen:
• Select All. Select all entries in the table.
• Delete. Delete the selected entry or entries from the table.
• Enable. Enable the selected entry or entries in the table.
• Disable. Disable the selected entry or entries in the table.
• Add.
• Edit. Edit the selected entry.
• Up. Move the selected entry up in the table.
• Down. Move the selected entry down in the table.
• Apply.
Add an entry to the table.
Apply the selected entry.
Almost all screens and sections of screens have an accompanying help screen.
help screen, click the (question mark) icon.
To open the
Requirements for Entering IP Addresses
To connect to the VPN firewall, your computer needs to be configured to obtain an IP address
automatically from the VPN firewall, either an IPv4 address through DHCP or an IPv6
address through DHCPv6, or both.
IPv4
The fourth octet of an IP address needs to be between 0 and 255 (both inclusive). This
requirement applies to any IP address that you enter on a screen of the web management
interface.
IPv6
IPv6 addresses are denoted by eight groups of hexadecimal quartets that are separated by
colons. Any four-digit group of zeroes within an IPv6 address can be reduced to a single zero
or altogether omitted.
The following errors invalidate an IPv6 address:
• More than eight groups of hexadecimal quartets
• More than four hexadecimal characters in a quartet
• More than two colons in a row
Introduction
25
Page 26
2. IPv4 and IPv6 Internet and WAN
Settings
This chapter explains how to configure the IPv4 and IPv6 Internet and WAN settings. The
chapter contains the following sections:
• Internet and WAN Configuration Tasks
• Configure the IPv4 Internet Connection and WAN Settings
• Configure the IPv6 Internet Connection and WAN Settings
• Configure Advanced WAN Options and Other Tasks
• Configure WAN QoS Profiles
• Additional WAN-Related Configuration Tasks
• What to Do Next
2
26
Page 27
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Internet and WAN Configuration Tasks
• Roadmap to Setting Up IPv4 Internet Connections to Your ISPs
• Roadmap to Setting Up IPv6 Internet Connections to Your ISPs
Typically, the VPN firewall is installed as a network gateway to function as a combined LAN
switch and firewall to protect the network from incoming threats and provide secure
connections.
gateway security appliance such as a NETGEAR ProSecure STM appliance.
The tasks that are required to complete the Internet connection of your VPN firewall depend
on whether you use an IPv4 connection, an IPv6 connection, or both to your Internet service
provider (ISP).
Note: The VPN firewall supports simultaneous IPv4 and IPv6 connections.
o complement the firewall protection, NETGEAR advises that you use a
T
Roadmap to Setting Up IPv4 Internet Connections to Your ISPs
Setting up IPv4 Internet connections to your ISP or ISPs includes seven tasks, five of which
are optional.
Complete these tasks:
1. Configure the IPv4 routing mode. Select either NAT or classical routing.
This task is described in
2. Configure the IPv4 Internet connections to your ISPs. Connect to one or more ISPs by
configuring up to four WAN interfaces.
Y
ou have two configuration options. These tasks are described in the following sections:
• Let the VPN Firewall Automatically Detect and Configure an IPv4 Internet Connection
on page 31
• Manually Configure an IPv4 Internet Connection on page 34
3. (Optional) Configure either load balancing or auto-rollover.
interfaces are configured for primary (single) WAN mode. You can select load balancing
or auto-rollover and a failure detection method. If you configure load balancing, you can also
configure protocol binding.
This task is described in Configure Load Balancing or Auto-Rollover for IPv4 Interfaces
on page 40.
Configure the IPv4 WAN Mode on page 29.
By default, the WAN
4. (Optional) Configure secondary WAN addresses on the WAN interfaces. Configure
aliases for each WAN interface.
This task is described in Configure Secondary WAN Addresses on page 47.
IPv4 and IPv6 Internet and WAN Settings
27
Page 28

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
5. (Optional) Configure Dynamic DNS on the WAN interfaces. If necessary, configure your
fully qualified domain names.
This task is described in Configure Dynamic DNS on page 49.
6. (Optional) Configure the WAN options. If necessary
port speed, and MAC address of the VPN firewall. These are advanced features, and you
usually do not need to change the settings.
This task is described in Configure Advanced WAN Options and Other Tasks on page 71.
7. (Optional) Configure the WAN traffic meters.
This task is described in
Configure and Enable the WAN Traffic Meter on page 356.
, change the factory default MTU size,
Roadmap to Setting Up IPv6 Internet Connections to Your ISPs
Setting up IPv6 Internet connections to your ISP or ISPs includes six tasks, four of which are
optional.
Complete these tasks:
1. Configure the IPv6 routing mode. Configure the VPN firewall to support both devices
with IPv4 addresses and devices with IPv6 addresses.
This task is described in Configure the IPv6 Routing Mode on page 53.
2. Configure the IPv6 Internet connections to your ISPs. Connect to an ISP by configuring
a W
AN interface.
ou have three configuration options. These tasks are described in the following sections:
Y
• Use a DHCPv6 Server to Configure an IPv6 Internet Connection on page 55
• Configure a Static IPv6 Internet Connection on page 58
• Configure a PPPoE IPv6 Internet Connection on page 61
3. (Optional) Configure the IPv6 tunnels. Enable 6to4 tunnels and configure ISA
These tasks are described in the following sections:
• Configure 6to4 Automatic Tunneling on page 64
• Configure ISATAP Automatic Tunneling on page 65
4. (Optional) Configure Stateless IP/ICMP T
not have permanently assigned IPv4 addresses to communicate with IPv4-only devices.
This task is described in
5. (Optional) Configure auto-rollover. By default, the WAN interfaces are configured for
primary (single) W
settings.
These tasks are described in Configure Auto-Rollover for IPv6 Interfaces on page 68.
AN mode. You can enable auto-rollover and configure the failure detection
Configure Stateless IP/ICMP Translation on page 67.
ranslation (SIIT). Enable IPv6 devices that do
AP tunnels.
T
IPv4 and IPv6 Internet and WAN Settings
28
Page 29

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
6. (Optional) Configure the WAN options. If necessary , change the factory default MTU size,
port speed, and MAC address of the VPN firewall. These are advanced features, and you
usually do not need to change the settings.
These tasks are described in Configure Advanced WAN Options and Other Tasks on
page 71.
Configure the IPv4 Internet Connection and WAN Settings
• Configure the IPv4 WAN Mode
• Let the VPN Firewall Automatically Detect and Configure an IPv4 Internet Connection
• Manually Configure an IPv4 Internet Connection
• Configure Load Balancing or Auto-Rollover for IPv4 Interfaces
• Configure Secondary WAN Addresses
• Configure Dynamic DNS
To set up your VPN firewall for secure IPv4 Internet connections, you need to determine the
IPv4 W
your ISP on the W
configuration options, described in the following sections:
• Let the VPN Firewall Automatically Detect and Configure an IPv4 Internet Connection on
• Manually Configure an IPv4 Internet Connection on page 34
AN mode (see the next section) and then configure the IPv4 Internet connection to
AN port. The web management interface offers two connection
page 31
Configure the IPv4 WAN Mode
By default, IPv4 is supported and functions in NAT mode but can also function in classical
routing mode. IPv4 functions the same way in IPv4-only mode that it does in IPv4 / IPv6
mode. The latter mode adds IPv6 functionality (see Configure the IPv6 Routing Mode on
page 53).
Network Address Translation
Network Address T ranslation (NA T) allows all computers on your LAN to share a single public
Internet IP address. From the Internet, there is only a single device (the VPN firewall) and a
single IP address. Computers on your LAN can use any private IP address range, and these
IP addresses are not visible from the Internet.
Note the following about NAT:
• The VPN firewall uses NAT to select the correct computer (on your LAN) to receive any
incoming data.
• If you have only a single public Internet IP address, you need to use NAT (the default
setting).
IPv4 and IPv6 Internet and WAN Settings
29
Page 30
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• If your ISP has provided you with multiple public IP addresses, you can use one address
as the primary shared address for Internet access by your computers, and you can map
incoming traffic on the other public IP addresses to specific computers on your LAN. This
one-to-one inbound mapping is configured using an inbound firewall rule.
Classical Routing
In classical routing mode, the VPN firewall performs routing, but without NA T. To gain Internet
access, each computer on your LAN needs to have a valid static Internet IP address.
If your ISP has allocated a number of static IP addresses to you, and you have assigned one
of these addresses to each computer, you can choose classical routing. Or you can use
classical routing for routing private IP addresses within a campus environment.
To view the status of the WAN ports, you can view the Router Status screen (see View the
System Status on page 369).
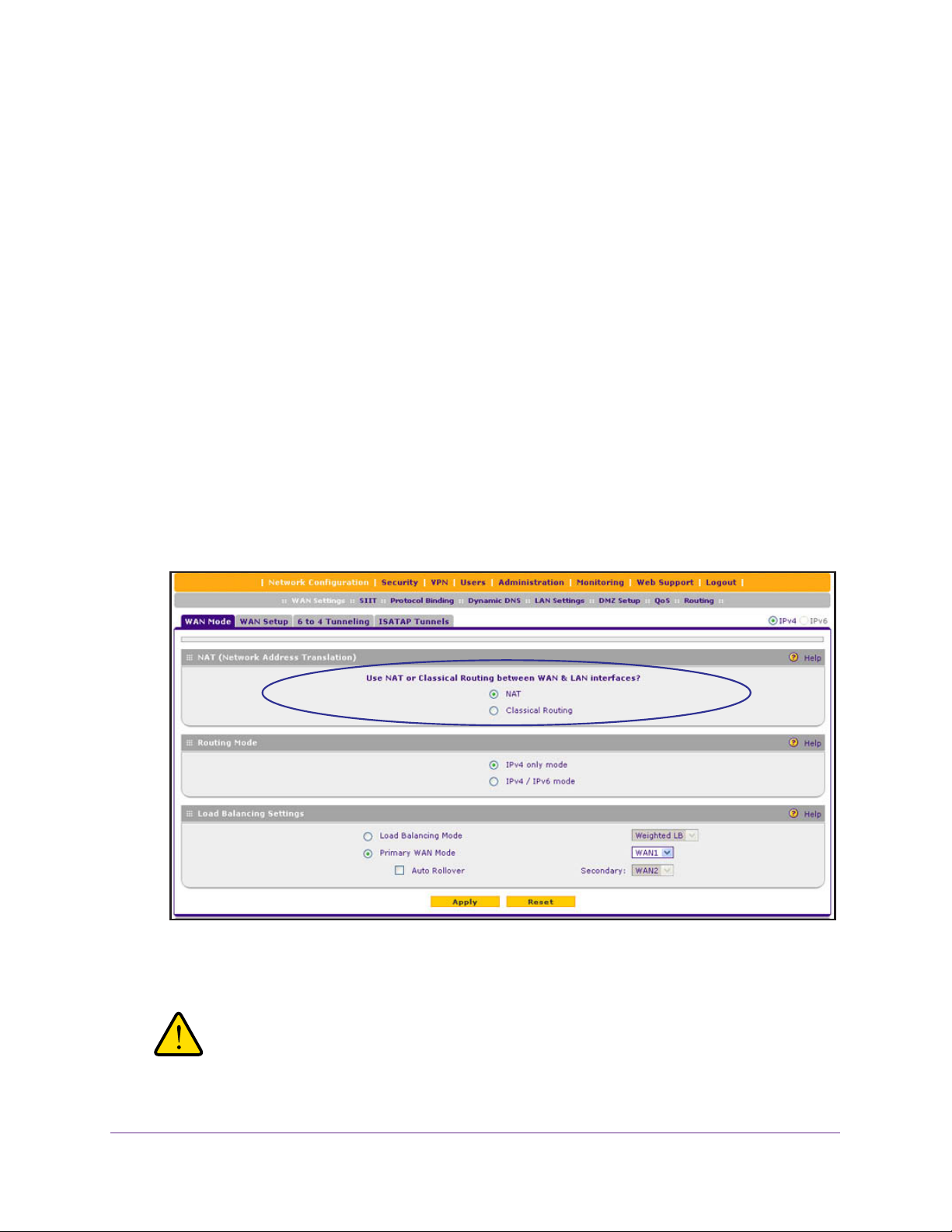
Configure the IPv4 Routing Mode
To configure the IPv4 routing mode:
1. Select Network Configuration > WAN Settings > W
displays:
Figure 10.
AN Mode. The WAN Mode screen
2. In the NAT (Network Address Translation) section of the screen, select the NAT radio button
or the Classical Routing radio button.
WARNING:
Changing the WAN mode causes all LAN WAN and DMZ WAN
inbound rules to revert to default settings.
IPv4 and IPv6 Internet and WAN Settings
30
Page 31

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
3. Click Apply to save your settings. These settings apply to all WAN ports.
Let the VPN Firewall Automatically Detect and Configure an IPv4 Internet Connection
To automatically configure a WAN port for an IPv4 connection to the Internet:
1. Select Network Configuration > WAN Settings > W
screen, the IPv4 radio button is selected by default. The WAN Setup screen displays the
IPv4 settings:
Figure 11.
The IPv4 WAN Settings table displays the following fields:
• WAN.
• Status. The status of the W
• WAN IP.
• Failure Detection Method. The failure detection method that is active for the W
interface. The following methods can be displayed:
- None
- DNS Lookup (W
-
- PING (the configured IP address is displayed)
The WAN interface (WAN1, WAN2, WAN3, and WAN4).
AN interface (UP or DOWN).
The IPv4 address of the WAN interface.
AN DNS Servers)
DNS Lookup (the configured IP address is displayed)
AN Setup. In the upper right of the
AN
You can set the failure detection method for each WAN interface on its corresponding
W
AN
Advanced Options screen (see Configure the Auto-Rollover Mode and Failure
Detection Method for IPv4 Interfaces on page 45).
• Action. The Edit table button provides access to the W
(see Step 2) for the corresponding WAN interface; the Status button provides access
to the Connection Status screen (see Step 4) for the corresponding WAN interface.
2. Click the Edit table button in the Action column of the WAN interface for which you want to
automatically configure the connection to the Internet. The WAN IPv4 ISP Settings screen
displays. (The following figure shows the WAN2 IPv4 ISP Settings screen as an example.)
IPv4 and IPv6 Internet and WAN Settings
31
AN IPv4 ISP Settings screen
Page 32

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 12.
3. Click the Auto Detect button at the bottom of the screen. The autodetect process probes
the WAN port for a range of connection methods and suggests one that your ISP is most
likely to support.
The autodetect process returns one of the following results:
• If the autodetect process is successful, a status bar at the top of the screen displays
the results (for example, DHCP service detected).
• If the autodetect process senses a connection method that requires input from you, it
prompts you for the information.
The following table explains the settings that you
might have to enter:
IPv4 and IPv6 Internet and WAN Settings
32
Page 33

