NEC Express5800-R120f-2M, Express5800-R120e-2M, Express5800-R120e-1M, Express5800-R120d-2M, Express5800-R120d-1M User Guide
...Page 1

EXPRESSSCOPE Engine 3
User’s Guide
4
4
1. Overview
2. Configuring the Host System
3. Configuring a Management PC
4. Networking
5. Using Remote Management
6. Command Line Interface
7. WS-Management (Web Service for Management)
8. Troubleshooting
NEC Express Server
Express5800 Series
1-1th Edition Sep, 201
© NEC Corporation 2011-201
Page 2

TRADEMARKS AND PATENTS
EXPRESSSCOPE is registered trademarks of NEC Corporation.
EXPRESSBUILDER and ESMPRO are registered trademarks of NEC Corporation.
Microsoft, Windows and Windows Vista, Windows Media Player are registered trademarks of
Microsoft Corporation in the United States and other countries.
Firefox is registered trad emarks of the Mozilla Foundation.
Java is registered trademarks of Oracle and/or its affiliates .
NOTES
(1) No part of this manual may be reproduced in any form without the prior written permission of
NEC Corporation.
(2) The contents of this User’s Guide may be revised without prior notice.
(3) The contents of this User's Guide shall not be copied or altered without the prior written
permission of NEC Corporation.
(4) All efforts have been made to ensure the accuracy of all information in this User's Guide. If you
notice any part unclear, incorrect, or omitted in this User's Guide, contact the sales agent where
you purchased this product.
(5) NEC assumes no liability arising from the use of this product, nor any liability for incidental or
consequential damages arising from the use of this User's Guide regardless of Item (4).
ABOUT THIS USER' S GUIDE
This User's Guide provides the instructions for properly using the EXPRESSSCOPE Engine 3. Please
keep this document at hand for a quick reference and use it when you encounter any questions or
troubles while using the EXPRESSSCOPE Engine 3 for remote control, monitoring, and management
of the host system.
Page 3

Tabl e of Cont e nts
Trademarks and Patents .............................................................................................................................. 2
Notes ........................................................................................................................................................... 2
About This User' s Guide ............................................................................................................................. 2
Symbols ....................................................................................................................................................... 5
Preface ........................................................................................................................................................ 6
1. Overview ..................................................................................................................................... 7
2. Configuring the Host System ................................................................................................... 8
Default Network Settings ............................................................................................................................. 8
Management LAN Settings .......................................................................................................................... 9
3. Configuring a Management PC .............................................................................................. 12
Setting your browser .................................................................................................................................. 12
Supported browsers ................................................................................................................................... 12
J2SE Runtime Environment ....................................................................................................................... 13
4. Networking ............................................................................................................................... 14
TCP/IP Ports .............................................................................................................................................. 14
5. Using Remote Management ................................................................................................... 15
Overview .................................................................................................................................................... 15
Connecting to the web server .................................................................................................................... 15
Login and logout ........................................................................................................................................ 17
HEADER MENU ........................................................................................................................................ 18
SERVER PANEL ........................................................................................................................................ 20
SYSTEM .................................................................................................................................................... 21
REMOTE ACCESS .................................................................................................................................... 23
Remote KVM/media ................................................................................................................................... 24
CONFIGURATION ..................................................................................................................................... 27
UPDATE..................................................................................................................................................... 34
6. Command Line Interface ......................................................................................................... 35
Overview .................................................................................................................................................... 35
Connecting to BMC .................................................................................................................................... 35
Login and logout ........................................................................................................................................ 36
Login ..................................................................................................................................................... 36
Logout ................................................................................................................................................... 36
Basic Commands ....................................................................................................................................... 37
Remote Control .......................................................................................................................................... 41
Power ON ............................................................................................................................................. 41
Forced Power OFF ............................................................................................................................... 41
OS Shutdown ........................................................................................................................................ 41
System Reset ....................................................................................................................................... 41
Remote Console ................................................................................................................................... 42
UID Switch Control ............................................................................................................................... 44
System Event Log ...................................................................................................................................... 46
Viewing system event log ..................................................................................................................... 46
Setting of system event log ................................................................................................................... 47
Access Log ................................................................................................................................................ 48
Viewing access log ............................................................................................................................... 48
Clearing access log .............................................................................................................................. 50
Setting access log ................................................................................................................................. 50
User Settings ............................................................................................................................................. 52
Network Settings ........................................................................................................................................ 53
Power Consumption Control ...................................................................................................................... 59
Confirming System Information .................................................................................................................. 62
Page 4

Special Extended Commands .................................................................................................................... 66
Stat e Acquisition ................................................................................................................................... 66
Power State acquisition .................................................................................................................... 66
Lamp State acq uis iti on ..................................................................................................................... 66
Interrupt Generation for OS Dump ........................................................................................................ 68
7. WS-Management (Web Service fo r Management) ................................................................ 69
Overview .................................................................................................................................................... 69
Power Control ............................................................................................................................................ 69
Power ON ............................................................................................................................................. 70
Forced Power OFF ............................................................................................................................... 70
OS Shutdown ........................................................................................................................................ 72
System Reset ....................................................................................................................................... 73
Interrupt Generation for OS Dump ........................................................................................................ 74
Sensor Information ..................................................................................................................................... 76
Enumeration of All Sensors .................................................................................................................. 76
Retrieving Specified Sensor .................................................................................................................. 76
8. Troubleshooting ...................................................................................................................... 78
Error messages .......................................................................................................................................... 78
About ECO Setting ..................................................................................................................................... 78
About Network information ......................................................................................................................... 78
Others Tips ................................................................................................................................................. 78
License Notes ................................................................................................................................ 80
GNU General Public License ................................................................................................................ 80
GNU Lesser General Public Licsense .................................................................................................. 86
OpenSSL Toolkit ................................................................................................................................... 94
MIT License .......................................................................................................................................... 97
BSD License ......................................................................................................................................... 98
SHA2 ................................................................................................................................................ 98
HMAC-SHA2 .................................................................................................................................... 98
lighttpd .............................................................................................................................................. 99
NET-SNMP ..................................................................................................................................... 100
TCP Wrapper ................................................................................................................................. 106
Other open source software programs ............................................................................................... 106
OpenSSH ....................................................................................................................................... 106
OpenSLP ........................................................................................................................................ 111
OpenLDAP ..................................................................................................................................... 111
sblim-sfcb ....................................................................................................................................... 112
SQLite ............................................................................................................................................ 113
MD2 ................................................................................................................................................ 113
MD5 ................................................................................................................................................ 114
ExploerCanvas ............................................................................................................................... 114
js-tables .......................................................................................................................................... 114
IPA Font License Agreement v1.0 .................................................................................................. 118
Oracle Code sample License Note ................................................................................................. 120
Page 5
Notice
Items to be observed or points to be noted when using this product.
Items to be checked when using this product or software.
Information useful or convenient for you.
Example of troubles occurred.
SYMBOLS
The following symbols are used throughout this manual.
- 5 -
Page 6

PREFACE
The EXPRESSSCOPE Engine 3 enables you to monitor the operating status of the host
system (power supplies, fans, temperature and so forth), to operate the host system’s
keyboard, video, and mouse (KVM) from a remote console* and to access to
CD-ROM/Floppy disk drives on a remote site*. The EXPRESSSCOPE Engine 3 is enabled
by a system management LSI called “BMC (Baseboard Management Controller)” and thus
referred to as the “BMC” hereinafter in this User’s Guide.
*The Remote KVM and Remote Media functions are optional.
- 6 -
Page 7

1. Overview
The host system comes standard with the BMC (system management LSI) and a
management LAN port dedicated to the BMC. By connecting the management LAN port to
your network, you can monitor and control the host system from a remote site via a Web
browser and SSH client.
With the optional N8115-04 Remote KVM and Media License, you can operate the host
system’s KVM (keyboard, video, and mouse) from a remote console and access
CD-ROM/DVD-ROM/floppy disk drives and USB memory in a remote site(Remote
KVM/media).
- 7-
Page 8
For security reasons, change the above default settings (IP address, User
Refer to “Chapter 5: Using Remote Management” for details.
2. Configuring the Host System
This chapter describes the settings necessary to configure the BMC in the host system.
DEFAULT NETWORK SETTINGS
The B MC’s default network settings are as follows:
IP Address: 192.168.1.1
User Name: Administrator
Password: Administrator
• Connect the management LAN port to the private network on which the default IP
address “192.168.1.1”is reachable. If the default IP address is not reachable on the
network, assign a new IP address to the management LAN by using the Server
Configuration Utility of the Off-line Tool in the host system. Refer to “Management LAN
Settings” in the next page for the settings.
Name, and Password) to the ones appropriate in your network environment.
• The remot e management function is enabled by default. (In some systems, the remote
management function is disabled by default.) So, If the remote management function is
not used, disable this settings by using the Server Configuration Utilit y of the Off-line
Tool. Refer to "Management LAN Settings" in the next page for the settings.
- 8-
Page 9
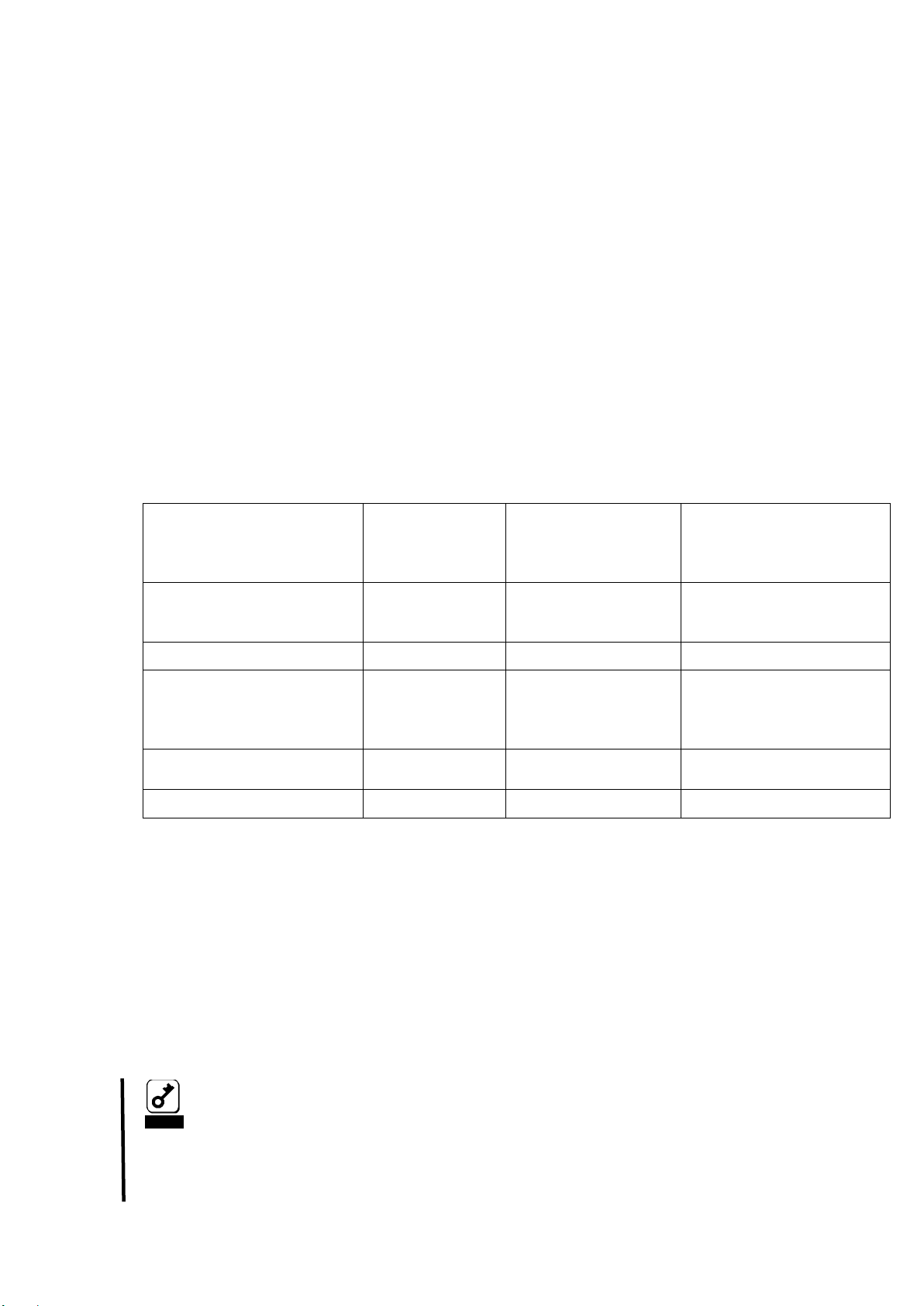
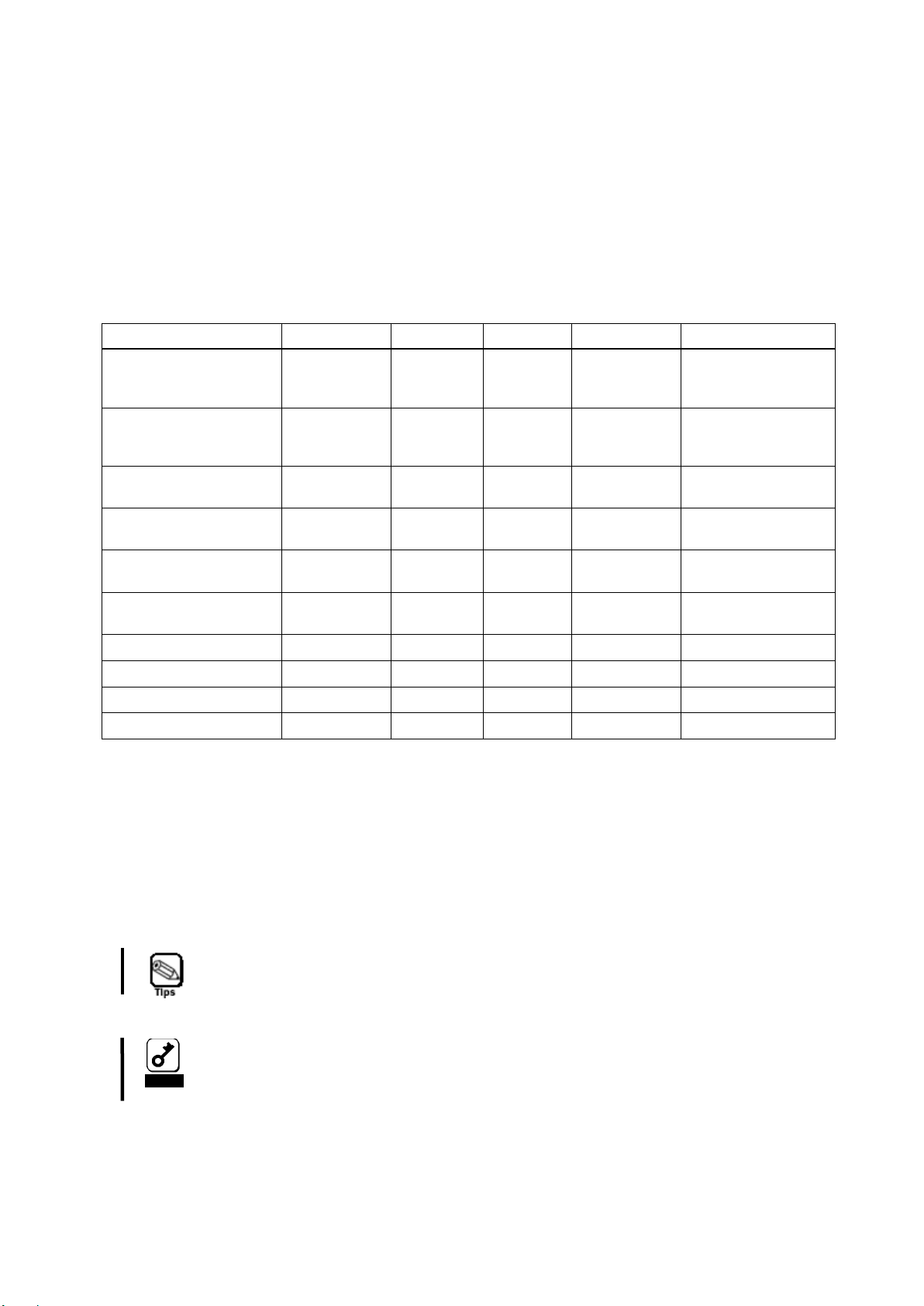
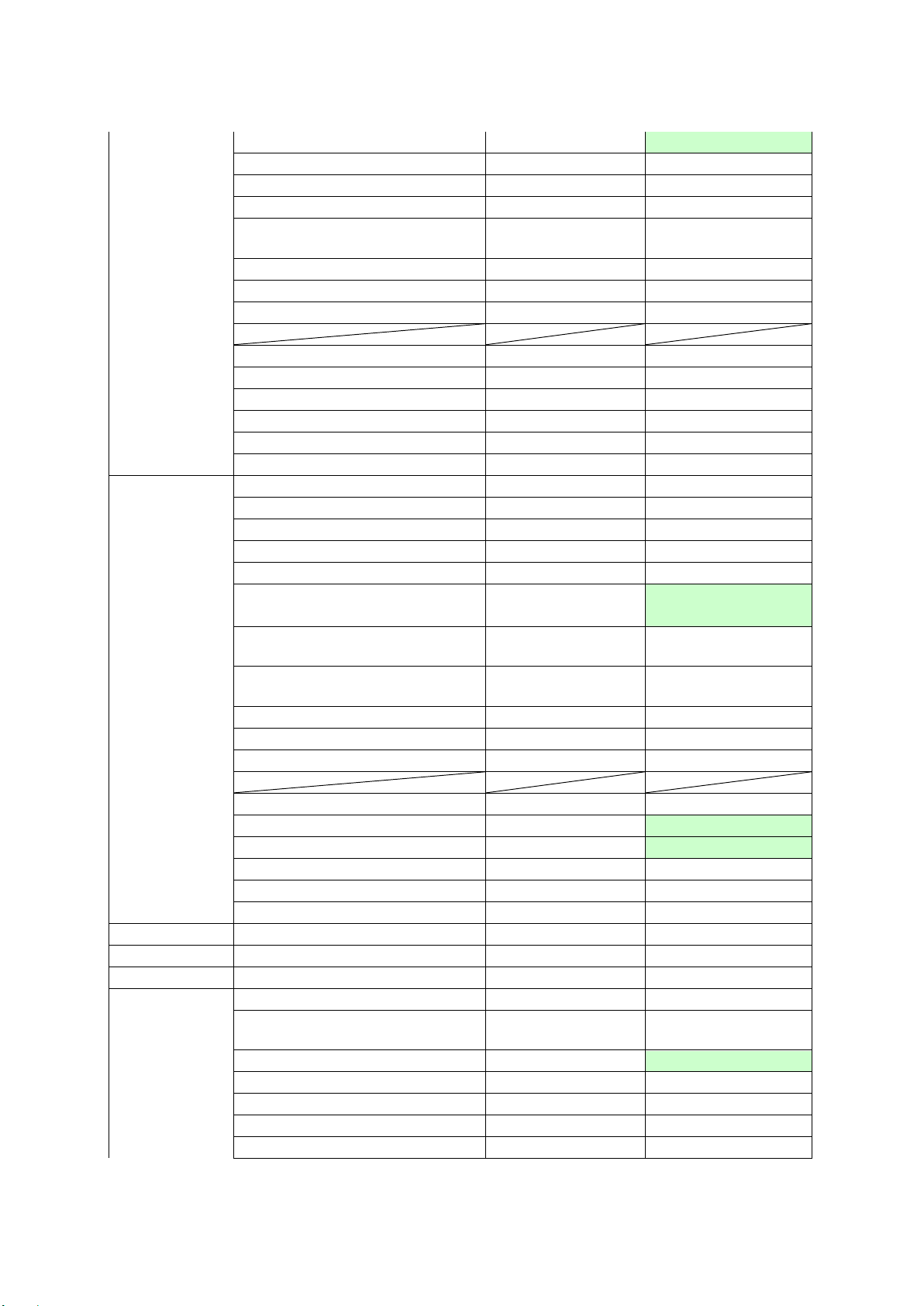
Setting item
Web Brows er
Off-line
On-line
(Windows/Linux)
BMC LAN Setting
Management LAN Port
NG
OK
NG
Connection Type
OK
OK
OK
IP Address
DHCP
OK
OK
OK
Service Settings
HTTP/HTTPS/SSH
OK
OK
OK
BMC Initialization
NG
OK
OK
Notice
If you set [Enabled] the ‘Shared BMC LAN’, the system LAN port that
please select [Disabled] to disable ‘Shared BMC LAN’ .
MANAGEMENT LAN SETTINGS
You can configure basic setting of management LAN set tings of BMC for remote
management using Web server function and command line interface of BMC by using some
tools
• Web Brows er
Please refer to Chapter 5 for details.
• Server Configuration Utility (Off-line)
Press the F4 key during POST(Power on Self test) or displaying logo immediately
after p ower on or reset the host system to enter the Server Configuration Utility.
• Server Configuration Utility (On-line Windows/Linux).
It is possible to install it from NEC EXPRESSBUILDER of the host system
attachment.
The item that can be set with each tool is different. Please refer to help of each tool for
details of a set item.
Shared LAN Port or
Subnet Mask
Default Gateway
Management LAN / Shared BMC LAN
The function for BMC to use operation LAN of the host system is called Shared
BMC LAN.
Select [Enabled] to share a system LAN port with BMC LAN. If you use a
management LAN port for the BMC, select [Disabled]. The management LAN port is
not available when this setting is set [Enabled]. (Default setting is [Enabled]. In
some systems, this menu is not supported. Please refer to the User's Guide of your
host system for more details.)
Server Configuration
Utility
Server Configuration
Utility
is shared and BMC are not able to communicate directly. To the
system LAN port that is shared be able to communicate with BMC,
- 9-
Page 10
Notice
Select [Auto Negotiation] if the link speed and duplex mode
the management LAN.
Connection Type
Select appropriate setting for link speed and duplex mode which you need.
Following settings are available. (Default setting is [Auto Negotiation].)
- Auto Negotiation
- 100Mbps Full Duplex
- 100Mbps Half Duplex
- 10Mbps Full Duplex
- 10Mbps Half Duplex
(Connection Type) of the switch (such as HUB) connected to the
Management LAN is [Auto Negotiation]. If you would like to use the
other setting (not “Auto Negotiation”), at first, select the other setting
of the switch (such as HUB) connected to the management LAN, and
then select the same setting as the switch to the Connection Type of
IP Address
If DHCP is not used to automatically obtain an IP address, enter the BMC’s IP
address.
If DHCP has been used, an automatically obtained IP address will appear.
(Default setting is 192.168.1.1.)
Subnet Mask
If DHCP is not used to automatically obtain a subnet mask IP address, enter the
subnet mask of your management LAN.
If DHCP has been used, an automatically obtained subnet mask IP address will
appear. (Default setting is 255.255.255.0.)
Default Gateway
If DHCP is not used to automatically obtain a default gateway IP address, enter the
default gateway of your management LAN.
If DHCP has been used, an automatically obtained default gateway will appear.
(Default setting is 0.0.0.0.)
DHCP
If you want to obtain an IP address, choose [Enabled].
If you want to manually configure an IP address, choose [Disabled].
(Default setting is [Disabled](*).)
Web Inte r face:
HTTP Interface
Select [Enabled] to use the Web Server function using the HTTP. If not, select
[Disabled]. (Default setting is [Enabled](*). )
HTTP Port Number
Specify the HTTP port number. (Default setting is 80.)
HTTPS Interface
Select [Enabled] to use the Web Server function using the HTTPS(SSL). If not,
select [Disabled]. (Default setting is [Enabled](*).)
HTTPS Port Number
Specify the HTTPS(SSL)port number. (Default setting is 443.)
- 10-
Page 11
Notice
These BMC Management LAN-related settings of BMC are not
the BMC reset button,
The BMC Initialization also deletes the settings for NEC ESMPRO
you change the BMC settings.
Command Line Interface:
SSH
Select [Enabled] to use the Command Line Interface using SSH. If not, select
[Disabled]. (Default setting is [Enabled](*).)
SSH Port Number
Specify the BMC’s SSH port number. (Default setting is 22.)
BMC Initialization
The BMC Configuration will be cleared. Please use this function when you forgot
your user name and password, etc. for remote management via a Web browser and
command line interface. This function will be executed when you select "YES" on
confirmation menu which appears after pressing the “Enter” key. This menu invokes
the BMC configuration clear operation after selecting the "YES".
•
changed to default settings by executing the "Load Setup Default"
of BIOS Setup Utility. (Execute the "BMC Initialization" to set
default settings to the BMC Management LAN settings.)
• When "BMC Initialization" is executed, BMC is reset. It will take
about two minutes by the time initialization is completed after it
executes it. During the initialization , D o not shutdown the system,
reboot the system, or perform any switch operation after pressing
Manager(a software application bundled for remote management). Be
sure to perform a backup for the NEC ESMPRO Manager settings before
* In some systems, the default settings are different for DCHP, HTTP, HTTPS, and/or SSH.
- 11-
Page 12

