Page 1
Log Management Utility
User’s Guide
Page 2

Contents
About this Product ..........................................................................................iii
Trademarks and registered trademarks .......................................................iii
LICENSE ISSUES .............................................................................................iv
1 Introduction
1.1 Operating Environment .................................................................... 1-1
1.2 Supported MFP Devices .................................................................. 1-1
1.3 Introduction to Functions ................................................................ 1-2
Overview ........................................................................................ 1-2
Log Data that can be Acquired ...................................................... 1-2
2 Installation of Log Management Utility
2.1 Installation ......................................................................................... 2-1
To install ......................................................................................... 2-1
2.2 Items that are Installed .................................................................... 2-3
2.3 Uninstallation .................................................................................... 2-4
3 Starting Log Management Utility
3.1 To Start .............................................................................................. 3-1
3.2 Main Window ..................................................................................... 3-2
3.3 To Exit ................................................................................................ 3-2
4 Log Confirmation
4.1 Device Registration .......................................................................... 4-1
4.1.1 Specify as reception target ............................................................ 4-1
Specify as reception target ............................................................ 4-1
4.2 Receive Log from Device ................................................................. 4-4
4.2.1 Receive .......................................................................................... 4-4
4.2.2 Receive From Specified Devices ................................................... 4-7
4.2.3 Receive Log Periodically From Specified Devices ......................... 4-8
4.3 Confirm Logs ..................................................................................... 4-9
4.3.1 Select the Target History ............................................................... 4-9
4.3.2 Details of Log Display .................................................................. 4-10
Log Management Utility i
Page 3

Audit logs: .................................................................................... 4-10
Communication History (Scan): ................................................... 4-11
Communication History (Fax): ...................................................... 4-11
4.4 Log Operations ............................................................................... 4-13
4.4.1 Sorting .......................................................................................... 4-13
4.4.2 Filter ............................................................................................. 4-15
Specifying a Filter ......................................................................... 4-16
Deleting a Filter ............................................................................ 4-17
4.4.3 Log Search ................................................................................... 4-18
Searching ..................................................................................... 4-18
4.4.4 Detailed Information ..................................................................... 4-21
4.4.5 Log Deletion ................................................................................. 4-23
5 Log Management Utility Settings
5.1 File Menu ........................................................................................... 5-1
5.1.1 Open/Close Log File ...................................................................... 5-1
5.1.2 Export ............................................................................................. 5-2
5.1.3 Properties ....................................................................................... 5-6
5.2 Edit Menu .......................................................................................... 5-7
5.2.1 Copy ............................................................................................... 5-7
5.2.2 Search ............................................................................................ 5-7
5.2.3 Log Deletion ................................................................................... 5-7
5.2.4 Detailed Log Information ................................................................ 5-7
5.3 Display Menu ..................................................................................... 5-8
5.3.1 Toolbar Display ON/OFF ................................................................ 5-8
5.3.2 Separation ...................................................................................... 5-8
5.3.3 Record Display (Filter) .................................................................... 5-8
5.3.4 Sorting ............................................................................................ 5-8
5.3.5 Moving ........................................................................................... 5-9
5.3.6 Displayed Item Settings ................................................................. 5-9
5.3.7 General Settings ........................................................................... 5-10
5.4 Options ............................................................................................ 5-11
Reception Log: ............................................................................. 5-11
Auto export: ................................................................................. 5-12
Periodic Reception: ...................................................................... 5-14
6 Error message list
Log Management Utility ii
Page 4
About this Product
“KONICA MINOLTA Log Management Utility”, as plug-in of Device Set-Up,
accesses MFP products on the network, and displays log files (operations
and processing records that include monitoring logs and communications
history) stored on these devices. These can be used in management of device usage status, and in troubleshooting.
Trademarks and registered trademarks
Trademark acknowledgements
KONICA MINOLTA and the KONICA MINOLTA logo are either registered
trademarks or trademarks of KONICA MINOLTA HOLDINGS, INC.
PageScope is a registered trademark or trademark of KONICA MINOLTA
BUSINESS TECHNOLOGIES, INC.
®
Microsoft
Microsoft Corporation in the United States and/or other countries.
Intel and Pentium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries.
All other company and product names are trademarks or registered trademarks of their respective companies.
Dialog boxes
The dialog boxes shown in this manual are those that appear in Windows XP.
and Windows® are either registered trademarks or trademarks of
2
Note
The dialog boxes that appear in this document may differ from those that
appear on your computer, depending on the installed devices and specified settings.
2
Note
Unauthorized reproduction, translation or duplication of this document
whether in its entirety or in part, is strictly prohibited.
The content of this document is subject to change without notice.
Copyright © 2007 KONICA MINOLTA BUSINESS TECHNOLOGIES, INC.
All rights reserved.
Log Management Utility iii
Page 5

LICENSE ISSUES
The OpenSSL toolkit stays under a dual license, i.e. both the conditions of
the OpenSSL License and the original SSLeay license apply to the toolkit.
See below for the actual license texts. Actually both licenses are BSD-style
Open Source licenses. In case of any license issues related to OpenSSL
please contact openssl-core@openssl.org.
OpenSSL License
Copyright © 1998-2004 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the above copyright notice,
this list of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must
display the following acknowledgment:
“This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit. (http://www.openssl.org/)”
4. The names “OpenSSL Toolkit” and “OpenSSL Project” must not be used
to endorse or promote products derived from this software without prior
written permission. For written permission, please contact opensslcore@openssl.org.
5. Products derived from this software may not be called “OpenSSL” nor
may “OpenSSL” appear in their names without prior written permission
of the OpenSSL Project.
6. Redistributions of any form whatsoever must retain the following acknowledgment:
“This product includes software developed by the OpenSSL Project for
use in the OpenSSL Toolkit (http://www.openssl.org/)”
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS” AND
ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT
SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR
ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR
PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON
ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY,
OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY
Log Management Utility iv
Page 6

WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE
POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com). This product includes software written by Tim Hudson
(tjh@cryptsoft.com).
Original SSLeay License
Copyright © 1995-1998 Eric Young (eay@cryptsoft.com) All rights reserved.
This package is an SSL implementation written by Eric Young (eay@cryptsoft.com).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as the following conditions are adhered to. The following conditions apply to all code
found in this distribution, be it the RC4, RSA, lhash, DES, etc., code; not just
the SSL code. The SSL documentation included with this distribution is covered by the same copyright terms except that the holder is Tim Hudson
(tjh@cryptsoft.com).
Copyright remains Eric Young’s, and as such any Copyright notices in the
code are not to be removed.
If this package is used in a product, Eric Young should be given attribution
as the author of the parts of the library used.
This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
1. Redistributions of source code must retain the copyright notice, this list
of conditions and the following disclaimer.
2. Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
3. All advertising materials mentioning features or use of this software must
display the following acknowledgement:
“This product includes cryptographic software written by Eric Young
(eay@cryptsoft.com)”
The word ‘cryptographic’ can be left out if the routines from the library
being used are not cryptographic related.
4. If you include any Windows specific code (or a derivative thereof) from
the apps directory (application code) you must include an acknowledgement:
“This product includes software written by Tim Hudson (tjh@cryptsoft.com)”
Log Management Utility v
Page 7

THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO,
THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A
PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES
(INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE
GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS
INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING
NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE
OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH
DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution licence [including the GNU Public
Licence.]
Log Management Utility vi
Page 8
Introduction
1 Introduction
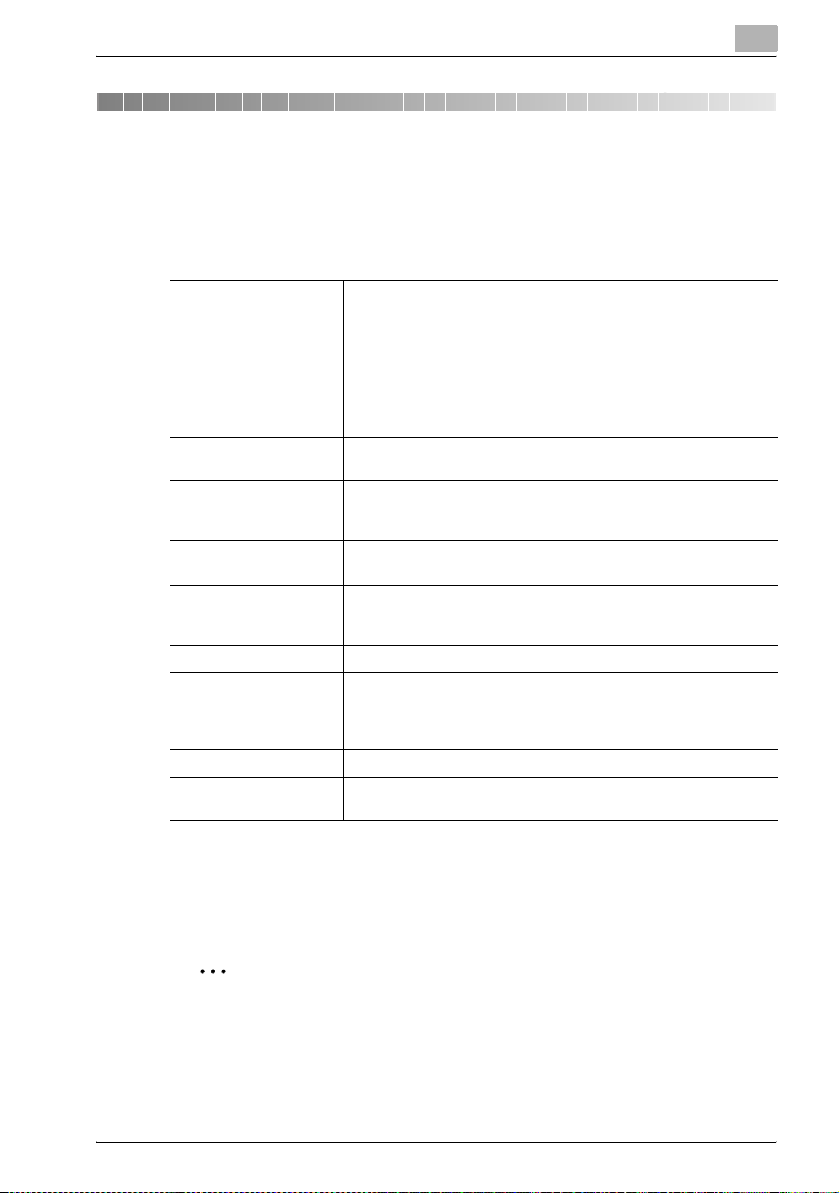
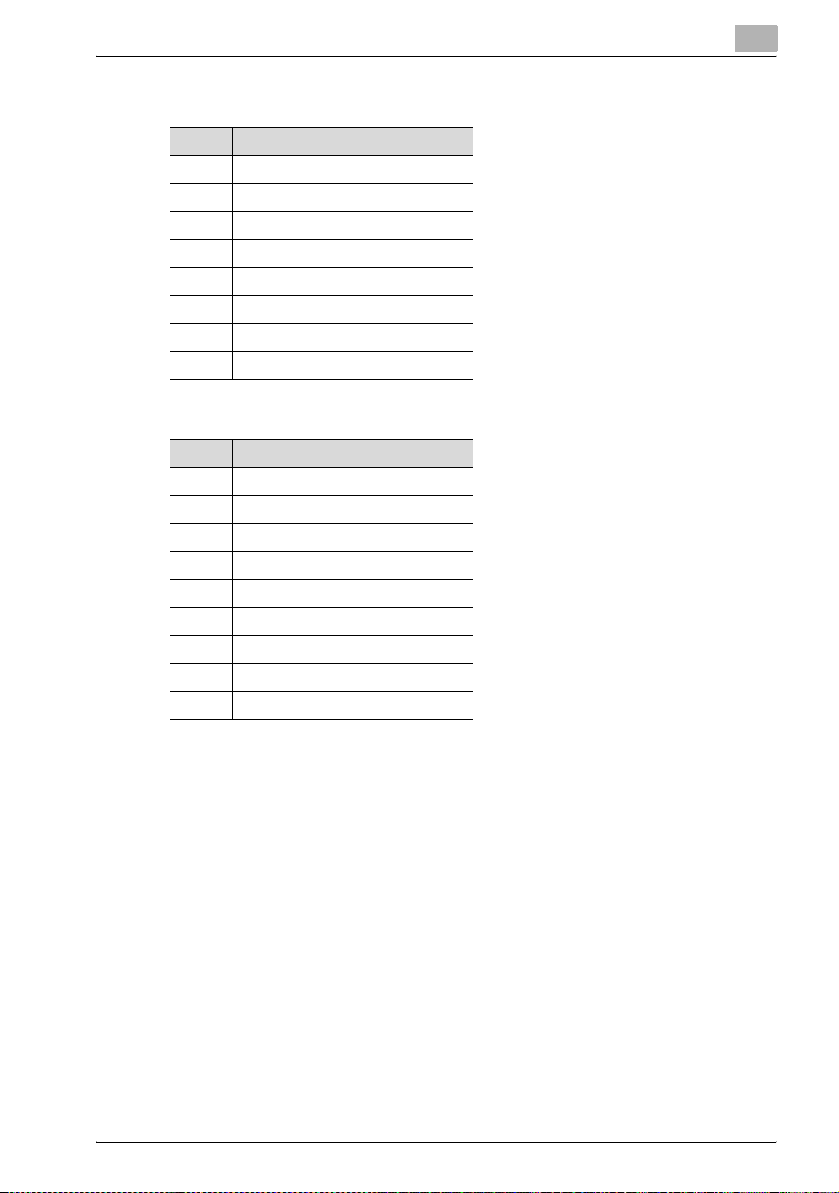
1.1 Operating Environment
The operating environment for Log Management Utility is described below.
1
Supported operating
systems
CPU According to the recommended system requirements of your oper-
Free hard disk space 100 MB or more
Memory According to the recommended system requirements of your oper-
File system NTFS
Web browser Microsoft Internet Explorer 6.0 (SP1) or later
Libraries Microsoft .NET Framework 2.0 (SP2 or later) <Windows XP>
Network Computer with properly configured TCP/IP and SNMP protocols.
Display 800 × 600 pixel or better.
Windows XP Professional (SP3 or later)
Windows XP Professional x64 Edition (SP2 or later)
Windows Vista Enterprise (SP2 or later)*
Windows Vista Business (SP2 or later)*
Windows Vista Ultimate (SP2 or later)*
Windows 7 Enterprise (SP1 or later)*
Windows 7 Professional (SP1 or later)*
Windows 7 Ultimate (SP1 or later)*
* 32-bit(x86) and 64-bit(x64) editions are supported.
ating system.
However, a separate area for saving acquired log files is also required.
ating system.
The location for saving reception logs cannot be specified on FAT or
FAT32 file systems.
Microsoft .NET Framework 3.5 (SP1 or later) <Windows Vista>
* The edition of .NET Framework required for this software is
pre-installed on Windows 7.
16 bit color or better
Refer to the Readme file for the latest information about service packs and
so on.
1.2 Supported MFP Devices
2
Reminder
Please refer to the Readme to confirm if your MFP is supported by Log
