Keri Systems Doors16 User Manual
Doors™ for use with Windows™
Access Control Software
Users Guide v2.1
© 1998 Keri Systems, Inc. – ALL RIGHTS RESERVED Document Number 01821-001, Revision 2.1 – October, 1998
Keri Systems, PXL-250, SB-293, Tiger Controller, and Doors are trademarks of Keri Systems, Inc. Other product names are trademarks or registered trademarks of their owners.
Keri Systems, Inc. reserves the right to change, without notice, product offerings or specifications.
No part of this publication may be reproduced in any form without written permission from Keri Systems, Inc.
Keri Systems, Inc. Doors™ Users Guide
Table of Contents
Table of Contents |
3 |
Introduction to Doors™ |
9 |
The Host Computer |
11 |
System Requirements |
11 |
COMTEST Serial Port Test |
12 |
The Loop-Back Plugs |
12 |
Starting COMTEST In Windows 95 |
12 |
Starting COMTEST In Windows 3.11 |
12 |
Running COMTEST |
12 |
If the Host Computer Fails COMTEST |
14 |
If the Host Computer Passes COMTEST, but there are Still Problems |
14 |
Setting the Host Computer Date and Time |
15 |
Setting the Date and Time in Windows '95 |
15 |
Setting the Date and Time in Windows 3.11 |
15 |
Software Installation |
17 |
Upgrade Installation |
17 |
Backing Up in Windows 95 |
17 |
Backing Up in Windows 3.11 |
17 |
New Installation |
17 |
To Install Doors using Windows 95 |
17 |
To Install Doors using Windows 3.11 |
18 |
Troubleshooting |
19 |
Low System Resources |
19 |
Verifying System Resources in Windows 95 |
19 |
Verifying System Resources in Windows 3.11 |
19 |
Missing DLL Files |
19 |
To Copy the Missing DLL Files in Windows 95 |
20 |
To Copy the Missing DLL Files in Windows 3.11 |
20 |
Recovering an Original Doors Installation |
20 |
Recovery Using Windows 95 |
20 |
Recovery Using Windows 3.11 |
21 |
Deleting a Backed Up Doors Installation |
21 |
Deleting Using Windows 95 |
21 |
Deleting Using Windows 3.11 |
21 |
Users Guide |
23 |
Users Guide Conventions |
24 |
Windows Conventions |
25 |
On-Line Help |
25 |
01821-001 |
October 1998 |
Revision 2.1 |
Page 3 |
Doors™ Users Guide |
Keri Systems, Inc. |
The Order of Operation |
25 |
Logging On the Doors Program |
25 |
Setup and Verify Network Communication |
25 |
Set Communication Parameters |
25 |
Auto-Config |
25 |
Set Time |
26 |
Perform Smart Update |
26 |
Get Controller Status |
26 |
Begin Database Programming |
26 |
Setup Operators |
26 |
Setup Time Zones |
26 |
Setup Doors |
26 |
Setup Access Groups |
26 |
Setup Cards |
26 |
Setup Monitor Windows |
26 |
Download Information to the Network |
27 |
System Operation |
27 |
Advanced Features |
27 |
Logging On |
29 |
Starting the Doors Program |
29 |
Starting the Program in Windows 95 |
29 |
Starting the Program in Windows 3.11 |
30 |
System Logon |
30 |
Network Update |
31 |
Introducing the Doors Desktop |
33 |
The Desktop |
33 |
The Tool Bar |
34 |
On-Line Help |
34 |
Exiting a Doors Window |
35 |
Exiting in Windows 95 |
35 |
Exiting in Windows 3.11 |
35 |
Setup/Verify Network Communication |
37 |
Set Communication Parameters |
37 |
Set the COM Port |
37 |
Set the Communication Speed |
38 |
Set the Modem Parameters |
39 |
Save the Communication Parameters |
39 |
Auto-Config |
39 |
Successful Auto-Config |
41 |
Failed Auto-Config |
41 |
Set Controller Time and Date |
42 |
Network Update – Default Parameters |
43 |
Get Controller Status |
45 |
Get Status For All Controllers |
45 |
Get Status For One Controller |
47 |
Database Programming |
49 |
October 1998 |
01821-001 |
Page 4 |
Revision 2.1 |
Keri Systems, Inc. Doors™ Users Guide
Setup Operators |
49 |
Editing the Default Operator |
49 |
Creating a New Operator |
50 |
Setup Time Zones |
53 |
Day-Shift Time Zone Example |
53 |
Janitorial Shift Time Zone Example |
56 |
Grave Shift Time Zone Example (Crossing Midnight) |
57 |
Holiday Schedules |
58 |
Display/Edit a Time Zone |
60 |
Delete a Time Zone |
61 |
Setup Doors/Controllers |
63 |
Set Controller Dial-Out Parameters |
63 |
Enable Controller Dial-Out |
63 |
Set the Dial-Out Threshold Percentage |
64 |
Disable Controller Dial-Out |
64 |
Assign a Door Name |
65 |
Assign a Door Class |
66 |
Disable/Enable a Reader |
67 |
Set a Door Unlock Time |
68 |
Set a Door Open Time |
69 |
Set an Unlock/Lock Time Zone |
70 |
First Person In |
71 |
Alarm Output |
72 |
Setup Access Groups |
75 |
Create a New Access Group |
75 |
Edit an Existing Access Group |
80 |
Add/Remove a Door from the Access Group |
81 |
Change the Time Zone on an Access Group Door |
82 |
Delete an Access Group |
84 |
Setup Cards |
87 |
Card Enrollment – Dialog Box Method |
87 |
Enroll Tab |
87 |
Block Enrollment by Card Number Range |
87 |
Enrolling by Presenting to a Reader |
90 |
Card Data Tab |
91 |
Entering Card Data for a Cardholder |
92 |
Editing Card Data for a Cardholder |
94 |