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 2. IPv4 Internet connection methods
Connection Method Manual Data Input Required
DHCP (Dynamic IP) No manual data input is required.
PPPoE The following fields are required:
•
Login
• Password
• Account Name
• Domain Name
PPTP The following fields are required:
• Login
• Password
• Account Name
• Domain Name
• My IP Address
• Server IP Address
Fixed (Static) IP The following fields are required:
• IP Address
• IP Subnet Mask
• Gateway IP Address
• Primary DNS Server
• Secondary DNS Server
• If the autodetect process does not find a connection, you are prompted either to
check the physical connection between your VPN firewall and the cable, DSL line, or
satellite or wireless Internet dish, or to check your VPN firewall’s MAC address. For
more information, see Configure Advanced WAN Options and Other Tasks on
page 71 and Troubleshoot the ISP Connection on page 396.
4. Verify the connection:
a. Select
Network Configuration > WAN Settings > W
AN Setup. The WAN Setup
screen displays the IPv4 settings (see Figure 11 on page 31).
b. In the Action column, click the Status
button of the WAN interface for which you
want to display the Connection Status pop-up screen. (The following figure shows a
static IP address configuration.)
IPv4 and IPv6 Internet and WAN Settings
33
Page 34

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 13.
The Connection Status screen should show a valid IP address and gateway , and you are
connected to the Internet. If the configuration was not successful, skip ahead to Manually
Configure an IPv4 Internet Connection on page 34, or see Troubleshoot the ISP
Connection on page 396.
Note: For more information about the Connection Status screen, see View
the WAN Port Status on page 382.
Manually Configure an IPv4 Internet Connection
Unless your ISP automatically assigns your configuration through a DHCP server, you need
to obtain configuration parameters from your ISP to manually establish an Internet
connection. The required parameters for various connection types are listed in Table 2 on
page 33.
To manually configure the WAN IPv4 ISP settings:
1. Select Network Configuration > WAN Settings > W
screen, the IPv4 radio button is selected by default. The WAN Setup screen displays the
IPv4 settings:
AN Setup. In the upper right of the
Figure 14.
IPv4 and IPv6 Internet and WAN Settings
34
Page 35

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The IPv4 WAN Settings table displays the following fields:
• WAN. The WAN interface (WAN1, WAN2, WAN3, and WAN4).
• Status. The status of the W
• WAN IP.
The IPv4 address of the WAN interface.
AN interface (UP or DOWN).
• Failure Detection Method. The failure detection method that is active for the W
interface. The following methods can be displayed:
- None
- DNS Lookup (W
DNS Lookup (the configured IP address is displayed)
-
AN DNS Servers)
- PING (the configured IP address is displayed)
You can set the failure detection method for each WAN interface on its corresponding
W
AN
Advanced Options screen (see Configure the Auto-Rollover Mode and Failure
Detection Method for IPv4 Interfaces on page 45).
AN
• Action. The Edit table button provides access to the W
AN IPv4 ISP Settings screen
(see Step 2) for the corresponding WAN interface; the Status button provides access
to the Connection Status screen (see Step 11) for the corresponding WAN interface.
2. Click the Edit table button in the Action column of the WAN interface for which you want to
manually configure the connection to the Internet. The WAN IPv4 ISP Settings screen
displays (see Figure 12 on page 32, which shows the WAN2 IPv4 ISP Settings screen as an
example).
3. Locate the ISP Login section on the screen:
Figure 15.
In the ISP Login section, select one of the following options:
• If your ISP requires an initial login to establish an Internet connection, select Yes.
(The default is No.)
• If a login is not required, select
4. If you selected
es, enter the login name in the Login field and the password in the
Y
No, and ignore the Login and Password fields.
Password field. This information is provided by your ISP.
5. In the ISP T
ype section of the screen, select the type of ISP connection that you use from
the two listed options. By default, Austria (PPTP) is selected, as shown in the following
figure:
IPv4 and IPv6 Internet and WAN Settings
35
Page 36

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 16.
6. If your connection is PPTP or PPPoE, your ISP requires an initial login. Enter the settings as
described in the following table:
Table 3. PPTP and PPPoE settings
Setting Description
Austria (PPTP)
Note: For login
and password
information, see
Step 3 and Step 4.
If your ISP is
radio button, and enter the following settings:
Account Name The account name is also known as the host name or system name.
Domain Name Your domain name or workgroup name assigned by your ISP, or
Idle Timeout Select the Keep Connected radio button to keep the connection
My IP Address The IP address assigned by the ISP to make the connection with the
Server IP
Address
Austria
Telecom or any other ISP that uses PPTP for login, select this
Enter the valid account name for the PPTP connection (usually your
email ID assigned by your ISP). Some ISPs require you to enter
your full email address here.
your ISP’s domain name. You can leave this field blank.
always on. To log out after the connection is idle for a period, select
the Idle Timeout radio button and, in the Idle T imeout field, enter the
number of minutes to wait before disconnecting. This is useful if your
ISP charges you based on the period that you have logged in.
ISP server.
The IP address of the PPTP server.
IPv4 and IPv6 Internet and WAN Settings
36
Page 37

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 3. PPTP and PPPoE settings (continued)
Setting Description
Other (PPPoE)
Note: For login
and password
information, see
Step 3 and Step 4.
If you have installed login software, your connection type is PPPoE. Select this radio
button, and enter the following settings:
Account Name The valid account name for the PPPoE connection.
Domain Name The name of your ISP’s domain or your domain name if your ISP
has assigned one. You can leave this field blank.
Idle Timeout Select the Keep Connected radio button to keep the connection
always on. To log out after the connection is idle for a period, select
the Idle Timeout radio button and, in the Idle T imeout field, enter the
number of minutes to wait before disconnecting. This is useful if your
ISP charges you based on the period that you have logged in.
Connection
Reset
Select the Connection Reset check box to specify a time when the
PPPoE WAN connection is reset, that is, the connection is
disconnected momentarily and then reestablished. Then specify the
disconnect time and delay.
Disconnect
Time
Delay Specify the period in seconds after which the
Specify the hour and minutes when the connection
should be disconnected.
connection should be reestablished.
7. In the Internet (IP) Address section of the screen (see the following figure), configure the IP
address settings as described in the following table. Click the Current IP Address link to
see the assigned IP address.
Figure 17.
IPv4 and IPv6 Internet and WAN Settings
37
Page 38

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 4. Internet IP address settings
Setting Description
Get Dynamically
from ISP
Use Static IP
Address
If your ISP has not assigned you a static IP address, select the Get Dynamically from
ISP radio button. The ISP automatically assigns an IP address to the VPN firewall using
DHCP network protocol.
Client Identifier
Vendor Class Identifier If your ISP requires the vendor class identifier information to
If your ISP has assigned you a fixed (static or permanent) IP address, select the Use
Static IP Address radio button, and enter the following settings:
IP Address The static IP address assigned to you. This address identifies
IP Subnet Mask The subnet mask is usually provided by your ISP.
Gateway IP Address The IP address of the ISP’s gateway is usually provided by
If your ISP requires client identifier information to assign an IP
address using DHCP, select the Client Identifier check box,
and enter the client identifier information in the field.
assign an IP address using DHCP, select the Vendor Class
Identifier check box.
the VPN firewall to your ISP.
your ISP.
8. In the Domain Name Server (DNS) Servers section of the screen (see the following figure),
specify the DNS settings as described in the following table.
Figure 18.
IPv4 and IPv6 Internet and WAN Settings
38
Page 39

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 5. DNS server settings
Setting Description
Get Automatically
from ISP
Use These
Servers
DNS
If your ISP has not assigned any Domain Name Server (DNS) addresses, select the
Get Automatically from ISP radio button.
If your ISP has assigned DNS addresses, select the Use These DNS Servers radio
button. Make sure that you fill in valid DNS server IP addresses in the fields. Incorrect
DNS entries might cause connectivity issues.
Primary DNS Server The IP address of the primary DNS server.
Secondary DNS Server The IP address of the secondary DNS server.
9. Click Apply to save your changes.
10. Click Test to evaluate your entries. The VPN firewall attempts to make a connection
according to the settings that you entered.
11. Verify the connection:
a. Select
Network Configuration > WAN Settings > W
AN Setup. The WAN Setup
screen displays the IPv4 settings (see Figure 14 on page 34).
b. In the Action column, click the Status
button of the WAN interface for which you
want to display the Connection Status pop-up screen. (The following figure shows a
PPPoE configuration; the IP addresses are not related to any other examples in this
manual.)
Figure 19.
The Connection Status screen should show a valid IP address and gateway , and you are
connected to the Internet. If the configuration was not successful, see Troubleshoot the
ISP Connection on page 396.
IPv4 and IPv6 Internet and WAN Settings
39
Page 40

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: If your ISP requires MAC authentication and another MAC address has
been previously registered with your ISP, you need to enter that
address on the WAN Advanced Options screen for the WAN interface
(see Configure Advanced WAN Options and Other Tasks on page 71).
Configure Load Balancing or Auto-Rollover for IPv4 Interfaces
You can configure the VPN firewall’s IPv4 interfaces on a mutually exclusive basis for either
auto-rollover (for increased system reliability) or load balancing (for maximum bandwidth
efficiency). If you do not select load balancing, you need to specify one WAN interface as the
primary interface.
The VPN firewall supports the following modes for IPv4 interfaces:
• Load balancing mode. The VPN firewall distributes the outbound traf
the WAN interfaces that are functional. You can configure up to four WAN interfaces. The
VPN firewall supports weighted load balancing and round-robin load balancing (see
Configure Load Balancing Mode and Optional Protocol Binding for IPv4 Interfaces on
page 41).
Note: Scenarios could arise in which load balancing needs to be bypassed
for certain traffic or applications. If certain traffic needs to travel on a
specific WAN interface, configure protocol binding rules for that
WAN interface. The rule should match the desired traffic.
• Primary WAN mode
other three interfaces are disabled.
• Auto-rollover mode. The selected W
another interface needs to be defined as the rollover link. The remaining two interfaces
are disabled. As long as the primary link is up, all traffic is sent over the primary link.
When the primary link goes down, the rollover link is brought up to send the traffic. When
the primary link comes back up, traffic automatically rolls back to the original primary link.
If you want to use a redundant ISP link for backup purposes, select the WAN port that
should function as the primary link for this mode. Ensure that the backup W
also been configured and that you configure the W
WAN Advanced Options screen to support auto-rollover (see Configure the Auto-Rollover
Mode and Failure Detection Method for IPv4 Interfaces on page 45).
. The selected WAN interface is made the primary interface. The
AN interface is defined as the primary link, and
AN failure detection method on the
fic equally among
AN port has
Note: If the VPN firewall functions in IPv4 / IPv6 mode, you cannot
configure load balancing.
IPv4 and IPv6 Internet and WAN Settings
40
Page 41

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure Load Balancing Mode and Optional Protocol Binding for
IPv4 Interfaces
To use multiple ISP links simultaneously, configure load balancing. In load balancing mode,
any WAN port carries any outbound protocol unless protocol binding is configured.
When a protocol is bound to a particular WAN port, all outgoing traffic of that protocol is
directed to the bound WAN port. For example, if the HTTPS protocol is bound to the WAN1
port and the FTP protocol is bound to the WAN2 port, the VPN firewall automatically routes
all outbound HTTPS traffic from the computers on the LAN through the WAN1 port. All
outbound FTP traffic is routed through the WAN2 port.
Protocol binding addresses two issues:
• Segregation of traffic between links that are not of the same speed.
High-volume traf
and low-volume traffic can be routed through the W
link.
• Continuity of source IP address for secure connections.
Some services, particularly HTTPS, cease to respond when a client’s source IP address
changes shortly after a session has been established.
fic can be routed through the WAN port connected to a high-speed link,
AN port connected to the low-speed
Configure Load Balancing Mode for IPv4 Interfaces
To configure load balancing mode:
1. Select Network Configuration > WAN Settings > W
displays:
AN Mode. The WAN Mode screen
Figure 20.
2. In the Load Balancing Settings section of the screen, configure the following settings:
a. Select the Load Balancing Mode radio button.
IPv4 and IPv6 Internet and WAN Settings
41
Page 42

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
b. From the corresponding drop-down list on the right, select one of the following load
balancing methods:
eighted LB. With weighted load balancing, balance weights are calculated
• W
based on W
AN link speed and available WAN bandwidth. This is the default
setting and most efficient load balancing algorithm.
• Round-robin. With round-robin load balancing, new traffic connections are sent
over a W
AN link in a serial method irrespective of bandwidth or link speed. For
example, if the WAN1, W AN2, and W AN3 interfaces are active in round-robin load
balancing mode, an HTTP request could first be sent over the WAN1 interface,
then a new FTP session could start on the WAN2 interface, and then any new
connection to the Internet could be made on the WAN3 interface. This
load balancing method ensures that a single WAN interface does not carry a
disproportionate distribution of sessions.
3. Click Apply to save your settings.
Configure Protocol Binding for IPv4 Interfaces (Optional)
To configure protocol binding and add protocol binding rules:
1. Select Network Configuration > Protocol Binding.
2. Select the Load Balancing radio button.
The Protocol Bindings screen displays. (The
following figure shows two examples in the Protocol Bindings table.)
Figure 21.
The Protocol Bindings table displays the following fields:
• Check box. Allows you to select the protocol binding rule in the table.
• Status icon. Indicates the status of the protocol binding rule:
- Green circle.
-
Gray circle. The protocol binding rule is disabled.
• Service
. The service or protocol for which the protocol binding rule is set up.
• Local Gateway. The W
The protocol binding rule is enabled.
AN interface to which the service or protocol is bound.
• Source Network. The computers or groups on your network that are af
protocol binding rule.
fected by the
IPv4 and IPv6 Internet and WAN Settings
42
Page 43

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• Destination Network. The Internet locations (based on their IP address) or groups
that are covered by the protocol binding rule.
• Action. The Edit table button, which provides access to the Edit Protocol Binding
screen for the corresponding service.
3. Click the Add
table button below the Protocol Binding table. The
Add Protocol Binding
screen displays:
Figure 22.
4. Configure the protocol binding settings as described in the following table:
Table 6. Add Protocol Binding screen settings
Setting Description
Service From the drop-down list, select a service or application to be covered by this rule. If the
service or application does not appear in the list, you need to define it using the Services
screen (see Add Customized Services on page 177).
Local Gateway
Source Network The source network settings determine which computers on your network are affected by
From the drop-down list, select one of the W
this rule. Select one of the following options from the drop-down list:
Any All devices on your LAN.
Single address In the Start IP field, enter the IP address to which the rule is applied.
Address Range In the Start IP field and End IP field, enter the IP addresses for the
range to which the rule is applied.
Group If this option is selected, the rule is applied to the selected group.
The group can be a LAN group or an IP (LAN) group.
Note: For information about LAN groups, see Manage IPv4 Groups
and Hosts (IPv4 LAN Groups) on page 96. For information about IP
groups, see Create IP Groups on page 179.
IPv4 and IPv6 Internet and WAN Settings
AN interfaces.
43
Page 44