Management Utility.
Log Management Utility 1-1
Page 9
Introduction
1.3 Introduction to Functions
Overview
The main functions of Log Management Utility are described below.
- Acquisition of logs in devices
Acquire device audit logs, scan communication histories, and fax communication histories, and display these on the screen. Contents of the log
can be used to confirm the date and time of operations, operation users,
and operation results. Additionally, logs from multiple devices can be acquired.
- Management of acquired logs
The log display can be sorted by date or number, and searched using parameters such as transmission type and destination, allowing confirmation of device usage and errors status information. This is effective in
collective management of usage status information.
- Log export
Export an acquired log as a different file (log file). This enables ongoing
management through periodic saving of logs.
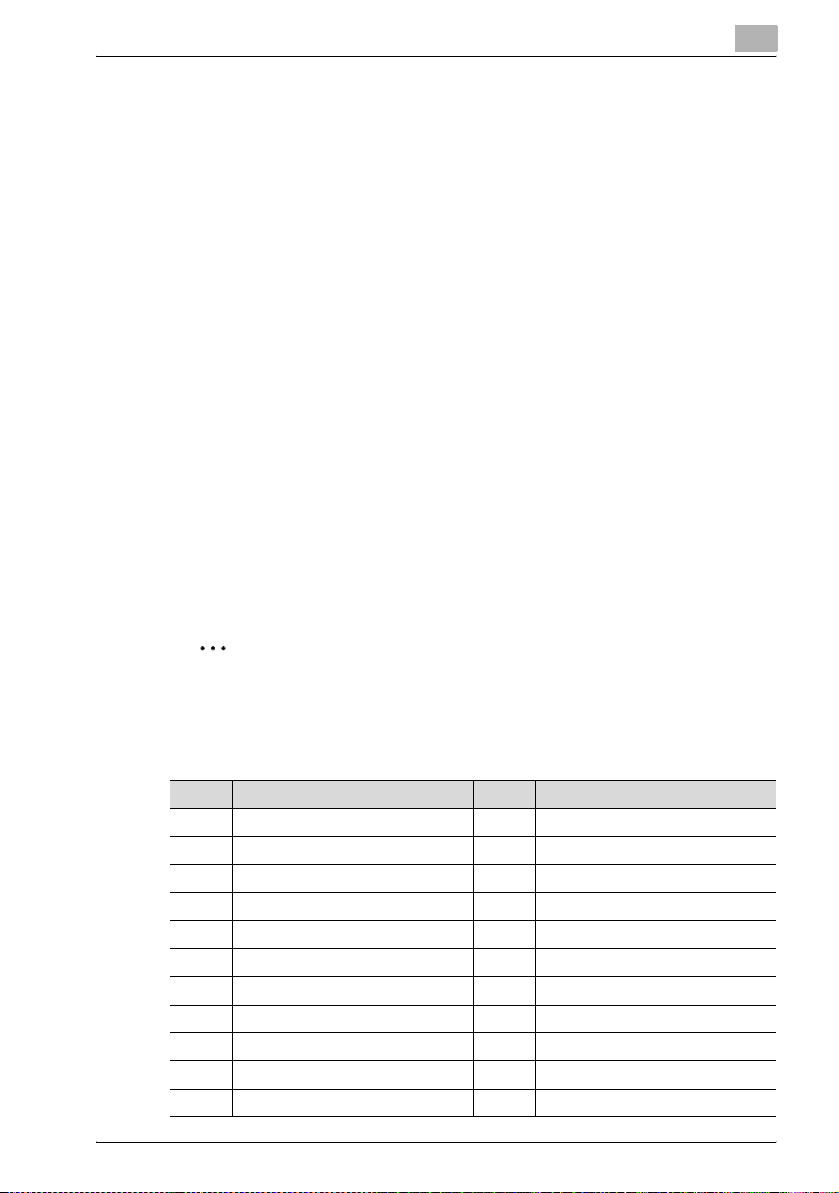
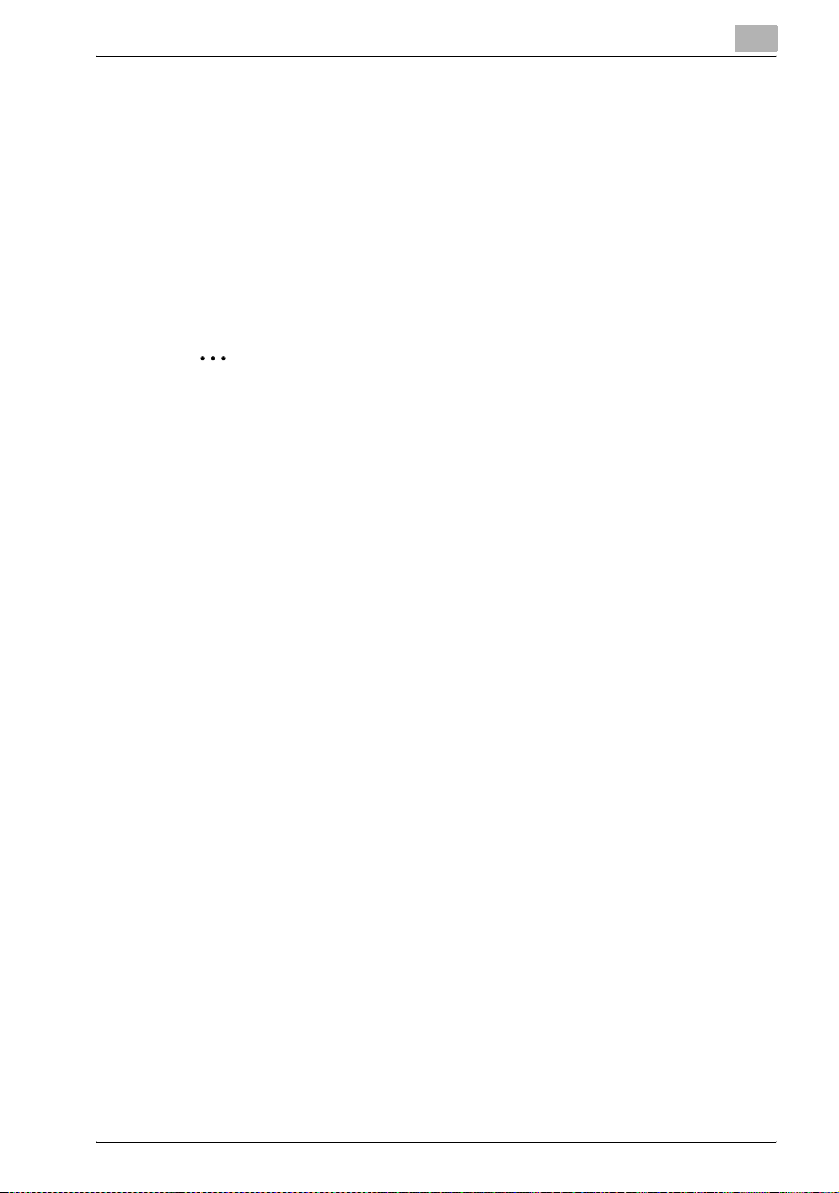
Log Data that can be Acquired
Log data that can be acquired by Log Management Utility is described below.
1
2
Note
Items to display, and the width of the display can be changed in [Displayed Item Settings].
Audit logs:
No. Item No. Item
1 Result 12 Individual Job Number
2 Result Code 13 Type
3 Operation 14 Address
4 Date and Time of Implementation 15 File Name
5 IF Number 16 Own Box Number
6 Operator Information 17 Box Number of Other Machine
7 Settings/Status 18 Relay User Box Number
8 User/Account Number 19 TSI Table Number
9 Operation Box Number 20 Received Fax Number
10 Security print ID 21 User/Account Name
11 User Job Number 22 External Server Information
Log Management Utility 1-2
Page 10
Introduction
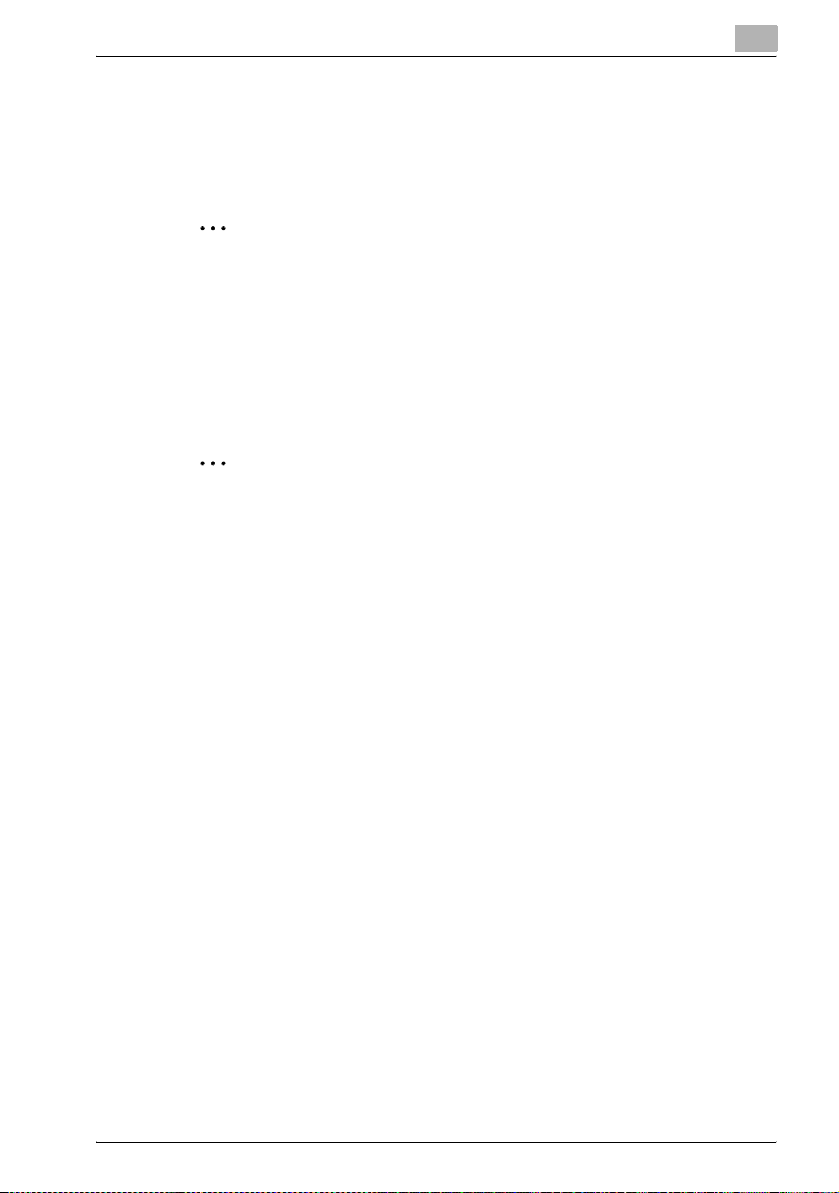
Communication History (Scan) logs:
Communication History (Fax) logs:
1
No. Item
1 Communication Result
2Result Code
3Number
4Destination
5Time
6 Type
7Number of Originals
8Remarks
No. Item
1 Communication Result
2Result Code
3Log Type
4Number
5Destination
6Time
7 Transmission Time
8Number of Originals
9Remarks
Log Management Utility 1-3
Page 11