Voiding a Card |
94 |
Deleting a Card |
96 |
More Card Data |
97 |
Preferences |
98 |
Personal Setup |
99 |
Personal |
101 |
01821-001 |
October 1998 |
Revision 2.1 |
Page 5 |
Doors™ Users Guide |
Keri Systems, Inc. |
Card Enrollment – Spreadsheet Method |
103 |
Enrolling Cards |
103 |
Entering Card Data for a Cardholder |
104 |
Voiding Cards |
107 |
Deleting Cards |
109 |
Sorting Data |
110 |
Block Copying Data |
111 |
Personal Data Fields |
113 |
Editing Cardholder Data |
114 |
Resizing Columns and Rows |
116 |
To Resize a Column |
116 |
To Resize a Row |
116 |
Printing Cardholder Data from the Spreadsheet (Quick Print) |
116 |
Setup Monitor and Events |
117 |
Enable/Disable Auto-Collection |
117 |
Configure Event Monitoring Windows |
118 |
Naming Event Monitoring Windows |
118 |
Message Text Strings |
119 |
Message Text String Definitions |
121 |
Assigning Events to be Monitored |
126 |
Save to File |
128 |
Controller Reports Events |
130 |
Update the Network |
133 |
System Operation |
135 |
Locking, Unlocking, and Updating Doors |
135 |
Lock Doors |
136 |
Lock All Doors |
136 |
Lock All Doors in a Door Class |
136 |
Lock a Single Door |
137 |
Unlock Doors |
138 |
Unlock All Doors |
138 |
Unlock All Doors in a Door Class |
139 |
Unlock a Single Door |
140 |
Timed Unlock |
140 |
Timed Unlock All Doors |
140 |
Timed Unlock All Doors in a Door Class |
141 |
Timed Unlock a Single Door |
142 |
Update Doors |
142 |
Update All Doors |
142 |
Update All Doors in a Door Class |
143 |
Update a Single Door in a Door Class |
144 |
Monitor and Collect Events from the Controllers |
147 |
Verifying Communication Status |
147 |
Starting Monitoring |
147 |
Collecting Events |
148 |
Stopping Monitoring |
148 |
October 1998 |
01821-001 |
Page 6 |
Revision 2.1 |
Keri Systems, Inc. |
Doors™ Users Guide |
Create Event Reports |
149 |
Quick Search Event Report |
149 |
Clear all Fields |
149 |
Select Doors |
150 |
Select Cardholders |
151 |
Select Events |
152 |
Select Dates |
152 |
Generate Report Output |
153 |
View Report on Screen |
153 |
Print Report |
154 |
Save Report to File |
154 |
Power Search Event Reports |
155 |
Field Type and Field Value |
156 |
Boolean Operators |
157 |
Boolean Links |
159 |
Power Search Example |
160 |
Generate the Report |
163 |
Library Tab |
163 |
Save a Search Expression |
164 |
Get a Search Expression |
164 |
Options Tab |
165 |
Reverse Order of Sort |
165 |
Save Card ID Numbers in the Report File |
166 |
Identify an Unknown Card |
167 |
ID by Reading the Card |
167 |
ID by Entering the Internal Number |
168 |
ID by Entering the Card Number |
168 |
Disconnect from the Access Control Network |
169 |
Window Management |
169 |
Cascading Windows |
169 |
Tiling Windows |
170 |
Tiling Windows Horizontally |
170 |
Arranging Icons |
171 |
Cycling Windows |
172 |
Retrieving the Software Revision and Logged Operator |
172 |
System Maintenance |
175 |
Secure Storage of Source Disks |
175 |
Periodic Doors Software Backup |
175 |
In Windows 95 |
175 |
In Windows 3.11 |
175 |
Archiving the Event Logs |
176 |
In Windows 95 |
176 |
In Windows 3.11 |
176 |
Generating Reports from an Archived Event Log |
177 |
01821-001 |
October 1998 |
Revision 2.1 |
Page 7 |
Doors™ Users Guide Keri Systems, Inc.
Advanced Features |
179 |
Multiple Site Control |
179 |
Enable Sites |
179 |
Enter Site Configuration Information |
181 |
Assign a Site Name |
182 |
Enter the Site Address |
182 |
Site Number |
182 |
Site Personal Identification Number (PIN) |
182 |
Site Phone Number |
183 |
Site Modem Initialization String |
183 |
Site Global Secure Time |
184 |
Site Global Unlock Enable |
184 |
Site Comment |
184 |
Adding a New Site |
185 |
Changes in Database Entry and Program Operation |
186 |
Cardholder Spreadsheet Changes |
186 |
Access Group Changes |
187 |
For a New Access Group |
187 |
Update Site |
189 |
Select a Site |
189 |
Quick Search Reports by Site |
190 |
Power Search Reports by Site |
191 |
I/O Control |
193 |
I/O Configuration |
193 |
Link Configuration |
194 |
Link Parameters |
195 |
I/O Link Example |
197 |
Manual Output Control |
202 |
Appendix |
203 |
Database File Field Definitions |
205 |
Data Format in Single Site Mode – Using the Cardholder’s Name |
206 |
Data Format in Single Site Mode – Using the Cardholder’s Card Number |
207 |
Data Format in Multiple Site Mode – Using the Cardholder’s Name |
208 |
Data Format in Multiple Site Mode – Using the Cardholder’s Card Number |
209 |
Glossary |
211 |
Index |
215 |
October 1998 |
01821-001 |
Page 8 |
Revision 2.1 |
Keri Systems, Inc. Doors™ Users Guide
Introduction to Doors™
Doors™ for use with Windows™ is a software program that configures and manages an access control system utilizing Keri Systems' PXL-250 Tiger Controllers or PXL-100 Smart Entry Controllers.