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 6. Add Protocol Binding screen settings (continued)
Setting Description
Destination
Network
The destination network settings determine which Internet locations (based on their IP
address) are covered by the rule. Select one of the following options from the drop-down
list:
Any All Internet IP address.
Single address In the Start IP field, enter the IP address to which the rule is applied.
Address range In the Start IP field and Finish field, enter the IP addresses for the
range to which the rule is applied.
Group If this option is selected, the rule is applied to the selected IP (WAN)
group.
Note: For information about IP groups, see Create IP Groups on
page 179.
5. Click Apply to save your settings. The protocol binding rule is added to the Protocol Binding
table. The rule is automatically enabled, which is indicated by the ! status icon that displays
a green circle.
To edit a protocol binding:
1. On the Protocol Bindings screen (see Figure 21 on page 42), in the Protocol Bindings
table, click the Edit table button to the right of the binding that you want to edit. The Edit
Protocol Bindings screen displays. This screen shows the same fields as the
Add Protocol
Bindings screen (see the previous figure).
2. Modify the settings as described in the previous table.
3. Click Apply to save your settings.
To enable, disable, or delete one or more protocol bindings:
1. On the Protocol Bindings screen (see Figure 21 on page 42), select the check box to the
left of the protocol binding that you want to enable, disable, or delete, or click the Select
All table button to select all bindings.
2. Click one of the following table buttons:
• Enable. Enables the binding or bindings. The ! status icon changes from a gray circle
to a green circle, indicating that the selected binding or bindings are enabled. (By
default, when a binding is added to the table, it is automatically enabled.)
• Disable. Disables the binding or bindings. The ! status icon changes from a green
circle to a gray circle, indicating that the selected binding or bindings are disabled.
• Delete
. Deletes the binding or bindings.
IPv4 and IPv6 Internet and WAN Settings
44
Page 45

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure the Auto-Rollover Mode and Failure Detection Method for
IPv4 Interfaces
To use a redundant ISP link for backup purposes, ensure that the backup WAN interface has
already been configured. Then select the WAN interface that should function as the primary
link for this mode, and configure the WAN failure detection method on the W AN Mode screen
to support auto-rollover.
When the VPN firewall is configured in auto-rollover mode, it uses the selected WAN failure
detection method to detect the status of the primary link connection at regular intervals. For
IPv4 interfaces, the VPN firewall detects link failure in one of the following ways:
• By sending DNS queries to a DNS server
• By sending a ping request to an IP address
From the primary WAN interface, DNS queries or ping requests are sent to the specified IP
address. If replies are not received, after a specified number of retries, the primary WAN
interface is considered down and a rollover to the backup W
primary WAN interface comes back up, another rollover occurs from the backup WAN
interface back to the primary WAN interface. The WAN failure detection method that you
select applies only to the primary WAN interface, that is, it monitors the primary link only.
AN interface occurs. When the
Configure Auto-Rollover Mode for IPv4 Interfaces
To configure auto-rollover mode:
1. Select Network Configuration > WAN Settings > W
displays:
AN Mode. The WAN Mode screen
Figure 23.
IPv4 and IPv6 Internet and WAN Settings
45
Page 46

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
2. In the Load Balancing Settings section of the screen, configure the following settings:
a. Select the Primary WAN Mode
radio button.
b. From the corresponding drop-down list on the right, select a WAN interface to
function as the primary W
AN interface. The other WAN interfaces become disabled.
c. Select the Auto Rollover check box.
d. From the corresponding drop-down list on the right, select a W
function as the backup W
AN interface.
AN interface to
Note: Ensure that the backup WAN interface is configured before enabling
auto-rollover mode.
3. Click Apply to save your settings.
Configure the Failure Detection Method for IPv4 Interfaces
To configure the failure detection method:
1. Select Network Configuration > WAN Settings > W
AN Setup. In the upper right of the
screen, the IPv4 radio button is selected by default. The WAN Setup screen displays the
IPv4 settings (see Figure 11 on page 31).
2. Click the Edit table button in the Action column of the W
AN interface that you selected as
the primary WAN interface. The WAN IPv4 ISP Settings screen displays (see Figure 12 on
page 32, which shows the WAN2 IPv4 ISP Settings screen as an example).
3. Click the Advanced option arrow in the upper right of the screen. The W
AN Advanced
Options screen displays for the WAN interface that you selected. (For an image of the entire
screen, see Figure 46 on page 73).
4. Locate the Failure Detection Method section on the screen. Enter the settings as described
in the following table.
Figure 24.
IPv4 and IPv6 Internet and WAN Settings
46
Page 47

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 7. Failure detection method settings
Setting Description
Failure Detection
Method
DNS Server
IP Address The IP address of the interface that should receive the ping request. The interface
Retry Interval is The retry interval in seconds. The DNS query or ping is sent after every retry interval.
Failover after The number of failover attempts. The primary WAN interface is considered down after
Select a failure detection method from the drop-down list:
• W
AN DNS. DNS queries are sent to the DNS server that is configured in the
Domain Name Server (DNS) Servers section of the W
Manually Configure an IPv4 Internet Connection on page 34).
• Custom DNS. DNS queries are sent to a DNS server that you need to specify in
the DNS Server fields.
• Ping. Pings are sent to a public IP address that you need to specify in the IP
Address field.
Note: DNS queries or pings are sent through the WAN interface that is being
monitored. The retry interval and number of failover attempts determine how quickly
the VPN firewall switches from the primary link to the backup link if the primary link
fails, or when the primary link comes back up, switches back from the backup link to
the primary link.
The IP address of the DNS server
should not reject the ping request and should not consider ping traffic to be abusive.
The default retry interval is 30 seconds.
the specified number of queries have failed to elicit a reply. The backup interface is
brought up after this situation has occurred. The failover default is 4 failures.
.
AN ISP screen (see
Note: The default time to roll over after the primary WAN interface has
failed is 2 minutes. The minimum test period is 30 seconds, and the
minimum number of tests is 2.
5. Click Apply to save your settings.
You can configure the VPN firewall to generate a WAN status log and email this log to a
specified address (see Configure Logging, Alerts, and Event Notifications on page 362).
Configure Secondary WAN Addresses
You can set up a single WAN Ethernet port to be accessed through multiple IPv4 addresses
by adding aliases to the port. An alias is a secondary WAN address. One advantage is, for
example, that you can assign different virtual IP addresses to a web server and an FTP
server, even though both servers use the same physical IP address. You can add several
secondary IP addresses to a single WAN port.
IPv4 and IPv6 Internet and WAN Settings
47
Page 48

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
After you have configured secondary WAN addresses, these addresses are displayed on the
following firewall rule screens:
• In the WAN Destination IP Address drop-down lists of the following inbound firewall rule
screens:
- Add LAN WAN Inbound Service screen
- Add DMZ WAN Inbound Service screen
• In the NAT IP drop-down lists of the following outbound firewall rule screens:
- Add LAN WAN Outbound Service screen
- Add DMZ WAN Outbound Service screen
For more information about firewall rules, see
Overview of Rules to Block or Allow Specific
Kinds of Traffic on page 136).
Note: It is important that you ensure that any secondary WAN addresses
are different from the primary WAN, LAN, and DMZ IP addresses
that are already configured on the VPN firewall. However, primary
and secondary WAN addresses can be in the same subnet.
The following is an example of correctly configured IP addresses:
Primary WAN1 IP address: 10.0.0.1 with subnet 255.0.0.0
Secondary WAN1 IP: 30.0.0.1 with subnet 255.0.0.0
Primary WAN2 IP address: 20.0.0.1 with subnet 255.0.0.0
Secondary WAN2 IP: 40.0.0.1 with subnet 255.0.0.0
DMZ IP address: 192.168.10.1 with subnet 255.255.255.0
Primary LAN IP address: 192.168.1.1 with subnet 255.255.255.0
Secondary LAN IP: 192.168.20.1 with subnet 255.255.255.0
To add a secondary WAN address to a WAN port:
1. Select Network Configuration > WAN Settings > W
AN Setup. In the upper right of the
screen, the IPv4 radio button is selected by default. The WAN Setup screen displays the
IPv4 settings (see Figure 11 on page 31).
2. Click the Edit table button in the Action column of the W
AN interface for which you want to
add a secondary WAN address. The WAN IPv4 ISP Settings screen displays (see Figure 12
on page 32, which shows the WAN2 IPv4 ISP Settings screen as an example).
3. Click the Secondary Addresses option arrow in the upper right of the screen. The W
Secondary Addresses screen displays for the WAN interface that you selected. (The
following figure shows the WAN1 Secondary Addresses screen as an example and includes
one entry in the List of Secondary WAN addresses table.)
IPv4 and IPv6 Internet and WAN Settings
48
AN
Page 49

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 25.
The List of Secondary WAN addresses table displays the secondary LAN IP addresses
added for the selected WAN interface.
4. In the Add WAN Secondary Addresses section of the screen, enter the following settings:
• IP Address
• Subnet Mask
. Enter the secondary address that you want to assign to the WAN port.
. Enter the subnet mask for the secondary IP address.
5. Click the Add table button in the rightmost column to add the secondary IP address to the
List of Secondary W
6. (Optional) Repeat
AN addresses table.
Step 4 and Step 5 for each secondary IP address that you want to add to
the List of Secondary WAN addresses table.
To delete one or more secondary addresses:
1. In the List of Secondary WAN addresses table, select the check box to the left of the
address that you want to delete, or click the
Select All table button to select all
addresses.
2. Click the Delete table button.
Configure Dynamic DNS
Dynamic DNS (DDNS) is an Internet service that allows devices with varying public IPv4
addresses to be located using Internet domain names. To use DDNS, you need to set up an
account with a DDNS provider such as DynDNS.org, TZO.com, Oray.net, or 3322.org. (Links
to DynDNS, TZO, Oray, and 3322 are provided for your convenience as option arrows on the
DDNS configuration screens.) The VPN firewall firmware includes software that notifies
DDNS servers of changes in the WAN IP address so that the services running on this
network can be accessed by others on the Internet.
If your network has a permanently assigned IP address, you can register a domain name and
have that name linked with your IP address by public Domain Name Servers (DNS).
However
in advance what your IP address will be, and the address can change frequently—hence, the
need for a commercial DDNS service, which allows you to register an extension to its
domain, and restores DNS requests for the resulting fully qualified domain name (FQDN) to
your frequently changing IP address.
, if your Internet account uses a dynamically assigned IP address, you do not know
IPv4 and IPv6 Internet and WAN Settings
49
Page 50

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
After you have configured your account information on the VPN firewall, when your
ISP-assigned IP address changes, your VPN firewall automatically contacts your DDNS
service provider, logs in to your account, and registers your new IP address. Consider the
following:
• For auto-rollover mode, you need a fully qualified domain name (FQDN) to implement
features such as exposed hosts and virtual private networks regardless of whether you
have a fixed or dynamic IP address.
• For load balancing mode, you might still need a fully qualified domain name (FQDN)
either for convenience or if you have a dynamic IP address.
Note: If your ISP assigns a private WAN IP address such as 192.168.x.x or
10.x.x.x, the DDNS service does not work because private
addresses are not routed on the Internet.
To configure DDNS:
1. Select Network Configuration > Dynamic DNS. The Dynamic DNS screen displays
(see the following figure).
The W
Single Port WAN1, Load Balancing, or
AN Mode section on the screen reports the configured WAN mode (for example,
Auto Rollover). Only those options that match the
configured WAN mode are accessible on the screen.
2. Click the submenu tab for your DDNS service provider:
• Dynamic DNS for DynDNS.org (which is shown in the following figure)
• DNS TZO for TZO.com
• DNS Oray
• 3322 DDNS
for Oray.net
for 3322.org
IPv4 and IPv6 Internet and WAN Settings
50
Page 51

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 26.
3. Click the Information option arrow in the upper right of a DNS screen for registration
information (for example, DynDNS Information).
Figure 27.
4. Access the website of the DDNS service provider, and register for an account (for example,
for DynDNS.org, go to http://www.dyndns.com/).
IPv4 and IPv6 Internet and WAN Settings
51
Page 52

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
5. Configure the DDNS service settings as described in the following table:
Table 8. DDNS service settings
Setting Description
WAN1 (... Status: ...)
Select the Yes radio button to enable the DDNS service.
the DDNS service provider that you have selected. Enter the following settings:
Host and Domain Name The host and domain name for the DDNS service.
Username or
User Email Address
Password or User Key The password that is used for DDNS server authentication.
Use wildcards If your DDNS provider allows the use of wildcards in resolving your URL, you
Update every 30 days If your WAN IP address does not often change, you might need to force a
WAN2 (... Status: ...)
WAN3 (... Status: ...)
WAN4 (... Status: ...)
See the information for W
different WAN interfaces.
The user name or email address for DDNS server authentication.
can select the Use wildcards check box to activate this feature. For example,
the wildcard feature causes *.yourhost.dyndns.org to be aliased to the same IP
address as yourhost.dyndns.org.
periodic update to the DDNS service to prevent your account from expiring. If
the Update every 30 days check box displays, select it to enable a periodic
update.
AN1 about how to enter the settings.
The fields that display on the screen depend on
You can select different DDNS services for
6. Click Apply to save your configuration.
Configure the IPv6 Internet Connection and WAN Settings
• Configure the IPv6 Routing Mode
• Use a DHCPv6 Server to Configure an IPv6 Internet Connection
• Configure a Static IPv6 Internet Connection
• Configure a PPPoE IPv6 Internet Connection
• Configure 6to4 Automatic Tunneling
• Configure ISATAP Automatic Tunneling
• View the Tunnel Status and IPv6 Addresses
• Configure Stateless IP/ICMP Translation
IPv4 and IPv6 Internet and WAN Settings
52
Page 53

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: You can configure only one WAN interface for IPv6. This restriction
might be lifted in a later release. You can configure the other three
WAN interfaces for IPv4.
The nature of your IPv6 network determines how you need to configure the IPv6 Internet
connections:
• Native IPv6 network. Y
IPv6 address and is connected to an IPv6 ISP and if your network consists of IPv6-only
devices. However, because we are in a IPv4-to-IPv6 transition period, native IPv6 is not
yet common.
• Isolated IPv6 network. If your network is an isolated IPv6 network that is not connected
to an IPv6 ISP
Internet backbone; you do this by enabling automatic 6to4 tunneling (see Configure 6to4
Automatic T
• Mixed network with IPv4 and IPv6 devices. If your network is an IPv4 network that
consists of both IPv4 and IPv6 devices, you need to make sure that the IPv6 packets can
travel over the IPv4 intranet; you do this by enabling and configuring ISAT
(see Configure ISATAP Automatic Tunneling on page 65).
Note: A network can be both an isolated IPv6 network and a mixed
After you have configured the IPv6 routing mode (see the next section), you need to
configure one or more WAN interfaces with a global unicast address to enable secure IPv6
Internet connections on your VPN firewall.
IPv6 WAN address that can be statically or dynamically assigned. The web management
interface offers two connection configuration options:
, you need to make sure that the IPv6 packets can travel over the IPv4
unneling on page 64).
network with IPv4 and IPv6 devices.
our network is a native IPv6 network if the VPN firewall has an
AP tunneling
A global unicast address is a public and routable
• Automatic configuration of the network connection (see Use a DHCPv6 Server to
Configure an IPv6 Internet Connection on page 55)
• Manual configuration of the network connection (see Configure a Static IPv6 Internet
Connection on page 58 or Configure a PPPoE IPv6 Internet Connection on page 61)
Configure the IPv6 Routing Mode
By default the VPN firewall supports IPv4 only. To use IPv6, you need to enable the VPN
firewall to support both devices with IPv4 addresses and devices with IPv6 addresses. The
routing mode does not include an IPv6-only option; however, you can still configure a native
IPv6 network if your ISP supports IPv6.
IPv4 and IPv6 Internet and WAN Settings
53
Page 54