Installation of Log Management Utility
2 Installation of Log Management Utility
2.1 Installation
Install Log Management Utility using the following procedure.
2
Note
When installing, login as a user that has administrator privileges.
Be sure to quit all programs (including virus check programs) that are running.
When installing the Log Management Utility, the Microsoft .NET Framework is required to have been installed in advance.
The version of Microsoft .NET Framework is based on the OS to be used.
Refer to page 1-1 for details.
When the Device Set-up is not installed, the Device Set-up installer is activated. Be sure, first of all, to install the Device Set-up.
To install
2
1 Double-click [Setup.exe] to start the installation program.
The installer starts.
2 Select the language, then click [OK].
3 Follow the on-screen instructions to install.
Log Management Utility 2-1
Page 12

Installation of Log Management Utility
2
Note
If [Start this tool when the PC is started] is selected in the following
screen, then Log Management Utility will be started when the computer
starts.
2
Log Management Utility 2-2
Page 13
Installation of Log Management Utility
2.2 Items that are Installed
When installing Log Management Utility, the following items are installed in
the Start Menu and on the Desktop.
Items registered in the Start Menu
- Program
- Online help
- Readme
Items registered on the Desktop
- Shortcut to the program
2
Note
It can also be specified that the “Readme” not be installed in the Start
Menu. When installing, select the [Custom] setup type, and specify the
items to install.
When installing, select whether or not to create registered shortcuts to
the program on the desktop.
2
Log Management Utility 2-3
Page 14
Installation of Log Management Utility
2.3 Uninstallation
Uninstall Log Management Utility using the following procedure.
- Use [Add or Remove Programs].
- Run [setup.exe] again
2
Note
When uninstalling Log Management Utility, ensure that the program is
closed.
Please note that the use of the Log Management Utility becomes unavailable if the Device Set-Up is uninstalled with the Log Management Utility
installed. On an occasion like this, reinstall it with the installer of the Log
Management Utility to install the Device Set-Up.
2
Note
When uninstalling, a message to confirm whether or not to delete user
settings data will be displayed.
2
Log Management Utility 2-4
Page 15