Doors is a fully functional Windows program, making full use of all popular Windows features such as resizing and relocating windows, drag-and-drop functions, multiple windows open simultaneously, background operation, and "real-time" operation. Doors operates under
Windows 3.11, Windows 95, or Windows NT.
Doors provides the operator with a user-friendly interface for defining system parameters, managing card and transaction files, setting timing functions, and preparing reports. For operators who are familiar with spreadsheet programs (such as Microsoft Excel™ ), many operations can be performed in spreadsheet format, with simple sorting, block, and copy functions. A wizard provides the operator a step-by-step walk-through procedure for creating Access Groups (a method for associating access doors with time periods of operation). An extensive on-line help file places assistance at the operator's fingertips.
A dedicated PC is not needed to run Doors. The PC is only needed for entering and uploading information to the controllers, downloading information from the controllers, or for real-time system monitoring. Doors uses a propriatary communications protocol to automatically check all controllers on the network and configures itself according to the connected hardware, greatly simplifying the system setup procedure.
Doors is capable of managing a single site via a direct connect line or a modem, and is capable of managing up to 255 remote sites, each via modem. Remote multiple site management features automatic dial-up of remote sites, global and site specific card enrollment, global and site specific event reporting, and configurable automatic downloads of events from controllers.
The Doors software can handle:
•Up to 32 system operators, each with password protection and configurable privileges.
•Up to 32 time zones, each with 4 start/stop intervals.
•3 holiday schedules, each with up to 32 definable holiday dates.
•An unlimited number of Access Groups (subject to available hard disk space).
•Up to 6 sortable user definable text fields for individual cardholder information in addition to last name, card number, access group, and department group fields.
•Up to 255 sites.
•Up to 128 controllers per site.
•Up to 128 doors (one per controller), or up to 256 doors (two per controller) if using optional Satellite boards with every controller.
•Up to 6,400 cards/cardholders.
01821-001 |
October 1998 |
Revision 2.1 |
Page 9 |
Doors™ Users Guide |
Keri Systems, Inc. |
This page is intentionally left blank.
October 1998 |
01821-001 |
Page 10 |
Revision 2.1 |
Keri Systems, Inc |
Doors™ Users Guide |
The Host Computer
System Requirements
For proper operation of the Doors access control software, the host computer operating the software must meet the following requirements.
•PC compatible computer using a Pentium-90 or faster microprocessor
•minimum of 16 MB of system RAM(1)
•520 KB of free, conventional memory
•VGA color monitor with VGA graphics card
•3.5 inch floppy disk drive
•keyboard
•mouse or other pointing device
•20 MB of hard disc space
•COM port(2) with a 16550 UART to support an external modem or a direct RS-232 serial connection, or an internal 9600 baud (or faster) modem
•one of the following operating systems:
Windows 3.11(3) with MS-DOS 6.2 (or greater)
Windows 95 Windows NT
NOTES
(1)The larger the number of cards being enrolled, the larger the system RAM should be to efficiently handle the card database.
(2)Since all communication between controllers and the Doors software is done through the host computer's COM port, Doors cannot work if the host computer's COM port is not working correctly. Keri Systems cannot be held responsible for host computer COM port or hardware problems. With the Doors software package, Keri Systems, Inc. provides a simple COM port test that can verify basic operation of the COM port. Please refer to the COMTEST Program section below for instructions on operating the program.
(3)This must be the Windows 3.11 upgrade version and not the older Windows 3.0 or 3.1 versions. There are features and improvements made in the 3.11 revision that the Doors program needs for proper operation. To determine which revision of Windows is on a host computer, click on the Help/About pull-down menu in the main program window. A text box will appear listing a variety of information regarding the host computer, including the revision of the Windows software. If necessary, contact Microsoft or a computer software vendor for operating system upgrades.
01821-001 |
October 1998 |
Revision 2.1 |
Page 11 |
Doors™ Users Guide |
Keri Systems, Inc. |
COMTEST Serial Port Test
The Keri Systems, Inc. COMTEST program is a simple program. It is designed to send a string of characters out the host computer's COM port output and see if they are echoed back to the host computer's COM port input.
It is not designed to determine if the COM port has more serious problems such as conflicts with other devices on the host computer. For these types of problems, troubleshooting by a computer technician is required.
The Loop-Back Plugs
To use the COM Test utility program, unplug the connection made from the access control system to the host computer's COM port. Plug in the correct loop-back plug. The loop-back plug routes the output signal from the serial port back to the input signal. Two plugs are provided – one with 9 pins and one with 25 pins. Virtually every serial COM port will use one of these two plugs.
Starting COMTEST In Windows 95
1.Open the Windows Explorer program.
2.Locate the COMTEST.EXE program. For a default software installation, the program can be found in the "\kerisys\doors\utils" subdirectory.
3.Double-click on the COMTEST.EXE program icon, or click on the COMTEST.EXE icon
and then click on the File Run pull-down menu option.
4.Skip to the Running COMTEST section below.
Starting COMTEST In Windows 3.11
1.Open the FILE MANAGER program.