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
These are the options:
• IPv4-only mode. The VPN firewall communicates only with devices that have IPv4
addresses.
• IPv4/IPv6 mode. The VPN firewall communicates with both devices that have IPv4
addresses and devices that have IPv6 addresses.
Note: IPv6 always functions in classical routing mode between the WAN
interface and the LAN interfaces; NAT does not apply to IPv6.
Note: When the Load Balancing Mode radio button is selected in the Load
Balancing Settings section of the WAN Mode screen, the IPv4 / IPv6
mode radio button is dimmed, preventing you from selecting it. You
can select the IPv4 / IPv6 mode radio button only when the Primary
WAN Mode radio button is selected.
To configure the IPv6 routing mode:
1. Select Network Configuration > WAN Settings > W
displays:
Figure 28.
AN Mode. The WAN Mode screen
2. In the Routing Mode section of the screen, select the IPv4 / IPv6 mode radio button. By
default, the IPv4 only mode radio button is selected, and IPv6 is disabled.
IPv4 and IPv6 Internet and WAN Settings
54
Page 55

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
WARNING:
Changing the IP routing mode causes the VPN firewall to reboot.
3. Click Apply to save your changes.
Use a DHCPv6 Server to Configure an IPv6 Internet Connection
The VPN firewall can autoconfigure its ISP settings through a DHCPv6 server by using either
stateless or stateful address autoconfiguration:
• Stateless address autoconfiguration. The VPN firewall generates its own IP address
by using a combination of locally available information and router advertisements, but
receives DNS server information from a DHCPv6 server.
Router advertisements include a prefix that identifies the subnet that is associated with
the WAN port.
the WAN port. The IP address is a dynamic address.
The IP address is formed by combining this prefix and the MAC address of
As an option for stateless address autoconfiguration, the ISP’s stateful DHCPv6 server
can assign a prefix through prefix delegation. The VPN firewall’
server can assign this prefix to its IPv6 LAN clients. For more information about prefix
delegation, see Stateless DHCPv6 Server With Prefix Delegation on page 103.
• Stateful address autoconfiguration. The VPN firewall obtains an interface address,
configuration information such as DNS server information, and other parameters from a
DHCPv6 server
To automatically configure a WAN interface for an IPv6 connection to the Internet:
1. Select Network Configuration > WAN Settings > W
2. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings:
. The IP address is a dynamic address.
AN Setup.
s own stateless DHCPv6
Figure 29.
IPv4 and IPv6 Internet and WAN Settings
55
Page 56

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The IPv6 WAN Settings table displays the following fields:
• WAN. The WAN interface (WAN1, WAN2, WAN3, and WAN4).
• Status. The status of the W
• WAN IP.
The IPv6 address of the WAN interface.
• Action. The Edit table button provides access to the W
AN interface (UP or DOWN).
AN IPv6 ISP Settings screen
(see Step 3) for the corresponding WAN interface; the Status button provides access
to the Connection Status screen (see Step 8) for the corresponding WAN interface.
3. Click the Edit table button in the Action column of the WAN interface for which you want to
automatically configure the connection to the Internet. The WAN IPv6 ISP Settings screen
displays. (The following figure shows the WAN2 IPv6 ISP Settings screen as an example.)
Figure 30.
4. In the Internet Address section of the screen, from the IPv6 drop-down list, select DHCPv6.
5. In the DHCPv6 section of the screen, select one of the following radio buttons:
• Stateless Address Auto Configuration
• Stateful Address Auto Configuration
IPv4 and IPv6 Internet and WAN Settings
56
Page 57

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
6. As an optional step: If you have selected the Stateless Address Auto Configuration radio
button, you can select the Prefix Delegation check box:
• Prefix delegation check box is selected.
A prefix is assigned by the ISP’
s stateful
DHCPv6 server through prefix delegation, for example, 2001:db8:: /64. The VPN
firewall’s own stateless DHCPv6 server can assign this prefix to its IPv6 LAN clients.
For more information about prefix delegation, see Stateless DHCPv6 Server With
Prefix Delegation on page 103.
• Prefix delegation check box is cleared. Prefix delegation is disabled. This is the
default setting.
7. Click Apply
8. V
erify the connection:
a. Select
to save your changes.
Network Configuration > WAN Settings > W
AN Setup.
b. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings (see Figure 29
c. In the Action column, click the Status
on page 55).
button of the WAN interface for which you
want to display the Connection Status pop-up screen. (The following figure shows a
dynamic IP address configuration.)
Figure 31.
The Connection Status screen should show a valid IP address and gateway , and you are
connected to the Internet. If the configuration was not successful, see Troubleshoot the
ISP Connection on page 396.
Note: For more information about the Connection Status screen, see View
the WAN Port Status on page 382.
IPv4 and IPv6 Internet and WAN Settings
57
Page 58

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure a Static IPv6 Internet Connection
To configure a static IPv6 or PPPoE IPv6 Internet connection, you need to enter the IPv6
address information that you should have received from your ISP.
To configure static IPv6 ISP settings for a WAN interface:
1. Select Network Configuration > WAN Settings > W
AN Setup.
2. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings:
Figure 32.
The IPv6 WAN Settings table displays the following fields:
• WAN.
• Status. The status of the W
• WAN IP.
• Action. The Edit table button provides access to the W
The WAN interface (WAN1, WAN2, WAN3, and WAN4).
AN interface (UP or DOWN).
The IPv6 address of the WAN interface.
AN IPv6 ISP Settings screen
(see Step 3) for the corresponding WAN interface; the Status button provides access
to the Connection Status screen (see Step 7) for the corresponding WAN interface.
3. Click the Edit table button in the Action column of the WAN interface for which you want to
automatically configure the connection to the Internet. The WAN IPv6 ISP Settings screen
displays. (The following figure shows the WAN2 IPv6 ISP Settings screen as an example.)
IPv4 and IPv6 Internet and WAN Settings
58
Page 59

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 33.
4. In the Internet Address section of the screen, from the IPv6 drop-down list, select Static
IPv6.
5. In the Static IP Address section of the screen, enter the settings as described in the following
table.
You should have received static IPv6 address information from your IPv6 ISP:
Table 9. WAN ISP IPv6 Settings screen settings for a static IPv6 address
Setting Description
IPv6 Address The IP address that your ISP assigned to you. Enter the address in one of the
following formats (all four examples specify the same IPv6 address):
• 2001:db8:0000:0000:020f:24ff:febf:dbcb
• 2001:db8:0:0:20f:24ff:febf:dbcb
• 2001:db8::20f:24ff:febf:dbcb
• 2001:db8:0:0:20f:24ff:128.141.49.32
IPv6 Prefix Length The prefix length that your ISP assigned to you, typically 64.
Default IPv6 Gateway
Primary DNS Server The IPv6 IP address of the ISP’s primary DNS server.
Secondary DNS Server The IPv6 IP address of the ISP’s secondary DNS server.
The IPv6 IP address of the ISP’
s default IPv6 gateway.
IPv4 and IPv6 Internet and WAN Settings
59
Page 60

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
6. Click Apply to save your changes.
7. Verify the connection:
a. Select
Network Configuration > WAN Settings > W
AN Setup.
b. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings (see
c. In the Action column, click the Status
Figure 32 on page 58).
button of the WAN interface for which you
want to display the Connection Status pop-up screen. (The following figure shows a
static IP address configuration; the IP addresses are not related to any other
examples in this manual.)
Figure 34.
The Connection Status screen should show a valid IP address and gateway , and you are
connected to the Internet. If the configuration was not successful, see Troubleshoot the
ISP Connection on page 396.
Note: For more information about the Connection Status screen, see View
the WAN Port Status on page 382.
Note: If your ISP requires MAC authentication and another MAC address
has been previously registered with your ISP, you need to enter that
address on the WAN Advanced Options screen for the
corresponding WAN interface (see Configure Advanced WAN
Options and Other Tasks on page 71).
IPv4 and IPv6 Internet and WAN Settings
60
Page 61

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Configure a PPPoE IPv6 Internet Connection
To configure a PPPoE IPv6 Internet connection, you need to enter the PPPoE IPv6
information that you should have received from your ISP.
To configure PPPoE IPv6 ISP settings for a WAN interface:
1. Select Network Configuration > WAN Settings > W
AN Setup.
2. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings:
Figure 35.
The IPv6 WAN Settings table displays the following fields:
• WAN.
• Status. The status of the W
• WAN IP.
• Action. The Edit table button provides access to the W
The WAN interface (WAN1, WAN2, WAN3, and WAN4).
AN interface (UP or DOWN).
The IPv6 address of the WAN interface.
AN IPv6 ISP Settings screen
(see Step 3) for the corresponding WAN interface; the Status button provides access
to the Connection Status screen (see Step 7) for the corresponding WAN interface.
3. Click the Edit table button in the Action column of the WAN interface for which you want to
automatically configure the connection to the Internet. The WAN IPv6 ISP Settings screen
displays. (The following figure shows the WAN2 IPv6 ISP Settings screen as an example.)
IPv4 and IPv6 Internet and WAN Settings
61
Page 62

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 36.
4. In the Internet Address section of the screen, from the IPv6 drop-down list, select PPPoE.
5. In the PPPoE IPv6 section of the screen, enter the settings as described in the following
table. Y
Table 10. WAN IPv6 ISP Settings screen settings for a PPPoE IPv6 connection
Setting Description
User Name The PPPoE user name that is provided by your ISP.
Password The PPPoE password that is provided by your ISP
ou should have received PPPoE IPv6 information from your ISP:
.
IPv4 and IPv6 Internet and WAN Settings
62
Page 63

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 10. WAN IPv6 ISP Settings screen settings for a PPPoE IPv6 connection (continued)
Setting Description
DHCPv6 Option From the DHCPv6 Option drop-down list, select one of the following DHCPv6
server options, as directed by your ISP:
• Disable-DHCPv6. DHCPv6 is disabled.
in the Primary DNS Server and Secondary DNS Server fields in order to
receive an IP address from the ISP.
• DHCPv6 StatelessMode.
using a combination of locally available information and router
advertisements, but receives DNS server information from the ISP’
server. Router advertisements include a prefix that identifies the subnet that
is associated with the WAN port. The IP address is formed by combining this
prefix and the MAC address of the WAN port. The IP address is a dynamic
address.
• DHCPv6 StatefulMode.
configuration information such as DNS server information, and other
parameters from the ISP’
address.
• DHCPv6 Prefix Delegation. The VPN firewall obtains a prefix from the ISP’
DHCPv6 server through prefix delegation, for example, 2001:db8:: /64. The
VPN firewall’s own stateless DHCPv6 server can assign this prefix to its IPv6
LAN clients. For more information about prefix delegation, see Stateless
DHCPv6 Server With Prefix Delegation on page 103.
The VPN firewall generates its own IP address by
The VPN firewall obtains an interface address,
s DHCPv6 server. The IP address is a dynamic
ou need to specify the DNS servers
Y
s DHCPv6
s
Primary DNS Server If you have selected the Disable-DHCPv6 from the DHCPv6 Options drop-down
list, the IPv6 IP address of the ISP’s primary DNS server.
Secondary DNS Server If you have selected the Disable-DHCPv6 from the DHCPv6 Options drop-down
list, the IPv6 IP address of the ISP’s secondary DNS server.
6. Click Apply to save your changes.
7. Verify the connection:
a. Select
Network Configuration > WAN Settings > W
AN Setup.
b. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings (see Figure 35
c. In the Action column, click the Status
on page 61).
button of the WAN interface for which you
want to display the Connection Status pop-up screen. (See Figure 34 on page 60,
which shows a static IP address configuration; the screen for PPPoE is similar.)
The Connection Status screen should show a valid IP address and gateway , and you are
connected to the Internet. If the configuration was not successful, see Troubleshoot the
ISP Connection on page 396.
Note: For more information about the Connection Status screen, see View
the WAN Port Status on page 382.
IPv4 and IPv6 Internet and WAN Settings
63
Page 64

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: If your ISP requires MAC authentication and another MAC address
has been previously registered with your ISP, you need to enter that
address on the WAN Advanced Options screen for the
corresponding WAN interface (see Configure Advanced WAN
Options and Other Tasks on page 71).
Configure 6to4 Automatic Tunneling
If your network is an isolated IPv6 network that is not connected to an IPv6 ISP, you need to
make sure that the IPv6 packets can travel over the IPv4 Internet backbone by enabling
automatic 6to4 tunneling.
6to4 is a WAN tunnel mechanism for automatic tunneling of IPv6 traffic between a device with
an IPv6 address and a device with an IPv4 address, or the other way around. 6to4 tunneling
is used to transfer IPv6 traffic between LAN IPv6 hosts and W
network.
AN IPv6 networks over the IPv4
With 6to4 tunnels, IPv6 packets are embedded within the IPv4 packet and then transported
over the IPv4 network. Y
ou do not need to specify remote tunnel endpoints, which are
automatically determined by relay routers on the Internet. You cannot use 6to4 tunnels for
traffic between IPv4-only devices and IPv6-only devices.
Note: If the VPN firewall functions as the endpoint for 6to4 tunnels in your
network, make sure that the VPN firewall has a static IPv4 address
(see Manually Configure an IPv4 Internet Connection on page 34). A
dynamic IPv4 address can cause routing problems on the 6to4
tunnels.
Note: If you do not use a stateful DHCPv6 server in your LAN, you need to
configure the Router Advertisement Daemon (RADVD), and set up
6to4 advertisement prefixes for 6to4 tunneling to function correctly.
For more information, see Manage the IPv6 LAN on page 102.
Typically, 6to4 tunnel addresses start with a 2002 prefix (decimal notification). On the VPN
firewall, a 6to4 tunnel is indicated by sit0-WAN1 (see V
iew the Tunnel Status and IPv6
Addresses on page 67).
To enable 6to4 automatic tunneling:
1. Select Network Configuration > WAN Settings > 6 to 4 T
Tunneling screen displays.
IPv4 and IPv6 Internet and WAN Settings
64
unneling. The 6 to 4
Page 65