Starting Log Management Utility
3 Starting Log Management Utility
3.1 To Start
Start Log Management Utility using the following procedure.
- Start from the Windows Start Menu
In Windows, click Start, then All Programs — KONICA MINOLTA —
Log Management Utility — Log Management Utility.
- Start using the shortcut on the desktop
Double click the “Log Management Utility” icon that has been created on
the desktop.
- Automatically start when the computer is started
When the software is started, the main dialog box will be displayed, and a
“Log Management Utility” icon will be displayed on the tasktray.
2
Note
During installation, you can select whether or not to create a “Log Management Utility” icon on the desktop.
Configure the program to start automatically with the computer either
during installation, or from the options dialog box. For details, please refer to “Options” on page 5-11.
3
At startup, a Protect Function dialog box will be displayed.
For details about auto protect function, refer to “Device Set-Up User’s
Guide”.
Log Management Utility 3-1
Page 16

Starting Log Management Utility
3.2 Main Window
When the Log Management Utility is activated, the main window is displayed.
!
Detail
Refer to “Device Set-Up User’s Guide” for more information about main
window.
3
3.3 To Exit
Exit Log Management Utility using the following procedure.
- On the main window, select [File], then [Exit].
- Click the [x] (Close) button at the top right of the main dialog box.
- Shut down or log off from the computer.
Log Management Utility 3-2
Page 17

Log Confirmation
4 Log Confirmation
4.1 Device Registration
When using the Log Management Utility, it is necessary to make a search for
a supported device on the network for registration.
As a method for the search/registration of a supported device, the following
are available.
- Method for searching a supported device on the network
- Method for searching a supported device with the IP address specified.
- Method for registering a supported device from the Function access re-
striction file
!
Detail
For details of the method for search/registration of the supported device,
refer to the user’s guide of the Device Set-up.
4.1.1 Specify as reception target
Specify as reception target
0 The setting of [Log Management Settings] is available only for a device
supported by the log management function.
4
1 Start Log Management Utility.
2 Click .
Log Management Utility 4-1
Page 18

Log Confirmation
3 Select from the list a device from which you want to receive a log and
then click [Edit].
4 Select [Log Management Settings] from the Setup Group area.
– When a device is selected that is not supported by the log manage-
4
ment function, [Log Management Settings] is not displayed.
Log Management Utility 4-2
Page 19

Log Confirmation
5 Select [Enable log reception from this device] and click [OK].
– [Log Reception Enabled Setting] may not be disabled for some de-
– In order to use [Receive Log from a specified device] or [Receive
– Set the operation of [Action when HDD is full] as necessary.
– The [Save non-supported logs] option is available for some devic-
4
vices.
Log periodically from a specified device], select also [Set as specified device for log reception].
es. To save logs other than audit logs and communication history,
select this option.
6 Click [Close].
A device selected is set as a reception target.
Log Management Utility 4-3
Page 20

Log Confirmation
4.2 Receive Log from Device
There are two ways to receive logs. “Receive”, for receiving logs from a selected device only; and “Receive From Specified Devices”, for receiving logs
from all devices that are set as specified device for log reception.
2
Note
While receiving logs, ensure that the power to the target device is not
switched off.
Depending on the number of logs, some time may be required for log reception.
2
Note
Periodic, automatic reception of logs can be specified in “Options”. For
details, please refer to “Options” on page 5-11.
4.2.1 Receive
1 Start Log Management Utility.
4
2 From the Device list, select the devices from which to acquire logs.
3 Click [Receive Log] from the Function Selection field.
Log Management Utility 4-4
Page 21

Log Confirmation
4 Check the location into which the log is saved and then click [OK].
5 Check if the log has been received and then click [Close].
4
6 Click [Log Viewer] from the Function Selection field of main window.
Log Management Utility 4-5
Page 22

Log Confirmation
7 Check the location into which the log is saved and then click [OK].
8 Confirm the log.
4
9 Click [X] to close Log Viewer.
Log Management Utility 4-6
Page 23

Log Confirmation
4.2.2 Receive From Specified Devices
Logs are collectively received from two or more devices set to [Set as specified device for log reception].
1 Start Log Management Utility.
The main window will be displayed.
2 Click [Log] tab and select [Receive Log from a specified device].
4
– Alternatively, select [Log] - [Receive Log from a specified device]
from the [Function] menu.
3 Confirm the log.
2
Note
Even if devices are registered, logs cannot be received from these unless
they are set as specified devices for log reception. For details, please refer to “Specify as reception target” on page 4-1.
Log Management Utility 4-7
Page 24