2.Click on the File Run pull-down menu.
3.Click on the Browse button and locate the COMTEST.EXE program. For a default software installation, the program can be found in the "\kerisys\doors\utils" subdirectory.
4.Click on the Run button.
Running COMTEST
1.When the program begins, the following screen will appear.
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Untested
October 1998 |
01821-001 |
Page 12 |
Revision 2.1 |
Keri Systems, Inc |
Doors™ Users Guide |
2.Press the letter C. The following screen will appear.
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Untested
Enter |
1 = COM1, 2 = COM2, 3 = COM3, 4 = COM4 |
3.Press the number corresponding to the COM port the host computer is using for communication with the access control network (in this example, 2 was pressed).The following screen will appear.
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Untested
4.Press the letter T. The following screen will appear.
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Untested
Testing, please wait . . .
01821-001 |
October 1998 |
Revision 2.1 |
Page 13 |
Doors™ Users Guide |
Keri Systems, Inc. |
5.The COM port test takes just a few seconds. When complete, if the COM port has passed the test it is able to send and receive data. The following screen will appear.
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Passed
6.If the COM port has failed the test, the following screen will appear (the error message will vary depending upon what type of error was detected).
KERI SYSTEMS INC. COMM TEST UTILITY
Plug in the Keri Loopback Test plug before starting the test.
Type C to set COM port
Type T to test COM port
Use icon in upper left to quit the program
PORT: COM2
STATUS: Failed
An error has occurred <type of error>
Press any key to continue
7.To rerun the COMTEST, press any key to return to the beginning of the program.
8.To exit the program, either click on the  box in the upper-right corner of the COMTEST window, or click on the Windows icon in the upper-left corner of the program window and a pull-down menu will appear. In the menu, click on Close.
box in the upper-right corner of the COMTEST window, or click on the Windows icon in the upper-left corner of the program window and a pull-down menu will appear. In the menu, click on Close.
9.Remove the loop-back plug from the serial port and reinstall the communication cable.
If the Host Computer Fails COMTEST
If the host computer failed COMTEST, there is a basic problem in transferring data through the COM port. A computer technician should examine the computer.
If the Host Computer Passes COMTEST, but there are Still Problems
Some COM port problems are beyond the scope of this COM test program. These types of problems tend to involve several devices within the computer that are trying to use the same resources within the computer, each device affecting the others. A computer technician should examine the computer to resolve these kinds of problems.
October 1998 |
01821-001 |
Page 14 |
Revision 2.1 |
Keri Systems, Inc |
Doors™ Users Guide |
Setting the Host Computer Date and Time
To ensure that the date and time assigned to events on the access control system are correct, the date and time kept by the host computer should be checked for accuracy. Part of the controller configuration process, later in this manual, will be to set the time and date of the controllers to match that of the host computer.
Setting the Date and Time in Windows '95
The Windows Help file provides instructions on setting the date and time.
1.Click on the Start button on the Windows Task Bar. A menu will appear.
2.Click on Help and a help topics window will appear.
3.Click on the Index tab and in the first field type Date/Time. This will automatically search for and highlight the Date/Time help entry.
4.Click on the display button and a list of hyperlinks to the instructions for setting the date and time will appear.
Setting the Date and Time in Windows 3.11
The Windows Help file provides instructions on setting the date and time.
1.Double-click on the Main window icon to open the Main window.
2.Double-click on the Control Panel icon to open the Control Panel.
3.On the Control Panel window’s menu bar click on Help. A pull-down menu will appear.
4.Click on the Contents menu option and a list of selections will appear.
5.Under the "How to . . ." heading, click on Change the System Date and Time.
6.A window will appear with instructions for setting the date and time.
01821-001 |
October 1998 |
Revision 2.1 |
Page 15 |
Doors™ Users Guide |
Keri Systems, Inc. |
This page is intentionally left blank.
October 1998 |
01821-001 |
Page 16 |
Revision 2.1 |
Keri Systems, Inc. |
Doors™ Users Guide |
Software Installation
This section covers upgrading an existing Doors software installation, performing a brandnew installation, troubleshooting some basic installation problems, and deleting an old software installation. For a brand-new installation, please skip to the New Installation section below.
Upgrade Installation
If you have an original revision of the Doors software and you're upgrading to a new revision, you should make a complete copy of the original Doors installation into a backup location for recovery if there is an issue with the new software installation. You must perform this step before installing the new revision of Doors as the installation process will overwrite critical files in the original revision making recovery of the original revision impossible.
Backing Up in Windows 95
1.Open the Windows EXPLORER program.
2.Click on the "kerisys" folder icon (typically c:).
3. Click on File New Folder, or right-click the mouse, scroll down the displayed list of available commands, and click on New Folder.
4.Enter a name for the backup folder (such as "backup").
5. Locate and click on the "kerisys\Doors" folder and then click on Edit Copy.
6.Click on the "backup" folder.
7.Click on Edit Paste. All files in the "kerisys\Doors" folder will be copied to the "kerisys\backup" folder.
8.When the copy process is complete, skip to the New Installation section below for instructions on the new installation of Doors software.
Backing Up in Windows 3.11
1.Enter the FILE MANAGER program.
2. Locate and click on the "Doors" directory and then click on FILE COPY. A prompt box will appear asking for a destination path.
3.Click in the text box within the prompt box and type the name of the destination path (such as "c:\kerisys\backup") into which the backup copy can be saved.
4.Click on the Copy button. All files in the "kerisys\Doors" folder will be copied to the "kerisys\backup" folder.