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 37.
2. Select the Enable Automatic T unneling check box.
3. Click Apply to save your changes.
Configure ISATAP Automatic Tunneling
If your network is an IPv4 network or IPv6 network that consists of both IPv4 and IPv6
devices, you need to make sure that the IPv6 packets can travel over the IPv4 intranet by
enabling and configuring Intra-Site Automatic Tunnel Addressing Protocol (ISATAP)
tunneling.
ISATAP is a LAN tunnel mechanism in which the IPv4 network functions as a virtual IPv6
local link. Each IPv4 address is mapped to a link-local IPv6 address, that is, the IPv4 address
is used in the interface portion of the IPv6 address. ISAT
AP tunneling is used intra-site, that
is, between addresses in the LAN. For more information about link-local addresses, see
Manage the IPv6 LAN on page 102.
Note: If you do not use a stateful DHCPv6 server in your LAN, you need to
configure the Router Advertisement Daemon (RADVD), and set up
ISATAP advertisement prefixes (which are referred to as
Global/Local/ISATAP prefixes) for ISATAP tunneling to function
correctly. For more information, see Manage the IPv6 LAN on
page 102.
The VPN firewall determines the link-local address by concatenating the IPv6 address with
the 32 bits of the IPv4 host address:
• For a unique global address:
fe80:0000:0000:0000:0000:5efe (or fe80::5efe) is concatenated with the IPv4 address.
For example, fe80::5efe with 10.29.33.4 becomes fe80::5efe:10.29.33.4, or in
hexadecimal format, fe80::5efe:a1d:2104.
• For a private address:
fe80:0000:0000:0000:0200:5efe (or fe80::200:5efe) is concatenated with the IPv4
address. For example, fe80::200:5efe with 192.168.1.1 becomes
fe80::200:5efe:192.168.1.1, or in hexadecimal format, fe80::200:5efe:c0a8:101.
IPv4 and IPv6 Internet and WAN Settings
65
Page 66

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
To configure an ISATAP tunnel:
1. Select Network Configuration > WAN Settings > ISATAP Tunnels. The ISATAP
Tunnels screen displays. (The following figure shows some examples.)
Figure 38.
2. Click the Add table button under the List of Available ISATAP Tunnels table. The Add
ISATAP Tunnel screen displays:
Figure 39.
3. Specify the tunnel settings as described in the following table.
Table 11. Add ISATAP Tunnel screen settings
Setting Description
ISATAP Subnet Prefix The IPv6 prefix for the tunnel.
Local End Point
Address
IPv4 Address If you select Other IP from the Local End Point Address drop-down list, enter the
From the drop-down list, select the type of local address:
• LAN.
• Other IP. The local endpoint address is another LAN IP address that you
IPv4 address.
The local endpoint address is the address of the default VLAN.
need to specify in the IPv4
Address fields.
4. Click Apply to save your changes.
IPv4 and IPv6 Internet and WAN Settings
66
Page 67

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
To edit an ISATAP tunnel:
1. On the ISATAP Tunnels screen, click the Edit button in the Action column for the tunnel
that you want to modify. The Edit ISATAP Tunnel screen displays. This screen is
identical to the Add ISATAP Tunnel screen.
2. Modify the settings as described in the previous table.
3. Click Apply to save your settings.
To delete one or more tunnels:
1. On the ISAT
want to delete, or click the Select All table button to select all tunnels.
2. Click the Delete table button.
AP Tunnels screen, select the check box to the left of each tunnel that you
View the Tunnel Status and IPv6 Addresses
The IPv6 Tunnel Status screen displays the status of all active 6to4 and ISATAP tunnels and
their IPv6 addresses.
To view the status of the tunnels and IPv6 addresses:
Select Monitoring > Router Status > Tunnel Status.
Figure 40.
The Tunnel Status screen displays:
The IPv6 Tunnel Status table shows the following fields:
• Tunnel Name. The tunnel name for the 6to4 tunnel is always sit0-WAN1 (SIT stands for
simple Internet transition); the tunnel name for an ISA
x is an integer.
• IPv6 Address. The IPv6 address of the local tunnel endpoint.
T AP tunnel is isatapx-LAN, in which
Configure Stateless IP/ICMP Translation
Stateless IP/ICMP Translation (SIIT) is a transition mechanism algorithm that translates
between IPv4 and IPv6 packet headers. Using SIIT, an IPv6 device that does not have a
permanently assigned IPv4 addresses can communicate with an IPv4-only device.
SIIT functions with IPv4-translated addresses, which are addresses of the format
ff:0:0:0/96 for IPv6-enabled devices. You can substitute an IPv4 address in the format
0::ff
IPv4 and IPv6 Internet and WAN Settings
67
Page 68

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
a.b.c.d for part of the IPv6 address so that the IPv4-translated address becomes
0::ffff:0:a.b.c.d/96.
For SIIT to function, the routing mode needs to be IPv4 / IPv6. NETGEAR’s implementation of
SIIT lets you enter a single IPv4 address on the SIIT screen. This IPv4 address is then used
in the IPv4-translated address for IPv6 devices to enable communication between IPv4-only
devices on the VPN firewall’s LAN and IPv6-only devices on the WAN.
To configure SIIT:
1. Select Network Configuration > SIIT. The SIIT
Figure 41.
screen displays:
2. Select the Enable SIIT check box.
3. In the SIIT Address fields, enter the IPv4 address that should be used i
n the IPv4-translated
address for IPv6 devices.
4. Click Apply to save your changes.
Configure Auto-Rollover for IPv6 Interfaces
You can configure the VPN firewall’s IPv6 interfaces for auto-rollover for increased system
reliability. You need to specify one WAN interface as the primary interface.
The VPN firewall supports the following modes for IPv6 interfaces:
• Primary WAN mode
. The selected WAN interface is made the primary interface. The
other three interfaces are disabled.
• Auto-rollover mode. The selected W
AN interface is defined as the primary link, and
another interface needs to be defined as the rollover link. The remaining two interfaces
are disabled. As long as the primary link is up, all traffic is sent over the primary link.
When the primary link goes down, the rollover link is brought up to send the traffic. When
the primary link comes back up, traffic automatically rolls back to the original primary link.
If you want to use a redundant ISP link for backup purposes, select the WAN port that
should function as the primary link for this mode. Ensure that the backup W
also been configured and that you configure the W
AN failure detection method on the
AN port has
WAN Advanced Options screen to support auto-rollover.
IPv4 and IPv6 Internet and WAN Settings
68
Page 69

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
To use a redundant ISP link for backup purposes, ensure that the backup WAN interface has
already been configured. Then select the WAN interface that should function as the primary
link for this mode, and configure the WAN failure detection method on the W AN Mode screen
to support auto-rollover.
When the VPN firewall is configured in auto-rollover mode, it uses the WAN failure detection
method to detect the status of the primary link connection at regular intervals. For IPv6
interfaces, the VPN firewall detects link failure by sending a ping request to an IP address
From the primary WAN interface, ping requests are sent to the specified IP address. If replies
are not received, after a specified number of retries, the primary W
down and a rollover to the backup W
AN interface occurs. When the primary WAN interface
AN interface is considered
comes back up, another rollover occurs from the backup WAN interface back to the primary
WAN interface. WAN failure detection applies only to the primary WAN interface, that is, it
monitors the primary link only.
Configure Auto-Rollover Mode for IPv6 Interfaces
To configure auto-rollover mode:
1. Select Network Configuration > WAN Settings > W
AN Mode. The WAN Mode screen
displays:
Figure 42.
2. In the Load Balancing Settings section of the screen, configure the following settings:
a. Select the Primary WAN Mode
radio button.
b. From the corresponding drop-down list on the right, select a WAN interface to
function as the primary W
AN interface. The other WAN interfaces become disabled.
c. Select the Auto Rollover check box.
d. From the corresponding drop-down list on the right, select a W
function as the backup W
AN interface.
AN interface to
IPv4 and IPv6 Internet and WAN Settings
69
Page 70

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: Ensure that the backup WAN interface is configured before enabling
auto-rollover mode.
3. Click Apply to save your settings.
Configure the Failure Detection Method for IPv6 Interfaces
To configure the failure detection method:
1. Select Network Configuration > WAN Settings > W
AN Setup.
2. In the upper right of the screen, select the IPv6 radio button. The WAN Setup screen
displays the IPv6 settings (See Figure 29
3. Click the Edit table button in the Action column of the W
on page 55).
AN interface that you selected as
the primary WAN interface. The WAN IPv6 ISP Settings screen displays (see Figure 30 on
page 56, which shows the WAN2 IPv6 ISP Settings screen as an example).
4. Click the Advanced option arrow in the upper right of the screen. The W
AN IPv6 Advanced
Options screen displays for the WAN interface that you selected:
Figure 43.
5. Enter the settings as described in the following table.
Table 12. Failure detection settings
Setting Description
Ping IP Address The IP address of the interface that should receive the ping request. The interface
should not reject the ping request and should not consider ping traffic to be abusive.
Note:
Pings are sent through the WAN interface that is being monitored. The retry
interval and number of failover attempts determine how quickly the VPN firewall
switches from the primary link to the backup link if the primary link fails, or when the
primary link comes back up, switches back from the backup link to the primary link.
Retry Interval is The retry interval in seconds. A ping is sent after every retry interval. The default retry
interval is 30 seconds.
Failover after The number of failover attempts. The primary WAN interface is considered down after
the specified number of queries have failed to elicit a reply. The backup interface is
brought up after this situation has occurred. The failover default is 4 failures.
IPv4 and IPv6 Internet and WAN Settings
70
Page 71

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: The default time to roll over after the primary WAN interface has
failed is 2 minutes. The minimum test period is 30 seconds, and the
minimum number of tests is 2.
6. Click Apply to save your settings.
You can configure the VPN firewall to generate a WAN status log and email this log to a
specified address (see Configure Logging, Alerts, and Event Notifications on page 362).
Configure Advanced WAN Options and Other Tasks
The advanced options include configuring the maximum transmission unit (MTU) size, port
speed, and VPN firewall’s MAC address, and setting a rate limit on the traffic that is being
forwarded by the VPN firewall. You can also configure the failure detection method for the
auto-rollover mode.
Note: Although you can access the WAN Advanced Options screen for a
WAN interface only through the WAN IPv4 ISP Settings screen, the
advanced options apply to both IPv4 and IPv6 WAN connections.
However, the failure detection method applies only to IPv4 settings.
To configure advanced WAN options:
1. Select Network Configuration > WAN Settings > W
screen, the IPv4 radio button is selected by default. The WAN Setup screen displays the
IPv4 settings:
Figure 44.
AN Setup. In the upper right of the
2. Click the Edit table button in the Action column of the WAN interface for which you want to
configure the advanced WAN options. The WAN IPv4 ISP Settings screen displays. (The
following figure shows the WAN2 IPv4 ISP Settings screen as an example.)
IPv4 and IPv6 Internet and WAN Settings
71
Page 72

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 45.
3. Click the Advanced option arrow in the upper right of the screen. The WAN Advanced
Options screen displays for the WAN interface that you selected. (The following figure shows
the WAN2 Advanced Options screen as an example.)
IPv4 and IPv6 Internet and WAN Settings
72
Page 73

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 46.
4. Enter the settings as described in the following table:
Table 13. WAN Advanced Options screen settings
Setting Description
MTU Size
Make one of the following selections:
Default
Custom Select the Custom radio button, and enter an MTU value in the Bytes field. For
Select the Default
value. For most Ethernet networks, this value is 1500 bytes, or 1492 bytes for
PPPoE connections.
some ISPs, you might need to reduce the MTU. This is rarely required, and
should not be done unless you are sure that it is necessary for your ISP
connection.
radio button for the normal maximum transmit unit (MTU)
IPv4 and IPv6 Internet and WAN Settings
73
Page 74
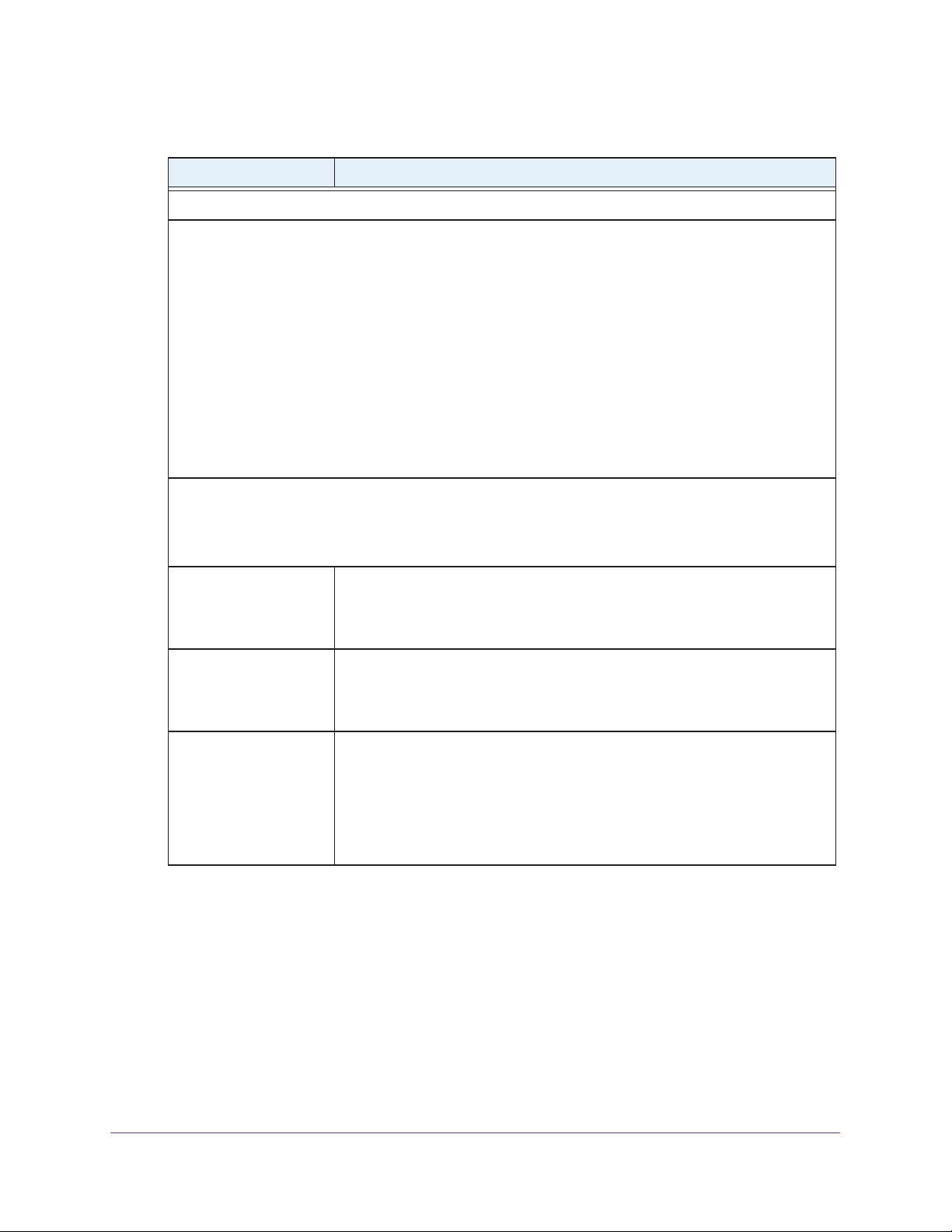
ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 13. WAN Advanced Options screen settings (continued)
Setting Description
Speed
In most cases, the VPN firewall can automatically determine the connection speed of the WAN port of the
device (modem, dish, or router) that provides the WAN connection. If you cannot establish an Internet
connection, you might need to manually select the port speed. If you know the Ethernet port speed of the
modem, dish, or router
settings do not function correctly.
Select one of the following speeds from the drop-down list:
• AutoSense. Speed autosensing.
duplex modes, including 1000BASE-T speed at full duplex.
• 10BaseT Half_Duplex
• 10BaseT Full_Duplex. Ethernet speed at full duplex.
• 100BaseT Half_Duplex. Fast Ethernet speed at half duplex.
• 100BaseT Full_Duplex. Fast Ethernet speed at full duplex.
• 1000BaseT Full_Duplex. Gigabit Ethernet speed at full duplex.
, select it from the drop-down list. Use the half-duplex settings only if the full-duplex
This is the default setting, which can sense all Ethernet speeds and
. Ethernet speed at half duplex.
Router’s MAC Address
Each computer or router on your network has a unique 48-bit local Ethernet address. This is also referred to
as the computer’s Media Access Control (MAC) address. The default is set to Use Default Address.
Make one of the following selections:
Use Default Address Each computer or router on your network has a unique 32-bit local Ethernet
address. This is also referred to as the computer’s Media Access Control (MAC)
address. To use the VPN firewall’s own MAC address, select the Use Default
Address radio button.
Use this computer’s MAC
Address
Use this MAC Address Select the Use this MAC Address radio button, and manually enter the MAC
Select the Use this computer’s MAC Address radio button to allow the VPN
firewall to use the MAC address of the computer you are now using to access
the web management interface. This setting is useful if your ISP requires MAC
authentication.
address in the field next to the radio button. You would typically enter the MAC
address that your ISP is requiring for MAC authentication.
Note: The format for the MAC address is 01:23:45:67:89:AB (numbers
0–9 and either uppercase or lowercase letters A–F). If you enter a MAC
address, the existing entry is overwritten.
IPv4 and IPv6 Internet and WAN Settings
74
Page 75