3. Configuring a Management PC
This chapter describes the settings necessary for the remote management PC that will be
connected to the host system.
SETTING YOUR BROWSER
Configure the following settings:
- Enable SSL.
- Allow Java Script execution.
- Allow Java execution.
- Accept Cookies.
- Allow Popup.
- Enable Stylesheet.
- Enable HTTP1.1.
* If you use Microsoft Internet Explorer, the following configurations are required.
- Add BMC’s address to Trusted Sites.
- Set Trusted Site's security level to Medium.
- If Enhanced Security is enabled, adding [about:blank] to Trusted Sites is required.
- If the “Do Not Save Encrypted Pages To Disk” of [Internet Options]-[Advanced]-[Security]
Is check on, un-check this item is required.
- If the “Play animations in web pages” of [Internet Options]-[Advanced]-[Multimedia] is
check off, check this item is required.
* If you use Mozilla Firefox (Supported only on Linux OS), below configuration is required.
- Enter URL "about:config" and change the value of
"network.http.max-persistent-connections-per-server" to 4 .
SUPPORTED BROWSERS
The following browsers are supported by Windows Vista (SP2), Windows 7, Windows 8,
Windows 8.1, Windows Server 2008, Windows Server 2008 R2 (SP1), Windows Server 2012
and Windows Server 2012 R2:
- Microsoft Internet Explorer 8.0
- Microsoft Internet Explorer 9.0
- Microsoft Internet Explorer 10.0
- Microsoft Internet Explorer 11.0
The following browser is supported by Red Hat Enterprise Linux WS (version 6.5 or more)
and Red Hat Enterprise Linux Client (version 6.5 or more):
- Firefox ESR 17 or ESR 24
It’s recommended that a brow ser be applied the latest service pack and the security patch.
- 12-
Page 13
Notice
If you open multiple BMC Web using Tab browser, you may not use
Notice
If you use Java7, you may see the dialog of ‘Running this application
Notice
If you use Java7, you may see the dialog of ‘Block potentially unsafe
panel.
Notice
If you use Java7, it may take some time to start for certificate
again from the browser.
J2SE RUNTIME ENVIRONMENT
The management PC requires Java2 Runtime Environment (JRE), Standard Edition 7.0.
JRE is available free of charge from Oracle Corporation. For security reasons, you are
recommended to use the latest JRE update. In addition, it is recommended to use the 32 bit
JRE on the 64 bit Browser.
It is necessary to set the following in the Java control panel.
- Add BMC’s IP address (both HTTP/HTTPS) to [Exception Site List]-[Security].
- If the [Enable the next-generation Java Plug-in (requires browser restart)]-[Java
Plug-in]-[Advanced] is not checked, please check. This item is req u ir e d.
Remote KVM/Media successfully. I n this case, please use another
browser instead of browser’s tab.
may be a security risk’. In this case, you need to check ‘I accept the
risk and want to run this application’ and press Run button.
components from being run?’. In this case, you need to press ‘Don’t
Block’ button or please choose the ‘Enable-hide warning and run with
protections’ from the Mixed code of Advanced menu of Java control
revocation checking of the signed Java Applet/Application. In this
case, once you need to close the browser and choose the ‘Do not
check (not recommended)’ from the [Perform certificate revocation
checks on] of Advanced menu of Java control panel and then login
- 13-
Page 14
Module name
Port #
Protocol
Direction
Module name
Port #
5123(FD) (*2)
5127(FD) (*2)
(Non-Encryption)
(Encryption)
(Non-Encryption)
(Encryption)
SSH client
Dynamic(*1)
TCP
BMC
22(*3)
SMTP server
25(*4)
TCP
BMC
Dynamic
LDAP server
389(*5)
TCP
BMC
Dynamic
SNMP server
162
UDP
BMC
Dynamic
BMC doesn't support connection via HTTP proxy server.
Notice
It is recommended to use the network in more than 100BASE-TX
4. Networking
TCP/IP PORTS
The BMC uses the TCP/IP ports listed below. If you use the BMC in a firewall environment,
you need to allocate the port numbers (shown in the right column) to the individual non-block
ports.
Remote Media
(Non-Encryption)
Remote Media
(Encryption)
Web browser
Web browser
Remote KVM Console
Remote KVM Console
Dynamic(*1) TCP
Dynamic(*1) TCP
Dynamic(*1) TCP
Dynamic(*1) TCP
Dynamic(*1) TCP
Dynamic(*1) TCP
BMC 5120(CD/DVD)
5122(USB MEM)
BMC 5124(CD/DVD)
5126(USB MEM)
BMC 80(*3)
BMC 443(*3)
BMC 7578(*2)
BMC 7582(*2)
*1 The Dynamic ports are dynamically allocated ports and usually ranged from 1024 to
65535.
*2 Go to [Configuration]-[System Operation] to change the port number.
*3 Go to [Configuration]-[Network]-[Service] to change the port number.
*4 Go to [Configuration]-[Alert:]-[Mail Alert] to change the port number.
*5 Go to [Configuration]-[User Management]-[LDAP] to change the port number.
(10Mbps bandwidth or more) for remote management feature.
- 14-
Page 15
The “BMC_HostPort” URL includes the BMC’s IP address or host name
(default), you may omit the port number.
For security reasons, you are recommended to use HTTPS (SSL)
When you connect via SSL, security warning messages may appear.
5. Using Remote Management
OVERVIEW
The B MC Web Server function allows you to control the host system’s power and KVM from
a remote console via a Web browser.
Part of the above function is implemented by Java Applet.
CONNECTING TO THE WEB SERVER
Access the following URL from the Web browser on the remote management PC:
http://BMC_HostPort or https://BMC_HostPort
and a colon followed by a port number for HTTP or HTTPS connection:
e.g. 192.168.1.1:80 If the port number is 80 for HTTP or 443 for HTTPS
connection. For better communication performance, use HTTP on a
secured network.
- 15-
Page 16
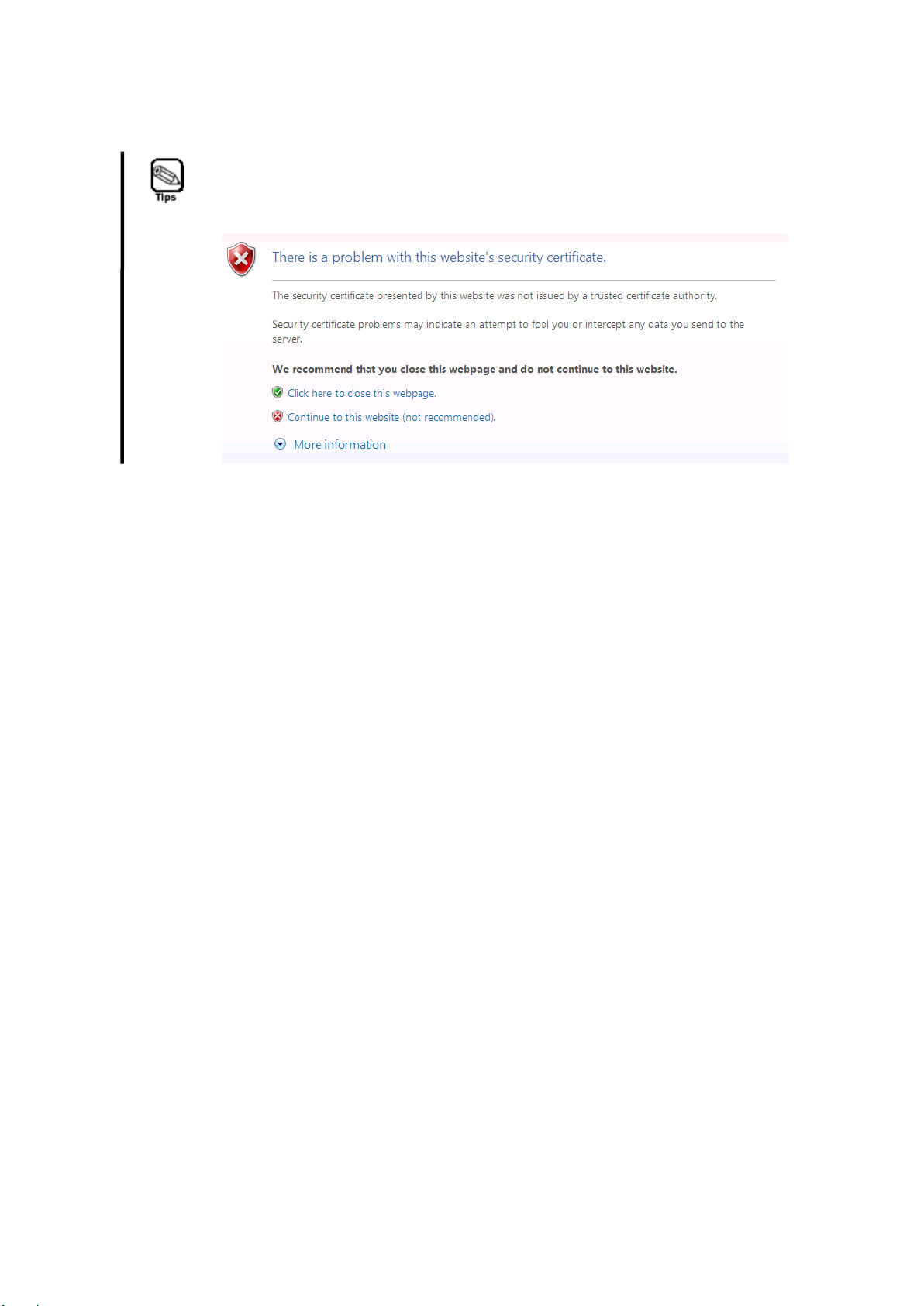
If you did not register the SSL server certificate, the following page is
displayed and HTTPS connection is blocked. In this case, select
"Continue to this website" to continue (The image if you are using
Internet Explorer is as follows).
- 16-
Page 17
Notice
You can select the display language only in the login page. If you
language in the login page.
Notice
Do not use the “Reload” button in your browser after login.
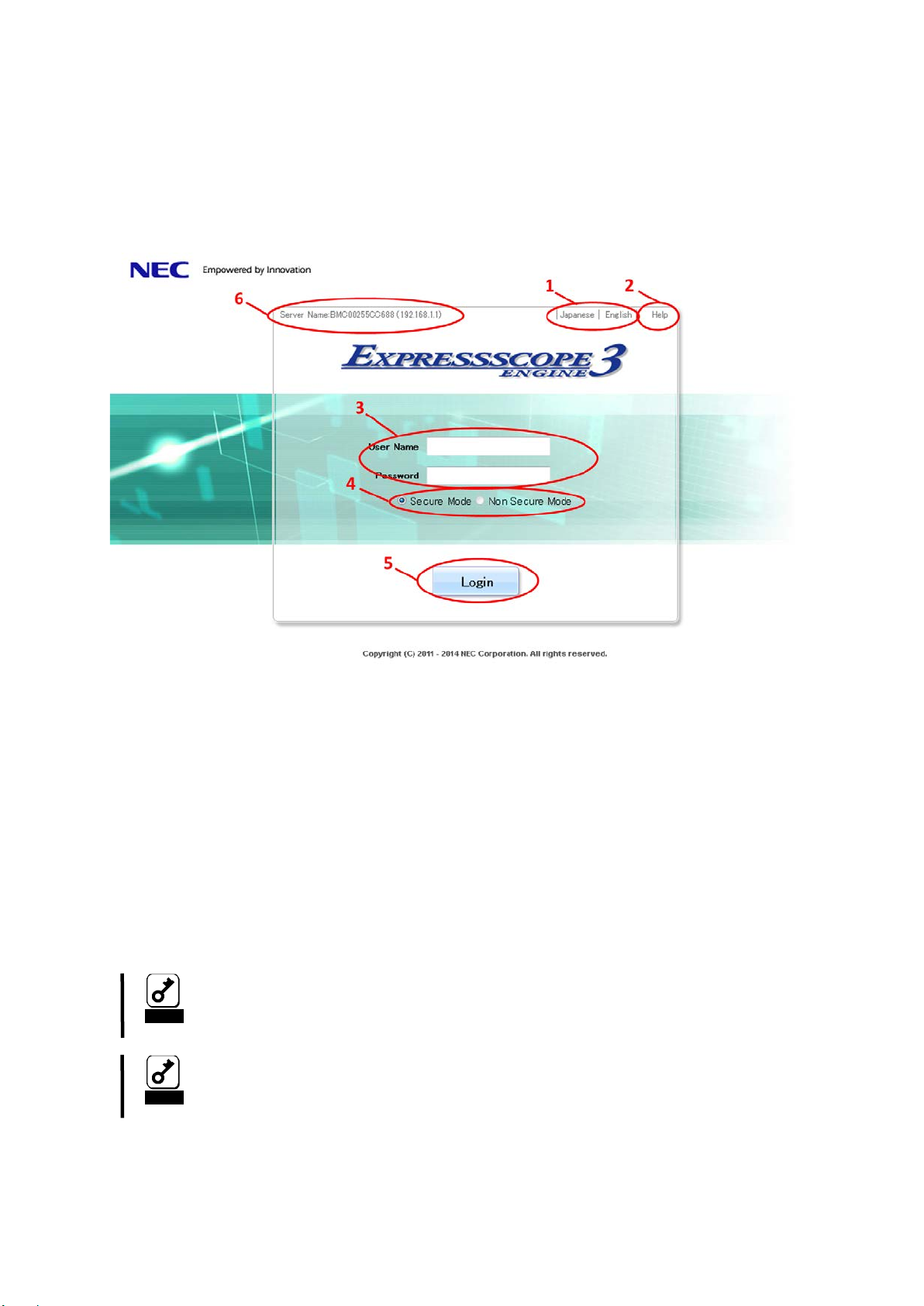
LOGIN AND LOGOUT
Login
When the login page appears, input the user name and password, and then click [Login].
1. The display language can be selected to English or Japanese.
2. The online help is displayed.
3. Please input username and password.
4. Secure Mode(HTTPS) or Non Secure Mode(HTTP) can be selected.
5. Please push "Login" button.
6. Server Name (BMC’s IP address) is displayed (*).
(*) Even if you use IPv6 address to login to BMC, BMC’s IP address is displayed as IPv4
address.
want to change the language after login, log out once and change the
- 17-
Page 18
Notice
If the browser is slow during login procedure, please restart your
Notice
BMC FW will be restarted very rare. In this case, it does not affect the
use it via network.
Notice
If it is repeatedly login to the BMC without logout normally, you
and try again or press BMC reset button of the host system.
Notice
Login failure may occur very rarely after network setting to the BMC
543
2
1
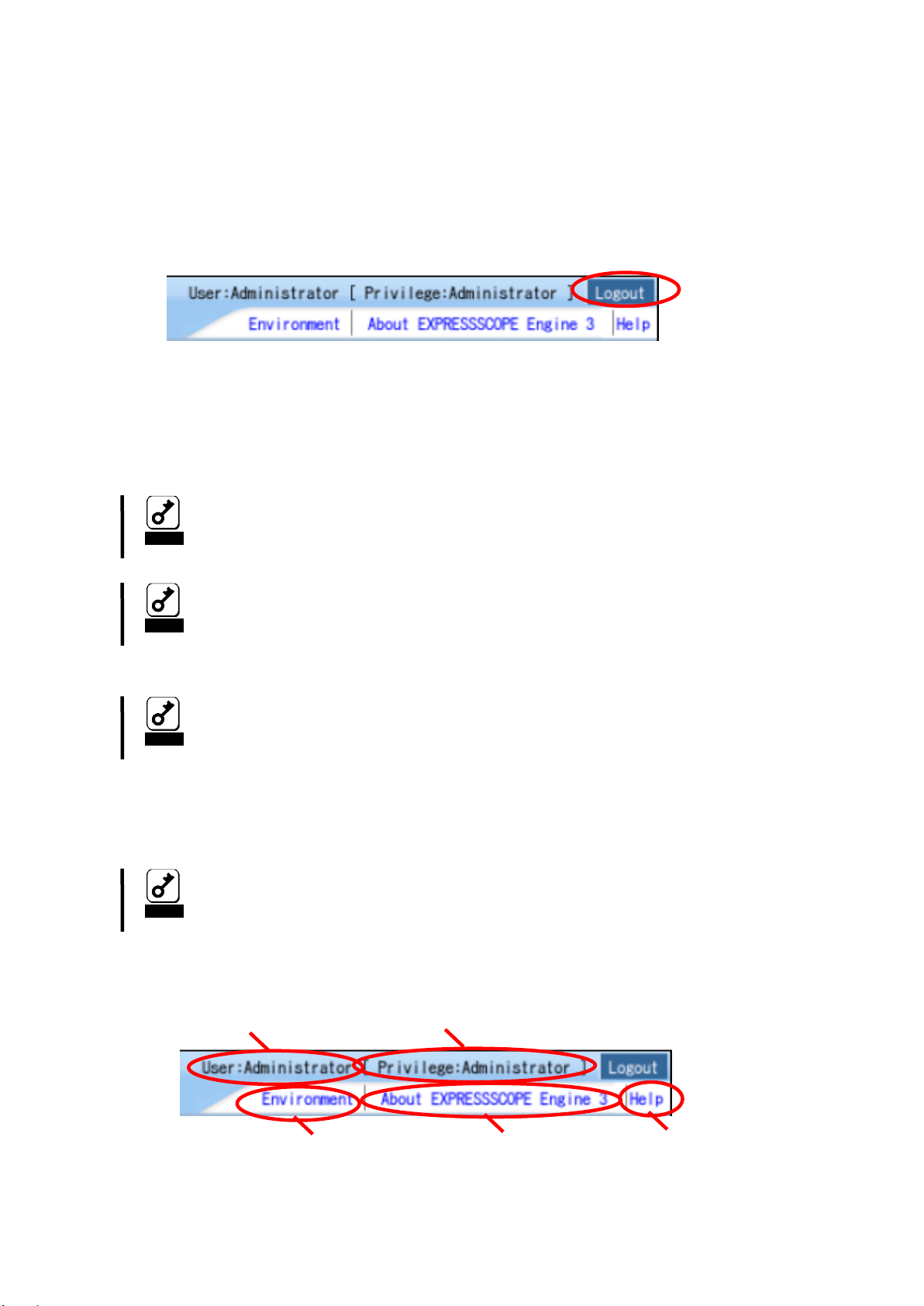
Logout
Click “Logout” in the upper right corner of the window. When a confirmation dialog appears,
click [OK] to log out.
After you log out, y ou return to the login page. Besides, all the remote device windows that
were opened during login will be closed.
brower or logout.
software on the host system OS, but an existing network connection
to the BMC will be disconnected, so, please connect again when you
cannot login to the BMC because it is reached to the maximum
number of simultaneous login users caused by the HTTPS sessions
that are not terminated and are remained or because it is reached to
the maximum number of simultaneous login users (4). In this case,
please wait for the BMC’s automatic logout time (30 minutes or more),
or shortly after the BMC reset. In this case, please try to login again.
HEADER MENU
- 18-
Page 19