Log Confirmation
4.2.3 Receive Log Periodically From Specified Devices
While in the activation of the Log Management Utility, logs are collectively received periodically from all the devices that are set to [Set as specified device
for log reception].
1 Start Log Management Utility.
The main window will be displayed.
2 Click [Log] tab and select [Receive Log periodically from a specified
device].
4
– Alternatively, select [Log] - [Receive Log periodically from a speci-
fied device] from the [Function] menu.
2
Note
For details of the Periodic reception interval, refer to page 5-14.
It is possible to activate the periodic reception while in the Windows logon. For details, refer to page 5-14.
Log Management Utility 4-8
Page 25

Log Confirmation
4.3 Confirm Logs
Received “Audit logs”, “Scan communications histories”, and “Fax communications histories” are displayed by year and month. The target history can
be specified in Selection View.
4.3.1 Select the Target History
1 Start Log Management Utility, and acquire logs as required.
2 Click [Log Viewer] from the Function Selection field of main window.
3 Select [Target] and [History] in the Selection View given to the left.
– Target:
Select target devices and log files.
Devices are displayed with a printer icon, and log files with a text
icon.
– History:
Select the log type. Further selection of each log type can be carried out by year and month.
A list of logs that corresponds to the selected Target and History is
displayed in the Log Information View at right.
If a log type is selected, then all records of that type will be displayed.
If year and month are selected, then records from that selected period
will be displayed.
4
Log Management Utility 4-9
Page 26

Log Confirmation
4.3.2 Details of Log Display
In each of the displayed log records, you can confirm results of operations,
as well as the date these were carried out and by which user. Items displayed
will differ depending on the log type.
2
Note
Log type items to display, and the width of the display can be changed
in [Displayed Item Settings]. For details, please refer to “Displayed Item
Settings” on page 5-9.
Audit logs:
Displays logs of operations carried out on the device. This allows confirmation of information such as results of operations, details of operations, and
users, etc.
4
2
Note
Operations results may be preceded by a blank space, and those that are
indented indicate that they are associated with the record above them in
the hierarchy. For these, the user job number is the same, with each operation being differentiated using an individual job number.
Associated
operations
Individual
operations
Log Management Utility 4-10
Page 27

Log Confirmation
Communication History (Scan):
Displays scan job logs. This allows confirmation of information such as communication results, job numbers, and destinations, etc.
Communication History (Fax):
Displays fax job logs. This allows confirmation of information such as communication results, job numbers, and destinations, etc.
4
Results status indicates the following.
History Type Item Status Condition
Audit log Result Successful The operation was successful
Error Error in the operation
Log Management Utility 4-11
Page 28

Log Confirmation
History Type Item Status Condition
Communication
History
(Scan)
Communication
History
(Fax)
Use the vertical scroll bar to confirm records on the page, and to scroll the
page.
Communication
Result
4
Successful The communication was successful
Error Error in the operation
Information Cancelled in the operation
To first page
To previous
page
Content of
page
To next page
To last page
2
Note
Movement between pages can be carried out either with the icons on the
page bar, or by selecting [Move] from the [Display] menu.
Log Management Utility 4-12
Page 29

Log Confirmation
4.4 Log Operations
Log records can be sorted, selected using conditions, searched, and deleted.
4.4.1 Sorting
Records can be sorted in descending or ascending order for different items,
by clicking each item name.
The + mark indicates that items are sorted in ascending order: click this
again to sort in descending order.
4
Items that can be sorted differ as follows depending on the log type.
History Type Items that can be sorted
Audit log Date and Time of Implementation
Communication History (Scan) Time
Communication History (Fax) Time
User Job Number
Individual Job Number
Log Management Utility 4-13
Page 30

Log Confirmation
2
Note
Depending on the number of records, some time may be required for
processing.
2
Note
If logs take up multiple pages, then information on all pages is sorted.
Log type items to display, and the width of the display can be changed
in Displayed Item Settings. For details, please refer to “Displayed Item
Settings” on page 5-9.
4
Log Management Utility 4-14
Page 31

Log Confirmation
4.4.2 Filter
Extract and display only records that match certain conditions.
Conditions that can be specified differ as follows depending on the log type.
4
Item Detail Audit log Commu-
Start Specify the target start date and
End Specify the target end date and
Result Specify the target operations re-
Communication Result
Operation* Specify the target operation.
Operator Information Specify the target operator in-
Type / Transmission
Type
Log Type Specify the target log type. o
Address* Specify the target address. o
Destination* Specify the target destination. oo
File Name* Specify the target file name. o
User/Account Name* Specify the target user names
External Server Information*
Remarks* Specify text for the target re-
Distinguish upper
case and lower case
letters
* For items that have text input, records that include input text are displayed as those which
match certain conditions (partial matching).
time.
time.
sult.
Specify the target communication result.
If no operation is specified, then
this is “No Conditions”
formation.
Specify the target transmission
type.
and/or account names.
Specify the target external server information.
marks.
Specify whether a distinction is
made between upper and lower
case for input text strings.
ooo
ooo
o
o
o
oo
o
o
ooo
nication
History
(Scan)
oo
oo
Communication
History
(Fax)
Log Management Utility 4-15
Page 32

Log Confirmation
Specifying a Filter
1 Open the Log Viewer and click on the Toolbar.
– Alternatively, select [Filter] from the [Display] menu.
2 Specify conditions, then click [Configure].
– Dialog boxes for configuring conditions will differ depending on the
Audit logs:
4
log type.
Communication History (Scan):
Log Management Utility 4-16
Page 33

Log Confirmation
Communication History (Fax):
Displays only records that match certain conditions.
2
Note
Depending on the number of records, some time may be required for
processing.
4
2
Note
Items in which text is input cannot use characters that are used in wildcards (* and ?).
Click [Restore Standard Values] on the screen where conditions are configured in order to restore original settings.
Deleting a Filter
To delete a filter, either click on the Toolbar, or select [Record All] from
the [Display] menu.
Log Management Utility 4-17
Page 34

Log Confirmation
4.4.3 Log Search
Search records that match certain conditions.
Conditions that can be specified differ as follows depending on the log type.
4
Item Detail Audit log Commu-
Result / Communication Result
Operation* Specify the target operation.
Operator Information Specify the target operator in-
Type/Transmission
Type
Log Type Specify the target log type. o
Address* Specify the target address. o
Destination* Specify the target destination. oo
File Name* Specify the target file name. o
User/Account Name* Specify the target user names
External Server Information*
Remarks* Specify text for the target re-
Distinguish upper
case and lower case
letters
Search Direction Specify the search direction. ooo
* For items that have text input, records that include input text are displayed as those which
match certain conditions (partial matching).
Specify the target operations result.
If no operation is specified, then
this is “No Conditions”
formation.
Specify the target transmission
type.
and/or account names.
Specify the target external server information.
marks.
Specify whether a distinction is
made between upper and lower
case for input text strings.
ooo
o
o
oo
o
o
ooo
nication
History
(Scan)
oo
Communication
History
(Fax)
Searching
1 Open the Log Viewer and select the types of log, and periods for target
logs from Selection View at left.
2 On the Toolbar, click .
– Alternatively, select [Find] from the [Edit] menu.
3 Specify conditions, then click [Find Next].
Log Management Utility 4-18
Page 35