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 13. WAN Advanced Options screen settings (continued)
Setting Description
Failure Detection Method
Note: This is the failure detection method for IPv4 interfaces. For information about failure detection for
IPfv6 interfaces, see Configure the Failure Detection Method for IPv6 Interfaces on page 70.
Failure Detection Method Select a failure detection method from the drop-down list:
• W
AN DNS. DNS queries are sent to the DNS server that is configured in
the Domain Name Server (DNS) Servers section of the W
(see Manually Configure an IPv4 Internet Connection on page 34).
• Custom DNS. DNS queries are sent to a DNS server that you need to
specify in the DNS Server fields.
• Ping. Pings are sent to a server with a public IP address that you need to
specify in the IP
request and should not consider ping traffic to be abusive.
Note: DNS queries or pings are sent through the WAN interface that is being
monitored. The retry interval and number of failover attempts determine how
quickly the VPN firewall switches from the primary link to the backup link if the
primary link fails, or when the primary link comes back up, switches back from
the backup link to the primary link.
Address fields.
The server should not reject the ping
AN ISP screen
DNS Server
IP Address The IP address of the interface that should receive the ping request. The
Retry Interval is The retry interval in seconds. The DNS query or ping is sent after every retry
Failover after The number of failover attempts. The primary WAN interface is considered down
Upload/Download Settings
These settings rate-limit the traffic that is being forwarded by the VPN firewall.
WAN Connection Type From the drop-down list, select the type of connection that the VPN firewall uses
WAN Connection Speed
Upload
WAN Connection Speed
Download
The IP address of the DNS server
interface should not reject the ping request and should not consider ping traffic
to be abusive
interval. The default retry interval is 30 seconds.
after the specified number of queries have failed to elicit a reply. The backup
interface is brought up after this situation has occurred. The failover default is
4 failures.
to connect to the Internet: DSL, ADLS, T1, T3, or Other.
From the drop-down list, select the maximum upload speed that is provided by
your ISP. You can select from 56 Kbps to 1 Gbps, or you can select Custom and
enter the speed in Kbps in the field below the drop-down list.
From the drop-down list, select the maximum download speed that is provided
by your ISP. You can select from 56 Kbps to 1 Gbps, or you can select Custom
and enter the speed in Kbps in the field below the drop-down list.
.
5. Click Apply to save your changes.
IPv4 and IPv6 Internet and WAN Settings
75
Page 76

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
WARNING:
Depending on the changes that you made, when you click Apply,
the VPN firewall might restart, or services such as HTTP and
SMTP might restart.
If you want to configure the advanced settings for an additional WAN interface, select
another W
AN interface and repeat these steps.
Configure WAN QoS Profiles
The VPN firewall can support multiple Quality of Service (QoS) profiles for each WAN
interface. You can assign profiles to services such as HTTP, FTP, and DNS and to LAN
groups or IP addresses. Profiles enforce either rate control with bandwidth allocation or
priority queue control. You can configure both types of profiles, but either all profiles on the
VPN firewall enforce rate control and the profiles that you configured for priority queue control
are inactive, or the other way around. Both types of profiles cannot be active simultaneously.
types
• Rate control with bandwidth allocation. These
is distributed among the services and hosts. A profile with a high priority is of fered excess
bandwidth while the required bandwidth is still allocated to profiles that specify minimum
and maximum bandwidth rates. The congestion priority represents the classification level
of the packets among the priority queues within the system. If you select a default
congestion priority, traffic is mapped based on the Type of Service (ToS) field in the
packet’s IP header.
• Priority queue control.
Y
ou can select a high-priority queue or a low-priority queue. Services in the high-priority
queue share 60 percent of the interface bandwidth; services in the low-priority queue
share 10 percent of the interface bandwidth. By default, all services are assigned the
medium-priority queue in which they share 30 percent of the interface bandwidth.
Both types of profiles let you allocate the Differentiated Services (DiffServ) QoS packet
matching and QoS packet marking settings, which you configure by specifying Dif
Services Code Point (DSCP) values, from 0 to 63.
Note: Before you enable WAN QoS, make sure that the WAN connection
type and speeds are configured correctly in the Upload/Download
Settings section of the WAN Advanced Options screen for the WAN
interface (see Configure Advanced WAN Options and Other Tasks
on page 71).
These types of profiles specify the priority levels of the services.
of profiles specify how bandwidth
ferentiated
IPv4 and IPv6 Internet and WAN Settings
76
Page 77

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Note: To configure and apply QoS profiles successfully, familiarity with
QoS concepts such QoS priority queues, IP precedence, DHCP, and
their values is helpful.
To enable and configure QoS for the WAN interfaces:
1. Select Network Configuration > QoS. The QoS
screen displays. (The following screen
shows some profiles in the List of QoS Profiles table).
Figure 47.
2. To enable QoS, select the Yes radio button. By default, the No radio button is selected.
3. Specify the profile type that should be active by selecting one of the following radio buttons:
• Rate control. All rate control QoS profiles that you configure are active, but priority
QoS profiles are not.
• Priority. All priority QoS profiles that you configure are active, but rate control QoS
profiles are not.
4. Click Apply
to save your settings.
The List of QoS Profiles table shows the following columns, all of which are described in
detail in the following table and Table 15 on page 80.
• QoS Type. The type of profile, either Rate Control or Priority.
• Interface Name
. The W
AN interface to which the profile applies (WAN1, WAN2,
WAN3, or WAN4).
• Service. The service to which the profile applies.
• Direction
. The W
AN direction to which the profile applies (inbound, outbound, or
both).
• Rate. The bandwidth rate in Kbps, or the priority.
IPv4 and IPv6 Internet and WAN Settings
77
Page 78

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• Hosts. The IP address, IP addresses, or group to which the rate control profile
applies. (The information in this column does not apply to priority profiles).
• Action. The Edit table button provides access to the Edit QoS screen for the
corresponding profile.
To add a rate control QoS profile:
1. Select Network Configuration > QoS. The QoS
screen displays.
2. Under the List of QoS Profiles table, click the Add table button. The
displays. The following figure shows settings for a rate control QoS profile:
Add QoS screen
Figure 48.
3. Enter the settings as described in the following table:
Table 14. Add QoS screen settings for a rate control profile
Setting Description
QoS Type Rate Control (for Priority, see Figure 49 on page 80 and T
Interface From the drop-down list, select one of the WAN interfaces.
Service From the drop-down list, select a service or application to be covered by this
profile. If the service or application does not appear in the list, you need to
define it using the Services screen (see Add Customized Services on
page 177).
Direction From the drop-down list, select the direction to which rate control is applied:
• Inbound T
• Outbound Traffic. Rate control is applied to outbound traf
• Both. Rate control is applied to both outbound and inbound traffic.
IPv4 and IPv6 Internet and WAN Settings
raffic. Rate control is applied to inbound traf
able 15 on page 80).
fic only.
fic only.
78
Page 79

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 14. Add QoS screen settings for a rate control profile (continued)
Setting Description
Diffserv QoS Match Enter a DSCP value in the range of 0 through 63. Packets are classified against
this value. Leave this field blank to disable packet matching.
Congestion Priority From the drop-down list, select the priority queue that determines the allocation
of excess bandwidth and the classification level of the packets among other
priority queues on the VPN firewall:
• Default. Traffic is mapped based on the ToS field in the packet’s IP header.
• High. This queue
AF44, and CS4.
• Medium-high. This
AF32, AF33, AF34, and CS3.
• Medium.
AF23, AF24, and CS2.
• Low.
AF14, CS1, 0, and all other values.
Hosts From the drop-down list, select the IP address, range of IP addresses, or group
to which the profile is applied:
• Single IP
address in the Start IP field.
• IP Address
start address of the range in the Start IP field and the end address of the
range in the End IP field, and specify how the bandwidth is allocated by
making a selection from the Bandwidth Allocation drop-down list.
• Group. The profile is applied to a group. Select the group from the Select
Group drop-down list, and specify how the bandwidth is allocated by
making a selection from the Bandwidth
This queue includes the following DSCP values:
This queue includes the following DSCP values: AF11, AF12, AF13,
Address.
includes the following DSCP values: AF41, AF42, AF43,
includes the following DSCP values: AF31,
queue
AF21, AF22,
The profile is applied to a single IP address. Enter the
Range.
The profile is applied to an IP address range. Enter the
Allocation drop-down list.
Outbound Minimum
Bandwidth
Outbound Maximum
Bandwidth
Inbound Minimum
Bandwidth
Start IP The IP address for a single IP address or the start IP
address for an IP address range.
End IP
Select Group
Bandwidth Allocation From the drop-down list, specify how the bandwidth is
Enter the outbound minimum bandwidth in Kbps that is allocated to the host.
Enter the outbound maximum bandwidth in Kbps that is allocated to the host.
Enter the inbound minimum bandwidth in Kbps that is allocated to the host.
The end IP address for an IP address range.
From the drop-down list, select the LAN group to which
the profile is applied. For information about LAN groups,
see Manage IPv4 Groups and Hosts (IPv4 LAN Groups)
on page 96.
allocated:
• Shared.
addresses in a range or all members of a group.
• Individual. The
address in the range or each member of a group.
The bandwidth is shared among all IP
bandwidth
is allocated to each IP
IPv4 and IPv6 Internet and WAN Settings
79
Page 80

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 14. Add QoS screen settings for a rate control profile (continued)
Setting Description
Inbound Maximum
Bandwidth
Diffserv QoS Remark Enter a DSCP value in the range of 0 through 63. Packets are marked with this
Enter the inbound maximum bandwidth in Kbps that is allocated to the host.
value. Leave this field blank to disable packet marking.
4. Click Apply to save your settings. The profile is added to the List of QoS Profiles table on
the QoS screen.
To add a priority queue QoS profile:
1. Select Network Configuration > QoS. The QoS
2. Under the List of QoS Profiles table, click the Add table button. The
screen displays.
Add QoS screen
displays. The following figure shows settings for a priority QoS profile:
Figure 49.
3. Enter the settings as described in the following table:
Table 15. Add QoS screen settings for a priority profile
Setting Description
QoS Type Priority (for Rate Control, see Figure 48 on page 78 and Table 14 on page 78).
Interface From the drop-down list, select one of the WAN interfaces.
IPv4 and IPv6 Internet and WAN Settings
80
Page 81

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 15. Add QoS screen settings for a priority profile (continued)
Setting Description
Service From the drop-down list, select a service or application to be covered by this
profile. If the service or application does not appear in the list, you need to
define it using the Services screen (see Add Customized Services on
page 177).
Direction From the drop-down list, select the direction to which the priority queue is
applied:
• Outbound T
• Inbound Traffic.
Diffserv QoS Match Enter a DSCP value in the range of 0 through 63. Packets are classified against
this value. Leave this field blank to disable packet matching.
Priority From the drop-down list, select the priority queue that determines the allocation
of bandwidth:
• Low. All services that are assigned a low-priority queue share 10 percent
of interface bandwidth.
• High.
of interface bandwidth.
raffic. The
All services that are assigned a high-priority queue share 60 percent
priority queue is applied to outbound traffic only.
The priority queue is applied to inbound traffic only.
Note: By default, all services are assigned the medium-priority queue in which
they share 30 percent of the interface bandwidth.
Hosts
Start IP
End IP
Select Group
Bandwidth Allocation
Outbound Minimum
Bandwidth
Outbound Maximum
Bandwidth
Inbound Minimum
Bandwidth
Inbound Maximum
Bandwidth
Diffserv QoS Remark Enter a DSCP value in the range of 0 through 63. Packets are marked with this
These settings do not apply to a priority profile.
value. Leave this field blank to disable packet marking.
4. Click Apply to save your settings. The profile is added to the List of QoS Profiles table on
the QoS screen.
IPv4 and IPv6 Internet and WAN Settings
81
Page 82