5.When the directory copy process is complete, skip to the New Installation section below for instructions on the new installation of Doors software.
New Installation
A new installation of the Doors software requires 20 MB of free space on the hard disc drive for program and database storage.
To Install Doors using Windows 95
1.Insert Disk 1 into the host computer's floppy disk drive.
2.Click on the Windows Start button.
3.In the start menu, click on the RUN button. A run window appears on screen.
4.Click in the "Open:" text box and type a:\winstall.exe.
5.Click on the OK button. Program installation now begins.
01821-001 |
October 1998 |
Revision 2.1 |
Page 17 |
Doors™ Users Guide |
Keri Systems, Inc. |
6.A text window appears with the README.TXT file for the Doors software. Please read the README.TXT file for late-breaking information regarding this revision of Doors
software. When you are finished reading, click on the File Exit pull-down menu or click on the  box in the upper-right corner of the window.
box in the upper-right corner of the window.
7.The installation program will then verify that the host computer has at least 20 MB of available space before allowing the file copying process to begin.
8.The installation program will request a directory name into which the software should be loaded. The Doors program uses "\kerisys\doors" as the default directory path for installing software. If another directory path is desired, click in this text field and enter that path now. If this installation is an upgrade to an existing installation and the existing installation is in a different directory path, enter that directory path now.
9.Click on the OK button.
10.The installation program will request an icon name. The default icon name is Doors. If desired, enter a more descriptive name at this time (perhaps a name including the software revision).
11.Click on the OK button.
12.A number of files will be copied to the host computer. When disk 1 is complete, the installation program will prompt for disk 2. Remove disk 1, insert disk 2, and click the OK button.
13.A few more files will be copied to the host computer. When the installation is complete, an "Installation Successful" banner will appear. Remove disk 2.
14.Click on the OK button and the Doors software is now ready for use.
To Install Doors using Windows 3.11
1.Insert Disk 1 into the host computer's floppy disk drive.
2.Open the Main window.
3.Open the FILE MANAGER program.
4.Click on the File Run pull-down menu.
5.Click in the text box and type a:\winstall.exe.
6.Click on the OK button. Program installation now begins.
7.A text box will appear with the README.TXT file for the Doors software. Please read the README.TXT file for late-breaking information regarding this revision of Doors
software. When you are finished reading, click on the File Exit pull-down menu or click on the  box in the upper-right corner of the window.
box in the upper-right corner of the window.
8.The installation program will then verify that the host computer has at least 20 MB of available space before allowing the file copying process to begin.
9.The installation program will request a directory name into which the software should be loaded. The Doors program uses "\kerisys\doors" as the default directory path for installing software. If another directory path is desired, click in this text field and enter that path now. If this installation is an upgrade to an existing installation and the existing installation is in a different directory path, enter that directory path now.
10.Click on the OK button.
11.The installation program will request an icon name. The default icon name is Doors. If desired, enter a more descriptive name at this time (perhaps a name including the software revision).
12.Click on the OK button.
13.A number of files will be copied to the host computer. When disk 1 is complete, the installation program will prompt for disk 2. Remove disk 1, insert disk 2, and click the OK button.
14.A few more files will be copied to the host computer. When the installation is complete, an "Installation Successful" banner will appear. Remove disk 2.
15.Click on the OK button and the Doors software is now ready for use.
October 1998 |
01821-001 |
Page 18 |
Revision 2.1 |
Keri Systems, Inc. |
Doors™ Users Guide |
Troubleshooting
The following section provides information on correcting two basic program installation/ operation problems and for recovering an original saved installation.
Low System Resources
Sporadic problems in operating the Doors software can be due to an inadequate amount of the host computer's resources being available for use by the Doors software. The greater the number of programs open concurrently, the less the amount of system resources available for any one program. Doors needs approximately 65% of the computer system's resources free for proper operation.
Verifying System Resources in Windows 95
1.Click on the Start button on the Task Bar. A menu of selections will appear.
2. Click on Settings Control Panel.
3.When the Control Panel window appears, double-click on the System icon.
4.When the System Properties window appears, click on the Performance tab.
5.A list of system performance status values will appear; one of which is the system resources value.
6.The system resources value should be above 65% to ensure proper operation of the Doors program. If it is not, close other unneeded programs to release the system resources they are using.
7.When you have finished viewing the system performance values, click on the OK button or click on the  box in the upper-right corner of the window.
box in the upper-right corner of the window.
8.If closing programs does not release enough system resources, close all programs, re-boot the host computer, and then start the Doors program. This will release all system resources for reallocation.
Verifying System Resources in Windows 3.11
1. In the Program Manager window, click on Help About.
2.A list of information about this Windows installation will appear. One of the items listed is the system resources value.
3.The system resources value should be above 65% to ensure proper operation of the Doors program. If it is not, close other unneeded programs to release the system resources they are using.
4.When you have finished viewing the installation information, click on the OK button or click on the  box in the upper-right corner of the window.
box in the upper-right corner of the window.
5.If closing programs does not release enough system resources, close all programs, re-boot the host computer, restart Windows, and then start the Doors program. This will release all system resources for reallocation.
Missing DLL Files
Sporadic problems with the screens and buttons in the Doors software in older Windows 3.11 installations can be due to two files that are required for proper operation of the Doors software but are missing from the Windows installation. In Windows 95 use WINDOWS EXPLORER and in Windows 3.11 use FILE MANAGER to verify these two files exist in the "Windows/System" directory.