1. Login user name is displayed.
2. Login user’s privilege is displayed.
3. The environment of management PC is displayed, and set by clicking "Environment"..
4. License information is displayed.
5. The online help is displayed.
- 19-
Page 20
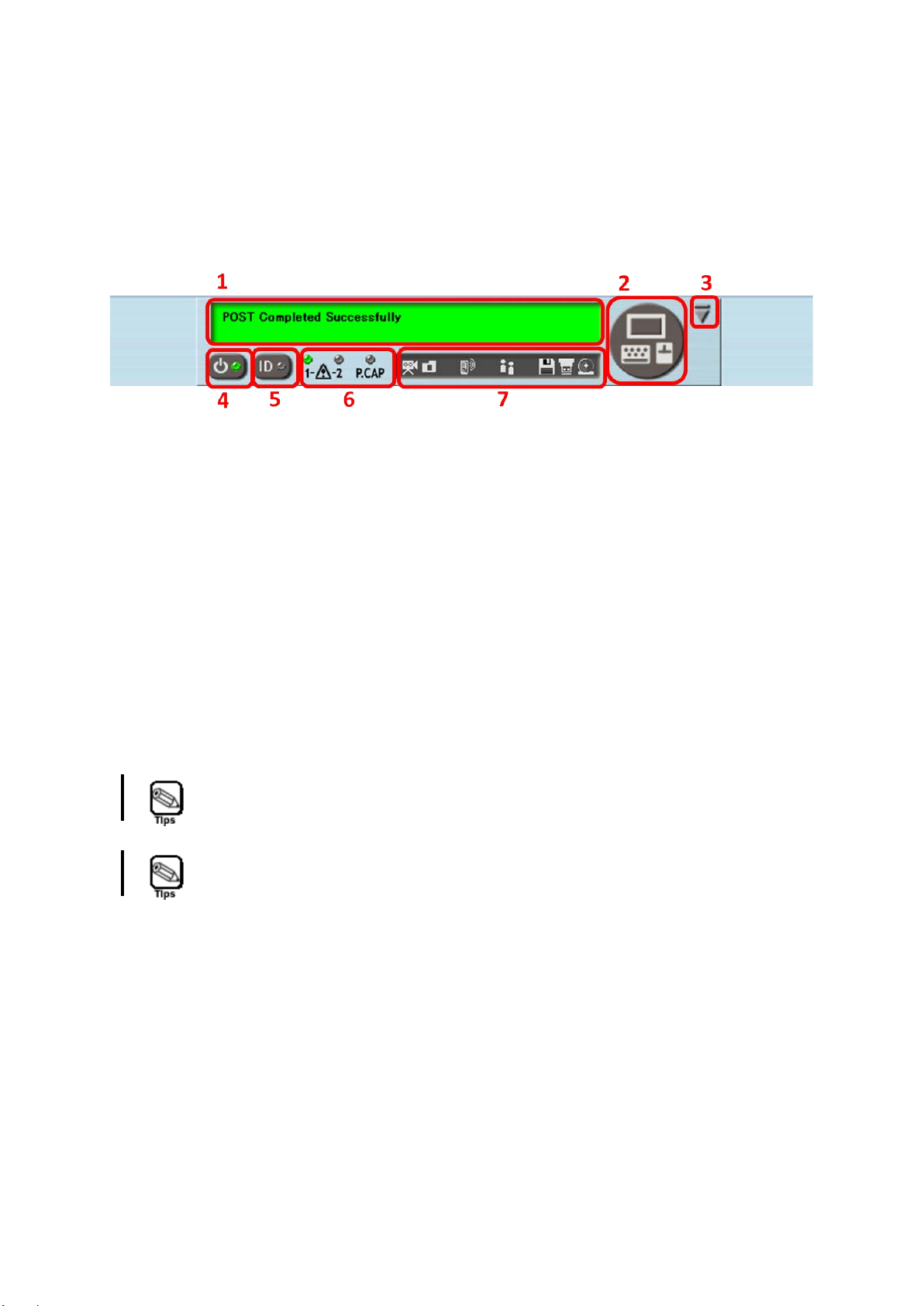
Even if actual UID LED is not mounted into the host system, the UID
LED indicator of the Server Panel functions as virtual UID LED.
Refer to Maintenance Guide of the system for the message displayed
in the Virtual LCD.
SERVER PANEL
The server panel is displayed under a browser after log in. The server panel has following
functions.
1. The virtual LCD that displays the state of the host system.
2. The Button to start RemoteKVM/Media
3. The button that minimizes the server panel.
4. The power switch and a lamp of the host system. The state of the power supply of the
host system is shown.
5. The UID(Unit ID) switch and a lamp of the host system.
6. The status lamp and power capping lamp of the host system. The state of the host
system is shown.
7. The login status to the BMC, the remote media usage condition and automatic video
record setting, whether the video data is recorded or not, and alert setting are displayed.
- 20-
Page 21
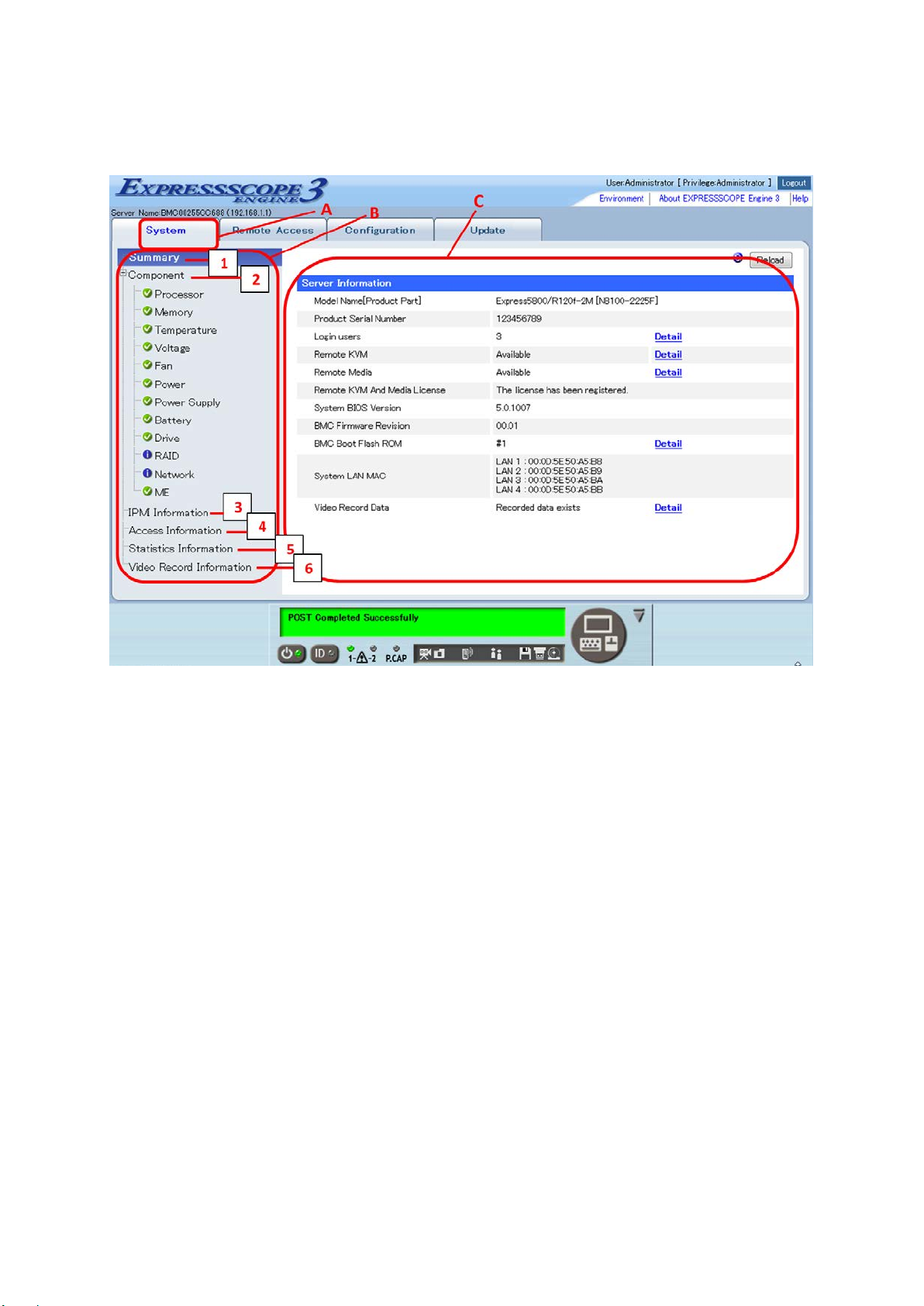
SYSTEM
A. The system tab. BMC supported functions are displayed.
B. The menu that can be selected in the system tab is displayed.
C. Information selected by B is displayed. The screen of "Summary" is displayed in the
above-mentioned example.
Menu
1 Summary
The state of information and BMC of the host system is displayed.
2 Component
Only items supported with the host system are displayed for each item of composition
information. (processor, memory, temper ature, voltage, fan, power, power supply, battery,
drive, RAID, network and ME). Moreover, the item supported with the host system might
not be displayed depending on the state of the system power supply and the presence
state of the components such as devices.
3 IPMI Information
Information (SEL,SDR,FRU,MC) is displayed in accordance with IPMI and it backs up.
The preserved backup data can be referred to from the server management software
(ESRAS utility and off-line maintenance utility).
4 Access Information
- 21-
Page 22
Notice
If the hardware clock setting (RTC) is set by the host system OS to
occur.
Notice
When the AC power of the host system is turned off, the video record
erased.
Notice
The video record data during BIOS POST will be overwritten at next
is deleted manually.
Notice
If the automatic video recording is run opening the Remote
video recording without opening the Remote KVM/Media.
Notice
If the host system power on by the AC-LINK with the automatic video
(recommends 70 seconds or more).
Login/Logout information and operation log are displayed.
5 Statistics Information
The Power Graph which shows power consumption changes of latest 10 minutes or 24
hours are displayed.
6 Video Record Information(*)
If the automatic video recording function is enabled from configuration tab, the video
records which were recorded at the time of BIOS POST or OS stall are displayed. Also
you can playback or download or delete them.
(*) The video length is maximum 5 minutes but it might be shorter than 5 minutes depending
on the size limit of regions of video record data or the size of the resolution of screen to be
recorded.
the time in UTC offset, The timestamp of SEL (System Event Log) will
be set to the time in UTC offset instead of local timestamp. Please
notice that the time difference between UTC time and local time will
data that was saved by the automatic video recording function will be
collection time. On the other hand, the video record data during OS
stall will be saved and not be collected at next collection time until it
KVM/Media, the video record data on the playback screen might be
displayed broken very rarely. In this case, please run the automatic
recording is enabled, the video record data during BIOS POST might
not be collected even if the AC-LINK delay time to the DC ON is short.
In this case, please set the AC-LINK delay time to 65 seconds or more
- 22-
Page 23
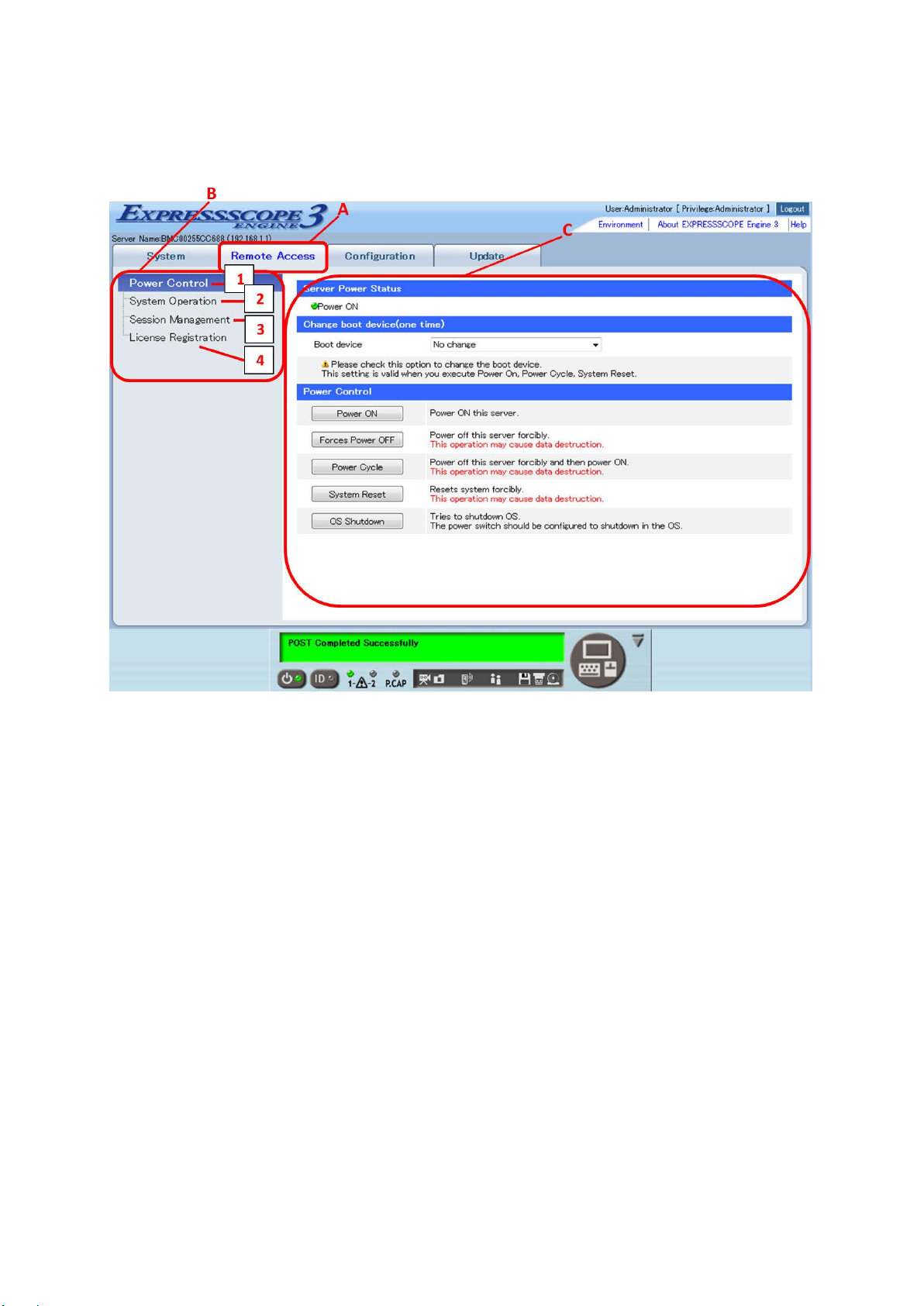
REMOTE ACCESS
A. The remote access tab. BMC supported functions are displayed.
B. The menu that can be selected in the remote acces s tab is displayed
C. Information selected by B is displayed. The screen of "Power Control" is displayed in the
above-mentioned example.
Menu
1 Power Control
Select Boot device of the host system, powering on/off, power cycle, reset the system,
and shutdown the OS.
2 System Operation
Start RemoteKVM/Media, turn on/off of UID lamp, press Dump switch and reset BMC.
3 Session Management
The user who is logging in BMC can be managed.
4 License Information
The license to use remote KVM/media is registered.
- 23-
Page 24
Notice
If you execute “power cycle” under the condition that the “Power
button of the host system.
Notice
Click “BMC Reset” only if a problem occurs in EXPRESSSCOPE
operation after clicking the “BMC Res et” for approximately 3 minutes.
The connections with Web browser and SSH client are disconnected
if you reset the BMC.
Clicking the “BMC Reset” cannot reboot the server.
Save” is enabled by BIOS Setup Utility, the powering on after the
powering off will not work. In this case, please try to press power
Engine 3 (BMC). Do not click “BMC Reset” in usual operation. Do not
shutdown the system, reboot the system, or perform any switch
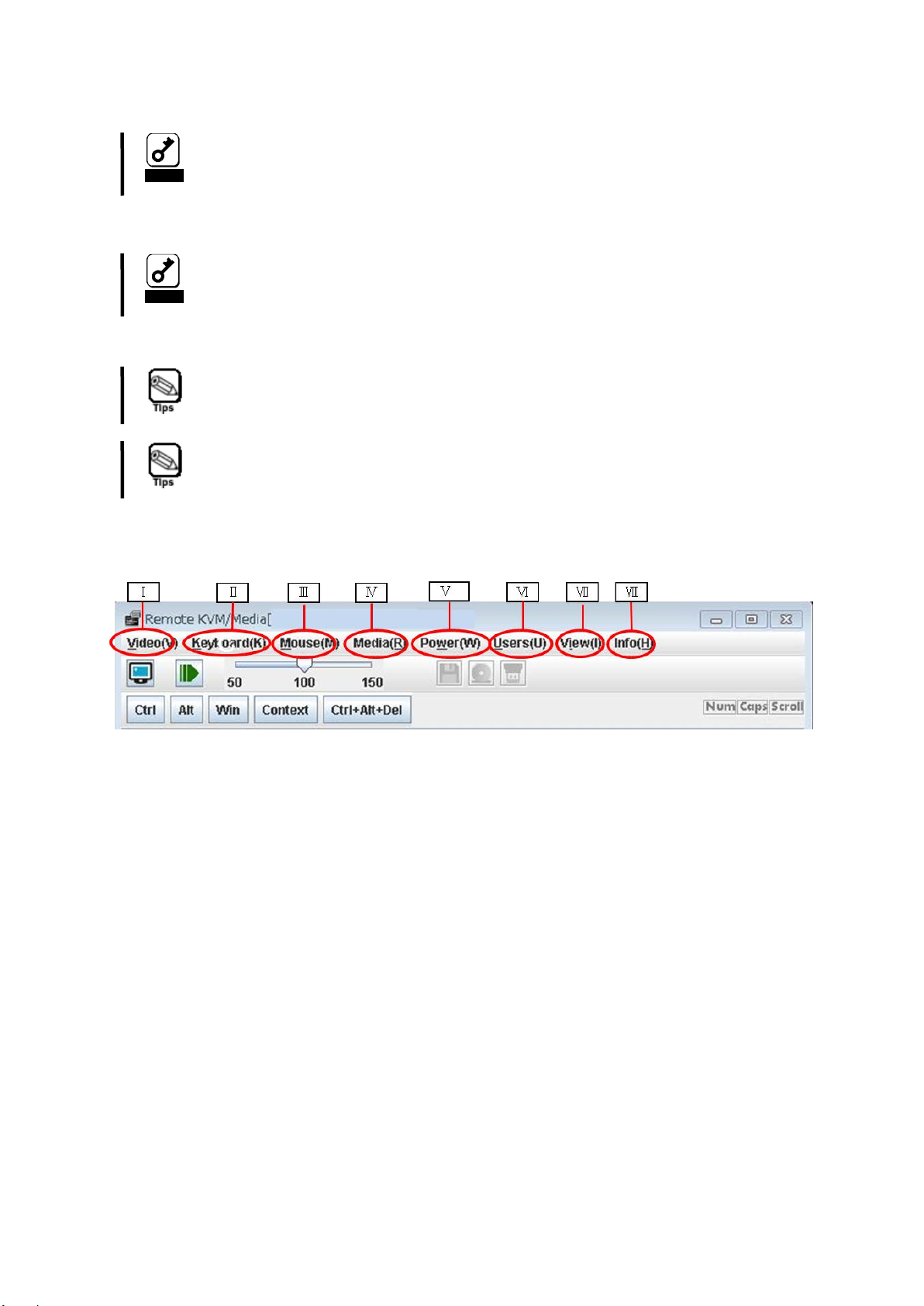
REMOTE KVM/MEDIA
Menu
I. Video
The features such as Refresh screen, Low bandwidth mode (Normal, 8bpp, 8bpp
B&W, 16bpp display mode are supported depending on the network bandwidth.),
manual video recording, capture screen, full screen are available.
II. Keyboard
The features such as user defined macros, virtual keyboard (software keyboard) for
Japanese/English/French/German are available.
III. Mouse
The features such as changing or synchronizing the mouse cursor, changing the
mouse coordinate mode are available.
IV. Media
Enable or disable the remote device and open the rem ote med i a window to connect
or disconnect the remote media.
V. Power
You can do the power on, power off, power cycle, reset, OS Shutdown, NMI dump (If
the memory dump is set on the host system OS.) to the host system.
- 24-
Page 25
The host system detects remote media as following devices: Remote
AMI Remote USB Mem
The access lamp comes to remain lighting after it connects it
according to the kind of the floppy disk drive of management PC.
Notice
When the operation into which the resolution on the host system side
KVM again.
Notice
When you log on to the BMC from the host system, do not access the
will not be able to use keyboard and mouse.
Notice
On some browsers, if you want to start the Remote KVM/Media, you
please download again by pressing ‘Retry’.
Notice
If the mouse pointer is not displayed properly on Remote KVM/Media,
box for [Display pointer trails]-[Visibility].
VI. Users
Display the user information that is using the Remote KVM/Media. Up to 2 users can
use Remote KVM/Media simultaneously.
VII. View
Control the visibility of tool bar (control box area and hot key area). The ‘Request Full
Control’ menu will be displayed for the Remote KVM/Media that is launched as view
only mode and it is possible to request for permission to the Remote KVM/Media that
is launched as full control mode.
VIII. Info
Display the version information.
devices are disabled just after the remote KVM/Media is started. It is
displayed only when they are enabled from the “Media” menu.
• AMI Remote FD
• AMI Remote CD/DVD
•
frequently changes after remote KVM is started, the remote KVM
connection might be disconnect. In that case, please start remote
Remote KVM Console from a Web browser in the host system. You
may see the dialog ‘jviewer.jnlp couldn’t be downloaded’. In this case,
please try the following setting on the host system OS.
- Lowered one scale from "Full" to "None" side on the [Hardware
acceleration]-[Troubleshoot]-[Advanced settings]-[Screen
Resolution]-[Display] of Control Panel.
- Uncheck the box for [Enhance pointer precision]-[Motion]-[Pointer
Options]-[Mouse Properties] of Control Panel. Also, try to check the
- 25-
Page 26
Notice
If you change keyboard language after adding user defined macro on
language.
Notice
If the manual video recording is run under ‘8bpp B&W’ mode which
software.
the Remote KVM/Media, the user defined macro that was created with
the previous keyboard language might not work well because some
keyboard key has different key code depending on the language. In
this case, please create the macro again with the current keyboard
was set by Low bandwidth mode, the created video file (AVI
formatted) might not be playback by Windows Media Player. In this
case, please try to install the codec pack which includes Motion
JPEG codec to the management PC or try the other playback
- 26-
Page 27
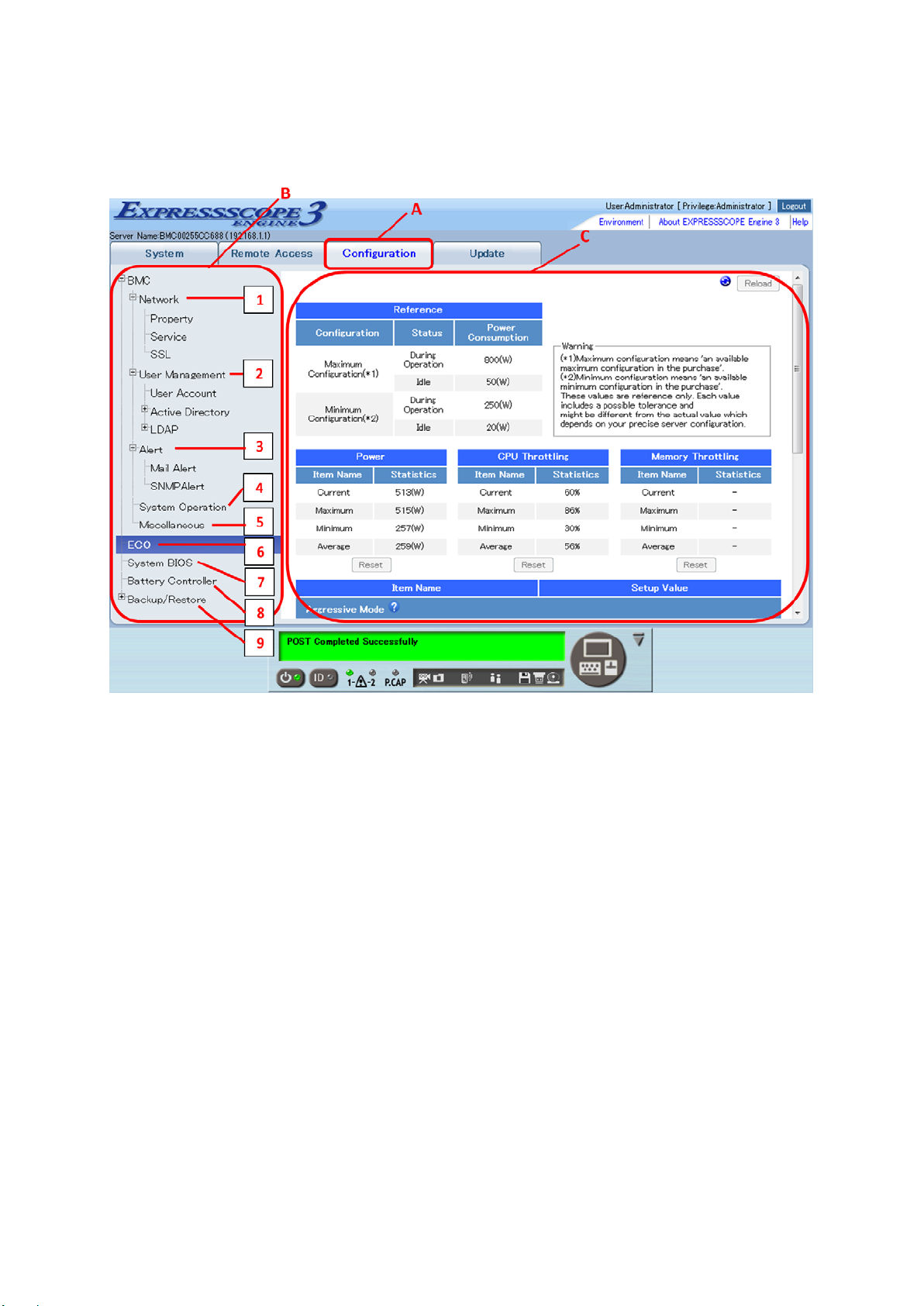
CONFIGURATION
A. The configuration tab. BMC supported functions are displayed.
B. The menu that can be selected in the configuration tab is displayed
C. Information selected by B is displayed. The screen of "ECO" is displayed in the
above-mentioned example.
Menu
1 Network
Set IP address and the service of the BMC and the SSL public key can be made.
2 User Management
Maintain user and Active directory/LDAP setting, register the SSH public Key.
3 Alert
The setting of which it alerts by using E-mail and SNMP from BMC can be done.
4 System Operation
Set the RemoteKVM/Media configuration.
5 Miscellaneous
- 27-
Page 28
Notice
The strings “InternalUseOnly”, “MWA”, “AccessByEM-Poem”,
IPMI command tool, you can use User ID from 6 to 16.
Web Br owser
Management LAN
Management LAN
Management LAN
Connection Type
Auto Negotiation
Auto Negotiation
DHCP
Disable
Disable
IP address
192.168.1.1
192.168.1.1
Subnet Mask
255.255.255.0
255.255.255.0
Default Gateway
0.0.0.0
0.0.0.0
DNS Server
0.0.0.0
0.0.0.0
Host Name
Blank
"BMC" + MAC
Set the behavior when the SEL repository is full, the access log setting, AC-LINK setting,
PEF setting, management setting from the management software, and the automatic
video recording setting.
6 ECO
Power consumption and the throttling situation are displayed and the power capping can
be set.
7 System BIOS
Some functions of System BIOS can be set.
8 Battery Controller
If the host system is equipped with a battery, various functions of Battery Controller can
be set.
9 Backup/Restore
Backup and Restore each item that was set.
“Administrator” are reserved by BMC. Please do not add or remove
these characters as User Name. The user account is synchronized
with the IPMI user account. If you want to add or remove users in the
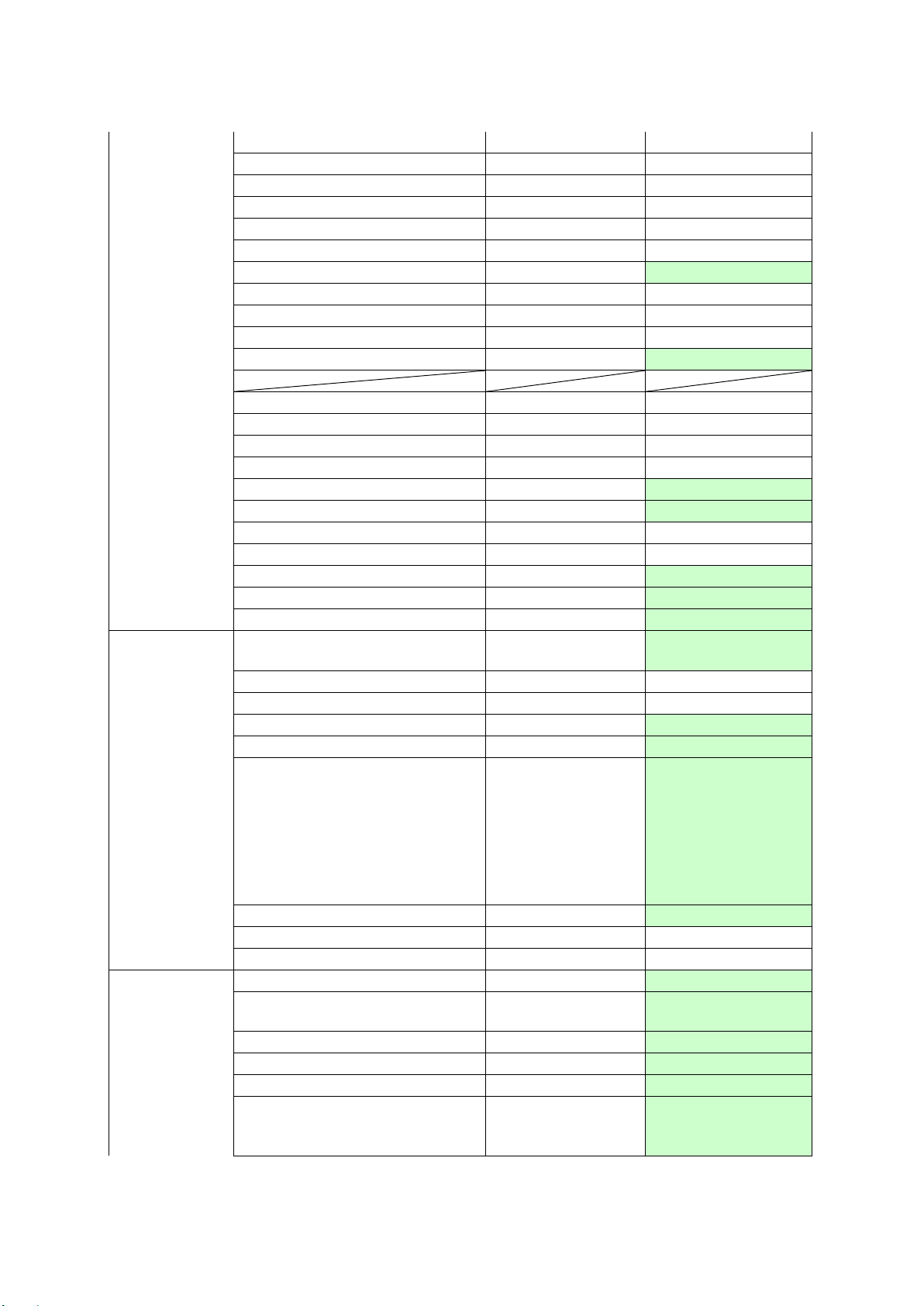
For each BMC setting, the “Default” value of the setting from Web browser of BMC, Server
Configuration Utility, NEC ESMPRO Manager and the initial value of BMC Initialization are as
the following table (There are some items of Server Configuration Utility, NEC ESMPRO
Manager that are not displayed in the Menu.). “No change” in “BMC Initial izat io n ” means that
the setting values from the Web Browser/Server Configuration Utility/NEC ESMPRO
manager are preserved by executing BMC Initialization.
Server
Configuration
Menu Setting
Utility
NEC ESMPRO
BMC Initialization
Manager
“Default” value
Network
- 28-
Page 29
address
Domain Name
Blank
Blank
Limitation Type
Allow All
Allow All
IPv6
Disable
Disable
IPv6 Address Assignment
Mode
IPv6 Static Address
0::0
0::0
IPv6 Prefix Length
64
64
IPv6 Gateway Address
0::0
0::0 HTTPS
Enable
Enable
HTTPS Port
443
443
HTTP
Enable
Enable
HTTP Port
80
80
SSH
Enable
Enable
SSH Port
22
22
Active Directory Authentication
Disable
Disable
Authentication User
Blank
Blank
Authentication Password
Blank
Blank
User Domain Name
Blank
Blank
Timeout
120
120
Domain Controller Server
Address1
Domain Controller Server
Address2
Domain Controller Server
Address3
Group Name
Blank
Blank
Group Domain
Blank
Blank
Privilege
Administrator
Administrator
LDAP Authentication
Disable
Disable
IP address
0.0.0.0
Blank
Port
389
389
Search Base
Blank
Blank
Bind Domain Name
Blank
Blank
Bind Password
Blank
Blank
Group Name
Blank
Blank
Group Search Base
Blank
Blank Privilege
Administrator
Administrator
Mail Alert
Disable
Disable
Waiting time for SMTP server's
response
To:1
Enable
Blank
To:2
Disable
Blank
To:3
Disable
Blank
From
Blank
Blank
Reply-To
Blank
Blank
Dynamic Dynamic
User
Management
0.0.0.0 Blank
Blank Blank
Blank Blank
30 30
Alert
- 29-
Page 30
Subject
Blank
Blank
Subject Option
Disable
Disable
X-Priority
Enable
Enable
Date Formats
MM/DD/YYYY
MM/DD/YYYY
SMTP Server
0.0.0.0
0.0.0.0
Port
25
25
Authentication
Disable
Enable
Authentication Type
All checked
All checked
User Name
Blank
Blank
Password
Blank
Blank
Alert Level
Error, Warning
Separate Setting
SNMP Alert
Disable
Disable
Computer Name
Blank
Blank
Community Name
public
public
Alert Process
One Alert Receiver
One Alert Receiver
Alert Acknowledge
Enable
Disable
Alert Receiver1
Enable
Disable
Alert Receiver2
Disable
Disable
Alert Receiver3
Disable
Disable
Alert Level
Error, Warning
Separate Setting
Alert Retry Count
3 0 Alert Timeout
6
0
Remote KVM Console
Encryption
Port (No Encryption)
7578
7578
Port (Encryption)
7582
7582
Cursor Mode
Dual
Single
Coordinate Mode
Absolute(*4)
Absolute
Remote Media Encryption
Enable
Disable
Port (No Encryption)
5120
5120
Port (Encryption)
5124
5124
Aggressive Mode(*1)
Disable
Disable(*10)
Maximum Power
Consumption(*5)
Maximum Power
Consumption(*10)
Correction time limit
2(*6)
2(*10)
Shutdown System
Disable
Disable(*10)
Non-Aggressive Mode(*2)
Disable
Disable(*10)
Maxim um Power
10(*7)
Maximum Power
10(*10)
System
Operation
ECO
Keyboard Language
Power Threshold(Pa)
Enable Disable
When login in
Japanese;
Japanese, When
login in English;
English
English
Power Threshold(Pn)
- 30-
Consumption -
Consumption -
Page 31