Log Confirmation
– Dialog boxes for configuring conditions will differ depending on the
– Audit logs:
– Communication History (Scan):
4
log type.
Log Management Utility 4-19
Page 36

Log Confirmation
– Communication History (Fax):
– Records that match certain conditions are sequentially searched,
The Filter configuration dialog box will remain displayed, from where
additional searches of records can be carried out.
4
and the found records selected.
4 To end searches, click [Close].
2
Note
Depending on the number of records, some time may be required for
processing.
2
Note
The target for searches will be the log types and periods specified in “Selection View”. To change the target, re-select these in Selection View.
Items in which text is input cannot use characters that are used in wildcards (* and ?).
Click [Restore Standard Values] on the screen where conditions are configured in order to restore original settings.
Log Management Utility 4-20
Page 37

Log Confirmation
4.4.4 Detailed Information
Confirm detailed information regarding selected records.
Either double click the records to confirm, or select the records, then select
Detailed Log Information from the Edit menu.
Audit logs:
Communication History (Scan):
4
Communication History (Fax):
Log Management Utility 4-21
Page 38

Log Confirmation
2
Note
Switch between displayed records using [Previous] and [Next].
Click [Copy] to copy the text contents to the clipboard.
4
Log Management Utility 4-22
Page 39

Log Confirmation
4.4.5 Log Deletion
Delete unnecessary log records.
2
Note
Deleted logs cannot be restored.
2
Note
Records within log files cannot be deleted.
Selected records only cannot be deleted. Select using a range.
If the range for deletion corresponds to a record that is at the top of a hierarchy, then all records included within this will be deleted.
1 Select the types of log, and periods for target logs from Selection View
at left.
2 Select [Delete Log] from the [Edit] menu.
3 Specify the records to delete, then click [Delete].
4
4 Click [Yes].
The logs within the specified range will be deleted.
Log Management Utility 4-23
Page 40

Log Management Utility Settings
5 Log Management Utility Settings
5.1 File Menu
5.1.1 Open/Close Log File
Open an exported file and confirm the log records.
1 Start the Log Management Utility to display main window.
– For details of the method for displaying the main window, refer to
page 3-1.
2 Click [Log] tab and select [Open Log File].
5
– Alternatively, select [Log] - [Open Log File] from the [Function]
menu.
3 Select log to open and click [Open].
– The log file will be opened.
– Sorting and filtering functions can be used on records in opened log
files, in the same way as with logs received from devices.
2
Note
Up to ten log files can be opened at the same time.
To close opened log files, either click the “Close Log File” icon on the
Toolbar, or select [Close Log File] from the [File] menu. If [Close Log File]
Log Management Utility 5-1
Page 41

Log Management Utility Settings
is not available, then confirm that the “Target” is the log file in Selection
View at left.
5.1.2 Export
Save logs received from devices as log files.
1 Start the Log Management Utility to display main window.
– For details of the method for displaying the main window, refer to
page 3-1.
2 Click [Log] tab and select [Export Log].
5
– Alternatively, select [Log] - [Export Log] from the [Function] menu.
3 Select the device from which to export the log, then click [Next].
– Only one device can be selected.
Log Management Utility 5-2
Page 42

Log Management Utility Settings
4 Select the log type, then click [Next].
– Only one log can be selected.
– Logs without records will not be displayed.
5 Specify the range of the log, then click [Next].
5
Log Management Utility 5-3
Page 43

Log Management Utility Settings
6 Specify the destination folder, file name, and file type.
– If [Delete the saved record from the received log] is selected, then
after saving, the record will be deleted from the received log.
– “MFP operation log file” is a file type that can be displayed using
Log Management Utility. If a different format is selected when saving the file, then it will not be possible to view this using Log Management Utility.
– If saved while using the filter functions to select the number of logs
to display, then all logs (including those that are not displayed) in
“MFP operation log file” format will be saved; whereas if these are
saved in other file formats, then only records that are displayed will
be saved.
5
7 Click [Next].
8 Confirm details, then click [Start].
Log Management Utility 5-4
Page 44

Log Management Utility Settings
9 Click [Finish].
– To save more logs, click [Continue], and repeat from step 3.
2
Note
Records are saved sorted into “Date and Time of Implementation” and
“Time”.
5
Log Management Utility 5-5
Page 45

Log Management Utility Settings
5.1.3 Properties
Display detailed information about devices and log files selected as “Targets” in the Selection View at left.
1 Open the Log Viewer and select the target devices and log files in Se-
lection View at left.
2 From the [File] menu, select [Properties].
Properties will be displayed.
5
Log Management Utility 5-6
Page 46

Log Management Utility Settings
5.2 Edit Menu
5.2.1 Copy
Copy the contents of a selected record to the clipboard.
1 Select the record.
2 From the [Edit] menu, select [Copy].
The content of the displayed record is copied to the clipboard as text.
This text can be used by pasting it into other applications.
Example of copied text (Audit log):
Result: Successful
Operation: User information write in administrator mode
Date and Time of Implementation: 12/27/2006 11:28:12 PM
Operator Information: Account: 1
User/Account Name:
5.2.2 Search
Select [Find] from the [Edit] menu in order to search for records that match
certain conditions. For details, please refer to “Log Search” on page 4-18.
5
(network) (0x032A)
5.2.3 Log Deletion
Select [Delete Log] from the [Edit] menu in order to delete unnecessary log
records. For details, please refer to “Log Deletion” on page 4-23.
5.2.4 Detailed Log Information
Select [Detailed Log Information] from the [Edit] menu in order to confirm detailed information regarding selected records. For details, please refer to
“Detailed Information” on page 4-21.
Log Management Utility 5-7
Page 47

Log Management Utility Settings
5.3 Display Menu
5.3.1 Toolbar Display ON/OFF
From the [Display] menu, select ON/OFF for display of the “Toolbar”, “Status
Bar”, and “Page Bar”.
5.3.2 Separation
Select the proportions for display of Selection View on the left, and Log In-
formation View on the right.
Select [Separation] from the [Display] menu in order to move the border between the left and right parts of the screen. Move this with the mouse, and
click to fix the position.
2
Note
Alternatively, move the line between the left and right parts of the screen
by dragging it with the mouse.
5
5.3.3 Record Display (Filter)
Select [Filter] from the [Display] menu in order to extract and display only
records that match certain conditions. For details, please refer to “Filter” on
page 4-15.
Select [Record All] from the [Display] menu in order to cancel the filter, and
to display all records.
5.3.4 Sorting
Select [List By] from the [Display] menu, and then select an item from the
menu that is displayed in order to use that parameter to sort records in ascending order. Select this item again to sort in descending order.
Alternatively, sorting using the “Item name” in Log Information View. For
details, please refer to “Sorting” on page 4-13.
Log Management Utility 5-8
Page 48