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
To edit a QoS profile:
1. In the List of QoS Profiles table, click the Edit table button to the right of the profile that
you want to edit. The Edit QoS screen displays. This screen shows the same fields as the
Add QoS screen (see the previous two figures).
2. Modify the settings as described in the previous two tables.
3. Click Apply to save your settings.
To delete a QoS profile:
1. In the List of QoS Profiles table, select the check box to the left of the QoS profile that
you want to delete, or click the Select All table button to select all profiles.
2. Click the Delete table button.
Additional WAN-Related Configuration Tasks
If you want the ability to manage the VPN firewall remotely , enable remote management (see
Configure Remote Management Access on page 338). If you enable remote management,
NETGEAR strongly recommends that you change your password (see Change Passwords
and Administrator and Guest Settings on page 336).
As an option, you can also set up the traffic meter for each WAN interface (see Configure and
Enable the WAN Traffic Meter on page 356).
Verify the Connection
Test the VPN firewall before deploying it in a live production environment. Verify that network
traffic can pass through the VPN firewall:
• Ping an Internet URL.
• Ping the IP address of a device on either side of the VPN firewall.
What to Do Next
You have completed setting up the WAN connection for the VPN firewall. The following
chapters and sections describe important tasks that you need to address before you deploy
the VPN firewall in your network:
• Chapter 3, LAN Configuration
• Configure Authentication Domains, Groups, and Users on page 303
• Manage Digital Certificates for VPN Connections on page 320
• Use the IPSec VPN Wizard for Client and Gateway Configurations on page 203
• Chapter 6, Virtual Private Networking Using SSL Connections
IPv4 and IPv6 Internet and WAN Settings
82
Page 83

3. LAN Configuration
This chapter describes how to configure the LAN features of your VPN firewall. The chapter
contains the following sections:
• Manage IPv4 Virtual LANs and DHCP Options
• Configure IPv4 Multihome LAN IP Addresses on the Default VLAN
• Manage IPv4 Groups and Hosts (IPv4 LAN Groups)
• Manage the IPv6 LAN
• Configure IPv6 Multihome LAN IP Addresses on the Default VLAN
• Enable and Configure the DMZ Port for IPv4 and IPv6 Traffic
• Manage Static IPv4 Routing
• Manage Static IPv6 Routing
3
83
Page 84

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Manage IPv4 Virtual LANs and DHCP Options
• Port-Based VLANs
• Assign and Manage VLAN Profiles
• VLAN DHCP Options
• Configure a VLAN Profile
• Configure VLAN MAC Addresses and LAN Advanced Settings
A local area network (LAN) can generally be defined as a broadcast domain. Hubs, bridges,
or switches in the same physical segment or segments connect all end node devices.
Endpoints can communicate with each other without the need for a router
LANs together, routing the traffic to the appropriate port.
A virtual LAN (VLAN) is a local area network with a definition that maps workstations on some
basis other than geographic location (for example, by department, type of user, or primary
application).
if the VLANs were on two separate LANs.
To enable traffic to flow between VLANs, traffic needs to go through a router, as
. Routers connect
A VLAN is a group of computers, servers, and other network resources that behave as if they
were connected to a single network segment—even though they might not be. For example,
all marketing personnel might be spread throughout a building. Y
a single VLAN, they can share resources and bandwidth as if they were connected to the
same segment. The resources of other departments can be invisible to the marketing VLAN
members, accessible to all, or accessible only to specified individuals, depending on how the
IT manager has set up the VLANs.
VLANs have a number of advantages:
• It is easy to set up network segmentation. Users who communicate most frequently with
each other can be grouped into common VLANs, regardless of physical location. Each
s traf
group’
improving the efficiency of the whole network.
• They are easy to manage. The addition of nodes, as well as moves and other changes,
can be dealt with quickly and conveniently from a management interface rather than from
the wiring closet.
• They provide increased performance. VLANs free up bandwidth by limiting node-to-node
and broadcast traffic throughout the network.
• They ensure enhanced network security. VLANs create virtual boundaries that can be
crossed only through a router
to restrict access to each VLAN.
fic is contained largely within the VLAN, reducing extraneous traffic and
. So standard, router-based security measures can be used
et if they are all assigned to
LAN Configuration
84
Page 85

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Port-Based VLANs
The VPN firewall supports port-based VLANs. Port-based VLANs help to confine broadcast
traffic to the LAN ports. Even though a LAN port can be a member of more than one VLAN,
the port can have only one VLAN ID as its port VLAN identifier (PVID). By default, all four
LAN ports of the VPN firewall are assigned to the default VLAN, or VLAN 1. Therefore, by
default, all four LAN ports have the default PVID 1. However, you can assign another PVID to
a LAN port by selecting a VLAN profile from the drop-down list on the LAN Setup screen.
After you have created a VLAN profile and assigned one or more ports to the profile, you
need to enable the profile to activate it.
The VPN firewall’s default VLAN cannot be deleted. All untagged traffic is routed through the
default VLAN (VLAN1), which you need to assign to at least one LAN port.
Note the following about VLANs and PVIDs:
• One physical port is assigned to at least one VLAN.
• One physical port can be assigned to multiple VLANs.
• When one port is assigned to multiple VLANs, the port is used as a trunk port to connect
to another switch or router.
• When a port receives an untagged packet, this packet is forwarded to a VLAN based on
the PVID.
• When a port receives a tagged packet, this packet is forwarded to a VLAN based on the
ID that is extracted from the tagged packet.
When you create a VLAN profile, assign LAN ports to the VLAN, and enable the VLAN, the
LAN ports that are members of the VLAN can send and receive both tagged and untagged
packets. Untagged packets that enter these LAN ports are assigned to the default PVID 1;
packets that leave these LAN ports with the same default PVID 1 are untagged. All other
packets are tagged according to the VLAN ID that you assigned to the VLAN when you
created the VLAN profile.
This is a typical scenario for a configuration with an IP phone that has two Ethernet ports, one
of which is connected to the VPN firewall, the other one to another device:
Packets coming from the IP phone to the VPN firewall LAN port are tagged. Packets passing
through the IP phone from the connected device to the VPN firewall LAN port are untagged.
When you assign the VPN firewall LAN port to a VLAN, packets entering and leaving the port
are tagged with the VLAN ID. However
are forwarded to the default VLAN with PVID 1; packets that leave the LAN port with the
same default PVID 1 are untagged.
Note: The configuration of the DHCP options for the default VLAN is
described in Configure the IPv4 Internet Connection and WAN
Settings on page 29. For information about how to add and edit a
VLAN profile, including its DHCP options, see Configure a VLAN
Profile on page 88.
, untagged packets entering the VPN firewall LAN port
LAN Configuration
85
Page 86

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Assign and Manage VLAN Profiles
To assign VLAN profiles to the LAN ports and manage VLAN profiles:
1. Select Network Configuration > LAN Setting. In the upper right of the screen, the IPv4
radio button is selected by default. The LAN submenu tabs display
screen in view, displaying the IPv4 settings. (The following figure contains some VLAN
profiles as an example.)
, with the LAN Setup
Figure 50.
For each VLAN profile, the following fields display in the VLAN Profiles table:
• Check box. Allows you to select the VLAN profile in the table.
• Status icon. Indicates the status of the VLAN profile:
- Green circle.
-
Gray circle. The VLAN profile is disabled.
• Profile Name
• VLAN ID
. The unique ID (or tag) assigned to the VLAN profile.
The VLAN profile is enabled.
. The unique name assigned to the VLAN profile.
• Subnet IP. The subnet IP address for the VLAN profile.
• DHCP Status
. The DHCP server status for the VLAN profile, which can be either
DHCP Enabled or DHCP Disabled.
• Action
. The Edit table button, which provides access to the Edit VLAN Profile screen.
2. Assign a VLAN profile to a LAN port by selecting a VLAN profile from the drop-down list. The
enabled VLAN profiles are displayed in the drop-down lists.
3. Click Apply to save your settings.
LAN Configuration
86
Page 87

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
VLAN DHCP Options
For each VLAN, you need to specify the Dynamic Host Configuration Protocol (DHCP)
options (see Configure a VLAN Profile on page 88). The configuration of the DHCP options
for the VPN firewall’s default VLAN, or VLAN 1, is described in Configure the IPv4 Internet
Connection and WAN Settings on page 29.
the DHCP options.
DHCP Server
The default VLAN (VLAN 1) has the DHCP server option enabled by default, allowing the
VPN firewall to assign IP, DNS server, WINS server, and default gateway addresses to all
computers connected to the VPN firewall’s LAN. The assigned default gateway address is
the LAN address of the VPN firewall. IP addresses are assigned to the attached computers
from a pool of addresses that you need to specify. Each pool address is tested before it is
assigned to avoid duplicate addresses on the LAN. When you create a VLAN, the DHCP
server option is disabled by default.
For most applications, the default DHCP server and TCP/IP settings of the VPN firewall are
satisfactory
.
This section provides further information about
The VPN firewall delivers the following settings to any LAN device that requests DHCP:
• An IP address from the range that you have defined
• Subnet mask
• Gateway IP address (the VPN firewall’
• Primary DNS server (the VPN firewall’s LAN IP address)
• WINS server (if you entered a WINS server address in the DHCP Setup screen)
• Lease time (the date obtained and the duration of the lease)
s LAN IP address)
DHCP Relay
DHCP relay options allow you to make the VPN firewall a DHCP relay agent for a VLAN. The
DHCP relay agent makes it possible for DHCP broadcast messages to be sent over routers
that do not support forwarding of these types of messages. The DHCP relay agent is
therefore the routing protocol that enables DHCP clients to obtain IP addresses from a DHCP
server on a remote subnet. If you do not configure a DHCP relay agent for a VLAN, its clients
can obtain IP addresses only from a DHCP server that is on the same subnet. To enable
clients to obtain IP addresses from a DHCP server on a remote subnet, you need to
configure the DHCP relay agent on the subnet that contains the remote clients, so that the
DHCP relay agent can relay DHCP broadcast messages to your DHCP server.
DNS Proxy
When the DNS proxy option is enabled for a VLAN, the VPN firewall acts as a proxy for all
DNS requests and communicates with the ISP’s DNS servers (as configured on the WAN
IPv4 ISP Settings screens). All DHCP clients receive the primary and secondary DNS IP
addresses along with the IP address where the DNS proxy is located (that is, the VPN
LAN Configuration
87
Page 88

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
firewall’s LAN IP address). When the DNS proxy option is disabled for a VLAN, all DHCP
clients receive the DNS IP addresses of the ISP but without the DNS proxy IP address.
LDAP Server
A Lightweight Directory Access Protocol (LDAP) server allows a user to query and modify
directory services that run over TCP/IP. For example, clients can query email addresses,
contact information, and other service information using an LDAP server. For each VLAN,
you can specify an LDAP server and a search base that defines the location in the directory
(that is, the directory tree) from which the LDAP search begins.
Configure a VLAN Profile
For each VLAN on the VPN firewall, you can configure its profile, port membership, LAN
TCP/IP settings, DHCP options, DNS server, and inter-VLAN routing capability.
To add a VLAN profile:
1. Select Network Configuration > LAN Settings. In the upper right of the screen, the
IPv4 radio button is selected by default. The LAN submenu tabs display
Setup screen in view, displaying the IPv4 settings. (The following figure contains some
VLAN profiles as an example.)
, with the LAN
Note: For information about how to manage VLANs, see Port-Based
VLANs on page 85. The following information describes how to
configure a VLAN profile.
Figure 51.
2. Click the Add table button under the VLAN Profiles table. The Add VLAN Profile screen
displays:
LAN Configuration
88
Page 89

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 52.
3. Enter the settings as described in the following table:
Table 16. Add VLAN Profile screen settings
Setting Description
VLAN Profile
Profile Name Enter a unique name for the VLAN profile.
VLAN ID Enter a unique ID number for the VLAN profile. No two VLANs can have the same
VLAN ID number
Note: You can enter VLAN IDs from 2 to 4089. VLAN ID 1 is reserved for the
default VLAN; VLAN ID 4094 is reserved for the DMZ interface.
.
LAN Configuration
89
Page 90

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 16. Add VLAN Profile screen settings (continued)
Setting Description
Port Membership
Port 1, Port 2, Port 3,
Port 4 / DMZ
IP Setup
IP Address Enter the IP address of the VPN firewall (the factory default address is
Subnet
DHCP
Mask Enter the IP subnet mask.
Select one, several, or all port check boxes to make the ports members of this
VLAN.
Note: A port that is defined as a member of a VLAN profile can send and receive
data frames that are tagged with the VLAN ID.
192.168.1.1).
Note: Ensure that the LAN port IP address and DMZ port IP address are in
different subnets.
Note: If you change the LAN IP address of the VLAN while being connected
through the browser to the VLAN, you are disconnected. You then need to open
a new connection to the new IP address and log in again. For example, if you
change the default IP address 192.168.1.1 to 10.0.0.1, you now need to enter
https://10.0.0.1 in your browser to reconnect to the web management interface.
The subnet mask specifies the network number portion
of an IP address. Based on the IP address that you assign, the VPN firewall
automatically calculates the subnet mask. Unless you are implementing
subnetting, use 255.255.255.0 as the subnet mask (computed by the VPN
firewall).
Disable DHCP Server If another device on your network is the DHCP server for the VLAN, or if you
intend to manually configure the network settings of all of your computers, select
the Disable DHCP Server radio button to disable the DHCP server. Except for
the default VLAN for which the DHCP server is enabled, this is the default setting.
LAN Configuration
90
Page 91

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 16. Add VLAN Profile screen settings (continued)
Setting Description
Enable DHCP Server Select the Enable DHCP Server radio button to enable the VPN firewall to
function as a Dynamic Host Configuration Protocol (DHCP) server, providing
TCP/IP configuration for all computers connected to the VLAN. (For the default
VLAN, the DHCP server is enabled by default.) Enter the following settings:
Domain Name This setting is optional. Enter the domain name of the VPN
firewall.
Start IP Address Enter the start IP address. This address specifies the first of
the contiguous addresses in the IP address pool. Any new
DHCP client joining the LAN is assigned an IP address
between this address and the end IP address. For the default
VLAN, the default start IP address is 192.168.1.100.
End IP Address Enter the end IP address. This address specifies the last of
the contiguous addresses in the IP address pool. Any new
DHCP client joining the LAN is assigned an IP address
between the start IP address and this IP address. For the
default VLAN, the default end IP address is 192.168.1.254.
The start and end DHCP IP addresses should be in the same
network as the LAN IP address of the VPN firewall (that is, the
IP address in the IP Setup section as described earlier in this
table).
Primary DNS
Server
Secondary DNS
Server
WINS Server This setting is optional. Enter a WINS server IP address to
Lease Time Enter a lease time. This specifies the duration for which IP
DHCP Relay To use the VPN firewall as a DHCP relay agent for a DHCP server somewhere
else in your network, select the DHCP Relay radio button. Enter the following
setting:
Relay Gateway The IP address of the DHCP server for which the VPN firewall
This setting is optional. If an IP address is specified, the VPN
firewall provides this address as the primary DNS server IP
address. If no address is specified, the VPN firewall uses the
VLAN IP address as the primary DNS server IP address.
This setting is optional. If an IP address is specified, the VPN
firewall provides this address as the secondary DNS server IP
address.
specify the Windows NetBIOS server, if one is present in your
network.
addresses are leased to clients.
serves as a relay.
LAN Configuration
91
Page 92