Correction time limit
10(*8)
10(*10)
Safe Power Capping
Disable
Disable(*10)
Boot Time Configuration(*3)
Disable
Disable(*10)
Performance
Optimized
Performance
Optimized(*10)
Disable CPU Cores
0
0(*10)
Behavior when SEL repository
is full
Overwrite oldest
SEL
Overwrite oldest
SEL (*9)
Access Log HTTP
Disable
Disable
HTTPS
Disable
Disable
SSH
Disable
Disable
Operation
Disable
Disable
Power Restore Delay AC-LINK
Last state
No change
Minimum
configurable time
Platform Event Filtering
Enable
Disable
ESMPRO Management
no change
Disable
Authentication Key
guest
Blank
Redirection (LAN)
Enable
Disable
Automatic Video Recording
Disable
Disable
POST Error Pause
Enable/Disable
Enable
Memory Error
Boot/Halt
Boot
CLI SETUP
Enable/Disable
Disable
Miscellaneous
Performance Mode
Delay Time
No change
*1: This menu is shown as “Critical Power Capping” in some host system.
*2: This menu is not supported in some host system.
*3: This menu is not supported in some host system.
*4: This value is “Relative” in some host system or depending on the revision of the BMC.
*5: The default value is ‘settable maximum’ in some host system. The ‘settable maximum’ is
equal to ’Maximum Configuration’ in some host system.
*6: The default value is ‘settable minimum’ in some host system.
*7: The default value is ‘Power Threshold(Pa) -10’ or ‘The settable minimum +10’ ,whichever
is greater in some host system. The ‘settable minimum’ is equal to ‘Minimum Configuration’ in
some host system.
*8: The default value is ‘settable minimum’ in some host system.
*9: This value is “Stop logging SEL ” in some host system or depending on the revision of the
BMC.
*10: This value is “Blank” in some host system or depending on the revision of the BMC.
For each System BIOS setting, the possible values and the value of BIOS Initialization are as
the following table.
Item N ame Setting Possible Values(*1)
BIOS Basic
BIOS Initialization
(*2)
- 31-
Page 32

Power Save (*3)
Enable/Disable
Disable
Serial Port A
Enable/Disable
Enable
2E8h
3F8hBlank
IRQ 3
IRQ 4
Serial Port B
Enable/Disable
Enable
2E8h
3F8h
IRQ 3
IRQ 4
Disabled
Serial Port B
VT100+
PC-ANSI
9600
115200
7
8
None
Odd
1
2
None
Hardware RTS/CTS
Continue C.R. after POST
Enable/Disable
Enable
Serial Port A
Serial Port B
Console
Redirection
Serial A Base I/O
Serial A Interrupt
Serial B Base I/O
Serial B Interrupt
BIOS Redirection Port
Terminal Type
Baud Rate
Data Bits
2F8h
3E8h
2F8h
3E8h
Serial Port A
VT-UTF8
19200
57600
3F8h
IRQ 4
2F8h
IRQ 3
Disabled
VT100+
115200
8
Parity
Stop Bits
Flow Control
Even
None
1
Hardware RTS/CTS
*1: The value might be different according to the system.
*2: The value that is set when shipping. The value might be different according to the syst em.
*3: If the “Power Save” is enabled, then Power ON following Power OFF by the Power Cycle
will not be performed.
- 32-
Page 33

Example of an E-mail alert:
Virtual LCD Message:
Asset Tag: xxx-xxxxxx-xxx
Notice
Following contents are sent as E-mail alert.
System Rear FAN4 Lower Non-Critical
Event Information:
Record ID: 0AA0h
Timestamp: 10/13/2011 17:59:23
Severity: Non-critical
Description:
Fan(Speed) - Error
Lower Non-critical - going low
Dump:
A0 0A 02 FB 26 97 4E 20 00 04 04 43 01 57 FF B6
URL:
http://192.168.1.11:80
https://192.168.1.11:443
BMC Network Information:
BMC IP Address: 192.168.1.1
BMC Host Name: BMCxxxxxxxxxxxx
Firmware Revision:
System BIOS Revision: x.x.xxxx
BMC Firmware Revision: xx.xx
SDR Revision: SDR Version xx.xx
Product Information:
Manufacturer: xxx
Product Name: xxxxxxxxxxx/xxxxx-xx
Part/Model Number: [xxxxx-xxxxx]
Version: FR1.0
Serial Number: xxxxxxx
• You should use a straight through ethernet cable if you set
10Mbps or 100Mbps as ‘Connection Type’ of Network.
- 33-
Page 34

Notice
When you update the BMC firmware, you need to check “Apply
UPDATE
A. The update tab. BMC supported functions are displayed.
B. The menu that can be selected in the update tab is displayed
C. Information selected by B is displayed. The screen of "BMC Firmware" is displayed in the
above-mentioned example.
Menu
1 BMC Firmware
Update the BMC firmware regardless of power-off/on of the host system.
2 System BIOS
Update the System BIOS regardless of power-off/on of the host system.
Immediate” befor e proceeding to “Start Update”.
- 34-
Page 35

To use Command Line Interface, you need to change the
You can change the BMC’s SSH port number by using the Off-line
SSH: 22
A security warning messages regarding your server certificate may
6. Command Line Interface
OVERVIEW
With the BMC Command Line Interface, you can control the host system from a remote SSH
client. The BMC supports SSH (Version 2) protocol.
CONNECTING TO BMC
Access the BMC IP address or DNS host name from SSH client on the remote management
PC.
configuration of the command line interface (SSH) to be enabled by
any of the setting of the Off-line Server Configuration Utility or
On-line Server Configuration Utility or Setting of Web browser. Refer
to the “
Host System”.
Management LAN Settings” in the “Chapter 2: Configuring the
Server Configuration Utility, On-line Server Configuration Utility or a
web browser. The default settings are as follows:
be displayed when you access the BMC from a SSH client.
- 35-
Page 36

The user account is common to the one for a remote management
function via web browser.
The number of users who can log in the system using the command
in via the command line interface.
Only a single user among users who are using the command line
cannot use a character-based remote console.
LOGIN AND LOGOUT
Login
Enter your user name and passwo rd at login prompt. A command prompt will be displayed
after l ogin. Also you can login by using public key authentication.
line interface at the same time is four users or less. Therefore, you
cannot log in the system when other four users have been logging in
the system using SSH clients via the command line interface. Check
whether other three users are logging in the system, if you cannot log
interface or NEC ESMPRO Manager can use a character-based
remote console via the command line interface. Check whether
another user is using a character-based remote console, if you
Refer to the “CONFIGURATION” in the Chapter 5: Using Remote
Management” for registering SSH public key.
Logout
Enter the “exit” command at the comma nd prompt. The SSH client will be disconnected from
the BMC after logout.
- 36-
Page 37

The user must have an account as the following user level to use the
command.
BASIC COMMANDS
This section describes basic commands to use them as the command line interface. These
basic commands manage the host system by using the concept of command (verb) and
target (Managed Element) proposed by DMTF (Distributed Management Task Force).
Each basic command functions to a specified target. The target points the managed element
by address path much like the path to a file in a file system.
Both absolute path, which is started from "/", and relative path are available for pointing the
target. Specifically, "." and ".." are supported. The "." means the current default target and the
".." means the parent target.
Each basic command functions to the current default target when the <target>, which is an
argument pointing a target for the command, is not specified to the basic command. The
current default target can be changed by the cd command. The current default target is
"/admin1" when the command line interface session is started.
The current default target is displayed at the left side of the command prompt ( "->").
Help string, command syntax, of each command appears when "-h" option is specified as the
<options> of the command. The argument placed between "[" and "]" is omissible.
basic commands:
• cd, exit, help, show and version can be used under an account as
all user levels.
• stop, start and reset are needed an account as operator or
administrator user level to use these commands.
• set is needed an account as administrator user level to use this
Maximum number of input character for command line interface is 250.
cd
Syntax:
cd [<options>] [<target>]
Description:
The cd command changes the current default target to the target specified by the
<targe t > argument.
exit
Syntax:
exit [<options>]
Description:
The exit command terminates and logs out the user session.
- 37-
Page 38