CTL3D.DLL
CTL3DV2.DLL
01821-001 |
October 1998 |
Revision 2.1 |
Page 19 |
Doors™ Users Guide |
Keri Systems, Inc. |
If these files do not exist, they may be copied from Disk 1 of the Doors installation disks. Perform the following steps to copy these files to your Windows/System directory.
To Copy the Missing DLL Files in Windows 95
1.Exit the Doors program.
2.Insert Doors installation disk number 1 into the floppy disk drive.
3.Start the WINDOWS EXPLORER program.
4.Click on the floppy disk drive icon, typically a:\.
5.When its file directory appears, click on the CTL3D.DLL file. This file name should now be highlighted.
6.Hold down the CTRL key and click on the CTL3DV2.DLL file. Both file names should now be highlighted.
7.Click on Edit Copy, or click on the right mouse button, scroll down the displayed list of available commands, and click on Copy.
8.Scroll down the list of folders and locate the "windows\system" directory. Click on the "windows\system" directory.
9.Click on Edit Paste, or click on the right mouse button, scroll down the displayed list of available commands, and click on Paste.
10.Restart the Doors program and the DLLs will be applied to the program.
To Copy the Missing DLL Files in Windows 3.11
1.Exit the Doors program.
2.Insert Doors installation disk number 1 into the floppy disk drive.
3.Double-click on the Main window icon and then double-click on the FILE MANAGER program.
4.Click on the floppy disk drive icon, typically a:\.
5.When its file directory appears, click on the CTL3D.DLL file in the right-side of the window. This file name should now be highlighted.
6.Hold down the CTRL key and click on the CTL3DV2.DLL file. Both file names should now be highlighted.
7.Click on File Copy, or click on the right mouse button, scroll down the displayed list of available commands, and click on Copy.
8.Click on the hard disk drive icon, typically c:\.
9.When its file directory appears, scroll down the list of folders in the left-side of the window and locate the "windows\system" directory. Click on the "windows\system" directory.
10.Click on File Paste, or click on the right mouse button, scroll down the displayed list of available commands, and click on Paste.
11.Restart the Doors program and the DLLs will be applied to the program.
Recovering an Original Doors Installation
At times following an upgrade installation, it can become necessary to restore the original installation of Doors software. Restoration is simply a matter of copying the original installation back over the new installation.
October 1998 |
01821-001 |
Page 20 |
Revision 2.1 |

Keri Systems, Inc. |
Doors™ Users Guide |
Recovery Using Windows 95
1.Open the WINDOWS EXPLORER program.
2. Locate and click on the backup folder and then click on EDIT COPY.
3.Click on the folder to which the original installation should be restored (typically c:\kerisys\doors).
4.Click on EDIT PASTE, or click on the right mouse button, scroll down the displayed list of available commands, and click on Paste.
5.When the folder copy process is complete, the original revision of Doors software has been restored and is ready for use.
Recovery Using Windows 3.11
1.Enter the FILE MANAGER program.
2. Locate and click on the backup directory and then click on FILE COPY. A prompt box will appear asking for a destination path.
3.Click in the text box within the prompt box and type the name of the destination path (typically c:\kerisys\doors) into which the original installation should be restored.
4.Click on the OK button.
5.When the directory copy process is complete, the original revision of Doors software has been restored and is ready for use.
Deleting a Backed Up Doors Installation
If the new installation has been operating correctly for an extended period of time and if disc storage space is at a premium, the backed up installation can be deleted.
Be sure the new installation is working to your satisfaction before deleting the backed up installation. Once deleted, the backed up installation cannot be recovered.
Deleting Using Windows 95
1.Open the WINDOWS EXPLORER program.
2. Locate and click on the backup folder and then click on FILE DELETE.
3.A file deletion confirmation window will appear. Click on the Yes button.
4.At some point during the file deletion process a prompt box will appear asking if executable files should be deleted. Click on the Yes to All button.
5.When the file deletion progress window disappears, the original installation has been deleted and disc storage space has been recovered.
Deleting Using Windows 3.11
1.Open the FILE MANAGER program.
2. Locate and click on the backup folder and then click on EDIT DELETE.
3.A file deletion confirmation window will appear. Click on the Yes button.
4.When the file deletion progress window disappears, the original installation has been deleted and disc storage space has been recovered.
01821-001 |
October 1998 |
Revision 2.1 |
Page 21 |
Doors™ Users Guide |
Keri Systems, Inc. |
This page is intentionally left blank.
October 1998 |
01821-001 |
Page 22 |
Revision 2.1 |

Keri Systems, Inc. |
Doors™ Users Guide |
Users Guide
Doors is designed to make the access control system configuration and operation as simple as possible. This is done by breaking the configuration and operation processes into logical sections. Each section is responsible for a specific operation; whether it is entering information regarding how some aspect of the system is to be used or physically performing some operation.
The Users Guide is written for the novice user, learning how to navigate the Doors software menus and how to use the commands within the menus. The Users Guide presents the configuration and operation process in a recommended order of implementation. An operator can configure the system in almost any order, but the order described in the Users Guide provides the most sequential and complete path for the first time installer and for a new installation. Generally speaking, each section of the Users Guide builds upon what has been completed in the previous section.
To present this information, the Users Guide provides "real-world" examples of a new installation for a small company in an order that logically builds a complete access control database. By using real-world examples, this Users Guide will reveal the extensive power and simplicity of the Doors software.