Log Management Utility Settings
5.3.5 Moving
Select [Move] from the [Display] menu, and then select a destination from the
menu that is displayed in order to move the cursor (currently selected target).
Move the page either using the vertical scroll bar, or with the icons on the
page bar.
5.3.6 Displayed Item Settings
Change items to display for each log type, and the width of the display.
1 From the [Display] menu, select [Displayed Item Settings].
2 Select the “History Type” for which to configure items.
5
3 From the [Details] list, select [Show]/[Hide].
– If selected, an item will be shown.
– Settings can also be changed using [Show]/[Hide] at the right of the
dialog box.
4 Specify other conditions as required.
– Width of selected column (pixels):
Specify the display width in pixels. The range is 0 to 999.
– Move Up: Move an item up in the display.
– Move Down: Move an item down in the display.
Log Management Utility 5-9
Page 49

Log Management Utility Settings
– In Audit Log, the display order for “Result” and “Communication
Result” cannot be changed.
5 Click [Setting].
Display items will be changed.
5.3.7 General Settings
Specify the maximum number of records to display on one page.
1 From the [Display] menu, select [General Settings].
2 Specify the maximum number of records to display on one page.
3 Click [Setup].
The display settings will be changed.
5
Log Management Utility 5-10
Page 50

Log Management Utility Settings
5.4 Options
Select [Options] - [Log Management Options] from the [Tool] menu to specify
Log Management Utility reception logs, and conditions for operation.
The Options settings dialog box has a Reception Log, Auto export, and a
Periodic Reception.
Reception Log:
5
Settings Item Description
Reception Log
Folder
Folder for non-supported logs
Change Folder Specify the save location for logs acquired from
Display reception
log folder at startup
Change the Folder If [Save non-supported logs] is selected in the
devices.
Specify whether or not to display the reception log
folder at startup.
[Log Management Settings] dialog box, specify
the save location for logs other than audit logs and
communication history.
2
Note
If there are already reception logs, then the save location for reception
logs cannot be changed. In order to change the save location, ensure this
has no logs stored, by either exporting or deleting any existing logs.
Log Management Utility 5-11
Page 51

Log Management Utility Settings
Auto export:
Settings Item Description
Operation when reception log is at maximum capacity
Operation when log version is changed Specify handling of received logs when the ver-
Auto export Change Folder Specify the save location for the automatically ex-
Specify the operation when the reception log is at
maximum capacity.
Specify maximum size for each device and
overwrite log:
Overwrite the log when the reception log has
reached its maximum capacity. Click Detail to
specify the maximum disk capacity.
Automatically export log:
Automatically export the log when the reception
log has reached its maximum capacity. Click De-
tail to specify the proportion of the log to be auto-
matically exported.
The folder for automatic export of logs can be
specified in Auto export at the bottom of the dialog box.
sion of the log for the registered device has
changed.
Delete old version of log:
Deletes saved old versions of reception logs.
Automatically export old version of log:
Automatically exports saved old versions of reception logs.
ported file.
5
Log Management Utility 5-12
Page 52

Log Management Utility Settings
2
Note
If the log version for registered devices has changed, then Log Management Utility cannot bulk manage reception logs that are created using log
versions from before the change together with those created using log
versions from after the change.
If [Delete old version of log] is specified in [Operation when log version is
changed], then the deleted reception logs cannot be restored.
!
Detail
File names for automatically exported files are as follows.
LOG - Text string indicating the log type - date and time of first record date and time of last record
For example, when exporting an audit log for the period “2004/11/5
13:00:24 to 2005/2/25 04:39:12” the file name will be “LOG-AUD-200411-05-130024-2005-02-25-043912.lmu”.
The part of the string above indicating “AUD” for audit logs is replaced
with “SCAN” for communications (scan) logs, and “FAX” for communications (fax) logs.
5
Log Management Utility 5-13
Page 53

Log Management Utility Settings
Periodic Reception:
Settings Item Description
Periodic reception interval Periodically acquires logs while Log Management
Start periodic reception when logging onto
Windows
Minimize on start-up Start Log Management Utility minimized.
Display only on the Task Tray when minimized
Utility is running. Specify the interval for receiving
logs.
Start Log Management Utility at Windows logon.
Shows Log Management Utility only in the task
tray, and not on the Taskbar when minimized.
5
2
Note
The [Receive Log Periodically] function cannot be configured to be enabled at the same time as “Auto Protect Functions”.
!
Detail
Even if [Receive Log Periodically] is set, logs cannot be received from devices unless they are specified as targets for reception processing. For
details, please refer to “Specify as reception target” on page 4-1.
Log Management Utility 5-14
Page 54

Error message list
6 Error message list
An error message may appear while Log Management Utility is being used.
An error code appears after the message describing the error.
The corrective measures for the various error codes are described below.
Follow the described procedure.
Error Code Number Description
22, 23, 101, 102, 201, 221, 245,
9110.
28 Take action as an administrator.
9024, 9109 A memory error has occurred.
9002, 9017, 9018, 9021, 90289030, 9032, 9035-9039, 9043,
9103, 9105, 9106
220, 287, 9003, 9102, 9107, 9108 Not supported by this device.
286, 9006, 9008, 9013, 9015,
9044
9007 The device is in security protect status.
303, 306, 3200, 4000-4010, 9004,
9011, 9014
9005, 9012 Wait a short period, then try again.
20, 21, 24-27, 30-39, 222-244,
246-267, 270-274, 277-283, 285,
288-302, 304, 307-317, 400-413,
450-470, 472, 500, 700-716,
3100, 3101, 3110, 4011, 9000,
9001, 9010, 9019, 9020, 9100,
9101, 40039, 40041
9009, 9016, 9022, 9023, 90259027, 9031, 9033, 9034, 90409042, 9104
29, 268, 269, 275, 284 Restart the Utility.
305, 471 Unsupported log file.
Reinstall the Utility.
A communications error has occurred.
Change device settings, then try again.
Change settings, then try again.
Try again.
Consult with an administrator.
6
Log Management Utility 6-1
Page 55

Error message list
Error Code Number Description
1 The process has been cancelled by the user.
6
Log Management Utility 6-2
Page 56

2007
http://konicaminolta.com
Copyright
2011.74343-PS312-11
 Loading...
Loading...