Notice
Reset the BMC only if a problem occurs in the BMC and don't reset
and SSH client are disconnected if you reset the BMC.
help
Syntax:
help [<options>] [<help topics>]
Description:
A basic command, <command>, can be specified for the <help topics>. The help
command displays the help string for specified basic command when <command>
argument is specified.
reset
Syntax:
reset [<options>] [<target>]
Description:
The reset command performs a hardware reset on the <target>.
/admin1/system1 and /admin1/sp1 are available for the <target> of the reset command.
For /admin1/system1, the host system is reset. For /admin1/sp1, the BMC is reset.
the BMC in normal operation. Also the connections with Web browser
set
Syntax:
set [<options>] [<target>] <propertyname>=<value>
Description:
The set command is used to set the value of one or more properties of target specified
by the <target>. The command accepts a target specified by the <target> and series of
<propertyname>=<value> pairs which is will try and apply. The <propertyname> means
a name of property set by the command. The <value> means a new value set by the
command.
One or more <propertyname>=<value> pairs can be specified by delimiting between
each pair in space.
The set command requires <propertyname>=<value> command line argument except
when -h is specified as the <options>.
show
Syntax:
show [<options>] [<target>] [<properties>]
Description:
- 38-
Page 39

Notice
It may take about 1 minute to display the target information
The show command is used to display information about the target specified by the
<targe t > argument.
The command displays the target specified by the <target> as the first line of the
information. It displays the current default target in the first line if <target> is not
specified.
The default behavior of the command for the target specified by the <target> is as
follows. The command display targets which are contained by the specified target after
the "Targets" string. The command displays properties which are contained by the
specified target after the "Properties" string. The properties are displayed in the form of
property=value. The command displays basic commands (verbs) and special extended
commands which are available for the specified target after the "Verbs" string.
The command displays the property specified by the <properties> in the form of
property=value if the <properties> is specified. The command displays all properties
which are contained by the specified target if the <properties> is not specified.
There is -display <arg values> option which can be specified by the <options> for the
show command. The option can control the type of information that is displayed about
the target specified by the <target>. Valid option argument values as the <arg values>
for this option include "targets", "properties", "verbs", and "all". The option argument
values can select the above "Targets", "Propert ies" and "Verbs" information that is
displayed. “all” displays the whole. The default for the -display option control is "all".
depending on the configuration of the host system.
start
Syntax:
start [<options>] [<target>]
Description:
/admin1/system1 and /admin1/system1/textredirectsvc1 are available for the target of
the start command.
The start command performs a power on to the host system if /admin1/system1 is
specified by the <target>.
The start command starts a character-based remote console if /admin1/system1/
textredirectsvc1 is specified by the <target>.
stop
Syntax:
stop [<options>] [<target>]
Description:
The stop command performs a normal power off request (OS shutdown request) or a
forced power off request.
/admin1/system1 is available for the target of the stop command. The stop command
- 39-
Page 40

with no option as the <options> performs a normal power off request (OS shutdown
request) to the host system if /admin1/system1 is specified by the <target>. The
command with -f (or -force) as the <options> performs a forced power off request to the
host system if /admin1/system1 is specified by the <target>.
version
Syntax:
version [<options>]
Description:
The version command is used to display the version of the command line protocol
specification which is supported.
- 40-
Page 41

Notice
Performing remote control when the operating system is running may
The user must have an account as operator or administrator for
remote control.
The above OS shutdown is equivalent to pressing the POWER switch
must be set to shut down when you power off the system.
An above system reset is failed when the power of the host system is
REMOTE CONTROL
You can perform remote control of the host system at the command prompt.
cause the loss of data in the host system.
Power ON
Enter the following command at the command prompt.
start /admin1/system1
Forced Power OFF
Enter the following command at the command prompt.
stop -force /admin1/system1
or
stop -f /admin1/system1
OS Shutdown
Enter the following command at the command prompt.
stop /admin1/system1
when the power of the host system is o n. Your operating system
System Reset
Enter the following command at the command prompt.
reset /admin1/system1
off.
- 41-
Page 42

Notice
The standard serial port B (COM B) on the host system cannot be
occupies the serial port B.
To use a character-based remote console, set appropriate settings for
your host system.
Only a single user among users who are using the command line
remote console.
Remote Console
To start a character-based remote console, enter the following command at the command
prompt.
start /admin1/system1/textredirectsvc1
To return f rom the character-based remote console to the command interface session, enter
the <ESC>stop keys (<ESC>key, <s>key, <t>key, <o>key and <p>key) during the
character-based remote console.
used for connecting another device in this cases because the BMC
the console redirection function of the host system's serial port on
the BIOS Setup Utility in advance.
Especially, please use the following items by the following setting:
• BI O S Redirection Port : Serial Port B
• Baud Rate : 19.2K
• Flow Control: CTS/RTS
• Terminal Type: PC ANSI
For the system BIOS Setup Utility, please refer to the User's Guide of
interface or NEC ESMPRO Manager (a software application bundled
for remote management) can use a character-based remote console
via the command line interface or NEC ESMPRO Manager. Once the
first user uses the character-based remote console, other users
cannot use any character-based remote console from any SSH clients
or NEC ESMPRO Manager. Check whether another user is using a
character-based remote console, if you cannot use a character-based
To show the usage status of the character-based remote console by other users of the
command line interface or NEC ESMPRO Manager, enter the following command at the
command prompt.
show /admin1/system1/textredirectsvc1/textredirectsap1
You can confirm the usage state by value of EnabledState of the "Properties" which is
displayed by the command.
EnabledState=2 : Using the character-based remote console by current user or other
user.
EnabledState=6 : Not in use.
- 42-
Page 43

Please confirm in advance whether it is OK to stop the
The user must have an account as administrator for stopping the
To stop t he character-based remote console using by other user forcibly, enter the following
command at the command prompt.
set /admin1/system1/textredirectsvc1/textredirectsap1 EnabledState=6
character-based remote console using by other user forcibly.
character-based remote console forcibly.
- 43-
Page 44

Notice
The user must have an account as administrator for UID Switch
set command for the UID Switch Control.
If the UID LED is not mounted into the host system, the “UID Switch
description of the UID LED.
UID Switch Control
You can turn on/off the UID (Unit ID) LED on the host system by the virtual UID switch
throug h the command line interface. T his function is available only in the host system with
UID LED.
Control (turning on or turning off the UID LED) because of using the
Tur ni ng on UID LED
Enter the following command at the command prompt. State of the UID LED becomes same
state of turning on the LED by using UID (Unit ID) switch of the host system.
set /admin1/system1/led1 ActivateState=2
Tur ni ng of f UID LED
Enter the following command at the command prompt. State of the UID LED becomes same
state of turning off the LED by using UID (Unit ID) switch of the host system.
set /admin1/system1/led1 ActivateState=4
Confirmation of state of turning on UID LED
Enter the following command at the command prompt.
show /admin1/system1/led1
You can conf irm the state of the UID LED by value of ActivateState of the "Properties" which
is displayed by the command.
ActivateState=2 : UID LED state is turned on by UID switch .
ActivateState=3 : UID LED sate is blinking by the management software .
ActivateState=4 : UID LED state is turned off by UI D switch .
Control” function works only to the virtual UID LED of the Server
Panel. Please refer to the User’s Guide of your host system for the
- 44-
Page 45

state) only by the UID switch control.
• The UID LED will blink (flash) when it is controlled by Chassis
Identify function of management software such as NEC ESMPRO
Manager. The UID LED will turn on when it is controlled by
pushing the UID switch of the host system or using UID switch
control function of BMC's web server or command line interface.
For actual display state of the UID LED, blinking (flashing) the UID
LED is higher priority than turning on it when it is controlled at a
same time (blinking state AND turning on state).
• Blinking (flashing) UID LED by management software can be
turned off (release the blinking state) only by management
software. Turning on UID LED by UID switch control (actual switch
of the host system or the function of BMC's web server or
command line interface) can be turned off (release turning on
- 45-
Page 46

To show the total number of system event log records more than 1000
SYSTEM EVENT LOG
You can display system event log and modify setting of the system event log through the
command line interface.
Viewing system event log
To move the current default target to /admin1/system1/log1, enter the following command at
the command prompt.
cd /admin1/system1/log1
Here, to confirm the total number of system event log records, enter the following command.
The "Targets" section reported by the following command indicates the "record<N>" target(s).
<N> means any value between 1 and the total number of the system event log records.
show
event logs, it may take about tens of seconds.
Next, when the following command is input, information of a specific record is displayed at
"Properties" section: Here, <N> means record number which you would like to confirm.
show record<N>
For example, enter the following command when you would like to confirm the number 1
record.
show record1
The example of displaying information in this case is shown below.
-> show record1
Command Status: COMMAND COMPLET ED
ufip=/admin1/system1/log1/record1
Properties:
RecordID=1
CreationTimeStamp=20110324130745.000000+000
RecordFormat=*RecordID*RecordType*TimeStamp*GeneratorID*EvMRev*Sens
orType*SensorNumber*EventType*EventData1*EventData2*EventData3*
RecordData=*1*2*1300972065*32*4*16*9*111*66*143*255*
Verbs:
cd
exit
help
show
version
- 46-
Page 47

The user must have an account as administrator for modifying the
Setting of s ystem event log
To move the current default target to /admin1/system1/log1, enter the following command at
the command prompt.
cd /admin1/system1/log1
The "Properties" section reported by the following command indicates the current setting of
system event log.
show
Enter the following command if you would like to modify a property of the setting of system
event log .
set <Property>=<New value>
The properties which the system event log target contains are as follows:
• oemnec_selbehavior
This specifies the behavior when the system event log repository is full. The valid
values for this property are followings. This is the dynamic setting.
0 : Stop logging the system event log. The system event log is not recorded any more
when the system event log is full.
1: Clear all system event logs. All system event logs are cleared when the system
event log is full.
2: Overwrite oldest system event log. Oldest system event log is overwritten with new
system event log when the system event log is full.
For example, enter the following command when you would like to enable the auto clear of
system event log.
set oemnec_selbehavior=1
setting of the system event log.
- 47-
Page 48
The user must have an account as administrator for clearing and
The following are events supported by the Access Log function.
Start the remote KVM
User Information is not registered by logout events for SSH
ACCESS LOG
You can display, clear, and set the access log for the management LAN.
setting the access log.
• Login and logout events for HTTP, HTTPS, and SSH connections
• System control (Power OFF/ON, system reset, etc…) via Web
browser.
• Modify the setting (Network setting, etc…) via Web browser.
•
connections.
Vie win g ac ce ss lo g
To move the current default target to /admin1/sp1/log1/record1, enter the following command
at the command prompt.
cd /admin1/sp1/log1/record1
Enter the following command, if you would like to confirm the access log.
show
The example of displaying the access log is shown below.
timestamp user ipaddress protocol event
----------------+-----------+-----------------------+--------------+-----------------------------------------06/10/2009 ope 192.168.2.14 SSH Login Successful
----------------------------------------------------------------------------------------------------------------06/10/2009 admin 192.168.2.14 SSH Login Successful 13:53:14
----------------------------------------------------------------------------------------------------------------06/10/2009 user 192.168.2.14 HTTP Login Successful 13:55:49
-----------------------------------------------------------------------------------------------------------------
13:52:19
- 48-
Page 49

You can display only access log that corresponded to the specified from following condition.
• timestamp
Specify the date by the following format: MM/DD/YYYY
• user
Specify the user name.
• ipaddress
Specify the IP address on the remote management PC by the following format:
XXX.XXX.XXX.XXX
• protocol
Specify the following protocol: HTTP, HTTPS, SSH
• event
Specify the following event: normal, error
“normal” means not error event. ”error” means error event.
You can change the displaying sequence of access log and display the specified number of
access log by the specified from following options.
• oemnec_headlog <number>
Display from <number> head of the access log.
• oemnec_taillog <number>
Display from <number> back of the access log.
Enter the following command when you would like to use the above condition.
e.g.1) Display the access log whose username is Administrator.
show user==Administrator
e.g.2) Display the access log whose IP address is 192.168.1.100 and protocol is HTTP and
event is error.
show ipaddress==192.168.1.100,protocol==HTTP,event==error
e.g.3) Display from 100 back of the access log whose timestamp is 10/10/2010 and protocol
is HTTPS.
show –oemnec_taillog 100 timestamp==01/01/2010,protocol==HTTPS
- 49-
Page 50

Access log might not be correctly displayed with timestamp condition
about the log of recorded from AC ON to DC ON on host system.
Clearing ac cess log
To move the current default target to /admin1/sp1/log1/record1, enter the following command
at the command prompt.
cd /admin1/sp1/log1/record1
Enter the following command, if you would like to clear the access log.
delete
Setting acce ss log
To move the current default target to /admin1/sp1/log1, enter the following command at the
command prompt.
cd /admin1/sp1/log1
Enter the following command, if you would like to confirm the access log as properties of the
access log target which is /admin1/sp1/log1.
show
Enter the following command if you would like to modify a property of the setting access log.
set <Property>=<New value>
The properties which the access log target contains are as follows:
• oemnec_operationlog_enable
This specifies whether access log for the system control and the BMC setting
modification via Web browser is enabled. The valid values for this property are "2" and
"3". "2" means that the access log is enabled. "3" means that the access log is
disabled. This is the dynamic setting.
• oemnec_sshlog_enable
This specifies whether access log for login/logout of SSH is enabled. The valid values
for this property are "2" and "3". "2" means that the access log is enabled. "3" means
that the access log is disabled. This is the dynamic setting.
• oemnec_httpslog_enable
This specifies whether access log for login/logout of HTTP S is enabled. The valid
values for this property are "2" and "3". "2" means that the access log is enabled. "3"
- 50-
Page 51

means that the access log is disabled. This is the dynamic setting.
• oemnec_httplog_enable
This specifies whether access log for login/logout of HTTP is enabled. The valid
values for this property are "2" and "3". "2" means that the access log is enabled. "3"
means that the access log is disabled. This is the dynamic setting.
For example, enter the following command when you would like to use the access log for
login/logout of HTTPS.
set oemnec_httpslog_enable=2
- 51-
Page 52

Notice
IPMI command tool, you can use User ID from 6 to 16.
Notice
A user name can contain up to 15 alphanumeric characters, including
except for “ (space)”, ““(quotation marks)”, “&”, “?”, “=”, “¥”, “#”.
Notice
You should set appropriate value to all properties for the user to login
USER SETTINGS
This section describes how to confirm and modify the user account through the command
line interface. To move the current default target to an user account target which you would
like to confi rm or (and) modify, enter the following command at the command prompt. <N>
means any value between 1 and 12: Therefore you can select a user account between
account1 and account12. The <N> corresponds to an order from the list of user accounts top
on the user account configuration page through a Web browser.
cd /admin1/sp1/account<N>
Enter the following command, if you would like to confirm the information which the selected
user account has as its pr operties.
show
Enter the following command if you would like to modify a property of the selected user
account.
set <Property>=<New value>
The properties which the selected user account target contains are as follows:
• UserID
This corresponds to a user name (login name). It becomes effective at next login if you
change it.
• UserPassword
This is the user password (only can be changed). "UserPassword=" is displayed but
the password setting, value of this property, is not displayed when this property is
displayed. It becomes effective at next login if you change it.
• oemnec_Group
This specifies the user level. The valid values for this property are "User", "Operator"
and "Administrator". It becomes effective at next login if you change it.
The strings “InternalUseOnly”, “MWA”, “AccessByEM-Poem”,
“Administrator” are reserved by BMC. Please do not add or remove
these characters as User Name. The user account is synchronized
with the IPMI user account. If you want to add or remove users in the
“- (minus)” and “_ (underscore)”. “- (minus)” can not be used for the
top of a user name. The password accepts up to 19 ASCII characters,
with it.
- 52-
Page 53

NETWORK SETTINGS
This section describes how to confirm and modify the network setting for management LAN
through the command line interface. To move the current default target to
/admin1/sp1/enetport1, enter the following command at the command prompt:
cd /admin1/sp1/enetport1
Enter the following command, if you would like to confirm properties of the Ethernet port
target which is /admin1/sp1/enetport1.
show
The properties which the Ethernet port target contains are as follows:
• PermanentAddress
This specifies the MAC address for the management LAN. This property is read-only.
• AutoSense
This indicates whether Auto Negotiation is enabled for the LAN Connection T y pe
setting of the management LAN. Note that, the valid values for this property are
"TRUE" and "FALSE". "TRUE" means that the Auto Negotiation is enabled. "FALSE"
means that the Auto Negotiation is disabled. This property is read-only.
• FullDuplex
This indicates whether Full Duplex Mode is enabled for the LAN Connection Type
setting of the management LAN when the Auto Negotiation (AutoSense) is disabled
(FALSE). The value of this property is not displayed when the Auto Negotiation
(AutoSense) is enabled (TRUE). This property is read-only.
• PortType
This indicates Link Speed ("10Base-T" or "100Base-TX") for the LAN Connection Type
setting of the management LAN when the Auto Negotiation (AutoSense) is disabled
(FALSE). The value of this property is not displayed when the Auto Negotiation
(AutoSense) is enabled (TRUE). This property is read-only.
Followings describe how to confirm and modify the access limitation setting for management
LAN through the command line interface. To move the current default target to
/admin1/sp1/enetport1/lanendpt1, enter the following command at the command prompt:
cd /admin1/sp1/enetport1/lanendpt1
Enter the following command, if you would like to confirm properties of th e access limitation
target which is /admin1/sp1/enetport1/lanendpt1.
show
Enter the following command if you would like to modify a property of the access limitation
target.
set <Property>=<New value>
- 53-
Page 54

Clear all oemnec_allowedaccessips/oemnec_deniedaccessips values,
management LAN.
The communication with NEC ESMPRO Manager is also restricted by
Manager.
To r est r i ct access by IP address used by logging in to the BMC's SSH
IP address which is previously used by the BMC's SSH server.
You can set the access restriction settings to 222 characters. The
characters.
The properties which the access limitation target contains are as follows:
• oemnec_allowedaccessips
This specifies the IP addresses that permit a ccess to the management LAN. Divide IP
address by "," (ex. 192.168.1.2, 192.168.1.2, …) or use asterisk (ex. 192.168.1.*), if
you would like to set multiple permit IP address. Set "0.0.0.0" or no <value> (*) to this
property, if you would like to clear the value of this property, It becomes effective at
next login if you change it. The value of this property is cleared if
oemnec_deniedaccessips is set.
* "Set no <value>" means to input [Enter] key next to "=" key like following example.
set oemnec_allowedaccessips=[Enter]
• oemnec_deniedaccessips
This specifies the IP addresses that reject access to the management LAN. Divide IP
address by "," (ex. 192.168.1.2, 192.168.1.2, …) or use asterisk (ex. 192.168.1.*), if
you would like to set multiple reject IP address. Set "0.0.0.0" or no <value> (*) to this
property, if you would like to clear the value of this property, It becomes effective at
next login if you change it. The value of this property is cleared if
oemnec_allowedaccessips is set.
* "Set no <value>" means to input [Enter] key next to "=" key like following example.
set oemnec_deniedaccessips=[Enter]
For example, enter the following command when you would like to permit access from
192.168.1.* and 192.168.3.4.
set oemnec_allowedaccessips=192.168.1.*,192.168.3.4
if you would like NOT to restrict access by IP address for the
this configuration. Permit the IP address used by the communication
with NEC ESMPRO Manager if you would like to use NEC ESMPRO
server is impossible. So, if you would like to restrict the IP address,
the following procedures are necessary.
At first, log out of current BMC's SSH session using the IP address
and lo g in to the B MC's SSH server once again by using other IP
address permitted by oemnec_allowedaccessips /
oemnec_deniedaccessips (Access Permission Address)
Configuration. Then change the configuration for NOT permitting the
indication by the show command is displayed to 255 characters. The
access restriction settings from Web browser are possible to 255
- 54-
Page 55

Followings describe how to confirm and modify the DHCP setting for management LAN
through the command line interface. To move the current default target to
/admin1/sp1/enetport1/lanendpt1/ipendpt1, enter the following command at the command
prompt:
cd /admin1/sp1/enetport1/lanendpt1/ipendpt1
Enter the following command, if you would like to confirm properties of th e DHCP target
which is /admin1/sp1/enetport1/lanendpt1/ipendpt1.
show
Enter the following command if you would like to modify a property of the DHCP target.
set <Property>=<New value>
The properties which the DHCP target contains are as follows:
• AddressOrigin
This specifies whether DHCP is enabled for the management LAN. Note that, the valid
values for this property are "3" and "4". "3" means that the DHCP is disabled. "4"
means that the DHCP is enabled. This is the dynamic setting.
• IPv4Address
This specifies the IP address for the management LAN. This property is read-only.
• SubnetMask
This specifies the subnet mask for the management LAN. This property is read-only.
For example, enter the following command when you would like to enable DHCP.
set AddressOrigin=4
Followings describe how to confirm the gateway setting for management LAN through the
command line interface. To move the current default target to
/admin1/sp1/enetport1/lanendpt1/ipendpt1/gateway1, enter the following command at the
command prompt:
cd /admin1/sp1/enetport1/lanendpt1/ipendpt1/gateway1
Enter the following command, if you would like to confirm properties of th e gateway target
which is /admin1/sp1/enetport1/lanendpt1/ipendpt1/gateway1.
show
The properties which the gateway target contains are as follows:
• InfoFormat
The value is "3". This specifies the AccessInf o is IPv4 address. This property is
read-only.
- 55-
Page 56