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 16. Add VLAN Profile screen settings (continued)
Setting Description
Enable LDAP
information
DNS Proxy
Enable DNS Proxy This setting is optional. To enable the VPN firewall to provide a LAN IP address
To enable the DHCP server to provide Lightweight Directory Access Protocol
(LDAP) server information, select the Enable LDAP information check box.
Enter the following settings:
LDAP Server The IP address or name of the LDAP server.
Search Base The search objects that specify the location in the directory
tree from which the LDAP search begins. You can specify
multiple search objects, separated by commas. The search
objects include:
• CN (for common name)
• OU (for organizational unit)
• O (for organization)
• C (for country)
• DC (for domain)
For example, to search the Netgear.net domain for all last
names of Johnson, you would enter:
cn=Johnson,dc=Netgear
Port The port number for the LDAP server
(zero).
for DNS address name resolution, select the Enable DNS Proxy check box.
setting is disabled by default.
,dc=net
. The default setting is 0
This
When the DNS proxy option is disabled for a VLAN, all DHCP clients
Note:
receive the DNS IP addresses of the ISP but without the DNS proxy IP address.
Inter VLAN Routing
Enable Inter VLAN
Routing
This setting is optional. To ensure that traffic is routed only to VLANs for which
inter-VLAN routing is enabled, select the Enable Inter VLAN Routing check box.
This setting is disabled by default. When the Enable Inter VLAN Routing check
box is not selected, traffic from this VLAN is not routed to other VLANs, and traffic
from other VLANs is not routed to this VLAN.
4. Click Apply to save your settings.
Note: Once you have completed the LAN setup, all outbound traffic is
allowed and all inbound traffic is discarded except responses to
requests from the LAN side. For information about how to change
these default traffic rules, see Chapter 4, Firewall Protection.
LAN Configuration
92
Page 93

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
To edit a VLAN profile:
1. On the LAN Setup screen for IPv4 (see Figure 51 on page 88), click the Edit button in
the Action column for the VLAN profile that you want to modify. The Edit VLAN Profile
screen displays. This screen is identical to the
on page 89).
2. Modify the settings as described in the previous table.
3. Click Apply to save your settings.
To enable, disable, or delete one or more VLAN profiles:
1. On the LAN Setup screen for IPv4 (see Figure 51 on page 88), select the check box to
the left of each VLAN profile that you want to enable, disable, or delete, or click the
Select All table button to select all profiles. (You cannot select the default VLAN profile.)
2. Click one of the following table buttons:
• Enable
a green circle, indicating that the selected VLAN or VLANs are enabled. (By default,
when a VLAN is added to the table, it is automatically enabled.)
• Disable
to a gray circle, indicating that the selected VLAN or VLANs are disabled.
• Delete.
. Enables the VLAN or VLANs. The ! status icon changes from a gray circle to
. Disables the VLAN or VLANs. The ! status icon changes from a green circle
Deletes the VLAN or VLANs.
Add VLAN Profile screen (see Figure 52
Configure VLAN MAC Addresses and LAN Advanced Settings
By default, all configured VLAN profiles share the same single MAC address as the LAN
ports. (All LAN ports share the same MAC address.) However, you can change the VLAN
MAC settings to allow up to 16 VLANs to each be assigned a unique MAC address.
You can also enable or disable the broadcast of Address Resolution Protocol (ARP) packets
for the default VLAN. If the broadcast of ARP packets is enabled, IP addresses can be
mapped to physical addresses (that is, MAC addresses).
To configure a VLAN to have a unique MAC address:
1. Select Network Configuration > LAN Settings. In the upper right of the screen, the
IPv4 radio button is selected by default. The LAN submenu tabs display
Setup screen in view, displaying the IPv4 settings (see Figure 51 on page 88).
2. Click the Advanced option arrow in the upper middle of the LAN Setup screen. The IPv4
LAN Advanced
screen displays:
, with the LAN
LAN Configuration
93
Page 94

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 53.
3. From the MAC Address for VLANs drop-down list, select Unique. (The default is Same.)
4. As an option, you can disable the broadcast of ARP packets for the default VLAN by
clearing the Enable ARP
by default for the default VLAN.)
5. Click Apply to save your settings.
Broadcast check box. (The broadcast of ARP packets is enabled
Note: If you attempt to configure more than 16 VLANs while the MAC
address for VLANs is set to Unique on the IPv4 LAN Advanced
screen, the MAC addresses that are assigned to each VLAN might
no longer be distinct.
Note: For information about how to configure and enable the LAN traffic
meter, see Configure and Enable the LAN Traffic Meter on
page 359.
Configure IPv4 Multihome LAN IP Addresses on the Default VLAN
If you have computers using different IPv4 networks in the LAN (for example, 172.124.10.0 or
192.168.200.0), you can add aliases to the LAN ports and give computers on those networks
access to the Internet, but you can do so only for the default VLAN. The IP address that is
assigned as a secondary IP address needs to be unique and cannot be assigned to a VLAN.
Make sure that any secondary LAN addresses are different from the primary LAN, WAN, and
DMZ IP addresses and subnet addresses that are already configured on the VPN firewall.
LAN Configuration
94
Page 95

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The following is an example of correctly configured IPv4 addresses:
• WAN IP address. 10.0.0.1 with subnet 255.0.0.0
• DMZ IP address. 176.16.2.1 with subnet 255.255.255.0
• Primary LAN IP address. 192.168.1.1 with subnet 255.255.255.0
• Secondary LAN IP address. 192.168.20.1 with subnet 255.255.255.0
To add a secondary LAN IPv4 address:
1. Select Network Configuration > LAN Settings > LAN Multi-homing. In the upper
right of the screen, the IPv4 radio button is selected by default. The LAN Multi-homing
screen displays the IPv4 settings. (The following figure contains one example.)
Figure 54.
The A vailable Secondary LAN IPs table displays the secondary LAN IP addresses added
to the VPN firewall.
2. In the Add Secondary LAN IP Address section of the screen, enter the following settings:
• IP Address. Enter the secondary address that you want to assign to the LAN ports.
• Subnet Mask. Enter the subnet mask for the secondary IP address.
3. Click the Add table button in the rightmost column to add the secondary IP address to the
Available Secondary LAN IPs table.
Repeat Step 2
and Step 3 for each secondary IP address that you want to add to the
Available Secondary LAN IPs table.
Note: Secondary IP addresses cannot be configured in the DHCP server.
The hosts on the secondary subnets need to be manually configured
with the IP addresses, gateway IP address, and DNS server IP
addresses.
To edit a secondary LAN IP address:
1. On the LAN Multi-homing screen for IPv4 (see the previous figure), click the Edit button
in the Action column for the secondary IP address that you want to modify
. The Edit
LAN Multi-homing screen displays.
LAN Configuration
95
Page 96

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
2. Modify the IP address or subnet mask, or both.
3. Click Apply to save your settings.
To delete one or more secondary LAN IP addresses:
1. On the LAN Multi-homing screen for IPv4 (see the previous figure), select the check box
to the left of each secondary IP address that you want to delete, or click the Select All
table button to select secondary IP addresses.
2. Click the Delete table button.
Manage IPv4 Groups and Hosts (IPv4 LAN Groups)
• Manage the Network Database
• Change Group Names in the Network Database
• Set Up DHCP Address Reservation
The Known PCs and Devices table on the LAN Groups (IPv4) screen (see Figure 55 on
page 97) contains a list of all known computers and network devices that are assigned
dynamic IP addresses by the VPN firewall, have been discovered by other means, or were
entered manually
. Collectively
, these entries make up the network database.
The network database is updated by these methods:
• DHCP client requests. When the DHCP server is enabled, it accepts and responds to
DHCP client requests from computers and other network devices. These requests also
generate an entry in the network database.
server feature.
• Scanning the network.
(ARP) requests. The ARP scan detects active devices that are not DHCP clients.
Note: In large networks, scanning the network might generate unwanted
traffic.
Note: When the VPN firewall receives a reply to an ARP request, it might
not be able to determine the device name if the software firewall of
the device blocks the name.
• Manual entry. Y
These are some advantages of the network database:
ou can manually enter information about a network device.
The local network is scanned using
This is an advantage of enabling the DHCP
Address Resolution Protocol
• Generally, you do not need to enter an IP address or a MAC address. Instead, you can
select the name of the desired computer or device.
LAN Configuration
96
Page 97

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
• There is no need to reserve an IP address for a computer in the DHCP server. All IP
address assignments made by the DHCP server are maintained until the computer or
device is removed from the network database, either by expiration (inactive for a long
time) or by you.
• There is no need to use a fixed IP address on a computer
. Because the IP address
allocated by the DHCP server never changes, you do not need to assign a fixed IP
address to a computer to ensure that it always has the same IP address.
• A computer is identified by its MAC address—not its IP address. The network database
uses the MAC address to identify each computer or device. Therefore, changing a
computer’s IP address does not affect any restrictions applied to that computer.
• Control over computers can be assigned to groups and individuals:
- You can assign computers to groups (see Manage the Network Database on this
page) and apply restrictions (outbound rules and inbound rules) to each group (see
Overview of Rules to Block or
Allow Specific Kinds of Traffic on page 136).
- You can select groups that are allowed access to URLs that you have blocked for
other groups, or the other way around, block access to URLs that you have allowed
access to for groups (see
Configure Content Filtering on page 186).
- If necessary, you can also create firewall rules to apply to a single computer (see
Enable Source MAC Filtering
on page 190). Because the MAC address is used to
identify each computer, users cannot avoid these restrictions by changing their IP
address.
Manage the Network Database
You can view the network database, manually add or remove database entries, and edit
database entries.
To view the network database, select Network Configuration > LAN Settings > LAN
Groups. The LAN Groups screen displays. (The following figure shows some manually
added devices in the Known PCs and Devices table as an example.)
Figure 55.
LAN Configuration
97
Page 98

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
The Known PCs and Devices table lists the entries in the network database. For each
computer or device, the following fields display:
• Check box. Allows you to select the computer or device in the table.
• Name. The name of the computer or device. For computers that do not support the
NetBIOS protocol, the name is displayed as Unknown (you can edit the entry manually to
add a meaningful name). If the computer or device was assigned an IP address by the
DHCP server, the name is appended by an asterisk.
• IP Address.
The current IP address of the computer or device. For DHCP clients of the
VPN firewall, this IP address does not change. If a computer or device is assigned a static
IP address, you need to update this entry manually after the IP address on the computer
or device has changed.
• MAC Address
The MAC address of the computer or device’
.
s network interface.
• Group. Each computer or device can be assigned to a single LAN group. By default, a
computer or device is assigned to Group 1. Y
ou can select a different LAN group from the
Group drop-down list in the Add Known PCs and Devices section or on the Edit Groups
and Hosts screen.
• Profile Name. Each computer or device can be assigned to a single VLAN. By default, a
ou can select a different
computer or device is assigned to the default VLAN (VLAN 1).
Y
VLAN profile name from the Profile Name drop-down list in the Add Known PCs and
Devices section or on the Edit Groups and Hosts screen.
• Action.
The Edit table button, which provides access to the Edit Groups and Hosts
screen.
Add Computers or Devices to the Network Database
To add computers or devices manually to the network database:
1. In the Add Known PCs and Devices section of the LAN Groups screen (see the previous
figure), enter the settings as described in the following table:
Table 17. Add Known PCs and Devices section settings
Setting Description
Name Enter the name of the computer or device.
IP Address T
ype From the drop-down list, select how the computer or device receives its IP address:
• Fixed (set on PC). The IP address is statically assigned on the computer or
device.
• Reserved (DHCP Client).
assigns the specified IP address to this client during the DHCP negotiation
(see also Set Up DHCP
The DHCP server of the VPN firewall always
Address Reservation on page 101).
Note: For both types of IP addresses, the VPN firewall reserves the IP address for
the associated MAC address.
LAN Configuration
98
Page 99

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Table 17. Add Known PCs and Devices section settings (continued)
Setting Description
IP Address Enter the IP address that this computer or device is assigned to:
• If the IP address type is Fixed (set on PC), the IP address needs to be outside
of the address range that is allocated to the DHCP server pool to prevent the
IP address from also being allocated by the DHCP server.
•
If the IP address type is Reserved (DHCP Client), the IP address can be inside
or outside the address range that is allocated to the DHCP server pool.
Note: Make sure that the IP address is in the IP subnet for the VLAN profile that
you select from the Profile Name drop-down list.
MAC Address Enter the MAC address of the computer’s or device’s network interface. The MAC
address format is six colon-separated pairs of hexadecimal characters (0–9 and
a–f), such as 01:23:d2:6f:89:ab.
Group From the drop-down list, select the group to which the computer or device is
assigned. (Group 1 is the default group.)
Profile Name From the drop-down list, select the name of the VLAN profile to which the computer
or device is assigned.
2. Click the Add table button to add the computer or device to the Known PCs and Devices
table.
3. As an optional step: T
o save the binding between the IP address and MAC address for the
entry that you just added to the Known PCs and Devices table, select the check box for the
table entry, and click the Save Binding button.
Note: The saved binding is also displayed on the IP/MAC Binding screen
(see Figure 116 on page 193).
Edit Computers or Devices in the Network Database
To edit computers or devices manually in the network database:
1. In the Known PCs and Devices table of the LAN Groups screen (see Figure 55 on
page 97), click the Edit table button of a table entry.
displays (see the following figure, which contains an example).
The Edit LAN Groups screen
LAN Configuration
99
Page 100

ProSAFE Gigabit Quad WAN SSL VPN Firewall SRX5308
Figure 56.
2. Modify the settings as described in Table 17 on page 98.
3. Click Apply to save your settings in the Known PCs and Devices table.
Deleting Computers or Devices from the Network Database
To delete one or more computers or devices from the network database:
1. On the LAN Groups screen (see Figure 55 on page 97), select the check box to the left
of each computer or device that you want to delete, or click the Select All table button
to select all computers and devices.
2. Click the Delete table button.
Note: If you delete a saved binding between an IP and MAC address on
the LAN Groups screen, make sure that you also delete the binding
on the IP/MAC Binding screen (see Figure 116 on page 193).
Change Group Names in the Network Database
By default, the groups are named Group1 through Group8. You can change these group
names to be more descriptive, such as GlobalMarketing and GlobalSales.
To edit the name of one of the eight available groups:
1. Select Network Configuration > LAN Settings > LAN Groups. The LAN Groups
screen displays (see Figure 55 on page 97, which shows some examples in the Known
PCs and Devices table).
2. Click the Edit Group Names option arrow to the right of the LAN submenu tabs. The
Network Database Group Names screen displays. (The following figure shows some
examples.)
LAN Configuration
100
 Loading...
Loading...