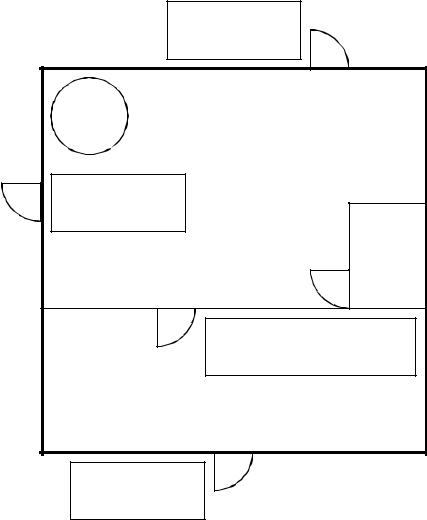
The scenario for these real-world examples consists of a small building with 4 controllers controlling 5 doors. Figure 1 provides a floor-plan of this building. Access control will be provided for three exterior doors and for two interior doors. The people working in this building have a variety of jobs: manufacturing, stockroom, sales, technical, janitorial, management, so the time of access and area of access requirements differ depending upon the personnel.
Older revisions of Doors software and controller firmware do not have all the features described in this Users Guide. This Users Guide is written to describe the capabilities of the current Doors software and controller firmware, and might not accurately reflect the capabilities of previous software/firmware revisions.
01821-001 |
October 1998 |
Revision 2.1 |
Page 23 |
Doors™ Users Guide |
Keri Systems, Inc. |
Back Door
PXL-250 |
Slave Controller (4) |
Host |
Computer |
MANUFACTURING AREA |
Emergency Exit |
PXL-250 |
Master Controller (1) |
STOCK |
ROOM |
Manufacturing/Stockroom Doors |
PXL-250 w/ SB-293 |
Slave Controller (3) |
CUSTOMER AREA |
Front/Customer Door |
PXL-250
Slave Controller (2)
Figure 1 - Users Guide Site Layout
Users Guide Conventions
There are certain conventions the Users Guide follows for presenting information and for indicating when an operator needs to perform an action on the computer.
Folder or directory names are identified in the text as "folder/subfolder."
Locating an item under a pull-down menu is identified as Menu Option Sub-Menu Option.
Program names are identified in all UPPER-CASE.
Information to be typed by an operator is identified in Boldface.
If a button is clicked to perform an operation, the button icon is displayed or the button name is shown in Boldface.
October 1998 |
01821-001 |
Page 24 |
Revision 2.1 |

Keri Systems, Inc. |
Doors™ Users Guide |
Operation notes are shown in italics. These are things of which to be aware while using the Doors software.
Items that require special attention or that can dramatically affect the access control network are prefaced with a caution sign.
Windows Conventions
Doors is a fully compliant Windows program; providing complete operability in Windows and allowing its program window to be opened, closed, resized, and multi-tasked as any other Windows compliant program. Please refer to the help file within the Windows operating system for information on working in Windows.
On-Line Help
To assist the end user there is a "point-and-tell" on-line help file in the Doors software. Once in the help file, simply point and click on a menu option, command, or selection and a description of that item is displayed. To call-up the help file when in the Doors program,
Click on the Help/Contents pull-down menu or click on the  button on the Doors tool bar (see the Tool Bar section under Introducing the Desk Top) to open the help file.
button on the Doors tool bar (see the Tool Bar section under Introducing the Desk Top) to open the help file.
The Order of Operation
This section provides a summary of the major sections in the order that they are presented in the Users Guide.
Logging On the Doors Program
Each operator has a unique log on password that allows the Doors program to identify the operator logging on to the program and to track the actions the operator takes while logged on.
Setup and Verify Network Communication
The setup and verify network communication section describes the process for configuring the Doors operating parameters to meet those of the host computer and then verifying that basic communication is indeed happening between host computer and all the controllers on the access control network.
Set Communication Parameters
Four tasks are performed to set the Doors communication parameters.
1.Set the program’s COM port to match the host computer.
2.Set the program’s communication speed.
3.Set the remote phone number (for remote access via modem).
4.Restart the program to configure Doors with the communication parameters.
Auto-Config
The Doors program polls the access control network and receives information identifying which controllers are communicating on the network. It then inserts this information into the appropriate databases within the Doors program.
01821-001 |
October 1998 |
Revision 2.1 |
Page 25 |
Doors™ Users Guide |
Keri Systems, Inc. |
Set Time
The Doors program then needs to synchronize the time/date between the host computer and all controllers so that all event can be tracked correctly.
Perform Smart Update
The Doors program downloads default operating information to the access control network.
Get Controller Status
The Doors program polls the access control network and receives information regarding controller/door configuration. It then inserts this information into the appropriate databases within the Doors program. This is the quickest way to verify that all controllers/doors are recognized by the access control system.
Begin Database Programming
Database programming is where the day-to-day operating parameters for the access control system are entered.
Setup Operators
The setup operators commands allow for the creation of system operators and the assignment of operator privileges. It is the operators that will be performing the work: creating the databases required by the Doors software to do its job and monitoring the access control network once everything has been downloaded to the network.
Setup Time Zones
The setup time zones commands allow an operator to create the various daily time periods and holiday time periods to be applied to access groups, the auto unlock/lock door function, and for input/output operations.
Setup Doors
The setup doors commands allow an operator to define the configuration and operation parameters for all the controllers/doors on the access control network.
Setup Access Groups
The setup access groups commands allow an operator to combine time zones and doors into a superset of information that is applied to cardholders. In conjunction with time zones, access groups allow an operator to define which doors an employee is allowed to use at what times.
Setup Cards
The setup cards commands allow an operator to enroll cards into the system and enter cardholder information, and to void cards from the system. Each cardholder has a card that identifies that individual to the access control network. When a cardholder presents a card to a reader requesting access, information associated with the card is compared to information in the databases stored at the controller to determine if that cardholder should be allowed access through that door.