• AccessInfo
This specifies the IP address of the default gateway for the management LAN. This
property is read-only.
Followings describe how to confirm and modify the network setting with disabling DHCP for
management LAN through the command line interface. To move the current default target to
/admin1/sp1/enetport1/lanendpt1/ipendpt1/staticipsettings1, enter the following command at
the command prompt:
cd /admin1/sp1/enetport1/lanendpt1/ipendpt1/staticipsettings1
Enter the following command, if you would like to confirm properties of th e static network
setting target which is /admin1/sp1/enetport1/lanendpt1/ipendpt1/staticipsettings1.
show
Enter the following command if you would like to modify a property of the static network
setting target.
set <Property>=<New value>
The properties which the static network setting target contains are as follows:
• IPv4Address
This specifies the IP address for the management LAN when DHCP is disabled. This
is the dynamic setting.
• SubnetMask
This specifies the subnet mask for the management LAN when DHCP is disabled.
This is the dynamic setting.
• GatewayIPv4Address
This specifies the IP address of the default gateway for the management LAN when
DHCP is disabled. This is the dynamic setting
Followings describe how to confirm and modify the HTTP service for management LAN
through the command line interface. To move the current default target to
/admin1/sp1/httpsvc1, enter the following command at the command prompt:
cd /admin1/sp1/httpsvc1
Enter the following command, if you would like to confirm properties of th e HTTP servi ce
target which is /admin1/sp1/httpsvc1.
show
Enter the following command if you would like to modify a property of the HTTP service
target.
- 56-
Page 57

set <Property>=<New value>
The properties which the HTTP service target contains are as follows:
• EnabledState
This specifies whether HTTP port is enabled for the management LAN. The valid
values for this property are "2" and "3". "2" means that the HTTP port is enabled. "3"
means that the HTTP port is disabled. This is the dynamic setting.
• oemnec_httpport
This specifies the HTTP port for the management LAN. This is the dynamic setting.
Followings describe how to confirm and modify the HTTPS service for management LAN
through the command line interface. To move the current default target to
/admin1/sp1/httpssvc1, enter the following command at the command prompt:
cd /admin1/sp1/httpssvc1
Enter the following command, if you would like to confirm properties of th e HTTPS service
target which is /admin1/sp1/httpssvc1.
show
Enter the following command if you would like to modify a property of the HTTPS service
target.
set <Property>=<New value>
The properties which the HTTPS service target contains are as follows:
• EnabledState
This specifies whether HTTPS port is enabled for the management LAN. The valid
values for this property are "2" and "3". "2" means that the HTTPS port is enabled. "3"
means that the HTTPS port is disabled. This is the dynamic setting.
• oemnec_httpsport
This specifies the HTTPS port for the management LAN. This is the dynamic setting.
Followings describe how to confirm and modify the SSH service for management LAN
through the command line interface. To move the current default target to
/admin1/sp1/sshsvc1, enter the following command at the command prompt:
cd /admin1/sp1/sshsvc1
Enter the following command, if you would like to confirm properties of the SSH service
target which is /admin1/sp1/sshsvc1.
show
- 57-
Page 58

Enter the following command if you would like to modify a property of the SSH service target.
set <Property>=<New value>
The properties which the SSH service target contains are as follows:
• EnabledState
This specifies whether SSH por t is enabled for the management LAN. The valid
values for this property are "2" and "3". "2" means that the SSH port is enabled. "3"
means that the SSH port is disabled. This is the dynamic setting.
• oemnec_sshport
This specifies the SSH port for the management LAN. This is the dynamic setting.
- 58-
Page 59

The user must have an account as administrator for controlling the
power consumption.
POWER CONSUMPTION CONTROL
You can control the power consumption of the host system through the command line
interface.
To move the current default target to /admin1/system1, enter the following command at the
command prompt:
cd /admin1/system1
State confirmation and modification of Power Consumption Control
Enter the following command, if you would like to confirm properties related to the power
consumption.
show
Enter the following command if you would like to modify a property related to the power
consumption.
set <Property>=<New value>
The properties related to power consumption on /admin1/system1 are as follows. The “()” of
the property name is a property name in the specific product.
“oemnec_ProcessorCoreDisableMax”, “oemnec_ProcessorCoreDisable”,
“oemnec_BootPerfomanceOptimized”, “oemnec_BootTimeConfig”,
“oemnec_NonAggressiveModeCorrectionTimeLimit”,
“oemnec_NonAggressiveModeCapvalue”, “oemnec_NonAggressiveModeSetableCapvalue”,
“oemnec_NonAggressiveMode” don’t display at specific product:
• EnabledState
The value is always "2".This specifies whether SSH port is enabled for the
management LAN. This property is read-only.
• oemnec_SafePowerCapping
This specifies whether fault check of the power consumption sensor is enabled. The
valid values for this property are "enabled" and "disabled". "enabled" means that the
fault check is enabled. "disable" means that t he fault check is disabled. Default setting
is "disabled".
• oemnec_ProcessorCoreDisableMax
This specifies Max Core number which can be set from
oemnec_ProcessorCoreDisable property. This property is not displayed if
oemnec_BootTimeConfig is disabled.
• oemnec_ProcessorCoreDisable
This specifies the number of CPU core to disable. This is the dynamic setting. This
property is not displayed if oemnec_BootTimeConfig is disabled.
- 59-
Page 60

• oemnec_BootPerformanceOptimized
This specifies whether Performance Optimized mode is enabled. This is the dynamic
setting. This property is not displayed if oemnec_BootTimeConfig is disabled.
• oemnec_BootTimeConfig
This specifies whether BootingMode is enabled. This is the dynamic setting. Default
value is “disabled”. This property supported by specific product.
• oemnec_NonAggressiveModeCorrectionTimeLimit
Specify the maximum time to take corrective actions in order to bring the system
power consumption back to the specified ‘Power Threshold (Pn)’ before generating
System Event Log and sending alert. This is the dynamic setting. This property is not
displayed if oemnec_NonAggressiveMode is disabled.
• oemnec_NonAggresiveModeCapvalue
This specifies the value of the power consumption starting he power consumption
control. This is the dynamic setting. This property is not displayed if
oemnec_NonAggressiveMode is disabled.
• oemnec_NonAggressiveModeSetableCapvalue
This specifies the value range of the settable oemnec_NonAggressiveModeCapvalue.
This property is read-only. This property is not displayed if
oemnec_NonAggressiveMode is disabled.
• oemnec_NonAggressiveMode
Non-Aggressive Mode brings the system power consumption under the specified
upper limit threshold without extremely decreasing system performance. The valid
values for this property are "enabled" and "disabled". "enabled" means that the power
control is enabled. "disable" means that the power control is disabled. Default setting
is "disabled".
• oemnec_ExceptionAction_Shutdown_Enable
This specifies whether the shutdown function of the system is enabled when power
consumption control is of no effect within a given
oemnec_AggressiveModeCorrectionTimeLimit after the power consumption pass
oemnec_AggressiveModeCapvalue. The valid values for this property are "enabled"
and "disabled". "enabled" means that the shutdown function is enabled. "disable"
means that the shutdown function is disabled. This is the dynamic setting. This
property is not displayed if oemnec_AggressiveMode is disabled.
• oemnec_AggressiveModeCorrectionTimeLimit (oemnec_CorrectionTimeLimit)
The shutdown of the system will be done according to setting of
oemnec_ExceptionAction_Shutdown_Enable when power consumption control is of
no effect within a given oemnec_AggressiveModeCorrectionTimeLimit (seconds) after
the power consumption pass oemnec_AggresiveModeCapvalue. This is the dynamic
setting. This property is not displayed if oemnec_AggressiveMode is disabled.
• oemnec_AggresiveModeCapvalue (oemnec_PowerCapvalue)
- 60-
Page 61

Notice
The system performance, such as frequency of CPU, decreases for
This specifies the value of the power consumption starting he power consumption
control. This is the dynamic setting. This property is not displayed if
oemnec_AggressiveMode is disabled.
• oemnec_AggressiveModeSetablePowerCapvalue (oemnec_setablePowerCapvalue)
This specifies the value range of the settable oemnec_AggressiveModeCapvalue.
This property is read-only. This property is not displayed if oemnec_AggressiveMode
is disabled.
• oemnec_AggressiveMode (oemnec_CriticalPowerCapSensor)
This specifies whether the power consumption control under the specified upper limit
threshold is enabled. The valid values for this property are "enabled" and "disabled".
"enabled" means that the power control is enabled. "disable" means that the power
control is disabled. Default setting is "disabled".
reducing power consumption when the power control is enabled.
- 61-
Page 62

The values of the properties for items not supported by the host
a power supply and mounting such as a device of the system either.
CONFIRMING SYSTEM INFORMATION
This section describes how to confirm the system information (product, BIOS/BMC firmware
revision, MAC address of System LAN, CPU, Memory) through the command line interface.
system is not displayed for the system information. Moreover, the
values of the properties for items supported with the host system
might not be displayed the system information according to a state of
Confirming Product Information
You can confirm the product information through the command line interface by entering
following the basic command at the command prompt.
show /admin1/system1
In this case, value of oemnec_productname property indicates "Product Name" information at
the "Properties" section. Also value of oemnec_modelnumber property indicates "Part /
Model Number" information and value of oemnec_serialnumber property indicates "Product
Serial Number" information. These properties for the product information are read-only.
Confirming MAC address of System LAN
To move the current default target to /admin1/system1, enter the following command at the
command prompt.
cd /admin1/system1
Here, to confirm all the targets for System LAN (onboard LAN), enter the following command
at the command prompt. All the System LAN targets are represented as enetport<N> strings
at "Targets" section. <N> means value of one-origin integer.
show
Next, when the following command is input, the MAC address of the System LAN target is
appeared at the right side of "PermanentAddress=" string. <N> means the number of the
System LAN target which you would like to confirm.
show enetport<N>
For example, enter the following command when you would like to confirm the MAC address
of LAN P ort1.
show enetport1
- 62-
Page 63

Confirming System BIOS revision
You can confirm the System BIOS revision through the command line interface by entering
following the basic command at the command prompt.
show /admin1/system1/swid1
In this case, the System BIOS revision is appeared at the right side of "VersionString=" string
in the "Properties" section.
Confirming BMC firmware revision
You can confirm the BMC firmware revision through the command line interface by entering
following the basic command at the command prompt.
show /admin1/sp1/swid1
In this case, the BMC firmware revision is appeared at the right side of "VersionString="
string in the "Properties" section. Also the SDR revision is appeared at the right side of "
oemnec_sdrversion =" string.
Confirming CPU Information
To move the current default target to /admin1/system1, enter the following command at the
command prompt.
cd /admin1/system1
Here, to confirm all the targets for CPU, enter the following command at the command
prompt. All the CPU targets are represented as cpu<N> strings at "Targets" section. <N>
means value of one-origin integer.
show
Next, when the following command is input, information of a specific CPU target is displayed
at "Properties" section. Here, <N> means CPU target number which you would like to
confirm.
show cpu<N>
The EnabledState property of the CPU target indicates the CPU status. "2" indicates CPU
installed. No value (Only "EnabledState=" string is displayed.) indicates CPU not installed. "3"
indicates that the CPU is defected. The values of the other properties (such as
oemnec_clock) are not displayed (Only property name with "=" string is displayed.). if the
CPU is not installed (Only "EnabledState=" string is displayed.). Also, the values of the
properties not supported by the host system are not displayed.
- 63-
Page 64

For example, enter the following command when you would like to confirm the infor mation of
CPU1.
show cpu1
The example of displaying information in this case is shown below.
ufip=/admin1/system1/cpu1
Properties:
EnabledState=enabled
oemnec_clock=2660MHz
oemnec_validcore=4
oemnec_maxcore=4
oemnec_validthread=8
oemnec_maxthread=8
oemnec_l1cache=256KB
oemnec_l2cache=1024KB
oemnec_l3cache=8192KB
Verbs:
cd
exit
help
show
version
- 64-
Page 65

Confirming Memory Information
To move the current default target to /admin1/system1, enter the following command at the
command prompt.
cd /admin1/system1
Here, to confirm all the targets for memory (DIMM), enter the following command at the
command prompt. All the memory (DIMM) targets are represented as memory<N> strings at
"Targets" section. <N> means value of one-origin integer.
show
Next, when the following command is input, information of a specific memory (DIMM) target
is displayed at "Properties" section. Here, <N> means memory (DIMM) target number which
you would like to confirm.
show memory<N>
The EnabledState property of the memory target indicates the memory (DIMM) status. "2"
indicates memory (DIMM) installed. "3" indicates memory (DIMM) error. If the memory
(DIMM) is not installed the target will not be displayed. Also, the values of the properties not
supported by the host system are not displayed.
For example, enter the following command when you would like to confirm the information of
memory1 (CPU1_DIMM1).
show memory1
The example of displaying information in this case is shown below.
ufip=/admin1/system1/memory1
Properties:
enabledstate=2
oemnec_slotname=CPU1_DIMM1
oemnec_clocksize=1024MB 1066MHz
Verbs:
cd
exit
help
show
version
- 65-
Page 66

Commands to acquire the state are executable in all user levels.
SPECIAL EXTENDED COMMANDS
This section describes the special extended command which can do state acquisition
(powerstate, lampstate) and interrupt generation for OS dump (nmidump). The special
extended commands use the syntaxes different from the basic command's ones.
S tate Acqui sition
You can acquire the state of the system at the command prompt:
Power State acquisition
Power state acquisition command (powerstate) is executable only when current default target
is "/admin1" or "/admin1/system1".
Enter the following command, if the current default target is not "/admin1" and
"/admin1/system1".
cd /admin1
or
cd /admin1/system1
Enter the following command at the command prompt:
powerstate
One of the following responses is returned according to the power state.
power on
System power is on.
power off
System power is off.
Lamp State acquisition
Lamp state acquisition command (lampstate) is executable only when current default target is
"/admin1", "/admin1/system1" or “/admin1/system1/led1”.
Enter the following command, if the current default target is not "/admin1", "/admin1/system1"
or “/admin1/system1/led1”.
cd /admin1
or
cd /admin1/system1
or
cd /admin1/system1/led1
- 66-
Page 67

The state of the STATUS LED and the meaning are different according
to the system. Refer to the User’s Guide of the system for details.
If the UID LED is not mounted into the host system, the “UID LED
the description of the UID LED.
Status LED state acquisition
Enter the following command at the command prompt:
lampstate -statuslamp
One of the following responses is returned according to the ST ATUS LED state.
off
STATUS LED is turned off.
green on
STATUS LED lights in green.
green blink
STATUS LED is blinking in green.
amber on
STATUS LED lights in amber.
amber blink
STATUS LED is blinking in amber.
red on
STATUS LED lights in red.
red blink
STATUS LED is blinking in red.
UID LED State acquisition
Enter the following command at the command prompt:
lampstate -uidlamp
One of the following responses is returned according to actual display state of the UID LED.
off
UID LED is turned off.
on
UID LED is turned on (lights).
blink
UID LED is blinking (flashing ).
State acquisition” function works only to the virtual UID LED of the
Server Panel. Please refer to the User’s Guide of your host system for
- 67-
Page 68

Notice
The user must have an account as operator or administrator for
The above command behavior is equivalent to pressing the DUMP
Interrupt Generation for OS Dump
You can execute OS dump by entering following command at the command prompt.
nmidump /admin1/system1
executing the nmidump command.
switch on the host system.
- 68-
Page 69

EXPRESSSCOPE Engine 3 implementation of WS-Management
1.0.0.
EXPRESSSCOPE Engine 3 is confirmed the WS-Management operation
Windows Remote Management (WinRM) 2.0
Notice
To use WS-Management, you need to configure HTTPS connection to
2: Configuring the Host System”.
The user must have an account as operator or administrator for
power control.
Notice
Performing power control when the operating system is running may
7. WS-Management (Web Service for Management)
OVERVIEW
With the WS-Management Protocol, you can control the host system and check the sensor of
host system.
complies with the specification, DTMF Web Services for Management
with the following tools that support the WS-Management protocol.
•
be enabled. Refer to the “Management LAN Settings” in the “Chapter
POWER CONTROL
You can perform power control of the host system.
cause the loss of data in the host system.
- 69-
Page 70

Please change according to your environment.
Engine 3.
Power ON
Create the file input-RequestPowerStateChange2.xml and enter the following command, if
you use WinRM.
winrm invoke RequestPowerStateChange
“http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_PowerManagementSer
vice?__cimnamespace=root/cimv2+Name=Host Power Management
Service+CreationClassName=CIM_PowerManagementService+SystemName=Unkn
own.IPMI_BMC_DeviceID.136+SystemCreationClassName=CIM_HostComputerSyst
em” -r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -format:xml -file:input-RequestPowerStateChange2.xml
-skipCAcheck -skipCNcheck -skipRevocationcheck
input-RequestPowerStateChange2.xml
<n1:RequestPowerStateChange_INPUT
xmlns:n1="http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Power
ManagementService"
xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing"
xmlns:wsman="http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd">
<n1:PowerState>2</n1:PowerState>
<n1:ManagedElement>
<wsa:ReferenceParameters>
<wsman:ResourceURI>http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/
CIM_HostComputerSystem</wsman:ResourceURI>
<wsman:SelectorSet>
<wsman:Selector Name='__cimnamespace'>root/cimv2</wsman:Selector>
<wsman:Selector
Name='CreationClassName'>CIM_HostComputerSystem</wsman:Selector>
<wsman:Selector Name='Name'>Unknown.IPMI BMC
DeviceID.136</wsman:Selector>
</wsman:SelectorSet>
</wsa:ReferenceParameters>
</n1:ManagedElement>
</n1:RequestPowerStateChange_INPUT>
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
Forced Power OFF
Create the file input-RequestPowerStateChange6.xml and enter the following command, if
you use WinRM.
winrm invoke RequestPowerStateChange
“http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_PowerManagementSer
vice?__cimnamespace=root/cimv2+Name=Host Power Management
Service+CreationClassName=CIM_PowerManagementService+SystemName=Unkn
- 70-
Page 71

Please change according to your environment.
Engine 3.
own.IPMI_BMC_DeviceID.136+SystemCreationClassName=CIM_HostComputerSyst
em” -r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -format:xml -file:input-RequestPowerStateChange6.xml
-skipCNcheck -skipCAcheck -skipRevocationcheck
input-RequestPowerStateChange6.xml
<n1:RequestPowerStateChange_INPUT
xmlns:n1="http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Power
ManagementService"
xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing"
xmlns:wsman="http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd">
<n1:PowerState>6</n1:PowerState>
<n1:ManagedElement>
<wsa:ReferenceParameters>
<wsman:ResourceURI>http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/
CIM_HostComputerSystem</wsman:ResourceURI>
<wsman:SelectorSet>
<wsman:Selector Name='__cimnamespace'>root/cimv2</wsman:Selector>
<wsman:Selector
Name='CreationClassName'>CIM_HostComputerSystem</wsman:Selector>
<wsman:Selector Name='Name'>Unknown.IPMI BMC
DeviceID.136</wsman:Selector>
</wsman:SelectorSet>
</wsa:ReferenceParameters>
</n1:ManagedElement>
</n1:RequestPowerStateChange_INPUT>
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
- 71-
Page 72

The above OS shutdown is equivalent to pressing the POWER switch
must be set to shut down when you power off the system.
Please change according to your environment.
Engine 3.
OS Shutdown
Create the file input-RequestPowerStateChange8.xml and enter the following command, if
you use WinRM.
winrm invoke RequestPowerStateChange
“http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_PowerManagementSer
vice?__cimnamespace=root/cimv2+Name=Host Power Management
Service+CreationClassName=CIM_PowerManagementService+SystemName=Unkn
own.IPMI_BMC_DeviceID.136+SystemCreationClassName=CIM_HostComputerSyst
em” -r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -format:xml -file:input-RequestPowerStateChange8.xml
-skipCAcheck -skipCNcheck -skipRevocationcheck
input-RequestPowerStateChange8.xml
<n1:RequestPowerStateChange_INPUT
xmlns:n1="http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Power
ManagementService"
xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing"
xmlns:wsman="http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd">
<n1:PowerState>8</n1:PowerState>
<n1:ManagedElement>
<wsa:ReferenceParameters>
<wsman:ResourceURI>http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/
CIM_HostComputerSystem</wsman:ResourceURI>
<wsman:SelectorSet>
<wsman:Selector Name='__cimnamespace'>root/cimv2</wsman:Selector>
<wsman:Selector
Name='CreationClassName'>CIM_HostComputerSystem</wsman:Selector>
<wsman:Selector Name='Name'>Unknown.IPMI BMC
DeviceID.136</wsman:Selector>
</wsman:SelectorSet>
</wsa:ReferenceParameters>
</n1:ManagedElement>
</n1:RequestPowerStateChange_INPUT>
when the power of the host system is on. Your operating system
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
- 72-
Page 73

Please change according to your environment.
Engine 3.
System Reset
Create the file input-RequestPowerStateChange10.xml and enter the following command, if
you use WinRM.
winrm invoke RequestPowerStateChange
“http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_PowerManagementServic
e?__cimnamespace=root/cimv2+Name=Host Power Management
Service+CreationClassName=CIM_PowerManagementService+SystemName=Unknown
.IPMI_BMC_DeviceID.136+SystemCreationClassName=CIM_HostComputerSystem”
-r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -format:xml -file:input-RequestPowerStateChange10.xml
-skipCAcheck -skipCNcheck -skipRevocationcheck
input-RequestPowerStateChange10.xml
<n1:RequestPowerStateChange_INPUT
xmlns:n1="http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Power
ManagementService"
xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing"
xmlns:wsman="http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd">
<n1:PowerState>10</n1:PowerState>
<n1:ManagedElement>
<wsa:ReferenceParameters>
<wsman:ResourceURI>http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/
CIM_HostComputerSystem</wsman:ResourceURI>
<wsman:SelectorSet>
<wsman:Selector Name='__cimnamespace'>root/cimv2</wsman:Selector>
<wsman:Selector
Name='CreationClassName'>CIM_HostComputerSystem</wsman:Selector>
<wsman:Selector Name='Name'>Unknown.IPMI BMC
DeviceID.136</wsman:Selector>
</wsman:SelectorSet>
</wsa:ReferenceParameters>
</n1:ManagedElement>
</n1:RequestPowerStateChange_INPUT>
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
- 73-
Page 74

The above command behavior is equivalent to pressing the DUMP
switch on the host system.
Change according to your environment.
Engine 3.
Notice
Performing interrupt generation for OS dump when the operating
Interrupt Generation for O S Dump
Create the file input-RequestPowerStateChange11.xml and enter the following command, if
you use WinRM.
winrm invoke RequestPowerStateChange
“http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_PowerManagementServic
e?__cimnamespace=root/cimv2+Name=Host Power Management
Service+CreationClassName=CIM_PowerManagementService+SystemName=Unknown
.IPMI_BMCDeviceID.136+SystemCreationClassName=CIM_HostComputerSystem”
-r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -format:xml -file:input-RequestPowerStateChange11.xml
-skipCAcheck -skipCNcheck -skipRevocationcheck
input-RequestPowerStateChange11.xml
<n1:RequestPowerStateChange_INPUT
xmlns:n1="http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Power
ManagementService"
xmlns:wsa="http://schemas.xmlsoap.org/ws/2004/08/addressing"
xmlns:wsman="http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd">
<n1:PowerState>11</n1:PowerState>
<n1:ManagedElement>
<wsa:ReferenceParameters>
<wsman:ResourceURI>http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/
CIM_HostComputerSystem</wsman:ResourceURI>
<wsman:SelectorSet>
<wsman:Selector Name='__cimnamespace'>root/cimv2</wsman:Selector>
<wsman:Selector
Name='CreationClassName'>CIM_HostComputerSystem</wsman:Selector>
<wsman:Selector Name='Name'>Unknown.IPMI BMC
DeviceID.136</wsman:Selector>
</wsman:SelectorSet>
</wsa:ReferenceParameters>
</n1:ManagedElement>
</n1:RequestPowerStateChange_INPUT>
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
system is running may cause the loss of data in the host system.
- 74-
Page 75

- 75-
Page 76

Change according to your environment.
Engine 3.
SENSOR INFORMATION
You can get sensor information either by enumeration of all sensors or by retrieving specified
sensor.
Enumeration of All Sensors
Enter the following command, if you enumerate numeric sensors (e.g.: temperature, voltage)
with WinRM.
winrm enumerate
http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_NumericSensor
-username:USERNAME -password:PASSWORD -r:https://IP_ADDRESS/wsman
-auth:basic -encoding:utf-8 -skipCAcheck -skipCNcheck -skipRevocationcheck
Enter the following command, if you enumerate non-numeric sensors (e.g.: PSU, HDD) with
WinRM.
winrm enumerate
http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_Sensor
-username:USERNAME -password:PASSWORD -r:https://IP_ADDRESS/wsman
-auth:basic -encoding:utf-8 -skipCAcheck -skipCNcheck -skipRevocationcheck
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
Retrieving Specified Sensor
You can retrieve the sensor by specifying sensor number.
Enter the following command, if you retrieve the sensor of sensor number 48 with the
WinRM.
winrm get
"http://schemas.dmtf.org/wbem/wscim/1/cim-schema/2/CIM_NumericSensor?Syste
mCreationClassName=CIM_ComputerSystem+CreationClassName=CIM_NumericS
ensor+SystemName=Unknown.IPMI BMC DeviceID.136+DeviceID=1.48.0.136.1.99"
-r:https://IP_ADDRESS/wsman -username:USERNAME -password:PASSWORD
-auth:basic -encoding:utf-8 -skipCAcheck -skipCNcheck -skipRevocationcheck
- 76-
Page 77

Change according to your environment.
Engine 3.
Specify the “Device ID” returned in the response of enumerating all
“IP_ADDRESS” : IP address of EXPRESSSCOPE Engine 3.
“USERNAME/PASSWORD”: username/password of EXPRESSSCOPE
sensors.
- 77-
Page 78
8. Troubleshooting
ERROR MESSAGES
Abnormality occurs while using remote management, and the error dialog might be displayed
in management PC. Please refer to the list of the message of the online help for the main
message and the coping process.
ABOUT ECO SETTING
The electric power value may not be reached to Power Cap Value.
The electric power value might not necessarily reach even the value of Power Cap value.
The electric power control lowers the power consumption of the system by lowering the
frequency of CPU/Memory.
When CPU/Memory Throttling value reaches 100%, the electric power value doesn't fall any
more.
“Failed to access BMC.” error has occurred while executing ECO setting.
If you execute ECO setting during shutdown the OS of the host system, ECO setting may
not be set correctly. I n this case, please execute again after shutdown process is finished.
For more detail about the Power Monitoring and Power Control Function, please reference
the following site.
http://www.58support.nec.co.jp/global/download/index.html
[Others] - [Technology papers]
ABOUT NETWORK INFORMATION
Please note that the “Link stat us”(*) may not be displayed correctly depending on the O S of
the host sys tem, because the link status of the system LAN can not get properly depending
on the version of the LAN drivers that are used by the OS.
(*) [System] - [Component] - [Network] - [System LAN Information]
OTHERS TIPS
Should you have troubles while using the BMC for remote control, monitoring, and
management of the host system, please first check the system according to the online help
to troubleshoot your issue prior to sending it for repair.
For the issues regarding your system operation, please refer to the User’s Guide attached to
your system.
If your issue is not described below, or should the provided instructions do not resolve your
- 78-
Page 79

issue, please contact your service center.
- 79-
Page 80

License Notes
This product includes open source software programs described below.
GNU General Public License
• Busybox
• Linux Kernel
• U-Boot
• stunnel
GNU GENERAL PUBLIC LICENSE
Version 2, June 1991
Copyright (C) 1989, 1991 Free Software Foundation, Inc.,
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
Preamble
The licenses for most software are designed to take away your
freedom to share and change it. By contrast, the GNU General Public
License is intended to guarantee your freedom to share and change free
software--to make sure the software is free for all its users. This
General Public License applies to most of the Free Software
Foundation's software and to any other program whose authors commit to
using it. (Some other Free Software Foundation software is covered by
the GNU Lesser General Public License instead.) You can apply it to
your programs, too.
When we speak of free software, we are referring to freedom, not
price. Our General Public Licenses are designed to make sure that you
have the freedom to distribute copies of free software (and charge for
this service if you wish), that you receive source code or can get it
if you want it, that you can change the software or use pieces of it
in new free p rograms; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid
anyone to deny you these rights or to ask you to surrender the rights.
These restrictions translate to c e r tain responsibil ities for you if you
distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether
gratis or for a fee, you must give the recipients all the rights that
you have. You must make s ure that they, too, receive or can get the
source code. And you mus t show them t hese terms so they know their
rights.
We protect your rights with two steps: (1) copyright the software, and
(2) offer you this license which gives you legal p ermission to copy,
distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain
that ever yone understa nds that there is no warranty for this free
- 80-
Page 81

software. If the software is modified by someone else and passed on, we
want its recipients to know that wha t they have i s not the original, so
that any problems introduced by other s will not reflect on the original
authors' reputations.
Finally, any free program is threatened constantly by software
patents. We wish to avoid the danger that redistributors of a free
program wil l individua lly obtain p atent licenses, in effec t making the
program proprietary. To prevent this, we have made it clear that any
patent must be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and
modification follow.
GNU GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License applies to any program or other work which contains
a notice placed by the copyright holder saying it may be distributed
under the terms of this General Public License. The "Program", below,
refers to any such program or work, and a "work based on the Program"
means eithe r the Program or any derivative work under copyright law:
that is to say, a work containing the Pr ogram or a portion of it,
either verbatim or with modifications and/or translated into another
language. (Hereinafter, translation is included without limitation in
the term "modification".) Each licensee is addressed as "you".
Activities other than copying, distribution and modification are no t
covered by this License; they are outside its scope. The act of
running the Program is not restricted, and the output fro m the Program
is covered only if its co ntents constitute a work based on the
Program (independent of having be en made by running the Program).
Whether that is true depends on what the Program does.
1. You may copy and distribute verbatim copies of the Program's
source code as you receive it, in any medium, provided that you
conspicuously and appropriately publish on each copy an appropriate
copyright notice and disclaimer of warranty; keep intact all the
notices that refer to this License and to the absence of any warranty;
and give any other recipients of the Program a copy of this License
along with the Program.
You may charge a fee for the physical act of transferring a copy, and
you may at your option offer warranty protection in exchange for a fee.
2. You may modify your copy or copies of the Program or any portion
of it, thus forming a work based on the Program, and copy and
distribute such modifications o r wor k u nde r the terms of Section 1
above, provided that you also meet all of these conditions:
a) You must cause the modified files to carry prominent notices
stating that you changed t he files and t he date of any change.
b) You must cause any work t hat you distri bute or publish, that in
whole or in part contains or is derived from the Program or any
part thereof, to be licensed as a whole at no charge to all third
parties under the terms of this License.
- 81-
Page 82

c) If the modified program normally reads commands interactively
when run, you must cause it, when started running for such
interactive use in the most ordinary way, to print or display an
announceme nt including an appropriate copyright notice a nd a
notice that there is no warranty (or else, sa yin g tha t you provide
a warranty) and that users may redistribute the program under
these conditions, and telling the use r how to view a copy of thi s
License. (Exception: if the Program itself is interactive but
does not normally print such an announcement, your work based on
the Program is not required to print an announcement.)
These requirements apply to the modified work as a whole. If
identifiable sections of that work are not derived from the Program,
and can be reasonably considered independent and separate works in
themselves, then this License, and its terms, do not apply to those
sections whe n you di str ib ute them as separate wor ks. But when you
distribute the same sections as part of a whole which is a work based
on the Program, the distribution o f t he whole must be on the terms of
this License, whose permissions for other licensees extend to the
entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to cla im rights or contest
your rights to work written entire ly by you; rather, the intent is to
exercise the right to control the d istr ibution of derivative or
collective works based on the Program.
In addition, mere aggregation of another work not based on the Program
with the Pr ogram (or with a work ba sed on the Program) on a volume of
a storage or distribution medium does not bring the other work under
the scope of this License.
3. You may copy and distribute the Program (or a work based on it,
under Section 2) in object code or executable form under the terms of
Sections 1 and 2 above provided that you also do one of the following:
a) Accompany it with the complete corresponding machine-readable
source code, which must be distributed under the terms of Sections
1 and 2 above on a medium customarily used for software inter change; or ,
b) Accompany it with a written offer, valid for a t le a st three
years, to give any third pa rty, for a charge no more than your
cost of physically performing source distribution, a complete
machine-readable copy of the corresponding source code, to be
distributed under the terms of Sections 1 and 2 above on a medium
customarily used for software interchange; or,
c) Accompany it with the information you received as to the offer
to distribute corresponding source code. (This alternative is
allowed only for noncommercial distribution and only if you
received the program in object code or executable form with such
an offer, in accord with Subsection b above.)
The source code for a work means the preferred form of the work for
making modifications to it. For an executable work, complete source
code means all the source code for all modules it contains, plus any
associated interface definitio n files, plus the scripts used to
control compilation and installation of the executable. However, as a
special exception, the source code distributed need not include
- 82-
Page 83

anything that is normally distributed (in either source or binary
form) with the major components (compiler, kernel, and so on) of the
operating system on which the executable runs, unless that component
itself accompanies the executable.
If distribution of executable or object code is made by offering
access to copy from a designated place, then offering equivalent
access to copy the source code from the same place counts as
distribution of the source code, even though t hird partie s are not
compelled to copy the source along with the object code.
4. You may not copy, modify, sublicense, or distribute the Program
except as expressly provided under this License. Any attempt
otherwise to copy, modify, sublicense or distribute the Program is
void, and will automatically terminate your rights under this License.
However, parties who have received copies, or rights, from you under
this License will not have their licenses terminated so long as such
parties remain in full compliance.
5. You are not required to accept this License, since you have not
signed it. However, nothing else grants you permission to modify or
distribute the Program or its derivative works. These actions are
prohibited by law if you do not accept this License. Therefore, by
modifying or distributing the Program (or any work based on the
Program), you indicate your acceptance of this License to do so, and
all its terms and conditions for copying, distributing or modifying
the Program or works based on it.
6. Each time you redistribute the Program (or any work based on the
Program), the recipient automatically receives a license from the
original licensor to copy, distrib ute or modify the Program subject to
these terms and conditions. You may not impose any further
restrictions on the recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties to
this License.
7. If, as a consequence of a court judgment or allegation of patent
infringement or for any other rea son (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot
distribute so as to satisfy simultaneo usly your obligations under this
License and any other pertinent obligations, then as a cons equence you
may not distribute the Program at all. For example, if a patent
license would not permit royalt y-free redistribution of the Program by
all those who receive copies directly or indirectly through you, then
the only wa y you could satisfy bot h it and this License would be to
refrain entirely from distributi on of the Program.
If any portion of this section is held invalid or unenforceable under
any particular circumstance, the balance of the section is intended to
apply and the section as a whole is intende d to apply in other
circumstances.
It is not the purpose of this section t o induce you to infringe any
patents or other property right c la ims or to contest validity of any
such claims; this section has the sole purpose of protecting t he
integrity of the free software distribution system, which is
- 83-
Page 84

implemented by public license practices. Many people have made
generous contributions to the wide range of software distributed
through that system in reliance o n consistent application of that
system; it is up to the author/donor to decide if he or she is willing
to distribute software through any other system and a licensee cannot
impose that choice.
This section is intended to make thor oughly clear what is believed to
be a consequence of the rest of this License.
8. If the distribution and/or use of the Program is restricted in
certain countries either by patents or by copyrighted interfaces, the
original copyright holder who pla ces the Program under this License
may add an explicit geographica l distribution limitation excluding
those countries, so that distrib ution is permitted only in or among
countries not thus excluded. In suc h case, this Li cense incorporates
the limitation as if written in the body of this License.
9. The Free Software Foundation may publish revised and/or new versions
of the General Public License from time to time. Such new versions will
be similar in spirit to the present ver sion, but may differ in detail to
address new problems or concerns.
Each version is given a distinguishing version number. If the Program
specifies a version number of this License which applies to it and "any
later version", you have the option of following the terms and conditions
either of that version or of any later version published by the Free
Software Foundation. If the Program does not specify a version number of
this License, you may choose any version ever published by the Free Software
Foundation.
10. If you wish to incorporate parts of the Program into other free
programs whose distribution conditions are different, write to the author
to ask for permission. For software which is copyrighted by the Free
Software Foundation, write to the Free Software Foundation; we sometimes
make exceptions for this. Our decision will be guided by the two goals
of preserving the free status of all derivatives of our free software and
of promoting the shari ng and reuse of software generally.
NO WARRANTY
11. BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY
FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN
OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIE S
PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED
OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIE S OF
MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS
TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE
PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING,
REPAIR OR COR RECTION.
12. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR
REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR D AM AGE S,
INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTI AL DAM AGES ARISING
OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED
TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY
YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER
- 84-
Page 85

PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE
POSSIBILITY OF SUCH DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest
possible use to the public, the be st way to achieve this is to make it
free software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest
to attach them to the start of each source file to most effectively
convey the exclusion o f warranty; and each file s hould have a t least
the "copyright" line and a pointer to where the full notice is found.
<one line to gi ve the program's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This program is free software; you can redistribute it and/or modify
it under the terms of the GNU General Public License as published by
the Free Software Foundation; either version 2 of the License, or
(at your option) any later version.
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU General Public License for more details.
You should have received a copy of the GNU General Public License along
with this program; if not, write to the Free Software Foundation, Inc.,
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
Also add information on how to contact you by electronic and paper mail.
If the program is interactive, make it output a short notice like this
when it starts in an interactive mode :
Gnomovision version 69, Copyright (C) year name of author
Gnomovision comes with ABSOLUTELY NO WARRANTY; for details type `show w'.
This is free software, and you are welcome to redistribute it
under certain conditions; type `show c' for de ta ils.
The hypothetical com mands `show w' and `show c' should show the appropriate
parts of the General Public License. Of course, the commands you use may
be called s omething other than `show w' and `show c'; they could even be
mouse-clicks or menu items--whatever suits your program.
You should also get your employer ( i f you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the program, if
necessary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the program
`Gnomovision' (which makes passes at compilers) written by James Hacker.
<signature of Ty Coon>, 1 April 1989
Ty Coon, President of Vice
- 85-
Page 86

This General Public License does not permit incorporating your program into
proprietary programs. If your program is a subroutine library, you may
consider it more useful to permit linking proprietary applications wit h the
library. If this is what you want to do, use the GNU Lesser General
Public License instead of this License.
GNU Lesser Ge neral Public Licsense
• glibc
GNU LESSER GENERAL PUBLIC LICENSE
Version 2.1, February 1999
Copyright (C) 1991, 1999 Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts
as the successor of the GNU Library Public License, version 2, hence
the version number 2.1.]
Preamble
The licenses for most software are designed to take away your
freedom to share and change it. By contrast, the GNU General Public
Licenses are intended to guarantee your freedom to share and change
free software--to make sure the software is free for all its users.
This license, the Lesser General Public License, applies to some
specially designated software packages--typically libraries--of the
Free Software Foundation and other authors who decide to use it. You
can use it too, but we suggest you first think carefully about whe ther
this license or the ordinary General Public License is the better
strategy to use in any particular case, based on the explanations below.
When we speak of free software, we are referring to freedom of use,
not price. Our General Public Licenses are designed to make sure that
you have the freedom to distribute copies of free software (and charge
for this service if you wish); that you receive source code or can get
it if you want it; that you can change the software and use pieces of
it in new free programs; and that you are infor med that you ca n do
these thing s .
To protect your rights, we need to make restrictions that forbid
distributo rs to deny you these rights or to ask you to surrender these
rights. These re str ic tions translate to certain responsibili ties for
you if you distribute copies of the libra ry or if you modify it.
For example, if you distribute copie s o f the libr a ry, whether gratis
or for a fee, you must give the recipie nts all the rights that we ga ve
you. You must make sure that they, too, receive or can get the source
code. If you link other code with the library, you must provide
complete object files to the recipie nts, so that they can relink them
with the library after making changes to the library and recompiling
it. And you must show them these ter ms s o they know their rights.
- 86-
Page 87

We protect your rights wit h a two-step method: (1) we copyright the
library, and (2) we offer you this license, which g ives you legal
permission to copy, distribute and/or modify the library.
To protect each distributor, we want to make it very clear that
there is no warranty for the free libr a ry. Also, if the library is
modified by someone else and passed on, the recipients should know
that what they have is not the original ve rsion, so tha t the origi nal
author's reputation will not be affected b y pro blems that might be
introduced by others.
Finally, software patents pose a constant threat to the existence of
any free program. We wish to make sure that a company cannot
effectively restrict the users of a free program by obtaining a
restrictive license from a patent holder. Therefore, we insist that
any patent license obtained for a version of the library must be
consistent with the ful l freedom of use specified in this license.
Most GNU software, including some libraries, is covered by the
ordinary GNU General Public License. This license, the GNU Lesser
General Public License, applies to certain designated libraries, and
is quite different from the ordinary General Public License. We use
this license for certain librarie s in or der to permit linking those
libraries into non-free programs.
When a program is linked with a library, whether statically or using
a shared library, the combination of the two is legally speaki ng a
combined work, a derivative of the original library. The ordinary
General Public License therefore permits such linking only if the
entire combination fits its criteria of freedom. The Lesser General
Public License permits more lax criteria for linking other code with
the library.
We call this license the "Lesser" General Public License because it
does Less to protect the user's freedom than the ordinary General
Public License. It also provides other free software developers Less
of an advantage over competing non-free programs. These disadvantages
are the reason we use the ordinary General Public License for many
libraries. However, the Lesser license provides advantages in certain
special circumstances.
For example, on rare occasions, there may be a special need to
encourage the widest possible use of a certain library, so that it becomes
a de-facto standard. To achieve this, non-free programs must be
allowed to use the library. A more frequent case is that a free
library does the same job as widely used non-free libraries. In this
case, there is little to gain by limitin g the free library to free
software only, so we use the Lesser General Public License.
In other cases, permission to use a particular library in non-free
programs enables a greater number of people to use a large body of
free software. For example, permission to use the GNU C Library in
non-free programs enables many more people to use the whole GNU
operating system, as well as its variant, the GNU/Linux operating
system.
Although the Lesser General Public License is Less protective of the
users' freedom, it does ensure that the user of a program that is
- 87-
Page 88

linked with the Library has the freed om and the wherewithal to run
that program using a modified version of the Library.
The precise terms and conditions for copying, distribution and
modification follow. Pay close attention to the difference between a
"work based on the libra ry" and a "work that uses the library". The
former contains code derived from the library, whereas the latter must
be combined with the library in order to run.
GNU LESSER GENERAL PUBLIC LICENSE
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
0. This License Agreement applies to any software library or other
program which contains a notice placed by the copyright holder or
other authorized party saying it may be distributed under the terms of
this Lesser General Public License (a lso c a lle d "this License").
Each licensee is addressed as "you".
A "library" means a collection of software functions and/or data
prepared so as to be conveniently linked with application programs
(which use some of those functions and data) to form executables.
The "Library", below, refers to any such software library or work
which has been distributed under these terms. A "work based on the
Library" means either the Library or any derivative work under
copyright law: that is to say, a work containing the Library or a
portion of it, either verbatim or with modifications and/or translated
straightforwardly into another language. (Hereinafter, translation is
included without limitation in the term "modification".)
"Source code" for a work means the preferred form of the work for
making modifications to it. For a library, complete source code means
all the source code for all modules it contains, plus any associated
interface definition files, plus the scripts used to control compilatio n
and installation of the library.
Activities other than copying, distr ibution and modification are not
covered by this License; they are outside its scope. The act of
running a pr ogram using the Library is not restricted, and output from
such a program is covered only if its contents constitute a work based
on the Library (independent of the use of the Library in a tool for
writing it). Whether that is true de pends on what the Library does
and what the program that uses the Library does.
1. You may copy and distribute verbatim copies of the Library's
complete source code as you receive it, in any medium, provided that
you conspicuously and appropriately publish on each copy an
appropriate copyright notice and disclaimer of warranty; keep intact
all the notices that refer to this License and to the absence of any
warranty; and distribute a copy of t his License along with the
Library.
You may charge a fee for the physical act of transferring a copy,
and you may at your option offer warranty protection in exchange for a
fee.
2. You may modify your copy or copies of the Library or any portion
of it, thus forming a work based on the Library, and copy and
- 88-
Page 89