Setup Monitor Windows
The setup monitor window commands allow an operator to configure up to three different monitoring windows to allow filtered, real-time tracking of events on the access control network.
October 1998 |
01821-001 |
Page 26 |
Revision 2.1 |
Keri Systems, Inc. |
Doors™ Users Guide |
Download Information to the Network
The download information to the network command allows an operator to download information from the program database to the access control network. This information is used by the controllers in the network to run the access control system.
System Operation
The system operation commands allow an operator to manually, immediately perform specific functions such as:
•unlock and lock doors
•monitor and collect events from controllers
•override regularly programmed door controls
•create and view event reports
Advanced Features
The Doors program is capable of several advanced features that expand the program’s capabilities. These features include:
•Remote communication with one or more access control networks via modems.
•I/O control – the linking of input events to drive output responses (i.e. an input connected to a vibration sensor on a window that is linked to an alarm output so that a broken window will sound an alarm).
01821-001 |
October 1998 |
Revision 2.1 |
Page 27 |
Doors™ Users Guide |
Keri Systems, Inc. |
This page is intentionally left blank.
October 1998 |
01821-001 |
Page 28 |
Revision 2.1 |
Keri Systems, Inc. |
Doors™ Users Guide |
Logging On
The first step is to start the Doors program and log onto the system. In normal operation, the log on process identifies to the software which operator is entering the program. With this identification, the program is able to limit the operator’s actions to those that operator has been approved to perform.
Starting the Doors Program
For both Windows 95 and Windows 3.11, there are several ways to start the Doors program. The easiest, most common methods are described below.
Starting the Program in Windows 95
1.From the Windows 95 Task Bar.
•Click on the Start button. A pop-up menu of commands appears.
•Click on the Programs menu option. A pop-up menu of program folders appears.
•Click on the Kerisys program folder. A pop-up menu of programs appears.
•Click on the Doors program icon.
•The program now begins.
2.Using WINDOWS EXPLORER.
•Run the WINDOWS EXPLORER program.
•Locate the DOORS.EXE program (it is typically found under the "\kerisys\doors" folder.
• Either double-click on the DOORS.EXE program icon or click on the File Open pull-down menu.
•The program now begins.
3.Using WINDOWS EXPLORER to create a Windows desk top shortcut.
•Run the WINDOWS EXPLORER program.
•Locate the DOORS.EXE program (it is typically found under the "\kerisys\doors" folder.
•Click on the DOORS.EXE program icon. It should now be highlighted.
•Either click on the File Create Shortcut menu option or right-click on the DOORS.EXE program icon, scroll down the list of menu options, and select the Create Shortcut option.
•A new file is created titled "Shortcut to Doors.exe".
• Click on the "Shortcut to Doors.exe" icon and then click on either File Copy or right-click on the "Shortcut to Doors.exe" icon, scroll down the list of menu options, and select the Copy option.
•Close the WINDOWS EXPLORER program and click on the main Windows desk top.
•Right-click the mouse, scroll down the list of menu options, and select the Paste option. The new icon for the Doors program will be placed on the desk top.
•This icon will now appear on the desk top every time the Windows program is entered. Simply double-click on the icon to start the Doors program.
01821-001 |
October 1998 |
Revision 2.1 |
Page 29 |
Doors™ Users Guide |
Keri Systems, Inc. |
Starting the Program in Windows 3.11
1.Run the program from the Doors program group.
•Locate the Doors program group on the main window.
•Double-click on the Doors program group icon. A window will open with icons for all the programs within the Doors program group.
•Locate the DOORS.EXE program icon.
•Double-click on the DOORS.EXE program icon.
•The program now begins.
2.Using FILE MANAGER.
•Run the FILE MANAGER program.
•Locate the DOORS.EXE program (it is typically found under the "\kerisys\doors" subdirectory.
• Either double-click on the DOORS.EXE program listing or click on the File Open pull-down menu.
•The program now begins.
System Logon
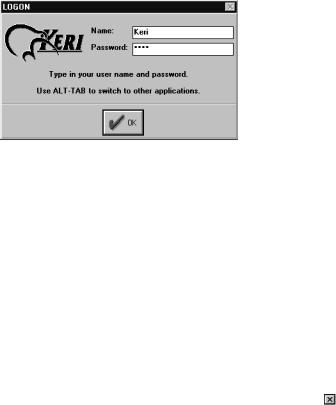
Once the program begins, it will prompt for an operator Logon (see Figure 2). This is an identifying name and password for the operator entering the program. The first time the program is entered, the default Logon information must be used. Until changed, the default password provides access to everything in the Doors program. Later in the Doors configuration process, each authorized operator is assigned identifying names and passwords.
Figure 2 – Logon Screen
To logon the program:
1.Click in the Name box, type Keri and press ENTER.
2.Click in the Password Box, type Keri. Asterisks will appear in the password box instead of letters so that someone looking over your shoulder during Logon cannot steal your password.
3.Press ENTER or click on the  button.
button.
The program will now verify the user name and password. If both are correct, the Logon window disappears allowing access to the Doors program. If either are incorrect, the user name and password fields are cleared and the Logon window remains. To leave the Logon
process and return to Windows, for Windows 95 click on the |
box in the upper-right corner |
of the Logon window, for Windows 3.11 click on the File |
Exit pull-down menu option. |
October 1998 |
01821-001 |
Page 30 |
Revision 2.1 |
 Loading...
Loading...