distribute such modifications o r wor k u nde r the terms of Section 1
above, provided that you also meet all of these conditions:
a) The modified work must itself be a software library.
b) You must cause the files modified to carry prominent notices
stating that you changed t he files and t he date of any change.
c) You must cause the whole of the work to be licensed at no
charge to all third parties under the terms of this Lice ns e .
d) If a facility in the modified Library refers to a function or a
table of data to be supplied by an application program that uses
the facility, other than as an argument passed when the facility
is invoked, then you must make a good fait h effort to ensure that,
in the event an a pplication does not s upply such f unction or
table, the facility still operates, and per forms whatever part of
its purpose remains meaningful.
(For example, a function in a library to compute square roots has
a purpose that is entirely well-defined independent of the
application. Therefore, Subsection 2d requires that any
application-supplied function or table used by this function must
be optional: if the application does not supply it, the square
root function must still compute square roots.)
These requirements apply to the modified work as a whole. If
identifiable sections of that work are not derived from the Library,
and can be reasonably considered independent and separate works in
themselves, then this License, and its terms, do not apply to those
sections whe n you di str ib ute them as separate wor ks. But when you
distribute the same sections as part of a whole which is a work based
on the Library, the distribution of the whole must be on the terms of
this License, whose permissions for other licensees extend to the
entire whole, and thus to each and every part regardless of who wrote
it.
Thus, it is not the intent of this section to c laim rights or contest
your rights to work written entire ly by you; rather, the intent is to
exercise the right to control the d istr ibution of derivative or
collective works based on the Library.
In addition, mere aggregation of another work not based on the Library
with the Library (or with a work based on the Library) on a volume of
a storage or distribution medium does not bring the other work under
the scope of this License.
3. You may opt to apply the terms of the ordinary GNU General Public
License instead of this License to a given copy of the Library. To do
this, you must alter all the notices that refer to this License, so
that they refer to the ordinary GNU General Public License, version 2,
instead of to this License . (If a newe r version than version 2 of the
ordinary GNU General Public License has appeared, then you can specify
that versio n instead if you wish.) Do not make any other change in
these notices.
Once this change is made in a given co py, it is irreversible for
that copy, so the ordinary GNU General Public License applies to all
- 89-
Page 90

subsequent copies and derivative works made from that copy.
This option is useful when you wish to copy part of the code of
the Library into a program that is not a library.
4. You may copy and distribute the Library (or a portion or
derivative of it, under Section 2) in object code or executable form
under the terms of Sections 1 and 2 above provided that you accompany
it with the complete corresponding machine-readable source code, which
must be distributed under the terms of Sections 1 and 2 above on a
medium customarily used for software interchange.
If distribution of object code is made by offering access to copy
from a designated place, then offering equivalent access to copy the
source code from the same place satisfies the requirement to
distribute the source code, even though third parties are not
compelled to copy the source along with the object code.
5. A program that contains no derivative of any portion of the
Library, but is designed to work with the Library by being compiled or
linked with it, is called a "work that uses the Library". Such a
work, in isol ation, is not a derivative work of t he Library, and
therefore falls outside the scope of this License.
However, linking a "work that uses the Library" with the Library
creates an executable that is a derivative of the Library (because it
contains portions of the Library), rather tha n a "work that uses the
library". The executable is therefore covered by this License.
Section 6 states terms for distr ibution of such executables.
When a "work that uses the Library" uses material from a header file
that is part of the Library, the object code for the work may be a
derivative work of the Library even though the source code is not.
Whether this is true is especially significant if the work can be
linked without the Library, or if the work is itself a library. The
threshold for this to be true is not prec isely defined by law.
If such an object file uses only numerical parameters, data
structure layouts and accessors, and small macros and small inline
functions (ten lines or less in length), then the use of the object
file is unrestricted, regardless of whether it is legally a derivative
work. (Exec utables cont aining this object code plus portions of the
Library will still fall under Section 6.)
Otherwise, if the work is a derivative of the Library, you may
distribute the object code for the work under the terms of Section 6.
Any executa bles containing that work also fall under Section 6,
whether or not they are linked directly with the Library itself.
6. As an exception to the Sections above, you may also combine or
link a "work that uses the Library" with the Library to produce a
work containing portions of the Library, a nd distribute that work
under terms of your choice, provided that the terms permit
modification of the work for the customer's own use and reverse
engineering for debugging such modifications.
You must give prominent notice with eac h copy of the work that the
Library is used in it and that the Library and its use are covered by
- 90-
Page 91

this License. You must supply a copy of this License. If the work
during execution disp l ays copyright notices, you must include the
copyright notice for the Library among them, as well as a reference
directing the user to the copy of this License. Also, you must do one
of these thi ngs:
a) Accompany the work with the complete corresponding
machine-readable source code for the Library including whatever
changes were used in the work (which must be distributed under
Sections 1 and 2 above); and, if the work is an executable linked
with the Library, with the complete machine-readable "work that
uses the Library", as object code and/or source code, so that the
user can modify the Library and then relink to produce a modified
executable containing the modified Libra ry. (It is understood
that the user who changes the contents of definitions files in the
Library will not necessarily be able to recompile the application
to use the modi fi ed definit ions.)
b) Use a suitab l e shared library mechanism for lin king with the
Library. A suitable mechanism is one that (1) uses at run time a
copy of the library already present on the user's computer syst em,
rather than copying library functions into the executable, and (2)
will operate properly with a modified version of the library, if
the user installs one, as long as the modified ver sio n is
interface-compatible with the version that the work wa s made wit h.
c) Accompany the work with a written offer, valid for at
least three years, to give the same user the materials
specified in Subsection 6a, above, for a charge no more
than the cost of performi ng this distribution.
d) If distribution of the work is made by offering access to copy
from a designated place, offer equivalent access to copy the above
specified materials from the same place.
e) Verify that the user has already received a copy of these
materials or that you have already sent this user a copy.
For an executable, the required form of the "work that uses the
Library" must include any data and utility programs needed for
reproducing the executable from it. However, as a special exception,
the materials to be distributed need not include anything that is
normally distributed (in either source or binary form) with the major
components (compiler, kernel, and so on) of the operating system on
which the executable r uns, unless that component itself accompanies
the executable.
It may happen that this requirement contra dicts the license
restrictions of other propr ie ta ry libra r ie s that d o not normally
accompany the operating system. Such a contradiction means you cannot
use both them and the Library together in an executable that you
distribute.
7. You may place library facilities that are a work based on the
Library side-by-side in a single library together wit h o ther library
facilities not covered by this License, and distribute such a combined
library, provided that the separate distribution of the work based on
the Library and of the other libra ry facilities is otherwise
- 91-
Page 92

permitted, and provided that you do these two things:
a) Accompany the combined library with a copy of the same work
based on the Library, unco mbined with any other library
facilities. This must be distributed under the te rms of the
Sections above.
b) Give prominent notice with the combined library of the fact
that part of it is a work based on the Library, and expla ining
where to find the accompanying uncombined form of the same work.
8. You may not copy, modify, sublicense, link with, or distribute
the Library except as expressly provided under this License. Any
attempt otherwise to copy, modify, sublicense, link with, or
distribute the Library is void, and will automatically terminate your
rights under this License. However, parties who have received copies,
or rights, from you unde r this License will not have their licenses
terminated so long as such parties remain in full compliance.
9. You are not required to accept this License, since you have not
signed it. However, nothing else grants you permission to modify or
distribute the Library or its der ivative works. These actions are
prohibited by law if you do not accept this License. Therefore, by
modifying or distributing the Library (or any work based on the
Library), you indicate your acceptance of this License to do so, and
all its terms and conditions for co pying, distributing or modifying
the Library or works based on it.
10. Each time you redistribute the Library (or any work based on the
Library), the recipient automatically receives a license from the
original licensor to copy, distribute, link with or modify the Library
subject to these terms and conditions. You may not impose any further
restrictions on the recipients' exercise of the rights granted herein.
You are not responsible for enforcing compliance by third parties with
this License.
11. If, as a consequence of a court judgment or allegation of patent
infringement or for any other rea son (not limited to patent issues),
conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot
distribute so as to satisfy simultaneo usly your obligations under this
License and any other pertinent obligations, then as a cons equence you
may not distribute the Librar y at all. For example, if a patent
license would not permit royalt y-free redistribution of the Library by
all those who receive copies directly or indirectly through you, then
the only wa y you could satisfy bot h it and this License would be to
refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any
particular circumstance, the balance of the section is intended to apply,
and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infr inge any
patents or other property right c la ims or to contest validity of any
such claims; this section has the sole purpose of protecting t he
integrity of the free software distribution system which is
implemented by public license practices. Many people have made
- 92-
Page 93

generous contributions to the wide range of software distributed
through that system in reliance o n consistent application of that
system; it is up to the author/donor to decide if he or she is willing
to distribute software through any other system and a licensee cannot
impose that choice.
This section is intended to make thor oughly clear what is believed to
be a consequence of the rest of this License.
12. If the distribution and/or use of the Library is restricted in
certain countries either by patents or by copyrighted interfaces, the
original copyright holder who places the Library under this License may add
an explicit geographical distri bution limitation excluding those countries,
so that distribution is permitted only in or among countries not thus
excluded. In such case, this License incorporates the limitation as if
written in the body of this License.
13. The Free Software Foundation may publish revised and/or new
versions of the Lesser General Public License from time to time.
Such new versions will be similar in spir it to the present version,
but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Library
specifies a version number of this License which applies to it and
"any later version", you have the option of following the terms and
conditions either of that version or of any later version published by
the Free Software Foundation. If the Library does not specify a
license version number, you may choose any version ever published by
the Free Software Foundation.
14. If you wish to incorporate parts of the Library into other free
programs whose distribution conditions are incompatible with these ,
write to the author to ask for pe rmission. For software which is
copyrighted by the Free Software Foundation, write to the Free
Software Foundation; we sometimes make exceptions for this. Our
decision will be guided by the two goals of preserving the free status
of all derivatives of our free software and of promoting the sharing
and reuse of software generally.
NO WARRANTY
15. BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE, THERE IS NO
WARRANTY FOR THE LIBRARY, TO THE EXTENT PERMITTED BY APPLICABLE LAW.
EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR
OTHER PARTIES PROVIDE THE LIBRARY "AS IS" WITHOUT WARRANTY OF ANY
KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PART I CULAR
PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND P E RFO RMANCE OF THE
LIBRARY I S WITH YOU. SHOULD THE LIBRARY PROVE DEFECTIVE, YOU ASSUME
THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN
WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY
AND/OR REDISTRIBUTE THE LIBRARY AS PERMITTED ABOVE, BE LIABLE TO YOU
FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE
LIBRARY ( I NCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING
RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A
- 93-
Page 94

FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF
SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH
DAMAGES.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Libraries
If you develop a new library, and you want it to be of the greatest
possible use to the public, we recommend making it free software that
everyone can redistribute and change. You can do so by permitting
redistribution under these ter ms (o r, alternatively, under the terms of the
ordinary General Public License).
To apply these terms, attach the followi ng notices to the library. It is
safest to attach them to the start of each source file to most effectively
convey the exclusion o f warranty; and each file s hould have a t least the
"copyright" line and a pointer to where the full notice is found.
<one line to give the library's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This library is free software; you can redistribute it and/or
modify it under the terms of the GNU Lesser General Public
License as published by the Free Software Foundation; either
version 2.1 of the License, or (at your option) any later version.
This library is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty o f
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU
Lesser General Public License for more details.
You should have received a copy of the GNU Lesser General Public
License along with this library; if not, write to the Free Software
Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Also add information on how to contact you by electronic and paper mail.
You should also get your employer (if you work as a programmer) or your
school, if any, to sign a "copyright disclaimer" for the library, if
necessary. Here is a sample; alter the names:
Yoyodyne, Inc., hereby disclaims all copyright interest in the
library `Frob' (a library for tweaking knobs) written by James Random Hacker.
<signature of Ty Coon>, 1 April 1990
Ty Coon, President of Vice
That's all there is to it!
OpenSSL Toolkit
This product includes software developed by the OpenSSL Project for use in the OpenSSL
Toolkit (
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
http://www.openssl.org/).
- 94-
Page 95

LICENSE ISSUES
==============
The OpenSSL toolkit stays under a dual license, i.e. both the conditions o f
the OpenSSL License and the original SSLeay license appl y to the toolkit.
See below for the actual license texts. Actually both licenses are BSD-style
Open Source licenses. In case of any license issues related to OpenSSL
please contact openssl-core@openssl.org.
OpenSSL License
---------------
/* ====================================================================
* Copyright (c) 1998-2011 The OpenSSL Project. All rights reserved.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
*
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions a nd the following disclaimer.
*
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions a nd the following disclaimer in
* the documentation and/or other materials provided with the
* distribution.
*
* 3. All advertising materials mentioning features or use of this
* software must display the following acknowledgment:
* "This product includes software developed by the OpenSSL Project
* for use in the OpenSSL Toolkit. (http://www.openssl.org/)"
*
* 4. The names "OpenSS L Toolkit" and "OpenSSL Project" must not be used to
* endorse or promote products derived from this software without
* prior written permission. For written permission, please contact
* openssl-core@openssl.org.
*
* 5. Products derived from this software may not be called "OpenSSL"
* nor may "OpenSSL" appear in their names without prior written
* permission of the OpenSSL Project.
*
* 6. Redistributions of any form whatsoever must retain the following
* acknowledgment:
* "This product includes software developed by the OpenSSL Project
* for use in the OpenSSL Toolkit (http://www.openssl.org/)"
*
* THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT ``AS IS'' AND ANY
* EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, T HE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
* PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR
* ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENT AL,
* SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT
* NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES;
* LOSS OF USE, DATA, OR PROFITS; OR BUSINESS I N TERRUPTION)
* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHE R IN CONTRACT,
* STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
* ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED
- 95-
Page 96

* OF THE POSSIBILITY OF SUCH DAMAGE.
* ====================================================================
*
* This product includes cryptographic software written by Eric Young
* (eay@cryptsoft.com). This product includes software written by Tim
* Hudson (tjh@cryptsoft.com).
*
*/
Original SSLeay License
-----------------------
/* Copyright (C) 1995-1998 Eric Young (eay@cryptsoft.com)
* All rights reserved.
*
* This package is an SSL imple mentatio n written
* by Eric Young (eay@cryptsoft.com).
* The implementation was written so as to conform with Netscapes SSL.
*
* This library is free for commercial and non-commercial use as long as
* the following conditions ar e a hea r e d to. The following conditions
* apply to all code found in this distribution, be it the RC4, RSA,
* lhash, DES, etc., code; not just the SSL code. The SSL documentation
* included with this distribution is covered by the same copyright terms
* except that the holder is Tim Hudson (tjh@cryptsoft.com).
*
* Copyright remains Eric Young's, and as such any Copyright notices in
* the code are not to be removed.
* If this package is used i n a product, Eric Young should be given attribution
* as the author of the parts of the library used.
* This can be in the form of a textual message at program star tup or
* in documentation (online or textual) provided with the package.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the copyright
* notice, this list of conditions a nd the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions a nd the following disclaimer in the
* documentation and/or other materials provided with the distribu tion.
* 3. All advertising materials mentioning features or use of this software
* must display the following acknowledgement:
* "This product includes cryptographic software written by
* Eric Young (eay@cryptsoft.com)"
* The word 'cryptographic' can be left out if the rouines from the library
* being used are not cryptographic related :-).
* 4. If you include any Windows specific code (or a derivative thereof) from
* the apps directory (application code) you must include an acknowledgement:
* "This product includes software written by Tim Hudson (tjh@cryptsoft.com)"
*
* THIS SOFTWARE IS PROVIDED BY ERIC YOUNG ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE
* ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE
* FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL
* DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS
* OR SERVICES; LOSS OF USE, DATA, OR PROFITS; O R BUSINESS INTERRUPTION)
- 96-
Page 97

* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHE R IN CONTRACT, STRICT
* LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY W AY
* OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILIT Y OF
* SUCH DAMAGE.
*
* The licence and distribution terms for any publically available version or
* derivative of this code cannot be changed. i.e. this code cannot simply be
* copied and put under another distribution licence
* [including the GNU Public Licence.]
*/
MIT License
• iniParser
Copyright (c) 2000-2011 by Nicolas Devillard.
• jQuery
Copyright (c) 2011 John Resig, http://jquery.com/
• canvas-text
Copyright (c) 2008 Fabien Menager
• jQuery TreeView
Copyright (c) 2007 Jorn Zaefferer
• jQuery tablesorter
Copyright (c) 2007 Christian Bach
• typeface.js
Copyright (c) 2008, David Chester (davidchester@gmx.net)
• JSDeferred
Copyright (c) 2007 cho45 ( www.lowreal.net )
• jQuery uploa d
Copyright (c) 2010 lagos
• jQuery LoadMask
Copyright (c) 2009 Sergiy Kovalchuk (serg472@gmail.com)
• flot
Copyright (c) 2007-2009 IOLA and Ole Laursen (http://code.google.com/p/flot)
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
in the Software without re str iction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in
all copies or substantial portio ns of t he Software.
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIE S OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. I N NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN
THE SOFTWARE.
- 97-
Page 98

BSD License
SHA2
/*
* FIPS 180-2 SHA-224/256/384/512 implementation
* Last update: 02/02/2007
* Issue date: 04/30/2005
*
* Copyright (C) 2005, 2007 Olivier Gay <olivier.gay@a3.epfl.ch>
* All rights re serv ed.
*
* Redistribution and use in source and binary forms, with or without
* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.
* 3. Neither the name of the project nor the names of its contributors
* may be used to endorse or promote products derived from this software
* without specific prior written permission.
*
* THIS SOFTWARE IS PROVIDED BY THE PROJECT AND CONTRIBUTORS ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE
* ARE DISCLAIMED. IN NO EVENT SHALL THE PROJECT OR CONTRIBUTORS BE LIABLE
* FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL
* DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS
* OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
STRICT
* LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
* OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
* SUCH DAMAGE.
*/
HMAC-SHA2
/*
* HMAC-SHA-224/256/384/512 implementation
* Last update: 06/15/2005
* Issue date: 06/15/2005
*
* Copyright (C) 2005 Olivier Gay <olivier.gay@a3.epfl.ch>
* All rights re serv ed.
*
* Redistribution and use in source and binary forms, with or without
- 98-
Page 99

* modification, are permitted provided that the following conditions
* are met:
* 1. Redistributions of source code must retain the above copyright
* notice, this list of conditions and the following disclaimer.
* 2. Redistributions in binary form must reproduce the above copyright
* notice, this list of conditions and the following disclaimer in the
* documentation and/or other materials provided with the distribution.
* 3. Neither the name of the project nor the names of its contributors
* may be used to endorse or promote products derived from this software
* without specific prior written permission.
*
* THIS SOFTWARE IS PROVIDED BY THE PROJECT AND CONTRIBUTORS ``AS IS'' AND
* ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
* IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE
* ARE DISCLAIMED. IN NO EVENT SHALL THE PROJECT OR CONTRIBUTORS BE LIABLE
* FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL
* DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS
* OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION)
* HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT,
STRICT
* LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY
* OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF
* SUCH DAMAGE.
*/
lighttpd
Copyright (c) 2004, Jan Kneschke, incremental
All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this
list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice,
this list of conditions and the following disclaimer in the documentation
and/or other materials provided with the distribution.
- Neither the name of the 'incremental' nor the names of its contributors may
be used to endorse or promote products derived from this software without
specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS
IS"
AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE
- 99-
Page 100

ARE DISCLAIMED. IN NO EV ENT SHALL THE COPYRIGHT OWNER OR CONTR IBUTORS
BE
LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR
CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF
SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN
CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE)
ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF
THE POSSIBILITY OF SUCH DAMAGE.
NET-SNMP
Various copyrights apply to this package, listed in various separate
parts below. Please make sure that you read all the parts.
---- Part 1: CMU/UCD copyright notice: (BSD like) -----
Copyright 1989, 1991, 1992 by Carnegie Mellon University
Derivative Work - 1996, 1998-2000
Copyright 1996, 1998-2000 The Regents of the University of California
All Rights Reserved
Permission to use, copy , modify and distribute this software and its
documentation for any purpose and without fee is hereby granted,
provided that the above copyright notice appears in all copies and
that both that copyright notice and this permission notice appear in
supporting documentation, and that the name of CMU and The Regents of
the University of California not be used in advertising or publicity
pertaining to distribution of the software without specific written
permission.
CMU AND THE REGENTS OF THE UNIVERSITY OF CALIFORNIA DISCLAIM ALL
WARRANTIES WITH REGARD TO THIS SOFTWARE, INCLUDING ALL IMPLIED
WARRANTIES OF MERCHANTABILITY AND FITNESS. IN NO EVENT SHALL CMU OR
THE REGENTS OF THE UNIVERSITY OF CALIFORNIA BE LIABLE FOR ANY SPECIAL,
INDIRECT OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER
RESULTING
FROM THE LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF
CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN
CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
---- Part 2: Networks Associates Technology, Inc copyright notice (BSD) -----
Copyright (c) 2001-2003, Networks Associates Techn ology , Inc
All rights reserved.
Redistribution and use in source and binary forms, with or without
modification, are permitted provided that the following conditions are met:
- 100-
 Loading...
Loading...